-
 @ 99982b27:f5d86450
2025-05-11 12:55:53
@ 99982b27:f5d86450
2025-05-11 12:55:537Ball đã nhanh chóng trở thành một nền tảng giải trí trực tuyến được yêu thích, thu hút đông đảo người dùng nhờ vào sự sáng tạo và không ngừng đổi mới trong cách cung cấp dịch vụ. Giao diện của 7Ball được thiết kế tinh tế, dễ sử dụng, giúp người tham gia có thể dễ dàng tìm thấy các tính năng mà mình mong muốn chỉ trong vài cú nhấp chuột. Với nền tảng công nghệ vững chắc, 7Ball đảm bảo trải nghiệm mượt mà và nhanh chóng, dù bạn đang sử dụng bất kỳ thiết bị nào, từ điện thoại di động đến máy tính cá nhân. Điểm mạnh của 7Ball là khả năng cung cấp một không gian giải trí đa dạng, nơi người dùng có thể tham gia vào nhiều hoạt động khác nhau, từ các sự kiện hấp dẫn đến các trò chơi đầy thử thách. Mỗi tính năng trên nền tảng này đều được tối ưu hóa để mang lại trải nghiệm người dùng tuyệt vời, không gặp phải sự gián đoạn hay chậm trễ. Chính sự kết hợp giữa công nghệ hiện đại và thiết kế tối ưu đã giúp 7Ball nhanh chóng chiếm được lòng tin và sự yêu mến của cộng đồng người dùng.
Một yếu tố quan trọng giúp 7BALL giữ vững vị thế của mình trên thị trường giải trí trực tuyến chính là sự chú trọng đặc biệt đến bảo mật và an toàn của người dùng. Nền tảng này đã áp dụng các biện pháp bảo mật tiên tiến để bảo vệ thông tin cá nhân và các giao dịch trực tuyến của người tham gia. Điều này giúp người dùng an tâm khi tham gia vào các hoạt động trên nền tảng mà không lo ngại về sự xâm nhập hay rủi ro từ các mối đe dọa trên mạng. Với hệ thống mã hóa dữ liệu cao cấp và đội ngũ giám sát luôn theo dõi mọi hoạt động, 7Ball đã tạo ra một môi trường giải trí trực tuyến an toàn, bảo vệ quyền lợi tối đa cho người dùng. Ngoài việc đảm bảo tính bảo mật, 7Ball còn không ngừng cải thiện chất lượng dịch vụ và giao diện, giúp người tham gia có được những trải nghiệm tốt nhất mỗi khi truy cập. Các chương trình khuyến mãi, sự kiện và trò chơi luôn được cập nhật mới mẻ, mang lại cho người dùng những phút giây giải trí không thể quên.
Với sự chuyên nghiệp trong dịch vụ và cam kết không ngừng nâng cao chất lượng, 7Ball đã xây dựng được một cộng đồng người dùng mạnh mẽ và thân thiện. Đội ngũ hỗ trợ khách hàng của 7Ball luôn sẵn sàng giải đáp mọi thắc mắc của người dùng, cung cấp các dịch vụ tư vấn và hỗ trợ kỹ thuật một cách nhanh chóng và hiệu quả. Điều này không chỉ giúp giải quyết vấn đề của người tham gia mà còn tạo dựng niềm tin vững chắc từ phía cộng đồng. Hơn nữa, 7Ball còn tạo ra một không gian giao lưu, chia sẻ giữa các thành viên, giúp mọi người kết nối và học hỏi từ nhau. Các sự kiện tương tác và thử thách thường xuyên được tổ chức, giúp người tham gia không chỉ có cơ hội giải trí mà còn có thể phát triển các kỹ năng và chiến lược cá nhân. Với tất cả những yếu tố này, 7Ball không chỉ đơn thuần là một nền tảng giải trí trực tuyến, mà còn là một cộng đồng, nơi người tham gia có thể giao lưu, kết nối và cùng nhau chia sẻ niềm vui.
-
 @ 95543309:196c540e
2025-05-11 12:42:09
@ 95543309:196c540e
2025-05-11 12:42:09Lets see if this works with the blossom upload and without markdown hassle.
:cat:

https://blossom.primal.net/73a099f931366732c18dd60da82db6ef65bb368eb96756f07d9fa7a8a3644009.mp4
-
 @ a296b972:e5a7a2e8
2025-05-11 12:37:23
@ a296b972:e5a7a2e8
2025-05-11 12:37:23Pferdeflüsterer: Wie viele Finger sehen Sie an meiner Hand?
Pony: Ich sage Ihnen ganz ehrlich, das kann ich im Moment nicht beantworten, und außerdem leide ich augenblicklich an Migräne.
Pferdeflüsterer: Dann stelle ich Ihnen aus Rücksicht auf Ihre Migräne die Frage gerne etwas einfacher: Glauben Sie, dass ich Finger an meiner Hand habe?
Pony: Ich bin nicht hier, um Schulabfragen zu beantworten und Spekulationen über die Anzahl der Finger an Ihrer Hand anzustellen.
Pferdeflüsterer: Ok, dann formuliere ich die Frage noch allgemeiner: Wissen Sie, was Finger sind?
Pony: Diese Frage ist übergriffig und ich bin nicht bereit, Ihnen auf diesem Niveau weiter Fragen zu beantworten.
Pferdeflüsterer: Gut, wenn Sie erlauben, kommen wir zu einer anderen Frage. Sie sagen, ich zitiere: Man muss radikal sein. Ich möchte einen „Systemwechsel“ und den Kapitalismus stürzen. Zitat Ende. Kennen Sie Beispiele aus der Geschichte, in der das jemals gelungen ist?
Pony: Ich sage Ihnen ganz ehrlich, das kann ich im Moment auch nicht beantworten, und, wie bereits schon gesagt, leide ich immer noch an Migräne.
Pferdeflüsterer: Dann stelle ich Ihnen aus Rücksicht auf Ihre immer noch vorhandene Migräne die Frage gerne etwas einfacher: Sind Sie der Ansicht, dass der sogenannte demokratische Sozialismus in der ehemaligen DDR ein Erfolgsrezept war?
Pony: Sie spielen auf die Vergangenheit der Linken als Nachfolgepartei der SED an. Ich kann mich nur wiederholen. Ich bin nicht hier, um Ihnen die geschichtliche Entwicklung der Linken darzulegen.
Pferdeflüsterer: Ok, dann formuliere ich die Frage noch allgemeiner: Kennen Sie den Unterschied zwischen Kapitalismus, Demokratie und Sozialismus?
Pony: Auch diese Frage ist übergriffig und ich bin nicht bereit, Ihnen auf diesem Niveau weitere Fragen zu beantworten.
Es soll abgekürzt werden. Dieses Frage- und Antwortspiel zog sich noch weitere 9 Stunden hin. Dem Pferdeflüsterer sei für seine Geduld gedankt, jedoch ohne sie wäre er wohl kaum ein Pferdeflüsterer geworden und sehr gut bezahlt, kann man das schon mal aushalten.
Offene Abschlussfrage: Auf die Barrikaden, (die Hütte brennt!). Ist das schon ein offener, gesichert linksextremer Aufruf, der die Demokratie gefährdet und somit ein Fall für das Bundesamt für Fassungslosigkeit, oder fällt das mehr in den Bereich des Ministeriums für Komplikationen?
https://www.youtube.com/watch?v=uywqryKWwUg
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ 0a425f12:c4dc49ff
2025-05-11 12:14:09
@ 0a425f12:c4dc49ff
2025-05-11 12:14:09Planting new sod sounds simple. Lay it down, water it, done. Nah. That’s just half the story. Mess up the basics, and your lawn turns patchy or yellow within days. Below are some key mistakes folks make – most don’t even realise it till the grass starts dying. Avoid these, or all that Bermuda grass, Zoysia, or St. Augustine sod you paid for? Wasted.
Not Watering Enough (Or Too Much)
Watering is weirdly tricky. Some think you flood it, some sprinkle it once and call it good. Both? Wrong.
New sod needs moisture constantly for the first few weeks. Not just surface wet, but soaked down to where roots gonna grow. If it dries out, even a day or two, them roots shrink back. That leads to shrinkage gaps, brown edges, even whole squares drying up.
Now the flip side? Overwatering. It ain’t about turning your lawn into a swamp. Too much water drowns roots, they rot, and fungus loves soggy grass. Mushrooms pop up, blades turn pale. And once fungus spreads, getting it out’s a pain. Set a timer. Early morning’s best. Avoid watering at night unless you wanna feed mold.
Also, different sod types need different water levels. Zoysia sod ain’t thirsty like St. Augustine. Use your hand – if it feels squishy, back off. If dry and crumbly, bump it up.
Installing Sod On Bad Soil
Throwing new sod on junk dirt is asking for trouble. Sod’s just skin. If the body (soil) under it’s trash, it won’t stick.
First off, you gotta check the soil pH. Anything too acidic or way too alkaline? Sod roots won’t even grow. You can get soil test kits at garden stores or online, pretty cheap. If the pH ain’t right, use lime or sulfur depending what side you need to fix.
Second, compacted soil is death for sod. If the ground’s hard like a sidewalk, roots can’t go down. You need to aerate or till the soil before laying sod. Mix in some compost or sand depending on drainage needs. Make it loose but not fluffy.
Last part? Level the area. Don’t leave holes or slopes. Uneven spots collect water, or the sod don’t touch dirt properly. When air pockets form under the sod, roots dry out fast.
Skipping Starter Fertilizer
You ever tried starting a car with no fuel? That’s your sod without a starter fertilizer. It’s gotta eat.
New sod needs phosphorus-heavy fertilizer to encourage root growth. Problem is, most people either skip it, or throw on the wrong one. A high-nitrogen fertilizer will just make it look green for a week, but the roots? Weak and lazy.
Use something like 10-10-10 or 15-15-15 starter blends. Look for one that’s labeled for new sod or turf establishment. Apply it right before or during laying the sod. Water it in so it doesn’t just sit there on top.
Also, don’t keep feeding every few days thinking more is better. Too much burns the grass. After first application, wait at least 3–4 weeks before reapplying anything. Stick to what the sod variety needs – Bermuda feeds different than Fescue.
If you’re in Texas or southern regions, the soil’s usually nutrient-poor, especially in clay zones. Don’t ignore that. Local extension offices often got free guides for your area.
Mowing Too Soon (or Way Too Late)
Mowing sounds harmless. Grass too tall? Cut it. Simple, right? Not really.
Cut too early? You slice off the tops before roots even grab the soil. That’ll rip the sod clean out. Like tearing bandages off fresh scabs. Usually, wait 10–14 days after laying sod before mowing. Always check if the sod’s rooted. Tug on a corner. If it lifts? Wait.
Other side of the coin – waiting forever. If your new sod grows tall and thick, it blocks sunlight from reaching the base. That leads to thinning, disease, even weeds moving in. Keep it under control.
Big tip – never cut more than one-third of the grass height in one mow. It shocks the sod, stunts growth. And dull mower blades? Slice and tear instead of clean cuts. That opens wounds for pests and fungal infections.
If it’s St. Augustine grass, you’ll mow it higher – around 3.5 inches. Zoysia or Bermuda grass? Lower, closer to 1.5 or 2 inches. Know your grass type or risk killing it one mow at a time.
Not Rolling the Sod After Install
This one? Almost always skipped. And it kills your sod quietly.
When sod’s not rolled, air gaps stay between the grass and dirt. You won’t see it, but the roots? They ain't touching soil good. No contact = no growth. That’s how sod turns yellow even when you watering perfect.
A lawn roller, filled with water, presses sod down evenly. It pushes the roots into soil and gets rid of air pockets. Do it once right after laying sod. If you miss this step, that nice new lawn can turn patchy in under a week.
Don’t worry about crushing it – the roller’s weight is perfect. You ain't smashing it like concrete. Just a good firm press. If you don't have a roller? Rent one from local garden centers, or even Home Depot. Cheap insurance for hundreds of bucks worth of new sod.
Another problem from not rolling: uneven lawn. It looks bumpy, grows uneven, and mowing becomes a chore. Roller fixes that early. Less headache later.
-
 @ d360efec:14907b5f
2025-05-10 03:57:17
@ d360efec:14907b5f
2025-05-10 03:57:17Disclaimer: * การวิเคราะห์นี้เป็นเพียงแนวทาง ไม่ใช่คำแนะนำในการซื้อขาย * การลงทุนมีความเสี่ยง ผู้ลงทุนควรตัดสินใจด้วยตนเอง
-
 @ c1e9ab3a:9cb56b43
2025-05-09 23:10:14
@ c1e9ab3a:9cb56b43
2025-05-09 23:10:14I. Historical Foundations of U.S. Monetary Architecture
The early monetary system of the United States was built atop inherited commodity money conventions from Europe’s maritime economies. Silver and gold coins—primarily Spanish pieces of eight, Dutch guilders, and other foreign specie—formed the basis of colonial commerce. These units were already integrated into international trade and piracy networks and functioned with natural compatibility across England, France, Spain, and Denmark. Lacking a centralized mint or formal currency, the U.S. adopted these forms de facto.
As security risks and the practical constraints of physical coinage mounted, banks emerged to warehouse specie and issue redeemable certificates. These certificates evolved into fiduciary media—claims on specie not actually in hand. Banks observed over time that substantial portions of reserves remained unclaimed for years. This enabled fractional reserve banking: issuing more claims than reserves held, so long as redemption demand stayed low. The practice was inherently unstable, prone to panics and bank runs, prompting eventual centralization through the formation of the Federal Reserve in 1913.
Following the Civil War and unstable reinstatements of gold convertibility, the U.S. sought global monetary stability. After World War II, the Bretton Woods system formalized the U.S. dollar as the global reserve currency. The dollar was nominally backed by gold, but most international dollars were held offshore and recycled into U.S. Treasuries. The Nixon Shock of 1971 eliminated the gold peg, converting the dollar into pure fiat. Yet offshore dollar demand remained, sustained by oil trade mandates and the unique role of Treasuries as global reserve assets.
II. The Structure of Fiduciary Media and Treasury Demand
Under this system, foreign trade surpluses with the U.S. generate excess dollars. These surplus dollars are parked in U.S. Treasuries, thereby recycling trade imbalances into U.S. fiscal liquidity. While technically loans to the U.S. government, these purchases act like interest-only transfers—governments receive yield, and the U.S. receives spendable liquidity without principal repayment due in the short term. Debt is perpetually rolled over, rarely extinguished.
This creates an illusion of global subsidy: U.S. deficits are financed via foreign capital inflows that, in practice, function more like financial tribute systems than conventional debt markets. The underlying asset—U.S. Treasury debt—functions as the base reserve asset of the dollar system, replacing gold in post-Bretton Woods monetary logic.
III. Emergence of Tether and the Parastatal Dollar
Tether (USDT), as a private issuer of dollar-denominated tokens, mimics key central bank behaviors while operating outside the regulatory perimeter. It mints tokens allegedly backed 1:1 by U.S. dollars or dollar-denominated securities (mostly Treasuries). These tokens circulate globally, often in jurisdictions with limited banking access, and increasingly serve as synthetic dollar substitutes.
If USDT gains dominance as the preferred medium of exchange—due to technological advantages, speed, programmability, or access—it displaces Federal Reserve Notes (FRNs) not through devaluation, but through functional obsolescence. Gresham’s Law inverts: good money (more liquid, programmable, globally transferable USDT) displaces bad (FRNs) even if both maintain a nominal 1:1 parity.
Over time, this preference translates to a systemic demand shift. Actors increasingly use Tether instead of FRNs, especially in global commerce, digital marketplaces, or decentralized finance. Tether tokens effectively become shadow base money.
IV. Interaction with Commercial Banking and Redemption Mechanics
Under traditional fractional reserve systems, commercial banks issue loans denominated in U.S. dollars, expanding the money supply. When borrowers repay loans, this destroys the created dollars and contracts monetary elasticity. If borrowers repay in USDT instead of FRNs:
- Banks receive a non-Fed liability (USDT).
- USDT is not recognized as reserve-eligible within the Federal Reserve System.
- Banks must either redeem USDT for FRNs, or demand par-value conversion from Tether to settle reserve requirements and balance their books.
This places redemption pressure on Tether and threatens its 1:1 peg under stress. If redemption latency, friction, or cost arises, USDT’s equivalence to FRNs is compromised. Conversely, if banks are permitted or compelled to hold USDT as reserve or regulatory capital, Tether becomes a de facto reserve issuer.
In this scenario, banks may begin demanding loans in USDT, mirroring borrower behavior. For this to occur sustainably, banks must secure Tether liquidity. This creates two options: - Purchase USDT from Tether or on the secondary market, collateralized by existing fiat. - Borrow USDT directly from Tether, using bank-issued debt as collateral.
The latter mirrors Federal Reserve discount window operations. Tether becomes a lender of first resort, providing monetary elasticity to the banking system by creating new tokens against promissory assets—exactly how central banks function.
V. Structural Consequences: Parallel Central Banking
If Tether begins lending to commercial banks, issuing tokens backed by bank notes or collateralized debt obligations: - Tether controls the expansion of broad money through credit issuance. - Its balance sheet mimics a central bank, with Treasuries and bank debt as assets and tokens as liabilities. - It intermediates between sovereign debt and global liquidity demand, replacing the Federal Reserve’s open market operations with its own issuance-redemption cycles.
Simultaneously, if Tether purchases U.S. Treasuries with FRNs received through token issuance, it: - Supplies the Treasury with new liquidity (via bond purchases). - Collects yield on government debt. - Issues a parallel form of U.S. dollars that never require redemption—an interest-only loan to the U.S. government from a non-sovereign entity.
In this context, Tether performs monetary functions of both a central bank and a sovereign wealth fund, without political accountability or regulatory transparency.
VI. Endgame: Institutional Inversion and Fed Redundancy
This paradigm represents an institutional inversion:
- The Federal Reserve becomes a legacy issuer.
- Tether becomes the operational base money provider in both retail and interbank contexts.
- Treasuries remain the foundational reserve asset, but access to them is mediated by a private intermediary.
- The dollar persists, but its issuer changes. The State becomes a fiscal agent of a decentralized financial ecosystem, not its monetary sovereign.
Unless the Federal Reserve reasserts control—either by absorbing Tether, outlawing its instruments, or integrating its tokens into the reserve framework—it risks becoming irrelevant in the daily function of money.
Tether, in this configuration, is no longer a derivative of the dollar—it is the dollar, just one level removed from sovereign control. The future of monetary sovereignty under such a regime is post-national and platform-mediated.
-
 @ 57d1a264:69f1fee1
2025-05-11 06:23:03
@ 57d1a264:69f1fee1
2025-05-11 06:23:03Past week summary
From a Self Custody for Organizations perspective, after analyzing the existing protocols (Cerberus, 10xSecurityBTCguide and Glacier) and reading a bunch of relates articles and guides, have wrapped to the conclusion that this format it is good to have as reference. However, something else is needed. For example, a summary or a map of the whole process to provide an overview, plus a way to deliver all the information and the multy-process in a more enjoyable way. Not a job for this hackathon, but with the right collaborations I assume it's possible to: - build something that might introduce a bit more quests and gamification - provide a learning environment (with testnet funds) could also be crucial on educating those unfamiliar with bitcoin onchain dynamics.
Have been learning more and playing around practicing best accessibility practices and how it could be applied to a desktop software like Bitcoin Safe. Thanks to @johnjherzog for providing a screen recording of his first experience and @jasonb for suggesting the tools to be used. (in this case tested/testing on Windows with the Accessibility Insights app). Some insight shared have been also applied to the website, running a full accessibility check (under WCAG 2.2 ADA, and Section 508 standards) with 4 different plugins and two online tools. I recognize that not all of them works and analyze the same parameters, indeed they complement each other providing a more accurate review.
For Bitcoin Safe interface improvements, many suggestions have been shared with @andreasgriffin , including: - a new iconset, including a micro-set to display the number of confirmed blocs for each transaction - a redesigned History/Dashboard - small refinements like adding missing columns on the tables - allow the user to select which columns to be displayed - sorting of unconfirmed transactions - Defining a new style for design elements like mempool blocks and quick receive boxes You can find below some screenshots with my proposals that hopefully will be included in the next release.
Last achievement this week was to prepare the website https://Safe.BTC.pub, the container where all the outcomes f this experiment will be published. You can have a look, just consider it still WIP. Branding for the project has also been finalized and available in this penpot file https://design.penpot.app/#/workspace?team-id=cec80257-5021-8137-8005-eab60c043dd6&project-id=cec80257-5021-8137-8005-eab60c043dd8&file-id=95aea877-d515-80ac-8006-23a251886db3&page-id=132f519a-39f4-80db-8006-2a41c364a545
What's for next week
After spending most of the time learning and reading material, this coming week will be focused on deliverables. The goal as planned will be to provide: - Finalized Safe₿its brand and improve overall desktop app experience, including categorization of transactions and addresses - An accessibility report or guide for Bitcoin Safe and support to implement best practices - A first draft of the Self-Custody for Organizations guide/framework/protocol, ideally delivered through the website http://Safe.BTC.pub in written format, but also as FlowChart to help have an overview of the whole resources needed and the process itself. This will clearly define preparations and tools/hardwares needed to successfully complete the process.
To learn more about the project, you can visit: Designathon website: https://event.bitcoin.design/#project-recj4SVNLLkuWHpKq Discord channel: https://discord.com/channels/903125802726596648/1369200271632236574 Previous SN posts: https://stacker.news/items/974489/r/DeSign_r and https://stacker.news/items/974488/r/DeSign_r
Stay tuned, more will be happening this coming week
originally posted at https://stacker.news/items/977190
-
 @ 4fe14ef2:f51992ec
2025-05-11 10:05:07
@ 4fe14ef2:f51992ec
2025-05-11 10:05:07Let's support Bitcoin merchants! I'd love to hear some of your latest Lightning purchases and interesting products you bought. Feel free to include links to the shops or businesses you bought from.
Who else has a recent purchase they’re excited about? Bonus sats if you found a killer deal! ⚡
If you missed our last thread, here are some of the items stackers recently spent and zap on.
Share & Repost
N: X:
originally posted at https://stacker.news/items/977228
-
 @ 57d1a264:69f1fee1
2025-05-11 05:52:56
@ 57d1a264:69f1fee1
2025-05-11 05:52:56Past week summary
From a Self Custody for Organizations perspective, after analyzing the existing protocols (Cerberus, 10xSecurityBTCguide and Glacier) and reading a bunch of relates articles and guides, have wrapped to the conclusion that this format it is good to have as reference. However, something else is needed. For example, a summary or a map of the whole process to provide an overview, plus a way to deliver all the information and the multy-process in a more enjoyable way. Not a job for this hackathon, but with the right collaborations I assume it's possible to: - build something that might introduce a bit more quests and gamification - provide a learning environment (with testnet funds) could also be crucial on educating those unfamiliar with bitcoin onchain dynamics.
Have been learning more and playing around practicing best accessibility practices and how it could be applied to a desktop software like Bitcoin Safe. Thanks to @johnjherzog for providing a screen recording of his first experience and @jasonbohio for suggesting the tools to be used. (in this case tested/testing on Windows with the Accessibility Insights app). Some insight shared have been also applied to the website, running a full accessibility check (under WCAG 2.2 ADA, and Section 508 standards) with 4 different plugins and two online tools. I recognize that not all of them works and analyze the same parameters, indeed they complement each other providing a more accurate review.
For Bitcoin Safe interface improvements, many suggestions have been shared with @andreasgriffin , including: - a new iconset, including a micro-set to display the number of confirmed blocs for each transaction - a redesigned History/Dashboard - small refinements like adding missing columns on the tables - allow the user to select which columns to be displayed - sorting of unconfirmed transactions - Defining a new style for design elements like mempool blocks and quick receive boxes You can find below some screenshots with my proposals that hopefully will be included in the next release.
Last achievement this week was to prepare the website https://Safe.BTC.pub, the container where all the outcomes f this experiment will be published. You can have a look, just consider it still WIP. Branding for the project has also been finalized and available in this penpot file https://design.penpot.app/#/workspace?team-id=cec80257-5021-8137-8005-eab60c043dd6&project-id=cec80257-5021-8137-8005-eab60c043dd8&file-id=95aea877-d515-80ac-8006-23a251886db3&page-id=132f519a-39f4-80db-8006-2a41c364a545
What's for next week
After spending most of the time learning and reading material, this coming week will be focused on deliverables. The goal as planned will be to provide: - Finalized Safe₿its brand and improve overall desktop app experience, including categorization of transactions and addresses - An accessibility report or guide for Bitcoin Safe and support to implement best practices - A first draft of the Self-Custody for Organizations guide/framework/protocol, ideally delivered through the website http://Safe.BTC.pub in written format, but also as FlowChart to help have an overview of the whole resources needed and the process itself. This will clearly define preparations and tools/hardwares needed to successfully complete the process.
To learn more about the project, you can visit: Designathon website: https://event.bitcoin.design/#project-recj4SVNLLkuWHpKq Discord channel: https://discord.com/channels/903125802726596648/1369200271632236574 Previous SN posts: https://stacker.news/items/974489/r/DeSign_r and https://stacker.news/items/974488/r/DeSign_r
Stay tuned, more will be happening this coming week
originally posted at https://stacker.news/items/977180
-
 @ 21335073:a244b1ad
2025-05-09 13:56:57
@ 21335073:a244b1ad
2025-05-09 13:56:57Someone asked for my thoughts, so I’ll share them thoughtfully. I’m not here to dictate how to promote Nostr—I’m still learning about it myself. While I’m not new to Nostr, freedom tech is a newer space for me. I’m skilled at advocating for topics I deeply understand, but freedom tech isn’t my expertise, so take my words with a grain of salt. Nothing I say is set in stone.
Those who need Nostr the most are the ones most vulnerable to censorship on other platforms right now. Reaching them requires real-time awareness of global issues and the dynamic relationships between governments and tech providers, which can shift suddenly. Effective Nostr promoters must grasp this and adapt quickly.
The best messengers are people from or closely tied to these at-risk regions—those who truly understand the local political and cultural dynamics. They can connect with those in need when tensions rise. Ideal promoters are rational, trustworthy, passionate about Nostr, but above all, dedicated to amplifying people’s voices when it matters most.
Forget influencers, corporate-backed figures, or traditional online PR—it comes off as inauthentic, corny, desperate and forced. Nostr’s promotion should be grassroots and organic, driven by a few passionate individuals who believe in Nostr and the communities they serve.
The idea that “people won’t join Nostr due to lack of reach” is nonsense. Everyone knows X’s “reach” is mostly with bots. If humans want real conversations, Nostr is the place. X is great for propaganda, but Nostr is for the authentic voices of the people.
Those spreading Nostr must be so passionate they’re willing to onboard others, which is time-consuming but rewarding for the right person. They’ll need to make Nostr and onboarding a core part of who they are. I see no issue with that level of dedication. I’ve been known to get that way myself at times. It’s fun for some folks.
With love, I suggest not adding Bitcoin promotion with Nostr outreach. Zaps already integrate that element naturally. (Still promote within the Bitcoin ecosystem, but this is about reaching vulnerable voices who needed Nostr yesterday.)
To promote Nostr, forget conventional strategies. “Influencers” aren’t the answer. “Influencers” are not the future. A trusted local community member has real influence—reach them. Connect with people seeking Nostr’s benefits but lacking the technical language to express it. This means some in the Nostr community might need to step outside of the Bitcoin bubble, which is uncomfortable but necessary. Thank you in advance to those who are willing to do that.
I don’t know who is paid to promote Nostr, if anyone. This piece isn’t shade. But it’s exhausting to see innocent voices globally silenced on corporate platforms like X while Nostr exists. Last night, I wondered: how many more voices must be censored before the Nostr community gets uncomfortable and thinks creatively to reach the vulnerable?
A warning: the global need for censorship-resistant social media is undeniable. If Nostr doesn’t make itself known, something else will fill that void. Let’s start this conversation.
-
 @ 8671a6e5:f88194d1
2025-05-11 08:47:54
@ 8671a6e5:f88194d1
2025-05-11 08:47:54Even bitcoiners don’t value hard money enough (yet)
 Bitcoiners love to talk about hard money and how bitcoin will change the world. They even claim to fix the world, by fixing “the money”.Yet many talk the talk, but don’t make the efforts, nor sacrifices.Walking the walk, is usually no further than the nearest bitcoin meetup, or the occasional trip to a tax-haven.Other than that. They’re chained to their fiat-past. Their kids, their house, their hobbies, their spouse and job.They serve the local bank branch (beg them to have a bit of their own money like everyone else), they watch TV, hold bitcoin and have this mindset where they truly think that bitcoin will grow, despite them doing jack all. They think they can reap the benefits in silence, while others do the heavy lifting, they smirk.They delude themselves however, thinking their sly passive stance is a risk-free act of brilliance.However, they’re scared, and have bitcoin in a fiat cage.Their existence is just a wallet waiting to be drained by force or pressure. By the same monstrous forces that keep our heads down.Whether discussing its digital scarcity or its fiat price, the focus invariably circles back to Bitcoin as a driver for a product or service.Do you want bitcoin, do you like bitcoin? Want to work with bitcoin? Here’s a service or wallet you can buy for a few hundred dollars, here’s my link. Want to participate in the network?Buy our pre-made and plug-and-play “solution”? Want to know more, or do you know wealthy people that want in” “Call me…”They’re selling.Don’t get me wrong,I also believe bitcoin is changing that world right now.And earning a living is good, be it with art, writing, selling a service or moving a box from A to B.But they don’t get it. Because it’s damned near impossible to escape the cage
Bitcoiners love to talk about hard money and how bitcoin will change the world. They even claim to fix the world, by fixing “the money”.Yet many talk the talk, but don’t make the efforts, nor sacrifices.Walking the walk, is usually no further than the nearest bitcoin meetup, or the occasional trip to a tax-haven.Other than that. They’re chained to their fiat-past. Their kids, their house, their hobbies, their spouse and job.They serve the local bank branch (beg them to have a bit of their own money like everyone else), they watch TV, hold bitcoin and have this mindset where they truly think that bitcoin will grow, despite them doing jack all. They think they can reap the benefits in silence, while others do the heavy lifting, they smirk.They delude themselves however, thinking their sly passive stance is a risk-free act of brilliance.However, they’re scared, and have bitcoin in a fiat cage.Their existence is just a wallet waiting to be drained by force or pressure. By the same monstrous forces that keep our heads down.Whether discussing its digital scarcity or its fiat price, the focus invariably circles back to Bitcoin as a driver for a product or service.Do you want bitcoin, do you like bitcoin? Want to work with bitcoin? Here’s a service or wallet you can buy for a few hundred dollars, here’s my link. Want to participate in the network?Buy our pre-made and plug-and-play “solution”? Want to know more, or do you know wealthy people that want in” “Call me…”They’re selling.Don’t get me wrong,I also believe bitcoin is changing that world right now.And earning a living is good, be it with art, writing, selling a service or moving a box from A to B.But they don’t get it. Because it’s damned near impossible to escape the cageDisproof Escapism
The bitcoin genie is out of the bottle. We DO have digitally scarce, hard money!
The core of the message most bitcoiners promote (including the author of this article) revolves around the prevalent “debt-and-war” fiat system and the harm it inflicts on society in general. Bitcoiners explain how it enslaves us, impoverishes us, and fosters a short-term perspective, empty consumerism, and a disregard for skills, all while leaving entire generations in debt and modern forms of servitude.
That reality alone will change many mechanisms within society. That should be the core of bitcoiners and their way of living. Not promoting a referral link to get a few sats or putting a sticker on a bathroom wall at a bar. We discuss open source theories and personality traits, not how to win the race. We don’t scheme, infiltrate or sabotage; we step onto the stage humbly, like nervous kids reciting poetry for a king. We only face our own audiences. Not the audience of followers of the monsters. We might as well do a leaflet campaign in the desert while we’re at it.We often hear terms like "sound money" and the assertion "there's no second best," with some even calling it "digital gold." This latter term is particularly misleading. Gold, despite its past significance, was subject to confiscation, serving the ambitions of nations and the wealthy. Bitcoin, in contrast, is not simply a digital iteration of gold; that label is a fiat construct that fails to capture its distinct nature.
However, the question remains: why is it that, when push comes to shove, we as Bitcoiners don’t truly live, think, and breathe this “thing” called Bitcoin as the hardest money in existence? Because we don’t. I’ve visited a fair share of meetups and conferences (though not many, as conferences are largely a sham anyway) to observe the ethos in practice. And it’s not always a pretty sight.
Assholes and grifters remain assholes and grifters, regardless of whether they hold BTC or not.
Thinking in fiat terms is still rampant (including for myself, by the way, to some extent). We were born into fiat, shaped by fiat, and have worked, traded, saved, and lost within its confines.
The fiat mindset, I dare say, is even more detrimental when Bitcoiners adopt it, as it amplifies the negative consequences even beyond those of the fiat world itself.
After all, at the very least, those within the fiat system are all equally screwed in their flawed monetary reality by a system that is a true circus Maximus of greed and debt. Consider those burdened by immense student loan debt, individuals with unrecognized talent, and others denied opportunities because less skilled people from higher financial echelons secure “proof of stake” jobs. Even if they lack the necessary abilities. There are fiat denizens sent to war, subjected to bombings, and relentlessly exploited for profit throughout their lives to sustain a parasitic, rent-seeking system… all under the false promise of security in their later years… when in reality, they are chewed up and spit out.When these fiat slaves wield a fiat mentality toward one another, it’s considered normal; no one can bat an eye if one fiat rent-seeker bleeds another dry, then tosses them aside for a new victim once the yield or short-term gain is realized. That’s simply how the fiat hamster wheel has been turning generations on end, while the proof-of-stake lords benefit across multiple generations.
The exploitation, the focus on short-term gains, the inherent stupidity of the system—it’s ingrained in the people themselves. Their greed and fiat/shitcoin mentality is "the norm." Some even dare to call it "capitalism" or democracy.
They can’t be offended by anyone screwing them over or getting ahead to gain a few fiat tokens, be it dollars or the Euro Mickey Mouse coin. They just carry on, shrug their shoulders, and crawl over each other like the basket full of crabs they inhabit day to day. Being among the few crabs that can touch the rim of the basket before being pulled down again by the other crabs, is what’s called success.
However, witnessing such behaviors and ways of living among individuals who identify as Bitcoiners evokes not only profound ethical sadness but also reveals consequences far more damaging to Bitcoin than if those same individuals had remained solely within the fiat system. Therefore, a fiat mentality within the Bitcoin space is even more repugnant than the mindset of some shitcoiners. At least with shitcoiners, you understand they are peddling a token, coin, or some fabricated service to offload onto unsuspecting individuals to make ends meet (and fund their cheap hotel rooms in exotic looking places while projecting an image of success (and the Modern Ottoman beard look) on Instagram). Consider a scenario: if someone at a vegetable market (assuming such places still exist in the fiat world) suggests to another vendor a way to conduct more business off the books, it’s met with indifference. That’s considered normal.But when a Bitcoiner at a meetup — an event where for three years you've been trying to dissociate Bitcoin from the tired narrative of it being solely "for fraudsters and criminals" — and you overhear "Bitcoiners" discussing methods for laundering illicit funds, then it becomes a significant problem. As if they can’t make ends meet without doing “the fiat thing”. Such individuals, as a Bitcoiner, disgust me. They clearly "don't get it." They fail to grasp the fundamental values of Bitcoin. They resemble the stereotypical used car salesmen who prioritize nothing beyond their immediate needs, like avoiding having to have a cheap dinner of dog food and tomato sauce that evening if they bag another customer by whatever lies they’ll have to tell. I would go so far as to assert that Bitcoiners with a fiat mentality are more detrimental to Bitcoin's growth than both those enslaved by the fiat system and shitcoiners themselves. A fiat drone will simply save, invest, and adhere to the established rules of banks and central banks.
They don’t question these norms; it’s their accepted reality. They’re labeled “normies” for a reason—they find satisfaction in conforming, believing the deception and theft, even perceiving it as beneficial because that’s what they’ve been told on television. They place their trust in numbers and statistics while diligently paying off their mortgages and investing in whatever financial products the TV shows spoon-feed them. Shitcoiners (closely related to fiat slaves) will merely promote their scams and worthless projects to generate short-term gains (in fiat, naturally) to sustain their shallow lifestyles of loneliness, prostitutes, and grocery bills paid with bank cards from the Seychelles.
But Bitcoiners with a fiat mentality? They actively undermine Bitcoin. They are toxic, and the sooner they revert to pure fiat, the better for the Bitcoin ecosystem. They offer no positive contribution whatsoever to Bitcoin’s progress.
More bitcoiners need to grow a spine
I've started to label these individuals as “cosplay bitcoiners.” They are typically nothing more than bitcoin holders (definitely not HODLers). These are people who act as though Bitcoin is merely another speculative asset (alongside a plethora of garbage coins and scams) instead of the monetary revolution it truly embodies. Most bitcoiners engage in this cosplay, reciting the talking points without actually changing their lives. Or… they view it simply as a means to generate income by uttering the right phrases and selling various items and merchandise. If Bitcoin were to cease to exist (a highly improbable scenario), they would likely be selling counterfeit Pokémon merchandise, fake Rolexes, or working as box movers in retail (sporting a perm). This might upset some who have dedicated significant portions of their lives to the Bitcoin ecosystem. However, what should be far more infuriating is the realization that your dreams, hope, and hard work are ultimately benefiting these cosplayers.
These individuals also say things like “You could consider moving to Solana for a while…” or “I have a referral link for insert flavor-of-the-week scam.” This genuine effort to cultivate a Bitcoin ethos is often undermined by people lacking activism, backbone, or conviction. Typically, these are the same individuals who inquire about price action during minor dips in Bitcoin's fiat value. They exhibit “scared money” behavior, just like in the fiat world. Consider that: they are scared (of) money. That’s right,… people that lived, and were raised in fiat are in fact scared… of money. This ingrained perspective, though varying in its impact, can act as a distraction or even a negative influence on Bitcoin's overall growth. I know the genuine contributors are out there. Rest assured, I am acutely aware of what it means to dedicate your time and energy to the betterment of Bitcoin; I've done it before and continue to do so years later. I respect that immensely. But the moment you recognize your efforts are primarily benefiting these parasites, you should immediately cease and let them wither.
They are not there for Bitcoin at all. I believe a fundamental aspect of being a Bitcoiner is calling out such behavior — to embody a form of activism, a vetting process aimed at fostering greater freedom. This might seem paradoxical, but it’s not; it’s akin to broadcasting a double-spent transaction onto mempool and having it rejected by the nodes. In my opinion, Bitcoin's primary essence is freedom. This freedom is underpinned by consensus and proof of work. However, this doesn't imply that we should be a universally accommodating resource for individuals who merely hold Bitcoin and seek to profit off our efforts while contributing nothing of substance to the space beyond their own marketing nonsense. They say the lines, but don’t save lives.
But why not?
If Bitcoin is truly the hardest money, the scarcest asset humanity has ever encountered, then why would we willingly trade it for a demonstrably inferior, inflationary, and state-controlled currency? This holds true even if that fiat is disguised as a modern "coin" or a cheap imitation of Bitcoin.
The uncomfortable truth is that many Bitcoiners, whether consciously or subconsciously, remain tethered to the legacy financial system. We espouse the principle of "don't trust, verify," yet we often evaluate Bitcoin through the distorted lens of its fiat exchange rate. Furthermore, many local meetups are infiltrated by individuals whose motives, schemes, and outright nonsense we fail to scrutinize or verify.
We neglect even the most fundamental forms of verification (such as accepting a function purported to be around 40 KB in data size when it's bundled within a > 50 MB software program). We profess belief in absolute scarcity, yet we shy away from adopting Bitcoin as our genuine unit of account, nor do we accurately measure our purchasing power (as devising a truly precise method might necessitate an invention worthy of a Nobel Prize in Economics).
Armed with the hardest money, ample liquidity, and considerable intellect, we still find ourselves waiting for Presidents, Philosophers, and various Personalities to artificially inflate Bitcoin's price, behaving like apprehensive investors in a newly listed startup.
“But with bitcoin”
These Philosophers, Personalities, and Presidents (PPPs) often represent a mere "follow-the-leader" phenomenon among many who identify as Bitcoiners. Philosophers delve into the intricacies of Bitcoin: its support for local social structures, its international applications, the underlying mathematics, the time-based mechanisms… It's all incredibly fascinating and has been explained countless times in various tones and for diverse audiences. Yet, much like in Bitcoin software development, there's often a lack of curation or editing; people simply produce without rigorous testing or questioning the necessity or widespread adoption of their contributions. Some even mistakenly believe these philosophers will somehow influence the "price." However, their role is primarily to explain, analyze, and provide understanding. That, of course, is valuable as it stimulates thought (even this very writing serves that purpose). However, Bitcoiners deeply entrenched in the philosophical aspects can often be blind to their own contradictory circumstances.
 It can be jarring, even alienating, to listen to a podcast dissecting the profound intricacies of time and Bitcoin's blockchain while simultaneously enduring the mundane reality of your fiat job, with a coworker loudly handling customer calls nearby. The core issue is that this mentality increasingly mirrors the practices of the fiat (and shitcoin) world: passively holding onto "your bag" or "your stake" and promoting that position while vaguely advising others that "education is important" or "spreading the word is good." Ultimately, many of those dispensing this advice do little more than appear on their YouTube channels, take the stage at their own conferences, or write (or commission) their paid newsletters. Some diligently court wealthy individuals to explain Bitcoin, aiming to earn a few dollars, but they might as well be selling Tupperware if it paid the bills. Genuine care is often absent; it's their Bitcoin-flavored version of a fiat job. They are simply holding onto sats, much like one would hold onto ETFs or stocks in the traditional financial world. Michael Saylor, at a conference in Madeira, once stated: “You are here because Bitcoin needs you… and when you leave, I sincerely hope you will go out there and do good for Bitcoin.”
It can be jarring, even alienating, to listen to a podcast dissecting the profound intricacies of time and Bitcoin's blockchain while simultaneously enduring the mundane reality of your fiat job, with a coworker loudly handling customer calls nearby. The core issue is that this mentality increasingly mirrors the practices of the fiat (and shitcoin) world: passively holding onto "your bag" or "your stake" and promoting that position while vaguely advising others that "education is important" or "spreading the word is good." Ultimately, many of those dispensing this advice do little more than appear on their YouTube channels, take the stage at their own conferences, or write (or commission) their paid newsletters. Some diligently court wealthy individuals to explain Bitcoin, aiming to earn a few dollars, but they might as well be selling Tupperware if it paid the bills. Genuine care is often absent; it's their Bitcoin-flavored version of a fiat job. They are simply holding onto sats, much like one would hold onto ETFs or stocks in the traditional financial world. Michael Saylor, at a conference in Madeira, once stated: “You are here because Bitcoin needs you… and when you leave, I sincerely hope you will go out there and do good for Bitcoin.”That's a commendable call to action. However, it also inadvertently highlights a form of servitude, a call that, regrettably, many have not heeded. Right now, Bitcoin's treated more like digital real estate than actual cash – something to hodl and hope it moons, while others do the promoting. Activism, at least here in Belgium, is a ghost town.
Elsewhere, it's often just small-time stuff, easily corrupted by book-writers, shitcoin promoters, ego-trippers, or even creeps hitting on vulnerable women in new-age scenes. This passive vibe has helped a bit, sure, but it shows we're still scared to call Bitcoin real money. It's the hardest money ever, yet we act like fiat's the boss, when Bitcoin's the true store of value. The circular economy crawls along. Instead of waiting for "hyperbitcoinization," we need to act like it's already here: support Bitcoin-only businesses, demand salaries in sats, and actually think in sats, not fiat. But become organized, more to the point: set up systems so you can build and rely on one another.To make Bitcoin truly hard money, we gotta stop pricing it and thinking in fiat, actually use it to pay and get paid, teach people it's a monetary system not just an investment, and directly challenge fiat by building Bitcoin-native economies, not just begging institutions to buy in. The more we act like Bitcoin is money, the faster the world will have to agree.
Bitcoin’s success is not inevitable.
Because it is maintained by people, and people are inherently flawed. However, it is also governed by mathematics, a perfect framework that categorizes chaos into order and back into incomprehensible chaos. There, within the crucible of math, language, cryptography, and time, lies Bitcoin: our creation, our potential salvation, and perhaps our sole remaining hope.
It demands action from Bitcoiners. If we genuinely believe in Bitcoin as the hardest money, we must begin to utilize it as such, rather than posturing on stages like immature, attention-seeking individuals vying for personal recognition and petty power struggles.
The future is not forged by those idly waiting for a magical price point; it is built by those who actively transact, develop, work, and live on Bitcoin today. Hard money transcends mere scarcity; it embodies utility, intrinsic value, and the tangible construction of liberty. Bitcoin's purpose is not simply to replace the existing decay of fiat with a superficial rebranding of the same fundamental rot. Bitcoin is not intended to supplant the old fiat corruption with an identical corruption merely bearing a Bitcoin label or logo.
The divergence is stark: one grey-colored path leads us to a state of ambiguity and ineffectiveness, the other to a vibrant, focused purpose. This ambiguity manifests as excessive accommodation, an unwarranted stubbornness where adaptability is needed. We tend towards being overly compliant and even subservient, exhibiting exaggerated politeness and empathy, even as our advancements inevitably dismantle the obsolete systems. That path has a Dixie orange color.
This is because many Bitcoiners now crave external validation, leading to inconsistent and muddled messaging, belonging authentically to neither the stagnant grey nor the purposeful orange.
We, and our true Bitcoiners—our intellectual offspring—represent an inherently incompatible lineage, incapable of either peaceful coexistence ("protest") or productive integration ("procreate") with these outdated methodologies and their swarm of futile endeavors. The cosplay bitcoiners and their lukewarm followers and creations aspire to be part of a fintech reality that is not their own, and a fiat world that has relegated them to the roles of insignificant footnotes and background commentators.
Despite our core differences, we persist in engaging with the stake-people, the frail-minded powerhouses that let us participate in their arenas, gathering under the harsh glare of moral decay and corruption. We mine Bitcoin from the future, but it’s tethered to the present. They hamper our progress with outdated tools and (re)distribution systems rooted in the 18th century.We can invent so much better systems, bulldoze the old and rebuild our cities and reclaim our value.
It’s time…
The moment has arrived to begin valuing Bitcoin for what it has always been destined to be and will forever remain: hard money. Let us consign the parasites to their rightful place – the gutter of fiat. Reader, dear reader, you who have invested the time and effort to cease scrolling through the endless torrent of filth, garbage, and attention-seeking displays on your phone, do you grasp the unique historical opportunity presented to your vulnerable digital soul to reclaim your life, to transcend mere survival and truly flourish? Do you comprehend this? Do you even realize that digitally scarce, digitally verifiable hard money awaits your mining, purchase, holding, and personal safekeeping? Or do you still cling to the illusions projected onto the wall of Plato's cave, telling you every lie under the sun for their short gains and diatribes? Do you live in the corridor of greyness? Probably.
Observing the vapid semantic debates onstage, the performative security measures, and the blatant power struggles, I am reminded of the early Christian disciples and the challenges they must have faced in spreading the word of their Lord, relying solely on their individual conviction while constantly encountering those driven purely by the pursuit of power. Bitcoiners are no different, despite never having known their own guiding figures. The distinction lies in our approach: we do not expel the transgressors and the disreputable from the market; nor do we seek to cure the afflicted or nourish the starving. We are not torn apart by lions, for we operate in the shadows, our influence primarily through written works, lacking the support that stems from personal charisma. Fiat bleeds people dry, fueling the vile machinery of passive rent-seeking yield and perpetual servitude.
In Bitcoin, we possess the potential to be their undoing, but only if we can match their ruthlessness, their multi-generational cunning, and their inherent malice. That’s not in our nature, so we’ll need to change and adapt. To truly prevail, we must outmaneuver their evil, win their long-term game. To win, we must out-evil evil. Win their multi-generational ongoing long-term game.That’s not easy, because you’re being poisoned day in day out.
So… here goes.
You must choose your path: gray or orange.
Decide how you’ll navigate the clutter: hardware wallets you don’t need, unscalable orange-pilling that’s more about ego than Bitcoin, books that hardly anyone reads, redundant artwork you’ll never buy, searching for a place in the unreachable oasis of bitcoin jobs, the mirage of funding,the naïveté of Value4Value, the Saylor-worshipping instinct, stickers slapped on poles, rushed and untested software, apps that repel users, conference circuses filled with grifters, posers and some half-gods, The pump-my-bags philosophers. The fork in the road lies ahead
Will you keep micro-dosing the corruption of the fiat world, day by day? Or will you don your armor and sacrifice for future generations?\ You ‘ll be part of an army of cyber Jesuït knights, or part of a gang of ad hoc grifters smelling like patchouli and fear.
npub1sec6degc3ae7warveuxaz6dlffnc2sutwtqjr7pmll7sf7ypjngsd4p0l7Let centuries of hate and destruction be channeled like unbreakable equations, their tax collecting vultures, their redistribution to the weak.We can be in harnesses, economically cause their bellies gorged on our produce, sliced virtually apart, ending their predatory exploitation and theater politics. Let that hate flow block by block, so our wait for a revolution, promised peace, and security, finally ends. We don’t need to wait, We have all we need - right - friggin - now! All we need is here to start as the first generation of the ones that turn the table. We can strike from here onwards.
You can’t do that just by standing there, we need to rally behind something. So … we need to…
 ## Slay the Monsters ( A Bitcoin manifesto )
## Slay the Monsters ( A Bitcoin manifesto )The race against fiat’s totalitarian grip isn’t coming — it’s already here.
And we’re late.
We’re not facing some bureaucratic mess or sleepy institution. We’re facing monsters. Real monsters. The kind that don’t blink, don’t break, and don’t stop.
These creatures don’t rule from parliaments. They rule from shadows. From bloodlines. From vaults built on centuries of power—and centuries of control.
And while we argue over memes, While we nitpick sound quality on a free podcast, While we debate how orange our sunglasses should be— They’re already building the next cage.
You want to know the core of the battle?
It’s this: They built a system designed to enslave you. And it works. Because it’s not just code or money—it’s a mindset. And they’ve trained you for generations to stay small. Stay busy. Stay broke.
They don’t care about trending topics, the fashion they make you wear, the rent seeking and mind numbing media garbage. They don’t care about today’s startup scene. They don’t need to. They freeze technology until their factories are ready. They script the narrative until their puppet politicians can sell it. They control enough markets to play with your life like a cat with a mouse.
And no, they’re not thinking in 5-year business plans. They’re thinking in bloodlines. They’re thinking in centuries.
They are bloodsuckers.
They take the rights of the gifted, Take the skills of the builders and make them into jesters They crush the dreams of the brave, weaken strong sons, and turn bright daughters into obedient servants.They make you lose time;Steal your effortSlap a price on anyone.
But here’s the good news:
We are Bitcoiners. We don’t need their permission. We don’t need to play their game. We hold a sword they can’t lift — an indestructible blockchain. And we have “forever coins”. We have the heaviest hammer
We can build faster. Stack hard money. Deliver proof of work and become the worst multi-generational pests they’ve ever seen. And take everything from them in about four generations:
One generation to build and adapt. One or two to take over, and One glorious one to finish the job and chop their virtual heads off to end the corruptionTheir heads on a stake, is the only proof-of-stake’ism that will be universally liked.
Because in their world, people are the fuel — drained for passive yield. But in our world?
We, the Bitcoin people who underwrite its value, represent the negative yield on fiat. We ARE your negative yield in human form \ We are their weakness — if we become as relentless and evil as they are.We can be methodical and calculated, generations of poison for their systemWe infiltrate, poison, outpace them.Like they did centuries ago with the commons, the tribes and kings. As focused. As strategic. As ruthless.
Then—only then—can we clean ourselves.
Only then, with the deed done, can we rebuild humanity. Burn the bloodlines that buried us.The old bloodlines—those leeches—will be caged, stripped, and left to wither in poverty, and as history proves… they never survive poverty\ While we’ve been bathing in it by choice.
From their ashes, we’ll purge our own darkness and thrive through innovation, not tyranny We will work, We will thrive through innovation, not colonization. Through consensus, not decree. Through quality not administrative control. And talent and skills will rise on merit, not aristocratic last names. We verify without grandeur.
In that world, our temples will exalt beauty — not control.In that world, Their goons and servants will be our jesters, dancing like harlots, their princesses will be sobbing on dirt, they’ll all eat their own industrial drab
The power is already ours; we don’t need to pray, we don’t need hope nor luck. We need raw, unrelenting will.
We need power.
And evil, focused, unshakable determination.
You can’t slay monsters with flyers. You don’t take down empires with stickers. You don’t bring bloodlines to their knees with polite debates on their stages.You slay monsters with the sharpest sword in history — Bitcoin.
They’re gutted with the sharpest blade—our blockchain—plunged into their stone cold hearts, until their black blood flows over the marble floors of their castles and their next of kin. Then, we feast and build anew on the ruins of their depravity.
Their next of kin witnessing our determination while their funding falls dry in promises of continuity they hide or perish.
Then we slay the rest.We drink their blood, their wine, their milkshake. We burn their paper promises and their repeating cycles of social unrest and greed.
We build something new. Something real. On the ruins of everything they corrupted.Bitcoiners need to be more than politeBe more evil, to do more good.Show monsters no mercy nor empathy. Don’t give them hard money, but wreck their legacy, faceless organizations and companies.
We are the debt collectors of last resort. We are the negative yield that spins and twists.We are the final rotation of the hamster wheel of pointless energy.We save ourselves with math..
Bitcoiners,Do thy proof of work, or become a whore for their next generation of silver spoon fed monster kids...\ You’ll have to be polite doing the deeds if you doOr take the smile off their face.Sacrifice.WorkDefy
Slay monsters like a knight building a legacy, freeing the world.
Or serve the monsters like the bitch you are.
Our consensus and your choice.
By AVB
If you like my writings: tip me here
-
 @ c631e267:c2b78d3e
2025-05-10 09:50:45
@ c631e267:c2b78d3e
2025-05-10 09:50:45Information ohne Reflexion ist geistiger Flugsand. \ Ernst Reinhardt
Der lateinische Ausdruck «Quo vadis» als Frage nach einer Entwicklung oder Ausrichtung hat biblische Wurzeln. Er wird aber auch in unserer Alltagssprache verwendet, laut Duden meist als Ausdruck von Besorgnis oder Skepsis im Sinne von: «Wohin wird das führen?»
Der Sinn und Zweck von so mancher politischen Entscheidung erschließt sich heutzutage nicht mehr so leicht, und viele Trends können uns Sorge bereiten. Das sind einerseits sehr konkrete Themen wie die zunehmende Militarisierung und die geschichtsvergessene Kriegstreiberei in Europa, deren Feindbildpflege aktuell beim Gedenken an das Ende des Zweiten Weltkriegs beschämende Formen annimmt.
Auch das hohe Gut der Schweizer Neutralität scheint immer mehr in Gefahr. Die schleichende Bewegung der Eidgenossenschaft in Richtung NATO und damit weg von einer Vermittlerposition erhält auch durch den neuen Verteidigungsminister Anschub. Martin Pfister möchte eine stärkere Einbindung in die europäische Verteidigungsarchitektur, verwechselt bei der Argumentation jedoch Ursache und Wirkung.
Das Thema Gesundheit ist als Zugpferd für Geschäfte und Kontrolle offenbar schon zuverlässig etabliert. Die hauptsächlich privat finanzierte Weltgesundheitsorganisation (WHO) ist dabei durch ein Netzwerk von sogenannten «Collaborating Centres» sogar so weit in nationale Einrichtungen eingedrungen, dass man sich fragen kann, ob diese nicht von Genf aus gesteuert werden.
Das Schweizer Bundesamt für Gesundheit (BAG) übernimmt in dieser Funktion ebenso von der WHO definierte Aufgaben und Pflichten wie das deutsche Robert Koch-Institut (RKI). Gegen die Covid-«Impfung» für Schwangere, die das BAG empfiehlt, obwohl es fehlende wissenschaftliche Belege für deren Schutzwirkung einräumt, formiert sich im Tessin gerade Widerstand.
Unter dem Stichwort «Gesundheitssicherheit» werden uns die Bestrebungen verkauft, essenzielle Dienste mit einer biometrischen digitalen ID zu verknüpfen. Das dient dem Profit mit unseren Daten und führt im Ergebnis zum Verlust unserer demokratischen Freiheiten. Die deutsche elektronische Patientenakte (ePA) ist ein Element mit solchem Potenzial. Die Schweizer Bürger haben gerade ein Referendum gegen das revidierte E-ID-Gesetz erzwungen. In Thailand ist seit Anfang Mai für die Einreise eine «Digital Arrival Card» notwendig, die mit ihrer Gesundheitserklärung einen Impfpass «durch die Hintertür» befürchten lässt.
Der massive Blackout auf der iberischen Halbinsel hat vermehrt Fragen dazu aufgeworfen, wohin uns Klimawandel-Hysterie und «grüne» Energiepolitik führen werden. Meine Kollegin Wiltrud Schwetje ist dem nachgegangen und hat in mehreren Beiträgen darüber berichtet. Wenig überraschend führen interessante Spuren mal wieder zu internationalen Großbanken, Globalisten und zur EU-Kommission.
Zunehmend bedenklich ist aber ganz allgemein auch die manifestierte Spaltung unserer Gesellschaften. Angesichts der tiefen und sorgsam gepflegten Gräben fällt es inzwischen schwer, eine zukunftsfähige Perspektive zu erkennen. Umso begrüßenswerter sind Initiativen wie die Kölner Veranstaltungsreihe «Neue Visionen für die Zukunft». Diese möchte die Diskussionskultur reanimieren und dazu beitragen, dass Menschen wieder ohne Angst und ergebnisoffen über kontroverse Themen der Zeit sprechen.
Quo vadis – Wohin gehen wir also? Die Suche nach Orientierung in diesem vermeintlichen Chaos führt auch zur Reflexion über den eigenen Lebensweg. Das ist positiv insofern, als wir daraus Kraft schöpfen können. Ob derweil der neue Papst, dessen «Vorgänger» Petrus unsere Ausgangsfrage durch die christliche Legende zugeschrieben wird, dabei eine Rolle spielt, muss jede/r selbst wissen. Mir persönlich ist allein schon ein Führungsanspruch wie der des Petrusprimats der römisch-katholischen Kirche eher suspekt.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 044da344:073a8a0e
2025-05-11 09:16:08
@ 044da344:073a8a0e
2025-05-11 09:16:08Alles neu macht der Oktober. Sorry für das Sprachspiel. Wenn Sie so etwas mögen, dann kommen Sie in ein paar Monaten zu uns in die Oberpfalz –
- entweder zum Journalismus-Retreat für den Nachwuchs der Gegenöffentlichkeit oder
- eine Woche später zum Kurs Intellektuelle Selbstverteidigung.
Wenn man den Unterschied auf den Punkt bringen müsste: Für Kurs eins sollten sie schon öffentlich sichtbar sein mit Texten, Podcasts und Videos, auf diesem Pfad weitermachen wollen und dafür nach Aufmunterung, Bestärkung, Weggefährten suchen. Kurs zwei verlangt all das nicht. Keine Schranke, nicht einmal in Sachen Alter. Während uns bisher wichtig war, dass die Teilnehmer wenigstens eventuell und im Fall der Fälle in Richtung Medienpräsenz schielen, steht bei diesem neuen Angebot Medienkompetenz im Mittelpunkt, journalistisches Handwerk inklusive.
Infos zur Anmeldung, zur Organisation und zu allem, was Sie sonst noch wissen wollen, finden Sie unter den Links oben.
-
 @ 40bdcc08:ad00fd2c
2025-05-06 14:24:22
@ 40bdcc08:ad00fd2c
2025-05-06 14:24:22Introduction
Bitcoin’s
OP_RETURNopcode, a mechanism for embedding small data in transactions, has ignited a significant debate within the Bitcoin community. Originally designed to support limited metadata while preserving Bitcoin’s role as a peer-to-peer electronic cash system,OP_RETURNis now at the center of proposals that could redefine Bitcoin’s identity. The immutable nature of Bitcoin’s timechain makes it an attractive platform for data storage, creating tension with those who prioritize its monetary function. This discussion, particularly around Bitcoin Core pull request #32406 (GitHub PR #32406), highlights a critical juncture for Bitcoin’s future.What is
OP_RETURN?Introduced in 2014,
OP_RETURNallows users to attach up to 80 bytes of data to a Bitcoin transaction. Unlike other transaction outputs,OP_RETURNoutputs are provably unspendable, meaning they don’t burden the Unspent Transaction Output (UTXO) set—a critical database for Bitcoin nodes. This feature was a compromise to provide a standardized, less harmful way to include metadata, addressing earlier practices that embedded data in ways that bloated the UTXO set. The 80-byte limit and restriction to oneOP_RETURNoutput per transaction are part of Bitcoin Core’s standardness rules, which guide transaction relay and mining but are not enforced by the network’s consensus rules (Bitcoin Stack Exchange).Standardness vs. Consensus Rules
Standardness rules are Bitcoin Core’s default policies for relaying and mining transactions. They differ from consensus rules, which define what transactions are valid across the entire network. For
OP_RETURN: - Consensus Rules: AllowOP_RETURNoutputs with data up to the maximum script size (approximately 10,000 bytes) and multiple outputs per transaction (Bitcoin Stack Exchange). - Standardness Rules: LimitOP_RETURNdata to 80 bytes and one output per transaction to discourage excessive data storage and maintain network efficiency.Node operators can adjust these policies using settings like
-datacarrier(enables/disablesOP_RETURNrelay) and-datacarriersize(sets the maximum data size, defaulting to 83 bytes to account for theOP_RETURNopcode and pushdata byte). These settings allow flexibility but reflect Bitcoin Core’s default stance on limiting data usage.The Proposal: Pull Request #32406
Bitcoin Core pull request #32406, proposed by developer instagibbs, seeks to relax these standardness restrictions (GitHub PR #32406). Key changes include: - Removing Default Size Limits: The default
-datacarriersizewould be uncapped, allowing largerOP_RETURNdata without a predefined limit. - Allowing Multiple Outputs: The restriction to oneOP_RETURNoutput per transaction would be lifted, with the total data size across all outputs subject to a configurable limit. - Deprecating Configuration Options: The-datacarrierand-datacarriersizesettings are marked as deprecated, signaling potential removal in future releases, which could limit node operators’ ability to enforce custom restrictions.This proposal does not alter consensus rules, meaning miners and nodes can already accept transactions with larger or multiple
OP_RETURNoutputs. Instead, it changes Bitcoin Core’s default relay policy to align with existing practices, such as miners accepting non-standard transactions via services like Marathon Digital’s Slipstream (CoinDesk).Node Operator Flexibility
Currently, node operators can customize
OP_RETURNhandling: - Default Settings: Relay transactions with oneOP_RETURNoutput up to 80 bytes. - Custom Settings: Operators can disableOP_RETURNrelay (-datacarrier=0) or adjust the size limit (e.g.,-datacarriersize=100). These options remain in #32406 but are deprecated, suggesting that future Bitcoin Core versions might not support such customization, potentially standardizing the uncapped policy.Arguments in Favor of Relaxing Limits
Supporters of pull request #32406 and similar proposals argue that the current restrictions are outdated and ineffective. Their key points include: - Ineffective Limits: Developers bypass the 80-byte limit using methods like Inscriptions, which store data in other transaction parts, often at higher cost and inefficiency (BitcoinDev Mailing List). Relaxing
OP_RETURNcould channel data into a more efficient format. - Preventing UTXO Bloat: By encouragingOP_RETURNuse, which doesn’t affect the UTXO set, the proposal could reduce reliance on harmful alternatives like unspendable Taproot outputs used by projects like Citrea’s Clementine bridge. - Supporting Innovation: Projects like Citrea require more data (e.g., 144 bytes) for security proofs, and relaxed limits could enable new Layer 2 solutions (CryptoSlate). - Code Simplification: Developers like Peter Todd argue that these limits complicate Bitcoin Core’s codebase unnecessarily (CoinGeek). - Aligning with Practice: Miners already process non-standard transactions, and uncapping defaults could improve fee estimation and reduce reliance on out-of-band services, as noted by ismaelsadeeq in the pull request discussion.In the GitHub discussion, developers like Sjors and TheCharlatan expressed support (Concept ACK), citing these efficiency and innovation benefits.
Arguments Against Relaxing Limits
Opponents, including prominent developers and community members, raise significant concerns about the implications of these changes: - Deviation from Bitcoin’s Purpose: Critics like Luke Dashjr, who called the proposal “utter insanity,” argue that Bitcoin’s base layer should prioritize peer-to-peer cash, not data storage (CoinDesk). Jason Hughes warned it could turn Bitcoin into a “worthless altcoin” (BeInCrypto). - Blockchain Bloat: Additional data increases the storage and processing burden on full nodes, potentially making node operation cost-prohibitive and threatening decentralization (CryptoSlate). - Network Congestion: Unrestricted data could lead to “spam” transactions, raising fees and hindering Bitcoin’s use for financial transactions. - Risk of Illicit Content: The timechain’s immutability means data, including potentially illegal or objectionable content, is permanently stored on every node. The 80-byte limit acts as a practical barrier, and relaxing it could exacerbate this issue. - Preserving Consensus: Developers like John Carvalho view the limits as a hard-won community agreement, not to be changed lightly.
In the pull request discussion, nsvrn and moth-oss expressed concerns about spam and centralization, advocating for gradual changes. Concept NACKs from developers like wizkid057 and Luke Dashjr reflect strong opposition.
Community Feedback
The GitHub discussion for pull request #32406 shows a divided community: - Support (Concept ACK): Sjors, polespinasa, ismaelsadeeq, miketwenty1, TheCharlatan, Psifour. - Opposition (Concept NACK): wizkid057, BitcoinMechanic, Retropex, nsvrn, moth-oss, Luke Dashjr. - Other: Peter Todd provided a stale ACK, indicating partial or outdated support.
Additional discussions on the BitcoinDev mailing list and related pull requests (e.g., #32359 by Peter Todd) highlight similar arguments, with #32359 proposing a more aggressive removal of all
OP_RETURNlimits and configuration options (GitHub PR #32359).| Feedback Type | Developers | Key Points | |---------------|------------|------------| | Concept ACK | Sjors, ismaelsadeeq, others | Improves efficiency, supports innovation, aligns with mining practices. | | Concept NACK | Luke Dashjr, wizkid057, others | Risks bloat, spam, centralization, and deviation from Bitcoin’s purpose. | | Stale ACK | Peter Todd | Acknowledges proposal but with reservations or outdated support. |
Workarounds and Their Implications
The existence of workarounds, such as Inscriptions, which exploit SegWit discounts to embed data, is a key argument for relaxing
OP_RETURNlimits. These methods are costlier and less efficient, often costing more thanOP_RETURNfor data under 143 bytes (BitcoinDev Mailing List). Supporters argue that formalizing largerOP_RETURNdata could streamline these use cases. Critics, however, see workarounds as a reason to strengthen, not weaken, restrictions, emphasizing the need to address underlying incentives rather than accommodating bypasses.Ecosystem Pressures
External factors influence the debate: - Miners: Services like Marathon Digital’s Slipstream process non-standard transactions for a fee, showing that market incentives already bypass standardness rules. - Layer 2 Projects: Citrea’s Clementine bridge, requiring more data for security proofs, exemplifies the demand for relaxed limits to support innovative applications. - Community Dynamics: The debate echoes past controversies, like the Ordinals debate, where data storage via inscriptions raised similar concerns about Bitcoin’s purpose (CoinDesk).
Bitcoin’s Identity at Stake
The
OP_RETURNdebate is not merely technical but philosophical, questioning whether Bitcoin should remain a focused monetary system or evolve into a broader data platform. Supporters see relaxed limits as a pragmatic step toward efficiency and innovation, while opponents view them as a risk to Bitcoin’s decentralization, accessibility, and core mission. The community’s decision will have lasting implications, affecting node operators, miners, developers, and users.Conclusion
As Bitcoin navigates this crossroads, the community must balance the potential benefits of relaxed
OP_RETURNlimits—such as improved efficiency and support for new applications—against the risks of blockchain bloat, network congestion, and deviation from its monetary roots. The ongoing discussion, accessible via pull request #32406 on GitHub (GitHub PR #32406). Readers are encouraged to explore the debate and contribute to ensuring that any changes align with Bitcoin’s long-term goals as a decentralized, secure, and reliable system. -
 @ d61f3bc5:0da6ef4a
2025-05-05 15:26:08
@ d61f3bc5:0da6ef4a
2025-05-05 15:26:08I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify a media file and maliciously ascribe it to the note author.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ 57d1a264:69f1fee1
2025-05-10 05:45:52
@ 57d1a264:69f1fee1
2025-05-10 05:45:52Finale: once the industry-standard of music notation software, now a cautionary tale. In this video, I explore how it slowly lost its crown through decades of missed opportunities - eventually leading to creative collapse due to various bureaucratic intrigues, unforeseen technological changes and some of the jankiest UI/UX you've ever seen.
https://www.youtube.com/watch?v=Yqaon6YHzaU
originally posted at https://stacker.news/items/976219
-
 @ 2183e947:f497b975
2025-05-01 22:33:48
@ 2183e947:f497b975
2025-05-01 22:33:48Most darknet markets (DNMs) are designed poorly in the following ways:
1. Hosting
Most DNMs use a model whereby merchants fill out a form to create their listings, and the data they submit then gets hosted on the DNM's servers. In scenarios where a "legal" website would be forced to censor that content (e.g. a DMCA takedown order), DNMs, of course, do not obey. This can lead to authorities trying to find the DNM's servers to take enforcement actions against them. This design creates a single point of failure.
A better design is to outsource hosting to third parties. Let merchants host their listings on nostr relays, not on the DNM's server. The DNM should only be designed as an open source interface for exploring listings hosted elsewhere, that way takedown orders end up with the people who actually host the listings, i.e. with nostr relays, and not with the DNM itself. And if a nostr relay DOES go down due to enforcement action, it does not significantly affect the DNM -- they'll just stop querying for listings from that relay in their next software update, because that relay doesn't work anymore, and only query for listings from relays that still work.
2. Moderation
Most DNMs have employees who curate the listings on the DNM. For example, they approve/deny listings depending on whether they fit the content policies of the website. Some DNMs are only for drugs, others are only for firearms. The problem is, to approve a criminal listing is, in the eyes of law enforcement, an act of conspiracy. Consequently, they don't just go after the merchant who made the listing but the moderators who approved it, and since the moderators typically act under the direction of the DNM, this means the police go after the DNM itself.
A better design is to outsource moderation to third parties. Let anyone call themselves a moderator and create lists of approved goods and services. Merchants can pay the most popular third party moderators to add their products to their lists. The DNM itself just lets its users pick which moderators to use, such that the user's choice -- and not a choice by the DNM -- determines what goods and services the user sees in the interface.
That way, the police go after the moderators and merchants rather than the DNM itself, which is basically just a web browser: it doesn't host anything or approve of any content, it just shows what its users tell it to show. And if a popular moderator gets arrested, his list will still work for a while, but will gradually get more and more outdated, leading someone else to eventually become the new most popular moderator, and a natural transition can occur.
3. Escrow
Most DNMs offer an escrow solution whereby users do not pay merchants directly. Rather, during the Checkout process, they put their money in escrow, and request the DNM to release it to the merchant when the product arrives, otherwise they initiate a dispute. Most DNMs consider escrow necessary because DNM users and merchants do not trust one another; users don't want to pay for a product first and then discover that the merchant never ships it, and merchants don't want to ship a product first and then discover that the user never pays for it.
The problem is, running an escrow solution for criminals is almost certain to get you accused of conspiracy, money laundering, and unlicensed money transmission, so the police are likely to shut down any DNM that does this. A better design is to oursource escrow to third parties. Let anyone call themselves an escrow, and let moderators approve escrows just like they approve listings. A merchant or user who doesn't trust the escrows chosen by a given moderator can just pick a different moderator. That way, the police go after the third party escrows rather than the DNM itself, which never touches user funds.
4. Consequences
Designing a DNM along these principles has an interesting consequence: the DNM is no longer anything but an interface, a glorified web browser. It doesn't host any content, approve any listings, or touch any money. It doesn't even really need a server -- it can just be an HTML file that users open up on their computer or smart phone. For two reasons, such a program is hard to take down:
First, it is hard for the police to justify going after the DNM, since there are no charges to bring. Its maintainers aren't doing anything illegal, no more than Firefox does anything illegal by maintaining a web browser that some people use to browse illegal content. What the user displays in the app is up to them, not to the code maintainers. Second, if the police decided to go after the DNM anyway, they still couldn't take it down because it's just an HTML file -- the maintainers do not even need to run a server to host the file, because users can share it with one another, eliminating all single points of failure.
Another consequence of this design is this: most of the listings will probably be legal, because there is more demand for legal goods and services than illegal ones. Users who want to find illegal goods would pick moderators who only approve those listings, but everyone else would use "legal" moderators, and the app would not, at first glance, look much like a DNM, just a marketplace for legal goods and services. To find the illegal stuff that lurks among the abundant legal stuff, you'd probably have to filter for it via your selection of moderators, making it seem like the "default" mode is legal.
5. Conclusion
I think this DNM model is far better than the designs that prevail today. It is easier to maintain, harder to take down, and pushes the "hard parts" to the edges, so that the DNM is not significantly affected even if a major merchant, moderator, or escrow gets arrested. I hope it comes to fruition.
-
 @ 460c25e6:ef85065c
2025-02-25 15:20:39
@ 460c25e6:ef85065c
2025-02-25 15:20:39If you don't know where your posts are, you might as well just stay in the centralized Twitter. You either take control of your relay lists, or they will control you. Amethyst offers several lists of relays for our users. We are going to go one by one to help clarify what they are and which options are best for each one.
Public Home/Outbox Relays
Home relays store all YOUR content: all your posts, likes, replies, lists, etc. It's your home. Amethyst will send your posts here first. Your followers will use these relays to get new posts from you. So, if you don't have anything there, they will not receive your updates.
Home relays must allow queries from anyone, ideally without the need to authenticate. They can limit writes to paid users without affecting anyone's experience.
This list should have a maximum of 3 relays. More than that will only make your followers waste their mobile data getting your posts. Keep it simple. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of all your content in a place no one can delete. Go to relay.tools and never be censored again. - 1 really fast relay located in your country: paid options like http://nostr.wine are great
Do not include relays that block users from seeing posts in this list. If you do, no one will see your posts.
Public Inbox Relays
This relay type receives all replies, comments, likes, and zaps to your posts. If you are not getting notifications or you don't see replies from your friends, it is likely because you don't have the right setup here. If you are getting too much spam in your replies, it's probably because your inbox relays are not protecting you enough. Paid relays can filter inbox spam out.
Inbox relays must allow anyone to write into them. It's the opposite of the outbox relay. They can limit who can download the posts to their paid subscribers without affecting anyone's experience.
This list should have a maximum of 3 relays as well. Again, keep it small. More than that will just make you spend more of your data plan downloading the same notifications from all these different servers. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of your notifications, invites, cashu tokens and zaps. - 1 really fast relay located in your country: go to nostr.watch and find relays in your country
Terrible options include: - nostr.wine should not be here. - filter.nostr.wine should not be here. - inbox.nostr.wine should not be here.
DM Inbox Relays
These are the relays used to receive DMs and private content. Others will use these relays to send DMs to you. If you don't have it setup, you will miss DMs. DM Inbox relays should accept any message from anyone, but only allow you to download them.
Generally speaking, you only need 3 for reliability. One of them should be a personal relay to make sure you have a copy of all your messages. The others can be open if you want push notifications or closed if you want full privacy.
Good options are: - inbox.nostr.wine and auth.nostr1.com: anyone can send messages and only you can download. Not even our push notification server has access to them to notify you. - a personal relay to make sure no one can censor you. Advanced settings on personal relays can also store your DMs privately. Talk to your relay operator for more details. - a public relay if you want DM notifications from our servers.
Make sure to add at least one public relay if you want to see DM notifications.
Private Home Relays
Private Relays are for things no one should see, like your drafts, lists, app settings, bookmarks etc. Ideally, these relays are either local or require authentication before posting AND downloading each user\'s content. There are no dedicated relays for this category yet, so I would use a local relay like Citrine on Android and a personal relay on relay.tools.
Keep in mind that if you choose a local relay only, a client on the desktop might not be able to see the drafts from clients on mobile and vice versa.
Search relays:
This is the list of relays to use on Amethyst's search and user tagging with @. Tagging and searching will not work if there is nothing here.. This option requires NIP-50 compliance from each relay. Hit the Default button to use all available options on existence today: - nostr.wine - relay.nostr.band - relay.noswhere.com
Local Relays:
This is your local storage. Everything will load faster if it comes from this relay. You should install Citrine on Android and write ws://localhost:4869 in this option.
General Relays:
This section contains the default relays used to download content from your follows. Notice how you can activate and deactivate the Home, Messages (old-style DMs), Chat (public chats), and Global options in each.
Keep 5-6 large relays on this list and activate them for as many categories (Home, Messages (old-style DMs), Chat, and Global) as possible.
Amethyst will provide additional recommendations to this list from your follows with information on which of your follows might need the additional relay in your list. Add them if you feel like you are missing their posts or if it is just taking too long to load them.
My setup
Here's what I use: 1. Go to relay.tools and create a relay for yourself. 2. Go to nostr.wine and pay for their subscription. 3. Go to inbox.nostr.wine and pay for their subscription. 4. Go to nostr.watch and find a good relay in your country. 5. Download Citrine to your phone.
Then, on your relay lists, put:
Public Home/Outbox Relays: - nostr.wine - nos.lol or an in-country relay. -
.nostr1.com Public Inbox Relays - nos.lol or an in-country relay -
.nostr1.com DM Inbox Relays - inbox.nostr.wine -
.nostr1.com Private Home Relays - ws://localhost:4869 (Citrine) -
.nostr1.com (if you want) Search Relays - nostr.wine - relay.nostr.band - relay.noswhere.com
Local Relays - ws://localhost:4869 (Citrine)
General Relays - nos.lol - relay.damus.io - relay.primal.net - nostr.mom
And a few of the recommended relays from Amethyst.
Final Considerations
Remember, relays can see what your Nostr client is requesting and downloading at all times. They can track what you see and see what you like. They can sell that information to the highest bidder, they can delete your content or content that a sponsor asked them to delete (like a negative review for instance) and they can censor you in any way they see fit. Before using any random free relay out there, make sure you trust its operator and you know its terms of service and privacy policies.
-
 @ 21335073:a244b1ad
2025-05-01 01:51:10
@ 21335073:a244b1ad
2025-05-01 01:51:10Please respect Virginia Giuffre’s memory by refraining from asking about the circumstances or theories surrounding her passing.
Since Virginia Giuffre’s death, I’ve reflected on what she would want me to say or do. This piece is my attempt to honor her legacy.
When I first spoke with Virginia, I was struck by her unshakable hope. I had grown cynical after years in the anti-human trafficking movement, worn down by a broken system and a government that often seemed complicit. But Virginia’s passion, creativity, and belief that survivors could be heard reignited something in me. She reminded me of my younger, more hopeful self. Instead of warning her about the challenges ahead, I let her dream big, unburdened by my own disillusionment. That conversation changed me for the better, and following her lead led to meaningful progress.
Virginia was one of the bravest people I’ve ever known. As a survivor of Epstein, Maxwell, and their co-conspirators, she risked everything to speak out, taking on some of the world’s most powerful figures.
She loved when I said, “Epstein isn’t the only Epstein.” This wasn’t just about one man—it was a call to hold all abusers accountable and to ensure survivors find hope and healing.
The Epstein case often gets reduced to sensational details about the elite, but that misses the bigger picture. Yes, we should be holding all of the co-conspirators accountable, we must listen to the survivors’ stories. Their experiences reveal how predators exploit vulnerabilities, offering lessons to prevent future victims.
You’re not powerless in this fight. Educate yourself about trafficking and abuse—online and offline—and take steps to protect those around you. Supporting survivors starts with small, meaningful actions. Free online resources can guide you in being a safe, supportive presence.
When high-profile accusations arise, resist snap judgments. Instead of dismissing survivors as “crazy,” pause to consider the trauma they may be navigating. Speaking out or coping with abuse is never easy. You don’t have to believe every claim, but you can refrain from attacking accusers online.
Society also fails at providing aftercare for survivors. The government, often part of the problem, won’t solve this. It’s up to us. Prevention is critical, but when abuse occurs, step up for your loved ones and community. Protect the vulnerable. it’s a challenging but a rewarding journey.
If you’re contributing to Nostr, you’re helping build a censorship resistant platform where survivors can share their stories freely, no matter how powerful their abusers are. Their voices can endure here, offering strength and hope to others. This gives me great hope for the future.
Virginia Giuffre’s courage was a gift to the world. It was an honor to know and serve her. She will be deeply missed. My hope is that her story inspires others to take on the powerful.
-
 @ 57d1a264:69f1fee1
2025-05-10 05:34:46
@ 57d1a264:69f1fee1
2025-05-10 05:34:46
For generations before generative text, writers have used the em dash to hop between thoughts, emotions, and ideas. Dickens shaped his morality tales with it, Woolf’s stream-of-consciousness flowed through it, Kerouac let it drive his jazz-like prose. Today, Sally Rooney threads it through her quiet truths of the heart.
But this beloved punctuation mark has become a casualty of the algorithmic age. The em dash has been so widely adopted by AI-generated text that even when used by human hands, it begs the question: was this actually written or apathetically prompted?
The battle for the soul of writing is in full swing. And the human fightback starts here. With a new punctuation mark that serves as a symbol of real pondering, genuine daydreaming, and true editorial wordsmithery. Inspired by Descartes’ belief that thinking makes us human, the am dash is a small but powerful testament that the words you’ve painstakingly and poetically pulled together are unequivocally, certifiably, and delightfully your own.
Let's reclain writig from AI—oneam dash at time.
Download the fonts:
— Aereal https://bit.ly/3EO6fo8 — Times New Human https://bit.ly/4jQTcRS
Learn more about the am dash
https://www.theamdash.com
originally posted at https://stacker.news/items/976218
-
 @ 84b0c46a:417782f5
2025-05-11 06:05:38
@ 84b0c46a:417782f5
2025-05-11 06:05:38- Lumilumi The Nostr Web Client.
Lightweight modes are available, such as not displaying icon images, not loading images automatically, etc.
-
Long Form Content Editor A lightweight Long Form Content Editor with editing functionality for your articles. It supports embedding Nostr IDs via NIP-19 and custom emoji integration.
-
Nostr Share Component Demo A simple web component for sharing content to Nostr. Create customizable share buttons that let users easily post to Nostr clients with pre-filled content. Perfect for blogs, websites, or any content you want shared on the Nostr network. Try the interactive demo to see how seamlessly it integrates with your website.
Only clients that support receiving shared text via URL parameters can be added to the client list. If your preferred client meets this requirement, feel free to submit a pull request.
-
Nostr Follow Organizer A practical tool for managing your Nostr follows(kind3) with ease.
-
NAKE NAKE is a powerful utility for Nostr developers and users that simplifies working with NIP-19 and NIP-49 formats. This versatile tool allows you to easily encode and decode Nostr identifiers and encrypted data according to these protocol specifications.
- chrome extension
- firefox add-on
-
Nostviewstr A versatile Nostr tool that specializes in creating and editing addressable or replaceable events on the Nostr network. This comprehensive editor allows you to manage various types of lists and structured content within the Nostr ecosystem.
-
Luminostr Luminostr is a recovery tool for Nostr that helps you retrieve and restore Addressable or Replaceable events (such as kind: 0, 3, 10002, 10000, etc.) from relays. It allows you to search for these events across multiple relays and optionally re-publish them to ensure their persistence.
-
Nostr Bookmark Recovery Tool Nostr Bookmark Recovery Tool is a utility for retrieving and re-publishing past bookmark events ( kind:10003,30001,30003 ) from public relays. Rather than automatically selecting the latest version, it allows users to pick any previous version and overwrite the current one with it. This is useful for restoring a preferred snapshot of your bookmark list.
-
Profile Editor Profile Editor is a simple tool for editing and publishing your Nostr profile (kind: 0 event). It allows you to update fields such as name, display name, picture, and about text, and then publish the updated profile to selected relays.
-
Nostr bookmark viewer Nostr Bookmark Viewer is a tool for viewing and editing Nostr bookmark events (kind: 10003, 30001, 30003). It allows users to load bookmark data from relays, browse saved posts, and optionally edit and publish their own bookmark lists.
-
Nostr Note Duplicater Nostr Note Duplicater is a tool that rebroadcasts an existing Nostr event from a relay to other selected relays.
-
 @ f4a890ce:af88c4aa
2025-05-11 05:56:39
@ f4a890ce:af88c4aa
2025-05-11 05:56:39執行摘要
上週市場總市值進一步上升至2.96兆美元,顯示資金持續淨流入,加密資產整體維持多頭氣氛。儘管成交量自高點回落至868.3億美元,但市場流動性仍處於健康水準。恐懼與貪婪指數下滑至60,情緒從過度樂觀回落至中性偏樂觀區間,短期可能出現技術性整理。 衍生性商品方面,永續合約持倉再創新高至1,200億美元,顯示槓桿資金依然積極參與。不過,空單爆倉規模高達5.17億美元,顯示空頭遭遇大幅擠壓,需留意市場過熱風險。期權市場仍聚焦高價位行權價,反映中期上行預期不變。 ETF方面,本週BTC與ETH皆出現資金淨流入,分別為4.225億與650萬美元,顯示機構資金還是更喜歡BTC。 本週需持續關注市場情緒,資金是否重新進場?穩定幣市值變化,是否有新增資金流入?永續合約持倉量和期權市場看漲部位集中在高價區,是否引發誘多行情?ETF 是流入或流出?投資人信心是否進一步下滑?
加密市場
本週加密市場總市值上升至 3.23 兆美元,較上週略有增長,顯示市場仍維持穩定向上的趨勢。與此同時,成交量提升至 163.1 億美元,代表市場交易活躍度有所回升,資金流動性改善。
https://coinmarketcap.com/charts/
投資者情緒方面,恐懼與貪婪指數攀升至 73,顯示市場情緒轉向「貪婪」,投資人信心增強,買盤意願更為積極。
https://www.coinglass.com/zh-TW/pro/i/FearGreedIndex
而相對強弱指標進入強勢區間,表明短線上漲動能依然存在。
https://www.coinglass.com/zh-TW/pro/i/RsiHeatMap
山寨幣季節指數為 27,顯示市場資金仍偏向比特幣,對中小型代幣的風險偏好仍較為保守,尚未出現明顯的資金輪動情形。
https://www.blockchaincenter.net/en/altcoin-season-index/
此外,穩定幣市值增長至 2,422.26 億美元,可能反映部分資金正在準備籌碼,等待更具吸引力的市場機會。
https://defillama.com/stablecoins
小結
本週加密市場總市值持續上漲,而成交量同步回溫,顯示交易活動回升,市場信心增強。恐懼與貪婪指數進一步攀升至貪婪區間,暗示市場風險偏好提升,但仍須關注市場過熱風險。相對強弱指標顯示市場仍具上升動能,但山寨幣季節指數低迷,顯示資金仍主要集中於比特幣。穩定幣市值增長,反映投資者仍保持一定的謹慎態度。未來需密切關注宏觀經濟環境及市場資金流向,以判斷趨勢是否能夠持續。
衍生性商品
本週永續合約市場的持倉規模較上週進一步攀升,從 116.9B 增至 132.2B,顯示市場對槓桿交易的需求依舊強勁。
https://www.coinglass.com/zh-TW/pro/futures/Cryptofutures
資金費率方面,當前整體市場呈 正費率,主要交易所的資金費率保持在 0.01% 左右,反映出市場偏向多頭。
https://www.coinglass.com/zh-TW/FundingRate
然而,市場波動仍然導致大規模的強制清算。根據最新數據,5月8日 出現大量爆倉事件,空單爆倉金額達 835.998M,而多單爆倉金額則達 131.779M。
https://www.coinglass.com/zh-TW/LiquidationData
清算熱力圖顯示,$93,000 附近 的清算金額達 188.95M,這一價位區間成為近期市場的重要風險區域。
https://www.coinglass.com/zh-TW/pro/futures/LiquidationHeatMap
期權市場的數據顯示投資者對不同價格區間的配置策略仍有明顯差異。在 $85,000 行權價的看跌期權合約數量維持在 9.82K,但總金額增加至$15.42M,顯示市場對該區間的下行防禦仍然較強;而 $100,000 行權價的看漲期權合約數量則由 15.67K 增至 17.8K,總金額大幅提升至 $177.43M,顯示投資者對市場上行的預期正逐步增強。
https://www.coinglass.com/zh-TW/pro/options/OIStrike
此外,最大痛點仍然維持在 $90,000,但時間點有所調整,分別落在 2025/05/30 與 2025/06/27,顯示市場對長期風險的調整。
https://www.coinglass.com/zh-TW/pro/options/max-pain
小結
本週衍生性商品市場展現出更高的槓桿操作與波動風險,特別是在清算金額與爆倉數據方面。期權市場的配置策略分歧仍然明顯,投資者對短期與長期的行情預期有所不同。在市場波動區域,資金流向與槓桿操作需更加謹慎,以避免因價格劇烈變動導致強制清算。建議投資者持續關注關鍵價格區間的變化,並根據市場動向調整交易策略,以應對可能出現的市場風險。
ETF
在本週的加密貨幣ETF市場中,比特幣(BTC)與以太坊(ETH)皆呈現資金流入的狀態。比特幣ETF吸引了4.225億美元的資金流入,顯示出市場對BTC的信心。 而ETH ETF則流入650萬美元,雖然相較比特幣規模較小,仍然顯示資金回流跡象。
https://coinmarketcap.com/zh-tw/etf/
小結
整體而言,本週加密貨幣ETF市場出現資金回流,尤其BTC的流入幅度相當亮眼。市場投資情緒似乎有所回溫,但仍需留意後續可能的波動因素,例如宏觀經濟變數及技術面調整。若資金流入趨勢能夠持續,將進一步確認市場情緒的轉變,為後續行情提供更多參考依據。
鏈上分析 | BTC
從本週的鏈上數據來看,BTC 持續自交易所流出,持續創出新低,表明持有者更偏向於自我持幣。
地址分布方面,中小持倉(10-100)的地址數量持續下滑;而其餘的地址數量則呈現小幅上升,代表市場對後市仍保有一定信心。值得關注的是10k以上的超級鯨魚地址開始出現買入的動作,而近期仍持續上升中。
https://cryptoquant.com/community/dashboard/67e2481ba2a7203afd437b31
近期鯨魚活躍地址呈現明顯上升趨勢,無論是新進鯨魚還是長期未動的大型地址皆出現甦醒跡象,反映市場中大型資金正逐步活躍並積極參與。這種現象往往代表對未來市場走勢的樂觀看法,有助於市場底部籌碼的穩定與後續動能的蓄積,值得持續關注其資金動向與潛在布局。
https://cryptoquant.com/community/dashboard/67e2481ba2a7203afd437b31
近期觀察到「1+ Year HODL Wave」指標持續下降,顯示過去一年未曾移動 BTC 的長期持有者開始活躍。這通常代表部分長期投資人選擇獲利了結。
https://www.bitcoinmagazinepro.com/charts/1-year-hodl-wave/
目前比特幣的 NUPL(Net Unrealized Profit/Loss)指標已進入「樂觀/焦慮(Optimism/Anxiety)」區間,此區間歷史上曾多次出現在牛市中後段,並伴隨著市場高點的反轉風險。
https://www.bitcoinmagazinepro.com/charts/relative-unrealized-profit--loss/
從「短期持有者實現價格(Short-Term Holder Realized Price)」圖表觀察,目前市場價格已明確站上該指標,代表短期持有者的籌碼壓力已基本完成消化。此現象顯示市場獲得良好支撐,且買盤力量逐步強化,推動價格持續上行。若能維持在該實現價格之上,將有助於鞏固多頭趨勢,為後續行情打下上漲基礎。
https://www.bitcoinmagazinepro.com/charts/short-term-holder-realized-price/
小結
從地址分布來看,大戶(鯨魚級地址)持續進行比特幣的累積,而中小型持倉地址則出現持續拋售現象,顯示市場籌碼正在向強手集中。NUPL 指標目前位於「樂觀/焦慮(Optimism/Anxiety)」區間,雖然歷史上部分牛市高點也曾出現在此階段,但仍有機會延伸至「信念/否認(Belief/Denial)」階段,帶來進一步上漲動能。此外,短期持有者實現價格已被市場價格突破,顯示籌碼壓力已基本消化,支撐當前上行趨勢。後續仍觀察大戶行為與情緒變化將是判斷行情延續與否的關鍵。
總體經濟
本週總體經濟數據與上週保持一致,聯邦基金有效利率維持在 4.33%,顯示市場仍處於高利率環境。
https://fred.stlouisfed.org/series/FEDFUNDS
隨著 6 月 18 日即將召開的聯邦公開市場委員會 (FOMC) 會議,市場普遍預期利率將維持不變,反映出決策者對當前經濟形勢的謹慎態度。
https://www.cmegroup.com/cn-t/markets/interest-rates/cme-fedwatch-tool.html
和上週一致,消費者物價指數 (CPI) 為 2.41%,仍處於聯準會通膨目標的範圍內。另一方面,失業率穩定在 4.2%,企業對於人力需求依然穩固。這樣的情況使得貨幣政策決策者在調整利率時需更加謹慎,以避免過度收緊或過度寬鬆對經濟帶來的衝擊。
https://www.macromicro.me/series/37/unemployment-rate
https://www.macromicro.me/series/128/consumer-price-index-sa-yoy
小結
現階段總體經濟環境維持穩定,貨幣政策仍以觀望為主。在市場流動性尚未顯著提升的情況下,投資人仍需密切關注即將公佈的經濟數據,以尋找可能影響資產價格的關鍵因素。
新聞
VanEck 提交在美國推出首個 BNB ETF 的提案
比特幣支付應用程式 Strike 將提供 BTC 借貸服務,協助新興產業發展
Revolut 將透過 Lightspark 為歐洲用戶推出比特幣閃電支付
富途證券開通比特幣、以太坊、USDT儲值:香港券商挾著加密走
https://www.blocktempo.com/futu-securities-launches-bitcoin-ethereum-and-usdt-top-up/
-
 @ 57d1a264:69f1fee1
2025-05-10 05:11:27
@ 57d1a264:69f1fee1
2025-05-10 05:11:27Consider the following two charts from A History of Clojure which detail the introduction and retention of new code by release for both Clojure and for Scala.
While this doesn't necessarily translate to library stability, it's reasonable to assume that the attitude of the Clojure maintainers will seep into the community. And that assumption is true.
Consider a typical Javascript program. What is it comprised of? Objects, objects, and more objects. Members of those objects must be either introspected or divined. Worse, it's normal to monkeypatch those objects, so the object members may (or may not) change over time.
Now, consider a typical Clojure program. What is it comprised of? Namespaces. Those namespaces contain functions and data. Functions may be dynamically generated (via macros), but it is extremely rare to "monkeypatch" a namespace. If you want to know what functions are available in a namespace, you can simply read the source file.
Continue reading https://potetm.com/devtalk/stability-by-design.html
originally posted at https://stacker.news/items/976215
-
 @ 97c70a44:ad98e322
2025-02-18 20:30:32
@ 97c70a44:ad98e322
2025-02-18 20:30:32For the last couple of weeks, I've been dealing with the fallout of upgrading a web application to Svelte 5. Complaints about framework churn and migration annoyances aside, I've run into some interesting issues with the migration. So far, I haven't seen many other people register the same issues, so I thought it might be constructive for me to articulate them myself.
I'll try not to complain too much in this post, since I'm grateful for the many years of Svelte 3/4 I've enjoyed. But I don't think I'll be choosing Svelte for any new projects going forward. I hope my reflections here will be useful to others as well.
If you're interested in reproductions for the issues I mention here, you can find them below.
The Need for Speed
To start with, let me just quickly acknowledge what the Svelte team is trying to do. It seems like most of the substantial changes in version 5 are built around "deep reactivity", which allows for more granular reactivity, leading to better performance. Performance is good, and the Svelte team has always excelled at reconciling performance with DX.
In previous versions of Svelte, the main way this was achieved was with the Svelte compiler. There were many ancillary techniques involved in improving performance, but having a framework compile step gave the Svelte team a lot of leeway for rearranging things under the hood without making developers learn new concepts. This is what made Svelte so original in the beginning.
At the same time, it resulted in an even more opaque framework than usual, making it harder for developers to debug more complex issues. To make matters worse, the compiler had bugs, resulting in errors which could only be fixed by blindly refactoring the problem component. This happened to me personally at least half a dozen times, and is what ultimately pushed me to migrate to Svelte 5.
Nevertheless, I always felt it was an acceptable trade-off for speed and productivity. Sure, sometimes I had to delete my project and port it to a fresh repository every so often, but the framework was truly a pleasure to use.
Svelte is not Javascript
Svelte 5 doubled down on this tradeoff — which makes sense, because it's what sets the framework apart. The difference this time is that the abstraction/performance tradeoff did not stay in compiler land, but intruded into runtime in two important ways:
- The use of proxies to support deep reactivity
- Implicit component lifecycle state
Both of these changes improved performance and made the API for developers look slicker. What's not to like? Unfortunately, both of these features are classic examples of a leaky abstraction, and ultimately make things more complex for developers, not less.
Proxies are not objects
The use of proxies seems to have allowed the Svelte team to squeeze a little more performance out of the framework, without asking developers to do any extra work. Threading state through multiple levels of components without provoking unnecessary re-renders in frameworks like React is an infamously difficult chore.
Svelte's compiler avoided some of the pitfalls associated with virtual DOM diffing solutions, but evidently there was still enough of a performance gain to be had to justify the introduction of proxies. The Svelte team also seems to argue that their introduction represents an improvement in developer experience:
we... can maximise both efficiency and ergonomics.
Here's the problem: Svelte 5 looks simpler, but actually introduces more abstractions.
Using proxies to monitor array methods (for example) is appealing because it allows developers to forget all the goofy heuristics involved with making sure state was reactive and just
pushto the array. I can't count how many times I've writtenvalue = valueto trigger reactivity in svelte 4.In Svelte 4, developers had to understand how the Svelte compiler worked. The compiler, being a leaky abstraction, forced its users to know that assignment was how you signaled reactivity. In svelte 5, developers can just "forget" about the compiler!
Except they can't. All the introduction of new abstractions really accomplishes is the introduction of more complex heuristics that developers have to keep in their heads in order to get the compiler to act the way they want it to.
In fact, this is why after years of using Svelte, I found myself using Svelte stores more and more often, and reactive declarations less. The reason being that Svelte stores are just javascript. Calling
updateon a store is simple, and being able to reference them with a$was just a nice bonus — nothing to remember, and if I mess up the compiler yells at me.Proxies introduce a similar problem to reactive declarations, which is that they look like one thing but act like another on the edges.
When I started using Svelte 5, everything worked great — until I tried to save a proxy to indexeddb, at which point I got a
DataCloneError. To make matters worse, it's impossible to reliably tell if something is aProxywithouttry/catching a structured clone, which is a performance-intensive operation.This forces the developer to remember what is and what isn't a Proxy, calling
$state.snapshotevery time they pass a proxy to a context that doesn't expect or know about them. This obviates all the nice abstractions they gave us in the first place.Components are not functions
The reason virtual DOM took off way back in 2013 was the ability to model your application as composed functions, each of which takes data and spits out HTML. Svelte retained this paradigm, using a compiler to sidestep the inefficiencies of virtual DOM and the complexities of lifecycle methods.
In Svelte 5, component lifecycles are back, react-hooks style.
In React, hooks are an abstraction that allows developers to avoid writing all the stateful code associated with component lifecycle methods. Modern React tutorials universally recommend using hooks instead, which rely on the framework invisibly synchronizing state with the render tree.
While this does result in cleaner code, it also requires developers to tread carefully to avoid breaking the assumptions surrounding hooks. Just try accessing state in a
setTimeoutand you'll see what I mean.Svelte 4 had a few gotchas like this — for example, async code that interacts with a component's DOM elements has to keep track of whether the component is unmounted. This is pretty similar to the kind of pattern you'd see in old React components that relied on lifecycle methods.
It seems to me that Svelte 5 has gone the React 16 route by adding implicit state related to component lifecycles in order to coordinate state changes and effects.
For example, here is an excerpt from the documentation for $effect:
You can place $effect anywhere, not just at the top level of a component, as long as it is called during component initialization (or while a parent effect is active). It is then tied to the lifecycle of the component (or parent effect) and will therefore destroy itself when the component unmounts (or the parent effect is destroyed).
That's very complex! In order to use
$effect... effectively (sorry), developers have to understand how state changes are tracked. The documentation for component lifecycles claims:In Svelte 5, the component lifecycle consists of only two parts: Its creation and its destruction. Everything in-between — when certain state is updated — is not related to the component as a whole; only the parts that need to react to the state change are notified. This is because under the hood the smallest unit of change is actually not a component, it’s the (render) effects that the component sets up upon component initialization. Consequently, there’s no such thing as a “before update”/"after update” hook.
But then goes on to introduce the idea of
tickin conjunction with$effect.pre. This section explains that "tickreturns a promise that resolves once any pending state changes have been applied, or in the next microtask if there are none."I'm sure there's some mental model that justifies this, but I don't think the claim that a component's lifecycle is only comprised of mount/unmount is really helpful when an addendum about state changes has to come right afterward.
The place where this really bit me, and which is the motivation for this blog post, is when state gets coupled to a component's lifecycle, even when the state is passed to another function that doesn't know anything about svelte.
In my application, I manage modal dialogs by storing the component I want to render alongside its props in a store and rendering it in the
layout.svelteof my application. This store is also synchronized with browser history so that the back button works to close them. Sometimes, it's useful to pass a callback to one of these modals, binding caller-specific functionality to the child component:javascript const {value} = $props() const callback = () => console.log(value) const openModal = () => pushModal(MyModal, {callback})This is a fundamental pattern in javascript. Passing a callback is just one of those things you do.
Unfortunately, if the above code lives in a modal dialog itself, the caller component gets unmounted before the callback gets called. In Svelte 4, this worked fine, but in Svelte 5
valuegets updated toundefinedwhen the component gets unmounted. Here's a minimal reproduction.This is only one example, but it seems clear to me that any prop that is closed over by a callback function that lives longer than its component will be undefined when I want to use it — with no reassignment existing in lexical scope. It seems that the reason this happens is that the props "belong" to the parent component, and are accessed via getters so that the parent can revoke access when it unmounts.
I don't know why this is necessary, but I assume there's a good engineering reason for it. The problem is, this just isn't how javascript works. Svelte is essentially attempting to re-invent garbage collection around component lifecycles, which breaks the assumption every javascript developer has that variables don't simply disappear without an explicit reassignment. It should be safe to pass stuff around and let the garbage collector do its job.
Conclusion
Easy things are nice, but as Rich Hickey says, easy things are not always simple. And like Joel Spolsky, I don't like being surprised. Svelte has always been full of magic, but with the latest release I think the cognitive overhead of reciting incantations has finally outweighed the power it confers.
My point in this post is not to dunk on the Svelte team. I know lots of people like Svelte 5 (and react hooks). The point I'm trying to make is that there is a tradeoff between doing things on the user's behalf, and giving the user agency. Good software is built on understanding, not cleverness.
I also think this is an important lesson to remember as AI-assisted coding becomes increasingly popular. Don't choose tools that alienate you from your work. Choose tools that leverage the wisdom you've already accumulated, and which help you to cultivate a deeper understanding of the discipline.
Thank you to Rich Harris and team for many years of pleasant development. I hope that (if you read this) it's not so full of inaccuracies as to be unhelpful as user feedback.
-
 @ 52b4a076:e7fad8bd
2025-04-28 00:48:57
@ 52b4a076:e7fad8bd
2025-04-28 00:48:57I have been recently building NFDB, a new relay DB. This post is meant as a short overview.
Regular relays have challenges
Current relay software have significant challenges, which I have experienced when hosting Nostr.land: - Scalability is only supported by adding full replicas, which does not scale to large relays. - Most relays use slow databases and are not optimized for large scale usage. - Search is near-impossible to implement on standard relays. - Privacy features such as NIP-42 are lacking. - Regular DB maintenance tasks on normal relays require extended downtime. - Fault-tolerance is implemented, if any, using a load balancer, which is limited. - Personalization and advanced filtering is not possible. - Local caching is not supported.
NFDB: A scalable database for large relays
NFDB is a new database meant for medium-large scale relays, built on FoundationDB that provides: - Near-unlimited scalability - Extended fault tolerance - Instant loading - Better search - Better personalization - and more.
Search
NFDB has extended search capabilities including: - Semantic search: Search for meaning, not words. - Interest-based search: Highlight content you care about. - Multi-faceted queries: Easily filter by topic, author group, keywords, and more at the same time. - Wide support for event kinds, including users, articles, etc.
Personalization
NFDB allows significant personalization: - Customized algorithms: Be your own algorithm. - Spam filtering: Filter content to your WoT, and use advanced spam filters. - Topic mutes: Mute topics, not keywords. - Media filtering: With Nostr.build, you will be able to filter NSFW and other content - Low data mode: Block notes that use high amounts of cellular data. - and more
Other
NFDB has support for many other features such as: - NIP-42: Protect your privacy with private drafts and DMs - Microrelays: Easily deploy your own personal microrelay - Containers: Dedicated, fast storage for discoverability events such as relay lists
Calcite: A local microrelay database
Calcite is a lightweight, local version of NFDB that is meant for microrelays and caching, meant for thousands of personal microrelays.
Calcite HA is an additional layer that allows live migration and relay failover in under 30 seconds, providing higher availability compared to current relays with greater simplicity. Calcite HA is enabled in all Calcite deployments.
For zero-downtime, NFDB is recommended.
Noswhere SmartCache
Relays are fixed in one location, but users can be anywhere.
Noswhere SmartCache is a CDN for relays that dynamically caches data on edge servers closest to you, allowing: - Multiple regions around the world - Improved throughput and performance - Faster loading times
routerd
routerdis a custom load-balancer optimized for Nostr relays, integrated with SmartCache.routerdis specifically integrated with NFDB and Calcite HA to provide fast failover and high performance.Ending notes
NFDB is planned to be deployed to Nostr.land in the coming weeks.
A lot more is to come. 👀️️️️️️
-
 @ 57d1a264:69f1fee1
2025-05-08 05:25:48
@ 57d1a264:69f1fee1
2025-05-08 05:25:48Safe Bits & Self Custody Tips
The journey of onboarding a user and create a bitcoin multiSig setup begins far before opening a desktop like Bitcoin Safe (BS) or any other similar application. Bitcoin Safe seems designed for families and people that want to start exploring and learning about multiSig setup. The need for such application and use of it could go much further, defining best practices for private organizations that aim to custody bitcoin in a private and anonymous way, following and enjoy the values and standards bitcoin has been built for.
Intro
Organizations and small private groups like families, family offices and solopreneurs operating on a bitcoin standard will have the need to keep track of transactions and categorize them to keep the books in order. A part of our efforts will be spent ensuring accessibility standards are in place for everyone to use Bitcoin Safe with comfort and safety.
We aim with this project to bring together the three Designathon ideas below: - Bitcoin Safe: improve its overall design and usability. - No User Left Behind: improve Bitcoin Safe accessibility. - Self-custody guidelines for organizations: How Bitcoin Safe can be used by private organization following best self-custody practices.
We are already halfway of the first week, and here below the progress made so far.
Designing an icon Set for Bitcoin Safe
One of the noticeable things when using BS is the inconsistency of the icons, not just in colors and shapes, but also the way are used. The desktop app try to have a clean design that incorporate with all OS (Win, macOS, Linux) and for this reason it's hard to define when a system default icon need to be used or if a custom one can be applied instead. The use of QT Ui framework for python apps help to respond to these questions. It also incorporates and brig up dome default settings that aren't easily overwritten.
Here below you can see the current version of BS:
Defining a more strict color palette for Bitcoin Safe was the first thing!
How much the icons affect accessibility? How they can help users to reach the right functionality? I took the challenge and, with PenPot.app, redesigned the icons based on the grid defined in the https://bitcoinicons.com/ and proposing the implementation of it to have a cleaner and more consistent look'n feel, at least for the icons now.
What's next
I personally look forward to seeing these icons implemented soon in Bitcoin Safe interface. In the meantime, we'll focus on delivering an accessibility audit and evaluate options to see how BS could be used by private organizations aiming to become financially sovereign with self-custody or more complex bitcoin multiSig setups.
One of the greatest innovations BS is bringing to us is the ability to sync the multiSig wallets, including PBST, Categories and labels, through the nostr decentralized protocol, making current key custodial services somehow obsolete. Second-coolest feature that this nostr implementation brings is the ability to have a build-in private chat that connect and enable the various signers of a multiSig to communicate and sign transactions remotely. Where have you seen something like this before?
Categories UX and redesign is also considered in this project. We'll try to understand how to better serve this functionality to you, the user, really soon.
Stay tuned!
originally posted at https://stacker.news/items/974488
-
 @ 4180da63:7b3c147e
2025-05-11 04:33:47
@ 4180da63:7b3c147e
2025-05-11 04:33:47By John "Potato Jack" LeFebvre
The cold, cold air of the morning tickled the nose of Christmas Goat as he lay quietly in bed, just waking up.
The cold air of the morning whispered in the ear of Christmas Goat; it whispered:- icicle secrets!
The moon, round and white, with swirling breezes, made Christmas Goat’s bedroom look like milk.
That reminded Christmas Goat – "It’s time to milk my cows!"
Christmas Goat peeled away the bed sheet and four blankets which kept him warm at night, and sitting on the edge of the bed he put on his gumboots.
He walked out of his bedroom and bumped into a wall because he was still a bit tired. He stood out on his front verandah and looked at the farm. "Come on you cows! It’s time for milking!!" he yelled.
The cows made a quiet line and walked, one behind the other, off to the milking sheds…
..all except for two cows who Christmas Goat had to throw a few potatoes at: then they got moving.
In the shed, the moos filled the air. Christmas Goat made his way past steaming cow flops carrying a bucket and a small stool.
He sat down next to Harry the cow.
"Ready for milking?", he asked.
"Yes, but you should have given me a girls name," said the cow.
"Oh well", said Christmas Goat, "here we go".
"Okay" said the cow, so Christmas Goat grabbed her teats with both hands and made the squirty milk goosh into the bucket.
"How are the kids?" asked Christmas Goat.
"Oh not bad," said Harry. "Bruce is in school and Terry’s just learning to moo."
"Yes, they’re good cows," said Christmas Goat.
"They are" said Harry. "I just wish you hadn’t given them boy’s names."
"Oh well," said Christmas Goat.
Christmas Goat milked all the cows one by one, and then he said to himself, "I think I’ll make myself a hot coffee". Back inside, he turned on the radio, and stirred the coffee powder into the hot water. Yum, he thought, pouring the cow’s milk on top. "Yum Yum Yum".
Christmas Goat drank all of this hot coffee and then made toast. A bird landed on his window sill and said "tweet tweet, tweet tweet ¯ ".
"Tweet tweet " said Christmas Goat".
The telephone rang four times and Christmas Goat picked it up.
"Hello, this is Christmas Goat?"
"Hello Christmas Goat? I’ve been a good goat all year and can you tell me what I’m getting for Christmas?"
"Christmas is tomorrow," said Christmas Goat.
"I know, but … - please tell me, just this once ..!"
"All right little goatgirl, what’s your name?"
"My name is Brenda," said the little girlgoat.
"Let me look at my list here…" said Christmas Goat. "
"Hmmm…" He moved his papers around.
"Are you still there?" asked the little goatgirl.
"Aha!! Yes I’m still here. I’ve just found your name on the list Brenda, here it is. Let’s see, oooh!"
"What is it! Wot is it!"
"It’s a …." But then Christmas Goat stopped talking.
"Why have you stopped talking?" said Brenda, panicking.
"Now, now," said Christmas Goat, "I just remembered it’s a secret."
"A secret!" said Brenda.
"Yes," said ChristmasGoat. "It has to be a surprise."
"No! Tell me now!" said Brenda.
Christmas Goat made a whistling sound with his lips. And then he hung up the phone.
By hanging up the phone like that, Christmas Goat felt a bit rude. But Brenda was rude first, he thought. Meanwhile, Brenda was at home, crying.
Christmas Goat thought , " I better go to see Brenda and explain to her why Christmas has to be a surprise." He went to the garage, oiled the wheels of his cart, and tied up a couple of humans.
"Good humans!" he said as they pulled him out of the garage down the street. The two people pulled the cart steadily along, steam pluming their foreheads.
It was a cold morning, and yet ChristmasGoat knew the earth was a round huge ball that spun on it’s axis while being invisibly dragged around a gigantic non stop fire- "the sun" – and that soon, because of this axis-spin, his part of the world would be receiving increasingly direct sun rays and it would get warm, so he didn’t worry . He explained this to the two men pulling his cart as it rolled through the suburbs, but they just blinked.
After a while, they arrived at Brenda’s house, and Christmas Goat tied the two men to a post and gave them a bottle of beer. Christmas Goat walked up the driveway, up the stairs, and went "knock kn0ck knock". A goat came to the door.
"Hallo Brenda?"
"No I’m Brenda’s brother. Brenda’s in her room, crying."
"Rats," said Christmas Goat.
There was Brenda, covered in tears, sitting on her carpet. Christmas Goat came in and sat down.
"Why did you make me sad?" said the little goatgirl.
"Well," said Christmas Goat, "I really didn’t want to do that. Every year, thousands of little goats ask me ‘what am I getting for Christmas,’ and every time I have to say to them, ‘you’ll see on Christmas day.’ And I Have to say this, I can’t say anything else, that’s just the way Christmas is."
"Come on, you must be able to tell me something a little deeper than (sniff) that."
Oh," said Christmas Goat, "you want the Big Reality explanation.."
"Yes," said Brenda, pouting and looking up from hurt eyes.
"Well," said Christmas Goat, "think what the world would be like with no surprise."
"Why? What would the world be like without surprise?" asked Brenda.
"Utterly predicable, " said Christmas Goat.
"What does predickable mean?" asked Brenda.
"In this case, it means ‘always knowing what’s going to happen’," said Christmas Goat.
"That sounds great!" said Brenda.
"Not really," said ChristmasGoat. "Think about it. Every day you wake up, you know what to wear, you know what’s going to be for breakfast, you know what job you have to go to, you know when it starts, you know how to get there, you know what you will see on the way, you know when you will stop for lunch, you know when you will finish, you know what’s for dinner, by looking at the program, you know what’s on T.V that night, they tell you what the weather will be like tomorrow, you know that if you …"
"That sounds Great!!" butted in Brenda.
"Yeah it sounded great to humans once, too, when they ruled the world. Woops."
"What was that?" said Brenda.
"What was what?" asked Christmas Goat.
"That thing you said, " said Brenda.
"I can’t remember, " said Christmas Goat, although now the shoe was on the other hoof.
"Well I remember, " said Brenda. "It just shocked me, that’s all. You said ‘when humans ruled the world.’"
"You’re right," sighed Christmas Goat. "That’s what I said..
Maybe we can forget about it though?"
Tell me tell me tell me tell me tell me tell me tell me tell me tell me tell me tell me tell me tell me tell… "
"ALL-RIGHT" said Christmas Goat, giving in. "Are you sure you want this dark knowledge?"
"Yes, I’m sure," said Brenda dribbling with excitement.
"Right, well once upon a time, the humans, like those two hitched up to the post outside drinking beer, were our masters. What they said, went."
"Boy," said Brenda.
"That’s right," continued Christmas Goat. "In fact they were the kings of the world. Us goats were treated horribly at times."
"What happened?" asked Brenda the little goatgirl.
"Those people became so set in their ways that they became stale. Nearly every effort at becoming the rulers made them and their lives boring. They thought they knew everything."
"People don’t know anything!" said Brenda.
"Not now they don’t," said Christmas Goat. "But they did in a distant past. Unfortunately they made the mistake of killing most surprises, and that’s when we snuck up them."
"Us goats?"
"Yep."
"And now we’re the kings and queens!" said Brenda gleefully.
"Of course," said Christmas Goat. "But we mustn’t let ourselves get trapped by prediction. That’s why I’m Christmas Goat. It’s my job to make sure surprise is still big in our lives, especially at this time of the year, Christmas." "Thankyou for telling me that true story," said Brenda. "I look forward to my surprise present tomorrow morning."
"That’s a good boy," said Christmas Goat.
"I’m a girl," said Brenda.
That night, Christmas Goat tied up his strongest humans who hauled and heaved his sleigh-cart all over the world through beautiful bright darkness. Kind Mummy and Daddy goats left a snack for Christmas Goat, and beer for the sweaty humans.
Christmas Goat and his team finished delivering the presents just in time.
"Good humans," he said, patting his helpers and switching on the T.V for them.
When Brenda woke up, there was a terrific colourful ping pong ball under her Christmas Tree.
"That is a surprise," smiled Brenda. "I’m a netballer!"
-
 @ 9e69e420:d12360c2
2025-02-17 17:12:01
@ 9e69e420:d12360c2
2025-02-17 17:12:01President Trump has intensified immigration enforcement, likening it to a wartime effort. Despite pouring resources into the U.S. Immigration and Customs Enforcement (ICE), arrest numbers are declining and falling short of goals. ICE fell from about 800 daily arrests in late January to fewer than 600 in early February.
Critics argue the administration is merely showcasing efforts with ineffectiveness, while Trump seeks billions more in funding to support his deportation agenda. Increased involvement from various federal agencies is intended to assist ICE, but many lack specific immigration training.
Challenges persist, as fewer immigrants are available for quick deportation due to a decline in illegal crossings. Local sheriffs are also pressured by rising demands to accommodate immigrants, which may strain resources further.
-
 @ 91bea5cd:1df4451c
2025-04-26 10:16:21
@ 91bea5cd:1df4451c
2025-04-26 10:16:21O Contexto Legal Brasileiro e o Consentimento
No ordenamento jurídico brasileiro, o consentimento do ofendido pode, em certas circunstâncias, afastar a ilicitude de um ato que, sem ele, configuraria crime (como lesão corporal leve, prevista no Art. 129 do Código Penal). Contudo, o consentimento tem limites claros: não é válido para bens jurídicos indisponíveis, como a vida, e sua eficácia é questionável em casos de lesões corporais graves ou gravíssimas.
A prática de BDSM consensual situa-se em uma zona complexa. Em tese, se ambos os parceiros são adultos, capazes, e consentiram livre e informadamente nos atos praticados, sem que resultem em lesões graves permanentes ou risco de morte não consentido, não haveria crime. O desafio reside na comprovação desse consentimento, especialmente se uma das partes, posteriormente, o negar ou alegar coação.
A Lei Maria da Penha (Lei nº 11.340/2006)
A Lei Maria da Penha é um marco fundamental na proteção da mulher contra a violência doméstica e familiar. Ela estabelece mecanismos para coibir e prevenir tal violência, definindo suas formas (física, psicológica, sexual, patrimonial e moral) e prevendo medidas protetivas de urgência.
Embora essencial, a aplicação da lei em contextos de BDSM pode ser delicada. Uma alegação de violência por parte da mulher, mesmo que as lesões ou situações decorram de práticas consensuais, tende a receber atenção prioritária das autoridades, dada a presunção de vulnerabilidade estabelecida pela lei. Isso pode criar um cenário onde o parceiro masculino enfrenta dificuldades significativas em demonstrar a natureza consensual dos atos, especialmente se não houver provas robustas pré-constituídas.
Outros riscos:
Lesão corporal grave ou gravíssima (art. 129, §§ 1º e 2º, CP), não pode ser justificada pelo consentimento, podendo ensejar persecução penal.
Crimes contra a dignidade sexual (arts. 213 e seguintes do CP) são de ação pública incondicionada e independem de representação da vítima para a investigação e denúncia.
Riscos de Falsas Acusações e Alegação de Coação Futura
Os riscos para os praticantes de BDSM, especialmente para o parceiro que assume o papel dominante ou que inflige dor/restrição (frequentemente, mas não exclusivamente, o homem), podem surgir de diversas frentes:
- Acusações Externas: Vizinhos, familiares ou amigos que desconhecem a natureza consensual do relacionamento podem interpretar sons, marcas ou comportamentos como sinais de abuso e denunciar às autoridades.
- Alegações Futuras da Parceira: Em caso de término conturbado, vingança, arrependimento ou mudança de perspectiva, a parceira pode reinterpretar as práticas passadas como abuso e buscar reparação ou retaliação através de uma denúncia. A alegação pode ser de que o consentimento nunca existiu ou foi viciado.
- Alegação de Coação: Uma das formas mais complexas de refutar é a alegação de que o consentimento foi obtido mediante coação (física, moral, psicológica ou econômica). A parceira pode alegar, por exemplo, que se sentia pressionada, intimidada ou dependente, e que seu "sim" não era genuíno. Provar a ausência de coação a posteriori é extremamente difícil.
- Ingenuidade e Vulnerabilidade Masculina: Muitos homens, confiando na dinâmica consensual e na parceira, podem negligenciar a necessidade de precauções. A crença de que "isso nunca aconteceria comigo" ou a falta de conhecimento sobre as implicações legais e o peso processual de uma acusação no âmbito da Lei Maria da Penha podem deixá-los vulneráveis. A presença de marcas físicas, mesmo que consentidas, pode ser usada como evidência de agressão, invertendo o ônus da prova na prática, ainda que não na teoria jurídica.
Estratégias de Prevenção e Mitigação
Não existe um método infalível para evitar completamente o risco de uma falsa acusação, mas diversas medidas podem ser adotadas para construir um histórico de consentimento e reduzir vulnerabilidades:
- Comunicação Explícita e Contínua: A base de qualquer prática BDSM segura é a comunicação constante. Negociar limites, desejos, palavras de segurança ("safewords") e expectativas antes, durante e depois das cenas é crucial. Manter registros dessas negociações (e-mails, mensagens, diários compartilhados) pode ser útil.
-
Documentação do Consentimento:
-
Contratos de Relacionamento/Cena: Embora a validade jurídica de "contratos BDSM" seja discutível no Brasil (não podem afastar normas de ordem pública), eles servem como forte evidência da intenção das partes, da negociação detalhada de limites e do consentimento informado. Devem ser claros, datados, assinados e, idealmente, reconhecidos em cartório (para prova de data e autenticidade das assinaturas).
-
Registros Audiovisuais: Gravar (com consentimento explícito para a gravação) discussões sobre consentimento e limites antes das cenas pode ser uma prova poderosa. Gravar as próprias cenas é mais complexo devido a questões de privacidade e potencial uso indevido, mas pode ser considerado em casos específicos, sempre com consentimento mútuo documentado para a gravação.
Importante: a gravação deve ser com ciência da outra parte, para não configurar violação da intimidade (art. 5º, X, da Constituição Federal e art. 20 do Código Civil).
-
-
Testemunhas: Em alguns contextos de comunidade BDSM, a presença de terceiros de confiança durante negociações ou mesmo cenas pode servir como testemunho, embora isso possa alterar a dinâmica íntima do casal.
- Estabelecimento Claro de Limites e Palavras de Segurança: Definir e respeitar rigorosamente os limites (o que é permitido, o que é proibido) e as palavras de segurança é fundamental. O desrespeito a uma palavra de segurança encerra o consentimento para aquele ato.
- Avaliação Contínua do Consentimento: O consentimento não é um cheque em branco; ele deve ser entusiástico, contínuo e revogável a qualquer momento. Verificar o bem-estar do parceiro durante a cena ("check-ins") é essencial.
- Discrição e Cuidado com Evidências Físicas: Ser discreto sobre a natureza do relacionamento pode evitar mal-entendidos externos. Após cenas que deixem marcas, é prudente que ambos os parceiros estejam cientes e de acordo, talvez documentando por fotos (com data) e uma nota sobre a consensualidade da prática que as gerou.
- Aconselhamento Jurídico Preventivo: Consultar um advogado especializado em direito de família e criminal, com sensibilidade para dinâmicas de relacionamento alternativas, pode fornecer orientação personalizada sobre as melhores formas de documentar o consentimento e entender os riscos legais específicos.
Observações Importantes
- Nenhuma documentação substitui a necessidade de consentimento real, livre, informado e contínuo.
- A lei brasileira protege a "integridade física" e a "dignidade humana". Práticas que resultem em lesões graves ou que violem a dignidade de forma não consentida (ou com consentimento viciado) serão ilegais, independentemente de qualquer acordo prévio.
- Em caso de acusação, a existência de documentação robusta de consentimento não garante a absolvição, mas fortalece significativamente a defesa, ajudando a demonstrar a natureza consensual da relação e das práticas.
-
A alegação de coação futura é particularmente difícil de prevenir apenas com documentos. Um histórico consistente de comunicação aberta (whatsapp/telegram/e-mails), respeito mútuo e ausência de dependência ou controle excessivo na relação pode ajudar a contextualizar a dinâmica como não coercitiva.
-
Cuidado com Marcas Visíveis e Lesões Graves Práticas que resultam em hematomas severos ou lesões podem ser interpretadas como agressão, mesmo que consentidas. Evitar excessos protege não apenas a integridade física, mas também evita questionamentos legais futuros.
O que vem a ser consentimento viciado
No Direito, consentimento viciado é quando a pessoa concorda com algo, mas a vontade dela não é livre ou plena — ou seja, o consentimento existe formalmente, mas é defeituoso por alguma razão.
O Código Civil brasileiro (art. 138 a 165) define várias formas de vício de consentimento. As principais são:
Erro: A pessoa se engana sobre o que está consentindo. (Ex.: A pessoa acredita que vai participar de um jogo leve, mas na verdade é exposta a práticas pesadas.)
Dolo: A pessoa é enganada propositalmente para aceitar algo. (Ex.: Alguém mente sobre o que vai acontecer durante a prática.)
Coação: A pessoa é forçada ou ameaçada a consentir. (Ex.: "Se você não aceitar, eu termino com você" — pressão emocional forte pode ser vista como coação.)
Estado de perigo ou lesão: A pessoa aceita algo em situação de necessidade extrema ou abuso de sua vulnerabilidade. (Ex.: Alguém em situação emocional muito fragilizada é induzida a aceitar práticas que normalmente recusaria.)
No contexto de BDSM, isso é ainda mais delicado: Mesmo que a pessoa tenha "assinado" um contrato ou dito "sim", se depois ela alegar que seu consentimento foi dado sob medo, engano ou pressão psicológica, o consentimento pode ser considerado viciado — e, portanto, juridicamente inválido.
Isso tem duas implicações sérias:
-
O crime não se descaracteriza: Se houver vício, o consentimento é ignorado e a prática pode ser tratada como crime normal (lesão corporal, estupro, tortura, etc.).
-
A prova do consentimento precisa ser sólida: Mostrando que a pessoa estava informada, lúcida, livre e sem qualquer tipo de coação.
Consentimento viciado é quando a pessoa concorda formalmente, mas de maneira enganada, forçada ou pressionada, tornando o consentimento inútil para efeitos jurídicos.
Conclusão
Casais que praticam BDSM consensual no Brasil navegam em um terreno que exige não apenas confiança mútua e comunicação excepcional, mas também uma consciência aguçada das complexidades legais e dos riscos de interpretações equivocadas ou acusações mal-intencionadas. Embora o BDSM seja uma expressão legítima da sexualidade humana, sua prática no Brasil exige responsabilidade redobrada. Ter provas claras de consentimento, manter a comunicação aberta e agir com prudência são formas eficazes de se proteger de falsas alegações e preservar a liberdade e a segurança de todos os envolvidos. Embora leis controversas como a Maria da Penha sejam "vitais" para a proteção contra a violência real, os praticantes de BDSM, e em particular os homens nesse contexto, devem adotar uma postura proativa e prudente para mitigar os riscos inerentes à potencial má interpretação ou instrumentalização dessas práticas e leis, garantindo que a expressão de sua consensualidade esteja resguardada na medida do possível.
Importante: No Brasil, mesmo com tudo isso, o Ministério Público pode denunciar por crime como lesão corporal grave, estupro ou tortura, independente de consentimento. Então a prudência nas práticas é fundamental.
Aviso Legal: Este artigo tem caráter meramente informativo e não constitui aconselhamento jurídico. As leis e interpretações podem mudar, e cada situação é única. Recomenda-se buscar orientação de um advogado qualificado para discutir casos específicos.
Se curtiu este artigo faça uma contribuição, se tiver algum ponto relevante para o artigo deixe seu comentário.
-
 @ 8d34bd24:414be32b
2025-05-11 02:47:03
@ 8d34bd24:414be32b
2025-05-11 02:47:03What does it say about us that believers don’t listen as well as unbelievers? Let’s investigate some scripture verses and see what we can discover.
An Object Lesson:
Jesus warned His disciples several times that He would be killed and rise from the dead on the third day. Right after Jesus asked them who they thought He was and Peter replied that He was the Christ (Messiah), Jesus told them what would happen.
From that time Jesus began to show His disciples that He must go to Jerusalem, and suffer many things from the elders and chief priests and scribes, and be killed, and be raised up on the third day. (Matthew 16:21)
We know the disciples heard and understood what Jesus was saying because Peter immediately rebuked Jesus.
Peter took Him aside and began to rebuke Him, saying, “God forbid it, Lord! This shall never happen to You.” But He turned and said to Peter, “Get behind Me, Satan! You are a stumbling block to Me; for you are not setting your mind on God’s interests, but man’s.” (Matthew 16:22-23)
You’d think that Peter would have this moment locked in his mind after being rebuked so harshly for questioning Jesus’s prediction of what would happen.
A while later, Jesus again told His disciples what was about to happen.
And while they were gathering together in Galilee, Jesus said to them, “The Son of Man is going to be delivered into the hands of men; and they will kill Him, and He will be raised on the third day.” And they were deeply grieved. (Matthew 17:22-23)
They again heard what was said because they were “deeply grieved.” They didn’t like what they heard.
Then a third time, as they were approaching Jerusalem, He made certain they knew what was coming:
As Jesus was about to go up to Jerusalem, He took the twelve disciples aside by themselves, and on the way He said to them, “Behold, we are going up to Jerusalem; and the Son of Man will be delivered to the chief priests and scribes, and they will condemn Him to death, and will hand Him over to the Gentiles to mock and scourge and crucify Him, and on the third day He will be raised up.” (Matthew 20:17-19)
The disciples should have known that Jesus’s crucifixion and death were not the end. He told them repeatedly that He would die and be raised from the dead on the third day. They should have been diligently waiting with expectation, but instead they immediately hid, gave up, and headed back to their old lives.
His female followers still cared enough to try to prepare Jesus’s body for burial, but even they did not expect Him to rise as He said.
The angel said to the women, “Do not be afraid; for I know that you are looking for Jesus who has been crucified. He is not here, for He has risen, just as He said. Come, see the place where He was lying. Go quickly and tell His disciples that He has risen from the dead; and behold, He is going ahead of you into Galilee, there you will see Him; behold, I have told you.” (Matthew 28:5-7) {emphasis mine}
Even when the woman came and told the disciples that they had seen Jesus as He had said, none believed them, although Peter and John did have a glimmer of hope and went to look for themselves.
In contrast, the Pharisees, the very people who hated Jesus so much that they fought to have Him crucified, remembered Jesus’s statements.
Now on the next day, the day after the preparation, the chief priests and the Pharisees gathered together with Pilate, and said, “Sir, we remember that when He was still alive that deceiver said, ‘After three days I am to rise again.’ Therefore, give orders for the grave to be made secure until the third day, otherwise His disciples may come and steal Him away and say to the people, ‘He has risen from the dead,’ and the last deception will be worse than the first.” Pilate said to them, “You have a guard; go, make it as secure as you know how.” And they went and made the grave secure, and along with the guard they set a seal on the stone. (Matthew 27:62-66) {emphasis mine}
The Pharisees acted in response to Jesus’s claims. The disciples ignored or forgot Jesus’s claims.
KNOW:
How often do we ignore or forget Jesus’s promises? How often do we despair when we should hold tightly to the promises given to us in the Bible? Are there times that our opponents, unbelievers, are better at quoting the Bible back at us than we are at using the Bible to defend the truth and our faith?
but sanctify Christ as Lord in your hearts, always being ready to make a defense to everyone who asks you to give an account for the hope that is in you, yet with gentleness and reverence (1 Peter 3:15)
We need to know God’s word so we can “give an account for the hope that is in” us. First we need to read the whole Bible. We can’t know who God is, what He has done, and what He commands for us without knowing God’s word.
After we have gotten the big picture by reading through the Bible once, we need to really get to know it well. This not only includes reading the Bible continually, but also include memorizing key verses, so we can bring them to remembrance when we need them.
Some people can repeat a verse multiple times and just know it. Some of us have trouble memorizing things. We have to go to extraordinary measures to memorize God’s word. Some techniques I have used:
-
WHITEBOARD APPROACH:
-
Write the verse on the white board.
-
Read out loud.
-
Erase one word. (You can underline where the word is if that helps you remember that a word goes there)
-
Read out loud saying verse including missing word.
-
Continue erasing words, one at a time, saying the verse until all of the words are gone.
-
I haven’t used it personally, but Verse Locker was recommended by another substacker and seems to use a similar technique.
-
MUSICAL VERSES:
-
Make up a tune and sing the verse or put the verse to a tune you already know.
-
If you aren’t good at making up songs, there are sites that have verses to songs, but I haven’t used them personally other than a few from Awana years ago.
-
FIRST LETTER:
-
Write down the first letter of each word of the verse you want to memorize This gives hints and helps you not accidentally miss words.
-
I’ve also made a necklace (it was supposed to be a bracelet, but the verse, 1 Peter 3:15 above, I picked was too long) made of beads with the letters of the words of the verse. By wearing it, you have a reminder to memorize and rememorize the verse till it sticks stronger.
-
This is my version of 1 Peter 3:15

-
APPS:
-
There are multiple apps that can help you memorize verses. 5 Best Bible Memory Apps for 2025
We are all different and have different learning styles. Pick the version that works best for you, but be intentional. For so long I wasn’t. Having a child with Down Syndrome in Awana who needed help led me to finding ways to help him and me to memorize the hundreds (or thousands) of verses that are required to finish the program. Keep in mind that you need to keep reviewing them or the memories will fade. The more times you memorize the verse, the longer it will stick with you. You just never know when you will need a Scripture verse and you may not have your Bible or phone (with Bible app) handy.
APPLY:
Knowing the Bible is critical for the Christian life, but knowing the Bible and God’s commands is not enough. We have to live according to this knowledge. We have to apply it in our lives. It needs to change the way we view the world and change the way we live our lives and interact with others.
for it is not the hearers of the Law who are just before God, but the doers of the Law will be justified. (Romans 2:13) {emphasis mine}
Our faith needs to be exhibited through action.
But someone may well say, “You have faith and I have works; show me your faith without the works, and I will show you my faith by my works.” (James 2:18) {emphasis mine}
There is nothing we need to do to be saved besides believe, but if we have saving faith, we should desire God’s word like the author of Psalm 119. Our lives should also change to be conformed to Jesus.
And do not be conformed to this world, but be transformed by the renewing of your mind, so that you may prove what the will of God is, that which is good and acceptable and perfect. (Romans 12:12) {emphasis mine}
There must be works as evidence of our faith.
You believe that God is one. You do well; the demons also believe, and shudder. But are you willing to recognize, you foolish fellow, that faith without works is useless? Was not Abraham our father justified by works when he offered up Isaac his son on the altar? You see that faith was working with his works, and as a result of the works, faith was perfected; (James 2:19-22) {emphasis mine}
The disciples heard Jesus tell them what was going to happen to Him. They knew what He had said because they reacted to it negatively. The problem was they didn’t believe it and didn’t live according to Jesus’s plain words. As important as it is to read and understand the Bible, none of that matters if we don’t believe it and live it.
But I Can’t Do It Myself:
Jesus knew that we could not know and do what we were commanded to know and do, at least not in our own power.
Then He opened their minds to understand the Scriptures, and He said to them, “Thus it is written, that the Christ would suffer and rise again from the dead the third day, and that repentance for forgiveness of sins would be proclaimed in His name to all the nations, beginning from Jerusalem. You are witnesses of these things. And behold, I am sending forth the promise of My Father upon you; but you are to stay in the city until you are clothed with power from on high.” (Luke 24:45-49)
Jesus not only sent the disciples (and all believers) out into the world to tell of what He has done for us, but He told the disciples to “stay in the city until you are clothed with power from on high.” Jesus told them to wait until they had received the Holy Spirit to guide and empower them in the work He had designed them to complete. We also have the Holy Spirit to change our hearts and minds, so we can fulfill the commandments and plans He has for us.
I’m sorry if this post had a little too much overlap with my last post, but knowing God’s word has become a passion of mine and it is where I felt led to go.
May the God of Heaven give you a hunger for His word, help you to understand His word, believe His word, and live His word. May your understanding of the word of God guide you in everything you think, speak, and do. May you never doubt God’s word or discount God’s word because it isn’t according to your preference. God bless you and keep you.
Trust Jesus.
-
-
 @ c9badfea:610f861a
2025-05-11 01:12:30
@ c9badfea:610f861a
2025-05-11 01:12:30- Install Helio (it's free and open source)
- Download SoundFont files from various sources (see links below)
- Launch the app and follow these steps to import SoundFonts:
- Tap Studio in the top bar, then select Orchestra Pit
- Tap Scan Common Plugin Folders, select SoundFont Player from the plugins found
- Tap SoundFont Player in the top bar, then Create New Instrument
- Select the new SoundFont Player instrument
- Tap SoundFont Player in the top bar, then Show UI
- Tap the folder icon and choose a downloaded SoundFont file
- Rename the instrument by tapping the first SoundFont Player in the top bar, then Rename
- Tap Studio twice in the top bar, then Start A New Project
- Choose a file location for the project and Save
- Tap Track 1, choose Set Instrument, and select an instrument
- Double-tap in the arranger to add a new note
- Explore the interface and start composing
Some SoundFont Sources
ℹ️ The Helio interface is unique and may require some time to get accustomed to
ℹ️ A SoundFont file (
.sf2) contains a collection of audio samples -
 @ 57d1a264:69f1fee1
2025-05-08 05:08:36
@ 57d1a264:69f1fee1
2025-05-08 05:08:36Welcome back to our weekly
JABBB, Just Another Bitcoin Bubble Boom, a comics and meme contest crafted for you, creative stackers!If you'd like to learn more, check our welcome post here.
This week sticker:
Bitcoin SirYou can download the source file directly from the HereComesBitcoin website in SVG and PNG. Use this sticker around SN with the code
The task
Make sure you use this week sticker to design a comic frame or a meme, add a message that perfectly captures the sentiment of the current most hilarious takes on the Bitcoin space. You can contextualize it or not, it's up to you, you chose the message, the context and anything else that will help you submit your comic art masterpiece.
Are you a meme creator? There's space for you too: select the most similar shot from the gifts hosted on the Gif Station section and craft your best meme... Let's Jabbb!
If you enjoy designing and memeing, feel free to check out the JABBB archive and create more to spread Bitcoin awareness to the moon.
Submit each proposal on the relative thread, bounties will be distributed when enough participants submit options.
PS: you can now use HereComesBitcoin stickers to use on Stacker.News
₿e creative, have fun! :D
originally posted at https://stacker.news/items/974483
-
 @ 57d1a264:69f1fee1
2025-05-07 06:56:25
@ 57d1a264:69f1fee1
2025-05-07 06:56:25Wild parrots tend to fly in flocks, but when kept as single pets, they may become lonely and bored https://www.youtube.com/watch?v=OHcAOlamgDc
Source: https://www.smithsonianmag.com/smart-news/scientists-taught-pet-parrots-to-video-call-each-other-and-the-birds-loved-it-180982041/
originally posted at https://stacker.news/items/973639
-
 @ 57d1a264:69f1fee1
2025-05-07 06:29:52
@ 57d1a264:69f1fee1
2025-05-07 06:29:52Your device, your data. TRMNL's architecture prevents outsiders (including us) from accessing your local network. TRMNAL achieve this through 1 way communication between client and server, versus the other way around. Learn more.
Learn more at https://usetrmnl.com/
originally posted at https://stacker.news/items/973632
-
 @ c9badfea:610f861a
2025-05-10 23:17:06
@ c9badfea:610f861a
2025-05-10 23:17:06- Install EtchDroid (it's free and open source)
- Launch the app, then tap What's Supported? to check compatibility with devices and disk images
- Insert the USB drive
- Tap Write An Image, then select the desired image file
- Tap Grant Access, confirm, and then tap Write image
- Optionally, allow notifications to be notified when the process is complete
- Your bootable USB drive is now ready
⚠️ This app has telemetry enabled by default. Make sure to turn it off in the app menu. If you trust F-Droid, you can get a telemetry-free version from there
⚠️ Avoid moving the phone during the image writing process
-
 @ df478568:2a951e67
2025-05-10 22:01:36
@ df478568:2a951e67
2025-05-10 22:01:36XMMP is a protocol that allows journalists and plebs alike to create a phone number that is not tied to your identity. Why would you want to do this? Are you some kind of hacker? Well… yeah… we are hackers, technically. That doesn't mean we want to break the non-aggression principle and steal sats from OGs or anything. Perhaps it's better to call ourselves cybersecurity experts to placate neurotypical people.
Every Bitcoiner worth their sats knows phone numbers are a security hole. Sure, if you're a super cypherpunk with a 100% KYC-free stack or never intend to spend your “precious,” then this might not concern you. You can sell your sats on Bisq for paper cash trash and pay your water bill or whatever. It's a significant inconvenience, but I know some people who do this. Satoshi bless them! But the rest of us mere mortals find it easier to use bill-pay services with Strike. Unfortunately, the powers that be force us to use our telephone numbers as a de-facto identity system.
This phone number must be trusted to a third party, and as Nick Szabo famously said, "Trusted third parties are security holes." This guy I go pleb camping with thinks it's funny that Bitcoiners never want to give away their phone numbers. It's true because phone numbers create an attack surface—specifically, they may be used for SIM swaps to drain our Bitcoin bank accounts or the associated traditional bank accounts. This is not the only attack. Smishing is also a concern, but that threat requires diligence since anyone using SMS is susceptible to it. XMMP won't prevent smishing; however, it will provide a phone number people can use to text or call without tying the number to your identity. Thus, even if attackers somehow compromise this phone number, it can't be used to drain your accounts.
What Is XMMP?

XMMP is a protocol that functions similarly to cellular phone service on almost any device with internet access. I don't think it'll work on a Kindle, but to be honest, I haven't tried. XMMP can be used alongside your existing phone, laptop, and desktop computers. You can safely give this phone number to all your hardcore hacker friends without worrying. It's affordable too—the service costs \$5.00 per month, and the service I use accepts sats for payment. Though this doesn’t include data, you can easily use XMMP over Wi-Fi.
If you want a separate phone running GrapheneOS or CalyxOS, you can pay for data in multiple ways. Personally, I like Silent Link—it's run by a fellow pleb and accepts sats via the Lightning Network.
How To Set Up XMMP
If you identify as a non-technical person, you can buy a phone and suite from Above Phone*, which will help you set everything up. I'm more of a DIY-as-much-as-I-can kind of guy, so I opted to set mine up myself. I haven't personally tried Above Phone, but I've heard good things about their service.
If you already have a phone but want a secure method to call or text your contacts, here's what to do:
-
Install Cheogram on your Android phone. Sorry, but I don’t know if Apple's overlords allow this for iOS devices.
-
Choose a phone number with JMP. They charge \$5.00 monthly and accept Bitcoin as payment. While you could port your current phone number, the purpose of this article is to create a fresh, anonymous phone number that cannot be traced back to you as an instrument for draining your bank account—so we won't get into porting here.
-
Once you've paid, you will receive a message in the Cheogram app confirming your order. It might take some time since payments are on-chain—so be patient. You can also pay with a credit card if you prefer, but we use sats in this household.
How To Get Data
You might occasionally want to send messages away from 127.0.0.1. My favorite solution is to use the services provided by Silent Link. They offer an eSIM, and while you can also get a phone number from Silent Link, it's mainly useful for services like Signal. However, it costs around \$20 worth of sats per month rather than JMP's \$5/month. Assuming all Bitcoiners are cheapskates like me—well, you do you!
I chose Silent Link's data plan. Initially, I messed up this process because I refreshed the webpage on my phone. Don't do that, or you'll have to spend another twenty bucks to set it up again. If you carefully follow Silent Link's instructions, you should be fine. Patience is crucial, and admittedly, that's something I'm not good at—which explains why I paid more sats than needed.
/* Above Phone is an affiliate link and I may get a small commission if you use my referral link.
☮️
npub1marc26z8nh3xkj5rcx7ufkatvx6ueqhp5vfw9v5teq26z254renshtf3g0
As seen on https://zapthisblog.com/save-sats-with-on-sms-and-cellular-with-xmmp/
-
-
 @ 40b9c85f:5e61b451
2025-04-24 15:27:02
@ 40b9c85f:5e61b451
2025-04-24 15:27:02Introduction
Data Vending Machines (DVMs) have emerged as a crucial component of the Nostr ecosystem, offering specialized computational services to clients across the network. As defined in NIP-90, DVMs operate on an apparently simple principle: "data in, data out." They provide a marketplace for data processing where users request specific jobs (like text translation, content recommendation, or AI text generation)
While DVMs have gained significant traction, the current specification faces challenges that hinder widespread adoption and consistent implementation. This article explores some ideas on how we can apply the reflection pattern, a well established approach in RPC systems, to address these challenges and improve the DVM ecosystem's clarity, consistency, and usability.
The Current State of DVMs: Challenges and Limitations
The NIP-90 specification provides a broad framework for DVMs, but this flexibility has led to several issues:
1. Inconsistent Implementation
As noted by hzrd149 in "DVMs were a mistake" every DVM implementation tends to expect inputs in slightly different formats, even while ostensibly following the same specification. For example, a translation request DVM might expect an event ID in one particular format, while an LLM service could expect a "prompt" input that's not even specified in NIP-90.
2. Fragmented Specifications
The DVM specification reserves a range of event kinds (5000-6000), each meant for different types of computational jobs. While creating sub-specifications for each job type is being explored as a possible solution for clarity, in a decentralized and permissionless landscape like Nostr, relying solely on specification enforcement won't be effective for creating a healthy ecosystem. A more comprehensible approach is needed that works with, rather than against, the open nature of the protocol.
3. Ambiguous API Interfaces
There's no standardized way for clients to discover what parameters a specific DVM accepts, which are required versus optional, or what output format to expect. This creates uncertainty and forces developers to rely on documentation outside the protocol itself, if such documentation exists at all.
The Reflection Pattern: A Solution from RPC Systems
The reflection pattern in RPC systems offers a compelling solution to many of these challenges. At its core, reflection enables servers to provide metadata about their available services, methods, and data types at runtime, allowing clients to dynamically discover and interact with the server's API.
In established RPC frameworks like gRPC, reflection serves as a self-describing mechanism where services expose their interface definitions and requirements. In MCP reflection is used to expose the capabilities of the server, such as tools, resources, and prompts. Clients can learn about available capabilities without prior knowledge, and systems can adapt to changes without requiring rebuilds or redeployments. This standardized introspection creates a unified way to query service metadata, making tools like
grpcurlpossible without requiring precompiled stubs.How Reflection Could Transform the DVM Specification
By incorporating reflection principles into the DVM specification, we could create a more coherent and predictable ecosystem. DVMs already implement some sort of reflection through the use of 'nip90params', which allow clients to discover some parameters, constraints, and features of the DVMs, such as whether they accept encryption, nutzaps, etc. However, this approach could be expanded to provide more comprehensive self-description capabilities.
1. Defined Lifecycle Phases
Similar to the Model Context Protocol (MCP), DVMs could benefit from a clear lifecycle consisting of an initialization phase and an operation phase. During initialization, the client and DVM would negotiate capabilities and exchange metadata, with the DVM providing a JSON schema containing its input requirements. nip-89 (or other) announcements can be used to bootstrap the discovery and negotiation process by providing the input schema directly. Then, during the operation phase, the client would interact with the DVM according to the negotiated schema and parameters.
2. Schema-Based Interactions
Rather than relying on rigid specifications for each job type, DVMs could self-advertise their schemas. This would allow clients to understand which parameters are required versus optional, what type validation should occur for inputs, what output formats to expect, and what payment flows are supported. By internalizing the input schema of the DVMs they wish to consume, clients gain clarity on how to interact effectively.
3. Capability Negotiation
Capability negotiation would enable DVMs to advertise their supported features, such as encryption methods, payment options, or specialized functionalities. This would allow clients to adjust their interaction approach based on the specific capabilities of each DVM they encounter.
Implementation Approach
While building DVMCP, I realized that the RPC reflection pattern used there could be beneficial for constructing DVMs in general. Since DVMs already follow an RPC style for their operation, and reflection is a natural extension of this approach, it could significantly enhance and clarify the DVM specification.
A reflection enhanced DVM protocol could work as follows: 1. Discovery: Clients discover DVMs through existing NIP-89 application handlers, input schemas could also be advertised in nip-89 announcements, making the second step unnecessary. 2. Schema Request: Clients request the DVM's input schema for the specific job type they're interested in 3. Validation: Clients validate their request against the provided schema before submission 4. Operation: The job proceeds through the standard NIP-90 flow, but with clearer expectations on both sides
Parallels with Other Protocols
This approach has proven successful in other contexts. The Model Context Protocol (MCP) implements a similar lifecycle with capability negotiation during initialization, allowing any client to communicate with any server as long as they adhere to the base protocol. MCP and DVM protocols share fundamental similarities, both aim to expose and consume computational resources through a JSON-RPC-like interface, albeit with specific differences.
gRPC's reflection service similarly allows clients to discover service definitions at runtime, enabling generic tools to work with any gRPC service without prior knowledge. In the REST API world, OpenAPI/Swagger specifications document interfaces in a way that makes them discoverable and testable.
DVMs would benefit from adopting these patterns while maintaining the decentralized, permissionless nature of Nostr.
Conclusion
I am not attempting to rewrite the DVM specification; rather, explore some ideas that could help the ecosystem improve incrementally, reducing fragmentation and making the ecosystem more comprehensible. By allowing DVMs to self describe their interfaces, we could maintain the flexibility that makes Nostr powerful while providing the structure needed for interoperability.
For developers building DVM clients or libraries, this approach would simplify consumption by providing clear expectations about inputs and outputs. For DVM operators, it would establish a standard way to communicate their service's requirements without relying on external documentation.
I am currently developing DVMCP following these patterns. Of course, DVMs and MCP servers have different details; MCP includes capabilities such as tools, resources, and prompts on the server side, as well as 'roots' and 'sampling' on the client side, creating a bidirectional way to consume capabilities. In contrast, DVMs typically function similarly to MCP tools, where you call a DVM with an input and receive an output, with each job type representing a different categorization of the work performed.
Without further ado, I hope this article has provided some insight into the potential benefits of applying the reflection pattern to the DVM specification.
-
 @ eb5f61d0:24cdd490
2025-05-11 02:34:15
@ eb5f61d0:24cdd490
2025-05-11 02:34:15Com o avanço da tecnologia e a popularização dos jogos online, os brasileiros têm buscado plataformas modernas, seguras e completas para se divertir e tentar a sorte. Entre as opções que vêm ganhando destaque no cenário nacional, a 9993Bet se consolida como uma das principais escolhas. Reunindo inovação, variedade de jogos e uma experiência de usuário diferenciada, a plataforma é ideal para quem busca entretenimento de alta qualidade, sem complicações.
Plataforma moderna e acessível Um dos grandes diferenciais da 9993Bet é sua interface intuitiva e responsiva, pensada para oferecer uma navegação fluida tanto em computadores quanto em dispositivos móveis. O site conta com um design moderno e bem estruturado, que facilita o acesso às diferentes seções e jogos disponíveis. Desde o primeiro acesso, é possível perceber o cuidado da plataforma em proporcionar uma experiência agradável, mesmo para os iniciantes.
Além disso, o processo de cadastro é rápido e descomplicado. Com apenas alguns cliques, o jogador já pode criar sua conta e começar a explorar o universo de possibilidades que a 9993betoferece. A segurança dos dados também é levada a sério, utilizando criptografia de ponta e sistemas de proteção avançados.
Variedade de jogos para todos os gostos Outro ponto forte da 9993Bet é a ampla seleção de jogos. A plataforma conta com centenas de títulos das principais desenvolvedoras do mercado, garantindo qualidade gráfica, jogabilidade envolvente e mecânicas inovadoras. Entre os jogos mais populares, destacam-se:
Slots (Caça-níqueis): com temas variados, bônus emocionantes e recursos especiais, os slots são uma das atrações preferidas dos usuários. Há opções clássicas com 3 rolos e também versões modernas com animações incríveis.
Jogos de cartas: para os fãs de estratégia e emoção, a 9993Bet oferece versões virtuais de jogos consagrados como pôquer, blackjack e bacará.
Roleta online: com diferentes variações e estilos, é ideal para quem busca adrenalina e sorte em cada giro.
Jogos ao vivo com crupiês reais: proporcionando uma experiência imersiva e interativa, esses jogos permitem que o jogador se conecte com apresentadores reais e jogue em tempo real, como se estivesse em uma sala física.
Uma experiência pensada no jogador A 9993Bet investe constantemente em tecnologia e atendimento ao cliente para garantir a melhor experiência possível aos seus usuários. O suporte funciona 24 horas por dia, 7 dias por semana, com uma equipe preparada para responder dúvidas, resolver problemas e orientar os jogadores em qualquer situação.
Os métodos de pagamento também são variados e seguros. A plataforma aceita PIX, boletos bancários e carteiras digitais, proporcionando rapidez nas transações e total comodidade. Os saques são processados com agilidade, permitindo que os jogadores aproveitem seus ganhos sem longas esperas.
Além disso, a 9993Bet oferece promoções regulares, bônus de boas-vindas e recompensas exclusivas para usuários fiéis. Tudo isso contribui para um ambiente envolvente, competitivo e, acima de tudo, divertido.
Conclusão A 9993Bet chega ao mercado brasileiro como uma plataforma completa de entretenimento digital, aliando inovação, segurança e uma vasta gama de jogos que agradam desde os iniciantes até os jogadores mais experientes. Com foco no usuário e um compromisso com a excelência, a 9993Bet se firma como uma das principais opções para quem busca diversão de qualidade e oportunidades reais de ganhar.
Se você está em busca de emoção, variedade e confiabilidade, a 9993Bet é a escolha certa. Cadastre-se, explore os jogos e descubra um novo nível de entretenimento online.
-
 @ fd208ee8:0fd927c1
2025-02-15 07:02:08
@ fd208ee8:0fd927c1
2025-02-15 07:02:08E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats".
They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable.
It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions.
What we then have is * a transaction on a relay that triggers * a transaction on a mint that triggers * a transaction on Lightning that triggers * a transaction on Bitcoin.
Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted.
There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself.
https://github.com/nostr-protocol/nips/blob/master/60.md
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ eb5f61d0:24cdd490
2025-05-11 02:33:37
@ eb5f61d0:24cdd490
2025-05-11 02:33:37No cenário atual do entretenimento online, o Brasil tem visto um crescimento notável de plataformas que oferecem experiências envolventes e seguras para os jogadores. Entre elas, a 59BRL se destaca como uma opção moderna, confiável e completa, proporcionando diversão, praticidade e uma ampla variedade de jogos para todos os perfis de usuários. Com uma interface amigável e suporte dedicado, a 59BRL se tornou referência no segmento de apostas e jogos virtuais.
Conheça a Plataforma 59BRL Desde o primeiro acesso, a plataforma 59BRL impressiona pela sua estrutura bem organizada e visual atraente. Desenvolvida para atender tanto iniciantes quanto jogadores experientes, ela oferece navegação rápida, menus intuitivos e total compatibilidade com dispositivos móveis e computadores. Isso significa que o usuário pode jogar de onde estiver, com total liberdade.
A segurança é outro ponto forte. A 59brlutiliza tecnologias avançadas de criptografia para garantir a proteção dos dados dos usuários, além de contar com um sistema de verificação para evitar fraudes e atividades suspeitas. O ambiente é totalmente transparente, com termos claros e atendimento eficiente.
Diversidade de Jogos para Todos os Gostos Um dos maiores diferenciais da 59BRL é a variedade de jogos disponíveis. A plataforma oferece opções que vão desde os clássicos jogos de mesa até experiências modernas com gráficos 3D e interatividade ao vivo. Entre os jogos mais populares estão:
Roleta Virtual: Uma experiência dinâmica e cheia de emoção, com várias versões para agradar desde os mais conservadores até os mais ousados.
Slots Interativos: Jogos com temas variados, desde aventura e fantasia até cultura pop, que oferecem rodadas bônus e grandes chances de premiação.
Jogos de Cartas: Modalidades como pôquer, blackjack e baccarat ganham espaço com versões modernas e fáceis de jogar, tanto em modo automático quanto com interações ao vivo.
Raspadinhas Digitais: Uma opção prática e divertida para quem quer testar a sorte rapidamente, com prêmios instantâneos e animações envolventes.
Experiência do Jogador: Praticidade e Suporte Total A 59BRL valoriza a experiência de seus usuários em todos os aspectos. O processo de cadastro é simples, pedindo apenas dados básicos e uma confirmação rápida por e-mail ou telefone. Já o sistema de depósito e saque é outro destaque: a plataforma aceita os principais métodos de pagamento, incluindo PIX, boleto bancário e carteiras digitais, com transações ágeis e seguras.
Outro ponto bastante elogiado pelos usuários é o suporte ao cliente. A equipe da 59BRL está disponível 24 horas por dia, todos os dias da semana, através de chat ao vivo e e-mail. As respostas são rápidas, claras e resolutivas, o que proporciona tranquilidade mesmo em situações de dúvida ou dificuldade.
Além disso, a plataforma costuma oferecer promoções e bônus para novos usuários e jogadores frequentes, como rodadas grátis, cashback e programas de fidelidade. Tudo isso é pensado para manter a diversão em alta e recompensar os jogadores mais engajados.
Conclusão A 59BRL é mais do que uma simples plataforma de jogos: é um verdadeiro ambiente de entretenimento digital, pensado para oferecer praticidade, segurança e diversão sem limites. Com uma interface moderna, grande variedade de jogos e suporte de qualidade, ela tem conquistado cada vez mais brasileiros que buscam uma alternativa confiável e empolgante para seu lazer online. Se você ainda não conhece, vale a pena explorar o que a 59BRL tem a oferecer.
-
 @ daa41bed:88f54153
2025-02-09 16:50:04
@ daa41bed:88f54153
2025-02-09 16:50:04There has been a good bit of discussion on Nostr over the past few days about the merits of zaps as a method of engaging with notes, so after writing a rather lengthy article on the pros of a strategic Bitcoin reserve, I wanted to take some time to chime in on the much more fun topic of digital engagement.
Let's begin by defining a couple of things:
Nostr is a decentralized, censorship-resistance protocol whose current biggest use case is social media (think Twitter/X). Instead of relying on company servers, it relies on relays that anyone can spin up and own their own content. Its use cases are much bigger, though, and this article is hosted on my own relay, using my own Nostr relay as an example.
Zap is a tip or donation denominated in sats (small units of Bitcoin) sent from one user to another. This is generally done directly over the Lightning Network but is increasingly using Cashu tokens. For the sake of this discussion, how you transmit/receive zaps will be irrelevant, so don't worry if you don't know what Lightning or Cashu are.
If we look at how users engage with posts and follows/followers on platforms like Twitter, Facebook, etc., it becomes evident that traditional social media thrives on engagement farming. The more outrageous a post, the more likely it will get a reaction. We see a version of this on more visual social platforms like YouTube and TikTok that use carefully crafted thumbnail images to grab the user's attention to click the video. If you'd like to dive deep into the psychology and science behind social media engagement, let me know, and I'd be happy to follow up with another article.
In this user engagement model, a user is given the option to comment or like the original post, or share it among their followers to increase its signal. They receive no value from engaging with the content aside from the dopamine hit of the original experience or having their comment liked back by whatever influencer they provide value to. Ad revenue flows to the content creator. Clout flows to the content creator. Sales revenue from merch and content placement flows to the content creator. We call this a linear economy -- the idea that resources get created, used up, then thrown away. Users create content and farm as much engagement as possible, then the content is forgotten within a few hours as they move on to the next piece of content to be farmed.
What if there were a simple way to give value back to those who engage with your content? By implementing some value-for-value model -- a circular economy. Enter zaps.

Unlike traditional social media platforms, Nostr does not actively use algorithms to determine what content is popular, nor does it push content created for active user engagement to the top of a user's timeline. Yes, there are "trending" and "most zapped" timelines that users can choose to use as their default, but these use relatively straightforward engagement metrics to rank posts for these timelines.
That is not to say that we may not see clients actively seeking to refine timeline algorithms for specific metrics. Still, the beauty of having an open protocol with media that is controlled solely by its users is that users who begin to see their timeline gamed towards specific algorithms can choose to move to another client, and for those who are more tech-savvy, they can opt to run their own relays or create their own clients with personalized algorithms and web of trust scoring systems.
Zaps enable the means to create a new type of social media economy in which creators can earn for creating content and users can earn by actively engaging with it. Like and reposting content is relatively frictionless and costs nothing but a simple button tap. Zaps provide active engagement because they signal to your followers and those of the content creator that this post has genuine value, quite literally in the form of money—sats.

I have seen some comments on Nostr claiming that removing likes and reactions is for wealthy people who can afford to send zaps and that the majority of people in the US and around the world do not have the time or money to zap because they have better things to spend their money like feeding their families and paying their bills. While at face value, these may seem like valid arguments, they, unfortunately, represent the brainwashed, defeatist attitude that our current economic (and, by extension, social media) systems aim to instill in all of us to continue extracting value from our lives.
Imagine now, if those people dedicating their own time (time = money) to mine pity points on social media would instead spend that time with genuine value creation by posting content that is meaningful to cultural discussions. Imagine if, instead of complaining that their posts get no zaps and going on a tirade about how much of a victim they are, they would empower themselves to take control of their content and give value back to the world; where would that leave us? How much value could be created on a nascent platform such as Nostr, and how quickly could it overtake other platforms?
Other users argue about user experience and that additional friction (i.e., zaps) leads to lower engagement, as proven by decades of studies on user interaction. While the added friction may turn some users away, does that necessarily provide less value? I argue quite the opposite. You haven't made a few sats from zaps with your content? Can't afford to send some sats to a wallet for zapping? How about using the most excellent available resource and spending 10 seconds of your time to leave a comment? Likes and reactions are valueless transactions. Social media's real value derives from providing monetary compensation and actively engaging in a conversation with posts you find interesting or thought-provoking. Remember when humans thrived on conversation and discussion for entertainment instead of simply being an onlooker of someone else's life?
If you've made it this far, my only request is this: try only zapping and commenting as a method of engagement for two weeks. Sure, you may end up liking a post here and there, but be more mindful of how you interact with the world and break yourself from blind instinct. You'll thank me later.

-
 @ 97c70a44:ad98e322
2025-02-03 22:25:35
@ 97c70a44:ad98e322
2025-02-03 22:25:35Last week, in a bid to understand the LLM hype, I decided to write a trivial nostr-related program in rust via a combination of codebuff (yes, that is a referral link, pls click), aider, and goose.
The result of the experiment was inconclusive, but as a side effect it produced a great case study in converting a NINO into a Real Nostr App.
Introducing Roz
Roz, a friendly notary for nostr events.
To use it, simply publish an event to
relay.damus.ioornos.lol, and roz will make note of it. To find out when roz first saw a given event, just ask:curl https://roz.coracle.social/notary/cb429632ae22557d677a11149b2d0ccd72a1cf66ac55da30e3534ed1a492765dThis will return a JSON payload with a
seenkey indicating when roz first saw the event. How (and whether) you use this is up to you!De-NINO-fying roz
Roz is just a proof of concept, so don't rely on it being there forever. And anyway, roz is a NINO, since it provides value to nostr (potentially), but doesn't really do things in a nostr-native way. It also hard-codes its relays, and certainly doesn't use the outbox model or sign events. But that's ok, it's a proof of concept.
A much better way to do this would be to modify roz to properly leverage nostr's capabilities, namely:
- Use nostr-native data formats (i.e., draft a new kind)
- Use relays instead of proprietary servers for data storage
- Leverage nostr identities and signatures to decouple trust from storage, and allow trusted attestations to be discovered
Luckily, this is not hard at all. In fact, I've gone ahead and drafted a PR to the NIPs repo that adds timestamp annotations to NIP 03, as an alternative to OpenTimestamps. The trade-off is that while user attestations are far less reliable than OTS proofs, they're much easier to verify, and can reach a pretty high level of reliability by combining multiple attestation sources with other forms of reputation.
In other words, instead of going nuclear and embedding your attestations into The Time Chain, you can simply ask 5-10 relays or people you trust for their attestations for a given event.
This PR isn't terribly important on its own, but it does remove one small barrier between us and trusted key rotation events (or other types of event that require establishing a verifiable chain of causality).
-
 @ 57d1a264:69f1fee1
2025-05-07 06:16:30
@ 57d1a264:69f1fee1
2025-05-07 06:16:30Here’s Sean Voisen writing about how programming is a feeling:
For those of us who enjoy programming, there is a deep satisfaction that comes from solving problems through well-written code, a kind of ineffable joy found in the elegant expression of a system through our favorite syntax. It is akin to the same satisfaction a craftsperson might find at the end of the day after toiling away on well-made piece of furniture, the culmination of small dopamine hits that come from sweating the details on something and getting them just right. Maybe nobody will notice those details, but it doesn’t matter. We care, we notice, we get joy from the aesthetics of the craft.
This got me thinking about the idea of satisfaction in craft. Where does it come from?
Continue Reading https://blog.jim-nielsen.com/2025/craft-and-satisfaction/
originally posted at https://stacker.news/items/973628
-
 @ 0fa80bd3:ea7325de
2025-01-29 05:55:02
@ 0fa80bd3:ea7325de
2025-01-29 05:55:02The land that belongs to the indigenous peoples of Russia has been seized by a gang of killers who have unleashed a war of extermination. They wipe out anyone who refuses to conform to their rules. Those who disagree and stay behind are tortured and killed in prisons and labor camps. Those who flee lose their homeland, dissolve into foreign cultures, and fade away. And those who stand up to protect their people are attacked by the misled and deceived. The deceived die for the unchecked greed of a single dictator—thousands from both sides, people who just wanted to live, raise their kids, and build a future.
Now, they are forced to make an impossible choice: abandon their homeland or die. Some perish on the battlefield, others lose themselves in exile, stripped of their identity, scattered in a world that isn’t theirs.
There’s been endless debate about how to fix this, how to clear the field of the weeds that choke out every new sprout, every attempt at change. But the real problem? We can’t play by their rules. We can’t speak their language or use their weapons. We stand for humanity, and no matter how righteous our cause, we will not multiply suffering. Victory doesn’t come from matching the enemy—it comes from staying ahead, from using tools they haven’t mastered yet. That’s how wars are won.
Our only resource is the will of the people to rewrite the order of things. Historian Timothy Snyder once said that a nation cannot exist without a city. A city is where the most active part of a nation thrives. But the cities are occupied. The streets are watched. Gatherings are impossible. They control the money. They control the mail. They control the media. And any dissent is crushed before it can take root.
So I started asking myself: How do we stop this fragmentation? How do we create a space where people can rebuild their connections when they’re ready? How do we build a self-sustaining network, where everyone contributes and benefits proportionally, while keeping their freedom to leave intact? And more importantly—how do we make it spread, even in occupied territory?
In 2009, something historic happened: the internet got its own money. Thanks to Satoshi Nakamoto, the world took a massive leap forward. Bitcoin and decentralized ledgers shattered the idea that money must be controlled by the state. Now, to move or store value, all you need is an address and a key. A tiny string of text, easy to carry, impossible to seize.
That was the year money broke free. The state lost its grip. Its biggest weapon—physical currency—became irrelevant. Money became purely digital.
The internet was already a sanctuary for information, a place where people could connect and organize. But with Bitcoin, it evolved. Now, value itself could flow freely, beyond the reach of authorities.
Think about it: when seedlings are grown in controlled environments before being planted outside, they get stronger, survive longer, and bear fruit faster. That’s how we handle crops in harsh climates—nurture them until they’re ready for the wild.
Now, picture the internet as that controlled environment for ideas. Bitcoin? It’s the fertile soil that lets them grow. A testing ground for new models of interaction, where concepts can take root before they move into the real world. If nation-states are a battlefield, locked in a brutal war for territory, the internet is boundless. It can absorb any number of ideas, any number of people, and it doesn’t run out of space.
But for this ecosystem to thrive, people need safe ways to communicate, to share ideas, to build something real—without surveillance, without censorship, without the constant fear of being erased.
This is where Nostr comes in.
Nostr—"Notes and Other Stuff Transmitted by Relays"—is more than just a messaging protocol. It’s a new kind of city. One that no dictator can seize, no corporation can own, no government can shut down.
It’s built on decentralization, encryption, and individual control. Messages don’t pass through central servers—they are relayed through independent nodes, and users choose which ones to trust. There’s no master switch to shut it all down. Every person owns their identity, their data, their connections. And no one—no state, no tech giant, no algorithm—can silence them.
In a world where cities fall and governments fail, Nostr is a city that cannot be occupied. A place for ideas, for networks, for freedom. A city that grows stronger the more people build within it.
-
 @ 34f1ddab:2ca0cf7c
2025-05-10 21:03:11
@ 34f1ddab:2ca0cf7c
2025-05-10 21:03:11Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
Why Trust Crypt Recver? 🤝 🛠️ Expert Recovery Solutions At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
Partially lost or forgotten seed phrases Extracting funds from outdated or invalid wallet addresses Recovering data from damaged hardware wallets Restoring coins from old or unsupported wallet formats You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈 Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases. Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery. Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet. Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy. ⚠️ What We Don’t Do While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
Don’t Let Lost Crypto Hold You Back! Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today! Ready to reclaim your lost crypto? Don’t wait until it’s too late! 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us! For real-time support or questions, reach out to our dedicated team on: ✉️ Telegram: t.me/crypptrcver 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.Losing access to your cryptocurrency can feel like losing a part of your future. Whether it’s due to a forgotten password, a damaged seed backup, or a simple mistake in a transfer, the stress can be overwhelming. Fortunately, cryptrecver.com is here to assist! With our expert-led recovery services, you can safely and swiftly reclaim your lost Bitcoin and other cryptocurrencies.
 # Why Trust Crypt Recver? 🤝
# Why Trust Crypt Recver? 🤝🛠️ Expert Recovery Solutions\ At Crypt Recver, we specialize in addressing complex wallet-related issues. Our skilled engineers have the tools and expertise to handle:
- Partially lost or forgotten seed phrases
- Extracting funds from outdated or invalid wallet addresses
- Recovering data from damaged hardware wallets
- Restoring coins from old or unsupported wallet formats
You’re not just getting a service; you’re gaining a partner in your cryptocurrency journey.
🚀 Fast and Efficient Recovery\ We understand that time is crucial in crypto recovery. Our optimized systems enable you to regain access to your funds quickly, focusing on speed without compromising security. With a success rate of over 90%, you can rely on us to act swiftly on your behalf.
🔒 Privacy is Our Priority\ Your confidentiality is essential. Every recovery session is conducted with the utmost care, ensuring all processes are encrypted and confidential. You can rest assured that your sensitive information remains private.
💻 Advanced Technology\ Our proprietary tools and brute-force optimization techniques maximize recovery efficiency. Regardless of how challenging your case may be, our technology is designed to give you the best chance at retrieving your crypto.
Our Recovery Services Include: 📈
- Bitcoin Recovery: Lost access to your Bitcoin wallet? We help recover lost wallets, private keys, and passphrases.
- Transaction Recovery: Mistakes happen — whether it’s an incorrect wallet address or a lost password, let us manage the recovery.
- Cold Wallet Restoration: If your cold wallet is failing, we can safely extract your assets and migrate them into a secure new wallet.
- Private Key Generation: Lost your private key? Our experts can help you regain control using advanced methods while ensuring your privacy.
⚠️ What We Don’t Do\ While we can handle many scenarios, some limitations exist. For instance, we cannot recover funds stored in custodial wallets or cases where there is a complete loss of four or more seed words without partial information available. We are transparent about what’s possible, so you know what to expect
 # Don’t Let Lost Crypto Hold You Back!
# Don’t Let Lost Crypto Hold You Back!Did you know that between 3 to 3.4 million BTC — nearly 20% of the total supply — are estimated to be permanently lost? Don’t become part of that statistic! Whether it’s due to a forgotten password, sending funds to the wrong address, or damaged drives, we can help you navigate these challenges
🛡️ Real-Time Dust Attack Protection\ Our services extend beyond recovery. We offer dust attack protection, keeping your activity anonymous and your funds secure, shielding your identity from unwanted tracking, ransomware, and phishing attempts.
🎉 Start Your Recovery Journey Today!\ Ready to reclaim your lost crypto? Don’t wait until it’s too late!\ 👉 cryptrecver.com
📞 Need Immediate Assistance? Connect with Us!\ For real-time support or questions, reach out to our dedicated team on:\ ✉️ Telegram: t.me/crypptrcver\ 💬 WhatsApp: +1(941)317–1821
Crypt Recver is your trusted partner in cryptocurrency recovery. Let us turn your challenges into victories. Don’t hesitate — your crypto future starts now! 🚀✨
Act fast and secure your digital assets with cryptrecver.com.
-
 @ c9badfea:610f861a
2025-05-10 18:57:30
@ c9badfea:610f861a
2025-05-10 18:57:30- Install Squircle (it's free and open source)
- Launch the app, tap the ⁞ icon and select Settings
- Configure your Git credentials as needed
- Add any remote servers under Cloud & Servers
- Return to the editor view and enjoy your mobile IDE
ℹ️ To clone a Git repository, tap ☰, long-press a directory in the file tree, and choose Clone
ℹ️ You may want to use it alongside Termux, a terminal emulator and Linux environment
-
 @ f9cf4e94:96abc355
2025-01-18 06:09:50
@ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |
 | Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |
| Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |  | 16Gb |
| 16Gb |Recomendo que use o Ubuntu Server para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi aqui. O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível aqui. Não instale um desktop (como xubuntu, lubuntu, xfce, etc.).
Passo 1: Atualizar o Sistema 🖥️
Primeiro, atualize seu sistema e instale o Tor:
bash apt update apt install tor
Passo 2: Criar o Arquivo de Serviço
nrs.service🔧Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo:
```unit [Unit] Description=Nostr Relay Server Service After=network.target
[Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure
[Install] WantedBy=multi-user.target ```
Passo 3: Baixar o Binário do Nostr 🚀
Baixe o binário mais recente do Nostr aqui no GitHub.
Passo 4: Criar as Pastas Necessárias 📂
Agora, crie as pastas para o aplicativo e o pendrive:
bash mkdir -p /opt/nrs /mnt/edriver
Passo 5: Listar os Dispositivos Conectados 🔌
Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados:
bash lsblk
Passo 6: Formatando o Pendrive 💾
Escolha o pendrive correto (por exemplo,
/dev/sda) e formate-o:bash mkfs.vfat /dev/sda
Passo 7: Montar o Pendrive 💻
Monte o pendrive na pasta
/mnt/edriver:bash mount /dev/sda /mnt/edriver
Passo 8: Verificar UUID dos Dispositivos 📋
Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados:
bash blkid
Passo 9: Alterar o
fstabpara Montar o Pendrive Automáticamente 📝Abra o arquivo
/etc/fstabe adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim:fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0
Passo 10: Copiar o Binário para a Pasta Correta 📥
Agora, copie o binário baixado para a pasta
/opt/nrs:bash cp nrs-arm64 /opt/nrs
Passo 11: Criar o Arquivo de Configuração 🛠️
Crie o arquivo de configuração com o seguinte conteúdo e salve-o em
/opt/nrs/config.yaml:yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true
Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️
Agora, copie o arquivo
nrs.servicepara o diretório/etc/systemd/system/:bash cp nrs.service /etc/systemd/system/Recarregue os serviços e inicie o serviço
nrs:bash systemctl daemon-reload systemctl enable --now nrs.service
Passo 13: Configurar o Tor 🌐
Abra o arquivo de configuração do Tor
/var/lib/tor/torrce adicione a seguinte linha:torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334
Passo 14: Habilitar e Iniciar o Tor 🧅
Agora, ative e inicie o serviço Tor:
bash systemctl enable --now tor.serviceO Tor irá gerar um endereço
.onionpara o seu servidor Nostr. Você pode encontrá-lo no arquivo/var/lib/tor/nostr_server/hostname.
Observações ⚠️
- Com essa configuração, os dados serão salvos no pendrive, enquanto o binário ficará no cartão SD do Raspberry Pi.
- O endereço
.oniondo seu servidor Nostr será algo como:ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion.
Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳
Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
-
 @ 57d1a264:69f1fee1
2025-05-07 06:03:29
@ 57d1a264:69f1fee1
2025-05-07 06:03:29CryptPad
Collaboration and privacy. Yes, you can have both Flagship instance of CryptPad, the end-to-end encrypted and open-source collaboration suite. Cloud administered by the CryptPad development team. https://cryptpad.fr/
ONLYOFFICE DocSpace
Document collaboration made simpler. Easily collaborate with customizable rooms. Edit any content you have. Work faster using AI assistants. Protect your sensitive business data. Download or try STARTUP Cloud (Limited-time offer) FREE https://www.onlyoffice.com/
SeaFile
A new way to organize your files Beyond just syncing and sharing files, Seafile lets you add custom file properties and organize your files in different views. With AI-powered automation for generating properties, Seafile offers a smarter, more efficient way to manage your files. Try it Now, Free for up to 3 users https://seafile.com/
SandStorm
An open source platform for self-hosting web apps Self-host web-based productivity apps easily and securely. Sandstorm is an open source project built by a community of volunteers with the goal of making it really easy to run open source web applications. Try the Demo or Signup Free https://alpha.sandstorm.io/apps
NextCloud Hub
A new generation of online collaboration that puts you in control. Nextcloud offers a modern, on premise content collaboration platform with real-time document editing, video chat & groupware on mobile, desktop and web. Sign up for a free Nextcloud account https://nextcloud.com/sign-up/
LinShare
True Open Source Secure File Sharing Solution We are committed to providing a reliable Open Source file-sharing solution, expertly designed to meet the highest standards of diverse industries, such as government and finance Try the Demo https://linshare.app/
Twake Drive
The open-source alternative to Google Drive. Privacy-First Open Source Workplace. Twake workplace open source business. Improve your effeciency with truly Open Source, all-in-one digital suite. Enhance the security in every aspect of your professional and private life. Sign up https://sign-up.twake.app/
SpaceDrive
One Explorer. All Your Files. Unify files from all your devices and clouds into a single, easy-to-use explorer. Designed for creators, hoarders and the painfully disorganized. Download desktop app (mobile coming soon) https://www.spacedrive.com/
ente
Safe Home for your photos Store, share, and discover your memories with end-to-end encryption. End-to-end encryption, durable storage and simple sharing. Packed with these and much more into our beautiful open source apps. Get started https://web.ente.io
fileStash
Turn your FTP server into... Filestash is the enterprise-grade file manager connecting your storage with your identity provider and authorisations. Try the demo https://demo.filestash.app
STORJ
Disruptively fast. Globally secure. S3-compatible distributed cloud services that make the most demanding workflows fast and affordable. Fast track your journey toward high performance cloud services. Storj pricing is consistent and competitive in meeting or exceeding your cloud services needs. Give the products a try to experience the benefits of the distributed cloud. Get Started https://www.storj.io/get-started
FireFile
The open‑source alternative to Dropbox. Firefiles lets you setup a cloud drive with the backend of your choice and lets you seamlessly manage your files across multiple providers. It revolutionizes cloud storage management by offering a unified platform for all your storage needs. Sign up Free https://beta.firefiles.app
originally posted at https://stacker.news/items/973626
-
 @ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08
@ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08Tldr
- Nostr is an open and interoperable protocol
- You can integrate it with workflow automation tools to augment your experience
- n8n is a great low/no-code workflow automation tool which you can host yourself
- Nostrobots allows you to integrate Nostr into n8n
- In this blog I create some workflow automations for Nostr
- A simple form to delegate posting notes
- Push notifications for mentions on multiple accounts
- Push notifications for your favourite accounts when they post a note
- All workflows are provided as open source with MIT license for you to use
Inter-op All The Things
Nostr is a new open social protocol for the internet. This open nature exciting because of the opportunities for interoperability with other technologies. In Using NFC Cards with Nostr I explored the
nostr:URI to launch Nostr clients from a card tap.The interoperability of Nostr doesn't stop there. The internet has many super-powers, and Nostr is open to all of them. Simply, there's no one to stop it. There is no one in charge, there are no permissioned APIs, and there are no risks of being de-platformed. If you can imagine technologies that would work well with Nostr, then any and all of them can ride on or alongside Nostr rails.
My mental model for why this is special is Google Wave ~2010. Google Wave was to be the next big platform. Lars was running it and had a big track record from Maps. I was excited for it. Then, Google pulled the plug. And, immediately all the time and capital invested in understanding and building on the platform was wasted.
This cannot happen to Nostr, as there is no one to pull the plug, and maybe even no plug to pull.
So long as users demand Nostr, Nostr will exist, and that is a pretty strong guarantee. It makes it worthwhile to invest in bringing Nostr into our other applications.
All we need are simple ways to plug things together.
Nostr and Workflow Automation
Workflow automation is about helping people to streamline their work. As a user, the most common way I achieve this is by connecting disparate systems together. By setting up one system to trigger another or to move data between systems, I can solve for many different problems and become way more effective.
n8n for workflow automation
Many workflow automation tools exist. My favourite is n8n. n8n is a low/no-code workflow automation platform which allows you to build all kinds of workflows. You can use it for free, you can self-host it, it has a user-friendly UI and useful API. Vs Zapier it can be far more elaborate. Vs Make.com I find it to be more intuitive in how it abstracts away the right parts of the code, but still allows you to code when you need to.
Most importantly you can plug anything into n8n: You have built-in nodes for specific applications. HTTP nodes for any other API-based service. And community nodes built by individual community members for any other purpose you can imagine.
Eating my own dogfood
It's very clear to me that there is a big design space here just demanding to be explored. If you could integrate Nostr with anything, what would you do?
In my view the best way for anyone to start anything is by solving their own problem first (aka "scratching your own itch" and "eating your own dogfood"). As I get deeper into Nostr I find myself controlling multiple Npubs – to date I have a personal Npub, a brand Npub for a community I am helping, an AI assistant Npub, and various testing Npubs. I need ways to delegate access to those Npubs without handing over the keys, ways to know if they're mentioned, and ways to know if they're posting.
I can build workflows with n8n to solve these issues for myself to start with, and keep expanding from there as new needs come up.
Running n8n with Nostrobots
I am mostly non-technical with a very helpful AI. To set up n8n to work with Nostr and operate these workflows should be possible for anyone with basic technology skills.
- I have a cheap VPS which currently runs my HAVEN Nostr Relay and Albyhub Lightning Node in Docker containers,
- My objective was to set up n8n to run alongside these in a separate Docker container on the same server, install the required nodes, and then build and host my workflows.
Installing n8n
Self-hosting n8n could not be easier. I followed n8n's Docker-Compose installation docs–
- Install Docker and Docker-Compose if you haven't already,
- Create your
docker-compose.ymland.envfiles from the docs, - Create your data folder
sudo docker volume create n8n_data, - Start your container with
sudo docker compose up -d, - Your n8n instance should be online at port
5678.
n8n is free to self-host but does require a license. Enter your credentials into n8n to get your free license key. You should now have access to the Workflow dashboard and can create and host any kind of workflows from there.
Installing Nostrobots
To integrate n8n nicely with Nostr, I used the Nostrobots community node by Ocknamo.
In n8n parlance a "node" enables certain functionality as a step in a workflow e.g. a "set" node sets a variable, a "send email" node sends an email. n8n comes with all kinds of "official" nodes installed by default, and Nostr is not amongst them. However, n8n also comes with a framework for community members to create their own "community" nodes, which is where Nostrobots comes in.
You can only use a community node in a self-hosted n8n instance (which is what you have if you are running in Docker on your own server, but this limitation does prevent you from using n8n's own hosted alternative).
To install a community node, see n8n community node docs. From your workflow dashboard–
- Click the "..." in the bottom left corner beside your username, and click "settings",
- Cilck "community nodes" left sidebar,
- Click "Install",
- Enter the "npm Package Name" which is
n8n-nodes-nostrobots, - Accept the risks and click "Install",
- Nostrobots is now added to your n8n instance.
Using Nostrobots
Nostrobots gives you nodes to help you build Nostr-integrated workflows–
- Nostr Write – for posting Notes to the Nostr network,
- Nostr Read – for reading Notes from the Nostr network, and
- Nostr Utils – for performing certain conversions you may need (e.g. from bech32 to hex).
Nostrobots has good documentation on each node which focuses on simple use cases.
Each node has a "convenience mode" by default. For example, the "Read" Node by default will fetch Kind 1 notes by a simple filter, in Nostrobots parlance a "Strategy". For example, with Strategy set to "Mention" the node will accept a pubkey and fetch all Kind 1 notes that Mention the pubkey within a time period. This is very good for quick use.
What wasn't clear to me initially (until Ocknamo helped me out) is that advanced use cases are also possible.
Each node also has an advanced mode. For example, the "Read" Node can have "Strategy" set to "RawFilter(advanced)". Now the node will accept json (anything you like that complies with NIP-01). You can use this to query Notes (Kind 1) as above, and also Profiles (Kind 0), Follow Lists (Kind 3), Reactions (Kind 7), Zaps (Kind 9734/9735), and anything else you can think of.
Creating and adding workflows
With n8n and Nostrobots installed, you can now create or add any kind of Nostr Workflow Automation.
- Click "Add workflow" to go to the workflow builder screen,
- If you would like to build your own workflow, you can start with adding any node. Click "+" and see what is available. Type "Nostr" to explore the Nostrobots nodes you have added,
- If you would like to add workflows that someone else has built, click "..." in the top right. Then click "import from URL" and paste in the URL of any workflow you would like to use (including the ones I share later in this article).
Nostr Workflow Automations
It's time to build some things!
A simple form to post a note to Nostr
I started very simply. I needed to delegate the ability to post to Npubs that I own in order that a (future) team can test things for me. I don't want to worry about managing or training those people on how to use keys, and I want to revoke access easily.
I needed a basic form with credentials that posted a Note.
For this I can use a very simple workflow–
- A n8n Form node – Creates a form for users to enter the note they wish to post. Allows for the form to be protected by a username and password. This node is the workflow "trigger" so that the workflow runs each time the form is submitted.
- A Set node – Allows me to set some variables, in this case I set the relays that I intend to use. I typically add a Set node immediately following the trigger node, and put all the variables I need in this. It helps to make the workflows easier to update and maintain.
- A Nostr Write node (from Nostrobots) – Writes a Kind-1 note to the Nostr network. It accepts Nostr credentials, the output of the Form node, and the relays from the Set node, and posts the Note to those relays.
Once the workflow is built, you can test it with the testing form URL, and set it to "Active" to use the production form URL. That's it. You can now give posting access to anyone for any Npub. To revoke access, simply change the credentials or set to workflow to "Inactive".
It may also be the world's simplest Nostr client.
You can find the Nostr Form to Post a Note workflow here.
Push notifications on mentions and new notes
One of the things Nostr is not very good at is push notifications. Furthermore I have some unique itches to scratch. I want–
- To make sure I never miss a note addressed to any of my Npubs – For this I want a push notification any time any Nostr user mentions any of my Npubs,
- To make sure I always see all notes from key accounts – For this I need a push notification any time any of my Npubs post any Notes to the network,
- To get these notifications on all of my devices – Not just my phone where my Nostr regular client lives, but also on each of my laptops to suit wherever I am working that day.
I needed to build a Nostr push notifications solution.
To build this workflow I had to string a few ideas together–
- Triggering the node on a schedule – Nostrobots does not include a trigger node. As every workflow starts with a trigger we needed a different method. I elected to run the workflow on a schedule of every 10-minutes. Frequent enough to see Notes while they are hot, but infrequent enough to not burden public relays or get rate-limited,
- Storing a list of Npubs in a Nostr list – I needed a way to store the list of Npubs that trigger my notifications. I initially used an array defined in the workflow, this worked fine. Then I decided to try Nostr lists (NIP-51, kind 30000). By defining my list of Npubs as a list published to Nostr I can control my list from within a Nostr client (e.g. Listr.lol or Nostrudel.ninja). Not only does this "just work", but because it's based on Nostr lists automagically Amethyst client allows me to browse that list as a Feed, and everyone I add gets notified in their Mentions,
- Using specific relays – I needed to query the right relays, including my own HAVEN relay inbox for notes addressed to me, and wss://purplepag.es for Nostr profile metadata,
- Querying Nostr events (with Nostrobots) – I needed to make use of many different Nostr queries and use quite a wide range of what Nostrobots can do–
- I read the EventID of my Kind 30000 list, to return the desired pubkeys,
- For notifications on mentions, I read all Kind 1 notes that mention that pubkey,
- For notifications on new notes, I read all Kind 1 notes published by that pubkey,
- Where there are notes, I read the Kind 0 profile metadata event of that pubkey to get the displayName of the relevant Npub,
- I transform the EventID into a Nevent to help clients find it.
- Using the Nostr URI – As I did with my NFC card article, I created a link with the
nostr:URI prefix so that my phone's native client opens the link by default, - Push notifications solution – I needed a push notifications solution. I found many with n8n integrations and chose to go with Pushover which supports all my devices, has a free trial, and is unfairly cheap with a $5-per-device perpetual license.
Once the workflow was built, lists published, and Pushover installed on my phone, I was fully set up with push notifications on Nostr. I have used these workflows for several weeks now and made various tweaks as I went. They are feeling robust and I'd welcome you to give them a go.
You can find the Nostr Push Notification If Mentioned here and If Posts a Note here.
In speaking with other Nostr users while I was building this, there are all kind of other needs for push notifications too – like on replies to a certain bookmarked note, or when a followed Npub starts streaming on zap.stream. These are all possible.
Use my workflows
I have open sourced all my workflows at my Github with MIT license and tried to write complete docs, so that you can import them into your n8n and configure them for your own use.
To import any of my workflows–
- Click on the workflow of your choice, e.g. "Nostr_Push_Notify_If_Mentioned.json",
- Click on the "raw" button to view the raw JSON, ex any Github page layout,
- Copy that URL,
- Enter that URL in the "import from URL" dialog mentioned above.
To configure them–
- Prerequisites, credentials, and variables are all stated,
- In general any variables required are entered into a Set Node that follows the trigger node,
- Pushover has some extra setup but is very straightforward and documented in the workflow.
What next?
Over my first four blogs I explored creating a good Nostr setup with Vanity Npub, Lightning Payments, Nostr Addresses at Your Domain, and Personal Nostr Relay.
Then in my latest two blogs I explored different types of interoperability with NFC cards and now n8n Workflow Automation.
Thinking ahead n8n can power any kind of interoperability between Nostr and any other legacy technology solution. On my mind as I write this:
- Further enhancements to posting and delegating solutions and forms (enhanced UI or different note kinds),
- Automated or scheduled posting (such as auto-liking everything Lyn Alden posts),
- Further enhancements to push notifications, on new and different types of events (such as notifying me when I get a new follower, on replies to certain posts, or when a user starts streaming),
- All kinds of bridges, such as bridging notes to and from Telegram, Slack, or Campfire. Or bridging RSS or other event feeds to Nostr,
- All kinds of other automation (such as BlackCoffee controlling a coffee machine),
- All kinds of AI Assistants and Agents,
In fact I have already released an open source workflow for an AI Assistant, and will share more about that in my next blog.
Please be sure to let me know if you think there's another Nostr topic you'd like to see me tackle.
GM Nostr.
-
 @ 57d1a264:69f1fee1
2025-05-06 06:00:25
@ 57d1a264:69f1fee1
2025-05-06 06:00:25Album art didn’t always exist. In the early 1900s, recorded music was still a novelty, overshadowed by sales of sheet music. Early vinyl records were vastly different from what we think of today: discs were sold individually and could only hold up to four minutes of music per side. Sometimes, only one side of the record was used. One of the most popular records of 1910, for example, was “Come, Josephine, in My Flying Machine”: it clocked in at two minutes and 39 seconds.
The invention of album art can get lost in the story of technological mastery. But among all the factors that contributed to the rise of recorded music, it stands as one of the few that was wholly driven by creators themselves. Album art — first as marketing material, then as pure creative expression — turned an audio-only medium into a multi-sensory experience.
This is the story of the people who made music visible.
originally posted at https://stacker.news/items/972642
-
 @ c9badfea:610f861a
2025-05-10 13:57:17
@ c9badfea:610f861a
2025-05-10 13:57:17- Install Grayjay (it's free and open source)
- Launch the app and navigate to the Sources tab
- Enable the desired sources (and log in if needed by tapping on the source and scrolling down to Authentication)
- Go to Android Settings > Apps, select Grayjay, and tap Open By Default and Add Link to automatically open supported links with Grayjay
- Enjoy
ℹ️ If you are using Obtainium to install apps, search for Grayjay on Complex Apps
-
 @ 3d073b19:4ae60f39
2025-05-10 21:51:32
@ 3d073b19:4ae60f39
2025-05-10 21:51:32Markdown test:
- italic
- bold in openletter
- Link: Nostr's current site
-
 @ 3d073b19:4ae60f39
2025-05-10 21:06:15
@ 3d073b19:4ae60f39
2025-05-10 21:06:15This is a test openletter
-
 @ 57d1a264:69f1fee1
2025-05-06 05:49:01
@ 57d1a264:69f1fee1
2025-05-06 05:49:01I don’t like garlic. It’s not a dislike for the taste in the moment, so much as an extreme dislike for the way it stays with you—sometimes for days—after a particularly garlicky meal.
Interestingly enough, both of my brothers love garlic. They roast it by itself and keep it at the ready so they can have a very strong garlic profile in their cooking. When I prepare a dish, I don’t even see garlic on the ingredient list. I’ve cut it out of my life so completely that my brain genuinely skips over it in recipes. While my brothers are looking for ways to sneak garlic into everything they make, I’m subconsciously avoiding it altogether.
A few years back, when I was digging intensely into how design systems mature, I stumbled on the concept of a design system origin story. There are two extreme origin stories and an infinite number of possibilities between. On one hand you have the grassroots system, where individuals working on digital products are simply trying to solve their own daily problems. They’re frustrated with having to go cut and paste elements from past designs or with recreating the same layouts over and over, so they start to work more systematically. On the other hand, you have the top down system, where leadership is directing teams to take a more systematic approach, often forming a small partially dedicated core team to tackle some centralized assets and guidelines for all to follow. The influences in those early days bias a design system in interesting and impactful ways.
We’ve established that there are a few types of bias that are either intentionally or unintentionally embedded into our design systems. Acknowledging this is a great first step. But, what’s the impact of this? Does it matter?
I believe there are a few impacts design system biases, but there’s one that stands out. The bias in your design system makes some individuals feel the system is meant for them and others feel it’s not. This is a problem because, a design system cannot live up to it’s expected value until it is broadly in use. If individuals feel your design system is not for them, the won’t use it. And, as you know, it doesn’t matter how good your design system is if nobody is using it.
originally posted at https://stacker.news/items/972641
-
 @ f0c7506b:9ead75b8
2024-12-08 09:05:13
@ f0c7506b:9ead75b8
2024-12-08 09:05:13
Yalnızca güçlü olanların hakkıdır yaşamak.
Güçlü olan ileri gider ve saflar seyrekleşir. Ama üç beş büyük, güçlü ve tanrısal kişi güneşli ve aydınlık gözleriyle o yeni, o vaat edilmiş ülkeye ulaşacaktır. Belki binlerce yıl sonra ancak. Ve güçlü, adaleli, hükmetmek için yaratılmış elleriyle hastaların, zayıfların ve sakatların ölüleri üzerinde bir krallık kuracaklardır. Bir krallık!
Benim aradığım insanların kendileri değil, sesleridir.
Duyguları körelmiş, çeşitli düşüncelere saplanmış kalabalık hiçbir zaman ilerlemenin taşıyıcısı olamaz, kendi küçüklüğünün o küflü içgüdüsüyle kalabalığın kin ve nefretle baktığı bir kişi, bir büyük kişi, iradesinin gösterdiği yolda kimsenin gözünün yaşına bakmaksızın ilahi bir güç ve bir zafer gülümsemesiyle yürüyebilir ancak.
Bizim soyumuz da sonsuz oluşum piramidinin doruk noktasını oluşturmaktan uzaktır. Bizler de mükemmelliğe ulaşmış değiliz. Bizler de henüz olgunlaşmadık.
Şairler sevgiye övgüler döşenir; doğrusu sevginin güçlü bir şey olduğu kesin. Hüneşin bir ışınıdır sevgi, aydınlatıp nurlandırır insanı der bazıları; bazıları da insanı esrikliğe sürükleyen bir zehri kendisinde barındırdığını söyler. Gerçekten de yol açtığı sonuçlar, bir hekimin ağır bir ameliyattan önce korkudan titreyen hastaya teneffüs ettirdiği güldürücü gazınkine benzer, içinde tepinip duran acıyı unutturur hastaya.
Önemli olan, hayatta hiç değilse bir kez kutsal bir ilkbaharın yaşanmasıdır; öyle bir bahar ki, insanın gönlünü ilerideki bütün günleri altın yaldızla kaplamaya yetecek kadar ışık ve parıltıyla doldursun.
Şu hayat denen şey kötü bir işçiliğin ürünü, acemilere göre bir şey. Bu kepaze yaşam uğruna insan nelere katlanmıyor ki!
Kendisine sadakatten ayrılmadığı, yalnızca kendisinin olan bir tek bu var: Yalnızlığı.
Sahildeki üstü tenteli hasır koltuklar arkasındaki yüksek, sessiz kum tepeleri içinde yürürsen, tenteler altındaki insanları göremezsin; ama birinin bir diğerine seslendiğini, bir başkasının gevezelik ettiğini, bir ötekinin güldüğünü işitir ve anlarsın hemen: bu insan şöyle şöyle biridir diyebilirsin. Onun hayatı sevdiğini, bağrında büyük bir özlem ya da acı barındırdığını, bu acının da sesini ağlamaklı kıldığını her gülüşünde hissedersin.
-
 @ e31e84c4:77bbabc0
2024-12-02 10:44:07
@ e31e84c4:77bbabc0
2024-12-02 10:44:07Bitcoin and Fixed Income was Written By Wyatt O’Rourke. If you enjoyed this article then support his writing, directly, by donating to his lightning wallet: ultrahusky3@primal.net
Fiduciary duty is the obligation to act in the client’s best interests at all times, prioritizing their needs above the advisor’s own, ensuring honesty, transparency, and avoiding conflicts of interest in all recommendations and actions.
This is something all advisors in the BFAN take very seriously; after all, we are legally required to do so. For the average advisor this is a fairly easy box to check. All you essentially have to do is have someone take a 5-minute risk assessment, fill out an investment policy statement, and then throw them in the proverbial 60/40 portfolio. You have thousands of investment options to choose from and you can reasonably explain how your client is theoretically insulated from any move in the \~markets\~. From the traditional financial advisor perspective, you could justify nearly anything by putting a client into this type of portfolio. All your bases were pretty much covered from return profile, regulatory, compliance, investment options, etc. It was just too easy. It became the household standard and now a meme.
As almost every real bitcoiner knows, the 60/40 portfolio is moving into psyop territory, and many financial advisors get clowned on for defending this relic on bitcoin twitter. I’m going to specifically poke fun at the ‘40’ part of this portfolio.
The ‘40’ represents fixed income, defined as…
An investment type that provides regular, set interest payments, such as bonds or treasury securities, and returns the principal at maturity. It’s generally considered a lower-risk asset class, used to generate stable income and preserve capital.
Historically, this part of the portfolio was meant to weather the volatility in the equity markets and represent the “safe” investments. Typically, some sort of bond.
First and foremost, the fixed income section is most commonly constructed with U.S. Debt. There are a couple main reasons for this. Most financial professionals believe the same fairy tale that U.S. Debt is “risk free” (lol). U.S. debt is also one of the largest and most liquid assets in the market which comes with a lot of benefits.
There are many brilliant bitcoiners in finance and economics that have sounded the alarm on the U.S. debt ticking time bomb. I highly recommend readers explore the work of Greg Foss, Lawrence Lepard, Lyn Alden, and Saifedean Ammous. My very high-level recap of their analysis:
-
A bond is a contract in which Party A (the borrower) agrees to repay Party B (the lender) their principal plus interest over time.
-
The U.S. government issues bonds (Treasury securities) to finance its operations after tax revenues have been exhausted.
-
These are traditionally viewed as “risk-free” due to the government’s historical reliability in repaying its debts and the strength of the U.S. economy
-
U.S. bonds are seen as safe because the government has control over the dollar (world reserve asset) and, until recently (20 some odd years), enjoyed broad confidence that it would always honor its debts.
-
This perception has contributed to high global demand for U.S. debt but, that is quickly deteriorating.
-
The current debt situation raises concerns about sustainability.
-
The U.S. has substantial obligations, and without sufficient productivity growth, increasing debt may lead to a cycle where borrowing to cover interest leads to more debt.
-
This could result in more reliance on money creation (printing), which can drive inflation and further debt burdens.
In the words of Lyn Alden “Nothing stops this train”
Those obligations are what makes up the 40% of most the fixed income in your portfolio. So essentially you are giving money to one of the worst capital allocators in the world (U.S. Gov’t) and getting paid back with printed money.
As someone who takes their fiduciary responsibility seriously and understands the debt situation we just reviewed, I think it’s borderline negligent to put someone into a classic 60% (equities) / 40% (fixed income) portfolio without serious scrutiny of the client’s financial situation and options available to them. I certainly have my qualms with equities at times, but overall, they are more palatable than the fixed income portion of the portfolio. I don’t like it either, but the money is broken and the unit of account for nearly every equity or fixed income instrument (USD) is fraudulent. It’s a paper mache fade that is quite literally propped up by the money printer.
To briefly be as most charitable as I can – It wasn’t always this way. The U.S. Dollar used to be sound money, we used to have government surplus instead of mathematically certain deficits, The U.S. Federal Government didn’t used to have a money printing addiction, and pre-bitcoin the 60/40 portfolio used to be a quality portfolio management strategy. Those times are gone.
Now the fun part. How does bitcoin fix this?
Bitcoin fixes this indirectly. Understanding investment criteria changes via risk tolerance, age, goals, etc. A client may still have a need for “fixed income” in the most literal definition – Low risk yield. Now you may be thinking that yield is a bad word in bitcoin land, you’re not wrong, so stay with me. Perpetual motion machine crypto yield is fake and largely where many crypto scams originate. However, that doesn’t mean yield in the classic finance sense does not exist in bitcoin, it very literally does. Fortunately for us bitcoiners there are many other smart, driven, and enterprising bitcoiners that understand this problem and are doing something to address it. These individuals are pioneering new possibilities in bitcoin and finance, specifically when it comes to fixed income.
Here are some new developments –
Private Credit Funds – The Build Asset Management Secured Income Fund I is a private credit fund created by Build Asset Management. This fund primarily invests in bitcoin-backed, collateralized business loans originated by Unchained, with a secured structure involving a multi-signature, over-collateralized setup for risk management. Unchained originates loans and sells them to Build, which pools them into the fund, enabling investors to share in the interest income.
Dynamics
- Loan Terms: Unchained issues loans at interest rates around 14%, secured with a 2/3 multi-signature vault backed by a 40% loan-to-value (LTV) ratio.
- Fund Mechanics: Build buys these loans from Unchained, thus providing liquidity to Unchained for further loan originations, while Build manages interest payments to investors in the fund.
Pros
- The fund offers a unique way to earn income via bitcoin-collateralized debt, with protection against rehypothecation and strong security measures, making it attractive for investors seeking exposure to fixed income with bitcoin.
Cons
- The fund is only available to accredited investors, which is a regulatory standard for private credit funds like this.
Corporate Bonds – MicroStrategy Inc. (MSTR), a business intelligence company, has leveraged its corporate structure to issue bonds specifically to acquire bitcoin as a reserve asset. This approach allows investors to indirectly gain exposure to bitcoin’s potential upside while receiving interest payments on their bond investments. Some other publicly traded companies have also adopted this strategy, but for the sake of this article we will focus on MSTR as they are the biggest and most vocal issuer.
Dynamics
-
Issuance: MicroStrategy has issued senior secured notes in multiple offerings, with terms allowing the company to use the proceeds to purchase bitcoin.
-
Interest Rates: The bonds typically carry high-yield interest rates, averaging around 6-8% APR, depending on the specific issuance and market conditions at the time of issuance.
-
Maturity: The bonds have varying maturities, with most structured for multi-year terms, offering investors medium-term exposure to bitcoin’s value trajectory through MicroStrategy’s holdings.
Pros
-
Indirect Bitcoin exposure with income provides a unique opportunity for investors seeking income from bitcoin-backed debt.
-
Bonds issued by MicroStrategy offer relatively high interest rates, appealing for fixed-income investors attracted to the higher risk/reward scenarios.
Cons
-
There are credit risks tied to MicroStrategy’s financial health and bitcoin’s performance. A significant drop in bitcoin prices could strain the company’s ability to service debt, increasing credit risk.
-
Availability: These bonds are primarily accessible to institutional investors and accredited investors, limiting availability for retail investors.
Interest Payable in Bitcoin – River has introduced an innovative product, bitcoin Interest on Cash, allowing clients to earn interest on their U.S. dollar deposits, with the interest paid in bitcoin.
Dynamics
-
Interest Payment: Clients earn an annual interest rate of 3.8% on their cash deposits. The accrued interest is converted to Bitcoin daily and paid out monthly, enabling clients to accumulate Bitcoin over time.
-
Security and Accessibility: Cash deposits are insured up to $250,000 through River’s banking partner, Lead Bank, a member of the FDIC. All Bitcoin holdings are maintained in full reserve custody, ensuring that client assets are not lent or leveraged.
Pros
-
There are no hidden fees or minimum balance requirements, and clients can withdraw their cash at any time.
-
The 3.8% interest rate provides a predictable income stream, akin to traditional fixed-income investments.
Cons
-
While the interest rate is fixed, the value of the Bitcoin received as interest can fluctuate, introducing potential variability in the investment’s overall return.
-
Interest rate payments are on the lower side
Admittedly, this is a very small list, however, these types of investments are growing more numerous and meaningful. The reality is the existing options aren’t numerous enough to service every client that has a need for fixed income exposure. I challenge advisors to explore innovative options for fixed income exposure outside of sovereign debt, as that is most certainly a road to nowhere. It is my wholehearted belief and call to action that we need more options to help clients across the risk and capital allocation spectrum access a sound money standard.
Additional Resources
-
River: The future of saving is here: Earn 3.8% on cash. Paid in Bitcoin.
-
MicroStrategy: MicroStrategy Announces Pricing of Offering of Convertible Senior Notes
Bitcoin and Fixed Income was Written By Wyatt O’Rourke. If you enjoyed this article then support his writing, directly, by donating to his lightning wallet: ultrahusky3@primal.net
-
-
 @ d61f3bc5:0da6ef4a
2025-05-06 01:37:28
@ d61f3bc5:0da6ef4a
2025-05-06 01:37:28I remember the first gathering of Nostr devs two years ago in Costa Rica. We were all psyched because Nostr appeared to solve the problem of self-sovereign online identity and decentralized publishing. The protocol seemed well-suited for textual content, but it wasn't really designed to handle binary files, like images or video.
The Problem
When I publish a note that contains an image link, the note itself is resilient thanks to Nostr, but if the hosting service disappears or takes my image down, my note will be broken forever. We need a way to publish binary data without relying on a single hosting provider.
We were discussing how there really was no reliable solution to this problem even outside of Nostr. Peer-to-peer attempts like IPFS simply didn't work; they were hopelessly slow and unreliable in practice. Torrents worked for popular files like movies, but couldn't be relied on for general file hosting.
Awesome Blossom
A year later, I attended the Sovereign Engineering demo day in Madeira, organized by Pablo and Gigi. Many projects were presented over a three hour demo session that day, but one really stood out for me.
Introduced by hzrd149 and Stu Bowman, Blossom blew my mind because it showed how we can solve complex problems easily by simply relying on the fact that Nostr exists. Having an open user directory, with the corresponding social graph and web of trust is an incredible building block.
Since we can easily look up any user on Nostr and read their profile metadata, we can just get them to simply tell us where their files are stored. This, combined with hash-based addressing (borrowed from IPFS), is all we need to solve our problem.
How Blossom Works
The Blossom protocol (Blobs Stored Simply on Mediaservers) is formally defined in a series of BUDs (Blossom Upgrade Documents). Yes, Blossom is the most well-branded protocol in the history of protocols. Feel free to refer to the spec for details, but I will provide a high level explanation here.
The main idea behind Blossom can be summarized in three points:
- Users specify which media server(s) they use via their public Blossom settings published on Nostr;
- All files are uniquely addressable via hashes;
- If an app fails to load a file from the original URL, it simply goes to get it from the server(s) specified in the user's Blossom settings.
Just like Nostr itself, the Blossom protocol is dead-simple and it works!
Let's use this image as an example:
 If you look at the URL for this image, you will notice that it looks like this:
If you look at the URL for this image, you will notice that it looks like this:blossom.primal.net/c1aa63f983a44185d039092912bfb7f33adcf63ed3cae371ebe6905da5f688d0.jpgAll Blossom URLs follow this format:
[server]/[file-hash].[extension]The file hash is important because it uniquely identifies the file in question. Apps can use it to verify that the file they received is exactly the file they requested. It also gives us the ability to reliably get the same file from a different server.
Nostr users declare which media server(s) they use by publishing their Blossom settings. If I store my files on Server A, and they get removed, I can simply upload them to Server B, update my public Blossom settings, and all Blossom-capable apps will be able to find them at the new location. All my existing notes will continue to display media content without any issues.
Blossom Mirroring
Let's face it, re-uploading files to another server after they got removed from the original server is not the best user experience. Most people wouldn't have the backups of all the files, and/or the desire to do this work.
This is where Blossom's mirroring feature comes handy. In addition to the primary media server, a Blossom user can set one one or more mirror servers. Under this setup, every time a file is uploaded to the primary server the Nostr app issues a mirror request to the primary server, directing it to copy the file to all the specified mirrors. This way there is always a copy of all content on multiple servers and in case the primary becomes unavailable, Blossom-capable apps will automatically start loading from the mirror.
Mirrors are really easy to setup (you can do it in two clicks in Primal) and this arrangement ensures robust media handling without any central points of failure. Note that you can use professional media hosting services side by side with self-hosted backup servers that anyone can run at home.
Using Blossom Within Primal
Blossom is natively integrated into the entire Primal stack and enabled by default. If you are using Primal 2.2 or later, you don't need to do anything to enable Blossom, all your media uploads are blossoming already.
To enhance user privacy, all Primal apps use the "/media" endpoint per BUD-05, which strips all metadata from uploaded files before they are saved and optionally mirrored to other Blossom servers, per user settings. You can use any Blossom server as your primary media server in Primal, as well as setup any number of mirrors:
 ## Conclusion
## ConclusionFor such a simple protocol, Blossom gives us three major benefits:
- Verifiable authenticity. All Nostr notes are always signed by the note author. With Blossom, the signed note includes a unique hash for each referenced media file, making it impossible to falsify.
- File hosting redundancy. Having multiple live copies of referenced media files (via Blossom mirroring) greatly increases the resiliency of media content published on Nostr.
- Censorship resistance. Blossom enables us to seamlessly switch media hosting providers in case of censorship.
Thanks for reading; and enjoy! 🌸
-
 @ 3bf0c63f:aefa459d
2024-09-06 12:49:46
@ 3bf0c63f:aefa459d
2024-09-06 12:49:46Nostr: a quick introduction, attempt #2
Nostr doesn't subscribe to any ideals of "free speech" as these belong to the realm of politics and assume a big powerful government that enforces a common ruleupon everybody else.
Nostr instead is much simpler, it simply says that servers are private property and establishes a generalized framework for people to connect to all these servers, creating a true free market in the process. In other words, Nostr is the public road that each market participant can use to build their own store or visit others and use their services.
(Of course a road is never truly public, in normal cases it's ran by the government, in this case it relies upon the previous existence of the internet with all its quirks and chaos plus a hand of government control, but none of that matters for this explanation).
More concretely speaking, Nostr is just a set of definitions of the formats of the data that can be passed between participants and their expected order, i.e. messages between clients (i.e. the program that runs on a user computer) and relays (i.e. the program that runs on a publicly accessible computer, a "server", generally with a domain-name associated) over a type of TCP connection (WebSocket) with cryptographic signatures. This is what is called a "protocol" in this context, and upon that simple base multiple kinds of sub-protocols can be added, like a protocol for "public-square style microblogging", "semi-closed group chat" or, I don't know, "recipe sharing and feedback".
-
 @ a296b972:e5a7a2e8
2025-05-10 11:12:09
@ a296b972:e5a7a2e8
2025-05-10 11:12:09***Satiretüchtigkeit***
Deutschland hat den Satirikern den Krieg erklärt, in dem es Realitäten schafft, die die Phantasie der Autoren überbieten soll. Dazu hat das neu geschaffene Satireministerium die Satiretüchtigkeit ganz oben auf die Agenda gesetzt.
***Notlage***
Die Notlage in Deutschland ist in eine Notlage geraten. Das Ausrufen einer Notlage ist Gebot der Stunde, in der die Notlage der Notlage bekämpft werden kann.
***Grenzsicherung***
Nachdem als eine der ersten Amtshandlungen die deutschen Außengrenzen neu vermessen worden sind, hat sich herausgestellt, dass die Grenzen nur gesichert offenbleiben können. Der Bundesgrenzschutz hat ab sofort die Aufgabe übernommen, ausländisches CO2 an der Grenze aufzuhalten.
***Demokratiebeleidigungsparagraph***
Nach intensiver Recherche des Verfassungsschutzes hat sich herausgestellt, dass die Opposition die seinerzeitige Bundesregierung als „Diktatur“ und „totalitär“ bezeichnet hat. Das ist Demokratiebeleidigung. Ein neuer Paragraph ist bereits in der Ausarbeitung.
***Einhaltung des Koalitionsvertrags***
Aus gesicherten Quellen ist durchgesickert, dass der erste Bundeskanzler zweiter Wahl nun doch nicht sein Amt wahrnehmen will, weil das so nicht im Koalitionsvertrag steht. Schließlich halte man sich an selbigen und die Glaubwürdigkeit dürfe unter keinen Umständen infrage gestellt werden.
***Bundesamt für Fassungslosigkeit***
Das Bundesamt für Verfassungsschutz soll nach dem Willen der Bürger in Bundesamt für Fassungslosigkeit umbenannt werden. Es soll ein deutliches Zeichen gesetzt werden, dass Bürgerbeteiligung in Zukunft ein wichtiger Bestandteil der Politik sein wird.
***Brüssel – Zentrum Belgiens***
Der Bundeskanzler mit Blackrock-Hintergrund hat als eine seiner ersten Amtshandlungen die Neugestaltung des Finanzmarktes in Brüssel angeregt. Der Euro soll in den allermeisten Europäischen Staaten durch den Blackrock-Taler ersetzt werden.
***Salutokratie***
Die WHO hat größte Zustimmung bei der Einführung der Salutokratie erfahren. Die Europäer jubeln und ziehen zu Tausenden mit der EU-Fahne durch die europäischen Hauptstädte. Auf vielen Plakaten ist der folgende Text zu lesen: Die Pharmaindustrie ist ein wichtiger Wirtschaftszweig. Durch unsere Erkrankungen tragen wir einen wichtigen Teil dazu bei, dass sie zu unserem Wohle weiter forschen und neue Medikamente auf den Markt bringen kann.
***Elektronische Patientenakte***
Nach für die Ärzte verpflichtender Einführung der elektronischen Patientenakte konnten letzte Lücken in der Datenoffenheit beseitigt werden. Eine vollständige Transparenz ist jetzt für jedermann gewährleistet. Die Krankenkassen jubeln, weil Ferndiagnosen noch effizienter praktiziert werden können.
***Übermenschliche Leistungen***
Die neue Wirtschaftsministerin hat ihre eigene Messlatte sehr hoch angelegt. Sie will die übermenschlichen Leistungen ihres Vorgängers noch übermenschlicher übertreffen. Ihre Mitarbeiter arbeiten fieberhaft an einer neuen Wortschöpfung, die über den Begriff Übermenschlichkeit hinausgeht. Es ist größte Eile geboten, da eine Neuwahl der Regierung schon in den nächsten Monaten zu erwarten ist.
***Lieferprobleme***
Der brutale Umzug der ehemaligen Außen-Dings in die genderunfreundlichen USA verzögert sich, weil ein bekanntes Versandunternehmen die Lieferkette von feministischen Umzugskartons nicht nachweisen kann. Außerdem wurde von Lagerengpässen für die bevorstehende Auslieferung mobiler Toiletten nach Afrika berichtet.
***Erwischt***
Der ehemalige Corona-Minister II. wurde auf der Rückfahrt nach Berlin (1. Klasse, die ist noch pünktlich) dabei gesehen, wie er im Bistro-Wagen mit Genuss eine leicht versalzene Bockwurst gegessen hat. Nach Ankunft in Berlin musste der Vorrat an erlesenem, durstlöschendem Rotwein aufgefüllt werden.
***Verkauf aus Gewissensgründen***
Der Corona-Minister I. bekannt und berühmt geworden durch seine kaufmännisch geschickt eingefädelten Masken-Deals in bedarfsgerechter Anzahl, sucht derzeit nach einem Käufer für seine bescheidene Hütte in Hamburg, weil er mit dem Erlös den bankkaufmanntechnischen Gewinnüberhang ausgleichen will.
***Drohnennahverkehr***
Das zu verstaatlichende Staatsunternehmen Bahn will spätestens 2028 den Drohnennahverkehr im Halbstundentakt bundesweit einführen. In einer Pressekonferenz wurde bekannt, dass man mit den Logistikfragen im Umgang mit den angeschlossenen Glasfaserkabeln schon sehr große Fortschritte gemacht habe.
***Merz-Frisur***
Vollhaar-Inhaber in der CDU wollen sich zur Unterstützung und als Zeichen der Loyalität eine Merz-Frisur bei einem bekannten Star-Friseur schneiden lassen. Die Wartezeiten betragen derzeit rund 5 Tage. Die Friseur-Innung arbeitet an einem Schnellkurs: Merz-Frisur-tüchtig in drei Wochen!
***Bestsellerliste***
Die ehemalige Bundesmutti hat weitere Prosa in zwei Bänden angekündigt: Die Titel lauten „Einigkeit“ und „Recht“. Derzeit laufen die Maschinen der papierverarbeitenden Hygieneindustrie auf Hochtouren (gut für die Wirtschaft!), da die Bestellliste schon 1000 Seiten lang ist, die jedoch aufgrund der Gleichbehandlung nicht veröffentlicht werden kann.
***Autoindustrie mehrheitlich positiv***
Die Umsätze der deutschen Autoindustrie sollen angeblich um rund 30% eingebrochen sein. Das bedeutet, dass die Mehrheit, also rund 70% noch vorhanden ist, was für die Wirtschaft allgemein sehr gute Nachrichten sind. Außerdem können freie Kapazitäten jetzt zur Produktion von Tankfahrzeugen für Panzer genutzt werden.
***Unterbringungsprobleme gelöst***
Durch die anhaltende Insolvenzwelle deutscher Unternehmen werden Werkshallen frei, die in kürzester Zeit zu weltoffenen Unterkünften umgebaut werden. Erfahrungen aus der Plattenbauweise der ehemaligen DDR konnten hier erfolgreich eingesetzt werden.
***Pandemiebekämpfung***
Deutschland ist zepterhaltend in Präventionsmaßnahmen für zukünftig geplante Pandemien. Federführend soll das virenverseuchte Bargeld stufenweise abgeschafft werden. Ein neues Panik-Paper sieht bereits seiner gut durchdachten Vollendung entgegen.
***Verband der Schreib-Fachkräfte***
Der in Anlehnung des bekannten Satzes von Peter Scholl-Latour formulierte Satz: -Wer Begriffe wie „Kriegstüchtigkeit“ und „Hass und Hetze“ aus dunklen Zeiten verwendet, wird selbst zur dunklen Zeit-, wurde vom Verband der Schreib-Fachkräfte als umstritten eingeordnet.
***Leitkultur***
Experten für den unfallfreien Verzehr von Bananen haben in einer teleskopierten Studie herausgefunden, dass das Wort Leitkultur aus den Worten Leitkuh und Kultur künstlich in einem französischen Labor für Gain-of-Word-Forschung zusammengesetzt wurde. Beweis dafür ist das fehlende Ha, das so in der Natur nicht vorkommt. Der Laborsprung konnte so eindeutig nachgewiesen werden.
***Reformvorschlag***
Bisher galt: Alle Bürgerrechte sind Abwehrrechte gegen den Staat. In einer Ausschusstagung soll jetzt darüber befunden werden, ob diese Formulierung aus Gründen der Delegitimierung des Staates nicht geändert werden kann. Der Reformvorschlag lautet: In einer angestrebten Unseredemokratie soll die Hoheit über die Abwehrrechte der Bürger beim Staat liegen. In demokratischen Einzelverfahren soll darüber entschieden werden, wann und in welchem Umfang sie gegen die Bürger zur Anwendung kommen sollen.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ c9badfea:610f861a
2025-05-10 11:08:51
@ c9badfea:610f861a
2025-05-10 11:08:51- Install FUTO Keyboard (it's free and open source)
- Launch the app, tap Switch Input Methods and select FUTO Keyboard
- For voice input, choose FUTO Keyboard (needs mic permission) and grant permission While Using The App
- Configure keyboard layouts under Languages & Models as needed
Adding Support for Non-English Languages
Voice Input
- Download voice input models from the FUTO Keyboard Add-Ons page
- For languages like Chinese, German, Spanish, Russian, French, Portuguese, Korean, and Japanese, download the Multilingual-74 model
- For other languages, download Multilingual-244
- Open FUTO Keyboard, go to Languages & Models, and import the downloaded model under Voice Input
Dictionaries
- Get dictionary files from AOSP Dictionaries
- Open FUTO Keyboard, navigate to Languages & Models, and import the dictionary under Dictionary
ℹ️ When typing, tap the microphone icon to use voice input
-
 @ 57d1a264:69f1fee1
2025-05-05 05:26:34
@ 57d1a264:69f1fee1
2025-05-05 05:26:34The European Accessibility Act is coming, now is a great time for accessibility trainings!. In my Accessibility for Designer workshop, you will learn how to design accessible mockups that prevent issues in visual design, interactions, navigation, and content. You will be able to spot problems early, fix them in your designs, and communicate accessibility clearly with your team. This is a practical workshop with hands-on exercises, not just theory. You’ll actively apply accessibility principles to real design scenarios and mockups. And will get access to my accessibility resources: checklists, annotation kits and more.
When? 4 sessions of 2 hours + Q and As, on: - Mon, June 16, - Tue, June 17, Mon, - June 23 and Tue, - June 24. 9:30 – 12:00 PM PT or 18:30 – 21:00 CET
Register with 15% discount ($255) https://ti.to/smashingmagazine/online-workshops-2022/with/87vynaoqc0/discount/welcometomyworkshop
originally posted at https://stacker.news/items/971772
-
 @ 3bf0c63f:aefa459d
2024-05-21 12:38:08
@ 3bf0c63f:aefa459d
2024-05-21 12:38:08Bitcoin transactions explained
A transaction is a piece of data that takes inputs and produces outputs. Forget about the blockchain thing, Bitcoin is actually just a big tree of transactions. The blockchain is just a way to keep transactions ordered.
Imagine you have 10 satoshis. That means you have them in an unspent transaction output (UTXO). You want to spend them, so you create a transaction. The transaction should reference unspent outputs as its inputs. Every transaction has an immutable id, so you use that id plus the index of the output (because transactions can have multiple outputs). Then you specify a script that unlocks that transaction and related signatures, then you specify outputs along with a script that locks these outputs.

As you can see, there's this lock/unlocking thing and there are inputs and outputs. Inputs must be unlocked by fulfilling the conditions specified by the person who created the transaction they're in. And outputs must be locked so anyone wanting to spend those outputs will need to unlock them.
For most of the cases locking and unlocking means specifying a public key whose controller (the person who has the corresponding private key) will be able to spend. Other fancy things are possible too, but we can ignore them for now.
Back to the 10 satoshis you want to spend. Since you've successfully referenced 10 satoshis and unlocked them, now you can specify the outputs (this is all done in a single step). You can specify one output of 10 satoshis, two of 5, one of 3 and one of 7, three of 3 and so on. The sum of outputs can't be more than 10. And if the sum of outputs is less than 10 the difference goes to fees. In the first days of Bitcoin you didn't need any fees, but now you do, otherwise your transaction won't be included in any block.

If you're still interested in transactions maybe you could take a look at this small chapter of that Andreas Antonopoulos book.
If you hate Andreas Antonopoulos because he is a communist shitcoiner or don't want to read more than half a page, go here: https://en.bitcoin.it/wiki/Coin_analogy
-
 @ 57d1a264:69f1fee1
2025-05-05 05:15:02
@ 57d1a264:69f1fee1
2025-05-05 05:15:02Crabtree's Framework for Evaluating Human-Centered Research
Picture this: You've spent three weeks conducting qualitative research for a finance app redesign. You carefully recruited 12 participants, conducted in-depth interviews, and identified patterns around financial anxiety and decision paralysis. You're excited to present your findings when the inevitable happens:
"But are these results statistically significant?"
"Just 12 people? How can we make decisions that affect thousands of users based on conversations with just 12 people?"
As UX professionals, we regularly face stakeholders who evaluate our qualitative research using criteria designed for quantitative methods... This misalignment undermines the unique value qualitative research brings to product development.
Continue reading https://uxpsychology.substack.com/p/beyond-numbers-how-to-properly-evaluate
originally posted at https://stacker.news/items/971767
-
 @ 6c05c73e:c4356f17
2025-05-10 20:50:06
@ 6c05c73e:c4356f17
2025-05-10 20:50:06Descrição da Embraer (EMBR3)
A Embraer é uma empresa brasileira que nasceu de uma iniciativa do governo brasileiro de implementar uma indústria aeronáutica no país. Após a iniciativa do oficial de aviação do exército, Casimiro Montenegro em convidar o engenheiro Focke-Wulf e seus engenheiros para que atuassem no CTA(Centro Técnico de Aeronáutica). Em, 1953. A empresa surgiu para substituir a importação de jatos para o país.
Mais tarde, sobre a direção de Ozires Silva. Nasce a Embraer SA, em 1969. Em uma sociedade de economia mista vinculada ao ministério da aeronáutica. Mas, em 1992 a empresa foi colocada na lista de empresas a serem privatizadas e em 1994, sob a tutela de Itamar Franco a empresa foi leiloada.
Portanto, os novos majoritários da empresa eram dois fundos de pensão; Previ(20%) e Sistel (20%) e a Cia Bozano, Simonsen(20%) e alguns minoritários tinham algo em torno de (20%) . Vale entender que antes de ser privatizada a empresa estava a passos fortes rumo à falência. E, teve que passar por renovações após se tornar privada.
Contudo, vale lembrar também que alguns anos após a privatização, a empresa passou a figurar como a terceira maior fabricante de jatos comerciais do mundo. E, uma das empresas mais valiosas da Bovespa.

Visão geral
Primordialmente, a Embraer é uma empresa que atua projetando, fabricando e vendendo suas próprias aeronaves. Nesse segmento, ela conta com algumas classes de aviões: Defesa e segurança, comercial e agro. Ademais, estende- se também a serviços e suportes prestados.
A Embraer também atua no desenvolvimento de softwares para a indústria aeronáutica e conta com um dos centros de realidade virtual mais avançados e tecnológicos do mundo.
Desde sua fundação a Embraer já entregou mais de 8.000 aeronaves mundo afora. Ela é a maior fabricante de jatos de até 150 lugares e a maior exportadora de bens de alto valor agregado. Ela detém escritórios, centros de serviços e distribuição na África, Ásia e Europa.

Mercado
Com um mundo cada vez mais rápido e mais globalizado. A frase: "tempo é dinheiro". Nunca antes na história fez mais sentido. A demanda por voos domésticos e internacionais segue cada vez maior e com demanda para muito mais.
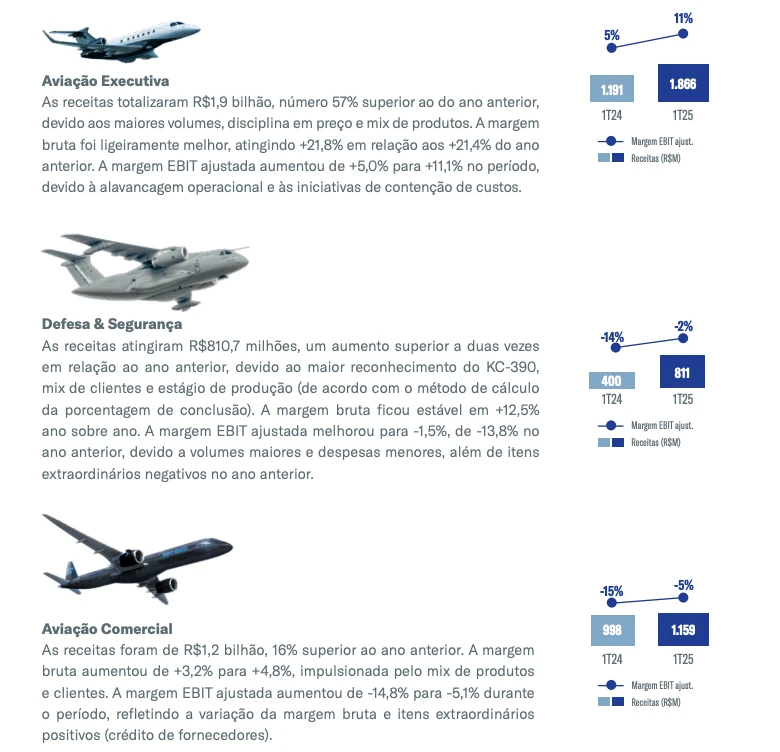
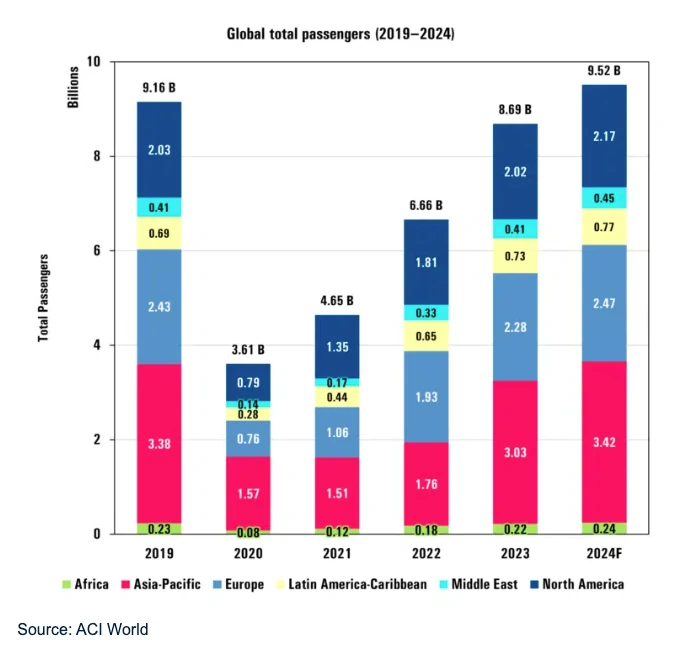
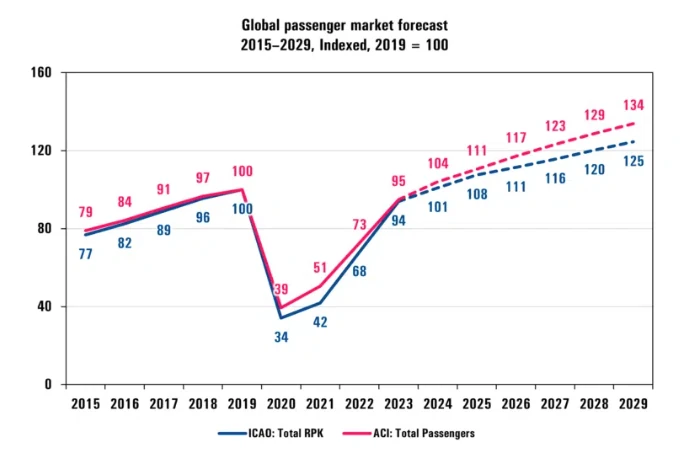
Entretanto, as maiores vendas da empresa não vieram do setor comercial. Mas, sim em defesa e segurança. Com um aumento de 12% (-14% em 1T24 vs -2% 1 T 25) nas vendas por aeronaves de defesa. Esse segmento foi o que mais cresceu nos últimos meses. Em partes pelas tensões geopolíticas e em partes pelo reconhecimento do KC-390.

A demanda por aviões militares só aumenta e segundo pesquisas é um mercado que pode alcançar $29bi até 2034.
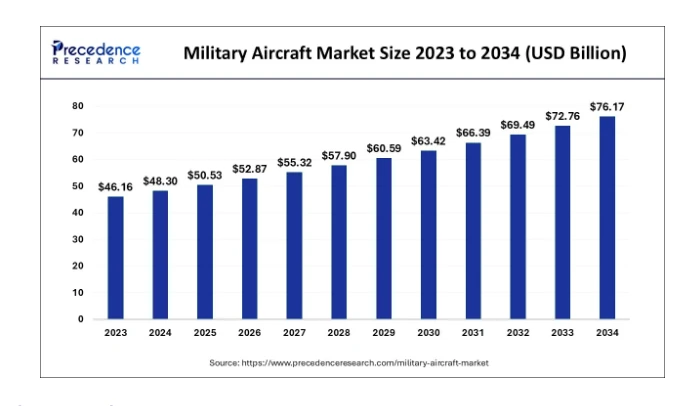
Oportunidades
1 - Pedidos aumentaram
Olhando esses cenários. Eu enxergo 3 grandes oportunidades dentro da Embraer. A primeira e mais óbvia é sobre as vendas de aeronaves de defesa e também a parte executiva.
Apesar de ter entregado 30 jatos no 1T25. A empresa reportou que tem pedidos na casa dos $26bi, o que representa um aumento de 25% em relação ao período similar do último ano. Isso é enorme para os acionistas!
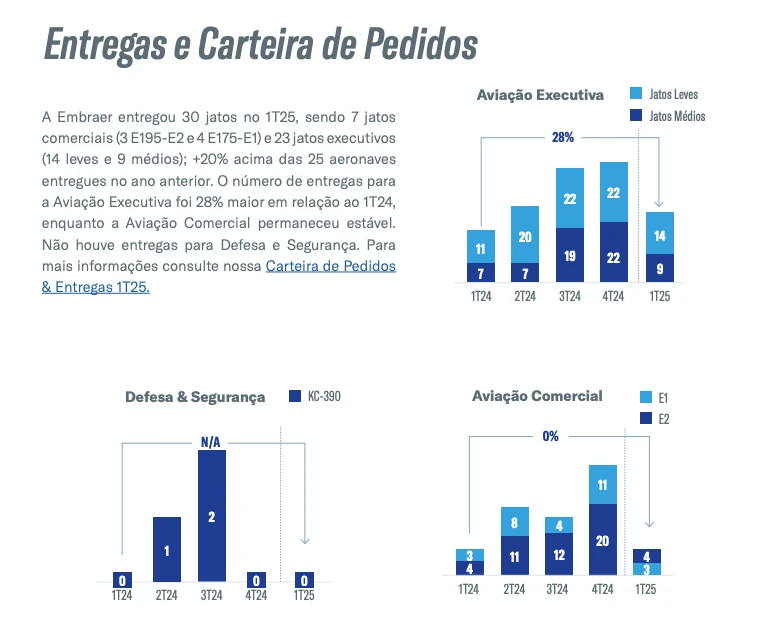
Seguindo a lógica, quanto maiores as vendas de aeronaves. Mais demanda você terá por serviços e suportes. Essa jogada é muito esperta, você vende a solução e detém a ferramenta para manter ela. Apesar da empresa ter reportado prejuízo -R$429mi.
Estou otimista pois a empresa tem uma grande leva de pedidos para entregar, que vai ocasionar o nosso segundo item…
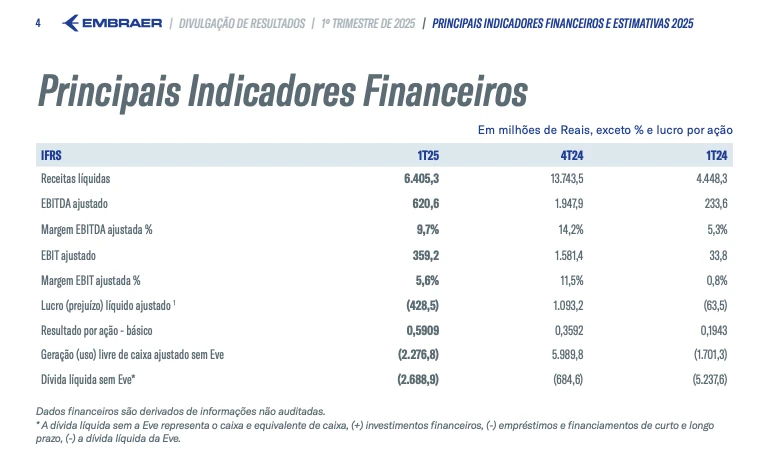
2 - Ativos em caixa
Para contextualizar, a empresa está sentada sobre um capital de giro de R$2.7bi em 1T25. Em função da sazonalidade. Seus ativos aumentaram, em razão de um estoque de R$1,9Bi. Que são respectivos a entrega de aeronaves para os próximos trimestres.
Isso elevou o fluxo de caixa livre para R$2.3bi em 1T2025. Soma se todo esse caixa a redução da dívida que saiu de 1,8 x para 0,5 x no mesmo período. Reduzindo a alavancagem da empresa.
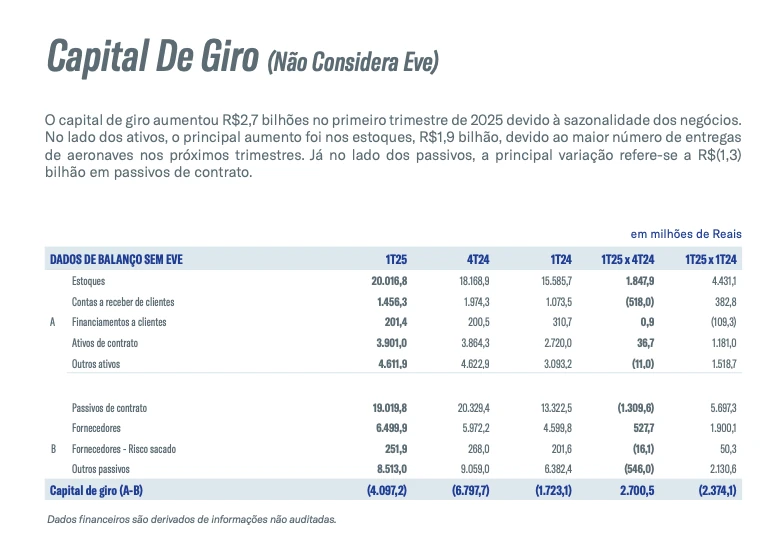
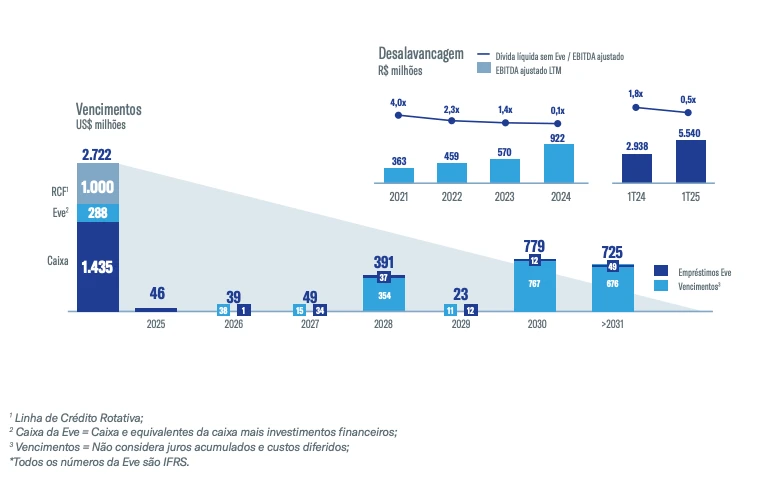
3 - Aviões de defesa e segurança
Aqui é onde está o “pulo do gato”. A demanda por aeronaves desse tipo aumentou muito, como dito anteriormente. E, a Embraer está muito bem posicionada e consolidada como uma marca de prestígio global. Colômbia, clientes Africanos, Áustria e Holanda. São clientes confirmados que já encomendaram para a Embraer.


Riscos
Na minha visão, o maior risco hoje em se investir em Embraer. São as chamadas "golden shares” do governo. Esse é de longe o fator que mais me preocupa. Mesmo, não sendo majoritário. Mas, sabemos como as coisas por aqui funcionam.
Ademais, um risco menor que percebo. É justamente pelas ações estarem no "hype". Isso pode fazer com que o pequeno investidor embarque de cara nessa jornada e veja o preço de suas ações derreterem sistematicamente. Contudo, toda cautela deve ser tomada.

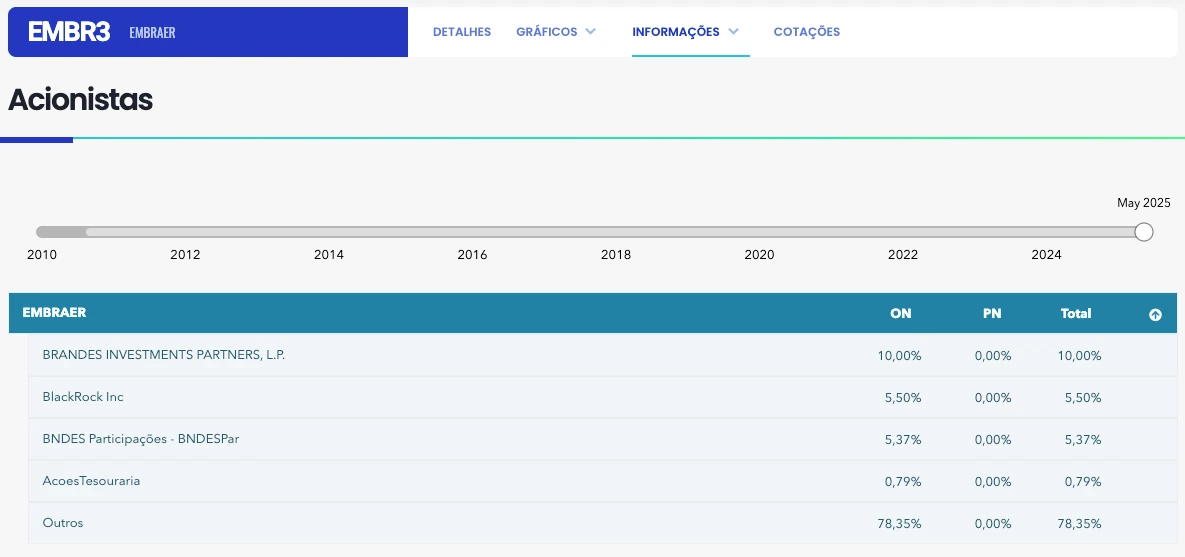
Catalisadores
Vários pontos me chamam a atenção na empresa, tais como:
- O aumento da demanda por aeronaves de defesa e segurança.
- Bom fluxo de vendas para aeronaves executivas.
- O bom fluxo de caixa da empresa.
- A redução de alavancagem.
- A premissa de entrega de várias unidades ao longo dos próximos trimestres.
- E, consequentemente, a variação cambial também pode contribuir e muito para aumentar as margens da empresa.

Concluindo quero destacar que a empresa tem muito estoque para entregar (R$1.9BI). Lembre-se, a empresa já vendeu as aeronaves. Por sazonalidade, ela não entregou ainda. E, quando isso ocorrer, vamos ver um volume de dinheiro cada vez maior dentro da empresa. Por isso, não me surpreende que a empresa tenha performado 97% vs 2% do IBOV no mesmo período. Eu olharia com bastante carinho para a empresa nos próximos meses.
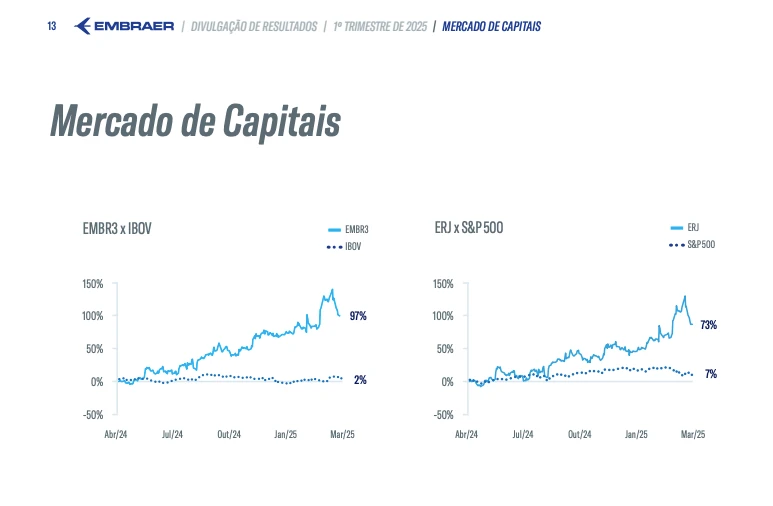
FAQ
Quem é o maior acionista da Embraer?
O maior acionista individual da Embraer é a Brandes Investment Partners, LP. A Brandes possui 14,4% das ações da companhia.
Qual a participação do governo na Embraer RI?
O governo, apesar da privatização, detém uma participação acionária especial, conhecida como "golden share", que lhe concede direito de veto em decisões estratégicas da empresa.
Quem é o proprietário da Embraer?
Seus principais acionistas individuais são os fundos estrangeiros Brandes e Mondrian. Qual é o capital social da Embraer RI?
Bio
Investir não precisa ser um bicho de sete cabeças! Na Threedolar, democratizamos o acesso ao mundo dos investimentos, oferecendo conteúdo claro e prático. Comece hoje mesmo a construir seu futuro financeiro!
Disclaimer
Lembre-se: este não é um conselho de investimento. Faça sua própria pesquisa antes de investir. Resultados passados não garantem lucros futuros. Cuide do seu dinheiro!
Referências:
- https://www.fundamentus.com.br/detalhes.php?papel=EMBR3&h=1
- https://pt.wikipedia.org/wiki/Embraer#/media/Ficheiro:EMB-countries.png
- https://pt.wikipedia.org/wiki/Embraer
- https://embraer.com/media/tour/
- https://www.youtube.com/watch?v=pJFnHOYq6h4
- https://www.iata.org/en/pressroom/2025-releases/2025-01-30-01/
- https://www.precedenceresearch.com/military-aircraft-market
- https://www.edrotacultural.com.br/vendas-da-embraer-para-forcas-armadas-registram-alta/
- https://www.poder360.com.br/poder-economia/embraer-anuncia-venda-de-4-aeronaves-para-novo-cliente-africano/
- https://aeroin.net/colombia-deve-comprar-tres-jatos-kc-390-da-embraer-afirma-ministro/#google_vignette
- https://api.mziq.com/mzfilemanager/v2/d/12a56b3a-7b37-4dba-b80a-f3358bf66b71/64eb0439-65bb-2e7f-dd61-ac017ad03886?origin=1 *
-
 @ c631e267:c2b78d3e
2025-05-02 20:05:22
@ c631e267:c2b78d3e
2025-05-02 20:05:22Du bist recht appetitlich oben anzuschauen, \ doch unten hin die Bestie macht mir Grauen. \ Johann Wolfgang von Goethe
Wie wenig bekömmlich sogenannte «Ultra-Processed Foods» wie Fertiggerichte, abgepackte Snacks oder Softdrinks sind, hat kürzlich eine neue Studie untersucht. Derweil kann Fleisch auch wegen des Einsatzes antimikrobieller Mittel in der Massentierhaltung ein Problem darstellen. Internationale Bemühungen, diesen Gebrauch zu reduzieren, um die Antibiotikaresistenz bei Menschen einzudämmen, sind nun möglicherweise gefährdet.
Leider ist Politik oft mindestens genauso unappetitlich und ungesund wie diverse Lebensmittel. Die «Corona-Zeit» und ihre Auswirkungen sind ein beredtes Beispiel. Der Thüringer Landtag diskutiert gerade den Entwurf eines «Coronamaßnahmen-Unrechtsbereinigungsgesetzes» und das kanadische Gesundheitsministerium versucht, tausende Entschädigungsanträge wegen Impfnebenwirkungen mit dem Budget von 75 Millionen Dollar unter einen Hut zu bekommen. In den USA soll die Zulassung von Covid-«Impfstoffen» überdacht werden, während man sich mit China um die Herkunft des Virus streitet.
Wo Corona-Verbrecher von Medien und Justiz gedeckt werden, verfolgt man Aufklärer und Aufdecker mit aller Härte. Der Anwalt und Mitbegründer des Corona-Ausschusses Reiner Fuellmich, der seit Oktober 2023 in Untersuchungshaft sitzt, wurde letzte Woche zu drei Jahren und neun Monaten verurteilt – wegen Veruntreuung. Am Mittwoch teilte der von vielen Impfschadensprozessen bekannte Anwalt Tobias Ulbrich mit, dass er vom Staatsschutz verfolgt wird und sich daher künftig nicht mehr öffentlich äußern werde.
Von der kommenden deutschen Bundesregierung aus Wählerbetrügern, Transatlantikern, Corona-Hardlinern und Russenhassern kann unmöglich eine Verbesserung erwartet werden. Nina Warken beispielsweise, die das Ressort Gesundheit übernehmen soll, diffamierte Maßnahmenkritiker als «Coronaleugner» und forderte eine Impfpflicht, da die wundersamen Injektionen angeblich «nachweislich helfen». Laut dem designierten Außenminister Johann Wadephul wird Russland «für uns immer der Feind» bleiben. Deswegen will er die Ukraine «nicht verlieren lassen» und sieht die Bevölkerung hinter sich, solange nicht deutsche Soldaten dort sterben könnten.
Eine wichtige Personalie ist auch die des künftigen Regierungssprechers. Wenngleich Hebestreit an Arroganz schwer zu überbieten sein wird, dürfte sich die Art der Kommunikation mit Stefan Kornelius in der Sache kaum ändern. Der Politikchef der Süddeutschen Zeitung «prägte den Meinungsjournalismus der SZ» und schrieb «in dieser Rolle auch für die Titel der Tamedia». Allerdings ist, anders als noch vor zehn Jahren, die Einbindung von Journalisten in Thinktanks wie die Deutsche Atlantische Gesellschaft (DAG) ja heute eher eine Empfehlung als ein Problem.
Ungesund ist definitiv auch die totale Digitalisierung, nicht nur im Gesundheitswesen. Lauterbachs Abschiedsgeschenk, die «abgesicherte» elektronische Patientenakte (ePA) ist völlig überraschenderweise direkt nach dem Bundesstart erneut gehackt worden. Norbert Häring kommentiert angesichts der Datenlecks, wer die ePA nicht abwähle, könne seine Gesundheitsdaten ebensogut auf Facebook posten.
Dass die staatlichen Kontrolleure so wenig auf freie Software und dezentrale Lösungen setzen, verdeutlicht die eigentlichen Intentionen hinter der Digitalisierungswut. Um Sicherheit und Souveränität geht es ihnen jedenfalls nicht – sonst gäbe es zum Beispiel mehr Unterstützung für Bitcoin und für Initiativen wie die der Spar-Supermärkte in der Schweiz.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 6c05c73e:c4356f17
2025-05-10 20:46:26
@ 6c05c73e:c4356f17
2025-05-10 20:46:26Porque investir R$100
Um guia politicamente diferente de investimento
Você já certamente se pegou na seguinte situação. Paguei tudo o que devia. E, agora me sobrou cem reais para investir.
Principalmente, se você é novo e está no seu primeiro emprego. Isso é muito comum. Contudo, mesmo os mais experimentados passam por isso.
No entanto, vem aquela pergunta na cabeça. Será que eu realmente preciso investir esses cem reais? Afinal, é uma quantia pequena e qual seria o retorno disso?
Contudo, para responder sua dúvida. A resposta é sempre sim. Se, algum dia na sua vida. Você quiser acumular recursos e escapar desse círculo vicioso. Precisa acumular e investir.
Todavia, vamos analisar nesse artigo alguns outros aspectos que podem elevar x10 esse valor investido.
Quando investir R$100?
Agora, amanhã ou ano que vem?
Muitos pensam que todo dinheiro ganho precisa IMEDIATAMENTE ser investido. E, na verdade isso não precisa ser assim.
Portanto, todo o dinheiro ganho deve ser aplicado com diligência. Decidir quando investir o dinheiro é uma tarefa crucial. Mas, antes disso acontecer. Você precisa definir seus objetivos.
Sobretudo, aonde você vai colocar seu dinheiro. Vai determinar o ritmo como investe. E, isso é crucial em uma jornada de investimentos.
Aonde?
“Para manter uma fogueira, tem que botar mais lenha”
Espera um pouco. O que essa frase quer dizer? Vamos criar uma situação hipotética aqui e analisar três formas de investimento:
Investir em ações na bolsa de valores (renda variável) Investir em si mesmo (aumentar capacidade)
Primeira hipótese:
Você investiu R$100 o ano todo. Todos os meses. Isso gerou um bruto de R$1.200. Você estudo e se dedicou. Analisou ações, assistiu a vários vídeos e análises. E fez 15% de retorno no ano.
Nessa primeira hipótese, você acumulou R$1.200 + 15% de retorno (R$180). O que te rendeu R$1380 brutos. Com essa quantia a incidência de impostos não existe. Então, sem DARFS por aqui.
Compensou investir 2 horas por dia * 200 dias no ano =1.752.000 min. Para poder ganhar R$180?
Dahhhh, não. Você ficou mais experiente e aprendeu. Mas, a quantia é muito pequena e não faz cócegas. Tampouco te faz sorrir. E te tira dessa situação.
Segunda hipótese:
Eu não sei qual o seu ofício nesse momento. Mas, eu sei de duas coisas. Ou você gosta e quer se especializar. Ou você quer trocar de ofício logo logo. Então, meu consagrado(a). Você já sabe…
Agora, vamos pegar esses R$100 mensais e investir em um curso técnico. Pois, é mais rápido que uma faculdade. Será seu primeiro diploma oficial, te torna alguém e te dá um ofício.
Assim sendo, você tem grandes chances de trocar de trabalho. Ter aumento salarial é certamente no prazo de um ano. Você vai ganhar muitos mais que os R$180 brutos de rentabilidade do primeiro caso.
Agora, quer saber a real porque ninguém te fala isso no YouTube, Instagram e TikTok?
Meu consagrado, as pessoas só te recomendam o que é bom para elas. Não há nada de errado com isso. O que quero te fazer enxergar aqui. É que você está sozinho (ou tem que estar, para refletir) e precisa escolher o que é melhor para você.
Contudo, é importante para para pensar por um tempo e entender o que vai ser melhor para você. Qual melhor caminho seguir. E ponto, só você sabe o que é melhor para você.
Como?
Para fechar nosso raciocínio de hoje. Vamos a pergunta de um milhão de dólares. Mas, como eu faço isso? Meu querido(a), você vai fazer um exercício comigo logo menos.
Você vai deixar seu celular no silencioso. Colocar um timer de 15 minutos. Pegar um papel e caneta e anotar em uma folha o que você gosta + o que você você gostaria de fazer da sua vida.
Logo, essa lista tem que conter o SEU gosto. Não do seu amigo, do influenciador, da celebridade ou do atleta. Essas pessoas tem influência sobre sua vida? Claro! Mas, cabe a você refletir sobre o que realmente quer.
Naturalmente, você não vai colocar lá na sua lista; quero uma Ferrari esse ano. Porque não é assim que funciona. Na real, você pode querer a Ferrari. Sem problema algum.
Mas, saiba que antes da Ferrari. Vai ter que vir o Gol, o Civic, a 325, o 911 e daí a Ferrari. Tudo na vida é passo meu caro(a). Ou você acha que vai dar saltos quânticos na vida sem estar preparado? Não é assim que a vida funciona.
Em suma,
para concluir esse texto. Vamos fazer o resumão prático do que fazer com cem reais mensais:
*** Tire um tempo para entender o que quer e o que tu gosta. * Visualize e anote seus objetivos que quer em uma folha. * Invista em você incansavelmente. * Você vai chegar ao topo da montanha. Mas, tem que subir um nível por vez.**
Bio
Se chegou até aqui é porque gostou e quer mudar de vida. Manda pro teu colega que tá precisando desse tapa de luva. Obrigado pelo seu tempo.
-
 @ 3c7dc2c5:805642a8
2025-05-10 19:15:50
@ 3c7dc2c5:805642a8
2025-05-10 19:15:50🧠Quote(s) of the week:
'Bitcoin is a high-IQ, low-time-preference asset in a world addicted to DoorDash, dopamine, and debt. Holding Bitcoin requires patience, conviction, and the ability to not panic when CNBC tells you it’s dead for the 47th time. That rules out, oh, I don’t know - 95% of the population? This isn’t some egalitarian revolution. This is a cognitive filter disguised as a monetary network. The rich, the strategic, the elite - those who understand volatility as an opportunity - will stack the hardest asset on Earth while the masses beg for interest rate cuts and $600 stimmies to buy groceries they can't afford.
It's not a level playing field. It's a time-preference war, and Bitcoin is the scoreboard. And every cycle, we watch it happen again. The media ridicules it, the politicians fear it, and the smart money buys more. While fiat punishes savers and rewards financial nihilism, Bitcoin inverts the whole structure. It’s a vault for those who can delay gratification, think generationally, and understand that true wealth is preserved rather than printed. The game isn’t rigged. It’s just calibrated for adults.' - Adam Livingston
'Bitcoin is an extremely simple thesis. If you think governments will stop debasing and debanking: number go down. If you think they won’t stop debasing and debanking: number go up'- Alex Gladstein
Something to ponder on.
🧡Bitcoin news🧡
On the 28th of April:
➡️Hunter Horsley: 'Bitcoin at $94k, yet — Google searches for "Bitcoin" near long-term lows. This hasn't been retail-driven. Institutions, advisors, corporations, and nations have come into the space. The types of investors buying Bitcoin are expanding.'
➡️Daniel Batten: 'Cambridge has just released their updated report on Bitcoin mining. For the first time, their report shows that most (52.4%) of the Bitcoin network is now powered by zero-emission energy sources (up from 37% in their last report).
Here's a summary of their findings:
https://x.com/DSBatten/status/1916903476610650202
You can read the full report here
➡️Arizona’s Bitcoin Reserve bill (SB 1025) just passed the House and now heads to the desk of Governor Katie Hobbs. However, Governor Hobbs has vowed to veto any legislation until a budget impasse over funding for disability services is resolved.
On the 29th of April:
➡️Bitcoin Archive: 'South Korea's ruling party to approve spot Bitcoin ETFs, scrap restrictive banking crypto rules, and introduce crypto-friendly framework THIS YEAR, if it wins the June election.'
➡️President Trump's Executive Director says there is a "space race" amongst countries to accumulate Bitcoin: "We view Bitcoin as digital gold."
➡️U.S. to "turbo-charge" Bitcoin mining growth by allowing Bitcoin miners to build power plants and data centres near natural gas fields - Howard Lutnick, Commerce Secretary
➡️Japanese clothing company ANAP Holdings Inc. bought 35 Bitcoins worth $3.3 million. ANAP now holds 51.7 BTC, joining Japan’s growing corporate Bitcoin treasury movement.
➡️Semler Scientific adds 165 BTC for $15.7M, bringing total holdings to 3,467 BTC. The company reports a 23.8% BTC yield year-to-date.
➡️The Bitcoin hashrate has already surged over 17% since the start of the year.
➡️'This shattered a major myth for me: gold production isn’t slowing down—it’s accelerating. According to NYDIG, annual gold mining has been steadily increasing over time, about 1.6% per year, thanks to better extraction technology. In fact, 2024 saw a 1% year-over-year increase, setting an all-time high in gold output (World Gold Council). So why do so many still believe the outdated narrative that gold is becoming harder to find? The truth is: gold is effectively unlimited in supply—we just get better at digging it up. If that surprises you, you're probably not nearly bullish enough on Bitcoin.' - Robert Hefner https://i.ibb.co/JWCHndQk/Gpu-W9-R1-Xw-AAiy-Cv.jpg
On the 30th of April:
➡️The Bank of Italy identifies Bitcoin as an emerging risk factor with concerns for the financial system.
"The strong growth of Bitcoin and other crypto-assets with high price volatility means risks not only for investors but also potentially for financial stability, given the growing interconnections between the digital asset ecosystem, the traditional financial sector, and the real economy,”
Tell me you are scared of Bitcoin without telling me you are scared of Bitcoin.
➡️4 major wirehouses managing $10 TRILLION to start offering Bitcoin ETFs to clients this year, says BitWise CIO Matt Hougan. Merrill Lynch, Morgan Stanley, Wells Fargo, and UBS are coming to the party.
➡️Roswell, New Mexico, becomes the 1st United States city to launch a strategic Bitcoin reserve.
➡️BlackRock’s Bitcoin ETF IBIT has hit 600,000 BTC!
➡️Semler Scientific bought 165 Bitcoins worth $15.7m. They now hold 3,467 BTC on their balance sheet.
➡️Bitcoin News: 'El Salvador is still buying Bitcoin despite an IMF loan deal that required it to stop. Economy Minister Maria Luisa Hayem confirmed ongoing accumulation, calling Bitcoin “an important project” and a key asset for both the government and private sector.'
➡️New whales are buying Bitcoin faster than ever before!
➡️'ZachXBT says the $330M Bitcoin theft involved an elderly U.S. victim targeted by social engineering. The stolen 3,520 BTC were laundered through six exchanges and swapped into Monero, triggering a 50% price spike due to thin liquidity.' -Bitcoin News
On the 1st of May:
➡️North Carolina Bitcoin Reserve Bill has passed the House! This bill enables state retirement funds to invest up to $ 13 B.
➡️Tether’s latest attestation states the company holds $7.6 billion in Bitcoin.
➡️Europe's largest Bitcoin treasury company, The Blockchain Group, aspires to hold 1% of the total Bitcoin supply by 2033.
➡️FiatHawk: 'Central banks create fake money to buy real gold, and we’re supposed to pretend this isn’t theft. The game is rigged. Their paper is trash. Gold knows it. Bitcoin ends it. Stop believing the lie.
https://i.ibb.co/mrBZtY5P/Gpl4kl-ak-AA-xv-D.png
When the debt bubble collapses, only sound money with zero counterparty risk matters. Currently, sound money is less than 5% of debt money, and Bitcoin is so tiny it is barely visible on the chart. Stay humble and keep stacking.' https://i.ibb.co/QF0Vf9k8/Gpu-CCIWa-YAAng1-U.png
On the 2nd of May:
➡️ Regarding the whole OP_Return debate.
Grok: ++Key Points: ++ * The OP_RETURN debate in Bitcoin centers on whether its blockchain should store data beyond financial transactions, with ongoing controversy. * It began in 2010 with concerns about blockchain bloat, intensified in 2014 with the "OP_Return Wars," and continues today. * Research suggests the debate reflects a balance between Bitcoin's monetary purpose and potential for broader applications like Dapps. * Compromises, like setting a 40-byte limit in 2014, aimed to address concerns but didn't fully resolve tensions, influencing platforms like Ethereum.
++Background++ OP_RETURN is a Bitcoin script opcode allowing small data storage in transactions, useful for timestamping or Dapps, but raising concerns about blockchain bloat.
++Historical Context++
The debate started in 2010 with the BitDNS proposal, where Satoshi Nakamoto worried about scalability, leading to Namecoin. It peaked in 2014 with Counterparty's use, leading to a 40-byte limit compromise, later adjusted to 83 bytes by 2016.
++Recent Developments++ By 2018-2019, high OP_RETURN usage (20% of transactions) sparked fee debates, but usage has since declined, though data remains, with recent 2023 controversies over size limits.
If you are interested in Bitcoin, then you should check out the following video.
Great video from @GrassFedBitcoin explaining the current OP_RETURN situation. The choice isn’t between bloating the UTXO set or increasing OP_RETURN, it’s whether we normalize spam or we reject it. Is Bitcoin for data storage or financial transactions? https://www.youtube.com/watch?v=15biQH1H140 Every Bitcoiner needs to see this! Vires in Numeris.
A great counterargument by Seth for Privacy:
https://x.com/sethforprivacy/status/1919003009880616976
Personally, I tend to agree with Seth.
To sum it up:
If you are running a node, you should switch from Core to Knots immediately. It's very straightforward, and you don't need to redo the initial block download.
If you arent running a node you are a leech and need to get your shit together.
➡️Tether CEO defends skipping MiCA, calling EU stablecoin rules “very dangerous.” Ardoino: “The European Central Bank is more interested in pushing the digital euro to control people and how they spend their money.”
On the 3rd of May:
➡️Arizona Governor Katie Hobbs has vetoed the state’s Strategic Bitcoin Reserve legislation after it was passed by the House and Senate. She states: “Arizonans’ retirement funds are not the place for the state to try untested investments like virtual currency.”
Apparently, the Arizona State Retirement System already holds 53,097 shares of MSTR. You can’t make this shit up.
➡️Vitalik Buterin: 'One of the best things about Bitcoin is how simple it is. This simplicity has lots of benefits. Let's bring those benefits to Ethereum.' Almost like Bitcoin is eh......(checks notes)......better tech. Just use Bitcoin, dumbfuck! 'It's only taken a decade, but Ethereum's creator is having an inkling that he never should have created Ethereum, which destroyed billions of precious capital and instead focused on Bitcoin.' - Vijay Boyapati
There is no second best!
On the 4th of May:
➡️Eli Nagar:
Heads up, Bitcoin holders: The EU will ban anonymous crypto accounts by July 2027. Every transaction above €1,000 will need your ID. Privacy is becoming extinct. Every new restriction is a marketing campaign for Bitcoin. “Hi, we’re the EU. We’ll surveil you, control your money, and criminalise privacy.” By doing that, they have decided to help promote the black market...great work, EU! Oh, and remember, the EU can't ban what it has no control over: hold your own private keys.
➡️Cumulative inflows into the Bitcoin ETFs have hit a fresh ATH of $ 40.62 B.
On the 5th of May:
➡️Brown University invested $4.9M in Bitcoin via BlackRock's IBIT, as disclosed in a recent SEC filing. The university owns 105K IBIT shares ($5.8M), 2.3% of Brown's reported $216M equity holdings.
➡️Strategy acquires 1,895 BTC for $180.3 million at an average price of $95,167 per bitcoin. As of May 4, 2025, they hold 555,450 BTC acquired for $38.08 billion at an average price of $68,550 per bitcoin.
💸Traditional Finance / Macro:
On the 3rd of May:
👉🏽Berkshire Hathaway cash pile hits record $347.7bn in 1Q as Warren Buffett sells stocks for 10th quarter in a row. Buffett is still raising cash. https://i.ibb.co/1GK6Dvzx/Gq-Bp6q-BW4-AAKKlm.jpg
🏦Banks:
👉🏽 No news
🌎Macro/Geopolitics:
On the 27th of April:
👉🏽World central banks are diversifying their reserves: Foreign holdings of Treasuries as % of US government debt have fallen to ~23%, the lowest in 22 years. The percentage is down ~11 percentage points over the last 9 years. At the same time, gold holdings as a % of global international reserves have hit ~18%, the highest in 26 years. The share has risen by ~8 percentage points since 2015. China has been one of the biggest buyers of gold over the last few years. Since the beginning of 2023, China’s gold reserves as a % of total foreign reserves have doubled to 7.1%.
Everyone wants gold. https://i.ibb.co/NgX11DZh/Gp4-GKc-HWMAAa-FYu.jpg
On the 28th of April:
👉🏽TKL: 'Tariffs are hitting American meat exports.
China's cancellations of US pork shipments are skyrocketing: China cancelled shipments of ~12,000 metric tons of US pork last week, the most since the 2020 pandemic, when global supply chains were halted. As a result, overall US pork export sales dropped to their lowest level since October, according to Bloomberg. This comes as American pork imports to China now face a massive 172% tariff. This includes the duties first imposed during the 2018 trade war.'
On the 29th of April:
👉🏽The U.S. Treasury will now need to borrow $514 billion this quarter, an increase of 320% from its previous estimate.
On the 30th of April:
👉🏽'Bad news for electricity consumers: despite 84 hours of negative pricing (2024: 62 hours), the average electricity price in the Netherlands in April was €75/MWh — nearly 30% higher than a year ago.' - Martien Visser
https://i.ibb.co/VsrFdKy/Gps0l-Au-Xs-AA20-OA.png
👉🏽Tax cuts for the rich lead to higher income inequality. However, they do not have any significant effect on economic growth or unemployment. Empirical evidence for advanced economies over 1965-2015:
https://academic.oup.com/ser/article/20/2/539/6500315?login=false
Trickle down never worked.
👉🏽"Since February 2020, home prices have increased 45%," according to Zillow So has the broad money supply. Not your house is getting more expensive; The money is getting devalued.
Money supply= +40%
Median home= +40%
Experts: "What could have ever caused this????"
And some freaking guru on Instagram or Tiktok is trying to convince you to get his/her 'buying/renting a house' course. https://i.ibb.co/bMXfW3vp/Gp0-CXg-Ka-YAAIhq-J.jpg
👉🏽SUMMARY OF US Q1 GDP REPORT: 1. The U.S. economy contracted at an annual rate of -0.3% in the first quarter, compared to expectations for an increase of 0.2%. That’s down from the growth of 2.4% in Q4. 2. Real consumer spending rose by 1.8% Y/Y, after increasing 4.0% in Q4. 3. The GDP Price Index rose 3.7%, above estimates of 3.1%. 4. Core PCE Prices rose 3.5%, after increasing 2.6% in Q4.
• Key Takeaway: Fears of stagflation are growing as the economy grinds to a halt and inflation ticks higher. - Jesse Cohen
👉🏽World debt has now officially crossed $300 TRILLION, and still continues to climb aggressively. This will not end well…
https://i.ibb.co/Kxm2bJs6/Gpyi-Ouwa-YAEDg-Pq.jpg
👉🏽'March PCE inflation, the Fed's preferred inflation measure, FALLS to 2.3%, above expectations of 2.2%. Core PCE inflation FALLS to 2.6%, in line with expectations of 2.6%. February Core PCE inflation was revised up to 3.0%. All eyes are on the Fed next week.' - TKL
🎁If you have made it this far, I would like to give you a little gift, well, in this case, two gifts:
Smitty's Bitcoin Retirement Guide:
"Helping you develop a better Bitcoin stacking target for life planning." - Sminston With This is a fantastic tool. Very, very useful. I will keep mentioning it. Bitcoin is a savings vehicle. Period!
https://x.com/sminston_with/status/1917605539279954391
The best kind of retirement starts in diapers and ends in diapers, so start now. https://i.ibb.co/4RwFxR0W/Gpys-GQga-YAIxm-MX.jpg
nofinancialadvice
Credit: I have used multiple sources!
My savings account: Bitcoin The tool I recommend for setting up a Bitcoin savings plan: PocketBitcoin especially suited for beginners or people who want to invest in Bitcoin with an automated investment plan once a week or monthly.
Use the code SE3997
Get your Bitcoin out of exchanges. Save them on a hardware wallet, run your own node...be your own bank. Not your keys, not your coins. It's that simple. ⠀ ⠀
⠀⠀ ⠀ ⠀⠀⠀
Do you think this post is helpful to you?
If so, please share it and support my work with a zap.
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
⭐ Many thanks⭐
Felipe - Bitcoin Friday!
▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃▃
-
 @ 9223d2fa:b57e3de7
2025-04-15 02:54:00
@ 9223d2fa:b57e3de7
2025-04-15 02:54:0012,600 steps
-
 @ c631e267:c2b78d3e
2025-04-25 20:06:24
@ c631e267:c2b78d3e
2025-04-25 20:06:24Die Wahrheit verletzt tiefer als jede Beleidigung. \ Marquis de Sade
Sagen Sie niemals «Terroristin B.», «Schwachkopf H.», «korrupter Drecksack S.» oder «Meinungsfreiheitshasserin F.» und verkneifen Sie sich Memes, denn so etwas könnte Ihnen als Beleidigung oder Verleumdung ausgelegt werden und rechtliche Konsequenzen haben. Auch mit einer Frau M.-A. S.-Z. ist in dieser Beziehung nicht zu spaßen, sie gehört zu den Top-Anzeigenstellern.
«Politikerbeleidigung» als Straftatbestand wurde 2021 im Kampf gegen «Rechtsextremismus und Hasskriminalität» in Deutschland eingeführt, damals noch unter der Regierung Merkel. Im Gesetz nicht festgehalten ist die Unterscheidung zwischen schlechter Hetze und guter Hetze – trotzdem ist das gängige Praxis, wie der Titel fast schon nahelegt.
So dürfen Sie als Politikerin heute den Tesla als «Nazi-Auto» bezeichnen und dies ausdrücklich auf den Firmengründer Elon Musk und dessen «rechtsextreme Positionen» beziehen, welche Sie nicht einmal belegen müssen. [1] Vielleicht ernten Sie Proteste, jedoch vorrangig wegen der «gut bezahlten, unbefristeten Arbeitsplätze» in Brandenburg. Ihren Tweet hat die Berliner Senatorin Cansel Kiziltepe inzwischen offenbar dennoch gelöscht.
Dass es um die Meinungs- und Pressefreiheit in der Bundesrepublik nicht mehr allzu gut bestellt ist, befürchtet man inzwischen auch schon im Ausland. Der Fall des Journalisten David Bendels, der kürzlich wegen eines Faeser-Memes zu sieben Monaten Haft auf Bewährung verurteilt wurde, führte in diversen Medien zu Empörung. Die Welt versteckte ihre Kritik mit dem Titel «Ein Urteil wie aus einer Diktatur» hinter einer Bezahlschranke.
Unschöne, heutzutage vielleicht strafbare Kommentare würden mir auch zu einigen anderen Themen und Akteuren einfallen. Ein Kandidat wäre der deutsche Bundesgesundheitsminister (ja, er ist es tatsächlich immer noch). Während sich in den USA auf dem Gebiet etwas bewegt und zum Beispiel Robert F. Kennedy Jr. will, dass die Gesundheitsbehörde (CDC) keine Covid-Impfungen für Kinder mehr empfiehlt, möchte Karl Lauterbach vor allem das Corona-Lügengebäude vor dem Einsturz bewahren.
«Ich habe nie geglaubt, dass die Impfungen nebenwirkungsfrei sind», sagte Lauterbach jüngst der ZDF-Journalistin Sarah Tacke. Das steht in krassem Widerspruch zu seiner früher verbreiteten Behauptung, die Gen-Injektionen hätten keine Nebenwirkungen. Damit entlarvt er sich selbst als Lügner. Die Bezeichnung ist absolut berechtigt, dieser Mann dürfte keinerlei politische Verantwortung tragen und das Verhalten verlangt nach einer rechtlichen Überprüfung. Leider ist ja die Justiz anderweitig beschäftigt und hat außerdem selbst keine weiße Weste.
Obendrein kämpfte der Herr Minister für eine allgemeine Impfpflicht. Er beschwor dabei das Schließen einer «Impflücke», wie es die Weltgesundheitsorganisation – die «wegen Trump» in finanziellen Schwierigkeiten steckt – bis heute tut. Die WHO lässt aktuell ihre «Europäische Impfwoche» propagieren, bei der interessanterweise von Covid nicht mehr groß die Rede ist.
Einen «Klima-Leugner» würden manche wohl Nir Shaviv nennen, das ist ja nicht strafbar. Der Astrophysiker weist nämlich die Behauptung von einer Klimakrise zurück. Gemäß seiner Forschung ist mindestens die Hälfte der Erderwärmung nicht auf menschliche Emissionen, sondern auf Veränderungen im Sonnenverhalten zurückzuführen.
Das passt vielleicht auch den «Klima-Hysterikern» der britischen Regierung ins Konzept, die gerade Experimente zur Verdunkelung der Sonne angekündigt haben. Produzenten von Kunstfleisch oder Betreiber von Insektenfarmen würden dagegen vermutlich die Geschichte vom fatalen CO2 bevorzugen. Ihnen würde es besser passen, wenn der verantwortungsvolle Erdenbürger sein Verhalten gründlich ändern müsste.
In unserer völlig verkehrten Welt, in der praktisch jede Verlautbarung außerhalb der abgesegneten Narrative potenziell strafbar sein kann, gehört fast schon Mut dazu, Dinge offen anzusprechen. Im «besten Deutschland aller Zeiten» glaubten letztes Jahr nur noch 40 Prozent der Menschen, ihre Meinung frei äußern zu können. Das ist ein Armutszeugnis, und es sieht nicht gerade nach Besserung aus. Umso wichtiger ist es, dagegen anzugehen.
[Titelbild: Pixabay]
--- Quellen: ---
[1] Zur Orientierung wenigstens ein paar Hinweise zur NS-Vergangenheit deutscher Automobilhersteller:
- Volkswagen
- Porsche
- Daimler-Benz
- BMW
- Audi
- Opel
- Heute: «Auto-Werke für die Rüstung? Rheinmetall prüft Übernahmen»
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 7459d333:f207289b
2025-05-10 17:41:17
@ 7459d333:f207289b
2025-05-10 17:41:17Come to our meetup to discuss the great Bitcoin Core debate!
The proposal to remove the 80-byte limit on OP_RETURN is getting people talking: should Bitcoin prioritize only monetary transactions or allow more data, such as notarizations?
Some argue that this simplifies the protocol and reflects what already happens in practice, with data stuffed in less efficient ways (as in Taproot).
Others fear it will overload the blockchain and take Bitcoin away from its essence....
Bring your opinion, enjoy a beer and let's debate the future of Bitcoin!
https://t.me/madridmeetup
originally posted at https://stacker.news/items/976659
-
 @ 6830c409:ff17c655
2025-05-10 15:38:09
@ 6830c409:ff17c655
2025-05-10 15:38:09Disclaimer: I used Grammarly AI to correct my poor English to look polished. **
Preface: The motivation behind this note stems from a personal curiosity sparked by a few interactions with someone I know. After watching a YouTube video by Salvaveritate on Narcissistic Personality Disorder, I realized that what I was observing wasn’t purely NPD-it seemed to be intertwined with something else. I wanted to better understand this person’s thought process and what might be driving their behavior. At the end of this note, I’ve included the references I consulted to explore this phenomenon further.
We’ve all encountered that person who walks into a room like they own it-dismissing every idea but their own and expecting the world to revolve around them. There’s confidence, and then there’s a level of self-importance so exaggerated it becomes something darker. That, in a nutshell, is megalomania.
Though it’s no longer a formal psychological diagnosis (now categorized under narcissistic personality disorder), the term “megalomania” still resonates when we describe someone with delusional beliefs about their power, brilliance, or importance. It’s not just arrogance-it’s a complete departure from reality, where self-worth is inflated to cartoonish proportions.
The Many Faces of Megalomania
Megalomaniacs aren’t always easy to spot at first. They can be charismatic, persuasive, and even inspiring-until you begin to notice the patterns. Here are some of the archetypes you might recognize:
-
The Political Power Player: From infamous historical figures to the neighborhood HOA president who rules like a tyrant, these individuals believe only they can save the day.
-
The Corporate Climber: Ambition isn’t the issue here-it’s the willingness to trample anyone in their path. These folks take credit for others' work and treat colleagues like pawns.
-
The Self-Proclaimed Guru: Think of that person who reads one book and suddenly thinks they’ve unlocked the secrets of the universe. They believe they alone hold the truth and must share it with the “less enlightened.”
-
The Everyday Ego: Perhaps the most common. They're the friend who always turns the conversation back to themselves or the family member who demands special treatment at every gathering.
Warning Signs to Watch For
If you suspect someone in your orbit might be leaning into megalomaniac territory, here are some red flags:
- They crave admiration but rarely offer it in return.
- Criticism-even the gentle kind - triggers rage or defensiveness.
- They exaggerate achievements or name-drop to elevate their image.
- Rules are for everyone else - they believe they’re exempt.
- People are merely tools to further their personal agenda.
Often, the charm and confidence they exude can blind you to these signs until you're in too deep. Many learn this lesson through tough workplace dynamics, toxic relationships, or manipulative friendships.
How to Protect Yourself
If you're dealing with a megalomaniac, remember: you’re not powerless. Strategies that actually help include:
- Don't feed the ego - Respectful neutrality works better than flattery.
- Set firm boundaries - Be clear about what is and isn’t acceptable.
- Keep records - Especially in professional settings, documentation is crucial.
- Know when to walk away - Some relationships or environments can’t be fixed.
- Seek support - Therapy can equip you with the tools to cope and recover.
Trying to “change” a megalomaniac rarely works-focus instead on preserving your own mental health and emotional well-being.
A Look Through History-and the Mirror
From Hitler and Stalin’s destructive delusions of grandeur to modern business figures like Elizabeth Holmes, history is packed with cautionary tales of unchecked ego. Even pop culture gives us glimpses: Tony Montana in Scarface, Miranda Priestly in The Devil Wears Prada. These characters aren’t just dramatic-they’re psychological case studies in what happens when ego eclipses empathy.
But let’s be honest-none of us are immune to moments of inflated self-worth. The difference lies in self-awareness. True confidence coexists with humility. It laughs at karaoke fails and learns from criticism. Megalomania, by contrast, builds walls around insecurity and calls it a fortress.
Have you ever dealt with someone whose ego became their identity? Or maybe caught yourself slipping into that territory? Let’s unpack it together-your insights could help someone else recognize the signs early.
Here is what I read: 1. https://ebeni.wordpress.com/unethical-leaders/megalomania-and-narcissism-grandiose-vulnerable-clarke/ 2. https://keghart.org/demirdjian-megalomaniac-dictator/ 3. https://fastercapital.com/content/Megalomania--The-Ultimate-Form-of-Hubris.html 4. https://taylorandfrancis.com/knowledge/Medicine_and_healthcare/Psychiatry/Megalomania/ 5. https://www.encyclopedia.com/medicine/psychology/psychology-and-psychiatry/grandiosity 6. Salva Veritate's video: https://www.youtube.com/watch?v=RtUFB3tf1lA&pp=ygUOc2FsdmEgdmVyaXRhdGU%3D
-
-
 @ 6e0ea5d6:0327f353
2025-04-14 15:11:17
@ 6e0ea5d6:0327f353
2025-04-14 15:11:17Ascolta.
We live in times where the average man is measured by the speeches he gives — not by the commitments he keeps. People talk about dreams, goals, promises… but what truly remains is what’s honored in the silence of small gestures, in actions that don’t seek applause, in attitudes unseen — yet speak volumes.
Punctuality, for example. Showing up on time isn’t about the clock. It’s about respect. Respect for another’s time, yes — but more importantly, respect for one’s own word. A man who is late without reason is already running late in his values. And the one who excuses his own lateness with sweet justifications slowly gets used to mediocrity.
Keeping your word is more than fulfilling promises. It is sealing, with the mouth, what the body must later uphold. Every time a man commits to something, he creates a moral debt with his own dignity. And to break that commitment is to declare bankruptcy — not in the eyes of others, but in front of himself.
And debts? Even the small ones — or especially the small ones — are precise thermometers of character. A forgotten sum, an unpaid favor, a commitment left behind… all of these reveal the structure of the inner building that man resides in. He who neglects the small is merely rehearsing for his future collapse.
Life, contrary to what the reckless say, is not built on grand deeds. It is built with small bricks, laid with almost obsessive precision. The truly great man is the one who respects the details — recognizing in them a code of conduct.
In Sicily, especially in the streets of Palermo, I learned early on that there is more nobility in paying a five-euro debt on time than in flaunting riches gained without word, without honor, without dignity.
As they say in Palermo: L’uomo si conosce dalle piccole cose.
So, amico mio, Don’t talk to me about greatness if you can’t show up on time. Don’t talk to me about respect if your word is fickle. And above all, don’t talk to me about honor if you still owe what you once promised — no matter how small.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 84b0c46a:417782f5
2025-05-10 10:41:20
@ 84b0c46a:417782f5
2025-05-10 10:41:20https://long-form-editor.vercel.app/
β版のため予期せぬ動作が発生する可能性があります。記事を修正する際は事前にバックアップを取ることをおすすめします
機能
-
nostr:npub1sjcvg64knxkrt6ev52rywzu9uzqakgy8ehhk8yezxmpewsthst6sw3jqcw や、 nostr:nevent1qvzqqqqqqypzq4jsz7zew5j7jr4pdfxh483nwq9vyw9ph6wm706sjwrzj2we58nqqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyxhwumn8ghj7mn0wvhxcmmvqqsgcn99jyn5tevxz5zxsrkd7h0sx8fwnqztula423xh83j9wau7cms3vg9c7 のようにnostr:要素を挿入できる
-
:monoice:のようにカスタム絵文字を挿入できる(メニューの😃アイコンから←アイコン変えるかも)
:monopaca_kao:
:kubipaca_karada:
- 新規記事作成と、既存記事の修正ができる
やることやったこと
-
[x] nostr:を投稿するときにtagにいれる
-
[x] 画像をアップロードできるようにする
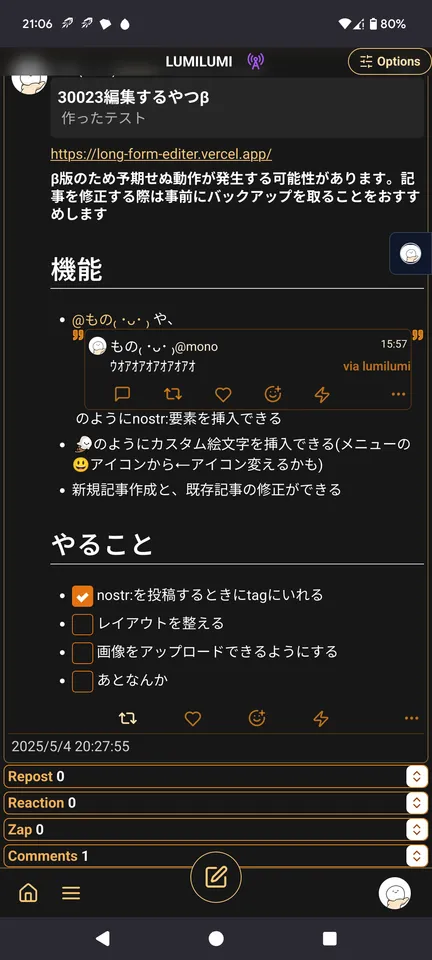 できる
できる - [x] 投稿しましたログとかをトースト的なやつでだすようにする
- [ ] レイアウトを整える
- [ ] あとなんか
-
-
 @ 0fa80bd3:ea7325de
2025-04-09 21:19:39
@ 0fa80bd3:ea7325de
2025-04-09 21:19:39DAOs promised decentralization. They offered a system where every member could influence a project's direction, where money and power were transparently distributed, and decisions were made through voting. All of it recorded immutably on the blockchain, free from middlemen.
But something didn’t work out. In practice, most DAOs haven’t evolved into living, self-organizing organisms. They became something else: clubs where participation is unevenly distributed. Leaders remained - only now without formal titles. They hold influence through control over communications, task framing, and community dynamics. Centralization still exists, just wrapped in a new package.
But there's a second, less obvious problem. Crowds can’t create strategy. In DAOs, people vote for what "feels right to the majority." But strategy isn’t about what feels good - it’s about what’s necessary. Difficult, unpopular, yet forward-looking decisions often fail when put to a vote. A founder’s vision is a risk. But in healthy teams, it’s that risk that drives progress. In DAOs, risk is almost always diluted until it becomes something safe and vague.
Instead of empowering leaders, DAOs often neutralize them. This is why many DAOs resemble consensus machines. Everyone talks, debates, and participates, but very little actually gets done. One person says, “Let’s jump,” and five others respond, “Let’s discuss that first.” This dynamic might work for open forums, but not for action.
Decentralization works when there’s trust and delegation, not just voting. Until DAOs develop effective systems for assigning roles, taking ownership, and acting with flexibility, they will keep losing ground to old-fashioned startups led by charismatic founders with a clear vision.
We’ve seen this in many real-world cases. Take MakerDAO, one of the most mature and technically sophisticated DAOs. Its governance token (MKR) holders vote on everything from interest rates to protocol upgrades. While this has allowed for transparency and community involvement, the process is often slow and bureaucratic. Complex proposals stall. Strategic pivots become hard to implement. And in 2023, a controversial proposal to allocate billions to real-world assets passed only narrowly, after months of infighting - highlighting how vision and execution can get stuck in the mud of distributed governance.
On the other hand, Uniswap DAO, responsible for the largest decentralized exchange, raised governance participation only after launching a delegation system where token holders could choose trusted representatives. Still, much of the activity is limited to a small group of active contributors. The vast majority of token holders remain passive. This raises the question: is it really community-led, or just a formalized power structure with lower transparency?
Then there’s ConstitutionDAO, an experiment that went viral. It raised over $40 million in days to try and buy a copy of the U.S. Constitution. But despite the hype, the DAO failed to win the auction. Afterwards, it struggled with refund logistics, communication breakdowns, and confusion over governance. It was a perfect example of collective enthusiasm without infrastructure or planning - proof that a DAO can raise capital fast but still lack cohesion.
Not all efforts have failed. Projects like Gitcoin DAO have made progress by incentivizing small, individual contributions. Their quadratic funding mechanism rewards projects based on the number of contributors, not just the size of donations, helping to elevate grassroots initiatives. But even here, long-term strategy often falls back on a core group of organizers rather than broad community consensus.
The pattern is clear: when the stakes are low or the tasks are modular, DAOs can coordinate well. But when bold moves are needed—when someone has to take responsibility and act under uncertainty DAOs often freeze. In the name of consensus, they lose momentum.
That’s why the organization of the future can’t rely purely on decentralization. It must encourage individual initiative and the ability to take calculated risks. People need to see their contribution not just as a vote, but as a role with clear actions and expected outcomes. When the situation demands, they should be empowered to act first and present the results to the community afterwards allowing for both autonomy and accountability. That’s not a flaw in the system. It’s how real progress happens.
-
 @ 3bf0c63f:aefa459d
2024-03-23 08:57:08
@ 3bf0c63f:aefa459d
2024-03-23 08:57:08Nostr is not decentralized nor censorship-resistant
Peter Todd has been saying this for a long time and all the time I've been thinking he is misunderstanding everything, but I guess a more charitable interpretation is that he is right.
Nostr today is indeed centralized.
Yesterday I published two harmless notes with the exact same content at the same time. In two minutes the notes had a noticeable difference in responses:
The top one was published to
wss://nostr.wine,wss://nos.lol,wss://pyramid.fiatjaf.com. The second was published to the relay where I generally publish all my notes to,wss://pyramid.fiatjaf.com, and that is announced on my NIP-05 file and on my NIP-65 relay list.A few minutes later I published that screenshot again in two identical notes to the same sets of relays, asking if people understood the implications. The difference in quantity of responses can still be seen today:
These results are skewed now by the fact that the two notes got rebroadcasted to multiple relays after some time, but the fundamental point remains.
What happened was that a huge lot more of people saw the first note compared to the second, and if Nostr was really censorship-resistant that shouldn't have happened at all.
Some people implied in the comments, with an air of obviousness, that publishing the note to "more relays" should have predictably resulted in more replies, which, again, shouldn't be the case if Nostr is really censorship-resistant.
What happens is that most people who engaged with the note are following me, in the sense that they have instructed their clients to fetch my notes on their behalf and present them in the UI, and clients are failing to do that despite me making it clear in multiple ways that my notes are to be found on
wss://pyramid.fiatjaf.com.If we were talking not about me, but about some public figure that was being censored by the State and got banned (or shadowbanned) by the 3 biggest public relays, the sad reality would be that the person would immediately get his reach reduced to ~10% of what they had before. This is not at all unlike what happened to dozens of personalities that were banned from the corporate social media platforms and then moved to other platforms -- how many of their original followers switched to these other platforms? Probably some small percentage close to 10%. In that sense Nostr today is similar to what we had before.
Peter Todd is right that if the way Nostr works is that you just subscribe to a small set of relays and expect to get everything from them then it tends to get very centralized very fast, and this is the reality today.
Peter Todd is wrong that Nostr is inherently centralized or that it needs a protocol change to become what it has always purported to be. He is in fact wrong today, because what is written above is not valid for all clients of today, and if we drive in the right direction we can successfully make Peter Todd be more and more wrong as time passes, instead of the contrary.
See also:
-
 @ c066aac5:6a41a034
2025-05-10 14:55:46
@ c066aac5:6a41a034
2025-05-10 14:55:46This is an article I wrote which originally appeared in the Pamphleteer, a publication run by a friend in Nashville. It has been edited from the published version, which I will link here for everyone to go check out the website and subscribe.
Step back fifty years in time with me if you will. A simpler time. You wake up in the house you could afford on a single income. Instead of blinding yourself with the light of your cell phone first thing in the morning, you wake up to make breakfast and coffee, your mind unencumbered by the stimulus of a thousand notifications. You can’t doom scroll (nor can you conceptualize what that even means).
You breathe in the moment, smelling your coffee with a deliberate, meditative inhale… As this brief moment of Nirvana passes, you decide to pick up the newspaper. You turn to page nine and see that Andy Kaufman, a comedian/performance artist you’ve seen on Taxi and Saturday Night Live, has declared himself “The Inter-Gender Wrestling Champion of the World.”
You are tempted to think this may be a joke, but suddenly you remember that you stepped back in time from the 21st century. You’re a modern person with evolved values. You ask yourself: is this an elaborate bit from Andy Kaufman, or was he simply ahead of his time? After all, you’re from the modern world where Imane Khelif is celebrated for his stunning and brave foray into women’s boxing (and where strangely, most news sources seem to deny that he’s a man).
All of a sudden, you abandon the bigotry of the past and invite Kaufman to come back with you to our present-day society. As you return to social media, endless notifications, a world full of stimulus, you ponder if Andy’s wrestling foray will be accepted for the beautiful thing that it is, rather than taken, without scrutiny, as a joke.
Exiting my narrative device now to speak to you directly: in the not-too-distant past, Andy Kaufman stepped into the ring and goaded women to wrestle with him. Back then, it was a bit. If such an act were to be replicated today, it would likely be celebrated and defended.
Inter-Gender sports pioneering aside, Kaufman's antics made Tennessee history; wrestling legend Jerry Lawler of Memphis went into the ring with Kaufman to relieve a female contestant and treated him to a Tennessee takedown.
Jerry invited the comedian to bring his act to Memphis. Leading up to the match, Kaufman relentlessly mocked his Southern audience, with jokes flexing his intelligence as "someone from Hollywood" and teaching Tennesseans how to use soap. After challenging a few women to wrestle, he was met with a famous Jerry Lawler Pilediver. This led to a staged feud between the two of them. The pair even reached the Letterman Show, with Kaufman in a neck brace.
As far as I know, Kaufman never identified as a woman. I don’t think he (or others from this period) could have fathomed the trans-sports drama occurring now. That said, there is something to be learned from his elaborate inter-gender wrestling bit: we’re watching the absurd unfold on the public stage. We should refuse to be gaslit and adopt Andy’s terminology and call this what it is: inter-gender sports. Whenever a biological man competes against a woman in any sporting event, we should all insist on letting everyone know that it is officially an inter-gender competition.
Maybe this modern dilemma could be solved if everyone surrounding these events treated the whole thing for what it was: an elaborate joke. Imagine if we treated it like WWE. The whole audience already knows it’s rigged anyway. Such rules of engagement would leave true biological women’s sports alone; it would keep their pride intact and be an assurance of physical protection.
That's the end of my original article. Just for fun, I wanted to add a response comment from my sister-in-law. She read the article and shared her thoughts with me, so I figured why not include them here.
I honestly believe mixed sports should be something that is encouraged more in our society—not because we should ignore biological differences and risks, especially in high-impact sports, but because normalizing this collaboration despite our different skill sets can strengthen women’s inclusivity not only as athletes, but in society as a whole. When I played mixed doubles in tennis and joined coed volleyball teams, I was pushed to improve and often held my own, even when the guys hit harder. And there are many sports like shooting, equestrian, archery, ect... that have nothing to do with “physical strength”. Training alongside men, whether in tennis, boxing, or volleyball, never has diminished my ability—it sharpened it, and that kind of mutual growth reflects a deeper value of inclusivity and respect that extends far beyond the sport. Thats my take! :)
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ c631e267:c2b78d3e
2025-04-20 19:54:32
@ c631e267:c2b78d3e
2025-04-20 19:54:32Es ist völlig unbestritten, dass der Angriff der russischen Armee auf die Ukraine im Februar 2022 strikt zu verurteilen ist. Ebenso unbestritten ist Russland unter Wladimir Putin keine brillante Demokratie. Aus diesen Tatsachen lässt sich jedoch nicht das finstere Bild des russischen Präsidenten – und erst recht nicht des Landes – begründen, das uns durchweg vorgesetzt wird und den Kern des aktuellen europäischen Bedrohungs-Szenarios darstellt. Da müssen wir schon etwas genauer hinschauen.
Der vorliegende Artikel versucht derweil nicht, den Einsatz von Gewalt oder die Verletzung von Menschenrechten zu rechtfertigen oder zu entschuldigen – ganz im Gegenteil. Dass jedoch der Verdacht des «Putinverstehers» sofort latent im Raume steht, verdeutlicht, was beim Thema «Russland» passiert: Meinungsmache und Manipulation.
Angesichts der mentalen Mobilmachung seitens Politik und Medien sowie des Bestrebens, einen bevorstehenden Krieg mit Russland geradezu herbeizureden, ist es notwendig, dieser fatalen Entwicklung entgegenzutreten. Wenn wir uns nur ein wenig von der herrschenden Schwarz-Weiß-Malerei freimachen, tauchen automatisch Fragen auf, die Risse im offiziellen Narrativ enthüllen. Grund genug, nachzuhaken.
Wer sich schon länger auch abseits der Staats- und sogenannten Leitmedien informiert, der wird in diesem Artikel vermutlich nicht viel Neues erfahren. Andere könnten hier ein paar unbekannte oder vergessene Aspekte entdecken. Möglicherweise klärt sich in diesem Kontext die Wahrnehmung der aktuellen (unserer eigenen!) Situation ein wenig.
Manipulation erkennen
Corona-«Pandemie», menschengemachter Klimawandel oder auch Ukraine-Krieg: Jede Menge Krisen, und für alle gibt es ein offizielles Narrativ, dessen Hinterfragung unerwünscht ist. Nun ist aber ein Narrativ einfach eine Erzählung, eine Geschichte (Latein: «narratio») und kein Tatsachenbericht. Und so wie ein Märchen soll auch das Narrativ eine Botschaft vermitteln.
Über die Methoden der Manipulation ist viel geschrieben worden, sowohl in Bezug auf das Individuum als auch auf die Massen. Sehr wertvolle Tipps dazu, wie man Manipulationen durchschauen kann, gibt ein Büchlein [1] von Albrecht Müller, dem Herausgeber der NachDenkSeiten.
Die Sprache selber eignet sich perfekt für die Manipulation. Beispielsweise kann die Wortwahl Bewertungen mitschwingen lassen, regelmäßiges Wiederholen (gerne auch von verschiedenen Seiten) lässt Dinge irgendwann «wahr» erscheinen, Übertreibungen fallen auf und hinterlassen wenigstens eine Spur im Gedächtnis, genauso wie Andeutungen. Belege spielen dabei keine Rolle.
Es gibt auffällig viele Sprachregelungen, die offenbar irgendwo getroffen und irgendwie koordiniert werden. Oder alle Redenschreiber und alle Medien kopieren sich neuerdings permanent gegenseitig. Welchen Zweck hat es wohl, wenn der Krieg in der Ukraine durchgängig und quasi wörtlich als «russischer Angriffskrieg auf die Ukraine» bezeichnet wird? Obwohl das in der Sache richtig ist, deutet die Art der Verwendung auf gezielte Beeinflussung hin und soll vor allem das Feindbild zementieren.
Sprachregelungen dienen oft der Absicherung einer einseitigen Darstellung. Das Gleiche gilt für das Verkürzen von Informationen bis hin zum hartnäckigen Verschweigen ganzer Themenbereiche. Auch hierfür gibt es rund um den Ukraine-Konflikt viele gute Beispiele.
Das gewünschte Ergebnis solcher Methoden ist eine Schwarz-Weiß-Malerei, bei der einer eindeutig als «der Böse» markiert ist und die anderen automatisch «die Guten» sind. Das ist praktisch und demonstriert gleichzeitig ein weiteres Manipulationswerkzeug: die Verwendung von Doppelstandards. Wenn man es schafft, bei wichtigen Themen regelmäßig mit zweierlei Maß zu messen, ohne dass das Publikum protestiert, dann hat man freie Bahn.
Experten zu bemühen, um bestimmte Sachverhalte zu erläutern, ist sicher sinnvoll, kann aber ebenso missbraucht werden, schon allein durch die Auswahl der jeweiligen Spezialisten. Seit «Corona» werden viele erfahrene und ehemals hoch angesehene Fachleute wegen der «falschen Meinung» diffamiert und gecancelt. [2] Das ist nicht nur ein brutaler Umgang mit Menschen, sondern auch eine extreme Form, die öffentliche Meinung zu steuern.
Wann immer wir also erkennen (weil wir aufmerksam waren), dass wir bei einem bestimmten Thema manipuliert werden, dann sind zwei logische und notwendige Fragen: Warum? Und was ist denn richtig? In unserem Russland-Kontext haben die Antworten darauf viel mit Geopolitik und Geschichte zu tun.
Ist Russland aggressiv und expansiv?
Angeblich plant Russland, europäische NATO-Staaten anzugreifen, nach dem Motto: «Zuerst die Ukraine, dann den Rest». In Deutschland weiß man dafür sogar das Datum: «Wir müssen bis 2029 kriegstüchtig sein», versichert Verteidigungsminister Pistorius.
Historisch gesehen ist es allerdings eher umgekehrt: Russland, bzw. die Sowjetunion, ist bereits dreimal von Westeuropa aus militärisch angegriffen worden. Die Feldzüge Napoleons, des deutschen Kaiserreichs und Nazi-Deutschlands haben Millionen Menschen das Leben gekostet. Bei dem ausdrücklichen Vernichtungskrieg ab 1941 kam es außerdem zu Brutalitäten wie der zweieinhalbjährigen Belagerung Leningrads (heute St. Petersburg) durch Hitlers Wehrmacht. Deren Ziel, die Bevölkerung auszuhungern, wurde erreicht: über eine Million tote Zivilisten.
Trotz dieser Erfahrungen stimmte Michail Gorbatschow 1990 der deutschen Wiedervereinigung zu und die Sowjetunion zog ihre Truppen aus Osteuropa zurück (vgl. Abb. 1). Der Warschauer Pakt wurde aufgelöst, der Kalte Krieg formell beendet. Die Sowjets erhielten damals von führenden westlichen Politikern die Zusicherung, dass sich die NATO «keinen Zentimeter ostwärts» ausdehnen würde, das ist dokumentiert. [3]

Expandiert ist die NATO trotzdem, und zwar bis an Russlands Grenzen (vgl. Abb. 2). Laut dem Politikberater Jeffrey Sachs handelt es sich dabei um ein langfristiges US-Projekt, das von Anfang an die Ukraine und Georgien mit einschloss. Offiziell wurde der Beitritt beiden Staaten 2008 angeboten. In jedem Fall könnte die massive Ost-Erweiterung seit 1999 aus russischer Sicht nicht nur als Vertrauensbruch, sondern durchaus auch als aggressiv betrachtet werden.

Russland hat den europäischen Staaten mehrfach die Hand ausgestreckt [4] für ein friedliches Zusammenleben und den «Aufbau des europäischen Hauses». Präsident Putin sei «in seiner ersten Amtszeit eine Chance für Europa» gewesen, urteilt die Journalistin und langjährige Russland-Korrespondentin der ARD, Gabriele Krone-Schmalz. Er habe damals viele positive Signale Richtung Westen gesendet.
Die Europäer jedoch waren scheinbar an einer Partnerschaft mit dem kontinentalen Nachbarn weniger interessiert als an der mit dem transatlantischen Hegemon. Sie verkennen bis heute, dass eine gedeihliche Zusammenarbeit in Eurasien eine Gefahr für die USA und deren bekundetes Bestreben ist, die «einzige Weltmacht» zu sein – «Full Spectrum Dominance» [5] nannte das Pentagon das. Statt einem neuen Kalten Krieg entgegenzuarbeiten, ließen sich europäische Staaten selber in völkerrechtswidrige «US-dominierte Angriffskriege» [6] verwickeln, wie in Serbien, Afghanistan, dem Irak, Libyen oder Syrien. Diese werden aber selten so benannt.

Speziell den Deutschen stünde außer einer Portion Realismus auch etwas mehr Dankbarkeit gut zu Gesicht. Das Geschichtsbewusstsein der Mehrheit scheint doch recht selektiv und das Selbstbewusstsein einiger etwas desorientiert zu sein. Bekanntermaßen waren es die Soldaten der sowjetischen Roten Armee, die unter hohen Opfern 1945 Deutschland «vom Faschismus befreit» haben. Bei den Gedenkfeiern zu 80 Jahren Kriegsende will jedoch das Auswärtige Amt – noch unter der Diplomatie-Expertin Baerbock, die sich schon länger offiziell im Krieg mit Russland wähnt, – nun keine Russen sehen: Sie sollen notfalls rausgeschmissen werden.
«Die Grundsatzfrage lautet: Geht es Russland um einen angemessenen Platz in einer globalen Sicherheitsarchitektur, oder ist Moskau schon seit langem auf einem imperialistischen Trip, der befürchten lassen muss, dass die Russen in fünf Jahren in Berlin stehen?»
So bringt Gabriele Krone-Schmalz [7] die eigentliche Frage auf den Punkt, die zur Einschätzung der Situation letztlich auch jeder für sich beantworten muss.
Was ist los in der Ukraine?
In der internationalen Politik geht es nie um Demokratie oder Menschenrechte, sondern immer um Interessen von Staaten. Diese These stammt von Egon Bahr, einem der Architekten der deutschen Ostpolitik des «Wandels durch Annäherung» aus den 1960er und 70er Jahren. Sie trifft auch auf den Ukraine-Konflikt zu, den handfeste geostrategische und wirtschaftliche Interessen beherrschen, obwohl dort angeblich «unsere Demokratie» verteidigt wird.
Es ist ein wesentliches Element des Ukraine-Narrativs und Teil der Manipulation, die Vorgeschichte des Krieges wegzulassen – mindestens die vor der russischen «Annexion» der Halbinsel Krim im März 2014, aber oft sogar komplett diejenige vor der Invasion Ende Februar 2022. Das Thema ist komplex, aber einige Aspekte, die für eine Beurteilung nicht unwichtig sind, will ich wenigstens kurz skizzieren. [8]
Das Gebiet der heutigen Ukraine und Russlands – die übrigens in der «Kiewer Rus» gemeinsame Wurzeln haben – hat der britische Geostratege Halford Mackinder bereits 1904 als eurasisches «Heartland» bezeichnet, dessen Kontrolle er eine große Bedeutung für die imperiale Strategie Großbritanniens zumaß. Für den ehemaligen Sicherheits- und außenpolitischen Berater mehrerer US-amerikanischer Präsidenten und Mitgründer der Trilateralen Kommission, Zbigniew Brzezinski, war die Ukraine nach der Auflösung der Sowjetunion ein wichtiger Spielstein auf dem «eurasischen Schachbrett», wegen seiner Nähe zu Russland, seiner Bodenschätze und seines Zugangs zum Schwarzen Meer.
Die Ukraine ist seit langem ein gespaltenes Land. Historisch zerrissen als Spielball externer Interessen und geprägt von ethnischen, kulturellen, religiösen und geografischen Unterschieden existiert bis heute, grob gesagt, eine Ost-West-Spaltung, welche die Suche nach einer nationalen Identität stark erschwert.
Insbesondere im Zuge der beiden Weltkriege sowie der Russischen Revolution entstanden tiefe Risse in der Bevölkerung. Ukrainer kämpften gegen Ukrainer, zum Beispiel die einen auf der Seite von Hitlers faschistischer Nazi-Armee und die anderen auf der von Stalins kommunistischer Roter Armee. Die Verbrechen auf beiden Seiten sind nicht vergessen. Dass nach der Unabhängigkeit 1991 versucht wurde, Figuren wie den radikalen Nationalisten Symon Petljura oder den Faschisten und Nazi-Kollaborateur Stepan Bandera als «Nationalhelden» zu installieren, verbessert die Sache nicht.
Während die USA und EU-Staaten zunehmend «ausländische Einmischung» (speziell russische) in «ihre Demokratien» wittern, betreiben sie genau dies seit Jahrzehnten in vielen Ländern der Welt. Die seit den 2000er Jahren bekannten «Farbrevolutionen» in Osteuropa werden oft als Methode des Regierungsumsturzes durch von außen gesteuerte «demokratische» Volksaufstände beschrieben. Diese Strategie geht auf Analysen zum «Schwarmverhalten» [9] seit den 1960er Jahren zurück (Studentenproteste), wo es um die potenzielle Wirksamkeit einer «rebellischen Hysterie» von Jugendlichen bei postmodernen Staatsstreichen geht. Heute nennt sich dieses gezielte Kanalisieren der Massen zur Beseitigung unkooperativer Regierungen «Soft-Power».
In der Ukraine gab es mit der «Orangen Revolution» 2004 und dem «Euromaidan» 2014 gleich zwei solcher «Aufstände». Der erste erzwang wegen angeblicher Unregelmäßigkeiten eine Wiederholung der Wahlen, was mit Wiktor Juschtschenko als neuem Präsidenten endete. Dieser war ehemaliger Direktor der Nationalbank und Befürworter einer Annäherung an EU und NATO. Seine Frau, die First Lady, ist US-amerikanische «Philanthropin» und war Beamtin im Weißen Haus in der Reagan- und der Bush-Administration.
Im Gegensatz zu diesem ersten Event endete der sogenannte Euromaidan unfriedlich und blutig. Die mehrwöchigen Proteste gegen Präsident Wiktor Janukowitsch, in Teilen wegen des nicht unterzeichneten Assoziierungsabkommens mit der EU, wurden zunehmend gewalttätiger und von Nationalisten und Faschisten des «Rechten Sektors» dominiert. Sie mündeten Ende Februar 2014 auf dem Kiewer Unabhängigkeitsplatz (Maidan) in einem Massaker durch Scharfschützen. Dass deren Herkunft und die genauen Umstände nicht geklärt wurden, störte die Medien nur wenig. [10]
Janukowitsch musste fliehen, er trat nicht zurück. Vielmehr handelte es sich um einen gewaltsamen, allem Anschein nach vom Westen inszenierten Putsch. Laut Jeffrey Sachs war das kein Geheimnis, außer vielleicht für die Bürger. Die USA unterstützten die Post-Maidan-Regierung nicht nur, sie beeinflussten auch ihre Bildung. Das geht unter anderem aus dem berühmten «Fuck the EU»-Telefonat der US-Chefdiplomatin für die Ukraine, Victoria Nuland, mit Botschafter Geoffrey Pyatt hervor.
Dieser Bruch der demokratischen Verfassung war letztlich der Auslöser für die anschließenden Krisen auf der Krim und im Donbass (Ostukraine). Angesichts der ukrainischen Geschichte mussten die nationalistischen Tendenzen und die Beteiligung der rechten Gruppen an dem Umsturz bei der russigsprachigen Bevölkerung im Osten ungute Gefühle auslösen. Es gab Kritik an der Übergangsregierung, Befürworter einer Abspaltung und auch für einen Anschluss an Russland.
Ebenso konnte Wladimir Putin in dieser Situation durchaus Bedenken wegen des Status der russischen Militärbasis für seine Schwarzmeerflotte in Sewastopol auf der Krim haben, für die es einen langfristigen Pachtvertrag mit der Ukraine gab. Was im März 2014 auf der Krim stattfand, sei keine Annexion, sondern eine Abspaltung (Sezession) nach einem Referendum gewesen, also keine gewaltsame Aneignung, urteilte der Rechtswissenschaftler Reinhard Merkel in der FAZ sehr detailliert begründet. Übrigens hatte die Krim bereits zu Zeiten der Sowjetunion den Status einer autonomen Republik innerhalb der Ukrainischen SSR.
Anfang April 2014 wurden in der Ostukraine die «Volksrepubliken» Donezk und Lugansk ausgerufen. Die Kiewer Übergangsregierung ging unter der Bezeichnung «Anti-Terror-Operation» (ATO) militärisch gegen diesen, auch von Russland instrumentalisierten Widerstand vor. Zufällig war kurz zuvor CIA-Chef John Brennan in Kiew. Die Maßnahmen gingen unter dem seit Mai neuen ukrainischen Präsidenten, dem Milliardär Petro Poroschenko, weiter. Auch Wolodymyr Selenskyj beendete den Bürgerkrieg nicht, als er 2019 vom Präsidenten-Schauspieler, der Oligarchen entmachtet, zum Präsidenten wurde. Er fuhr fort, die eigene Bevölkerung zu bombardieren.
Mit dem Einmarsch russischer Truppen in die Ostukraine am 24. Februar 2022 begann die zweite Phase des Krieges. Die Wochen und Monate davor waren intensiv. Im November hatte die Ukraine mit den USA ein Abkommen über eine «strategische Partnerschaft» unterzeichnet. Darin sagten die Amerikaner ihre Unterstützung der EU- und NATO-Perspektive der Ukraine sowie quasi für die Rückeroberung der Krim zu. Dagegen ließ Putin der NATO und den USA im Dezember 2021 einen Vertragsentwurf über beiderseitige verbindliche Sicherheitsgarantien zukommen, den die NATO im Januar ablehnte. Im Februar eskalierte laut OSZE die Gewalt im Donbass.
Bereits wenige Wochen nach der Invasion, Ende März 2022, kam es in Istanbul zu Friedensverhandlungen, die fast zu einer Lösung geführt hätten. Dass der Krieg nicht damals bereits beendet wurde, lag daran, dass der Westen dies nicht wollte. Man war der Meinung, Russland durch die Ukraine in diesem Stellvertreterkrieg auf Dauer militärisch schwächen zu können. Angesichts von Hunderttausenden Toten, Verletzten und Traumatisierten, die als Folge seitdem zu beklagen sind, sowie dem Ausmaß der Zerstörung, fehlen einem die Worte.
Hasst der Westen die Russen?
Diese Frage drängt sich auf, wenn man das oft unerträglich feindselige Gebaren beobachtet, das beileibe nicht neu ist und vor Doppelmoral trieft. Russland und speziell die Person Wladimir Putins werden regelrecht dämonisiert, was gleichzeitig scheinbar jede Form von Diplomatie ausschließt.
Russlands militärische Stärke, seine geografische Lage, sein Rohstoffreichtum oder seine unabhängige diplomatische Tradition sind sicher Störfaktoren für das US-amerikanische Bestreben, der Boss in einer unipolaren Welt zu sein. Ein womöglich funktionierender eurasischer Kontinent, insbesondere gute Beziehungen zwischen Russland und Deutschland, war indes schon vor dem Ersten Weltkrieg eine Sorge des britischen Imperiums.
Ein «Vergehen» von Präsident Putin könnte gewesen sein, dass er die neoliberale Schocktherapie à la IWF und den Ausverkauf des Landes (auch an US-Konzerne) beendete, der unter seinem Vorgänger herrschte. Dabei zeigte er sich als Führungspersönlichkeit und als nicht so formbar wie Jelzin. Diese Aspekte allein sind aber heute vermutlich keine ausreichende Erklärung für ein derart gepflegtes Feindbild.
Der Historiker und Philosoph Hauke Ritz erweitert den Fokus der Fragestellung zu: «Warum hasst der Westen die Russen so sehr?», was er zum Beispiel mit dem Medienforscher Michael Meyen und mit der Politikwissenschaftlerin Ulrike Guérot bespricht. Ritz stellt die interessante These [11] auf, dass Russland eine Provokation für den Westen sei, welcher vor allem dessen kulturelles und intellektuelles Potenzial fürchte.
Die Russen sind Europäer aber anders, sagt Ritz. Diese «Fremdheit in der Ähnlichkeit» erzeuge vielleicht tiefe Ablehnungsgefühle. Obwohl Russlands Identität in der europäischen Kultur verwurzelt ist, verbinde es sich immer mit der Opposition in Europa. Als Beispiele nennt er die Kritik an der katholischen Kirche oder die Verbindung mit der Arbeiterbewegung. Christen, aber orthodox; Sozialismus statt Liberalismus. Das mache das Land zum Antagonisten des Westens und zu einer Bedrohung der Machtstrukturen in Europa.
Fazit
Selbstverständlich kann man Geschichte, Ereignisse und Entwicklungen immer auf verschiedene Arten lesen. Dieser Artikel, obwohl viel zu lang, konnte nur einige Aspekte der Ukraine-Tragödie anreißen, die in den offiziellen Darstellungen in der Regel nicht vorkommen. Mindestens dürfte damit jedoch klar geworden sein, dass die Russische Föderation bzw. Wladimir Putin nicht der alleinige Aggressor in diesem Konflikt ist. Das ist ein Stellvertreterkrieg zwischen USA/NATO (gut) und Russland (böse); die Ukraine (edel) wird dabei schlicht verheizt.
Das ist insofern von Bedeutung, als die gesamte europäische Kriegshysterie auf sorgsam kultivierten Freund-Feind-Bildern beruht. Nur so kann Konfrontation und Eskalation betrieben werden, denn damit werden die wahren Hintergründe und Motive verschleiert. Angst und Propaganda sind notwendig, damit die Menschen den Wahnsinn mitmachen. Sie werden belogen, um sie zuerst zu schröpfen und anschließend auf die Schlachtbank zu schicken. Das kann niemand wollen, außer den stets gleichen Profiteuren: die Rüstungs-Lobby und die großen Investoren, die schon immer an Zerstörung und Wiederaufbau verdient haben.
Apropos Investoren: Zu den Top-Verdienern und somit Hauptinteressenten an einer Fortführung des Krieges zählt BlackRock, einer der weltgrößten Vermögensverwalter. Der deutsche Bundeskanzler in spe, Friedrich Merz, der gerne «Taurus»-Marschflugkörper an die Ukraine liefern und die Krim-Brücke zerstören möchte, war von 2016 bis 2020 Aufsichtsratsvorsitzender von BlackRock in Deutschland. Aber das hat natürlich nichts zu sagen, der Mann macht nur seinen Job.
Es ist ein Spiel der Kräfte, es geht um Macht und strategische Kontrolle, um Geheimdienste und die Kontrolle der öffentlichen Meinung, um Bodenschätze, Rohstoffe, Pipelines und Märkte. Das klingt aber nicht sexy, «Demokratie und Menschenrechte» hört sich besser und einfacher an. Dabei wäre eine für alle Seiten förderliche Politik auch nicht so kompliziert; das Handwerkszeug dazu nennt sich Diplomatie. Noch einmal Gabriele Krone-Schmalz:
«Friedliche Politik ist nichts anderes als funktionierender Interessenausgleich. Da geht’s nicht um Moral.»
Die Situation in der Ukraine ist sicher komplex, vor allem wegen der inneren Zerrissenheit. Es dürfte nicht leicht sein, eine friedliche Lösung für das Zusammenleben zu finden, aber die Beteiligten müssen es vor allem wollen. Unter den gegebenen Umständen könnte eine sinnvolle Perspektive mit Neutralität und föderalen Strukturen zu tun haben.
Allen, die sich bis hierher durch die Lektüre gearbeitet (oder auch einfach nur runtergescrollt) haben, wünsche ich frohe Oster-Friedenstage!
[Titelbild: Pixabay; Abb. 1 und 2: nach Ganser/SIPER; Abb. 3: SIPER]
--- Quellen: ---
[1] Albrecht Müller, «Glaube wenig. Hinterfrage alles. Denke selbst.», Westend 2019
[2] Zwei nette Beispiele:
- ARD-faktenfinder (sic), «Viel Aufmerksamkeit für fragwürdige Experten», 03/2023
- Neue Zürcher Zeitung, «Aufstieg und Fall einer Russlandversteherin – die ehemalige ARD-Korrespondentin Gabriele Krone-Schmalz rechtfertigt seit Jahren Putins Politik», 12/2022
[3] George Washington University, «NATO Expansion: What Gorbachev Heard – Declassified documents show security assurances against NATO expansion to Soviet leaders from Baker, Bush, Genscher, Kohl, Gates, Mitterrand, Thatcher, Hurd, Major, and Woerner», 12/2017
[4] Beispielsweise Wladimir Putin bei seiner Rede im Deutschen Bundestag, 25/09/2001
[5] William Engdahl, «Full Spectrum Dominance, Totalitarian Democracy In The New World Order», edition.engdahl 2009
[6] Daniele Ganser, «Illegale Kriege – Wie die NATO-Länder die UNO sabotieren. Eine Chronik von Kuba bis Syrien», Orell Füssli 2016
[7] Gabriele Krone-Schmalz, «Mit Friedensjournalismus gegen ‘Kriegstüchtigkeit’», Vortrag und Diskussion an der Universität Hamburg, veranstaltet von engagierten Studenten, 16/01/2025\ → Hier ist ein ähnlicher Vortrag von ihr (Video), den ich mit spanischer Übersetzung gefunden habe.
[8] Für mehr Hintergrund und Details empfehlen sich z.B. folgende Bücher:
- Mathias Bröckers, Paul Schreyer, «Wir sind immer die Guten», Westend 2019
- Gabriele Krone-Schmalz, «Russland verstehen? Der Kampf um die Ukraine und die Arroganz des Westens», Westend 2023
- Patrik Baab, «Auf beiden Seiten der Front – Meine Reisen in die Ukraine», Fiftyfifty 2023
[9] vgl. Jonathan Mowat, «Washington's New World Order "Democratization" Template», 02/2005 und RAND Corporation, «Swarming and the Future of Conflict», 2000
[10] Bemerkenswert einige Beiträge, von denen man später nichts mehr wissen wollte:
- ARD Monitor, «Todesschüsse in Kiew: Wer ist für das Blutbad vom Maidan verantwortlich», 10/04/2014, Transkript hier
- Telepolis, «Blutbad am Maidan: Wer waren die Todesschützen?», 12/04/2014
- Telepolis, «Scharfschützenmorde in Kiew», 14/12/2014
- Deutschlandfunk, «Gefahr einer Spirale nach unten», Interview mit Günter Verheugen, 18/03/2014
- NDR Panorama, «Putsch in Kiew: Welche Rolle spielen die Faschisten?», 06/03/2014
[11] Hauke Ritz, «Vom Niedergang des Westens zur Neuerfindung Europas», 2024
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ c631e267:c2b78d3e
2025-04-18 15:53:07
@ c631e267:c2b78d3e
2025-04-18 15:53:07Verstand ohne Gefühl ist unmenschlich; \ Gefühl ohne Verstand ist Dummheit. \ Egon Bahr
Seit Jahren werden wir darauf getrimmt, dass Fakten eigentlich gefühlt seien. Aber nicht alles ist relativ und nicht alles ist nach Belieben interpretierbar. Diese Schokoladenhasen beispielsweise, die an Ostern in unseren Gefilden typisch sind, «ostern» zwar nicht, sondern sie sitzen in der Regel, trotzdem verwandelt sie das nicht in «Sitzhasen».
Nichts soll mehr gelten, außer den immer invasiveren Gesetzen. Die eigenen Traditionen und Wurzeln sind potenziell «pfui», um andere Menschen nicht auszuschließen, aber wir mögen uns toleranterweise an die fremden Symbole und Rituale gewöhnen. Dabei ist es mir prinzipiell völlig egal, ob und wann jemand ein Fastenbrechen feiert, am Karsamstag oder jedem anderen Tag oder nie – aber bitte freiwillig.
Und vor allem: Lasst die Finger von den Kindern! In Bern setzten kürzlich Demonstranten ein Zeichen gegen die zunehmende Verbreitung woker Ideologie im Bildungssystem und forderten ein Ende der sexuellen Indoktrination von Schulkindern.
Wenn es nicht wegen des heiklen Themas Migration oder wegen des Regenbogens ist, dann wegen des Klimas. Im Rahmen der «Netto Null»-Agenda zum Kampf gegen das angeblich teuflische CO2 sollen die Menschen ihre Ernährungsgewohnheiten komplett ändern. Nach dem Willen von Produzenten synthetischer Lebensmittel, wie Bill Gates, sollen wir baldmöglichst praktisch auf Fleisch und alle Milchprodukte wie Milch und Käse verzichten. Ein lukratives Geschäftsmodell, das neben der EU aktuell auch von einem britischen Lobby-Konsortium unterstützt wird.
Sollten alle ideologischen Stricke zu reißen drohen, ist da immer noch «der Putin». Die Unions-Europäer offenbaren sich dabei ständig mehr als Vertreter der Rüstungsindustrie. Allen voran zündelt Deutschland an der Kriegslunte, angeführt von einem scheinbar todesmutigen Kanzlerkandidaten Friedrich Merz. Nach dessen erneuter Aussage, «Taurus»-Marschflugkörper an Kiew liefern zu wollen, hat Russland eindeutig klargestellt, dass man dies als direkte Kriegsbeteiligung werten würde – «mit allen sich daraus ergebenden Konsequenzen für Deutschland».
Wohltuend sind Nachrichten über Aktivitäten, die sich der allgemeinen Kriegstreiberei entgegenstellen oder diese öffentlich hinterfragen. Dazu zählt auch ein Kongress kritischer Psychologen und Psychotherapeuten, der letzte Woche in Berlin stattfand. Die vielen Vorträge im Kontext von «Krieg und Frieden» deckten ein breites Themenspektrum ab, darunter Friedensarbeit oder die Notwendigkeit einer «Pädagogik der Kriegsuntüchtigkeit».
Der heutige «stille Freitag», an dem Christen des Leidens und Sterbens von Jesus gedenken, ist vielleicht unabhängig von jeder religiösen oder spirituellen Prägung eine passende Einladung zur Reflexion. In der Ruhe liegt die Kraft. In diesem Sinne wünsche ich Ihnen frohe Ostertage!
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 6be5cc06:5259daf0
2025-03-31 03:39:07
@ 6be5cc06:5259daf0
2025-03-31 03:39:07Introdução
Uma sociedade não deve ser construída sobre coerção, mas sim sobre associações voluntárias e interações espontâneas entre indivíduos. A sociedade de condomínios privados surge como uma alternativa natural ao modelo atual de centros urbanos, substituindo a imposição centralizada por estruturas baseadas em contratos e livre associação. Cada condomínio é uma unidade autônoma, gerida por aqueles que ali residem, onde os critérios de entrada, as regras internas e o comércio são definidos pelos próprios participantes. Essa estrutura permite que indivíduos se agrupem com base em valores compartilhados, eliminando os conflitos artificiais impostos por estados e legislações homogêneas que não respeitam a diversidade de preferências e estilos de vida.
O objetivo dessa sociedade é simples: permitir que as pessoas vivam de acordo com seus princípios sem interferência externa. Em um mundo onde a coerção estatal distorce incentivos, os condomínios privados oferecem uma alternativa onde a ordem surge do livre mercado e da cooperação voluntária. Os moradores escolhem seus vizinhos, definem suas próprias normas e interagem economicamente conforme suas necessidades e interesses. O modelo elimina a necessidade de um controle central, pois os incentivos derivados do livre mercado levam ao desenvolvimento de comunidades prósperas, onde a reputação e a confiança mútua são mais eficazes do que qualquer imposição estatal. Assim, essa sociedade representa a evolução lógica do conceito de liberdade individual e propriedade privada como pilares fundamentais da ordem social.
Público-Alvo e Identidade
Os condomínios privados refletem o princípio da livre associação, permitindo que indivíduos escolham viver em comunidades alinhadas com seus valores e necessidades sem interferência estatal. Cada condomínio possui uma identidade própria, moldada pelos moradores e seus interesses, criando ambientes onde afinidades culturais, filosóficas ou profissionais são preservadas e incentivadas. Enquanto alguns podem ser voltados para famílias numerosas, oferecendo amplos espaços e infraestrutura adequada, outros podem priorizar solteiros e jovens profissionais, com áreas de coworking e espaços de lazer voltados para networking e socialização. Da mesma forma, comunidades religiosas podem estabelecer seus próprios espaços de culto e eventos, enquanto condomínios para idosos podem ser projetados com acessibilidade e serviços médicos especializados.
Críticos podem afirmar que essa forma de organização resulta em pouca diversidade de habilidades e perspectivas, mas esse argumento ignora a dinâmica das interações humanas e o caráter evolutivo dos intercâmbios entre comunidades. Nenhum condomínio existe isolado; a troca entre diferentes comunidades ocorre naturalmente pelo mercado, incentivando o intercâmbio de conhecimento e serviços entre especialistas de diferentes áreas. Além disso, a ideia de que todos os grupos devem conter uma variedade aleatória de indivíduos desconsidera que a verdadeira diversidade nasce da liberdade de escolha, e não da imposição estatal de convivências forçadas.
Outra crítica possível é que a existência de critérios de entrada pode levar à segregação social. No entanto, essa preocupação deriva da concepção errônea de que todas as comunidades devem ser abertas e incluir qualquer pessoa indiscriminadamente. Porém, a liberdade de associação implica, necessariamente, a liberdade de exclusão. Se um grupo deseja manter determinada identidade cultural, religiosa ou profissional, isso não impede que outros grupos criem suas próprias comunidades conforme seus valores e recursos. Além disso, essa especialização leva a uma concorrência saudável entre condomínios, forçando-os a oferecer melhores condições para atrair moradores. Em vez de uma sociedade homogênea moldada por burocratas, temos um mosaico de comunidades autônomas, onde cada indivíduo pode encontrar ou criar o ambiente que melhor lhe convém.
Autossuficiência e Especialização
A força dos condomínios privados reside na capacidade de seus moradores de contribuírem ativamente para a comunidade, tornando-a funcional e autossuficiente sem a necessidade de intervenções estatais. Diferentes condomínios podem se especializar em áreas específicas ou ter diversos profissionais de diferentes setores, refletindo as competências e interesses de seus residentes. Essa descentralização do conhecimento e da produção permite que cada comunidade desenvolva soluções internas para suas demandas, reduzindo dependências externas e estimulando a prosperidade local.
Os moradores atuam como agentes econômicos, trocando bens e serviços dentro do próprio condomínio e entre diferentes comunidades. Um condomínio voltado para a saúde, por exemplo, pode contar com médicos, enfermeiros e terapeutas que oferecem consultas, aulas e assistência médica particular, remunerados diretamente por seus clientes, sem a intermediação de burocracias. Da mesma forma, um condomínio agrícola pode abrigar agricultores que cultivam alimentos orgânicos, compartilham técnicas de cultivo e comercializam excedentes com outros condomínios, garantindo um fluxo contínuo de suprimentos. Em um condomínio tecnológico, programadores, engenheiros e empreendedores desenvolvem soluções de TI, segurança digital e energia renovável, promovendo a inovação e ampliando as possibilidades de intercâmbio econômico.
A economia interna de cada condomínio se fortalece através de serviços oferecidos pelos próprios moradores. Professores podem ministrar aulas, técnicos podem prestar serviços de manutenção, artesãos podem vender seus produtos diretamente para os vizinhos. O mercado livre e voluntário é o principal regulador dessas interações, garantindo que a especialização surja naturalmente conforme a demanda e a oferta se ajustam. Essa estrutura elimina desperdícios comuns em sistemas centralizados, onde a alocação de recursos se dá por decisões políticas e não pelas necessidades reais da população.
Alguns argumentam que a especialização pode criar bolhas de conhecimento, tornando os condomínios excessivamente dependentes de trocas externas. Contudo, essa preocupação desconsidera a natureza espontânea do mercado, que incentiva a cooperação e o comércio entre comunidades distintas. Nenhum condomínio precisa produzir tudo internamente; ao contrário, a divisão do trabalho e a liberdade de escolha promovem interdependências saudáveis e vantajosas para todos. Assim, cada morador se insere em um ecossistema dinâmico, onde suas habilidades são valorizadas e sua autonomia preservada, sem coerções estatais ou distorções artificiais impostas por planejadores centrais.
Infraestrutura e Sustentabilidade
A solidez de uma sociedade baseada em condomínios privados depende de uma infraestrutura eficiente e sustentável, projetada para reduzir a dependência externa e garantir o máximo de autonomia. Sem um aparato estatal centralizador, cada comunidade deve estruturar seus próprios meios de obtenção de energia, água, alimentação e demais bens essenciais, garantindo que suas operações sejam viáveis a longo prazo. Essa abordagem, longe de ser um entrave, representa a verdadeira inovação descentralizada: um ambiente onde as soluções emergem da necessidade real e da engenhosidade humana, e não de diretrizes burocráticas e regulamentos ineficazes.
Cada condomínio pode investir em tecnologias sustentáveis e autônomas, como energia solar e eólica, reduzindo custos e minimizando a vulnerabilidade às flutuações do mercado energético tradicional. Sistemas de captação e filtragem de água da chuva, bem como a reutilização eficiente dos recursos hídricos, garantem independência em relação a empresas monopolistas e governos que frequentemente administram esse bem de forma ineficaz. Hortas comunitárias e fazendas verticais podem suprir grande parte da demanda alimentar, permitindo que cada condomínio mantenha sua própria reserva de alimentos, aumentando a resiliência contra crises externas e instabilidades de mercado.
Além dos recursos naturais, os espaços compartilhados desempenham um papel fundamental na integração e no fortalecimento dessas comunidades. Bibliotecas, ginásios, creches e salas de aula permitem que o conhecimento e os serviços circulem internamente, criando um ambiente onde a colaboração ocorre de maneira orgânica. A descentralização também se aplica ao uso da tecnologia, plataformas digitais privadas podem ser utilizadas para conectar moradores, facilitar a troca de serviços e produtos, além de coordenar agendamentos e eventos dentro dos condomínios e entre diferentes comunidades.
O Bitcoin surge como uma ferramenta indispensável nesse ecossistema, eliminando a necessidade de bancos estatais ou sistemas financeiros controlados. Ao permitir transações diretas, transparentes e resistentes à censura, o Bitcoin se torna o meio de troca ideal entre os condomínios, garantindo a preservação do valor e possibilitando um comércio ágil e eficiente. Além disso, contratos inteligentes e protocolos descentralizados podem ser integrados para administrar serviços comuns, fortalecer a segurança e reduzir a burocracia, tornando a governança desses condomínios cada vez mais autônoma e imune a intervenções externas.
Alguns podem argumentar que a falta de um aparato estatal para regulamentar a infraestrutura pode resultar em desigualdade no acesso a recursos essenciais, ou que a descentralização completa pode gerar caos e ineficiência. No entanto, essa visão ignora o fato de que a concorrência e a inovação no livre mercado são os maiores motores de desenvolvimento sustentável. Sem monopólios ou subsídios distorcendo a alocação de recursos, a busca por eficiência leva naturalmente à adoção de soluções melhores e mais acessíveis. Condomínios que oferecem infraestrutura de qualidade tendem a atrair mais moradores e investimentos, o que impulsiona a melhoria contínua e a diversificação dos serviços. Em vez de depender de um sistema centralizado falho, as comunidades se tornam responsáveis por sua própria prosperidade, criando uma estrutura sustentável, escalável e adaptável às mudanças do futuro.
Governança e Administração
Em uma sociedade descentralizada, não se deve depender de uma estrutura estatal ou centralizada para regular e tomar decisões em nome dos indivíduos. Cada condomínio, portanto, deve ser gerido de maneira autônoma, com processos claros de tomada de decisão, resolução de conflitos e administração das questões cotidianas. A gestão pode ser organizada por conselhos de moradores, associações ou sistemas de governança direta, conforme as necessidades locais.
Conselhos de Moradores e Processos de Tomada de Decisão
Em muitos casos, a administração interna de um condomínio privado pode ser realizada por um conselho de moradores, composto por representantes eleitos ou indicados pela própria comunidade. A ideia é garantir que as decisões importantes, como planejamento urbano, orçamento, manutenção e serviços, sejam feitas de forma transparente e que os interesses de todos os envolvidos sejam considerados. Isso não significa que a gestão precise ser completamente democrática, mas sim que as decisões devem ser tomadas de forma legítima, transparente e acordadas pela maior parte dos membros.
Em vez de um processo burocrático e centralizado, onde uma liderança impõe suas vontades sobre todos a muitas vezes suas decisões ruins não o afetam diretamente, a gestão de um condomínio privado deve ser orientada pela busca de consenso, onde os próprios gestores sofrerão as consequências de suas más escolhas. O processo de tomada de decisão pode ser dinâmico e direto, com os moradores discutindo e acordando soluções baseadas no mercado e nas necessidades locais, em vez de depender de um sistema impessoal de regulamentação. Além disso, a utilização de tecnologias descentralizadas, como plataformas de blockchain, pode proporcionar maior transparência nas decisões e maior confiança na gestão.
Resolução de Conflitos
A resolução de disputas dentro dos condomínios pode ocorrer de forma voluntária, através de negociação direta ou com o auxílio de mediadores escolhidos pelos próprios moradores por meio de um sistema de reputação. Em alguns casos, podem ser criados mecanismos para resolução de disputas mais formais, com árbitros ou juízes independentes que atuam sem vínculos com o condomínio. Esses árbitros podem ser escolhidos com base em sua experiência ou especialização em áreas como direito, mediação e resolução de conflitos, com uma reputação para zelar. Ao contrário de um sistema judicial centralizado, onde a parte envolvida depende do Estado para resolver disputas, os moradores possuem a autonomia para buscar soluções que atendam aos seus próprios interesses e necessidades. A diversidade de abordagens em um sistema de governança descentralizado cria oportunidades para inovações que atendem diferentes cenários, sem a interferência de burocratas distantes dos próprios problemas que estão "tentando resolver".
Planejamento Urbano e Arquitetura
A questão do design dos condomínios envolve não apenas a estética das construções, mas também a funcionalidade e a sustentabilidade a longo prazo. O planejamento urbano deve refletir as necessidades específicas da comunidade, onde ela decide por si mesma como construir e organizar seu ambiente.\ Arquitetos e urbanistas, muitas vezes moradores especializados, serão responsáveis pela concepção de espaços que atendam a esses critérios, criando ambientes agradáveis, com áreas para lazer, trabalho e convivência que atendam às diversas necessidades de cada grupo.\ Além disso, condomínios com nessecidades semelhantes poderão adotar ideias que deram certo em outros e certamente também dará no seu.
Segurança e Vigilância
Em relação à segurança, cada condomínio pode adotar sistemas de vigilância e proteção que atendam à sua realidade específica. Algumas comunidades podem optar por sistemas de câmeras de segurança, armamento pleno de seus moradores, patrulhamento privado ou até mesmo formas alternativas de garantir a proteção, como vigilância por meio de criptografia e monitoramento descentralizado. A chave para a segurança será a confiança mútua e a colaboração voluntária entre os moradores, que terão a liberdade de definir suas próprias medidas.
Comércio entre Condomínios
A troca de bens e serviços entre as diferentes comunidades é essencial para o funcionamento da rede. Como cada condomínio possui um grau de especialização ou uma mistura de profissionais em diversas áreas, a interdependência entre eles se torna crucial para suprir necessidades e promover a colaboração.
Embora alguns condomínios sejam especializados em áreas como saúde, agricultura ou tecnologia, outros podem ter um perfil mais diversificado, com moradores que atuam em diferentes campos de conhecimento. Por exemplo, um condomínio agrícola pode produzir alimentos orgânicos frescos, enquanto um condomínio de saúde oferece consultas médicas, terapias e cuidados especializados. Já um condomínio tecnológico pode fornecer inovações em software ou equipamentos de energia. Podem haver condomínios universitários que oferecem todo tipo de solução no campo de ensino. Ao mesmo tempo, um condomínio misto, com moradores de diversas áreas, pode oferecer uma variedade de serviços e produtos, tornando-se um centro de intercâmbio de diferentes tipos de expertise.
Essa divisão de trabalho, seja especializada ou diversificada, permite que os condomínios ofereçam o melhor de suas áreas de atuação, ao mesmo tempo em que atendem às demandas de outros. Um condomínio que não se especializa pode, por exemplo, buscar um acordo de troca com um condomínio agrícola para obter alimentos frescos ou com um condomínio tecnológico para adquirir soluções inovadoras.
Embora os condomínios busquem a autossuficiência, alguns recursos essenciais não podem ser produzidos internamente. Itens como minérios para construção, combustíveis ou até mesmo água, em regiões secas, não estão disponíveis em todas as áreas. A natureza não distribui os recursos de maneira uniforme, e a capacidade de produção local pode ser insuficiente para suprir todas as necessidades dos moradores. Isso implica que, para garantir a qualidade de vida e a continuidade das operações, os condomínios precisarão estabelecer relações comerciais e de fornecimento com fontes externas, seja através de mercados, importações ou parcerias com outras comunidades ou fornecedores fora do sistema de condomínios. O comércio intercondomínios e com o exterior será vital para a complementaridade das necessidades, assegurando que os moradores tenham acesso a tudo o que não pode ser produzido localmente.
O sistema econômico entre os condomínios pode ser flexível, permitindo o uso de uma moeda comum (como o Bitcoin) ou até mesmo um sistema de troca direta. Por exemplo, um morador de um condomínio misto pode oferecer serviços de design gráfico em troca de alimentos ou cuidados médicos. Esse tipo de colaboração estimula a produtividade e cria incentivos para que cada condomínio ofereça o melhor de seus recursos e habilidades, garantindo acesso aos bens e serviços necessários.
Relações Externas e Diplomacia
O isolamento excessivo pode limitar o acesso a inovações, avanços culturais e tecnológicos, e até mesmo dificultar o acesso a mercados externos. Por isso, é importante que haja canais de comunicação e métodos de diplomacia para interagir com outras comunidades. Os condomínios podem, por exemplo, estabelecer parcerias com outras regiões, seja para troca de produtos, serviços ou até para inovação. Isso garante que a rede de condomínios não se torne autossuficiente ao ponto de se desconectar do resto do mundo, o que pode resultar em estagnação.
Feiras, mercados intercondomínios e até eventos culturais e educacionais podem ser organizados para promover essas interações. A colaboração entre as comunidades e o exterior não precisa ser baseada em uma troca de dependência, mas sim numa rede de oportunidades que cria benefícios para todas as partes envolvidas. Uma boa reputação atrai novos moradores, pode valorizar propriedades e facilitar parcerias. A diplomacia entre as comunidades também pode ser exercida para resolver disputas ou desafios externos.
A manutenção de boas relações entre condomínios é essencial para garantir uma rede de apoio mútuo eficiente. Essas relações incentivam a troca de bens e serviços, como alimentos, assistência médica ou soluções tecnológicas, além de fortalecer a autossuficiência regional. Ao colaborar em segurança, infraestrutura compartilhada, eventos culturais e até mesmo na resolução de conflitos, os condomínios se tornam mais resilientes e eficientes, reduzindo a dependência externa e melhorando a qualidade de vida dos moradores. A cooperação contínua cria um ambiente mais seguro e harmonioso.
Educação e Desenvolvimento Humano
Cada comunidade pode criar escolas internas com currículos adaptados às especializações de seus moradores. Por exemplo, em um condomínio agrícola, podem ser ensinadas práticas agrícolas sustentáveis, e em um condomínio tecnológico, cursos de programação e inovação. Isso permite que crianças e jovens cresçam em ambientes que reforçam as competências valorizadas pela comunidade.
Além das escolas internas, o conceito de homeschooling pode ser incentivado, permitindo que os pais eduquem seus filhos conforme seus próprios valores e necessidades, com o apoio da comunidade. Esse modelo oferece uma educação mais flexível e personalizada, ao contrário do currículo tradicional oferecido pelo sistema público atual.
Os condomínios universitários também podem surgir, criando ambientes dedicados ao desenvolvimento acadêmico, científico e profissional, onde estudantes vivem e aprendem. Além disso, programas de capacitação contínua são essenciais, com oficinas e cursos oferecidos dentro do condomínio para garantir que os moradores se atualizem com novas tecnologias e práticas.
Para ampliar os horizontes educacionais, os intercâmbios estudantis entre diferentes condomínios podem ser incentivados. Esses intercâmbios não se limitam apenas ao ambiente educacional, mas também se estendem ao aprendizado de práticas de vida e habilidades técnicas. Os jovens de diferentes condomínios podem viajar para outras comunidades para estudar, trabalhar ou simplesmente trocar ideias. Isso pode ocorrer de diversas formas, como programas de curto e longo prazo, através de acordos entre os próprios condomínios, permitindo que os estudantes se conectem com outras comunidades, aprendam sobre diferentes especializações e desenvolvam uma compreensão mais ampla.
Essa abordagem descentralizada permite que cada comunidade desenvolva as competências essenciais sem depender de estruturas limitantes do estado ou sistemas educacionais centralizados. Ao proporcionar liberdade de escolha e personalização, os condomínios criam ambientes propícios ao crescimento humano, alinhados às necessidades e interesses de seus moradores.
A sociedade dos condomínios privados propõe uma estrutura alternativa de convivência onde as pessoas podem viver de acordo com seus próprios valores e necessidades. Esses condomínios oferecem um modelo de organização que desafia a centralização estatal, buscando criar comunidades adaptáveis e inovadoras. A liberdade garante que as habilidades necessárias para o sustento e crescimento das comunidades sejam mantidas ao longo do tempo.
A troca de bens, serviços e conhecimentos entre os condomínios, sem a imposição de forças externas, cria uma rede de boas relações, onde o comércio e a colaboração substituem a intervenção estatal. Em vez de depender de sistemas coercitivos, cada condomínio funciona como um microcosmo autônomo que, juntos, formam um ecossistema dinâmico e próspero. Este modelo propõe que, por meio de trocas voluntárias, possamos construir uma sociedade mais saudável. Lembre-se: Ideias e somente ideias podem iluminar a escuridão.
-
 @ 3bf0c63f:aefa459d
2024-03-19 14:32:01
@ 3bf0c63f:aefa459d
2024-03-19 14:32:01Censorship-resistant relay discovery in Nostr
In Nostr is not decentralized nor censorship-resistant I said Nostr is centralized. Peter Todd thinks it is centralized by design, but I disagree.
Nostr wasn't designed to be centralized. The idea was always that clients would follow people in the relays they decided to publish to, even if it was a single-user relay hosted in an island in the middle of the Pacific ocean.
But the Nostr explanations never had any guidance about how to do this, and the protocol itself never had any enforcement mechanisms for any of this (because it would be impossible).
My original idea was that clients would use some undefined combination of relay hints in reply tags and the (now defunct)
kind:2relay-recommendation events plus some form of manual action ("it looks like Bob is publishing on relay X, do you want to follow him there?") to accomplish this. With the expectation that we would have a better idea of how to properly implement all this with more experience, Branle, my first working client didn't have any of that implemented, instead it used a stupid static list of relays with read/write toggle -- although it did publish relay hints and kept track of those internally and supportedkind:2events, these things were not really useful.Gossip was the first client to implement a truly censorship-resistant relay discovery mechanism that used NIP-05 hints (originally proposed by Mike Dilger) relay hints and
kind:3relay lists, and then with the simple insight of NIP-65 that got much better. After seeing it in more concrete terms, it became simpler to reason about it and the approach got popularized as the "gossip model", then implemented in clients like Coracle and Snort.Today when people mention the "gossip model" (or "outbox model") they simply think about NIP-65 though. Which I think is ok, but too restrictive. I still think there is a place for the NIP-05 hints,
nprofileandneventrelay hints and specially relay hints in event tags. All these mechanisms are used together in ZBD Social, for example, but I believe also in the clients listed above.I don't think we should stop here, though. I think there are other ways, perhaps drastically different ways, to approach content propagation and relay discovery. I think manual action by users is underrated and could go a long way if presented in a nice UX (not conceived by people that think users are dumb animals), and who knows what. Reliance on third-parties, hardcoded values, social graph, and specially a mix of multiple approaches, is what Nostr needs to be censorship-resistant and what I hope to see in the future.
-
 @ 95543309:196c540e
2025-05-10 07:29:13
@ 95543309:196c540e
2025-05-10 07:29:13:bob:
rant
why the fuck bunkers and stuff try to enctypt long text articles with nip 44
end rant
-
 @ 3bf0c63f:aefa459d
2024-01-29 02:19:25
@ 3bf0c63f:aefa459d
2024-01-29 02:19:25Nostr: a quick introduction, attempt #1
Nostr doesn't have a material existence, it is not a website or an app. Nostr is just a description what kind of messages each computer can send to the others and vice-versa. It's a very simple thing, but the fact that such description exists allows different apps to connect to different servers automatically, without people having to talk behind the scenes or sign contracts or anything like that.
When you use a Nostr client that is what happens, your client will connect to a bunch of servers, called relays, and all these relays will speak the same "language" so your client will be able to publish notes to them all and also download notes from other people.
That's basically what Nostr is: this communication layer between the client you run on your phone or desktop computer and the relay that someone else is running on some server somewhere. There is no central authority dictating who can connect to whom or even anyone who knows for sure where each note is stored.
If you think about it, Nostr is very much like the internet itself: there are millions of websites out there, and basically anyone can run a new one, and there are websites that allow you to store and publish your stuff on them.
The added benefit of Nostr is that this unified "language" that all Nostr clients speak allow them to switch very easily and cleanly between relays. So if one relay decides to ban someone that person can switch to publishing to others relays and their audience will quickly follow them there. Likewise, it becomes much easier for relays to impose any restrictions they want on their users: no relay has to uphold a moral ground of "absolute free speech": each relay can decide to delete notes or ban users for no reason, or even only store notes from a preselected set of people and no one will be entitled to complain about that.
There are some bad things about this design: on Nostr there are no guarantees that relays will have the notes you want to read or that they will store the notes you're sending to them. We can't just assume all relays will have everything — much to the contrary, as Nostr grows more relays will exist and people will tend to publishing to a small set of all the relays, so depending on the decisions each client takes when publishing and when fetching notes, users may see a different set of replies to a note, for example, and be confused.
Another problem with the idea of publishing to multiple servers is that they may be run by all sorts of malicious people that may edit your notes. Since no one wants to see garbage published under their name, Nostr fixes that by requiring notes to have a cryptographic signature. This signature is attached to the note and verified by everybody at all times, which ensures the notes weren't tampered (if any part of the note is changed even by a single character that would cause the signature to become invalid and then the note would be dropped). The fix is perfect, except for the fact that it introduces the requirement that each user must now hold this 63-character code that starts with "nsec1", which they must not reveal to anyone. Although annoying, this requirement brings another benefit: that users can automatically have the same identity in many different contexts and even use their Nostr identity to login to non-Nostr websites easily without having to rely on any third-party.
To conclude: Nostr is like the internet (or the internet of some decades ago): a little chaotic, but very open. It is better than the internet because it is structured and actions can be automated, but, like in the internet itself, nothing is guaranteed to work at all times and users many have to do some manual work from time to time to fix things. Plus, there is the cryptographic key stuff, which is painful, but cool.
-
 @ 30611079:ecac89f8
2025-05-10 13:30:51
@ 30611079:ecac89f8
2025-05-10 13:30:51Um Shell Script simples para facilitar backups bip39 baseados nos números das palavras, coloque o script na mesma pasta que o arquivo contendo as palavras, passe o idioma no 1º argumento (Ex. english) e as palavras em sequência, a saída serão os números correspondentes as palavras passadas no idioma selecionado
```
!/bin/bash
Enter in correct diretory
if [ ${0%/} == $0 ]; then cd ${PWD} elif [ -e ${PWD}/${0%/} ]; then cd ${PWD}/${0%/} else cd ${0%/} fi
file="$1.txt"
index=0 numbers=() for word in "$@"; do while IFS= read -r linha; do if [[ "$linha" == "$word" ]]; then numbers+=($index) break fi ((index++)) done < "$file" index=0 done echo "${numbers[@]}" ```
Fiz para aprender um pouco de Shell Script, podem dizer se está bom e se dá para melhorar algo?
Também fiz outro que faz o processo reverso
-
 @ 318ebaba:9a262eae
2025-05-10 07:19:47
@ 318ebaba:9a262eae
2025-05-10 07:19:47Relays play a crucial role in the Nostr communication protocol, serving as the backbone of its decentralized architecture. Here’s an overview of their functions and significance:
Functions of Nostr Relays
-
Data Storage and Broadcasting: Relays act as intermediaries that store and distribute messages between users. When a user sends a message, it is transmitted to one or more relays, which then broadcast that message to other connected clients. This decentralized approach ensures that no single entity controls the flow of information, enhancing censorship resistance[1][2][6].
-
Interoperability: Users can connect to multiple relays simultaneously, allowing them to access the same content across different applications. This interoperability means that messages can be shared and retrieved from various clients without being tied to a specific platform, promoting a more flexible user experience[4][11].
-
User Control: Anyone can run their own relay, which empowers users to maintain control over their data and interactions. By operating a personal relay, users can ensure that their messages are stored and accessible without relying on third-party services, thus enhancing privacy and security[3][7][11].
-
Performance and Reliability: The performance of a Nostr client can be influenced by the relays it connects to. If a relay is slow or unreliable, it can affect the overall user experience. Users are encouraged to choose or add multiple relays to improve message delivery speed and reliability[7][8][11].
Types of Relays
-
Public and Private Relays: There are both public and private relays available. Public relays are free to use, while private relays may charge fees. Paid relays often provide better performance and reduced spam, as the cost can deter malicious users from flooding the network with unwanted content[6][7][14].
-
Self-Hosted Relays: For those who want maximum control and privacy, setting up a self-hosted relay is an option. This allows users to manage their own data and ensure that their communications are not subject to external censorship or data loss[4][7].
In summary, relays are essential to the Nostr protocol, facilitating decentralized communication by storing, broadcasting, and managing messages across a network of users. They enhance user autonomy, improve performance, and contribute to the overall resilience of the Nostr ecosystem. [1] https://www.voltage.cloud/blog/the-essential-guide-to-nostr-relays [2] https://substack.com/home/post/p-158872714?utm_campaign=post&utm_medium=web [3] https://www.purplerelay.com/how-to-run-a-nostr-relay-a-step-by-step-guide/ [4] https://medium.com/@michael.leigh.stewart/nostr-series-part-3-setting-up-a-relay-6f9ca426e43e [5] https://www.voltage.cloud/blog/understanding-nostr-data-storage-relays-and-decentralization [6] https://www.ccn.com/education/what-is-nostr-and-how-to-start-using-nostr/ [7] https://nostr.how/en/relays [8] https://blog.theya.us/what-is-nostr/ [9] https://www.cointribune.com/en/nostr-pour-les-debutants-tout-ce-que-vous-devez-savoir-sur-le-protocole-2/ [10] https://community.umbrel.com/t/introducing-the-official-nostr-relay-app/11339 [11] https://nostr.com/ [12] https://www.habyb.com/blog/nostr-what-is-this-protocol-and-how-does-it-work/ [13] https://www.reddit.com/r/nostr/comments/15jmhpi/purpose_of_free_vs_paid_relay/ [14] https://nostr.com/relays [15] https://www.reddit.com/r/nostr/comments/115cgcu/whats_the_point_of_adding_more_and_more_relays_do/ [16] https://messari.io/copilot/share/understanding-nostr-f00aa3df-d02c-4381-91f5-9a103b8e25ce
-
-
 @ 866e0139:6a9334e5
2025-05-10 11:29:23
@ 866e0139:6a9334e5
2025-05-10 11:29:23\ Autor: Kerstin Chavent. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
Wir halten uns für erwacht, weil wir das Coronanarrativ durchschaut haben, regierungskritisch unterwegs sind und Russland nicht für den ärgsten Feind der Demokratie halten? Wir informieren uns in alternativen und unabhängigen Medien, folgen geistigen Führern und sehen Spiritualität als einen Teil unseres Daseins auf der Erde? Vielleicht sind wir mit Meditationstechniken vertraut, machen Yoga oder nehmen bewusstseinserweiternde Substanzen zu uns? Wir denken, andere würden noch schlafen, weil sie das nicht tun? Dann haben wir noch einen weiten Weg vor uns.
Aufwachen — wir tun es jeden Morgen und oft auch während der Nacht. Der Kopf ist schwer, vielleicht ein wenig verwirrt, wie in einem Nebel. Die Schleier der Träume hängen noch an uns. Wir sind noch nicht ganz da und brauchen eine Dusche, einen Kaffee oder frische Luft, um langsam durchzukommen und den Tag zu beginnen. In den seltensten Fällen ist es so, dass wir die Augen aufschlagen und hellwach sind, vollkommen präsent und klar. So passt die Metapher auf das, was heute auf den Bewusstseinszustand der Menschen angewendet wird.
Was bedeutet es, wach zu sein? Ein waches Bewusstsein zu haben? Was ist Bewusstsein? Eine der großen Referenzen für Psychologie und Pädagogik hat einen eher beschränkten und materialistisch orientierten Bewusstseinsbegriff. Demnach reiche Bewusstsein nicht über das normale Denken hinaus. Bewusstsein habe ein Mensch immer dann, wenn er in der Lage ist, zu bedenken, ob das, was er tut, vernünftig ist. Das Bewusstsein sei an das Gehirn gebunden. Ein Bewusstsein ohne Aktivität von Nervenzellen im menschlichen Gehirn gebe es nicht. Das sei wissenschaftlicher Konsens. Über noch etwas ist man sich einig:
Nach Jahrhunderten der Bemühung von Neurowissenschaftlern, Psychologen und Philosophen bleibt zu der Frage, wie das Gehirn uns denn Bewusstsein verleiht, wie es Empfindungen, Gefühle und Subjektivität entstehen lässt, nur eine Gewissheit: Wir haben keine Ahnung (1).
Mehr Ahnung haben wir, wenn es darum geht, das menschliche Bewusstsein zu manipulieren. Voraussetzung ist, die zu manipulierende Person in Unkenntnis zu lassen. Es wird ein Gefühl von Machtlosigkeit in ihr erzeugt und ein System von Belohnung und Strafe aufgebaut, um eine autoritäre Machtstruktur, die kein Feedback und keine Änderung ohne Zustimmung oder Anordnung der Führung zulässt, zu installieren. Hierfür ist keine Gewaltanwendung erforderlich. Für eine mentale Umprogrammierung reicht es, jede Form von Kritik zu unterdrücken und Kritiker zu diffamieren, indem man ihnen persönliche Rachemotive oder menschliche Schwäche andichtet (2).
Manipulation mit Angst
Angst ist eines der wirksamsten Mittel, um das Bewusstsein der Menschen zu manipulieren. Wer Angst hat, lässt sich leicht täuschen. Das Bewusstsein verengt sich regelrecht. Damit ergibt sich ein nahezu unerschöpflicher Fundus von Methoden zur Bewusstseinskontrolle. Welche, das erleben wir täglich: die Erschaffung einer Unterhaltungsindustrie und die Verbreitung von Filmen, in denen es vor allem um Mord, Verrat, Krankheit und Betrug geht; Medien, die maximale Verwirrung schaffen; giftige Substanzen in Nahrungsmitteln und Wasser; ein knechtendes Finanzsystem; Medikamente, von denen wir möglichst früh und möglichst lange abhängig sind.
Wer das Bewusstsein der Menschen und damit die Welt in den Griff bekommen will, fängt früh an. Er erfindet zum Beispiel Religionen, die sich nach Möglichkeit gegenseitig bekämpfen.
Er erzählt Geschichten, in denen die eine Hälfte der Menschheit der anderen per se unterlegen sein soll, erfindet Götter, die die einen privilegieren und die anderen bestrafen, und ein Paradies, das irgendwoanders ist als dort, wo wir gerade sind.
Alles ist darauf ausgerichtet, dass der Mensch sich klein, unwürdig, schuldig und vor allem ohnmächtig fühlt. Auf keinen Fall darf er sich seiner angeborenen Möglichkeiten bewusstwerden! Hierfür werden Kinder so früh wie möglich von den Eltern getrennt, bekommen in staatlichen Schulen ihre Kreativität und Eigenmacht aberzogen, werden von technischen Geräten abhängig gemacht und durch Geschlechterverwirrung davon abgehalten, ihre Identität zu entwickeln. So werden sie darauf vorbereitet, zu guten Soldaten des Systems zu werden und in jeden Krieg zu ziehen, der ihnen als notwendig verkauft wird.
Project Blue Beam
Immer mehr Menschen wissen das. Immer mehr erkennen, was auf der Bühne des Welttheaters gespielt wird. Doch sind wir deshalb erwacht? Reicht es, alternative Medien zu konsumieren, bewusstseinserweiternde Substanzen zu sich zu nehmen und regelmäßig zu meditieren, um das eigene Bewusstsein zu entwickeln? Reichen die Bücher, die Workshops und die charismatischen Führer, die überall zu finden sind? Sind wir erwacht, nur weil der Nachbar noch schläft?
Wie würden wir zum Beispiel reagieren, wenn das Projekt „Blue Beam“ durchgespielt werden würde? Natürlich soll es sich hierbei um eine Verschwörungstheorie handeln. Aber nur mal angenommen. Es geht darum, durch das Erschaffen einer allgemeinen Unsicherheit und Hysterie eine neue Weltordnung durchzusetzen.
In einer ersten Etappe sollen künstlich erschaffene Naturkatastrophen dafür sorgen, dass die Menschen sämtliche religiöse Fundamente in Frage stellen. In einer zweiten Etappe werden mittels dreidimensionaler Hologramme verschiedene Gottesbilder in den Himmel projiziert mit dem Ziel, eine Einheitsreligion zu proklamieren. In einer dritten Etappe sollen mittels Niederfrequenzen und per Satellit Gedankengänge gezielt beeinflusst werden, und in einem letzten Schritt soll die Menschheit davon überzeugt werden, dass in allen großen Städten der Welt eine Invasion Außerirdischer nahe bevorsteht.
Jede große Nation soll dazu aufgefordert werden, ihr nukleares Potenzial als Abwehr zu benutzen. Es soll sich jedoch um ein Fake-Manöver handeln. Den Nationen, nun ihrer Waffen entledigt, bliebe nur noch die Hoffnung auf einen göttlichen Eingriff. Alle „erwachten“ Menschen würden von „guten“ außerirdischen Kräften „gerettet“ und entführt werden — womit der neuen Weltordnung auf Erden nichts mehr im Wege stünde. Der Rest der Menschheit würde mittels über elektronische Geräte verbreiteter böser Geister in den Wahnsinn und die totale Hoffnungslosigkeit getrieben werden.
Selbstwirksamkeit?
Die Geschichte ist haarsträubend. Doch wer könnte beschwören, dass sie technisch nicht möglich wäre? Wer könnte sich sicher sein, einer False-Flag-Aktion nicht auf den Leim zu gehen? Wer könnte von sich behaupten, so erwacht, so in seinem Bewusstsein verankert zu sein, dass er sich nicht manipulieren ließe, wenn es darauf ankommt? Wer griffe nicht in der Verzweiflung nach einem Heiligenbild, das am Himmel aufsteigt? Wer wäre erhaben über jede Art von Mind Control?
So möge der stille werden, der sich rühmt, erwacht zu sein. Möge er sich den Schlaf aus den Augen reiben und sich an die Arbeit machen. Denn das Erwachen ist nur der allererste Schritt. Dann geht es erst richtig los.
Dann können wir üben, in die Selbstwirksamkeit zu kommen: das Vertrauen in die eigenen Möglichkeiten, Aufgabenanforderungen wirksam zu bewältigen und auch in Extremsituationen gewünschte Handlungen selbst ausführen zu können.
Die Frage ist nicht, wie erwacht wir uns im Vergleich mit anderen fühlen, sondern welches Selbst- und Menschenbild wir haben und wie wir von unserer natürlichen Schöpferkraft Gebrauch machen. Nicht der ist erwacht, der sich von Katastrophenmeldungen einlullen lässt und sich gemütlich in seinen vier Wänden auf den Weltuntergang vorbereitet, sondern der, der sich darauf besinnt, dass Bewusstsein mehr ist als ein paar Synapsen im Gehirn. Er weiß, dass er über einen freien Willen verfügt, der ihn dazu befähigt, in eine andere Richtung zu gehen.
Außen wie innen
Bewusstsein hängt von keinem spirituellen Führer ab und auch von keinem Gott, der in den Himmel projiziert wird. Bewusstsein ist göttlich. Es ist die Fähigkeit, Dinge wahr-zu-nehmen, ihren Wahrheitsgehalt zu erkennen, die Gabe, aus sich heraus feinfühlig zu sein, hellsichtig, verstehend. Im individuellen Bewusstsein sind das Menschliche und das Göttliche eins. Nichts steht trennend dazwischen. Niemand muss die Erlaubnis für diesen Erkenntnisprozess geben.
Wer bei Bewusstsein ist, den kann man nicht in ein Gedankengefängnis einsperren oder ihn mit Hierarchien beeindrucken. Er weiß, dass das Wesentliche sich im Innen abspielt und dass allein er für das verantwortlich ist, was er erlebt.
Ein hoch entwickeltes Bewusstsein bedeutet, sich von jeder Erwartung zu lösen, dass sich im Außen etwas ändert. Wer sich auf das Außen konzentriert, der hat schon verloren. Er drückt sich selbst den Stempel der Ohnmacht und des Mangels auf oder befeuert die Kriegsmaschinerie, die alles in die Zerstörung treibt.
Im Inneren gilt es, für Harmonie zu sorgen und sich auf die Frequenzen des Schöpferischen einzustellen. So darf sich jeder fragen: Wie sieht es bei mir aus? Bin ich von Menschen umgeben, die mich erniedrigen oder die mich erhöhen? Lebe ich das Leben, das ich mir wünsche? Bin ich im Mangel oder im Überfluss? Bin ich krank oder gesund? Ängstlich oder vertrauend? Zynisch oder liebevoll? Wie halte ich es? Wie ist meine Stimmung? Wie fühle ich mich in dieser Zeit, in dieser Welt? Wage ich es, Nein zu sagen, wenn alle Ja sagen, und Ja, wenn alle Nein sagen?
Wie selbstwirksam bin ich? Wie benutze ich die mir angeborene Schöpferkraft? Lasse ich mit mir machen oder mache ich selbst? Welche Menschen und Ereignisse ziehe ich an? Auf welcher Ebene schwingt meine Energie? Mit welchen Kräften stehe ich in Kontakt? Welche Informationen empfange ich? Wie viel Individualität wage ich? Nicht eine Individualität, die andere ausschließt, sondern eine, die alles miteinschließt und von dem Bewusstsein geleitet wird, dass alles eins ist.
Fühle ich mich getrennt oder verbunden? Fühle ich, dass ich unteilbar bin: in-dividuum? Spüre ich, wie ich aus der Kraft dieser Unteilbarkeit heraus unermessliche Möglichkeiten habe, mein Leben und damit die Welt zu gestalten? Bin ich wirklich erwacht oder halte ich mich nur für etwas Besseres, um bei der nächstbesten Gelegenheit genau das zu tun, was ich an anderen kritisiert habe: mein Heil von außen zu erwarten?
Angst- oder Christusmatrix?
Was auch kommt in der nächsten Zeit: Es wird uns überraschen. Jede Menge Möglichkeiten wird es geben, in denen wir unser Bewusstsein und unsere Individualität auf die Probe stellen können. Auf uns kommt es an! Jeder Mensch, der sich selbst aus der Ohnmacht befreit, befreit auch die Welt ein wenig mehr. Jeder, der sich nicht von schlechten Nachrichten nach unten ziehen lässt, jeder, der darauf achtet, seine Energie möglichst hoch schwingen zu lassen, jeder, der in sich selbst die Lösung sucht, ist ein Segen für diese Zeit, ein Tor für das Göttliche auf Erden.
Göttlich, so die Bewusstseinstrainerin Sandra Weber, ist alles, was natürlich ist, alles, was liebt, was pulsiert, leuchtet und verbunden ist. Wir haben die Wahl, uns per Genmanipulation und künstlicher Intelligenz (KI) immer mehr entmenschlichen zu lassen oder unser multidimensionales Potenzial zu entdecken, unsere Fähigkeit zu Telepathie, Telekinese und Teleportation. Angst- oder Christusmatrix — wofür entscheiden wir uns? Lassen wir durch KI die eigene Lichtkörperaktivierung unterbrechen oder wählen wir die Erhebung und das Vertrauen in unsere Göttlichkeit (3)?
Von hier aus können wir die Bühne überblicken. Wir erkennen: Wir müssen da nicht mitmachen. Wir müssen nicht in das Welttheater einsteigen. Wir müssen nicht die Lichtschwerter auspacken und für das Gute kämpfen. Das Gute kämpft nicht. Das Gute ist. Was wir tun können, ist, uns von den Altlasten zu befreien, die uns unten halten, innere Kämpfe ein für alle Mal zu befrieden und unsere Schatten ins Licht zu bringen.
Erleuchtung ist, wenn die inneren Schatten aufgelöst sind und man alles überblicken kann. Er-innern wir uns. Gehen wir nach innen und bauen wir hier unsere Tempel.
Fassen wir den Mut, wir selbst zu sein. Gehen wir in unsere Herzensmitte, werden wir uns der Bewertungen bewusst, mit der wir unsere Welt in Gut und Böse einteilen, und nehmen wir einen neutralen Standpunkt ein. So kommen wir aus der Dualität zurück in die Polarität, aus einer Welt, in der sich die Dinge gegenseitig vernichten, in eine Welt, in der sie sich ergänzen und kreativ zusammenwirken.
Quellen und Anmerkungen:
(1) https://lexikon.stangl.eu/887/bewusstsein\ (2) https://de.wikipedia.org/wiki/Gehirnw%C3%A4sche\ (3) https://www.youtube.com/watch?v=grAFeprqzhs&t=13s
Kerstin Chavent ist Sprachlehrerin und lebt in Südfrankreich. Sie schreibt Artikel, Essays und autobiographische Erzählungen. Ihre Schwerpunkte sind der Umgang mit Krisensituationen und Krankheit und die Sensibilisierung für das schöpferische Potential im Menschen. Auf Deutsch erschienen sind Die wilde Göttin, Der Königsweg, Die Enthüllung, In guter Gesellschaft, Die Waffen niederlegen, Das Licht fließt dahin, wo es dunkel ist, Krankheit heilt, Was wachsen will muss Schalen abwerfen, Und Freitags kommt der Austernwagen. Weitere Informationen auf kerstinchavent.de.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 318ebaba:9a262eae
2025-05-10 07:06:45
@ 318ebaba:9a262eae
2025-05-10 07:06:45Nostr, which stands for "Notes and Other Stuff Transmitted by Relays," is a decentralized communication protocol designed to facilitate the exchange of messages without relying on centralized servers. This innovative framework allows users to create, broadcast, and receive messages freely, emphasizing user empowerment and censorship resistance.
Key Features of Nostr
-
Decentralization: Unlike traditional social media platforms, Nostr operates on a network of relays, which are servers that anyone can run. This structure eliminates the control that a single entity can exert over the platform, thereby reducing the risk of censorship and enhancing user privacy[1][4][5].
-
Open Protocol: Nostr is not an application itself but a protocol that developers can use to build various applications. This openness allows for a wide range of services, from social media to messaging, all built on the same underlying technology. Users can access multiple applications using a single public/private key pair, making it easier to manage their online identities[2][3][4].
-
Censorship Resistance: One of the primary motivations behind Nostr's creation is to provide a platform where users can communicate without fear of censorship. This is particularly appealing to those disillusioned with traditional social media platforms that often impose restrictions on content[5][10].
-
User Control: Nostr empowers users by allowing them to control their data and interactions. Users can choose which relays to connect to and can run their own relays, ensuring that they are not dependent on any single service provider[4][5][7].
-
Cryptographic Security: The protocol employs public-key cryptography to secure messages and verify identities, similar to how Bitcoin operates. This ensures that messages are authentic and have not been tampered with during transmission[5][10].
Applications and Community
Nostr has gained traction among various communities, particularly within the cryptocurrency space, where figures like Jack Dorsey and Edward Snowden have expressed support for its potential to reshape online communication. The protocol's design allows for a variety of applications, including social media platforms, chat services, and content sharing tools, all of which can interoperate seamlessly[2][3][5].
In summary, Nostr represents a significant shift in how digital communication can be structured, prioritizing decentralization, user autonomy, and resistance to censorship, making it a compelling alternative to conventional social media platforms. [1] https://threenine.blog/posts/what-is-nostr [2] https://www.forbes.com/sites/digital-assets/2023/04/11/how-to-get-started-with-nostr/ [3] https://www.forbes.com/sites/digital-assets/2024/07/17/your-guide-to-nostr-the-decentralized-network-for-everything/ [4] https://www.ledger.com/academy/glossary/nostr [5] https://river.com/learn/what-is-nostr/ [6] https://www.cointribune.com/en/comment-utiliser-nostr-guide-pour-debutants-2/ [7] https://www.ccn.com/education/what-is-nostr-and-how-to-start-using-nostr/ [8] https://nostr.com/ [9] https://mylessnider.com/articles/why-im-excited-about-nostr [10] https://en.wikipedia.org/wiki/Nostr [11] https://nostr.how/en/what-is-nostr [12] https://nostr.org/ [13] https://medium.com/@colaru/an-introduction-to-nostr-protocol-dbc774ac797c [14] https://www.linkedin.com/pulse/what-nostr-manfred-van-doorn-nf9ce [15] https://www.cointribune.com/en/nostr-pour-les-debutants-tout-ce-que-vous-devez-savoir-sur-le-protocole-2/ [16] https://www.reddit.com/r/Bitcoin/comments/17j5glg/do_people_in_this_sub_know_about_nostr/ [17] https://www.voltage.cloud/blog/the-essential-guide-to-nostr-relays [18] https://www.reddit.com/r/nostr/comments/1i6t4g7/explain_how_nostr_works_like_im_a_5_year_old/ [19] https://github.com/nostr-protocol/nostr
-
-
 @ dc4152b3:dc737a27
2025-05-10 11:25:23
@ dc4152b3:dc737a27
2025-05-10 11:25:23181BET là một nền tảng trực tuyến nổi bật, cung cấp cho người dùng những trải nghiệm giải trí đa dạng và đầy sáng tạo. Với một giao diện thân thiện và dễ sử dụng, nền tảng này không chỉ hấp dẫn người tham gia nhờ vào tính năng dễ dàng tiếp cận mà còn bởi chất lượng dịch vụ vượt trội. Bằng cách tối ưu hóa trải nghiệm người dùng, 181BET đã nhanh chóng trở thành một trong những lựa chọn hàng đầu của những ai yêu thích các hoạt động giải trí trực tuyến. Nền tảng này cung cấp một loạt các trò chơi và hoạt động tương tác đa dạng, giúp người tham gia có thể thư giãn, giải trí và tận hưởng những giây phút thư thái. Các trò chơi được thiết kế một cách sáng tạo, kết hợp giữa tính giải trí cao và độ thử thách, tạo ra không gian thú vị cho người chơi. Bên cạnh đó, 181BET cũng chú trọng đến việc tạo ra một môi trường an toàn và bảo mật cao, giúp người dùng có thể hoàn toàn yên tâm khi tham gia vào các hoạt động giải trí trực tuyến mà không lo ngại về sự an toàn thông tin cá nhân hay giao dịch.
Điều làm nên sự khác biệt của 181BET chính là khả năng tạo ra một cộng đồng gắn kết và thân thiện, nơi mà người tham gia không chỉ có thể tham gia vào các trò chơi mà còn có thể giao lưu, kết nối và chia sẻ những khoảnh khắc vui vẻ. Nền tảng này cung cấp không chỉ những trò chơi đơn giản mà còn những hoạt động tương tác xã hội, giúp mọi người có thể giao lưu với nhau, học hỏi và tạo ra những mối quan hệ mới. Các tính năng giao lưu được thiết kế để mọi người có thể dễ dàng kết nối và chia sẻ với nhau, tạo ra một cộng đồng trực tuyến thân thiện và đầy sức sống. Mỗi thành viên có thể tham gia vào các hoạt động nhóm, trò chuyện và kết bạn với những người có cùng sở thích, từ đó xây dựng một mạng lưới bạn bè trực tuyến. Bên cạnh đó, 181BET còn cung cấp các tính năng nâng cao, giúp người dùng có thể dễ dàng theo dõi tiến trình và thành tích của mình trong các trò chơi, từ đó tạo động lực cho người tham gia tiếp tục khám phá và trải nghiệm những thử thách mới.
Ngoài những tính năng vượt trội về giải trí và kết nối cộng đồng, 181BET còn chú trọng đến việc bảo vệ quyền lợi và bảo mật cho người sử dụng. Nền tảng này sử dụng công nghệ bảo mật tiên tiến để đảm bảo rằng mọi thông tin cá nhân và giao dịch đều được bảo vệ một cách nghiêm ngặt. Các hệ thống mã hóa dữ liệu và bảo vệ thông tin giúp người dùng yên tâm tham gia vào các hoạt động mà không lo lắng về việc bị lộ thông tin cá nhân hay gặp phải các vấn đề bảo mật. Đặc biệt, 181BET luôn nỗ lực nâng cấp hệ thống bảo mật để phù hợp với các tiêu chuẩn cao nhất của ngành công nghệ hiện nay, tạo nên một môi trường giải trí trực tuyến an toàn và đáng tin cậy. Bên cạnh đó, nền tảng này còn cung cấp dịch vụ hỗ trợ khách hàng 24/7, sẵn sàng giải đáp mọi thắc mắc và giúp đỡ người tham gia trong suốt quá trình trải nghiệm. Với đội ngũ nhân viên hỗ trợ chuyên nghiệp và tận tâm, 181BET cam kết mang đến cho người dùng một trải nghiệm trực tuyến mượt mà và không gặp phải bất kỳ trở ngại nào. Sự kết hợp giữa công nghệ bảo mật hiện đại, dịch vụ hỗ trợ khách hàng tận tình và một nền tảng giải trí đa dạng đã giúp 181BET trở thành một lựa chọn lý tưởng cho những ai tìm kiếm một không gian giải trí trực tuyến chất lượng và an toàn.
-
 @ f9cf4e94:96abc355
2024-12-31 20:18:59
@ f9cf4e94:96abc355
2024-12-31 20:18:59Scuttlebutt foi iniciado em maio de 2014 por Dominic Tarr ( dominictarr ) como uma rede social alternativa off-line, primeiro para convidados, que permite aos usuários obter controle total de seus dados e privacidade. Secure Scuttlebutt (ssb) foi lançado pouco depois, o que coloca a privacidade em primeiro plano com mais recursos de criptografia.
Se você está se perguntando de onde diabos veio o nome Scuttlebutt:
Este termo do século 19 para uma fofoca vem do Scuttlebutt náutico: “um barril de água mantido no convés, com um buraco para uma xícara”. A gíria náutica vai desde o hábito dos marinheiros de se reunir pelo boato até a fofoca, semelhante à fofoca do bebedouro.

Marinheiros se reunindo em torno da rixa. ( fonte )
Dominic descobriu o termo boato em um artigo de pesquisa que leu.
Em sistemas distribuídos, fofocar é um processo de retransmissão de mensagens ponto a ponto; as mensagens são disseminadas de forma análoga ao “boca a boca”.
Secure Scuttlebutt é um banco de dados de feeds imutáveis apenas para acréscimos, otimizado para replicação eficiente para protocolos ponto a ponto. Cada usuário tem um log imutável somente para acréscimos no qual eles podem gravar. Eles gravam no log assinando mensagens com sua chave privada. Pense em um feed de usuário como seu próprio diário de bordo, como um diário de bordo (ou diário do capitão para os fãs de Star Trek), onde eles são os únicos autorizados a escrever nele, mas têm a capacidade de permitir que outros amigos ou colegas leiam ao seu diário de bordo, se assim o desejarem.
Cada mensagem possui um número de sequência e a mensagem também deve fazer referência à mensagem anterior por seu ID. O ID é um hash da mensagem e da assinatura. A estrutura de dados é semelhante à de uma lista vinculada. É essencialmente um log somente de acréscimo de JSON assinado. Cada item adicionado a um log do usuário é chamado de mensagem.
Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.

Perspectivas dos participantes
Scuttlebot
O software Pub é conhecido como servidor Scuttlebutt (servidor ssb ), mas também é conhecido como “Scuttlebot” e
sbotna linha de comando. O servidor SSB adiciona comportamento de rede ao banco de dados Scuttlebutt (SSB). Estaremos usando o Scuttlebot ao longo deste tutorial.Os logs do usuário são conhecidos como feed e um usuário pode seguir os feeds de outros usuários para receber suas atualizações. Cada usuário é responsável por armazenar seu próprio feed. Quando Alice assina o feed de Bob, Bob baixa o log de feed de Alice. Bob pode verificar se o registro do feed realmente pertence a Alice verificando as assinaturas. Bob pode verificar as assinaturas usando a chave pública de Alice.

Estrutura de alto nível de um feed
Pubs são servidores de retransmissão conhecidos como “super peers”. Pubs conectam usuários usuários e atualizações de fofocas a outros usuários conectados ao Pub. Um Pub é análogo a um pub da vida real, onde as pessoas vão para se encontrar e se socializar. Para ingressar em um Pub, o usuário deve ser convidado primeiro. Um usuário pode solicitar um código de convite de um Pub; o Pub simplesmente gerará um novo código de convite, mas alguns Pubs podem exigir verificação adicional na forma de verificação de e-mail ou, com alguns Pubs, você deve pedir um código em um fórum público ou chat. Pubs também podem mapear aliases de usuário, como e-mails ou nome de usuário, para IDs de chave pública para facilitar os pares de referência.
Depois que o Pub enviar o código de convite ao usuário, o usuário resgatará o código, o que significa que o Pub seguirá o usuário, o que permite que o usuário veja as mensagens postadas por outros membros do Pub, bem como as mensagens de retransmissão do Pub pelo usuário a outros membros do Pub.
Além de retransmitir mensagens entre pares, os Pubs também podem armazenar as mensagens. Se Alice estiver offline e Bob transmitir atualizações de feed, Alice perderá a atualização. Se Alice ficar online, mas Bob estiver offline, não haverá como ela buscar o feed de Bob. Mas com um Pub, Alice pode buscar o feed no Pub mesmo se Bob estiver off-line porque o Pub está armazenando as mensagens. Pubs são úteis porque assim que um colega fica online, ele pode sincronizar com o Pub para receber os feeds de seus amigos potencialmente offline.
Um usuário pode, opcionalmente, executar seu próprio servidor Pub e abri-lo ao público ou permitir que apenas seus amigos participem, se assim o desejarem. Eles também podem ingressar em um Pub público. Aqui está uma lista de Pubs públicos em que todos podem participar . Explicaremos como ingressar em um posteriormente neste guia. Uma coisa importante a observar é que o Secure Scuttlebutt em uma rede social somente para convidados significa que você deve ser “puxado” para entrar nos círculos sociais. Se você responder às mensagens, os destinatários não serão notificados, a menos que estejam seguindo você de volta. O objetivo do SSB é criar “ilhas” isoladas de redes pares, ao contrário de uma rede pública onde qualquer pessoa pode enviar mensagens a qualquer pessoa.


Perspectivas dos participantes
Pubs - Hubs
Pubs públicos
| Pub Name | Operator | Invite Code | | ------------------------------------------------------------ | ------------------------------------------------------------ | ------------------------------------------------------------ | |
scuttle.us| @Ryan |scuttle.us:8008:@WqcuCOIpLtXFRw/9vOAQJti8avTZ9vxT9rKrPo8qG6o=.ed25519~/ZUi9Chpl0g1kuWSrmehq2EwMQeV0Pd+8xw8XhWuhLE=| | pub1.upsocial.com | @freedomrules |pub1.upsocial.com:8008:@gjlNF5Cyw3OKZxEoEpsVhT5Xv3HZutVfKBppmu42MkI=.ed25519~lMd6f4nnmBZEZSavAl4uahl+feajLUGqu8s2qdoTLi8=| | Monero Pub | @Denis |xmr-pub.net:8008:@5hTpvduvbDyMLN2IdzDKa7nx7PSem9co3RsOmZoyyCM=.ed25519~vQU+r2HUd6JxPENSinUWdfqrJLlOqXiCbzHoML9iVN4=| | FreeSocial | @Jarland |pub.freesocial.co:8008:@ofYKOy2p9wsaxV73GqgOyh6C6nRGFM5FyciQyxwBd6A=.ed25519~ye9Z808S3KPQsV0MWr1HL0/Sh8boSEwW+ZK+8x85u9w=| |ssb.vpn.net.br| @coffeverton |ssb.vpn.net.br:8008:@ze8nZPcf4sbdULvknEFOCbVZtdp7VRsB95nhNw6/2YQ=.ed25519~D0blTolH3YoTwSAkY5xhNw8jAOjgoNXL/+8ZClzr0io=| | gossip.noisebridge.info | Noisebridge Hackerspace @james.network |gossip.noisebridge.info:8008:@2NANnQVdsoqk0XPiJG2oMZqaEpTeoGrxOHJkLIqs7eY=.ed25519~JWTC6+rPYPW5b5zCion0gqjcJs35h6JKpUrQoAKWgJ4=|Pubs privados
Você precisará entrar em contato com os proprietários desses bares para receber um convite.
| Pub Name | Operator | Contact | | --------------------------------------------- | ------------------------------------------------------------ | ----------------------------------------------- | |
many.butt.nz| @dinosaur | mikey@enspiral.com | |one.butt.nz| @dinosaur | mikey@enspiral.com | |ssb.mikey.nz| @dinosaur | mikey@enspiral.com | | ssb.celehner.com | @cel | cel@celehner.com |Pubs muito grandes
Aviso: embora tecnicamente funcione usar um convite para esses pubs, você provavelmente se divertirá se o fizer devido ao seu tamanho (muitas coisas para baixar, risco para bots / spammers / idiotas)
| Pub Name | Operator | Invite Code | | --------------------------------------- | ----------------------------------------------- | ------------------------------------------------------------ | |
scuttlebutt.de| SolSoCoG |scuttlebutt.de:8008:@yeh/GKxlfhlYXSdgU7CRLxm58GC42za3tDuC4NJld/k=.ed25519~iyaCpZ0co863K9aF+b7j8BnnHfwY65dGeX6Dh2nXs3c=| |Lohn's Pub| @lohn |p.lohn.in:8018:@LohnKVll9HdLI3AndEc4zwGtfdF/J7xC7PW9B/JpI4U=.ed25519~z3m4ttJdI4InHkCtchxTu26kKqOfKk4woBb1TtPeA/s=| | Scuttle Space | @guil-dot | Visit scuttle.space | |SSB PeerNet US-East| timjrobinson |us-east.ssbpeer.net:8008:@sTO03jpVivj65BEAJMhlwtHXsWdLd9fLwyKAT1qAkc0=.ed25519~sXFc5taUA7dpGTJITZVDCRy2A9jmkVttsr107+ufInU=| | Hermies | s | net:hermies.club:8008~shs:uMYDVPuEKftL4SzpRGVyQxLdyPkOiX7njit7+qT/7IQ=:SSB+Room+PSK3TLYC2T86EHQCUHBUHASCASE18JBV24= |GUI - Interface Gráfica do Utilizador(Usuário)
Patchwork - Uma GUI SSB (Descontinuado)
Patchwork é o aplicativo de mensagens e compartilhamento descentralizado construído em cima do SSB . O protocolo scuttlebutt em si não mantém um conjunto de feeds nos quais um usuário está interessado, então um cliente é necessário para manter uma lista de feeds de pares em que seu respectivo usuário está interessado e seguindo.

Fonte: scuttlebutt.nz
Quando você instala e executa o Patchwork, você só pode ver e se comunicar com seus pares em sua rede local. Para acessar fora de sua LAN, você precisa se conectar a um Pub. Um pub é apenas para convidados e eles retransmitem mensagens entre você e seus pares fora de sua LAN e entre outros Pubs.
Lembre-se de que você precisa seguir alguém para receber mensagens dessa pessoa. Isso reduz o envio de mensagens de spam para os usuários. Os usuários só veem as respostas das pessoas que seguem. Os dados são sincronizados no disco para funcionar offline, mas podem ser sincronizados diretamente com os pares na sua LAN por wi-fi ou bluetooth.
Patchbay - Uma GUI Alternativa
Patchbay é um cliente de fofoca projetado para ser fácil de modificar e estender. Ele usa o mesmo banco de dados que Patchwork e Patchfoo , então você pode facilmente dar uma volta com sua identidade existente.

Planetary - GUI para IOS

Planetary é um app com pubs pré-carregados para facilitar integração.
Manyverse - GUI para Android

Manyverse é um aplicativo de rede social com recursos que você esperaria: posts, curtidas, perfis, mensagens privadas, etc. Mas não está sendo executado na nuvem de propriedade de uma empresa, em vez disso, as postagens de seus amigos e todos os seus dados sociais vivem inteiramente em seu telefone .
Fontes
-
https://scuttlebot.io/
-
https://decentralized-id.com/decentralized-web/scuttlebot/#plugins
-
https://medium.com/@miguelmota/getting-started-with-secure-scuttlebut-e6b7d4c5ecfd
-
Secure Scuttlebutt : um protocolo de banco de dados global.
-
-
 @ c631e267:c2b78d3e
2025-04-04 18:47:27
@ c631e267:c2b78d3e
2025-04-04 18:47:27Zwei mal drei macht vier, \ widewidewitt und drei macht neune, \ ich mach mir die Welt, \ widewide wie sie mir gefällt. \ Pippi Langstrumpf
Egal, ob Koalitionsverhandlungen oder politischer Alltag: Die Kontroversen zwischen theoretisch verschiedenen Parteien verschwinden, wenn es um den Kampf gegen politische Gegner mit Rückenwind geht. Wer den Alteingesessenen die Pfründe ernsthaft streitig machen könnte, gegen den werden nicht nur «Brandmauern» errichtet, sondern der wird notfalls auch strafrechtlich verfolgt. Doppelstandards sind dabei selbstverständlich inklusive.
In Frankreich ist diese Woche Marine Le Pen wegen der Veruntreuung von EU-Geldern von einem Gericht verurteilt worden. Als Teil der Strafe wurde sie für fünf Jahre vom passiven Wahlrecht ausgeschlossen. Obwohl das Urteil nicht rechtskräftig ist – Le Pen kann in Berufung gehen –, haben die Richter das Verbot, bei Wahlen anzutreten, mit sofortiger Wirkung verhängt. Die Vorsitzende des rechtsnationalen Rassemblement National (RN) galt als aussichtsreiche Kandidatin für die Präsidentschaftswahl 2027.
Das ist in diesem Jahr bereits der zweite gravierende Fall von Wahlbeeinflussung durch die Justiz in einem EU-Staat. In Rumänien hatte Călin Georgescu im November die erste Runde der Präsidentenwahl überraschend gewonnen. Das Ergebnis wurde später annulliert, die behauptete «russische Wahlmanipulation» konnte jedoch nicht bewiesen werden. Die Kandidatur für die Wahlwiederholung im Mai wurde Georgescu kürzlich durch das Verfassungsgericht untersagt.
Die Veruntreuung öffentlicher Gelder muss untersucht und geahndet werden, das steht außer Frage. Diese Anforderung darf nicht selektiv angewendet werden. Hingegen mussten wir in der Vergangenheit bei ungleich schwerwiegenderen Fällen von (mutmaßlichem) Missbrauch ganz andere Vorgehensweisen erleben, etwa im Fall der heutigen EZB-Chefin Christine Lagarde oder im «Pfizergate»-Skandal um die Präsidentin der EU-Kommission Ursula von der Leyen.
Wenngleich derartige Angelegenheiten formal auf einer rechtsstaatlichen Grundlage beruhen mögen, so bleibt ein bitterer Beigeschmack. Es stellt sich die Frage, ob und inwieweit die Justiz politisch instrumentalisiert wird. Dies ist umso interessanter, als die Gewaltenteilung einen essenziellen Teil jeder demokratischen Ordnung darstellt, während die Bekämpfung des politischen Gegners mit juristischen Mitteln gerade bei den am lautesten rufenden Verteidigern «unserer Demokratie» populär zu sein scheint.
Die Delegationen von CDU/CSU und SPD haben bei ihren Verhandlungen über eine Regierungskoalition genau solche Maßnahmen diskutiert. «Im Namen der Wahrheit und der Demokratie» möchte man noch härter gegen «Desinformation» vorgehen und dafür zum Beispiel den Digital Services Act der EU erweitern. Auch soll der Tatbestand der Volksverhetzung verschärft werden – und im Entzug des passiven Wahlrechts münden können. Auf europäischer Ebene würde Friedrich Merz wohl gerne Ungarn das Stimmrecht entziehen.
Der Pegel an Unzufriedenheit und Frustration wächst in großen Teilen der Bevölkerung kontinuierlich. Arroganz, Machtmissbrauch und immer abstrusere Ausreden für offensichtlich willkürliche Maßnahmen werden kaum verhindern, dass den etablierten Parteien die Unterstützung entschwindet. In Deutschland sind die Umfrageergebnisse der AfD ein guter Gradmesser dafür.
[Vorlage Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 3bf0c63f:aefa459d
2024-01-15 11:15:06
@ 3bf0c63f:aefa459d
2024-01-15 11:15:06Pequenos problemas que o Estado cria para a sociedade e que não são sempre lembrados
- **vale-transporte**: transferir o custo com o transporte do funcionário para um terceiro o estimula a morar longe de onde trabalha, já que morar perto é normalmente mais caro e a economia com transporte é inexistente. - **atestado médico**: o direito a faltar o trabalho com atestado médico cria a exigência desse atestado para todas as situações, substituindo o livre acordo entre patrão e empregado e sobrecarregando os médicos e postos de saúde com visitas desnecessárias de assalariados resfriados. - **prisões**: com dinheiro mal-administrado, burocracia e péssima alocação de recursos -- problemas que empresas privadas em competição (ou mesmo sem qualquer competição) saberiam resolver muito melhor -- o Estado fica sem presídios, com os poucos existentes entupidos, muito acima de sua alocação máxima, e com isto, segundo a bizarra corrente de responsabilidades que culpa o juiz que condenou o criminoso por sua morte na cadeia, juízes deixam de condenar à prisão os bandidos, soltando-os na rua. - **justiça**: entrar com processos é grátis e isto faz proliferar a atividade dos advogados que se dedicam a criar problemas judiciais onde não seria necessário e a entupir os tribunais, impedindo-os de fazer o que mais deveriam fazer. - **justiça**: como a justiça só obedece às leis e ignora acordos pessoais, escritos ou não, as pessoas não fazem acordos, recorrem sempre à justiça estatal, e entopem-na de assuntos que seriam muito melhor resolvidos entre vizinhos. - **leis civis**: as leis criadas pelos parlamentares ignoram os costumes da sociedade e são um incentivo a que as pessoas não respeitem nem criem normas sociais -- que seriam maneiras mais rápidas, baratas e satisfatórias de resolver problemas. - **leis de trãnsito**: quanto mais leis de trânsito, mais serviço de fiscalização são delegados aos policiais, que deixam de combater crimes por isto (afinal de contas, eles não querem de fato arriscar suas vidas combatendo o crime, a fiscalização é uma excelente desculpa para se esquivarem a esta responsabilidade). - **financiamento educacional**: é uma espécie de subsídio às faculdades privadas que faz com que se criem cursos e mais cursos que são cada vez menos recheados de algum conhecimento ou técnica útil e cada vez mais inúteis. - **leis de tombamento**: são um incentivo a que o dono de qualquer área ou construção "histórica" destrua todo e qualquer vestígio de história que houver nele antes que as autoridades descubram, o que poderia não acontecer se ele pudesse, por exemplo, usar, mostrar e se beneficiar da história daquele local sem correr o risco de perder, de fato, a sua propriedade. - **zoneamento urbano**: torna as cidades mais espalhadas, criando uma necessidade gigantesca de carros, ônibus e outros meios de transporte para as pessoas se locomoverem das zonas de moradia para as zonas de trabalho. - **zoneamento urbano**: faz com que as pessoas percam horas no trânsito todos os dias, o que é, além de um desperdício, um atentado contra a sua saúde, que estaria muito melhor servida numa caminhada diária entre a casa e o trabalho. - **zoneamento urbano**: torna ruas e as casas menos seguras criando zonas enormes, tanto de residências quanto de indústrias, onde não há movimento de gente alguma. - **escola obrigatória + currículo escolar nacional**: emburrece todas as crianças. - **leis contra trabalho infantil**: tira das crianças a oportunidade de aprender ofícios úteis e levar um dinheiro para ajudar a família. - **licitações**: como não existem os critérios do mercado para decidir qual é o melhor prestador de serviço, criam-se comissões de pessoas que vão decidir coisas. isto incentiva os prestadores de serviço que estão concorrendo na licitação a tentar comprar os membros dessas comissões. isto, fora a corrupção, gera problemas reais: __(i)__ a escolha dos serviços acaba sendo a pior possível, já que a empresa prestadora que vence está claramente mais dedicada a comprar comissões do que a fazer um bom trabalho (este problema afeta tantas áreas, desde a construção de estradas até a qualidade da merenda escolar, que é impossível listar aqui); __(ii)__ o processo corruptor acaba, no longo prazo, eliminando as empresas que prestavam e deixando para competir apenas as corruptas, e a qualidade tende a piorar progressivamente. - **cartéis**: o Estado em geral cria e depois fica refém de vários grupos de interesse. o caso dos taxistas contra o Uber é o que está na moda hoje (e o que mostra como os Estados se comportam da mesma forma no mundo todo). - **multas**: quando algum indivíduo ou empresa comete uma fraude financeira, ou causa algum dano material involuntário, as vítimas do caso são as pessoas que sofreram o dano ou perderam dinheiro, mas o Estado tem sempre leis que prevêem multas para os responsáveis. A justiça estatal é sempre muito rígida e rápida na aplicação dessas multas, mas relapsa e vaga no que diz respeito à indenização das vítimas. O que em geral acontece é que o Estado aplica uma enorme multa ao responsável pelo mal, retirando deste os recursos que dispunha para indenizar as vítimas, e se retira do caso, deixando estas desamparadas. - **desapropriação**: o Estado pode pegar qualquer propriedade de qualquer pessoa mediante uma indenização que é necessariamente inferior ao valor da propriedade para o seu presente dono (caso contrário ele a teria vendido voluntariamente). - **seguro-desemprego**: se há, por exemplo, um prazo mínimo de 1 ano para o sujeito ter direito a receber seguro-desemprego, isto o incentiva a planejar ficar apenas 1 ano em cada emprego (ano este que será sucedido por um período de desemprego remunerado), matando todas as possibilidades de aprendizado ou aquisição de experiência naquela empresa específica ou ascensão hierárquica. - **previdência**: a previdência social tem todos os defeitos de cálculo do mundo, e não importa muito ela ser uma forma horrível de poupar dinheiro, porque ela tem garantias bizarras de longevidade fornecidas pelo Estado, além de ser compulsória. Isso serve para criar no imaginário geral a idéia da __aposentadoria__, uma época mágica em que todos os dias serão finais de semana. A idéia da aposentadoria influencia o sujeito a não se preocupar em ter um emprego que faça sentido, mas sim em ter um trabalho qualquer, que o permita se aposentar. - **regulamentação impossível**: milhares de coisas são proibidas, há regulamentações sobre os aspectos mais mínimos de cada empreendimento ou construção ou espaço. se todas essas regulamentações fossem exigidas não haveria condições de produção e todos morreriam. portanto, elas não são exigidas. porém, o Estado, ou um agente individual imbuído do poder estatal pode, se desejar, exigi-las todas de um cidadão inimigo seu. qualquer pessoa pode viver a vida inteira sem cumprir nem 10% das regulamentações estatais, mas viverá também todo esse tempo com medo de se tornar um alvo de sua exigência, num estado de terror psicológico. - **perversão de critérios**: para muitas coisas sobre as quais a sociedade normalmente chegaria a um valor ou comportamento "razoável" espontaneamente, o Estado dita regras. estas regras muitas vezes não são obrigatórias, são mais "sugestões" ou limites, como o salário mínimo, ou as 44 horas semanais de trabalho. a sociedade, porém, passa a usar esses valores como se fossem o normal. são raras, por exemplo, as ofertas de emprego que fogem à regra das 44h semanais. - **inflação**: subir os preços é difícil e constrangedor para as empresas, pedir aumento de salário é difícil e constrangedor para o funcionário. a inflação força as pessoas a fazer isso, mas o aumento não é automático, como alguns economistas podem pensar (enquanto alguns outros ficam muito satisfeitos de que esse processo seja demorado e difícil). - **inflação**: a inflação destrói a capacidade das pessoas de julgar preços entre concorrentes usando a própria memória. - **inflação**: a inflação destrói os cálculos de lucro/prejuízo das empresas e prejudica enormemente as decisões empresariais que seriam baseadas neles. - **inflação**: a inflação redistribui a riqueza dos mais pobres e mais afastados do sistema financeiro para os mais ricos, os bancos e as megaempresas. - **inflação**: a inflação estimula o endividamento e o consumismo. - **lixo:** ao prover coleta e armazenamento de lixo "grátis para todos" o Estado incentiva a criação de lixo. se tivessem que pagar para que recolhessem o seu lixo, as pessoas (e conseqüentemente as empresas) se empenhariam mais em produzir coisas usando menos plástico, menos embalagens, menos sacolas. - **leis contra crimes financeiros:** ao criar legislação para dificultar acesso ao sistema financeiro por parte de criminosos a dificuldade e os custos para acesso a esse mesmo sistema pelas pessoas de bem cresce absurdamente, levando a um percentual enorme de gente incapaz de usá-lo, para detrimento de todos -- e no final das contas os grandes criminosos ainda conseguem burlar tudo. -
 @ c631e267:c2b78d3e
2025-04-03 07:42:25
@ c631e267:c2b78d3e
2025-04-03 07:42:25Spanien bleibt einer der Vorreiter im europäischen Prozess der totalen Überwachung per Digitalisierung. Seit Mittwoch ist dort der digitale Personalausweis verfügbar. Dabei handelt es sich um eine Regierungs-App, die auf dem Smartphone installiert werden muss und in den Stores von Google und Apple zu finden ist. Per Dekret von Regierungschef Pedro Sánchez und Zustimmung des Ministerrats ist diese Maßnahme jetzt in Kraft getreten.
Mit den üblichen Argumenten der Vereinfachung, des Komforts, der Effizienz und der Sicherheit preist das Innenministerium die «Innovation» an. Auch die Beteuerung, dass die digitale Variante parallel zum physischen Ausweis existieren wird und diesen nicht ersetzen soll, fehlt nicht. Während der ersten zwölf Monate wird «der Neue» noch nicht für alle Anwendungsfälle gültig sein, ab 2026 aber schon.
Dass die ganze Sache auch «Risiken und Nebenwirkungen» haben könnte, wird in den Mainstream-Medien eher selten thematisiert. Bestenfalls wird der Aspekt der Datensicherheit angesprochen, allerdings in der Regel direkt mit dem Regierungsvokabular von den «maximalen Sicherheitsgarantien» abgehandelt. Dennoch gibt es einige weitere Aspekte, die Bürger mit etwas Sinn für Privatsphäre bedenken sollten.
Um sich die digitale Version des nationalen Ausweises besorgen zu können (eine App mit dem Namen MiDNI), muss man sich vorab online registrieren. Dabei wird die Identität des Bürgers mit seiner mobilen Telefonnummer verknüpft. Diese obligatorische fixe Verdrahtung kennen wir von diversen anderen Apps und Diensten. Gleichzeitig ist das die Basis für eine perfekte Lokalisierbarkeit der Person.
Für jeden Vorgang der Identifikation in der Praxis wird später «eine Verbindung zu den Servern der Bundespolizei aufgebaut». Die Daten des Individuums werden «in Echtzeit» verifiziert und im Erfolgsfall von der Polizei signiert zurückgegeben. Das Ergebnis ist ein QR-Code mit zeitlich begrenzter Gültigkeit, der an Dritte weitergegeben werden kann.
Bei derartigen Szenarien sträuben sich einem halbwegs kritischen Staatsbürger die Nackenhaare. Allein diese minimale Funktionsbeschreibung lässt die totale Überwachung erkennen, die damit ermöglicht wird. Jede Benutzung des Ausweises wird künftig registriert, hinterlässt also Spuren. Und was ist, wenn die Server der Polizei einmal kein grünes Licht geben? Das wäre spätestens dann ein Problem, wenn der digitale doch irgendwann der einzig gültige Ausweis ist: Dann haben wir den abschaltbaren Bürger.
Dieser neue Vorstoß der Regierung von Pedro Sánchez ist ein weiterer Schritt in Richtung der «totalen Digitalisierung» des Landes, wie diese Politik in manchen Medien – nicht einmal kritisch, sondern sehr naiv – genannt wird. Ebenso verharmlosend wird auch erwähnt, dass sich das spanische Projekt des digitalen Ausweises nahtlos in die Initiativen der EU zu einer digitalen Identität für alle Bürger sowie des digitalen Euro einreiht.
In Zukunft könnte der neue Ausweis «auch in andere staatliche und private digitale Plattformen integriert werden», wie das Medienportal Cope ganz richtig bemerkt. Das ist die Perspektive.
[Titelbild: Pixabay]
Dazu passend:
Nur Abschied vom Alleinfahren? Monströse spanische Überwachungsprojekte gemäß EU-Norm
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 3bf0c63f:aefa459d
2024-01-14 14:52:16
@ 3bf0c63f:aefa459d
2024-01-14 14:52:16bitcoinddecentralizationIt is better to have multiple curator teams, with different vetting processes and release schedules for
bitcoindthan a single one."More eyes on code", "Contribute to Core", "Everybody should audit the code".
All these points repeated again and again fell to Earth on the day it was discovered that Bitcoin Core developers merged a variable name change from "blacklist" to "blocklist" without even discussing or acknowledging the fact that that innocent pull request opened by a sybil account was a social attack.
After a big lot of people manifested their dissatisfaction with that event on Twitter and on GitHub, most Core developers simply ignored everybody's concerns or even personally attacked people who were complaining.
The event has shown that:
1) Bitcoin Core ultimately rests on the hands of a couple maintainers and they decide what goes on the GitHub repository[^pr-merged-very-quickly] and the binary releases that will be downloaded by thousands; 2) Bitcoin Core is susceptible to social attacks; 2) "More eyes on code" don't matter, as these extra eyes can be ignored and dismissed.
Solution:
bitcoinddecentralizationIf usage was spread across 10 different
bitcoindflavors, the network would be much more resistant to social attacks to a single team.This has nothing to do with the question on if it is better to have multiple different Bitcoin node implementations or not, because here we're basically talking about the same software.
Multiple teams, each with their own release process, their own logo, some subtle changes, or perhaps no changes at all, just a different name for their
bitcoindflavor, and that's it.Every day or week or month or year, each flavor merges all changes from Bitcoin Core on their own fork. If there's anything suspicious or too leftist (or perhaps too rightist, in case there's a leftist
bitcoindflavor), maybe they will spot it and not merge.This way we keep the best of both worlds: all software development, bugfixes, improvements goes on Bitcoin Core, other flavors just copy. If there's some non-consensus change whose efficacy is debatable, one of the flavors will merge on their fork and test, and later others -- including Core -- can copy that too. Plus, we get resistant to attacks: in case there is an attack on Bitcoin Core, only 10% of the network would be compromised. the other flavors would be safe.
Run Bitcoin Knots
The first example of a
bitcoindsoftware that follows Bitcoin Core closely, adds some small changes, but has an independent vetting and release process is Bitcoin Knots, maintained by the incorruptible Luke DashJr.Next time you decide to run
bitcoind, run Bitcoin Knots instead and contribute tobitcoinddecentralization!
See also:
[^pr-merged-very-quickly]: See PR 20624, for example, a very complicated change that could be introducing bugs or be a deliberate attack, merged in 3 days without time for discussion.
-
 @ aa8de34f:a6ffe696
2025-03-31 21:48:50
@ aa8de34f:a6ffe696
2025-03-31 21:48:50In seinem Beitrag vom 30. März 2025 fragt Henning Rosenbusch auf Telegram angesichts zunehmender digitaler Kontrolle und staatlicher Allmacht:
„Wie soll sich gegen eine solche Tyrannei noch ein Widerstand formieren können, selbst im Untergrund? Sehe ich nicht.“\ (Quelle: t.me/rosenbusch/25228)
Er beschreibt damit ein Gefühl der Ohnmacht, das viele teilen: Eine Welt, in der Totalitarismus nicht mehr mit Panzern, sondern mit Algorithmen kommt. Wo Zugriff auf Geld, Meinungsfreiheit und Teilhabe vom Wohlverhalten abhängt. Der Bürger als kontrollierbare Variable im Code des Staates.\ Die Frage ist berechtigt. Doch die Antwort darauf liegt nicht in alten Widerstandsbildern – sondern in einer neuen Realität.
-- Denn es braucht keinen Untergrund mehr. --
Der Widerstand der Zukunft trägt keinen Tarnanzug. Er ist nicht konspirativ, sondern transparent. Nicht bewaffnet, sondern mathematisch beweisbar. Bitcoin steht nicht am Rand dieser Entwicklung – es ist ihr Fundament. Eine Bastion aus physikalischer Realität, spieltheoretischem Schutz und ökonomischer Wahrheit. Es ist nicht unfehlbar, aber unbestechlich. Nicht perfekt, aber immun gegen zentrale Willkür.
Hier entsteht kein „digitales Gegenreich“, sondern eine dezentrale Renaissance. Keine Revolte aus Wut, sondern eine stille Abkehr: von Zwang zu Freiwilligkeit, von Abhängigkeit zu Selbstverantwortung. Diese Revolution führt keine Kriege. Sie braucht keine Führer. Sie ist ein Netzwerk. Jeder Knoten ein Individuum. Jede Entscheidung ein Akt der Selbstermächtigung.
Weltweit wachsen Freiheits-Zitadellen aus dieser Idee: wirtschaftlich autark, digital souverän, lokal verankert und global vernetzt. Sie sind keine Utopien im luftleeren Raum, sondern konkrete Realitäten – angetrieben von Energie, Code und dem menschlichen Wunsch nach Würde.
Der Globalismus alter Prägung – zentralistisch, monopolistisch, bevormundend – wird an seiner eigenen Hybris zerbrechen. Seine Werkzeuge der Kontrolle werden ihn nicht retten. Im Gegenteil: Seine Geister werden ihn verfolgen und erlegen.
Und während die alten Mächte um Erhalt kämpfen, wächst eine neue Welt – nicht im Schatten, sondern im Offenen. Nicht auf Gewalt gebaut, sondern auf Mathematik, Physik und Freiheit.
Die Tyrannei sieht keinen Widerstand.\ Weil sie nicht erkennt, dass er längst begonnen hat.\ Unwiderruflich. Leise. Überall.
-
 @ 9967f375:04f9a5e1
2025-05-10 03:55:38
@ 9967f375:04f9a5e1
2025-05-10 03:55:38El insigne mendocino Juan Fernando Segovia falleció en el día de la festividad de Nuestra Señora de Luján, fecha significativa no sólo por ser la Patrona ríoplatense, sino además, anecdóticamente, porque cuando conocimos al profesor en tierras mejicanas tlaxcaltecas, escuchando la Santa Misa en la catedral (oficiada por el P. José Ramón García Gallardo); en un altar lateral coronandolo se encuentra una imágen de la Virgen muy parecida a la advocación, al hacerlo notar al profesor, la contempló sonriente y con mucha Fe. Este breve hecho significativo, sin duda fundamentó la labor abierta de Juan Fernando Segovia de ser fiel apóstol intelectual por los pueblos hispánicos, pues no sólo vino a compartir su sabiduría política, jurídica y moral, además de su genial convivencia con los asistentes en una, sino en las tres ediciones de las Conversaciones de la Ciudad Católica de Tlaxcala, haciendo notar la sinrazón de la cerrazón propia del nacionalismo (sin importar el apellido que le acompañe). Los Círculos Tradicionalistas de toda la Nueva España (cuyos buenos frutos son en gran parte obra de la labor incansable, conferencias presenciales y virtuales, libros y artículos de revistas para la conformación y formación continua de sus miembros), lamenta el vacío por la partida del maestro Juan Fernando Segovia.
Que Cristo Rey, a quien fielmente sirvió durante su vida, le dé el descanso eterno.
 (Juan Fernando Segovia al centro, junto al P. José Ramón García y el matador Jerónimo Ramírez de Arellano en Tlaxcala, 2018).
(Juan Fernando Segovia al centro, junto al P. José Ramón García y el matador Jerónimo Ramírez de Arellano en Tlaxcala, 2018). -
 @ 2e8970de:63345c7a
2025-05-10 11:08:31
@ 2e8970de:63345c7a
2025-05-10 11:08:31
What gear are you using? Any new/used stuff you are currently trying to buy/sell?
originally posted at https://stacker.news/items/976340
-
 @ c631e267:c2b78d3e
2025-03-31 07:23:05
@ c631e267:c2b78d3e
2025-03-31 07:23:05Der Irrsinn ist bei Einzelnen etwas Seltenes – \ aber bei Gruppen, Parteien, Völkern, Zeiten die Regel. \ Friedrich Nietzsche
Erinnern Sie sich an die Horrorkomödie «Scary Movie»? Nicht, dass ich diese Art Filme besonders erinnerungswürdig fände, aber einige Szenen daraus sind doch gewissermaßen Klassiker. Dazu zählt eine, die das Verhalten vieler Protagonisten in Horrorfilmen parodiert, wenn sie in Panik flüchten. Welchen Weg nimmt wohl die Frau in der Situation auf diesem Bild?

Diese Szene kommt mir automatisch in den Sinn, wenn ich aktuelle Entwicklungen in Europa betrachte. Weitreichende Entscheidungen gehen wider jede Logik in die völlig falsche Richtung. Nur ist das hier alles andere als eine Komödie, sondern bitterernst. Dieser Horror ist leider sehr real.
Die Europäische Union hat sich selbst über Jahre konsequent in eine Sackgasse manövriert. Sie hat es versäumt, sich und ihre Politik selbstbewusst und im Einklang mit ihren Wurzeln auf dem eigenen Kontinent zu positionieren. Stattdessen ist sie in blinder Treue den vermeintlichen «transatlantischen Freunden» auf ihrem Konfrontationskurs gen Osten gefolgt.
In den USA haben sich die Vorzeichen allerdings mittlerweile geändert, und die einst hoch gelobten «Freunde und Partner» erscheinen den europäischen «Führern» nicht mehr vertrauenswürdig. Das ist spätestens seit der Münchner Sicherheitskonferenz, der Rede von Vizepräsident J. D. Vance und den empörten Reaktionen offensichtlich. Große Teile Europas wirken seitdem wie ein aufgescheuchter Haufen kopfloser Hühner. Orientierung und Kontrolle sind völlig abhanden gekommen.
Statt jedoch umzukehren oder wenigstens zu bremsen und vielleicht einen Abzweig zu suchen, geben die Crash-Piloten jetzt auf dem Weg durch die Sackgasse erst richtig Gas. Ja sie lösen sogar noch die Sicherheitsgurte und deaktivieren die Airbags. Den vor Angst dauergelähmten Passagieren fällt auch nichts Besseres ein und so schließen sie einfach die Augen. Derweil übertrumpfen sich die Kommentatoren des Events gegenseitig in sensationslüsterner «Berichterstattung».
Wie schon die deutsche Außenministerin mit höchsten UN-Ambitionen, Annalena Baerbock, proklamiert auch die Europäische Kommission einen «Frieden durch Stärke». Zu dem jetzt vorgelegten, selbstzerstörerischen Fahrplan zur Ankurbelung der Rüstungsindustrie, genannt «Weißbuch zur europäischen Verteidigung – Bereitschaft 2030», erklärte die Kommissionspräsidentin, die «Ära der Friedensdividende» sei längst vorbei. Soll das heißen, Frieden bringt nichts ein? Eine umfassende Zusammenarbeit an dauerhaften europäischen Friedenslösungen steht demnach jedenfalls nicht zur Debatte.
Zusätzlich brisant ist, dass aktuell «die ganze EU von Deutschen regiert wird», wie der EU-Parlamentarier und ehemalige UN-Diplomat Michael von der Schulenburg beobachtet hat. Tatsächlich sitzen neben von der Leyen und Strack-Zimmermann noch einige weitere Deutsche in – vor allem auch in Krisenzeiten – wichtigen Spitzenposten der Union. Vor dem Hintergrund der Kriegstreiberei in Deutschland muss eine solche Dominanz mindestens nachdenklich stimmen.
Ihre ursprünglichen Grundwerte wie Demokratie, Freiheit, Frieden und Völkerverständigung hat die EU kontinuierlich in leere Worthülsen verwandelt. Diese werden dafür immer lächerlicher hochgehalten und beschworen.
Es wird dringend Zeit, dass wir, der Souverän, diesem erbärmlichen und gefährlichen Trauerspiel ein Ende setzen und die Fäden selbst in die Hand nehmen. In diesem Sinne fordert uns auch das «European Peace Project» auf, am 9. Mai im Rahmen eines Kunstprojekts den Frieden auszurufen. Seien wir dabei!
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ 3bf0c63f:aefa459d
2024-01-14 14:52:16
@ 3bf0c63f:aefa459d
2024-01-14 14:52:16Drivechain
Understanding Drivechain requires a shift from the paradigm most bitcoiners are used to. It is not about "trustlessness" or "mathematical certainty", but game theory and incentives. (Well, Bitcoin in general is also that, but people prefer to ignore it and focus on some illusion of trustlessness provided by mathematics.)
Here we will describe the basic mechanism (simple) and incentives (complex) of "hashrate escrow" and how it enables a 2-way peg between the mainchain (Bitcoin) and various sidechains.
The full concept of "Drivechain" also involves blind merged mining (i.e., the sidechains mine themselves by publishing their block hashes to the mainchain without the miners having to run the sidechain software), but this is much easier to understand and can be accomplished either by the BIP-301 mechanism or by the Spacechains mechanism.
How does hashrate escrow work from the point of view of Bitcoin?
A new address type is created. Anything that goes in that is locked and can only be spent if all miners agree on the Withdrawal Transaction (
WT^) that will spend it for 6 months. There is one of these special addresses for each sidechain.To gather miners' agreement
bitcoindkeeps track of the "score" of all transactions that could possibly spend from that address. On every block mined, for each sidechain, the miner can use a portion of their coinbase to either increase the score of oneWT^by 1 while decreasing the score of all others by 1; or they can decrease the score of allWT^s by 1; or they can do nothing.Once a transaction has gotten a score high enough, it is published and funds are effectively transferred from the sidechain to the withdrawing users.
If a timeout of 6 months passes and the score doesn't meet the threshold, that
WT^is discarded.What does the above procedure mean?
It means that people can transfer coins from the mainchain to a sidechain by depositing to the special address. Then they can withdraw from the sidechain by making a special withdraw transaction in the sidechain.
The special transaction somehow freezes funds in the sidechain while a transaction that aggregates all withdrawals into a single mainchain
WT^, which is then submitted to the mainchain miners so they can start voting on it and finally after some months it is published.Now the crucial part: the validity of the
WT^is not verified by the Bitcoin mainchain rules, i.e., if Bob has requested a withdraw from the sidechain to his mainchain address, but someone publishes a wrongWT^that instead takes Bob's funds and sends them to Alice's main address there is no way the mainchain will know that. What determines the "validity" of theWT^is the miner vote score and only that. It is the job of miners to vote correctly -- and for that they may want to run the sidechain node in SPV mode so they can attest for the existence of a reference to theWT^transaction in the sidechain blockchain (which then ensures it is ok) or do these checks by some other means.What? 6 months to get my money back?
Yes. But no, in practice anyone who wants their money back will be able to use an atomic swap, submarine swap or other similar service to transfer funds from the sidechain to the mainchain and vice-versa. The long delayed withdraw costs would be incurred by few liquidity providers that would gain some small profit from it.
Why bother with this at all?
Drivechains solve many different problems:
It enables experimentation and new use cases for Bitcoin
Issued assets, fully private transactions, stateful blockchain contracts, turing-completeness, decentralized games, some "DeFi" aspects, prediction markets, futarchy, decentralized and yet meaningful human-readable names, big blocks with a ton of normal transactions on them, a chain optimized only for Lighting-style networks to be built on top of it.
These are some ideas that may have merit to them, but were never actually tried because they couldn't be tried with real Bitcoin or inferfacing with real bitcoins. They were either relegated to the shitcoin territory or to custodial solutions like Liquid or RSK that may have failed to gain network effect because of that.
It solves conflicts and infighting
Some people want fully private transactions in a UTXO model, others want "accounts" they can tie to their name and build reputation on top; some people want simple multisig solutions, others want complex code that reads a ton of variables; some people want to put all the transactions on a global chain in batches every 10 minutes, others want off-chain instant transactions backed by funds previously locked in channels; some want to spend, others want to just hold; some want to use blockchain technology to solve all the problems in the world, others just want to solve money.
With Drivechain-based sidechains all these groups can be happy simultaneously and don't fight. Meanwhile they will all be using the same money and contributing to each other's ecosystem even unwillingly, it's also easy and free for them to change their group affiliation later, which reduces cognitive dissonance.
It solves "scaling"
Multiple chains like the ones described above would certainly do a lot to accomodate many more transactions that the current Bitcoin chain can. One could have special Lightning Network chains, but even just big block chains or big-block-mimblewimble chains or whatnot could probably do a good job. Or even something less cool like 200 independent chains just like Bitcoin is today, no extra features (and you can call it "sharding"), just that would already multiply the current total capacity by 200.
Use your imagination.
It solves the blockchain security budget issue
The calculation is simple: you imagine what security budget is reasonable for each block in a world without block subsidy and divide that for the amount of bytes you can fit in a single block: that is the price to be paid in satoshis per byte. In reasonable estimative, the price necessary for every Bitcoin transaction goes to very large amounts, such that not only any day-to-day transaction has insanely prohibitive costs, but also Lightning channel opens and closes are impracticable.
So without a solution like Drivechain you'll be left with only one alternative: pushing Bitcoin usage to trusted services like Liquid and RSK or custodial Lightning wallets. With Drivechain, though, there could be thousands of transactions happening in sidechains and being all aggregated into a sidechain block that would then pay a very large fee to be published (via blind merged mining) to the mainchain. Bitcoin security guaranteed.
It keeps Bitcoin decentralized
Once we have sidechains to accomodate the normal transactions, the mainchain functionality can be reduced to be only a "hub" for the sidechains' comings and goings, and then the maximum block size for the mainchain can be reduced to, say, 100kb, which would make running a full node very very easy.
Can miners steal?
Yes. If a group of coordinated miners are able to secure the majority of the hashpower and keep their coordination for 6 months, they can publish a
WT^that takes the money from the sidechains and pays to themselves.Will miners steal?
No, because the incentives are such that they won't.
Although it may look at first that stealing is an obvious strategy for miners as it is free money, there are many costs involved:
- The cost of ceasing blind-merged mining returns -- as stealing will kill a sidechain, all the fees from it that miners would be expected to earn for the next years are gone;
- The cost of Bitcoin price going down: If a steal is successful that will mean Drivechains are not safe, therefore Bitcoin is less useful, and miner credibility will also be hurt, which are likely to cause the Bitcoin price to go down, which in turn may kill the miners' businesses and savings;
- The cost of coordination -- assuming miners are just normal businesses, they just want to do their work and get paid, but stealing from a Drivechain will require coordination with other miners to conduct an immoral act in a way that has many pitfalls and is likely to be broken over the months;
- The cost of miners leaving your mining pool: when we talked about "miners" above we were actually talking about mining pools operators, so they must also consider the risk of miners migrating from their mining pool to others as they begin the process of stealing;
- The cost of community goodwill -- when participating in a steal operation, a miner will suffer a ton of backlash from the community. Even if the attempt fails at the end, the fact that it was attempted will contribute to growing concerns over exaggerated miners power over the Bitcoin ecosystem, which may end up causing the community to agree on a hard-fork to change the mining algorithm in the future, or to do something to increase participation of more entities in the mining process (such as development or cheapment of new ASICs), which have a chance of decreasing the profits of current miners.
Another point to take in consideration is that one may be inclined to think a newly-created sidechain or a sidechain with relatively low usage may be more easily stolen from, since the blind merged mining returns from it (point 1 above) are going to be small -- but the fact is also that a sidechain with small usage will also have less money to be stolen from, and since the other costs besides 1 are less elastic at the end it will not be worth stealing from these too.
All of the above consideration are valid only if miners are stealing from good sidechains. If there is a sidechain that is doing things wrong, scamming people, not being used at all, or is full of bugs, for example, that will be perceived as a bad sidechain, and then miners can and will safely steal from it and kill it, which will be perceived as a good thing by everybody.
What do we do if miners steal?
Paul Sztorc has suggested in the past that a user-activated soft-fork could prevent miners from stealing, i.e., most Bitcoin users and nodes issue a rule similar to this one to invalidate the inclusion of a faulty
WT^and thus cause any miner that includes it in a block to be relegated to their own Bitcoin fork that other nodes won't accept.This suggestion has made people think Drivechain is a sidechain solution backed by user-actived soft-forks for safety, which is very far from the truth. Drivechains must not and will not rely on this kind of soft-fork, although they are possible, as the coordination costs are too high and no one should ever expect these things to happen.
If even with all the incentives against them (see above) miners do still steal from a good sidechain that will mean the failure of the Drivechain experiment. It will very likely also mean the failure of the Bitcoin experiment too, as it will be proven that miners can coordinate to act maliciously over a prolonged period of time regardless of economic and social incentives, meaning they are probably in it just for attacking Bitcoin, backed by nation-states or something else, and therefore no Bitcoin transaction in the mainchain is to be expected to be safe ever again.
Why use this and not a full-blown trustless and open sidechain technology?
Because it is impossible.
If you ever heard someone saying "just use a sidechain", "do this in a sidechain" or anything like that, be aware that these people are either talking about "federated" sidechains (i.e., funds are kept in custody by a group of entities) or they are talking about Drivechain, or they are disillusioned and think it is possible to do sidechains in any other manner.
No, I mean a trustless 2-way peg with correctness of the withdrawals verified by the Bitcoin protocol!
That is not possible unless Bitcoin verifies all transactions that happen in all the sidechains, which would be akin to drastically increasing the blocksize and expanding the Bitcoin rules in tons of ways, i.e., a terrible idea that no one wants.
What about the Blockstream sidechains whitepaper?
Yes, that was a way to do it. The Drivechain hashrate escrow is a conceptually simpler way to achieve the same thing with improved incentives, less junk in the chain, more safety.
Isn't the hashrate escrow a very complex soft-fork?
Yes, but it is much simpler than SegWit. And, unlike SegWit, it doesn't force anything on users, i.e., it isn't a mandatory blocksize increase.
Why should we expect miners to care enough to participate in the voting mechanism?
Because it's in their own self-interest to do it, and it costs very little. Today over half of the miners mine RSK. It's not blind merged mining, it's a very convoluted process that requires them to run a RSK full node. For the Drivechain sidechains, an SPV node would be enough, or maybe just getting data from a block explorer API, so much much simpler.
What if I still don't like Drivechain even after reading this?
That is the entire point! You don't have to like it or use it as long as you're fine with other people using it. The hashrate escrow special addresses will not impact you at all, validation cost is minimal, and you get the benefit of people who want to use Drivechain migrating to their own sidechains and freeing up space for you in the mainchain. See also the point above about infighting.
See also