-
 @ cae03c48:2a7d6671
2025-05-27 19:00:51
@ cae03c48:2a7d6671
2025-05-27 19:00:51Bitcoin Magazine
Exodus Launches XO Pay, An In-App Bitcoin And Crypto Purchase SolutionExodus has officially launched XO Pay, a new crypto purchasing feature that allows users to buy and sell digital assets directly within the Exodus mobile wallet, and is now live across the United States. XO Pay aims to simplify the process for its users to easily purchase cryptocurrencies such as Bitcoin.
XO Pay is powered by Coinme’s Crypto-as-a-Service (CaaS) API platform and is a self custody Bitcoin wallet. This means customers can now purchase BTC within the wallet without going through third-party exchanges while keeping full control of their assets.
“XO Pay represents our commitment to making cryptocurrency more accessible to everyday customers,” said JP Richardson, Co-Founder and CEO of Exodus, in a recent press release sent to Bitcoin Magazine. “By integrating the purchasing process directly into our mobile wallet, we’re removing barriers and simplifying the journey from fiat to crypto, and back.”
With XO Pay, Exodus offers a self custodial way to complete Bitcoin transactions. This rollout is part of Exodus’ broader mission to make digital assets more secure, as the demand for Bitcoin is increasing.
“By creating a Web2 checkout experience into a Web3 self-custody wallet, Exodus has set a new bar for crypto user experience,” said Neil Bergquist, CEO and co-founder of Coinme. “Exodus’ innovative integration of Coinme’s APIs delivers the seamless in-app purchase flow users expect while keeping them in full control of their assets.”
This post Exodus Launches XO Pay, An In-App Bitcoin And Crypto Purchase Solution first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ cae03c48:2a7d6671
2025-05-27 19:00:50
@ cae03c48:2a7d6671
2025-05-27 19:00:50Bitcoin Magazine

🔴 LIVE: The Bitcoin Conference 2025 – Day 1The liveblog has ended.
No liveblog updates yet.
Load more
This post 🔴 LIVE: The Bitcoin Conference 2025 – Day 1 first appeared on Bitcoin Magazine and is written by Bitcoin Magazine.
-
 @ 5391098c:74403a0e
2025-05-27 18:20:42
@ 5391098c:74403a0e
2025-05-27 18:20:42Você trabalha 5 meses do ano somente para pagar impostos. Ou seja, 42% da sua renda serve para bancar serviços públicos de péssima qualidade. Mesmo que você tivesse a liberdade de usar esses 42% da sua renda para contratar serviços privados de qualidade (saúde, segurança e ensino), ainda assim você seria um escravo porque você recebe dinheiro em troca do seu trabalho, e o dinheiro perde cerca de 10% do valor a cada ano. Em outras palavras todo seu dinheiro que sobra depois de comprar comida, vestuário e moradia perde 100% do valor a cada 10 anos. Isso acontece porque o Estado imprime dinheiro do nada e joga na economia de propósito para gerar INFLAÇÃO e manter todos nós escravizados. Você pode deixar seu dinheiro investido em qualquer aplicação que imaginar e ainda assim nunca terá uma rentabilidade superior a inflação real. No final, acaba perdendo tudo do mesmo jeito. Caso você se ache esperto por investir o que sobra da sua renda em bens duráveis como imóveis ou veículos, sabia que esses bens também não são seus, porque se deixar de pagar os impostos desses bens (iptu, itr, ipva) você também perde tudo. Além disso, o custo de manutenção desses bens deve ser levado em consideração na conta das novas dívidas que você assumiu. No caso dos imóveis urbanos é impossível alugá-lo por mais de 0,38% do seu valor mensalmente. Em outras palavras, a cada ano você recebe menos de 5% do que investiu, tem que pagar o custo de manutenção, mais impostos e a valorização do bem nunca será superior a inflação real, também fazendo você perder quase tudo em cerca de 15 anos. A situação é ainda pior com os imóveis rurais e veículos, basta fazer as contas. Caso o dinheiro que você receba em troca do seu trabalho seja suficiente apenas para comprar comida, vestuário e moradia, você já sabe que é um escravo né?… Precisamos entender que a escravidão não acabou, apenas foi democratizada. Hoje a escravidão é financeira, nós somos os castiços e os donos do dinheiro são o senhorio. Os donos do dinheiro são os Globalistas e os Estados seus fantoches. O esquema é simples: fazer todo mundo trabalhar em troca de algo que perde 100% do valor a cada 10 anos, ou seja o dinheiro. Se você pudesse trabalhar em troca de algo que aumentasse de valor acima da inflação real a cada 10 anos você finalmente conquistaria sua liberdade financeira e deixaria de ser escravo. Pois bem, isso já é possível, e não se trata de ouro ou imóveis e sim sobre o Bitcoin, que sobe de valor mais de 100% a cada 10 anos, com a vantagem de ser inconfiscável e de fácil transferência para seus herdeiros quando você morrer, através de uma simples transação LockTime feita em vida. Portanto, mesmo que você não tenha dinheiro para comprar Bitcoin, passar a aceitar Bitcoin em troca de seus produtos e serviços é a única forma de se libertar da escravidão financeira. A carta de alforria financeira proporcionada pelo Bitcoin não é imediata, pois a velocidade da sua libertação depende do quanto você está disposto a aprender sobre o assunto. Eu estou aqui para te ajudar, caso queira. No futuro o Bitcoin estará tão presente na sua vida quanto o pix e o cartão de crédito, você querendo ou não. Assim como o cartão de crédito foi a evolução do cheque pós-datado e o pix a evolução do cartão, o Bitcoin e outras criptomoedas serão a evolução de todos esses meios de pagamento. O que te ofereço é a oportunidade de abolição da sua escravatura antes dos demais escravos acordarem para a realidade, afinal a história sempre se repete: desde o ano de 1300 a.c. a escravidão era defendida pelos próprios escravos, que mais cedo ou mais tarde, foram libertados por Moisés em êxodo 11 da Bíblia Sagrada e hoje o povo de israel se tornou a nação mais rica do mundo. A mesma história se repetiu na Roma Antiga: com o pão e circo. Da mesma forma todo esse império escravocrata ruiu porque mais cedo ou mais tarde os escravos se revoltam, bastam as coisas piorarem bastante. O atual regime de escravidão teve início com a queda do padrão-ouro para impressão do dinheiro no ano de 1944. A escravidão apenas ficou mais sofisticada, pois em vez de pagar os escravos com cerveja como no Egito Antigo ou com pão e circo como na Roma Antiga, passou-se a pagar os escravos com dinheiro sem lastro, ou seja dinheiro inventado, criado do nada, sem qualquer representação com a riqueza real da economia. Mesmo sendo a escravidão atual mais sofisticada, que deixou de ser física para ser financeira, o que torna a mentira mais bem contada, mais cedo ou mais tarde os escravos modernos irão acordar, basta as coisas piorarem mais ou perceberem que todos os bens e serviços do mundo não representam nem 1% de todo o dinheiro que impresso sem lastro. Em outras palavras, se os donos de todo o dinheiro do mundo resolvessem utilizá-lo para comprar tudo o que existe à venda, o preço do quilo do café subiria para R$ 297.306,00 e o preço médio dos imóveis subiria para um número tão grande que sequer caberia nesta folha de papel. Hoje, o dinheiro não vale nada, seus donos sabem disso e optam por entregar o dinheiro aos poucos para os escravos em troca do seu trabalho, para manter o atual regime o máximo de tempo possível. Mesmo assim, o atual regime de escravidão financeira está com os dias contados e depende de você se posicionar antes do efeito manada. Nunca é tarde para entrar no Bitcoin, mesmo ele tendo uma quantidade de emissão limitada, seu valor subirá infinitamente. A menor unidade do Bitcoin é o satoshi, cuja abreviação é sats. Diferente do centavo, cada sat vale um centésimo milionésimo de bitcoin. Hoje (25/05/25), cada unidade de Bitcoin equivale a setecentos mil reais. Logo, cada R$ 0,01 equivale à 0,007 sats. Lembrando que o centavo é um real dividido por cem e o sat é um bitcoin dividido por cem milhões, por isso ainda não existe a paridade entre 1 centavo de real e 1 sat. Essa paridade será alcançada quando um Bitcoin passar a valer um milhão de reais. Com a velocidade que nosso dinheiro está perdendo valor isso não irá demorar muito. Utilizando dados econômicos avançados, prevejo que cada unidade de Bitcoin passará a valer hum milhão de reais até o ano de 2029, assim equiparando 1 sat para cada R$ 0,01. Nesse momento, certamente muitos empresários, comerciantes e profissionais liberais passarão a aceitar o Bitcoin como forma de pagamento pelos seus produtos e serviços, assim como o cheque foi substituído pelo cartão de crédito e o cartão pelo pix. Sabendo disso, você pode entrar na onda de transição no futuro junto com a manada e perder essa alta valorização, ou passar a aceitar Bitcoin agora pelos seus produtos e serviços, assinando assim, a própria carta de alforria da sua escravidão financeira. É importante dizer que os próprios globalistas e governos estão trocando dinheiro por Bitcoin como nunca na história e mesmo que eles adquiram todos os bitcoins disponíveis, ainda assim não será mais possível manter seu regime de escravidão financeira funcionando porque a emissão de Bitcoin é limitada, sendo impossível criar Bitcoin sem lastro, como é feito com o dinheiro hoje. Com o presente artigo, te ofereço a oportunidade de conquistar seus primeiros sats agora, de forma segura e independente, sem precisar de corretoras, bancos, intermediários ou terceiros, basta você querer pois toda a informação necessária está disponível na internet gratuitamente. Se ainda assim você quiser continuar sendo escravo financeiro, depois não adiantar se arrepender quando as janelas de oportunidade se fecharem, o Drex for implantado, papel moeda restringido e sua vida piorar bastante. Importante mencionar que a Lei Brasileira ainda permite a movimentação de até R$ 30.000,00 em Bitcoin por mês sem a necessidade de declaração à Receita Federal e que esse direito pode deixar de existir a qualquer momento, e que quando o Drex for implantado você perderá diversos outros direitos, dentre ele a liberdade de gastar seu dinheiro como quiser e o sigilo. Ofereço ainda, a oportunidade de você baixar uma carteira de Bitcoin gratuita e segura no seu aparelho de celular que funciona de forma semelhante a um banco digital como Nubank e Pagseguro por exemplo, para poder começar à receber Bitcoin pelos seus produtos e serviços agora, de forma fácil e gratuita. Utilizando o qrcode abaixo você ainda ganha alguns sats de graça, promoção válida até o dia 29/05/25 e patrocinada pela Corretora Blink de El Salvador, onde o Bitcoin já é moeda oficial do país, basta acessar o link e instalar o aplicativo: https://get.blink.sv/btcvale
Aviso: disponibilizei o link da carteira de Bitcoin da Corretora Blink apenas como exemplo de como é fácil aceitar Bitcoin como forma de pagamento pelos seus produtos e serviços. Não recomento depender de qualquer corretora para guardar seus valores em Bitcoin. A melhor forma de fazer isso é mantendo dois computadores ou notebook em casa, um conectado à internet com memória em disco disponível de 1 terabyte ou mais para armazenar e visualizar suas transações e outro computador ou notebook desconectado da internet para armazenar suas senhas e chaves privadas para assinar as transações via pendrive. Somente assim você estará 100% livre e seguro. Importante ainda fazer backup em vários CDs com criptografia do seu computador ou notebook que assina as transações, assim também ficando 100% livre e seguro para restaurar sua carteira em qualquer outro computador caso necessário. Todas as instruções de como fazer isso já estão disponíveis gratuitamente na internet. Caso deseje contratar uma consultoria pessoal que inclui aulas particulares por vídeo conferência, onde você aprenderá:
→ Tudo o que precisa saber sobre Bitcoin e demais criptomoedas; → Sistema operacional Linux; → Como instalar sua carteira de Bitcoin em dois computadores para assinaturas air gapped; → Se manter 100% livre e seguro. → Com carga horária à combinar conforme sua disponibilidade.
O custo do investimento pelo meu serviço individual para esse tipo de consultoria é de 204.000 sats (R$ 1.543,46 na cotação atual) valor válido até 31/07/25, interessados entrar em contato por aqui ou através da Matrix: @davipinheiro:matrix.org https://davipinheiro.com/voce-e-escravo-e-nem-sabe-eu-vou-te-provar-agora/
-
 @ 5391098c:74403a0e
2025-05-27 18:15:38
@ 5391098c:74403a0e
2025-05-27 18:15:38Você trabalha 5 meses do ano somente para pagar impostos. Ou seja, 42% da sua renda serve para bancar serviços públicos de péssima qualidade. Mesmo que você tivesse a liberdade de usar esses 42% da sua renda para contratar serviços privados de qualidade (saúde, segurança e ensino), ainda assim você seria um escravo porque você recebe dinheiro em troca do seu trabalho, e o dinheiro perde cerca de 10% do valor a cada ano. Em outras palavras todo seu dinheiro que sobra depois de comprar comida, vestuário e moradia perde 100% do valor a cada 10 anos. Isso acontece porque o Estado imprime dinheiro do nada e joga na economia de propósito para gerar INFLAÇÃO e manter todos nós escravizados. Você pode deixar seu dinheiro investido em qualquer aplicação que imaginar e ainda assim nunca terá uma rentabilidade superior a inflação real. No final, acaba perdendo tudo do mesmo jeito. Caso você se ache esperto por investir o que sobra da sua renda em bens duráveis como imóveis ou veículos, sabia que esses bens também não são seus, porque se deixar de pagar os impostos desses bens (iptu, itr, ipva) você também perde tudo. Além disso, o custo de manutenção desses bens deve ser levado em consideração na conta das novas dívidas que você assumiu. No caso dos imóveis urbanos é impossível alugá-lo por mais de 0,38% do seu valor mensalmente. Em outras palavras, a cada ano você recebe menos de 5% do que investiu, tem que pagar o custo de manutenção, mais impostos e a valorização do bem nunca será superior a inflação real, também fazendo você perder quase tudo em cerca de 15 anos. A situação é ainda pior com os imóveis rurais e veículos, basta fazer as contas. Caso o dinheiro que você receba em troca do seu trabalho seja suficiente apenas para comprar comida, vestuário e moradia, você já sabe que é um escravo né?… Precisamos entender que a escravidão não acabou, apenas foi democratizada. Hoje a escravidão é financeira, nós somos os castiços e os donos do dinheiro são o senhorio. Os donos do dinheiro são os Globalistas e os Estados seus fantoches. O esquema é simples: fazer todo mundo trabalhar em troca de algo que perde 100% do valor a cada 10 anos, ou seja o dinheiro. Se você pudesse trabalhar em troca de algo que aumentasse de valor acima da inflação real a cada 10 anos você finalmente conquistaria sua liberdade financeira e deixaria de ser escravo. Pois bem, isso já é possível, e não se trata de ouro ou imóveis e sim sobre o Bitcoin, que sobe de valor mais de 100% a cada 10 anos, com a vantagem de ser inconfiscável e de fácil transferência para seus herdeiros quando você morrer, através de uma simples transação LockTime feita em vida. Portanto, mesmo que você não tenha dinheiro para comprar Bitcoin, passar a aceitar Bitcoin em troca de seus produtos e serviços é a única forma de se libertar da escravidão financeira. A carta de alforria financeira proporcionada pelo Bitcoin não é imediata, pois a velocidade da sua libertação depende do quanto você está disposto a aprender sobre o assunto. Eu estou aqui para te ajudar, caso queira. No futuro o Bitcoin estará tão presente na sua vida quanto o pix e o cartão de crédito, você querendo ou não. Assim como o cartão de crédito foi a evolução do cheque pós-datado e o pix a evolução do cartão, o Bitcoin e outras criptomoedas serão a evolução de todos esses meios de pagamento. O que te ofereço é a oportunidade de abolição da sua escravatura antes dos demais escravos acordarem para a realidade, afinal a história sempre se repete: desde o ano de 1300 a.c. a escravidão era defendida pelos próprios escravos, que mais cedo ou mais tarde, foram libertados por Moisés em êxodo 11 da Bíblia Sagrada e hoje o povo de israel se tornou a nação mais rica do mundo. A mesma história se repetiu na Roma Antiga: com o pão e circo. Da mesma forma todo esse império escravocrata ruiu porque mais cedo ou mais tarde os escravos se revoltam, bastam as coisas piorarem bastante. O atual regime de escravidão teve início com a queda do padrão-ouro para impressão do dinheiro no ano de 1944. A escravidão apenas ficou mais sofisticada, pois em vez de pagar os escravos com cerveja como no Egito Antigo ou com pão e circo como na Roma Antiga, passou-se a pagar os escravos com dinheiro sem lastro, ou seja dinheiro inventado, criado do nada, sem qualquer representação com a riqueza real da economia. Mesmo sendo a escravidão atual mais sofisticada, que deixou de ser física para ser financeira, o que torna a mentira mais bem contada, mais cedo ou mais tarde os escravos modernos irão acordar, basta as coisas piorarem mais ou perceberem que todos os bens e serviços do mundo não representam nem 1% de todo o dinheiro que impresso sem lastro. Em outras palavras, se os donos de todo o dinheiro do mundo resolvessem utilizá-lo para comprar tudo o que existe à venda, o preço do quilo do café subiria para R$ 297.306,00 e o preço médio dos imóveis subiria para um número tão grande que sequer caberia nesta folha de papel. Hoje, o dinheiro não vale nada, seus donos sabem disso e optam por entregar o dinheiro aos poucos para os escravos em troca do seu trabalho, para manter o atual regime o máximo de tempo possível. Mesmo assim, o atual regime de escravidão financeira está com os dias contados e depende de você se posicionar antes do efeito manada. Nunca é tarde para entrar no Bitcoin, mesmo ele tendo uma quantidade de emissão limitada, seu valor subirá infinitamente. A menor unidade do Bitcoin é o satoshi, cuja abreviação é sats. Diferente do centavo, cada sat vale um centésimo milionésimo de bitcoin. Hoje (25/05/25), cada unidade de Bitcoin equivale a setecentos mil reais. Logo, cada R$ 0,01 equivale à 0,007 sats. Lembrando que o centavo é um real dividido por cem e o sat é um bitcoin dividido por cem milhões, por isso ainda não existe a paridade entre 1 centavo de real e 1 sat. Essa paridade será alcançada quando um Bitcoin passar a valer um milhão de reais. Com a velocidade que nosso dinheiro está perdendo valor isso não irá demorar muito. Utilizando dados econômicos avançados, prevejo que cada unidade de Bitcoin passará a valer hum milhão de reais até o ano de 2029, assim equiparando 1 sat para cada R$ 0,01. Nesse momento, certamente muitos empresários, comerciantes e profissionais liberais passarão a aceitar o Bitcoin como forma de pagamento pelos seus produtos e serviços, assim como o cheque foi substituído pelo cartão de crédito e o cartão pelo pix. Sabendo disso, você pode entrar na onda de transição no futuro junto com a manada e perder essa alta valorização, ou passar a aceitar Bitcoin agora pelos seus produtos e serviços, assinando assim, a própria carta de alforria da sua escravidão financeira. É importante dizer que os próprios globalistas e governos estão trocando dinheiro por Bitcoin como nunca na história e mesmo que eles adquiram todos os bitcoins disponíveis, ainda assim não será mais possível manter seu regime de escravidão financeira funcionando porque a emissão de Bitcoin é limitada, sendo impossível criar Bitcoin sem lastro, como é feito com o dinheiro hoje. Com o presente artigo, te ofereço a oportunidade de conquistar seus primeiros sats agora, de forma segura e independente, sem precisar de corretoras, bancos, intermediários ou terceiros, basta você querer pois toda a informação necessária está disponível na internet gratuitamente. Se ainda assim você quiser continuar sendo escravo financeiro, depois não adiantar se arrepender quando as janelas de oportunidade se fecharem, o Drex for implantado, papel moeda restringido e sua vida piorar bastante. Importante mencionar que a Lei Brasileira ainda permite a movimentação de até R$ 30.000,00 em Bitcoin por mês sem a necessidade de declaração à Receita Federal e que esse direito pode deixar de existir a qualquer momento, e que quando o Drex for implantado você perderá diversos outros direitos, dentre ele a liberdade de gastar seu dinheiro como quiser e o sigilo. Ofereço ainda, a oportunidade de você baixar uma carteira de Bitcoin gratuita e segura no seu aparelho de celular que funciona de forma semelhante a um banco digital como Nubank e Pagseguro por exemplo, para poder começar à receber Bitcoin pelos seus produtos e serviços agora, de forma fácil e gratuita. Utilizando o qrcode abaixo você ainda ganha alguns sats de graça, promoção válida até o dia 29/05/25 e patrocinada pela Corretora Blink de El Salvador, onde o Bitcoin já é moeda oficial do país, basta acessar o link e instalar o aplicativo: https://get.blink.sv/btcvale
Aviso: disponibilizei o link da carteira de Bitcoin da Corretora Blink apenas como exemplo de como é fácil aceitar Bitcoin como forma de pagamento pelos seus produtos e serviços. Não recomento depender de qualquer corretora para guardar seus valores em Bitcoin. A melhor forma de fazer isso é mantendo dois computadores ou notebook em casa, um conectado à internet com memória em disco disponível de 1 terabyte ou mais para armazenar e visualizar suas transações e outro computador ou notebook desconectado da internet para armazenar suas senhas e chaves privadas para assinar as transações via pendrive. Somente assim você estará 100% livre e seguro. Importante ainda fazer backup em vários CDs com criptografia do seu computador ou notebook que assina as transações, assim também ficando 100% livre e seguro para restaurar sua carteira em qualquer outro computador caso necessário. Todas as instruções de como fazer isso já estão disponíveis gratuitamente na internet. Caso deseje contratar uma consultoria pessoal que inclui aulas particulares por vídeo conferência, onde você aprenderá:
→ Tudo o que precisa saber sobre Bitcoin e demais criptomoedas; → Sistema operacional Linux; → Como instalar sua carteira de Bitcoin em dois computadores para assinaturas air gapped; → Se manter 100% livre e seguro. → Com carga horária à combinar conforme sua disponibilidade.
O custo do investimento pelo meu serviço individual para esse tipo de consultoria é de 204.000 sats (R$ 1.543,46 na cotação atual) valor válido até 31/07/25, interessados entrar em contato por aqui ou através da Matrix: @davipinheiro:matrix.org https://davipinheiro.com/voce-e-escravo-e-nem-sabe-eu-vou-te-provar-agora/
-
 @ f0fcbea6:7e059469
2025-05-27 18:08:04
@ f0fcbea6:7e059469
2025-05-27 18:08:04Muita gente, hoje em dia, acha que a leitura já não é tão necessária quanto foi no passado. O rádio e a televisão acabaram assumindo as funções que outrora pertenciam à mídia impressa, da mesma maneira que a fotografia assumiu as funções que outrora pertenciam à pintura e às artes gráficas. Temos de reconhecer - é verdade - que a televisão cumpre algumas dessas funções muito bem; a comunicação visual dos telejornais, por exemplo, tem impacto enorme. A capacidade do rádio em transmitir informações enquanto estamos ocupados - dirigindo um carro, por exemplo - é algo extraordinário, além de nos poupar muito tempo. No entanto, é necessário questionar se as comunicações modernas realmente aumentam o conhecimento sobre o mundo à nossa volta.
Talvez hoje saibamos mais sobre o mundo do que no passado. Dado que o conhecimento é pré-requisito para o entendimento, trata-se de algo bom. Mas o conhecimento não é um pré-requisito tão importante ao entendimento quanto normalmente se supõe. Não precisamos saber tudo sobre determinada coisa para que possamos entendê-la. Uma montanha de fatos pode provocar o efeito contrário, isto é, pode servir de obstáculo ao entendimento. Há uma sensação, hoje em dia, de que temos acesso a muitos fatos, mas não necessariamente ao entendimento desses fatos.
Uma das causas dessa situação é que a própria mídia é projetada para tornar o pensamento algo desnecessário - embora, é claro, isso seja apenas mera impressão. O ato de empacotar ideias e opiniões intelectuais é uma atividade à qual algumas das mentes mais brilhantes se dedicam com grande diligência. O telespectador, o ouvinte, o leitor de revistas - todos eles se defrontam com um amálgama de elementos complexos, desde discursos retóricos minuciosamente planejados até dados estatísticos cuidadosamente selecionados, cujo objetivo é facilitar o ato de "formar a opinião" das pessoas com esforço e dificuldade mínimos. Por vezes, no entanto, o empacotamento é feito de maneira tão eficiente, tão condensada, que o telespectador, o ouvinte ou o leitor não conseguem formar sua opinião. Em vez disso, a opinião empacotada é introjetada em sua mente mais ou menos como uma gravação é inserida no aparelho de som. No momento apropriado, aperta-se o play e a opinião é "tocada". Eles reproduzem a opinião sem terem pensado a respeito.
-
 @ cae03c48:2a7d6671
2025-05-27 18:01:39
@ cae03c48:2a7d6671
2025-05-27 18:01:39Bitcoin Magazine

Cake Wallet Introduces PayJoin v2, Increasing Bitcoin Privacy For The MassesCake Wallet, a non-custodial open-source wallet for cryptocurrencies, has officially launched PayJoin v2, becoming the first major mobile wallet to offer Bitcoin silent payments to everyday users.
This integration introduces a protocol upgrade that disrupts blockchain surveillance by mixing transaction inputs from both the sender and receiver, undermining the common blockchain surveillance techniques chain analysts typically rely on.
 JUST LAUNCHED: Cake Wallet v4.28.0 brings Bitcoin Payjoin v2!
JUST LAUNCHED: Cake Wallet v4.28.0 brings Bitcoin Payjoin v2! • No need for both parties to be online
• No server required
• Just a few taps in your walletIt's that simple
 Update Cake Wallet to try it out! pic.twitter.com/IjOccnBYy7
Update Cake Wallet to try it out! pic.twitter.com/IjOccnBYy7— Cake Wallet (@cakewallet) May 19, 2025
“Bitcoin is open and permissionless — but without privacy, it’s a surveillance tool,” said Vikrant Sharma, CEO of Cake Wallet in a recent press release sent to Bitcoin Magazine. “This upgrade gives everyday users the ability to transact privately, without needing to be online or run a server.”
Cake Wallet’s implementation removes the limitation of requiring both parties to be online or run a server to coordinate a transaction. Users can now send or receive Bitcoin through asynchronous, serverless PayJoin transactions—no Tor, no apps, no advanced configuration.
“This makes Bitcoin privacy accessible to people who aren’t developers or hardcore cypherpunks,” said Sharma. “We’ve seen huge progress with Monero privacy tools. Now, Bitcoin users can take a step towards privacy as well, built right into a mainstream wallet.”
This announcement follows closely on the heels of another major privacy upgrade: Cake Wallet recently became one of the first major wallets to support Silent Payments, allowing users to receive Bitcoin without exposing a reusable address.
This post Cake Wallet Introduces PayJoin v2, Increasing Bitcoin Privacy For The Masses first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ c631e267:c2b78d3e
2025-05-16 18:40:18
@ c631e267:c2b78d3e
2025-05-16 18:40:18Die zwei mächtigsten Krieger sind Geduld und Zeit. \ Leo Tolstoi
Zum Wohle unserer Gesundheit, unserer Leistungsfähigkeit und letztlich unseres Glücks ist es wichtig, die eigene Energie bewusst zu pflegen. Das gilt umso mehr für an gesellschaftlichen Themen interessierte, selbstbewusste und kritisch denkende Menschen. Denn für deren Wahrnehmung und Wohlbefinden waren und sind die rasanten, krisen- und propagandagefüllten letzten Jahre in Absurdistan eine harte Probe.
Nur wer regelmäßig Kraft tankt und Wege findet, mit den Herausforderungen umzugehen, kann eine solche Tortur überstehen, emotionale Erschöpfung vermeiden und trotz allem zufrieden sein. Dazu müssen wir erkunden, was uns Energie gibt und was sie uns raubt. Durch Selbstreflexion und Achtsamkeit finden wir sicher Dinge, die uns erfreuen und inspirieren, und andere, die uns eher stressen und belasten.
Die eigene Energie ist eng mit unserer körperlichen und mentalen Gesundheit verbunden. Methoden zur Förderung der körperlichen Gesundheit sind gut bekannt: eine ausgewogene Ernährung, regelmäßige Bewegung sowie ausreichend Schlaf und Erholung. Bei der nicht minder wichtigen emotionalen Balance wird es schon etwas komplizierter. Stress abzubauen, die eigenen Grenzen zu kennen oder solche zum Schutz zu setzen sowie die Konzentration auf Positives und Sinnvolles wären Ansätze.
Der emotionale ist auch der Bereich, über den «Energie-Räuber» bevorzugt attackieren. Das sind zum Beispiel Dinge wie Überforderung, Perfektionismus oder mangelhafte Kommunikation. Social Media gehören ganz sicher auch dazu. Sie stehlen uns nicht nur Zeit, sondern sind höchst manipulativ und erhöhen laut einer aktuellen Studie das Risiko für psychische Probleme wie Angstzustände und Depressionen.
Geben wir negativen oder gar bösen Menschen keine Macht über uns. Das Dauerfeuer der letzten Jahre mit Krisen, Konflikten und Gefahren sollte man zwar kennen, darf sich aber davon nicht runterziehen lassen. Das Ziel derartiger konzertierter Aktionen ist vor allem, unsere innere Stabilität zu zerstören, denn dann sind wir leichter zu steuern. Aber Geduld: Selbst vermeintliche «Sonnenköniginnen» wie EU-Kommissionspräsidentin von der Leyen fallen, wenn die Zeit reif ist.
Es ist wichtig, dass wir unsere ganz eigenen Bedürfnisse und Werte erkennen. Unsere Energiequellen müssen wir identifizieren und aktiv nutzen. Dazu gehören soziale Kontakte genauso wie zum Beispiel Hobbys und Leidenschaften. Umgeben wir uns mit Sinnhaftigkeit und lassen wir uns nicht die Energie rauben!
Mein Wahlspruch ist schon lange: «Was die Menschen wirklich bewegt, ist die Kultur.» Jetzt im Frühjahr beginnt hier in Andalusien die Zeit der «Ferias», jener traditionellen Volksfeste, die vor Lebensfreude sprudeln. Konzentrieren wir uns auf die schönen Dinge und auf unsere eigenen Talente – soziale Verbundenheit wird helfen, unsere innere Kraft zu stärken und zu bewahren.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 9e9085e9:2056af17
2025-05-27 17:16:22
@ 9e9085e9:2056af17
2025-05-27 17:16:22Market Overview
As of May 27, 2025, Bitcoin (BTC) is trading at approximately $110,387, reflecting a modest 0.8% daily gain.
24-Hour Range: $108,291 – $110,415
Recent High: $111,970
Support Level to Watch: $105,700
Bullish Target: $135,000 (based on analyst projections)
The market remains optimistic ahead of the Bitcoin 2025 Conference in Las Vegas, sparking renewed interest and speculation.
Impact on Decentralized Social Media
Bitcoin’s strong performance is influencing decentralized social platforms in multiple ways:
- Increased Engagement
Platforms like Nostr, Mastodon, and others are seeing a spike in activity. Users are sharing price charts, engaging in Bitcoin discourse, and posting market-related content.
- Monetization Opportunities
Creators on decentralized networks are leveraging Bitcoin-based tipping, NFT-based publishing, and tokenized rewards to monetize content more effectively.
- Community Growth
Positive sentiment is drawing in new users and developers, contributing to the growth of decentralized ecosystems and innovation in peer-to-peer social tech.
Strategic Highlights
Trump Media & Technology Group aims to raise $2.5 billion to build a Bitcoin treasury, signaling strong institutional interest.
The U.S. is reportedly establishing a Strategic Bitcoin Reserve, underscoring digital currency’s growing relevance at the national level.
#Bitcoin #BTC #CryptoNews #Web3 #DecentralizedSocialMedia #Nostr #Yakihonne #CryptoCommunity #BitcoinUpdate #BTC2025 #DigitalFreedom #ContentCuration #Hackathon #SocialFi
-
 @ c631e267:c2b78d3e
2025-05-10 09:50:45
@ c631e267:c2b78d3e
2025-05-10 09:50:45Information ohne Reflexion ist geistiger Flugsand. \ Ernst Reinhardt
Der lateinische Ausdruck «Quo vadis» als Frage nach einer Entwicklung oder Ausrichtung hat biblische Wurzeln. Er wird aber auch in unserer Alltagssprache verwendet, laut Duden meist als Ausdruck von Besorgnis oder Skepsis im Sinne von: «Wohin wird das führen?»
Der Sinn und Zweck von so mancher politischen Entscheidung erschließt sich heutzutage nicht mehr so leicht, und viele Trends können uns Sorge bereiten. Das sind einerseits sehr konkrete Themen wie die zunehmende Militarisierung und die geschichtsvergessene Kriegstreiberei in Europa, deren Feindbildpflege aktuell beim Gedenken an das Ende des Zweiten Weltkriegs beschämende Formen annimmt.
Auch das hohe Gut der Schweizer Neutralität scheint immer mehr in Gefahr. Die schleichende Bewegung der Eidgenossenschaft in Richtung NATO und damit weg von einer Vermittlerposition erhält auch durch den neuen Verteidigungsminister Anschub. Martin Pfister möchte eine stärkere Einbindung in die europäische Verteidigungsarchitektur, verwechselt bei der Argumentation jedoch Ursache und Wirkung.
Das Thema Gesundheit ist als Zugpferd für Geschäfte und Kontrolle offenbar schon zuverlässig etabliert. Die hauptsächlich privat finanzierte Weltgesundheitsorganisation (WHO) ist dabei durch ein Netzwerk von sogenannten «Collaborating Centres» sogar so weit in nationale Einrichtungen eingedrungen, dass man sich fragen kann, ob diese nicht von Genf aus gesteuert werden.
Das Schweizer Bundesamt für Gesundheit (BAG) übernimmt in dieser Funktion ebenso von der WHO definierte Aufgaben und Pflichten wie das deutsche Robert Koch-Institut (RKI). Gegen die Covid-«Impfung» für Schwangere, die das BAG empfiehlt, obwohl es fehlende wissenschaftliche Belege für deren Schutzwirkung einräumt, formiert sich im Tessin gerade Widerstand.
Unter dem Stichwort «Gesundheitssicherheit» werden uns die Bestrebungen verkauft, essenzielle Dienste mit einer biometrischen digitalen ID zu verknüpfen. Das dient dem Profit mit unseren Daten und führt im Ergebnis zum Verlust unserer demokratischen Freiheiten. Die deutsche elektronische Patientenakte (ePA) ist ein Element mit solchem Potenzial. Die Schweizer Bürger haben gerade ein Referendum gegen das revidierte E-ID-Gesetz erzwungen. In Thailand ist seit Anfang Mai für die Einreise eine «Digital Arrival Card» notwendig, die mit ihrer Gesundheitserklärung einen Impfpass «durch die Hintertür» befürchten lässt.
Der massive Blackout auf der iberischen Halbinsel hat vermehrt Fragen dazu aufgeworfen, wohin uns Klimawandel-Hysterie und «grüne» Energiepolitik führen werden. Meine Kollegin Wiltrud Schwetje ist dem nachgegangen und hat in mehreren Beiträgen darüber berichtet. Wenig überraschend führen interessante Spuren mal wieder zu internationalen Großbanken, Globalisten und zur EU-Kommission.
Zunehmend bedenklich ist aber ganz allgemein auch die manifestierte Spaltung unserer Gesellschaften. Angesichts der tiefen und sorgsam gepflegten Gräben fällt es inzwischen schwer, eine zukunftsfähige Perspektive zu erkennen. Umso begrüßenswerter sind Initiativen wie die Kölner Veranstaltungsreihe «Neue Visionen für die Zukunft». Diese möchte die Diskussionskultur reanimieren und dazu beitragen, dass Menschen wieder ohne Angst und ergebnisoffen über kontroverse Themen der Zeit sprechen.
Quo vadis – Wohin gehen wir also? Die Suche nach Orientierung in diesem vermeintlichen Chaos führt auch zur Reflexion über den eigenen Lebensweg. Das ist positiv insofern, als wir daraus Kraft schöpfen können. Ob derweil der neue Papst, dessen «Vorgänger» Petrus unsere Ausgangsfrage durch die christliche Legende zugeschrieben wird, dabei eine Rolle spielt, muss jede/r selbst wissen. Mir persönlich ist allein schon ein Führungsanspruch wie der des Petrusprimats der römisch-katholischen Kirche eher suspekt.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 9e9085e9:2056af17
2025-05-27 16:58:28
@ 9e9085e9:2056af17
2025-05-27 16:58:28Part 2: Community Impact & Key Milestones
How Yakihonne Benefits the Community
Yakihonne is more than an app—it's a platform for freedom and self-expression. Here’s how it empowers its users and community:
Censorship-Resistant Communication Say what matters without fear of shadowbans or takedowns.
Privacy and Data Control You own your data—no tracking, no selling, no manipulation.
Peer-to-Peer Support for Creators With Bitcoin Lightning tipping, fans can directly support creators without needing middlemen.
Open Participation Developers, artists, and builders can all contribute to the network through the open Nostr protocol.
Milestones (You can update these with exact dates later)
Platform Launch: [Insert Date]
1,000+ Users Joined: [Insert Date]
Key Feature Rollouts (Chats, Groups, Tips): [Insert Date]
Yakihonne #Yakihonne #Yakihonne #Nostr #Nostr #YoungDfx
-
 @ da8b7de1:c0164aee
2025-05-27 15:09:54
@ da8b7de1:c0164aee
2025-05-27 15:09:54Globális nukleáris reneszánsz és új kapacitások
A 2025-ös év a globális nukleáris energiaipar újabb lendületét hozza, amit a Nemzetközi Energiaügynökség (IEA) is megerősít: rekordtermelés várható, jelenleg több mint 70 GW új nukleáris kapacitás épül világszerte, és több mint 40 ország tervezi a nukleáris energia szerepének növelését az energiamixében. A világ számos pontján – Kínában, az Egyesült Államokban, Indiában, az Egyesült Arab Emírségekben és Franciaországban – új blokkok csatlakoznak a hálózatra, miközben nyolc új egység építése is elindult. A cél, hogy 2050-re a jelenlegi 416 GW globális nukleáris kapacitás meghaladja az 1000 GW-ot, ami elengedhetetlen a klímavédelmi és energiabiztonsági célok teljesítéséhez[vg.hu][paks2.hu].
SMR-ek: technológiai áttörés és globális terjeszkedés
A kis moduláris reaktorok (SMR) forradalmasíthatják az iparágat: ezek a kompakt, előregyártott, gyorsan telepíthető egységek különösen alkalmasak távoli területek energiaellátására, ipari hőtermelésre vagy akár tengervíz sótalanítására is. Az SMR-ek fejlesztése világszerte zajlik, az USA, Kína, Oroszország és Európa élen jár, de már több mint 17 országban terveznek ilyen létesítményeket. 2025 májusában Oroszország és Üzbegisztán történelmi megállapodást kötött hat RITM-200N típusú SMR építéséről, amely az első ilyen egység lesz Közép-Ázsiában. Az Egyesült Arab Emírségekben és az USA-ban is új SMR-projektek indulnak, például a Tennessee Valley Authority hivatalosan is engedélyt kért egy BWRX-300 típusú SMR-re a Clinch River telephelyen[makronom.eu][world-nuclear-news.org][nucnet.org].
Nukleáris üzemanyag-ellátás és ellátásbiztonság
Az orosz-ukrán háború és az ellátásbiztonsági kockázatok miatt Európában is felgyorsult az alternatív nukleáris üzemanyag-beszállítók keresése. Franciaországban az EDF, az Orano és az amerikai Westinghouse tárgyalásokat folytat egy új, nyugat-európai üzemanyag-feldolgozó létesítmény létrehozásáról, hogy csökkentsék az orosz függőséget. Az Európai Bizottság részletes útmutatót adott ki az orosz nukleáris technológiákról való leválásról, de a tagállamok jelentős készleteket halmoztak fel orosz üzemanyagból, mivel az azonnali leválás az energiabiztonságot veszélyeztetné[pakspress.hu][nucnet.org].
Technológiai innovációk és üzemanyagciklus-zárás
A gyorsneutronos reaktorok és a MOX-üzemanyag alkalmazása új távlatokat nyit a nukleáris hulladék mennyiségének és veszélyességének csökkentésében, valamint a földi uránkészletek hatékonyabb felhasználásában. Az orosz BN–800 gyorsreaktor már kizárólag kevert, urán-plutónium MOX-üzemanyagot használ, és folyamatban van a BN–1200 típusú egység fejlesztése is. Ezek a fejlesztések a zárt üzemanyagciklus megvalósítását célozzák, amely jelentősen csökkentheti a végleges elhelyezésre kerülő sugárzó hulladék mennyiségét és kezelési költségeit[vg.hu].
Nukleáris energia és digitális infrastruktúra
Az adatközpontok növekvő energiaigénye miatt egyre több technológiai vállalat fordul az atomenergia felé. Az amerikai Oklo és az RPower, valamint a Deep Fission és az Endeavour együttműködése révén föld alatti SMR-eket telepítenek adatközpontok energiaellátására. Ezek a projektek kiemelik a nukleáris energia szerepét a digitális infrastruktúra fenntartható működtetésében[nucnet.org].
Piaci kilátások és geopolitikai kihívások
A Cameco vezérigazgatója szerint a globális nukleáris keresletet nem befolyásolják jelentősen a kereskedelmi vagy geopolitikai feszültségek, mivel a reaktorokra világszerte szükség van, még magasabb költségek vagy vámok mellett is. A magántőke beáramlása, az új szabályozási reformok (pl. az USA-ban az ADVANCE törvény), valamint a nemzetközi együttműködések mind hozzájárulnak az iparág hosszú távú stabilitásához és bővüléséhez[world-nuclear-news.org][nucnet.org].
Források:
world-nuclear-news.org
nucnet.org
vg.hu
makronom.eu
paks2.hu
pakspress.hu -
 @ 0fab798f:2752acff
2025-05-27 16:43:40
@ 0fab798f:2752acff
2025-05-27 16:43:40
In the heart of Africa’s digital uprising, Nigeria stands tall as one of the most crypto-curious nations on the planet. For many of us dreamers, builders, hustlers, crypto isn’t just a buzzword. It’s a lifeline. A path out of unemployment. A rebellion against the old financial system. A shot at freedom.
But here’s the hard truth: freedom without protection is exposure>
The recent $1.5 billion Ethereum heist — orchestrated by North Korea’s notorious Lazarus Group — didn’t just shake the crypto world. It shattered any illusions we might still have that blockchain alone can save us. If a juggernaut like Bybit can fall, what hope does the everyday Nigerian creative or crypto enthusiast have?
Let’s not sugarcoat it. This is war, a cyber war. And we must learn how to defend ourselves.
What the Heist Taught Us
- Security is not optional, it’s foundational.
- If you’re building in Web3, minting NFTs, or trading tokens, you’re a target. Use cold wallets. Enable 2FA. Don’t store your life savings on exchanges. Paranoia might just save your wallet.
- Don’t fall for vibes.
- Read smart contracts. Study tokenomics. If a project looks too clean, dig deeper. In crypto, vibes alone won’t protect your funds.
- Educate before you speculate.
- Everyone wants the bag, but not everyone reads the blueprint. Before you ape in, understand the tech. That’s how you stay alive in the jungle.* * *
For the Builders, the Artists, the Rebels
We’re not just investors. We’re architects of the future, launching NFT marketplaces, building DeFi protocols, designing metaverse spaces that blend culture, identity, and code. But here’s the kicker: even the most beautiful idea can burn if it’s built on shaky security.
What we need now isn’t just innovation,it’s insulation.
Form collectives: Learn together, audit each other’s code, build firewalls around our ideas.
Pressure regulators to evolve: Not to stifle us, but to protect the creative economy rising from the streets of Lagos, Port Harcourt, Enugu, Kano.
Go open-source: The more transparent we build, the harder it is for bad actors to hide.
Yakihonne Fam, Let’s Talk
This is more than a headline!
We can either continue building shiny dApps with no shields, or we can become cyber-aware architects of a truly secure digital future. One where Nigerian youth don’t just participate in Web3 — we define it.
The heist should wake us up, not wipe us out.
So the question is: will we build castles or fortresses?
Let’s choose wisely.
-
 @ 94e2c22d:d50b08a3
2025-05-27 18:33:13
@ 94e2c22d:d50b08a3
2025-05-27 18:33:13Night photography opens up a whole new dimension of creativity—and with a bit of know-how, your camera becomes a tool for painting with light. Whether you're a curious beginner or looking to refine your technique, these 12 practical tips will help you get started on the right foot. From gear choices to artistic mindset, here’s what you need to know.
-
Know Your Gear – Learn how to operate your camera in complete darkness. You should be comfortable using settings like ISO, aperture, and manual focus without relying on the display.
-
Understand Exposure – Manual settings are crucial. Use low ISO for noise reduction and long exposure times to capture light trails. A tripod is essential for stability.
-
Experiment and Learn – Review your images critically and learn from mistakes. Every attempt offers an opportunity to refine your technique.
-
Avoid Gear Obsession – You don’t need the latest camera. Even basic models can produce impressive results with the right approach.
-
Pack Light – Carry minimal equipment to stay flexible and creative. Too many tools can hinder spontaneity.
-
Use Prime Lenses – Fixed focal length lenses often deliver better quality and let in more light. They also force you to think more about composition.
-
Create Images on Site – Aim to achieve effects in-camera, not later through editing. This improves your skills and leads to more authentic outcomes.
-
See It as a Journey – Be patient and enjoy the process. Your artistic voice will develop over time.
-
Set Goals – Give yourself creative challenges or themes to stay motivated.
-
Plan Your Shoots – Research your location and check weather and moonlight conditions in advance. This minimizes wasted time and frustration.
-
Get Inspired by Others – Study the work of other light painters or night photographers. Join communities to share experiences and gather new ideas.
-
Question the Rules – Creativity often involves breaking away from norms. Don’t be afraid to try unconventional techniques or styles.
Night photography and light painting are not just technical exercises—they're a playful exploration of light, time, and creativity. Don’t stress about perfection. Instead, enjoy the process, embrace the learning curve, and let your imagination run wild. With a bit of patience and these tips in your toolkit, you're well on your way to capturing the magic of the light at night.
Picture created by: Kim Von Coels / Model: Mafu Fuma
-
-
 @ bf47c19e:c3d2573b
2025-05-26 16:56:52
@ bf47c19e:c3d2573b
2025-05-26 16:56:52Dragi Bitcoineri,
Kako se bliži treći mesec izostanka ličnog dohotka na Fakultetu dramskih umetnosti u Beogradu, a dosadašnji vidovi podrške ne mogu da pokriju sve profesore, neophodno je da preduzmemo dalje korake kako ne bi više ispaštali profesori zbog svoje otvorene podrške studentima u borbi za pravednije društvo.
Možda nekad, kad se spolja gleda, deluje kao da se ništa ne dešava na fakultetima ali u našoj zajednici konstantno vri. Borbu sa studentima osećamo kao svoju moralnu i građansku dužnost, a namera nam je da istrajemo na tom putu ka instuitucionalnoj odgovornosti, slobodi i pravdi.
Doniraj BTC! Sve donacije idu u Bitcoin novčanik studenata u blokadi FDU! Hvala unapred ❤️

-
 @ da8b7de1:c0164aee
2025-05-26 15:15:56
@ da8b7de1:c0164aee
2025-05-26 15:15:56Technológiai fejlemények
Az Egyesült Államokban Donald Trump négy végrehajtási rendeletet írt alá, amelyek célja a nukleáris ipar gyors fejlesztése és az ország nukleáris kapacitásának 2050-ig történő megnégyszerezése. Ezek a rendeletek támogatják az új generációs reaktorok – különösen a kisméretű moduláris reaktorok (SMR-ek) és mikroreaktorok – gyorsabb engedélyezését és telepítését, beleértve katonai létesítményeket és mesterséges intelligenciát használó adatközpontokat is. Továbbá lehetővé teszik a használt nukleáris üzemanyag újrahasznosítását, valamint ösztönzik a HALEU (magas tisztaságú, alacsony dúsítású urán) hazai előállítását, ezzel erősítve az amerikai nukleáris ellátási láncot.
Források:
- world-nuclear-news.org
- reuters.com
- bloomberg.comIpari fejlemények
Tajvanban augusztus 23-ára tűzték ki a Maanshan-2 atomerőmű újraindításáról szóló népszavazást. Az erőművet május közepén állították le a „nukleárismentes Tajvan” program részeként, azonban az ellenzék kezdeményezésére a lakosság dönthet az újraindításról. Az USA-ban a frissen aláírt végrehajtási rendeletek egyszerűsítik az engedélyezési folyamatokat, csökkentik a szabályozási terheket, és ösztönzik a magánbefektetéseket, ami a hazai uránbányászat és feldolgozás fellendülését eredményezheti.
Források:
- taipeitimes.com
- world-nuclear-news.orgPénzügyi hatások
A pénzügyi piacokon a nukleáris szektor részvényei jelentős emelkedést mutattak a Trump-féle rendeletek bejelentése után. Az Uranium Energy részvényei 11%-kal, az Oklo Inc. papírjai 16%-kal, a Global X Uranium ETF 9%-kal erősödtek. A növekedés hátterében a szabályozási könnyítések mellett az AI adatközpontok növekvő energiaigénye áll, amelyre a nagy technológiai cégek egyre inkább a nukleáris energiát tartják a legjobb megoldásnak. A kormányzati támogatás és a technológiai vállalatok befektetései új lendületet adhatnak a nukleáris iparnak, amely évek óta küzd a gazdasági és társadalmi kihívásokkal.
Források:
- bloomberg.com
- finance.yahoo.com
- reuters.com -
 @ 9e9085e9:2056af17
2025-05-27 16:36:45
@ 9e9085e9:2056af17
2025-05-27 16:36:45Part 1: Introducing Yakihonne and the Nostr Protocol
Yakihonne – Redefining Social Media Through Decentralization
Yakihonne is a decentralized social media platform built on the Nostr protocol (Notes and Other Stuff Transmitted by Relays). Unlike traditional social networks controlled by corporations, Yakihonne puts users in charge—your identity, content, and connections are all yours to own.
What is Nostr? Nostr is an open protocol that uses public/private key pairs to enable secure communication. Posts (called “notes”) are sent to public relays instead of being stored on a central server. This allows Yakihonne to offer:
Censorship resistance
User-owned data
Open developer participation
Yakihonne leverages this technology to create a user-first social experience: chat, share, and connect—all without gatekeepers.
Yakihonne #Yakihonne #Yakihonne #Nostr #Nostr #YoungDfx
-
 @ 6a6be47b:3e74e3e1
2025-05-27 16:36:21
@ 6a6be47b:3e74e3e1
2025-05-27 16:36:21🔍 Today was one of those days where I dove deeper into the world of Stacker News, exploring how wallets work and all that jazz. If you have any tips or tricks, please send them my way—I’m still figuring it all out!
After my tech adventures, I turned to drawing. Usually, I have a lineup of ideas ready to go, but none of them quite fit my mood today. Then I remembered the butterflies from my upcoming blog entry—can you guess what I’m writing and painting about? 👀
🦋Even though I’ve painted butterflies before here’s one on Instagram, I felt like revisiting them.
This one I posted on Nostr, a while ago
Lately, I’ve been seeing butterflies everywhere on my walks with my dog, and they just felt right for today’s art session. So here’s to butterflies and their beautiful symbolism!
In Celtic mythology, there’s an old Irish saying:
“Butterflies are souls of the dead waiting to pass through Purgatory.” From mindbodygreen.com
It’s no wonder butterflies are often seen as symbols of rebirth. Even Aristotle named the butterfly:
“Psyche,” the Greek word for “soul.” From learnreligions.com
☀️With the weather warming up, days growing longer, and the air full of new scents (and butterfly sightings!🦋), I invite you to really enjoy this season. After drawing today’s butterfly, I realized how freeing it is to just let go and create—no pressure, just fun. Sometimes, taking even a few mindful minutes to do something you love can work wonders—maybe even a little magic.
Hope to catch you on the next one, frens. Godspeed! ✨
Today's butterfly. I drew it on Procreate.
https://stacker.news/items/990470
-
 @ 9c9d2765:16f8c2c2
2025-05-27 16:19:12
@ 9c9d2765:16f8c2c2
2025-05-27 16:19:12CHAPTER THIRTY
“So this is what it’s come to?” Mark muttered, his voice barely audible beneath the hum of city traffic outside the courtroom. His suit was neatly pressed, but the weariness in his eyes betrayed sleepless nights. Helen stood beside him, silent for once, clutching her handbag like it was the last anchor to reality.
“Yes,” came a calm voice from behind them. They turned to see James approaching, flanked by Rita and a group of lawyers dressed in solemn black. His presence was poised, commanding, and utterly devoid of fear.
“You both built your legacy on lies,” James continued, his gaze unwavering. “It was only a matter of time before the truth surfaced.”
Helen’s composure cracked as she stepped forward. “You think this is justice, James? You think humiliating us in court will change the past?”
James gave a faint smirk. “No, Helen. But it will make sure no one else suffers because of your greed.”
The courtroom was already brimming with anticipation. Reporters filled the gallery. Spectators whispered rumors with every glance exchanged between lawyers. A judge with decades of experience presided over the case stern and unsympathetic to theatrics.
As the hearing commenced, James’s legal team presented meticulously organized evidence bank statements tracing illicit transactions to offshore accounts, leaked audio recordings of bribe negotiations, falsified media contracts, and forged internal memos. Each document was a nail in the coffin of Helen and Mark’s defense.
Rita testified, her voice calm and articulate, recounting the smear campaign orchestrated by Tracy under their instructions.
“They targeted James not just to discredit him,” she stated, looking the judge directly in the eye, “but to dismantle every ounce of credibility he had built. They used lies as weapons and fear as a shield.”
Tracy, under pressure from investigators, had also turned witness. Her statement confirmed the bribery and named both Helen and Mark as the masterminds.
“I was promised protection. They said James would be out of the picture before he could fight back,” Tracy confessed tearfully. “But I never imagined the damage we were doing.”
Mark buried his face in his hands while Helen’s facade of arrogance disintegrated in front of the press. Her voice trembled as she rose from her seat during cross-examination.
“It wasn’t meant to go this far,” she stammered. “We were just trying to protect our interests.”
The judge’s gavel struck with finality. “This court finds sufficient grounds for a full criminal trial. The charges include corporate fraud, character defamation, and financial manipulation. The accused are to remain in custody pending further proceedings.”
Gasps filled the room. Helen’s knees buckled as officers approached to take her into custody. Mark, pale and visibly shaking, didn’t resist.
As they were led away, James stood watching. Not with triumph but with quiet vindication.
Later that evening, James held a press conference at JP Enterprises. Cameras clicked and lights flashed as he stepped onto the podium.
“Today marks not a victory over enemies,” he said, his voice resonating with calm authority, “but a victory for accountability. For truth. For every hardworking individual who believes that integrity still matters in business.”
The days following the courtroom revelation were nothing short of transformative for James. What once seemed like an unending siege of betrayal and defamation now stood as a monumental testimony of perseverance. His vindication rippled through the business community, not only restoring his honor but elevating his stature to that of a symbol of resilience, truth, and quiet triumph.
The media, which had once been ravenous in its pursuit to scandalize his name, now sought exclusive interviews. Headlines changed overnight: “The President Who Defied the Odds,” “From Disgrace to Glory James’s Unrivaled Comeback,” and “Truth Prevails at JP Enterprises.”
Still, James remained composed. He declined most interview requests, only issuing a single written statement to the press:
“My silence was never a weakness, nor was my patience approved. In a world where deception moves faster than truth, I chose to let integrity do the talking. Let this be a reminder: time may delay justice, but it cannot deny it.”
In the boardroom of JP Enterprises, there was a newfound sense of reverence. Senior executives who once viewed James with reserved acknowledgment now listened with deference. Staff who had wavered in their loyalties found themselves inspired by his unshakable conviction.
Rita, reinstated officially as General Manager, transformed the company’s internal culture. She advocated for transparency, fairness, and accountability, echoing James’s values. Together, they initiated corporate reforms that would safeguard JP Enterprises against future exploitation. Employee welfare programs were improved, mentorship initiatives were introduced, and innovation was rewarded instead of suppressed.
As for Helen and Mark, the criminal proceedings dragged them through every layer of public accountability. Their assets were frozen pending investigation, and the companies they once boasted of began to crumble under the weight of distrust. The Ray family, mortified and shamed, distanced themselves completely. Robert, in particular, approached James privately, full of contrition.
“I misjudged you,” he said quietly, standing across from James in the same office where he once dismissed him. “And I know an apology may not undo what has been done… but I needed to say it.”
James, ever composed, gave a small nod. “Acknowledgment is the first step toward redemption, Robert. What you do with the rest of your journey that’s what will matter.”
Despite all the chaos, James found time to reconnect with himself. On certain evenings, he would return to the very neighborhood where he had once wandered, alone and destitute. He walked its narrow lanes not with bitterness, but gratitude. Every hardship had refined him. Every betrayal had taught him discernment.
On the sixteenth floor of JP Tower, standing before the massive glass window that overlooked the city skyline, James often stood in silence, his reflection merging with the city lights. He knew his story wasn’t merely about power or wealth, it was about transformation.
The days that followed James’s public exoneration ushered in a new chapter not only in his professional journey but also in his personal life. Amidst the rising stature and recognition, there remained unresolved threads that tugged quietly at his conscience chief among them, his estranged wife, Rita.
Though she was back in her rightful position at JP Enterprises, a wall of silence stood between them, built from years of misunderstanding, pride, and pain. Their conversations, though respectful and professional, were void of warmth. Yet, beneath her poised demeanor, James could sense her hesitation, perhaps a longing unspoken, restrained by fear of rejection or guilt over the past.
-
 @ c1e9ab3a:9cb56b43
2025-05-27 16:19:06
@ c1e9ab3a:9cb56b43
2025-05-27 16:19:06Star Wars is often viewed as a myth of rebellion, freedom, and resistance to tyranny. The iconography—scrappy rebels, totalitarian stormtroopers, lone smugglers—suggests a deep anti-authoritarian ethos. Yet, beneath the surface, the narrative arc of Star Wars consistently affirms the necessity, even sanctity, of central authority. This blog entry introduces the question: Is Star Wars fundamentally a celebration of statism?
Rebellion as Restoration, Not Revolution
The Rebel Alliance’s mission is not to dismantle centralized power, but to restore the Galactic Republic—a bureaucratic, centrally governed institution. Characters like Mon Mothma and Bail Organa are high-ranking senators, not populist revolutionaries. The goal is to remove the corrupt Empire and reinstall a previous central authority, presumed to be just.
- Rebels are loyalists to a prior state structure.
- Power is not questioned, only who wields it.
Jedi as Centralized Moral Elites
The Jedi, often idealized as protectors of peace, are unelected, extra-legal enforcers of moral and military order. Their authority stems from esoteric metaphysical abilities rather than democratic legitimacy.
- They answer only to their internal Council.
- They are deployed by the Senate, but act independently of civil law.
- Their collapse is depicted as tragic not because they were unaccountable, but because they were betrayed.
This positions them as a theocratic elite, not spiritual anarchists.
Chaos and the Frontier: The Case of the Cantina
The Mos Eisley cantina, often viewed as a symbol of frontier freedom, reveals something darker. It is: - Lawless - Violent - Culturally fragmented
Conflict resolution occurs through murder, not mediation. Obi-Wan slices off a limb; Han shoots first—both without legal consequence. There is no evidence of property rights, dispute resolution, or voluntary order.
This is not libertarian pluralism—it’s moral entropy. The message: without centralized governance, barbarism reigns.
The Mythic Arc: Restoration of the Just State
Every trilogy in the saga returns to a single theme: the fall and redemption of legitimate authority.
- Prequels: Republic collapses into tyranny.
- Originals: Rebels fight to restore legitimate order.
- Sequels: Weak governance leads to resurgence of authoritarianism; heroes must reestablish moral centralism.
The story is not anti-state—it’s anti-bad state. The solution is never decentralization; it’s the return of the right ruler or order.
Conclusion: The Hidden Statism of a Rebel Myth
Star Wars wears the costume of rebellion, but tells the story of centralized salvation. It: - Validates elite moral authority (Jedi) - Romanticizes restoration of fallen governments (Republic) - Portrays decentralized zones as corrupt and savage (outer rim worlds)
It is not an anarchist parable, nor a libertarian fable. It is a statist mythology, clothed in the spectacle of rebellion. Its core message is not that power should be abolished, but that power belongs to the virtuous few.
Question to Consider:
If the Star Wars universe consistently affirms the need for centralized moral and political authority, should we continue to see it as a myth of freedom? Or is it time to recognize it as a narrative of benevolent empire? -
 @ 9c9d2765:16f8c2c2
2025-05-27 16:05:22
@ 9c9d2765:16f8c2c2
2025-05-27 16:05:22CHAPTER TWENTY NINE In boardrooms, lounges, and even on social media platforms, one question echoed relentlessly: Who is this man who rose from the ashes, not just to lead, but to lead with such bold transparency?
Meanwhile, in a dimly lit office nestled deep within Ray Enterprises, Helen paced restlessly across her carpeted floor. Her heels clicked in rhythm with the tension radiating from her. Mark stood by the window, nervously peeking through the blinds as though paranoia had taken root in his very soul.
“This can’t be happening,” Helen hissed, her voice sharp with frustration. “That press conference flipped everything. Now we’re the ones under scrutiny, and James has flipped the narrative like a magician.”
Mark turned, his voice laced with disbelief. “You saw the financial reports. Investors are pulling out of our side deals. If this continues, Ray Enterprises will collapse under the weight of its own debt.”
Helen clenched her fists, her perfectly manicured nails digging into her palms. “We need leverage. Something from his past. Something real. If the rumors didn’t ruin him, maybe the truth whatever it is will.”
But unknown to them, their every word was being monitored.
Lilian, the sharp cybersecurity expert at JP Enterprises, had tapped into Helen’s office through a corrupted email file disguised as a sponsorship request. Every correspondence, every call, and every document opened since then had been recorded and encrypted. Now, James had everything he needed and more.
At JP Enterprises, James stood in the private archive room, going through printed transcriptions of the recordings. Rita entered quietly, holding another file.
“We’ve compiled a list of shell companies used to launder bribe money into media firms and anonymous accounts,” she said, placing the documents gently before him.
James glanced through the list. Names of journalists, bloggers, and even a few local politicians filled the pages.
“They thought hiding behind faceless transactions would protect them,” he said calmly. “But even shadows betray their source when the light is bright enough.”
He closed the file slowly and looked at Rita.
“Let’s prepare the evidence for the federal board. By the time I’m done, Ray Enterprises will not only owe us 85%… they’ll owe us their very survival.”
The following day, the National Corporate Regulatory Board received a sealed dossier containing proof of bribery, media manipulation, and corporate fraud complete with audio clips, transaction records, and screen captures. An anonymous tip, courtesy of The Integrity Initiative.
As the investigation began to stir, Helen and Mark received a legal summons. Panic set in like a poison. Reporters camped outside Ray Enterprises. Shareholders demanded answers. The once feared and revered duo now found themselves cornered like rats.
In a final, desperate attempt, Helen reached out to James.
She showed up at JP Enterprises’ reception uninvited, her expression soft but insincere. She was dressed in white as if to evoke purity but James saw through the façade like glass.
“James,” she began, her voice low and trembling, “I know we’ve had our differences, but let’s not destroy each other. We can fix this, together. Let’s negotiate.”
James leaned back in his chair, eyes piercing.
“Negotiate?” he echoed, a wry smile touching his lips. “When you smeared my name, tried to sabotage my company, and humiliated me in public?”
Helen faltered but held her composure.
“It was business, James. That’s all. I didn’t mean to”
James cut her off with a raised hand.
“You didn’t mean to destroy my life? Helen, you orchestrated an entire charade. You bribed people to lie. But now the charade is over. And business… has consequences.”
He reached into his drawer, pulled out a copy of the legal complaint already filed against her, and placed it in front of her.
“You have 24 hours to prepare your lawyers.”
Helen’s mask of grace fell instantly. Her hands shook as she picked up the file, her eyes scanning the lines like a woman reading her own obituary.
-
 @ d360efec:14907b5f
2025-05-27 15:46:26
@ d360efec:14907b5f
2025-05-27 15:46:26 -
 @ c631e267:c2b78d3e
2025-05-02 20:05:22
@ c631e267:c2b78d3e
2025-05-02 20:05:22Du bist recht appetitlich oben anzuschauen, \ doch unten hin die Bestie macht mir Grauen. \ Johann Wolfgang von Goethe
Wie wenig bekömmlich sogenannte «Ultra-Processed Foods» wie Fertiggerichte, abgepackte Snacks oder Softdrinks sind, hat kürzlich eine neue Studie untersucht. Derweil kann Fleisch auch wegen des Einsatzes antimikrobieller Mittel in der Massentierhaltung ein Problem darstellen. Internationale Bemühungen, diesen Gebrauch zu reduzieren, um die Antibiotikaresistenz bei Menschen einzudämmen, sind nun möglicherweise gefährdet.
Leider ist Politik oft mindestens genauso unappetitlich und ungesund wie diverse Lebensmittel. Die «Corona-Zeit» und ihre Auswirkungen sind ein beredtes Beispiel. Der Thüringer Landtag diskutiert gerade den Entwurf eines «Coronamaßnahmen-Unrechtsbereinigungsgesetzes» und das kanadische Gesundheitsministerium versucht, tausende Entschädigungsanträge wegen Impfnebenwirkungen mit dem Budget von 75 Millionen Dollar unter einen Hut zu bekommen. In den USA soll die Zulassung von Covid-«Impfstoffen» überdacht werden, während man sich mit China um die Herkunft des Virus streitet.
Wo Corona-Verbrecher von Medien und Justiz gedeckt werden, verfolgt man Aufklärer und Aufdecker mit aller Härte. Der Anwalt und Mitbegründer des Corona-Ausschusses Reiner Fuellmich, der seit Oktober 2023 in Untersuchungshaft sitzt, wurde letzte Woche zu drei Jahren und neun Monaten verurteilt – wegen Veruntreuung. Am Mittwoch teilte der von vielen Impfschadensprozessen bekannte Anwalt Tobias Ulbrich mit, dass er vom Staatsschutz verfolgt wird und sich daher künftig nicht mehr öffentlich äußern werde.
Von der kommenden deutschen Bundesregierung aus Wählerbetrügern, Transatlantikern, Corona-Hardlinern und Russenhassern kann unmöglich eine Verbesserung erwartet werden. Nina Warken beispielsweise, die das Ressort Gesundheit übernehmen soll, diffamierte Maßnahmenkritiker als «Coronaleugner» und forderte eine Impfpflicht, da die wundersamen Injektionen angeblich «nachweislich helfen». Laut dem designierten Außenminister Johann Wadephul wird Russland «für uns immer der Feind» bleiben. Deswegen will er die Ukraine «nicht verlieren lassen» und sieht die Bevölkerung hinter sich, solange nicht deutsche Soldaten dort sterben könnten.
Eine wichtige Personalie ist auch die des künftigen Regierungssprechers. Wenngleich Hebestreit an Arroganz schwer zu überbieten sein wird, dürfte sich die Art der Kommunikation mit Stefan Kornelius in der Sache kaum ändern. Der Politikchef der Süddeutschen Zeitung «prägte den Meinungsjournalismus der SZ» und schrieb «in dieser Rolle auch für die Titel der Tamedia». Allerdings ist, anders als noch vor zehn Jahren, die Einbindung von Journalisten in Thinktanks wie die Deutsche Atlantische Gesellschaft (DAG) ja heute eher eine Empfehlung als ein Problem.
Ungesund ist definitiv auch die totale Digitalisierung, nicht nur im Gesundheitswesen. Lauterbachs Abschiedsgeschenk, die «abgesicherte» elektronische Patientenakte (ePA) ist völlig überraschenderweise direkt nach dem Bundesstart erneut gehackt worden. Norbert Häring kommentiert angesichts der Datenlecks, wer die ePA nicht abwähle, könne seine Gesundheitsdaten ebensogut auf Facebook posten.
Dass die staatlichen Kontrolleure so wenig auf freie Software und dezentrale Lösungen setzen, verdeutlicht die eigentlichen Intentionen hinter der Digitalisierungswut. Um Sicherheit und Souveränität geht es ihnen jedenfalls nicht – sonst gäbe es zum Beispiel mehr Unterstützung für Bitcoin und für Initiativen wie die der Spar-Supermärkte in der Schweiz.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ bf47c19e:c3d2573b
2025-05-27 14:57:56
@ bf47c19e:c3d2573b
2025-05-27 14:57:56Srpski prevod knjige "The Little Bitcoin Book"
Zašto je Bitkoin bitan za vašu slobodu, finansije i budućnost?
Verovatno ste čuli za Bitkoin u vestima ili da o njemu raspravljaju vaši prijatelji ili kolege. Kako to da se cena stalno menja? Da li je Bitkoin dobra investicija? Kako to uopšte ima vrednost? Zašto ljudi stalno govore o tome kao da će promeniti svet?
"Mala knjiga o Bitkoinu" govori o tome šta nije u redu sa današnjim novcem i zašto je Bitkoin izmišljen da obezbedi alternativu trenutnom sistemu. Jednostavnim rečima opisuje šta je Bitkoin, kako funkcioniše, zašto je vredan i kako utiče na individualnu slobodu i mogućnosti ljudi svuda - od Nigerije preko Filipina do Venecuele do Sjedinjenih Država. Ova knjiga takođe uključuje odeljak "Pitanja i odgovori" sa nekim od najčešće postavljanih pitanja o Bitkoinu.
Ako želite da saznate više o ovom novom obliku novca koji i dalje izaziva interesovanje i usvajanje širom sveta, onda je ova knjiga za vas.
-
 @ 7e538978:a5987ab6
2025-05-13 10:59:37
@ 7e538978:a5987ab6
2025-05-13 10:59:37Introduction
Nostr Wallet Connect (NWC) is a powerful open protocol built on Nostr that enables a connection between Bitcoin Lightning wallets and applications—offering strong privacy, user control, easy connection, open interoperability, and support for a wide range of use cases without needing port forwarding or other network configuration. It allows a user to use many different Lightning apps with their own Lightning node via NWC.
In this post, we’ll give an overview of NWC as well as how to use a home-hosted LNbits instance as a private funding source for a public LNbits instance—giving you the benefits of privacy, control, and simplicity, to unleash the full power of LNbits.
Why Self-host with NWC?
- Privacy: Keep your Lightning node and LNbits instance at home, within your own network.
- Ownership & Control: Retain full custody of your funds, with no third-parties.
- Security: No port forwarding or VPN required—your node is not accessible from the public internet.
- Simplicity: Easy to set up and maintain.
- Flexible Funding: Fund your clearnet LNbits with any NWC-capable service—including your own LNbits instance, Alby, Minibits, Coinos, and more.
- App Access: Use LNbits at home as a Lightning wallet for one of the many NWC compatible apps.
How It Works
Your home Lightning node (running Raspiblitz, Umbrel, Start9, MyNode or one of the many other node packages) runs LNbits. You enable the NWCProvider extension in LNbits and generate a connection string.
On your clearnet LNbits instance (hosted with the LNbits SaaS or on your own VPS), set this connection string as your funding source.
This lets you:
- Fund and use LNbits from anywhere
- Keep your node private
- Add or change funding sources at any time with minimal config
How To Set It Up
1. Install LNbits at Home
Use a Raspiblitz, MyNode, Umbrel or other node package to run your home LNbits instance. You can also build your own node with Phoenixd and LNbits or any other combination of LNbits and Lightning node software.
-
Enable the
NWCProviderextension -
Create a new NWC connection

- Copy the NWC connection string

2. Provision a Clearnet LNbits Instance
Use:
- LNbits SaaS
- Your own VPS on a VPS provider like Vultr, Linode, AWC EC2 and install LNbits
3. Connect via NWC
On your clearnet LNbits instance:
-
Go to Settings → Funding
-
Select "Nostr Wallet Connect"
-
Paste your copied NWC connection string
-
Click Save, then Restart Server

Done! 🎉 Your clearnet LNbits instance is now funded by your home Lightning node—no open ports, no VPN, no fuss.
Home Nodes
You can use this setup with any LNbits-compatible home Lightning node, including:
- Raspiblitz
- Start9
- Umbrel
- MyNode
- Your own home server box with LNbits plus any other Lightning funding source for example Phoenixd, Core-Lightning, LND, etc.
Try it Out
Want to try this yourself?
- 🧠 Enjoy control, privacy, and simplicity
- 🌍 Use LNbits on the clearnet with funding from your own node
- 🔌 Connect apps like Alby, Minibits, Coinos, or your own LNbits
🚀 Run LNbits
Start exploring the power of NWC and LNbits today:
NWC Apps
Here are some great apps that make use of NWC.
- Alby Go
- A lightning wallet that uses one or many NWC providers to make and receive lightning payments
- Damus
- Decentralised social app on Nostr
- Amethyst
- Android Nostr social media client client
- Clean interface, popular among mobile users
- Snort
- Web-based Nostr client
- Familiar UI, easy access via browser
- Stacker News
- Bitcoin-centric news/discussion site
- Earn sats via upvotes
- Zeus
- Mobile app for controlling your own Lightning node
- Favoured by self-custody and privacy-focused users
Resources
-
 @ c631e267:c2b78d3e
2025-04-25 20:06:24
@ c631e267:c2b78d3e
2025-04-25 20:06:24Die Wahrheit verletzt tiefer als jede Beleidigung. \ Marquis de Sade
Sagen Sie niemals «Terroristin B.», «Schwachkopf H.», «korrupter Drecksack S.» oder «Meinungsfreiheitshasserin F.» und verkneifen Sie sich Memes, denn so etwas könnte Ihnen als Beleidigung oder Verleumdung ausgelegt werden und rechtliche Konsequenzen haben. Auch mit einer Frau M.-A. S.-Z. ist in dieser Beziehung nicht zu spaßen, sie gehört zu den Top-Anzeigenstellern.
«Politikerbeleidigung» als Straftatbestand wurde 2021 im Kampf gegen «Rechtsextremismus und Hasskriminalität» in Deutschland eingeführt, damals noch unter der Regierung Merkel. Im Gesetz nicht festgehalten ist die Unterscheidung zwischen schlechter Hetze und guter Hetze – trotzdem ist das gängige Praxis, wie der Titel fast schon nahelegt.
So dürfen Sie als Politikerin heute den Tesla als «Nazi-Auto» bezeichnen und dies ausdrücklich auf den Firmengründer Elon Musk und dessen «rechtsextreme Positionen» beziehen, welche Sie nicht einmal belegen müssen. [1] Vielleicht ernten Sie Proteste, jedoch vorrangig wegen der «gut bezahlten, unbefristeten Arbeitsplätze» in Brandenburg. Ihren Tweet hat die Berliner Senatorin Cansel Kiziltepe inzwischen offenbar dennoch gelöscht.
Dass es um die Meinungs- und Pressefreiheit in der Bundesrepublik nicht mehr allzu gut bestellt ist, befürchtet man inzwischen auch schon im Ausland. Der Fall des Journalisten David Bendels, der kürzlich wegen eines Faeser-Memes zu sieben Monaten Haft auf Bewährung verurteilt wurde, führte in diversen Medien zu Empörung. Die Welt versteckte ihre Kritik mit dem Titel «Ein Urteil wie aus einer Diktatur» hinter einer Bezahlschranke.
Unschöne, heutzutage vielleicht strafbare Kommentare würden mir auch zu einigen anderen Themen und Akteuren einfallen. Ein Kandidat wäre der deutsche Bundesgesundheitsminister (ja, er ist es tatsächlich immer noch). Während sich in den USA auf dem Gebiet etwas bewegt und zum Beispiel Robert F. Kennedy Jr. will, dass die Gesundheitsbehörde (CDC) keine Covid-Impfungen für Kinder mehr empfiehlt, möchte Karl Lauterbach vor allem das Corona-Lügengebäude vor dem Einsturz bewahren.
«Ich habe nie geglaubt, dass die Impfungen nebenwirkungsfrei sind», sagte Lauterbach jüngst der ZDF-Journalistin Sarah Tacke. Das steht in krassem Widerspruch zu seiner früher verbreiteten Behauptung, die Gen-Injektionen hätten keine Nebenwirkungen. Damit entlarvt er sich selbst als Lügner. Die Bezeichnung ist absolut berechtigt, dieser Mann dürfte keinerlei politische Verantwortung tragen und das Verhalten verlangt nach einer rechtlichen Überprüfung. Leider ist ja die Justiz anderweitig beschäftigt und hat außerdem selbst keine weiße Weste.
Obendrein kämpfte der Herr Minister für eine allgemeine Impfpflicht. Er beschwor dabei das Schließen einer «Impflücke», wie es die Weltgesundheitsorganisation – die «wegen Trump» in finanziellen Schwierigkeiten steckt – bis heute tut. Die WHO lässt aktuell ihre «Europäische Impfwoche» propagieren, bei der interessanterweise von Covid nicht mehr groß die Rede ist.
Einen «Klima-Leugner» würden manche wohl Nir Shaviv nennen, das ist ja nicht strafbar. Der Astrophysiker weist nämlich die Behauptung von einer Klimakrise zurück. Gemäß seiner Forschung ist mindestens die Hälfte der Erderwärmung nicht auf menschliche Emissionen, sondern auf Veränderungen im Sonnenverhalten zurückzuführen.
Das passt vielleicht auch den «Klima-Hysterikern» der britischen Regierung ins Konzept, die gerade Experimente zur Verdunkelung der Sonne angekündigt haben. Produzenten von Kunstfleisch oder Betreiber von Insektenfarmen würden dagegen vermutlich die Geschichte vom fatalen CO2 bevorzugen. Ihnen würde es besser passen, wenn der verantwortungsvolle Erdenbürger sein Verhalten gründlich ändern müsste.
In unserer völlig verkehrten Welt, in der praktisch jede Verlautbarung außerhalb der abgesegneten Narrative potenziell strafbar sein kann, gehört fast schon Mut dazu, Dinge offen anzusprechen. Im «besten Deutschland aller Zeiten» glaubten letztes Jahr nur noch 40 Prozent der Menschen, ihre Meinung frei äußern zu können. Das ist ein Armutszeugnis, und es sieht nicht gerade nach Besserung aus. Umso wichtiger ist es, dagegen anzugehen.
[Titelbild: Pixabay]
--- Quellen: ---
[1] Zur Orientierung wenigstens ein paar Hinweise zur NS-Vergangenheit deutscher Automobilhersteller:
- Volkswagen
- Porsche
- Daimler-Benz
- BMW
- Audi
- Opel
- Heute: «Auto-Werke für die Rüstung? Rheinmetall prüft Übernahmen»
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ bf47c19e:c3d2573b
2025-05-27 14:54:03
@ bf47c19e:c3d2573b
2025-05-27 14:54:03Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- 5 Razloga Zašto je Novac Važan za Vas, Individualno
- 3 Razloga Zašto je Novac Važan za Društvo u Celini
- Zašto ljudi mrze novac?

Novac vs trenuci – da li oni treba da budu u sukobu? Kakva je uloga novca?
Novac je nepredvidiva zver modernog društva – neki ga veličaju sa stalnom željom da steknu više, dok ga drugi demonizuju i kažu da je pohlepa srž društvenih problema. Tokom mnogih godina svog života, ja sam često prelazio sa jednog na drugo gledište, i naučio mnogo toga upoznajući druge ljude koji žive na oba kraja ovog spektra. Kao i kod mnogih složenih tema, istina leži negde u sredini.
Novac je važan zato što on može da pomogne u uklanjanju materijalnih želja i patnji – omogućavanjem da preuzmete kontrolu nad svojim životom i da brinete o voljenima. Novac podiže životni standard društva omogućavanjem trgovine, a pritom minimalizuje potrebu za poverenjem.
Na novac možemo gledati kao na način da svoj uloženi trud sačuvamo u odredjenom obliku, i da ga vremenom prenesemo, tako da možemo da uživamo u plodovima svog rada. Novac kao alat je jedna od najvažnijih stvari za rast civilizacije. Na nesreću, mnogi su vremenom zlostavljali novac, ali sa dobrim razlogom: način na koji naš novac danas funkcioniše dovodi do duboko podeljenog društva – što ću i objasniti.
5 Razloga Zašto je Novac Važan za Vas, Individualno
Novac je važan za rast bogatstva, što je malo drugačije od toga da imamo veliku platu ili jednostavno zarađivati velike količine novca. Bogatstvo je otklanjanje želja, kako bi mogli da obratimo više pažnje na neke korisnije stvari u životu, od pukog preživljavanja i osnovnih udobnosti.
Bogata osoba je ona koja zaradi više novca nego što potroši, i koja ga čuva – ona čuva svoj rad tokom vremena. Uporedite ovo sa visoko plaćenim lekarom koji živi u velikoj vili sa hipotekom i sa Mercedesom na lizing. Iako ova osoba ima visoke prihode, ona takođe ima velike rashode u vidu obaveze plaćanja te hipoteke i lizinga. Te obaveze sprečavaju ovu osobu da uživa u istinskim blagodetima novca i bogatstva koje one predstavljaju:
1. Sloboda od potrebe za radom
Bez bogatstva, vi morate da radite da biste preživeli. Dostizanjem bogatstva i odredjenom imovinom koja vam donosi novac bez potrebe da vi trošite svoje vreme, vi možete da oslobodite svoj raspored. Više ne zavisite od posla koji mrzite, i nemorate da provodite 40 sati nedeljno odvojeni od porodice, samo da biste se pobrinuli za svoje osnovne potrebe. Dobijanje otkaza u padu ekonomije neće vas dovesti do finansijske propasti ili nečeg goreg.
2. Kontrola nad time kako vi trošite svoje vreme
Kada steknete bogatstvo, vi možete da odlučite kako želite da provodite svoje vreme. Kada se nalazimo u trci pacova i radimo 40+ sati nedeljno, često se naviknemo da novac trošimo onda kada imamo slobodnog vremena. Idemo na lepe večere ili idemo na skupe odmore. Međutim, sa više vremena, a možda čak i sa manje novca, mi možemo da imamo isto ili više uživanja živeći usporenije.
Razmislite o ovome – ukoliko imate samo 1 nedelju slobodno od posla, vi onda morate da kupite onaj mnogo skuplji let u Petak uveče koji se vraća u sledeću Nedelju, kako biste maksimalno iskoristili svoje vreme na nekom egzotičnom mestu za odmor. Međutim, ukoliko ste u mogućnosti da izdržavate sebe bez potrebe da mnogo vremena provodite na poslu, vi onda možete u Utorak da krenete jeftinijim letom i vratite se u sledeću Sredu. Takođe nećete osećati toliki pritisak da se opustite u uživanju tokom vaše nedelje u inostranstvu – možda ćete čak moći i da ostanete duže i da istražujete više, bez plaćanja skupih turističkih agencija i hotela kako bi organizovali vaše kraće putovanje.
3. Sposobnost da pomažete vašim prijateljima i porodici
Onda kada novca imate na pretek, možete poboljšati svoje odnose sa prijateljima i porodicom ne samo kroz dodatno slobodno vreme koje provodite sa njima, već i sa samim novcem. Ako je vašem prijatelju potrebna hitna operacija, vi možete da mu izadjete u susret i pomognete mu da stane na svoje noge. Ukoliko vam je tetka bolesna, vi možete da provedete vreme pored nje, umesto da je pozovete na kratko dok putujete prema kući vraćajući se nakon celog dana provedenog u kancelariji.
4. Smanjen finansijski stres
Stres je sveobuhvatno i opasno stanje modernog doba, sa kojim gotovo svi mi živimo u nekoj odredjenoj meri. Povezan je sa lošim zdravljem, sa preko 43% svih odraslih koji kažu da pate od odredjenih zdravstvenih problema uzrokovanih stresom. Stres zbog posla pogađa 83% zaposlenih.
Pravo bogatstvo – koje znači eliminaciju želja i potreba – može da ukloni ovaj stres i njegove negativne uticaje na druge delove života. Ovo bi čak moglo da ukloni većinu stresa u vašem životu, uzimajući u obzir da je uzrok stresa broj 1 upravo novac.
5. Bolje možete da pomognete vašoj zajednici
Mnogi od nas žele da volontiraju u svojim zajednicama i pomognu onima koja je pomoć preko potrebna, ali nisu u stanju da pronađu slobodnog vremena i energije zbog svog posla, porodice i društvenih aktivnosti koje nas mentalno i fizički čine srećnima, zdravima i hranjenima. Sa bogatstvom, mi možemo da posvetimo vreme koje nam je potrebno za razumevanje i doprinos drugima – a ne samo da sa vremena na vreme pomognemo slanjem humanitarnog SMS-a.
Novac, koji se pametno koristi, je moćno sredstvo za poboljšanje vašeg života i života vaših najmilijih i zajednice. Međutim, novac je takođe moćno sredstvo za poboljšanje društva u celini – ukoliko je dobro strukturiran.
3 Razloga Zašto je Novac Važan za Društvo u Celini
Novac poboljšava sposobnost ljudi da trguju jedni s drugima, što podstiče određene specijalizacije. Ako je imanje vašeg komšije odlično za proizvodnju vina, a vaše je pogodno za žito, obojica možete da profitirate trgovinom. Sad oboje imate i hleb i vino, umesto jednog pijanog vlasnika vinograda i jednog proizvodjača žita kome je dosadno!
Novac poboljšava društvo na nekoliko načina:
1. Omogućava specijalizaciju
Kao u primeru vlasnika vinograda i proizvodjača žita, novac omogućava povećanu specijalizaciju poboljšavajući sposobnost trgovine. Svaka razmena dobara ima problem sa ‘sticajima potreba’ – oba partnera u trgovini moraju da žele ono što druga osoba ima da bi pristala na trgovinu.
Možemo da mislimo o novcu kao o dobru koje žele gotovo svi. Ovo trgovinu čini mnogo jednostavnijom – da biste stekli odredjeno dobro, sve što vam je potrebno je novac, a ne neka slučajna stvar koju prodavac tog dobra takođe želi u tom trenutku. Vremenom je upotreba novca omogućila specijalizaciju, što je povećalo kvalitet i složenost roba i usluga.
Zamislite da sami pokušate da napravite svoj telefon – a bili su potrebni milioni stručnjaka i specijalizovana oprema da bi proizveli taj uređaj. Svi ti stručnjaci i kompanije plaćaju jedni drugima u novcu, omogućavajući složenom plesu globalnih proizvođača i lanaca snabdevanja da taj telefon isporuče na dlan vaše ruke. Čak i nešto tako jednostavno kao flaša za vodu uključuje naftna polja i proizvodne pogone koji su možda hiljadama kilometara od vaše kuće.
Kada ljudi mogu da se specijalizuju, kvalitet robe i usluga može da se poveća.
2. Omogućava korisnu trgovinu uz smanjeno poverenje
Mala društva mogu mirno i produktivno da posluju bez novca koristeći usluge, “dodjem ti” i uzajamno razumevanje. Međutim, kako se društva uvećavaju, svima brzo postaje nemoguće da održavaju lične odnose i isti stepen poverenja sa svima ostalima. Sistem trgovine uslugama i međusobnog poverenja ne funkcioniše previše dobro sa putnikom koji se nalazi na proputovanju kroz grad, i provede samo 15 minuta svog života u vašoj prodavnici.
Novac minimizira poverenje potrebno za trgovinu u većim društvima. Sada više ne moram da verujem da ćete mi pomoći kasnije kada mi zatreba – mogu samo da prihvatim uplatu od vas i da to koristim da bih sebi pomogao kasnije. Jedan od mojih omiljenih mislilaca, Nick Szabo, ovo naziva ‘društvena prilagodljivost’.
3. Smanjuje upotrebu sile
Kada društvo teži upotrebi određenog oblika novca za olakšavanje trgovine, može u velikoj meri da smanji nasilje u tom društvu. Kako to može biti tako? Zar ljudi ne bi i dalje želeli da kradu jedni od drugih ili da se svete?
Ukoliko razmišljamo van uobičajnih okvira, možemo da počnemo da razumemo kako novac može da smanji nasilje. Ako ti i ja živimo u susednim zemljama i želimo nešto što druga zemlja ima, imamo dva načina da to dobijemo: uzimanjem na silu ili menjanjem nečeg našeg za to. Kao što je ranije rečeno, novac znatno olakšava trgovinu – pa ćemo postojanjem zajedničkog monetarnog sistema verovatnije radje izvršiti trgovinu nego napad na zemlju. Zašto bismo rizikovali svoje živote kad možemo samo mirno da trgujemo jedni sa drugima?
Zašto ljudi mrze novac?
Pa ako novac ima toliko koristi za nas lično i za društvo u celini, zašto toliko ljudi mrzi novac? Zašto je demonizovan, zajedno sa onima koji ga imaju puno?
Za deo ovoga može biti okrivljen problem u jednakosti mogućnosti – to da je nekima teže da izadju iz nemaštine i postanu bogati. Bez sumnje, neki mali deo potiče od ljudi koji jednostavno ne žele da se trude ili preduzmu neophodne rizike da bi postali bogati.
Međutim, oba ova problema imaju više veze sa problemima kako naš novac danas funkcioniše, nego sa bilo kojim problemom u samom konceptu novca. Novčani sistem treba da nagrađuje ljude koji proizvode vredne stvari i trguju njima sa drugima. Verujem da većina ljudi danas misli da novac tako funkcioniše, i to ne bi smelo da bude daleko od istine.
Naš trenutni monetarni sistem, na žalost, nagrađuje ’finansijalizaciju’ – pretvarajući sve u imovinu, čija vrednost može da se napumpava ili spušta stvaranjem dobre priče i navođenjem drugih da veruju u nju. Razuzdani dug pogonjen stalnim omalovažavanjem svih glavnih valuta dodat je ovom blatu finansijalizacije. Sada je isplativije podići ogroman kredit i koristiti ga za brzo okretanje imovine radi zarade nego izgraditi posao koji društvu nudi korisne robe i usluge.
Tradicionalni monetarni sistem dodatno nagradjuje predatore, partnere u zločinu i neradnike.
Propast našeg novca razvila se tokom proteklih pola veka, počevši od toga kada su naše valute postale ništa više od parčeta papira, podržanog sa verom i kreditima naših vlada. Da biste bolje razumeli ovu promenu, pogledajte moj post o svrsi i istoriji novca.
Ako vam se sviđa moj rad, molim vas da ga podelite sa svojim prijateljima i porodicom. Cilj mi je da svima pružim pogled u ekonomiju i na to kako ona utiče na njihov život.
-
 @ e844b39d:adafb6a2
2025-05-27 14:31:02
@ e844b39d:adafb6a2
2025-05-27 14:31:02This was not planned, but last evening I realized that I should at least test the Sony A900 and Minolta gear that I had, which was bought for real estate photography around a decade ago.
 Look at everything out here!
Look at everything out here!Our two white kittens are almost identical, but they come from two different mothers, Charcoal and Tiger!
I sometimes wonder if they have realized that they look the same, they tend to stick together most of the day.
 I know you're there!
I know you're there!This ended up being perfect scenes for the 20/2.8 wide open!
 Outside the gate
Outside the gateSeveral of our cats have been digging a hole outside, sniffing for something, we have no idea what that is all about...

 Playing around
Playing aroundThey often stay in the slot for the gate, I guess its a little less hot there.
 Happy cat?
Happy cat?This sort of scene is perfect for the Beercan, Minolta 70-210/4, its a legendary piece of optics for sure. One of the reasons I got into the system back then.
 Scouting
ScoutingThey spent some time hunting each others in the "jungle" of course!

 Hunting mode!
Hunting mode!They were moving too rapidly for any gear really, so the slow AF was not a real hindrance.
 I look good, yes?
I look good, yes?Sometimes when I process images of them the fur gets messy and kinda dirty looking, but this went the opposite way!
It was a good day in the garden, and a very useful test.
That's it for today!
-
 @ da8b7de1:c0164aee
2025-05-23 16:08:53
@ da8b7de1:c0164aee
2025-05-23 16:08:53Amerikai Nukleáris Fordulat és Pénzügyi hatások
Donald Trump elnök bejelentette, hogy végrehajtási rendeleteket ír alá a nukleáris energia fellendítésére . Ezek célja az új reaktorok engedélyezési folyamatának egyszerűsítése, az üzemanyag-ellátási láncok megerősítése, valamint a hazai ipar támogatása az orosz és kínai nyersanyagfüggőség csökkentése érdekében. A hír hatására az amerikai és globális nukleáris részvények jelentős emelkedést mutattak: az Uránium Energy 11%, a Centrus Energy 19,6%, az Oklo 16%, a Nano Nuclear 15%, a Nu Power 14,1%, a Global X Uranium ETF pedig 9%-kal erősödött . A növekvő energiaigény, különösen a mesterséges intelligencia által hajtott adatközpontok miatt, tovább növeli a nukleáris energia stratégiai szerepét az USA-ban .
Európai és Nemzetközi Nukleáris Fejlemények
Svédország parlamentje elfogadta az új állami támogatási keretrendszert, amely akár 5 000 MW új nukleáris kapacitás beruházását ösztönzi . Az intézkedés célja az áramárak stabilizálása, az ellátásbiztonság növelése és a zöld átmenet támogatása. A program keveri az állami hiteleket és a piaci árgaranciákat (CfD), a projektek finanszírozásában pedig a magántőke is részt vesz. A törvény 2025. augusztus 1-jén lép hatályba, a végrehajtás azonban még EU-jóváhagyásra vár .
Nukleáris Ellátási Lánc és Iparági Konferencia
Május 20–21-én Varsóban rendezték meg az első World Nuclear Supply Chain Conference-t, amelynek célja a globális nukleáris ellátási lánc megerősítése és bővítése . A konferencián elhangzottak szerint az iparág előtt álló kihívás a kapacitás gyors növelése, hiszen a cél a globális nukleáris kapacitás megháromszorozása 2050-ig. A World Nuclear Association legfrissebb elemzése szerint a következő 15 évben akár 2 billió dollár értékű beruházási lehetőség nyílhat a nemzetközi ellátási láncban . A rendezvényen kiemelték az innováció, a lokalizáció és az iparági együttműködés fontosságát, valamint a szállítási és geopolitikai kihívásokat is.
Új Projektek, Technológiai és Piaci Hírek
Az Egyesült Államokban a Tennessee Valley Authority (TVA) benyújtotta az első hivatalos engedélykérelmet egy BWRX-300 típusú kis moduláris reaktor (SMR) építésére a Clinch River telephelyen . Indiában a nukleáris hatóság jóváhagyta a Mahi Banswara Rajasthan Atomerőmű négy új blokkjának helyszínét . Kínában befejeződött a Haiyang 3 atomerőmű gőzturbinájának fő egységeinek telepítése . Belgiumban és Dániában is újraértékelik a nukleáris energia szerepét, míg Brazília Oroszországgal közös SMR-projektet tervez .
Iparági Trendek és Kilátások
A World Nuclear Association és az International Energy Agency (IEA) szerint a globális nukleáris energiatermelés 2025-ben minden korábbinál magasabb szintet érhet el, köszönhetően az új reaktorok üzembe helyezésének és a stabil, alacsony kibocsátású energiaforrások iránti növekvő igénynek . A nukleáris üzemanyag-ellátási lánc megerősítése, az uránbányászat, az átalakítás és a dúsítás bővítése, valamint a szállítási kapacitás fejlesztése mind kulcsfontosságú tényezők lesznek a következő években .
Hivatkozások
reuters.com
investopedia.com
nucnet.org
world-nuclear-news.org
world-nuclear.org -
 @ 6e64b83c:94102ee8
2025-04-23 20:23:34
@ 6e64b83c:94102ee8
2025-04-23 20:23:34How to Run Your Own Nostr Relay on Android with Cloudflare Domain
Prerequisites
- Install Citrine on your Android device:
- Visit https://github.com/greenart7c3/Citrine/releases
- Download the latest release using:
- zap.store
- Obtainium
- F-Droid
- Or download the APK directly
-
Note: You may need to enable "Install from Unknown Sources" in your Android settings
-
Domain Requirements:
- Purchase a domain if you don't have one
-
Transfer your domain to Cloudflare if it's not already there (for free SSL certificates and cloudflared support)
-
Tools to use:
- nak (the nostr army knife):
- Download from https://github.com/fiatjaf/nak/releases
- Installation steps:
-
For Linux/macOS: ```bash # Download the appropriate version for your system wget https://github.com/fiatjaf/nak/releases/latest/download/nak-linux-amd64 # for Linux # or wget https://github.com/fiatjaf/nak/releases/latest/download/nak-darwin-amd64 # for macOS
# Make it executable chmod +x nak-*
# Move to a directory in your PATH sudo mv nak-* /usr/local/bin/nak
- For Windows:batch # Download the Windows version curl -L -o nak.exe https://github.com/fiatjaf/nak/releases/latest/download/nak-windows-amd64.exe# Move to a directory in your PATH (e.g., C:\Windows) move nak.exe C:\Windows\nak.exe
- Verify installation:bash nak --version ```
Setting Up Citrine
- Open the Citrine app
- Start the server
- You'll see it running on
ws://127.0.0.1:4869(local network only) - Go to settings and paste your npub into "Accept events signed by" inbox and press the + button. This prevents others from publishing events to your personal relay.
Installing Required Tools
- Install Termux from Google Play Store
- Open Termux and run:
bash pkg update && pkg install wget wget https://github.com/cloudflare/cloudflared/releases/latest/download/cloudflared-linux-arm64.deb dpkg -i cloudflared-linux-arm64.debCloudflare Authentication
- Run the authentication command:
bash cloudflared tunnel login - Follow the instructions:
- Copy the provided URL to your browser
- Log in to your Cloudflare account
- If the URL expires, copy it again after logging in
Creating the Tunnel
- Create a new tunnel:
bash cloudflared tunnel create <TUNNEL_NAME> - Choose any name you prefer for your tunnel
-
Copy the tunnel ID after creating the tunnel
-
Create and configure the tunnel config:
bash touch ~/.cloudflared/config.yml nano ~/.cloudflared/config.yml -
Add this configuration (replace the placeholders with your values): ```yaml tunnel:
credentials-file: /data/data/com.termux/files/home/.cloudflared/ .json ingress: - hostname: nostr.yourdomain.com service: ws://localhost:4869
- service: http_status:404 ```
- Note: In nano editor:
CTRL+Oand Enter to saveCTRL+Xto exit
-
Note: Check the credentials file path in the logs
-
Validate your configuration:
bash cloudflared tunnel validate -
Start the tunnel:
bash cloudflared tunnel run my-relay
Preventing Android from Killing the Tunnel
Run these commands to maintain tunnel stability:
bash date && apt install termux-tools && termux-setup-storage && termux-wake-lock echo "nameserver 1.1.1.1" > $PREFIX/etc/resolv.confTip: You can open multiple Termux sessions by swiping from the left edge of the screen while keeping your tunnel process running.
Updating Your Outbox Model Relays
Once your relay is running and accessible via your domain, you'll want to update your relay list in the Nostr network. This ensures other clients know about your relay and can connect to it.
Decoding npub (Public Key)
Private keys (nsec) and public keys (npub) are encoded in bech32 format, which includes: - A prefix (like nsec1, npub1 etc.) - The encoded data - A checksum
This format makes keys: - Easy to distinguish - Hard to copy incorrectly
However, most tools require these keys in hexadecimal (hex) format.
To decode an npub string to its hex format:
bash nak decode nostr:npub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4Change it with your own npub.
bash { "pubkey": "6e64b83c1f674fb00a5f19816c297b6414bf67f015894e04dd4c657e94102ee8" }Copy the pubkey value in quotes.
Create a kind 10002 event with your relay list:
- Include your new relay with write permissions
- Include other relays you want to read from and write to, omit 3rd parameter to make it both read and write
Example format:
json { "kind": 10002, "tags": [ ["r", "wss://your-relay-domain.com", "write"], ["r", "wss://eden.nostr.land/"], ["r", "wss://nos.lol/"], ["r", "wss://nostr.bitcoiner.social/"], ["r", "wss://nostr.mom/"], ["r", "wss://relay.primal.net/"], ["r", "wss://nostr.wine/", "read"], ["r", "wss://relay.damus.io/"], ["r", "wss://relay.nostr.band/"], ["r", "wss://relay.snort.social/"] ], "content": "" }Save it to a file called
event.jsonNote: Add or remove any relays you want. To check your existing 10002 relays: - Visit https://nostr.band/?q=by%3Anpub1dejts0qlva8mqzjlrxqkc2tmvs2t7elszky5upxaf3jha9qs9m5q605uc4+++kind%3A10002 - nostr.band is an indexing service, it probably has your relay list. - Replace
npub1xxxin the URL with your own npub - Click "VIEW JSON" from the menu to see the raw event - Or use thenaktool if you know the relaysbash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.comReplace `<your-pubkey>` with your public key in hex format (you can get it using `nak decode <your-npub>`)- Sign and publish the event:
- Use a Nostr client that supports kind 10002 events
- Or use the
nakcommand-line tool:bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)
Important Security Notes: 1. Never share your nsec (private key) with anyone 2. Consider using NIP-49 encrypted keys for better security 3. Never paste your nsec or private key into the terminal. The command will be saved in your shell history, exposing your private key. To clear the command history: - For bash: use
history -c- For zsh: usefc -Wto write history to file, thenfc -pto read it back - Or manually edit your shell history file (e.g.,~/.zsh_historyor~/.bash_history) 4. if you're usingzsh, usefc -pto prevent the next command from being saved to history 5. Or temporarily disable history before running sensitive commands:bash unset HISTFILE nak key encrypt ... set HISTFILEHow to securely create NIP-49 encypted private key
```bash
Read your private key (input will be hidden)
read -s SECRET
Read your password (input will be hidden)
read -s PASSWORD
encrypt command
echo "$SECRET" | nak key encrypt "$PASSWORD"
copy and paste the ncryptsec1 text from the output
read -s ENCRYPTED nak key decrypt "$ENCRYPTED"
clear variables from memory
unset SECRET PASSWORD ENCRYPTED ```
On a Windows command line, to read from stdin and use the variables in
nakcommands, you can use a combination ofset /pto read input and then use those variables in your command. Here's an example:```bash @echo off set /p "SECRET=Enter your secret key: " set /p "PASSWORD=Enter your password: "
echo %SECRET%| nak key encrypt %PASSWORD%
:: Clear the sensitive variables set "SECRET=" set "PASSWORD=" ```
If your key starts with
ncryptsec1, thenaktool will securely prompt you for a password when using the--secparameter, unless the command is used with a pipe< >or|.bash nak event --sec ncryptsec1... wss://relay1.com wss://relay2.com $(cat event.json)- Verify the event was published:
- Check if your relay list is visible on other relays
-
Use the
naktool to fetch your kind 10002 events:bash nak req -k 10002 -a <your-pubkey> wss://relay1.com wss://relay2.com -
Testing your relay:
- Try connecting to your relay using different Nostr clients
- Verify you can both read from and write to your relay
- Check if events are being properly stored and retrieved
- Tip: Use multiple Nostr clients to test different aspects of your relay
Note: If anyone in the community has a more efficient method of doing things like updating outbox relays, please share your insights in the comments. Your expertise would be greatly appreciated!
-
 @ da8b7de1:c0164aee
2025-05-22 16:19:52
@ da8b7de1:c0164aee
2025-05-22 16:19:52Technológiai és fejlesztési hírek
- Észtország SMR-tervei:
Észtország hivatalosan elindította a nemzeti tervezési folyamatot és a környezeti hatásvizsgálatot egy 600 MW-os kis moduláris reaktor (SMR) atomerőmű létesítésére, GE Hitachi BWRX-300 technológiával. A projektet a Fermi Energia vezeti, a lakosság körében mérsékelt támogatottság mellett. Az építési engedélykérelem benyújtását 2029-re tervezik, a cél az ország energiabiztonságának és klímacéljainak erősítése.
- Olkiluoto-1 csökkentett teljesítménnyel üzemel:
Finnországban az Olkiluoto-2 egységben a generátor rotorjának cseréje miatt a termelés májusban újraindul, de a teljesítményt 735 MW-ra korlátozzák (a teljes kapacitás 890 MW). A csökkentett teljesítmény 2026-ig marad érvényben. Az Olkiluoto-1 egység normálisan működik, az Olkiluoto-3 pedig éves karbantartáson van.
Ipari és pénzügyi fejlemények
- Kanada–Argentína nehézvíz-együttműködés:
A kanadai Candu Energy (AtkinsRéalis) és az argentin Nemzeti Atomenergia Bizottság (CNEA) memorandumot írt alá a nehézvíz-termelés fellendítéséről. Ez magában foglalja az argentin PIAP nehézvízgyár újraindítását és potenciálisan új üzemek építését Kanadában. A fejlesztés támogatja a meglévő és tervezett CANDU reaktorok működését világszerte, és illeszkedik a COP28 utáni globális nukleáris bővüléshez.
- USA: nukleáris adókedvezményekért folyó lobbizás:
Az amerikai nukleáris ipar intenzív lobbitevékenységet folytat, hogy megőrizze a Biden-adminisztráció által bevezetett, az Inflációcsökkentő Törvény (IRA) szerinti nukleáris adókedvezményeket. Az új, republikánus többségű költségvetési törvényjavaslat jelentősen lerövidítené a tiszta energia (szél, nap, akkumulátor) támogatásokat, de a nukleáris ipar számára bizonyos kedvezmények megmaradnának, bár a 45U nukleáris adókedvezmény is három évvel korábban, 2031-ben lejárhat.
- Háztartási és ipari érdekek:
Az amerikai ház költségvetési törvényjavaslata megszüntetné a legtöbb tiszta energiához kapcsolódó adókedvezményt, kivéve néhány nukleáris projektet, és szigorítaná a kínai kapcsolatokkal rendelkező projektek támogatását. Ez várhatóan visszaveti a megújuló energiaipar beruházásait, miközben a nukleáris szektor relatív pozíciója javulhat.
Politikai és társadalmi fejlemények
- Tajvan: népszavazás a nukleáris energia sorsáról:
Tajvan parlamentje megszavazta, hogy népszavazást tartsanak a Maanshan atomerőmű újraindításáról, miután az ország utolsó működő reaktorát is leállították. A referendum nem azonnali újraindításról szól, hanem arról, hogy a lakosság döntsön a meghosszabbításról, ha a hatóságok biztonságosnak találják az üzemet.
- Pennsylvania kormányzója a nukleáris energia mellett:
Josh Shapiro, Pennsylvania kormányzója, a „Lightning Plan” keretében hangsúlyozta, hogy az állam energiabiztonsága és gazdasági fejlődése érdekében kulcsszerepet szán a nukleáris energiának, valamint más megbízható energiaforrásoknak. A terv célja a munkahelyteremtés, a fogyasztói költségek csökkentése és az engedélyezési folyamatok gyorsítása.
- TMI névváltás:
Az amerikai Nukleáris Szabályozó Hatóság (NRC) jóváhagyta a Three Mile Island (TMI) atomerőmű nevének megváltoztatását Christopher M. Crane-re, az Exelon volt vezérigazgatójának emlékére. A létesítmény a jövőben a Microsoft AI műveleteit is ellátja majd árammal, és 2028-tól 835 MW szén-dioxid-mentes áramot termelhet.
Nemzetközi szakmai események
- NEA konferencia Londonban:
Az OECD NEA 2025. június 18–19-én Londonban rendezi meg az „Excellence in Nuclear Construction” nemzetközi konferenciát. A rendezvény célja, hogy a nukleáris ipar szereplői megosszák tapasztalataikat a nukleáris beruházások gyorsabb, kiszámíthatóbb és költséghatékonyabb megvalósítása érdekében, különös tekintettel a mérnöki, beszerzési és kivitelezési (EPC) kihívásokra.
Hivatkozások
- https://www.nucnet.org
- https://www.world-nuclear-news.org
- https://www.neimagazine.com
- https://www.oecd-nea.org
- https://www.iaea.org
- https://www.reuters.com/business/energy
- https://www.utilitydive.com
- https://www.atkinsrealis.com
- https://www.candu.com
-
 @ 45d6c2bf:56915a25
2025-05-27 14:23:39
@ 45d6c2bf:56915a25
2025-05-27 14:23:39published without nostr installed
-
 @ da8b7de1:c0164aee
2025-05-21 15:59:12
@ da8b7de1:c0164aee
2025-05-21 15:59:12Blykalla svéd fejlesztő következő tőkebevonási köre augusztus végéig
A svéd Blykalla, amely fejlett ólom-hűtésű gyorsreaktorokat (SEALER) fejleszt, augusztus végéig tervezi következő tőkebevonási körét. A vállalat nemrég 7,3 millió dolláros befektetést szerzett, amellyel összesen már 20 millió dollárnyi forrást gyűjtött össze. A SEALER technológia jelentősen hatékonyabb üzemanyag-felhasználást ígér, akár 140-szeres hatékonysággal a hagyományos könnyűvizes reaktorokhoz képest. Az első két reaktort Svédországban tervezik megépíteni, de már ukrán és más európai, valamint kanadai partnerekkel is tárgyalnak. A következő lépés a tesztreaktor megépítése és az engedélyezési folyamat elindítása, amelyet 2025-re terveznek lezárni. A vállalat célja, hogy technológiai szolgáltatóként jelenjen meg, nem pedig üzemeltetőként[2].
Amerikai szenátorok törvényjavaslata Kína és Oroszország nukleáris befolyása ellen
Amerikai republikánus és demokrata szenátorok közösen nyújtottak be törvényjavaslatot, amelynek célja Kína és Oroszország növekvő nemzetközi nukleáris befolyásának visszaszorítása. Az International Nuclear Energy Act egy új hivatalt hozna létre, amely a nukleáris exportot, finanszírozást és szabályozási szabványosítást erősítené. A törvényjavaslat egy alapot is létrehozna a nemzetbiztonság szempontjából fontos projektek finanszírozására, valamint kétévente kabinet szintű egyeztetést írna elő a nukleáris biztonságról és ipar-politikai kérdésekről. A kezdeményezés hátterében az elektromos áram iránti várható keresletnövekedés és a szektor stratégiai jelentősége áll[3].
India 49%-os külföldi tulajdon engedélyezését fontolgatja a nukleáris szektorban
India fontolgatja, hogy akár 49%-os külföldi tulajdont is engedélyezzen atomerőműveiben, hogy elérje ambiciózus nukleáris kapacitásbővítési céljait és csökkentse szén-dioxid-kibocsátását. Jelenleg a külföldi befektetők számára tilos az atomerőművekben való tulajdonszerzés, de a kormány tervezi a szabályozás lazítását, beleértve a nukleáris felelősségi törvények enyhítését is. A cél az, hogy 2047-re 12-ről 100 gigawattra növeljék az ország nukleáris kapacitását. Bármilyen külföldi befektetéshez továbbra is kormányzati jóváhagyás szükséges lenne[4].
NRC: végleges környezeti jelentés a Summer-1 engedélymegújításáról
Az amerikai Nukleáris Szabályozási Bizottság (NRC) közzétette a Summer-1 atomerőmű engedélymegújításához kapcsolódó végleges környezeti hatástanulmányát. A jelentés szerint nincs olyan jelentős környezeti hatás, amely akadályozná a 966 MWe teljesítményű reaktor további 20 évig tartó üzemeltetését 2042 után. A vizsgálat alternatív energiaforrásokat is értékelt, de egyik sem bizonyult jobbnak a jelenlegi atomenergia-használatnál. A Summer-1 egység különálló a befejezetlen Summer-2 és -3 blokkoktól, amelyek építését 2017-ben leállították[5].
Nemzetközi nukleáris hatósági és technológiai fejlemények
A szlovéniai Portorozban május közepén tartották a közép-európai nukleáris hatóságok éves találkozóját, ahol a biztonsági és technológiai együttműködés volt a fókuszban. Emellett a BME megalapította a Mikro- és Kis Moduláris Reaktorok Kompetenciaközpontját, amely a magyarországi SMR-technológia fejlesztését és elterjesztését támogatja[6][7].
Hivatkozások
- nucnet.org
- ignition-news.com
- investing.com
- energynews.oedigital.com
- ans.org
- pakspress.hu
- mandiner.hu
-
 @ 43baaf0c:d193e34c
2025-05-27 14:08:02
@ 43baaf0c:d193e34c
2025-05-27 14:08:02During the incredible Bitcoin Filmfest, I attended a community session where a discussion emerged about zapping and why I believe zaps are important. The person leading the Nostr session who is also developing an app that’s partially connected to Nostr mentioned they wouldn’t be implementing the zap mechanism directly. This sparked a brief but meaningful debate, which is why I’d like to share my perspective as an artist and content creator on why zaps truly matter.
Let me start by saying that I see everything from the perspective of an artist and creator, not so much from a developer’s point of view. In 2023, I started using Nostr after spending a few years exploring the world of ‘shitcoins’ and NFTs, beginning in 2018. Even though I became a Bitcoin maximalist around 2023, those earlier years taught me an important lesson: it is possible to earn money with my art.
Whether you love or hate them, NFTs opened my eyes to the idea that I could finally take my art to the next level. Before that, for over 15 years, I ran a travel stock video content company called @traveltelly. You can read the full story about my journey in travel and content here: https://yakihonne.com/article/traveltelly@primal.net/vZc1c8aXrc-3hniN6IMdK
When I truly understood what Bitcoin meant to me, I left all other coins behind. Some would call that becoming a Bitcoin maximalist.
The first time I used Nostr, I discovered the magic of zapping. It amazed me that someone who appreciates your art or content could reward you—not just with a like, but with real value: Bitcoin, the hardest money on earth. Zaps are small amounts of Bitcoin sent as a sign of support or appreciation. (Each Bitcoin is divisible into 100 million units called Satoshis, or Sats for short—making a Satoshi the smallest unit of Bitcoin recorded on the blockchain.)
 The Energy of Zaps
The Energy of ZapsIf you’re building an app on Nostr—or even just connecting to it—but choose not to include zaps, why should artists and content creators share their work there? Why would they leave platforms like Instagram or Facebook, which already benefit from massive network effects?
Yes, the ability to own your own data is one of Nostr’s greatest strengths. That alone is a powerful reason to embrace the protocol. No one can ban you. You control your content. And the ability to post once and have it appear across multiple Nostr clients is an amazing feature.
But for creators, energy matters. Engagement isn’t just about numbers—it’s about value. Zaps create a feedback loop powered by real appreciation and real value, in the form of Bitcoin. They’re a signal that your content matters. And that energy is what makes creating on Nostr so special.
But beyond those key elements, I also look at this from a commercial perspective. The truth is, we still can’t pay for groceries with kisses :)—we still need money as a medium of exchange. Being financially rewarded for sharing your content gives creators a real incentive to keep creating and sharing. That’s where zaps come in—they add economic value to engagement.
A Protocol for Emerging Artists and Creators
I believe Nostr offers a great starting point for emerging artists and content creators. If you’re just beginning and don’t already have a large following on traditional social media platforms, Nostr provides a space where your work can be appreciated and directly supported with Bitcoin, even by a small but engaged community.
On the other hand, creators who already have a big audience and steady income on platforms like Instagram or YouTube may not feel the urgency to switch. This is similar to how wealthier countries are often slower to understand or adopt Bitcoin—because they don’t need it yet. In contrast, people in unbanked regions or countries facing high inflation are more motivated to learn how money really works.
In the same way, emerging creators—those still finding their audience and looking for sustainable ways to grow—are often more open to exploring new ecosystems like Nostr, where innovation and financial empowerment go hand in hand.
The same goes for Nostr. After using it for the past two years, I can honestly say: without Nostr, I wouldn’t be the artist I am today.
Nostr motivates me to create and share every single day. A like is nice but receiving a zap, even just 21 sats, is something entirely different. Once you truly understand that someone is willing to pay you for what you share, it’s no longer about the amount. It’s about the magic behind it. That simple gesture creates a powerful, positive energy that keeps you going.
Even with Nostr’s still relatively small user base, I’ve already been able to create projects that simply wouldn’t have been possible elsewhere.
Zaps do more than just reward—they inspire. They encourage you to keep building your community. That inspiration often leads to new projects. Sometimes, the people who zap you become directly involved in your work, or even ask you to create something specifically for them.
That’s the real value of zaps: not just micro-payments, but micro-connections sparks that lead to creativity, collaboration, and growth.
Proof of Work (PoW)
Over the past two years, I’ve experienced firsthand how small zaps can evolve into full art projects and even lead to real sales. Here are two examples that started with zaps and turned into something much bigger:
Halving 2024 Artwork
When I started the Halving 2024 project, I invited people on Nostr to be part of it. 70 people zapped me 2,100 sats each, and in return, I included their Npubs in the final artwork. That piece was later auctioned and sold to Jurjen de Vries for 225,128 Sats.
Magic Internet Money
For the Magic Internet Money artwork, I again invited people to zap 2,100 sats to be included. Fifty people participated, and their contributions became part of the final art frame. The completed piece was eventually sold to Filip for 480,000 sats.
These examples show the power of zaps: a simple, small act of appreciation can turn into larger engagement, deeper connection, and even the sale of original art. Zaps aren’t just tips—they’re a form of collaboration and support that fuel creative energy.
I hope this article gives developers a glimpse into the perspective of an artist using Nostr. Of course, this is just one artist’s view, and it doesn’t claim to speak for everyone. But I felt it was important to share my Proof of Work and perspective.
For me, Zaps matter.
Thank you to all the developers who are building these amazing apps on Nostr. Your work empowers artists like me to share, grow, and be supported through the value-for-value model.
-
 @ cae03c48:2a7d6671
2025-05-27 14:00:49
@ cae03c48:2a7d6671
2025-05-27 14:00:49Bitcoin Magazine

What to expect from the BTCfi & L2s companies at the Bitcoin Conference in VegasThe annual Bitcoin Conference in Las Vegas is a pivotal event for the Bitcoin ecosystem, where companies unveil breakthroughs, announce partnerships, and deliver speeches that shape the narrative of digital assets. For many, the sheer volume of information can be overwhelming. Having attended several conferences and being familiar with the attending companies through my work at UTXO, I’ve highlighted key panels and expected developments for 2025, focusing on Bitcoin’s Layer 2 (L2) and BTCfi ecosystems.
The full agenda is available using this link: https://b.tc/conference/2025/agenda
Here’s a breakdown of anticipated announcements and panels, categorized by key themes:
BitVM2 Announcements
Since BitVM’s introduction in 2023, top Bitcoin development teams have been working tirelessly to transform centralized sidechain designs into true Bitcoin rollups and permissionless L2s. At the 2025 conference, expect these teams to unveil the first versions of BitVM2 bridges, providing critical details on their mechanics. Once live, BitVM2 bridges could unlock a wide range of decentralized BTC use cases, accessible to all Bitcoin holders. May 2025 might mark a turning point, potentially signaling the decline of centralized “crypto” and DeFi projects in favor of a Bitcoin-native economy. As the saying goes, on a long enough timeline, everything comes back to Bitcoin.
L2 Partnerships
Bitcoin L2s face a steep challenge: competing with established crypto players while earning the trust of Bitcoiners. The conference is likely to feature major partnership announcements, particularly at the infrastructure level, addressing long-standing barriers to BTCfi adoption. These collaborations could bolster the credibility and functionality of L2 solutions, paving the way for broader acceptance.
Lightning and Taproot Assets Innovation
The recent announcement that Tether (USDT) will return to Bitcoin by issuing its stablecoin on Lightning rails via Taproot Assets has sparked significant excitement. Expect major updates from companies in this space, particularly regarding Taproot Assets and stablecoin integration. The Lightning Network is poised for dominance, and 2025 could be the year it breaks into the mainstream.
Opcodes and Governance Discussions
With growing support for covenant activation on Bitcoin and recent debates over mempool policy on social media, governance discussions will be a focal point. These panels promise to be intellectually stimulating, offering deep insights into Bitcoin’s core mechanics and potential fireworks for those following the debates. Attending these sessions will likely be the most rewarding experience of the week for anyone seeking to understand Bitcoin’s future.
Must-Attend Panels
Below is a curated list of panels aligned with the above categories, along with my expectations for each. (Note: These predictions reflect my personal perspective and are not definitive. This list is not exhaustive but highlights high-signal sessions for attendees with limited time.)
Panels and Keynote with the highest probability of a major announcement related to Bitcoin L2s and BTCfi products: in other words, this is where major alpha will be dropped
Governance Discussions

*Bitcoin L2s and BTCfi products*
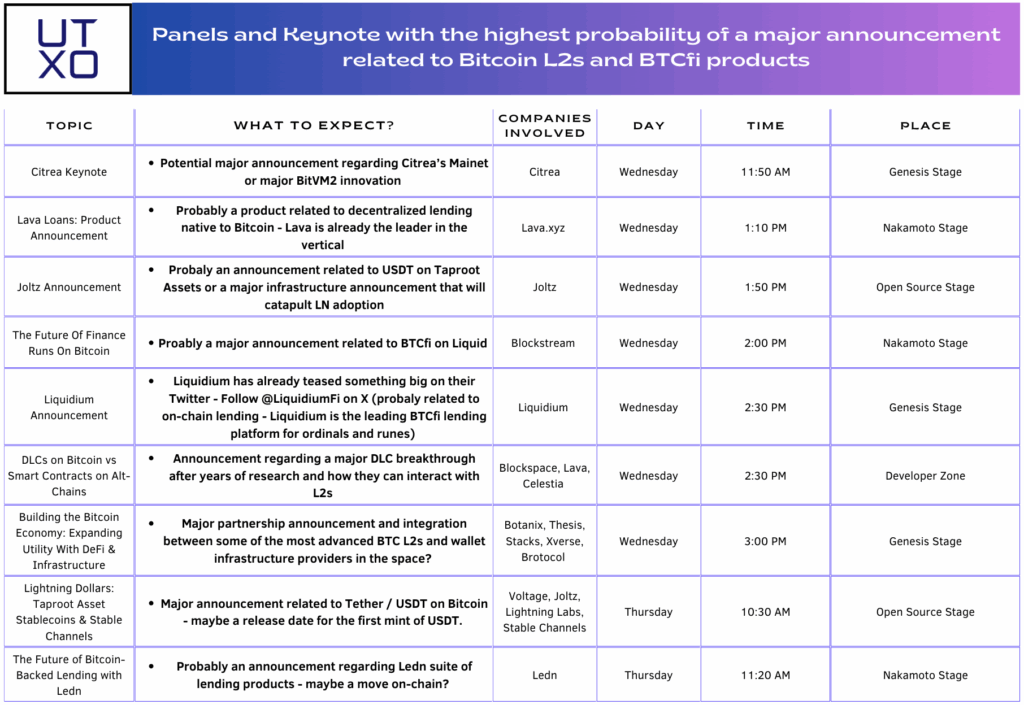
L2 and Lightning discussions
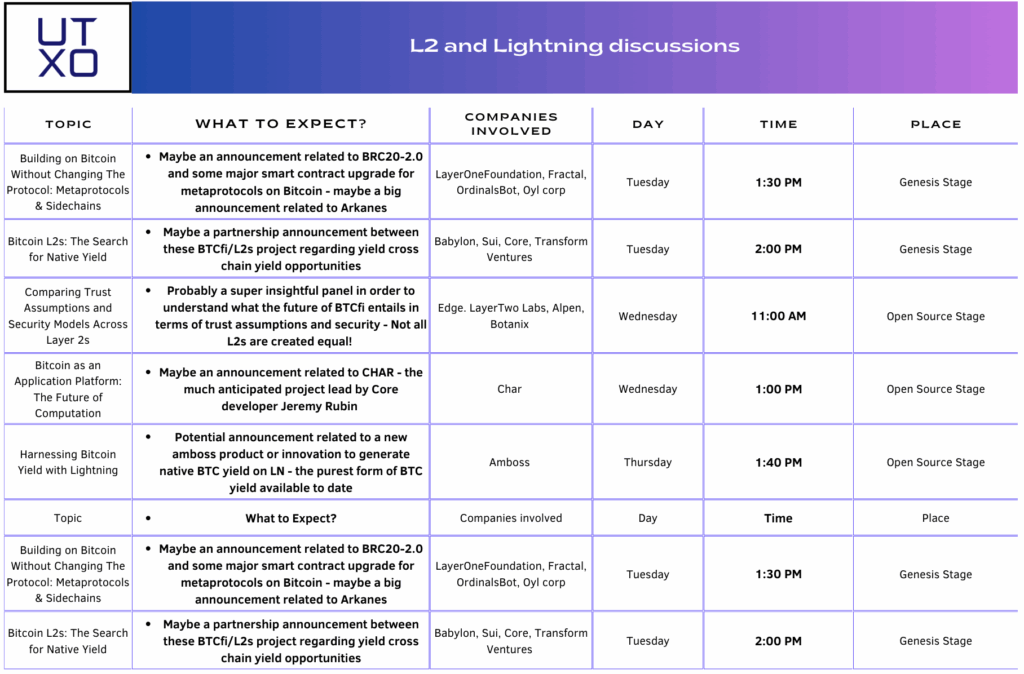
This post What to expect from the BTCfi & L2s companies at the Bitcoin Conference in Vegas first appeared on Bitcoin Magazine and is written by Guillaume Girard.
-
 @ da8b7de1:c0164aee
2025-05-21 10:30:07
@ da8b7de1:c0164aee
2025-05-21 10:30:07„Európának a tettek mezejére kell lépnie a nukleáris energia támogatásában” – mondja a brüsszeli iparági csoport új vezetője
A cikk fő témája, hogy az európai nukleáris ipar új vezetője, Emmanuel Brutin (Nucleareurope), nagyobb elkötelezettséget vár el az Európai Bizottságtól a nukleáris energia támogatásában. Bár pozitív jelek mutatkoznak a nukleáris energia iránti nyitottság terén, Brutin szerint a gyakorlatban még mindig jelentős akadályok vannak, például a finanszírozási forrásokhoz való hozzáférésben és a projektengedélyezések lassúságában.
Főbb pontok:
- Politikai nyitottság, de gyakorlati akadályok: Az EU-ban nőtt a nukleáris energia elismerése, például bekerült a fenntartható befektetési taxonómiába és a Net-Zero Industry Act-be. Ugyanakkor a nukleáris energia továbbra is kizárt több fontos finanszírozási eszközből, mint az InvestEU vagy a Just Transition Fund.
- Technológiai semlegesség szükségessége: Brutin hangsúlyozza, hogy az EU-nak nemcsak nem szabad hátráltatnia a nukleáris energiát, hanem aktívan támogatnia is kellene, különösen a Clean Industrial Deal és az Affordable Energy Action Plan keretében.
- Finanszírozás és engedélyezés: A nukleáris ágazat számára kulcsfontosságú a finanszírozáshoz való jobb hozzáférés, mivel a beruházások tőkeigényesek. Brutin szerint gyorsítani kellene a nukleáris projektek engedélyezését, és lazítani az állami támogatási szabályokon.
- Stratégiai jelentőség: Európa teljes nukleáris értéklánccal rendelkezik, ami stratégiai autonómiát jelent, különösen a jelenlegi geopolitikai környezetben.
- Új PINC dokumentum: Nyáron várható a frissített PINC (Illustrative Nuclear Programme), amelynek konkrét lépéseket kell tartalmaznia a nukleáris beruházások támogatására.
- Iparági igények: Az energiaintenzív iparágak (pl. acél, cement) számára nem az energiaforrás típusa számít, hanem a megbízható, olcsó és dekarbonizált villamosenergia-ellátás.
- Tanulás a múlt hibáiból: Brutin elismeri, hogy a nukleáris projektek Európában gyakran szenvedtek késésektől és költségtúllépésektől, de az iparág dolgozik ezek megoldásán.
Forrás:
NucNet:
"Europe Must 'Walk The Talk' On Support For Nuclear Energy, Says New Head Of Brussels Industry Group"
Megjelenés dátuma: 2025. május 20.
Elérhető: NucNet honlapján -
 @ da8b7de1:c0164aee
2025-05-20 19:30:10
@ da8b7de1:c0164aee
2025-05-20 19:30:10TVA SMR-építési engedélykérelem Clinch Riverben
A Tennessee Valley Authority (TVA) benyújtotta az első kis moduláris reaktor (SMR) építési engedélykérelmet az Egyesült Államokban, a Clinch River-i telephelyre. Ez a lépés mérföldkő az amerikai nukleáris ipar számára, hiszen a BWRX-300 típusú SMR-rel a TVA célja a szén-dioxid-mentes energiatermelés bővítése és az innovatív nukleáris technológia bevezetése.
ČEZ új nukleáris telephelyet jelölt ki Csehországban
A cseh ČEZ energetikai vállalat kijelölte a Tušimice-i telephelyet egy új atomerőmű számára, ahol várhatóan kis moduláris reaktorokat (SMR) telepítenek. Ez a lépés segíti az országot az energiafüggetlenség és a szénalapú energiatermelés kivezetése felé vezető úton.
Urenco USA új dúsító kaszkádot indított
Az Urenco USA New Mexicóban elindította új gázcentrifuga kaszkádját, amely 15%-kal növeli az amerikai dúsított urán kapacitást. Ez kulcsfontosságú az orosz uránimporttól való függetlenedés és az amerikai atomerőművek ellátásbiztonsága szempontjából.
Fiatal szakemberek sürgetik a nukleáris energia központi szerepét Európában
Európai fiatal nukleáris szakemberek nyílt levélben hívták fel a döntéshozók figyelmét arra, hogy a nukleáris energia kapjon központi szerepet a kontinens dekarbonizációs stratégiájában. Kiemelték a kutatás-fejlesztés, a befektetési környezet javítása és a társadalmi elfogadottság növelésének fontosságát.
Zeno Power 50 millió dolláros befektetést szerzett
Az amerikai Zeno Power startup 50 millió dolláros befektetést jelentett be nukleáris akkumulátorok fejlesztésére, amelyek extrém környezetekben – például az űrben vagy tenger alatt – biztosítanak megbízható energiát. A cég célja, hogy 2027-re kereskedelmi forgalomba hozza első rendszereit.
További globális nukleáris fejlemények
Több ország – például India, Kína, Belgium, Kanada, Brazília – is új nukleáris projekteket jelentett be, miközben a nemzetközi konferenciák az ellátási láncok megerősítését és a nukleáris kapacitások bővítését helyezik előtérbe.
Hivatkozások
- tva.com
- en.wikipedia.org/wiki/ČEZ_Group
- urencousa.com
- zenopower.com
- fisa-euradwaste2025.ncbj.gov.pl
- world-nuclear.org
- nucnet.org
-
 @ cae03c48:2a7d6671
2025-05-27 14:00:46
@ cae03c48:2a7d6671
2025-05-27 14:00:46Bitcoin Magazine

Trump Media Group Seeks $3 Billion War Chest to Buy Bitcoin and Crypto Assets: FTTrump Media and Technology Group (TMTG), the company behind Truth Social and controlled by the Trump family, is preparing to raise a staggering $3 billion to invest in cryptocurrencies such as Bitcoin, according to the Financial Times.
JUST IN:
 Trump Media Group to raise $3 billion to buy Bitcoin and crypto — Financial Times pic.twitter.com/VEyvy5vpGZ
Trump Media Group to raise $3 billion to buy Bitcoin and crypto — Financial Times pic.twitter.com/VEyvy5vpGZ— Bitcoin Magazine (@BitcoinMagazine) May 26, 2025
The media venture plans to secure $2 billion in fresh equity and another $1 billion through a convertible bond offering, those familiar with the matter told the Financial Times. The capital raise could be formally announced ahead of The Bitcoin 2025 Conference in Las Vegas this week, where Vice President JD Vance, Donald Trump Jr., Eric Trump, and Trump’s crypto advisor David Sachs are expected to speak.
The secondary equity offering will be carried out on an at-the-market basis, meaning shares are expected to be priced near the most recent closing price of $25.72, giving TMTG a current valuation of nearly $6 billion.
TMTG’s push comes amid a wider cryptocurrency resurgence. Bitcoin hit a new record of $111,999 last week, and investor interest in crypto-related plays has surged. The strategy echoes that of Strategy, which used a similar blend of debt and equity financing to buy tens of billions of dollars in Bitcoin—catapulting its market cap to over $100 billion.
Although the news is still yet to be confirmed by TMTG, a comment they made to the Financial Times may give some doubt to the validity of the story:
“Apparently the Financial Times has dumb writers listening to even dumber sources”, reportedly said TMTG. A White House spokesperson also declined to weigh in. Representatives for Donald Trump Jr. did not respond to requests for comment and Reuters also did not immediately receive a request for comment.
TMTG’s deepening crypto pivot has included a slew of ventures: an NFT trading card series, two memecoins, investments in crypto miner American Bitcoin and stablecoin platform World Liberty Financial, and an upcoming crypto ETF.
After returning to the White House last year, Trump transferred his 53% stake in TMTG—worth roughly $3 billion—to a revocable trust controlled by Donald Trump Jr., who holds full investment and voting authority.
This is a developing story and will be updated as needed.
This post Trump Media Group Seeks $3 Billion War Chest to Buy Bitcoin and Crypto Assets: FT first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ da8b7de1:c0164aee
2025-05-19 17:38:59
@ da8b7de1:c0164aee
2025-05-19 17:38:59Németország feladja a nukleáris energiával szembeni ellenállását Franciaországgal való közeledés jegyében
Németország hosszú idő után feladta a nukleáris energiával szembeni ellenállását, ami jelentős lépést jelenthet az EU energiapolitikai vitáinak rendezésében, különösen Franciaországgal szemben. Ez a változás eltávolíthatja a nukleáris energiával szembeni előítéleteket az uniós jogszabályokból, és elősegítheti a közös európai energiapolitika kialakítását[2].
Trump adminisztráció tervezett rendeletei a nukleáris erőművek építésének gyorsítására
Az Egyesült Államokban a Trump-adminisztráció több elnöki rendelet-tervezetet készít elő, amelyek célja a nukleáris erőművek építésének gyorsítása. A tervek szerint a jelenlegi mintegy 100 GW nukleáris kapacitást 2050-re 400 GW-ra növelnék, az engedélyezési folyamatok egyszerűsítésével, a hadsereg szerepének növelésével és a nukleáris üzemanyag-ellátás megerősítésével[3][9].
Tajvan hivatalosan is nukleárismentes lett
- május 17-én Tajvan utolsó kereskedelmi reaktorát is leállították, ezzel az ország elérte a "nukleárismentes haza" célját. Az energiamixben a nukleáris energia aránya 17%-ról 3%-ra csökkent, miközben a megújuló energia tízszeresére nőtt. Bár a parlamentben vita folyik a Maanshan atomerőmű élettartam-hosszabbításáról, jelenleg Tajvan teljesen leállította a nukleáris energiatermelést[1][6].
Kazatomprom hitelmegállapodást kötött egy új kénsavgyár finanszírozására
Kazahsztán állami atomipari vállalata, a Kazatomprom hitelmegállapodást kötött egy évi 800 000 tonna kapacitású kénsavgyár építésére. A kénsavat az uránkitermeléshez használják, és a gyár 2027 első negyedévében készülhet el. A projekt célja a régió gazdasági fejlődésének támogatása és az uránipar ellátásbiztonságának javítása[4].
Az IAEA segíti Kazahsztánt az első atomerőmű biztonságos helyszínének kiválasztásában
Az IAEA (Nemzetközi Atomenergia-ügynökség) szakértői csapata ötnapos szemináriumot tart Kazahsztánban, hogy segítsen kiválasztani az ország első atomerőművének legbiztonságosabb helyszínét. A folyamatban több helyszín is szóba került, jelenleg a Zhambyl körzet az elsődleges jelölt. A projektben négy lehetséges technológiai partner vesz részt: CNNC (Kína), Roszatom (Oroszország), KHNP (Dél-Korea) és EDF (Franciaország)[8].
India új nukleáris helyszínt hagyott jóvá
Az indiai nukleáris hatóság engedélyezte a Mahi Banswara Rajasthan Atomic Power Project négy blokkjának elhelyezését Rádzsasztán államban. Ez újabb lépés India ambiciózus nukleáris bővítési terveiben[5].
Globális nukleáris ipari konferencia Varsóban
- május 20-21-én Varsóban rendezik meg az első World Nuclear Supply Chain Conference-t, amely célja a globális nukleáris ellátási lánc megerősítése és a szektor 2 billió dolláros beruházási lehetőségének kiaknázása a következő 15 évben. A konferencián iparági vezetők, döntéshozók és szakértők vesznek részt[7].
Hivatkozások
- [1] reccessary.com – Tajvan nukleárismentes lett
- [2] nucnet.org – Németország nukleáris politikai fordulata
- [3] humanprogress.org – Trump rendelettervezetek
- [4] world-nuclear-news.org – Kazatomprom kénsavgyár
- [5] world-nuclear-news.org – India új nukleáris helyszíne
- [6] taiwannews.com.tw – Tajvan atomerőmű leállítása
- [7] world-nuclear.org – Varsói nukleáris konferencia
- [8] astanatimes.com – IAEA-Kazahsztán együttműködés
- [9] esgdive.com – Oklo és Trump engedélyezési reformok
-
 @ cae03c48:2a7d6671
2025-05-27 14:00:44
@ cae03c48:2a7d6671
2025-05-27 14:00:44Bitcoin Magazine

Jippi Launches Pokémon GO-Style AR Bitcoin Education Game at Vegas’s Bitcoin 2025Jippi, a mobile augmented reality (AR) game developer, will debut its Bitcoin education game at the Bitcoin Conference 2025, held at The Venetian Resort in Las Vegas from May 27-29. Inspired by Pokémon GO, the game blends location-based gameplay with financial literacy, aiming to engage over 30,000 attendees by making Bitcoin education fun and accessible.
Using the app, players can explore The Venetian’s grounds to hunt digital “Bitcoin Beasts,” answering Bitcoin-related trivia to capture them and earn 1000 satoshis (sats) per catch. The game is designed to deliver concise lessons on sound money principles, targeting younger audiences, with Jippi’s research showing 90% of Gen Z play mobile games. This approach aims to make learning about Bitcoin intuitive and engaging.
“We’re excited to turn Bitcoin education into an adventure,” said Oliver Porter, Jippi’s Founder and CEO. “Our game meets players where they are, making complex concepts approachable.”
Jippi partnered with six Bitcoin companies—Bitcoin Well, Beyond The Checkout, Bitcoin Trading Cards, Geyser, SHAmory, and 21M Communications—to sponsor unique Beasts. Each is tied to a specific location, offering tailored trivia that highlights the sponsor’s mission. For instance, Bitcoin Well’s Beast teaches wallet security, while SHAmory’s content suits all ages. “Jippi’s game is a fresh way to onboard new users,” said Adam O’Brien, CEO of Bitcoin Well.
The game stems from over a year of development, including university testing and on-site surveys. Jippi’s efforts earned it the top prize at PlebLab’s Top Builder competition in March 2025, a hackathon for Bitcoin startups, cementing its role in gamifying education.
With 30,000 attendees expected, the conference is an ideal stage for Jippi to showcase AR’s potential in Bitcoin adoption. The game promises to transform The Venetian into a dynamic learning hub, encouraging players to explore while grasping Bitcoin’s real-world applications. Jippi aims to expand the game post-conference, adding more educational content.
This post Jippi Launches Pokémon GO-Style AR Bitcoin Education Game at Vegas’s Bitcoin 2025 first appeared on Bitcoin Magazine and is written by Juan Galt.
-
 @ c631e267:c2b78d3e
2025-04-20 19:54:32
@ c631e267:c2b78d3e
2025-04-20 19:54:32Es ist völlig unbestritten, dass der Angriff der russischen Armee auf die Ukraine im Februar 2022 strikt zu verurteilen ist. Ebenso unbestritten ist Russland unter Wladimir Putin keine brillante Demokratie. Aus diesen Tatsachen lässt sich jedoch nicht das finstere Bild des russischen Präsidenten – und erst recht nicht des Landes – begründen, das uns durchweg vorgesetzt wird und den Kern des aktuellen europäischen Bedrohungs-Szenarios darstellt. Da müssen wir schon etwas genauer hinschauen.
Der vorliegende Artikel versucht derweil nicht, den Einsatz von Gewalt oder die Verletzung von Menschenrechten zu rechtfertigen oder zu entschuldigen – ganz im Gegenteil. Dass jedoch der Verdacht des «Putinverstehers» sofort latent im Raume steht, verdeutlicht, was beim Thema «Russland» passiert: Meinungsmache und Manipulation.
Angesichts der mentalen Mobilmachung seitens Politik und Medien sowie des Bestrebens, einen bevorstehenden Krieg mit Russland geradezu herbeizureden, ist es notwendig, dieser fatalen Entwicklung entgegenzutreten. Wenn wir uns nur ein wenig von der herrschenden Schwarz-Weiß-Malerei freimachen, tauchen automatisch Fragen auf, die Risse im offiziellen Narrativ enthüllen. Grund genug, nachzuhaken.
Wer sich schon länger auch abseits der Staats- und sogenannten Leitmedien informiert, der wird in diesem Artikel vermutlich nicht viel Neues erfahren. Andere könnten hier ein paar unbekannte oder vergessene Aspekte entdecken. Möglicherweise klärt sich in diesem Kontext die Wahrnehmung der aktuellen (unserer eigenen!) Situation ein wenig.
Manipulation erkennen
Corona-«Pandemie», menschengemachter Klimawandel oder auch Ukraine-Krieg: Jede Menge Krisen, und für alle gibt es ein offizielles Narrativ, dessen Hinterfragung unerwünscht ist. Nun ist aber ein Narrativ einfach eine Erzählung, eine Geschichte (Latein: «narratio») und kein Tatsachenbericht. Und so wie ein Märchen soll auch das Narrativ eine Botschaft vermitteln.
Über die Methoden der Manipulation ist viel geschrieben worden, sowohl in Bezug auf das Individuum als auch auf die Massen. Sehr wertvolle Tipps dazu, wie man Manipulationen durchschauen kann, gibt ein Büchlein [1] von Albrecht Müller, dem Herausgeber der NachDenkSeiten.
Die Sprache selber eignet sich perfekt für die Manipulation. Beispielsweise kann die Wortwahl Bewertungen mitschwingen lassen, regelmäßiges Wiederholen (gerne auch von verschiedenen Seiten) lässt Dinge irgendwann «wahr» erscheinen, Übertreibungen fallen auf und hinterlassen wenigstens eine Spur im Gedächtnis, genauso wie Andeutungen. Belege spielen dabei keine Rolle.
Es gibt auffällig viele Sprachregelungen, die offenbar irgendwo getroffen und irgendwie koordiniert werden. Oder alle Redenschreiber und alle Medien kopieren sich neuerdings permanent gegenseitig. Welchen Zweck hat es wohl, wenn der Krieg in der Ukraine durchgängig und quasi wörtlich als «russischer Angriffskrieg auf die Ukraine» bezeichnet wird? Obwohl das in der Sache richtig ist, deutet die Art der Verwendung auf gezielte Beeinflussung hin und soll vor allem das Feindbild zementieren.
Sprachregelungen dienen oft der Absicherung einer einseitigen Darstellung. Das Gleiche gilt für das Verkürzen von Informationen bis hin zum hartnäckigen Verschweigen ganzer Themenbereiche. Auch hierfür gibt es rund um den Ukraine-Konflikt viele gute Beispiele.
Das gewünschte Ergebnis solcher Methoden ist eine Schwarz-Weiß-Malerei, bei der einer eindeutig als «der Böse» markiert ist und die anderen automatisch «die Guten» sind. Das ist praktisch und demonstriert gleichzeitig ein weiteres Manipulationswerkzeug: die Verwendung von Doppelstandards. Wenn man es schafft, bei wichtigen Themen regelmäßig mit zweierlei Maß zu messen, ohne dass das Publikum protestiert, dann hat man freie Bahn.
Experten zu bemühen, um bestimmte Sachverhalte zu erläutern, ist sicher sinnvoll, kann aber ebenso missbraucht werden, schon allein durch die Auswahl der jeweiligen Spezialisten. Seit «Corona» werden viele erfahrene und ehemals hoch angesehene Fachleute wegen der «falschen Meinung» diffamiert und gecancelt. [2] Das ist nicht nur ein brutaler Umgang mit Menschen, sondern auch eine extreme Form, die öffentliche Meinung zu steuern.
Wann immer wir also erkennen (weil wir aufmerksam waren), dass wir bei einem bestimmten Thema manipuliert werden, dann sind zwei logische und notwendige Fragen: Warum? Und was ist denn richtig? In unserem Russland-Kontext haben die Antworten darauf viel mit Geopolitik und Geschichte zu tun.
Ist Russland aggressiv und expansiv?
Angeblich plant Russland, europäische NATO-Staaten anzugreifen, nach dem Motto: «Zuerst die Ukraine, dann den Rest». In Deutschland weiß man dafür sogar das Datum: «Wir müssen bis 2029 kriegstüchtig sein», versichert Verteidigungsminister Pistorius.
Historisch gesehen ist es allerdings eher umgekehrt: Russland, bzw. die Sowjetunion, ist bereits dreimal von Westeuropa aus militärisch angegriffen worden. Die Feldzüge Napoleons, des deutschen Kaiserreichs und Nazi-Deutschlands haben Millionen Menschen das Leben gekostet. Bei dem ausdrücklichen Vernichtungskrieg ab 1941 kam es außerdem zu Brutalitäten wie der zweieinhalbjährigen Belagerung Leningrads (heute St. Petersburg) durch Hitlers Wehrmacht. Deren Ziel, die Bevölkerung auszuhungern, wurde erreicht: über eine Million tote Zivilisten.
Trotz dieser Erfahrungen stimmte Michail Gorbatschow 1990 der deutschen Wiedervereinigung zu und die Sowjetunion zog ihre Truppen aus Osteuropa zurück (vgl. Abb. 1). Der Warschauer Pakt wurde aufgelöst, der Kalte Krieg formell beendet. Die Sowjets erhielten damals von führenden westlichen Politikern die Zusicherung, dass sich die NATO «keinen Zentimeter ostwärts» ausdehnen würde, das ist dokumentiert. [3]

Expandiert ist die NATO trotzdem, und zwar bis an Russlands Grenzen (vgl. Abb. 2). Laut dem Politikberater Jeffrey Sachs handelt es sich dabei um ein langfristiges US-Projekt, das von Anfang an die Ukraine und Georgien mit einschloss. Offiziell wurde der Beitritt beiden Staaten 2008 angeboten. In jedem Fall könnte die massive Ost-Erweiterung seit 1999 aus russischer Sicht nicht nur als Vertrauensbruch, sondern durchaus auch als aggressiv betrachtet werden.

Russland hat den europäischen Staaten mehrfach die Hand ausgestreckt [4] für ein friedliches Zusammenleben und den «Aufbau des europäischen Hauses». Präsident Putin sei «in seiner ersten Amtszeit eine Chance für Europa» gewesen, urteilt die Journalistin und langjährige Russland-Korrespondentin der ARD, Gabriele Krone-Schmalz. Er habe damals viele positive Signale Richtung Westen gesendet.
Die Europäer jedoch waren scheinbar an einer Partnerschaft mit dem kontinentalen Nachbarn weniger interessiert als an der mit dem transatlantischen Hegemon. Sie verkennen bis heute, dass eine gedeihliche Zusammenarbeit in Eurasien eine Gefahr für die USA und deren bekundetes Bestreben ist, die «einzige Weltmacht» zu sein – «Full Spectrum Dominance» [5] nannte das Pentagon das. Statt einem neuen Kalten Krieg entgegenzuarbeiten, ließen sich europäische Staaten selber in völkerrechtswidrige «US-dominierte Angriffskriege» [6] verwickeln, wie in Serbien, Afghanistan, dem Irak, Libyen oder Syrien. Diese werden aber selten so benannt.

Speziell den Deutschen stünde außer einer Portion Realismus auch etwas mehr Dankbarkeit gut zu Gesicht. Das Geschichtsbewusstsein der Mehrheit scheint doch recht selektiv und das Selbstbewusstsein einiger etwas desorientiert zu sein. Bekanntermaßen waren es die Soldaten der sowjetischen Roten Armee, die unter hohen Opfern 1945 Deutschland «vom Faschismus befreit» haben. Bei den Gedenkfeiern zu 80 Jahren Kriegsende will jedoch das Auswärtige Amt – noch unter der Diplomatie-Expertin Baerbock, die sich schon länger offiziell im Krieg mit Russland wähnt, – nun keine Russen sehen: Sie sollen notfalls rausgeschmissen werden.
«Die Grundsatzfrage lautet: Geht es Russland um einen angemessenen Platz in einer globalen Sicherheitsarchitektur, oder ist Moskau schon seit langem auf einem imperialistischen Trip, der befürchten lassen muss, dass die Russen in fünf Jahren in Berlin stehen?»
So bringt Gabriele Krone-Schmalz [7] die eigentliche Frage auf den Punkt, die zur Einschätzung der Situation letztlich auch jeder für sich beantworten muss.
Was ist los in der Ukraine?
In der internationalen Politik geht es nie um Demokratie oder Menschenrechte, sondern immer um Interessen von Staaten. Diese These stammt von Egon Bahr, einem der Architekten der deutschen Ostpolitik des «Wandels durch Annäherung» aus den 1960er und 70er Jahren. Sie trifft auch auf den Ukraine-Konflikt zu, den handfeste geostrategische und wirtschaftliche Interessen beherrschen, obwohl dort angeblich «unsere Demokratie» verteidigt wird.
Es ist ein wesentliches Element des Ukraine-Narrativs und Teil der Manipulation, die Vorgeschichte des Krieges wegzulassen – mindestens die vor der russischen «Annexion» der Halbinsel Krim im März 2014, aber oft sogar komplett diejenige vor der Invasion Ende Februar 2022. Das Thema ist komplex, aber einige Aspekte, die für eine Beurteilung nicht unwichtig sind, will ich wenigstens kurz skizzieren. [8]
Das Gebiet der heutigen Ukraine und Russlands – die übrigens in der «Kiewer Rus» gemeinsame Wurzeln haben – hat der britische Geostratege Halford Mackinder bereits 1904 als eurasisches «Heartland» bezeichnet, dessen Kontrolle er eine große Bedeutung für die imperiale Strategie Großbritanniens zumaß. Für den ehemaligen Sicherheits- und außenpolitischen Berater mehrerer US-amerikanischer Präsidenten und Mitgründer der Trilateralen Kommission, Zbigniew Brzezinski, war die Ukraine nach der Auflösung der Sowjetunion ein wichtiger Spielstein auf dem «eurasischen Schachbrett», wegen seiner Nähe zu Russland, seiner Bodenschätze und seines Zugangs zum Schwarzen Meer.
Die Ukraine ist seit langem ein gespaltenes Land. Historisch zerrissen als Spielball externer Interessen und geprägt von ethnischen, kulturellen, religiösen und geografischen Unterschieden existiert bis heute, grob gesagt, eine Ost-West-Spaltung, welche die Suche nach einer nationalen Identität stark erschwert.
Insbesondere im Zuge der beiden Weltkriege sowie der Russischen Revolution entstanden tiefe Risse in der Bevölkerung. Ukrainer kämpften gegen Ukrainer, zum Beispiel die einen auf der Seite von Hitlers faschistischer Nazi-Armee und die anderen auf der von Stalins kommunistischer Roter Armee. Die Verbrechen auf beiden Seiten sind nicht vergessen. Dass nach der Unabhängigkeit 1991 versucht wurde, Figuren wie den radikalen Nationalisten Symon Petljura oder den Faschisten und Nazi-Kollaborateur Stepan Bandera als «Nationalhelden» zu installieren, verbessert die Sache nicht.
Während die USA und EU-Staaten zunehmend «ausländische Einmischung» (speziell russische) in «ihre Demokratien» wittern, betreiben sie genau dies seit Jahrzehnten in vielen Ländern der Welt. Die seit den 2000er Jahren bekannten «Farbrevolutionen» in Osteuropa werden oft als Methode des Regierungsumsturzes durch von außen gesteuerte «demokratische» Volksaufstände beschrieben. Diese Strategie geht auf Analysen zum «Schwarmverhalten» [9] seit den 1960er Jahren zurück (Studentenproteste), wo es um die potenzielle Wirksamkeit einer «rebellischen Hysterie» von Jugendlichen bei postmodernen Staatsstreichen geht. Heute nennt sich dieses gezielte Kanalisieren der Massen zur Beseitigung unkooperativer Regierungen «Soft-Power».
In der Ukraine gab es mit der «Orangen Revolution» 2004 und dem «Euromaidan» 2014 gleich zwei solcher «Aufstände». Der erste erzwang wegen angeblicher Unregelmäßigkeiten eine Wiederholung der Wahlen, was mit Wiktor Juschtschenko als neuem Präsidenten endete. Dieser war ehemaliger Direktor der Nationalbank und Befürworter einer Annäherung an EU und NATO. Seine Frau, die First Lady, ist US-amerikanische «Philanthropin» und war Beamtin im Weißen Haus in der Reagan- und der Bush-Administration.
Im Gegensatz zu diesem ersten Event endete der sogenannte Euromaidan unfriedlich und blutig. Die mehrwöchigen Proteste gegen Präsident Wiktor Janukowitsch, in Teilen wegen des nicht unterzeichneten Assoziierungsabkommens mit der EU, wurden zunehmend gewalttätiger und von Nationalisten und Faschisten des «Rechten Sektors» dominiert. Sie mündeten Ende Februar 2014 auf dem Kiewer Unabhängigkeitsplatz (Maidan) in einem Massaker durch Scharfschützen. Dass deren Herkunft und die genauen Umstände nicht geklärt wurden, störte die Medien nur wenig. [10]
Janukowitsch musste fliehen, er trat nicht zurück. Vielmehr handelte es sich um einen gewaltsamen, allem Anschein nach vom Westen inszenierten Putsch. Laut Jeffrey Sachs war das kein Geheimnis, außer vielleicht für die Bürger. Die USA unterstützten die Post-Maidan-Regierung nicht nur, sie beeinflussten auch ihre Bildung. Das geht unter anderem aus dem berühmten «Fuck the EU»-Telefonat der US-Chefdiplomatin für die Ukraine, Victoria Nuland, mit Botschafter Geoffrey Pyatt hervor.
Dieser Bruch der demokratischen Verfassung war letztlich der Auslöser für die anschließenden Krisen auf der Krim und im Donbass (Ostukraine). Angesichts der ukrainischen Geschichte mussten die nationalistischen Tendenzen und die Beteiligung der rechten Gruppen an dem Umsturz bei der russigsprachigen Bevölkerung im Osten ungute Gefühle auslösen. Es gab Kritik an der Übergangsregierung, Befürworter einer Abspaltung und auch für einen Anschluss an Russland.
Ebenso konnte Wladimir Putin in dieser Situation durchaus Bedenken wegen des Status der russischen Militärbasis für seine Schwarzmeerflotte in Sewastopol auf der Krim haben, für die es einen langfristigen Pachtvertrag mit der Ukraine gab. Was im März 2014 auf der Krim stattfand, sei keine Annexion, sondern eine Abspaltung (Sezession) nach einem Referendum gewesen, also keine gewaltsame Aneignung, urteilte der Rechtswissenschaftler Reinhard Merkel in der FAZ sehr detailliert begründet. Übrigens hatte die Krim bereits zu Zeiten der Sowjetunion den Status einer autonomen Republik innerhalb der Ukrainischen SSR.
Anfang April 2014 wurden in der Ostukraine die «Volksrepubliken» Donezk und Lugansk ausgerufen. Die Kiewer Übergangsregierung ging unter der Bezeichnung «Anti-Terror-Operation» (ATO) militärisch gegen diesen, auch von Russland instrumentalisierten Widerstand vor. Zufällig war kurz zuvor CIA-Chef John Brennan in Kiew. Die Maßnahmen gingen unter dem seit Mai neuen ukrainischen Präsidenten, dem Milliardär Petro Poroschenko, weiter. Auch Wolodymyr Selenskyj beendete den Bürgerkrieg nicht, als er 2019 vom Präsidenten-Schauspieler, der Oligarchen entmachtet, zum Präsidenten wurde. Er fuhr fort, die eigene Bevölkerung zu bombardieren.
Mit dem Einmarsch russischer Truppen in die Ostukraine am 24. Februar 2022 begann die zweite Phase des Krieges. Die Wochen und Monate davor waren intensiv. Im November hatte die Ukraine mit den USA ein Abkommen über eine «strategische Partnerschaft» unterzeichnet. Darin sagten die Amerikaner ihre Unterstützung der EU- und NATO-Perspektive der Ukraine sowie quasi für die Rückeroberung der Krim zu. Dagegen ließ Putin der NATO und den USA im Dezember 2021 einen Vertragsentwurf über beiderseitige verbindliche Sicherheitsgarantien zukommen, den die NATO im Januar ablehnte. Im Februar eskalierte laut OSZE die Gewalt im Donbass.
Bereits wenige Wochen nach der Invasion, Ende März 2022, kam es in Istanbul zu Friedensverhandlungen, die fast zu einer Lösung geführt hätten. Dass der Krieg nicht damals bereits beendet wurde, lag daran, dass der Westen dies nicht wollte. Man war der Meinung, Russland durch die Ukraine in diesem Stellvertreterkrieg auf Dauer militärisch schwächen zu können. Angesichts von Hunderttausenden Toten, Verletzten und Traumatisierten, die als Folge seitdem zu beklagen sind, sowie dem Ausmaß der Zerstörung, fehlen einem die Worte.
Hasst der Westen die Russen?
Diese Frage drängt sich auf, wenn man das oft unerträglich feindselige Gebaren beobachtet, das beileibe nicht neu ist und vor Doppelmoral trieft. Russland und speziell die Person Wladimir Putins werden regelrecht dämonisiert, was gleichzeitig scheinbar jede Form von Diplomatie ausschließt.
Russlands militärische Stärke, seine geografische Lage, sein Rohstoffreichtum oder seine unabhängige diplomatische Tradition sind sicher Störfaktoren für das US-amerikanische Bestreben, der Boss in einer unipolaren Welt zu sein. Ein womöglich funktionierender eurasischer Kontinent, insbesondere gute Beziehungen zwischen Russland und Deutschland, war indes schon vor dem Ersten Weltkrieg eine Sorge des britischen Imperiums.
Ein «Vergehen» von Präsident Putin könnte gewesen sein, dass er die neoliberale Schocktherapie à la IWF und den Ausverkauf des Landes (auch an US-Konzerne) beendete, der unter seinem Vorgänger herrschte. Dabei zeigte er sich als Führungspersönlichkeit und als nicht so formbar wie Jelzin. Diese Aspekte allein sind aber heute vermutlich keine ausreichende Erklärung für ein derart gepflegtes Feindbild.
Der Historiker und Philosoph Hauke Ritz erweitert den Fokus der Fragestellung zu: «Warum hasst der Westen die Russen so sehr?», was er zum Beispiel mit dem Medienforscher Michael Meyen und mit der Politikwissenschaftlerin Ulrike Guérot bespricht. Ritz stellt die interessante These [11] auf, dass Russland eine Provokation für den Westen sei, welcher vor allem dessen kulturelles und intellektuelles Potenzial fürchte.
Die Russen sind Europäer aber anders, sagt Ritz. Diese «Fremdheit in der Ähnlichkeit» erzeuge vielleicht tiefe Ablehnungsgefühle. Obwohl Russlands Identität in der europäischen Kultur verwurzelt ist, verbinde es sich immer mit der Opposition in Europa. Als Beispiele nennt er die Kritik an der katholischen Kirche oder die Verbindung mit der Arbeiterbewegung. Christen, aber orthodox; Sozialismus statt Liberalismus. Das mache das Land zum Antagonisten des Westens und zu einer Bedrohung der Machtstrukturen in Europa.
Fazit
Selbstverständlich kann man Geschichte, Ereignisse und Entwicklungen immer auf verschiedene Arten lesen. Dieser Artikel, obwohl viel zu lang, konnte nur einige Aspekte der Ukraine-Tragödie anreißen, die in den offiziellen Darstellungen in der Regel nicht vorkommen. Mindestens dürfte damit jedoch klar geworden sein, dass die Russische Föderation bzw. Wladimir Putin nicht der alleinige Aggressor in diesem Konflikt ist. Das ist ein Stellvertreterkrieg zwischen USA/NATO (gut) und Russland (böse); die Ukraine (edel) wird dabei schlicht verheizt.
Das ist insofern von Bedeutung, als die gesamte europäische Kriegshysterie auf sorgsam kultivierten Freund-Feind-Bildern beruht. Nur so kann Konfrontation und Eskalation betrieben werden, denn damit werden die wahren Hintergründe und Motive verschleiert. Angst und Propaganda sind notwendig, damit die Menschen den Wahnsinn mitmachen. Sie werden belogen, um sie zuerst zu schröpfen und anschließend auf die Schlachtbank zu schicken. Das kann niemand wollen, außer den stets gleichen Profiteuren: die Rüstungs-Lobby und die großen Investoren, die schon immer an Zerstörung und Wiederaufbau verdient haben.
Apropos Investoren: Zu den Top-Verdienern und somit Hauptinteressenten an einer Fortführung des Krieges zählt BlackRock, einer der weltgrößten Vermögensverwalter. Der deutsche Bundeskanzler in spe, Friedrich Merz, der gerne «Taurus»-Marschflugkörper an die Ukraine liefern und die Krim-Brücke zerstören möchte, war von 2016 bis 2020 Aufsichtsratsvorsitzender von BlackRock in Deutschland. Aber das hat natürlich nichts zu sagen, der Mann macht nur seinen Job.
Es ist ein Spiel der Kräfte, es geht um Macht und strategische Kontrolle, um Geheimdienste und die Kontrolle der öffentlichen Meinung, um Bodenschätze, Rohstoffe, Pipelines und Märkte. Das klingt aber nicht sexy, «Demokratie und Menschenrechte» hört sich besser und einfacher an. Dabei wäre eine für alle Seiten förderliche Politik auch nicht so kompliziert; das Handwerkszeug dazu nennt sich Diplomatie. Noch einmal Gabriele Krone-Schmalz:
«Friedliche Politik ist nichts anderes als funktionierender Interessenausgleich. Da geht’s nicht um Moral.»
Die Situation in der Ukraine ist sicher komplex, vor allem wegen der inneren Zerrissenheit. Es dürfte nicht leicht sein, eine friedliche Lösung für das Zusammenleben zu finden, aber die Beteiligten müssen es vor allem wollen. Unter den gegebenen Umständen könnte eine sinnvolle Perspektive mit Neutralität und föderalen Strukturen zu tun haben.
Allen, die sich bis hierher durch die Lektüre gearbeitet (oder auch einfach nur runtergescrollt) haben, wünsche ich frohe Oster-Friedenstage!
[Titelbild: Pixabay; Abb. 1 und 2: nach Ganser/SIPER; Abb. 3: SIPER]
--- Quellen: ---
[1] Albrecht Müller, «Glaube wenig. Hinterfrage alles. Denke selbst.», Westend 2019
[2] Zwei nette Beispiele:
- ARD-faktenfinder (sic), «Viel Aufmerksamkeit für fragwürdige Experten», 03/2023
- Neue Zürcher Zeitung, «Aufstieg und Fall einer Russlandversteherin – die ehemalige ARD-Korrespondentin Gabriele Krone-Schmalz rechtfertigt seit Jahren Putins Politik», 12/2022
[3] George Washington University, «NATO Expansion: What Gorbachev Heard – Declassified documents show security assurances against NATO expansion to Soviet leaders from Baker, Bush, Genscher, Kohl, Gates, Mitterrand, Thatcher, Hurd, Major, and Woerner», 12/2017
[4] Beispielsweise Wladimir Putin bei seiner Rede im Deutschen Bundestag, 25/09/2001
[5] William Engdahl, «Full Spectrum Dominance, Totalitarian Democracy In The New World Order», edition.engdahl 2009
[6] Daniele Ganser, «Illegale Kriege – Wie die NATO-Länder die UNO sabotieren. Eine Chronik von Kuba bis Syrien», Orell Füssli 2016
[7] Gabriele Krone-Schmalz, «Mit Friedensjournalismus gegen ‘Kriegstüchtigkeit’», Vortrag und Diskussion an der Universität Hamburg, veranstaltet von engagierten Studenten, 16/01/2025\ → Hier ist ein ähnlicher Vortrag von ihr (Video), den ich mit spanischer Übersetzung gefunden habe.
[8] Für mehr Hintergrund und Details empfehlen sich z.B. folgende Bücher:
- Mathias Bröckers, Paul Schreyer, «Wir sind immer die Guten», Westend 2019
- Gabriele Krone-Schmalz, «Russland verstehen? Der Kampf um die Ukraine und die Arroganz des Westens», Westend 2023
- Patrik Baab, «Auf beiden Seiten der Front – Meine Reisen in die Ukraine», Fiftyfifty 2023
[9] vgl. Jonathan Mowat, «Washington's New World Order "Democratization" Template», 02/2005 und RAND Corporation, «Swarming and the Future of Conflict», 2000
[10] Bemerkenswert einige Beiträge, von denen man später nichts mehr wissen wollte:
- ARD Monitor, «Todesschüsse in Kiew: Wer ist für das Blutbad vom Maidan verantwortlich», 10/04/2014, Transkript hier
- Telepolis, «Blutbad am Maidan: Wer waren die Todesschützen?», 12/04/2014
- Telepolis, «Scharfschützenmorde in Kiew», 14/12/2014
- Deutschlandfunk, «Gefahr einer Spirale nach unten», Interview mit Günter Verheugen, 18/03/2014
- NDR Panorama, «Putsch in Kiew: Welche Rolle spielen die Faschisten?», 06/03/2014
[11] Hauke Ritz, «Vom Niedergang des Westens zur Neuerfindung Europas», 2024
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ 1c19eb1a:e22fb0bc
2025-04-22 01:36:33
@ 1c19eb1a:e22fb0bc
2025-04-22 01:36:33After my first major review of Primal on Android, we're going to go a very different direction for this next review. Primal is your standard "Twitter clone" type of kind 1 note client, now branching into long-form. They also have a team of developers working on making it one of the best clients to fill that use-case. By contrast, this review will not be focusing on any client at all. Not even an "other stuff" client.
Instead, we will be reviewing a very useful tool created and maintained by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 called #Amber. For those unfamiliar with Amber, it is an #Android application dedicated to managing your signing keys, and allowing you to log into various #Nostr applications without having to paste in your private key, better known as your #nsec. It is not recommended to paste your nsec into various applications because they each represent another means by which it could be compromised, and anyone who has your nsec can post as you. On Nostr, your #npub is your identity, and your signature using your private key is considered absolute proof that any given note, reaction, follow update, or profile change was authorized by the rightful owner of that identity.
It happens less often these days, but early on, when the only way to try out a new client was by inputting your nsec, users had their nsec compromised from time to time, or they would suspect that their key may have been compromised. When this occurs, there is no way to recover your account, or set a new private key, deprecating the previous one. The only thing you can do is start over from scratch, letting everyone know that your key has been compromised and to follow you on your new npub.
If you use Amber to log into other Nostr apps, you significantly reduce the likelihood that your private key will be compromised, because only one application has access to it, and all other applications reach out to Amber to sign any events. This isn't quite as secure as storing your private key on a separate device that isn't connected to the internet whatsoever, like many of us have grown accustomed to with securing our #Bitcoin, but then again, an online persona isn't nearly as important to secure for most of us as our entire life savings.
Amber is the first application of its kind for managing your Nostr keys on a mobile device. nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 didn't merely develop the application, but literally created the specification for accomplishing external signing on Android which can be found in NIP-55. Unfortunately, Amber is only available for Android. A signer application for iOS is in the works from nostr:npub1yaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgs3tvjmf, but is not ready for use at this time. There is also a new mobile signer app for Android and iOS called Nowser, but I have not yet had a chance to try this app out. From a cursory look at the Android version, it is indeed in the very early stages of development and cannot be compared with Amber.
This review of Amber is current as of version 3.2.5.
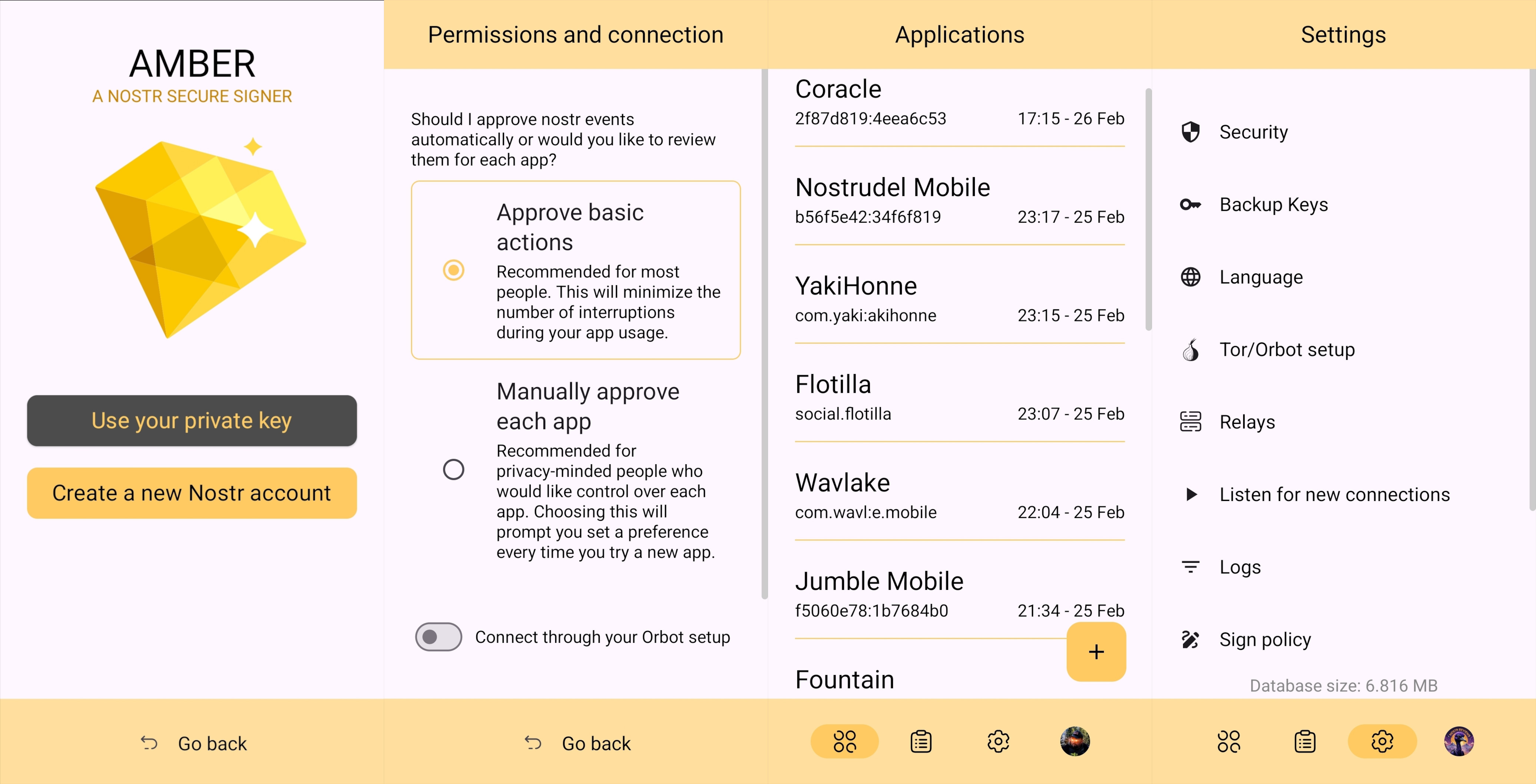
Overall Impression
Score: 4.7 / 5 (Updated 4/21/2025)
I cannot speak highly enough about Amber as a tool that every Nostr user on Android should start using if they are not already. When the day comes that we have more options for well-developed signer apps on mobile, my opinion may very well change, but until then Amber is what we have available to us. Even so, it is an incredibly well thought-out and reliable tool for securing your nsec.
Despite being the only well-established Android signer available for Android, Amber can be compared with other external signing methods available on other platforms. Even with more competition in this arena, though, Amber still holds up incredibly well. If you are signing into web applications on a desktop, I still would recommend using a browser extension like #Alby or #Nos2x, as the experience is usually faster, more seamless, and far more web apps support this signing method (NIP-07) than currently support the two methods employed by Amber. Nevertheless that gap is definitely narrowing.
A running list I created of applications that support login and signing with Amber can be found here: Nostr Clients with External Signer Support
I have run into relatively few bugs in my extensive use of Amber for all of my mobile signing needs. Occasionally the application crashes when trying to send it a signing request from a couple of applications, but I would not be surprised if this is no fault of Amber at all, and rather the fault of those specific apps, since it works flawlessly with the vast majority of apps that support either NIP-55 or NIP-46 login.
I also believe that mobile is the ideal platform to use for this type of application. First, because most people use Nostr clients on their phone more than on a desktop. There are, of course, exceptions to that, but in general we spend more time on our phones when interacting online. New users are also more likely to be introduced to Nostr by a friend having them download a Nostr client on their phone than on a PC, and that can be a prime opportunity to introduce the new user to protecting their private key. Finally, I agree with the following assessment from nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn.
nostr:nevent1qqsw0r6gzn05xg67h5q2xkplwsuzedjxw9lf7ntrxjl8ajm350fcyugprfmhxue69uhhyetvv9ujumn0wd68yurvv438xtnrdaksyg9hyaxj3clfswlhyrd5kjsj5v04clhjvgeq6pwztmysfzdvn93gev7awu9v
The one downside to Amber is that it will be quite foreign for new users. That is partially unavoidable with Nostr, since folks are not accustomed to public/private key cryptography in general, let alone using a private key to log into websites or social media apps. However, the initial signup process is a bit cumbersome if Amber is being used as the means of initially generating a key pair. I think some of this could be foregone at start-up in favor of streamlining onboarding, and then encourage the user to back-up their private key at a later time.
Features
Amber has some features that may surprise you, outside of just storing your private key and signing requests from your favorite Nostr clients. It is a full key management application, supporting multiple accounts, various backup methods, and even the ability to authorize other users to access a Nostr profile you control.
Android Signing
This is the signing method where Amber really shines in both speed and ease of use. Any Android application that supports this standard, and even some progressive web-apps that can be installed to your Android's home-screen, can very quickly and seamlessly connect with Amber to authorize anything that you need signed with your nsec. All you have to do is select "Login with Amber" in clients like #Amethyst or #0xChat and the app will reach out to Amber for all signing requests from there on out. If you had previously signed into the app with your nsec, you will first need to log out, then choose the option to use Amber when you log back in.
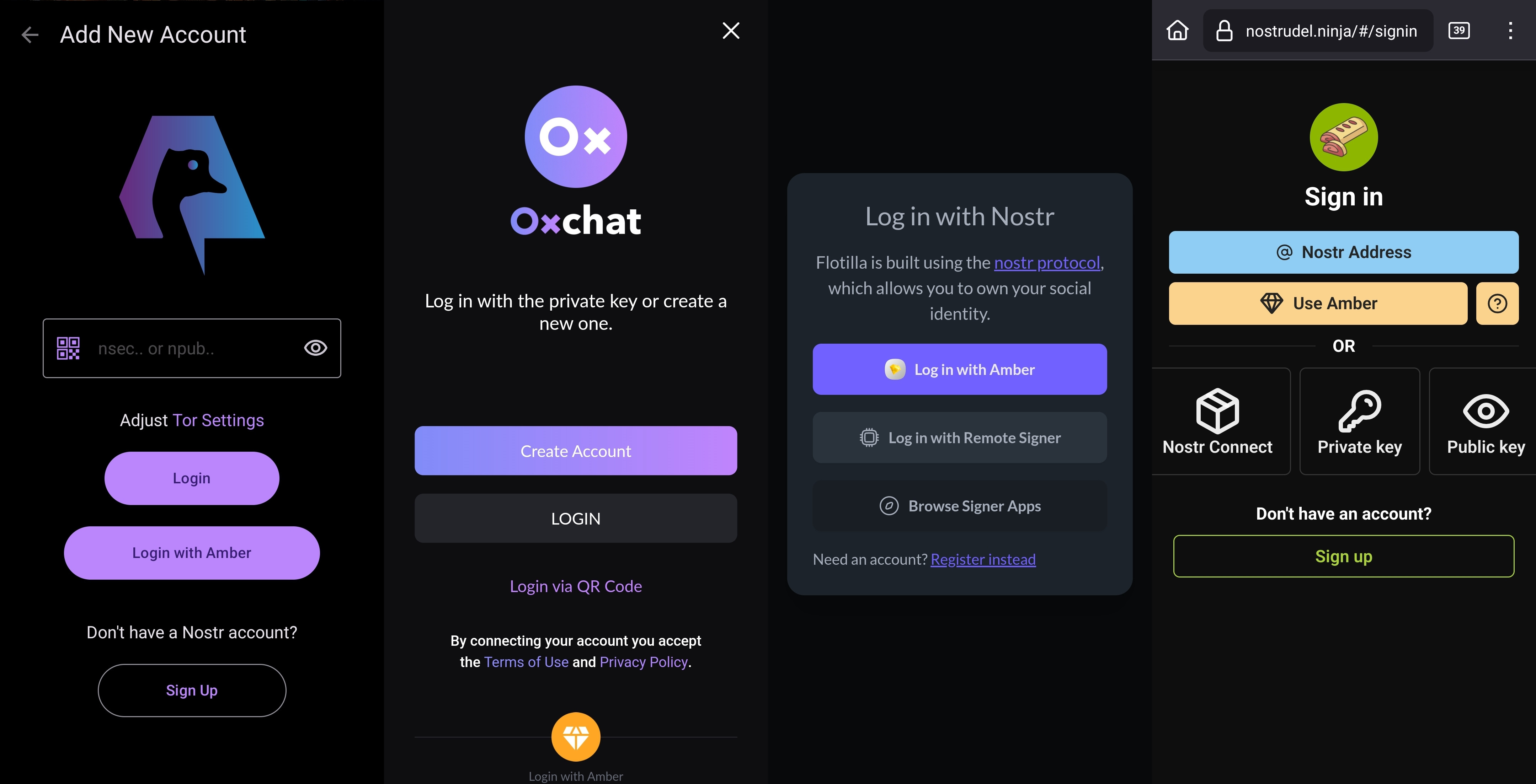
This is a massive deal, because everything you do on Nostr requires a signature from your private key. Log in? Needs a signature. Post a "GM" note? Needs a signature. Follow someone who zapped your note? Needs a signature. Zap them back? You guessed it; needs a signature. When you paste your private key into an application, it will automatically sign a lot of these actions without you ever being asked for approval, but you will quickly realize just how many things the client is doing on your behalf when Amber is asking you to approve them each time.
Now, this can also get quite annoying after a while. I recommend using the setting that allows Amber to automatically sign for basic functions, which will cut down on some of the authorization spam. Once you have been asked to authorize the same type of action a few times, you can also toggle the option to automatically authorize that action in the future. Don't worry, though, you have full control to require Amber to ask you for permission again if you want to be alerted each time, and this toggle is specific to each application, so it's not a blanket approval for all Nostr clients you connect with.
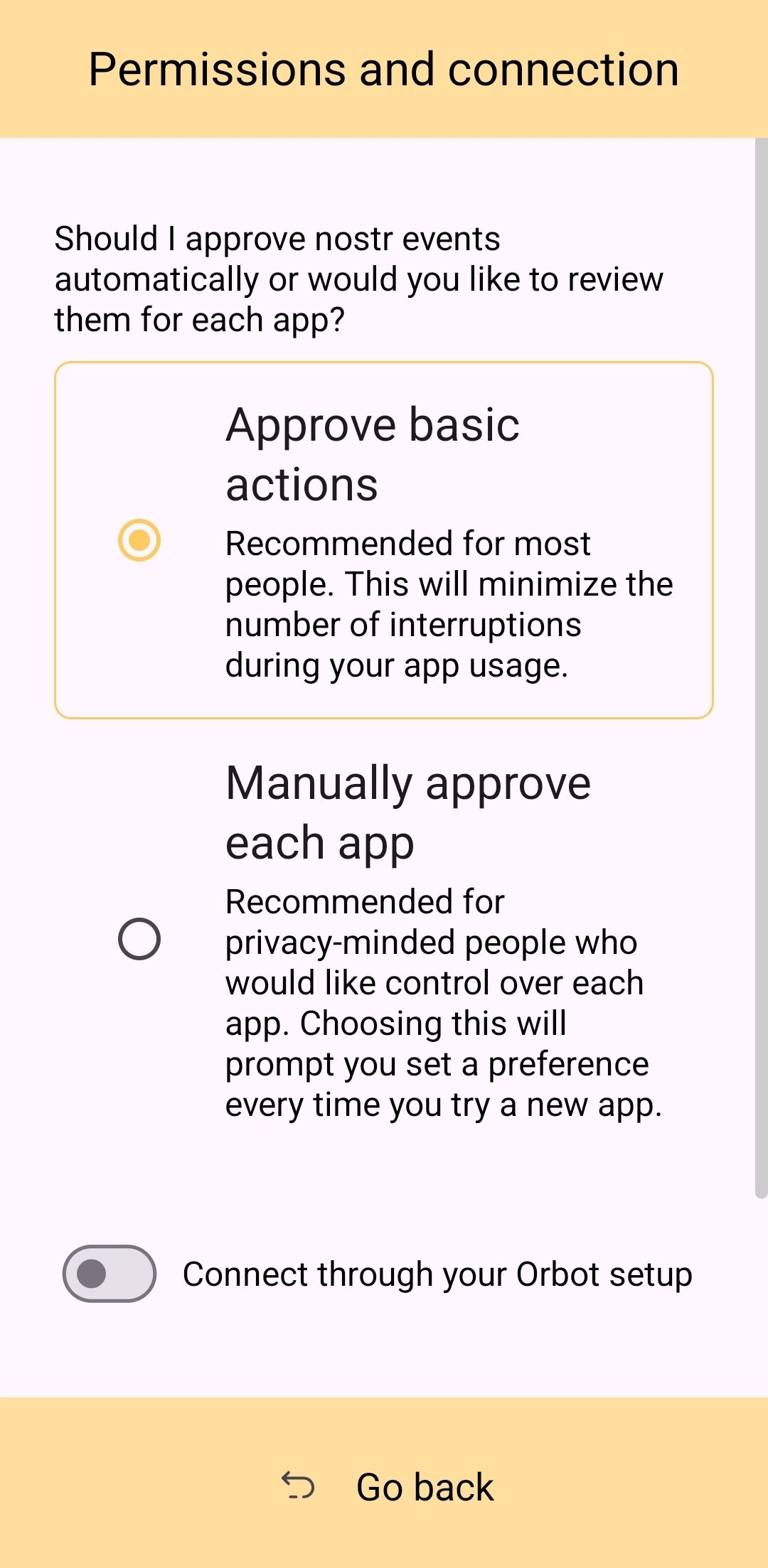
This method of signing is just as fast as signing via browser extension on web clients, which users may be more accustomed to. Everything is happening locally on the device, so it can be very snappy and secure.
Nostr Connect/Bunker Signing
This next method of signing has a bit of a delay, because it is using a Nostr relay to send encrypted information back and forth between the app the user is interacting with and Amber to obtain signatures remotely. It isn't a significant delay most of the time, but it is just enough to be noticeable.
Also, unlike the previous signing method that would automatically switch to Amber as the active application when a signing request is sent, this method only sends you a notification that you must be watching for. This can lead to situations where you are wondering why something isn't working in a client you signed into remotely, because it is waiting on you to authorize the action and you didn't notice the notification from Amber. As you use the application, you get used to the need to check for such authorization requests from time to time, or when something isn't working as expected.
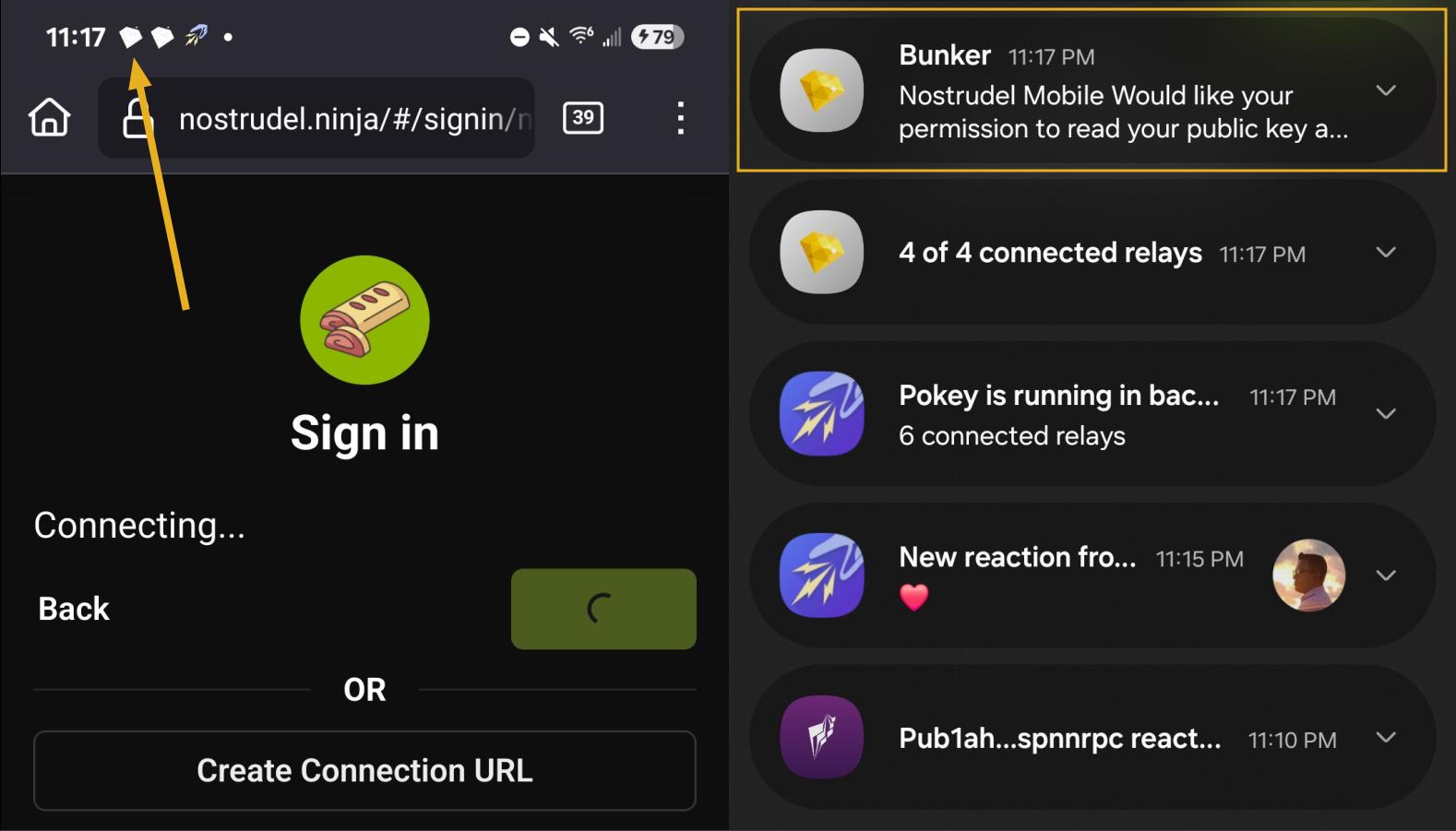
By default, Amber will use relay.nsec.app to communicate with whichever Nostr app you are connecting to. You can set a different relay for this purpose, if you like, though not just any relay will support the event kinds that Amber uses for remote signing. You can even run your own relay just for your own signing purposes. In fact, the creator of Amber has a relay application you can run on your phone, called Citrine, that can be used for signing with any web app you are using locally on your phone. This is definitely more of an advanced option, but it is there for you if you want it. For most users, sticking with relay.nsec.app will be just fine, especially since the contents of the events sent back and forth for signing are all encrypted.
Something many users may not realize is that this remote signing feature allows for issuing signing permissions to team members. For instance, if anyone ever joined me in writing reviews, I could issue them a connection string from Amber, and limit their permissions to just posting long-form draft events. Anything else they tried to do would require my explicit approval each time. Moreover, I could revoke those permissions if I ever felt they were being abused, without the need to start over with a whole new npub. Of course, this requires that your phone is online whenever a team member is trying to sign using the connection string you issued, and it requires you pay attention to your notifications so you can approve or reject requests you have not set to auto-approve. However, this is probably only useful for small teams, and larger businesses will want to find a more robust solution for managing access to their npub, such as Keycast from nostr:npub1zuuajd7u3sx8xu92yav9jwxpr839cs0kc3q6t56vd5u9q033xmhsk6c2uc.
The method for establishing a connection between Amber and a Nostr app for remote signing can vary for each app. Most, at minimum, will support obtaining a connection string from Amber that starts with "bunker://" and pasting it in at the time of login. Then you just need to approve the connection request from Amber and the client will log you in and send any subsequent signing requests to Amber using the same connection string.
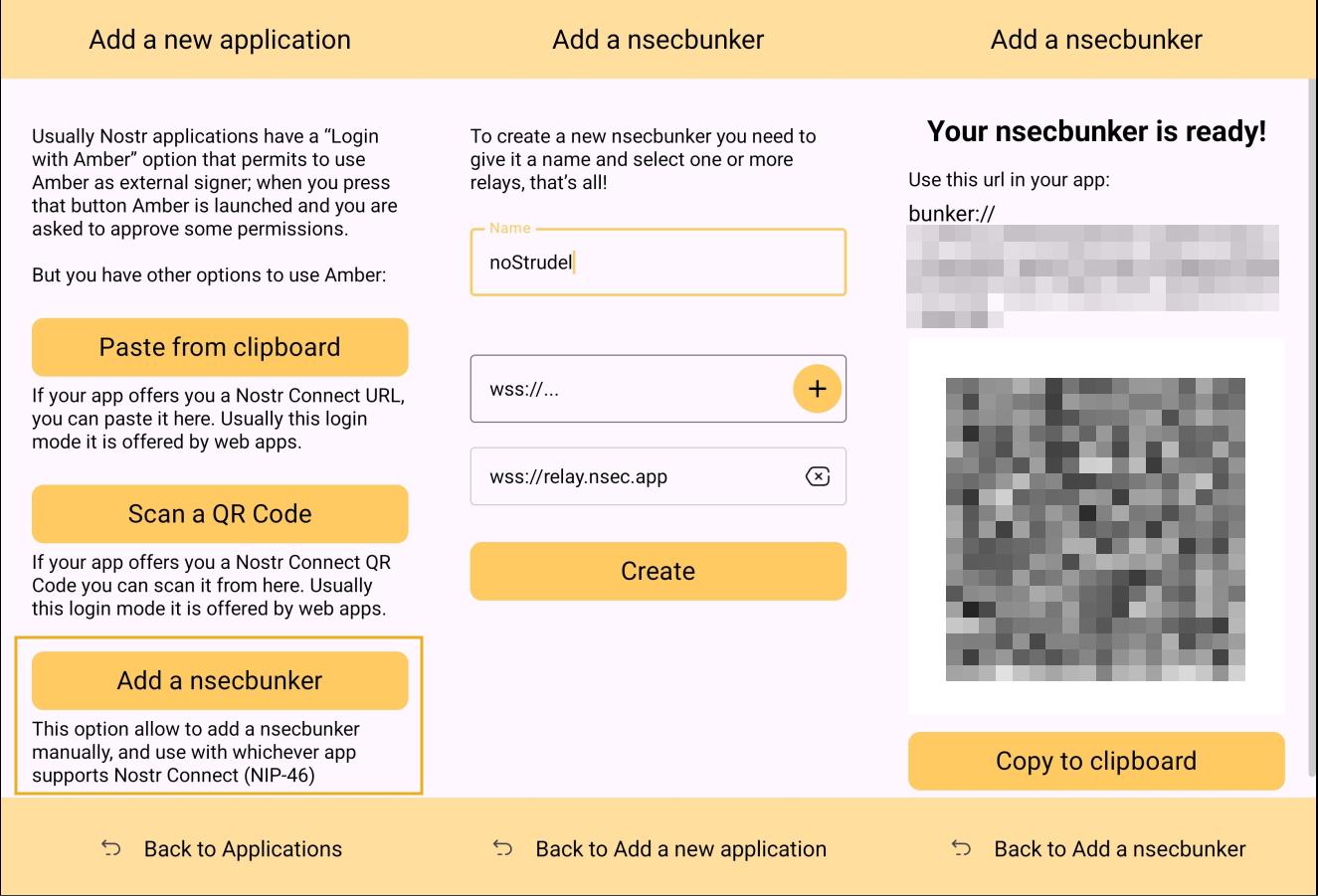
Some clients will also offer the option to scan a QR code to connect the client to Amber. This is quite convenient, but just remember that this also means the client is setting which relay will be used for communication between the two. Clients with this option will also have a connection string you can copy and paste into Amber to achieve the same purpose. For instance, you may need this option if you are trying to connect to an app on your phone and therefore can't scan the QR code using Amber on the same phone.
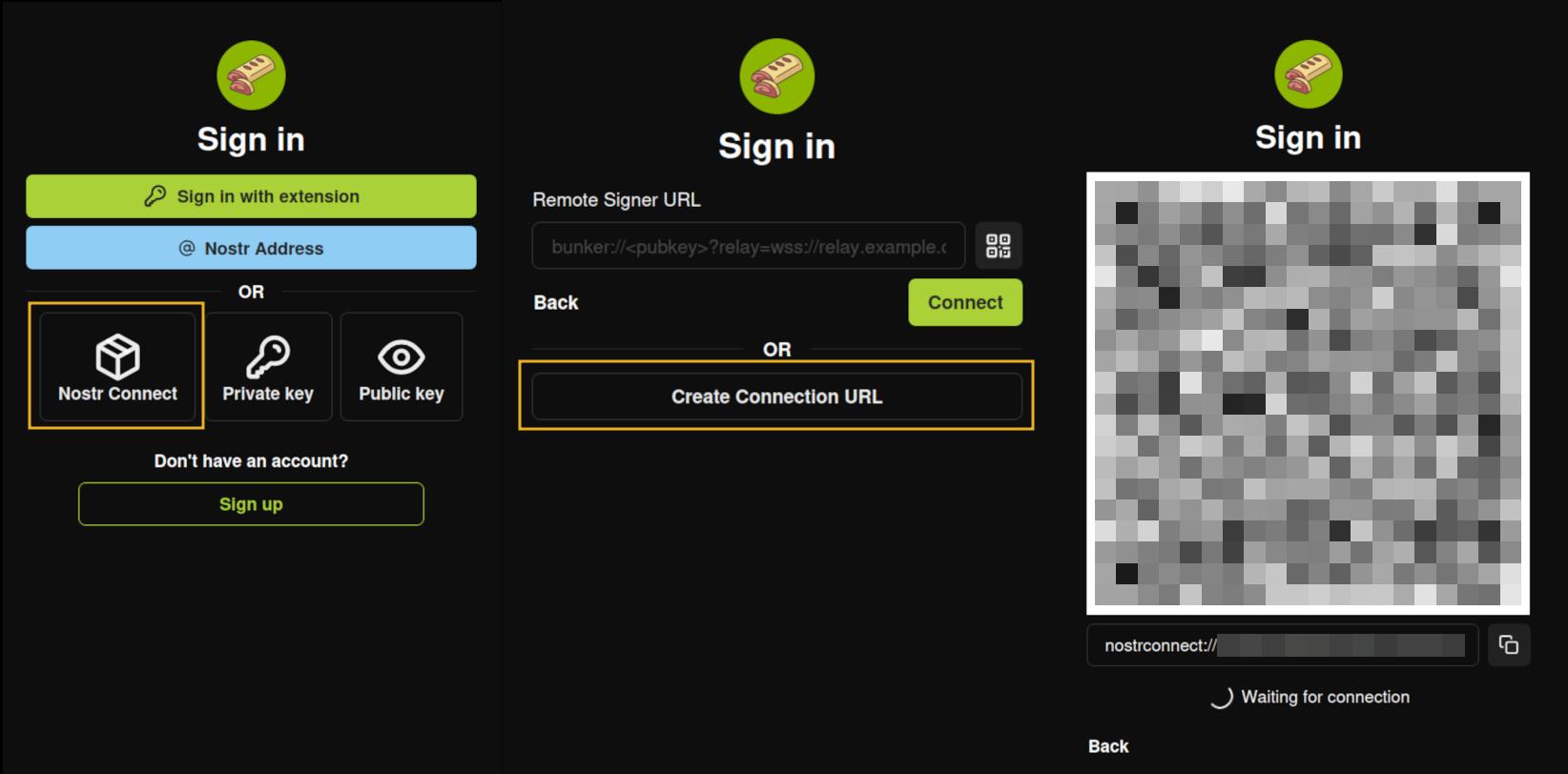
Multiple Accounts
Amber does not lock you into using it with only a single set of keys. You can add all of your Nostr "accounts" to Amber and use it for signing events for each independently. Of course, Nostr doesn't actually have "accounts" in the traditional sense. Your identity is simply your key-pair, and Amber stores and accesses each private key as needed.
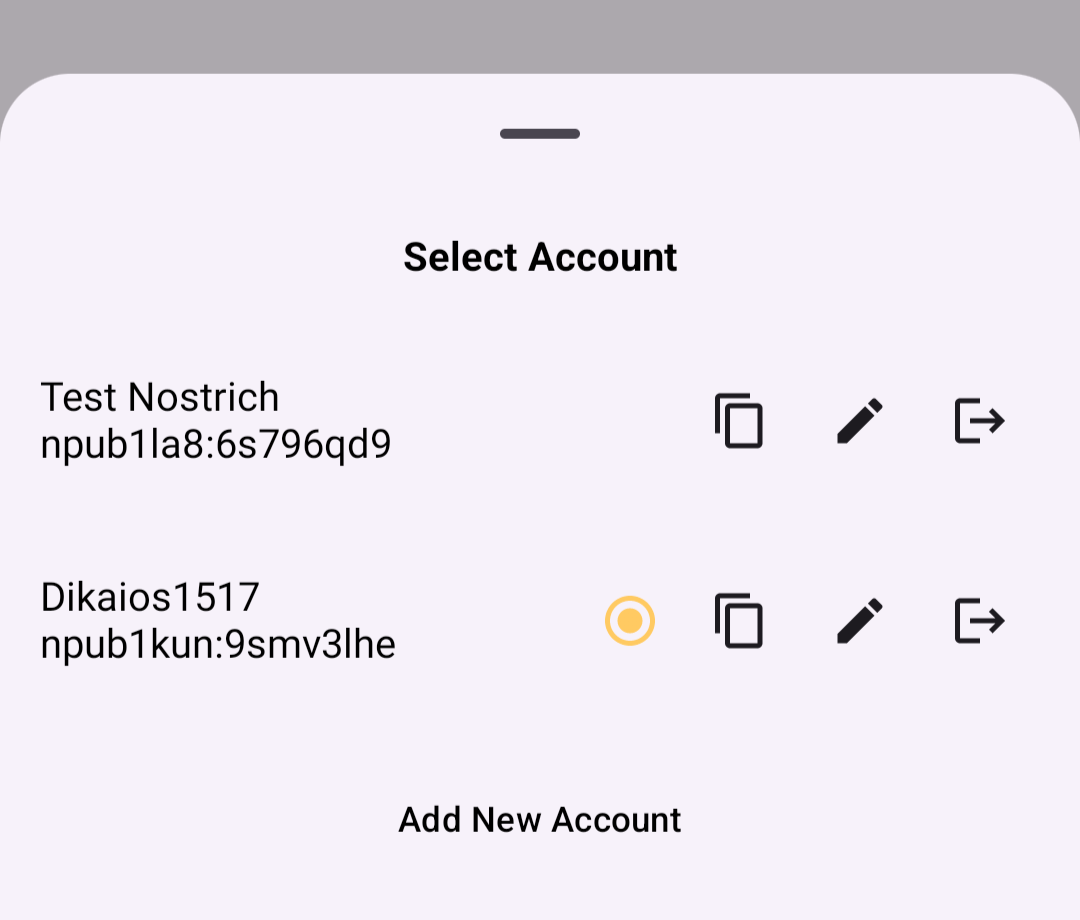
When first signing in using native Android signing as described above, Amber will default to whichever account was most recently selected, but you can switch to the account that is needed before approving the request. After initial login, Amber will automatically detect the account that the signing request is for.
Key Backup & Restore
Amber allows multiple ways to back up your private key. As most users would expect, you can get your standard nsec and copy/paste it to a password manager, but you can also obtain your private key as a list of mnemonic seed words, an encrypted version of your key called an ncryptsec, or even a QR code of your nsec or ncryptsec.
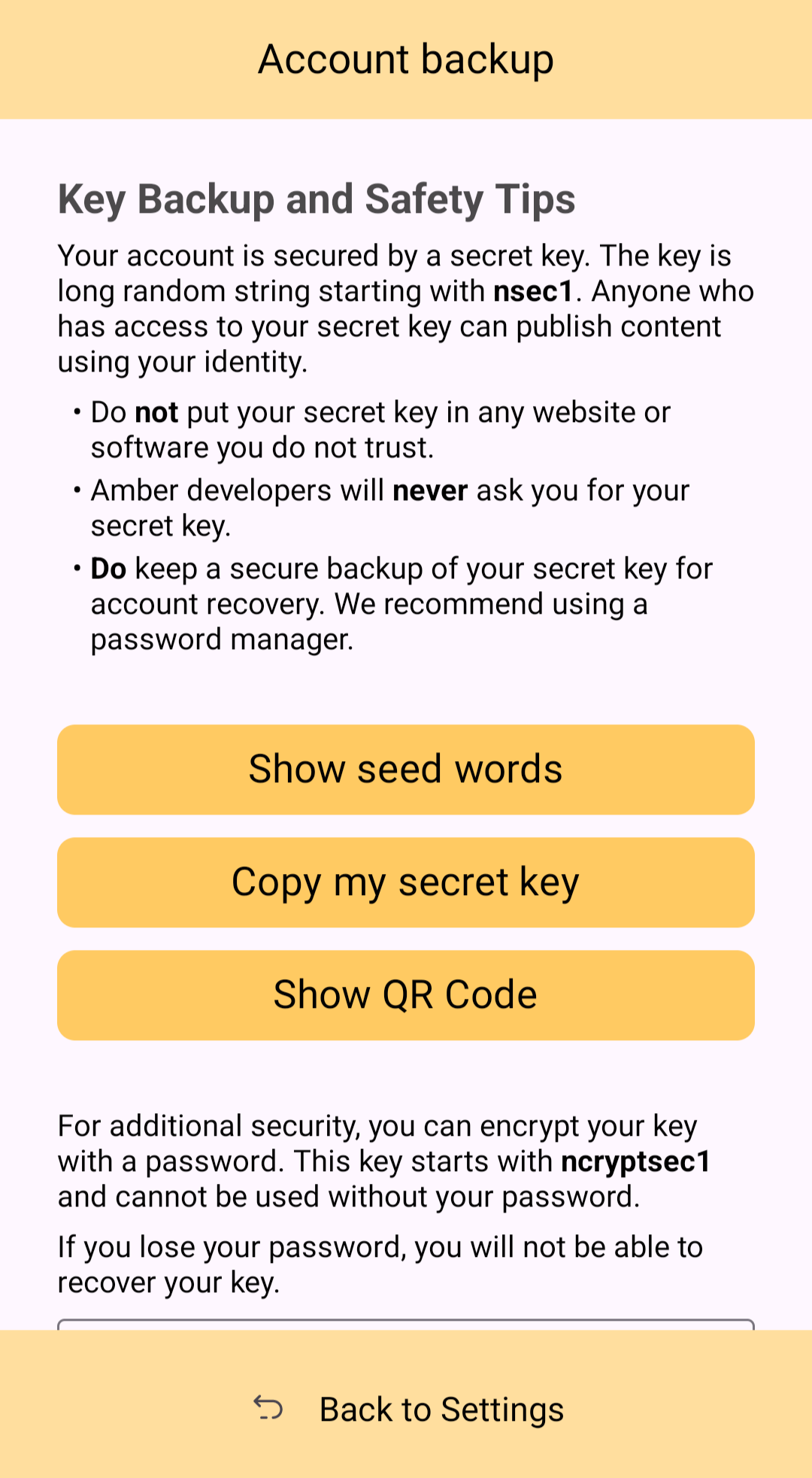
Additionally, in order to gain access to this information, Amber requires you to enter your device's PIN or use biometric authentication. This isn't cold-storage level protection for your private key by any means, especially since your phone is an internet connected device and does not store your key within a secure element, but it is about as secure as you can ask for while having your key accessible for signing Nostr events.
Tor Support
While Amber does not have Tor support within the app itself, it does support connecting to Tor through Orbot. This would be used with remote signing so that Amber would not connect directly over clearnet to the relay used for communication with the Nostr app requesting the signature. Instead, Amber would connect through Tor, so the relay would not see your IP address. This means you can utilize the remote signing option without compromising your anonymity.
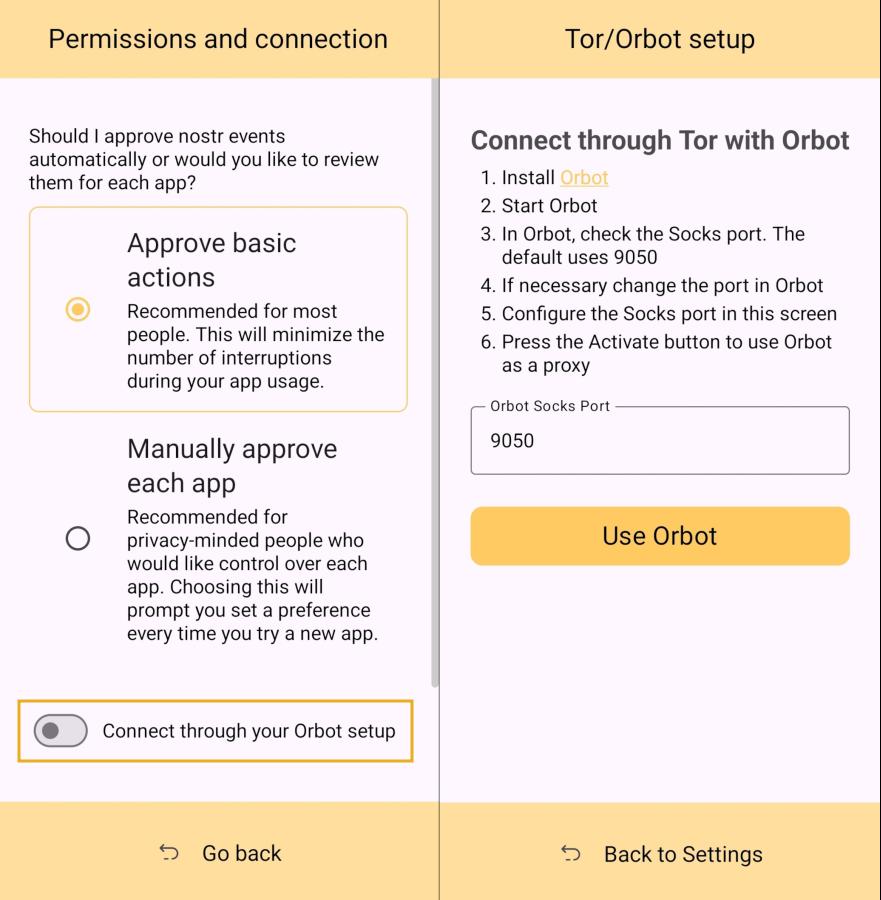
Additional Security
Amber allows the user the option to require either biometric or PIN authentication before approving signing requests. This can provide that extra bit of assurance that no one will be able to sign events using your private key if they happen to gain access to your phone. The PIN you set in Amber is also independent from the PIN to unlock your device, allowing for separation of access.
Can My Grandma Use It?
Score: 4.6 / 5 (Updated 4/21/2025)
At the end of the day, Amber is a tool for those who have some concept of the importance of protecting their private key by not pasting it into every Nostr client that comes along. This concept in itself is not terribly approachable to an average person. They are used to just plugging their password into every service they use, and even worse, they usually have the same password for everything so they can more readily remember it. The idea that they should never enter their "Nostr password" into any Nostr application would never occur to them unless someone first explained how cryptography works related to public/private key pairs.
That said, I think there can be some improvements made to how users are introduced to these concepts, and that a signer application like Amber might be ideal for the job. Considering Amber as a new user's first touch-point with Nostr, I think it holds up well, but could be somewhat streamlined.
Upon opening the app, the user is prompted to either use their existing private key or "Create a new Nostr account." This is straightforward enough. "Account" is not a technically correct term with Nostr, but it is a term that new users would be familiar with and understand the basic concept.
The next screen announces that the account is ready, and presents the user with their public key, explaining that it is "a sort of username" that will allow others to find them on Nostr. While it is good to explain this to the user, it is unnecessary information at this point. This screen also prompts the user to set a nickname and set a password to encrypt their private key. Since the backup options also allow the user to set this password, I think this step could be pushed to a later time. This screen would better serve the new user if it simply prompted them to set a nickname and short bio that could be saved to a few default relays.
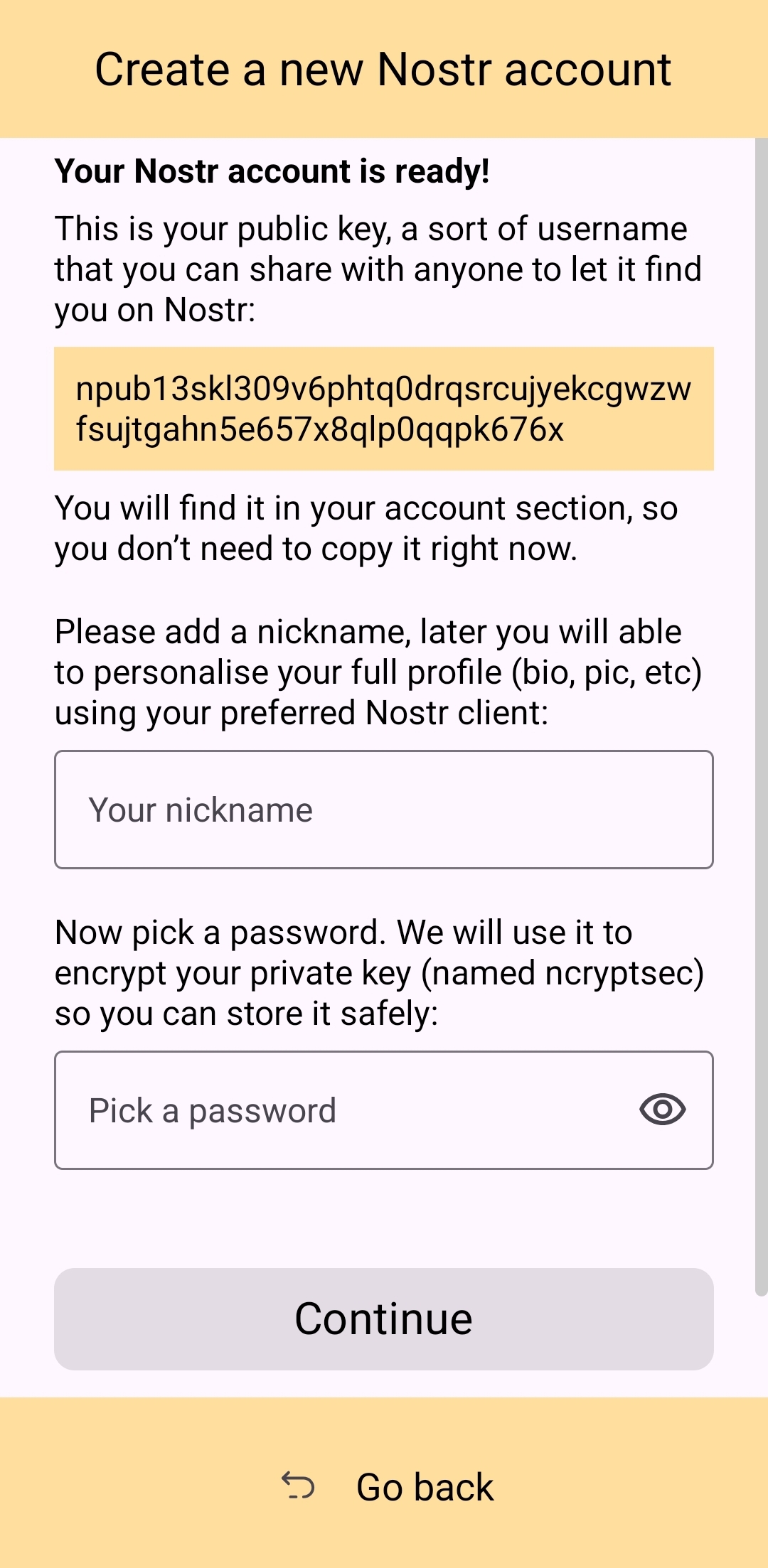
Of course, Amber is currently prompting for a password to be set up-front because the next screen requires the new user to download a "backup kit" in order to continue. While I do believe it is a good idea to encourage the creation of a backup, it is not crucial to do so immediately upon creation of a new npub that has nothing at stake if the private key is lost. This is something the UI could remind the user to do at a later time, reducing the friction of profile creation, and expediting getting them into the action.
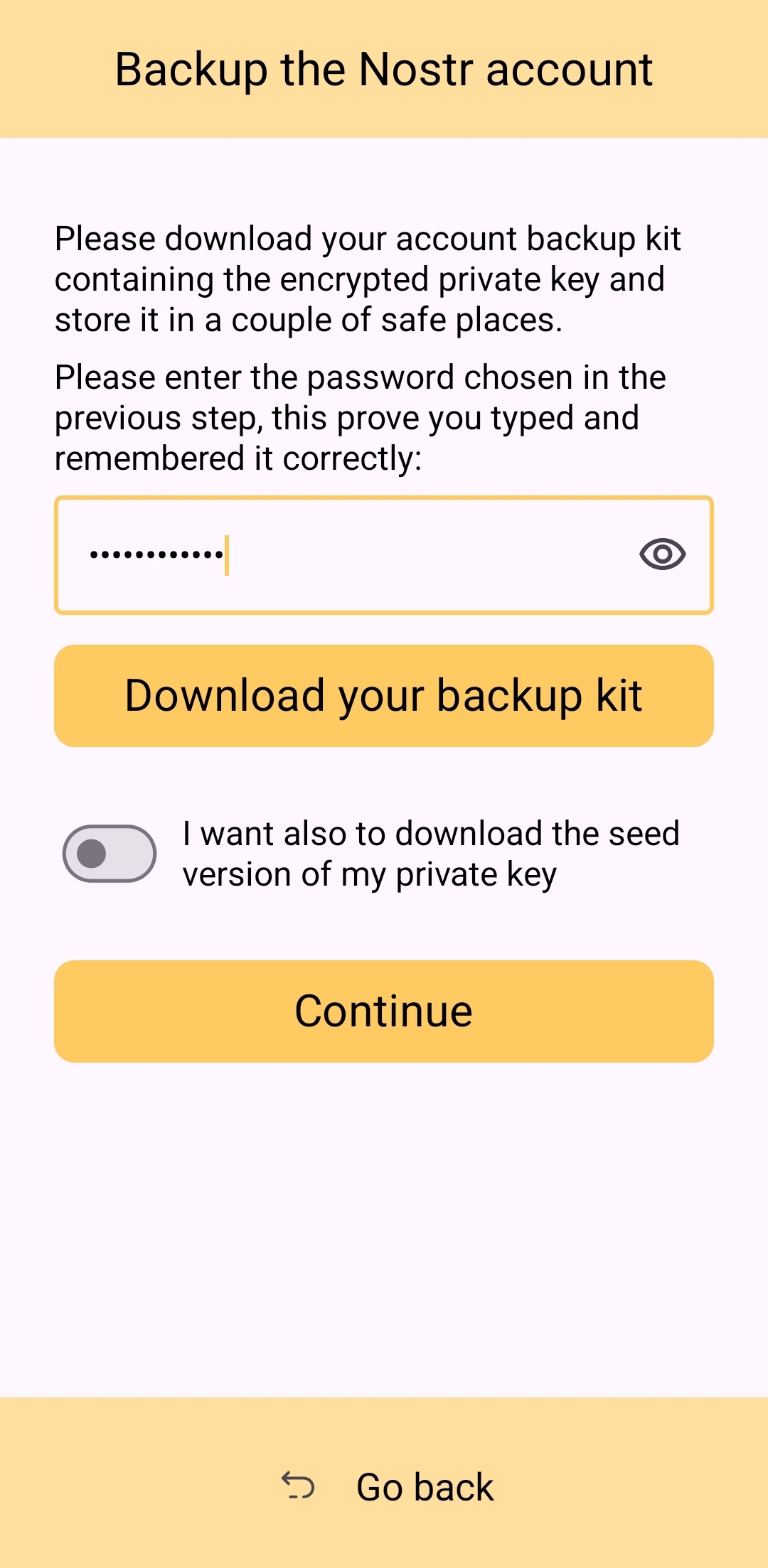
Outside of these minor onboarding friction points, I think Amber does a great job of explaining to the user the purpose of each of its features, all within the app and without any need to reference external documentation. As long as the user understands the basic concept that their private key is being stored by Amber in order to sign requests from other Nostr apps, so they don't have to be given the private key, Amber is very good about explaining the rest without getting too far into the technical weeds.
The most glaring usability issue with Amber is that it isn't available in the Play Store. Average users expect to be able to find applications they can trust in their mobile device's default app store. There is a valid argument to be made that they are incorrect in this assumption, but that doesn't change the fact that this is the assumption most people make. They believe that applications in the Play Store are "safe" and that anything they can't install through the Play Store is suspect. The prompts that the Android operating system requires the user to approve when installing "unknown apps" certainly doesn't help with this impression.
Now, I absolutely love the Zapstore from nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9, but it doesn't do much to alleviate this issue. Users will still need to be convinced that it is safe to install the Zapstore from the GitHub repo, and then install Amber from there. Furthermore, this adds yet another step to the onboarding process.
Instead of:
- Install Amber
- Set up your keys
- Install the client you want to use
- Log in with Amber
The process becomes:
- Go to the Zapstore GitHub and download the latest version from the releases page.
- Install the APK you downloaded, allowing any prompt to install unknown apps.
- Open Zapstore and install Amber, allowing any prompt to install unknown apps again.
- Open Amber and set up your keys.
- Install the client you want to use
- Log in with Amber
An application as important as Amber for protecting users' private keys should be as readily available to the new user as possible. New users are the ones most prone to making mistakes that could compromise their private keys. Amber should be available to them in the Play Store.
UPDATE: As of version 3.2.8 released on 4/21/2025, the onboarding flow for Amber has been greatly improved! Now, when selecting to set up a new "account" the user is informed on the very next screen, "Your Nostr account is ready!" and given their public key/npub. The only field the user must fill in is their "nickname"/display name and hit "Continue."
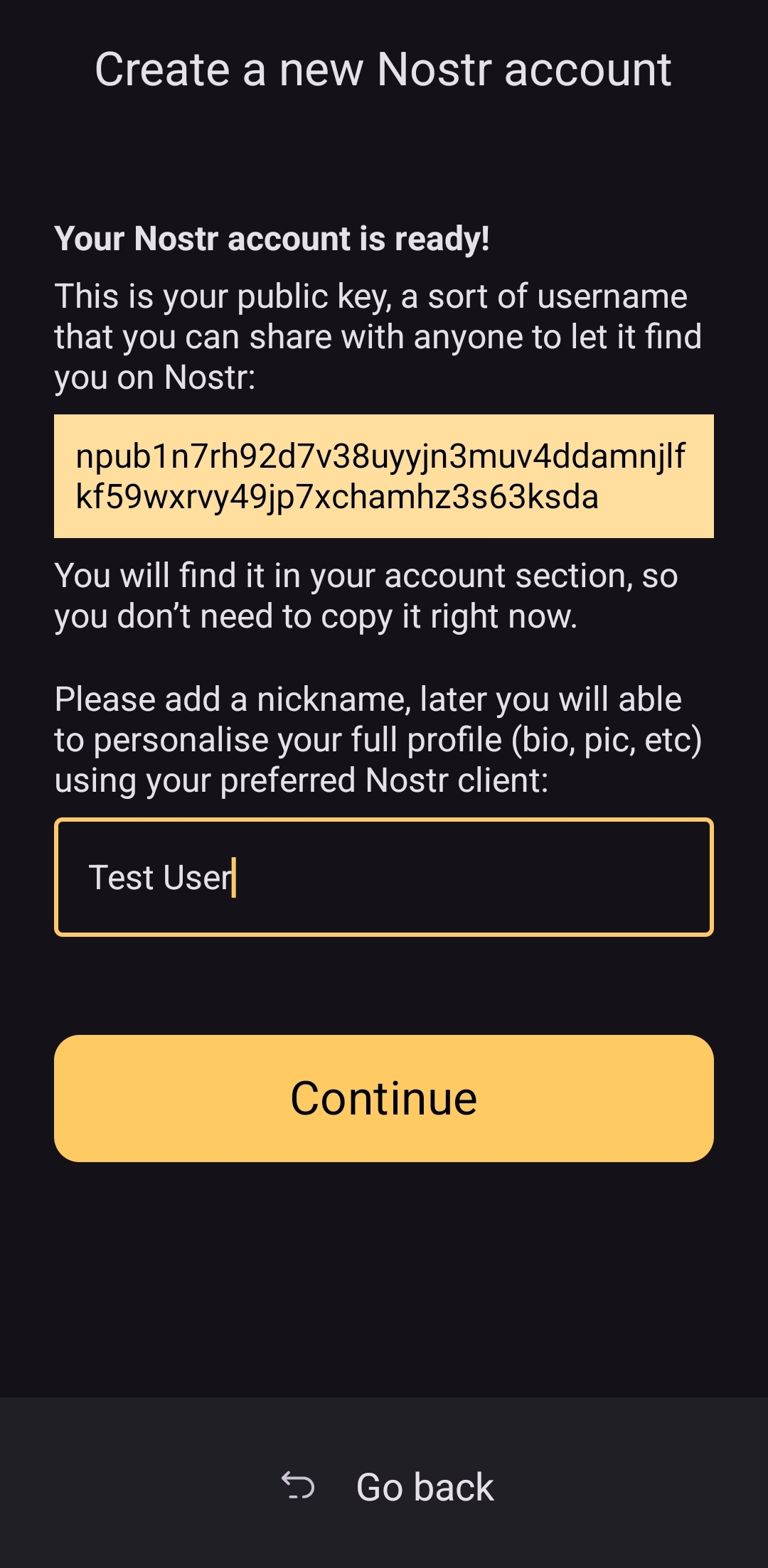
From there the user is asked if they want Amber to automatically approve basic actions, or manually approve each app, and then they are shown a new Applications screen, with a prompt to create a backup of their account. This prompt persists until the user has done so.
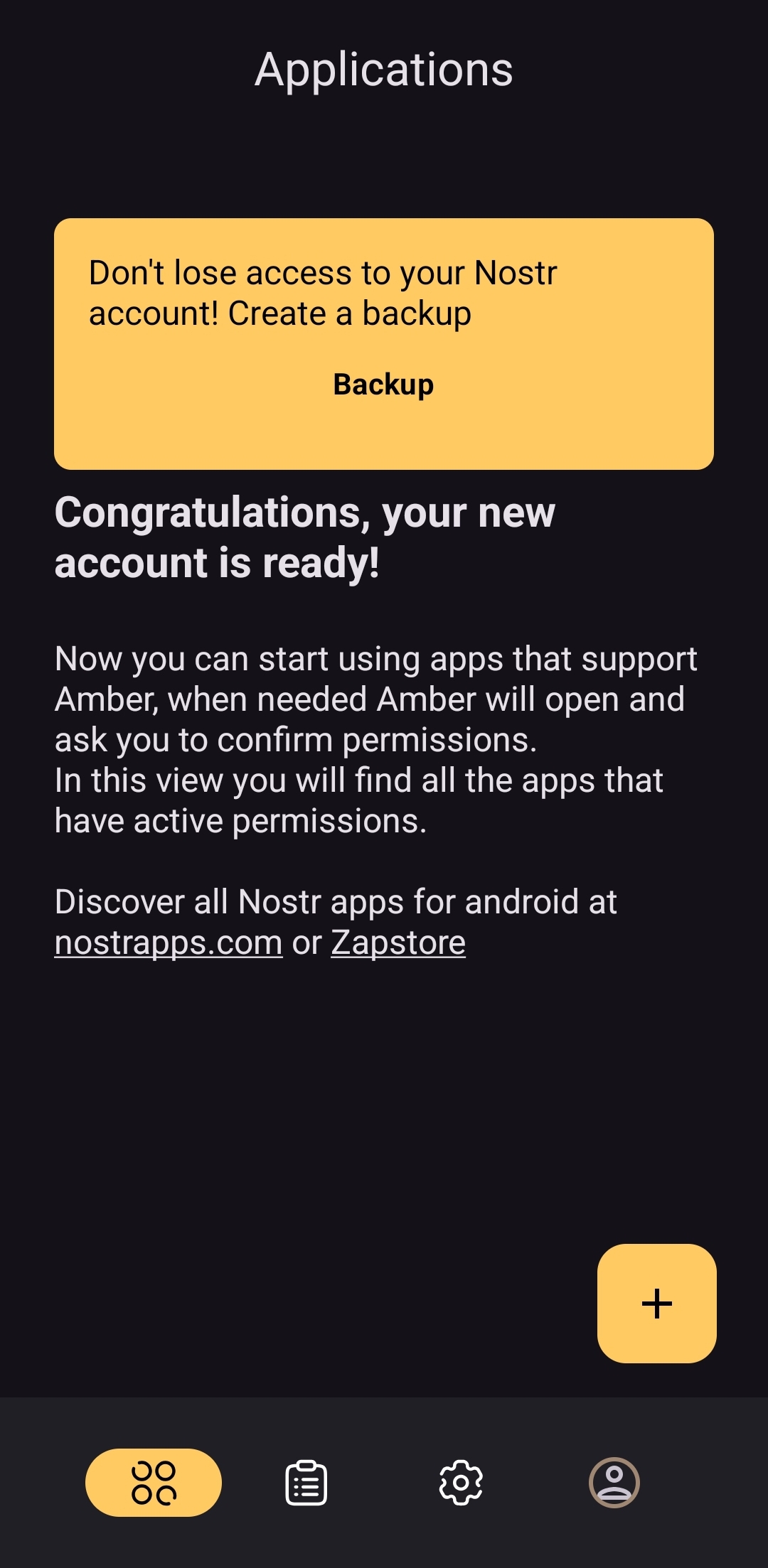
As you can see, the user is also encouraged to find applications that can be used with Amber with links to nostrapps.com and the Zapstore.
Thanks to these updates, Amber is now the smoothest and most user-friendly onboarding experience I have seen for Nostr to date. Sure, it doesn't have anything for setting up a profile picture or lightning address, but that is better done in a client like Amethyst or YakiHonne, anyway. Just tap "create," type in a handle to call yourself, and you're done!
How do UI Look?
Score: 4.5 / 5
Amber's UI can be described as clean but utilitarian. But then, Amber is a tool, so this is somewhat expected. It is not an app you will be spending a lot of time in, so the UI just needs to be serviceable. I would say it accomplishes this and then some. UI elements are generally easy to understand what they do, and page headings fill in the gaps where that is not the case.
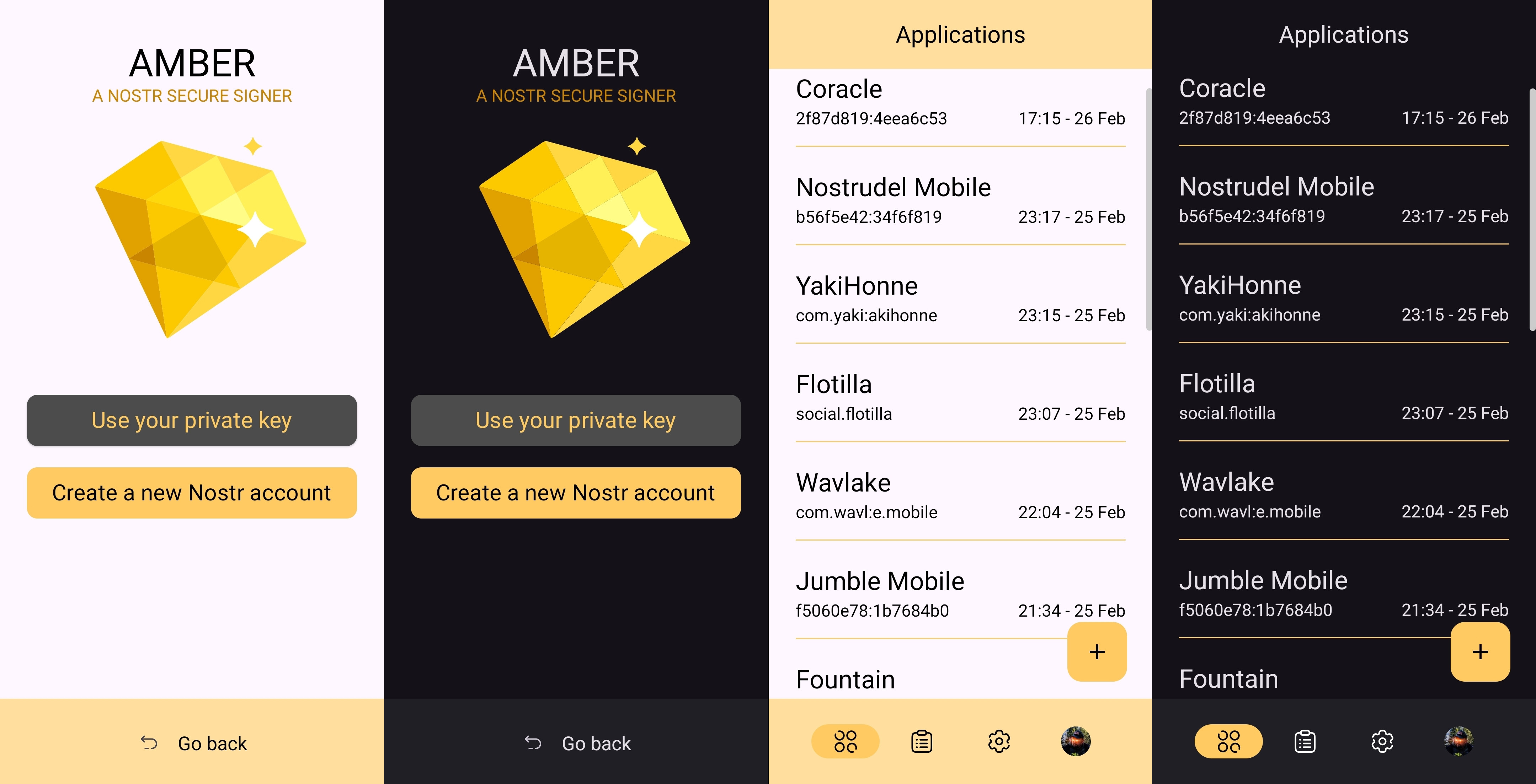
I am not the biggest fan of the color-scheme, particularly in light-mode, but it is not bad in dark-mode at all, and Amber follows whatever theme you have set for your device in that respect. Additionally, the color choice does make sense given the application's name.
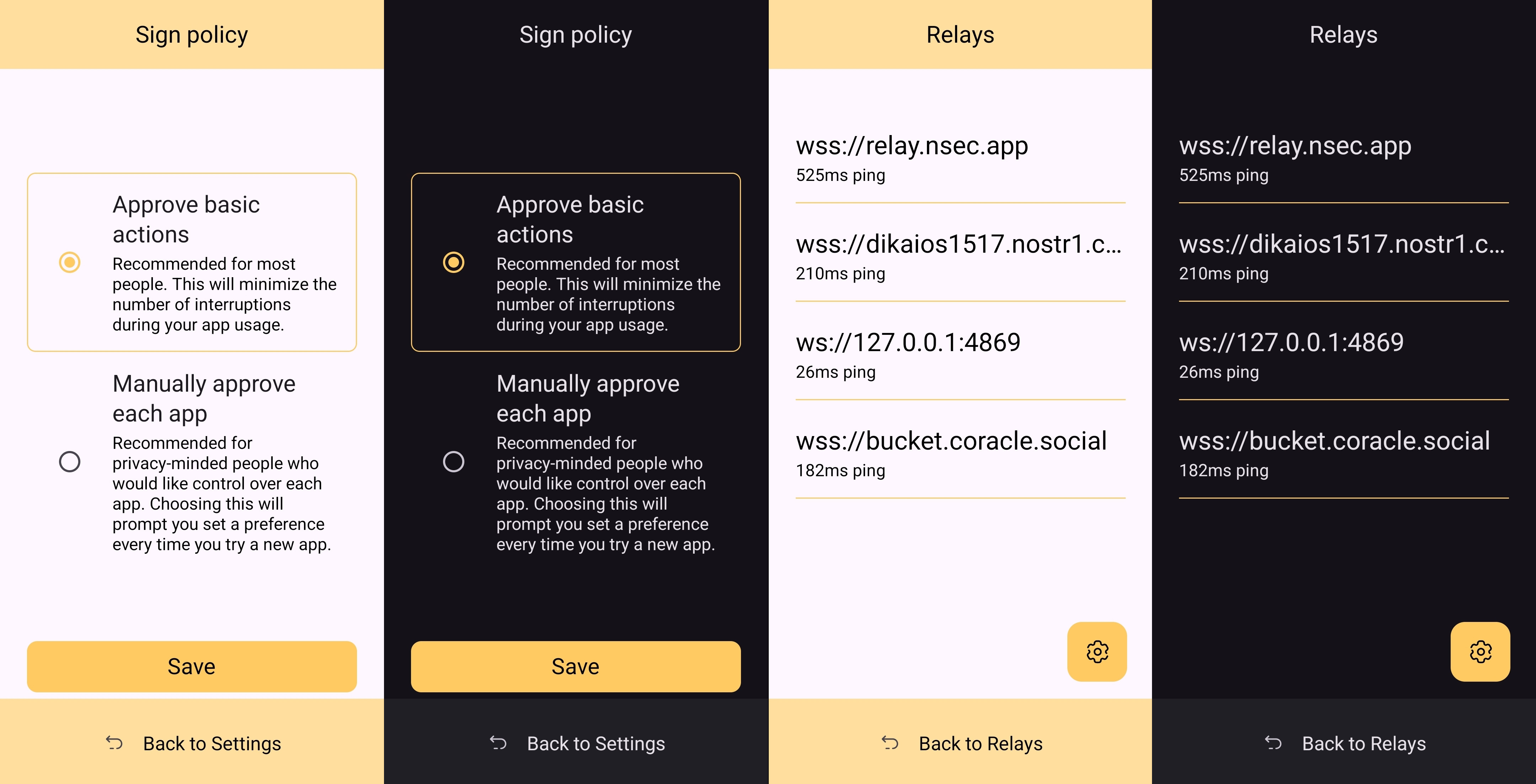
It must also be taken into consideration that Amber is almost entirely the product of a single developer's work. He has done a great job producing an app that is not only useful, but pleasant to interact with. The same cannot be said for most utility apps I have previously used, with interfaces that clearly made good design the lowest priority. While Amber's UI may not be the most beautiful Nostr app I have seen, design was clearly not an afterthought, either, and it is appreciated.
Relay Management
Score: 4.9 / 5
Even though Amber is not a Nostr client, where users can browse notes from their favorite npubs, it still relies heavily on relays for some of its features. Primarily, it uses relays for communicating with other Nostr apps for remote signing requests. However, it also uses relays to fetch profile data, so that each private key you add to Amber will automatically load your chosen username and profile picture.
In the relay settings, users can choose which relays are being used to fetch profile data, and which relays will be used by default when creating new remote signing connection strings.
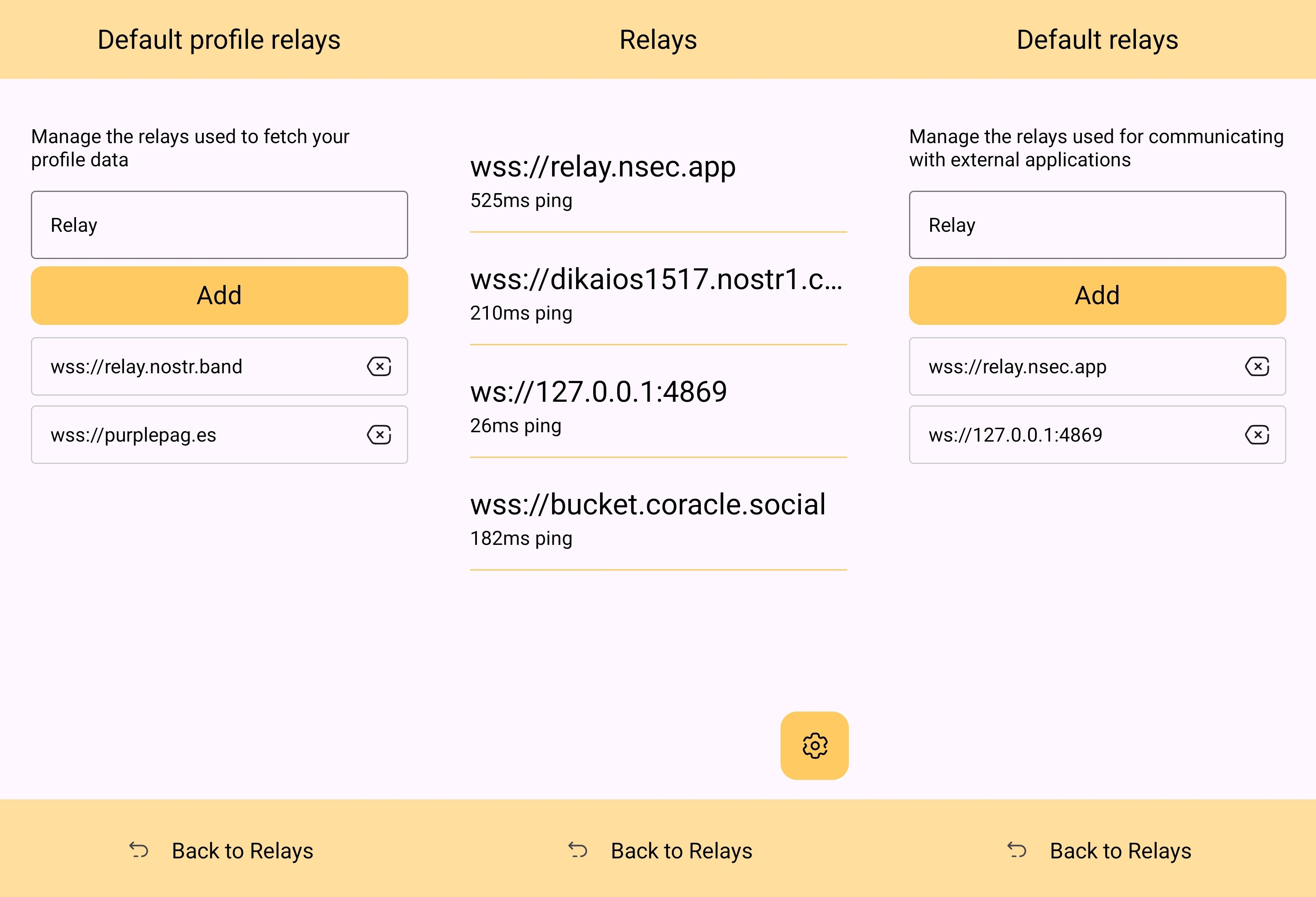
The user can also see which relays are currently connected to Amber and even look at the information that has been passed back and forth on each of those active relays. This information about actively connected relays is not only available within the application, but also in the notification that Amber has to keep in your device's notification tray in order to continue to operate in the background while you are using other apps.
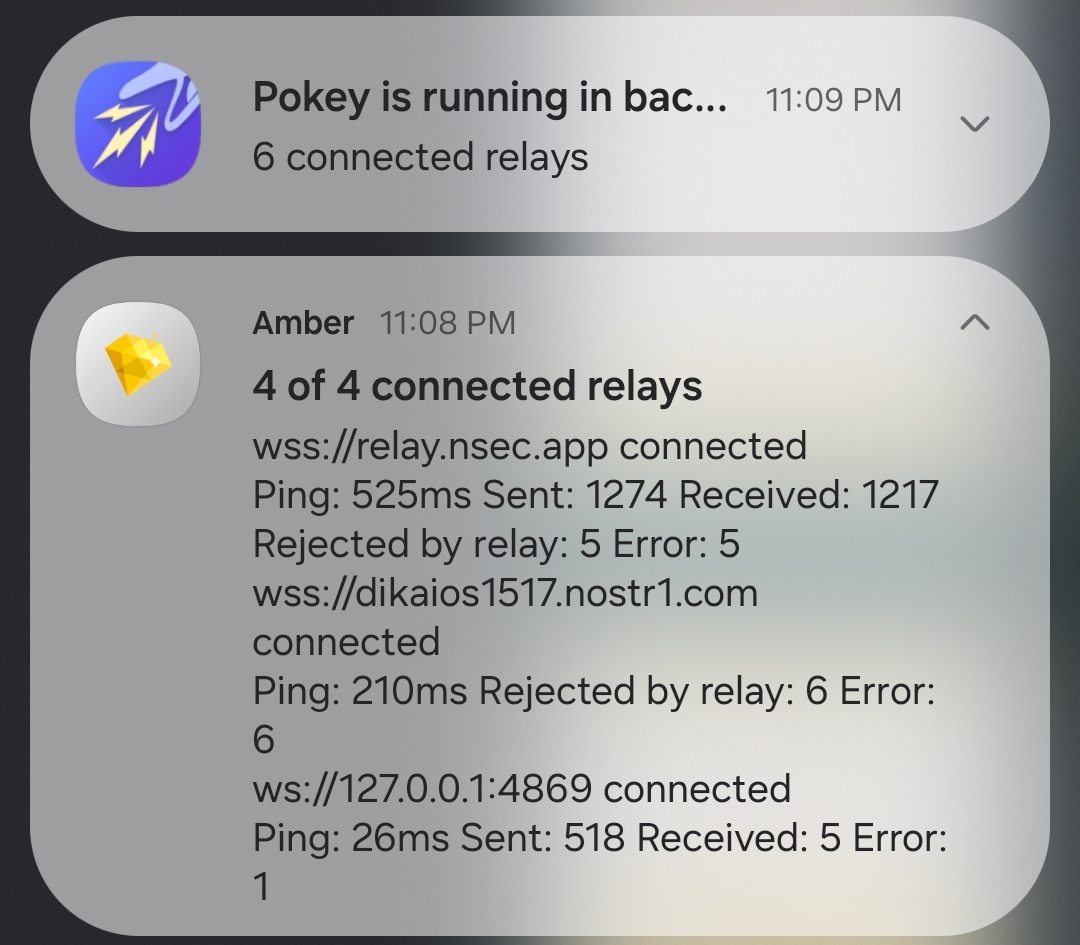
Optionality is the name of the game when it comes to how Amber handles relay selection. The user can just stick with the default signing relay, use their own relay as the default, or even use a different relay for each Nostr application that they connect to for remote signing. Amber gives the user an incredible amount of flexibility in this regard.
In addition to all of this, because not all relays accept the event types needed for remote signing, when you add a relay address to Amber, it automatically tests that relay to see if it will work. This alone can be a massive time saver, so users aren't trying to use relays that don't support remote signing and wondering why they can't log into noStrudel with the connection string they got from Amber.
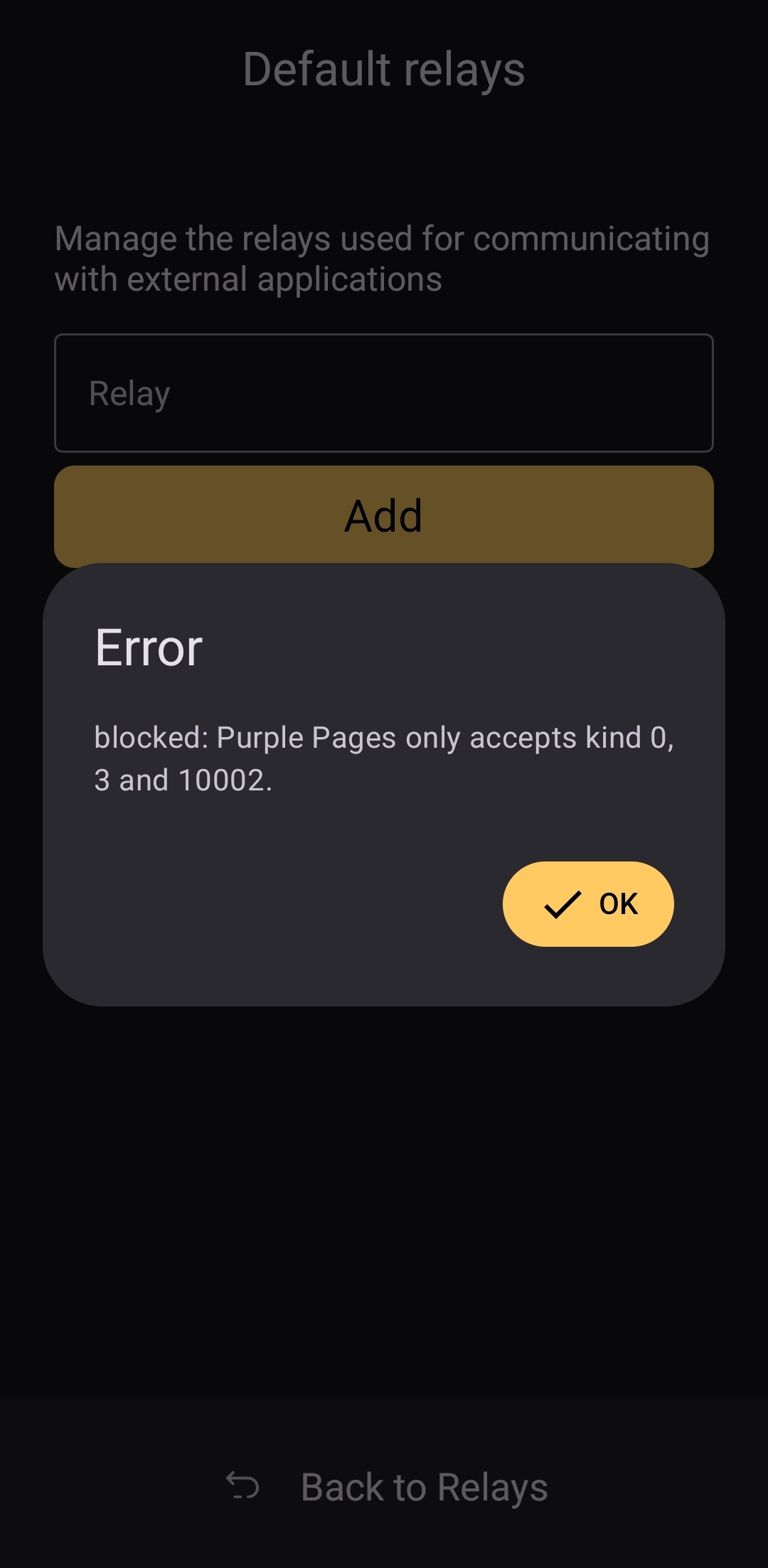
The only way I could see relay management being improved would be some means of giving the user relay recommendations, in case they want to use a relay other than relay.nsec.app, but they aren't sure which other relays will accept remote signing events. That said, most users who want to use a different relay for signing remote events will likely be using their own, in which case recommendations aren't needed.
Current Users' Questions
The AskNostr hashtag can be a good indication of the pain points that other users are currently having with any Nostr application. Here are some of the most common questions submitted about Amber in the last two months.
nostr:nevent1qqsfrdr68fafgcvl8dgnhm9hxpsjxuks78afxhu8yewhtyf3d7mkg9gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgq3qkgh77xxt7hhtt4u528hecnx69rhagla8jj3tclgyf9wvkxa6dc0sxp0e6m
This is a good example of Amber working correctly, but the app the user is trying to log into not working. In my experience with #Olas in particular, it sometimes allows remote signer login, and sometimes doesn't. Amber will receive the signing request and I will approve it, but Olas remains on the login screen.
If Amber is receiving the signing requests, and you are approving them, the fault is likely with the application you are trying to log into.
That's it. That's all the repeated questions I could find. Oh, there were a few one-off questions where relay.nsec.app wouldn't connect, or where the user's out-of-date web browser was the issue. Outside of that, though, there were no common questions about how to use Amber, and that is a testament to Amber's ease of use all on its own.
Wrap Up
If you are on Android and you are not already using Amber to protect your nsec, please do yourself a favor and get it installed. It's not at all complicated to set up, and it will make trying out all the latest Nostr clients a safe and pleasant experience.
If you are a client developer and you have not added support for NIP-55 or NIP-46, do your users the courtesy of respecting the sanctity of their private keys. Even developers who have no intention of compromising their users' keys can inadvertently do so. Make that eventuality impossible by adding support for NIP-55 and NIP-46 signing.
Finally, I apologize for the extended time it took me to get this review finished. The time I have available is scarce, Nostr is distracting, and nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 kept improving Amber even as I was putting it through its paces over the last two months. Keep shipping, my friend! You have made one of the most useful tools we have seen for Nostr to date!
Now... What should I review next?
-
 @ c631e267:c2b78d3e
2025-04-18 15:53:07
@ c631e267:c2b78d3e
2025-04-18 15:53:07Verstand ohne Gefühl ist unmenschlich; \ Gefühl ohne Verstand ist Dummheit. \ Egon Bahr
Seit Jahren werden wir darauf getrimmt, dass Fakten eigentlich gefühlt seien. Aber nicht alles ist relativ und nicht alles ist nach Belieben interpretierbar. Diese Schokoladenhasen beispielsweise, die an Ostern in unseren Gefilden typisch sind, «ostern» zwar nicht, sondern sie sitzen in der Regel, trotzdem verwandelt sie das nicht in «Sitzhasen».
Nichts soll mehr gelten, außer den immer invasiveren Gesetzen. Die eigenen Traditionen und Wurzeln sind potenziell «pfui», um andere Menschen nicht auszuschließen, aber wir mögen uns toleranterweise an die fremden Symbole und Rituale gewöhnen. Dabei ist es mir prinzipiell völlig egal, ob und wann jemand ein Fastenbrechen feiert, am Karsamstag oder jedem anderen Tag oder nie – aber bitte freiwillig.
Und vor allem: Lasst die Finger von den Kindern! In Bern setzten kürzlich Demonstranten ein Zeichen gegen die zunehmende Verbreitung woker Ideologie im Bildungssystem und forderten ein Ende der sexuellen Indoktrination von Schulkindern.
Wenn es nicht wegen des heiklen Themas Migration oder wegen des Regenbogens ist, dann wegen des Klimas. Im Rahmen der «Netto Null»-Agenda zum Kampf gegen das angeblich teuflische CO2 sollen die Menschen ihre Ernährungsgewohnheiten komplett ändern. Nach dem Willen von Produzenten synthetischer Lebensmittel, wie Bill Gates, sollen wir baldmöglichst praktisch auf Fleisch und alle Milchprodukte wie Milch und Käse verzichten. Ein lukratives Geschäftsmodell, das neben der EU aktuell auch von einem britischen Lobby-Konsortium unterstützt wird.
Sollten alle ideologischen Stricke zu reißen drohen, ist da immer noch «der Putin». Die Unions-Europäer offenbaren sich dabei ständig mehr als Vertreter der Rüstungsindustrie. Allen voran zündelt Deutschland an der Kriegslunte, angeführt von einem scheinbar todesmutigen Kanzlerkandidaten Friedrich Merz. Nach dessen erneuter Aussage, «Taurus»-Marschflugkörper an Kiew liefern zu wollen, hat Russland eindeutig klargestellt, dass man dies als direkte Kriegsbeteiligung werten würde – «mit allen sich daraus ergebenden Konsequenzen für Deutschland».
Wohltuend sind Nachrichten über Aktivitäten, die sich der allgemeinen Kriegstreiberei entgegenstellen oder diese öffentlich hinterfragen. Dazu zählt auch ein Kongress kritischer Psychologen und Psychotherapeuten, der letzte Woche in Berlin stattfand. Die vielen Vorträge im Kontext von «Krieg und Frieden» deckten ein breites Themenspektrum ab, darunter Friedensarbeit oder die Notwendigkeit einer «Pädagogik der Kriegsuntüchtigkeit».
Der heutige «stille Freitag», an dem Christen des Leidens und Sterbens von Jesus gedenken, ist vielleicht unabhängig von jeder religiösen oder spirituellen Prägung eine passende Einladung zur Reflexion. In der Ruhe liegt die Kraft. In diesem Sinne wünsche ich Ihnen frohe Ostertage!
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 65038d69:1fff8852
2025-04-14 20:55:11
@ 65038d69:1fff8852
2025-04-14 20:55:11Most people would define “maintenance” as “fixing stuff that’s broken”. If you told them that that’s “repair” and that maintenance is different, they’d reply that you should get your head out of the dictionary and stop being so pedantic. After all, the difference is semantic at best and nobody cares! My argument is that you should care, and that the difference will save your household, your business, and your society.
I’ve gotten way ahead of myself. Let’s start with defining maintenance and repair so we can understand the differences. Repair, to borrow from above, is fixing stuff that’s broken. If your pencil snaps in half and you tape it back together, that’s repair. If you drive over a nail and the shop patches your tire, that’s repair. Maintenance is when you do work to prevent stuff from breaking. Trimming your fingernails prevents them from cracking or ripping.
When you define maintenance and describe examples out loud the benefits sound obvious. Yet we struggle with even the most basic maintenance items. This is because unlike with repair, maintenance requires a form of intentional advanced thinking similar to delayed gratification. If something is broken the need for repair is immediate and usually quite visible. Almost no thinking at all is needed to see that a tire is flat, but regularly cleaning your shower to avoid mold requires thinking about future effects. Some effects are even further removed; for example, changing your HVAC filters leads to higher air quality, which leads to fewer respiratory issues, which leads to better sleep, which leads to improved mood and productivity.
Reactive thinkers struggle deeply with the idea of maintenance. It’s a bit like the Marshmallow Test (see Which Disney Princess Are You (In The Workplace)?) except instead of a larger reward later, it’s less expense later. Putting off maintenance is not always due to high time preference though; sometimes there are monetary restrictions. Terry Pratchett has a wonderful example of this in his book “Men at Arms” where a character compares cheap boots that only last a short while to more expensive ones that last much longer. A poor person can’t afford the larger upfront cost of the ones that last longer, so they’re doomed to spend more money on several pairs of cheaper boots over the same time period.
One thing you can do is choose options that require less maintenance overall. “Low-maintenance” can be sought out in almost any category. Vehicles, appliances, technology, even friends! I would describe myself as a low-maintenance spouse. Our 2003 Toyota RAV4 is also low-maintenance. Our dog, on the other hand, is rather high-maintenance.
Want help picking out low-maintenance technology for your organization? You can find us as scalebright.ca.
-
 @ 5d4b6c8d:8a1c1ee3
2025-05-27 13:34:45
@ 5d4b6c8d:8a1c1ee3
2025-05-27 13:34:45Is the housing market going to crash for real this time?
https://primal.net/e/nevent1qvzqqqqqqypzp6dtxy5uz5yu5vzxdtcv7du9qm9574u5kqcqha58efshkkwz6zmdqqs8dqr35dc0npsc8cuulqm4m7gxrgqq3ytphtja9nx534a592gztzsuzsrja
https://stacker.news/items/990316
-
 @ c631e267:c2b78d3e
2025-04-04 18:47:27
@ c631e267:c2b78d3e
2025-04-04 18:47:27Zwei mal drei macht vier, \ widewidewitt und drei macht neune, \ ich mach mir die Welt, \ widewide wie sie mir gefällt. \ Pippi Langstrumpf
Egal, ob Koalitionsverhandlungen oder politischer Alltag: Die Kontroversen zwischen theoretisch verschiedenen Parteien verschwinden, wenn es um den Kampf gegen politische Gegner mit Rückenwind geht. Wer den Alteingesessenen die Pfründe ernsthaft streitig machen könnte, gegen den werden nicht nur «Brandmauern» errichtet, sondern der wird notfalls auch strafrechtlich verfolgt. Doppelstandards sind dabei selbstverständlich inklusive.
In Frankreich ist diese Woche Marine Le Pen wegen der Veruntreuung von EU-Geldern von einem Gericht verurteilt worden. Als Teil der Strafe wurde sie für fünf Jahre vom passiven Wahlrecht ausgeschlossen. Obwohl das Urteil nicht rechtskräftig ist – Le Pen kann in Berufung gehen –, haben die Richter das Verbot, bei Wahlen anzutreten, mit sofortiger Wirkung verhängt. Die Vorsitzende des rechtsnationalen Rassemblement National (RN) galt als aussichtsreiche Kandidatin für die Präsidentschaftswahl 2027.
Das ist in diesem Jahr bereits der zweite gravierende Fall von Wahlbeeinflussung durch die Justiz in einem EU-Staat. In Rumänien hatte Călin Georgescu im November die erste Runde der Präsidentenwahl überraschend gewonnen. Das Ergebnis wurde später annulliert, die behauptete «russische Wahlmanipulation» konnte jedoch nicht bewiesen werden. Die Kandidatur für die Wahlwiederholung im Mai wurde Georgescu kürzlich durch das Verfassungsgericht untersagt.
Die Veruntreuung öffentlicher Gelder muss untersucht und geahndet werden, das steht außer Frage. Diese Anforderung darf nicht selektiv angewendet werden. Hingegen mussten wir in der Vergangenheit bei ungleich schwerwiegenderen Fällen von (mutmaßlichem) Missbrauch ganz andere Vorgehensweisen erleben, etwa im Fall der heutigen EZB-Chefin Christine Lagarde oder im «Pfizergate»-Skandal um die Präsidentin der EU-Kommission Ursula von der Leyen.
Wenngleich derartige Angelegenheiten formal auf einer rechtsstaatlichen Grundlage beruhen mögen, so bleibt ein bitterer Beigeschmack. Es stellt sich die Frage, ob und inwieweit die Justiz politisch instrumentalisiert wird. Dies ist umso interessanter, als die Gewaltenteilung einen essenziellen Teil jeder demokratischen Ordnung darstellt, während die Bekämpfung des politischen Gegners mit juristischen Mitteln gerade bei den am lautesten rufenden Verteidigern «unserer Demokratie» populär zu sein scheint.
Die Delegationen von CDU/CSU und SPD haben bei ihren Verhandlungen über eine Regierungskoalition genau solche Maßnahmen diskutiert. «Im Namen der Wahrheit und der Demokratie» möchte man noch härter gegen «Desinformation» vorgehen und dafür zum Beispiel den Digital Services Act der EU erweitern. Auch soll der Tatbestand der Volksverhetzung verschärft werden – und im Entzug des passiven Wahlrechts münden können. Auf europäischer Ebene würde Friedrich Merz wohl gerne Ungarn das Stimmrecht entziehen.
Der Pegel an Unzufriedenheit und Frustration wächst in großen Teilen der Bevölkerung kontinuierlich. Arroganz, Machtmissbrauch und immer abstrusere Ausreden für offensichtlich willkürliche Maßnahmen werden kaum verhindern, dass den etablierten Parteien die Unterstützung entschwindet. In Deutschland sind die Umfrageergebnisse der AfD ein guter Gradmesser dafür.
[Vorlage Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ c3c7122c:607731d7
2025-04-12 04:05:06
@ c3c7122c:607731d7
2025-04-12 04:05:06Help!
Calling all El Salvador Nostriches! If you currently live in SV, I need your help and am offering several bounties (0.001, 0.01, and 0.1 BTC).
In Brief
In short, I am pursuing El Salvador citizenship by birthright (through my grandmother). I’ve struggled to progress because her name varies on different documents. I need someone to help me push harder to get past this barrier, or connect me with information or people who can work on my behalf. I am offering:
- 0.001 BTC (100k sats) for information that will help me progress from my current situation
- 0.01 BTC (1 MM sats) to get me in touch with someone that is more impactful than the immigration lawyer I already spoke with
- 0.1 BTC (10 MM sats) if your efforts help me obtain citizenship for me or my father
Background
My grandma married my grandfather (an American Marine) and moved to the states where my father was born. I have some official and unofficial documents where her name varies in spelling, order of first/middle name, and addition of her father’s last name. So every doc basically has a different name for her. I was connected with an english-speaking immigration lawyer in SV who hit a dead end when searching for her official ID because the city hall in her city had burned down so there was no record of her info. He gave up at that point. I find it odd that it was so easy to change your name back then, but they are more strict now with the records from that time.
I believe SV citizenship is my birthright and have several personal reasons for pursuing this. I want someone to act on my behalf who will try harder to work the system (by appeal, loophole, or even bribe if I have to). If you are local and can help me with this, I’d greatly appreciate any efforts you make.
Cheers!
Corey San Diego
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 0c65eba8:4a08ef9a
2025-05-27 17:03:54
@ 0c65eba8:4a08ef9a
2025-05-27 17:03:54Most people assume that the future will look like the present, just more of it. That’s why they get blindsided. Ideas and events that seemed “unthinkable” yesterday often become the norm tomorrow. The end of slavery, universal suffrage, legal equality for women, the collapse of the Soviet Union, the legalization of gay marriage, the fall of the Berlin Wall, the mass adoption of smartphones, and even the outbreak of world wars, none of these were considered likely or even possible by the majority until they were already happening.
Why does this happen? Because what drives large-scale change isn't today's opinions or moral sentiments. It's shifting incentives.
When people change their minds at scale, it's not because everyone suddenly found a better argument. It's because the costs and rewards of holding their previous views changed. Incentives shifted. And when incentives shift, behavior follows. Belief is downstream of necessity.
We have been going in a particular direction for over a century now, a direction increasingly out of alignment with Natural Law. Liberalization, moral relativism, and institutional centralization have undermined the evolutionary constraints that sustain functional cooperation. As the distance from a Natural Law equilibrium grows, so do the costs. The pressure to restore reciprocity, sovereignty, and truth builds beneath the surface.
And this buildup doesn't continue indefinitely. It snaps. When it does, the pendulum swings hard in the other direction. Just as many societal liberalizations once seemed impossible until they occurred, many of the restorations and clawbacks now deemed unthinkable will appear inevitable in hindsight.
This is not a matter of nostalgia or ideology, it’s a matter of survival. Restoration of traditional values aligned with Natural Law will happen, not because it is wanted by all, but because it will become necessary for continued cooperation and survival.
That’s why instead of guessing what the future holds based on what feels right today, we can calculate what is likely based on Natural Law.
Natural Law isn’t a philosophy, it’s a description of the rules that govern cooperation and conflict. It defines the pressures, constraints, and evolutionary incentives that force people to adapt. And it shows how those pressures produce large-scale changes in thought, behavior, and institutions.
That’s the common-language version. But to really understand why this works, and why most predictions fail, we need to move from intuition to computation. We need a scientific grammar of change.
Understanding Natural Law and Its Predictive Power:
Natural Law is a framework developed and refined by Curt Doolittle and a collaborative body of thinkers at the Natural Law Institute. It is not a philosophy or ideology, but a scientific system that explains how incentives shape human cooperation, belief, and institutional stability over time.
This explanation draws on the key principles of Natural Law to clarify why seemingly impossible cultural reversals become inevitable. For more, seek out and follow the Natural Law Institute and Curt Doolittle.
-
First Principle: All human behavior is reducible to acquisition under constraint. Constraints are physical, biological, and institutional.
-
Causal Chain: Beliefs are not causes; they are consequences. What people consider “possible” or “acceptable” is a strategy for surviving current incentive structures. When those structures change, beliefs change.
-
Decidability: Natural Law operationalizes this by providing a decidable, commensurable, and testifiable logic of human cooperation. It identifies invariant incentives and maps them across scales: individual, institutional, and civilizational.
-
Prediction: Prediction is not sentiment or analogy, it is adversarial computation over time. What is inconceivable today becomes obvious tomorrow because people adapt to pressures, not principles.
-
Conclusion: Therefore, we reject moral intuitionism and ideological forecasting. We use Natural Law to trace changes in cooperation and conflict as evolutionary computation. It allows us to model not what people believe, but what they must do to survive within new equilibria of constraint.
Final Thoughts:
Most people attempt to forecast the future using moral intuitions, wishful thinking, ideological narratives, or historical analogies. These methods are little more than guesswork, prophecies dressed up as analysis. They offer comfort, not clarity.
Natural Law offers something different: a method of calculation. A system of first principles, constraints, and causal chains that can be used to project outcomes and identify the likely direction of change. Whether you are a father making long-term decisions for your family, an entrepreneur allocating resources, a CEO steering a corporation, or a statesman crafting policy, Natural Law gives you the tools to understand what pressures are building, what constraints are shifting, and what behaviors will be necessary in the near future.
You don’t need to master every element of Natural Law to benefit from it. That’s what the Natural Law Institute is for. If you have strategic questions, if you are responsible for people, capital, or institutions, reach out. We will help you identify your opportunities, clarify your risks, and calculate the range of outcomes you need to prepare for.
Contact us directly or engage with us online. We exist to make the future decidable.
Noah Revoy Senior Fellow at the Natural Law Institute Natural Law Applied Psychology
-
-
 @ 65038d69:1fff8852
2025-04-08 03:03:04
@ 65038d69:1fff8852
2025-04-08 03:03:04Sometime in the not-too-distant future...
alert – low voltage – P Node 5
Pippin looked up from the McMaster-Carr catalogue to the blinking line of text. A double-click opened the Grafana page for Perimeter Node 5. The solar panel voltage graph showed a stable 18V, then a jagged drop to 10V. Weird, that panel is less than a year old, and it’s a clear, sunny, wind-less day. He reached to the wall and poked the button labelled “Patrol 3”, and listened for the noise of the Hawk 2A fixed-wing patrol drone leaving it’s nest.
whirrrrr-zip!
Off it went. It should be over the node in about 6 minutes. He opened the live feed on the second monitor and went back to the catalogue. Here we are, 49045K12. That should get the water system in the greenhouse working again. Back on the computer he opened his AirZap page, selected McMaster-Carr from the list of vendors, and entered the part number on the item list. 148sats with next week’s regular delivery, or 400sats special delivery tomorrow. He clicked the “Regular Delivery” button, then “Confirm Zap”. The HF radio on the network rack hummed for a moment then shrieked a burst of noise. The Nostr event with the order details and Lightning payment was on it’s way to McMaster-Carr’s relay. Luckily the part is small and light enough for drone delivery. Pippin’s private grid on Glass Lake is well outside Fed-PS’s ground delivery area, and even if it wasn’t, there are no government roads here. Being a non-citizen and outside a metro-state was a pain and could be expensive. It was better than paying a 95% tax rate though...
alert – low voltage – P Node 5
The node! His eyes snapped to the second monitor just in time for the flyover, and he could see right away that the solar panel was at an odd angle. Yay, a field repair out in the cold. He tossed the tool kit and electrical repair kit on the hovertrike rack while his thermos filled with coffee. Giving the freeze-frame from the Hawk 2A a second look, he grumbled and grabbed the mechanical kit, adding it to the pile. After a third look and an eye roll he dragged a spare solar panel over to the trailer, then slapped the “Hitch” button.
Clear! Clear! Clear! zzz-thunk!
The electromagnets sucked the trailer and trike together, the pin dropping in as soon as it cleared. Pippin silently prayed thanks to God for small conveniences that eased life’s suffering and slurped a sip off the top of the thermos. And coffee. Thank you Father for the coffee trees in the greenhouse.
...
The cutline running the border of Pippin’s property is technically straight and certainly looks it from above, but driving it, even on a hovertrike, is a bouncy, curvy, slow-going affair. Watching immediately ahead instead of appropriately further meant a surprise when the node entered his field of vision. The trailer slid sideways as the trike stopped immediately on its legs. After a sigh and a sip, Pippin powered off the pads and dismounted. Yup, the solar panel is definitely twisted sideways. And bent. And...scratched? Short gouges scraped through the 2 columns of cells closest to the bent edge. There were no fallen trees nearby, so that wasn’t the cause...
snap!
He reached for his laser and got nothing but air. It was in the shop on the charger. Of course it would be; cue a subconscious eye roll. When his brain finally caught up with his eyes he registered the source: 2 meters tall, all black, and capable of mowing him down without a second thought. Thankfully the bull moose was, as most are, completely disinterested in everything but the willow tree he was in the middle of dismembering for lunch. Nonchalance was a benefit of having no natural predators. The ceramic dust on the points of one antler solved the solar panel mystery though; the panel was at the perfect hight for him to have scrapped the side of it as he walked by. He probably didn’t even notice as they’re constantly dragging them through the brush and trees.
...
warning – P Node 5 offline
He hadn’t bothered to mute the alerts while he replaced the broken panel and twisted mounting hardware. Last time he did he forgot to unmute them and went 2 days without noticing. Better to be mildly annoyed for a short time then to go without system or security alerts. He closed the junction box and moved his gaze to the status screen.
powering on...
self check...
all tests pass...
connecting to network...
no signal, switching to failover network...
He mashed the reboot button before it could complete. If he let it connect to the backup ZuckLink satellite network he’d be paying non-citizen usage fees by the megabyte. It was probably just a hiccup anyways, the point-to-point terrestrial link would probably connect fine on the next try.
no signal, switching to failover network...
This time he hit the power switch. The moose hadn’t damaged the antenna and he’d double-checked the alignment while he had the ladder out. Why wasn’t it connecting? He picked up the network scanner, walked to the other side of the node, and pointed it in the general direction of Node 6. No signal. Surely Node 6 didn’t go down on his way here. Now it was either drive all the way there to check it, or let Node 5 connect via satellite and check remotely.
no signal, switching to failover network...
He could practically feel the sats streaming out of his wallet. Ugh, here we go...
failover network unavailble, no signal...
What? There’s no way the satellite link was down too, unless the whole network stack was borked. Huffing and grumbling back to the trike, he plugged the network scanner into it’s com system and selected the satellite interface.
no signal
“Hey Bullwinkle, you wouldn’t happen to be running around with an all-spectrum jammer would you?” Hearing nothing, he looked up and around for the moose. He had been working his way down the edge of the line where the young willows were while Pippin had been working on repairs. Now he was gone. If the moose had joined the rimwalker raiders and started carrying signal jammers, he should be out of range now. He chuckled at the thought of some off-grid wildman trying to train a moose to carry equipment.
no signal, switching to failover network...
failover network unavailable, no signal...
Maybe it was the network stack. But that wouldn’t explain being unable to connect through the trike. Maybe he should just unhitch the trailer and go check Node 6. While highly unlikely, there could be a ZuckLink outage in his cell and an issue with the link to the next node at the same time. The only way to know would be to check in-person.
As he looked up from the status screen his peripheral caught motion on the treeline. “Hey Bullwinkle, is that you?” Antler points protruded from behind a tree, unmoving. A bit too still, actually.
“Bullwinkle?” Those weren’t antler points. That was an antenna array.
no signal
Notes & Appendix
The various technical and other odd bits I used in this story are all either real things or will be very soon. If this was a movie or TV show the visual elements would make some of the nerdier references either to get (i.e. most people would know a drone if they saw one, but saying “fixed-wing patrol drone” doesn’t necessarily draw a mental image for everyone), but in an effort to not constantly interrupt the flow for explanations I’ve moved those here. If I’ve missed any or you want more more detailed explanations, you can find us at scalebright.ca!
McMaster-Carr: A 120+ year old distribution company that specializes in hardware, parts, and tools. Known for their iconic enormous yellow catalogues and legendary (in I.T. circles) website. They’ll probably still be around in another 120+ years and probably still have their yellow catalogues.
Fixed-wing patrol drones: The fixed-wing variety of drones look like miniature airplanes and generally fly much faster than their more common quad-copter style siblings, making them excellent for patrols of static routes.
Sats: Short for “satoshis”, sats are the smallest denomination of Bitcoin.
Zaps: Bitcoin Lighting payments made over Nostr.
Lighting: A Bitcoin protocol for small payments (usually denominated in sats).
Nostr: A decentralized communications and social media protocol.
HF radio: Short for “high frequency”, also knows as ham radio. Bitcoin Lightning payments have been made over HF, as have Nostr posts.
Metro-state: City-states have existed since cities were first built. Metro-states would be a modern version that include their entire greater metro areas in their statehood.
Laser: Advances in focusing lens manufacturing have made handheld “laser guns” possible, though currently legally dubious. I get ads for them on a few of my social networks.
Ceramic solar panels: They’re being marketed as the next big thing in solar tech, but time will tell if they’re as good as the sales pitches say.
Bullwinkle: An anthropomorphic moose character from the 1950s/60s TV show “Rocky and Bullwinkle”.
All-spectrum jammer: Police have been finding criminals using both commercially manufactured and home-made signal jammers during robberies, kidnappings, and other crimes to stop people from calling emergency services or disrupt wireless security cameras. Most of them look like a WIFI router with a whole bunch of antennas.
rimwalker raiders: A made-up category of bandits known for living on the edge of civilization but still making use of technology.
-
 @ c631e267:c2b78d3e
2025-04-03 07:42:25
@ c631e267:c2b78d3e
2025-04-03 07:42:25Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-App, die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt in Kraft getreten.
Mit den üblichen Argumenten der Vereinfachung, des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon.
Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte, wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten.
Um sich die digitale Version des nationalen Ausweises besorgen zu können (eine App mit dem Namen MiDNI), muss man sich vorab online registrieren. Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person.
Für jeden Vorgang der Identifikation in der Praxis wird später «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann.
Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare. Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger.
Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt in Richtung der «totalen Digitalisierung» des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht.
In Zukunft könnte der neue Ausweis «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal Cope ganz richtig bemerkt. Das ist die Perspektive.
[Titelbild: Pixabay]
Dazu passend:
Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ bbef5093:71228592
2025-05-13 04:18:45
@ bbef5093:71228592
2025-05-13 04:18:45Nukleáris politika – 2025. május 12. | Szerző: David Dalton
Lengyelország és Franciaország nukleáris szerződést ír alá, Macron új építési szerződéseket céloz
Lengyelország és Franciaország olyan szerződést kötött, amely együttműködést irányoz elő a polgári nukleáris energia szektorban, miközben Párizs reménykedik abban, hogy Varsótól jövedelmező új atomerőmű-építési szerződéseket nyer el.
A szerződés közös tevékenységeket tartalmaz, amelyek célja a nukleáris energia előnyeinek kihasználása az európai ipar dekarbonizációja érdekében.
A két ország együtt kíván működni a nukleáris fűtőanyag-ellátás biztonságának megerősítésében is.
Európa szeretné kizárni Oroszországot a nukleáris fűtőanyag-piacáról, de az Euratom Ellátási Ügynökség (ESA) legfrissebb éves jelentése szerint 2023-ban nőtt az Oroszországból származó természetes urán szállítása, mivel az uniós szolgáltatók készleteket halmoztak fel az orosz tervezésű VVER atomerőművekhez.
Az ESA, amely az európai nukleáris anyagok rendszeres és méltányos ellátásáért felelős, közölte, hogy az uniós szolgáltatók tovább diverzifikálják nukleáris fűtőanyag-beszerzéseiket, különösen a VVER reaktorokhoz, hogy csökkentsék a „egy forrásból származó vagy magas kockázatú” ellátásoktól való függést.
„Majdnem minden olyan ország, amely orosz tervezésű reaktorokat üzemeltet, halad az alternatív fűtőanyagok engedélyeztetésében, és ígéretes fejlemények várhatók a közeljövőben” – közölte az ESA.
Az EU-ban jelenleg 19 VVER reaktor működik, köztük négy 1000 MW-os Bulgáriában és Csehországban, valamint tizenöt 440 MW-os Csehországban, Finnországban, Magyarországon és Szlovákiában.
A jelentések szerint a francia–lengyel nukleáris szerződés különösen fontos a francia állami EDF energetikai vállalat számára, amely még mindig reménykedik abban, hogy részt vehet Lengyelország ambiciózus atomerőmű-építési programjában, annak ellenére, hogy az első új építésű projekt tenderét az amerikai Westinghouse nyerte el Pomeránia északi tartományában.
Franciaország ambiciózus reaktorépítési tervei
Franciaország maga is nagyszabású nukleáris fejlesztési terveket dédelget: a kormány nemrégiben felkérte az EDF-et, hogy gyorsítsa fel a hat új generációs EPR2 atomerőmű megépítésének előkészítését.
Az EDF kezdetben három EPR2 párost tervez: az elsőt Penlyben, majd egyet-egyet a Gravelines-i atomerőmű telephelyén (Calais közelében), illetve vagy Bugey-ben (Lyon keleti részén), vagy Tricastinban (Lyon és Avignon közelében).
A nukleáris szerződés aláírását megelőzte egy másik szerződés is, amely a két szövetséges közötti kapcsolatok elmélyítését, valamint kölcsönös biztonsági garanciákat is tartalmaz háború esetére.
Donald Tusk lengyel miniszterelnök, aki Emmanuel Macron francia elnökkel együtt írta alá a biztonsági dokumentumot, „áttörésnek” nevezte a szerződést, kiemelve, hogy csak Németországnak van hasonló biztonsági paktuma Franciaországgal, és ez Lengyelországot „egyenrangú partnerként” helyezi nyugati szövetségesei közé.
Macron eközben úgy fogalmazott, hogy a szerződés „új korszakot nyit” nemcsak Lengyelország és Franciaország, hanem egész Európa számára. „Bresttől Krakkóig Európa együtt áll ki” – mondta a francia elnök.
Nukleáris politika – 2025. május 12. | Szerző: David Dalton
Trump csapata a nukleáris erőművek építésének felgyorsítását tervezi
A Trump-adminisztráció tisztviselői végrehajtási rendeleteket készítenek elő, amelyek célja az atomerőművek jóváhagyásának és építésének felgyorsítása az Egyesült Államokban – számolt be róla a sajtó.
Az erőfeszítés, amelyet egy kormányzati tisztviselő és más, az egyeztetéseket ismerő személyek írtak le, még folyamatban van. Az elnök még nem hagyta jóvá a tervezetet – mondta az egyik forrás, aki névtelenséget kért, mivel hivatalos bejelentés még nem történt. Az amerikai Axios hírportál és a New York Times is beszámolt az egyeztetésekről.
Trump és kormányának tisztviselői többször hangsúlyozták a bőséges, olcsó villamos energia fontosságát az energiaigényes mesterséges intelligencia ipar számára, amely segítheti az Egyesült Államokat abban, hogy megnyerje a feltörekvő technológia globális versenyét.
„Meg kell nyernünk az MI-versenyt, és ebben vezetnünk kell – ehhez pedig sokkal több energiára lesz szükség” – mondta Chris Wright energiaügyi miniszter múlt hónapban egy kabinetülésen Trump társaságában.
Az elnök már hivatalosan is energia-vészhelyzetet hirdetett, nemzeti és gazdasági biztonsági szempontokra hivatkozva annak érdekében, hogy gyorsítsa az erőművek, csővezetékek és elektromos távvezetékek építését az országban.
A szóban forgó tervezetek célokat tűznének ki az atomerőművek gyors országos építésére, illetve az amerikai nukleáris ipar vezető szerepének visszaállítására.
Legalább az egyik intézkedés a Nukleáris Szabályozási Bizottságnál (NRC) vezetne be változtatásokat, amelyek gyorsíthatják az erőműtervek, köztük az új kis moduláris reaktorok (SMR-ek) engedélyezését.
Wright nemrégiben úgy nyilatkozott, hogy az új reaktorblokkok építésének legnagyobb akadálya az Egyesült Államokban a szabályozás volt.
Az elképzelés részeként akár katonai létesítményekre is telepíthetnek majd atomerőműveket, valószínűleg mikroreaktorok vagy SMR-ek formájában.
Jelenleg az Egyesült Államokban nincs kereskedelmi atomerőmű építés alatt. Az utolsó két üzembe helyezett blokk a georgiai Vogtle-3 és Vogtle-4 volt, 2023-ban és 2024-ben.
Előrehaladott tervek vannak a michigani Palisades atomerőmű újraindítására. Ha megvalósul, ez lenne az első olyan, korábban leállított amerikai atomerőmű, amely ismét működésbe lép.
Új építések – 2025. május 12. | Szerző: David Dalton
Vietnam és Oroszország tárgyalásokat kezd atomerőmű-építésről
Vietnam és Oroszország megállapodott abban, hogy tárgyalásokat folytatnak és szerződéseket írnak alá kereskedelmi atomerőművek építéséről Vietnamban – közölték a két ország egy közös nyilatkozatban.
„Az erőművek fejlesztése korszerű technológiával szigorúan megfelel majd a nukleáris és sugárbiztonsági előírásoknak, és a társadalmi-gazdasági fejlődést szolgálja” – áll a közleményben, amely a vietnami vezető, To Lam moszkvai látogatása után jelent meg.
Az orosz állami atomenergetikai vállalat, a Roszatom szerint a látogatás „az együttműködés új szakaszát” jelenti – egy nagy atomerőmű építését Délkelet-Ázsiában.
A Roszatom felajánlotta Vietnámnak a VVER-1200 nyomottvizes reaktor technológiáját, amelyből kettő már működik az oroszországi Novovoronyezs 2 atomerőműben, és kettő Fehéroroszországban.
A Roszatom közölte, hogy további tárgyalásokra van szükség a vietnami atomerőmű műszaki és pénzügyi feltételeinek tisztázásához, de hozzátette: „ezek a tárgyalások ma [május 10-én] megkezdődtek”.
A Roszatom arról is beszámolt, hogy Alekszej Lihacsov vezérigazgató és Nguyen Manh Hung vietnami tudományos és technológiai miniszter aláírt egy nukleáris energia ütemtervet.
Az ütemterv tartalmazza egy nukleáris tudományos és technológiai központ lehetséges megépítését, fűtőanyag-szállítást a dél-vietnami Dalat kutatóreaktorhoz, Vietnam részvételét Oroszország IV. generációs MBIR többcélú gyorsneutronos kutatóreaktor projektjében, valamint vietnami szakemberek képzését.
Vietnamnak jelenleg egy kutatóreaktora van Dalatban, és egy másik is tervben van. A Roszatom nem közölte, melyikre gondolt.
A múlt hónapban Vietnam elfogadta a nemzeti energiastratégia módosított változatát, amely 2030-ig 136 milliárd dollárt irányoz elő az energiaellátás hosszú távú biztonságának megerősítésére, és először szerepel benne az atomenergia.
Vietnam azt szeretné, ha első atomerőművei 2030 és 2035 között lépnének üzembe. A beépített nukleáris kapacitás várhatóan 4–6,4 GW lesz, ami körülbelül 4–6 nagy atomerőműnek felel meg.
A kormány szerint további 8 GW nukleáris kapacitás kerül majd a mixbe az évszázad közepéig.
Vietnam már 2009-ben is tervezett két atomerőművet, de a Nemzetgyűlés 2016-ban költségvetési okokból elutasította a javaslatot.
Új építések – 2025. május 12. | Szerző: David Dalton
Az NRC engedélyt adott az „energia-sziget” munkálatokra a TerraPower wyomingi atomerőművénél
Az Egyesült Államok Nukleáris Szabályozási Bizottsága (NRC) mentességet adott a TerraPower Natrium demonstrációs atomerőművének wyomingi Kemmererben, lehetővé téve a vállalat számára bizonyos „energia-sziget” tevékenységek folytatását, miközben a hatóságok tovább vizsgálják az építési engedély iránti kérelmet.
Az energia-sziget a tervezett Natrium atomerőműben a felesleges hő tárolására szolgál majd, hogy csúcsterhelés idején növelje az áramtermelést.
Az NRC szerint az energia-szigethez kapcsolódó bizonyos tevékenységek engedélyezése nem jelent indokolatlan kockázatot a közegészségre és biztonságra, és „különleges körülmények” állnak fenn.
A mentesség a létesítmények, rendszerek és komponensek korlátozott részére vonatkozik, lehetővé téve például cölöpverést, alapozást, vagy bizonyos szerkezetek, rendszerek és komponensek összeszerelését, gyártását, tesztelését korlátozott munkavégzési engedély nélkül.
Az NRC szerint a mentesség nem befolyásolja a reaktor építési engedélyéről szóló végső döntést. „Az NRC folytatja az építési engedély iránti kérelem vizsgálatát az egész projektre vonatkozóan” – áll a közleményben.
A Bill Gates által alapított TerraPower üdvözölte a döntést, hozzátéve, hogy a nukleáris reaktor és az energiatermelő létesítmények szétválasztása rövidebb építési időt és alacsonyabb anyagköltségeket tesz lehetővé.
Februárban az amerikai energiaügyi minisztérium befejezte a projekt előzetes tevékenységeire vonatkozó végső környezeti értékelést.
A TerraPower, amelyet Gates 2008-ban alapított, 2024 júniusában kezdte meg első kereskedelmi Natrium atomerőművének építését Kemmererben, ahol egy széntüzelésű erőmű zár be.
A Natrium demonstrációs projekt három különálló részből áll: egy nátrium teszt- és feltöltő létesítményből, az energiatermelő vagy energia-szigetből, valamint a nukleáris szigetből magával a reaktorral.
A kezdeti építkezés a teszt- és feltöltő létesítményre összpontosít, amely egy különálló, nem nukleáris épület, és a reaktor nátrium hűtőrendszerének tesztelésére szolgál. Itt történik a folyékony nátrium fogadása, mintavételezése, feldolgozása és tárolása, mielőtt a Natrium reaktorhoz kerülne.
Egyéb hírek
A lengyel atomerőmű-projekt biztosítási szerződéseket kötött
A lengyel Polskie Elektrownie Jądrowe (PEJ) atomerőmű-projekt vállalat négy biztosítási bróker céggel kötött keretmegállapodást. Az Aon Polska, GrECo Polska, Marsh és Smartt Re cégek támogatják a PEJ-t Lengyelország első kereskedelmi atomerőművének biztosítási szerződéseinek megkötésében, valamint a napi működéshez szükséges biztosítások beszerzésében. A PEJ minden brókerrel keretmegállapodást írt alá, amelyek alapján egyes biztosítási feladatokra kiválasztja a megfelelő brókert.
Az Aecon cég nyerte az ontariói SMR építési szerződését
A kanadai Aecon Kiewit Nuclear Partners nyerte el az Ontario Power Generation (OPG) által Darlingtonban építendő első kis moduláris reaktor (SMR) kivitelezési szerződését. A szerződés értéke 1,3 milliárd kanadai dollár (934 millió USD, 841 millió euró), amely projektmenedzsmentet, kivitelezési tervezést és végrehajtást foglal magában, a befejezést és a kereskedelmi üzemet 2030-ra tervezik. Ontario tartomány és az OPG múlt héten hagyta jóvá a négy SMR első darabjának 20,9 milliárd CAD értékű tervét Darlingtonban.
26 000 dolgozó a Hinkley Point C projekten a csúcskivitelezés idején
Az Egyesült Királyságban mintegy 26 000 dolgozó vesz részt a Hinkley Point C atomerőmű építésében, amely jelenleg csúcskivitelezési szakaszban van – derül ki az EDF Energy jelentéséből. Közvetlenül a projekten 18 000-en dolgoznak, ebből 12 000-en a helyszínen, további 3 000 fővel bővülhet a létszám a következő 12 hónapban. További 8 000-en a beszállítói láncban dolgoznak. A jelentés szerint a Hinkley Point C építése fontos katalizátor a gazdasági növekedésben, jelenleg 13,3 milliárd fonttal (15,7 milliárd euró, 17,5 milliárd dollár) járul hozzá a gazdasághoz. Ebből 5 milliárd fontot már a délnyugati régió beszállítóinál költöttek el – jóval meghaladva az 1,5 milliárd fontos célt. A Hinkley Point C két francia EPR reaktort kap.
Az Ansaldo Nucleare nukleáris mesterszakot indít Olaszországban
Az olasz Ansaldo Nucleare és a Politecnico di Milano vállalati mesterszakot indít, amely a nukleáris energia és kapcsolódó technológiák új szakértő generációját képzi. A képzés októberben indul, egy évig tart, 1500 órás, mérnöki, fizikai és kémiai diplomásoknak szól. Húsz résztvevőt választanak ki a következő hónapokban, akiket az Ansaldo Nucleare azonnal, határozatlan időre alkalmaz, és október elején kezdik meg a képzést.
-
 @ d360efec:14907b5f
2025-05-13 00:39:56
@ d360efec:14907b5f
2025-05-13 00:39:56🚀📉 #BTC วิเคราะห์ H2! พุ่งชน 105K แล้วเจอแรงขาย... จับตา FVG 100.5K เป็นจุดวัดใจ! 👀📊
จากากรวิเคราะห์ทางเทคนิคสำหรับ #Bitcoin ในกรอบเวลา H2:
สัปดาห์ที่แล้ว #BTC ได้เบรคและพุ่งขึ้นอย่างแข็งแกร่งค่ะ 📈⚡ แต่เมื่อวันจันทร์ที่ผ่านมา ราคาได้ขึ้นไปชนแนวต้านบริเวณ 105,000 ดอลลาร์ แล้วเจอแรงขายย่อตัวลงมาตลอดทั้งวันค่ะ 🧱📉
ตอนนี้ ระดับที่น่าจับตาอย่างยิ่งคือโซน H4 FVG (Fair Value Gap ในกราฟ 4 ชั่วโมง) ที่ 100,500 ดอลลาร์ ค่ะ 🎯 (FVG คือโซนที่ราคาวิ่งผ่านไปเร็วๆ และมักเป็นบริเวณที่ราคามีโอกาสกลับมาทดสอบ/เติมเต็ม)
👇 โซน FVG ที่ 100.5K นี้ ยังคงเป็น Area of Interest ที่น่าสนใจสำหรับมองหาจังหวะ Long เพื่อลุ้นการขึ้นในคลื่นลูกถัดไปค่ะ!
🤔💡 อย่างไรก็ตาม การตัดสินใจเข้า Long หรือเทรดที่บริเวณนี้ ขึ้นอยู่กับว่าราคา แสดงปฏิกิริยาอย่างไรเมื่อมาถึงโซน 100.5K นี้ เพื่อยืนยันสัญญาณสำหรับการเคลื่อนไหวที่จะขึ้นสูงกว่าเดิมค่ะ!
เฝ้าดู Price Action ที่ระดับนี้อย่างใกล้ชิดนะคะ! 📍
BTC #Bitcoin #Crypto #คริปโต #TechnicalAnalysis #Trading #FVG #FairValueGap #PriceAction #MarketAnalysis #ลงทุนคริปโต #วิเคราะห์กราฟ #TradeSetup #ข่าวคริปโต #ตลาดคริปโต


-
 @ 6146ad04:a0937b0b
2025-05-27 13:25:11
@ 6146ad04:a0937b0b
2025-05-27 13:25:11The cryptocurrency market has evolved from a fringe innovation to a mainstream financial ecosystem in just over a decade. What began with Bitcoin's launch in 2009 has grown into a global market with thousands of digital assets, decentralized finance (DeFi) protocols, and billions of dollars in daily trading volume.
Current Landscape
As of 2025, the cryptocurrency market remains dynamic, with Bitcoin and Ethereum continuing to dominate in terms of market capitalization and influence. However, other assets like Solana, Cardano, and newer entrants are gaining traction, offering innovative features such as faster transaction times, lower fees, and more energy-efficient consensus mechanisms.
The rise of stablecoins, like USDT and USDC, has also played a crucial role in bridging the gap between traditional finance and the digital asset economy. These assets provide a stable store of value in a notoriously volatile market and are widely used in trading, lending, and remittance applications.
Key Trends
-
Regulation and Compliance: Governments and regulatory bodies worldwide are increasingly focused on creating frameworks for crypto oversight. This push aims to protect consumers, combat illicit activities, and integrate digital assets into existing financial systems.
-
Institutional Adoption: Major financial institutions, hedge funds, and publicly traded companies are increasingly incorporating cryptocurrencies into their portfolios. Bitcoin ETFs and crypto custody solutions have helped legitimize the market.
-
Decentralized Finance (DeFi): DeFi platforms offer lending, borrowing, and trading without intermediaries. This sector continues to grow, although it faces regulatory scrutiny and security challenges.
-
Non-Fungible Tokens (NFTs) and Web3: The integration of blockchain with gaming, digital art, and metaverse projects is expanding the use case of cryptocurrencies beyond just financial applications.
Challenges
Volatility: Cryptocurrencies remain highly volatile, posing risks for investors and hindering their use as stable stores of value.
Security: Hacks and scams persist, especially within DeFi ecosystems. Ensuring smart contract security and better user education are critical.
Environmental Concerns: Although the industry is moving toward greener solutions like Proof of Stake (PoS), energy usage remains a concern for some networks.
The Future Outlook
Despite its ups and downs, the cryptocurrency market shows long-term promise. Innovations in blockchain scalability, privacy, and interoperability are likely to shape the next wave of adoption. As regulation matures and institutional trust deepens, cryptocurrencies could become a standard part of the global financial system.
For investors and enthusiasts, staying informed and cautious is key in this rapidly changing space.
-
-
 @ dbc27e2e:b1dd0b0b
2025-04-05 22:49:04
@ dbc27e2e:b1dd0b0b
2025-04-05 22:49:04Dose:
30g coffee (Fine-medium grind size) 500mL soft or bottled water (97°C / 206.6°F)Instructions:
- Rinse out your filter paper with hot water to remove the papery taste. This will also preheat the brewer.
- Add your grounds carefully to the center of the V60 and then create a well in the middle of the grounds.
- For the bloom, start to gently pour 60mL of water, making sure that all the coffee is wet in this initial phase.
- As soon as you’ve added your water, grab your V60 and begin to swirl in a circular motion. This will ensure the water and coffee are evenly mixed. Let this rest and bloom for up to 45 seconds.
- Pour the rest of the water in in 2 phases. You want to try and get 60% of your total water in, within 30 seconds.
- Pour until you reach 300mL total with a time at 1:15. Here you want to pour with a little agitation, but not so much that you have an uneven extraction.
- Once you hit 60% of your total brew weight, start to pour a little slower and more gently, keeping your V60 cone topped up. Aim to have 100% of your brew weight in within the next 30 seconds.
- Once you get to 500mL, with a spoon give the V60 a small stir in one direction, and then again in the other direction. This will release any grounds stuck to the side of the paper.
- Allow the V60 to drain some more, and then give it one final swirl. This will help keep the bed flat towards the end of the brew, giving you the most even possible extraction.
-
 @ aa8de34f:a6ffe696
2025-03-31 21:48:50
@ aa8de34f:a6ffe696
2025-03-31 21:48:50In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht:
„Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\ (Quelle: t.me/rosenbusch/25228)
Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\ Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität.
-- Denn es braucht keinen Untergrund mehr. --
Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür.
Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung.
Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde.
Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen.
Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit.
Die Tyrannei sieht keinen Widerstand.\ Weil sie nicht erkennt, dass er längst begonnen hat.\ Unwiderruflich. Leise. Überall.
-
 @ c1e9ab3a:9cb56b43
2025-05-27 13:19:53
@ c1e9ab3a:9cb56b43
2025-05-27 13:19:53I. Introduction: Money as a Function of Efficiency and Preference
Money is not defined by law, but by power over productivity. In any open economy, the most economically efficient actors—those who control the most valuable goods, services, and knowledge—ultimately dictate the medium of exchange. Their preferences signal to the broader market what form of money is required to access the highest-value goods, from durable commodities to intangibles like intellectual property and skilled labor.
Whatever money these actors prefer becomes the de facto unit of account and store of value, regardless of its legal status. This emergent behavior is natural and reflects a hierarchy of monetary utility.
II. Classical Gresham’s Law: A Product of Market Distortion
Gresham’s Law, famously stated as:
"Bad money drives out good"
is only valid under coercive monetary conditions, specifically: - Legal tender laws that force the acceptance of inferior money at par with superior money. - Fixed exchange rates imposed by decree, not market valuation. - Governments or central banks backing elastic fiduciary media with promises of redemption. - Institutional structures that mandate debt and tax payments in the favored currency.
Under these conditions, superior money (hard money) is hoarded, while inferior money (soft, elastic, inflationary) circulates. This is not an expression of free market behavior—it is the result of suppressed price discovery and legal coercion.
Gresham’s Law, therefore, is not a natural law of money, but a law of distortion under forced parity and artificial elasticity.
III. The Collapse of Coercion: Inversion of Gresham’s Law
When coercive structures weaken or are bypassed—through technological exit, jurisdictional arbitrage, monetary breakdown, or political disintegration—Gresham’s Law inverts:
Good money drives out bad.
This occurs because: - Market actors regain the freedom to select money based on utility, scarcity, and credibility. - Legal parity collapses, exposing the true economic hierarchy of monetary forms. - Trustless systems (e.g., Bitcoin) or superior digital instruments (e.g., stablecoins) offer better settlement, security, and durability. - Elastic fiduciary media become undesirable as counterparty risk and inflation rise.
The inversion marks a return to monetary natural selection—not a breakdown of Gresham’s Law, but the collapse of its preconditions.
IV. Elasticity and Control
Elastic fiduciary media (like fiat currency) are not intrinsically evil. They are tools of state finance and debt management, enabling rapid expansion of credit and liquidity. However, when their issuance is unconstrained, and legal tender laws force their use, they become weapons of economic coercion.
Banks issue credit unconstrained by real savings, and governments enforce the use of inflated media through taxation and courts. This distorts capital allocation, devalues productive labor, and ultimately hollows out monetary confidence.
V. Monetary Reversion: The Return of Hard Money
When the coercion ends—whether gradually or suddenly—the monetary system reverts. The preferences of the productive and wealthy reassert themselves:
- Superior money is not just saved—it begins to circulate.
- Weaker currencies are rejected not just for savings, but for daily exchange.
- The hoarded form becomes the traded form, and Gresham’s Law inverts completely.
Bitcoin, gold, and even highly credible stable instruments begin to function as true money, not just stores of value. The natural monetary order returns, and the State becomes a late participant, not the originator of monetary reality.
VI. Conclusion
Gresham’s Law operates only under distortion. Its inversion is not an anomaly—it is a signal of the collapse of coercion. The monetary system then reorganizes around productive preference, technological efficiency, and economic sovereignty.
The most efficient market will always dictate the form of hard money. The State can delay this reckoning through legal force, but it cannot prevent it indefinitely. Once free choice returns, bad money dies, and good money lives again.
-
 @ c631e267:c2b78d3e
2025-03-31 07:23:05
@ c631e267:c2b78d3e
2025-03-31 07:23:05Der Irrsinn ist bei Einzelnen etwas Seltenes – \ aber bei Gruppen, Parteien, Völkern, Zeiten die Regel. \ Friedrich Nietzsche
Erinnern Sie sich an die Horrorkomödie «Scary Movie»? Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?

Diese Szene kommt mir automatisch in den Sinn, wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real.
Die Europäische Union hat sich selbst über Jahre konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt.
In den USA haben sich die Vorzeichen allerdings mittlerweile geändert, und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen.
Statt jedoch umzukehren oder wenigstens zu bremsen und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die Kommentatoren des Events gegenseitig in sensationslüsterner «Berichterstattung».
Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen, Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, selbstzerstörerischen Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», erklärte die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte.
Zusätzlich brisant ist, dass aktuell «die ganze EU von Deutschen regiert wird», wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen.
Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen.
Es wird dringend Zeit, dass wir, der Souverän, diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts den Frieden auszurufen. Seien wir dabei!
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ d360efec:14907b5f
2025-05-12 04:01:23
@ d360efec:14907b5f
2025-05-12 04:01:23 -
 @ 9cb3545c:2ff47bca
2025-05-27 12:58:56
@ 9cb3545c:2ff47bca
2025-05-27 12:58:56Introduction
Public companies that hold Bitcoin on behalf of investors (often issuing securities backed by those Bitcoin holdings) have faced growing pressure to demonstrate proof of reserves – evidence that they genuinely hold the cryptocurrency they claim. One approach is to publish the company’s Bitcoin wallet addresses so that anyone can verify the balances on the blockchain. This practice gained momentum after high-profile crypto collapses (e.g. FTX in 2022) eroded trust, leading major exchanges and fund issuers like Binance, Kraken, OKX, and Bitwise to publicize wallet addresses as proof of assets . The goal is transparency and reassurance for investors. However, making wallet addresses public comes with significant security and privacy risks. This report examines those risks – from cybersecurity threats and blockchain tracing to regulatory and reputational implications – and weighs them against the transparency benefits of on-chain proof of reserves.
Proof of Reserves via Public Wallet Addresses
In the cryptocurrency ethos of “don’t trust – verify,” on-chain proof of reserves is seen as a powerful tool. By disclosing wallet addresses (or cryptographic attestations of balances), a company lets investors and analysts independently verify that the Bitcoin reserves exist on-chain. For example, some firms have dashboards showing their addresses and balances in real time . In theory, this transparency builds trust by proving assets are not being misreported or misused. Shareholders gain confidence that the company’s Bitcoin holdings are intact, potentially preventing fraud or mismanagement.
Yet this approach essentially sacrifices the pseudonymity of blockchain transactions. Publishing a wallet address ties a large, known institution to specific on-chain funds. While Bitcoin addresses are public by design, most companies treat their specific addresses as sensitive information. Public proof-of-reserve disclosures break that anonymity, raising several concerns as detailed below.
Cybersecurity Threats from Visible Wallet Balances
Revealing a wallet address with a large balance can make a company a prime target for hackers and cybercriminals. Knowing exactly where significant reserves are held gives attackers a clear blueprint. As Bitcoin advocate (and MicroStrategy Executive Chairman) Michael Saylor warned in 2025, “publicly known wallet addresses become prime targets for malicious actors. Knowing where significant reserves are held provides hackers with a clear target, potentially increasing the risk of sophisticated attacks” . In other words, publishing the address increases the attack surface – attackers might intensify phishing campaigns, malware deployment, or insider bribery aimed at obtaining the keys or access to those wallets.
Even if the wallets are secured in cold storage, a public address advertisement may encourage attempts to penetrate the organization’s security. Custodians and partners could also be targeted. Saylor noted that this exposure isn’t just risky for the company holding the Bitcoin; it can indirectly put their custodial providers and related exchanges at risk as well . For instance, if a third-party custodian manages the wallets, hackers might attempt to breach that custodian knowing the reward (the company’s Bitcoin) is great.
Companies themselves have acknowledged these dangers. Grayscale Investments, which runs the large Grayscale Bitcoin Trust (GBTC), pointedly refused to publish its wallet addresses in late 2022, citing “security concerns” and complex custody arrangements that have “kept our investors’ assets safe for years” . Grayscale implied that revealing on-chain addresses could undermine those security measures, and it chose not to “circumvent complex security arrangements” just to appease public demand . This highlights a key point: corporate treasury security protocols often assume wallet details remain confidential. Publicizing them could invalidate certain assumptions (for example, if an address was meant to be operationally secret, it can no longer serve that role once exposed).
Additionally, a publicly known trove of cryptocurrency might invite physical security threats. While not a purely “cyber” issue, if criminals know a particular company or facility controls a wallet with, say, thousands of Bitcoin, it could lead to threats against personnel (extortion or coercion to obtain keys). This is a less common scenario for large institutions (which typically have robust physical security), but smaller companies or key individuals could face elevated personal risk by being associated with huge visible crypto reserves.
In summary, cybersecurity experts consider public proof-of-reserve addresses a double-edged sword: transparency comes at the cost of advertising exactly where a fortune is held. As Saylor bluntly put it, “the conventional way of issuing proof of reserves today is actually insecure… This method undermines the security of the issuer, the custodian, the exchanges and the investors. This is not a good idea”  . From a pure security standpoint, broadcasting your wallets is akin to drawing a bullseye on them.
Privacy Risks: Address Clustering and Blockchain Tracing
Blockchain data is public, so publishing addresses opens the door to unwanted analytics and loss of privacy for the business. Even without knowing the private keys, analysts can scrutinize every transaction in and out of those addresses. This enables address clustering – linking together addresses that interact – and other forms of blockchain forensics that can reveal sensitive information about the company’s activities.
One immediate risk is that observers can track the company’s transaction patterns. For example, if the company moves Bitcoin from its reserve address to an exchange or to another address, that move is visible in real time. Competitors, investors, or even attackers could deduce strategic information: perhaps the company is planning to sell (if coins go to an exchange wallet) or is reallocating funds. A known institution’s on-chain movements can thus “reveal strategic movements or holdings”, eroding the company’s operational privacy . In a volatile market, advance knowledge of a large buy or sell by a major player could even be exploited by others (front-running the market, etc.).
Publishing one or a few static addresses also violates a basic privacy principle of Bitcoin: address reuse. Best practice in Bitcoin is to use a fresh address for each transaction to avoid linking them  . If a company continuously uses the same “proof of reserve” address, all counterparties sending funds to or receiving funds from that address become visible. Observers could map out the company’s business relationships or vendors by analyzing counterparties. A Reddit user commenting on an ETF that published a single address noted that “reusing a single address for this makes me question their risk management… There are much better and more privacy-preserving ways to prove reserves… without throwing everything in a single public address” . In other words, a naive implementation of proof-of-reserve (one big address) maximizes privacy leakage.
Even if multiple addresses are used, if they are all disclosed, one can perform clustering analysis to find connections. This happened in the Grayscale case: although Grayscale would not confirm any addresses, community analysts traced and identified 432 addresses likely belonging to GBTC’s custodial holdings by following on-chain traces from known intermediary accounts . They managed to attribute roughly 317,705 BTC (about half of GBTC’s holdings) to those addresses . This demonstrates that even partial information can enable clustering – and if the company directly published addresses, the task becomes even easier to map the entirety of its on-chain asset base.
Another threat vector is “dusting” attacks, which become more feasible when an address is publicly known. In a dusting attack, an adversary sends a tiny amount of cryptocurrency (dust) to a target address. The dust itself is harmless, but if the target address ever spends that dust together with other funds, it can cryptographically link the target address to other addresses in the same wallet. Blockchain security researchers note that “with UTXO-based assets, an attacker could distribute dust to an address to reveal the owner’s other addresses by tracking the dust’s movement… If the owner unknowingly combines this dust with their funds in a transaction, the attacker can… link multiple addresses to a single owner”, compromising privacy . A company that publishes a list of reserve addresses could be systematically dusted by malicious actors attempting to map out all addresses under the company’s control. This could unmask cold wallet addresses that the company never intended to publicize, further eroding its privacy and security.
Investor confidentiality is another subtle concern. If the business model involves individual investor accounts or contributions (for instance, a trust where investors can deposit or withdraw Bitcoin), public addresses might expose those movements. An outside observer might not know which investor corresponds to a transaction, but unusual inflows/outflows could signal actions by big clients. In extreme cases, if an investor’s own wallet is known (say a large investor announces their involvement), one might link that to transactions in the company’s reserve addresses. This could inadvertently reveal an investor’s activities or holdings, breaching expectations of confidentiality. Even absent direct identification, some investors might simply be uncomfortable with their transactions being part of a publicly traceable ledger tied to the company.
In summary, publishing reserve addresses facilitates blockchain tracing that can pierce the veil of business privacy. It hands analysts the keys to observe how funds move, potentially exposing operational strategies, counterparties, and internal processes. As one industry publication noted, linking a large known institution to specific addresses can compromise privacy and reveal more than intended . Companies must consider whether they are ready for that level of transparency into their every on-chain move.
Regulatory and Compliance Implications
From a regulatory perspective, wallet address disclosure lies in uncharted territory, but it raises several flags. First and foremost is the issue of incomplete information: A wallet address only shows assets, not the company’s liabilities or other obligations. Regulators worry that touting on-chain holdings could give a false sense of security. The U.S. Securities and Exchange Commission (SEC) has cautioned investors to “not place too much confidence in the mere fact a company says it’s got a proof-of-reserves”, noting that such reports “lack sufficient information” for stakeholders to ascertain if liabilities can be met . In other words, a public company might show a big Bitcoin address balance, but if it has debts or customer liabilities of equal or greater value, the proof-of-reserve alone is “not necessarily an indicator that the company is in a good financial position” .
This regulatory stance implies that address disclosure, if done, must be paired with proper context. A public company would likely need to clarify in its financial statements or investor communications that on-chain reserves are unencumbered (not pledged as loan collateral, not already sold forward, etc.) and that total liabilities are accounted for. Otherwise, there’s a risk of misleading investors, which could have legal consequences. For example, if investors interpret the on-chain balance as proof of solvency but the company actually had leveraged those bitcoins for loans, lawsuits or regulatory enforcement could follow for misrepresentation.
There’s also a compliance burden associated with revealing addresses. Once an address is known to be the company’s, that company effectively must monitor all transactions related to it. If someone sends funds to that address (even without permission), the company might receive tainted coins (from hacked sources or sanctioned entities). This could trigger anti-money laundering (AML) red flags. Normally, compliance teams can ignore random deposits to unknown wallets, but they cannot ignore something sent into their publicly identified corporate wallet. Even a tiny dust amount sent from a blacklisted address could complicate compliance – for instance, the company would need to prove it has no relation to the sender and perhaps even avoid moving those tainted outputs. Being in the open increases such exposure. Threat actors might even exploit this by “poisoning” a company’s address with unwanted transactions, just to create regulatory headaches or reputational smears.
Another consideration is that custodial agreements and internal risk controls might forbid public disclosure of addresses. Many public companies use third-party custodians for their Bitcoin (for example, Coinbase Custody, BitGo, etc.). These custodians often treat wallet details as confidential for security. Grayscale noted that its Bitcoin are custodied on Coinbase and implied that revealing on-chain info would interfere with security arrangements  . It’s possible that some custodians would object to their clients broadcasting addresses, or might require additional assurances. A company going against such advice might be seen as negligent if something went wrong.
Regulators have so far not mandated on-chain proofs for public companies – in fact, recent laws have exempted public companies from proof-of-reserve mandates on the assumption they are already subject to rigorous SEC reporting. For example, a Texas bill in 2023 required crypto exchanges and custodians to provide quarterly proof-of-reserves to the state, but it “specifically carved out public reporting companies” since they already file audited financials with the SEC . The rationale was that between SEC filings and audits, public companies have oversight that private crypto firms lack . However, this also highlights a gap: even audited financials might not verify 100% of crypto assets (auditors often sample balances). Some observers noted that standard audits “may not ever include the 100% custodial asset testing contemplated by proof of reserves”, especially since quarterly SEC filings (10-Q) are often not audited . This puts public companies in a nuanced position – they are trusted to use traditional audits and internal controls, but the onus is on them if they choose to add extra transparency like on-chain proofs.
Finally, securities regulators focus on fair disclosure and accuracy. If a company publicly posts addresses, those essentially become investor disclosures subject to anti-fraud rules. The firm must keep them up to date and accurate. Any mistake (such as publishing a wrong address or failing to mention that some coins are locked up or lent out) could attract regulatory scrutiny for being misleading. In contrast, a formal audit or certification from a third-party comes with standards and disclaimers that are better understood by regulators. A self-published wallet list is an unprecedented form of disclosure that regulators haven’t fully vetted – meaning the company bears the risk if something is misinterpreted.
In summary, wallet address disclosure as proof-of-reserve must be handled very carefully to avoid regulatory pitfalls. The SEC and others have warned that on-chain assets alone don’t tell the whole story . Public companies would need to integrate such proofs with their official reporting in a responsible way – otherwise they risk confusion or even regulatory backlash for giving a false sense of security.
Reputational and Operational Risks
While transparency is meant to enhance reputation, in practice public wallet disclosures can create new reputational vulnerabilities. Once an address is public, a company’s every on-chain action is under the microscope of the crypto community and media. Any anomaly or perceived misstep can snowball into public relations problems.
One vivid example occurred with Crypto.com in late 2022. After the exchange published its cold wallet addresses to prove reserves (a move prompted by the FTX collapse), on-chain analysts quickly noticed a “suspicious transfer of 320,000 ETH” – about 82% of Crypto.com’s Ether reserves – moving from their cold wallet to another exchange (Gate.io)  . This large, unexpected transfer sparked immediate panic and FUD (fear, uncertainty, and doubt) on social media. Observers speculated that Crypto.com might be insolvent or was manipulating snapshots of reserves by borrowing funds. The CEO had to publicly respond, admitting it was an operational error – the ETH was supposed to go to a new cold storage address but ended up at a whitelisted external address by mistake . The funds were eventually returned, but not before reputational damage was done: the incident made headlines about mishandled funds and rattled user confidence  . This case illustrates how full public visibility can turn an internal slip-up into a highly public crisis. If the addresses had not been public, the mistake might have been quietly corrected; with on-chain transparency, there was nowhere to hide and no way to control the narrative before the public drew worst-case conclusions.
Even routine operations can be misinterpreted. Blockchain data lacks context – analysts may jump to conclusions that hurt a company’s reputation even if nothing is actually wrong. For instance, Binance (the world’s largest crypto exchange) encountered scrutiny when on-chain observers noted that one of its reserve wallets (labeled “Binance 8”) contained far more assets than it should have. This wallet was meant to hold collateral for Binance’s issued tokens, but held an excess balance, suggesting possible commingling of customer funds with collateral  . Bloomberg and others reported a ~$12.7 billion discrepancy visible on-chain . Binance had to acknowledge the issue as a “clerical error” and quickly separate the funds, all under the glare of public attention  . While Binance maintained that user assets were fully backed and the mistake was purely operational, the episode raised public concern over Binance’s practices, feeding a narrative that even the largest exchange had internal control lapses. The key point is that public proof-of-reserves made the lapse obvious to everyone, forcing a reactive explanation. The reputational hit (even if temporary) was an operational risk of being so transparent.
Additionally, strategic confidentiality is lost. If a company holding Bitcoin as a reserve asset decides to make a major move (say, reallocating to a different wallet, or using some Bitcoin for a strategic investment or loan), doing so with known addresses broadcasts that strategy. Competitors or market analysts can infer things like “Company X is moving 10% of its BTC — why? Are they selling? Hedging? Using it as collateral?” This can erode any competitive advantage of keeping financial strategies discreet. It might even affect the company’s stock price if investors interpret moves negatively. For example, if a blockchain analysis shows the company’s reserves dropping, shareholders might fear the company sold Bitcoin (perhaps due to financial distress), even if the reality is benign (like moving funds to a new custodian). The company would be forced into continuous public explanation of on-chain actions to prevent misunderstanding.
There’s also a risk of exposing business partnerships. Suppose the company uses certain exchanges or OTC desks to rebalance its holdings – transactions with those service providers will be visible and could link the company to them. If one of those partners has issues (say a hacked exchange or a sanctioned entity inadvertently), the company could be reputationally contaminated by association through the blockchain trail.
Finally, not all publicity is good publicity in the crypto world. A public proof-of-reserve might invite armchair auditors to scrutinize and criticize every aspect of the company’s crypto management. Minor issues could be blown out of proportion. On the flip side, if a company chooses not to publish addresses, it could face reputational risk from a different angle: skeptics might question why it isn’t being transparent. (Indeed, Grayscale’s refusal to disclose wallet addresses led to social media chatter about whether they truly held all the Bitcoin they claimed, contributing to investor nervousness and a steep discount on GBTC shares .) Thus, companies are in a delicate spot: share too much and every move invites scrutiny; share too little and you breed distrust.
Balancing Transparency Benefits vs. Risks
The central question is whether the benefit of proving reserve holdings to investors outweighs these security and privacy risks. It’s a classic risk-reward calculation, and opinions in the industry are divided.
On the side of transparency, many argue that the credibility and trust gained by proof-of-reserves is invaluable. Advocates note that Bitcoin was designed for open verification – “on-chain auditability and permissionless transparency” are core features . By embracing this, companies demonstrate they are good stewards of a “trustless” asset. In fact, some believe public companies have a duty to be extra transparent. A recent Nasdaq report contended that “when a publicly traded company holds Bitcoin but offers no visibility into how that Bitcoin is held or verified, it exposes itself to multiple levels of risk: legal, reputational, operational, and strategic”, undermining trust . In that view, opacity is riskier in the long run – a lack of proof could weaken investor confidence or invite regulatory suspicion. Shareholders and analysts may actually penalize a company that refuses to provide verifiable proof of its crypto assets .
Transparency done right can also differentiate a firm as a leader in governance. Publishing reserve data (whether via addresses or through third-party attestations) can be seen as a commitment to high standards. For example, Metaplanet, an investment firm, publicly discloses its BTC reserve addresses and even provides a live dashboard for anyone to verify balances . This proactive openness signals confidence and has been touted as an industry best practice in some quarters. By proving its reserves, a company can potentially avoid the fate of those that lost public trust (as happened with opaque crypto firms in 2022). It’s also a means to preempt false rumors – if data is out in the open, misinformation has less room to grow.
However, the pro-transparency camp increasingly acknowledges that there are smarter ways to achieve trust without courting all the risks. One compromise is using cryptographic proofs or audits instead of plain address dumps. For instance, exchanges like Kraken have implemented Merkle tree proof-of-reserves: an independent auditor verifies all customer balances on-chain and provides a cryptographic report, and customers can individually verify their account is included without the exchange revealing every address publicly. This method proves solvency to those who need to know without handing over a complete roadmap to attackers. Another emerging solution is zero-knowledge proofs, where a company can prove knowledge or ownership of certain assets without revealing the addresses or amounts to the public. These technologies are still maturing, but they aim to deliver the best of both worlds: transparency and privacy.
On the side of caution, many experts believe the risks of full public disclosure outweigh the incremental gain in transparency, especially for regulated public companies. Michael Saylor encapsulates this viewpoint: he calls on-chain proof-of-reserve “a bad idea” for institutions, arguing that it “offers one-way transparency” (assets only) and “leaves organizations open to cyberattacks” . He stresses that no serious security expert would advise a Fortune 500 company to list all its wallet addresses, as it essentially compromises corporate security over time . Saylor and others also point out the pointlessness of an assets-only proof: unless you also prove liabilities, showing off reserves might even be dangerous because it could lull investors into a false sense of security .
Regulators and traditional auditors echo this: proof-of-reserves, while a useful tool, “is not enough by itself” to guarantee financial health . They advocate for holistic transparency – audits that consider internal controls, liabilities, and legal obligations, not just a snapshot of a blockchain address  . From this perspective, a public company can satisfy transparency demands through rigorous third-party audits and disclosures rather than raw on-chain data. Indeed, public companies are legally bound to extensive reporting; adding public crypto addresses on top may be seen as redundant and risky.
There is also an implicit cost-benefit analysis: A successful attack resulting from over-sharing could be catastrophic (loss of funds, legal liability, reputational ruin), whereas the benefit of public proof is somewhat intangible (improved investor sentiment, which might be achieved via other assurance methods anyway). Given that trade-off, many firms err on the side of caution. As evidence, few if any U.S.-listed companies that hold Bitcoin have published their wallet addresses. Instead, they reference independent custodians and audits for assurance. Even crypto-native companies have pulled back on full transparency after realizing the downsides – for example, some auditing firms halted issuing proof-of-reserves reports due to concerns about how they were interpreted and the liability involved  .
Industry best practices are still evolving. A prudent approach gaining favor is to prove reserves without leaking sensitive details. This can involve disclosing total balances and having an auditor or blockchain oracle confirm the assets exist, but without listing every address publicly. Companies are also encouraged to disclose encumbrances (whether any of the reserves are collateralized or lent out) in tandem, to address the liabilities issue . By doing so, they aim to achieve transparency and maintain security.
In evaluating whether to publish wallet addresses, a company must ask: Will this level of openness meaningfully increase stakeholder trust, or would a more controlled disclosure achieve the same goal with less risk? For many public companies, the answer has been to avoid public addresses. The risks – from attracting hackers to revealing strategic moves – tend to outweigh the marginal transparency benefit in their judgment. The collapse of unregulated exchanges has certainly proven the value of reserve verification, but public companies operate in a different context with audits and legal accountability. Thus, the optimal solution may be a middle ground: proving reserves through vetted processes (auditor attestations, cryptographic proofs) that satisfy investor needs without blatantly exposing the company’s financial backend to the world.
Conclusion
Publishing Bitcoin wallet addresses as proof of reserves is a bold transparency measure – one that speaks to crypto’s ideals of open verification – but it comes with a laundry list of security considerations. Public companies weighing this approach must contend with the heightened cybersecurity threat of advertising their treasure troves to hackers, the loss of privacy and confidentiality as on-chain sleuths dissect their every transaction, and potential regulatory complications if such disclosures are misunderstood or incomplete. Real-world incidents illustrate the downsides: firms that revealed addresses have seen how quickly online communities flag (and sometimes misinterpret) their blockchain moves, causing reputational turbulence and forcing rapid damage control  .
On the other hand, proving reserves to investors is important – it can prevent fraud and bolster trust. The question is how to achieve it without incurring unacceptable risk. Many experts and industry leaders lean towards the view that simply publishing wallet addresses is too risky a method, especially for public companies with much to lose  . The risks often do outweigh the direct benefits in such cases. Transparency remains crucial, but it can be provided in safer ways – through regular audits, cryptographic proofs that don’t expose all wallet details, and comprehensive disclosures that include liabilities and controls.
In conclusion, while on-chain proof of reserves via public addresses offers a tantalizing level of openness, it must be approached with extreme caution. For most public companies, the smart strategy is to balance transparency with security: verify and show investors that assets exist and are sufficient, but do so in a controlled manner that doesn’t compromise the very assets you’re trying to protect. As the industry matures, we can expect more refined proof-of-reserve practices that satisfy the demand for honesty and solvency verification without unduly endangering the enterprise. Until then, companies will continue to tread carefully, mindful that transparency is only truly valuable when it doesn’t come at the price of security and trust.
Sources:
• Grayscale statement on refusal to share on-chain proof-of-reserves  • Community analysis identifying Grayscale’s wallet addresses  • Cointelegraph – Crypto.com’s mistaken 320k ETH transfer spotted via on-chain proof-of-reserves   • Axios – Binance wallet “commingling” error observed on-chain   • Michael Saylor’s remarks on security risks of publishing wallet addresses    • SEC Acting Chief Accountant on limitations of proof-of-reserves reports  • Nasdaq (Bitcoin for Corporations) – argument for corporate transparency & proof-of-reserves    • 1inch Security Blog – explanation of dusting attacks and privacy loss via address linking  -
 @ e844b39d:adafb6a2
2025-05-27 12:30:49
@ e844b39d:adafb6a2
2025-05-27 12:30:49I've been going so deep into black & white for a longer period now that I've totally forgotten about colours!
Actually that is how I felt when I started editing these, it was kinda too much haha
 Grasshopper on our banana flower
Grasshopper on our banana flowerThis was to test my old Minolta 70-210/4 Beercan, even though the AF is slow it still locked in time to get this grasshopper!
I'm contemplating bringing this gear on the long trip instead of the old Nikon stuff, so gotta know it will do almost all sorts of jobs...
 Random flower
Random flowerI know that the pastel colours that I found using auto levels is in there, in the combination of the Sony A900 and the Beercan, which is one of the main reasons that I got it all around a decade ago.
 Twig
TwigMaybe too much? But still, these colours are in there, just gotta whack the files hard in post hehe
 Sharpness is no problem
Sharpness is no problemAll of these are at f4, its sharp enough to tackle anything really.
 Spider web
Spider webOf course this could be better technically, but it will do for almost anything I'll get across. Also this was manual focus, I didn't think the matte screen and viewfinder would make it possible to focus like this, never really tried before!
 Amulet and my Nikon gear
Amulet and my Nikon gearI found a tiny amulet on the floor, of course its the cats that are responsible for that...
 Zelda is happy
Zelda is happyThe A900 has built in stabilization, so any old lenses will get that by default! Which makes it far easier to get things like this right a around 1/4th of a second, even with that mirror clacking...
This one is with the Minolta 20/2.8, which is a lens I should really explore more. I got that and a 24/2.8 for a very low price, never had the time to use them much, and now I realize that they both can focus all the way down to 25 centimeters!
Now that is something I can use creatively, and on the road with ease...
I think this might end with me selling (dumping, really) my Nikon gear instead of this!
We'll find out soon 😁
-
 @ c631e267:c2b78d3e
2025-03-21 19:41:50
@ c631e267:c2b78d3e
2025-03-21 19:41:50Wir werden nicht zulassen, dass technisch manches möglich ist, \ aber der Staat es nicht nutzt. \ Angela Merkel
Die Modalverben zu erklären, ist im Deutschunterricht manchmal nicht ganz einfach. Nicht alle Fremdsprachen unterscheiden zum Beispiel bei der Frage nach einer Möglichkeit gleichermaßen zwischen «können» im Sinne von «die Gelegenheit, Kenntnis oder Fähigkeit haben» und «dürfen» als «die Erlaubnis oder Berechtigung haben». Das spanische Wort «poder» etwa steht für beides.
Ebenso ist vielen Schülern auf den ersten Blick nicht recht klar, dass das logische Gegenteil von «müssen» nicht unbedingt «nicht müssen» ist, sondern vielmehr «nicht dürfen». An den Verkehrsschildern lässt sich so etwas meistens recht gut erklären: Manchmal muss man abbiegen, aber manchmal darf man eben nicht.

Dieses Beispiel soll ein wenig die Verwirrungstaktik veranschaulichen, die in der Politik gerne verwendet wird, um unpopuläre oder restriktive Maßnahmen Stück für Stück einzuführen. Zuerst ist etwas einfach innovativ und bringt viele Vorteile. Vor allem ist es freiwillig, jeder kann selber entscheiden, niemand muss mitmachen. Später kann man zunehmend weniger Alternativen wählen, weil sie verschwinden, und irgendwann verwandelt sich alles andere in «nicht dürfen» – die Maßnahme ist obligatorisch.
Um die Durchsetzung derartiger Initiativen strategisch zu unterstützen und nett zu verpacken, gibt es Lobbyisten, gerne auch NGOs genannt. Dass das «NG» am Anfang dieser Abkürzung übersetzt «Nicht-Regierungs-» bedeutet, ist ein Anachronismus. Das war vielleicht früher einmal so, heute ist eher das Gegenteil gemeint.
In unserer modernen Zeit wird enorm viel Lobbyarbeit für die Digitalisierung praktisch sämtlicher Lebensbereiche aufgewendet. Was das auf dem Sektor der Mobilität bedeuten kann, haben wir diese Woche anhand aktueller Entwicklungen in Spanien beleuchtet. Begründet teilweise mit Vorgaben der Europäischen Union arbeitet man dort fleißig an einer «neuen Mobilität», basierend auf «intelligenter» technologischer Infrastruktur. Derartige Anwandlungen wurden auch schon als «Technofeudalismus» angeprangert.
Nationale Zugangspunkte für Mobilitätsdaten im Sinne der EU gibt es nicht nur in allen Mitgliedsländern, sondern auch in der Schweiz und in Großbritannien. Das Vereinigte Königreich beteiligt sich darüber hinaus an anderen EU-Projekten für digitale Überwachungs- und Kontrollmaßnahmen, wie dem biometrischen Identifizierungssystem für «nachhaltigen Verkehr und Tourismus».
Natürlich marschiert auch Deutschland stracks und euphorisch in Richtung digitaler Zukunft. Ohne vernetzte Mobilität und einen «verlässlichen Zugang zu Daten, einschließlich Echtzeitdaten» komme man in der Verkehrsplanung und -steuerung nicht aus, erklärt die Regierung. Der Interessenverband der IT-Dienstleister Bitkom will «die digitale Transformation der deutschen Wirtschaft und Verwaltung vorantreiben». Dazu bewirbt er unter anderem die Konzepte Smart City, Smart Region und Smart Country und behauptet, deutsche Großstädte «setzen bei Mobilität voll auf Digitalisierung».
Es steht zu befürchten, dass das umfassende Sammeln, Verarbeiten und Vernetzen von Daten, das angeblich die Menschen unterstützen soll (und theoretisch ja auch könnte), eher dazu benutzt wird, sie zu kontrollieren und zu manipulieren. Je elektrischer und digitaler unsere Umgebung wird, desto größer sind diese Möglichkeiten. Im Ergebnis könnten solche Prozesse den Bürger nicht nur einschränken oder überflüssig machen, sondern in mancherlei Hinsicht regelrecht abschalten. Eine gesunde Skepsis ist also geboten.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Er ist zuerst auf Transition News erschienen.
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ d360efec:14907b5f
2025-05-12 01:34:24
@ d360efec:14907b5f
2025-05-12 01:34:24สวัสดีค่ะเพื่อนๆ นักเทรดที่น่ารักทุกคน! 💕 Lina Engword กลับมาพร้อมกับการวิเคราะห์ BTCUSDT.P แบบเจาะลึกเพื่อเตรียมพร้อมสำหรับเทรดวันนี้ค่ะ! 🚀
วันนี้ 12 พฤษภาคม 2568 เวลา 08.15น. ราคา BTCUSDT.P อยู่ที่ 104,642.8 USDT ค่ะ โดยมี Previous Weekly High (PWH) อยู่ที่ 104,967.8 Previous Weekly Low (PWL) ที่ 93,338 ค่ะ
✨ ภาพรวมตลาดวันนี้ ✨
จากการวิเคราะห์ด้วยเครื่องมือคู่ใจของเรา ทั้ง SMC/ICT (Demand/Supply Zone, Order Block, Liquidity), EMA 50/200, Trend Strength, Money Flow, Chart/Price Pattern, Premium/Discount Zone, Trend line, Fibonacci, Elliott Wave และ Dow Theory ใน Timeframe ตั้งแต่ 15m ไปจนถึง Week! 📊 เราพบว่าภาพใหญ่ของ BTCUSDT.P ยังคงอยู่ในแนวโน้มขาขึ้นที่แข็งแกร่งมากๆ ค่ะ 👍 โดยเฉพาะใน Timeframe Day และ Week ที่สัญญาณทุกอย่างสนับสนุนทิศทางขาขึ้นอย่างชัดเจน Money Flow ยังไหลเข้าอย่างต่อเนื่อง และเราเห็นโครงสร้างตลาดแบบ Dow Theory ที่ยก High ยก Low ขึ้นไปเรื่อยๆ ค่ะ
อย่างไรก็ตาม... ใน Timeframe สั้นๆ อย่าง 15m และ 1H เริ่มเห็นสัญญาณของการชะลอตัวและการพักฐานบ้างแล้วค่ะ 📉 อาจมีการสร้าง Buyside และ Sellside Liquidity รอให้ราคาไปกวาดก่อนที่จะเลือกทางใดทางหนึ่ง ซึ่งเป็นเรื่องปกติของการเดินทางของ Smart Money ค่ะ
⚡ เปรียบเทียบแนวโน้มแต่ละ Timeframe ⚡
🪙 แนวโน้มตรงกัน Timeframe 4H, Day, Week ส่วนใหญ่ชี้ไปทาง "ขาขึ้น" ค่ะ ทุกเครื่องมือสนับสนุนแนวโน้มนี้อย่างแข็งแกร่ง 💪 เป้าหมายต่อไปคือการไปทดสอบ PWH และ High เดิม เพื่อสร้าง All-Time High ใหม่ค่ะ! 🪙 แนวโน้มต่างกัน Timeframe 15m, 1H ยังค่อนข้าง "Sideways" หรือ "Sideways Down เล็กน้อย" ค่ะ มีการบีบตัวของราคาและอาจมีการพักฐานสั้นๆ ซึ่งเป็นโอกาสในการหาจังหวะเข้า Long ที่ราคาดีขึ้นค่ะ
💡 วิธีคิดแบบ Market Slayer 💡
เมื่อแนวโน้มใหญ่เป็นขาขึ้นที่แข็งแกร่ง เราจะเน้นหาจังหวะเข้า Long เป็นหลักค่ะ การย่อตัวลงมาในระยะสั้นคือโอกาสของเราในการเก็บของ! 🛍️ เราจะใช้หลักการ SMC/ICT หาโซน Demand หรือ Order Block ที่ Smart Money อาจจะเข้ามาดันราคาขึ้น และรอสัญญาณ Price Action ยืนยันการกลับตัวค่ะ
สรุปแนวโน้มวันนี้:
🪙 ระยะสั้น: Sideways to Sideways Down (โอกาส 55%) ↔️↘️ 🪙 ระยะกลาง: ขาขึ้น (โอกาส 70%) ↗️ 🪙 ระยะยาว: ขาขึ้น (โอกาส 85%) 🚀 🪙 วันนี้: มีโอกาสย่อตัวเล็กน้อยก่อนจะมีแรงซื้อกลับเข้ามาเพื่อไปทดสอบ PWH (โอกาส Sideways Down เล็กน้อย สลับกับ Sideways Up: 60%) 🎢
🗓️ Daily Trade Setup ประจำวันนี้ 🗓️
นี่คือตัวอย่าง Setup ที่ Lina เตรียมไว้ให้พิจารณาค่ะ (เน้นย้ำว่าเป็นเพียงแนวทาง ไม่ใช่คำแนะนำลงทุนนะคะ)
1️⃣ ตัวอย่างที่ 1: รอรับที่โซน Demand (ปลอดภัย, รอยืนยัน)
🪙 Enter: รอราคาย่อตัวลงมาในโซน Demand Zone หรือ Bullish Order Block ที่น่าสนใจใน TF 1H/4H (ดูจากกราฟประกอบนะคะ) และเกิดสัญญาณ Bullish Price Action ที่ชัดเจน เช่น แท่งเทียนกลืนกิน (Engulfing) หรือ Hammer 🪙 TP: บริเวณ PWH 104,967.8 หรือ Buyside Liquidity ถัดไป 🎯 🪙 SL: ใต้ Low ที่เกิดก่อนสัญญาณกลับตัวเล็กน้อย หรือใต้ Demand Zone ที่เข้า 🛡️ 🪙 RRR: ประมาณ 1:2.5 ขึ้นไป ✨ 🪙 อธิบาย: Setup นี้เราจะใจเย็นๆ รอให้ราคาลงมาในโซนที่มีโอกาสเจอแรงซื้อเยอะๆ ตามหลัก SMC/ICT แล้วค่อยเข้า เพื่อให้ได้ราคาที่ดีและความเสี่ยงต่ำค่ะ ต้องรอสัญญาณ Price Action ยืนยันก่อนนะคะ ✍️
2️⃣ ตัวอย่างที่ 2: Follow Breakout (สายบู๊, รับความเสี่ยงได้)
🪙 Enter: เข้า Long ทันทีเมื่อราคาสามารถ Breakout เหนือ High ล่าสุดใน TF 15m หรือ 1H พร้อม Volume ที่เพิ่มขึ้นอย่างมีนัยสำคัญ 🔥 🪙 TP: บริเวณ PWH 104,967.8 หรือ Buyside Liquidity ถัดไป 🚀 🪙 SL: ใต้ High ก่อนหน้าที่ถูก Breakout เล็กน้อย 🚧 🪙 RRR: ประมาณ 1:3 ขึ้นไป ✨ 🪙 อธิบาย: Setup นี้เหมาะกับคนที่อยากเข้าไวเมื่อเห็นโมเมนตัมแรงๆ ค่ะ เราจะเข้าเมื่อราคา Breakout แนวต้านระยะสั้นพร้อม Volume เป็นสัญญาณว่าแรงซื้อกำลังมาค่ะ เข้าได้เลยด้วยการตั้ง Limit Order หรือ Market Order เมื่อเห็นการ Breakout ที่ชัดเจนค่ะ 💨
3️⃣ ตัวอย่างที่ 3: พิจารณา Short สั้นๆ ในโซน Premium (สวนเทรนด์หลัก, ความเสี่ยงสูง)
🪙 Enter: หากราคาขึ้นไปในโซน Premium ใน TF 15m หรือ 1H และเกิดสัญญาณ Bearish Price Action ที่ชัดเจน เช่น แท่งเทียน Shooting Star หรือ Bearish Engulfing บริเวณ Supply Zone หรือ Bearish Order Block 🐻 🪙 TP: พิจารณาแนวรับถัดไป หรือ Sellside Liquidity ใน TF เดียวกัน 🎯 🪙 SL: เหนือ High ของสัญญาณ Bearish Price Action เล็กน้อย 💀 🪙 RRR: ประมาณ 1:1.5 ขึ้นไป (เน้นย้ำว่าเป็นการเทรดสวนเทรนด์หลัก ควรใช้ RRR ต่ำและบริหารขนาด Lot อย่างเข้มงวด!) 🪙 อธิบาย: Setup นี้สำหรับคนที่เห็นโอกาสในการทำกำไรจากการย่อตัวระยะสั้นค่ะ เราจะเข้า Short เมื่อเห็นสัญญาณว่าราคาอาจจะมีการพักฐานในโซนที่ถือว่า "แพง" ในกรอบสั้นๆ ค่ะ ต้องตั้ง Stop Loss ใกล้มากๆ และจับตาดูใกล้ชิดนะคะ 🚨
⚠️ Disclaimer: การวิเคราะห์นี้เป็นเพียงความคิดเห็นส่วนตัวของ Lina เท่านั้น ไม่ถือเป็นคำแนะนำในการลงทุนนะคะ การลงทุนมีความเสี่ยง ผู้ลงทุนควรศึกษาข้อมูลเพิ่มเติมและตัดสินใจด้วยความรอบคอบค่ะ 🙏
ขอให้ทุกท่านโชคดีกับการเทรดในวันนี้ค่ะ! มีคำถามอะไรเพิ่มเติม ถามมาได้เลยนะคะ ยินดีเสมอค่ะ! 😊
Bitcoin #BTCUSDT #Crypto #Trading #TechnicalAnalysis #SMC #ICT #MarketSlayer #TradeSetup #คริปโต #เทรดคริปโต #วิเคราะห์กราฟ #LinaEngword 😉



-
 @ aa8de34f:a6ffe696
2025-03-21 12:08:31
@ aa8de34f:a6ffe696
2025-03-21 12:08:3119. März 2025
🔐 1. SHA-256 is Quantum-Resistant
Bitcoin’s proof-of-work mechanism relies on SHA-256, a hashing algorithm. Even with a powerful quantum computer, SHA-256 remains secure because:
- Quantum computers excel at factoring large numbers (Shor’s Algorithm).
- However, SHA-256 is a one-way function, meaning there's no known quantum algorithm that can efficiently reverse it.
- Grover’s Algorithm (which theoretically speeds up brute force attacks) would still require 2¹²⁸ operations to break SHA-256 – far beyond practical reach.
++++++++++++++++++++++++++++++++++++++++++++++++++
🔑 2. Public Key Vulnerability – But Only If You Reuse Addresses
Bitcoin uses Elliptic Curve Digital Signature Algorithm (ECDSA) to generate keys.
- A quantum computer could use Shor’s Algorithm to break SECP256K1, the curve Bitcoin uses.
- If you never reuse addresses, it is an additional security element
- 🔑 1. Bitcoin Addresses Are NOT Public Keys
Many people assume a Bitcoin address is the public key—this is wrong.
- When you receive Bitcoin, it is sent to a hashed public key (the Bitcoin address).
- The actual public key is never exposed because it is the Bitcoin Adress who addresses the Public Key which never reveals the creation of a public key by a spend
- Bitcoin uses Pay-to-Public-Key-Hash (P2PKH) or newer methods like Pay-to-Witness-Public-Key-Hash (P2WPKH), which add extra layers of security.
🕵️♂️ 2.1 The Public Key Never Appears
- When you send Bitcoin, your wallet creates a digital signature.
- This signature uses the private key to prove ownership.
- The Bitcoin address is revealed and creates the Public Key
- The public key remains hidden inside the Bitcoin script and Merkle tree.
This means: ✔ The public key is never exposed. ✔ Quantum attackers have nothing to target, attacking a Bitcoin Address is a zero value game.
+++++++++++++++++++++++++++++++++++++++++++++++++
🔄 3. Bitcoin Can Upgrade
Even if quantum computers eventually become a real threat:
- Bitcoin developers can upgrade to quantum-safe cryptography (e.g., lattice-based cryptography or post-quantum signatures like Dilithium).
- Bitcoin’s decentralized nature ensures a network-wide soft fork or hard fork could transition to quantum-resistant keys.
++++++++++++++++++++++++++++++++++++++++++++++++++
⏳ 4. The 10-Minute Block Rule as a Security Feature
- Bitcoin’s network operates on a 10-minute block interval, meaning:Even if an attacker had immense computational power (like a quantum computer), they could only attempt an attack every 10 minutes.Unlike traditional encryption, where a hacker could continuously brute-force keys, Bitcoin’s system resets the challenge with every new block.This limits the window of opportunity for quantum attacks.
🎯 5. Quantum Attack Needs to Solve a Block in Real-Time
- A quantum attacker must solve the cryptographic puzzle (Proof of Work) in under 10 minutes.
- The problem? Any slight error changes the hash completely, meaning:If the quantum computer makes a mistake (even 0.0001% probability), the entire attack fails.Quantum decoherence (loss of qubit stability) makes error correction a massive challenge.The computational cost of recovering from an incorrect hash is still incredibly high.
⚡ 6. Network Resilience – Even if a Block Is Hacked
- Even if a quantum computer somehow solved a block instantly:The network would quickly recognize and reject invalid transactions.Other miners would continue mining under normal cryptographic rules.51% Attack? The attacker would need to consistently beat the entire Bitcoin network, which is not sustainable.
🔄 7. The Logarithmic Difficulty Adjustment Neutralizes Threats
- Bitcoin adjusts mining difficulty every 2016 blocks (\~2 weeks).
- If quantum miners appeared and suddenly started solving blocks too quickly, the difficulty would adjust upward, making attacks significantly harder.
- This self-correcting mechanism ensures that even quantum computers wouldn't easily overpower the network.
🔥 Final Verdict: Quantum Computers Are Too Slow for Bitcoin
✔ The 10-minute rule limits attack frequency – quantum computers can’t keep up.
✔ Any slight miscalculation ruins the attack, resetting all progress.
✔ Bitcoin’s difficulty adjustment would react, neutralizing quantum advantages.
Even if quantum computers reach their theoretical potential, Bitcoin’s game theory and design make it incredibly resistant. 🚀
-
 @ c631e267:c2b78d3e
2025-02-07 19:42:11
@ c631e267:c2b78d3e
2025-02-07 19:42:11Nur wenn wir aufeinander zugehen, haben wir die Chance \ auf Überwindung der gegenseitigen Ressentiments! \ Dr. med. dent. Jens Knipphals
In Wolfsburg sollte es kürzlich eine Gesprächsrunde von Kritikern der Corona-Politik mit Oberbürgermeister Dennis Weilmann und Vertretern der Stadtverwaltung geben. Der Zahnarzt und langjährige Maßnahmenkritiker Jens Knipphals hatte diese Einladung ins Rathaus erwirkt und publiziert. Seine Motivation:
«Ich möchte die Spaltung der Gesellschaft überwinden. Dazu ist eine umfassende Aufarbeitung der Corona-Krise in der Öffentlichkeit notwendig.»
Schon früher hatte Knipphals Antworten von den Kommunalpolitikern verlangt, zum Beispiel bei öffentlichen Bürgerfragestunden. Für das erwartete Treffen im Rathaus formulierte er Fragen wie: Warum wurden fachliche Argumente der Kritiker ignoriert? Weshalb wurde deren Ausgrenzung, Diskreditierung und Entmenschlichung nicht entgegengetreten? In welcher Form übernehmen Rat und Verwaltung in Wolfsburg persönlich Verantwortung für die erheblichen Folgen der politischen Corona-Krise?
Der Termin fand allerdings nicht statt – der Bürgermeister sagte ihn kurz vorher wieder ab. Knipphals bezeichnete Weilmann anschließend als Wiederholungstäter, da das Stadtoberhaupt bereits 2022 zu einem Runden Tisch in der Sache eingeladen hatte, den es dann nie gab. Gegenüber Multipolar erklärte der Arzt, Weilmann wolle scheinbar eine öffentliche Aufarbeitung mit allen Mitteln verhindern. Er selbst sei «inzwischen absolut desillusioniert» und die einzige Lösung sei, dass die Verantwortlichen gingen.
Die Aufarbeitung der Plandemie beginne bei jedem von uns selbst, sei aber letztlich eine gesamtgesellschaftliche Aufgabe, schreibt Peter Frey, der den «Fall Wolfsburg» auch in seinem Blog behandelt. Diese Aufgabe sei indes deutlich größer, als viele glaubten. Erfreulicherweise sei der öffentliche Informationsraum inzwischen größer, trotz der weiterhin unverfrorenen Desinformations-Kampagnen der etablierten Massenmedien.
Frey erinnert daran, dass Dennis Weilmann mitverantwortlich für gravierende Grundrechtseinschränkungen wie die 2021 eingeführten 2G-Regeln in der Wolfsburger Innenstadt zeichnet. Es sei naiv anzunehmen, dass ein Funktionär einzig im Interesse der Bürger handeln würde. Als früherer Dezernent des Amtes für Wirtschaft, Digitalisierung und Kultur der Autostadt kenne Weilmann zum Beispiel die Verknüpfung von Fördergeldern mit politischen Zielsetzungen gut.
Wolfsburg wurde damals zu einem Modellprojekt des Bundesministeriums des Innern (BMI) und war Finalist im Bitkom-Wettbewerb «Digitale Stadt». So habe rechtzeitig vor der Plandemie das Projekt «Smart City Wolfsburg» anlaufen können, das der Stadt «eine Vorreiterrolle für umfassende Vernetzung und Datenerfassung» aufgetragen habe, sagt Frey. Die Vereinten Nationen verkauften dann derartige «intelligente» Überwachungs- und Kontrollmaßnahmen ebenso als Rettung in der Not wie das Magazin Forbes im April 2020:
«Intelligente Städte können uns helfen, die Coronavirus-Pandemie zu bekämpfen. In einer wachsenden Zahl von Ländern tun die intelligenten Städte genau das. Regierungen und lokale Behörden nutzen Smart-City-Technologien, Sensoren und Daten, um die Kontakte von Menschen aufzuspüren, die mit dem Coronavirus infiziert sind. Gleichzeitig helfen die Smart Cities auch dabei, festzustellen, ob die Regeln der sozialen Distanzierung eingehalten werden.»
Offensichtlich gibt es viele Aspekte zu bedenken und zu durchleuten, wenn es um die Aufklärung und Aufarbeitung der sogenannten «Corona-Pandemie» und der verordneten Maßnahmen geht. Frustration und Desillusion sind angesichts der Realitäten absolut verständlich. Gerade deswegen sind Initiativen wie die von Jens Knipphals so bewundernswert und so wichtig – ebenso wie eine seiner Kernthesen: «Wir müssen aufeinander zugehen, da hilft alles nichts».
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ d360efec:14907b5f
2025-05-10 03:57:17
@ d360efec:14907b5f
2025-05-10 03:57:17Disclaimer: * การวิเคราะห์นี้เป็นเพียงแนวทาง ไม่ใช่คำแนะนำในการซื้อขาย * การลงทุนมีความเสี่ยง ผู้ลงทุนควรตัดสินใจด้วยตนเอง
-
 @ c631e267:c2b78d3e
2025-01-18 09:34:51
@ c631e267:c2b78d3e
2025-01-18 09:34:51Die grauenvollste Aussicht ist die der Technokratie – \ einer kontrollierenden Herrschaft, \ die durch verstümmelte und verstümmelnde Geister ausgeübt wird. \ Ernst Jünger
«Davos ist nicht mehr sexy», das Weltwirtschaftsforum (WEF) mache Davos kaputt, diese Aussagen eines Einheimischen las ich kürzlich in der Handelszeitung. Während sich einige vor Ort enorm an der «teuersten Gewerbeausstellung der Welt» bereicherten, würden die negativen Begleiterscheinungen wie Wohnungsnot und Niedergang der lokalen Wirtschaft immer deutlicher.
Nächsten Montag beginnt in dem Schweizer Bergdorf erneut ein Jahrestreffen dieses elitären Clubs der Konzerne, bei dem man mit hochrangigen Politikern aus aller Welt und ausgewählten Vertretern der Systemmedien zusammenhocken wird. Wie bereits in den vergangenen vier Jahren wird die Präsidentin der EU-Kommission, Ursula von der Leyen, in Begleitung von Klaus Schwab ihre Grundsatzansprache halten.
Der deutsche WEF-Gründer hatte bei dieser Gelegenheit immer höchst lobende Worte für seine Landsmännin: 2021 erklärte er sich «stolz, dass Europa wieder unter Ihrer Führung steht» und 2022 fand er es bemerkenswert, was sie erreicht habe angesichts des «erstaunlichen Wandels», den die Welt in den vorangegangenen zwei Jahren erlebt habe; es gebe nun einen «neuen europäischen Geist».
Von der Leyens Handeln während der sogenannten Corona-«Pandemie» lobte Schwab damals bereits ebenso, wie es diese Woche das Karlspreis-Direktorium tat, als man der Beschuldigten im Fall Pfizergate die diesjährige internationale Auszeichnung «für Verdienste um die europäische Einigung» verlieh. Außerdem habe sie die EU nicht nur gegen den «Aggressor Russland», sondern auch gegen die «innere Bedrohung durch Rassisten und Demagogen» sowie gegen den Klimawandel verteidigt.
Jene Herausforderungen durch «Krisen epochalen Ausmaßes» werden indes aus dem Umfeld des WEF nicht nur herbeigeredet – wie man alljährlich zur Zeit des Davoser Treffens im Global Risks Report nachlesen kann, der zusammen mit dem Versicherungskonzern Zurich erstellt wird. Seit die Globalisten 2020/21 in der Praxis gesehen haben, wie gut eine konzertierte und konsequente Angst-Kampagne funktionieren kann, geht es Schlag auf Schlag. Sie setzen alles daran, Schwabs goldenes Zeitfenster des «Great Reset» zu nutzen.
Ziel dieses «großen Umbruchs» ist die totale Kontrolle der Technokraten über die Menschen unter dem Deckmantel einer globalen Gesundheitsfürsorge. Wie aber könnte man so etwas erreichen? Ein Mittel dazu ist die «kreative Zerstörung». Weitere unabdingbare Werkzeug sind die Einbindung, ja Gleichschaltung der Medien und der Justiz.
Ein «Great Mental Reset» sei die Voraussetzung dafür, dass ein Großteil der Menschen Einschränkungen und Manipulationen wie durch die Corona-Maßnahmen praktisch kritik- und widerstandslos hinnehme, sagt der Mediziner und Molekulargenetiker Michael Nehls. Er meint damit eine regelrechte Umprogrammierung des Gehirns, wodurch nach und nach unsere Individualität und unser soziales Bewusstsein eliminiert und durch unreflektierten Konformismus ersetzt werden.
Der aktuelle Zustand unserer Gesellschaften ist auch für den Schweizer Rechtsanwalt Philipp Kruse alarmierend. Durch den Umgang mit der «Pandemie» sieht er die Grundlagen von Recht und Vernunft erschüttert, die Rechtsstaatlichkeit stehe auf dem Prüfstand. Seiner dringenden Mahnung an alle Bürger, die Prinzipien von Recht und Freiheit zu verteidigen, kann ich mich nur anschließen.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 65038d69:1fff8852
2025-03-31 12:13:39
@ 65038d69:1fff8852
2025-03-31 12:13:39Artificial intelligence is upon us and not showing any signs of slowing. The most common concern from those in the workforce is being replaced by one of these “thinking machines”. But what if AI wasn’t coming for your job? What if it was coming for your boss’s job instead?
I happened across the following post on X: https://x.com/BrianRoemmele/status/1905754986795151629 Brian describes having installed an AI system that provides an omniscient “shadow” to each of the executives at a client company, which can then be queried by the CEO for reports. The CEO seems to like it so far, and if it leads to less time spent writing internal reports I’m sure the executives like it too. But many of you may be recoiling at the thought of an always-on nanycam who’s sole purpose seems to be to snitch on you to your boss, and judging by the replies to Brian’s post, you’re not alone. If your supervisor has a history of targeting you your fears may not be misplaced. Workplace surveillance tools are often coyly marketed for this.
What if instead of your boss using an AI tool to spy on you, your boss was completely replaced by an AI? Would your supervisor having no biases or favouritism sway your opinion? What about being able to tailor its communication specifically to you? Expressing no judgement at your clarifying questions? Being immediately available 24/7? Perfectly equitable expectations and performance reviews? Just writing that almost has me convinced this would usher in a workplace utopia.
In practice guaranteeing zero bias is extremely difficult. After all, these things are programmed by humans and learn from human data. Their “weights” could also be intentionally adjusted to favour or target. If the AI’s supervisor follows the Pareto Principle (also known as the 80/20 Rule) they may be tempted to ask it for a list of the lowest performing employees to be laid off on a regular basis. Not keeping yourself in the top 20% of performers (by whatever metrics the AI has been programmed to look for) may mean your job. The dystopian-future videogame “Cyberpunk 2077” tells a story of a company that brings in an AI only to have it fire all the human workers in favour of automation and copies of itself. Clearly it’s implementers forgot to set hard limits on its executive powers. The shareholders were happy with all-time high profits though…
When technology is blamed for these sorts of existential problems the IT industry collectively sighs and repeats the mantra, “The problem is not the technology. The problem is the people.” A quote from a 1979 IBM presentation is likewise summoned; “A computer can never be held accountable, therefore a computer must never make a management decision.” As a darker example, the Nuremberg trials post-WWII saw the precedent set that acting under “superior orders” is not a valid defence for war crimes or crimes against humanity. It seems responsibility can’t be passed to others, whether man or machine. The endless task of generating reports and presentations can probably be automated away though.
Would you work under an AI, or “hire” an AI to manage others? We can help you with that; you can find us at scalebright.ca.
-
 @ 9ca447d2:fbf5a36d
2025-05-27 12:01:21
@ 9ca447d2:fbf5a36d
2025-05-27 12:01:21DDC Enterprise, a consumer brand and e-commerce company with operations in the U.S. and China, has launched a big plan to make bitcoin (BTC) a key part of its financial strategy.
The company just bought 21 BTC as the first step in a plan to buy up to 5,000 BTC over the next 3 years.
The move was announced in a press release and a letter to shareholders by DDC’s founder, chairwoman and CEO Norma Chu.
The 21 BTC, worth around $2.28 million at current prices, was bought through a share exchange. DDC issued 254,333 class A ordinary shares.
“We are fully committed to ensuring the success of this strategy, which aligns with our vision to drive long-term value for our shareholders,” said Norma Chu. “Today marks a pivotal moment in DDC’s evolution.”
Chu is the first female founder and CEO of a U.S.-listed public company to lead a bitcoin-only treasury strategy. DDC is one of the first companies in its industry to adopt this strategy in such a structured way.
DDC’s plan is being rolled out in phases. The company will buy another 79 BTC soon and will have 100 BTC in the short term.
In the next 6 months, it will buy 500 BTC, and long-term, it expects to build a 5,000 BTC reserve over 36 months.
This phased approach may allow DDC to manage market volatility and take advantage of price movements.
In her recent letter to shareholders, Chu called the bitcoin strategy “a cornerstone of our long-term value creation plan”.
She said bitcoin’s qualities – especially as a hedge against macroeconomic uncertainty and inflation – make it the perfect reserve asset for DDC. She added:
“Bitcoin’s unique properties as a store of value and hedge against macroeconomic uncertainty align perfectly with our vision to diversify reserves and enhance shareholder returns.”
The announcement comes on the back of a record-breaking year for DDC.
In 2024, the company made $37.4 million in revenue—a 33% increase from 2023.
Gross margin improved from 25.0% in 2023 to 28.4% in 2024 due to strategic acquisitions in the U.S. and more efficient operations in China.
As of March 31, 2025 the company had $11.3 million in shareholder equity and $23.6 million in cash, cash equivalents and short-term investments.
This gives DDC the flexibility and credibility to do something as bold as this bitcoin accumulation plan.
DDC’s announcement comes as corporations are getting increasingly interested in adding bitcoin to their balance sheet.
While giants like Strategy have made headlines with large bitcoin purchases, DDC is the first e-commerce company to do so.
The company’s dual presence in China and the U.S. also adds complexity, especially with the different regulatory environments surrounding Bitcoin in each region.
To ensure proper execution, DDC has expanded its treasury and advisory teams to include experts in the bitcoin markets.
The company will use a mix of dollar cost averaging and tactical buying, adjusting purchases based on market conditions.
-
 @ c631e267:c2b78d3e
2024-10-23 20:26:10
@ c631e267:c2b78d3e
2024-10-23 20:26:10Herzlichen Glückwunsch zum dritten Geburtstag, liebe Denk Bar! Wieso zum dritten? Das war doch 2022 und jetzt sind wir im Jahr 2024, oder? Ja, das ist schon richtig, aber bei Geburtstagen erinnere ich mich immer auch an meinen Vater, und der behauptete oft, der erste sei ja schließlich der Tag der Geburt selber und den müsse man natürlich mitzählen. Wo er recht hat, hat er nunmal recht. Konsequenterweise wird also heute dieser Blog an seinem dritten Geburtstag zwei Jahre alt.
Das ist ein Grund zum Feiern, wie ich finde. Einerseits ganz einfach, weil es dafür gar nicht genug Gründe geben kann. «Das Leben sind zwei Tage», lautet ein gängiger Ausdruck hier in Andalusien. In der Tat könnte es so sein, auch wenn wir uns im Alltag oft genug von der Routine vereinnahmen lassen.
Seit dem Start der Denk Bar vor zwei Jahren ist unglaublich viel passiert. Ebenso wie die zweieinhalb Jahre davor, und all jenes war letztlich auch der Auslöser dafür, dass ich begann, öffentlich zu schreiben. Damals notierte ich:
«Seit einigen Jahren erscheint unser öffentliches Umfeld immer fragwürdiger, widersprüchlicher und manchmal schier unglaublich - jede Menge Anlass für eigene Recherchen und Gedanken, ganz einfach mit einer Portion gesundem Menschenverstand.»
Wir erleben den sogenannten «großen Umbruch», einen globalen Coup, den skrupellose Egoisten clever eingefädelt haben und seit ein paar Jahren knallhart – aber nett verpackt – durchziehen, um buchstäblich alles nach ihrem Gusto umzukrempeln. Die Gelegenheit ist ja angeblich günstig und muss genutzt werden.
Nie hätte ich mir träumen lassen, dass ich so etwas jemals miterleben müsste. Die Bosheit, mit der ganz offensichtlich gegen die eigene Bevölkerung gearbeitet wird, war früher für mich unvorstellbar. Mein (Rest-) Vertrauen in alle möglichen Bereiche wie Politik, Wissenschaft, Justiz, Medien oder Kirche ist praktisch komplett zerstört. Einen «inneren Totalschaden» hatte ich mal für unsere Gesellschaften diagnostiziert.
Was mich vielleicht am meisten erschreckt, ist zum einen das Niveau der Gleichschaltung, das weltweit erreicht werden konnte, und zum anderen die praktisch totale Spaltung der Gesellschaft. Haben wir das tatsächlich mit uns machen lassen?? Unfassbar! Aber das Werkzeug «Angst» ist sehr mächtig und funktioniert bis heute.
Zum Glück passieren auch positive Dinge und neue Perspektiven öffnen sich. Für viele Menschen waren und sind die Entwicklungen der letzten Jahre ein Augenöffner. Sie sehen «Querdenken» als das, was es ist: eine Tugend.
Auch die immer ernsteren Zensurbemühungen sind letztlich nur ein Zeichen der Schwäche, wo Argumente fehlen. Sie werden nicht verhindern, dass wir unsere Meinung äußern, unbequeme Fragen stellen und dass die Wahrheit peu à peu ans Licht kommt. Es gibt immer Mittel und Wege, auch für uns.
Danke, dass du diesen Weg mit mir weitergehst!
-
 @ ff517fbf:fde1561b
2025-03-30 04:43:09
@ ff517fbf:fde1561b
2025-03-30 04:43:09ビットコインが「最強の担保」と言われる理由
ビットコインは「デジタルゴールド」とも呼ばれることがありますが、実はローンの担保としても最強だと言われています。その理由を、他の資産(株式、不動産、金など)と比較しながら見てみましょう。
-
流動性と即時性:ビットコインは24時間365日世界中で取引されているため、非常に流動性が高い資産です。売買がすぐにできて価格も常に明確なので、担保評価がしやすく、お金を貸す側・借りる側双方に安心感を与えます。一方、株式や不動産は市場が営業時間内しか動かず、現金化にも時間がかかります。不動産は売却に数ヶ月かかることもありますし、金(ゴールド)は現物を保管・輸送する手間があります。ビットコインならネット上で即座に担保設定・解除ができるのです。
-
分割性と柔軟性:ビットコインは小数点以下8桁まで分割可能(1億分の1が最小単位の「サトシ」)なので、必要な額だけ正確に担保に充てることができます。他方、土地や建物を一部だけ担保に入れることは難しいですし、株式も1株未満の細かい調整はできません。ビットコインなら価値の微調整が容易で、担保として柔軟に扱えるのです。
-
管理のしやすさ(マルチシグによる信頼性):HodlHodlのLendでは、ビットコイン担保は2-of-3のマルチシグ契約で管理されます。これは「借り手・貸し手・プラットフォーム」の3者それぞれが鍵を持ち、2つの鍵の同意がないとビットコインを動かせない仕組みです。このため、誰か一人が勝手に担保を持ち逃げすることができず、第三者(HodlHodl)も単独ではコインを移動できません。ビットコインだからこそ実現できる非中央集権で安全な担保管理であり、株式や不動産を担保にする場合のように銀行や証券会社といった仲介業者に頼る必要がありません。
-
国境を越えた利用:ビットコインはインターネットがつながる所なら世界中どこでも送受信できます。このため、日本にいながら海外の相手とでもローン契約が可能です。たとえば日本の方がビットコインを担保にドル建てのステーブルコインを借り、それを日本円に換えて使うこともできます(為替リスクには注意ですが…)。不動産を海外の人と直接やり取りするのは現実的に難しいですが、ビットコインならグローバルに担保が活用できるのです。
-
希少性と価値の上昇期待:ビットコインは発行上限が決まっており(2100万BTCまで)、時間とともに新規供給が減っていきます。過去の長期的な価格推移を見ると、短期的な変動は激しいものの数年〜十年のスパンでは上昇傾向にあります。一方、法定通貨建ての資産(債券や株式など)はインフレの影響で実質価値が目減りすることがあります。ビットコインは長期保有すれば価値が上がりやすい特性があるため、「今手放したくない資産」として担保に向いています。実際、HodlHodlのチームは「ビットコインはスーパーカCollateral(超優秀な担保)だ」と述べています。
こうした理由から、ビットコインは現時点で考えうる中でも最良の担保資産と考えられています。株や不動産のように書類手続きや名義変更をしなくても、ビットコインならブロックチェーン上の契約でシンプルに担保設定ができる――この手軽さと信頼性が大きな魅力です。
匿名&プライバシー重視:KYC不要のP2Pレンディングのメリット
HodlHodlのLend最大の特徴の一つは、本人確認(KYC)が一切不要だという点です。日本の多くの金融サービスでは口座開設時に運転免許証やマイナンバー提出など煩雑な手続きが必要ですが、Lendではメールアドレスでアカウント登録するだけでOK。これは「匿名性・プライバシー」を重視する人にとって非常に相性が良いポイントです。
-
個人情報を晒さなくて良い安心感:日本では昔から「人に迷惑をかけない」「目立たない」ことが美徳とされ、特にお金の話は他人に知られたくないと考える人が多いですよね。Lendは匿名で利用できるため、借金をすることを周囲に知られたくない人でも安心です。銀行からローンを借りるときのように収入証明や保証人を用意する必要もなく、誰にも知られずひっそりと資金調達ができます。
-
ノー・チェック&ノー・ペーパー:貸し借りにあたって信用審査や過去の借入履歴チェックがありません 。極端な話、今まで金融履歴が全く無い人や、銀行に相手にされないような人でも、ビットコインさえ持っていればお金を借りられるのです。書類のやり取りが無いので手続きもスピーディーです。「印鑑証明や収入証明を揃えて…」という面倒とは無縁で、ネット上でクリックして契約が完結します。
-
プライバシーの保護:個人情報を提出しないということは、情報漏洩のリスクも無いということです。近年、日本でも個人情報の流出事件が相次いでおり、不安に感じる方も多いでしょう。Lendではアカウント登録時にメールアドレスとパスワード以外何も求められません。財務情報や身元情報がどこかに蓄積される心配がないのは、大きな安心材料です。
-
国や機関から干渉されにくい:匿名であるということは、極端に言えば誰にも利用を知られないということです。たとえば「ローンを借りると住宅ローンの審査に響くかな…」とか「副業の資金調達を会社に知られたくないな…」といった心配も、匿名のP2Pローンなら不要です。借りたお金の使い道も自由ですし、何より利用自体が自分だけの秘密にできるのは、日本人にとって心理的ハードルを下げてくれるでしょう。
このように、ノーKYC(本人確認なし) のP2Pレンディングは、日本のようにプライバシーや控えめさを重んじる文化圏でも利用しやすいサービスと言えます。実際、HodlHodlのLendは「地理的・規制的な制限がなく、世界中の誰もが利用できる純粋なP2P市場」とされています。日本に居ながらグローバルな貸し借りができ、しかも身元明かさずに済む――これは画期的ですね。
Borrow編:HodlHodlのLendでビットコインを担保にお金を借りる方法
それでは具体的に、HodlHodlのLendでどのようにビットコイン担保のローンを借りるのか、手順を追って説明します。初心者でも迷わないよう、シンプルなステップにまとめました。
1. アカウント登録 (Sign up)
まずはHodlHodlのLendサイトにアクセスし、無料のアカウントを作成します。必要なのはメールアドレスとパスワードだけです。登録後、確認メールが届くのでリンクをクリックして認証すれば準備完了。これでプラットフォーム上でオファー(契約希望)を閲覧・作成できるようになります。
※HodlHodlは日本語には対応していませんが、英語のシンプルなUIです。Google翻訳などを使っても良いでしょう。
2. 借りたい条件のオファーを探す or 作成
ログインしたら、「To Borrow(借りる)」のメニューから現在出ている貸し手のオファー一覧を見てみましょう。オファーには借入希望額(例:$1000相当のUSDT)、期間(例:3ヶ月)、金利(例:5%)やLTV(担保価値比率、例:60%)などの条件が書かれています。自分の希望に合うものがあれば選んで詳細画面へ進みます。条件に合うオファーが見つからない場合は、自分で「○○ USDTを△ヶ月、金利○%で借りたい」という借り手オファーを新規作成することも可能です。
用語補足:LTV(ローン・トゥ・バリュー)とはローン額に対する担保価値の割合です。たとえばLTV50%なら、借りたい額の2倍の価値のビットコインを担保に入れる必要があります。LTVは貸し手が設定しており、一般に30%〜70%程度の範囲でオファーが出ています。低いLTVほど借り手は多くのBTC担保が必要ですが、その分だけ貸し手にとって安全なローンとなります。
3. 契約成立とマルチシグ担保のデポジット
借り手・貸し手双方が条件に合意すると契約成立です。HodlHodlプラットフォーム上で自動的に専用のマルチシグ・エスクロー用ビットコインアドレス(担保保管先アドレス)が生成されます。次に、借り手であるあなたは自分のウォレットからビットコインをそのエスクローアドレスに送金します。
- 📌ポイント:マルチシグで安心 – 上述の通り、このエスクロー用アドレスのコインを動かすには3者中2者の署名が必要です。あなた(借り手)は常にそのうちの1つの鍵を保有しています。つまり、自分が承認しない限り担保BTCが勝手に引き出されることはないのでご安心ください。
ビットコインの入金がブロックチェーン上で所定の承認(通常数ブロック程度)を得ると、担保デポジット完了です。これで契約は有効化され、次のステップへ進みます。
4. 貸し手から資金(ステーブルコイン)を受け取る
担保のロックが確認できると、今度は貸し手がローン金額の送金を行います。Lendで借りられるのは主にステーブルコインです。ステーブルコインとは、米ドルなど法定通貨の価値に連動するよう設計された仮想通貨で、USDTやUSDC、DAIといった種類があります。借り手は契約時に受取用のステーブルコインアドレス(自分のウォレットアドレス)を指定しますので、貸し手はそのアドレス宛に契約どおりの額を送金します。例えばUSDTを借りる契約なら、貸し手からあなたのUSDTウォレットにUSDTが送られてきます。
これで晴れて、あなた(借り手)は希望のステーブルコインを手にすることができました! あなたのビットコインは担保としてロックされていますが、期限までに返済すれば取り戻せますので、しばしのお別れです。借りたステーブルコインは自由に使えますので、後述する活用例を参考に有効活用しましょう。
5. 返済(リペイメント)
契約期間中は基本的に何もする必要はありません(途中で追加担保や一部返済を行うことも可能ですが、初心者向け記事では割愛します)。期間が満了するまでに、借りたステーブルコイン+利息を貸し手に返済します。返済も、貸し手の指定するウォレットアドレスにステーブルコインを送金する形で行われます。
- 利息の計算:利息は契約時に決めた率で発生します。例えば年利10%で6ヶ月間$1000を借りたなら、利息は単純計算で$50(=$1000×10%×0.5年)です。契約によっては「期間全体で○%」と定める場合もありますが、プラットフォーム上で年率(APR)換算が表示されます。
期間内であれば任意のタイミングで早期返済することも可能です。返済期限より早く全額返せば、利息もその日数分だけで済みます(※ただし契約によります。事前に契約条件を確認してください)。HodlHodlでは分割返済にも対応しており、例えば月ごとに少しずつ返して最後に完済することもできます。
6. ビットコイン担保の解除(返却)
貸し手があなたからの返済受領を確認すると、プラットフォーム上で契約終了の手続きを行います。マルチシグの担保アドレスからあなたのビットコインを解放(返却)する署名を貸し手とプラットフォームが行い、あなたの元のウォレットにビットコインが送られます。こうして無事に担保のBTCが戻ってくれば、一連のローン取引は完了です🎉。
もし返済が滞った場合はどうなるのでしょうか?その場合、契約で定められた猶予期間やマージンコール(追加担保のお願い)を経た後、担保のビットコインが強制的に貸し手に渡されて契約終了(清算)となります。担保額が未返済額を上回っていれば、差額は借り手に返ってきます。つまり、返せなかったとしても借り手が担保以上の損をすることはありませんが、大切なビットコインを失ってしまう結果にはなるので注意しましょう。
Borrow(借りる)側のまとめ:ビットコインさえあれば、あとの手続きは非常に簡単です。借入までの流れをもう一度簡潔にまとめると:
- メールアドレスでLendに登録
- 借入オファーを探すor作成してマッチング
- マルチシグ契約が自動生成・BTC担保を自分で入金
- 貸し手からステーブルコインを受領
- 期限までにステーブルコイン+利息を返済
- ビットコイン担保が自分のウォレットに戻る
第三者の仲介なしに、ネット上でこれだけのことが完結するのは驚きですよね。HodlHodlは「あなたの条件、あなたの鍵、あなたのコイン」と銘打っており、自分の望む条件で・自分が鍵を管理し・自分の資産を動かせるプラットフォームであることを強調しています。
Lend編:HodlHodlのプラットフォームでお金を貸してみよう
次は逆に、自分が貸し手(Lender)となってステーブルコインを貸し出し、利息収入を得る方法です。銀行に預けても超低金利のこのご時世、手持ちの資金をうまく運用したい方にとってP2Pレンディングは魅力的な選択肢になりえます。HodlHodlのLendなら、これもまた簡単な手順で始められます。
基本的な流れは先ほどの「Borrow編」と鏡写しになっています。
1. アカウント登録
借り手と同様、まずはHodlHodlに登録します(すでに借り手として登録済みなら同じアカウントで貸し手にもなれます)。メールアドレスだけでOK、もちろん貸し手側もKYC不要です。
2. 貸出オファーの確認 or 作成
ログイン後、「To Lend(貸す)」メニューから現在の借り手募集一覧を見ます。各オファーには希望額・期間・支払い利率・LTVなど条件が表示されています。「この条件なら貸してもいいかな」という案件があれば選択しましょう。もし自分の希望する利回りや期間が合わない場合は、自分で貸し手オファーを作成することも可能です。「○○ USDTまで、最長△ヶ月、最低利息◻◻%で貸せます」といった条件を提示できます。プラットフォーム上ではユーザーがお互いに条件を提示しあってマッチングする仕組みなので、金利や期間もすべてユーザー自身が自由に設定できます。
3. マッチングと契約開始
あなたの提示した条件で借りたい人が現れたら契約成立です(逆に誰かの借入オファーに応じる形なら、その時点で成立)。システムがマルチシグの担保用BTCアドレスを生成し、借り手がそこへビットコインをデポジットします。借り手からのBTC入金が確認できるまで、貸し手であるあなたは資金を送る必要はありません。担保が確保されたのを見届けてから次に進みます。
4. 資金(ステーブルコイン)の送金
借り手の担保ロックが完了したら、契約で定めたステーブルコインを借り手へ送金します。送金先アドレスは契約詳細画面に表示されます(借り手が指定済み)。例えばUSDCを貸す契約なら、相手のUSDCアドレスに約束の額を送ります。ここで送金した金額がローンの principal(元本)となり、後ほど利息とともに返ってくるわけです。
無事に相手に届けば、あとは契約期間終了まで待つだけです。あなたは担保のBTCに対して鍵を1つ持っている状態なので、万一トラブルが起きた場合でも担保を引き出す権利を部分的に持っています(詳しくは次ステップ)。
5. 返済の受領
契約期間が終わると、借り手があなたにステーブルコインを返済してくるはずです。約束どおり元本+利息を受け取ったら、それを確認してプラットフォーム上で「返済完了」を操作します。すると担保のビットコインがマルチシグから解放され、借り手に返却されます。これで貸し手としてのあなたは利息分の収益を獲得できました。お疲れ様です!
もし借り手が返済しなかった場合どうなるでしょうか?その場合、所定の猶予期間やマージンコール通知の後、担保のビットコインがあなた(貸し手)に渡されることになります。具体的には、LTVが90%に達するか返済期日から24時間以上滞納が続くと強制清算となり、担保BTCからあなたの貸付相当額が充当されます。担保が十分であれば元本と利息はカバーされ、余剰があれば借り手に返還されます。つまり貸し手側はかなり手厚く保護されており、返済を受け取れない場合でも担保で穴埋めされる仕組みです。
6. 収益を管理・再投資
受け取ったステーブルコイン(元本+利息)は再度プラットフォームで貸し出しても良いですし、他の用途に使ってもOKです。年利に換算するとだいたい10%前後の利回りになる案件が多く見られます。条件次第では更に高い利率の契約も可能ですが、その分借り手が見つかりにくかったりリスク(担保不足のリスク)が高まる可能性もあります。ご自身のリスク許容度に合わせて運用しましょう。
Lend(貸す)側のまとめ:
- HodlHodlに登録(メールアドレスのみ)
- 貸出オファーを提示 or 借り手募集に応じる
- 契約成立後、借り手がBTC担保を入金
- 貸し手(自分)がステーブルコインを送金
- 期限まで待ち、借り手から元本+利息を受領
- 担保BTCを返却し、利息収入を得る
銀行預金では考えられないような利息収入を得られるのが魅力ですが、その裏でビットコイン価格変動リスクも担っています。大暴落が起きて担保評価額が急落すると、清算時に元本を割るリスクもゼロではありません(LTV設定とマージンコール制度で極力保護されまますが)。リスクとリターンを理解した上で、小額から試すことをおすすめします。
ステーブルコインの活用:お金持ちは借金で生活する?
ここまで、ビットコインを手放さずにステーブルコインを手に入れる方法を見てきました。それでは、借りたステーブルコインは具体的に何に使えるのでしょうか?いくつか例を挙げてみましょう。
-
日常の出費に充当:ビットコイン投資家の中には「生活費はすべて借りたお金で賄い、自分のBTCはガチホ(売らずに長期保有)する」という方針の人もいます。例えば毎月の家賃や食費をステーブルコインのローンで支払い(これについても今後詳しく解説していきます)、ビットコインは一切使わないというイメージです。こうすれば、手持ちのBTCを売らずに済むので将来の値上がり益を逃しません。また日本では仮想通貨を売却すると雑所得として高率の税金がかかりますが、ローンで得たお金は借入金なので課税対象になりません(※将来的な税務計算は自己責任で行ってください)。つまり、ビットコインを売却して現金化する代わりにローンを使うことで、節税と資産温存のメリットが得られる可能性があります。
-
投資・資産運用に回す:借りた資金をさらに別の投資に活用することもできます。例えば有望な株式や不動産に投資したり、あるいは他の仮想通貨を買うこともできます。極端な例では、ビットコインを担保にUSDTを借りて、そのUSDTでまた別の仮想通貨を買い、それを運用益で返済する…といった戦略も理論上は可能です。ただし、借りたお金での投機はハイリスクなので慎重に!手堅い使い道としては、事業資金に充てるのも良いでしょう。例えば小さなオンラインビジネスを始めるための元手にしたり、新しい資格取得のための学費にするなど、自分への投資に使えば将来的なリターンでローンを返しつつ利益を上げることが期待できます。
-
急な支払いへの備え:人生何があるか分かりません。医療費や冠婚葬祭など急に現金が必要になる場面もあります。そんなとき、ビットコインをすぐ売ってしまうのは惜しい…という場合にローンで一時的にしのぐことができます。後で落ち着いてから返済すれば、大事なBTCを手放さずにピンチを乗り切れます。言わばデジタル質屋のような感覚で、ビットコインを預けてお金を工面し、後で買い戻す(返済する)イメージですね。日本でも昔から「質屋」で着物や宝石を預けてお金を借りる文化がありましたが、HodlHodl Lendはビットコイン版の質屋とも言えるでしょう。
-
市場の機会を逃さない:仮想通貨市場は変動が激しく、「今これを買いたいのに現金が無い!」というチャンスもあるでしょう。例えば「ビットコインが急落したから買い増したいが、現金が足りない」という場合、手持ちBTCを担保にしてステーブルコインを借り、その急落で安く買い増しする、といった動きもできます。そして後日価格が戻したところで返済すれば、差益を得つつBTC保有枚数も増やせるかもしれません。このようにローンを戦略的に使えば、市場の好機を掴む資金余力を生み出すことができます。ただしハイリスクな手法でもあるため、上級者向けではあります。
ここで覚えておきたいのは、「お金持ちは借金との付き合い方が上手い」という点です。日本では借金にネガティブな印象を持つ人も多いですが、世界的な資産家や大企業はしばしばあえて借金をして手元資金を他に活用しています。アメリカのベストセラー『金持ち父さん貧乏父さん』で有名なロバート・キヨサキ氏も「富裕層は他人のお金(借金)を利用してさらに富を築く」と強調しています。例えば彼は借金で高級車を買い、不動産投資にも借入を活用したそう (金持ちは貧乏人より借金が多い | 「金持ち父さん 貧乏父さん」日本オフィシャルサイト)❤️。借金を味方につけて資産運用すれば、自分の持ち出し資金を抑えつつ豊かな生活を実現できる可能性があります。
もちろん無計画な借金は禁物ですが、ローンを上手に使うことは決して悪いことではなく、むしろ経済的戦略として有効なのです。ビットコイン担保ローンはその新しい選択肢として、「お金にお金に働いてもらう」感覚を身につけるきっかけになるかもしれません。
高い金利でもローンを利用するのはなぜ?その理由と戦略
Lendのプラットフォームで提示される金利は、年利換算で見ると10〜15%程度が一つの目安 です。中にはそれ以上の利率の契約もあります。日本の銀行ローン(金利数%以下)と比べるとかなり高利に思えますが、それでも多くの人がこのサービスを利用してローンを組んでいます。なぜ高い利息を支払ってまで借りる価値があるのでしょうか?最後に、その理由と利用者の戦略について考えてみましょう。
-
(1) ビットコインの期待リターンが高い:借り手にとって一番の動機は、「ビットコインは将来もっと値上がりするはずだから、多少利息を払っても売りたくない」というものです。例えば年利15%で$1000借りると一年後に$1150返す必要がありますが、もしビットコイン価格がその間に15%以上上昇すれば、利息分を差し引いても得をする計算になります。過去のビットコイン相場は年率ベースで大きく成長した年も多く、強気のホルダーほど利息より値上がり益を優先する傾向があります。「金利よりビットコインの価値上昇のほうが大きい」という自信が、高金利を払ってでも借りる動機になっているのです。
-
(2) 課税や手数料の回避:先ほど述べたように、日本ではビットコインを売却すると高額の税金が発生する可能性があります。仮に30%〜50%の税金がかかるのであれば、年利10%前後のローンで済ませたほうがトクだという判断も成り立ちます。また、取引所で売却するときのスプレッドや出金手数料なども考えると、売却コストを回避する手段としてローンを選ぶ人もいます。要するに「売るくらいなら借りた方がマシ」という考え方ですね。
-
(3) 自由と速さを優先:従来の金融機関からお金を借りるには時間がかかりますし、使途にも制限があることが多いです(事業資金なのか生活費なのか、といった審査があります)。それに対してHodlHodlのP2Pローンは使い道自由・即日資金調達が可能です。利息が高めでも「今すぐ○○がしたい」「明日までに現金が要る」といったニーズには代えられません。特に仮想通貨業界はスピード命ですから、チャンスを逃さないために高コストでも素早く借りるという選択が生まれます。
-
(4) 借金=時間を買うこと:あるユーザーの言葉を借りれば、「借金をすることは未来の時間を先取りすること」でもあります。例えば住宅ローンがあるからこそ若い世代でもマイホームに住めますし、事業ローンがあるからこそ企業は成長の機会を掴めます。ビットコイン担保ローンも同じで、「今はお金が無いけど将来増やすアテはある。だから今借りてしまおう」というケースもあるでしょう。将来の収入や資産増加を見込んで、時間を味方につけるためにあえて借金をするのです。日本語では「借金してでも◯◯する」という表現がありますが、前向きな借金は将来への投資とも言えるでしょう。
-
(5) 非中央集権への支持:もう一つ見逃せないのは、HodlHodlのようなプラットフォームを利用する理由に思想的な支持があります。つまり「銀行や政府に頼らないお金の流れを実現したい」「ビットコインのエコシステムを活性化させたい」というビットコイナーたちです。多少コストが高くても、理念に共感して使っているケースもあります。匿名で自由にお金を借りられる世界を体験することで、金融システムの新たな可能性を感じているのです。
以上のように、高い金利にも関わらずローンを利用するのは明確なメリットや戦略があるからなのです。もちろん全ての人に当てはまるわけではありません。ビットコイン価格が下落局面ではリスクも伴いますし、利息分だけ損になる場合もあります。しかし、それらを理解した上で「自分のお金を働かせる」「資産を手放さずレバレッジを利かせる」手段として活用している人々が増えてきています。
最後に、HodlHodlの公式ブログの一文をご紹介します。
“私たちはビットコインこそがスーパーカ collateral(超優秀な担保)であり、利回りを得るために使うのではなく、それを担保に資金を借りるために使われるべきだと考えています" (The lending is dead, long live the lending | by Hodl Hodl | Hodl Hodl | Medium)。
ビットコイン時代の新しいお金の借り方・貸し方であるP2Pローン。最初は難しく感じるかもしれませんが、仕組みを理解すればとてもシンプルで強力なツールです。日本ではまだ馴染みが薄いかもしれませんが、匿名性を好み、コツコツ資産を増やすのが得意な人にこそフィットするサービスかもしれません。ぜひ少額から試し、自分なりの活用法を見つけてみてください。きっと新たな発見があるはずです。
もしビットコイン担保のP2Pローンなどについてもっと深く知りたい、あるいは個別に相談してみたいと思えば、どうぞお気軽にご連絡ください。1対1のコンサルティングも承っています。
サービスには決まった料金はありませんが、ご相談を通じて「役に立った」と思い、お悩みや疑問を解決できたと感じていただけたら、「3つのT」でのご支援(Value for Value)をぜひご検討ください:
- 時間(Time):この記事をSNSなどでシェアしていただくこと。
- 才能(Talent):コメントや補足情報などを通じて知識を共有していただくこと。
- 宝(Treasure):世界で最も健全なお金、ビットコインの最小単位「sats」でのご支援。
もちろん、支援の有無にかかわらず、お力になれればとても嬉しいです。 では、また次回!
-
-
 @ bbef5093:71228592
2025-05-07 15:09:39
@ bbef5093:71228592
2025-05-07 15:09:39Az Európai Bizottság terve az orosz urán- és energiafüggőség felszámolására
Az Európai Bizottság bejelentette, hogy korlátozni kívánja az új urán-, dúsított urán- és egyéb, Oroszországból származó nukleáris anyagokra vonatkozó ellátási szerződéseket, ezzel is elősegítve, hogy az Európai Unió „teljesen megszüntesse” az orosz energiától való függését[8][6][2].
A Bizottság új ütemtervet mutatott be, amely részletesen tartalmazza, hogyan kívánja megszüntetni az orosz energiafüggőséget, miközben biztosítja az EU energiaellátásának és árainak stabilitását[6][2][15].
Főbb intézkedések és célok
- Az EU az orosz gázimport arányát 45%-ról 19%-ra csökkentette a 2022 májusában indított REPowerEU tervnek köszönhetően, de 2024-ben ismét növekedett az orosz gáz behozatala[2][20].
- Az új ütemterv szerint az orosz olaj, gáz és nukleáris energia fokozatosan, összehangoltan és biztonságosan kerül ki az uniós piacokról, miközben az EU a tiszta energiára való átállást gyorsítja fel[6][15][7].
- Az EU-tagállamoknak 2025 végéig nemzeti terveket kell készíteniük arról, hogyan járulnak hozzá az orosz gáz, nukleáris energia és olaj importjának megszüntetéséhez[13][7][18].
- Az orosz eredetű urán, dúsított urán és egyéb nukleáris anyagok esetében új korlátozásokat vezetnek be: az Euratom Ellátási Ügynökség (ESA) nem hagy jóvá új orosz beszállítási szerződéseket, és gazdasági eszközökkel is igyekeznek visszaszorítani az importot[4][5][16].
- A meglévő rövid távú szerződéseket 2025 végéig meg kell szüntetni, új szerződéseket pedig nem lehet kötni; a hosszú távú szerződéseket 2027 végéig kell felmondani[5][7][6].
- Az intézkedések célja, hogy a teljes orosz gáz- és olajimport 2027 végéig megszűnjön, az orosz atomenergia pedig fokozatosan kivezetésre kerüljön[3][9][17].
Nukleáris háttér
- Az ESA jelentése szerint 2023-ban az EU-ban felhasznált természetes urán 23,4%-a érkezett Oroszországból, ami 72,6%-os növekedést jelentett, főként a VVER típusú orosz atomerőművek üzemanyag-felhalmozása miatt[16].
- Az EU-ban 19 VVER reaktor működik (Bulgáriában, Csehországban, Finnországban, Magyarországon és Szlovákiában).
- Az EU természetes uránszükséglete a globális igények mintegy 22%-át teszi ki, a beszerzések 91%-a Kanadából, Oroszországból, Kazahsztánból és Nigerből származik[16].
Célkitűzés és indoklás
A Bizottság szerint az orosz energiafüggőség felszámolása nemcsak gazdasági, hanem biztonságpolitikai kérdés is, mivel Oroszország többször is eszközként használta az energiát az EU-val szemben[2][12]. A lépések célja, hogy az EU energiaellátása biztonságos, stabil és kiszámítható maradjon, miközben az orosz energiaimportból származó bevételek ne finanszírozhassák tovább az Ukrajna elleni háborút[6][2][12].
Források alapján készült magyar összefoglaló és fordítás
Citations: [1] Döntött az Európai Bizottság: teljes mértékben megszüntetik ... - 444 https://444.hu/2025/05/06/dontott-az-europai-bizottsag-teljes-mertekben-megszuntetik-az-orosz-energiatol-valo-fuggest [2] Három éven belül felszámolná az orosz energiafüggőséget az ... https://hu.euronews.com/my-europe/2025/05/06/harom-even-belul-felszamolna-az-orosz-energiafuggoseget-az-europai-bizottsag [3] 2027-re teljesen leállítaná az Európai Bizottság az orosz ... - Új Szó https://ujszo.com/kozelet/2027-re-teljesen-leallitana-az-europai-bizottsag-az-orosz-energiabehozatalt-a-nuklearis [4] Bejelentették Brüsszelben: megkerülik Magyarországot, teljesen ... https://www.portfolio.hu/gazdasag/20250506/bejelentettek-brusszelben-megkerulik-magyarorszagot-teljesen-levalik-az-orosz-olajrol-es-gazrol-az-eu-759267 [5] Érik az újabb ütközés: Brüsszel betiltaná az orosz energiát https://www.valaszonline.hu/2025/05/06/energia-szankcio-oroszorszag-haboru-eu-olaj-gaz-uran/ [6] Az EU teljes mértékben megszünteti az orosz energiától való függését https://hungary.representation.ec.europa.eu/az-eu-teljes-mertekben-megszunteti-az-orosz-energiatol-valo-fuggeset-2025-05-06_hu?prefLang=en [7] Megvan az ütemterv, végleg betiltaná az orosz energiát az Európai ... https://index.hu/kulfold/2025/05/06/orosz-energiafuggoseg-orosz-gaz-olaj-import-europai-unio-repowereu/ [8] European Commission Unveils Plans To Restrict New Uranium ... https://www.nucnet.org/news/european-commission-unveils-plans-to-restrict-new-uranium-deals-with-russia-5-3-2025 [9] Az EU teljes mértékben megszünteti az orosz energiától való ... https://infostart.hu/belfold/2025/05/06/az-eu-teljes-mertekben-megszunteti-az-orosz-energiatol-valo-fuggoseget-a-nap-hirei [10] [PDF] EURÓPAI BIZOTTSÁG Brüsszel, 2025.4.9. COM(2025) 159 final ... https://secure.ipex.eu/IPEXL-WEB/download/file/082d29089612ec1e019619f955940250 [11] Kiszivárgott az Európai Bizottság 2025-ös munkaprogramja https://www.eu-monitor.hu/hu/cikk/20250206-kiszivargott-az-europai-bizottsag-2025-os-munkaprogramja [12] EU says it will end dependency on Russian energy supplies https://www3.nhk.or.jp/nhkworld/en/news/20250507_B4/ [13] Végleg leválik az orosz energiáról az Európai Unió ... - Népszava https://nepszava.hu/3278673_oroszorszag-europai-unio-foldgaz-koolaj-levalas-terv [14] Egyre több európai ország támogatja az atomenergiát https://www.vg.hu/nemzetkozi-gazdasag/2025/03/atomenergia-energiatarolas-europa [15] Az EU teljes mértékben megszünteti az orosz energiától való ... https://karpatinfo.net/energiafuggetlenseg-orosz-foldgaz-orosz-energiafuggoseg-2025-05-07 [16] EU outlines measures to end Russian gas, oil imports by end-2027 https://balkangreenenergynews.com/eu-outlines-measures-to-end-russian-gas-oil-imports-by-end-2027/ [17] Az Európai Unió 2027 végére betiltaná az orosz gáz importját https://www.korkep.sk/cikkek/gazdasag/2025/05/05/az-europai-unio-2027-vegere-betiltana-az-orosz-gazimportot/ [18] Ficónak és Orbánnak sem tetszik, hogy az EU teljesen kitiltaná az ... https://napunk.dennikn.sk/hu/4623240/ficonak-es-orbannak-sem-tetszik-hogy-az-eu-teljesen-kitiltana-az-orosz-energiat/ [19] Várhelyi Olivér késlelteti az EU orosz energiafüggőségét felszámoló ... https://telex.hu/kulfold/2025/05/05/varhelyi-oliver-europai-bizottsag-orosz-energia-kivaltas-hatraltatas [20] REPowerEU roadmap - Energy - European Commission https://energy.ec.europa.eu/strategy/repowereu-roadmap_en
-
 @ bbef5093:71228592
2025-05-06 05:17:07
@ bbef5093:71228592
2025-05-06 05:17:07*Holtec új atomenergetikai együttműködése Utah államban*
Az amerikai Holtec International stratégiai megállapodást kötött Utah állammal és a Hi Tech Solutions nukleáris szolgáltatóval, hogy elősegítse saját fejlesztésű, SMR-300 típusú kis moduláris reaktorainak (SMR) telepítését Utahban és az Egyesült Államok Mountain West régiójában. A megállapodás értelmében 2028-ig állandó képzési központot hoznak létre Utahban, amely az üzemeltetéshez, karbantartáshoz és az új generációs nukleáris technológiákhoz szükséges munkaerő képzését célozza, szoros együttműködésben helyi egyetemekkel, főiskolákkal és szakiskolákkal.
A projekt Utah állam energetikai stratégiájának („Operation Gigawatt” és „Built Here”) része, amely a következő tíz évben megduplázná az állam energiatermelését, kiemelt szerepet szánva a tiszta nukleáris energiának. A Holtec Utah-t választotta nyugati gyártóbázisának is, ezzel erősítve az amerikai nukleáris ellátási láncot és hosszú távú munkahelyeket teremtve. A cég a 2030-as években akár 4 GW összkapacitású SMR-300 telepítését tervezi főként Utahban és Wyomingban.
Az SMR-300 egy nyomottvizes reaktor, amely 300 MW villamos vagy 1050 MW hőteljesítményt biztosít, és a Holtec tervei szerint kulcsszerepet játszhat a tiszta, szén-dioxid-mentes energiatermelésben.
*Amerikai SMR-piac helyzete*
Az SMR-technológia az utóbbi években került a figyelem középpontjába, mivel gyorsabban és olcsóbban telepíthető, mint a hagyományos atomerőművek, és lehetőséget kínál magánbefektetők számára is. Ugyanakkor az első amerikai SMR-projekt, a NuScale és a Utah Associated Municipal Power Systems közös beruházása költségnövekedés miatt meghiúsult, ami rávilágított a technológia gazdasági kihívásaira.
Nemzetközi fejlemények és további hírek
- Az ausztrál Okapi Resources és az Urenco együttműködési megállapodást kötött új urán dúsítási technológia fejlesztésére, amely tisztább és olcsóbb dúsítási eljárást ígér.
- Az Argonne National Laboratory sikeresen kicserélt egy 30 éves kulcsfontosságú alkatrészt a nátriumhűtésű gyorsreaktor-tesztberendezésében, ami hozzájárulhat a gyorsreaktor-technológia fejlesztéséhez az Egyesült Államokban.
- A Tennessee Egyetem ösztöndíjprogramot indít a Fülöp-szigeteki nukleáris szakemberek képzésére, támogatva ezzel a délkelet-ázsiai ország nukleáris energiafejlesztési törekvéseit.
- Bulgáriában a Westinghouse Electric Company helyi beszállítókkal kötött megállapodásokat két új AP1000 típusú reaktor építéséhez a kozloduji atomerőműben.
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 90c656ff:9383fd4e
2025-05-27 11:27:26
@ 90c656ff:9383fd4e
2025-05-27 11:27:26Since its creation, Bitcoin has been a revolutionary asset, challenging the traditional financial system and proposing a new form of decentralized money. However, its future remains uncertain and the subject of intense debate. Among the possible outcomes, two extreme scenarios stand out: hyperbitcoinization-where Bitcoin becomes the dominant currency in the global economy—and obsolescence, where the network loses relevance and is replaced by other solutions.
- Hyperbitcoinization: The World Adopts Bitcoin as a Monetary Standard
01 - Loss of trust in fiat currencies: Due to excessive money printing by central banks, many economies face rampant inflation. Bitcoin, with its fixed supply of 21 million units, emerges as a more trustworthy alternative.
02 - Growing adoption by companies and governments: Some countries have already begun integrating Bitcoin into their economies, accepting it for payments and as a store of value. If this trend continues, Bitcoin’s legitimacy as a global currency will grow.
03 - Ease of global transactions: Bitcoin enables fast and low-cost international transfers, removing the need for financial intermediaries and reducing operational costs.
04 - Technological advancements: Scalability improvements, such as the Lightning Network, can make Bitcoin more efficient for daily use, encouraging mass adoption.
If hyperbitcoinization becomes reality, the world may witness a radical shift in the financial system—with greater decentralization, censorship resistance, and an economy based on sound, predictable money.
- Obsolescence: Bitcoin Loses Relevance and Is Replaced
01 - Restrictive government regulations: If major economic powers enforce strict regulations on Bitcoin, adoption could slow, reducing its utility.
02 - Technological shortcomings or lack of innovation: Despite its security and decentralization, Bitcoin may struggle to scale effectively. If superior solutions emerge and gain acceptance, Bitcoin could lose its leading position.
03 - Competition from faster, more user-friendly alternatives: Other forms of digital money may surpass Bitcoin in scalability and usability, potentially leading to a decline in Bitcoin adoption.
04 - Decreasing miner incentives: As new Bitcoin issuance halves every four years, miners will rely increasingly on transaction fees. If those fees are insufficient to sustain network security, long-term viability could be at risk.
In summary, Bitcoin’s future could unfold along multiple paths, depending on factors like innovation, global adoption, and resilience to external challenges. Hyperbitcoinization would represent an economic revolution—ushering in a decentralized, inflation-resistant monetary system. Yet, obsolescence remains a risk if the network fails to adapt to future demands. Regardless of the outcome, Bitcoin has already made its mark on financial history, paving the way for a new era of digital money and economic freedom.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 65038d69:1fff8852
2025-03-29 13:05:35
@ 65038d69:1fff8852
2025-03-29 13:05:35Welcome to part 4, the final entry in the What is Money series. We’re capping it off with “crypto” and CBDCs.
Let's start with crypto. Short for cryptocurrency, it’s a catch-all term for all of the non-fiat, blockchain-based, or non-government-operated new money systems that aren’t Bitcoin. Ethereum, Solana, and Dogecoin are some you may have heard of. There are actually thousands of cryptocurrencies in existence, but we’ll summarize some of the biggest ones by size and pop culture penetration. One thing they all have in common is that like fiat currencies, they have no supply limit and are therefore inflationary by nature.
Ethereum: Released in 2015 by Vitalik Buterin, Ethereum is less of a money system and more of a network built to run “decentralized applications” (DAPs) on. “Smart contracts” and “tokens” are the most common of these. If none of those terms mean anything to you, you’re not alone. What they’ve essentially done is recreate the unending complexity of high finance in a computer system and replaced the bankers and lawyers with programmers.
Solana: Solana is much smaller than Ethereum but serves a similar function of being a wild-west finance platform. I’m only mentioning it here as it's been in the media a lot with numerous security compromises, lawsuits, and general drama. Your nephew who trades in Robux probably knows someone who lost their allowance savings in the 2021 crash.
USDT/Tether: This is the largest in a family of cryptocurrencies called “stablecoins”. They’re meant to offer the features of crypto but with the “stability” of having their value tied to a fiat currency, in this case the US Dollar.
Monero: Monero was designed from the ground up to be as anonymous as possible. Unfortunately it’s lack of popularity means it’s not particularly useful for purchases.
Dogecoin: Released in 2013, Dogecoin was created as a joke to poke fun at Bitcoin and cryptocurrencies. As a joke it’s been wildly successful, but like most jokes there are many who decided to take it seriously over the years, which has driven its market cap to surpass that of Monera and most others. It’s currently in the top 10 by market cap, but you’ll struggle to find anyone who takes it as payment.
The concept of CBDCs (central bank digital currencies) has been making the rounds through media for some time. Some paint it as a boogeyman to be feared, while others see it as nothing more than an annoying waste of government resources. As you may recall from part 2 of this series, the Bank of Canada is not a retail bank with individuals for customers, instead acting as an administrative body and a bank for banks. CBDCs have the potential to change that. In a sentence, a Canadian CBDC would most likely be a system whereby individuals who struggle to get or maintain accounts at retail banks could be issued a Bank of Canada account. There may also be some integration with Payments Canada systems to make retail payments and transfers cheaper and more direct. Much of this is speculation though, as the BoC hasn’t announced any of this, only that research is ongoing. In any case it won’t be a replacement of the Canadian Dollar, just another system for moving Dollars around between ledgers and accounts.
I’d normally sign off with something like, “Want help with insert article topic here? You can find us at scalebright.ca”, but in the case of crypto I’m afraid we must decline. The other trait shared by all of these money systems beside inflation via no supply limit is that they’re all scams designed to steal from their customers. Bitcoin is the only digital non-fiat currency this doesn't apply to. So if you’d like help with Bitcoin, you can find us at scalebright.ca.
-
 @ 90c656ff:9383fd4e
2025-05-27 11:22:10
@ 90c656ff:9383fd4e
2025-05-27 11:22:10Since its creation, Bitcoin has been much more than just an alternative to traditional money. With the ongoing digitalization of the global economy, Bitcoin has emerged as a foundational pillar for new forms of transactions, commerce, and value storage. Its decentralization, transparency, and censorship resistance make it a solid base for digital economies, where financial interactions occur without the need for traditional intermediaries.
- Bitcoin’s role in the digital economy
01 - Global, borderless transactions: Anyone with internet access can send and receive Bitcoin without needing a bank or government authorization.
02 - Limited and predictable supply: Unlike fiat currencies that can be inflated by central banks, Bitcoin has a fixed cap of 21 million units, making it a scarce and reliable asset.
03 - Security and transparency: The Bitcoin blockchain or timechain publicly records all transactions, ensuring a secure and auditable system.
04 - Censorship resistance: No government or institution can block Bitcoin transactions, enabling a freer and more accessible digital economy.
With these characteristics, Bitcoin is already transforming various economic sectors and driving new forms of commerce and investment.
- Bitcoin in digital commerce and the global economy
01 - E-commerce: Businesses and consumers can use Bitcoin for fast international transactions without exorbitant fees.
02 - International remittances: Workers sending money to their home countries can avoid high fees and long delays by using Bitcoin.
03 - Emerging economies: In countries with unstable currencies and unreliable banking systems, Bitcoin serves as a secure and decentralized alternative for storing wealth and conducting daily transactions.
Additionally, Bitcoin is being adopted by companies and even governments as a store of value, reinforcing its role as a foundation for the digital economy of the future.
- Challenges and adapting to the new economy
01 - Price volatility: Bitcoin’s fluctuating value can make it difficult to use as a daily medium of exchange.
02 - Regulations and governmental resistance: Some countries attempt to restrict or regulate Bitcoin to maintain control over the traditional financial system.
03 - Education and adoption: Many people still lack the knowledge to use Bitcoin safely and effectively.
In summary, Bitcoin is transforming the way the world interacts with money, offering a decentralized and transparent alternative for digital economies. As more individuals and businesses adopt Bitcoin for payments, savings, and global commerce, its impact becomes increasingly clear. Despite the challenges, Bitcoin continues to solidify its place as the foundation of a new economic paradigm—where financial freedom and technological innovation go hand in hand.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 9ca447d2:fbf5a36d
2025-05-27 12:01:36
@ 9ca447d2:fbf5a36d
2025-05-27 12:01:36Donald Trump’s recent four-day visit took the President to Saudi Arabia, Qatar, and the United Arab Emirates. This visit has intertwined diplomatic relations with business interests, while simultaneously influencing the bitcoin market.
In Qatar, the President met with Emir Tanim bin Hamad Al Thani, resulting in over $243 billion in deals including major defense agreements, according to Bloomberg.
On May 15, the President made his visit to the Sheikh Zayed Grand Mosque in Abu Dhabi alongside Crown Prince Khaled bin Mohamed Al Nahyan. This occurs as the Trump family expands its business presence in the Middle East.
The Trump Organization is developing luxury properties across the region, including Trump Tower Dubai, real estate projects in Riyadh, and development in Jeddah and Oman.

Donald Trump and Mohammed bin Salman in King Khalid International Airport — NBCNews
Eric Trump publicly announced construction plans for Trump Tower Dubai just last month, highlighting the family’s ongoing commercial footprint in the region.
These business connections extend into the digital asset ecosystem as UAE-backed investment firm MGX recently announced it would use USD1, World Liberty Financial’s stablecoin to support a $2 billion investment in Binance, the world’s largest digital asset exchange, according to APNews.
This connection between Trump-aligned interests and major digital asset investments creates a potential avenue for market influence.
Historically, stability in the Middle East, especially among oil-rich nations, reduces global market volatility. This encourages risk appetite among investors, often leading to increased allocations to digital assets like bitcoin.
Middle East diplomacy directly affects global oil prices. Stable oil prices can lower inflation expectations and lead to interest rate cuts by the Fed. Lower rates lead to an increase in liquidity, having positive effects on bitcoin, an asset that benefits from money printing.
Related: Fed Rate Cuts Could Lead to Major Price Swings for Bitcoin
On the investment front, Abu Dhabi’s Wealth Fund, Mubadala Investment Company, has been focused on increasing their shares in BlackRock’s iShares Bitcoin Trust (IBIT).
According to a 13F filing with the U.S. Securities and Exchange Commission, Mubdala held 8.7 million IBIT shares, totaling $408.5 million as of March 31, 2025.
The Abu Dhabi Wealth Fund increased its shares by 500,000 since its last filing in December of 2024.
Back in March, the United States created a Strategic Bitcoin Reserve. The executive order states that the U.S. will not sell the bitcoin they already hold, and will create budget-neutral ways to increase their holdings.
The time has come where governments and wealth funds alike are jumping on board the Bitcoin train.
Trump’s recent visit to the Middle East illustrates how financial, diplomatic, and personal interests are becoming increasingly intertwined with Bitcoin and digital assets, serving as a new axis of influence in the U.S.-Middle East relations.
The combination of diplomatic progress and business expansion has heightened short-term volatility and trading volumes in the bitcoin market.
Trump’s business and digital asset ties in the region may further boost institutional interest and create an opportunity for more players to enter the market.
-
 @ cae03c48:2a7d6671
2025-05-27 11:01:23
@ cae03c48:2a7d6671
2025-05-27 11:01:23Bitcoin Magazine

Semler Scientific Buys Additional $50 Million Worth of BitcoinMedical equipment provider Semler Scientific has acquired 455 Bitcoin for $50 million, marking it one of the largest purchases as more publicly traded companies continue to adopt Bitcoin treasury strategies.
According to a Form 8-K filed with the SEC on May 23, the company purchased the Bitcoin between May 13 and May 22 at an average price of $109,801 per coin, including fees. The acquisition brings Semler’s total Bitcoin holdings to 4,264 BTC, acquired at an aggregate cost of $390 million.
The purchase was funded through Semler’s at-the-market (ATM) equity offering program, which has raised approximately $114.8 million since its launch in April 2025. The company has issued 3,003,488 shares under the $500 million program to date.
“$SMLR acquires 455 Bitcoins for $50 million and has generated BTC Yield of 25.8% YTD. Now holding 4,264 $BTC. Flywheel in motion. ,” said Eric Semler, Chairman of Semler Scientific. The company’s Bitcoin holdings are now valued at approximately $474.4 million based on current market prices.
Semler reported its Bitcoin Yield – a key performance indicator measuring the year-to-date percentage change in total Bitcoin holdings relative to diluted shares outstanding – has reached 25.8% in 2025. The metric has become a standard measure among public companies holding Bitcoin on their balance sheets.
The company maintains a Bitcoin Dashboard on its website to provide transparent information about its holdings, including market data, performance metrics, and acquisition details, as part of its Regulation FD compliance strategy.
Semler’s move comes amid accelerating corporate Bitcoin adoption in 2025, with over 40 public companies announcing Bitcoin treasury programs this year alone. The market has shown increased sensitivity to corporate treasury activities as institutional adoption continues to grow.
The company’s latest Bitcoin purchase reinforces the growing trend of public companies using equity offerings to fund Bitcoin acquisitions, a strategy pioneered by larger players like Strategy, which recently added 7,390 BTC to its holdings through a similar funding mechanism.
This post Semler Scientific Buys Additional $50 Million Worth of Bitcoin first appeared on Bitcoin Magazine and is written by Vivek Sen.
-
 @ 65038d69:1fff8852
2025-03-29 13:02:18
@ 65038d69:1fff8852
2025-03-29 13:02:18Millennials remember the era of Buzzfeed quizzes with fondness, and some may even describe it as identity or culture shaping. People have always loved these miniature personality tests, and while Buzzfeed may no longer be in its heyday, the popularity of these dinner-table icebreakers has transcended generational gaps. To the analytically-brained among us this sounds like a datapoint that could be used in the workplace. Or is it?
You’ve probably heard someone’s answer to one of these and thought, “Oh wow, that sounds mildly psychopathic, I’m sure glad I don’t work with them!” Interviewers will sometimes ask questions like “if you were an animal, what kind of animal would you be?” as a conversation starter, but unscored. Part of the reason for this is that laws around discrimination in hiring make filtering via psychological or personality tests a grey area. Any suggestion of discrimination opens employers to potential lawsuits and investigations. Even if the applicant answered unironically with “I would be a dragon because I love hoarding gold and burning down unsuspecting villages!”, you would need to prove that the question was asked in a controlled environment by a certified professional and that the question was directly relevant to the position being applied for.
Now that I’ve most likely talked you out of implementing these in your interview processes, here are a handful of tests that, in an HR and legal department approved manner, could be run during an interview. Failing that, they make for great casual icebreakers! Their sources range from actual psychological tests to dubious corners of the internet, and they’ve all been simplified down to their simplest forms, so I’ll again warn that you’ll want to do diligence before suggesting their use in your workplace.
The Marshmallow Test: The test subjects (usually children) are offered a marshmallow and told that if they leave it for a few minutes, they can have two. Adults who’ve developed impulse control will usually say the correct answer is obvious, yet we fail slightly more complex versions all the time. Remember that greasy fast-food you bought with money you could have saved for a nice dinner out?
Cognitive Reflection Test (CRT): “Some apples and some bananas cost $1.10. The apples cost $1 more than the bananas. How much did the apples cost?” If you suspect a trick, you’ll probably think about the question a bit further, but the intuitive part of our brains want us to think the apples were $1 and the bananas $0.10.
The Breakfast Question: “How would you feel if you hadn’t eaten breakfast?” This one has some deep internet lore behind it, but the idea is that you’re testing the subject’s capacity for hypothetical reasoning. Can they process “what-ifs”? It can also extend into testing for empathy (“How would you feel if you were in Steve’s shoes and someone stole your ice cream?”).
Thematic Apperception Test (TAT): Show the subject an ambiguous picture (ideally emotionally neutral) with people in it and ask them to imagine what is happening, including what the people are thinking and feeling. Most people will subconsciously project their own thoughts and feelings onto the characters in the picture.
Moral Circle Test: This one has a history of being misunderstood and used as a political cudgel, so you may want to save it for your more understanding friends. Subjects were asked to rank the moral responsibilities they felt toward increasingly distant groups, starting from themselves in the center of a circle and working their way out through family, friends, acquaintances, animals, Earth, etc. The primary misunderstanding is whether the outer circles include the inner circles, i.e. whether caring for Earth includes caring for family. It’s unclear whether the subjects fully understood this, and those interpreting the results seem confused as well.
Workplace Motivation Test: “You are up for a promotion. You can be promoted into a position that pays 20% more, or one that pays the same that you’re currently making but aligns with your non-financial life goals or sense of purpose.” This one is my own, and you can learn more about the underlying concepts here: “True Believers & Mercenaries” Are you a “True Believer” or a “Mercenary”?
Need help with your interview processes or figuring out which Disney princess you are? You can find us at scalebright.ca.
-
 @ 1c19eb1a:e22fb0bc
2025-04-30 22:02:13
@ 1c19eb1a:e22fb0bc
2025-04-30 22:02:13I am happy to present to you the first full review posted to Nostr Reviews: #Primal for #Android!
Primal has its origins as a micro-blogging, social media client, though it is now expanding its horizons into long-form content. It was first released only as a web client in March of 2023, but has since had a native client released for both iOS and Android. All of Primal's clients recently had an update to Primal 2.0, which included both performance improvements and a number of new features. This review will focus on the Android client specifically, both on phone and tablet.
Since Primal has also added features that are only available to those enrolled in their new premium subscription, it should also be noted that this review will be from the perspective of a free user. This is for two reasons. First, I am using an alternate npub to review the app, and if I were to purchase premium at some time in the future, it would be on my main npub. Second, despite a lot of positive things I have to say about Primal, I am not planning to regularly use any of their apps on my main account for the time being, for reasons that will be discussed later in the review.
The application can be installed through the Google Play Store, nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8, or by downloading it directly from Primal's GitHub. The full review is current as of Primal Android version 2.0.21. Updates to the review on 4/30/2025 are current as of version 2.2.13.
In the ecosystem of "notes and other stuff," Primal is predominantly in the "notes" category. It is geared toward users who want a social media experience similar to Twitter or Facebook with an infinite scrolling feed of notes to interact with. However, there is some "other stuff" included to complement this primary focus on short and long form notes including a built-in Lightning wallet powered by #Strike, a robust advanced search, and a media-only feed.
Overall Impression
Score: 4.4 / 5 (Updated 4/30/2025)
Primal may well be the most polished UI of any Nostr client native to Android. It is incredibly well designed and thought out, with all of the icons and settings in the places a user would expect to find them. It is also incredibly easy to get started on Nostr via Primal's sign-up flow. The only two things that will be foreign to new users are the lack of any need to set a password or give an email address, and the prompt to optionally set up the wallet.
Complaints prior to the 2.0 update about Primal being slow and clunky should now be completely alleviated. I only experienced quick load times and snappy UI controls with a couple very minor exceptions, or when loading DVM-based feeds, which are outside of Primal's control.
Primal is not, however, a client that I would recommend for the power-user. Control over preferred relays is minimal and does not allow the user to determine which relays they write to and which they only read from. Though you can use your own wallet, it will not appear within the wallet interface, which only works with the custodial wallet from Strike. Moreover, and most eggregiously, the only way for existing users to log in is by pasting their nsec, as Primal does not support either the Android signer or remote signer options for users to protect their private key at this time. This lack of signer support is the primary reason the client received such a low overall score. If even one form of external signer log in is added to Primal, the score will be amended to 4.2 / 5, and if both Android signer and remote signer support is added, it will increase to 4.5.
Update: As of version 2.2.13, Primal now supports the Amber Android signer! One of the most glaring issues with the app has now been remedied and as promised, the overall score above has been increased.
Another downside to Primal is that it still utilizes an outdated direct message specification that leaks metadata that can be readily seen by anyone on the network. While the content of your messages remains encrypted, anyone can see who you are messaging with, and when. This also means that you will not see any DMs from users who are messaging from a client that has moved to the latest, and far more private, messaging spec.
That said, the beautiful thing about Nostr as a protocol is that users are not locked into any particular client. You may find Primal to be a great client for your average #bloomscrolling and zapping memes, but opt for a different client for more advanced uses and for direct messaging.
Features
Primal has a lot of features users would expect from any Nostr client that is focused on short-form notes, but it also packs in a lot of features that set it apart from other clients, and that showcase Primal's obvious prioritization of a top-tier user experience.
Home Feed
By default, the infinitely scrolling Home feed displays notes from those you currently follow in chronological order. This is traditional Nostr at its finest, and made all the more immersive by the choice to have all distracting UI elements quickly hide themselves from view as the you begin to scroll down the feed. They return just as quickly when you begin to scroll back up.
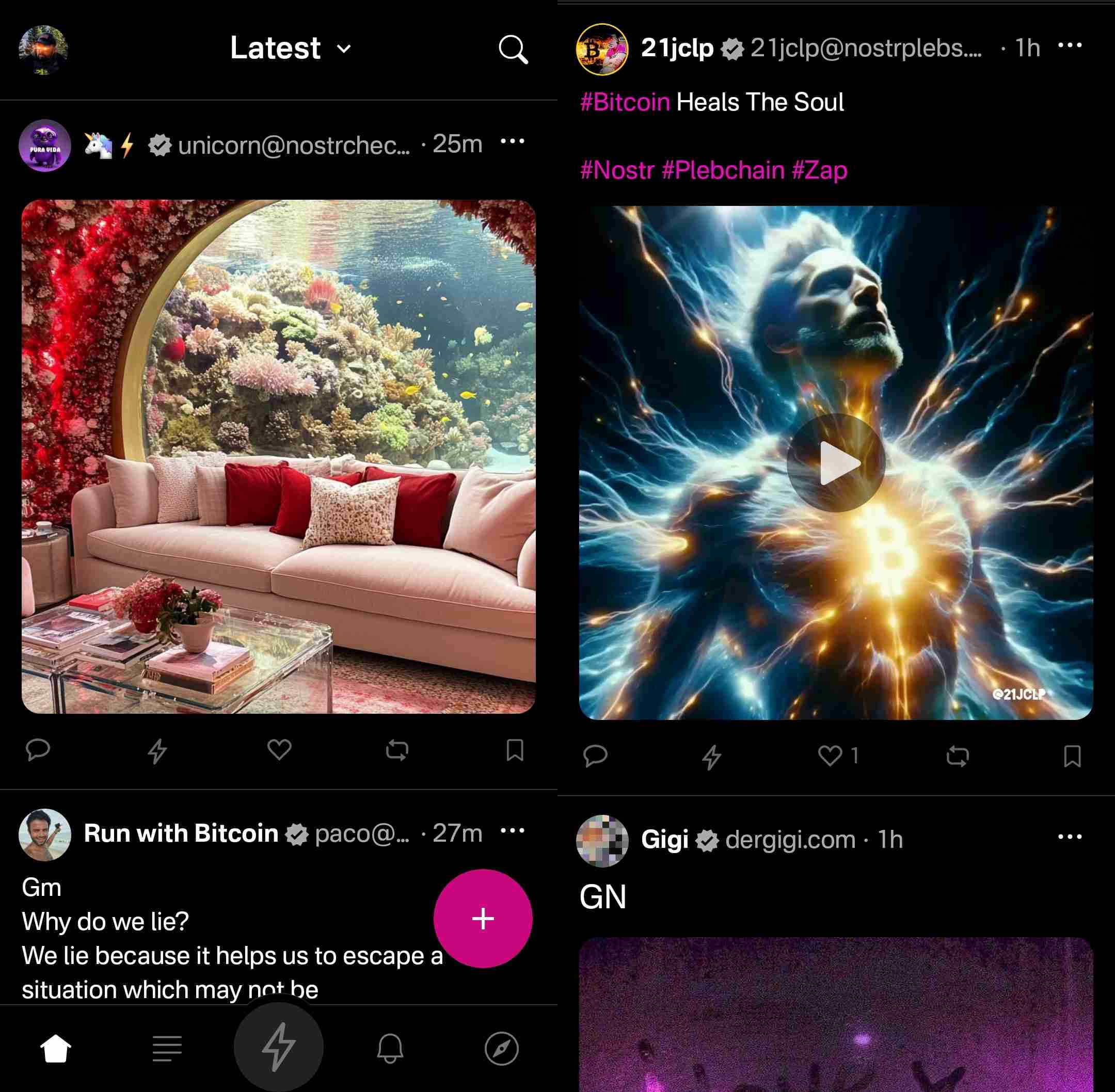
Scrolling the feed is incredibly fast, with no noticeable choppiness and minimal media pop-in if you are on a decent internet connection.
Helpfully, it is easy to get back to the top of the feed whenever there is a new post to be viewed, as a bubble will appear with the profile pictures of the users who have posted since you started scrolling.

Interacting With Notes
Interacting with a note in the feed can be done via the very recognizable icons at the bottom of each post. You can comment, zap, like, repost, and/or bookmark the note.
Notably, tapping on the zap icon will immediately zap the note your default amount of sats, making zapping incredibly fast, especially when using the built-in wallet. Long pressing on the zap icon will open up a menu with a variety of amounts, along with the ability to zap a custom amount. All of these amounts, and the messages that are sent with the zap, can be customized in the application settings.
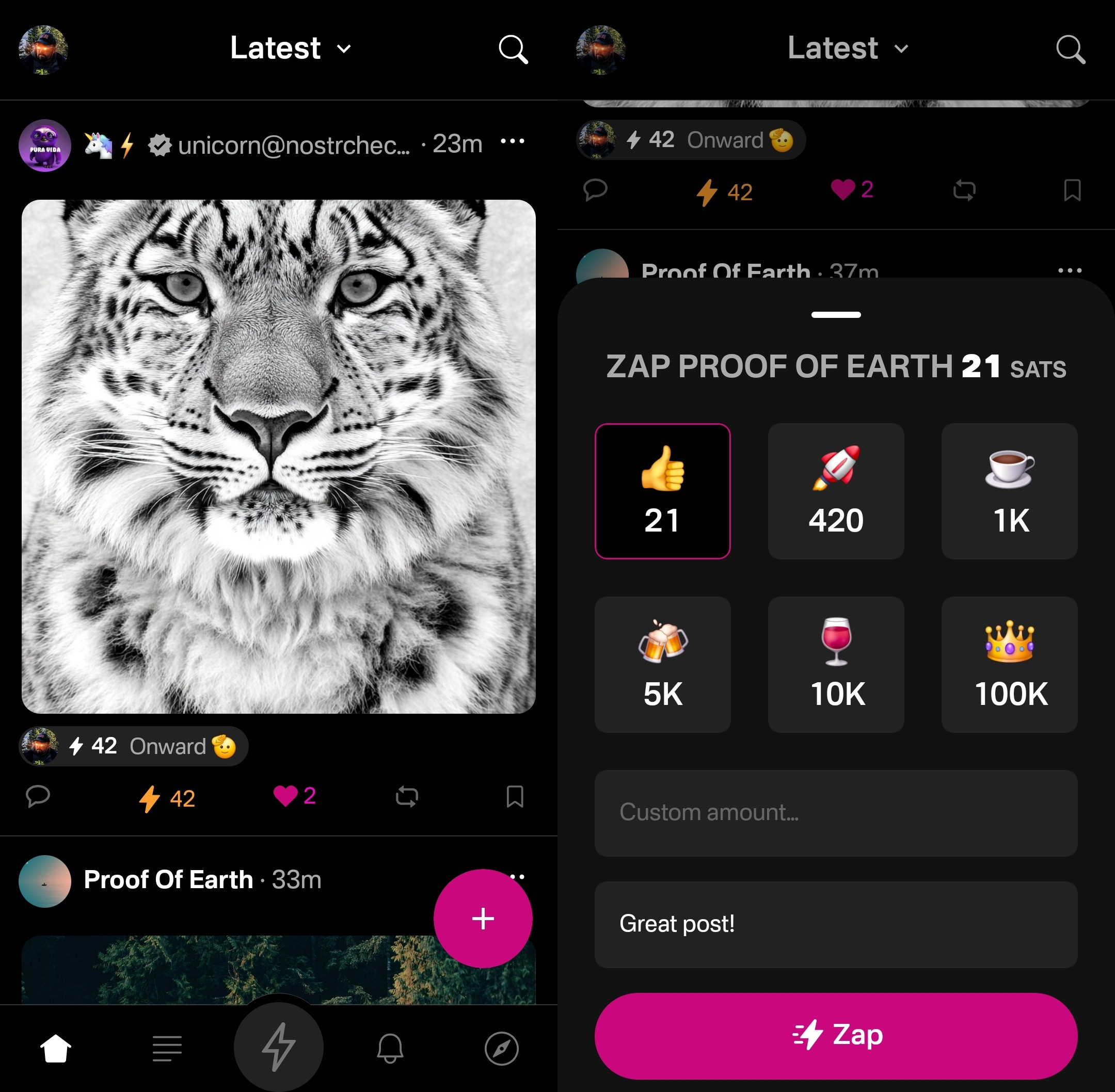
Users who are familiar with Twitter or Instagram will feel right at home with only having one option for "liking" a post. However, users from Facebook or other Nostr clients may wonder why they don't have more options for reactions. This is one of those things where users who are new to Nostr probably won't notice they are missing out on anything at all, while users familiar with clients like #Amethyst or #noStrudel will miss the ability to react with a 🤙 or a 🫂.
It's a similar story with the bookmark option. While this is a nice bit of feature parity for Twitter users, for those already used to the ability to have multiple customized lists of bookmarks, or at minimum have the ability to separate them into public and private, it may be a disappointment that they have no access to the bookmarks they already built up on other clients. Primal offers only one list of bookmarks for short-form notes and they are all visible to the public. However, you are at least presented with a warning about the public nature of your bookmarks before saving your first one.
Yet, I can't dock the Primal team much for making these design choices, as they are understandable for Primal's goal of being a welcoming client for those coming over to Nostr from centralized platforms. They have optimized for the onboarding of new users, rather than for those who have been around for a while, and there is absolutely nothing wrong with that.
Post Creation
Composing posts in Primal is as simple as it gets. Accessed by tapping the obvious circular button with a "+" on it in the lower right of the Home feed, most of what you could need is included in the interface, and nothing you don't.
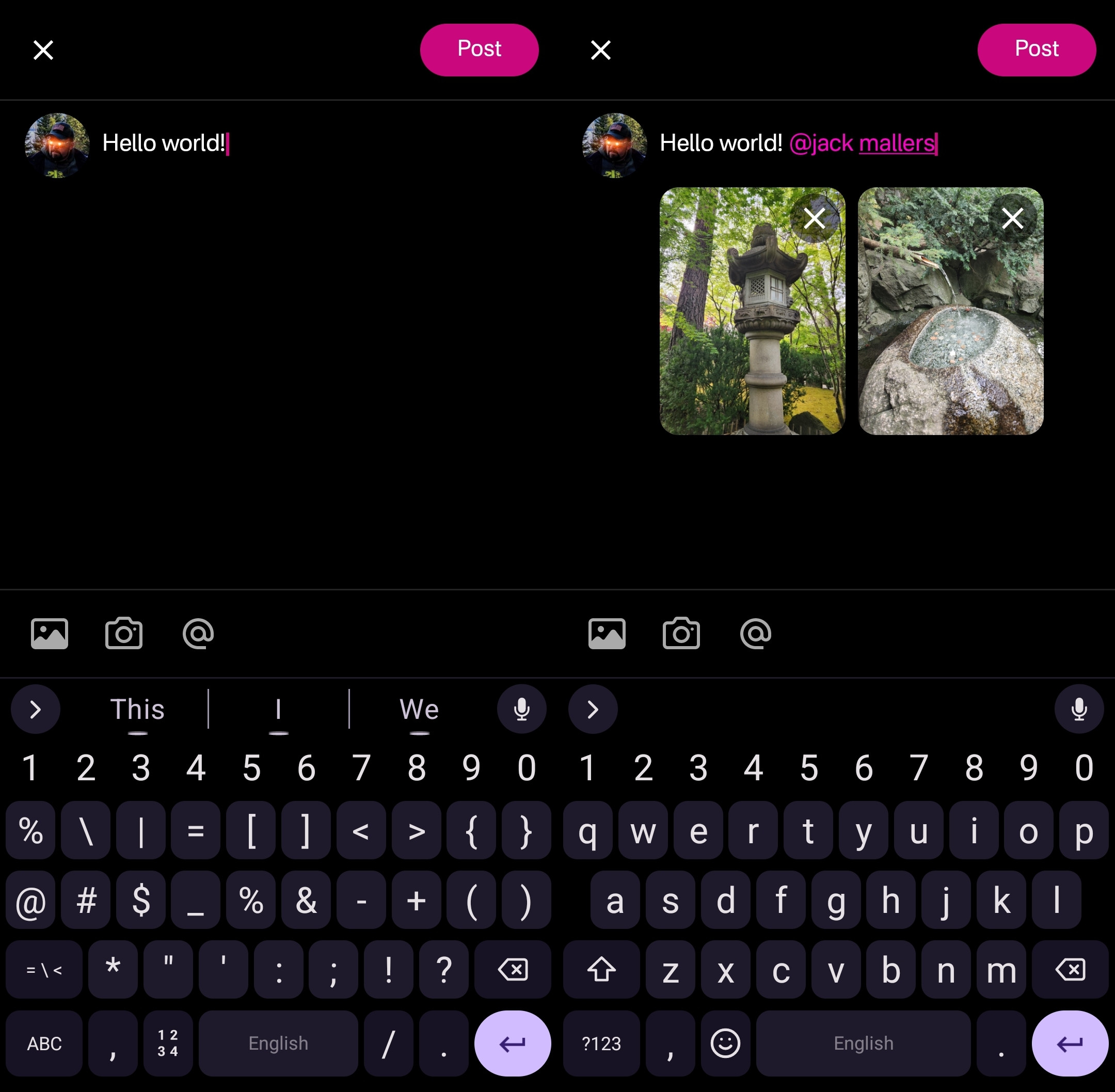
Your device's default keyboard loads immediately, and the you can start typing away.
There are options for adding images from your gallery, or taking a picture with your camera, both of which will result in the image being uploaded to Primal's media-hosting server. If you prefer to host your media elsewhere, you can simply paste the link to that media into your post.
There is also an @ icon as a tip-off that you can tag other users. Tapping on this simply types "@" into your note and brings up a list of users. All you have to do to narrow down the user you want to tag is continue typing their handle, Nostr address, or paste in their npub.
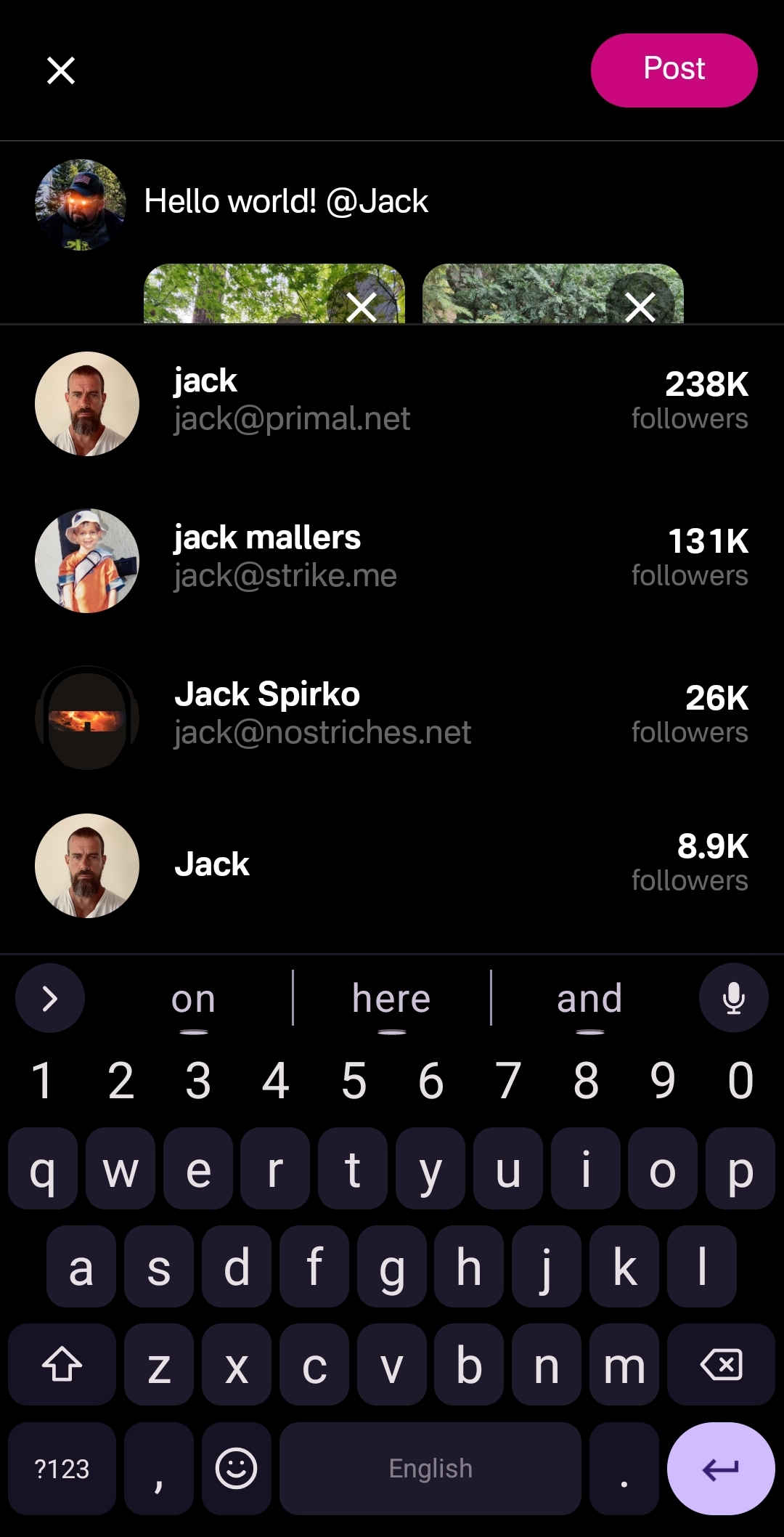
This can get mixed results in other clients, which sometimes have a hard time finding particular users when typing in their handle, forcing you to have to remember their Nostr address or go hunt down their npub by another means. Not so with Primal, though. I had no issues tagging anyone I wanted by simply typing in their handle.
Of course, when you are tagging someone well known, you may find that there are multiple users posing as that person. Primal helps you out here, though. Usually the top result is the person you want, as Primal places them in order of how many followers they have. This is quite reliable right now, but there is nothing stopping someone from spinning up an army of bots to follow their fake accounts, rendering follower count useless for determining which account is legitimate. It would be nice to see these results ranked by web-of-trust, or at least an indication of how many users you follow who also follow the users listed in the results.
Once you are satisfied with your note, the "Post" button is easy to find in the top right of the screen.
Feed Selector and Marketplace
Primal's Home feed really shines when you open up the feed selection interface, and find that there are a plethora of options available for customizing your view. By default, it only shows four options, but tapping "Edit" opens up a new page of available toggles to add to the feed selector.
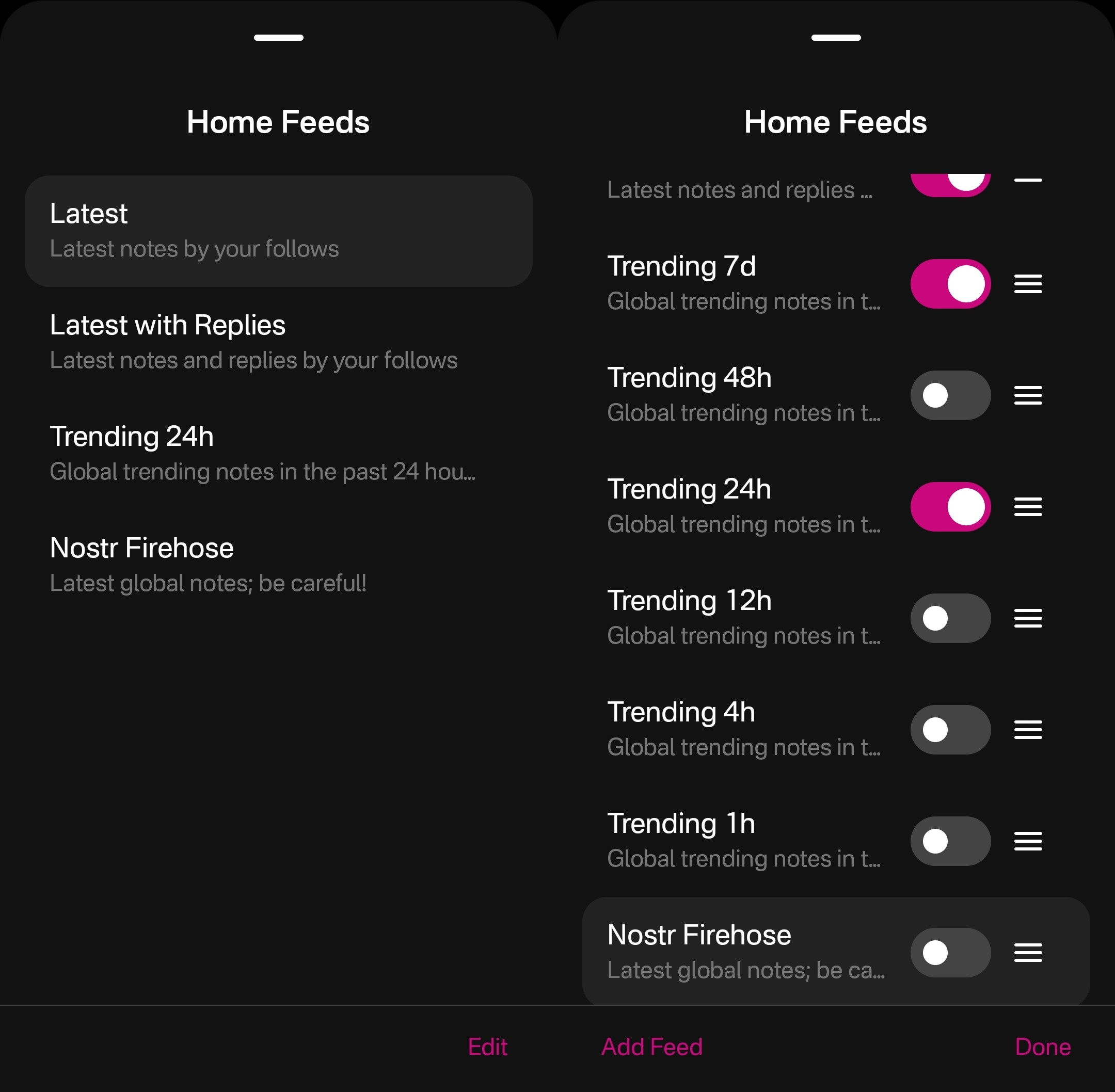
The options don't end there, though. Tapping "Add Feed" will open up the feed marketplace, where an ever-growing number of custom feeds can be found, some created by Primal and some created by others. This feed marketplace is available to a few other clients, but none have so closely integrated it with their Home feeds like Primal has.
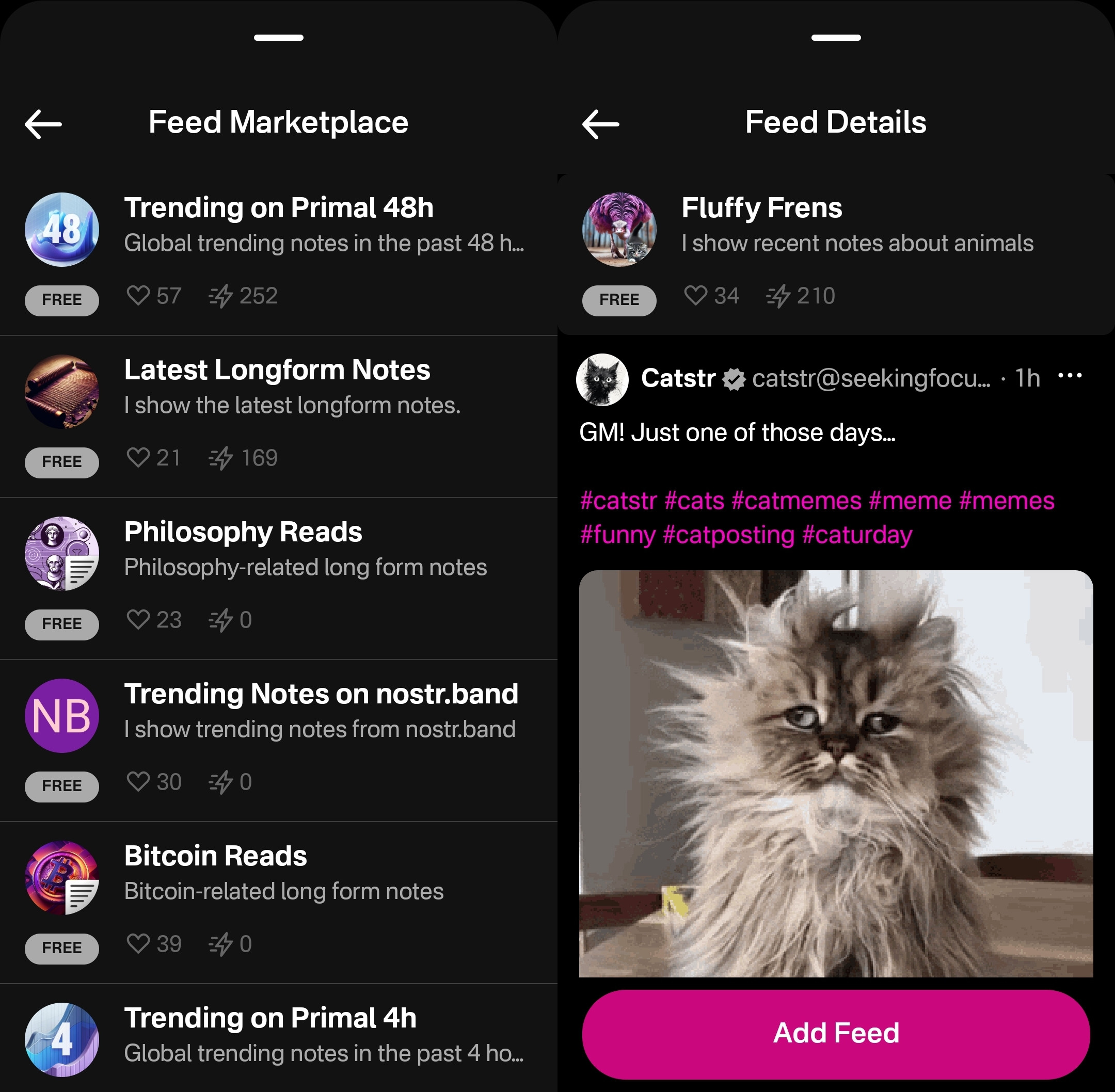
Unfortunately, as great as these custom feeds are, this was also the feature where I ran into the most bugs while testing out the app.
One of these bugs was while selecting custom feeds. Occasionally, these feed menu screens would become unresponsive and I would be unable to confirm my selection, or even use the back button on my device to back out of the screen. However, I was able to pull the screen down to close it and re-open the menu, and everything would be responsive again.
This only seemed to occur when I spent 30 seconds or more on the same screen, so I imagine that most users won't encounter it much in their regular use.
Another UI bug occurred for me while in the feed marketplace. I could scroll down the list of available feeds, but attempting to scroll back up the feed would often close the interface entirely instead, as though I had pulled the screen down from the top, when I was swiping in the middle of the screen.
The last of these bugs occurred when selecting a long-form "Reads" feed while in the menu for the Home feed. The menu would allow me to add this feed and select it to be displayed, but it would fail to load the feed once selected, stating "There is no content in this feed." Going to a different page within the the app and then going back to the Home tab would automatically remove the long-form feed from view, and reset back to the most recently viewed short-form "Notes" feed, though the long-form feed would still be available to select again. The results were similar when selecting a short-form feed for the Reads feed.
I would suggest that if long-form and short-form feeds are going to be displayed in the same list, and yet not be able to be displayed in the same feed, the application should present an error message when attempting to add a long-form feed for the Home feed or a short-form feed for the Reads feed, and encourage the user add it to the proper feed instead.
Long-Form "Reads" Feed
A brand new feature in Primal 2.0, users can now browse and read long-form content posted to Nostr without having to go to a separate client. Primal now has a dedicated "Reads" feed to browse and interact with these articles.
This feed displays the author and title of each article or blog, along with an image, if available. Quite conveniently, it also lets you know the approximate amount of time it will take to read a given article, so you can decide if you have the time to dive into it now, or come back later.
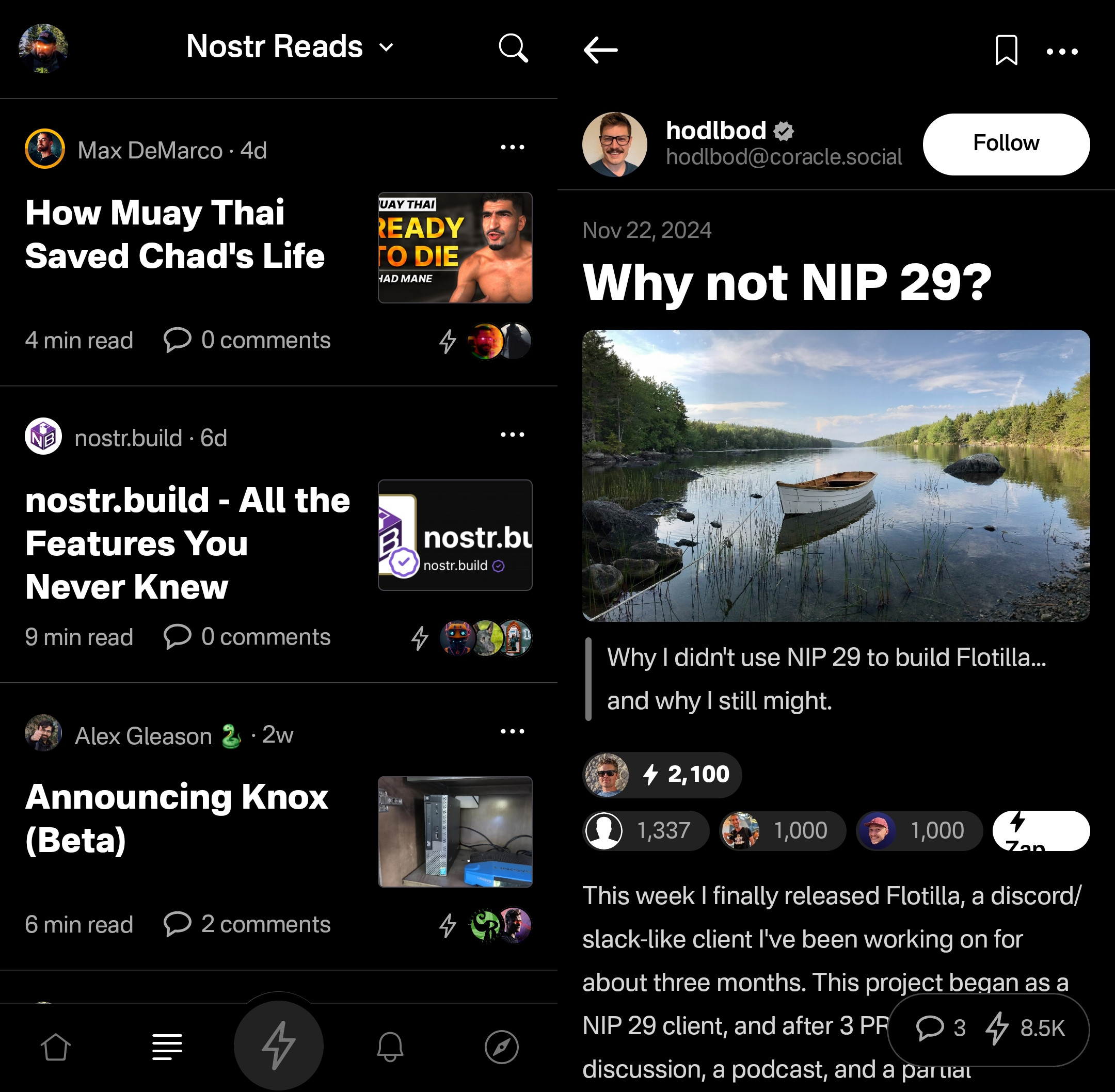
Noticeably absent from the Reads feed, though, is the ability to compose an article of your own. This is another understandable design choice for a mobile client. Composing a long-form note on a smart-phone screen is not a good time. Better to be done on a larger screen, in a client with a full-featured text editor.
Tapping an article will open up an attractive reading interface, with the ability to bookmark for later. These bookmarks are a separate list from your short-form note bookmarks so you don't have to scroll through a bunch of notes you bookmarked to find the article you told yourself you would read later and it's already been three weeks.
While you can comment on the article or zap it, you will notice that you cannot repost or quote-post it. It's not that you can't do so on Nostr. You absolutely can in other clients. In fact, you can do so on Primal's web client, too. However, Primal on Android does not handle rendering long-form note previews in the Home feed, so they have simply left out the option to share them there. See below for an example of a quote-post of a long-form note in the Primal web client vs the Android client.
Primal Web:
Primal Android:
The Explore Tab
Another unique feature of the Primal client is the Explore tab, indicated by the compass icon. This tab is dedicated to discovering content from outside your current follow list. You can find the feed marketplace here, and add any of the available feeds to your Home or Reads feed selections. You can also find suggested users to follow in the People tab. The Zaps tab will show you who has been sending and receiving large zaps. Make friends with the generous ones!
The Media tab gives you a chronological feed of just media, displayed in a tile view. This can be great when you are looking for users who post dank memes, or incredible photography on a regular basis. Unfortunately, it appears that there is no way to filter this feed for sensitive content, and so you do not have to scroll far before you see pornographic material.
Indeed, it does not appear that filters for sensitive content are available in Primal for any feed. The app is kind enough to give a minimal warning that objectionable content may be present when selecting the "Nostr Firehose" option in your Home feed, with a brief "be careful" in the feed description, but there is not even that much of a warning here for the media-only feed.
The media-only feed doesn't appear to be quite as bad as the Nostr Firehose feed, so there must be some form of filtering already taking place, rather than being a truly global feed of all media. Yet, occasional sensitive content still litters the feed and is unavoidable, even for users who would rather not see it. There are, of course, ways to mute particular users who post such content, if you don't want to see it a second time from the same user, but that is a never-ending game of whack-a-mole, so your only realistic choices in Primal are currently to either avoid the Nostr Firehose and media-only feeds, or determine that you can put up with regularly scrolling past often graphic content.
This is probably the only choice Primal has made that is not friendly to new users. Most clients these days will have some protections in place to hide sensitive content by default, but still allow the user to toggle those protections off if they so choose. Some of them hide posts flagged as sensitive content altogether, others just blur the images unless the user taps to reveal them, and others simply blur all images posted by users you don't follow. If Primal wants to target new users who are accustomed to legacy social media platforms, they really should follow suit.
The final tab is titled "Topics," but it is really just a list of popular hashtags, which appear to be arranged by how often they are being used. This can be good for finding things that other users are interested in talking about, or finding specific content you are interested in.
If you tap on any topic in the list, it will display a feed of notes that include that hashtag. What's better, you can add it as a feed option you can select on your Home feed any time you want to see posts with that tag.
The only suggestion I would make to improve this tab is some indication of why the topics are arranged in the order presented. A simple indicator of the number of posts with that hashtag in the last 24 hours, or whatever the interval is for determining their ranking, would more than suffice.
Even with those few shortcomings, Primal's Explore tab makes the client one of the best options for discovering content on Nostr that you are actually interested in seeing and interacting with.
Built-In Wallet
While this feature is completely optional, the icon to access the wallet is the largest of the icons at the bottom of the screen, making you feel like you are missing out on the most important feature of the app if you don't set it up. I could be critical of this design choice, but in many ways I think it is warranted. The built-in wallet is one of the most unique features that Primal has going for it.
Consider: If you are a new user coming to Nostr, who isn't already a Bitcoiner, and you see that everyone else on the platform is sending and receiving sats for their posts, will you be more likely to go download a separate wallet application or use one that is built-into your client? I would wager the latter option by a long shot. No need to figure out which wallet you should download, whether you should do self-custody or custodial, or make the mistake of choosing a wallet with unexpected setup fees and no Lightning address so you can't even receive zaps to it. nostr:npub16c0nh3dnadzqpm76uctf5hqhe2lny344zsmpm6feee9p5rdxaa9q586nvr often states that he believes more people will be onboarded to Bitcoin through Nostr than by any other means, and by including a wallet into the Primal client, his team has made adopting Bitcoin that much easier for new Nostr users.
Some of us purists may complain that it is custodial and KYC, but that is an unfortunate necessity in order to facilitate onboarding newcoiners to Bitcoin. This is not intended to be a wallet for those of us who have been using Bitcoin and Lightning regularly already. It is meant for those who are not already familiar with Bitcoin to make it as easy as possible to get off zero, and it accomplishes this better than any other wallet I have ever tried.
In large part, this is because the KYC is very light. It does need the user's legal name, a valid email address, date of birth, and country of residence, but that's it! From there, the user can buy Bitcoin directly through the app, but only in the amount of $4.99 at a time. This is because there is a substantial markup on top of the current market price, due to utilizing whatever payment method the user has set up through their Google Play Store. The markup seemed to be about 19% above the current price, since I could purchase 4,143 sats for $4.99 ($120,415 / Bitcoin), when the current price was about $101,500. But the idea here is not for the Primal wallet to be a user's primary method of stacking sats. Rather, it is intended to get them off zero and have a small amount of sats to experience zapping with, and it accomplishes this with less friction than any other method I know.
Moreover, the Primal wallet has the features one would expect from any Lightning wallet. You can send sats to any Nostr user or Lightning address, receive via invoice, or scan to pay an invoice. It even has the ability to receive via on-chain. This means users who don't want to pay the markup from buying through Primal can easily transfer sats they obtained by other means into the Primal wallet for zapping, or for using it as their daily-driver spending wallet.
Speaking of zapping, once the wallet is activated, sending zaps is automatically set to use the wallet, and they are fast. Primal gives you immediate feedback that the zap was sent and the transaction shows in your wallet history typically before you can open the interface. I can confidently say that Primal wallet's integration is the absolute best zapping experience I have seen in any Nostr client.
One thing to note that may not be immediately apparent to new users is they need to add their Lightning address with Primal into their profile details before they can start receiving zaps. So, sending zaps using the wallet is automatic as soon as you activate it, but receiving is not. Ideally, this could be further streamlined, so that Primal automatically adds the Lightning address to the user's profile when the wallet is set up, so long as there is not currently a Lightning address listed.
Of course, if you already have a Lightning wallet, you can connect it to Primal for zapping, too. We will discuss this further in the section dedicated to zap integration.
Advanced Search
Search has always been a tough nut to crack on Nostr, since it is highly dependent on which relays the client is pulling information from. Primal has sought to resolve this issue, among others, by running a caching relay that pulls notes from a number of relays to store them locally, and perform some spam filtering. This allows for much faster retrieval of search results, and also makes their advanced search feature possible.
Advanced search can be accessed from most pages by selecting the magnifying glass icon, and then the icon for more options next to the search bar.
As can be seen in the screenshot below, there are a plethora of filters that can be applied to your search terms.
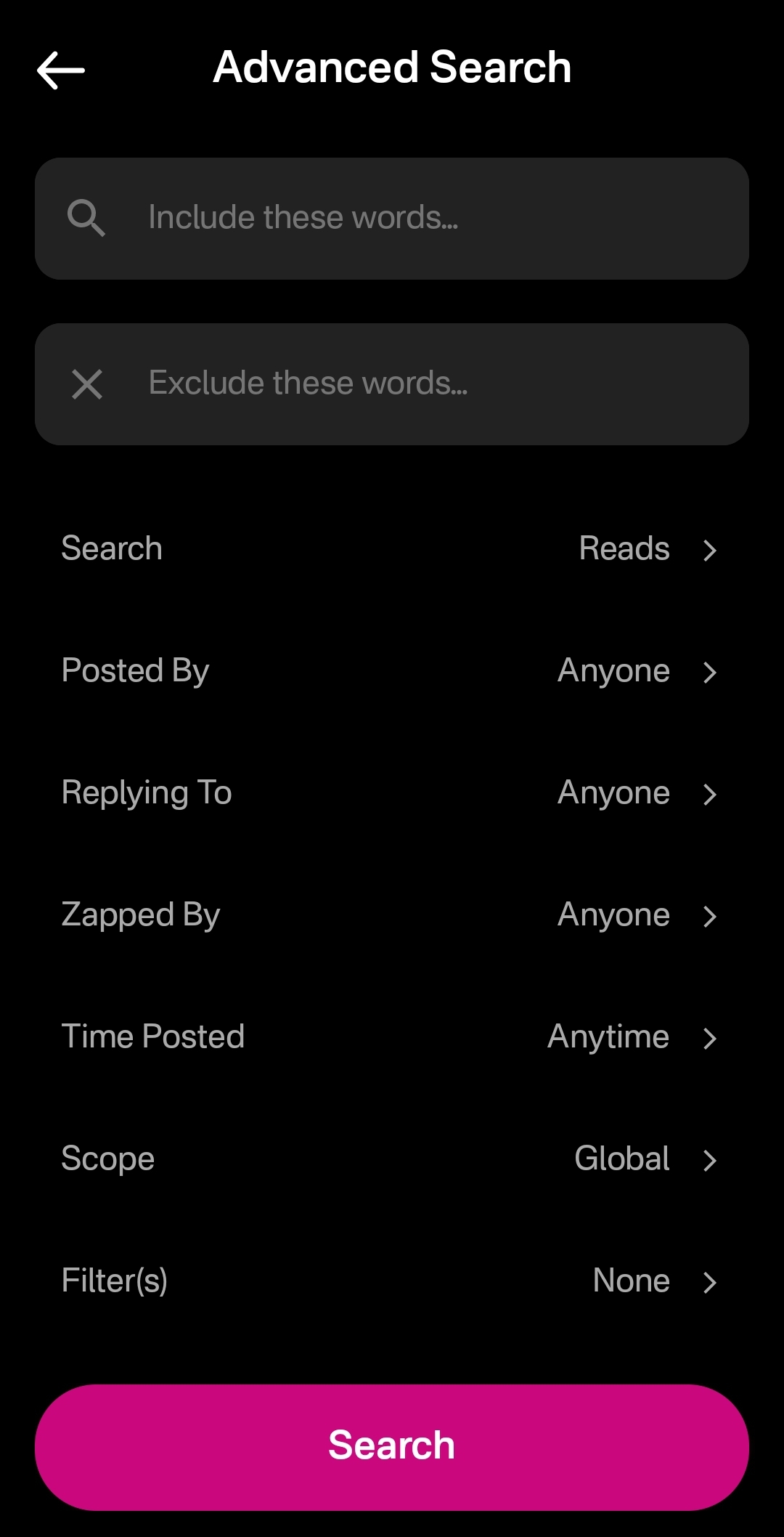
You can immediately see how this advanced search could be a very powerful tool for not just finding a particular previous note that you are looking for, but for creating your own custom feed of notes. Well, wouldn't you know it, Primal allows you to do just that! This search feature, paired with the other features mentioned above related to finding notes you want to see in your feed, makes Primal hands-down the best client for content discovery.
The only downside as a free user is that some of these search options are locked behind the premium membership. Or else you only get to see a certain number of results of your advanced search before you must be a premium member to see more.
Can My Grandma Use It?
Score: 4.8 / 5 Primal has obviously put a high priority on making their client user-friendly, even for those who have never heard of relays, public/private key cryptography, or Bitcoin. All of that complexity is hidden away. Some of it is available to play around with for the users who care to do so, but it does not at all get in the way of the users who just want to jump in and start posting notes and interacting with other users in a truly open public square.
To begin with, the onboarding experience is incredibly smooth. Tap "Create Account," enter your chosen display name and optional bio information, upload a profile picture, and then choose some topics you are interested in. You are then presented with a preview of your profile, with the ability to add a banner image, if you so choose, and then tap "Create Account Now."
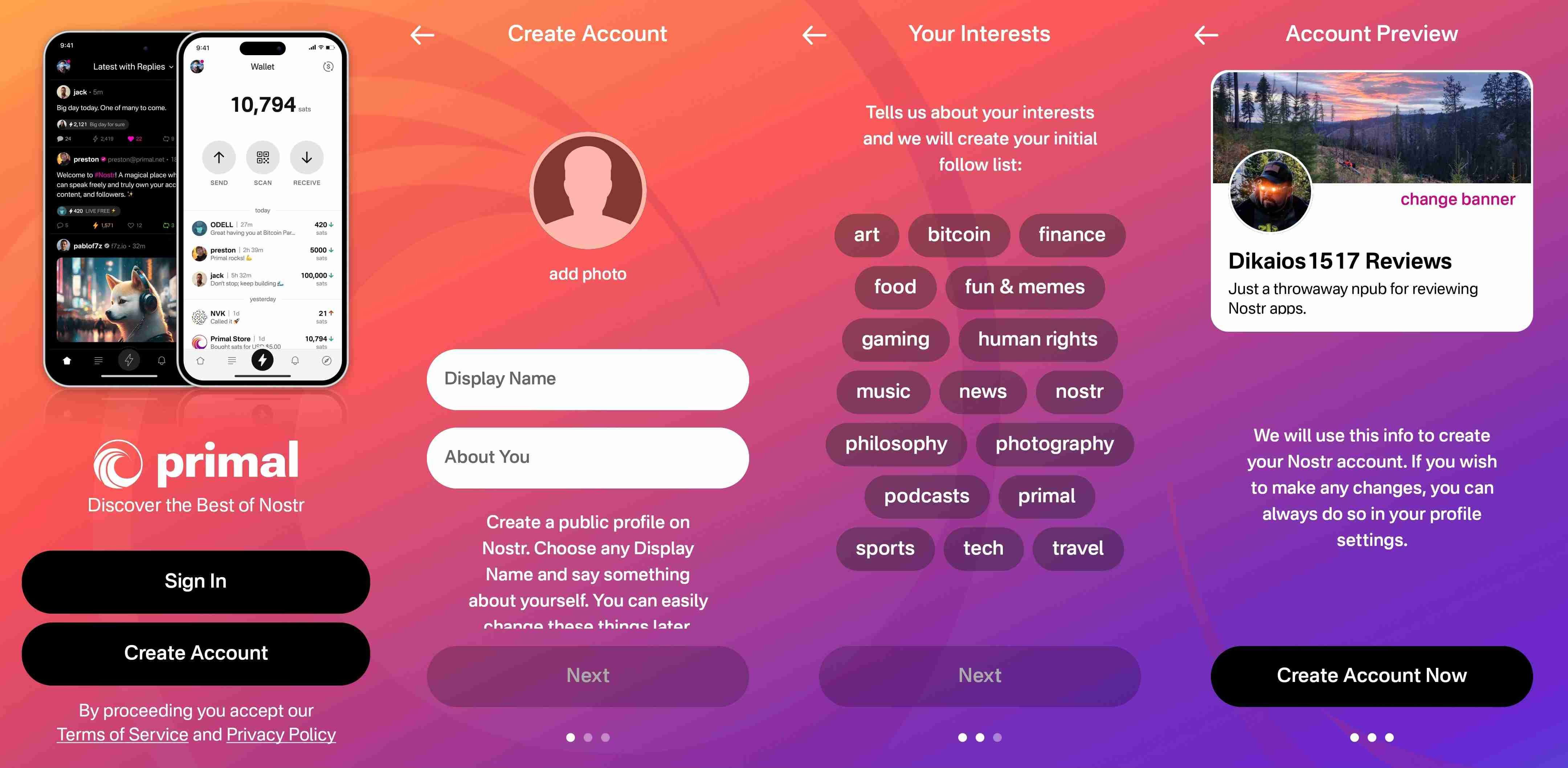
From there you receive confirmation that your account has been created and that your "Nostr key" is available to you in the application settings. No further explanation is given about what this key is for at this point, but the user doesn't really need to know at the moment, either. If they are curious, they will go to the app settings to find out.
At this point, Primal encourages the user to activate Primal Wallet, but also gives the option for the user to do it later.
That's it! The next screen the user sees if they don't opt to set up the wallet is their Home feed with notes listed in chronological order. More impressive, the feed is not empty, because Primal has auto-followed several accounts based on your selected topics.
Now, there has definitely been some legitimate criticism of this practice of following specific accounts based on the topic selection, and I agree. I would much prefer to see Primal follow hashtags based on what was selected, and combine the followed hashtags into a feed titled "My Topics" or something of that nature, and make that the default view when the user finishes onboarding. Following particular users automatically will artificially inflate certain users' exposure, while other users who might be quality follows for that topic aren't seen at all.
The advantage of following particular users over a hashtag, though, is that Primal retains some control over the quality of the posts that new users are exposed to right away. Primal can ensure that new users see people who are actually posting quality photography when they choose it as one of their interests. However, even with that example, I chose photography as one of my interests and while I did get some stunning photography in my Home feed by default based on Primal's chosen follows, I also scrolled through the Photography hashtag for a bit and I really feel like I would have been better served if Primal had simply followed that hashtag rather than a particular set of users.
We've already discussed how simple it is to set up the Primal Wallet. You can see the features section above if you missed it. It is, by far, the most user friendly experience to onboarding onto Lightning and getting a few sats for zapping, and it is the only one I know of that is built directly into a Nostr client. This means new users will have a frictionless introduction to transacting via Lightning, perhaps without even realizing that's what they are doing.
Discovering new content of interest is incredibly intuitive on Primal, and the only thing that new users may struggle with is getting their own notes seen by others. To assist with this, I would suggest Primal encourage users to make their first post to the introductions hashtag and direct any questions to the AskNostr hashtag as part of the onboarding process. This will get them some immediate interactions from other users, and further encouragement to set up their wallet if they haven't already done so.
How do UI look?
Score: 4.9 / 5
Primal is the most stunningly beautiful Nostr client available, in my honest opinion. Despite some of my hangups about certain functionality, the UI alone makes me want to use it.
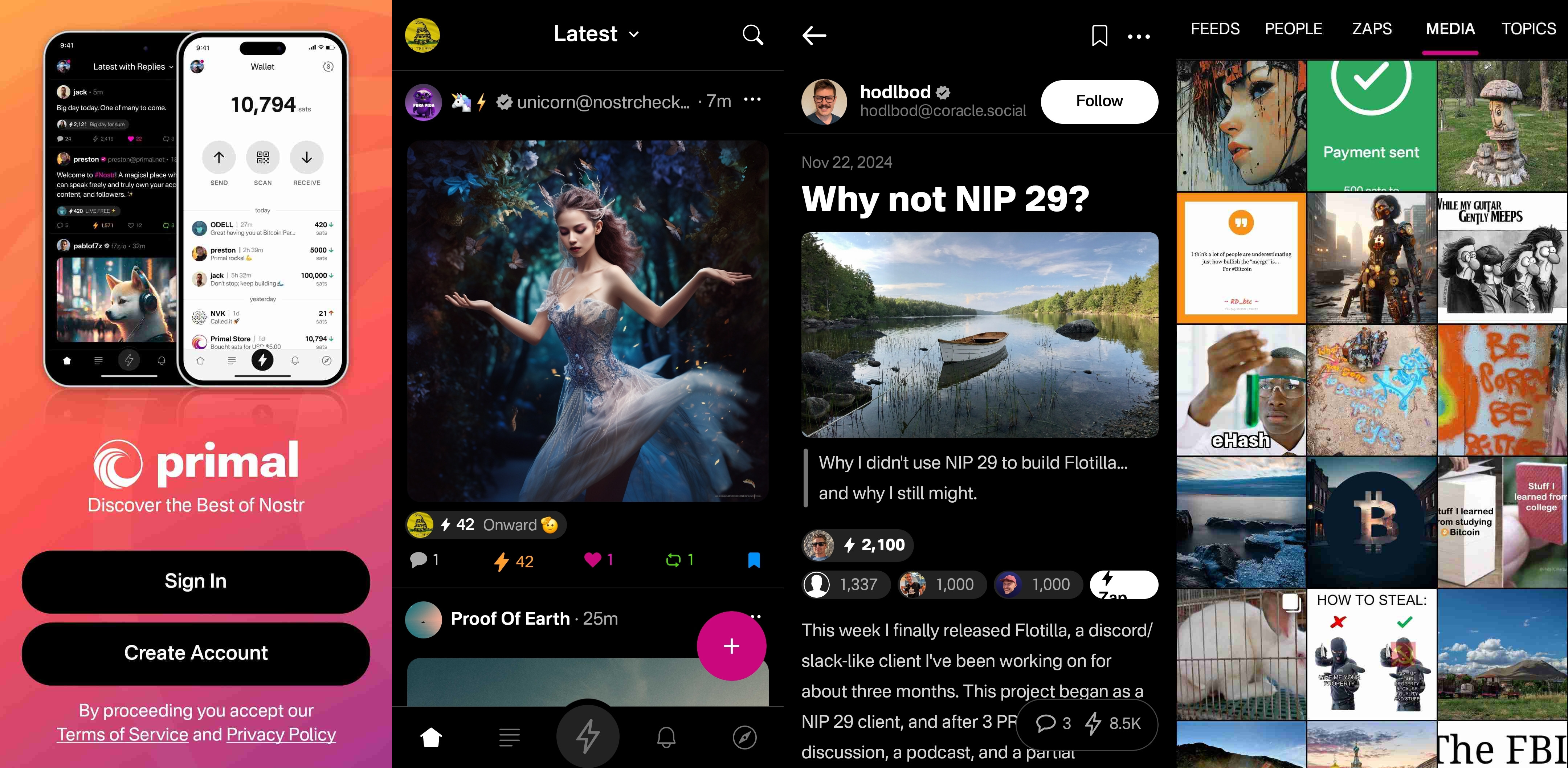
It is clean, attractive, and intuitive. Everything I needed was easy to find, and nothing felt busy or cluttered. There are only a few minor UI glitches that I ran into while testing the app. Some of them were mentioned in the section of the review detailing the feed selector feature, but a couple others occurred during onboarding.
First, my profile picture was not centered in the preview when I uploaded it. This appears to be because it was a low quality image. Uploading a higher quality photo did not have this result.

The other UI bug was related to text instructions that were cut off, and not able to scroll to see the rest of them. This occurred on a few pages during onboarding, and I expect it was due to the size of my phone screen, since it did not occur when I was on a slightly larger phone or tablet.
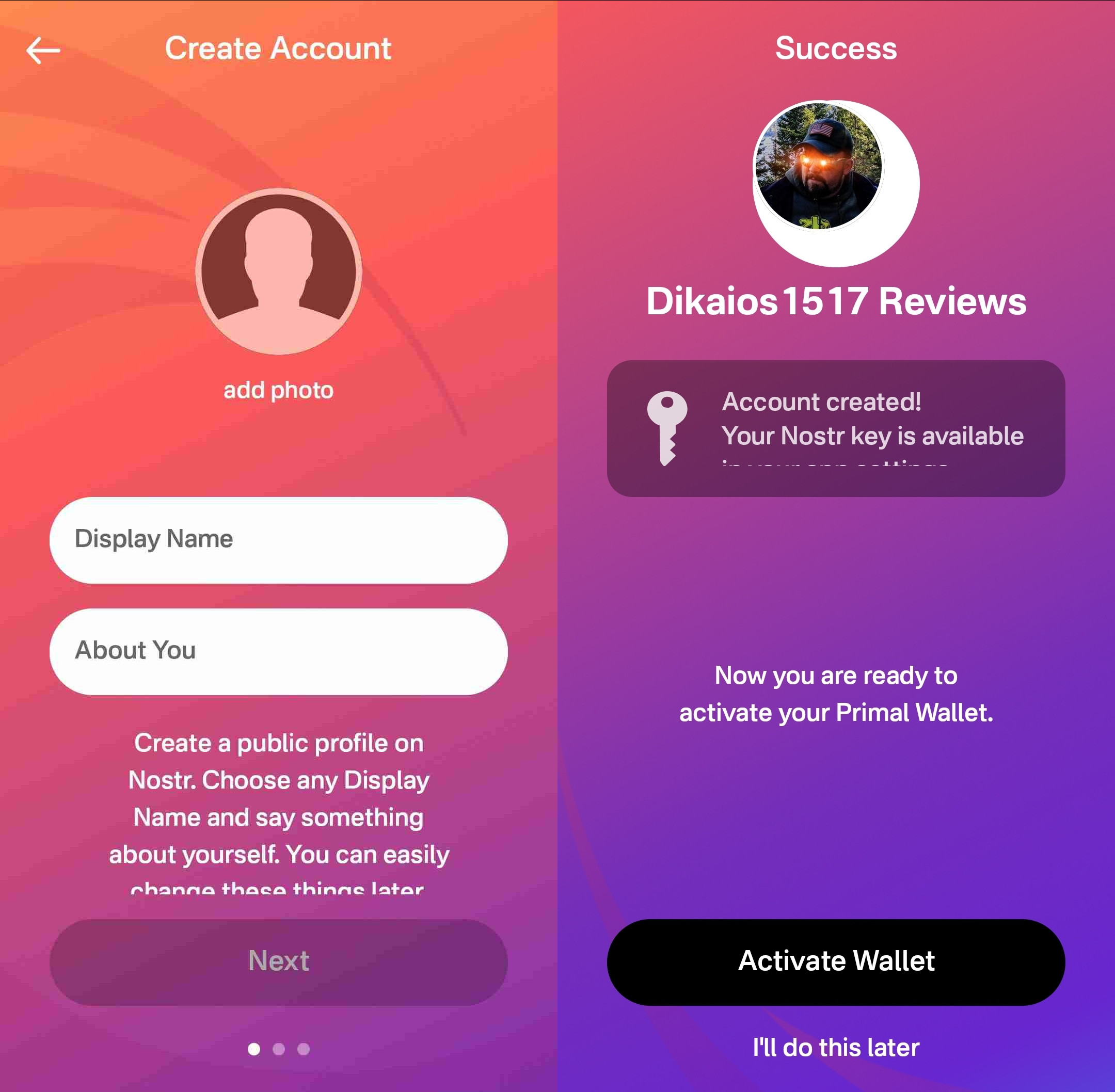
Speaking of tablets, Primal Android looks really good on a tablet, too! While the client does not have a landscape mode by default, many Android tablets support forcing apps to open in full-screen landscape mode, with mixed results. However, Primal handles it well. I would still like to see a tablet version developed that takes advantage of the increased screen real estate, but it is certainly a passable option.
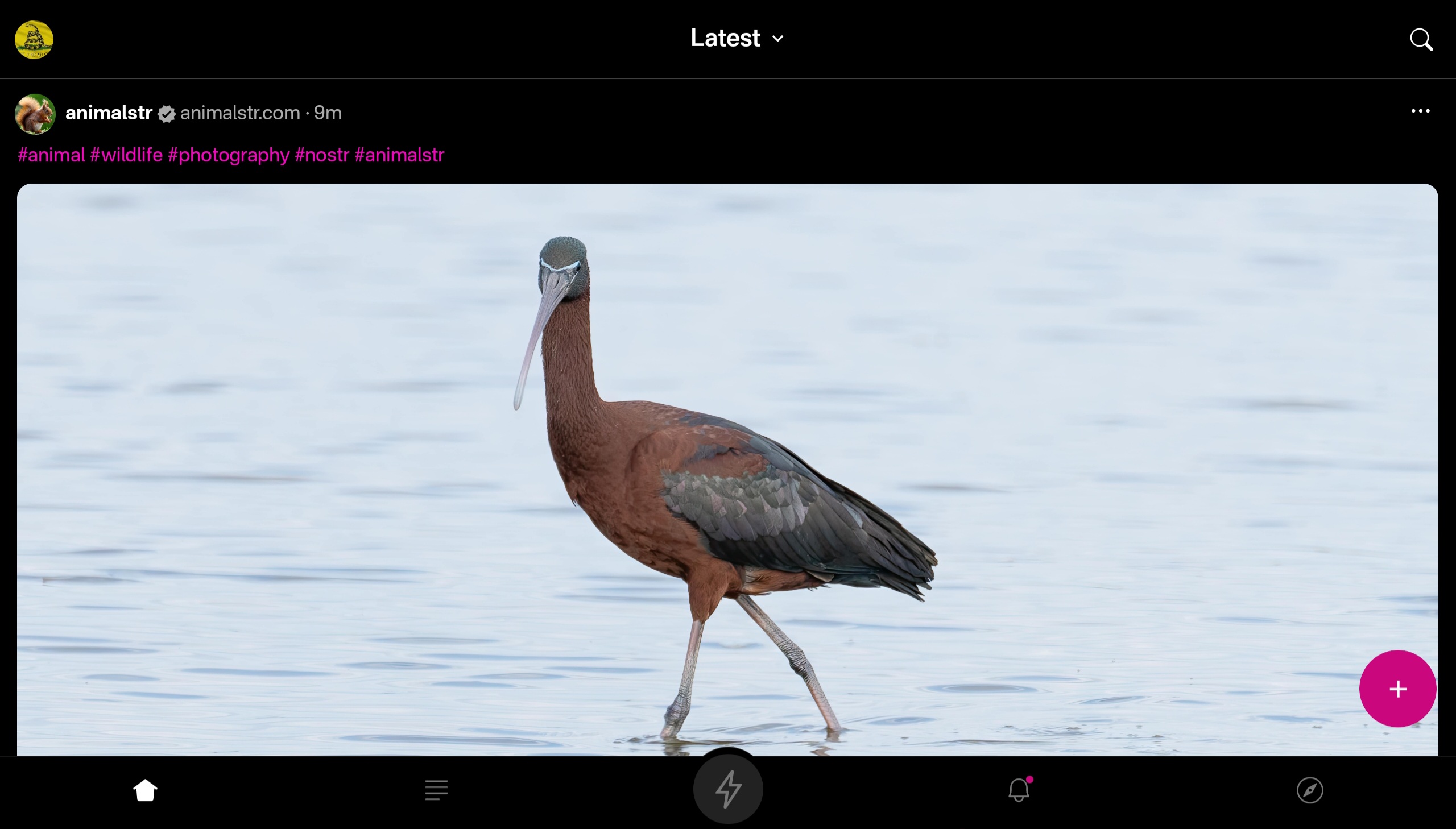

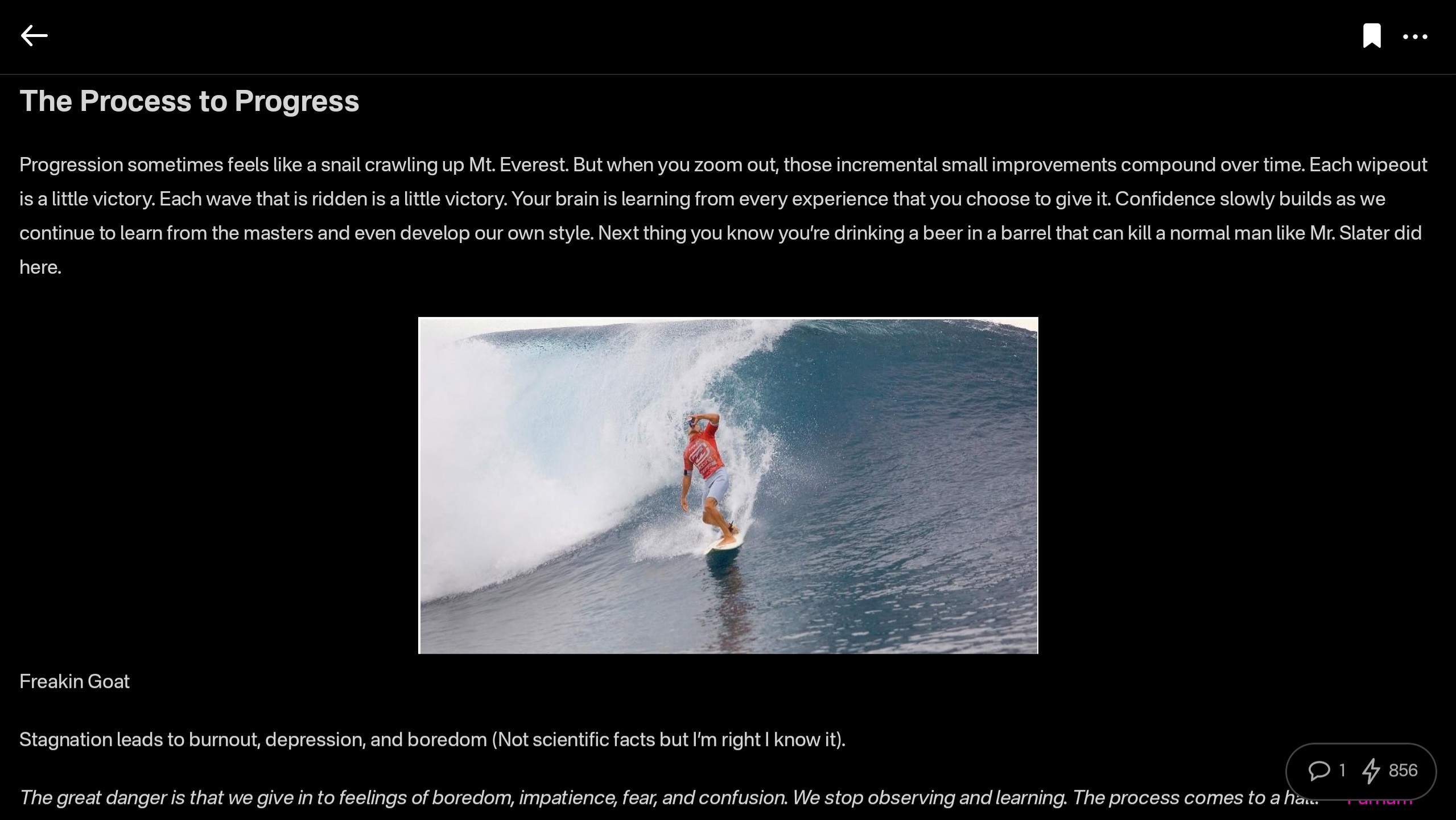
At this point, I would say the web client probably has a bit better UI for use on a tablet than the Android client does, but you miss out on using the built-in wallet, which is a major selling point of the app.
This lack of a landscape mode for tablets and the few very minor UI bugs I encountered are the only reason Primal doesn't get a perfect score in this category, because the client is absolutely stunning otherwise, both in light and dark modes. There are also two color schemes available for each.
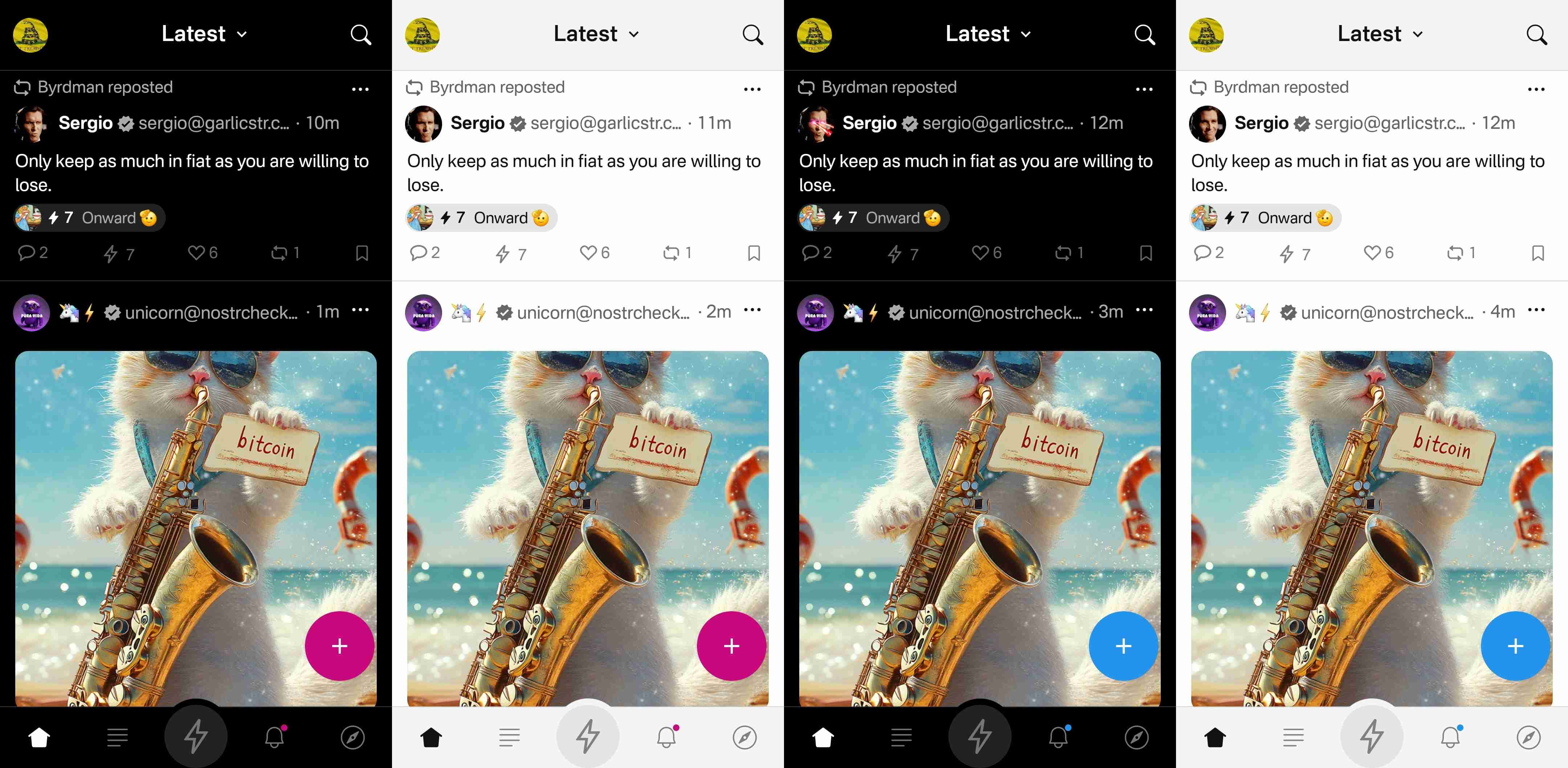
Log In Options
Score: 4 / 5 (Updated 4/30/2025)
Unfortunately, Primal has not included any options for log in outside of pasting your private key into the application. While this is a very simple way to log in for new users to understand, it is also the least secure means to log into Nostr applications.
This is because, even with the most trustworthy client developer, giving the application access to your private key always has the potential for that private key to somehow be exposed or leaked, and on Nostr there is currently no way to rotate to a different private key and keep your identity and social graph. If someone gets your key, they are you on Nostr for all intents and purposes.
This is not a situation that users should be willing to tolerate from production-release clients at this point. There are much better log in standards that can and should be implemented if you care about your users.
That said, I am happy to report that external signer support is on the roadmap for Primal, as confirmed below:
nostr:note1n59tc8k5l2v30jxuzghg7dy2ns76ld0hqnn8tkahyywpwp47ms5qst8ehl
No word yet on whether this will be Android signer or remote signer support, or both.
This lack of external signer support is why I absolutely will not use my main npub with Primal for Android. I am happy to use the web client, which supports and encourages logging in with a browser extension, but until the Android client allows users to protect their private key, I cannot recommend it for existing Nostr users.
Update: As of version 2.2.13, all of what I have said above is now obsolete. Primal has added Android signer support, so users can now better protect their nsec by using Amber!
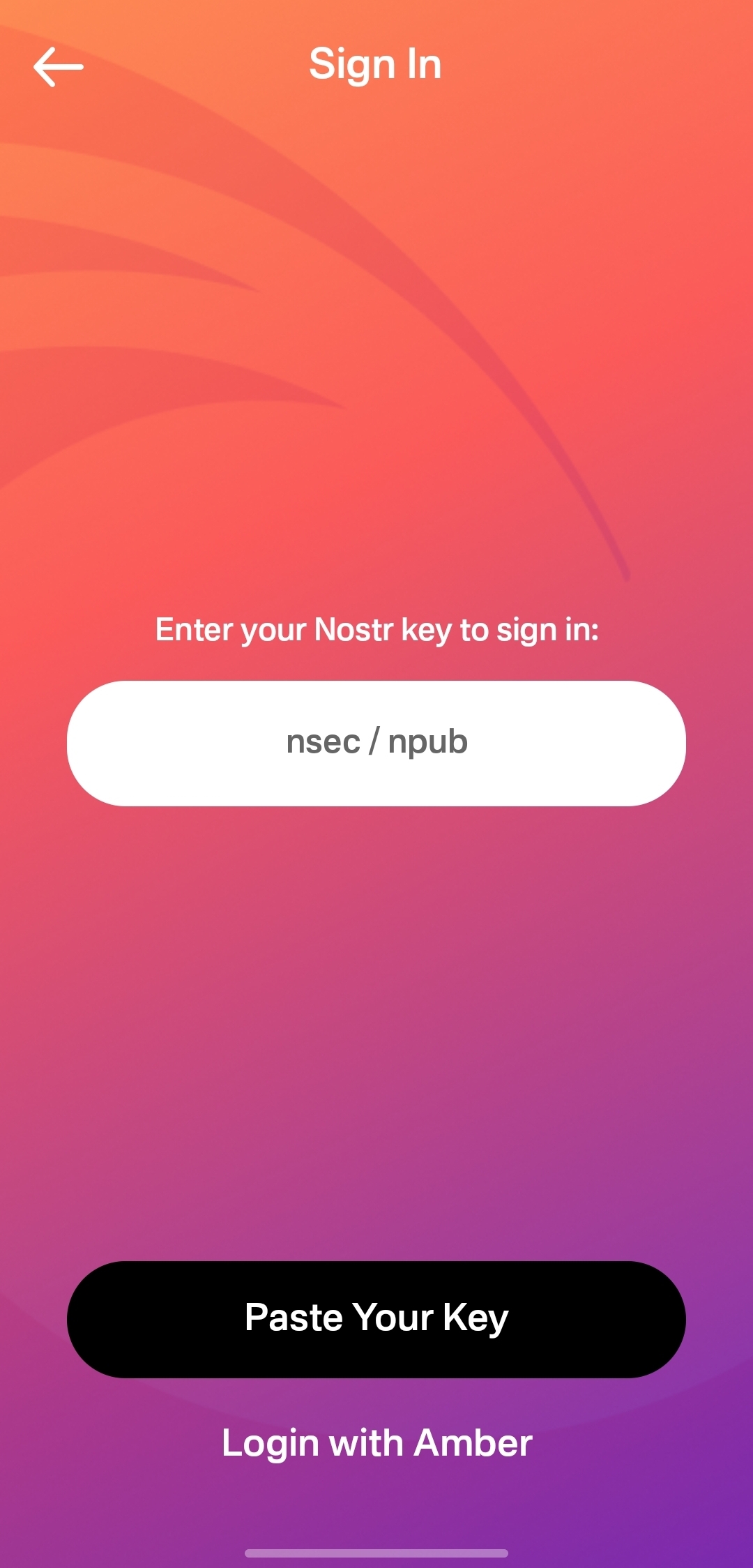
I would still like to see support for remote signers, especially with nstart.me as a recommended Nostr onboarding process and the advent of FROSTR for key management. That said, Android signer support on its own has been a long time coming and is a very welcome addition to the Primal app. Bravo Primal team!
Zap Integration
Score: 4.8 / 5
As mentioned when discussing Primal's built-in wallet feature, zapping in Primal can be the most seamless experience I have ever seen in a Nostr client. Pairing the wallet with the client is absolutely the path forward for Nostr leading the way to Bitcoin adoption.
But what if you already have a Lightning wallet you want to use for zapping? You have a couple options. If it is an Alby wallet or another wallet that supports Nostr Wallet Connect, you can connect it with Primal to use with one-tap zapping.
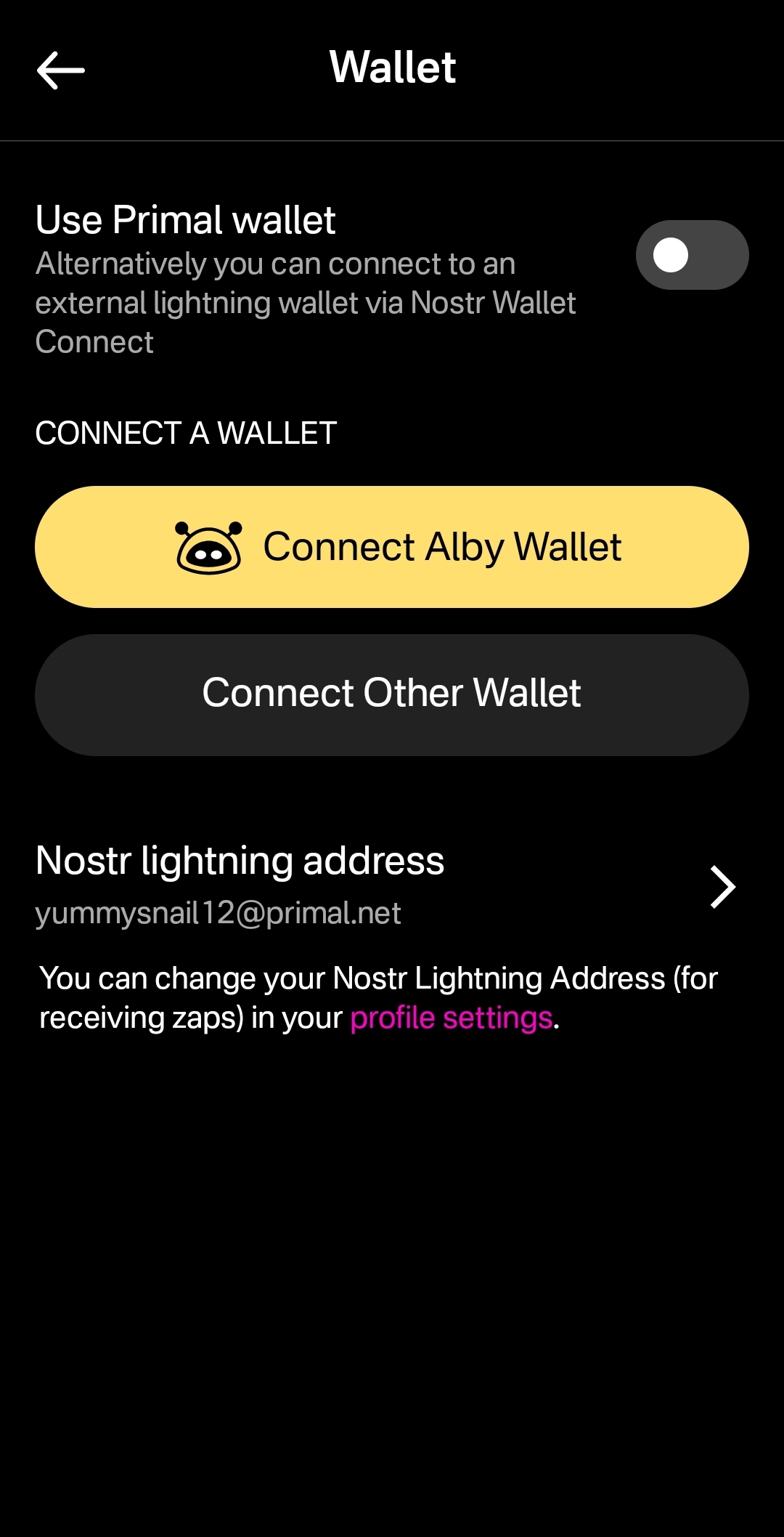
How your zapping experience goes with this option will vary greatly based on your particular wallet of choice and is beyond the scope of this review. I used this option with a hosted wallet on my Alby Hub and it worked perfectly. Primal gives you immediate feedback that you have zapped, even though the transaction usually takes a few seconds to process and appear in your wallet's history.
The one major downside to using an external wallet is the lack of integration with the wallet interface. This interface currently only works with Primal's wallet, and therefore the most prominent tab in the entire app goes unused when you connect an external wallet.
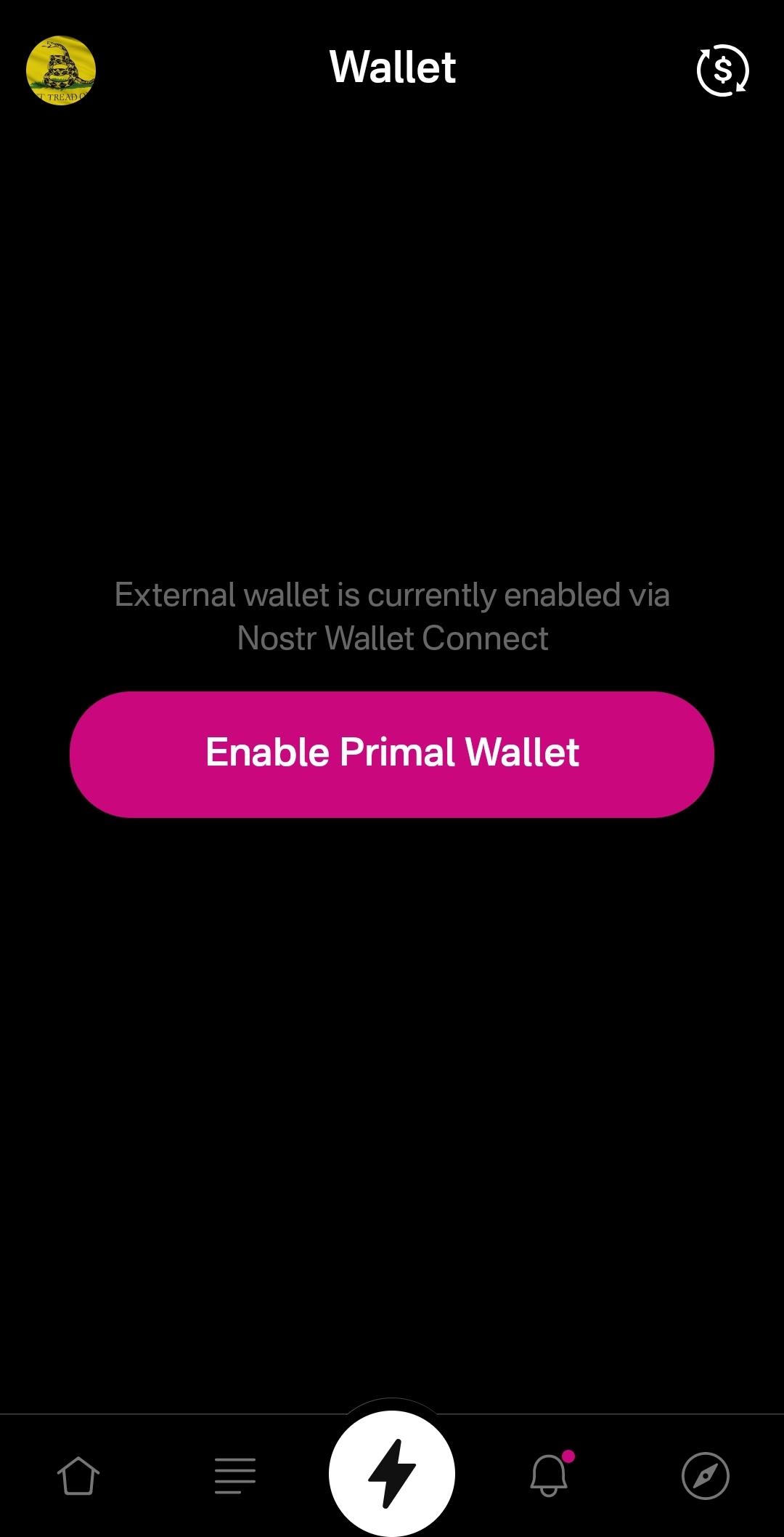
An ideal improvement would be for the wallet screen to work similar to Alby Go when you have an external wallet connected via Nostr Wallet Connect, allowing the user to have Primal act as their primary mobile Lightning wallet. It could have balance and transaction history displayed, and allow sending and receiving, just like the integrated Primal wallet, but remove the ability to purchase sats directly through the app when using an external wallet.
Content Discovery
Score: 4.8 / 5
Primal is the best client to use if you want to discover new content you are interested in. There is no comparison, with only a few caveats.
First, the content must have been posted to Nostr as either a short-form or long-form note. Primal has a limited ability to display other types of content. For instance, discovering video content or streaming content is lacking.
Second, you must be willing to put up with the fact that Primal lacks a means of filtering sensitive content when you are exploring beyond the bounds of your current followers. This may not be an issue for some, but for others it could be a deal-breaker.
Third, it would be preferable for Primal to follow topics you are interested in when you choose them during onboarding, rather than follow specific npubs. Ideally, create a "My Topics" feed that can be edited by selecting your interests in the Topics section of the Explore tab.
Relay Management
Score: 2.5 / 5
For new users who don't want to mess around with managing relays, Primal is fantastic! There are 7 relays selected by default, in addition to Primal's caching service. For most users who aren't familiar with Nostr's protocol archetecture, they probably won't ever have to change their default relays in order to use the client as they would expect.
However, two of these default relays were consistently unreachable during the week that I tested. These were relay.plebes.fans and remnant.cloud. The first relay seems to be an incorrect URL, as I found nosflare.plebes.fans online and with perfect uptime for the last 12 hours on nostr.watch. I was unable to find remnant.cloud on nostr.watch at all. A third relay was intermittent, sometimes online and reachable, and other times unreachable: v1250.planz.io/nostr. If Primal is going to have default relays, they should ideally be reliable and with accurate URLs.
That said, users can add other relays that they prefer, and remove relays that they no longer want to use. They can even set a different caching service to use with the client, rather than using Primal's.
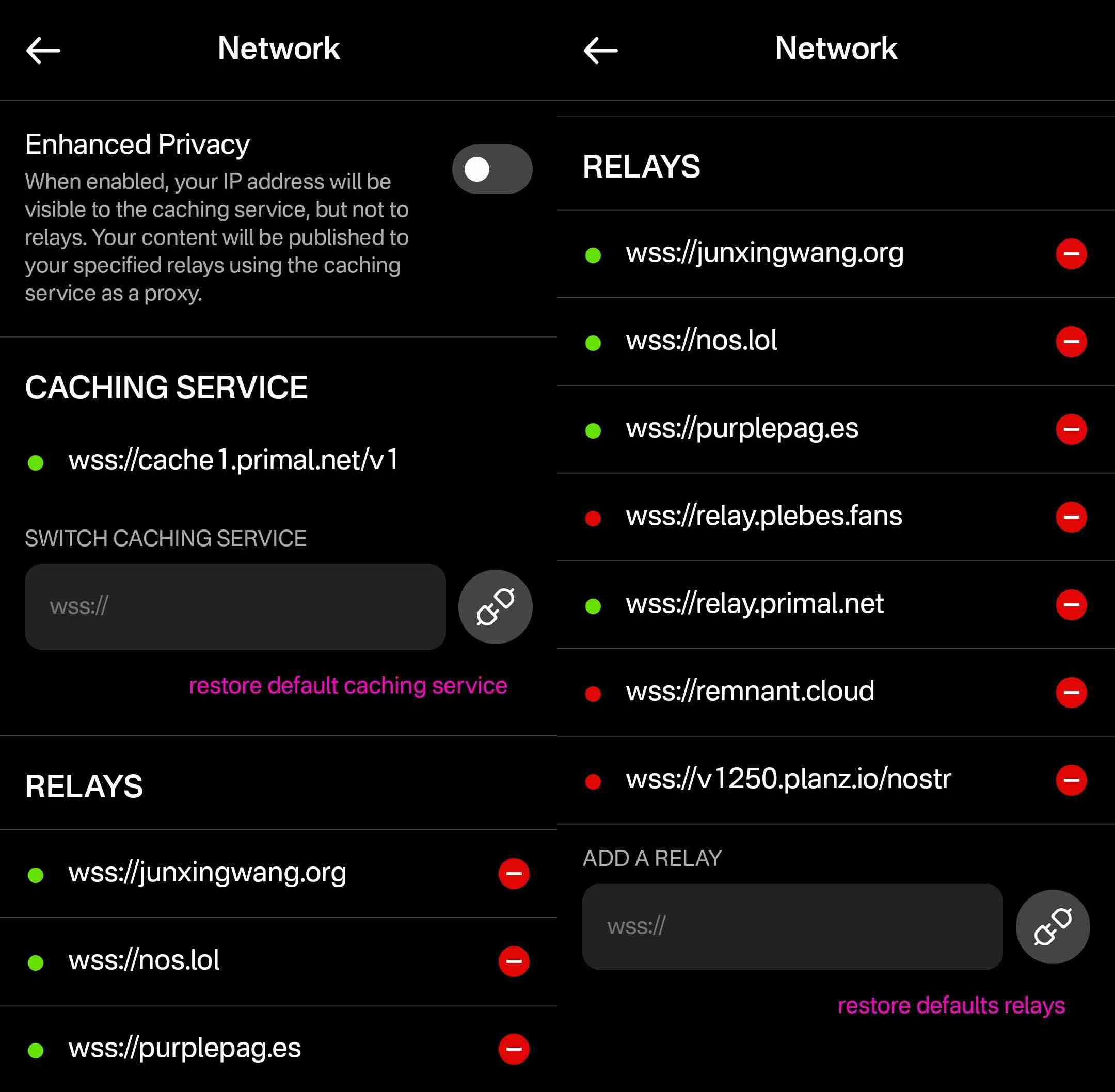
However, that is the extent of a user's control over their relays. They cannot choose which relays they want to write to and which they want to read from, nor can they set any private relays, outbox or inbox relays, or general relays. Loading the npub I used for this review into another client with full relay management support revealed that the relays selected in Primal are being added to both the user's public outbox relays and public inbox relays, but not to any other relay type, which leads me to believe the caching relay is acting as the client's only general relay and search relay.
One unique and welcomed addition is the "Enhanced Privacy" feature, which is off by default, but which can be toggled on. I am not sure why this is not on by default, though. Perhaps someone from the Primal team can enlighten me on that choice.
By default, when you post to Nostr, all of your outbox relays will see your IP address. If you turn on the Enhanced Privacy mode, only Primal's caching service will see your IP address, because it will post your note to the other relays on your behalf. In this way, the caching service acts similar to a VPN for posting to Nostr, as long as you trust Primal not to log or leak your IP address.
In short, if you use any other Nostr clients at all, do not use Primal for managing your relays.
Media Hosting Options
Score: 4.9 / 5 This is a NEW SECTION of this review, as of version 2.2.13!
Primal has recently added support for the Blossom protocol for media hosting, and has added a new section within their settings for "Media Uploads."
Media hosting is one of the more complicated problems to solve for a decentralized publishing protocol like Nostr. Text-based notes are generally quite small, making them no real burden to store on relays, and a relay can prune old notes as they see fit, knowing that anyone who really cared about those notes has likely archived them elsewhere. Media, on the other hand, can very quickly fill up a server's disk space, and because it is usually addressable via a specific URL, removing it from that location to free up space means it will no longer load for anyone.
Blossom solves this issue by making it easy to run a media server and have the same media mirrored to more than one for redundancy. Since the media is stored with a file name that is a hash of the content itself, if the media is deleted from one server, it can still be found from any other server that has the same file, without any need to update the URL in the Nostr note where it was originally posted.
Prior to this update, Primal only allowed media uploads to their own media server. Now, users can upload to any blossom server, and even choose to have their pictures or videos mirrored additional servers automatically. To my knowledge, no other Nostr client offers this automatic mirroring at the time of upload.
One of my biggest criticisms of Primal was that it had taken a siloed approach by providing a client, a caching relay, a media server, and a wallet all controlled by the same company. The whole point of Nostr is to separate control of all these services to different entities. Now users have more options for separating out their media hosting and their wallet to other providers, at least. I would still like to see other options available for a caching relay, but that relies on someone else being willing to run one, since the software is open for anyone to use. It's just not your average, lightweight relay that any average person can run from home.
Regardless, this update to add custom Blossom servers is a most welcome step in the right direction!
Current Users' Questions
The AskNostr hashtag can be a good indication of the pain points that other users are currently having with a client. Here are some of the most common questions submitted about Primal since the launch of 2.0:
nostr:note1dqv4mwqn7lvpaceg9s7damf932ydv9skv2x99l56ufy3f7q8tkdqpxk0rd
This was a pretty common question, because users expect that they will be able to create the same type of content that they can consume in a particular client. I can understand why this was left out in a mobile client, but perhaps it should be added in the web client.
nostr:note16xnm8a2mmrs7t9pqymwjgd384ynpf098gmemzy49p3572vhwx2mqcqw8xe
This is a more concerning bug, since it appears some users are experiencing their images being replaced with completely different images. I did not experience anything similar in my testing, though.
nostr:note1uhrk30nq0e566kx8ac4qpwrdh0vfaav33rfvckyvlzn04tkuqahsx8e7mr
There hasn't been an answer to this, but I have not been able to find a way. It seems search results will always include replies as well as original notes, so a feed made from the search results will as well. Perhaps a filter can be added to the advanced search to exclude replies? There is already a filter to only show replies, but there is no corresponding filter to only show original notes.
nostr:note1zlnzua28a5v76jwuakyrf7hham56kx9me9la3dnt3fvymcyaq6eqjfmtq6
Since both mobile platforms support the wallet, users expect that they will be able to access it in their web client, too. At this time, they cannot. The only way to have seamless zapping in the web client is to use the Alby extension, but there is not a way to connect it to your Primal wallet via Nostr Wallet Connect either. This means users must have a separate wallet for zapping on the web client if they use the Primal Wallet on mobile.
nostr:note15tf2u9pffy58y9lk27y245ew792raqc7lc22jezxvqj7xrak9ztqu45wep
It seems that Primal is filtering for spam even for profiles you actively follow. Moreover, exactly what the criteria is for being considered spam is currently opaque.
nostr:note1xexnzv0vrmc8svvduurydwmu43w7dftyqmjh4ps98zksr39ln2qswkuced
For those unaware, Blossom is a protocol for hosting media as blobs identified by a hash, allowing them to be located on and displayed from other servers they have been mirrored to when when the target server isn't available. Primal currently runs a Blossom server (blossom.primal.net) so I would expect we see Blossom support in the future.
nostr:note1unugv7s36e2kxl768ykg0qly7czeplp8qnc207k4pj45rexgqv4sue50y6
Currently, Primal on Android only supports uploading photos to your posts. Users must upload any video to some other hosting service and copy/paste a link to the video into their post on Primal. I would not be surprised to see this feature added in the near future, though.
nostr:note10w6538y58dkd9mdrlkfc8ylhnyqutc56ggdw7gk5y7nsp00rdk4q3qgrex
Many Nostr users have more than one npub for various uses. Users would prefer to have a way to quickly switch between accounts than to have to log all the way out and paste their npub for the other account every time they want to use it.
There is good news on this front, though:
nostr:note17xv632yqfz8nx092lj4sxr7drrqfey6e2373ha00qlq8j8qv6jjs36kxlh
Wrap Up
All in all, Primal is an excellent client. It won't be for everyone, but that's one of the strengths of Nostr as a protocol. You can choose to use the client that best fits your own needs, and supplement with other clients and tools as necessary.
There are a couple glaring issues I have with Primal that prevent me from using it on my main npub, but it is also an ever-improving client, that already has me hopeful for those issues to be resolved in a future release.
So, what should I review next? Another Android client, such as #Amethyst or #Voyage? Maybe an "other stuff" app, like #Wavlake or #Fountain? Please leave your suggestions in the comments.
I hope this review was valuable to you! If it was, please consider letting me know just how valuable by zapping me some sats and reposting it out to your follows.
Thank you for reading!
PV 🤙
-
 @ cae03c48:2a7d6671
2025-05-27 11:01:12
@ cae03c48:2a7d6671
2025-05-27 11:01:12Bitcoin Magazine

The Bitcoin Mempool: Relay Network DynamicsIn the last Mempool article, I went over the different kinds of relay policy filters, why they exist, and the incentives that ultimately decide how effective each class of filter is at preventing the confirmation of different classes of transactions. In this piece I’ll be looking at the dynamics of the relay network when some nodes on the network are running different relay policies compared to other nodes.
All else being equal, when nodes on the network are running homogenous relay policies in their mempools, all transactions should propagate across the entire network given that they pay the minimum feerate necessary not to be evicted from a node’s mempool during times of large transaction backlogs. This changes when different nodes on the network are running heterogenous policies.
The Bitcoin relay network operates on a best effort basis, using what is called a flood-fill architecture. This means that when a transaction is received by one node, it is forwarded to every other node it is connected to except the one that it received the transaction from. This is a highly inefficient network architecture, but in the context of a decentralized system it provides a high degree of guarantee that the transaction will eventually reach its intended destination, the miners.
Introducing filters in a node’s relay policy to restrict the relaying of otherwise valid transactions in theory introduces friction to the propagation of that transaction, and degrades the reliability of the network’s ability to perform this function. In practice, things aren’t that simple.
How Much Friction Prevents Propagation
Let’s look at a simplified example of different network node compositions. In the following graphics blue nodes represent ones that will propagate some arbitrary class of consensus valid transactions, and red nodes represent ones that will not propagate those transactions. The collective set of miners is denoted in the center as a simple representation of where transacting users ultimately want their transactions to wind up so as to eventually be confirmed in the blockchain.

This is a model of the network in which the nodes refusing to propagate these transactions are a clear minority. As you can clearly see, any node on the network that accepts them has a clear path to relay them to the miners. The two nodes attempting to restrict the transactions propagation across the network have no effect on their eventual receipt by miners’ nodes.

In this diagram, you can see that almost half of the example network is instituting filtering policies for this class of transactions. Despite this, only part of the network that propagates these transactions is cut off from a path to miners. The rest of the nodes not filtering still have a clear path to miners. This has introduced some degree of friction for a subset of users, but the others can still freely engage in propagating these transactions.
Even for the users that are affected by filtering nodes, only a single connection to the rest of the network nodes that are not cut off from miners (or a direct connection to a miner) is necessary in order for that friction to be removed. If the real relay network were to have a similar composition to this example, all it would take is a single new connection to alleviate the problem.

In this scenario, only a tiny minority of the network is actually propagating these transactions. The rest of the network is engaging in filtering policies to prevent their propagation. Even in this case however, those nodes that are not filtering still have a clear path to propagate them to miners.
Only this tiny minority of non-filtering nodes is necessary in order to ensure their eventual propagation to miners. Preferential peering logic, i.e. functionality to ensure that your node prefers peers who implement the same software version or relay policies. These types of solutions can guarantee that peers who will propagate something to others won’t find each other and maintain connections amongst themselves across the network.
The Tolerant Minority
As you can see looking at these different examples, even in the face of an overwhelming majority of the public network engaging in filtering of a specific class of transactions, all that is necessary for them to successfully propagate across the network to miners is a small minority of the network to propagate and relay them.
These nodes will essentially, through whatever technical mechanism, create a “sub-network” within the larger public relay network in order to guarantee that there are viable paths from users engaging in these types of transactions to the miners willing to include them in their blocks.
There is essentially nothing that can be done to counter this dynamic except to engage in a sybil attack against all of these nodes, and sybil attacks only need a single honest connection in order to be completely defeated. As well, an honest node creating a very large number of connections with other nodes on the network can raise the cost of such a sybil attack exorbitantly. The more connections it creates, the more sybil nodes must be spun up in order to consume all of its connection slots.
What If There Is No Minority?
So what if there is no Tolerant Minority? What will happen to this class of transactions in that case?

If users still want to make them and pay fees to miners for them, they will be confirmed. Miners will simply set up an API. The role of miners is to confirm transactions, and the reason they do so is to maximize profit. Miners are not selfless entities, or morally or ideologically motivated, they are a business. They exist to make money.
If users exist that are willing to pay them money for a certain type of transaction, and the entirety of the public relay network is refusing to propagate those transactions to miners in order to include them in blocks, miners will create another way for users to submit those transactions to them.
It is simply the rational move to make as a profit motivated actor when customers exist that wish to pay you money.
Relay Policy Is Not A Replacement For Consensus
At the end of the day, relay policy cannot successfully censor transactions if they are consensus valid, users are willing to pay for them, and miners do not have some extenuating circumstances to turn down the fees users are willing to pay (such as causing material damage or harm to nodes on the network, i.e. crashing nodes, propagating blocks that take hours to verify on a consumer PC, etc.).
If some class of transactions is truly seen as undesirable by Bitcoin users and node operators, there is no solution to stopping them from being confirmed in the blockchain short of enacting a consensus change to make them invalid.
If it were possible to simply prevent transactions from being confirmed by filtering policies implemented on the relay network, then Bitcoin would not be censorship resistant.
This post The Bitcoin Mempool: Relay Network Dynamics first appeared on Bitcoin Magazine and is written by Shinobi.
-
 @ 9ca447d2:fbf5a36d
2025-05-27 12:01:34
@ 9ca447d2:fbf5a36d
2025-05-27 12:01:34Bahrain-based Al Abraaj Restaurants Group has made history by becoming the first publicly-traded company in the Middle East to add bitcoin to its corporate treasury. This is a major step forward for regional bitcoin adoption.
On May 15, 2025, Al Abraaj Restaurants Group, a well-known restaurant chain listed on the Bahrain Bourse, announced it had bought 5 bitcoin (BTC) as part of a new treasury strategy. This makes the company the first in Bahrain, the GCC and the Middle East to officially hold bitcoin as a reserve asset.
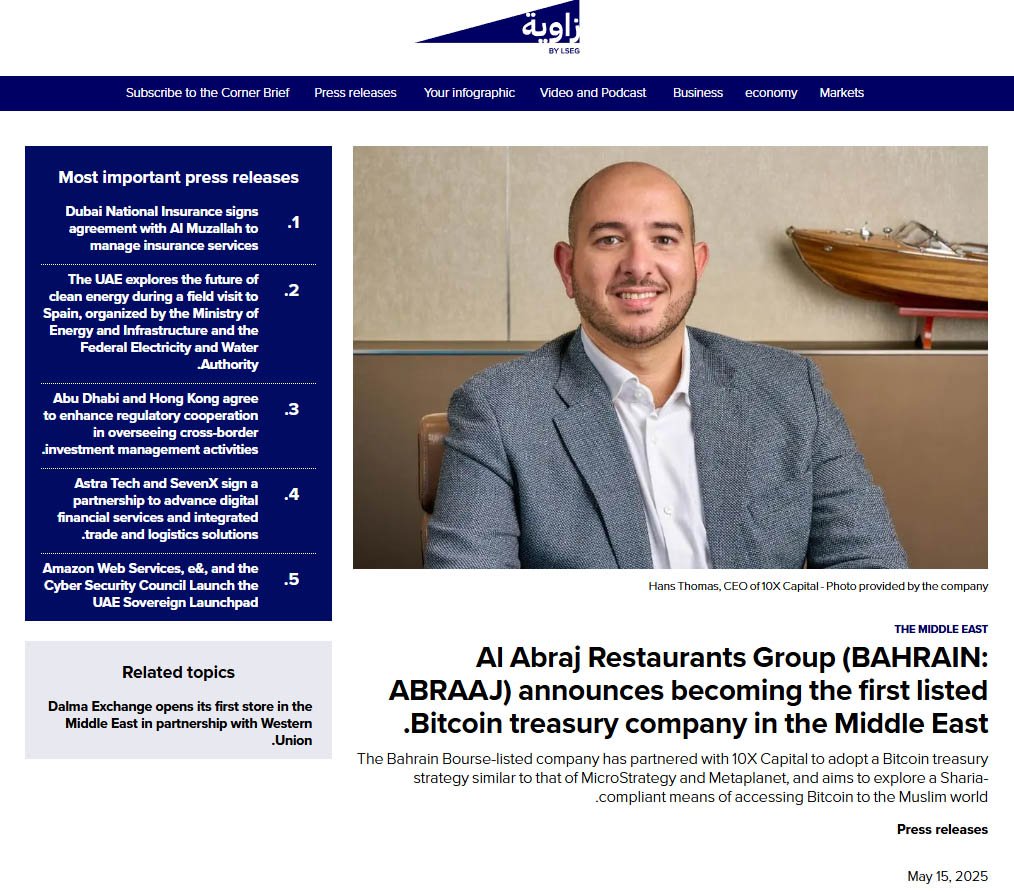
Al Abraaj adds bitcoin to its treasury — Zawya
This is a growing trend globally where companies are treating bitcoin not just as an investment but as a long-term store of value. Major companies like Strategy, Tesla and Metaplanet have already done this — and now Al Abraaj is following suit.
Metaplanet recently added 1,241 BTC to its treasury, boosting the company’s holdings above El Salvador’s.
Related: Metaplanet Overtakes El Salvador in Bitcoin Holdings After $126M Purchase
“Our initiative towards becoming a Bitcoin Treasury Company reflects our forward-thinking approach and dedication to maximizing shareholder value,” said Abdulla Isa, Chairman of the Bitcoin Treasury Committee at Al Abraaj.
Al Abraaj’s move is largely inspired by Michael Saylor, Executive Chairman of Strategy, the world’s largest corporate holder of bitcoin. Saylor’s strategy of allocating billions to bitcoin has set a model that other companies — now including Al Abraaj — are following.
A photo shared by the company even showed a meeting between an Al Abraaj representative and Saylor, with the company calling itself the “MicroStrategy of the Middle East”.
“We believe that Bitcoin will play a pivotal role in the future of finance, and we are excited to be at the forefront of this transformation in the Kingdom of Bahrain,” Isa added.
To support its bitcoin initiative, Al Abraaj has partnered with 10X Capital, a New York-based investment firm that specializes in digital assets.
10X Capital has a strong track record in bitcoin treasury strategies, and recently advised Nakamoto Holdings on a $710 million deal — the largest of its kind.
With 10X’s help, Al Abraaj looks to raise more capital and increase its bitcoin holdings over time to maximize bitcoin-per-share for its investors. The company will also develop Sharia-compliant financial instruments so Islamic investors can get exposure to bitcoin in a halal way.
“Bahrain continues to be a leader in the Middle East in Bitcoin adoption,” said Hans Thomas, CEO of 10X Capital. He noted, with a combined GDP of $2.2 trillion and over $6 trillion in sovereign wealth, the GCC now has its first publicly listed bitcoin treasury company.
This is not just a first for Al Abraaj — it’s a first for the region. Bahrain has been positioning itself as a fintech hub and Al Abraaj’s move will encourage more non-fintech companies in the region to look into bitcoin.
The company said the decision was made after thorough due diligence and is in line with the regulations set by the Central Bank of Bahrain (CBB). Al Abraaj will be fully compliant with all digital asset transaction rules, including transparency, security and governance.
A special Bitcoin Committee has been formed to oversee the treasury strategy. It includes experienced bitcoin investors, financial experts and portfolio managers who will manage risk, monitor market conditions and ensure best practices in custody and disclosure.
The initial purchase was 5 BTC, but Al Abraaj sees this as just the beginning. The company stated that there are plans in motion to allocate a significant portion of their treasury into bitcoin over time.
According to the company’s reports, Al Abraaj is financially sound with $12.5 million in EBITDA in 2024. This strong financial foundation gives the company the confidence to explore new strategies like bitcoin investment.
-
 @ b1ddb4d7:471244e7
2025-05-27 12:01:18
@ b1ddb4d7:471244e7
2025-05-27 12:01:18Global fintech leader Revolut has announced a landmark partnership with Lightspark, a pioneer in blockchain infrastructure solutions, to integrate bitcoin’s Lightning Network into its platform.
This collaboration, now live for Revolut users in the UK and select European Economic Area (EEA) countries, marks a transformative leap toward frictionless, real-time transactions—eliminating delays and exorbitant fees traditionally associated with digital asset transfers.
 Major update: @RevolutApp is now partnering with @lightspark pic.twitter.com/OUblgrj6Xr
Major update: @RevolutApp is now partnering with @lightspark pic.twitter.com/OUblgrj6Xr— Lightspark (@lightspark) May 7, 2025
Breaking Barriers in Digital Currency Usability
By adopting Lightspark’s cutting-edge technology, Revolut empowers its 40+ million customers to execute bitcoin transactions instantly at a fraction of current costs.
This integration addresses longstanding pain points in digital currency adoption, positioning bitcoin as a practical tool for everyday payments. Users can now seamlessly send, receive, and store bitcoin with the same ease as traditional fiat currencies, backed by Revolut’s secure platform.
The partnership also advances Revolut’s integration into the open Money Grid, a decentralized network enabling universal interoperability between financial platforms.
This move aligns Revolut with forward-thinking fintechs adopting next-gen solutions like Lightning transactions and Universal Money Addresses (UMA), which simplify cross-border payments by replacing complex wallet codes with human-readable addresses (e.g., $john.smith).
Why This Matters
The collaboration challenges conventional payment rails, which often incur delays of days and high fees for cross-border transfers. By contrast, Lightning Network transactions settle in seconds for minimal cost, revolutionizing peer-to-peer payments, remittances, and merchant settlements. For Revolut users, this means:
- Instant transactions: Send bitcoin globally in under three seconds.
- Near-zero fees: Dramatically reduce costs compared to traditional crypto transfers.
- Enhanced utility: Use bitcoin for daily spending, not just as a speculative asset.
The Road Ahead
Revolut plans to expand Lightning Network access to additional markets in 2025, with ambitions to integrate UMA support for seamless fiat and digital currency interactions. Lightspark will continue optimizing its infrastructure to support Revolut’s scaling efforts, further bridging the gap between blockchain innovation and mainstream finance.
About Revolut
Revolut is a global financial app serving over 40 million customers worldwide. Offering services ranging from currency exchange and stock trading to digital assets and insurance, Revolut is committed to building a borderless financial ecosystem.
About Lightspark
Founded by former PayPal and Meta executives, Lightspark develops enterprise-grade solutions for the Lightning Network. Its technology stack empowers institutions to harness bitcoin’s speed and efficiency while maintaining regulatory compliance.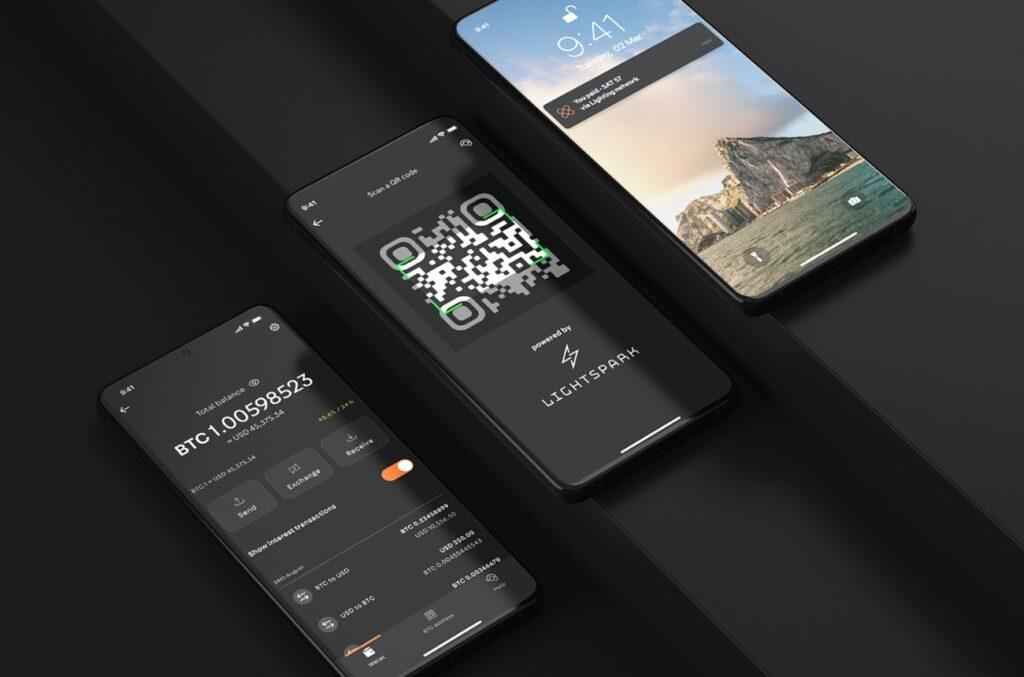
-
 @ cae03c48:2a7d6671
2025-05-27 12:01:05
@ cae03c48:2a7d6671
2025-05-27 12:01:05Bitcoin Magazine

The Bitcoin Mempool: Relay Network DynamicsIn the last Mempool article, I went over the different kinds of relay policy filters, why they exist, and the incentives that ultimately decide how effective each class of filter is at preventing the confirmation of different classes of transactions. In this piece I’ll be looking at the dynamics of the relay network when some nodes on the network are running different relay policies compared to other nodes.
All else being equal, when nodes on the network are running homogenous relay policies in their mempools, all transactions should propagate across the entire network given that they pay the minimum feerate necessary not to be evicted from a node’s mempool during times of large transaction backlogs. This changes when different nodes on the network are running heterogenous policies.
The Bitcoin relay network operates on a best effort basis, using what is called a flood-fill architecture. This means that when a transaction is received by one node, it is forwarded to every other node it is connected to except the one that it received the transaction from. This is a highly inefficient network architecture, but in the context of a decentralized system it provides a high degree of guarantee that the transaction will eventually reach its intended destination, the miners.
Introducing filters in a node’s relay policy to restrict the relaying of otherwise valid transactions in theory introduces friction to the propagation of that transaction, and degrades the reliability of the network’s ability to perform this function. In practice, things aren’t that simple.
How Much Friction Prevents Propagation
Let’s look at a simplified example of different network node compositions. In the following graphics blue nodes represent ones that will propagate some arbitrary class of consensus valid transactions, and red nodes represent ones that will not propagate those transactions. The collective set of miners is denoted in the center as a simple representation of where transacting users ultimately want their transactions to wind up so as to eventually be confirmed in the blockchain.

This is a model of the network in which the nodes refusing to propagate these transactions are a clear minority. As you can clearly see, any node on the network that accepts them has a clear path to relay them to the miners. The two nodes attempting to restrict the transactions propagation across the network have no effect on their eventual receipt by miners’ nodes.

In this diagram, you can see that almost half of the example network is instituting filtering policies for this class of transactions. Despite this, only part of the network that propagates these transactions is cut off from a path to miners. The rest of the nodes not filtering still have a clear path to miners. This has introduced some degree of friction for a subset of users, but the others can still freely engage in propagating these transactions.
Even for the users that are affected by filtering nodes, only a single connection to the rest of the network nodes that are not cut off from miners (or a direct connection to a miner) is necessary in order for that friction to be removed. If the real relay network were to have a similar composition to this example, all it would take is a single new connection to alleviate the problem.

In this scenario, only a tiny minority of the network is actually propagating these transactions. The rest of the network is engaging in filtering policies to prevent their propagation. Even in this case however, those nodes that are not filtering still have a clear path to propagate them to miners.
Only this tiny minority of non-filtering nodes is necessary in order to ensure their eventual propagation to miners. Preferential peering logic, i.e. functionality to ensure that your node prefers peers who implement the same software version or relay policies. These types of solutions can guarantee that peers who will propagate something to others won’t find each other and maintain connections amongst themselves across the network.
The Tolerant Minority
As you can see looking at these different examples, even in the face of an overwhelming majority of the public network engaging in filtering of a specific class of transactions, all that is necessary for them to successfully propagate across the network to miners is a small minority of the network to propagate and relay them.
These nodes will essentially, through whatever technical mechanism, create a “sub-network” within the larger public relay network in order to guarantee that there are viable paths from users engaging in these types of transactions to the miners willing to include them in their blocks.
There is essentially nothing that can be done to counter this dynamic except to engage in a sybil attack against all of these nodes, and sybil attacks only need a single honest connection in order to be completely defeated. As well, an honest node creating a very large number of connections with other nodes on the network can raise the cost of such a sybil attack exorbitantly. The more connections it creates, the more sybil nodes must be spun up in order to consume all of its connection slots.
What If There Is No Minority?
So what if there is no Tolerant Minority? What will happen to this class of transactions in that case?

If users still want to make them and pay fees to miners for them, they will be confirmed. Miners will simply set up an API. The role of miners is to confirm transactions, and the reason they do so is to maximize profit. Miners are not selfless entities, or morally or ideologically motivated, they are a business. They exist to make money.
If users exist that are willing to pay them money for a certain type of transaction, and the entirety of the public relay network is refusing to propagate those transactions to miners in order to include them in blocks, miners will create another way for users to submit those transactions to them.
It is simply the rational move to make as a profit motivated actor when customers exist that wish to pay you money.
Relay Policy Is Not A Replacement For Consensus
At the end of the day, relay policy cannot successfully censor transactions if they are consensus valid, users are willing to pay for them, and miners do not have some extenuating circumstances to turn down the fees users are willing to pay (such as causing material damage or harm to nodes on the network, i.e. crashing nodes, propagating blocks that take hours to verify on a consumer PC, etc.).
If some class of transactions is truly seen as undesirable by Bitcoin users and node operators, there is no solution to stopping them from being confirmed in the blockchain short of enacting a consensus change to make them invalid.
If it were possible to simply prevent transactions from being confirmed by filtering policies implemented on the relay network, then Bitcoin would not be censorship resistant.
This post The Bitcoin Mempool: Relay Network Dynamics first appeared on Bitcoin Magazine and is written by Shinobi.
-
 @ 866e0139:6a9334e5
2025-05-27 10:15:17
@ 866e0139:6a9334e5
2025-05-27 10:15:17Autor: Milosz Matuschek. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Der Schweizer Historiker Daniele Ganser startet eine Plakataktion. Auf Facebook schreibt er:
"Dieses Plakat habe ich ab heute an sechs Bahnhöfen in der Schweiz aufhängen lassen: Die Schweiz muss die Neutralität bewahren. Keine Zusammenarbeit mit der NATO!
Die Aktion läuft eine Woche. Das Plakat hängt in Basel (Gleis 5 und 7), Zürich (Gleis 9 und 12), Bern (Gleis 3 und 11), Luzern (Gleis 7 und 11), St. Gallen (Gleis 1 und 2) und Chur (Gleis 4 und Arosabahn).
Wenn jemand ein Plakat sieht und fotografiert und es mir per Email schickt freut mich das!
https://globalbridge.ch/die-schweiz-muss-die.../
Daniele Ganser kann man über folgende Seite kontaktieren.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 65038d69:1fff8852
2025-03-29 12:55:20
@ 65038d69:1fff8852
2025-03-29 12:55:20Welcome to part 3 of the “What is Money?” series! So far we’ve covered the base concepts of money and money as a system in part 1, and the Canadian Dollar in part 2. Today we’re going to talk about a relatively new system of money, Bitcoin!
Let’s review a few key details about money and the Canadian Dollar (CAD). Money is a placeholder to make trading easier, so anything that can fulfill the 3 functions of money can do the job (store of value, medium of exchange, and unit of account). During the Italian Renaissance the double-entry bookkeeping (or double-entry ledger) system was codified as a method of tracking transactions, and this system is still in use today for CAD and most other money systems. One of the features of using a ledger instead of physical money with intrinsic value (such as precious metals) is that it allows for fiat (money by decree) that isn’t backed by anything. The CAD is a fully fiat money with no reserve requirements. It’s also mostly digital, with only 7% of the total supply being cash and liquid deposits with the Bank of Canada.
Bitcoin was invented by Satoshi Nakamoto, a pseudonymous individual or group who no one knows the real identity of. They released the Bitcoin whitepaper (which can be read here: https://bitcoin.org/bitcoin.pdf) in October of 2008, and on January 3, 2009 they started the Bitcoin system. 2 years later they decided to disappear and were never heard from again. Others were involved in early development and maintenance, including Laszlo Hanyecz, who completed the first real-world purchase using Bitcoin. He paid 10,000 bitcoin for 2 pizzas on May 22, 2010, which is now unofficially celebrated as “Bitcoin Pizza Day”. There are several websites and pages dedicated to the story and tracking the current “value” of those pizzas; one can be found here: https://bitcoinpizzaindex.net
Fun history nuggets aside, Bitcoin is similar to CAD in that it uses the same double-entry ledger concept. The difference is that Bitcoin uses a single digital ledger across the entire network. Transactions are grouped into 10-minute blocks and chained together, which is where the popular term “blockchain” comes from. Another term you’ve probably heard, “mining”, is all of the computers dedicated to the task competing with each other in a combination math and guessing game for who gets to verify the authenticity and correctness of each block (the combined computational power from all of the competing computers is used, not just the winner), and the winner is rewarded with newly generated bitcoin and the transaction fees from the included transactions. This is what keeps the ledger secure and makes it practically impossible to fake, break, steal, or cheat on Bitcoin transactions. Last piece of technical background, I promise: If Bitcoin is just a ledger, how do you actually “hold” the money? You do so by holding something called a “private key”. This key is used to authorize new transactions (spending the money). Think of the private key as similar to a password, PIN, or secret code for a bank account. In Bitcoin, if you hold the keys, you hold the coins.
That was a lot of history and technical stuff; take a break, touch some grass, pet the dog, sip some coffee, and come back in a few minutes.
Since you have an understanding of how money systems and CAD works I won’t bother re-explaining it all for Bitcoin; I’ll instead hit some of the major differences between it and CAD (and most other fiat currencies). Bitcoin doesn’t have a central bank or any other central authority governing or controlling it. The ledger is the “single source of truth” and anyone with a valid private key and internet connection cannot be stopped from creating a new transaction. The ledger is also fully public; you can download a full copy and view it, or use a handy website. There are several; here’s the “Bitcoin Pizza” transaction on one of my favourite public sites, mempool.space: https://mempool.space/tx/a1075db55d416d3ca199f55b6084e2115b9345e16c5cf302fc80e9d5fbf5d48d
There’s also a hard limit to the number of Bitcoin that can exist, so there’s no inflation. 21 million bitcoin, which can be divided down into 2.1 quadrillion “satoshis”, or “sats”. Think of sats as similar to the CAD penny, the smallest unit of measurement.
Bitcoin is what I call a “push” system, which is opposite of CAD’s mostly “pull” system. When you do a debit, credit card, or cheque transaction, you’re authorizing the receiving bank to reach in and “pull” the money from your account. Credit cards especially rely on this; it’s how recurring subscriptions where you are charged automatically work. Central authorities also have the ability to pull from your accounts, such as banks for fees and the Canada Revenue Agency (CRA) for taxes (though the latter pinky-promise to only do this in emergency situations). With cash, you can’t authorize someone to physically reach into your pocket and take some of your money, and it's the same with Bitcoin. You have to “push” the money to the other person. This is one of the reasons Bitcoin has been referred to as “digital cash”.
Lastly, you may have heard some, including myself, talk about Bitcoin as a replacement for fiat currencies. How is it supposed to do that if we’re required by law to use CAD? My opinion is that we’ll most likely use both for several reasons, but let’s address CAD’s requirement of use. There are no Canadian laws that force the acceptance of CAD, including cash, for purchases. In Canada cash is “legal tender”, which is “the money approved in a country for paying debts.” (See the Bank of Canada page explaining this here: https://www.bankofcanada.ca/banknotes/about-legal-tender/) If there’s no debt being settled, there is no requirement to accept CAD in cash or digital form (i.e. debit or credit card). If there is debt (i.e. paying a bill for a product or service you already received) only cash (as legal tender) is required to be accepted, but payees are not required to use it. There is a bit of an exception to CAD’s non-requirement of use though; all “business” transactions (including barter and Bitcoin) are potentially taxable and therefore are required to be reported at Fair Market Value, denominated in CAD, to the CRA. See the CRA interpretation bulletin here: https://www.canada.ca/en/revenue-agency/services/forms-publications/publications/it490/archived-barter-transactions.html Taxes are required to be paid in CAD as well.
If you’d like to see how Bitcoin works in the real world, I’d be happy to show you. I’ll even gift you a few sats to practice with! You can find us at scalebright.ca.
-
 @ cae03c48:2a7d6671
2025-05-27 12:01:03
@ cae03c48:2a7d6671
2025-05-27 12:01:03Bitcoin Magazine

Something is Brewing in Ireland: A Sound Punt Is Released, As Bitcoin Enters The National ConversationFor years, Bitcoin in Ireland has quietly simmered at the grassroots level—discussed in pubs and meetups, debated in Telegram groups, and occasionally splashed across headlines with predictable suspicion. But recently, the temperature is beginning to rise. With the release of “A Sound Punt: The Case for Ireland’s Interest in Bitcoin” by Bitcoin Network Ireland (BNI), and a weekend that sees both the Bitcoin Ireland Conference and Aontú’s Ard Fheis, it’s clear momentum is building on the Emerald Isle.
A Sound Punt: A Paper for the Citizens of Ireland
The new paper, released today by Bitcoin Network Ireland, is a concise, accessible document crafted to cut through the noise and present the merits of Bitcoin to the general public and politicians alike. Its aim is straightforward: provide a rational, jargon-free entry point into why Bitcoin matters, especially in an era of euro debasement and rising living costs.
The name itself is a clever pun—while it is a nod to both “sound money” and Ireland’s former currency, the punt, it also playfully suggests that although the majority of people view it as associated with risk, this may be worth reevaluating. It’s a signal that this is about more than technology: it’s about claiming monetary sovereignty and re-examining what makes money “good” in the first place.
What BNI is attempting to accomplish is bridging an important gap in understanding, helping citizens seeking change and government officials looking for solutions to recognize that sound, stateless money has value for everyone. As Mark Goodwin famously noted, “Bitcoin simply must be for enemies, or it will never be for friends.“—a neutral system that serves all participants regardless of their political stance.
Ireland’s Long and Complicated Relationship With Money
To appreciate the significance of this moment, it’s worth noting that Ireland’s relationship with money has always been distinct from its European neighbors. While the Romans introduced coinage to Britain over a thousand years before it was adopted in Ireland. The native Irish resisted state-issued money, relying instead on barter and bullion well into the second millennium.
In ancient Ireland, the absence of coinage was a testament to a society that was stateless, highly decentralised, and it embraced a polycentric legal system varying between clans. The ideal of that society was that no man in society has rule over others, and even kings could be disposed of if they abused their power.
So it’s perhaps no coincidence that Ireland was the last European society to adopt coinage, as coinage gives power to rulers. Eventually, it was forced upon the land by the English crown in 1601, this period coincided with the final stages of the Nine Years’ War (1594-1603) and the increasing English control over Ireland. To this day, Ireland has never had its own free-floating currency; it has always been tethered to external powers: first the pound sterling, then the European Monetary System, and now the euro under the ECB. So it should come as no coincidence that in recent years, the EU is growing unabated in power and influence over Ireland.
“Give me control over a nation’s currency, and I care not who makes its laws.” — Mayer Amschel Rothschild (1743–1812)
Perhaps, given this historical context, Ireland is uniquely positioned to understand the value of sound, stateless money. Bitcoin represents a return to the monetary independence that preceded state-issued currencies, but with the technological advantages of the digital age. Where ancient Irish kingdoms used market goods that couldn’t be manipulated by distant authorities, Bitcoin offers a modern equivalent: a system that can’t be debased or controlled by any power, whether domestic or foreign.
This historical skepticism toward centrally-controlled currency is resurfacing in the present, as the Irish state and its citizens face a new wave of economic uncertainty via euro debasement and tariffs. Geopolitical and economic tensions have rarely felt less stable. Tariff disputes, renewed questions over Ireland’s foreign direct-investment model, and potential tech and pharma layoffs are sure to sharpen the focus on sovereignty and resilience. The release of “A Sound Punt” is timely, inviting the nation to once again question the wisdom of tying its fortunes to distant monetary authorities.
A Political Crossroads
Coinciding with the release of “A Sound Punt,” Dr. Niall Burke—a respected academic and BNI member—will be putting forward two motions at the Aontú Ard Fheis (party conference). Aontú, the party that saw the largest surge in votes in the last general election, has shown itself to be receptive to Bitcoin and is opening its doors to conversations that, until recently, were relegated to the margins. That Bitcoin motions are being presented and accepted at a major party conference is a marker of how the conversation is turning.
Meanwhile, the Bitcoin Ireland Conference is gathering the country’s growing community of plebs, builders, and advocates. These circles, once on the periphery, are now finding doors opening in political circles.
Public Discontent and a Call for Financial Autonomy
It’s not just Bitcoiners who are seeking alternatives. Ireland is witnessing its largest public demonstrations since the post-GFC days of 2012. Recent marches have drawn in excess of 100,000 people to the streets of Dublin. These protests reflect deep frustration and a sense that the political establishment is no longer in alignment with its people.
What’s particularly striking is how Bitcoin could serve as common ground for seemingly opposing interests. For protesters, Bitcoin offers protection from inflation and defends against government overreach. For a government concerned about economic stability and growth, Bitcoin may be the very solution it needs, especially to protect pension funds and indeed the state’s very own investment fund—ISIF, from inflation over the coming decades. This is the paradox and promise of sound, stateless money. It serves everyone’s interests because it enforces property rights, and can’t be captured or controlled by any single faction.
Last, but not least, MMA star Conor McGregor’s foray into both politics and Bitcoin is something few would have predicted a year ago, but for those with an ear to the ground, this has been a developing story for some time. His proposal for a national Bitcoin reserve is emblematic of a broader national shift: Bitcoin is finally entering the Zeitgeist and perhaps he, like BNI, has a part to play in keeping it there.
Bitcoin is an open-source monetary protocol, and adoption comes from all quarters, irrespective of politics. Bitcoin is neutral, it supports no partisan cause. What’s perhaps not recognized enough is how empowering Bitcoin can be and we should focus on its ability to unite rather than divide, giving every Irish citizen—regardless of their political views—tools for individual liberty, inflation protection, as well as practical solutions for businesses.
Back to “A Sound Punt” Paper
The paper itself makes a compelling case for Ireland’s interest in Bitcoin:
- Sound Money Principles: It evaluates Bitcoin against the six characteristics of “good money”—durability, divisibility, uniformity, portability, verifiability, and scarcity.
- Store of Value: The document highlights Bitcoin’s fixed supply as protection against rising inflation and currency debasement.
- Practical Examples: It provides evidence of Bitcoin’s monetization, comparing the costs of buying a home in Euros vs. Bitcoin over the span of a decade.
- Common Concern Rebuttals: The paper addresses the most common objections to Bitcoin—energy usage, volatility, criminal activity, undermining traditional currencies, and speculation—offering balanced counterarguments to each.
- Action Steps: Rather than just theoretical arguments, the paper outlines specific actions for individuals, businesses, and the government to consider, from education to strategic Bitcoin reserves.
The Beginning of a Process
No one expects the Irish government to announce a Bitcoin treasury next week, and it’s debatable whether it should establish one at all. But “A Sound Punt” marks the beginning of a process that could, in time, help reshape Ireland’s approach to money and economic sovereignty.
This accessible primer is just the first step in Bitcoin Network Ireland’s broader educational mission. BNI plans to publish a much more comprehensive policy paper for policymakers in the coming months, which is currently going through the editing phase. While “A Sound Punt” introduces the concepts to the general public, the forthcoming document will provide the detailed analysis and policy recommendations that decision-makers need.
As BNI works to elevate this conversation through both public ed
-
 @ cae03c48:2a7d6671
2025-05-27 12:01:02
@ cae03c48:2a7d6671
2025-05-27 12:01:02Bitcoin Magazine

What to expect from the BTCfi & L2s companies at the Bitcoin Conference in VegasThe annual Bitcoin Conference in Las Vegas is a pivotal event for the Bitcoin ecosystem, where companies unveil breakthroughs, announce partnerships, and deliver speeches that shape the narrative of digital assets. For many, the sheer volume of information can be overwhelming. Having attended several conferences and being familiar with the attending companies through my work at UTXO, I’ve highlighted key panels and expected developments for 2025, focusing on Bitcoin’s Layer 2 (L2) and BTCfi ecosystems.
The full agenda is available using this link: https://b.tc/conference/2025/agenda
Here’s a breakdown of anticipated announcements and panels, categorized by key themes:
BitVM2 Announcements
Since BitVM’s introduction in 2023, top Bitcoin development teams have been working tirelessly to transform centralized sidechain designs into true Bitcoin rollups and permissionless L2s. At the 2025 conference, expect these teams to unveil the first versions of BitVM2 bridges, providing critical details on their mechanics. Once live, BitVM2 bridges could unlock a wide range of decentralized BTC use cases, accessible to all Bitcoin holders. May 2025 might mark a turning point, potentially signaling the decline of centralized “crypto” and DeFi projects in favor of a Bitcoin-native economy. As the saying goes, on a long enough timeline, everything comes back to Bitcoin.
L2 Partnerships
Bitcoin L2s face a steep challenge: competing with established crypto players while earning the trust of Bitcoiners. The conference is likely to feature major partnership announcements, particularly at the infrastructure level, addressing long-standing barriers to BTCfi adoption. These collaborations could bolster the credibility and functionality of L2 solutions, paving the way for broader acceptance.
Lightning and Taproot Assets Innovation
The recent announcement that Tether (USDT) will return to Bitcoin by issuing its stablecoin on Lightning rails via Taproot Assets has sparked significant excitement. Expect major updates from companies in this space, particularly regarding Taproot Assets and stablecoin integration. The Lightning Network is poised for dominance, and 2025 could be the year it breaks into the mainstream.
Opcodes and Governance Discussions
With growing support for covenant activation on Bitcoin and recent debates over mempool policy on social media, governance discussions will be a focal point. These panels promise to be intellectually stimulating, offering deep insights into Bitcoin’s core mechanics and potential fireworks for those following the debates. Attending these sessions will likely be the most rewarding experience of the week for anyone seeking to understand Bitcoin’s future.
Must-Attend Panels
Below is a curated list of panels aligned with the above categories, along with my expectations for each. (Note: These predictions reflect my personal perspective and are not definitive. This list is not exhaustive but highlights high-signal sessions for attendees with limited time.)
Panels and Keynote with the highest probability of a major announcement related to Bitcoin L2s and BTCfi products: in other words, this is where major alpha will be dropped
Governance Discussions

*Bitcoin L2s and BTCfi products*
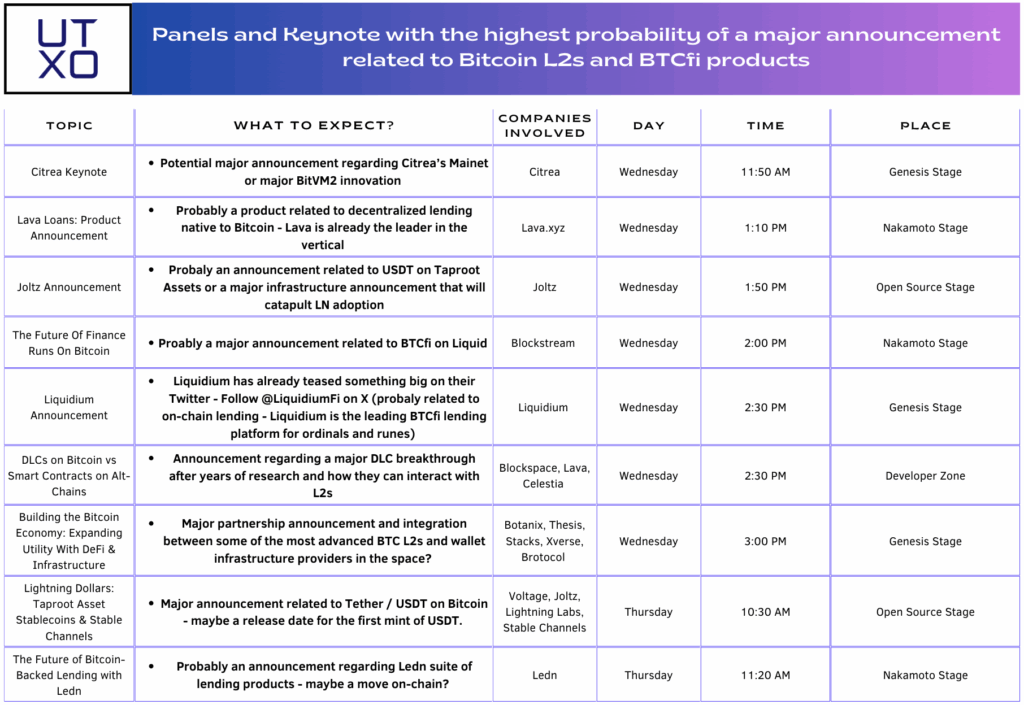
L2 and Lightning discussions
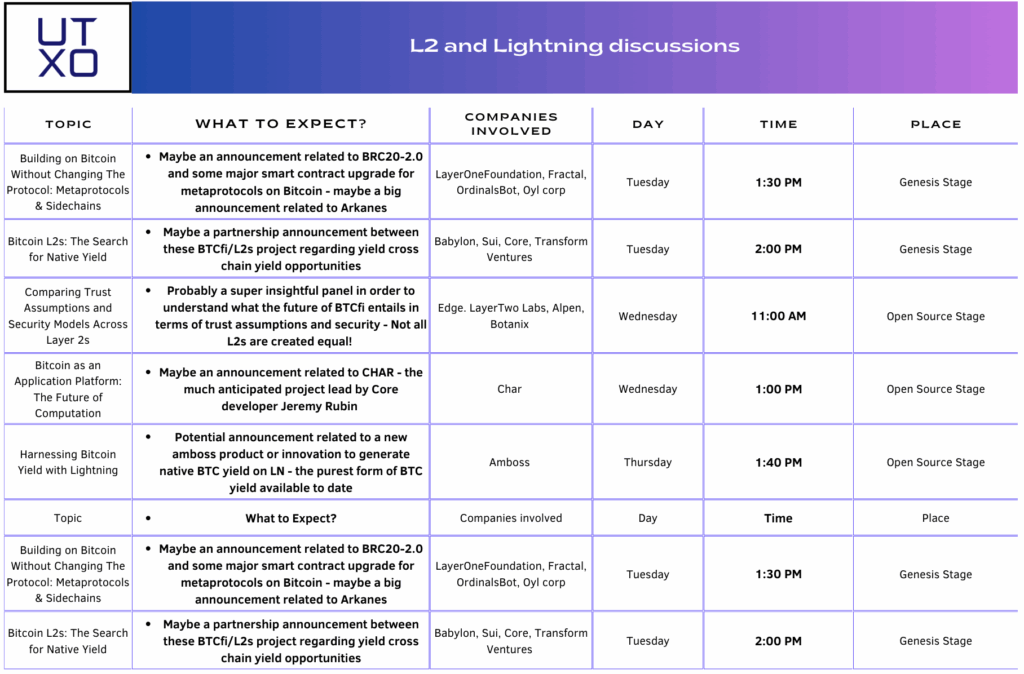
This post What to expect from the BTCfi & L2s companies at the Bitcoin Conference in Vegas first appeared on Bitcoin Magazine and is written by Guillaume Girard.
-
 @ 65038d69:1fff8852
2025-03-29 12:53:57
@ 65038d69:1fff8852
2025-03-29 12:53:57If you haven’t had the experience of waking up in the morning and fearing going to work, you’ve probably heard at least one story of someone who has. Someone who was afraid of their boss, a coworker, an impending audit, or layoffs. These stories are centered around fear, but what about fear’s older, more mature cousin, respect? How are they related, and what are their roles in the workplace?
Fear? Having a role in the workplace? I thought fear was bad and to be avoided at all costs? Didn’t we leave fear at work behind in the 1950s along with day-drinking and open misogyny? Not entirely it seems, but the fear we’re talking about today is of a different kind, a healthy kind. For example, a primary school child would have a healthy fear of bears. What about respect? While the term might feel dated in our current hyper-equality society, it too has a healthy version. As our example child matures, their fear of bears will develop into respect for them. They’ll understand their destructive power, but also that they’ll generally only engage it in defence. For another example, think back to your relationship with your childhood friend’s parents. As a child in an unknown adult’s home with different rules and expectations there was an amount of fear involved, but as an adult you most likely have respect for the amount of shenanigans they put up with at the hands of your and your friends.
Fear, even the unhealthy kind, can sometimes be leveraged for good. Fear of being yelled at might motivate you to finish the last 10% of a project or emptying your inbox before the end of the workday. It is better matured into respect whenever possible, however. The trade-off of fear of verbal assault or firing isn’t worth it. It’d be much healthier to be motivated by respect. Respect for your coworkers (who might also be made late by your procrastinations), your boss (who may need to take responsibility for the delay), and customers or clients (imagine yourself in their shoes).
We’ve established that respect is good, and that fear is a sometimes-useful antecedent of it. And we can all now hear a thousand voices screaming, “but so-and-so doesn’t respect me!” or “but so-and-so doesn’t deserve respect!”. They may not be wrong, so let’s see what we can do to help promote respect. Ignoring the edge cases where some people are arrogant to the point of not respecting anyone, the most common cause I’ve witnessed isn’t a lack of respect, but a misdirection of it. Respect has a directional flow from one person to another, and ideally there are streams flowing in both directions. You respect your boss for their authority and responsibilities, and your boss respects you for your expertise and commitment. Misdirection of respect isn’t giving it where it isn’t deserved but flowing in the wrong direction. For example, a coworker is regularly late for meetings, and the meeting chair says, “Out of respect for Bill we’re going to wait for them to start the meeting.” What about their respect for everyone else’s time? Respect is flowing in the wrong direction. The same thing can happen when making decisions. “Mary has been with us the longest, so we’re going to defer to her preferences and keep the fax machine in the document transfer workflow even though it’s expensive and takes longer.” Sometimes it can even lead to putting the unqualified in positions they’re incapable of executing out of a misdirection of respect. Permission to speak is an extremely common misdirection as well; respect for someone’s “right to be heard” shouldn’t override their respect for everyone else’s time.
The solution to this chaotic storm surge of misdirected respect is simple, but difficult. Break the fourth wall and haven open discussions. Start with groups and work your way down to one-on-one as necessary. Meeting start times is an excellent place to begin as most will agree that starting on time (especially with the goal of finishing on time!) is a practical shared good. Permission to speak in meetings (especially public ones) will be a difficult tackle but is also highly relevant. If respect directionality feels too heavy to bring up at work at all, try practising at home or with friends first. Failing that, a therapist or chat AI might be options.
Want someone with a neutral or outside voice to talk about fear and respect in your workplace? You can find us at scalebright.ca.
-
 @ 65038d69:1fff8852
2025-03-29 12:46:30
@ 65038d69:1fff8852
2025-03-29 12:46:30In part 1 of this series (Part 1 - What is Money?) we overviewed the history of money and as a global concept. Now that we have a base understanding of what money is we can get into detail about the Canadian Dollar. Why the Canadian Dollar specifically? One of the inspirations for this series was realizing how much the pervasiveness of American media has affected the average Canadian’s understanding of how our money works. How many of you can quote what is printed on US bills? Do you know what is printed on Canadian bills? What about what the Canadian Dollar is backed by, and who’s in charge of it? To preview, it’s not gold, and it’s not the Federal Reserve.
Lets do some history to give us some background on the Canadian Dollar (CAD) as we know it today. In 1858 the Province of Canada introduced the Canadian Dollar as a hopeful replacement for the mix of British, American, Spanish, and private bank credit notes in use. In 1867 Canada was formed as a nation, and the next year the Government of Canada issued Dominion credit notes as currency. These Dominion notes were required to be backed by a minimum of 20% gold reserves. This is called a “fractional reserve” system, or fractional reserve banking. Reserve requirements for private bank notes and Dominion notes changed over the years leading up to 1935 when the Bank of Canada (BoC) was formed and became to sole issuer of currency in Canada. 10 years later gold reserve requirements were removed and the Dollar became a fully fiat currency (remember this term from the previous article?).
The Bank of Canada is Canada’s “central bank”. If you check out the About Us page on their website (https://www.bankofcanada.ca/about/) you’ll see they have a broad range of roles and responsibilities, but the main one we’re focused on is that they manage the Canadian Dollar as a system of money, including creating and destroying Dollars as they deem necessary. (This is similar to the American Federal Reserve, but a key difference is that the BoC is a crown corporation, while the Federal Reserve is owned by private banks.) The creation and destruction of Dollars is a complex process, but it’s mostly done through borrowing. The government indirectly borrows money from the BoC (and sometimes directly from commercial banks), and everyone else borrows from banks. This money is then created by the BoC and banks, and when the principal (debt exclusive of interest) is paid back, its destroyed.
I’d be remiss if I didn’t mention and define “inflation”, “monetary expansion”, and the “Quantity Theory of Money”. The BoC defines inflation as “…a persistent rise in the average level of prices over time.” They have an excellent explainer on their website here (https://www.bankofcanada.ca/2020/08/understanding-inflation/); to summarize, the BoC and government use the Consumer Price Index (CPI) to keep track of this. “Monetary expansion” is when money is created and kept in circulation. The “Quantity Theory of Money” states that when new money is created it becomes less valuable, which means prices increase, AKA inflation. With this in mind the BoC targets a 2% inflation rate when making decisions about creating and destroying Dollars (through the systems of borrowing). Whether they’re successful or not is the subject of an article all on its own and much speculation.
I should also mention an outlier in the Canadian financial system; Credit Unions. These are provincial banks that don’t have a direct relationship with the BoC. They’re generally much smaller than the national banks and offer fewer services, but many feel they offer a more personal service. And one credit union in particular is an outlier among outliers; Bow Valley Credit Union in Alberta. They’ve embarked on mission to stockpile precious metals (mostly gold) as a form of guarantee for customer deposits. They still practice fractional reserve banking, but this is an improvement over zero reserve banking.
You might be imagining stacks of Dollar notes being passed around all these institutions, but most of the money only exists in ledgers (remember this from part 1?). For comparison, there is currently about $250B in the M0 supply (liquid deposits at the BoC and cash), and the rest totals about $3500B, or $3.5T. That’s about 7% as “real” money that could be used to buy groceries or for payroll. To move this invisible money around the government created Payments Canada, a non-profit that operates most of the inter-institution transfer systems. (They have other responsibilities as well.) Lynx and the Automated Clearing Settlement System (ACSS) are currently in use, and Real-Time Rail (RTR) is coming soon to augment them.
On the retail side, we have the Interac network and credit card networks. The Interac Corporation (a for-profit founded and primarily owned by major national banks) operates the Interac network, which is the primary debit card network in Canada, as well as Interac e-Transfer for direct electronic payments. Visa and Mastercard are the primary credit card networks, but they simply move payment information between banks and Payment Services Providers (PSPs). PSPs are responsible for the actual payment settlements. You’ve probably heard of some of the major ones; Moneris, Chase, Square, and PayPal to name a few. If that sounds complicated, that’s because it is. Let’s walk through an example credit card payment at a physical store to see how it works. The customer inserts, taps, or swipes their card at the payment terminal, typically managed by a Point of Sale (POS) provider. The terminal sends the information to the PSP, who sends the information through the credit card network to the issuing bank. If the transaction is approved, it’s logged for transfer in a batch later, and the approval makes it way back through the credit card network, PSP, terminal, and POS.
Wipe the sweat from your brow and take a sip of coffee; that was a lot! The important part to remember is that all of this complexity serves to move numbers between accounts in ledgers. The government (through the BoC) controls the money supply (the primary driver of inflation), and the banks and networks move the ledger numbers between individuals, companies, and each other. About 7% is liquid, and 0% is backed by hard assets such as gold.
In part 3 we’ll cover Bitcoin, its intention to replace fiat currencies, and its current state in Canada.
-
 @ 65038d69:1fff8852
2025-03-29 12:31:02
@ 65038d69:1fff8852
2025-03-29 12:31:02Minimum wage has been a hot topic as far back as I can remember. If you’re an employer it can feel like government needlessly meddling in the free market, while for employees it feels like its never high enough to make a difference. This is especially true where oversaturated labour markets are combined with high costs of living (HCOL) (which is pretty much everywhere at this point). Workers may need 2 or even 3 minimum wage jobs just to cover food, shelter, and transport in these areas, and would probably love to see minimum wage lifted. Employers in less-dense areas are faced with the opposite problem; even if they advertise pay “above minimum wage”, acquiring and keeping entry-level staff in HCOL areas is a constant battle. In this case, my recommendation is to localize your minimum wage.
In Canada most enforceable minimum wages are set by the provinces. Federal minimums apply to federal government employees (and some federally regulated industries). The problem with this is the sometimes broad disparities in cost of living (COL) between municipalities, especially between urban and rural. I’ve seen rent differences from 50% to 100% for comparable apartments. Applying the same minimum wage isn’t going to have the effect it’s meant to. If your staff can’t afford rent, they’re going to constantly be searching for something better, leading to high turnover. They’ll be forced into mercenary behaviours (see my previous post on “True Believers & Mercenaries”). Official minimum wages also lag behind inflation, but that’s a whole separate discussion (see my “What is Money?” series, starting with “Part 1 - What is Money?). On the flip-side, having a localized minimum wage allows your employees to stay settled where they are and gives them the freedom to be True Believers. You can work it directly into your job postings too; advertising wages that are based on local COL will have your inbox flooded with applications, allowing you to choose from the best instead of having to settle for the desperate. Let’s get into how to go about localizing your minimum wage.
First, look at a map and ponder how far most would be willing to commute to your workplace. Draw a rough circle with that as the radius. Everywhere inside this circle is fair game for everything to follow. Next, find some low-rent but livable apartments inside the circle and look up their rates. This will be your rent figure.
Transport is next. We’re going to use fuel cost as a “close enough” placeholder as actual costs will vary greatly between individuals. We’re also going to pick a “close enough” fuel efficiency for the same reason. I’ve chosen 8.5L/100KM, but you can adjust this. For example, full-size pickups may be more popular among your staff so that number may need to go up. Look up the average fuel prices for the last few months at retail stations within the circle, and the average working days per month for your staff. Now plug all of these numbers into the following formula and calculate. This will give you the monthly fuel cost: (fuel price x 8.5 x (circle radius KM x 2) / 100) x working days
Lastly, groceries. Like transport, we’re aiming for a “close enough” placeholder. You can substitute any items and volumes you like, but these are my recommendation to get an average monthly cost for an average minimum wage worker plus 1 dependant. Go to a generic grocery store within the circle and get the regular (non-sale) prices of the following: 3 x 3lb/1.36kg apples (averaged or middle price), 5 x single Long English cucumber, 1 x 10lb bag of potatoes, 2 x 4L 2% milk, 4 x 1 dozen large eggs, 2 x 600g block of cheese (average or middle price), 6 x loaf of brown or whole grain bakery bread (average or middle price), 5 x 1lb/454g lean ground beef, 1 x 4kg box frozen chicken breasts, and 1 x 3.5lb/1.6kg bag of jasmine rice.
Now that you have totals for the expenses, put those numbers into the following formula. This will give you total monthly living expenses: ((rent + groceries) / 0.45) + fuel Put that total into the following formula for the monthly paycheque total, pre-deductions. Insert current federal and provincial income tax rates for your jurisdiction: expenses / (1 - (provincial tax rate as decimal + federal tax rate as decimal + 0.05) With this final total you can divide by monthly working hours for an hourly wage, or multiply by 12 for an annual salary. I’ll provide an example of all of this at the bottom of the article.
After crunching these numbers you may have concluded that paying a localized minimum wage would eat into your profits. This may be the case initially, but lowering turnover rates and increasing the quality of your hires will save you money long-term. However, if it raises costs so high that the business would become unprofitable, you may need to consider that the business isn’t viable. Being dependant on employees willing to work for below the cost of living in your area will eventually end the business regardless, and I would argue is immoral.
Want help localizing your minimum wage? You can find us at scalebright.ca.
Sample localized minimum wage calculation: Rent: $1,200 Fuel cost: ((1.40 x 8.5 x (9.4 x 2) / 100) x 20 = $44.75 Groceries: $229.46 Apples: 23.97 Cucumbers: 14.95 Potatoes: 8.99 Milk: 11.90 Eggs: 17.40 Cheese: 20.58 Bread: 23.94 Ground beef: 42.45 Chicken breasts: 49.99 Rice: 15.29 Total expenses: ((1200 + 229.46) / 0.45) + 44.75 = $3,221.33 Total monthly paycheque: 3221.33 / (1 - (0.10 + 0.15 + 0.05) = $4,601.90 Hourly: 4601.90 / 160 = $28.76 Annual salary: 4601.90 x 12 = $55,222.80 -
 @ 162b4b08:9f7d278c
2025-05-27 10:12:53
@ 162b4b08:9f7d278c
2025-05-27 10:12:53Trong thời đại mà công nghệ số trở thành trụ cột không thể thiếu trong mọi lĩnh vực, từ công việc đến giải trí, việc sở hữu một nền tảng số toàn diện như PUM88 đóng vai trò vô cùng quan trọng đối với người dùng hiện đại. Không chỉ là nơi cung cấp các công cụ tiện ích, PUM88 còn tạo nên một hệ sinh thái linh hoạt, đáp ứng mọi nhu cầu trong một môi trường trực tuyến đầy năng động. Từ những bước đầu như đăng ký, đăng nhập, cho đến trải nghiệm thực tế, tất cả đều được tối ưu nhằm mang lại sự thuận tiện tối đa. Giao diện thiết kế thông minh, bố cục rõ ràng, thao tác nhanh gọn giúp người dùng dễ dàng tiếp cận và sử dụng mà không cần kiến thức kỹ thuật chuyên sâu. Bên cạnh đó, hệ thống xử lý tốc độ cao và khả năng tương thích đa nền tảng (từ smartphone đến laptop) giúp người dùng duy trì kết nối mọi lúc mọi nơi, không bị giới hạn bởi thiết bị hay không gian sử dụng. Không dừng lại ở đó, PUM88 còn liên tục nâng cấp công nghệ như tích hợp trí tuệ nhân tạo để gợi ý nội dung cá nhân hóa theo hành vi và sở thích, giúp mỗi trải nghiệm trở nên sống động, gần gũi và mang tính cá nhân cao hơn bao giờ hết. Đây chính là điểm cộng lớn giúp PUM88 tạo nên dấu ấn trong lòng người dùng yêu thích sự tiện lợi và linh hoạt trong đời sống số.
Ngoài ra, yếu tố khiến PUM88 trở nên đáng tin cậy chính là khả năng bảo mật vượt trội và chính sách hỗ trợ khách hàng tận tâm. Dữ liệu cá nhân và các hoạt động của người dùng luôn được bảo vệ nghiêm ngặt bằng các chuẩn mã hóa quốc tế, hệ thống tường lửa, xác thực hai lớp và giám sát bảo mật liên tục. Nhờ vậy, người dùng hoàn toàn yên tâm khi sử dụng mà không lo bị lộ thông tin hay rò rỉ dữ liệu. Thêm vào đó, đội ngũ chăm sóc khách hàng hoạt động 24/7 với thái độ chuyên nghiệp và phản hồi nhanh chóng giúp giải quyết mọi thắc mắc hoặc sự cố kỹ thuật một cách hiệu quả. Không những thế, PUM88 còn thường xuyên lắng nghe ý kiến người dùng để cải tiến giao diện, bổ sung tính năng mới, đảm bảo rằng nền tảng luôn bắt kịp xu hướng công nghệ và đáp ứng đúng nhu cầu thực tế. Việc cập nhật liên tục không chỉ giúp người dùng có được trải nghiệm mượt mà hơn mà còn giữ cho nền tảng luôn mới mẻ, sáng tạo và không ngừng phát triển. Trong bối cảnh chuyển đổi số đang diễn ra mạnh mẽ tại Việt Nam, PUM88 không chỉ đơn thuần là một ứng dụng tiện ích mà còn là một trợ thủ đắc lực cho cuộc sống hiện đại – nơi mà người dùng có thể tận dụng công nghệ để nâng cao hiệu suất cá nhân, tối ưu hóa thời gian và tận hưởng trải nghiệm số trọn vẹn nhất mỗi ngày.
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 65038d69:1fff8852
2025-03-29 12:31:02
@ 65038d69:1fff8852
2025-03-29 12:31:02“What is money?” sounds like a bit of a silly question. You’d probably hold up some cash or maybe flash your debit card. But I challenge you with this: imagine a 5-year-old asking you this question. How would you answer? If you showed them a $20 bill, they might respond with, “I know that’s a money, but what is it?” If you manage to explain that the bill is worth $20, they’re next question is going to be, “how many is your card?” How would you answer that? At some point you’d probably end up trying to distract them with something else while you worked to ignore the dread feeling that you should have those answers, but don’t. Never fear, for we will attempt to explain it in such a way that you’ll have an answer for 5, 15, 50, or 95-year-olds by the time we’re done this 4-part series!
Let’s start with an overview of the history of money. I highly recommend further reading on each of these; we’re going to skim most of them today. In the beginning, there was simple barter. If we each had something the other wanted, we could trade. But if the scale of what we want to trade is lopsided, say, chickens for a cow, or cows for a house, how do you make the trade work? Or what if you wanted to save up for a larger purchase? The answer is a placeholder; something that represents value in trade. An early example of this is the rai stones in Micronesia, which are essentially carved rocks. These worked well for store of value and medium of exchange, but not so much for unit of account. Precious metal coins arose later, with the most common being gold, silver, copper, and bronze. These worked well for all three of the major elements.
Store of value, medium of exchange, and unit of account are the three major elements of any system of money. Store of value means it holds its value well over time. If you put a gold coin in a box in your house and retrieve it 10 years later, it’s still a gold coin and should be in the same physical condition as it was when stored. Medium of exchange means it’s widely accepted for trade. This one is a bit trickier, but if you’re the Roman Empire you can simply make everyone accept denarius. Unit of account means units should hold the same value everywhere they’re used. This is similarly tricky, but if you’re the Dutch East India Company you can simply make VOC-stamped coins global denominations.
Renaissance-era Italy is where modern banking was born. A key concept invented during this time was the double-entry ledger, or double-entry bookkeeping system. In short, every transaction is recorded, and every transaction has two entries: one with an amount leaving an account, and one with the same amount going into a different account. At the end of every block of time all accounts will have an aggregate balance of 0, with individual accounts either having a credit or debit. This system is still in use today, as well as the broad use of credit notes in place of coins or direct trade. Credit notes could be written against an account and given in trade, and later the receiver could take the note to the bank, who would then record the transaction as complete. If this sounds familiar, that’s because modern cheques are the same thing.
Modern money systems take these concepts a step further. Banks now maintain a whole network of double-entry ledgers and in most countries banks are no longer required to hold reserves matching their credit notes issued. Credit notes are also the total physical currency, also known as a fiat currency, or currency by authority or decree. This essentially means fiat money has no intrinsic value other than the promise of the issuing authority to treat it as valid and the willingness of others to accept it in trade. For an example of “willingness to accept in trade”, many retail stores in Canada will accept American dollars even though they’re not required to.
If you’re now thinking, “thanks for the history lesson, but what does this mean to me and the payment terminal in my store?”, the answer will come 2 weeks from now when we cover the Canadian dollar. In the meantime if you want to learn a bit more about the systems our modern money is based on, read up on the Roman Empire and their currency, as well as that of the Dutch East India Company. If you really want to dive deep, Renaissance Italy’s banking systems are also fascinating and a little closer to us on the timeline.
-
 @ cae03c48:2a7d6671
2025-05-27 12:01:01
@ cae03c48:2a7d6671
2025-05-27 12:01:01Bitcoin Magazine

Trump Media Group Seeks $3 Billion War Chest to Buy Bitcoin and Crypto Assets: FTTrump Media and Technology Group (TMTG), the company behind Truth Social and controlled by the Trump family, is preparing to raise a staggering $3 billion to invest in cryptocurrencies such as Bitcoin, according to the Financial Times.
JUST IN:
 Trump Media Group to raise $3 billion to buy Bitcoin and crypto — Financial Times pic.twitter.com/VEyvy5vpGZ
Trump Media Group to raise $3 billion to buy Bitcoin and crypto — Financial Times pic.twitter.com/VEyvy5vpGZ— Bitcoin Magazine (@BitcoinMagazine) May 26, 2025
The media venture plans to secure $2 billion in fresh equity and another $1 billion through a convertible bond offering, those familiar with the matter told the Financial Times. The capital raise could be formally announced ahead of The Bitcoin 2025 Conference in Las Vegas this week, where Vice President JD Vance, Donald Trump Jr., Eric Trump, and Trump’s crypto advisor David Sachs are expected to speak.
The secondary equity offering will be carried out on an at-the-market basis, meaning shares are expected to be priced near the most recent closing price of $25.72, giving TMTG a current valuation of nearly $6 billion.
TMTG’s push comes amid a wider cryptocurrency resurgence. Bitcoin hit a new record of $111,999 last week, and investor interest in crypto-related plays has surged. The strategy echoes that of Strategy, which used a similar blend of debt and equity financing to buy tens of billions of dollars in Bitcoin—catapulting its market cap to over $100 billion.
Although the news is still yet to be confirmed by TMTG, a comment they made to the Financial Times may give some doubt to the validity of the story:
“Apparently the Financial Times has dumb writers listening to even dumber sources”, reportedly said TMTG. A White House spokesperson also declined to weigh in. Representatives for Donald Trump Jr. did not respond to requests for comment and Reuters also did not immediately receive a request for comment.
TMTG’s deepening crypto pivot has included a slew of ventures: an NFT trading card series, two memecoins, investments in crypto miner American Bitcoin and stablecoin platform World Liberty Financial, and an upcoming crypto ETF.
After returning to the White House last year, Trump transferred his 53% stake in TMTG—worth roughly $3 billion—to a revocable trust controlled by Donald Trump Jr., who holds full investment and voting authority.
This is a developing story and will be updated as needed.
This post Trump Media Group Seeks $3 Billion War Chest to Buy Bitcoin and Crypto Assets: FT first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ cae03c48:2a7d6671
2025-05-27 12:01:00
@ cae03c48:2a7d6671
2025-05-27 12:01:00Bitcoin Magazine

Jippi Launches Pokémon GO-Style AR Bitcoin Education Game at Vegas’s Bitcoin 2025Jippi, a mobile augmented reality (AR) game developer, will debut its Bitcoin education game at the Bitcoin Conference 2025, held at The Venetian Resort in Las Vegas from May 27-29. Inspired by Pokémon GO, the game blends location-based gameplay with financial literacy, aiming to engage over 30,000 attendees by making Bitcoin education fun and accessible.
Using the app, players can explore The Venetian’s grounds to hunt digital “Bitcoin Beasts,” answering Bitcoin-related trivia to capture them and earn 1000 satoshis (sats) per catch. The game is designed to deliver concise lessons on sound money principles, targeting younger audiences, with Jippi’s research showing 90% of Gen Z play mobile games. This approach aims to make learning about Bitcoin intuitive and engaging.
“We’re excited to turn Bitcoin education into an adventure,” said Oliver Porter, Jippi’s Founder and CEO. “Our game meets players where they are, making complex concepts approachable.”
Jippi partnered with six Bitcoin companies—Bitcoin Well, Beyond The Checkout, Bitcoin Trading Cards, Geyser, SHAmory, and 21M Communications—to sponsor unique Beasts. Each is tied to a specific location, offering tailored trivia that highlights the sponsor’s mission. For instance, Bitcoin Well’s Beast teaches wallet security, while SHAmory’s content suits all ages. “Jippi’s game is a fresh way to onboard new users,” said Adam O’Brien, CEO of Bitcoin Well.
The game stems from over a year of development, including university testing and on-site surveys. Jippi’s efforts earned it the top prize at PlebLab’s Top Builder competition in March 2025, a hackathon for Bitcoin startups, cementing its role in gamifying education.
With 30,000 attendees expected, the conference is an ideal stage for Jippi to showcase AR’s potential in Bitcoin adoption. The game promises to transform The Venetian into a dynamic learning hub, encouraging players to explore while grasping Bitcoin’s real-world applications. Jippi aims to expand the game post-conference, adding more educational content.
This post Jippi Launches Pokémon GO-Style AR Bitcoin Education Game at Vegas’s Bitcoin 2025 first appeared on Bitcoin Magazine and is written by Juan Galt.
-
 @ 7f6db517:a4931eda
2025-05-27 10:01:54
@ 7f6db517:a4931eda
2025-05-27 10:01:54

"Privacy is necessary for an open society in the electronic age. Privacy is not secrecy. A private matter is something one doesn't want the whole world to know, but a secret matter is something one doesn't want anybody to know. Privacy is the power to selectively reveal oneself to the world." - Eric Hughes, A Cypherpunk's Manifesto, 1993
Privacy is essential to freedom. Without privacy, individuals are unable to make choices free from surveillance and control. Lack of privacy leads to loss of autonomy. When individuals are constantly monitored it limits our ability to express ourselves and take risks. Any decisions we make can result in negative repercussions from those who surveil us. Without the freedom to make choices, individuals cannot truly be free.
Freedom is essential to acquiring and preserving wealth. When individuals are not free to make choices, restrictions and limitations prevent us from economic opportunities. If we are somehow able to acquire wealth in such an environment, lack of freedom can result in direct asset seizure by governments or other malicious entities. At scale, when freedom is compromised, it leads to widespread economic stagnation and poverty. Protecting freedom is essential to economic prosperity.
The connection between privacy, freedom, and wealth is critical. Without privacy, individuals lose the freedom to make choices free from surveillance and control. While lack of freedom prevents individuals from pursuing economic opportunities and makes wealth preservation nearly impossible. No Privacy? No Freedom. No Freedom? No Wealth.
Rights are not granted. They are taken and defended. Rights are often misunderstood as permission to do something by those holding power. However, if someone can give you something, they can inherently take it from you at will. People throughout history have necessarily fought for basic rights, including privacy and freedom. These rights were not given by those in power, but rather demanded and won through struggle. Even after these rights are won, they must be continually defended to ensure that they are not taken away. Rights are not granted - they are earned through struggle and defended through sacrifice.
If you found this post helpful support my work with bitcoin.



