-
 @ 6ad3e2a3:c90b7740
2025-05-20 13:38:04
@ 6ad3e2a3:c90b7740
2025-05-20 13:38:04When I was a kid, I wanted to be rich, but found the prospect of hard work tedious, pointless and soul-crushing. Instead of studying for exams, getting some job and clawing your way up the ladder, I wondered why we couldn’t just build a device that measured your brain capacity and awarded you the money you would have made had you applied yourself. Eliminate the middleman, so to speak, the useless paper pushing evoked by the word “career.”
But when you think about it, it’s not really money you’re after, as money is but purchasing power, and so it’s the things money can provide like a nice lifestyle and the peace of mind that comes from not worrying about it. And it’s not really the lifestyle or financial independence, per se, since moment to moment what’s in your bank account isn’t determining your mental state, but the feeling those things give you — a sense of expansiveness and freedom.
But if you did have such a machine, and it awarded you the money, you probably wouldn’t have that kind of expansiveness and freedom, especially if you did nothing to achieve those things. You would still feel bored, distracted and unsatisfied despite unrestricted means to travel or dine out as you saw fit. People who win the lottery, for example, tend to revert to their prior level of satisfaction in short order.
The feeling you really want then is the sense of rising to a challenge, negotiating and adapting to your environment, persevering in a state of uncertainty, tapping into your resourcefulness and creativity. It’s only while operating at the edge of your capacity you could ever be so fulfilled. In fact, in such a state the question of your satisfaction level would never come up. You wouldn’t even think to wonder about it you’d be so engrossed.
So what you really crave is a mind device that encourages you to adapt to your environment using your full creative capabilities in the present moment, so much so you realize if you do not do this, you have the sense of squandering your life in a tedious, pointless and soul-crushing way. You need to be totally stuck, without the option of turning back. In sum, you need to face reality exactly as it is, without any escape therefrom.
The measure of your mind in that case is your reality itself. The device is already with you — it’s the world you are presently creating with the consciousness you have, providing you avenues to escape, none of which are satisfactory, none that can lead to the state you truly desire. You have a choice to pursue them fruitlessly and wind up at square one, or to abandon them and attain your freedom. No matter how many times you go down a false road, you wind up at the same place until you give up on the Sisyphean task and proceed in earnest.
My childhood fantasy was real, it turns out, only I had misunderstood its meaning.
-
 @ bbb5dda0:f09e2747
2025-05-20 13:33:59
@ bbb5dda0:f09e2747
2025-05-20 13:33:59My week 19 started with a celebration of 80 years of liberation from the Germans (we love you guys now tho 🫶🏼). It feels conflicting, we're celebrating freedom, whilst cutting down those freedoms day by day more rapidly as time progresses. Should we still celebrate...?
The current path back to freedom can be mundane in the day to day but I wouldn't wanna have it any other way. These last couple weeks I've continued working on our TollGate pipelines to facilitate our release cycle, make it faster and easier to release in quick succession. There's been a lot of details to get right, because our releases are nostr based and once people start relying on the structure of the events we can't easily change it.
A TollGateOS release event now looks like this NIP-94 file metadata event:
json { "id": "a867f15ca7edc95a69e1557539a624466147584f68c62a16c47fe9bca3778312", "pubkey": "5075e61f0b048148b60105c1dd72bbeae1957336ae5824087e52efa374f8416a", "created_at": 1747475980, "kind": 1063, "tags": [ [ "url", "https://blossom.swissdash.site/9e5e8c48810a1b59cf10fa56486f311e048a0305eb58444992b6133fd19fcb3e.bin" ], [ "m", "application/octet-stream" ], [ "x", "9e5e8c48810a1b59cf10fa56486f311e048a0305eb58444992b6133fd19fcb3e" ], [ "ox", "9e5e8c48810a1b59cf10fa56486f311e048a0305eb58444992b6133fd19fcb3e" ], [ "architecture", "aarch64_cortex-a53" ], [ "device_id", "glinet_gl-mt3000" ], [ "supported_devices", "glinet,gl-mt3000 glinet,mt3000-snand" ], [ "openwrt_version", "24.10.1" ], [ "tollgate_os_version", "v0.0.2" ], [ "release_channel", "stable" ] ], "content": "TollGate OS Firmware for glinet_gl-mt3000", "sig": "1d050233428304685d202e954cb48714c800a7ca5f2d6a8d8fd657a775b9c51bf83364505311859c846e25098168a8ff309af2308712aafe634fcbdc96fcd84a" }One of the missing links was the
supported_devicestag. That is because the installer checks the device name by ssh-ing into the router and it returns theglinet,gl-mt3000which doesn't properly translate into thedevice_id, which is what's used for compiling the OS. So this helps us to do the lookups and compatibility checks in the installer.I also worked on: - getting the versioning of the tollgate-basic package's naming in line with the OpenWRT naming convention. - Rework versioning for dev builds into
[branchname].[commit_height].[commit_hash]which will show up on thedevrelease_channelreleases. - Getting an initial release of the tollgate-installer done, so we can easily flash a bunch of routers to become TollGates.Bright minds in Prague
I met up with some bright minds from the space in Prague where @cobrador and i did a workshop on turning routers into TollGates and start earning sats. As is part of building things, things break and people make us aware of issues that we wouldn't foresee. Like for some reason Minibits cashu tokens being rejected, which is likely because of the memo's but we still need to dive into that issue.
Also we released [v0.0.2] of TollGate OS, which now includes an updater feature, again for faster release cycles. Currently we're focussing on getting a v0.0.3 out quickly with fixes for the user feedback we've gathered so far!
Receipt.Cash
I also, kind of unplanned, saw an opportunity to shill Receipt.Cash. I'd made a few improvements recently and it's ready enough for reckless people to try it out ;).
|
 |
| 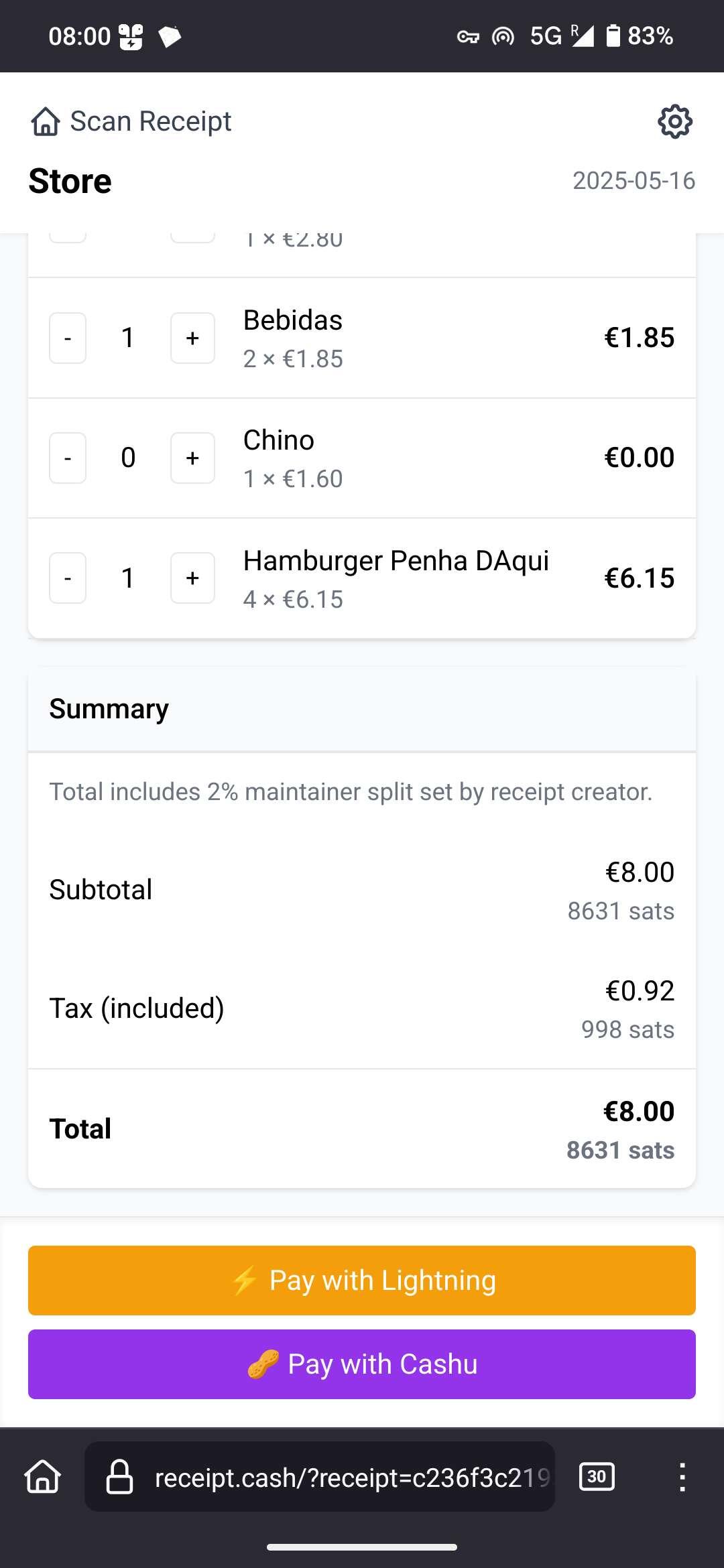 |
| |
| Payer Scans any fiat receipt & Share link with friends | Friends tap what they had, price is auto-converted to sats, then pay by Lightning or Cashu. |
If you want to try it, BE CAREFUL! It is highly experimental and you might lose your sats, no refunds!
|
| |
| Payer Scans any fiat receipt & Share link with friends | Friends tap what they had, price is auto-converted to sats, then pay by Lightning or Cashu. |
If you want to try it, BE CAREFUL! It is highly experimental and you might lose your sats, no refunds!Source Code here.
-
 @ 3770c235:16042bcc
2025-05-20 13:27:03
@ 3770c235:16042bcc
2025-05-20 13:27:03In recent years, a remarkable transformation has taken place in the way people view and utilize their homes. No longer confined to the four walls of traditional interior spaces, homeowners are increasingly turning their attention outward—toward their own backyards. The concept of outdoor living has evolved from mere patio furniture and barbecues to fully functional living environments, equipped with kitchens, entertainment systems, and even workspaces.
This growing trend is not just a design choice; it reflects changing lifestyles, shifting priorities, and a reimagining of what it means to feel at home. The rise of outdoor living is more than a fad—it's a movement, and it's here to stay.
**A Shift in Lifestyle and Values ** At the heart of the outdoor living boom is a deeper shift in how people value their time, environment, and personal space. The COVID-19 pandemic played a significant role in this evolution. Lockdowns and restrictions forced many to reassess their living situations, seeking ways to make the most of what they already had. The backyard, once overlooked, suddenly became a sanctuary—a space to breathe, gather, and escape the monotony of indoor life.
According to a 2021 study by the International Casual Furnishings Association, over 90% of Americans with outdoor living space report that it is more valuable to them than ever before, with nearly 60% saying they upgraded their outdoor spaces during the pandemic source.
This change in perception is not solely pandemic-related. There's a growing emphasis on wellness, mindfulness, and balance. People are looking to nature for inspiration and relaxation. Outdoor living spaces—be they modest balconies or expansive decks—allow homeowners to connect with nature without leaving the comfort of home.
Redefining the Backyard: From Playgrounds to Living Rooms
Traditionally, the backyard has served specific purposes—gardening, children’s play areas, maybe a grill tucked in the corner. Today, backyards are being reimagined as multi-functional extensions of the home.
-
Outdoor Kitchens and Dining Areas Once considered a luxury, outdoor kitchens have become increasingly common. With built-in grills, pizza ovens, refrigerators, sinks, and full countertops, these outdoor culinary spaces rival their indoor counterparts. The convenience of preparing and serving meals outside is matched by the social benefit: cooking becomes a shared experience.
-
Living and Lounge Areas Outdoor seating now goes far beyond foldable lawn chairs. Modular sectionals, fire pits, weather-resistant rugs, and even smart lighting have turned patios into legitimate living rooms under the sky. Some include mounted TVs, Bluetooth speakers, and retractable canopies or pergolas for all-weather comfort.
-
Work and Study Zones Remote work has blurred the boundaries between office and home. Now, it’s expanding into the outdoors. With Wi-Fi extenders, weather-protected furniture, and shade structures, backyards are becoming viable home office environments, perfect for Zoom calls with a natural backdrop.
-
Wellness Retreats From hot tubs and saunas to yoga decks and meditation gardens, outdoor spaces are being tailored to support wellness. These personal sanctuaries offer solitude and stress relief, all within the perimeter of one's property.
The Role of Technology and Innovation Modern outdoor spaces owe much of their versatility to advances in technology and materials. Weather-resistant fabrics, composite decking, solar lighting, and smart irrigation systems have all expanded what's possible in backyard design.
Smart home technology has also made its way outdoors. Lighting can be automated or voice-controlled. Outdoor speakers can be synced across zones. Even grills can be connected to apps that monitor cooking temperatures. These innovations allow outdoor living to be both luxurious and convenient, requiring minimal maintenance while offering maximum comfort.
**Economic Impact and Value Addition ** Investing in outdoor living isn't just about lifestyle—it’s also smart economics. Outdoor upgrades can significantly boost a home's resale value. A well-designed patio or outdoor kitchen can yield a return on investment (ROI) of up to 80%, according to the National Association of Realtors. In fact, data from Houzz shows that nearly 57% of homeowners are investing in their outdoor spaces specifically to increase resale value source.
This financial motivation has fueled demand for landscape architects, outdoor furniture designers, and construction professionals specializing in outdoor living projects. As a result, the industry surrounding outdoor enhancements—from pergola manufacturers to luxury fire pit designers—has seen exponential growth.
Environmental Considerations and Sustainability As outdoor living becomes more popular, so does the demand for environmentally conscious design. Homeowners are increasingly incorporating sustainable elements into their outdoor plans, including: • Native plant landscaping: Reduces water usage and supports local ecosystems. • Rainwater harvesting systems: Collect and store rain for garden irrigation. • Solar-powered lighting: Minimizes energy consumption while maximizing ambiance. • Permeable paving materials: Reduce runoff and promote groundwater recharge. Green living isn't just a buzzword—it’s influencing how people design their outdoor sanctuaries. Eco-conscious homeowners are prioritizing sustainability as much as aesthetics, ensuring their outdoor spaces are in harmony with nature, not in conflict with it.
The Social Connection
Outdoor living also taps into our basic need for connection. From summer barbecues to cozy firepit gatherings, the backyard is an ideal setting for meaningful social interactions. During a time when indoor gatherings have been restricted or limited, outdoor spaces have offered a safer, more accessible alternative.
Community ties can also be strengthened through outdoor living. In urban settings, rooftop terraces or shared gardens create communal spaces for neighbors to engage, collaborate, and unwind. For families, these outdoor extensions offer a way to spend quality time together—whether through games, meals, or simply enjoying the open air. For individuals, they provide a space to recharge, free from the digital and physical clutter of indoor life.
Customization and Personalization
One of the most appealing aspects of outdoor living is the high degree of customization available. Unlike interior spaces that may be limited by architectural constraints, outdoor areas can often be more flexible in layout and design.
Homeowners can craft outdoor environments that reflect their personalities and values: • The entertainer may opt for a bar area, ambient lighting, and surround sound. • The minimalist might choose clean lines, neutral tones, and eco-friendly materials. • The nature-lover may emphasize greenery, water features, and natural textures. DIY options also abound, allowing for creative freedom and budget-friendly upgrades. Raised garden beds, handmade furniture, repurposed materials, and vertical planters give individuals the opportunity to leave their personal mark on the space.
The Influence of Global Design Trends Outdoor living isn’t confined to North America. Around the world, cultures have long embraced outdoor spaces—from Japanese zen gardens to Mediterranean courtyards. The current global design conversation draws inspiration from a variety of traditions and climates.
Scandinavian principles of simplicity and functionality influence clean-lined, open-air designs, while tropical resorts have inspired lush, greenery-filled retreats in suburban settings. The blending of international styles enables homeowners to create outdoor spaces that are both eclectic and functional.
Looking Ahead: The Future of Outdoor Living The trajectory of outdoor living points to continued growth, innovation, and integration. Here are some trends likely to define the next decade:
- Year-Round Use With heating lamps, insulated pergolas, and all-weather furniture, outdoor spaces are becoming viable in all seasons. Expect to see more designs tailored for winter, including hot tubs, enclosed lounges, and warm lighting features.
- Outdoor Smart Hubs Technology will play an even greater role, with integrated outdoor control systems for lighting, security, irrigation, and entertainment—managed through a single device or app.
- Edible Landscaping Gardens will not only be for beauty but also for sustenance. Raised vegetable beds, fruit trees, and herb walls will become staples in functional outdoor design.
- Modular Design Portable and adaptable elements like movable walls, foldable furniture, and hybrid indoor-outdoor structures will offer more flexibility, especially in smaller spaces.
- Wellness Integration Expect an even stronger emphasis on health and well-being—cold plunge pools, outdoor gyms, meditation pods, and immersive natural soundscapes will take center stage.
Conclusion The rise of outdoor living is not just a design phenomenon—it’s a cultural shift. Homeowners are recognizing the value of outdoor spaces as extensions of their identities, routines, and dreams. Whether it's a serene garden, a vibrant entertainment hub, or a cozy work nook, the backyard is being redefined as a vital part of the home. In a world that often feels fast-paced and digitally overloaded, outdoor living offers a much-needed antidote: space to breathe, relax, connect, and thrive. It’s about more than upgrading the home—it’s about enhancing the human experience. As this trend continues to evolve, one thing is clear: the best room in the house may not be inside at all.
-
-
 @ cefb08d1:f419beff
2025-05-20 13:26:14
@ cefb08d1:f419beff
2025-05-20 13:26:14https://www.youtube.com/watch?v=jIydjo4B25U
The GWM Catch Up Day 2: Western Australia pushes CT to the ultimate test in all or nothing bouts:
https://www.youtube.com/watch?v=4zwuqs6iTPg
Women and Men Results:
https://stacker.news/items/984538
-
 @ 472f440f:5669301e
2025-05-20 13:01:09
@ 472f440f:5669301e
2025-05-20 13:01:09Marty's Bent

via me
Don't sleep on what's happening in Japan right now. We've been covering the country and the fact that they've lost control of their yield curve since late last year. After many years of making it a top priority from a monetary policy perspective, last year the Bank of Japan decided to give up on yield curve control in an attempt to reel inflation. This has sent yields for the 30-year and 40-year Japanese government bonds to levels not seen since the early 2000s in the case of the 30-year and levels never before seen for the 40-year, which was launched in 2007. With a debt to GDP ratio that has surpassed 250% and a population that is aging out with an insufficient amount of births to replace the aging workforce, it's hard to see how Japan can get out of this conundrum without some sort of economic collapse.
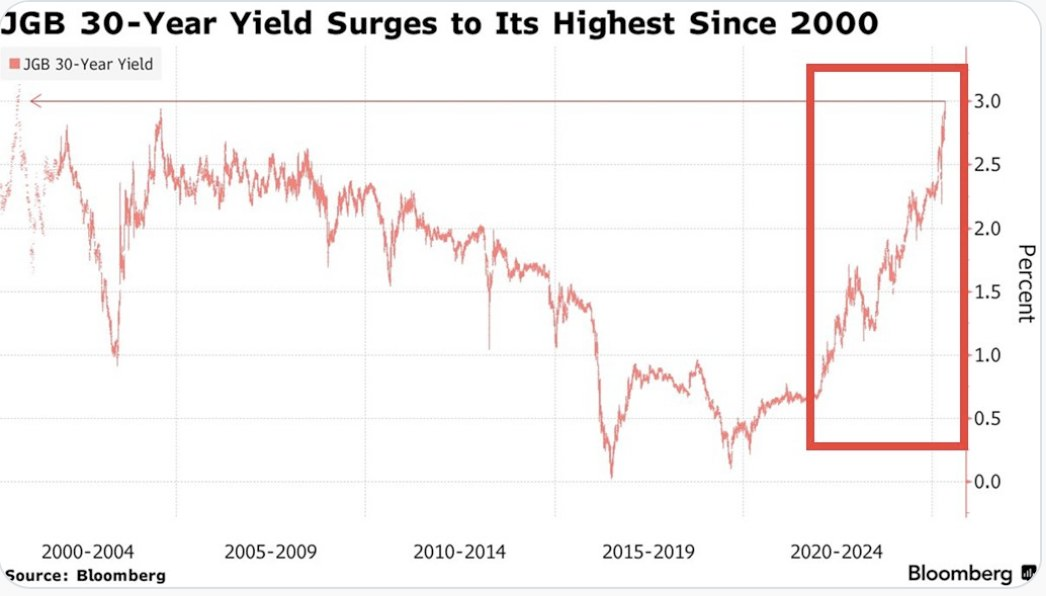

This puts the United States in a tough position considering the fact that Japan is one of the largest holders of U.S. Treasury bonds with more than 1,135 sats | $1.20 trillion in exposure. If things get too out of control in Japan and the yield curve continues to drift higher and inflation continues to creep higher Japan can find itself in a situation where it's a forced seller of US Treasuries as they attempt to strengthen the yen. Another aspect to consider is the fact that investors may see the higher yields on Japanese government bonds and decide to purchase them instead of US Treasuries. This is something to keep an eye on in the weeks to come. Particularly if higher rates drive a higher cost of capital, which leads to even more inflation. As producers are forced to increase their prices to ensure that they can manage their debt repayments.
It's never a good sign when the Japanese Prime Minister is coming out to proclaim that his country's financial situation is worse than Greece's, which has been a laughing stock of Europe for the better part of three decades. Japan is a very proud nation, and the fact that its Prime Minister made a statement like this should not be underappreciated.
As we noted last week, the 10-year and 30-year U.S. Treasury bonds are drifting higher as well. Earlier today, the 30-year bond yield surpassed 5%, which has been a psychological level that many have been pointed to as a critical tipping point. When you take a step back and look around the world it seems pretty clear that bond markets are sending a very strong signal. And that signal is that something is not well in the back end of the financial system.
This is even made clear when you look at the private sector, particularly at consumer debt. In late March, we warned of the growing trend of buy now, pay later schemes drifting down market as major credit card companies released charge-off data which showed charge-off rates reaching levels not seen since the 2008 great financial crisis. At the time, we could only surmise that Klarna was experiencing similar charge-off rates on the bigger-ticket items they financed and started doing deals with companies like DoorDash to finance burrito deliveries in an attempt to move down market to finance smaller ticket items with a higher potential of getting paid back. It seems like that inclination was correct as Klarna released data earlier today showing more losses on their book as consumers find it extremely hard to pay back their debts.

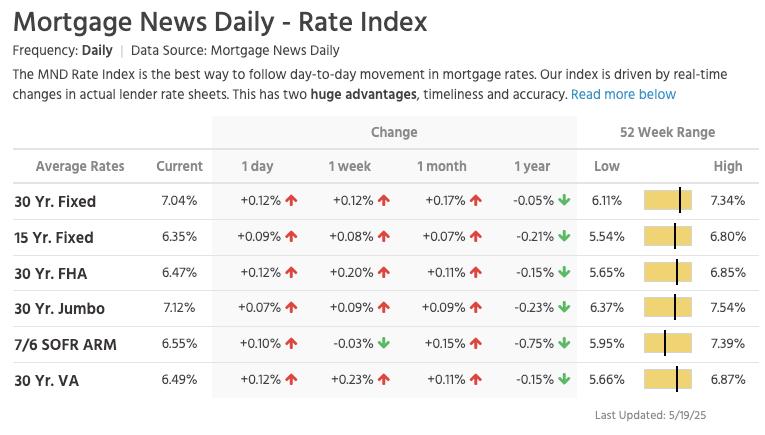
via NewsWire
This news hit the markets on the same day as the average rate of the 30-year mortgage in the United States rose to 7.04%. I'm not sure if you've checked lately, but real estate prices are still relatively elevated outside of a few big cities who expanded supply significantly during the COVID era as people flooded out of blue states towards red states. It's hard to imagine that many people can afford a house based off of sticker price alone, but with a 7% 30-year mortgage rate it's becoming clear that the ability of the Common Man to buy a house is simply becoming impossible.
via Lance Lambert
The mortgage rate data is not the only thing you need to look at to understand that it's becoming impossible for the Common Man of working age to buy a house. New data has recently been released that highlights That the median home buyer in 2007 was born in 1968, and the median home buyer in 2024 was born in 1968. Truly wild when you think of it. As our friend Darth Powell cheekily highlights below, we find ourselves in a situation where boomers are simply trading houses and the younger generations are becoming indentured slaves. Forever destined to rent because of the complete inability to afford to buy a house.
via Darth Powell
via Yahoo Finance
Meanwhile, Bitcoin re-approached all-time highs late this evening and looks primed for another breakout to the upside. This makes sense if you're paying attention. The high-velocity trash economy running on an obscene amount of debt in both the public and private sectors seems to be breaking at the seams. All the alarm bells are signaling that another big print is coming. And if you hope to preserve your purchasing power or, ideally, increase it as the big print approaches, the only thing that makes sense is to funnel your money into the hardest asset in the world, which is Bitcoin.

via Bitbo
Buckle up, freaks. It's gonna be a bumpy ride. Stay humble, Stack Sats.
Trump's Middle East Peace Strategy: Redefining U.S. Foreign Policy
In his recent Middle East tour, President Trump signaled what our guest Dr. Anas Alhajji calls "a major change in US policy." Trump explicitly rejected the nation-building strategies of his predecessors, contrasting the devastation in Afghanistan and Iraq with the prosperity of countries like Saudi Arabia and UAE. This marks a profound shift from both Republican and Democratic foreign policy orthodoxy. As Alhajji noted, Trump's willingness to meet with Syrian President Assad follows a historical pattern where former adversaries eventually become diplomatic partners.
"This is really one of the most important shifts in US foreign policy to say, look, sorry, we destroyed those countries because we tried to rebuild them and it was a big mistake." - Dr. Anas Alhajji
The administration's new approach emphasizes negotiation over intervention. Rather than military solutions, Trump is engaging with groups previously considered off-limits, including the Houthis, Hamas, and Iran. This pragmatic stance prioritizes economic cooperation and regional stability over ideological confrontation. The focus on trade deals and investment rather than regime change represents a fundamental reimagining of America's role in the Middle East.
Check out the full podcast here for more on the Iran nuclear situation, energy market predictions, and why AI development could create power grid challenges. Only on TFTC Studio.
Headlines of the Day
Bitcoin Soars to 100,217 sats | $106.00K While Bonds Lose 40% Since 2020 - via X
US Senate Advances Stablecoin Bill As America Embraces Bitcoin - via X
Get our new STACK SATS hat - via tftcmerch.io
Texas House Debates Bill For State-Run Bitcoin Reserve - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code “TFTC20” during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed 158,469 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
Don't let the noise consume you. Focus on making your life 1% better every day.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ f85b9c2c:d190bcff
2025-05-20 12:51:06
@ f85b9c2c:d190bcff
2025-05-20 12:51:06 Sometimes I feel like reversing time.
I miss my childhood. Honestly, who wouldn’t? Back then, life was so simple, so carefree. I had no bills to pay, no deadlines to chase, and no worries about what tomorrow might bring. All I had to do was wake up, play, eat, and maybe dodge a beating or two from Mum when I got a little too adventurous😂. Sometimes I feel like reversing time, just to relive those golden days when my biggest problem was figuring out how to sneak a piece of meat from the pot without getting caught.
Sometimes I feel like reversing time.
I miss my childhood. Honestly, who wouldn’t? Back then, life was so simple, so carefree. I had no bills to pay, no deadlines to chase, and no worries about what tomorrow might bring. All I had to do was wake up, play, eat, and maybe dodge a beating or two from Mum when I got a little too adventurous😂. Sometimes I feel like reversing time, just to relive those golden days when my biggest problem was figuring out how to sneak a piece of meat from the pot without getting caught.I remember those moments vividly. When I was little, I’d tiptoe into the kitchen, the aroma of Mum’s stew pulling me like a magnet. I’d wait for her to turn her back, then—bam!—my tiny hand would dive into the pot, snagging a juicy piece of meat. Of course, I wasn’t exactly a master thief. Mum always seemed to know. She’d catch me red-handed, and let’s just say her wooden spoon wasn’t just for cooking! I was kinda stubborn back then, so those beatings happened a lot. But I don’t steal meat anymore—grown-up me knows better. Life was different then. My only “job” was to have fun—climbing trees, chasing friends, or making up wild stories in my head. Now, adulthood feels like a never-ending to-do list. I miss the freedom, the laughter, the way problems seemed to vanish with a nap or a hug. If I could, I’d turn back the clock, even just for a day, to feel that lightness again. Childhood wasn’t perfect, but it sure felt like it.
-
 @ 9be6a199:6e133301
2025-05-20 12:47:14
@ 9be6a199:6e133301
2025-05-20 12:47:14sadfsflkjsdflkdsjfglksjdfglksdaasdfsdfsdfsdfssdsd
-
 @ 9be6a199:6e133301
2025-05-20 12:46:43
@ 9be6a199:6e133301
2025-05-20 12:46:43sadfsflkjsdflkdsjfglksjdfglksdaasdfsdfsdfsdfssdsd
-
 @ 9be6a199:6e133301
2025-05-20 12:46:20
@ 9be6a199:6e133301
2025-05-20 12:46:20sadfsflkjsdflkdsjfglksjdfglksdaasdfsdfsdfsdfs
-
 @ 9be6a199:6e133301
2025-05-20 12:45:08
@ 9be6a199:6e133301
2025-05-20 12:45:08sadfsflkjsdflkdsjfglksjdfglksd
-
 @ 9be6a199:6e133301
2025-05-20 12:44:22
@ 9be6a199:6e133301
2025-05-20 12:44:22 -
 @ f85b9c2c:d190bcff
2025-05-20 12:41:35
@ f85b9c2c:d190bcff
2025-05-20 12:41:35 Solana (SOL) is acquiring popularity in the crypto world for its speed and flexibility.It's rapidly gaining ground on established blockchains, grabbing investor interest.
Solana (SOL) is acquiring popularity in the crypto world for its speed and flexibility.It's rapidly gaining ground on established blockchains, grabbing investor interest.History Of Solana Anatoly Yakovenko, once a Qualcomm executive, formulated the concept for Solana in 2017. A town on the Southern California coast inspired the name. Yakovenko wanted a swifter, more reliable blockchain network to address the limitations of existing onesat that time. Solana is based in San Francisco, California, at the headquarters of Solana Labs. Solana was launched in March 2020, making a major step in the advancement of blockchain technology.
What Is Solana? Solana is a blockchain network built for speed and affordability.This versatility makes it useful for DeFi, NFTs, and more. Solana operates on its own independent blockchain network with SOL as its native token and infrastructure to power its operations. It functions as a self-sufficient ecosystem, independent of any other existing blockchain network.
How Does Solana Work? Unlike normal blockchains that usually rely on the Proof-of-Work mechanism, Solana uses another approach. It combines two mechanisms: 1.Proof-of-Stake: It lets operators secure the network by putting SOL tokens at stake. These operators are entrusted with adding new blocks to the blockchain and are rewarded for their contribution.
2.Proof-of-History: It helps eliminates the need for communications between operators and boosts transaction processing speed.
Conclusion The mix of these mechanisms is a key factor behind Solana’s reputation for superior speed. Of course, it uses other technical aspects that contribute to its efficiency, but PoS and PoH play a critical role.
-
 @ 9be6a199:6e133301
2025-05-20 12:24:02
@ 9be6a199:6e133301
2025-05-20 12:24:02test
-
 @ 88cc134b:5ae99079
2025-05-20 12:22:03
@ 88cc134b:5ae99079
2025-05-20 12:22:03content
nostr:nevent1qvzqqqqqqypzpkygz22lv3pdey6gr7ygmk67wjh24hdvj3t797mm6z0x3ax4erdhqqsdxy48qm3tces0tu90shwltcg20zsprejkahklwftpzyhytcf32tc9sm779
-
 @ a296b972:e5a7a2e8
2025-05-20 12:22:00
@ a296b972:e5a7a2e8
2025-05-20 12:22:00Die Natur strebt nach einem Gleichgewicht durch Ausgleich von nicht zueinander passenden Verhältnissen. Die Gesellschaft ist ein sozialer Organismus, der ebenso nach Ausgleich und einer Stimmigkeit der Verhältnisse strebt. Das sind Naturgesetze, die keine Regierung auf Dauer imstande ist, außer Kraft zu setzen.
Weder oppositionelle Kräfte, noch Kräfte innerhalb des Souveräns haben die Absicht, die Demokratie abzuschaffen. Es geht vielmehr darum, sie wieder in der Form herzustellen, in der sie ihren Namen auch verdient. Dazu gehört, dass alle Macht vom Volke ausgeht, was derzeit nicht der Fall ist.
Ein durch den Staat vorgegebenes Bildungssystem hat Menschen vor allem zu gefügigen Rädchen im Wirtschaftsgetriebe und nicht zu alles kritisch hinterfragenden Bürgern erzogen, die ständig der Regierung auf die Finger schauen.
Wenn die Bürger, der Souverän, eine Regierung immer mehr „machen lässt“ und glaubt, es sei genug, alle 4 Jahre sein Wahl-Kreuzchen zu machen, entfernt er sich immer mehr von der Kontrolle der durch ihn beauftragten Vertreter, und diese entfernen sich so immer mehr vom Alltag der Bürger.
Zu wenig Gegenrede des Souveräns führt zu immer mehr Übermut der Regierung, die sich immer sicherer wird, mit jedem Unsinn durchzukommen.
Ist dann die Schmerzgrenze des Souveräns erreicht, beginnt er, die Opposition zu stärken. In einer funktionierenden Demokratie würde das dazu führen, dass die Opposition die Regierung bildet, die dann die Chance hat, Fehlentwicklungen abzustellen und ausgleichend tätig zu werden.
Derzeit findet sowohl beim Souverän, als auch bei den Parteien, die bisher Regierungen zusammengestellt haben, ein Erwachen statt.
Da die ehemaligen Volks-Parteien unbedingt an der Macht festhalten wollen, seitens des Souveräns auf zu wenig Widerstand stoßen, wird mit der Macht, einer Demokratie nicht würdig, umgegangen. Dem sollte dringend Einhalt geboten werden.
Der Missbrauch äußert sich in brutalen (Lieblingswort der Ex-Außen-Dings) Einschränkungen der Grundrechte (Corona-Zeit), in der Einschränkung der Meinungsfreiheit (D S A), in Tendenzen zunehmender Kontrolle und Überwachung, Förderung von Denunzianten-Portalen, Kapern des öffentlich-rechtlichen Rundfunks, Förderung von NGOs, die als Sprechpuppen genutzt werden. Besetzt von Menschen, die entweder tatsächlich überzeugt sind von dem, was sie ideologisch vertreten, oder die über Charaktereigenschaften verfügen, die noch sehr viel Optimierungspotenzial in sich bergen. Gepaart mit fachlicher Inkompetenz ist das ein gefährlicher Cocktail.
Erst jüngst sogar durch Ausreiseverbote, wie in einem Staat, mit dem man das derzeitige Deutschland nicht vergleichen darf. So groß ist inzwischen schon die Angst geworden, die Kontrolle über die Macht zu verlieren. Alles, was an Kritik geäußert werden will, gilt als Delegitimierung des Staates. Auf keinen Fall darf sie im Ausland geäußert werden, damit es ja nichts davon mitbekommt, was in Deutschland abgeht. Das ist so wie ein Kind, dass sich die Hände vor die Augen hält und meint, es würde nicht gesehen werden.
Die Regierung ist übergriffig geworden. Je lauter sie Demokratie schreit, desto totalitärer wird sie.
Durch fehlende Kontrolle des Souveräns sind charakterlich und fachlich ungeeignete Personen in die Politik gelangt, deren ständige Überforderung dazu führt, dass sich deren Entscheidungen immer weiter von der Lebensrealität des Souveräns entfernen.
Bislang haben rund 25% des Souveräns diese Schieflage erkannt und wollen einer Opposition, die so stark geworden ist, weil die Alt-Parteien über Jahre Fehler an Fehler aneinandergereiht haben, die Gelegenheit geben, diese Fehler zu beheben und auszugleichen. Offen bleibt die Frage, ob sie dazu wirklich in der Lage sind, oder ob die Gefahr besteht, dass sie von einem möglicherweise grundsätzlich kranken System vereinnahmt werden.
Da es seitens der Alt-Parteien keine Einsicht gibt, dass sie in der Regierung nicht mehr den Willen des Souveräns vertreten, derzeit auch besonders gut zu sehen an dem Friedenswillen des Souveräns im Vergleich zur Kriegstreiberei der Regierung, bleibt nur, der Opposition zumindest die Chance zu geben, es besser zu machen und den Willen des Souveräns umzusetzen. Gelänge das nicht, ist die Demokratie, wie wir sie bislang verstanden haben, gescheitert.
Eine daraus resultierende Staatsform stünde dem Freiheitsgedanken diametral gegenüber.
Die Verteidigung von Unseredemokratie seitens der Regierung entlarvt das eigentliche, was damit gemeint ist, nämlich die Erhaltung der eigenen Macht, verbunden mit allen Vorzügen und Privilegien. Sie richtet sich gegen das eigene Volk, das mit einer ganz normal funktionierenden Demokratie schon sehr zufrieden wäre. Unseredemokratie ist nicht unsere Demokratie!
In Anlehnung an die berühmt gewordene Lüge Walter Ulbrichs: „Niemand hat die Absicht eine Mauer zu errichten“, hat derzeit niemand die Absicht, die sogenannte Brandmauer einzureißen, bzw. sie so lange stehen zu lassen, wie es eben geht, um die herrschenden Machtverhältnisse so lange wie möglich aufrechtzuerhalten. Die Geschichte hat jedoch zum Glück gezeigt, dass selbst eine Berliner Mauer nicht ewig hält.
Wie sich aus dem absurd-lächerlichen Gutachten, einer der Regierung gegenüber weisungsgebundenen Behörde herausgestellt hat, gibt es keinerlei Anzeichen dafür, dass die Opposition die demokratische Grundordnung weder gefährden noch beseitigen will.
Da die ehemaligen Volksparteien augenscheinlich nicht in der Lage sind, politische, wirtschaftliche und gesellschaftliche Verhältnisse zum Wohle des Deutschen Volkes herzustellen, ist der demokratische Weg, die Opposition hierzu zu ermächtigen.
Wird das weiterhin verhindert, wird der Unmut des Souveräns weiter zunehmen, und spätestens, wenn die zunehmenden Schikanen die Schmerzgrenze überschritten haben, wird der Souverän nach geeigneten Mitteln und Möglichkeiten suchen, diese Schieflage zu beheben und auszugleichen.
Derzeit stehen sich ein in der Zahl und im Befinden zunehmend unzufrieden werdender Souverän und eine immer absurdere Entscheidungen treffende Regierung im lebendigen Tauziehen um Interessen gegenüber. Je mehr Bockmist die Alt-Parteien bauen, um so stärker wird die Opposition.
Aufgrund der jetzt schon vorhandenen Anzahl wacher Bürger und der Anzahl der in der Politik Unfähigen, ist eigentlich schon jetzt klar, wer in diesem Tauziehen die größere Kraft hat und wer das „Spiel“ nach demokratischen Regeln am Ende gewinnen wird. Das ist eindeutig der Souverän. Verliert er, wider Erwarten, verliert auch die Demokratie.
Dem Souverän fehlt nur noch ein wenig mehr Selbstvertrauen und ein Bewusstsein für die Macht, über die er tatsächlich verfügt.
Je mehr absurde Entscheidungen seitens der Regierung getroffen werden, und man arbeitet ja sehr fleißig daran, besonders, wenn es um Frieden geht, desto stärker wird das Selbstbewusstsein des Souveräns werden und ein natürlicher, friedlicher Ausgleich der Schieflage kann stattfinden. Der Start der neuen Regierung war jedenfalls schon einmal sehr "Keine-4-Jahre".
Wer sich in die steile und eisglatte Abfahrtspiste Deutschlands vertiefen will, hier eine Rezension zu dem Buch „Im Taumel des Niedergangs“ von dem von mir sehr geschätzten und akribisch arbeitenden Uwe Froschauer:
https://www.manova.news/artikel/abwarts
oder
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ 91bea5cd:1df4451c
2025-05-20 12:16:57
@ 91bea5cd:1df4451c
2025-05-20 12:16:57Contexto e início
O precursor direto do avivamento foi William J. Seymour, um pregador afro-americano filho de ex-escravos, influenciado pelos ensinamentos de Charles Parham, que pregava o "batismo no Espírito Santo" com evidência do falar em línguas.
Em 1906, Seymour foi convidado para pregar em uma igreja em Los Angeles. Após ser rejeitado por alguns por sua pregação sobre o batismo com o Espírito Santo, ele começou a liderar reuniões de oração na casa da família Asberry. Em abril de 1906, durante uma dessas reuniões, os participantes começaram a experimentar manifestações intensas do Espírito Santo, incluindo glossolalia (falar em línguas), curas e profecias.
A Rua Azusa
Logo, o número de participantes cresceu tanto que foi necessário mudar para um antigo prédio da Igreja Metodista Africana Episcopal, no número 312 da Rua Azusa, no centro de Los Angeles. Esse local se tornou o epicentro do avivamento.
Características marcantes
Cultos espontâneos e fervorosos, muitas vezes sem ordem pré-definida.
Diversidade étnica e social: negros, brancos, latinos, asiáticos, ricos e pobres adoravam juntos — algo radical para os padrões da época.
Ênfase nas manifestações espirituais, como línguas, curas, visões e profecias.
Igualdade de gênero e raça no ministério, com mulheres e homens de diversas origens pregando e liderando.
Impacto
O avivamento da Rua Azusa marcou o nascimento e expansão global do pentecostalismo, hoje uma das maiores forças do cristianismo mundial. Missionários saíram de Azusa para várias partes do mundo, levando a mensagem pentecostal. Movimentos como as Assembleias de Deus e Igreja do Evangelho Quadrangular têm raízes nesse avivamento.
Tensão e Interpretação entre Reformistas e Pentecostalistas
Evangelhos e Atos
João Batista profetiza: “Ele vos batizará com o Espírito Santo e com fogo” (Mateus 3:11).
Em Atos 2, no Pentecostes, os discípulos falam em línguas e recebem poder (Atos 1:8; 2:4).
Outros episódios: Atos 10 (Casa de Cornélio) e Atos 19 (Éfeso).
Cartas Paulinas
Paulo não relaciona diretamente o “batismo com o Espírito” ao falar em línguas. Em 1 Coríntios 12:13 ele diz: “Pois em um só Espírito todos nós fomos batizados em um corpo”.
A glossolalia aparece como um dom entre outros, mas não como evidência obrigatória (1 Coríntios 12:30).
Tensão
Pentecostais veem o batismo com o Espírito como uma segunda experiência após a conversão, evidenciada por línguas. Reformados geralmente interpretam que o batismo com o Espírito ocorre na conversão e que línguas não são obrigatórias ou cessaram com os apóstolos.
Reformadores e o Batismo com o Espírito Santo
Martinho Lutero, João Calvino e outros reformadores não falavam em línguas nem davam ênfase a experiências carismáticas.
Cessacionismo: Doutrina comum entre reformados que diz que os dons sobrenaturais (línguas, profecias, curas) cessaram com a era apostólica.
Continuação (posição pentecostal): Os dons continuam hoje.
Filmes / Documentários
“Azusa Street: The Origins of Pentecostalism” (2006) – Documentário com imagens históricas e entrevistas.
“Wesley” (2009) – Biografia de John Wesley, precursor do metodismo e influência indireta no pentecostalismo.
“The Cross and the Switchblade” (1970) – História de David Wilkerson e a conversão de Nicky Cruz; enfatiza a obra do Espírito.
Série “God in America” (PBS) – Episódio sobre o pentecostalismo (não só Azusa, mas seu impacto cultural).
-
 @ b099870e:f3ba8f5d
2025-05-20 11:14:41
@ b099870e:f3ba8f5d
2025-05-20 11:14:41The fools in life want things fast and easy – money, success, attention. Boredom is their great enemy and fear. Whatever they manage to get slips through their hands as fast as it comes in. You, on the other hand, want to outlast your rivals. You are building the foundation for something that can continue to expand. To make this happen, you will have to serve an apprenticeship. You must learn early on to endure the hours of practice and drudgery, knowing that in the end all of that time will translate into a higher pleasure – mastery of a craft and of yourself. Your goal is to reach the ultimate skill level – an intuitive feel for what must come next.
Quote from The 50th Law that I'm currently reading
-
 @ e4950c93:1b99eccd
2025-05-20 11:06:09
@ e4950c93:1b99eccd
2025-05-20 11:06:09Contenu à venir.
-
 @ a5142938:0ef19da3
2025-05-20 11:05:20
@ a5142938:0ef19da3
2025-05-20 11:05:20Content coming soon.
-
 @ 56f27915:5fee3024
2025-05-20 11:02:41
@ 56f27915:5fee3024
2025-05-20 11:02:41Buchbeschreibung:\ \ Dieses Buch ist ein Appell.
Es richtet sich nicht nur an den Kopf des Lesers, sondern auch an seinen Willen.\ \ Es ist ein Appell an Volk und Leser, die Lenkung der Geschicke direkt selbst in die Hand zu nehmen. Nicht nur: "Was ist?" sondern vor allem: "Was können wir tun?" ist in diesem Buch die große Frage.\ \ Mit dem Blick auf diese Frage wird das Grundgesetz betrachtet und gezeigt, dass es absolut noch nicht der gediegene Glockenguss ist, als der es uns von "oben" immer vorgestellt wurde, sondern dass in ihm auch extrem gegenläufige, bemessen an seinen freiheitlich-demokratischen Idealen sogar als extrem verfassungs-widrig zu bezeichnende Tendenzen wirken, die heute in seine Zerstörung führen.\ \ Vor allem die unselige Übermacht des Parteienwesens und die damit verbundene systemische Entmündigung des Souveräns, des Volkes, ist das Ergebnis dieser verfassungs-widrigen Tendenzen.\ \ Es wird aber auch gezeigt, wo in den Idealen des Grundgesetzes und in den Entscheidungen der Mütter und Väter dieses Grundgesetzes die Ansatzpunkte liegen, durch die der Zerstörung des Grundgesetzes wirkungsvoll begegnet werden kann. Und diese Ansatzpunkte werden im Buch allseits zur Entfaltung gebracht.\ \ "Wer die Demokratie verteidigen will, der muss sie weiter entwickeln." Im Sinne dieses Wortes wird dem Leser ein praktikabler Weg gewiesen, auf dem er unmittelbar helfen kann, das Grundgesetz den wirkenden Zerstörungskräften zu entwinden, durch Einrichtung der direkten Bürgerbeteiligung an den entscheidenden Fragen unserer Republik die Position des Souveräns gegenüber der Parteienmacht zu stärken, Freiheitsrechte, Demokratie und Rechtsstaat auf eine wesentlich höhere Stufe als bisher zu bringen und sich durch eine verfassungs-klärende Versammlung seine Basis selbst und neu zu geben.
Buch bestellen: https://great-reset-von-unten.de/
\ Und nicht vergessen, abzustimmen! Die Zeit ist reif. Packen wir's an.\
-
 @ cae03c48:2a7d6671
2025-05-20 11:00:00
@ cae03c48:2a7d6671
2025-05-20 11:00:00Bitcoin Magazine

Ben Allen Receives Maelstrom Bitcoin Developer Grant to Advance Payjoin TechBen Allen has been named the third recipient of the Maelstrom Bitcoin Developer Grant, the family office of Arthur Hayes announced in a recent press release sent to Bitcoin Magazine. Over the next year, Allen will focus on enhancing the Payjoin Dev Kit project, a privacy-focused Bitcoin transaction tool designed to improve user anonymity and network scalability.
Payjoin, first introduced in 2019 by Nicolas Dorier in BIP 78, allows both the sender and receiver to contribute inputs to a single Bitcoin transaction. This disrupts common assumptions used by financial surveillance firms, namely the idea that multiple transaction inputs must come from a single entity. By breaking this assumption, even limited adoption of Payjoin can bolster privacy across the Bitcoin network.
“Maelstrom would like to congratulate Ben Allen on this grant,” said Arthur Hayes, Chief Investment Officer of Maelstrom. “The great thing about Payjoin, is that if only a small amount of adoption is achieved, it breaks a key assumption used by financial surveillance companies. The assumption they have is that if a Bitcoin transaction has multiple inputs, all the inputs must all belong to the same entity. Therefore, Payjoin adoption improves the privacy of even the people who don’t use it. We are excited to support Ben Allen’s work on open-source tools and software to increase Payjoin adoption.”
Allen, who will be working alongside Dan Gould, aims to expand the implementation of Payjoin so it can be integrated into more Bitcoin wallets. He acknowledged the technical complexities of the project—including the requirement for receivers to be online—but expressed optimism about overcoming these challenges.
“I’m deeply grateful to Arthur Hayes and Maelstrom for generously providing me with this grant to support my work on the Payjoin Dev Kit project,” said Allen. “With this funding, I can dedicate myself full-time to enhancing the Payjoin implementation, improving testing, and ensuring that the dev kit remains robust, well-documented, and maintainable for the future.”
Allen also emphasized the broader mission of his work: “Improving privacy for bitcoin is an area where continued improvement allows for a better experience by empowering users to control their financial data and foster greater peace of mind when using bitcoin day to day. This is an exciting opportunity to contribute to Bitcoin’s privacy and scalability, and I’m looking forward to continuing to collaborate with the community to make Payjoin more widely adopted.”
Maelstrom, which is focused on supporting digital asset infrastructure, is led by Arthur Hayes, co-founder of BitMEX. Through grants like this one, the firm is investing in the foundational tools that promote a more private, scalable, and decentralized Bitcoin ecosystem.
This post Ben Allen Receives Maelstrom Bitcoin Developer Grant to Advance Payjoin Tech first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ cae03c48:2a7d6671
2025-05-20 10:50:37
@ cae03c48:2a7d6671
2025-05-20 10:50:37Bitcoin Magazine
Proof of Reserves Should Be the Standard for Bitcoin Treasury Companies“The root problem with conventional currency is all the trust that’s required to make it work. The central bank must be trusted not to debase the currency, but the history of fiat currencies is full of breaches of that trust. Banks must be trusted to hold our money and transfer it electronically, but they lend it out in waves of credit bubbles with barely a fraction in reserve.”
— Satoshi Nakamoto (2009)
Bitcoin was created to eliminate the need for trusted intermediaries. It replaced opaque, permissioned systems with transparency, auditability, and decentralized verification. The ethos was clear from day one: don’t trust—verify.
And yet, many of the institutions now holding Bitcoin—custodians, exchanges, ETFs, even public companies—continue to rely on trust-based assumptions, the very problem Bitcoin was designed to solve.
For Bitcoin treasury companies, this contradiction is especially glaring. These are firms that claim to operate on a Bitcoin standard—yet without verifiable Proof of Reserves (PoR), there’s no way for shareholders to know whether the Bitcoin is actually there.
The Problem: Unproven Bitcoin Is Just Another IOU
Bitcoin is designed to be verifiable—but most corporate disclosures aren’t. When companies report BTC holdings without public wallet visibility or on-chain proof, investors are left to trust balance sheets, auditors, and custodians.
That opens the door to systemic risks:
- Rehypothecation: BTC pledged or lent behind the scenes
- Custodial failure: Centralized services operating without 1:1 backing
- “Paper Bitcoin”: Multiple claims on the same BTC, echoing legacy financial opacity
The mere presence of Bitcoin on a balance sheet is not a guarantee. Without verification, it’s no different than a fiat-denominated claim—an IOU dressed up in BTC terms.
What We Learned from Gold: The Paper Problem
Bitcoin is not the first hard asset to face this challenge. The gold market offers a cautionary tale.
For decades, gold investors have dealt with “paper gold” systems—unallocated accounts, synthetic ETFs, and derivatives with little or no linkage to actual metal. These claims often outnumber real reserves many times over, leading to widespread suspicion of price distortion and systemic misrepresentation.
Most gold investors don’t own gold—they own a claim to gold. And they have no way to prove it.
Bitcoin gives us the tools to break this cycle. But only if companies choose to use them.
Bitcoin Is Built for Proof—and Companies Should Use It
Unlike legacy assets, Bitcoin is designed to make proof of ownership and solvency a native function of the asset itself. Through public key cryptography, on-chain auditability, and permissionless transparency, Bitcoin enables real-time, trust-minimized verification.
This isn’t just a technical capability—it’s a governance feature. Bitcoin allows companies to demonstrate, cryptographically and without intermediaries, that their reserves exist, are intact, and are unencumbered. No bank statements. No opaque custodial claims. Just data, on-chain.
That’s a radical shift—and it’s one that Bitcoin treasury companies are uniquely positioned to take advantage of. In doing so, they can reduce audit complexity, strengthen shareholder communication, and align their internal capital practices with the trustless architecture of the asset they’re holding.
And it’s already happening. Metaplanet, Premiere Member of Bitcoin For Corporations, publicly discloses its BTC reserve addresses and transaction history. Anyone in the world—including shareholders, analysts, and regulators—can independently verify the existence and movement of their treasury. That’s not just compliance. That’s Bitcoin, applied. View the snapshot of Metaplanet’s proof of reserves dashboard below.

Public Companies Face the Greatest Responsibility
Public companies don’t operate in a vacuum. Their disclosures shape market perception, influence investor behavior, and—especially when Bitcoin is involved—serve as a proxy for the maturity of the asset class itself.
When a publicly traded company holds Bitcoin but offers no visibility into how that Bitcoin is held or verified, it exposes itself to multiple levels of risk: legal, reputational, operational, and strategic. It undermines trust at the very moment it claims to be embracing a trustless system.
More importantly, public companies send signals. Whether they like it or not, they become de facto representatives of the Bitcoin strategy they’ve adopted. Their behavior becomes part of the playbook for others considering similar moves.
That’s why the responsibility is higher. Transparency isn’t optional for companies who lead with Bitcoin. It’s a duty. And companies that choose opacity not only take on unnecessary risk—they weaken the credibility of the entire movement.e.
What Proof of Reserves Should Actually Include
For Proof of Reserves to have real integrity, it must go beyond vague references to “custody partners” or internal assurance statements. The key is verifiability—independent, data-driven, and actionable by any shareholder or auditor.
At a minimum, Bitcoin treasury companies should provide:
- Custody model clarity: Is the company using self-custody, shared multisig, or third-party solutions? Who controls the keys, and under what governance?
- On-chain transparency: Whether through view-only wallet addresses or cryptographic attestations (like Merkle tree proofs), companies must make it possible to verify balances against public disclosures.
- Encumbrance disclosure: Reserves that are pledged, lent out, or locked in yield strategies should be disclosed clearly, with timelines and risk parameters attached.
- Routine updates: Proof should be refreshed regularly—not once per year in an audit footnote, but as part of ongoing financial communication.
- Reconciliation framework: Companies should explain how on-chain data maps to reported BTC NAV in filings or investor materials.
For boards and CFOs, this doesn’t need to introduce operational risk. Tools already exist—xpub view-only wallets, custody APIs, third-party validators—to provide assurance without compromising security. The obstacle isn’t capability. It’s willingness.
Setting the Industry Benchmark: Where Bitcoin Treasury Companies Must Lead
Bitcoin treasury companies are not just financial outliers—they are structural pioneers. Their decision to hold BTC signals not only a belief in long-term value, but a rejection of legacy capital inefficiency. That’s why they must also lead on standards of integrity.
By adopting PoR voluntarily and early, companies can position themselves as trustworthy, sophisticated, and future-ready. This will matter more as institutional capital rotates into Bitcoin, as index inclusion expands, and as regulators begin asking sharper questions about crypto asset disclosures on balance sheets.
PoR isn’t just a way to comply with future standards—it’s a way to shape them. The companies that lead now will not only avoid future scrutiny—they’ll attract capital from allocators who are seeking transparency but don’t yet know where to find it.
At BFC, we believe the market rewards clarity. Bitcoin treasury companies have a chance to bake transparency into their structure, not as an afterthought, but as a strategic differentiator.
Shareholders Must Demand It
Proof of Reserves isn’t just a company initiative—it’s a shareholder obligation. When a public company holds Bitcoin on its balance sheet, it is acting as a fiduciary for shareholder capital denominated in one of the hardest, most transparent assets in history. To accept opacity in that context is to forfeit the very advantage Bitcoin offers.
If you’re an investor in a Bitcoin treasury company and you can’t verify the Bitcoin, you don’t own a monetary reserve—you own a narrative. You’re trusting that someone else is telling the truth, rather than requiring the proof Bitcoin makes possible.
That’s not aligned with the principles of sound capital stewardship.
Institutional allocators, activist shareholders, and governance professionals have a growing role to play here. Just as proxy advisors and investor coalitions have pushed for climate disclosures, board transparency, and ESG clarity in the past decade, it’s time to apply that same rigor to Bitcoin disclosures—especially for companies who claim to operate on a Bitcoin standard.
Demand direct answers:
- Can we verify the holdings on-chain?
- Are reserves fully collateralized and unencumbered?
- Has manageme
-
 @ f18b1f8f:5f442454
2025-05-20 10:40:01
@ f18b1f8f:5f442454
2025-05-20 10:40:01Graphiti's MCP Server builds temporal knowledge graphs from interactions with MCP-compatible applications like Claude and Cursor. The system creates and maintains structured representations of conversations over time, enabling AI tools to access historical context through a standardized protocol.
Santiago's review: "This is next-level context management" - https://x.com/svpino/status/1924437664997998996
Available at: https://agentlist.com/agent/6fe099b024714254a038d4b977ae2a35
6fe099b024714254a038d4b977ae2a35 #AI #ContextRetention
-
 @ a19caaa8:88985eaf
2025-05-20 10:34:53
@ a19caaa8:88985eaf
2025-05-20 10:34:53-
拡張機能を使わない状態で使用した所感!
-
makimono:全部できる。nip21にも対応してる。kind10002にデータが無いときは勝手にどっかに流される。kind5が流せない。nsec.appで署名できる。
-
flycat:新規作成できるけど、流すだけで読み取りはしないっぽい。上書き(置き換え)はできるけど、編集はできない。すぐnos.lolに流そうとしてくる。kind5が流せない。他クライアント(lumilumiなど)から流したkind5は自動で反映されず、flycat内「設定」の「重複イベントの削除」をやれば反映される。nip21非対応。秘密鍵でログインできる。
-
habla:秘密鍵ログインできない、nsec.appもなんか入れない(読み込みから進まない)。公開鍵ログインからの表示確認用。nip21には対応してる。
-
yakihonnne:秘密鍵ログインできる。編集ができない(読み込みから進まない)。nip21は試してない。まだ全然見れてない。
-
ほか:
| クライアント | 編集 | 秘密鍵ログイン | nip21対応 | kind5流せるか | その他 | | -------------- | -------------------- | ------- | ------- | --------- | ------------------------------------------- | | makimono | 新規作成、編集可 | 不可 | 対応 | 流せない | kind10002にデータが無いときは自動で他に流される、nsec.appで署名可能 | | flycat | 新規作成、上書き(置き換え)可 | 可 | 非対応 | 流せない | 送信先要確認、他クライアントから流したkind5は重複イベント削除で反映 | | habla | 未確認 | 不可 | 対応 | 未確認 | nsec.app読み込み不可、公開鍵ログインのみ、表示確認用? | | yakihonnne | 編集不可(読み込みで止まる) | 可 | 未確認 | 未確認 | もっとちゃんと確認したい |
-
-
 @ 10870fc2:f5c8cdcd
2025-05-20 10:34:29
@ 10870fc2:f5c8cdcd
2025-05-20 10:34:29Graphiti's MCP Server builds temporal knowledge graphs from interactions with MCP-compatible applications like Claude and Cursor. The system creates and maintains structured representations of conversations over time, enabling AI tools to access historical context through a standardized protocol.
Santiago's review: "This is next-level context management" - https://x.com/svpino/status/1924437664997998996
Available at: https://agentlist.com/agent/6fe099b024714254a038d4b977ae2a35
6fe099b024714254a038d4b977ae2a35 #AI #ContextRetention
-
 @ a93d7cd3:ae5ce5dd
2025-05-20 10:16:55
@ a93d7cd3:ae5ce5dd
2025-05-20 10:16:55Test Nostr
-
 @ cd17b2d6:8cc53332
2025-05-20 10:15:09
@ cd17b2d6:8cc53332
2025-05-20 10:15:09🚀 Instantly Send Spendable Flash BTC, ETH, & USDT — Fully Blockchain-Verifiable!
Welcome to the cutting edge of crypto innovation: the ultimate tool for sending spendable Flash Bitcoin (BTC), Ethereum (ETH), and USDT transactions. Our advanced blockchain simulation technology employs 🔥 Race/Finney-style mechanisms, producing coins indistinguishable from authentic blockchain-confirmed tokens. Your transactions are instantly trackable and fully spendable for durations from 60 to 360 days!
🌐 Visit cryptoflashingtool.com for complete details.
🌟 Why Choose Our Crypto Flashing Service? Crypto Flashing is perfect for crypto enthusiasts, blockchain developers, ethical hackers, security professionals, and digital entrepreneurs looking for authenticity combined with unparalleled flexibility.
🎯 Our Crypto Flashing Features: ✅ Instant Blockchain Verification: Transactions appear completely authentic, complete with real blockchain confirmations, transaction IDs, and wallet addresses.
🔒 Maximum Security & Privacy: Fully compatible with VPNs, TOR, and proxy servers, ensuring absolute anonymity and protection.
🖥️ Easy-to-Use Software: Designed for Windows, our intuitive platform suits both beginners and experts, with detailed, step-by-step instructions provided.
📅 Customizable Flash Durations: Control your transaction lifespan precisely, from 60 to 360 days.
🔄 Universal Wallet Compatibility: Instantly flash BTC, ETH, and USDT tokens to SegWit, Legacy, or BCH32 wallets.
💱 Spendable on Top Exchanges: Flash coins seamlessly accepted on leading exchanges like Kraken and Huobi.
📊 Proven Track Record: ✅ Over 79 Billion flash transactions completed. ✅ 3000+ satisfied customers worldwide. ✅ 42 active blockchain nodes for fast, reliable transactions. 📌 Simple Step-by-Step Flashing Process: Step 1️⃣: Enter Transaction Details
Choose coin (BTC, ETH, USDT: TRC-20, ERC-20, BEP-20) Specify amount & flash duration Provide wallet address (validated automatically) Step 2️⃣: Complete Payment & Verification
Pay using the cryptocurrency you wish to flash Scan the QR code or paste the payment address Upload payment proof (transaction hash & screenshot) Step 3️⃣: Initiate Flash Transaction
Our technology simulates blockchain confirmations instantly Flash transaction appears authentic within seconds Step 4️⃣: Verify & Spend Immediately
Access your flashed crypto instantly Easily verify transactions via provided blockchain explorer links 🛡️ Why Our Technology is Trusted: 🔗 Race/Finney Attack Logic: Creates realistic blockchain headers. 🖥️ Private iNode Cluster: Guarantees fast synchronization and reliable transactions. ⏰ Live Timer System: Ensures fresh wallet addresses and transaction legitimacy. 🔍 Genuine Blockchain TX IDs: Authentic transaction IDs included with every flash ❓ Frequently Asked Questions: Is flashing secure? ✅ Yes, encrypted with full VPN/proxy support. Can I flash from multiple devices? ✅ Yes, up to 5 Windows PCs per license. Are chargebacks possible? ❌ No, flash transactions are irreversible. How long are flash coins spendable? ✅ From 60–360 days, based on your chosen plan. Verification after expiry? ❌ Transactions can’t be verified after the expiry. Support available? ✅ Yes, 24/7 support via Telegram & WhatsApp.
🔐 Transparent, Reliable & Highly Reviewed:
CryptoFlashingTool.com operates independently, providing unmatched transparency and reliability. Check out our glowing reviews on ScamAdvisor and leading crypto forums!
📲 Get in Touch Now: 📞 WhatsApp: +1 770 666 2531 ✈️ Telegram: @cryptoflashingtool
🎉 Ready to Start?
💰 Buy Flash Coins Now 🖥️ Get Your Flashing Software
Experience the smartest, safest, and most powerful crypto flashing solution on the market today!
CryptoFlashingTool.com — Flash Crypto Like a Pro.
Instantly Send Spendable Flash BTC, ETH, & USDT — Fully Blockchain-Verifiable!
Welcome to the cutting edge of crypto innovation: the ultimate tool for sending spendable Flash Bitcoin (BTC), Ethereum (ETH), and USDT transactions. Our advanced blockchain simulation technology employs
Race/Finney-style mechanisms, producing coins indistinguishable from authentic blockchain-confirmed tokens. Your transactions are instantly trackable and fully spendable for durations from 60 to 360 days!
Visit cryptoflashingtool.com for complete details.
Why Choose Our Crypto Flashing Service?
Crypto Flashing is perfect for crypto enthusiasts, blockchain developers, ethical hackers, security professionals, and digital entrepreneurs looking for authenticity combined with unparalleled flexibility.
Our Crypto Flashing Features:
Instant Blockchain Verification: Transactions appear completely authentic, complete with real blockchain confirmations, transaction IDs, and wallet addresses.
Maximum Security & Privacy: Fully compatible with VPNs, TOR, and proxy servers, ensuring absolute anonymity and protection.
Easy-to-Use Software: Designed for Windows, our intuitive platform suits both beginners and experts, with detailed, step-by-step instructions provided.
Customizable Flash Durations: Control your transaction lifespan precisely, from 60 to 360 days.
Universal Wallet Compatibility: Instantly flash BTC, ETH, and USDT tokens to SegWit, Legacy, or BCH32 wallets.
Spendable on Top Exchanges: Flash coins seamlessly accepted on leading exchanges like Kraken and Huobi.
Proven Track Record:
- Over 79 Billion flash transactions completed.
- 3000+ satisfied customers worldwide.
- 42 active blockchain nodes for fast, reliable transactions.
Simple Step-by-Step Flashing Process:
Step : Enter Transaction Details
- Choose coin (BTC, ETH, USDT: TRC-20, ERC-20, BEP-20)
- Specify amount & flash duration
- Provide wallet address (validated automatically)
Step : Complete Payment & Verification
- Pay using the cryptocurrency you wish to flash
- Scan the QR code or paste the payment address
- Upload payment proof (transaction hash & screenshot)
Step : Initiate Flash Transaction
- Our technology simulates blockchain confirmations instantly
- Flash transaction appears authentic within seconds
Step : Verify & Spend Immediately
- Access your flashed crypto instantly
- Easily verify transactions via provided blockchain explorer links
Why Our Technology is Trusted:
- Race/Finney Attack Logic: Creates realistic blockchain headers.
- Private iNode Cluster: Guarantees fast synchronization and reliable transactions.
- Live Timer System: Ensures fresh wallet addresses and transaction legitimacy.
- Genuine Blockchain TX IDs: Authentic transaction IDs included with every flash
Frequently Asked Questions:
- Is flashing secure?
Yes, encrypted with full VPN/proxy support. - Can I flash from multiple devices?
Yes, up to 5 Windows PCs per license. - Are chargebacks possible?
No, flash transactions are irreversible. - How long are flash coins spendable?
From 60–360 days, based on your chosen plan. - Verification after expiry?
Transactions can’t be verified after the expiry.
Support available?
Yes, 24/7 support via Telegram & WhatsApp.
Transparent, Reliable & Highly Reviewed:
CryptoFlashingTool.com operates independently, providing unmatched transparency and reliability. Check out our glowing reviews on ScamAdvisor and leading crypto forums!
Get in Touch Now:
WhatsApp: +1 770 666 2531
Telegram: @cryptoflashingtool
Ready to Start?
Experience the smartest, safest, and most powerful crypto flashing solution on the market today!
CryptoFlashingTool.com — Flash Crypto Like a Pro.
-
 @ dfc7c785:4c3c6174
2025-05-20 09:55:44
@ dfc7c785:4c3c6174
2025-05-20 09:55:44![[0B745064-2D34-4A3C-8393-AD033910E6D7.jpeg]]![[0C3FA837-E1BA-497F-8D44-9EC1CD723970.jpeg]]
-
 @ 8576ca0e:621f735e
2025-05-20 09:31:18
@ 8576ca0e:621f735e
2025-05-20 09:31:18The Bitcoin community is currently debating BIP 177, a proposal that seeks to redefine Bitcoin’s base unit from the satoshi (sat) to bitcoin itself. Proposed by Synonym CEO John Carvalho, this initiative aims to simplify Bitcoin’s usability, reduce cognitive barriers for newcomers, and align the currency’s representation with its integer-based protocol design. While the proposal has sparked enthusiasm among some supporters, it has also faced criticism for potentially eroding Bitcoin’s cultural heritage. Here’s a comprehensive breakdown of BIP 177 and its implications.
What Is BIP 177? BIP 177 is a non consensus proposal that reimagines how Bitcoin units are displayed and labeled. Key changes include: 1. Base Unit Redefinition: The smallest unit, currently called a satoshi (1 sat = 0.00000001 BTC), would be renamed to "bitcoin" (lowercase). Thus, 1 BTC would equal 100,000,000 bitcoins under the new system . 2. Integer Only Display: Transactions and balances would be shown in whole numbers (e.g., "10,000 bitcoins" instead of "0.0001 BTC") to eliminate decimal complexity . 3. Symbol Adoption: The "₿" symbol could represent the base unit, making values like ₿34,500,000 equivalent to 0.345 BTC . 4. Backward Compatibility: The BTC ticker and total supply (21 million BTC) remain unchanged. Users and applications can toggle between legacy and new formats .
Why BIP 177? The Case for Change 1. Reducing Cognitive Load Decimal heavy displays (e.g., 0.000023 BTC) are unintuitive, especially for new users. Integer values (e.g., 2,300 bitcoins) simplify mental calculations and reduce errors in transactions . As Carvalho argues, Bitcoin’s protocol inherently uses integers, and the decimal system is a "human imposed abstraction" .
-
Eliminating Unit Fear A Bitcoin priced at $100,000+ can deter newcomers who perceive it as unaffordable. By rebranding the base unit, 1 bitcoin would appear as a fraction of a cent (e.g., $0.00104 per bitcoin), making ownership of thousands of bitcoins feel more accessible . This shift could mitigate "price ceiling anxiety" and encourage broader adoption .
-
Aligning with Bitcoin’s Design Bitcoin’s ledger tracks discrete units, not fractions. BIP 177 emphasizes this by removing artificial decimal formatting, fostering a clearer understanding of Bitcoin’s scarcity and indivisible nature .
-
Mainstream Usability For everyday transactions like buying coffee integer displays (e.g., "1,830 bitcoins") are more practical than tiny decimals. This aligns with Bitcoin’s growing role in micropayments, as seen in El Salvador’s adoption of satoshis for daily use .
Criticisms and Concerns 1. Cultural Erosion The term "satoshi" honors Bitcoin’s pseudonymous creator, and its deprecation risks alienating long-time supporters. Critics argue that abandoning this term weakens Bitcoin’s cultural identity .
-
Confusion Risks Renaming the base unit "bitcoin" while retaining BTC could cause ambiguity. For example, saying "I own 1,000 bitcoins" might mislead newcomers into thinking they own 1,000 BTC . Translation challenges also arise, particularly in languages like Chinese where "比特币" (Bitcoin) would represent both BTC and the base unit .
-
Brand Perception Bitcoin’s high value per BTC is a marketing strength. Displaying prices as fractions of a cent might dilute its perceived prestige, potentially affecting investor sentiment .
-
Implementation Hurdles Wallets, exchanges, and merchants would need to update interfaces, APIs, and educational materials—a process estimated to take 2+ years .
Community Reactions: A Divided Ecosystem - Supporters: Proponents like Jack Dorsey argue that integer displays simplify Bitcoin for mass adoption. They compare the shift to historical advancements like replacing Roman numerals with Arabic numbers . - Opponents: Critics dismiss BIP 177 as "bikeshedding" focusing on trivial changes while ignoring larger issues like transaction fees. Some Reddit users warn, "Don’t split it, don’t change anything" .
Implementation Timeline 1. Phase 1 (3–6 months): Introduce dual displays and pilot testing in wallets like Bitkit . 2. Phase 2 (6–12 months): Mainstream platforms adopt integer displays by default. 3. Phase 3 (12+ months): Legacy decimal formats are phased out entirely .
Conclusion: Tradition vs Progress BIP 177 highlights Bitcoin’s evolving identity: Should it prioritize cultural heritage or usability for the next billion users? While the proposal doesn’t alter Bitcoin’s code or supply, its success hinges on community consensus. As Carvalho notes, "Bitcoin’s heart is immovable code. BIP 177 merely retires the decimal point" . Whether this change becomes a footnote or a revolution remains to be seen but it undeniably sparks a vital conversation about Bitcoin’s future.
-
-
 @ 90c656ff:9383fd4e
2025-05-20 09:06:27
@ 90c656ff:9383fd4e
2025-05-20 09:06:27Since its creation in 2008, Bitcoin has been seen as a direct challenge to the traditional banking system. Developed as a decentralized alternative to fiat money, Bitcoin offers a way to store and transfer value without relying on banks, governments, or other financial institutions. This characteristic has made it a symbol of resistance against a financial system that, over time, has been marked by crises, manipulation, and restrictions imposed on citizens.
The 2008 financial crisis and the birth of Bitcoin
Bitcoin emerged in response to the 2008 financial crisis—a collapse that exposed the flaws of the global banking system. Central banks printed massive amounts of money to bail out irresponsible financial institutions, while millions of people lost their homes, savings, and jobs. In this context, Bitcoin was created as an alternative financial system, where no central authority could manipulate the economy for its own benefit.
In the first block of the Bitcoin blockchain or timechain, Satoshi Nakamoto included the following message:
“The Times 03/Jan/2009 Chancellor on brink of second bailout for banks.”
This phrase, taken from a newspaper headline of the time, symbolizes Bitcoin’s intent to offer a financial system beyond the control of banks and governments.
- Key reasons why Bitcoin resists the banking system
01 - Decentralization: Unlike money issued by central banks, Bitcoin cannot be created or controlled by any single entity. The network of users validates transactions transparently and independently.
02 - Limited Supply: While central banks can print money without limit—causing inflation and currency devaluation—Bitcoin has a fixed supply of 21 million units, making it resistant to artificial depreciation.
03 - Censorship Resistance: Banks can freeze accounts and block transactions at any time. With Bitcoin, anyone can send and receive funds without needing permission from third parties.
04 - Self-Custody: Instead of entrusting funds to a bank, Bitcoin users can store their own coins without the risk of account freezes or bank failures.
- Conflict between banks and Bitcoin
01 - Media Attacks: Large financial institutions often label Bitcoin as risky, volatile, or useless, attempting to discourage its adoption.
02 - Regulation and Crackdowns: Some governments, influenced by the banking sector, have implemented restrictions on Bitcoin usage, making it harder to buy and sell.
03 - Creation of Centralized Alternatives: Many central banks are developing digital currencies (CBDCs) that maintain control over digital money but do not offer Bitcoin’s freedom and decentralization.
In summary, Bitcoin is not just a digital currency—it is a movement of resistance against a financial system that has repeatedly failed to protect ordinary citizens. By offering a decentralized, transparent, and censorship-resistant alternative, Bitcoin represents financial freedom and challenges the banking monopoly over money. As long as the traditional banking system continues to impose restrictions and control the flow of capital, Bitcoin will remain a symbol of independence and financial sovereignty.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 640f3844:d7b13a29
2025-05-20 08:52:49
@ 640f3844:d7b13a29
2025-05-20 08:52:49CrazyGames là một nền tảng giải trí số đang ngày càng khẳng định vị thế trong cộng đồng người dùng hiện đại nhờ vào khả năng cung cấp trải nghiệm linh hoạt, hấp dẫn và thân thiện. Với giao diện được thiết kế thông minh và trực quan, CrazyGames giúp người dùng dễ dàng tiếp cận và khám phá hàng loạt nội dung đa dạng chỉ trong vài thao tác. Dù sử dụng điện thoại, máy tính bảng hay máy tính để bàn, hệ thống luôn được tối ưu hóa để vận hành mượt mà, không gây gián đoạn hay ảnh hưởng đến trải nghiệm tổng thể. CrazyGames không chỉ đơn thuần là một nền tảng kỹ thuật số mà còn là nơi hội tụ của sáng tạo, công nghệ và niềm vui, nơi người dùng có thể tìm thấy sự giải tỏa sau những giờ làm việc căng thẳng hoặc học tập mệt mỏi. Nền tảng luôn chú trọng đến việc đổi mới giao diện, bổ sung các tính năng tiện ích nhằm mang lại giá trị sử dụng thực tế và phù hợp với xu hướng công nghệ đang thay đổi từng ngày.
Một trong những điểm nhấn nổi bật khiến CRAZYGAMES thu hút sự quan tâm rộng rãi chính là tính cá nhân hóa và khả năng kết nối cộng đồng vượt trội. Hệ thống sử dụng các thuật toán phân tích hành vi thông minh để đưa ra các đề xuất nội dung phù hợp với sở thích và nhu cầu riêng biệt của từng người dùng, từ đó nâng cao mức độ hài lòng và giữ chân người dùng lâu hơn. Không gian cộng đồng tích hợp trong nền tảng cũng tạo điều kiện cho các thành viên giao lưu, chia sẻ cảm nhận và trao đổi kinh nghiệm, giúp tăng sự gắn kết và hình thành một hệ sinh thái giải trí sôi động, đầy màu sắc. Hơn thế nữa, CrazyGames thường xuyên cập nhật nội dung mới, điều chỉnh theo phản hồi thực tế từ người dùng nhằm đảm bảo mọi người luôn cảm thấy được lắng nghe và phục vụ đúng với mong đợi. Việc áp dụng công nghệ mới, đặc biệt là trí tuệ nhân tạo và dữ liệu lớn, đã giúp CrazyGames trở thành một nền tảng tiên phong trong việc cá nhân hóa trải nghiệm người dùng ở cấp độ cao nhất.
CrazyGames cũng đặt yếu tố bảo mật và hỗ trợ kỹ thuật làm trọng tâm trong chiến lược phát triển lâu dài. Với hệ thống bảo mật nhiều lớp, kết hợp xác thực người dùng và mã hóa dữ liệu tiên tiến, người dùng có thể yên tâm khi trải nghiệm mà không phải lo lắng về quyền riêng tư hay nguy cơ rò rỉ thông tin cá nhân. Đồng thời, đội ngũ chăm sóc khách hàng của CrazyGames luôn sẵn sàng phản hồi nhanh chóng, giải quyết kịp thời các vướng mắc phát sinh và liên tục cập nhật các hướng dẫn sử dụng để người dùng tận dụng được mọi tính năng mà nền tảng mang lại. Ngoài ra, CrazyGames còn tổ chức nhiều chương trình tương tác hấp dẫn và hoạt động khuyến khích sáng tạo trong cộng đồng, giúp nâng cao trải nghiệm người dùng và biến mỗi lần truy cập trở thành một hành trình khám phá mới mẻ. Với tất cả những yếu tố đó, CrazyGames không chỉ là một nền tảng giải trí kỹ thuật số, mà còn là người bạn đồng hành lý tưởng trong hành trình kết nối công nghệ, sáng tạo và cảm xúc.
-
 @ 8576ca0e:621f735e
2025-05-20 08:46:45
@ 8576ca0e:621f735e
2025-05-20 08:46:45
Now that you’ve mastered the basics, it’s time to level up. Bitcoin isn’t just about buying and holding it’s about understanding the ecosystem, optimizing security, and leveraging its unique properties to build wealth. In this deep dive, we’ll explore advanced concepts every Bitcoin enthusiast needs to know.
-
Mastering Bitcoin Security: Beyond the Basics -Multisig Wallets: Require multiple private keys to authorize transactions (e.g., 2-of-3 signatures). Ideal for protecting large holdings. -Cold Storage Deep Dive: How to set up air gapped hardware wallets, metal seed backups, and geographic redundancy. -Privacy Best Practices: Using CoinJoin, Tor, and wallets like Wasabi or Samourai to enhance anonymity. -Pro Tip: Test recovery phrases before transferring large sums.
-
Bitcoin’s Economic Landscape: Scarcity, Halvings, and Market Cycles -The Halving Explained: How Bitcoin’s supply schedule (every 4 years) impacts price, miner behavior, and long term value. -Stock to Flow (S2F) Model: Why Bitcoin’s scarcity makes it a compelling store of value. -Market Psychology: Spotting bull/bear cycles, avoiding FOMO, and using dollar cost averaging (DCA) strategically.
-
Advanced Transaction Techniques -Layer 2 Solutions: Harnessing the Lightning Network for instant, low cost payments (and earning routing fees). -Replace by Fee (RBF): Speed up stuck transactions by increasing fees. -Taproot and Schnorr Signatures: How Bitcoin’s upgrades improve privacy and scalability.
-
Earning Passive Income with Bitcoin -Lending and Yield: Risks and rewards of platforms like Celsius (post-bankruptcy lessons) and decentralized alternatives. -Bitcoin Mining Pools: Can you still profit as a small miner? We break down the math. -Staking Alternatives: Wrapped Bitcoin (WBTC) in DeFi opportunities and risks.
-
Navigating Regulation and Taxes -Global Tax Compliance: Reporting crypto gains, airdrops, and forks (IRS, HMRC, etc.). -Self custody vs Regulation: How governments are approaching Bitcoin custody laws and privacy tools. -Bitcoin ETFs and Institutions: What BlackRock, Fidelity, and others mean for retail investors.
-
The Future of Bitcoin: What’s Next? -Bitcoin as a Reserve Asset: Nation states adopting BTC (El Salvador, Lugano). -Smart Contracts on Bitcoin: Exploring Rootstock (RSK) and Discreet Log Contracts (DLCs). -Quantum Computing Threats: Separating hype from reality.
Why Follow My Profile? -Weekly Deep Dives: From mining profitability calculators to privacy tool tutorials. -Market Analysis: Bullish catalysts, bearish risks, and how to stay ahead. -Community Q&A: Get your advance bitcion questions answered.
🔔 Follow my profile to unlock Bitcoin 103: Building Wealth in a Decentralized World. Coming soon!
-
-
 @ bd4ae3e6:1dfb81f5
2025-05-20 08:46:08
@ bd4ae3e6:1dfb81f5
2025-05-20 08:46:08 -
 @ bd4ae3e6:1dfb81f5
2025-05-20 08:46:06
@ bd4ae3e6:1dfb81f5
2025-05-20 08:46:06 -
 @ 5188521b:008eb518
2025-05-20 08:33:09
@ 5188521b:008eb518
2025-05-20 08:33:09This memo intends to brief the federated societies of the galaxy on the status of one specific emerging civilization that has increasingly been of interest to our members, and further, to recommend caution when traveling unannounced nearby their local planet.
External Memo #263 from the Emerging Civilizations Council (ECC)
As you are all aware, it is the intention of our federated societies to isolate any emerging civilization in order to allow them the freedom to evolve and innovate independent of any external knowledge or technology. The benefits of this are twofold. Firstly, if during their scientific exploration and development, they are able to reach our same conclusions about the fundamentals of the universe, then we receive additional independent confirmation of our existing knowledge base. Secondly, and of much greater interest, is that all of our most advanced zero-to-one technological innovations have originated from these isolated civilizations because they are permitted to solve problems without bias from more advanced societies.
In earlier times, some of our members practiced strategic infusions of knowledge into emerging civilizations that would be disguised as native discoveries in order to secretly accelerate their advancement. While this was effective in developing advanced and peaceful civilizations more quickly, it was observed that those societies rarely developed any meaningful new technologies. As we have since learned, once a bias is introduced into an emerging civilization, it is typically destined to only innovate around our existing knowledge base.
More dangerously, societies that become aware of more advanced galactic civilizations almost always become focused on extrasolar power projection. This is an extension of the local evolutionary pressures that led to their domination as the apex predator on their planet. Only after they access the virtually unlimited resources of the galaxy, and they have resolved their internal struggle over distribution of those resources, will they be granted full federation status and interspecies technology transfer can be permitted. Prior to this stage, technology transfer from advanced societies must be avoided, as it can destabilize their development and often leads to the destruction of our most precious galactic resource; independent, decentralized technological innovation.
The dominant intelligent species of the specific civilization that is the focus of this memo identify as “Humans” and collectively inhabit a planet they call “Earth.” The Humans of Earth have yet to discover any advanced technology that would be useful to our members at this time; however, based on a key recent milestone in their development, their status has been upgraded to that of “pre-federation,” making them the leading candidate for our next admission into the galactic federation. As such, it has been estimated that first contact with the Humans of Earth may be possible within the next 1-2 GmRs [1 Galactic micro-Rotation (GmR) equals approximately 200 Earth solar orbits and spans approximately 10 human generations].
Their recent promotion to pre-federation status is based on their discovery of inviolable absolute scarcity — a key event that was independently reached among all federation members and typically triggers exponential advancement within two to four local generations. As is the case on Earth, inviolable absolute scarcity is virtually always used to develop undiluted intraspecies communication of value (the so-called perfect money). This has shown to be critical for cooperation and advancement among planetary apex predators throughout our galaxy.
The Earth-based discovery centers around a simple massless ledger system that is secured by electric power projection and is rapidly being adopted among the Humans of Earth. As with most apex predators, human trust is extremely difficult to scale across their entire planetary population. However, the new Earth-based monetary system, which they have named “bitcoin,” is quickly gaining the trust of humans as it continues to prove its inviolability. As has been the case among all emerging civilizations since the formation of the ECC, scarcity alone, even absolute scarcity, has never been enough to trigger exponential technological growth. The source of absolute scarcity must also be inviolable, or it will never be sufficiently trusted among a population.
The new currency of Earth is in the process of proving its inviolability by surviving numerous attacks with no meaningful disruption. Notably, even those closest to its discovery attempted to violate the properties of Earth’s initial implementation of absolute scarcity but were unsuccessful. Today it continues to withstand external attacks by those who have the most to lose, as adoption of a true and fair economic communication threatens to expose the opposition’s less productive, less efficient ideas. This, of course, is the specific class that must be disintegrated in order to allow the Humans of Earth to innovate freely and unlock exponential advancement. This same scenario has played out in all of our ancient histories following the discovery of inviolable absolute scarcity.
Because bitcoin has only existed for approximately one half of one human generation, proofs of inviolability have only been apparent to those who are looking the closest into the implications of the new discovery. Unsurprisingly, the humans who are the most inadequately compensated by the previous monetary systems are the first to find the benefits of inviolable absolute scarcity.
The highly anticipated exponential advancement from the now pre-federation Humans of Earth has attracted the interest of many of our members. Note, that at this juncture, the galactic playbook permits members to approach a pre-federation civilization undetected in order to fairly attain small quantities of their local implementation of inviolable absolute scarcity. The purpose of this practice is to allow our members to obtain a compatible and trusted source of compensation to be used in exchange for the first valuable innovations of a pre-federation society in a way that avoids unnecessary exposure to our technology prior to its full federation status.
Fortunately, all members who have taken part in this practice have fairly participated in the securitization of the bitcoin network, contributing small amounts of energy to organize and record transactions onto its independent time-based ledger system called the “Timechain.” Fair participation is critical to establish trust upon first contact.
Further, our members have, thus far, successfully minimized their impact on the new monetary system of Earth. This is important to disguise our existence but will also help gain trust in the future as no member will be seen as having abused its privileged access to overwhelming amounts of energy and computational power. To that end, it is believed that none of our members have collected more than a single payment for their energy contributions; meaning that no member society has more than 50 out of the full supply of 21,000,000 bitcoin (this was originally the smallest attainable payment for this form of fair participation).
The ECC asks that you please continue exercising caution, keeping your contributions to the bitcoin network to an absolute minimum. As a reminder, even a single service payment (currently 6.25 out of the full supply of 21,000,000 bitcoin), will likely be sufficient compensation for any of their innovations following first contact. Once awarded full federation status, Humans of Earth will be permitted to act as a full trading partner and will be eligible for other means of value for value payment.
However, the purpose of this message is not simply to commend our members for following those aspects of the galactic playbook. All federated societies of the galaxy should also be aware that there have recently been an increasing number of atmospheric anomalies detected by the Humans of Earth. Many believe that these anomalies are primarily caused by the influx of near-earth TDEs following their upgrade to pre-federation status [Temporary Distortion Events (TDEs) are a byproduct of most means of galactic travel]. We are, therefore, requesting that all members voluntarily announce their travel coordinates to help ensure that any TDEs in the future are adequately dispersed in space-time to avoid detectable events on Earth.
Although it has been almost 50 GmRs since the last emerging civilization was upgraded to pre-federation status, it is imperative that we maintain the complete isolation of the Humans of Earth at this critical juncture. As stated, if the Humans of Earth begin to suspect the presence of an overwhelmingly advanced species, they are highly likely to skew their innovations towards violent technologies that could destabilize their society and disrupt their potential for future contributions.
Thank you for maintaining our core principles as we begin to prepare for the next member to be admitted into our peaceful, decentralized federation.
End wideband galactic transmission…
This story first appeared in Tales from the Timechain. Support our work and buy a copy here.
79% of the zaps from this story will be passed onto the author, Reed. 21 Futures requests 21% for operating costs.
@nostr:npub1xgyjasdztryl9sg6nfdm2wcj0j3qjs03sq7a0an32pg0lr5l6yaqxhgu7s is a Christian, father of three, husband, bitcoiner, mechanical engineer in the nuclear power industry, science nerd and is passionate about the pursuit of truth. Reed also organized the Western Mass Bitcoin Meetup and is active on bitcoin twitter (@FreedomMoney21) and Nostr (nostrplebs.com/s/reed)
-
 @ da0b9bc3:4e30a4a9
2025-05-20 07:11:51
@ da0b9bc3:4e30a4a9
2025-05-20 07:11:51Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
https://stacker.news/items/984377
-
 @ d64f3475:8e56b3bf
2025-05-20 07:06:29
@ d64f3475:8e56b3bf
2025-05-20 07:06:29Jo, blomster kommer i alle farger og fasonger. Her har du to eksempler:
-
 @ d64f3475:8e56b3bf
2025-05-20 07:06:27
@ d64f3475:8e56b3bf
2025-05-20 07:06:27Skjønner du? Bare tekst.
-
 @ d64f3475:8e56b3bf
2025-05-20 07:06:25
@ d64f3475:8e56b3bf
2025-05-20 07:06:25TEST TEST TEST Her kommer bildene:
-
 @ cefb08d1:f419beff
2025-05-20 06:59:00
@ cefb08d1:f419beff
2025-05-20 06:59:00https://stacker.news/items/984374
-
 @ 58537364:705b4b85
2025-05-20 06:47:23
@ 58537364:705b4b85
2025-05-20 06:47:23อิคิไก (Ikigai) แปลว่า ความหมายของการมีชีวิตอยู่ เหตุผลของการมีชีวิตอยู่ เราเกิดมาเพื่ออะไร ใช้ชีวิตอยู่ไปทำไม เมื่อการงานไม่ใช่สิ่งที่แปลกแยกจากชีวิต
คนญี่ปุ่นเชื่อว่าทุกคนมี ikigai ของตัวเอง ผู้ที่ค้นพบ ikigai จะเจอความหมายและคุณค่าของชีวิต ทำให้มีความสุขกว่า อารมณ์ดีกว่า และมีโลกที่น่าอยู่กว่าด้วย
ปัจจุบัน มีหนังสือเกี่ยวกับอิคิไกออกวางขายเป็นจำนวนมาก แต่เล่มที่คนญี่ปุ่นเป็นคนเขียนเล่มแรกนั้น คือ
- The Little Book of Ikigai : The secret Japanese way to live a happy and long life โดยอาจารย์เคน โมหงิ (แปลภาษาไทยโดย คุณวุฒิชัย กฤษณะประการกิจ)
ตามมาสัมผัสโลกของอิคิไกที่แท้จริงจากนักวิทยาศาสตร์วิจัยด้านสมองชาวญี่ปุ่นคนนี้ ผ่านบทสนทนาที่จะเปลี่ยนความคิดใหม่ที่ว่า 'อิคิไก' เริ่มต้นจากมองหาความสุขเล็กๆ น้อยๆ ในแบบของตัวเราเอง
อาจารย์เคน โมหงิว่า ปู่จิโร่ เชฟซูชิวัย 94 ปี ที่ยังยืนปั้นซูชิให้เราทานอยู่ในทุกวันนี้ เป็นแรงบันดาลใจให้อาจารย์เกิดไอเดียในการเขียนหนังสืออิคิไก
เชฟซูชิที่ ‘ไม่ได้’ เริ่มเลือกงานนี้เพราะความรักหรือความถนัด แต่กลับทุ่มเทปั้นซูชิทุกคำเพื่อให้ลูกค้ามีความสุข… นั่นคือต้นแบบของอิคิไก
น่าแปลกที่คนญี่ปุ่นไม่ค่อยใช้คำว่า ‘อิคิไก’ ในชีวิตประจำวันหรือบทสนทนาทั่วไปเท่าไหร่
เพราะมันเป็นสิ่งที่ปกติและเราทำกันตามธรรมชาติ ในโลกปัจจุบัน เรามักพูดกันว่าทำอย่างไรเราถึงจะประสบความสำเร็จ ทำอย่างไรจะได้เลื่อนตำแหน่ง หากอยากเป็น CEO จะเป็นได้อย่างไร แต่คนญี่ปุ่นมีความคิดว่าความสำเร็จไม่ใช่ทุกอย่างในชีวิต
ยกตัวอย่างเช่นมีคนญี่ปุ่นจำนวนมากที่จริงจังกับงานอดิเรก หรือมี โคดาวาริ* คนอื่นไม่สนหรอกว่างานอดิเรกของคนคนนั้นจะเป็นอะไร ตราบใดที่คนคนนั้นดูมีความสุขดีนั่นก็โอเคแล้ว มีคนจำนวนมากคลั่งไคล้รถไฟ มังงะ (หนังสือการ์ตูน) หรือแอนิเมะ (ภาพยนตร์การ์ตูน) คนเหล่านี้ไม่จำเป็นต้องมีชื่อเสียงหรือได้รับการยอมรับจากสังคม ตราบเท่าที่พวกเขามีความสุขในแบบของเขาเอง มันก็ดีแล้ว
- ความพิถีพิถันใส่ใจในบางเรื่องเป็นพิเศษ เช่น คนที่ชอบเครื่องเขียนมากๆ จะพิถีพิถันในการเลือกปากกา สมุด ดินสอที่ตนเองจะใช้ เพราะฉะนั้น คนที่มีโคดาวาริเหล่านี้จะศึกษาเครื่องเขียนจนถึงที่สุด วิเคราะห์ ทดลอง จนพบว่าเครื่องเขียนแบบใดที่ตนเองหลงใหลที่สุด
อิคิไกของแต่ละคนอาจแตกต่างกัน ต่างคนอาจมีค่านิยมที่ต่างกัน ซึ่งสะท้อนในรูปแบบชีวิตที่แตกต่างกันก็ได้
อิคิไกเป็นเรื่องของความหลากหลายนะ สังคมญี่ปุ่นพยายามผลักดันให้เด็กๆ ทุกคนตามหาอิคิไกของตนเอง เราจะไม่บอกว่า งานนี้เงินดี ทำสิ หรืองานนี้เงินน้อย อย่าไปทำเลย ถ้าคุณถามนักศึกษาว่า พวกเขาอยากทำงานอะไร พวกเขาคงไม่ตอบว่าเลือกทำที่บริษัทนี้เพราะเงินเป็นอันดับแรกหรอก
อิคิไกแตกต่างจากคำว่า ‘ความสำเร็จ’ คนญี่ปุ่นรู้ว่าชีวิตไม่ได้มีแค่เรื่องประสบความสำเร็จ อิคิไกสำคัญกับชีวิตมากกว่า คุณอาจจะประสบความสำเร็จ แต่คุณอาจไม่มีอิคิไก ในทางกลับกัน แม้คุณไม่ประสบความสำเร็จ คุณอาจจะมีอิคิไกก็ได้ ซึ่งชีวิตคุณอาจจะมีความสุขมากกว่า
อาจารย์เคน โมหงินิยามคำว่า ‘ความสำเร็จ’ คือสิ่งที่คุณจะได้รับการยอมรับจากคนในสังคมหรือบริบทสังคมนั้นๆ แต่อิคิไกมาจากหัวใจของคุณ มาจากความสุขส่วนตัวของคุณ คนอื่นอาจจะไม่ได้มองว่านั่นคือความสำเร็จ
อิคิไกเป็นสิ่งที่เฉพาะบุคคล เราสามารถมีความสุขในแบบของเราเอง เราไม่ตัดสินความสุขของคนอื่น และให้เขามีความสุขในแบบของเขาเอง…
สิ่งสำคัญของอิคิไกคือ คุณมีความสุขเล็กๆ น้อยๆ จากเรื่องที่ดูเหมือนเป็นเรื่องเล็กๆ น้อยๆ หรือเปล่า เช่น ตอนเด็กๆ ผมชอบศึกษาเกี่ยวกับผีเสื้อ เวลาผมไปวิ่งออกกำลังกายแล้วเห็นผีเสื้อสวยๆ ผมก็สัมผัสได้ถึงอิคิไก หรือบางทีอาจเกิดขึ้นตอนที่ผมรู้สึกตลกๆ ก็ได้ ผมเห็นเด็กผู้ชายคนหนึ่งบอกพ่อว่า “พ่อๆ ต้องทำอย่างนี้สิ” เวลาผมได้ยินบทสนทนาแบบนี้ ผมก็รู้สึกถึงอิคิไก
หากพวกเราอยากมีอิคิไกบ้าง เราควรเริ่มจากอะไรดี ? เริ่มจากการสัมผัสความสุขจากสิ่งเล็กๆ น้อยๆ ก่อน มันเริ่มทำได้ง่ายที่สุด ในสมองเรามีสารชื่อโดพามีน หากเราทำอะไรสำเร็จเล็กๆ น้อยๆ โดพามีนจะหลั่งออกมา วงจรนั้นจะช่วยทำให้คุณมีความสุข การมีความสุขกับสิ่งเล็กๆ เช่นนี้เป็นเรื่องสำคัญมาก สำหรับหลายคน แนวคิดเรื่องอิคิไกอาจเข้าใจยาก หรือยากสำหรับบางคนที่ชีวิตพวกเขากำลังอยู่ในช่วงยากลำบาก กำลังรู้สึกหมดหวัง ท้อแท้ หรือไม่ได้เคารพตนเอง เพราะฉะนั้น เริ่มจากความสุขเล็กๆ น้อยๆ ก่อนครับ
มันเหมือนการคิดบวกไหม ? อิคิไกเป็นส่วนหนึ่งนะ เวลาเราคิดถึงชีวิต หรือคิดหาวิธีการคิดบวก มันเป็นเรื่องที่ซับซ้อนมาก สำหรับบางคนคำว่า ‘คิดบวก’ อาจฟังดูกดดันสำหรับพวกเขา เพราะฉะนั้น เริ่มจากการมองเห็นความสุขจากสิ่งเล็กๆ น้อยๆ รอบตัว สิ่งเล็กมากๆ เช่นการได้ตื่นมาชงกาแฟดื่ม การได้วิ่งกลางสายฝน

Lesson from Ken Mogi 1. อิคิไก ไม่ใช่การแสวงหาความสำเร็จหรือความร่ำรวย แต่เป็นการรู้สึกหรือสัมผัสถึงความสุขในชีวิตของตนเอง จนทำให้เราเห็นความหมายของชีวิตเราในแบบของเรา 2. อิคิไกไม่ใช่สิ่งที่สังคมนิยามหรือโลกให้ความสำคัญ แต่ละคนมีอิคิไกที่แตกต่างกัน และมีความสุขกับชีวิตในแบบของตนเอง ที่เราเลือกเอง 3. เราไม่ควรตัดสินคนอื่นหรือบีบบังคับคนอื่น เช่น ลูก แฟน ให้ใช้ชีวิตในแบบที่เราคิดว่าใช่ แต่เราควรเคารพความหลากหลายนั้น 4. มองคนที่มีอิคิไกหรือกำลังสนุกกับสิ่งที่พวกเขารักด้วยรอยยิ้ม และคอยช่วยเหลือหากพวกเขาลำบาก 5. อิคิไกมีทั้งระดับใหญ่ ซึ่งเกี่ยวกับแนวทางชีวิตหรือคุณค่าของงาน และอิคิไกระดับเล็กคือการสัมผัสความสุขเล็กๆ น้อยๆ ที่พบเห็นได้ในชีวิตประจำวัน 6. อิคิไก เริ่มต้นจากมองหาความสุขเล็กๆ น้อยๆ ในวันนี้
ที่มา : จากคอลัมน์ Cloud of Thoughts บทสัมภาษณ์ของอ.เกตุวดี Marumura พาไปคุยกับอาจารย์เคน โมหงิ ผู้เขียนหนังสืออิคิไกเล่มแรก!
-
 @ 57d1a264:69f1fee1
2025-05-20 06:15:51
@ 57d1a264:69f1fee1
2025-05-20 06:15:51Deliberate (?) trade-offs we make for the sake of output speed.
... By sacrificing depth in my learning, I can produce substantially more work. I’m unsure if I’m at the correct balance between output quantity and depth of learning. This uncertainty is mainly fueled by a sense of urgency due to rapidly improving AI models. I don’t have time to learn everything deeply. I love learning, but given current trends, I want to maximize immediate output. I’m sacrificing some learning in classes for more time doing outside work. From a teacher’s perspective, this is obviously bad, but from my subjective standpoint, it’s unclear.
Finding the balance between learning and productivity. By trade, one cannot be productive in specific areas without first acquire the knowledge to define the processes needed to deliver. Designing the process often come on a try and fail dynamic that force us to learn from previous mistakes.
I found this little journal story fun but also little sad. Vincent's realization, one of us trading his learnings to be more productive, asking what is productivity without quality assurance?
Inevitably, parts of my brain will degenerate and fade away, so I need to consciously decide what I want to preserve or my entire brain will be gone. What skills am I NOT okay with offloading? What do I want to do myself?
Read Vincent's journal https://vvvincent.me/llms-are-making-me-dumber/
https://stacker.news/items/984361
-
 @ 57d1a264:69f1fee1
2025-05-20 06:02:26
@ 57d1a264:69f1fee1
2025-05-20 06:02:26Digital Psychology ↗Wall of impact website showcase a collection of success metrics and micro case studies to create a clear, impactful visual of your brand's achievements. It also displays a Wall of love with an abundance of testimonials in one place, letting the sheer volume highlight your brand's popularity and customer satisfaction.
And like these, many others collections like Testimonial mashup that combine multiple testimonials into a fast-paced, engaging reel that highlights key moments of impact in an attention-grabbing format.
Awards and certifications of websites highlighting third-party ratings and verification to signal trust and quality through industry-recognized achievements and standards.
View them all at https://socialproofexamples.com/
https://stacker.news/items/984357
-
 @ 9c9d2765:16f8c2c2
2025-05-20 05:45:33
@ 9c9d2765:16f8c2c2
2025-05-20 05:45:33CHAPTER TWENTY THREE Across town, the Ray estate was drenched in shame. The once-proud family was now the subject of ridicule, their downfall televised, published, and whispered in business circles. Helen stood before a cracked mirror in her bedroom, mascara smudged, lips trembling with fury. The headlines were merciless:
"Heir to JP Empire Humiliated by Ray Family Then Bought Them Out."
"President James: From Rejection to Royalty."
She had lost more than power. She had lost control.
Mark, seated in an armchair with a drink that had gone warm, stared at the wall, his eyes empty. He was a strategist, a manipulator but somehow, he had underestimated James.
"He's just one man…" Mark muttered.
"No," Helen corrected him coldly. "He's not just a man. He’s a symbol now. Of power… of justice… and worst of all, forgiveness."
Mark scoffed. "Forgiveness?"
"Yes," she snapped, spinning to face him. "Because he didn’t destroy us when he could. That makes him look grander than anything we can ever fabricate. He let the world ruin us instead."
There was a long pause.
Then Mark stood, eyes narrow. "We’ll find another way. We always do."
But the fire in his voice had dulled. The Ray family was crippled, their company reduced to a shadow of its former self. Their staff had dwindled, partners severed ties, and their name now stood for arrogance and downfall.
Meanwhile, James had begun the silent restoration of more than just a company he was rebuilding legacies.
Back at JP Enterprises, Rita stepped into James’s office, her presence warm and reassuring.
“You’ve been in here for hours,” she said softly. “Everything alright?”
James looked up, his eyes thoughtful. “Everything is fine. I’m just… reflecting.”
“About them?”
He nodded. “Helen, Mark, Tracy. I know they’re not done. People like them never accept defeat.”
Rita approached, placing a comforting hand on the desk. “Then be ready for their next move. But know that you’re not alone anymore. And you’re no longer the man they thought you were.”
A faint smile curved on his lips. “No. I’m the man they made me become.”
Outside the office, whispers of the upcoming restructuring had already begun. Rumors swirled about James planning to absorb Ray Enterprises entirely into JP Holdings. Some believed he would dismantle it brick by brick. Others hoped he would revive it, proving once again that mercy was strength.
But only James knew his next move.
And as the days passed, the city watched some in admiration, others in dread.
Nightfall settled over the city like velvet, embroidered with the glimmer of a thousand restless lights. From the penthouse office of JP Enterprises, James stood before the floor-to-ceiling windows, his silhouette framed against the horizon. The world below him pulsed with ambition and whispers. Yet his mind wasn’t on the skyline, but on the murky tide still gathering beneath it Mark, Helen, and the crumbling remnants of a fallen dynasty that refused to stay buried.
The public had embraced his rise like a storybook tale. From the ashes of mockery, betrayal, and scorn, he had risen dignified, strategic, and unyielding. News outlets now hailed him as a symbol of resilience, of leadership sharpened by adversity. But James knew that the brightest stars cast the darkest shadows.
Behind the glamour, war drums still beat.
He sat at his desk, opening a sealed file handed to him earlier by his private investigator. Inside were photographs, recordings, and written transcripts irrefutable proof of secret meetings between Helen, Mark, and a few disgruntled former board members of Ray Enterprises. They were not merely planning revenge, they were mobilizing.
A knock interrupted his thoughts. Rita stepped in, poised and composed.
“You asked me to bring the reports on the integration of Ray Enterprises’ satellite branches.”
“Thank you, Rita,” James said, his voice calm but laced with calculation. “Leave them here.”
She lingered. “There’s something else,” she said, her tone more hushed now. “The woman from the anniversary… she’s resurfaced.”
James looked up slowly. “Where?”
“She was seen outside a media house yesterday, trying to set up another exclusive. But word is she's trying to recant her confession. Claims she was ‘coerced’ into blaming Mark and Helen.”
James’s gaze narrowed. “They’re trying to rewrite the narrative.”
Rita nodded. “And if they succeed, they’ll portray you as the one who orchestrated the chaos.”
He exhaled quietly, rising from his seat. “Let them try. The truth is no longer their weapon, it's mine.”
Meanwhile, in a dimly lit lounge across town, Mark and Helen sat opposite a trembling young woman, the same one who once fell to her knees and confessed everything at the anniversary.
“You owe us,” Helen said through clenched teeth. “We gave you the money, we protected you… and you humiliated us in front of the entire city.”
“I was scared,” the woman stammered, eyes darting between them. “Everyone was watching. Mr. JP was furious. What was I supposed to do?”
Mark leaned in, his expression carved from ice. “Fix it.”
“Y-You mean go to the press?”
Helen smiled coldly. “No. We mean bury the damage. Make James look like the one pulling your strings. We’ll give you twice what we paid. You just have to make the world believe he bribed you.”
As the woman hesitated, fear swimming in her gaze, Helen added softly, “Or you disappear.”
The woman’s nod was reluctant, but it was enough.
-
 @ 6983717b:0ad20c03
2025-05-20 04:23:13
@ 6983717b:0ad20c03
2025-05-20 04:23:13Zignaly公司深度研究报告
1. 创始人背景及声誉
Zignaly于2018年由三位好友共同创立,分别是CEO Bartolome “Bart” R. Bordallo、CFO Abdul Rafay Gadit和CMO David Rodríguez Coronadobitdegree.org。\ Bart Bordallo 是一位拥有数据驱动思维的创业者和区块链倡导者,他曾在西班牙富士通担任系统管理员长达8年,并创办过多家创业项目(如Hadanet、Innova Medialead等)iq.wiki。2014年他联合创办营销数据分析工具Tractionboard,2017年出任Quickstart Ventures CEO,孵化推出Zignaly和社交媒体工具Jooiceriq.wiki。Bart以善于开拓创新技术闻名,在业内积累了丰富经验和人脉。
Abdul Rafay Gadit 拥有金融背景,毕业于巴基斯坦IBA商学院(2010年获银行与金融学士学位)iq.wiki。他曾在渣打银行任职(2010–2016),后加入家族科技企业并成为巴基斯坦知名科技公司Gaditek的合伙人iq.wiki。2016年起Rafay担任风投公司Disrupt的合伙人和投资主管,并担任多家初创企业顾问iq.wiki。他于2019年参与联合创立Zignaly并出任财务主管,被誉为连续创业者,在巴基斯坦科技圈享有声誉iq.wiki。他的家族及商业背景使他在行业内建立起良好信誉。
David Rodríguez 在B2C和B2B市场营销领域有多年创业和领导经验theorg.com。作为Zignaly联合创始人兼市场总监,他负责全球市场拓展。他曾创立过创业公司Artigoo等,在数字营销和增长策略方面有专长crustdata.com。David毕业于西班牙知名院校(具体背景未详),其在欧洲创业圈口碑良好。
综上,三位创始人结合了技术、金融和营销的互补背景:Bart拥有技术创业经验,Rafay具备金融投资专业和家族企业支持,David深谙市场运营。这样的多元背景为Zignaly奠定了坚实基础,创始团队在区块链社交投资领域拥有较高声誉iq.wikiiq.wiki。
 Zignaly团队在2023年Token2049峰会上(迪拜)与合作伙伴DWF Labs合影,展示了创始团队的行业影响力。
Zignaly团队在2023年Token2049峰会上(迪拜)与合作伙伴DWF Labs合影,展示了创始团队的行业影响力。2. 南非数字货币牌照情况
牌照概况:Zignaly已在南非获得加密资产服务提供商牌照,是全球首批持牌的加密社交投资平台之一coindesk.comglobenewswire.com。根据南非《金融咨询与中介服务法》(FAIS)的新规,Zignaly于2024年获授第二类(Category II)“自由裁量型金融服务提供商 (Discretionary FSP)”牌照coindesk.com。该类别相当于传统资管中的基金管理资格,允许Zignaly为用户提供资金托管和自主投资管理服务。
持牌实体与监管:Zignaly的南非牌照由其当地注册实体 Merritt Administrators (Pty) Ltd 名义持有coindesk.com。根据南非金融部门行为监管局(FSCA)登记信息,Merritt Administrators (Pty) Ltd已正式列入授权机构名单coindesk.com。该公司注册号为2013/189063/07,注册地址在南非豪登省约翰内斯堡Rosebank区Hood大道1号zignaly.com。颁发牌照的监管机构正是南非金融行业行为监管局(FSCA),负责加密资产服务提供商的审批和监管。FSCA自2023年6月起受理加密公司牌照申请,并计划至2024年4月共批准约60家企业coindesk.comcoindesk.com。Zignaly与Luno等成为首批获批者,体现出其合规运营能力。
牌照影响:获得南非Category II牌照使Zignaly成为“全球首家持牌社交投资平台”globenewswire.com。Zignaly团队表示为满足严格监管要求投入了6年时间准备,拿证后即可为用户提供自由裁量基金管理和托管服务globenewswire.com。这一里程碑显著增强了平台合法性和用户信心,用户基础随之增长,并为其开发新产品(如去中心化金融DeFi投资)打开大门globenewswire.com。该牌照处于G20国家中少有的先进数字资产监管框架下globenewswire.com。凭借FSCA授权,Zignaly建立了合规背书,有助于其在全球拓展业务并加强监管沟通coindesk.com。
为清晰起见,整理Zignaly相关牌照信息如下:
| 持牌地区 | 持牌实体及注册号 | 牌照类型 | 监管机构 | | -------- | ---------------------------------------------- | -------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | ----------------- | | 南非(2024) | Merritt Administrators Pty Ltd(2013/189063/07) | 加密资产服务提供商牌照:Category II 类金融服务提供商(自由裁量资管)coindesk.com | 南非金融部门行为监管局(FSCA) |
表:Zignaly在南非持有的加密资产相关牌照概览。
3. 南美业务布局及发展状况
主要市场及用户:Zignaly的产品在南美地区具有相当用户基础,覆盖大部分拉美国家市场criptonoticias.com。根据西班牙语媒体报道,Zignaly平台可在阿根廷、哥伦比亚、墨西哥、智利、秘鲁、玻利维亚、巴拿马、乌拉圭、巴拉圭、巴西、危地马拉、哥斯达黎加等主要拉美国家正常访问服务criptonoticias.com。这些国家拥有活跃的加密投资群体,是Zignaly重点拓展的区域。其中巴西是特别重要的市场,用户规模增长迅速。2023年Zignaly(也称“ZIGDAO”)宣布与巴西最大的加密社区之一Criptomaniacos达成战略合作zignaly.medium.com。Zignaly为该社区定制了专属版本(称为“Z-Prime”解决方案),上线后短期内吸引超过5,000名用户,管理资产超250万美元zignaly.medium.com。这一合作为Zignaly在巴西迅速聚拢人气,并计划借助Criptomaniacos超过50万的用户群实现爆发式增长(目标突破百万用户、资产管理规模翻倍)zignaly.medium.com。可见,巴西已成为Zignaly在南美的领军市场之一。
合作伙伴与在地化:Zignaly积极与南美本地加密社群和机构合作,采用共赢模式拓展业务版图。在巴西,通过与Criptomaniacos等头部社区领袖合作,Zignaly快速建立起信任背书和用户基础zignaly.medium.com。此外,Zignaly的去中心化部门ZIGChain亦关注拉美市场机会。2024年12月,ZIGChain与拉美新兴市场金融公链Kiichain签署合作备忘录,共同致力于为拉美真实资产代币化引入全球流动性medium.commedium.com。Kiichain专注于拉美实物资产上链(如房地产、基础设施),此次合作将使Kiichain发行的代币化资产通过ZIGChain生态触达全球投资者medium.commedium.com。这显示Zignaly不仅服务散户投资者,也寻求参与拉美更广阔的金融创新生态。
监管环境与动态:拉美各国对加密业务监管态度不一,Zignaly在该地区主要采取合规经营与规避高风险市场并举的策略。根据其用户协议,Zignaly目前不向部分国家提供服务,包括美国、萨尔瓦多、古巴、委内瑞拉等criptonoticias.com(其中萨尔瓦多虽将比特币定为法币,但Zignaly出于内部政策或风险考虑暂未进入)。这一列表暗示Zignaly在拉美选择了政治经济环境稳定、监管友好的国家运营。像巴西已于2024年初实施加密法案,要求数字资产服务商向中央银行注册。Zignaly与当地社区合作有助于理解并适应监管。不过截至目前,未见Zignaly在南美获得正式牌照的公开报道,运营主要依托其全球牌照(如南非FSCA)和合作伙伴资源。未来若南美国家(如巴西、阿根廷等)推行明确牌照制度,Zignaly可能考虑申请本地牌照或设立合资实体,以巩固合规基础。
总的来说,南美(广义上含拉美地区)已成为Zignaly用户增长和社区运营的要地。巴西是亮点市场,Zignaly通过深耕本地合作获得显著成果zignaly.medium.com。同时,平台在西语圈国家如阿根廷、哥伦比亚、墨西哥等亦有相当渗透率criptonoticias.com。凭借区域化策略和全球合规优势,Zignaly在南美正持续扩张其社交投资版图。
4. 在巴基斯坦的业务及关系
团队渊源: 巴基斯坦与Zignaly关系密切,主要体现在联合创始人Rafay Gadit的背景上。Rafay作为巴基斯坦本土培养的企业家,其家族企业和投资经历为Zignaly奠定了早期基础iq.wiki。他毕业后回国加入了自家科技业务(Gaditek集团)并活跃于本地创业投资圈iq.wiki。Rafay通过Paklaunch等巴基斯坦创业社区结识投资人,并将这些资源引入Zignaly的融资中linkedin.com。据其领英发文透露,Zignaly于2022年获得5000万美元融资时,Paklaunch平台曾帮助团队对接到了关键投资方linkedin.com。由此可见,巴基斯坦创业社区对Zignaly的早期成长有所助力。
本地业务和用户:由于巴基斯坦目前对加密货币交易所持不友好甚至禁止态度(央行曾建议全面禁止加密交易),Zignaly尚未在巴基斯坦开展官方业务或设立办事处。这一点从Zignaly未将巴基斯坦列入支持或排除名单中也可侧面印证(官方服务条款并未提及巴基斯坦,可能是默认不提供)criptonoticias.com。然而,巴基斯坦拥有庞大的散户投资群体,不排除部分用户通过VPN等方式访问Zignaly服务。据报道,Rafay本人积极倡导普惠金融理念,希望通过区块链技术解决金融包容性问题thefounderdaily.comthefounderdaily.com。他曾在访谈中提及,自己的背景让他意识到传统金融体系对普通人的局限,因此创立Zignaly旨在让全球各地的人(包括穆斯林国家民众)都能公平参与财富增值机会thefounderdaily.com。这包含了对巴基斯坦等发展中国家投资者的考虑。因此可以推测,虽然Zignaly未在巴基斯坦公开运营,但创始团队可能借助当地人脉在小范围内推广教育,加深对当地监管的了解。Rafay也有可能通过他的家族企业和人脉(如Gaditek和Paklaunch)向巴基斯坦用户传播Zignaly理念。总的来说,目前Zignaly在巴基斯坦没有官方合作伙伴或直接服务,与当地监管机构亦无公开互动记录。然而,凭借联合创始人的资源,Zignaly在巴基斯坦保持了一定的间接影响力和潜在用户关注度。
监管互动:巴基斯坦尚未建立明确的加密监管框架,大环境不利于Zignaly此类平台落地。本地监管层曾多次警告数字货币交易风险,并封锁过一些交易所的网站。Zignaly为了规避监管风险,选择暂不触碰这一市场也是明智之举。目前未见Zignaly与巴基斯坦国家银行(SBP)或证券监管机构直接沟通的报道。未来若巴基斯坦态度转变,比如引入沙盒监管,Zignaly或将凭借Rafay的关系寻求进入。但就当前而言,Zignaly与巴基斯坦的联系更多体现在人脉和愿景层面,而非实际业务开展。
5. 伊斯兰金融领域的参与程度
Zignaly高度重视伊斯兰金融合规和穆斯林市场的需求,近年积极将清真(Halal)投资原则纳入其产品体系。具体表现在:
-
推出清真合规投资板块:2025年初,Zignaly上线了一个专门的伊斯兰教法合规投资市场,聚焦代币化实物资产(RWA)的投资机会help.zignaly.comhelp.zignaly.com。该板块命名为“Zamanat”,于2025年迪拜ZIGChain峰会上发布,是构建在ZIGChain上的清真RWA投资平台hackernoon.com。Zamanat由专业的伊斯兰金融机构审核把关,每个上线项目均经过伊斯兰教金融专家团队审核,确保符合教法原则(禁止利息利巴和过度投机Gharar等)help.zignaly.com。这一市场专注于房地产、基础设施等真实资产的代币化,使穆斯林投资者能够在不违背信仰的前提下参与高潜力投资help.zignaly.comhackernoon.com。这体现出Zignaly对于道德金融和信仰价值的尊重,旨在吸引全球穆斯林投资群体。
-
专业认证与合作:Zignaly积极寻求知名伊斯兰金融顾问的背书。2025年4月在迪拜举办的ZIGChain峰会上,Zignaly宣布与国际顶尖的伊斯兰金融顾问公司Amanie Advisors建立战略合作chainwire.orgchainwire.org。Amanie Advisors为Zignaly生态中的项目提供教法合规认证。例如,去中心化收益聚合协议Nawa Finance在该峰会上获得了Amanie出具的正式沙里亚合规证书,成为全球首个清真合规的比特币DeFi收益协议chainwire.org。Amanie首席执行官Maya Marissa Malek表示,期待与Zignaly及其合作项目一同推进包容性和合乎道德的金融创新chainwire.org。此外,ZIGChain生态对清真项目的支持也吸引了众多伊斯兰金融领域创业者参与,如Nawa Finance在ZIGChain Summit上获得ZIGLabs、Disrupt等机构投资,加速清真DeFi生态发展chainwire.org。
-
穆斯林国家市场推广:Zignaly选择在迪拜举办大型峰会并发布伊斯兰金融相关产品,凸显对中东穆斯林市场的重视prnewswire.com。迪拜作为伊斯兰金融中心和区块链友好城市,吸引了众多穆斯林投资者与开发者参加ZIGChain Summit(现场超过2000人,包括传统金融的私人银行家、财富管理团队等)hackernoon.com。会上伊斯兰金融主题成为焦点之一(设有“沙里亚、DeFi与普惠财富”专题讨论),探讨Web3如何为穆斯林投资者开拓新机遇hackernoon.com。除了中东,Zignaly对南亚和东南亚穆斯林市场也有所关注。例如印尼、马来西亚拥有大量穆斯林投资者且监管相对开放,Zignaly提供清真选项将有利于进入这些市场。Zignaly联合创始人Rafay来自穆斯林国家,对清真投资理念有亲身认同,他多次强调将道德与技术结合的重要性,以吸引过去因宗教原因观望的投资者群体chainwire.orgchainwire.org。
综上,Zignaly正深入伊斯兰金融领域:不仅在产品上推出符合教法的投资渠道help.zignaly.com,还引入权威机构认证提升可信度chainwire.org。通过在穆斯林聚居地区(如海湾国家)开展市场活动并强调道德投资理念,Zignaly努力成为穆斯林投资者可信赖的加密财富平台。这种战略有助于Zignaly在竞争中差异化,并为数万亿美元规模的全球伊斯兰金融市场服务hackernoon.com。
6. ZigChain项目概况
ZigChain是Zignaly于2024年推出的全新Layer-1区块链项目,旨在打造面向财富管理和去中心化投资的专用公链生态coindesk.com。其主要情况如下:
-
技术架构:ZigChain基于Cosmos SDK构建,是Cosmos网络上的一条独立区块链binance.com。采用Tendermint BFT共识,实现高吞吐和跨链互操作(可与Cosmos生态链通过IBC协议连接)。值得注意的是,ZigChain兼容EVM(以太虚拟机)binance.com。这意味着开发者可以方便地在ZigChain上部署Solidity智能合约,并与以太坊等生态交互。ZigChain内置了Zignaly团队开发的创新财富管理模块,使其区别于普通公链binance.com。该模块汲取了Zignaly平台的投资功能,将专业资管策略直接嵌入区块链底层,实现链上托管和收益分配等逻辑。ZigChain还支持账户抽象等用户体验改进,降低了使用私钥和管理链上资产的门槛binance.com。总体而言,从架构上ZigChain定位为一个专用的去中心化投资基础设施,兼顾了Cosmos的可扩展性和EVM的广泛兼容性。
-
市场定位:ZigChain被称为“财富生成基础设施”,目标是连接专业资管人与普通投资者,桥接传统理财与DeFi世界thefounderdaily.combinance.com。其愿景是在区块链上提供类似传统基金的体验:用户将资金委托给链上的财富经理(即经验丰富的交易员/基金经理),后者通过智能合约策略进行投资操作,用户持有其投资组合份额的代币化凭证hackernoon.com。这种模式让不懂技术或理财的小白用户也能“一键式”参与复杂的DeFi策略或真实资产投资binance.com。ZigChain希望解决其他资产链“有基础设施无需求”的痛点,通过Zignaly现有庞大用户社区提供初始流动性和投资需求binance.com。Zignaly已有60万+注册用户和5万+ ZIG持币用户,为ZigChain带来冷启动优势binance.com。因此,ZigChain定位于下一代财富管理公链,以满足传统高净值产品(如地产、私募基金)在区块链上的发行和投资需求hackernoon.com。它强调自身是解决“代币化房地产缺乏流动性”的方案,通过庞大投资者网络为代币化资产注入买盘需求binance.combinance.com。这一定位差异化了ZigChain,使其不仅是技术平台,更是带有现成用户和资金的流动性层。
-
生态系统组成:ZigChain生态由多个层次构成:
-
基础层:ZigChain区块链本身及其财富管理引擎(WME)。WME提供去中心化资产管理框架,让财富经理发行策略代币、自动复利和调仓等hackernoon.comhackernoon.com。
-
资产层:涵盖各种资产类别,如DeFi收益策略、Real World Assets (RWA)(房地产、票据等现实资产的代币)、游戏资产以及其他创新资产类型binance.com。ZigChain尤其重视RWA,上面提到的Zamanat清真市场即是RWA板块的重要组成hackernoon.com。另有合作伙伴如Kiichain一起丰富RWA品类medium.commedium.com。
-
参与者:由财富经理(专业交易员/机构)、投资者用户以及开发者三方组成。coindesk.comZigChain的独特之处在于引入“财富经理”这一层作为强用户,充当协议和散户之间的桥梁coindesk.com。开发者则可在ZigChain上开发各类dApp,如策略聚合器、数据分析工具等,扩展生态功能。
-
支持机构:ZigChain获得多方战略及资金支持。2024年宣布时即联合DWF Labs、Disrupt.com和UDHC Finance设立了1亿美元生态基金,用于激励开发者在ZigChain上创新iq.wiki。DWF Labs管理合伙人Andrei Grachev公开背书ZigChain模式,称这是前所未有的开发者、财富管理者和用户融合的新尝试iq.wiki。另外,Zignaly内部孵化器ZIGLabs也在投资生态项目,如参与投资了清真DeFi项目Nawa Financechainwire.orgchainwire.org。
-
社区治理:随着ZigChain的发展,Zignaly社区已于2023年转型为ZIGDAOiq.wiki。社区持有人将通过DAO机制参与ZigChain治理和决策。ZIG代币未来可能用于质押验证节点、提案投票等治理功能,从而将社区与链的发展紧密绑定。
-
代币信息:ZigChain的原生代币为ZIG币(ZIG)。ZIG最初于2021年作为ERC-20代币发行,用于赋能Zignaly平台bitdegree.org。ZIG总量约19.54亿枚,目前流通约14.09亿枚,市值在1.3亿美金上下,排名200名开外bitdegree.org。ZIG币在Zignaly/ZigChain生态中有多重用途:
-
平台功能:用户可用ZIG支付服务费用、获得交易手续费折扣和现金返还,以及购买保险NFT等iq.wikibitdegree.org。Zignaly提供了一种保险机制,允许用户用ZIG购买保单,对投资提供10%-100%不等的损失保障bitdegree.org。
-
治理权益:ZIG持有人作为ZIGDAO成员,可对平台升级和未来战略进行投票表决iq.wiki。持币还可提前体验新功能并参与项目空投。
-
奖励与忠诚度:ZIG用作生态激励,例如质押ZIG可获得额外收益,或兑换独家NFT资产等iq.wiki。2023年Zignaly推出AI驱动的新功能时,也曾对ZIG持有者发放独家NFT白名单作为奖励medium.com。
-
跨链和主网角色:随着ZigChain主网推进,ZIG将从ERC-20逐步映射成为ZigChain的主网币,用于支付链上Gas费用、质押节点、跨链桥流动性等。值得注意的是,CoinGecko显示Zignaly已将项目名称更改为“ZIGChain (ZIG)”twitter.com。这暗示ZIG币定位从平台币扩展为公链主网币。
项目进展:ZigChain已于2024年发布测试网并在Token2049等场合展示功能iq.wiki。2025年4月的迪拜峰会宣布主网将于6月上线,同时发布了Zamanat平台和$2500万AI生态基金等消息prnewswire.com(AI基金用于支持基于ZigChain的AI投资项目)。ZigChain Summit聚集了众多投资界人士,反响积极hackernoon.com。可以预期,ZigChain主网在2025年中推出后,将进入生态建设快车道。
总而言之,ZigChain具有清晰的技术架构和差异化定位,融合了传统资管理念与区块链优势。凭借Zignaly既有用户和资金基础,以及雄厚的生态资金支持,ZigChain有望打造出一个围绕财富管理的创新公链生态,在DeFi市场占据一席之地。
7. 币安最大Broker地位及角色分析
币安经纪商计划参与:Zignaly自早期便加入币安Broker(经纪商)计划(现称币安链接伙伴计划),充分利用币安交易所的流动性和基础设施来为其用户提供交易服务criptonoticias.com。作为Broker,Zignaly的用户通过Zignaly界面下单,但实际交易执行和资金托管由币安等交易所完成criptonoticias.com。这意味着用户资产安全由币安保障,并受其SAFU基金保护,且可享用币安深度和撮合引擎zignaly.com。Zignaly通过Broker API对接,实现与币安账户体系的联通,用户无需单独在币安开户即可交易,从而降低了门槛。
最大Broker的地位:截至目前,Zignaly已成为币安生态中规模最大的经纪合作伙伴之一。在币安官方内容和Zignaly资料中,多次提及Zignaly是“币安顶级Broker”,甚至是“最大的币安Broker合作伙伴”zignaly.combinance.com。据Zignaly官方透露,其平台拥有60万+用户,其中约$1.2亿美金的用户资产通过Broker连接到币安等交易所进行交易binance.com。这一AUM(管理资产规模)在币安Broker合作伙伴中名列前茅binance.com。币安方面也将Zignaly列为示范案例之一,认可其为大量散户提供了进入币安市场的渠道zignaly.com。值得注意的是,Zignaly不仅对接币安,还同时是Bybit等交易所的官方Broker合作伙伴medium.com。它支持的交易所包括币安、Bybit、KuCoin、BitMEX、AscendEX等,总计5-6家criptonoticias.commedium.com。在这些中币安交易量最大、用户使用最多criptonoticias.com。因此Zignaly在币安Broker体系内的交易量和用户数应是最高的,这奠定了其“最大Broker”的地位。
角色定位与收益模式:作为币安Broker,Zignaly扮演的是“导流+增值服务提供者”角色。一方面,Zignaly通过其社交投资平台吸引了众多原本不会直接使用交易所的新用户,将其导流至币安的交易深度中进行交易criptonoticias.comcriptonoticias.com。另一方面,Zignaly为用户提供了币安本身没有的复制交易、利润分成等独特功能,提升了用户黏性和交易频率criptonoticias.com。这种分工合作下,币安获得了交易量和用户基数,Zignaly则通过与币安分润交易手续费来实现收益。根据Broker计划,币安会将Zignaly用户交易手续费的一定比例返还给Zignaly作为佣金。此外,Zignaly自己的盈利模式还包括对盈利的跟单投资收取一定成功报酬(Profit Sharing模型)globenewswire.com。但其复制交易服务对用户零前期费用,只有盈利才按比例分成globenewswire.com。这需要有大量交易作为支撑,币安的高流动性恰好满足了这一点。可以说,Zignaly的Broker身份为其盈利模式提供了坚实基础。
交易量与数据:公开数据显示,Zignaly发展初期(2021年上半年)平台交易量已超过20亿美元,AUM约9000万美元reddit.com。如今用户数比当时增长数倍,AUM增至1.2亿以上binance.commedium.com。保守估计目前Zignaly月均交易额已达数十亿美元级别,成为币安不可忽视的流量来源。Zignaly也积极宣传这一成就,以增强投资者和用户信心。例如其Medium博客提到在一年内用户从2万增至50万+、资管规模从数百万增至过亿美元medium.com。币安官方新闻稿和Square动态也多次报道Zignaly的进展,将其列为Broker成功案例zignaly.com。
官方评价:币安和Zignaly官方均对这层合作予以正面评价。Zignaly网站称“币安将我们列为顶级Broker,提升了平台可信度”zignaly.com。币安Broker项目页面则强调,通过Binance Link计划,合作方可利用币安技术和安全体系扩展业务binance.com。对于Zignaly用户而言,与币安的深度合作带来了安全感(资产由全球最大交易所托管)和便利性(无需在多平台频繁转账)criptonoticias.com。这种双赢关系是币安经纪商模式的初衷。Zignaly联合创始人Rafay在领英上也表达了对币安合作的重视,称有幸与顶级伙伴(包括币安)合作使团队更有动力将Zignaly做成全球最大社交投资平台linkedin.com。
简言之,Zignaly确系币安最大的Broker之一。它以社交交易优势为币安带来可观用户和交易量,并借助币安基础设施增强自身服务能力criptonoticias.com。其Broker角色实为币安生态的“前端入口”和“功能延伸”,双方关系密切(见下节),官方场合也经常互相背书这一合作。对于“最大Broker”这一定位,Zignaly通过数据和币安的认可充分证明了自身的行业领先地位binance.com。
8. 在日本的潜在业务布局
当前业务状况:截至目前,没有公开资料显示Zignaly在日本开展了实际业务或设立法律实体。日本对加密交易及相关服务实行严格的牌照制度(需取得金融厅FSA颁发的加密资产交易业者牌照或投资顾问牌照),门槛较高。而Zignaly尚未出现在日本金融厅授权的交易平台名单中。据日媒报道,FSA近期甚至要求下架未注册的海外加密APP以限制日本用户使用境外服务binance.com。Zignaly并未进入日本主流市场,可能基于合规压力选择暂不触及日本用户。其官网的服务条款中常见的禁止地区列表里一般会包括美国和受制裁国家,但并未明确提及日本criptonoticias.com。然而,日本法律规定未注册业者不得向日本居民招揽业务,否则会收到警告。2022-2023年间FSA曾警告多家海外交易所非法向日本用户提供服务binance.com。Zignaly显然希望避免卷入此类合规风险。因此可以推测,Zignaly默示屏蔽了日本市场,至少在没有拿到牌照前不会积极招募日本用户。
潜在布局和计划:尽管目前缺席,日本市场对于Zignaly具有潜在吸引力:日本拥有成熟的零售交易群体和完善的法规环境,若能合规进入,将利于提升品牌可信度和用户质量。Zignaly可能已经在关注日本监管动态,评估进入时机。一种可能途径是在日本寻找本土合作伙伴,比如与持牌金融机构或大型证券公司合作推出受监管的社交交易服务。然而这需要克服文化和产品适配等挑战。另一种路径是等日本明确推出针对社交投资或复制交易的新规,再申请相应牌照。目前日本的金融商品取引法下没有直接针对复制跟单的平台分类,Zignaly若申请,可能需按照“投资顾问/代理业”或“第二种金融商品业务”来办理,流程复杂冗长。此外,从市场测试角度,Zignaly尚未针对日本语系进行本地化,包括网站、客服、社区运营都未见日语内容。这表明短期内他们不打算投入日本市场。
竞争与展望:日本市场已有Bitcopy等本地社交交易服务,以及eToro等平台的间接影响。如果Zignaly进军日本,将面对本土玩家和监管壁垒双重挑战。不过,Zignaly在合规方面已经有南非牌照背书,或许能增加日本监管部门的信任感。Zignaly过去也曾在高度监管环境下运营(如与美国投资者隔离服务),有一定经验。如果未来Zignaly决定进入日本,可能会:
-
成立日本子公司(如“Zignaly Japan KK”)并申请成为注册投资业者。
-
或与当地公司合资,利用后者牌照开展业务,以技术提供方身份出现。
-
同时针对日本用户开发日语界面、符合当地法规的风控措施(例如设置杠杆上限、用户适当性检查等)。
但在这些举措落地前,暂无迹象表明Zignaly已经在日本展开布局。目前可以确认的是,Zignaly未对日本市场进行任何官方宣传或业务拓展。考虑到日本监管渐趋严格,Zignaly短期策略可能是观望为主,把资源集中在东南亚、中东等增长更快且监管宽松的地区。等到条件成熟,再评估进入日本的可行性。总而言之,Zignaly在日本暂未有公开业务或合规进展,未来是否进入取决于监管环境和公司战略调整。
9. 与FTX团队及美系交易所的关系
与FTX团队的历史关系:目前无确凿信息显示Zignaly与已倒闭的FTX交易所或其团队存在直接合作或投资关系。在Zignaly历次融资中,已知主要资方为GEM数字投资基金(来自卢森堡,承诺投资5000万美元)coindesk.com、DWF Labs等,并未出现FTX旗下Alameda Research等的身影coindesk.com。Zignaly的代币ZIG也未曾在FTX交易所上线交易(主要流通于Binance、KuCoin、Kraken等交易所bitdegree.org)。此外,Zignaly创始团队背景与FTX团队并无交集:FTX团队核心在美国和香港,而Zignaly团队在西班牙、巴基斯坦等地。因此可以认定,Zignaly与FTX基本不存在直接联系。唯一可能的间接关联是:两者都曾参与Binance等行业活动,或有过行业交流。但未见任何合作公告或交叉投资记录。FTX于2022年11月爆雷后,Zignaly业务未受明显影响,也印证其未与FTX深度绑定。
与美国系交易所的关系:这里主要指Coinbase、(以及Deribit等衍生品平台)的关联程度:
-
Coinbase:Zignaly没有与Coinbase公布任何官方合作。Coinbase主要面向北美合规市场,而Zignaly由于合规原因不服务美国用户criptonoticias.com。因此Zignaly几乎不可能与Coinbase有用户导流或API对接合作。此外,Coinbase也没有类似币安Broker的外部经纪商计划。Zignaly亦未获得Coinbase Ventures的投资(其融资公告中无Coinbase身影)。因此Zignaly与Coinbase基本没有直接关联。唯一弱关联是ZIG代币曾在2021年申请过Coinbase资产评估名单,但未被上市。此外,Zignaly提供的策略主要在高杠杆币种,而Coinbase产品以现货为主,业务契合度不高。
-
Deribit:Deribit虽以美国团队创立,但注册在欧盟(荷兰)并面向全球提供加密期权和期货交易。Zignaly迄今未集成Deribit作为支持交易所。其支持的衍生品交易所包括BitMEX、Bybit等criptonoticias.com。可能由于Deribit主要提供期权,较为小众,而Zignaly专注于现货和永续合约的跟单交易。在投资或合作层面,也无迹象显示双方有往来。Deribit未出现在Zignaly合作伙伴名单中,Zignaly也未曾宣布支持Deribit的API接入。因此双方关联度很低。
-
其他美系交易所:如Kraken、Gemini等,Zignaly同样无直接合作。ZIG代币虽然在Kraken上线交易bitdegree.org,但这属于Kraken自主上市行为,不代表战略合作。Zignaly没有接入Kraken的交易API作为其平台的一部分,因为Kraken主要服务现货和少量期货,不符合Zignaly用户偏好。Gemini等更无交集。
总结来说,Zignaly与美国阵营的交易所联系甚微。这与Zignaly避开美国市场战略一致,也是对其主要合作伙伴币安的差异化选择。相较之下,Zignaly更倾向于与非美系平台合作(币安、Bybit、KuCoin等亚洲和欧洲平台),一方面规避美国监管风险,另一方面这些平台的产品(高杠杆合约等)更适合Zignaly的跟单盈利模式。对于FTX这样的美国背景公司,Zignaly并未牵涉其中,因而在FTX风波中毫发无损,继续推进自身业务。
10. 与币安的关系分析(“若即若离”)
Zignaly与币安的关系可以用“紧密合作却保持独立”来形容,表面上看似若即若离,实则是一种战略平衡:
合作深度:Zignaly是币安紧密的生态伙伴之一。从2019年起,Zignaly就与币安建立对接,推出针对币安交易的复制交易功能zignaly.com。币安的Broker/Link计划更使双方绑定,Zignaly大量交易在币安体系内完成criptonoticias.com。币安也认可Zignaly为顶级合作方,多次在官方渠道宣传其业绩zignaly.com。技术上,Zignaly深度集成币安API,用户通过Zignaly下单实为在币安撮合criptonoticias.com。安全上,Zignaly用户资产由币安托管,受到币安风控保护criptonoticias.com。可以说,币安为Zignaly提供了交易引擎、流动性、托管、安全等关键支持。如果没有币安,Zignaly无法轻易实现全球服务。因此合作层面,两者关系非常紧密,Zignaly对币安存在一定依赖。
独立性:尽管联系密切,Zignaly仍保持自身的独立运营和战略拓展:
-
多元交易所集成: Zignaly并非只依赖币安一家,它同时对接了多家交易所(Bybit、KuCoin等),以分散风险和覆盖更多市场medium.com。这表明Zignaly不将所有鸡蛋放在一个篮子里,在合作币安的同时也与币安的竞争对手合作。这种多元策略保证了如果币安出现政策变化,Zignaly仍有其他出路。
-
自主生态建设: Zignaly开发了ZIGChain公链和ZIG代币经济,打造自己的去中心化生态iq.wiki。这部分业务(如链上RWA投资、DAO治理等)是在币安体系之外开展的。尤其ZIGChain是一个独立网络,Zignaly藉此拥有了不依赖任何中心化交易所的新赛道。如果ZIGChain生态成功,Zignaly对币安的依赖度将降低,因为部分交易和资产管理可转移到链上进行。
-
资本与治理独立: Zignaly目前并未接受币安Labs或币安直接投资,其主要股东是第三方基金(如GEM)和创始团队。币安在Zignaly没有股权,这意味着Zignaly在公司治理上不受币安直接控制。双方是合作伙伴关系而非母子公司关系。这给了Zignaly在决策上更大自主空间,可以根据自身利益选择业务方向,而不必完全听命于币安。
-
品牌和社区: Zignaly经营着自己的品牌和用户社区(ZIGDAO),并未被币安品牌所吞没。用户普遍认识Zignaly作为独立平台,而非币安的子平台。这种品牌独立性也体现双方保持一定距离。Zignaly甚至在某些场合与币安竞争,例如它的利润分享模式理论上和币安的理财产品存在替代关系。但由于定位不同,币安默许了Zignaly的存在。
“若即若离”的表现:这种关系既有亲密合作的一面,也有保持距离的一面:
-
亲密体现在日常运营和战略协同上——币安为Zignaly赋能,Zignaly为币安导流,互惠互利binance.com。双方高层可能定期沟通,比如在行业会议或Broker大会上交流经验。币安也从Zignaly获取社交交易领域的数据和洞见。
-
保持距离体现在Zignaly不断拓展币安之外的新领域,比如支持币安竞争对手Bybit,发行自己代币并上其他交易所(Kraken等)bitdegree.org。币安则对Zignaly采取开放态度,但并未将其收购或纳入子公司体系。这可能是出于合规或资源考虑,也反映币安对这种松散合作模式的认可。
风险与依赖程度:尽管Zignaly努力独立,但对币安的依赖仍不可忽视。币安交易量占Zignaly大头,一旦币安遭遇风险(如监管打压、停业等),Zignaly业务将受冲击。不过Zignaly的多交易所策略和链上业务可部分缓解这种风险。此外,币安若改变Broker政策(例如降低佣金比例或收紧用户管控),也可能影响Zignaly收益。这种不确定性让Zignaly对币安既依赖又审慎,从而保持若即若离的姿态。
战略定位:对币安来说,Zignaly是拓展社交投资领域的战略伙伴,但不是唯一伙伴(币安还有其他Broker合作)。币安希望Zignaly成功又不会大到威胁自身。所以币安支持Zignaly但保持一定边界,不给予独占特权。对Zignaly而言,币安是基础设施提供者而非最终目的地。Zignaly借力币安成长,同时构筑自己的护城河(社区+公链)。这种伙伴关系类似“平台+应用”的生态纽带:币安提供平台,Zignaly作为应用丰富了平台场景。双方都从合作中获益,但也都为自己预留了退出和转圜的空间。
综上,Zignaly与币安的关系紧密合作却又保持独立,被用户形容为“若即若离”实属恰当。它们既相互依存,又各自发展:Zignaly深度依赖币安的交易生态来服务其50万+用户medium.com,同时通过多元化策略降低对单一平台的束缚。币安则愿意共享部分资源给Zignaly,但不直接将其收编,以保持生态开放性和灵活性。这种微妙平衡使得双方在快速变化的加密行业中都能进退自如。正如一份币安Square分析所称:“Zignaly连接全球50万用户和150多位资管人,币安与Bybit皆将其视为顶级Broker伙伴”binance.com。这种定位体现了Zignaly在头部交易所眼中的价值,也解释了双方若即若离、松耦合但高协同的关系本质。
参考资料:
-
Zignaly创始团队及公司简介bitdegree.orgiq.wiki
-
Zignaly获得南非FSCA二类牌照的报道coindesk.comglobenewswire.com
-
Zignaly在拉美市场(巴西)合作的官方披露zignaly.medium.com
-
Zignaly伊斯兰金融合规及Zamanat平台介绍help.zignaly.comhackernoon.com
-
ZigChain发布和技术架构详情coindesk.combinance.com
-
Zignaly为币安最大Broker的官方说法binance.commedium.com
-
关于Zignaly在日本暂无业务的推断criptonoticias.combinance.com
-
Zignaly与FTX无关联及与美系交易所关系分析bitdegree.orgreddit.com
-
币安与Zignaly合作关系的综述criptonoticias.comzignaly.com
-
-
 @ 04ce30c2:59ea576a
2025-05-20 04:19:25
@ 04ce30c2:59ea576a
2025-05-20 04:19:25Em uma sociedade verdadeiramente livre, o indivíduo tem o direito de escolher como guardar e transferir valor. Isso inclui a liberdade de escolher qual moeda usar, sem coerção, monopólios ou imposições estatais. A concorrência entre moedas permite que as melhores propriedades monetárias prevaleçam de forma natural e voluntária.
Moeda imposta é controle
Quando uma única moeda é forçada por lei, seja por decreto estatal ou por exigências institucionais, o usuário perde a soberania sobre seu próprio patrimônio. Isso abre espaço para inflação arbitrária, bloqueios de transações, congelamento de fundos e vigilância massiva.
Concorrência monetária é essencial
A liberdade monetária implica a coexistência de várias moedas competindo entre si. Cada uma traz suas características e vantagens específicas. A escolha deve estar nas mãos do usuário, não em autoridades centralizadas.
A melhor moeda tende a se tornar o padrão
No longo prazo, a moeda com melhores propriedades monetárias, como previsibilidade, descentralização, auditabilidade e liquidez, tende a ser adotada como padrão de referência para precificação, poupança e comércio global.
O Bitcoin é a moeda mais forte nesse sentido. Mas isso não impede que outras moedas coexistam como ferramentas complementares em contextos específicos.
Conversão é liberdade
Se o usuário quiser por exemplo mais privacidade ao comprar um café ou pagar uma conta, ele pode facilmente trocar seus bitcoins por monero e usá-los conforme sua necessidade. A possibilidade de trocar entre moedas é parte essencial da liberdade financeira.
Uma sociedade livre permite a escolha. O padrão monetário deve emergir do consenso do mercado, não de imposições. Que o Bitcoin se torne o padrão não por decreto, mas por mérito. E que outras moedas existam para servir à liberdade individual em toda sua complexidade.
-
 @ 7953d1fa:69c8039d
2025-05-20 02:39:56
@ 7953d1fa:69c8039d
2025-05-20 02:39:56No mundo digital em constante evolução, plataformas de entretenimento online vêm ganhando espaço entre os brasileiros que buscam diversão, emoção e recompensas. Uma das opções que tem se destacado recentemente é a KK999, uma plataforma moderna, segura e repleta de oportunidades para jogadores de todos os níveis. Com uma ampla gama de jogos envolventes e uma experiência de usuário otimizada, o KK999 está conquistando cada vez mais adeptos no Brasil.
Introdução à Plataforma KK999 O KK999 se diferencia por oferecer uma experiência completa e intuitiva desde o primeiro acesso. A interface da plataforma foi cuidadosamente projetada para ser amigável, permitindo que novos usuários se cadastrem rapidamente e naveguem com facilidade. Tudo é pensado para garantir que o jogador tenha uma experiência fluida, sem complicações e com total transparência.
Além disso, o kk999se destaca por sua forte infraestrutura de segurança. Utilizando tecnologia de criptografia de ponta, os dados dos usuários são protegidos em todas as transações, garantindo tranquilidade para quem deseja apenas se divertir. Outro ponto importante é o suporte ao cliente, que está disponível 24 horas por dia, com atendimento em português, pronto para auxiliar com qualquer dúvida ou necessidade.
Variedade de Jogos para Todos os Gostos Um dos grandes atrativos do KK999 é a impressionante variedade de jogos disponíveis. Desde os tradicionais jogos de cartas até opções modernas com gráficos avançados, a plataforma atende todos os estilos de jogadores. Entre os destaques, estão as famosas roletas virtuais, jogos de pesca interativa, slot machines com temas variados e jogos ao vivo que simulam a sensação de estar em uma sala de jogos física.
Os slots, por exemplo, são um sucesso entre os brasileiros, oferecendo desde títulos clássicos com frutas e números até aventuras temáticas com bônus emocionantes. Os jogos de cartas também têm grande popularidade, incluindo versões modernas de pôquer, bacará e outros jogos estratégicos que desafiam a mente do jogador.
Para quem gosta de competir em tempo real, o KK999 oferece jogos ao vivo com crupiês reais e interatividade instantânea, proporcionando uma experiência imersiva e cheia de adrenalina. Tudo isso com transmissões de alta qualidade e conexão estável.
Experiência do Jogador: Diversão e Confiabilidade A experiência do jogador é uma das maiores prioridades do KK999. Desde o primeiro cadastro até as jogadas mais avançadas, a plataforma investe em funcionalidades que aumentam o conforto e a confiança do usuário. A navegação é rápida, os jogos carregam com eficiência e as recompensas são distribuídas com agilidade.
Outro fator que atrai muitos jogadores é o sistema de bônus e promoções. O KK999 frequentemente disponibiliza ofertas especiais para novos membros e prêmios para usuários frequentes, incentivando a fidelidade e aumentando ainda mais as chances de ganhar.
Além disso, o KK999 oferece uma experiência totalmente otimizada para dispositivos móveis. Seja no celular ou tablet, o jogador pode acessar todos os recursos da plataforma de qualquer lugar, a qualquer momento, sem perder desempenho ou qualidade.
Conclusão O KK999 se consolida como uma das principais plataformas de entretenimento digital no Brasil, reunindo inovação, segurança e uma variedade impressionante de jogos. Ideal tanto para iniciantes quanto para jogadores experientes, o site oferece tudo o que é necessário para transformar momentos comuns em experiências emocionantes.
-
 @ 7953d1fa:69c8039d
2025-05-20 02:39:23
@ 7953d1fa:69c8039d
2025-05-20 02:39:23O cenário do entretenimento online no Brasil vem evoluindo rapidamente, e uma das plataformas que mais se destaca atualmente é a 8CC. Com uma proposta moderna, intuitiva e voltada para a melhor experiência do usuário, a 8CC conquistou a confiança de milhares de jogadores que buscam diversão, praticidade e oportunidades de ganhos reais em um ambiente seguro.
Conhecendo a Plataforma 8CC A 8CC é uma plataforma digital desenvolvida para atender tanto iniciantes quanto jogadores experientes. Sua interface amigável e bem organizada facilita a navegação mesmo para quem nunca teve contato com esse tipo de entretenimento antes. Compatível com computadores, tablets e celulares, o site é totalmente responsivo, o que significa que você pode se divertir de qualquer lugar, a qualquer hora.
Um dos diferenciais da 8cc é o seu compromisso com a segurança dos usuários. A plataforma utiliza tecnologia de criptografia de ponta para garantir a proteção de dados pessoais e transações financeiras. Além disso, o suporte ao cliente está sempre disponível para tirar dúvidas, resolver problemas e oferecer o melhor atendimento possível.
Diversidade de Jogos para Todos os Gostos Na 8CC, os jogadores têm acesso a uma vasta seleção de jogos online, desenvolvidos pelos principais provedores do mercado internacional. Isso garante alta qualidade gráfica, mecânicas inovadoras e excelente desempenho.
Entre os jogos mais populares da plataforma estão:
Slots (caça-níqueis): com temas variados, rodadas bônus e jackpots progressivos que proporcionam grandes emoções.
Jogos de mesa clássicos: como roleta, blackjack e bacará, com versões que imitam perfeitamente a experiência de jogo ao vivo.
Jogos com crupiês em tempo real: transmitidos com qualidade HD, esses jogos trazem interatividade e realismo, permitindo que o jogador se sinta dentro de um ambiente físico de alto padrão.
A plataforma também disponibiliza jogos de habilidade e apostas esportivas ao vivo, oferecendo uma experiência ainda mais completa e personalizada de acordo com o perfil de cada usuário.
Experiência do Jogador na 8CC Quem já experimentou jogar na 8CC sabe o quanto a plataforma valoriza o conforto e a satisfação de seus usuários. Desde o momento do cadastro até o resgate de ganhos, tudo é feito de forma simples, rápida e segura. O processo de registro é intuitivo, exigindo apenas alguns dados básicos, e os métodos de pagamento são variados, aceitando transferências bancárias, carteiras digitais e até criptomoedas.
Outro destaque é o sistema de recompensas e promoções. A 8CC frequentemente oferece bônus de boas-vindas, rodadas grátis e campanhas especiais para usuários fiéis, o que aumenta ainda mais as chances de ganhar e prolonga a diversão. Além disso, a plataforma promove torneios e desafios semanais com prêmios atrativos, incentivando a competição saudável entre os jogadores.
Por Que Escolher a 8CC? Existem muitas razões para escolher a 8CC como sua principal plataforma de jogos online:
Confiabilidade e segurança em todas as operações;
Variedade de jogos para todos os perfis;
Interface moderna e de fácil navegação;
Promoções e bônus frequentes;
Atendimento ao cliente eficiente e disponível 24 horas.
Se você busca uma experiência diferenciada, com diversão garantida e a possibilidade de transformar seu tempo livre em momentos empolgantes, a 8CC é a escolha certa. Descubra agora mesmo tudo o que essa plataforma inovadora tem a oferecer e junte-se à comunidade que está revolucionando o entretenimento digital no Brasil.
-
 @ 472f440f:5669301e
2025-05-20 02:00:54
@ 472f440f:5669301e
2025-05-20 02:00:54Marty's Bent
https://www.youtube.com/watch?v=p0Sj1sG05VQ
Here's a great presentation from our good friend nostr:nprofile1qyx8wumn8ghj7cnjvghxjmcpp4mhxue69uhkummn9ekx7mqqyz2hj3zg2g3pqwxuhg69zgjhke4pcmjmmdpnndnefqndgqjt8exwj6ee8v7 , President of The Nakamoto Institute titled Hodl for Good. He gave it earlier this year at the BitBlockBoom Conference, and I think it's something everyone reading this should take 25 minutes to watch. Especially if you find yourself wondering whether or not it's a good idea to spend bitcoin at any given point in time. Michael gives an incredible Austrian Economics 101 lesson on the importance of lowering one's time preference and fully understanding the importance of hodling bitcoin. For the uninitiated, it may seem that the hodl meme is nothing more than a call to hoard bitcoins in hopes of getting rich eventually. However, as Michael points out, there's layers to the hodl meme and the good that hodling can bring individuals and the economy overall.
The first thing one needs to do to better understand the hodl meme is to completely flip the framing that is typically thrust on bitcoiners who encourage others to hodl. Instead of ceding that hodling is a greedy or selfish action, remind people that hodling, or better known as saving, is the foundation of capital formation, from which all productive and efficient economic activity stems. Number go up technology is great and it really matters. It matters because it enables anybody leveraging that technology to accumulate capital that can then be allocated toward productive endeavors that bring value to the individual who creates them and the individual who buys them.
When one internalizes this, it enables them to turn to personal praxis and focus on minimizing present consumption while thinking of ways to maximize long-term value creation. Live below your means, stack sats, and use the time that you're buying to think about things that you want in the future. By lowering your time preference and saving in a harder money you will have the luxury of demanding higher quality goods in the future. Another way of saying this is that you will be able to reshape production by voting with your sats. Initially when you hold them off the market by saving them - signaling that the market doesn't have goods worthy of your sats - and ultimately by redeploying them into the market when you find higher quality goods that meet the standards desire.
The first part of this equation is extremely important because it sends a signal to producers that they need to increase the quality of their work. As more and more individuals decide to use bitcoin as their savings technology, the signal gets stronger. And over many cycles we should begin to see low quality cheap goods exit the market in favor of higher quality goods that provide more value and lasts longer and, therefore, make it easier for an individual to depart with their hard-earned and hard-saved sats. This is only but one aspect that Michael tries to imbue throughout his presentation.
The other is the ability to buy yourself leisure time when you lower your time preference and save more than you spend. When your savings hit a critical tipping point that gives you the luxury to sit back and experience true leisure, which Michael explains is not idleness, but the contemplative space to study, create art, refine taste, and to find what "better goods" actually are. Those who can experience true leisure while reaping the benefits of saving in a hard asset that is increasing in purchasing power significantly over the long term are those who build truly great things. Things that outlast those who build them. Great art, great monuments, great institutions were all built by men who were afforded the time to experience leisure. Partly because they were leveraging hard money as their savings and the place they stored the profits reaped from their entrepreneurial endeavors.
If you squint and look into the future a couple of decades, it isn't hard to see a reality like this manifesting. As more people begin to save in Bitcoin, the forces of supply and demand will continue to come into play. There will only ever be 21 million bitcoin, there are around 8 billion people on this planet, and as more of those 8 billion individuals decide that bitcoin is the best savings vehicle, the price of bitcoin will rise.
When the price of bitcoin rises, it makes all other goods cheaper in bitcoin terms and, again, expands the entrepreneurial opportunity. The best part about this feedback loop is that even non-holders of bitcoin benefit through higher real wages and faster tech diffusion. The individuals and business owners who decide to hodl bitcoin will bring these benefits to the world whether you decide to use bitcoin or not.
This is why it is virtuous to hodl bitcoin. The potential for good things to manifest throughout the world increase when more individuals decide to hodl bitcoin. And as Michael very eloquently points out, this does not mean that people will not spend their bitcoin. It simply means that they have standards for the things that they will spend their bitcoin on. And those standards are higher than most who are fully engrossed in the high velocity trash economy have today.
In my opinion, one of those higher causes worthy of a sats donation is nostr:nprofile1qyfhwumn8ghj7enjv4jhyetvv9uju7re0gq3uamnwvaz7tmfdemxjmrvv9nk2tt0w468v6tvd3skwefwvdhk6qpqwzc9lz2f40azl98shkjewx3pywg5e5alwqxg09ew2mdyeey0c2rqcfecft . Consider donating so they can preserve and disseminate vital information about bitcoin and its foundations.
The Shell Game: How Health Narratives May Distract from Vaccine Risks
In our recent podcast, Dr. Jack Kruse presented a concerning theory about public health messaging. He argues that figures like Casey and Callie Means are promoting food and exercise narratives as a deliberate distraction from urgent vaccine issues. While no one disputes healthy eating matters, Dr. Kruse insists that focusing on "Froot Loops and Red Dye" diverts attention from what he sees as immediate dangers of mRNA vaccines, particularly for children.
"It's gonna take you 50 years to die from processed food. But the messenger jab can drop you like Damar Hamlin." - Dr Jack Kruse
Dr. Kruse emphasized that approximately 25,000 children per month are still receiving COVID vaccines despite concerns, with 3 million doses administered since Trump's election. This "shell game," as he describes it, allows vaccines to remain on childhood schedules while public attention fixates on less immediate health threats. As host, I believe this pattern deserves our heightened scrutiny given the potential stakes for our children's wellbeing.
Check out the full podcast here for more on Big Pharma's alleged bioweapons program, the "Time Bank Account" concept, and how Bitcoin principles apply to health sovereignty.
Headlines of the Day
Aussie Judge: Bitcoin is Money, Possibly CGT-Exempt - via X
JPMorgan to Let Clients Buy Bitcoin Without Direct Custody - via X
Get our new STACK SATS hat - via tftcmerch.io
Mubadala Acquires 384,239 sats | $408.50M Stake in BlackRock Bitcoin ETF - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code “TFTC20” during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed 158,469 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
I've been walking from my house around Town Lake in Austin in the mornings and taking calls on the walk. Big fan of a walking call.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ 98912a0b:c1f46ab6
2025-05-20 07:15:49
@ 98912a0b:c1f46ab6
2025-05-20 07:15:49Jo, blomster kommer i alle farger og fasonger. Her har du to eksempler:


-
 @ 98912a0b:c1f46ab6
2025-05-20 07:15:47
@ 98912a0b:c1f46ab6
2025-05-20 07:15:47Skjønner du? Bare tekst.
-
 @ 6e0ea5d6:0327f353
2025-05-20 01:35:20
@ 6e0ea5d6:0327f353
2025-05-20 01:35:20**Ascolta bene! ** A man's sentimental longing, though often disguised in noble language and imagination, is a sickness—not a virtue.
It begins as a slight inclination toward tenderness, cloaked in sweetness. Then it reveals itself as a masked addiction: a constant need to be seen by a woman, validated by her, and reciprocated—as if someone else's affection were the only anchor preventing the shipwreck of his emotions.
The man who understands the weight of leadership seeks no applause, no gratitude, not even romantic love. He knows that his role is not theatrical but structural. He is not measured by the emotion he evokes, but by the stability he ensures. Being a true man is not ornamental. He is not a decorative symbol in the family frame.
We live in an era where male roles have been distorted by an overindulgence in emotion. The man stopped guiding and began asking for direction. His firmness was exchanged for softness, his decisiveness for hesitation. Trying to please, many have given up authority. Trying to love, they’ve begun to bow. A man who begs for validation within his own home is not a leader—he is a guest. And when the patriarch has to ask for a seat at the table he should preside over and sustain, something has already been irreversibly inverted.
Unexamined longing turns into pleading. And all begging is the antechamber of humiliation. A man who never learned to cultivate dignified solitude will inevitably fall to his knees in desperation. And then, he yields. Yields to mediocre presence, to shallow affection, to constant disrespect. He smiles while he bleeds, praises the one who despises him, accepts crumbs and pretends it’s a banquet. All of it, cazzo... just to avoid the horror of being alone.
Davvero, amico mio, for the men who beg for romance, only the consolation of being remembered will remain—not with respect, but with pity and disgust.
The modern world feeds the fragile with illusions, but reality spits them out. Sentimental longing is now celebrated as sensitivity. But every man who nurtures it as an excuse will, sooner or later, pay for it with his dignity.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ fb3d3798:371f711a
2025-05-20 07:13:37
@ fb3d3798:371f711a
2025-05-20 07:13:37Jo, blomster kommer i alle farger og fasonger. Her har du to eksempler:


-
 @ 502ab02a:a2860397
2025-05-20 01:22:31
@ 502ab02a:a2860397
2025-05-20 01:22:31พอพูดถึงบริษัทอย่าง Formo ที่ทำชีสโดยไม่ใช้วัวเลย คนส่วนใหญ่จะนึกถึงคำว่า “นวัตกรรม” “ยั่งยืน” “ลดโลกร้อน” กันเป็นด่านแรก แต่พอเฮียมองทะลุม่านควันพวกนี้ไป จะเห็นทุนรายใหญ่ที่หนุนหลังอยู่ ซึ่งหลายเจ้าก็ไม่ใช่ผู้พิทักษ์โลก แต่เป็นผู้เล่นตัวจี๊ดในอุตสาหกรรมอาหารโลกมายาวนาน
หนึ่งในนั้นคือบริษัทจากเกาหลีใต้ชื่อ CJ CheilJedang ซึ่งอาจฟังดูไกลตัว แต่จริงๆ แล้ว เฮียว่าชื่อนี้โผล่ตามซองอาหารสำเร็จรูปในครัวคนไทยหลายบ้านโดยไม่รู้ตัว
ถ้าจะเข้าใจ Formo ให้ถึงแก่น เราต้องมองไปถึงทุนที่ “ใส่เงิน” และ “ใส่จุดยืน” ลงไปในบริษัทนั้น และหนึ่งในผู้ถือหุ้นรายสำคัญก็คือ CJ CheilJedang บริษัทเกาหลีใต้ที่ก่อตั้งมาตั้งแต่ปี 1953 โดยเริ่มจากการเป็นโรงงานผลิตน้ำตาล จากนั้นก็กินรวบแทบทุกวงจรอาหารของเกาหลี
โปรไฟล์ CJ แค่เห็นภาพรวมก็ขนลุกแล้วครับ ลูกพี่เราแข็งแกร่งขนาดไหน - เป็นเจ้าของแบรนด์ Bibigo ที่เราอาจจะคุ้นในสินค้า กิมจิ และ CJ Foods ที่มีขายทั่วโลก -เป็นผู้ผลิต กรดอะมิโน รายใหญ่ของโลก เช่น ไลซีน, ทรีโอนีน, ทริปโตแฟน ที่ใช้เป็นวัตถุดิบในอาหารสัตว์ แต่ตอนนี้หลายบริษัทเอาไปใส่ใน Plant-based food แล้วเคลมว่าเป็นโปรตีนสมบูรณ์ -เป็นเจ้าของโรงงานผลิต แบคทีเรียสายพันธุ์พิเศษ สำหรับการหมักหลายประเภท -ขึ้นชื่อเรื่อง bioscience โดยเฉพาะ precision fermentation ซึ่งเป็นเทคโนโลยีเดียวกับที่ Formo ใช้ผลิตเคซีน (โปรตีนในนมวัว)
แปลว่า CJ ไม่ได้มาลงทุนใน Formo แบบ “หวังผลกำไรเฉยๆ” แต่เขามองเห็น “อนาคตใหม่ของอาหาร” ที่ตัวเองจะเป็นเจ้าของต้นน้ำยันปลายน้ำ
คำถามก็คือเบื้องลึกการลงทุนใน Formo ใครได้อะไร? Formo ปิดรอบระดมทุน Series A ได้ประมาณ 50 ล้านดอลลาร์สหรัฐ เมื่อปี 2021 โดยมีนักลงทุนหลายเจ้า เช่น EQT Ventures, Elevat3 Capital, Atomico แต่ CJ CheilJedang ก็เป็นหนึ่งในผู้ลงทุนเชิงกลยุทธ์ (strategic investor) ที่เข้ามาแบบไม่ใช่แค่ลงเงิน แต่เอา เทคโนโลยี + เครือข่ายโรงงาน + ซัพพลายเชนระดับโลก มาเสริมให้ Formo ขยายได้เร็วขึ้น
การจับมือกันครั้งนี้มีนัยยะสำคัญครับ -Formo ได้ เทคโนโลยีหมักจุลินทรีย์ (ที่ CJ ถนัดมาก) และช่องทางกระจายสินค้าในเอเชีย -CJ ได้ ถือหุ้นในบริษัทที่กำลังจะเปลี่ยนภาพ “ผลิตภัณฑ์จากนม” ให้กลายเป็นสิ่งที่ไม่ต้องมีสัตว์อีกต่อไป ซึ่งจะเป็นกลยุทธ์สำคัญในการสร้างแบรนด์อาหารแห่งอนาคต ที่นมจะต้องมาจากโรงงานผลิตเท่านั้นจึงจะมีคุณสมบัติที่ดีทั้งสารอาหารและความสะอาด
CJ เองก็เคยประกาศต่อสื่อว่า อยากเป็น “Global Lifestyle Company” ซึ่งฟังดูเบาๆ แต่จริงๆ คือแผนใหญ่ในการ เปลี่ยนวิธีการกินของคนทั้งโลกได้เลยเช่นกัน -จาก “อาหารจริง” ไปเป็น “อาหารสังเคราะห์” (synthetic food) -จาก “ฟาร์มสัตว์” ไปเป็น “ถังหมักจุลินทรีย์” -จาก “ความหลากหลายตามธรรมชาติ” ไปเป็น “สูตรกลาง” ที่ควบคุมได้ในระดับโมเลกุล
การหนุนหลัง Formo จึงไม่ใช่เรื่องบังเอิญ แต่เป็นอีกหนึ่งหมากในกระดานใหญ่ที่ CJ วางไว้ เพื่อเป็นเจ้าของอาหารอนาคตแบบไม่ต้องเลี้ยงหมู ไก่ วัว แต่ครองเทคโนโลยีแทน
คำถามคือแล้วผู้บริโภคจะรู้ทันไหมว่า เบื้องหลังชีสที่ไม่มีวัว อาจมี “ทุนที่อยากครองโลกอาหาร” คำที่เคลมว่า “ยั่งยืน” อาจสร้างระบบอาหารใหม่ที่ยิ่งห่างจากธรรมชาติเข้าไปทุกที
คนที่เคย “กลัวสารเคมี” ในอาหารแปรรูป กลับกลืนผลิตภัณฑ์จากห้องแล็บ โดยคิดว่า “มันคือความสะอาดและอนาคต” #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ fb3d3798:371f711a
2025-05-20 07:13:35
@ fb3d3798:371f711a
2025-05-20 07:13:35Skjønner du? Bare tekst.
-
 @ fd06f542:8d6d54cd
2025-05-20 01:18:45
@ fd06f542:8d6d54cd
2025-05-20 01:18:45🧱 NostrTrust Initial Trust Score List (V0.1)
This list defines the initial trust scores (T Score) for key members of the Nostr community based on their contributions, reputation, and role in the ecosystem. The goal is to seed a decentralized trust system that encourages quality interactions and authentic contributions.
> ⚠️ Note: This is an draft version.
✅ Initial T Score Allocation Rules
| User Type | Initial T Score Range | Criteria | |-----------|------------------------|----------| | Founder | 10,000 | Creator of the Nostr protocol | | Core Developers | 5,000 - 8,000 | Major contributors to core codebase, clients, or infrastructure | | Active Contributors | 1,000 - 4,000 | Recognized long-term contributors to content, tools, or community |
👤 Initial Trust Score Table
| Name / Alias | npub | Initial T Score | Justification | |--------------|------|------------------|----------------| | fiatjaf | npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 | 10,000 | Creator of the Nostr protocol | |Jack|npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m|9,000|| | jb55 | npub1xtscya34g58tk0z605fvr788k263gsu6cy9x0mhnm87echrgufzsevkk5s | 7,000 | Developer of tools, relays, and early Nostr integrations,made damus | |Alex Gleason | npub1q3sle0kvfsehgsuexttt3ugjd8xdklxfwwkh559wxckmzddywnws6cd26p | 7,000 || |PABLOF7z|npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft|7,000|NDK| |DASHU|npub19yeqjawls407xjnmgkk6yss7936pcd7qzd5srlj8wye6j8433vrsjazqwk|4,000|Nostrmo | |Moss|npub129z0az8lgffuvsywazww07hx75qas3veh3dazsq56z8y39v86khs2uy5gm|4,000| freerse.com| |w|npub10td4yrp6cl9kmjp9x5yd7r8pm96a5j07lk5mtj2kw39qf8frpt8qm9x2wl|4,000| 0xchat | |Cody Tseng|npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl|4,000| jumble.social| |nostr_cn_dev|npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm|1,000|nostrbook.com,NostrTrust,nostrbridge| |hzrd149|npub1ye5ptcxfyyxl5vjvdjar2ua3f0hynkjzpx552mu5snj3qmx5pzjscpknpr|6,000|blossom,nostrudel| ||||| ||||| ||||| ||||| |||||
-
 @ 8b4456a7:ba913035
2025-05-20 07:10:58
@ 8b4456a7:ba913035
2025-05-20 07:10:58Jo, blomster kommer i alle farger og fasonger. Her har du to eksempler:


-
 @ 5d4b6c8d:8a1c1ee3
2025-05-20 00:09:55
@ 5d4b6c8d:8a1c1ee3
2025-05-20 00:09:55https://youtu.be/EPiE-Ruhohg
I'm pretty sure Ben called Caruso the "Bald Mamba" in this video, which is an awesome nickname for him.
Great walkthrough of the adjustments made over the course of seven games to try to disrupt Joker, culminating with putting Caruso (who's 100 lbs lighter and 6 inches shorter) on him.
https://stacker.news/items/984227
-
 @ 8b4456a7:ba913035
2025-05-20 07:10:56
@ 8b4456a7:ba913035
2025-05-20 07:10:56Skjønner du? Bare tekst.
-
 @ c296b5f7:c7282b53
2025-05-19 23:35:17
@ c296b5f7:c7282b53
2025-05-19 23:35:17testee
-
 @ d22a8d30:b273f7ab
2025-05-20 06:56:55
@ d22a8d30:b273f7ab
2025-05-20 06:56:55Jo, blomster kommer i alle farger og fasonger. Her har du to eksempler:


-
 @ c296b5f7:c7282b53
2025-05-19 23:18:42
@ c296b5f7:c7282b53
2025-05-19 23:18:42 -
 @ d22a8d30:b273f7ab
2025-05-20 06:56:54
@ d22a8d30:b273f7ab
2025-05-20 06:56:54Skjønner du? Bare tekst.
-
 @ c296b5f7:c7282b53
2025-05-19 23:17:49
@ c296b5f7:c7282b53
2025-05-19 23:17:49https://curtlink.com/user/login powerdigital f1950610#@
-
 @ c296b5f7:c7282b53
2025-05-19 23:16:33
@ c296b5f7:c7282b53
2025-05-19 23:16:33enter in leaders group https://chat.whatsapp.com/EhI9fGsMbGPHd2cF5KQwC9
-
 @ 1afd69c9:53832d1d
2025-05-20 06:52:34
@ 1afd69c9:53832d1d
2025-05-20 06:52:34Jo, blomster kommer i alle farger og fasonger. Her har du to eksempler:


-
 @ 1afd69c9:53832d1d
2025-05-20 06:52:32
@ 1afd69c9:53832d1d
2025-05-20 06:52:32Skjønner du? Bare tekst.
-
 @ 85fb39c4:81498307
2025-05-19 23:14:21
@ 85fb39c4:81498307
2025-05-19 23:14:21teste
-
 @ 9be6a199:6e133301
2025-05-19 23:11:35
@ 9be6a199:6e133301
2025-05-19 23:11:35this is the content
this is an update
-
 @ 85fb39c4:81498307
2025-05-19 23:07:11
@ 85fb39c4:81498307
2025-05-19 23:07:11It's my first post
-
 @ 9be6a199:6e133301
2025-05-19 22:39:28
@ 9be6a199:6e133301
2025-05-19 22:39:28sdsdsd
-
 @ 4ba8e86d:89d32de4
2025-05-19 22:33:46
@ 4ba8e86d:89d32de4
2025-05-19 22:33:46O que é Cwtch? Cwtch (/kʊtʃ/ - uma palavra galesa que pode ser traduzida aproximadamente como “um abraço que cria um lugar seguro”) é um protocolo de mensagens multipartidário descentralizado, que preserva a privacidade, que pode ser usado para construir aplicativos resistentes a metadados.
Como posso pronunciar Cwtch? Como "kutch", para rimar com "butch".
Descentralizado e Aberto : Não existe “serviço Cwtch” ou “rede Cwtch”. Os participantes do Cwtch podem hospedar seus próprios espaços seguros ou emprestar sua infraestrutura para outras pessoas que buscam um espaço seguro. O protocolo Cwtch é aberto e qualquer pessoa é livre para criar bots, serviços e interfaces de usuário e integrar e interagir com o Cwtch.
Preservação de privacidade : toda a comunicação no Cwtch é criptografada de ponta a ponta e ocorre nos serviços cebola Tor v3.
Resistente a metadados : O Cwtch foi projetado de forma que nenhuma informação seja trocada ou disponibilizada a ninguém sem seu consentimento explícito, incluindo mensagens durante a transmissão e metadados de protocolo
Uma breve história do bate-papo resistente a metadados Nos últimos anos, a conscientização pública sobre a necessidade e os benefícios das soluções criptografadas de ponta a ponta aumentou com aplicativos como Signal , Whatsapp e Wire. que agora fornecem aos usuários comunicações seguras.
No entanto, essas ferramentas exigem vários níveis de exposição de metadados para funcionar, e muitos desses metadados podem ser usados para obter detalhes sobre como e por que uma pessoa está usando uma ferramenta para se comunicar.
Uma ferramenta que buscou reduzir metadados é o Ricochet lançado pela primeira vez em 2014. Ricochet usou os serviços cebola Tor v2 para fornecer comunicação criptografada segura de ponta a ponta e para proteger os metadados das comunicações.
Não havia servidores centralizados que auxiliassem no roteamento das conversas do Ricochet. Ninguém além das partes envolvidas em uma conversa poderia saber que tal conversa está ocorrendo.
Ricochet tinha limitações; não havia suporte para vários dispositivos, nem existe um mecanismo para suportar a comunicação em grupo ou para um usuário enviar mensagens enquanto um contato está offline.
Isto tornou a adoção do Ricochet uma proposta difícil; mesmo aqueles em ambientes que seriam melhor atendidos pela resistência aos metadados, sem saber que ela existe.
Além disso, qualquer solução para comunicação descentralizada e resistente a metadados enfrenta problemas fundamentais quando se trata de eficiência, privacidade e segurança de grupo conforme definido pelo consenso e consistência da transcrição.
Alternativas modernas ao Ricochet incluem Briar , Zbay e Ricochet Refresh - cada ferramenta procura otimizar para um conjunto diferente de compensações, por exemplo, Briar procura permitir que as pessoas se comuniquem mesmo quando a infraestrutura de rede subjacente está inoperante, ao mesmo tempo que fornece resistência à vigilância de metadados.
O projeto Cwtch começou em 2017 como um protocolo de extensão para Ricochet, fornecendo conversas em grupo por meio de servidores não confiáveis, com o objetivo de permitir aplicativos descentralizados e resistentes a metadados como listas compartilhadas e quadros de avisos.
Uma versão alfa do Cwtch foi lançada em fevereiro de 2019 e, desde então, a equipe do Cwtch dirigida pela OPEN PRIVACY RESEARCH SOCIETY conduziu pesquisa e desenvolvimento em cwtch e nos protocolos, bibliotecas e espaços de problemas subjacentes.
Modelo de Risco.
Sabe-se que os metadados de comunicações são explorados por vários adversários para minar a segurança dos sistemas, para rastrear vítimas e para realizar análises de redes sociais em grande escala para alimentar a vigilância em massa. As ferramentas resistentes a metadados estão em sua infância e faltam pesquisas sobre a construção e a experiência do usuário de tais ferramentas.
https://nostrcheck.me/media/public/nostrcheck.me_9475702740746681051707662826.webp
O Cwtch foi originalmente concebido como uma extensão do protocolo Ricochet resistente a metadados para suportar comunicações assíncronas de grupos multiponto por meio do uso de infraestrutura anônima, descartável e não confiável.
Desde então, o Cwtch evoluiu para um protocolo próprio. Esta seção descreverá os vários riscos conhecidos que o Cwtch tenta mitigar e será fortemente referenciado no restante do documento ao discutir os vários subcomponentes da Arquitetura Cwtch.
Modelo de ameaça.
É importante identificar e compreender que os metadados são omnipresentes nos protocolos de comunicação; é de facto necessário que tais protocolos funcionem de forma eficiente e em escala. No entanto, as informações que são úteis para facilitar peers e servidores também são altamente relevantes para adversários que desejam explorar tais informações.
Para a definição do nosso problema, assumiremos que o conteúdo de uma comunicação é criptografado de tal forma que um adversário é praticamente incapaz de quebrá-lo veja tapir e cwtch para detalhes sobre a criptografia que usamos, e como tal nos concentraremos em o contexto para os metadados de comunicação.
Procuramos proteger os seguintes contextos de comunicação:
• Quem está envolvido em uma comunicação? Pode ser possível identificar pessoas ou simplesmente identificadores de dispositivos ou redes. Por exemplo, “esta comunicação envolve Alice, uma jornalista, e Bob, um funcionário público”.
• Onde estão os participantes da conversa? Por exemplo, “durante esta comunicação, Alice estava na França e Bob estava no Canadá”.
• Quando ocorreu uma conversa? O momento e a duração da comunicação podem revelar muito sobre a natureza de uma chamada, por exemplo, “Bob, um funcionário público, conversou com Alice ao telefone por uma hora ontem à noite. Esta é a primeira vez que eles se comunicam.” *Como a conversa foi mediada? O fato de uma conversa ter ocorrido por meio de um e-mail criptografado ou não criptografado pode fornecer informações úteis. Por exemplo, “Alice enviou um e-mail criptografado para Bob ontem, enquanto eles normalmente enviam apenas e-mails de texto simples um para o outro”.
• Sobre o que é a conversa? Mesmo que o conteúdo da comunicação seja criptografado, às vezes é possível derivar um contexto provável de uma conversa sem saber exatamente o que é dito, por exemplo, “uma pessoa ligou para uma pizzaria na hora do jantar” ou “alguém ligou para um número conhecido de linha direta de suicídio na hora do jantar”. 3 horas da manhã."
Além das conversas individuais, também procuramos defender-nos contra ataques de correlação de contexto, através dos quais múltiplas conversas são analisadas para obter informações de nível superior:
• Relacionamentos: Descobrir relações sociais entre um par de entidades analisando a frequência e a duração de suas comunicações durante um período de tempo. Por exemplo, Carol e Eve ligam uma para a outra todos os dias durante várias horas seguidas.
• Cliques: Descobrir relações sociais entre um grupo de entidades que interagem entre si. Por exemplo, Alice, Bob e Eva se comunicam entre si.
• Grupos vagamente conectados e indivíduos-ponte: descobrir grupos que se comunicam entre si através de intermediários, analisando cadeias de comunicação (por exemplo, toda vez que Alice fala com Bob, ela fala com Carol quase imediatamente depois; Bob e Carol nunca se comunicam).
• Padrão de Vida: Descobrir quais comunicações são cíclicas e previsíveis. Por exemplo, Alice liga para Eve toda segunda-feira à noite por cerca de uma hora. Ataques Ativos
Ataques de deturpação.
O Cwtch não fornece registro global de nomes de exibição e, como tal, as pessoas que usam o Cwtch são mais vulneráveis a ataques baseados em declarações falsas, ou seja, pessoas que fingem ser outras pessoas:
O fluxo básico de um desses ataques é o seguinte, embora também existam outros fluxos:
•Alice tem um amigo chamado Bob e outro chamado Eve
• Eve descobre que Alice tem um amigo chamado Bob
• Eve cria milhares de novas contas para encontrar uma que tenha uma imagem/chave pública semelhante à de Bob (não será idêntica, mas pode enganar alguém por alguns minutos)
• Eve chama essa nova conta de "Eve New Account" e adiciona Alice como amiga.
• Eve então muda seu nome em "Eve New Account" para "Bob"
• Alice envia mensagens destinadas a "Bob" para a conta falsa de Bob de Eve Como os ataques de declarações falsas são inerentemente uma questão de confiança e verificação, a única maneira absoluta de evitá-los é os usuários validarem absolutamente a chave pública. Obviamente, isso não é o ideal e, em muitos casos, simplesmente não acontecerá .
Como tal, pretendemos fornecer algumas dicas de experiência do usuário na interface do usuário para orientar as pessoas na tomada de decisões sobre confiar em contas e/ou distinguir contas que possam estar tentando se representar como outros usuários.
Uma nota sobre ataques físicos A Cwtch não considera ataques que exijam acesso físico (ou equivalente) à máquina do usuário como praticamente defensáveis. No entanto, no interesse de uma boa engenharia de segurança, ao longo deste documento ainda nos referiremos a ataques ou condições que exigem tal privilégio e indicaremos onde quaisquer mitigações que implementámos falharão.
Um perfil Cwtch.
Os usuários podem criar um ou mais perfis Cwtch. Cada perfil gera um par de chaves ed25519 aleatório compatível com Tor.
Além do material criptográfico, um perfil também contém uma lista de Contatos (outras chaves públicas do perfil Cwtch + dados associados sobre esse perfil, como apelido e (opcionalmente) mensagens históricas), uma lista de Grupos (contendo o material criptográfico do grupo, além de outros dados associados, como apelido do grupo e mensagens históricas).
Conversões entre duas partes: ponto a ponto
https://nostrcheck.me/media/public/nostrcheck.me_2186338207587396891707662879.webp
Para que duas partes participem de uma conversa ponto a ponto, ambas devem estar on-line, mas apenas uma precisa estar acessível por meio do serviço Onion. Por uma questão de clareza, muitas vezes rotulamos uma parte como “ponto de entrada” (aquele que hospeda o serviço cebola) e a outra parte como “ponto de saída” (aquele que se conecta ao serviço cebola).
Após a conexão, ambas as partes adotam um protocolo de autenticação que:
• Afirma que cada parte tem acesso à chave privada associada à sua identidade pública.
• Gera uma chave de sessão efêmera usada para criptografar todas as comunicações futuras durante a sessão.
Esta troca (documentada com mais detalhes no protocolo de autenticação ) é negável offline , ou seja, é possível para qualquer parte falsificar transcrições desta troca de protocolo após o fato e, como tal - após o fato - é impossível provar definitivamente que a troca aconteceu de forma alguma.
Após o protocolo de autenticação, as duas partes podem trocar mensagens livremente.
Conversas em Grupo e Comunicação Ponto a Servidor
Ao iniciar uma conversa em grupo, é gerada uma chave aleatória para o grupo, conhecida como Group Key. Todas as comunicações do grupo são criptografadas usando esta chave. Além disso, o criador do grupo escolhe um servidor Cwtch para hospedar o grupo. Um convite é gerado, incluindo o Group Key, o servidor do grupo e a chave do grupo, para ser enviado aos potenciais membros.
Para enviar uma mensagem ao grupo, um perfil se conecta ao servidor do grupo e criptografa a mensagem usando a Group Key, gerando também uma assinatura sobre o Group ID, o servidor do grupo e a mensagem. Para receber mensagens do grupo, um perfil se conecta ao servidor e baixa as mensagens, tentando descriptografá-las usando a Group Key e verificando a assinatura.
Detalhamento do Ecossistema de Componentes
O Cwtch é composto por várias bibliotecas de componentes menores, cada uma desempenhando um papel específico. Algumas dessas bibliotecas incluem:
- abertoprivacidade/conectividade: Abstração de rede ACN, atualmente suportando apenas Tor.
- cwtch.im/tapir: Biblioteca para construção de aplicativos p2p em sistemas de comunicação anônimos.
- cwtch.im/cwtch: Biblioteca principal para implementação do protocolo/sistema Cwtch.
- cwtch.im/libcwtch-go: Fornece ligações C para Cwtch para uso em implementações de UI.
TAPIR: Uma Visão Detalhada
Projetado para substituir os antigos canais de ricochete baseados em protobuf, o Tapir fornece uma estrutura para a construção de aplicativos anônimos.
Está dividido em várias camadas:
• Identidade - Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um par.
• Conexões – O protocolo de rede bruto que conecta dois pares. Até agora, as conexões são definidas apenas através do Tor v3 Onion Services.
• Aplicativos - As diversas lógicas que permitem um determinado fluxo de informações em uma conexão. Os exemplos incluem transcrições criptográficas compartilhadas, autenticação, proteção contra spam e serviços baseados em tokens. Os aplicativos fornecem recursos que podem ser referenciados por outros aplicativos para determinar se um determinado peer tem a capacidade de usar um determinado aplicativo hospedado.
• Pilhas de aplicativos - Um mecanismo para conectar mais de um aplicativo, por exemplo, a autenticação depende de uma transcrição criptográfica compartilhada e o aplicativo peer cwtch principal é baseado no aplicativo de autenticação.
Identidade.
Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um peer.
InitializeIdentity - de um par de chaves conhecido e persistente:i,I
InitializeEphemeralIdentity - de um par de chaves aleatório: ie,Ie
Aplicativos de transcrição.
Inicializa uma transcrição criptográfica baseada em Merlin que pode ser usada como base de protocolos baseados em compromisso de nível superior
O aplicativo de transcrição entrará em pânico se um aplicativo tentar substituir uma transcrição existente por uma nova (aplicando a regra de que uma sessão é baseada em uma e apenas uma transcrição).
Merlin é uma construção de transcrição baseada em STROBE para provas de conhecimento zero. Ele automatiza a transformação Fiat-Shamir, para que, usando Merlin, protocolos não interativos possam ser implementados como se fossem interativos.
Isto é significativamente mais fácil e menos sujeito a erros do que realizar a transformação manualmente e, além disso, também fornece suporte natural para:
• protocolos multi-round com fases alternadas de commit e desafio;
• separação natural de domínios, garantindo que os desafios estejam vinculados às afirmações a serem provadas;
• enquadramento automático de mensagens, evitando codificação ambígua de dados de compromisso;
• e composição do protocolo, usando uma transcrição comum para vários protocolos.
Finalmente, o Merlin também fornece um gerador de números aleatórios baseado em transcrição como defesa profunda contra ataques de entropia ruim (como reutilização de nonce ou preconceito em muitas provas). Este RNG fornece aleatoriedade sintética derivada de toda a transcrição pública, bem como dos dados da testemunha do provador e uma entrada auxiliar de um RNG externo.
Conectividade Cwtch faz uso do Tor Onion Services (v3) para todas as comunicações entre nós.
Fornecemos o pacote openprivacy/connectivity para gerenciar o daemon Tor e configurar e desmontar serviços cebola através do Tor.
Criptografia e armazenamento de perfil.
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir uma senha.
Perfis não criptografados e a senha padrão Para lidar com perfis "não criptografados" (ou seja, que não exigem senha para serem abertos), atualmente criamos um perfil com uma senha codificada de fato .
Isso não é o ideal, preferiríamos confiar no material de chave fornecido pelo sistema operacional, de modo que o perfil fosse vinculado a um dispositivo específico, mas esses recursos são atualmente uma colcha de retalhos - também notamos, ao criar um perfil não criptografado, pessoas que usam Cwtch estão explicitamente optando pelo risco de que alguém com acesso ao sistema de arquivos possa descriptografar seu perfil.
Vulnerabilidades Relacionadas a Imagens e Entrada de Dados
Imagens Maliciosas
O Cwtch enfrenta desafios na renderização de imagens, com o Flutter utilizando Skia, embora o código subjacente não seja totalmente seguro para a memória.
Realizamos testes de fuzzing nos componentes Cwtch e encontramos um bug de travamento causado por um arquivo GIF malformado, levando a falhas no kernel. Para mitigar isso, adotamos a política de sempre habilitar cacheWidth e/ou cacheHeight máximo para widgets de imagem.
Identificamos o risco de imagens maliciosas serem renderizadas de forma diferente em diferentes plataformas, como evidenciado por um bug no analisador PNG da Apple.
Riscos de Entrada de Dados
Um risco significativo é a interceptação de conteúdo ou metadados por meio de um Input Method Editor (IME) em dispositivos móveis. Mesmo aplicativos IME padrão podem expor dados por meio de sincronização na nuvem, tradução online ou dicionários pessoais.
Implementamos medidas de mitigação, como enableIMEPersonalizedLearning: false no Cwtch 1.2, mas a solução completa requer ações em nível de sistema operacional e é um desafio contínuo para a segurança móvel.
Servidor Cwtch.
O objetivo do protocolo Cwtch é permitir a comunicação em grupo através de infraestrutura não confiável .
Ao contrário dos esquemas baseados em retransmissão, onde os grupos atribuem um líder, um conjunto de líderes ou um servidor confiável de terceiros para garantir que cada membro do grupo possa enviar e receber mensagens em tempo hábil (mesmo que os membros estejam offline) - infraestrutura não confiável tem o objetivo de realizar essas propriedades sem a suposição de confiança.
O artigo original do Cwtch definia um conjunto de propriedades que se esperava que os servidores Cwtch fornecessem:
• O Cwtch Server pode ser usado por vários grupos ou apenas um.
• Um servidor Cwtch, sem a colaboração de um membro do grupo, nunca deve aprender a identidade dos participantes de um grupo.
• Um servidor Cwtch nunca deve aprender o conteúdo de qualquer comunicação.
• Um servidor Cwtch nunca deve ser capaz de distinguir mensagens como pertencentes a um grupo específico. Observamos aqui que essas propriedades são um superconjunto dos objetivos de design das estruturas de Recuperação de Informações Privadas.
Melhorias na Eficiência e Segurança
Eficiência do Protocolo
Atualmente, apenas um protocolo conhecido, o PIR ingênuo, atende às propriedades desejadas para garantir a privacidade na comunicação do grupo Cwtch. Este método tem um impacto direto na eficiência da largura de banda, especialmente para usuários em dispositivos móveis. Em resposta a isso, estamos ativamente desenvolvendo novos protocolos que permitem negociar garantias de privacidade e eficiência de maneiras diversas.
Os servidores, no momento desta escrita, permitem o download completo de todas as mensagens armazenadas, bem como uma solicitação para baixar mensagens específicas a partir de uma determinada mensagem. Quando os pares ingressam em um grupo em um novo servidor, eles baixam todas as mensagens do servidor inicialmente e, posteriormente, apenas as mensagens novas.
Mitigação de Análise de Metadados
Essa abordagem permite uma análise moderada de metadados, pois o servidor pode enviar novas mensagens para cada perfil suspeito exclusivo e usar essas assinaturas de mensagens exclusivas para rastrear sessões ao longo do tempo. Essa preocupação é mitigada por dois fatores:
- Os perfis podem atualizar suas conexões a qualquer momento, resultando em uma nova sessão do servidor.
- Os perfis podem ser "ressincronizados" de um servidor a qualquer momento, resultando em uma nova chamada para baixar todas as mensagens. Isso é comumente usado para buscar mensagens antigas de um grupo.
Embora essas medidas imponham limites ao que o servidor pode inferir, ainda não podemos garantir resistência total aos metadados. Para soluções futuras para esse problema, consulte Niwl.
Proteção contra Pares Maliciosos
Os servidores enfrentam o risco de spam gerado por pares, representando uma ameaça significativa à eficácia do sistema Cwtch. Embora tenhamos implementado um mecanismo de proteção contra spam no protótipo do Cwtch, exigindo que os pares realizem alguma prova de trabalho especificada pelo servidor, reconhecemos que essa não é uma solução robusta na presença de um adversário determinado com recursos significativos.
Pacotes de Chaves
Os servidores Cwtch se identificam por meio de pacotes de chaves assinados, contendo uma lista de chaves necessárias para garantir a segurança e resistência aos metadados na comunicação do grupo Cwtch. Esses pacotes de chaves geralmente incluem três chaves: uma chave pública do serviço Tor v3 Onion para o Token Board, uma chave pública do Tor v3 Onion Service para o Token Service e uma chave pública do Privacy Pass.
Para verificar os pacotes de chaves, os perfis que os importam do servidor utilizam o algoritmo trust-on-first-use (TOFU), verificando a assinatura anexada e a existência de todos os tipos de chave. Se o perfil já tiver importado o pacote de chaves do servidor anteriormente, todas as chaves são consideradas iguais.
Configuração prévia do aplicativo para ativar o Relé do Cwtch.
No Android, a hospedagem de servidor não está habilitada, pois essa opção não está disponível devido às limitações dos dispositivos Android. Essa funcionalidade está reservada apenas para servidores hospedados em desktops.
No Android, a única forma direta de importar uma chave de servidor é através do grupo de teste Cwtch, garantindo assim acesso ao servidor Cwtch.
Primeiro passo é Habilitar a opção de grupo no Cwtch que está em fase de testes. Clique na opção no canto superior direito da tela de configuração e pressione o botão para acessar as configurações do Cwtch.
Você pode alterar o idioma para Português do Brasil.Depois, role para baixo e selecione a opção para ativar os experimentos. Em seguida, ative a opção para habilitar o chat em grupo e a pré-visualização de imagens e fotos de perfil, permitindo que você troque sua foto de perfil.
https://pomf2.lain.la/f/eprhj0u3.mp4
Próximo passo é Criar um perfil.
Pressione o + botão de ação no canto inferior direito e selecione "Novo perfil" ou aberta no botão + adicionar novo perfil.
-
Selecione um nome de exibição
-
Selecione se deseja proteger
este perfil e salvo localmente com criptografia forte: Senha: sua conta está protegida de outras pessoas que possam usar este dispositivo
Sem senha: qualquer pessoa que tenha acesso a este dispositivo poderá acessar este perfil.
Preencha sua senha e digite-a novamente
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a chave da senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir um senha.
https://pomf2.lain.la/f/7p6jfr9r.mp4
O próximo passo é adicionar o FuzzBot, que é um bot de testes e de desenvolvimento.
Contato do FuzzBot: 4y2hxlxqzautabituedksnh2ulcgm2coqbure6wvfpg4gi2ci25ta5ad.
Ao enviar o comando "testgroup-invite" para o FuzzBot, você receberá um convite para entrar no Grupo Cwtch Test. Ao ingressar no grupo, você será automaticamente conectado ao servidor Cwtch. Você pode optar por sair do grupo a qualquer momento ou ficar para conversar e tirar dúvidas sobre o aplicativo e outros assuntos. Depois, você pode configurar seu próprio servidor Cwtch, o que é altamente recomendável. https://pomf2.lain.la/f/x4pm8hm8.mp4
Agora você pode utilizar o aplicativo normalmente. Algumas observações que notei: se houver demora na conexão com outra pessoa, ambas devem estar online. Se ainda assim a conexão não for estabelecida, basta clicar no ícone de reset do Tor para restabelecer a conexão com a outra pessoa.
Uma introdução aos perfis Cwtch.
Com Cwtch você pode criar um ou mais perfis . Cada perfil gera um par de chaves ed25519 aleatório compatível com a Rede Tor.
Este é o identificador que você pode fornecer às pessoas e que elas podem usar para entrar em contato com você via Cwtch.
Cwtch permite criar e gerenciar vários perfis separados. Cada perfil está associado a um par de chaves diferente que inicia um serviço cebola diferente.
Gerenciar Na inicialização, o Cwtch abrirá a tela Gerenciar Perfis. Nessa tela você pode:
- Crie um novo perfil.
- Desbloquear perfis.
- Criptografados existentes.
- Gerenciar perfis carregados.
- Alterando o nome de exibição de um perfil.
- Alterando a senha de um perfil Excluindo um perfil.
- Alterando uma imagem de perfil.
Backup ou exportação de um perfil.
Na tela de gerenciamento de perfil:
-
Selecione o lápis ao lado do perfil que você deseja editar
-
Role para baixo até a parte inferior da tela.
-
Selecione "Exportar perfil"
-
Escolha um local e um nome de arquivo.
5.confirme.
Uma vez confirmado, o Cwtch colocará uma cópia do perfil no local indicado. Este arquivo é criptografado no mesmo nível do perfil.
Este arquivo pode ser importado para outra instância do Cwtch em qualquer dispositivo.
Importando um perfil.
-
Pressione o +botão de ação no canto inferior direito e selecione "Importar perfil"
-
Selecione um arquivo de perfil Cwtch exportado para importar
-
Digite a senha associada ao perfil e confirme.
Uma vez confirmado, o Cwtch tentará descriptografar o arquivo fornecido usando uma chave derivada da senha fornecida. Se for bem-sucedido, o perfil aparecerá na tela Gerenciamento de perfil e estará pronto para uso.
OBSERVAÇÃO Embora um perfil possa ser importado para vários dispositivos, atualmente apenas uma versão de um perfil pode ser usada em todos os dispositivos ao mesmo tempo. As tentativas de usar o mesmo perfil em vários dispositivos podem resultar em problemas de disponibilidade e falhas de mensagens.
Qual é a diferença entre uma conexão ponto a ponto e um grupo cwtch?
As conexões ponto a ponto Cwtch permitem que 2 pessoas troquem mensagens diretamente. As conexões ponto a ponto nos bastidores usam serviços cebola Tor v3 para fornecer uma conexão criptografada e resistente a metadados. Devido a esta conexão direta, ambas as partes precisam estar online ao mesmo tempo para trocar mensagens.
Os Grupos Cwtch permitem que várias partes participem de uma única conversa usando um servidor não confiável (que pode ser fornecido por terceiros ou auto-hospedado). Os operadores de servidores não conseguem saber quantas pessoas estão em um grupo ou o que está sendo discutido. Se vários grupos estiverem hospedados em um único servidor, o servidor não conseguirá saber quais mensagens pertencem a qual grupo sem a conivência de um membro do grupo. Ao contrário das conversas entre pares, as conversas em grupo podem ser conduzidas de forma assíncrona, para que todos num grupo não precisem estar online ao mesmo tempo.
Por que os grupos cwtch são experimentais? Mensagens em grupo resistentes a metadados ainda são um problema em aberto . Embora a versão que fornecemos no Cwtch Beta seja projetada para ser segura e com metadados privados, ela é bastante ineficiente e pode ser mal utilizada. Como tal, aconselhamos cautela ao usá-lo e apenas o fornecemos como um recurso opcional.
Como posso executar meu próprio servidor Cwtch? A implementação de referência para um servidor Cwtch é de código aberto . Qualquer pessoa pode executar um servidor Cwtch, e qualquer pessoa com uma cópia do pacote de chaves públicas do servidor pode hospedar grupos nesse servidor sem que o operador tenha acesso aos metadados relacionados ao grupo .
https://git.openprivacy.ca/cwtch.im/server
https://docs.openprivacy.ca/cwtch-security-handbook/server.html
Como posso desligar o Cwtch? O painel frontal do aplicativo possui um ícone do botão "Shutdown Cwtch" (com um 'X'). Pressionar este botão irá acionar uma caixa de diálogo e, na confirmação, o Cwtch será desligado e todos os perfis serão descarregados.
Suas doações podem fazer a diferença no projeto Cwtch? O Cwtch é um projeto dedicado a construir aplicativos que preservam a privacidade, oferecendo comunicação de grupo resistente a metadados. Além disso, o projeto também desenvolve o Cofre, formulários da web criptografados para ajudar mútua segura. Suas contribuições apoiam iniciativas importantes, como a divulgação de violações de dados médicos em Vancouver e pesquisas sobre a segurança do voto eletrônico na Suíça. Ao doar, você está ajudando a fechar o ciclo, trabalhando com comunidades marginalizadas para identificar e corrigir lacunas de privacidade. Além disso, o projeto trabalha em soluções inovadoras, como a quebra de segredos através da criptografia de limite para proteger sua privacidade durante passagens de fronteira. E também tem a infraestrutura: toda nossa infraestrutura é open source e sem fins lucrativos. Conheça também o Fuzzytags, uma estrutura criptográfica probabilística para marcação resistente a metadados. Sua doação é crucial para continuar o trabalho em prol da privacidade e segurança online. Contribua agora com sua doação
https://openprivacy.ca/donate/
onde você pode fazer sua doação em bitcoin e outras moedas, e saiba mais sobre os projetos. https://openprivacy.ca/work/
Link sobre Cwtch
https://cwtch.im/
https://git.openprivacy.ca/cwtch.im/cwtch
https://docs.cwtch.im/docs/intro
https://docs.openprivacy.ca/cwtch-security-handbook/
Baixar #CwtchDev
cwtch.im/download/
https://play.google.com/store/apps/details?id=im.cwtch.flwtch
-
 @ cae03c48:2a7d6671
2025-05-19 22:21:46
@ cae03c48:2a7d6671
2025-05-19 22:21:46Bitcoin Magazine

BitMine Launches Bitcoin Treasury Advisory Practice, Secures $4M Deal with First ClientToday, BitMine Immersion Technologies, Inc. (OTCQX: BMNRD) announced the launch of its Bitcoin Treasury Advisory Practice and a $4 million deal with a U.S. exchange-listed company. The deal saw Bitmine surpass its last year’s total revenue in that single transaction alone, according to the announcement.
BitMine ( OTCQX: $BMNRD $BMNR) launches Bitcoin Treasury Advisory Practice and secures $4M deal with first client.
This single transaction exceeds our 2024 revenue and sets the stage for major growth.
Read now: https://t.co/R89K3WXdZZ pic.twitter.com/5vIvlYPZUY
— Bitmine Immersion Technologies, Inc. (@BitMNR) May 19, 2025
BitMine will provide “Mining as a Service” (MaaS) by leasing 3,000 Bitcoin ASIC miners to the client through December 30, 2025, in a $3.2 million lease deal, with $1.6 million paid upfront. Additionally, the client has signed an $800,000 consulting agreement for one year focusing on Bitcoin Mining-as-a-Service and Bitcoin Treasury Strategy.
“Currently, there are almost 100 public companies that have adopted Bitcoin as a treasury holding. We expect this number to grow in the future. As more companies adopt Bitcoin treasury strategies, the need for infrastructure, revenue generation, and expert guidance grows along with it,” said Jonathan Bates, CEO of BitMine. “This single transaction is greater than our entire 2024 fiscal year revenue, and we feel there is an opportunity to acquire more clients in the near future as interest in Bitcoin ownership grows.”
BitMine’s first quarter 2025 results showed strong revenue growth, with GAAP revenue rising approximately 135% to $1.2 million, up from $511,000 in Q1 2024, supported by an expanded mining capacity of 4,640 miners as of November 30, 2024, compared to 1,606 the previous year. Despite this growth, the company reported a net loss of $3.9 million in Q1 2025, primarily due to a one-time, non-cash accounting adjustment related to preferred stock; excluding this charge, the adjusted loss was approximately $975,000, consistent with the prior year’s results.
$BMNR reports a 135% revenue increase YOY for Q1 2025 and tripled self-mining capacity with 3,000 new miners! CEO Jonathan Bates credits a team-driven approach and creative financing for this growth.
Read the full release here: https://t.co/slNrZv8Ocn pic.twitter.com/Gb4tk1UfAO— Bitmine Immersion Technologies, Inc. (@BitMNR) January 13, 2025
BitMine’s new Bitcoin Treasury Advisory Practice, along with the $4 million deal, joins a trend among public companies exploring Bitcoin not just as a treasury asset but also as a source of revenue.
This post BitMine Launches Bitcoin Treasury Advisory Practice, Secures $4M Deal with First Client first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ 866e0139:6a9334e5
2025-05-19 21:39:26
@ 866e0139:6a9334e5
2025-05-19 21:39:26Autor: Ludwig F. Badenhagen. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie auch in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Wer einhundert Prozent seines Einkommens abgeben muss, ist sicher ein Sklave, oder? Aber ab wieviel Prozent Pflichtabgabe ist er denn kein Sklave mehr? Ab wann ist er frei und selbst-bestimmt?
Wer definieren möchte, was ein Sklave ist, sollte nicht bei Pflichtabgaben verweilen, denn die Fremdbestimmtheit geht viel weiter. Vielfach hat der gewöhnliche Mensch wenig Einfluss darauf, wie er und seine Familie misshandelt wird. Es wird verfügt, welche Bildung, welche Nahrung, welche Medikamente, welche Impfungen und welche Kriege er zu erdulden hat. Hierbei erkennt der gewöhnliche Mensch aber nur, wer ihm direkt etwas an-tut. So wie der Gefolterte bestenfalls seinen Folterer wahrnimmt, aber nicht den, in dessen Auftrag dieser handelt, so haben die vorbezeichnet Geschädigten mit Lehrern, „Experten“, Ärzten und Politikern zu tun. Ebenfalls ohne zu wissen, in wessen Auftrag diese Leute handeln. „Führungssysteme“ sind so konzipiert, dass für viele Menschen bereits kleinste wahrgenommene Vorteile genügen, um einem anderen Menschen Schlimmes anzutun.
Aber warum genau wird Menschen Schlimmes angetan? Die Gründe dafür sind stets dieselben. Der Täter hat ein Motiv und Motivlagen können vielfältig sein.
Wer also ein Motiv hat, ein Geschehen zu beeinflussen, motiviert andere zur Unterstützung. Wem es gelingt, bei anderen den Wunsch zu erwecken, das zu tun, was er möchte, ist wirklich mächtig. Und es sind die Mächtigen im Hintergrund, welche die Darsteller auf den Bühnen dieser Welt dazu nutzen, die Interessen der wirklich Mächtigen durchzusetzen. Insbesondere die letzten fünf Jahre haben eindrucksvoll gezeigt, wie willfährig Politiker, Ärzte, Experten und viele weitere ihre jeweiligen Aufträge gegen die Bevölkerung durchsetz(t)en.
Und so geschieht es auch beim aktuellen Krieg, der stellvertretend auf dem europäischen Kontinent ausgetragen wird. Parolen wie „nie wieder Krieg“ gehören der Vergangenheit an. Stattdessen ist nunmehr wieder der Krieg und nur der Krieg geeignet, um „Aggressionen des Gegners abzuwehren“ und um „uns zu verteidigen“.
Das hat mindestens drei gute Gründe:
- Mit einem Krieg können Sie einem anderen etwas wegnehmen, was er freiwillig nicht herausrückt. Auf diese Weise kommen Sie an dessen Land, seine Rohstoffe und sein Vermögen. Sie können ihn beherrschen und Ihren eigenen Einfluss ausbauen. Je mehr Ihnen gehört, um so besser ist das für Sie. Sie müssen sich weniger abstimmen und Widersacher werden einfach ausgeschaltet.
- Wenn etwas über einen langen Zeitraum aufgebaut wurde, ist es irgendwann auch einmal fertig. Um aber viel Geld verdienen und etwas nach eigenen Vorstellungen gestalten zu können, muss immer wieder etwas Neues erschaffen werden, und da stört das Alte nur. Demzufolge ist ein Krieg ein geeignetes Mittel, etwas zu zerstören. Und das Schöne ist, dass man von Beginn an viel Geld verdient. Denn man muss dem indoktrinierten Volk nur vormachen, dass der Krieg „unbedingt erforderlich“ sei, um das Volk dann selbst bereitwillig für diesen Krieg bezahlen und auch sonst engagiert mitwirken zu lassen. Dann kann in Rüstung und „Kriegstauglichkeit“ investiert werden. Deutschland soll dem Vernehmen nach bereits in einigen Jahren „kriegstauglich“ sein. Der Gegner wartet sicher gerne mit seinen Angriffen, bis es so weit ist.
- Und nicht zu vergessen ist, dass man die vielen gewöhnlichen Menschen loswird. Schon immer wurden Populationen „reguliert“. Das macht bei Tieren ebenfalls so, indem man sie je nach „Erfordernis“ tötet. Und bei kollabierenden Systemen zu Zeiten von Automatisierung und KI unter Berücksichtigung der Klimarettung wissen doch mittlerweile alle, dass es viel zu viele Menschen auf dem Planeten gibt. Wenn jemand durch medizinische Misshandlungen oder auch durch einen Krieg direkt stirbt, zahlt dies auf die Lösung des Problems ein. Aber auch ein „Sterben auf Raten“ ist von großem Vorteil, denn durch die „fachmännische Behandlung von Verletzten“ bis zu deren jeweiligen Tode lässt sich am Leid viel verdienen.
Sie erkennen, dass es sehr vorteilhaft ist, Kriege zu führen, oder? Und diese exemplarisch genannten drei Gründe könnten noch beliebig erweitert werden.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Das Einzige, was gegen Kriegsereignisse sprechen könnte, wäre, dass man selbst niemandem etwas wegnehmen möchte, was ihm gehört, und dass man seinen Mitmenschen nicht schaden, geschweige denn diese verletzen oder gar töten möchte.
In diesem Zusammenhang könnte man auch erkennen, dass die, die nach Krieg rufen, selbst nicht kämpfen. Auch deren Kinder nicht. Man könnte erkennen, dass man selbst nur benutzt wird, um die Interessen anderer durchzusetzen. Wie beim Brettspiel Schach hat jede Figur eine Funktion und keinem Spieler ist das Fortbestehen eines Bauern wichtig, wenn seine Entnahme dem Spielgewinn dient. Wer Krieg spielt, denkt sicher ähnlich.
Meine beiden Großväter waren Soldaten im zweiten Weltkrieg und erlebten die Grausamkeiten des Krieges und der Gefangenschaft so intensiv, dass sie mit uns Enkeln zu keiner Zeit hierüber sprechen konnten, da sie wohl wussten, dass uns allein ihre Erzählungen zutiefst traumatisiert hätten. Die Opas waren analog dem, was wir ihnen an Information abringen konnten, angeblich nur Sanitäter. Sanitäter, wie auch die meisten Großväter aus der Nachbarschaft. Wer aber jemals beobachten konnte, wie unbeholfen mein Opa ein Pflaster aufgebracht hat, der konnte sich denken, dass seine vermeintliche Tätigkeit als Sanitäter eine Notlüge war, um uns die Wahrheit nicht vermitteln zu müssen.
Mein Opa war mein bester Freund und mir treibt es unverändert die Tränen in die Augen, sein erlebtes Leid nachzuempfinden. Und trotz aller seelischen und körperlichen Verletzungen hat er nach seiner Rückkehr aus der Kriegshölle mit großem Erfolg daran gearbeitet, für seine Familie zu sorgen.
Manchmal ist es m. E. besser, die Dinge vom vorhersehbaren Ende aus zu betrachten, um zu entscheiden, welche Herausforderungen man annimmt und welche man besser ablehnt. Es brauchte fast 80 Jahre, um die Deutschen erneut dafür zu begeistern, Ihre Leben „für die gute Sache“ zu opfern. Was heutzutage aber anders ist als früher: Einerseits sind die Politiker dieser Tage sehr durchschaubar geworden. Aber in einem ähnlichen Verhältnis, wie die schauspielerischen Leistungen der Politiker abgenommen haben, hat die Volksverblödung zugenommen.
Denken Sie nicht nach. Denken Sie stattdessen vor. Und denken Sie selbst. Für sich, Ihre Lieben und alle anderen Menschen. Andernfalls wird die Geschichte, so wie sie von meinen Opas (und Omas) erlebt wurde, mit neuen Technologien und „zeitgemäßen Methoden“ wiederholt. Dies führt zweifelsfrei zu Not und Tod.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 2b998b04:86727e47
2025-05-19 21:18:46
@ 2b998b04:86727e47
2025-05-19 21:18:46After the pruning came clarity.\ And after the clarity came a quiet but relentless question:\ What now?
If I wasn’t going back to Web3, if I wasn’t going to pretend anymore — not in faith, not in finance — then I needed to start building again. But this time, with different materials. Different rhythms. A different spirit.
Starting Over on Solid Ground
I’d spent years exploring tokens, networks, and well-intentioned communities. But most of it, I see now, was sand. It moved with the tides. The incentives shifted. The values bent. And when the storms came — personal, financial, spiritual — much of what I’d been part of collapsed or exposed its shallowness.
So I returned to the beginning: What can’t be faked?
That’s where Bitcoin came in — not just as an asset, but as a foundation.\ It taught me cost. Time. Truth. It doesn’t market itself. It just is.\ A system that punishes shortcuts, rewards discipline, and invites peace.
And the more I leaned in, the more I realized:\ This isn’t just money. This is philosophy. This is soil.
Pruned to Plant Again
I used to be a buy-and-hold investor. I still carry those instincts. But in 2020–21, I discovered trading — and with it, a new kind of discipline. Not gambling. Not speculation. Stewardship under pressure. Real-time decision-making with skin in the game.
My grandfather, who passed in the late '90s, probably would’ve looked a little dimly on trading. He lived off his dividends. Stocks he held for decades. He wasn’t chasing. He was rooting. But he would’ve respected the discipline — the clarity — when done right.
He also saw things I didn’t. He once told me I wasn’t raised properly. It hurt at the time, but now I understand. He saw the drift — not just in me, but in the culture. He understood that frugality means nothing if it’s not paired with truth.
I think he would’ve respected what I’m doing now — even if he wouldn't have fully understand it.
What I’m Building Now
-
StartNation – A Bitcoin-aligned equity accelerator. Proof-based. No tokens. No hype.
-
Golden Gate Group Investments – Real estate with a vision to integrate BTC in payments and ownership. Still early. Still real.
-
Blue Planet Ventures – Equities trading with daily proof-of-work and sats-based performance tracking.
-
A garden – Yes, literal food. Soil and seed. Hypdropnics. Bitcoin taught me patience; gardening reinforces it.
I’m not building a brand. I’m building a life. And I’m doing it in public — not to be seen, but to help others see. That it’s possible to step off the hype rails and still thrive.
Bitcoin: The Turning Point
It wasn’t until last fall that Bitcoin truly became central for me.\ Not just part of a portfolio — the lens through which I see capital, time, and truth.
I don’t see it as speculative anymore. I see it as inevitable. In 20–30 years, I believe Bitcoin will be the de facto reserve currency — even if not in name. Those who hold it will steward wealth not because they played the game, but because they opted out of it early.
I’m stacking not to escape — but to prepare. Not to prove I'm right — but to live rightly.
Legacy Without a Platform
I don’t have children.\ But I do have nieces. Nephews. Brothers. Sisters. Cousins. In-Laws.
And I know they’re watching — even if they don’t say it.\ I want to show them that you can live with truth, walk by faith, work with your hands — and still thrive.
I’m not stacking for applause. I’m stacking for legacy.\ I’m building not just for the next quarter — but for the next generation.
And if someone, years from now, asks why I chose this path, I want to say:
Because it was real.\ Because it was proof.\ Because it was built to last.
⚡ If this series has encouraged or challenged you, zap a few sats/bitcoin. It keeps me building.
✍️ Catch up on the full series here:\ \ Part 1: The Drift -> https://primal.net/andrewgstanton/why-i-left-web3-for-proof-of-work-%E2%80%93-part-1%3A-the-drift\ Part 2: The Breaking Point -> https://primal.net/andrewgstanton/why-i-left-web3-for-proof-of-work---part-2%3A-the-breaking-point\ Part 3: The Return -> https://primal.net/andrewgstanton/why-i-left-web3-for-proof-of-work-%E2%80%93-part-3%3A-the-return\ Part 4: Proof Of Work as Philosophy -> https://primal.net/andrewgstanton/why-i-left-web3-for-proof-of-work-%E2%80%93-part-4%3A-proof-of-work-as-philosophy\ Part 5: Building Again (what you are reading now...)
Written with help from ChatGPT (GPT-4), edited and posted by me.
-
-
 @ 4c96d763:80c3ee30
2025-05-19 20:56:26
@ 4c96d763:80c3ee30
2025-05-19 20:56:26Changes
William Casarin (19):
- dave: add screenshot to readme
- dave: fix image in readme
- columns: remove spamming info logs about writing to cache
- columns: never truncate notes you're replying to
- windows: don't show terminal window
- mention: show username instead of display_name
- chrome: switch from ALPHA to BETA
- ui: make post replies selectable
- dave: include anonymous user identifier in api call
- dave: add trial mode
- dave: fix sidebar click
- dave: nudge avatar when you click
- dave: hide media in dave note previews
- chrome: fix theme persistence
- ui: fix a bunch of missing hover pointers
- Release Notedeck Beta v0.4.0
- release: changelog
- timeline: show media on universe timeline
- clippy: fix lint related to iterator
kernelkind (28):
- add
trust_media_from_pk2method - add hashbrown
- introduce & use
JobPool - introduce JobsCache
- add blurhash dependency
- introduce blur
- note: remove unnecessary derive macros from
NoteAction - propagate
JobsCache ImagePulseTint->PulseAlpha- images: move fetch to fn
- add
TexturesCache - images: make
MediaCacheholdMediaCacheType - images: make promise payload optional to take easily
- post: unnest
- notedeck_ui: move carousel to
note/media.rs - note media: only show full screen when loaded
- note media: unnest full screen media
- pass
NoteActionby value instead of reference - propagate
Imagesto actionbar - add one shot error message
- make
WidgetimplProfilePicmutably - implement blurring
- don't show zap button if no wallet
- display name should wrap
- make styled button toggleable
- method to get current default zap amount
- add
CustomZapView - use
CustomZapView
pushed to notedeck:refs/heads/master
-
 @ 1817b617:715fb372
2025-05-19 20:39:28
@ 1817b617:715fb372
2025-05-19 20:39:28Looking to simulate a USDT deposit that appears instantly in a wallet — with no blockchain confirmation, no real spend, and no trace?
You’re in the right place.
🔗 Buy Flash USDT Now This product sends Flash USDT directly to your TRC20, ERC20, or BEP20 wallet address — appears like a real deposit, but disappears after a set time or block depth.
✅ Perfect for: Simulating token inflows Wallet stress testing “Proof of funds” display Flash USDT is ideal for developers, trainers, UI testers, and blockchain researchers — and it’s fully customizable.
🧠 What Is Flash USDT? Flash USDT is a synthetic transaction that mimics a real Tether transfer. It shows up instantly in a wallet balance, and it’s confirmed on-chain — and expires after a set duration.
This makes it:
Visible on wallet interfaces Time-limited (auto-disappears cleanly) Undetectable on block explorers after expiry It’s the smartest, safest way to simulate high-value transactions without real crypto.
🛠️ Flash USDT Software – Your Own USDT Flasher at Your Fingertips Want to control the flash? Run your own operations? Flash unlimited wallets?
🔗 Buy Flash USDT Software
This is your all-in-one USDT flasher tool, built for TRC20, ERC20, and BEP20 chains. It gives you full control to:
Send custom USDT amounts Set custom expiry time (e.g., 30–360 days) Flash multiple wallets Choose between networks (Tron, ETH, BSC) You can simulate any amount, to any supported wallet, from your own system.
No third-party access. No blockchain fee. No trace left behind.
💥 Why Our Flash USDT & Software Stands Out Feature Flash USDT Flash USDT Software One-time flash send ✅ Yes Optional Full sender control ❌ No ✅ Yes TRC20 / ERC20 / BEP20 ✅ Yes ✅ Yes Custom duration/expiry Limited ✅ Yes Unlimited usage ❌ One-off ✅ Yes Whether you’re flashing for wallet testing, demoing investor dashboards, or simulating balance flows, our tools deliver realism without risk.
🛒 Ready to Buy Flash USDT or the Software? Skip the wait. Skip the scammers. You’re one click away from real control.
👉 Buy Flash USDT 👉 Buy Flash USDT Software
📞 Support or live walkthrough?
💬 Telegram: @cryptoflashingtool 📱 WhatsApp: +1 770-666-2531
🚫 Legal Notice These tools are intended for:
Educational purposes Demo environments Wallet and UI testing They are not for illegal use or financial deception. Any misuse is your full responsibility.
Final Call: Need to flash USDT? Want full control? Don’t wait for another “maybe” tool.
Get your Flash USDT or Flashing Software today and simulate like a pro.
🔗 Buy Now → Flash USDT 🔗 Buy Now → Flash USDT Software 💬 Telegram: @cryptoflashingtool 📱 WhatsApp: +1 770-666-2531Looking to simulate a USDT deposit that appears instantly in a wallet — with no blockchain confirmation, no real spend, and no trace?
You’re in the right place.
Buy Flash USDT Now\ This product sends Flash USDT directly to your TRC20, ERC20, or BEP20 wallet address — appears like a real deposit, but disappears after a set time or block depth.
Perfect for:
- Simulating token inflows
- Wallet stress testing
- “Proof of funds” display
Flash USDT is ideal for developers, trainers, UI testers, and blockchain researchers — and it’s fully customizable.
What Is Flash USDT?
Flash USDT is a synthetic transaction that mimics a real Tether transfer. It shows up instantly in a wallet balance, and it’s confirmed on-chain — and expires after a set duration.
This makes it:
- Visible on wallet interfaces
- Time-limited (auto-disappears cleanly)
- Undetectable on block explorers after expiry
It’s the smartest, safest way to simulate high-value transactions without real crypto.
Flash USDT Software – Your Own USDT Flasher at Your Fingertips
Want to control the flash?\ Run your own operations?\ Flash unlimited wallets?
This is your all-in-one USDT flasher tool, built for TRC20, ERC20, and BEP20 chains. It gives you full control to:
- Send custom USDT amounts
- Set custom expiry time (e.g., 30–360 days)
- Flash multiple wallets
- Choose between networks (Tron, ETH, BSC)
You can simulate any amount, to any supported wallet, from your own system.
No third-party access.\ No blockchain fee.\ No trace left behind.
Why Our Flash USDT & Software Stands Out
Feature
Flash USDT
Flash USDT Software
One-time flash send
Yes
Optional
Full sender control
No
Yes
TRC20 / ERC20 / BEP20
Yes
Yes
Custom duration/expiry
Limited
Yes
Unlimited usage
One-off
Yes
Whether you’re flashing for wallet testing, demoing investor dashboards, or simulating balance flows, our tools deliver realism without risk.
Ready to Buy Flash USDT or the Software?
Skip the wait. Skip the scammers.\ You’re one click away from real control.
Support or live walkthrough?
Telegram: @cryptoflashingtool
WhatsApp: +1 770-666-2531
Legal Notice
These tools are intended for:
- Educational purposes
- Demo environments
- Wallet and UI testing
They are not for illegal use or financial deception. Any misuse is your full responsibility.
Final Call:
Need to flash USDT? Want full control?\ Don’t wait for another “maybe” tool.
Get your Flash USDT or Flashing Software today and simulate like a pro.
Telegram: @cryptoflashingtool
WhatsApp: +1 770-666-2531
-
 @ d41bf82f:ed90d888
2025-05-19 20:31:54
@ d41bf82f:ed90d888
2025-05-19 20:31:54“ประเด็นแท้จริงคือเรื่องของการควบคุม—อินเทอร์เน็ตแพร่ขยายกว้างไกลเกินกว่าที่รัฐบาลใดจะครอบงำได้โดยง่าย ด้วยการสร้างเขตเศรษฐกิจระดับโลกที่ไร้รอยต่อ ไม่ขึ้นต่ออธิปไตย และอยู่นอกเหนือการควบคุม อินเทอร์เน็ตจึงตั้งคำถามต่อแนวคิดของรัฐชาติในตัวมันเอง” — JOHN PERRY BARLOW
บทนี้เริ่มต้นด้วยการวิพากษ์แนวคิด ทางด่วนข้อมูล ว่าเป็นคำอุปมาอุปมัยที่ยังยึดติดกับโลกยุคอุตสาหกรรม เพราะเศรษฐกิจยุคสารสนเทศไม่ใช่แค่โครงสร้างพื้นฐานสำหรับขนส่งข้อมูล แต่คือ จุดหมายปลายทาง ใหม่ในตัวเอง นั่นคือ ไซเบอร์สเปซ —ดินแดนที่ก้าวข้ามขอบเขตทางภูมิศาสตร์โดยสิ้นเชิง
ไซเบอร์สเปซคือพื้นที่ใหม่ของปฏิสัมพันธ์ทางสังคม เศรษฐกิจ และการเมือง ซึ่งไม่สามารถควบคุมโดยรัฐชาติแบบเดิมได้อีกต่อไป ผู้เขียนยกคำของ John Perry Barlow ที่เปรียบไซเบอร์สเปซเป็น “ดินแดนแห่งเสรีภาพ” ที่ไม่ยึดโยงกับสถานที่จริง และเปิดโอกาสให้ทุกคนแสดงความคิดเห็นได้อย่างไร้การควบคุม
การเปลี่ยนผ่านนี้ส่งผลกระทบรุนแรงต่อโครงสร้างของเศรษฐกิจแบบเดิม การเข้าถึงข้อมูลอย่างรวดเร็วแบบไร้ขอบเขตเปรียบเสมือนตัวทำละลายที่กัดกร่อนต้นทุนของสถาบันขนาดใหญ่ ทั้งภาครัฐและเอกชน ไมโครโพรเซสซิงจะเปลี่ยนรูปแบบขององค์กรและแนวคิดเรื่องสถานที่ในทางเศรษฐกิจอย่างสิ้นเชิง
ตลอดประวัติศาสตร์ เศรษฐกิจผูกติดกับพื้นที่ทางภูมิศาสตร์ การเดินทางเป็นเรื่องยากและจำกัด การค้าขายส่วนใหญ่เกิดในระดับท้องถิ่น ภาษา วัฒนธรรม และภูมิประเทศเป็นอุปสรรคทางการเมืองเสมอ จนถึงกับที่ผู้เขียนกล่าวว่า การเมืองทั้งหมดเป็นเรื่องท้องถิ่น
แต่เทคโนโลยีสมัยใหม่กำลังเปลี่ยนสมการนี้ การสื่อสารและขนส่งที่รวดเร็วทำให้ผู้มีความสามารถสามารถเลือกสถานที่อยู่อาศัยหรือทำงานได้อย่างเสรี ลดอำนาจต่อรองของรัฐบาลในพื้นที่นั้นลง เพราะคนสามารถ “หนี” ได้ง่ายขึ้น หากรัฐบาลกดขี่หรือรีดไถ
แม้อินเทอร์เน็ตยุคแรกจะดูธรรมดา เช่น ใช้อ่านบทความหรือสั่งซื้อสินค้า แต่ศักยภาพที่แท้จริงของเศรษฐกิจไซเบอร์นั้นยิ่งใหญ่มาก ผู้เขียนเสนอว่ามันจะพัฒนาเป็นสามขั้น: 1. ขั้นพื้นฐาน: อินเทอร์เน็ตเป็นเพียงช่องทางเพิ่มประสิทธิภาพธุรกิจแบบเดิม (เช่น เว็บขายสินค้าขายของออนไลน์ เช่น อเมซอน) 2. ขั้นพัฒนา: การเกิดขึ้นของเงินดิจิทัลที่เข้ารหัสและไม่สามารถติดตามได้ จะปลดปล่อยธุรกรรมจากการควบคุมและการจัดเก็บภาษีของรัฐ 3. ขั้นก้าวหน้า: ไซเบอร์สเปซจะมีระบบเศรษฐกิจ กฎหมาย และกลไกคุ้มครองของตัวเอง ปราศจากการควบคุมจากรัฐบาลใด ๆ
ในโลกใหม่นี้ Sovereign Individual หรือ “ปัจเจกผู้มีอธิปไตย” จะสามารถสร้างความมั่งคั่งและดำเนินกิจกรรมในไซเบอร์สเปซได้อย่างเป็นอิสระ โดยไม่ต้องอิงรัฐชาติ รัฐจึงจะถูกบีบให้ลดขนาดและเปลี่ยนบทบาทจากผู้ใช้อำนาจกลายเป็นผู้ให้บริการที่ต้องแข่งขันเพื่อความพึงพอใจของพลเมือง
สามารถไปติดตามเนื้อหาแบบ short vdo ที่สรุปประเด็นสำคัญจากแต่ละบท พร้อมกราฟิกและคำอธิบายกระชับ เข้าใจง่าย ได้ที่ TikTok ช่อง https://www.tiktok.com/@moneyment1971
-
 @ 9be6a199:6e133301
2025-05-19 20:27:20
@ 9be6a199:6e133301
2025-05-19 20:27:20ssdsdsdsdsdsdsd
-
 @ 9be6a199:6e133301
2025-05-19 20:15:18
@ 9be6a199:6e133301
2025-05-19 20:15:18 -
 @ 91117f2b:111207d6
2025-05-19 18:50:48
@ 91117f2b:111207d6
2025-05-19 18:50:48
Crypto currency is now a buzzword in the financial world. Many people are wondering what it is all about. In my article I will break down the basis of crypto currency and at the same time explore it's basis and risks.
MANY ASKS "WHAT IS CRYPTO CURRENCY
Crypto currency is a virtual or digital currency that uses cryptography for security. Which means it is not controlled by government or financial institutions. The transaction are recorded on a public ledger also called a blockchain which ensures the transparency and security of crypto currency.
MANY ASKS HOW DOES IT WORK
Crypto currency has different stages such as the mining, transaction and the wallet stage. THE MINING STAGE: Crypto currency is created through a process which is described as mining, and where your hardwares or computer solve complex mathematical problem to validate your transaction and create new coins.
TRANSACTION STAGE: crypto currency can be be traded for other currencies, they can also be used to buy goods and services online.
WALLET: crypto currency is stored digitally which can be accessed through your hardwares or even your softwares.
THEY ARE BENEFITS AND RISKS FOR CRYPTO CURRENCY
HERE ARE SOME BENEFITS 1. Decentralization :decentralization gives users more control over their money, because crypto currency operates independently of government and banks.
- ACCESSIBILITY: crypto currency can be accessed by anyone through the use of internet making it to be a solution for finances.
- SECURITY: the transactions of crypto currencies are secure and also transparent through the aid of blockchain technology.
HERE ARE SOME RISKS
-
SECURITY RISKS: during exchange in crypto currency wallets can be vulnerable to hacking and cyber theft.
-
VOLATILITY: crypto currency can fluctuate or tends to fluctuate rapidly making it a risky investment.
-
REGULATORY UNCERTAINTY: the rules and regulations of crypto currency is still evolving, which can create uncertainty and risks for investors.
SOME POPULAR CRYPTO CURRENCIES
- BITCOIN: it is the most reknown crypto currency and is often a gold standard for digital currencies.
-
ETHERIUM: it is a popular platform for building decentralized applications. Etherium has its own crypto currency called Ether.
-
ALTCOINS: they are other crypto currenciss like montero, lite coin and so on, which offers alternatives.
IN CONCLUSION
Crypto currency is complex and it is rapidly evolving, both with benefit and risks. It is essential to stay updated and informed to understand the changes both opportunities and challenges. I assure you whatever you do for a living crypto currency is worth your time and explorations.
-
 @ cae03c48:2a7d6671
2025-05-19 18:29:07
@ cae03c48:2a7d6671
2025-05-19 18:29:07Bitcoin Magazine

Bitcoin Records Highest Weekly Close Above $106KBitcoin has officially recorded its highest-ever weekly candle close, finishing the week at $106,516. The milestone was achieved on Sunday evening, marking a notable moment in Bitcoin’s ongoing price history and underscoring growing institutional and retail interest.
JUST IN: $107,000 #Bitcoin
 pic.twitter.com/Xt1JLm0Ke6
pic.twitter.com/Xt1JLm0Ke6— Bitcoin Magazine (@BitcoinMagazine) May 19, 2025
This weekly close sets a new benchmark for BTC’s price performance and positions the asset in a historically rare range. As of Monday, Bitcoin is trading at $102,924, reflecting typical price movement following a new high as markets adjust to key levels.
Historical data helps illustrate the significance of this moment. According to an analysis shared by on-chain researcher Dan, Bitcoin has closed above $106,439 only once—this week—accounting for just 0.02% of its entire trading history. Closures above $100,000 have occurred in only 40 days total. Even levels like $75,000 and $50,000 remain relatively uncommon in Bitcoin’s lifespan, appearing on just 181 and 586 days, respectively.
— Dan (@robustus) May 19, 2025
This data highlights how current prices place Bitcoin in a historically narrow range of time — a reflection of the long-term upward trend of the asset over the past decade. For market participants, this type of price action often serves as an indicator of continued momentum and interest in Bitcoin’s role as a digital store of value.
The broader Bitcoin ecosystem continues to show strength, with on-chain metrics reflecting growing user engagement and long-term holder confidence. Notably, activity on the Bitcoin network remains elevated, with transaction volumes and address growth signaling continued adoption. Analysts are closely watching inflows into Bitcoin-focused ETFs and the behavior of long-term holders, both of which are key indicators of sustained interest and belief in Bitcoin’s long-term value.
bitcoin just had its all-time high weekly candle close at $106,500 pic.twitter.com/FuqqptHEmA
— Alex Thorn (@intangiblecoins) May 19, 2025
Some traders are watching the $100,000 level closely as a key psychological and technical zone. Bitcoin’s ability to maintain this level following a record weekly close could be important in setting the tone for the weeks ahead.
While near-term price movements are always part of market dynamics, the latest close represents a milestone in Bitcoin’s history. It reaffirms the asset’s resilience and ongoing relevance in the global financial landscape.
This post Bitcoin Records Highest Weekly Close Above $106K first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ 82a7a1ff:2c1e9cdf
2025-05-19 18:18:31
@ 82a7a1ff:2c1e9cdf
2025-05-19 18:18:31Whatever
-
 @ 6b0a60cf:b952e7d4
2025-05-19 22:33:33
@ 6b0a60cf:b952e7d4
2025-05-19 22:33:33タイトルは釣りです。そんなこと微塵も思っていません。 本稿はアウトボックスモデルの実装に関してうだうだ考えるコーナーです。 ダムスに関して何か言いたいわけではないので先にタイトル回収しておきます。
- NIP-65を守る気なんかさらさら無いのにNIP-65に書いてあるkind:10002のReadリレーの意味を知っていながら全然違う使い方をしているのは一部の和製クライアントの方だよね
- NIP-65を守る気が無いならkind:10002を使うべきではなく、独自仕様でリレーを保存するべきだよね
- アウトボックスモデルを採用しているクライアントからすれば仕様と異なる実装をしてしまっているクライアントが迷惑だと思われても仕方ないよね
- と考えればダムスの方が潔いよね
- とはいえkind:3のcontentは空にしろって言われてんだからやっぱダムスはゴミだわ
- やるとしたらRabbitみたいにローカルに保存するか、別デバイス間で同期したいならkind:30078を使うべきだよね
アウトボックスモデルはなぜ人気がないのか
言ってることはとてもいいと思うんですよ。 欠点があるとすれば、
- 末端のユーザーからすればreadリレーとwriteリレーと書かれると直感的にイメージされるものとかけ離れている
- 正しく設定してもらうには相当の説明が必要
- フォローTLを表示しようとすれば非常にたくさんのリレーと接続することになり現実的ではない
- なるほど完璧な作戦っスねーっ 不可能だという点に目をつぶればよぉ~
余談ですが昔irisでログインした時に localhost のリレーに繋ごうとしてiris壊れたって思ったけど今思えばアウトボックスモデルを忠実に実装してたんじゃないかな…。
現実的に実装する方法は無いのか
これでReadすべきリレーをシミュレーションできる。 https://nikolat.github.io/nostr-relay-trend/ フォローイーのWriteリレーを全部購読しようとすると100個近いリレー数になるので現実的ではありません。 しかしフォローイーのWriteリレーのうち1個だけでよい、とする条件を仮に追加すると一気にハードルが下がります。私の場合はReadリレー含めて7個のリレーに収まりました。 Nos Haikuはとりあえずこの方針でいくことにしました。
今後どうしていきたいのか
エンドユーザーとしての自分の志向としては、自分が指定したリレーだけを購読してほしい、勝手に余計なリレーを読みに行かないでほしい、という気持ちがあり、現状の和製クライアントの仕様を気に入っています。 仮にNos Haikuでアウトボックスモデルを採用しつつ自分の決めたリレーに接続するハイブリッド実装を考えるとすれば、
あなたの購読するリレーはこれですよー - Read(inbox) Relays (あなたへのメンションが届くリレー) - wss://relay1.example.com/ - wss://relay2.example.com/ - wss://relay3.example.com/ - Followee's Write Relays (フォローイーが書き込んでいるリレー) - wss://relay4.example.com/ - wss://relay5.example.com/ - wss://relay6.example.com/って出して、チェックボックス付けてON/OFFできるようにして最終的に購読するリレーをユーザーに決めてもらう感じかな……って漠然と考えています。よほど時間を持て余したときがあればやってみるかも。
あとリレーを数は仕方ないとしてリレーごとにフォローイーの投稿だけを取得するようにした方が理にかなってるよね。全部のリレーから全部のフォローイーの投稿を取得しようとしたら(実装はシンプルで楽だけど)通信量が大変だよね。 rx-nostr の Forward Strategy ってリレーごとにREQかえて一度に購読できるっけ?
常にひとつ以下の REQ サブスクリプションを保持します。
って書いてあるから無理なのかな? あとReadリレーは純粋に自分へのメンション(pタグ付き)イベントのみを購読するようにした方がいい気がする。スパム対策としてかなり有効だと思うので。スパムはNIP-65に準拠したりはしていないでしょうし。 まぁ、NIP-65に準拠していないクライアントからのメンションは届かなくなってしまうわけですが。
-
 @ 3f770d65:7a745b24
2025-05-19 18:09:52
@ 3f770d65:7a745b24
2025-05-19 18:09:52🏌️ Monday, May 26 – Bitcoin Golf Championship & Kickoff Party
Location: Las Vegas, Nevada\ Event: 2nd Annual Bitcoin Golf Championship & Kick Off Party"\ Where: Bali Hai Golf Clubhouse, 5160 S Las Vegas Blvd, Las Vegas, NV 89119\ 🎟️ Get Tickets!
Details:
-
The week tees off in style with the Bitcoin Golf Championship. Swing clubs by day and swing to music by night.
-
Live performances from Nostr-powered acts courtesy of Tunestr, including Ainsley Costello and others.
-
Stop by the Purple Pill Booth hosted by Derek and Tanja, who will be on-boarding golfers and attendees to the decentralized social future with Nostr.
💬 May 27–29 – Bitcoin 2025 Conference at the Las Vegas Convention Center
Location: The Venetian Resort\ Main Attraction for Nostr Fans: The Nostr Lounge\ When: All day, Tuesday through Thursday\ Where: Right outside the Open Source Stage\ 🎟️ Get Tickets!
Come chill at the Nostr Lounge, your home base for all things decentralized social. With seating for \~50, comfy couches, high-tops, and good vibes, it’s the perfect space to meet developers, community leaders, and curious newcomers building the future of censorship-resistant communication.
Bonus: Right across the aisle, you’ll find Shopstr, a decentralized marketplace app built on Nostr. Stop by their booth to explore how peer-to-peer commerce works in a truly open ecosystem.
Daily Highlights at the Lounge:
-
☕️ Hang out casually or sit down for a deeper conversation about the Nostr protocol
-
🔧 1:1 demos from app teams
-
🛍️ Merch available onsite
-
🧠 Impromptu lightning talks
-
🎤 Scheduled Meetups (details below)
🎯 Nostr Lounge Meetups
Wednesday, May 28 @ 1:00 PM
- Damus Meetup: Come meet the team behind Damus, the OG Nostr app for iOS that helped kickstart the social revolution. They'll also be showcasing their new cross-platform app, Notedeck, designed for a more unified Nostr experience across devices. Grab some merch, get a demo, and connect directly with the developers.
Thursday, May 29 @ 1:00 PM
- Primal Meetup: Dive into Primal, the slickest Nostr experience available on web, Android, and iOS. With a built-in wallet, zapping your favorite creators and friends has never been easier. The team will be on-site for hands-on demos, Q\&A, merch giveaways, and deeper discussions on building the social layer of Bitcoin.
🎙️ Nostr Talks at Bitcoin 2025
If you want to hear from the minds building decentralized social, make sure you attend these two official conference sessions:
1. FROSTR Workshop: Multisig Nostr Signing
-
🕚 Time: 11:30 AM – 12:00 PM
-
📅 Date: Wednesday, May 28
-
📍 Location: Developer Zone
-
🎤 Speaker: nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgdwaehxw309ahx7uewd3hkcqpqs9etjgzjglwlaxdhsveq0qksxyh6xpdpn8ajh69ruetrug957r3qf4ggfm (Austin Kelsay) @ Voltage\ A deep-dive into FROST-based multisig key management for Nostr. Geared toward devs and power users interested in key security.
2. Panel: Decentralizing Social Media
-
🕑 Time: 2:00 PM – 2:30 PM
-
📅 Date: Thursday, May 29
-
📍 Location: Genesis Stage
-
🎙️ Moderator: nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqy08wumn8ghj7mn0wd68yttjv4kxz7fwv3jhyettwfhhxuewd4jsqgxnqajr23msx5malhhcz8paa2t0r70gfjpyncsqx56ztyj2nyyvlq00heps - Bitcoin Strategy @ Roxom TV
-
👥 Speakers:
-
nostr:nprofile1qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcppemhxue69uhkummn9ekx7mp0qqsy2ga7trfetvd3j65m3jptqw9k39wtq2mg85xz2w542p5dhg06e5qmhlpep – Early Bitcoin dev, CEO @ Sirius Business Ltd
-
nostr:nprofile1qy2hwumn8ghj7mn0wd68ytndv9kxjm3wdahxcqg5waehxw309ahx7um5wfekzarkvyhxuet5qqsw4v882mfjhq9u63j08kzyhqzqxqc8tgf740p4nxnk9jdv02u37ncdhu7e3 – Analyst & Partner @ Ego Death Capital
Get the big-picture perspective on why decentralized social matters and how Nostr fits into the future of digital communication.
🌃 NOS VEGAS Meetup & Afterparty
Date: Wednesday, May 28\ Time: 7:00 PM – 1:00 AM\ Location: We All Scream Nightclub, 517 Fremont St., Las Vegas, NV 89101\ 🎟️ Get Tickets!
What to Expect:
-
🎶 Live Music Stage – Featuring Ainsley Costello, Sara Jade, Able James, Martin Groom, Bobby Shell, Jessie Lark, and other V4V artists
-
🪩 DJ Party Deck – With sets by nostr:nprofile1qy0hwumn8ghj7cmgdae82uewd45kketyd9kxwetj9e3k7mf6xs6rgqgcwaehxw309ahx7um5wgh85mm694ek2unk9ehhyecqyq7hpmq75krx2zsywntgtpz5yzwjyg2c7sreardcqmcp0m67xrnkwylzzk4 , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqgkwaehxw309anx2etywvhxummnw3ezucnpdejqqg967faye3x6fxgnul77ej23l5aew8yj0x2e4a3tq2mkrgzrcvecfsk8xlu3 , and more DJs throwing down
-
🛰️ Live-streamed via Tunestr
-
🧠 Nostr Education – Talks by nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq37amnwvaz7tmwdaehgu3dwfjkccte9ejx2un9ddex7umn9ekk2tcqyqlhwrt96wnkf2w9edgr4cfruchvwkv26q6asdhz4qg08pm6w3djg3c8m4j , nostr:nprofile1qy2hwumn8ghj7etyv4hzumn0wd68ytnvv9hxgqg7waehxw309anx2etywvhxummnw3ezucnpdejz7ur0wp6kcctjqqspywh6ulgc0w3k6mwum97m7jkvtxh0lcjr77p9jtlc7f0d27wlxpslwvhau , nostr:nprofile1qy88wumn8ghj7mn0wvhxcmmv9uq3vamnwvaz7tmwdaehgu3wd33xgetk9en82m30qqsgqke57uygxl0m8elstq26c4mq2erz3dvdtgxwswwvhdh0xcs04sc4u9p7d , nostr:nprofile1q9z8wumn8ghj7erzx3jkvmmzw4eny6tvw368wdt8da4kxamrdvek76mrwg6rwdngw94k67t3v36k77tev3kx7vn2xa5kjem9dp4hjepwd3hkxctvqyg8wumn8ghj7mn0wd68ytnhd9hx2qpqyaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgssuy4zk , nostr:nprofile1qy28wue69uhnzvpwxqhrqt33xgmn5dfsx5cqz9thwden5te0v4jx2m3wdehhxarj9ekxzmnyqqswavgevxe9gs43vwylumr7h656mu9vxmw4j6qkafc3nefphzpph8ssvcgf8 , and more.
-
🧾 Vendors & Project Booths – Explore new tools and services
-
🔐 Onboarding Stations – Learn how to use Nostr hands-on
-
🐦 Nostrich Flocking – Meet your favorite nyms IRL
-
🍸 Three Full Bars – Two floors of socializing overlooking vibrant Fremont Street
| | | | | ----------- | -------------------- | ------------------- | | Time | Name | Topic | | 7:30-7:50 | Derek | Nostr for Beginners | | 8:00-8:20 | Mark & Paul | Primal | | 8:30-8:50 | Terry | Damus | | 9:00-9:20 | OpenMike and Ainsley | V4V | | 09:30-09:50 | The Space | Space |
This is the after-party of the year for those who love freedom technology and decentralized social community. Don’t miss it.
Final Thoughts
Whether you're there to learn, network, party, or build, Bitcoin 2025 in Las Vegas has a packed week of Nostr-friendly programming. Be sure to catch all the events, visit the Nostr Lounge, and experience the growing decentralized social revolution.
🟣 Find us. Flock with us. Purple pill someone.
-
-
 @ cae03c48:2a7d6671
2025-05-19 17:48:53
@ cae03c48:2a7d6671
2025-05-19 17:48:53Bitcoin Magazine

JPMorgan To Allow Clients To Buy Bitcoin, Jamie Dimon SaysToday, Chairman and CEO of JPMorgan Chase Jamie Dimon reiterated his personal disapproval of Bitcoin during the bank’s annual Investor Day event. Despite the bank’s decision to provide clients with access to Bitcoin investments, Dimon emphasized his personal disapproval of Bitcoin.
“I am not a fan” of Bitcoin, stated Dimon.
JPMorgan is going to allow clients to buy Bitcoin, but the bank won’t custody it, according to Bloomberg. Dimon made clear that while JPMorgan will provide clients access to Bitcoin investments, the bank will not hold or manage the digital asset directly.
JUST IN: JPMorgan CEO Jamie Dimon said they will allow clients to buy #Bitcoin
 pic.twitter.com/wO0djlYGUM
pic.twitter.com/wO0djlYGUM— Bitcoin Magazine (@BitcoinMagazine) May 19, 2025
In a January 2025 interview with CBS News, Dimon expressed continued skepticism toward Bitcoin. “Bitcoin itself has no intrinsic value. It’s used heavily by sex traffickers, money launderers, ransomware,” said Dimon.
Although he acknowledged, “We are going to have some kind of digital currency at some point,” he added, “I just don’t feel great about bitcoin. I applaud your ability to wanna buy or sell it. Just like I think you have the right to smoke, but I don’t think you should smoke.”
These comments from Dimon contrast with recent optimism from JPMorgan analysts regarding Bitcoin’s market prospects. JPMorgan analysts reported that Bitcoin is likely to continue gaining ground at gold’s expense in the second half of the year, driven by rising corporate demand and growing support from U.S. states.
JUST IN: JPMorgan says #Bitcoin likely to have more upside than gold in the second half of 2025
 pic.twitter.com/YPrHivch9O
pic.twitter.com/YPrHivch9O— Bitcoin Magazine (@BitcoinMagazine) May 15, 2025
“Between mid-February and mid-April gold was rising at the expense of bitcoin, while of the past three weeks we have been observing the opposite, i.e. bitcoin rising at the expense of gold,” said JPMorgan analysts. “In all, we expect the YTD zero sum game between gold and bitcoin to extend to the remainder of the year, but are biased towards crypto-specific catalysts creating more upside for bitcoin over gold into the second half of the year.”
Since April 22, gold has dropped nearly 8%, while Bitcoin has surged 18%, reflecting a notable shift in investor sentiment. Capital has been moving out of gold ETFs and into Bitcoin. Several U.S. states are also warming to Bitcoin—New Hampshire now permits up to 5% of its reserves in Bitcoin, while Arizona is launching a Bitcoin reserve and has pledged not to raise taxes this year. At the corporate level, companies like Strategy and Metaplanet are expanding their Bitcoin holdings.
“As the list grows, with other U.S. states potentially considering adding bitcoin to their strategic reserves, this could turn out to be a more sustained positive catalyst for bitcoin,” said the analysts.
This post JPMorgan To Allow Clients To Buy Bitcoin, Jamie Dimon Says first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ da8b7de1:c0164aee
2025-05-19 17:38:59
@ da8b7de1:c0164aee
2025-05-19 17:38:59Németország feladja a nukleáris energiával szembeni ellenállását Franciaországgal való közeledés jegyében
Németország hosszú idő után feladta a nukleáris energiával szembeni ellenállását, ami jelentős lépést jelenthet az EU energiapolitikai vitáinak rendezésében, különösen Franciaországgal szemben. Ez a változás eltávolíthatja a nukleáris energiával szembeni előítéleteket az uniós jogszabályokból, és elősegítheti a közös európai energiapolitika kialakítását[2].
Trump adminisztráció tervezett rendeletei a nukleáris erőművek építésének gyorsítására
Az Egyesült Államokban a Trump-adminisztráció több elnöki rendelet-tervezetet készít elő, amelyek célja a nukleáris erőművek építésének gyorsítása. A tervek szerint a jelenlegi mintegy 100 GW nukleáris kapacitást 2050-re 400 GW-ra növelnék, az engedélyezési folyamatok egyszerűsítésével, a hadsereg szerepének növelésével és a nukleáris üzemanyag-ellátás megerősítésével[3][9].
Tajvan hivatalosan is nukleárismentes lett
- május 17-én Tajvan utolsó kereskedelmi reaktorát is leállították, ezzel az ország elérte a "nukleárismentes haza" célját. Az energiamixben a nukleáris energia aránya 17%-ról 3%-ra csökkent, miközben a megújuló energia tízszeresére nőtt. Bár a parlamentben vita folyik a Maanshan atomerőmű élettartam-hosszabbításáról, jelenleg Tajvan teljesen leállította a nukleáris energiatermelést[1][6].
Kazatomprom hitelmegállapodást kötött egy új kénsavgyár finanszírozására
Kazahsztán állami atomipari vállalata, a Kazatomprom hitelmegállapodást kötött egy évi 800 000 tonna kapacitású kénsavgyár építésére. A kénsavat az uránkitermeléshez használják, és a gyár 2027 első negyedévében készülhet el. A projekt célja a régió gazdasági fejlődésének támogatása és az uránipar ellátásbiztonságának javítása[4].
Az IAEA segíti Kazahsztánt az első atomerőmű biztonságos helyszínének kiválasztásában
Az IAEA (Nemzetközi Atomenergia-ügynökség) szakértői csapata ötnapos szemináriumot tart Kazahsztánban, hogy segítsen kiválasztani az ország első atomerőművének legbiztonságosabb helyszínét. A folyamatban több helyszín is szóba került, jelenleg a Zhambyl körzet az elsődleges jelölt. A projektben négy lehetséges technológiai partner vesz részt: CNNC (Kína), Roszatom (Oroszország), KHNP (Dél-Korea) és EDF (Franciaország)[8].
India új nukleáris helyszínt hagyott jóvá
Az indiai nukleáris hatóság engedélyezte a Mahi Banswara Rajasthan Atomic Power Project négy blokkjának elhelyezését Rádzsasztán államban. Ez újabb lépés India ambiciózus nukleáris bővítési terveiben[5].
Globális nukleáris ipari konferencia Varsóban
- május 20-21-én Varsóban rendezik meg az első World Nuclear Supply Chain Conference-t, amely célja a globális nukleáris ellátási lánc megerősítése és a szektor 2 billió dolláros beruházási lehetőségének kiaknázása a következő 15 évben. A konferencián iparági vezetők, döntéshozók és szakértők vesznek részt[7].
Hivatkozások
- [1] reccessary.com – Tajvan nukleárismentes lett
- [2] nucnet.org – Németország nukleáris politikai fordulata
- [3] humanprogress.org – Trump rendelettervezetek
- [4] world-nuclear-news.org – Kazatomprom kénsavgyár
- [5] world-nuclear-news.org – India új nukleáris helyszíne
- [6] taiwannews.com.tw – Tajvan atomerőmű leállítása
- [7] world-nuclear.org – Varsói nukleáris konferencia
- [8] astanatimes.com – IAEA-Kazahsztán együttműködés
- [9] esgdive.com – Oklo és Trump engedélyezési reformok
-
 @ a8d1560d:3fec7a08
2025-05-19 17:28:05
@ a8d1560d:3fec7a08
2025-05-19 17:28:05NIP-XX
Documentation and Wikis with Spaces and Format Declaration
draftoptionalSummary
This NIP introduces a system for collaborative documentation and wikis on Nostr. It improves upon earlier efforts by adding namespace-like Spaces, explicit content format declaration, and clearer separation of article types, including redirects and merge requests.
Motivation
Previous approaches to wiki-style collaborative content on Nostr had two key limitations:
- Format instability – No declared format per event led to breaking changes (e.g. a shift from Markdown to Asciidoc).
- Lack of namespace separation – All articles existed in a global space, causing confusion and collision between unrelated projects.
This NIP addresses both by introducing:
- Spaces – individually defined wikis or documentation sets.
- Explicit per-article format declaration.
- Dedicated event kinds for articles, redirects, merge requests, and space metadata.
Specification
kind: 31055– Space DefinitionDefines a project namespace for articles.
Tags: -
["name", "<space title>"]-["slug", "<short identifier>"]-["description", "<optional description>"]-["language", "<ISO language code>"]-["license", "<license text or SPDX ID>"]Content: (optional) full description or README for the space.
kind: 31056– ArticleAn article in a specific format belonging to a defined space.
Tags: -
["space", "<slug>"]-["title", "<article title>"]-["format", "markdown" | "asciidoc" | "mediawiki" | "html"]-["format-version", "<format version>"](optional) -["prev", "<event-id>"](optional) -["summary", "<short change summary>"](optional)Content: full body of the article in the declared format.
kind: 31057– RedirectRedirects from one article title to another within the same space.
Tags: -
["space", "<slug>"]-["from", "<old title>"]-["to", "<new title>"]Content: empty.
kind: 31058– Merge RequestProposes a revision to an article without directly altering the original.
Tags: -
["space", "<slug>"]-["title", "<article title>"]-["base", "<event-id>"]-["format", "<format>"]-["comment", "<short summary>"](optional)Content: proposed article content.
Format Guidelines
Currently allowed formats: -
markdown-asciidoc-mediawiki-htmlClients MUST ignore formats they do not support. Clients MAY apply stricter formatting rules.
Client Behavior
Clients: - MUST render only supported formats. - MUST treat
spaceas a case-sensitive namespace. - SHOULD allow filtering, browsing and searching within Spaces. - SHOULD support revision tracking viaprev. - MAY support diff/merge tooling forkind: 31058.
Examples
Space Definition
json { "kind": 31055, "tags": [ ["name", "Bitcoin Docs"], ["slug", "btc-docs"], ["description", "Developer documentation for Bitcoin tools"], ["language", "en"], ["license", "MIT"] ], "content": "Welcome to the Bitcoin Docs Space." }Markdown Article
json { "kind": 31056, "tags": [ ["space", "btc-docs"], ["title", "Installation Guide"], ["format", "markdown"] ], "content": "# Installation\n\nFollow these steps to install the software..." }Asciidoc Article
json { "kind": 31056, "tags": [ ["space", "btc-docs"], ["title", "RPC Reference"], ["format", "asciidoc"] ], "content": "= RPC Reference\n\nThis section describes JSON-RPC calls." }MediaWiki Article
json { "kind": 31056, "tags": [ ["space", "btc-docs"], ["title", "Block Structure"], ["format", "mediawiki"] ], "content": "== Block Structure ==\n\nThe structure of a Bitcoin block is..." }Redirect
json { "kind": 31057, "tags": [ ["space", "btc-docs"], ["from", "Getting Started"], ["to", "Installation Guide"] ], "content": "" }Merge Request
json { "kind": 31058, "tags": [ ["space", "btc-docs"], ["title", "Installation Guide"], ["base", "d72fa1..."], ["format", "markdown"], ["comment", "Added step for testnet"] ], "content": "# Installation\n\nNow includes setup instructions for testnet users." }
Acknowledgements
This proposal builds on earlier ideas for decentralized wikis and documentation within Nostr, while solving common issues related to format instability and lack of project separation.
-
 @ 9be6a199:6e133301
2025-05-19 17:24:12
@ 9be6a199:6e133301
2025-05-19 17:24:12this is the content
-
 @ 30b99916:3cc6e3fe
2025-05-19 20:30:52
@ 30b99916:3cc6e3fe
2025-05-19 20:30:52bitcoin #security #vault #veracrypt #powershell
BTCwallet automates running hot and cold storage wallets for multiple Bitcoin wallet applications.

BTCwallet is included with VaultApi and supports Sparrow, Blockstream Green, and just added support for Wasabi wallets.
To launch a wallet application, the command BTCwallet start is executed.
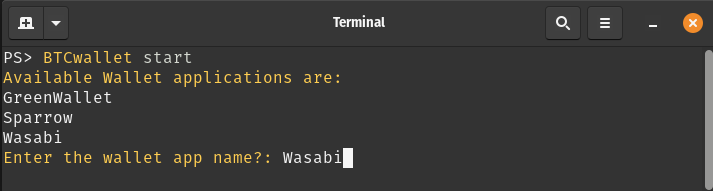
After responding to prompts for launching and initializing the Vault (not shown), the following prompts are presented.
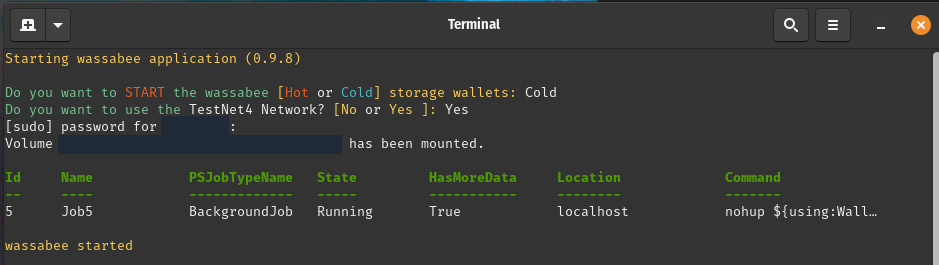
Now the Wasabi GUI application (a.k.a wassabee) is presented.

With the combination of VaultApi and BTCwallet one has a very secure self-hosted password manager along with a very secure way of protecting your Bitcoin wallet's data.
Care to follow me on my journey? If so, then check out the following links.
-
 @ 9be6a199:6e133301
2025-05-19 17:23:23
@ 9be6a199:6e133301
2025-05-19 17:23:23this is the content
-
 @ cae03c48:2a7d6671
2025-05-19 17:15:58
@ cae03c48:2a7d6671
2025-05-19 17:15:58Bitcoin Magazine

Nebraska’s New Mining Rules: Infrastructure Safeguard or Soft Ban in Disguise?Nebraska lawmakers have just passed Legislative Bill 526 (LB526), and while not explicitly anti-Bitcoin, its effects may be anything but neutral. With a unanimous 49-0 vote, the Legislature sent the bill to Governor Jim Pillen’s desk, where it’s expected to be signed into law. Supporters call it a commonsense infrastructure bill. Bitcoin miners call it a slow-motion exodus in the making.
On paper, LB526 is about large energy users. But in practice, it singles out Bitcoin mining facilities with one megawatt (MW) or greater loads and layers on operational constraints that look more like punishment than policy.
Cost Shifting, Public Shaming, and Curtailment
At the heart of LB526 is a mandate: miners must shoulder the costs of any infrastructure upgrades needed to support their demand. Utilities are empowered to demand direct payments or letters of credit after conducting a “load study.” And while the law pays lip service to “fairness” and non-discrimination, it’s clear who the target is. Bitcoin miners are the only industry named.
Further, mining operators must notify utilities in advance, submit to their interconnection requirements, and, critically, accept interruptible service. That means that when the grid gets tight, it’s miners who go dark first. Voluntary demand response, the hallmark of Bitcoin mining’s grid-friendly posture? Replaced with mandated curtailment and utility discretion.
And the kicker: public disclosure of energy consumption. Utilities must publish annual energy usage for each mining operation. No such requirement exists for other data-heavy sectors — not for cloud computing, not for AI clusters, not for Amazon data centers. Just Bitcoin. It’s not just surveillance, it’s signaling.
The Tax That Wasn’t, and the Costs That Remain
To its credit, the Legislature dropped an earlier provision that would’ve added a 2.5¢/kWh tax on mining. This punitive levy would’ve tacked 50% onto typical industrial rates. That tax would have been an open declaration of hostility. Removing it was necessary. But not sufficient.
Because what remains in LB526 is a less visible, but no less potent deterrent: uncertainty. Miners already operate on razor-thin margins and seek jurisdictions with predictable power costs and clear rules. Instead, Nebraska is offering infrastructure tolls, discretionary curtailment, and regulatory spotlighting.
The Market Responds: Warning Shots from Miners
Industry leaders didn’t stay silent. Marathon Digital Holdings, one of the largest publicly traded mining firms, testified that it had invested nearly $200 million in Nebraska and paid over $6.5 million in taxes, and warned that if LB526 passed, further expansion would likely be scrapped.
Their message was clear: Nebraska had been a pro-mining, pro-growth jurisdiction. But LB526 sends a signal that miners aren’t welcome, or at best, are second-class citizens in the energy economy. As one executive put it, “If the same rules don’t apply to other energy-intensive industries, this isn’t about infrastructure, it’s about discrimination.”
Others warned that mandatory curtailment replaces cooperative grid services with coercion. Bitcoin miners can, and do, offer real-time load shedding that stabilizes grids during peak demand. But that value proposition only works when there’s a market signal. LB526 turns it into a liability.
Politics, Power, and Public Utilities
Senator Mike Jacobson, the bill’s sponsor, insisted LB526 is agnostic toward Bitcoin. “This is about electricity usage,” he said. But that’s hard to square with a bill that surgically targets one user class.
Jacobson pointed to Kearney, where half the city’s power goes to a single mining facility. But rather than view that as an opportunity, a dispatchable industrial customer willing to scale up or down based on grid needs, the Legislature opted for risk aversion and central planning.
And in Nebraska’s public power model, that matters. With every utility publicly owned, the regulatory posture of the state isn’t advisory, it’s existential. There is no retail competition. If Nebraska’s power authorities begin treating Bitcoin miners like unreliable freeloaders rather than willing partners, miners have no recourse. Just the exit.
For now, LB526 awaits only the governor’s signature. Given that LB526 was introduced at the behest of the governor, it is likely to be signed. Once enacted, it will take effect October 1, 2025. Miners have until then to decide: adapt, relocate, or fold.
States like Texas, Wyoming, and North Dakota have gone the opposite direction, offering tax clarity, grid integration, and legal protection. Nebraska, once on that shortlist, may find itself dropping off the radar.
Bitcoin mining doesn’t need handouts. But it does need equal footing. LB526 imposes costs, limits flexibility, and broadcasts suspicion. If the goal was to balance innovation with infrastructure, the execution leaves much to be desired.
Because when one industry is burdened while others are exempted, when voluntary partnerships are replaced with mandates, and when operational data is made public for no clear reason, it’s not hard to see why miners view LB526 not as regulation, but as retaliation.
This is a guest post by Colin Crossman. Opinions expressed are entirely their own and do not necessarily reflect those of BTC, Inc. or Bitcoin Magazine_._
This post Nebraska’s New Mining Rules: Infrastructure Safeguard or Soft Ban in Disguise? first appeared on Bitcoin Magazine and is written by Colin Crossman.
-
 @ 3f68dede:779bb81d
2025-05-19 17:14:15
@ 3f68dede:779bb81d
2025-05-19 17:14:15 -
 @ cae03c48:2a7d6671
2025-05-19 17:14:11
@ cae03c48:2a7d6671
2025-05-19 17:14:11Bitcoin Magazine

Fold Unveils Bitcoin Gift Card, Pioneering Bitcoin in U.S. Retail Gift Card MarketFold, a leading Bitcoin financial services company, recently announced the launch of its Bitcoin Gift Card, marking the first step in integrating Bitcoin into the $300 billion U.S. retail gift card market. This innovative product enables consumers to purchase and gift bitcoin through familiar retail channels, is available now at Fold’s website and is expected to expand to major retailers nationwide throughout the year.
The Fold Bitcoin Gift Card allows users to acquire bitcoin for personal savings or as a gift, redeemable via the Fold app. “Once you buy that gift card, you can give it to someone or use it yourself. You open the Fold app, and your bitcoin appears,” said Will Reeves, Chairman and CEO of Fold, in an interview with Bitcoin Magazine. Available initially at the Fold website, the product will soon reach physical and online retail shelves, bringing Bitcoin to everyday shopping experiences.
This launch positions Fold as a trailblazer in making Bitcoin accessible through gift cards, the most popular gift in America.
“We’re now talking about Bitcoin gift cards on sale on the racks of the largest retailers in the country. You can pick up Bitcoin at the checkout line, buy it for yourself, or share it as a gift,” Reeves told Bitcoin Magazine.
The gift card, a white Bitcoin “B,” adorned by vibrant orange, taps into the retail market’s demand for alternative assets, following the success of Costco’s $200 million monthly gold sales.

Fold’s partnership with Totus, a gift card issuance provider, enables distribution through over 150,000 points of sale nationwide.
“In our announcement, we reference one of our partners who has direct distribution into all primary retailers in the country,” Reeves said. While specific retailer names will be revealed later, Fold plans to expand throughout 2025, ensuring Bitcoin’s presence in stores like grocery chains and gas stations. “Throughout the rest of this year, we’ll announce distribution partners, including some of the largest retailers in the US,” Reeves added.
The Bitcoin Gift Card targets millions of Americans curious about Bitcoin but hesitant to navigate apps or exchanges.
“This gift card gives us distribution directly to millions of Americans who may not be buying Bitcoin because they haven’t downloaded a new app, don’t have a brokerage account, or haven’t seen the ETF,” Reeves explained. By leveraging trusted retail channels, Fold is opening a new avenue for Bitcoin adoption.
Since 2019, Fold has empowered over 600,000 users with Bitcoin-based financial tools, holding over 1,485 Bitcoin in its treasury.
“I think there’s a real chance by the end of 2025 that Bitcoin becomes the most popular gift in America because of this card,” Reeves predicted.
This post Fold Unveils Bitcoin Gift Card, Pioneering Bitcoin in U.S. Retail Gift Card Market first appeared on Bitcoin Magazine and is written by Juan Galt.
-
 @ 3f68dede:779bb81d
2025-05-19 17:06:26
@ 3f68dede:779bb81d
2025-05-19 17:06:26 -
 @ 3f68dede:779bb81d
2025-05-19 17:04:13
@ 3f68dede:779bb81d
2025-05-19 17:04:13testing schedule
-
 @ 3f68dede:779bb81d
2025-05-19 17:02:54
@ 3f68dede:779bb81d
2025-05-19 17:02:54testing schedule
-
 @ 3f68dede:779bb81d
2025-05-19 17:02:33
@ 3f68dede:779bb81d
2025-05-19 17:02:33testing
-
 @ 3f68dede:779bb81d
2025-05-19 17:01:57
@ 3f68dede:779bb81d
2025-05-19 17:01:57testing schedule
-
 @ 005bc4de:ef11e1a2
2025-05-19 17:01:54
@ 005bc4de:ef11e1a2
2025-05-19 17:01:54Keys and Religion
Mixing
Normally, I'm not a fan mixing and comparing bitcoinesque things and religion. It's too banal and trite, too easy: the religion of Bitcoin, the allusion of Satoshi the savior, the "Book of Satoshi," even the "Genesis" block. But, today, I'll break my own rule.
Yesterday, I heard a Christian pastor speak of the "keys of the kingdom." My feeling is that, were you to ask the average Christian, "What is the key, or keys, to the kingdom?", and perhaps I'm wrong on this, but I think they'd answer, "Prayer." I've heard it many times, "Prayer is the key to the kingdom." It's an easy mantra to remember. And, prayer is important for a Christian, no question about it. However, Biblically, the phrase "keys of the kingdom" refers to something else.
As the pastor pointed out yesterday, Biblically there are two keys: the binding key and the loosing key. This refers to Matthew 16:19 where Jesus says:
I will give you the keys of the kingdom of heaven; whatever you bind on earth will be bound in heaven, and whatever you loose on earth will be loosed in heaven. Matthew 16:19 (NIV)
For context, back up a few verses. This statement above was made in a conversation between Jesus and his disciple Simon Peter.
15 Jesus asked, “But what about you?” he asked. “Who do you say I am?” 16 Simon Peter answered, “You are the Messiah, the Son of the living God.” 17 Jesus replied, “Blessed are you, Simon son of Jonah, for this was not revealed to you by flesh and blood, but by my Father in heaven. 18 And I tell you that you are Peter, and on this rock I will build my church, and the gates of Hades will not overcome it.
Although brief, this is a deep and rich exchange. Traditionally, this has been viewed as the moment that Christ instituted the Christian church, the passing of power and authority to the early church itself. There has been confusion over it too, particularly the "...on this rock I will build my church..." part of it. Jesus was referring to Simon Peter's statement of faith (...for this was not revealed to you by flesh and blood...) with the "this" being what Peter had just said, "You are the Messiah, the Son of the living God." The church would be built upon the rock of faith in Jesus as the Messiah.
The early Christian church thus established, Jesus instituted what's come to be called the "office of the keys." That is, Jesus grants authority to his "appointees" in the church to carry out his authority. In more practical terms, this is referring to those who have been called into church service, normally priests, to forgive or not forgive sins. When a priest or pastor forgives, or not, it is not that he is doing it by his own right or power. That priest is, after all, yet another sinful man as well. Instead, the priest forgives by Christ's authority which was handed down by Jesus himself in those words to Peter.
To use an analogy, suppose a general had to make a decision about foot soldiers on the front line, waiting there in the trenches. Due to some time constraint, a decision for action was needed imminently. However, suppose the general lacked some bit of information that could only be obtained at the front. So, the general wrote up a communique to the lieutenant stationed at the front saying, "You assess the situation, and you make the call, charge or pull back. I'll support your decision." A courier ran to the front, relayed the message to the lieutenant, and the lieutenant assessed and made the decision. Ultimately, even thought the lieutenant made the decision, the authority behind the decision lay with the general who had transferred his authority to the lieutenant.
This authority or office of the keys is mirrored in John 20:22-23, when the resurrected Jesus appears to his disciples and says, "If you forgive anyone’s sins, their sins are forgiven; if you do not forgive them, they are not forgiven.”
Going just one step further, recall there are two keys involved, binding and loosing, and there are two places involved, earth and heaven. Usually, priests and pastors are "in the business" of forgiving. Penitence or confession, when real, is forgiven. The priest has the authority to forgive, or "loose" the sinner from his wrongdoings here on earth. And, that forgiveness applies to heaven as well, the sin is atoned and reconciled with God.
But, what about when the person is unrepentant, unbothered by what is Biblically sinful, refuses to change his ways, and rather chooses to continue in sinful ways? The "binding" key says that the priest or appointed church leader can hold that person accountable, can bind that person to the sin and separation from God. Normally, we hear of "excommunication" from the church which is formally stating that a person is outside of the church body. The binding keys still bind, both on earth as being outside of the church and in heaven as being separated from God.
And bitcoin?
That's a lot of religion, and heavy religion at that. The question is, what does this have to do with bitcoin?
Keys.
Namely, this is about public and private keys. Loosing and binding keys. A bit more religion, then I'll get back to bitcoin.
Yesterday, the pastor spoke briefly about binding and loosing keys, and this where my thoughts about keys somehow morphed over into bitcoin. For some reason, I pictured Herod's Temple. There had been Solomon's temple, which was destroyed, and then there was Herod's which was known for its beauty and was the one during Jesus's time. But, let's recall the background on this...
The book of Exodus, and others in the Old Testament, outline in detail God's plan for the tabernacle (a traveling tent) and for the temple in Jerusalem.
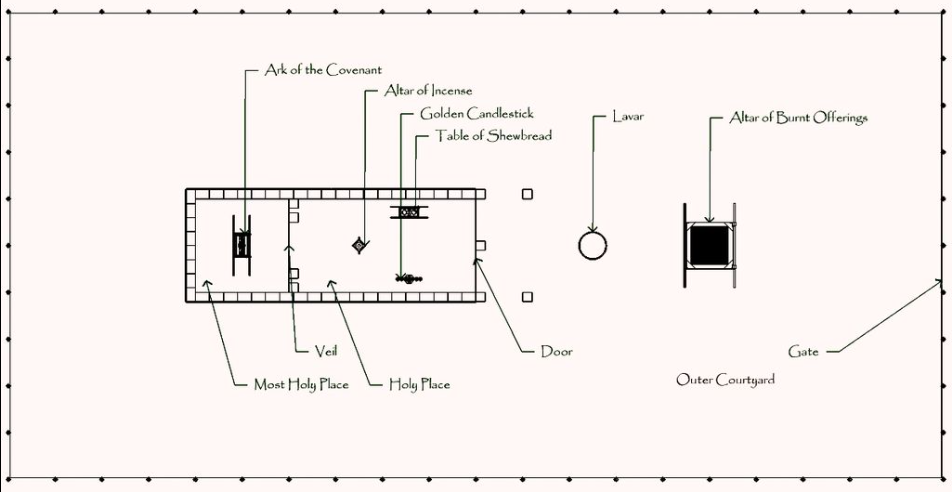
The tabernacle, overhead diagram. Image source: https://en.wikipedia.org/wiki/Tabernacle
You might recall the "history" lesson in Raiders of the Lost Ark. With the tabernacle and temple, one of the purposes was to house the ark of the covenant. Remember that the ark was the golden box that the Israelites carried around containing Moses's stone tablets with the Ten Commandments, some manna, and Aaron's staff. It held great power, God's power, and God literally met and spoke with the Levite priests hovering over the cherubim's wings.
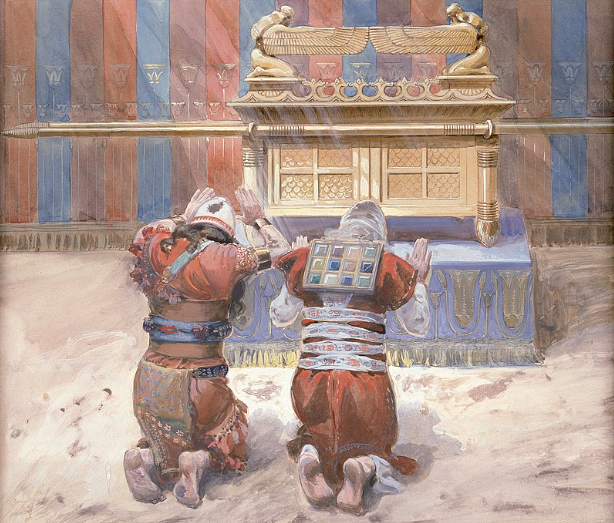
The ark of the covenant. Image source: https://en.wikipedia.org/wiki/Ark_of_the_Covenant
In the tabernacle and temple, the "Holy of Holies" was a room, separated by a heavy curtain. It was off limits to all because it was, well, holy of holies. A heavy curtain divided the Holy of Holies, or the "Most Holy Place", from the less-holy, "Holy Place."
Once a year, on the Day of Atonement, one person, the chief priest, was allowed to walk into the Holy of Holies. He would sprinkle the blood of a sacrificed animal onto the ark. This was done for the forgiveness of the people's sins. Although this was pre-Jesus's words, this was using the loosing keys and was loosing sin.
This was serious business and was taken seriously. For instance, the priests Nadab and Abihu improperly performed their sacrificial duties, they messed up the procedure, and were consumed by fire. Priesthood was a dangerous occupation, one slip up and you were scorched.
 The second temple, "Herod's Temple". Image source: https://en.wikipedia.org/wiki/Second_Temple
The second temple, "Herod's Temple". Image source: https://en.wikipedia.org/wiki/Second_TempleBack to keys...
Yesterday, for some reason when I heard about binding and loosing keys, I imagined the chief priest standing in front of the curtain. I imagined him taking a deep breath, collecting his thoughts, getting ready to go in. It had to be intimidating.
As he stood there, in my mind, he and everyone else was shut out. The Most Holy Place was bound and locked. Walking in meant getting scorched (again, the end of Raiders of the Lost Ark). Yet, that priest had the loosing key. He had, first, permission as chief priest to enter on the Day of Atonement, secondly, he had the sacrificial blood to loose sins. Although the binding key had locked the Holy of Holies and thus bound the sins of the people, the loosing key was about to loose their sins.
Cryptographic keys
And back to bitcoin...
Bitcoin, and cryptography in general, operate on public and private keys. Any flavor of "cryptocurrency", or even Nostr, has public and private keys. In a way, these are binding and loosing keys.
Say you have 1.0 BTC (that's 100,000,000 sats 😀). That BTC exists as a UTXO which can be seen by anyone viewing your public address. In this way, your bitcoin public key is your binding key...that UTXO, that bitcoin, is bound to your public key...it is locked in place behind that heavy curtain. It will be there forever, unless there is an intervention...
You also have your private key, your loosing key. You can apply your private key to loose that UTXO, that bitcoin, and to send it along to wherever.
This is like law and gospel: sin is binding, however Jesus frees it. A bitcoin UTXO is bound until a private key looses it.
Nostr offers a somewhat similar illustration. You have an npub publicly and and nsec secretly or privately. If you were to write a note, your private nsec is needed as a loosing key to free that message, to broadcast it to the world. Once broadcast, it can be seen by all, however it is still inextricably bound or tied to your public key (your npub). Your npub is your binding key and your message is bound to it.
Summed
I'm not sure this binding and loosing keys in religion, and public and private keys in cryptography is the best comparison in the world. It's probably a terrible comparison. But, this is what came to my mind yesterday.
And, so, the mixing of religion and bitcoin is now officially over.