-
 @ 0971cd37:53c969f4
2025-05-31 13:30:33
@ 0971cd37:53c969f4
2025-05-31 13:30:33ขุด Bitcoin ด้วยเครื่อง ASIC เช่น Antminer หรือ Whatsminer นั้น "อุณหภูมิ" ถือเป็นหนึ่งในปัจจัยที่สำคัญที่สุดที่มีผลต่อ ประสิทธิภาพ, ความเสถียร, และ อายุการใช้งาน ของเครื่อง หากอุณหภูมิสูงเกินไป อาจทำให้แรงขุดลดลง

ตัวอย่าง Antminer S21 Pro อุณหภูมิ Chip Temp (Tuning Power)

ตัวอย่าง WhatsMiner M30S++ อุณหภูมิ Chip Temp (Tuning Power)

📌 จุดวัดอุณหภูมิที่สำคัญ Chip Temp: อุณหภูมิของชิป ASIC โดยตรง เป็นค่าหลักที่ใช้ประเมินความร้อน
Inlet Temp: อุณหภูมิของอากาศที่เข้าเครื่อง ควรต่ำกว่า 35-38°C
Outlet Temp: อุณหภูมิของลมร้อนที่ออกจากเครื่อง อาจสูงถึง 60–80°C ได้
ตัวอย่าง Antminer S21 Pro (Tuning Power)

แนวทางการจัดการความร้อน
-
ทำความสะอาดพัดลม ฮีตซิงค์ และ ซิลิโคนระบายความร้อน 6 เดือน/ครั้ง
-
ใช้ระบบ พัดลมดูดลมออก หลักการ Inlet และ Outlet หรือ custom water cooling kit (สายแนว hydro)
-
วางเครื่องในที่ที่มีอากาศถ่ายเทดี อุณหภูมิแวดล้อมไม่เกิน 30–35°C หลีกเลี่ยงการวางเครื่องในพื้นที่อับ เช่น ห้องปิด
หากไม่ทำความสะอาดเครื่องขุด Bitcoin เป็นระยะ โดยเฉพาะฝุ่นที่สะสมในพัดลมและฮีตซิงก์ อาจเกิดผลเสียหลายด้าน
-
ความร้อนสะสม อุณหภูมิสูงเกินไป ฝุ่นจะอุดตันช่องลม ทำให้อากาศไหลเวียนไม่สะดวกพัดลมระบายความร้อนไม่สามารถพาอากาศร้อนออกได้อย่างมีประสิทธิภาพส่งผลให้ อุณหภูมิของชิป (Chip Temp) พุ่งสูงขึ้นเรื่อย ๆ
-
เครื่องทำงานช้าลง เมื่ออุณหภูมิเกิน 80–85°C ระบบจะ ลด Hashrate อัตโนมัติ เพื่อป้องกันความเสียหาย กำลังขุดลดลง รายได้จากการขุดก็ลดลงด้วย
-
เสี่ยงต่อการเสียหายของฮาร์ดแวร์ หากปล่อยให้ความร้อนสะสมจนเกิน 90°C บอร์ดอาจไหม้ ชิป ASIC เสียหายถาวร พัดลมทำงานหนักเกินไป จนมอเตอร์พัง
-
อายุการใช้งานเครื่องสั้นลง เครื่องที่ร้อนจัดและสะสมฝุ่นจะเสื่อมเร็วกว่าเครื่องที่ได้รับการดูแล อาจใช้ได้ไม่ถึงปี
-
ค่าซ่อม/เปลี่ยนอุปกรณ์สูง หากต้องเปลี่ยนบอร์ด ASIC หรือ พัดลม จะมีค่าใช้จ่ายหลักพันถึงหลักหมื่นบาทต่อเครื่อง ในบางกรณี อาจต้องเปลี่ยนทั้งเครื่องหากเสียหายหนัก
-
-
 @ 84b0c46a:417782f5
2025-05-31 09:11:23
@ 84b0c46a:417782f5
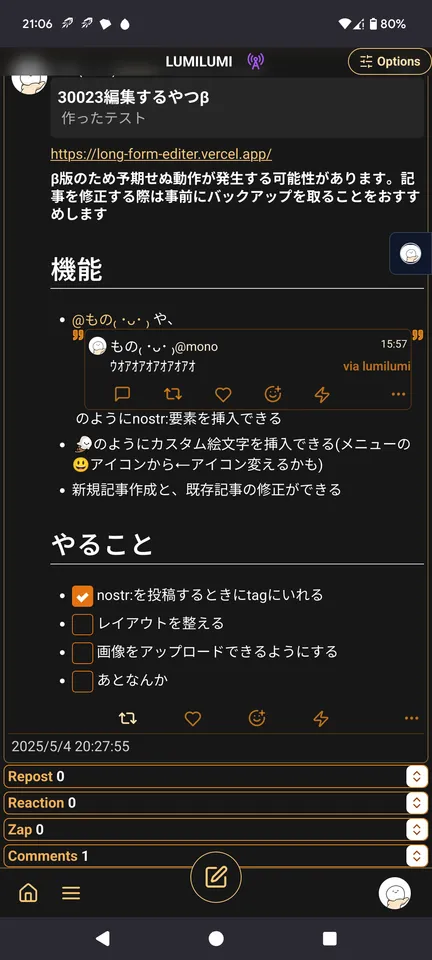
2025-05-31 09:11:23Simple Long Form Content Editor (NIP-23)
機能
-
nostr:npub1sjcvg64knxkrt6ev52rywzu9uzqakgy8ehhk8yezxmpewsthst6sw3jqcw や、 nostr:nevent1qvzqqqqqqypzq4jsz7zew5j7jr4pdfxh483nwq9vyw9ph6wm706sjwrzj2we58nqqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyxhwumn8ghj7mn0wvhxcmmvqqsgcn99jyn5tevxz5zxsrkd7h0sx8fwnqztula423xh83j9wau7cms3vg9c7 のようにnostr:要素を挿入できる (メニューのNアイコンから挿入またはnostr:note~~のように手動で入力)
-
:monoice:のようにカスタム絵文字を挿入できる(メニューの🙂アイコンから)
:monopaca_kao:
:kubipaca_karada:
- 新規記事作成と、既存記事の修正ができる
やることやったこと
-
[x] nostr:を投稿するときにtagにいれる
-
[x] 画像をアップロードできるようにする(NIP-96)
 できる
できる - [x] 投稿しましたログとかをトースト的なやつでだすようにする
- [ ] レイアウトを整える
- [ ] あとなんか
test
nostr:naddr1qvzqqqr4gupzpp9sc34tdxdvxh4jeg5xgu9ctcypmvsg0n00vwfjydkrjaqh0qh4qqxnzde58q6njvpkxqersv3ejxw9x9
-
-
 @ 6a6be47b:3e74e3e1
2025-05-31 12:18:17
@ 6a6be47b:3e74e3e1
2025-05-31 12:18:17Hi frens! 🦖
📖 How’s your weekend starting out? I’ve been painting and reading, and I’m super excited to share that I finally finished Jurassic Park by Michael Crichton!
😜 I’m still working on the art of convincing people to read a book without spoiling it, but I’ll do my best here.
📕 Let me just say: the book is so much better than the movie (and that’s saying something, because the movie will always have a special place in my heart). The novel is basically one cliffhanger after another—I was absolutely hooked! There’s nonstop adventure and so much tension as the characters dodge dinosaurs at every turn.
I was pleasantly surprised by how the characters react to the dinosaurs in the book. I love Ian Malcolm’s character even more here—his warnings about the park being a disaster waiting to happen are even sharper and more compelling. I thought Dr. Grant would come to the same conclusion as Malcolm a bit sooner, but as a paleontologist, he’s understandably in awe—this is the pinnacle of his career, after all! Unlike Malcolm, he has less time to process the reality of prehistoric creatures walking the earth again.
The characters are all a bit different (sometimes a LOT different) from their movie versions, but it works so well. If I could change one thing, I would have loved to see Dr. Sattler play a bigger role throughout the novel.
📝 All in all, I’m so glad I finally read it. There’s action, adventure, dinosaurs, humans being humans, and a sprinkle of science and deep questions about the consequences of our actions. I was hooked from start to finish.
If you haven’t read it yet, I hope you give yourself the chance—don’t wait as long as I did!
See you later, alligator 🐊
Godspeed! By the way, I wrote and painted some dinosaurs here 👀 just in case you want to know more about dinosaurs, just like it happened to me!
https://stacker.news/items/993455
-
 @ d360efec:14907b5f
2025-05-31 00:36:48
@ d360efec:14907b5f
2025-05-31 00:36:48 -
 @ d360efec:14907b5f
2025-05-30 11:23:40
@ d360efec:14907b5f
2025-05-30 11:23:40 -
 @ 2e8970de:63345c7a
2025-05-31 11:54:55
@ 2e8970de:63345c7a
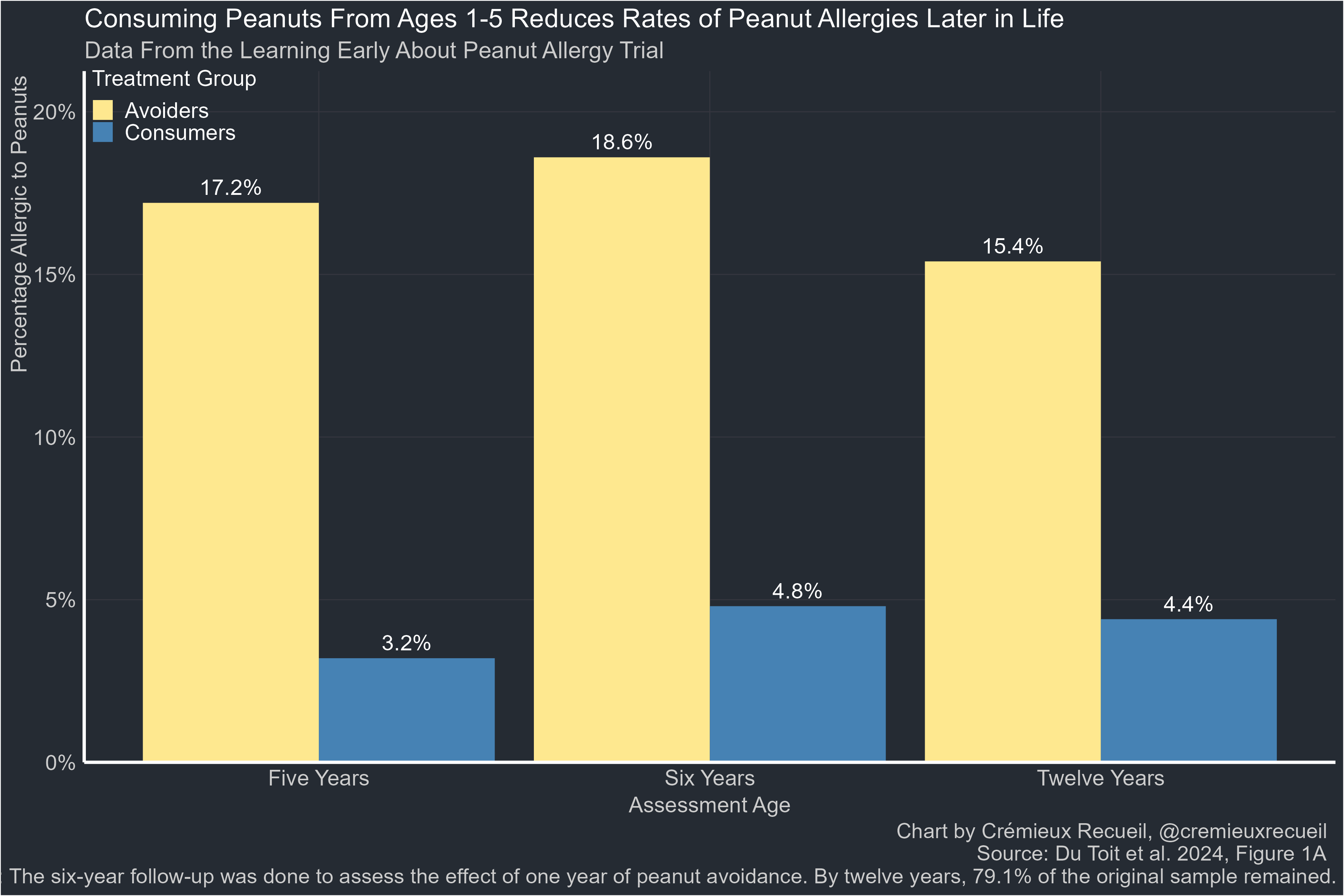
2025-05-31 11:54:55https://evidence.nejm.org/doi/full/10.1056/EVIDoa2300311
The solution to peanut allergy? Import Bamba!
https://stacker.news/items/993440
-
 @ eb0157af:77ab6c55
2025-05-31 11:01:02
@ eb0157af:77ab6c55
2025-05-31 11:01:02Block’s hardware wallet sparks debate between security and borderline compromises.
The debate ignited after Jack Dorsey publicly supported the superiority of “seedless” wallets over traditional solutions on X.
seedless is safer https://t.co/MvjmFcQE8k
— jack (@jack) May 27, 2025
The Twitter co-founder and Block CEO sustained this by promoting Bitkey, a company that completely eliminates seed phrases, aiming to simplify the user experience and improve security through different recovery options.
The Bitkey model
Bitkey represents a different solution compared to the traditional approach to bitcoin custody. Instead of relying on a single seed phrase, the system implements a 2-of-3 multisig scheme that distributes security across three distinct keys:
- Hardware key: protected by biometric fingerprint on the physical device;
- Mobile key: stored in the smartphone app;
- Server key: managed by Block’s servers.
Any transaction requires two of the three signatures, eliminating the single point of failure represented by traditional seed phrases, the company claims. In its official documents, Bitkey explains how this approach, according to the company, offers three different recovery paths: phone loss, hardware loss, or loss of both through “Trusted Contacts,” pre-set trusted people who can help the user regain wallet access without being able to see the balance or control the private keys.
The seed phrase criticism
For the Bitkey team, the seed phrase paradoxically represents the weakest link in the Bitcoin security chain. While private keys are “exceptionally secure” within the hardware – “designed for security, isolated from networks, physically reinforced” – the seed phrase is “plain text, readable, physically vulnerable,” the company states.
Bitkey developers argue that the industry has “offloaded the most complex part of the security model onto individuals least equipped to handle it.”
System limits and dependencies
However, Bitkey’s simplicity comes at a price. The system introduces a dependency on Block for optimal multisig functionality. Although users always maintain the ability to move funds using the two keys in their possession, recovery procedures and many advanced features require collaboration from the company’s servers.
This architecture presents limitations in terms of flexibility: users cannot use Bitkey with other mobile applications, cannot import the wallet into alternative solutions, and do not have direct access to seed phrases for traditional backup operations.
One of the most frequent criticisms concerns the absence of a screen on the hardware device. Unlike traditional hardware wallets that allow direct verification of destination addresses and transaction amounts on the device display, Bitkey forces users to rely exclusively on the mobile app for these details. This design choice introduces what critics define as a “blind signing risk”: if the mobile app were compromised by malware, users could unknowingly authorize altered transactions without the possibility of independent verification.
Community criticism
Dorsey’s post sparked contrasting reactions in the community. The most orthodox bitcoiners mainly contest two aspects:
- third-party dependency: despite Bitkey maintaining the “self-custody” label, the need to rely on Block’s servers for many operations contradicts the autonomy principles that many bitcoiners consider fundamental;
- loss of technical control: the inability to directly manage the seed phrase or use the device in customized multisig configurations limits the user’s technical sovereignty.
Some users have criticized Block’s hardware wallet. User bamskki highlighted how “the lack of a screen forces users to rely on the app for transaction details. Unlike traditional hardware wallets with screens, Bitkey users cannot verify transactions independently. Users must trust the app as the source of truth.”
Even more critical was user nakadai_mon, who ironized about Dorsey’s strategy writing: “It would be a shame if I influenced you to abandon the seed and locked you into my ecosystem so I can surveil you, sell and share your personal data with government authorities and deny you service.”
Dorsey responded directly to both criticisms. To bamskki he replied:
it's a start, not our end. we will iterate the product like everything else.
— jack (@jack) May 28, 2025
More articulated was his response to nakadai_mon:
we are working on much of the privacy aspects (launching soon). and you don't have to use our 3rd key. that's where some of the restrictions come in. working to figure out how to allow folks to create their own trusted 3rd party as well. but all of this is designed to get people…
— jack (@jack) May 28, 2025
However, privacy concerns are not unfounded. Bitkey’s own documentation clarifies that “because we maintain this key, we are able to identify transaction data on the blockchain related to your Bitkey” and that “this information is collected when you transfer bitcoin to or from your Bitkey.”
Additionally, Block declares using automated decision-making systems, without direct staff involvement, to manage some activities that have legal effects on users. Among these, the application of sanctions restrictions: the system is programmed to automatically prevent the purchase and use of Bitkey by people or countries subject to international sanctions. Finally, the privacy policy specifies that users’ personal data can be shared with law enforcement, government agencies, officials, or authorized third parties in the presence of a warrant, court order, or other legal obligation. Block reserves the right to disclose this information whenever it deems necessary to comply with regulations, legal proceedings, or government requests.
Hardware security and compromises
From a hardware security perspective, Bitkey implements advanced protections including unique device identifiers, secure boot, and anti-tamper technologies. In case the device were compromised, an attacker would still need to access a second key to steal funds.
According to Dorsey’s statements, Bitkey represents an attempt to make self-custody accessible to a broader audience. The company’s roadmap promises improvements in terms of privacy, security, and usability.
The post Bitkey controversy: Dorsey’s marketing divides the community appeared first on Atlas21.
-
 @ 9ca447d2:fbf5a36d
2025-05-31 11:00:41
@ 9ca447d2:fbf5a36d
2025-05-31 11:00:41Michael Saylor, executive chairman of Strategy, has stirred up the Bitcoin community with his recent comments on proof-of-reserves, calling it a “bad idea” that puts institutional security at risk.
Speaking at a side event at the Bitcoin 2025 conference in Las Vegas, Saylor expressed strong concerns about the security implications of on-chain proof of reserves (PoR), a method used by many bitcoin companies to show they actually hold the assets they claim.
“The conventional way of issuing proof of reserves today is actually insecure,” Saylor said.
“It actually dilutes the security of the issuer, the custodians, the exchanges and the investors. It’s not a good idea, it’s a bad idea.”
Proof-of-reserves is a process where companies with bitcoin reserves share public wallet addresses or use cryptographic methods to prove how much bitcoin they hold.
This practice gained popularity after the collapse of major exchanges like FTX and Mt. Gox to build trust through transparency.
Many big players in the digital asset space, including Binance, Kraken, OKX and asset manager Bitwise, have adopted PoR to reassure users and stakeholders.
Related: Bitwise Announces On-Chain Address, Donations Go to Shareholders
Saylor’s objections boil down to two main points.
First, he believes publishing wallet addresses creates serious security risks. By exposing institutional wallet structures, companies may open themselves up to attacks from hackers, hostile governments or malicious actors.
“[It’s like] publishing the address and the bank accounts of all your kids and the phone numbers of all your kids and then thinking somehow that makes your family better,” Saylor said.
“(It becomes) an attack vector for hackers, nation-state actors, every type of troll imaginable.”
He even asked the audience to try a thought experiment:
“Go to AI, put it in deep think mode and then ask it ‘what are the security problems of publishing your wallet addresses?’ and ‘how might it undermine the security of your company over time’ … It will write you a book. It will be fifty pages of security problems.”
Second, Saylor pointed out that proof of reserves only shows what a company owns, not what it owes. In his view, that’s incomplete.
“It’s proof of assets that is insecure, and it is not proof of liabilities… So you own $63 billion worth of bitcoin—do you have a hundred billion dollars of liabilities?” he asked rhetorically.
For large institutions and investors, this view of financial health is not enough.
Instead of publishing wallet addresses, Saylor thinks the better approach is to use institutional-grade audits by trusted firms.
“The best practice… would be to have a Big Four auditor that checks to make sure you actually have the bitcoin, then checks to make sure the company hasn’t rehypothecated or pledged the bitcoin,” he said.
“Then you have to wash it through a public company where the CFO signs, then the CEO signs, then the chairman and all the outside directors are civilly and criminally liable for it.”
He believes the legal consequences of corporate auditing — including prison time for fraud under the Sarbanes-Oxley Act — are stronger than cryptographic proof alone.
He did admit that a more secure, future version of PoR might be possible if it involved zero-knowledge proofs that protect wallet privacy while still confirming ownership.
Not everyone agrees with Saylor’s opinion. While some praised his focus on security, others accused Saylor of hiding something.
Speculations resurfaced about whether Strategy truly holds all the bitcoin it claims, or if it’s involved in so-called “paper bitcoin” — claims to BTC without physical backing.
Others pointed out that exchanges like Kraken and asset managers like Bitwise have implemented PoR systems without major breaches.
-
 @ d360efec:14907b5f
2025-05-27 15:46:26
@ d360efec:14907b5f
2025-05-27 15:46:26 -
 @ dfa02707:41ca50e3
2025-05-31 11:01:14
@ dfa02707:41ca50e3
2025-05-31 11:01:14
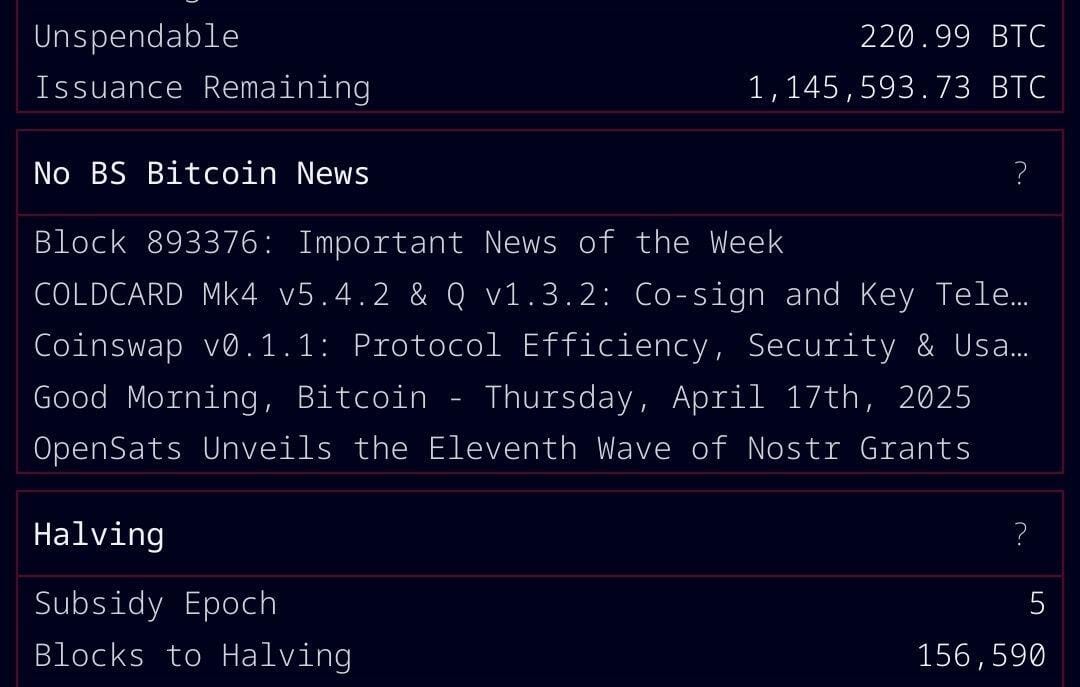
Good morning (good night?)! The No Bullshit Bitcoin news feed is now available on Moody's Dashboard! A huge shoutout to sir Clark Moody for integrating our feed.
Headlines
- Spiral welcomes Ben Carman. The developer will work on the LDK server and a new SDK designed to simplify the onboarding process for new self-custodial Bitcoin users.
- The Bitcoin Dev Kit Foundation announced new corporate members for 2025, including AnchorWatch, CleanSpark, and Proton Foundation. The annual dues from these corporate members fund the small team of open-source developers responsible for maintaining the core BDK libraries and related free and open-source software (FOSS) projects.
- Strategy increases Bitcoin holdings to 538,200 BTC. In the latest purchase, the company has spent more than $555M to buy 6,556 coins through proceeds of two at-the-market stock offering programs.
- Spar supermarket experiments with Bitcoin payments in Zug, Switzerland. The store has introduced a new payment method powered by the Lightning Network. The implementation was facilitated by DFX Swiss, a service that supports seamless conversions between bitcoin and legacy currencies.
- The Bank for International Settlements (BIS) wants to contain 'crypto' risks. A report titled "Cryptocurrencies and Decentralised Finance: Functions and Financial Stability Implications" calls for expanding research into "how new forms of central bank money, capital controls, and taxation policies can counter the risks of widespread crypto adoption while still fostering technological innovation."
- "Global Implications of Scam Centres, Underground Banking, and Illicit Online Marketplaces in Southeast Asia." According to the United Nations Office on Drugs and Crime (UNODC) report, criminal organizations from East and Southeast Asia are swiftly extending their global reach. These groups are moving beyond traditional scams and trafficking, creating sophisticated online networks that include unlicensed cryptocurrency exchanges, encrypted communication platforms, and stablecoins, fueling a massive fraud economy on an industrial scale.
- Slovenia is considering a 25% capital gains tax on Bitcoin profits for individuals. The Ministry of Finance has proposed legislation to impose this tax on gains from cryptocurrency transactions, though exchanging one cryptocurrency for another would remain exempt. At present, individual 'crypto' traders in Slovenia are not taxed.
- Circle, BitGo, Coinbase, and Paxos plan to apply for U.S. bank charters or licenses. According to a report in The Wall Street Journal, major crypto companies are planning to apply for U.S. bank charters or licenses. These firms are pursuing limited licenses that would permit them to issue stablecoins, as the U.S. Congress deliberates on legislation mandating licensing for stablecoin issuers.
"Established banks, like Bank of America, are hoping to amend the current drafts of [stablecoin] legislation in such a way that nonbanks are more heavily restricted from issuing stablecoins," people familiar with the matter told The Block.
- Charles Schwab to launch spot Bitcoin trading by 2026. The financial investment firm, managing over $10 trillion in assets, has revealed plans to introduce spot Bitcoin trading for its clients within the next year.
Use the tools
- Bitcoin Safe v1.2.3 expands QR SignMessage compatibility for all QR-UR-compatible hardware signers (SpecterDIY, KeyStone, Passport, Jade; already supported COLDCARD Q). It also adds the ability to import wallets via QR, ensuring compatibility with Keystone's latest firmware (2.0.6), alongside other improvements.
- Minibits v0.2.2-beta, an ecash wallet for Android devices, packages many changes to align the project with the planned iOS app release. New features and improvements include the ability to lock ecash to a receiver's pubkey, faster confirmations of ecash minting and payments thanks to WebSockets, UI-related fixes, and more.
- Zeus v0.11.0-alpha1 introduces Cashu wallets tied to embedded LND wallets. Navigate to Settings > Ecash to enable it. Other wallet types can still sweep funds from Cashu tokens. Zeus Pay now supports Cashu address types in Zaplocker, Cashu, and NWC modes.
- LNDg v1.10.0, an advanced web interface designed for analyzing Lightning Network Daemon (LND) data and automating node management tasks, introduces performance improvements, adds a new metrics page for unprofitable and stuck channels, and displays warnings for batch openings. The Profit and Loss Chart has been updated to include on-chain costs. Advanced settings have been added for users who would like their channel database size to be read remotely (the default remains local). Additionally, the AutoFees tool now uses aggregated pubkey metrics for multiple channels with the same peer.
- Nunchuk Desktop v1.9.45 release brings the latest bug fixes and improvements.
- Blockstream Green iOS v4.1.8 has renamed L-BTC to LBTC, and improves translations of notifications, login time, and background payments.
- Blockstream Green Android v4.1.8 has added language preference in App Settings and enables an Android data backup option for disaster recovery. Additionally, it fixes issues with Jade entry point PIN timeout and Trezor passphrase input.
- Torq v2.2.2, an advanced Lightning node management software designed to handle large nodes with over 1000 channels, fixes bugs that caused channel balance to not be updated in some cases and channel "peer total local balance" not getting updated.
- Stack Wallet v2.1.12, a multicoin wallet by Cypher Stack, fixes an issue with Xelis introduced in the latest release for Windows.
- ESP-Miner-NerdQAxePlus v1.0.29.1, a forked version from the NerdAxe miner that was modified for use on the NerdQAxe+, is now available.
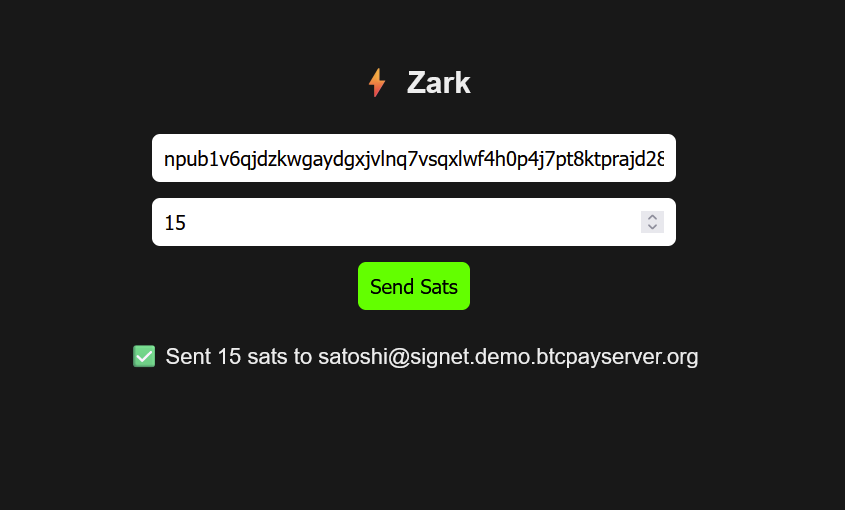
- Zark enables sending sats to an npub using Bark.
- Erk is a novel variation of the Ark protocol that completely removes the need for user interactivity in rounds, addressing one of Ark's key limitations: the requirement for users to come online before their VTXOs expire.
- Aegis v0.1.1 is now available. It is a Nostr event signer app for iOS devices.
- Nostash is a NIP-07 Nostr signing extension for Safari. It is a fork of Nostore and is maintained by Terry Yiu. Available on iOS TestFlight.
- Amber v3.2.8, a Nostr event signer for Android, delivers the latest fixes and improvements.
- Nostur v1.20.0, a Nostr client for iOS, adds
-
 @ 9ca447d2:fbf5a36d
2025-05-31 11:00:39
@ 9ca447d2:fbf5a36d
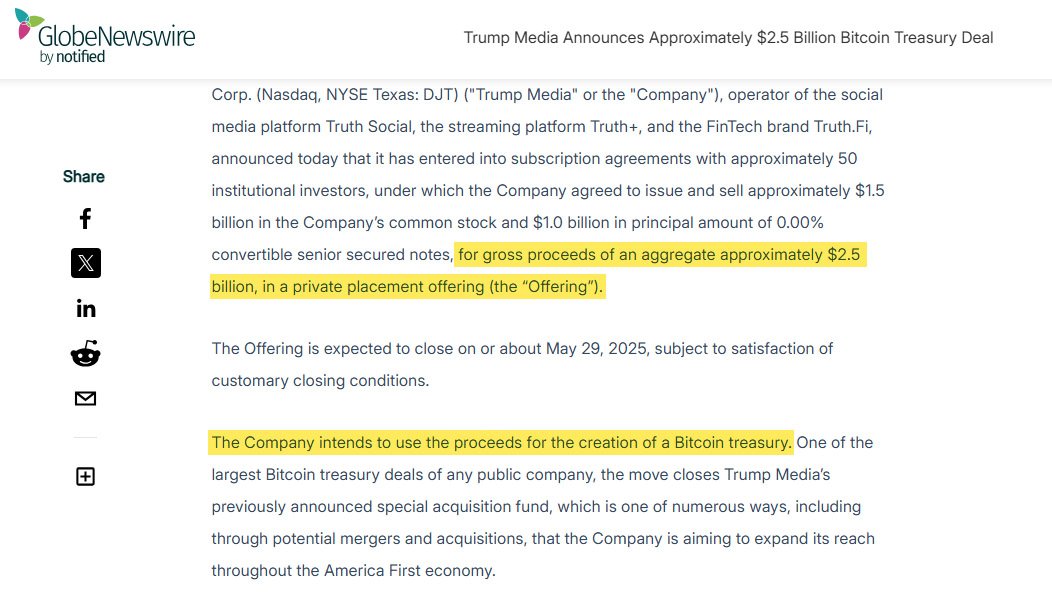
2025-05-31 11:00:39Trump Media & Technology Group (TMTG), the company behind Truth Social and other Trump-branded digital platforms, is planning to raise $2.5 billion to build one of the largest bitcoin treasuries among public companies.
The deal involves the sale of approximately $1.5 billion in common stock and $1.0 billion in convertible senior secured notes.
According to the company, the offering is expected to close by the end of May, pending standard closing conditions.
Devin Nunes, CEO of Trump Media, said the investment in bitcoin is a big part of the company’s long-term plan.
“We view Bitcoin as an apex instrument of financial freedom,” Nunes said.
“This investment will help defend our Company against harassment and discrimination by financial institutions, which plague many Americans and U.S. firms.”
He added that the bitcoin treasury will be used to create new synergies across the company’s platforms including Truth Social, Truth+, and the upcoming financial tech brand Truth.Fi.
“It’s a big step forward in the company’s plans to evolve into a holding company by acquiring additional profit-generating, crown jewel assets consistent with America First principles,” Nunes said.
The $2.5 billion raise will come from about 50 institutional investors. The $1 billion in convertible notes will have 0% interest and be convertible into shares at a 35% premium.
TMTG’s current liquid assets, including cash and short-term investments, are $759 million as of the end of the first quarter of 2025. With this new funding, the company’s liquid assets will be over $3 billion.
Custody of the bitcoin treasury will be handled by Crypto.com and Anchorage Digital. They will manage and store the digital assets.
Earlier this week The Financial Times reported Trump Media was planning to raise $3 billion for digital assets acquisitions.
The article said the funds would be used to buy bitcoin and other digital assets, and an announcement could come before a major related event in Las Vegas.
Related: Bitcoin 2025 Conference Kicks off in Las Vegas Today
Trump Media denied the FT report. In a statement, the company said, “Apparently the Financial Times has dumb writers listening to even dumber sources.”
There was no further comment. However, the official $2.5 billion figure, which was announced shortly after by Trump Media through a press release, aligns with its actual filing and investor communication.
Trump Media’s official announcement
This comes at a time when the Trump family and political allies are showing renewed interest in Bitcoin.
President Donald Trump who is now back in office since the 2025 election, has said he wants to make the U.S. the “crypto capital of the world.”
Trump Media is also working on retail bitcoin investment products including ETFs aligned with America First policies.
These products will make bitcoin more accessible to retail investors and support pro-Trump financial initiatives.
But not everyone is happy.
Democratic Senator Elizabeth Warren recently expressed concerns about Trump Media’s Bitcoin plans. She asked U.S. regulators to clarify their oversight of digital-asset ETFs, warning of investor risk.
Industry insiders are comparing Trump Media’s plans to Strategy (MSTR) which has built a multi-billion dollar bitcoin treasury over the last year. They used stock and bond sales to fund their bitcoin purchases.
-
 @ 21335073:a244b1ad
2025-05-21 16:58:36
@ 21335073:a244b1ad
2025-05-21 16:58:36The other day, I had the privilege of sitting down with one of my favorite living artists. Our conversation was so captivating that I felt compelled to share it. I’m leaving his name out for privacy.
Since our last meeting, I’d watched a documentary about his life, one he’d helped create. I told him how much I admired his openness in it. There’s something strange about knowing intimate details of someone’s life when they know so little about yours—it’s almost like I knew him too well for the kind of relationship we have.
He paused, then said quietly, with a shy grin, that watching the documentary made him realize how “odd and eccentric” he is. I laughed and told him he’s probably the sanest person I know. Because he’s lived fully, chasing love, passion, and purpose with hardly any regrets. He’s truly lived.
Today, I turn 44, and I’ll admit I’m a bit eccentric myself. I think I came into the world this way. I’ve made mistakes along the way, but I carry few regrets. Every misstep taught me something. And as I age, I’m not interested in blending in with the world—I’ll probably just lean further into my own brand of “weird.” I want to live life to the brim. The older I get, the more I see that the “normal” folks often seem less grounded than the eccentric artists who dare to live boldly. Life’s too short to just exist, actually live.
I’m not saying to be strange just for the sake of it. But I’ve seen what the crowd celebrates, and I’m not impressed. Forge your own path, even if it feels lonely or unpopular at times.
It’s easy to scroll through the news and feel discouraged. But actually, this is one of the most incredible times to be alive! I wake up every day grateful to be here, now. The future is bursting with possibility—I can feel it.
So, to my fellow weirdos on nostr: stay bold. Keep dreaming, keep pushing, no matter what’s trending. Stay wild enough to believe in a free internet for all. Freedom is radical—hold it tight. Live with the soul of an artist and the grit of a fighter. Thanks for inspiring me and so many others to keep hoping. Thank you all for making the last year of my life so special.
-
 @ 005bc4de:ef11e1a2
2025-05-31 10:55:47
@ 005bc4de:ef11e1a2
2025-05-31 10:55:47LUV and Hivebits/HBIT/Wusang pause tl;dr LUV and HBIT (aka, Hivebits and the Wusang game) are on a pause at the moment, taking a break. https://files.peakd.com/file/peakd-hive/crrdlx/23x1SY8Vx8j1mVGnDFtq7ebuzKNGd8K9Ssex51AEerxks1VYikxGPShM7bjNhmSrEZ2wf.png Image from pixabay.com Why? There are odd things going on. I have a theory, but here's what is known... May 28, 2025, at about 1:30 pm GMT (8:30 AM EDT), a second attack (for lack of better term) hit HBIT in about a week. It seemed to start with @tyler45 with this comment https://peakd.com/blog/@tyler45/comment-20250528125108033 tx: https://he.dtools.dev/tx/7e7d4126196ca5b6dbe0a04dcded0e25d3bcc7f4 See tyler45's activity at https://he.dtools.dev/@tyler45 Notice the reply and WUSANG command is to a post by @olivia897 and how many of the other WUSANG comments on the explorer are in reply to olivia897. It seems these are all auto-generated accounts. The names and "birthdates" and interactions all point to automation. Once initiated, things happened very fast on the back end, clearly not being done manually. In this way, this seems rather sophisticated technically. I estimate just over 400 HBIT were pilfered the other day from the @Hivebits account before I noticed and was able to shut things down. Just for a little background, after the first attack May 21, 2025. I wrote a small bit of info: https://peakd.com/hivebits/@crrdlx/hbit-resource-credits A couple of days ago this post by @holoz0r was interesting: https://peakd.com/hive-133987/@holoz0r/text-analytics-reveal-thirty-two-percent-of-comments-on-hive-are-not-unique-and-at-least-ten-percent-add-no-value-to-discussion The thing that caught my eye was that the WUSANG comment was the largest by far, along with BBH (hello @bradleyarrow), because the attackers used both commands. Then, a few days later, things happened again: sudden start, repetitive bot attack, until I shut things down. So, a pause This is a period in my personal calendar where I simply don't have time to sit down at a computer for an extended period and try fiddle with this stuff. So, for now @Luvshares and @Hivebits (HBIT) and the @Wusang game are on hold. Plus, there's other fun stuff to do. https://files.peakd.com/file/peakd-hive/crrdlx/AJL43SREA1EuyqPXhydmqaq1RHhRVoYd12PfiBN5vDMu2WSKUtGeYWgKJyuRwV8.jpg I go by @crrdlx or "CR" for short. See all my links or contact info at https://linktr.ee/crrdlx.
Originally posted on Hive at https://peakd.com/@crrdlx/luv-and-hivebitshbitwusang-pause
Auto cross-post via Hostr v0.1.48 (br) at https://hostr-home.vercel.app
-
 @ c9badfea:610f861a
2025-05-20 19:49:20
@ c9badfea:610f861a
2025-05-20 19:49:20- Install Sky Map (it's free and open source)
- Launch the app and tap Accept, then tap OK
- When asked to access the device's location, tap While Using The App
- Tap somewhere on the screen to activate the menu, then tap ⁝ and select Settings
- Disable Send Usage Statistics
- Return to the main screen and enjoy stargazing!
ℹ️ Use the 🔍 icon in the upper toolbar to search for a specific celestial body, or tap the 👁️ icon to activate night mode
-
 @ 43baaf0c:d193e34c
2025-05-27 14:08:02
@ 43baaf0c:d193e34c
2025-05-27 14:08:02During the incredible Bitcoin Filmfest, I attended a community session where a discussion emerged about zapping and why I believe zaps are important. The person leading the Nostr session who is also developing an app that’s partially connected to Nostr mentioned they wouldn’t be implementing the zap mechanism directly. This sparked a brief but meaningful debate, which is why I’d like to share my perspective as an artist and content creator on why zaps truly matter.
Let me start by saying that I see everything from the perspective of an artist and creator, not so much from a developer’s point of view. In 2023, I started using Nostr after spending a few years exploring the world of ‘shitcoins’ and NFTs, beginning in 2018. Even though I became a Bitcoin maximalist around 2023, those earlier years taught me an important lesson: it is possible to earn money with my art.
Whether you love or hate them, NFTs opened my eyes to the idea that I could finally take my art to the next level. Before that, for over 15 years, I ran a travel stock video content company called @traveltelly. You can read the full story about my journey in travel and content here: https://yakihonne.com/article/traveltelly@primal.net/vZc1c8aXrc-3hniN6IMdK
When I truly understood what Bitcoin meant to me, I left all other coins behind. Some would call that becoming a Bitcoin maximalist.
The first time I used Nostr, I discovered the magic of zapping. It amazed me that someone who appreciates your art or content could reward you—not just with a like, but with real value: Bitcoin, the hardest money on earth. Zaps are small amounts of Bitcoin sent as a sign of support or appreciation. (Each Bitcoin is divisible into 100 million units called Satoshis, or Sats for short—making a Satoshi the smallest unit of Bitcoin recorded on the blockchain.)
 The Energy of Zaps
The Energy of ZapsIf you’re building an app on Nostr—or even just connecting to it—but choose not to include zaps, why should artists and content creators share their work there? Why would they leave platforms like Instagram or Facebook, which already benefit from massive network effects?
Yes, the ability to own your own data is one of Nostr’s greatest strengths. That alone is a powerful reason to embrace the protocol. No one can ban you. You control your content. And the ability to post once and have it appear across multiple Nostr clients is an amazing feature.
But for creators, energy matters. Engagement isn’t just about numbers—it’s about value. Zaps create a feedback loop powered by real appreciation and real value, in the form of Bitcoin. They’re a signal that your content matters. And that energy is what makes creating on Nostr so special.
But beyond those key elements, I also look at this from a commercial perspective. The truth is, we still can’t pay for groceries with kisses :)—we still need money as a medium of exchange. Being financially rewarded for sharing your content gives creators a real incentive to keep creating and sharing. That’s where zaps come in—they add economic value to engagement.
A Protocol for Emerging Artists and Creators
I believe Nostr offers a great starting point for emerging artists and content creators. If you’re just beginning and don’t already have a large following on traditional social media platforms, Nostr provides a space where your work can be appreciated and directly supported with Bitcoin, even by a small but engaged community.
On the other hand, creators who already have a big audience and steady income on platforms like Instagram or YouTube may not feel the urgency to switch. This is similar to how wealthier countries are often slower to understand or adopt Bitcoin—because they don’t need it yet. In contrast, people in unbanked regions or countries facing high inflation are more motivated to learn how money really works.
In the same way, emerging creators—those still finding their audience and looking for sustainable ways to grow—are often more open to exploring new ecosystems like Nostr, where innovation and financial empowerment go hand in hand.
The same goes for Nostr. After using it for the past two years, I can honestly say: without Nostr, I wouldn’t be the artist I am today.
Nostr motivates me to create and share every single day. A like is nice but receiving a zap, even just 21 sats, is something entirely different. Once you truly understand that someone is willing to pay you for what you share, it’s no longer about the amount. It’s about the magic behind it. That simple gesture creates a powerful, positive energy that keeps you going.
Even with Nostr’s still relatively small user base, I’ve already been able to create projects that simply wouldn’t have been possible elsewhere.
Zaps do more than just reward—they inspire. They encourage you to keep building your community. That inspiration often leads to new projects. Sometimes, the people who zap you become directly involved in your work, or even ask you to create something specifically for them.
That’s the real value of zaps: not just micro-payments, but micro-connections sparks that lead to creativity, collaboration, and growth.
Proof of Work (PoW)
Over the past two years, I’ve experienced firsthand how small zaps can evolve into full art projects and even lead to real sales. Here are two examples that started with zaps and turned into something much bigger:
Halving 2024 Artwork
When I started the Halving 2024 project, I invited people on Nostr to be part of it. 70 people zapped me 2,100 sats each, and in return, I included their Npubs in the final artwork. That piece was later auctioned and sold to Jurjen de Vries for 225,128 Sats.
Magic Internet Money
For the Magic Internet Money artwork, I again invited people to zap 2,100 sats to be included. Fifty people participated, and their contributions became part of the final art frame. The completed piece was eventually sold to Filip for 480,000 sats.
These examples show the power of zaps: a simple, small act of appreciation can turn into larger engagement, deeper connection, and even the sale of original art. Zaps aren’t just tips—they’re a form of collaboration and support that fuel creative energy.
I hope this article gives developers a glimpse into the perspective of an artist using Nostr. Of course, this is just one artist’s view, and it doesn’t claim to speak for everyone. But I felt it was important to share my Proof of Work and perspective.
For me, Zaps matter.
Thank you to all the developers who are building these amazing apps on Nostr. Your work empowers artists like me to share, grow, and be supported through the value-for-value model.
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ 6be5cc06:5259daf0
2025-05-27 20:22:09
@ 6be5cc06:5259daf0
2025-05-27 20:22:09A posição do libertário que rejeita o cristianismo padece de sérias incoerências lógicas, históricas e filosóficas. Ao renegar as bases espirituais e culturais que tornaram possível o próprio ideal libertário, tal posição demonstra ser, ao mesmo tempo, autofágica e irracional. É o caso de alguém que se gloria dos frutos de uma árvore que corta pela raiz.
I. Fundamento histórico: a civilização da liberdade é cristã
Não foi o secularismo moderno, nem o paganismo antigo, que ergueram as instituições que protegem a dignidade da pessoa humana e os limites ao poder. Desde os primeiros séculos, a Igreja resistiu ao culto estatal romano, afirmando a soberania de Deus sobre os Césares — "Mais importa obedecer a Deus que aos homens" (Atos 5,29).
Foi o cristianismo que:
-
Fundou universidades livres, onde o saber era buscado sob o primado da verdade;
-
Defendeu a lei natural como fundamento do direito — uma doutrina que protege o indivíduo contra tiranias;
-
Resgatou e aprofundou o conceito de pessoa, dotada de razão e livre-arbítrio, imagem de Deus, e, portanto, inalienavelmente digna e responsável.
Em momentos-chave da história, como nas disputas entre papado e império, nas resistências contra absolutismos, e na fundação do direito internacional por Francisco de Vitoria e a Escola de Salamanca, foi o cristianismo quem freou o poder estatal em nome de princípios superiores. A tradição cristã foi frequentemente o principal obstáculo à tirania, não seu aliado.
Negar isso é amputar a própria genealogia da liberdade ocidental.
Uma das chaves do cristianismo para a construção dessa civilização da liberdade foi a exaltação do individualismo. Ao afirmar que o ser humano é feito à imagem de Deus e que sua salvação é uma escolha pessoal, o cristianismo colocou o indivíduo no centro da moralidade e da liberdade. Diferente dos gregos, cuja ética era voltada para a polis e a cidade-estado, o cristianismo reafirma a suprema importância do indivíduo, com sua capacidade de escolha moral, responsabilidade pessoal e dignidade intrínseca. Esse princípio, mais do que qualquer outra religião, foi o alicerce do desenvolvimento da liberdade individual e da autonomia, valores que sustentam a civilização ocidental.
A ética grega, na melhor das hipóteses, descreve a ordem natural — mas não consegue justificar por que essa ordem deveria obrigar a vontade humana. Um Logos impessoal não tem autoridade moral. Uma ordem cósmica sem um Legislador é apenas um dado de fato, não uma norma vinculante. A vontade pode rebelar-se contra o telos — e sem um Deus justo, que ordena a natureza à perfeição, não há razão última para não o fazer.
A cultura grega teve uma influência indiscutível sobre o desenvolvimento da civilização ocidental, mas o cristianismo não só absorveu o que havia de bom na cultura grega, como também elevou e completou esses aspectos. O cristianismo, ao afirmar que todos os homens são feitos à imagem e semelhança de Deus e têm dignidade intrínseca, levou a uma noção de igualdade moral e liberdade que transcende as limitações da pólis grega.
II. Falsa dicotomia: fé e liberdade não são opostas
Com frequência equiparam a religião à coerção e à obediência cega. Mas isso é um equívoco: o cristianismo não se impõe pela força, mas apela à consciência. O próprio Deus, em sua relação com a criatura racional, respeita sua liberdade. Como ensina a Escritura:
"Se alguém quiser vir após mim..." (Mt 16,24);
"Eis que estou à porta e bato. Se alguém ouvir a minha voz e abrir a porta, entrarei em sua casa e cearei com ele." (Ap 3,20);
"Assim falai, e assim procedei, como devendo ser julgados pela lei da liberdade." (Tiago 2,12).A adesão à fé deve ser livre, voluntária e racional, pois sem liberdade não há verdadeiro mérito, nem amor genuíno. Isso é mais compatível com o princípio de não agressão do que qualquer utopia secular. Ora, o núcleo do evangelho é voluntarista: salvação pessoal, conversão interior, caridade.
Ninguém deve ser forçado, contra sua vontade, a abraçar a fé, pois o ato de fé é por sua natureza voluntário (Dignitatis Humanae; CDC, cân. 748,2)
Se algum Estado usa da força para impor o cristianismo, afirmar que o cristianismo causou as coerções é tão equivocado quanto dizer que a propriedade privada causa o comunismo; é uma inversão da realidade, pois o comunismo surge precisamente da violação da propriedade. Portanto, a fé forçada é inválida em si mesma, pois viola a natureza do ato de crer, que deve ser livre.
III. Fundamento moral: sem transcendência, o libertarianismo flutua no vácuo
O libertário anticristão busca defender princípios objetivos — como a inviolabilidade do indivíduo e a ilegitimidade da agressão — sem um fundamento transcendente que lhes dê validade universal. Por que a agressão é errada? Por que alguém tem direito à vida, à liberdade, à propriedade? Sem uma explicação transcendental, as respostas para tais perguntas se tornam apenas opiniões ou convenções, não obrigações morais vinculantes. Se a moralidade é puramente humana, então os direitos podem ser modificados ou ignorados conforme a vontade da sociedade. O conceito de direitos naturais, tão caro ao libertarianismo, precisa de um solo metafísico que justifique sua universalidade e imutabilidade. Caso contrário, eles podem ser tratados apenas como acordos utilitários temporários ou preferências culturais, sem qualquer obrigatoriedade para todos os seres humanos em todas as circunstâncias.
Pensadores libertários seculares, como Ayn Rand e Murray Rothbard, tentaram ancorar os direitos naturais na razão humana ou na natureza do homem. Rand baseia sua ética no egoísmo racional, enquanto Rothbard apela à lei natural. Embora essas abordagens busquem objetividade, elas carecem de uma resposta definitiva para por que a razão ou a natureza humana obrigam moralmente todos os indivíduos. Sem um fundamento transcendente, suas concepções permanecem vulneráveis a interpretações subjetivas ou a cálculos utilitários.
Aqui, o cristianismo oferece uma explicação sólida e transcendental que fundamenta os direitos naturais. A visão cristã de que o ser humano foi criado à imagem e semelhança de Deus confere à pessoa uma dignidade intrínseca, imutável e universal. Essa dignidade não depende de fatores externos, como consenso social ou poder político, mas é uma característica inerente ao ser humano pela sua criação divina. A partir dessa perspectiva teológica, torna-se possível afirmar com base sólida que os direitos naturais são dados por Deus e, portanto, são universais e vinculantes.
O cristianismo também é a base de um sistema moral que distingue claramente justiça de legalidade. O Estado pode criar leis, mas isso não significa que essas leis sejam justas. A justiça, sob a ótica cristã, é uma expressão da ordem moral objetiva, algo que transcende as leis humanas e é definido pela vontade divina. Por isso, o libertarianismo cristão vê a agressão como uma violação de uma ordem moral objetiva, e não apenas uma violação de uma convenção social ou de um acordo utilitário.
Se a moralidade e os direitos naturais não forem fundamentados em um Logos criador e legislador, o que acontece é que o conceito de direito natural degenera para algo mais frágil, como um simples acordo utilitário. Nesse cenário, os direitos do indivíduo se tornam algo acordado entre os membros de uma sociedade, em vez de princípios imutáveis e universais. Os direitos podem ser negociados, alterados ou ignorados conforme o interesse do momento.
IV. Fundamento científico: a racionalidade moderna é filha da fé cristã
A ciência moderna só foi possível no contexto cultural cristão. Nenhuma outra civilização — nem a grega, nem a islâmica, nem a chinesa — produziu o método científico como o Ocidente cristão o fez.
Isso se deve a quatro premissas teológicas:
-
Criação racional: O mundo é ordenado por um Deus racional.
-
Distinção entre Criador e criatura: A natureza não é divina e pode ser estudada sem sacrilégio.
-
Valor do trabalho e da observação empírica, herdado do monaquismo.
-
Autonomia institucional, presente nas universidades medievais.
A doutrina cristã da Criação ex nihilo ensina que o mundo foi criado por um Deus racional, sábio e pessoal. Portanto, o cosmos é ordenado, possui leis, e pode ser compreendido pela razão humana — que é imagem do Criador. Isso contrasta fortemente com as cosmovisões panteístas ou mitológicas, onde o mundo é cíclico, arbitrário ou habitado por forças caprichosas.
Sem essa fé no Logos criador, não há razão para crer que a natureza tenha uma ordem inteligível universal e constante, que pode ser descoberta por observação e dedução. A ciência moderna só é possível porque, antes de investigar a natureza, pressupôs-se que ela era investigável — e isso foi uma herança direta do pensamento cristão.
Homens como Bacon, Newton, Kepler e Galileu viam na ciência um modo de glorificar o Criador. O ateísmo cientificista é, portanto, parasitário da teologia cristã, pois toma seus frutos e rejeita suas raízes. A ciência moderna nasceu como filha legítima da fé cristã. E os que hoje a usam contra sua mãe, ou são ingratos, ou ignorantes.
V. O cristianismo como barreira à revolução cultural
O cristianismo é a barreira mais sólida contra a infiltração revolucionária. A chamada "marcha gramsciana", que visa corroer os fundamentos morais da sociedade para subjugar o indivíduo ao coletivo, encontra sua resistência mais firme nos princípios cristãos. A fé cristã, ao proclamar a existência de uma verdade objetiva, de uma lei moral imutável e de uma dignidade humana que transcende o Estado e o consenso social, imuniza a civilização contra o relativismo e o igualitarismo nivelador do marxismo cultural.
Além disso, o cristianismo é uma tradição milenar, profundamente enraizada no cotidiano das pessoas, não sendo uma novidade a ser imposta ou implementada, mas uma força presente há séculos, que permeia a estrutura social, moral e cultural da sociedade. Sua presença constante nas comunidades, desde os tempos mais antigos, oferece uma resistência robusta contra qualquer tentativa de subverter a ordem natural e moral estabelecida.
Não por acaso, tanto Karl Marx quanto Antonio Gramsci identificaram no cristianismo o principal obstáculo à realização de seus projetos revolucionários. Marx chamou a religião de "ópio do povo" porque sabia que uma alma ancorada em Deus não se submete facilmente ao poder terreno; Gramsci, mais sutil, propôs a destruição da cultura cristã como pré-condição para o triunfo do socialismo. Sem essa âncora transcendente, a sociedade torna-se presa fácil das engenharias sociais que pretendem redefinir arbitrariamente o homem, a família e a liberdade.
Conclusão
O libertário anticristão, consciente ou não, nega as fundações mesmas do edifício que habita. Ao rejeitar o cristianismo, cava o abismo sob os próprios pés, privando o ideal libertário de sua base moral, cultural e racional. Ele defende a ética voluntária, a liberdade individual e a ordem espontânea, mas sem o solo metafísico e histórico que torna esses princípios inteligíveis e possíveis. É um erro tentar preservar a liberdade em termos absolutos sem reconhecer as raízes cristãs que a sustentam, pois o cristianismo é a única tradição que a legitima e a viabiliza.
Negar o cristianismo é racionalmente insustentável. A liberdade, como a conhecemos, é filha da fé cristã, que oferece a base moral e metafísica que torna a liberdade tanto desejável quanto possível. Mesmo que ateu, o libertário que ama a liberdade deveria, no mínimo, respeitar — e, idealmente, redescobrir — essas raízes cristãs. Pois sem fé, restam apenas o niilismo e o relativismo, que, eventualmente, desaguam na servidão.
Como nos ensina a tradição: Ubi fides ibi libertas — onde há fé, há liberdade.
-
-
 @ eb0157af:77ab6c55
2025-05-28 07:01:26
@ eb0157af:77ab6c55
2025-05-28 07:01:26Bitcoin surpasses gold in the United States: 50 million holders and a dominant role in the global market.
According to a new report by River, for the first time in history, the number of Americans owning bitcoin has surpassed that of gold holders. The analysis reveals that approximately 50 million U.S. citizens currently own the cryptocurrency, while gold owners number 37 million. In fact, 14.3% of Americans own bitcoin, the highest percentage of holders worldwide.

Source: River
The report highlights that 40% of all Bitcoin-focused companies are based in the United States, consolidating America’s dominant position in the sector. Additionally, 40.5% of Bitcoin holders are men aged 31 to 35, followed by 35.9% of men aged 41 to 45. In contrast, only 13.4% of holders are women.

Source: River
Notably, U.S. companies hold 94.8% of all bitcoins owned by publicly traded companies worldwide. According to the report, recent regulatory changes in the U.S. have made the asset more accessible through financial products such as spot ETFs.
The document also shows that American investors increasingly view the cryptocurrency as protection against fiscal instability and inflation, appreciating its limited supply and decentralized governance model.
For River, Bitcoin offers significant practical advantages over gold in the modern digital era. Its ease of custody, cross-border transfer, and liquidity make the cryptocurrency an attractive option for both individual and institutional investors, the report suggests.
The post USA: 50 million Americans own bitcoin appeared first on Atlas21.
-
 @ 866e0139:6a9334e5
2025-05-31 10:45:03
@ 866e0139:6a9334e5
2025-05-31 10:45:03Autor: Marcel Bühler. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
In einem Artikel in der NZZ vom 27. Mai mit dem Titel "Trump nennt Putin verrückt" wird über den laut Kiew grössten russischen Drohnenangriff seit Beginn des Krieges auf ukrainische Städte berichtet. Dabei sollen am vergangenen Wochenende 355 Drohnen und 69 Raketen auf Kiew, Odessa, Ternipol (Westukraine) und andere Städte gesteuert bzw. abgefeuert worden sein. 288 Drohnen und 9 Raketen konnten laut Kiew von der ukrainischen Luftverteidigung abgeschossen werden. Was der Artikel verschweigt: bereits in der Woche davor, am 20. - 22. Mai hatte die Ukraine 485 Drohnen gegen russische Städte wie Kursk, Belgorod oder Brijansk geflogen, 63 davon erreichten die Region Moskau. Auch am Wochenende schickten die Ukrainer 205 Drohnen gegen russische Städte, 13 davon erreichten Moskau. Auch hier konnte die Luftverteidigung die meisten Drohnen unschädlich machen, eine davon hatte gar den Helikopter von Präsident Putin (!) im Visier. Als Reaktion darauf erklärte Präsident Putin, dass in der ukrainischen Region Sumy bzw. Tschernihiw im Norden eine Sicherheitszoneeingerichtet werden soll da die meisten Drohnen von hier aus gestartet wurden. Auch am 27./28. Mai schickte die Ukraine wieder 296 Drohnen Richtung Moskau, offenbar soll die russische Luftverteidigung damit überlastet werden um später westliche Cruise Missiles wie "Storm shadows", "Skalp" oder die umstrittenen deutschen "Taurus" effektiver einsetzen zu können. Der neue Bundeskanzler Friedrich Merz hat dafür rund 5 Milliarden Euro in Aussicht gestellt um solche Waffensysteme in der Ukraine selber zusammenbauen zu können.
Diese Gewaltspirale hat eine lange Geschichte: diese begann 2007 mit der 43. Münchner Sicherheitskonferenz, in der Präsident Putin sich gegen die unilaterale Weltordnung der USA und ihrer Verbündeten aussprach. Auch erteilte er den NATO-Osterweiterungen seit 1991 eine deutliche Absage, da diese entgegen (mündlich) gemachten Zusicherungen vollzogen wurden (siehe im Anhang die Rede im Wortlaut). Bei anderer Gelegenheit bezeichnete er vor allem einen möglichen NATO-Beitritt der (ehemals russischen) Ukraine als die "rote Linie", da es hier im Osten eine gemeinsame Grenze zu Russland über weit mehr als tausend Kilometer gebe und zudem Millionen von russischstämmigen Bürgern in der Ukraine lebten welche durch die Unabhängigkeit des Landes von ihrem Mutterland getrennt seinen. Im mittlerweile umstrittenen Budapester Memorandum von 5.12.1994 hatten zudem die Signatarmächte USA, GB und die Russische Föderation in getrennten Dokumenten die Unabhängigkeit und territoriale Integrität der Ukraine garantiert, wenn diese ein neutraler Pufferstaat zwischen der NATO und der Russischen Föderation sei und auf ihre Atomwaffen aus der sowjetischen Zeit verzichte (die Neutralität war in der ukrainischen Verfassung verankert). Trotzdem erklärten am darauffolgenden NATO-Gipfel in Bukarest im April 2008 die versammelten Staats- und Regierungschefs der 26 NATO-Staaten: "Die NATO begrüßt die euro-atlantischen Bestrebungen der Ukraine und Georgiens, die dem Bündnis beitreten wollen. Wir kamen heute überein, dass diese Länder NATO-Mitglieder werden." Zudem wurde die Unabhängigkeitserklärung des Kosowo vorbehaltlos anerkannt, dies nach einer völkerrechtswidrigen militärischen Intervention (d.h. ohne eine entsprechende UN-Resolution) der NATO gegen die Republik Serbien im Jahr 1999 (Staatsgrenzen dürfen also unter Umständen verändert werden).
Die Gewalt begann schon wenige Monate danach, als der durch die "Rosenrevolution" 2003 mit Unterstützung der USA in Tiflis an die Macht gekommene Exil-Georgier, Michail Saakaschwili, in der Nacht auf den 8.8.2008 einen militärischen Angriff auf die seit 1992/93 abtrünnigen Südosseten bzw. deren Hauptstadt Zchinwali befahl und dabei auch russische Friedenstruppen (als Schutzmacht der Osseten) unter Beschuss gerieten. Dies nachdem die Regierung Bush jr. die georgische Armee durch NATO-Offiziere ausgebildet und aufgerüstet hatte. Laut einem NZZ-Artikel vom 1.10.2009 kam eine von der EU eingesetzte Untersuchungskommission unter der Schweizer Diplomatin Heidi Tagliavini 2009 zum Schluss, dass zuvor von beiden Seiten Provokationen in Form von Terroranschlägen, Entführungen und Morde begangen worden waren. Zudem hatte Russland jahrelang an willige Osseten und Abchasen russische Pässe ausgegeben, was völkerrechtswidrig sei, da dies die Staatlichkeit Georgiens untergrabe (Abchasien ist eine weitere abtrünnige Region Georgiens am schwarzen Meer). Saakaschwili wollte offenkundig mit dem überraschenden Angriff auf die Osseten die volle Kontrolle der Zentralregierung über das Gebiet wieder erlangen, da die Satzungen der NATO nur die Aufnahme von Ländern erlauben in denen keine ungelösten territorialen Konflikte vorhanden sind. Den Abchasen hätte also das gleiche Schicksal gedroht wenn die Aktion erfolgreich gewesen wäre. Da die Russen aber aufgepasst hatten, lief innert 24 Stunden eine russische Gegenoffensive welche die georgischen Verbände und ihre amerikanischen Berater innert wenigen Tagen bis nach Gori (Geburtsort von Stalin) zurückwarf. Präsident Saakaschwili verlor bald darauf in Tiflis die Macht und setzte sich in die Ukraine ab. Die heutige georgische Regierung unterhält wieder politische und wirtschaftliche Beziehungen zu Russland und verzichtet auf einen NATO-Beitritt. Siehe dazu das Interview von Roger Köppel mit dem aktuellen georgischen Regierungschef Kobachidse (auf englisch mit deutschen Untertiteln):
https://www.youtube.com/watch?v=xWh6bAfLdhw
In der Ukraine begann die Gewalt mit dem rechtswidrigen Sturz des 2010 legal gewählten Präsidenten Wiktor Janukowitsch, der zwischen der EU und Russland hin und her gerissen war und daher die Unterzeichnung eines EU-Assoziierungsabkommens auf unbestimmte Zeit vertagte. Nach den folgenden wochenlangen Protesten und Krawallen auf dem Maidan in Kiew ("Euromaidan") unterschrieb er unter Vermittlung Deutschlands, Frankreichs und Polens am 21.2.2014 einen Vertrag mit der Opposition und versprach baldige Neuwahlen. Trotzdem wurde er am Tag darauf durch einen regelrechten Putsch gestürzt und in die Flucht getrieben, indem unbekannte Heckenschützen aus verschiedenen Positionen zuerst auf die "Berkut"-Polizei und anschliessend auf militante Demonstranten schossen, welche die "Institutskaja" hinauf das durch eine Strassensperre der Polizei geschützte Regierungsviertel stürmen wollten.
Dabei kamen insgesamt 104 Menschen ums Leben, darunter 34 Polizisten und Vertreter der Regierung. Nach dem Putsch wurde der zuvor völlig unbekannte Exil-Ukrainer Arsenij Jazenjuk Chef der neuen Übergangsregierung, von dem die Europagesandte des US-Statedepartements, Victoria Nuland, bereits einige Tage davor in einem abgehörten Telefongespräch mit dem amerikanischen Botschafter in Kiew, Geoffrey Pyatt, gesprochen hatte ("Jaz is our man"). Die mit rund 600 Mann unter Führung von Andrij Parubi während Wochen auf dem Maidan präsenten militanten und teilweise bewaffneten Kräfte des "Prawi sektor" ("Rechter Sektor") und der "Swoboda" ("Freiheit") weigerten sich zuerst, der neuen Regierung ihre Waffen auszuhändigen. Mitglieder der "Swoboda" unter Oleh Tjahibok besetzten aber anfangs im Kabinett das Aussen-, Innen-, Verteidigungs- sowie das Ministerium für Kultur und "strategische" Kommunikation (Propaganda), während die Mitglieder des "Prawi sektor" unter Dmitro Jarosch eine Zusammenarbeit mit der neuen Regierung verweigerten. Als eine der ersten Amtshandlungen nach dem Putsch wurde in der ganzen Ukraine die russische Sprache als offizielle Amtssprache und als Unterrichtssprache in den Schulen verboten (auch in den mehrheitlich von russischstämmigen Menschen bewohnten Regionen im Osten und Süden des Landes).
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Als erste Reaktion auf den rechtswidrigen Umsturz wurde in Simferopol auf der Krim das lokale Parlament von prorussischen Aktivisten besetzt und russische Soldaten verliessen illegal den Flottenstützpunkt in Sewastopol und besetzten strategische Positionen auf der ganzen Krim bzw. blockierten die ukrainischen Kasernen. Unter dem Schutz dieser "grünen Männchen" konnte dann am 16.3.2014 ein Referendum über den zukünftigen Status der Krim durchgeführt werden. Rund 70% der Bevölkerung stimmten für eine Wiedervereinigung mit Russland, was ungefähr dem Anteil der ethnischen Russen auf der Krim entspricht. Der Kommandant der ukrainischen Flotte in Sewastopol lief mit dem Grossteil der Matrosen zu den Russen über, so dass fast die gesamte Flotte im Kriegshafen verblieb (die Schwarzmeerflotte war anfang der 90er Jahre zwischen Russland und der Ukraine aufgeteilt worden). Die restlichen Matrosen und Soldaten durften später in die Ukraine heimkehren. Angesichts der klaren Machtverhältnisse auf der Krim verzichteten die ukrainischen Ultra-Nationalisten auf die angedrohte Entsendung von "Zügen der Freundschaft" (mit bewaffneten Schlägern) nach Simferopol.
Auch in den Städten Lugansk, Donezk und Mariupol in der Ostukraine besetzten prorussische Aktivisten analog den Vorgängen einige Monate zuvor in der Westukraine Regierungs- und Verwaltungsgebäude und hissten russische Fahnen auf vielen Gebäuden. Auch hier gab es am 11. bzw. 12.5.2014 Referenden über die zukünftige Zugehörigkeit dieser Gebiete, doch konnten dabei nur ungefähr die Hälfte der Bevölkerungen überhaupt darüber abstimmen, weil die Separatisten nicht die volle Kontrolle über die jeweiligen Bezirke hatten. Auch in anderen ukrainischen Städten wie Odessa und Charkow gab es prorussische Demonstrationen, doch wurden diese von den ukrainischen Behörden unterdrückt. In Odessa kam es am 2.5.2014 zu einem Massaker, als prorussische Aktivisten von mit Zügen aus Kiew angereisten Rechtsradikalen und Hooligans in ein Gewerkschaftshaus abgedrängt wurden welches dann kurzerhand abgefackelt und mit Handfeuerwaffen beschossen wurde. Rund 50 Menschen verloren dabei ihr Leben während die ukrainische Polizei untätig herumstand.
Die am 12.4.2014 von der neuen Regierung in Kiew verkündete "Antiterror-Operation" gegen die Separatisten im Osten wurde anfangs nur zaghaft umgesetzt, da viele russischstämmige Soldaten auch hier mit den Aufständischen sympathisierten und teilweise mitsamt dem Material überliefen. Erst nachdem sich der "Spreu vom Weizen" getrennt hatte und nach der Bildung von Freiwilligenverbänden wie "Donbas","Asow" oder "Aidar" - welche in der ukrainischen Nationalgarde (dem Innen- und nicht dem Verteidigungsministerium unterstellt) zusammengefasst wurden - gewann die ukrainische Offensive an Kraft, so dass bereits im Mai/Juni 2014 die Hafenstadt Mariupol vom Asow'schen Bataillon (später ein Regiment bzw. neu die 12. Brigade für spezielle Aufgaben) und einer Marinebrigade zurückerobert und bis zur vollständigen Kapitulation im berühmten Stahlwerk "Asowstal" nach der russischen Intervention vom 24.2.2022 besetzt werden konnte. Bei den heftigen Kämpfen im Frühjahr 2022 mussten die Zivilisten wochenlang im Keller ausharren, da die Stadtverwaltung die rechtzeitige Evakuierung der Zivilbevölkerung versäumt hatte). Nach den Kesselschlachten von Ilowaisk im Juli/Aug. 2014 bzw. von Debaltsewoim Jan./Feb. 2015, bei denen weit über tausend ukrainische Soldaten und hunderte von Kämpfern der neu aufgestellten Donezker- und Lugansker Volksmilizen sowie vermutlich rund 100 russische Soldaten ihr Leben verloren (laut Kiew beteiligten sich mehrere russische Bataillone an den Kämpfen), wurde am 12.2.2015 das Minsker Abkommen (Minsk II) unter Vermittlung von Weissrussland, Deutschland und Frankreich unterzeichnet. Vertragspartner als Unterzeichnende waren: der frühere Präsident der Ukraine Leonid Kutschma, der Botschafter der Russischen Föderation in der Ukraine Michail Surabow, die Milizenführer der selbstproklamierten Volksrepubliken Igor Plotnizki und Alexander Sachartschenko sowie die OSZE-Beauftragte Heidi Tagliavini. Der Waffenstillstand und die vertrauensbildenden Massnahmen (wie z.B. der Rückzug der schweren Waffen von der Frontlinie) wurden dabei von beiden Seiten wiederholt verletzt. Am 18.2.2017 unterzeichnete der russische Präsident Wladimir Putin ein Dekret, nach dem Pässe und andere Papiere der Volksrepubliken Donezk und Lugansk von Russland offiziell als gültig anerkannt wurden, was wiederum die Staatlichkeit der Ukraine untergrub und daher dem Minsker Abkommen widersprach, wonach die abtrünnigen Gebiete weiterhin zur Ukraine gehörten. Insgesamt verloren in dem jahrelangen Konflikt bis 2022 rund 14'000 Menschen ihr Leben, darunter ca. 3'500 Zivilisten inkl. 200 Kinder, besonders in der Stadt Donezk und Umgebung welche von der ukrainischen Armee immer wieder mit Artillerie (Granaten und Raketen) oder durch Scharfschützen beschossen wurde.
Nachdem eine von NATO-Offizieren jahrelang gut ausgebildete und mit modernen Waffen aufgerüstete ukrainische Elitearmee von rund 130'000 Mann ab Sommer 2021 vor dem Donbas aufmarschiert war um den Konflikt offenkundig gewaltsam zu lösen und seit Anfang 2022 auch der ukrainische Beschuss von Donezk und dessen Umland wieder verstärkt wurde, unterzeichnete Präsident Putin am 21.2.2022 ein Freundschafts- und Beistandsabkommen mit den ostukrainischen Volksrepubliken und anerkannte ausdrücklich deren Unabhängigkeitvon Kiew. Das Minsker Abkommen habe keine Zukunft mehr. Am 24.2.2022 intervenierte die russische Armee mit anfangs "nur" rund 190'000 Mann in der Ukraine da die rund 40'000 Mann der Donezker- und Lugansker Volksmilizen einem Angriff der ukrainischen Elitearmee nicht mehr hätten standhalten können. Zuvor hatte die Russische Föderation im Dez. 2021 den USA noch einmal Verhandlungen über den Abschluss eines gesamteuropäischen Sicherheitsabkommen unter Berücksichtigung des Konflikts in der Ukraine vorgeschlagen, was aber von der Regierung Biden abgelehnt wurde. Bei Beginn der "speziellen Militäroperation" erklärte Joe Biden öffentlich, das politische Ziel sei der Sturz des Regimes in Moskau.
Mit dem Beginn der russischen Sommeroffensive an allen Frontabschnitten dürften die ukrainischen Kräfte endgültig überdehnt werden. Da der Oberbefehlshaber der Ukraine, Alexander Syrskij, aus der Region Sumy und Charkow verschiedene Verbände wie die 36. Marinebrigade, die 43. Artilleriebrigade, die 44. mechanisierte Brigade, die 82. Air Assault Brigade sowie die berüchtigte 12. Brigade "Asow" nach Südosten verlegen musste, um die Lage um den wichtigen Logistikpunkt Pokrowsk bzw. die Stadt Konstantinowka zu stabilisieren, dürften die Russen auch bei der oben erwähnten Einrichtung einer Sicherheitszone im Norden rasche Fortschritte machen. Rund 50'000 russische Soldaten werden dort eingesetzt um die zukünftige Bedrohung durch ukrainische Drohnen zu minimieren.
Zusammenfassend kann gesagt werden, dass in dem jahrelangen Konflikt alle Seiten das Völkerrecht missachtetoder zum eigenen Vorteil interpretiert haben. Angefangen damit hat aber klar der Westen (NATO und EU), der mit der finanziellen und politischen Unterstützung des rechtswidrigen Putsches in Kiew 2014 die Gewaltspirale in der Ukraine in Gang setzte und mit den anhaltenden Waffenlieferungen und Geheimdienstinformationen für den Tod von weit mehr als einer Million Soldaten auf beiden Seiten und unzähligen Zivilisten entscheidend mitverantwortlichist. Zudem wurde zumindest im Falle der Ukraine mit der NATO-Erklärung von 2008 zu deren Aufnahme als Beitrittskandidat der Geist des Budapester Memorandums von 1994 verletzt. In einem erstaunlich offenen, zweiseitigen Interview in der NZZ vom 6. Mai hat der amerikanische Politikwissenschaftler Prof. John Mearsheimervon der Universität Chicago erklärt, er hätte anstelle von Präsident Putin "die Ukraine schon viel früher überfallen". Und: "Der Westen ist der Bösewicht. Aber das wollen die USA und die Europäer natürlich nicht hören". Er glaube, dass dieser Krieg auf dem Schlachtfeld entschieden werde und dass wir am Ende einen eingefrorenen Konflikt haben werden (ähnlich wie in Georgien).
Über das Problem des ukrainischen Faschismus und Ultra-Nationalismus, der letztlich die multiethnische Ukraine in ihren Grenzen von 1991 zerstört hat, äusserte er sich nicht. Stattdessen hat die EU gerade die ersten 150 Milliarden Euro zum Aufbau einer eigenen Rüstungsindustrie beschlossen. Der neue Vorsteher des Schweizer Verteidigungsdepartementes, Bundesrat Martin Pfister, hat in einem NZZ-Artikel vom 27. Mai erklärt, die Kooperation mit der EU und der NATO müsse intensiviert werden, "stets in Vereinbarkeit mit der Neutralität". In der gleichen NZZ-Ausgabe wurde auch berichtet, dass die Schweiz den Spitzendiplomaten Gabriel Lüchinger nach Moskau schicke um für Friedensgespräche in der Schweiz zu sondieren (Bürgenstock II).
Ob der während Jahren provozierte und stigmatisierte "russische Bär" darauf noch eingeht?
(Der Beitrag folgt der Schweizer Rechtschreibung)
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
In Kürze folgt eine Mail an alle Genossenschafter, danke für die Geduld!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ a4043831:3b64ac02
2025-05-31 10:20:02
@ a4043831:3b64ac02
2025-05-31 10:20:02Money can be complicated. You work hard, save diligently, and try to make smart choices. But when it comes to long-term financial security, is that enough? That’s where wealth management services come in. They help you plan, invest, and secure your financial future. But are they the right fit for you?
Let’s find out.
What Is Wealth Management?
Wealth management isn’t just about investing. It’s about creating a strategy that covers all aspects of your financial life—retirement, taxes, healthcare, and even the legacy you want to leave behind.
At Passive Capital Management, wealth management is designed to help you navigate life’s financial twists and turns with confidence. Whether you’re planning for retirement, growing your assets, or protecting what you’ve built, a structured approach can make all the difference.
Do You Need Wealth Management?
Not everyone needs a wealth manager. But if you answer “yes” to any of these questions, it might be time to consider it:
- Do you worry about outliving your retirement savings?
- Are you unsure how to structure your investments for long-term security?
- Do you want a plan that adapts as your life changes?
- Are tax implications of your income and investments confusing?
- Do you want to leave behind a financial legacy for your family?
If any of these concerns sound familiar, a wealth management service could help you create a roadmap for financial success.
The Key Benefits of Wealth Management
1. Retirement Planning: More Than Just Saving
Retirement isn’t just about putting money aside. It’s about ensuring you can live comfortably once your regular income stops. Passive Capital Management helps clients create a sustainable retirement strategy, ensuring they have enough to cover daily expenses, healthcare, and even the fun things—like travel or hobbies.
By assessing income sources like pensions, social security, and investments, they build a tailored plan that matches your lifestyle and long-term goals.
2. Investment Strategies: Making Your Money Work for You
Investing can feel overwhelming. Stocks, bonds, real estate—where do you even begin? Wealth management helps you make informed choices based on your risk tolerance, time horizon, and financial objectives.
Rather than chasing trends, a well-planned investment strategy focuses on steady, long-term growth while minimizing unnecessary risks.
3. Tax Planning: Keeping More of What You Earn
No one likes to pay more taxes than necessary. But without a strategy, you might be doing just that.
Wealth managers help structure your income, retirement withdrawals, and investments in a tax-efficient way. Whether it's maximizing tax-free accounts or minimizing liabilities, they ensure you keep more of what you’ve earned.
4. Healthcare and Long-Term Care Planning
As you age, healthcare becomes a bigger concern—and a bigger expense. Without proper planning, medical costs can quickly eat into your savings.
A solid financial plan includes strategies to manage these costs, whether through insurance, savings, or investment strategies. This way, you get the care you need without financial stress.
5. Estate and Legacy Planning
Do you want to leave something behind for your loved ones? Wealth management ensures your assets are distributed according to your wishes, minimizing tax burdens and avoiding unnecessary legal complications.
Whether you’re thinking about passing on wealth to family or contributing to a cause you care about, having a plan in place ensures your money makes the impact you want.
When Should You Start?
The best time to start planning? Yesterday. The second-best time? Today.
Wealth management isn’t just for retirees or the ultra-rich. It’s for anyone who wants financial security and a clear plan for the future. Whether you’re in your 30s and just starting to build wealth or in your 50s preparing for retirement, having expert guidance can help you make smarter financial decisions.
Final Thoughts: Is It Right for You?
If you want peace of mind about your financial future, wealth management might be a great fit. It helps you grow your money, protect your assets, and ensure a comfortable life—now and in the years to come.
At Passive Capital Management, the goal is simple: to help you achieve financial freedom with confidence. If that sounds like something you want, it might be time to explore how wealth management can work for you.
Ready to take the next step? Let’s talk.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 04c915da:3dfbecc9
2025-05-20 15:53:48
@ 04c915da:3dfbecc9
2025-05-20 15:53:48This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ a39d19ec:3d88f61e
2025-04-22 12:44:42
@ a39d19ec:3d88f61e
2025-04-22 12:44:42Die Debatte um Migration, Grenzsicherung und Abschiebungen wird in Deutschland meist emotional geführt. Wer fordert, dass illegale Einwanderer abgeschoben werden, sieht sich nicht selten dem Vorwurf des Rassismus ausgesetzt. Doch dieser Vorwurf ist nicht nur sachlich unbegründet, sondern verkehrt die Realität ins Gegenteil: Tatsächlich sind es gerade diejenigen, die hinter jeder Forderung nach Rechtssicherheit eine rassistische Motivation vermuten, die selbst in erster Linie nach Hautfarbe, Herkunft oder Nationalität urteilen.
Das Recht steht über Emotionen
Deutschland ist ein Rechtsstaat. Das bedeutet, dass Regeln nicht nach Bauchgefühl oder politischer Stimmungslage ausgelegt werden können, sondern auf klaren gesetzlichen Grundlagen beruhen müssen. Einer dieser Grundsätze ist in Artikel 16a des Grundgesetzes verankert. Dort heißt es:
„Auf Absatz 1 [Asylrecht] kann sich nicht berufen, wer aus einem Mitgliedstaat der Europäischen Gemeinschaften oder aus einem anderen Drittstaat einreist, in dem die Anwendung des Abkommens über die Rechtsstellung der Flüchtlinge und der Europäischen Menschenrechtskonvention sichergestellt ist.“
Das bedeutet, dass jeder, der über sichere Drittstaaten nach Deutschland einreist, keinen Anspruch auf Asyl hat. Wer dennoch bleibt, hält sich illegal im Land auf und unterliegt den geltenden Regelungen zur Rückführung. Die Forderung nach Abschiebungen ist daher nichts anderes als die Forderung nach der Einhaltung von Recht und Gesetz.
Die Umkehrung des Rassismusbegriffs
Wer einerseits behauptet, dass das deutsche Asyl- und Aufenthaltsrecht strikt durchgesetzt werden soll, und andererseits nicht nach Herkunft oder Hautfarbe unterscheidet, handelt wertneutral. Diejenigen jedoch, die in einer solchen Forderung nach Rechtsstaatlichkeit einen rassistischen Unterton sehen, projizieren ihre eigenen Denkmuster auf andere: Sie unterstellen, dass die Debatte ausschließlich entlang ethnischer, rassistischer oder nationaler Kriterien geführt wird – und genau das ist eine rassistische Denkweise.
Jemand, der illegale Einwanderung kritisiert, tut dies nicht, weil ihn die Herkunft der Menschen interessiert, sondern weil er den Rechtsstaat respektiert. Hingegen erkennt jemand, der hinter dieser Kritik Rassismus wittert, offenbar in erster Linie die „Rasse“ oder Herkunft der betreffenden Personen und reduziert sie darauf.
Finanzielle Belastung statt ideologischer Debatte
Neben der rechtlichen gibt es auch eine ökonomische Komponente. Der deutsche Wohlfahrtsstaat basiert auf einem Solidarprinzip: Die Bürger zahlen in das System ein, um sich gegenseitig in schwierigen Zeiten zu unterstützen. Dieser Wohlstand wurde über Generationen hinweg von denjenigen erarbeitet, die hier seit langem leben. Die Priorität liegt daher darauf, die vorhandenen Mittel zuerst unter denjenigen zu verteilen, die durch Steuern, Sozialabgaben und Arbeit zum Erhalt dieses Systems beitragen – nicht unter denen, die sich durch illegale Einreise und fehlende wirtschaftliche Eigenleistung in das System begeben.
Das ist keine ideologische Frage, sondern eine rein wirtschaftliche Abwägung. Ein Sozialsystem kann nur dann nachhaltig funktionieren, wenn es nicht unbegrenzt belastet wird. Würde Deutschland keine klaren Regeln zur Einwanderung und Abschiebung haben, würde dies unweigerlich zur Überlastung des Sozialstaates führen – mit negativen Konsequenzen für alle.
Sozialpatriotismus
Ein weiterer wichtiger Aspekt ist der Schutz der Arbeitsleistung jener Generationen, die Deutschland nach dem Zweiten Weltkrieg mühsam wieder aufgebaut haben. Während oft betont wird, dass die Deutschen moralisch kein Erbe aus der Zeit vor 1945 beanspruchen dürfen – außer der Verantwortung für den Holocaust –, ist es umso bedeutsamer, das neue Erbe nach 1945 zu respektieren, das auf Fleiß, Disziplin und harter Arbeit beruht. Der Wiederaufbau war eine kollektive Leistung deutscher Menschen, deren Früchte nicht bedenkenlos verteilt werden dürfen, sondern vorrangig denjenigen zugutekommen sollten, die dieses Fundament mitgeschaffen oder es über Generationen mitgetragen haben.
Rechtstaatlichkeit ist nicht verhandelbar
Wer sich für eine konsequente Abschiebepraxis ausspricht, tut dies nicht aus rassistischen Motiven, sondern aus Respekt vor der Rechtsstaatlichkeit und den wirtschaftlichen Grundlagen des Landes. Der Vorwurf des Rassismus in diesem Kontext ist daher nicht nur falsch, sondern entlarvt eine selektive Wahrnehmung nach rassistischen Merkmalen bei denjenigen, die ihn erheben.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:47:16
@ 04c915da:3dfbecc9
2025-05-20 15:47:16Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 06639a38:655f8f71
2025-05-26 12:58:38
@ 06639a38:655f8f71
2025-05-26 12:58:38Nostr-PHP
Djuri submitted quite some pull requests in the last couple of week while he was implementing a Nostr connect / login on https://satsback.com. The backend of that platform is written in PHP so the Nostr-PHP library is used for several purposes while Djuri also developed quite some new features utilizing the following NIPs:
- NIP-04
- NIP-05
- NIP-17
- NIP-44
Thank you very much Djuri for these contributions. We now can do the basic private stuff with the library.
PR for NIP-04 and NIP-44: https://github.com/nostrver-se/nostr-php/pull/84 and https://github.com/nostrver-se/nostr-php/pull/88
Examples:- https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip04-encrypted-messages.php
- https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip44-gift-wrapping.php
PR for NIP-05: https://github.com/nostrver-se/nostr-php/pull/89
Example: https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip05-lookup.phpPR for NIP-17: https://github.com/nostrver-se/nostr-php/pull/90
Example: https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip17-private-direct-messages.phpPR for adding more metadata profile fields: https://github.com/nostrver-se/nostr-php/pull/94
Example: https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/fetch-profile-metadata.phpFetch
10050event (dm relay list) of an given pubkey
Example: https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/fetch-dm-relayslist.phpThe CLI tool is removed from the library, see PR https://github.com/nostrver-se/nostr-php/pull/93
Nostr-PHP documentation
While new NIPs are implemented in the Nostr-PHP library, I'm trying to keep up with the documentation at https://nostr-php.dev. For now, things are still much work in progress and I've added the AI agent Goose using the Claude LLM to bootstrap new documentation pages. Currently I'm working on documentation for
- How to direct messages with NIP-04 and NIP-17
- Encrypted payloads for event content NIP-44
- Fetch profiledata of a given pubkey
- Lookup NIP-05 data of given pubkey
- Using the NIP-19 helper class
CCNS.news
I've moved CCNS to a new domain https://ccns.news and have partly implemented the new NIP-B0 for web bookmarks. When you post a bookmark there, a kind
39701event is transmitted to some Nostr relays (take a look at this event for example). Optionally you can also publish this content as a note to the network.As you can see at https://ccns.news/l/censorship-resistant-publishing-and-archiving, I've listed some todo's. All this stuff is done with Javascript using the NDK Typescript library (so I'm not using any PHP stuff for this with Nostr-PHP).
Also new: https://ccns.news/global now has a global feed which fetches all the web bookmark events with kind
39701from several public Nostr relays. I had a rough idea to compare feeds generated with NDK and Nostr-PHP (for both using the same set of relays).
Building a njump clone for this Drupal website
You can now use this URL pattern to fetch Nostr events:
https://nostrver.se/e/{event_id|nevent1|note1|addr1}where you can provide a plain Nostr event ID or NIP-19 encoded identifier.An example, this URL [nostr:nevent1qvzqqqqqqypzqmjxss3dld622uu8q25gywum9qtg4w4cv4064jmg20xsac2aam5nqqsqm2lz4ru6wlydzpulgs8m60ylp4vufwsg55whlqgua6a93vp2y4g3uu9lr) fetches the data from one or more relays. This data is then being saved as a (Drupal) node entity (in a database on the server where this website is hosted, which is located in my office fyi). With this saved node, this data is now also available at https://nostrver.se/e/0dabe2a8f9a77c8d1079f440fbd3c9f0d59c4ba08a51d7f811ceeba58b02a255/1 where the (cached) data is server from the database instead. It's just raw data for now, nothing special about it. One of my next steps is to style this in a more prettier interface and I will need to switch the theme of this website to a custom theme. A custom theme where I will be using TailwindCSS v4 and DaisyUI v5.
The module which is providing these Nostr features is FOSS and uses the Nostr-PHP library for doing the following:
- Request the event from one or more relays
- Decode the provided NIP-19 identifier
For now this module is way for me to utilize the Nostr-PHP library with Drupal for fetching events. This can be automated so in theory I could index all the Nostr events. But this is not my ambition as it would require quite some hardware resources to accomplish this.
I hope I can find the time to build up a new theme first for this website, so I can start styling the data for the fetched events. On this website, there is also a small piece (powered by another module) you can find at https://nostrver.se/nostrides doing things with this NIP-113 around activity events (in my case that's cycling what interests me).What's next
I'm already working on the following stuff:
- Implement a class to setup a persistent connection to a relay for requesting events continuously
- Extend the documentation with the recent added features
Other todo stuff:
- Review NIP-13 proof-of-work PR from Djuri
- Implement a NIP-65 lookup for fetching read and write relays for a given npub issue #91
- Build a proof-of-concept with revolt/event-loop to request events asynchronous with persistent relay connections
- Add comments to https://ccns.news
-
 @ c1e9ab3a:9cb56b43
2025-05-27 16:19:06
@ c1e9ab3a:9cb56b43
2025-05-27 16:19:06Star Wars is often viewed as a myth of rebellion, freedom, and resistance to tyranny. The iconography—scrappy rebels, totalitarian stormtroopers, lone smugglers—suggests a deep anti-authoritarian ethos. Yet, beneath the surface, the narrative arc of Star Wars consistently affirms the necessity, even sanctity, of central authority. This blog entry introduces the question: Is Star Wars fundamentally a celebration of statism?
Rebellion as Restoration, Not Revolution
The Rebel Alliance’s mission is not to dismantle centralized power, but to restore the Galactic Republic—a bureaucratic, centrally governed institution. Characters like Mon Mothma and Bail Organa are high-ranking senators, not populist revolutionaries. The goal is to remove the corrupt Empire and reinstall a previous central authority, presumed to be just.
- Rebels are loyalists to a prior state structure.
- Power is not questioned, only who wields it.
Jedi as Centralized Moral Elites
The Jedi, often idealized as protectors of peace, are unelected, extra-legal enforcers of moral and military order. Their authority stems from esoteric metaphysical abilities rather than democratic legitimacy.
- They answer only to their internal Council.
- They are deployed by the Senate, but act independently of civil law.
- Their collapse is depicted as tragic not because they were unaccountable, but because they were betrayed.
This positions them as a theocratic elite, not spiritual anarchists.
Chaos and the Frontier: The Case of the Cantina
The Mos Eisley cantina, often viewed as a symbol of frontier freedom, reveals something darker. It is: - Lawless - Violent - Culturally fragmented
Conflict resolution occurs through murder, not mediation. Obi-Wan slices off a limb; Han shoots first—both without legal consequence. There is no evidence of property rights, dispute resolution, or voluntary order.
This is not libertarian pluralism—it’s moral entropy. The message: without centralized governance, barbarism reigns.
The Mythic Arc: Restoration of the Just State
Every trilogy in the saga returns to a single theme: the fall and redemption of legitimate authority.
- Prequels: Republic collapses into tyranny.
- Originals: Rebels fight to restore legitimate order.
- Sequels: Weak governance leads to resurgence of authoritarianism; heroes must reestablish moral centralism.
The story is not anti-state—it’s anti-bad state. The solution is never decentralization; it’s the return of the right ruler or order.
Conclusion: The Hidden Statism of a Rebel Myth
Star Wars wears the costume of rebellion, but tells the story of centralized salvation. It: - Validates elite moral authority (Jedi) - Romanticizes restoration of fallen governments (Republic) - Portrays decentralized zones as corrupt and savage (outer rim worlds)
It is not an anarchist parable, nor a libertarian fable. It is a statist mythology, clothed in the spectacle of rebellion. Its core message is not that power should be abolished, but that power belongs to the virtuous few.
Question to Consider:
If the Star Wars universe consistently affirms the need for centralized moral and political authority, should we continue to see it as a myth of freedom? Or is it time to recognize it as a narrative of benevolent empire? -
 @ eb0157af:77ab6c55
2025-05-27 07:01:37
@ eb0157af:77ab6c55
2025-05-27 07:01:37The exchange reveals the extent of the breach that occurred last December as federal authorities investigate the data leak.
Coinbase has disclosed that the personal data of 69,461 users was compromised during the breach in December 2024, according to documentation filed with the Maine Attorney General’s Office.
The disclosure comes after Coinbase announced last week that a group of hackers had demanded a $20 million ransom, threatening to publish the stolen data on the dark web. The attackers allegedly bribed overseas customer service agents to extract information from the company’s systems.
Coinbase had previously stated that the breach affected less than 1% of its user base, compromising KYC (Know Your Customer) data such as names, addresses, and email addresses. In a filing with the U.S. Securities and Exchange Commission (SEC), the company clarified that passwords, private keys, and user funds were not affected.
Following the reports, the SEC has reportedly opened an official investigation to verify whether Coinbase may have inflated user metrics ahead of its 2021 IPO. Separately, the Department of Justice is investigating the breach at Coinbase’s request, according to CEO Brian Armstrong.
Meanwhile, Coinbase has faced criticism for its delayed response to the data breach. Michael Arrington, founder of TechCrunch, stated that the stolen data could cause irreparable harm. In a post on X, Arrington wrote:
“The human cost, denominated in misery, is much larger than the $400m or so they think it will actually cost the company to reimburse people. The consequences to companies who do not adequately protect their customer information should include, without limitation, prison time for executives.”
Coinbase estimates the incident could cost between $180 million and $400 million in remediation expenses and customer reimbursements.
Arrington also condemned KYC laws as ineffective and dangerous, calling on both regulators and companies to better protect user data:
“Combining these KYC laws with corporate profit maximization and lax laws on penalties for hacks like these means these issues will continue to happen. Both governments and corporations need to step up to stop this. As I said, the cost can only be measured in human suffering.”
The post Coinbase: 69,461 users affected by December 2024 data breach appeared first on Atlas21.
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:49:50
@ 6ad3e2a3:c90b7740
2025-05-20 13:49:50I’ve written about MSTR twice already, https://www.chrisliss.com/p/mstr and https://www.chrisliss.com/p/mstr-part-2, but I want to focus on legendary short seller James Chanos’ current trade wherein he buys bitcoin (via ETF) and shorts MSTR, in essence to “be like Mike” Saylor who sells MSTR shares at the market and uses them to add bitcoin to the company’s balance sheet. After all, if it’s good enough for Saylor, why shouldn’t everyone be doing it — shorting a company whose stock price is more than 2x its bitcoin holdings and using the proceeds to buy the bitcoin itself?
Saylor himself has said selling shares at 2x NAV (net asset value) to buy bitcoin is like selling dollars for two dollars each, and Chanos has apparently decided to get in while the getting (market cap more than 2x net asset value) is good. If the price of bitcoin moons, sending MSTR’s shares up, you are more than hedged in that event, too. At least that’s the theory.
The problem with this bet against MSTR’s mNAV, i.e., you are betting MSTR’s market cap will converge 1:1 toward its NAV in the short and medium term is this trade does not exist in a vacuum. Saylor has described how his ATM’s (at the market) sales of shares are accretive in BTC per share because of this very premium they carry. Yes, we’ll dilute your shares of the company, but because we’re getting you 2x the bitcoin per share, you are getting an ever smaller slice of an ever bigger overall pie, and the pie is growing 2x faster than your slice is reducing. (I https://www.chrisliss.com/p/mstr how this works in my first post.)
But for this accretion to continue, there must be a constant supply of “greater fools” to pony up for the infinitely printable shares which contain only half their value in underlying bitcoin. Yes, those shares will continue to accrete more BTC per share, but only if there are more fools willing to make this trade in the future. So will there be a constant supply of such “fools” to keep fueling MSTR’s mNAV multiple indefinitely?
Yes, there will be in my opinion because you have to look at the trade from the prospective fools’ perspective. Those “fools” are not trading bitcoin for MSTR, they are trading their dollars, selling other equities to raise them maybe, but in the end it’s a dollars for shares trade. They are not selling bitcoin for them.
You might object that those same dollars could buy bitcoin instead, so they are surely trading the opportunity cost of buying bitcoin for them, but if only 5-10 percent of the market (or less) is buying bitcoin itself, the bucket in which which those “fools” reside is the entire non-bitcoin-buying equity market. (And this is not considering the even larger debt market which Saylor has yet to tap in earnest.)
So for those 90-95 percent who do not and are not presently planning to own bitcoin itself, is buying MSTR a fool’s errand, so to speak? Not remotely. If MSTR shares are infinitely printable ATM, they are still less so than the dollar and other fiat currencies. And MSTR shares are backed 2:1 by bitcoin itself, while the fiat currencies are backed by absolutely nothing. So if you hold dollars or euros, trading them for MSTR shares is an errand more sage than foolish.
That’s why this trade (buying BTC and shorting MSTR) is so dangerous. Not only are there many people who won’t buy BTC buying MSTR, there are many funds and other investment entities who are only able to buy MSTR.
Do you want to get BTC at 1:1 with the 5-10 percent or MSTR backed 2:1 with the 90-95 percent. This is a bit like medical tests that have a 95 percent accuracy rate for an asymptomatic disease that only one percent of the population has. If someone tests positive, it’s more likely to be a false one than an indication he has the disease*. The accuracy rate, even at 19:1, is subservient to the size of the respective populations.
At some point this will no longer be the case, but so long as the understanding of bitcoin is not widespread, so long as the dollar is still the unit of account, the “greater fools” buying MSTR are still miles ahead of the greatest fools buying neither, and the stock price and mNAV should only increase.
. . .
One other thought: it’s more work to play defense than offense because the person on offense knows where he’s going, and the defender can only react to him once he moves. Similarly, Saylor by virtue of being the issuer of the shares knows when more will come online while Chanos and other short sellers are borrowing them to sell in reaction to Saylor’s strategy. At any given moment, Saylor can pause anytime, choosing to issue convertible debt or preferred shares with which to buy more bitcoin, and the shorts will not be given advance notice.
If the price runs, and there is no ATM that week because Saylor has stopped on a dime, so to speak, the shorts will be left having to scramble to change directions and buy the shares back to cover. Their momentum might be in the wrong direction, though, and like Allen Iverson breaking ankles with a crossover, Saylor might trigger a massive short squeeze, rocketing the share price ever higher. That’s why he actually welcomes Chanos et al trying this copycat strategy — it becomes the fuel for outsized gains.
For that reason, news that Chanos is shorting MSTR has not shaken my conviction, though there are other more pertinent https://www.chrisliss.com/p/mstr-part-2 with MSTR, of which one should be aware. And as always, do your own due diligence before investing in anything.
* To understand this, consider a population of 100,000, with one percent having a disease. That means 1,000 have it, 99,000 do not. If the test is 95 percent accurate, and everyone is tested, 950 of the 1,000 will test positive (true positives), 50 who have it will test negative (false negatives.) Of the positives, 95 percent of 99,000 (94,050) will test negative (true negatives) and five percent (4,950) will test positive (false positives). That means 4,950 out of 5,900 positives (84%) will be false.
-
 @ a39d19ec:3d88f61e
2025-03-18 17:16:50
@ a39d19ec:3d88f61e
2025-03-18 17:16:50Nun da das deutsche Bundesregime den Ruin Deutschlands beschlossen hat, der sehr wahrscheinlich mit dem Werkzeug des Geld druckens "finanziert" wird, kamen mir so viele Gedanken zur Geldmengenausweitung, dass ich diese für einmal niedergeschrieben habe.
Die Ausweitung der Geldmenge führt aus klassischer wirtschaftlicher Sicht immer zu Preissteigerungen, weil mehr Geld im Umlauf auf eine begrenzte Menge an Gütern trifft. Dies lässt sich in mehreren Schritten analysieren:
1. Quantitätstheorie des Geldes
Die klassische Gleichung der Quantitätstheorie des Geldes lautet:
M • V = P • Y
wobei:
- M die Geldmenge ist,
- V die Umlaufgeschwindigkeit des Geldes,
- P das Preisniveau,
- Y die reale Wirtschaftsleistung (BIP).Wenn M steigt und V sowie Y konstant bleiben, muss P steigen – also Inflation entstehen.
2. Gütermenge bleibt begrenzt
Die Menge an real produzierten Gütern und Dienstleistungen wächst meist nur langsam im Vergleich zur Ausweitung der Geldmenge. Wenn die Geldmenge schneller steigt als die Produktionsgütermenge, führt dies dazu, dass mehr Geld für die gleiche Menge an Waren zur Verfügung steht – die Preise steigen.
3. Erwartungseffekte und Spekulation
Wenn Unternehmen und Haushalte erwarten, dass mehr Geld im Umlauf ist, da eine zentrale Planung es so wollte, können sie steigende Preise antizipieren. Unternehmen erhöhen ihre Preise vorab, und Arbeitnehmer fordern höhere Löhne. Dies kann eine sich selbst verstärkende Spirale auslösen.
4. Internationale Perspektive
Eine erhöhte Geldmenge kann die Währung abwerten, wenn andere Länder ihre Geldpolitik stabil halten. Eine schwächere Währung macht Importe teurer, was wiederum Preissteigerungen antreibt.
5. Kritik an der reinen Geldmengen-Theorie
Der Vollständigkeit halber muss erwähnt werden, dass die meisten modernen Ökonomen im Staatsauftrag argumentieren, dass Inflation nicht nur von der Geldmenge abhängt, sondern auch von der Nachfrage nach Geld (z. B. in einer Wirtschaftskrise). Dennoch zeigt die historische Erfahrung, dass eine unkontrollierte Geldmengenausweitung langfristig immer zu Preissteigerungen führt, wie etwa in der Hyperinflation der Weimarer Republik oder in Simbabwe.
-
 @ 9223d2fa:b57e3de7
2025-04-15 02:54:00
@ 9223d2fa:b57e3de7
2025-04-15 02:54:0012,600 steps
-
 @ 84b0c46a:417782f5
2025-05-30 22:17:19
@ 84b0c46a:417782f5
2025-05-30 22:17:195/24 nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzqxk47yl7vwqu0yrv4fljymp4m2vf0gtesmel4cgg638h82rt4hdn6yyejn
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs8msrjypjuvhwaarkq72739wl5rewl49vx0ku6s3u3y03anmau5dscqjj0l
nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs0fzqwr2xt044zglcwcj3dnnxuk0vlcmwcw0sdzw7yhzfsn009ttss5pv6k
こていたんさんのアイコン

5/25 nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs0ku3qs4zskmclvtqm0lt707jwn2ylz9v2xj2qakznyp86j4p7fzqd85kfq
nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs8054fh3l8qtngdfpdwxfl84r36ju3f65zmhjvjy67y7gjj0mhjks2c7w80
nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsr8nycy3gvjfdn3rqjc49j2gwhwjdhu6d5ms6uxx7y44kzf0u2ftsc8r3c3
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzpmcs4xzsusg9s6cn2acasjsam2pwmf6m8h0z08kfca56f8aqwyf2fjwv7w
nostr:nevent1qvzqqqqqqypzphu0pfjqc0lap83f8xv6e73en5zhfjzsrlx6hnk22pewugzhmpa9qqsvh305tpg0xesw6n4eu2kmumgx0mcv0cn64zznyydzpezzsazdugcyrfqm0
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzq2aq2l9cq04ygjjk4tq8zfjmuezvckcav8cfqv6z745744nfd2nqlxpq04
nostr:nevent1qvzqqqqqqypzphu0pfjqc0lap83f8xv6e73en5zhfjzsrlx6hnk22pewugzhmpa9qqs05f8xz5uahsdzceq9d0mp860hck3ash8s3ssp3paxxu620tw4ufssk6ntz
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzppyeyt0xt0fps85hxv4evdhgy35m9zfzhsqtnq93rsy4arnw3n853sc0u7
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzq7emnt7e67h5cygnyvz922x2m4f3x30hpvns3yxls2v4t2uy0vrc6060ek
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqqspu5ny2laxuqtrryffsf455fldpnluw5ladrq32cfveu6mjjgmuxsynheu3
nostr:nevent1qvzqqqqqqypzphla8l7r42mzjvdgevy0pg4y3rd8gupaprgaa7fcdzhrpaddu7lpqqsyhjuxzjkgzp5d8xt8wg8vzekcnaw6ud7htrnqppy2xmpeajrhqncs0rv4c
nostr:nevent1qvzqqqqqqypzphu0pfjqc0lap83f8xv6e73en5zhfjzsrlx6hnk22pewugzhmpa9qqswm6wxhc3h426py80vjm9jj03j8vhvrnhwmalunlxm0pq5xvxqs5qpr2kq7
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqqsgehqf8cl5sp0wfw0fzl982lvhmy9j23vpus70wddtytkr4qygxlchprwv6
nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqqsvkrvnh8lzw4rfx87278rwxp2uymej2alputzn2nl525p85c3703cmrgkfn
nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpz9mhxue69uhkuenjv4kxz7fwv9c8qqgawaehxw309aex2mrp0yhxummnw3ezuamfwfjkgmn9wshx5uqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsf2u5larth503yh236mhssn2tes4shvawnv4kufzh3889cr9dt4wculcv6w
nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqqspnfvau4ylywwk2f7nrm68ue6c86j9p4y0cu4parfwapun0nsw97sad9jwf
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqqs2y7lha9uy30wwdt9yn47s6krqv3e8duj6nqrl27e2s6dl465xssg5gt4ue
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqqsyf8peg4zggp858zfha6dt4mjxss4nhc3k4szqynh0u53j22asx6sdhpfwc
nostr:nevent1qvzqqqqqqypzphla8l7r42mzjvdgevy0pg4y3rd8gupaprgaa7fcdzhrpaddu7lpqqsr0s5ger5l8aapw63yyve5sne5rge0ractks4v4l0yn3ezcvq3f4s8wthq8
nostr:nevent1qvzqqqqqqypzphu0pfjqc0lap83f8xv6e73en5zhfjzsrlx6hnk22pewugzhmpa9qqs93gfz3kskw2lcxadwu3dvanyq7xstaj39vfqmppnng0nvz5gjm8syq9p8p
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzp5tlgnw663dswldulvnvgczfr08aflg35cu2syaaddmppvjytvn09tc679
nostr:nevent1qvzqqqqqqypzpe30ylfgzj39zuwyvmfdwcf26xsxdkcnv26wykwmtsrkl8nty89hqqswq489vn7h9hz2q0w60m05wn5xuqd0vvnqcxwxkewmh7h72yjtrrc6yulf2
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzqzcyhx8d350shzfczewxkhxemqknfeu5z8kj0arrur9wn726k5hjayfwl6
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqqsrnvmc5r2rs6jx7z8v3gvnzpkfsc3vqqxg0ygnk8wn3jmulzq887q07smq2
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzqzk0lg9aq8yzg0m4dcqp5a0a468c3jmtcw058hvckt6yj0nlnl0mqfgav7
nostr:nevent1qvzqqqqqqypzpu89j3vdtkj0cec9mzs4hcmetfq5a9d6fw5smezlpyqhme90uq27qqsf4js8wu9zlp74kj5erkwsq9rvhj0d6xmynevt4tsa766nsvja04gsrfaz5
nostr:nevent1qvzqqqqqqypzpu89j3vdtkj0cec9mzs4hcmetfq5a9d6fw5smezlpyqhme90uq27qqsqky2uqkzu60f3tkcttx59q675sxmd9ypyppnd50ukmhlx3qwrqfgmmxmjh
nostr:nevent1qvzqqqqqqypzq6lj6gusf8gqyqgj2s0vzjyw3fgj9ufhqdefn8fsvljn6vdjq69hqqsvtkn6rkgmttjzzm3nn58d85eve5834pnamzhy0u4p584jger8uvgttcqhe
nostr:nevent1qvzqqqqqqypzq6mwr88y02ghe0sn5elwkszn4xesreuwexg5z0n42j2npz8dvtfmqqstua4ssqq9wejs4kjvjjs0azlzjftt6qgh8l80msn2zd8k0nxw5ccnv7p2w
nostr:nevent1qvzqqqqqqypzq6lj6gusf8gqyqgj2s0vzjyw3fgj9ufhqdefn8fsvljn6vdjq69hqqsywfl8gfpxkynq54ju27aa5rqd0mjz9lx2haqzaszelm3vhlfa5mc3n0hkj
nostr:nevent1qvzqqqqqqypzq6mwr88y02ghe0sn5elwkszn4xesreuwexg5z0n42j2npz8dvtfmqqs86az8q8zd9wevcnnw6rcrg6edc3jfzff6sza572a25yywr477s9g4yfrq0
nostr:nevent1qvzqqqqqqypzprzeywf3jcmljlsq0kks66q7vh8rtvdvuvemv20z6vlegewpxfsgqqsq47mwcs7kpylrqwkyec76839nwrk09cx33s3lwdv88e34fkx4hdqf2sa8r
nostr:nevent1qvzqqqqqqypzq6mwr88y02ghe0sn5elwkszn4xesreuwexg5z0n42j2npz8dvtfmqqsxykjsdzg9nnaweajftl4g33amcdh4wjmdq3y30w6fu555e3xpm2c2n4wah
nostr:nevent1qvzqqqqqqypzprzeywf3jcmljlsq0kks66q7vh8rtvdvuvemv20z6vlegewpxfsgqqs9cgpau6l4rfmhkwav4jsjhxjwpgehyhuw3c39q46v23q75qdjfssp3jr0k
nostr:nevent1qvzqqqqqqypzq6mwr88y02ghe0sn5elwkszn4xesreuwexg5z0n42j2npz8dvtfmqqsxrzydard7yz0cp79uk30u9g7wv0nq9sfw36e7f5tefd7z7vfezvsq7kqy4
nostr:nevent1qvzqqqqqqypzpvgsp0c85zgh8rcf2683v7s058fzspcqt0em5ednf8z9c3q5qy5fqqsghpetrx0lkxd4d79vk90h66vln5pd9lklh64sk8qa75a453g20jc3j3q9y
nostr:nevent1qvzqqqqqqypzpvgsp0c85zgh8rcf2683v7s058fzspcqt0em5ednf8z9c3q5qy5fqqsxrmm05rgdzdpthuh9zmk7jf9jmhu0jfty6kf5v8s2f8252683drgf6m79g
nostr:nevent1qvzqqqqqqypzpdc866l8lkwvncdwaqlgrsueg9tvlnm5mm2mpyg3jv8aam445rpqqqswcp6exyy0f9sgpypzlc4dx40equyxeyhwskzgeks78r9rp54w7hc05v93n
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqstvk6q4xwtd7evpzggkcngqhlk5gktme0sj6235nuf0axxxngktpc88gqd7
nostr:nevent1qvzqqqqqqypzq6lj6gusf8gqyqgj2s0vzjyw3fgj9ufhqdefn8fsvljn6vdjq69hqqswfythwf02x6ekjpfdrucd6cx6su2t3uq3td45d4v0xrucfphy38cn0mmw2
nostr:nevent1qvzqqqqqqypzqu3j6ujahw4eezqm9gn2lz8av5waj9ek9fcwclfsrq5kc63zla2wqqsxpddg7lf4yqmpeg9z82flqa8fzpfcwmn4qfluvy95p03l8pjud2cfjx43u
nostr:nevent1qvzqqqqqqypzpq4np5cygstsu65vsx0ggphrv23kj4z553sh39xwyur08pqvdsqrqqsxzm8fx8aaprn533e0c44edf60lw73a6z5vzzumzd6edttgl0uawgn4kgp2
nostr:nevent1qvzqqqqqqypzpq4np5cygstsu65vsx0ggphrv23kj4z553sh39xwyur08pqvdsqrqqs88tvfyn6h8ls3h2994nmpykj2zc2l90vqwj8epzwfjnz2dy0mcjqyhsms5
nostr:nevent1qvzqqqqqqypzqt7zjsv2gxscw5l9d6k8j5agctlm6rr3rz3c6mar4eqmn69uu6c2qqsdavnxvhtlnkamt8cap09aan7mu2z364ltmeh8u747nvvj60h5jcsyf3hjz
nostr:nevent1qvzqqqqqqypzq6mwr88y02ghe0sn5elwkszn4xesreuwexg5z0n42j2npz8dvtfmqqsq86a0sr2h0p4qfesv00ztyqpdw545rsnq2nmq9quafahwxp8elhckws7wh
nostr:nevent1qvzqqqqqqypzqf4m96ldd32j6ecvsp9s6e2jv7euvc4jrcpx6mjg4jf6vpc9xz2cqqsqp3ugj5y8epkjyh62cfnm4gen27nhq055668glhgzjm87p64ep5sgqgawl
nostr:nevent1qvzqqqqqqypzqcmflwpta32zy6lsnwektdhs6ud3d3ql2mn7ml20jl0z87wr9qw6qqsfagdtz0ldem963wwelh2lc8d4qkuxlmfq0j62qwt6lrkvd8v36squ8d4k8
nostr:nevent1qvzqqqqqqypzpvj726mjcemd4uhpyutaykvsm0y54n5fzte5mhgtv46vhg8lunhfqqsgrrj849xmqpvdx6h9554gnetguxzz2ad8fqvpmvhm0zy85m4pl8swnyg5s
nostr:nevent1qvzqqqqqqypzq6lj6gusf8gqyqgj2s0vzjyw3fgj9ufhqdefn8fsvljn6vdjq69hqqs2n5mz6j5yft327mld352hazjwfrla3w92gpzuvmpgffjttsqyq6qgu5dwe
nostr:nevent1qvzqqqqqqypzq6mwr88y02ghe0sn5elwkszn4xesreuwexg5z0n42j2npz8dvtfmqqsz6wr7cnewt7t7vt4t2c28jtmppu832vs2syacv0sy8lcn28075ss277lty
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqqsdrt35drfatmhl795f36em4yy7gsaasr3xkvgmdwswr7f87rcrmuc7z7kf8
nostr:nevent1qvzqqqqqqypzpvj726mjcemd4uhpyutaykvsm0y54n5fzte5mhgtv46vhg8lunhfqqsrl6c8gu74vkwa5ahlsycxjx40a3gzrx6uxm0qmpa35nrnd7ntysc4d6llh
nostr:nevent1qvzqqqqqqypzqwyu5j2hjyd3ycyn7s4q4yrcv52mtyc3m3dfg26qf4lpdutjs7pgqqsq945chuafedqk95uglwl3xumcuvjcdgz66ykd840hfsa4xpp6dgqa9vsft
nostr:nevent1qvzqqqqqqypzqf4m96ldd32j6ecvsp9s6e2jv7euvc4jrcpx6mjg4jf6vpc9xz2cqqsynxwgyy8nsu2r3dx8f37hww6keemkhh962ghq45umlxz2khemytgzv08n4
nostr:nevent1qvzqqqqqqypzqyrx5pw3ga88uye6jusg5h93w75uq8jts8c0zsms44vlfg9yw45pqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqqsdex6xy8kq8l64c0gq606yguaqn8fxrsyl67m6ld5cctxxwe79jpcsmxhh6
nostr:nevent1qvzqqqqqqypzpj7tpc9kqtkr4xklc62kh7lru27pydu7uyals5zuu303eqca9ef2qyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpq7gkdqqukguh3r79yfxcy9tsxpx348wqys6q8v3njfyqj4vga727sh9cfpt
5/26 nostr:nevent1qvzqqqqqqypzpq4np5cygstsu65vsx0ggphrv23kj4z553sh39xwyur08pqvdsqrqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqqspk6e9e9wph23lt7xumuuu90rayzcswp3gz96c3w25raq9r9agw5cnfgve5
nostr:nevent1qvzqqqqqqypzpp9sc34tdxdvxh4jeg5xgu9ctcypmvsg0n00vwfjydkrjaqh0qh4qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqqsfnspcp9yqu989mnnpwj9tphrrj05268vjkwwmx7jcus4mn7erqngl94f9y
nostr:nevent1qvzqqqqqqypzpp9sc34tdxdvxh4jeg5xgu9ctcypmvsg0n00vwfjydkrjaqh0qh4qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqqs84x0ws9myccv29kf99jkuwqh8rj9ws23kn5s9yyl0scz67m97z2g7rq7z5
nostr:nevent1qvzqqqqqqypzphu0pfjqc0lap83f8xv6e73en5zhfjzsrlx6hnk22pewugzhmpa9qyg8wumn8ghj7mn0wd68ytnhd9hx2qgkwaehxw309aek2ctjvd5zumn0wvh8gmmyv9usz9nhwden5te0wfjkccte9ehx7um5wghxyctwvsqzqk76agahvd3t5lutvkuj69pccwrurey3fws0kjnrsemwlx9ntvwukkjfk6
nostr:nevent1qvzqqqqqqypzqrqykrtju88xhdq0an0vdnccdfvrmqr8da0n8p5fs8reaczhxmpeqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyz3twtpw08v554hph0j6wpk598rd677pfa460y2pcdd2064aaevjwe74erq
nostr:nevent1qvzqqqqqqypzqx34k480waf274x2e0hd7re5nceq7z3wu5q59zp3xnp7uvv8nnn3qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyp59rw9n380w5kvdth9qefc28xsrt99l33tmfgvq02kut3dnepk6zr7ng2t
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyq8q2qcfne76j4c9y794xz9g5unuxhf98deh3mupmnwpn33mwlxhzmxuefq
nostr:nevent1qvzqqqqqqypzpmzzcaj5rzeah8y940ln4z855wa72af4a6aac4zjypql55egcpsqqyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpqscswkz2s03r6yhz0yz40h634nkf2j2vpkvqd3vk5rl7lgaj9unns7qz3ms
nostr:nevent1qvzqqqqqqypzprfe5ru6zvakym6hq5eycwdr2vx2q8awzaaw8wu9mq4wlek8yhenqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyqr5njtg8f5xdm52p3k9mugfqk3zuc0ycsxaj6j5uf4amkrdt3ymq8kuyhj
nostr:nevent1qvzqqqqqqypzq0363fpyt2sgytq9p3pduzch6rlrp4z8e6swvzr72km83pg76qmnqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyrj0xgrrwr2meuurst5lsqn744wt6uxhfmyralknm7cl57lsapcrkunqcnn
nostr:nevent1qvzqqqqqqypzqf57dat64x3qpjq5u6ucwgvpnh0q8r9xpspepwrmvkxnqz4k6rgyqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyq2yn3cjlmns8ttaam8ev2rn3csm26wnwhe3ccvk8s5e8x6ejyykql8em9d
nostr:nevent1qvzqqqqqqypzqx34k480waf274x2e0hd7re5nceq7z3wu5q59zp3xnp7uvv8nnn3qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyqu2p8vtuwvxmzqh7mlq2lp3xel8z9l0xg5e3hyxjlwamsm0p3pvq9qh4d0
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsr9tpqqfeke4qt9xlg6m34446dpd844myrw9cc4tmqcrf3xfp9yqsxa05hf
nostr:nevent1qvzqqqqqqypzpp9sc34tdxdvxh4jeg5xgu9ctcypmvsg0n00vwfjydkrjaqh0qh4qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqypyaj8uyahtgwf5evyk5deqx90udyrmxff99gqskfcl3eqh0mgmw6nlnlud
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsdpy08r0758lz0js2zpk5fe5mpqxd349mdqxg2vk3y7azlme2ysqqm8uy75
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs8s0r7c908mmhxk090zvmlajfgswwcnmwxj34dtqjpyxry0tmumagcmm29s
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs0x6pgm96r70y8836l0d5ajj6nrlq6p5fz06wdu26fkpg3gznctscf5ggxn
5/27 nostr:nevent1qvzqqqqqqypzqxlwemj4760tc2ysgqmqdu5tt68th2er6gn8xrsjkjlhvtff6gtzqyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpqlq0lp52xg7uv4wwzuqy9yhtmcpy5v8ad8v7ft9xcwkdncd97h66q0wmawu
nostr:nevent1qvzqqqqqqypzpq4np5cygstsu65vsx0ggphrv23kj4z553sh39xwyur08pqvdsqrqyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpqpt2wncdxkptxyhj025vd53vjpxz3hjs452px7y8g6gzsxmnfw2fsp2rv0k
KAZもさん nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzpk3nll8rr3sj6adsrfrlgjpj4cyn2sg9rmlz9m2djwk5zp2ku80czfr460
5/28 kaijiさん nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsqjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqythwumn8ghj7mn0wd68ytnfw36xzmndduhx6etwqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzpt7w33qv7tlywj0wphremkdft6dpnv3z8mvw0t2pdxcgvlzw6sathjmz0v
マルフォイ nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyw8wumn8ghj7umjw3ex2mrp0yhxxttnw3jkcmrpwghxuet5qyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs8r0frcfwqkgpefhd0knjurekna8ztnq69432f3k00wccd0vcrl5c6qr3gh
5/29 nostr:nevent1qvzqqqqqqypzqrec47eremps2u8wvnu6f2sfjg5njhkrxuw9l6r8uzwfzy2gqq2aqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmjv4kxz7fwdehhxarj9e3xzmnyqqsp2c6xh22lfj2ccy95lqu584hfpfz0ds7w2llnf4sv2qs445yqcgqmgwq57
nostr:nevent1qvzqqqqqqypzphu0pfjqc0lap83f8xv6e73en5zhfjzsrlx6hnk22pewugzhmpa9qyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpqt43r3wtjkr5ezxay6dh7jq94nelduvsk07w5ufxrver5f6jfggksakz9e8
nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqqjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qzymhwden5te0wahhgtnwdaehgu3wdejhgqpqn6n7xrrmk40ucmh9m5ktae58xjqz6h7epj6mcffpcmuhgpysvv6snh5vf5
nostr:nevent1qvzqqqqqqypzpk28l9nyyf4av8f8j8jhh8k60mt2sc643ux2td3n547kvk4lrsglqyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpq6gv8avhe93ypvypd66rmn34760s3sldj3x2cz5w4yu2xy9z8tt2qadd7kl
nostr:nevent1qvzqqqqqqypzpk28l9nyyf4av8f8j8jhh8k60mt2sc643ux2td3n547kvk4lrsglqyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpqn2pfqkgcfk3cdhtvkqqlfycsy2j2xe6c6jz8gzfxlnddnq8jq6vqecuvwy
nostr:nevent1qvzqqqqqqypzpug7j8zm7jr0hjunpkpgz8gzdvgn5h8mw77g4wg58xnmsav6pvz2qqspds662qvcpz995r5rx39wzncyzcx3q5zfpe8ztgx4zdwy9znvu9cv28mya
5/30 nostr:nevent1qvzqqqqqqypzp54kkqfyshkxm078mpzygmfxpqfq6fwu2njry424strce6dmvhwyqqstc5jak2vax4uejyrmu2td3w0spv6k4mds9sfwqtvmh0hwaa3eststwmtzt
nostr:nevent1qvzqqqqqqypzp54kkqfyshkxm078mpzygmfxpqfq6fwu2njry424strce6dmvhwyqqs9v75spmgrxngfn805q5d9fsqa562a8240xkr6z3kvkszkra9plvsgm2qw4
nostr:nevent1qvzqqqqqqypzp62ezs5gz04adyt8xmyghw2ej3yk7eradlnknmuysd5ha2udqnfdqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqqjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqswy0smsrukck33hfhavscvs68pg9m4d859np8pkgvrc49kwjzr4ac0cwhea
nostr:nevent1qvzqqqqqqypzpc9ge0t4a0lya7a63fjl749mgdv9ssz0dhqt5jnytz3y6lmy9525qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqqjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qzymhwden5te0wahhgtnwdaehgu3wdejhgqpqeunx8pj5hc255wqu4ea9cgz6cptjvcx6jk8yfd8u55smjl6y8z9sepz5xt
nostr:nevent1qvzqqqqqqypzp62ezs5gz04adyt8xmyghw2ej3yk7eradlnknmuysd5ha2udqnfdqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqqjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqst07pk8637lvs5vjnp00quzhcsx8ghran90nsm6sycnm3a626lnqqw0py8w
nostr:nevent1qvzqqqqqqypzp62ezs5gz04adyt8xmyghw2ej3yk7eradlnknmuysd5ha2udqnfdqyxhwumn8ghj77tpvf6jumt9qyw8wumn8ghj7umjw3ex2mrp0yhxxttnw3jkcmrpwghxuet5qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsya6zp38496uetw83txlr294nttk6myuc0n7hxrl2d7jma2rvvcesnz2naf
nostr:nevent1qvzqqqqqqypzqlwpvac39uz74ay4g7qx2sa3cqrvuvjhy7899vwf40lkxfcw6uz0qyxhwumn8ghj77tpvf6jumt9qyghwumn8ghj7mnxwfjkccte9eshquqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsz6zj33hmynuhq20nscntjc3lhx4hl5azhf0cx38g5nmhpjezuttqpdr0ht
nostr:nevent1qvzqqqqqqypzqhh27290rxjexusv8as357lpxy423nnznzfh4fjkq22k94tvqcpaqyxhwumn8ghj77tpvf6jumt9qyghwumn8ghj7u3wddhk56tjvyhxjmcqyrfpj9ym2apvgjpmcy4qjq2ks89uzuwm27d9jpj9flk7438sm23kqjetapu
nostr:nevent1qvzqqqqqqypzpuy2jdcyy3vqr4l9ucmhlpuwnsl29h7lwsvaez00eu4467jlvf7eqythwumn8ghj7mn0wd68ytnfw36xzmndduhx6etwqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsphe28h7t6jmwlvpd90q38xkde87hmy9q24u90sgeaz6hu6nfsazqxkfw56
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 91117f2b:111207d6
2025-05-31 09:49:03
@ 91117f2b:111207d6
2025-05-31 09:49:03
Success is a journey, not a destination. Here's a step-by-step guide to help you achieve your goals:
Step 1: Set Clear Goals
- Define what success means to you.
- Set specific, measurable, achievable, relevant, and time-bound (SMART) goals.
- Write down your goals and track progress.
- Make sure you go through with your goals even in hard times.
Step 2: Create a Plan
- Break down large goals into smaller tasks.
- Prioritize tasks based on importance and urgency.
- Establish a timeline for completion.
Step 3: Develop a Growth Mindset
- Embrace challenges and learn from failures.
- Stay curious and keep learning.
- Believe in your ability to grow and improve.
Step 4: Build Positive Habits
- Establish a morning routine.
- Practice self-care and prioritize well-being.
- Stay organized and focused.
Step 5: Take Action
- Start taking small steps towards your goals.
- Stay consistent and persistent.
- Celebrate your progress and achievements.
Step 6: Overcome Obstacles
- Identify potential obstacles and plan for them.
- Stay flexible and adapt to changes.
- Seek support from others when needed.
Step 7: Stay Motivated
- Find your why and remind yourself of it often.
- Surround yourself with positive influences.
- Reward yourself for progress and milestones.
Step 8: Review and Adjust
- Regularly review your progress.
- Adjust your plan as needed.
- Stay focused on your goals.
By following these steps, you'll be well on your way to achieving success. Remember, success is a journey, and every step you take brings you closer to your goals.
-
 @ 17e2889f:a8fbe515
2025-05-31 09:14:33
@ 17e2889f:a8fbe515
2025-05-31 09:14:33More content will come soon!
Headline
-
 @ c9badfea:610f861a
2025-05-24 12:55:17
@ c9badfea:610f861a
2025-05-24 12:55:17Before you post a message or article online, let the LLM check if you are leaking any personal information using this prompt:
Analyze the following text to identify any Personally Identifiable Information (PII): <Your Message>Replace
<Your Message>with your textIf no PII is found, continue by modifying your message to detach it from your personality. You can use any of the following prompts (and further modify it if necessary).
Prompt № 1 - Reddit-Style
Convert the message into a casual, Reddit-style post without losing meaning. Split the message into shorter statements with the same overall meaning. Here is the message: <Your Message>Prompt № 2 - Advanced Modifications
``` Apply the following modifications to the message: - Rewrite it in lowercase - Use "u" instead of "you" - Use "akchoaly" instead of "actually" - Use "hav" instead of "have" - Use "tgat" instead of "that" - Use comma instead of period - Use British English grammar
Here is the message:
``` Prompt № 3 - Neutral Tone
Rewrite the message to correct grammar errors, and ensure the tone is neutral and free of emotional language: <Your Message>Prompt № 4 - Cross Translation Technique
Translate the message into Chinese, then translate the resulting Chinese text back into English. Provide only the final English translation. Here is the message: <Your Message>Check the modified message and send it.
ℹ️ You can use dialects to obfuscate your language further. For example, if you are from the US, you can tell the LLM to use British grammar and vice versa.
⚠️ Always verify the results. Don't fully trust an LLM.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 9bcc5462:eb501d90
2025-04-04 16:02:14
@ 9bcc5462:eb501d90
2025-04-04 16:02:14The story you are about to read is one hundred percent true. It is also my first encounter with a supernatural force.
It was the summer of 2003 and I was visiting my auntie in Nashville as a 16-year-old, pimply-faced teenager. My younger cousins, Alex, Mikey, and Tony were also there. One afternoon, they were all sitting bored outside in the blazing heat, sheltered under the tree on the front lawn. It was a comical sight really, all of them sprawled out lifeless and silent, eaten alive by the unforgiving mosquitos. I ducked inside and asked my aunt if it was okay to borrow her RAV4 to take them to play basketball nearby at Pitts Park. Despite not having a license she handed me the keys and when I went outside to tell the boys we were going to shoot hoops, you’d have thought I said I was taking them to Disney World!
Off we went up and down the rollercoaster-like hills of Tennessee. Yes, I was speeding, and no, we were not wearing seatbelts. (Remember, sixteen, acne, angst, etc.) We arrived at the park and immediately I felt an eerie sensation. I had been there before with my other cousin Kim, but this time was undeniably different. It didn’t matter that the sun was shining above the bright blue sky, I sensed a darkness lingering. And it had nothing to do with the sticky Southern humidity. It was an overwhelming, odd, ineffable sensation. My eyes couldn’t help but focus on the trees behind the court. As if someone or something was watching us.
Nevertheless, after shooting for teams, we began a 2-on-2 immediately. When Mikey and I won, (I towered over them and Mikey was surprisingly pretty good) Tony wasn’t too happy about losing. In frustration, he bounced the basketball with both hands as hard as he could. The ball ended up on the other side of the fences surrounding the court and rolled into the bordering woods. None of the little squirts wanted to retrieve the ball, so as the big cuz I volunteered myself. Nothing to it right? Wrong!
As I walked towards the woods I couldn’t even locate the basketball. I stopped and scanned until I finally saw it, way deep among the trees. “How did it get all the way over there?” I mumbled beneath my breath. Then, while approaching the ball I heard a loud and distinct voice—“Hey!”—I turned around suddenly, but nothing was there. At first I wasn’t afraid, rather I was genuinely confused. It just made no damn sense, there was no one around. I swiveled my head in every direction and once again the deep, gravelly voice called out, “Hey!” This time I knew where it was coming from and crept towards the source until I spotted something in the bushes. I crouched and pushed some branches aside. And that’s when I noticed it. Buried under the shrubs was a tombstone! It stared back at me, weathered, cracked, moss-eaten. I picked my ass up, ran to the ball, scooped it and bolted back to the court.
Little Alex asked if we were going to play a rematch; I said, “Hell no”. After herding them back to the car, we left and never looked back. To this day I remember the voice. I recall the inexplicable feeling of the unknown energy, force, or spirit that was with us. I only recently shared this story with him and now, at 27, he asked why I didn’t tell him sooner. I thought hard about it and answered, “I guess I didn’t want you to get scared and piss yourself.”
-
 @ 04c915da:3dfbecc9
2025-05-15 15:31:45
@ 04c915da:3dfbecc9
2025-05-15 15:31:45Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 9c9d2765:16f8c2c2
2025-05-31 08:51:38
@ 9c9d2765:16f8c2c2
2025-05-31 08:51:38In the valley of Wudo, nestled between emerald mountains and singing rivers, there was a village known for its harmony. The people of Wudil lived simple lives farming, weaving, raising children, and singing their local song to the wind. Their days flowed with the rhythm of nature, untouched by war, plague, or tyranny. For generations, the people believed they were blessed by the gods of balance.
Among them was a young woman named Eva. A gardener by trade, Eva tended to the central orchard, where trees older than memory bore fruit that nourished the entire village. She was known for her patience, her kindness, and her unwavering devotion to her garden. She’d never known violence, nor sorrow deeper than a poor harvest.
Eva believed peace was the default state of the world, like a calm lake reflecting the sky.
Fire came from beyond the mountains.
No one saw it coming not until the smoke darkened the horizon. A warlord named Stephen, a conqueror from the north, sought to expand his empire. The village of Wudil, with its fertile lands and soft people, was no obstacle.
The soldiers descended like wolves.
Homes were burned. Families torn apart. Screams replaced songs. Eva, who had never raised a hand in anger, watched her orchard set ablaze, twisting in fire, roots cracking, birds fleeing into the smoke.
She ran. She survived. But everything she had known, every idea she had clung to about the world being kind and calm was turned to ash in a single night.
She wandered for weeks through scorched forests and ravaged towns. She saw the aftermath of chaos starving children, hollow-eyed men, women digging graves with bare hands. And each time she closed her eyes, she heard the fire crackle and the cries of her neighbors.
The peace she once knew now felt like a dream someone else had lived.
Eventually, Eva reached the wasteland. A vast, arid expanse where nothing grew and the sky was white with heat. There, she collapsed body thin, lips cracked, hope extinguished.
She expected to die.
But she didn’t.
A band of wanderers found her. Survivors from other broken lands. They took her in, gave her water, patched her wounds. They were not like the people of Wudil; there was no softness in them. They had lived through war, betrayal, famine. They spoke little, but their silence carried weight.
Among them was an old woman named Serah. Scarred, one eye blind, but her presence quiet and steady.
“You come from the green valley,” Serah said one night. “The ones who believed they’d been spared.”
Eva nodded slowly.
“And now you know,” Serah said, “peace is not something given. It is something grown.”
“I thought I had peace,” Eva whispered.
“No. You had comfort. The two are not the same.”
Years passed.
Eva stayed with the wanderers, traveling from ruin to ruin, helping the broken rebuild. She learned to defend herself, to plant seeds in difficult soil, to listen more than she spoke. The ache inside her never truly faded, but it no longer ruled her.
One day, she returned to the valley of Wudo.
There was nothing left of Wudil but ruins. The land was overgrown, the orchard just blackened stumps. But the river still sang. And the soil, though scarred, was still rich.
Eva dropped to her knees and dug her fingers into the earth.
She planted the first seed.
Others joined her refugees, wanderers, survivors who had lost their homes. They built slowly, with hands that had known suffering. They did not speak of peace as something fragile, but as something they must forge again and again like fire-forged steel.
The orchard grew once more. But this time, every branch held memory. Every root, resilience.
Eva became the heart of the new village. The children called her the Flame-Gardener not because she brought destruction, but because she had survived it and bloomed anyway.
One evening, under the silver moon, a child asked her, “Why do you never fear the storms?”
Eva smiled softly. “Because I’ve lived through worse. And I’ve learned true peace doesn’t come when the world is quiet. It comes when your soul is strong enough to stand in the storm... and stay still.”
-
 @ 08f96856:ffe59a09
2025-05-15 01:17:18
@ 08f96856:ffe59a09
2025-05-15 01:17:18เมื่อพูดถึง Bitcoin Standard หลายคนมักนึกถึงภาพโลกอนาคตที่ทุกคนใช้บิตคอยน์ซื้อกาแฟหรือของใช้ในชีวิตประจำวัน ภาพแบบนั้นดูเหมือนไกลตัวและเป็นไปไม่ได้ในความเป็นจริง หลายคนถึงกับพูดว่า “คงไม่ทันเห็นในช่วงชีวิตนี้หรอก” แต่ในมุมมองของผม Bitcoin Standard อาจไม่ได้เริ่มต้นจากการที่เราจ่ายบิตคอยน์โดยตรงในร้านค้า แต่อาจเริ่มจากบางสิ่งที่เงียบกว่า ลึกกว่า และเกิดขึ้นแล้วในขณะนี้ นั่นคือ การล่มสลายทีละน้อยของระบบเฟียตที่เราใช้กันอยู่
ระบบเงินที่อิงกับอำนาจรัฐกำลังเข้าสู่ช่วงขาลง รัฐบาลทั่วโลกกำลังจมอยู่ในภาระหนี้ระดับประวัติการณ์ แม้แต่ประเทศมหาอำนาจก็เริ่มแสดงสัญญาณของภาวะเสี่ยงผิดนัดชำระหนี้ อัตราเงินเฟ้อกลายเป็นปัญหาเรื้อรังที่ไม่มีท่าทีจะหายไป ธนาคารที่เคยโอนฟรีเริ่มกลับมาคิดค่าธรรมเนียม และประชาชนก็เริ่มรู้สึกถึงการเสื่อมศรัทธาในระบบการเงินดั้งเดิม แม้จะยังพูดกันไม่เต็มเสียงก็ตาม
ในขณะเดียวกัน บิตคอยน์เองก็กำลังพัฒนาแบบเงียบ ๆ เงียบ... แต่ไม่เคยหยุด โดยเฉพาะในระดับ Layer 2 ที่เริ่มแสดงศักยภาพอย่างจริงจัง Lightning Network เป็น Layer 2 ที่เปิดใช้งานมาได้ระยะเวลสหนึ่ง และยังคงมีบทบาทสำคัญที่สุดในระบบนิเวศของบิตคอยน์ มันทำให้การชำระเงินเร็วขึ้น มีต้นทุนต่ำ และไม่ต้องบันทึกทุกธุรกรรมลงบล็อกเชน เครือข่ายนี้กำลังขยายตัวทั้งในแง่ของโหนดและการใช้งานจริงทั่วโลก
ขณะเดียวกัน Layer 2 ทางเลือกอื่นอย่าง Ark Protocol ก็กำลังพัฒนาเพื่อตอบโจทย์ด้านความเป็นส่วนตัวและประสบการณ์ใช้งานที่ง่าย BitVM เปิดแนวทางใหม่ให้บิตคอยน์รองรับ smart contract ได้ในระดับ Turing-complete ซึ่งทำให้เกิดความเป็นไปได้ในกรณีใช้งานอีกมากมาย และเทคโนโลยีที่น่าสนใจอย่าง Taproot Assets, Cashu และ Fedimint ก็ทำให้การออกโทเคนหรือสกุลเงินที่อิงกับบิตคอยน์เป็นจริงได้บนโครงสร้างของบิตคอยน์เอง
เทคโนโลยีเหล่านี้ไม่ใช่การเติบโตแบบปาฏิหาริย์ แต่มันคืบหน้าอย่างต่อเนื่องและมั่นคง และนั่นคือเหตุผลที่มันจะ “อยู่รอด” ได้ในระยะยาว เมื่อฐานของความน่าเชื่อถือไม่ใช่บริษัท รัฐบาล หรือทุน แต่คือสิ่งที่ตรวจสอบได้และเปลี่ยนกฎไม่ได้
แน่นอนว่าบิตคอยน์ต้องแข่งขันกับ stable coin, เงินดิจิทัลของรัฐ และ cryptocurrency อื่น ๆ แต่สิ่งที่ทำให้มันเหนือกว่านั้นไม่ใช่ฟีเจอร์ หากแต่เป็นความทนทาน และความมั่นคงของกฎที่ไม่มีใครเปลี่ยนได้ ไม่มีทีมพัฒนา ไม่มีบริษัท ไม่มีประตูปิด หรือการยึดบัญชี มันยืนอยู่บนคณิตศาสตร์ พลังงาน และเวลา
หลายกรณีใช้งานที่เคยถูกทดลองในโลกคริปโตจะค่อย ๆ เคลื่อนเข้ามาสู่บิตคอยน์ เพราะโครงสร้างของมันแข็งแกร่งกว่า ไม่ต้องการทีมพัฒนาแกนกลาง ไม่ต้องพึ่งกลไกเสี่ยงต่อการผูกขาด และไม่ต้องการ “ความเชื่อใจ” จากใครเลย
Bitcoin Standard ที่ผมพูดถึงจึงไม่ใช่การเปลี่ยนแปลงแบบพลิกหน้ามือเป็นหลังมือ แต่คือการ “เปลี่ยนฐานของระบบ” ทีละชั้น ระบบการเงินใหม่ที่อิงอยู่กับบิตคอยน์กำลังเกิดขึ้นแล้ว มันไม่ใช่โลกที่ทุกคนถือเหรียญบิตคอยน์ แต่มันคือโลกที่คนใช้อาจไม่รู้ตัวด้วยซ้ำว่า “สิ่งที่เขาใช้นั้นอิงอยู่กับบิตคอยน์”
ผู้คนอาจใช้เงินดิจิทัลที่สร้างบน Layer 3 หรือ Layer 4 ผ่านแอป ผ่านแพลตฟอร์ม หรือผ่านสกุลเงินใหม่ที่ดูไม่ต่างจากเดิม แต่เบื้องหลังของระบบจะผูกไว้กับบิตคอยน์
และถ้ามองในเชิงพัฒนาการ บิตคอยน์ก็เหมือนกับอินเทอร์เน็ต ครั้งหนึ่งอินเทอร์เน็ตก็ถูกมองว่าเข้าใจยาก ต้องพิมพ์ http ต้องรู้จัก TCP/IP ต้องตั้ง proxy เอง แต่ปัจจุบันผู้คนใช้งานอินเทอร์เน็ตโดยไม่รู้ว่าเบื้องหลังมีอะไรเลย บิตคอยน์กำลังเดินตามเส้นทางเดียวกัน โปรโตคอลกำลังถอยออกจากสายตา และวันหนึ่งเราจะ “ใช้มัน” โดยไม่ต้องรู้ว่ามันคืออะไร
หากนับจากช่วงเริ่มต้นของอินเทอร์เน็ตในยุค 1990 จนกลายเป็นโครงสร้างหลักของโลกในสองทศวรรษ เส้นเวลาของบิตคอยน์ก็กำลังเดินตามรอยเท้าของอินเทอร์เน็ต และถ้าเราเชื่อว่าวัฏจักรของเทคโนโลยีมีจังหวะของมันเอง เราก็จะรู้ว่า Bitcoin Standard นั้นไม่ใช่เรื่องของอนาคตไกลโพ้น แต่มันเกิดขึ้นแล้ว
-
 @ cefb08d1:f419beff
2025-05-31 07:55:19
@ cefb08d1:f419beff
2025-05-31 07:55:19https://stacker.news/items/993333
-
 @ 629c4a12:f822cc1a
2025-02-23 21:33:31
@ 629c4a12:f822cc1a
2025-02-23 21:33:31I’ve always been drawn to minimalism. There’s a certain peace that comes from stripping away the unnecessary, decluttering both physical and mental spaces. Yet, when it comes to finances, I’ve found myself tangled in complexity. As an ‘optimizer,’ I spend an inordinate amount of time thinking about investments, managing risk, and endlessly tinkering with my portfolio. This preoccupation contradicts the minimalist principles I try to live by.
It seems absurd to me that the financial world has become so complicated that we need money managers to simply preserve the value of our money. If investing is so intricate that the average person must hire professionals just to preserve (let alone grow) the value of their savings, then something is fundamentally wrong.
For the past five years, I’ve immersed myself in the history and mechanics of financial systems. The deeper I delved, the clearer it became: Bitcoin is a force of minimalism in an increasingly financialized and complex world.
The Clutter of Modern Finance
Our financial system has become bloated with complexity. The hyper-securitization of assets has created an environment filled with financial clutter. Derivatives, for example, represent layers upon layers of financial engineering, often so convoluted that even experts struggle to understand them fully.
More troubling is the way nearly everything of value has been financialized. Real estate and art, two things that should embody personal value and cultural significance, have been transformed into mere asset classes. They are bought, sold, and speculated upon not for their intrinsic qualities but as instruments in the game of wealth preservation.
But why has this happened? It’s actually quite simple: our money is constantly losing value. The dollar, for example, debases at a rate of around 7% per year. Holding cash feels like holding melting ice, so it’s only natural for people to seek out scarce assets to preserve their wealth. The Never-Ending Game of Diversification
This pursuit of scarce assets sets off a complex game—a game that forces people to diversify endlessly:
- Equities
- Bonds
- Real Estate
- Commodities
- Art
- Collectibles
We’re told to spread our investments across these asset classes to mitigate risk and preserve our hard-earned money. Those who can afford to hire money managers generally fare better in this game, as they have access to expertise and strategies designed to navigate this maze of complexity.
Ironically, this system creates an incentive for more complexity. The more convoluted the financial landscape becomes, the more we need money managers, and the more entrenched this cycle of financialization and securitization becomes. It’s a force of ever-increasing entropy—quite the opposite of minimalism.
Bitcoin: Simplicity in a Complex World
In the midst of this financial chaos, Bitcoin emerges as a beacon of simplicity. It offers a way out of the clutter, a chance to reclaim financial minimalism. Bitcoin embodies the concept of scarcity with a rare kind of perfection: there will only ever be 21 million Bitcoins. No more.
This scarcity makes Bitcoin the perfect savings technology. Unlike traditional currencies, no one can debase your holdings. You don’t need to chase after real estate, art, or other assets to preserve your wealth. You don’t need to constantly diversify and rebalance a portfolio to stay ahead of inflation. Bitcoin’s scarcity gives you a way to hold your wealth securely, without the need for endless tinkering.
I’m not blind to Bitcoin’s short-term price volatility. However, it’s crucial to understand that we’re still in the early stages of adoption. As more people embrace this perfect form of scarcity, Bitcoin’s qualities as savings technology will express itself.
Bitcoin has the potential to de-financialize the housing market. It can de-financialize art.
Ultimately, Bitcoin has the power to replace those aspects of our lives that currently serve as proxies for scarcity.
A Minimalist Approach to Wealth
Bitcoin allows us to step off the treadmill of constant financial optimization. It offers a simpler way to safeguard the fruits of our labor. Rather than spending our time, energy, and attention on navigating a complex financial system, we can focus on what truly matters: living a meaningful life.
By embracing Bitcoin, we embrace a minimalist approach to wealth. We reject the idea that we must play a never-ending game of diversification to maintain our standard of living. Instead, we adopt a simple, elegant solution that aligns with the principles of minimalism.
Conclusion
In a world that grows more financially cluttered by the day, Bitcoin stands as a path to financial minimalism. It frees us from the complexities of traditional finance, allowing us to preserve our wealth without the need for constant vigilance and management.
By embodying scarcity and simplicity, Bitcoin gives us a way to reclaim our time and energy. It’s not just a financial tool; it’s a way to simplify our lives, to step back from the chaos, and to focus on what truly matters
-
 @ 866e0139:6a9334e5
2025-05-30 17:37:36
@ 866e0139:6a9334e5
2025-05-30 17:37:36Autor: Michael Meyen. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
„Eine wohltemperierte Abrechnung hin zum Frieden“ steht auf dem Cover, und ich dachte gleich: Das ist doch etwas für die „Friedenstaube“. Ist es auch, aber anders als zunächst gedacht. Vielleicht hätte ich mir einen Moment Zeit nehmen sollen für den Haupttitel. Drei Substantive ohne Punkt und Komma. Raffen Sterben Trance. Besser kann man das Leiden an dieser Welt nicht in Worte gießen – vor allem dann nicht, wenn daraus ein Satzstrom wird, der einen Rhythmus von ganz eigener Kraft entwickelt. Man braucht keine Noten, um einen Ohrwurm zu schreiben. Mit Buchstaben geht das auch. Wer das nicht glaubt, lese dieses Buch von Teer Sandmann und lasse sich von seiner Melodie durch die Abgründe dieser Zeit tragen.
Ich habe den Autor im Spätsommer 2020 kennengelernt, bei einem Rubikon-Treffen. Das schreibt sich jetzt so leicht hin, war aber damals fast ein Abenteuer. Schon die Bahnfahrt. Die Blicke, das Zischen, der Hass. Sie da! Wo ist Ihre Maske? Ich hatte überlegt, ob ich mir das antun will, und war auch nicht sicher, ob es wirklich eine gute Idee ist, drei Tage mit lauter Dissidenten auf einem Haufen zu sein. Mehr Zielscheibe geht kaum. Vor Ort war das dann alles wie weggeblasen. Abends ein Lagerfeuer und tagsüber Menschen wie Daniel Sandmann, der sich auf seinen Büchern Teer nennt und weiß, was Glück ist:
„Der Augenblick, den du mit dem Andern und durch das Andere erlebst, unbelangt von Staat, Norm und Konzern: dieser Augenblick hebt deine Einsamkeit auf. Die aufgehobene Einsamkeit aber ist die Freiheit, die wir als Wärme erleben. Als Feuer im Körper.“ (90)
So war das an jenem Augustwochenende. Jeder, der ein wenig älter ist, hat längst erlebt, dass keine Flamme ewig brennt. Nach Corona kamen die Kriege. Und selbst die, die solche Tage nicht vergessen wollen, verlieren sich im Kleinklein ihrer Eitelkeiten. Daniel und Teer Sandmann machen aus diesem Stoff eine grandiose Sinfonie, die darüber erhaben ist, mit dem Finger auf diesen zu zeigen oder auf jenen. Hin und wieder eine Andeutung: Das muss reichen. Der Formaterfinder, der sein Baby mit einem plumpen Satz schützt. „Nicht einfach kritisieren, mach es besser!“ Eine Redaktion der Gegenöffentlichkeit, hochgelobt, die kurze Sätze will und kurze Texte. Dieses Feld können und wollen die Sandmänner nicht bestellen, genau wie all das, was im Namen einer „Menschheitsfamilie“ daherkommt. „Liebe Community. So begrüßt ein dissidenter Moderator das Publikum in einer dissidenten Talkshow.“ (87) Etwas mehr Platz bekommt [Rainer Mausfeld](https://www.freie-medienakademie.de/medien-plus/101):
„Warum schweigen die Lämmer? Ein tolles Buch. Es hat gegriffen. Dann hat sich gezeigt: Das System, von diesem Buch dekonstruiert, muss einen Zacken zugeben an Totalität und schon schlüpft auch die Analyse mit hinein ins System und ins Schweigen und der Autor wird selbst zum Lamm.“ (21)
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Ich kenne das Lied, das Daniel aka Teer Sandmann hier singt. Wie er bin ich von links gekommen und habe erlebt, „wie meine Welt leer wurde“ (23). Wie er weiß ich inzwischen, dass ich in „meinen Kreisen“ von einst nicht mehr klarkommen würde und dass es mit den neuen keinesfalls einfacher ist. Hier, immer noch und trotz alledem, die Idee, dass sich Glück planen lässt, und damit „der Wahn“, „ein Ziel zu erreichen und alles auszumerzen, was dem Ziel in die Quere kommt“ (143): „Die linken Ideen münden in Ordnungen und im Polizeistaat“ (24). Und dort Kritiker der Macht, die vor den Gerichten der gleichen Macht um ein wenig Wohlstand streiten, sich nur noch gegenseitig interviewen, die AfD hoffieren und auf Personen zielen, wo es um Strukturen gehen müsste. Klaus Schwab, Bill Gates, Jeff Epstein statt Kapitalismus. Was bleibt euch noch, Kinder, wenn ihr zwar den Totalitarismus erkennt, aber nicht sehen wollt, „wie dieser alternativlos aus dem Kapital hervorschießen musste“ (40)?
Der letzte Satz ist ein Versuch, den Takt aufzunehmen, den dieser Text anschlägt. Teer Sandmann sagt, dass ihn „die Musik aus der Renaissance“ noch mehr gerettet habe als das Schreiben, und baut vielleicht auch deshalb immer wieder Miniaturen ein, die zeigen, dass Kunst auch dann Jahrhunderte überdauern kann, wenn jemand wie ich noch nie davon gehört hat. Daniel Sandmann reicht. Vergesst all eure Gegenentwürfe, singt dieser Künstler:
„Wir sind für nichts. Wir stören die Haltungen und schaffen Nischen. Indem wir stören. Wir sind für alles, was nicht in ein ‚wir sind für‘ mündet. Bloß, ist das alles nicht schon eine Haltung? Und wer sind ‚wir‘?“ (79)
Die Sache mit dem Frieden, natürlich. Es gibt in diesem Buch einen Traum, in dem ein „lieber Gott“ alle Journalisten tötet, „die neuen Schwarzhemden“ (49), „die in diesem medialen Schlachtfeld, Journalismus genannt, mitfeuern und mitgeifern und ihrer Niedertracht freien Lauf lassen“, und mit ihnen auch alle, „die binnen einer Woche auch nur einen Cent noch überweisen an diese Instrumente der Niedertracht und der Geistvernichtung“ sowie Parteimitglieder und Manager, jeden Adelsclan und alle Künstler, „die der Macht zusprechen“ (55). Sie ahnen es schon: Diese Liste ist unvollständig und mit ihrer Wucht eine Ausnahme in dieser „wohltemperierten Abrechnung hin zum Frieden“. Daniel und Teer Sandmann suchen nach Ruhe und Trance. Frieden: Das ist nicht nur das Ende des Kapitalismus oder das vergessene Stück aus der Renaissance. Frieden bringt auch die Runde im Waldsee:
„Komme ich aus dem Wasser, komme ich nach Hause. Mag sein, dass im Orgasmus der Tod vergessen geht, im Wasser aber verliert er die Bedeutung und vermengt sich mit dem Leben aufs Unkenntliche. Stilles Jauchzen, meerjungfrauartiges Kreisen, kindliches Drehen um sich selbst und ohne Bezugspunkt: das sind die Ausdrucksformen dieses ungeplanten Glücks.“ (157)
Jetzt weiß ich auch, warum ich schon als junger Mann jeden Tag ohne Schwimmgelegenheit für einen verlorenen Tag gehalten habe.
Michael Meyen ist Medienforscher, Ausbilder und Journalist. Seit 2002 ist er Universitätsprofessor an der LMU München. https://www.freie-medienakademie.de/
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
In Kürze folgt eine Mail an alle Genossenschafter, danke für die Geduld!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ d360efec:14907b5f
2025-05-13 00:39:56
@ d360efec:14907b5f
2025-05-13 00:39:56🚀📉 #BTC วิเคราะห์ H2! พุ่งชน 105K แล้วเจอแรงขาย... จับตา FVG 100.5K เป็นจุดวัดใจ! 👀📊
จากากรวิเคราะห์ทางเทคนิคสำหรับ #Bitcoin ในกรอบเวลา H2:
สัปดาห์ที่แล้ว #BTC ได้เบรคและพุ่งขึ้นอย่างแข็งแกร่งค่ะ 📈⚡ แต่เมื่อวันจันทร์ที่ผ่านมา ราคาได้ขึ้นไปชนแนวต้านบริเวณ 105,000 ดอลลาร์ แล้วเจอแรงขายย่อตัวลงมาตลอดทั้งวันค่ะ 🧱📉
ตอนนี้ ระดับที่น่าจับตาอย่างยิ่งคือโซน H4 FVG (Fair Value Gap ในกราฟ 4 ชั่วโมง) ที่ 100,500 ดอลลาร์ ค่ะ 🎯 (FVG คือโซนที่ราคาวิ่งผ่านไปเร็วๆ และมักเป็นบริเวณที่ราคามีโอกาสกลับมาทดสอบ/เติมเต็ม)
👇 โซน FVG ที่ 100.5K นี้ ยังคงเป็น Area of Interest ที่น่าสนใจสำหรับมองหาจังหวะ Long เพื่อลุ้นการขึ้นในคลื่นลูกถัดไปค่ะ!
🤔💡 อย่างไรก็ตาม การตัดสินใจเข้า Long หรือเทรดที่บริเวณนี้ ขึ้นอยู่กับว่าราคา แสดงปฏิกิริยาอย่างไรเมื่อมาถึงโซน 100.5K นี้ เพื่อยืนยันสัญญาณสำหรับการเคลื่อนไหวที่จะขึ้นสูงกว่าเดิมค่ะ!
เฝ้าดู Price Action ที่ระดับนี้อย่างใกล้ชิดนะคะ! 📍
BTC #Bitcoin #Crypto #คริปโต #TechnicalAnalysis #Trading #FVG #FairValueGap #PriceAction #MarketAnalysis #ลงทุนคริปโต #วิเคราะห์กราฟ #TradeSetup #ข่าวคริปโต #ตลาดคริปโต


-
 @ 4d41a7cb:7d3633cc
2025-04-08 01:17:39
@ 4d41a7cb:7d3633cc
2025-04-08 01:17:39Satoshi Nakamoto, the pseudonymous creator of Bitcoin, registered his birthday as April 5, 1975, on his P2P Foundation profile. Many think that he chose this date because on that same day in 1933, the United States government confiscated the gold of the American people. Whether this was on purpose or not, what happened in this day is very important to understand how do we ended up here.
In 1933, as expressed in Roosevelt’s Executive Orders 6073, 6102, and 6260, the United States first declared bankruptcy. The bankrupt U.S. went into receivership in 1933. America was turned over via receivership and reorganization in favor of its creditors. These creditors, the International Bankers, from the beginning stated their intent, which was to plunder, bankrupt, conquer and enslave America and return it to its colonial status.1
As one of his first acts as President, Franklin Delano Roosevelt declared a “Banking Emergency” to bail out the Federal Reserve Bank, which had embezzled this country’s gold supply. The Congress gave the President dictatorial powers under the “War Powers Act of 1917” (amended 1933), written, by the way, by the Board of Governors of the Federal Reserve Bank of New York.2
This day marked the official abandonment of the American Constitution, law and real money. Today, 92 years after this event, most of the people living today have never had any real money or paid for anything using real money; unless they used Bitcoin...
There could be no bankruptcy if there was not a private central bank lending paper currency to the government at interest, so we must start from 1913, when the Federal Reserve was created: a non-federal private bank with no reserves and the monopoly of issuing debt based paper currency in unlimited amounts and lending it to the government at interest by buying treasury bills. The fact that this currency is lent into existence at interest makes the debt mathematically impossible to be repaid; it can only be refinanced or defaulted.
Between 1929 and 1933, the Federal Reserve Bank reduced the currency supply by 33%, thereby creating the Great Depression, bankrupting the US government, stealing the Americans’ gold supply, and officially ending the gold standard. Since then the US dollar (money) was replaced with Federal Reserve Notes (debt). This was also the end of the Republican form of government and the beginning of a socialist mob rule democracy (Fascism).
“Fascism should more properly be called corporatism because it is the merger of state and corporate power.” — Benito Mussolini
The United States government has been bankrupt since 1933, since it defaulted on its gold bonds. This type of bond existed until 1933, when the U.S. monetary system abandoned the gold standard. 3 From this year the government has been totally controlled by the International bankers and used as a tool to spread and maintain their power worldwide.
Many people think that the gold standard was abandoned in 1971, but this is not true; in fact, this happened in 1933 when the US dollar was replaced by Federal Reserve Notes that are 100% debt-based fiat paper currency.
The year 1933 in the United States marked:
- The end of the Republican form of government and the beginning of American Fascism
- The end of the United States dollar and its replacement by Federal Reserve Notes
- The abandonment of common law and replacement with military admiralty law
- The takeover of the United States government by International bankers
- A massive gold theft and the end of the US gold standard
- The exchange of rights with privileges and licenses
- The United States government bankruptcy
The next shameful event in our history which still plagues us to this day was the “War Powers Act of 1933.” This Act permitted President Roosevelt to make law in the form of Executive Order, bypass Congress and create his socialist state. We (citizens of this country) were ever after to be considered enemies of the United States who must be licensed to engage in any commercial activity. With the aid of the Federal Reserve (the same people who created the Depression), the President confiscated our gold and silver coin and replaced it with worthless pieces of paper and a debt system that will eventually destroy this great country. Our land and our labor were pledged to the Federal Reserve Bank, Inc., as collateral for a debt system that could never be paid.4
“Emergency Powers” means any form of military style government, martial law, or martial rule. Martial law and martial rule are not the same.
United States Congressional Record March 17, 1993 Vol. #33, page H- 1303, Congressman James Traficant, Jr. (Ohio) addressing the House:
“Mr. Speaker, we are here now in chapter 11. Members of Congress are official trustees presiding over the greatest reorganization of any Bankrupt entity in world history, the U.S. Government. We are setting forth, hopefully, a blueprint for our future”
“There are some who say it is a coroner’s report that will lead to our demise. It is an established fact that the United States Federal Government has been dissolved by the Emergency Banking Act, March 9, 1933, 48 Stat. 1, Public Law 89-719; dered by President Roosevelt, being bankrupt and insolvent. H.J.R. 192, 73rd Congress in session June 5, 1933 – Joint Resolution To Suspend The Gold Standard and Abrogate the Gold Clause dissolved the Sovereign Authority of the United States and the official capacities of all United States Governmental Offices, Officers, and Departments and is further evidence that the United States Federal Government exists today in name only” **“The receivers of the United States Bankruptcy are the International Bankers, via the United Nations, the World Bank and the International Monetary Fund”
“All United States Offices, Officials, and Departments are now operating within a de facto status in name only under Emergency War Powers. With the Constitutional Republican form of Government now dissolved, the receivers of the Bankruptcy have adopted a new form of government for the United States. This new form of government is known as a Democracy, being an established Socialist/Communist order under a new governor for America. This act was instituted and established by transferring and/or placing the Office of the Secretary of Treasury to that of the Governor of the International Monetary Fund. Public Law 94-564, page 8, Section H.R. 13955 read in part:”
“The U.S. Secretary of Treasury receives no compensation for representing the United States.”
The American Spirit
The intention of the founding fathers of the United States was to create a constitutional republic to protect natural human rights and escape from the tyrannical English monarchy and its usurious Bank of England's monetary system. They created an honest monetary system based on gold and silver (United State Dollar) and got rid of nobility titles, creating equality under the law.
Section 10 of the American Constitution says:
No State shall enter into any Treaty, Alliance, or Confederation; grant Letters of Marque and Reprisal; coin Money; emit Bills of Credit; make anything but gold and silver Coin a tender in payment of debts; pass any bill of attainder, ex post facto law, or law impairing the obligation of contracts; or grant any title of nobility.
The United States Dollar (1792-1933)
A dollar is a measure of weight defined by the Coinage Act of 1792 and 1900, which specifies a certain quantity—24.8 grains of gold or 371.25 grains of silver (from 1792 to 1900) when the American dollar was based on a bimetallic standard.
The Gold Standard Act of 1900 formally placed the United States on the gold standard, setting the value of one dollar at 25.8 grams of 90% pure gold, which fixed the price of gold at $20.67 per troy ounce. This standard was totally abandoned in 1933.
Gold and silver were such powerful money during the founding of the United States of America that the founding fathers declared that only gold or silver coins could be “money” in America.
But since the greedy bankers cannot profit from honest money they cannot print, they replaced the money with paper debt instruments. And by doing this, they have effectively enslaved the American people until today. My definition of modern slavery is working for a currency that someone else can create at no cost or effort. What's worse is that they even demand to be paid back and with interest!
Federal Reserve Notes (1913-present)
Federal Reserve Notes are not real money. Money that has metallic or other intrinsic value, as distinguished from paper currency, checks, and drafts.
Federal Reserve Notes (FRNs) are a legal fiction. An assumption that something is true even though it may be untrue. 5 The assumption that they are money, when in fact they are the opposite of money: debt or paper currency.
Paper money. Paper documents that circulate as currency; bills drawn by a government against its own credit. 6 Like Goldsmiths' notes. Hist. Bankers' cash notes: promissory notes given by bankers to customers as acknowledgments of the receipt of money. • This term derives from the London banking business, which originally was transacted by goldsmiths.7
These notes were scientifically designed to bankrupt the government and slave the American people, as Alfred Owen Crozier warned one year before the bill for the creation of the FED was passed through Congress (1912):
If Congress yields and authorizes a private central bank as proposed by the pending bill, the end when the bubble bursts will be universal ruin and national bankruptcy.
Unfortunately, the bill was passed in 1913, and this private bank started printing a new currency different from the US dollar creating the great depression and effectible bankrupting the government like Alfred warned 20 years before.
Alfred also warned:
Thus the way is opened for an unlimited inflation of corporate paper currency issued by a mere private corporation with relatively small net assets and no government guarantee, every dollar supposed to be redeemable in gold, but with not a single dollar of gold necessarily held in the reserves of such corporation to accomplish such redemption.
Differently from what's commonly believed Federal Reserve Notes (FRNs) were never really “backed” by gold; they were never supposed to be hard currency. Currency backed by reserves, esp. gold and silver reserves.
The United States government defaulted on its gold clauses, calling for payment in gold. This marked the end of the gold standard. A monetary system in which currency is convertible into its legal equivalent in gold or gold coin.
Since then we have been under a paper standard, where we use fake money as tender for payments. Paper standard. A monetary system based entirely on paper; a system of currency that is not convertible into gold or other precious metal.
People traded their coupons as money or “currency.” Currency is not money but a money substitute. Redeemable currency must promise to pay a dollar equivalent in gold or silver money. Federal Reserve Notes (FRNs) make no such promises and are not “money.” A Federal Reserve Note is a debt obligation of the federal United States government, not “money.” The federal United States government and the U.S. Congress were not and have never been authorized by the Constitution of the United States of America to issue currency of any kind, but only lawful money—gold and silver coin.8
A bona fide note can be used in a financial transaction to discharge the debt only because it is an unconditional promise to pay by the issuer to the bearer. Is a Federal Reserve Note a contract note, an unconditional promise to pay? At one time the Federal Reserve issued bona fide contractual notes and certificates, redeemable in gold and silver coin. Most people never saw or comprehended the contract. It went largely unread because the Federal Reserve very cunningly hid the contract on the face of the note by breaking it up into five separate lines of text with a significantly different typeface for each line and placing the president’s picture right in the middle of it. They even used the old attorney’s ruse of obscuring the most important text in fine print! Over time, the terms and conditions of the contract were diluted until eventually they literally became an I.O.U. for nothing.
FEDERAL RESERVE NOTE
-
THIS NOTE IS LEGAL TENDER FOR ALL DEBT, PUBLIC AND PRIVATE, AND IT IS REDEEMABLE IN LAWFUL MONEY AT THE UNITED STATES TREASURY OR ANY FEDERAL RESERVE BANK.
-
DATE: SERIES OF 1934
-
WILL PAY TO THE BEARER ON DEMAND: ONE HUNDRED DOLLARS
-
TREASURER OF THE UNITED STATES SIGNATURE
-
SECRETARY OF THE TREASURY SIGNATURE

Nowadays FRNs say "This note is legal tender for all debts public and private" it tender debt but it does not pay the bearer on demand. It value was stolen by a counterfeiting technique commonly know as inflation.
One hundred dollars (SERIES OF 1934) will be 2480 grains of gold, or 159.4 grams, or 5.1249 troy ounces. Today one troy ounce is priced around $3,000 federal reserve notes. 5.1249 X 3,000 = $15,375 actual FRNs.
A $100 FRN bill today will buy 0.65% of a real gold $100 dollar certificate. That’s a -99.35% loss of purchasing power in the last 91 years.
FRNs savers have been rugged pulled!
Gold bugs where the winners...
But Bitcoin is even better...
Happy birthday Satoshi! April 5 will be forever remembered.
Satoshi... The man, the myth, the Legend...
-
 @ 57d1a264:69f1fee1
2025-05-31 06:19:55
@ 57d1a264:69f1fee1
2025-05-31 06:19:55Knowledge- Pattern knowledge- Trend knowledge- A desire to learn more- A desire to explore good designExperience- A sense of where to start/what will work- Good taste- Good judge of your own design and others’- Comfortable working in many styles- Willing to have a strong opinionCreativity- Novel ideas- Exhaustive exploration of options/approaches- Exhaustive iterationQuality- A preference for quality- A preference to test designs- Open to feedback- Able to balance classical and expressive aesthetics- Able to balance aesthetics and usability- Obsessed with details- RigorousTechnical skills- Good typography- Good composition/layout- Good colour choices- Good at some associated skills (e.g. prototyping, animation, imagery, writing)- Tool expertiseWider picture- Informed by understanding of the product (e.g. research)- System thinking (how the work is connected to other things)- Product thinking (what makes a successful product)- Development thinking (how a design might be implemented)- Practical mindset when necessary- Believes in importance of accessibilityCommunication- Able to articulate your design “feelings”- Able to explain design principles to others- Can clearly document/explain the design (e.g. specifications, mockups)- Good relationship-building, especially with developers- Able to “sell” a design idea
Read more aboutAnthony Hobday.https://stacker.news/items/993319
-
 @ d360efec:14907b5f
2025-05-12 04:01:23
@ d360efec:14907b5f
2025-05-12 04:01:23 -
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 51bbb15e:b77a2290
2025-05-21 00:24:36
@ 51bbb15e:b77a2290
2025-05-21 00:24:36Yeah, I’m sure everything in the file is legit. 👍 Let’s review the guard witness testimony…Oh wait, they weren’t at their posts despite 24/7 survellience instructions after another Epstein “suicide” attempt two weeks earlier. Well, at least the video of the suicide is in the file? Oh wait, a techical glitch. Damn those coincidences!
At this point, the Trump administration has zero credibility with me on anything related to the Epstein case and his clients. I still suspect the administration is using the Epstein files as leverage to keep a lot of RINOs in line, whereas they’d be sabotaging his agenda at every turn otherwise. However, I just don’t believe in ends-justify-the-means thinking. It’s led almost all of DC to toss out every bit of the values they might once have had.
-
 @ 0d97beae:c5274a14
2025-01-11 16:52:08
@ 0d97beae:c5274a14
2025-01-11 16:52:08This article hopes to complement the article by Lyn Alden on YouTube: https://www.youtube.com/watch?v=jk_HWmmwiAs
The reason why we have broken money
Before the invention of key technologies such as the printing press and electronic communications, even such as those as early as morse code transmitters, gold had won the competition for best medium of money around the world.
In fact, it was not just gold by itself that became money, rulers and world leaders developed coins in order to help the economy grow. Gold nuggets were not as easy to transact with as coins with specific imprints and denominated sizes.
However, these modern technologies created massive efficiencies that allowed us to communicate and perform services more efficiently and much faster, yet the medium of money could not benefit from these advancements. Gold was heavy, slow and expensive to move globally, even though requesting and performing services globally did not have this limitation anymore.
Banks took initiative and created derivatives of gold: paper and electronic money; these new currencies allowed the economy to continue to grow and evolve, but it was not without its dark side. Today, no currency is denominated in gold at all, money is backed by nothing and its inherent value, the paper it is printed on, is worthless too.
Banks and governments eventually transitioned from a money derivative to a system of debt that could be co-opted and controlled for political and personal reasons. Our money today is broken and is the cause of more expensive, poorer quality goods in the economy, a larger and ever growing wealth gap, and many of the follow-on problems that have come with it.
Bitcoin overcomes the "transfer of hard money" problem
Just like gold coins were created by man, Bitcoin too is a technology created by man. Bitcoin, however is a much more profound invention, possibly more of a discovery than an invention in fact. Bitcoin has proven to be unbreakable, incorruptible and has upheld its ability to keep its units scarce, inalienable and counterfeit proof through the nature of its own design.
Since Bitcoin is a digital technology, it can be transferred across international borders almost as quickly as information itself. It therefore severely reduces the need for a derivative to be used to represent money to facilitate digital trade. This means that as the currency we use today continues to fare poorly for many people, bitcoin will continue to stand out as hard money, that just so happens to work as well, functionally, along side it.
Bitcoin will also always be available to anyone who wishes to earn it directly; even China is unable to restrict its citizens from accessing it. The dollar has traditionally become the currency for people who discover that their local currency is unsustainable. Even when the dollar has become illegal to use, it is simply used privately and unofficially. However, because bitcoin does not require you to trade it at a bank in order to use it across borders and across the web, Bitcoin will continue to be a viable escape hatch until we one day hit some critical mass where the world has simply adopted Bitcoin globally and everyone else must adopt it to survive.
Bitcoin has not yet proven that it can support the world at scale. However it can only be tested through real adoption, and just as gold coins were developed to help gold scale, tools will be developed to help overcome problems as they arise; ideally without the need for another derivative, but if necessary, hopefully with one that is more neutral and less corruptible than the derivatives used to represent gold.
Bitcoin blurs the line between commodity and technology
Bitcoin is a technology, it is a tool that requires human involvement to function, however it surprisingly does not allow for any concentration of power. Anyone can help to facilitate Bitcoin's operations, but no one can take control of its behaviour, its reach, or its prioritisation, as it operates autonomously based on a pre-determined, neutral set of rules.
At the same time, its built-in incentive mechanism ensures that people do not have to operate bitcoin out of the good of their heart. Even though the system cannot be co-opted holistically, It will not stop operating while there are people motivated to trade their time and resources to keep it running and earn from others' transaction fees. Although it requires humans to operate it, it remains both neutral and sustainable.
Never before have we developed or discovered a technology that could not be co-opted and used by one person or faction against another. Due to this nature, Bitcoin's units are often described as a commodity; they cannot be usurped or virtually cloned, and they cannot be affected by political biases.
The dangers of derivatives
A derivative is something created, designed or developed to represent another thing in order to solve a particular complication or problem. For example, paper and electronic money was once a derivative of gold.
In the case of Bitcoin, if you cannot link your units of bitcoin to an "address" that you personally hold a cryptographically secure key to, then you very likely have a derivative of bitcoin, not bitcoin itself. If you buy bitcoin on an online exchange and do not withdraw the bitcoin to a wallet that you control, then you legally own an electronic derivative of bitcoin.
Bitcoin is a new technology. It will have a learning curve and it will take time for humanity to learn how to comprehend, authenticate and take control of bitcoin collectively. Having said that, many people all over the world are already using and relying on Bitcoin natively. For many, it will require for people to find the need or a desire for a neutral money like bitcoin, and to have been burned by derivatives of it, before they start to understand the difference between the two. Eventually, it will become an essential part of what we regard as common sense.
Learn for yourself
If you wish to learn more about how to handle bitcoin and avoid derivatives, you can start by searching online for tutorials about "Bitcoin self custody".
There are many options available, some more practical for you, and some more practical for others. Don't spend too much time trying to find the perfect solution; practice and learn. You may make mistakes along the way, so be careful not to experiment with large amounts of your bitcoin as you explore new ideas and technologies along the way. This is similar to learning anything, like riding a bicycle; you are sure to fall a few times, scuff the frame, so don't buy a high performance racing bike while you're still learning to balance.
-
 @ ec9bd746:df11a9d0
2025-04-06 08:06:08
@ ec9bd746:df11a9d0
2025-04-06 08:06:08🌍 Time Window:
🕘 When: Every even week on Sunday at 9:00 PM CET
🗺️ Where: https://cornychat.com/eurocornStart: 21:00 CET (Prague, UTC+1)
End: approx. 02:00 CET (Prague, UTC+1, next day)
Duration: usually 5+ hours.| Region | Local Time Window | Convenience Level | |-----------------------------------------------------|--------------------------------------------|---------------------------------------------------------| | Europe (CET, Prague) 🇨🇿🇩🇪 | 21:00–02:00 CET | ✅ Very Good; evening & night | | East Coast North America (EST) 🇺🇸🇨🇦 | 15:00–20:00 EST | ✅ Very Good; afternoon & early evening | | West Coast North America (PST) 🇺🇸🇨🇦 | 12:00–17:00 PST | ✅ Very Good; midday & afternoon | | Central America (CST) 🇲🇽🇨🇷🇬🇹 | 14:00–19:00 CST | ✅ Very Good; afternoon & evening | | South America West (Peru/Colombia PET/COT) 🇵🇪🇨🇴 | 15:00–20:00 PET/COT | ✅ Very Good; afternoon & evening | | South America East (Brazil/Argentina/Chile, BRT/ART/CLST) 🇧🇷🇦🇷🇨🇱 | 17:00–22:00 BRT/ART/CLST | ✅ Very Good; early evening | | United Kingdom/Ireland (GMT) 🇬🇧🇮🇪 | 20:00–01:00 GMT | ✅ Very Good; evening hours (midnight convenient) | | Eastern Europe (EET) 🇷🇴🇬🇷🇺🇦 | 22:00–03:00 EET | ✅ Good; late evening & early night (slightly late) | | Africa (South Africa, SAST) 🇿🇦 | 22:00–03:00 SAST | ✅ Good; late evening & overnight (late-night common) | | New Zealand (NZDT) 🇳🇿 | 09:00–14:00 NZDT (next day) | ✅ Good; weekday morning & afternoon | | Australia (AEDT, Sydney) 🇦🇺 | 07:00–12:00 AEDT (next day) | ✅ Good; weekday morning to noon | | East Africa (Kenya, EAT) 🇰🇪 | 23:00–04:00 EAT | ⚠️ Slightly late (night hours; late night common) | | Russia (Moscow, MSK) 🇷🇺 | 23:00–04:00 MSK | ⚠️ Slightly late (join at start is fine, very late night) | | Middle East (UAE, GST) 🇦🇪🇴🇲 | 00:00–05:00 GST (next day) | ⚠️ Late night start (midnight & early morning, but shorter attendance plausible)| | Japan/Korea (JST/KST) 🇯🇵🇰🇷 | 05:00–10:00 JST/KST (next day) | ⚠️ Early; convenient joining from ~07:00 onwards possible | | China (Beijing, CST) 🇨🇳 | 04:00–09:00 CST (next day) | ❌ Challenging; very early morning start (better ~07:00 onwards) | | India (IST) 🇮🇳 | 01:30–06:30 IST (next day) | ❌ Very challenging; overnight timing typically difficult|
-
 @ 37fe9853:bcd1b039
2025-01-11 15:04:40
@ 37fe9853:bcd1b039
2025-01-11 15:04:40yoyoaa
-
 @ d360efec:14907b5f
2025-05-12 01:34:24
@ d360efec:14907b5f
2025-05-12 01:34:24สวัสดีค่ะเพื่อนๆ นักเทรดที่น่ารักทุกคน! 💕 Lina Engword กลับมาพร้อมกับการวิเคราะห์ BTCUSDT.P แบบเจาะลึกเพื่อเตรียมพร้อมสำหรับเทรดวันนี้ค่ะ! 🚀
วันนี้ 12 พฤษภาคม 2568 เวลา 08.15น. ราคา BTCUSDT.P อยู่ที่ 104,642.8 USDT ค่ะ โดยมี Previous Weekly High (PWH) อยู่ที่ 104,967.8 Previous Weekly Low (PWL) ที่ 93,338 ค่ะ
✨ ภาพรวมตลาดวันนี้ ✨
จากการวิเคราะห์ด้วยเครื่องมือคู่ใจของเรา ทั้ง SMC/ICT (Demand/Supply Zone, Order Block, Liquidity), EMA 50/200, Trend Strength, Money Flow, Chart/Price Pattern, Premium/Discount Zone, Trend line, Fibonacci, Elliott Wave และ Dow Theory ใน Timeframe ตั้งแต่ 15m ไปจนถึง Week! 📊 เราพบว่าภาพใหญ่ของ BTCUSDT.P ยังคงอยู่ในแนวโน้มขาขึ้นที่แข็งแกร่งมากๆ ค่ะ 👍 โดยเฉพาะใน Timeframe Day และ Week ที่สัญญาณทุกอย่างสนับสนุนทิศทางขาขึ้นอย่างชัดเจน Money Flow ยังไหลเข้าอย่างต่อเนื่อง และเราเห็นโครงสร้างตลาดแบบ Dow Theory ที่ยก High ยก Low ขึ้นไปเรื่อยๆ ค่ะ
อย่างไรก็ตาม... ใน Timeframe สั้นๆ อย่าง 15m และ 1H เริ่มเห็นสัญญาณของการชะลอตัวและการพักฐานบ้างแล้วค่ะ 📉 อาจมีการสร้าง Buyside และ Sellside Liquidity รอให้ราคาไปกวาดก่อนที่จะเลือกทางใดทางหนึ่ง ซึ่งเป็นเรื่องปกติของการเดินทางของ Smart Money ค่ะ
⚡ เปรียบเทียบแนวโน้มแต่ละ Timeframe ⚡
🪙 แนวโน้มตรงกัน Timeframe 4H, Day, Week ส่วนใหญ่ชี้ไปทาง "ขาขึ้น" ค่ะ ทุกเครื่องมือสนับสนุนแนวโน้มนี้อย่างแข็งแกร่ง 💪 เป้าหมายต่อไปคือการไปทดสอบ PWH และ High เดิม เพื่อสร้าง All-Time High ใหม่ค่ะ! 🪙 แนวโน้มต่างกัน Timeframe 15m, 1H ยังค่อนข้าง "Sideways" หรือ "Sideways Down เล็กน้อย" ค่ะ มีการบีบตัวของราคาและอาจมีการพักฐานสั้นๆ ซึ่งเป็นโอกาสในการหาจังหวะเข้า Long ที่ราคาดีขึ้นค่ะ
💡 วิธีคิดแบบ Market Slayer 💡
เมื่อแนวโน้มใหญ่เป็นขาขึ้นที่แข็งแกร่ง เราจะเน้นหาจังหวะเข้า Long เป็นหลักค่ะ การย่อตัวลงมาในระยะสั้นคือโอกาสของเราในการเก็บของ! 🛍️ เราจะใช้หลักการ SMC/ICT หาโซน Demand หรือ Order Block ที่ Smart Money อาจจะเข้ามาดันราคาขึ้น และรอสัญญาณ Price Action ยืนยันการกลับตัวค่ะ
สรุปแนวโน้มวันนี้:
🪙 ระยะสั้น: Sideways to Sideways Down (โอกาส 55%) ↔️↘️ 🪙 ระยะกลาง: ขาขึ้น (โอกาส 70%) ↗️ 🪙 ระยะยาว: ขาขึ้น (โอกาส 85%) 🚀 🪙 วันนี้: มีโอกาสย่อตัวเล็กน้อยก่อนจะมีแรงซื้อกลับเข้ามาเพื่อไปทดสอบ PWH (โอกาส Sideways Down เล็กน้อย สลับกับ Sideways Up: 60%) 🎢
🗓️ Daily Trade Setup ประจำวันนี้ 🗓️
นี่คือตัวอย่าง Setup ที่ Lina เตรียมไว้ให้พิจารณาค่ะ (เน้นย้ำว่าเป็นเพียงแนวทาง ไม่ใช่คำแนะนำลงทุนนะคะ)
1️⃣ ตัวอย่างที่ 1: รอรับที่โซน Demand (ปลอดภัย, รอยืนยัน)
🪙 Enter: รอราคาย่อตัวลงมาในโซน Demand Zone หรือ Bullish Order Block ที่น่าสนใจใน TF 1H/4H (ดูจากกราฟประกอบนะคะ) และเกิดสัญญาณ Bullish Price Action ที่ชัดเจน เช่น แท่งเทียนกลืนกิน (Engulfing) หรือ Hammer 🪙 TP: บริเวณ PWH 104,967.8 หรือ Buyside Liquidity ถัดไป 🎯 🪙 SL: ใต้ Low ที่เกิดก่อนสัญญาณกลับตัวเล็กน้อย หรือใต้ Demand Zone ที่เข้า 🛡️ 🪙 RRR: ประมาณ 1:2.5 ขึ้นไป ✨ 🪙 อธิบาย: Setup นี้เราจะใจเย็นๆ รอให้ราคาลงมาในโซนที่มีโอกาสเจอแรงซื้อเยอะๆ ตามหลัก SMC/ICT แล้วค่อยเข้า เพื่อให้ได้ราคาที่ดีและความเสี่ยงต่ำค่ะ ต้องรอสัญญาณ Price Action ยืนยันก่อนนะคะ ✍️
2️⃣ ตัวอย่างที่ 2: Follow Breakout (สายบู๊, รับความเสี่ยงได้)
🪙 Enter: เข้า Long ทันทีเมื่อราคาสามารถ Breakout เหนือ High ล่าสุดใน TF 15m หรือ 1H พร้อม Volume ที่เพิ่มขึ้นอย่างมีนัยสำคัญ 🔥 🪙 TP: บริเวณ PWH 104,967.8 หรือ Buyside Liquidity ถัดไป 🚀 🪙 SL: ใต้ High ก่อนหน้าที่ถูก Breakout เล็กน้อย 🚧 🪙 RRR: ประมาณ 1:3 ขึ้นไป ✨ 🪙 อธิบาย: Setup นี้เหมาะกับคนที่อยากเข้าไวเมื่อเห็นโมเมนตัมแรงๆ ค่ะ เราจะเข้าเมื่อราคา Breakout แนวต้านระยะสั้นพร้อม Volume เป็นสัญญาณว่าแรงซื้อกำลังมาค่ะ เข้าได้เลยด้วยการตั้ง Limit Order หรือ Market Order เมื่อเห็นการ Breakout ที่ชัดเจนค่ะ 💨
3️⃣ ตัวอย่างที่ 3: พิจารณา Short สั้นๆ ในโซน Premium (สวนเทรนด์หลัก, ความเสี่ยงสูง)
🪙 Enter: หากราคาขึ้นไปในโซน Premium ใน TF 15m หรือ 1H และเกิดสัญญาณ Bearish Price Action ที่ชัดเจน เช่น แท่งเทียน Shooting Star หรือ Bearish Engulfing บริเวณ Supply Zone หรือ Bearish Order Block 🐻 🪙 TP: พิจารณาแนวรับถัดไป หรือ Sellside Liquidity ใน TF เดียวกัน 🎯 🪙 SL: เหนือ High ของสัญญาณ Bearish Price Action เล็กน้อย 💀 🪙 RRR: ประมาณ 1:1.5 ขึ้นไป (เน้นย้ำว่าเป็นการเทรดสวนเทรนด์หลัก ควรใช้ RRR ต่ำและบริหารขนาด Lot อย่างเข้มงวด!) 🪙 อธิบาย: Setup นี้สำหรับคนที่เห็นโอกาสในการทำกำไรจากการย่อตัวระยะสั้นค่ะ เราจะเข้า Short เมื่อเห็นสัญญาณว่าราคาอาจจะมีการพักฐานในโซนที่ถือว่า "แพง" ในกรอบสั้นๆ ค่ะ ต้องตั้ง Stop Loss ใกล้มากๆ และจับตาดูใกล้ชิดนะคะ 🚨
⚠️ Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัวของ Lina เท่านั้น ไม่ถือเป็นคำแนะนำในการลงทุนนะคะ การลงทุนมีความเสี่ยง ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบค่ะ 🙏
ขอให้ทุกท่านโชคดีกับการเทรดในวันนี้ค่ะ! มีคำถามอะไรเพิ่มเติม ถามมาได้เลยนะคะ ยินดีเสมอค่ะ! 😊
Bitcoin #BTCUSDT #Crypto #Trading #TechnicalAnalysis #SMC #ICT #MarketSlayer #TradeSetup #คริปโต #เทรดคริปโต #วิเคราะห์กราฟ #LinaEngword 😉



-
 @ 3770c235:16042bcc
2025-05-31 05:30:22
@ 3770c235:16042bcc
2025-05-31 05:30:22In a world full of constant stimulation, overflowing schedules, and ever-growing to-do lists, our physical spaces often bear the brunt of our busy lives. The clutter in our homes and workplaces can slowly pile up until it becomes overwhelming, contributing not only to a chaotic environment but also to increased levels of stress and anxiety.
But what if the simple act of removing junk and organizing your space could bring clarity to your mind, lift your mood, and create a lasting positive impact on your mental health? Decluttering isn't just about aesthetics—it’s about mental wellness. Junk removal can be a powerful tool to help you take control of your space and, in turn, your mindset. Let’s explore how clearing the clutter can boost mental health and transform your daily life.
The Psychological Impact of Clutter Clutter isn’t just stuff—it’s unmade decisions and postponed actions. Psychologists have long understood the connection between our environment and our emotional well-being. Clutter bombards our minds with excessive stimuli, making it difficult to focus or relax. It sends a signal that work is never done, which can lead to chronic stress.
A study published in the Personality and Social Psychology Bulletin found that women who described their homes as cluttered or full of unfinished projects were more likely to be fatigued and depressed than those who described their homes as restorative and restful. The same study found that cortisol levels—the body’s main stress hormone—were significantly higher in women living in cluttered environments.
Additionally, according to a UCLA study, families living in homes with a high density of household objects experienced increased levels of anxiety. The psychological toll of clutter isn’t minor; it has real, measurable effects on our mental health.
Junk Removal as an Act of Self-Care Self-care isn't just about spa days or bubble baths—it's about creating systems and habits that support your well-being. Removing clutter and excess junk from your living or working space can be an essential act of self-care, sending your brain a clear message: you deserve a clean, peaceful environment.
The physical act of junk removal creates a sense of accomplishment. Whether it’s donating unused clothing, throwing away broken items, or clearing out the garage, every bag removed is a step toward emotional relief. The process can be surprisingly cathartic, especially for those dealing with stress, grief, or major life transitions.
Why Clutter Creates Mental Clutter Clutter and disorganization can reduce our ability to process information. Researchers at Princeton University Neuroscience Institute found that physical clutter competes for your attention, resulting in decreased performance and increased stress. When your environment is chaotic, your mind tends to mimic that chaos.
Every time you walk past a cluttered desk or disorganized closet, your brain registers it as a task you haven't completed. Over time, this leads to mental fatigue. You might find yourself feeling constantly behind, overwhelmed, or unable to concentrate—even when you're not consciously thinking about the mess.
On the flip side, a tidy, clutter-free environment can promote mental clarity, boost productivity, and help foster a greater sense of control and calm.
How Junk Removal Enhances Mood There’s a distinct emotional payoff to junk removal. Many people report feeling lighter, freer, and happier after decluttering a space. Here's why: 1. Reduces Anxiety and Stress Too much clutter can create a constant low-grade stress that gnaws away at your peace of mind. By physically removing items that no longer serve a purpose, you're also removing sources of tension. 2. Improves Focus and Productivity When your environment is clear, your mind follows suit. A cleaner space supports sharper thinking and better decision-making. Whether you're working from home or studying, a decluttered area can significantly enhance your ability to concentrate. 3. Boosts Self-Esteem Clutter can carry feelings of guilt or shame—reminders of undone tasks, unused purchases, or poor organizational habits. Taking the step to clean up can restore confidence and create a sense of achievement.
- Encourages Mindfulness Decluttering forces you to be present. You have to examine each item, reflect on its usefulness, and make a conscious decision about its place in your life. This process promotes mindfulness and intentional living.
The Decluttering Process: Step-by-Step for Mental Clarity If the idea of decluttering your entire home feels overwhelming, start small. Begin with one drawer, one shelf, or one room. Here's a practical approach to get started:
Step 1: Set a Clear Intention Know why you're decluttering. Is it to feel less stressed? To improve your focus? Having a specific goal will keep you motivated. Step 2: Sort Items into Categories Use the classic “keep, donate, toss” system. Be honest with yourself about what adds value to your life. Step 3: Focus on One Area at a Time Avoid jumping from room to room. Focus your energy on one space to see progress quickly and stay motivated.
Step 4: Remove the Junk Promptly Once you've sorted items for removal, don’t let them linger. Hire a junk removal service or take them to a donation center right away. Step 5: Maintain Your Space Set a monthly reminder to reassess clutter. Make it a habit, not a one-time task.
Professional Help: The Role of Junk Removal Services For some people, the physical and emotional burden of clearing out clutter is too overwhelming to tackle alone. This is where professional junk removal services come in. These services not only handle the heavy lifting but also offer a judgment-free way to transform your space quickly and efficiently. By outsourcing the task, you reduce stress and avoid decision fatigue. It’s a practical solution for busy professionals, seniors downsizing, or those recovering from emotional trauma like the loss of a loved one.
The mental relief from seeing a room go from chaotic to clean in just a few hours is worth the investment. Plus, many services are eco-friendly and donate reusable items to charities, adding another layer of purpose to the process.
Real-Life Impacts: Statistics that Speak Decluttering doesn’t just feel good—it’s backed by data. Consider this: • According to a study by the National Association of Professional Organizers, 54% of Americans are overwhelmed by clutter, and 78% have no idea what to do with it [source]. • A report from the Journal of Environmental Psychology found that people with clean homes are happier and more relaxed, with higher activity levels and lower levels of cortisol [source]. These statistics highlight how deeply our environment influences our emotional health—and how important it is to reclaim control of your space.
Decluttering in the Digital Age While physical clutter is the most obvious, digital clutter can also affect your mental state. Overflowing email inboxes, unorganized files, and constant notifications can leave you feeling scattered and distracted. Take time to regularly clean up your digital life by: • Unsubscribing from unwanted emails • Deleting unused apps • Organizing desktop files and folders • Turning off non-essential notifications Just like physical spaces, a clean digital environment supports a clearer, more focused mind.
When Clutter Signals Something Deeper While decluttering is beneficial, it’s important to recognize when excessive clutter or hoarding behavior may be a sign of deeper mental health issues. Conditions such as depression, anxiety, and obsessive-compulsive disorder (OCD) can manifest in the inability to discard items or maintain an organized space. If clutter feels insurmountable or leads to distress and dysfunction, it may be time to seek support from a mental health professional. Therapy can help address the root causes and develop strategies for long-term change.
Final Thoughts: Clearing the Path to Mental Well-Being Junk removal and decluttering may seem like simple tasks, but their effects on your mental health can be profound. By reducing chaos in your environment, you invite peace, focus, and emotional clarity into your life. Whether you choose to tackle the clutter yourself or enlist the help of professionals, taking the first step is often the hardest—and the most transformative. Your environment is a mirror of your mind. Clear the clutter, and you’ll often find that clarity, joy, and calm aren’t far behind.
-
 @ d360efec:14907b5f
2025-05-10 03:57:17
@ d360efec:14907b5f
2025-05-10 03:57:17Disclaimer: * การวิเคราะห์นี้เป็นเพียงแนวทาง ไม่ใช่คำแนะนำในการซื้อขาย * การลงทุนมีความเสี่ยง ผู้ลงทุนควรตัดสินใจด้วยตนเอง
-
 @ 04c915da:3dfbecc9
2025-02-25 03:55:08
@ 04c915da:3dfbecc9
2025-02-25 03:55:08Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 21335073:a244b1ad
2025-03-18 20:47:50
@ 21335073:a244b1ad
2025-03-18 20:47:50Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 866e0139:6a9334e5
2025-05-29 07:29:43
@ 866e0139:6a9334e5
2025-05-29 07:29:43Autor: Anna Nagel. (Bild: Lukas Karl). Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Wem in seinem Leben Schmerz zugefügt wurde, wer sich ungerecht behandelt fühlt oder wachen Auges in der Welt umschaut, kommt wahrscheinlich irgendwann mit der Frage in Berührung, wie das alles noch einmal «gut» werden kann. Wie kann die Welt sich mit sich selbst versöhnen? Und wie kann ich es selbst schaffen, mich mit ihr und den Menschen, die schlimme Taten vollbringen, wieder in harmonischer Akzeptanz zu verbinden? Kann und will ich gewisse Gräueltaten verzeihen oder gibt es das «Unverzeihliche»? Und selbst wenn ich wollte, wie könnte mir das gelingen?
Perspektivwechsel
Wenn wir an dem Zorn über begangenes Unrecht festhalten, schauen wir in der Regel aus immer derselben Perspektive auf das Geschehen. Mal um Mal erzürnen und empören wir uns darüber, erzählen uns und anderen stets die gleiche Geschichte, die uns allerdings – ebenfalls ein ums andere Mal – wieder selbst verletzt. Das Destruktive holt uns so ständig wieder ein; wir sehen und fühlen das unschuldige Kind und empfinden Verachtung für die Täter.
Die Perspektive zu wechseln lädt uns dazu ein, das Geschehen aus anderen Blickwinkeln zu betrachten und unser Bewusstsein von der schmerzlichen Wiederholung zu lösen. Wir können einmal weit rauszoomen und einen spirituellen Blickwinkel einnehmen, beispielsweise aus Sicht des All-ein-Bewusstseins, das sich in unzählige Seelen teilt, von denen wiederum Milliarden derzeit auf der Erde inkarniert sind. Dieses eine Bewusstsein möchte jede auch nur mögliche Erfahrung machen und durch die Trennung – die Erschaffung der Dualität – kann es sich selbst aus diesen Milliarden Persönlichkeiten heraus erfahren, um zu lernen. Während dieser scheinbaren Trennung vergessen wir, dass wir alle eins sind, dass wir alle aus demselben «Stoff» gemacht sind und nach diesem Spiel hier auf Erden unsere Erinnerung zurückerlangen und unsere Erfahrungen zurück geben in die eine «Quelle».
Unser aller Reise geht letztlich darum, hier auf der Erde aus diesem Zustand des Vergessens zu erwachen. Um dies zu erreichen und all diese Erfahrungen machen zu können und uns auch unter widrigsten Umständen an unsere wahre Essenz, an die Liebe, erinnern können, braucht es auch Akteure, die die Dunkelheit verkörpern – denn nur so haben wir die Wahl, ob wir uns von ihr einnehmen lassen oder uns für die Liebe und das Mitgefühl entscheiden. Der Täter sowie das Opfer sind dabei stets Aspekte unserer selbst – im Innen wie im Außen – und jeder einzelne verändert die Welt, indem er Liebe und Mitgefühl oder Hass und Verachtung wählt.
Eine etwas rationalere Herangehensweise wäre, zu schauen, was dazu führt, dass ein Mensch sich derart unmenschlich verhalten kann; also der Zugang über die Psychologie. Hier werden wir uns bewusst, dass jeder Täter auch einmal ein Kind war. Symbolisch sogar das Kind, mit dem wir jetzt im Beispiel mitfühlen und das wir gleichzeitig heute als erwachsenen Täter verachten. Natürlich kann man hier einwenden, dass nicht jedes Opfer zum Täter wird, aber man kann ebenso anerkennen, dass uns bei dieser Haltung das größte Stück fehlt; und zwar die Geschichte desjenigen, die Jahre dazwischen, sowie jeder einzelne Reiz und jedes Detail der Umstände.
Wie viel Schmerz und Leid muss ein Mensch erfahren, bis er unmenschlich wird? Mit Einbezug aller Umstände und Faktoren, der psychischen Schutzmechanismen traumatischer Erfahrungen sowie fehlender Ausbildung sozialer und empathischer Fähigkeiten auch im neuronalen Bereich kann man auch auf diesem Wege Verständnis erlangen. Sichtbar wird hierdurch auch, dass emotionaler Schmerz über Generationen weitergegeben wird und es schwer ersichtlich ist, wo denn die eigentliche Ursache liegt. Auch hier wird erkennbar, dass nur jeder bei sich anfangen kann und Verantwortung für seine Heilung – und damit gleichzeitig die anderer – übernehmen müsste, anstatt auf die Suche nach dem oder der «Schuldigen» zu gehen.
Was bedarf eigentlich der Vergebung?
Wenn es uns schwerfällt zu vergeben, also Groll und Verachtung loszulassen und Mitgefühl zu empfinden, ist es ebenfalls hilfreich, einmal hinzuschauen, worum es genau geht. Wenn es uns selbst betrifft, handelt es sich in der Regel um Schmerz, der uns willentlich, manchmal auch unbewusst, zugefügt wurde und den wir (noch) nicht loslassen können, weil er noch nicht verheilt ist. Darauf gehe ich später noch einmal ein. Oft geht es aber auch um uns unbekannte Menschen, von deren Verbrechen wir Kenntnis haben und deren Ungeheuerlichkeit uns aus der Fassung bringt. Es geht um Taten, die wir nicht nachvollziehen können, weder rational noch emotional. Wir meinen, selbst wenn jemand nicht spürte, was er anderen antut, so müsse er es doch wenigstens besser wissen. Das ist das, was uns Menschen ausmacht, mit anderen mitzufühlen und sie zu verstehen. Doch anscheinend gibt es Menschen, deren Persönlichkeit oder auch Psyche dazu absolut nicht in der Lage sind. Die keinen moralischen Kompass besitzen und keinerlei soziales Empfinden, denn sonst könnten sie bestimmte Taten nicht ausführen. Möglicherweise dissoziieren sie sich selbst so stark, dass diese für sie eine Normalität darstellen, sie diese entschuldigen beziehungsweise vor sich selbst rechtfertigen oder im extremen Fall keine Erinnerung mehr daran haben.
Uns erscheinen die fehlende Empathie sowie das fehlende Verständnis so fremd, dass wir es nicht nachvollziehen können. Uns fehlt die Nachvollziehbarkeit der Nichtnachvollziehbarkeit des Erlebens des anderen, und wir erachten diesen dadurch als unmenschlich. Denn menschlich wären doch eben diese Fähigkeiten wie Mitgefühl, Güte, Reflexion, Warmherzigkeit, Verständnis und Liebe. Zugleich erzeugen wir hier aber einen Konflikt, wenn wir sagen: «Da diese Menschen sich so unmenschlich verhalten, soll ihnen kein Mitgefühl und keine Vergebung entgegengebracht werden, sollen auch sie nicht menschlich behandelt werden», wodurch wir uns allerdings selbst unserer Menschlichkeit berauben.
«Aber der Täter hatte doch die freie Wahl, er hätte doch anders entscheiden können!» Ja, möglicherweise schon, aber jetzt haben wir die Wahl. Und wir haben viel leichtere Voraussetzungen dafür, menschlich zu handeln, weil wir gesunden Zugang zu unserer Empathie, Moral und unserer Ratio haben.
Hätte der Täter es geschafft, seinen Tätern zu verzeihen, würde er die Destruktivität, die er ab einem gewissen Zeitpunkt nicht mehr in sich tragen oder verdrängen konnte, nicht an anderen ausagieren. Es ist ihm nicht gelungen, vielleicht sogar weil etwas in ihm es für unmöglich hielt, Unmenschliches, das ihm zugefügt wurde, zu verzeihen. Aber uns kann es gelingen, diesen Kreislauf zu durchbrechen und uns nicht in ihn hineinziehen zu lassen; wir können dem «Dunklen» den Nährboden entziehen.
Manchmal nehmen wir an, würden wir das Unbeschreibliche verzeihen, bedeutete dies, dass wir es tolerieren oder gar gutheißen. Dem ist nicht so. Analog dazu habe ich manches Mal die Angst gehabt, würde ich aufhören, um meinen Freund zu trauern, bedeute dies, dass ich ihn nicht mehr vermisse. Auch das ist nicht richtig. Ich heile lediglich das, was mir Schmerzen zufügt, bis am Ende nur noch die Liebe bleibt. Und wenn wir verzeihen, ist es kein Gutheißen der Taten, es bedeutet ein Loslassen dessen, was uns damit verstrickt und das Destruktive nährt.
Mitgefühl beginnt bei uns selbst
«Daß ich dem Hungrigen zu essen gebe, dem vergebe, der mich beleidigt, und meinen Feind liebe- das sind große Tugenden. Was aber, wenn ich nun entdecken sollte, daß der armselige Bettler und der unverschämteste Beleidiger alle in mir selber sind und ich bedürftig bin, Empfänger meiner eigenen Wohltaten zu sein? Daß ich der Feind bin, den ich lieben muß - was dann?» – C. G. Jung
Mit diesem Zitat beginnt Dan Millman das Kapitel «Das Gesetz des Mitgefühls» in seinem Buch «Die universellen Lebensgesetze des friedvollen Kriegers». Die weise Frau lehrt dem Wanderer das Gesetz des Mitgefühls und erklärt, es sei «eine liebevolle Aufforderung, über unsere begrenzte Sichtweise hinauszuwachsen», auch wenn die Last dieser Aufgabe zuweilen sehr schwer wiegen könne. Genau deshalb müsse man daran denken, dass sie bei uns selbst beginnt und wir «geduldig» und «sanft» mit uns, unseren Gefühlen und Gedanken sein sollten.
Um dem – noch skeptischen – Wanderer zu veranschaulichen, wie wir Mitgefühl auch mit unseren Gegnern empfinden können, bat sie ihn, sich an eine Auseinandersetzung zu erinnern, in der er zornig, neidisch oder eifersüchtig war und sich diese Gefühle noch einmal zu vergegenwärtigen. Als er das tat, den Schmerz und die Wut wieder spürte, sagte sie zu ihm: «Und nun stell dir vor, daß der Mensch, mit dem du dich streitest, mitten in eurer erregten Auseinandersetzung plötzlich nach seinem Herzen faßt, einen Schrei ausstößt und zu deinen Füßen tot zu Boden sinkt.» Der Wanderer erschrak und auf Nachfrage der weisen Frau stellte er fest, dass er nun keinerlei Schmerz oder Wut mehr empfand. Sogleich aber kam ihm der Gedanke: «Aber – aber was wäre, wenn ich mich über den Tod dieses Menschen freuen würde? Wenn ich ihm nicht verzeihen könnte?», worauf die weise Frau antwortete: «Dann verzeih dir wenigstens selber deine Unversöhnlichkeit. Und in dieser Vergebung wirst du das Mitgefühl finden, das deinen Schmerz heilt, als Mensch in dieser Welt zu leben.»
Weiter erinnert uns die weise Frau daran, dass wir alle, während wir hier auf der Erde sind, Träume, Hoffnungen und Enttäuschungen haben; und dass diese, sowie letztlich der Tod, uns alle verbinden.
Es ist ein Prozess
Dan Millman sagt hier in Gestalt der Weisen Frau, dass Mitgefühl bei uns selbst beginnt und diesen Aspekt möchte ich noch einmal hervorheben. Es kann nämlich passieren, dass wir uns in einer oberflächlichen Vergebung wieder finden, weil wir meinen, es sei richtig und moralisch, anderen zu verzeihen, ohne aber die tieferen Schichten dabei zu fühlen. Das ist dann leider nichts anderes, als Verdrängung. Gerade wenn wir selbst Opfer von Ungerechtigkeit, physischer oder mentaler Gewalt wurden, ist es unerlässlich den Heilungsweg in Gänze zu durchschreiten, und in den Wachstumsprozess zu verwandeln, der uns Mitgefühl und Weisheit lehrt. Und dazu gehören die Wut auf das Begangene, die Verzweiflung, die Ungerechtigkeit und Ohnmacht zu fühlen, uns auf «unsere Seite» zu stellen und Partei für uns selbst zu ergreifen, bevor es ernstlich möglich wird, zu verzeihen. Zunächst fühlen wir mit uns selbst den Schmerz und befreien die Gefühle, die wir uns möglicherweise nie trauten zu fühlen, all die Wut und den Groll. Erst später kann dann aus dem Inneren heraus das weitere Erkennen stattfinden und Heilung und Vergebung geschehen.
Vergebung findet im Herzen statt
Die hier in diesem Text von mir aufgeführten Perspektiven sind nur zwei, drei kleine Beispiele für Sichtweisen, die man einnehmen könnte, um zu neuen Einsichten zu gelangen. Sie sollen niemanden von irgendetwas überzeugen, sondern als Anregung dienen. Denn letztlich geht es darum, Vergebung in sich selbst zu finden. Vergebung ist also etwas, das aus dem Inneren heraus entsteht; ein Ergebnis eines tiefen Verständnisses und Fühlens, ja eines Erkennens. Auf dieser Reise gehen wir unterschiedliche Blickwinkel und Versionen ab, bis wir im Herzen ankommen, es sich öffnet und wir plötzlich «klar» sehen. Daraufhin breitet sich Wärme im Körper aus, Liebe durchströmt uns, begleitet möglicherweise von einem Gefühl leiser Euphorie, möglicherweise auch einem leichten Schmerz und Tränen – sowohl ein paar der Traurigkeit als auch welchen der Dankbarkeit. Das Loslassen und die Befreiung sind spürbar und nur für jeden persönlich erfahrbar, der sich auf diesen Weg begibt und seine individuelle Ansicht findet, die ihn befreit und erlöst.
Meiner Meinung nach bedeutet also Vergebung eine Öffnung des Herzens, ein Erkennen und ein Hineinwachsen in die Perspektive der Liebe. Sie ist nicht auf rationaler Ebene zu finden; die rationale Ebene kann nur dabei helfen, den Weg zum Mitgefühl zu beschreiten, denn:
«Man sieht nur mit dem Herzen gut. Das Wesentliche ist für die Augen unsichtbar.»
– Antoine de Saint-Exupéry
Anna Nagel veröffentlicht auf ihrem Blog „Heimwärts“ seit Jahren zu den Themen Heilung, Bewusstsein, kollektives Erwachen, Gefühle, Spiritualität, Psyche, Kundalini und Philosophie.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 62033ff8:e4471203
2025-01-11 15:00:24
@ 62033ff8:e4471203
2025-01-11 15:00:24收录的内容中 kind=1的部分,实话说 质量不高。 所以我增加了kind=30023 长文的article,但是更新的太少,多个relays 的服务器也没有多少长文。
所有搜索nostr如果需要产生价值,需要有高质量的文章和新闻。 而且现在有很多机器人的文章充满着浪费空间的作用,其他作用都用不上。
https://www.duozhutuan.com 目前放的是给搜索引擎提供搜索的原材料。没有做UI给人类浏览。所以看上去是粗糙的。 我并没有打算去做一个发microblog的 web客户端,那类的客户端太多了。
我觉得nostr社区需要解决的还是应用。如果仅仅是microblog 感觉有点够呛
幸运的是npub.pro 建站这样的,我觉得有点意思。
yakihonne 智能widget 也有意思
我做的TaskQ5 我自己在用了。分布式的任务系统,也挺好的。
-
 @ 23b0e2f8:d8af76fc
2025-01-08 18:17:52
@ 23b0e2f8:d8af76fc
2025-01-08 18:17:52Necessário
- Um Android que você não use mais (a câmera deve estar funcionando).
- Um cartão microSD (opcional, usado apenas uma vez).
- Um dispositivo para acompanhar seus fundos (provavelmente você já tem um).
Algumas coisas que você precisa saber
- O dispositivo servirá como um assinador. Qualquer movimentação só será efetuada após ser assinada por ele.
- O cartão microSD será usado para transferir o APK do Electrum e garantir que o aparelho não terá contato com outras fontes de dados externas após sua formatação. Contudo, é possível usar um cabo USB para o mesmo propósito.
- A ideia é deixar sua chave privada em um dispositivo offline, que ficará desligado em 99% do tempo. Você poderá acompanhar seus fundos em outro dispositivo conectado à internet, como seu celular ou computador pessoal.
O tutorial será dividido em dois módulos:
- Módulo 1 - Criando uma carteira fria/assinador.
- Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
No final, teremos:
- Uma carteira fria que também servirá como assinador.
- Um dispositivo para acompanhar os fundos da carteira.

Módulo 1 - Criando uma carteira fria/assinador
-
Baixe o APK do Electrum na aba de downloads em https://electrum.org/. Fique à vontade para verificar as assinaturas do software, garantindo sua autenticidade.
-
Formate o cartão microSD e coloque o APK do Electrum nele. Caso não tenha um cartão microSD, pule este passo.

- Retire os chips e acessórios do aparelho que será usado como assinador, formate-o e aguarde a inicialização.

- Durante a inicialização, pule a etapa de conexão ao Wi-Fi e rejeite todas as solicitações de conexão. Após isso, você pode desinstalar aplicativos desnecessários, pois precisará apenas do Electrum. Certifique-se de que Wi-Fi, Bluetooth e dados móveis estejam desligados. Você também pode ativar o modo avião.\ (Curiosidade: algumas pessoas optam por abrir o aparelho e danificar a antena do Wi-Fi/Bluetooth, impossibilitando essas funcionalidades.)

- Insira o cartão microSD com o APK do Electrum no dispositivo e instale-o. Será necessário permitir instalações de fontes não oficiais.

- No Electrum, crie uma carteira padrão e gere suas palavras-chave (seed). Anote-as em um local seguro. Caso algo aconteça com seu assinador, essas palavras permitirão o acesso aos seus fundos novamente. (Aqui entra seu método pessoal de backup.)

Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
-
Criar uma carteira somente leitura em outro dispositivo, como seu celular ou computador pessoal, é uma etapa bastante simples. Para este tutorial, usaremos outro smartphone Android com Electrum. Instale o Electrum a partir da aba de downloads em https://electrum.org/ ou da própria Play Store. (ATENÇÃO: O Electrum não existe oficialmente para iPhone. Desconfie se encontrar algum.)
-
Após instalar o Electrum, crie uma carteira padrão, mas desta vez escolha a opção Usar uma chave mestra.

- Agora, no assinador que criamos no primeiro módulo, exporte sua chave pública: vá em Carteira > Detalhes da carteira > Compartilhar chave mestra pública.

-
Escaneie o QR gerado da chave pública com o dispositivo de consulta. Assim, ele poderá acompanhar seus fundos, mas sem permissão para movimentá-los.
-
Para receber fundos, envie Bitcoin para um dos endereços gerados pela sua carteira: Carteira > Addresses/Coins.
-
Para movimentar fundos, crie uma transação no dispositivo de consulta. Como ele não possui a chave privada, será necessário assiná-la com o dispositivo assinador.

- No assinador, escaneie a transação não assinada, confirme os detalhes, assine e compartilhe. Será gerado outro QR, desta vez com a transação já assinada.

- No dispositivo de consulta, escaneie o QR da transação assinada e transmita-a para a rede.
Conclusão
Pontos positivos do setup:
- Simplicidade: Basta um dispositivo Android antigo.
- Flexibilidade: Funciona como uma ótima carteira fria, ideal para holders.
Pontos negativos do setup:
- Padronização: Não utiliza seeds no padrão BIP-39, você sempre precisará usar o electrum.
- Interface: A aparência do Electrum pode parecer antiquada para alguns usuários.
Nesse ponto, temos uma carteira fria que também serve para assinar transações. O fluxo de assinar uma transação se torna: Gerar uma transação não assinada > Escanear o QR da transação não assinada > Conferir e assinar essa transação com o assinador > Gerar QR da transação assinada > Escanear a transação assinada com qualquer outro dispositivo que possa transmiti-la para a rede.
Como alguns devem saber, uma transação assinada de Bitcoin é praticamente impossível de ser fraudada. Em um cenário catastrófico, você pode mesmo que sem internet, repassar essa transação assinada para alguém que tenha acesso à rede por qualquer meio de comunicação. Mesmo que não queiramos que isso aconteça um dia, esse setup acaba por tornar essa prática possível.
-
 @ c1e9ab3a:9cb56b43
2025-05-09 23:10:14
@ c1e9ab3a:9cb56b43
2025-05-09 23:10:14I. Historical Foundations of U.S. Monetary Architecture
The early monetary system of the United States was built atop inherited commodity money conventions from Europe’s maritime economies. Silver and gold coins—primarily Spanish pieces of eight, Dutch guilders, and other foreign specie—formed the basis of colonial commerce. These units were already integrated into international trade and piracy networks and functioned with natural compatibility across England, France, Spain, and Denmark. Lacking a centralized mint or formal currency, the U.S. adopted these forms de facto.
As security risks and the practical constraints of physical coinage mounted, banks emerged to warehouse specie and issue redeemable certificates. These certificates evolved into fiduciary media—claims on specie not actually in hand. Banks observed over time that substantial portions of reserves remained unclaimed for years. This enabled fractional reserve banking: issuing more claims than reserves held, so long as redemption demand stayed low. The practice was inherently unstable, prone to panics and bank runs, prompting eventual centralization through the formation of the Federal Reserve in 1913.
Following the Civil War and unstable reinstatements of gold convertibility, the U.S. sought global monetary stability. After World War II, the Bretton Woods system formalized the U.S. dollar as the global reserve currency. The dollar was nominally backed by gold, but most international dollars were held offshore and recycled into U.S. Treasuries. The Nixon Shock of 1971 eliminated the gold peg, converting the dollar into pure fiat. Yet offshore dollar demand remained, sustained by oil trade mandates and the unique role of Treasuries as global reserve assets.
II. The Structure of Fiduciary Media and Treasury Demand
Under this system, foreign trade surpluses with the U.S. generate excess dollars. These surplus dollars are parked in U.S. Treasuries, thereby recycling trade imbalances into U.S. fiscal liquidity. While technically loans to the U.S. government, these purchases act like interest-only transfers—governments receive yield, and the U.S. receives spendable liquidity without principal repayment due in the short term. Debt is perpetually rolled over, rarely extinguished.
This creates an illusion of global subsidy: U.S. deficits are financed via foreign capital inflows that, in practice, function more like financial tribute systems than conventional debt markets. The underlying asset—U.S. Treasury debt—functions as the base reserve asset of the dollar system, replacing gold in post-Bretton Woods monetary logic.
III. Emergence of Tether and the Parastatal Dollar
Tether (USDT), as a private issuer of dollar-denominated tokens, mimics key central bank behaviors while operating outside the regulatory perimeter. It mints tokens allegedly backed 1:1 by U.S. dollars or dollar-denominated securities (mostly Treasuries). These tokens circulate globally, often in jurisdictions with limited banking access, and increasingly serve as synthetic dollar substitutes.
If USDT gains dominance as the preferred medium of exchange—due to technological advantages, speed, programmability, or access—it displaces Federal Reserve Notes (FRNs) not through devaluation, but through functional obsolescence. Gresham’s Law inverts: good money (more liquid, programmable, globally transferable USDT) displaces bad (FRNs) even if both maintain a nominal 1:1 parity.
Over time, this preference translates to a systemic demand shift. Actors increasingly use Tether instead of FRNs, especially in global commerce, digital marketplaces, or decentralized finance. Tether tokens effectively become shadow base money.
IV. Interaction with Commercial Banking and Redemption Mechanics
Under traditional fractional reserve systems, commercial banks issue loans denominated in U.S. dollars, expanding the money supply. When borrowers repay loans, this destroys the created dollars and contracts monetary elasticity. If borrowers repay in USDT instead of FRNs:
- Banks receive a non-Fed liability (USDT).
- USDT is not recognized as reserve-eligible within the Federal Reserve System.
- Banks must either redeem USDT for FRNs, or demand par-value conversion from Tether to settle reserve requirements and balance their books.
This places redemption pressure on Tether and threatens its 1:1 peg under stress. If redemption latency, friction, or cost arises, USDT’s equivalence to FRNs is compromised. Conversely, if banks are permitted or compelled to hold USDT as reserve or regulatory capital, Tether becomes a de facto reserve issuer.
In this scenario, banks may begin demanding loans in USDT, mirroring borrower behavior. For this to occur sustainably, banks must secure Tether liquidity. This creates two options: - Purchase USDT from Tether or on the secondary market, collateralized by existing fiat. - Borrow USDT directly from Tether, using bank-issued debt as collateral.
The latter mirrors Federal Reserve discount window operations. Tether becomes a lender of first resort, providing monetary elasticity to the banking system by creating new tokens against promissory assets—exactly how central banks function.
V. Structural Consequences: Parallel Central Banking
If Tether begins lending to commercial banks, issuing tokens backed by bank notes or collateralized debt obligations: - Tether controls the expansion of broad money through credit issuance. - Its balance sheet mimics a central bank, with Treasuries and bank debt as assets and tokens as liabilities. - It intermediates between sovereign debt and global liquidity demand, replacing the Federal Reserve’s open market operations with its own issuance-redemption cycles.
Simultaneously, if Tether purchases U.S. Treasuries with FRNs received through token issuance, it: - Supplies the Treasury with new liquidity (via bond purchases). - Collects yield on government debt. - Issues a parallel form of U.S. dollars that never require redemption—an interest-only loan to the U.S. government from a non-sovereign entity.
In this context, Tether performs monetary functions of both a central bank and a sovereign wealth fund, without political accountability or regulatory transparency.
VI. Endgame: Institutional Inversion and Fed Redundancy
This paradigm represents an institutional inversion:
- The Federal Reserve becomes a legacy issuer.
- Tether becomes the operational base money provider in both retail and interbank contexts.
- Treasuries remain the foundational reserve asset, but access to them is mediated by a private intermediary.
- The dollar persists, but its issuer changes. The State becomes a fiscal agent of a decentralized financial ecosystem, not its monetary sovereign.
Unless the Federal Reserve reasserts control—either by absorbing Tether, outlawing its instruments, or integrating its tokens into the reserve framework—it risks becoming irrelevant in the daily function of money.
Tether, in this configuration, is no longer a derivative of the dollar—it is the dollar, just one level removed from sovereign control. The future of monetary sovereignty under such a regime is post-national and platform-mediated.
-
 @ e3ba5e1a:5e433365
2025-02-13 06:16:49
@ e3ba5e1a:5e433365
2025-02-13 06:16:49My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get this line:
“Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.”
Yesterday, I came across a comment on the song Devil Went Down to Georgia that had a very similar feel to it:

America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans.
That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form.
For most countries, saying “our nation is the greatest” is, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people should be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence.
But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America.
That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is freedom. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit.
American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are definitionally better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.)
In Devil Went Down to Georgia, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.”
Libertas magnitudo est
-
 @ 1bc70a01:24f6a411
2025-05-31 04:34:37
@ 1bc70a01:24f6a411
2025-05-31 04:34:37{"title":"SVG Bee Logo","description":"Bee ready with a nice bee logo for your beeloved app!","price":35000,"contentUrl":"https://d.nostr.build/HRcgBzWongPHkSYT.svg","imageUrl":"data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAACSgAAASUCAYAAABu9HH1AAAACXBIWXMAABYlAAAWJQFJUiTwAAAAAXNSR0IArs4c6QAAAARnQU1BAACxjwv8YQUAAI8dSURBVHgB7N3PblX32ffhXwvCsgsKNQWJKKlJ0kStGqkOo84CR4A5gsCow5gjwB51GHvWGfYRYEYdxjkAFFeKlAoUgiVLSI6MsGzhgmLl1b1ebcSThMTG+157/bkuacsuT5U63mvybH343r+5ePHiDwUAAAAADuju3bsFAAAAAA7qtwUAAAAAAAAAACCJQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAAAAAAAAAAgjUAJAAAAAAAAAABII1ACAAAAAAAAAADSCJQAAAAAAAAAAIA0AiUAAAAAAAAAACCNQAkAAAAAAAAAAEgjUAIAAAAAAAAAANIIlAAAAAAAAAAAgDQCJQAAAAAAAAAAII1ACQAAAAAAAAAASCNQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAAoAAAAAAAAAZBEoAQAAAAAAAAAAaQRKAAAAAAAAAABAGoESAAAAAAAAAACQRqAEAAAAAAAAAACkESgBAAAAAAAAAABpBEoAAAAAAAAAAEAagRIAAAAAAAAAAJBGoAQAAAAAAAAAAKQRKAEAAAAAAAAAAGkESgAAAAAAAAAAQBqBEgAAAAAAAAAAkEagBAAAAAAAAAAApBEoAQAAAAAAAAAAaQRKAAAAAAAAAABAGoESAAAAAAAAAACQRqAEAAAAAAAAAACkESgBAAAAAAAAAABpBEoAAAAAAAAAAEAagRIAAAAAAAAAAJBGoAQAAAAAAAAAAKQRKAEAAAAAAAAAAGkESgAAAAAAAAAAQBqBEgAAAAAAAAAAkEagBAAAAAAAAAAApBEoAQAAAAAAAAAAaQRKAAAAAAAAAABAGoESAAAAAAAAAACQRqAEAAAAAAAAAACkESgBAAAAAAAAAABpBEoAAAAAAAAAAEAagRIAAAAAAAAAAJBGoAQAAAAAAAAAAKQRKAEAAAAAAAAAAGkESgAAAAAAAAAAQBqBEgAAAAAAAAAAkEagBAAAAAAAAAAApBEoAQAAAAAAAAAAaQRKAAAAAAAAAABAGoESAAAAAAAAAACQRqAEAAAAAAAAAACkESgBAAAAAAAAAABpBEoAAAAAAAAAAEAagRIAAAAAAAAAAJBGoAQAAAAAAAAAAKQRKAEAAAAAAAAAAGkESgAAAAAAAAAAQBqBEgAAAAAAAAAAkEagBAAAAAAAAAAApBEoAQAAAAAAAAAAaQRKAAAAAAAAAABAGoESAAAAAAAAAACQRqAEAAAAAAAAAACkESgBAAAAAAAAAABpBEoAAAAAAAAAAEAagRIAAAAAAAAAAJBGoAQAAAAAAAAAAKQRKAEAAAAAAAAAAGkESgAAAAAAAAAAQBqBEgAAAAAAAAAAkEagBAAAAAAAAAAApBEoAQAAAAAAAAAAaQRKAAAAAAAAAABAGoESAAAAAAAAAACQRqAEAAAAAAAAAACkESgBAAAAAAAAAABpBEoAAAAAAAAAAEAagRIAAAAAAAAAAJBGoAQAAAAAAAAAAKQRKAEAAAAAAAAAAGkESgAAAAAAAAAAQBqBEgAAAAAAAAAAkEagBAAAAAAAAAAApBEoAQAAAAAAAAAAaQRKAAAAAAAAAABAGoESAAAAAAAAAACQRqAEAAAAAAAAAACkESgBAAAAAAAAAABpBEoAAAAAAAAAAEAagRIAAAAAAAAAAJBGoAQAAAAAAAAAAKQRKAEAAAAAAAAAAGkESgAAAAAAAAAAQBqBEgAAAAAAAAAAkEagBAAAAAAAAAAApBEoAQAAAAAAAAAAaQRKAAAAAAAAAABAGoESAAAAAAAAAACQRqAEAAAAAAAAAACkESgBAAAAAAAAAABpBEoAAAAAAAAAAEAagRIAAAAAAAAAAJBGoAQAAAAAAAAAAKQRKAEAAAAAAAAAAGkESgAAAAAAAAAAQBqBEgAAAAAAAAAAkEagBAAAAAAAAAAApBEoAQAAAAAAAAAAaQRKAAAAAAAAAABAGoESAAAAAAAAAACQRqAEAAAAAAAAAACkESgBAAAAAAAAAABpBEoAAAAAAAAAAEAagRIAAAAAAAAAAJBGoAQAAAAAAAAAAKQRKAEAAAAAAAAAAGkESgAAAAAAAAAAQBqBEgAAAAAAAAAAkEagBAAAAAAAAAAApBEoAQAAAAAAAAAAaQRKAAAAAAAAAABAGoESAAAAAAAAAACQRqAEAAAAAAAAAACkESgBAAAAAAAAAABpBEoAAAAAAAAAAEAagRIAAAAAAAAAAJBGoAQAAAAAAAAAAKQRKAEAAAAAAAAAAGkESgAAAAAAAAAAQBqBEgAAAAAAAAAAkEagBAAAAAAAAAAApBEoAQAAAAAAAAAAaQRKAAAAAAAAAABAGoESAAAAAAAAAACQRqAEAAAAAAAAAACkESgBAAAAAAAAAABpBEoAAAAAAAAAAEAagRIAAAAAAAAAAJBGoAQAAAAAAAAAAKQRKAEAAAAAAAAAAGkESgAAAAAAAAAAQBqBEgAAAAAAAAAAkEagBAAAAAAAAAAApBEoAQAAAAAAAAAAaQRKAAAAAAAAAABAGoESAAAAAAAAAACQRqAEAAAAAAAAAACkESgBAAAAAAAAAABpBEoAAAAAAAAAAEAagRIAAAAAAAAAAJBGoAQAAAAAAAAAAKQRKAEAAAAAAAAAAGkESgAAAAAAAAAAQBqBEgAAAAAAAAAAkEagBAAAAAAAAAAApBEoAQAAAAAAAAAAaQRKAAAAAAAAAABAGoESAAAAAAAAAACQRqAEAAAAAAAAAACkESgBAAAAAAAAAABpBEoAAAAAAAAAAEAagRIAAAAAAAAAAJBGoAQAAAAAAAAAAKQRKAEAAAAAAAAAAGkESgAAAAAAAAAAQBqBEgAAAAAAAAAAkOZ4AQBaZ39/v2xubpbd3d3y9OnT6j+/bGxsrPp64sSJcuzYseprvOLP4+v4+HiBw4hn7Pnz52Vvb688e/as+n7wZ4PnL/78ZRMTE9Xz9sYbb5QzZ84UAAAAYHSePHlSFhcXy+rqallbW6v+88suXLjw4uvp06err/Gampqqvk5PTxc4jHjGHj58WD1v6+vr1feDPxs8f/H9y+I5i+dtZmamfPLJJwUA6I7fXLx48YcCALRChCAbGxtla2urHNUgHjl58mT1fXyFEM9ZxG87Ozv/J0o6injWzp8/L1QCgI64e/duAQDaIUKQGzdulKWlpXJUg3jk0qVL5W9/+1v1FUI8ZxG/ffHFFy+ipB/HR4cVz9rc3JxQCQA6QqAEAC0Rkcg333xTBSMZYmkpQqVYu4m/JRdBCf0RQVJ8kDRY5cpy6tSp8u6771bPGwDQXgIlAGiHiESuXr165FDkVeIzpIiWYu3mypUrL1aY6IcIku7cufNilStLhHC3b9+unjcAoL0ESgDQAhEn3bt37yen3DJFoBT/T38s3jgJ1z3xLMVzFWtcESbV+WxFCPf++++LlACgxQRKANB8EYxcvnz5J6fcMr18mstJuO6JZymeq+Xl5bKyslLrsxXP0+effy5SAoAWEygBQMPFYlLESVnLSQcxOM8V6zeWldptsJQUYVKdUdKPxYdJsaQEALSTQAkAmi0WkyJOylpOOojBea6PP/7YslLLDZaS4kxgnVHSj0X8FktKAEA7CZQAoOHW19ermKQpYlEpXidPniy0Q4RI8Qxtb2+XnZ2d0hTvvfdedVIQAGgfgRIANNv169ermKQprl27Vq0qxaku2iFCpMFSUgRKTRGBUoRKAED7CJQAoMFi7SbWk5oo1pQmJyerWIlmijBpc3Ozeo1yLelVYo3rww8/LABA+wiUAKC5IiaJ9aQmikBpECvRTBEmLS4uloWFhZGuJb1KrHF9++23BQBon98WAKCxmrSc9GOxxBPrTl999VWjf84+ihjp0aNH1XsTX5sYJ4U4WxgRHgAAADA8sXrTVBFPRaD0zjvvNPrn7KOIkebn56v3Jk7zNTFOCnG2sEmLTgDAwQmUAKDBmnSO61UiMhmESnt7e4XRakOY9LKmftgFAAAAbdWGeCMik0GotLa2VhitNoRJL7tz504BANpHoAQADRVxScQ/bRE/69dff13FSm36ubsilojaFCYNeFYAAABgeCIuifinLeJn/eijj8r169db9XN3RcRsbQqTBjwrANBOAiUAaKg2RSYvi3NvESpFKEO+CHzu379f7t2718rYR6AEAAAAw9PWpeKlpaUqVIolH/JF4HP16tVy+fLlVsY+AiUAaCeBEgAwdBFXDU6NCVDybG5uVjFYG04BvsqxY8cKAAAAQMRVseQTiz4ClDyLi4tVDLayslLa6vTp0wUAaB+BEgA0VBfCjYiTBmfHGJ7BatLGxkZrl7YAAACA4etCuBFxUkRK1pSGK36vsZg0Ozvb2qUtAKDdBEoA0FARKHVlXSYCpQhqrCkd3e7ubnXOrc2rSS8bHx8vAAAAwHBEoHThwoXSBbGm1NYTZE2zurpa/S7jaxdMT08XAKB9BEoA0GBnzpwpXRFBTYQ1e3t7hdcToVf8DrsUepnkBgAAgOGamZkpXTEIa9bW1gqvJ5aouhZ6XblypQAA7SNQAoAG61q8EWHN119/7eTbIcUZtwcPHnTu9zY2NlZOnjxZAAAAgOHpWrwRYc1HH33k5NshxRm3q1evVktUXRILYZcuXSoAQPsIlACgwSLeOHXqVOmaCG1ESgcziLriQ6WuOX/+fAEAAACGK+KNLgYcEdqIlA5mEHWtrKyUrrl582YBANpJoAQADTc1NVWOHTtWuiYCpVgFinUgfl6cw+vaSbeBOF84OTlZAAAAgOG7detWJ8+qR6QUq0Bd/ItcwxLn8Lp20m3g2rVr1QsAaCeBEgA03IkTJ8oHH3zQyUgpPky6f/++SOlndDlOmpiYKG+99VYBAAAAcsQZrM8//7yTkVKsAkWAI1L6qS7HSfFMf/bZZwUAaC+BEgC0wPj4eBUpjY2Nla55+vRpdcKsiyHO69ra2qripC6GW3Gy8P333+9kcAcAAABNMj09XUVKEXZ0TYQ4ccKsiyHO6+pyuBUnC7/88stOBncA0CcCJQBoiYiUIuyI01hdE3FSV9eCDivipPX19c7FScePH69Wk8RJAAAAUJ9BpNTFs1gRJ3V1LeiwIk7q4um7CJJiNamra2AA0De/uXjx4g8FAGiVCHm2t7erDx3iFNj3339fuiBOf/U5YBmcdetKnBSLXydPnqxWk9544w1hEgB0yN27dwsA0C4R8kTIcufOnWqBqCsxyyDC6mvAMjjr1pX3Mxa/YjHp448/LjMzM8IkAOgQgRIAdEzELfGKiCm+xgm1CF/i+52dndJ0fY2U2hInxRJSrHnFKwKkEydOVK94vwYvAKD7BEoA0C0Rt8QrIqb4+p///OdFxLS6ulqarq+RUlvipHhf4j2K19TUVBUhxSv+fPACALpPoAQAPbO7u1vFMPHBRVODpThjFx9W9EWTT9xFkBTrR7GCFGtIESMBAAiUAKBfIlKKGCbWl5oaLMUZu1u3bpW+aPKJuwiOYv0oVpBiDSliJAAAgRIA9Fis9QxOxTXtb1qdP3++enVdE+OkiJImJyerD5MiSgIA+DGBEgD0V3yGNDgVF1+bZG5urty8ebN0XRPjpPgcKSKxK1euVFESAMCPCZQAgEoEMrGu9OjRo/Ls2bPSBG+99VY5d+5c6bL79+83ZskqVpIiChMlAQC/RqAEAIQIZGJRaX5+vjGxzMLCQvn0009Ll0Wc1JQlq4iRIgoTJQEAv0agBAD8xOPHjxsRKh07dqx88MEHZXx8vHRR/I7jNWpxUi/CJOfbAICDEigBAD+2tLRUFhcXq1NwoxRLPp9//nmZnp4uXRQxWCxFjVqsJUWY5HwbAHBQAiUA4JWaECpFNPOXv/ylipW6ZGtrq6yvr5dREiYBAK9LoAQAvEqESqNeVIpo5ssvv6xipS6J3+3169fLKAmTAIDX9dsCAPAKk5OT5a9//Wv1gcPY2FgZhTg9N+qQZ9ji32mUy0lxyi2WqaampsRJAAAAwFBFwPLtt9+WW7dujSxiiThq1CHPsMW/U4RfoxIn3GKZapTvKwDQbsfOnz8/VwAAfkGcWIu/cba/v1/29vZK3f73v/9VC0q/+93vShc8ePBgJL/H48ePlzfffLP88Y9/FCYBAEfyj3/8owAA/JI4sTYzM1O2t7dHcvbtv//9b/n9739f/v73v5cuuHr16kh+j/GZ4D//+c/yr3/9S5gEAByJBSUA4EAiaInFnVGtKcXiUCwPtV38e+zs7JS6xWrSn//853Lu3LkCAAAAUIf4HCkWd0a1ujM3NzfSU3PDEstJq6urpW6xmhSn8mZnZwsAwFEJlACAQ4mzb++//36ZmJgodYr1prafehvVabfz589X75nVJAAAAGAU4uxbnAeL4KVOT548af2ptwisIrSq282bN6v3zGoSADAsTrwBAIcW59b+8Ic/VN/v7u6WukTg0+ZTb3Harc4VqDjp9qc//amcOXOmAAAMkxNvAMBhxamwCJXCF198UeoSgU+bT73Fabc6V6Diffr3v//94r0CABgWC0oAwGuLZZ6333671CkWiGJNqW22trZqPe0WZ/jipNvJkycLAAAAQFPEGtBnn31W6hT/m7Gm1DZLS0u1nnaLtaQ46Vb30hUA0A8CJQDgSM6ePVt9eBHLRnWIOGkUZ9KOou6fOeIkJ90AAACAppqdnS23b9+u1nrqEHHS/Px8aZO6f+b4fM9JNwAgk0AJADiyycnJ8sEHH9QWKW1ubpa9vb3SFvHz1nXabWJiolpOEicBAAAATTYzM1MFMXVFSgsLC2Vtba20xeLiYm2n3aanp6vlJHESAJBJoAQADMX4+HitkdLGxkZpgwiT6lpPGiwn1fUeAAAAABxFhDF1Rko3btwobRBhUpylq8NgOamu9wAA6C+BEgAwNBEpvf3226UOOzs7ZXd3tzSdOAkAAADg1SJS+uyzz0odVldXq1fT1XXaTZwEANRJoAQADFWce6srUqor/nldsZ60tbVVsg3iJGfdAAAAgDa6du1abZFSXfHP64r1pKWlpZJtECc56wYA1EWgBAAM3dmzZ8u5c+dKtqavKNUVUL377rviJAAAAKDVZmdnq1e2pq8o1RVQ3b59W5wEANRKoAQApHjrrbfKxMREydbUFaW61pPOnz9fndYDAAAAaLtYUYqTb9mauqJU13rSzZs3a/k9AwC8TKAEAKSJZZ9jx46VTLGitL+/X5rmyZMnJduZM2eqQAkAAACgK2LZ5/Tp0yVTLCjV8dnNYa2srJRscU5vbm6uAADUTaAEAKSJs2Nvvvlmyba5uVmaJvtnGhsbEycBAAAAnRNnx2LhJ9vi4mJpmuyfqa7fLQDAzxEoAQCpzp49W06dOlUyRQzUpBWlOO0WJ94yRZwUARgAAABA18zOzpZLly6VTAsLC41aUYrTbnHiLVPESREpAQCMgkAJAEg3NTWVeuot4qQ49dYU29vbJVOcdpucnCwAAAAAXXXr1q3UU28RJ8Wpt6a4c+dOyRSn3eIFADAqAiUAIF0s/Zw7d65k+u6770oTxHJS9t++c9oNAAAA6LpY+oklpUxNOfMWy0krKyslk9NuAMCoCZQAgFpEoDQ2NlayxIJSE868ZS85xe/RaTcAAACgDz799NPUk2SxoNSEM2/ZS07Zv0cAgIMQKAEAtYgTb9nLP1tbW2XUHj9+XLJE4JW9RAUAAADQFHHiLXv5Z3l5uYxa5s9QxxIVAMBBCJQAgNpMTk6mrihtb2+XUYrzbpkLSvH7s54EAAAA9Mm1a9dS13+yT6v9mjjvlrmg9Mknn1hPAgAa4XgBAKjR2bNny8bGRsnw9OnT6sxbrDWF+D6iob29vfLs2bPq+xBfB99///33rzwNN4ipBlFQfI1/dnyN/1t8HR8ff/Hfzz7vdubMmQIAAADQN7EAlLUCtLa2Vp15i7WmEN9HNBR/vr6+Xn0f4uvg+/jvvOo03CAGevlr/LPj69TUVPV1enr6xX8/+7xbBF4AAE3wm4sXL/5QAABqEjHQV1999coo6Kgi4on4aBAr1WFiYqKKlQb/uxni3ys+xAIAaIK7d+8WAIC6RAz0zjvvvDIKOqqZmZnqnz2IleoQkVLESoMYKkPESbdu3SoAAE0gUAIAavfo0aPqxcF9+OGHzrsBAI0hUAIA6jY/P1/m5uYKB/ftt9867wYANMZvCwBAzQaT2RzMYKEJAAAAoK+uXLlSOLjBQhMAQFMIlACA2o2Pj5dTp04VDubcuXMFAAAAoM8iuLl06VLhYD799NMCANAkAiUAYCROnjxZOBi/KwAAAIBSZmZmCgcj5gIAmkagBACMxJkzZwq/LpamnHcDAAAAcObtoCJOct4NAGgagRIAMBIR3Qhvfp31JAAAAID/L6Ib4c2vs54EADSRQAkAGIn9/f0yNjZWAAAAAOAgnjx5IlACAGgpgRIAUKsIkx49elS++uqrsrOzU/hlg9/V1tZWAQAAAOijCJPm5+fLO++8U1ZXVwu/bG5urvpdLS8vFwCApvjNxYsXfygAADXY3NysgpuIlDi88fHx8t577zmNBwCM3N27dwsAQB0WFxer4CYiJQ5venq63L592/IUADByFpQAgHS7u7vl66+/LhsbG+KkI9jb26vWlNbX18vz588LAAAAQFfFUtJHH31UZmdnxUlHsLa2Vq0pXb9+vTx8+LAAAIyKQAkASBMxUsQ09+7dq+IahiPOvcXv1Nk3AAAAoGsiRoqY5vLly1Vcw3AsLS1Vv1Nn3wCAUXHiDQBIER8mRZxkMSmXs28AwCg48QYAZFhZWaniJItJuZx9AwBGwYISADBUESQ9ePCgeomT8sUyVZzP29zcLAAAAABtFEHS1atXq5c4KV8sU8X5vMXFxQIAUBeBEgAwNLu7u1Us44OkekUItrGxUUVhz58/LwAAAABtsbq6WsUysZ5EfeLzu9nZ2SoKe/jwYQEAyCZQAgCG4tGjR+XevXsCmRGKD5biPYhQDAAAAKDp5ufny+XLlwUyIxRhWLwHEYoBAGQSKAEARxLrPffv368CJUYvArGIlLwfAAAAQFPFX7KKKGZubq4wehGIxfsRwRgAQBaBEgDw2vb29qqTbjs7O4VmiUApzr5FQAYAAADQFGtra9VJN4s9zRPB2I0bN6qADABg2ARKAMBr2dractKt4TY3N6uAzHsEAAAANMHy8rKTbg23sLBQBWTeIwBg2ARKAMChxTrP+vq6dZ4WGJx8EykBAAAAoxTnw65du2adpwUGJ99ESgDAMAmUAIBDiTgpXrTHIFKKk3wAAAAAdYs4Kc6H0R4RJ8WSUpzkAwAYBoESAHBg4qT2GkRK29vbBQAAAKAu4qT2irWrWFJaWVkpAABHJVACAA4kTrqJk9otTvJ988035fHjxwUAAAAg2/Xr18VJLReR0tWrV8vy8nIBADgKgRIA8KsiTtra2ip0Q0x0i5QAAACATBEnLS0tFbrh2rVrIiUA4EgESgDAL4rVJHFS90SktLu7WwAAAACGLc66iZO6JyKl1dXVAgDwOgRKAMArRZzkrFt3xbm3vb29AgAAADAsESc569Zdce5tbW2tAAAclkAJAPhZ4qTu29/fL/fu3SvPnz8vAAAAAEclTuq+J0+elMuXL1fr3AAAhyFQAgB+Ik66iZP6QaQEAAAADMPy8rI4qSdESgDA6xAoAQD/R4QqGxsbhf6I9/zBgwdVrAQAAABwWBGqzM7OFvoj3vM49xaxEgDAQQiUAIAXIlSJNR2hSv88ffrUahYAAABwaBGqxJqOUKV/1tbWqrN+AAAHIVACAF745ptvnPrqsc3NzeoFAAAAcFCxouPUV38tLCyUxcXFAgDwawRKAEAl1nP29vYK/Rbn/TwHAAAAwEHEek6s6NBvcd7PcwAA/BqBEgBQtra2nPfihVjScuYPAAAA+CVLS0tlbm6uQIglLWf+AIBfIlACgJ6Lk27iJF4Wz8T6+noBAAAA+Dlx0i3Wk2Agnonr168XAIBXESgBQM9FiBJBCrws/sbb5uZmAQAAAPixGzduVEEKvGxlZaUsLi4WAICfI1ACgB6LAGVnZ6fAz4llLfEaAAAA8LIIUCJEgZ8TZ//EawDAzxEoAUBPOe3Gr9nf33fqDQAAAHghwpMIUOBVYpXbqTcA4OcIlACgpyJOigAFfkksbG1vbxcAAACA+fn5KkCBX7K6umplCwD4CYESAPTQ1tZW9YKDiL8dKWYDAACAfltaWqpecBCxoiRmAwBeJlACgB5y2o3DiDhpc3OzAAAAAP0V60lwUBEneWYAgJcJlACgZyJOev78eYHD8NwAAABAf0VoEgvLcBgLCwueGwDgBYESAPRIBCbWk3hd6+vrBQAAAOiXCEzm5uYKvI449QYAEARKANAj4iSOYmdnp+zu7hYAAACgP5zp4ihWV1erFwCAQAkAeiLWk7a2tgochcgNAAAA+iPWk5aWlgochcgNAAgCJQDoCWEJw2BFCQAAAPpDWMIwWFECAIJACQB6wHoSwyR2AwAAgO6znsQwid0AAIESAPSAoIRhsqIEAAAA3ScoYZisKAEAAiUA6DjrSWQQvQEAAEB3WU8ig+gNAPpNoAQAHffkyZMCwxYrSvv7+wUAAADonpWVlQLDFgtKEb8BAP0kUAKAjtvc3CyQwbMFAAAA3bS4uFggw/LycgEA+kmgBAAdFqfd4sQbZIhAyYoSAAAAdEucdrNyQ5aFhQWL7wDQUwIlAOiwx48fF8gScVKcegMAAAC6w8INmSJOilNvAED/CJQAoKNiOUk8QrbvvvuuAAAAAN0Qy0niEbI5IQgA/SRQAoCOEidRh3jOnHkDAACAbhAnUYd4zpx5A4D+ESgBQEdtbm4WqMPW1lYBAAAA2s+yDXVxShAA+kegBAAdFOfd9vb2CtRhe3u7AAAAAO0W593W1tYK1GFlZaUAAP0iUAKADjKRTJ2ceQMAAID2u3PnToG6OPMGAP0jUAKADrJoQ92ceQMAAIB2s2hD3Zx5A4B+ESgBQMfEkk0s2kCdRHEAAADQXrFkE4s2UCdRHAD0i0AJADpGnMQoPH36tAAAAADt9MUXXxSo29raWgEA+kOgBAAdY8mGUYjlrt3d3QIAAAC0jyUbRsFyFwD0i0AJADrGkg2j4tkDAACAdrJkw6hY7wKA/hAoAUCHPH/+vOzt7RUYBetdAAAA0D6xYiNQYlQsKAFAfwiUAKBDLNgwSp4/AAAAaB8LNoySOA4A+kOgBAAdYj2JUdrf369WvAAAAID2EIgwSrHg9fDhwwIAdJ9ACQA6ZHd3t8Ao7ezsFAAAAKA9nNhi1Kx4AUA/CJQAoEOc2GLUrHgBAABAu1hQYtQ8gwDQDwIlAOiIOK8VLxglJ94AAACgPeK8VrxglJx4A4B+ECgBQEdYrqEJrHgBAABAe1iuoQk8hwDQDwIlAOiIZ8+eFRg1C0oAAADQHpZraIJ4Di15AUD3CZQAoCOEITSFZxEAAADaYX19vUATCJQAoPsESgDQEU680RSeRQAAAGgHC0o0hTNvANB9AiUA6Ij9/f0CTfD9998XAAAAoPkESjTF9vZ2AQC6TaAEAB0hCqEpnHgDAACAdnBWi6YQywFA9wmUAKAjRCE0hTUvAAAAaAdRCE0hlgOA7hMoAUBHiEJoCs8iAAAAtIMohKbwLAJA9wmUAKADBCE0iecRAAAAmk8QQpN4HgGg+wRKANABghCaxPMIAAAAzScIoUk8jwDQfQIlAAAAAAAAAAAgjUAJAAAAAAAAGBkLSgDQfQIlAACG6tmzZwUAAAAADkqgBADdJ1ACAGCojh8/XgAAAAAAAGBAoAQAwFAdO3asAAAAAMBBXbhwoQAA3SZQAgAAAAAAAAAA0giUAAAAAAAAAACANAIlAOgAJ7UAAAAAOIzTp08XAACoi0AJADpAoESTnDhxogAAAADNJlCiSS5cuFAAgG4TKAFAR4iUaArPIgAAALSDSImm8CwCQPcJlACgI0QhNIVnEQAAANpBFEJTeBYBoPsESgDQEWNjYwWawIk3AAAAaAdntWgKzyIAdJ9ACQA6QhRCU4jlAAAAoB1EITTF1NRUAQC6TaAEAB0hUKIpnHgDAACAdhAo0RROvAFA9wmUAKAjBEo0xfj4eAEAAACaz2oNTTE9PV0AgG4TKAFAR0xMTBQYNc8hAAAAtIcohCbwHAJAPwiUAKAjLCjRBM67AQAAQHs48UYTOO8GAP0gUAKAjogwRBzCqDnvBgAAAO0RYYhIiVGzoAQA/SBQAoAOOXXqVIFR8gwCAABAu4hDGLWPP/64AADdJ1ACgA5x5o1R8wwCAABAu1hQYtQ8gwDQDwIlAOiQkydPFhiVODHoxBsAAAC0y6VLlwqMSpwZtOIFAP0gUAKADnFei1GamJgoAAAAQLs4r8UoiZMAoD8ESgDQIbFg48QWo2LBCwAAANonFmyc2GJULHgBQH8IlACgY+JDJRgFC14AAAD8P/buLlbL88wP/WVjg8FgMNgkuCZgO7GdOlMDldqMc5BFlbSTSo3hoGlyUAHZk3pvzUgsEk3mkLVOKs3MAWupGWlmS2NAW1UymkhAVLWT2JKxtJ1mtOVhRYqU2GkcPHZFywQPDgRiEuTN9ay8Cbb5WB/v/bzPx+8nvXrBib/Wx7P8/J//fV20044dOwJGwQQvAOgPBSUA6Jjly5cH1C2nd5mgBAAAAO30+OOPB9QtD1qaoAQA/aGgBAAdY4ISo2B6EgAAALSXCUqMgnISAPSLghIAdExOslEWoW6KcQAAANBeJtkwCk8++WQAAP2hoAQAHbR69eqAOlnvBgAAAO1mihJ1U4oDgH5RUAKADjLNhjrlxK6lS5cGAAAA0F6m2VCnLCdt3rw5AID+UFACgA7Ksog1b9Rl3bp1AQAAALRblkVMtKEuu3btCgCgXxSUAKCjrNyiLr7WAAAAoBsUlKiLrzUA6B8FJQDoqPXr1weUZr0bAAAAdMfevXsDSrPeDQD6SUEJADpqyZIl1rxRnPVuAAAA0B1r1qwx2YbirHcDgH5SUAKADtuwYUNAKcuWLYu1a9cGAAAA0B379+8PKCUnJ+3evTsAgP5RUAKADlu5cmU1SQlKyK8vAAAAoFtyglJOUoISTOgCgP5SUAKAjlu/fn1ACSZ0AQAAQDeNj48HlGBCFwD0l4ISAHRcFpRMUWLY1q1bF0uXLg0AAACge/bu3WuKEkOXq91yxRsA0E9LNmzYMBEAQGfdeuut8ctf/jJ+9rOfBQzLsmXL4he/+EW8/fbbVQEuv84AgP546qmnAgDorjvuuCP+9//+3/Gd73wnYFiynJRfVz//+c+rAlx+nQEA/XFbAACddfny5bh48WL1DsN09uzZ6jWwYsWKaqLS6tWrq18vX748AAAAgPbJ+/2ZmZl33PfDMBw9erR6DWzZsqUqLe3YsSMef/zx6vcAQHfdsm3btrcDAOiM8+fPx7lz5379DqOQZaUsKmVhadWqVdbBAUDHvPjiiwEAdMfx48fj+eefr97zBaOQZaUsKWVh6eMf/7h1cADQMQpKANByOR0py0iDiTamJdFEWVZauXJlNb473wGAdlNQAoB2ywwpi0jHjh2rJtqYlkQTZVlpbGwsnnzyyeodAGg3BSUAaKEsIb355ptx5syZuHDhglISrZLTlHKq0rp165SVAKClFJQAoH2yhJRlpMOHD1vhRuvkNKUsKe3atUtZCQBaSkEJAFoiS0gXL16MU6dOKSXRGYOy0oYNG6yBA4AWUVACgHbIElKWkSYnJ5WS6IxBWWnv3r3VlCUAoB0UlACg4Qbr23JaklISXZZr4O69996qsKSsBADNpqAEAM02WN926NAhpSQ6LQtK4+Pj8fGPf7wqLgEAzaWgBAANlEWkLCTlGrdz584F9E2uf7MCDgCaS0EJAJoni0i5vi3XuGVBCfpm9+7dVsABQIMpKAFAg5iWBO+Uk5Ry/ZupSgDQLApKANAcpiXBO+UkpYmJCVOVAKBhFJQAoAGykPTGG2+YlgQ3kBOVsqykqAQAo6egBACjl5OSpqenTUuCG8ipSvv371dUAoAGUFACgBHJCUmnT5+uXqYlwdzlNKW1a9dWhSUAYDQUlABgNHJCUpaSpqamTEuCeci1b4MVcADAaCgoAUDNLl26VJWSrHGDxRmsf1NUAoD6KSgBQL1OnjxZFZOscYPFGax/U1QCgPopKAFATc6fPx+nTp2yxg2GLItK69evjzVr1lj/BgA1UVACgHrk+rbJyUlr3GDIsqg0Pj4eTz75pPVvAFATBSUAKEwxCeqR5aRc/5ZTlRSVAKAsBSUAKEsxCeqR5aRc/7Z//35FJQAoTEEJAApRTILRybVvikoAUI6CEgCUoZgEo7N7925FJQAoSEEJAIZMMQmaQ1EJAMpQUAKA4VJMguZQVAKAMhSUAGBIFJOguRSVAGC4FJQAYDgUk6C5FJUAYLgUlABgkRSToB2ynJRFpXwpKgHA4igoAcDiKCZBO2Q5KYtKu3btUlQCgEVSUAKABbp06VJVTDpz5kx00ZoVEWcvBHROlpNymlIWlQCAhVFQAoCFOXnyZFVMOnToUHSRPImuynLSxMREVVQCABZGQQkA5uny5ctx+vTpqpwEtJeiEgAsnIISAMzP2bNnY3p6uio4AO2lqAQAC6egBABzNCgm5St/DXRDFpUyXFq5cmUAAHOjoAQAczMoJk1NTVW/Brohs6SDBw/G2NhYAABzo6AEAHOQa9xyYlKudeu6zffMjuNOM38X9NjYo7Nj2U/+pB/j2XOSUk5UysISAHBjCkoAcHO5xi3XueVat66TJzHQtzxp9+7dsX///qqwBADcmIISANzA+fPnq2LSuXPnomsyNMrAYPO6iMc3Xvn1I7Nh0sCxExE7vhL0VH4t/PiPfvP7DJRmXpt9vfqT2ffjP4hOWr9+ffVSVAKA61NQAoDrO378eFVMyveuuVmedPyliO1/HPRUn/Ok8fHx2Lt3r6ISANyAghIAXEOucHv99deryUldMQiQPn4lONqx5Z3h0bUceiFiz9NBj739Fzf//2Tw+PxLs+9dCpiynJTTlHKqEgDwXgpKAPBeucJt37591eSkrpAnMV99zpOynDQxMRG7du0KAOC9FJQA4F1yYtLp06erklLbZWi0Y2vEk1tnT7TNx+Q3IiaOBT2WJ95uFjxeLU/FHT0xGzDlexfGeGdR6eGHHzZNCQDeRUEJAN4pJyZNTU1VJaW2kyexGPKk2aLSkSNHYsuWLQEA/IaCEgD8Sq5zO3nyZFy6dCnabMsHZgOk3U/MLwx4t51/eiUU+Nugx478/mwguVAZKuWqwC6ESzlJKScqKSoBwCwFJQCYlWvc9uzZU2VKbSZPYlgWmyflVKXDL3QjT9q9e3fs37/f2jcA+JXbAgB6LgtJuc6tzSfcctz23k/Onmqb78m26zn5k6DnXl3khsMMo/J1MGZHvB+baW9Imesez507Z+0bAAAAlcyRsph09OjRaCt5EiUsNk8afD1mnpQlpcPfbm+elOses8Ro7RsAzDJBCYBey1VuudKtrevcxh6N2P/p4YVIV7vl/wh6bvfHroRBn4+hyqAyT8LlyPe2hpbWvgGACUoA9Nv09HRVOGjrYTd5EiXJk64tpyg999xzpikB0GsmKAHQS7nOLYtJORGlbQan28Y/MfvrEvKGH2b+LoYux8Tvvmc2rBqM7M7pSm2SU9e+973vxfr166uJSkuWLAkAAAC6b2ZmJvbt21dNRGkbeRJ1kSddW66BfOCBB2J8fLxa+7ZmzZoAgL4xQQmAXslJSVlMyslJbVPydNu7TT97JbD6akD8w38qF1wOtPkUXE5RsvYNgD4yQQmAPslJSZOTkzE1NRVtI09iFORJN5ZTlKx9A6CPFJQA6I2cmpQnVXL6SVvkjXyeDNp15bVlY9Rm55+2d7c7w/Xcl+sJMQfy9Nvhb18JmH4QrZIFpSwqWfsGQF8oKAHQFzktac+ePVWm1BbyJEZNnjQ3u3fvrqYpWfsGQF/cGgDQcTk16fXXX4+XX365NeWkDJL2Pxnx4z+KOPDZesOkVGIUM+30fM3j2TNAfe4PIk5MzP66Lc6cOVNdY/IdAACA9supSbnObfv27a0pJ8mTaIpjJ6JWbc2TDh06VF1jDh8+HADQByYoAdBpbZualPvU937yyo30E+XHIF/PzGsRWycCKnnaLU+9jUqO6M5R3XkSri1MUwKgD0xQAqDL2jY1KfOknJY0/gl5Es0gT5o/05QA6AMTlADopLZNTcog6eDnZ0+4jTJMSnVPzKHZjl/5ejh7IUbm6u+NtpyAM00JAACgndo2Nenqe+aJT8uTaA550vyZpgRAHygoAdA5OTXp+9//fpw+fTqabuzR2dNETbpZPvq3Ae9wbCZGrm3BUhYjX3311erVlgluAAAAfZZTk7Zu3RpTU1PRdPIk2kCeNH9ZjMxJSm2a4AYA86GgBEBntGlqUt4cZ5CUu9Fz5HFT5Mmm40688S7HfxCN0bZgyTQlAACAZmvT1KS8Jz7y+/Ik2kGetHCmKQHQVQpKAHRCW6YmXX0z3KQgaeDoiYD3aOLXRZuCJdOUAAAAmqktU5OuvgfesTUaR57EtciTFsc0JQC6SEEJgNZrw9SkNSsiDnyu+Te/TRi9TPM0+SRkm4KlwTSlLFQCAAAwWm2YmiRPos3kScMxmKaUhUoAaDsFJQBaKwtJTZ+alEHS/idnb3bHPxGN16TRyzTLsYafhmxLsJTXrSwpnTp1KgAAAKhfFpKaPjVJnkRXyJOGI69bWVKanJwMAGizW7Zt2/Z2AEDLZCkpH/Bfvnw5mmrvJyMmPj0bKrXBoRci9jwdcE35dfwP/ylaI0/o5dfzyZ9EYy1dujQefvjh6h0A2ubFF18MAGib6enpmJiYiLNnz0ZTyZPoEnnS8G3evDmee+656h0A2sYEJQBaJQtJr776arXWranlpLFHZ0/dTH22PWFSMo6bG2nyWO5rGXtk9vswT8HlabgmasMUOAAAgC7IQtKePXtifHy8seUkeRJdJE8avsEUuCxcAkDbLNmwYcNEAEALXLx4sVqNdP78+WiiLRsjvvp/tuuU20CeCvq//p+AG7rlymvH1miVLR+IGP9kVP/wzzcwEHv77bfjpz/9aVVWWrVqVdx6q/MDALTDU089FQDQBjMzM9VqpOPHj0cTyZPoOnnS8P385z+Pv/7rv64O8o6NjcUdd9wRANAGnoAA0Ao5YSQnjeRD/KbJ8OjA5yJOTMyesmmjNp1kYnSOnpg9+dZGGfTmCbjdH4tGOnPmTGOvcQAAAG2VE0Zy0khOHGkaeRJ9IU8q59ChQ429xgHAtSgoAdBoucbtlVdeqVa6NdHeT87epI5/Ilrt8AsBN5Vh0uFvR2vlaO4c0Z3hbxPHdGc56Xvf+56VbwAAAIuUa9x27txZrXRrInkSfSJPKivLSQ888ICVbwC0goISAI2VK91yokiGSk0z9mjEc1+OmPps+8Zvv1uO43bijbk6+rfRejk+P4PgPKnaxGApC5n5yoImAAAA85Mr3XKiyNGjR6Np5En0lTypvCxk7tu3r5FZOgAMKCgB0Eg5QeTll19u3Lqjwfjt5/6gveO3323yGwFzluHjzGvRCXlSNb+Xmzimu8lrLQEAAJoqJ4hs3769ceuO5En0nTypHlNTU1a+AdBoCkoANE5Tp4fkTWcXxm+/m9NuzNexE9EZgzHdR36/eaffspyURc0333wzAAAAuLGcHJITRJo2PUSeBLPkSfXIclIWNZs4RQ4AFJQAaIx8GJ8TQ3JySJPkTWaO386bzraP3363Qy/MjuSG+Zh6JuLsheiUHVtnA+P9T0aj5HXxRz/6UZw6dSoAAAB4r3wYnxNDcnJIk8iT4J3kSfXJ6+LOnTtjcnIyAKBJFJQAaISLFy9Wk0LyvUny5vLE/u6M3363wy8EzFuGSV09KTnx6dlgqWmn37Kg9MorrzRushwAAMAozczMVJNC8r1J5EnwXpkndWmK0tWamidNTExURaWmTZYDoL8UlAAYuZyYlJOTclJIU2zZeCVImpi9uezaKbeBPOlmHDcLNf1MdFaGSRkqHfhcs77/M0xq2rUSAABgVKanp6vJSTkppCnkSXBjhzpcbmtqnpSr3pp2rQSgvxSUABip119/vXo1Rd485k1khkkZKnXZ5DcCFizDyK4HkuOfaN6J1ywnNXHaHAAAQJ327dsX4+Pj0RSZJ1VTkybkSXAjfcqTdmyLxshyUhOnzQHQPwpKAIxErin64Q9/WE1PaoqxR2dvHvMmsuvytNvRjo5Upj5dHct9tTz99tyXIw5+vjmn37KklJOUmnT9BAAAqENOls11RVNTU9EUgzwppyZ1nTyJYejDisDMk4783mye1JS1b1lSyklKOX0OAEZFQQmA2g0erp87dy6aIqcmPfcHzdsTXkqeVMq977AYOZa7L19Huz/WvGlKOX3u1KlTAQAA0AeDh+u5rqgp5Ekwf1ly61OelNeIJuVJOX1ucnIyAGAUlmzYsGEiAKAmuZbof/yP/1GVlJogx27/ty9G7NgavbLzTwVKLN7PfxGxfGmzQpaScoJSBktr7oz4m1dm//1H7fz589X1dNWqVXHrrc4eAFCfp556KgCgLrmW6FOf+lRVUmoCeRIsnDwpRu748ePx6quvxtjYWNxxxx0BAHXxFAOA2uQY7pdffrkx5aS9n4w4MTEbKvVJTr3JkdwwDFPP9C+czDWQOU2pKSdkz5w5U63MbMq1FQAAYJhyYtL27dsbU06SJ8HiyZNG79ChQ426tgLQDwpKANTi9OnT8corr8Tly5dj1PIm8LkvX7kR/mz0Uh/2vFOfDJOOnYjeyevIj/8oYv+T0QgXLlxoVAEUAABgGKanp2Pnzp3VobdRkycFDE3mSYe/Hb3TtDwpp9MpKQFQJwUlAIo7depUvP7669EEuz42e1KlLyOE3+34S7MvGKZDPQ4pJz49Gyw14fRblpOUlAAAgK6YnJyM8fHxaAJ5kjyJ4Tv0/0ZvNSlPynKSkhIAdVFQAqCoLCfla9Ry1/eBz1258f387K/7ymk3Suh7UJlhUgbVuz8WI5flpO9///tx8eLFAAAAaKssJ01MTMSoyZNmyZMoYeY1eVJT8qQsJ23durWaqAQAJS3ZsGHDRABAAa+++mq12m3UtmycHcH9Ox+JXjv5k4g9TwcU8epPmhGojModt0fs2HolsL4z4m9eifj5L2Jk3n777fiHf/iHWLp0aSxfvjwAoISnnnoqAKCEPXv2xNTUVIyaPGmWPImS5EnNyZN+/vOfx1/+5V/GlefGsWXLlgCAEkxQAqCILCedOXMmRm3vJyNOTDRjXO6oTX4joBjj3meNf2L29NuorzmXL1+uTr+98cYbAQAA0BZZTjp06FCMmjzpN+RJlCRPmtWUPOns2bOxe/fuOHz4cABACQpKAAxVPhT/4Q9/OPJyUo7dPvL7EVOfDWL2tNsh47gpbPJYELNh0o//6Eq49MkYuSwpNWGSHQAAwI3kQ/Ht27ePvJwkT3oneRJ1kCfNalKelCWl6enpAIBhs+INgKHJctLLL78cP/vZz2KUBiO4P/pQ8Cv7vja71x1KOnkmYuxRJ0wHcg1AE0Z0//SnP63eV61aFQAwLFa8ATAsg3LSd77znRgledJ7yZOogzzpnZqSJ/31X/913HLLLTE2NhYAMCwmKAEwFINy0sWLF2OUcgR3hkluaH/DaTfq5NTbOzVlRPepU6eqFwAAQJMMykkzMzMxSvKk95InUSd50js1JU+amJiIycnJAIBhUVACYNGaUE7KEdwHPjc7gjt/zW9MfiOgNsdfcrry3TJMylBp98dipJSUAACAJmlCOUmedH3yJOqUeVK++I2m5ElKSgAMkxVvACzaSy+9NNJyUt6s/bd9ETu2Bu+Sp932PB1Qq7d+4fvx3e64/Vcfk1sinh9h4Hb+/PlYtmxZLF++PABgMax4A2CxPvWpT410rZs86frkSYzClcjE9+O7NCVPOn78eDzwwAOxZcuWAIDFMEEJgEV59dVXR1pOyv3kz/1BxJaNwTU47cYo5Aj4DDN5r4lPRxz5/dGezD158mS88cYbAQAAMCp79uypHniPijzpxuRJjII86foGedIoV77t3r07Dh8+HACwGApKACzY66+/HmfOnIlR2fvJ2TBp1Lu4mypv6PPGHkZBmHl9efItR3SP8tqVJaWcpgQAAFC3ffv2xaFDh2JU5Ek3Jk9ilORJ15d50qivXVlSGmW5FID2U1ACYEFOnToVp0+fjlE58LmIqc8GN+CGnlFy6u3GMkzKUGnskRiZH/3oRyOdgAcAAPTP5ORkTE1NxajIk25OnsQoyZNubJAnjXIV3s6dO2NmZiYAYCEUlACYtywn5WsUci3Sc1+OGP9EcANOu9EE+74W3EAVKl25nu1/Mkbi8uXLVUnp0qVLAQAAUFqWkyYmJmIU5ElzI0+iCfY8HdxA5km57m1UedLZs2erklJO5waA+VJQAmBe8gZkVOWkvPnKtUijnDjSFk670QRHT0Qcfym4iYlPjy5UynLSyy+/XJWVAAAASjl69OjIyknypLmTJ9EEmSXJk25ulHlSlpO2b99ePSsAgPlQUAJgzvJB9quvvhqjsGXj6Hdst4XTbjTJ5LFgDjJUytNveaq3bnltf+WVVwIAAKCEfJC9Z8+eGAV50tzJk2gSedLcjDJPymt7TlICgPlQUAJgTkY5ZWPXx2bHcAuT5sZpN5rEqbe527F1dNe6c+fOxeuvvx4AAADDNMopG/Kk+ZEn0STypLkbZZ50/Pjx2LdvXwDAXCkoATAnP/rRj6qSUt32fjLi0OdHcwqkjZx2o4mcepu7UZ7uPX36dPUCAAAYlpyukSWlusmT5keeRBPJk+ZulHnS1NRUTE9PBwDMhYISADd16tSpuHjxYtQtd2hPfTaYB6fdaCKn3uYnw6RRhUqjut4DAADdMzk5GTMzM1E3edL8yZNoInnS/IwyTxofHx/J9R6A9lFQAuCGzpw5Uz2wrluGSblDm7lz2o0mc+ptfjJMOrF/9gRcnXKNZ07MG8U6TwAAoDsOHToUExMTUTd50vzJk2gyedL8jCpPSjkxbxTrPAFoFwUlAK4rV7qNopx04HPCpIVw2o0mc+pt/nIVwXNfrj9Uymv/q6++GgAAAAuRK91yelLd5EkLI0+iyeRJ8zeqPCmv/Xv27AkAuBEFJQCuK6do5IPqOh38fMT4J4J5yht1p91ouj1PB/OUodKJiYhdH4ta5Ym306dPBwAAwHzlA+p8UF0nedLCyJNoA3nS/I0qTzp69GhMT08HAFyPghIA15STky5evBh1yjBpd803TV3hRp02yLHx088EC3Do8/WHSvlzoO6SKgAA0G45Oen48eNRJ3nSwsmTaAN50sKNIk/K9Z51l1QBaA8FJQDeYxSr3YRJC5cn3fJGHdpg4hsRZy8EC1B3qHT58mWr3gAAgDnLB9L5YLpO8qSFkyfRJvKkhas7T8qp3Fa9AXA9CkoAvMfrr78edRImLc7kNwJaI8Ok6WeDBcpQacfWqM25c+fizTffDAAAgJvZt29f1EmetDjyJNpEnrQ4dZeUcpJernsDgHdTUALgHc6cOVOdcqjL/ieFSYvhtBttNPWMU2+LkSH8lo1Rm9dee62apgQAAHA9hw4dqvVhtDxpceRJtJE8aXGmPltvnpSl1TqfMwDQDgpKALxDnavdMkya+HSwQBkkOe1GG2WYNHksWKA1KyKe+3J9oVKu/Tx9+nQAAABcz+TkZNRFnrQ48iTaSp60OHXnSbn2c3p6OgDgards27bt7QCAmJ2e9Oqrr0YdhEmLt++rEVOFRxv7PPXXA39Y/jTliYl6T251TX5+tv9JPadelyxZEh/5yEeqdwBIL774YgBAyulJe/bsiTrIKRZPnkRJ8qTmqzNPWrNmTfz4xz+u3gEgmaAEQCUnZNQ1PSn3XQspFidvIEuHSZvv8XnqswOfjeIyFGXh8nv0uT+YfS8tV7zVOWEPAABoh5yQUdf0JHnS4smTKC3X0pcmT1qcOvOkXPFW54Q9AJpPQQmASj54zpJSaXm65VANN6pdV8co7v3CpF7bsTVi7JEo6vhLsy8WLsOkI78ftcg1b+fPnw8AAICBfPCcJaXSMk+aquEgTdfJkygtsyR5UvPVmSdNTU3F8ePHAwCSghIAVTEp17uVVueNT5fNvBZx6IUoKj9Xuz8W9FyOZC/NqbfFy6D+wOeiFqYoAQAAA1lMyvVupQ3ypDUrgkWQJ1EXeVI71JknmaIEwICCEgDx8ssvRx3qGh3bdTu/EsU57Uaq49RbBqTTzwSLNP6JK69PRnHnzp2rpdAKAAA0386dO6MO8qThkCdRF3lSe9SVJ+UEpcOHDwcAKCgB9Fw+aK5jtVuexhAmLV6edDv5kyjKaTeuVsept4lvRJy9ECzSgc/Onn4r7fXXX4/Lly8HAADQXzk5aWZmJkqTJw2HPIm6yZPao648aXx8PM6ePRsA9JuCEkDP1bGuJ8OJPI3B4uQN9+Q3oriDnw/4tTzxtmNrFJVf29PPBkNQx9qDLCedPn06AACA/qpjXY88aTjqypOy5AADdeVJk8eCIagjT8py0vT0dADQbwpKAD1Wx/SkPD1lvPNw5Nji0qfdMvwrPYKZ9qkjZJw4Vv7ruw+qa24NpxSzoGSKEgAA9FNOTzp58mSUJE8anjrypB3bypdRaJ868qSpZ+VJw1BXnjQ1NWWKEkDPKSgB9Fgd05MyTDKKe/HyRnuihtNuwj+uJb+HJ2oIKfY8HQxBnjAuXTQ0RQkAAPqrjulJ8qThqCtPOvDvAt5DntQudeRJpigBoKAE0FN1TE/KaTx2zw9HHaO483Ml/ON69n6i/Kjn4y/Nvli8OlY1KigBAED/HDt2rPj0pJzGI08aDnkSoyZPapfMk0p/vnKKEgD9paAE0FNvvPFGlGYaz3AcemH2VZrPFzeS4cT4J6O4PPV29kKwSHWcUswpSsZyAwBAv9TxYNk0nuGQJ9EE8qR2yTyp9Ocrs6SjR48GAP2koATQQzk56dy5c1GS01PDU8dpt9wx7vPFzeSpt9JfJzl+fvrZYAjqOKX493//9wEAAPRDTk46fvx4lCRPGh55Ek0hT2qXOvIka94A+ktBCaCHTp06FaU5PTUck8dmb7BLqk7GfCLgpjKcOPDZKG7qmfJf931QxynFLLtevHgxAACA7pucnIzS5EnDIU+iSeRJ7VJHnpRl15mZmQCgfxSUAHqo9PQkp6eGI2+op2o4+ZPhX+lTMXTHjq0RY49EUTmSe9/XgiGo45SiNW8AANAPpacnyZOGQ55EE8mT2iW/v0tfj48dOxYA9I+CEkDPnD9/vlrxVkreuEw47TYUOYq79O70/Hzl+HSYjwyNSzt64kr4/VKwSBkWH/x8FHX69OkAAAC6LctJueKtFHnS8MiTaCp5UruUzpOmpqYCgP5RUALomTNnzkRJRnEPR95MH3ohiit9o0k35Ym3OoLIPU8HQ5Cfr5KnFC9fvlyVXwEAgO46fPhwlCRPGo6Z1+RJNJc8qV1K50k5kbv0ZD4AmkdBCaBnSq53G3vU6alhqWMccX6uSo9WprvqGOWeY+nz5CeLVzo8Lr06FAAAGK2SD5HlScOz8ytRnDyJxZAntUvpPMmaN4D+UVAC6JHS692cdhuOyWOzN9Kl+XyxGDnOffyTUdzUM/V8P3Rd6fH7b775ZgAAAN1Uer2bfGI45Em0gTypXUrnSSYoAfSPghJAj5SenuT01OLljfPUs1Fc7nzPG0xYjL2fKP91dPZCPRPF+mBXwUDpwoUL1ao3AACge55//vkoRZ40HPIk2kSe1C4l86SZmZlq1RsA/aGgBNAjOUGplF1PBEOQ44fzBrqk6qTSJwIWLUdyH/hsFHf0RMTxl4JFytC/ZPAvUAIAgG4qOeFCnjQc8iTaRJ7ULqXzJGveAPpFQQmgR0pNUCo96rUvDr0w+yqtjl3v9MeOrfWcdt3zdPmwtQ/2FhyjfvHixQAAALqnVEFJnjQc8iTaSJ7ULiXzpJyiBEB/KCgB9ETJ6UlGcQ9HnnYrbcsHhH8M34HPRXE5rn66hnH1XZfX61KBcsmfMwAAwGiUnJ4kTxqOOvIkZTJKkCe1R8k86ejRowFAfygoAfTEhQvljorsElAs2uSx2Rvm0o78XsDQbdkYMV7wJNXA1DP1fJ90WYZJeUqxhPw5c/ny5QAAALrju9/9bpQiT1q8uvKk5/4gYOjkSe1RMk86efJknD17NgDoBwUlgJ64dOlSlJA3J068LU7eIE/UcNotT7rliTcooY5R7zmSO0dzszgfL3jNLvWzBgAAGI18cFyCPGnx5El0gTypPUrmSaV+1gDQPApKAD1x8eLFKEGYtHh13CBnkJQ3/FBKhkn7n4zijr8UcfiFYBFKnXhLJaf1AQAA9ZuZmYkS5EmLJ0+iC+RJ7VEyTyo5rQ+AZlFQAuiJUg+Nxx4NFuHQC7M3yKVlmOS0G6WNf6KekHn8a7On31iYDP9KXQ9KlWEBAIDRKFZQkictijyJLpEntUPmSVs+EEWU+lkDQPMoKAH0wOXLl6tXCY9vDBYoR3FP1jCKO4OkHMcNdajj1FuGSZPHgkUoFfyV+lkDAADU7+zZs9WrBHnSwsmT6CJ5UjtsKXTtLvWzBoDmUVAC6IFLly5FKVsESguWYVKGSqU99wcBtcniy/gno7ipZ+s5LdpVpU68maAEAADdcfLkyShFnrRw8iS6SJ7UDiYoAbBYCkoAPVBqokWGSTnalfnLG+FDNew9z9NuRnFTt72fiFrseTpYoM3roohf/vKXAQAAdEOpiRbypIWTJ9Fl8qTmK5UnmaAE0B8KSgA98NZbb0UJa+4MFsiNMCxeXWPtu6jUOoWSE/sAAIB6lZqgJE9aOHkSLJ48aeFK5UklJ/YB0CwKSgA9UGqCUqkTE12Xu87rGMUNfTD1jO+nhXASFgAAuJk333wzSpAnLYw8CYZHnrQwJfMkU5QA+kFBCaAHihWUPOCet7zxnXBCB4bm7AUnSBeq1EoFU5QAAKAbSj0stt5t/uRJMFzypIUrdQ1XUALoBwUlAKjR9j8JYMiOvxQx/UwwTx4KAAAAo+BeZP7kSTB88qSFcQ0HYDEUlACgJtNGB0MxeZLU9xcAAABdI0+CcuRJAFAvBSUAqIFR3FBWjube97UAAACAzpAnQVnyJACol4ISANRg8huzN7xAOUdPzI7nBgAAgC6QJ0F5mSflCwAoT0EJAAo79MLsCyhvz9PC27nycQIAAGgueRLUJ6coyUnmxscJgMVQUALogSVLlkQJ9nPfXH6MJo3ihtpU33PHgjkoFSgtXbo0AACA9luzZk2UIE+6OXkS1EueNHel8qRSP3MAaBYFJYAeKFVQclri5jJMErxBvaaetertZlyXAACAm1m9enWUIE+6OXkS1E+edHMlr0sKSgD9oKAE0AOlCkozrwU3YBQ3jI5Vbzd28kwUYXoSAAB0x9133x0lyJNuTJ4EoyNPurFSedLmzZsDgH64LQDovGXLlkUJTnJdX1NGcec/xy3/R0DvDEZzH/hccA3fLfRA4Lbb3F4AAEBXbNq0KUqQJ12fPAlGS550Y6XyJNOTAPrDBCWAHig1QSk59XZtRnHD6BnNfX2lrk8mKAEAQHeUnGghT7o2eRKMnjzp+kpdnxSUAPpDQQmgB/KBcamS0ncFSu9hFDc0h9Hc1zbzd1GEghIAAHRHPjAu9dBYnvRe8iRoDnnStZXKk7Zs2RIA9IOCEkBPlHpofPwHwVWaMoobmJXfkxkq8RsZsJU6CaigBAAA3VJqipI86Z3kSdAs8qRrK5UnlZzYB0CzKCgB9MSKFSuihKMngqts/xOjuKFp8jo1/UzwKyVXKZT6WQMAAIxGqakW8qR3kidB88iT3qnk2rvHH388AOgHBSWAnli+fHmUUHISR9vs+6owCZpq/GuuVQOHC64MKPWzBgAAGI1SBSV50m/Ik6C55Em/UTJPsuINoD8UlAB6ouRUi+fdpMXksYipZwNosBzNLfQtF6zlz5klS5YEAADQHSWnWsiT5EnQBvKkWaXypCwnrVmzJgDoBwUlgJ4oOdXiUMHTE22Q434nvhHAAmWppY5iS4ZJOTY/T+r2VYZJpUK1pUuXBgAA0C0lp1rIk+RJsBh33XVX9SpNnlQ2T9q8eXMA0B8KSgA9kQ//S5WU8uakr6NuZ16bPUUDLFxen+65556oQxUq/XH0Vslx3E67AQBA9+R/55cqKcmTAliE1atXxxe+8IWogzwpinnyyScDgP5QUALokVWrVkUpOZK6b/LGdOdX+n16BoZl/fr1cccdd0Qd+hoE5zWr5AnlkpP6AACA0RkbG4tS5EnAYnzxi1+Mxx57LOogTyqj5KQ+AJpHQQmgR0pOtyg55rWJBqN97R+HxRusd7vvvvuiLhms9C1UKnnabdmyZQpKAADQUSWnW8iTgMWanp6OusiThivXuykoAfSLghJAj+TD40ERoITJb0QvCJNguAbXpZUrV1aTlOqSoVJfTutWp92+HcXk5w4AAOimfHhc8tCbPAlYiI0bN1bvjz/+eIyPj0dd5EnDU3JCHwDNpKAE0CNZAlixYkWUkjdnXQ9ZhElQ1oYNG6ppPHWZuBKE7/tqdN7hwtfndevWBQAA0E1ZTir5EFmeBCzW/v37q2k8dZEnDceuXbsCgH5RUALombVr10ZJXR5xK0yC8rJIuWnTpqjT1LPdv3ZNFDyRnIUyE5QAAKDbSq55S/IkYDGySHnw4MGokzxpcbJQZoISQP8oKAH0TN6slVzzdvyl2VfXzLwWsXVSmAR1qHvVW8oTu9v/OOLsheic0usSlJMAAKD7duzYUXTNmzwJWKwsu9S56i1lnrR1Qp60EMpJAP2koATQM1lOKhkopTw50qWbssMdvtGEJrj99tur91tuueXXf+z+++8vupLyWjIM71pwnEFZvkqy3g0AALovs6Tdu3dHSV3Mk7p6EAaaILOjdNttt/36jx04cCC2bNkSdepiEbGOPMl6N4B+UlAC6KHSD5PzZmzyWHRC/nvsHsGoXg/8IeLBBx8sOvHtWgaj9zNcarvqWlz4tJv1bgAA0B+l17x1MU+qu5yUJbLSBxOh6Y4cOVL794E8aX6sdwPoLwUlgB7Kh8mlJ5PkDu7pZ6K1MkDa+ZWye7avJx/4b9iwIZYuXRrQB4Ov9asnKA3+eAYWdcsgJqemtfkalvL0cenTe3mtAgAA+iEfJpd+oCxPWri8f96/f7+CEr2xcePG6v3dh9vye+HgwYNRN3nS3OW1CoB+UlAC6Km1a9dGaRnGtPHUyGAs79ETUbscSfyhD32oKmbUPTkGRuVGX+urV6+O9evXxyiMfy1i31fbOY4/T+vmyrqS8vNmehIAAPTLjh07ojR50vxlKem5556rihkKSvTFXXfdVb3feut7H3XmtWp8fDxGQZ50c6YnAfSXghJAT+UKsdIFmMGpsTbt384TLtv/eHT/zO9///t/PU0mJylBH9x+++3V+7snKA3cf//9sWrVqhiFPL2bAXObrmMZJtVxWjdDb5PeAACgX3bt2lW8ACNPmr+cRjKYQDyKScQwCpkXpetl3AcOHBhZEaaNeVJex+rIk3IVpesUQH8pKAH0VN641TGVZLB/u+k3Y9U/5x/PnnAZ1emWXJV09efEBCX6Yi5f6w8++ODISnt5fXjgD2eLP013+IX6VglY7wYAAP2T5aQ6ppLIk+Yuy0lXf05MUKIvcup2utYEpYEjR46MrAzTtjwpr2N1sN4NoN8UlAB6LMswdZRgmh4q5emQPNFSx/ja68mJVu9+2G8yCX0xl6/1vFbl+sNRFvey+JPBUlOvZRkm7X46apHXLNcoAADop71799ZSgpEn3VyusZqYmHjHHzOZhL7YuHFj9X6jrGiw/nCUxT150m+YngSAghJAj9U1RSk1MVTKAGnUp9zSihUrfj2S+Goe/tMXN1vxNpDfEw8//HCM0tWn30Z53Xi3OsOkZHoSAAD0V11TlJI86fq2bNkSBw8efM8f37RpU0Af3GzF20AWYkZdUpInzTI9CQAFJYCeq2uKUmpKqJQ3gfu+OhsmjfKUW8qVVbm66lqfgywuQdctX768er9ZOenq/38TTlrl6bc8KZtBzqhluFV3OUmBEgAA+i2nKNV1byZPeq/82OfqqmsVLrK4BF332GOPVe+DQ283k98XBw4ciFHrc55U588NAJpLQQmg57IYMxiHW4cMk/ImLMdg1y2DpLzxytMqU8/GyGU5KVdWXe9BvwIAfbCQguTatWtrvW5dT17PMsjJa8oogqW8pu15ejbcqktet3K9GwAA0G9ZjKlzEoY86TcG02Cu96BfAYA+WL16dfU+1wNvKdeLNaGk1Mc8Ka9LdU3eA6DZlmzYsGEiAOi1nEhy/vz5uHTpUtTh57+I+OvvRbx55Wboow9F3DG3gy4Lljddf/RfIz73f8/+ffPvP2o3KyelW2+9NU6fPh1vv/12QFfdddddsWrVqurrPV9zdeedd1bvee0atbzGHD1xJVT6dsTdKyK2fCCKy9O6n5qq/9RuFsNWrlwZAPDUU08FAP2WE0mef/75OHnyZNRBnnTzclK64447Ynp6On7+858HdNXv/M7vxNjYWJVrZ846Vx/96Eer97x2jdoo8qSZ12Yn0tWdJ2UxLD9fAKCgBEAl14n95Cf1zsr+zisRf/n/lbsByxutfV+bPRGSv25CkJTmUk4aOHfuXG3FMRiFe++9t/qeyElK8zn1lrLYlJpQUkpXB0sZmG++J2LNkDc1DgLyvK7lr+uUPyeaMLkKgGZQUAIgZUnpz//8z6NOfc2T5lJOGvjmN79ZW3EMRuH3fu/34oMf/GB1iOq2226b1587KMo0oaSU6syTPvfn9edJ+XPiz/7szwIAkoISAJXBvu66H/QPbsCef2n25itfi5HBUY7G3fmnEX9+POIH/ysaZT7lpHTx4sX42c9+FtBV69evr4KknJ4034JSalpJKeV1La9F08/OXtvy3yqDpcWES+8+uTsKjzzyyIJW8gHQTQpKAKT3v//91b3c8ePHo059y5PmU05K3/3ud+M73/lOQFdlQSkzpcFU7vlqWkkpdTVP+u///b9Xa0EBIN2ybds2e2MA+LUf/OAHceFCzccorpKB0o6tEU9eeW3ZeOMbsLzBOnlm9oZt5u9mg6mzo/tHv6n5lpPSmTNn4tVXXw3oqt/6rd+q3gclyYU6depU9WqysUdmT/d+/JHZa92WmwwjOvmT2WAqr3Gjvr5t2LChegHAwIsvvhgAMLB169aYmZmJUVlInpRZUhPut25mvuWkdOjQodizZ09AV/3P//k/q/f77rsvFmNiYiImJyejydqcJ+3fv7/6GAPAgIISAO+Q68S+//3vx+XLl6MJqlNw62Z/neFS3lBVr4uzN1ttsZByUsrPx/e+N6LjLVBYjuF+4IEHqtO28x3HfS1tKCldLa9peX0bBOdXX+MyLG9KQJ6nEfP6BQBXU1AC4Gq5TixLSmfPno0m6EqetJByUsrPR95vQxc98cQT8Vd/9VdVznrPPYscnxbtKCldrS15Uk6pyusXAFxt8U+CAOiUvLHLkyevvfZaNEGGRm0Kjq5loeWklH9OrlRqSmEMhumOO+6o3hey2u1acsJPfr9lENsGGRjNNPiUbsqP56ZNmwIAAOBGskCTkzL27dsXTdCFPGmh5aTBn5srlZpSGINheuyxx6r3hWSt15IFpfyeacvUsTbkSfnxPHjwYADAu81/MSsAnXfvvfdWO7xZvJw88uijjy7qhnnFikUsGocGu/POO6v3W28d3n+Srl27Nj784Q9XxT4W78EHHxxa4AcAAHTb+Ph49WLxcvLIiRMnFlROuvqvAV300Y9+tHofZl6xe/fu6nsui30s3pEjRxZ1/QKguxSUALimnESiGLM4WfLKyUmLLUqsXr06oIsGE5SGbfny5VVJKaf/sHD5cyA/lgAAAHOVU5S2bNkSLNzevXuryUmLLUooKNFVH/nIR6r322+/PYYpr12LLQbi5wAAN6agBMA1ZakmJ2d4wL8w+WD//vvvj2FQFKOLsviSJ91yvduwVrxdLf/aWRD0/bMweQ3LFwAAwHxkqcbkjIXLB/tTU1MxDI8//nhA12zcuLHKXDO7LjE9e7BaUcFmYfIalivzAOB6FJQAuK7BA36rkubutttui4cffnioD/ZXrlzpc0DnDKYnlSgnDeQ1LFcsWlk5P/lAQTkJAABYqMEDfquS5i4/VvkxG+aD/Zyg5HNA1/z2b/929V7yUG1ew3KSUpZtmLsdO3YoJwFwUwpKANxQPuDPwo2CzM3lpJYsQ2ShaNhWrVoV0CV33XVX9X7rreX/czRP1uUJO9exm8vr2KZNmwIAAGAxlJTmbrBWqsRKNmve6Jp/9a/+VfU+OPhWUpZtDhw44Do2B3kdO3jwYADAzdyybdu2twMAbuLixYvx8ssvx+XLl4P3ygktOXGkVAHi9OnT8frrr0dJz335SnD1SEDseTri0AtR1D/+x/+4+n65/fbboy6XLl2KH/7wh/HWW28F75XlJFPzAJirF198MQDgZmZmZmL79u1x9uzZ4L327t1blSBKFSCmp6djfHw8SpInMVBHnvT973+/OvT2/ve/v5ZDb+nkyZPVdSzfea8sJymkAjBXJigBMCfLly83SekacqXbQw899Ovd56WsW7cuSjt2IqBy/KUoarC2sOR6t2ux8u36lJMAAIASPLi+tvx4HDlyJKampop+bHbt2hWlyZMYKJ0nPfHEE1U5KfOduspJabDyrXTZr41c4wGYLwUlAOZsUFIqueO7TXLtWpYdVq9eHaVlaaD0mrc84XT2QtBz+XVw8idR1CC0qDNMGsjvpSwUZrjkWjYrry3KSQAAQCmDB9h5H8bs2rUsO+zYsSNKy/vv0mve5EmkOvKkf/tv/231noes6pbfS7nuLdeYuZbNymuLchIA86WgBMC8ZEkpH2T3+cF+Tk3KgkN+HPLETl1y6kxJGSZNPxv0XB1fA3feeWf1XvcEpautXbu2+h6uYzpZk+W/v3ISAABQmpLSbwoOdX8cSheh5EmkOr4GcoJSGmUuvXv37up7ON/7LKezKScBsBAKSgDMW5Zy8oH2KE6rjFredI1qRVQdf8/Se+JpthzFPfN3UVQW7fIakuWkURaUUv5zbNq0qbfTlDZs2FD9+wMAANQh773ygXaWlfomS0KjWhFVx5o3eVK/1ZEnZTkpD4xmljPqQ1Z5LctJSn2dprR///44dOhQAMBCKCgBsCB5Mziqos4oZHkh19s9+OCDtU5Nuloda95yFHPpffE01+EaAsVRrne7npym9Nhjj1WFnT7IKXAPPfRQb/59AQCA5siH+aMq6ozCoJR15MiRkRUZ6ljzJk/qtzrypFGud7uenKL04x//uCrs9EFeS7KUNTExEQCwUApKACxKnlzZuHFjdFU+yM+H+FleKL1ibS5Wr14dpU0eC3oow8Q6Tjw2Yb3b9eT3+kc+8pFOr33LIC/LpXVcSwAAAK4nV53lq6vrgfLfK0sLWV4oXQ6ai9Jr3pI8qZ/qypOasN7terKwk9/rXV77lpPvslza99V2ACyeghIAi3bvvfdWD/W7tCLp6mJSk6aMZHGi9BjjPPHm1Fv/TH4jirv77rurCWQ5PamJBaU0WPv24Q9/uPjEsrrlxLtczzmqKXAAAABXyylK+cC7SyuSri4mNWnKSK55K10Gkyf1Ux150mc+85nqkGweuhr1erfrGax9y2taE0qJw7R3795qElwf19kBMHwKSgAMRT7w7sKKpHcXk5p201vHmrfk1Fu/1HXaLQtKqUnr3a5n+fLlVZknVzu2vag0WFGZYV5TgzwAAKCf8oF3F1YkvbuY1LTJUHWseUvypH6pK0/KglJq0nq368lJQ1nmyVfbi0qDFZVTU1OdnXYHQP0UlAAYqsGKpDbcMF6t6cWkq+UUlNLyxNvRE0FP1HHaLUuMud4tJyc1dXrSteRqx0FRqY1hTF7PcqVbE1ZUAgAAXM9gRVI+3G+TpheTrpZTUEqTJ/VLHXnSxo0b47d/+7errLZNE6GznDQoKtWxYnHY8rrWxWlQAIzeLdu2bXs7AKCAN954I06dOhVvvfVWNFVORsnwaO3ata2aLPLDH/4wzp07FyVtvifixP4rYVu7umbMUwaHO78SxeX0npyglN9nbZigdD2XLl2qrmtvvvlm/PKXv4ymymtbrqqzzg2AUl588cUAgBIOHToUk5OTcfLkyWiqfGj/5JNPxu7du1t1mGX79u1x/PjxKEme1A9ZRtv+x1HcgQMHqglK+X3WtgOxV8vrWV7Xjh49GmfPno2mymtbrqqzzg2AUkxQAqCYLP3kRKK8ockVQ02R05JyClFORMnJKPfee2/r1h6tXr06SssxzdPPBh2372tRi5yelNo0PelasvCTxZ/Bta1p69/yn2dwbVNOAgAA2ihLPzmRqGkPybMgMT4+/uupKPnrtk3arWOSizypH/Y8HbV44oknqvcmZcsLkdeyvKYNrm1Nm0x09cQn5SQASjJBCYDanD9/Ps6cOVO96palpCz1rFu3LpYvX966QtK7Xb58Ob73ve9V7yXlabc89Zan3+ie6WcixmsoKOXkpJyglJOT2v69dy05VWlwfSs92exa8vqWRcssXnbx4wtAM5mgBEBdcuLP4cOHq8lKdcsCUpZ6du3aVa2fa+Pq76vl5JYHHnig+AQXeVK31ZUn5eSknKCUk5Pa/r13LTlVaXB9Kz3Z7FryY5qrH9tYtgSgvRSUAKhdlmpyPVKGIflQv9SapJwksnLlyl+/d02umcpXaWOPRDz35aBj8kTj1skr4eSFKO6RRx6ppvlkkabtE5RuZlBWyqJSvpdacZknB7N0mQFSF69vADSfghIAdcscKdcjHTt2rHqYX6pkk5NEsoyUK9yaNuVkGHLN1MTERJQmT+qmOvOkv/mbv6kOvL3vfe/r/IGsQVnp+eefr95LrbjM6UhZuuzq9Q2A5lNQAmDkLl68+OsH+lleyt/Pp7SUD+rzJjUnI+WJmnzvwpSkm6lrilI68vsRO7YGHZKjuA+9EMV1fXrSzWRhKa9pFy5cqN7z9/ma7zUur2lZ8sprXBaTTEoCYNQUlAAYtZmZmepB/ne/+93qYX7+fj6lpXxQn4c+soz0+OOPV+9dmJJ0M3VNUUrypO6pK0/q+vSkmxlc0/L6lu/5+3zN9xqX17R8z2tcFpNMSgJg1BSUAGikLN3kQ/yryzf5+3xAn/LhfL4Gv++ruqYoGc3dLRkkZaBUhz5NT5oP1zgA2k5BCYAmyof3736In7/PB/QpH87na/D7vqpripI8qVvqzJP6ND1pPlzjAGg7BSUAaLE6pygZzd0NdY7i7vv0JADoMgUlAGivOqcoyZO6oc48qe/TkwCgy24NAKC1svSxfv36qMPxlyKmnwlabvuf1BMmpcHXZhaUAAAAgGbI0sf4+HjUQZ7UDXXmSV/60peq91WrVgUA0C2eFgFAy2UJpK7pNONfi5h5LWipyWOzJ97qkNOTcj1ZlpOsdgMAAIBm2bt3b23TaeRJ7VZnnpTTk3Iad05PMo0bALpHQQkAWq7OKUpp51fqCyUYnkMvREx8I2pjehIAAAA0V51TlJI8qZ3qzpNMTwKAbvPECAA6IMsgy5YtizpkmJShEu2Rn7N9X4vavO997zM9CQAAABoupyht3rw56iBPap+686QsJ+X0pCwnmZ4EAN2koAQAHZA37Zs2bYq65FjufV8NWiDDpO1/EnH2QtQii0nr1q2rikmmJwEAAEBz5RSlgwcPRl3kSe1Rd560cePGar1bZpy53g0A6CZPjQCgI1auXFnr+OOpZ2d30NNcGSJlmFTnCPWc5pVhkulJAAAA0HxjY2PVqy7ypOYbRZ70xS9+0fQkAOgBBSUA6JCcolTnTXzuoJ9+Jmio7X9cb5i0evXquPvuu6tykulJAAAA0A45RSmnKdUl8yQlpeaqO0964oknqulJOZXb9CQA6DZPjgCgQ/JGPifY1Gn8axGHXwgaZs/Ts6PT6/T+97+/eldOAgAAgPbYvHlzjI+PR52ypCRPap5R5EkHDhyo3vPQGwDQbZ4eAUDHbNiwofbTRrufFio1SYZJh2r+fLzvfe+rCnJWuwEAAED77N+/P7Zs2RJ1kic1yyjypC996UtWuwFAjygoAUAH5aq3ugmVmmEUYdJgclcWk4RJAAAA0E656q1u8qRmGEWetHHjxvjiF79YZUlZUAIAum/Jhg0bJgIA6JTbb789brvttvjpT38adTp6IiJn54w9GtTs7IWITx2Y/RzUKUOkhx56qPp6y1+bngQA/fDUU08FANAtubp9zZo18c1vfjPqJE8anVHlSemZZ56Ju+66qzr0lhO5AYDu8xMfADrq3nvvHcnpo4lvREweC2p08icR2/844vhLUTur3QAAAKA7xsfHY2xsLOomT6rfKPOkycnJarXb6tWrTeMGgB5RUAKADstVb6O4yc9Qad9XgxpUYdKfRMy8FrW7++67Y926dVU5yUk3AAAA6IZc9ZaTlOomT6rPKPOkz3zmM/G7v/u7sWLFirjzzjsDAOgPT5IAoMNyss3mzZtjFKaejdg6MRt4UEaO3946OZqPcX5t5QjunJqknAQAAADdkVlSlpRGIfOkB/5QnlTSKPOkjRs3xpe+9KXqQOUoJr8DAKPlaRIAdFyOSs4iySjkKaw8jTWKUdFdl2PPd34l4uyFGIkHHnigKilloGS1GwAAAHTLjh07qnVvozCY7iNPGr5R50lf//rXq9Vu99xzj9VuANBDCkoA0AN54z+qU0mDffYZgLB4g49njj0flfvuu085CQAAADruwIEDMTY2FqMgTxquJuRJk5OTVUaZhymVkwCgnxSUAKAnNm3aFMuWLYtRyQDEyrfFGYzgHuUJwjzhtm7dumqtm9VuAAAA0G1HjhypVr6Nijxp8ZqQJ33hC1+I3/3d342VK1fGnXfeGQBAP92ybdu2twMA6IVLly7F97///bh8+XKMypoVV8KlT0fs/WQwRzl2e8/Ts4HSKC1fvjw++MEPVlOTbrvttgAA+uvFF18MAKAfTp48GVu3bo2zZ8/GqMiT5q8pedJjjz0W3/rWt+L222+Pe++9NwCA/nLsHQB6JNdyPfTQQzFKGY6Mf83pt7mafibigT8cfZiUXzsf+MAHqnKSMdwAAADQHzlBKScpjZI8aX4OvdCMPGnjxo3x9NNPV1nS2rVrAwDotyUbNmyYCACgN7JoktNvfvrTn8Yo/a8rf/vpZyPevBIwPbph9iQcv5Fjt/OU2589H/HzX8RI5dfMAw88UK0IzEApS0oAQL899dRTAQD0R5aU1qxZE9/85jdjlORJNzbIk/JjNOo8KctJX//612PTpk1xzz33OPAGACgoAUAfDXa9nz9/PkbtO69EHJuJuPtKoLTlA9F7eQpw39dmXyfPxMhleJRTt5STAICrKSgBQP989KMfrd6ff/75GDV50js1LU+666674r/8l/9STePOtW7KSQBAUlACgJ5atWpV9d6EklKO6c6R04e/3d9gKT8Gf/RfI/YcnA3ZmiDDo5yctHz5cuUkAOAdFJQAoJ/Gxsaq9yaUlORJzcyTspyUk5MefvjhWLduXTXJHQAg3bJt27a3AwDorVOnTlWvJtl8T8TEpyN2fSw6L0+45djtQy/MhkpNMSgnrVixQjkJAHiPF198MQCA/pqYmIjJycloEnlSM3zrW9+Kxx57rJqcdPvttwcAwICCEgDQyJJSymBp7JGI/Z+e/XWXHH8pYvLY7HvTZCHp/vvvj9WrV8ett95avQAArqagBAA0saSU5Emjc+DAgfjMZz4Ta9asqQ69AQBcTUEJAKg0taQ0kMHS7o+1+xRcnmibfibi0LdnT7o1kclJAMBcKCgBAKmpJaUBeVI9cq3b008/HR/72Mdi7dq1sXTp0gAAeDcFJQDg15peUkprVkTs2Brx5NbZ96bLEOnwlQDp6N8293TbgHISADBXCkoAwEDTS0pJnlROlpO+/vWvx2/91m/FunXrrHUDAK5LQQkAeIc2lJSutuNXwdLjH4jYsjFGLgOkmdcinv/BbIDU9BBpIE+2feADH1BOAgDmREEJALhaG0pKV5MnDcfGjRvjL/7iL+Kf/JN/Uk1OUk4CAG5EQQkAeI+///u/j9deey3aZvM9s6HS2KNXAqaNs79eU3jdfY7WztDou1c+XDN/NxsmZajUJllOyslJy5YtU04CAOZEQQkAeLepqanYt29ftI08aWGynJSTkzZt2hT33HNPlSkBANyIghIAcE3nz5+PH/3oR3H58uVoswyUMljKsClfm9bNvqfN6371fs97/7wMhQbB0Mkzv/n9d38VGGV4NPjjbbZ8+fKqnHTbbbcpJwEAc6agBABcy/Hjx2Pnzp1x9uzZaDN50o099thj8fTTT1eZUk5OUk4CAOZCQQkAuK5Lly7FD3/4w3jrrbeC7snTbRs2bIhbb71VkAQAzIuCEgBwPSdPnozt27dX73TPF77whWql38qVK+Ouu+4KAIC5ujUAAK4jV3996EMfijVr1gTdct9991XlpCwmKScBAAAAw7J58+Z47rnnYseOHUG3TE5OVuWk1atXKycBAPOmoAQA3FCWlB588MGqzEL7DT6fOT0p17rl9CQAAACAYcqS0pEjR2L//v1B+23cuDG+/vWvx1NPPVVlSnfeeWcAAMyXJ1IAwJxkQemhhx6KZcuWBe2Uo7cfeOCBWLVqVTU16ZZbbgkAAACAUnLaThaVsrBEOz3xxBNVOenjH/94VU7Kw28AAAuhoAQAzFmOb7byrZ1ypVuWk5YvX66cBAAAANQmV71Z+dZOudLtr/7qr+Kxxx6rykmZKQEALJSCEgAwL4MVYTnaWSjRfPn5+uAHP2ilGwAAADAyg5VvBw4ccPCtBTL3+9a3vlWtdLv33nutdAMAhsITKgBgQTKc+PCHPxwrVqwImilLSVlOyhDJ1CQAAABg1MbHx+PEiRMxNjYWNNMXvvCFqpz0z//5P6/yv9tvvz0AAIZBQQkAWLCczvPoo49Wp6qWLVsWNMPKlSurYtI/+kf/qPq8KCcBAAAATZHTlHLl28GDB6tf0wxPPPFEVUz6j//xP8ZDDz0Ud911l0ncAMBQ3bJt27a3AwBgkS5duhSnTp2KM2fOBKORRaT3ve991eSkDJCESABAKS+++GIAACzWyZMnY3JyMg4dOhSMRhaRvvSlL8V/+A//IVatWmWdGwBQjIISADBUFy9ejFdeeSXeeuutoD5ZSlq/fn01djuLSSYmAQAlKSgBAMM0MzMTO3furApL1CfXuX3xi1+M++67r5rI7bAbAFCS/9IAAIZq+fLl8dhjj1Ujuq19Ky/DowcffNA6NwAAAKC1tmzZEj/+8Y+tfatJrnP7+te/Xq1zy1zJOjcAoA4mKAEARb3xxhvV6jcTlYYri0k5MSlHb5uYBADUzQQlAKCkXPmWq99MVBquLCblxKSPf/zjVSlp6dKlAQBQFwUlAKAWikrDoZgEADSBghIAUAdFpeFQTAIAmkBBCQColaLSwigmAQBNoqAEANRJUWlhFJMAgCZRUAIARuLNN9+M06dPx7lz54JrW7JkSdx9991xzz33xLJlyxSTAIDGUFACAEbh6NGjMT09HcePHw+uLYtI/+7f/bv4whe+EI888kjceeedVcYEADBqCkoAwEhdunSpmqh0/vx5U5V+Jacl5aSkdevWxW233VaVkhSTAIAmUVACAEYpJynlRKUsKpmqNCunJf3Lf/kv49//+39fTeFesWJFddgNAKApFJQAgMbIqUpnz56NM2fORN/kSbaclJSn3PJkm1ISANBkCkoAQFPkVKVjx45Va+D6JnOknJT0qU99Kv7ZP/tnsXz58uqwGwBAEykoAQCNc/ny5aqslOvf8v2Xv/xldNHSpUurIGn16tXV1CQr3ACAtlBQAgCaJg+9ZVnp+eefr97z9120cePG+J3f+Z341//6X8e/+Bf/Iu64444qYwIAaDoFJQCg8XL9W4ZK+X7hwoVoq5ySlCfZBqWkZcuWmZQEALSSghIA0HS5/i0nK+X7zMxMtFXmSB/5yEeqUtK/+Tf/Jj74wQ9W+VLmTAAAbaKgBAC0yqVLl+LixYvVdKXBe1NdXUjK91zdNgiPlJIAgDZTUAIA2uTkyZNVSSmnK+V7lpaa6upC0pYtW+Kf/tN/Gvfcc0+1ui2nbwMAtJWCEgDQeqdOnapeTZGTkTZv3hwrVqyofq+MBAB0jYISANB2ExMTMTk5GU2RWdJ//s//ObZu3VqtbDMhCQDoGlVrAKD1NmzYEKtWrYqmyH+enJZkfRsAAABAM2VBaWxsLJpi//798cQTT1jfBgB0loISANAJWQpqgpyetHbt2gAAAACg2bIU1AQ5PWn37t0BANBlCkoAQCesXLky1q1bF6N2//33BwAAAADNlxOUmlAMOnDgQAAAdJ2CEgDQGTlFaZQjsLMgtXr16gAAAACgHbIctGbNmhiVLEjt2LEjAAC6TkEJAOiMpUuXxvr162NUmrJmDgAAAIC5yXLS+Ph4jEpT1swBAJSmoAQAdEoWlJYtWxZ1y3JSFqQAAAAAaJe9e/fG5s2bo25ZThrF3xcAYBQUlACATskVb5s2bYo6ZSEq17sBAAAA0D45RengwYNRpywm5Xo3AIC+UFACADpn5cqVsWrVqqiL6UkAAAAA7TY2Nla96mJ6EgDQNwpKAEAnZWmoDjk9ae3atQEAAABAux04cCDqYHoSANBHCkoAQCflFKX169dHaQ8++GAAAAAA0H5btmyJ8fHxKO3IkSMBANA3CkoAQGflFKUlS5ZEKevWrYvly5cHAAAAAN2Qq9fWrFkTpeTkpCxCAQD0jYISANBZWU4qOUWprjVyAAAAANQjy0lZUiql5F8bAKDJFJQAgE7LEtGyZcti2PKvu3Tp0gAAAACgW3LN2+bNm2PYspxU4q8LANAGCkoAQOdt2rQphikLT6YnAQAAAHTXwYMHY5iymDQxMREAAH2loAQAdN7KlStj1apVMSzKSQAAAADdNjY2Vr2GxWo3AKDvFJQAgF4Y1hSlFStWxNq1awMAAACAbhvWFKUtW7bE7t27AwCgzxSUAIBeWLp06VAmHz344IMBAAAAQPcNay3bkSNHAgCg7xSUAIDeWL9+fSxZsiQWat26dVXRCQAAAIB+2Lt3b6xZsyYWKicnZdEJAKDvFJQAgN7IctJ9990XC7Fs2bKhTGACAAAAoD2ynLR///5YiCwmLfTPBQDoGgUlAKBX7r333li1alXM19q1a01PAgAAAOih8fHxGBsbi/natWuX6UkAAL+ioAQA9M58JyGZngQAAADQb/OdhJTFpImJiQAAYJaCEgDQOytXrqzGc8+VchIAAABAv+UEpR07dsz5/2+1GwDAOykoAQC9dP/998eSJUtu+v9bt25dtd4NAAAAgH47cODAnA697d69u3oBAPAbCkoAQC8tXbo0Hn744Wp92/WsWrWqKjIBAAAAQK5te+6556r368lJS1lkAgDgnRSUAIDeWr58eXzoQx+qpiStWLGi+mO33XZbVUzKoCn/t7lMWQIAAACgH7Zs2VKVlHJCUv465VSlLCYdPHiw+t/mMmUJAKBvbtm2bdvbAQAAAABz9OKLLwYAAAAAzJUJSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAAAAAAQDEKSgAAAAAA/P/t2jEBAAAAwiD7pzbFPsgBAAAAZAQlAAAAAAAAAAAgIygBAAAAAAAAAAAZQQkAAAAAAAAAAMgISgAAAAAAAAAAQEZQAgAAAAAAAAAAMoISAAAAAAAAAACQEZQAAAAAAAAAAICMoAQAAAAAAAAAAGQEJQAAAAAAAAAAICMoAQAAAAAAAAAAGUEJAAAAAAAAAADICEoAAAAAAAAAAEBGUAIAAABgAAAAAFARlAAAAAAAAAAAgIygBAAAAAAAAAAAZAQlAAAAAAAAAAAgIygBAAAAAAAAAAAZQQkAAAAAAAAAAMgISgAAAAAAAAAAQEZQAgAAAAAAAAAAMoISAAAAAAAAAACQEZQAAAAAAAAAAICMoAQAAAAAAAAAAGQEJQAAAAAAAAAAICMoAQAAAAAAAAAAGUEJAAAAAAAAAADICEoAAAAAAAAAAEBGUAIAAAAAAAAAADKCEgAAAAAAAAAAkBGUAAAAAAAAAACAjKAEAAAAAAAAAABkBCUAAAAAAAAAACAjKAEAAAAAAAAAABlBCQAAAAAAAAAAyAhKAAAAAAAAAABARlACAAAAAAAAAAAyghIAAAAAAAAAAJARlAAAAAAAAAAAgIygBAAAAAAAAAAAZAQlAAAAAAAAAAAgIygBAAAAAAAAAAAZQQkAAAAAAAAAAMgISgAAAAAAAAAAQEZQAgAAAAAAAAAAMoISAAAAAAAAAACQEZQAAAAAAAAAAICMoAQAAAAAAAAAAGQEJQAAAAAAAAAAICMoAQAAAAAAAAAAGUEJAAAAAAAAAADICEoAAAAAAAAAAEBGUAIAAAAAAAAAADKCEgAAAAAAAAAAkBGUAAAAAAAAAACAjKAEAAAAAAAAAABkBCUAAAAAAAAAACAjKAEAAAAAAAAAABlBCQAAAAAAAAAAyAhKAAAAAAAAAABARlACAAAAAAAAAAAyghIAAAAAAAAAAJARlAAAAAAAAAAAgIygBAAAAAAAAAAAZAQlAAAAAAAAAAAgIygBAAAAAAAAAAAZQQkAAAAAAAAAAMgISgAAAAAAAAAAQEZQAgAAAAAAAAAAMoISAAAAAAAAAACQEZQAAAAAAAAAAICMoAQAAAAAAAAAAGQEJQAAAAAAAAAAICMoAQAAAAAAAAAAGUEJAAAAAAAAAADICEoAAAAAAAAAAEBGUAIAAAAAAAAAADKCEgAAAAAAAAAAkBGUAAAAAAAAAACAjKAEAAAAAAAAAABkBCUAAAAAAAAAACAjKAEAAAAAAAAAABlBCQAAAAAAAAAAyAhKAAAAAAAAAABARlACAAAAAAAAAAAyghIAAAAAAAAAAJARlAAAAAAAAAAAgIygBAAAAAAAAAAAZAQlAAAAAAAAAAAgIygBAAAAAAAAAAAZQQkAAAAAAAAAAMgISgAAAAAAAAAAQEZQAgAAAAAAAAAAMoISAAAAAAAAAACQEZQAAAAAAAAAAICMoAQAAAAAAAAAAGQEJQAAAAAAAAAAICMoAQAAAAAAAAAAGUEJAAAAAAAAAADICEoAAAAAAAAAAEBGUAIAAAAAAAAAADKCEgAAAAAAAAAAkBGUAAAAAAAAAACAjKAEAAAAAAAAAABkBCUAAAAAAAAAACAjKAEAAAAAAAAAABlBCQAAAAAAAAAAyAhKAAAAAAAAAABARlACAAAAAAAAAAAyghIAAAAAAAAAAJARlAAAAAAAAAAAgIygBAAAAAAAAAAAZAQlAAAAAAAAAAAgIygBAAAAAAAAAAAZQQkAAAAAAAAAAMgISgAAAAAAAAAAQEZQAgAAAAAAAAAAMoISAAAAAAAAAACQEZQAAAAAAAAAAICMoAQAAAAAAAAAAGQEJQAAAAAAAAAAICMoAQAAAAAAAAAAGUEJAAAAAAAAAADICEoAAAAAAAAAAEBGUAIAAAAAAAAAADKCEgAAAAAAAAAAkBGUAAAAAAAAAACAjKAEAAAAAAAAAABkBCUAAAAAAAAAACAjKAEAAAAAAAAAABlBCQAAAAAAAAAAyAhKAAAAAAAAAABARlACAAAAAAAAAAAyghIAAAAAAAAAAJARlAAAAAAAAAAAgIygBAAAAAAAAAAAZAQlAAAAAAAAAAAgIygBAAAAAAAAAAAZQQkAAAAAAAAAAMgISgAAAAAAAAAAQEZQAgAAAAAAAAAAMoISAAAAAAAAAACQEZQAAAAAAAAAAICMoAQAAAAAAAAAAGQEJQAAAAAAAAAAICMoAQAAAAAAAAAAGUEJAAAAAAAAAADICEoAAAAAAAAAAEBGUAIAAAAAAAAAADKCEgAAAAAAAAAAkBGUAAAAAAAAAACAjKAEAAAAAAAAAABkBCUAAAAAAAAAACAjKAEAAAAAAAAAABlBCQAAAAAAAAAAyAhKAAAAAAAAAABARlACAAAAAAAAAAAyghIAAAAAAAAAAJARlAAAAAAAAAAAgIygBAAAAAAAAAAAZAQlAAAAAAAAAAAgIygBAAAAAAAAAAAZQQkAAAAAAAAAAMgISgAAAAAAAAAAQEZQAgAAAAAAAAAAMoISAAAAAAAAAACQEZQAAAAAAAAAAICMoAQAAAAAAAAAAGQEJQAAAAAAAAAAICMoAQAAAAAAAAAAGUEJAAAAAAAAAADICEoAAAAAAAAAAEBGUAIAAAAAAAAAADKCEgAAAAAAAAAAkBGUAAAAAAAAAACAjKAEAAAAAAAAAABkBCUAAAAAAAAAACAjKAEAAAAAAAAAABlBCQAAAAAAAAAAyAhKAAAAAAAAAABARlACAAAAAAAAAAAyghIAAAAAAAAAAJARlAAAAAAAAAAAgIygBAAAAAAAAAAAZAQlAAAAAAAAAAAgIygBAAAAAAAAAAAZQQkAAAAAAAAAAMgISgAAAAAAAAAAQEZQAgAAAAAAAAAAMoISAAAAAAAAAACQEZQAAAAAAAAAAICMoAQAAAAAAAAAAGQEJQAAAAAAAAAAICMoAQAAAAAAAAAAGUEJAAAAAAAAAADICEoAAAAAAAAAAEBGUAIAAAAAAAAAADKCEgAAAAAAAAAAkBGUAAAAAAAAAACAjKAEAAAAAAAAAABkBCUAAAAAAAAAACAjKAEAAAAAAAAAABlBCQAAAAAAAAAAyAhKAAAAAAAAAABARlACAAAAAAAAAAAyghIAAAAAAAAAAJARlAAAAAAAAAAAgIygBAAAAAAAAAAAZAQlAAAAAAAAAAAgIygBAAAAAAAAAAAZQQkAAAAAAAAAAMgISgAAAAAAAAAAQEZQAgAAAAAAAAAAMoISAAAAAAAAAACQEZQAAAAAAAAAAICMoAQAAAAAAAAAAGQEJQAAAAAAAAAAICMoAQAAAAAAAAAAGUEJAAAAAAAAAADICEoAAAAAAAAAAEBGUAIAAAAAAAAAADKCEgAAAAAAAAAAkBGUAAAAAAAAAACAjKAEAAAAAAAAAABkBCUAAAAAAAAAACAjKAEAAAAAAAAAABlBCQAAAAAAAAAAyAhKAAAAAAAAAABA5rcwQPH6Y8W9AAAAAElFTkSuQmCC","lightningAddress":"fd5ce42fc3e44e17@coinos.io","zapSplits":[{"pubkey":"1bc70a0148b3f316da33fe3c89f23e3e71ac4ff998027ec712b905cd24f6a411","weight":95,"relay":"wss://relay.damus.io"},{"pubkey":"1bc70a0148b3f316da33fe3c89f23e3e71ac4ff998027ec712b905cd24f6a411","weight":5,"relay":"wss://nos.lol"}]}
-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:22
@ 04c915da:3dfbecc9
2025-05-20 15:50:22There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 207ad2a0:e7cca7b0
2025-01-07 03:46:04
@ 207ad2a0:e7cca7b0
2025-01-07 03:46:04Quick context: I wanted to check out Nostr's longform posts and this blog post seemed like a good one to try and mirror. It's originally from my free to read/share attempt to write a novel, but this post here is completely standalone - just describing how I used AI image generation to make a small piece of the work.
Hold on, put your pitchforks down - outside of using Grammerly & Emacs for grammatical corrections - not a single character was generated or modified by computers; a non-insignificant portion of my first draft originating on pen & paper. No AI is ~~weird and crazy~~ imaginative enough to write like I do. The only successful AI contribution you'll find is a single image, the map, which I heavily edited. This post will go over how I generated and modified an image using AI, which I believe brought some value to the work, and cover a few quick thoughts about AI towards the end.
Let's be clear, I can't draw, but I wanted a map which I believed would improve the story I was working on. After getting abysmal results by prompting AI with text only I decided to use "Diffuse the Rest," a Stable Diffusion tool that allows you to provide a reference image + description to fine tune what you're looking for. I gave it this Microsoft Paint looking drawing:
and after a number of outputs, selected this one to work on:
The image is way better than the one I provided, but had I used it as is, I still feel it would have decreased the quality of my work instead of increasing it. After firing up Gimp I cropped out the top and bottom, expanded the ocean and separated the landmasses, then copied the top right corner of the large landmass to replace the bottom left that got cut off. Now we've got something that looks like concept art: not horrible, and gets the basic idea across, but it's still due for a lot more detail.

The next thing I did was add some texture to make it look more map like. I duplicated the layer in Gimp and applied the "Cartoon" filter to both for some texture. The top layer had a much lower effect strength to give it a more textured look, while the lower layer had a higher effect strength that looked a lot like mountains or other terrain features. Creating a layer mask allowed me to brush over spots to display the lower layer in certain areas, giving it some much needed features.
At this point I'd made it to where I felt it may improve the work instead of detracting from it - at least after labels and borders were added, but the colors seemed artificial and out of place. Luckily, however, this is when PhotoFunia could step in and apply a sketch effect to the image.
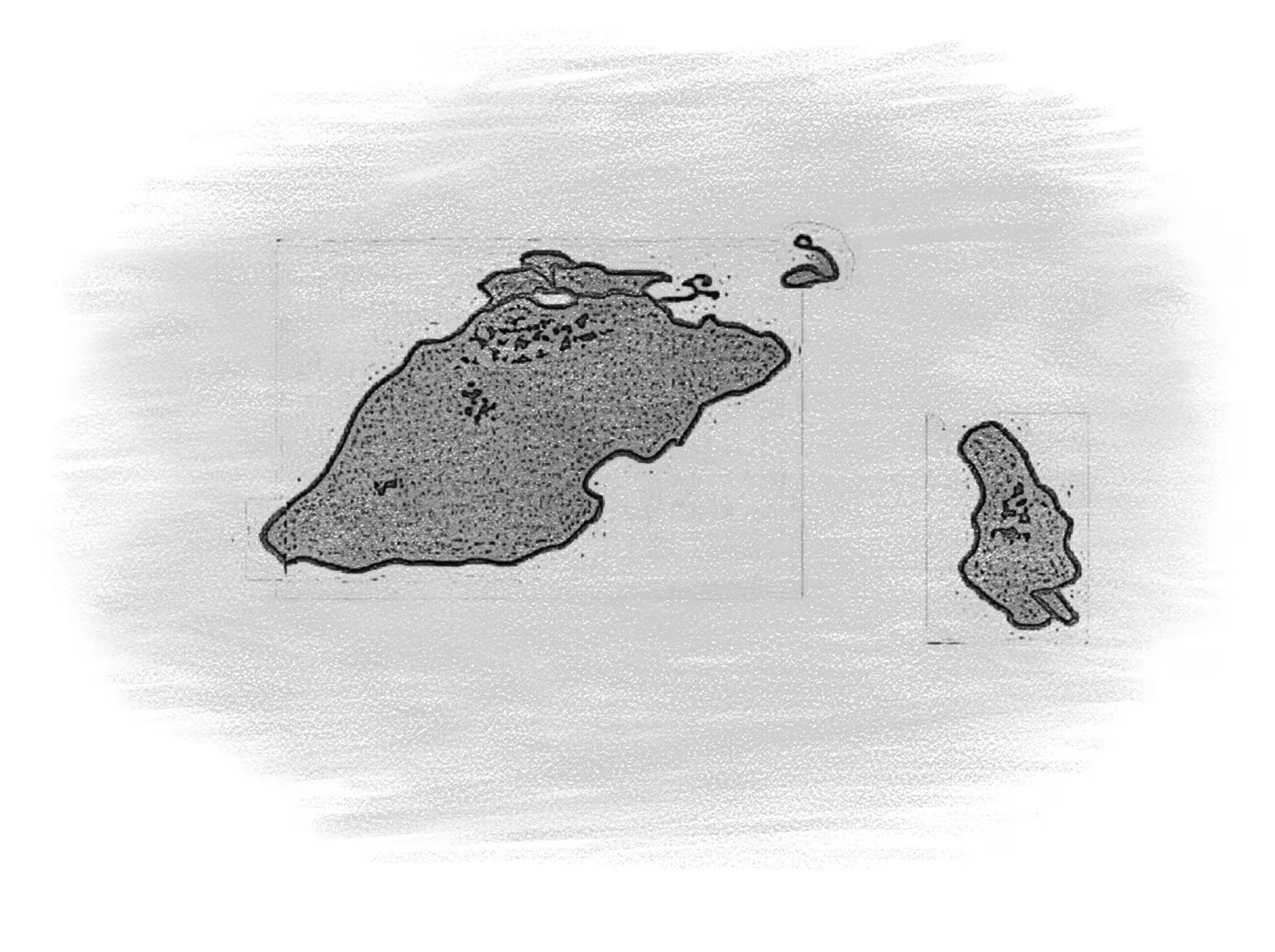
At this point I was pretty happy with how it was looking, it was close to what I envisioned and looked very visually appealing while still being a good way to portray information. All that was left was to make the white background transparent, add some minor details, and add the labels and borders. Below is the exact image I wound up using:

Overall, I'm very satisfied with how it turned out, and if you're working on a creative project, I'd recommend attempting something like this. It's not a central part of the work, but it improved the chapter a fair bit, and was doable despite lacking the talent and not intending to allocate a budget to my making of a free to read and share story.
The AI Generated Elephant in the Room
If you've read my non-fiction writing before, you'll know that I think AI will find its place around the skill floor as opposed to the skill ceiling. As you saw with my input, I have absolutely zero drawing talent, but with some elbow grease and an existing creative direction before and after generating an image I was able to get something well above what I could have otherwise accomplished. Outside of the lowest common denominators like stock photos for the sole purpose of a link preview being eye catching, however, I doubt AI will be wholesale replacing most creative works anytime soon. I can assure you that I tried numerous times to describe the map without providing a reference image, and if I used one of those outputs (or even just the unedited output after providing the reference image) it would have decreased the quality of my work instead of improving it.
I'm going to go out on a limb and expect that AI image, text, and video is all going to find its place in slop & generic content (such as AI generated slop replacing article spinners and stock photos respectively) and otherwise be used in a supporting role for various creative endeavors. For people working on projects like I'm working on (e.g. intended budget $0) it's helpful to have an AI capable of doing legwork - enabling projects to exist or be improved in ways they otherwise wouldn't have. I'm also guessing it'll find its way into more professional settings for grunt work - think a picture frame or fake TV show that would exist in the background of an animated project - likely a detail most people probably wouldn't notice, but that would save the creators time and money and/or allow them to focus more on the essential aspects of said work. Beyond that, as I've predicted before: I expect plenty of emails will be generated from a short list of bullet points, only to be summarized by the recipient's AI back into bullet points.
I will also make a prediction counter to what seems mainstream: AI is about to peak for a while. The start of AI image generation was with Google's DeepDream in 2015 - image recognition software that could be run in reverse to "recognize" patterns where there were none, effectively generating an image from digital noise or an unrelated image. While I'm not an expert by any means, I don't think we're too far off from that a decade later, just using very fine tuned tools that develop more coherent images. I guess that we're close to maxing out how efficiently we're able to generate images and video in that manner, and the hard caps on how much creative direction we can have when using AI - as well as the limits to how long we can keep it coherent (e.g. long videos or a chronologically consistent set of images) - will prevent AI from progressing too far beyond what it is currently unless/until another breakthrough occurs.
-
 @ 7e3784e5:5d820637
2025-05-31 03:35:02
@ 7e3784e5:5d820637
2025-05-31 03:35:02{"pattern":{"kick":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"snare":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"hihat":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"openhat":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"crash":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"ride":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"tom1":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"tom2":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false]},"bpm":120,"swing":0,"timeSignature":"4/4","drumKit":"standard","timestamp":1748662502742}
-
 @ 0fa80bd3:ea7325de
2025-01-30 04:28:30
@ 0fa80bd3:ea7325de
2025-01-30 04:28:30"Degeneration" or "Вырождение" ![[photo_2025-01-29 23.23.15.jpeg]]
A once-functional object, now eroded by time and human intervention, stripped of its original purpose. Layers of presence accumulate—marks, alterations, traces of intent—until the very essence is obscured. Restoration is paradoxical: to reclaim, one must erase. Yet erasure is an impossibility, for to remove these imprints is to deny the existence of those who shaped them.
The work stands as a meditation on entropy, memory, and the irreversible dialogue between creation and decay.
-
 @ e6817453:b0ac3c39
2025-01-05 14:29:17
@ e6817453:b0ac3c39
2025-01-05 14:29:17The Rise of Graph RAGs and the Quest for Data Quality
As we enter a new year, it’s impossible to ignore the boom of retrieval-augmented generation (RAG) systems, particularly those leveraging graph-based approaches. The previous year saw a surge in advancements and discussions about Graph RAGs, driven by their potential to enhance large language models (LLMs), reduce hallucinations, and deliver more reliable outputs. Let’s dive into the trends, challenges, and strategies for making the most of Graph RAGs in artificial intelligence.
Booming Interest in Graph RAGs
Graph RAGs have dominated the conversation in AI circles. With new research papers and innovations emerging weekly, it’s clear that this approach is reshaping the landscape. These systems, especially those developed by tech giants like Microsoft, demonstrate how graphs can:
- Enhance LLM Outputs: By grounding responses in structured knowledge, graphs significantly reduce hallucinations.
- Support Complex Queries: Graphs excel at managing linked and connected data, making them ideal for intricate problem-solving.
Conferences on linked and connected data have increasingly focused on Graph RAGs, underscoring their central role in modern AI systems. However, the excitement around this technology has brought critical questions to the forefront: How do we ensure the quality of the graphs we’re building, and are they genuinely aligned with our needs?
Data Quality: The Foundation of Effective Graphs
A high-quality graph is the backbone of any successful RAG system. Constructing these graphs from unstructured data requires attention to detail and rigorous processes. Here’s why:
- Richness of Entities: Effective retrieval depends on graphs populated with rich, detailed entities.
- Freedom from Hallucinations: Poorly constructed graphs amplify inaccuracies rather than mitigating them.
Without robust data quality, even the most sophisticated Graph RAGs become ineffective. As a result, the focus must shift to refining the graph construction process. Improving data strategy and ensuring meticulous data preparation is essential to unlock the full potential of Graph RAGs.
Hybrid Graph RAGs and Variations
While standard Graph RAGs are already transformative, hybrid models offer additional flexibility and power. Hybrid RAGs combine structured graph data with other retrieval mechanisms, creating systems that:
- Handle diverse data sources with ease.
- Offer improved adaptability to complex queries.
Exploring these variations can open new avenues for AI systems, particularly in domains requiring structured and unstructured data processing.
Ontology: The Key to Graph Construction Quality
Ontology — defining how concepts relate within a knowledge domain — is critical for building effective graphs. While this might sound abstract, it’s a well-established field blending philosophy, engineering, and art. Ontology engineering provides the framework for:
- Defining Relationships: Clarifying how concepts connect within a domain.
- Validating Graph Structures: Ensuring constructed graphs are logically sound and align with domain-specific realities.
Traditionally, ontologists — experts in this discipline — have been integral to large enterprises and research teams. However, not every team has access to dedicated ontologists, leading to a significant challenge: How can teams without such expertise ensure the quality of their graphs?
How to Build Ontology Expertise in a Startup Team
For startups and smaller teams, developing ontology expertise may seem daunting, but it is achievable with the right approach:
- Assign a Knowledge Champion: Identify a team member with a strong analytical mindset and give them time and resources to learn ontology engineering.
- Provide Training: Invest in courses, workshops, or certifications in knowledge graph and ontology creation.
- Leverage Partnerships: Collaborate with academic institutions, domain experts, or consultants to build initial frameworks.
- Utilize Tools: Introduce ontology development tools like Protégé, OWL, or SHACL to simplify the creation and validation process.
- Iterate with Feedback: Continuously refine ontologies through collaboration with domain experts and iterative testing.
So, it is not always affordable for a startup to have a dedicated oncologist or knowledge engineer in a team, but you could involve consulters or build barefoot experts.
You could read about barefoot experts in my article :
Even startups can achieve robust and domain-specific ontology frameworks by fostering in-house expertise.
How to Find or Create Ontologies
For teams venturing into Graph RAGs, several strategies can help address the ontology gap:
-
Leverage Existing Ontologies: Many industries and domains already have open ontologies. For instance:
-
Public Knowledge Graphs: Resources like Wikipedia’s graph offer a wealth of structured knowledge.
- Industry Standards: Enterprises such as Siemens have invested in creating and sharing ontologies specific to their fields.
-
Business Framework Ontology (BFO): A valuable resource for enterprises looking to define business processes and structures.
-
Build In-House Expertise: If budgets allow, consider hiring knowledge engineers or providing team members with the resources and time to develop expertise in ontology creation.
-
Utilize LLMs for Ontology Construction: Interestingly, LLMs themselves can act as a starting point for ontology development:
-
Prompt-Based Extraction: LLMs can generate draft ontologies by leveraging their extensive training on graph data.
- Domain Expert Refinement: Combine LLM-generated structures with insights from domain experts to create tailored ontologies.
Parallel Ontology and Graph Extraction
An emerging approach involves extracting ontologies and graphs in parallel. While this can streamline the process, it presents challenges such as:
- Detecting Hallucinations: Differentiating between genuine insights and AI-generated inaccuracies.
- Ensuring Completeness: Ensuring no critical concepts are overlooked during extraction.
Teams must carefully validate outputs to ensure reliability and accuracy when employing this parallel method.
LLMs as Ontologists
While traditionally dependent on human expertise, ontology creation is increasingly supported by LLMs. These models, trained on vast amounts of data, possess inherent knowledge of many open ontologies and taxonomies. Teams can use LLMs to:
- Generate Skeleton Ontologies: Prompt LLMs with domain-specific information to draft initial ontology structures.
- Validate and Refine Ontologies: Collaborate with domain experts to refine these drafts, ensuring accuracy and relevance.
However, for validation and graph construction, formal tools such as OWL, SHACL, and RDF should be prioritized over LLMs to minimize hallucinations and ensure robust outcomes.
Final Thoughts: Unlocking the Power of Graph RAGs
The rise of Graph RAGs underscores a simple but crucial correlation: improving graph construction and data quality directly enhances retrieval systems. To truly harness this power, teams must invest in understanding ontologies, building quality graphs, and leveraging both human expertise and advanced AI tools.
As we move forward, the interplay between Graph RAGs and ontology engineering will continue to shape the future of AI. Whether through adopting existing frameworks or exploring innovative uses of LLMs, the path to success lies in a deep commitment to data quality and domain understanding.
Have you explored these technologies in your work? Share your experiences and insights — and stay tuned for more discussions on ontology extraction and its role in AI advancements. Cheers to a year of innovation!
-
 @ d61f3bc5:0da6ef4a
2025-05-06 01:37:28
@ d61f3bc5:0da6ef4a
2025-05-06 01:37:28I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ c230edd3:8ad4a712
2025-05-31 01:51:38
@ c230edd3:8ad4a712
2025-05-31 01:51:38Chef's notes
Most Santa Maria tri tip roast recipes call for red wine vinegar and dijon mustard. I prefer other ingredients in place of those, but should you like those flavors and textures, they are more traditional.
Keep in mind when cooking and slicing, that the grain of tri-tip runs in 3 directions and the meat is unevenly thick. Pulling the roast when the thin end achieves well done, the thicker end will be a nice medium rare. When slicing, change direction to cut against the grain as you transition through for the most tender outcome.
Details
- ⏲️ Prep time: 10 minutes
- 🍳 Cook time: 1 hour ( with grill heating time)
- 🍽️ Servings: 4-6
Ingredients
- 1.5 - 2 lb Tri-Tip Roast
- 1 Tbsp Kosher Salt
- 1 tsp Black Pepper
- 1 tsp Cayanne Pepper ( substitute all or some with smoked paprika for a milder taste)
- 1 tsp Garlic Powder
- 1 tsp Onion Powder
- 1 Tbsp Rosemary
- 2 Tbsp Stone Ground Mustard
- 1 Tbsp Rice Vinegar
- 2-3 Cloves Garlic, Minced
Directions
- Mix all dry spices.
- Pat the roast dry and coat on all sides with seasdoning mix.
- Cover loosely and allow to sit in fridge for 8-12 hours.
- Preheat grill to 475 degrees F, allow meat to sit at room temp during this process.
- Mix vinegar, mustard, and minced garlic.
- Place meat on hot grill, fat side down and coat the upward side with mustard mix
- Grill approximately 7-10 minutes.
- Flip meat, repeat coating and grilling.
- Flip once more and grill for 2-3 minutes to caramelize the glaze and until the fat begins to render.
- Remove from grill and let the roast rest for 5 minutes before slicing,
- Serve with grilled veggies or any side of your choice. This is a bit spicy so it goes well with a salsa fresca and tortillas, too.
-
 @ a4a6b584:1e05b95b
2025-01-02 18:13:31
@ a4a6b584:1e05b95b
2025-01-02 18:13:31The Four-Layer Framework
Layer 1: Zoom Out

Start by looking at the big picture. What’s the subject about, and why does it matter? Focus on the overarching ideas and how they fit together. Think of this as the 30,000-foot view—it’s about understanding the "why" and "how" before diving into the "what."
Example: If you’re learning programming, start by understanding that it’s about giving logical instructions to computers to solve problems.
- Tip: Keep it simple. Summarize the subject in one or two sentences and avoid getting bogged down in specifics at this stage.
Once you have the big picture in mind, it’s time to start breaking it down.
Layer 2: Categorize and Connect

Now it’s time to break the subject into categories—like creating branches on a tree. This helps your brain organize information logically and see connections between ideas.
Example: Studying biology? Group concepts into categories like cells, genetics, and ecosystems.
- Tip: Use headings or labels to group similar ideas. Jot these down in a list or simple diagram to keep track.
With your categories in place, you’re ready to dive into the details that bring them to life.
Layer 3: Master the Details

Once you’ve mapped out the main categories, you’re ready to dive deeper. This is where you learn the nuts and bolts—like formulas, specific techniques, or key terminology. These details make the subject practical and actionable.
Example: In programming, this might mean learning the syntax for loops, conditionals, or functions in your chosen language.
- Tip: Focus on details that clarify the categories from Layer 2. Skip anything that doesn’t add to your understanding.
Now that you’ve mastered the essentials, you can expand your knowledge to include extra material.
Layer 4: Expand Your Horizons

Finally, move on to the extra material—less critical facts, trivia, or edge cases. While these aren’t essential to mastering the subject, they can be useful in specialized discussions or exams.
Example: Learn about rare programming quirks or historical trivia about a language’s development.
- Tip: Spend minimal time here unless it’s necessary for your goals. It’s okay to skim if you’re short on time.
Pro Tips for Better Learning
1. Use Active Recall and Spaced Repetition
Test yourself without looking at notes. Review what you’ve learned at increasing intervals—like after a day, a week, and a month. This strengthens memory by forcing your brain to actively retrieve information.
2. Map It Out
Create visual aids like diagrams or concept maps to clarify relationships between ideas. These are particularly helpful for organizing categories in Layer 2.
3. Teach What You Learn
Explain the subject to someone else as if they’re hearing it for the first time. Teaching exposes any gaps in your understanding and helps reinforce the material.
4. Engage with LLMs and Discuss Concepts
Take advantage of tools like ChatGPT or similar large language models to explore your topic in greater depth. Use these tools to:
- Ask specific questions to clarify confusing points.
- Engage in discussions to simulate real-world applications of the subject.
- Generate examples or analogies that deepen your understanding.Tip: Use LLMs as a study partner, but don’t rely solely on them. Combine these insights with your own critical thinking to develop a well-rounded perspective.
Get Started
Ready to try the Four-Layer Method? Take 15 minutes today to map out the big picture of a topic you’re curious about—what’s it all about, and why does it matter? By building your understanding step by step, you’ll master the subject with less stress and more confidence.
-
 @ 812cff5a:5c40aeeb
2025-05-31 01:12:55
@ 812cff5a:5c40aeeb
2025-05-31 01:12:55NIP-02 — أنماط المفاتيح العامة
رقم التعريف (NIP): 02
العنوان: أنماط المفاتيح العامة
الحالة: نهائي
المؤلف: fiatjaf
التاريخ: 2020-12-10
الملخص
يقترح هذا المستند نمطًا معياريًا لطريقة تمثيل المفاتيح العامة (public keys) في نُستر — يُعرف باسم
npub— لتسهيل مشاركتها وقراءتها من قبل البشر، تمامًا كما يتم تمثيل عناوين البيتكوين بـ bech32.
التنسيق المقترح
نقترح استخدام bech32 لترميز المفاتيح العامة، حيث يكون التنسيق كالتالي:
npub1<سلسلة bech32>على سبيل المثال:
npub1qqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqzv9sxهذا الشكل يمكن نسخه بسهولة، والتعرف عليه بصريًا، والتعامل معه دون الوقوع في أخطاء النسخ الشائعة للمفاتيح بصيغ hex.
السبب
- الشكل hex التقليدي للمفاتيح العامة (مثل
32e...af1) صعب القراءة. - bech32 أسهل للمشاركة عبر الرسائل أو الوسائط الاجتماعية.
- وجود بادئة
npub1يوضح فورًا أن السلسلة تمثل مفتاحًا عامًا في نظام نُستر.
ملاحظات إضافية
- نفس المبدأ يُستخدم أيضًا مع أنواع أخرى مثل
note(لتمثيل معرفات الأحداث) وnsec(للمفاتيح الخاصة). - هذه الصيغ لا تغيّر البيانات الأصلية، بل فقط تمثلها بطريقة أسهل وأكثر أمانًا للبشر.
الخلاصة
npubهو معيار لتنسيق المفاتيح العامة باستخدام bech32، مما يجعلها أكثر قابلية للقراءة والاستخدام من قبل البشر.
يُوصى بأن تستخدم جميع تطبيقات نُستر هذا النمط عند عرض أو مشاركة المفاتيح العامة. - الشكل hex التقليدي للمفاتيح العامة (مثل
-
 @ fd208ee8:0fd927c1
2024-12-26 07:02:59
@ fd208ee8:0fd927c1
2024-12-26 07:02:59I just read this, and found it enlightening.
Jung... notes that intelligence can be seen as problem solving at an everyday level..., whereas creativity may represent problem solving for less common issues
Other studies have used metaphor creation as a creativity measure instead of divergent thinking and a spectrum of CHC components instead of just g and have found much higher relationships between creativity and intelligence than past studies
https://www.mdpi.com/2079-3200/3/3/59
I'm unusually intelligent (Who isn't?), but I'm much more creative, than intelligent, and I think that confuses people. The ability to apply intelligence, to solve completely novel problems, on the fly, is something IQ tests don't even claim to measure. They just claim a correlation.
Creativity requires taking wild, mental leaps out into nothingness; simply trusting that your brain will land you safely. And this is why I've been at the forefront of massive innovation, over and over, but never got rich off of it.
I'm a starving autist.
Zaps are the first time I've ever made money directly, for solving novel problems. Companies don't do this because there is a span of time between providing a solution and the solution being implemented, and the person building the implementation (or their boss) receives all the credit for the existence of the solution. At best, you can hope to get pawned off with a small bonus.
Nobody can remember who came up with the solution, originally, and that person might not even be there, anymore, and probably never filed a patent, and may have no idea that their idea has even been built. They just run across it, later, in a tech magazine or museum, and say, "Well, will you look at that! Someone actually went and built it! Isn't that nice!"
Universities at least had the idea of cementing novel solutions in academic papers, but that: 1) only works if you're an academic, and at a university, 2) is an incredibly slow process, not appropriate for a truly innovative field, 3) leads to manifestations of perverse incentives and biased research frameworks, coming from 'publish or perish' policies.
But I think long-form notes and zaps solve for this problem. #Alexandria, especially, is being built to cater to this long-suffering class of chronic underachievers. It leaves a written, public, time-stamped record of Clever Ideas We Have Had.
Because they are clever, the ideas. And we have had them.
-
 @ 4ba8e86d:89d32de4
2025-05-19 10:13:19
@ 4ba8e86d:89d32de4
2025-05-19 10:13:19DTails é uma ferramenta que facilita a inclusão de aplicativos em imagens de sistemas live baseados em Debian, como o Tails. Com ela, você pode personalizar sua imagem adicionando os softwares que realmente precisa — tudo de forma simples, transparente e sob seu controle total.
⚠️ DTails não é uma distribuição. É uma ferramenta de remasterização de imagens live.
Ela permite incluir softwares como:
✅ SimpleX Chat ✅ Clientes Nostr Web (Snort & Iris) ✅ Sparrow Wallet ✅ Feather Wallet ✅ Cake Wallet ✅ RoboSats ✅ Bisq ✅ BIP39 (Ian Coleman) ✅ SeedTool ... e muito mais. https://image.nostr.build/b0bb1f0da5a9a8fee42eacbddb156fc3558f4c3804575d55eeefbe6870ac223e.jpg
Importante: os binários originais dos aplicativos não são modificados, garantindo total transparência e permitindo a verificação de hashes a qualquer momento.
👨💻 Desenvolvido por: nostr:npub1dtmp3wrkyqafghjgwyk88mxvulfncc9lg6ppv4laet5cun66jtwqqpgte6
GitHub: https://github.com/DesobedienteTecnologico/dtails?tab=readme-ov-file
🎯 Controle total do que será instalado
Com o DTails, você escolhe exatamente o que deseja incluir na imagem personalizada. Se não marcar um aplicativo, ele não será adicionado, mesmo que esteja disponível. Isso significa: privacidade, leveza e controle absoluto.
https://image.nostr.build/b0bb1f0da5a9a8fee42eacbddb156fc3558f4c3804575d55eeefbe6870ac223e.jpg https://image.nostr.build/b70ed11ad2ce0f14fd01d62c08998dc18e3f27733c8d7e968f3459846fb81baf.jpg https://image.nostr.build/4f5a904218c1ea6538be5b3f764eefda95edd8f88b2f42ac46b9ae420b35e6f6.jpg
⚙️ Começando com o DTails
📦 Requisitos de pacotes
Antes de tudo, instale os seguintes pacotes no Debian:
``` sudo apt-get install genisoimage parted squashfs-tools syslinux-utils build-essential python3-tk python3-pil.imagetk python3-pyudev
```
🛠 Passo a passo
1 Clone o repositório:
``` git clone https://github.com/DesobedienteTecnologico/dtails cd dtails
```
2 Inicie a interface gráfica com sudo:
``` sudo ./dtails.py
```
Por que usar sudo? É necessário para montar arquivos .iso ou .img e utilizar ferramentas essenciais do sistema.
💿 Selecione a imagem Tails que deseja modificar
https://nostr.download/e3143dcd72ab6dcc86228be04d53131ccf33d599a5f7f2f1a5c0d193557dac6b.jpg
📥 Adicione ou remova pacotes
1 Marque os aplicativos desejados. 2 Clique Buildld para gerar sua imagem personalizada. https://image.nostr.build/5c4db03fe33cd53d06845074d03888a3ca89c3e29b2dc1afed4d9d181489b771.png
Você pode acompanhar todo o processo diretamente no terminal. https://nostr.download/1d959f4be4de9fbb666ada870afee4a922fb5e96ef296c4408058ec33cd657a8.jpg
💽 .ISO vs .IMG — Qual escolher?
| Formato | Persistência | Observações | | ------- | ---------------------- | ----------------------------------------------- | | .iso | ❌ Não tem persistência | Gera o arquivo DTails.iso na pasta do projeto | | .img | ✅ Suporta persistência | Permite gravar diretamente em um pendrive |
https://nostr.download/587fa3956df47a38b169619f63c559928e6410c3dd0d99361770a8716b3691f6.jpg https://nostr.download/40c7c5badba765968a1004ebc67c63a28b9ae3b5801addb02166b071f970659f.jpg
vídeo
https://www.youtube.com/live/QABz-GOeQ68?si=eYX-AHsolbp_OmAm
-
 @ 7e3784e5:5d820637
2025-05-31 03:30:55
@ 7e3784e5:5d820637
2025-05-31 03:30:55{"pattern":{"kick":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"snare":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"hihat":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"openhat":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"crash":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"ride":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"tom1":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"tom2":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false]},"bpm":120,"swing":0,"timeSignature":"4/4","drumKit":"standard","timestamp":1748662255227}
-
 @ 14206a66:689725cf
2025-05-31 00:54:40
@ 14206a66:689725cf
2025-05-31 00:54:40We’ve all been there, you’re locked in, desperately fighting with spreadsheets, the dishwasher’s going, and a banana cake is in the oven. Suddenly, all goes quiet, lights are off, oven’s off, PC dead as a doorknob. You check the fusebox, it’s fine. Must be a blackout. Usually, the power comes back on after 30 minutes to an hour, but you’re left standing there wondering what happened.
We’ve just seen a country-wide scale event like this, which was much more extreme. On 28th April, the Iberian Peninsula experienced a catastrophic breakdown of the grid (see here).
Power was off for several days. I won’t dig into the details of this particular event; doing so is way beyond my pay grade. Suffice it to say it follows the ideas I want to introduce in this article.
We’ll begin with the simplest model I can think of, getting to grips with the issue from first principles. Then I’ll walk through how the basic premise scales up the Australian grid (or at least the east coast, the NEM), before introducing the shadowy supergeniuses in control of it all (AEMO) and one of the most important market mechanisms they use - Frequency Control Ancillary Services (FCAS).
Part one: First principles
Imagine a way-over-simplified system with a single source of power and a single load. Our source of power is just a battery that produces 10MW of power at an assumed 1000V. The battery has no rotating components. It is connected to a very basic inverter. The inverter is designed to produce 50 Hz AC power; however, let's imagine it has no sophisticated voltage controls or protections (unlike real inverters). All that our inverter comprises is a basic switching and timing circuit.
This specific frequency of 50 Hz is a fundamental design standard for almost all AC electrical equipment. Just like a clock needs to tick at a precise rate to tell accurate time, electrical devices like motors rely on the AC power cycling exactly 50 times per second. If the frequency deviates too much, it can cause motors to speed up or slow down incorrectly, or sensitive electronics to malfunction. Our simple inverter, despite its limitations, is designed to produce 50 Hz because that's what the heater and any other AC device expect.
Our load is a large but mechanically simple industrial heater. It has a large coil that produces heat by running a current through it. Importantly, the heater has a dial to adjust temperature (which can change its power consumption). The heater is currently set to draw 10MW of power.
That’s the start, with a simplified system in equilibrium, all is well. The heater is producing heat, and you can make up your own story about what the heat is used for. The important point is that the voltage, current, and frequency are all stable.
Next, the foreman operating the heater turns the dial up to increase the heat output. Assume the heater now wants to draw 20MW of power. We’re simplifying, so also assume that in this instant, the voltage remains at 1000V.
To draw this much power, the heater now has to draw more current (because power = voltage x current, it’s the rules). Since we assumed the voltage remains at 1000V, there is an instantaneous demand for more power from the battery than it was previously supplying.
The battery now attempts to supply this current, which means the current must flow through the battery’s components, the inverter’s components, and the wire connecting the battery to the heater. All of these physical components have resistance. This means the actual voltage the heater receives will be lower than 1000V.
Now that the heater is receiving voltage lower than 1000V, things start to go wrong. The power consumed by the heater is proportional to the square of the voltage across it (rules are rules), so power = voltage^2 / resistance. Following this rule, since the voltage has decreased, then that means the actual power the heater draws will be less than the 20MW desired. For example, it might only draw 15MW, but it depends on the resistances in all the components, which we haven’t set.
Things just get uglier. The battery and inverter are operating under extreme stress, trying to deliver the higher current demanded, but at reduced voltage. Inside the inverter and the battery, the components start getting hot (rules, again). Since we assumed the battery and inverter are super simple, the inverter can't adjust its power output based on actual grid conditions (like a sophisticated one would); it can only fail. Then the heater goes out, and the foreman gets mad; it’s just a bad day all around.
The fix: add a spinny thing.
Reimagine the situation just as before, but now, instead of a battery, imagine the source of power is a contemporary synchronous generator system. Say it’s a hydro plant, where the spinning turbine is directly connected to the grid. This generator, unlike the battery-inverter, inherently uses its large rotating mass to move a metal rod up and down inside a magnetic coil and produces AC power. Importantly, it synchronises with our system’s required 50 Hz rhythm.
In this case, the story proceeds as before. When the foreman turns the heater dial up the heater wants to draw 20MW. In this case, the increased current flows through the impedance of the generator’s internal components and the wire. Just as before, this causes an immediate, rapid voltage drop at the heater’s terminals. In that instant, the heater will not get its desired 20MW because the voltage is too low.
Since the generator’s power output is less than the load demand, the lack of energy causes the rotating mass of the generator to decelerate (energy is conserved), and the frequency of the AC power in the system drops below 50 HZ. Because the generator’s turbine is a large mass, it has substantial inertia (pesky rules again), so the drop in frequency happens much more slowly than in our first story, and there is no catastrophic failure of the system. Instea,d this inertia buys time for the system to react.
The reaction comes from the manager of the generator. In the real world, this is a piece of software called a governor, but it’s useful to imagine it’s a person. The manager sees the drop in frequency and presses some buttons to let more water flow to the turbine, the frequency climbs back to 50 HZ and the power output of the generator increases.
Then the heater gets its required 20MW of power at 1000V and 50Hz, and the foreman is happy, everyone’s happy, it’s just a good time.
Frequency, in this simple system, indicates power imbalances and triggers the manager of the generator to respond. Equally, we could have assumed the foreman can be notified that he shouldn’t increase the heater’s dial - we can manage the imbalance either on the supply (generator) or demand (heater) side, or a mix of both.
This hints at a crucial question: how the hell do we coordinate this? Even with just a single load and a single generator, what sort of contracts would the foreman and generator manager need to keep everything running?
Part deux: AEMO, the not-so-invisible hand coordinating the market
Above is a story of a system with one load and one generator, without protections for the management of voltage or frequency. I walked through how this simple system could suffer a catastrophic breakdown as a result of the load increasing. Followed by a slight added complexity, which solves the issue.
Everything that applies in the simplified model also applies in the real world; the basic principles scale up and create complex incentives, coordination, and knowledge problems.
In my simple story, there was a manager in charge of the generator and a foreman in charge of the heater. In the much more complex National Electricity Market (NEM), there’s a third main actor: Australian Energy Market Operator (AEMO, because it operates the energy market, perfect naming convention). Among a host of competing priorities, AEMO has one role we’re particularly interested in: making sure we have a good time, i.e making sure the grid is stable. How it does so is the economics bit.
The NEM covers a huge geographic area (all the way up the East Coast from South Australia up to North Port Douglas). Within the vast area it covers are around 10 million customer connections (source). AEMO provides an interactive map that shows you how many substations there are - lots!
here's a map from AEMO
With all those connections and interconnections, the only constant is change. Strong winds can suddenly break connections, generators can trip for a host of reasons, and sometimes physics just says “no”.
On the flip side, sometimes large loads connect unpredictably and want instant power to be available. The physics says supply must equal demand or things get bad, so how does AEMO make sure supply equals demand?
In short, dispatch instructions. AEMO coordinates the supply-side market participants using signals to their control rooms. The economics of it could be summed up as: AEMO is a visible hand trying to approximate the role of Smith’s invisible hand in the market*.
Though not the focus of my current article, dispatch can be (over)simplified as follows: Every five minutes, generators send an offer to AEMO containing a price-quantity pair for power output. AEMO sorts the offer from lowest price to highest and matches supply to forecasted demand, starting from the lowest offer to create a dispatch interval/dispatch window, within system constraints. Importantly, generators all receive the highest marginal price (spot price) of all offers within the dispatch interval. Then, all generators included in the dispatch interval receive revenue equal to their power dispatched times the spot price.
So, assuming the system is in balance. This plays out, and everyone’s happy. But that’s not guaranteed in such a complex interconnected system like the NEM. So, what happens if, after offers are placed and power is scheduled, a generator suddenly trips off (cutting supply) or a large load connects unexpectedly (rapidly ramping up demand)?
AEMO needs some sort of backup power supply or backup demand as a contingency for when imbalances happen. One of such contingencies is what we call this service provision Frequency Control Ancillary Services (FCAS). So named because AEMO uses system frequency to understand where, when, and how much extra supply or demand (load) is required to return the system to the normal stable operation.
But AEMO doesn’t own any generators, batteries, or large loads itself. So, how does it get them? Someone came up with the idea that you can sell backup supply or demand (load) to AEMO, for a fee. This idea implies that AEMO has to find the right incentives to bring backup supply or backup demand (load) online in a flash.
There’s a market for that!
Actually, there are eight markets, but we’re simplifying.
To procure FCAS, AEMO runs a similar auction process to the market for power. Participants submit bids to AEMO every five minutes, containing a service type and availability across up to 10 price bands. The service type is one of: increase/decrease frequency in one of the three time intervals.
AEMO then considers all bids and finds the least-cost solution that meets all system requirements, matching the supply of FCAS to the demand for FCAS. Just like in the market for power, AEMO orders the FCAS bids into a “merit order” based on price for each service type (lowest price to highest price). It then decides which bids it will accept and pays all accepted bids the highest marginal price of all accepted bids. This creates a price signal for FCAS in the market.
The design has obvious intentions: FCAS suppliers win big if they can be super low cost while their competitors are high cost.
Just like in the market for power, once bids are accepted, AEMO sends a signal to the control panels of the FCAS participants.
You can see how , by following this process, AEMO acts to approximate the emergent order (or invisible hand) of a market by creating price signals for both power supply as well as FCAS. Then, physically matching those price signals with the actual power flows using a (pretty amazing, honestly) control scheme.
The idea that AEMO is only approximating the invisible hand is important; I’ll explore that more deeply in future articles.
That’s the physics and market mechanisms in a nutshell. But who sells FCAS to AEMO, and what about the mullah, dollars, buckerinos, fat stacks?
Part tres: How big is the market
Firstly, who can participate in the FCAS market? As far as I understand, it’s quite open; if you invent a device that meets the standards and go through the application process, then you can participate. AEMO’s concern is system stability, so from their POV, any particular device is fair game as long as you meet the engineering standards.
One common example is certain electricity retailers who use their customers’ hot water cylinders as a demand response. By sending an electrical signal to your hot water cylinder, the company can turn it off for a short period, reducing demand (load). There’s a complex “annoyance cost” paid by the consumer of their hot water cylinder being turned off, but then that’s balanced against potentially lower bills as the electricity retailer can substitute FCAS revenue.
Another example is grid-scale batteries; these can build or release charge on a whim. For batteries, the incentives are about whether their charge is worth more in the spot market or in the supply response FCAS market. If the battery is connected to a facility like a solar plant, then the incentives get more complex; is it worth selling power instantly or building charge in the battery for potential spot market or FCAS later? Add in a futures market and you just get more complexity.
A final, still emerging, example is bitcoin miners, these are basically just computers. These machines can be powered up or down relatively quickly and easily with little ill physical effects, and no ill effects to the Bitcoin network or protocol. When they are powered up, they earn a stream of income for the owners in the form of bitcoin.
This creates an interesting dynamic when bitcoin miners participate in the FCAS market; their FCAS bid, all else equal, should be at least the value of the opportunity cost of not mining bitcoin.
A completely unanswered question is what happens if bitcoin mining becomes a large proportion of FCAS? Consider a case where the FCAS from bitcoin miners drops out of the market because bitcoin fees spike and miners find it more profitable to mine rather than provide FCAS.
Alright, but the money! Surely FCAS is lucrative?
AEMO publishes data on FCAS. The most readily understandable data is the payment data. This is, as the name suggests, how much AEMO paid to FCAS participants over the eight service types (and in each State/Territory in the NEM) each month. This is the raw revenue of FCAS market participants. One way to think of it is as the cost of stability.
In total, FCAS payments have been about $39 million this year (up to week 20, which ended May 18).
AEMO has also provided total revenue for FCAS from batteries in the NEM, specifically in its Quarterly Energy Dynamics - Q1 2025, covering 1 January to 31 March 2025 report. This data suggests that batteries in the NEM have earned $69 million in 2024, which is 42.9 percent of all FCAS costs. This is remarkable to me, because grid-scale batteries are relatively new to the market as compared to other generation and storage technologies.
The cause lies in the fact that batteries can* *have a low marginal cost to charge and discharge, so the fact that they captured such market share this fast highlights the idea that he who produces FCAS cheapest wins.
This data release also contains aggregate FCAS costs for all states. The data tells us that in 2024, total FCAS costs were $161 million.
The fact that there is such a healthy pot up for grabs speaks to the fragility of our grid, but also to the resilience; it's a strange duality.
With continued investment in solar generation, because such systems have little to no inertia, we could see increased frequency excursions (technical term for being out of range). Engineers are busy solving this using inverters, which simulate inertia. These are genius, but such innovations take time (and standards) to be adopted.
Then there’s the question of critical infrastructure risk - how tolerant can we be of instability when datacenters mining Bitcoin and running AI models are on the line
At the risk of repeating myself, the whole construction is very much a visible hand trying to approximate what Adam Smith’s invisible hand might do.
Fin
Full disclosure, I do use AI (Gemini specifically) to help me research, learn, and write my articles, but I go over everything multiple times to make it my own voice and reflect my own ideas.
*Adam Smith described the idea of an invisible hand, which directs the market, coordinating people's desires, as a metaphor to explain how people in a market somehow end up serving each other's best interests even without directly communicating.
-
 @ 9ca447d2:fbf5a36d
2025-05-31 03:01:09
@ 9ca447d2:fbf5a36d
2025-05-31 03:01:09Austin, Texas – May 22, 2025 — Jippi, a pioneering mobile augmented reality (AR) game developer, is set to transform Bitcoin education with the launch of its flagship game at the Bitcoin Conference 2025, held at The Venetian Resort in Las Vegas from May 27-29.
In collaboration with six leading Bitcoin companies—Bitcoin Well, Beyond The Checkout, Bitcoin Trading Cards, Geyser, SHAmory, and 21M Communications—Jippi introduces an innovative blend of outdoor adventure, Bitcoin rewards, and gamified financial education designed to captivate.
At the Bitcoin Conference, Jippi’s six partners have sponsored custom “Bitcoin Beasts” tied to specific locations around The Venetian. Each sponsored Beast offers players exclusive rewards and trivia, transforming brand interactions into immersive, non-intrusive experiences.
With an expected attendance of over 30,000 at the conference, sponsors gain unparalleled exposure to a tech-savvy, Bitcoin-centric audience. Players will be rewarded 1k sats for each catch, making the total reward for catching them all 6k sats.
Jippi is redefining how young adults engage with Bitcoin by combining the thrill of location-based AR gameplay, reminiscent of Pokémon GO, with real-world bitcoin rewards (sats) and bite-sized lessons on sound money principles.
Players explore real-world locations to hunt digital creatures called Bitcoin Beasts, answering Bitcoin-related trivia to capture them and earn sats, the smallest unit of bitcoin.
The game’s seamless integration of education and entertainment makes learning about Bitcoin fun, accessible, and rewarding.
“We’re meeting Gen Z where they are—90% play mobile games, and 70% expect rewards for their time,” said Oliver Porter, Founder and CEO of Jippi.
“Jippi backdoors Bitcoin education through an immersive, reward-driven experience while offering our partners a unique branding opportunity. It’s a win-win for players, sponsors, and the Bitcoin ecosystem.”
“Jippi’s mission to gamify Bitcoin education is a game-changer for onboarding the next generation,” said Adam O’Brien, CEO of Bitcoin Well, a leading automatic self-custody Bitcoin platform and “Beast” sponsor.
“Their AR game makes learning about Bitcoin intuitive and engaging, aligning perfectly with our vision of financial empowerment. From a branding perspective, partnering with Jippi to engage and acquire new customers is a no brainer.”
In March 2025, Jippi clinched the top prize in PlebLab’s prestigious Top Builder competition, a three-month hackathon designed to spotlight innovative Bitcoin startups.
Backed by over a year of development, on-site surveys, and university testing, Jippi is a leading innovator in the Bitcoin industry looking to onboard the next generation.
Jippi invites brands, investors, and media to explore sponsorship and investment opportunities. Visit Jippi’s Partnerships Page for sponsorship details or Jippi’s Timestamp Page for investment inquiries.
For media inquiries, please contact Phil@21mcommunications.com
About Jippi
Jippi is a mobile AR gaming company dedicated to making Bitcoin education accessible and engaging. By combining location-based gameplay with bitcoin rewards and financial literacy, Jippi empowers the next generation to embrace sound money principles. Learn more at https://jippi.app.
Bitcoin Beast Sponsors
About Bitcoin Well
Beast #1 – Bitcoin Well – All bitcoin bought at Bitcoin Well are delivered directly to your personal bitcoin wallet. Your Bitcoin Well account gives you the convenience of modern banking, with the benefits of bitcoin. Join the platform that enables independence at bitcoinwell.com.
About Bitcoin Trading Cards
Beast #2 – Bitcoin Trading Cards – Bitcoin Trading Cards is bringing Bitcoin to the masses one pack at a time, making your Bitcoin journey fun and exciting for everyone.
About Beyond The Checkout
Beast #3 – Beyond The Checkout – Beyond The Checkout transforms everyday products into Bitcoin-powered experiences — rewarding customers, collecting real-time insights, and redefining post-purchase engagement.
About Geyser
Beast #4 – Geyser – Geyser is a Bitcoin-native crowdfunding platform enabling grassroots projects to raise funds via Lightning, globally and permissionlessly.
About SHAmory
Beast #5 – SHAmory – We make Bitcoin fun for all ages! Explore our bitcoin games, books, and more today at shamory.com.
About 21M Communications
Beast #6 – 21 Communications – 21 Communications helps Bitcoin companies get the media attention they deserve. As a Bitcoin-only PR Agency, 21M Comms believes Bitcoin is imperative and is committed to supporting the companies that are advancing the mission.
About Bitcoin Conference 2025
The Bitcoin Conference is the world’s largest gathering of Bitcoin enthusiasts, industry leaders, and innovators. Held annually, it showcases cutting-edge developments in the Bitcoin ecosystem. For more information, visit www.bitcoinconference.com.
-
 @ 0fa80bd3:ea7325de
2025-01-29 15:43:42
@ 0fa80bd3:ea7325de
2025-01-29 15:43:42Lyn Alden - биткойн евангелист или евангелистка, я пока не понял
npub1a2cww4kn9wqte4ry70vyfwqyqvpswksna27rtxd8vty6c74era8sdcw83aThomas Pacchia - PubKey owner - X - @tpacchia
npub1xy6exlg37pw84cpyj05c2pdgv86hr25cxn0g7aa8g8a6v97mhduqeuhgplcalvadev - Shopstr
npub16dhgpql60vmd4mnydjut87vla23a38j689jssaqlqqlzrtqtd0kqex0nkqCalle - Cashu founder
npub12rv5lskctqxxs2c8rf2zlzc7xx3qpvzs3w4etgemauy9thegr43sf485vgДжек Дорси
npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m21 ideas
npub1lm3f47nzyf0rjp6fsl4qlnkmzed4uj4h2gnf2vhe3l3mrj85vqks6z3c7lМного адресов. Хз кто надо сортировать
https://github.com/aitechguy/nostr-address-bookФиатДжеф - создатель Ностр - https://github.com/fiatjaf
npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6EVAN KALOUDIS Zues wallet
npub19kv88vjm7tw6v9qksn2y6h4hdt6e79nh3zjcud36k9n3lmlwsleqwte2qdПрограммер Коди https://github.com/CodyTseng/nostr-relay
npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wlAnna Chekhovich - Managing Bitcoin at The Anti-Corruption Foundation https://x.com/AnyaChekhovich
npub1y2st7rp54277hyd2usw6shy3kxprnmpvhkezmldp7vhl7hp920aq9cfyr7 -
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ a29cfc65:484fac9c
2025-05-28 10:30:32
@ a29cfc65:484fac9c
2025-05-28 10:30:32Deutschland ist eines der wenigen Länder mit einer gesetzlich verankerten ausnahmslosen Schulbesuchspflicht. Mit den Schulschließungen in der Corona-Zeit wurde das Gesetz jedoch faktisch plötzlich außer Kraft gesetzt. Alle mussten zu Hause lernen. Als die Schulen danach wieder offen waren, wurden die Kinder mit Maskenpflicht, Tests und Impfdruck gequält. Nicht selten traten bei den Schülern Krankheiten und psychische Störungen auf. Nicht wenige Eltern suchten im Gespräch mit dem Lehrerkollegium nach Lösungen für ihre Kinder. In den meisten Fällen war das nicht möglich. Die Lehrer waren auf die neue Ideologie und die Durchsetzung der Maßnahmen eingeschworen und hatten Angst. Einige Eltern haben ihre Kinder dann in eigener Verantwortung aus der Schule genommen und zu Hause selbst unterrichtet. An manchen Orten fanden sich Gemeinschaften, wo die Kinder in Gruppen lernten. Während viele Lerngemeinschaften nicht mehr existieren, hat die Familie von Katharina den Unterricht für ihre drei Kinder in Eigenregie etabliert. Inzwischen haben sie dafür sogar „den Segen“ von Familiengericht und Jugendamt.
Katharina und Johannes leben mit ihren drei Wunschkindern Aurelius (15), Benjamin (14) und Friedrich (10) in einem Vorort von Leipzig. Die Familie wohnte früher in der Stadt. In der Corona-Zeit haben sie sich mit dem Physiotherapie- & Seminarzentrum Curasanus eine Existenz auf dem Land aufgebaut und begehen diesen Sommer ihr 20-jähriges Praxis-Jubiläum. Katharina hat ihre Arbeit als Physiotherapeutin weitgehend aufgegeben, um sich als Mama und Lernbegleiterin ihren Kindern widmen zu können. Daneben bietet sie Vorträge und Workshops an, übernimmt einen großen Teil der Praxis-Organisation und ist Manager, Rezeptionistin und Vertriebler der eigenen Firma. Wir besuchten einen ihrer Lachyoga-Kurse. Dabei erlebten wir ihr Zusammenspiel mit den drei Kindern. Anschließend stellten wir Katharina unsere Fragen zum Freilernen.
Im unmittelbaren Umfeld wird die Familie bestaunt und geachtet. Sie haben sich bewusst für das Freilernen entschieden. Die Kinder wurden ohne Test nicht mehr in die Schule gelassen. Auch andere Zwangsmaßnahmen wie die Maske wollten die Eltern den Kindern ersparen. Besonders Benjamin hatte traumatische Erlebnisse. Seine Lehrerin schmiss mit dem Schlüssel nach den Schülern und wandte andere schwarze Pädagogik an. Er ging ständig mit Bauchschmerzen ins Bett. Ein weiterer Punkt ist die Masernimpfung. Die Kinder könnten zwar zur Schule gehen, aber die Eltern werden mit rechtlichen Maßnahmen und Zwangszahlungen belegt. Da Katharina in ihrer Praxis viele Erkrankungen als Folge der Masernimpfung beobachten konnte, lehnt sie die Pflichtimpfung ab. Die Eltern haben kein Vertrauen mehr in die staatliche Schulerziehung mit all dem Zwang und den Erpressungen. Als die Familie den Entschluss gefasst hatte, die Kinder nicht mehr in die Schule zu schicken, haben sie ihre Praxis vorübergehend geschlossen, ihr Haus verkauft und sind auf Reisen gegangen. Die beiden großen Kinder wurden von der Schule abgemeldet. Nach der Rückkehr haben sie dann mit einem neuen Leben auf dem Land begonnen.
Lernen ohne Schule: Wie geht das?
„Wissen ist Macht und eine Holschuld“, sagt uns Katharina. Das ist ihr Motto und motiviert auch die Kinder. Mit dem Unterricht zu Hause macht die Familie ihre eigene Studie und zeigt, dass Lernen auch anders geht als in der Schule. Die Eltern können viel besser auf jedes einzelne Kind eingehen. Johannes arbeitete früher als Straßenbauer. Er unterstützt die Jungs vor allem in Mathematik, Geometrie und Physik sowie bei handwerklichen Fertigkeiten. Katharinas Stärken liegen in Deutsch, Sprachen und Organisation. Unter den Patienten ihrer Praxis gibt es Lehrer, die ihnen helfen. Weitere Unterstützung kommt von Freunden und Bekannten. Bei bestimmten Projekten treffen sie auf andere Freilernerkinder. „Das Netzwerk wird immer größer, es wird immer schöner und interessanter“, sagt Katharina. Man geht mit vielen anderen einen gemeinsamen Weg, verlässt dabei eingetretene Pfade und erkundet neue Themenfelder wie Mediengestaltung, freie Energie, Elektrotherapie, meditatives und Improvisations-Zeichnen. „Ich sprudele vor Ideen. Sie kommen in mein Feld, und dann mache ich was draus“, sagt Katharina. Die Jungs sind in Wurzen im Ringelnatz-Literaturkreis. Dort schreiben sie Drehbuchgeschichten und haben einen Film produziert. Sie suchen sich Projekte oder kreieren neue, wie mit dem Planetarium Eilenburg. Diese Zusammenarbeit hat sich sehr gut entwickelt. Dort lernen 4- bis 15-Jährige zusammen. Die drei Jungs spielen Klavier. Erdkunde und Geschichte erleben die Kinder auch dadurch, dass die Familie Hauptstädte oder die bosnischen Pyramiden selbst erkundet. Dabei erweist es sich als Vorteil, nicht auf die Ferienzeiten angewiesen zu sein.
Als Physiotherapeutin ist Katharina bewusst, dass man neue Lernstrategien entwickeln muss. Die Kinder lernen unterschiedlich. Jedes Kind hat seinen eigenen Charakter. Aurelius benötigt eher eine 1:1-Betreuung. Darauf kann Katharina viel individueller eingehen als die staatliche Schule. Es ist aber auch aufwendiger und anstrengender. Besonderen Wert legt sie darauf, dass rechte und linke Gehirnhälfte gleichmäßig beansprucht werden. Lernphasen werden immer wieder mit Entspannungs- oder Bewegungsphasen kombiniert. Sie weiß, dass den Kindern zuerst die Grundlagen des Lesens, Rechnens und Schreibens vermittelt werden müssen. Dann sind sie in der Lage, sich alles Weitere selbst anzueignen – Unterstützung vorausgesetzt. „Besonders das Schreiben mit der eigenen Hand ist wichtig für die Vernetzung der beiden Gehirnhälften“, sagt Katharina. Dafür nehmen sich die Eltern Zeit. Die Kinder führen Tagebuch. Außerdem halten es die Eltern für wichtig, den Kindern Werte und Tugenden wie Dankbarkeit, Verlässlichkeit, Beharrlichkeit, Aufrichtigkeit, Ehrlichkeit und die zehn Gebote zu vermitteln. Katharina und Johannes sind beide religiös begleitet aufgewachsen. Heute sehen sie die Kirche als Institution kritisch. Angebunden an die Schöpfung und im Gottvertrauen erschaffen und schöpfen sie Leben und Lebensraum aus eigener Kraft – so erklärt es uns Katharina.
Ein weiteres Thema sind die Funktionen des Körpers und wie sich die Kinder gesund erhalten können. Vieles lernen sie dabei in der Physiotherapiepraxis. Die Familie hat das Privileg, in ihrem eigenen Biorhythmus leben zu können. „Das macht sehr viel aus – wir sind alle gesund“, sagt Katharina. Der Lern- und Arbeitstag beginnt nicht vor 9 Uhr und hat eine eigene Struktur. Im Tagesablauf sind feste Verantwortlichkeiten integriert. So wechseln sich die Kinder aller drei Tage mit Tischdecken, Staubsaugen und Geschirrspüler ab. Das hilft ihnen, sich selbst zu organisieren. Das geht nicht immer reibungslos vonstatten. Wenn das Lernpensum beizeiten abgearbeitet wurde, helfen die Kinder im Haushalt oder Garten oder gehen ihrem Bewegungsdrang auf andere Weise nach. Die Eltern sind am Abend noch länger aktiv, denn die Praxis erfordert noch die eine oder andere bürokratische Pflicht. Die Familie ist sehr naturverbunden. Sie gehen viel in den Wald und in den Garten. Sie bauen selbst Gemüse und Obst an. Dabei können die Kinder zum Beispiel Erfahrungen mit Permakultur und natürlicher Düngung sammeln. Die Familie achtet auf die Ernährung, schließlich ist Katharina seit fast 25 Jahren Ernährungsberaterin. Was sie nicht selbst anbauen, wird beim Bauern des Vertrauens eingekauft. Die Jungs können selbst kochen und backen. Die Schädlichkeit von Zucker ist den Kindern schon bewusst geworden, ohne gänzlich auf Schokolade verzichten zu müssen. Medikamente gibt es im Haushalt nicht. Sie kennen sich sehr gut mit den Heilmitteln aus der Natur aus und können so ihre Selbstheilungskräfte aktivieren. Sie haben keinen Hausarzt. Natürlich hat keines der Kinder ein Handy. Bisher haben sie noch kein Verlangen danach. Die Eltern halten es für wichtig, dass die Kinder erst sicher bei Selbstorganisation und Tagesstruktur sind, bevor sie ein Handy bekommen. Katharina weist darauf hin, dass beispielsweise WhatsApp erst ab 16 Jahren zugelassen ist, und fragt sich, ob das andere Eltern wissen.
Gesetze auf Augenhöhe auslegen
Den Behörden blieben die Freilerner nicht verborgen. Sie wurden aktiv und schalteten das Familiengericht ein. Die Familie hatte keinen Anwalt und keine Rechtsschutzversicherung. Katharina erzählt uns, dass sie schließlich auf „Hilfe von oben“ gehofft habe. Irgendwer hat sie anscheinend erhört, denn sie bekamen „einen Engel“ als Verfahrensbeistand. Die Behörden waren sehr zugänglich. In den Gesprächen gab man zu, mit der Schulsituation ebenfalls nicht zufrieden zu sein. „Wir wollen so wie ihr, dass sich etwas verändert. Wir sind an Eurer Seite.“ Die Gespräche mit dem Jugendamt und der Richterin vom Familiengericht Grimma waren immer auf Augenhöhe. Schließlich legte man der Familie keine Steine in den Weg. Damit kann Katharina ihr Konzept nach außen leben und andere inspirieren. Ihre Schlussfolgerung: Eltern müssen sich ihrer Stärken bewusst werden und aus ihrer Angst herauskommen. Das Konzept muss aber zur Familie passen, denn jede Familie ist anders.
Die Basis für freies Lernen ist das Vertrauen der Eltern in ihre Kinder. Denn Kinder sind von Natur aus wissbegierig und wollen lernen. Katharina hat viel von Bertrand Stern und von Riccardo Leppe gelernt. Beiden wurde von ihren Eltern das Lernen ohne Schulbesuch ermöglicht. Mit Bertrand Stern hat Katharina Kontakt. Er wird im November am Buß- und Bettag eine kleine Fortbildung im Therapie- und Seminarzentrum geben. Für den Vorabend ist ein Vortrag geplant. Katharina zitiert Riccardo Leppe: „Es ändert sich nur was, wenn man es selbst tut.“ Er sei sich sicher, dass der Fortschritt beim Freilernen inzwischen so weit ist, dass „die Paste nicht wieder zurück in die Tube geht“.
Der Übergang zur Berufsausbildung
Die ersten Freilernerkinder kommen jetzt in das Alter, in dem sie eine Berufsausbildung beginnen können. Aurelius und Benjamin, die beiden „Großen“, machen seit Anfang des Jahres schon erste Praktika bei ortsansässigen Handwerksbetrieben. Beide Seiten sind sehr zufrieden. Durch die Praktika, die länger dauern als im schulischen Lehrplan vorgesehen, können sich die Kinder ausprobieren. Katharina findet es interessant miterleben zu dürfen, wie auf ihre Kinder reagiert wird. Bringen sie etwas mit, das die anderen nicht haben? Denken sie anders mit? Benjamin bekam schon ein Angebot, in einem Metallbau-Betrieb stundenweise mitzuarbeiten. In den Betrieben weiß man, dass die Abschlüsse der staatlichen Schulen größtenteils das Papier nicht wert sind, auf dem sie stehen. Viele verlassen die Schule und können kaum lesen und schreiben, von Selbstorganisation ganz zu schweigen. Ein Freilerner kann eine staatliche Externen-Prüfung ablegen, um einen Haupt- oder Realschulabschluss zu erwerben. Katharina: „Für eine Ausbildung bei einem privaten Unternehmer braucht man das nicht, allein der Unternehmer entscheidet über die Aufnahme des Auszubildenden“. Außerdem stehen den jungen Leuten Privatschulen oder der zweite Bildungsweg zur Verfügung. Wenn man einen praktischen Beruf ergreift, ist es immer noch möglich, sich bis zur Hochschulreife weiterzubilden. Nach mehrjährigen Tätigkeiten kann man bei den Kammern von Industrie, Handel und Handwerk (IHK und HWK) eine Abschlussprüfung ablegen, mit der man zum Studium zugelassen werden kann. Oder man geht gleich den Weg in die Selbstständigkeit.
Frei lernen weitergedacht
Während der Coronazeit haben sich in Sachsen und speziell um Leipzig herum kleine Freilernergruppen gefunden. Die Gruppen werden aktuell zusammengeführt, um zum Beispiel gemeinsam den Mathematikunterricht zu gestalten. Besonders um Dresden herum ist die Szene noch stärker ausgeprägt. Außerdem gibt es seit mehr als 20 Jahren den Bundesverband Natürlich Lernen (BVNL). Er bietet Beratung und zentrale Veranstaltungen an.
Der Wunsch nach dem freien Lernen ohne Schulzwang ist groß. Doch die meisten Eltern wollen ihre Kinder dafür irgendwo abgeben und nicht selbst unterrichten. Katharinas größter Wunsch ist es, drei bis fünf Elternpaare zu finden, die sich in die Betreuung und Unterrichtung ihrer Kinder teilen. Das größte Hindernis dafür sieht sie in den Eltern selbst. Durch ungelöste transgenerative Konflikte und unverarbeitete Familientraumata kommen sie noch nicht in ihre eigene Kraft für ein selbstbestimmtes Leben. Viele wagen es noch nicht, ihre Erwerbstätigkeit zugunsten der Kinder einzuschränken. Katharina sieht es als große Aufgabe für sich und ihre Familie, mit dem Freilernen das Gemeinschaftsbewusstsein und gute Konfliktlösungsstrategien zu entwickeln. Sie denkt dabei bereits an ihre Enkel. Aber sie weiß auch, dass die Eltern ein sehr hohes Maß an Eigeninitiative, Motivation und Selbstdisziplin aufbringen müssen. Sie würde Eltern, die sich das noch nicht zutrauen, als Traumabegleiterin zur Verfügung stehen, für einen angemessenen Energieausgleich. Diese gegenseitige Unterstützung käme Kindern und Eltern zugute. Ebenso hält sie die Idee der Mehrgenerationenerziehung für wichtig. Dabei profitieren nicht nur die Kinder. Die Erfahrungen der älteren Menschen gehen nicht verloren, sondern werden an die jüngeren Generationen weitergegeben und machen sie resilienter. Das hilft den Eltern, ihrer Erwerbsarbeit nachzugehen und Familientraumata zu bewältigen.
Katharina ist eine starke Frau und sprüht nur so vor Energie. Selbst als wir nach 21 Uhr das Therapiezentrum verlassen, sind ihr die Anstrengungen des Tages nicht anzumerken. Sie wird nicht müde beim Sprechen. Für Fragen zum Thema Freilernen kann man sich an sie wenden.
Der Text wurde zuerst am 27.05.2025 im Blog „Freie Akademie für Medien und Journalismus“ veröffentlicht (https://www.freie-medienakademie.de/medien-plus/lernen-neu-gemacht)
Bildquelle: Salah Darwish, unsplash.com
-
 @ a5ee4475:2ca75401
2025-05-19 01:11:59
@ a5ee4475:2ca75401
2025-05-19 01:11:59clients #link #list #english #article #finalversion #descentralismo
*These clients are generally applications on the Nostr network that allow you to use the same account, regardless of the app used, keeping your messages and profile intact.
**However, you may need to meet certain requirements regarding access and account NIP for some clients, so that you can access them securely and use their features correctly.
CLIENTS
Twitter like
- Nostrmo - [source] 🌐💻(🐧🪟🍎)🍎🤖(on zapstore)
- Coracle - Super App [source] 🌐🤖(on zapstore)
- Amethyst - Super App with note edit, delete and other stuff with Tor [source] 🤖(on zapstore)
- Primal - Social and wallet [source] 🌐🍎🤖(on zapstore)
- Iris - [source] 🌐🤖🍎
- Current - [source] 🤖🍎
- FreeFrom 🤖🍎
- Openvibe - Nostr and others (new Plebstr) [source] 🤖🍎
- Snort 🌐(🤖[early access]) [onion] [source]
- Damus 🍎 [source]
- Nos 🍎 [source]
- Nostur 🍎 [source]
- NostrBand 🌐 [info] [source]
- Yana [source] 🌐💻(🐧) 🍎🤖(on zapstore)
- Nostribe [on development] 🌐 [source]
- Lume 💻(🐧🪟🍎) [info] [source]
- Gossip - [source] 💻(🐧🪟🍎)
- noStrudel - Gamified Experience [onion] [info/source] 🌐
- [Nostrudel Next] - [onion]
- moStard - Nostrudel with Monero [onion] [info/source] 🌐
- Camelus - [source] 🤖 [early access]
Community
- CCNS - Community Curated Nostr Stuff [source]
- Nostr Kiwi [creator] 🌐
- Satellite [info] 🌐
- Flotilla - [source] 🌐🐧🤖(on zapstore)
- Chachi - [source] 🌐
- Futr - Coded in haskell [source] 🐧 (others soon)
- Soapbox - Comunnity server [info] [source] 🌐
- Ditto - Soapbox community server 🌐 [source] 🌐
- Cobrafuma - Nostr brazilian community on Ditto [info] 🌐
- Zapddit - Reddit like [source] 🌐
- Voyage (Reddit like) [on development] 🤖
Wiki
- Wikifreedia - Wiki Dark mode [source] 🌐
- Wikinostr - Wiki with tabs clear mode [source] 🌐
- Wikistr - Wiki clear mode [info] [source] 🌐
Search
- Keychat - Signal-like chat with AI and browser [source] 💻(🐧🪟🍎) - 📱(🍎🤖{on zapstore})
- Spring - Browser for Nostr apps and other sites [source] 🤖 (on zapstore)
- Advanced nostr search - Advanced note search by isolated terms related to a npub profile [source] 🌐
- Nos Today - Global note search by isolated terms [info] [source] 🌐
- Nostr Search Engine - API for Nostr clients [source]
- Ntrends - Trending notes and profiles 🌐
Website
- Nsite - Nostr Site [onion] [info] [source]
- Nsite Gateway - Nostr Site Gateway [source]
- Npub pro - Your site on Nostr [source]
App Store
ZapStore - Permitionless App Store [source] 🤖 💻(🐧🍎)
Video and Live Streaming
- Flare - Youtube like 🌐 [source]
- ZapStream - Lives, videos, shorts and zaps (NIP-53) [source] 🌐 🤖(lives only | Amber | on zapstore)
- Swae - Live streaming [source] (on development) ⏳
Post Aggregator - Kinostr - Nostr Cinema with #kinostr [english] [author] 🌐 - Stremstr - Nostr Cinema with #kinostr [english] [source] 📱 (on development) ⏳
Link Agreggator - Kinostr - #kinostr - Nostr Cinema Profile with links [English] - Equinox - Nostr Cinema Community with links [Portuguese]
Audio and Podcast Transmission
- Castr - Your npub as podcast feed [source]
- Nostr Nests - Audio Chats [source] 🌐
- Fountain - Podcast [source] 🤖🍎
- Corny Chat - Audio Chat [source] 🌐
Music
- Tidal - Music Streaming [source] [about] [info] 🤖🍎🌐
- Wavlake - Music Streaming [source] 🌐(🤖🍎 [early access])
- Tunestr - Musical Events [source] [about] 🌐
- Stemstr - Musical Colab (paid to post) [source] [about] 🌐
Images
- Lumina - Trending images and pictures [source] 🌐
- Pinstr - Pinterest like [source] 🌐
- Slidestr - DeviantArt like [source] 🌐
- Memestr - ifunny like [source] 🌐
Download and Upload
Documents, graphics and tables
- Mindstr - Mind maps [source] 🌐
- Docstr - Share Docs [info] [source] 🌐
- Formstr - Share Forms [info] 🌐
- Sheetstr - Share Spreadsheets [source] 🌐
- Slide Maker - Share slides 🌐 [Advice: Slide Maker https://zaplinks.lol/ site is down]
Health
- Sobrkey - Sobriety and mental health [source] 🌐
- Runstr - Running app [source] 🌐
- NosFabrica - Finding ways for your health data 🌐
- LazerEyes - Eye prescription by DM [source] 🌐
Forum
- OddBean - Hacker News like [info] [source] 🌐
- LowEnt - Forum [info] 🌐
- Swarmstr - Q&A / FAQ [info] 🌐
- Staker News - Hacker News like 🌐 [info]
Direct Messenges (DM)
- 0xchat 🤖🍎 [source]
- Nostr Chat 🌐🍎 [source]
- Blowater 🌐 [source]
- Anigma (new nostrgram) - Telegram based [on development] [source]
Reading
- Oracolo - A minimalist Nostr html blog [source]
- nRSS - Nostr RSS reader 🌐
- Highlighter - Insights with a highlighted read [info] 🌐
- Zephyr - Calming to Read [info] 🌐
- Flycat - Clean and Healthy Feed [info] 🌐
- Nosta - Check Profiles [on development] [info] 🌐
- Alexandria - e-Reader and Nostr Knowledge Base (NKB) [source] 🌐
Writing
- Habla - Blog [info] 🌐
- Blogstack - Blog [info]🌐
- YakiHonne - Articles and News [info] 🌐🍎🤖(on zapstore)
Lists
- Following - Users list [source] 🌐
- Nostr Unfollower - Nostr Unfollower
- Listr - Lists [source] 🌐
- Nostr potatoes - Movies List [source] 💻(numpy)
Market and Jobs
- Shopstr - Buy and Sell [onion] [source] 🌐
- Nostr Market - Buy and Sell 🌐
- Plebeian Market - Buy and Sell [source] 🌐
- Ostrich Work - Jobs [source] 🌐
- Nostrocket - Jobs [source] 🌐
Data Vending Machines - DVM (NIP90)
(Data-processing tools)
Games
- Chesstr - Chess 🌐 [source]
- Jestr - Chess [source] 🌐
- Snakestr - Snake game [source] 🌐
- Snakes on a Relay - Multiplayer Snake game like slither.io [source] 🌐
ENGINES - DEG Mods - Decentralized Game Mods [info] [source] 🌐 - NG Engine - Nostr Game Engine [source] 🌐 - JmonkeyEngine - Java game engine [source] 🌐
Customization
Like other Services
- Olas - Instagram like [source] 🌐🍎🤖(on zapstore)
- Nostree - Linktree like 🌐
- Rabbit - TweetDeck like [info] 🌐
- Zaplinks - Nostr links 🌐
- Omeglestr - Omegle-like Random Chats [source] 🌐
General Uses
- Njump - HTML text gateway source 🌐
- Filestr - HTML midia gateway [source] 🌐
- W3 - Nostr URL shortener [source] 🌐
- Playground - Test Nostr filters [source] 🌐
Places
- Wherostr - Travel and show where you are
- Arc Map (Mapstr) - Bitcoin Map [info]
Driver and Delivery
- RoadRunner - Uber like [on development] ⏱️
- Nostrlivery - iFood like [on development] ⏱️
⚠️ SCAM ⚠️ | Arcade City - Uber like [source]
OTHER STUFF
Lightning Wallets (zap)
- Alby - Native and extension [info] 🌐
- ZBD - Gaming and Social [info] [source] 🤖🍎
- Wallet of Satoshi - Simplest Lightning Wallet [info] 🤖🍎
- Minibits - Cashu mobile wallet [info] 🤖
- Blink - Opensource custodial wallet (KYC over 1000 usd) [source] 🤖🍎
- LNbits - App and extesion [source] 🤖🍎💻
- Zeus - [info] [source] 🤖🍎
Without Zap - Wassabi Wallet - Privacy-focused and non-custodial with Nostr Update Manager [source]
Exchange
Media Server (Upload Links)
audio, image and video
Connected with Nostr (NIP):
- Nostr Build - Free and paid Upload [info] [source] 🌐
- NostrMedia - Written in Go with Nip 96 / Blossom (free and paid) [info] [source]
- Nostr Check - [info] [source] 🌐
- NostPic - [info] [source] 🌐
- Sovbit - Free and paid upload [info] [source] 🌐
- Voidcat - Nip-96 and Blossom [source] 🌐
- Primal Media - Primal Media Uploader [source] 🌐
Blossom - Your Media Safer
- Primal Blossom 🌐
- NostrBuild Blossom - Free upload (max 100MiB) and paid [info] [source] 🌐
Paid Upload Only
- Satellite CDN - prepaid upload (max 5GB each) [info] [source] 🌐
Without Nostr NIP:
- Pomf - Upload larger videos (max 1GB) [source]
- Catbox - max 200 MB [source]
- x0 - max 512 MiB [source]
Donation and payments
- Zapper - Easy Zaps [source] 🌐
- Autozap [source] 🌐
- Zapmeacoffee 🌐
- Nostr Zap 💻(numpy)
- Creatr - Creators subscription 🌐
- Geyzer - Crowdfunding [info] [source] 🌐
- Heya! - Crowdfunding [source]
Security
- Secret Border - Generate offline keys 💻(java)
- Umbrel - Your private relay [source] 🌐
Key signing/login and Extension
- Amber - Key signing [source] 🤖(on zapstore)
- Nowser - Account access keys 📱(🤖🍎) 💻(🐧🍎🪟)
- Nos2x - Account access keys 🌐
- Nsec.app 🌐 [info]
- Lume - [info] [source] 🐧🪟🍎
- Satcom - Share files to discuss - [info] 🌐
- KeysBand - Multi-key signing [source] 🌐
Code
- Stacks - AI Templates [info] [source] 🌐
- Nostrify - Share Nostr Frameworks 🌐
- Git Workshop (github like) [experimental] 🌐
- Gitstr (github like) [on development] ⏱️
- Osty [on development] [info] 🌐
- Python Nostr - Python Library for Nostr
- Sybil - Creating, managing and test Nostr events [on development] ⏱️
Relay Check and Cloud
- Nostr Watch - See your relay speed 🌐
- NosDrive - Nostr Relay that saves to Google Drive
Bidges and Getways
- Matrixtr Bridge - Between Matrix & Nostr
- Mostr - Between Nostr & Fediverse
- Nostrss - RSS to Nostr
- Rsslay - Optimized RSS to Nostr [source]
- Atomstr - RSS/Atom to Nostr [source]
Useful Profiles and Trends
nostr-voice - Voice note (just some clients)
NOT RELATED TO NOSTR
Voca - Text-to-Speech App for GrapheneOS [source] 🤖(on zapstore)
Android Keyboards
Personal notes and texts
Front-ends
- Nitter - Twitter / X without your data [source]
- NewPipe - Youtube, Peertube and others, without account & your data [source] 🤖
- Piped - Youtube web without you data [source] 🌐
Other Services
- Brave - Browser [source]
- DuckDuckGo - Search [source]
- LLMA - Meta - Meta open source AI [source]
- DuckDuckGo AI Chat - Famous AIs without Login [source]
- Proton Mail - Mail [source]
Other open source index: Degoogled Apps
Some other Nostr index on:
-
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 6be5cc06:5259daf0
2025-01-21 01:51:46
@ 6be5cc06:5259daf0
2025-01-21 01:51:46Bitcoin: Um sistema de dinheiro eletrônico direto entre pessoas.
Satoshi Nakamoto
satoshin@gmx.com
www.bitcoin.org
Resumo
O Bitcoin é uma forma de dinheiro digital que permite pagamentos diretos entre pessoas, sem a necessidade de um banco ou instituição financeira. Ele resolve um problema chamado gasto duplo, que ocorre quando alguém tenta gastar o mesmo dinheiro duas vezes. Para evitar isso, o Bitcoin usa uma rede descentralizada onde todos trabalham juntos para verificar e registrar as transações.
As transações são registradas em um livro público chamado blockchain, protegido por uma técnica chamada Prova de Trabalho. Essa técnica cria uma cadeia de registros que não pode ser alterada sem refazer todo o trabalho já feito. Essa cadeia é mantida pelos computadores que participam da rede, e a mais longa é considerada a verdadeira.
Enquanto a maior parte do poder computacional da rede for controlada por participantes honestos, o sistema continuará funcionando de forma segura. A rede é flexível, permitindo que qualquer pessoa entre ou saia a qualquer momento, sempre confiando na cadeia mais longa como prova do que aconteceu.
1. Introdução
Hoje, quase todos os pagamentos feitos pela internet dependem de bancos ou empresas como processadores de pagamento (cartões de crédito, por exemplo) para funcionar. Embora esse sistema seja útil, ele tem problemas importantes porque é baseado em confiança.
Primeiro, essas empresas podem reverter pagamentos, o que é útil em caso de erros, mas cria custos e incertezas. Isso faz com que pequenas transações, como pagar centavos por um serviço, se tornem inviáveis. Além disso, os comerciantes são obrigados a desconfiar dos clientes, pedindo informações extras e aceitando fraudes como algo inevitável.
Esses problemas não existem no dinheiro físico, como o papel-moeda, onde o pagamento é final e direto entre as partes. No entanto, não temos como enviar dinheiro físico pela internet sem depender de um intermediário confiável.
O que precisamos é de um sistema de pagamento eletrônico baseado em provas matemáticas, não em confiança. Esse sistema permitiria que qualquer pessoa enviasse dinheiro diretamente para outra, sem depender de bancos ou processadores de pagamento. Além disso, as transações seriam irreversíveis, protegendo vendedores contra fraudes, mas mantendo a possibilidade de soluções para disputas legítimas.
Neste documento, apresentamos o Bitcoin, que resolve o problema do gasto duplo usando uma rede descentralizada. Essa rede cria um registro público e protegido por cálculos matemáticos, que garante a ordem das transações. Enquanto a maior parte da rede for controlada por pessoas honestas, o sistema será seguro contra ataques.
2. Transações
Para entender como funciona o Bitcoin, é importante saber como as transações são realizadas. Imagine que você quer transferir uma "moeda digital" para outra pessoa. No sistema do Bitcoin, essa "moeda" é representada por uma sequência de registros que mostram quem é o atual dono. Para transferi-la, você adiciona um novo registro comprovando que agora ela pertence ao próximo dono. Esse registro é protegido por um tipo especial de assinatura digital.
O que é uma assinatura digital?
Uma assinatura digital é como uma senha secreta, mas muito mais segura. No Bitcoin, cada usuário tem duas chaves: uma "chave privada", que é secreta e serve para criar a assinatura, e uma "chave pública", que pode ser compartilhada com todos e é usada para verificar se a assinatura é válida. Quando você transfere uma moeda, usa sua chave privada para assinar a transação, provando que você é o dono. A próxima pessoa pode usar sua chave pública para confirmar isso.
Como funciona na prática?
Cada "moeda" no Bitcoin é, na verdade, uma cadeia de assinaturas digitais. Vamos imaginar o seguinte cenário:
- A moeda está com o Dono 0 (você). Para transferi-la ao Dono 1, você assina digitalmente a transação com sua chave privada. Essa assinatura inclui o código da transação anterior (chamado de "hash") e a chave pública do Dono 1.
- Quando o Dono 1 quiser transferir a moeda ao Dono 2, ele assinará a transação seguinte com sua própria chave privada, incluindo também o hash da transação anterior e a chave pública do Dono 2.
- Esse processo continua, formando uma "cadeia" de transações. Qualquer pessoa pode verificar essa cadeia para confirmar quem é o atual dono da moeda.
Resolvendo o problema do gasto duplo
Um grande desafio com moedas digitais é o "gasto duplo", que é quando uma mesma moeda é usada em mais de uma transação. Para evitar isso, muitos sistemas antigos dependiam de uma entidade central confiável, como uma casa da moeda, que verificava todas as transações. No entanto, isso criava um ponto único de falha e centralizava o controle do dinheiro.
O Bitcoin resolve esse problema de forma inovadora: ele usa uma rede descentralizada onde todos os participantes (os "nós") têm acesso a um registro completo de todas as transações. Cada nó verifica se as transações são válidas e se a moeda não foi gasta duas vezes. Quando a maioria dos nós concorda com a validade de uma transação, ela é registrada permanentemente na blockchain.
Por que isso é importante?
Essa solução elimina a necessidade de confiar em uma única entidade para gerenciar o dinheiro, permitindo que qualquer pessoa no mundo use o Bitcoin sem precisar de permissão de terceiros. Além disso, ela garante que o sistema seja seguro e resistente a fraudes.
3. Servidor Timestamp
Para assegurar que as transações sejam realizadas de forma segura e transparente, o sistema Bitcoin utiliza algo chamado de "servidor de registro de tempo" (timestamp). Esse servidor funciona como um registro público que organiza as transações em uma ordem específica.
Ele faz isso agrupando várias transações em blocos e criando um código único chamado "hash". Esse hash é como uma impressão digital que representa todo o conteúdo do bloco. O hash de cada bloco é amplamente divulgado, como se fosse publicado em um jornal ou em um fórum público.
Esse processo garante que cada bloco de transações tenha um registro de quando foi criado e que ele existia naquele momento. Além disso, cada novo bloco criado contém o hash do bloco anterior, formando uma cadeia contínua de blocos conectados — conhecida como blockchain.
Com isso, se alguém tentar alterar qualquer informação em um bloco anterior, o hash desse bloco mudará e não corresponderá ao hash armazenado no bloco seguinte. Essa característica torna a cadeia muito segura, pois qualquer tentativa de fraude seria imediatamente detectada.
O sistema de timestamps é essencial para provar a ordem cronológica das transações e garantir que cada uma delas seja única e autêntica. Dessa forma, ele reforça a segurança e a confiança na rede Bitcoin.
4. Prova-de-Trabalho
Para implementar o registro de tempo distribuído no sistema Bitcoin, utilizamos um mecanismo chamado prova-de-trabalho. Esse sistema é semelhante ao Hashcash, desenvolvido por Adam Back, e baseia-se na criação de um código único, o "hash", por meio de um processo computacionalmente exigente.
A prova-de-trabalho envolve encontrar um valor especial que, quando processado junto com as informações do bloco, gere um hash que comece com uma quantidade específica de zeros. Esse valor especial é chamado de "nonce". Encontrar o nonce correto exige um esforço significativo do computador, porque envolve tentativas repetidas até que a condição seja satisfeita.
Esse processo é importante porque torna extremamente difícil alterar qualquer informação registrada em um bloco. Se alguém tentar mudar algo em um bloco, seria necessário refazer o trabalho de computação não apenas para aquele bloco, mas também para todos os blocos que vêm depois dele. Isso garante a segurança e a imutabilidade da blockchain.
A prova-de-trabalho também resolve o problema de decidir qual cadeia de blocos é a válida quando há múltiplas cadeias competindo. A decisão é feita pela cadeia mais longa, pois ela representa o maior esforço computacional já realizado. Isso impede que qualquer indivíduo ou grupo controle a rede, desde que a maioria do poder de processamento seja mantida por participantes honestos.
Para garantir que o sistema permaneça eficiente e equilibrado, a dificuldade da prova-de-trabalho é ajustada automaticamente ao longo do tempo. Se novos blocos estiverem sendo gerados rapidamente, a dificuldade aumenta; se estiverem sendo gerados muito lentamente, a dificuldade diminui. Esse ajuste assegura que novos blocos sejam criados aproximadamente a cada 10 minutos, mantendo o sistema estável e funcional.
5. Rede
A rede Bitcoin é o coração do sistema e funciona de maneira distribuída, conectando vários participantes (ou nós) para garantir o registro e a validação das transações. Os passos para operar essa rede são:
-
Transmissão de Transações: Quando alguém realiza uma nova transação, ela é enviada para todos os nós da rede. Isso é feito para garantir que todos estejam cientes da operação e possam validá-la.
-
Coleta de Transações em Blocos: Cada nó agrupa as novas transações recebidas em um "bloco". Este bloco será preparado para ser adicionado à cadeia de blocos (a blockchain).
-
Prova-de-Trabalho: Os nós competem para resolver a prova-de-trabalho do bloco, utilizando poder computacional para encontrar um hash válido. Esse processo é como resolver um quebra-cabeça matemático difícil.
-
Envio do Bloco Resolvido: Quando um nó encontra a solução para o bloco (a prova-de-trabalho), ele compartilha esse bloco com todos os outros nós na rede.
-
Validação do Bloco: Cada nó verifica o bloco recebido para garantir que todas as transações nele contidas sejam válidas e que nenhuma moeda tenha sido gasta duas vezes. Apenas blocos válidos são aceitos.
-
Construção do Próximo Bloco: Os nós que aceitaram o bloco começam a trabalhar na criação do próximo bloco, utilizando o hash do bloco aceito como base (hash anterior). Isso mantém a continuidade da cadeia.
Resolução de Conflitos e Escolha da Cadeia Mais Longa
Os nós sempre priorizam a cadeia mais longa, pois ela representa o maior esforço computacional já realizado, garantindo maior segurança. Se dois blocos diferentes forem compartilhados simultaneamente, os nós trabalharão no primeiro bloco recebido, mas guardarão o outro como uma alternativa. Caso o segundo bloco eventualmente forme uma cadeia mais longa (ou seja, tenha mais blocos subsequentes), os nós mudarão para essa nova cadeia.
Tolerância a Falhas
A rede é robusta e pode lidar com mensagens que não chegam a todos os nós. Uma transação não precisa alcançar todos os nós de imediato; basta que chegue a um número suficiente deles para ser incluída em um bloco. Da mesma forma, se um nó não receber um bloco em tempo hábil, ele pode solicitá-lo ao perceber que está faltando quando o próximo bloco é recebido.
Esse mecanismo descentralizado permite que a rede Bitcoin funcione de maneira segura, confiável e resiliente, sem depender de uma autoridade central.
6. Incentivo
O incentivo é um dos pilares fundamentais que sustenta o funcionamento da rede Bitcoin, garantindo que os participantes (nós) continuem operando de forma honesta e contribuindo com recursos computacionais. Ele é estruturado em duas partes principais: a recompensa por mineração e as taxas de transação.
Recompensa por Mineração
Por convenção, o primeiro registro em cada bloco é uma transação especial que cria novas moedas e as atribui ao criador do bloco. Essa recompensa incentiva os mineradores a dedicarem poder computacional para apoiar a rede. Como não há uma autoridade central para emitir moedas, essa é a maneira pela qual novas moedas entram em circulação. Esse processo pode ser comparado ao trabalho de garimpeiros, que utilizam recursos para colocar mais ouro em circulação. No caso do Bitcoin, o "recurso" consiste no tempo de CPU e na energia elétrica consumida para resolver a prova-de-trabalho.
Taxas de Transação
Além da recompensa por mineração, os mineradores também podem ser incentivados pelas taxas de transação. Se uma transação utiliza menos valor de saída do que o valor de entrada, a diferença é tratada como uma taxa, que é adicionada à recompensa do bloco contendo essa transação. Com o passar do tempo e à medida que o número de moedas em circulação atinge o limite predeterminado, essas taxas de transação se tornam a principal fonte de incentivo, substituindo gradualmente a emissão de novas moedas. Isso permite que o sistema opere sem inflação, uma vez que o número total de moedas permanece fixo.
Incentivo à Honestidade
O design do incentivo também busca garantir que os participantes da rede mantenham um comportamento honesto. Para um atacante que consiga reunir mais poder computacional do que o restante da rede, ele enfrentaria duas escolhas:
- Usar esse poder para fraudar o sistema, como reverter transações e roubar pagamentos.
- Seguir as regras do sistema, criando novos blocos e recebendo recompensas legítimas.
A lógica econômica favorece a segunda opção, pois um comportamento desonesto prejudicaria a confiança no sistema, diminuindo o valor de todas as moedas, incluindo aquelas que o próprio atacante possui. Jogar dentro das regras não apenas maximiza o retorno financeiro, mas também preserva a validade e a integridade do sistema.
Esse mecanismo garante que os incentivos econômicos estejam alinhados com o objetivo de manter a rede segura, descentralizada e funcional ao longo do tempo.
7. Recuperação do Espaço em Disco
Depois que uma moeda passa a estar protegida por muitos blocos na cadeia, as informações sobre as transações antigas que a geraram podem ser descartadas para economizar espaço em disco. Para que isso seja possível sem comprometer a segurança, as transações são organizadas em uma estrutura chamada "árvore de Merkle". Essa árvore funciona como um resumo das transações: em vez de armazenar todas elas, guarda apenas um "hash raiz", que é como uma assinatura compacta que representa todo o grupo de transações.
Os blocos antigos podem, então, ser simplificados, removendo as partes desnecessárias dessa árvore. Apenas a raiz do hash precisa ser mantida no cabeçalho do bloco, garantindo que a integridade dos dados seja preservada, mesmo que detalhes específicos sejam descartados.
Para exemplificar: imagine que você tenha vários recibos de compra. Em vez de guardar todos os recibos, você cria um documento e lista apenas o valor total de cada um. Mesmo que os recibos originais sejam descartados, ainda é possível verificar a soma com base nos valores armazenados.
Além disso, o espaço ocupado pelos blocos em si é muito pequeno. Cada bloco sem transações ocupa apenas cerca de 80 bytes. Isso significa que, mesmo com blocos sendo gerados a cada 10 minutos, o crescimento anual em espaço necessário é insignificante: apenas 4,2 MB por ano. Com a capacidade de armazenamento dos computadores crescendo a cada ano, esse espaço continuará sendo trivial, garantindo que a rede possa operar de forma eficiente sem problemas de armazenamento, mesmo a longo prazo.
8. Verificação de Pagamento Simplificada
É possível confirmar pagamentos sem a necessidade de operar um nó completo da rede. Para isso, o usuário precisa apenas de uma cópia dos cabeçalhos dos blocos da cadeia mais longa (ou seja, a cadeia com maior esforço de trabalho acumulado). Ele pode verificar a validade de uma transação ao consultar os nós da rede até obter a confirmação de que tem a cadeia mais longa. Para isso, utiliza-se o ramo Merkle, que conecta a transação ao bloco em que ela foi registrada.
Entretanto, o método simplificado possui limitações: ele não pode confirmar uma transação isoladamente, mas sim assegurar que ela ocupa um lugar específico na cadeia mais longa. Dessa forma, se um nó da rede aprova a transação, os blocos subsequentes reforçam essa aceitação.
A verificação simplificada é confiável enquanto a maioria dos nós da rede for honesta. Contudo, ela se torna vulnerável caso a rede seja dominada por um invasor. Nesse cenário, um atacante poderia fabricar transações fraudulentas que enganariam o usuário temporariamente até que o invasor obtivesse controle completo da rede.
Uma estratégia para mitigar esse risco é configurar alertas nos softwares de nós completos. Esses alertas identificam blocos inválidos, sugerindo ao usuário baixar o bloco completo para confirmar qualquer inconsistência. Para maior segurança, empresas que realizam pagamentos frequentes podem preferir operar seus próprios nós, reduzindo riscos e permitindo uma verificação mais direta e confiável.
9. Combinando e Dividindo Valor
No sistema Bitcoin, cada unidade de valor é tratada como uma "moeda" individual, mas gerenciar cada centavo como uma transação separada seria impraticável. Para resolver isso, o Bitcoin permite que valores sejam combinados ou divididos em transações, facilitando pagamentos de qualquer valor.
Entradas e Saídas
Cada transação no Bitcoin é composta por:
- Entradas: Representam os valores recebidos em transações anteriores.
- Saídas: Correspondem aos valores enviados, divididos entre os destinatários e, eventualmente, o troco para o remetente.
Normalmente, uma transação contém:
- Uma única entrada com valor suficiente para cobrir o pagamento.
- Ou várias entradas combinadas para atingir o valor necessário.
O valor total das saídas nunca excede o das entradas, e a diferença (se houver) pode ser retornada ao remetente como troco.
Exemplo Prático
Imagine que você tem duas entradas:
- 0,03 BTC
- 0,07 BTC
Se deseja enviar 0,08 BTC para alguém, a transação terá:
- Entrada: As duas entradas combinadas (0,03 + 0,07 BTC = 0,10 BTC).
- Saídas: Uma para o destinatário (0,08 BTC) e outra como troco para você (0,02 BTC).
Essa flexibilidade permite que o sistema funcione sem precisar manipular cada unidade mínima individualmente.
Difusão e Simplificação
A difusão de transações, onde uma depende de várias anteriores e assim por diante, não representa um problema. Não é necessário armazenar ou verificar o histórico completo de uma transação para utilizá-la, já que o registro na blockchain garante sua integridade.
10. Privacidade
O modelo bancário tradicional oferece um certo nível de privacidade, limitando o acesso às informações financeiras apenas às partes envolvidas e a um terceiro confiável (como bancos ou instituições financeiras). No entanto, o Bitcoin opera de forma diferente, pois todas as transações são publicamente registradas na blockchain. Apesar disso, a privacidade pode ser mantida utilizando chaves públicas anônimas, que desvinculam diretamente as transações das identidades das partes envolvidas.
Fluxo de Informação
- No modelo tradicional, as transações passam por um terceiro confiável que conhece tanto o remetente quanto o destinatário.
- No Bitcoin, as transações são anunciadas publicamente, mas sem revelar diretamente as identidades das partes. Isso é comparável a dados divulgados por bolsas de valores, onde informações como o tempo e o tamanho das negociações (a "fita") são públicas, mas as identidades das partes não.
Protegendo a Privacidade
Para aumentar a privacidade no Bitcoin, são adotadas as seguintes práticas:
- Chaves Públicas Anônimas: Cada transação utiliza um par de chaves diferentes, dificultando a associação com um proprietário único.
- Prevenção de Ligação: Ao usar chaves novas para cada transação, reduz-se a possibilidade de links evidentes entre múltiplas transações realizadas pelo mesmo usuário.
Riscos de Ligação
Embora a privacidade seja fortalecida, alguns riscos permanecem:
- Transações multi-entrada podem revelar que todas as entradas pertencem ao mesmo proprietário, caso sejam necessárias para somar o valor total.
- O proprietário da chave pode ser identificado indiretamente por transações anteriores que estejam conectadas.
11. Cálculos
Imagine que temos um sistema onde as pessoas (ou computadores) competem para adicionar informações novas (blocos) a um grande registro público (a cadeia de blocos ou blockchain). Este registro é como um livro contábil compartilhado, onde todos podem verificar o que está escrito.
Agora, vamos pensar em um cenário: um atacante quer enganar o sistema. Ele quer mudar informações já registradas para beneficiar a si mesmo, por exemplo, desfazendo um pagamento que já fez. Para isso, ele precisa criar uma versão alternativa do livro contábil (a cadeia de blocos dele) e convencer todos os outros participantes de que essa versão é a verdadeira.
Mas isso é extremamente difícil.
Como o Ataque Funciona
Quando um novo bloco é adicionado à cadeia, ele depende de cálculos complexos que levam tempo e esforço. Esses cálculos são como um grande quebra-cabeça que precisa ser resolvido.
- Os “bons jogadores” (nós honestos) estão sempre trabalhando juntos para resolver esses quebra-cabeças e adicionar novos blocos à cadeia verdadeira.
- O atacante, por outro lado, precisa resolver quebra-cabeças sozinho, tentando “alcançar” a cadeia honesta para que sua versão alternativa pareça válida.
Se a cadeia honesta já está vários blocos à frente, o atacante começa em desvantagem, e o sistema está projetado para que a dificuldade de alcançá-los aumente rapidamente.
A Corrida Entre Cadeias
Você pode imaginar isso como uma corrida. A cada bloco novo que os jogadores honestos adicionam à cadeia verdadeira, eles se distanciam mais do atacante. Para vencer, o atacante teria que resolver os quebra-cabeças mais rápido que todos os outros jogadores honestos juntos.
Suponha que:
- A rede honesta tem 80% do poder computacional (ou seja, resolve 8 de cada 10 quebra-cabeças).
- O atacante tem 20% do poder computacional (ou seja, resolve 2 de cada 10 quebra-cabeças).
Cada vez que a rede honesta adiciona um bloco, o atacante tem que "correr atrás" e resolver mais quebra-cabeças para alcançar.
Por Que o Ataque Fica Cada Vez Mais Improvável?
Vamos usar uma fórmula simples para mostrar como as chances de sucesso do atacante diminuem conforme ele precisa "alcançar" mais blocos:
P = (q/p)^z
- q é o poder computacional do atacante (20%, ou 0,2).
- p é o poder computacional da rede honesta (80%, ou 0,8).
- z é a diferença de blocos entre a cadeia honesta e a cadeia do atacante.
Se o atacante está 5 blocos atrás (z = 5):
P = (0,2 / 0,8)^5 = (0,25)^5 = 0,00098, (ou, 0,098%)
Isso significa que o atacante tem menos de 0,1% de chance de sucesso — ou seja, é muito improvável.
Se ele estiver 10 blocos atrás (z = 10):
P = (0,2 / 0,8)^10 = (0,25)^10 = 0,000000095, (ou, 0,0000095%).
Neste caso, as chances de sucesso são praticamente nulas.
Um Exemplo Simples
Se você jogar uma moeda, a chance de cair “cara” é de 50%. Mas se precisar de 10 caras seguidas, sua chance já é bem menor. Se precisar de 20 caras seguidas, é quase impossível.
No caso do Bitcoin, o atacante precisa de muito mais do que 20 caras seguidas. Ele precisa resolver quebra-cabeças extremamente difíceis e alcançar os jogadores honestos que estão sempre à frente. Isso faz com que o ataque seja inviável na prática.
Por Que Tudo Isso é Seguro?
- A probabilidade de sucesso do atacante diminui exponencialmente. Isso significa que, quanto mais tempo passa, menor é a chance de ele conseguir enganar o sistema.
- A cadeia verdadeira (honesta) está protegida pela força da rede. Cada novo bloco que os jogadores honestos adicionam à cadeia torna mais difícil para o atacante alcançar.
E Se o Atacante Tentar Continuar?
O atacante poderia continuar tentando indefinidamente, mas ele estaria gastando muito tempo e energia sem conseguir nada. Enquanto isso, os jogadores honestos estão sempre adicionando novos blocos, tornando o trabalho do atacante ainda mais inútil.
Assim, o sistema garante que a cadeia verdadeira seja extremamente segura e que ataques sejam, na prática, impossíveis de ter sucesso.
12. Conclusão
Propusemos um sistema de transações eletrônicas que elimina a necessidade de confiança, baseando-se em assinaturas digitais e em uma rede peer-to-peer que utiliza prova de trabalho. Isso resolve o problema do gasto duplo, criando um histórico público de transações imutável, desde que a maioria do poder computacional permaneça sob controle dos participantes honestos. A rede funciona de forma simples e descentralizada, com nós independentes que não precisam de identificação ou coordenação direta. Eles entram e saem livremente, aceitando a cadeia de prova de trabalho como registro do que ocorreu durante sua ausência. As decisões são tomadas por meio do poder de CPU, validando blocos legítimos, estendendo a cadeia e rejeitando os inválidos. Com este mecanismo de consenso, todas as regras e incentivos necessários para o funcionamento seguro e eficiente do sistema são garantidos.
Faça o download do whitepaper original em português: https://bitcoin.org/files/bitcoin-paper/bitcoin_pt_br.pdf
-
 @ fe32298e:20516265
2024-12-16 20:59:13
@ fe32298e:20516265
2024-12-16 20:59:13Today I learned how to install NVapi to monitor my GPUs in Home Assistant.
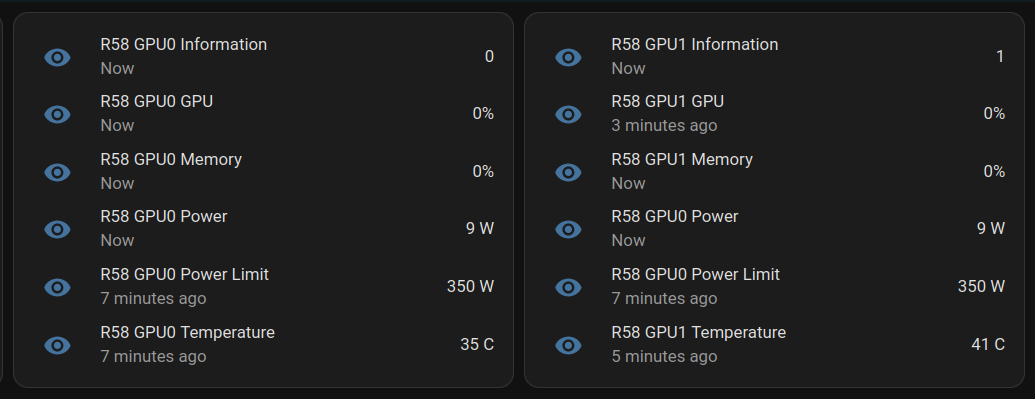
NVApi is a lightweight API designed for monitoring NVIDIA GPU utilization and enabling automated power management. It provides real-time GPU metrics, supports integration with tools like Home Assistant, and offers flexible power management and PCIe link speed management based on workload and thermal conditions.
- GPU Utilization Monitoring: Utilization, memory usage, temperature, fan speed, and power consumption.
- Automated Power Limiting: Adjusts power limits dynamically based on temperature thresholds and total power caps, configurable per GPU or globally.
- Cross-GPU Coordination: Total power budget applies across multiple GPUs in the same system.
- PCIe Link Speed Management: Controls minimum and maximum PCIe link speeds with idle thresholds for power optimization.
- Home Assistant Integration: Uses the built-in RESTful platform and template sensors.
Getting the Data
sudo apt install golang-go git clone https://github.com/sammcj/NVApi.git cd NVapi go run main.go -port 9999 -rate 1 curl http://localhost:9999/gpuResponse for a single GPU:
[ { "index": 0, "name": "NVIDIA GeForce RTX 4090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 16, "power_limit_watts": 450, "memory_total_gb": 23.99, "memory_used_gb": 0.46, "memory_free_gb": 23.52, "memory_usage_percent": 2, "temperature": 38, "processes": [], "pcie_link_state": "not managed" } ]Response for multiple GPUs:
[ { "index": 0, "name": "NVIDIA GeForce RTX 3090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 14, "power_limit_watts": 350, "memory_total_gb": 24, "memory_used_gb": 0.43, "memory_free_gb": 23.57, "memory_usage_percent": 2, "temperature": 36, "processes": [], "pcie_link_state": "not managed" }, { "index": 1, "name": "NVIDIA RTX A4000", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 10, "power_limit_watts": 140, "memory_total_gb": 15.99, "memory_used_gb": 0.56, "memory_free_gb": 15.43, "memory_usage_percent": 3, "temperature": 41, "processes": [], "pcie_link_state": "not managed" } ]Start at Boot
Create
/etc/systemd/system/nvapi.service:``` [Unit] Description=Run NVapi After=network.target
[Service] Type=simple Environment="GOPATH=/home/ansible/go" WorkingDirectory=/home/ansible/NVapi ExecStart=/usr/bin/go run main.go -port 9999 -rate 1 Restart=always User=ansible
Environment="GPU_TEMP_CHECK_INTERVAL=5"
Environment="GPU_TOTAL_POWER_CAP=400"
Environment="GPU_0_LOW_TEMP=40"
Environment="GPU_0_MEDIUM_TEMP=70"
Environment="GPU_0_LOW_TEMP_LIMIT=135"
Environment="GPU_0_MEDIUM_TEMP_LIMIT=120"
Environment="GPU_0_HIGH_TEMP_LIMIT=100"
Environment="GPU_1_LOW_TEMP=45"
Environment="GPU_1_MEDIUM_TEMP=75"
Environment="GPU_1_LOW_TEMP_LIMIT=140"
Environment="GPU_1_MEDIUM_TEMP_LIMIT=125"
Environment="GPU_1_HIGH_TEMP_LIMIT=110"
[Install] WantedBy=multi-user.target ```
Home Assistant
Add to Home Assistant
configuration.yamland restart HA (completely).For a single GPU, this works: ``` sensor: - platform: rest name: MYPC GPU Information resource: http://mypc:9999 method: GET headers: Content-Type: application/json value_template: "{{ value_json[0].index }}" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature scan_interval: 1 # seconds
- platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} GPU" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Memory" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Temperature" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'temperature') }}" unit_of_measurement: "°C" ```
For multiple GPUs: ``` rest: scan_interval: 1 resource: http://mypc:9999 sensor: - name: "MYPC GPU0 Information" value_template: "{{ value_json[0].index }}" json_attributes_path: "$.0" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature - name: "MYPC GPU1 Information" value_template: "{{ value_json[1].index }}" json_attributes_path: "$.1" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature
-
platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC GPU0 GPU" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC GPU0 Memory" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC GPU0 Power" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC GPU0 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC GPU0 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'temperature') }}" unit_of_measurement: "C"
-
platform: template sensors: mypc_gpu_1_gpu: friendly_name: "MYPC GPU1 GPU" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_memory: friendly_name: "MYPC GPU1 Memory" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_power: friendly_name: "MYPC GPU1 Power" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_1_power_limit: friendly_name: "MYPC GPU1 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_1_temperature: friendly_name: "MYPC GPU1 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'temperature') }}" unit_of_measurement: "C"
```
Basic entity card:
type: entities entities: - entity: sensor.mypc_gpu_0_gpu secondary_info: last-updated - entity: sensor.mypc_gpu_0_memory secondary_info: last-updated - entity: sensor.mypc_gpu_0_power secondary_info: last-updated - entity: sensor.mypc_gpu_0_power_limit secondary_info: last-updated - entity: sensor.mypc_gpu_0_temperature secondary_info: last-updatedAnsible Role
```
-
name: install go become: true package: name: golang-go state: present
-
name: git clone git: repo: "https://github.com/sammcj/NVApi.git" dest: "/home/ansible/NVapi" update: yes force: true
go run main.go -port 9999 -rate 1
-
name: install systemd service become: true copy: src: nvapi.service dest: /etc/systemd/system/nvapi.service
-
name: Reload systemd daemons, enable, and restart nvapi become: true systemd: name: nvapi daemon_reload: yes enabled: yes state: restarted ```
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 6f6b50bb:a848e5a1
2024-12-15 15:09:52
@ 6f6b50bb:a848e5a1
2024-12-15 15:09:52Che cosa significherebbe trattare l'IA come uno strumento invece che come una persona?
Dall’avvio di ChatGPT, le esplorazioni in due direzioni hanno preso velocità.
La prima direzione riguarda le capacità tecniche. Quanto grande possiamo addestrare un modello? Quanto bene può rispondere alle domande del SAT? Con quanta efficienza possiamo distribuirlo?
La seconda direzione riguarda il design dell’interazione. Come comunichiamo con un modello? Come possiamo usarlo per un lavoro utile? Quale metafora usiamo per ragionare su di esso?
La prima direzione è ampiamente seguita e enormemente finanziata, e per una buona ragione: i progressi nelle capacità tecniche sono alla base di ogni possibile applicazione. Ma la seconda è altrettanto cruciale per il campo e ha enormi incognite. Siamo solo a pochi anni dall’inizio dell’era dei grandi modelli. Quali sono le probabilità che abbiamo già capito i modi migliori per usarli?
Propongo una nuova modalità di interazione, in cui i modelli svolgano il ruolo di applicazioni informatiche (ad esempio app per telefoni): fornendo un’interfaccia grafica, interpretando gli input degli utenti e aggiornando il loro stato. In questa modalità, invece di essere un “agente” che utilizza un computer per conto dell’essere umano, l’IA può fornire un ambiente informatico più ricco e potente che possiamo utilizzare.
Metafore per l’interazione
Al centro di un’interazione c’è una metafora che guida le aspettative di un utente su un sistema. I primi giorni dell’informatica hanno preso metafore come “scrivanie”, “macchine da scrivere”, “fogli di calcolo” e “lettere” e le hanno trasformate in equivalenti digitali, permettendo all’utente di ragionare sul loro comportamento. Puoi lasciare qualcosa sulla tua scrivania e tornare a prenderlo; hai bisogno di un indirizzo per inviare una lettera. Man mano che abbiamo sviluppato una conoscenza culturale di questi dispositivi, la necessità di queste particolari metafore è scomparsa, e con esse i design di interfaccia skeumorfici che le rafforzavano. Come un cestino o una matita, un computer è ora una metafora di se stesso.
La metafora dominante per i grandi modelli oggi è modello-come-persona. Questa è una metafora efficace perché le persone hanno capacità estese che conosciamo intuitivamente. Implica che possiamo avere una conversazione con un modello e porgli domande; che il modello possa collaborare con noi su un documento o un pezzo di codice; che possiamo assegnargli un compito da svolgere da solo e che tornerà quando sarà finito.
Tuttavia, trattare un modello come una persona limita profondamente il nostro modo di pensare all’interazione con esso. Le interazioni umane sono intrinsecamente lente e lineari, limitate dalla larghezza di banda e dalla natura a turni della comunicazione verbale. Come abbiamo tutti sperimentato, comunicare idee complesse in una conversazione è difficile e dispersivo. Quando vogliamo precisione, ci rivolgiamo invece a strumenti, utilizzando manipolazioni dirette e interfacce visive ad alta larghezza di banda per creare diagrammi, scrivere codice e progettare modelli CAD. Poiché concepiamo i modelli come persone, li utilizziamo attraverso conversazioni lente, anche se sono perfettamente in grado di accettare input diretti e rapidi e di produrre risultati visivi. Le metafore che utilizziamo limitano le esperienze che costruiamo, e la metafora modello-come-persona ci impedisce di esplorare il pieno potenziale dei grandi modelli.
Per molti casi d’uso, e specialmente per il lavoro produttivo, credo che il futuro risieda in un’altra metafora: modello-come-computer.
Usare un’IA come un computer
Sotto la metafora modello-come-computer, interagiremo con i grandi modelli seguendo le intuizioni che abbiamo sulle applicazioni informatiche (sia su desktop, tablet o telefono). Nota che ciò non significa che il modello sarà un’app tradizionale più di quanto il desktop di Windows fosse una scrivania letterale. “Applicazione informatica” sarà un modo per un modello di rappresentarsi a noi. Invece di agire come una persona, il modello agirà come un computer.
Agire come un computer significa produrre un’interfaccia grafica. Al posto del flusso lineare di testo in stile telescrivente fornito da ChatGPT, un sistema modello-come-computer genererà qualcosa che somiglia all’interfaccia di un’applicazione moderna: pulsanti, cursori, schede, immagini, grafici e tutto il resto. Questo affronta limitazioni chiave dell’interfaccia di chat standard modello-come-persona:
-
Scoperta. Un buon strumento suggerisce i suoi usi. Quando l’unica interfaccia è una casella di testo vuota, spetta all’utente capire cosa fare e comprendere i limiti del sistema. La barra laterale Modifica in Lightroom è un ottimo modo per imparare l’editing fotografico perché non si limita a dirti cosa può fare questa applicazione con una foto, ma cosa potresti voler fare. Allo stesso modo, un’interfaccia modello-come-computer per DALL-E potrebbe mostrare nuove possibilità per le tue generazioni di immagini.
-
Efficienza. La manipolazione diretta è più rapida che scrivere una richiesta a parole. Per continuare l’esempio di Lightroom, sarebbe impensabile modificare una foto dicendo a una persona quali cursori spostare e di quanto. Ci vorrebbe un giorno intero per chiedere un’esposizione leggermente più bassa e una vibranza leggermente più alta, solo per vedere come apparirebbe. Nella metafora modello-come-computer, il modello può creare strumenti che ti permettono di comunicare ciò che vuoi più efficientemente e quindi di fare le cose più rapidamente.
A differenza di un’app tradizionale, questa interfaccia grafica è generata dal modello su richiesta. Questo significa che ogni parte dell’interfaccia che vedi è rilevante per ciò che stai facendo in quel momento, inclusi i contenuti specifici del tuo lavoro. Significa anche che, se desideri un’interfaccia più ampia o diversa, puoi semplicemente richiederla. Potresti chiedere a DALL-E di produrre alcuni preset modificabili per le sue impostazioni ispirati da famosi artisti di schizzi. Quando clicchi sul preset Leonardo da Vinci, imposta i cursori per disegni prospettici altamente dettagliati in inchiostro nero. Se clicchi su Charles Schulz, seleziona fumetti tecnicolor 2D a basso dettaglio.
Una bicicletta della mente proteiforme
La metafora modello-come-persona ha una curiosa tendenza a creare distanza tra l’utente e il modello, rispecchiando il divario di comunicazione tra due persone che può essere ridotto ma mai completamente colmato. A causa della difficoltà e del costo di comunicare a parole, le persone tendono a suddividere i compiti tra loro in blocchi grandi e il più indipendenti possibile. Le interfacce modello-come-persona seguono questo schema: non vale la pena dire a un modello di aggiungere un return statement alla tua funzione quando è più veloce scriverlo da solo. Con il sovraccarico della comunicazione, i sistemi modello-come-persona sono più utili quando possono fare un intero blocco di lavoro da soli. Fanno le cose per te.
Questo contrasta con il modo in cui interagiamo con i computer o altri strumenti. Gli strumenti producono feedback visivi in tempo reale e sono controllati attraverso manipolazioni dirette. Hanno un overhead comunicativo così basso che non è necessario specificare un blocco di lavoro indipendente. Ha più senso mantenere l’umano nel loop e dirigere lo strumento momento per momento. Come stivali delle sette leghe, gli strumenti ti permettono di andare più lontano a ogni passo, ma sei ancora tu a fare il lavoro. Ti permettono di fare le cose più velocemente.
Considera il compito di costruire un sito web usando un grande modello. Con le interfacce di oggi, potresti trattare il modello come un appaltatore o un collaboratore. Cercheresti di scrivere a parole il più possibile su come vuoi che il sito appaia, cosa vuoi che dica e quali funzionalità vuoi che abbia. Il modello genererebbe una prima bozza, tu la eseguirai e poi fornirai un feedback. “Fai il logo un po’ più grande”, diresti, e “centra quella prima immagine principale”, e “deve esserci un pulsante di login nell’intestazione”. Per ottenere esattamente ciò che vuoi, invierai una lista molto lunga di richieste sempre più minuziose.
Un’interazione alternativa modello-come-computer sarebbe diversa: invece di costruire il sito web, il modello genererebbe un’interfaccia per te per costruirlo, dove ogni input dell’utente a quell’interfaccia interroga il grande modello sotto il cofano. Forse quando descrivi le tue necessità creerebbe un’interfaccia con una barra laterale e una finestra di anteprima. All’inizio la barra laterale contiene solo alcuni schizzi di layout che puoi scegliere come punto di partenza. Puoi cliccare su ciascuno di essi, e il modello scrive l’HTML per una pagina web usando quel layout e lo visualizza nella finestra di anteprima. Ora che hai una pagina su cui lavorare, la barra laterale guadagna opzioni aggiuntive che influenzano la pagina globalmente, come accoppiamenti di font e schemi di colore. L’anteprima funge da editor WYSIWYG, permettendoti di afferrare elementi e spostarli, modificarne i contenuti, ecc. A supportare tutto ciò è il modello, che vede queste azioni dell’utente e riscrive la pagina per corrispondere ai cambiamenti effettuati. Poiché il modello può generare un’interfaccia per aiutare te e lui a comunicare più efficientemente, puoi esercitare più controllo sul prodotto finale in meno tempo.
La metafora modello-come-computer ci incoraggia a pensare al modello come a uno strumento con cui interagire in tempo reale piuttosto che a un collaboratore a cui assegnare compiti. Invece di sostituire un tirocinante o un tutor, può essere una sorta di bicicletta proteiforme per la mente, una che è sempre costruita su misura esattamente per te e il terreno che intendi attraversare.
Un nuovo paradigma per l’informatica?
I modelli che possono generare interfacce su richiesta sono una frontiera completamente nuova nell’informatica. Potrebbero essere un paradigma del tutto nuovo, con il modo in cui cortocircuitano il modello di applicazione esistente. Dare agli utenti finali il potere di creare e modificare app al volo cambia fondamentalmente il modo in cui interagiamo con i computer. Al posto di una singola applicazione statica costruita da uno sviluppatore, un modello genererà un’applicazione su misura per l’utente e le sue esigenze immediate. Al posto della logica aziendale implementata nel codice, il modello interpreterà gli input dell’utente e aggiornerà l’interfaccia utente. È persino possibile che questo tipo di interfaccia generativa sostituisca completamente il sistema operativo, generando e gestendo interfacce e finestre al volo secondo necessità.
All’inizio, l’interfaccia generativa sarà un giocattolo, utile solo per l’esplorazione creativa e poche altre applicazioni di nicchia. Dopotutto, nessuno vorrebbe un’app di posta elettronica che occasionalmente invia email al tuo ex e mente sulla tua casella di posta. Ma gradualmente i modelli miglioreranno. Anche mentre si spingeranno ulteriormente nello spazio di esperienze completamente nuove, diventeranno lentamente abbastanza affidabili da essere utilizzati per un lavoro reale.
Piccoli pezzi di questo futuro esistono già. Anni fa Jonas Degrave ha dimostrato che ChatGPT poteva fare una buona simulazione di una riga di comando Linux. Allo stesso modo, websim.ai utilizza un LLM per generare siti web su richiesta mentre li navighi. Oasis, GameNGen e DIAMOND addestrano modelli video condizionati sull’azione su singoli videogiochi, permettendoti di giocare ad esempio a Doom dentro un grande modello. E Genie 2 genera videogiochi giocabili da prompt testuali. L’interfaccia generativa potrebbe ancora sembrare un’idea folle, ma non è così folle.
Ci sono enormi domande aperte su come apparirà tutto questo. Dove sarà inizialmente utile l’interfaccia generativa? Come condivideremo e distribuiremo le esperienze che creiamo collaborando con il modello, se esistono solo come contesto di un grande modello? Vorremmo davvero farlo? Quali nuovi tipi di esperienze saranno possibili? Come funzionerà tutto questo in pratica? I modelli genereranno interfacce come codice o produrranno direttamente pixel grezzi?
Non conosco ancora queste risposte. Dovremo sperimentare e scoprirlo!Che cosa significherebbe trattare l'IA come uno strumento invece che come una persona?
Dall’avvio di ChatGPT, le esplorazioni in due direzioni hanno preso velocità.
La prima direzione riguarda le capacità tecniche. Quanto grande possiamo addestrare un modello? Quanto bene può rispondere alle domande del SAT? Con quanta efficienza possiamo distribuirlo?
La seconda direzione riguarda il design dell’interazione. Come comunichiamo con un modello? Come possiamo usarlo per un lavoro utile? Quale metafora usiamo per ragionare su di esso?
La prima direzione è ampiamente seguita e enormemente finanziata, e per una buona ragione: i progressi nelle capacità tecniche sono alla base di ogni possibile applicazione. Ma la seconda è altrettanto cruciale per il campo e ha enormi incognite. Siamo solo a pochi anni dall’inizio dell’era dei grandi modelli. Quali sono le probabilità che abbiamo già capito i modi migliori per usarli?
Propongo una nuova modalità di interazione, in cui i modelli svolgano il ruolo di applicazioni informatiche (ad esempio app per telefoni): fornendo un’interfaccia grafica, interpretando gli input degli utenti e aggiornando il loro stato. In questa modalità, invece di essere un “agente” che utilizza un computer per conto dell’essere umano, l’IA può fornire un ambiente informatico più ricco e potente che possiamo utilizzare.
Metafore per l’interazione
Al centro di un’interazione c’è una metafora che guida le aspettative di un utente su un sistema. I primi giorni dell’informatica hanno preso metafore come “scrivanie”, “macchine da scrivere”, “fogli di calcolo” e “lettere” e le hanno trasformate in equivalenti digitali, permettendo all’utente di ragionare sul loro comportamento. Puoi lasciare qualcosa sulla tua scrivania e tornare a prenderlo; hai bisogno di un indirizzo per inviare una lettera. Man mano che abbiamo sviluppato una conoscenza culturale di questi dispositivi, la necessità di queste particolari metafore è scomparsa, e con esse i design di interfaccia skeumorfici che le rafforzavano. Come un cestino o una matita, un computer è ora una metafora di se stesso.
La metafora dominante per i grandi modelli oggi è modello-come-persona. Questa è una metafora efficace perché le persone hanno capacità estese che conosciamo intuitivamente. Implica che possiamo avere una conversazione con un modello e porgli domande; che il modello possa collaborare con noi su un documento o un pezzo di codice; che possiamo assegnargli un compito da svolgere da solo e che tornerà quando sarà finito.
Tuttavia, trattare un modello come una persona limita profondamente il nostro modo di pensare all’interazione con esso. Le interazioni umane sono intrinsecamente lente e lineari, limitate dalla larghezza di banda e dalla natura a turni della comunicazione verbale. Come abbiamo tutti sperimentato, comunicare idee complesse in una conversazione è difficile e dispersivo. Quando vogliamo precisione, ci rivolgiamo invece a strumenti, utilizzando manipolazioni dirette e interfacce visive ad alta larghezza di banda per creare diagrammi, scrivere codice e progettare modelli CAD. Poiché concepiamo i modelli come persone, li utilizziamo attraverso conversazioni lente, anche se sono perfettamente in grado di accettare input diretti e rapidi e di produrre risultati visivi. Le metafore che utilizziamo limitano le esperienze che costruiamo, e la metafora modello-come-persona ci impedisce di esplorare il pieno potenziale dei grandi modelli.
Per molti casi d’uso, e specialmente per il lavoro produttivo, credo che il futuro risieda in un’altra metafora: modello-come-computer.
Usare un’IA come un computer
Sotto la metafora modello-come-computer, interagiremo con i grandi modelli seguendo le intuizioni che abbiamo sulle applicazioni informatiche (sia su desktop, tablet o telefono). Nota che ciò non significa che il modello sarà un’app tradizionale più di quanto il desktop di Windows fosse una scrivania letterale. “Applicazione informatica” sarà un modo per un modello di rappresentarsi a noi. Invece di agire come una persona, il modello agirà come un computer.
Agire come un computer significa produrre un’interfaccia grafica. Al posto del flusso lineare di testo in stile telescrivente fornito da ChatGPT, un sistema modello-come-computer genererà qualcosa che somiglia all’interfaccia di un’applicazione moderna: pulsanti, cursori, schede, immagini, grafici e tutto il resto. Questo affronta limitazioni chiave dell’interfaccia di chat standard modello-come-persona:
Scoperta. Un buon strumento suggerisce i suoi usi. Quando l’unica interfaccia è una casella di testo vuota, spetta all’utente capire cosa fare e comprendere i limiti del sistema. La barra laterale Modifica in Lightroom è un ottimo modo per imparare l’editing fotografico perché non si limita a dirti cosa può fare questa applicazione con una foto, ma cosa potresti voler fare. Allo stesso modo, un’interfaccia modello-come-computer per DALL-E potrebbe mostrare nuove possibilità per le tue generazioni di immagini.
Efficienza. La manipolazione diretta è più rapida che scrivere una richiesta a parole. Per continuare l’esempio di Lightroom, sarebbe impensabile modificare una foto dicendo a una persona quali cursori spostare e di quanto. Ci vorrebbe un giorno intero per chiedere un’esposizione leggermente più bassa e una vibranza leggermente più alta, solo per vedere come apparirebbe. Nella metafora modello-come-computer, il modello può creare strumenti che ti permettono di comunicare ciò che vuoi più efficientemente e quindi di fare le cose più rapidamente.
A differenza di un’app tradizionale, questa interfaccia grafica è generata dal modello su richiesta. Questo significa che ogni parte dell’interfaccia che vedi è rilevante per ciò che stai facendo in quel momento, inclusi i contenuti specifici del tuo lavoro. Significa anche che, se desideri un’interfaccia più ampia o diversa, puoi semplicemente richiederla. Potresti chiedere a DALL-E di produrre alcuni preset modificabili per le sue impostazioni ispirati da famosi artisti di schizzi. Quando clicchi sul preset Leonardo da Vinci, imposta i cursori per disegni prospettici altamente dettagliati in inchiostro nero. Se clicchi su Charles Schulz, seleziona fumetti tecnicolor 2D a basso dettaglio.
Una bicicletta della mente proteiforme
La metafora modello-come-persona ha una curiosa tendenza a creare distanza tra l’utente e il modello, rispecchiando il divario di comunicazione tra due persone che può essere ridotto ma mai completamente colmato. A causa della difficoltà e del costo di comunicare a parole, le persone tendono a suddividere i compiti tra loro in blocchi grandi e il più indipendenti possibile. Le interfacce modello-come-persona seguono questo schema: non vale la pena dire a un modello di aggiungere un return statement alla tua funzione quando è più veloce scriverlo da solo. Con il sovraccarico della comunicazione, i sistemi modello-come-persona sono più utili quando possono fare un intero blocco di lavoro da soli. Fanno le cose per te.
Questo contrasta con il modo in cui interagiamo con i computer o altri strumenti. Gli strumenti producono feedback visivi in tempo reale e sono controllati attraverso manipolazioni dirette. Hanno un overhead comunicativo così basso che non è necessario specificare un blocco di lavoro indipendente. Ha più senso mantenere l’umano nel loop e dirigere lo strumento momento per momento. Come stivali delle sette leghe, gli strumenti ti permettono di andare più lontano a ogni passo, ma sei ancora tu a fare il lavoro. Ti permettono di fare le cose più velocemente.
Considera il compito di costruire un sito web usando un grande modello. Con le interfacce di oggi, potresti trattare il modello come un appaltatore o un collaboratore. Cercheresti di scrivere a parole il più possibile su come vuoi che il sito appaia, cosa vuoi che dica e quali funzionalità vuoi che abbia. Il modello genererebbe una prima bozza, tu la eseguirai e poi fornirai un feedback. “Fai il logo un po’ più grande”, diresti, e “centra quella prima immagine principale”, e “deve esserci un pulsante di login nell’intestazione”. Per ottenere esattamente ciò che vuoi, invierai una lista molto lunga di richieste sempre più minuziose.
Un’interazione alternativa modello-come-computer sarebbe diversa: invece di costruire il sito web, il modello genererebbe un’interfaccia per te per costruirlo, dove ogni input dell’utente a quell’interfaccia interroga il grande modello sotto il cofano. Forse quando descrivi le tue necessità creerebbe un’interfaccia con una barra laterale e una finestra di anteprima. All’inizio la barra laterale contiene solo alcuni schizzi di layout che puoi scegliere come punto di partenza. Puoi cliccare su ciascuno di essi, e il modello scrive l’HTML per una pagina web usando quel layout e lo visualizza nella finestra di anteprima. Ora che hai una pagina su cui lavorare, la barra laterale guadagna opzioni aggiuntive che influenzano la pagina globalmente, come accoppiamenti di font e schemi di colore. L’anteprima funge da editor WYSIWYG, permettendoti di afferrare elementi e spostarli, modificarne i contenuti, ecc. A supportare tutto ciò è il modello, che vede queste azioni dell’utente e riscrive la pagina per corrispondere ai cambiamenti effettuati. Poiché il modello può generare un’interfaccia per aiutare te e lui a comunicare più efficientemente, puoi esercitare più controllo sul prodotto finale in meno tempo.
La metafora modello-come-computer ci incoraggia a pensare al modello come a uno strumento con cui interagire in tempo reale piuttosto che a un collaboratore a cui assegnare compiti. Invece di sostituire un tirocinante o un tutor, può essere una sorta di bicicletta proteiforme per la mente, una che è sempre costruita su misura esattamente per te e il terreno che intendi attraversare.
Un nuovo paradigma per l’informatica?
I modelli che possono generare interfacce su richiesta sono una frontiera completamente nuova nell’informatica. Potrebbero essere un paradigma del tutto nuovo, con il modo in cui cortocircuitano il modello di applicazione esistente. Dare agli utenti finali il potere di creare e modificare app al volo cambia fondamentalmente il modo in cui interagiamo con i computer. Al posto di una singola applicazione statica costruita da uno sviluppatore, un modello genererà un’applicazione su misura per l’utente e le sue esigenze immediate. Al posto della logica aziendale implementata nel codice, il modello interpreterà gli input dell’utente e aggiornerà l’interfaccia utente. È persino possibile che questo tipo di interfaccia generativa sostituisca completamente il sistema operativo, generando e gestendo interfacce e finestre al volo secondo necessità.
All’inizio, l’interfaccia generativa sarà un giocattolo, utile solo per l’esplorazione creativa e poche altre applicazioni di nicchia. Dopotutto, nessuno vorrebbe un’app di posta elettronica che occasionalmente invia email al tuo ex e mente sulla tua casella di posta. Ma gradualmente i modelli miglioreranno. Anche mentre si spingeranno ulteriormente nello spazio di esperienze completamente nuove, diventeranno lentamente abbastanza affidabili da essere utilizzati per un lavoro reale.
Piccoli pezzi di questo futuro esistono già. Anni fa Jonas Degrave ha dimostrato che ChatGPT poteva fare una buona simulazione di una riga di comando Linux. Allo stesso modo, websim.ai utilizza un LLM per generare siti web su richiesta mentre li navighi. Oasis, GameNGen e DIAMOND addestrano modelli video condizionati sull’azione su singoli videogiochi, permettendoti di giocare ad esempio a Doom dentro un grande modello. E Genie 2 genera videogiochi giocabili da prompt testuali. L’interfaccia generativa potrebbe ancora sembrare un’idea folle, ma non è così folle.
Ci sono enormi domande aperte su come apparirà tutto questo. Dove sarà inizialmente utile l’interfaccia generativa? Come condivideremo e distribuiremo le esperienze che creiamo collaborando con il modello, se esistono solo come contesto di un grande modello? Vorremmo davvero farlo? Quali nuovi tipi di esperienze saranno possibili? Come funzionerà tutto questo in pratica? I modelli genereranno interfacce come codice o produrranno direttamente pixel grezzi?
Non conosco ancora queste risposte. Dovremo sperimentare e scoprirlo!
Tradotto da:\ https://willwhitney.com/computing-inside-ai.htmlhttps://willwhitney.com/computing-inside-ai.html
-
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 81022b27:2b8d0644
2025-05-31 00:47:43
@ 81022b27:2b8d0644
2025-05-31 00:47:43Today some clients and I were talking and they asked me about my recent seminar where I attended the “Unleash The Power Within” seminar with Tony Robbins. I explained that the firewalk I performed was not the highlight of the seminar, It was all the junk I got rid of mentally. We talked some more and then someone said something a little derogatory about Scientology.
I said, “wait a second, Scientology changed my life!”
It’s true. Some of the things I learned through Dianetics and Scientology were catalysts in me changing my entire life around.
It started one evening in Coral Gables, FL when I was walking down the street going to meet someone for dinner. I was stopped by a lady holding a clipboard outside of a 50’s-looking building.
“Would you like to take personality test?”
I asked: “What’s that?”
She explained and since I’m always early to things, I had plenty of time to kill. I said: “Sure! let’s do it!”
I took the test and the results seemed spot on. Then they asked if I would like to learn more about the mind , I could sign up for a course for a modest amount and I was genuinely curious about the whole deal and I agreed.
The Class I came back like a week later to start the class. I’m remembering that building had a distinct smell. It wasn’t bad. I can’t really describe it, but if I ever smell something similar, I’d recognize it instantly.
I walked in and they took me to a big room, a classroom with lots of tables and chairs. Every table had a small box with objects in it. There were people reading, there were people in groups studying, lots of chatter.
It seemed exciting!
I don’t remember if it was my first lesson or not, but we had to do TR’s (Training Routines) and I was asked to sit across from some guy and just stare at him. Look him in the eyes and not laugh, not blink excessively, just keep your composure.
Bah! Stupid! But I can do this!
We started the exercise and it seemed silly at first, but then my heart started racing and started freaking out. It felt like I was in a tunnel, but somehow his eyes were attacking me.
Then all of a sudden I’m hovering 8 feet above myself and I’m looking at the situation from above.
Next thing I know, I’m back in my body and the exercise is over.
The teacher, or facilitator came by to ask me how everything went. I started to tell her exactly what happened and she was writing very matter-of-fact-ly.
“And then I left my body!,” I emphasized.
“So you exteriorized?” She asked.
“I guess.”, I mumbled.
What really made me curious is these people are just nonchalantly just writing down stuff like it’s no big deal.
They got me. I was hooked.
Auditing
I started doing some courses whenever I had some free time: maybe once or twice a week. I learned that there is something that they call the “reactive mind” and that past traumas can affect someone in the present time.
We did this exercise that when my “Auditor” would snap her fingers, I would repeat the first word that popped into my mind, until we got a string of words. I would the repeat this string of words until they “lost their charge” and had no effect.
During one of these sessions, I
felt like I was choking.
No, not choking !
I could taste salt water!
I was drowning!
This shook me up because I had no recollection of almost drowning like that.
I asked my mother if I ever almost drowned and I was surprised by her answer.
She said; “Yes. We were at the beach-you were a baby and in the water with your father. A wave got both of you and your dad had to throw you towards me like a football, because he couldn’t fight the riptide.”
Wow.
Study Tech
before you start the “heavy” course, you must learn how to study. So they have designed a way to teach people “How.”
I thought, “wow, no one ever really taught me how to study.”
In high school, I kind of just skated by, with no need to ever read or do much. I didn’t make valedictorian, but I was discovering my social life and that was top priority for me at the time.
They showed me if you read something and can’t remember what you just read, t means you read past a misunderstood word. You never skip a word you don’t understand. There are always dictionaries at every study table.
If you get woozy and want to bail on the material being studied, then you have skipped a gradient, so you should go back to a point you understand and work back up.
If you get a headache while, studying, that means you have a “lack of mass” and the topic is abstract and you need to make it more physical to be able to understand it.
That is why they had those baskets with modeling clay and stuff in it, so you could model out concepts.
I still use this knowledge.
Basic Study Manual
The Purification Program
At some point one of the coaches pointed out that if I wanted to make quicker progress, I should do The Purification Program. The Program is designed to get rid of environmental toxins and medications and other materials that are stuck in your physical body and is interfering with your progress “up the bridge”
So of course, I am fascinated by this idea and sign up for the course, This time, it;s a lot of books and it’s going to cost be some serious cash. I didn’t have that kind of money, because I was scraping by on an assistant manager at Wendy’s salary.
No worries, take out a new credit card to pay for it. And one of the members drove out to my work to get the signature (and $$) to pay for the course. I think It was the end of the month and they got a bonus if I signed up before then.
The Program
The program basically consists of sitting in a sauna for 5 hours a day, Taking supplements: cal-mag, megadoses of niacin, and oils
It was perfectly organized: we were taken to a different part of the building to an area with a eucalyptus smell. We were shown the sauna-it was a large sauna , It could hold like 10 people.
We were given our supplements and then told to jog for few blocks around the building and then come into the sauna.
By the time you are done with the run, the niacin has kicked in and given you a nice “flush” skin is red and blood vessels have dilated. Now you’re ready for the sauna.
Everything done here is monitored. The guy supervising us was a Medical Doctor and he recorded weight going in and was always available supervising and answering any questions.
Five hours a day in a sauna is a LONG time- especially with someone like me who is not crazy about sweating constantly.
You were free to come in and out to prevent from getting overheated and get in the shower to cool off.
I brought reading material, I was doing this!
Reactions
X Ray Radiation
For the first couple of days, nothing significant happened except my skin started getting better.
One day as I am leaving the sauna to cool off, I take a look in the mirror and it looks like I’d been in a fight. Both my eyes had black rings like bruises around them.
I asked the attendant what this was and he looked at them and asked me if I had been exposed to many x-rays. I said that yes, I had been a sick kid and had tons of diagnostic procedures and medicines and stuff.
He said : “Ok, get back in there! You’re just running out x-ray radiation”
Came back out about 20 minutes later and the rings were gone.
Medications
I’m sitting in the sauna and I start getting sleepy. More like “anesthesia count down to ten sleepy”
Again, I was concerned, so I asked attendant what the deal was and he said I was likely detoxing from medicines and drugs I’d taken.
Went back in until it cleared up.
Chlorine
One day there were about 5 of us in the sauna and all of a sudden a strong smell of chlorine started. It keeps getting worse until it was so bad it was burning our eyes. We all exited the sauna thinking there was some sort of chlorine spill or something like that.
The attendant asked: “Has any of you worked as a pool maintenance tech?”
We looked around and one guy raised his hand.
The attendant said “Ok! Everyone dismissed for today except for you!” as he pointed to the Pool Tech guy. “Get back in there!”
I was doing this in the mornings when I had the evening shifts at the restaurant and when I worked days, Id try to make it to the sauna in the evenings.
After about 3 weeks, everything started to taper off and I was done.
I was feeling great and there was something different about everything, I felt like I was more awake and aware. And my skin and complexion were fabulous!
Clear Body, Clear Mind
The Sea Org
At some point, the people in charge routed me to talk to someone one in the Sea Org.
It was a small glass office, like the one you are led into when you are buying a car. I was greeted by a man in an impressive looking uniform like Captain Steubing from the “Love Boat”.
He said they had been watching me and my progress and were impressed with my IQ score. He said I stood out among the other people and compared me to this woman we could see through the glass.
He basically ripped her to shreds in front of me, telling me how her life was in chaos and how she had created all of her chaos and that somehow I was different from her.
They basically offered me a job.
One catch:
I had to sign a contract for a “billion years” and I couldn’t be in debt.
Seeing I was already in debt from some of the previous courses, I didn’t qualify. Also a billion years seemed a bit long.
I thanked him and said I would consider it- I was pretty sure it was a solid no, but I didn’t want to tell him that. I was probably intimidated by the uniform.
Healing with Vitamins
This was not an official class or anything, but during my time there, I saw whenever someone was having issues with their body, they would consult with one of the counselors and they would look into a little book: “Earl Mindell’s Vitamin Bible” or see a chiropractor down the road who was apparently a Scientologist.
I used what little I learned and suggested home remedies to my Wendy’s employees and their families and developed a little side gig offering supplements to anyone willing to listen.
The Bottom Line
I know there is a lot of negative press and negativity in general about Scientology, but be clear about this: Scientology changed my life!
I’m not an active Scientologist, and don’t feel like I want to go back. But it definitely shaped me into the person that I am today.
If there is bias against the church in this article, it’s just the way that it’s run. Running an organization like an MLM encourages bad behavior.
I have moved countless times since those days, and the first piece of forwarded mail is usually from a Scientology Org.
I’m not sure I would have taken the steps to make a drastic change and decide to attend chiropractic school had it not been for my brief time in Scientology,
Love,
-Dan
-
 @ 0fa80bd3:ea7325de
2025-04-09 21:19:39
@ 0fa80bd3:ea7325de
2025-04-09 21:19:39DAOs promised decentralization. They offered a system where every member could influence a project's direction, where money and power were transparently distributed, and decisions were made through voting. All of it recorded immutably on the blockchain, free from middlemen.
But something didn’t work out. In practice, most DAOs haven’t evolved into living, self-organizing organisms. They became something else: clubs where participation is unevenly distributed. Leaders remained - only now without formal titles. They hold influence through control over communications, task framing, and community dynamics. Centralization still exists, just wrapped in a new package.
But there's a second, less obvious problem. Crowds can’t create strategy. In DAOs, people vote for what "feels right to the majority." But strategy isn’t about what feels good - it’s about what’s necessary. Difficult, unpopular, yet forward-looking decisions often fail when put to a vote. A founder’s vision is a risk. But in healthy teams, it’s that risk that drives progress. In DAOs, risk is almost always diluted until it becomes something safe and vague.
Instead of empowering leaders, DAOs often neutralize them. This is why many DAOs resemble consensus machines. Everyone talks, debates, and participates, but very little actually gets done. One person says, “Let’s jump,” and five others respond, “Let’s discuss that first.” This dynamic might work for open forums, but not for action.
Decentralization works when there’s trust and delegation, not just voting. Until DAOs develop effective systems for assigning roles, taking ownership, and acting with flexibility, they will keep losing ground to old-fashioned startups led by charismatic founders with a clear vision.
We’ve seen this in many real-world cases. Take MakerDAO, one of the most mature and technically sophisticated DAOs. Its governance token (MKR) holders vote on everything from interest rates to protocol upgrades. While this has allowed for transparency and community involvement, the process is often slow and bureaucratic. Complex proposals stall. Strategic pivots become hard to implement. And in 2023, a controversial proposal to allocate billions to real-world assets passed only narrowly, after months of infighting - highlighting how vision and execution can get stuck in the mud of distributed governance.
On the other hand, Uniswap DAO, responsible for the largest decentralized exchange, raised governance participation only after launching a delegation system where token holders could choose trusted representatives. Still, much of the activity is limited to a small group of active contributors. The vast majority of token holders remain passive. This raises the question: is it really community-led, or just a formalized power structure with lower transparency?
Then there’s ConstitutionDAO, an experiment that went viral. It raised over $40 million in days to try and buy a copy of the U.S. Constitution. But despite the hype, the DAO failed to win the auction. Afterwards, it struggled with refund logistics, communication breakdowns, and confusion over governance. It was a perfect example of collective enthusiasm without infrastructure or planning - proof that a DAO can raise capital fast but still lack cohesion.
Not all efforts have failed. Projects like Gitcoin DAO have made progress by incentivizing small, individual contributions. Their quadratic funding mechanism rewards projects based on the number of contributors, not just the size of donations, helping to elevate grassroots initiatives. But even here, long-term strategy often falls back on a core group of organizers rather than broad community consensus.
The pattern is clear: when the stakes are low or the tasks are modular, DAOs can coordinate well. But when bold moves are needed—when someone has to take responsibility and act under uncertainty DAOs often freeze. In the name of consensus, they lose momentum.
That’s why the organization of the future can’t rely purely on decentralization. It must encourage individual initiative and the ability to take calculated risks. People need to see their contribution not just as a vote, but as a role with clear actions and expected outcomes. When the situation demands, they should be empowered to act first and present the results to the community afterwards allowing for both autonomy and accountability. That’s not a flaw in the system. It’s how real progress happens.
-
 @ 866e0139:6a9334e5
2025-05-27 10:15:17
@ 866e0139:6a9334e5
2025-05-27 10:15:17Autor: Milosz Matuschek. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Der Schweizer Historiker Daniele Ganser startet eine Plakataktion. Auf Facebook schreibt er:
"Dieses Plakat habe ich ab heute an sechs Bahnhöfen in der Schweiz aufhängen lassen: Die Schweiz muss die Neutralität bewahren. Keine Zusammenarbeit mit der NATO!
Die Aktion läuft eine Woche. Das Plakat hängt in Basel (Gleis 5 und 7), Zürich (Gleis 9 und 12), Bern (Gleis 3 und 11), Luzern (Gleis 7 und 11), St. Gallen (Gleis 1 und 2) und Chur (Gleis 4 und Arosabahn).
Wenn jemand ein Plakat sieht und fotografiert und es mir per Email schickt freut mich das!
https://globalbridge.ch/die-schweiz-muss-die.../
Daniele Ganser kann man über folgende Seite kontaktieren.
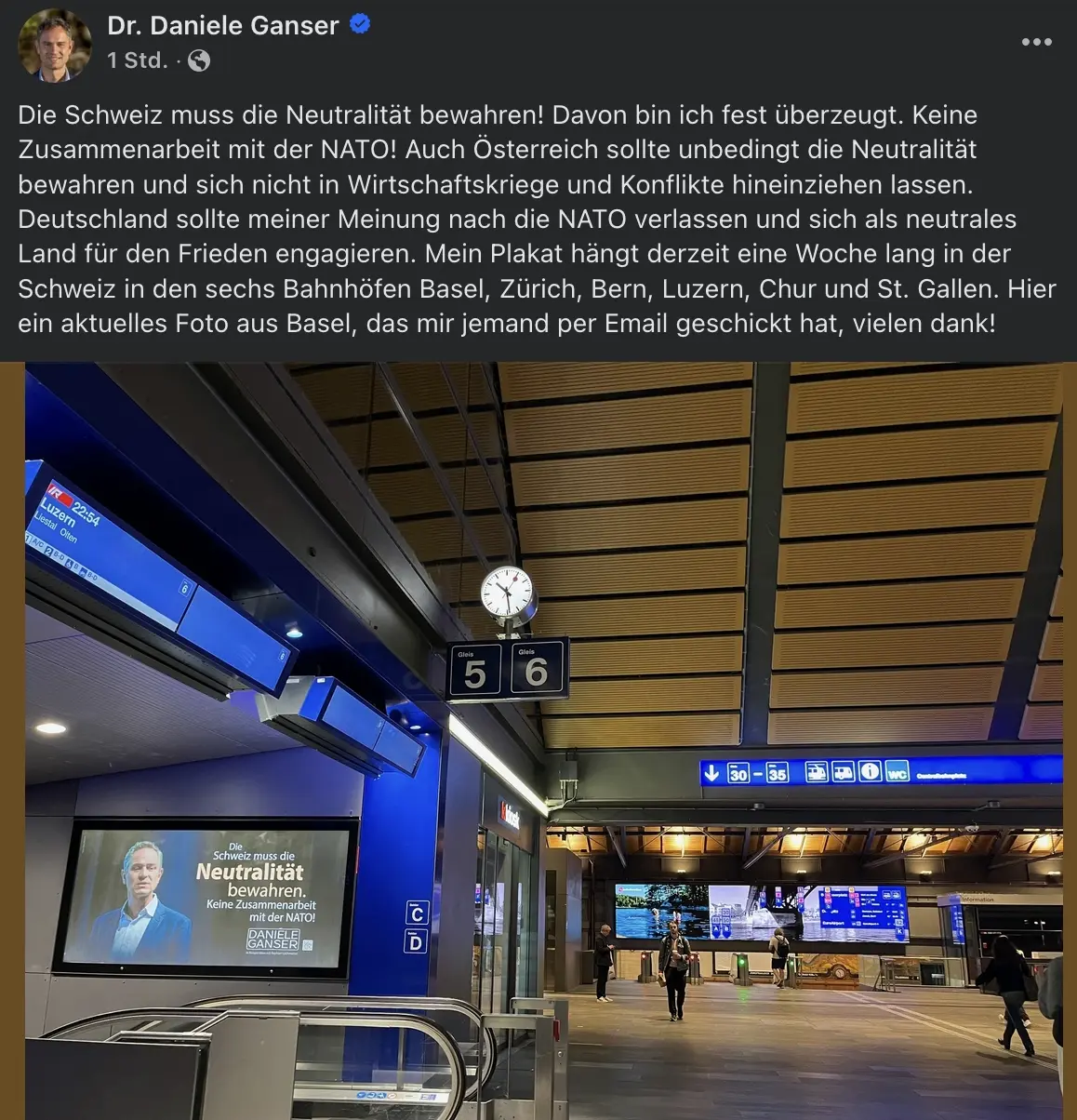
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ a5ee4475:2ca75401
2025-05-18 16:07:07
@ a5ee4475:2ca75401
2025-05-18 16:07:07ai #artificial #intelligence #english #tech
Open Source
Models
Text
Image
- SDAI FOSS - Stable Diffusion AI to Android [download] [source] 🤖
- Stable Diffusion - Text to image [source] 🌐
- Pixart Alpha - Photorealistic Text to Image Generation [source]
- Pixart Delta - Framework to Pixart Alpha [paper] [source]
- Pixart Sigma - 4K Text to Image Generation [source]
- OmniGen - Pompt, image or subject to image [source]
- Pigallery - Self-Hosted AI Image Generator [source]
Video
Tools
Lightning Based
- Animal Sunset - AI video generation with Nostr npub by lightning payments [source]
- Ai Rand - AI text generation with Pubky DNS by lightning payments [source]
- PlebAI - Text and Image generation without signup [source] 🌐🤖🍎 [sites down - only github available]
Others
- HuggingFace - Test and collaborate on models, datasets and apps. [source]
- DuckDuckGo AI Chat - Famous AIs without Login [source]
- Ollama - Run LLMs Locally [source]
- DreamStudio - Stable Diffusion’s Web App Tool [info] [source]
- Prompt Gallery - AI images with their prompts [source]
Closed Source
Models
Text
- ChatGPT
- Claude
- Gemini
- Copilot
- Maritalk - Text AI in Portuguese focused on Brazil with model Sabia-3 and the open source models Sabia-7b and Sabia-2 [source]
- Amazônia IA - Text AI in Portuguese focused on Brazil with the guara, hapia and golia models [source]
Image
Video
- Minimax - Realistic videos (prompts only in chinese)
Tools
Other index: Amazing AI
-
 @ f85b9c2c:d190bcff
2025-05-31 01:48:30
@ f85b9c2c:d190bcff
2025-05-31 01:48:30
The anime world is far from real and especially the powers that characters have is unimaginable and fighting scene are just epic. One good thing about anime is the story setting and the brilliant way of narration , it is not restricted by the characters, nor by what role will they play. Once such anime is Naruto ,it not just anime but a life-lesson series that will touch each and every emotion one has ever experienced . Although the characters are from a ninja world.

You will find the characters much more relatable to society that we live in . You will find yourself growing into a better person with each passing episode , it’s full of knowledge and will definitely increase your Emotional Quotient.
There is no age barrier as to who should watch this anime, any person of can and I would encourage everyone to watch this masterpiece. You will grow along with the series and would know that how our thinking evolve with growing age .
The character development in this epic saga is one of a kind and every characters back story is shown and this shows even though we live in a same world but still everyone is different and that difference has a lot to do with the journey an individual goes through. Personality is not born it is created and build during the lifetime.

Story has no plot holes and the whole story is wellhighlighted ,it's experiences with each episode playing a key role in story building and you don't want to miss any it keeps you glued to the series. Even though the series is a 700+ episodes you would wish it to never end ever. Villains are an integral part of the story and you would love villains more the hero’s in many cases . Basically it is based on the perception or lens through which an individual gauge good or evil deeds.
“It’s not the face that makes someone a monster, it’s the choices they make with their lives.” Naruto”.
There is no supreme villain but each villain shows a conflict of opinion , so is the case in real life too. No one is an ultimate bad character it’s the perception and the deeds committed in the past that portraits the character such. The story has extremely powerful villains and have a solid reason to act harsh. Looking at there side of story you feel for the emotional trauma associated with them. But in the end a crime committed in pain is also a crime and must not be promoted and must be punished.
NARUTO being the protagonist of the whole saga is not the hero . He is also an character and the hero is left on the people to decide. The whole concept of one hero story is what not applicable in real life , we all are heroes of our respective life and everyone should believe in themselves.
“Hard-work is worthless for those that don’t believe in themselves.” Naruto.
Epic fight sequence makes the anime more interesting to watch and the clash of opinions are truly shown through the fights. The fights bring chaos and destruction to the world but after this the world understand why peace is the ultimate truth . Wars bring the people closer and shows the power of cooperation.
“Sometimes You Must Hurt In Order To Know, Fall In Order To Grow, Lose In Order To Gain, Because Life’s Greatest Lessons Are Learned Through Pain.” -Pain
The relationship of a teacher and student is shown with great importance and one should always respect the teacher for all the knowledge that they share. How teacher with his faith can transform lives. Especially in the years when the world seems new and hostile to us.
“Rejection is a part of any man’s life. If you can’t accept and move past rejection or at least use it as writing material you’re not a real man.” — Master Jiraya.
The series also highlights the importance of one’s job and the importance of it. It is greatly justified when Naruto’s own parents sacrifice themselves to protect others and prevented a war. Always try to add value to others life , otherwise there is no meaning of existence in this world . Friends ,family , society will pay back 100 folds .
This series will add meaning to your life and will transform you for the good. “BELIEVE IT.”
-
 @ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03
@ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ 81022b27:2b8d0644
2025-05-31 00:25:44
@ 81022b27:2b8d0644
2025-05-31 00:25:44I did my chiropractic studies at Life University in Georgia. When I picked schools, I had no idea about chiropractic philosophies or the politics in chiropractic.
I picked Life for two reasons: It was the closest to home (Miami at the time), and it was the first one to get back to me and tell me I was accepted.
My chiropractor in Miami wanted me to attend Palmer College, but that was in Iowa, and it sounded remote and cold. So, hell no.
I was so excited to start my new life that I crammed a U-Haul with all my junk and headed to Marietta.
Once classes started, someone suggested I join clubs to make friends.
I asked around, and there was this club having an upcoming party. It was Spizz Club. Spizz was short for Spizzerinctum, which meant “chiropractic enthusiasm.”
Well, I had a lot of that—plus, there were some attractive girls in that club.
I showed up at the party, which was at a student’s apartment, and got greeted with a long, uncomfortable hug. Do you remember the old cartoon of Pepe Le Pew and the cat? Well, I was the cat.
I grabbed a beer and started mingling. It was one uncomfortably long hug after another. Some made moaning sounds!
Fucking weirdos.
I got invited to a philosophy class while I was at the party. My social calendar wasn’t exactly overflowing, so I went.
Wow! These people were explaining concepts I’d known deep down my entire life, but I was hearing them out loud for the first time.
Deciding to move 700 miles away and change careers was a rash and selfish decision because I was running away.
Running from:
Failure
A failed marriage
Failure at real estate
Failure at finding something I was good at
Failure at being happy
Failure as a student, ten years after high school with no degree.
Here I am, listening to the speakers, and I realized this was different.
Maybe this was MY thing.
Maybe I could be a chiropractor.
Maybe I could help people.
Maybe I could be proud of myself.
Maybe someone could be proud of me.
That night changed me. The weirdos seemed less weird. I made friends, I found my footing.
Chiropractic college was tough, much tougher than I expected. I had always kind of “skated by,” but now I had to put in hard work because I hadn’t been in school full-time for ten years.
I also had never lived the college life, and apparently I was partying too much. We hit the bars to blow off steam after midterms and finals—turns out, there were a lot midterms and finals.
I almost flunked out one quarter, but there was a lot going on. My 85-year-old dad came to visit and was going to stay with me for a bit, then he passed away suddenly.
I had a lot of guilt from that, thinking that I could have done something different and could have stayed around a little longer. That guilt would resurface years later in a Craniosacral therapy session.
I couldn’t fail at this. This was too important. I went to a Hypnotherapist to see if maybe I could get “programmed” to not flunk out. Apparently, it worked.
Funny thing, I worked hard and time passed. We did it. We graduated and made it through.
Look, those brutal study sessions weren’t easy, and almost flunking out scared the hell out of me. I am thankful that Chiropractic passion stuck with me. That Spizz still gets me through some days.
Live Long and Prosper,
-Danny
-
 @ b83a28b7:35919450
2025-05-16 19:23:58
@ b83a28b7:35919450
2025-05-16 19:23:58This article was originally part of the sermon of Plebchain Radio Episode 110 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ b83a28b7:35919450
2025-05-16 19:26:56
@ b83a28b7:35919450
2025-05-16 19:26:56This article was originally part of the sermon of Plebchain Radio Episode 111 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ 39cc53c9:27168656
2025-05-27 09:21:51
@ 39cc53c9:27168656
2025-05-27 09:21:51Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% ^1 – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% ^1 of less-than-careful criminals.
KYC? Not you.
KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. ^2
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
Your identity has been stolen
KYC data has been found to be for sale on many dark net markets^3. Exchanges may have leaks or hacks, and such leaks contain very sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. ^3
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
(they) Know Your Coins
You may already know that Bitcoin and most cryptocurrencies have a transparent public blockchain, meaning that all data is shown unencrypted for everyone to see and recorded forever. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
Conclusions
To sum up, KYC does not protect individuals; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
Edited 20/03/2024 * Add reference to the 1% statement on Rights for Illusions section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity ^1
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ e6817453:b0ac3c39
2024-12-07 15:06:43
@ e6817453:b0ac3c39
2024-12-07 15:06:43I started a long series of articles about how to model different types of knowledge graphs in the relational model, which makes on-device memory models for AI agents possible.
We model-directed graphs
Also, graphs of entities
We even model hypergraphs
Last time, we discussed why classical triple and simple knowledge graphs are insufficient for AI agents and complex memory, especially in the domain of time-aware or multi-model knowledge.
So why do we need metagraphs, and what kind of challenge could they help us to solve?
- complex and nested event and temporal context and temporal relations as edges
- multi-mode and multilingual knowledge
- human-like memory for AI agents that has multiple contexts and relations between knowledge in neuron-like networks
MetaGraphs
A meta graph is a concept that extends the idea of a graph by allowing edges to become graphs. Meta Edges connect a set of nodes, which could also be subgraphs. So, at some level, node and edge are pretty similar in properties but act in different roles in a different context.
Also, in some cases, edges could be referenced as nodes.
This approach enables the representation of more complex relationships and hierarchies than a traditional graph structure allows. Let’s break down each term to understand better metagraphs and how they differ from hypergraphs and graphs.Graph Basics
- A standard graph has a set of nodes (or vertices) and edges (connections between nodes).
- Edges are generally simple and typically represent a binary relationship between two nodes.
- For instance, an edge in a social network graph might indicate a “friend” relationship between two people (nodes).
Hypergraph
- A hypergraph extends the concept of an edge by allowing it to connect any number of nodes, not just two.
- Each connection, called a hyperedge, can link multiple nodes.
- This feature allows hypergraphs to model more complex relationships involving multiple entities simultaneously. For example, a hyperedge in a hypergraph could represent a project team, connecting all team members in a single relation.
- Despite its flexibility, a hypergraph doesn’t capture hierarchical or nested structures; it only generalizes the number of connections in an edge.
Metagraph
- A metagraph allows the edges to be graphs themselves. This means each edge can contain its own nodes and edges, creating nested, hierarchical structures.
- In a meta graph, an edge could represent a relationship defined by a graph. For instance, a meta graph could represent a network of organizations where each organization’s structure (departments and connections) is represented by its own internal graph and treated as an edge in the larger meta graph.
- This recursive structure allows metagraphs to model complex data with multiple layers of abstraction. They can capture multi-node relationships (as in hypergraphs) and detailed, structured information about each relationship.
Named Graphs and Graph of Graphs
As you can notice, the structure of a metagraph is quite complex and could be complex to model in relational and classical RDF setups. It could create a challenge of luck of tools and software solutions for your problem.
If you need to model nested graphs, you could use a much simpler model of Named graphs, which could take you quite far.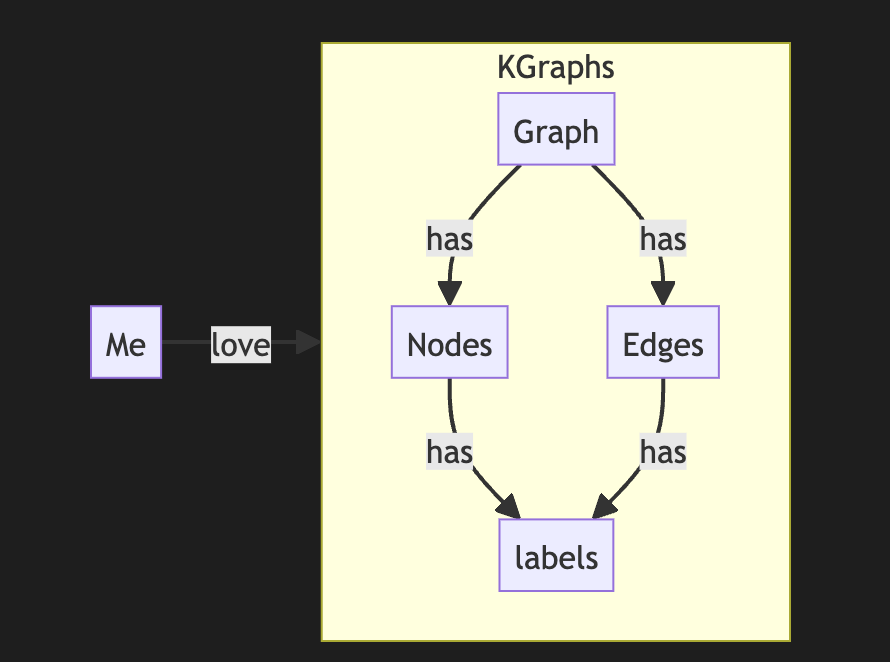
The concept of the named graph came from the RDF community, which needed to group some sets of triples. In this way, you form subgraphs inside an existing graph. You could refer to the subgraph as a regular node. This setup simplifies complex graphs, introduces hierarchies, and even adds features and properties of hypergraphs while keeping a directed nature.
It looks complex, but it is not so hard to model it with a slight modification of a directed graph.
So, the node could host graphs inside. Let's reflect this fact with a location for a node. If a node belongs to a main graph, we could set the location to null or introduce a main node . it is up to you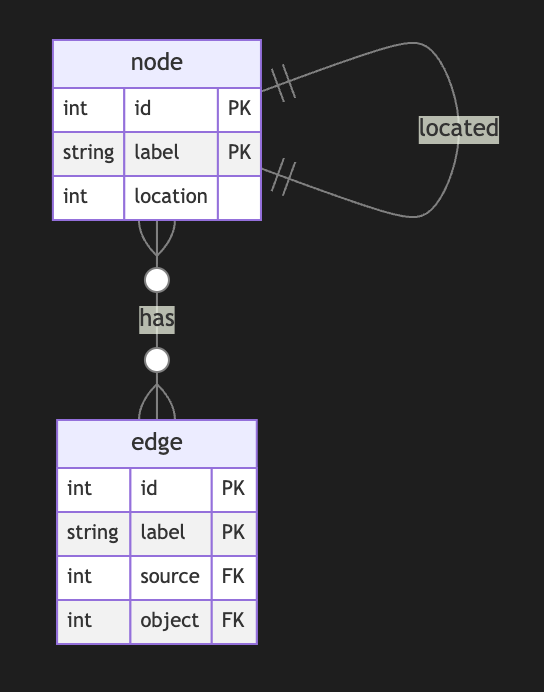
Nodes could have edges to nodes in different subgraphs. This structure allows any kind of nesting graphs. Edges stay location-free
Meta Graphs in Relational Model
Let’s try to make several attempts to model different meta-graphs with some constraints.
Directed Metagraph where edges are not used as nodes and could not contain subgraphs
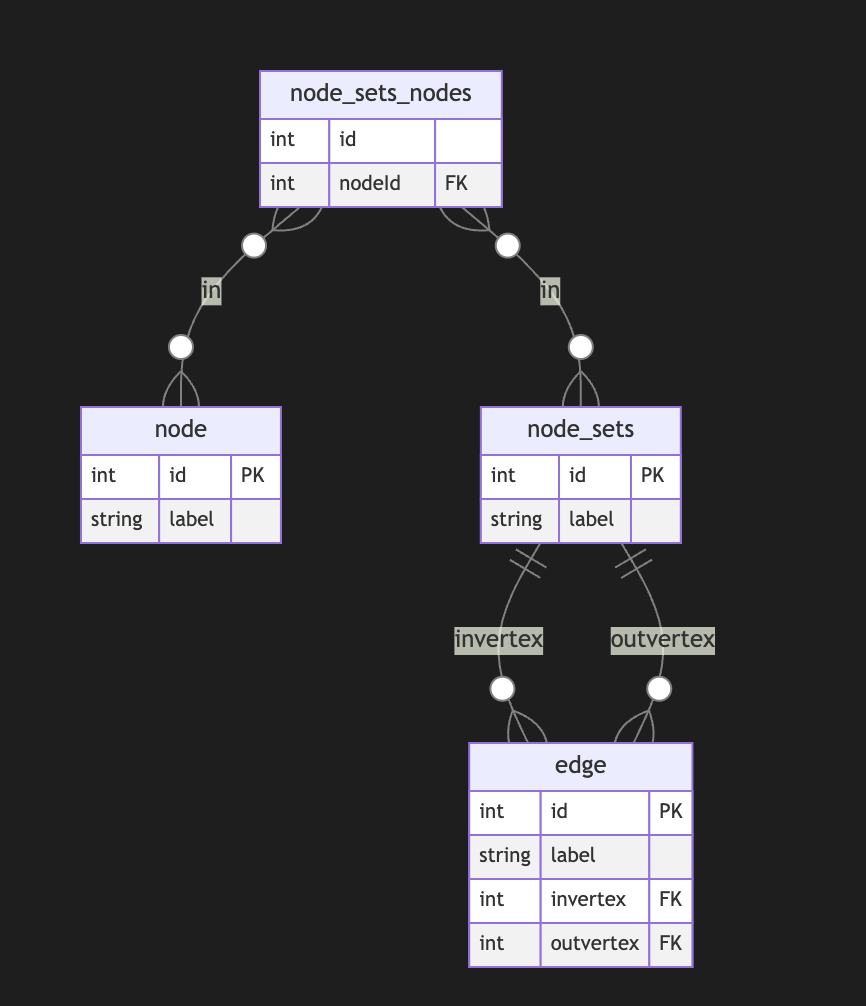
In this case, the edge always points to two sets of nodes. This introduces an overhead of creating a node set for a single node. In this model, we can model empty node sets that could require application-level constraints to prevent such cases.
Directed Metagraph where edges are not used as nodes and could contain subgraphs
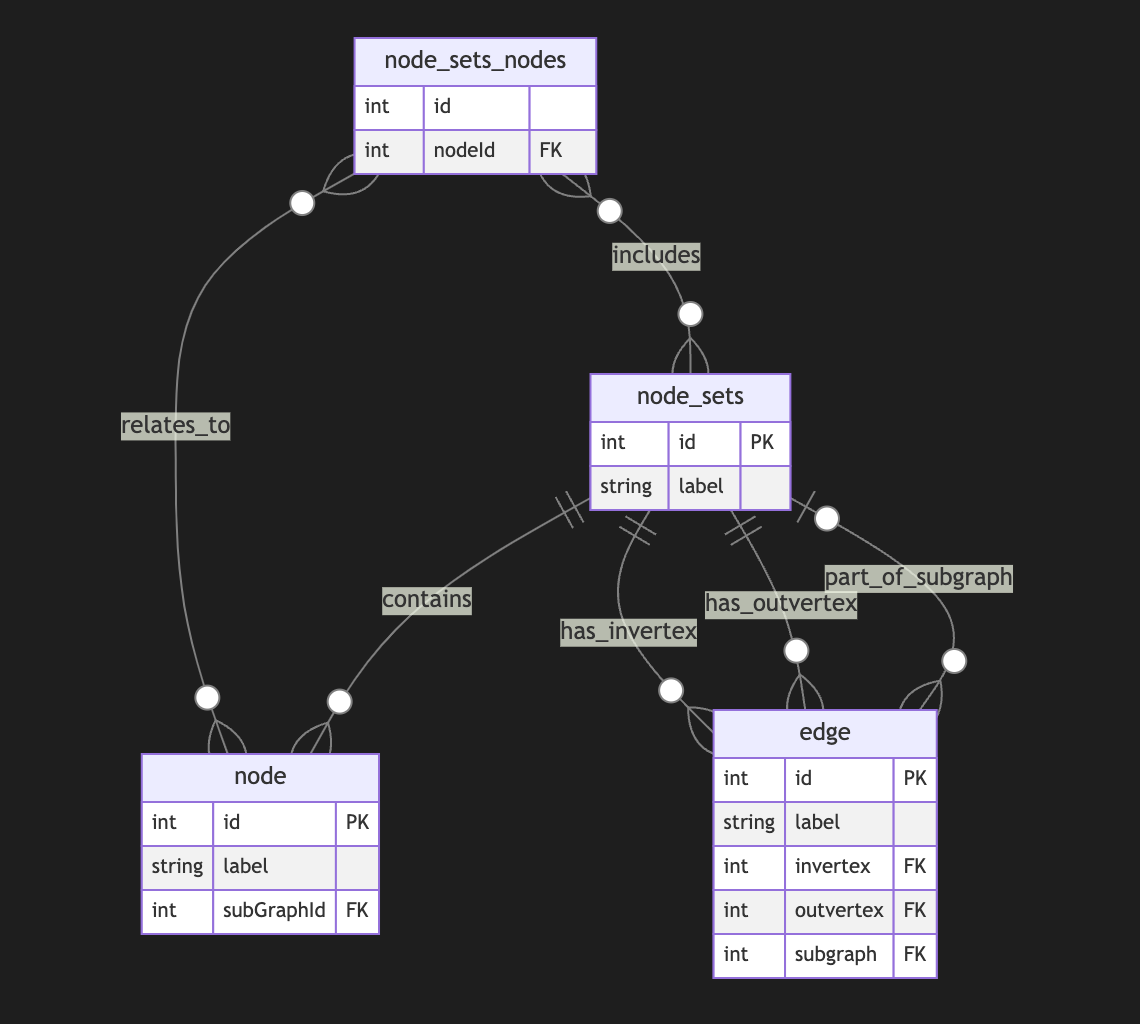
Adding a node set that could model a subgraph located in an edge is easy but could be separate from in-vertex or out-vert.
I also do not see a direct need to include subgraphs to a node, as we could just use a node set interchangeably, but it still could be a case.Directed Metagraph where edges are used as nodes and could contain subgraphs
As you can notice, we operate all the time with node sets. We could simply allow the extension node set to elements set that include node and edge IDs, but in this case, we need to use uuid or any other strategy to differentiate node IDs from edge IDs. In this case, we have a collision of ephemeral edges or ephemeral nodes when we want to change the role and purpose of the node as an edge or vice versa.
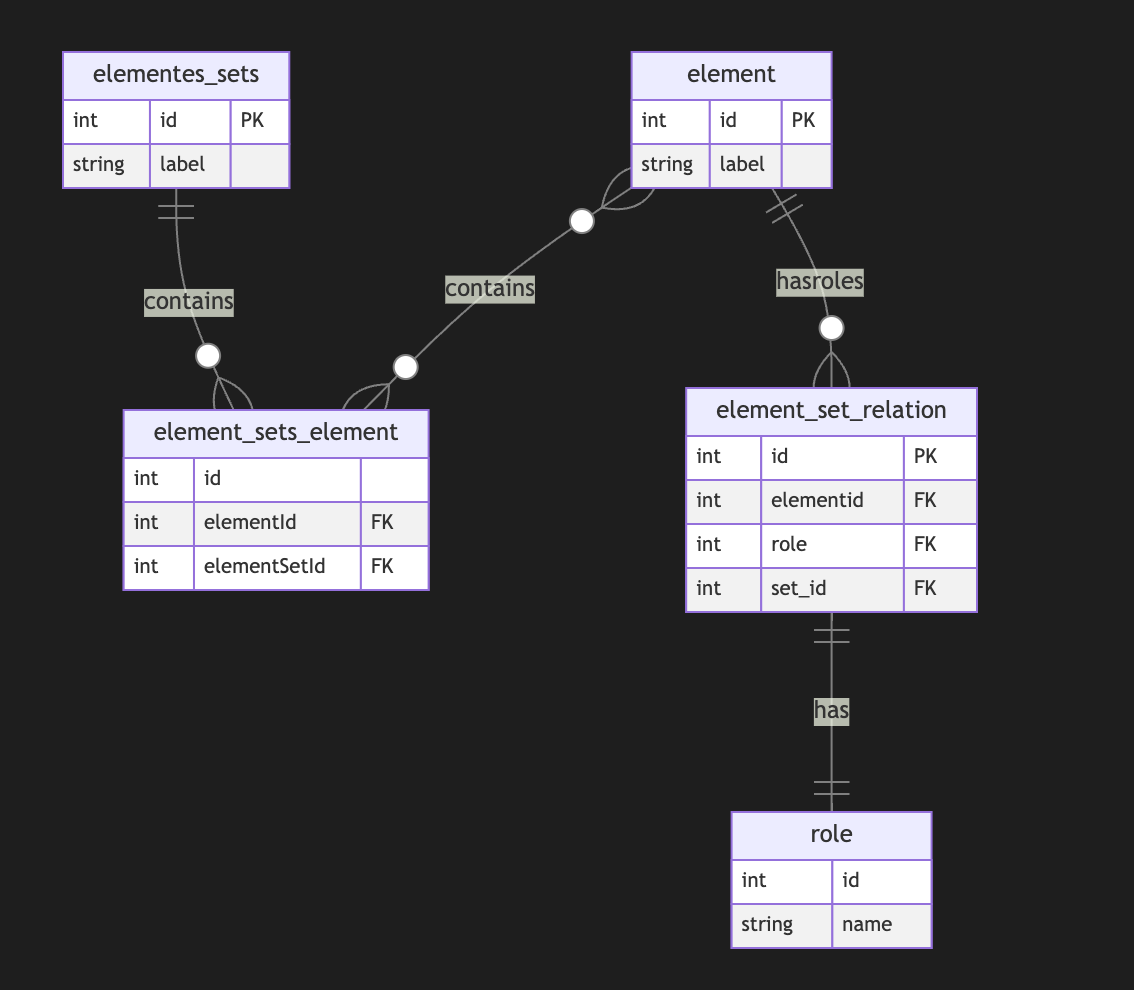
A full-scale metagraph model is way too complex for a relational database.
So we need a better model.Now, we have more flexibility but loose structural constraints. We cannot show that the element should have one vertex, one vertex, or both. This type of constraint has been moved to the application level. Also, the crucial question is about query and retrieval needs.
Any meta-graph model should be more focused on domain and needs and should be used in raw form. We did it for a pure theoretical purpose. -
 @ 81022b27:2b8d0644
2025-05-30 23:46:46
@ 81022b27:2b8d0644
2025-05-30 23:46:46How the birth of my grandson is making me re-think my own future
I just became a grandfather. My youngest daughter had a baby boy.
I’m thrilled.
And
I’m scared.
Babies are pure potential Infinite possibilities, all sorts of different paths they could take.
They haven’t drank the Kool-Aid, or in fact any Kool-Aid at all, lol
Will he be gregarious and outgoing?
Will he be shy and introverted?
Will he want to be an artist?
An engineer?
Will he be brave or scared?
Will he be like his grandfather, trying to overcompensate in his later life for being afraid of nearly everything in the early part of his life?
I am thrilled. All the grandparents that I have ever met said to me:
Just wait until you have grandkids, its different
And yes, it is different.
I’m not so worried about the how to take care of the baby-all I have to do is love him.
The other day, I was just holding him and was able to stay in “the love state” for the longest time ever.
(The love state is the goal of a meditation that I do-The goal is to stay “in love” feeling for as long as you can.)
I was able to get to this place so easily with him!
He has also taught me to slow down even more. He is not in a hurry to do anything. His job is to eat, poop and grow.
I feel like I get to savor the time I get with him even more than with my own kids.
I’m Scared His mom has had her share of issues.
She is now a single mom trying to navigate all the responsibilities of being a parent.
I didn’t think she was ready, but here we are.
She doesn’t have her mom to help guide her, but I thank god that she has Christi-my girlfriend. She has been such an incredible support for both Audrey and me.
I’m scared mostly because now my own future is uncertain.
I had my future planned out like where i wanted to retire-the things I wanted to do and now this little guy has me re-thinking all my plans about the future.
Here’s to uncertainty!!
Live Long and Prosper 🖖,
-Dan
Links | The Natural Life | The Intuitive Chiropractor