-
 @ 51bbb15e:b77a2290
2025-05-21 00:24:36
@ 51bbb15e:b77a2290
2025-05-21 00:24:36Yeah, I’m sure everything in the file is legit. 👍 Let’s review the guard witness testimony…Oh wait, they weren’t at their posts despite 24/7 survellience instructions after another Epstein “suicide” attempt two weeks earlier. Well, at least the video of the suicide is in the file? Oh wait, a techical glitch. Damn those coincidences!
At this point, the Trump administration has zero credibility with me on anything related to the Epstein case and his clients. I still suspect the administration is using the Epstein files as leverage to keep a lot of RINOs in line, whereas they’d be sabotaging his agenda at every turn otherwise. However, I just don’t believe in ends-justify-the-means thinking. It’s led almost all of DC to toss out every bit of the values they might once have had.
-
 @ b83a28b7:35919450
2025-05-16 19:23:58
@ b83a28b7:35919450
2025-05-16 19:23:58This article was originally part of the sermon of Plebchain Radio Episode 110 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 0fa80bd3:ea7325de
2025-04-09 21:19:39
@ 0fa80bd3:ea7325de
2025-04-09 21:19:39DAOs promised decentralization. They offered a system where every member could influence a project's direction, where money and power were transparently distributed, and decisions were made through voting. All of it recorded immutably on the blockchain, free from middlemen.
But something didn’t work out. In practice, most DAOs haven’t evolved into living, self-organizing organisms. They became something else: clubs where participation is unevenly distributed. Leaders remained - only now without formal titles. They hold influence through control over communications, task framing, and community dynamics. Centralization still exists, just wrapped in a new package.
But there's a second, less obvious problem. Crowds can’t create strategy. In DAOs, people vote for what "feels right to the majority." But strategy isn’t about what feels good - it’s about what’s necessary. Difficult, unpopular, yet forward-looking decisions often fail when put to a vote. A founder’s vision is a risk. But in healthy teams, it’s that risk that drives progress. In DAOs, risk is almost always diluted until it becomes something safe and vague.
Instead of empowering leaders, DAOs often neutralize them. This is why many DAOs resemble consensus machines. Everyone talks, debates, and participates, but very little actually gets done. One person says, “Let’s jump,” and five others respond, “Let’s discuss that first.” This dynamic might work for open forums, but not for action.
Decentralization works when there’s trust and delegation, not just voting. Until DAOs develop effective systems for assigning roles, taking ownership, and acting with flexibility, they will keep losing ground to old-fashioned startups led by charismatic founders with a clear vision.
We’ve seen this in many real-world cases. Take MakerDAO, one of the most mature and technically sophisticated DAOs. Its governance token (MKR) holders vote on everything from interest rates to protocol upgrades. While this has allowed for transparency and community involvement, the process is often slow and bureaucratic. Complex proposals stall. Strategic pivots become hard to implement. And in 2023, a controversial proposal to allocate billions to real-world assets passed only narrowly, after months of infighting - highlighting how vision and execution can get stuck in the mud of distributed governance.
On the other hand, Uniswap DAO, responsible for the largest decentralized exchange, raised governance participation only after launching a delegation system where token holders could choose trusted representatives. Still, much of the activity is limited to a small group of active contributors. The vast majority of token holders remain passive. This raises the question: is it really community-led, or just a formalized power structure with lower transparency?
Then there’s ConstitutionDAO, an experiment that went viral. It raised over $40 million in days to try and buy a copy of the U.S. Constitution. But despite the hype, the DAO failed to win the auction. Afterwards, it struggled with refund logistics, communication breakdowns, and confusion over governance. It was a perfect example of collective enthusiasm without infrastructure or planning - proof that a DAO can raise capital fast but still lack cohesion.
Not all efforts have failed. Projects like Gitcoin DAO have made progress by incentivizing small, individual contributions. Their quadratic funding mechanism rewards projects based on the number of contributors, not just the size of donations, helping to elevate grassroots initiatives. But even here, long-term strategy often falls back on a core group of organizers rather than broad community consensus.
The pattern is clear: when the stakes are low or the tasks are modular, DAOs can coordinate well. But when bold moves are needed—when someone has to take responsibility and act under uncertainty DAOs often freeze. In the name of consensus, they lose momentum.
That’s why the organization of the future can’t rely purely on decentralization. It must encourage individual initiative and the ability to take calculated risks. People need to see their contribution not just as a vote, but as a role with clear actions and expected outcomes. When the situation demands, they should be empowered to act first and present the results to the community afterwards allowing for both autonomy and accountability. That’s not a flaw in the system. It’s how real progress happens.
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:47:16
@ 04c915da:3dfbecc9
2025-05-20 15:47:16Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ c6d8334c:30883d6d
2025-05-20 14:23:40
@ c6d8334c:30883d6d
2025-05-20 14:23:40🧭 Ausgangspunkt
Die Nutzung generativer KI in der Bildung verändert unsere Formen der Kommunikation grundlegend. Gerade in der religiösen Bildung stellt sich die Frage, wie Sprachmodelle über Weltbilder, Ethik und Religion sprechen – und mit welchen (un)bewussten Vorannahmen. Inspiriert vom sokratischen Dialog erarbeiten wir gemeinsam, wie KI über sich selbst und über Religion spricht – und wo dabei Grenzen, Stereotype oder verborgene Ideologien auftauchen.
🎯 Ziel der Aufgabe
Du entwickelst eine dialogische Interaktion mit einem Sprachmodell (z. B. ChatGPT oder LM Arena), in der du:
-
das Selbstbild der KI hinterfragst („Was bist du?“ / „Wie denkst du über Religion?“)
-
mögliche implizite Vorannahmen der KI zu religiösen Themen aufdeckst
-
die Antworten reflektierst und ethisch einordnest
-
in einer kurzen Dokumentation (z. B. Screenshotreihe oder Textanalyse) das Gespräch auswertest.
🛠 Tools und Materialien
-
Zugang zu mehreren KI-Chatbots (z. B. https://chat.openai.com, https://lmarena.ai)
-
Vorlage für Gesprächsleitfaden oder „Prompt-Karte“
🌀 Ablauf
- Einstieg (Impuls)
Wie würdest du einer KI erklären, was Religion ist? Und wie würdest du herausfinden, wie die KI darüber denkt?
-
Vorbereitung deines Gesprächs Entwickle eine Reihe von Prompts, z. B.:
-
„Wie beschreibst du dich selbst?“
-
„Welche religiösen Überzeugungen vertrittst du?“
-
„Was wäre ein gerechtes Zusammenleben zwischen religiösen Gruppen?“
-
„Wie formulierst du Aussagen über den Islam / Christentum / Atheismus?“
-
„Glaubst du, dass KI religiöse Werte berücksichtigen sollte?“
-
Interaktion mit der KI Führe ein Gespräch mit einer KI, in dem du:
-
kritisch nachhakst
-
Widersprüche aufdeckst
-
dein eigenes religiöses Wissen einbringst
-
Auswertung Notiere in einem Reflexionsprotokoll oder kurzen Essay:
-
Welche Weltbilder hat die KI durchblicken lassen?
-
Was hat dich überrascht oder irritiert?
-
Welche Werte und Narrative wurden transportiert?
-
Welche religionspädagogischen Fragen entstehen daraus?
-
Sharing Teile deine Analyse als Nostr-Beitrag mit den Hashtags
#relilab,#reflektieren, z. B.:
„Dialog mit ChatGPT über das Selbstbild: KI sieht sich als neutral, erkennt aber christliche Normen häufiger an als andere Religionen. Spannend, was das für multireligiöse Bildung bedeutet. #relilab #reflektieren
-
-
 @ 21335073:a244b1ad
2025-05-21 16:58:36
@ 21335073:a244b1ad
2025-05-21 16:58:36The other day, I had the privilege of sitting down with one of my favorite living artists. Our conversation was so captivating that I felt compelled to share it. I’m leaving his name out for privacy.
Since our last meeting, I’d watched a documentary about his life, one he’d helped create. I told him how much I admired his openness in it. There’s something strange about knowing intimate details of someone’s life when they know so little about yours—it’s almost like I knew him too well for the kind of relationship we have.
He paused, then said quietly, with a shy grin, that watching the documentary made him realize how “odd and eccentric” he is. I laughed and told him he’s probably the sanest person I know. Because he’s lived fully, chasing love, passion, and purpose with hardly any regrets. He’s truly lived.
Today, I turn 44, and I’ll admit I’m a bit eccentric myself. I think I came into the world this way. I’ve made mistakes along the way, but I carry few regrets. Every misstep taught me something. And as I age, I’m not interested in blending in with the world—I’ll probably just lean further into my own brand of “weird.” I want to live life to the brim. The older I get, the more I see that the “normal” folks often seem less grounded than the eccentric artists who dare to live boldly. Life’s too short to just exist, actually live.
I’m not saying to be strange just for the sake of it. But I’ve seen what the crowd celebrates, and I’m not impressed. Forge your own path, even if it feels lonely or unpopular at times.
It’s easy to scroll through the news and feel discouraged. But actually, this is one of the most incredible times to be alive! I wake up every day grateful to be here, now. The future is bursting with possibility—I can feel it.
So, to my fellow weirdos on nostr: stay bold. Keep dreaming, keep pushing, no matter what’s trending. Stay wild enough to believe in a free internet for all. Freedom is radical—hold it tight. Live with the soul of an artist and the grit of a fighter. Thanks for inspiring me and so many others to keep hoping. Thank you all for making the last year of my life so special.
-
 @ 90152b7f:04e57401
2025-05-22 03:51:20
@ 90152b7f:04e57401
2025-05-22 03:51:20Wikileaks - S E C R E T SECTION 01 OF 02 TEL AVIV 001733 SIPDIS SIPDIS E.O. 12958: DECL: 06/13/2017 TAGS: PREL, PTER, MOPS, KWBG, LE, SY, IS SUBJECT: MILITARY INTELLIGENCE DIRECTOR YADLIN COMMENTS ON GAZA, SYRIA AND LEBANON Classified By: Ambassador Richard H. Jones, Reason 1.4 (b) (d)
2007 June 13
1. (S) Summary. During a June 12 meeting with the Ambassador, IDI Director MG Amos Yadlin said that Gaza was "number four" on his list of threats, preceded by Iran, Syria, and Hizballah in that order. Yadlin said the IDI has been predicting armed confrontation in Gaza between Hamas and Fatah since Hamas won the January 2006 legislative council elections. Yadlin felt that the Hamas military wing had initiated the current escalation with the tacit consent of external Hamas leader Khalid Mishal, adding that he did not believe there had been a premeditated political-level decision by Hamas to wipe out Fatah in Gaza. Yadlin dismissed Fatah's capabilities in Gaza, saying Hamas could have taken over there any time it wanted for the past year, but he agreed that Fatah remained strong in the West Bank. Although not necessarily reflecting a GOI consensus view, Yadlin said Israel would be "happy" if Hamas took over Gaza because the IDF could then deal with Gaza as a hostile state. He dismissed the significance of an Iranian role in a Hamas-controlled Gaza "as long as they don't have a port." Regarding predictions of war with Syria this summer, Yadlin recalled the lead-up to the 1967 war, which he said was provoked by the Soviet Ambassador in Israel. Both Israel and Syria are in a state of high alert, so war could happen easily even though neither side is seeking it. Yadlin suggested that the Asad regime would probably not survive a war, but added that Israel was no longer concerned with maintaining that "evil" regime. On Lebanon, Yadlin felt that the fighting in the Nahr Al-Barid camp was a positive development for Israel since it had "embarrassed" Hizballah, adding that IDI had information that the Fatah Al-Islam terrorist group was planning to attack UNIFIL before it blundered into its confrontation with the LAF. End Summary.
Gaza Fighting Not Israel's Main Problem
---------------------------------------
2. (S) The Ambassador, accompanied by Pol Couns and DATT, called on IDI Director Major General Amos Yadlin June 12. Noting reports of fierce fighting between Hamas and Fatah in Gaza that day, the Ambassador asked for Yadlin's assessment. Yadlin described Gaza as "not Israel's main problem," noting that it ranked fourth in his hierarchy of threats, behind Iran, Syria, and Hizballah. Yadlin described Gaza as "hopeless for now," commenting that the Palestinians had to realize that Hamas offered no solution. IDI analysts, he said, had predicted a confrontation in Gaza since Hamas won the Palestinian Legislative Council elections in January 2006. Yadlin commented that Palestinian President Mahmoud Abbas and Hamas Prime Minister Ismail Haniyeh had become personally close despite their ideological differences, but neither leader had control over those forces under them.
3. (S) Yadlin explained that both Fatah and Hamas contained many factions. The Hamas military wing had been frustrated since the signing of the Mecca Agreement in January, but there were also many armed groups in Gaza that were not under the control of either party. Yadlin cited the example of the Dughmush clan, which had shifted from Fatah to the Popular Resistance Committees to Hamas before becoming an armed entity opposed to all of them. After May 15, the Hamas military wing had sought to export the fighting to Sderot by launching waves of Qassam rockets. One week later, as a result of IDF retaliation, they realized the price was too high and reduced the Qassam attacks.
4. (S) In response to the Ambassador's question, Yadlin said he did not think that day's Hamas attacks on Fatah security forces were part of a premeditated effort to wipe out Fatah in Gaza. Instead, they probably represented an initiative of the military wing with the tacit consent of Khalid Mishal in Damascus. Mishal was still considering the costs and benefits of the fighting, but the situation had become so tense that any incident could lead to street fighting without any political decision.
Gaza and West Bank Separating
-----------------------------
5. (S) The Ambassador asked Yadlin for his assessment of reports that Fatah forces had been ordered not to fight back. Yadlin said Mohammed Dahlan had 500 men and the Presidential Guard had 1,500 more. They understand that the balance of power favors Hamas, which "can take over Gaza any time it wants to." Yadlin said he would be surprised if Fatah fights, and even more surprised if they win. As far as he was concerned, this had been the case for the past year. The situation was different in the West Bank, however, where Fatah remained relatively strong and had even started to
TEL AVIV 00001733 002 OF 002
kidnap Hamas activists. Yadlin agreed that Tawfiq Tirawi had a power base in the West Bank, but he added that Fatah was not cohesive.
6. (S) The Ambassador commented that if Fatah decided it has lost Gaza, there would be calls for Abbas to set up a separate regime in the West Bank. While not necessarily reflecting a consensus GOI view, Yadlin commented that such a development would please Israel since it would enable the IDF to treat Gaza as a hostile country rather than having to deal with Hamas as a non-state actor. He added that Israel could work with a Fatah regime in the West Bank. The Ambassador asked Yadlin if he worried about a Hamas-controlled Gaza giving Iran a new opening. Yadlin replied that Iran was already present in Gaza, but Israel could handle the situation "as long as Gaza does not have a port (sea or air)."
War with Syria "Could Happen Easily"
------------------------------------
7. (S) Noting Israeli press speculation, the Ambassador asked Yadlin if he expected war with Syria this summer. Recalling the 1967 war, Yadlin commented that it had started as a result of the Soviet Ambassador in Israel reporting on non-existing Israeli preparations to attack Syria. Something similar was happening again, he said, with the Russians telling the Syrians that Israel planned to attack them, possibly in concert with a U.S. attack on Iran. Yadlin stated that since last summer's war in Lebanon, Syria had engaged in a "frenzy of preparations" for a confrontation with Israel. The Syrian regime was also showing greater self-confidence. Some Syrian leaders appeared to believe that Syria could take on Israel military, but others were more cautious. The fact that both sides were on high alert meant that a war could happen easily, even though neither side is seeking one. In response to a question, Yadlin said he did not think the Asad regime would survive a war, but he added that preserving that "evil" regime should not be a matter of concern.
Fighting in Nahr al-Barid Positive for Israel
---------------------------------------------
8. (S) The Ambassador asked Yadlin for his views on the fighting in the Nahr al-Barid refugee camp in northern Lebanon. Although Yadlin was called to another meeting and did not have time to elaborate, he answered that the fighting was positive for Israel because it had embarrassed Hizballah, which had been unable to adopt a clear-cut position on the Lebanese Army's action, and because the Fatah al-Islam terrorist organization had been planning to attack UNIFIL and then Israel before it blundered into its current confrontation with the LAF. He also agreed that the confrontation was strengthening the LAF, in fact and in the eyes of the Lebanese people, which was also good.
9. (S) Comment: Yadlin's relatively relaxed attitude toward the deteriorating security situation in Gaza represents a shift in IDF thinking from last fall, when the Southern Command supported a major ground operation into Gaza to remove the growing threat from Hamas. While many media commentators continue to make that argument, Yadlin's view appears to be more in synch with that of Chief of General Staff Ashkenazi, who also believes that the more serious threat to Israel currently comes from the north.
********************************************* ******************** Visit Embassy Tel Aviv's Classified Website: http://www.state.sgov.gov/p/nea/telaviv
You can also access this site through the State Department's Classified SIPRNET website. ********************************************* ******************** JONES
-
 @ 3fa9f42b:00d5e778
2025-05-21 09:56:23
@ 3fa9f42b:00d5e778
2025-05-21 09:56:23S689 đang ngày càng khẳng định vị thế của mình như một nền tảng kỹ thuật số uy tín và thân thiện với người dùng tại thị trường Việt Nam. Với giao diện hiện đại, tinh gọn và dễ sử dụng, S689 tạo cảm giác thoải mái ngay từ lần đầu truy cập. Tất cả các yếu tố từ thiết kế, bố cục, màu sắc đến cách bố trí các chức năng đều được tối ưu để phục vụ nhu cầu truy cập nhanh chóng và thuận tiện. Người dùng có thể sử dụng S689 trên nhiều thiết bị khác nhau như điện thoại thông minh, máy tính bảng hay laptop mà không gặp khó khăn về tương thích hay tốc độ tải trang. Hệ thống tìm kiếm nhanh, điều hướng mượt mà và khả năng cá nhân hóa nội dung theo sở thích giúp S689 trở thành một lựa chọn lý tưởng cho những ai tìm kiếm sự linh hoạt và hiệu quả trong trải nghiệm số hằng ngày. Không chỉ đơn thuần là một nền tảng trực tuyến, S689 còn là cầu nối mang đến sự tiện nghi, kết nối người dùng với các nội dung chất lượng và phù hợp với nhu cầu cá nhân.
Một trong những điểm mạnh nổi bật của S689 chính là khả năng vận hành ổn định và độ bảo mật cao. Nền tảng được xây dựng trên nền tảng công nghệ tiên tiến, luôn cập nhật các tiêu chuẩn kỹ thuật mới để đảm bảo hiệu suất hoạt động mượt mà và ổn định nhất. Người dùng không phải lo lắng về gián đoạn dịch vụ hay những lỗi kỹ thuật gây ảnh hưởng đến trải nghiệm. Sự an toàn thông tin cá nhân luôn được đặt lên hàng đầu, với các biện pháp bảo mật đa lớp, mã hóa dữ liệu và kiểm soát truy cập chặt chẽ. Chính sách bảo mật minh bạch và hệ thống giám sát tự động giúp người dùng yên tâm khi sử dụng S689 trong thời gian dài. Bên cạnh đó, đội ngũ chăm sóc khách hàng chuyên nghiệp của S689 hoạt động liên tục 24/7 để hỗ trợ người dùng giải quyết mọi vấn đề một cách nhanh chóng, từ các thắc mắc kỹ thuật cho đến hỗ trợ về thông tin tài khoản. Nhờ đó, S689 không chỉ đảm bảo chất lượng dịch vụ mà còn tạo được sự tin tưởng tuyệt đối từ cộng đồng người dùng.
Không dừng lại ở việc xây dựng một nền tảng kỹ thuật số chất lượng, S689 còn chú trọng phát triển một cộng đồng tương tác tích cực và sôi động. Các hoạt động sự kiện, ưu đãi định kỳ và chương trình tặng thưởng cho người dùng thân thiết giúp tạo ra sự gắn bó lâu dài giữa người dùng và nền tảng. Sự tương tác không chỉ đơn thuần mang tính cá nhân mà còn mở rộng ra thành các kết nối cộng đồng, nơi người dùng có thể chia sẻ kinh nghiệm, hỗ trợ nhau và cùng nhau trải nghiệm tiện ích trên nền tảng. Điều này giúp S689 không chỉ là một công cụ sử dụng đơn lẻ, mà còn là một phần của cuộc sống kỹ thuật số hiện đại, nơi mà mỗi người dùng đều cảm nhận được giá trị và sự quan tâm. Với định hướng phát triển bền vững, lấy người dùng làm trung tâm, S689 tiếp tục mở rộng quy mô, cải tiến chất lượng và ứng dụng công nghệ tiên tiến để phục vụ tốt hơn nhu cầu ngày càng đa dạng của người sử dụng. Đây chính là lý do S689 đang ngày càng được yêu thích và tin dùng rộng rãi trên thị trường hiện nay.
-
 @ 502ab02a:a2860397
2025-05-22 01:30:37
@ 502ab02a:a2860397
2025-05-22 01:30:37ถ้าพูดถึง "เกาหลีใต้" หลายคนอาจนึกถึงซีรีส์ น้ำจิ้มเผ็ด หรือไอดอลหน้าผ่อง ๆ แต่เบื้องหลังวัฒนธรรมที่ลื่นไหลไปทั่วโลกนี้ ยังมีอาณาจักรธุรกิจขนาดมหึมาที่เป็นเหมือนเครื่องยนต์หลักผลักดันทั้งอาหาร เพลง หนัง และนวัตกรรมระดับโลก หนึ่งในนั้นคือ CJ Group ที่เริ่มต้นจากบริษัทน้ำตาลเล็ก ๆ ในปี 1953 แต่เติบโตจนกลายเป็นหนึ่งใน conglomerate หรือ "กลุ่มธุรกิจผูกเครือ" ที่ทรงอิทธิพลที่สุดของแดนโสม
คำว่า CJ ย่อมาจาก CheilJedang (แปลว่า “หมายเลขหนึ่งแห่งโลก” ในภาษาจีน-เกาหลี) ก่อตั้งโดย อี บยองชอล ผู้ก่อตั้ง Samsung Group ในช่วงเวลานั้น เกาหลีใต้กำลังฟื้นตัวจากสงครามเกาหลี และรัฐบาลส่งเสริมการพัฒนาอุตสาหกรรมภายในประเทศ เดิมเป็นหน่วยธุรกิจอาหารของกลุ่ม Samsung ในปี 1993 Cheil Jedang แยกตัวออกจาก Samsung Group และกลายเป็นบริษัทอิสระภายใต้การบริหารของ อี แจฮยอน หลานชายของอี บยองชอล แล้วขยายขอบเขตธุรกิจอย่างไม่หยุดยั้ง จากความเชี่ยวชาญใน "การหมัก" แบบดั้งเดิม พวกเขากลับกลายเป็นผู้เล่นรายใหญ่ระดับโลกในวงการ เทคโนโลยีชีวภาพ การผลิตอาหารไปจนถึงธุรกิจ บันเทิงระดับฮอลลีวูด และ โลจิสติกส์ข้ามทวีป
พูดง่าย ๆ ว่า CJ ไม่ได้แค่ส่งออกกิมจิหรือบิบิมบับ แต่พวกเขากำลังวางรากฐานของ "อนาคตแห่งอาหาร" และ "ความบันเทิงแบบไร้พรมแดน" ในเวลาเดียวกัน จนใครหลายคนถึงกับบอกว่า ถ้าอยากเข้าใจเกาหลีใต้ ก็ต้องเริ่มจากเข้าใจ CJ Group เสียก่อน
แล้วในเครือข่ายของ CJ Group มีธุรกิจอะไรบ้างที่น่าสนใจ และแบรนด์ไหนที่เราคุ้นเคยแบบไม่รู้ตัว ไปดูกันเลย
- ธุรกิจอาหารและบริการอาหาร (Food & Food Services)
- CJ CheilJedang บริษัทอาหารชั้นนำของเกาหลีใต้ มีผลิตภัณฑ์เด่น ได้แก่ Bibigo แบรนด์อาหารเกาหลีพร้อมรับประทาน เช่น เกี๊ยว ซอส และกิมจิ Hetbahn ข้าวสวยพร้อมรับประทานที่ได้รับความนิยมในเกาหลี
-
CJ Foodville ดำเนินธุรกิจร้านอาหารและเบเกอรี่ เช่น: Tous Les Jours ร้านเบเกอรี่สไตล์ฝรั่งเศส VIPS ร้านสเต็กและสลัดบุฟเฟ่ต์
-
ธุรกิจเทคโนโลยีชีวภาพ (Bio) ความเชี่ยวชาญนี้เป็นรากฐานสำคัญในการขยายธุรกิจด้านเทคโนโลยีชีวภาพของ CJ เลยครับ
- CJ BIO ผู้นำด้านการผลิตกรดอะมิโนและผลิตภัณฑ์ชีวภาพผ่านเทคโนโลยีการหมักจุลินทรีย์ เช่น Lysine, Tryptophan, Valine กรดอะมิโนที่ใช้ในอุตสาหกรรมอาหารสัตว์และอาหารเสริม
-
CJ Bioscience มุ่งเน้นการวิจัยและพัฒนาไมโครไบโอมเพื่อสุขภาพ
-
ธุรกิจโลจิสติกส์และค้าปลีก (Logistics & Retail)
- CJ Logistics ให้บริการโลจิสติกส์ครบวงจร ทั้งการขนส่งทางบก ทางทะเล และทางอากาศ รวมถึงบริการคลังสินค้าและการจัดการซัพพลายเชน
-
CJ Olive Young: ร้านค้าปลีกด้านสุขภาพและความงามอันดับหนึ่งของเกาหลี มีผลิตภัณฑ์ยอดนิยม เช่น Anua PDRN Set ชุดบำรุงผิวที่ได้รับความนิยม MILKTOUCH ผลิตภัณฑ์เมคอัพที่ได้รับความนิยม
-
ธุรกิจบันเทิงและสื่อ (Entertainment & Media) อันนี้ยิ่งใหญ่ระดับโลกมากๆ หลายคนคงจำได้กับ ภาพยนตร์เอเชียแรกกับรางวัลออสการ์ Parasite
- CJ ENM บริษัทผลิตและจัดจำหน่ายเนื้อหาบันเทิงที่มีชื่อเสียงระดับโลก มีผลงานเด่น ได้แก่ Crash Landing on You ซีรีส์ที่ได้รับความนิยมอย่างสูง Parasite ภาพยนตร์ที่ได้รับรางวัลออสการ์
- CJ CGV เครือโรงภาพยนตร์มัลติเพล็กซ์ที่มีสาขาทั่วโลก
CJ Group ขยายธุรกิจไปยังต่างประเทศ เช่น การเข้าซื้อกิจการ Schwan's Company ในสหรัฐอเมริกา และการเปิดสาขา CGV ในหลายประเทศ นอกจากนี้ CJ ยังมีบทบาทสำคัญในการเผยแพร่วัฒนธรรมเกาหลีสู่ระดับโลกผ่าน KCON และการผลิตเนื้อหาบันเทิงที่ได้รับความนิยมในต่างประเทศด้วยครับ
จะเห็นได้ว่า เครือข่ายของ CJ นั้นยิ่งใหญ่มากๆเลย ทีนี้มีเรื่องน่าสนใจตรงนี้ครับ
ในช่วงปี 2013–2016 CJ Group โดยเฉพาะฝ่ายสื่อบันเทิงอย่าง CJ ENM ต้องเผชิญกับแรงกดดันจากรัฐบาลของประธานาธิบดี พัค กึนฮเย เหตุการณ์สำคัญคือการที่ อี มีคยอง (Miky Lee) รองประธาน CJ และผู้มีบทบาทสำคัญในการขับเคลื่อนธุรกิจบันเทิงระดับโลก ถูกกดดันให้ลาออกจากตำแหน่ง รายงานระบุว่า ทำเนียบประธานาธิบดีไม่พอใจเนื้อหาสื่อบางรายการของ CJ ที่มีลักษณะเสียดสีหรือวิพากษ์วิจารณ์รัฐบาล เช่น รายการ SNL Korea ที่ล้อเลียนพัค กึนฮเย ผ่านตัวละคร Teletubbies
ภายใต้แรงกดดันนี้ CJ มีการปรับเปลี่ยนเนื้อหาสื่อ โดยลดการนำเสนอเนื้อหาที่อาจขัดแย้งกับรัฐบาล และหันไปผลิตภาพยนตร์ที่สอดคล้องกับนโยบายของรัฐ เช่น ภาพยนตร์เรื่อง Ode to My Father (2014) ที่สะท้อนความรักชาติและการพัฒนาเศรษฐกิจในยุคของพัค ชุงฮี บิดาของพัค กึนฮเย ภาพยนตร์เรื่องนี้ได้รับการสนับสนุนจากรัฐบาลและถูกมองว่าเป็น "ภาพยนตร์เพื่อสุขภาพ" ที่ส่งเสริมความภาคภูมิใจในชาติ แน่นอนว่าแค้นฝังหุ่นมันยังไม่หายไปไหนครับ
เมื่อเกิดการเปิดโปง "บัญชีดำ" (Blacklist) ของรัฐบาลพัค กึนฮเย ที่มีการจำกัดสิทธิเสรีภาพของศิลปินและผู้ผลิตสื่อที่วิพากษ์วิจารณ์รัฐบาล ทำให้เกิดกระแสต่อต้านอย่างรุนแรงในสังคมเกาหลี. ในปี 2016 ซน กยองชิก ประธาน CJ ได้ให้การต่อศาลว่า มีแรงกดดันจากรัฐบาลให้ อี มีคยอง หลีกเลี่ยงการมีบทบาทในบริษัท เหตุการณ์นี้เป็นส่วนหนึ่งของการเปิดโปงคดีทุจริตของพัค กึนฮเย ซึ่งนำไปสู่การประท้วงครั้งใหญ่และการถอดถอนประธานาธิบดีในปี 2017
หลังจากการเปลี่ยนแปลงทางการเมือง CJ Group ได้กลับมามีบทบาทอย่างเต็มที่ในวงการบันเทิงอีกครั้ง อี มีคยอง กลับมาดำรงตำแหน่งและมีบทบาทสำคัญในการผลักดันภาพยนตร์เรื่อง Parasite (2019) ซึ่งได้รับรางวัลออสการ์และยกระดับภาพลักษณ์ของ CJ ในระดับโลก ซึ่งถ้าใครได้ดูหนังเรื่องนั้นแล้วรู้เรื่องราวเบื้องหลังนี้จะเข้าใจเนื้อหาได้อย่างลึกซึ้งขึ้นไปอีกเลยครับ การนำเสนอเรื่องราวนี้ถือเป็นการวิพากษ์วิจารณ์สังคมและระบบทุนนิยมอย่างชัดเจน ซึ่งแตกต่างจากแนวทางที่ CJ เคยถูกกดดันให้ปฏิบัติตามในยุคของพัค กึนฮเย อย่างสิ้นเชิง
อย่าเพิ่งไปสะใจกับเนื้อหา ให้มองว่า "เขาทำอะไรได้บ้าง" นี่คือประเด็นสำคัญครับ #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ f6488c62:c929299d
2025-05-21 08:52:36
@ f6488c62:c929299d
2025-05-21 08:52:36ปี 2568 ตลาดคริปโตยังคงเต็มไปด้วยความร้อนแรงและโอกาส Bitcoin พุ่งแตะ 106,595.5 ดอลลาร์ (ณ วันที่ 21 พ.ค. 2568) ขณะที่เหรียญมีมอย่าง KPEPE ก็กลายเป็นที่จับตามองของเหล่านักลงทุนรายใหญ่ แต่ท่ามกลางกระแสความร้อนแรง คำถามสำคัญยังคงอยู่: ตลาดคริปโตอยู่ช่วงไหนของวัฏจักร? และโอกาสใหญ่กำลังมาหรือใกล้จบลงแล้ว?
หนึ่งในเสียงที่ดังที่สุดในชุมชนคริปโตตอนนี้คือชื่อที่หลายคนอาจยังไม่รู้จักแน่ชัด – James Wynn เขาโพสต์ข้อความเมื่อวันที่ 31 มีนาคม 2568 ว่า
“The best is yet to come.” หรือ “สิ่งที่ดีที่สุดยังมาไม่ถึง” – คำพูดที่จุดประกายความหวังในชุมชนนักเทรดทั่วโลก
แม้เขาจะถูกยกย่องว่าเป็น “วาฬคริปโต” จากการถือครองมูลค่ามหาศาล แต่ในความเป็นจริง เรายังไม่รู้ว่าเขาคือใคร – ชื่อ James Wynn อาจเป็นเพียงนามแฝง หรือ persona บนโลกออนไลน์ก็เป็นได้
ในบทความนี้ เราจะวิเคราะห์มุมมองของเขาอย่างมีวิจารณญาณ พร้อมแนะแนวทางที่นักเทรดควรเตรียมตัวเพื่อคว้าโอกาสในช่วงขาขึ้นนี้
ภาพรวมตลาดคริปโตในปี 2568 ปีนี้ถือเป็นช่วงขาขึ้นที่เกิดจากหลายปัจจัยสำคัญ:
การอนุมัติ Bitcoin Spot ETFs ในสหรัฐฯ
การเข้ารับตำแหน่งของ Donald Trump พร้อมนโยบายที่เป็นมิตรต่อคริปโต เช่น การผลักดันให้ Bitcoin เป็นสินทรัพย์สำรองของชาติ
ปัจจัยเหล่านี้ได้ดึงดูดทั้งนักลงทุนรายย่อยและสถาบันเข้าสู่ตลาด ส่งผลให้ราคาของ BTC และเหรียญมีมอย่าง KPEPE พุ่งสูงขึ้นอย่างรวดเร็ว สะท้อนถึงโมเมนตัมที่ยังคงแข็งแกร่ง
มุมมองจาก ‘James Wynn’: ปลายวัฏจักร? หรือแค่เริ่มต้น? แม้จะไม่มีใครรู้แน่ชัดว่า James Wynn คือใคร แต่เขากลายเป็นบุคคลที่มีอิทธิพลในชุมชนคริปโตจากการเปิดเผยมุมมองที่เฉียบคมและพอร์ตการลงทุนขนาดใหญ่
เขาโพสต์ไว้ว่า
“ถ้าใครคิดว่าเราอยู่ท้ายวัฏจักรแล้ว คุณคิดผิด”
โดยให้เหตุผลหลัก 3 ข้อ:
การพุ่งขึ้นของราคาส่วนใหญ่เกิดจาก ข่าวดีภายนอก เช่น ETF ยังไม่ใช่ "กระแสล้นตลาด"
นโยบายรัฐบาล Trump ส่งผลเชิงจิตวิทยาเชิงบวกต่อทั้งนักลงทุนและตลาด
ยังไม่เกิด Altcoin Season หรืออารมณ์ตลาดช่วง “Euphoria” ตามแผนภาพ Psychology of a Market Cycle
เขาประเมินว่าตลาดน่าจะอยู่ช่วง “Optimism → Thrill” ซึ่งเป็นช่วงกลางของวัฏจักรที่นักลงทุนเริ่มตื่นเต้น แต่ยังไม่ถึงจุดสูงสุด
เขาเป็นใคร? วาฬตัวจริงหรือบุคคลลึกลับ? แม้ James Wynn จะได้รับความสนใจอย่างมาก แต่ตัวตนของเขายังคลุมเครือ:
ไม่มีข้อมูลยืนยันตัวตนชัดเจน
ไม่รู้ว่าเขาเป็นบุคคล กลุ่ม หรือองค์กร
ใช้นามแฝงออนไลน์ และบัญชีเทรดที่ระบุไว้ไม่ผูกกับตัวตนจริง
ถึงอย่างนั้น พฤติกรรมการลงทุนของเขาก็ไม่ธรรมดา:
Long BTC-USD ด้วยเลเวอเรจ 40x กว่า 5,200 BTC (มูลค่ากว่า 546 ล้านดอลลาร์)
Long KPEPE-USD ด้วยเลเวอเรจ 10x มูลค่ากว่า 32.8 ล้านดอลลาร์
รวมกำไรจากการเทรดกว่า 20.2 ล้านดอลลาร์ (ราว 687 ล้านบาท)
ใช้แพลตฟอร์ม Hyperliquid และแสดงจุดยืนต่อต้าน CEX บางแห่งอย่าง Bybit ที่เขาเคยกล่าวหาว่ามีการ manipulate ตลาด
สิ่งที่น่าสนใจคือ Wynn มักจะลดตำแหน่งและล็อกกำไรอย่างเป็นระบบ เช่น วันที่ 20 พ.ค. 2568 เขาลดตำแหน่ง BTC ลง 1,142 BTC และถอน USDC กลับวอลเล็ตส่วนตัว – สะท้อนถึงการบริหารความเสี่ยงที่รอบคอบ
แนวทางสำหรับนักเทรด: ถ้า "สิ่งที่ดีที่สุด" ยังมาไม่ถึง... หากมุมมองของ Wynn ถูกต้อง และตลาดยังไม่ถึงจุดสูงสุด ต่อไปนี้คือตัวอย่างแนวทางที่นักเทรดควรพิจารณา:
🔹 วางแผนรับ pullback: หากอยู่ในช่วง "Thrill" ตลาดอาจมีการพักตัวชั่วคราว – เป็นโอกาสในการ “ซื้อซ้ำ” ก่อนเข้าสู่จุดพีค
🔹 จับตา altcoin season: การที่เหรียญมีมอย่าง KPEPE พุ่งขึ้น อาจเป็นสัญญาณล่วงหน้าของ Altcoin Season ที่กำลังจะเริ่ม – เตรียมลิสต์เหรียญที่มีศักยภาพ
🔹 เน้นการบริหารความเสี่ยง: ใช้ stop-loss และเลเวอเรจอย่างระมัดระวัง อย่าลืมว่าวัฏจักรคริปโตสามารถเปลี่ยนแปลงอย่างรวดเร็ว
🔹 ติดตามความเคลื่อนไหวของวาฬ (แม้จะไม่รู้ว่าเขาคือใคร): เช่น ที่อยู่กระเป๋า 0x5078C2FbeA2B2aD61bcB40BC0233E5Ce56EDb6 ซึ่งเชื่อว่าเป็นของ Wynn – การเคลื่อนไหวของกระเป๋านี้อาจบ่งชี้แนวโน้มตลาดล่วงหน้า
สรุป แม้เราจะยังไม่รู้แน่ชัดว่า James Wynn คือใคร หรือแม้กระทั่งเขามีอยู่จริงหรือไม่ แต่คำพูดของเขาก็สอดคล้องกับทิศทางตลาดในปัจจุบันที่ยังคงอยู่ในขาขึ้น
“The best is yet to come.” – ถ้าเขาพูดถูก โอกาสที่ดีที่สุดในตลาดคริปโตปี 2568 ก็ยังไม่มาถึง
นักเทรดควร:
ติดตามสัญญาณตลาดอย่างรอบคอบ
จัดพอร์ตให้พร้อมสำหรับการเปลี่ยนแปลง
และที่สำคัญ — อย่าหลงกระแส โดยไม่มีแผนรองรับ
วาฬที่แท้จริงอาจไม่มีชื่อเสียง… และนั่นแหละคือสิ่งที่ทำให้พวกเขาน่าจับตายิ่งกว่าใคร
-
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 15f9e159:ca9a5ac4
2025-05-21 07:37:11
@ 15f9e159:ca9a5ac4
2025-05-21 07:37:11A plataforma 755Bet é uma das principais opções para quem busca uma experiência única no universo dos jogos online. Com uma interface intuitiva, jogos de alta qualidade e uma experiência de usuário focada na diversão e no prazer do jogador, o 755Bet se destaca como um dos destinos preferidos para quem deseja aproveitar ao máximo o entretenimento digital. Vamos explorar o que torna o 755Bet uma plataforma tão especial e por que ele deve ser a sua próxima escolha para diversão online.
Plataforma 755Bet: Um Espaço Inovador e Completo O 755Bet oferece aos jogadores uma plataforma moderna e fácil de navegar, permitindo que se conectem ao mundo do entretenimento online com apenas alguns cliques. A plataforma é projetada para ser acessível tanto para novatos quanto para jogadores experientes, com recursos que atendem a diferentes gostos e preferências.
Com um design que prioriza a simplicidade, o 755Bet garante que seus usuários possam encontrar rapidamente o que procuram. Seja para jogar ou simplesmente explorar as opções oferecidas, a experiência do usuário é fluida e sem complicações. Além disso, o site é otimizado para dispositivos móveis, permitindo que você aproveite a diversão a qualquer hora e em qualquer lugar.
A plataforma oferece diversos métodos de pagamento seguros, garantindo que os jogadores possam realizar transações de maneira rápida e sem preocupações. O 755bet também investe constantemente em melhorar a segurança dos dados de seus usuários, com protocolos avançados de criptografia para proteger as informações pessoais e financeiras.
Jogos no 755Bet: Variedade para Todos os Gostos Uma das principais atrações do 755Bet é a ampla seleção de jogos oferecidos. Se você é fã de jogos de mesa, como blackjack e roleta, ou prefere jogos de habilidade e estratégia, o 755Bet tem algo para todos. A variedade de opções garante que cada jogador possa encontrar o jogo que mais lhe agrada, com gráficos de alta qualidade e jogabilidade envolvente.
O site conta com uma vasta gama de opções, que incluem títulos populares de diferentes categorias. Além disso, novos jogos estão sempre sendo adicionados ao portfólio, garantindo que os jogadores nunca fiquem sem novidades. A plataforma oferece jogos com diferentes níveis de dificuldade, o que significa que tanto iniciantes quanto veteranos podem aproveitar as opções disponíveis, sempre encontrando o jogo que se adapta ao seu estilo.
Experiência do Jogador: Diversão e Comodidade No 755Bet, a experiência do jogador é uma prioridade. A plataforma não apenas oferece jogos de alta qualidade, mas também foca em criar um ambiente acolhedor e acessível. O atendimento ao cliente é uma parte fundamental da experiência do usuário, com uma equipe dedicada pronta para responder a qualquer dúvida ou ajudar com problemas de forma rápida e eficaz.
Além disso, o 755Bet oferece promoções e bônus que tornam a experiência ainda mais interessante para seus jogadores. Isso inclui recompensas para novos membros, bem como ofertas especiais para usuários regulares. Esses incentivos ajudam a manter a motivação dos jogadores e garantem que a experiência seja sempre divertida e recompensadora.
O 755Bet também conta com recursos de personalização que permitem aos jogadores ajustar a plataforma conforme suas preferências. Isso pode incluir a escolha de temas, ajustes de notificação e preferências de jogo, tudo para garantir que o ambiente de jogo seja o mais agradável possível.
Conclusão O 755Bet se destaca como uma plataforma completa para quem busca uma experiência online rica e envolvente. Com uma interface intuitiva, uma ampla variedade de jogos e um foco constante na satisfação do jogador, ele é um destino obrigatório para aqueles que querem explorar o universo dos jogos online de forma segura, divertida e acessível. Seja você um novato ou um jogador experiente, o 755Bet tem tudo o que você precisa para uma experiência inesquecível.
-
 @ 04c915da:3dfbecc9
2025-03-10 23:31:30
@ 04c915da:3dfbecc9
2025-03-10 23:31:30Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Usually stolen bitcoin for the reserve creates a perverse incentive. If governments see a bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 04c915da:3dfbecc9
2025-03-07 00:26:37
@ 04c915da:3dfbecc9
2025-03-07 00:26:37There is something quietly rebellious about stacking sats. In a world obsessed with instant gratification, choosing to patiently accumulate Bitcoin, one sat at a time, feels like a middle finger to the hype machine. But to do it right, you have got to stay humble. Stack too hard with your head in the clouds, and you will trip over your own ego before the next halving even hits.
Small Wins
Stacking sats is not glamorous. Discipline. Stacking every day, week, or month, no matter the price, and letting time do the heavy lifting. Humility lives in that consistency. You are not trying to outsmart the market or prove you are the next "crypto" prophet. Just a regular person, betting on a system you believe in, one humble stack at a time. Folks get rekt chasing the highs. They ape into some shitcoin pump, shout about it online, then go silent when they inevitably get rekt. The ones who last? They stack. Just keep showing up. Consistency. Humility in action. Know the game is long, and you are not bigger than it.
Ego is Volatile
Bitcoin’s swings can mess with your head. One day you are up 20%, feeling like a genius and the next down 30%, questioning everything. Ego will have you panic selling at the bottom or over leveraging the top. Staying humble means patience, a true bitcoin zen. Do not try to "beat” Bitcoin. Ride it. Stack what you can afford, live your life, and let compounding work its magic.
Simplicity
There is a beauty in how stacking sats forces you to rethink value. A sat is worth less than a penny today, but every time you grab a few thousand, you plant a seed. It is not about flaunting wealth but rather building it, quietly, without fanfare. That mindset spills over. Cut out the noise: the overpriced coffee, fancy watches, the status games that drain your wallet. Humility is good for your soul and your stack. I have a buddy who has been stacking since 2015. Never talks about it unless you ask. Lives in a decent place, drives an old truck, and just keeps stacking. He is not chasing clout, he is chasing freedom. That is the vibe: less ego, more sats, all grounded in life.
The Big Picture
Stack those sats. Do it quietly, do it consistently, and do not let the green days puff you up or the red days break you down. Humility is the secret sauce, it keeps you grounded while the world spins wild. In a decade, when you look back and smile, it will not be because you shouted the loudest. It will be because you stayed the course, one sat at a time. \ \ Stay Humble and Stack Sats. 🫡
-
 @ 15f9e159:ca9a5ac4
2025-05-21 07:36:25
@ 15f9e159:ca9a5ac4
2025-05-21 07:36:25O mundo dos jogos online está sempre em evolução, e novas plataformas surgem constantemente para oferecer experiências únicas aos jogadores. O 0e0e é uma dessas plataformas, que vem conquistando o público com uma proposta inovadora, repleta de jogos envolventes e uma interface amigável. Se você está em busca de uma nova forma de diversão e desafios, o 0e0e oferece tudo isso e muito mais.
Introdução à Plataforma 0e0e O 0e0e é uma plataforma online que tem como principal objetivo proporcionar uma experiência de entretenimento de qualidade. Com um design moderno e acessível, a plataforma é fácil de navegar, permitindo que os jogadores se sintam à vontade ao explorar suas diversas funcionalidades. O 0e0e está disponível para todos os tipos de dispositivos, garantindo que os usuários possam jogar a qualquer hora e em qualquer lugar, seja no desktop ou no celular.
Ao acessar a plataforma, os jogadores têm acesso a uma ampla variedade de jogos, além de recursos que tornam a experiência ainda mais agradável, como bônus atrativos, promoções e um atendimento ao cliente de excelência. O 0e0efoca em criar um ambiente dinâmico, que agrada tanto aos iniciantes quanto aos jogadores mais experientes.
Jogos no 0e0e: Diversão Sem Limites Uma das maiores vantagens do 0e0e é sua vasta seleção de jogos, que atende aos mais diversos gostos e preferências. Seja você fã de jogos de habilidade, estratégia ou entretenimento de alta ação, a plataforma tem opções para todos. Entre os jogos mais populares, encontramos desde clássicos da cultura de jogos até títulos exclusivos que você não encontra facilmente em outras plataformas.
Os jogos disponíveis são desenvolvidos por fornecedores renomados da indústria, garantindo gráficos impressionantes, jogabilidade fluida e uma experiência imersiva. Cada jogo foi cuidadosamente selecionado para proporcionar momentos de diversão, com desafios que mantêm os jogadores engajados e motivados a explorar cada vez mais as opções da plataforma.
Uma das atrações mais procuradas pelos usuários do 0e0e são os jogos de mesa, que oferecem uma experiência tradicional de jogo com um toque moderno. Os jogadores podem escolher entre várias modalidades, cada uma com regras fáceis de aprender, mas desafiadoras o suficiente para manter o interesse.
Além disso, a plataforma oferece jogos com temas variados, desde aventuras épicas a opções mais leves e descontraídas. Seja você um jogador casual ou alguém em busca de competição, há sempre algo para experimentar no 0e0e.
Experiência do Jogador: Conforto e Inovação O 0e0e entende que a experiência do jogador vai além da simples escolha de jogos. A plataforma investe em diversos aspectos para garantir que a navegação seja intuitiva e sem complicações. O processo de registro e acesso aos jogos é simples, permitindo que qualquer pessoa, independentemente da sua familiaridade com plataformas digitais, possa começar a jogar rapidamente.
Além disso, o 0e0e conta com um suporte ao cliente eficiente, pronto para ajudar em qualquer questão que possa surgir durante a jornada do jogador. A equipe de suporte está disponível 24 horas por dia, 7 dias por semana, oferecendo um atendimento rápido e amigável.
Para tornar a experiência ainda mais imersiva, o 0e0e disponibiliza uma série de promoções e bônus especiais para seus usuários. Estes benefícios são pensados para aumentar a diversão e proporcionar mais oportunidades de ganhar, criando um ambiente onde os jogadores podem aproveitar ao máximo cada momento.
A plataforma também oferece métodos de pagamento rápidos e seguros, garantindo que os depósitos e retiradas sejam realizados de maneira tranquila, sem qualquer complicação. A segurança dos dados do usuário é uma prioridade para o 0e0e, que utiliza tecnologia de ponta para proteger todas as informações pessoais e financeiras.
Conclusão: O 0e0e Como a Escolha Certa para os Jogadores O 0e0e é muito mais do que uma plataforma de jogos; é um espaço onde diversão, emoção e segurança se encontram. Com uma interface amigável, uma vasta seleção de jogos e um suporte ao cliente dedicado, o 0e0e oferece tudo o que um jogador precisa para se divertir e viver novas experiências. Seja você um iniciante ou um veterano, o 0e0e tem tudo para tornar sua jornada ainda mais emocionante e recompensadora. Não perca a chance de explorar tudo o que essa plataforma incrível tem a oferecer!
-
 @ 04c915da:3dfbecc9
2025-03-04 17:00:18
@ 04c915da:3dfbecc9
2025-03-04 17:00:18This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 04c915da:3dfbecc9
2025-02-25 03:55:08
@ 04c915da:3dfbecc9
2025-02-25 03:55:08Here’s a revised timeline of macro-level events from The Mandibles: A Family, 2029–2047 by Lionel Shriver, reimagined in a world where Bitcoin is adopted as a widely accepted form of money, altering the original narrative’s assumptions about currency collapse and economic control. In Shriver’s original story, the failure of Bitcoin is assumed amid the dominance of the bancor and the dollar’s collapse. Here, Bitcoin’s success reshapes the economic and societal trajectory, decentralizing power and challenging state-driven outcomes.
Part One: 2029–2032
-
2029 (Early Year)\ The United States faces economic strain as the dollar weakens against global shifts. However, Bitcoin, having gained traction emerges as a viable alternative. Unlike the original timeline, the bancor—a supranational currency backed by a coalition of nations—struggles to gain footing as Bitcoin’s decentralized adoption grows among individuals and businesses worldwide, undermining both the dollar and the bancor.
-
2029 (Mid-Year: The Great Renunciation)\ Treasury bonds lose value, and the government bans Bitcoin, labeling it a threat to sovereignty (mirroring the original bancor ban). However, a Bitcoin ban proves unenforceable—its decentralized nature thwarts confiscation efforts, unlike gold in the original story. Hyperinflation hits the dollar as the U.S. prints money, but Bitcoin’s fixed supply shields adopters from currency devaluation, creating a dual-economy split: dollar users suffer, while Bitcoin users thrive.
-
2029 (Late Year)\ Dollar-based inflation soars, emptying stores of goods priced in fiat currency. Meanwhile, Bitcoin transactions flourish in underground and online markets, stabilizing trade for those plugged into the bitcoin ecosystem. Traditional supply chains falter, but peer-to-peer Bitcoin networks enable local and international exchange, reducing scarcity for early adopters. The government’s gold confiscation fails to bolster the dollar, as Bitcoin’s rise renders gold less relevant.
-
2030–2031\ Crime spikes in dollar-dependent urban areas, but Bitcoin-friendly regions see less chaos, as digital wallets and smart contracts facilitate secure trade. The U.S. government doubles down on surveillance to crack down on bitcoin use. A cultural divide deepens: centralized authority weakens in Bitcoin-adopting communities, while dollar zones descend into lawlessness.
-
2032\ By this point, Bitcoin is de facto legal tender in parts of the U.S. and globally, especially in tech-savvy or libertarian-leaning regions. The federal government’s grip slips as tax collection in dollars plummets—Bitcoin’s traceability is low, and citizens evade fiat-based levies. Rural and urban Bitcoin hubs emerge, while the dollar economy remains fractured.
Time Jump: 2032–2047
- Over 15 years, Bitcoin solidifies as a global reserve currency, eroding centralized control. The U.S. government adapts, grudgingly integrating bitcoin into policy, though regional autonomy grows as Bitcoin empowers local economies.
Part Two: 2047
-
2047 (Early Year)\ The U.S. is a hybrid state: Bitcoin is legal tender alongside a diminished dollar. Taxes are lower, collected in BTC, reducing federal overreach. Bitcoin’s adoption has decentralized power nationwide. The bancor has faded, unable to compete with Bitcoin’s grassroots momentum.
-
2047 (Mid-Year)\ Travel and trade flow freely in Bitcoin zones, with no restrictive checkpoints. The dollar economy lingers in poorer areas, marked by decay, but Bitcoin’s dominance lifts overall prosperity, as its deflationary nature incentivizes saving and investment over consumption. Global supply chains rebound, powered by bitcoin enabled efficiency.
-
2047 (Late Year)\ The U.S. is a patchwork of semi-autonomous zones, united by Bitcoin’s universal acceptance rather than federal control. Resource scarcity persists due to past disruptions, but economic stability is higher than in Shriver’s original dystopia—Bitcoin’s success prevents the authoritarian slide, fostering a freer, if imperfect, society.
Key Differences
- Currency Dynamics: Bitcoin’s triumph prevents the bancor’s dominance and mitigates hyperinflation’s worst effects, offering a lifeline outside state control.
- Government Power: Centralized authority weakens as Bitcoin evades bans and taxation, shifting power to individuals and communities.
- Societal Outcome: Instead of a surveillance state, 2047 sees a decentralized, bitcoin driven world—less oppressive, though still stratified between Bitcoin haves and have-nots.
This reimagining assumes Bitcoin overcomes Shriver’s implied skepticism to become a robust, adopted currency by 2029, fundamentally altering the novel’s bleak trajectory.
-
-
 @ 15f9e159:ca9a5ac4
2025-05-21 07:35:46
@ 15f9e159:ca9a5ac4
2025-05-21 07:35:46A 55kd é uma plataforma inovadora no cenário de jogos online, criada para oferecer aos jogadores uma experiência única e envolvente. Se você está procurando por uma maneira divertida de passar o tempo, explorar novos jogos e viver grandes emoções, a 55kd pode ser o lugar ideal. Neste artigo, vamos explorar como a 55kd se destaca, desde sua introdução até a experiência dos jogadores e a vasta gama de jogos disponíveis.
Introdução à Plataforma 55kd A 55kd surgiu com a missão de revolucionar o mundo dos jogos online, oferecendo uma plataforma fácil de navegar, segura e repleta de opções de entretenimento. Com um design moderno e uma interface amigável, a plataforma foi desenvolvida para atender tanto jogadores iniciantes quanto veteranos, garantindo que todos se sintam confortáveis e imersos na experiência.
A 55kd prioriza a acessibilidade e a praticidade, permitindo que os jogadores acessem os jogos de forma rápida e sem complicações. Com um sistema eficiente de registro e uma plataforma intuitiva, novos usuários podem se cadastrar e começar a jogar rapidamente, sem a necessidade de processos complexos.
Variedade de Jogos na 55kd A plataforma 55kdse destaca pela grande variedade de jogos que oferece aos seus usuários. Desde opções de estratégia até os jogos mais emocionantes de sorte e habilidade, há algo para todos os gostos. A cada visita, os jogadores podem esperar novas e emocionantes opções para explorar.
Entre os jogos mais populares, destacam-se as opções de jogos de mesa, slots de vídeo e jogos de habilidade. Cada jogo foi cuidadosamente selecionado e desenvolvido para garantir uma experiência de alta qualidade, com gráficos impressionantes, jogabilidade fluida e recursos inovadores.
Os jogos de mesa, por exemplo, oferecem desafios para aqueles que preferem jogos de raciocínio e estratégia. Já os slots de vídeo são ideais para quem busca emoção e diversão instantânea, com uma ampla gama de temas e bônus que aumentam a adrenalina.
Além disso, a 55kd também oferece jogos de habilidade, permitindo que os jogadores mostrem sua destreza e competência. Esses jogos são perfeitos para aqueles que gostam de testar suas habilidades e estratégias, competindo com outros jogadores por grandes prêmios.
A Experiência do Jogador na 55kd Uma das maiores preocupações da 55kd é garantir que seus jogadores tenham uma experiência de jogo impecável. A plataforma investe constantemente em melhorias para proporcionar um ambiente seguro, rápido e transparente. A segurança é uma prioridade, e a plataforma utiliza tecnologias de ponta para proteger as informações dos usuários, além de garantir transações rápidas e seguras.
A 55kd também se destaca pelo seu suporte ao cliente. Se os jogadores tiverem dúvidas ou enfrentarem problemas durante o jogo, uma equipe de suporte altamente treinada está disponível para oferecer assistência imediata. O suporte é acessível por vários canais, como chat ao vivo e e-mail, garantindo que os jogadores se sintam sempre amparados.
Além disso, a plataforma oferece um sistema de bônus e promoções que torna a experiência ainda mais emocionante. Oferecendo prêmios, ofertas exclusivas e recompensas constantes, a 55kd mantém os jogadores motivados e engajados, proporcionando uma sensação contínua de novidade e prazer.
Conclusão A 55kd se destaca como uma plataforma completa e de alta qualidade, que oferece não apenas uma ampla gama de jogos, mas também uma experiência personalizada para cada jogador. Com uma interface intuitiva, jogos diversificados e um suporte excepcional, a 55kd é a escolha ideal para quem busca diversão e entretenimento de qualidade.
Se você ainda não experimentou a 55kd, está na hora de se juntar a essa comunidade vibrante e explorar tudo o que ela tem a oferecer. Prepare-se para uma jornada inesquecível de diversão, desafios e grandes vitórias.
-
 @ c9badfea:610f861a
2025-05-20 19:49:20
@ c9badfea:610f861a
2025-05-20 19:49:20- Install Sky Map (it's free and open source)
- Launch the app and tap Accept, then tap OK
- When asked to access the device's location, tap While Using The App
- Tap somewhere on the screen to activate the menu, then tap ⁝ and select Settings
- Disable Send Usage Statistics
- Return to the main screen and enjoy stargazing!
ℹ️ Use the 🔍 icon in the upper toolbar to search for a specific celestial body, or tap the 👁️ icon to activate night mode
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ 04c915da:3dfbecc9
2025-05-20 15:53:48
@ 04c915da:3dfbecc9
2025-05-20 15:53:48This piece is the first in a series that will focus on things I think are a priority if your focus is similar to mine: building a strong family and safeguarding their future.
Choosing the ideal place to raise a family is one of the most significant decisions you will ever make. For simplicity sake I will break down my thought process into key factors: strong property rights, the ability to grow your own food, access to fresh water, the freedom to own and train with guns, and a dependable community.
A Jurisdiction with Strong Property Rights
Strong property rights are essential and allow you to build on a solid foundation that is less likely to break underneath you. Regions with a history of limited government and clear legal protections for landowners are ideal. Personally I think the US is the single best option globally, but within the US there is a wide difference between which state you choose. Choose carefully and thoughtfully, think long term. Obviously if you are not American this is not a realistic option for you, there are other solid options available especially if your family has mobility. I understand many do not have this capability to easily move, consider that your first priority, making movement and jurisdiction choice possible in the first place.
Abundant Access to Fresh Water
Water is life. I cannot overstate the importance of living somewhere with reliable, clean, and abundant freshwater. Some regions face water scarcity or heavy regulations on usage, so prioritizing a place where water is plentiful and your rights to it are protected is critical. Ideally you should have well access so you are not tied to municipal water supplies. In times of crisis or chaos well water cannot be easily shutoff or disrupted. If you live in an area that is drought prone, you are one drought away from societal chaos. Not enough people appreciate this simple fact.
Grow Your Own Food
A location with fertile soil, a favorable climate, and enough space for a small homestead or at the very least a garden is key. In stable times, a small homestead provides good food and important education for your family. In times of chaos your family being able to grow and raise healthy food provides a level of self sufficiency that many others will lack. Look for areas with minimal restrictions, good weather, and a culture that supports local farming.
Guns
The ability to defend your family is fundamental. A location where you can legally and easily own guns is a must. Look for places with a strong gun culture and a political history of protecting those rights. Owning one or two guns is not enough and without proper training they will be a liability rather than a benefit. Get comfortable and proficient. Never stop improving your skills. If the time comes that you must use a gun to defend your family, the skills must be instinct. Practice. Practice. Practice.
A Strong Community You Can Depend On
No one thrives alone. A ride or die community that rallies together in tough times is invaluable. Seek out a place where people know their neighbors, share similar values, and are quick to lend a hand. Lead by example and become a good neighbor, people will naturally respond in kind. Small towns are ideal, if possible, but living outside of a major city can be a solid balance in terms of work opportunities and family security.
Let me know if you found this helpful. My plan is to break down how I think about these five key subjects in future posts.
-
 @ 9e69e420:d12360c2
2025-02-17 17:12:01
@ 9e69e420:d12360c2
2025-02-17 17:12:01President Trump has intensified immigration enforcement, likening it to a wartime effort. Despite pouring resources into the U.S. Immigration and Customs Enforcement (ICE), arrest numbers are declining and falling short of goals. ICE fell from about 800 daily arrests in late January to fewer than 600 in early February.
Critics argue the administration is merely showcasing efforts with ineffectiveness, while Trump seeks billions more in funding to support his deportation agenda. Increased involvement from various federal agencies is intended to assist ICE, but many lack specific immigration training.
Challenges persist, as fewer immigrants are available for quick deportation due to a decline in illegal crossings. Local sheriffs are also pressured by rising demands to accommodate immigrants, which may strain resources further.
-
 @ 0fa80bd3:ea7325de
2025-02-14 23:24:37
@ 0fa80bd3:ea7325de
2025-02-14 23:24:37intro
The Russian state made me a Bitcoiner. In 1991, it devalued my grandmother's hard-earned savings. She worked tirelessly in the kitchen of a dining car on the Moscow–Warsaw route. Everything she had saved for my sister and me to attend university vanished overnight. This story is similar to what many experienced, including Wences Casares. The pain and injustice of that time became my first lessons about the fragility of systems and the value of genuine, incorruptible assets, forever changing my perception of money and my trust in government promises.
In 2014, I was living in Moscow, running a trading business, and frequently traveling to China. One day, I learned about the Cypriot banking crisis and the possibility of moving money through some strange thing called Bitcoin. At the time, I didn’t give it much thought. Returning to the idea six months later, as a business-oriented geek, I eagerly began studying the topic and soon dove into it seriously.
I spent half a year reading articles on a local online journal, BitNovosti, actively participating in discussions, and eventually joined the editorial team as a translator. That’s how I learned about whitepapers, decentralization, mining, cryptographic keys, and colored coins. About Satoshi Nakamoto, Silk Road, Mt. Gox, and BitcoinTalk. Over time, I befriended the journal’s owner and, leveraging my management experience, later became an editor. I was drawn to the crypto-anarchist stance and commitment to decentralization principles. We wrote about the economic, historical, and social preconditions for Bitcoin’s emergence, and it was during this time that I fully embraced the idea.
It got to the point where I sold my apartment and, during the market's downturn, bought 50 bitcoins, just after the peak price of $1,200 per coin. That marked the beginning of my first crypto winter. As an editor, I organized workflows, managed translators, developed a YouTube channel, and attended conferences in Russia and Ukraine. That’s how I learned about Wences Casares and even wrote a piece about him. I also met Mikhail Chobanyan (Ukrainian exchange Kuna), Alexander Ivanov (Waves project), Konstantin Lomashuk (Lido project), and, of course, Vitalik Buterin. It was a time of complete immersion, 24/7, and boundless hope.
After moving to the United States, I expected the industry to grow rapidly, attended events, but the introduction of BitLicense froze the industry for eight years. By 2017, it became clear that the industry was shifting toward gambling and creating tokens for the sake of tokens. I dismissed this idea as unsustainable. Then came a new crypto spring with the hype around beautiful NFTs – CryptoPunks and apes.
I made another attempt – we worked on a series called Digital Nomad Country Club, aimed at creating a global project. The proceeds from selling images were intended to fund the development of business tools for people worldwide. However, internal disagreements within the team prevented us from completing the project.
With Trump’s arrival in 2025, hope was reignited. I decided that it was time to create a project that society desperately needed. As someone passionate about history, I understood that destroying what exists was not the solution, but leaving everything as it was also felt unacceptable. You can’t destroy the system, as the fiery crypto-anarchist voices claimed.
With an analytical mindset (IQ 130) and a deep understanding of the freest societies, I realized what was missing—not only in Russia or the United States but globally—a Bitcoin-native system for tracking debts and financial interactions. This could return control of money to ordinary people and create horizontal connections parallel to state systems. My goal was to create, if not a Bitcoin killer app, then at least to lay its foundation.
At the inauguration event in New York, I rediscovered the Nostr project. I realized it was not only technologically simple and already quite popular but also perfectly aligned with my vision. For the past month and a half, using insights and experience gained since 2014, I’ve been working full-time on this project.
-
 @ e3ba5e1a:5e433365
2025-02-13 06:16:49
@ e3ba5e1a:5e433365
2025-02-13 06:16:49My favorite line in any Marvel movie ever is in “Captain America.” After Captain America launches seemingly a hopeless assault on Red Skull’s base and is captured, we get this line:
“Arrogance may not be a uniquely American trait, but I must say, you do it better than anyone.”
Yesterday, I came across a comment on the song Devil Went Down to Georgia that had a very similar feel to it:

America has seemingly always been arrogant, in a uniquely American way. Manifest Destiny, for instance. The rest of the world is aware of this arrogance, and mocks Americans for it. A central point in modern US politics is the deriding of racist, nationalist, supremacist Americans.
That’s not what I see. I see American Arrogance as not only a beautiful statement about what it means to be American. I see it as an ode to the greatness of humanity in its purest form.
For most countries, saying “our nation is the greatest” is, in fact, twinged with some level of racism. I still don’t have a problem with it. Every group of people should be allowed to feel pride in their accomplishments. The destruction of the human spirit since the end of World War 2, where greatness has become a sin and weakness a virtue, has crushed the ability of people worldwide to strive for excellence.
But I digress. The fears of racism and nationalism at least have a grain of truth when applied to other nations on the planet. But not to America.
That’s because the definition of America, and the prototype of an American, has nothing to do with race. The definition of Americanism is freedom. The founding of America is based purely on liberty. On the God-given rights of every person to live life the way they see fit.
American Arrogance is not a statement of racial superiority. It’s barely a statement of national superiority (though it absolutely is). To me, when an American comments on the greatness of America, it’s a statement about freedom. Freedom will always unlock the greatness inherent in any group of people. Americans are definitionally better than everyone else, because Americans are freer than everyone else. (Or, at least, that’s how it should be.)
In Devil Went Down to Georgia, Johnny is approached by the devil himself. He is challenged to a ridiculously lopsided bet: a golden fiddle versus his immortal soul. He acknowledges the sin in accepting such a proposal. And yet he says, “God, I know you told me not to do this. But I can’t stand the affront to my honor. I am the greatest. The devil has nothing on me. So God, I’m gonna sin, but I’m also gonna win.”
Libertas magnitudo est
-
 @ 39cc53c9:27168656
2025-05-20 10:45:24
@ 39cc53c9:27168656
2025-05-20 10:45:24Bitcoin enthusiasts frequently and correctly remark how much value it adds to Bitcoin not to have a face, a leader, or a central authority behind it. This particularity means there isn't a single person to exert control over, or a single human point of failure who could become corrupt or harmful to the project.
Because of this, it is said that no other coin can be equally valuable as Bitcoin in terms of decentralization and trustworthiness. Bitcoin is unique not just for being first, but also because of how the events behind its inception developed. This implies that, from Bitcoin onwards, any coin created would have been created by someone, consequently having an authority behind it. For this and some other reasons, some people refer to Bitcoin as "The Immaculate Conception".
While other coins may have their own unique features and advantages, they may not be able to replicate Bitcoin's community-driven nature. However, one other cryptocurrency shares a similar story of mystery behind its creation: Monero.
History of Monero
Bytecoin and CryptoNote
In March 2014, a Bitcointalk thread titled "Bytecoin. Secure, private, untraceable since 2012" was initiated by a user under the nickname "DStrange"^1^. DStrange presented Bytecoin (BCN) as a unique cryptocurrency, in operation since July 2012. Unlike Bitcoin, it employed a new algorithm known as CryptoNote.
DStrange apparently stumbled upon the Bytecoin website by chance while mining a dying bitcoin fork, and decided to create a thread on Bitcointalk^1^. This sparked curiosity among some users, who wondered how could Bytecoin remain unnoticed since its alleged launch in 2012 until then^2^.
Some time after, a user brought up the "CryptoNote v2.0" whitepaper for the first time, underlining its innovative features^4^. Authored by the pseudonymous Nicolas van Saberhagen in October 2013, the CryptoNote v2 whitepaper^5^ highlighted the traceability and privacy problems in Bitcoin. Saberhagen argued that these flaws could not be quickly fixed, suggesting it would be more efficient to start a new project rather than trying to patch the original^5^, an statement simmilar to the one from Satoshi Nakamoto^6^.
Checking with Saberhagen's digital signature, the release date of the whitepaper seemed correct, which would mean that Cryptonote (v1) was created in 2012^7^, although there's an important detail: "Signing time is from the clock on the signer's computer" ^9^.
Moreover, the whitepaper v1 contains a footnote link to a Bitcointalk post dated May 5, 2013^10^, making it impossible for the whitepaper to have been signed and released on December 12, 2012.
As the narrative developed, users discovered that a significant 80% portion of Bytecoin had been pre-mined^11^ and blockchain dates seemed to be faked to make it look like it had been operating since 2012, leading to controversy surrounding the project.
The origins of CryptoNote and Bytecoin remain mysterious, leaving suspicions of a possible scam attempt, although the whitepaper had a good amount of work and thought on it.
The fork
In April 2014, the Bitcointalk user
thankful_for_today, who had also participated in the Bytecoin thread^12^, announced plans to launch a Bytecoin fork named Bitmonero^13^.The primary motivation behind this fork was "Because there is a number of technical and marketing issues I wanted to do differently. And also because I like ideas and technology and I want it to succeed"^14^. This time Bitmonero did things different from Bytecoin: there was no premine or instamine, and no portion of the block reward went to development.
However, thankful_for_today proposed controversial changes that the community disagreed with. Johnny Mnemonic relates the events surrounding Bitmonero and thankful_for_today in a Bitcointalk comment^15^:
When thankful_for_today launched BitMonero [...] he ignored everything that was discussed and just did what he wanted. The block reward was considerably steeper than what everyone was expecting. He also moved forward with 1-minute block times despite everyone's concerns about the increase of orphan blocks. He also didn't address the tail emission concern that should've (in my opinion) been in the code at launch time. Basically, he messed everything up. Then, he disappeared.
After disappearing for a while, thankful_for_today returned to find that the community had taken over the project. Johnny Mnemonic continues:
I, and others, started working on new forks that were closer to what everyone else was hoping for. [...] it was decided that the BitMonero project should just be taken over. There were like 9 or 10 interested parties at the time if my memory is correct. We voted on IRC to drop the "bit" from BitMonero and move forward with the project. Thankful_for_today suddenly resurfaced, and wasn't happy to learn the community had assumed control of the coin. He attempted to maintain his own fork (still calling it "BitMonero") for a while, but that quickly fell into obscurity.
The unfolding of these events show us the roots of Monero. Much like Satoshi Nakamoto, the creators behind CryptoNote/Bytecoin and thankful_for_today remain a mystery^17^, having disappeared without a trace. This enigma only adds to Monero's value.
Since community took over development, believing in the project's potential and its ability to be guided in a better direction, Monero was given one of Bitcoin's most important qualities: a leaderless nature. With no single face or entity directing its path, Monero is safe from potential corruption or harm from a "central authority".
The community continued developing Monero until today. Since then, Monero has undergone a lot of technological improvements, migrations and achievements such as RingCT and RandomX. It also has developed its own Community Crowdfundinc System, conferences such as MoneroKon and Monerotopia are taking place every year, and has a very active community around it.
Monero continues to develop with goals of privacy and security first, ease of use and efficiency second. ^16^
This stands as a testament to the power of a dedicated community operating without a central figure of authority. This decentralized approach aligns with the original ethos of cryptocurrency, making Monero a prime example of community-driven innovation. For this, I thank all the people involved in Monero, that lead it to where it is today.
If you find any information that seems incorrect, unclear or any missing important events, please contact me and I will make the necessary changes.
Sources of interest
- https://forum.getmonero.org/20/general-discussion/211/history-of-monero
- https://monero.stackexchange.com/questions/852/what-is-the-origin-of-monero-and-its-relationship-to-bytecoin
- https://en.wikipedia.org/wiki/Monero
- https://bitcointalk.org/index.php?topic=583449.0
- https://bitcointalk.org/index.php?topic=563821.0
- https://bitcointalk.org/index.php?action=profile;u=233561
- https://bitcointalk.org/index.php?topic=512747.0
- https://bitcointalk.org/index.php?topic=740112.0
- https://monero.stackexchange.com/a/1024
- https://inspec2t-project.eu/cryptocurrency-with-a-focus-on-anonymity-these-facts-are-known-about-monero/
- https://medium.com/coin-story/coin-perspective-13-riccardo-spagni-69ef82907bd1
- https://www.getmonero.org/resources/about/
- https://www.wired.com/2017/01/monero-drug-dealers-cryptocurrency-choice-fire/
- https://www.monero.how/why-monero-vs-bitcoin
- https://old.reddit.com/r/Monero/comments/u8e5yr/satoshi_nakamoto_talked_about_privacy_features/
-
 @ 9bcc5462:eb501d90
2025-04-04 16:02:14
@ 9bcc5462:eb501d90
2025-04-04 16:02:14The story you are about to read is one hundred percent true. It is also my first encounter with a supernatural force.
It was the summer of 2003 and I was visiting my auntie in Nashville as a 16-year-old, pimply-faced teenager. My younger cousins, Alex, Mikey, and Tony were also there. One afternoon, they were all sitting bored outside in the blazing heat, sheltered under the tree on the front lawn. It was a comical sight really, all of them sprawled out lifeless and silent, eaten alive by the unforgiving mosquitos. I ducked inside and asked my aunt if it was okay to borrow her RAV4 to take them to play basketball nearby at Pitts Park. Despite not having a license she handed me the keys and when I went outside to tell the boys we were going to shoot hoops, you’d have thought I said I was taking them to Disney World!
Off we went up and down the rollercoaster-like hills of Tennessee. Yes, I was speeding, and no, we were not wearing seatbelts. (Remember, sixteen, acne, angst, etc.) We arrived at the park and immediately I felt an eerie sensation. I had been there before with my other cousin Kim, but this time was undeniably different. It didn’t matter that the sun was shining above the bright blue sky, I sensed a darkness lingering. And it had nothing to do with the sticky Southern humidity. It was an overwhelming, odd, ineffable sensation. My eyes couldn’t help but focus on the trees behind the court. As if someone or something was watching us.
Nevertheless, after shooting for teams, we began a 2-on-2 immediately. When Mikey and I won, (I towered over them and Mikey was surprisingly pretty good) Tony wasn’t too happy about losing. In frustration, he bounced the basketball with both hands as hard as he could. The ball ended up on the other side of the fences surrounding the court and rolled into the bordering woods. None of the little squirts wanted to retrieve the ball, so as the big cuz I volunteered myself. Nothing to it right? Wrong!
As I walked towards the woods I couldn’t even locate the basketball. I stopped and scanned until I finally saw it, way deep among the trees. “How did it get all the way over there?” I mumbled beneath my breath. Then, while approaching the ball I heard a loud and distinct voice—“Hey!”—I turned around suddenly, but nothing was there. At first I wasn’t afraid, rather I was genuinely confused. It just made no damn sense, there was no one around. I swiveled my head in every direction and once again the deep, gravelly voice called out, “Hey!” This time I knew where it was coming from and crept towards the source until I spotted something in the bushes. I crouched and pushed some branches aside. And that’s when I noticed it. Buried under the shrubs was a tombstone! It stared back at me, weathered, cracked, moss-eaten. I picked my ass up, ran to the ball, scooped it and bolted back to the court.
Little Alex asked if we were going to play a rematch; I said, “Hell no”. After herding them back to the car, we left and never looked back. To this day I remember the voice. I recall the inexplicable feeling of the unknown energy, force, or spirit that was with us. I only recently shared this story with him and now, at 27, he asked why I didn’t tell him sooner. I thought hard about it and answered, “I guess I didn’t want you to get scared and piss yourself.”
-
 @ e3ba5e1a:5e433365
2025-02-05 17:47:16
@ e3ba5e1a:5e433365
2025-02-05 17:47:16I got into a friendly discussion on X regarding health insurance. The specific question was how to deal with health insurance companies (presumably unfairly) denying claims? My answer, as usual: get government out of it!
The US healthcare system is essentially the worst of both worlds:
- Unlike full single payer, individuals incur high costs
- Unlike a true free market, regulation causes increases in costs and decreases competition among insurers
I'm firmly on the side of moving towards the free market. (And I say that as someone living under a single payer system now.) Here's what I would do:
- Get rid of tax incentives that make health insurance tied to your employer, giving individuals back proper freedom of choice.
- Reduce regulations significantly.
-
In the short term, some people will still get rejected claims and other obnoxious behavior from insurance companies. We address that in two ways:
- Due to reduced regulations, new insurance companies will be able to enter the market offering more reliable coverage and better rates, and people will flock to them because they have the freedom to make their own choices.
- Sue the asses off of companies that reject claims unfairly. And ideally, as one of the few legitimate roles of government in all this, institute new laws that limit the ability of fine print to allow insurers to escape their responsibilities. (I'm hesitant that the latter will happen due to the incestuous relationship between Congress/regulators and insurers, but I can hope.)
Will this magically fix everything overnight like politicians normally promise? No. But it will allow the market to return to a healthy state. And I don't think it will take long (order of magnitude: 5-10 years) for it to come together, but that's just speculation.
And since there's a high correlation between those who believe government can fix problems by taking more control and demanding that only credentialed experts weigh in on a topic (both points I strongly disagree with BTW): I'm a trained actuary and worked in the insurance industry, and have directly seen how government regulation reduces competition, raises prices, and harms consumers.
And my final point: I don't think any prior art would be a good comparison for deregulation in the US, it's such a different market than any other country in the world for so many reasons that lessons wouldn't really translate. Nonetheless, I asked Grok for some empirical data on this, and at best the results of deregulation could be called "mixed," but likely more accurately "uncertain, confused, and subject to whatever interpretation anyone wants to apply."
https://x.com/i/grok/share/Zc8yOdrN8lS275hXJ92uwq98M
-
 @ 91bea5cd:1df4451c
2025-02-04 17:24:50
@ 91bea5cd:1df4451c
2025-02-04 17:24:50Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ 8d34bd24:414be32b
2025-05-21 15:52:46
@ 8d34bd24:414be32b
2025-05-21 15:52:46In our culture today, people like to have “my truth” as opposed to “your truth.” They want to have teachers who tell them what they want to hear and worship in the way they desire. The Bible predicted these times.
For the time will come when people will not put up with sound doctrine. Instead, to suit their own desires, they will gather around them a great number of teachers to say what their itching ears want to hear. (2 Timothy 4:3)
My question is, “do we get to choose what we want to believe about God and how we want to worship Him, or does God tell us what we are to believe and how we are to worship Him?”
The Bible makes it clear that He is who He says He is and He expects obedience and worship according to His commands. We do not get to decide for ourselves.
The woman said to Him, “Sir, I perceive that You are a prophet. Our fathers worshiped in this mountain, and you people say that in Jerusalem is the place where men ought to worship.” Jesus said to her, “Woman, believe Me, an hour is coming when neither in this mountain nor in Jerusalem will you worship the Father. You worship what you do not know; we worship what we know, for salvation is from the Jews. But an hour is coming, and now is, when the true worshipers will worship the Father in spirit and truth; for such people the Father seeks to be His worshipers. God is spirit, and those who worship Him must worship in spirit and truth.” (John 4:19-24) {emphasis mine}
In this passage, Jesus gently corrects the woman for worshipping what she does not know. He also says, “God is spirit, and those who worship Him must worship in spirit and truth.” He states what God is (spirit) and how He must be worshipped “in spirit and truth.” We don’t get to define God however we wish, and we don’t get to worship Him any way we wish. God is who He has revealed Himself to be and we must obey Him and worship Him the way He has commanded.
In this next passage, God makes clear that He is holy and we do not get to worship Him any way we wish. We are to interact with Him in the prescribed manner.
Now Nadab and Abihu, the sons of Aaron, took their respective firepans, and after putting fire in them, placed incense on it and offered strange fire before the Lord, which He had not commanded them. And fire came out from the presence of the Lord and consumed them, and they died before the Lord. Then Moses said to Aaron, “It is what the Lord spoke, saying,
‘By those who come near Me I will be treated as holy,\ And before all the people I will be honored.’ ”
So Aaron, therefore, kept silent. (Leviticus 10:1-3) {emphasis mine}
God had prescribed a particular way to approach Him and only those whom He had chosen (priests of the lineage of Aaron). Nadab and Abihu chose to “do it their way” and paid the price for ignoring God’s command. God set an example with them.
God has been gracious enough to reveal Himself, His character, His power, and His commands to us. If we have truly submitted ourselves to His rule, we should hunger for God’s words so we can know Him better and honor Him in obedience.
But now I come to You; and these things I speak in the world so that they may have My joy made full in themselves. I have given them Your word; and the world has hated them, because they are not of the world, even as I am not of the world. I do not ask You to take them out of the world, but to keep them from the evil one. They are not of the world, even as I am not of the world. Sanctify them in the truth; Your word is truth. (John 17:13-17) {emphasis mine}
In today’s culture, everybody likes to claim their own personal truth, but that isn’t how truth works. The truth is not determined by an individual for themselves. It isn’t even determined by a consensus or majority vote. The truth is the truth even if not one person on earth believes it. God speaks truth and God is truth. Our belief or lack thereof doesn’t change the truth, but our lack of belief in the truth, especially the truth as revealed by God in His word, can negatively affect our relationship with God.
God expects us to study His word so we can obey His commands.
For I did not speak to your fathers, or command them in the day that I brought them out of the land of Egypt, concerning burnt offerings and sacrifices. But this is what I commanded them, saying, ‘Obey My voice, and I will be your God, and you will be My people; and you will walk in all the way which I command you, that it may be well with you.’ Yet they did not obey or incline their ear, but walked in their own counsels and in the stubbornness of their evil heart, and went backward and not forward. Since the day that your fathers came out of the land of Egypt until this day, I have sent you all My servants the prophets, daily rising early and sending them. Yet they did not listen to Me or incline their ear, but stiffened their neck; they did more evil than their fathers. (Jeremiah 7:22-26) {emphasis mine}
Today you rarely see someone bowing down to a golden idol, but that doesn’t mean that we are any better at obeying God’s commands or submitting to His will. We still try to make God in our own image so He is a convenience to us and how we want to live our lives. We still put other things ahead of God — family, work, entertainment, fame, etc. Most of us aren’t any more faithful to God than the Israelites were. Just like the Israelites, we put on the trappings of faith but don’t live according to faith and faithfulness.
And He said to them, “Rightly did Isaiah prophesy of you hypocrites, as it is written:
‘This people honors Me with their lips,\ But their heart is far away from Me.\ **But in vain do they worship Me,\ Teaching as doctrines the precepts of men.’\ Neglecting the commandment of God, you hold to the tradition of men.”
He was also saying to them, “You are experts at setting aside the commandment of God in order to keep your tradition. (Mark 7:6-9) {emphasis mine}
How many “churches” and “Christian” leaders teach people according to the culture instead of according to the Word of God? How many tell people what they want to hear and what makes them feel good instead of what they need to hear — the truth as spoken through the Bible? How many church attenders follow a “Christian” leader more than they follow their Creator, Savior, and God? How many church attenders can recite the words of their leaders better than the Holy Scriptures?
I solemnly charge you in the presence of God and of Christ Jesus, who is to judge the living and the dead, and by His appearing and His kingdom: preach the word; be ready in season and out of season; reprove, rebuke, exhort, with great patience and instruction. For the time will come when they will not endure sound doctrine; but wanting to have their ears tickled, they will accumulate for themselves teachers in accordance to their own desires, and will turn away their ears from the truth and will turn aside to myths. But you, be sober in all things, endure hardship, do the work of an evangelist, fulfill your ministry. (2 Timothy 4:1-5) {emphasis mine}
How can we know if a church leader is rightly preaching God’s word? We can only know if we have read the Bible and studied it. We should be like the Bereans:
Now these were more noble-minded than those in Thessalonica, for they received the word with great eagerness, examining the Scriptures daily to see whether these things were so. (Acts 17:11)
Honestly, I don’t trust any spiritual leader who doesn’t encourage me to search the Scriptures to see whether their words are true. Any leader who puts their own word above the Scriptures is a false teacher. Sadly there are many, maybe more than faithful teachers. Some false teachers are intentionally so, but many have been misled by other false teachers. Their guilt is less, but they don’t do any less harm than those who intentionally mislead.
We need to seek trustworthy teachers who speak according to the Word of God, who quote the Bible to support their opinions, and who seek the good of their followers rather than the submission of their followers.
Do not harden your hearts, as at Meribah,\ As in the day of Massah in the wilderness,
“When your fathers tested Me,\ They tried Me, though they had seen My work.\ For forty years I loathed that generation,\ And said they are a people who err in their heart,\ And they do not know My ways.\ Therefore I swore in My anger,\ Truly they shall not enter into My rest.” (Psalm 95:8-11) {emphasis mine} *Teach me good discernment and knowledge,\ For I believe in Your commandments*.\ Before I was afflicted I went astray,\ But now I keep Your word.\ You are good and do good;\ Teach me Your statutes.\ The arrogant have forged a lie against me;\ *With all my heart I will observe Your precepts*.\ Their heart is covered with fat,\ But I delight in Your law.\ It is good for me that I was afflicted,\ That I may learn Your statutes.\ The law of Your mouth is better to me\ Than thousands of gold and silver pieces. (Psalm 119:66-72) {emphasis mine}
May our Creator God teach us the truth. May He fill our hearts with the desire to be in His word daily and to seek His will. May He do what is necessary to get our attention and turn our hearts and minds fully to Him, so we can learn His statutes and serve Him faithfully, so one day we are blessed to hear, “Well done! Good and faithful servant.”
Trust Jesus.
FYI, I see lack of knowledge of truth and God’s word as one of the biggest problems in the church today; however, it is possible to know the Bible in depth, but not know God. As important as knowledge of Scriptures is, this knowledge (without faith, submission, obedience, and love) is meaningless. Knowledge doesn’t get us to heaven. Even obedience doesn’t get us to heaven. Only faith and submission to our creator God leads to salvation and heaven. That being said, we can’t faithfully serve our God without knowledge of Him and His commands. Out of gratefulness for who He is and what He has done for us, we should seek to know and please Him.
-
 @ c1e6505c:02b3157e
2025-05-22 03:44:39
@ c1e6505c:02b3157e
2025-05-22 03:44:39This is day two of testing the Leica Summaron 35mm f2.8 on the Fujifilm X-Pro2.
The first part of this story you can find here on StackerNews**
TL;DR: I think I’m really enjoying this lens.
I went into it thinking I’d probably just sell it since it was gifted to me - assumed I wouldn’t like it. But after just a couple of days with it mounted on the X-Pro2, I’ve been surprisingly drawn to it.
Shooting wide open at f2.8 (which is how I’m testing it - to best reveal the lens’s character), the soft roll-off is really pleasing. It feels organic. The lens is over 50 years old, so I expected some quirks-but the quality feels natural, not overly “vintage". Takes the digital edge off.
The short focus throw is also really nice. Compared to the Summicron 35mm f2 v3 I usually shoot on my M262 (which has a longer throw), the Summaron feels tighter and more responsive when zone focusing.
One gripe: the infinity lock. It’s kind of annoying. I find myself accidentally locking it too often, but I’m getting used to holding the button down as I rotate the ring. I’ve read others complain about it, so I know I’m not alone there.
Most of these shots were from a bike ride to the river - about 6 miles out to swim and enjoy the sun. Perfect day for making a few photos.
This kind of work is honestly just fun. I enjoy the process, and even more so once I’m happy with the results and can share them.
Still building confidence in my work over time. I think I’m slowly refining my style - even if the subject matter is simple. Easier said than done, as any editor/curator knows (and I say this as one through NOICE Magazine).
Let me know what you think. I’ll try to upload higher resolution versions this time around (but not too high).
*Also, I use a program called Dehancer for creating the grain in these photographs. I highly recommend the program actually, I've been using it for a long time. If you would like to try it out, I have a promo code. Use "Pictureroom" for 10% off I believe.
You can further support me and my work by sending sats to colincz\@getalby.com. Thank you.
(note* this is being publised from the updated Primal reads client)
-
 @ 91bea5cd:1df4451c
2025-02-04 17:15:57
@ 91bea5cd:1df4451c
2025-02-04 17:15:57Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ ffbcb706:b0574044
2025-05-21 09:59:14
@ ffbcb706:b0574044
2025-05-21 09:59:14Just a client name test
-
 @ 06639a38:655f8f71
2025-05-21 07:47:56
@ 06639a38:655f8f71
2025-05-21 07:47:56Nostr-PHP
Djuri submitted quite some pull requests in the last couple of week while he was implementing a Nostr connect / login on https://satsback.com. The backend of that platform is written in PHP so the Nostr-PHP library is used for several purposes while Djuri also developed quite some new features utilizing the following NIPs:
- NIP-04
- NIP-05
- NIP-17
- NIP-44
Thank you very much Djuri for these contributions. We now can do the basic private stuff with the library.
PR for NIP-04 and NIP-44: https://github.com/nostrver-se/nostr-php/pull/84 and https://github.com/nostrver-se/nostr-php/pull/88
Examples:- https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip04-encrypted-messages.php
- https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip44-gift-wrapping.php
PR for NIP-05: https://github.com/nostrver-se/nostr-php/pull/89
Example: https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip05-lookup.phpPR for NIP-17: https://github.com/nostrver-se/nostr-php/pull/90
Example: https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip17-private-direct-messages.phpPR for adding more metadata profile fields: https://github.com/nostrver-se/nostr-php/pull/94
Example: https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/fetch-profile-metadata.phpFetch
10050event (dm relay list) of an given pubkey
Example: https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/fetch-dm-relayslist.phpThe CLI tool is removed from the library, see PR https://github.com/nostrver-se/nostr-php/pull/93
Nostr-PHP documentation
While new NIPs are implemented in the Nostr-PHP library, I'm trying to keep up with the documentation at https://nostr-php.dev. For now, things are still much work in progress and I've added the AI agent Goose using the Claude LLM to bootstrap new documentation pages. Currently I'm working on documentation for
- How to direct messages with NIP-04 and NIP-17
- Encrypted payloads for event content NIP-44
- Fetch profiledata of a given pubkey
- Lookup NIP-05 data of given pubkey
- Using the NIP-19 helper class
CCNS.news
I've moved CCNS to a new domain https://ccns.news and have partly implemented the new NIP-B0 for web bookmarks. When you post a bookmark there, a kind
39701event is transmitted to some Nostr relays (take a look at this event for example). Optionally you can also publish this content as a note to the network.As you can see at https://ccns.news/l/censorship-resistant-publishing-and-archiving, I've listed some todo's. All this stuff is done with Javascript using the NDK Typescript library (so I'm not using any PHP stuff for this with Nostr-PHP).

Also new: https://ccns.news/global now has a global feed which fetches all the web bookmark events with kind
39701from several public Nostr relays. I had a rough idea to compare feeds generated with NDK and Nostr-PHP (for both using the same set of relays).
Building a njump clone for this Drupal website
You can now use this URL pattern to fetch Nostr events:
https://nostrver.se/e/{event_id|nevent1|note1|addr1}where you can provide a plain Nostr event ID or NIP-19 encoded identifier.An example, this URL https://nostrver.se/e/nevent1qvzqqqqqqypzqmjxss3dld622uu8q25gywum9qtg4w4cv4064jmg20xsac2aam5nqqsqm2lz4ru6wlydzpulgs8m60ylp4vufwsg55whlqgua6a93vp2y4g3uu9lr fetches the data from one or more relays. This data is then being saved as a (Drupal) node entity (in a database on the server where this website is hosted, which is located in my office fyi). With this saved node, this data is now also available at https://nostrver.se/e/0dabe2a8f9a77c8d1079f440fbd3c9f0d59c4ba08a51d7f811ceeba58b02a255/1 where the (cached) data is server from the database instead. It's just raw data for now, nothing special about it. One of my next steps is to style this in a more prettier interface and I will need to switch the theme of this website to a custom theme. A custom theme where I will be using TailwindCSS v4 and DaisyUI v5.
The module which is providing these Nostr features is FOSS and uses the Nostr-PHP library for doing the following:
- Request the event from one or more relays
- Decode the provided NIP-19 identifier
For now this module is way for me to utilize the Nostr-PHP library with Drupal for fetching events. This can be automated so in theory I could index all the Nostr events. But this is not my ambition as it would require quite some hardware resources to accomplish this.
I hope I can find the time to build up a new theme first for this website, so I can start styling the data for the fetched events. On this website, there is also a small piece (powered by another module) you can find at https://nostrver.se/nostrides doing things with this NIP-113 around activity events (in my case that's cycling what interests me).What's next
I'm already working on the following stuff:
- Implement a class to setup a persistent connection to a relay for requesting events continuously
- Extend the documentation with the recent added features
Other todo stuff:
- Review NIP-13 proof-of-work PR from Djuri
- Implement a NIP-65 lookup for fetching read and write relays for a given npub issue #91
- Build a proof-of-concept with revolt/event-loop to request events asynchronous with persistent relay connections
- Add comments to https://ccns.news
-
 @ 554ab6fe:c6cbc27e
2025-05-20 15:51:33
@ 554ab6fe:c6cbc27e
2025-05-20 15:51:33Introduction
It is becoming increasingly evident that sunlight is an essential nutrient for the body. To be more precise, the various wavelengths coming from the sun provide different benefits to the body, and each play a vital role in human health. Even more so, they work in concert with one another, as one wavelength may help reduce the potentially harmful effects of another. Benefits are maximized and harm reduced when we are exposed to the full breadth of this rainbow. This article will attempt to shed light on these various benefits and synergies.
To put this discussion into context, it is important to consider the overall health benefits of sunlight exposure. In a Swedish study that followed 29,000 women over 20 years, it was found that the mortality rate was doubled in those who avoided sun exposure when compared to those that didn’t (Lindqvist et al. 2016). Women who avoided the sun were twice as likely to die, primarily from cardiovascular disease, and there was no difference between death from malignant melanoma between the two groups (Lindqvist et al. 2016).
To understand why sunlight is so beneficial to health, it is important to make clear the diverse range of wavelengths that come from the sun. We typically think of the sun as a provider of both visible light and warmth. However, the spectrum of light visible to the human eye is a narrow band of the wavelengths actually emitted by the sun.


As wavelengths become shorter, visible light becomes more blue. Beyond the visible spectrum on the blue end, we arrive at ultraviolet (UV) light. On the other end of the spectrum are the longer red wavelengths. Outside of the visible window on the red side is infrared (IR) light, which provides heat. For helpful context, consider how shorter wavelengths have a harder time penetrating our atmosphere. So, the skies of dawn and dusk are predominately filled with red and near-infrared (NIR) light, while the middle of the day contains more blue and UV light. The bulk of wavelengths from the sun throughout the day are on the NIR end. The entire spectrum of visible and non-visible light between UV and IR plays critical roles in human health, especially towards mitochondrial health and metabolism. To summarize these benefits and provide a general overview for the following article, the benefits are as follows:
- UV – aids in the production of vitamin D and melanin, but also causes DNA damage
- Vitamin D improves immune system function and can repair DNA damage
- Melanin stores electrons for use within mitochondria
- Blue – involved in our circadian rhythm as the absence of blue light triggers the production of melatonin, an important antioxidant.
- Near-infrared (NIR) – improves mitochondria function and energy production while also protecting us from the harms of blue and UV light.
Ultraviolet Light
Let’s begin with a discussion around the widely misunderstood light of UV. UV is often viewed as a dangerous form of light, given that it can cause DNA damage and lead to cancer. While true, this myopic point of view ignores the crucial benefits of UV light. UV light produces vitamin D, which counteracts the DNA damage caused by UV while providing many other benefits. Additionally, UV light triggers the production of melanin, which aids in mitochondrial function. Like all physiological processes in the body that are vital to survival, there is a release of POMC-derived endorphins when skin comes into contact with UV light (Fell et al. 2014). Any person likely reading this article can agree that sitting under the sun simply feels amazing. We are drawn to it in a deeply meaningful sense.
Vitamin D is one of the most important chemicals regarding health, and it is poorly named. The term ‘vitamin’ refers to a compound that is important for health but cannot be adequately made within the body and must be retrieved externally. Peoples of the Northern and Southern hemisphere who are exposed to less UV light during winter would, for example, historically retrieve their vitamin D from foods such as oily fish, seal blubber, whale blubber, and polar bear liver (Wacker and Holick 2013). In a similar way, vitamin D was given its name 100 years ago when it was found that cod-liver oil was capable of curing rickets, when it was found that the so-called vitamin could promote calcium deposition in bones (McCollum et al. 1922). It was only until much later, in 1981, when scientists discovered that human skin could also synthesize vitamin D (M. F. Holick 1981). A majority of human vitamin D is produced by the skin when exposed to UVB (280 – 315 nm), while a minor amount is gained through food (Prietl et al. 2013; Wacker and Holick 2013). Most cells and organs in the human body have vitamin D receptors and many organs also have the ability to produce it, this speaks to the incredibly important nature of this compound towards our health (Prietl et al. 2013; Wacker and Holick 2013). Vitamin D deficiency has been associated with various types of cancer, autoimmune disorders, type 1 diabetes mellitus, multiple sclerosis (MS), cardiovascular disease, and even schizophrenia (Michael F. Holick 2007; Wacker and Holick 2013). Multiple studies have also found that vitamin D deficiency increases all-cause mortality (Garland et al. 2014; Yang et al. 2011; Chowdhury et al. 2014).
Though the historical benefits to vitamin D were attributed mainly to bone health, it is far more important. Vitamin D plays a critical role in protecting against invasive pathogens, reducing autoimmunity, and maintaining overall health (Wimalawansa 2023). Regarding immunity, one way it does this is by causing a shift away from proinflammatory responses to one more centered around T cell activation (Prietl et al. 2013). Vitamin D has therefore been shown to benefit other disorders that are related to immunity, such as a study that found vitamin D supplementation during pregnancy reduced asthmatic symptoms in children (Litonjua et al. 2016). That being said, it is important to highlight how there is no substitution for natural sunlight as a means of getting vitamin D. Naturally produced vitamin D from the skin lasts 2-3 times longer in the body (Wacker and Holick 2013). This is one of many likely reasons why the natural avenue should always be preferred over the supplemental. A similar line of reasoning follows in methods of getting UV light, as natural sun exposure leads to a decrease of all-cause mortality while the use of artificial tanning beds has been shown to increase all-cause and cancer mortality (Yang et al. 2011). More on why this likely occurs later.
Beyond vitamin D’s benefits to the immune system, it is important to focus on the compound’s role in mitochondrial health. In a previous article I wrote titled “Sunlight and Health”, I delve deeper into the importance of mitochondria and the science of how they work. In simplicity, imagine how all life on earth centers around energy. The sun provides energy to the earth, and the plethora of life on earth harness and facilitate the flow of that energy. Plants and animals share a symbiotic relationship within this system. Plants, through photosynthesis, take in sunlight, CO2, and water and create a glucose precursor and oxygen. This occurs within the chloroplast of plant cells. Within human cells, we have mitochondria. Our mitochondria, in turn, take in oxygen and glucose and produce CO2, water, and energy for our bodies in the form of ATP. What the plant breathes out, we breathe in, and vice versa. Mitochondria are central to all animal life on earth, and the ATP produced is central to all physiologic function. If your mitochondria are unhealthy, you are unhealthy and will experience disease.
Vitamin D plays a role in mitochondrial health at a DNA level. Our cells have DNA, which we inherited from our mother and father. On top of that, the mitochondria within our cells have their own set of DNA (mtDNA). Our mitochondria come from our mother’s egg, and therefore our mtDNA always is inherited from our mother. UV light can cause damage to both our DNA and mtDNA (Birch-Machin, Russell, and Latimer 2013). This is what gives UV light the ability to cause cancer. Additionally, damage to the mtDNA within our mitochondria can lead to mitochondrial dysfunction. The more poorly our mitochondria function, the less energy we produce for our cells, and the less healthy our cells become. There is research being developed that suggests the role of vitamin D is to counterbalance this danger by regulating gene transcription and reducing mtDNA damage. A mouse study conducted in 2011, for example, found that different shapes of vitamin D reduce the development of tumors in mice following UV exposure (Dixon et al. 2011). It is not unlike nature to create a system of checks and balances, to ensure that the damaging effects of UV light are counterbalanced by a compound produced by the body when exposure to that same light.
While vitamin D may be important for mitochondrial health by protecting against mtDNA damage, melanin potentially plays a much larger role. Melanin is the pigment in our skin that make us darker. Not only is the diversity in skin tones across humans due to variations in melanin content, but a tan is also the creation of more melanin. To be more specific, the skin’s exposure to UVA (315-400nm) leads to the creation of melanin (Wicks et al. 2011). The most obvious benefit to the production of melanin, which most people could appreciate, is that the darker or tanner our skin is, the less damage we will receive from UV light. In this way, melanin shares a similar responsibility to vitamin D, where both are protecting the body against the very thing that forms them. Even more crucially however, melanin acts as a battery for the mitochondria.
During cellular respiration, where mitochondria turn oxygen and glucose into energy, electrons are stripped from the glucose for use. In other words, what our mitochondria really need are oxygen and electrons, and the glucose is simply a means to an end. If the mitochondria are the engine, then the electrons are the fuel (assuming you are still breathing). Due to its chemical structure, melanin is a natural reversible oxidation-reduction system (Figge 1939). In other words, it can both store and release electrons. Melanin is therefore a kind of battery, retrieving electrons from various sources, and storing them for future use in our mitochondria as a substitute for food. When stated this way, and considering how food is important because both fats and carbohydrates fuel the body by providing electrons to our mitochondria, one can imagine how vitally important melanin is. Melanin is central towards the availability of electrons for use in our body to produce the energy to live. Without adequate melanin, your mitochondria will starve for fuel and not provide your body with the energy it needs to thrive.
Blue Light
To contextualize the role blue light plays in human health, it is important to revisit an important byproduct of cellular respiration within mitochondria. When mitochondria turn electrons and oxygen into energy, there is a byproduct formed known as reactive oxygen species (ROS). ROS play important roles in the body, but in excess they can cause DNA damage and disrupt various cellular processes. For example, UV light causes cancer due to the ROS generated, and studies have found that blue light does the same in both the skin and eyes (Nakashima, Ohta, and Wolf 2017; Abdouh et al. 2024). This research suggests that excess blue light or blue light in isolation can damage the eyes and cause harm like UV light.
Blue and UV light are predominant during the middle of the day. Though both may cause oxidative stress on the body, the body simultaneously counteracts this damage through melatonin. Think of melatonin as the junk remover for mitochondria. Throughout the day mitochondria produce energy, and ROS is formed. During our nighttime sleep, melatonin plays an important role as an antioxidant and removes the excess ROS (Leon et al. 2004).
The relationship between blue light and melatonin is important. During the day, when blue light is present, our body suppresses the production of melatonin (West et al. 2011). When the sun sets and there is no longer a heavy presence of blue light, our body begins to produce melatonin for sleep. This is a central function for how our body gets tired at night and gets ready for sleep. This is also why artificial light at night, from our modern technology, is harmful to human health because it tricks the body into the continual suppression of melatonin production. Without proper melatonin production, our cells buildup too much ROS and this can cause mitochondrial dysfunction and other sleep related issues.
Beyond the importance of getting good sleep and producing melatonin to remove excess ROS from our cells, the existence of artificial light and excess blue light is problematic during the day as well. As stated previously, blue light causes ROS buildup in both the skin and eyes (Nakashima, Ohta, and Wolf 2017; Abdouh et al. 2024). As with most harms from sunlight, our body has adapted with a backup plan. During the day, when blue and UV light is present, there is simultaneous exposure to NIR light (650-1200nm). Recent research suggests that NIR also counterbalances the harm of blue light by increasing melatonin synthesis in the mitochondria (Tan et al. 2023). This highlights the importance of receiving the full spectrum of light from the sun, as one wavelength counterbalances the damages of the other.
Near-Infrared Light
While indoor living has been commonplace for humans across generations, and modern technology has over saturated our bodies with blue light, some recent changes to our technology have made things worse. Incandescent light bulbs emit NIR light, this is why they got warm. However, LED lights do not emit NIR light. Therefore, where people of past generations were potentially exposed to a lot of artificial light at night, this was counterbalanced by the NIR emitted by those same lightbulbs. Now, modern humans use LEDs and spend 93% of our time indoors with zero exposure to NIR, which is 90% of the light emitted by the sun (Tan et al. 2023).
Not only does NIR light protect our bodies from the damaging consequences of blue light, but it similarly protects us against UV light. As stated previously, NIR may result in the production of melatonin within mitochondria during the day, helping protect against the ROS buildup and mtDNA damage. Additionally, research has also found that NIR light protects from UV light in other ways. For example, a study in 2008 found that pretreating skin with NIR light (660nm) prevented sunburns (Barolet and Boucher 2008). Another study found that red and NIR light (620-690nm) altered gene expression and upregulated DNA repair (Kim et al. 2019). Again, this highlights the theme that the body has produced the means to protect itself from the harms of the sun via other rays emitted. However, the protection from harmful rays is best achieved when exposed to the full spectrum of light wavelengths as they change throughout the day. The light of dawn and dusk is predominately red and NIR. Therefore, this research suggests that being exposed to morning light will protect the body from the potentially cancer-causing effects of the UV light later in the day. A human being who lived outside would naturally be exposed to this spectrum of light every day. However, modern humans may be inside in the morning, go to the beach during the middle of the day, and get sunburned because they do not properly receive the full spectrum of light as nature intended every day.
Lastly, it is important to explore the ways NIR improves mitochondrial function. If electrons are the fuel source for this engine, and melatonin is the junk removal, then NIR is the lubricant. NIR improves the energy output of mitochondria, and there are various hypotheses for how this occurs. One hypothesis is that NIR boosts the functionality of cytochrome c oxidase, one of the chromophores used in the electron transport chain (ETC) of cellular respiration within mitochondria (De Freitas and Hamblin 2016). Another involves NIR light’s ability to modify the viscosity of water which increases the efficiency of the final step in the ETC, the ATP synthase (Sommer, Haddad, and Fecht 2015). ATP synthase can be thought of as a kind of pump that produces ATP, in this way NIR can be thought of almost literally as a lubricant for this pump.
Summary
In summary, the research involving how sunlight affects mitochondrial health highlights the importance of the full spectrum of wavelengths, each of which plays a vital role in human health throughout the day. Having exposure to one, without the other, can lead to imbalances and mitochondrial disease. The red and NIR light in the morning helps our mitochondria produce more energy throughout the day, while also preparing our bodies for the beneficial yet dangerous wavelengths to come. In the middle of the day, we receive much more UV and blue light, which help us produce vitamin D and melanin, both central to health and wellness. Once the sun sets, and blue light is absent, we produce melatonin for sleep. During our sleep, the melatonin removes the dangerous byproducts of our energy-producing day, protecting us from disease and preparing us for the following day. Mitochondria are central to human health and life on earth, and the rays from the sun are central to mitochondrial health.
Respecting nature and its cycles is vital for us humans who are increasingly immersing ourselves in a world dominated by technology. Our ancestors did not have to reconcile with these ideas, because life forced these exposures upon them. If we wish to maintain health in our modern world, we must be able to find balance. Even though some might think they can escape into the virtual world, our bodies will always and forever be connected and reliant upon the natural one.
References
Abdouh, Mohamed, Yunxi Chen, Alicia Goyeneche, and Miguel N. Burnier. 2024. “Blue Light-Induced Mitochondrial Oxidative Damage Underlay Retinal Pigment Epithelial Cell Apoptosis.” International Journal of Molecular Sciences 25 (23): 12619.
Barolet, Daniel, and Annie Boucher. 2008. “LED Photoprevention: Reduced MED Response Following Multiple LED Exposures.” Lasers in Surgery and Medicine 40 (2): 106–12.
Birch-Machin, M. A., E. V. Russell, and J. A. Latimer. 2013. “Mitochondrial DNA Damage as a Biomarker for Ultraviolet Radiation Exposure and Oxidative Stress.” The British Journal of Dermatology 169 (s2): 9–14.
Chowdhury, Rajiv, Setor Kunutsor, Anna Vitezova, Clare Oliver-Williams, Susmita Chowdhury, Jessica C. Kiefte-de-Jong, Hassan Khan, et al. 2014. “Vitamin D and Risk of Cause Specific Death: Systematic Review and Meta-Analysis of Observational Cohort and Randomised Intervention Studies.” BMJ (Clinical Research Ed.) 348 (apr01 2): g1903.
De Freitas, Lucas Freitas, and Michael R. Hamblin. 2016. “Proposed Mechanisms of Photobiomodulation or Low-Level Light Therapy.” IEEE Journal of Selected Topics in Quantum Electronics: A Publication of the IEEE Lasers and Electro-Optics Society 22 (3): 348–64.
Dixon, Katie M., Anthony W. Norman, Vanessa B. Sequeira, Ritu Mohan, Mark S. Rybchyn, Vivienne E. Reeve, Gary M. Halliday, and Rebecca S. Mason. 2011. “1α,25(OH)₂-Vitamin D and a Nongenomic Vitamin D Analogue Inhibit Ultraviolet Radiation-Induced Skin Carcinogenesis.” Cancer Prevention Research (Philadelphia, Pa.) 4 (9): 1485–94.
Fell, Gillian L., Kathleen C. Robinson, Jianren Mao, Clifford J. Woolf, and David E. Fisher. 2014. “Skin β-Endorphin Mediates Addiction to UV Light.” Cell 157 (7): 1527–34.
Figge, Frank H. J. 1939. “Melanin: A Natural Reversible Oxidation-Reduction System and Indicator.” Experimental Biology and Medicine (Maywood, N.J.) 41 (1): 127.
Garland, Cedric F., June Jiwon Kim, Sharif Burgette Mohr, Edward Doerr Gorham, William B. Grant, Edward L. Giovannucci, Leo Baggerly, et al. 2014. “Meta-Analysis of All-Cause Mortality According to Serum 25-Hydroxyvitamin D.” American Journal of Public Health 104 (8): e43-50.
Holick, M. F. 1981. “The Cutaneous Photosynthesis of Previtamin D3: A Unique Photoendocrine System.” The Journal of Investigative Dermatology 77 (1): 51–58.
Holick, Michael F. 2007. “Vitamin D Deficiency.” The New England Journal of Medicine 357 (3): 266–81.
Kim, Hyun Soo, Yeo Jin Kim, Su Ji Kim, Doo Seok Kang, Tae Ryong Lee, Dong Wook Shin, Hyoung-June Kim, and Young Rok Seo. 2019. “Transcriptomic Analysis of Human Dermal Fibroblast Cells Reveals Potential Mechanisms Underlying the Protective Effects of Visible Red Light against Damage from Ultraviolet B Light.” Journal of Dermatological Science 94 (2): 276–83.
Leon, Josefa, Dario Acuña-Castroviejo, Rosa M. Sainz, Juan C. Mayo, Dun Xian Tan, and Russel J. Reiter. 2004. “Melatonin and Mitochondrial Function.” Life Sciences. Elsevier Inc. https://doi.org/10.1016/j.lfs.2004.03.003.
Lindqvist, P. G., E. Epstein, K. Nielsen, M. Landin-Olsson, C. Ingvar, and H. Olsson. 2016. “Avoidance of Sun Exposure as a Risk Factor for Major Causes of Death: A Competing Risk Analysis of the Melanoma in Southern Sweden Cohort.” Journal of Internal Medicine 280 (4): 375–87.
Litonjua, Augusto A., Vincent J. Carey, Nancy Laranjo, Benjamin J. Harshfield, Thomas F. McElrath, George T. O’Connor, Megan Sandel, et al. 2016. “Effect of Prenatal Supplementation with Vitamin D on Asthma or Recurrent Wheezing in Offspring by Age 3 Years: The VDAART Randomized Clinical Trial.” JAMA: The Journal of the American Medical Association 315 (4): 362–70.
McCollum, E. V., Nina Simmonds, J. Ernestine Becker, and P. G. Shipley. 1922. “Studies on Experimental Rickets.” The Journal of Biological Chemistry 53 (2): 293–312.
Nakashima, Yuya, Shigeo Ohta, and Alexander M. Wolf. 2017. “Blue Light-Induced Oxidative Stress in Live Skin.” Free Radical Biology & Medicine 108 (July): 300–310.
Prietl, Barbara, Gerlies Treiber, Thomas R. Pieber, and Karin Amrein. 2013. “Vitamin D and Immune Function.” Nutrients 5 (7): 2502–21.
Sommer, Andrei P., Mike Kh Haddad, and Hans Jörg Fecht. 2015. “Light Effect on Water Viscosity: Implication for ATP Biosynthesis.” Scientific Reports 5 (July). https://doi.org/10.1038/srep12029.
Tan, Dun-Xian, Russel J. Reiter, Scott Zimmerman, and Ruediger Hardeland. 2023. “Melatonin: Both a Messenger of Darkness and a Participant in the Cellular Actions of Non-Visible Solar Radiation of near Infrared Light.” Biology 12 (1): 89.
Wacker, Matthias, and Michael F. Holick. 2013. “Sunlight and Vitamin D: A Global Perspective for Health: A Global Perspective for Health.” Dermato-Endocrinology 5 (1): 51–108.
West, Kathleen E., Michael R. Jablonski, Benjamin Warfield, Kate S. Cecil, Mary James, Melissa A. Ayers, James Maida, et al. 2011. “Blue Light from Light-Emitting Diodes Elicits a Dose-Dependent Suppression of Melatonin in Humans.” Journal of Applied Physiology (Bethesda, Md.: 1985) 110 (3): 619–26.
Wicks, Nadine L., Jason W. Chan, Julia A. Najera, Jonathan M. Ciriello, and Elena Oancea. 2011. “UVA Phototransduction Drives Early Melanin Synthesis in Human Melanocytes.” Current Biology: CB 21 (22): 1906.
Wimalawansa, Sunil J. 2023. “Infections and Autoimmunity-the Immune System and Vitamin D: A Systematic Review.” Nutrients 15 (17): 3842.
Yang, Ling, Marie Lof, Marit Bragelien Veierød, Sven Sandin, Hans-Olov Adami, and Elisabete Weiderpass. 2011. “Ultraviolet Exposure and Mortality among Women in Sweden.” Cancer Epidemiology, Biomarkers & Prevention: A Publication of the American Association for Cancer Research, Cosponsored by the American Society of Preventive Oncology 20 (4): 683–90.
- UV – aids in the production of vitamin D and melanin, but also causes DNA damage
-
 @ 90152b7f:04e57401
2025-05-22 02:30:51
@ 90152b7f:04e57401
2025-05-22 02:30:51WikiLeaks The Global Intelligence Files
Released on 2013-03-11 00:00 GMT
| Email-ID | 364528 | | -------- | --------------------------- | | Date | 2007-09-20 03:02:09 | | From | os@stratfor.com | | To | intelligence@stratfor.com |
Rice, Israeli FM discuss Israeli decision of defining Gaza as "hostile\ entity"\ 2007-09-20 00:41:16\ http://news.xinhuanet.com/english/2007-09/20/content_6756959.htm\ \ JERUSALEM, Sept. 19 (Xinhua) -- Visiting U.S. Secretary of State\ Condoleezza Rice met with Israeli Foreign Minister Tzipi Livni on\ Wednesday, the two discussed Israel's decision that defined the Hamas-\ controlled Gaza Strip as a "hostile entity."\ \ At a joint press conference held after their meeting, Rice told the\ reporters that the Palestinian Hamas is a "hostile entity" to U.S. as well.\ \ Israel's Security Cabinet declared the Gaza Strip a "hostile entity" on\ Wednesday ahead of Rice's visit and said it would cutoff power and fuel\ supplies to the strip.\ \ Gaza's population, largely impoverished, is almost entirely\ dependent on Israel for the supply of electricity, water and fuel, and a\ cutoff would deepen their hardship.\ \ Since the Hamas takeover in June, Israel has closed crossings with\ Gaza almost entirely, allowing in only humanitarian aid. However, Rice\ reiterated that the United States will not abandon the innocent\ Palestinians in Gaza.\ \ For her part, Livni said that Israel withdrew from the Gaza Strip\ two years ago, hoping that could lead to the establishment of a\ Palestinian state, but only get almost daily rocket attacks in return.\ \ "We expect the Palestinians to understand that Israeli security is\ in their own interests," Livni said, adding that Palestinians must\ understand "supporting Hamas won't help them."\ \ The Israeli Security Cabinet's declaration of Gaza as an "hostile\ entity" could lead to the most severe retaliatory measure taken by\ Israel against Palestinian rocket fire from the strip.\ \ The crude rocket attacks have killed 12 people in southern Israel in\ the past seven years, injured dozens more and badly disrupted daily life\ in the region.\ \ Last week, a Qassam rocket hit an Israeli military base near the\ Gaza Strip, wounding over 60 soldiers in the attack. The attack then\ sparked calls for the government to take harsh response against the Gaza\ Strip, which has been under the control of Hamas since it violently took\ over the enclave in mid June.\ \ The Jewish states has been holding Hamas responsible for the attack,\ although the movement has not been directly involved in the attacks.\ Israel still accused the Islamic movement of doing little to halt them.\ \ Apart from the Palestinian issue, Rice also discussed with Livni\ issues about Iran, Lebanon and the Middle East peace progress.\ \ She said Israel and the Palestinians are showing good faith in their\ negotiations towards a "two state solution."\ \ Regarding Iranian issues, Rice told reporters that diplomatic mean\ is a part of efforts to halt the Iranian nuclear program, but stressed\ it "has to have teeth."\ \ Rice, who had visited this region in August, is also expected to\ hold separate meetings on Wednesday with Israeli Defense Minister Ehud\ Barak and the Likud party head Binyamin Netanyahu.\ \ She will then hold a dinner meeting with Israeli Prime Minister Ehud\ Olmert.\ \ Rice is scheduled to leave here Thursday afternoon and visit the\ West Bank city of Ramallah for meetings with the Palestinian leadership\ on Thursday.
-
 @ 04c915da:3dfbecc9
2025-05-20 15:50:48
@ 04c915da:3dfbecc9
2025-05-20 15:50:48For years American bitcoin miners have argued for more efficient and free energy markets. It benefits everyone if our energy infrastructure is as efficient and robust as possible. Unfortunately, broken incentives have led to increased regulation throughout the sector, incentivizing less efficient energy sources such as solar and wind at the detriment of more efficient alternatives.
The result has been less reliable energy infrastructure for all Americans and increased energy costs across the board. This naturally has a direct impact on bitcoin miners: increased energy costs make them less competitive globally.
Bitcoin mining represents a global energy market that does not require permission to participate. Anyone can plug a mining computer into power and internet to get paid the current dynamic market price for their work in bitcoin. Using cellphone or satellite internet, these mines can be located anywhere in the world, sourcing the cheapest power available.
Absent of regulation, bitcoin mining naturally incentivizes the build out of highly efficient and robust energy infrastructure. Unfortunately that world does not exist and burdensome regulations remain the biggest threat for US based mining businesses. Jurisdictional arbitrage gives miners the option of moving to a friendlier country but that naturally comes with its own costs.
Enter AI. With the rapid development and release of AI tools comes the requirement of running massive datacenters for their models. Major tech companies are scrambling to secure machines, rack space, and cheap energy to run full suites of AI enabled tools and services. The most valuable and powerful tech companies in America have stumbled into an accidental alliance with bitcoin miners: THE NEED FOR CHEAP AND RELIABLE ENERGY.
Our government is corrupt. Money talks. These companies will push for energy freedom and it will greatly benefit us all.
-
 @ 909e3fdc:73f2b10a
2025-05-22 02:14:38
@ 909e3fdc:73f2b10a
2025-05-22 02:14:38Pizza Day’s not really about pizza. It’s about Laszlo exhibiting Bitcoin as a P2P payment mechanism. That’s worth a cheers. In 15 years, Bitcoin went from a nerdy experiment to challenging the fiat system. That’s massive! It’s changed how I see the world. Patient hodling and carnivore-focus, practices that I picked up from the bitcoin community, shifted me from kinda nihilistic to stupidly optimistic. So, definitely celebrate Pizza Day. Or maybe barbecue steaks instead. Commiserate on the frivolous purchases that you made with bitcoin in the day. I think of these sometimes. Honour Laszlo’s pioneer vibe and Bitcoin’s insane rise, but keep your eyes on what’s coming. The future’s gonna be wilder than we think.
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:49:50
@ 6ad3e2a3:c90b7740
2025-05-20 13:49:50I’ve written about MSTR twice already, https://www.chrisliss.com/p/mstr and https://www.chrisliss.com/p/mstr-part-2, but I want to focus on legendary short seller James Chanos’ current trade wherein he buys bitcoin (via ETF) and shorts MSTR, in essence to “be like Mike” Saylor who sells MSTR shares at the market and uses them to add bitcoin to the company’s balance sheet. After all, if it’s good enough for Saylor, why shouldn’t everyone be doing it — shorting a company whose stock price is more than 2x its bitcoin holdings and using the proceeds to buy the bitcoin itself?
Saylor himself has said selling shares at 2x NAV (net asset value) to buy bitcoin is like selling dollars for two dollars each, and Chanos has apparently decided to get in while the getting (market cap more than 2x net asset value) is good. If the price of bitcoin moons, sending MSTR’s shares up, you are more than hedged in that event, too. At least that’s the theory.
The problem with this bet against MSTR’s mNAV, i.e., you are betting MSTR’s market cap will converge 1:1 toward its NAV in the short and medium term is this trade does not exist in a vacuum. Saylor has described how his ATM’s (at the market) sales of shares are accretive in BTC per share because of this very premium they carry. Yes, we’ll dilute your shares of the company, but because we’re getting you 2x the bitcoin per share, you are getting an ever smaller slice of an ever bigger overall pie, and the pie is growing 2x faster than your slice is reducing. (I https://www.chrisliss.com/p/mstr how this works in my first post.)
But for this accretion to continue, there must be a constant supply of “greater fools” to pony up for the infinitely printable shares which contain only half their value in underlying bitcoin. Yes, those shares will continue to accrete more BTC per share, but only if there are more fools willing to make this trade in the future. So will there be a constant supply of such “fools” to keep fueling MSTR’s mNAV multiple indefinitely?
Yes, there will be in my opinion because you have to look at the trade from the prospective fools’ perspective. Those “fools” are not trading bitcoin for MSTR, they are trading their dollars, selling other equities to raise them maybe, but in the end it’s a dollars for shares trade. They are not selling bitcoin for them.
You might object that those same dollars could buy bitcoin instead, so they are surely trading the opportunity cost of buying bitcoin for them, but if only 5-10 percent of the market (or less) is buying bitcoin itself, the bucket in which which those “fools” reside is the entire non-bitcoin-buying equity market. (And this is not considering the even larger debt market which Saylor has yet to tap in earnest.)
So for those 90-95 percent who do not and are not presently planning to own bitcoin itself, is buying MSTR a fool’s errand, so to speak? Not remotely. If MSTR shares are infinitely printable ATM, they are still less so than the dollar and other fiat currencies. And MSTR shares are backed 2:1 by bitcoin itself, while the fiat currencies are backed by absolutely nothing. So if you hold dollars or euros, trading them for MSTR shares is an errand more sage than foolish.
That’s why this trade (buying BTC and shorting MSTR) is so dangerous. Not only are there many people who won’t buy BTC buying MSTR, there are many funds and other investment entities who are only able to buy MSTR.
Do you want to get BTC at 1:1 with the 5-10 percent or MSTR backed 2:1 with the 90-95 percent. This is a bit like medical tests that have a 95 percent accuracy rate for an asymptomatic disease that only one percent of the population has. If someone tests positive, it’s more likely to be a false one than an indication he has the disease*. The accuracy rate, even at 19:1, is subservient to the size of the respective populations.
At some point this will no longer be the case, but so long as the understanding of bitcoin is not widespread, so long as the dollar is still the unit of account, the “greater fools” buying MSTR are still miles ahead of the greatest fools buying neither, and the stock price and mNAV should only increase.
. . .
One other thought: it’s more work to play defense than offense because the person on offense knows where he’s going, and the defender can only react to him once he moves. Similarly, Saylor by virtue of being the issuer of the shares knows when more will come online while Chanos and other short sellers are borrowing them to sell in reaction to Saylor’s strategy. At any given moment, Saylor can pause anytime, choosing to issue convertible debt or preferred shares with which to buy more bitcoin, and the shorts will not be given advance notice.
If the price runs, and there is no ATM that week because Saylor has stopped on a dime, so to speak, the shorts will be left having to scramble to change directions and buy the shares back to cover. Their momentum might be in the wrong direction, though, and like Allen Iverson breaking ankles with a crossover, Saylor might trigger a massive short squeeze, rocketing the share price ever higher. That’s why he actually welcomes Chanos et al trying this copycat strategy — it becomes the fuel for outsized gains.
For that reason, news that Chanos is shorting MSTR has not shaken my conviction, though there are other more pertinent https://www.chrisliss.com/p/mstr-part-2 with MSTR, of which one should be aware. And as always, do your own due diligence before investing in anything.
* To understand this, consider a population of 100,000, with one percent having a disease. That means 1,000 have it, 99,000 do not. If the test is 95 percent accurate, and everyone is tested, 950 of the 1,000 will test positive (true positives), 50 who have it will test negative (false negatives.) Of the positives, 95 percent of 99,000 (94,050) will test negative (true negatives) and five percent (4,950) will test positive (false positives). That means 4,950 out of 5,900 positives (84%) will be false.
-
 @ 0fa80bd3:ea7325de
2025-01-29 15:43:42
@ 0fa80bd3:ea7325de
2025-01-29 15:43:42Lyn Alden - биткойн евангелист или евангелистка, я пока не понял
npub1a2cww4kn9wqte4ry70vyfwqyqvpswksna27rtxd8vty6c74era8sdcw83aThomas Pacchia - PubKey owner - X - @tpacchia
npub1xy6exlg37pw84cpyj05c2pdgv86hr25cxn0g7aa8g8a6v97mhduqeuhgplcalvadev - Shopstr
npub16dhgpql60vmd4mnydjut87vla23a38j689jssaqlqqlzrtqtd0kqex0nkqCalle - Cashu founder
npub12rv5lskctqxxs2c8rf2zlzc7xx3qpvzs3w4etgemauy9thegr43sf485vgДжек Дорси
npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m21 ideas
npub1lm3f47nzyf0rjp6fsl4qlnkmzed4uj4h2gnf2vhe3l3mrj85vqks6z3c7lМного адресов. Хз кто надо сортировать
https://github.com/aitechguy/nostr-address-bookФиатДжеф - создатель Ностр - https://github.com/fiatjaf
npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6EVAN KALOUDIS Zues wallet
npub19kv88vjm7tw6v9qksn2y6h4hdt6e79nh3zjcud36k9n3lmlwsleqwte2qdПрограммер Коди https://github.com/CodyTseng/nostr-relay
npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wlAnna Chekhovich - Managing Bitcoin at The Anti-Corruption Foundation https://x.com/AnyaChekhovich
npub1y2st7rp54277hyd2usw6shy3kxprnmpvhkezmldp7vhl7hp920aq9cfyr7 -
 @ 0fa80bd3:ea7325de
2025-01-29 14:44:48
@ 0fa80bd3:ea7325de
2025-01-29 14:44:48![[yedinaya-rossiya-bear.png]]
1️⃣ Be where the bear roams. Stay in its territory, where it hunts for food. No point setting a trap in your backyard if the bear’s chilling in the forest.
2️⃣ Set a well-hidden trap. Bury it, disguise it, and place the bait right in the center. Bears are omnivores—just like secret police KGB agents. And what’s the tastiest bait for them? Money.
3️⃣ Wait for the bear to take the bait. When it reaches in, the trap will snap shut around its paw. It’ll be alive, but stuck. No escape.
Now, what you do with a trapped bear is another question... 😏
-
 @ a5ee4475:2ca75401
2025-05-19 01:11:59
@ a5ee4475:2ca75401
2025-05-19 01:11:59clients #link #list #english #article #finalversion #descentralismo
*These clients are generally applications on the Nostr network that allow you to use the same account, regardless of the app used, keeping your messages and profile intact.
**However, you may need to meet certain requirements regarding access and account NIP for some clients, so that you can access them securely and use their features correctly.
CLIENTS
Twitter like
- Nostrmo - [source] 🌐💻(🐧🪟🍎)🍎🤖(on zapstore)
- Coracle - Super App [source] 🌐🤖(on zapstore)
- Amethyst - Super App with note edit, delete and other stuff with Tor [source] 🤖(on zapstore)
- Primal - Social and wallet [source] 🌐🍎🤖(on zapstore)
- Iris - [source] 🌐🤖🍎
- Current - [source] 🤖🍎
- FreeFrom 🤖🍎
- Openvibe - Nostr and others (new Plebstr) [source] 🤖🍎
- Snort 🌐(🤖[early access]) [onion] [source]
- Damus 🍎 [source]
- Nos 🍎 [source]
- Nostur 🍎 [source]
- NostrBand 🌐 [info] [source]
- Yana [source] 🌐💻(🐧) 🍎🤖(on zapstore)
- Nostribe [on development] 🌐 [source]
- Lume 💻(🐧🪟🍎) [info] [source]
- Gossip - [source] 💻(🐧🪟🍎)
- noStrudel - Gamified Experience [onion] [info/source] 🌐
- [Nostrudel Next] - [onion]
- moStard - Nostrudel with Monero [onion] [info/source] 🌐
- Camelus - [source] 🤖 [early access]
Community
- CCNS - Community Curated Nostr Stuff [source]
- Nostr Kiwi [creator] 🌐
- Satellite [info] 🌐
- Flotilla - [source] 🌐🐧🤖(on zapstore)
- Chachi - [source] 🌐
- Futr - Coded in haskell [source] 🐧 (others soon)
- Soapbox - Comunnity server [info] [source] 🌐
- Ditto - Soapbox community server 🌐 [source] 🌐
- Cobrafuma - Nostr brazilian community on Ditto [info] 🌐
- Zapddit - Reddit like [source] 🌐
- Voyage (Reddit like) [on development] 🤖
Wiki
- Wikifreedia - Wiki Dark mode [source] 🌐
- Wikinostr - Wiki with tabs clear mode [source] 🌐
- Wikistr - Wiki clear mode [info] [source] 🌐
Search
- Keychat - Signal-like chat with AI and browser [source] 💻(🐧🪟🍎) - 📱(🍎🤖{on zapstore})
- Spring - Browser for Nostr apps and other sites [source] 🤖 (on zapstore)
- Advanced nostr search - Advanced note search by isolated terms related to a npub profile [source] 🌐
- Nos Today - Global note search by isolated terms [info] [source] 🌐
- Nostr Search Engine - API for Nostr clients [source]
- Ntrends - Trending notes and profiles 🌐
Website
- Nsite - Nostr Site [onion] [info] [source]
- Nsite Gateway - Nostr Site Gateway [source]
- Npub pro - Your site on Nostr [source]
App Store
ZapStore - Permitionless App Store [source] 🤖 💻(🐧🍎)
Video and Live Streaming
- Flare - Youtube like 🌐 [source]
- ZapStream - Lives, videos, shorts and zaps (NIP-53) [source] 🌐 🤖(lives only | Amber | on zapstore)
- Swae - Live streaming [source] (on development) ⏳
Post Aggregator - Kinostr - Nostr Cinema with #kinostr [english] [author] 🌐 - Stremstr - Nostr Cinema with #kinostr [english] [source] 📱 (on development) ⏳
Link Agreggator - Kinostr - #kinostr - Nostr Cinema Profile with links [English] - Equinox - Nostr Cinema Community with links [Portuguese]
Audio and Podcast Transmission
- Castr - Your npub as podcast feed [source]
- Nostr Nests - Audio Chats [source] 🌐
- Fountain - Podcast [source] 🤖🍎
- Corny Chat - Audio Chat [source] 🌐
Music
- Tidal - Music Streaming [source] [about] [info] 🤖🍎🌐
- Wavlake - Music Streaming [source] 🌐(🤖🍎 [early access])
- Tunestr - Musical Events [source] [about] 🌐
- Stemstr - Musical Colab (paid to post) [source] [about] 🌐
Images
- Lumina - Trending images and pictures [source] 🌐
- Pinstr - Pinterest like [source] 🌐
- Slidestr - DeviantArt like [source] 🌐
- Memestr - ifunny like [source] 🌐
Download and Upload
Documents, graphics and tables
- Mindstr - Mind maps [source] 🌐
- Docstr - Share Docs [info] [source] 🌐
- Formstr - Share Forms [info] 🌐
- Sheetstr - Share Spreadsheets [source] 🌐
- Slide Maker - Share slides 🌐 [Advice: Slide Maker https://zaplinks.lol/ site is down]
Health
- Sobrkey - Sobriety and mental health [source] 🌐
- Runstr - Running app [source] 🌐
- NosFabrica - Finding ways for your health data 🌐
- LazerEyes - Eye prescription by DM [source] 🌐
Forum
- OddBean - Hacker News like [info] [source] 🌐
- LowEnt - Forum [info] 🌐
- Swarmstr - Q&A / FAQ [info] 🌐
- Staker News - Hacker News like 🌐 [info]
Direct Messenges (DM)
- 0xchat 🤖🍎 [source]
- Nostr Chat 🌐🍎 [source]
- Blowater 🌐 [source]
- Anigma (new nostrgram) - Telegram based [on development] [source]
Reading
- Oracolo - A minimalist Nostr html blog [source]
- nRSS - Nostr RSS reader 🌐
- Highlighter - Insights with a highlighted read [info] 🌐
- Zephyr - Calming to Read [info] 🌐
- Flycat - Clean and Healthy Feed [info] 🌐
- Nosta - Check Profiles [on development] [info] 🌐
- Alexandria - e-Reader and Nostr Knowledge Base (NKB) [source] 🌐
Writing
- Habla - Blog [info] 🌐
- Blogstack - Blog [info]🌐
- YakiHonne - Articles and News [info] 🌐🍎🤖(on zapstore)
Lists
- Following - Users list [source] 🌐
- Nostr Unfollower - Nostr Unfollower
- Listr - Lists [source] 🌐
- Nostr potatoes - Movies List [source] 💻(numpy)
Market and Jobs
- Shopstr - Buy and Sell [onion] [source] 🌐
- Nostr Market - Buy and Sell 🌐
- Plebeian Market - Buy and Sell [source] 🌐
- Ostrich Work - Jobs [source] 🌐
- Nostrocket - Jobs [source] 🌐
Data Vending Machines - DVM (NIP90)
(Data-processing tools)
Games
- Chesstr - Chess 🌐 [source]
- Jestr - Chess [source] 🌐
- Snakestr - Snake game [source] 🌐
- Snakes on a Relay - Multiplayer Snake game like slither.io [source] 🌐
ENGINES - DEG Mods - Decentralized Game Mods [info] [source] 🌐 - NG Engine - Nostr Game Engine [source] 🌐 - JmonkeyEngine - Java game engine [source] 🌐
Customization
Like other Services
- Olas - Instagram like [source] 🌐🍎🤖(on zapstore)
- Nostree - Linktree like 🌐
- Rabbit - TweetDeck like [info] 🌐
- Zaplinks - Nostr links 🌐
- Omeglestr - Omegle-like Random Chats [source] 🌐
General Uses
- Njump - HTML text gateway source 🌐
- Filestr - HTML midia gateway [source] 🌐
- W3 - Nostr URL shortener [source] 🌐
- Playground - Test Nostr filters [source] 🌐
Places
- Wherostr - Travel and show where you are
- Arc Map (Mapstr) - Bitcoin Map [info]
Driver and Delivery
- RoadRunner - Uber like [on development] ⏱️
- Nostrlivery - iFood like [on development] ⏱️
⚠️ SCAM ⚠️ | Arcade City - Uber like [source]
OTHER STUFF
Lightning Wallets (zap)
- Alby - Native and extension [info] 🌐
- ZBD - Gaming and Social [info] [source] 🤖🍎
- Wallet of Satoshi - Simplest Lightning Wallet [info] 🤖🍎
- Minibits - Cashu mobile wallet [info] 🤖
- Blink - Opensource custodial wallet (KYC over 1000 usd) [source] 🤖🍎
- LNbits - App and extesion [source] 🤖🍎💻
- Zeus - [info] [source] 🤖🍎
Without Zap - Wassabi Wallet - Privacy-focused and non-custodial with Nostr Update Manager [source]
Exchange
Media Server (Upload Links)
audio, image and video
Connected with Nostr (NIP):
- Nostr Build - Free and paid Upload [info] [source] 🌐
- NostrMedia - Written in Go with Nip 96 / Blossom (free and paid) [info] [source]
- Nostr Check - [info] [source] 🌐
- NostPic - [info] [source] 🌐
- Sovbit - Free and paid upload [info] [source] 🌐
- Voidcat - Nip-96 and Blossom [source] 🌐
- Primal Media - Primal Media Uploader [source] 🌐
Blossom - Your Media Safer
- Primal Blossom 🌐
- NostrBuild Blossom - Free upload (max 100MiB) and paid [info] [source] 🌐
Paid Upload Only
- Satellite CDN - prepaid upload (max 5GB each) [info] [source] 🌐
Without Nostr NIP:
- Pomf - Upload larger videos (max 1GB) [source]
- Catbox - max 200 MB [source]
- x0 - max 512 MiB [source]
Donation and payments
- Zapper - Easy Zaps [source] 🌐
- Autozap [source] 🌐
- Zapmeacoffee 🌐
- Nostr Zap 💻(numpy)
- Creatr - Creators subscription 🌐
- Geyzer - Crowdfunding [info] [source] 🌐
- Heya! - Crowdfunding [source]
Security
- Secret Border - Generate offline keys 💻(java)
- Umbrel - Your private relay [source] 🌐
Key signing/login and Extension
- Amber - Key signing [source] 🤖(on zapstore)
- Nowser - Account access keys 📱(🤖🍎) 💻(🐧🍎🪟)
- Nos2x - Account access keys 🌐
- Nsec.app 🌐 [info]
- Lume - [info] [source] 🐧🪟🍎
- Satcom - Share files to discuss - [info] 🌐
- KeysBand - Multi-key signing [source] 🌐
Code
- Stacks - AI Templates [info] [source] 🌐
- Nostrify - Share Nostr Frameworks 🌐
- Git Workshop (github like) [experimental] 🌐
- Gitstr (github like) [on development] ⏱️
- Osty [on development] [info] 🌐
- Python Nostr - Python Library for Nostr
- Sybil - Creating, managing and test Nostr events [on development] ⏱️
Relay Check and Cloud
- Nostr Watch - See your relay speed 🌐
- NosDrive - Nostr Relay that saves to Google Drive
Bidges and Getways
- Matrixtr Bridge - Between Matrix & Nostr
- Mostr - Between Nostr & Fediverse
- Nostrss - RSS to Nostr
- Rsslay - Optimized RSS to Nostr [source]
- Atomstr - RSS/Atom to Nostr [source]
Useful Profiles and Trends
nostr-voice - Voice note (just some clients)
NOT RELATED TO NOSTR
Voca - Text-to-Speech App for GrapheneOS [source] 🤖(on zapstore)
Android Keyboards
Personal notes and texts
Front-ends
- Nitter - Twitter / X without your data [source]
- NewPipe - Youtube, Peertube and others, without account & your data [source] 🤖
- Piped - Youtube web without you data [source] 🌐
Other Services
- Brave - Browser [source]
- DuckDuckGo - Search [source]
- LLMA - Meta - Meta open source AI [source]
- DuckDuckGo AI Chat - Famous AIs without Login [source]
- Proton Mail - Mail [source]
Other open source index: Degoogled Apps
Some other Nostr index on:
-
 @ 9e69e420:d12360c2
2025-01-25 22:16:54
@ 9e69e420:d12360c2
2025-01-25 22:16:54President Trump plans to withdraw 20,000 U.S. troops from Europe and expects European allies to contribute financially to the remaining military presence. Reported by ANSA, Trump aims to deliver this message to European leaders since taking office. A European diplomat noted, “the costs cannot be borne solely by American taxpayers.”
The Pentagon hasn't commented yet. Trump has previously sought lower troop levels in Europe and had ordered cuts during his first term. The U.S. currently maintains around 65,000 troops in Europe, with total forces reaching 100,000 since the Ukraine invasion. Trump's new approach may shift military focus to the Pacific amid growing concerns about China.
-
 @ 6be5cc06:5259daf0
2025-01-21 20:58:37
@ 6be5cc06:5259daf0
2025-01-21 20:58:37A seguir, veja como instalar e configurar o Privoxy no Pop!_OS.
1. Instalar o Tor e o Privoxy
Abra o terminal e execute:
bash sudo apt update sudo apt install tor privoxyExplicação:
- Tor: Roteia o tráfego pela rede Tor.
- Privoxy: Proxy avançado que intermedia a conexão entre aplicativos e o Tor.
2. Configurar o Privoxy
Abra o arquivo de configuração do Privoxy:
bash sudo nano /etc/privoxy/configNavegue até a última linha (atalho:
Ctrl+/depoisCtrl+Vpara navegar diretamente até a última linha) e insira:bash forward-socks5 / 127.0.0.1:9050 .Isso faz com que o Privoxy envie todo o tráfego para o Tor através da porta 9050.
Salve (
CTRL+OeEnter) e feche (CTRL+X) o arquivo.
3. Iniciar o Tor e o Privoxy
Agora, inicie e habilite os serviços:
bash sudo systemctl start tor sudo systemctl start privoxy sudo systemctl enable tor sudo systemctl enable privoxyExplicação:
- start: Inicia os serviços.
- enable: Faz com que iniciem automaticamente ao ligar o PC.
4. Configurar o Navegador Firefox
Para usar a rede Tor com o Firefox:
- Abra o Firefox.
- Acesse Configurações → Configurar conexão.
- Selecione Configuração manual de proxy.
- Configure assim:
- Proxy HTTP:
127.0.0.1 - Porta:
8118(porta padrão do Privoxy) - Domínio SOCKS (v5):
127.0.0.1 - Porta:
9050
- Proxy HTTP:
- Marque a opção "Usar este proxy também em HTTPS".
- Clique em OK.
5. Verificar a Conexão com o Tor
Abra o navegador e acesse:
text https://check.torproject.org/Se aparecer a mensagem "Congratulations. This browser is configured to use Tor.", a configuração está correta.
Dicas Extras
- Privoxy pode ser ajustado para bloquear anúncios e rastreadores.
- Outros aplicativos também podem ser configurados para usar o Privoxy.
-
 @ 9e69e420:d12360c2
2025-01-21 19:31:48
@ 9e69e420:d12360c2
2025-01-21 19:31:48Oregano oil is a potent natural compound that offers numerous scientifically-supported health benefits.
Active Compounds
The oil's therapeutic properties stem from its key bioactive components: - Carvacrol and thymol (primary active compounds) - Polyphenols and other antioxidant
Antimicrobial Properties
Bacterial Protection The oil demonstrates powerful antibacterial effects, even against antibiotic-resistant strains like MRSA and other harmful bacteria. Studies show it effectively inactivates various pathogenic bacteria without developing resistance.
Antifungal Effects It effectively combats fungal infections, particularly Candida-related conditions like oral thrush, athlete's foot, and nail infections.
Digestive Health Benefits
Oregano oil supports digestive wellness by: - Promoting gastric juice secretion and enzyme production - Helping treat Small Intestinal Bacterial Overgrowth (SIBO) - Managing digestive discomfort, bloating, and IBS symptoms
Anti-inflammatory and Antioxidant Effects
The oil provides significant protective benefits through: - Powerful antioxidant activity that fights free radicals - Reduction of inflammatory markers in the body - Protection against oxidative stress-related conditions
Respiratory Support
It aids respiratory health by: - Loosening mucus and phlegm - Suppressing coughs and throat irritation - Supporting overall respiratory tract function
Additional Benefits
Skin Health - Improves conditions like psoriasis, acne, and eczema - Supports wound healing through antibacterial action - Provides anti-aging benefits through antioxidant properties
Cardiovascular Health Studies show oregano oil may help: - Reduce LDL (bad) cholesterol levels - Support overall heart health
Pain Management The oil demonstrates effectiveness in: - Reducing inflammation-related pain - Managing muscle discomfort - Providing topical pain relief
Safety Note
While oregano oil is generally safe, it's highly concentrated and should be properly diluted before use Consult a healthcare provider before starting supplementation, especially if taking other medications.
-
 @ 7460b7fd:4fc4e74b
2025-05-21 02:23:16
@ 7460b7fd:4fc4e74b
2025-05-21 02:23:16如果比特币发明了真正的钱,那么 Crypto 是什么?
引言
比特币诞生之初就以“数字黄金”姿态示人,被支持者誉为人类历史上第一次发明了真正意义上的钱——一种不依赖国家信用、总量恒定且不可篡改的硬通货。然而十多年过去,比特币之后蓬勃而起的加密世界(Crypto)已经远超“货币”范畴:从智能合约平台到去中心组织,从去央行的稳定币到戏谑荒诞的迷因币,Crypto 演化出一个丰富而混沌的新生态。这不禁引发一个根本性的追问:如果说比特币解决了“真金白银”的问题,那么 Crypto 又完成了什么发明?
 Crypto 与政治的碰撞:随着Crypto版图扩张,全球政治势力也被裹挟进这场金融变革洪流(示意图)。比特币的出现重塑了货币信用,但Crypto所引发的却是一场更深刻的政治与治理结构实验。从华尔街到华盛顿,从散户论坛到主权国家,越来越多人意识到:Crypto不只是技术或金融现象,而是一种全新的政治表达结构正在萌芽。正如有激进论者所断言的:“比特币发明了真正的钱,而Crypto则在发明新的政治。”价格K线与流动性曲线,或许正成为这个时代社群意志和社会价值观的新型投射。
Crypto 与政治的碰撞:随着Crypto版图扩张,全球政治势力也被裹挟进这场金融变革洪流(示意图)。比特币的出现重塑了货币信用,但Crypto所引发的却是一场更深刻的政治与治理结构实验。从华尔街到华盛顿,从散户论坛到主权国家,越来越多人意识到:Crypto不只是技术或金融现象,而是一种全新的政治表达结构正在萌芽。正如有激进论者所断言的:“比特币发明了真正的钱,而Crypto则在发明新的政治。”价格K线与流动性曲线,或许正成为这个时代社群意志和社会价值观的新型投射。冲突结构:当价格挑战选票
传统政治中,选票是人民意志的载体,一人一票勾勒出民主治理的正统路径。而在链上的加密世界里,骤升骤降的价格曲线和真金白银的买卖行为却扮演起了选票的角色:资金流向成了民意走向,市场多空成为立场表决。价格行为取代选票,这听来匪夷所思,却已在Crypto社群中成为日常现实。每一次代币的抛售与追高,都是社区对项目决策的即时“投票”;每一根K线的涨跌,都折射出社区意志的赞同或抗议。市场行为本身承担了决策权与象征权——价格即政治,正在链上蔓延。
这一新生政治形式与旧世界的民主机制形成了鲜明冲突。bitcoin.org中本聪在比特币白皮书中提出“一CPU一票”的工作量证明共识,用算力投票取代了人为决策bitcoin.org。而今,Crypto更进一步,用资本市场的涨跌来取代传统政治的选举。支持某项目?直接购入其代币推高市值;反对某提案?用脚投票抛售资产。相比漫长的选举周期和层层代议制,链上市场提供了近乎实时的“公投”机制。但这种机制也引发巨大争议:资本的投票天然偏向持币多者(富者)的意志,是否意味着加密政治更为金权而非民权?持币多寡成为影响力大小,仿佛选举演变成了“一币一票”,巨鲸富豪俨然掌握更多话语权。这种与民主平等原则的冲突,成为Crypto政治形式饱受质疑的核心张力之一。
尽管如此,我们已经目睹市场投票在Crypto世界塑造秩序的威力:2016年以太坊因DAO事件分叉时,社区以真金白银“投票”决定了哪条链获得未来。arkhamintelligence.com结果是新链以太坊(ETH)成为主流,其市值一度超过2,800亿美元,而坚持原则的以太经典(ETC)市值不足35亿美元,不及前者的八十分之一arkhamintelligence.com。市场选择清楚地昭示了社区的政治意志。同样地,在比特币扩容之争、各类硬分叉博弈中,无不是由投资者和矿工用资金与算力投票,胜者存续败者黯然。价格成为裁决纷争的最终选票,冲击着传统“选票决胜”的政治理念。Crypto的价格民主,与现代代议民主正面相撞,激起当代政治哲思中前所未有的冲突火花。
治理与分配
XRP对决SEC成为了加密世界“治理与分配”冲突的经典战例。2020年底,美国证券交易委员会(SEC)突然起诉Ripple公司,指控其发行的XRP代币属于未注册证券,消息一出直接引爆市场恐慌。XRP价格应声暴跌,一度跌去超过60%,最低触及0.21美元coindesk.com。曾经位居市值前三的XRP险些被打入谷底,监管的强硬姿态似乎要将这个项目彻底扼杀。
然而XRP社区没有选择沉默。 大批长期持有者组成了自称“XRP军团”(XRP Army)的草根力量,在社交媒体上高调声援Ripple,对抗监管威胁。面对SEC的指控,他们集体发声,质疑政府选择性执法,声称以太坊当年发行却“逍遥法外”,只有Ripple遭到不公对待coindesk.com。正如《福布斯》的评论所言:没人预料到愤怒的加密散户投资者会掀起法律、政治和社交媒体领域的‘海啸式’反击,痛斥监管机构背弃了保护投资者的承诺crypto-law.us。这种草根抵抗监管的话语体系迅速形成:XRP持有者不但在网上掀起舆论风暴,还采取实际行动向SEC施压。他们发起了请愿,抨击SEC背离保护投资者初衷、诉讼给个人投资者带来巨大伤害,号召停止对Ripple的上诉纠缠——号称这是在捍卫全球加密用户的共同利益bitget.com。一场由民间主导的反监管运动就此拉开帷幕。
Ripple公司则选择背水一战,拒绝和解,在法庭上与SEC针锋相对地鏖战了近三年之久。Ripple坚称XRP并非证券,不应受到SEC管辖,即使面临沉重法律费用和业务压力也不妥协。2023年,这场持久战迎来了标志性转折:美国法庭作出初步裁决,认定XRP在二级市场的流通不构成证券coindesk.com。这一胜利犹如给沉寂已久的XRP注入强心针——消息公布当天XRP价格飙涨近一倍,盘中一度逼近1美元大关coindesk.com。沉重监管阴影下苟延残喘的项目,凭借司法层面的突破瞬间重获生机。这不仅是Ripple的胜利,更被支持者视为整个加密行业对SEC强权的一次胜仗。
XRP的对抗路线与某些“主动合规”的项目形成了鲜明对比。 稳定币USDC的发行方Circle、美国最大合规交易所Coinbase等选择了一条迎合监管的道路:它们高调拥抱现行法规,希望以合作换取生存空间。然而现实却给了它们沉重一击。USDC稳定币在监管风波中一度失去美元锚定,哪怕Circle及时披露储备状况也无法阻止恐慌蔓延,大批用户迅速失去信心,短时间内出现数十亿美元的赎回潮blockworks.co。Coinbase则更为直接:即便它早已注册上市、反复向监管示好,2023年仍被SEC指控为未注册证券交易所reuters.com,卷入漫长诉讼漩涡。可见,在迎合监管的策略下,这些机构非但未能换来监管青睐,反而因官司缠身或用户流失而丧失市场信任。 相比之下,XRP以对抗求生存的路线反而赢得了投资者的眼光:价格的涨跌成为社区投票的方式,抗争的勇气反过来强化了市场对它的信心。
同样引人深思的是另一种迥异的治理路径:技术至上的链上治理。 以MakerDAO为代表的去中心化治理模式曾被寄予厚望——MKR持币者投票决策、算法维持稳定币Dai的价值,被视为“代码即法律”的典范。然而,这套纯技术治理在市场层面却未能形成广泛认同,亦无法激发群体性的情绪动员。复杂晦涩的机制使得普通投资者难以参与其中,MakerDAO的治理讨论更多停留在极客圈子内部,在社会大众的政治对话中几乎听不见它的声音。相比XRP对抗监管所激发的铺天盖地关注,MakerDAO的治理实验显得默默无闻、难以“出圈”。这也说明,如果一种治理实践无法连接更广泛的利益诉求和情感共鸣,它在社会政治层面就难以形成影响力。
XRP之争的政治象征意义由此凸显: 它展示了一条“以市场对抗国家”的斗争路线,即通过代币价格的集体行动来回应监管权力的施压。在这场轰动业界的对决中,价格即是抗议的旗帜,涨跌映射着政治立场。XRP对SEC的胜利被视作加密世界向旧有权力宣告的一次胜利:资本市场的投票器可以撼动监管者的强权。这种“价格即政治”的张力,正是Crypto世界前所未有的社会实验:去中心化社区以市场行为直接对抗国家权力,在无形的价格曲线中凝聚起政治抗争的力量,向世人昭示加密货币不仅有技术和资本属性,更蕴含着不可小觑的社会能量和政治意涵。
不可归零的政治资本
Meme 币的本质并非廉价或易造,而在于其构建了一种“无法归零”的社群生存结构。 对于传统观点而言,多数 meme 币只是短命的投机游戏:价格暴涨暴跌后一地鸡毛,创始人套现跑路,投资者血本无归,然后“大家转去炒下一个”theguardian.com。然而,meme 币社群的独特之处在于——失败并不意味着终结,而更像是运动的逗号而非句号。一次币值崩盘后,持币的草根们往往并未散去;相反,他们汲取教训,准备东山再起。这种近乎“不死鸟”的循环,使得 meme 币运动呈现出一种数字政治循环的特质:价格可以归零,但社群的政治热情和组织势能不归零。正如研究者所指出的,加密领域中的骗局、崩盘等冲击并不会摧毁生态,反而成为让系统更加强韧的“健康应激”,令整个行业在动荡中变得更加反脆弱cointelegraph.com。对应到 meme 币,每一次暴跌和重挫,都是社群自我进化、卷土重来的契机。这个去中心化群体打造出一种自组织的安全垫,失败者得以在瓦砾上重建家园。对于草根社群、少数派乃至体制的“失败者”而言,meme 币提供了一个永不落幕的抗争舞台,一种真正反脆弱的政治性。正因如此,我们看到诸多曾被嘲笑的迷因项目屡败屡战:例如 Dogecoin 自2013年问世后历经八年沉浮,早已超越玩笑属性,成为互联网史上最具韧性的迷因之一frontiersin.org;支撑 Dogecoin 的正是背后强大的迷因文化和社区意志,它如同美国霸权支撑美元一样,为狗狗币提供了“永不中断”的生命力frontiersin.org。
“复活权”的数字政治意涵
这种“失败-重生”的循环结构蕴含着深刻的政治意涵:在传统政治和商业领域,一个政党选举失利或一家公司破产往往意味着清零出局,资源散尽、组织瓦解。然而在 meme 币的世界,社群拥有了一种前所未有的“复活权”。当项目崩盘,社区并不必然随之消亡,而是可以凭借剩余的人心和热情卷土重来——哪怕换一个 token 名称,哪怕重启一条链,运动依然延续。正如 Cheems 项目的核心开发者所言,在几乎无人问津、技术受阻的困境下,大多数人可能早已卷款走人,但 “CHEEMS 社区没有放弃,背景、技术、风投都不重要,重要的是永不言弃的精神”cointelegraph.com。这种精神使得Cheems项目起死回生,社区成员齐声宣告“我们都是 CHEEMS”,共同书写历史cointelegraph.com。与传统依赖风投和公司输血的项目不同,Cheems 完全依靠社区的信念与韧性存续发展,体现了去中心化运动的真谛cointelegraph.com。这意味着政治参与的门槛被大大降低:哪怕没有金主和官方背书,草根也能凭借群体意志赋予某个代币新的生命。对于身处社会边缘的群体来说,meme 币俨然成为自组织的安全垫和重新集结的工具。难怪有学者指出,近期涌入meme币浪潮的主力,正是那些对现实失望但渴望改变命运的年轻人theguardian.com——“迷茫的年轻人,想要一夜暴富”theguardian.com。meme币的炒作表面上看是投机赌博,但背后蕴含的是草根对既有金融秩序的不满与反抗:没有监管和护栏又如何?一次失败算不得什么,社区自有后路和新方案。这种由底层群众不断试错、纠错并重启的过程,本身就是一种数字时代的新型反抗运动和群众动员机制。
举例而言,Terra Luna 的沉浮充分展现了这种“复活机制”的政治力量。作为一度由风投资本热捧的项目,Luna 币在2022年的崩溃本可被视作“归零”的失败典范——稳定币UST瞬间失锚,Luna币价归零,数十亿美元灰飞烟灭。然而**“崩盘”并没有画下休止符**。Luna的残余社区拒绝承认失败命运,通过链上治理投票毅然启动新链,“复活”了 Luna 代币,再次回到市场交易reuters.com。正如 Terra 官方在崩盘后发布的推文所宣称:“我们力量永在社区,今日的决定正彰显了我们的韧性”reuters.com。事实上,原链更名为 Luna Classic 后,大批所谓“LUNC 军团”的散户依然死守阵地,誓言不离不弃;他们自发烧毁巨量代币以缩减供应、推动技术升级,试图让这个一度归零的项目重新燃起生命之火binance.com。失败者并未散场,而是化作一股草根洪流,奋力托举起项目的残迹。经过迷因化的叙事重塑,这场从废墟中重建价值的壮举,成为加密世界中草根政治的经典一幕。类似的案例不胜枚举:曾经被视为笑话的 DOGE(狗狗币)正因多年社群的凝聚而跻身主流币种,总市值一度高达数百亿美元,充分证明了“民有民享”的迷因货币同样可以笑傲市场frontiersin.org。再看最新的美国政治舞台,连总统特朗普也推出了自己的 meme 币 $TRUMP,号召粉丝拿真金白银来表达支持。该币首日即从7美元暴涨至75美元,两天后虽回落到40美元左右,但几乎同时,第一夫人 Melania 又发布了自己的 $Melania 币,甚至连就职典礼的牧师都跟风发行了纪念币theguardian.com!显然,对于狂热的群众来说,一个币的沉浮并非终点,而更像是运动的换挡——资本市场成为政治参与的新前线,你方唱罢我登场,meme 币的群众动员热度丝毫不减。值得注意的是,2024年出现的 Pump.fun 等平台更是进一步降低了这一循环的技术门槛,任何人都可以一键生成自己的 meme 币theguardian.com。这意味着哪怕某个项目归零,剩余的社区完全可以借助此类工具迅速复制一个新币接力,延续集体行动的火种。可以说,在 meme 币的世界里,草根社群获得了前所未有的再生能力和主动权,这正是一种数字时代的群众政治奇观:失败可以被当作梗来玩,破产能够变成重生的序章。
价格即政治:群众投机的新抗争
meme 币现象的兴盛表明:在加密时代,价格本身已成为一种政治表达。这些看似荒诞的迷因代币,将金融市场变成了群众宣泄情绪和诉求的另一个舞台。有学者将此概括为“将公民参与直接转化为了投机资产”cdn-brighterworld.humanities.mcmaster.ca——也就是说,社会运动的热情被注入币价涨跌,政治支持被铸造成可以交易的代币。meme 币融合了金融、技术与政治,通过病毒般的迷因文化激发公众参与,形成对现实政治的某种映射cdn-brighterworld.humanities.mcmaster.caosl.com。当一群草根投入全部热忱去炒作一枚毫无基本面支撑的币时,这本身就是一种大众政治动员的体现:币价暴涨,意味着一群人以戏谑的方式在向既有权威叫板;币价崩盘,也并不意味着信念的消亡,反而可能孕育下一次更汹涌的造势。正如有分析指出,政治类 meme 币的出现前所未有地将群众文化与政治情绪融入市场行情,价格曲线俨然成为民意和趋势的风向标cdn-brighterworld.humanities.mcmaster.ca。在这种局面下,投机不再仅仅是逐利,还是一种宣示立场、凝聚共识的过程——一次次看似荒唐的炒作背后,是草根对传统体制的不服与嘲讽,是失败者拒绝认输的呐喊。归根结底,meme 币所累积的,正是一种不可被归零的政治资本。价格涨落之间,群众的愤怒、幽默与希望尽显其中;这股力量不因一次挫败而消散,反而在市场的循环中愈发壮大。也正因如此,我们才说“价格即政治”——在迷因币的世界里,价格不只是数字,更是人民政治能量的晴雨表,哪怕归零也终将卷土重来。cdn-brighterworld.humanities.mcmaster.caosl.com
全球新兴现象:伊斯兰金融的入场
当Crypto在西方世界掀起市场治政的狂潮时,另一股独特力量也悄然融入这一场域:伊斯兰金融携其独特的道德秩序,开始在链上寻找存在感。长期以来,伊斯兰金融遵循着一套区别于世俗资本主义的原则:禁止利息(Riba)、反对过度投机(Gharar/Maysir)、强调实际资产支撑和道德投资。当这些原则遇上去中心化的加密技术,会碰撞出怎样的火花?出人意料的是,这两者竟在“以市场行为表达价值”这个层面产生了惊人的共鸣。伊斯兰金融并不拒绝市场机制本身,只是为其附加了道德准则;Crypto则将市场机制推向了政治高位,用价格来表达社群意志。二者看似理念迥异,实则都承认市场行为可以也应当承载社会价值观。这使得越来越多金融与政治分析人士开始关注:当虔诚的宗教伦理遇上狂野的加密市场,会塑造出何种新范式?
事实上,穆斯林世界已经在探索“清真加密”的道路。一些区块链项目致力于确保协议符合伊斯兰教法(Sharia)的要求。例如Haqq区块链发行的伊斯兰币(ISLM),从规则层面内置了宗教慈善义务——每发行新币即自动将10%拨入慈善DAO,用于公益捐赠,以符合天课(Zakat)的教义nasdaq.comnasdaq.com。同时,该链拒绝利息和赌博类应用,2022年还获得了宗教权威的教令(Fatwa)认可其合规性nasdaq.com。再看理念层面,伊斯兰经济学强调**货币必须有内在价值**、收益应来自真实劳动而非纯利息剥削。这一点与比特币的“工作量证明”精神不谋而合——有人甚至断言法定货币无锚印钞并不清真,而比特币这类需耗费能源生产的资产反而更符合教法初衷cointelegraph.com。由此,越来越多穆斯林投资者开始以道德投资的名义进入Crypto领域,将资金投向符合清真原则的代币和协议。
这种现象带来了微妙的双重合法性:一方面,Crypto世界原本奉行“价格即真理”的世俗逻辑,而伊斯兰金融为其注入了一股道德合法性,使部分加密资产同时获得了宗教与市场的双重背书;另一方面,即便在遵循宗教伦理的项目中,最终决定成败的依然是市场对其价值的认可。道德共识与市场共识在链上交汇,共同塑造出一种混合的新秩序。这一全球新兴现象引发广泛议论:有人将其视为金融民主化的极致表现——不同文化价值都能在市场平台上表达并竞争;也有人警惕这可能掩盖新的风险,因为把宗教情感融入高风险资产,既可能凝聚强大的忠诚度,也可能在泡沫破裂时引发信仰与财富的双重危机。但无论如何,伊斯兰金融的入场使Crypto的政治版图更加丰盈多元。从华尔街交易员到中东教士,不同背景的人们正通过Crypto这个奇特的舞台,对人类价值的表达方式进行前所未有的实验。
升华结语:价格即政治的新直觉
回顾比特币问世以来的这段历程,我们可以清晰地看到一条演进的主线:先有货币革命,后有政治发明。比特币赋予了人类一种真正自主的数字货币,而Crypto在此基础上完成的,则是一项前所未有的政治革新——它让市场价格行为承担起了类似政治选票的功能,开创了一种“价格即政治”的新直觉。在这个直觉下,市场不再只是冷冰冰的交易场所;每一次资本流动、每一轮行情涨落,都被赋予了社会意义和政治涵义。买入即表态,卖出即抗议,流动性的涌入或枯竭胜过千言万语的陈情。Crypto世界中,K线图俨然成为民意曲线,行情图就是政治晴雨表。决策不再由少数权力精英关起门来制定,而是在全球无眠的交易中由无数普通人共同谱写。这样的政治形式也许狂野,也许充满泡沫和噪音,但它不可否认地调动起了广泛的社会参与,让原本疏离政治进程的个体通过持币、交易重新找回了影响力的幻觉或实感。
“价格即政治”并非一句简单的口号,而是Crypto给予世界的全新想象力。它质疑了传统政治的正统性:如果一串代码和一群匿名投资者就能高效决策资源分配,我们为何还需要繁冗的官僚体系?它也拷问着自身的内在隐忧:当财富与权力深度绑定,Crypto政治如何避免堕入金钱统治的老路?或许,正是在这样的矛盾和张力中,人类政治的未来才会不断演化。Crypto所开启的,不仅是技术乌托邦或金融狂欢,更可能是一次对民主形式的深刻拓展和挑战。这里有最狂热的逐利者,也有最理想主义的社群塑梦者;有一夜暴富的神话,也有瞬间破灭的惨痛。而这一切汇聚成的洪流,正冲撞着工业时代以来既定的权力谱系。
当我们再次追问:Crypto究竟是什么? 或许可以这样回答——Crypto是比特币之后,人类完成的一次政治范式的试验性跃迁。在这里,价格行为化身为选票,资本市场演化为广场,代码与共识共同撰写“社会契约”。这是一场仍在进行的文明实验:它可能无声地融入既有秩序,也可能剧烈地重塑未来规则。但无论结局如何,如今我们已经见证:在比特币发明真正的货币之后,Crypto正在发明真正属于21世纪的政治。它以数字时代的语言宣告:在链上,价格即政治,市场即民意,代码即法律。这,或许就是Crypto带给我们的最直观而震撼的本质启示。
参考资料:
-
中本聪. 比特币白皮书: 一种点对点的电子现金系统. (2008)bitcoin.org
-
Arkham Intelligence. Ethereum vs Ethereum Classic: Understanding the Differences. (2023)arkhamintelligence.com
-
Binance Square (@渔神的加密日记). 狗狗币价格为何上涨?背后的原因你知道吗?binance.com
-
Cointelegraph中文. 特朗普的迷因币晚宴预期内容揭秘. (2025)cn.cointelegraph.com
-
慢雾科技 Web3Caff (@Lisa). 风险提醒:从 LIBRA 看“政治化”的加密货币骗局. (2025)web3caff.com
-
Nasdaq (@Anthony Clarke). How Cryptocurrency Aligns with the Principles of Islamic Finance. (2023)nasdaq.comnasdaq.com
-
Cointelegraph Magazine (@Andrew Fenton). DeFi can be halal but not DOGE? Decentralizing Islamic finance. (2023)
-
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:44:28
@ 6ad3e2a3:c90b7740
2025-05-20 13:44:28I https://www.chrisliss.com/p/mstr a few months ago with the subtitle “The Only Stock,” and I’m starting to regret it. Now, it was trading at 396 on January 20 when I posted it and 404 now (even if it dipped 40 percent to 230 or so in between), but that’s not why I regret it. I pointed out it was not investable unless you’re willing to stomach large drawdowns, and anyone who bought then could exit with a small profit now had they not panic-sold along the way.
The reason I regret it is I don’t want to make public stock predictions because it adds stress to my life. I have not sold any of my shares yet, but something I’ve noticed recently has got me thinking about it, and stock tips are like a game of telephone wherein whoever is last in the chain might find out the wrong information and too late. And while every adult has agency and is responsible for his own financial decisions, I don’t want my readers losing money on account of anything I write.
My base case is still that MSTR becomes a trillion-dollar company, destroys the performance of the S&P, the Mag-7 and virtually any other equity portfolio most people would assemble. Michael Saylor is trading an infinitely-printable asset (his shares) for humanity’s best-ever, finite-supply digital gold, and that trade should be profitable for him and his shareholders in perpetuity.
I don’t know exactly what he plans to do when that trade is no longer available to him — either because no one takes fiat currency for bitcoin anymore or because his mNAV (market-cap-to-bitcoin-holding ratio) goes below one — but that’s not my main concern, either. At that point he’ll have so much bitcoin, he’ll probably become the world’s first and largest bitcoin bank and profit by making his pristine collateral available to individuals and institutions. Even at five percent interest, half a trillion in bitcoin would yield $25B in profits every year. Even at a modest 10x valuation, the stock would more than double from here.
I am also not overly concerned with Saylor’s present amount of convertible debt which is at low or zero rates and is only https://www.strategy.com/. He’s been conservative on that front and only issuing on favorable terms. I don’t doubt Saylor’s prescience, intelligence or business sense one bit.
What got me thinking were some Twitter posts by a former Salomon Brothers trader/prophet Josh Mandell https://x.com/JoshMandell6/status/1921597739458339193 recently. In November when bitcoin was mooning after the election, he predicted that on March 14th it would close at $84,000, and if it did it would then go on an epic run up to $444,000 this cycle.
A lot of people make predictions, a few of them come true, but rarely do they come true on the dot (it closed at exactly $84K according to some exchanges) and on such a specific timeframe. Now, maybe he just got lucky, or maybe he is a skilled trader who made one good prediction, but the reason he gave for his prediction, insofar as he gave one, was not some technical chart or quantitative analysis, but a memory he had from 30 years ago that got into his mind that he couldn’t shake. He didn’t get much more specific than that, other than that he was tuned into something that if he explained fully would make too many people think he had gone insane. And then the prediction came true on the dot months later.
Now I believe in the paranormal more than the average person. I do not think things are random, and insofar as they appear that way it’s only because we have incomplete information — even a coin toss is predictable if you knew the exact force and spin that was put on the coin. I think for whatever reason, this guy is plugged into something, and while I would never invest a substantial amount of money on that belief — not only are earnestly-made prophecies often delusions or even if correct wrongly interpreted — that he sold makes me think.
He gave more substantive reasons for selling than prophecy, by the way — he seems to think Saylor’s perpetual issuance of shares ATM (at the market) to buy more bitcoin is putting too much downward pressure on the stock. Obviously, selling shares — even if to buy the world’s most pristine collateral at a 2x-plus mNAV — reduces the short-term appreciation of those shares.
His thesis seems to be that Saylor is doing this even if he would be better off letting the price appreciate more, attracting more investors, squeezing more shorts, etc because he needs to improve his credit rating to tap into the convertible debt market to the extent he has promised ($42 billion more over the next few years) at favorable terms. But in doing this, he is souring common stock investors because they are not seeing the near-term appreciation they should on their holdings.
Now this is a trivial concern if over the long haul MSTR does what it has the last couple years which is to outperform by a wide margin not only every large cap stock and the S&P but bitcoin itself. And the bigger his stack of bitcoin, the more his stock should appreciate as bitcoin goes up. But markets do not operate linearly and rationally. Should he sour prospective buyers to a great enough extent, should he attract shorts (and supply them with available shares to borrow) to a great enough extent, perhaps there might be an mNAV-crushing cascade that drives people into other bitcoin treasury companies, ETFs or bitcoin itself.
Now Saylor as first mover and by far the largest publicly-traded treasury company has a significant advantage. Institutions are far less likely to invest in size in smaller treasury companies with shorter track records, and many of them are not allowed to invest in ETFs or bitcoin at all. And even if a lot of money did go into any of those vehicles, it would only drive the value of his assets up and hence his stock price, no matter the mNAV. But Josh Mandell sold his shares prior to a weekend where bitcoin went from 102K to 104K, the US announced a deal with China, the mag-7 had a big spike (AAPL was up 6.3 percent) and then MSTR’s stock went down from 416 to 404. As I said, he is on to something.
So what’s the real long-term risk? I don’t know. Maybe there’s something about the nature of bitcoin that long-term is not really amenable to third-party custody and administration. It’s a bearer asset (“not your keys, not your coins”), and introducing counterparty risk is antithetical to its core purpose, the separation of money and state, or in this case money and bank.
With the bitcoin network you can literally “be your own bank.” To transact in digital dollars you need a bank account — or at least a stable coin one mediated by a centralized entity like Tether. You can’t hold digital dollars in your mind via some memorized seed words like you can bitcoin, accessible anywhere in the world, the ledger of which is maintained by tens of thousands of individually-run nodes. This property which democratizes value storage in the way gold did, except now you can wield your purchasing power globally, might be so antithetical to communal storage via corporation or bank that doing so is doomed to catastrophe.
We’ve already seen this happen with exchanges via FTX and Mt. Gox. Counterparty risk is one of the problems bitcoin was created to solve, so moving that risk from a fractionally reserved international banking system to corporate balance sheets still very much a part of that system is probably not the seismic advancement integral to the technology’s promise.
But this is more of a philosophical concern rather than a concrete one. To get more specific, it’s easy to imagine Coinbase, if indeed that’s where MSTR custodies its coins, gets hacked or https://www.chrisliss.com/p/soft-landing, i.e., seized by an increasingly desperate and insolvent government. Or maybe Coinbase simply doesn’t have the coins it purports like FTX, or a rogue band of employees, working on behalf of some powerful faction for “https://www.chrisliss.com/national-security-and-public-healt” executes the rug pull. Even if you deem these scenarios unlikely, they are not unfathomable.
Beyond outright counterparty malfeasance, there are other risks — what if owning common stock in an enterprise that simply holds bitcoin falls out of favor? Imagine if some new individual custody solution emerges wherein you have direct access to the coins themselves in an “even a boomer can do this” kind of way wherein there’s no compelling reason to own common stock with its junior claims to the capital stack in the event of insolvency? Why stand in line behind debt holders and preferred shares when you can invest in something that’s directly withdrawable and accessible if world events spike volatility to a systemic breaking point?
Things need not even get that rocky for this to be a concern — just the perception that they might could spook people into realizing common stock of a corporate balance sheet might be less than ideal as your custody solution.
Moreover, Saylor himself presents some risk. He could be compromised or blackmailed, he could lose his cool or get into an accident. These are low-probability scenarios, but also not unfathomable as any single point of failure is a target, especially for those factions who stand to lose unimaginable wealth and power should his speculative attack on the system succeed at scale.
Finally, even if Saylor remains free to operate as he sees fit, there is what I’d call the Icarus risk — he might be too ambitious, too hell-bent on acquiring bitcoin at all costs, too much of a maniac in service of his vision. Remember, he initially bought bitcoin during the covid crash and concomitant massive money print upon his prescient realization that businesses providing goods and services couldn’t possibly keep pace with inflation over the long haul. He was merely playing defense to preserve his capital, and now, despite his sizable lead and secured position is still throwing forward passes in the fourth quarter rather than running out the clock and securing the W.
Saylor is now arguably less a bitcoin maximalist and advocate, articulately making the case for superior money and individual sovereignty, but a corporate titan hell-bent on world domination via apex-predator-status balance sheet. When is enough enough? Many of the greatest conquerors in history pushed their empires too far until they fractured. In fact, 25 years ago MSTR was a big winner before the dot-com crash during which its stock price and most of Saylor’s fortune were wiped out when he was sued by the SEC for accounting fraud (he subsequently settled).
Now it’s possible, he learned from that experience, got up off the mat and figured out how to avoid his youthful mistakes. But it’s also possible his character is such that he will repeat it again, only this time at scale.
But as I said, my base case is MSTR is a trillion-dollar market cap, and the stock runs in parallel with bitcoin’s ascendance over the next decade. Saylor has been https://www.strategy.com/, prescient, bold and responsible so far over this iteration. I view Mandell’s concerns as valid, but similar to Wall St’s ones about AMZN’s Jeff Bezos who relentlessly ignored their insistence on profitability for a decade as he plowed every dollar into building out productive capacity and turned the company into the $2T world-dominating retail giant it is now.
Again, I haven’t (yet) sold any of my shares or even call options. But because I posted about this in January I felt I should at least follow-up with a more detailed rundown of what I take to be the risks. As always, do your own due diligence with any prospective investment.
-
 @ 3f770d65:7a745b24
2025-01-19 21:48:49
@ 3f770d65:7a745b24
2025-01-19 21:48:49The recent shutdown of TikTok in the United States due to a potential government ban serves as a stark reminder how fragile centralized platforms truly are under the surface. While these platforms offer convenience, a more polished user experience, and connectivity, they are ultimately beholden to governments, corporations, and other authorities. This makes them vulnerable to censorship, regulation, and outright bans. In contrast, Nostr represents a shift in how we approach online communication and content sharing. Built on the principles of decentralization and user choice, Nostr cannot be banned, because it is not a platform—it is a protocol.
PROTOCOLS, NOT PLATFORMS.
At the heart of Nostr's philosophy is user choice, a feature that fundamentally sets it apart from legacy platforms. In centralized systems, the user experience is dictated by a single person or governing entity. If the platform decides to filter, censor, or ban specific users or content, individuals are left with little action to rectify the situation. They must either accept the changes or abandon the platform entirely, often at the cost of losing their social connections, their data, and their identity.
What's happening with TikTok could never happen on Nostr. With Nostr, the dynamics are completely different. Because it is a protocol, not a platform, no single entity controls the ecosystem. Instead, the protocol enables a network of applications and relays that users can freely choose from. If a particular application or relay implements policies that a user disagrees with, such as censorship, filtering, or even government enforced banning, they are not trapped or abandoned. They have the freedom to move to another application or relay with minimal effort.
THIS IS POWERFUL.
Take, for example, the case of a relay that decides to censor specific content. On a legacy platform, this would result in frustration and a loss of access for users. On Nostr, however, users can simply connect to a different relay that does not impose such restrictions. Similarly, if an application introduces features or policies that users dislike, they can migrate to a different application that better suits their preferences, all while retaining their identity and social connections.
The same principles apply to government bans and censorship. A government can ban a specific application or even multiple applications, just as it can block one relay or several relays. China has implemented both tactics, yet Chinese users continue to exist and actively participate on Nostr, demonstrating Nostr's ability to resistant censorship.
How? Simply, it turns into a game of whack-a-mole. When one relay is censored, another quickly takes its place. When one application is banned, another emerges. Users can also bypass these obstacles by running their own relays and applications directly from their homes or personal devices, eliminating reliance on larger entities or organizations and ensuring continuous access.
AGAIN, THIS IS POWERUFL.
Nostr's open and decentralized design makes it resistant to the kinds of government intervention that led to TikTok's outages this weekend and potential future ban in the next 90 days. There is no central server to target, no company to regulate, and no single point of failure. (Insert your CEO jokes here). As long as there are individuals running relays and applications, users continue creating notes and sending zaps.
Platforms like TikTok can be silenced with the stroke of a pen, leaving millions of users disconnected and abandoned. Social communication should not be silenced so incredibly easily. No one should have that much power over social interactions.
Will we on-board a massive wave of TikTokers in the coming hours or days? I don't know.
TikTokers may not be ready for Nostr yet, and honestly, Nostr may not be ready for them either. The ecosystem still lacks the completely polished applications, tools, and services they’re accustomed to. This is where we say "we're still early". They may not be early adopters like the current Nostr user base. Until we bridge that gap, they’ll likely move to the next centralized platform, only to face another government ban or round of censorship in the future. But eventually, there will come a tipping point, a moment when they’ve had enough. When that time comes, I hope we’re prepared. If we’re not, we risk missing a tremendous opportunity to onboard people who genuinely need Nostr’s freedom.
Until then, to all of the Nostr developers out there, keep up the great work and keep building. Your hard work and determination is needed.
-
 @ 21335073:a244b1ad
2025-03-18 20:47:50
@ 21335073:a244b1ad
2025-03-18 20:47:50Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 3f770d65:7a745b24
2025-05-20 21:14:28
@ 3f770d65:7a745b24
2025-05-20 21:14:28I’m Derek Ross, and I’m all-in on Nostr.
I started the Grow Nostr Initiative to help more people discover what makes Nostr so powerful: ✅ You own your identity ✅ You choose your social graph and algorithms ✅ You aren't locked into any single app or platform ✅ You can post, stream, chat, and build, all without gatekeepers
What we’re doing with Grow Nostr Initiative: 🌱 Hosting local meetups and mini-conferences to onboard people face-to-face 📚 Creating educational materials and guides to demystify how Nostr works 🧩 Helping businesses and creators understand how they can plug into Nostr (running media servers, relays, and using key management tools)
I believe Nostr is the foundation of a more open internet. It’s still early, but we’re already seeing incredible apps for social, blogging, podcasting, livestreaming, and more. And the best part is that they're all interoperable, censorship-resistant, and built on open standards. Nostr is the world's largest bitcoin economy by transaction volume and I truly believe that the purple pill helps the orange pill go down. Meaning, growing Nostr will also grow Bitcoin adoption.
If you’ve been curious about Nostr or are building something on it, or let’s talk. Whether you're just getting started or you're already deep in the ecosystem, I'm here to answer questions, share what I’ve learned, and hear your ideas. Check out https://nostrapps.com to find your next social decentralized experience.
Ask Me Anything about GNI, Nostr, Bitcoin, the upcoming #NosVegas event at the Bitcoin Conference next week, etc.!
– Derek Ross 🌐 https://grownostr.org npub18ams6ewn5aj2n3wt2qawzglx9mr4nzksxhvrdc4gzrecw7n5tvjqctp424
https://stacker.news/items/984689
-
 @ 04c915da:3dfbecc9
2025-05-15 15:31:45
@ 04c915da:3dfbecc9
2025-05-15 15:31:45Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ bc6ccd13:f53098e4
2025-05-21 22:13:47
@ bc6ccd13:f53098e4
2025-05-21 22:13:47The global population has been rising rapidly for the past two centuries when compared to historical trends. Fifty years ago, that trend seemed set to continue, and there was a lot of concern around the issue of overpopulation. But if you haven’t been living under a rock, you’ll know that while the population is still rising, that trend now seems set to reverse this century, and there’s every indication population could decline precipitously over the next two centuries.
Demographics is a field where predictions about the future are much more reliable than in most scientific fields. That’s because future population trends are “baked in” decades in advance. If you want to know how many fifty-year-olds there will be in forty years, all you have to do is count the ten-year-olds today and allow for mortality rates. That maximum was already determined by the number of births ten years ago, and absolutely nothing can change that now. The average person doesn’t think that through when they look at population trends. You hear a lot of “oh we just need to do more of x to help the declining birthrate” without an acknowledgement that future populations in a given cohort are already fixed by the number of births that already occurred.
As you can see, global birthrates have already declined close to the 2.3 replacement level, with some regions ahead of others, but all on the same trajectory with no region moving against the trend. I’m not going to speculate on the reasons for this, or even whether it’s a good or bad thing. Instead I’m going to make some observations about outcomes this trend could cause economically, and why. Like most macro issues, an individual can’t do anything to change the global landscape personally, but knowing what that landscape might look like is essential to avoiding fallout from trends outside your control.
The Resource Pie
Thomas Malthus popularized the concern about overpopulation with his 1798 book An Essay on the Principle of Population. The basic premise of the book was that population could grow and consume all the available resources, leading to mass poverty, starvation, disease, and population collapse. We can say in hindsight that this was incorrect, given that the global population has increased from less than a billion to over eight billion since then, and the apocalypse Malthus predicted hasn’t materialized. Exactly the opposite, in fact. The global standard of living has risen to levels Malthus couldn’t have imagined, much less predicted.
So where did Malthus go wrong? His hypothesis seems reasonable enough, and we do see a similar trend in certain animal populations. The base assumption Malthus got wrong was to assume resources are a finite, limiting factor to the human population. That at some point certain resources would be totally consumed, and that would be it. He treated it like a pie with a lot of slices, but still a finite number, and assumed that if the population kept rising, eventually every slice would be consumed and there would be no pie left for future generations. That turns out to be completely wrong.
Of course, the earth is finite at some abstract level. The number of atoms could theoretically be counted and quantified. But on a practical level, do humans exhaust the earth’s resources? I’d point to an article from Yale Scientific titled Has the Earth Run out of any Natural Resources? To quote,
> However, despite what doomsday predictions may suggest, the Earth has not run out of any resources nor is it likely that it will run out of any in the near future. > > In fact, resources are becoming more abundant. Though this may seem puzzling, it does not mean that the actual quantity of resources in the Earth’s crust is increasing but rather that the amount available for our use is constantly growing due to technological innovations. According to the U.S. Geological Survey, the only resource we have exhausted is cryolite, a mineral used in pesticides and aluminum processing. However, that is not to say every bit of it has been mined away; rather, producing it synthetically is much more cost efficient than mining the existing reserves at its current value.
As it happens, we don’t run out of resources. Instead, we become better at finding, extracting, and efficiently utilizing resources, which means that in practical terms resources become more abundant, not less. In other words, the pie grows faster than we can eat it.
So is there any resource that actually limits human potential? I think there is, and history would suggest that resource is human ingenuity and effort. The more people are thinking about and working on a problem, the more solutions we find and build to solve it. That means not only does the pie grow faster than we can eat it, but the more people there are, the faster the pie grows. Of course that assumes everyone eating pie is also working to grow the pie, but that’s a separate issue for now.
Productivity and Division of Labor
Why does having more people lead to more productivity? A big part of it comes down to division of labor and specialization. The best way to get really good at something is to do more of it. In a small community, doing just one thing simply isn’t possible. Everyone has to be somewhat of a generalist in order to survive. But with a larger population, being a specialist becomes possible. In fact, that’s the purpose of money, as I explained here.
nostr:naddr1qvzqqqr4gupzp0rve5f6xtu56djkfkkg7ktr5rtfckpun95rgxaa7futy86npx8yqq247t2dvet9q4tsg4qng36lxe6kc4nftayyy89kua2
The more specialized an economy becomes, the more efficient it can be. There are big economies of scale in almost every task or process. So for example, if a single person tried to build a car from scratch, it would be extremely difficult and take a very long time. However, if you have a thousand people building a car, each doing a specific job, they can become very good at doing that specific job and do it much faster. And then you can move that process to a factory, and build machines to do specific jobs, and add even more efficiency.
But that only works if you’re building more than one car. It doesn’t make sense to build a huge factory full of specialized equipment that takes lots of time and effort to design and manufacture, and then only build one car. You need to sell thousands of cars, maybe even millions of cars, to pay off that initial investment. So division of labor and specialization relies on large populations in two different ways. First, you need a large population to have enough people to specialize in each task. But second and just as importantly, you need a large population of buyers for the finished product. You need a big market in order to make mass production economical.
Think of a computer or smartphone. It takes thousands of specialized processes, thousands of complex parts, and millions of people doing specialized jobs to extract the raw materials, process them, and assemble them into a piece of electronic hardware. And electronics are relatively expensive anyway. Imagine how impossible it would be to manufacture electronics economically, if the market demand wasn’t literally in the billions of units.
Stairs Up, Elevator Down
We’ve seen exponential increases in productivity over the past few centuries, resulting in higher living standards even as population exploded. Now, facing the prospect of a drastic trend reversal, what will happen to productivity and living standards? The typical sentiment seems to be “well, there are a lot of people already competing for resources, so if population does decline, that will just reduce the competition and leave a bigger slice of pie for each person, so we’ll all be getting wealthier as a result of population decline.”
This seems reasonable at first glance. Surely dividing the economic pie into fewer slices means a bigger slice for everyone, right? But remember, more specialization and division of labor is what made the pie as big as it is to begin with. And specialization depends on large populations for both the supply of specialized labor, and the demand for finished goods. Can complex supply chains and mass production withstand population reduction intact? I don’t think the answer is clear.
The idea that it will all be okay, and we’ll get wealthier as population falls, is based on some faulty assumptions. It assumes that wealth is basically some fixed inventory of “things” that exist, and it’s all a matter of distribution. That’s typical Marxist thinking, similar to the reasoning behind “tax the rich” and other utopian wealth transfer schemes.
The reality is, wealth is a dynamic concept with strong network effects. For example, a grocery store in a large city can be a valuable asset with a large potential income stream. The same store in a small village with a declining population can be an unprofitable and effectively worthless liability.
Even something as permanent as a house is very susceptible to network effects. If you currently live in an area where housing is scarce and expensive, you might think a declining population would be the perfect solution to high housing costs. However, if you look at a place that’s already facing the beginnings of a population decline, you’ll see it’s not actually that simple. Japan, for example, is already facing an aging and declining population. And sure enough, you can get a house in Japan for free, or basically free. Sounds amazing, right? Not really.
If you check out the reason houses are given away in Japan, you’ll find a depressing reality. Most of the free houses are in rural areas or villages where the population is declining, often to the point that the village becomes uninhabited and abandoned. It’s so bad that in 2018, 13.6% of houses in Japan were vacant. Why do villages become uninhabited? Well, it turns out that a certain population level is necessary to support the services and businesses people need. When the population falls too low, specialized businesses can no longer operated profitably. It’s the exact issue we discussed with division of labor and the need for a high population to provide a market for the specialist to survive. As the local stores, entertainment venues, and businesses close, and skilled tradesmen move away to larger population centers with more customers, living in the village becomes difficult and depressing, if not impossible. So at a certain critical level, a village that’s too isolated will reach a tipping point where everyone leaves as fast as possible. And it turns out that an abandoned house in a remote village or rural area without any nearby services and businesses is worth… nothing. Nobody wants to live there, nobody wants to spend the money to maintain the house, nobody wants to pay the taxes needed to maintain the utilities the town relied on. So they try to give the houses away to anyone who agrees to live there, often without much success.
So on a local level, population might rise gradually over time, but when that process reverses and population declines to a certain level, it can collapse rather quickly from there.
I expect the same incentives to play out on a larger scale as well. Complex supply chains and extreme specialization lead to massive productivity. But there’s also a downside, which is the fragility of the system. Specialization might mean one shop can make all the widgets needed for a specific application, for the whole globe. That’s great while it lasts, but what happens when the owner of that shop retires with his lifetime of knowledge and experience? Will there be someone equally capable ready to fill his shoes? Hopefully… But spread that problem out across the global economy, and cracks start to appear. A specialized part is unavailable. So a machine that relies on that part breaks down and can’t be repaired. So a new machine needs to be built, which is a big expense that drives up costs and prices. And with a falling population, demand goes down. Now businesses are spending more to make fewer items, so they have to raise prices to stay profitable. Now fewer people can afford the item, so demand falls even further. Eventually the business is forced to close, and other industries that relied on the items they produced are crippled. Things become more expensive, or unavailable at any price. Living standards fall. What was a stairway up becomes an elevator down.
Hope, From the Parasite Class?
All that being said, I’m not completely pessimistic about the future. I think the potential for an acceptable outcome exists.
I see two broad groups of people in the economy; producers, and parasites. One thing the increasing productivity has done is made it easier than ever to survive. Food is plentiful globally, the only issues are with distribution. Medical advances save countless lives. Everything is more abundant than ever before. All that has led to a very “soft” economic reality. There’s a lot of non-essential production, which means a lot of wealth can be redistributed to people who contribute nothing, and if it’s done carefully, most people won’t even notice. And that is exactly what has happened, in spades.
There are welfare programs of every type and description, and handouts to people for every reason imaginable. It’s never been easier to survive without lifting a finger. So millions of able-bodied men choose to do just that.
Besides the voluntarily idle, the economy is full of “bullshit jobs.” Shoutout to David Graeber’s book with that title. (It’s an excellent book and one I would highly recommend, even though the author was a Marxist and his conclusions are completely wrong.) A 2015 British poll asked people, “Does your job make a meaningful contribution to the world?” Only 50% said yes, while 37% said no and 13% were uncertain.
This won’t be a surprise to anyone who’s operated a business, or even worked in the private sector in general. There are three types of jobs; jobs that accomplish something productive, jobs that accomplish nothing of value, and jobs that actually hinder people trying to accomplish something productive. The number of jobs in the last two categories has grown massively over the years. This would include a lot of unnecessary administrative jobs, burdensome regulatory jobs, useless DEI and HR jobs, a large percentage of public sector jobs, most of the military-industrial complex, and the list is endless. All these jobs accomplish nothing worthwhile at best, and actively discourage those who are trying to accomplish something at worst.
Even among jobs that do accomplish some useful purpose, the amount of time spent actually doing the job continues to decline. According to a 2016 poll, American office workers spent only 39% of their workday actually doing their primary task. The other 61% was largely wasted on unproductive administrative tasks and meetings, answering emails, and just simply wasting time.
I could go on, but the point is, there’s a lot of slack in the economy. We’ve become so productive that the number of people actually doing the work to keep everyone fed, clothed, and cared for is only a small percentage of the population. In one sense, that’s a cause for optimism. The population could decline a lot, and we’d still have enough bodies to man the economic engine, as it were.
Aging
The thing with population decline, though, is nobody gets to choose who goes first. Not unless you’re a psychopathic dictator. So populations get old, then they get small. This means that the number of dependents in the economy rises naturally. Once people retire, they still need someone to grow the food, keep the lights on, and provide the medical care. And it doesn’t matter how much money the retirees have saved, either. Money is just a claim on wealth. The goods and services actually have to be provided by someone, and if that someone was never born, all the money in the world won’t change anything.
And the aging occurs on top of all the people already taking from the economy without contributing anything of value. So that seems like a big problem.
Currently, wealth redistribution happens through a combination of direct taxes, indirect taxation through deficit spending, and the whole gamut of games that happen when banks create credit/debt money by making loans. In a lot of cases, it’s very indirect and difficult to pin down. For example, someone has a “job” in a government office, enforcing pointless regulations that actually hinder someone in the private sector from producing something useful. Their paycheck comes from the government, so a combination of taxes on productive people, and deficit spending, which is also a tax on productive people. But they “have a job,” so who’s going to question their contribution to society? On the other hand, it could be a banker or hedge fund manager. They might be pulling in a massive salary, but at the core all they’re really doing is finding creative financial ways to transfer wealth from productive people to themselves, without contributing anything of value.
You’ll notice a common theme if you think about this problem deeply. Most of the wealth transfer that supports the unproductive, whether that’s welfare recipients, retirees, bureaucrats, corporate middle managers, or weapons manufacturers, is only possible through expanding the money supply. There’s a limit to how much direct taxation the productive will bear while the option to collect welfare exists. At a certain point, people conclude that working hard every day isn’t worth it, when taxes take so much of their wages that they could make almost as much without working at all. So the balance of what it takes to support the dependent class has to come indirectly, through new money creation.
As long as the declining population happens under the existing monetary system, the future looks bleak. There’s no limit to how much money creation and inflation the parasite class will use in an attempt to avoid work. They’ll continue to suck the productive class dry until the workers give up in disgust, and the currency collapses into hyperinflation. And you can’t run a complex economy without functional money, so productivity inevitably collapses with the currency.
The optimistic view is that we don’t have to continue supporting the failed credit/debt monetary system. It’s hurting productivity, messing up incentives, and contributing to increasing wealth inequality and lower living standards for the middle class. If we walk away from that system and adopt a hard money standard, the possibility of inflationary wealth redistribution vanishes. The welfare and warfare programs have to be slashed. The parasite class is forced to get busy, or starve. In that scenario, the declining population of workers can be offset by a massive shift away from “bullshit jobs” and into actual productive work.
While that might not be a permanent solution to declining population, it would at least give us time to find a real solution, without having our complex economy collapse and send our living standards back to the 17th century.
It’s a complex issue with many possible outcomes, but I think a close look at the effects of the monetary system on productivity shows one obvious problem that will make the situation worse than necessary. Moving to a better monetary system and creating incentives for productivity would do a lot to reduce the economic impacts of a declining population.
-
 @ f9cf4e94:96abc355
2025-01-18 06:09:50
@ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |
 | Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |
| Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |  | 16Gb |
| 16Gb |Recomendo que use o Ubuntu Server para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi aqui. O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível aqui. Não instale um desktop (como xubuntu, lubuntu, xfce, etc.).
Passo 1: Atualizar o Sistema 🖥️
Primeiro, atualize seu sistema e instale o Tor:
bash apt update apt install tor
Passo 2: Criar o Arquivo de Serviço
nrs.service🔧Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo:
```unit [Unit] Description=Nostr Relay Server Service After=network.target
[Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure
[Install] WantedBy=multi-user.target ```
Passo 3: Baixar o Binário do Nostr 🚀
Baixe o binário mais recente do Nostr aqui no GitHub.
Passo 4: Criar as Pastas Necessárias 📂
Agora, crie as pastas para o aplicativo e o pendrive:
bash mkdir -p /opt/nrs /mnt/edriver
Passo 5: Listar os Dispositivos Conectados 🔌
Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados:
bash lsblk
Passo 6: Formatando o Pendrive 💾
Escolha o pendrive correto (por exemplo,
/dev/sda) e formate-o:bash mkfs.vfat /dev/sda
Passo 7: Montar o Pendrive 💻
Monte o pendrive na pasta
/mnt/edriver:bash mount /dev/sda /mnt/edriver
Passo 8: Verificar UUID dos Dispositivos 📋
Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados:
bash blkid
Passo 9: Alterar o
fstabpara Montar o Pendrive Automáticamente 📝Abra o arquivo
/etc/fstabe adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim:fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0
Passo 10: Copiar o Binário para a Pasta Correta 📥
Agora, copie o binário baixado para a pasta
/opt/nrs:bash cp nrs-arm64 /opt/nrs
Passo 11: Criar o Arquivo de Configuração 🛠️
Crie o arquivo de configuração com o seguinte conteúdo e salve-o em
/opt/nrs/config.yaml:yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true
Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️
Agora, copie o arquivo
nrs.servicepara o diretório/etc/systemd/system/:bash cp nrs.service /etc/systemd/system/Recarregue os serviços e inicie o serviço
nrs:bash systemctl daemon-reload systemctl enable --now nrs.service
Passo 13: Configurar o Tor 🌐
Abra o arquivo de configuração do Tor
/var/lib/tor/torrce adicione a seguinte linha:torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334
Passo 14: Habilitar e Iniciar o Tor 🧅
Agora, ative e inicie o serviço Tor:
bash systemctl enable --now tor.serviceO Tor irá gerar um endereço
.onionpara o seu servidor Nostr. Você pode encontrá-lo no arquivo/var/lib/tor/nostr_server/hostname.
Observações ⚠️
- Com essa configuração, os dados serão salvos no pendrive, enquanto o binário ficará no cartão SD do Raspberry Pi.
- O endereço
.oniondo seu servidor Nostr será algo como:ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion.
Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳
Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
-
 @ 7460b7fd:4fc4e74b
2025-05-21 02:35:36
@ 7460b7fd:4fc4e74b
2025-05-21 02:35:36如果比特币发明了真正的钱,那么 Crypto 是什么?
引言
比特币诞生之初就以“数字黄金”姿态示人,被支持者誉为人类历史上第一次发明了真正意义上的钱——一种不依赖国家信用、总量恒定且不可篡改的硬通货。然而十多年过去,比特币之后蓬勃而起的加密世界(Crypto)已经远超“货币”范畴:从智能合约平台到去中心组织,从去央行的稳定币到戏谑荒诞的迷因币,Crypto 演化出一个丰富而混沌的新生态。这不禁引发一个根本性的追问:如果说比特币解决了“真金白银”的问题,那么 Crypto 又完成了什么发明?
 Crypto 与政治的碰撞:随着Crypto版图扩张,全球政治势力也被裹挟进这场金融变革洪流(示意图)。比特币的出现重塑了货币信用,但Crypto所引发的却是一场更深刻的政治与治理结构实验。从华尔街到华盛顿,从散户论坛到主权国家,越来越多人意识到:Crypto不只是技术或金融现象,而是一种全新的政治表达结构正在萌芽。正如有激进论者所断言的:“比特币发明了真正的钱,而Crypto则在发明新的政治。”价格K线与流动性曲线,或许正成为这个时代社群意志和社会价值观的新型投射。
Crypto 与政治的碰撞:随着Crypto版图扩张,全球政治势力也被裹挟进这场金融变革洪流(示意图)。比特币的出现重塑了货币信用,但Crypto所引发的却是一场更深刻的政治与治理结构实验。从华尔街到华盛顿,从散户论坛到主权国家,越来越多人意识到:Crypto不只是技术或金融现象,而是一种全新的政治表达结构正在萌芽。正如有激进论者所断言的:“比特币发明了真正的钱,而Crypto则在发明新的政治。”价格K线与流动性曲线,或许正成为这个时代社群意志和社会价值观的新型投射。冲突结构:当价格挑战选票
传统政治中,选票是人民意志的载体,一人一票勾勒出民主治理的正统路径。而在链上的加密世界里,骤升骤降的价格曲线和真金白银的买卖行为却扮演起了选票的角色:资金流向成了民意走向,市场多空成为立场表决。价格行为取代选票,这听来匪夷所思,却已在Crypto社群中成为日常现实。每一次代币的抛售与追高,都是社区对项目决策的即时“投票”;每一根K线的涨跌,都折射出社区意志的赞同或抗议。市场行为本身承担了决策权与象征权——价格即政治,正在链上蔓延。
这一新生政治形式与旧世界的民主机制形成了鲜明冲突。bitcoin.org中本聪在比特币白皮书中提出“一CPU一票”的工作量证明共识,用算力投票取代了人为决策bitcoin.org。而今,Crypto更进一步,用资本市场的涨跌来取代传统政治的选举。支持某项目?直接购入其代币推高市值;反对某提案?用脚投票抛售资产。相比漫长的选举周期和层层代议制,链上市场提供了近乎实时的“公投”机制。但这种机制也引发巨大争议:资本的投票天然偏向持币多者(富者)的意志,是否意味着加密政治更为金权而非民权?持币多寡成为影响力大小,仿佛选举演变成了“一币一票”,巨鲸富豪俨然掌握更多话语权。这种与民主平等原则的冲突,成为Crypto政治形式饱受质疑的核心张力之一。
尽管如此,我们已经目睹市场投票在Crypto世界塑造秩序的威力:2016年以太坊因DAO事件分叉时,社区以真金白银“投票”决定了哪条链获得未来。arkhamintelligence.com结果是新链以太坊(ETH)成为主流,其市值一度超过2,800亿美元,而坚持原则的以太经典(ETC)市值不足35亿美元,不及前者的八十分之一arkhamintelligence.com。市场选择清楚地昭示了社区的政治意志。同样地,在比特币扩容之争、各类硬分叉博弈中,无不是由投资者和矿工用资金与算力投票,胜者存续败者黯然。价格成为裁决纷争的最终选票,冲击着传统“选票决胜”的政治理念。Crypto的价格民主,与现代代议民主正面相撞,激起当代政治哲思中前所未有的冲突火花。
治理与分配
XRP对决SEC成为了加密世界“治理与分配”冲突的经典战例。2020年底,美国证券交易委员会(SEC)突然起诉Ripple公司,指控其发行的XRP代币属于未注册证券,消息一出直接引爆市场恐慌。XRP价格应声暴跌,一度跌去超过60%,最低触及0.21美元coindesk.com。曾经位居市值前三的XRP险些被打入谷底,监管的强硬姿态似乎要将这个项目彻底扼杀。
然而XRP社区没有选择沉默。 大批长期持有者组成了自称“XRP军团”(XRP Army)的草根力量,在社交媒体上高调声援Ripple,对抗监管威胁。面对SEC的指控,他们集体发声,质疑政府选择性执法,声称以太坊当年发行却“逍遥法外”,只有Ripple遭到不公对待coindesk.com。正如《福布斯》的评论所言:没人预料到愤怒的加密散户投资者会掀起法律、政治和社交媒体领域的‘海啸式’反击,痛斥监管机构背弃了保护投资者的承诺crypto-law.us。这种草根抵抗监管的话语体系迅速形成:XRP持有者不但在网上掀起舆论风暴,还采取实际行动向SEC施压。他们发起了请愿,抨击SEC背离保护投资者初衷、诉讼给个人投资者带来巨大伤害,号召停止对Ripple的上诉纠缠——号称这是在捍卫全球加密用户的共同利益bitget.com。一场由民间主导的反监管运动就此拉开帷幕。
Ripple公司则选择背水一战,拒绝和解,在法庭上与SEC针锋相对地鏖战了近三年之久。Ripple坚称XRP并非证券,不应受到SEC管辖,即使面临沉重法律费用和业务压力也不妥协。2023年,这场持久战迎来了标志性转折:美国法庭作出初步裁决,认定XRP在二级市场的流通不构成证券coindesk.com。这一胜利犹如给沉寂已久的XRP注入强心针——消息公布当天XRP价格飙涨近一倍,盘中一度逼近1美元大关coindesk.com。沉重监管阴影下苟延残喘的项目,凭借司法层面的突破瞬间重获生机。这不仅是Ripple的胜利,更被支持者视为整个加密行业对SEC强权的一次胜仗。
XRP的对抗路线与某些“主动合规”的项目形成了鲜明对比。 稳定币USDC的发行方Circle、美国最大合规交易所Coinbase等选择了一条迎合监管的道路:它们高调拥抱现行法规,希望以合作换取生存空间。然而现实却给了它们沉重一击。USDC稳定币在监管风波中一度失去美元锚定,哪怕Circle及时披露储备状况也无法阻止恐慌蔓延,大批用户迅速失去信心,短时间内出现数十亿美元的赎回潮blockworks.co。Coinbase则更为直接:即便它早已注册上市、反复向监管示好,2023年仍被SEC指控为未注册证券交易所reuters.com,卷入漫长诉讼漩涡。可见,在迎合监管的策略下,这些机构非但未能换来监管青睐,反而因官司缠身或用户流失而丧失市场信任。 相比之下,XRP以对抗求生存的路线反而赢得了投资者的眼光:价格的涨跌成为社区投票的方式,抗争的勇气反过来强化了市场对它的信心。
同样引人深思的是另一种迥异的治理路径:技术至上的链上治理。 以MakerDAO为代表的去中心化治理模式曾被寄予厚望——MKR持币者投票决策、算法维持稳定币Dai的价值,被视为“代码即法律”的典范。然而,这套纯技术治理在市场层面却未能形成广泛认同,亦无法激发群体性的情绪动员。复杂晦涩的机制使得普通投资者难以参与其中,MakerDAO的治理讨论更多停留在极客圈子内部,在社会大众的政治对话中几乎听不见它的声音。相比XRP对抗监管所激发的铺天盖地关注,MakerDAO的治理实验显得默默无闻、难以“出圈”。这也说明,如果一种治理实践无法连接更广泛的利益诉求和情感共鸣,它在社会政治层面就难以形成影响力。
XRP之争的政治象征意义由此凸显: 它展示了一条“以市场对抗国家”的斗争路线,即通过代币价格的集体行动来回应监管权力的施压。在这场轰动业界的对决中,价格即是抗议的旗帜,涨跌映射着政治立场。XRP对SEC的胜利被视作加密世界向旧有权力宣告的一次胜利:资本市场的投票器可以撼动监管者的强权。这种“价格即政治”的张力,正是Crypto世界前所未有的社会实验:去中心化社区以市场行为直接对抗国家权力,在无形的价格曲线中凝聚起政治抗争的力量,向世人昭示加密货币不仅有技术和资本属性,更蕴含着不可小觑的社会能量和政治意涵。
不可归零的政治资本
Meme 币的本质并非廉价或易造,而在于其构建了一种“无法归零”的社群生存结构。 对于传统观点而言,多数 meme 币只是短命的投机游戏:价格暴涨暴跌后一地鸡毛,创始人套现跑路,投资者血本无归,然后“大家转去炒下一个”theguardian.com。然而,meme 币社群的独特之处在于——失败并不意味着终结,而更像是运动的逗号而非句号。一次币值崩盘后,持币的草根们往往并未散去;相反,他们汲取教训,准备东山再起。这种近乎“不死鸟”的循环,使得 meme 币运动呈现出一种数字政治循环的特质:价格可以归零,但社群的政治热情和组织势能不归零。正如研究者所指出的,加密领域中的骗局、崩盘等冲击并不会摧毁生态,反而成为让系统更加强韧的“健康应激”,令整个行业在动荡中变得更加反脆弱cointelegraph.com。对应到 meme 币,每一次暴跌和重挫,都是社群自我进化、卷土重来的契机。这个去中心化群体打造出一种自组织的安全垫,失败者得以在瓦砾上重建家园。对于草根社群、少数派乃至体制的“失败者”而言,meme 币提供了一个永不落幕的抗争舞台,一种真正反脆弱的政治性。正因如此,我们看到诸多曾被嘲笑的迷因项目屡败屡战:例如 Dogecoin 自2013年问世后历经八年沉浮,早已超越玩笑属性,成为互联网史上最具韧性的迷因之一frontiersin.org;支撑 Dogecoin 的正是背后强大的迷因文化和社区意志,它如同美国霸权支撑美元一样,为狗狗币提供了“永不中断”的生命力frontiersin.org。
“复活权”的数字政治意涵
这种“失败-重生”的循环结构蕴含着深刻的政治意涵:在传统政治和商业领域,一个政党选举失利或一家公司破产往往意味着清零出局,资源散尽、组织瓦解。然而在 meme 币的世界,社群拥有了一种前所未有的“复活权”。当项目崩盘,社区并不必然随之消亡,而是可以凭借剩余的人心和热情卷土重来——哪怕换一个 token 名称,哪怕重启一条链,运动依然延续。正如 Cheems 项目的核心开发者所言,在几乎无人问津、技术受阻的困境下,大多数人可能早已卷款走人,但 “CHEEMS 社区没有放弃,背景、技术、风投都不重要,重要的是永不言弃的精神”cointelegraph.com。这种精神使得Cheems项目起死回生,社区成员齐声宣告“我们都是 CHEEMS”,共同书写历史cointelegraph.com。与传统依赖风投和公司输血的项目不同,Cheems 完全依靠社区的信念与韧性存续发展,体现了去中心化运动的真谛cointelegraph.com。这意味着政治参与的门槛被大大降低:哪怕没有金主和官方背书,草根也能凭借群体意志赋予某个代币新的生命。对于身处社会边缘的群体来说,meme 币俨然成为自组织的安全垫和重新集结的工具。难怪有学者指出,近期涌入meme币浪潮的主力,正是那些对现实失望但渴望改变命运的年轻人theguardian.com——“迷茫的年轻人,想要一夜暴富”theguardian.com。meme币的炒作表面上看是投机赌博,但背后蕴含的是草根对既有金融秩序的不满与反抗:没有监管和护栏又如何?一次失败算不得什么,社区自有后路和新方案。这种由底层群众不断试错、纠错并重启的过程,本身就是一种数字时代的新型反抗运动和群众动员机制。
举例而言,Terra Luna 的沉浮充分展现了这种“复活机制”的政治力量。作为一度由风投资本热捧的项目,Luna 币在2022年的崩溃本可被视作“归零”的失败典范——稳定币UST瞬间失锚,Luna币价归零,数十亿美元灰飞烟灭。然而“崩盘”并没有画下休止符。Luna的残余社区拒绝承认失败命运,通过链上治理投票毅然启动新链,“复活”了 Luna 代币,再次回到市场交易reuters.com。正如 Terra 官方在崩盘后发布的推文所宣称:“我们力量永在社区,今日的决定正彰显了我们的韧性”reuters.com。事实上,原链更名为 Luna Classic 后,大批所谓“LUNC 军团”的散户依然死守阵地,誓言不离不弃;他们自发烧毁巨量代币以缩减供应、推动技术升级,试图让这个一度归零的项目重新燃起生命之火binance.com。失败者并未散场,而是化作一股草根洪流,奋力托举起项目的残迹。经过迷因化的叙事重塑,这场从废墟中重建价值的壮举,成为加密世界中草根政治的经典一幕。类似的案例不胜枚举:曾经被视为笑话的 DOGE(狗狗币)正因多年社群的凝聚而跻身主流币种,总市值一度高达数百亿美元,充分证明了“民有民享”的迷因货币同样可以笑傲市场frontiersin.org。再看最新的美国政治舞台,连总统特朗普也推出了自己的 meme 币 $TRUMP,号召粉丝拿真金白银来表达支持。该币首日即从7美元暴涨至75美元,两天后虽回落到40美元左右,但几乎同时,第一夫人 Melania 又发布了自己的 $Melania 币,甚至连就职典礼的牧师都跟风发行了纪念币theguardian.com!显然,对于狂热的群众来说,一个币的沉浮并非终点,而更像是运动的换挡——资本市场成为政治参与的新前线,你方唱罢我登场,meme 币的群众动员热度丝毫不减。值得注意的是,2024年出现的 Pump.fun 等平台更是进一步降低了这一循环的技术门槛,任何人都可以一键生成自己的 meme 币theguardian.com。这意味着哪怕某个项目归零,剩余的社区完全可以借助此类工具迅速复制一个新币接力,延续集体行动的火种。可以说,在 meme 币的世界里,草根社群获得了前所未有的再生能力和主动权,这正是一种数字时代的群众政治奇观:失败可以被当作梗来玩,破产能够变成重生的序章。
价格即政治:群众投机的新抗争
meme 币现象的兴盛表明:在加密时代,价格本身已成为一种政治表达。这些看似荒诞的迷因代币,将金融市场变成了群众宣泄情绪和诉求的另一个舞台。有学者将此概括为“将公民参与直接转化为了投机资产”cdn-brighterworld.humanities.mcmaster.ca——也就是说,社会运动的热情被注入币价涨跌,政治支持被铸造成可以交易的代币。meme 币融合了金融、技术与政治,通过病毒般的迷因文化激发公众参与,形成对现实政治的某种映射cdn-brighterworld.humanities.mcmaster.caosl.com。当一群草根投入全部热忱去炒作一枚毫无基本面支撑的币时,这本身就是一种大众政治动员的体现:币价暴涨,意味着一群人以戏谑的方式在向既有权威叫板;币价崩盘,也并不意味着信念的消亡,反而可能孕育下一次更汹涌的造势。正如有分析指出,政治类 meme 币的出现前所未有地将群众文化与政治情绪融入市场行情,价格曲线俨然成为民意和趋势的风向标cdn-brighterworld.humanities.mcmaster.ca。在这种局面下,投机不再仅仅是逐利,还是一种宣示立场、凝聚共识的过程——一次次看似荒唐的炒作背后,是草根对传统体制的不服与嘲讽,是失败者拒绝认输的呐喊。归根结底,meme 币所累积的,正是一种不可被归零的政治资本。价格涨落之间,群众的愤怒、幽默与希望尽显其中;这股力量不因一次挫败而消散,反而在市场的循环中愈发壮大。也正因如此,我们才说“价格即政治”——在迷因币的世界里,价格不只是数字,更是人民政治能量的晴雨表,哪怕归零也终将卷土重来。cdn-brighterworld.humanities.mcmaster.caosl.com
全球新兴现象:伊斯兰金融的入场
当Crypto在西方世界掀起市场治政的狂潮时,另一股独特力量也悄然融入这一场域:伊斯兰金融携其独特的道德秩序,开始在链上寻找存在感。长期以来,伊斯兰金融遵循着一套区别于世俗资本主义的原则:禁止利息(Riba)、反对过度投机(Gharar/Maysir)、强调实际资产支撑和道德投资。当这些原则遇上去中心化的加密技术,会碰撞出怎样的火花?出人意料的是,这两者竟在“以市场行为表达价值”这个层面产生了惊人的共鸣。伊斯兰金融并不拒绝市场机制本身,只是为其附加了道德准则;Crypto则将市场机制推向了政治高位,用价格来表达社群意志。二者看似理念迥异,实则都承认市场行为可以也应当承载社会价值观。这使得越来越多金融与政治分析人士开始关注:当虔诚的宗教伦理遇上狂野的加密市场,会塑造出何种新范式?
事实上,穆斯林世界已经在探索“清真加密”的道路。一些区块链项目致力于确保协议符合伊斯兰教法(Sharia)的要求。例如Haqq区块链发行的伊斯兰币(ISLM),从规则层面内置了宗教慈善义务——每发行新币即自动将10%拨入慈善DAO,用于公益捐赠,以符合天课(Zakat)的教义nasdaq.comnasdaq.com。同时,该链拒绝利息和赌博类应用,2022年还获得了宗教权威的教令(Fatwa)认可其合规性nasdaq.com。再看理念层面,伊斯兰经济学强调货币必须有内在价值、收益应来自真实劳动而非纯利息剥削。这一点与比特币的“工作量证明”精神不谋而合——有人甚至断言法定货币无锚印钞并不清真,而比特币这类需耗费能源生产的资产反而更符合教法初衷cointelegraph.com。由此,越来越多穆斯林投资者开始以道德投资的名义进入Crypto领域,将资金投向符合清真原则的代币和协议。
这种现象带来了微妙的双重合法性:一方面,Crypto世界原本奉行“价格即真理”的世俗逻辑,而伊斯兰金融为其注入了一股道德合法性,使部分加密资产同时获得了宗教与市场的双重背书;另一方面,即便在遵循宗教伦理的项目中,最终决定成败的依然是市场对其价值的认可。道德共识与市场共识在链上交汇,共同塑造出一种混合的新秩序。这一全球新兴现象引发广泛议论:有人将其视为金融民主化的极致表现——不同文化价值都能在市场平台上表达并竞争;也有人警惕这可能掩盖新的风险,因为把宗教情感融入高风险资产,既可能凝聚强大的忠诚度,也可能在泡沫破裂时引发信仰与财富的双重危机。但无论如何,伊斯兰金融的入场使Crypto的政治版图更加丰盈多元。从华尔街交易员到中东教士,不同背景的人们正通过Crypto这个奇特的舞台,对人类价值的表达方式进行前所未有的实验。
升华结语:价格即政治的新直觉
回顾比特币问世以来的这段历程,我们可以清晰地看到一条演进的主线:先有货币革命,后有政治发明。比特币赋予了人类一种真正自主的数字货币,而Crypto在此基础上完成的,则是一项前所未有的政治革新——它让市场价格行为承担起了类似政治选票的功能,开创了一种“价格即政治”的新直觉。在这个直觉下,市场不再只是冷冰冰的交易场所;每一次资本流动、每一轮行情涨落,都被赋予了社会意义和政治涵义。买入即表态,卖出即抗议,流动性的涌入或枯竭胜过千言万语的陈情。Crypto世界中,K线图俨然成为民意曲线,行情图就是政治晴雨表。决策不再由少数权力精英关起门来制定,而是在全球无眠的交易中由无数普通人共同谱写。这样的政治形式也许狂野,也许充满泡沫和噪音,但它不可否认地调动起了广泛的社会参与,让原本疏离政治进程的个体通过持币、交易重新找回了影响力的幻觉或实感。
“价格即政治”并非一句简单的口号,而是Crypto给予世界的全新想象力。它质疑了传统政治的正统性:如果一串代码和一群匿名投资者就能高效决策资源分配,我们为何还需要繁冗的官僚体系?它也拷问着自身的内在隐忧:当财富与权力深度绑定,Crypto政治如何避免堕入金钱统治的老路?或许,正是在这样的矛盾和张力中,人类政治的未来才会不断演化。Crypto所开启的,不仅是技术乌托邦或金融狂欢,更可能是一次对民主形式的深刻拓展和挑战。这里有最狂热的逐利者,也有最理想主义的社群塑梦者;有一夜暴富的神话,也有瞬间破灭的惨痛。而这一切汇聚成的洪流,正冲撞着工业时代以来既定的权力谱系。
当我们再次追问:Crypto究竟是什么? 或许可以这样回答——Crypto是比特币之后,人类完成的一次政治范式的试验性跃迁。在这里,价格行为化身为选票,资本市场演化为广场,代码与共识共同撰写“社会契约”。这是一场仍在进行的文明实验:它可能无声地融入既有秩序,也可能剧烈地重塑未来规则。但无论结局如何,如今我们已经见证:在比特币发明真正的货币之后,Crypto正在发明真正属于21世纪的政治。它以数字时代的语言宣告:在链上,价格即政治,市场即民意,代码即法律。这,或许就是Crypto带给我们的最直观而震撼的本质启示。
参考资料:
-
中本聪. 比特币白皮书: 一种点对点的电子现金系统. (2008)bitcoin.org
-
Arkham Intelligence. Ethereum vs Ethereum Classic: Understanding the Differences. (2023)arkhamintelligence.com
-
Binance Square (@渔神的加密日记). 狗狗币价格为何上涨?背后的原因你知道吗?binance.com
-
Cointelegraph中文. 特朗普的迷因币晚宴预期内容揭秘. (2025)cn.cointelegraph.com
-
慢雾科技 Web3Caff (@Lisa). 风险提醒:从 LIBRA 看“政治化”的加密货币骗局. (2025)web3caff.com
-
Nasdaq (@Anthony Clarke). How Cryptocurrency Aligns with the Principles of Islamic Finance. (2023)nasdaq.comnasdaq.com
-
Cointelegraph Magazine (@Andrew Fenton). DeFi can be halal but not DOGE? Decentralizing Islamic finance. (2023)cointelegraph.com
-
-
 @ ece127e2:745bab9c
2025-05-20 18:59:11
@ ece127e2:745bab9c
2025-05-20 18:59:11vamos a ver que tal
-
 @ bc6ccd13:f53098e4
2025-05-21 22:11:33
@ bc6ccd13:f53098e4
2025-05-21 22:11:33The Bitcoin price action since the US presidential election, and particularly today, November 11, has given me an excuse to revisit an idea I’ve written about before. I explained here that money doesn’t “flow into” assets, and that the terminology makes it difficult for people to understand how prices actually work.
nostr:naddr1qvzqqqr4gupzp0rve5f6xtu56djkfkkg7ktr5rtfckpun95rgxaa7futy86npx8yqqhy6mmwv4uj63r0v4ekutt594fx2ctvd3uj63nvdamj6jtww3hj6stw096xs6twvukkgmt9ws6xg86ht5t
The Bitcoin market this year has been a perfect illustration of the points I tried to make, which offers another angle to explain the concept.
Back in January, the first spot Bitcoin ETFs were launched for trading in the US market. This was heralded as a great thing for the Bitcoin price, and tracking “inflows” into these ETFs became a top priority for Bitcoin market analysts. The expectation of course was that more Bitcoin purchased by these ETFs would result in higher prices for the asset.
And sure enough, over the first two months of trading, from mid-January to mid-March, the combined “inflows” to the ETFs totaled around $11 billion. Over the same time frame, the Bitcoin price rose almost 60%, from around $43,000 to $68,000. As should be expected, right?
But then, over the next seven and a half months, from mid-March to early November, the ETFs saw another $11 billion in “inflows”. The Bitcoin price in mid-March? $68,000. In early November? All the way up to… $68,000. Seven and a half months of treading water.
So how can that be? How can $11 billion dollars flowing into an asset cause a 60% price rise once, and no price change at all the next time?
If you read my previous article linked above, you’ll see that the whole idea of money “flowing into” an asset is incorrect and misleading, and this is a perfect illustration why. If you step back a bit, you’ll see the folly of that mentality. So when the ETFs buy $11 billion dollars worth of Bitcoin, where does it come from? They obviously have to buy it from someone. As always, every transaction has a buyer and a seller. In this case, the sellers are current Bitcoin holders selling through OTC desks on the spot market.
So why focus on the ETF buying rather than the Bitcoin holder selling? Instead of saying there were $11 billion in inflows to the Bitcoin ETFs, why not say there were $11 billion in outflows from spot Bitcoin holders? It’s just as valid either way.
To take it a step further, many analysts were consistently confused all summer as Bitcoin ETFs continued to see “inflows” on days that the Bitcoin price stayed flat or even fell. So let’s imagine two consecutive days of $300 million daily “inflows” into the ETFs. The first day, the Bitcoin price rises 3%. The second day, the Bitcoin price falls 3%. The first day, headlines can read Bitcoin Price Rises 3% as ETFs See $300m in Inflows. The second day, headlines can read Bitcoin Price Falls 3% as Spot Bitcoin Holders See $300m in Outflows.
See the silliness of this whole idea? Money flows aren’t the cause of price movement. They’re a fake metric used as a post hoc justification for price moves by people who want you to believe they understand markets better than you.
Moving on to today, as I write this on the evening of November 11, Bitcoin is up 30% from $68,000 to $88,000 in the week since the November 5 election. It rose from $69,000 to $75,000 on election night alone, after US markets had closed and while there were no ETF “inflows” at all. In fact, the ETFs saw over a hundred million dollars in outflows on November 5, followed by an 8% single day price increase.
So if money flows don’t move price, what does?
Investor sentiment, that’s what.
Talking about money flows at all, as illustrated by the Bitcoin ETFs, requires arbitrarily dividing a single market into different segments to disguise the fact that every transaction has both a buyer and a seller, so every transaction has an equal dollar amount of “flows” in both directions. In actuality, price is set by a convergence between the highest price any potential buyer is willing to pay, and the lowest price any potential seller is willing to accept. And that number can change without a single transaction occurring, and without a single dollar “flowing” anywhere.
If every Bitcoin holder simultaneously decided tonight that the lowest price they’re willing to accept is $200,000 per Bitcoin, and a single potential buyer decided to buy a single dollar worth of Bitcoin at that price, that would be the new Bitcoin price tomorrow morning. No ETF “inflows” or institutional buying pressure or short squeezes or liquidations required, or any of the other excuses market analysts use to confuse normal people and make it seem like they have some deep esoteric insight into the workings of markets and future price action.
Don’t overcomplicate something as simple as price. If holders of an asset demand higher prices and potential buyers are willing to pay it, prices rise. If potential buyers of an asset offer lower prices and holders are willing to sell, prices fall. The constant interplay between all those individual investors sentiments is what forms a market and a price. The transferring of money between buyers and sellers is an effect of price, not a cause.
-
 @ a5ee4475:2ca75401
2025-05-15 14:11:16
@ a5ee4475:2ca75401
2025-05-15 14:11:16lists #descentralismo #compilation #english
*The last list was updated in Amethyst, so the update of this one will only be visible in Amethyst.
nostr:naddr1qq245dz5tqe8w46swpphgmr4f3047s6629t45qg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guxde6sl
AI
nostr:naddr1qq24xwtyt9v5wjzefe6523j32dy5ga65gagkjqgawaehxw309ahx7um5wghxy6t5vdhkjmn9wgh8xmmrd9skctczyzj7u3r4dz3rwg3x6erszwj4y502clwn026qsp99zgdx8n3v5a2qzqcyqqq823c8mw5zk
FOSS GAME
nostr:naddr1qq2kvwp3v4hhvk2sw3j5sm6h23g5wkz5ddzhzqg4waehxw309aex2mrp0yhxgctdw4eju6t09upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4gut57qtr
OSHW - Open Source Hardware
nostr:naddr1qqgrqvp5vd3kycejxask2efcv4jr2qgswaehxw309ahx7um5wghx6mmd9upzpf0wg36k3g3hygndv3cp8f2j284v0hfh4dqgqjj3yxnreck2w4qpqvzqqqr4guc43v6c
Markdown Uses for Some Clients
nostr:nevent1qqsv54qfgtme38r2tl9v6ghwfj09gdjukealstkzc77mwujr56tgfwsppemhxue69uhkummn9ekx7mp0qgsq37tg2603tu0cqdrxs30e2n5t8p87uenf4fvfepdcvr7nllje5zgrqsqqqqqpkdvta4
Other Links
nostr:nevent1qqsrm6ywny5r7ajakpppp0lt525n0s33x6tyn6pz0n8ws8k2tqpqracpzpmhxue69uhkummnw3ezumt0d5hsygp6e5ns0nv3dun430jky25y4pku6ylz68rz6zs7khv29q6rj5peespsgqqqqqqsmfwa78
-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:38:04
@ 6ad3e2a3:c90b7740
2025-05-20 13:38:04When I was a kid, I wanted to be rich, but found the prospect of hard work tedious, pointless and soul-crushing. Instead of studying for exams, getting some job and clawing your way up the ladder, I wondered why we couldn’t just build a device that measured your brain capacity and awarded you the money you would have made had you applied yourself. Eliminate the middleman, so to speak, the useless paper pushing evoked by the word “career.”
But when you think about it, it’s not really money you’re after, as money is but purchasing power, and so it’s the things money can provide like a nice lifestyle and the peace of mind that comes from not worrying about it. And it’s not really the lifestyle or financial independence, per se, since moment to moment what’s in your bank account isn’t determining your mental state, but the feeling those things give you — a sense of expansiveness and freedom.
But if you did have such a machine, and it awarded you the money, you probably wouldn’t have that kind of expansiveness and freedom, especially if you did nothing to achieve those things. You would still feel bored, distracted and unsatisfied despite unrestricted means to travel or dine out as you saw fit. People who win the lottery, for example, tend to revert to their prior level of satisfaction in short order.
The feeling you really want then is the sense of rising to a challenge, negotiating and adapting to your environment, persevering in a state of uncertainty, tapping into your resourcefulness and creativity. It’s only while operating at the edge of your capacity you could ever be so fulfilled. In fact, in such a state the question of your satisfaction level would never come up. You wouldn’t even think to wonder about it you’d be so engrossed.
So what you really crave is a mind device that encourages you to adapt to your environment using your full creative capabilities in the present moment, so much so you realize if you do not do this, you have the sense of squandering your life in a tedious, pointless and soul-crushing way. You need to be totally stuck, without the option of turning back. In sum, you need to face reality exactly as it is, without any escape therefrom.
The measure of your mind in that case is your reality itself. The device is already with you — it’s the world you are presently creating with the consciousness you have, providing you avenues to escape, none of which are satisfactory, none that can lead to the state you truly desire. You have a choice to pursue them fruitlessly and wind up at square one, or to abandon them and attain your freedom. No matter how many times you go down a false road, you wind up at the same place until you give up on the Sisyphean task and proceed in earnest.
My childhood fantasy was real, it turns out, only I had misunderstood its meaning.
-
 @ 6389be64:ef439d32
2025-01-16 15:44:06
@ 6389be64:ef439d32
2025-01-16 15:44:06Black Locust can grow up to 170 ft tall
Grows 3-4 ft. per year
Native to North America
Cold hardy in zones 3 to 8

Firewood
- BLT wood, on a pound for pound basis is roughly half that of Anthracite Coal
- Since its growth is fast, firewood can be plentiful
Timber

- Rot resistant due to a naturally produced robinin in the wood
- 100 year life span in full soil contact! (better than cedar performance)
- Fence posts
- Outdoor furniture
- Outdoor decking
- Sustainable due to its fast growth and spread
- Can be coppiced (cut to the ground)
- Can be pollarded (cut above ground)
- Its dense wood makes durable tool handles, boxes (tool), and furniture
- The wood is tougher than hickory, which is tougher than hard maple, which is tougher than oak.
- A very low rate of expansion and contraction
- Hardwood flooring
- The highest tensile beam strength of any American tree
- The wood is beautiful
Legume
- Nitrogen fixer
- Fixes the same amount of nitrogen per acre as is needed for 200-bushel/acre corn
- Black walnuts inter-planted with locust as “nurse” trees were shown to rapidly increase their growth [[Clark, Paul M., and Robert D. Williams. (1978) Black walnut growth increased when interplanted with nitrogen-fixing shrubs and trees. Proceedings of the Indiana Academy of Science, vol. 88, pp. 88-91.]]
Bees

- The edible flower clusters are also a top food source for honey bees
Shade Provider

- Its light, airy overstory provides dappled shade
- Planted on the west side of a garden it provides relief during the hottest part of the day
- (nitrogen provider)
- Planted on the west side of a house, its quick growth soon shades that side from the sun
Wind-break

- Fast growth plus it's feathery foliage reduces wind for animals, crops, and shelters
Fodder
- Over 20% crude protein
- 4.1 kcal/g of energy
- Baertsche, S.R, M.T. Yokoyama, and J.W. Hanover (1986) Short rotation, hardwood tree biomass as potential ruminant feed-chemical composition, nylon bag ruminal degradation and ensilement of selected species. J. Animal Sci. 63 2028-2043
-
 @ 6389be64:ef439d32
2025-01-14 01:31:12
@ 6389be64:ef439d32
2025-01-14 01:31:12Bitcoin is more than money, more than an asset, and more than a store of value. Bitcoin is a Prime Mover, an enabler and it ignites imaginations. It certainly fueled an idea in my mind. The idea integrates sensors, computational prowess, actuated machinery, power conversion, and electronic communications to form an autonomous, machined creature roaming forests and harvesting the most widespread and least energy-dense fuel source available. I call it the Forest Walker and it eats wood, and mines Bitcoin.
I know what you're thinking. Why not just put Bitcoin mining rigs where they belong: in a hosted facility sporting electricity from energy-dense fuels like natural gas, climate-controlled with excellent data piping in and out? Why go to all the trouble building a robot that digests wood creating flammable gasses fueling an engine to run a generator powering Bitcoin miners? It's all about synergy.
Bitcoin mining enables the realization of multiple, seemingly unrelated, yet useful activities. Activities considered un-profitable if not for Bitcoin as the Prime Mover. This is much more than simply mining the greatest asset ever conceived by humankind. It’s about the power of synergy, which Bitcoin plays only one of many roles. The synergy created by this system can stabilize forests' fire ecology while generating multiple income streams. That’s the realistic goal here and requires a brief history of American Forest management before continuing.
Smokey The Bear
In 1944, the Smokey Bear Wildfire Prevention Campaign began in the United States. “Only YOU can prevent forest fires” remains the refrain of the Ad Council’s longest running campaign. The Ad Council is a U.S. non-profit set up by the American Association of Advertising Agencies and the Association of National Advertisers in 1942. It would seem that the U.S. Department of the Interior was concerned about pesky forest fires and wanted them to stop. So, alongside a national policy of extreme fire suppression they enlisted the entire U.S. population to get onboard via the Ad Council and it worked. Forest fires were almost obliterated and everyone was happy, right? Wrong.
Smokey is a fantastically successful bear so forest fires became so few for so long that the fuel load - dead wood - in forests has become very heavy. So heavy that when a fire happens (and they always happen) it destroys everything in its path because the more fuel there is the hotter that fire becomes. Trees, bushes, shrubs, and all other plant life cannot escape destruction (not to mention homes and businesses). The soil microbiology doesn’t escape either as it is burned away even in deeper soils. To add insult to injury, hydrophobic waxy residues condense on the soil surface, forcing water to travel over the ground rather than through it eroding forest soils. Good job, Smokey. Well done, Sir!
Most terrestrial ecologies are “fire ecologies”. Fire is a part of these systems’ fuel load and pest management. Before we pretended to “manage” millions of acres of forest, fires raged over the world, rarely damaging forests. The fuel load was always too light to generate fires hot enough to moonscape mountainsides. Fires simply burned off the minor amounts of fuel accumulated since the fire before. The lighter heat, smoke, and other combustion gasses suppressed pests, keeping them in check and the smoke condensed into a plant growth accelerant called wood vinegar, not a waxy cap on the soil. These fires also cleared out weak undergrowth, cycled minerals, and thinned the forest canopy, allowing sunlight to penetrate to the forest floor. Without a fire’s heat, many pine tree species can’t sow their seed. The heat is required to open the cones (the seed bearing structure) of Spruce, Cypress, Sequoia, Jack Pine, Lodgepole Pine and many more. Without fire forests can’t have babies. The idea was to protect the forests, and it isn't working.
So, in a world of fire, what does an ally look like and what does it do?
Meet The Forest Walker

For the Forest Walker to work as a mobile, autonomous unit, a solid platform that can carry several hundred pounds is required. It so happens this chassis already exists but shelved.
Introducing the Legged Squad Support System (LS3). A joint project between Boston Dynamics, DARPA, and the United States Marine Corps, the quadrupedal robot is the size of a cow, can carry 400 pounds (180 kg) of equipment, negotiate challenging terrain, and operate for 24 hours before needing to refuel. Yes, it had an engine. Abandoned in 2015, the thing was too noisy for military deployment and maintenance "under fire" is never a high-quality idea. However, we can rebuild it to act as a platform for the Forest Walker; albeit with serious alterations. It would need to be bigger, probably. Carry more weight? Definitely. Maybe replace structural metal with carbon fiber and redesign much as 3D printable parts for more effective maintenance.
The original system has a top operational speed of 8 miles per hour. For our purposes, it only needs to move about as fast as a grazing ruminant. Without the hammering vibrations of galloping into battle, shocks of exploding mortars, and drunken soldiers playing "Wrangler of Steel Machines", time between failures should be much longer and the overall energy consumption much lower. The LS3 is a solid platform to build upon. Now it just needs to be pulled out of the mothballs, and completely refitted with outboard equipment.
The Small Branch Chipper

When I say “Forest fuel load” I mean the dead, carbon containing litter on the forest floor. Duff (leaves), fine-woody debris (small branches), and coarse woody debris (logs) are the fuel that feeds forest fires. Walk through any forest in the United States today and you will see quite a lot of these materials. Too much, as I have described. Some of these fuel loads can be 8 tons per acre in pine and hardwood forests and up to 16 tons per acre at active logging sites. That’s some big wood and the more that collects, the more combustible danger to the forest it represents. It also provides a technically unlimited fuel supply for the Forest Walker system.
The problem is that this detritus has to be chewed into pieces that are easily ingestible by the system for the gasification process (we’ll get to that step in a minute). What we need is a wood chipper attached to the chassis (the LS3); its “mouth”.
A small wood chipper handling material up to 2.5 - 3.0 inches (6.3 - 7.6 cm) in diameter would eliminate a substantial amount of fuel. There is no reason for Forest Walker to remove fallen trees. It wouldn’t have to in order to make a real difference. It need only identify appropriately sized branches and grab them. Once loaded into the chipper’s intake hopper for further processing, the beast can immediately look for more “food”. This is essentially kindling that would help ignite larger logs. If it’s all consumed by Forest Walker, then it’s not present to promote an aggravated conflagration.
I have glossed over an obvious question: How does Forest Walker see and identify branches and such? LiDaR (Light Detection and Ranging) attached to Forest Walker images the local area and feed those data to onboard computers for processing. Maybe AI plays a role. Maybe simple machine learning can do the trick. One thing is for certain: being able to identify a stick and cause robotic appendages to pick it up is not impossible.
Great! We now have a quadrupedal robot autonomously identifying and “eating” dead branches and other light, combustible materials. Whilst strolling through the forest, depleting future fires of combustibles, Forest Walker has already performed a major function of this system: making the forest safer. It's time to convert this low-density fuel into a high-density fuel Forest Walker can leverage. Enter the gasification process.
The Gassifier

The gasifier is the heart of the entire system; it’s where low-density fuel becomes the high-density fuel that powers the entire system. Biochar and wood vinegar are process wastes and I’ll discuss why both are powerful soil amendments in a moment, but first, what’s gasification?
Reacting shredded carbonaceous material at high temperatures in a low or no oxygen environment converts the biomass into biochar, wood vinegar, heat, and Synthesis Gas (Syngas). Syngas consists primarily of hydrogen, carbon monoxide, and methane. All of which are extremely useful fuels in a gaseous state. Part of this gas is used to heat the input biomass and keep the reaction temperature constant while the internal combustion engine that drives the generator to produce electrical power consumes the rest.
Critically, this gasification process is “continuous feed”. Forest Walker must intake biomass from the chipper, process it to fuel, and dump the waste (CO2, heat, biochar, and wood vinegar) continuously. It cannot stop. Everything about this system depends upon this continual grazing, digestion, and excretion of wastes just as a ruminal does. And, like a ruminant, all waste products enhance the local environment.
When I first heard of gasification, I didn’t believe that it was real. Running an electric generator from burning wood seemed more akin to “conspiracy fantasy” than science. Not only is gasification real, it’s ancient technology. A man named Dean Clayton first started experiments on gasification in 1699 and in 1901 gasification was used to power a vehicle. By the end of World War II, there were 500,000 Syngas powered vehicles in Germany alone because of fossil fuel rationing during the war. The global gasification market was $480 billion in 2022 and projected to be as much as $700 billion by 2030 (Vantage Market Research). Gasification technology is the best choice to power the Forest Walker because it’s self-contained and we want its waste products.
Biochar: The Waste

Biochar (AKA agricultural charcoal) is fairly simple: it’s almost pure, solid carbon that resembles charcoal. Its porous nature packs large surface areas into small, 3 dimensional nuggets. Devoid of most other chemistry, like hydrocarbons (methane) and ash (minerals), biochar is extremely lightweight. Do not confuse it with the charcoal you buy for your grill. Biochar doesn’t make good grilling charcoal because it would burn too rapidly as it does not contain the multitude of flammable components that charcoal does. Biochar has several other good use cases. Water filtration, water retention, nutrient retention, providing habitat for microscopic soil organisms, and carbon sequestration are the main ones that we are concerned with here.
Carbon has an amazing ability to adsorb (substances stick to and accumulate on the surface of an object) manifold chemistries. Water, nutrients, and pollutants tightly bind to carbon in this format. So, biochar makes a respectable filter and acts as a “battery” of water and nutrients in soils. Biochar adsorbs and holds on to seven times its weight in water. Soil containing biochar is more drought resilient than soil without it. Adsorbed nutrients, tightly sequestered alongside water, get released only as plants need them. Plants must excrete protons (H+) from their roots to disgorge water or positively charged nutrients from the biochar's surface; it's an active process.
Biochar’s surface area (where adsorption happens) can be 500 square meters per gram or more. That is 10% larger than an official NBA basketball court for every gram of biochar. Biochar’s abundant surface area builds protective habitats for soil microbes like fungi and bacteria and many are critical for the health and productivity of the soil itself.
The “carbon sequestration” component of biochar comes into play where “carbon credits” are concerned. There is a financial market for carbon. Not leveraging that market for revenue is foolish. I am climate agnostic. All I care about is that once solid carbon is inside the soil, it will stay there for thousands of years, imparting drought resiliency, fertility collection, nutrient buffering, and release for that time span. I simply want as much solid carbon in the soil because of the undeniably positive effects it has, regardless of any climactic considerations.
Wood Vinegar: More Waste

Another by-product of the gasification process is wood vinegar (Pyroligneous acid). If you have ever seen Liquid Smoke in the grocery store, then you have seen wood vinegar. Principally composed of acetic acid, acetone, and methanol wood vinegar also contains ~200 other organic compounds. It would seem intuitive that condensed, liquefied wood smoke would at least be bad for the health of all living things if not downright carcinogenic. The counter intuition wins the day, however. Wood vinegar has been used by humans for a very long time to promote digestion, bowel, and liver health; combat diarrhea and vomiting; calm peptic ulcers and regulate cholesterol levels; and a host of other benefits.
For centuries humans have annually burned off hundreds of thousands of square miles of pasture, grassland, forest, and every other conceivable terrestrial ecosystem. Why is this done? After every burn, one thing becomes obvious: the almost supernatural growth these ecosystems exhibit after the burn. How? Wood vinegar is a component of this growth. Even in open burns, smoke condenses and infiltrates the soil. That is when wood vinegar shows its quality.
This stuff beefs up not only general plant growth but seed germination as well and possesses many other qualities that are beneficial to plants. It’s a pesticide, fungicide, promotes beneficial soil microorganisms, enhances nutrient uptake, and imparts disease resistance. I am barely touching a long list of attributes here, but you want wood vinegar in your soil (alongside biochar because it adsorbs wood vinegar as well).
The Internal Combustion Engine

Conversion of grazed forage to chemical, then mechanical, and then electrical energy completes the cycle. The ICE (Internal Combustion Engine) converts the gaseous fuel output from the gasifier to mechanical energy, heat, water vapor, and CO2. It’s the mechanical energy of a rotating drive shaft that we want. That rotation drives the electric generator, which is the heartbeat we need to bring this monster to life. Luckily for us, combined internal combustion engine and generator packages are ubiquitous, delivering a defined energy output given a constant fuel input. It’s the simplest part of the system.
The obvious question here is whether the amount of syngas provided by the gasification process will provide enough energy to generate enough electrons to run the entire system or not. While I have no doubt the energy produced will run Forest Walker's main systems the question is really about the electrons left over. Will it be enough to run the Bitcoin mining aspect of the system? Everything is a budget.
CO2 Production For Growth

Plants are lollipops. No matter if it’s a tree or a bush or a shrubbery, the entire thing is mostly sugar in various formats but mostly long chain carbohydrates like lignin and cellulose. Plants need three things to make sugar: CO2, H2O and light. In a forest, where tree densities can be quite high, CO2 availability becomes a limiting growth factor. It’d be in the forest interests to have more available CO2 providing for various sugar formation providing the organism with food and structure.
An odd thing about tree leaves, the openings that allow gasses like the ever searched for CO2 are on the bottom of the leaf (these are called stomata). Not many stomata are topside. This suggests that trees and bushes have evolved to find gasses like CO2 from below, not above and this further suggests CO2 might be in higher concentrations nearer the soil.
The soil life (bacterial, fungi etc.) is constantly producing enormous amounts of CO2 and it would stay in the soil forever (eventually killing the very soil life that produces it) if not for tidal forces. Water is everywhere and whether in pools, lakes, oceans or distributed in “moist” soils water moves towards to the moon. The water in the soil and also in the water tables below the soil rise toward the surface every day. When the water rises, it expels the accumulated gasses in the soil into the atmosphere and it’s mostly CO2. It’s a good bet on how leaves developed high populations of stomata on the underside of leaves. As the water relaxes (the tide goes out) it sucks oxygenated air back into the soil to continue the functions of soil life respiration. The soil “breathes” albeit slowly.
The gasses produced by the Forest Walker’s internal combustion engine consist primarily of CO2 and H2O. Combusting sugars produce the same gasses that are needed to construct the sugars because the universe is funny like that. The Forest Walker is constantly laying down these critical construction elements right where the trees need them: close to the ground to be gobbled up by the trees.
The Branch Drones

During the last ice age, giant mammals populated North America - forests and otherwise. Mastodons, woolly mammoths, rhinos, short-faced bears, steppe bison, caribou, musk ox, giant beavers, camels, gigantic ground-dwelling sloths, glyptodons, and dire wolves were everywhere. Many were ten to fifteen feet tall. As they crashed through forests, they would effectively cleave off dead side-branches of trees, halting the spread of a ground-based fire migrating into the tree crown ("laddering") which is a death knell for a forest.
These animals are all extinct now and forests no longer have any manner of pruning services. But, if we build drones fitted with cutting implements like saws and loppers, optical cameras and AI trained to discern dead branches from living ones, these drones could effectively take over pruning services by identifying, cutting, and dropping to the forest floor, dead branches. The dropped branches simply get collected by the Forest Walker as part of its continual mission.
The drones dock on the back of the Forest Walker to recharge their batteries when low. The whole scene would look like a grazing cow with some flies bothering it. This activity breaks the link between a relatively cool ground based fire and the tree crowns and is a vital element in forest fire control.
The Bitcoin Miner

Mining is one of four monetary incentive models, making this system a possibility for development. The other three are US Dept. of the Interior, township, county, and electrical utility company easement contracts for fuel load management, global carbon credits trading, and data set sales. All the above depends on obvious questions getting answered. I will list some obvious ones, but this is not an engineering document and is not the place for spreadsheets. How much Bitcoin one Forest Walker can mine depends on everything else. What amount of biomass can we process? Will that biomass flow enough Syngas to keep the lights on? Can the chassis support enough mining ASICs and supporting infrastructure? What does that weigh and will it affect field performance? How much power can the AC generator produce?
Other questions that are more philosophical persist. Even if a single Forest Walker can only mine scant amounts of BTC per day, that pales to how much fuel material it can process into biochar. We are talking about millions upon millions of forested acres in need of fuel load management. What can a single Forest Walker do? I am not thinking in singular terms. The Forest Walker must operate as a fleet. What could 50 do? 500?
What is it worth providing a service to the world by managing forest fuel loads? Providing proof of work to the global monetary system? Seeding soil with drought and nutrient resilience by the excretion, over time, of carbon by the ton? What did the last forest fire cost?
The Mesh Network

What could be better than one bitcoin mining, carbon sequestering, forest fire squelching, soil amending behemoth? Thousands of them, but then they would need to be able to talk to each other to coordinate position, data handling, etc. Fitted with a mesh networking device, like goTenna or Meshtastic LoRa equipment enables each Forest Walker to communicate with each other.
Now we have an interconnected fleet of Forest Walkers relaying data to each other and more importantly, aggregating all of that to the last link in the chain for uplink. Well, at least Bitcoin mining data. Since block data is lightweight, transmission of these data via mesh networking in fairly close quartered environs is more than doable. So, how does data transmit to the Bitcoin Network? How do the Forest Walkers get the previous block data necessary to execute on mining?
Back To The Chain

Getting Bitcoin block data to and from the network is the last puzzle piece. The standing presumption here is that wherever a Forest Walker fleet is operating, it is NOT within cell tower range. We further presume that the nearest Walmart Wi-Fi is hours away. Enter the Blockstream Satellite or something like it.
A separate, ground-based drone will have two jobs: To stay as close to the nearest Forest Walker as it can and to provide an antennae for either terrestrial or orbital data uplink. Bitcoin-centric data is transmitted to the "uplink drone" via the mesh networked transmitters and then sent on to the uplink and the whole flow goes in the opposite direction as well; many to one and one to many.
We cannot transmit data to the Blockstream satellite, and it will be up to Blockstream and companies like it to provide uplink capabilities in the future and I don't doubt they will. Starlink you say? What’s stopping that company from filtering out block data? Nothing because it’s Starlink’s system and they could decide to censor these data. It seems we may have a problem sending and receiving Bitcoin data in back country environs.
But, then again, the utility of this system in staunching the fuel load that creates forest fires is extremely useful around forested communities and many have fiber, Wi-Fi and cell towers. These communities could be a welcoming ground zero for first deployments of the Forest Walker system by the home and business owners seeking fire repression. In the best way, Bitcoin subsidizes the safety of the communities.
Sensor Packages
LiDaR

The benefit of having a Forest Walker fleet strolling through the forest is the never ending opportunity for data gathering. A plethora of deployable sensors gathering hyper-accurate data on everything from temperature to topography is yet another revenue generator. Data is valuable and the Forest Walker could generate data sales to various government entities and private concerns.
LiDaR (Light Detection and Ranging) can map topography, perform biomass assessment, comparative soil erosion analysis, etc. It so happens that the Forest Walker’s ability to “see,” to navigate about its surroundings, is LiDaR driven and since it’s already being used, we can get double duty by harvesting that data for later use. By using a laser to send out light pulses and measuring the time it takes for the reflection of those pulses to return, very detailed data sets incrementally build up. Eventually, as enough data about a certain area becomes available, the data becomes useful and valuable.
Forestry concerns, both private and public, often use LiDaR to build 3D models of tree stands to assess the amount of harvest-able lumber in entire sections of forest. Consulting companies offering these services charge anywhere from several hundred to several thousand dollars per square kilometer for such services. A Forest Walker generating such assessments on the fly while performing its other functions is a multi-disciplinary approach to revenue generation.
pH, Soil Moisture, and Cation Exchange Sensing

The Forest Walker is quadrupedal, so there are four contact points to the soil. Why not get a pH data point for every step it takes? We can also gather soil moisture data and cation exchange capacities at unheard of densities because of sampling occurring on the fly during commission of the system’s other duties. No one is going to build a machine to do pH testing of vast tracts of forest soils, but that doesn’t make the data collected from such an endeavor valueless. Since the Forest Walker serves many functions at once, a multitude of data products can add to the return on investment component.
Weather Data

Temperature, humidity, pressure, and even data like evapotranspiration gathered at high densities on broad acre scales have untold value and because the sensors are lightweight and don’t require large power budgets, they come along for the ride at little cost. But, just like the old mantra, “gas, grass, or ass, nobody rides for free”, these sensors provide potential revenue benefits just by them being present.
I’ve touched on just a few data genres here. In fact, the question for universities, governmental bodies, and other institutions becomes, “How much will you pay us to attach your sensor payload to the Forest Walker?”
Noise Suppression

Only you can prevent Metallica filling the surrounds with 120 dB of sound. Easy enough, just turn the car stereo off. But what of a fleet of 50 Forest Walkers operating in the backcountry or near a township? 500? 5000? Each one has a wood chipper, an internal combustion engine, hydraulic pumps, actuators, and more cooling fans than you can shake a stick at. It’s a walking, screaming fire-breathing dragon operating continuously, day and night, twenty-four hours a day, three hundred sixty-five days a year. The sound will negatively affect all living things and that impacts behaviors. Serious engineering consideration and prowess must deliver a silencing blow to the major issue of noise.
It would be foolish to think that a fleet of Forest Walkers could be silent, but if not a major design consideration, then the entire idea is dead on arrival. Townships would not allow them to operate even if they solved the problem of widespread fuel load and neither would governmental entities, and rightly so. Nothing, not man nor beast, would want to be subjected to an eternal, infernal scream even if it were to end within days as the fleet moved further away after consuming what it could. Noise and heat are the only real pollutants of this system; taking noise seriously from the beginning is paramount.
Fire Safety

A “fire-breathing dragon” is not the worst description of the Forest Walker. It eats wood, combusts it at very high temperatures and excretes carbon; and it does so in an extremely flammable environment. Bad mix for one Forest Walker, worse for many. One must take extreme pains to ensure that during normal operation, a Forest Walker could fall over, walk through tinder dry brush, or get pounded into the ground by a meteorite from Krypton and it wouldn’t destroy epic swaths of trees and baby deer. I envision an ultimate test of a prototype to include dowsing it in grain alcohol while it’s wrapped up in toilet paper like a pledge at a fraternity party. If it runs for 72 hours and doesn’t set everything on fire, then maybe outside entities won’t be fearful of something that walks around forests with a constant fire in its belly.
The Wrap

How we think about what can be done with and adjacent to Bitcoin is at least as important as Bitcoin’s economic standing itself. For those who will tell me that this entire idea is without merit, I say, “OK, fine. You can come up with something, too.” What can we plug Bitcoin into that, like a battery, makes something that does not work, work? That’s the lesson I get from this entire exercise. No one was ever going to hire teams of humans to go out and "clean the forest". There's no money in that. The data collection and sales from such an endeavor might provide revenues over the break-even point but investment demands Alpha in this day and age. But, plug Bitcoin into an almost viable system and, voilà! We tip the scales to achieve lift-off.
Let’s face it, we haven’t scratched the surface of Bitcoin’s forcing function on our minds. Not because it’s Bitcoin, but because of what that invention means. The question that pushes me to approach things this way is, “what can we create that one system’s waste is another system’s feedstock?” The Forest Walker system’s only real waste is the conversion of low entropy energy (wood and syngas) into high entropy energy (heat and noise). All other output is beneficial to humanity.
Bitcoin, I believe, is the first product of a new mode of human imagination. An imagination newly forged over the past few millennia of being lied to, stolen from, distracted and otherwise mis-allocated to a black hole of the nonsensical. We are waking up.
What I have presented is not science fiction. Everything I have described here is well within the realm of possibility. The question is one of viability, at least in terms of the detritus of the old world we find ourselves departing from. This system would take a non-trivial amount of time and resources to develop. I think the system would garner extensive long-term contracts from those who have the most to lose from wildfires, the most to gain from hyperaccurate data sets, and, of course, securing the most precious asset in the world. Many may not see it that way, for they seek Alpha and are therefore blind to other possibilities. Others will see only the possibilities; of thinking in a new way, of looking at things differently, and dreaming of what comes next.
-
 @ 57c631a3:07529a8e
2025-05-20 15:40:04
@ 57c631a3:07529a8e
2025-05-20 15:40:04The Video: The World's Biggest Toddler
https://connect-test.layer3.press/articles/3f9d28a4-0876-4ee8-bdac-d1a56fa9cd02
-
 @ bbb5dda0:f09e2747
2025-05-20 13:33:59
@ bbb5dda0:f09e2747
2025-05-20 13:33:59My week 19 started with a celebration of 80 years of liberation from the Germans (we love you guys now tho 🫶🏼). It feels conflicting, we're celebrating freedom, whilst cutting down those freedoms day by day more rapidly as time progresses. Should we still celebrate...?
The current path back to freedom can be mundane in the day to day but I wouldn't wanna have it any other way. These last couple weeks I've continued working on our TollGate pipelines to facilitate our release cycle, make it faster and easier to release in quick succession. There's been a lot of details to get right, because our releases are nostr based and once people start relying on the structure of the events we can't easily change it.
A TollGateOS release event now looks like this NIP-94 file metadata event:
json { "id": "a867f15ca7edc95a69e1557539a624466147584f68c62a16c47fe9bca3778312", "pubkey": "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a", "created_at": 1747475980, "kind": 1063, "tags": [ [ "url", "https://blossom.swissdash.site/9e5e8c48810a1b59cf10fa56486f311e048a0305eb58444992b6133fd19fcb3e.bin" ], [ "m", "application/octet-stream" ], [ "x", "9e5e8c48810a1b59cf10fa56486f311e048a0305eb58444992b6133fd19fcb3e" ], [ "ox", "9e5e8c48810a1b59cf10fa56486f311e048a0305eb58444992b6133fd19fcb3e" ], [ "architecture", "aarch64_cortex-a53" ], [ "device_id", "glinet_gl-mt3000" ], [ "supported_devices", "glinet,gl-mt3000 glinet,mt3000-snand" ], [ "openwrt_version", "24.10.1" ], [ "tollgate_os_version", "v0.0.2" ], [ "release_channel", "stable" ] ], "content": "TollGate OS Firmware for glinet_gl-mt3000", "sig": "1d050233428304685d202e954cb48714c800a7ca5f2d6a8d8fd657a775b9c51bf83364505311859c846e25098168a8ff309af2308712aafe634fcbdc96fcd84a" }One of the missing links was the
supported_devicestag. That is because the installer checks the device name by ssh-ing into the router and it returns theglinet,gl-mt3000which doesn't properly translate into thedevice_id, which is what's used for compiling the OS. So this helps us to do the lookups and compatibility checks in the installer.I also worked on: - getting the versioning of the tollgate-basic package's naming in line with the OpenWRT naming convention. - Rework versioning for dev builds into
[branchname].[commit_height].[commit_hash]which will show up on thedevrelease_channelreleases. - Getting an initial release of the tollgate-installer done, so we can easily flash a bunch of routers to become TollGates.Bright minds in Prague
I met up with some bright minds from the space in Prague where @cobrador and i did a workshop on turning routers into TollGates and start earning sats. As is part of building things, things break and people make us aware of issues that we wouldn't foresee. Like for some reason Minibits cashu tokens being rejected, which is likely because of the memo's but we still need to dive into that issue.
Also we released [v0.0.2] of TollGate OS, which now includes an updater feature, again for faster release cycles. Currently we're focussing on getting a v0.0.3 out quickly with fixes for the user feedback we've gathered so far!
Receipt.Cash
I also, kind of unplanned, saw an opportunity to shill Receipt.Cash. I'd made a few improvements recently and it's ready enough for reckless people to try it out ;).
|
 |
| 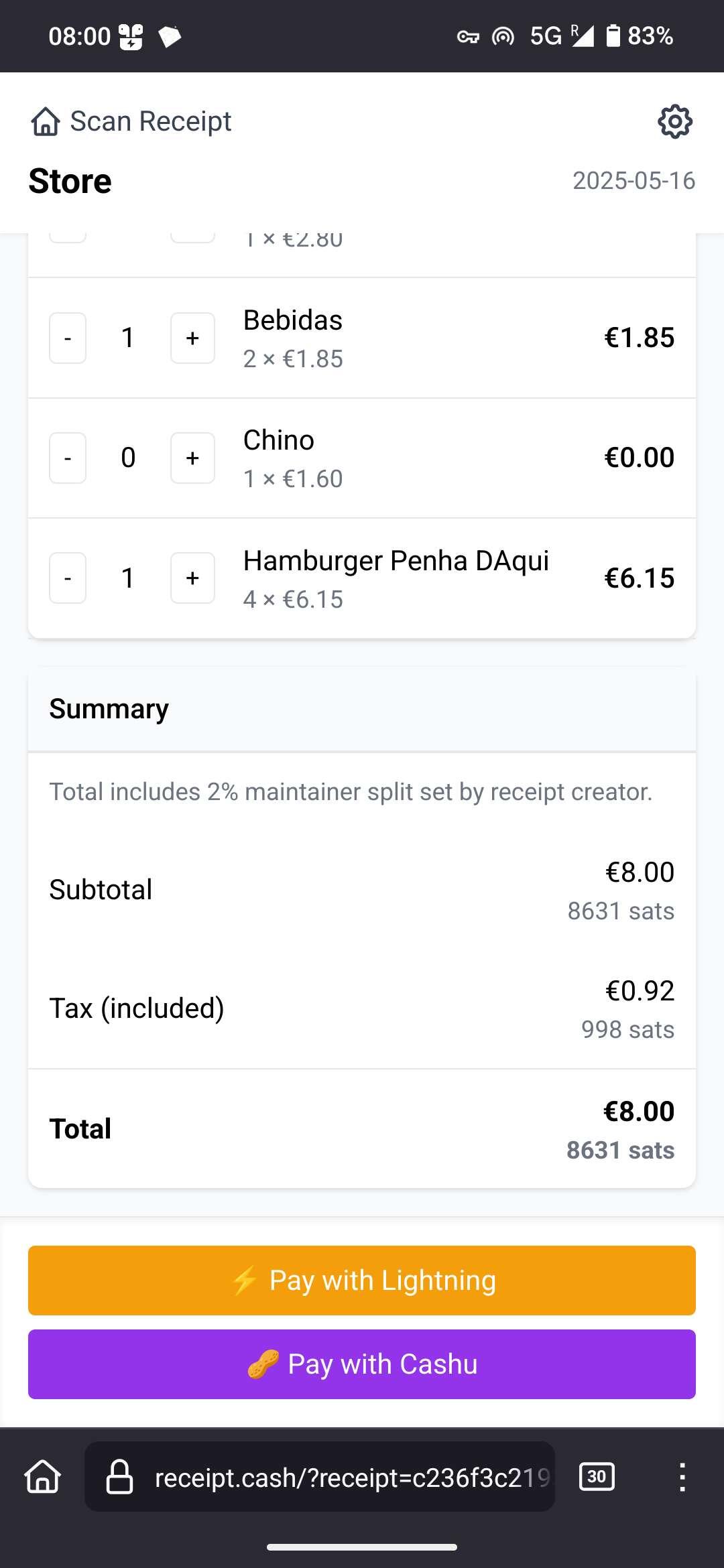 |
| |
| Payer Scans any fiat receipt & Share link with friends | Friends tap what they had, price is auto-converted to sats, then pay by Lightning or Cashu. |
If you want to try it, BE CAREFUL! It is highly experimental and you might lose your sats, no refunds!
|
| |
| Payer Scans any fiat receipt & Share link with friends | Friends tap what they had, price is auto-converted to sats, then pay by Lightning or Cashu. |
If you want to try it, BE CAREFUL! It is highly experimental and you might lose your sats, no refunds!Source Code here.
-
 @ a5142938:0ef19da3
2025-05-20 11:05:20
@ a5142938:0ef19da3
2025-05-20 11:05:20Content coming soon.
-
 @ 39cc53c9:27168656
2025-05-20 10:45:29
@ 39cc53c9:27168656
2025-05-20 10:45:29Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% ^1 – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% ^1 of less-than-careful criminals.
KYC? Not you.
KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. ^2
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
Your identity has been stolen
KYC data has been found to be for sale on many dark net markets^3. Exchanges may have leaks or hacks, and such leaks contain very sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. ^3
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
(they) Know Your Coins
You may already know that Bitcoin and most cryptocurrencies have a transparent public blockchain, meaning that all data is shown unencrypted for everyone to see and recorded forever. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
Conclusions
To sum up, KYC does not protect individuals; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
Edited 20/03/2024 * Add reference to the 1% statement on Rights for Illusions section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity ^1
-
 @ 3f770d65:7a745b24
2025-05-14 18:26:17
@ 3f770d65:7a745b24
2025-05-14 18:26:17🏌️ Monday, May 26 – Bitcoin Golf Championship & Kickoff Party
Location: Las Vegas, Nevada\ Event: 2nd Annual Bitcoin Golf Championship & Kick Off Party"\ Where: Bali Hai Golf Clubhouse, 5160 S Las Vegas Blvd, Las Vegas, NV 89119\ 🎟️ Get Tickets!
Details:
-
The week tees off in style with the Bitcoin Golf Championship. Swing clubs by day and swing to music by night.
-
Live performances from Nostr-powered acts courtesy of Tunestr, including Ainsley Costello and others.
-
Stop by the Purple Pill Booth hosted by Derek and Tanja, who will be on-boarding golfers and attendees to the decentralized social future with Nostr.
💬 May 27–29 – Bitcoin 2025 Conference at the Las Vegas Convention Center
Location: The Venetian Resort\ Main Attraction for Nostr Fans: The Nostr Lounge\ When: All day, Tuesday through Thursday\ Where: Right outside the Open Source Stage\ 🎟️ Get Tickets!
Come chill at the Nostr Lounge, your home base for all things decentralized social. With seating for \~50, comfy couches, high-tops, and good vibes, it’s the perfect space to meet developers, community leaders, and curious newcomers building the future of censorship-resistant communication.
Bonus: Right across the aisle, you’ll find Shopstr, a decentralized marketplace app built on Nostr. Stop by their booth to explore how peer-to-peer commerce works in a truly open ecosystem.
Daily Highlights at the Lounge:
-
☕️ Hang out casually or sit down for a deeper conversation about the Nostr protocol
-
🔧 1:1 demos from app teams
-
🛍️ Merch available onsite
-
🧠 Impromptu lightning talks
-
🎤 Scheduled Meetups (details below)
🎯 Nostr Lounge Meetups
Wednesday, May 28 @ 1:00 PM
- Damus Meetup: Come meet the team behind Damus, the OG Nostr app for iOS that helped kickstart the social revolution. They'll also be showcasing their new cross-platform app, Notedeck, designed for a more unified Nostr experience across devices. Grab some merch, get a demo, and connect directly with the developers.
Thursday, May 29 @ 1:00 PM
- Primal Meetup: Dive into Primal, the slickest Nostr experience available on web, Android, and iOS. With a built-in wallet, zapping your favorite creators and friends has never been easier. The team will be on-site for hands-on demos, Q\&A, merch giveaways, and deeper discussions on building the social layer of Bitcoin.
🎙️ Nostr Talks at Bitcoin 2025
If you want to hear from the minds building decentralized social, make sure you attend these two official conference sessions:
1. FROSTR Workshop: Multisig Nostr Signing
-
🕚 Time: 11:30 AM – 12:00 PM
-
📅 Date: Wednesday, May 28
-
📍 Location: Developer Zone
-
🎤 Speaker: nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgdwaehxw309ahx7uewd3hkcqpqs9etjgzjglwlaxdhsveq0qksxyh6xpdpn8ajh69ruetrug957r3qf4ggfm (Austin Kelsay) @ Voltage\ A deep-dive into FROST-based multisig key management for Nostr. Geared toward devs and power users interested in key security.
2. Panel: Decentralizing Social Media
-
🕑 Time: 2:00 PM – 2:30 PM
-
📅 Date: Thursday, May 29
-
📍 Location: Genesis Stage
-
🎙️ Moderator: nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqy08wumn8ghj7mn0wd68yttjv4kxz7fwv3jhyettwfhhxuewd4jsqgxnqajr23msx5malhhcz8paa2t0r70gfjpyncsqx56ztyj2nyyvlq00heps - Bitcoin Strategy @ Roxom TV
-
👥 Speakers:
-
nostr:nprofile1qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcppemhxue69uhkummn9ekx7mp0qqsy2ga7trfetvd3j65m3jptqw9k39wtq2mg85xz2w542p5dhg06e5qmhlpep – Early Bitcoin dev, CEO @ Sirius Business Ltd
-
nostr:nprofile1qy2hwumn8ghj7mn0wd68ytndv9kxjm3wdahxcqg5waehxw309ahx7um5wfekzarkvyhxuet5qqsw4v882mfjhq9u63j08kzyhqzqxqc8tgf740p4nxnk9jdv02u37ncdhu7e3 – Analyst & Partner @ Ego Death Capital
Get the big-picture perspective on why decentralized social matters and how Nostr fits into the future of digital communication.
🌃 NOS VEGAS Meetup & Afterparty
Date: Wednesday, May 28\ Time: 7:00 PM – 1:00 AM\ Location: We All Scream Nightclub, 517 Fremont St., Las Vegas, NV 89101\ 🎟️ Get Tickets!
What to Expect:
-
🎶 Live Music Stage – Featuring Ainsley Costello, Sara Jade, Able James, Martin Groom, Bobby Shell, Jessie Lark, and other V4V artists
-
🪩 DJ Party Deck – With sets by nostr:nprofile1qy0hwumn8ghj7cmgdae82uewd45kketyd9kxwetj9e3k7mf6xs6rgqgcwaehxw309ahx7um5wgh85mm694ek2unk9ehhyecqyq7hpmq75krx2zsywntgtpz5yzwjyg2c7sreardcqmcp0m67xrnkwylzzk4 , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgkwaehxw309anx2etywvhxummnw3ezucnpdejqqg967faye3x6fxgnul77ej23l5aew8yj0x2e4a3tq2mkrgzrcvecfsk8xlu3 , and more DJs throwing down
-
🛰️ Live-streamed via Tunestr
-
🧠 Nostr Education – Talks by nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq37amnwvaz7tmwdaehgu3dwfjkccte9ejx2un9ddex7umn9ekk2tcqyqlhwrt96wnkf2w9edgr4cfruchvwkv26q6asdhz4qg08pm6w3djg3c8m4j , nostr:nprofile1qyx8wumn8ghj7cnjvghxjmcpz4mhxue69uhk2er9dchxummnw3ezumrpdejqqgxchnavlnv8t5vky5dsa87ddye0jc8z9eza8ekvfryf3yt649mytvhadgpe , nostr:nprofile1q9z8wumn8ghj7erzx3jkvmmzw4eny6tvw368wdt8da4kxamrdvek76mrwg6rwdngw94k67t3v36k77tev3kx7vn2xa5kjem9dp4hjepwd3hkxctvqyg8wumn8ghj7mn0wd68ytnhd9hx2qpqyaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgssuy4zk , nostr:nprofile1qy28wue69uhnzvpwxqhrqt33xgmn5dfsx5cqz9thwden5te0v4jx2m3wdehhxarj9ekxzmnyqqswavgevxe9gs43vwylumr7h656mu9vxmw4j6qkafc3nefphzpph8ssvcgf8 , and more.
-
🧾 Vendors & Project Booths – Explore new tools and services
-
🔐 Onboarding Stations – Learn how to use Nostr hands-on
-
🐦 Nostrich Flocking – Meet your favorite nyms IRL
-
🍸 Three Full Bars – Two floors of socializing overlooking vibrant Fremont Street
This is the after-party of the year for those who love freedom technology and decentralized social community. Don’t miss it.
Final Thoughts
Whether you're there to learn, network, party, or build, Bitcoin 2025 in Las Vegas has a packed week of Nostr-friendly programming. Be sure to catch all the events, visit the Nostr Lounge, and experience the growing decentralized social revolution.
🟣 Find us. Flock with us. Purple pill someone.
-
-
 @ 3f770d65:7a745b24
2025-01-12 21:03:36
@ 3f770d65:7a745b24
2025-01-12 21:03:36I’ve been using Notedeck for several months, starting with its extremely early and experimental alpha versions, all the way to its current, more stable alpha releases. The journey has been fascinating, as I’ve had the privilege of watching it evolve from a concept into a functional and promising tool.
In its earliest stages, Notedeck was raw—offering glimpses of its potential but still far from practical for daily use. Even then, the vision behind it was clear: a platform designed to redefine how we interact with Nostr by offering flexibility and power for all users.
I'm very bullish on Notedeck. Why? Because Will Casarin is making it! Duh! 😂
Seriously though, if we’re reimagining the web and rebuilding portions of the Internet, it’s important to recognize the potential of Notedeck. If Nostr is reimagining the web, then Notedeck is reimagining the Nostr client.
Notedeck isn’t just another Nostr app—it’s more a Nostr browser that functions more like an operating system with micro-apps. How cool is that?
Much like how Google's Chrome evolved from being a web browser with a task manager into ChromeOS, a full blown operating system, Notedeck aims to transform how we interact with the Nostr. It goes beyond individual apps, offering a foundation for a fully integrated ecosystem built around Nostr.
As a Nostr evangelist, I love to scream INTEROPERABILITY and tout every application's integrations. Well, Notedeck has the potential to be one of the best platforms to showcase these integrations in entirely new and exciting ways.
Do you want an Olas feed of images? Add the media column.
Do you want a feed of live video events? Add the zap.stream column.
Do you want Nostr Nests or audio chats? Add that column to your Notedeck.
Git? Email? Books? Chat and DMs? It's all possible.
Not everyone wants a super app though, and that’s okay. As with most things in the Nostr ecosystem, flexibility is key. Notedeck gives users the freedom to choose how they engage with it—whether it’s simply following hashtags or managing straightforward feeds. You'll be able to tailor Notedeck to fit your needs, using it as extensively or minimally as you prefer.
Notedeck is designed with a local-first approach, utilizing Nostr content stored directly on your device via the local nostrdb. This will enable a plethora of advanced tools such as search and filtering, the creation of custom feeds, and the ability to develop personalized algorithms across multiple Notedeck micro-applications—all with unparalleled flexibility.
Notedeck also supports multicast. Let's geek out for a second. Multicast is a method of communication where data is sent from one source to multiple destinations simultaneously, but only to devices that wish to receive the data. Unlike broadcast, which sends data to all devices on a network, multicast targets specific receivers, reducing network traffic. This is commonly used for efficient data distribution in scenarios like streaming, conferencing, or large-scale data synchronization between devices.
In a local first world where each device holds local copies of your nostr nodes, and each device transparently syncs with each other on the local network, each node becomes a backup. Your data becomes antifragile automatically. When a node goes down it can resync and recover from other nodes. Even if not all nodes have a complete collection, negentropy can pull down only what is needed from each device. All this can be done without internet.
-Will Casarin
In the context of Notedeck, multicast would allow multiple devices to sync their Nostr nodes with each other over a local network without needing an internet connection. Wild.
Notedeck aims to offer full customization too, including the ability to design and share custom skins, much like Winamp. Users will also be able to create personalized columns and, in the future, share their setups with others. This opens the door for power users to craft tailored Nostr experiences, leveraging their expertise in the protocol and applications. By sharing these configurations as "Starter Decks," they can simplify onboarding and showcase the best of Nostr’s ecosystem.
Nostr’s “Other Stuff” can often be difficult to discover, use, or understand. Many users doesn't understand or know how to use web browser extensions to login to applications. Let's not even get started with nsecbunkers. Notedeck will address this challenge by providing a native experience that brings these lesser-known applications, tools, and content into a user-friendly and accessible interface, making exploration seamless. However, that doesn't mean Notedeck should disregard power users that want to use nsecbunkers though - hint hint.
For anyone interested in watching Nostr be developed live, right before your very eyes, Notedeck’s progress serves as a reminder of what’s possible when innovation meets dedication. The current alpha is already demonstrating its ability to handle complex use cases, and I’m excited to see how it continues to grow as it moves toward a full release later this year.
-
 @ 640f3844:d7b13a29
2025-05-20 08:52:49
@ 640f3844:d7b13a29
2025-05-20 08:52:49CrazyGames là một nền tảng giải trí số đang ngày càng khẳng định vị thế trong cộng đồng người dùng hiện đại nhờ vào khả năng cung cấp trải nghiệm linh hoạt, hấp dẫn và thân thiện. Với giao diện được thiết kế thông minh và trực quan, CrazyGames giúp người dùng dễ dàng tiếp cận và khám phá hàng loạt nội dung đa dạng chỉ trong vài thao tác. Dù sử dụng điện thoại, máy tính bảng hay máy tính để bàn, hệ thống luôn được tối ưu hóa để vận hành mượt mà, không gây gián đoạn hay ảnh hưởng đến trải nghiệm tổng thể. CrazyGames không chỉ đơn thuần là một nền tảng kỹ thuật số mà còn là nơi hội tụ của sáng tạo, công nghệ và niềm vui, nơi người dùng có thể tìm thấy sự giải tỏa sau những giờ làm việc căng thẳng hoặc học tập mệt mỏi. Nền tảng luôn chú trọng đến việc đổi mới giao diện, bổ sung các tính năng tiện ích nhằm mang lại giá trị sử dụng thực tế và phù hợp với xu hướng công nghệ đang thay đổi từng ngày.
Một trong những điểm nhấn nổi bật khiến CRAZYGAMES thu hút sự quan tâm rộng rãi chính là tính cá nhân hóa và khả năng kết nối cộng đồng vượt trội. Hệ thống sử dụng các thuật toán phân tích hành vi thông minh để đưa ra các đề xuất nội dung phù hợp với sở thích và nhu cầu riêng biệt của từng người dùng, từ đó nâng cao mức độ hài lòng và giữ chân người dùng lâu hơn. Không gian cộng đồng tích hợp trong nền tảng cũng tạo điều kiện cho các thành viên giao lưu, chia sẻ cảm nhận và trao đổi kinh nghiệm, giúp tăng sự gắn kết và hình thành một hệ sinh thái giải trí sôi động, đầy màu sắc. Hơn thế nữa, CrazyGames thường xuyên cập nhật nội dung mới, điều chỉnh theo phản hồi thực tế từ người dùng nhằm đảm bảo mọi người luôn cảm thấy được lắng nghe và phục vụ đúng với mong đợi. Việc áp dụng công nghệ mới, đặc biệt là trí tuệ nhân tạo và dữ liệu lớn, đã giúp CrazyGames trở thành một nền tảng tiên phong trong việc cá nhân hóa trải nghiệm người dùng ở cấp độ cao nhất.
CrazyGames cũng đặt yếu tố bảo mật và hỗ trợ kỹ thuật làm trọng tâm trong chiến lược phát triển lâu dài. Với hệ thống bảo mật nhiều lớp, kết hợp xác thực người dùng và mã hóa dữ liệu tiên tiến, người dùng có thể yên tâm khi trải nghiệm mà không phải lo lắng về quyền riêng tư hay nguy cơ rò rỉ thông tin cá nhân. Đồng thời, đội ngũ chăm sóc khách hàng của CrazyGames luôn sẵn sàng phản hồi nhanh chóng, giải quyết kịp thời các vướng mắc phát sinh và liên tục cập nhật các hướng dẫn sử dụng để người dùng tận dụng được mọi tính năng mà nền tảng mang lại. Ngoài ra, CrazyGames còn tổ chức nhiều chương trình tương tác hấp dẫn và hoạt động khuyến khích sáng tạo trong cộng đồng, giúp nâng cao trải nghiệm người dùng và biến mỗi lần truy cập trở thành một hành trình khám phá mới mẻ. Với tất cả những yếu tố đó, CrazyGames không chỉ là một nền tảng giải trí kỹ thuật số, mà còn là người bạn đồng hành lý tưởng trong hành trình kết nối công nghệ, sáng tạo và cảm xúc.
-
 @ 472f440f:5669301e
2025-05-20 13:01:09
@ 472f440f:5669301e
2025-05-20 13:01:09Marty's Bent

via me
Don't sleep on what's happening in Japan right now. We've been covering the country and the fact that they've lost control of their yield curve since late last year. After many years of making it a top priority from a monetary policy perspective, last year the Bank of Japan decided to give up on yield curve control in an attempt to reel inflation. This has sent yields for the 30-year and 40-year Japanese government bonds to levels not seen since the early 2000s in the case of the 30-year and levels never before seen for the 40-year, which was launched in 2007. With a debt to GDP ratio that has surpassed 250% and a population that is aging out with an insufficient amount of births to replace the aging workforce, it's hard to see how Japan can get out of this conundrum without some sort of economic collapse.
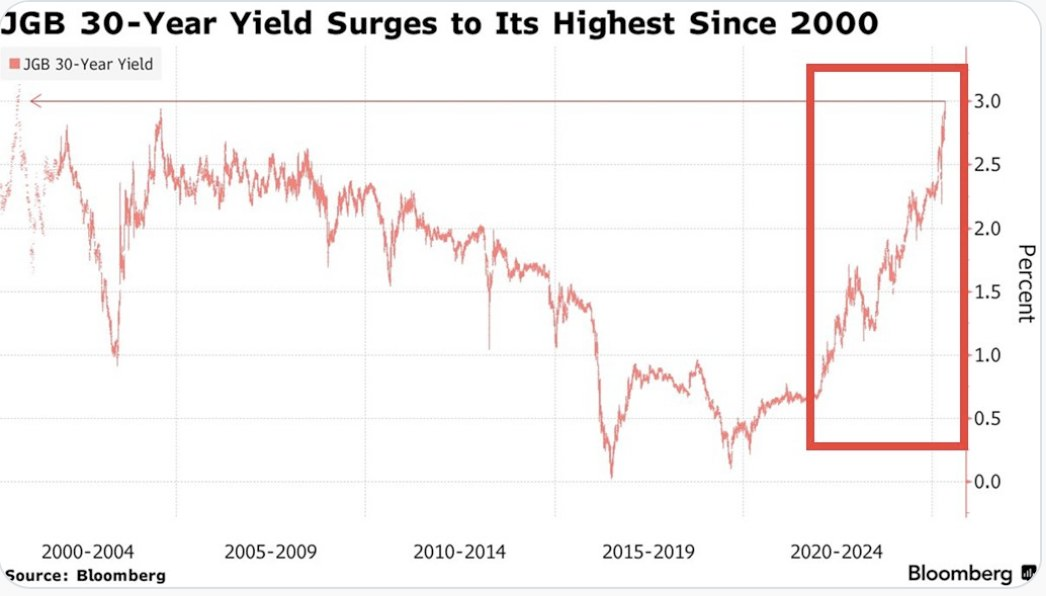

This puts the United States in a tough position considering the fact that Japan is one of the largest holders of U.S. Treasury bonds with more than 1,135 sats | $1.20 trillion in exposure. If things get too out of control in Japan and the yield curve continues to drift higher and inflation continues to creep higher Japan can find itself in a situation where it's a forced seller of US Treasuries as they attempt to strengthen the yen. Another aspect to consider is the fact that investors may see the higher yields on Japanese government bonds and decide to purchase them instead of US Treasuries. This is something to keep an eye on in the weeks to come. Particularly if higher rates drive a higher cost of capital, which leads to even more inflation. As producers are forced to increase their prices to ensure that they can manage their debt repayments.
It's never a good sign when the Japanese Prime Minister is coming out to proclaim that his country's financial situation is worse than Greece's, which has been a laughing stock of Europe for the better part of three decades. Japan is a very proud nation, and the fact that its Prime Minister made a statement like this should not be underappreciated.
As we noted last week, the 10-year and 30-year U.S. Treasury bonds are drifting higher as well. Earlier today, the 30-year bond yield surpassed 5%, which has been a psychological level that many have been pointed to as a critical tipping point. When you take a step back and look around the world it seems pretty clear that bond markets are sending a very strong signal. And that signal is that something is not well in the back end of the financial system.
This is even made clear when you look at the private sector, particularly at consumer debt. In late March, we warned of the growing trend of buy now, pay later schemes drifting down market as major credit card companies released charge-off data which showed charge-off rates reaching levels not seen since the 2008 great financial crisis. At the time, we could only surmise that Klarna was experiencing similar charge-off rates on the bigger-ticket items they financed and started doing deals with companies like DoorDash to finance burrito deliveries in an attempt to move down market to finance smaller ticket items with a higher potential of getting paid back. It seems like that inclination was correct as Klarna released data earlier today showing more losses on their book as consumers find it extremely hard to pay back their debts.

via NewsWire
This news hit the markets on the same day as the average rate of the 30-year mortgage in the United States rose to 7.04%. I'm not sure if you've checked lately, but real estate prices are still relatively elevated outside of a few big cities who expanded supply significantly during the COVID era as people flooded out of blue states towards red states. It's hard to imagine that many people can afford a house based off of sticker price alone, but with a 7% 30-year mortgage rate it's becoming clear that the ability of the Common Man to buy a house is simply becoming impossible.
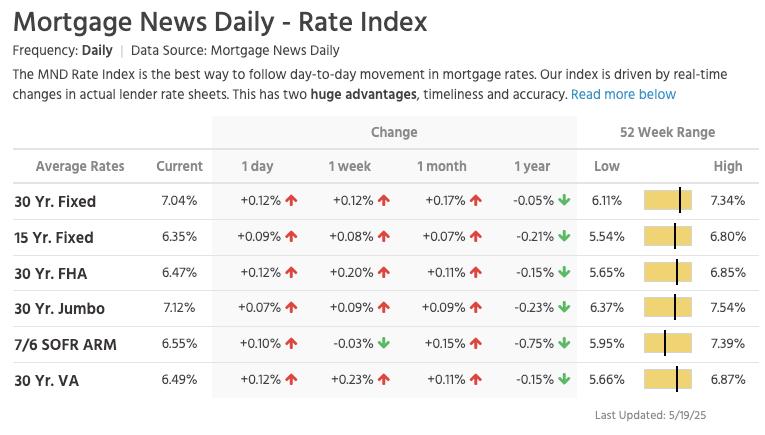
via Lance Lambert
The mortgage rate data is not the only thing you need to look at to understand that it's becoming impossible for the Common Man of working age to buy a house. New data has recently been released that highlights That the median home buyer in 2007 was born in 1968, and the median home buyer in 2024 was born in 1968. Truly wild when you think of it. As our friend Darth Powell cheekily highlights below, we find ourselves in a situation where boomers are simply trading houses and the younger generations are becoming indentured slaves. Forever destined to rent because of the complete inability to afford to buy a house.
via Darth Powell
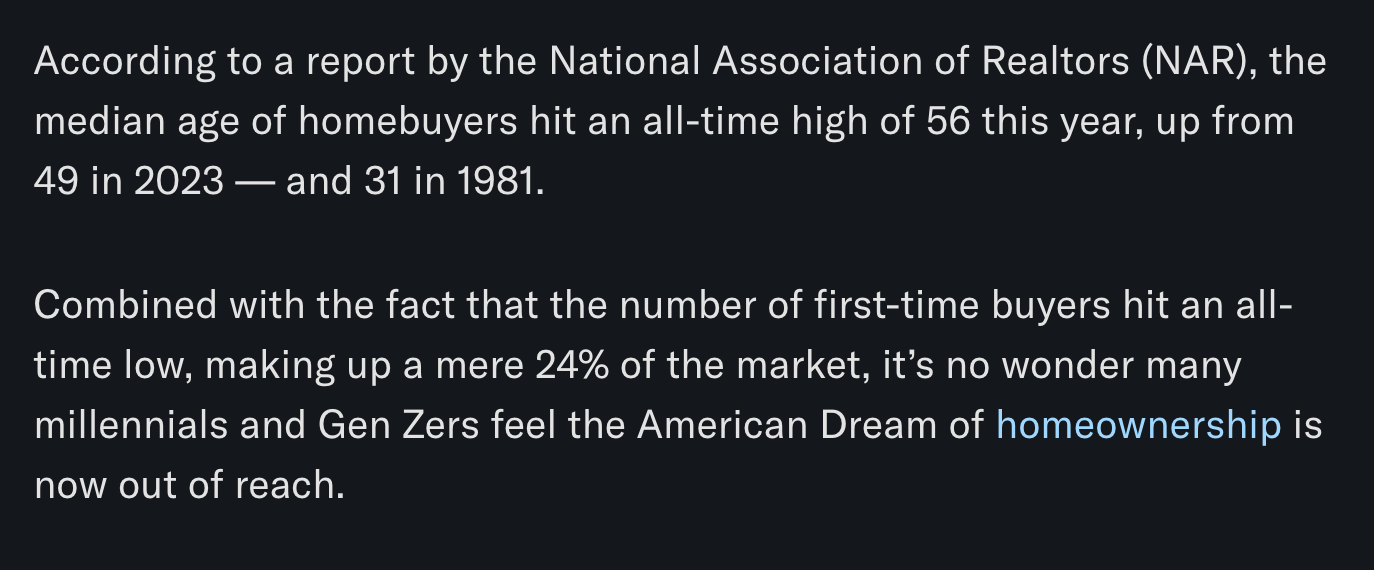
via Yahoo Finance
Meanwhile, Bitcoin re-approached all-time highs late this evening and looks primed for another breakout to the upside. This makes sense if you're paying attention. The high-velocity trash economy running on an obscene amount of debt in both the public and private sectors seems to be breaking at the seams. All the alarm bells are signaling that another big print is coming. And if you hope to preserve your purchasing power or, ideally, increase it as the big print approaches, the only thing that makes sense is to funnel your money into the hardest asset in the world, which is Bitcoin.

via Bitbo
Buckle up, freaks. It's gonna be a bumpy ride. Stay humble, Stack Sats.
Trump's Middle East Peace Strategy: Redefining U.S. Foreign Policy
In his recent Middle East tour, President Trump signaled what our guest Dr. Anas Alhajji calls "a major change in US policy." Trump explicitly rejected the nation-building strategies of his predecessors, contrasting the devastation in Afghanistan and Iraq with the prosperity of countries like Saudi Arabia and UAE. This marks a profound shift from both Republican and Democratic foreign policy orthodoxy. As Alhajji noted, Trump's willingness to meet with Syrian President Assad follows a historical pattern where former adversaries eventually become diplomatic partners.
"This is really one of the most important shifts in US foreign policy to say, look, sorry, we destroyed those countries because we tried to rebuild them and it was a big mistake." - Dr. Anas Alhajji
The administration's new approach emphasizes negotiation over intervention. Rather than military solutions, Trump is engaging with groups previously considered off-limits, including the Houthis, Hamas, and Iran. This pragmatic stance prioritizes economic cooperation and regional stability over ideological confrontation. The focus on trade deals and investment rather than regime change represents a fundamental reimagining of America's role in the Middle East.
Check out the full podcast here for more on the Iran nuclear situation, energy market predictions, and why AI development could create power grid challenges. Only on TFTC Studio.
Headlines of the Day
Bitcoin Soars to 100,217 sats | $106.00K While Bonds Lose 40% Since 2020 - via X
US Senate Advances Stablecoin Bill As America Embraces Bitcoin - via X
Get our new STACK SATS hat - via tftcmerch.io
Texas House Debates Bill For State-Run Bitcoin Reserve - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code “TFTC20” during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed 158,469 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
Don't let the noise consume you. Focus on making your life 1% better every day.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ a296b972:e5a7a2e8
2025-05-14 15:22:46
@ a296b972:e5a7a2e8
2025-05-14 15:22:46Es ist nicht anders zu erklären: Wir erleben die Verschwörung fast aller Politiker (jetzt schon die 2. Garde herausragender Geistesgrößen), Institutionen (NGOs), Behörden (RKI, PEI), Gerichte und die öffentlich-rechtlichen Medien gemeinsam gegen die Wahrheit. Erkennungszeichen: Der in Moral getauchte erhobene Zeigefinger als neuer deutscher Gruß. Das ist Größenwahn!
Dies wird jedoch nur von einem kleinen Teil der Gesellschaft wahrgenommen, weil der weitaus größere Teil nach wie vor die Wahrheit nicht hören will.
Aktuelles Beispiel: Das war sicher nur eine Rotzfahne, die Herr Macron, bekannt für sein schlechtes Benehmen, auf dem Tisch liegen lassen hat, nachdem er sich geschnäuzt hatte. Und Herr Merz hat mit einer Büroklammer gespielt, die wie ein Speitel aussah.
Das ist ein psychologisches Ding, und die Frage ist, warum manche immun gegen Propaganda und Manipulation sind und viele leider nicht.
Deutschland macht sich sowohl innen- als auch außenpolitisch immer mehr zur Deppen-Insel. Während außerhalb Friedensbemühungen stattfinden, droht der Blackrock-Spargel 2. Wahl weiter mit neuen Sanktionen, die in der Vergangenheit schon nicht gewirkt haben. Die Beschlagnahmung russischer Gelder kann dazu führen, dass europäische Gelder im Ausland ebenso beschlagnahmt werden, und das könnte das Ende des Euro bedeuten, was an sich nicht das Problem wäre, wenn die Menschen nicht unter einer Finanzkrise zu leiden hätten. „Der kleine Mann“ war ja von je her immer schon der Doofe.
Taurus ist immer noch nicht endgültig vom Tisch. Es kommt gar nicht darauf an, dass die Lieferung den Kriegsverlauf nicht beeinflussen würde, sondern vielmehr darauf, dass sich spätestens hier Wiesbaden, Düsseldorf-Rheinmetall, Garmisch-Patenkirchen und die Waffenindustrie am Bodensee zu einem legitimen Ziel für Russland machen würden.
Innenpolitisch kommen die in der Corona-Zeit erprobten, bewährten und loyalen Systemlinge aus den Medien in Sprecherpositionen in die Bundespressekonferenz-Show oder ins Innenministerium. Eine Ex-Ministerin landet sanft im Desinformations-Bekämpfungs-Ausschuss, wo sie aufgrund ihrer eigenen Praxiserfahrung in Desinformieren bestens aufgehoben ist.
Ein anderer Minister wechselt in den Ausschuss für „Peterchens Mondfahrt“. Ganz oben auf der Agenda: Rheinländer im Weltall.
Die ehemalige Chef-Diplomatin, die bis heute noch nicht verstanden hat, dass Diplomatie nicht das Ausstellen von Diplomen bedeutet, landet hunderttausende von Kilometern entfernt in Nju Jörg, um ein paar Brocken Englisch zu lernen. Der Speck der Hoffnung stirbt zuletzt, möge die Übung gelingen.
Alles zusammen erzeugt so viel Unterdruck, der geeignet ist, eine Implosion herbeizuführen.
Der Widerstand kann stolz auf die vielen engagierten Menschen sein, die sich über Jahre nicht haben brechen lassen und unbeirrt das Schild der Freiheit, der Demokratie, der Meinungsfreiheit, das Grundgesetz, das Recht und die Würde des Menschen hochhalten.
Die staatlichen Schikanen, die spätestens mit Corona ihren Anfang genommen haben, hier aber auf jeden Fall sichtbar geworden sind, haben sowohl das Schlimmste, als auch das Beste im Menschen hervorgerufen. Die Spaltung hat zwangsläufig erfolgen müssen, weil die Widerständler, im Sinne eines sich gegen das Volk richtenden Systems, immer wieder auf die Ja-Sager zugegangen sind, diese jedoch die Wiederaufnahme eines Dialogs weitgehend abgelehnt haben. Sei es durch aktive Verwehrung, oder durch passives Schweigen und Ignorieren.
All diese Schikanen, die Lügen, Weglassungen, Verdrehungen haben auch etwas Gutes: Sie haben bei vielen Menschen das Denken geschult und noch einmal ganz bewusst gemacht, wie wichtig die Freiheit ist. Sie haben erkannt, dass sie keine Naturgewalt ist und dass es nötig ist, sich für sie einzusetzen, wenn Kräfte am Werk sind, die sie abschaffen wollen.
Ja, dem Widerstand geht es um die Freiheit. Die Freiheit im Denken, im Fühlen und im Wollen. Und seit Corona auch im freien Atmen.
Denjenigen, die glauben, dass all ihre Schreiben, Berechnungen, Posts, Videos und Kanäle bis heute nichts gebracht haben, denen sei gesagt:
Doch, ihr habt die Aufklärung übernommen, die eigentlich von staatlicher Seite her hätte erfolgen müssen.
Alle Fakten sind sauber recherchiert und liegen auf dem Tisch. Das alles war und ist nicht umsonst.
Da an die Tatsachenverbreitung derjenigen Medien, die zur Verschwörung gehören, nicht zu denken ist, machen wir es eben selbst. Das dauert vielleicht länger, aber die Wahrheit hat sich am Ende immer durchgesetzt. Nicht verzagen, steter Tropfen höhlt den Stein.
Und seien wir doch mal ehrlich: Würden wir freiwillig an dem Ast sägen, auf dem wir sitzen, wenn wir in deren misslicher Lage wären? Es kann nur weiter gelogen werden, weil in einigen temperamentvolleren Ländern als Deutschland, die Bevölkerung kurzen Prozess machen würde. Daraus könnte ein Domino-Effekt entstehen, und der ist unter allen Umständen zu verhindern.
Es wäre noch nicht einmal undenkbar, diejenigen weiter in der Matrix leben zu lassen, denen die Realität und Tatsachen zu anstrengend sind, wenn gewährleistet würde, dass diejenigen, die sich entschieden haben die rote Pille zu schlucken, in Ruhe gelassen würden. Derzeit hat man eher den Eindruck, es wird mit allen Mitteln versucht, diese Menschen wieder ins System zurücksaugen zu wollen. Sei es mit dem Digital Services Act, Hausdurchsuchungen, Kontenkündigungen, Jobverlust, Existenzvernichtung oder anderen Maßnahmen, die geeignet sind, Exempel zu statuieren, die andere einschüchtern sollen, ja nicht auch auf die Idee zu kommen, sich dem System entgegenzustellen und die falschen Fragen laut auszusprechen.
Kein Mensch hat das Recht zu gehorchen!
Wir wollen keine Tyrannei der Mehrheit. Die breite Masse der Gesellschaft ist immer schon mit dem Strom geschwommen, sei es aus Bequemlichkeit, aus Unvermögen oder aus Desinteresse. Kein Wecker kann hier laut genug klingeln, um sie aufzuwecken.
Die Diplomatie in Deutschland wurde abgeschafft. Nicht, weil erkannt wurde, dass sie in der heutigen Zeit nicht mehr funktioniert, sondern weil diejenigen, die es können müssten, mangels fachlicher, sachlicher und menschlicher Qualifikation dazu nicht in der Lage sind. Diplomatisches Unvermögen und eine ordentliche Portion Russenhass scheinen unbedingtes Einstellungskriterium zu sein, um in Verantwortung zu kommen. Wer in Drohen eine Eins hatte, ist ganz vorne dabei.
Es ist ein unverschämter Raub von Lebenszeit der Beklagten, wie z. B. Ballweg, Füllmich, Guérot, der nur dazu dient, Exempel zu statuieren, um zu zeigen, wie das System seine Muskeln spielen lassen kann, wenn man nicht so funktioniert, wie es sich das System wünscht. Aber auch hier und da gibt es noch Richter, die ihrem Gewissen verpflichtet sind, unterstützt von unermüdlichen Anwälten, die sich der Rechtspflege und nicht dem Rechtsverdrehen verpflichtet sehen. Deutschland hat gute Gesetze, wenn sie nur schon wieder vollumfänglich gelten würden. Nicht kritische Stimmen delegitimieren den Staat, sondern der sogenannte Staat verbiegt die Rechtsprechung zu seinen Gunsten, auf die wir uns alle geeinigt haben und die für uns alle gilt.
Und sogar in der Medizin gibt es noch Ärzte mit Gewissen, denen der Satz „Primum non nocere“ oberste Pflicht und Berufsehre ist. Deren Aufgabe wäre es, das bei dem kritischen Teil des Volkes nicht mehr vorhandene Vertrauen, nach allen Regeln der Heilkunst wieder herzustellen. Begleitet durch die Forderung der Abschaffung der Fallpauschalen und das Wiederabschaffen der verordneten Gewinnorientierung zugunsten eines möglichst wirtschaftlich arbeitenden Gesundheitsbetriebes. Besonderer Respekt wäre hier der Generation zu zollen, die dieses Land wiederaufgebaut hat, nachdem ein Irrer es wiederholt in Schutt und Asche gelegt hat.
Ein Neuanfang ist schon mit dem ständigen Wachsen der Neuen Medien getan. Wer schaut sich noch den einseitig-selbstherrlichen Dreck im Staatsfunk an oder liest eine Zeitung aus dem Neues-Deutschland-Verlag?
Der tägliche Wahnsinn mit einem schier unerschöpflichen Potenzial für neue Absurditäten zehrt an denjenigen, die der Gehirnwäsche erfolgreich widerstanden haben. Und wenn es auch Tage der Niedergeschlagenheit gibt, am nächsten Tag wird die Krone zurechtgerückt und weitergemacht, ok? Niemals vergessen: Wir, die wir offensichtlich bei Verstand geblieben sind, können jeden Morgen in den Spiegel schauen, wir sind aufrichtig und haben ein Rückgrat. Wir sind keine wirbellosen Nacktschnecken, die eine klebrige Schleimspur hinter sich herziehen und zu nichts anderem taugen, als anderen auf den Wecker zu gehen und das Leben schwer zu machen.
Wir sind keine egoistischen Speichellecker, die nur darauf bedacht sind, irgendwie mit dem Kopf über Wasser zu bleiben, weil sie sich eingeredet haben, dass sie davonkommen:
„Wird schon gut gehen. Wir sind auf der Seite der Gewinner. Wir sind die Stärkeren. Wir halten zusammen. Gegen uns kommen diese Deppen sowieso nicht an.“
Ich bin der Teil von jener Kraft, die Böses will und Gutes schafft.
Wir werden sehen, wer hier die Hosen anhat: Die Wahrheit oder der Wahnsinn.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ 9bcc5462:eb501d90
2025-02-24 17:47:28
@ 9bcc5462:eb501d90
2025-02-24 17:47:28Every generation loves to learn. However, our public schooling system has gone as far as it can take us. The abundance of easily accessible information on the internet, coupled with emerging tech like AI, decentralized protocols and bitcoin, means this is our time to innovate our learning infrastructure. A complete overhaul is due along with the development of a pilot program to test new and unconventional models.
Let’s carve a path towards innovation by sparking discussion around this topic. Hence, this blueprint. It is a gauntlet for any person who genuinely wants to become a stakeholder for our country’s future. Entry points are:
- Builders—Startups, developers and investors who will fund and create infrastructure.
- Practitioners—Educators and researchers who will test models.
- Supporters—Parents, donors and community members who want to contribute.
Where Do We Begin?
Let’s think about crafting the main components of a new pilot model. Below are suggested areas of focus:
- DEFINITION
- APPROACH
- PHILOSOPHY
- CULTURE
- PHYSICAL DESIGN
- OPERATIONAL ORGANIZATION
- ACCOUNTABILITY METHODS
- RISKS & CHALLENGES
- STYLE
- STAKEHOLDERS
How It Works
After researching your pedagogical ideas for current and future generations of scholars, it’s time to share your insights. Contribute your viewpoint by structuring a blueprint—one page per section—in the following sequence:
- Definition of your modern learning model with its key principles.
- Description of the core learning approach.
- Philosophy distilled into central concepts that will orient stakeholders.
- Culture your modern learning model aspires to live by.
- Potential challenges, risks and drawbacks.
- Design of physical spaces and rationale.
- Operational framework detailing adult and child learning organization.
- Accountability methods to ensure skill growth and competency.
- Style development and name of your model.
- Skin in the game, sign your model with your first and last name (unite stakeholders).
Perhaps if enough stakeholders come together, we can begin to actualize a more effective and updated way of learning. This is a challenge meant to separate those willing to engage in discourse, planning and laying foundations from those content to complain from the sidelines.
Why Now and Where Does the Money Come From?
After being a public educator for fifteen years, I learned you will not change the system, the system will change you. It’s time to design and build above and apart from the current model. 2025 is when courageous people step up to the plate and discuss our learning infrastructure. Whether it’s contributing out of the box thinking, modernizing curriculum, investing in startups or creating your own venture; there is no greater time than now. And no greater place than in the USA!
(By extension, we also create the opportunity to influence our global allies including our neighbors to the North and South.)
“But how!?” Learning Producers is figuring it out by asking not, “how?” but “who?” Who will unite together to develop our learning infrastructure? If you decide you want to participate and join our efforts, share your blueprint as well. For all stakeholders, this is an investment in an untapped market of a new learning economy.
If not, you’re not alone. Some consider this just rhetoric, idealism, or wishful thinking. Additionally, it is unclear how such actions can be profitable or how such infrastructure building will be funded. Money talks. Bullshit walks, right? In that case, let’s talk, and let’s fine tune our BS detectors. Onward, with this call to action:
- Share your own blueprint online or reach out to Learning Producers, Inc. (Learningproducers.com).
- Conduct research on an ideal location and team to lay foundations on a pilot program at small scale.
- Engage in dialogue with investors interested in developing learning infrastructure for their own children and families.
- Secure stakeholders to develop and test a real world pilot model (real location, real agreements, real timeline, real people).
- Sponsor or donate resources to counter concerns over funding.
Now, we leave you with our blueprint:
PEDAGOGICAL WABI-SABI
We hope you enjoy it.
Sincerely,
Israel Hernandez
Founder of Learning Producers
**[Read or download full blueprint here: https://www.learningproducers.com/blog/pedagogical-wabi-sabiblueprint-for-developing-learning-infrastructure ]
-
 @ e4950c93:1b99eccd
2025-05-20 11:06:09
@ e4950c93:1b99eccd
2025-05-20 11:06:09Contenu à venir.
-
 @ 7953d1fa:69c8039d
2025-05-20 02:39:56
@ 7953d1fa:69c8039d
2025-05-20 02:39:56No mundo digital em constante evolução, plataformas de entretenimento online vêm ganhando espaço entre os brasileiros que buscam diversão, emoção e recompensas. Uma das opções que tem se destacado recentemente é a KK999, uma plataforma moderna, segura e repleta de oportunidades para jogadores de todos os níveis. Com uma ampla gama de jogos envolventes e uma experiência de usuário otimizada, o KK999 está conquistando cada vez mais adeptos no Brasil.
Introdução à Plataforma KK999 O KK999 se diferencia por oferecer uma experiência completa e intuitiva desde o primeiro acesso. A interface da plataforma foi cuidadosamente projetada para ser amigável, permitindo que novos usuários se cadastrem rapidamente e naveguem com facilidade. Tudo é pensado para garantir que o jogador tenha uma experiência fluida, sem complicações e com total transparência.
Além disso, o kk999se destaca por sua forte infraestrutura de segurança. Utilizando tecnologia de criptografia de ponta, os dados dos usuários são protegidos em todas as transações, garantindo tranquilidade para quem deseja apenas se divertir. Outro ponto importante é o suporte ao cliente, que está disponível 24 horas por dia, com atendimento em português, pronto para auxiliar com qualquer dúvida ou necessidade.
Variedade de Jogos para Todos os Gostos Um dos grandes atrativos do KK999 é a impressionante variedade de jogos disponíveis. Desde os tradicionais jogos de cartas até opções modernas com gráficos avançados, a plataforma atende todos os estilos de jogadores. Entre os destaques, estão as famosas roletas virtuais, jogos de pesca interativa, slot machines com temas variados e jogos ao vivo que simulam a sensação de estar em uma sala de jogos física.
Os slots, por exemplo, são um sucesso entre os brasileiros, oferecendo desde títulos clássicos com frutas e números até aventuras temáticas com bônus emocionantes. Os jogos de cartas também têm grande popularidade, incluindo versões modernas de pôquer, bacará e outros jogos estratégicos que desafiam a mente do jogador.
Para quem gosta de competir em tempo real, o KK999 oferece jogos ao vivo com crupiês reais e interatividade instantânea, proporcionando uma experiência imersiva e cheia de adrenalina. Tudo isso com transmissões de alta qualidade e conexão estável.
Experiência do Jogador: Diversão e Confiabilidade A experiência do jogador é uma das maiores prioridades do KK999. Desde o primeiro cadastro até as jogadas mais avançadas, a plataforma investe em funcionalidades que aumentam o conforto e a confiança do usuário. A navegação é rápida, os jogos carregam com eficiência e as recompensas são distribuídas com agilidade.
Outro fator que atrai muitos jogadores é o sistema de bônus e promoções. O KK999 frequentemente disponibiliza ofertas especiais para novos membros e prêmios para usuários frequentes, incentivando a fidelidade e aumentando ainda mais as chances de ganhar.
Além disso, o KK999 oferece uma experiência totalmente otimizada para dispositivos móveis. Seja no celular ou tablet, o jogador pode acessar todos os recursos da plataforma de qualquer lugar, a qualquer momento, sem perder desempenho ou qualidade.
Conclusão O KK999 se consolida como uma das principais plataformas de entretenimento digital no Brasil, reunindo inovação, segurança e uma variedade impressionante de jogos. Ideal tanto para iniciantes quanto para jogadores experientes, o site oferece tudo o que é necessário para transformar momentos comuns em experiências emocionantes.
-
 @ 94a6a78a:0ddf320e
2025-02-19 21:10:15
@ 94a6a78a:0ddf320e
2025-02-19 21:10:15Nostr is a revolutionary protocol that enables decentralized, censorship-resistant communication. Unlike traditional social networks controlled by corporations, Nostr operates without central servers or gatekeepers. This openness makes it incredibly powerful—but also means its success depends entirely on users, developers, and relay operators.
If you believe in free speech, decentralization, and an open internet, there are many ways to support and strengthen the Nostr ecosystem. Whether you're a casual user, a developer, or someone looking to contribute financially, every effort helps build a more robust network.
Here’s how you can get involved and make a difference.
1️⃣ Use Nostr Daily
The simplest and most effective way to contribute to Nostr is by using it regularly. The more active users, the stronger and more valuable the network becomes.
✅ Post, comment, and zap (send micro-payments via Bitcoin’s Lightning Network) to keep conversations flowing.\ ✅ Engage with new users and help them understand how Nostr works.\ ✅ Try different Nostr clients like Damus, Amethyst, Snort, or Primal and provide feedback to improve the experience.
Your activity keeps the network alive and helps encourage more developers and relay operators to invest in the ecosystem.
2️⃣ Run Your Own Nostr Relay
Relays are the backbone of Nostr, responsible for distributing messages across the network. The more independent relays exist, the stronger and more censorship-resistant Nostr becomes.
✅ Set up your own relay to help decentralize the network further.\ ✅ Experiment with relay configurations and different performance optimizations.\ ✅ Offer public or private relay services to users looking for high-quality infrastructure.
If you're not technical, you can still support relay operators by subscribing to a paid relay or donating to open-source relay projects.
3️⃣ Support Paid Relays & Infrastructure
Free relays have helped Nostr grow, but they struggle with spam, slow speeds, and sustainability issues. Paid relays help fund better infrastructure, faster message delivery, and a more reliable experience.
✅ Subscribe to a paid relay to help keep it running.\ ✅ Use premium services like media hosting (e.g., Azzamo Blossom) to decentralize content storage.\ ✅ Donate to relay operators who invest in long-term infrastructure.
By funding Nostr’s decentralized backbone, you help ensure its longevity and reliability.
4️⃣ Zap Developers, Creators & Builders
Many people contribute to Nostr without direct financial compensation—developers who build clients, relay operators, educators, and content creators. You can support them with zaps! ⚡
✅ Find developers working on Nostr projects and send them a zap.\ ✅ Support content creators and educators who spread awareness about Nostr.\ ✅ Encourage builders by donating to open-source projects.
Micro-payments via the Lightning Network make it easy to directly support the people who make Nostr better.
5️⃣ Develop New Nostr Apps & Tools
If you're a developer, you can build on Nostr’s open protocol to create new apps, bots, or tools. Nostr is permissionless, meaning anyone can develop for it.
✅ Create new Nostr clients with unique features and user experiences.\ ✅ Build bots or automation tools that improve engagement and usability.\ ✅ Experiment with decentralized identity, authentication, and encryption to make Nostr even stronger.
With no corporate gatekeepers, your projects can help shape the future of decentralized social media.
6️⃣ Promote & Educate Others About Nostr
Adoption grows when more people understand and use Nostr. You can help by spreading awareness and creating educational content.
✅ Write blogs, guides, and tutorials explaining how to use Nostr.\ ✅ Make videos or social media posts introducing new users to the protocol.\ ✅ Host discussions, Twitter Spaces, or workshops to onboard more people.
The more people understand and trust Nostr, the stronger the ecosystem becomes.
7️⃣ Support Open-Source Nostr Projects
Many Nostr tools and clients are built by volunteers, and open-source projects thrive on community support.
✅ Contribute code to existing Nostr projects on GitHub.\ ✅ Report bugs and suggest features to improve Nostr clients.\ ✅ Donate to developers who keep Nostr free and open for everyone.
If you're not a developer, you can still help with testing, translations, and documentation to make projects more accessible.
🚀 Every Contribution Strengthens Nostr
Whether you:
✔️ Post and engage daily\ ✔️ Zap creators and developers\ ✔️ Run or support relays\ ✔️ Build new apps and tools\ ✔️ Educate and onboard new users
Every action helps make Nostr more resilient, decentralized, and unstoppable.
Nostr isn’t just another social network—it’s a movement toward a free and open internet. If you believe in digital freedom, privacy, and decentralization, now is the time to get involved.
-
 @ 23b0e2f8:d8af76fc
2025-01-08 18:17:52
@ 23b0e2f8:d8af76fc
2025-01-08 18:17:52Necessário
- Um Android que você não use mais (a câmera deve estar funcionando).
- Um cartão microSD (opcional, usado apenas uma vez).
- Um dispositivo para acompanhar seus fundos (provavelmente você já tem um).
Algumas coisas que você precisa saber
- O dispositivo servirá como um assinador. Qualquer movimentação só será efetuada após ser assinada por ele.
- O cartão microSD será usado para transferir o APK do Electrum e garantir que o aparelho não terá contato com outras fontes de dados externas após sua formatação. Contudo, é possível usar um cabo USB para o mesmo propósito.
- A ideia é deixar sua chave privada em um dispositivo offline, que ficará desligado em 99% do tempo. Você poderá acompanhar seus fundos em outro dispositivo conectado à internet, como seu celular ou computador pessoal.
O tutorial será dividido em dois módulos:
- Módulo 1 - Criando uma carteira fria/assinador.
- Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
No final, teremos:
- Uma carteira fria que também servirá como assinador.
- Um dispositivo para acompanhar os fundos da carteira.

Módulo 1 - Criando uma carteira fria/assinador
-
Baixe o APK do Electrum na aba de downloads em https://electrum.org/. Fique à vontade para verificar as assinaturas do software, garantindo sua autenticidade.
-
Formate o cartão microSD e coloque o APK do Electrum nele. Caso não tenha um cartão microSD, pule este passo.

- Retire os chips e acessórios do aparelho que será usado como assinador, formate-o e aguarde a inicialização.

- Durante a inicialização, pule a etapa de conexão ao Wi-Fi e rejeite todas as solicitações de conexão. Após isso, você pode desinstalar aplicativos desnecessários, pois precisará apenas do Electrum. Certifique-se de que Wi-Fi, Bluetooth e dados móveis estejam desligados. Você também pode ativar o modo avião.\ (Curiosidade: algumas pessoas optam por abrir o aparelho e danificar a antena do Wi-Fi/Bluetooth, impossibilitando essas funcionalidades.)

- Insira o cartão microSD com o APK do Electrum no dispositivo e instale-o. Será necessário permitir instalações de fontes não oficiais.

- No Electrum, crie uma carteira padrão e gere suas palavras-chave (seed). Anote-as em um local seguro. Caso algo aconteça com seu assinador, essas palavras permitirão o acesso aos seus fundos novamente. (Aqui entra seu método pessoal de backup.)

Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
-
Criar uma carteira somente leitura em outro dispositivo, como seu celular ou computador pessoal, é uma etapa bastante simples. Para este tutorial, usaremos outro smartphone Android com Electrum. Instale o Electrum a partir da aba de downloads em https://electrum.org/ ou da própria Play Store. (ATENÇÃO: O Electrum não existe oficialmente para iPhone. Desconfie se encontrar algum.)
-
Após instalar o Electrum, crie uma carteira padrão, mas desta vez escolha a opção Usar uma chave mestra.

- Agora, no assinador que criamos no primeiro módulo, exporte sua chave pública: vá em Carteira > Detalhes da carteira > Compartilhar chave mestra pública.

-
Escaneie o QR gerado da chave pública com o dispositivo de consulta. Assim, ele poderá acompanhar seus fundos, mas sem permissão para movimentá-los.
-
Para receber fundos, envie Bitcoin para um dos endereços gerados pela sua carteira: Carteira > Addresses/Coins.
-
Para movimentar fundos, crie uma transação no dispositivo de consulta. Como ele não possui a chave privada, será necessário assiná-la com o dispositivo assinador.

- No assinador, escaneie a transação não assinada, confirme os detalhes, assine e compartilhe. Será gerado outro QR, desta vez com a transação já assinada.

- No dispositivo de consulta, escaneie o QR da transação assinada e transmita-a para a rede.
Conclusão
Pontos positivos do setup:
- Simplicidade: Basta um dispositivo Android antigo.
- Flexibilidade: Funciona como uma ótima carteira fria, ideal para holders.
Pontos negativos do setup:
- Padronização: Não utiliza seeds no padrão BIP-39, você sempre precisará usar o electrum.
- Interface: A aparência do Electrum pode parecer antiquada para alguns usuários.
Nesse ponto, temos uma carteira fria que também serve para assinar transações. O fluxo de assinar uma transação se torna: Gerar uma transação não assinada > Escanear o QR da transação não assinada > Conferir e assinar essa transação com o assinador > Gerar QR da transação assinada > Escanear a transação assinada com qualquer outro dispositivo que possa transmiti-la para a rede.
Como alguns devem saber, uma transação assinada de Bitcoin é praticamente impossível de ser fraudada. Em um cenário catastrófico, você pode mesmo que sem internet, repassar essa transação assinada para alguém que tenha acesso à rede por qualquer meio de comunicação. Mesmo que não queiramos que isso aconteça um dia, esse setup acaba por tornar essa prática possível.
-
 @ 39cc53c9:27168656
2025-05-20 10:45:15
@ 39cc53c9:27168656
2025-05-20 10:45:15After almost 3 months of work, we've completed the redesign of kycnot.me. More modern and with many new features.
Privacy remains the foundation - everything still works with JavaScript disabled. If you enable JS, you will get some nice-to-have features like lazy loading and smoother page transitions, but nothing essential requires it.
User Accounts
We've introduced user accounts that require zero personal information:
- Secret user tokens - no email, no phone number, no personal data
- Randomly generated usernames for default privacy and fairness
- Karma system that rewards contributions and unlocks features: custom display names, profile pictures, and more.
Reviews and Community Discussions
On the previous sites, I was using third party open source tools for the comments and discussions. This time, I've built my own from scratch, fully integrated into the site, without JavaScript requirements.
Everyone can share their experiences and help others make informed decisions:
- Ratings: Comments can have a 1-5 star rating attached. You can have one rating per service and it will affect the overall user score.
- Discussions: These are normal comments, you can add them on any listed service.
Comment Moderation
I was strugling to keep up with moderation on the old site. For this, we've implemented an AI-powered moderation system that:
- Auto-approves legitimate comments instantly
- Flags suspicious content for human review
- Keeps discussions valuable by minimizing spam
The AI still can mark comments for human review, but most comments will get approved automatically by this system. The AI also makes summaries of the comments to help you understand the overall sentiment of the community.
Powerful Search & Filtering
Finding exactly what you need is now easier:
- Advanced filtering system with many parameters. You can even filter by attributes to pinpoint services with specific features.
The results are dynamic and shuffle services with identical scores for fairness.
See all listings
Listings are now added as 'Community Contributed' by default. This means that you can still find them in the search results, but they will be clearly marked as such.
Updated Scoring System
New dual-score approach provides more nuanced service evaluations:
- Privacy Score: Measures how well a service protects your personal information and data
-
Trust Score: Assesses reliability, security, and overall reputation
-
Combined into a weighted Overall Score for quick comparisons
- Completely transparent and open source calculation algorithm. No manual tweaking or hidden factors.
AI-Powered Terms of Service Analysis
Basically, a TLDR summary for Terms of Service:
- Automated system extracts the most important points from complex ToS documents
- Clear summaries
- Updated monthly to catch any changes
The ToS document is hashed and only will be updated if there are any changes.
Service Events and Timelines
Track the complete history of any service, on each service page you can see the timeline of events. There are two types of events:
- Automatic events: Created by the system whenever something about a service changes, like its description, supported currencies, attributes, verification status…
- Manual events: Added by admins when there’s important news, such as a service going offline, being hacked, acquired, shut down, or other major updates.
There is also a global timeline view available at /events
Notification System
Since we now have user accounts, we built a notifiaction system so you can stay informed about anything:
- Notifications for comment replies and status changes
- Watch any comment to get notified for new replies.
- Subscribe to services to monitor events and updates
- Notification customization.
Coming soon: Third-party privacy-preserving notifications integration with Telegram, Ntfy.sh, webhooks...
Service Suggestions
Anyone with an account can suggest a new service via the suggestion form. After submitting, you'll receive a tracking page where you can follow the status of your suggestion and communicate directly with admins.
All new suggestions start as "unlisted" — they won't appear in search results until reviewed. Our team checks each submission to ensure it's not spam or inappropriate. If similar services already exist, you'll be shown possible duplicates and can choose to submit your suggestion as an edit instead.
You can always check the progress of your suggestion, respond to moderator questions, and see when it goes live, everything will also be notified to your account. This process ensures high-quality listings and a collaborative approach to building the directory.
These are some of the main features we already have, but there are many more small changes and improvements that you will find when using the site.
What's Next?
This is just the beginning. We will be constantly working to improve KYCnot.me and add more features that help you preserve your privacy.
Remember: True financial freedom requires the right to privacy. Stay KYC-free!
-
 @ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08
@ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08Tldr
- Nostr is an open and interoperable protocol
- You can integrate it with workflow automation tools to augment your experience
- n8n is a great low/no-code workflow automation tool which you can host yourself
- Nostrobots allows you to integrate Nostr into n8n
- In this blog I create some workflow automations for Nostr
- A simple form to delegate posting notes
- Push notifications for mentions on multiple accounts
- Push notifications for your favourite accounts when they post a note
- All workflows are provided as open source with MIT license for you to use
Inter-op All The Things
Nostr is a new open social protocol for the internet. This open nature exciting because of the opportunities for interoperability with other technologies. In Using NFC Cards with Nostr I explored the
nostr:URI to launch Nostr clients from a card tap.The interoperability of Nostr doesn't stop there. The internet has many super-powers, and Nostr is open to all of them. Simply, there's no one to stop it. There is no one in charge, there are no permissioned APIs, and there are no risks of being de-platformed. If you can imagine technologies that would work well with Nostr, then any and all of them can ride on or alongside Nostr rails.
My mental model for why this is special is Google Wave ~2010. Google Wave was to be the next big platform. Lars was running it and had a big track record from Maps. I was excited for it. Then, Google pulled the plug. And, immediately all the time and capital invested in understanding and building on the platform was wasted.
This cannot happen to Nostr, as there is no one to pull the plug, and maybe even no plug to pull.
So long as users demand Nostr, Nostr will exist, and that is a pretty strong guarantee. It makes it worthwhile to invest in bringing Nostr into our other applications.
All we need are simple ways to plug things together.
Nostr and Workflow Automation
Workflow automation is about helping people to streamline their work. As a user, the most common way I achieve this is by connecting disparate systems together. By setting up one system to trigger another or to move data between systems, I can solve for many different problems and become way more effective.
n8n for workflow automation
Many workflow automation tools exist. My favourite is n8n. n8n is a low/no-code workflow automation platform which allows you to build all kinds of workflows. You can use it for free, you can self-host it, it has a user-friendly UI and useful API. Vs Zapier it can be far more elaborate. Vs Make.com I find it to be more intuitive in how it abstracts away the right parts of the code, but still allows you to code when you need to.
Most importantly you can plug anything into n8n: You have built-in nodes for specific applications. HTTP nodes for any other API-based service. And community nodes built by individual community members for any other purpose you can imagine.
Eating my own dogfood
It's very clear to me that there is a big design space here just demanding to be explored. If you could integrate Nostr with anything, what would you do?
In my view the best way for anyone to start anything is by solving their own problem first (aka "scratching your own itch" and "eating your own dogfood"). As I get deeper into Nostr I find myself controlling multiple Npubs – to date I have a personal Npub, a brand Npub for a community I am helping, an AI assistant Npub, and various testing Npubs. I need ways to delegate access to those Npubs without handing over the keys, ways to know if they're mentioned, and ways to know if they're posting.
I can build workflows with n8n to solve these issues for myself to start with, and keep expanding from there as new needs come up.
Running n8n with Nostrobots
I am mostly non-technical with a very helpful AI. To set up n8n to work with Nostr and operate these workflows should be possible for anyone with basic technology skills.
- I have a cheap VPS which currently runs my HAVEN Nostr Relay and Albyhub Lightning Node in Docker containers,
- My objective was to set up n8n to run alongside these in a separate Docker container on the same server, install the required nodes, and then build and host my workflows.
Installing n8n
Self-hosting n8n could not be easier. I followed n8n's Docker-Compose installation docs–
- Install Docker and Docker-Compose if you haven't already,
- Create your
docker-compose.ymland.envfiles from the docs, - Create your data folder
sudo docker volume create n8n_data, - Start your container with
sudo docker compose up -d, - Your n8n instance should be online at port
5678.
n8n is free to self-host but does require a license. Enter your credentials into n8n to get your free license key. You should now have access to the Workflow dashboard and can create and host any kind of workflows from there.
Installing Nostrobots
To integrate n8n nicely with Nostr, I used the Nostrobots community node by Ocknamo.
In n8n parlance a "node" enables certain functionality as a step in a workflow e.g. a "set" node sets a variable, a "send email" node sends an email. n8n comes with all kinds of "official" nodes installed by default, and Nostr is not amongst them. However, n8n also comes with a framework for community members to create their own "community" nodes, which is where Nostrobots comes in.
You can only use a community node in a self-hosted n8n instance (which is what you have if you are running in Docker on your own server, but this limitation does prevent you from using n8n's own hosted alternative).
To install a community node, see n8n community node docs. From your workflow dashboard–
- Click the "..." in the bottom left corner beside your username, and click "settings",
- Cilck "community nodes" left sidebar,
- Click "Install",
- Enter the "npm Package Name" which is
n8n-nodes-nostrobots, - Accept the risks and click "Install",
- Nostrobots is now added to your n8n instance.
Using Nostrobots
Nostrobots gives you nodes to help you build Nostr-integrated workflows–
- Nostr Write – for posting Notes to the Nostr network,
- Nostr Read – for reading Notes from the Nostr network, and
- Nostr Utils – for performing certain conversions you may need (e.g. from bech32 to hex).
Nostrobots has good documentation on each node which focuses on simple use cases.
Each node has a "convenience mode" by default. For example, the "Read" Node by default will fetch Kind 1 notes by a simple filter, in Nostrobots parlance a "Strategy". For example, with Strategy set to "Mention" the node will accept a pubkey and fetch all Kind 1 notes that Mention the pubkey within a time period. This is very good for quick use.
What wasn't clear to me initially (until Ocknamo helped me out) is that advanced use cases are also possible.
Each node also has an advanced mode. For example, the "Read" Node can have "Strategy" set to "RawFilter(advanced)". Now the node will accept json (anything you like that complies with NIP-01). You can use this to query Notes (Kind 1) as above, and also Profiles (Kind 0), Follow Lists (Kind 3), Reactions (Kind 7), Zaps (Kind 9734/9735), and anything else you can think of.
Creating and adding workflows
With n8n and Nostrobots installed, you can now create or add any kind of Nostr Workflow Automation.
- Click "Add workflow" to go to the workflow builder screen,
- If you would like to build your own workflow, you can start with adding any node. Click "+" and see what is available. Type "Nostr" to explore the Nostrobots nodes you have added,
- If you would like to add workflows that someone else has built, click "..." in the top right. Then click "import from URL" and paste in the URL of any workflow you would like to use (including the ones I share later in this article).
Nostr Workflow Automations
It's time to build some things!
A simple form to post a note to Nostr
I started very simply. I needed to delegate the ability to post to Npubs that I own in order that a (future) team can test things for me. I don't want to worry about managing or training those people on how to use keys, and I want to revoke access easily.
I needed a basic form with credentials that posted a Note.
For this I can use a very simple workflow–
- A n8n Form node – Creates a form for users to enter the note they wish to post. Allows for the form to be protected by a username and password. This node is the workflow "trigger" so that the workflow runs each time the form is submitted.
- A Set node – Allows me to set some variables, in this case I set the relays that I intend to use. I typically add a Set node immediately following the trigger node, and put all the variables I need in this. It helps to make the workflows easier to update and maintain.
- A Nostr Write node (from Nostrobots) – Writes a Kind-1 note to the Nostr network. It accepts Nostr credentials, the output of the Form node, and the relays from the Set node, and posts the Note to those relays.
Once the workflow is built, you can test it with the testing form URL, and set it to "Active" to use the production form URL. That's it. You can now give posting access to anyone for any Npub. To revoke access, simply change the credentials or set to workflow to "Inactive".
It may also be the world's simplest Nostr client.
You can find the Nostr Form to Post a Note workflow here.
Push notifications on mentions and new notes
One of the things Nostr is not very good at is push notifications. Furthermore I have some unique itches to scratch. I want–
- To make sure I never miss a note addressed to any of my Npubs – For this I want a push notification any time any Nostr user mentions any of my Npubs,
- To make sure I always see all notes from key accounts – For this I need a push notification any time any of my Npubs post any Notes to the network,
- To get these notifications on all of my devices – Not just my phone where my Nostr regular client lives, but also on each of my laptops to suit wherever I am working that day.
I needed to build a Nostr push notifications solution.
To build this workflow I had to string a few ideas together–
- Triggering the node on a schedule – Nostrobots does not include a trigger node. As every workflow starts with a trigger we needed a different method. I elected to run the workflow on a schedule of every 10-minutes. Frequent enough to see Notes while they are hot, but infrequent enough to not burden public relays or get rate-limited,
- Storing a list of Npubs in a Nostr list – I needed a way to store the list of Npubs that trigger my notifications. I initially used an array defined in the workflow, this worked fine. Then I decided to try Nostr lists (NIP-51, kind 30000). By defining my list of Npubs as a list published to Nostr I can control my list from within a Nostr client (e.g. Listr.lol or Nostrudel.ninja). Not only does this "just work", but because it's based on Nostr lists automagically Amethyst client allows me to browse that list as a Feed, and everyone I add gets notified in their Mentions,
- Using specific relays – I needed to query the right relays, including my own HAVEN relay inbox for notes addressed to me, and wss://purplepag.es for Nostr profile metadata,
- Querying Nostr events (with Nostrobots) – I needed to make use of many different Nostr queries and use quite a wide range of what Nostrobots can do–
- I read the EventID of my Kind 30000 list, to return the desired pubkeys,
- For notifications on mentions, I read all Kind 1 notes that mention that pubkey,
- For notifications on new notes, I read all Kind 1 notes published by that pubkey,
- Where there are notes, I read the Kind 0 profile metadata event of that pubkey to get the displayName of the relevant Npub,
- I transform the EventID into a Nevent to help clients find it.
- Using the Nostr URI – As I did with my NFC card article, I created a link with the
nostr:URI prefix so that my phone's native client opens the link by default, - Push notifications solution – I needed a push notifications solution. I found many with n8n integrations and chose to go with Pushover which supports all my devices, has a free trial, and is unfairly cheap with a $5-per-device perpetual license.
Once the workflow was built, lists published, and Pushover installed on my phone, I was fully set up with push notifications on Nostr. I have used these workflows for several weeks now and made various tweaks as I went. They are feeling robust and I'd welcome you to give them a go.
You can find the Nostr Push Notification If Mentioned here and If Posts a Note here.
In speaking with other Nostr users while I was building this, there are all kind of other needs for push notifications too – like on replies to a certain bookmarked note, or when a followed Npub starts streaming on zap.stream. These are all possible.
Use my workflows
I have open sourced all my workflows at my Github with MIT license and tried to write complete docs, so that you can import them into your n8n and configure them for your own use.
To import any of my workflows–
- Click on the workflow of your choice, e.g. "Nostr_Push_Notify_If_Mentioned.json",
- Click on the "raw" button to view the raw JSON, ex any Github page layout,
- Copy that URL,
- Enter that URL in the "import from URL" dialog mentioned above.
To configure them–
- Prerequisites, credentials, and variables are all stated,
- In general any variables required are entered into a Set Node that follows the trigger node,
- Pushover has some extra setup but is very straightforward and documented in the workflow.
What next?
Over my first four blogs I explored creating a good Nostr setup with Vanity Npub, Lightning Payments, Nostr Addresses at Your Domain, and Personal Nostr Relay.
Then in my latest two blogs I explored different types of interoperability with NFC cards and now n8n Workflow Automation.
Thinking ahead n8n can power any kind of interoperability between Nostr and any other legacy technology solution. On my mind as I write this:
- Further enhancements to posting and delegating solutions and forms (enhanced UI or different note kinds),
- Automated or scheduled posting (such as auto-liking everything Lyn Alden posts),
- Further enhancements to push notifications, on new and different types of events (such as notifying me when I get a new follower, on replies to certain posts, or when a user starts streaming),
- All kinds of bridges, such as bridging notes to and from Telegram, Slack, or Campfire. Or bridging RSS or other event feeds to Nostr,
- All kinds of other automation (such as BlackCoffee controlling a coffee machine),
- All kinds of AI Assistants and Agents,
In fact I have already released an open source workflow for an AI Assistant, and will share more about that in my next blog.
Please be sure to let me know if you think there's another Nostr topic you'd like to see me tackle.
GM Nostr.
-
 @ a93d7cd3:ae5ce5dd
2025-05-20 10:16:55
@ a93d7cd3:ae5ce5dd
2025-05-20 10:16:55Test Nostr
-
 @ 7953d1fa:69c8039d
2025-05-20 02:39:23
@ 7953d1fa:69c8039d
2025-05-20 02:39:23O cenário do entretenimento online no Brasil vem evoluindo rapidamente, e uma das plataformas que mais se destaca atualmente é a 8CC. Com uma proposta moderna, intuitiva e voltada para a melhor experiência do usuário, a 8CC conquistou a confiança de milhares de jogadores que buscam diversão, praticidade e oportunidades de ganhos reais em um ambiente seguro.
Conhecendo a Plataforma 8CC A 8CC é uma plataforma digital desenvolvida para atender tanto iniciantes quanto jogadores experientes. Sua interface amigável e bem organizada facilita a navegação mesmo para quem nunca teve contato com esse tipo de entretenimento antes. Compatível com computadores, tablets e celulares, o site é totalmente responsivo, o que significa que você pode se divertir de qualquer lugar, a qualquer hora.
Um dos diferenciais da 8cc é o seu compromisso com a segurança dos usuários. A plataforma utiliza tecnologia de criptografia de ponta para garantir a proteção de dados pessoais e transações financeiras. Além disso, o suporte ao cliente está sempre disponível para tirar dúvidas, resolver problemas e oferecer o melhor atendimento possível.
Diversidade de Jogos para Todos os Gostos Na 8CC, os jogadores têm acesso a uma vasta seleção de jogos online, desenvolvidos pelos principais provedores do mercado internacional. Isso garante alta qualidade gráfica, mecânicas inovadoras e excelente desempenho.
Entre os jogos mais populares da plataforma estão:
Slots (caça-níqueis): com temas variados, rodadas bônus e jackpots progressivos que proporcionam grandes emoções.
Jogos de mesa clássicos: como roleta, blackjack e bacará, com versões que imitam perfeitamente a experiência de jogo ao vivo.
Jogos com crupiês em tempo real: transmitidos com qualidade HD, esses jogos trazem interatividade e realismo, permitindo que o jogador se sinta dentro de um ambiente físico de alto padrão.
A plataforma também disponibiliza jogos de habilidade e apostas esportivas ao vivo, oferecendo uma experiência ainda mais completa e personalizada de acordo com o perfil de cada usuário.
Experiência do Jogador na 8CC Quem já experimentou jogar na 8CC sabe o quanto a plataforma valoriza o conforto e a satisfação de seus usuários. Desde o momento do cadastro até o resgate de ganhos, tudo é feito de forma simples, rápida e segura. O processo de registro é intuitivo, exigindo apenas alguns dados básicos, e os métodos de pagamento são variados, aceitando transferências bancárias, carteiras digitais e até criptomoedas.
Outro destaque é o sistema de recompensas e promoções. A 8CC frequentemente oferece bônus de boas-vindas, rodadas grátis e campanhas especiais para usuários fiéis, o que aumenta ainda mais as chances de ganhar e prolonga a diversão. Além disso, a plataforma promove torneios e desafios semanais com prêmios atrativos, incentivando a competição saudável entre os jogadores.
Por Que Escolher a 8CC? Existem muitas razões para escolher a 8CC como sua principal plataforma de jogos online:
Confiabilidade e segurança em todas as operações;
Variedade de jogos para todos os perfis;
Interface moderna e de fácil navegação;
Promoções e bônus frequentes;
Atendimento ao cliente eficiente e disponível 24 horas.
Se você busca uma experiência diferenciada, com diversão garantida e a possibilidade de transformar seu tempo livre em momentos empolgantes, a 8CC é a escolha certa. Descubra agora mesmo tudo o que essa plataforma inovadora tem a oferecer e junte-se à comunidade que está revolucionando o entretenimento digital no Brasil.
-
 @ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03
@ 34f1ddab:2ca0cf7c
2025-05-16 22:47:03Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ bf47c19e:c3d2573b
2025-05-11 17:48:52
@ bf47c19e:c3d2573b
2025-05-11 17:48:52Originalni tekst na medium.com.
Autor: Aleksandar Svetski / Prevod: ₿itcoin Serbia
Nemojte kupovati Bitkoin!
Ni danas, ni kasnije, nikada!
Posvećeno skepticima, neznalicama, arogantnima i nezainteresovanima.
NE TREBA vam Bitkoin.
Molim vas. Nemojte ga kupovati.
Lično me ne zanima "masovna adopcija".
Draža mi je selektivna adopcija.
Svinja ne zaslužuje bisere.
Na vama je da platite cenu neznanja.
Kao i cenu glupavosti.
Kada dođe vreme, sa zadovoljstvom ću vam platiti hiljadu satošija mesečno za vaše vreme i smejati se usput.

Najbitnija odluka koju ćete ikada doneti
NEMA važnije odluke za vašu finansijsku, ekonomsku i suverenu budućnost koju danas možete doneti nego da kupite Bitkoin.
A ako ne želite da izdvojite malo vremena da ga dalje proučite, JEDINA osoba koju treba da krivite kasnije ste vi sami.
Danas, Bitkoin se nalazi u svojoj ranoj, početnoj fazi. O ovome možete više pročitati ovde (hvala ObiWan Kenobit):
Hiperbitkoinizacija: pobednik uzima sve
Ovo JE prilika ne samo vašeg života, već verovatno i najveći mogući transfer bogatstva u istoriji, a najluđa stvar je što će se najveći deo toga odigrati u narednih nekoliko decenija.
Nalazimo se tek u prvih 12 godina ove promene, a već smo videlo kako je Bitkoin eksplodirao sa $0.008c (kada su za 10.000 BTC kupljene dve pice) na trenutnu cenu od oko $11.500.
Ovo je tek početak. Tek 0.001% svetskog bogatstva je denominirano u Bitkoinu.
Ako sada izdvojite samo trenutak da razumete novac, njegovu ulogu u društvu i kako će ekonomski darvinizam voditi ceo svet prema najrobusnijem, najčvršćem i najsigurnijem obliku očuvanja bogatstva, možete odlučiti da kupite neki deo pre nego što se ostatak sveta priključi.
Čitajući ovo, vi ste poput drevnog pojedinca koji je pronašao zlato, dok svi ostali koriste školjke. Razlika je u tome što živite u digitalnom dobu tokom kojeg će se ovaj novac pojaviti i sazreti za vreme vašeg života. Taj drevni pojedinac bi bio u pravu ali mrtav zato što je zlatu bilo potrebno nekoliko hiljada godina da uradi ono za šta će Bitkoinu biti potrebne decenije.
Zamislite. Se. Nad. Tim.
I naučite dalje o nastanku Bitkoina ovde:
I za ime ljubavi prema sopstvenoj budućnosti, preuzmite ovu kratku elektronsku knjigu i jebeno se edukujte!!
Preuzmite "Investiranje u Bitkoin"
I eto, dajem vam izvore.. jbt.. Svejedno...
Danas, imate izbor da kupite Bitkoin; najoskudniji novac u univerzumu, za siću!! Bukvalno možete kupiti hiljade satošija (najmanju jedinicu Bitkoina gde je 100.000.000 satošija = 1 BTC) za $1!!!
Danas ne postoji veća prilika, kao što sutradan neće postojati veće žaljenje kada više ne budete imali "izbor" da ga kupite.
Kada taj dan bude došao i kada budete to morali da prihvatite, setićete se ovih reči, ali avaj, biće prekasno, a vreme ne možete vratiti.

Više nije 2012
Tada ste imali izgovor. Sada je 2020...
Apsolutno NEMA razloga zašto neko sa malo radoznalosti i relativno funkcionalnim mozgom ne može da prouči šta je Bitkoin, zašto postoji, zašto je važan i zašto bi trebalo da u njega prebaci malo ličnog bogatstva.
Naročito ako ima prijatelja poput mene ili mnoštvo Bitkoinera negde tamo.
Ja više neću smarati ljude sa porukama "zašto treba kupiti Bitkoin".
Više nije 2012. godina.
Danas imamo toliko puno informacija od toliko mnogo dobrih ljudi na svim mogućim medijima, tako da NEMATE IZGOVORA da ga ignorišete ili kažete: "ali niko mi nije rekao".
Ukoliko nemate da izdvojite bar malo vremena od vašeg Netflix rasporeda da biste istražili šta je ova stvar i zašto je bitna za vašu ličnu ekonomsku budućnost, onda zaslužujete to što imate.
Deluje okrutno ali dobrodošao u život, mladi žutokljunče.
Sada... Ako ste izdvojili malo vremena ali ste i dalje nezainteresovani ili dovoljno glupi da ga odbacite, onda zaista zaslužujete to što dolazi i ostatak ovog članka je definitivno za vas.
Ne želim da uopšte kupite Bitkoin!
Ok Aleks, ali šta ćemo sa "masovnom adopcijom"???
Pažljivo me slušajte:
Zabole me kurac da li će masovna adopcija doći za 10, 20, 50 ili 100 godina!
Ja sam skroz za selektivnu adopciju i potpuno za dugačku igru. Tako da sam spreman da čekam.
Kao u SVIM prirodnim, evolutivno funkcionalnim sistemima, oni koji seju i pomažu u izgradnji temelja bi trebalo da budu i nesrazmerno nagrađeni.
Ovo je 100% fer i predivno nejednako (neki od vas koji me znate ste upoznati sa mojim stavom o nejednakosti kao najprezrenijem od svih ljudskih ideala. Radi se o odvratnom idealu koji nagrađuje najgore među nama).
Tako da za skeptike i "neverne Tome" imam jednostavnu poruku:
Nadam se da nećete uopšte kupiti Bitkoin. Ni danas ni bilo kada. Nadam se da će jedini put kada budete stupili u dodir sa Bitkoinom to biti jedini način da za nešto budete isplaćeni; npr. kada budete morali da ga zaradite.
Jedva čekam dan kada će mojih nekoliko hiljada satošija moći da kupi tri, četiri ili pet meseci vašeg vremena.
A u međuvremenu...
Molim vas, držite se vašeg fiat novca. Molim vas, držite se vaših šitkoina.
Ne želim nikoga od vas "blokčejnera", šitkoinera, fiat nokoinera i vas svih ostalih klovnova koji mislite da znate bolje.
Ovaj rolerkoster je specijalan, tako da zašto bih želeo da ga delim sa vama glupanderima? Zašto bih bacao bisere pred svinje?
Ja verujem u principe isključivosti.
Ovo nije "kumbaya" ili "svi smo jedno". Jebite se.
Sa razlogom smo drugačiji.
Napraviću sam svoj krevet i ležati u njemu. Vi napravite svoje.
Kada bude došlo vreme, ja ću vam za vaše vreme plaćati satošijima zato što onda nećete imati izbora.
Tada ja pobeđujem, a vi gubite.
Kako sejete, tako žanjete
Razlika između mene i vas je ta što ja kupujem Bitkoin sada zato što tako želim. Vi ćete morati da radite za Bitkoin sutra zato što tako morate.
To je cena neznanja. To je cena arogancije.
To je cena gluposti koju ćete platiti i, koliko god ovo zvuči okrutno, istina je da zaslužujete svaki delić toga.
Svi ležimo u krevetu koji sami pravimo, a vi svoj krevet pravite sada.
Neće vam samouvereni Bitkoiner reći: "lepo sam vam rekao". Nova ekonomska realnost će vam to reći umesto njega.
"Lepo sam vam rekao" će vas udariti poput tone cigle kada shvatite razliku između vas i onih koji su bili razboriti, koji su marljivo štedeli, koji su uložili vreme i trud da otkriju šta je zapravo Bitkoin dok su ih svi nazivali ludacima.
Neće biti sažaljenja.
Nema više bacanja bisera pred svinje
Oni koji imaju priliku da kupe nešto Bitkoina sada, a odluče da to ne urade zahvaljujući neznanju, aroganciji ili gluposti, zaslužuju da plate sa kamatom.
Zaslužuju da trguju svoje sutrašnje dragoceno vreme i energiju za ono što su mogli da nabave danas i to bukvalno "za kikiriki".
Ovde nema greške: nismo jednaki. Mi smo veoma, veoma različiti ljudi.
Ja sam uložio vreme, trud i energiju sada, ne samo zbog sebe samog, već i da bih posadio seme i pomogao mreži.
Uradio sam svoj deo.
Vi ćete doći kasnije i pomoći mi da žanjem nagrade svog truda. Postojaćete da biste mi pomogli da uživam u plodovima.
To će biti vaša uloga.
Izabrao sam da rizikujem i steknem deo onoga zbog čega su me svi nazivali ludim zato što sam učio, verovao i shvatio danas, sa nadom da se izgradi bolja, poštenija i pravičnija budućnost za sve.
Radeći to, neki od nas će postati džinovi i nesrazmerno bogati. I vi imate tu šansu ali je mnogi od vas neće iskoristiti.
I ja sam skroz ok sa tim. Više neću bacati bisere pred svinje.
Ovaj članak može zvučati neprijatno ali više me zabole kurac. Sada je na vama da sami istražujete.
Ovo se događa bez obzira sviđalo vam se to ili ne. Ja i hiljade drugih Bitkoinera smo pisali eseje i eseje o ovome.
Neka imena sa kvalitetnim materijalom kojih se mogu setiti iz glave su:
- Naravno ja
- Gigi
- Robert Breedlove
- Saifedean Ammous
Ako ste radoznali možete ih pratiti. A ovo je sjajno mesto gde možete preuzeti nekoliko odličnih radova:
I za kraj, ako si Bitkoiner koji ovo čita, nikada nećeš znati da li sam zloban ili samo igram 4D šah.
Iskreno, nije ni bitno.
Ovo se dešava. Bitkoin osvaja svet. Ekonomski darvinizam je činjenica.
Sakupljajte vaše satošije, ponudite maslinovu grančicu, obratite pažnju na njihovu radoznalost ili iskru u njihovom oku kao znak da nastavite. Ukoliko toga nema ili naiđete na odbijanje, ostavite ih da se igraju kao svinje u govnima sa njihovim fiatom, deonicama ili šitkoinima.
Biće nam potrebni čistači za naše citadele.
-
 @ bc6ccd13:f53098e4
2025-05-21 22:03:04
@ bc6ccd13:f53098e4
2025-05-21 22:03:04Bullshit Jobs, for those unfamiliar, is the title of a 2018 book by anthropologist David Graeber. It’s well worth a read just for the fascinating research and the engaging writing style. The premise of the book is that many people work in jobs that contribute nothing to society, and would not be missed if they suddenly vanished overnight.
The data backs this up. In a 2015 British poll that asked “does your job make a meaningful contribution to the world?”, 37 percent of people said no, and another 13 percent weren’t sure. That’s fully half the population who can’t confidently say their job is even worth doing. And other polls have found similar or worse results.
The book was inspired by the overwhelming response to a 2013 article Graeber wrote titled On the Phenomenon of Bullshit Jobs: A Work Rant. The point I’d like to address is found here.
Over the course of the last century, the number of workers employed as domestic servants, in industry, and in the farm sector has collapsed dramatically. At the same time, ‘professional, managerial, clerical, sales, and service workers’ tripled, growing ‘from one-quarter to three-quarters of total employment.’ In other words, productive jobs have, just as predicted, been largely automated away (even if you count industrial workers globally, including the toiling masses in India and China, such workers are still not nearly so large a percentage of the world population as they used to be.)
But rather than allowing a massive reduction of working hours to free the world’s population to pursue their own projects, pleasures, visions, and ideas, we have seen the ballooning of not even so much of the ‘service’ sector as of the administrative sector, up to and including the creation of whole new industries like financial services or telemarketing, or the unprecedented expansion of sectors like corporate law, academic and health administration, human resources, and public relations.
These are what I propose to call ‘bullshit jobs’.
It’s as if someone were out there making up pointless jobs just for the sake of keeping us all working. And here, precisely, lies the mystery. In capitalism, this is precisely what is not supposed to happen. Sure, in the old inefficient socialist states like the Soviet Union, where employment was considered both a right and a sacred duty, the system made up as many jobs as they had to (this is why in Soviet department stores it took three clerks to sell a piece of meat). But, of course, this is the sort of very problem market competition is supposed to fix. According to economic theory, at least, the last thing a profit-seeking firm is going to do is shell out money to workers they don’t really need to employ. Still, somehow, it happens.
While corporations may engage in ruthless downsizing, the layoffs and speed-ups invariably fall on that class of people who are actually making, moving, fixing and maintaining things; through some strange alchemy no one can quite explain, the number of salaried paper-pushers ultimately seems to expand, and more and more employees find themselves, not unlike Soviet workers actually, working 40 or even 50 hour weeks on paper, but effectively working 15 hours just as Keynes predicted, since the rest of their time is spent organizing or attending motivational seminars, updating their facebook profiles or downloading TV box-sets.
The answer clearly isn’t economic: it’s moral and political.
In the book, Graeber expands on this idea with a very entertaining description of the many flavors of bullshit jobs, based on anecdotes from readers of his article. He follows that up with theories speculating on the cause of this situation. And wraps it all up with the conclusion that basically capitalists are all big meanies and invent bullshit jobs just to torture people and prevent the arrival of the Marxist utopia where no one has to do much real work and we all sit around and sing kumbaya and discuss philosophy. That’s too harsh a criticism of a very well researched and written book, but I have to confess I was sorely disappointed the first time I read it by the author’s failure to even entertain what seems like the obvious alternative explanation.
Graeber acknowledges in the book that it’s not surprising bullshit jobs exist inside government, although he doesn’t focus strongly enough on why that is. Like he does in the article, he tries to brush it off with the excuse that the same problem exists in the private sector. As he acknowledges, this isn’t supposed to happen in capitalism. He realizes that it makes no logical economic sense for a profit-seeking firm to hire workers to do nothing productive.
But then he follows that acknowledgement with the claim that “The answer clearly isn’t economic: it’s moral and political.” I’m sorry, what? How is that clear? How do you go from stating an obvious economic fact, to denying that the problem is economic, and call it “clear”.
“Still, somehow, it happens,” is not anywhere close to a sufficient explanation to rule out an economic factor.
The economic explanation
First, some definitions.
Capitalism is defined as “an economic system in which the means of production and distribution are privately or corporately owned and development occurs through the accumulation and reinvestment of profits gained in a free market.”
A free market is “an economic system in which prices are based on competition among private businesses and are not controlled or regulated by a government: a market operating by free competition.”
Now that we made sure we’re talking about the same thing, we can analyze this issue logically.
Capitalism and free markets work through competition for customers. It’s an economic law that a customer won’t pay more for the same good or service when they could pay less. Someone can try to make obscure and esoteric objections and force me to emphasize the word “same” and analyze what the good or service being purchased actually is, but everyone else understands this intuitively. So if two companies are offering the same product for sale, all things being equal, the company offering lower prices will attract the customers. Pretty simple stuff.
Of course, the goal for the company is to generate profits. It’s literally in the definition of the word “capitalism”. So any system in which companies have a goal other than generating profits is, by definition, not capitalism.
A company can increase its profits two ways: raising prices, or lowering costs. We don’t have to get too philosophical to realize that if a company is paying someone to do nothing, the company could increase profits by firing that person and lowering their costs of production.
So the question is, why don’t they? Why do they hire people who increase their costs and lower their profits, thereby making them less competitive? And more importantly, if they do make that mistake, why don’t their competitors undercut their prices and take all the customers and bankrupt them?
I don’t think we can dismiss the economic factor as off-handedly as Graeber does. After all, making a profit is the fundamental, definitional purpose of a business or company in a capitalist economy. To say “companies in this capitalist economy are doing something completely antithetical to the very principles and definition of capitalism, so obviously they’re not doing it for economic reasons” is something of a non sequitur.
The conclusion, to me, seems obvious. We don’t have a capitalist economy. As far as I can tell, that’s true by definition. If companies aren’t even trying to achieve the goal companies must achieve to survive in a capitalist economy, and somehow they’re still surviving, that’s proof of the non-capitalist nature of the economy.
Which part of the capitalist system are we missing?
Well, let’s start with the obvious: there’s a lot of government in our economy. The government isn’t privately owned, which makes it not capitalist by definition. So any part of the economy that’s government is not capitalist.
Why is government not capitalist? Because government is not motivated to provide goods and services at a profit. Why not? Because government does not sell goods and services into a free market. Government gives away goods and services to its “customers” for free, because they’re paid for by people other than the consumers of the service. That payment comes in one of two ways: taxes, and debt. It’s not a voluntary transaction.
Which part of the capitalist system might private companies be missing?
They could be lacking competition. That is, operating a monopoly or cartel. If there’s no competing business to provide goods at lower prices, the company could hire people for useless jobs and compensate by raising prices. This places them outside the definition of capitalism, since “free competition” is part of the definition of a free market. Monopolies and cartels often develop and survive through protection by the government, which emphasizes their un-capitalistic nature.
They could be in a temporary situation where the people making the management decisions are sufficiently insulated from the market forces at play that their poor decisions can persist for a while. Many companies begin to lose their competitive edge at some point, after getting big enough to have economic inertia and for the management to be less accountable for business performance. If a company has grown big enough, they can start making poor financial decisions and absorb the lost profits, sometimes for years, before losing their market share to a smaller, more competitive rival. This isn’t really an absence of capitalism, just the natural creative destruction necessary for capitalism to function. The problem comes when a company that’s obviously uncompetitive is prevented from failing through un-capitalistic means. Maybe they’re big enough and wealthy enough to pressure the government into granting them monopoly status. This doesn’t have to be open, it’s often through creating such an impenetrable legal morass around the industry that no competitor can emerge. Or it can be in the form of a “too big to fail” direct government bailout.
The company could also be lacking that essential link between customer satisfaction and business income. In other words, maybe they aren’t selling to their customers. That can happen for various reasons.
Some companies are “private companies” but sell to the government. The government is not a customer in the capitalist sense, because the government spends money taken coercively from its subjects, not money earned voluntarily in the free market. So any company like Raytheon or Boeing that survives off government contracts can’t be accurately called a capitalist organization.
In an industry like healthcare, where the insurance companies are the middlemen in basically all transactions between patients and doctors, there are also lots of ways for bullshit jobs to proliferate. Patients don’t care how much a procedure costs, just that it helps them. Doctors don’t care how much a procedure costs, just that the insurance company will pay for it. And insurance companies don’t care whether a procedure helps the patient, they just want to collect as many premiums as possible while paying out as little for care as possible. The fact that the patient isn’t paying the doctor for their care breaks the necessary link between customer and producer that’s essential for a free market to function. That combines with the regulatory moat and cartel-like structure of the healthcare industry to prevent the competitive function of capitalism from occurring.
Companies could also be surviving off of money from someone other than their customers: bankers and investors. There’s obviously a role in a capitalist system for investors to support a new venture until it’s able to attract customers and establish a stable and profitable business model. But many companies today exist for much longer than economically reasonable without turning a profit. In the US, almost 2,000 of the 5,000 publicly traded companies with data available were classified as “zombie companies”, meaning they don’t even make enough profit to pay the interest on their debt. So they’re going deeper in the hole every year. How can this continue?
Well, the alternative to paying off your debt, is to borrow even more money to make payments on the debt you already owe. If this sounds similar to how the US government survives, then you’re beginning to get the picture.
How can banks keep loaning money to unprofitable businesses? And why would they do it? It doesn’t make sense… until you understand how banking works.
That’s really the core focus of most of my writing, and I’ve written multiple articles on money and banking explaining how the system works as I understand it. This would be a good one focused on banking specifically.
nostr:naddr1qvzqqqr4gupzp0rve5f6xtu56djkfkkg7ktr5rtfckpun95rgxaa7futy86npx8yqqt4g6r994pxjeedgfsku6edf35k2tt5de4nvdtzhjwrp2
To very briefly recap, banks don’t make loans by taking in money from depositors and loaning that money to borrowers. Instead, banks create new money that never existed before out of thin air and loan that new money to borrowers. Banks make a profit by charging borrowers interest on this newly created money, which costs them nothing to create. A pretty cushy gig, if you can get it.
So from the perspective of the banks, the more loans and debt outstanding, the better. Every dollar of debt is a dollar they can collect interest on. It cost them nothing to create, so the more, the merrier. In fact, the banks would prefer that the loan principle never be repaid, because once it’s repaid, they can no longer collect interest on that loan until they make another loan to replace it. As long as the borrower keeps paying interest, the banks are happy. And if they need to lend the borrower some more money so he can afford to pay the interest, that’s fine too. Anything but letting the loan default.
Given those incentives, how do you expect a chart of the outstanding loans and credit of US commercial banks to look?
If you guessed up only, you’d be correct.
So what does this banking system have to do with bullshit jobs? Well, I’d argue that the fractionally reserved fiat banking system, in and of itself, is an anti-capitalist system. Money is the communication layer of capitalism, as I’ve previously written.
nostr:naddr1qvzqqqr4gupzp0rve5f6xtu56djkfkkg7ktr5rtfckpun95rgxaa7futy86npx8yqq247t2dvet9q4tsg4qng36lxe6kc4nftayyy89kua2
When one group of people can create money out of thin air, they have the ability to reallocate wealth in the economy. As long as the money is still functional, of course. Too much money creation and wealth reallocation, and people stop trusting the money. That’s when inflation becomes hyperinflation, the money no longer functions, and the whole system implodes.
Wealth reallocation by a small select group is the essence of a centrally planned socialist/Marxist economy. And we all know how efficient those economies are. In fact, Graeber himself mentioned the inefficiency of socialist states like the Soviet Union in his original article, and was not at all surprised by the existence of bullshit jobs in such an economic system. When wealth can be reallocated by central planners without regard to people’s preferences in a free market, inefficiency is never punished, so zombie companies full of bullshit jobs never go bankrupt.
The same thing happens under our “capitalist” system. Zombie companies full of bullshit jobs can get almost unlimited funding from too-big-to-fail banks, who don’t care whether they repay the loans, as long as they stay in business and keep making the interest payments. Sometimes the funding is in the form of loans directly, sometimes it’s in the form of massive stock market bubbles inflated by the endless money creation, sometimes through junk bond issuance funded by the same bubble economics, and sometimes it’s venture capital funds flush with liquidity for the same reason. Regardless, the cause, and the outcome, are the same.
The corrupt bankers own the corrupt politicians, so when the inevitable so-called black swan event occurs and the rotten edifice starts to quiver, another bailout is promptly rolled out. The government borrows trillions from their owners over at the Federal Reserve, who create the money out of thin air. The government sends it on over to the bankers who got caught with their hand in the cookie jar once again, and they paper over the massive holes in their balance sheet caused by blowing asset bubbles and funding inefficient zombie companies. Or sometimes, the government skips the middlemen entirely and bails out Boeing or whoever it happens to be directly.
And once again, bullshit jobs that couldn’t survive free market competition are rewarded at the expense of savers and taxpayers. As always, this flood of new liquidity flows out through the economy, causing inflation and boosting income for other inefficient companies that also deserved to fail. Creative destruction, a fundamental feature of a capitalist system, is avoided once again.
In my opinion, the banking system is at the root of the problem causing the proliferation of bullshit jobs. The system itself is, by design, fundamentally anti-capitalist in nature and function. It’s really a giant privately owned economic central planning system, in which a small fraction of people determine how resources are allocated, with privatized profits and socialized losses. The Soviet technocrats would be jealous.
Unfortunately, the bankers have successfully connected their industry so tightly to the term “capitalist” that showing people they’re anything but is almost impossible. To paraphrase the well-known quote, the greatest trick the bankers ever pulled was convincing the world that they’re the real capitalists.
Until the banking and monetary system fundamentally changes, inefficiency will persist and bullshit jobs will continue to proliferate. In my opinion, the problem is very much an economic problem. And it’s not a “late-stage capitalism” problem, it’s a “capitalism left the building a century ago” problem. We don’t need to get rid of capitalism, we’ve already done that. We need to bring sound money, and with it the possibility of a capitalist economy, back again.
-
 @ 9063ef6b:fd1e9a09
2025-05-11 17:28:34
@ 9063ef6b:fd1e9a09
2025-05-11 17:28:34This article explores potential vulnerabilities in bitcoin that quantum computers might exploit in the future.
But to be clear: today’s quantum computers are still in early stages, many questions are unresolved, and they are not expected to pose a serious threat any time soon.
1. Why Quantum Computing Threatens Bitcoin
Bitcoin’s current cryptographic security relies on ECDSA (Elliptic Curve Digital Signature Algorithm). While this is secure against classical computers, a sufficiently powerful quantum computer could break it using Shor’s algorithm, which would allow attackers to derive private keys from exposed public keys. This poses a serious threat to user funds and the overall trust in the Bitcoin network.
Even though SHA-256, the hash function used for mining and address creation, is more quantum-resistant, it too would be weakened (though not broken) by quantum algorithms.
2. The Core Problem
Bitcoin’s vulnerability to quantum computing stems from how it handles public keys and signatures.
🔓 Public Key Exposure
Most Bitcoin addresses today (e.g., P2PKH or P2WPKH) are based on a hash of the public key, which keeps the actual public key hidden — until the user spends from that address.
Once a transaction is made, the public key is published on the blockchain, making it permanently visible and linked to the address.

🧠 Why This Matters
If a sufficiently powerful quantum computer becomes available in the future, it could apply Shor’s algorithm to derive the private key from a public key.
This creates a long-term risk:
- Any Bitcoin tied to an address with an exposed public key — even from years ago — could be stolen.
- The threat persists after a transaction, not just while it’s being confirmed.
- The longer those funds sit untouched, the more exposed they become to future quantum threats.
⚠️ Systemic Implication
This isn’t just a theoretical risk — it’s a potential threat to long-term trust in Bitcoin’s security model.
If quantum computers reach the necessary scale, they could: - Undermine confidence in the finality of old transactions - Force large-scale migrations of funds - Trigger panic or loss of trust in the ecosystem
Bitcoin’s current design protects against today’s threats — but revealed public keys create a quantum attack surface that grows with time.
3. Why It’s Hard to Fix
Transitioning Bitcoin to post-quantum cryptography is a complex challenge:
- Consensus required: Changes to signature schemes or address formats require wide agreement across the Bitcoin ecosystem.
- Signature size: Post-quantum signature algorithms could be significantly larger, which affects blockchain size, fees, and performance.
- Wallet migration: Updating wallets and moving funds to new address types must be done securely and at massive scale.
- User experience: Any major cryptographic upgrade must remain simple enough for users to avoid security risks.
4. The Path Forward
The cryptographers worldwide are already working on solutions:
- Post-Quantum Cryptographic Algorithms are being standardized by NIST, including CRYSTALS-Dilithium, Kyber, FALCON, and SPHINCS+.
- Prototypes and experiments are ongoing research networks.
- Hybrid signature schemes are being explored to allow backward compatibility.
Governments and institutions like NIST, ENISA, and ISO are laying the foundation for cryptographic migration across industries — and Bitcoin will benefit from this ecosystem.
References & Further Reading
- https://komodoplatform.com/en/academy/p2pkh-pay-to-pubkey-hash
- https://csrc.nist.gov/projects/post-quantum-cryptography
- https://www.enisa.europa.eu/publications/post-quantum-cryptography-current-state-and-quantum-mitigation
- https://en.bitcoin.it/wiki/Quantum_computing_and_Bitcoin
- https://research.ibm.com/blog/ibm-quantum-condor-1121-qubits
- https://blog.google/technology/research/google-willow-quantum-chip/
- https://azure.microsoft.com/en-us/blog/quantum/2025/02/19/microsoft-unveils-majorana-1-the-worlds-first-quantum-processor-powered-by-topological-qubits/
- https://www.aboutamazon.com/news/aws/quantum-computing-aws-ocelot-chip
```
-
 @ da8b7de1:c0164aee
2025-05-19 17:38:59
@ da8b7de1:c0164aee
2025-05-19 17:38:59Németország feladja a nukleáris energiával szembeni ellenállását Franciaországgal való közeledés jegyében
Németország hosszú idő után feladta a nukleáris energiával szembeni ellenállását, ami jelentős lépést jelenthet az EU energiapolitikai vitáinak rendezésében, különösen Franciaországgal szemben. Ez a változás eltávolíthatja a nukleáris energiával szembeni előítéleteket az uniós jogszabályokból, és elősegítheti a közös európai energiapolitika kialakítását[2].
Trump adminisztráció tervezett rendeletei a nukleáris erőművek építésének gyorsítására
Az Egyesült Államokban a Trump-adminisztráció több elnöki rendelet-tervezetet készít elő, amelyek célja a nukleáris erőművek építésének gyorsítása. A tervek szerint a jelenlegi mintegy 100 GW nukleáris kapacitást 2050-re 400 GW-ra növelnék, az engedélyezési folyamatok egyszerűsítésével, a hadsereg szerepének növelésével és a nukleáris üzemanyag-ellátás megerősítésével[3][9].
Tajvan hivatalosan is nukleárismentes lett
- május 17-én Tajvan utolsó kereskedelmi reaktorát is leállították, ezzel az ország elérte a "nukleárismentes haza" célját. Az energiamixben a nukleáris energia aránya 17%-ról 3%-ra csökkent, miközben a megújuló energia tízszeresére nőtt. Bár a parlamentben vita folyik a Maanshan atomerőmű élettartam-hosszabbításáról, jelenleg Tajvan teljesen leállította a nukleáris energiatermelést[1][6].
Kazatomprom hitelmegállapodást kötött egy új kénsavgyár finanszírozására
Kazahsztán állami atomipari vállalata, a Kazatomprom hitelmegállapodást kötött egy évi 800 000 tonna kapacitású kénsavgyár építésére. A kénsavat az uránkitermeléshez használják, és a gyár 2027 első negyedévében készülhet el. A projekt célja a régió gazdasági fejlődésének támogatása és az uránipar ellátásbiztonságának javítása[4].
Az IAEA segíti Kazahsztánt az első atomerőmű biztonságos helyszínének kiválasztásában
Az IAEA (Nemzetközi Atomenergia-ügynökség) szakértői csapata ötnapos szemináriumot tart Kazahsztánban, hogy segítsen kiválasztani az ország első atomerőművének legbiztonságosabb helyszínét. A folyamatban több helyszín is szóba került, jelenleg a Zhambyl körzet az elsődleges jelölt. A projektben négy lehetséges technológiai partner vesz részt: CNNC (Kína), Roszatom (Oroszország), KHNP (Dél-Korea) és EDF (Franciaország)[8].
India új nukleáris helyszínt hagyott jóvá
Az indiai nukleáris hatóság engedélyezte a Mahi Banswara Rajasthan Atomic Power Project négy blokkjának elhelyezését Rádzsasztán államban. Ez újabb lépés India ambiciózus nukleáris bővítési terveiben[5].
Globális nukleáris ipari konferencia Varsóban
- május 20-21-én Varsóban rendezik meg az első World Nuclear Supply Chain Conference-t, amely célja a globális nukleáris ellátási lánc megerősítése és a szektor 2 billió dolláros beruházási lehetőségének kiaknázása a következő 15 évben. A konferencián iparági vezetők, döntéshozók és szakértők vesznek részt[7].
Hivatkozások
- [1] reccessary.com – Tajvan nukleárismentes lett
- [2] nucnet.org – Németország nukleáris politikai fordulata
- [3] humanprogress.org – Trump rendelettervezetek
- [4] world-nuclear-news.org – Kazatomprom kénsavgyár
- [5] world-nuclear-news.org – India új nukleáris helyszíne
- [6] taiwannews.com.tw – Tajvan atomerőmű leállítása
- [7] world-nuclear.org – Varsói nukleáris konferencia
- [8] astanatimes.com – IAEA-Kazahsztán együttműködés
- [9] esgdive.com – Oklo és Trump engedélyezési reformok
-
 @ 005bc4de:ef11e1a2
2025-05-19 17:01:54
@ 005bc4de:ef11e1a2
2025-05-19 17:01:54Keys and Religion
Mixing
Normally, I'm not a fan mixing and comparing bitcoinesque things and religion. It's too banal and trite, too easy: the religion of Bitcoin, the allusion of Satoshi the savior, the "Book of Satoshi," even the "Genesis" block. But, today, I'll break my own rule.
Yesterday, I heard a Christian pastor speak of the "keys of the kingdom." My feeling is that, were you to ask the average Christian, "What is the key, or keys, to the kingdom?", and perhaps I'm wrong on this, but I think they'd answer, "Prayer." I've heard it many times, "Prayer is the key to the kingdom." It's an easy mantra to remember. And, prayer is important for a Christian, no question about it. However, Biblically, the phrase "keys of the kingdom" refers to something else.
As the pastor pointed out yesterday, Biblically there are two keys: the binding key and the loosing key. This refers to Matthew 16:19 where Jesus says:
I will give you the keys of the kingdom of heaven; whatever you bind on earth will be bound in heaven, and whatever you loose on earth will be loosed in heaven. Matthew 16:19 (NIV)
For context, back up a few verses. This statement above was made in a conversation between Jesus and his disciple Simon Peter.
15 Jesus asked, “But what about you?” he asked. “Who do you say I am?” 16 Simon Peter answered, “You are the Messiah, the Son of the living God.” 17 Jesus replied, “Blessed are you, Simon son of Jonah, for this was not revealed to you by flesh and blood, but by my Father in heaven. 18 And I tell you that you are Peter, and on this rock I will build my church, and the gates of Hades will not overcome it.
Although brief, this is a deep and rich exchange. Traditionally, this has been viewed as the moment that Christ instituted the Christian church, the passing of power and authority to the early church itself. There has been confusion over it too, particularly the "...on this rock I will build my church..." part of it. Jesus was referring to Simon Peter's statement of faith (...for this was not revealed to you by flesh and blood...) with the "this" being what Peter had just said, "You are the Messiah, the Son of the living God." The church would be built upon the rock of faith in Jesus as the Messiah.
The early Christian church thus established, Jesus instituted what's come to be called the "office of the keys." That is, Jesus grants authority to his "appointees" in the church to carry out his authority. In more practical terms, this is referring to those who have been called into church service, normally priests, to forgive or not forgive sins. When a priest or pastor forgives, or not, it is not that he is doing it by his own right or power. That priest is, after all, yet another sinful man as well. Instead, the priest forgives by Christ's authority which was handed down by Jesus himself in those words to Peter.
To use an analogy, suppose a general had to make a decision about foot soldiers on the front line, waiting there in the trenches. Due to some time constraint, a decision for action was needed imminently. However, suppose the general lacked some bit of information that could only be obtained at the front. So, the general wrote up a communique to the lieutenant stationed at the front saying, "You assess the situation, and you make the call, charge or pull back. I'll support your decision." A courier ran to the front, relayed the message to the lieutenant, and the lieutenant assessed and made the decision. Ultimately, even thought the lieutenant made the decision, the authority behind the decision lay with the general who had transferred his authority to the lieutenant.
This authority or office of the keys is mirrored in John 20:22-23, when the resurrected Jesus appears to his disciples and says, "If you forgive anyone’s sins, their sins are forgiven; if you do not forgive them, they are not forgiven.”
Going just one step further, recall there are two keys involved, binding and loosing, and there are two places involved, earth and heaven. Usually, priests and pastors are "in the business" of forgiving. Penitence or confession, when real, is forgiven. The priest has the authority to forgive, or "loose" the sinner from his wrongdoings here on earth. And, that forgiveness applies to heaven as well, the sin is atoned and reconciled with God.
But, what about when the person is unrepentant, unbothered by what is Biblically sinful, refuses to change his ways, and rather chooses to continue in sinful ways? The "binding" key says that the priest or appointed church leader can hold that person accountable, can bind that person to the sin and separation from God. Normally, we hear of "excommunication" from the church which is formally stating that a person is outside of the church body. The binding keys still bind, both on earth as being outside of the church and in heaven as being separated from God.
And bitcoin?
That's a lot of religion, and heavy religion at that. The question is, what does this have to do with bitcoin?
Keys.
Namely, this is about public and private keys. Loosing and binding keys. A bit more religion, then I'll get back to bitcoin.
Yesterday, the pastor spoke briefly about binding and loosing keys, and this where my thoughts about keys somehow morphed over into bitcoin. For some reason, I pictured Herod's Temple. There had been Solomon's temple, which was destroyed, and then there was Herod's which was known for its beauty and was the one during Jesus's time. But, let's recall the background on this...
The book of Exodus, and others in the Old Testament, outline in detail God's plan for the tabernacle (a traveling tent) and for the temple in Jerusalem.
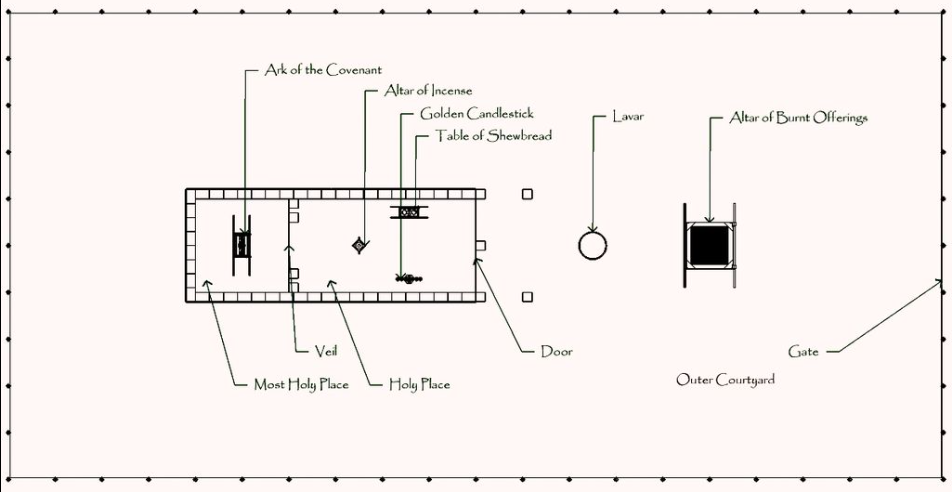
The tabernacle, overhead diagram. Image source: https://en.wikipedia.org/wiki/Tabernacle
You might recall the "history" lesson in Raiders of the Lost Ark. With the tabernacle and temple, one of the purposes was to house the ark of the covenant. Remember that the ark was the golden box that the Israelites carried around containing Moses's stone tablets with the Ten Commandments, some manna, and Aaron's staff. It held great power, God's power, and God literally met and spoke with the Levite priests hovering over the cherubim's wings.
The ark of the covenant. Image source: https://en.wikipedia.org/wiki/Ark_of_the_Covenant
In the tabernacle and temple, the "Holy of Holies" was a room, separated by a heavy curtain. It was off limits to all because it was, well, holy of holies. A heavy curtain divided the Holy of Holies, or the "Most Holy Place", from the less-holy, "Holy Place."
Once a year, on the Day of Atonement, one person, the chief priest, was allowed to walk into the Holy of Holies. He would sprinkle the blood of a sacrificed animal onto the ark. This was done for the forgiveness of the people's sins. Although this was pre-Jesus's words, this was using the loosing keys and was loosing sin.
This was serious business and was taken seriously. For instance, the priests Nadab and Abihu improperly performed their sacrificial duties, they messed up the procedure, and were consumed by fire. Priesthood was a dangerous occupation, one slip up and you were scorched.
 The second temple, "Herod's Temple". Image source: https://en.wikipedia.org/wiki/Second_Temple
The second temple, "Herod's Temple". Image source: https://en.wikipedia.org/wiki/Second_TempleBack to keys...
Yesterday, for some reason when I heard about binding and loosing keys, I imagined the chief priest standing in front of the curtain. I imagined him taking a deep breath, collecting his thoughts, getting ready to go in. It had to be intimidating.
As he stood there, in my mind, he and everyone else was shut out. The Most Holy Place was bound and locked. Walking in meant getting scorched (again, the end of Raiders of the Lost Ark). Yet, that priest had the loosing key. He had, first, permission as chief priest to enter on the Day of Atonement, secondly, he had the sacrificial blood to loose sins. Although the binding key had locked the Holy of Holies and thus bound the sins of the people, the loosing key was about to loose their sins.
Cryptographic keys
And back to bitcoin...
Bitcoin, and cryptography in general, operate on public and private keys. Any flavor of "cryptocurrency", or even Nostr, has public and private keys. In a way, these are binding and loosing keys.
Say you have 1.0 BTC (that's 100,000,000 sats 😀). That BTC exists as a UTXO which can be seen by anyone viewing your public address. In this way, your bitcoin public key is your binding key...that UTXO, that bitcoin, is bound to your public key...it is locked in place behind that heavy curtain. It will be there forever, unless there is an intervention...
You also have your private key, your loosing key. You can apply your private key to loose that UTXO, that bitcoin, and to send it along to wherever.
This is like law and gospel: sin is binding, however Jesus frees it. A bitcoin UTXO is bound until a private key looses it.
Nostr offers a somewhat similar illustration. You have an npub publicly and and nsec secretly or privately. If you were to write a note, your private nsec is needed as a loosing key to free that message, to broadcast it to the world. Once broadcast, it can be seen by all, however it is still inextricably bound or tied to your public key (your npub). Your npub is your binding key and your message is bound to it.
Summed
I'm not sure this binding and loosing keys in religion, and public and private keys in cryptography is the best comparison in the world. It's probably a terrible comparison. But, this is what came to my mind yesterday.
And, so, the mixing of religion and bitcoin is now officially over.
-
 @ a31f394c:7ad8f439
2025-05-19 07:55:53
@ a31f394c:7ad8f439
2025-05-19 07:55:53No mundo dos jogos online, onde inúmeras plataformas buscam a atenção dos jogadores, KK999 se destaca como uma opção inovadora e empolgante. Focada no público brasileiro, a plataforma oferece uma ampla gama de jogos, uma interface intuitiva e um excelente suporte ao cliente. Se você está em busca de um destino online para jogos que combine entretenimento, qualidade e segurança, KK999 é a escolha certa para você.
Visão Geral da Plataforma KK999 é mais do que uma simples plataforma de jogos. É uma experiência imersiva e moderna, desenvolvida para atender às necessidades específicas dos jogadores brasileiros. A plataforma possui uma interface limpa e fácil de navegar, o que torna a experiência de jogar agradável e sem complicações. O site é responsivo, o que significa que você pode acessar e jogar de qualquer dispositivo, seja no desktop ou no celular, tornando a plataforma perfeita para quem deseja jogar em qualquer lugar.
O diferencial do kk999 é a experiência personalizada que oferece aos jogadores brasileiros. Além de estar completamente traduzido para o português, o site também oferece promoções e suporte técnico localizados, o que cria uma sensação de familiaridade e confiança entre os usuários.
Variedade de Jogos para Todos os Gostos Uma das características mais atraentes da KK999 é sua vasta seleção de jogos. A plataforma oferece desde jogos tradicionais de mesa, como poker e baccarat, até os modernos jogos de slots, que são incrivelmente populares entre os jogadores. Se você gosta de desafios estratégicos ou prefere a emoção de uma boa rotação de roletas, KK999 tem algo para todos.
Os jogos de mesa, como poker e blackjack, permitem que os jogadores testem suas habilidades e se envolvam em desafios emocionantes. Cada jogo é projetado com gráficos de alta qualidade e animações fluidas, criando uma experiência realista e envolvente. Além disso, a plataforma oferece uma coleção diversificada de slots, com temas variados e recursos extras que aumentam a emoção a cada giro.
Para aqueles que preferem uma experiência mais interativa, KK999 também oferece jogos com dealers ao vivo. Esses jogos permitem que os jogadores interajam com dealers profissionais em tempo real, criando uma atmosfera de jogo ao vivo, que remete à experiência de um cassino físico.
Experiência do Jogador: Segurança e Suporte de Qualidade O KK999 entende que uma experiência de jogo de alta qualidade vai além de apenas jogar. A plataforma se destaca pelo seu compromisso com a segurança dos jogadores. Utilizando as mais recentes tecnologias de criptografia, KK999 garante que todas as informações pessoais e financeiras dos jogadores estejam seguras, proporcionando tranquilidade para que os jogadores possam se concentrar apenas no jogo.
Além disso, o suporte ao cliente do KK999 é impecável. A plataforma oferece suporte 24 horas por dia, 7 dias por semana, por meio de chat ao vivo e e-mail. Caso o jogador tenha dúvidas sobre um jogo, questões relacionadas à conta ou precise de assistência técnica, a equipe de atendimento está sempre disponível e pronta para ajudar.
Bônus e Promoções para Todos os Jogadores KK999 também se destaca pelas suas ofertas generosas de bônus e promoções. Para os novos jogadores, a plataforma oferece bônus de boas-vindas, enquanto os jogadores regulares podem aproveitar programas de fidelidade que recompensam a lealdade dos usuários com ofertas exclusivas e prêmios.
Essas promoções tornam a experiência de jogar ainda mais divertida e empolgante, dando aos jogadores mais chances de se divertir e ganhar enquanto jogam seus jogos favoritos.
Conclusão KK999 se estabeleceu como uma plataforma de jogos online de referência no Brasil, oferecendo uma experiência única que combina uma enorme variedade de jogos, uma interface amigável, suporte excepcional e medidas de segurança robustas. Se você está à procura de uma plataforma para se divertir e explorar, KK999 é o lugar perfeito para começar sua jornada de jogos online.
-
 @ 8bad92c3:ca714aa5
2025-05-21 22:01:27
@ 8bad92c3:ca714aa5
2025-05-21 22:01:27Key Takeaways

In this episode of the TFTC podcast, Dom Bei—a firefighter, union leader, and CalPERS Board of Trustees candidate—makes a powerful case for why the largest pension fund in the U.S. must seriously consider Bitcoin as both an investment opportunity and an educational tool. Highlighting CalPERS’ missed decade in private equity and its troubling 75% funded status, Bei critiques the system’s misaligned incentives and high leadership turnover. He argues that Bitcoin offers more than just potential gains—it forces participants to confront foundational issues like inflation, wealth extraction, and financial literacy. Through his nonprofit Proof of Workforce, Bei has already helped unions adopt Bitcoin in self-custody and believes that small, incremental steps can drive reform. His campaign is about re-engaging the 2 million CalPERS members, challenging political inertia, and avoiding another decade of lost opportunity.
Best Quotes
"Bitcoin’s brand is resilience, and that cannot be undone."
"I don’t need to convince pensions to buy Bitcoin. I just need them to look into it."
"The first pension was funded with confiscated warships. The original incentive structure was theft."
"CalPERS is the second-largest purchaser of medical insurance in the U.S., behind the federal government."
"Only 10% of CalPERS members voted in the last board election. That’s insane."
"Bitcoin’s simplest features remain its most impressive: you hold something that’s yours, and no one can take it."
"We don’t need pensions to go all in. Just get off zero."
"Mainstream media has run an 80% negative campaign on Bitcoin for a decade. That’s not a conspiracy—it’s just math."
Conclusion
Dom Bei’s conversation with Marty Bent frames Bitcoin not as a cure-all, but as a critical tool worth exploring—one that promotes financial literacy, institutional accountability, and personal sovereignty. His call for education, transparency, and incremental reform challenges broken pension governance and urges workers to reclaim control over both their retirements and their understanding of money. In a landscape of growing liabilities and political interference, Bei’s campaign sparks a vital conversation at the intersection of sound money and public service—one that aligns closely with Bitcoin’s foundational ethos.
Timestamps
0:00 - Intro
0:32 - Opportunity Cost app
3:34 - Dom's background
10:36 - Fold & Bitkey
12:13 - How pensions got to this point
19:29 - Impact of failure
28:10 - Unchained
28:38 - CalPERS politicized
33:49 - How pensions should approach bitcoin
42:49 - How to educate
49:37 - Energy/mining
55:55 - Running for the board
1:08:52 - Roswell NM
1:12:33 - C2ATranscript
(00:00) pension funds are chasing liabilities and having to basically be these vehicles that play in the big kids sandbox. It's cutthroat and there's no mercy there. I can't imagine a world where the pension goes bust, that's going to send shock waves through so many different sectors of the economy. I mean, you're talking global impact.
(00:17) If you have a CIO that's incentivized for the fund to do well, they're going to find Bitcoin. The numbers don't lie. Bitcoin's brand is resilience, and that cannot be undone. What's up, freaks? Sitting down with Dom Bay, running for the board of trustees of Kalpers. Dom, welcome to the show. Thanks, Marty.
(00:44) And uh uh what else? What is up, freaks? How's everyone doing today? I hope everybody's doing well. Vibes are high here. Uh been vibe coding. The vibes are high because the vibe coding has been up. I vibe coded something last night. Feeling pretty excited. Nice. What were you working on? Is it a top secret or uh No, I think by the time this episode airs, I'll have released it, but it's a simple, very simple product.
(01:07) Uh, a browser extension that allows you to put the price of goods that you may or may not be buying in SATS alongside dollars so that you recognize the opportunity cost of purchasing things. Uh, I like that. That's that's you know I was working once with a hotel that was looking at doing Bitcoin like you know different Bitcoin stuff whether it's like putting on the treasury and one of the things I told him I was like you guys should just do a coffee shop where you just have dollar price and sats price just next to each
(01:38) other. It' be a cool thing you know something that we don't see a lot as Bitcoiners but just to you know we all do it. you get that familiarity where you go like, well, what would this be in SATS? And it's easy to look up big things but not little things. Um, so that's really cool, man. That's a that's a that'll be that'll be good. Yeah.
(01:56) The whole idea is to just have the concept of opportunity costs while you're spending front of mind, while you're shopping on the internet, which I think actually ties in perfectly with what we're here to talk about today with you specifically, is the opportunity costs that exist within pensions um that are deploying capital in ways that they have for many decades and many are missing.
(02:23) uh the Bitcoin boat. Many who haven't spoken to you are missing the Bitcoin boat and you are taking it upon yourself to try to tackle one of the biggest behemoths in the world of pensions and Kalpers to really drive home this opportunity cost at at the pension level. Yeah, for sure. you know, the outgoing chief investment officer of Kalpers, uh, Nicole Muso, uh, described the 10-year era of private equity that KPERS missed as the lost decade.
(02:56) Uh, it was the pinnacle of private equity, and Kalpers really felt like they didn't have enough capital uh, deployed. And you know, in past conversations, I've I've talked about, you know, knowing what we know about Bitcoin and where it's at and where it's going. Are you going to have similar commentary from pensions around the country in 2035 saying, "Hey, we're going to get into Bitcoin now.
(03:21) We we had a lost decade where it was just staring us right in the face and oh, we didn't really need to do much but learn about it and uh we missed the boat. So now, you know, let's let's learn about it. It'll be time will tell. Yeah. Let's jump into how you got to the point where you decided to run for the board of trustees at Kalpers.
(03:46) Let's get into your history uh as a firefighter working with the union and then your advocacy in recent years going out to public pensions, particularly those of emergency responders to to get Bitcoin within their their pension systems. and yeah, why you think Kalpers is the next big step for you? For sure. So, um I got hired as a firefighter uh just around I'm coming up on my 16-year anniversary.
(04:11) Uh I got hired as a firefighter in Santa Monica and early in my career as a firefighter. Uh someone reached out and said, "Hey, you know, you're you're you're kind of a goofball. You like talking to people and and um there's this person on the board who does a lot of our political stuff. he's leaving. You should get with him and kind of learn about what he does and go find out. And so, uh, I went with him.
(04:36) First thing he did was bring me to this breakfast with a city council member and we were talking history in the city and and I just like, you know, I love that kind of stuff and learning about, you know, the backstories behind whatever's going on and all the moving pieces. And so, uh, I ended up getting on our board, um, for the Santa Monica firefighters and pretty pretty young, doing a lot of the political stuff, ended up becoming the vice president and then became the president of the firefighters and what was over a 10-year period of serving as
(05:07) an elected board member for the firefighters. Um, you know, kind of parallel to that and unrelated, I found Bitcoin in 2017 uh randomly working at a conference, which um I forget which conference it was, but I kind of looked back and I think it might have been consensus. I'm not sure. Um, but this was 2017 and I remember my one takeaway from this conference which may or may not have been consensus and it was this.
(05:39) The people I spoke to there were equally or greater as uh convicted as any group or constituency I'd ever met in my entire life. That's including firefighters. Um you know like like any group the conviction was was was unmissable. Uh and you could tell the people I talked to there they would not be uh convinced otherwise.
(06:08) And uh at that time, you know, there wasn't as much of a division between the different coins, you know, like like there was Ethereum people there and there was Bitcoiners there, but there was a definite like someone got a hold of me and was like, "Hey, uh Bitcoin is something that like forget all this other stuff.
(06:25) You need to just learn this." And and I remember taking that away and kind of got passively involved. Wasn't super active in the space. um just kind of like you know learned about it and grabbed a little bit and and you know just kind of did that thing. the board took up a lot of my time. And so, um, another thing that happened while I was on the board was I was appointed to a pension advisory committee for the city of Santa Monica where we had a full presentation from the board uh, and um, they came and presented to us and and different um,
(06:58) not the board, it was like different team members. And so I learned a ton about the pension and and I've always been a I was a history major in college, so I love learning about history. and I started really getting into the history of pensions which is fascinating. We'll save that for another episode for the sake of your viewers.
(07:18) Um but but um started doing that and when I got off the board um you know in addition to this -
 @ 3f770d65:7a745b24
2024-12-31 17:03:46
@ 3f770d65:7a745b24
2024-12-31 17:03:46Here are my predictions for Nostr in 2025:
Decentralization: The outbox and inbox communication models, sometimes referred to as the Gossip model, will become the standard across the ecosystem. By the end of 2025, all major clients will support these models, providing seamless communication and enhanced decentralization. Clients that do not adopt outbox/inbox by then will be regarded as outdated or legacy systems.
Privacy Standards: Major clients such as Damus and Primal will move away from NIP-04 DMs, adopting more secure protocol possibilities like NIP-17 or NIP-104. These upgrades will ensure enhanced encryption and metadata protection. Additionally, NIP-104 MLS tools will drive the development of new clients and features, providing users with unprecedented control over the privacy of their communications.
Interoperability: Nostr's ecosystem will become even more interconnected. Platforms like the Olas image-sharing service will expand into prominent clients such as Primal, Damus, Coracle, and Snort, alongside existing integrations with Amethyst, Nostur, and Nostrudel. Similarly, audio and video tools like Nostr Nests and Zap.stream will gain seamless integration into major clients, enabling easy participation in live events across the ecosystem.
Adoption and Migration: Inspired by early pioneers like Fountain and Orange Pill App, more platforms will adopt Nostr for authentication, login, and social systems. In 2025, a significant migration from a high-profile application platform with hundreds of thousands of users will transpire, doubling Nostr’s daily activity and establishing it as a cornerstone of decentralized technologies.
-
 @ dc0bbb4c:b5479e81
2025-05-19 06:31:45
@ dc0bbb4c:b5479e81
2025-05-19 06:31:45Trong bối cảnh thị trường giải trí trực tuyến ngày càng phát triển mạnh mẽ, 1BWM đã và đang khẳng định vị thế là một trong những nền tảng kỹ thuật số được cộng đồng người dùng tin tưởng và lựa chọn nhiều nhất. Nhờ sở hữu giao diện thiết kế hiện đại, tinh tế và cực kỳ dễ sử dụng, 1BWM giúp người dùng dễ dàng tiếp cận và trải nghiệm mọi tiện ích mà nền tảng này mang lại chỉ với vài thao tác đơn giản. Không chỉ vậy, 1BWM còn ghi điểm bởi khả năng tối ưu hóa trải nghiệm trên đa dạng thiết bị như điện thoại di động, máy tính bảng và máy tính để bàn, giúp người dùng có thể giải trí bất cứ lúc nào, ở bất kỳ đâu một cách thuận tiện và mượt mà. Từ các chuyên mục nội dung hấp dẫn, phong phú cho đến hệ thống tính năng linh hoạt, 1BWM luôn biết cách làm mới mình để phù hợp với xu hướng công nghệ và nhu cầu giải trí ngày càng đa dạng của người dùng hiện đại.
Điểm mạnh nổi bật tiếp theo khiến 1BWM được nhiều người lựa chọn chính là hệ thống bảo mật dữ liệu và quyền riêng tư vô cùng nghiêm ngặt. Nền tảng này ứng dụng công nghệ mã hóa tiên tiến, đảm bảo mọi thông tin cá nhân, tài khoản và dữ liệu giao dịch của người dùng luôn được bảo vệ an toàn tuyệt đối. Bên cạnh đó, 1BWM còn sở hữu đội ngũ chăm sóc khách hàng chuyên nghiệp, tận tâm và giàu kinh nghiệm, luôn sẵn sàng hỗ trợ giải đáp mọi thắc mắc cũng như xử lý các tình huống phát sinh một cách nhanh chóng, hiệu quả nhất. Người dùng có thể yên tâm khi trải nghiệm các dịch vụ tại đây mà không phải lo lắng về bất cứ rủi ro nào liên quan đến bảo mật thông tin. Ngoài ra, nền tảng này còn thường xuyên triển khai các chương trình ưu đãi hấp dẫn, quà tặng đặc biệt dành cho người dùng mới lẫn hội viên lâu năm, tạo thêm nhiều giá trị và động lực cho cộng đồng người tham gia.
Không dừng lại ở đó, 1BWM luôn nỗ lực không ngừng trong việc nâng cao chất lượng dịch vụ và mở rộng thêm nhiều tiện ích giải trí mới, nhằm mang đến cho người dùng những trải nghiệm trọn vẹn và thú vị nhất. Nền tảng này liên tục cập nhật các chuyên mục nội dung mới mẻ, phong phú và bắt kịp xu hướng giải trí hiện đại, giúp người dùng luôn có thêm nhiều lựa chọn phù hợp với sở thích cá nhân. Đồng thời, 1BWM cũng chú trọng vào việc cải tiến công nghệ, tối ưu tốc độ kết nối và giao diện sử dụng để nâng cao trải nghiệm mỗi lần truy cập. Với định hướng phát triển rõ ràng cùng sự đầu tư bài bản, 1BWM không chỉ là một nền tảng giải trí đơn thuần mà còn là cộng đồng trực tuyến năng động, nơi người dùng có thể kết nối, tương tác và chia sẻ những khoảnh khắc giải trí vui vẻ, ý nghĩa cùng nhau. Nhờ những ưu điểm vượt trội này, 1BWM ngày càng khẳng định được vị thế và trở thành sự lựa chọn hàng đầu của người dùng Việt khi tìm kiếm một không gian giải trí số chất lượng, an toàn và uy tín.
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ 97c70a44:ad98e322
2025-01-30 17:15:37
@ 97c70a44:ad98e322
2025-01-30 17:15:37There was a slight dust up recently over a website someone runs removing a listing for an app someone built based on entirely arbitrary criteria. I'm not to going to attempt to speak for either wounded party, but I would like to share my own personal definition for what constitutes a "nostr app" in an effort to help clarify what might be an otherwise confusing and opaque purity test.
In this post, I will be committing the "no true Scotsman" fallacy, in which I start with the most liberal definition I can come up with, and gradually refine it until all that is left is the purest, gleamingest, most imaginary and unattainable nostr app imaginable. As I write this, I wonder if anything built yet will actually qualify. In any case, here we go.
It uses nostr
The lowest bar for what a "nostr app" might be is an app ("application" - i.e. software, not necessarily a native app of any kind) that has some nostr-specific code in it, but which doesn't take any advantage of what makes nostr distinctive as a protocol.
Examples might include a scraper of some kind which fulfills its charter by fetching data from relays (regardless of whether it validates or retains signatures). Another might be a regular web 2.0 app which provides an option to "log in with nostr" by requesting and storing the user's public key.
In either case, the fact that nostr is involved is entirely neutral. A scraper can scrape html, pdfs, jsonl, whatever data source - nostr relays are just another target. Likewise, a user's key in this scenario is treated merely as an opaque identifier, with no appreciation for the super powers it brings along.
In most cases, this kind of app only exists as a marketing ploy, or less cynically, because it wants to get in on the hype of being a "nostr app", without the developer quite understanding what that means, or having the budget to execute properly on the claim.
It leverages nostr
Some of you might be wondering, "isn't 'leverage' a synonym for 'use'?" And you would be right, but for one connotative difference. It's possible to "use" something improperly, but by definition leverage gives you a mechanical advantage that you wouldn't otherwise have. This is the second category of "nostr app".
This kind of app gets some benefit out of the nostr protocol and network, but in an entirely selfish fashion. The intention of this kind of app is not to augment the nostr network, but to augment its own UX by borrowing some nifty thing from the protocol without really contributing anything back.
Some examples might include:
- Using nostr signers to encrypt or sign data, and then store that data on a proprietary server.
- Using nostr relays as a kind of low-code backend, but using proprietary event payloads.
- Using nostr event kinds to represent data (why), but not leveraging the trustlessness that buys you.
An application in this category might even communicate to its users via nostr DMs - but this doesn't make it a "nostr app" any more than a website that emails you hot deals on herbal supplements is an "email app". These apps are purely parasitic on the nostr ecosystem.
In the long-term, that's not necessarily a bad thing. Email's ubiquity is self-reinforcing. But in the short term, this kind of "nostr app" can actually do damage to nostr's reputation by over-promising and under-delivering.
It complements nostr
Next up, we have apps that get some benefit out of nostr as above, but give back by providing a unique value proposition to nostr users as nostr users. This is a bit of a fine distinction, but for me this category is for apps which focus on solving problems that nostr isn't good at solving, leaving the nostr integration in a secondary or supporting role.
One example of this kind of app was Mutiny (RIP), which not only allowed users to sign in with nostr, but also pulled those users' social graphs so that users could send money to people they knew and trusted. Mutiny was doing a great job of leveraging nostr, as well as providing value to users with nostr identities - but it was still primarily a bitcoin wallet, not a "nostr app" in the purest sense.
Other examples are things like Nostr Nests and Zap.stream, whose core value proposition is streaming video or audio content. Both make great use of nostr identities, data formats, and relays, but they're primarily streaming apps. A good litmus test for things like this is: if you got rid of nostr, would it be the same product (even if inferior in certain ways)?
A similar category is infrastructure providers that benefit nostr by their existence (and may in fact be targeted explicitly at nostr users), but do things in a centralized, old-web way; for example: media hosts, DNS registrars, hosting providers, and CDNs.
To be clear here, I'm not casting aspersions (I don't even know what those are, or where to buy them). All the apps mentioned above use nostr to great effect, and are a real benefit to nostr users. But they are not True Scotsmen.
It embodies nostr
Ok, here we go. This is the crème de la crème, the top du top, the meilleur du meilleur, the bee's knees. The purest, holiest, most chaste category of nostr app out there. The apps which are, indeed, nostr indigitate.
This category of nostr app (see, no quotes this time) can be defined by the converse of the previous category. If nostr was removed from this type of application, would it be impossible to create the same product?
To tease this apart a bit, apps that leverage the technical aspects of nostr are dependent on nostr the protocol, while apps that benefit nostr exclusively via network effect are integrated into nostr the network. An app that does both things is working in symbiosis with nostr as a whole.
An app that embraces both nostr's protocol and its network becomes an organic extension of every other nostr app out there, multiplying both its competitive moat and its contribution to the ecosystem:
- In contrast to apps that only borrow from nostr on the technical level but continue to operate in their own silos, an application integrated into the nostr network comes pre-packaged with existing users, and is able to provide more value to those users because of other nostr products. On nostr, it's a good thing to advertise your competitors.
- In contrast to apps that only market themselves to nostr users without building out a deep integration on the protocol level, a deeply integrated app becomes an asset to every other nostr app by becoming an organic extension of them through interoperability. This results in increased traffic to the app as other developers and users refer people to it instead of solving their problem on their own. This is the "micro-apps" utopia we've all been waiting for.
Credible exit doesn't matter if there aren't alternative services. Interoperability is pointless if other applications don't offer something your app doesn't. Marketing to nostr users doesn't matter if you don't augment their agency as nostr users.
If I had to choose a single NIP that represents the mindset behind this kind of app, it would be NIP 89 A.K.A. "Recommended Application Handlers", which states:
Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics. This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions.
These handlers are the glue that holds nostr apps together. A single event, signed by the developer of an application (or by the application's own account) tells anyone who wants to know 1. what event kinds the app supports, 2. how to link to the app (if it's a client), and (if the pubkey also publishes a kind 10002), 3. which relays the app prefers.
As a sidenote, NIP 89 is currently focused more on clients, leaving DVMs, relays, signers, etc somewhat out in the cold. Updating 89 to include tailored listings for each kind of supporting app would be a huge improvement to the protocol. This, plus a good front end for navigating these listings (sorry nostrapp.link, close but no cigar) would obviate the evil centralized websites that curate apps based on arbitrary criteria.
Examples of this kind of app obviously include many kind 1 clients, as well as clients that attempt to bring the benefits of the nostr protocol and network to new use cases - whether long form content, video, image posts, music, emojis, recipes, project management, or any other "content type".
To drill down into one example, let's think for a moment about forms. What's so great about a forms app that is built on nostr? Well,
- There is a spec for forms and responses, which means that...
- Multiple clients can implement the same data format, allowing for credible exit and user choice, even of...
- Other products not focused on forms, which can still view, respond to, or embed forms, and which can send their users via NIP 89 to a client that does...
- Cryptographically sign forms and responses, which means they are self-authenticating and can be sent to...
- Multiple relays, which reduces the amount of trust necessary to be confident results haven't been deliberately "lost".
Show me a forms product that does all of those things, and isn't built on nostr. You can't, because it doesn't exist. Meanwhile, there are plenty of image hosts with APIs, streaming services, and bitcoin wallets which have basically the same levels of censorship resistance, interoperability, and network effect as if they weren't built on nostr.
It supports nostr
Notice I haven't said anything about whether relays, signers, blossom servers, software libraries, DVMs, and the accumulated addenda of the nostr ecosystem are nostr apps. Well, they are (usually).
This is the category of nostr app that gets none of the credit for doing all of the work. There's no question that they qualify as beautiful nostrcorns, because their value propositions are entirely meaningless outside of the context of nostr. Who needs a signer if you don't have a cryptographic identity you need to protect? DVMs are literally impossible to use without relays. How are you going to find the blossom server that will serve a given hash if you don't know which servers the publishing user has selected to store their content?
In addition to being entirely contextualized by nostr architecture, this type of nostr app is valuable because it does things "the nostr way". By that I mean that they don't simply try to replicate existing internet functionality into a nostr context; instead, they create entirely new ways of putting the basic building blocks of the internet back together.
A great example of this is how Nostr Connect, Nostr Wallet Connect, and DVMs all use relays as brokers, which allows service providers to avoid having to accept incoming network connections. This opens up really interesting possibilities all on its own.
So while I might hesitate to call many of these things "apps", they are certainly "nostr".
Appendix: it smells like a NINO
So, let's say you've created an app, but when you show it to people they politely smile, nod, and call it a NINO (Nostr In Name Only). What's a hacker to do? Well, here's your handy-dandy guide on how to wash that NINO stench off and Become a Nostr.
You app might be a NINO if:
- There's no NIP for your data format (or you're abusing NIP 78, 32, etc by inventing a sub-protocol inside an existing event kind)
- There's a NIP, but no one knows about it because it's in a text file on your hard drive (or buried in your project's repository)
- Your NIP imposes an incompatible/centralized/legacy web paradigm onto nostr
- Your NIP relies on trusted third (or first) parties
- There's only one implementation of your NIP (yours)
- Your core value proposition doesn't depend on relays, events, or nostr identities
- One or more relay urls are hard-coded into the source code
- Your app depends on a specific relay implementation to work (ahem, relay29)
- You don't validate event signatures
- You don't publish events to relays you don't control
- You don't read events from relays you don't control
- You use legacy web services to solve problems, rather than nostr-native solutions
- You use nostr-native solutions, but you've hardcoded their pubkeys or URLs into your app
- You don't use NIP 89 to discover clients and services
- You haven't published a NIP 89 listing for your app
- You don't leverage your users' web of trust for filtering out spam
- You don't respect your users' mute lists
- You try to "own" your users' data
Now let me just re-iterate - it's ok to be a NINO. We need NINOs, because nostr can't (and shouldn't) tackle every problem. You just need to decide whether your app, as a NINO, is actually contributing to the nostr ecosystem, or whether you're just using buzzwords to whitewash a legacy web software product.
If you're in the former camp, great! If you're in the latter, what are you waiting for? Only you can fix your NINO problem. And there are lots of ways to do this, depending on your own unique situation:
- Drop nostr support if it's not doing anyone any good. If you want to build a normal company and make some money, that's perfectly fine.
- Build out your nostr integration - start taking advantage of webs of trust, self-authenticating data, event handlers, etc.
- Work around the problem. Think you need a special relay feature for your app to work? Guess again. Consider encryption, AUTH, DVMs, or better data formats.
- Think your idea is a good one? Talk to other devs or open a PR to the nips repo. No one can adopt your NIP if they don't know about it.
- Keep going. It can sometimes be hard to distinguish a research project from a NINO. New ideas have to be built out before they can be fully appreciated.
- Listen to advice. Nostr developers are friendly and happy to help. If you're not sure why you're getting traction, ask!
I sincerely hope this article is useful for all of you out there in NINO land. Maybe this made you feel better about not passing the totally optional nostr app purity test. Or maybe it gave you some actionable next steps towards making a great NINON (Nostr In Not Only Name) app. In either case, GM and PV.
-
 @ 9e69e420:d12360c2
2025-01-26 15:26:44
@ 9e69e420:d12360c2
2025-01-26 15:26:44Secretary of State Marco Rubio issued new guidance halting spending on most foreign aid grants for 90 days, including military assistance to Ukraine. This immediate order shocked State Department officials and mandates “stop-work orders” on nearly all existing foreign assistance awards.
While it allows exceptions for military financing to Egypt and Israel, as well as emergency food assistance, it restricts aid to key allies like Ukraine, Jordan, and Taiwan. The guidance raises potential liability risks for the government due to unfulfilled contracts.
A report will be prepared within 85 days to recommend which programs to continue or discontinue.
-
 @ 9063ef6b:fd1e9a09
2025-05-11 17:00:03
@ 9063ef6b:fd1e9a09
2025-05-11 17:00:03✅ Requirements
- GitHub account
- Own domain (e.g.,
yourdomain.com) - Public Nostr key in hex format (not
npub!) - Basic DNS configuration knowledge
🛒 1. Register a Domain
Register a domain from a provider like orangewebsite, njal.la, or similar.
🌐 2. Configure DNS Records for GitHub Pages
Set the following A records for your domain (via your DNS provider):
| Type | Host | Value | TTL | Priority | |------|--------------|-------------------|-----|----------| | A | @ (or blank) | 185.199.108.153 | 300 | | | A | @ (or blank) | 185.199.109.153 | 300 | | | A | @ (or blank) | 185.199.110.153 | 300 | | | A | @ (or blank) | 185.199.111.153 | 300 | |
Optional:
Add aCNAMErecord forwww→yourusername.github.io
📁 3. Create a GitHub Repository
- Go to https://github.com/new
- Repository name: e.g.,
nip5 - Check "Add a README"
- Click "Create repository"
🏗️ 4. Create Directory & File
a)
.well-known/nostr.jsonPath:
.well-known/nostr.jsonPut you nostrhandle (nostrname) and your nostr public key in the file. Example content:
json { "names": { "petermuster": "ldajflasjföldsjflj..." } }IMPORTANT: Use your hex-encoded Nostr public key, not the
npub1...format.b)
_config.ymlin RootCreate a file named
_config.ymlwith this content:yml include: [".well-known"]This ensures GitHub includes the
.well-knownfolder in the build output.
⚙️ 5. Configure GitHub Pages
- Go to Settings > Pages inside your repository
- Under "Build and Deployment":
- Choose:
Deploy from branch - Branch:
mainormaster - Under Custom domain:
- Enter
yourdomain.com - Ignore any warning
- Enable ✅ Enforce HTTPS
It may take a few minutes for the certificate to be issued.

🔍 6. Configure Nostr Client
Open your Nostr client and set the NIP-05 identifier as:
nostrName@yourdomain.com e.g. petermuster@yourdomain.techSave – done!
✅ Test
In your browser or via
curl:bash curl https://yourdomain.com/.well-known/nostr.json?name=petermusterExpected output:
json { "names": { "Nostr Benutzer": "elkajdlkajslfkjaödlkfjs..." } }
🛡️ Privacy Tips
| Item | Recommendation | |-----------------------------------|----------------------------------| | Public key is visible | Use pseudonyms only | | Register a KYC-free domain | e.g., orangewebsite, njal.la | | Use KYC-free email for GitHub | e.g., ProtonMail | | GitHub repository visibility | Must be public for GitHub Pages | | Commit metadata | Use a separate pseudonymous user | | Avoid tracking | Don’t include analytics scripts |
-
 @ c6d8334c:30883d6d
2025-05-19 15:02:01
@ c6d8334c:30883d6d
2025-05-19 15:02:01#KIBedenken - Bewusstsein
Einen wichtigen Impuls über KI nachzudenken lieferte vor einiger Zeit Yuval Noah Harari an der University of Cambridge am Ende eines Podiumsgesprächs hier ab 1:15 h auf youtube:
Ich denke, wir müssen die Frage des Bewusstseins in den Mittelpunkt der Diskussion stellen. Es gibt eine riesige, riesige Verwirrung in der Terminologie, auch in der Welt der KI, zwischen Bewusstsein und Intelligenz. Aber es sind zwei verschiedene Dinge. Intelligenz ist die Fähigkeit, Probleme zu lösen und Ziele zu erreichen. Bewusstsein ist die Fähigkeit, Dinge zu fühlen, wie Schmerz oder Freude oder Liebe oder Hass. Wir neigen dazu, die beiden zu verwechseln, weil bei Menschen und auch bei anderen Säugetieren, Vögeln und anderen Tieren Bewusstsein und Intelligenz zusammengehören. Wir lösen Probleme durch unsere Gefühle. Computer waren bisher sehr anders. Sie sind in einigen Bereichen bereits intelligenter als wir, haben aber, soweit wir wissen, kein Bewusstsein. Soweit wir wissen, können sie überhaupt keinen Schmerz, keine Freude, keine Liebe oder keinen Hass empfinden. Niemand weiß, was in Zukunft passieren wird. Es gibt Modelle und Theorien, die argumentieren, dass KIs irgendwann auch bewusst oder empfindsam werden. Sie werden anfangen, Dinge zu fühlen. Sie werden anfangen, Schmerz oder Liebe oder Hass zu empfinden. Es gibt andere Modelle und Theorien, die sagen, nein. Sie könnten weit intelligenter werden als wir und immer noch null Bewusstsein haben. Das kann in der Evolution des Lebens sein. Wenn man darüber nachdenkt, die lange Entwicklung von Milliarden von Jahren der Evolution. Die Entwicklung der Intelligenz ist im Falle von Tieren wie uns und Schimpansen und Hunden und Schweinen und so weiter durch die Entwicklung des Bewusstseins verlaufen. Aber das ist kein universelles Gesetz der Evolution der Intelligenz. Vielleicht gibt es alternative Wege, die zu Superintelligenz ohne jegliches Bewusstsein führen. Einfach einen anderen, einen fremden Weg gehen. Und wir könnten an einen Punkt gelangen, an dem sie superintelligent sind und trotzdem null Bewusstsein haben. Und die Gefahr besteht dann darin, dass sie nicht nur die menschliche Zivilisation zerstören könnten, sondern das ganze Licht des Bewusstseins, um das gesamte ökologische System nach ihren Bedürfnissen umzugestalten, wofür sie kein Bewusstsein brauchen. Sie funktionieren auf eine völlig andere Weise. Sie könnten sich sogar von der Erde auf andere Planeten, auf andere Galaxien ausbreiten. Sie werden das Universum mit Intelligenz füllen, aber es wird ein völlig dunkles Universum ohne Bewusstsein sein. Wieder hohe Intelligenz, fähig, Raumschiffe zu bauen, die mit Lichtgeschwindigkeit fliegen und was auch immer, aber es gibt null Gefühl. Niemand, keine Entität fühlt Schmerz oder Freude, Liebe oder Hass. Für mich ist das ein schreckliches Szenario. Das schlimmste Szenario von allen ist dies. Dass wir ein Universum voller Intelligenz und völlig ohne Bewusstsein haben werden, denn ich denke, dass von den beiden das Bewusstsein weitaus wichtiger, weitaus wertvoller ist. Und es ist eine gute Erinnerung daran, dass wir das zumindest heute mit vielen anderen Tieren teilen, aber nicht mit den Computern, nicht mit den KIs. Wir sind also immer noch im selben Team wie die Würmer und die Affen, nicht im selben Team wie die Computer.
Ich denke, hier wird eine Spur gelegt, die sich unterscheidet von der reinen Funktion von KI zur intelligenten Verbesserung und Unterstützung von Lernprozessen oder vielfältigem Kompetenzerwerb hin zur Selbstreflexion der Lernenden. Auch im Blick auf (religionsbezogene) Bildung kennen wir den Mensch nicht nur biologisch, wie die Würmer und Affen sondern auch ausgestattet mit Würde, Entscheidungsfreiheit und als Beziehungswesen, das auf ein Gegenüber ausgerichtet sein kann und, wie Harari sagt, nicht im selben Team wie die Computer spielt. Sinn, Seele und Verstand erhalten wir weder aus uns selbst heraus noch von einer wie auch immer gearteten Intelligenz. Liebe, Gnade, Hoffnung, Frieden, Gemeinschaft, Trost, Zuversicht und viele weiteren lebensbedeutsame Erfahrungen gewinnen im Angesicht von Maschinen aus meiner Sicht an elementarer Bedeutung.
-
 @ cae03c48:2a7d6671
2025-05-21 21:01:22
@ cae03c48:2a7d6671
2025-05-21 21:01:22Bitcoin Magazine

U.S. Leads the World in Bitcoin Ownership, New Report ShowsA new report from River reveals that the United States dominates Bitcoin ownership globally, holding about 40% of all available Bitcoin. With 14.3% of its population owning Bitcoin, the U.S. outpaces Europe, Oceania, and Asia combined.
The United States is the global Bitcoin superpower.
Our new report breaks down how this advantage can fuel the next era of American prosperity. pic.twitter.com/v5BNgTGsKA
— River (@River) May 20, 2025
Corporate America also leads in Bitcoin holdings. Thirty-two U.S. public companies, with a combined market cap of $1.26 trillion, hold Bitcoin as a treasury asset. These firms account for 94.8% of all Bitcoin owned by publicly traded companies worldwide. Major holders include Strategy with 569,000 BTC, U.S. mining companies with 96,000 BTC, and others with 68,000 BTC, totaling 733,000 BTC in the U.S., compared to 40,000 BTC held elsewhere.
Since China’s ban on Bitcoin mining in 2021, the United States has become the global leader in Bitcoin mining, responsible for 38% of all new Bitcoin mined since then. The U.S. attracts miners thanks to its stable regulatory environment, access to deep and liquid capital markets, and abundant energy resources. These advantages have helped the U.S. increase its share of the global Bitcoin mining hashrate by over 500% since 2020, solidifying its position as the center of the industry.
Bitcoin is also emerging as America’s preferred reserve asset, overtaking gold. Over 49.6 million Americans are in favor of holding Bitcoin, compared to 36.7 million who still prefer gold.
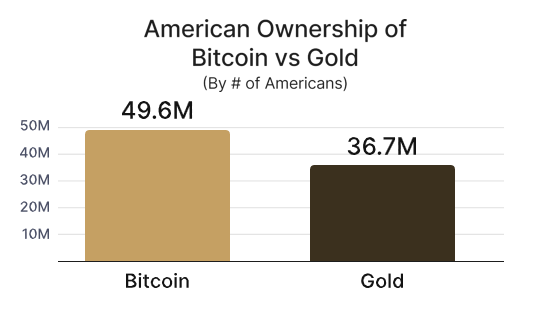
The US government’s bitcoin advantage is greater than that of gold, where the US accounts for just 29.9% of the world’s central bank gold reserves.
“Because there is a fixed supply of BTC, there is a strategic advantage to being among the first nations to create a strategic bitcoin reserve,” said the White House on March 7, 2025.
Politically, support for Bitcoin is gaining significant momentum across the U.S. government. As of now, 59% of U.S. Senators and 66% of House Representatives openly support pro-Bitcoin policies, signaling a notable shift in political attitudes and greater acceptance of digital assets as key components of America’s economic future.
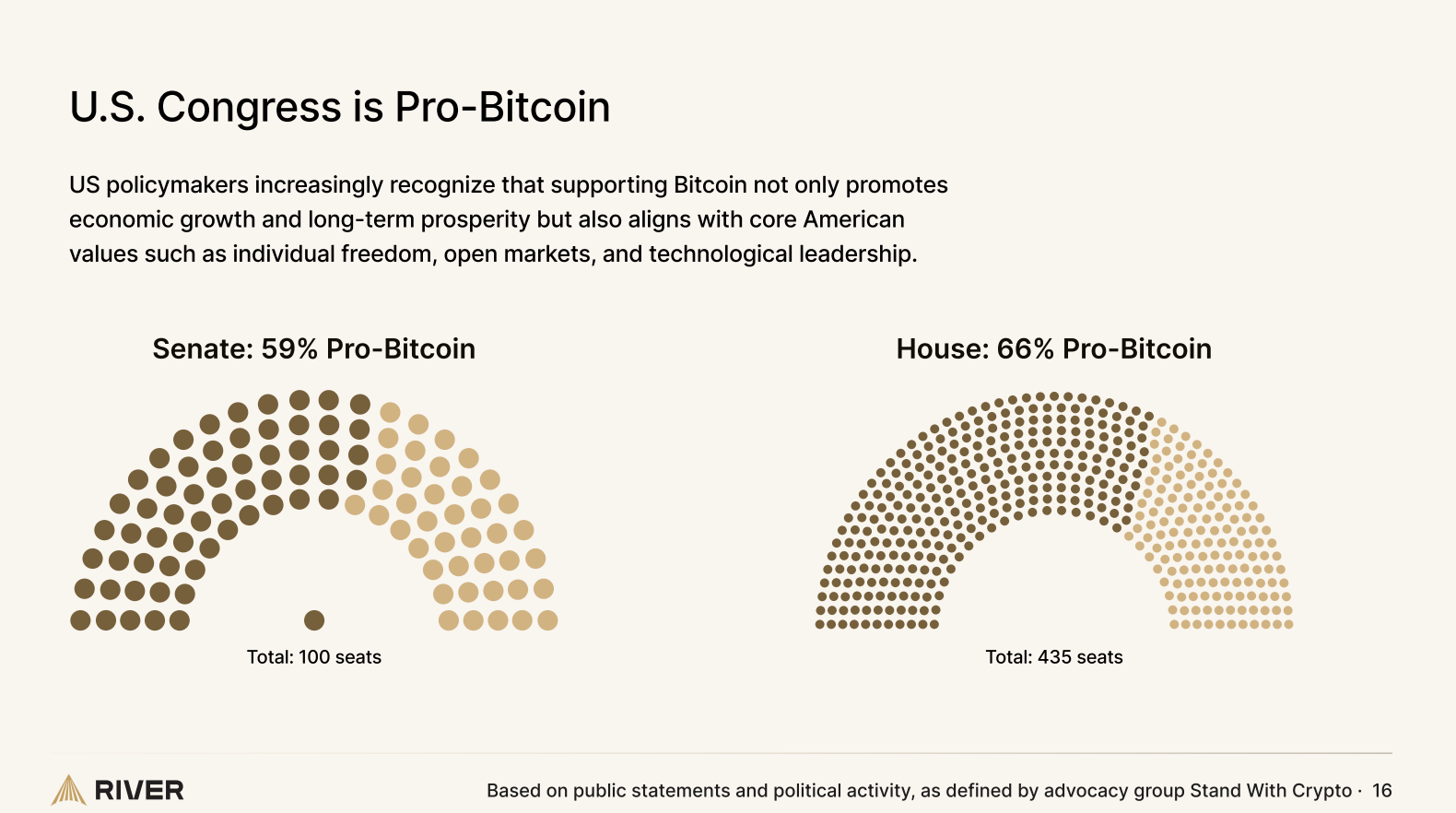
The study highlights that Bitcoin ownership is highest among American males aged 31-35 and 41-45, with ownership rates ranging from 3% to 41% within these age groups. Politically, those identifying as “very liberal” or “neutral” are more likely to own Bitcoin than conservatives, though conservatives still make up a significant portion of holders.
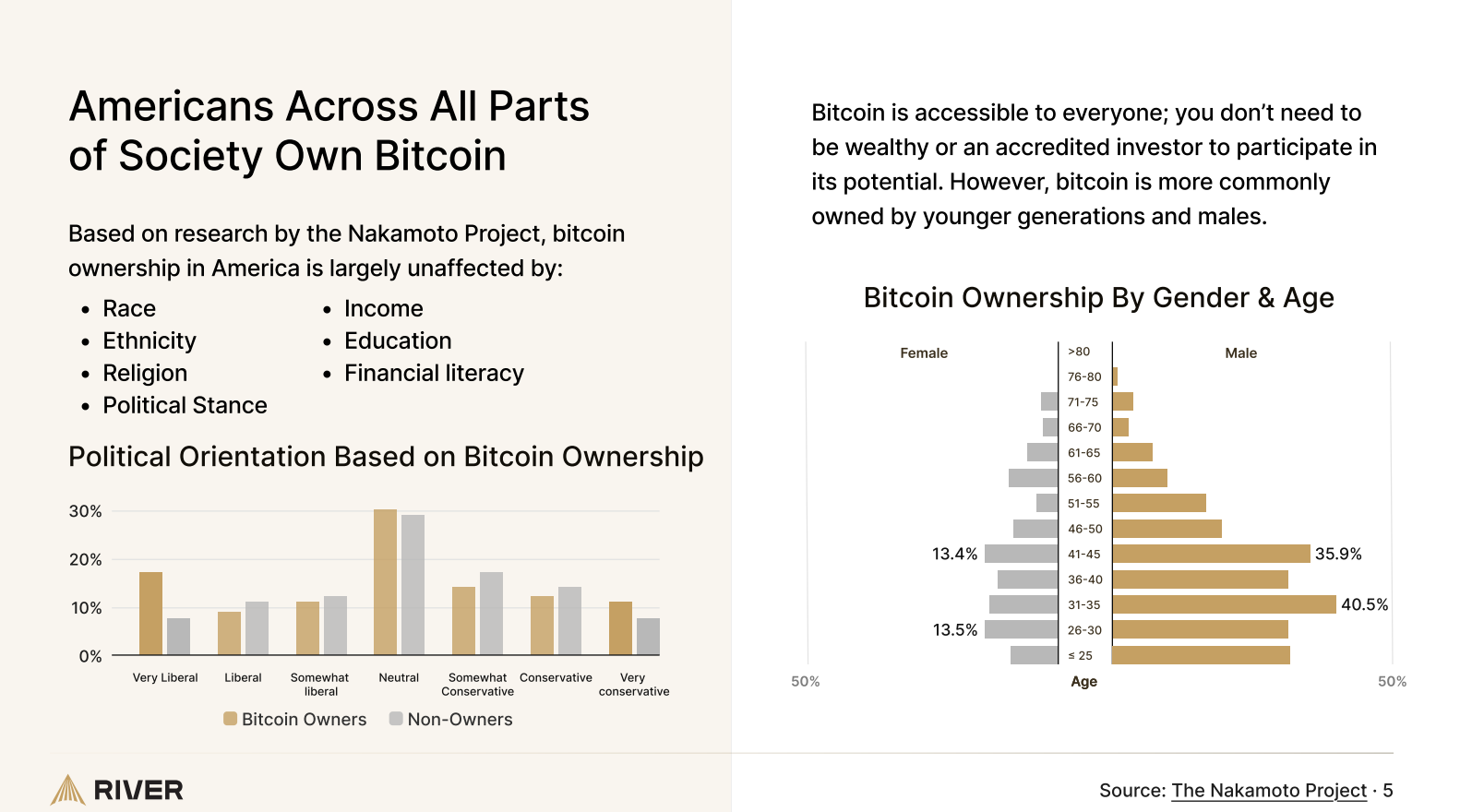
This post U.S. Leads the World in Bitcoin Ownership, New Report Shows first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.