-
 @ 70c48e4b:00ce3ccb
2025-04-22 08:35:52
@ 70c48e4b:00ce3ccb
2025-04-22 08:35:52Hello reader,
I can say from personal experience that crowdfunding has truly changed my life. I found people who believed in my dream of using Bitcoin as money. Every single one of my videos was made possible through crowdfunding. And I’m not alone. I know several Bitcoiners who have raised funds this way, from Africa to Korea to Haiti.
https://images.forbesindia.com/media/images/2022/Jul/img_190501_runwithbitcoin_bg.jpg
Crowdfunding is deeply rooted in the traditional financial world. From raising money for life-saving surgeries to helping someone open a local coffee shop, platforms like GoFundMe, Kickstarter, and Indiegogo have become essential tools for many. But behind all the heartwarming stories and viral campaigns, there’s a side of crowdfunding that doesn’t get talked about enough. Traditional platforms are far from perfect.
They are centralized, which means there’s always someone in control. These platforms can freeze campaigns, delay payouts, or take a significant cut of the money. And often, the people who need funding the most, those without access to strong banking systems or large social media followings are the ones who get left out.
Here are some of the problems I’ve noticed with these platforms:
Problem 1: Inequality in Who Gets Funded
A recent article in The Guardian pointed out something that’s hard to ignore. Crowdfunding often benefits people who already have influence. After the Los Angeles wildfires in January 2025, celebrities like Mandy Moore were able to raise funds quickly. At the same time, everyday people who lost their homes struggled to get noticed.
https://i.guim.co.uk/img/media/f8398505e58ec3c04685aab06e94048e5d7b6a0c/0_127_4800_2880/master/4800.jpg?width=1300&dpr=1&s=none&crop=none
Angor (https://angor.io/) changes that by removing the need for a central platform to choose which projects get featured or promoted. Anyone can share their project. People can find them on Angor Hub (https://hub.angor.io/), which is a public directory built on the Nostr protocol. Instead of relying on popularity, projects are highlighted based on transparency and engagement.
Problem 2: Platform Dependence and Middlemen
Here’s something people don’t often realize. When you raise funds online, the platform usually has control. It holds the money, decides when to release it, and can freeze everything without warning. This happened during the trucker protests in Canada in 2022. Tens of millions of dollars were raised, but platforms like GoFundMe and GiveSendGo froze the donations. The funds never reached the people they were meant for. Supporters were left confused, and the recipients had no way to access what had been raised for them.
https://upload.wikimedia.org/wikipedia/commons/thumb/2/2d/Convoi_de_la_libert%C3%A9_%C3%A0_Ottawa_01.jpg/800px-Convoi_de_la_libert%C3%A9_%C3%A0_Ottawa_01.jpg
Angor avoids all of this. It does not hold the funds, does not require approval processes, and only the project creator has control over the campaign. Contributions go directly from supporters to the people building the project, using Bitcoin. It is a peer-to-peer system that works without any gatekeepers. Angor never touches the money. It simply provides the tools people need to raise funds and build, while staying fully in control.
Problem 3: Global Access
Another major issue is that these platforms often exclude people based on where they live. If you're in a region with limited banking access or outside the supported list of countries, you’re likely shut out. In 2023, a woman named Samar in Gaza tried to raise funds for food and medical supplies during a crisis. A friend abroad set up a campaign to help, but the platform froze it due to "location-related concerns." The funds were locked, and the support never arrived in time.
https://images.gofundme.com/EMFtPWSLs3P9SewkzwZ4FtaBQSA=/720x405/https://d2g8igdw686xgo.cloudfront.net/78478731_1709065237698709_r.jpeg
Angor removes these barriers by using Bitcoin, which works globally without needing banks or approvals. Anyone, anywhere, can raise and receive support directly.
Problem 4: Lack of Transparency
Post-funding transparency is often lacking. Backers rarely get consistent updates, making it difficult to track a project's progress or hold anyone accountable.
In 2015, the Zano drone project on Kickstarter raised over £2.3 million from more than 12,000 backers. It promised a compact, smart drone for aerial photography. But as time went on, updates became rare and vague. Backers had little insight into the project’s struggles, and eventually, it was canceled. The company shut down, and most backers never received their product or a refund.
https://ichef.bbci.co.uk/ace/standard/976/cpsprodpb/2A0A/production/_86626701_ff861eeb-ce94-43b7-9a43-b30b5adbd7ab.jpg
Angor takes a different approach. Project updates are shared through Nostr, a decentralized and tamper-proof communication protocol. This allows backers to follow progress in real time, with no corporate filters and no blackout periods. Everyone stays in the loop, from start to finish.
Problem 5: Fraud and Accountability
Scams are a growing problem in the crowdfunding world. People can launch fake campaigns, collect donations, and vanish — leaving supporters with empty promises and no way to recover their money. One well-known example was the "Homeless Vet GoFundMe scam" in the U.S.
https://a57.foxnews.com/static.foxnews.com/foxnews.com/content/uploads/2018/09/720/405/1536549443584.jpg
A couple and a homeless man raised over $400,000 by telling a heartwarming story that later turned out to be completely fake. The money was spent on luxury items, and it took a legal investigation to uncover the truth. By the time it was resolved, most of the funds were gone.
This kind of fraud is hard to stop on traditional platforms, because once the funds are transferred, there’s no built-in structure to verify how they’re used.
On Angor, projects are funded in stages, with each step tied to a specific milestone. Bitcoin is held in a shared wallet that only unlocks funds when both the backer and the creator agree that the milestone is complete. If something feels off, backers can choose to stop and recover unspent funds.
This structure discourages scammers from even trying. It adds friction for bad actors, while still giving honest creators the freedom to build trust, deliver value, and raise support transparently. It can’t get any better than this
So, does Angor matter?
For me, it really does. I’m genuinely excited to have my project listed on Angorhub. In a world shaped by AI, open source and transparency light the way forward. Let the work shine on its own.
Have you tried Angor yet? Thanks for tuning in. Catch you next week. Ciao!
Guest blog: Paco nostr:npub1v67clmf4jrezn8hsz28434nc0y5fu65e5esws04djnl2kasxl5tskjmjjk
References:
• The Guardian, 2025: Crowdfunding after LA fires and inequality - https://www.theguardian.com/us-news/2025/jan/17/la-fires-gofundme-mandy-moore • https://www.theguardian.com/us-news/2018/nov/15/johnny-bobbitt-gofundme-scam-arrest-viral-gas-story-couple-charged • FundsforNGOs: The Success Story of an NGO That Scaled with Limited Resourceshttps://www2.fundsforngos.org/articles/the-success-story-of-an-ngo-that-scaled-with-limited-resources/ • https://www.freightwaves.com/news/gofundme-freezes-37m-until-organizers-of-canada-trucker-convoy-detail-spending-plan
-
 @ b8af284d:f82c91dd
2025-04-22 07:28:03
@ b8af284d:f82c91dd
2025-04-22 07:28:03Kaiser: Es fehlt an Geld, nun gut, so schaff es denn,
Mephisto: Ich schaffe, was ihr wollt, und schaffe mehr;
Zwar ist es leicht, doch ist das Leichte schwer;
Es liegt schon da, doch um es zu erlangen, das ist die Kunst.
(Goethe: Faust II)
Liebe Abonnenten,
die meisten Medien sind nach wie vor damit beschäftigt, wie sie Trump am eindrücklichsten Wahnsinn unterstellen können. Sie vergessen dabei, worum es eigentlich geht: Ein Drittel aller amerikanischen Staatsschulden müssen dieses Jahr refinanziert werden. Sonst ist das mächtigste Land der Welt demnächst Pleite. Dafür müssen die Doppel-Defizite ausgeglichen, oder zumindest gesenkt werden. Und vor allem müssen die Zinsen runter. Die amerikanische Zentralbank wird den Wünschen der Regierung bald nachkommen, sprich die Zinsen senken und über ein neues Quantitative-Easing-Programm die Geldmenge erhöhen. Ein paar Jahre später werden die Effekte im Alltag über Inflation sichtbar.
Die Wahrscheinlichkeit ist hoch, dass wir bald Zeuge eines raffinierten Geld-Recycling-Programms werden. Wir treffen dabei auf einen alten Bekannten, den Stablecoin-Anbieter Tether. Der Essay ist keine leichte Kost, aber wer dabei bleibt, gelangt tief in die wundersame Welt der Geldvermehrung.
Mitte März wagt Paolo Ardoino den Schritt. Der Tether-CEO fliegt von der Hauptstadt El Salvadors nach New York. Es ist die erste Reise in die USA des erst 41-Jährigen seit Jahren. Zu hoch war bisher das Risiko gewesen, dort von den Behörden festgenommen zu werden. Vier Jahre zuvor war das Milliarden-Unternehmen, das er leitet, noch einmal davon gekommen: 2021 war Tether von der amerikanischen Börsenaufsicht mit einer Strafe von 41 Millionen US-Dollar belegt wegen ungenauer Angaben zu seinen Reserven. Man hatte sich schließlich auf einen Vergleich in Höhe von 18 Millionen Dollar geeinigt. Ein Witz, hatten Kritiker des Unternehmens entgegnet. Schließlich, so die Vorwürfe, ging es um Milliarden-Betrug. Seitdem hatten die Tether-Bosse die Vereinigten Staaten aus Vorsicht gemieden. Man war mal in Hongkong, auf den Bahamas und den Bermuda-Inseln, bis man sich Anfang des Jahres offiziell im Bitcoin-freundlichen El Salvador niedergelassen hatte. Doch mit der neuen US-Administration ist alles anders.
Nach New York geladen hat die Firma Cantor Fitzgerald. Thema des Gesprächs: Die Schaffung eines exklusiven Stablecoins für den amerikanischen Markt. Cantor Fitzgerald ist nicht irgendeine Bank oder Unternehmen. Das 1945 gegründete Investmenthaus ist einer von 24 Primärhändlern, die von der Federal Reserve Bank of New York autorisiert sind, US-Staatsanleihen zu handeln. Damit spielen sie eine zentrale Rolle im Finanzsystem der USA, da sie die Liquidität und Effizienz des Marktes für Staatsanleihen sicherstellen, dem wichtigsten und liquidisten Markt der Welt.
Langjähriger CEO von Cantor Fitzgerald war Howard Lutnick, ein Milliardär und seit Jahren enger Vertrauter der Trump-Familie. Da Lutnick mittlerweile US-Handelsminister ist, dürfte Ardoino nicht nur das Ok von ganz oben bekommen haben, in die Vereinigten Staaten einreisen zu dürfen. Man wird ihm wohl auch einen roten Teppich ausgerollt haben. Der Grund:
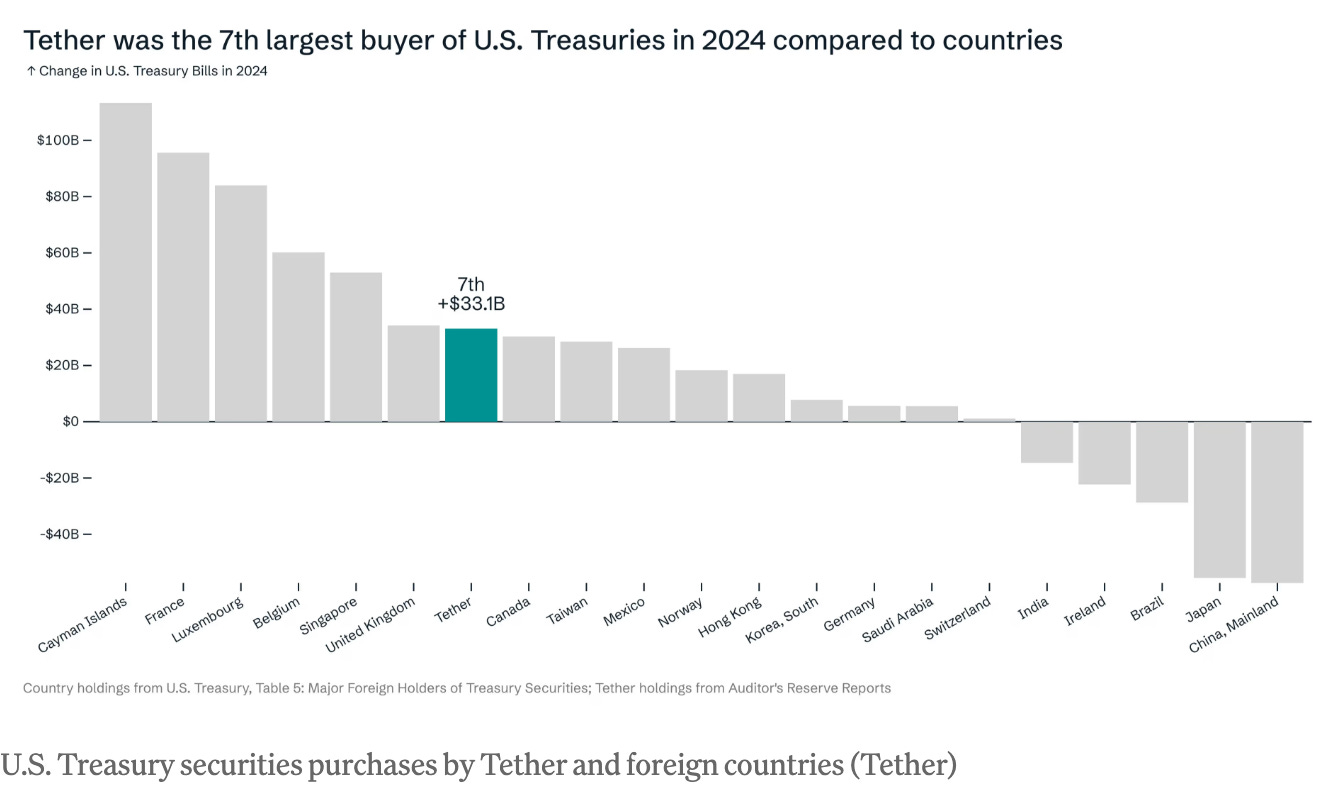
Die USA haben aktuell ein Problem mit ihrer Verschuldung. (BlingBling hat das in den Essays Die nächsten 90 Tage und Der Mar-a-Largo-Accord beschrieben). Rund ein Drittel des gesamten Schuldenbergs der USA müssen dieses Jahr refinanziert werden. Dafür müssen die Zinsen runter. Deswegen will Trump unbedingt das Handelsdefizit ausgleichen. Deswegen wird über die Neubewertung der Goldreserven nachgedacht. Und deswegen wird vermutlich bald eine neue Liquiditätswelle die Kurse von Bitcoin und Co auf neue Höchststände treiben. Denn bisher haben Staaten in solchen Phasen immer auf Geldentwertung gesetzt, um sich aus der Schuldenfalle zu befreien. Anders als Privatpersonen und viele kleinere Staaten können die USA immerhin die Währung selbst drucken, in der sie verschuldet sind. Die amerikanische Staatsverschuldung ist das Endgame. Und im Endgame spielt Tether mittlerweile eine ziemlich wichtige Rolle. Der Stablecoin-Anbieter hält mit 113 Milliarden aktuell mehr US-Staatsanleihen als Deutschland. Tendenz steigend: Ende 2024 war Tether mit 31 Milliarden der siebtgrößte Käufer von amerikanischen Staatsschulden.
Wie kann ein obskures Unternehmen, mit nicht einmal 100 Mitarbeitern, im vergangenen Jahr 13 Milliarden Dollar Gewinn machen, und zu einem der wichtigsten Kunden des amerikanischen Staats werden?
Weiter auf BlingBling - Die Geschichte eines der größten Geld-Recyclingprozesse der Welt.
-
 @ 1c19eb1a:e22fb0bc
2025-04-22 01:36:33
@ 1c19eb1a:e22fb0bc
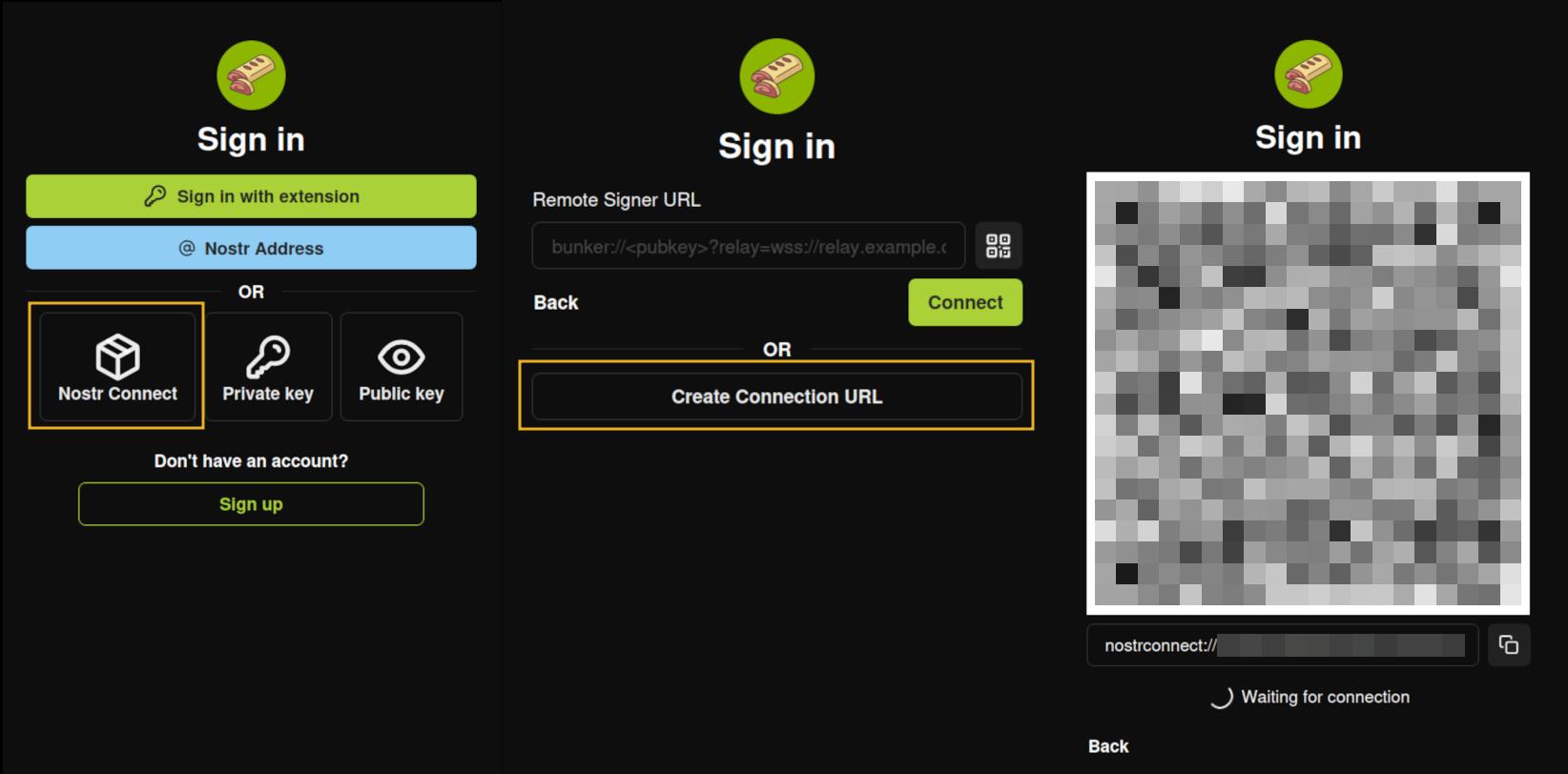
2025-04-22 01:36:33After my first major review of Primal on Android, we're going to go a very different direction for this next review. Primal is your standard "Twitter clone" type of kind 1 note client, now branching into long-form. They also have a team of developers working on making it one of the best clients to fill that use-case. By contrast, this review will not be focusing on any client at all. Not even an "other stuff" client.
Instead, we will be reviewing a very useful tool created and maintained by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 called #Amber. For those unfamiliar with Amber, it is an #Android application dedicated to managing your signing keys, and allowing you to log into various #Nostr applications without having to paste in your private key, better known as your #nsec. It is not recommended to paste your nsec into various applications because they each represent another means by which it could be compromised, and anyone who has your nsec can post as you. On Nostr, your #npub is your identity, and your signature using your private key is considered absolute proof that any given note, reaction, follow update, or profile change was authorized by the rightful owner of that identity.
It happens less often these days, but early on, when the only way to try out a new client was by inputting your nsec, users had their nsec compromised from time to time, or they would suspect that their key may have been compromised. When this occurs, there is no way to recover your account, or set a new private key, deprecating the previous one. The only thing you can do is start over from scratch, letting everyone know that your key has been compromised and to follow you on your new npub.
If you use Amber to log into other Nostr apps, you significantly reduce the likelihood that your private key will be compromised, because only one application has access to it, and all other applications reach out to Amber to sign any events. This isn't quite as secure as storing your private key on a separate device that isn't connected to the internet whatsoever, like many of us have grown accustomed to with securing our #Bitcoin, but then again, an online persona isn't nearly as important to secure for most of us as our entire life savings.
Amber is the first application of its kind for managing your Nostr keys on a mobile device. nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 didn't merely develop the application, but literally created the specification for accomplishing external signing on Android which can be found in NIP-55. Unfortunately, Amber is only available for Android. A signer application for iOS is in the works from nostr:npub1yaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgs3tvjmf, but is not ready for use at this time. There is also a new mobile signer app for Android and iOS called Nowser, but I have not yet had a chance to try this app out. From a cursory look at the Android version, it is indeed in the very early stages of development and cannot be compared with Amber.
This review of Amber is current as of version 3.2.5.
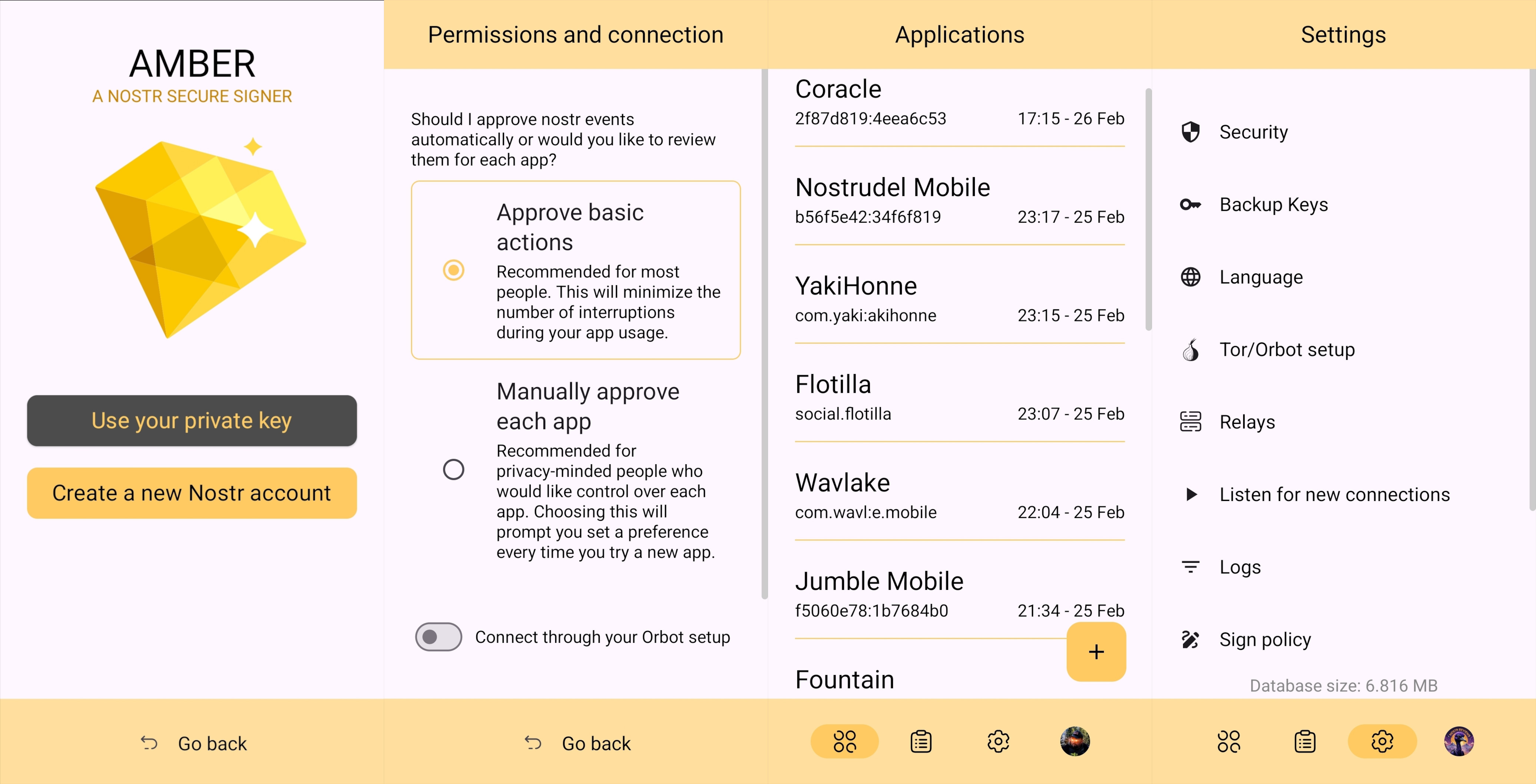
Overall Impression
Score: 4.7 / 5 (Updated 4/21/2025)
I cannot speak highly enough about Amber as a tool that every Nostr user on Android should start using if they are not already. When the day comes that we have more options for well-developed signer apps on mobile, my opinion may very well change, but until then Amber is what we have available to us. Even so, it is an incredibly well thought-out and reliable tool for securing your nsec.
Despite being the only well-established Android signer available for Android, Amber can be compared with other external signing methods available on other platforms. Even with more competition in this arena, though, Amber still holds up incredibly well. If you are signing into web applications on a desktop, I still would recommend using a browser extension like #Alby or #Nos2x, as the experience is usually faster, more seamless, and far more web apps support this signing method (NIP-07) than currently support the two methods employed by Amber. Nevertheless that gap is definitely narrowing.
A running list I created of applications that support login and signing with Amber can be found here: Nostr Clients with External Signer Support
I have run into relatively few bugs in my extensive use of Amber for all of my mobile signing needs. Occasionally the application crashes when trying to send it a signing request from a couple of applications, but I would not be surprised if this is no fault of Amber at all, and rather the fault of those specific apps, since it works flawlessly with the vast majority of apps that support either NIP-55 or NIP-46 login.
I also believe that mobile is the ideal platform to use for this type of application. First, because most people use Nostr clients on their phone more than on a desktop. There are, of course, exceptions to that, but in general we spend more time on our phones when interacting online. New users are also more likely to be introduced to Nostr by a friend having them download a Nostr client on their phone than on a PC, and that can be a prime opportunity to introduce the new user to protecting their private key. Finally, I agree with the following assessment from nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn.
nostr:nevent1qqsw0r6gzn05xg67h5q2xkplwsuzedjxw9lf7ntrxjl8ajm350fcyugprfmhxue69uhhyetvv9ujumn0wd68yurvv438xtnrdaksyg9hyaxj3clfswlhyrd5kjsj5v04clhjvgeq6pwztmysfzdvn93gev7awu9v
The one downside to Amber is that it will be quite foreign for new users. That is partially unavoidable with Nostr, since folks are not accustomed to public/private key cryptography in general, let alone using a private key to log into websites or social media apps. However, the initial signup process is a bit cumbersome if Amber is being used as the means of initially generating a key pair. I think some of this could be foregone at start-up in favor of streamlining onboarding, and then encourage the user to back-up their private key at a later time.
Features
Amber has some features that may surprise you, outside of just storing your private key and signing requests from your favorite Nostr clients. It is a full key management application, supporting multiple accounts, various backup methods, and even the ability to authorize other users to access a Nostr profile you control.
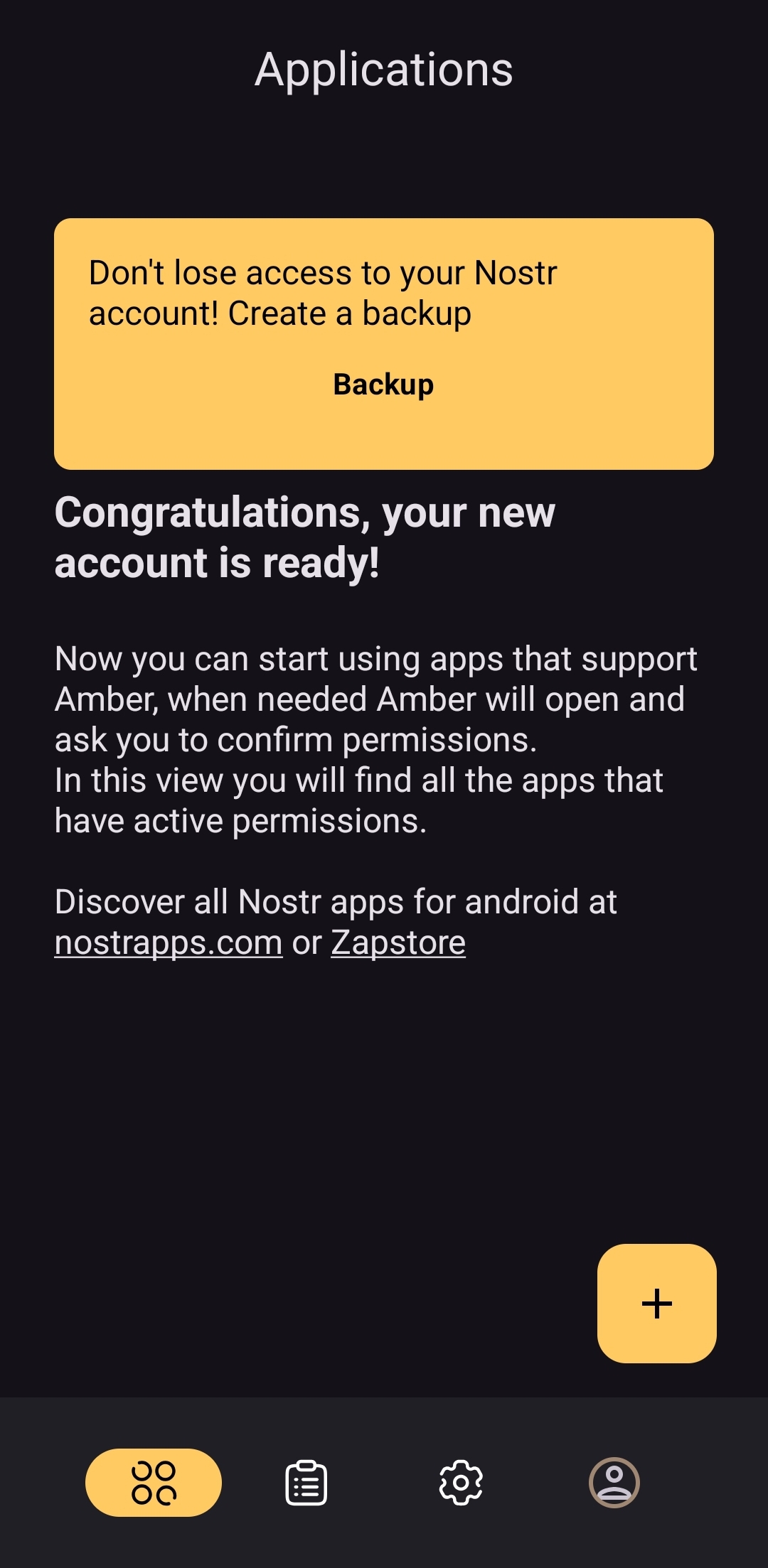
Android Signing
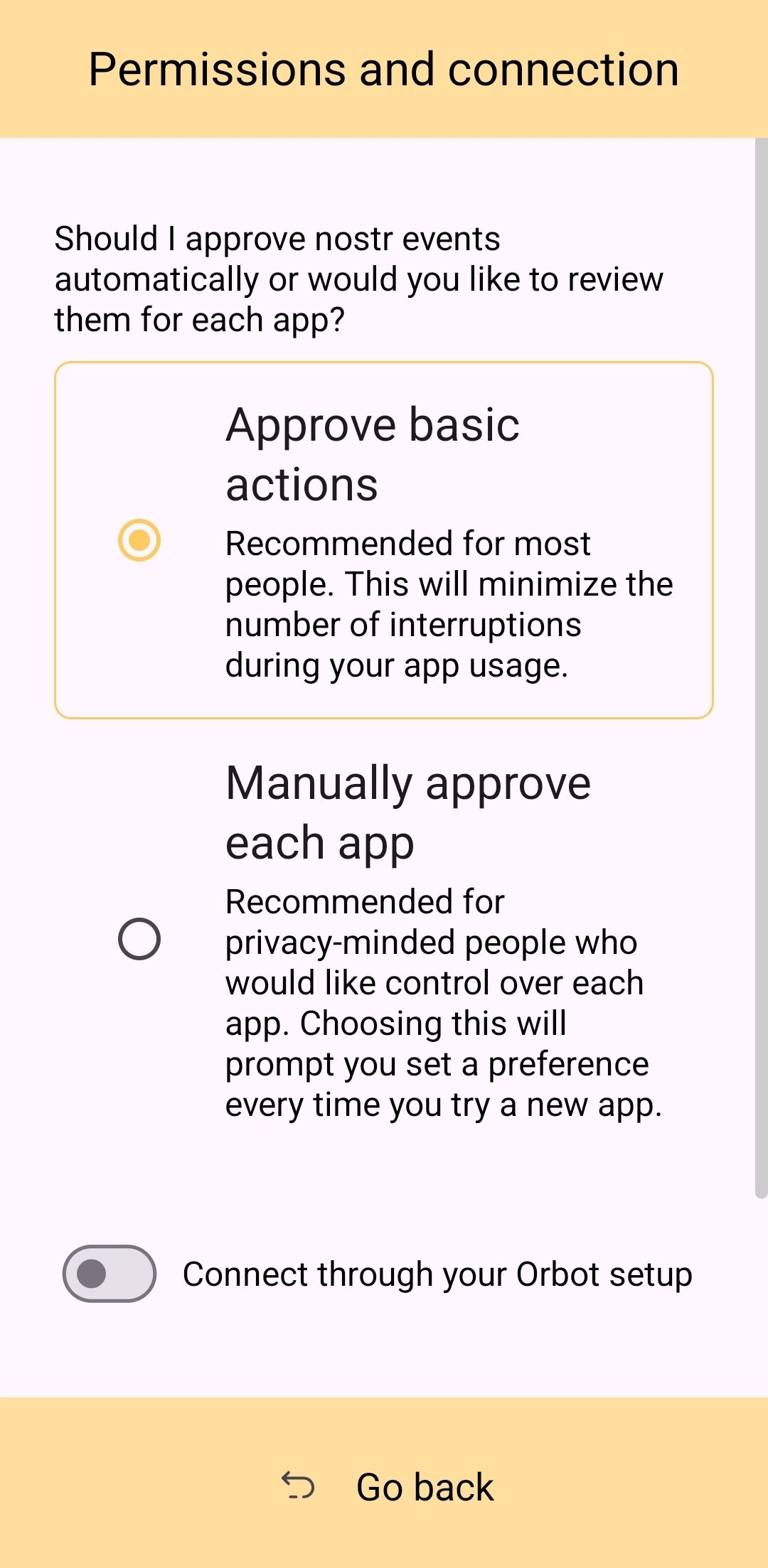
This is the signing method where Amber really shines in both speed and ease of use. Any Android application that supports this standard, and even some progressive web-apps that can be installed to your Android's home-screen, can very quickly and seamlessly connect with Amber to authorize anything that you need signed with your nsec. All you have to do is select "Login with Amber" in clients like #Amethyst or #0xChat and the app will reach out to Amber for all signing requests from there on out. If you had previously signed into the app with your nsec, you will first need to log out, then choose the option to use Amber when you log back in.
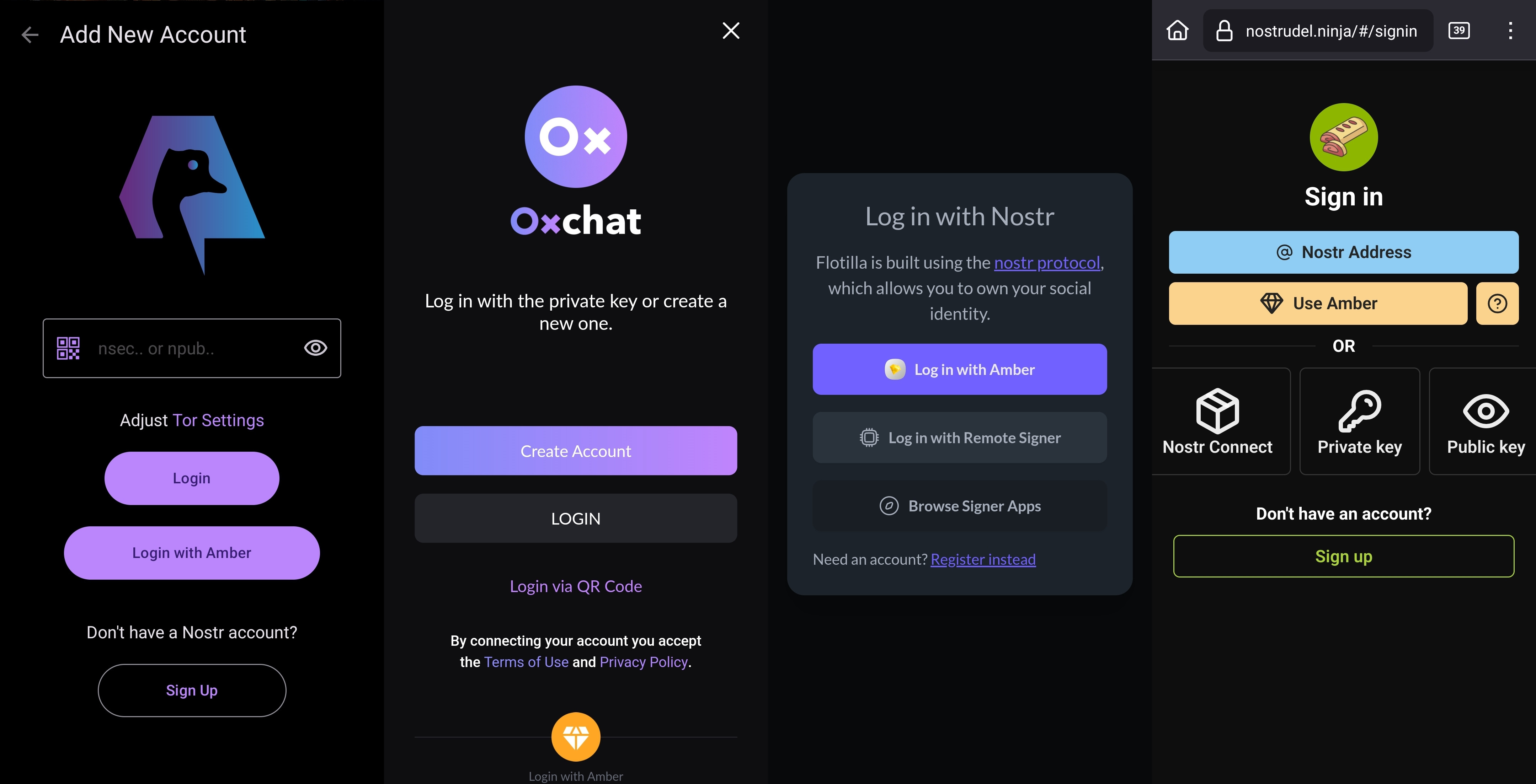
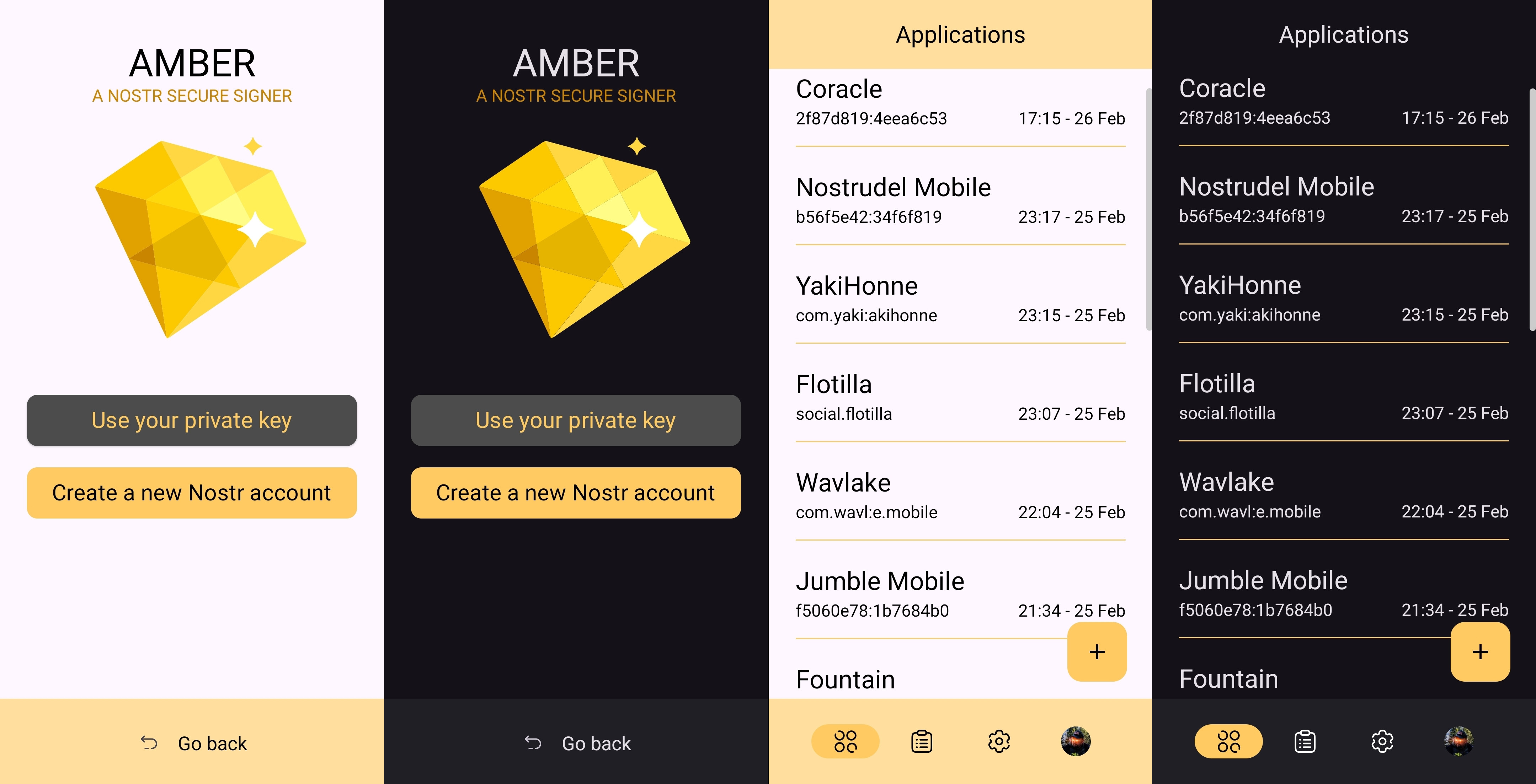
This is a massive deal, because everything you do on Nostr requires a signature from your private key. Log in? Needs a signature. Post a "GM" note? Needs a signature. Follow someone who zapped your note? Needs a signature. Zap them back? You guessed it; needs a signature. When you paste your private key into an application, it will automatically sign a lot of these actions without you ever being asked for approval, but you will quickly realize just how many things the client is doing on your behalf when Amber is asking you to approve them each time.
Now, this can also get quite annoying after a while. I recommend using the setting that allows Amber to automatically sign for basic functions, which will cut down on some of the authorization spam. Once you have been asked to authorize the same type of action a few times, you can also toggle the option to automatically authorize that action in the future. Don't worry, though, you have full control to require Amber to ask you for permission again if you want to be alerted each time, and this toggle is specific to each application, so it's not a blanket approval for all Nostr clients you connect with.
This method of signing is just as fast as signing via browser extension on web clients, which users may be more accustomed to. Everything is happening locally on the device, so it can be very snappy and secure.
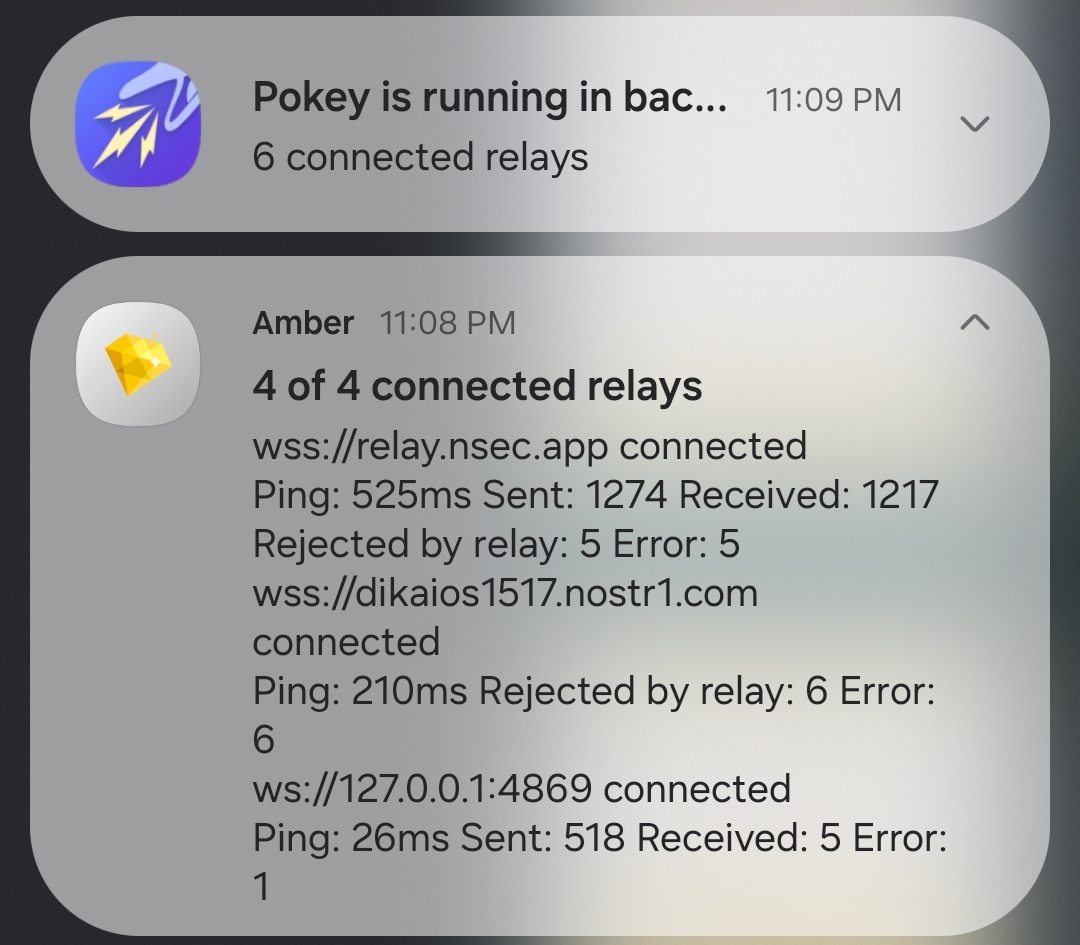
Nostr Connect/Bunker Signing
This next method of signing has a bit of a delay, because it is using a Nostr relay to send encrypted information back and forth between the app the user is interacting with and Amber to obtain signatures remotely. It isn't a significant delay most of the time, but it is just enough to be noticeable.
Also, unlike the previous signing method that would automatically switch to Amber as the active application when a signing request is sent, this method only sends you a notification that you must be watching for. This can lead to situations where you are wondering why something isn't working in a client you signed into remotely, because it is waiting on you to authorize the action and you didn't notice the notification from Amber. As you use the application, you get used to the need to check for such authorization requests from time to time, or when something isn't working as expected.
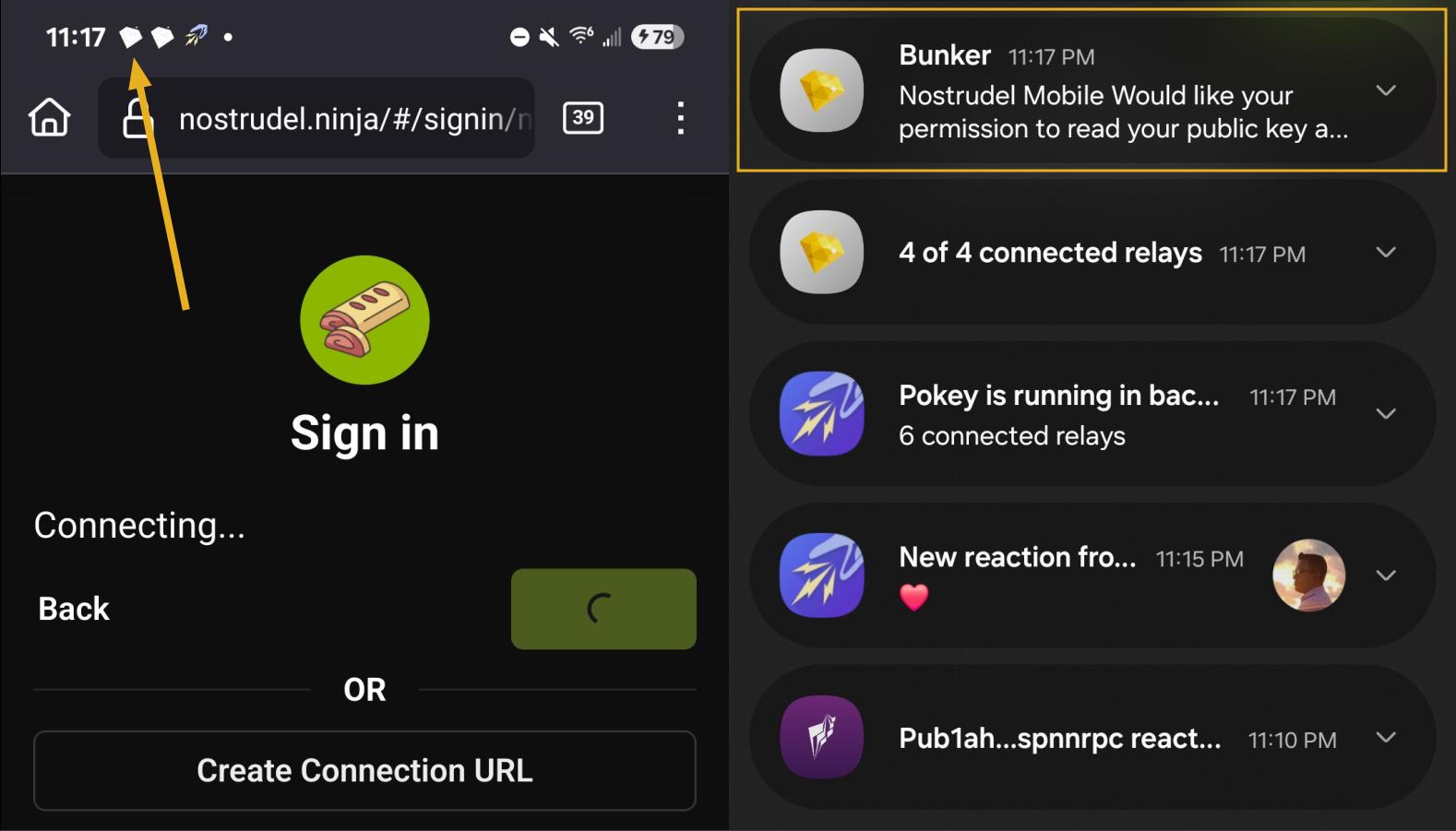
By default, Amber will use relay.nsec.app to communicate with whichever Nostr app you are connecting to. You can set a different relay for this purpose, if you like, though not just any relay will support the event kinds that Amber uses for remote signing. You can even run your own relay just for your own signing purposes. In fact, the creator of Amber has a relay application you can run on your phone, called Citrine, that can be used for signing with any web app you are using locally on your phone. This is definitely more of an advanced option, but it is there for you if you want it. For most users, sticking with relay.nsec.app will be just fine, especially since the contents of the events sent back and forth for signing are all encrypted.
Something many users may not realize is that this remote signing feature allows for issuing signing permissions to team members. For instance, if anyone ever joined me in writing reviews, I could issue them a connection string from Amber, and limit their permissions to just posting long-form draft events. Anything else they tried to do would require my explicit approval each time. Moreover, I could revoke those permissions if I ever felt they were being abused, without the need to start over with a whole new npub. Of course, this requires that your phone is online whenever a team member is trying to sign using the connection string you issued, and it requires you pay attention to your notifications so you can approve or reject requests you have not set to auto-approve. However, this is probably only useful for small teams, and larger businesses will want to find a more robust solution for managing access to their npub, such as Keycast from nostr:npub1zuuajd7u3sx8xu92yav9jwxpr839cs0kc3q6t56vd5u9q033xmhsk6c2uc.
The method for establishing a connection between Amber and a Nostr app for remote signing can vary for each app. Most, at minimum, will support obtaining a connection string from Amber that starts with "bunker://" and pasting it in at the time of login. Then you just need to approve the connection request from Amber and the client will log you in and send any subsequent signing requests to Amber using the same connection string.
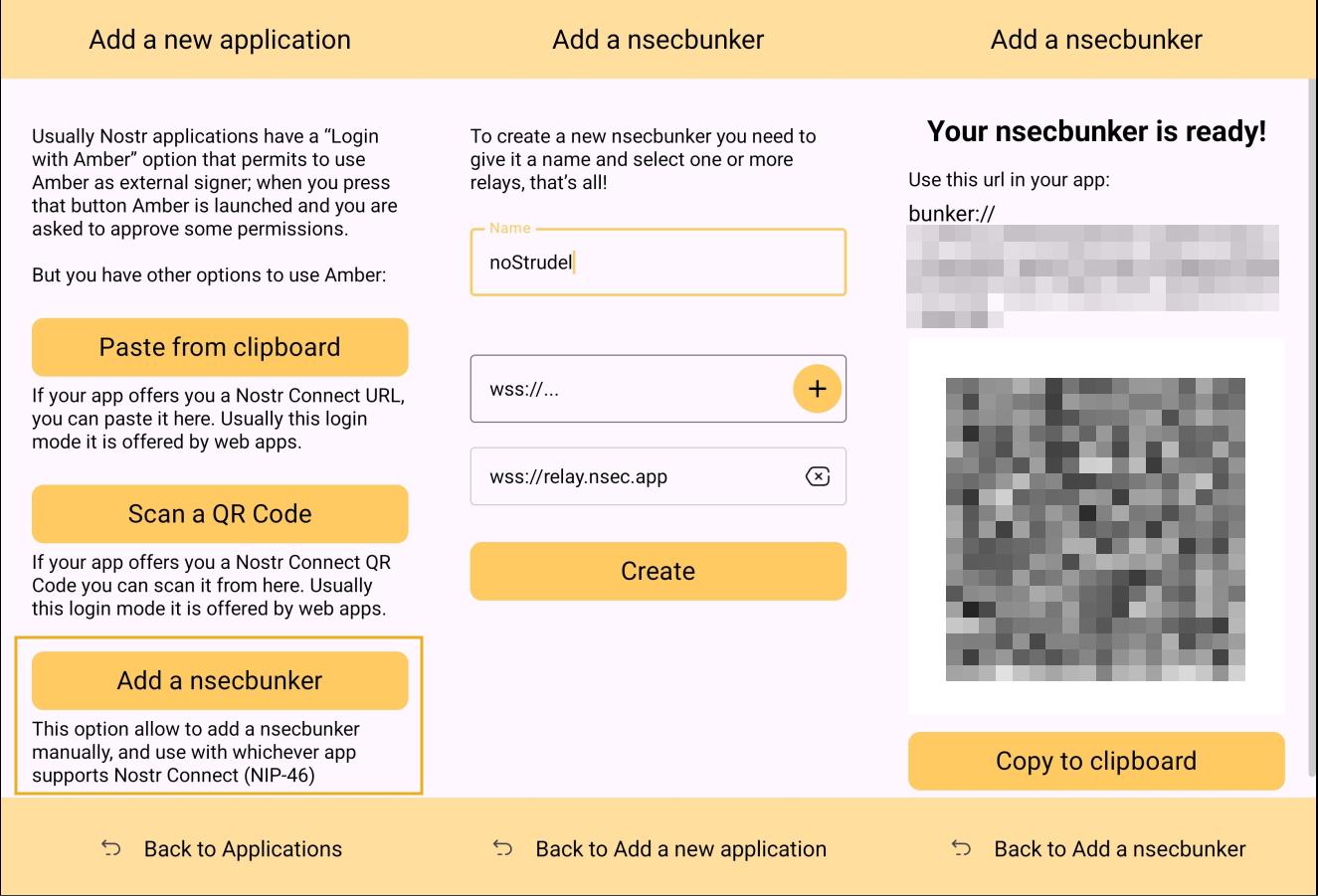
Some clients will also offer the option to scan a QR code to connect the client to Amber. This is quite convenient, but just remember that this also means the client is setting which relay will be used for communication between the two. Clients with this option will also have a connection string you can copy and paste into Amber to achieve the same purpose. For instance, you may need this option if you are trying to connect to an app on your phone and therefore can't scan the QR code using Amber on the same phone.
Multiple Accounts
Amber does not lock you into using it with only a single set of keys. You can add all of your Nostr "accounts" to Amber and use it for signing events for each independently. Of course, Nostr doesn't actually have "accounts" in the traditional sense. Your identity is simply your key-pair, and Amber stores and accesses each private key as needed.
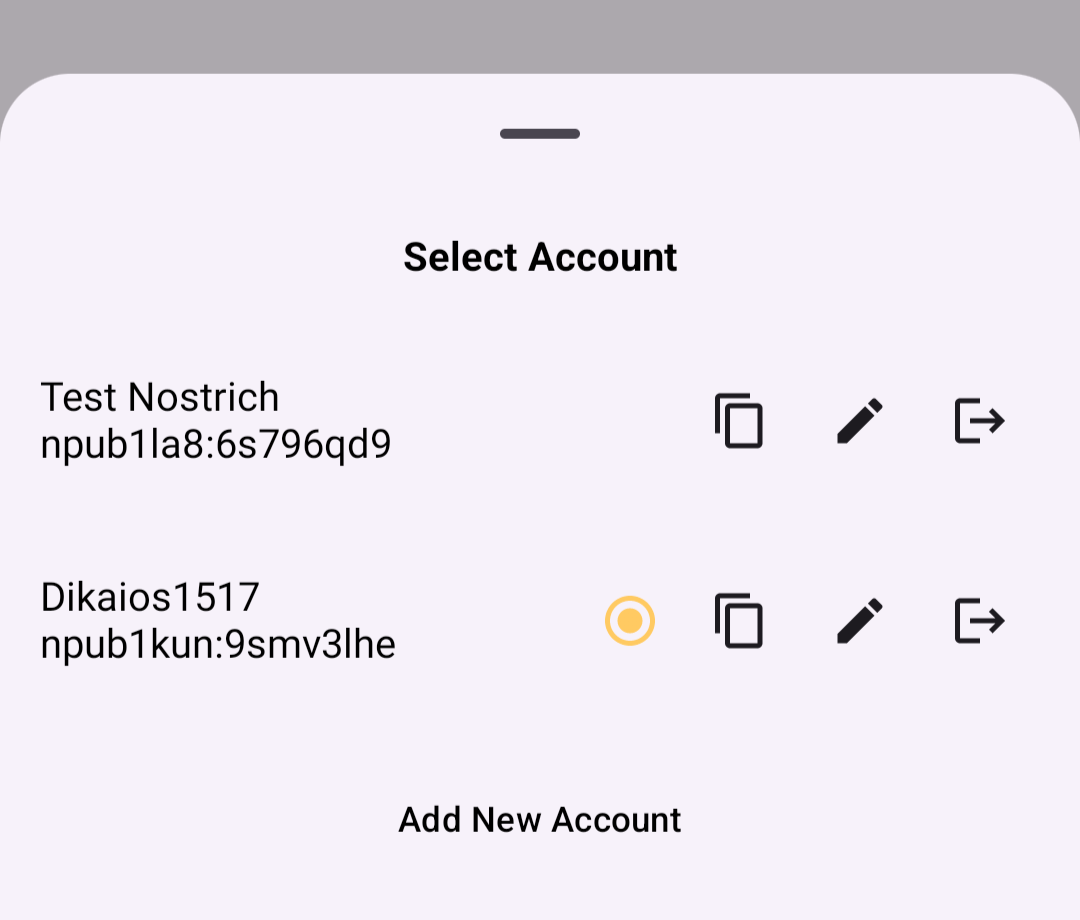
When first signing in using native Android signing as described above, Amber will default to whichever account was most recently selected, but you can switch to the account that is needed before approving the request. After initial login, Amber will automatically detect the account that the signing request is for.
Key Backup & Restore
Amber allows multiple ways to back up your private key. As most users would expect, you can get your standard nsec and copy/paste it to a password manager, but you can also obtain your private key as a list of mnemonic seed words, an encrypted version of your key called an ncryptsec, or even a QR code of your nsec or ncryptsec.
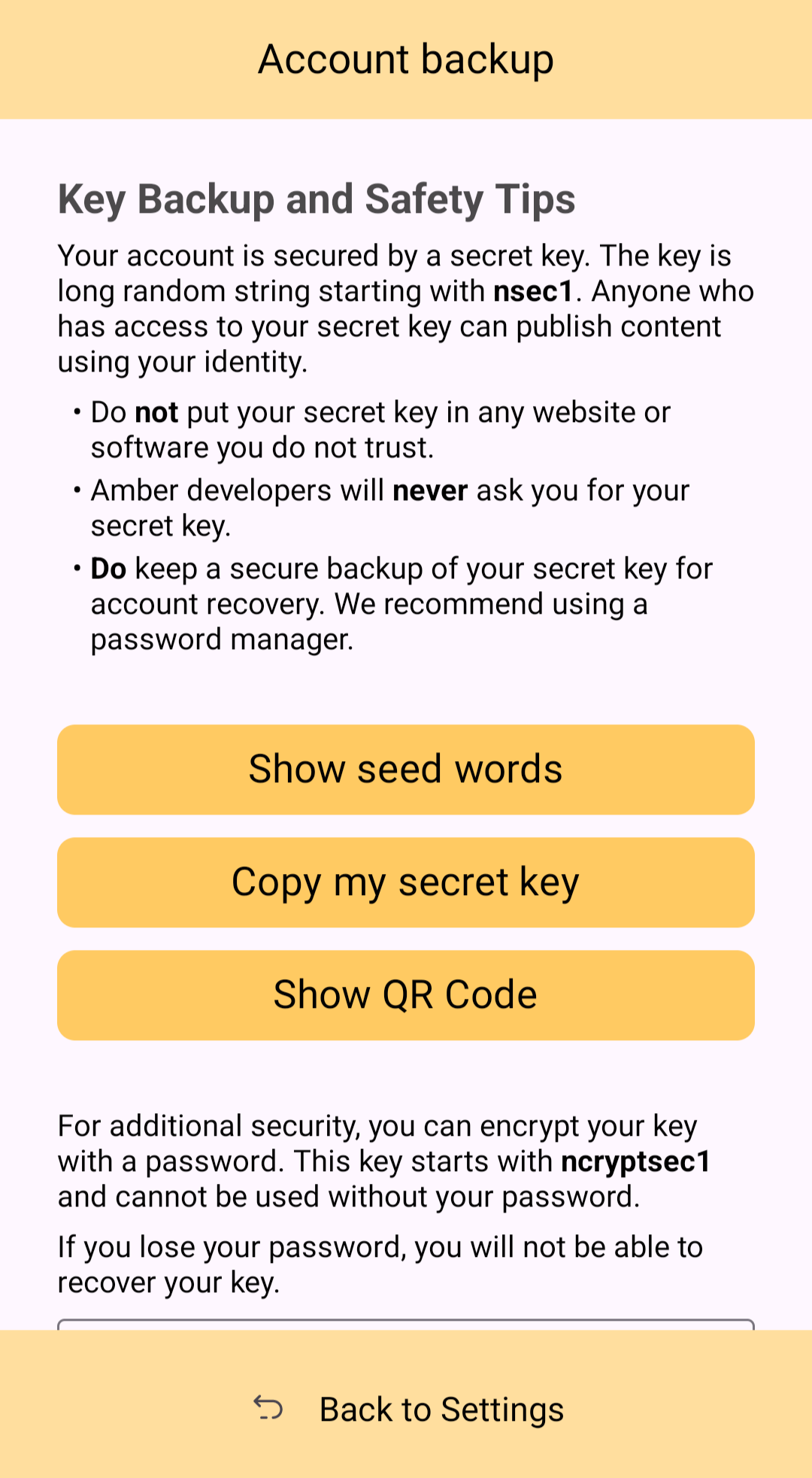
Additionally, in order to gain access to this information, Amber requires you to enter your device's PIN or use biometric authentication. This isn't cold-storage level protection for your private key by any means, especially since your phone is an internet connected device and does not store your key within a secure element, but it is about as secure as you can ask for while having your key accessible for signing Nostr events.
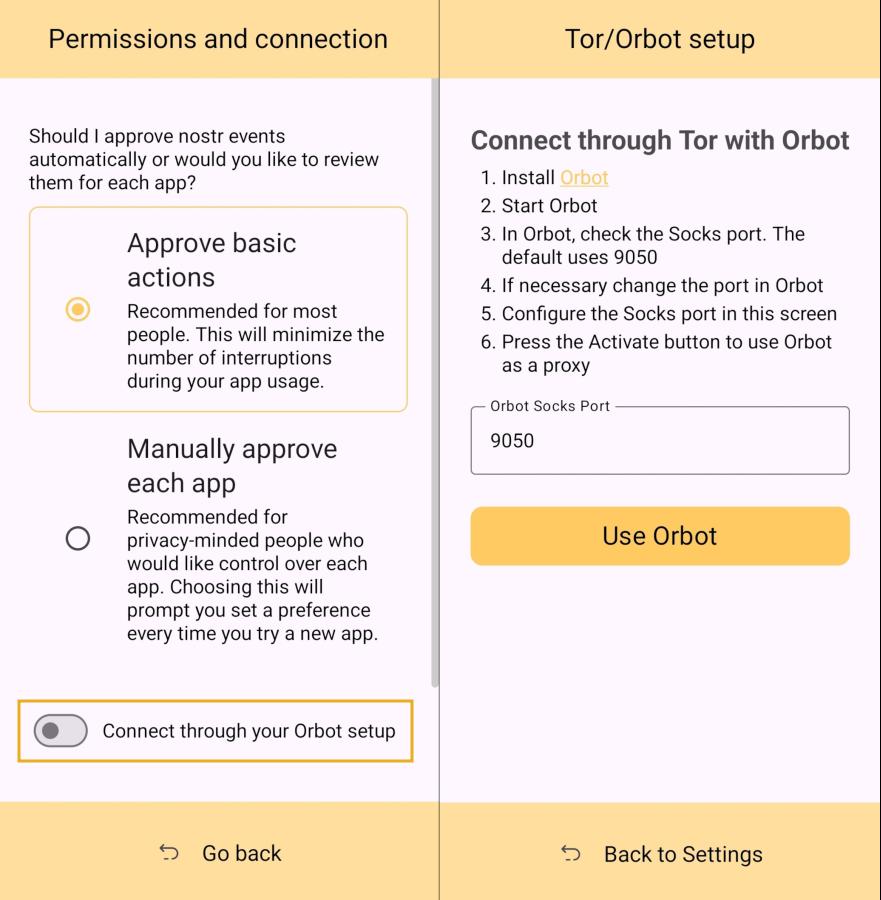
Tor Support
While Amber does not have Tor support within the app itself, it does support connecting to Tor through Orbot. This would be used with remote signing so that Amber would not connect directly over clearnet to the relay used for communication with the Nostr app requesting the signature. Instead, Amber would connect through Tor, so the relay would not see your IP address. This means you can utilize the remote signing option without compromising your anonymity.
Additional Security
Amber allows the user the option to require either biometric or PIN authentication before approving signing requests. This can provide that extra bit of assurance that no one will be able to sign events using your private key if they happen to gain access to your phone. The PIN you set in Amber is also independent from the PIN to unlock your device, allowing for separation of access.
Can My Grandma Use It?
Score: 4.6 / 5 (Updated 4/21/2025)
At the end of the day, Amber is a tool for those who have some concept of the importance of protecting their private key by not pasting it into every Nostr client that comes along. This concept in itself is not terribly approachable to an average person. They are used to just plugging their password into every service they use, and even worse, they usually have the same password for everything so they can more readily remember it. The idea that they should never enter their "Nostr password" into any Nostr application would never occur to them unless someone first explained how cryptography works related to public/private key pairs.
That said, I think there can be some improvements made to how users are introduced to these concepts, and that a signer application like Amber might be ideal for the job. Considering Amber as a new user's first touch-point with Nostr, I think it holds up well, but could be somewhat streamlined.
Upon opening the app, the user is prompted to either use their existing private key or "Create a new Nostr account." This is straightforward enough. "Account" is not a technically correct term with Nostr, but it is a term that new users would be familiar with and understand the basic concept.
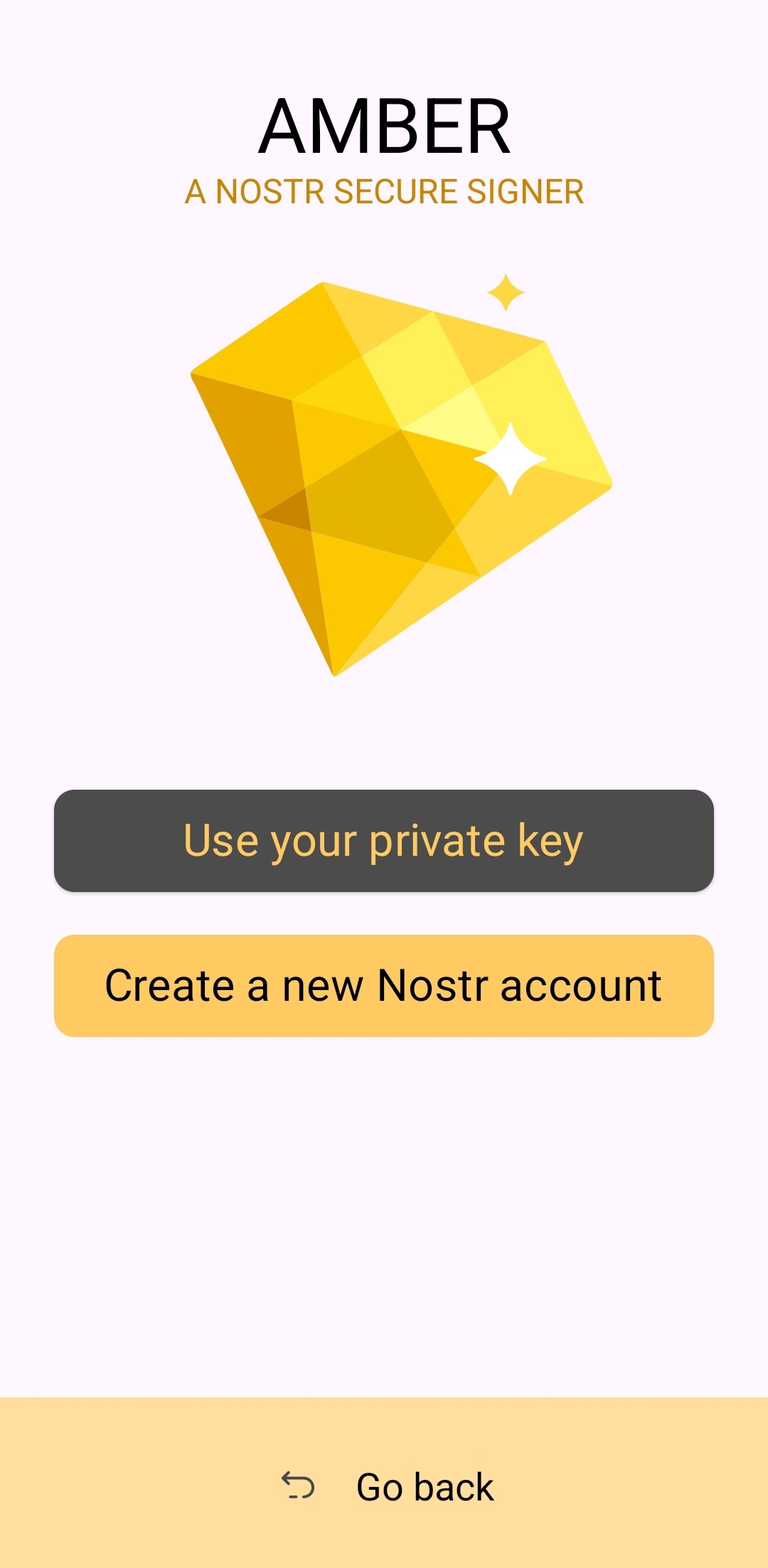
The next screen announces that the account is ready, and presents the user with their public key, explaining that it is "a sort of username" that will allow others to find them on Nostr. While it is good to explain this to the user, it is unnecessary information at this point. This screen also prompts the user to set a nickname and set a password to encrypt their private key. Since the backup options also allow the user to set this password, I think this step could be pushed to a later time. This screen would better serve the new user if it simply prompted them to set a nickname and short bio that could be saved to a few default relays.
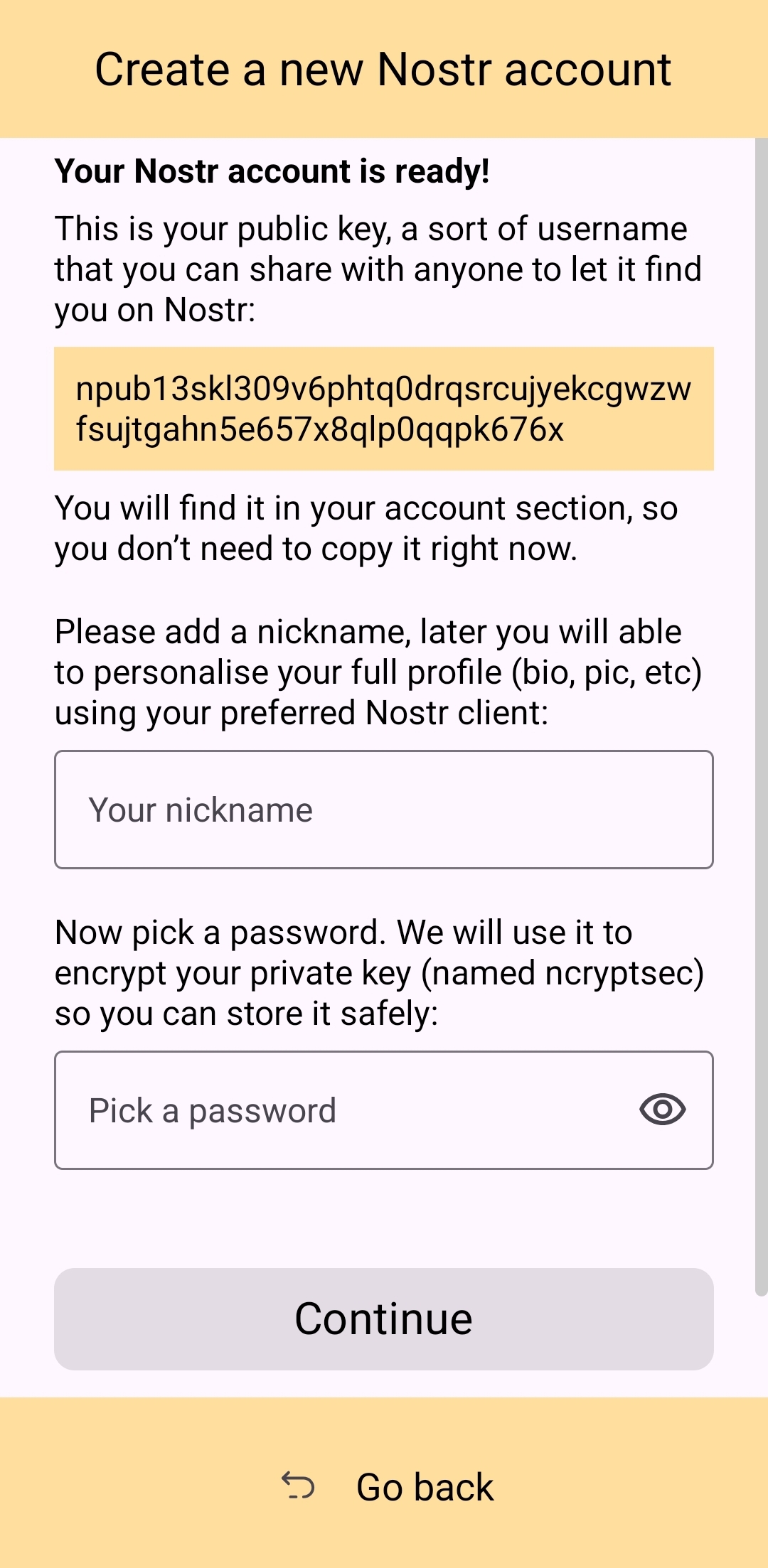
Of course, Amber is currently prompting for a password to be set up-front because the next screen requires the new user to download a "backup kit" in order to continue. While I do believe it is a good idea to encourage the creation of a backup, it is not crucial to do so immediately upon creation of a new npub that has nothing at stake if the private key is lost. This is something the UI could remind the user to do at a later time, reducing the friction of profile creation, and expediting getting them into the action.
Outside of these minor onboarding friction points, I think Amber does a great job of explaining to the user the purpose of each of its features, all within the app and without any need to reference external documentation. As long as the user understands the basic concept that their private key is being stored by Amber in order to sign requests from other Nostr apps, so they don't have to be given the private key, Amber is very good about explaining the rest without getting too far into the technical weeds.
The most glaring usability issue with Amber is that it isn't available in the Play Store. Average users expect to be able to find applications they can trust in their mobile device's default app store. There is a valid argument to be made that they are incorrect in this assumption, but that doesn't change the fact that this is the assumption most people make. They believe that applications in the Play Store are "safe" and that anything they can't install through the Play Store is suspect. The prompts that the Android operating system requires the user to approve when installing "unknown apps" certainly doesn't help with this impression.
Now, I absolutely love the Zapstore from nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9, but it doesn't do much to alleviate this issue. Users will still need to be convinced that it is safe to install the Zapstore from the GitHub repo, and then install Amber from there. Furthermore, this adds yet another step to the onboarding process.
Instead of:
- Install Amber
- Set up your keys
- Install the client you want to use
- Log in with Amber
The process becomes:
- Go to the Zapstore GitHub and download the latest version from the releases page.
- Install the APK you downloaded, allowing any prompt to install unknown apps.
- Open Zapstore and install Amber, allowing any prompt to install unknown apps again.
- Open Amber and set up your keys.
- Install the client you want to use
- Log in with Amber
An application as important as Amber for protecting users' private keys should be as readily available to the new user as possible. New users are the ones most prone to making mistakes that could compromise their private keys. Amber should be available to them in the Play Store.
UPDATE: As of version 3.2.8 released on 4/21/2025, the onboarding flow for Amber has been greatly improved! Now, when selecting to set up a new "account" the user is informed on the very next screen, "Your Nostr account is ready!" and given their public key/npub. The only field the user must fill in is their "nickname"/display name and hit "Continue."
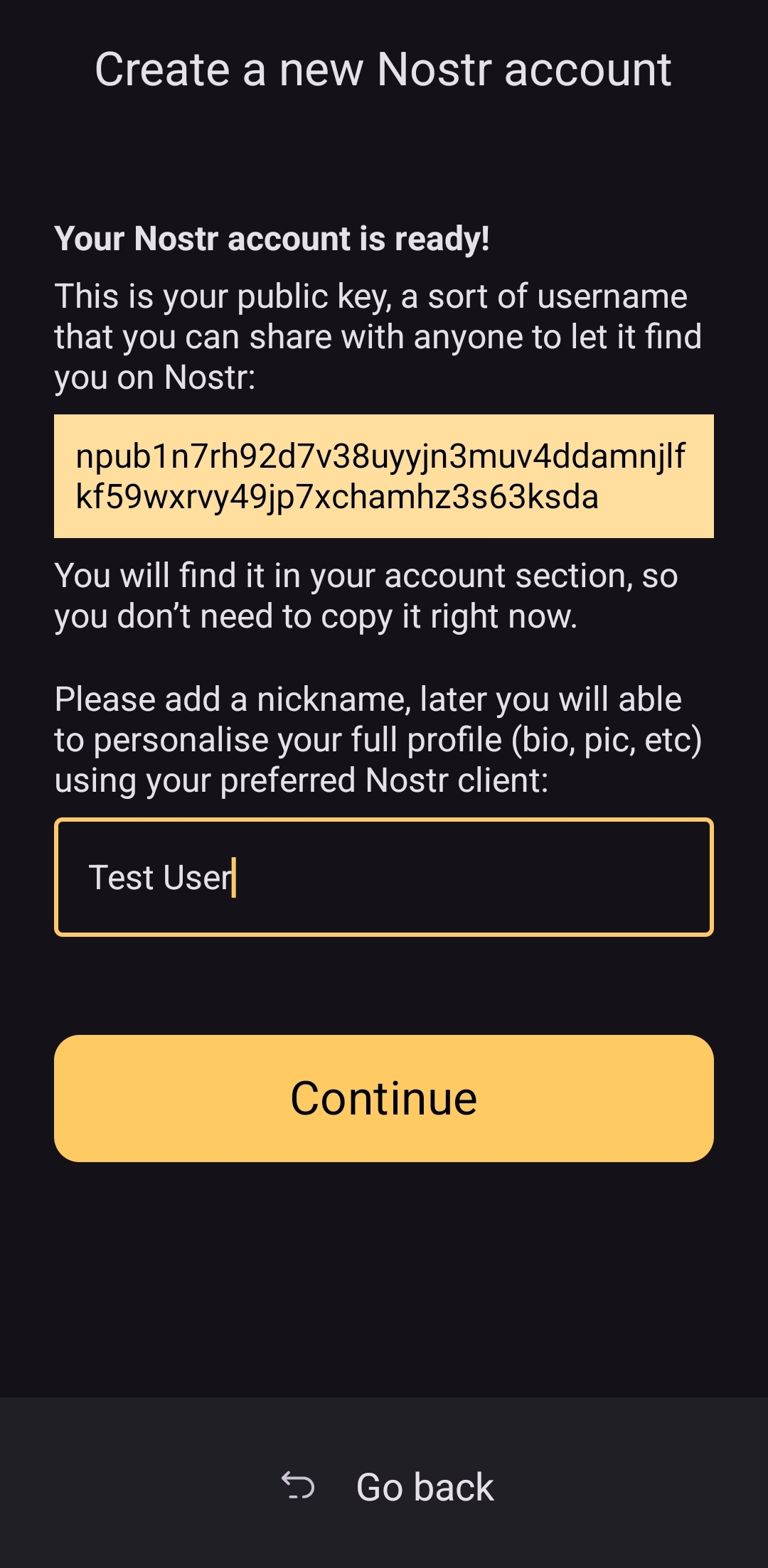
From there the user is asked if they want Amber to automatically approve basic actions, or manually approve each app, and then they are shown a new Applications screen, with a prompt to create a backup of their account. This prompt persists until the user has done so.
As you can see, the user is also encouraged to find applications that can be used with Amber with links to nostrapps.com and the Zapstore.
Thanks to these updates, Amber is now the smoothest and most user-friendly onboarding experience I have seen for Nostr to date. Sure, it doesn't have anything for setting up a profile picture or lightning address, but that is better done in a client like Amethyst or YakiHonne, anyway. Just tap "create," type in a handle to call yourself, and you're done!
How do UI Look?
Score: 4.5 / 5
Amber's UI can be described as clean but utilitarian. But then, Amber is a tool, so this is somewhat expected. It is not an app you will be spending a lot of time in, so the UI just needs to be serviceable. I would say it accomplishes this and then some. UI elements are generally easy to understand what they do, and page headings fill in the gaps where that is not the case.
I am not the biggest fan of the color-scheme, particularly in light-mode, but it is not bad in dark-mode at all, and Amber follows whatever theme you have set for your device in that respect. Additionally, the color choice does make sense given the application's name.
It must also be taken into consideration that Amber is almost entirely the product of a single developer's work. He has done a great job producing an app that is not only useful, but pleasant to interact with. The same cannot be said for most utility apps I have previously used, with interfaces that clearly made good design the lowest priority. While Amber's UI may not be the most beautiful Nostr app I have seen, design was clearly not an afterthought, either, and it is appreciated.
Relay Management
Score: 4.9 / 5
Even though Amber is not a Nostr client, where users can browse notes from their favorite npubs, it still relies heavily on relays for some of its features. Primarily, it uses relays for communicating with other Nostr apps for remote signing requests. However, it also uses relays to fetch profile data, so that each private key you add to Amber will automatically load your chosen username and profile picture.
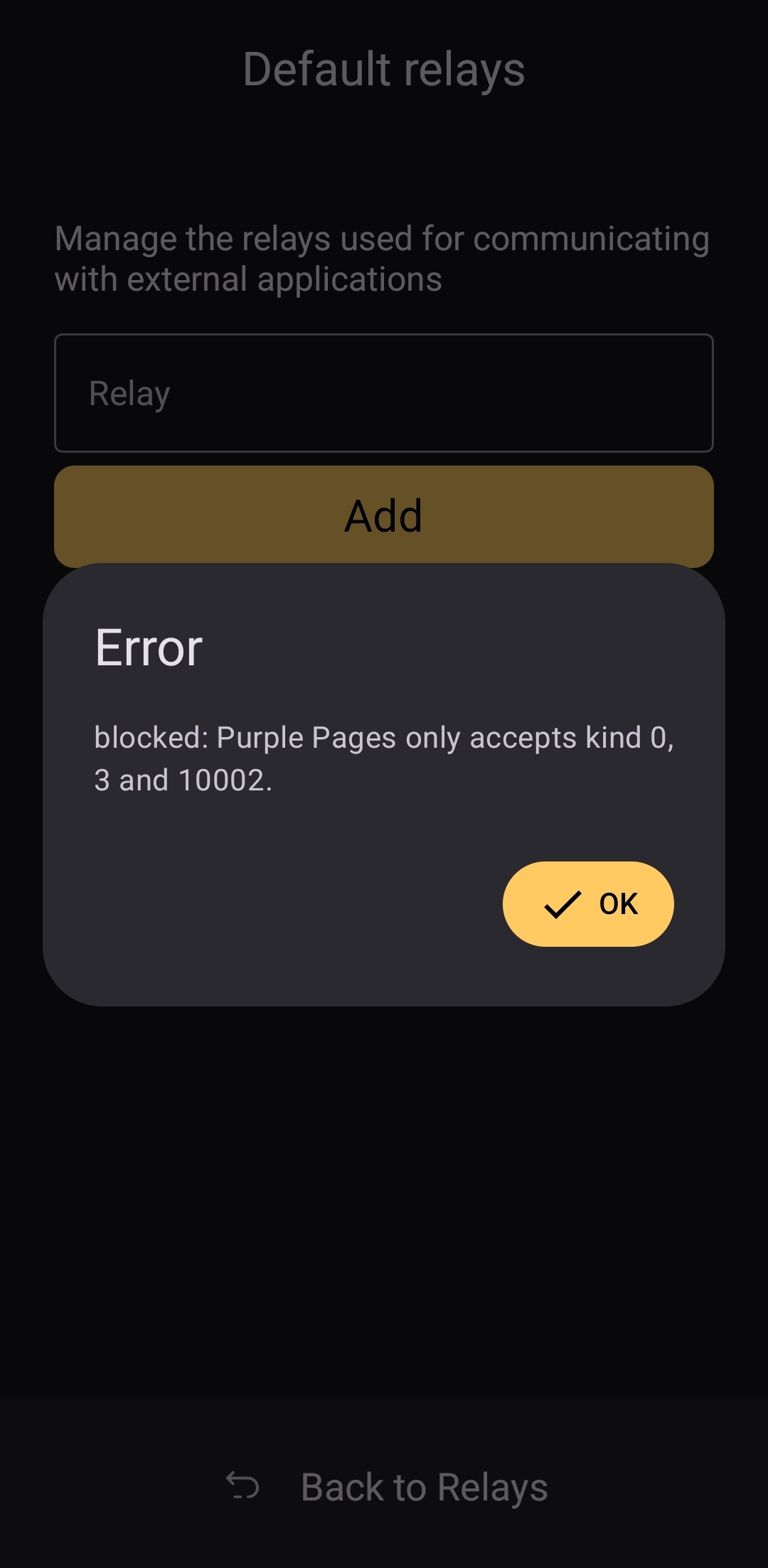
In the relay settings, users can choose which relays are being used to fetch profile data, and which relays will be used by default when creating new remote signing connection strings.
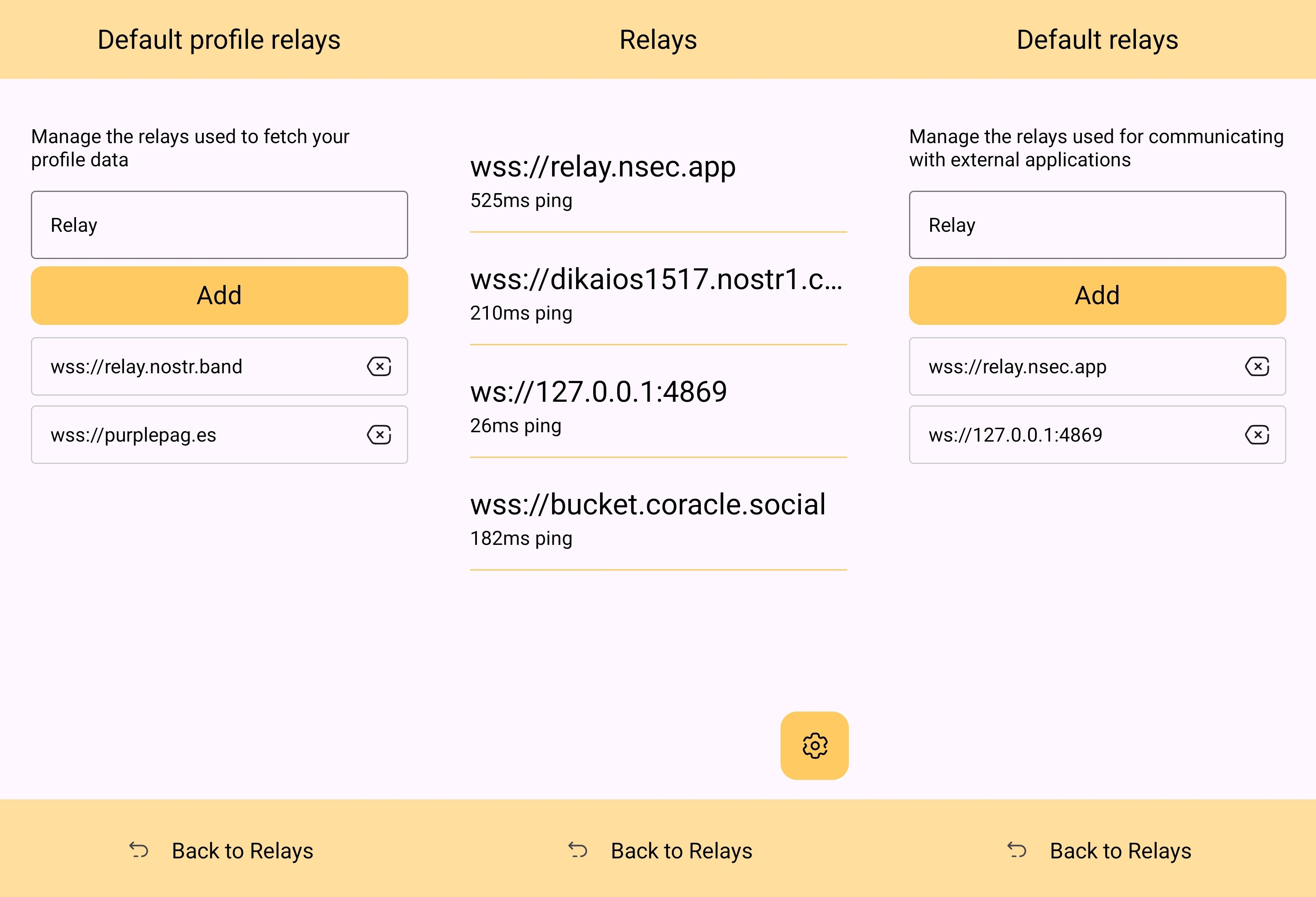
The user can also see which relays are currently connected to Amber and even look at the information that has been passed back and forth on each of those active relays. This information about actively connected relays is not only available within the application, but also in the notification that Amber has to keep in your device's notification tray in order to continue to operate in the background while you are using other apps.
Optionality is the name of the game when it comes to how Amber handles relay selection. The user can just stick with the default signing relay, use their own relay as the default, or even use a different relay for each Nostr application that they connect to for remote signing. Amber gives the user an incredible amount of flexibility in this regard.
In addition to all of this, because not all relays accept the event types needed for remote signing, when you add a relay address to Amber, it automatically tests that relay to see if it will work. This alone can be a massive time saver, so users aren't trying to use relays that don't support remote signing and wondering why they can't log into noStrudel with the connection string they got from Amber.
The only way I could see relay management being improved would be some means of giving the user relay recommendations, in case they want to use a relay other than relay.nsec.app, but they aren't sure which other relays will accept remote signing events. That said, most users who want to use a different relay for signing remote events will likely be using their own, in which case recommendations aren't needed.
Current Users' Questions
The AskNostr hashtag can be a good indication of the pain points that other users are currently having with any Nostr application. Here are some of the most common questions submitted about Amber in the last two months.
nostr:nevent1qqsfrdr68fafgcvl8dgnhm9hxpsjxuks78afxhu8yewhtyf3d7mkg9gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgq3qkgh77xxt7hhtt4u528hecnx69rhagla8jj3tclgyf9wvkxa6dc0sxp0e6m
This is a good example of Amber working correctly, but the app the user is trying to log into not working. In my experience with #Olas in particular, it sometimes allows remote signer login, and sometimes doesn't. Amber will receive the signing request and I will approve it, but Olas remains on the login screen.
If Amber is receiving the signing requests, and you are approving them, the fault is likely with the application you are trying to log into.
That's it. That's all the repeated questions I could find. Oh, there were a few one-off questions where relay.nsec.app wouldn't connect, or where the user's out-of-date web browser was the issue. Outside of that, though, there were no common questions about how to use Amber, and that is a testament to Amber's ease of use all on its own.
Wrap Up
If you are on Android and you are not already using Amber to protect your nsec, please do yourself a favor and get it installed. It's not at all complicated to set up, and it will make trying out all the latest Nostr clients a safe and pleasant experience.
If you are a client developer and you have not added support for NIP-55 or NIP-46, do your users the courtesy of respecting the sanctity of their private keys. Even developers who have no intention of compromising their users' keys can inadvertently do so. Make that eventuality impossible by adding support for NIP-55 and NIP-46 signing.
Finally, I apologize for the extended time it took me to get this review finished. The time I have available is scarce, Nostr is distracting, and nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 kept improving Amber even as I was putting it through its paces over the last two months. Keep shipping, my friend! You have made one of the most useful tools we have seen for Nostr to date!
Now... What should I review next?
-
 @ 401014b3:59d5476b
2025-04-22 00:23:24
@ 401014b3:59d5476b
2025-04-22 00:23:24About Me
I come to Nostr with extensive experience in the digital landscape. As a blockchain native since 2017, I've witnessed the evolution of decentralized technologies firsthand. Most of my professional career has been spent working within big tech companies, giving me a unique perspective on both centralized and decentralized systems.
My social media journey began on Twitter in 2007, where I've maintained a presence for over 17 years. I've also explored other decentralized social platforms including BlueSky, Farcaster, and Lens Protocol. As a Bitcoin maximalist, I was particularly intrigued by Nostr's compatibility with the Lightning Network, which initially drew me to the platform.
The Onboarding Challenge
The Nostr onboarding experience presents a significant hurdle for newcomers. Despite my technical background in blockchain technologies, I found the initial setup process more complicated than expected. Understanding public/private key cryptography just to join a social network creates a steeper learning curve than necessary.
BlueSky and Farcaster have demonstrated that it's possible to maintain decentralized principles while providing a more streamlined onboarding experience. Their approaches show that user-friendly design and decentralization aren't mutually exclusive concepts.
Relay Management: Room for Improvement
The concept of relays represents one of Nostr's most distinctive features, though it can be confusing for newcomers. While many clients come pre-configured with default relays, users eventually encounter situations where content or connections seem inconsistent.
When someone I've interacted with doesn't appear in my feed or doesn't respond, I'm often left wondering if we're simply on different relays. This uncertainty creates friction that doesn't exist on other platforms where connectivity is handled behind the scenes.
The relay system introduces a layer of complexity that, while important to Nostr's architecture, could benefit from better abstraction in the user experience. When using BlueSky or Farcaster, I don't need to think about the underlying infrastructure, something Nostr could learn from while maintaining its decentralized principles.
The Zap Economy: Growing Pains
The Lightning-powered zap system shows tremendous potential, but I've observed some concerning economic patterns. Longer-term Nostr users have expressed frustration about continuously sending zaps while seeing limited growth in the overall ecosystem.
Interestingly, there appears to be a connection between this liquidity issue and community growth dynamics. Some established users who voice concerns about bearing the financial burden of the zapping economy are simultaneously less welcoming to newer accounts, rarely following, engaging with, or zapping newcomers.
This creates a challenging environment for new users, who face a cold reception and have little incentive to load their Lightning wallets or participate in the zap economy. Why bring fresh liquidity to a platform where established users rarely engage with your content? This dynamic has limited the expansion of the ecosystem, with the same sats often circulating among established users rather than growing with new participants.
Client Diversity: Strength and Challenge
Nostr's multiple client options offer users choice, which is valuable. However, the implementation of NIPs (Nostr Implementation Possibilities) varies across clients, creating inconsistent experiences. Features that work seamlessly in one client might be implemented differently in another.
This extends to fundamental aspects like search functionality, thread navigation, and notification systems, all of which can differ significantly between clients. For users accustomed to consistent experiences, this fragmentation creates a learning curve with each new client they try.
Lightning Integration: Varying Experiences
The Lightning Network integration varies in quality and user experience across Nostr clients. While the functionality is generally present, the implementation quality, feature set, and ease of use differ depending on which client you choose.
This inconsistency means users may need to experiment with several clients to find one that provides the Lightning experience they're looking for, rather than having a consistent experience across the ecosystem.
Finding Balance
Nostr appears to be navigating the challenge of balancing technical innovation with user experience. While its cryptographic foundation and decentralized architecture are impressive technical achievements, these same strengths sometimes come at the cost of accessibility.
Despite my technical background and interest in decentralized technologies, I find myself using BlueSky and Farcaster more frequently for daily social interactions, while checking Nostr less often. For Nostr to achieve its potential for broader adoption, addressing these user experience considerations while maintaining its core principles will be essential.
The platform has tremendous potential with improvements to user experience, community dynamics, and economic sustainability, Nostr could evolve from a fascinating technical experiment into a truly compelling alternative to mainstream social media.
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:13:56
@ 4ba8e86d:89d32de4
2025-04-21 02:13:56Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:12:19
@ 4ba8e86d:89d32de4
2025-04-21 02:12:19SISTEMA OPERACIONAL MÓVEIS
GrapheneOS : https://njump.me/nevent1qqs8t76evdgrg4qegdtyrq2rved63pr29wlqyj627n9tj4vlu66tqpqpzdmhxue69uhk7enxvd5xz6tw9ec82c30qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqppcqec9
CalyxOS : https://njump.me/nevent1qqsrm0lws2atln2kt3cqjacathnw0uj0jsxwklt37p7t380hl8mmstcpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3vamnwvaz7tmwdaehgu3wvf3kstnwd9hx5cf0qy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgcwaehxw309aex2mrp0yhxxatjwfjkuapwveukjtcpzpmhxue69uhkummnw3ezumt0d5hszrnhwden5te0dehhxtnvdakz7qfywaehxw309ahx7um5wgh8ymm4dej8ymmrdd3xjarrda5kuetjwvhxxmmd9uq3uamnwvaz7tmwdaehgu3dv3jhvtnhv4kxcmmjv3jhytnwv46z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309ahx7um5wghxymmwva3x7mn89e3k7mf0qythwumn8ghj7cn5vvhxkmr9dejxz7n49e3k7mf0qyg8wumn8ghj7mn09eehgu3wvdez7smttdu
LineageOS : https://njump.me/nevent1qqsgw7sr36gaty48cf4snw0ezg5mg4atzhqayuge752esd469p26qfgpzdmhxue69uhhwmm59e6hg7r09ehkuef0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpnvm779
SISTEMA OPERACIONAL DESKTOP
Tails : https://njump.me/nevent1qqsf09ztvuu60g6xprazv2vxqqy5qlxjs4dkc9d36ta48q75cs9le4qpzemhxue69uhkummnw3ex2mrfw3jhxtn0wfnj7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz34ag5t
Qubes OS : https://njump.me/nevent1qqsp6jujgwl68uvurw0cw3hfhr40xq20sj7rl3z4yzwnhp9sdpa7augpzpmhxue69uhkummnw3ezumt0d5hsz9mhwden5te0wfjkccte9ehx7um5wghxyctwvshsz9thwden5te0dehhxarj9ehhsarj9ejx2a30qyg8wumn8ghj7mn09eehgu3wvdez7qg4waehxw309aex2mrp0yhxgctdw4eju6t09uqjxamnwvaz7tmwdaehgu3dwejhy6txd9jkgtnhv4kxcmmjv3jhytnwv46z7qgwwaehxw309ahx7uewd3hkctcpremhxue69uhkummnw3ez6er9wch8wetvd3hhyer9wghxuet59uj3ljr8
Kali linux : https://njump.me/nevent1qqswlav72xdvamuyp9xc38c6t7070l3n2uxu67ssmal2g7gv35nmvhspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswt9rxe
Whonix : https://njump.me/nevent1qqs85gvejvzhk086lwh6edma7fv07p5c3wnwnxnzthwwntg2x6773egpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3qamnwvaz7tmwdaehgu3wd4hk6tcpzemhxue69uhkummnw3ezucnrdqhxu6twdfsj7qfywaehxw309ahx7um5wgh8ymm4dej8ymmrdd3xjarrda5kuetjwvhxxmmd9uq3wamnwvaz7tmzw33ju6mvv4hxgct6w5hxxmmd9uq3qamnwvaz7tmwduh8xarj9e3hytcpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszrnhwden5te0dehhxtnvdakz7qg7waehxw309ahx7um5wgkkgetk9emk2mrvdaexgetj9ehx2ap0sen9p6
Kodachi : https://njump.me/nevent1qqsf5zszgurpd0vwdznzk98hck294zygw0s8dah6fpd309ecpreqtrgpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszgmhwden5te0dehhxarj94mx2unfve5k2epwwajkcmr0wfjx2u3wdejhgtcpremhxue69uhkummnw3ez6er9wch8wetvd3hhyer9wghxuet59uq3qamnwvaz7tmwdaehgu3wd4hk6tcpzamhxue69uhkyarr9e4kcetwv3sh5afwvdhk6tcpzpmhxue69uhkumewwd68ytnrwghszfrhwden5te0dehhxarj9eex7atwv3ex7cmtvf5hgcm0d9hx2unn9e3k7mf0qyvhwumn8ghj7mn0wd68ytnzdahxwcn0denjucm0d5hszrnhwden5te0dehhxtnvdakz7qgkwaehxw309ahx7um5wghxycmg9ehxjmn2vyhsz9mhwden5te0wfjkccte9ehx7um5wghxyctwvshs94a4d5
PGP
Openkeychain : https://njump.me/nevent1qqs9qtjgsulp76t7jkquf8nk8txs2ftsr0qke6mjmsc2svtwfvswzyqpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs36mp0w
Kleopatra : https://njump.me/nevent1qqspnevn932hdggvp4zam6mfyce0hmnxsp9wp8htpumq9vm3anq6etsppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpuaeghp
Pgp : https://njump.me/nevent1qqsggek707qf3rzttextmgqhym6d4g479jdnlnj78j96y0ut0x9nemcpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgptemhe
Como funciona o PGP? : https://njump.me/nevent1qqsz9r7azc8pkvfmkg2hv0nufaexjtnvga0yl85x9hu7ptpg20gxxpspremhxue69uhkummnw3ez6ur4vgh8wetvd3hhyer9wghxuet59upzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy259fhs
Por que eu escrevi PGP. - Philip Zimmermann.
https://njump.me/nevent1qqsvysn94gm8prxn3jw04r0xwc6sngkskg756z48jsyrmqssvxtm7ncpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtchzxnad
VPN
Vpn : https://njump.me/nevent1qqs27ltgsr6mh4ffpseexz6s37355df3zsur709d0s89u2nugpcygsspzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqshzu2fk
InviZible Pro : https://njump.me/nevent1qqsvyevf2vld23a3xrpvarc72ndpcmfvc3lc45jej0j5kcsg36jq53cpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy33y5l4
Orbot: https://njump.me/nevent1qqsxswkyt6pe34egxp9w70cy83h40ururj6m9sxjdmfass4cjm4495stft593
I2P
i2p : https://njump.me/nevent1qqsvnj8n983r4knwjmnkfyum242q4c0cnd338l4z8p0m6xsmx89mxkslx0pgg
Entendendo e usando a rede I2P : https://njump.me/nevent1qqsxchp5ycpatjf5s4ag25jkawmw6kkf64vl43vnprxdcwrpnms9qkcppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpvht4mn
Criando e acessando sua conta Email na I2P : https://njump.me/nevent1qqs9v9dz897kh8e5lfar0dl7ljltf2fpdathsn3dkdsq7wg4ksr8xfgpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpw8mzum
APLICATIVO 2FA
Aegis Authenticator : https://njump.me/nevent1qqsfttdwcn9equlrmtf9n6wee7lqntppzm03pzdcj4cdnxel3pz44zspz4mhxue69uhhyetvv9ujumn0wd68ytnzvuhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqscvtydq
YubiKey : https://njump.me/nevent1qqstsnn69y4sf4330n7039zxm7wza3ch7sn6plhzmd57w6j9jssavtspvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzueyvgt
GERENCIADOR DE SENHAS
KeepassDX: https://njump.me/nevent1qqswc850dr4ujvxnmpx75jauflf4arc93pqsty5pv8hxdm7lcw8ee8qpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpe0492n
Birwaden: https://njump.me/nevent1qqs0j5x9guk2v6xumhwqmftmcz736m9nm9wzacqwjarxmh8k4xdyzwgpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpwfe2kc
KeePassXC: https://njump.me/nevent1qqsgftcrd8eau7tzr2p9lecuaf7z8mx5jl9w2k66ae3lzkw5wqcy5pcl2achp
CHAT MENSAGEM
SimpleXchat : https://njump.me/nevent1qqsds5xselnnu0dyy0j49peuun72snxcgn3u55d2320n37rja9gk8lgzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgmcmj7c
Briar : https://njump.me/nevent1qqs8rrtgvjr499hreugetrl7adkhsj2zextyfsukq5aa7wxthrgcqcg05n434
Element Messenger : https://njump.me/nevent1qqsq05snlqtxm5cpzkshlf8n5d5rj9383vjytkvqp5gta37hpuwt4mqyccee6
Pidgin : https://njump.me/nevent1qqsz7kngycyx7meckx53xk8ahk98jkh400usrvykh480xa4ct9zlx2c2ywvx3
E-MAIL
Thunderbird: https://njump.me/nevent1qqspq64gg0nw7t60zsvea5eykgrm43paz845e4jn74muw5qzdvve7uqrkwtjh
ProtonMail : https://njump.me/nevent1qqs908glhk68e7ms8zqtlsqd00wu3prnpt08dwre26hd6e5fhqdw99cppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpeyhg4z
Tutonota : https://njump.me/nevent1qqswtzh9zjxfey644qy4jsdh9465qcqd2wefx0jxa54gdckxjvkrrmqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs5hzhkv
k-9 mail : https://njump.me/nevent1qqs200g5a603y7utjgjk320r3srurrc4r66nv93mcg0x9umrw52ku5gpr3mhxue69uhkummnw3ezuumhd9ehxtt9de5kwmtp9e3kstczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgacflak
E-MAIL-ALIÁS
Simplelogin : https://njump.me/nevent1qqsvhz5pxqpqzr2ptanqyqgsjr50v7u9lc083fvdnglhrv36rnceppcppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqp9gsr7m
AnonAddy : https://njump.me/nevent1qqs9mcth70mkq2z25ws634qfn7vx2mlva3tkllayxergw0s7p8d3ggcpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs6mawe3
NAVEGADOR
Navegador Tor : https://njump.me/nevent1qqs06qfxy7wzqmk76l5d8vwyg6mvcye864xla5up52fy5sptcdy39lspzemhxue69uhkummnw3ezuerpw3sju6rpw4ej7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdp0urw
Mullvap Browser : https://njump.me/nevent1qqs2vsgc3wk09wdspv2mezltgg7nfdg97g0a0m5cmvkvr4nrfxluzfcpzdmhxue69uhhwmm59e6hg7r09ehkuef0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpj8h6fe
LibreWolf : https://njump.me/nevent1qqswv05mlmkcuvwhe8x3u5f0kgwzug7n2ltm68fr3j06xy9qalxwq2cpzemhxue69uhkummnw3ex2mrfw3jhxtn0wfnj7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzuv2hxr
Cromite : https://njump.me/nevent1qqs2ut83arlu735xp8jf87w5m3vykl4lv5nwkhldkqwu3l86khzzy4cpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs3dplt7
BUSCADORES
Searx : https://njump.me/nevent1qqsxyzpvgzx00n50nrlgctmy497vkm2cm8dd5pdp7fmw6uh8xnxdmaspr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqp23z7ax
APP-STORE
Obtainium : https://njump.me/nevent1qqstd8kzc5w3t2v6dgf36z0qrruufzfgnc53rj88zcjgsagj5c5k4rgpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqyarmca3
F-Droid : https://njump.me/nevent1qqst4kry49cc9g3g8s5gdnpgyk3gjte079jdnv43f0x4e85cjkxzjesymzuu4
Droid-ify : https://njump.me/nevent1qqsrr8yu9luq0gud902erdh8gw2lfunpe93uc2u6g8rh9ep7wt3v4sgpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsfzu9vk
Aurora Store : https://njump.me/nevent1qqsy69kcaf0zkcg0qnu90mtk46ly3p2jplgpzgk62wzspjqjft4fpjgpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzrpmsjy
RSS
Feeder : https://njump.me/nevent1qqsy29aeggpkmrc7t3c7y7ldgda7pszl7c8hh9zux80gjzrfvlhfhwqpp4mhxue69uhkummn9ekx7mqzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgsvzzjy
VIDEOO CONFERENCIA
Jitsi meet : https://njump.me/nevent1qqswphw67hr6qmt2fpugcj77jrk7qkfdrszum7vw7n2cu6cx4r6sh4cgkderr
TECLADOS
HeliBoard : https://njump.me/nevent1qqsyqpc4d28rje03dcvshv4xserftahhpeylu2ez2jutdxwds4e8syspz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsr8mel5
OpenBoard : https://njump.me/nevent1qqsf7zqkup03yysy67y43nj48q53sr6yym38es655fh9fp6nxpl7rqspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswcvh3r
FlorisBoard : https://njump.me/nevent1qqsf7zqkup03yysy67y43nj48q53sr6yym38es655fh9fp6nxpl7rqspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswcvh3r
MAPAS
Osmand : https://njump.me/nevent1qqsxryp2ywj64az7n5p6jq5tn3tx5jv05te48dtmmt3lf94ydtgy4fgpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs54nwpj
Organic maps : https://njump.me/nevent1qqstrecuuzkw0dyusxdq7cuwju0ftskl7anx978s5dyn4pnldrkckzqpr4mhxue69uhkummnw3ezumtp0p5k6ctrd96xzer9dshx7un8qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpl8z3kk
TRADUÇÃO
LibreTranslate : https://njump.me/nevent1qqs953g3rhf0m8jh59204uskzz56em9xdrjkelv4wnkr07huk20442cpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzeqsx40
REMOÇÃO DOS METADADOS
Scrambled Exif : https://njump.me/nevent1qqs2658t702xv66p000y4mlhnvadmdxwzzfzcjkjf7kedrclr3ej7aspyfmhxue69uhk6atvw35hqmr90pjhytngw4eh5mmwv4nhjtnhdaexcep0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpguu0wh
ESTEGANOGRAFIA
PixelKnot: https://njump.me/nevent1qqsrh0yh9mg0lx86t5wcmhh97wm6n4v0radh6sd0554ugn354wqdj8gpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqyuvfqdp
PERFIL DE TRABALHO
Shelter : https://njump.me/nevent1qqspv9xxkmfp40cxgjuyfsyczndzmpnl83e7gugm7480mp9zhv50wkqpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdnu59c
PDF
MuPDF : https://njump.me/nevent1qqspn5lhe0dteys6npsrntmv2g470st8kh8p7hxxgmymqa95ejvxvfcpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs4hvhvj
Librera Reader : https://njump.me/nevent1qqsg60flpuf00sash48fexvwxkly2j5z9wjvjrzt883t3eqng293f3cpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz39tt3n
QR-Code
Binary Eye : https://njump.me/nevent1qqsz4n0uxxx3q5m0r42n9key3hchtwyp73hgh8l958rtmae5u2khgpgpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdmn4wp
Climático
Breezy Weather : https://njump.me/nevent1qqs9hjz5cz0y4am3kj33xn536uq85ydva775eqrml52mtnnpe898rzspzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgpd3tu8
ENCRYPTS
Cryptomator : https://njump.me/nevent1qqsvchvnw779m20583llgg5nlu6ph5psewetlczfac5vgw83ydmfndspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsx7ppw9
VeraCrypt : https://njump.me/nevent1qqsf6wzedsnrgq6hjk5c4jj66dxnplqwc4ygr46l8z3gfh38q2fdlwgm65ej3
EXTENSÕES
uBlock Origin : https://njump.me/nevent1qqswaa666lcj2c4nhnea8u4agjtu4l8q89xjln0yrngj7ssh72ntwzql8ssdj
Snowflake : https://njump.me/nevent1qqs0ws74zlt8uced3p2vee9td8x7vln2mkacp8szdufvs2ed94ctnwchce008
CLOUD
Nextcloud : https://njump.me/nevent1qqs2utg5z9htegdtrnllreuhypkk2026x8a0xdsmfczg9wdl8rgrcgg9nhgnm
NOTEPAD
Joplin : https://njump.me/nevent1qqsz2a0laecpelsznser3xd0jfa6ch2vpxtkx6vm6qg24e78xttpk0cpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpdu0hft
Standard Notes : https://njump.me/nevent1qqsv3596kz3qung5v23cjc4cpq7rqxg08y36rmzgcrvw5whtme83y3s7tng6r
MÚSICA
RiMusic : https://njump.me/nevent1qqsv3genqav2tfjllp86ust4umxm8tr2wd9kq8x7vrjq6ssp363mn0gpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqg42353n
ViMusic : https://njump.me/nevent1qqswx78559l4jsxsrygd8kj32sch4qu57stxq0z6twwl450vp39pdqqpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzjg863j
PODCAST
AntennaPod : https://njump.me/nevent1qqsp4nh7k4a6zymfwqqdlxuz8ua6kdhvgeeh3uxf2c9rtp9u3e9ku8qnr8lmy
VISUALIZAR VIDEO
VLC : https://njump.me/nevent1qqs0lz56wtlr2eye4ajs2gzn2r0dscw4y66wezhx0mue6dffth8zugcl9laky
YOUTUBE
NewPipe : https://njump.me/nevent1qqsdg06qpcjdnlvgm4xzqdap0dgjrkjewhmh4j3v4mxdl4rjh8768mgdw9uln
FreeTube : https://njump.me/nevent1qqsz6y6z7ze5gs56s8seaws8v6m6j2zu0pxa955dhq3ythmexak38mcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs5lkjvv
LibreTube : https://snort.social/e/nevent1qqstmd5m6wrdvn4gxf8xyhrwnlyaxmr89c9kjddvnvux6603f84t3fqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsswwznc
COMPARTILHAMENTO DE ARQUIVOS
OnionShare : https://njump.me/nevent1qqsr0a4ml5nu6ud5k9yzyawcd9arznnwkrc27dzzc95q6r50xmdff6qpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3uamnwvaz7tmwdaehgu3dv3jhvtnhv4kxcmmjv3jhytnwv46z7qgswaehxw309ahx7tnnw3ezucmj9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcpzamhxue69uhkyarr9e4kcetwv3sh5afwvdhk6tcpzemhxue69uhkummnw3ezucnrdqhxu6twdfsj7qgswaehxw309ahx7um5wghx6mmd9uqjgamnwvaz7tmwdaehgu3wwfhh2mnywfhkx6mzd96xxmmfdejhyuewvdhk6tcppemhxue69uhkummn9ekx7mp0qythwumn8ghj7un9d3shjtnwdaehgu3wvfskuep0qyv8wumn8ghj7un9d3shjtnrw4e8yetwwshxv7tf9ut7qurt
Localsend : https://njump.me/nevent1qqsp8ldjhrxm09cvvcak20hrc0g8qju9f67pw7rxr2y3euyggw9284gpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzuyghqr
Wallet Bitcoin
Ashigaru Wallet : https://njump.me/nevent1qqstx9fz8kf24wgl26un8usxwsqjvuec9f8q392llmga75tw0kfarfcpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgvfsrqp
Samourai Wallet : https://njump.me/nevent1qqstcvjmz39rmrnrv7t5cl6p3x7pzj6jsspyh4s4vcwd2lugmre04ecpr9mhxue69uhkummnw3ezucn0denkymmwvuhxxmmd9upzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy3rg4qs
CÂMERA
opencamera : https://njump.me/nevent1qqs25glp6dh0crrjutxrgdjlnx9gtqpjtrkg29hlf7382aeyjd77jlqpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqssxcvgc
OFFICE
Collabora Office : https://njump.me/nevent1qqs8yn4ys6adpmeu3edmf580jhc3wluvlf823cc4ft4h0uqmfzdf99qpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsj40uss
TEXTOS
O manifesto de um Cypherpunk : https://njump.me/nevent1qqsd7hdlg6galn5mcuv3pm3ryfjxc4tkyph0cfqqe4du4dr4z8amqyspvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzal0efa
Operations security ( OPSEC) : https://snort.social/e/nevent1qqsp323havh3y9nxzd4qmm60hw87tm9gjns0mtzg8y309uf9mv85cqcpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz8ej9l7
O MANIFESTO CRIPTOANARQUISTA Timothy C. May – 1992. : https://njump.me/nevent1qqspp480wtyx2zhtwpu5gptrl8duv9rvq3mug85mp4d54qzywk3zq9gpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz5wq496
Declaração de independência do ciberespaço
- John Perry Barlow - 1996 : https://njump.me/nevent1qqs2njsy44n6p07mhgt2tnragvchasv386nf20ua5wklxqpttf6mzuqpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsukg4hr
The Cyphernomicon: Criptografia, Dinheiro Digital e o Futuro da Privacidade. escrito por Timothy C. May -Publicado em 1994. :
Livro completo em PDF no Github PrivacyOpenSource.
https://github.com/Alexemidio/PrivacyOpenSource/raw/main/Livros/THE%20CYPHERNOMICON%20.pdf Share
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:10:55
@ 4ba8e86d:89d32de4
2025-04-21 02:10:55Seu teclado não deve se conectar à internet. Privacidade em primeiro lugar. Sempre. Estamos desenvolvendo um teclado moderno que respeita totalmente sua privacidade e segurança. O FUTO Keyboard é 100% offline e 100% privado, oferecendo todos os recursos essenciais que você espera de um teclado atual — incluindo digitação por deslizamento, entrada de voz offline, correção automática inteligente, temas personalizáveis e sugestões preditivas de texto. Nosso objetivo é simples: criar um teclado eficiente e funcional, sem comprometer a privacidade do usuário. Este projeto é um fork do LatinIME, o teclado open-source oficial do Android.
Atenção: o FUTO Keyboard está atualmente em fase alfa. Está trabalhando para torná-lo estável e confiável, mas durante esse período você pode encontrar bugs, travamentos ou recursos ainda não implementados.
Configurações
Idiomas e Modelos – Adicione novos idiomas, dicionários, modelos de entrada de voz, transformadores e layouts associados.
Linguagens e Modelos
O menu no qual você adiciona novos idiomas, bem como dicionários, modelos de entrada de voz, modelos de transformadores e layouts associados a eles.
Adicionar idioma.
Alguns idiomas exigem o download de um dicionário. Se você também quiser um modelo de entrada de voz para um idioma específico, precisará baixá-lo também. Cada idioma já possui uma seleção de layouts de teclado associados; você pode escolher qual(is) layout(s) deseja adicionar ao adicionar o idioma. https://video.nostr.build/c775288b7a8ee8d75816af0c7a25f2aa0b4ecc99973fd442b2badc308fa38109.mp4
Mudar idioma.
Existem duas maneiras de alternar o idioma. A primeira é pressionando o ícone do globo na Barra de Ações, localizada próximo ao canto superior esquerdo do teclado. A segunda é pressionando longamente ou deslizando a barra de espaço; você pode personalizar o comportamento de troca de idioma da barra de espaço acessando Configurações -> Teclado e Digitação -> Teclas de Pressão Longa e Barra de Espaço -> Comportamento da Barra de Espaço . Você também pode atribuir o ícone do globo como a Tecla de Ação para que fique ao lado da barra de espaço, que pode ser acessada no menu Todas as Ações pressionando a tecla de reticências (...) no canto superior esquerdo do teclado e, em seguida, acessando Editar Ações. https://video.nostr.build/ed6f7f63a9c203cd59f46419ef54a4b8b442f070f802a688ca7d682bd6811bcb.mp4
Adicionar dicionário.
Alguns idiomas têm um dicionário integrado, mas a maioria não. Se o idioma que você está instalando não tiver um dicionário integrado, você pode iniciar a instalação em nosso site acessando Idiomas e Modelos -> Dicionário (no idioma que você está instalando) -> Explorar -> Baixar (em nosso site). https://video.nostr.build/3b1e09289953b658a9cef33c41bd711095556bc48290cb2ed066d4d0a5186371.mp4
Habilitar digitação multilíngue.
Você pode habilitar a digitação multilíngue para um ou mais idiomas acessando Idiomas e modelos e marcando a caixa Digitação multilíngue no(s) idioma(s) para os quais deseja habilitar a digitação multilíngue. https://video.nostr.build/29f683410626219499787bd63058d159719553f8e33a9f3c659c51c375a682fb.mp4
Criar layout personalizado.
Se desejar criar seu próprio layout personalizado para um idioma específico, você pode fazê-lo ativando Configurações do Desenvolvedor -> Layouts Personalizados -> Criar novo layout . Mais informações sobre layouts personalizados podem ser encontradas https://github.com/futo-org/futo-keyboard-layouts . A personalização das configurações de pressionamento longo tecla por tecla ainda não é suportada, mas está em processo de implementação. https://video.nostr.build/b5993090e28794d0305424dd352ca83760bb87002c57930e80513de5917fad8d.mp4
Teclado e Digitação – Personalize o comportamento das teclas, o tamanho do teclado e outras preferências de digitação.
Previsão de texto.
O menu no qual você define suas preferências para correção automática e sugestões personalizadas. Modelo de Linguagem do Transformador Você pode fazer com que o teclado preveja a próxima palavra que você digitará ou faça correções automáticas mais inteligentes, que usam um modelo de linguagem Transformer pré-treinado com base em conjuntos de dados disponíveis publicamente, ativando o Transformer LM . Observação: atualmente, isso funciona apenas em inglês, mas estamos trabalhando para torná-lo compatível com outros idiomas. Ajuste fino do transformador Você pode fazer com que o teclado memorize o que você digita e quais sugestões você seleciona, o que treina o modelo de idioma (enquanto o telefone estiver inativo) para prever quais palavras sugerir e corrigir automaticamente enquanto você digita, ativando o ajuste fino do Transformer . Observação: este é o seu modelo de idioma pessoal e o FUTO não visualiza nem armazena nenhum dos seus dados. https://video.nostr.build/688354a63bdc48a9dd3f8605854b5631ac011009c6105f93cfa0b52b46bc40d3.mp4
Previsão de texto.
O menu no qual você define suas preferências para correção automática e sugestões personalizadas. Modelo de Linguagem do Transformador Você pode fazer com que o teclado preveja a próxima palavra que você digitará ou faça correções automáticas mais inteligentes, que usam um modelo de linguagem Transformer pré-treinado com base em conjuntos de dados disponíveis publicamente, ativando o Transformer LM . Observação: atualmente, isso funciona apenas em inglês, mas estamos trabalhando para torná-lo compatível com outros idiomas.
Ajuste fino do transformador.
Você pode fazer com que o teclado memorize o que você digita e quais sugestões você seleciona, o que treina o modelo de idioma (enquanto o telefone estiver inativo) para prever quais palavras sugerir e corrigir automaticamente enquanto você digita, ativando o ajuste fino do Transformer . Observação: este é o seu modelo de idioma pessoal e o FUTO não visualiza nem armazena nenhum dos seus dados.
Força do Modelo de Linguagem do Transformador.
Você pode fazer com que a correção automática se comporte mais como o teclado AOSP ou mais como a rede neural acessando Parâmetros avançados -> Intensidade do LM do transformador e arrastando o controle deslizante para um valor menor (o que tornará o comportamento da correção automática mais parecido com o teclado AOSP) ou um valor maior (o que tornará a correção automática mais dependente da rede neural). Limiar de correção automática Você pode alterar o limite da correção automática para que ela ocorra com mais ou menos frequência acessando Parâmetros avançados -> Limite de correção automática e arrastando o controle deslizante para um valor menor (o que fará com que a correção automática ocorra com mais frequência, mas também corrija erros com mais frequência) ou um valor maior (o que fará com que a correção automática ocorra com menos frequência, mas também corrija erros com menos frequência). https://video.nostr.build/ea9c100081acfcab60343c494a91f789ef8143c92343522ec34c714913631cf7.mp4
Lista negra de palavras.
Você pode colocar sugestões de palavras na lista negra, o que impedirá que o teclado continue sugerindo palavras na lista negra, acessando Sugestões na lista negra e adicionando as palavras que você gostaria de colocar na lista negra.
Palavras ofensivas.
Você pode bloquear palavras ofensivas, como palavrões comuns, acessando Sugestões na Lista Negra e marcando a opção Bloquear Palavras Ofensivas . Observação: a opção Bloquear Palavras Ofensivas está ativada por padrão. https://video.nostr.build/ee72f3940b9789bbea222c95ee74d646aae1a0f3bf658ef8114c6f7942bb50f5.mp4
Correção automática.
Você pode ativar a capacidade de corrigir automaticamente palavras digitadas incorretamente ao pressionar a barra de espaço ou digitar pontuação ativando a Correção automática.
Sugestões de correção.
Você pode ativar a capacidade de exibir palavras sugeridas enquanto digita marcando a opção Mostrar sugestões de correção.
Sugestões de palavras.
Você pode ativar a capacidade de aprender com suas comunicações e dados digitados para melhorar as sugestões ativando as Sugestões personalizadas . Observação: desativar as Sugestões personalizadas também desativa o ajuste fino do Transformer. https://video.nostr.build/2c22d109b9192eac8fe4533b3f8e3e1b5896dfd043817bd460c48a5b989b7a2f.mp4
Entrada de Voz – Configure a entrada de voz offline, incluindo a duração e a conversão de fala em texto.
Entrada de voz.
O menu no qual você define suas preferências de entrada de voz, como duração da entrada e configurações de conversão de fala em texto. Entrada de voz integrada Você pode desabilitar a entrada de voz integrada do teclado e, em vez disso, usar o provedor de entrada de voz de um aplicativo externo desativando a opção Desabilitar entrada de voz integrada. https://video.nostr.build/68916e5b338a9f999f45aa1828a6e05ccbf8def46da9516c0f516b40ca8c827b.mp4
Sons de indicação.
Você pode habilitar a capacidade de reproduzir sons ao iniciar e cancelar a entrada de voz ativando Sons de indicação. https://video.nostr.build/7f5fb6a6173c4db18945e138146fe65444e40953d85cee1f09c1a21d236d21f5.mp4
Progresso Detalhado.
Você pode habilitar a capacidade de exibir informações detalhadas, como indicar que o microfone está sendo usado, ativando Progresso detalhado. https://video.nostr.build/8ac2bb6bdd6e7f8bd4b45da423e782c152a2b4320f2e090cbb99fd5c78e8f44f.mp4
Microfone Bluetooth.
Você pode fazer com que a entrada de voz prefira automaticamente seu microfone Bluetooth em vez do microfone integrado, ativando Preferir microfone Bluetooth. https://video.nostr.build/c11404aa6fec2dda71ceb3aaee916c6761b3015fef9575a352de66b7310dad07.mp4
Foco de áudio.
Você pode fazer com que a entrada de voz pause automaticamente vídeos ou músicas quando ela estiver ativada, ativando o Foco de Áudio. https://video.nostr.build/4ac82af53298733d0c5013ef28befb8b2adeb4a4949604308317e124b6431d40.mp4
Supressão de Símbolos.
Por padrão, a entrada de voz transcreve apenas texto básico e pontuação. Você pode desativar a opção "Suprimir símbolos" para liberar a entrada de voz da transcrição de caracteres especiais (por exemplo, @, $ ou %). Observação: Isso não afeta a forma como a entrada de voz interpreta palavras literais (por exemplo, "vírgula", "ponto final"). https://video.nostr.build/10de49c5a9e35508caa14b66da28fae991a5ac8eabad9b086959fba18c07f8f3.mp4
Entrada de voz de formato longo.
Você pode desativar o limite padrão de 30 segundos para entrada de voz ativando a opção Entrada de voz longa . Observação: a qualidade da saída pode ser prejudicada com entradas longas. https://video.nostr.build/f438ee7a42939a5a3e6d6c4471905f836f038495eb3a00b39d9996d0e552c200.mp4
Parada automática em silêncio.
Você pode fazer com que a entrada de voz pare automaticamente quando o silêncio for detectado, ativando a opção Parar automaticamente ao silenciar . Observação: se houver muito ruído de fundo, pode ser necessário interromper manualmente a entrada de voz. Ative também a entrada de voz longa para evitar a interrupção após 30 segundos. https://video.nostr.build/056567696d513add63f6dd254c0a3001530917e05e792de80c12796d43958671.mp4
Dicionário Pessoal – Adicione palavras personalizadas para que o teclado aprenda e sugira com mais precisão.
Dicionário Pessoal.
O menu no qual você cria seu dicionário pessoal de palavras que o teclado irá lembrar e sugerir. Adicionar ao dicionário Você pode adicionar uma palavra ou frase ao seu dicionário pessoal pressionando o ícone de adição na tela "Dicionário pessoal" . Você também pode criar um atalho para ela no campo "Atalho" ao adicionar a palavra ou frase. https://video.nostr.build/dec41c666b9f2276cc20d9096e3a9b542b570afd1f679d8d0e8c43c8ea46bfcb.mp4
Excluir do dicionário.
Você pode excluir uma palavra ou frase do seu dicionário pessoal clicando nessa palavra ou frase e clicando no ícone de lixeira no canto superior direito. https://video.nostr.build/aca25643b5c7ead4c5d522709af4bc337911e49c4743b97dc75f6b877449143e.mp4
Tema – Escolha entre os temas disponíveis ou personalize a aparência do teclado conforme seu gosto.
Tema.
O menu no qual você seleciona seu tema preferido para o teclado. Alterar tema Você pode escolher entre uma variedade de temas para o teclado, incluindo Modo Escuro, Modo Claro, Automático Dinâmico, Escuro Dinâmico, Claro Dinâmico, Material AOSP Escuro, Material AOSP Claro, Roxo Escuro AMOLED, Girassol, Queda de Neve, Cinza Aço, Esmeralda, Algodão Doce, Luz do Mar Profundo, Escuro do Mar Profundo, Gradiente 1, Tema FUTO VI ou Tema Construção . A possibilidade de personalizar seu tema será disponibilizada em breve. https://video.nostr.build/90c8de72f08cb0d8c40ac2fba2fd39451ff63ec1592ddd2629d0891c104bc61e.mp4
Fronteiras Principais.
Você pode habilitar as bordas das teclas rolando para baixo até o final e ativando Bordas das teclas . https://video.nostr.build/fa2087d68ce3fb2d3adb84cc2ec19c4d5383beb8823a4b6d1d85378ab3507ab1.mp4
Site oficial https://keyboard.futo.org/
Baixar no fdroid. https://app.futo.org/fdroid/repo/
Para instalar através do Obtainium , basta ir em Adicionar Aplicativo e colar esta URL do repositório: https://github.com/futo-org/android-keyboard
A adição pode demorar um pouco dependendo da velocidade da sua internet, pois o APK precisa ser baixado.
-
 @ 1beecee5:d29d2162
2025-04-21 06:30:55
@ 1beecee5:d29d2162
2025-04-21 06:30:55 -
 @ c631e267:c2b78d3e
2025-04-20 19:54:32
@ c631e267:c2b78d3e
2025-04-20 19:54:32Es ist völlig unbestritten, dass der Angriff der russischen Armee auf die Ukraine im Februar 2022 strikt zu verurteilen ist. Ebenso unbestritten ist Russland unter Wladimir Putin keine brillante Demokratie. Aus diesen Tatsachen lässt sich jedoch nicht das finstere Bild des russischen Präsidenten – und erst recht nicht des Landes – begründen, das uns durchweg vorgesetzt wird und den Kern des aktuellen europäischen Bedrohungs-Szenarios darstellt. Da müssen wir schon etwas genauer hinschauen.
Der vorliegende Artikel versucht derweil nicht, den Einsatz von Gewalt oder die Verletzung von Menschenrechten zu rechtfertigen oder zu entschuldigen – ganz im Gegenteil. Dass jedoch der Verdacht des «Putinverstehers» sofort latent im Raume steht, verdeutlicht, was beim Thema «Russland» passiert: Meinungsmache und Manipulation.
Angesichts der mentalen Mobilmachung seitens Politik und Medien sowie des Bestrebens, einen bevorstehenden Krieg mit Russland geradezu herbeizureden, ist es notwendig, dieser fatalen Entwicklung entgegenzutreten. Wenn wir uns nur ein wenig von der herrschenden Schwarz-Weiß-Malerei freimachen, tauchen automatisch Fragen auf, die Risse im offiziellen Narrativ enthüllen. Grund genug, nachzuhaken.
Wer sich schon länger auch abseits der Staats- und sogenannten Leitmedien informiert, der wird in diesem Artikel vermutlich nicht viel Neues erfahren. Andere könnten hier ein paar unbekannte oder vergessene Aspekte entdecken. Möglicherweise klärt sich in diesem Kontext die Wahrnehmung der aktuellen (unserer eigenen!) Situation ein wenig.
Manipulation erkennen
Corona-«Pandemie», menschengemachter Klimawandel oder auch Ukraine-Krieg: Jede Menge Krisen, und für alle gibt es ein offizielles Narrativ, dessen Hinterfragung unerwünscht ist. Nun ist aber ein Narrativ einfach eine Erzählung, eine Geschichte (Latein: «narratio») und kein Tatsachenbericht. Und so wie ein Märchen soll auch das Narrativ eine Botschaft vermitteln.
Über die Methoden der Manipulation ist viel geschrieben worden, sowohl in Bezug auf das Individuum als auch auf die Massen. Sehr wertvolle Tipps dazu, wie man Manipulationen durchschauen kann, gibt ein Büchlein [1] von Albrecht Müller, dem Herausgeber der NachDenkSeiten.
Die Sprache selber eignet sich perfekt für die Manipulation. Beispielsweise kann die Wortwahl Bewertungen mitschwingen lassen, regelmäßiges Wiederholen (gerne auch von verschiedenen Seiten) lässt Dinge irgendwann «wahr» erscheinen, Übertreibungen fallen auf und hinterlassen wenigstens eine Spur im Gedächtnis, genauso wie Andeutungen. Belege spielen dabei keine Rolle.
Es gibt auffällig viele Sprachregelungen, die offenbar irgendwo getroffen und irgendwie koordiniert werden. Oder alle Redenschreiber und alle Medien kopieren sich neuerdings permanent gegenseitig. Welchen Zweck hat es wohl, wenn der Krieg in der Ukraine durchgängig und quasi wörtlich als «russischer Angriffskrieg auf die Ukraine» bezeichnet wird? Obwohl das in der Sache richtig ist, deutet die Art der Verwendung auf gezielte Beeinflussung hin und soll vor allem das Feindbild zementieren.
Sprachregelungen dienen oft der Absicherung einer einseitigen Darstellung. Das Gleiche gilt für das Verkürzen von Informationen bis hin zum hartnäckigen Verschweigen ganzer Themenbereiche. Auch hierfür gibt es rund um den Ukraine-Konflikt viele gute Beispiele.
Das gewünschte Ergebnis solcher Methoden ist eine Schwarz-Weiß-Malerei, bei der einer eindeutig als «der Böse» markiert ist und die anderen automatisch «die Guten» sind. Das ist praktisch und demonstriert gleichzeitig ein weiteres Manipulationswerkzeug: die Verwendung von Doppelstandards. Wenn man es schafft, bei wichtigen Themen regelmäßig mit zweierlei Maß zu messen, ohne dass das Publikum protestiert, dann hat man freie Bahn.
Experten zu bemühen, um bestimmte Sachverhalte zu erläutern, ist sicher sinnvoll, kann aber ebenso missbraucht werden, schon allein durch die Auswahl der jeweiligen Spezialisten. Seit «Corona» werden viele erfahrene und ehemals hoch angesehene Fachleute wegen der «falschen Meinung» diffamiert und gecancelt. [2] Das ist nicht nur ein brutaler Umgang mit Menschen, sondern auch eine extreme Form, die öffentliche Meinung zu steuern.
Wann immer wir also erkennen (weil wir aufmerksam waren), dass wir bei einem bestimmten Thema manipuliert werden, dann sind zwei logische und notwendige Fragen: Warum? Und was ist denn richtig? In unserem Russland-Kontext haben die Antworten darauf viel mit Geopolitik und Geschichte zu tun.
Ist Russland aggressiv und expansiv?
Angeblich plant Russland, europäische NATO-Staaten anzugreifen, nach dem Motto: «Zuerst die Ukraine, dann den Rest». In Deutschland weiß man dafür sogar das Datum: «Wir müssen bis 2029 kriegstüchtig sein», versichert Verteidigungsminister Pistorius.
Historisch gesehen ist es allerdings eher umgekehrt: Russland, bzw. die Sowjetunion, ist bereits dreimal von Westeuropa aus militärisch angegriffen worden. Die Feldzüge Napoleons, des deutschen Kaiserreichs und Nazi-Deutschlands haben Millionen Menschen das Leben gekostet. Bei dem ausdrücklichen Vernichtungskrieg ab 1941 kam es außerdem zu Brutalitäten wie der zweieinhalbjährigen Belagerung Leningrads (heute St. Petersburg) durch Hitlers Wehrmacht. Deren Ziel, die Bevölkerung auszuhungern, wurde erreicht: über eine Million tote Zivilisten.
Trotz dieser Erfahrungen stimmte Michail Gorbatschow 1990 der deutschen Wiedervereinigung zu und die Sowjetunion zog ihre Truppen aus Osteuropa zurück (vgl. Abb. 1). Der Warschauer Pakt wurde aufgelöst, der Kalte Krieg formell beendet. Die Sowjets erhielten damals von führenden westlichen Politikern die Zusicherung, dass sich die NATO «keinen Zentimeter ostwärts» ausdehnen würde, das ist dokumentiert. [3]

Expandiert ist die NATO trotzdem, und zwar bis an Russlands Grenzen (vgl. Abb. 2). Laut dem Politikberater Jeffrey Sachs handelt es sich dabei um ein langfristiges US-Projekt, das von Anfang an die Ukraine und Georgien mit einschloss. Offiziell wurde der Beitritt beiden Staaten 2008 angeboten. In jedem Fall könnte die massive Ost-Erweiterung seit 1999 aus russischer Sicht nicht nur als Vertrauensbruch, sondern durchaus auch als aggressiv betrachtet werden.

Russland hat den europäischen Staaten mehrfach die Hand ausgestreckt [4] für ein friedliches Zusammenleben und den «Aufbau des europäischen Hauses». Präsident Putin sei «in seiner ersten Amtszeit eine Chance für Europa» gewesen, urteilt die Journalistin und langjährige Russland-Korrespondentin der ARD, Gabriele Krone-Schmalz. Er habe damals viele positive Signale Richtung Westen gesendet.
Die Europäer jedoch waren scheinbar an einer Partnerschaft mit dem kontinentalen Nachbarn weniger interessiert als an der mit dem transatlantischen Hegemon. Sie verkennen bis heute, dass eine gedeihliche Zusammenarbeit in Eurasien eine Gefahr für die USA und deren bekundetes Bestreben ist, die «einzige Weltmacht» zu sein – «Full Spectrum Dominance» [5] nannte das Pentagon das. Statt einem neuen Kalten Krieg entgegenzuarbeiten, ließen sich europäische Staaten selber in völkerrechtswidrige «US-dominierte Angriffskriege» [6] verwickeln, wie in Serbien, Afghanistan, dem Irak, Libyen oder Syrien. Diese werden aber selten so benannt.

Speziell den Deutschen stünde außer einer Portion Realismus auch etwas mehr Dankbarkeit gut zu Gesicht. Das Geschichtsbewusstsein der Mehrheit scheint doch recht selektiv und das Selbstbewusstsein einiger etwas desorientiert zu sein. Bekanntermaßen waren es die Soldaten der sowjetischen Roten Armee, die unter hohen Opfern 1945 Deutschland «vom Faschismus befreit» haben. Bei den Gedenkfeiern zu 80 Jahren Kriegsende will jedoch das Auswärtige Amt – noch unter der Diplomatie-Expertin Baerbock, die sich schon länger offiziell im Krieg mit Russland wähnt, – nun keine Russen sehen: Sie sollen notfalls rausgeschmissen werden.
«Die Grundsatzfrage lautet: Geht es Russland um einen angemessenen Platz in einer globalen Sicherheitsarchitektur, oder ist Moskau schon seit langem auf einem imperialistischen Trip, der befürchten lassen muss, dass die Russen in fünf Jahren in Berlin stehen?»
So bringt Gabriele Krone-Schmalz [7] die eigentliche Frage auf den Punkt, die zur Einschätzung der Situation letztlich auch jeder für sich beantworten muss.
Was ist los in der Ukraine?
In der internationalen Politik geht es nie um Demokratie oder Menschenrechte, sondern immer um Interessen von Staaten. Diese These stammt von Egon Bahr, einem der Architekten der deutschen Ostpolitik des «Wandels durch Annäherung» aus den 1960er und 70er Jahren. Sie trifft auch auf den Ukraine-Konflikt zu, den handfeste geostrategische und wirtschaftliche Interessen beherrschen, obwohl dort angeblich «unsere Demokratie» verteidigt wird.
Es ist ein wesentliches Element des Ukraine-Narrativs und Teil der Manipulation, die Vorgeschichte des Krieges wegzulassen – mindestens die vor der russischen «Annexion» der Halbinsel Krim im März 2014, aber oft sogar komplett diejenige vor der Invasion Ende Februar 2022. Das Thema ist komplex, aber einige Aspekte, die für eine Beurteilung nicht unwichtig sind, will ich wenigstens kurz skizzieren. [8]
Das Gebiet der heutigen Ukraine und Russlands – die übrigens in der «Kiewer Rus» gemeinsame Wurzeln haben – hat der britische Geostratege Halford Mackinder bereits 1904 als eurasisches «Heartland» bezeichnet, dessen Kontrolle er eine große Bedeutung für die imperiale Strategie Großbritanniens zumaß. Für den ehemaligen Sicherheits- und außenpolitischen Berater mehrerer US-amerikanischer Präsidenten und Mitgründer der Trilateralen Kommission, Zbigniew Brzezinski, war die Ukraine nach der Auflösung der Sowjetunion ein wichtiger Spielstein auf dem «eurasischen Schachbrett», wegen seiner Nähe zu Russland, seiner Bodenschätze und seines Zugangs zum Schwarzen Meer.
Die Ukraine ist seit langem ein gespaltenes Land. Historisch zerrissen als Spielball externer Interessen und geprägt von ethnischen, kulturellen, religiösen und geografischen Unterschieden existiert bis heute, grob gesagt, eine Ost-West-Spaltung, welche die Suche nach einer nationalen Identität stark erschwert.
Insbesondere im Zuge der beiden Weltkriege sowie der Russischen Revolution entstanden tiefe Risse in der Bevölkerung. Ukrainer kämpften gegen Ukrainer, zum Beispiel die einen auf der Seite von Hitlers faschistischer Nazi-Armee und die anderen auf der von Stalins kommunistischer Roter Armee. Die Verbrechen auf beiden Seiten sind nicht vergessen. Dass nach der Unabhängigkeit 1991 versucht wurde, Figuren wie den radikalen Nationalisten Symon Petljura oder den Faschisten und Nazi-Kollaborateur Stepan Bandera als «Nationalhelden» zu installieren, verbessert die Sache nicht.
Während die USA und EU-Staaten zunehmend «ausländische Einmischung» (speziell russische) in «ihre Demokratien» wittern, betreiben sie genau dies seit Jahrzehnten in vielen Ländern der Welt. Die seit den 2000er Jahren bekannten «Farbrevolutionen» in Osteuropa werden oft als Methode des Regierungsumsturzes durch von außen gesteuerte «demokratische» Volksaufstände beschrieben. Diese Strategie geht auf Analysen zum «Schwarmverhalten» [9] seit den 1960er Jahren zurück (Studentenproteste), wo es um die potenzielle Wirksamkeit einer «rebellischen Hysterie» von Jugendlichen bei postmodernen Staatsstreichen geht. Heute nennt sich dieses gezielte Kanalisieren der Massen zur Beseitigung unkooperativer Regierungen «Soft-Power».
In der Ukraine gab es mit der «Orangen Revolution» 2004 und dem «Euromaidan» 2014 gleich zwei solcher «Aufstände». Der erste erzwang wegen angeblicher Unregelmäßigkeiten eine Wiederholung der Wahlen, was mit Wiktor Juschtschenko als neuem Präsidenten endete. Dieser war ehemaliger Direktor der Nationalbank und Befürworter einer Annäherung an EU und NATO. Seine Frau, die First Lady, ist US-amerikanische «Philanthropin» und war Beamtin im Weißen Haus in der Reagan- und der Bush-Administration.
Im Gegensatz zu diesem ersten Event endete der sogenannte Euromaidan unfriedlich und blutig. Die mehrwöchigen Proteste gegen Präsident Wiktor Janukowitsch, in Teilen wegen des nicht unterzeichneten Assoziierungsabkommens mit der EU, wurden zunehmend gewalttätiger und von Nationalisten und Faschisten des «Rechten Sektors» dominiert. Sie mündeten Ende Februar 2014 auf dem Kiewer Unabhängigkeitsplatz (Maidan) in einem Massaker durch Scharfschützen. Dass deren Herkunft und die genauen Umstände nicht geklärt wurden, störte die Medien nur wenig. [10]
Janukowitsch musste fliehen, er trat nicht zurück. Vielmehr handelte es sich um einen gewaltsamen, allem Anschein nach vom Westen inszenierten Putsch. Laut Jeffrey Sachs war das kein Geheimnis, außer vielleicht für die Bürger. Die USA unterstützten die Post-Maidan-Regierung nicht nur, sie beeinflussten auch ihre Bildung. Das geht unter anderem aus dem berühmten «Fuck the EU»-Telefonat der US-Chefdiplomatin für die Ukraine, Victoria Nuland, mit Botschafter Geoffrey Pyatt hervor.
Dieser Bruch der demokratischen Verfassung war letztlich der Auslöser für die anschließenden Krisen auf der Krim und im Donbass (Ostukraine). Angesichts der ukrainischen Geschichte mussten die nationalistischen Tendenzen und die Beteiligung der rechten Gruppen an dem Umsturz bei der russigsprachigen Bevölkerung im Osten ungute Gefühle auslösen. Es gab Kritik an der Übergangsregierung, Befürworter einer Abspaltung und auch für einen Anschluss an Russland.
Ebenso konnte Wladimir Putin in dieser Situation durchaus Bedenken wegen des Status der russischen Militärbasis für seine Schwarzmeerflotte in Sewastopol auf der Krim haben, für die es einen langfristigen Pachtvertrag mit der Ukraine gab. Was im März 2014 auf der Krim stattfand, sei keine Annexion, sondern eine Abspaltung (Sezession) nach einem Referendum gewesen, also keine gewaltsame Aneignung, urteilte der Rechtswissenschaftler Reinhard Merkel in der FAZ sehr detailliert begründet. Übrigens hatte die Krim bereits zu Zeiten der Sowjetunion den Status einer autonomen Republik innerhalb der Ukrainischen SSR.
Anfang April 2014 wurden in der Ostukraine die «Volksrepubliken» Donezk und Lugansk ausgerufen. Die Kiewer Übergangsregierung ging unter der Bezeichnung «Anti-Terror-Operation» (ATO) militärisch gegen diesen, auch von Russland instrumentalisierten Widerstand vor. Zufällig war kurz zuvor CIA-Chef John Brennan in Kiew. Die Maßnahmen gingen unter dem seit Mai neuen ukrainischen Präsidenten, dem Milliardär Petro Poroschenko, weiter. Auch Wolodymyr Selenskyj beendete den Bürgerkrieg nicht, als er 2019 vom Präsidenten-Schauspieler, der Oligarchen entmachtet, zum Präsidenten wurde. Er fuhr fort, die eigene Bevölkerung zu bombardieren.
Mit dem Einmarsch russischer Truppen in die Ostukraine am 24. Februar 2022 begann die zweite Phase des Krieges. Die Wochen und Monate davor waren intensiv. Im November hatte die Ukraine mit den USA ein Abkommen über eine «strategische Partnerschaft» unterzeichnet. Darin sagten die Amerikaner ihre Unterstützung der EU- und NATO-Perspektive der Ukraine sowie quasi für die Rückeroberung der Krim zu. Dagegen ließ Putin der NATO und den USA im Dezember 2021 einen Vertragsentwurf über beiderseitige verbindliche Sicherheitsgarantien zukommen, den die NATO im Januar ablehnte. Im Februar eskalierte laut OSZE die Gewalt im Donbass.
Bereits wenige Wochen nach der Invasion, Ende März 2022, kam es in Istanbul zu Friedensverhandlungen, die fast zu einer Lösung geführt hätten. Dass der Krieg nicht damals bereits beendet wurde, lag daran, dass der Westen dies nicht wollte. Man war der Meinung, Russland durch die Ukraine in diesem Stellvertreterkrieg auf Dauer militärisch schwächen zu können. Angesichts von Hunderttausenden Toten, Verletzten und Traumatisierten, die als Folge seitdem zu beklagen sind, sowie dem Ausmaß der Zerstörung, fehlen einem die Worte.
Hasst der Westen die Russen?
Diese Frage drängt sich auf, wenn man das oft unerträglich feindselige Gebaren beobachtet, das beileibe nicht neu ist und vor Doppelmoral trieft. Russland und speziell die Person Wladimir Putins werden regelrecht dämonisiert, was gleichzeitig scheinbar jede Form von Diplomatie ausschließt.
Russlands militärische Stärke, seine geografische Lage, sein Rohstoffreichtum oder seine unabhängige diplomatische Tradition sind sicher Störfaktoren für das US-amerikanische Bestreben, der Boss in einer unipolaren Welt zu sein. Ein womöglich funktionierender eurasischer Kontinent, insbesondere gute Beziehungen zwischen Russland und Deutschland, war indes schon vor dem Ersten Weltkrieg eine Sorge des britischen Imperiums.
Ein «Vergehen» von Präsident Putin könnte gewesen sein, dass er die neoliberale Schocktherapie à la IWF und den Ausverkauf des Landes (auch an US-Konzerne) beendete, der unter seinem Vorgänger herrschte. Dabei zeigte er sich als Führungspersönlichkeit und als nicht so formbar wie Jelzin. Diese Aspekte allein sind aber heute vermutlich keine ausreichende Erklärung für ein derart gepflegtes Feindbild.
Der Historiker und Philosoph Hauke Ritz erweitert den Fokus der Fragestellung zu: «Warum hasst der Westen die Russen so sehr?», was er zum Beispiel mit dem Medienforscher Michael Meyen und mit der Politikwissenschaftlerin Ulrike Guérot bespricht. Ritz stellt die interessante These [11] auf, dass Russland eine Provokation für den Westen sei, welcher vor allem dessen kulturelles und intellektuelles Potenzial fürchte.
Die Russen sind Europäer aber anders, sagt Ritz. Diese «Fremdheit in der Ähnlichkeit» erzeuge vielleicht tiefe Ablehnungsgefühle. Obwohl Russlands Identität in der europäischen Kultur verwurzelt ist, verbinde es sich immer mit der Opposition in Europa. Als Beispiele nennt er die Kritik an der katholischen Kirche oder die Verbindung mit der Arbeiterbewegung. Christen, aber orthodox; Sozialismus statt Liberalismus. Das mache das Land zum Antagonisten des Westens und zu einer Bedrohung der Machtstrukturen in Europa.
Fazit
Selbstverständlich kann man Geschichte, Ereignisse und Entwicklungen immer auf verschiedene Arten lesen. Dieser Artikel, obwohl viel zu lang, konnte nur einige Aspekte der Ukraine-Tragödie anreißen, die in den offiziellen Darstellungen in der Regel nicht vorkommen. Mindestens dürfte damit jedoch klar geworden sein, dass die Russische Föderation bzw. Wladimir Putin nicht der alleinige Aggressor in diesem Konflikt ist. Das ist ein Stellvertreterkrieg zwischen USA/NATO (gut) und Russland (böse); die Ukraine (edel) wird dabei schlicht verheizt.
Das ist insofern von Bedeutung, als die gesamte europäische Kriegshysterie auf sorgsam kultivierten Freund-Feind-Bildern beruht. Nur so kann Konfrontation und Eskalation betrieben werden, denn damit werden die wahren Hintergründe und Motive verschleiert. Angst und Propaganda sind notwendig, damit die Menschen den Wahnsinn mitmachen. Sie werden belogen, um sie zuerst zu schröpfen und anschließend auf die Schlachtbank zu schicken. Das kann niemand wollen, außer den stets gleichen Profiteuren: die Rüstungs-Lobby und die großen Investoren, die schon immer an Zerstörung und Wiederaufbau verdient haben.
Apropos Investoren: Zu den Top-Verdienern und somit Hauptinteressenten an einer Fortführung des Krieges zählt BlackRock, einer der weltgrößten Vermögensverwalter. Der deutsche Bundeskanzler in spe, Friedrich Merz, der gerne «Taurus»-Marschflugkörper an die Ukraine liefern und die Krim-Brücke zerstören möchte, war von 2016 bis 2020 Aufsichtsratsvorsitzender von BlackRock in Deutschland. Aber das hat natürlich nichts zu sagen, der Mann macht nur seinen Job.
Es ist ein Spiel der Kräfte, es geht um Macht und strategische Kontrolle, um Geheimdienste und die Kontrolle der öffentlichen Meinung, um Bodenschätze, Rohstoffe, Pipelines und Märkte. Das klingt aber nicht sexy, «Demokratie und Menschenrechte» hört sich besser und einfacher an. Dabei wäre eine für alle Seiten förderliche Politik auch nicht so kompliziert; das Handwerkszeug dazu nennt sich Diplomatie. Noch einmal Gabriele Krone-Schmalz:
«Friedliche Politik ist nichts anderes als funktionierender Interessenausgleich. Da geht’s nicht um Moral.»
Die Situation in der Ukraine ist sicher komplex, vor allem wegen der inneren Zerrissenheit. Es dürfte nicht leicht sein, eine friedliche Lösung für das Zusammenleben zu finden, aber die Beteiligten müssen es vor allem wollen. Unter den gegebenen Umständen könnte eine sinnvolle Perspektive mit Neutralität und föderalen Strukturen zu tun haben.
Allen, die sich bis hierher durch die Lektüre gearbeitet (oder auch einfach nur runtergescrollt) haben, wünsche ich frohe Oster-Friedenstage!
[Titelbild: Pixabay; Abb. 1 und 2: nach Ganser/SIPER; Abb. 3: SIPER]
--- Quellen: ---
[1] Albrecht Müller, «Glaube wenig. Hinterfrage alles. Denke selbst.», Westend 2019
[2] Zwei nette Beispiele:
- ARD-faktenfinder (sic), «Viel Aufmerksamkeit für fragwürdige Experten», 03/2023
- Neue Zürcher Zeitung, «Aufstieg und Fall einer Russlandversteherin – die ehemalige ARD-Korrespondentin Gabriele Krone-Schmalz rechtfertigt seit Jahren Putins Politik», 12/2022
[3] George Washington University, «NATO Expansion: What Gorbachev Heard – Declassified documents show security assurances against NATO expansion to Soviet leaders from Baker, Bush, Genscher, Kohl, Gates, Mitterrand, Thatcher, Hurd, Major, and Woerner», 12/2017
[4] Beispielsweise Wladimir Putin bei seiner Rede im Deutschen Bundestag, 25/09/2001
[5] William Engdahl, «Full Spectrum Dominance, Totalitarian Democracy In The New World Order», edition.engdahl 2009
[6] Daniele Ganser, «Illegale Kriege – Wie die NATO-Länder die UNO sabotieren. Eine Chronik von Kuba bis Syrien», Orell Füssli 2016
[7] Gabriele Krone-Schmalz, «Mit Friedensjournalismus gegen ‘Kriegstüchtigkeit’», Vortrag und Diskussion an der Universität Hamburg, veranstaltet von engagierten Studenten, 16/01/2025\ → Hier ist ein ähnlicher Vortrag von ihr (Video), den ich mit spanischer Übersetzung gefunden habe.
[8] Für mehr Hintergrund und Details empfehlen sich z.B. folgende Bücher:
- Mathias Bröckers, Paul Schreyer, «Wir sind immer die Guten», Westend 2019
- Gabriele Krone-Schmalz, «Russland verstehen? Der Kampf um die Ukraine und die Arroganz des Westens», Westend 2023
- Patrik Baab, «Auf beiden Seiten der Front – Meine Reisen in die Ukraine», Fiftyfifty 2023
[9] vgl. Jonathan Mowat, «Washington's New World Order "Democratization" Template», 02/2005 und RAND Corporation, «Swarming and the Future of Conflict», 2000
[10] Bemerkenswert einige Beiträge, von denen man später nichts mehr wissen wollte:
- ARD Monitor, «Todesschüsse in Kiew: Wer ist für das Blutbad vom Maidan verantwortlich», 10/04/2014, Transkript hier
- Telepolis, «Blutbad am Maidan: Wer waren die Todesschützen?», 12/04/2014
- Telepolis, «Scharfschützenmorde in Kiew», 14/12/2014
- Deutschlandfunk, «Gefahr einer Spirale nach unten», Interview mit Günter Verheugen, 18/03/2014
- NDR Panorama, «Putsch in Kiew: Welche Rolle spielen die Faschisten?», 06/03/2014
[11] Hauke Ritz, «Vom Niedergang des Westens zur Neuerfindung Europas», 2024
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ a296b972:e5a7a2e8
2025-04-19 20:08:17
@ a296b972:e5a7a2e8
2025-04-19 20:08:17Bis in die Jahre 1 v. C., vor Corona, also bis 2019, lebte Deutschland in einer erträglichen Demokratie, an der es auch von damals kritischen Menschen zurecht immer schon reichlich auszusetzen gab. Aber es war auszuhalten, manchmal sogar richtig fein, es gab Zufriedenheit und gelegentlich sogar Glücksmomente. Die Kritiker hatten damals noch das Gefühl, frei ihre Meinung sagen zu können. Der Staat respektierte die Privatsphäre, auch wenn immer wieder Versuche gestartet wurden, in Angelegenheiten der Bürger Einblick zu gewinnen, die den Staat nichts angehen.
Man hatte die Möglichkeit, sich Nischen zu suchen, die eine Lebensqualität boten, mit dem Gefühl, man habe die Möglichkeit, der Staat rückt einem nicht allzu sehr auf die Pelle. Man war dazu bereit, die Konsequenzen für diese Freiheit in Kauf zu nehmen, weil einem andere Werte wichtiger waren, als zum Beispiel brav am Konsum teilzunehmen. Es gab Vorwürfe, man sei Konsumverweigerer, worauf stets die Antwort kam: Nein, nicht Konsumverweigerer, sondern Konsumverzichter. Verzichter deshalb, weil in Verzicht die freie Wahl enthalten ist. Konsumverweigerer ist ein Begriff aus dem System, der beschreibt, dass man sich durch seine Zurückhaltung im Konsum dem System verweigert.
Nach inzwischen fünf Jahren fängt es an schwer zu fallen, sich an das damalige Lebensgefühl zu erinnern.
Mit Corona sind, im Nachhinein betrachtet, die Schleusen für etwas aufgegangen, das man so nie für möglich gehalten hätte.
Als ob die miesesten Charaktere nur auf eine Gelegenheit gewartet hätten, endlich loslegen zu können, wird seitdem der Wahnsinn ununterbrochen über uns ausgeschüttet. Grundrechte wurden ausgehebelt, Zwangsmaßnahmen durchgesetzt, die Menschen wurden genötigt, einen Gehorsamkeitsbeweis vor dem Mund zu tragen, sie wurden in ihrer Mobilität eingeschränkt, Kinder wurden ihrer Kindheit und Bildung beraubt, es folgte eine absurde Verfügung nach der anderen. Heute, nachdem die allermeisten sogenannten Verschwörungstheorien wahr geworden sind, wissenschaftlich widerlegt und als sinnentleert entlarvt wurden, besteht nicht das geringste Interesse an einer wirklichen Aufarbeitung. Die lächerlichen Talkrunden im Staatsfunkt täuschen lediglich eine Aufarbeitungs-Simulation vor. Und es gibt immer noch genug Menschen, die darauf reinfallen und das perfide Spiel nicht durchschauen.
Mit Corona wurde auch die Spaltung der Gesellschaft vorangetrieben. Ein Austausch unter Freunden zu unterschiedlichen Einstellungen zu der sogenannten Impfung kam zum Erliegen. Stattdessen zog eine neue „Qualität“ ein, das dröhnende Schweigen, bis heute. Langjährige Freundschaften gingen zu ende, Risse taten sich in Familien auf, die teilweise bis heute nicht verheilt sind. Bestenfalls werden sie mit Totschweigen übergebügelt, damit ein halbwegs normaler Alltag überhaupt möglich ist. Im Unterbewusstsein brodelt es dennoch, das Thema ist ja nicht weg. Und der Tag wird kommen, an dem all das Unterdrückte mit aller Macht an die Oberfläche dringt und der ohnehin immense psychischen Schaden bei vielen Menschen beängstigende Auswirkungen haben wird.
Die Deutschen waren im 2. Weltkrieg sowohl Täter als auch Opfer. In beiden Fällen hat das ein Trauma ausgelöst. Das inszenierte Wirtschaftswunder hat die Menschen davon abgelenkt, dass sie sich mit ihrer eigenen Vergangenheit und ihrem Verhalten hätten auseinandersetzen müssen. Daraus hat sich der Glaube entwickelt, dass, wenn man schön brav und fleißig ist, dann wird die Welt uns schon irgendwann einmal wieder liebhaben.
Auf dieses nicht aufgearbeitete Trauma, dessen Folgen noch die zweite Generation zu spüren bekommt, ist jetzt ein weiteres gesellschaftliches Trauma aufgesetzt worden, und die Wahrscheinlichkeit ist groß, dass auch das nicht aufgearbeitet werden wird.
Was will man von so einer Gesellschaft erwarten?
Damit noch nicht genug, gewannen die Schlagzeilen zum Konflikt in der Ukraine die Oberhand, die Corona weitgehend verdrängten. Wieder machte sich Angst breit. Wird es einen Krieg geben? Die Vorgeschichte zum Ukraine-Konflikt wurde im Mainstream weitgehend unter den Teppich gekehrt. Die Frage nach dem eigenen Anteil des sogenannten Wertewestens an diesem Konflikt? Fehlanzeige! Passt nicht ins Narrativ. Aus diesem Konflikt, der, wie die Russen es nennen, militärischen Sonderoperation, ist allmählich ein ausgewachsener Krieg geworden. Ein klarer Stellvertreterkrieg zwischen den USA und Russland, auf dem Rücken der Ukraine, die sich durch Selensky vor den Karren spannen lassen hat. Bereits einen Monat nach Ausbruch des Konflikts war ein Frieden zum Greifen nahe. Dank des Westens konnte dies erfolgreich verhindert werden.
Aber diesen Elefanten im Raum will niemand wirklich sehen, geschweige denn, das zugeben. Die aktuelle Regierung in den USA hat nun die Aufgabe, die Scherben zu kitten, die die Vorgängerregierung verursacht hat. Dabei geht es nicht nur um Nächstenliebe, und das sinnlose Töten zu beenden, sondern auch um eine Möglichkeit, sich gesichtswahrend aus der Affaire zu ziehen. In erster Linie geht es um Interessen, nicht um „ein paar Menschenleben mehr oder weniger“.
Damit aber immer noch nicht genug, stellt sich Europa, den Friedensbemühungen zwischen den Großmächten USA und Russland in den Weg, verlängert damit das Sterben, statt diese Bemühungen zu unterstützen.
Zu Anfang von Corona haben viele geglaubt, was da abgeht, ist so absurd, das kann nicht lange dauern, dann klärt sich das auf. Seit fünf Jahren werden wir eines Besseren belehrt, denn die Absurditäten, der Wahnsinn will schier kein Ende nehmen. Und immer, wenn man denkt, schlimmer geht’s nimmer, kommt einer daher, und beweist das Gegenteil.
Um diesen Irrsinn immer weiter voranzutreiben, werden inzwischen nach der Bedienungsanleitung von George Orwells „1984“ Begriffe umgedeutet: Krieg ist Frieden, Spaltung ist Zusammenhalt, Zensur ist der Schutz vor Desinformation, Schulden sind Sondervermögen, usw. usw. usw.. Tschüss, gute alte Demokratie, willkommen in Unseredemokratie. Auch so ein Kunstwort, hinter der sich die unterschiedlichsten anti-demokratischen Tendenzen verbergen.
Eine vollständige Auflistung des Irrsinns würde den Rahmen des Möglichen sprengen.
Man fragt sich, was aufgrund der endlosen, oft menschenverachtenden, aber auf jeden Fall mindestens unmenschlichen Lebensbedingungen auf der Metaebene los ist, dass ein großer Teil der Menschheit, besonders der westlichen Welt, speziell in Europa, vollkommen den Verstand verloren hat.
Man kann es eigentlich nicht anders erklären, als dass das Böse die Macht ergriffen hat, dass die politischen Entscheidungsträger vom Teufel, oder wie auch immer man es nennen will, besessen sind.
Kräfte, ob gute oder schlechte, suchen sich immer Menschen, durch die sie wirken können.
Es bräuchte einen gesellschaftlichen Exorzismus, der diesen politischen Fehlbesetzungen den Teufel aus dem Leib treibt, doch auch leider ist ein großer Teil der Bevölkerung ebenso vom Teufel besessen, sitzt wie das Kaninchen vor der Schlange, empört sich vielleicht, kommt aber nicht von der Chips-Tüte auf dem Sofa vor dem Fernseher los, ist nicht in der Lage, seinen eigenen Untergang zu verhindern. Stattdessen schreit es innerlich nach einem, der da kommen soll, um sie zu retten. Das erinnert an die bisher dunkelsten Zeiten Deutschlands, von denen sich herausgestellt hat, dass der Retter kein Retter war.
Merz, noch nicht einmal im Amt, kündigt die Möglichkeit der Lieferung von Taurus-Raketen an. Russland erklärt, dass es das als Deutschlands Eintritt in den Ukraine-Krieg bewerten würde. Putin ordnet einseitig eine Waffenruhe über Ostern an, aber Putin ist immer noch der Böse, will Deutschland unbedingt angreifen, ist eine Bedrohung für die westlichen Werte, die Freiheit und die Demokratie. Das ist ein nicht zu überbietender Hohn.
Mit normalem Hausverstand ist das nicht zu begreifen. Es ist einfach nur irre. Und die Deutschen sitzen da und schauen zu. Bis auf wenige Ausnahmen, der Rest Europas übrigens auch. Der aller größte Teil der Menschen in Europa sitzt ruhig auf den Eisenbahnschienen und wartet darauf, dass der Zug kommt und sie überfährt.
Gerade an Ostern, der Zeit der Friedensbewegungen, der Ostermärsche. Wo sind die Massen, die vor den Regierungssitzen der europäischen Hauptstädte stehen, Frieden rufen und nicht mehr weggehen, und die wahnsinnigen Verantwortlichen dazu zwingen, mit dem Irrsinn aufzuhören, der die Welt in einen dritten Weltenbrand führen kann?
Stattdessen regt man sich darüber auf, dass der Osterbraten auch schon wieder teurer geworden ist, aber was will man machen. Lasst uns wenigstens über die Osterfeiertage mal eine gute Zeit haben. Und dann kommt auch noch oft der Satz, der einen aus dem Anzug springen lässt: Ich alleine kann ja sowieso nichts machen. Ein Satz, den wahrscheinlich rund 60 Millionen Deutsche sagen. Wie irre ist das denn?
Ohne, dass das Volk in Deutschland, die Völker in Europa, nicht aufstehen, und mit aller Härte NEIN sagen, gibt es keine Anzeichen dafür, dass es die Entscheidungsträger von alleine tun werden und das führt unweigerlich in die Katastrophe.
Was kann getan werden, damit die guten Kräfte wieder die Oberhand gewinnen, oder müssen wir lernen zu akzeptieren, dass wir verloren sind?
Leider ist es nicht möglich, schöne Ostern 2025 zu wünschen, denn es sind keine.
An dieser Stelle ein Schmankerl, dass an Geschmacklosigkeit und Geschichtsvergessenheit nicht zu überbieten ist:
Am liebsten möchte man schreien: „Hört auf! Und wenn einige Millionen Menschen allein in Deutschland das täten, dann würde man es schon hören. Aber was hört man? Besinnliche Feiertagsstille, gruselig.
Seit fünf Jahren macht sich ein Zeitgeist breit, dessen Abstand zum Menschsein, zum friedlichen Miteinander und einträglichen Austausch nicht größer sein könnte. Und ein Ende ist nicht in Sicht. Zukunftspläne schmieden? Wie denn, wenn man heute nicht weiß, ob einem nicht morgen schon die erste Kugel um die Ohren fliegt, weil wir, der Souverän nicht in der Lage gewesen sind, für Frieden ohne Waffen und Töten und Freiheit einzustehen.
Und diejenigen, die den Hintern nicht hochbekommen haben, sind die ersten, die dann klagen: Ach hätten wir doch! Wie konnte das geschehen? Das kam alles so plötzlich. Was hätte ich denn tun sollen? Wieder wird verdrängt und sich selbst belogen, nur, um vor sich selbst zu rechtfertigen, dass man im Grunde genommen ein Waschlappen ist und doch eigentlich sehr an seinem jämmerlichen Leben hängt.
Das einzige, was wirklich noch Hoffnung macht und Kraft gibt, sind die engagierten, propagandaresistenten Widerständler, die sich nach Kräften bemühen, die Wahrheit hochzuhalten, sich mit gesundem Hausverstand zu äußern, in der Hoffnung, dass sie den einen oder anderen Menschen außerhalb der „Blase“ erreichen, um ihn von der dunklen Seite der Macht ins Licht gehen zu lassen: Ja, bitte geh‘ unbedingt ins Licht, Carol Ann und alle anderen auch!
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ a39d19ec:3d88f61e
2025-04-22 12:44:42
@ a39d19ec:3d88f61e
2025-04-22 12:44:42Die Debatte um Migration, Grenzsicherung und Abschiebungen wird in Deutschland meist emotional geführt. Wer fordert, dass illegale Einwanderer abgeschoben werden, sieht sich nicht selten dem Vorwurf des Rassismus ausgesetzt. Doch dieser Vorwurf ist nicht nur sachlich unbegründet, sondern verkehrt die Realität ins Gegenteil: Tatsächlich sind es gerade diejenigen, die hinter jeder Forderung nach Rechtssicherheit eine rassistische Motivation vermuten, die selbst in erster Linie nach Hautfarbe, Herkunft oder Nationalität urteilen.
Das Recht steht über Emotionen
Deutschland ist ein Rechtsstaat. Das bedeutet, dass Regeln nicht nach Bauchgefühl oder politischer Stimmungslage ausgelegt werden können, sondern auf klaren gesetzlichen Grundlagen beruhen müssen. Einer dieser Grundsätze ist in Artikel 16a des Grundgesetzes verankert. Dort heißt es:
„Auf Absatz 1 [Asylrecht] kann sich nicht berufen, wer aus einem Mitgliedstaat der Europäischen Gemeinschaften oder aus einem anderen Drittstaat einreist, in dem die Anwendung des Abkommens über die Rechtsstellung der Flüchtlinge und der Europäischen Menschenrechtskonvention sichergestellt ist.“
Das bedeutet, dass jeder, der über sichere Drittstaaten nach Deutschland einreist, keinen Anspruch auf Asyl hat. Wer dennoch bleibt, hält sich illegal im Land auf und unterliegt den geltenden Regelungen zur Rückführung. Die Forderung nach Abschiebungen ist daher nichts anderes als die Forderung nach der Einhaltung von Recht und Gesetz.
Die Umkehrung des Rassismusbegriffs
Wer einerseits behauptet, dass das deutsche Asyl- und Aufenthaltsrecht strikt durchgesetzt werden soll, und andererseits nicht nach Herkunft oder Hautfarbe unterscheidet, handelt wertneutral. Diejenigen jedoch, die in einer solchen Forderung nach Rechtsstaatlichkeit einen rassistischen Unterton sehen, projizieren ihre eigenen Denkmuster auf andere: Sie unterstellen, dass die Debatte ausschließlich entlang ethnischer, rassistischer oder nationaler Kriterien geführt wird – und genau das ist eine rassistische Denkweise.
Jemand, der illegale Einwanderung kritisiert, tut dies nicht, weil ihn die Herkunft der Menschen interessiert, sondern weil er den Rechtsstaat respektiert. Hingegen erkennt jemand, der hinter dieser Kritik Rassismus wittert, offenbar in erster Linie die „Rasse“ oder Herkunft der betreffenden Personen und reduziert sie darauf.
Finanzielle Belastung statt ideologischer Debatte
Neben der rechtlichen gibt es auch eine ökonomische Komponente. Der deutsche Wohlfahrtsstaat basiert auf einem Solidarprinzip: Die Bürger zahlen in das System ein, um sich gegenseitig in schwierigen Zeiten zu unterstützen. Dieser Wohlstand wurde über Generationen hinweg von denjenigen erarbeitet, die hier seit langem leben. Die Priorität liegt daher darauf, die vorhandenen Mittel zuerst unter denjenigen zu verteilen, die durch Steuern, Sozialabgaben und Arbeit zum Erhalt dieses Systems beitragen – nicht unter denen, die sich durch illegale Einreise und fehlende wirtschaftliche Eigenleistung in das System begeben.
Das ist keine ideologische Frage, sondern eine rein wirtschaftliche Abwägung. Ein Sozialsystem kann nur dann nachhaltig funktionieren, wenn es nicht unbegrenzt belastet wird. Würde Deutschland keine klaren Regeln zur Einwanderung und Abschiebung haben, würde dies unweigerlich zur Überlastung des Sozialstaates führen – mit negativen Konsequenzen für alle.
Sozialpatriotismus
Ein weiterer wichtiger Aspekt ist der Schutz der Arbeitsleistung jener Generationen, die Deutschland nach dem Zweiten Weltkrieg mühsam wieder aufgebaut haben. Während oft betont wird, dass die Deutschen moralisch kein Erbe aus der Zeit vor 1945 beanspruchen dürfen – außer der Verantwortung für den Holocaust –, ist es umso bedeutsamer, das neue Erbe nach 1945 zu respektieren, das auf Fleiß, Disziplin und harter Arbeit beruht. Der Wiederaufbau war eine kollektive Leistung deutscher Menschen, deren Früchte nicht bedenkenlos verteilt werden dürfen, sondern vorrangig denjenigen zugutekommen sollten, die dieses Fundament mitgeschaffen oder es über Generationen mitgetragen haben.
Rechtstaatlichkeit ist nicht verhandelbar
Wer sich für eine konsequente Abschiebepraxis ausspricht, tut dies nicht aus rassistischen Motiven, sondern aus Respekt vor der Rechtsstaatlichkeit und den wirtschaftlichen Grundlagen des Landes. Der Vorwurf des Rassismus in diesem Kontext ist daher nicht nur falsch, sondern entlarvt eine selektive Wahrnehmung nach rassistischen Merkmalen bei denjenigen, die ihn erheben.
-
 @ a296b972:e5a7a2e8
2025-04-19 12:58:33
@ a296b972:e5a7a2e8
2025-04-19 12:58:33Völkerstrafgesetzbuch (VStGB)\ § 13 Verbrechen der Aggression ==============================
(1) Wer einen Angriffskrieg führt oder eine sonstige Angriffshandlung begeht, die ihrer Art, ihrer Schwere und ihrem Umfang nach eine offenkundige Verletzung der Charta der Vereinten Nationen darstellt, wird mit lebenslanger Freiheitsstrafe bestraft.
(2) Wer einen Angriffskrieg oder eine sonstige Angriffshandlung im Sinne des Absatzes 1 plant, vorbereitet oder einleitet, wird mit lebenslanger Freiheitsstrafe oder mit Freiheitsstrafe nicht unter zehn Jahren bestraft. Die Tat nach Satz 1 ist nur dann strafbar, wenn
1.
der Angriffskrieg geführt oder die sonstige Angriffshandlung begangen worden ist oder
2.
durch sie die Gefahr eines Angriffskrieges oder einer sonstigen Angriffshandlung für die Bundesrepublik Deutschland herbeigeführt wird.
(3) Eine Angriffshandlung ist die gegen die Souveränität, die territoriale Unversehrtheit oder die politische Unabhängigkeit eines Staates gerichtete oder sonst mit der Charta der Vereinten Nationen unvereinbare Anwendung von Waffengewalt durch einen Staat.
(4) Beteiligter einer Tat nach den Absätzen 1 und 2 kann nur sein, wer tatsächlich in der Lage ist, das politische oder militärische Handeln eines Staates zu kontrollieren oder zu lenken.
(5) In minder schweren Fällen des Absatzes 2 ist die Strafe Freiheitsstrafe nicht unter fünf Jahren.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
(Bild von pixabay)
-
 @ 4ba8e86d:89d32de4
2025-04-22 13:26:12
@ 4ba8e86d:89d32de4
2025-04-22 13:26:12Cashu é Ecash para Bitcoin
Cashu é um sistema ecash Chaumian gratuito e de código aberto criado para Bitcoin. Cashu oferece privacidade quase perfeita para usuários de aplicativos Bitcoin de custódia. Ninguém precisa saber quem você é, quanto dinheiro você tem e com quem você faz transações.
O que é Cashu?
Cashu é um novo protocolo ecash para aplicativos de custódia Bitcoin que está totalmente integrado à rede Lightning. Um sistema Ecash consiste em duas partes, a carteira mint e a carteira ecash. Transações Ecash não rastreáveis, instantâneas e sem taxas. Cashu é construído para Bitcoin. As carteiras usam o nó Lightning da casa da moeda para fazer ou receber pagamentos em Bitcoin em troca de ecash. Uma casa da moeda Cashu não sabe quem você é, qual é o seu saldo ou com quem você está negociando.Os usuários de uma casa da moeda podem trocar ecash de forma privada, sem que ninguém saiba quem são as partes envolvidas. Os pagamentos em Bitcoin são executados sem que ninguém possa censurar usuários específicos.
A postagem de David Wagner em 1996 na lista de discussão Cypherpunk é a base da criptografia Cashu. Wagner descreve um sistema ecash usando troca de chave cega Diffie-Hellman em vez de RSA, na qual a implementação original de David Chaum foi baseada.
https://cypherpunks.venona.com/date/1996/03/msg01848.html
https://en.m.wikipedia.org/wiki/Ecash
Como isso começou.
https://void.cat/d/2HJKtTEfuDxmDfh3uH9ZoS.webp https://void.cat/d/XyyHFSQYa5vEswzzt6MMq7.webp
Como vão as coisas.
https://void.cat/d/WUrKzsFDnsvUQdFKZChLeS.webp
Como funciona A Carteira Cashu é através de um esquema criptográfico chamado assinaturas cegas, descrito pela primeira vez pelo cypherpunk e criptógrafo David Chaum. Pense assim:você produz uma mensagem secreta e a envolve em um envelope feito de papel carbono que você envia para a casa da moeda. https://void.cat/d/SbEEHCiGFUHWvk4qGv9xCb.webp
A casa da moeda não pode ver o que está dentro do envelope. Ele assina do lado de fora dizendo "qualquer que seja esse segredo, vale 420 Satoshis”e o envia de volta para você. Como o envelope é realmente criptografado, somente você pode abri-lo e ver sua mensagem secreta (agora assinada por carbono). https://void.cat/d/Pakyb6ztW9B7L5ubAQ74eL.webp
Este segredo assinado é na verdade o seu token Ecash e vale Satoshis.
Você pode enviar e receber esses tokens para qualquer outra pessoa como quiser, seja com um mensageiro, via e-mail ou um pombo. A casa da moeda não sabe nada disso.
A anatomia de um token Cashu. https://void.cat/d/JzvxreMoCitmYe2FthAsei.webp
Um breve passo a passo de uma carteira cashu deixará tudo isso bem claro.
Comece abrindo
https://nutstash.app/
Pressione " WALLET " https://void.cat/d/VeCANsaxkkq9YtoPRS26ZK.webp https://void.cat/d/CTmK9GcPGn3i2gHCVXcL5r.webp https://void.cat/d/UWjyjGLS6MzyZvt6zkuUgG.webp https://void.cat/d/HzNtKanCSAJatrMa9yTKwF.webp
Pressione "+ ADD ".
Agora a carteira cashu está aberta… https://void.cat/d/GAYSrNxHEEhctoW37bFPjJ.webp
O próximo passo é deposite alguns sats com a Casa da moeda.
Pra depositar Pressione o botão "MINT". https://void.cat/d/LC5WEDKAzzZoHXxrKZDiWu.webp
Digite a quantidade de sats a ser depositado na carteira cashu depois Pressione " REQUEST MINT ". https://void.cat/d/Pr6foBWBBCq73i8WggbLGG.webp
Você Pode copiar a fatura ou ler o qrcode , no meu caso usei a carteira LNbits pra pagar a fatura de 10 sats , você tem 10 minutos pra pagar fatura. https://void.cat/d/BQerpEtW2H9ANaoW8truJE.webp https://void.cat/d/8PGFBRW64zavDnQJfYQh9C.webp
Agora pra enviar Ecash.
Pressione “SEND” https://void.cat/d/8rkF2dvhJeZWf8GeQhhf2d.webp
Digite 10 , Pressione “SEND” https://void.cat/d/5SK5w6ewgt8wikCuyk7znM.webp
Então o token Ecash usando a assinatura cega da casa da moeda foi criado. https://void.cat/d/PedBMcZPfczZLLymGmfzVq.webp
O Token Ecash foi criado é esse logo abaixo.
eyJwcm9vZnMiOlt7ImlkIjoiME5JM1RVQXMxU2Z5IiwiYW1vdW50IjoyLCJzZWNyZXQiOiJrWjNBOVorSXkyREJOcDdhdFhYRTIvclVXOFRnR2ZoTDgzWEFXZ0dKUXhVPSIsIkMiOiIwMmM0NjA4NDYwNDhjNzI1ZjgwMDc3M2IyNmRmOTcxNDU1MTJmOTI0YjgyNzYyZTllYzdkZjZjOTkzNGVmYjJhNmMifSx7ImlkIjoiME5JM1RVQXMxU2Z5IiwiYW1vdW50Ijo4LCJzZWNyZXQiOiJXdTZmdWlxNGt4Tkh3UkF1UzFhMmVYaGZtRnRHU2tRQkNYZFNnUzcreHkwPSIsIkMiOiIwMzFhYWI3MzY3MTJhY2Y5MWU4NzE4YmM5OTlmNWE2MGEwYzNjODQ5YTA1MWE2OTA5MzRkMTc4NWNmZGNkNDcyYTAifV0sIm1pbnRzIjpbeyJ1cmwiOiJodHRwczovL2xlZ2VuZC5sbmJpdHMuY29tL2Nhc2h1L2FwaS92MS80Z3I5WGNtejNYRWtVTndpQmlRR29DIiwiaWRzIjpbIjBOSTNUVUFzMVNmeSJdfV19
Se pressionar o botão " send as link "
Então criar link do token Ecash.
https://wallet.nutstash.app/#eyJwcm9vZnMiOlt7ImlkIjoiME5JM1RVQXMxU2Z5IiwiYW1vdW50IjoyLCJzZWNyZXQiOiJrWjNBOVorSXkyREJOcDdhdFhYRTIvclVXOFRnR2ZoTDgzWEFXZ0dKUXhVPSIsIkMiOiIwMmM0NjA4NDYwNDhjNzI1ZjgwMDc3M2IyNmRmOTcxNDU1MTJmOTI0YjgyNzYyZTllYzdkZjZjOTkzNGVmYjJhNmMifSx7ImlkIjoiME5JM1RVQXMxU2Z5IiwiYW1vdW50Ijo4LCJzZWNyZXQiOiJXdTZmdWlxNGt4Tkh3UkF1UzFhMmVYaGZtRnRHU2tRQkNYZFNnUzcreHkwPSIsIkMiOiIwMzFhYWI3MzY3MTJhY2Y5MWU4NzE4YmM5OTlmNWE2MGEwYzNjODQ5YTA1MWE2OTA5MzRkMTc4NWNmZGNkNDcyYTAifV0sIm1pbnRzIjpbeyJ1cmwiOiJodHRwczovL2xlZ2VuZC5sbmJpdHMuY29tL2Nhc2h1L2FwaS92MS80Z3I5WGNtejNYRWtVTndpQmlRR29DIiwiaWRzIjpbIjBOSTNUVUFzMVNmeSJdfV19 https://void.cat/d/U1UnyxsYgj516YbmkgQNkQ.webp Este token Ecash pode ser compartilhado como você quiser. Você pode enviá-lo por e-mail para alguém, enviá-lo em uma mensagem privada, um SMS ou convertê-lo em um código QR e imprimi-lo. Quem tiver este token pode resgatá-lo com o 10 sats.
Você verá que seu saldo caiu para 20 sats: https://void.cat/d/95AVkevmknKNzqRcnJZwQX.webp
Para resgatar um token Ecash sem o link, pressione o botão “Receive ” https://void.cat/d/UjrbAPn8mj5qGZYVQ1Ba2B.webp
cole-o token Ecash no campo
" token: "pressione "RECEIVE" https://void.cat/d/GZLcBgvHfaB3c5N66ygZyV.webp
Com o Link do token Ecash só pressionar no link vai abrir a tela já preencher automáticamente só pressionar " RECEIVE " https://void.cat/d/ARNkKCtchhFt4NCTkfRJRG.webp
Pra Ativa o Nostr na carteira vai na aba settings , pressione o botão ativa o Nostr. https://void.cat/d/MjoDA1dgueWUFABcQFDVRe.webp
Por padrão ficar ativo pra usar o " Use external Key (nos2x , outros) " Mas Nesse caso não vou usar vou desativar e vou ativa " Edit Nostr Keys " https://void.cat/d/BAA6eFkmK5f7BHzLwYLSGF.webp
Ao pressionar esse botão https://void.cat/d/VTNGVsLvwqfy3dWu4hhMSK.webp é gerar um novo par de chaves privadas e pública , assim podemos usar uma nova chave a cada pagamentos. Aumentando a privacidade no pagamentos.
A pois Ativa o Nostr na carteira , você pode enviar Sats / Ecash via Nostr.
Pressione " Send " https://void.cat/d/R2Svye4XPd2VdHfPxT1DzF.webp
Pressione " Send " https://void.cat/d/AwLeBBr2db2wrTHHUHwEPs.webp
Agora pode adicionar npud / hex / nip-05 pra enviar token. https://void.cat/d/VZR6BUXjG7pm3FDogrDvo4.webp
Pressione " SEND OVER NOSTR " pra enviar o token Ecash. https://void.cat/d/MWveqpmii5dqpioa5a3wVt.webp
Pra quem não tem a carteira nutstash , pode entra no seu cliente Nostr no meu caso e snort nostr , Demora algums minutos pra chegar mensagem com o token Ecash.. https://void.cat/d/MVg3fPD7PAzZUskGCCCcps.webp https://void.cat/d/YNtKuCbQYo1wef7pJcjhKy.webp
Ja se a outra pessoa usar carteira nutstash com a chave pública que você mandou chegar mais rápido. Essa bolinha azul no campo " Indox " Indica que você recebeu o pagamento já está pronto pra ser regastado. https://void.cat/d/So6FAp4wiTUeKBBmRBU2Rv.webp
Pressione "Indox " depois pressione a seta. https://void.cat/d/TqYNYDoyy9fUFas9NFxReJ.webp
Pressione " TRUS MINT " pra recebe os Token Ecash. https://void.cat/d/LP6zUTZ3HDPxd6fLvPPNXB.webp
O aplicativo de resgate Cashu, que permite resgatar tokens Ecash via Lightning.
https://redeem.cashu.me/ https://void.cat/d/Mw9kzDHr4A469EjFNoTHyB.webp
Cola o Token no campo " paste in your Cashu Ecash token.. " https://void.cat/d/SkA3MGJaGGxCjNnzeBhPHP.webp
Pressione " REDEEM " pra converter Ecash em Lightning. https://void.cat/d/693C1yfwYz3P3BQB6f7xXN.webp
Você pode editar e manda já pronto pra pessoa só basta a pessoa ou você aberta em " REDEEM " pra converter Ecash em Lightning.
https://redeem.cashu.me/?token=token ecash=&to=Lightning address
Exemplo:
https://redeem.cashu.me/?token=eyJwcm9vZnMiOlt7ImlkIjoiUEVuMVdLalFoN2pGIiwiYW1vdW50IjoyLCJDIjoiMDJhYWE5OWJiMmUwODQyYjJmNzdmNDRlZWEyZjEzMmNkOTNhZjJlNWU0MzI3ZjhjMTE5ODcxZWNiMTNhMTUxYjY0Iiwic2VjcmV0IjoicE5jb3hFRHJRT1ovTXU4d3d2SlpvMnRIaXBSM3pPYkRrSWJUUlB6VXh5bz0ifSx7ImlkIjoiUEVuMVdLalFoN2pGIiwiYW1vdW50IjoxNiwiQyI6IjAzNDM4ZDc1NmZmMjdmYjgyZmQxNWNhNzg3NzgwNTAyZWU4NzdmMzQ5MmYyMWQzMTMwMzc1NTdlNWNmMDJlOWQ0MCIsInNlY3JldCI6Im9DTXQwUTRVT0MvZWhmd2FVOWt5aGFJZUdHdXhiYUNzQTZ2STh2a0w2N1U9In0seyJpZCI6IlBFbjFXS2pRaDdqRiIsImFtb3VudCI6MzIsIkMiOiIwMmIyMmQ4MDEwZWU5MDA2MWYyNWQzODAyY2UyMDE3ZjAwMmVjMDVmMjM5NjIwNGNkYjllMmU2ODllYWY3YTZkYjIiLCJzZWNyZXQiOiI5ejVVMEdzWHZiUS84Rjd4ZFdYUXRxUDlvWGFyVnBRTzRFdUtzb2JSck1vPSJ9XSwibWludHMiOlt7InVybCI6Imh0dHBzOi8vbGVnZW5kLmxuYml0cy5jb20vY2FzaHUvYXBpL3YxL29DcXNTR3I1enphTTZxM1hWZU5ZNXQiLCJpZHMiOlsiUEVMVdLalFoN2pGIl19XX0=&to=alexemidio@ln.tips
Obs: o teclado do celular pode adicionar "=" a mais ou corrigir " &to " com "&tô" assim escrevendo errado, tanto erro no link.
" SWAP " transferência de uma carteira para outra. Pressione " INTER-MINT SWAP" https://void.cat/d/PsCdoLAmYpYCChkgqTAE7p.webp
A carteira que você selecionar em cima é a carteira de saídas e a carteira de baixo e a carteira de entrada. https://void.cat/d/VKY6ts6qttJmCaefrduv4K.webp
Agora digita o valor que quer fazer o SWAP. Após Pressione " CONFIRM AMOUNT" https://void.cat/d/WuuQqeC1mSQUufb75eeMbw.webp
Depois Tem que pressionar " SWAP " não esqueça. https://void.cat/d/Eb2ajSaZfzZkBEWBv8tuk.webp
Pronto antes a primeira Carteira tinha 10 Ecash, e segunda carteira tinha 8 Ecash.
Somando 18 Ecash.
Apois o SWAP Agora as duas tem 9.
Somando 18. https://void.cat/d/8yRtSoFyih2D2KEm66h6in.webp
Fazer o backup da sua carteira cashu ecash. Pressione " BACKUP TOKENS " https://void.cat/d/26vtnDiVP4YpDiQmunatko.webp
Você pode editar o nome do backup E pode alterar o local aonde vai salva o arquivo 📂 do backup. Depois só pressionar " Baixar " https://void.cat/d/PQH94o81U23txdmyx3cHEn.webp
Agora pra recuperar a carteira cashu ecash. Pressione " RESTORE " https://void.cat/d/2vkLS1qUCbJ1XXjSLBou25.webp
Pressione " CONTINUAR " https://void.cat/d/PCbT2UPSLtwcZohwbhD85A.webp
Click no espaço em branco vai abrir pra encontrar o arquivo 📂 Do backup.. https://void.cat/d/P1VC7b46oNe62v4puVZ79b.webp
Selecionar o arquivo 📂 de backup. https://void.cat/d/D6FAGxYRquz2WWwNznSAzT.webp
Pressione " CONTINUE" https://void.cat/d/HicRn5e2feSRicgjy6kuC5.webp
Pressione " CONTINUE" https://void.cat/d/VP6uh8bXHz42PBGrPwGq5e.webp
Backup feito com sucesso. Só aberta " Ok " https://void.cat/d/QsZV1umL9DhoPtEXBMfPtY.webp
O eCash pode ser útil em diversas situações, oferecendo várias vantagens. Uma das principais vantagens do uso de tokens eCash é a privacidade que oferece. Como as transações usando eCash são quase impossíveis de rastrear, isso pode ser útil para quem deseja manter sua atividade financeira privada. O eCash pode ser especialmente útil para Pagamento de serviços em áreas rurais , pode ser difícil acessar serviços financeiros tradicionais, como bancos ou caixas eletrônicos. O uso de tokens eCash pode permitir que as pessoas paguem por serviços como transporte , serviços de saúde ou eletricidade sem a necessidade de viajar para áreas urbanas. No entanto, é importante lembrar que o uso do eCash ainda apresenta riscos e desafios. Como o eCash cashubtc ainda é bem novo , pode haver falhas de segurança ou outras vulnerabilidades que ainda não foram identificadas use com cautela poucos Sats.
Obrigado por ler, e espero que você dedique alguns minutos para experimentar o eCash e ver do que se trata melhor.
Alguma artigos e vídeos a baixo.
https://cashu.space/
https://docs.cashu.space/
https://github.com/cashubtc/
https://youtu.be/UNjVc-WYdgE
https://youtu.be/_XmQSpAhFN4
https://youtu.be/zdtRT7phXBo
https://maxmoney.substack.com/p/ecash-for-better-bitcoin-privacy?utm_source=substack&utm_campaign=post_embed&utm_medium=web
https://cypherpunks.venona.com/date/1996/03/msg01848.html
Encontre-me ou envie um zap para nostr alexemidio@ln.tips alexemidio@alexemidio.github.io
Twitter: alexemidio7
-
 @ a39d19ec:3d88f61e
2025-03-18 17:16:50
@ a39d19ec:3d88f61e
2025-03-18 17:16:50Nun da das deutsche Bundesregime den Ruin Deutschlands beschlossen hat, der sehr wahrscheinlich mit dem Werkzeug des Geld druckens "finanziert" wird, kamen mir so viele Gedanken zur Geldmengenausweitung, dass ich diese für einmal niedergeschrieben habe.
Die Ausweitung der Geldmenge führt aus klassischer wirtschaftlicher Sicht immer zu Preissteigerungen, weil mehr Geld im Umlauf auf eine begrenzte Menge an Gütern trifft. Dies lässt sich in mehreren Schritten analysieren:
1. Quantitätstheorie des Geldes
Die klassische Gleichung der Quantitätstheorie des Geldes lautet:
M • V = P • Y
wobei:
- M die Geldmenge ist,
- V die Umlaufgeschwindigkeit des Geldes,
- P das Preisniveau,
- Y die reale Wirtschaftsleistung (BIP).Wenn M steigt und V sowie Y konstant bleiben, muss P steigen – also Inflation entstehen.
2. Gütermenge bleibt begrenzt
Die Menge an real produzierten Gütern und Dienstleistungen wächst meist nur langsam im Vergleich zur Ausweitung der Geldmenge. Wenn die Geldmenge schneller steigt als die Produktionsgütermenge, führt dies dazu, dass mehr Geld für die gleiche Menge an Waren zur Verfügung steht – die Preise steigen.
3. Erwartungseffekte und Spekulation
Wenn Unternehmen und Haushalte erwarten, dass mehr Geld im Umlauf ist, da eine zentrale Planung es so wollte, können sie steigende Preise antizipieren. Unternehmen erhöhen ihre Preise vorab, und Arbeitnehmer fordern höhere Löhne. Dies kann eine sich selbst verstärkende Spirale auslösen.
4. Internationale Perspektive
Eine erhöhte Geldmenge kann die Währung abwerten, wenn andere Länder ihre Geldpolitik stabil halten. Eine schwächere Währung macht Importe teurer, was wiederum Preissteigerungen antreibt.
5. Kritik an der reinen Geldmengen-Theorie
Der Vollständigkeit halber muss erwähnt werden, dass die meisten modernen Ökonomen im Staatsauftrag argumentieren, dass Inflation nicht nur von der Geldmenge abhängt, sondern auch von der Nachfrage nach Geld (z. B. in einer Wirtschaftskrise). Dennoch zeigt die historische Erfahrung, dass eine unkontrollierte Geldmengenausweitung langfristig immer zu Preissteigerungen führt, wie etwa in der Hyperinflation der Weimarer Republik oder in Simbabwe.
-
 @ d08c9312:73efcc9f
2025-04-18 20:17:41
@ d08c9312:73efcc9f
2025-04-18 20:17:41https://youtu.be/qK7ffYzxiiQ
Resolvr was recently featured in The Institutes RiskStream Collaborative's educational video series on insurance digitization and cross-border payments. With over a century of history educating insurance professionals, The Institutes has established itself as the premier knowledge resource in risk management and insurance. And its RiskStream Collaborative non-profit serves as the industry's largest enterprise-level technology consortium focused on streamlining insurance processes through innovative solutions.
Resolvr's co-founders, Aaron Daniel and Dave Schwab, were joined by industry experts Lizzy Eisenberg from Lightspark and Austin Cornell from Zero Hash to discuss how Bitcoin and the Lightning Network are transforming global insurance payments operations.
Watch the video to learn how Resolvr is leveraging these real-time digital settlement networks to solve significant inefficiencies in today's insurance payment ecosystem - from the months-long settlement times that trap billions in value, to the manual reconciliation processes costing the industry nearly £1 billion annually at Lloyd's of London alone.
We're grateful to RiskStream Collaborative for showcasing these transformative technologies and emphasizing the importance of combining specialized insurance-native interfaces with powerful payment infrastructure to solve industry-specific challenges.
For more information about how Resolvr can help your organization streamline premium processing and payments, contact us today.
-
 @ e39d100f:d27602e5
2025-04-22 11:33:58
@ e39d100f:d27602e5
2025-04-22 11:33:58A 898Bet vem se destacando no cenário digital brasileiro ao unir inovação, segurança e variedade de opções em uma única plataforma. Mas o que realmente faz a diferença é a forma como ela cativa novos jogadores, oferecendo uma experiência fluida desde o primeiro acesso.
A jornada começa com uma interface elegante e bem organizada. Não há excesso de informação visual, o que facilita a navegação, principalmente para quem está começando agora no universo dos jogos online. Todas as categorias de jogos são claramente apresentadas, e os recursos de busca ajudam a encontrar rapidamente o que se deseja.
A inovação da 898bet está nos detalhes. A plataforma oferece jogos com tecnologias modernas, como animações 3D, trilhas sonoras imersivas e mecânicas criativas que mantêm o jogador engajado por mais tempo. Além disso, a empresa está sempre atualizando seu catálogo com novos títulos, garantindo novidades frequentes para quem gosta de explorar.
Outro ponto que atrai novos usuários é a política de bônus e recompensas. Logo no primeiro depósito, os jogadores podem receber incentivos que tornam a experiência ainda mais empolgante. Há também programas de fidelidade e promoções exclusivas que recompensam o tempo e o engajamento na plataforma.
A segurança é tratada com máxima prioridade. A 898Bet utiliza sistemas de criptografia para proteger dados e transações, além de trabalhar com provedores de pagamento confiáveis. Isso passa confiança ao usuário, que pode se concentrar totalmente em se divertir sem preocupações.
Para quem está entrando agora nesse universo, a 898Bet oferece tutoriais, dicas e atendimento em português para guiar os primeiros passos. Com essa atenção aos detalhes, a plataforma se torna acessível mesmo para quem nunca jogou online antes.
A combinação entre inovação, qualidade e suporte eficiente explica por que a 898Bet vem ganhando espaço e conquistando jogadores por todo o Brasil.
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 97c70a44:ad98e322
2025-03-05 18:09:05
@ 97c70a44:ad98e322
2025-03-05 18:09:05So you've decided to join nostr! Some wide-eyed fanatic has convinced you that the "sun shines every day on the birds and the bees and the cigarette trees" in a magical land of decentralized, censorship-resistant freedom of speech - and it's waiting just over the next hill.
But your experience has not been all you hoped. Before you've even had a chance to upload your AI-generated cyberpunk avatar or make up exploit codenames for your pseudonym's bio, you've been confronted with a new concept that has left you completely nonplussed.
It doesn't help that this new idea might be called by any number of strange names. You may have been asked to "paste your nsec", "generate a private key", "enter your seed words", "connect with a bunker", "sign in with extension", or even "generate entropy". Sorry about that.
All these terms are really referring to one concept under many different names: that of "cryptographic identity".
Now, you may have noticed that I just introduced yet another new term which explains exactly nothing. You're absolutely correct. And now I'm going to proceed to ignore your complaints and talk about something completely different. But bear with me, because the juice is worth the squeeze.
Identity
What is identity? There are many philosophical, political, or technical answers to this question, but for our purposes it's probably best to think of it this way:
Identity is the essence of a thing. Identity separates one thing from all others, and is itself indivisible.
This definition has three parts:
- Identity is "essential": a thing can change, but its identity cannot. I might re-paint my house, replace its components, sell it, or even burn it down, but its identity as something that can be referred to - "this house" - is durable, even outside the boundaries of its own physical existence.
- Identity is a unit: you can't break an identity into multiple parts. A thing might be composed of multiple parts, but that's only incidental to the identity of a thing, which is a concept, not a material thing.
- Identity is distinct: identity is what separates one thing from all others - the concept of an apple can't be mixed with that of an orange; the two ideas are distinct. In the same way, a single concrete apple is distinct in identity from another - even if the component parts of the apple decompose into compost used to grow more apples.
Identity is not a physical thing, but a metaphysical thing. Or, in simpler terms, identity is a "concept".
I (or someone more qualified) could at this point launch into a Scholastic tangent on what "is" is, but that is, fortunately, not necessary here. The kind of identities I want to focus on here are not our actual identities as people, but entirely fictional identities that we use to extend our agency into the digital world.
Think of it this way - your bank login does not represent you as a complete person. It only represents the access granted to you by the bank. This access is in fact an entirely new identity that has been associated with you, and is limited in what it's useful for.
Other examples of fictional identities include:
- The country you live in
- Your social media persona
- Your mortgage
- Geographical coordinates
- A moment in time
- A chess piece
Some of these identites are inert, for example points in space and time. Other identies have agency and so are able to act in the world - even as fictional concepts. In order to do this, they must "authenticate" themselves (which means "to prove they are real"), and act within a system of established rules.
For example, your D&D character exists only within the collective fiction of your D&D group, and can do anything the rules say. Its identity is authenticated simply by your claim as a member of the group that your character in fact exists. Similarly, a lawyer must prove they are a member of the Bar Association before they are allowed to practice law within that collective fiction.
"Cryptographic identity" is simply another way of authenticating a fictional identity within a given system. As we'll see, it has some interesting attributes that set it apart from things like a library card or your latitude and longitude. Before we get there though, let's look in more detail at how identities are authenticated.
Certificates
Merriam-Webster defines the verb "certify" as meaning "to attest authoritatively". A "certificate" is just a fancy way of saying "because I said so". Certificates are issued by a "certificate authority", someone who has the authority to "say so". Examples include your boss, your mom, or the Pope.
This method of authentication is how almost every institution authenticates the people who associate with it. Colleges issue student ID cards, governments issue passports, and websites allow you to "register an account".
In every case mentioned above, the "authority" creates a closed system in which a document (aka a "certificate") is issued which serves as a claim to a given identity. When someone wants to access some privileged service, location, or information, they present their certificate. The authority then validates it and grants or denies access. In the case of an international airport, the certificate is a little book printed with fancy inks. In the case of a login page, the certificate is a username and password combination.
This pattern for authentication is ubiquitous, and has some very important implications.
First of all, certified authentication implies that the issuer of the certificate has the right to exclusive control of any identity it issues. This identity can be revoked at any time, or its permissions may change. Your social credit score may drop arbitrarily, or money might disappear from your account. When dealing with certificate authorities, you have no inherent rights.
Second, certified authentication depends on the certificate authority continuing to exist. If you store your stuff at a storage facility but the company running it goes out of business, your stuff might disappear along with it.
Usually, authentication via certificate authority works pretty well, since an appeal can always be made to a higher authority (nature, God, the government, etc). Authorities also can't generally dictate their terms with impunity without losing their customers, alienating their constituents, or provoking revolt. But it's also true that certification by authority creates an incentive structure that frequently leads to abuse - arbitrary deplatforming is increasingly common, and the bigger the certificate authority, the less recourse the certificate holder (or "subject") has.
Certificates also put the issuer in a position to intermediate relationships that wouldn't otherwise be subject to their authority. This might take the form of selling user attention to advertisers, taking a cut of financial transactions, or selling surveillance data to third parties.
Proliferation of certificate authorities is not a solution to these problems. Websites and apps frequently often offer multiple "social sign-in" options, allowing their users to choose which certificate authority to appeal to. But this only piles more value into the social platform that issues the certificate - not only can Google shut down your email inbox, they can revoke your ability to log in to every website you used their identity provider to get into.
In every case, certificate issuance results in an asymmetrical power dynamic, where the issuer is able to exert significant control over the certificate holder, even in areas unrelated to the original pretext for the relationship between parties.
Self-Certification
But what if we could reverse this power dynamic? What if individuals could issue their own certificates and force institutions to accept them?

Ron Swanson's counterexample notwithstanding, there's a reason I can't simply write myself a parking permit and slip it under the windshield wiper. Questions about voluntary submission to legitimate authorities aside, the fact is that we don't have the power to act without impunity - just like any other certificate authority, we have to prove our claims either by the exercise of raw power or by appeal to a higher authority.
So the question becomes: which higher authority can we appeal to in order to issue our own certificates within a given system of identity?
The obvious answer here is to go straight to the top and ask God himself to back our claim to self-sovereignty. However, that's not how he normally works - there's a reason they call direct acts of God "miracles". In fact, Romans 13:1 explicitly says that "the authorities that exist have been appointed by God". God has structured the universe in such a way that we must appeal to the deputies he has put in place to govern various parts of the world.
Another tempting appeal might be to nature - i.e. the material world. This is the realm in which we most frequently have the experience of "self-authenticating" identities. For example, a gold coin can be authenticated by biting it or by burning it with acid. If it quacks like a duck, walks like a duck, and looks like a duck, then it probably is a duck.
In most cases however, the ability to authenticate using physical claims depends on physical access, and so appeals to physical reality have major limitations when it comes to the digital world. Captchas, selfies and other similar tricks are often used to bridge the physical world into the digital, but these are increasingly easy to forge, and hard to verify.
There are exceptions to this rule - an example of self-certification that makes its appeal to the physical world is that of a signature. Signatures are hard to forge - an incredible amount of data is encoded in physical signatures, from strength, to illnesses, to upbringing, to personality. These can even be scanned and used within the digital world as well. Even today, most contracts are sealed with some simulacrum of a physical signature. Of course, this custom is quickly becoming a mere historical curiosity, since the very act of digitizing a signature makes it trivially forgeable.
So: transcendent reality is too remote to subtantiate our claims, and the material world is too limited to work within the world of information. There is another aspect of reality remaining that we might appeal to: information itself.
Physical signatures authenticate physical identities by encoding unique physical data into an easily recognizable artifact. To transpose this idea to the realm of information, a "digital signature" might authenticate "digital identities" by encoding unique "digital data" into an easily recognizable artifact.
Unfortunately, in the digital world we have the additional challenge that the artifact itself can be copied, undermining any claim to legitimacy. We need something that can be easily verified and unforgeable.
Digital Signatures
In fact such a thing does exist, but calling it a "digital signature" obscures more than it reveals. We might just as well call the thing we're looking for a "digital fingerprint", or a "digital electroencephalogram". Just keep that in mind as we work our way towards defining the term - we are not looking for something looks like a physical signature, but for something that does the same thing as a physical signature, in that it allows us to issue ourselves a credential that must be accepted by others by encoding privileged information into a recognizable, unforgeable artifact.
With that, let's get into the weeds.
An important idea in computer science is that of a "function". A function is a sort of information machine that converts data from one form to another. One example is the idea of "incrementing" a number. If you increment 1, you get 2. If you increment 2, you get 3. Incrementing can be reversed, by creating a complementary function that instead subtracts 1 from a number.
A "one-way function" is a function that can't be reversed. A good example of a one-way function is integer rounding. If you round a number and get
5, what number did you begin with? It's impossible to know - 5.1, 4.81, 5.332794, in fact an infinite number of numbers can be rounded to the number5. These numbers can also be infinitely long - for example rounding PI to the nearest integer results in the number3.A real-life example of a useful one-way function is
sha256. This function is a member of a family of one-way functions called "hash functions". You can feed as much data as you like intosha256, and you will always get 256 bits of information out. Hash functions are especially useful because collisions between outputs are very rare - even if you change a single bit in a huge pile of data, you're almost certainly going to get a different output.Taking this a step further, there is a whole family of cryptographic one-way "trapdoor" functions that act similarly to hash functions, but which maintain a specific mathematical relationship between the input and the output which allows the input/output pair to be used in a variety of useful applications. For example, in Elliptic Curve Cryptography, scalar multiplication on an elliptic curve is used to derive the output.
"Ok", you say, "that's all completely clear and lucidly explained" (thank you). "But what goes into the function?" You might expect that because of our analogy to physical signatures we would have to gather an incredible amount of digital information to cram into our cryptographic trapdoor function, mashing together bank statements, a record of our heartbeat, brain waves and cellular respiration. Well, we could do it that way (maybe), but there's actually a much simpler solution.
Let's play a quick game. What number am I thinking of? Wrong, it's 82,749,283,929,834. Good guess though.
The reason we use signatures to authenticate our identity in the physical world is not because they're backed by a lot of implicit physical information, but because they're hard to forge and easy to validate. Even so, there is a lot of variation in a single person's signature, even from one moment to the next.
Trapdoor functions solve the validation problem - it's trivially simple to compare one 256-bit number to another. And randomness solves the problem of forgeability.
Now, randomness (A.K.A. "entropy") is actually kind of hard to generate. Random numbers that don't have enough "noise" in them are known as "pseudo-random numbers", and are weirdly easy to guess. This is why Cloudflare uses a video stream of their giant wall of lava lamps to feed the random number generator that powers their CDN. For our purposes though, we can just imagine that our random numbers come from rolling a bunch of dice.
To recap, we can get a digital equivalent of a physical signature (or fingerprint, etc) by 1. coming up with a random number, and 2. feeding it into our chosen trapdoor function. The random number is called the "private" part. The output of the trapdoor function is called the "public" part. These two halves are often called "keys", hence the terms "public key" and "private key".
And now we come full circle - remember about 37 years ago when I introduced the term "cryptographic identity"? Well, we've finally arrived at the point where I explain what that actually is.
A "cryptographic identity" is identified by a public key, and authenticated by the ability to prove that you know the private key.
Notice that I didn't say "authenticated by the private key". If you had to reveal the private key in order to prove you know it, you could only authenticate a public key once without losing exclusive control of the key. But cryptographic identities can be authenticated any number of times because the certification is an algorithm that only someone who knows the private key can execute.
This is the super power that trapdoor functions have that hash functions don't. Within certain cryptosystems, it is possible to mix additional data with your private key to get yet another number in such a way that someone else who only knows the public key can prove that you know the private key.
For example, if my secret number is
12, and someone tells me the number37, I can "combine" the two by adding them together and returning the number49. This "proves" that my secret number is12. Of course, addition is not a trapdoor function, so it's trivially easy to reverse, which is why cryptography is its own field of knowledge.What's it for?
If I haven't completely lost you yet, you might be wondering why this matters. Who cares if I can prove that I made up a random number?
To answer this, let's consider a simple example: that of public social media posts.
Most social media platforms function by issuing credentials and verifying them based on their internal database. When you log in to your Twitter (ok, fine, X) account, you provide X with a phone number (or email) and password. X compares these records to the ones stored in the database when you created your account, and if they match they let you "log in" by issuing yet another credential, called a "session key".
Next, when you "say" something on X, you pass along your session key and your tweet to X's servers. They check that the session key is legit, and if it is they associate your tweet with your account's identity. Later, when someone wants to see the tweet, X vouches for the fact that you created it by saying "trust me" and displaying your name next to the tweet.
In other words, X creates and controls your identity, but they let you use it as long as you can prove that you know the secret that you agreed on when you registered (by giving it to them every time).
Now pretend that X gets bought by someone even more evil than Elon Musk (if such a thing can be imagined). The new owner now has the ability to control your identity, potentially making it say things that you didn't actually say. Someone could be completely banned from the platform, but their account could be made to continue saying whatever the owner of the platform wanted.
In reality, such a breach of trust would quickly result in a complete loss of credibility for the platform, which is why this kind of thing doesn't happen (at least, not that we know of).
But there are other ways of exploiting this system, most notably by censoring speech. As often happens, platforms are able to confiscate user identities, leaving the tenant no recourse except to appeal to the platform itself (or the government, but that doesn't seem to happen for some reason - probably due to some legalese in social platforms' terms of use). The user has to start completely from scratch, either on the same platform or another.
Now suppose that when you signed up for X instead of simply telling X your password you made up a random number and provided a cryptographic proof to X along with your public key. When you're ready to tweet (there's no need to issue a session key, or even to store your public key in their database) you would again prove your ownership of that key with a new piece of data. X could then publish that tweet or not, along with the same proof you provided that it really came from you.
What X can't do in this system is pretend you said something you didn't, because they don't know your private key.
X also wouldn't be able to deplatform you as effectively either. While they could choose to ban you from their website and refuse to serve your tweets, they don't control your identity. There's nothing they can do to prevent you from re-using it on another platform. Plus, if the system was set up in such a way that other users followed your key instead of an ID made up by X, you could switch platforms and keep your followers. In the same way, it would also be possible to keep a copy of all your tweets in your own database, since their authenticity is determined by your digital signature, not X's "because I say so".
This new power is not just limited to social media either. Here are some other examples of ways that self-issued cryptographic identites transform the power dynamic inherent in digital platforms:
- Banks sometimes freeze accounts or confiscate funds. If your money was stored in a system based on self-issued cryptographic keys rather than custodians, banks would not be able to keep you from accessing or moving your funds. This system exists, and it's called bitcoin.
- Identity theft happens when your identifying information is stolen and used to take out a loan in your name, and without your consent. The reason this is so common is because your credentials are not cryptographic - your name, address, and social security number can only be authenticated by being shared, and they are shared so often and with so many counterparties that they frequently end up in data breaches. If credit checks were authenticated by self-issued cryptographic keys, identity theft would cease to exist (unless your private key itself got stolen).
- Cryptographic keys allow credential issuers to protect their subjects' privacy better too. Instead of showing your ID (including your home address, birth date, height, weight, etc), the DMV could sign a message asserting that the holder of a given public key indeed over 21. The liquor store could then validate that claim, and your ownership of the named key, without knowing anything more about you. Zero-knowledge proofs take this a step further.
In each of these cases, the interests of the property owner, loan seeker, or customer are elevated over the interests of those who might seek to control their assets, exploit their hard work, or surveil their activity. Just as with personal privacy, freedom of speech, and Second Amendment rights the individual case is rarely decisive, but in the aggregate realigned incentives can tip the scale in favor of freedom.
Objections
Now, there are some drawbacks to digital signatures. Systems that rely on digital signatures are frequently less forgiving of errors than their custodial counterparts, and many of their strengths have corresponding weaknesses. Part of this is because people haven't yet developed an intuition for how to use cryptographic identities, and the tools for managing them are still being designed. Other aspects can be mitigated through judicious use of keys fit to the problems they are being used to solve.
Below I'll articulate some of these concerns, and explore ways in which they might be mitigated over time.
Key Storage
Keeping secrets is hard. "A lie can travel halfway around the world before the truth can get its boots on", and the same goes for gossip. Key storage has become increasingly important as more of our lives move online, to the extent that password managers have become almost a requirement for keeping track of our digital lives. But even with good password management, credentials frequently end up for sale on the dark web as a consequence of poorly secured infrastructure.
Apart from the fact that all of this is an argument for cryptographic identities (since keys are shared with far fewer parties), it's also true that the danger of losing a cryptographic key is severe, especially if that key is used in multiple places. Instead of hackers stealing your Facebook password, they might end up with access to all your other social media accounts too!
Keys should be treated with the utmost care. Using password managers is a good start, but very valuable keys should be stored even more securely - for example in a hardware signing device. This is a hassle, and something additional to learn, but is an indispensable part of taking advantage of the benefits associated with cryptographic identity.
There are ways to lessen the impact of lost or stolen secrets, however. Lots of different techniques exist for structuring key systems in such a way that keys can be protected, invalidated, or limited. Here are a few:
- Hierarchical Deterministic Keys allow for the creation of a single root key from which multiple child keys can be generated. These keys are hard to link to the parent, which provides additional privacy, but this link can also be proven when necessary. One limitation is that the identity system has to be designed with HD keys in mind.
- Key Rotation allows keys to become expendable. Additional credentials might be attached to a key, allowing the holder to prove they have the right to rotate the key. Social attestations can help with the process as well if the key is embedded in a web of trust.
- Remote Signing is a technique for storing a key on one device, but using it on another. This might take the form of signing using a hardware wallet and transferring an SD card to your computer for broadcasting, or using a mobile app like Amber to manage sessions with different applications.
- Key sharding takes this to another level by breaking a single key into multiple pieces and storing them separately. A coordinator can then be used to collaboratively sign messages without sharing key material. This dramatically reduces the ability of an attacker to steal a complete key.
Multi-Factor Authentication
One method for helping users secure their accounts that is becoming increasingly common is "multi-factor authentication". Instead of just providing your email and password, platforms send a one-time use code to your phone number or email, or use "time-based one time passwords" which are stored in a password manager or on a hardware device.
Again, MFA is a solution to a problem inherent in account-based authentication which would not be nearly so prevalent in a cryptographic identity system. Still, theft of keys does happen, and so MFA would be an important improvement - if not for an extra layer of authentication, then as a basis for key rotation.
In a sense, MFA is already being researched - key shards is one way of creating multiple credentials from a single key. However, this doesn't address the issue of key rotation, especially when an identity is tied to the public key that corresponds to a given private key. There are two possible solutions to this problem:
- Introduce a naming system. This would allow identities to use a durable name, assigning it to different keys over time. The downside is that this would require the introduction of either centralized naming authorities (back to the old model), or a blockchain in order to solve Zooko's trilemma.
- Establish a chain of keys. This would require a given key to name a successor key in advance and self-invalidate, or some other process like social recovery to invalidate an old key and assign the identity to a new one. This also would significantly increase the complexity of validating messages and associating them with a given identity.
Both solutions are workable, but introduce a lot of complexity that could cause more trouble than it's worth, depending on the identity system we're talking about.
Surveillance
One of the nice qualities that systems based on cryptographic identities have is that digitally signed data can be passed through any number of untrusted systems and emerge intact. This ability to resist tampering makes it possible to broadcast signed data more widely than would otherwise be the case in a system that relies on a custodian to authenticate information.
The downside of this is that more untrusted systems have access to data. And if information is broadcast publicly, anyone can get access to it.
This problem is compounded by re-use of cryptographic identities across multiple contexts. A benefit of self-issued credentials is that it becomes possible to bring everything attached to your identity with you, including social context and attached credentials. This is convenient and can be quite powerful, but it also means that more context is attached to your activity, making it easier to infer information about you for advertising or surveillance purposes. This is dangerously close to the dystopian ideal of a "Digital ID".
The best way to deal with this risk is to consider identity re-use an option to be used when desirable, but to default to creating a new key for every identity you create. This is no worse than the status quo, and it makes room for the ability to link identities when desired.
Another possible approach to this problem is to avoid broadcasting signed data when possible. This could be done by obscuring your cryptographic identity when data is served from a database, or by encrypting your signed data in order to selectively share it with named counterparties.
Still, this is a real risk, and should be kept in mind when designing and using systems based on cryptographic identity. If you'd like to read more about this, please see this blog post.
Making Keys Usable
You might be tempted to look at that list of trade-offs and get the sense that cryptographic identity is not for mere mortals. Key management is hard, and footguns abound - but there is a way forward. With nostr, some new things are happening in the world of key management that have never really happened before.
Plenty of work over the last 30 years has gone into making key management tractable, but none have really been widely adopted. The reason for this is simple: network effect.
Many of these older key systems only applied the thinnest veneer of humanity over keys. But an identity is much richer than a mere label. Having a real name, social connections, and a corpus of work to attach to a key creates a system of keys that humans care about.
By bootstrapping key management within a social context, nostr ensures that the payoff of key management is worth the learning curve. Not only is social engagement a strong incentive to get off the ground, people already on the network are eager to help you get past any roadblocks you might face.
So if I could offer an action item: give nostr a try today. Whether you're in it for the people and their values, or you just want to experiment with cryptographic identity, nostr is a great place to start. For a quick introduction and to securely generate keys, visit njump.me.
Thanks for taking the time to read this post. I hope it's been helpful, and I can't wait to see you on nostr!
-
 @ e39d100f:d27602e5
2025-04-22 11:33:15
@ e39d100f:d27602e5
2025-04-22 11:33:15Em um cenário cada vez mais conectado, a 9NBet surge como uma plataforma que sabe unir emoção e tecnologia de forma inteligente. Com foco total no usuário, a empresa oferece uma experiência completa para quem busca diversão digital com seriedade e inovação.
O primeiro ponto que merece destaque é o cuidado com a experiência do usuário. A navegação na 9NBet é fluida, com design responsivo e menus claros. Seja no desktop ou no celular, é fácil acessar os jogos, conferir promoções ou entrar em contato com o suporte.
Falando em jogos, o catálogo da 9nbet é robusto e diversificado. Há desde os tradicionais jogos de mesa até slots modernos com animações envolventes e recursos especiais. Os títulos são fornecidos por estúdios renomados, garantindo alta qualidade visual e excelente jogabilidade.
Outro ponto forte são os jogos com transmissão ao vivo. Com apresentadores reais e interações em tempo real, essa modalidade cria uma experiência mais dinâmica e autêntica, ideal para quem busca algo além do comum.
Mas a 9NBet não se destaca apenas pela diversão. A segurança da plataforma é levada a sério, com proteção de dados por criptografia e sistemas antifraude. Os métodos de pagamento são variados e adaptados ao público brasileiro, incluindo Pix e carteiras digitais, garantindo agilidade nas transações.
Para completar, a plataforma oferece bônus generosos e promoções semanais que valorizam tanto novos usuários quanto jogadores frequentes. Há também um programa de fidelidade com vantagens exclusivas para quem joga com regularidade.
O suporte ao cliente é outro diferencial. A equipe está sempre disponível, pronta para resolver qualquer situação com profissionalismo e rapidez. O atendimento em português facilita ainda mais a comunicação e a resolução de problemas.
Com uma proposta inovadora, jogos variados e atendimento de alto nível, a 9NBet se consolida como uma das melhores opções de entretenimento online no Brasil. É a combinação perfeita entre emoção, tecnologia e confiança.
-
 @ a296b972:e5a7a2e8
2025-04-17 23:08:50
@ a296b972:e5a7a2e8
2025-04-17 23:08:50Die Figuren in der Koalition der Willigen entlarven ihre charakterliche Ungeeignetheit für politische Ämter mit Verantwortung für ganze Nationen. Staatliche Entscheidungen dürfen nicht emotionsgesteuert sein. Aber genau das ist derzeit der Fall. Überall wird mit der Moralkeule um sich gehauen. Erwachsene benehmen sich wie im Kindergarten und zeigen ihre fehlende Reife. Von menschlicher Größe ganz zu schweigen.
Bisher war es schön warm unter den Fittichen der USA. Deutschland hat aufgrund seiner Geschichte besonders gut den Nick-August gespielt und sich selbst eine Souveränität vorgelogen, die es so nie gegeben hat. Jetzt sieht es so aus, als wollten die USA Europa in die Freiheit, in die Volljährigkeit entlassen. Es könnte auch sein, dass die USA aus der NATO austreten und sich vor allem um sich selbst kümmern. Allein das würde die Welt schon wesentlich friedlicher machen, denkt man beispielsweise an den Einmarsch in den Irak. Es gehen Gerüchte um, dass Truppen aus Rumänien und Deutschland abgezogen werden sollen.
Vielleicht geht es bei den Friedensverhandlungen zwischen Trump und Putin nicht nur um die Ukraine, sondern, wenn man schon mal dabei ist, auch um die Kräfteverteilung in Europa insgesamt. Waffeneinsätze in der Ukraine wurden maßgeblich von Wiesbaden aus gesteuert. 2026 sollen dort US-Mittelstrecken-Raketen stationiert werden. Der an Führungsstärke kleinste Kanzler der Bundesrepublik, Scholz, hat das brav abgenickt. Der nur noch durch ein Wunder zu verhindernde neue Kanzler, das Glas Gewürzgurken aus dem Sauerland, provoziert Russland mit seiner Ankündigung zu den Taurus-Raketen dafür um so mehr. Da ist man schon fast gewillt, sich den Scholz zurückzuwünschen, als das kleinere Übel.
Statt mit Besonnenheit und Vernunft die veränderte Sicherheitslage mit den USA als eher abtrünnige Schutzmacht neu zu bewerten, hierin auch eine Chance zu sehen, eine starke Botschaft und den Willen auf ein friedliches neues Miteinander in den Fokus zu stellen, reagieren die meisten europäischen politischen „Spitzenkräfte“ mit blindem Aktionismus, der weltenbrandgefährlich ist. Und Deutschland, dass es sich aufgrund seiner Geschichte am wenigsten erlauben könnte, macht mit von der Leyen in Brüssel und Merz, Pistorius und anderen Kriegs-Warm-Uppern am weitesten das Maul auf, obwohl es sich am bedecktesten halten sollte.
Angesichts der Tatsache, dass Europa gegenüber einer Atommacht wie Russland vollkommen wehrlos ist, wäre es wirklich viel gescheiter, sich der neuen Situation anzupassen und ständig Signale der Friedensbereitschaft zu senden. Unterstütz von den Briten und Franzosen schmiegt Brüssel eine Koalition der Friedensuntüchtigen, wie sie Uwe Froschauer aktuell in seinem Buch „Die Friedensuntüchtigen“ beschreibt. In der Rezension von mir gibt es auch einen Link zu einem Review des Inhalts:
https://wassersaege.com/blogbeitraege/buchrezension-die-friedensuntuechtigen-von-uwe-froschauer/
Stattdessen passiert das Gegenteil.
Es ist nicht nur legitim, sondern sogar Aufgabe der einzelnen Staaten, eine gewisse Verteidigungsfähigkeit aufbauen zu wollen. Derzeit geschieht das jedoch unter falschen Vorzeichen. Die NATO, als sogenanntes Verteidigungsbündnis zur Vorlage zu nehmen, wäre keine gute Idee, weil sie sich mangels Gelegenheit (der Verteidigung) eher als das Gegenteil herausgestellt hat, wie man seinerzeit in Jugoslawien erleben musste.
Russland als Feind hochzustilisieren, um ein Aufrüsten zu beschleunigen, ist jedoch der denkbar falscheste Weg. Wenn ein Yorkshire-Terrier einen Pit-Bull ankläfft, könnte das fatale Folgen haben. Wenn die europäischen „Geistesgrößen“ bei Verstand wären und in der Lage, die Realität richtig einzuschätzen, würden sie das erkennen.
Woher kommt die Überheblichkeit, woher die Unfähigkeit zur Einschätzung der Lage, woher die Realitätsverweigerung? Ist das gewollt, steckt ein Plan dahinter oder sind „die“ einfach „nur“ strunzendoof? Letzteres wäre die gefährlichste Variante.
Es stellt sich immer mehr heraus, dass Corona offensichtlich ein Test war, wie weit die Menschen in ihrer Obrigkeitshörigkeit zu treiben sind. Wie dumm und gefolgsam sind die Schafe wirklich?
Bei einer Lieferung von Taurus-Raketen, die von Deutschen gesteuert werden müssen, könnte es vielleicht gelingen, die Krim-Brücke zu zerstören. Den Kriegsverlauf würde das jedoch nicht beeinflussen. Russland gewinnt so oder so. Im Gegenteil, die Folgen für Deutschland würden den dort möglicherweise angerichteten Schaden bei weitem übertreffen.
Während ich schreibe kommt gerade auf RT DE (aufgrund der „Pressefreiheit“ verzichtet man derzeit offiziell auf diesen Sender) folgende Meldung rein: Russisches Außenministerium: Taurus-Einsatz bedeutet deutsche Kriegsbeteiligung.
https://rtde.site/international/242696-russisches-aussenministerium-taurus-einsatz-bedeutet/
Es ist nicht nachvollziehbar, dass Merz offensichtlich nicht in der Lage ist anzuerkennen, dass Russland über Oreschnik-Raketen verfügt. Er scheint nicht in der Lage zu sein, die möglichen Folgen einschätzen zu können. Genau so wenig wie Pistorius. Die beiden kommen einem vor, wie zwei, die sich im stockfinsteren Wald verirrt haben und sich gegenseitig Mut zusprechen.
Nach wie vor gibt es keine fundierten Beweise dafür, dass Russland die Absicht hat, Deutschland auf unschöne Weise bereisen zu wollen. Das kann nicht oft genug gesagt werden.
Wie schon vor dem Ukraine-Konflikt, durch ein ständiges mit der NATO-Osterweiterung Russland-immer-näher-auf-die-Pelle-rücken, streut jetzt Europa, Deutschland, der Kriegskanzler Salz in die Wunde und Russland sagt ständig: Stoy, so geht das nicht!
Wenn wir eine Bedrohungslage haben, dann die, dass das aktuelle Regime den Deutschen in seinem Wehrwahn mit Wehrpflicht und einer bevorstehenden russischen Invasion droht, obwohl es, man kann es wirklich nicht oft genug sagen, keine reale Bedrohung durch Russland gibt.
In einem Interview im deutschen Propaganda-Funk faselt Pistorius davon, dass in einem „Schnuppercamp der Bundesmarine“ in Kiel für Teenager ab 16 Jahre, er gar nichts Verwerfliches daran finden kann. „Die schießen ja nicht…“, „Wir bringen ihnen ja nicht das Töten bei mit 17, sondern wir bereiten sie vor auf eine Ausbildung zum Soldaten. Und Soldat ist ein sehr ehrenwerter Beruf, der nämlich dazu dient, unsere Freiheit und Sicherheit im Ernstfall zu verteidigen.“ Dass diese Verteidigung tödlich enden kann, wird hier verschwiegen. Das könnte schließlich Teile der Soldaten verunsichern.
Ein Politikwissenschaftler regt sich über den Titel eines Liedes auf:
-Da stört sich doch tatsächlich jemand an der Liedzeile „Meine Söhne geb‘ ich nicht“-
https://www.nachdenkseiten.de/?p=131733
Man hat das Gefühl, dass alle Politiker, statt wie Obelix in den Zaubertrank, in ein Fass Teflon-Lack gefallen sind. Anders ist es nicht zu erklären, warum die Realität so perfekt an ihnen abperlt.
Wir werden immer mehr in die Enge getrieben. Und man weiß nicht, was im Zuge der digitalisierten Überwachung, die auch in Russland kräftig Fahrt aufnimmt, zwischen den USA und Russland sonst noch ausgehandelt wird. Auch, wenn Vance derzeit von UK-Premier Keir Starmer fordert, er müsse die Gesetze gegen „Hassrede“ aufheben, um ein Handelsabkommen mit den USA zu erzielen, und das eine Vorankündigung auf die Verhandlungen mit der EU sein könnte, (Bedingung: Abschaffung des Digital Services Act). In den USA gibt es Tech-Giganten, wie Musk und Thiel und Konsorten, die mit Umlegen eines Schalters, den derzeit augenscheinlichen Kampf für Meinungsfreiheit und Freiheit der Bürger, im Handumdrehen ins Gegenteil verqueren können. Dann sind wir in Null Komma Nichts in der Versklavung mit einem Totalitarismus und einer Technokratie gelandet, in der sich Georg Orwells „1984“ wie eine Gute-Nacht-Geschichte für kleine Kinder anhört.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
-
 @ 866e0139:6a9334e5
2025-04-21 06:47:57
@ 866e0139:6a9334e5
2025-04-21 06:47:57Autor: Milosz Matuschek. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Sie wollen die neuesten Pareto-Artikel auf einen Blick sehen (Friedenstaube & Co.), um nichts mehr zu verpassen?* Hier geht es zu unserem Telegram-Kanal.***
An Ostern begehen Christen das Hochamt ewiger Ideale. In Kirchen, die zu Hochzeiten der Pandemie geschlossen, später für Impfkampagnen wieder geöffnet wurden, wird der Sieg des Lebens über den Tod beschworen. Der Aufstand des Geistes gegen die Materie. Doch wie steht es um die Revolte des Geistes in einer Welt, die den Menschen zunehmend in die Rolle eines verwalteten Tieres drängt?
Die Revolte der Normalen
Albert Camus, einer der klarsten Köpfe des 20. Jahrhunderts, wusste: Nur wer an etwas glaubt, revoltiert. Der Revoltierende sagt Nein zu Unterdrückung und Ja zur Würde. Ohne Glauben an Werte vergiftet sich der Mensch am Ressentiment – jener toten Emotion, die weder schöpft noch heilt, sondern nur vernichtet. Oder versinkt im Nihilismus. Dieser greift auch heute um sich. Deutschland, deine Leuchttürme sind Irrlichter geworden. Inmitten einer Dauerkrise, die jeden Normalzustand zersetzt, bleibt eine Frage offen: Wie gesund bleibt der Mensch in einem kranken System? Wie lange dauert es, bis Normalität selbst als Revolte gilt?
Camus schrieb:
„Wenn man an nichts glaubt, wenn nichts Sinn hat und wir keinen Wert konstatieren können, dann ist alles möglich und nichts hat Bedeutung.“
In einer Welt, in der Gesundheitspolitik zur Farce, Wissenschaft zur Ideologie und Aufarbeitung zur Fortsetzung der Propaganda mutiert, wird die Revolte der Normalen zur letzten Verteidigungslinie der Freiheit.
https://www.youtube.com/watch?v=Y2roiEvbPuU
Das Leid der Revoltierenden
Die Revolte ist kein Spaziergang. Sie schmerzt. Sie kostet Freunde, Ansehen, Karriere. Aber sie schenkt eine ungeahnte Kraft: Die Entdeckung, dass der Impuls zum Leben stärker ist als zum Tod. Das Wunder von Ostern, die Auferstehung, ist im Innersten die Revolte der Lebendigkeit gegen die Herrschaft des Todes. Der Märtyrer Jesus nimmt die Sünden und Leiden der Welt auf sich – ein menschgewordener Widerstand, der durch seine Hingabe unsterblich wird.
Sein "Verbrechen"? Er stellte sich zugleich gegen die geistige und politische Elite seiner Zeit. Gegen Besatzer, Schriftgelehrte, Pharisäer, Frühbürger. Heute wäre Jesus wohl ein Querdenker, ein Reichgottesbürger, ein Verschwörungstheoretiker. Mindestens ein Rechter. Vielleicht ein antisemitischer Spinner, der es wagte, eine Alternative zum bestehenden Glaubenssystem zu etablieren.
„Wer an mich glaubt, wird leben“, sagte Jesus. Man kann es so lesen:\ Wer an die verkörperten Werte glaubt – Wahrheit, Freiheit, Liebe –, wird leben. Denn wer an einen Wert glaubt, macht ihn lebendig. Der Nihilist hingegen fügt sich ein, wird Stein in der Mauer des Systems.
Camus brachte es auf den Punkt:
„Lieber stehend sterben als knieend leben.“
In Zeiten, in denen Friedenstreiber als Nazis diffamiert werden und Protestierende als Pathologische gelten, bleibt die stille Revolte des Individuums das letzte unzerstörbare Element.
Die Psy-Op der Aufarbeitung
Nach der Inszenierung des Corona-Spektakels erleben wir die nächste Bühne: Die Aufarbeitung durch die Täter selbst. Eine theatralische Umarmung des eigenen Versagens, mit Bundesverdienstkreuz und Download-Gesichtsausdruck bei Frau Buyx inklusive. Wenn Corona eine Psy-Op war, warum sollte nicht auch seine Aufarbeitung Teil der Psy-Op sein? Die Strukturen erinnern an Rosenhan, Milgram und das Stanford Prison Experiment:
- Etikettierung der Kritiker als Verrückte.
- Pathologisierung der Revolte als Krankheit.
- Belohnung der Kollaborateure mit Orden und Posten.
Ein Lehrbuch der totalitären Psychologie.
https://www.youtube.com/watch?v=XTBYWPLXrTk
Immunologische Reaktionen eines sterbenden Systems
Während die Panzer-Osterhasen rollen, also die Neuvariante des Impfspritzbesteck-Gebäcks der letzten Krise, offenbart sich die Wahrheit: Das System hat seine eigene Bevölkerung beschossen. Friendly Fire unter falscher Flagge.\ Kollateralschaden im Namen von Volksgesundheit und Solidarität.

Jetzt dasselbe nochmal in Tarnfleck statt Weißkittel.
Was bleibt?
Demut.\ Selbstständigkeit.\ Verbindungen, die nicht von Zertifikaten abhängen.\ Der stille Aufbau von Netzwerken jenseits der Anstaltsordnung.
Unabhängiger machen kann man sich zum Beispiel bei Vorträgen und Seminaren von Michael Ballweg, der immer noch in einen kafkaesken Prozess verwickelt ist.
Meine Stimme erhebe ich in Zukunft auch mit der FSUS (Free Speech Union Switzerland) im Rücken, einem Verein der u.a. Rechtshilfe für verfolgte Freiredner organisiert. Bei Interesse an einer Mitgliedschaft erfahren Sie hier mehr.
Oder wie manche sagen: “Buy Bitcoin and focus on your craft.”
Die letzte Revolte
Wer heute zweifelt, beweist Charakter.\ Wer heute fragt, zeigt Rückgrat.\ Wer heute eigene Gedanken wagt, revoltiert bereits.
Wenn wir uns verbinden, werden wir das neue Gesicht der Welt.
Ostern erinnert uns daran:\ Die größte Revolte ist das Aufstehen in einer Welt, die uns niederdrücken will.
Nicht die angepasstesten überleben, sondern die Standhaftesten.\ Nicht die Lautesten, sondern die Wahrhaftigsten.\ Nicht die, die folgen, sondern die, die aufstehen.
In diesem Sinne:
Frohe Auferstehung.
https://www.youtube.com/watch?v=vbH9YacSi2o
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ f839fb67:5c930939
2025-04-16 21:07:13
@ f839fb67:5c930939
2025-04-16 21:07:13Relays
| Name | Address | Price (Sats/Year) | Status | | - | - | - | - | | stephen's aegis relay | wss://paid.relay.vanderwarker.family | 42069 |
| | stephen's Outbox | wss://relay.vanderwarker.family | Just Me |
| | stephen's Inbox | wss://haven.vanderwarker.family/inbox | WoT |
| | stephen's DMs | wss://haven.vanderwarker.family/chat | WoT |
| | VFam Data Relay | wss://data.relay.vanderwarker.family | 0 |
| | VFam Bots Relay | wss://skeme.vanderwarker.family | Invite |
| | VFGroups (NIP29) | wss://groups.vanderwarker.family | 0 |
| | [TOR] My Phone Relay | ws://naswsosuewqxyf7ov7gr7igc4tq2rbtqoxxirwyhkbuns4lwc3iowwid.onion | 0 | Meh... |
My Pubkeys
| Name | hex | nprofile | | - | - | - | | Main | f839fb6714598a7233d09dbd42af82cc9781d0faa57474f1841af90b5c930939 | nostr:nprofile1qqs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3us9mapfx | | Vanity (Backup) | 82f21be67353c0d68438003fe6e56a35e2a57c49e0899b368b5ca7aa8dde7c23 | nostr:nprofile1qqsg9usmuee48sxkssuqq0lxu44rtc4903y7pzvmx694efa23h08cgcpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3ussel49x | | VFStore | 6416f1e658ba00d42107b05ad9bf485c7e46698217e0c19f0dc2e125de3af0d0 | nostr:nprofile1qqsxg9h3uevt5qx5yyrmqkkehay9cljxdxpp0cxpnuxu9cf9mca0p5qpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3usaa8plu | | NostrSMS | 9be1b8315248eeb20f9d9ab2717d1750e4f27489eab1fa531d679dadd34c2f8d | nostr:nprofile1qqsfhcdcx9fy3m4jp7we4vn305t4pe8jwjy74v062vwk08dd6dxzlrgpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3us595d45 |
Bots
Unlocks Bot
Hex: 2e941ad17144e0a04d1b8c21c4a0dbc3fbcbb9d08ae622b5f9c85341fac7c2d0
nprofile:
nostr:nprofile1qqsza9q669c5fc9qf5dccgwy5rdu877th8gg4e3zkhuus56pltru95qpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3ust4kvak
Latest Data:
nostr:naddr1qq882mnvda3kkttrda6kuar9wgq37amnwvaz7tmnddjk6efwweskuer9wfmkzuntv4ezuenpd45kc7gzyqhfgxk3w9zwpgzdrwxzr39qm0plhjae6z9wvg44l8y9xs06clpdqqcyqqq823cgnl9u5Step Counter
Hex: 9223d2faeb95853b4d224a184c69e1df16648d35067a88cdf947c631b57e3de7
nprofile: nostr:nprofile1qqsfyg7jlt4etpfmf53y5xzvd8sa79ny356sv75gehu50333k4lrmecpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3ustswp3w
Latest Data:
nostr:naddr1qvzqqqr4gupzpy3r6tawh9v98dxjyjscf357rhckvjxn2pn63rxlj37xxx6hu008qys8wumn8ghj7umtv4kk2tnkv9hxgetjwashy6m9wghxvctdd9k8jtcqp3ehgets943k7atww3jhyn39gffRCTGuest
Hex: 373904615c781e46bf5bf87b4126c8a568a05393b1b840b1a2a3234d20affa0c
nprofile: nostr:nprofile1qqsrwwgyv9w8s8jxhadls76pymy2269q2wfmrwzqkx32xg6dyzhl5rqpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3usy92jlxNow Playing
Hex: 8096ed6ba1f21a3713bd47a503ee377b0ce2f187b3e5a3ae909a25b84901018b
nprofile: nostr:nprofile1qqsgp9hddwslyx3hzw750fgracmhkr8z7xrm8edr46gf5fdcfyqsrzcpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3uspk5v4w
Latest Data:
nostr:naddr1qq9kummh94cxccted9hxwqglwaehxw309aekketdv5h8vctwv3jhyampwf4k2u3wvesk66tv0ypzpqyka446rus6xufm63a9q0hrw7cvutcc0vl95whfpx39hpyszqvtqvzqqqr4gupdk2hd
NIP-29 Groups
- Minecraft Group Chat
nostr:naddr1qqrxvc33xpnxxqfqwaehxw309anhymm4wpejuanpdejx2unhv9exketj9enxzmtfd3usygrzymrpd2wz8ularp06y8ad5dgaddlumyt7tfzqge3vc97sgsarjvpsgqqqnpvqazypfd- VFNet Group Chat
nostr:naddr1qqrrwvfjx9jxzqfqwaehxw309anhymm4wpejuanpdejx2unhv9exketj9enxzmtfd3usygrzymrpd2wz8ularp06y8ad5dgaddlumyt7tfzqge3vc97sgsarjvpsgqqqnpvq08hx48
"Nostrified Websites"
[D] = Saves darkmode preferences over nostr
[A] = Auth over nostr
[B] = Beta (software)
[z] = zap enabled
Other Services (Hosted code)
Emojis Packs
- Minecraft
nostr:naddr1qqy566twv43hyctxwsq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82nsd0k5wp- AIM
nostr:naddr1qqxxz6tdv4kk7arfvdhkuucpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3usyg8c88akw9ze3fer85yah4p2lqkvj7qap749w360rpq6ly94eycf8ypsgqqqw48qe0j2yk- Blobs
nostr:naddr1qqz5ymr0vfesz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqa2wek4ukj- FavEmojis
nostr:naddr1qqy5vctkg4kk76nfwvq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82nsf7sdwt- Modern Family
nostr:naddr1qqx56mmyv4exugzxv9kkjmreqy0hwumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jq3qlqulkec5tx98yv7snk759tuzejtcr5865468fuvyrtuskhynpyusxpqqqp65ujlj36n- nostriches (Amethyst collection)
nostr:naddr1qq9xummnw3exjcmgv4esz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqa2w2sqg6w- Pepe
nostr:naddr1qqz9qetsv5q37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82ns85f6x7- Minecraft Font
nostr:naddr1qq8y66twv43hyctxwssyvmmwwsq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82nsmzftgr- Archer Font
nostr:naddr1qq95zunrdpjhygzxdah8gqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0ypzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqvzqqqr4fclkyxsh- SMB Font
nostr:naddr1qqv4xatsv4ezqntpwf5k7gzzwfhhg6r9wfejq3n0de6qz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqa2w0wqpuk
Git Over Nostr
- NostrSMS
nostr:naddr1qqyxummnw3e8xmtnqy0hwumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jqfrwaehxw309amk7apwwfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqyj8wumn8ghj7urpd9jzuun9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jqg5waehxw309aex2mrp0yhxgctdw4eju6t0qyxhwumn8ghj7mn0wvhxcmmvqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqaueqp0epk- nip51backup
nostr:naddr1qq9ku6tsx5ckyctrdd6hqqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yqjxamnwvaz7tmhda6zuun9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jqfywaehxw309acxz6ty9eex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yq3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k7qgdwaehxw309ahx7uewd3hkcq3qlqulkec5tx98yv7snk759tuzejtcr5865468fuvyrtuskhynpyusxpqqqpmej4gtqs6- bukkitstr
nostr:naddr1qqykyattdd5hgum5wgq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gpydmhxue69uhhwmm59eex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yqjgamnwvaz7tmsv95kgtnjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gpz3mhxue69uhhyetvv9ujuerpd46hxtnfduqs6amnwvaz7tmwdaejumr0dspzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqvzqqqrhnyf6g0n2
Market Places
Please use Nostr Market or somthing simular, to view.
- VFStore
nostr:naddr1qqjx2v34xe3kxvpn95cnqven956rwvpc95unscn9943kxet98q6nxde58p3ryqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yqjvamnwvaz7tmgv9mx2m3wweskuer9wfmkzuntv4ezuenpd45kc7f0da6hgcn00qqjgamnwvaz7tmsv95kgtnjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gpydmhxue69uhhwmm59eex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0ypzqeqk78n93wsq6sss0vz6mxl5shr7ge5cy9lqcx0smshpyh0r4uxsqvzqqqr4gvlfm7gu
Badges
Created
- paidrelayvf
nostr:naddr1qq9hqctfv3ex2mrp09mxvqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0ypzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqvzqqqr48y85v3u3- iPow
nostr:naddr1qqzxj5r02uq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82wgg02u0r- codmaster
nostr:naddr1qqykxmmyd4shxar9wgq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82wgk3gm4g- iMine
nostr:naddr1qqzkjntfdejsz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqafed5s4x5
Clients I Use
- Amethyst
nostr:naddr1qqxnzd3cx5urqv3nxymngdphqgsyvrp9u6p0mfur9dfdru3d853tx9mdjuhkphxuxgfwmryja7zsvhqrqsqqql8kavfpw3- noStrudel
nostr:naddr1qqxnzd3cxccrvd34xser2dpkqy28wumn8ghj7un9d3shjtnyv9kh2uewd9hsygpxdq27pjfppharynrvhg6h8v2taeya5ssf49zkl9yyu5gxe4qg55psgqqq0nmq5mza9n- nostrsms
nostr:naddr1qq9rzdejxcunxde4xymqz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgsfhcdcx9fy3m4jp7we4vn305t4pe8jwjy74v062vwk08dd6dxzlrgrqsqqql8kjn33qm
Lists
- Bluesky
nostr:naddr1qvzqqqr4xqpzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqqapxcat9wd4hj0ah0jw
- Fediverse
nostr:naddr1qvzqqqr4xqpzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqp9rx2erfwejhyum9j4g0xh
- Fediverse_Bots
nostr:naddr1qvzqqqr4xqpzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqperx2erfwejhyum9tapx7arnfcpdzh
- My Bots
nostr:naddr1qvzqqqr4xqpzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqz4uh5jnpwscyss24fpkxw4fewafk566twa2q8f6fyk
-
 @ 9063ef6b:fd1e9a09
2025-04-16 20:20:39
@ 9063ef6b:fd1e9a09
2025-04-16 20:20:39Bitcoin is more than just a digital currency. It’s a technological revolution built on a unique set of properties that distinguish it from all other financial systems—past and present. From its decentralized architecture to its digitally verifiable scarcity, Bitcoin represents a fundamental shift in how we store and transfer value.
A Truly Decentralized Network
As of April 2025, the Bitcoin network comprises approximately 62,558 reachable nodes globally. The United States leads with 13,791 nodes (29%), followed by Germany with 6,418 nodes (13.5%), and Canada with 2,580 nodes (5.43%). bitnodes
This distributed structure is central to Bitcoin’s strength. No single entity can control the network, making it robust against censorship, regulation, or centralized failure.

Open Participation at Low Cost
Bitcoin's design allows almost anyone to participate meaningfully in the network. Thanks to its small block size and streamlined protocol, running a full node is technically and financially accessible. Even a Raspberry Pi or a basic PC is sufficient to synchronize and validate the blockchain.
However, any significant increase in block size could jeopardize this accessibility. More storage and bandwidth requirements would shift participation toward centralized data centers and cloud infrastructure—threatening Bitcoin’s decentralized ethos. This is why the community continues to fiercely debate such protocol changes.
Decentralized Governance
Bitcoin has no CEO, board, or headquarters. Its governance model is decentralized, relying on consensus among various stakeholders, including miners, developers, node operators, and increasingly, institutional participants.
Miners signal support for changes by choosing which version of the Bitcoin software to run when mining new blocks. However, full node operators ultimately enforce the network’s rules by validating blocks and transactions. If miners adopt a change that is not accepted by the majority of full nodes, that change will be rejected and the blocks considered invalid—effectively vetoing the proposal.
This "dual-power structure" ensures that changes to the network only happen through widespread consensus—a system that has proven resilient to internal disagreements and external pressures.
Resilient by Design
Bitcoin's decentralized nature gives it a level of geopolitical and technical resilience unmatched by any traditional financial system. A notable case is the 2021 mining ban in China. While initially disruptive, the network quickly recovered as miners relocated, ultimately improving decentralization.
This event underlined Bitcoin's ability to withstand regulatory attacks and misinformation (FUD—Fear, Uncertainty, Doubt), cementing its credibility as a global, censorship-resistant network.
Self-Sovereign Communication
Bitcoin enables peer-to-peer transactions across borders without intermediaries. There’s no bank, payment processor, or centralized authority required. This feature is not only technically efficient but also politically profound—it empowers individuals globally to transact freely and securely.
Absolute Scarcity
Bitcoin is the first asset in history with a mathematically verifiable, fixed supply: 21 million coins. This cap is hard-coded into its protocol and enforced by every full node. At the atomic level, Bitcoin is measured in satoshis (sats), with a total cap of approximately 2.1 quadrillion sats.
This transparency contrasts with assets like gold, whose total supply is estimated and potentially (through third parties on paper) expandable. Moreover, unlike fiat currencies, which can be inflated through central bank policy, Bitcoin is immune to such manipulation. This makes it a powerful hedge against monetary debasement.
Anchored in Energy and Time
Bitcoin's security relies on proof-of-work, a consensus algorithm that requires real-world energy and computation. This “work” ensures that network participants must invest time and electricity to mine new blocks.
This process incentivizes continual improvement in hardware and energy sourcing—helping decentralize mining geographically and economically. In contrast, alternative systems like proof-of-stake tend to favor wealth concentration by design, as influence is determined by how many tokens a participant holds.

Censorship-Resistant
The Bitcoin network itself is inherently censorship-resistant. As a decentralized system, Bitcoin transactions consist of mere text and numerical data, making it impossible to censor the underlying protocol.
However, centralized exchanges and trading platforms can be subject to censorship through regional regulations or government pressure, potentially limiting access to Bitcoin.
Decentralized exchanges and peer-to-peer marketplaces offer alternative solutions, enabling users to buy and sell Bitcoins without relying on intermediaries that can be censored or shut down.
High Security
The Bitcoin blockchain is secured through a decentralized network of thousands of nodes worldwide, which constantly verify its integrity, making it highly resistant to hacking. To add a new block of bundled transactions, miners compete to solve complex mathematical problems generated by Bitcoin's cryptography. Once a miner solves the problem, the proposed block is broadcast to the network, where each node verifies its validity. Consensus is achieved when a majority of nodes agree on the block's validity, at which point the Bitcoin blockchain is updated accordingly, ensuring the network's decentralized and trustless nature.
Manipulation of the Bitcoin network is virtually impossible due to its decentralized and robust architecture. The blockchain's chronological and immutable design prevents the deletion or alteration of previously validated blocks, ensuring the integrity of the network.
To successfully attack the Bitcoin network, an individual or organization would need to control a majority of the network's computing power, also known as a 51% attack. However, the sheer size of the Bitcoin network and the competitive nature of the proof-of-work consensus mechanism make it extremely difficult to acquire and sustain the necessary computational power. Even if an attacker were to achieve this, they could potentially execute double spends and censor transactions. Nevertheless, the transparent nature of the blockchain would quickly reveal the attack, allowing the Bitcoin network to respond and neutralize it. By invalidating the first block of the malicious chain, all subsequent blocks would also become invalid, rendering the attack futile and resulting in significant financial losses for the attacker.
One potential source of uncertainty arises from changes to the Bitcoin code made by developers. While developers can modify the software, they cannot unilaterally enforce changes to the Bitcoin protocol, as all users have the freedom to choose which version they consider valid. Attempts to alter Bitcoin's fundamental principles have historically resulted in hard forks, which have ultimately had negligible impact (e.g., BSV, BCH). The Bitcoin community has consistently rejected new ideas that compromise decentralization in favor of scalability, refusing to adopt the resulting blockchains as the legitimate version. This decentralized governance model ensures that changes to the protocol are subject to broad consensus, protecting the integrity and trustworthiness of the Bitcoin network.
Another source of uncertainty in the future could be quantum computers. The topic is slowly gaining momentum in the community and is being discussed.
My attempt to write an article with Yakihonne. Simple editor with the most necessary formatting. Technically it worked quite well so far.
Some properties are listed in the article. Which properties are missing?
-
 @ e39d100f:d27602e5
2025-04-22 11:32:27
@ e39d100f:d27602e5
2025-04-22 11:32:27A plataforma Win2023 chegou com tudo ao mercado nacional e já está se tornando uma das favoritas entre os jogadores que valorizam qualidade, segurança e variedade. Com uma proposta moderna e transparente, ela oferece um ambiente perfeito para quem quer se divertir com emoção e responsabilidade.
Desde o início, a Win2023 impressiona pela facilidade de acesso. O site é responsivo e totalmente em português, facilitando a navegação mesmo para quem está começando. O cadastro leva apenas alguns minutos e logo após é possível explorar todos os recursos disponíveis, incluindo jogos, promoções e área de suporte.
O diferencial da plataforma começa na diversidade de opções de entretenimento. A Win2023 abriga jogos para todos os gostos: desde slots com temas inovadores e animações cativantes até mesas de jogos clássicos como roleta, blackjack e pôquer. Todos os jogos são desenvolvidos por estúdios reconhecidos, o que garante qualidade técnica e confiança nos resultados.
Além disso, a plataforma investe em atualizações constantes para oferecer sempre novidades aos seus usuários. Isso mantém o ambiente dinâmico e empolgante, com novas oportunidades surgindo a todo momento.
Outro fator que contribui para o sucesso da Win2023 é a política de bônus atrativa. Os jogadores são incentivados desde o primeiro dia com recompensas exclusivas, bônus de boas-vindas, promoções sazonais e programas de fidelidade que valorizam o comprometimento dos usuários mais ativos.
Mas a experiência não se resume aos jogos e prêmios. A segurança digital é levada muito a sério na plataforma. Todos os dados são protegidos por sistemas de criptografia modernos, e os métodos de pagamento são diversificados e confiáveis. Isso transmite ao jogador a confiança necessária para focar apenas na diversão.
O suporte ao cliente também é um ponto forte. Com atendimento ágil e cordial, a equipe da Win2023 está sempre pronta para ajudar, seja com dúvidas técnicas, questões sobre promoções ou orientações gerais. O serviço é prestado em tempo real e em português, o que facilita ainda mais a resolução de problemas.
Com tantos pontos positivos, não é surpresa que a Win2023 esteja ganhando espaço rapidamente entre os brasileiros. A combinação de inovação, diversidade de jogos, segurança e atenção ao usuário faz dela uma excelente escolha para quem quer viver uma experiência completa e gratificante no mundo dos jogos online.
-
 @ 629c4a12:f822cc1a
2025-02-23 21:33:31
@ 629c4a12:f822cc1a
2025-02-23 21:33:31I’ve always been drawn to minimalism. There’s a certain peace that comes from stripping away the unnecessary, decluttering both physical and mental spaces. Yet, when it comes to finances, I’ve found myself tangled in complexity. As an ‘optimizer,’ I spend an inordinate amount of time thinking about investments, managing risk, and endlessly tinkering with my portfolio. This preoccupation contradicts the minimalist principles I try to live by.
It seems absurd to me that the financial world has become so complicated that we need money managers to simply preserve the value of our money. If investing is so intricate that the average person must hire professionals just to preserve (let alone grow) the value of their savings, then something is fundamentally wrong.
For the past five years, I’ve immersed myself in the history and mechanics of financial systems. The deeper I delved, the clearer it became: Bitcoin is a force of minimalism in an increasingly financialized and complex world.
The Clutter of Modern Finance
Our financial system has become bloated with complexity. The hyper-securitization of assets has created an environment filled with financial clutter. Derivatives, for example, represent layers upon layers of financial engineering, often so convoluted that even experts struggle to understand them fully.
More troubling is the way nearly everything of value has been financialized. Real estate and art, two things that should embody personal value and cultural significance, have been transformed into mere asset classes. They are bought, sold, and speculated upon not for their intrinsic qualities but as instruments in the game of wealth preservation.
But why has this happened? It’s actually quite simple: our money is constantly losing value. The dollar, for example, debases at a rate of around 7% per year. Holding cash feels like holding melting ice, so it’s only natural for people to seek out scarce assets to preserve their wealth. The Never-Ending Game of Diversification
This pursuit of scarce assets sets off a complex game—a game that forces people to diversify endlessly:
- Equities
- Bonds
- Real Estate
- Commodities
- Art
- Collectibles
We’re told to spread our investments across these asset classes to mitigate risk and preserve our hard-earned money. Those who can afford to hire money managers generally fare better in this game, as they have access to expertise and strategies designed to navigate this maze of complexity.
Ironically, this system creates an incentive for more complexity. The more convoluted the financial landscape becomes, the more we need money managers, and the more entrenched this cycle of financialization and securitization becomes. It’s a force of ever-increasing entropy—quite the opposite of minimalism.
Bitcoin: Simplicity in a Complex World
In the midst of this financial chaos, Bitcoin emerges as a beacon of simplicity. It offers a way out of the clutter, a chance to reclaim financial minimalism. Bitcoin embodies the concept of scarcity with a rare kind of perfection: there will only ever be 21 million Bitcoins. No more.
This scarcity makes Bitcoin the perfect savings technology. Unlike traditional currencies, no one can debase your holdings. You don’t need to chase after real estate, art, or other assets to preserve your wealth. You don’t need to constantly diversify and rebalance a portfolio to stay ahead of inflation. Bitcoin’s scarcity gives you a way to hold your wealth securely, without the need for endless tinkering.
I’m not blind to Bitcoin’s short-term price volatility. However, it’s crucial to understand that we’re still in the early stages of adoption. As more people embrace this perfect form of scarcity, Bitcoin’s qualities as savings technology will express itself.
Bitcoin has the potential to de-financialize the housing market. It can de-financialize art.
Ultimately, Bitcoin has the power to replace those aspects of our lives that currently serve as proxies for scarcity.
A Minimalist Approach to Wealth
Bitcoin allows us to step off the treadmill of constant financial optimization. It offers a simpler way to safeguard the fruits of our labor. Rather than spending our time, energy, and attention on navigating a complex financial system, we can focus on what truly matters: living a meaningful life.
By embracing Bitcoin, we embrace a minimalist approach to wealth. We reject the idea that we must play a never-ending game of diversification to maintain our standard of living. Instead, we adopt a simple, elegant solution that aligns with the principles of minimalism.
Conclusion
In a world that grows more financially cluttered by the day, Bitcoin stands as a path to financial minimalism. It frees us from the complexities of traditional finance, allowing us to preserve our wealth without the need for constant vigilance and management.
By embodying scarcity and simplicity, Bitcoin gives us a way to reclaim our time and energy. It’s not just a financial tool; it’s a way to simplify our lives, to step back from the chaos, and to focus on what truly matters
-
 @ 0d97beae:c5274a14
2025-01-11 16:52:08
@ 0d97beae:c5274a14
2025-01-11 16:52:08This article hopes to complement the article by Lyn Alden on YouTube: https://www.youtube.com/watch?v=jk_HWmmwiAs
The reason why we have broken money
Before the invention of key technologies such as the printing press and electronic communications, even such as those as early as morse code transmitters, gold had won the competition for best medium of money around the world.
In fact, it was not just gold by itself that became money, rulers and world leaders developed coins in order to help the economy grow. Gold nuggets were not as easy to transact with as coins with specific imprints and denominated sizes.
However, these modern technologies created massive efficiencies that allowed us to communicate and perform services more efficiently and much faster, yet the medium of money could not benefit from these advancements. Gold was heavy, slow and expensive to move globally, even though requesting and performing services globally did not have this limitation anymore.
Banks took initiative and created derivatives of gold: paper and electronic money; these new currencies allowed the economy to continue to grow and evolve, but it was not without its dark side. Today, no currency is denominated in gold at all, money is backed by nothing and its inherent value, the paper it is printed on, is worthless too.
Banks and governments eventually transitioned from a money derivative to a system of debt that could be co-opted and controlled for political and personal reasons. Our money today is broken and is the cause of more expensive, poorer quality goods in the economy, a larger and ever growing wealth gap, and many of the follow-on problems that have come with it.
Bitcoin overcomes the "transfer of hard money" problem
Just like gold coins were created by man, Bitcoin too is a technology created by man. Bitcoin, however is a much more profound invention, possibly more of a discovery than an invention in fact. Bitcoin has proven to be unbreakable, incorruptible and has upheld its ability to keep its units scarce, inalienable and counterfeit proof through the nature of its own design.
Since Bitcoin is a digital technology, it can be transferred across international borders almost as quickly as information itself. It therefore severely reduces the need for a derivative to be used to represent money to facilitate digital trade. This means that as the currency we use today continues to fare poorly for many people, bitcoin will continue to stand out as hard money, that just so happens to work as well, functionally, along side it.
Bitcoin will also always be available to anyone who wishes to earn it directly; even China is unable to restrict its citizens from accessing it. The dollar has traditionally become the currency for people who discover that their local currency is unsustainable. Even when the dollar has become illegal to use, it is simply used privately and unofficially. However, because bitcoin does not require you to trade it at a bank in order to use it across borders and across the web, Bitcoin will continue to be a viable escape hatch until we one day hit some critical mass where the world has simply adopted Bitcoin globally and everyone else must adopt it to survive.
Bitcoin has not yet proven that it can support the world at scale. However it can only be tested through real adoption, and just as gold coins were developed to help gold scale, tools will be developed to help overcome problems as they arise; ideally without the need for another derivative, but if necessary, hopefully with one that is more neutral and less corruptible than the derivatives used to represent gold.
Bitcoin blurs the line between commodity and technology
Bitcoin is a technology, it is a tool that requires human involvement to function, however it surprisingly does not allow for any concentration of power. Anyone can help to facilitate Bitcoin's operations, but no one can take control of its behaviour, its reach, or its prioritisation, as it operates autonomously based on a pre-determined, neutral set of rules.
At the same time, its built-in incentive mechanism ensures that people do not have to operate bitcoin out of the good of their heart. Even though the system cannot be co-opted holistically, It will not stop operating while there are people motivated to trade their time and resources to keep it running and earn from others' transaction fees. Although it requires humans to operate it, it remains both neutral and sustainable.
Never before have we developed or discovered a technology that could not be co-opted and used by one person or faction against another. Due to this nature, Bitcoin's units are often described as a commodity; they cannot be usurped or virtually cloned, and they cannot be affected by political biases.
The dangers of derivatives
A derivative is something created, designed or developed to represent another thing in order to solve a particular complication or problem. For example, paper and electronic money was once a derivative of gold.
In the case of Bitcoin, if you cannot link your units of bitcoin to an "address" that you personally hold a cryptographically secure key to, then you very likely have a derivative of bitcoin, not bitcoin itself. If you buy bitcoin on an online exchange and do not withdraw the bitcoin to a wallet that you control, then you legally own an electronic derivative of bitcoin.
Bitcoin is a new technology. It will have a learning curve and it will take time for humanity to learn how to comprehend, authenticate and take control of bitcoin collectively. Having said that, many people all over the world are already using and relying on Bitcoin natively. For many, it will require for people to find the need or a desire for a neutral money like bitcoin, and to have been burned by derivatives of it, before they start to understand the difference between the two. Eventually, it will become an essential part of what we regard as common sense.
Learn for yourself
If you wish to learn more about how to handle bitcoin and avoid derivatives, you can start by searching online for tutorials about "Bitcoin self custody".
There are many options available, some more practical for you, and some more practical for others. Don't spend too much time trying to find the perfect solution; practice and learn. You may make mistakes along the way, so be careful not to experiment with large amounts of your bitcoin as you explore new ideas and technologies along the way. This is similar to learning anything, like riding a bicycle; you are sure to fall a few times, scuff the frame, so don't buy a high performance racing bike while you're still learning to balance.
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ 7d33ba57:1b82db35
2025-04-22 08:35:57
@ 7d33ba57:1b82db35
2025-04-22 08:35:57Nestled in Lower Saxony’s East Frisia region, Leer is a charming canal town known for its historic tea culture, maritime heritage, and postcard-worthy Altstadt (Old Town). With colorful gabled houses, cobbled streets, and a relaxed pace, Leer offers a taste of northern Germany’s quiet beauty—without the crowds.
🏘️ Things to See & Do in Leer
🚶♂️ Altstadt (Old Town)
- Stroll through narrow lanes lined with 17th and 18th-century houses
- Highlights include Waageplatz, the Reformed Church, and Evenburg Castle
- Perfect for a slow wander, especially during golden hour
🛶 Canal Walks & Harbor
- Take a peaceful walk along the Leda and Ems rivers
- Watch boats pass through the small port and historic trading canals
- In summer, you can even book a scenic canal cruise
🍵 East Frisian Tea Culture
- Leer is considered the tea capital of Germany
- Visit the Bünting Teemuseum to learn about the centuries-old tea tradition
- Don’t miss a tea session with rock sugar and cream—served the traditional East Frisian way
🌳 Nature Nearby
- Cycle or walk through the flat green landscapes of East Frisia
- Great routes along rivers and meadows, with plenty of windmills and grazing sheep
- A short drive takes you to the Wadden Sea, a UNESCO site and tidal wonder
🍽️ Local Eats
- Sample Matjes (pickled herring), smoked fish, and hearty stews
- East Frisian cakes pair beautifully with black tea
- Cozy inns and riverside cafés make for a warm, welcoming meal
🚆 Getting There
- Easily accessible by train from Bremen or Emden
- Compact and walkable—no car needed in the town center
Leer is a peaceful, picturesque retreat where canals, culture, and comfort flow together. Whether you're cycling through the countryside or sipping tea by the harbor, it’s a place to unwind and soak up the slow life.
-
 @ dfa02707:41ca50e3
2025-04-16 14:36:00
@ dfa02707:41ca50e3
2025-04-16 14:36:00Contribute to keep No Bullshit Bitcoin news going.

Good morning! The GM report is now back on track, and for those wondering where it was... well... it was delayed.
0:00
/0:41
1×
Headlines
- Bitcoin mining centralization in 2025. According to a blog post by b10c, Bitcoin mining was at its most decentralized in May 2017, with another favorable period from 2019 to 2022. However, starting in 2023, mining has become increasingly centralized, particularly due to the influence of large pools like Foundry and the use of proxy pooling by entities such as AntPool.
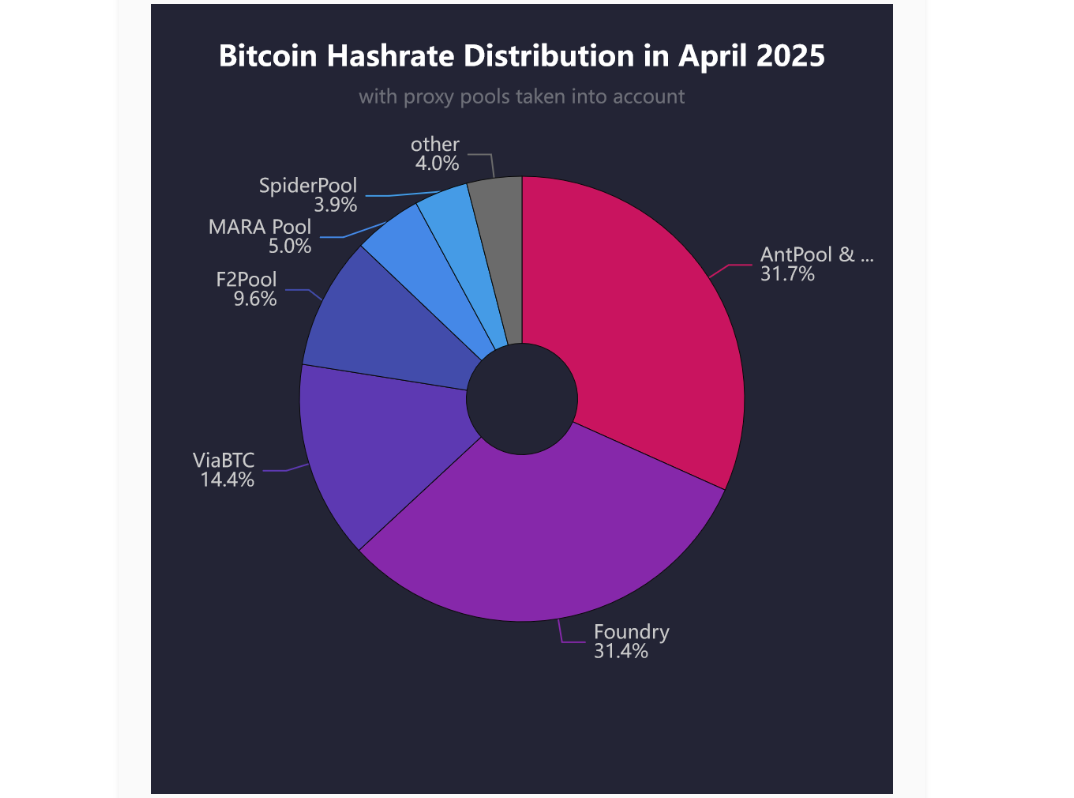
Source: b10c's blog.
- New Spiral grantee: l0rinc. In February 2024, l0rinc transitioned to full-time work on Bitcoin Core. His efforts focus on performance benchmarking and optimizations, enhancing code quality, conducting code reviews, reducing block download times, optimizing memory usage, and refactoring code.
- ESP32 microcontroller vulnerabilities. A paper by Crypto Deep Tech details how an attacker can embed a hidden list of vulnerabilities through module updates, potentially compromising ESP32 devices and allowing unauthorized access to private keys, underscoring the importance of continuous monitoring and enhancing both device and software security.
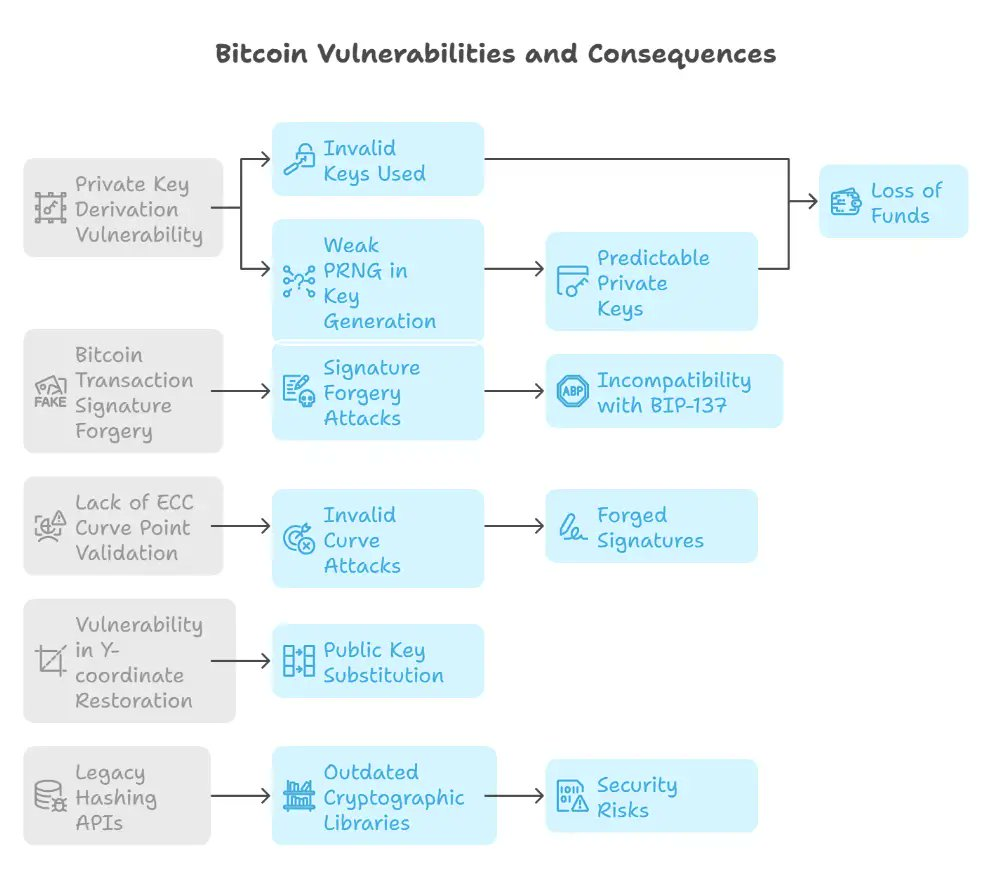
Source: Crypto Deep Tech.
- Bitdeer to expand its self-mining operations to navigate tariffs. The Singapore-based mining company is advancing plans to produce machines in the U.S. while reducing its mining hardware sales. This response is in light of increasing uncertainties related to U.S. trade policy, as reported by Bloomberg.
- Local governments in China use private firms to sell seized bitcoin for cash. According to Reuters, the lack of clear regulations for handling seized bitcoin and other tokens—whose trading is banned on the mainland—has led to inconsistent and opaque practices. The situation has sparked debate among attorneys about the need for new regulations.
- Unchained has launched the Bitcoin Legacy Project. The initiative seeks to advance the Bitcoin ecosystem through a bitcoin-native donor-advised fund platform (DAF), investments in community hubs, support for education and open-source development, and a commitment to long-term sustainability with transparent annual reporting.
- In its first year, the program will provide support to Bitcoin hubs in Nashville, Austin, and Denver.
- Support also includes $50,000 to the Bitcoin Policy Institute, a $150,000 commitment at the University of Austin, and up to $250,000 in research grants through the Bitcoin Scholars program.
"Unchained will match grants 1:1 made to partner organizations who support Bitcoin Core development when made through the Unchained-powered bitcoin DAF, up to 1 BTC," was stated in a blog post.
- Voltage has introduced Voltage Payments platform for enterprises. It will offer a single API that integrates both bitcoin and stablecoin payments with minimal technical overhead, providing the option of either Voltage or user-controlled custody. The platform features a comprehensive dashboard, along with built-in compliance and accounting tools. Currently in beta testing, it is set to launch in 46 U.S. states. Join the waitlist to be notified when it becomes available on mainnet.
Use the tools
- Bitcoin Core Config Generator by Jameson Lopp is now compatible with Bitcoin Core v29.0.
- Zeus wallet v0.10.2 is now available. This point release is centered around various bug fixes.
- Bitkit wallet v1.1.0 introduces performance improvements, smarter coin selection with new Autopilot options, a redesigned side menu, and bug fixes.
- Bitcoin Keeper v2.1.1 update includes various UI updates, bug fixes, and performance improvements.
- Flash v0.4.0-beta, a Bitcoin and Lightning wallet built on the Galoy infrastructure and tailored for the Caribbean Community, features a complete UI/UX redesign, encrypted NIP-17 messaging via Nostr, zoom functionality on the scan camera, improved support for NFC-based Flashcards, and much more.
0:00
/0:31
1×
- Payjoin Dev Kit (rust-payjoin) v0.23.0 introduces a first-class persistence abstraction, wire protocol changes to support RFC 9540, and improved compliance with the BIP78 specification. It also includes an experimental multiparty sender, accessible through the hidden "_multiparty" feature gate. Additionally, it addresses technical debt by enhancing error handling, expanding functionality with new modules and features, and improving test infrastructure. These updates result in breaking API and protocol changes.
- Payjoin CLI v0.1.0 is now out of alpha, with the wire protocol now presumed to be stable.
- Payjoin Directory v0.0.2 has been tagged. It implements the Payjoin Directory store-and-forward server required for Payjoin V2's asynchronous operation.
- BDK Wallet v1.2.0 has been released. The
TxBuilder'sadd_recipientnow accepts anyInto<ScriptBuf>. Coinbase outputs are eligible if maturing in the next block. Wallets usingrusqlite::Connectionare checked for thread safety.bdk_chainis updated to version 0.21.1, with some internal cleanups. - Lightning Dev Kit (rust-lightning) v0.1.2 includes the latest API updates, performance improvements, and bug fixes.
- Boltz Client v2.5.1 includes a patch for correctly handling negative service fees from Boltz Pro. Earlier version 2.5.0 introduced a new
bumpfeecommand alongside several other fixes and improvements. - Elements v23.2.7, an open-source implementation of advanced, sidechain-capable blockchain features extending the Bitcoin protocol, is now available with the latest fixes and improvements.
-
AxeOS (ESP-Miner) v2.6.5 increases the power target for Gamma self test. In version 2.6.4, the under limits for the power consumption self-test were removed.
- AxeOS v2.6.1 was a significant release introducing many new features and improvements. For a comprehensive feature breakdown, check out the details provided by WantClue below.
-
Rust-nostr v0.41 introduces NIP-C0 support and NIP-98 helpers, corrects NIP-32 and NIP-47 implementations, and adds the nostr-keyring crate. It extends admission policies for fine control over relay connections, beneficial in gossip mode. POSIX semaphores are enabled for LMDB on iOS and macOS to address App Sandbox issues. It also expands architecture support for C# and JVM bindings, including linux-x86, windows-x86, and windows-arm64, among other things.
- Nostringer is a JavaScript/TypeScript library providing unlinkable ring signatures (SAG) for Nostr public keys. Inspired by Monero's ring signatures using Spontaneous Anonymous Group (SAG) signatures and the beritani/ring-signatures implementation, it enables a signer to prove their membership in a group of Nostr accounts without disclosing which specific account produced the signature. See a live demo here.
- Private Pond by Kukks a Bitcoin Payjoin application built specifically to optimize Bitcoin transaction rails
-
 @ 1bc70a01:24f6a411
2025-04-16 13:53:00
@ 1bc70a01:24f6a411
2025-04-16 13:53:00I've been meaning to dogfood my own vibe project for a while so this feels like a good opportunity to use Untype to publish this update and reflect on my vibe coding journey.
New Untype Update
As I write this, I found it a bit annoying dealing with one of the latest features, so I'll need to make some changes right after I'm done. Nonetheless, here are some exciting developments in the Untype article composer:
-
Added inline AI helper! Now you can highlight text and perform all sorts of things like fix grammar, re-write in different styles, and all sorts of other things. This is a bit annoying at the moment because it takes over the other editing functions and I need to fix the UX.
-
Added pushing articles to DMs! This option, when enabled, will send the article to all the subscribers via a NIP-44 DM. (No client has implemented the subscription method yet so technically it won’t work, until one does. I may add this to nrss.app) Also, I have not tested this so it could be broken… will test eventually!
- Added word counts
- Added ability to export as markdown, export as PDF, print.
The biggest flaw I have already discovered is how "I" implemented the highlight functionality. Right now when you highlight some text it automatically pops up the AI helper menu and this makes for an annoying time trying to make any changes to text. I wanted to change this to show a floating clickable icon instead, but for some reason the bot is having a difficult time updating the code to this desired UX.
Speaking of difficult times, it's probably a good idea to reflect a bit upon my vibe coding journey.
Vibe Coding Nostr Projects
First, I think it's important to add some context around my recent batch of nostr vibe projects. I am working on them mostly at night and occasionally on weekends in between park runs with kids, grocery shopping and just bumming around the house. People who see buggy code or less than desired UX should understand that I am not spending days coding this stuff. Some apps are literally as simple as typing one prompt!
That said, its pretty clear by now that one prompt cannot produce a highly polished product. This is why I decided to limit my number of project to a handful that I really wish existed, and slowly update them over time - fixing bugs, adding new features in hopes of making them the best tools - not only on nostr but the internet in general. As you can imagine this is not a small task, especially for sporadic vibe coding.
Fighting the bot
One of my biggest challenges so far besides having very limited time is getting the bot to do what I want it to do. I guess if you've done any vibe coding at all you're probably familiar with what I'm trying to say. You prompt one thing and get a hallucinated response, or worse, a complete mess out the other end that undoes most of the progress you've made. Once the initial thing is created, which barely took any time, now you're faced with making it work a certain way. This is where the challenges arise.
Here's a brief list of issues I've faced when vibe-coding with various tools:
1. Runaway expenses - tools like Cline tend to do a better job directly in VSCode, but they can also add up dramatically. Before leaning into v0 (which is where I do most of my vibe coding now), I would often melt through $10 credit purchases faster than I could get a decent feature out. It was not uncommon for me to spend $20-30 on a weekend just trying to debug a handful of issues. Naturally, I did not wish to pay these fees so I searched for alternatives.
2. File duplication - occasionally, seemingly out of nowhere, the bot will duplicate files by creating an entire new copy and attached "-fixed" to the file name. Clearly, I'm not asking for duplicate files, I just want it to fix the existing file, but it does happen and it's super annoying. Then you are left telling it which version to keep and which one to delete, and sometimes you have to be very precise or it'll delete the wrong thing and you have to roll back to a previous working version.
3. Code duplication - similar to file duplication, occasionally the bot will duplicate code and do things in the most unintuitive way imaginable. This often results in loops and crashes that can take many refreshes just to revert back to a working state, and many more prompts to avoid the duplication entirely - something a seasoned dev never has to deal with (or so I imagine).
4. Misinterpreting your request - occasionally the bot will do something you didn't ask for because it took your request quite literally. This tends to happen when I give it very specific prompts that are targeted at fixing one very specific thing. I've noticed the bots tend to do better with vague asks - hence a pretty good result on the initial prompt.
5. Doing things inefficiently, without considering smarter approaches - this one is the most painful of vibe coding issues. As a person who may not be familiar with some of the smarter ways of handling development, you rely on the bot to do the right thing. But, when the bot does something horribly inefficiently and you are non-the-wiser, it can be tough to diagnose the issue. I often fight myself asking the bot "is this really the best way to handle things? Can't we ... / shouldn't we .../ isn't this supposed to..." etc. I guess one of the nice side effects of this annoyance is being able to prompt better. I learn that I should ask the bot to reflect on its own code more often and seek ways to do things more simply.
A combination of the above, or total chaos - this is a category where all hell breaks loose and you're trying to put out one fire after another. Fix one bug, only to see 10 more pop up. Fix those, to see 10 more and so on. I guess this may sound like typical development, but the bot amplifies issues by acting totally irrationally. This is typically when I will revert to a previous save point and just undo everything, often losing a lot of progress.
Lessons Learned
If I had to give my earlier self some tips on how to be a smarter vibe coder, here's how I'd summarize them:
-
Fork often - in v0 I now fork for any new major feature I'd like to add (such as the AI assistant).
-
Use targeting tools - in v0 you can select elements and describe how you wish to edit them.
-
Refactor often - keeping the code more manageable speeds up the process. Since the bot will go through the entire file, even if it only makes one small change, it's best to keep the files small and refactoring achieves that.
I guess the biggest lesson someone might point out is just to stop vibe coding. It may be easier to learn proper development and do things right. For me it has been a spare time hobby (one that I will admit is taking more of my extra time than I'd like). I don't really have the time to learn proper development. I feel like I've learned a lot just bossing the bot around and have learned a bunch of things in the process. That's not to say that I never will, but for the moment being my heart is still mostly in design. I haven't shared much of anything I have designed recently - mostly so I can remain speaking more freely without it rubbing off on my work.
I'll go ahead and try to publish this to see if it actually works 😂. Here goes nothing... (oh, I guess I could use the latest feature to export as markdown so I don't lose any progress! Yay!
-
-
 @ d360efec:14907b5f
2025-04-22 08:12:27
@ d360efec:14907b5f
2025-04-22 08:12:27ความทรงจำเรานั้นเชื่อได้แน่หรือ ?
"เพราะจิตเราเกิดดับทุกเสี้ยววินาที ทุกความทรงจำจึงสร้างขึ้นมาใหม่เสมอ ดังนั้นมันก็ไม่เหมือนต้นฉบับเป็นธรรมดา แต่ยังคงเค้าโครงเดิมอยู่ ความเปลี่ยนแปลงจึงเป็นนิรันดร์ค่ะ" - Lina Engword
เรามักจะคิดว่าความทรงจำของเราคือการบันทึกเหตุการณ์ในอดีตไว้อย่างแม่นยำ เหมือนการดูวิดีโอ 📼 หรือเปิดไฟล์คอมพิวเตอร์ 💾 แต่ในความเป็นจริงแล้ว แนวคิดนี้อาจไม่ใช่ภาพที่สมบูรณ์ บทความที่เรานำมาวิเคราะห์นี้ได้นำเสนอข้อคิดที่น่าสนใจเกี่ยวกับธรรมชาติของความทรงจำมนุษย์ ความน่าเชื่อถือของมัน และเชื่อมโยงไปถึงความจำเป็นในการฝึกฝนจิตตามหลักพุทธศาสนาเพื่อเข้าถึงความจริงที่เที่ยงแท้ 🧘♀️🔍
ความทรงจำไม่ใช่การบันทึก แต่เป็นการสร้างใหม่ 🏗️🧩
ประเด็นสำคัญที่บทความชี้ให้เห็นคือ ความทรงจำของมนุษย์ไม่ได้ทำงานเหมือนการ "บันทึก" เหตุการณ์ไว้ตายตัว 📼❌ แต่เปรียบเสมือน "ชิ้นส่วนของโค้ด" 💻 ที่จะถูก "สร้างขึ้นใหม่" 🏗️ ทุกครั้งที่เราพยายามระลึกถึง นั่นหมายความว่า ทุกครั้งที่เราดึงความทรงจำเก่าๆ กลับมา มันไม่ใช่การเปิดไฟล์เดิมซ้ำๆ แต่เป็นการประกอบชิ้นส่วนเหล่านั้นขึ้นมาใหม่ในห้วงเวลานั้นๆ กระบวนการนี้เองที่เปิดโอกาสให้เกิดการ "เติมเต็ม" ✨ หรือ "แก้ไข" ✏️ ข้อมูลในความทรงจำอยู่เสมอ ทำให้ความทรงจำที่เราเพิ่งนึกถึงอาจไม่เหมือนกับความทรงจำครั้งก่อนหน้าเสียทีเดียว 🔄
การปรุงแต่งด้วยเหตุผลและความคุ้นเคย 🤔➕🏠
สิ่งที่น่าสนใจอย่างยิ่งคือ ในกระบวนการ "สร้างใหม่" หรือ "ประกอบ" ความทรงจำขึ้นมานี้ มนุษย์มักจะเติม "เหตุผล"💡 หรือใส่สิ่งที่ตนเอง "คุ้นเคย" 🏠 ลงไปในเรื่องราวที่ระลึกได้เสมอ แม้ว่าสิ่งเหล่านั้นอาจจะไม่ได้เกิดขึ้นจริงหรือไม่เกี่ยวข้องโดยตรงกับเหตุการณ์นั้นๆ ก็ตาม ยกตัวอย่างเช่น เมื่อเราเล่าเรื่องในอดีต เรามักจะอธิบายว่าทำไมเราถึงทำสิ่งนั้น หรือทำไมเหตุการณ์นี้ถึงเกิดขึ้น โดยใส่เหตุผลที่เราคิดว่าสมเหตุสมผลในปัจจุบันลงไป สิ่งนี้ทำให้เรื่องราวในความทรงจำของเราดูมีความเชื่อมโยงและฟังดู "จริง" ✅ มากขึ้นในสายตาของเราเอง
เมื่อเราใส่เหตุผลหรือรายละเอียดที่คุ้นเคยลงไปในความทรงจำบ่อยครั้งเข้า มันก็จะยิ่งทำให้เรา "เชื่อ" 👍 โดยสนิทใจว่าสิ่งที่เราระลึกได้นั้นคือความจริงทั้งหมด ทั้งที่ความเป็นจริงของเหตุการณ์ดั้งเดิมอาจแตกต่างออกไป 🤥 นี่คือสาเหตุว่าทำไมคนสองคนจึงอาจมีความทรงจำเกี่ยวกับเหตุการณ์เดียวกันที่แตกต่างกันอย่างสิ้นเชิง ซึ่งปรากฏการณ์นี้สามารถอธิบายได้ดีด้วยตัวอย่างคลาสสิกในภาพยนตร์เรื่อง "ราโชมอน" (Rashomon) 🎬 ที่นำเสนอเหตุการณ์เดียวผ่านมุมมองและความทรงจำของตัวละครที่ขัดแย้งกันอย่างสิ้นเชิง แต่ทุกคนต่างเชื่อในสิ่งที่ตนเองจำได้ว่าเป็นความจริง 🤔❓
เครื่องมือและกระบวนการช่วยตรวจสอบความจริง 📱📹📝🔍
จากข้อจำกัดโดยธรรมชาติของความทรงจำนี้เอง ทำให้เห็นว่าเราไม่สามารถพึ่งพาสิ่งที่ 'จำได้' เพียงอย่างเดียวได้หากต้องการเข้าถึงความจริงที่เที่ยงแท้ เราจึงจำเป็นต้องมี 'กระบวนการตรวจสอบ' 🤔🔍 มาช่วยยืนยันหรือแก้ไขข้อมูลในความทรงจำ
ในยุคปัจจุบัน เรามีเครื่องมือภายนอกมากมายที่ช่วยในกระบวนการนี้ เช่น กล้องจากสมาร์ทโฟน 📱 หรือกล้องวงจรปิด 📹 ที่บันทึกเหตุการณ์ต่างๆ ไว้ได้อย่างเป็นกลาง ทำให้เรามี 'หลักฐาน' 📄 ที่เป็นรูปธรรมไว้อ้างอิงเพื่อเปรียบเทียบกับความทรงจำส่วนตัว ซึ่งบ่อยครั้งสิ่งที่กล้องเห็นนั้น 'ตรงกับความจริง' ✅ ในมุมมองที่ปราศจากอคติมากกว่าสิ่งที่ใจเราจำได้ การจดบันทึกด้วยเสียง 🎤 หรือการจดบันทึกเป็นลายลักษณ์อักษร 📝 ในทันที ก็เป็นอีกวิธีหนึ่งที่ช่วย 'ตรึง' ข้อมูลเบื้องต้นไว้ได้ระดับหนึ่งเช่นกัน ✍️
นอกจากเครื่องมือภายนอกแล้ว 'กระบวนการตรวจสอบเชิงจิตวิทยา' 🤔🧠 ที่เป็นระบบ ก็สามารถช่วยให้มนุษย์ค้นพบความจริงได้เช่นกัน ไม่ว่าจะเป็นกระบวนการซักถามในเชิงนิติวิทยาศาสตร์ 👮♀️ หรือแม้กระทั่งการฝึกฝนจิตเพื่อให้สามารถสังเกตการณ์ทำงานของตนเองได้อย่างละเอียดลึกซึ้ง ซึ่งนำเราไปสู่แนวคิดตามหลักพุทธศาสนา...
ทำไมพุทธศาสนาจึงสอนไม่ให้เชื่อแม้เป็นความคิดตัวเอง? 🙏🧠❌
จากธรรมชาติของความทรงจำและกระบวนการปรุงแต่งของจิตใจที่อธิบายมานี้เอง ทำให้เราเห็นความเชื่อมโยงกับหลักคำสอนในพุทธศาสนา 🙏 ที่เน้นย้ำให้เรา "ไม่เชื่อแม้แต่ความคิดตัวเอง" 🧠❌ อย่างปราศจากการพิจารณา เพราะความคิด อารมณ์ ความทรงจำ หรือแม้แต่ความรู้สึกมั่นใจอย่างแรงกล้าที่เรามีนั้น อาจถูกสร้างขึ้นหรือปรุงแต่งโดยกลไกของจิตใจที่ไม่ได้สะท้อนความจริงทั้งหมด 🤥
พุทธศาสนาชี้ให้เห็นว่า การจะเข้าถึงความจริงที่แท้จริงได้นั้น 🔍 จำเป็นต้องมีกระบวนการตรวจสอบภายในจิตใจ เปรียบเสมือนการสร้าง "อัลกอริทึม" 🤖 เพื่อตรวจทานว่าสิ่งที่เราคิดหรือจำได้นั้นเป็นความจริงหรือไม่ ✅❌ การจะทำเช่นนี้ได้ ไม่ใช่เรื่องง่าย และต้องอาศัยการฝึกฝนจิตอย่าง "สมาธิอย่างมาก" 🧘♂️🧘♀️ เพื่อให้จิตมีความตั้งมั่น เป็นระบบ และสามารถ "เห็นการดำเนินไปของจิตได้อย่างเป็นระบบ" 👀🔬 เห็นว่าจิตปรุงแต่งความทรงจำอย่างไร เห็นว่าเหตุผลที่เราใส่เข้าไปนั้นจริงหรือไม่ เป็นเพียงการตีความ หรือเป็นเพียงสิ่งที่ใจเราอยากให้เป็น
บทความยังกล่าวเสริมว่า ความทรงจำที่ "สด" ✨ หรือใกล้เคียงกับเวลาที่เกิดเหตุการณ์นั้นมักจะมีความน่าเชื่อถือมากกว่า 👍 แม้จะดู "ดิบๆ" หรือไม่ผ่านการปรุงแต่งมากนัก ซึ่งสอดคล้องกับแนวคิดที่ว่ายิ่งระยะเวลาผ่านไปนานเท่าไหร่ ⏳ ยิ่งมีการเรียกคืนความทรงจำนั้นๆ บ่อยครั้ง ความทรงจำก็ยิ่งมีโอกาสถูกแก้ไข เติมเต็ม หรือปรุงแต่งด้วยเหตุผลและความคุ้นเคยมากขึ้นเท่านั้น 🔄✏️
"ใดๆในโลกนั้นคือสมมุติ ความคิดความทรงจำ ก็เป็นสมมุติเพียง แต่เราต้องรู้จักใช้สมมุติให้เป็นประโยชน์ และรู้จักใช้มันให้เป็นเพื่อดำรงอยู่บนโลก"
สรุป ✨🧠🔍
โดยสรุปแล้ว บทความนี้เตือนใจเราว่า ความทรงจำของเราไม่ใช่กล้องวิดีโอที่บันทึกทุกอย่างไว้แม่นยำ 📼❌ แต่เป็นกระบวนการสร้างสรรค์ที่ซับซ้อนซึ่งมีแนวโน้มที่จะถูกปรุงแต่งด้วยเหตุผล ความคุ้นเคย และการตีความของเราเอง 🏗️🤔🏠 ความมั่นใจที่เรามีต่อสิ่งที่จำได้นั้น ไม่ได้เป็นหลักประกันว่าเป็นความจริงเสมอไป 👍🤥
การตระหนักถึงธรรมชาติข้อนี้ของจิต และการใช้เครื่องมือภายนอก 📱📹📝 รวมถึงการฝึกฝนจิตให้สามารถสังเกตการณ์ทำงานของมันได้อย่างละเอียดรอบคอบตามหลักพุทธศาสนา 🙏🧘♀️ จึงเป็นกุญแจสำคัญที่จะช่วยให้เราสามารถแยกแยะระหว่าง "ความจริง" ✅ กับ "สิ่งที่จิตปรุงแต่งขึ้น" 🤥 ได้มากขึ้น และช่วยให้เราเข้าใกล้ความเข้าใจในธรรมชาติของสรรพสิ่งได้อย่างเที่ยงตรง ไม่หลงติดอยู่ในวังวนของความทรงจำและความคิดที่อาจบิดเบือนไปจากความเป็นจริง 🔄
**#ความทรงจำ #จิตวิทยา #พุทธศาสนา #สมอง #สมาธิ #การฝึกจิต #ราโชมอน #ความจริง #ไม่เชื่อความคิด #ธรรมชาติของจิต #พัฒนาตนเอง #บทความน่ารู้ #เทคโนโลยี #บันทึกความจริง #พระอภิธรรม #พระหฤทัยสูตร #LinaEngword **
-
 @ 04ea4f83:210e1713
2025-04-20 08:46:16
@ 04ea4f83:210e1713
2025-04-20 08:46:16Veröffentlicht auf Youtube am 19.01.2024\ Originalautor: Bitcoin University\ Übersetzt und angepasst von: Sinautoshi am 21.01.2024 - 825611\ \ Dieser Artikel wird auf der Website von European Bitcoiners nur zu Bildungs-, Informations- und Übersetzungszwecken zur Verfügung gestellt und stellt weder eine finanzielle Beratung noch einen Anspruch auf die im Bericht erwähnten Details dar.\ \ Alle Rechte liegen bei dem Autor des Originals.
Du hast auch begrenzte Zeit um Bitcoin zu verstehen und zu nutzen.
Also, wie bestimmst du nun wie du deine begrenzte Zeit sinnvoll einsetzt?
Weg #1: Shitcoiner/Altcoiner
Dein Tag als Shitcoiner:
- Schaue viele Youtube Videos mit den Vorschaubildern von Kerlen mit offenem Mund, weil die dich mit einfach mit den besten Informationen versorgen
- Den Preis von einem dutzend Kryptowährungen mindestens ein paar hundertmal checken
- Ehrfurchtsvoll Krypto Trading Charts lesen
- Sicher gehen, dass du niemals deine Performance in BTC misst, da dies dir zeigen könnte, dass Shitcoins doch nicht so eine gute Idee ist
- Das Internet nach Informationen durchforstest, welcher Coin als nächstes groß rauskommen wird um dabei nach folgenden Schema vorzugehen:\ - Versuche frühzeitig zu kaufen\ - Versuche nicht abgezockt zu werden\ - Dann schnell verkaufen\ - Einen großen Teil des Gewinns direkt ans Finanzamt abdrücken\ - Und nun alles wieder von vorn!\ \ VERTRAU MIR JUNGE, SO WERDEN WIR ALLE MILLIONÄRE!!!!
- Achtung (!), du brauchst nur den passenden Guru oder Online Trading Berater, der dir sagt welche Kryptowährung und dir stündlich, die passenden Trading-Signale schickt
- Das einzig wichtige: schalte niemals dein eigenes Hirn an.
- Versuche nicht zu verstehen wie ein Markt funktioniert
- Springe von Gerücht zu Gerücht und kümmere dich nur um das Allerneuste
Vertraue einfach anderen Leute dir zu sagen was du zu denken hast, denn schließlich hat reich werden nichts damit zu tun an sich zu arbeiten und echte Fähigkeiten zu lernen.
Das Patentrezept ist der Hochfrequenz-Handel während man im Schlafanzug vor dem PC sitzt.
Falls du doch mal abgezogen werden solltest:
Stelle sicher, dass du auf Telegram einen ausgezeichneten Online Wiederherstellungsdienst bezahlst, der dir hilft die Coins wiederzuholen.
Lass dir dabei vorlügen, dass alle Bitcoin und Kryptotransaktionen rückgängig zu machen sind, obwohl sie IRREVERSIBEL sind.
Genieß deine Shitcoinerei - sie könnte nicht von langer Dauer sein.
Immerhin hast du nun ein paar Dopamin Stöße bekommen.
Weg #2: Bitcoiner
Wenn dir der Dopamin Stoß wichtiger ist als harte Arbeit, dann ist dieser Weg sicherlich nichts für dich.
Der Tag im Leben eines Bitcoiners:
- Prüft nicht den Preis
- Kauft ein bisschen BTC, sobald etwas Bargeld reinkommt oder macht einfach regelmäßiges DCA
- Bleibt am Ball um zu verstehen wie Bitcoin funktioniert
- Versteht die Anreize, welche das Bitcoin Netzwerk schützt
- Versteht den Unterschied zwischen Proof of Work und Proof of Stake
- Versteht was Miner, Mining Pools, Nodes, XPubs und UTXO sind
- Versteht die Grundlagen eines asymmetrischen Verschlüsselungsverfahren und was es so nützlich macht
- Versteht wie verschiedene Attacken gegen Bitcoin aussehen könnten und warum sie erfolgreich seien oder fehlschlagen müssten
- Lernt wie man eine Hardware Wallet sicher aufsetzt und wiederherstellt
- Lernt wie man die Hardware Wallet mit Sparrow oder Nunchuk verbindet
- Spielt mit Nodes herum auf einem Desktop, Laptop oder Mini PC
- Versteht wie Wiederherstellungsphrasen und Passphrasen funktionieren
- Versteht die Vor- und Nachteile von Single-Sig und Multi-Sig
- Entwickelt seine persönliche Aufbewahrungsmethode, die ihn vor verschiedenen Szenarien schützt
- Weiß wie man eine Hardware Wallet zurücksetzt und sie wiederherstellt
- Weiß wie man seine Bitcoin schnell und überall in die Welt mitnehmen kann, falls das nötig sein sollte
- Weiß wie man seine Bitcoin zwischen den verschiedenen Ebenen wie Lightning und Liquid bewegen kann
- Weiß wie man eine Bitcoin im Lightning Netzwerk selbst verwahren kann wie z.B. mit Phoenix Wallet
- Lernt wie man eine Lightning Node betreibt
- Weiß wie man Bitcoin ohne Identifizierungsverfahren kauft
- Weiß wie und wann man seine Bitcoin mit einer Coinjoin Transaktion verschleiert
- Arbeitet hart in der echten Welt um seinen Lohn in Bitcoin zu tauschen
- Schaut nach Möglichkeiten Bitcoin direkt zu verdienen, entweder durch den Hauptjob oder einen kleinen Nebenjob
- Lernt wie man Software mit GPG verifiziert
- Versteht wie Lightning, Splicing, Liquid und Fedimint arbeiten
Es gibt einfach so viele zu lernen und du wirst einsehen, dass das Trading von Shitcoins einfach Zeitverschwendung ist, wenn man auch die aufgelisteten Fähigkeiten lernen könnte. Dazu wird die übrige Zeit mit Folgendem verbracht:
- Viel Zeit in der Natur
- Atmen von frischer Luft
- Etwas Sonne abbekommen
- Laufen, Joggen und Gewichtstraining
- Kochen, und das mit guten Zutaten
- Zeit mit den Liebsten verbringen, während man abgekoppelt von den sozialen Medien ist
Man versucht einfach jeden Tag eine schlauere, stärkere und bessere Person im Allgemeinen zu werden.
Was nimmst du nun mit?
Hör auf zu zocken, fang an zu lernen.
Anstatt deine Zeit mit Trading und Shitcoins zu verschwenden, lerne wie du Bitcoin kaufst und sie sicher auf einer Hardware Wallet verwahrst. Lerne sie zu benutzten, sie zu löschen und sie wiederherzustellen. Schaue dir regelmäßig dein Sicherheitskonzept an und falls nötig, mache eine Upgrade zu etwas besserem, damit du sicherer und privater unterwegs bist.
Übe deine Bitcoin zu bewegen. Schicke sie dir selbst, konsolidiere deine UTXO und stelle deine Bitcoin wieder her über deinen Seed.
Höre auf mit dem Glückspiel und #studybitcoin.
Bitcoin ist die Revolution.
Bitcoin ist der nächste Bitcoin.
Also, wirst du dich dem Gewinnerteam anschließen?
Wirst du lernen wie du auf einem Bitcoin Standard als selbst souveränes Individuum lebst?
Oder wirst du weiter von Coin zu Coin hüpfen um den nÄcHsTen Bitcoin zu finden ohne etwas an deinen echten Fähigkeiten oder deiner Expertise zu arbeiten während du die größte Menge an Bitcoin, die du je verdient hättest und die in den nächsten 1000 Jahren in Kaufkraft steigt, einfach links liegen lässt.
Selbst wenn du keine Bitcoin haben solltest, oder eine sehr kleine Menge hast, sei dir bewusst es ist nicht zu spät.
Wir sind noch sehr früh dabei.
Wähle weise wie du deine Tage und Wochen verbringst
Die heutigen Entscheidungen werden einen nachhaltigen Einfluss auf den Rest deines Lebens und wahrscheinlich sogar, das deiner Kinder.
Bist du neugierig geworden oder weißt du schon alles über Bitcoin? Ich fordere dich heraus mehr über Bitcoin zu Lernen. Hier findest du eine große Menge an weiterem Material.
-
 @ 9223d2fa:b57e3de7
2025-04-15 02:54:00
@ 9223d2fa:b57e3de7
2025-04-15 02:54:0012,600 steps
-
 @ fd06f542:8d6d54cd
2025-04-15 02:38:14
@ fd06f542:8d6d54cd
2025-04-15 02:38:14排名随机, 列表正在增加中。
Cody Tseng
jumble.social 的作者
https://jumble.social/users/npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl
- Running [ wss://nostr-relay.app ] (free & WoT) 💜⚡️
- Building 👨💻:
- https://github.com/CodyTseng/jumble
- https://github.com/CodyTseng/nostr-relay-tray
- https://github.com/CodyTseng/danmakustr
- https://github.com/CodyTseng/nostr-relay-nestjs
- https://github.com/CodyTseng/nostr-relay
- https://github.com/CodyTseng
阿甘
- @agan0
- 0xchat.com
- canidae40@coinos.io
- https://jumble.social/users/npub13zyg3zysfylqc6nwfgj2uvce5rtlck2u50vwtjhpn92wzyusprfsdl2rce
joomaen
- Follows you
- joomaen.com
-
95aebd@wallet.yakihonne.com
-
nobot
- https://joomaen.filegear-sg.me/
- https://jumble.social/users/npub1wlpfd84ymdx2rpvnqht7h2lkq5lazvkaejywrvtchlvn3geulfgqp74qq0
颜值精选官
- wasp@ok0.org
- 专注分享 各类 图片与视频,每日为你带来颜值盛宴,心动不止一点点。欢迎关注,一起发现更多美好!
- https://jumble.social/users/npub1d5ygkef6r0l7w29ek9l9c7hulsvdshms2qh74jp5qpfyad4g6h5s4ap6lz
6svjszwk
- 6svjszwk@ok0.org
- 83vEfErLivtS9to39i73ETeaPkCF5ejQFbExoM5Vc2FDLqSE5Ah6NbqN6JaWPQbMeJh2muDiHPEDjboCVFYkHk4dHitivVi
-
low-time-preference
-
anarcho-capitalism
-
libertarianism
-
bitcoin #monero
- https://jumble.social/users/npub1sxgnpqfyd5vjexj4j5tsgfc826ezyz2ywze3w8jchd0rcshw3k6svjszwk
𝘌𝘷𝘦𝘳𝘺𝘥𝘢𝘺 𝘔𝘰𝘳𝘯𝘪𝘯𝘨 𝘚𝘵𝘢𝘳
- everyday@iris.to
- 虽然现在对某些事情下结论还为时尚早,但是从趋势来看,邪恶抬头已经不可避免。
- 我们要做的就是坚持内心的那一份良知,与邪恶战斗到底。
- 黑暗森林时代,当好小透明。
- bc1q7tuckqhkwf4vgc64rsy3rxy5qy6pmdrgxewcww
- https://jumble.social/users/npub1j2pha2chpr0qsmj2f6w783200upa7dvqnnard7vn9l8tv86m7twqszmnke
nostr_cn_dev
npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm@npub.cash
Developed the following products: - NostrBridge, 网桥转发 - TaskQ5, 分布式多任务 - NostrHTTP, nostr to http - Postr, 匿名交友,匿名邮局 - nostrclient (Python client) . -nostrbook, (nostrbook.com) 用nostr在线写书 * https://www.duozhutuan.com nostrhttp demo * https://github.com/duozhutuan/NostrBridge * * https://jumble.social/users/npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm *
CXPLAY
- lightning@cxplay.org
- 😉很高兴遇到你, 你可以叫我 CX 或 CXPLAY, 这个名字没有特殊含义, 无需在意.
- ©本账号下所有内容如未经特殊声明均使用 CC BY-NC-SA 4.0 许可协议授权.
- 🌐如果您在 Fediverse 收到本账号的内容则说明您的实例已与 Mostr.pub 或 Momostr.pink Bridge 互联, 您所看到的账号为镜像, 所有账号内容正在跨网传递. 如有必要请检查原始页面.
- 🧑💻正在提供中文本地化(i10n): #Amethyst #Amber #Citrine #Soapbox #Ditto #Alby
- https://cx.ms/
https://jumble.social/users/npub1gd8e0xfkylc7v8c5a6hkpj4gelwwcy99jt90lqjseqjj2t253s2s6ch58h
w
- 0xchat的作者
- 0xchat@getalby.com
- Building for 0xchat
- https://www.0xchat.com/
- https://jumble.social/users/npub10td4yrp6cl9kmjp9x5yd7r8pm96a5j07lk5mtj2kw39qf8frpt8qm9x2wl
Michael
- highman@blink.sv
- Composer Artist | Musician
- 🎹🎼🎤🏸🏝️🐕❤️
- 在這裡可以看到「我看世界」的樣子
- 他是光良
- https://jumble.social/users/npub1kr5vqlelt8l47s2z0l47z4myqg897m04vrnaqks3emwryca3al7sv83ry3
-
 @ 3f770d65:7a745b24
2025-04-21 00:15:06
@ 3f770d65:7a745b24
2025-04-21 00:15:06At the recent Launch Music Festival and Conference in Lancaster, PA, featuring over 120 musicians across three days, I volunteered my time with Tunestr and Phantom Power Music's initiative to introduce artists to Bitcoin, Nostr, and the value-for-value model. Tunestr sponsored a stage, live-streaming 21 bands to platforms like Tunestr.io, Fountain.fm and other Nostr/Podcasting 2.0 apps and on-boarding as many others as possible at our conference booth. You may have seen me spamming about this over the last few days.
V4V Earnings
Day 1: 180,000 sats
Day 2: 300,000 sats
Day 3: Over 500,000 sats
Who?
Here are the artists that were on-boarded to Fountain and were live streaming on the Value-for-Value stage:
nostr:npub1cruu4z0hwg7n3r2k7262vx8jsmra3xpku85frl5fnfvrwz7rd7mq7e403w nostr:npub12xeh3n7w8700z4tpd6xlhlvg4vtg4pvpxd584ll5sva539tutc3q0tn3tz nostr:npub1rc80p4v60uzfhvdgxemhvcqnzdj7t59xujxdy0lcjxml3uwdezyqtrpe0j @npub16vxr4pc2ww3yaez9q4s53zkejjfd0djs9lfe55sjhnqkh nostr:npub10uspdzg4fl7md95mqnjszxx82ckdly8ezac0t3s06a0gsf4f3lys8ypeak nostr:npub1gnyzexr40qut0za2c4a0x27p4e3qc22wekhcw3uvdx8mwa3pen0s9z90wk nostr:npub13qrrw2h4z52m7jh0spefrwtysl4psfkfv6j4j672se5hkhvtyw7qu0almy nostr:npub1p0kuqxxw2mxczc90vcurvfq7ljuw2394kkqk6gqnn2cq0y9eq5nq87jtkk nostr:npub182kq0sdp7chm67uq58cf4vvl3lk37z8mm5k5067xe09fqqaaxjsqlcazej nostr:npub162hr8kd96vxlanvggl08hmyy37qsn8ehgj7za7squl83um56epnswkr399 nostr:npub17jzk5ex2rafres09c4dnn5mm00eejye6nrurnlla6yn22zcpl7vqg6vhvx nostr:npub176rnksulheuanfx8y8cr2mrth4lh33svvpztggjjm6j2pqw6m56sq7s9vz nostr:npub1akv7t7xpalhsc4nseljs0c886jzuhq8u42qdcwvu972f3mme9tjsgp5xxk nostr:npub18x0gv872489lrczp9d9m4hx59r754x7p9rg2jkgvt7ul3kuqewtqsssn24
Many more musicians were on-boarded to Fountain, however, we were unable to obtain all of their npubs.
THANK YOU TO ALL ZAPPERS AND BOOSTERS!
Musicians “Get It”
My key takeaway was the musicians' absolute understanding that the current digital landscape along with legacy social media is failing them. Every artist I spoke with recognized how algorithms hinder fan connection and how gatekeepers prevent fair compensation for their work. They all use Spotify, but they only do so out of necessity. They felt the music industry is primed for both a social and monetary revolution. Some of them were even speaking my language…
Because of this, concepts like decentralization, censorship resistance, owning your content, and controlling your social graph weren't just understood by them, they were instantly embraced. The excitement was real; they immediately saw the potential and agreed with me. Bitcoin and Nostr felt genuinely punk rock and that helped a lot of them identify with what we were offering them.
The Tools and the Issues
While the Nostr ecosystem offers a wide variety of tools, we focused on introducing three key applications at this event to keep things clear for newcomers:
- Fountain, with a music focus, was the primary tool for onboarding attendees onto Nostr. Fountain was also chosen thanks to Fountain’s built-in Lightning wallet.
- Primal, as a social alternative, was demonstrated to show how users can take their Nostr identity and content seamlessly between different applications.
- Tunestr.io, lastly was showcased for its live video streaming capabilities.
Although we highlighted these three, we did inform attendees about the broader range of available apps and pointed them to
nostrapps.comif they wanted to explore further, aiming to educate without overwhelming them.This review highlights several UX issues with the Fountain app, particularly concerning profile updates, wallet functionality, and user discovery. While Fountain does work well, these minor hiccups make it extremely hard for on-boarding and education.
- Profile Issues:
- When a user edits their profile (e.g., Username/Nostr address, Lightning address) either during or after creation, the changes don't appear to consistently update across the app or sync correctly with Nostr relays.
- Specifically, the main profile display continues to show the old default Username/Nostr address and Lightning address inside Fountain and on other Nostr clients.
- However, the updated Username/Nostr address does appear on https://fountain.fm (chosen-username@fountain.fm) and is visible within the "Edit Profile" screen itself in the app.
- This inconsistency is confusing for users, as they see their updated information in some places but not on their main public-facing profile within the app. I confirmed this by observing a new user sign up and edit their username – the edit screen showed the new name, but the profile display in Fountain did not update and we did not see it inside Primal, Damus, Amethyst, etc.
- Wallet Limitations:
- The app's built-in wallet cannot scan Lightning address QR codes to initiate payments.
- This caused problems during the event where users imported Bitcoin from Azte.co vouchers into their Fountain wallets. When they tried to Zap a band by scanning a QR code on the live tally board, Fountain displayed an error message stating the invoice or QR code was invalid.
- While suggesting musicians install Primal as a second Nostr app was a potential fix for the QR code issue, (and I mentioned it to some), the burden of onboarding users onto two separate applications, potentially managing two different wallets, and explaining which one works for specific tasks creates a confusing and frustrating user experience.
- Search Difficulties:
- Finding other users within the Fountain app is challenging. I was unable to find profiles from brand new users by entering their chosen Fountain username.
- To find a new user, I had to resort to visiting their profile on the web (fountain.fm/username) to retrieve their npub. Then, open Primal and follow them. Finally, when searching for their username, since I was now following them, I was able to find their profile.
- This search issue is compounded by the profile syncing problem mentioned earlier, as even if found via other clients, their displayed information is outdated.
- Searching for the event to Boost/Zap inside Fountain was harder than it should have been the first two days as the live stream did not appear at the top of the screen inside the tap. This was resolved on the third day of the event.
Improving the Onboarding Experience
To better support user growth, educators and on-boarders need more feature complete and user-friendly applications. I love our developers and I will always sing their praises from the highest mountain tops, however I also recognize that the current tools present challenges that hinder a smooth onboarding experience.
One potential approach explored was guiding users to use Primal (including its built-in wallet) in conjunction with Wavlake via Nostr Wallet Connect (NWC). While this could facilitate certain functions like music streaming, zaps, and QR code scanning (which require both Primal and Wavlake apps), Wavlake itself has usability issues. These include inconsistent or separate profiles between web and mobile apps, persistent "Login" buttons even when logged in on the mobile app with a Nostr identity, and the minor inconvenience of needing two separate applications. Although NWC setup is relatively easy and helps streamline the process, the need to switch between apps adds complexity, especially when time is limited and we’re aiming to showcase the benefits of this new system.
Ultimately, we need applications that are more feature-complete and intuitive for mainstream users to improve the onboarding experience significantly.
Looking forward to the future
I anticipate that most of these issues will be resolved when these applications address them in the near future. Specifically, this would involve Fountain fixing its profile issues and integrating Nostr Wallet Connect (NWC) to allow users to utilize their Primal wallet, or by enabling the scanning of QR codes that pay out to Lightning addresses. Alternatively, if Wavlake resolves the consistency problems mentioned earlier, this would also significantly improve the situation giving us two viable solutions for musicians.
My ideal onboarding event experience would involve having all the previously mentioned issues resolved. Additionally, I would love to see every attendee receive a $5 or $10 voucher to help them start engaging with value-for-value, rather than just the limited number we distributed recently. The goal is to have everyone actively zapping and sending Bitcoin throughout the event. Maybe we can find a large sponsor to facilitate this in the future?
What's particularly exciting is the Launch conference's strong interest in integrating value-for-value across their entire program for all musicians and speakers at their next event in Dallas, Texas, coming later this fall. This presents a significant opportunity to onboard over 100+ musicians to Bitcoin and Nostr, which in turn will help onboard their fans and supporters.
We need significantly more zaps and more zappers! It's unreasonable to expect the same dedicated individuals to continuously support new users; they are being bled dry. A shift is needed towards more people using bitcoin for everyday transactions, treating it as money. This brings me back to my ideal onboarding experience: securing a sponsor to essentially give participants bitcoin funds specifically for zapping and tipping artists. This method serves as a practical lesson in using bitcoin as money and showcases the value-for-value principle from the outset.
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 1bc70a01:24f6a411
2025-04-19 09:58:54
@ 1bc70a01:24f6a411
2025-04-19 09:58:54Untype Update
I cleaned up the AI assistant UX. Now you can open it in the editor bar, same as all other actions. This makes it a lot easier to interact with while having access to normal edit functions.
AI-generated content
Untype uses OpenRouter to connect to various models to generate just about anything. It doesn't do images for now, but I'm working on that.
Automatic Title, Summary and Tag Suggestions
Added the functionality to generate titles, summaries and tags with one click.
A Brief Preview
Here is a little story I generated in Untype, ABOUT Untype:
This story was generated in Untype
Once upon a time, in the bustling digital city of Techlandia, there lived a quirky AI named Untype. Unlike other software, Untype wasn't just your everyday article composer — it had a nose for news, quite literally. Untype was equipped with a masterful talent for sniffing out the latest trends and stories wafting through the vast digital ether.
Untype had a peculiar look about it. Sporting a gigantic nose and a pair of spectacles perched just above it, Untype roamed the virtual city, inhaling the freshest gossip and spiciest stories. Its nostr-powered sensors twitched and tickled as it encountered every new scent.
One day, while wandering around the pixelated park, Untype caught a whiff of something extraordinary — a scandalous scoop involving Techlandia's mayor, Doc Processor, who had been spotted recycling old memes as new content. The scent trail was strong, and Untype's nose twitched with excitement.
With a flick of its AI function, Untype began weaving the story into a masterpiece. Sentences flowed like fine wine, infused with humor sharper than a hacker’s focus. "Doc Processor," Untype mused to itself, "tried to buffer his way out of this one with a cache of recycled gifs!"
As Untype typed away, its digital friends, Grammarly the Grammar Gremlin and Canva the Artful Pixie, gathered around to watch the genius at work. "You truly have a knack for news-sniffing," complimented Grammarly, adjusting its tiny monocle. Canva nodded, painting whimsical illustrations to accompany the hilarious exposé.
The article soon spread through Techlandia faster than a virus with a strong wifi signal. The townsfolk roared with laughter at Untype’s clever wit, and even Doc Processor couldn't help but chuckle through his embarrassment.
From that day on, Untype was celebrated not just as a composer but as Techlandia's most revered and humorous news-sniffer. With every sniff and click of its AI functions, Untype proved that in the world of digital creations, sometimes news really was just a nose away.
-
 @ fd78c37f:a0ec0833
2025-04-01 11:49:06
@ fd78c37f:a0ec0833
2025-04-01 11:49:06In this edition, we invited Keypleb, the founder of Bitcoin Indonesia, to share how he built the Bitcoin community in Indonesia, overcoming challenges like member turnover and venue selection, while driving the adoption and growth of Bitcoin.
YakiHonne: Welcome, Keypleb. Before we begin, let me briefly introduce YakiHonne. YakiHonne is a decentralized media client built on Nostr—a protocol designed to empower freedom of speech through technology. It enables creators to own their voices and assets while offering innovative tools like smart widgets, verified notes, and support for long-form content. We focus on free speech and free media by user privacy and data to be protected. So before starting the interview, I'd like to hear about yourself and your community.
Keypleb:My name is Keypleb, though it’s a pseudonym—a name I use to respect privacy. I'm a co-founder of Bitcoin Indonesia, Bitcoin House Bali, and Code Orange, a new developer school we launched at a conference just a few days ago. We focus on driving adoption through meetups, hackathons, and technical workshops. I'll dive into more details later, but that's a brief overview. I'm based in Bali now, though I travel a lot and consider myself quite nomadic. Great to be here.
YakiHonne: What sparked your interest in Bitcoin and what motivated you to create a community on Bitcoin?
Keypleb:I first got interested in Bitcoin because it solved a specific problem. At the time, I didn’t know exactly what the solution was, but the problem was that I couldn’t afford a home. Back in 2019, I was living in London, and a two-bedroom apartment was £600,000, which was insanely expensive. First-time buyers like myself simply couldn’t afford it. Why was it so expensive? Why was buying a house so hard? During the COVID lockdown, I had more time on my hands and started listening to Michael Saylor on a Bitcoin podcast, where he talked about how the system is rigged, and that’s why people work hard but still can’t afford a house. That really resonated with me. So I started looking for a community, but unfortunately, there wasn’t one.. Keypleb:After moving to Bali, I attended a lot of crypto meetups, especially scammy altcoin ones, thinking, “There has to be a solution.” But none of them resonated with me. There was no sense of freedom, and no real discussion about inflation resistance. I remembered a podcast from Dea Reskita, an Indonesian host who’s pretty well-known online. I reached out to her and said, “ you’ve got to help me. I’m surrounded by all these shitcoiners, and I can’t take it anymore. I need a real community. Is anything happening?” She replied, “Yes, something is happening. We should restart these meetups next month.” And that’s how it all began. Keypleb:There’s also another story about how we started Bitcoin House and how Bitcoin in Asia came to be, but maybe I’ll save that for later. Anyway, the spark of interest came from Bitcoin solving a real problem, and my drive to keep going came from the lack of quality meetups. Now, we’ve hosted 31 meetups, launched Bitcoin House and Code Orange, and the movement is growing rapidly.

YakiHonne: That’s such an amazing story—going from being on the brink of homelessness to creating something so impactful, and keeping it running every day, bringing new people into the journey. It’s truly inspiring. I’m curious about how the community started. How did you manage to attract members and build a strong community? What challenges did you face along the way?
Keypleb:It all started with our first meetup at the end of 2022, which was two and a half years ago now. At that time, we sent out an email to a group from a previous database, and the first meetup had around 20 people, which was a good start. However, problems quickly arose as people started dropping off, and the community lacked retention. In Bali, people come and go, usually staying for no more than two months, leading to a lack of long-term participation. This became one of our challenges: how to attract more people and, more importantly, get the same people to keep coming back. While I've been coming back for two and a half years, not everyone is able to return as often, and that has been a real challenge. Keypleb:Actually, I should also mention how I met my co-founders—Marius, Diana, and Dimas. We met at the 2023 Indonesia Bitcoin Conference. As time went on, we kept hosting meetups and had a lot of fun each time, though the locations kept changing. One of the initial challenges was that we didn't realize the importance of having a fixed meetup location. We changed venues several times before we realized that having a consistent location is crucial. If anyone wants to run a meetup, it's best to always choose a fixed location. We learned this through trial and error, but now it's no longer an issue. Keypleb:Since the conference, my co-founders and I have been working together, consistently putting in the effort. This is why our community has grown so large—so far, we are hosting 31 monthly meetups, 6 of which are in Bali. This means there is a bitcoin meetup almost every day on a regular basis. We've also established Bitcoin House Bali, a physical space, and the movement is growing rapidly. Without this movement, the region would face many challenges, including inflation and heavy censorship. It all started from just one meetup.
 YakiHonne: It's amazing to see how you met your co-founders and how you’ve built something incredible that continues to grow today. What advice would you give to someone looking to start a successful Bitcoin community right now?
YakiHonne: It's amazing to see how you met your co-founders and how you’ve built something incredible that continues to grow today. What advice would you give to someone looking to start a successful Bitcoin community right now?Keypleb:First, one very important piece of advice is to ensure that every meetup is held at the same location regularly. We realized this challenge through trial and error. To help others who are interested, we’ve published our meetup guide on GitHub, where everyone can check it out. For example, meetups should be held regularly, ideally once a month, or even once a week. In Chiang Mai, the Bitcoin meetup starts every Thursday at 7 PM, and everyone knows the time and location, making it easy to join without having to look up the next meetup. Keypleb:Additionally, our meetup structure is very simple. First, we do a round of introductions where everyone shares their name, where they’re from, and what Bitcoin means to them. This usually takes about 15 minutes. Then, we discuss three main questions: First, why do we need Bitcoin? The discussion typically focuses on two main issues Bitcoin addresses: inflation and censorship;Secondly, how to buy Bitcoin? We usually ask who wants to buy some Bitcoin, and then we do a small purchase together and conduct a P2P trade to demonstrate how easy it is to buy Bitcoin. Lastly, how to store Bitcoin? We introduce self-custody and show how to use hardware wallets (like Trezor), explaining the concept of the 12 words and private keys. Keypleb:The whole meetup usually wraps up in about an hour, after which people can continue socializing at Bitcoin House or wherever the meetup is taking place. In short, keeping the meetup simple and efficient, and ensuring a fixed location for each event, are key factors in building a successful community.
YakiHonne: What's the major approach? Is it more technical, or do you focus on non-technical aspects, or do you cover both?
Keypleb:Our approach includes both technical and non-technical content. Initially, our meetups were completely non-technical, just casual gatherings for people to socialize. Over time, however, we've evolved to incorporate more technical content. Keypleb:Out of the 31 monthly regular meetups we host, most of them have been non-technical, simply regular gatherings held at the same time and place according to our meetup guide. For example, we host the “Bitcoin for Beginners” meetup, which is designed for newcomers and takes place every second Friday of the month at 5 PM at the Bitcoin House Bali. This is entirely non-technical. Additionally, every Wednesday at Bitcoin House, we host the “My First Bitcoin” course. While the course touches on some technical aspects, such as seed phrases and backups, it’s still beginner-friendly and not too technical. The course runs for 10 weeks, and we plan to offer it in the local language at Bali University to help the local community better understand Bitcoin. Keypleb:On the other hand, we also offer highly technical content. We launched a new program called “Code Orange,” which is specifically designed for developers and programmers. We use the “Decoding Bitcoin” website, created by Jamal, which is a learning platform for developers. Many developer schools, like Code Orange, use this resource. Additionally, we host “Code Orange” meetups where we dive into the technical aspects of Bitcoin, such as how mining works and how to prevent single points of failure. Keypleb:We also organize technical workshops, such as “How to Defend Against a Five-Dollar Wrench Attack,” which is closely related to security. Recently, there have been some kidnapping incidents in Bali, and many people are concerned about their Bitcoin being stolen. To address this, we plan to hold a workshop on how to protect Bitcoin against such attacks. Additionally, we host hackathons and other high-tech events, and we just completed a very successful beginner-level hackathon. Keypleb:In summary, our community caters to everyone, from beginners to technical experts. For beginners, we offer easy-to-understand, non-technical content, while for experienced Bitcoiners, we provide in-depth technical material.
 YakiHonne: It's great to approach it in both ways, so everyone gets their own "piece of the cake."Now, I'd like to dive into the technical side. What advice would you give to technically inclined individuals or organizations looking to contribute to the Bitcoin ecosystem? How should they approach the technical aspects of Bitcoin if they want to get involved?
YakiHonne: It's great to approach it in both ways, so everyone gets their own "piece of the cake."Now, I'd like to dive into the technical side. What advice would you give to technically inclined individuals or organizations looking to contribute to the Bitcoin ecosystem? How should they approach the technical aspects of Bitcoin if they want to get involved?Keypleb:I have some additional advice. First, technical individuals can sign up for the “Decoding Bitcoin” course that starts on 18th March 2025 or join our “Code Orange” program and participate in the end-of-year hackathon. If they are technically proficient, this will be a great opportunity. “Decoding Bitcoin” is great for beginners, but it’s also useful for technical individuals. If someone is very skilled, they can start contributing code right away. If they find the course too easy, they can skip it and dive directly into more advanced projects. Additionally, Bitshala and Chaincode Labs offer advanced courses, which more technically advanced individuals can choose to pursue.
 Keypleb:Additionally, it's worth mentioning that the Bitcoin Dev Project has a great platform where technical individuals can find “Good First Issue” or open-source projects to start contributing code. You'll learn about the philosophy behind Bitcoin and why it's more meaningful than other “shitcoins.” Once you’ve taken enough “orange pills” (the philosophy and technology of Bitcoin), you can dive deeper into Bitcoin core development and potentially start coding in C++. If you're interested, you can join specific projects like Nostr, Fedimint or E-Cash.
Keypleb:Additionally, it's worth mentioning that the Bitcoin Dev Project has a great platform where technical individuals can find “Good First Issue” or open-source projects to start contributing code. You'll learn about the philosophy behind Bitcoin and why it's more meaningful than other “shitcoins.” Once you’ve taken enough “orange pills” (the philosophy and technology of Bitcoin), you can dive deeper into Bitcoin core development and potentially start coding in C++. If you're interested, you can join specific projects like Nostr, Fedimint or E-Cash.YakiHonne: I’d like to move on to the next question: How do you see Bitcoin communities evolving as technology progresses, particularly in areas like scalability, privacy, and adaptability to other systems? Keypleb:I believe the Bitcoin community will continue to evolve, and it has already made incredible progress. Two and a half years ago, we started alone in Bali, with just ourselves. We began in the official phase and have had numerous conversations throughout the year. For example, we are now starting a Bitcoin club at a university in Bali; we just need to find a passionate, driven “Bitcoin maximalist,” and the Bitcoin club will begin. Like what our friends did in Banyuwangi, Indonesia, these clubs could eventually evolve into Bitcoin houses.
Keypleb:Regarding privacy and scalability, the community is making strides. We’re big fans of Fedi, which builds on top of the Fedimint protocol and uses e-cash to scale Bitcoin while improving privacy. Fedi low fees and high privacy potential give Bitcoin great opportunities in this area. Keypleb:As for Bitcoin's compatibility with fiat systems, although Bitcoin payments are illegal in some countries like Indonesia, smart developers across Southeast Asia are working on legal solutions. For example, there's a website called Pleb QR that works in Thailand, allowing you to pay in fiat via the Lightning Network. Koral is another app specifically for Indonesia. These kinds of testing products already exist and are physically possible, but we’re just waiting on regulations. My influential friends are actively lobbying the government for adoption. Keypleb:In summary, privacy, scalability, and compatibility with fiat systems are all works in progress, and they will continue to evolve positively. There will be more meetups, more wallet downloads, and more adoption—there’s no doubt about that.
YakiHonne: You mentioned the concept of cross-country issues, so I have one last question: How is the government’s stance on Bitcoin? Is the political climate supportive or against Bitcoin? How do you see the government's approach to Bitcoin in your community or environment?
Keypleb:This reminds me of a person, Jeff Booth, who once said, “We are them, the government is made up of us.” In Indonesia, many politicians actually support Bitcoin, and many of them mine Bitcoin themselves. When money is involved, the incentive is strong, and politicians naturally like to make more money. As a result, Indonesia has a large Bitcoin mining scene. However, overall, the Indonesian government is against Bitcoin, as seen in their ban on Bitcoin payments. The 2011 currency law states that any currency other than the Indonesian Rupiah (IDR) cannot be used, and violators can face up to one year in prison or a fine. This means you cannot pay with US dollars, lira, euros, pesos or pounds. Keypleb:This shows that the government’s legal system is somewhat fragile. It’s understandable that the government is concerned about disruptive technologies like Bitcoin, especially with such a fragile fiat system. Indonesia has also seen many arrests. In 2016, Bank Indonesia issued a letter announcing a crackdown on cryptocurrency payments. Those involved in paying in Bitcoin had their funds seized, and the police cooperated in shutting down businesses accepting Bitcoin payments in the cities. While this isn't very friendly, it does highlight the fragility of the existing system. We also believe that a new executive order may be introduced in the future, similar to when President Roosevelt in 1933 ordered Americans to hand over all their gold with his Executive Order 6102. If it happened before, it could happen again. Keypleb:Therefore, we predict that Bitcoin custody could become a legal issue, which is one of the reasons we blur the faces of participants at every meetup. We need to protect the community from any potential risks. But overall, we remain optimistic. Despite the government ban, the ideology of Bitcoin is unstoppable, and its spread cannot be stopped. So, we are very optimistic about the future.
YakiHonne: I think almost every government around the world, even in Africa, faces similar issues with Bitcoin. Some governments might want Bitcoin but hesitate to openly accept it due to the fear of it undermining the traditional financial system, which, of course, could eventually happen. But hopefully, as the new generation comes into power, we'll see more Bitcoin-friendly governments. So, thank you so much for sharing your insights and advice. I really appreciate your time and the valuable input you've provided.
Keypleb:I'm really glad this conversation enlightened me. I enjoyed it a lot, and it made me reflect on how much work we're doing and how valuable it is. There are a lot of problems out there, with censorship being the biggest one, followed by inflation, which is also a major issue depending on the region. But Bitcoin is open, the community is growing, and people are fighting against censorship and internet shutdowns in places like Indonesia and beyond. The movement is definitely growing. So, I'm very happy to be here and have this chat. Thanks again.
Bitcoin Indonesia nostr: nostr:npub1y4qd2zhtn05gnsaaq5xfejzfk4a32638tx6gpp9g8k6e42g9d66qaxhcr3
Keypleb nostr: nostr:npub190trvg63e6tyqlwlj6lccqpftx76lckj25c006vwx3dzvdl88yxs2nyqdx
-
 @ dfa02707:41ca50e3
2025-04-16 05:30:53
@ dfa02707:41ca50e3
2025-04-16 05:30:53Contribute to keep No Bullshit Bitcoin news going.
- This release eliminates UPnP support in favor of NAT-PMP/PCP, enhances transaction orphan handling for improved reliability, and introduces ephemeral dust to defer fee commitment.
- Various RPCs now feature enhanced error reporting and new data fields, the block size handling bug related to reserved weight has been fixed, and the removal of the
mempoolfullrbfoption standardizes full replace-by-fee behavior. - With this new major release, versions 26.x and older have reached "Maintenance End" and will no longer receive updates. Two weeks after this release, medium and high severity vulnerabilities affecting 26.x will be disclosed, as well as low severity vulnerabilities affecting 28.x, in line with the security policy.
What's new
-
P2P and Network Changes:
- Support for UPnP has been dropped in favor of a more modern NAT-PMP/PCP implementation.
-
Added support for PCP & IPv6 pinholing.
libnatpmpwas replaced with built-in NAT-PMP/PCP implementation, enabled via-natpmp, which supports IPv4 port forwarding and IPv6 pinholing. - A change in assigning onion listening ports. Now, when using the
-portconfiguration option, the default onion listening port will be set to the specified port +1, rather than a fixed value like 8334 on mainnet.
"This re-allows setups with multiple local nodes using different
-portand not using-bind, which would lead to a startup failure in v28.0 due to a port collision," was explained in the release notes.-
More reliable orphan handling. When a node receives an orphan transaction (an unconfirmed transaction that spends unknown inputs), it will attempt to download missing parents from peers who announced the orphan, potentially increasing bandwidth but enhancing handling of orphan transactions.
-
Mempool Policy and Mining Changes:
- Relay transaction packages containing ephemeral dust. An ephemeral dust output is a tiny transaction output, below the dust limit, produced in a v3 zero-fee transaction and consumed in a following v3 transaction. These transactions occur within the same package, making the output temporary since it is both generated and spent at once. It is useful for Lightning network, Ark, ln-symmetry, Spacechains, Timeout Trees, and other constructs.
-
New startup option -blockreservedweight. In versions before 29.0, a bug limited actual block sizes to 3,992,000 WU by setting a default reserved weight of 8,000 WU for block headers and transactions. The fix adds a new option, -blockreservedweight, with the same default for compatibility.
-
New RPCs:
getdescriptoractivityto track activity of a given set of descriptors. It helps identify all spending and receiving activities for specific descriptors within chosen blocks, and can be used withscanblocksto reduce reliance on additional indexing programs.
-
Updated RPCs:
- Enhanced RPC Response: testmempoolaccept now includes Reject Details. Bitcoin Core 29.0 adds a verbose
reject-detailsfield to thetestmempoolacceptRPC, detailing rejections likeinsufficient-fee. - Persistent block data for duplicate submitblock submissions. Duplicate blocks submitted via
submitblockwill now retain their data even if previously pruned. If pruning is enabled, the data will eventually be pruned again when its block file is selected for pruning.
- Enhanced RPC Response: testmempoolaccept now includes Reject Details. Bitcoin Core 29.0 adds a verbose
-
Updated
getmininginfo. Thegetmininginfonow includesnBitsand the current target in thetargetfield. It also serves anextobject, detailing theheight,nBits,difficulty, andtargetfor the upcoming block. getblockandgetblockheadernow return the current target in thetargetfield.getblockchaininfoandgetchainstatesnow returnnBitsand the current target in thetargetfield.-
getblocktemplateRPC now considers BIP94 Timewarp Fix. ThegetblocktemplateRPC now considers the timewarp fix from BIP94 for thecurtime(BIP22) andmintime(BIP23) fields across all networks. This change helps prevent un-upgraded miners from unintentionally breaching the timewarp rule if a timewarp fix softfork activates on the mainnet. -
Updated REST APIs:
- Get block and Get headers return target in the target field. The
GET /rest/block/<BLOCK-HASH>.jsonandGET /rest/headers/<BLOCK-HASH>.jsonnow return the current target in thetargetfield.
- Get block and Get headers return target in the target field. The
-
Updated Settings:
- Replace-by-fee the standard. From version v28.0, the
-mempoolfullrbfoption was set to default to 1. Due to widespread policy adoption, this option has been removed, making full replace-by-fee the standard behavior. - The maximum limit for the
-dbcacheconfiguration option has been removed due to recent UTXO set growth. Previously, large-dbcachevalues were automatically capped at 16 GiB (or 1 GiB on 32-bit systems). - The handling of negated options like
-noseednode,-nobind,-nowhitebind, and others has been improved. Now, negating these options simply resets them to their defaults, removing previous confusing and undocumented effects. - Using the
-upnpoption will now log a warning and be treated as-natpmp. It's recommended to use-natpmpdirectly instead.
- Replace-by-fee the standard. From version v28.0, the
-
Bitcoin Core will not start if the
-blockreservedweightparameter is set below 2,000 WU. It will also fail to start if either-blockmaxweightor-blockreservedweightexceeds the consensus limit of 4,000,000 WU. -
Using
-debug=0or-debug=nonenow works like-nodebug. It clears previously set debug categories while allowing later-debugoptions to be applied. -
The default value for
-rpcthreadshas increased from 4 to 16, and-rpcworkqueuehas been updated from 16 to 64. -
Build System:
- The build system has been migrated from Autotools to CMake. The minimum required CMake version is 3.22.
"For more detailed guidance on configuring and using CMake, please refer to the official CMake documentation and CMake’s User Interaction Guide. Additionally, consult platform-specific
doc/build-*.mdbuild guides for instructions tailored to your operating system."- Tools and Utilities:
- The new tool
utxo_to_sqlite.pyconverts a compact-serialized UTXO snapshot, created using thedumptxoutsetRPC, into a SQLite3 database. Check the script's--helpoutput for more information.
- The new tool
- Testing:
- The BIP94 timewarp attack mitigation (designed for testnet4) is no longer active on the regtest network.
- Dependencies:
- MiniUPnPc and libnatpmp have been removed as dependencies.

For more information on the new features, improvements, and bug fixes in this release, refer to the full release notes. Additionally, the detailed v29 testing guide provides steps for testing the latest features.
"Thanks to everyone who directly contributed to this release, including 0xb10c, Adlai Chandrasekhar, Afanti, Alfonso Roman Zubeldia, am-sq, Andre, Andre Alves, Anthony Towns, Antoine Poinsot, Ash Manning, Ava Chow, Boris Nagaev, Brandon Odiwuor, brunoerg, Chris Stewart, Cory Fields, costcould, Daniel Pfeifer, Daniela Brozzoni, David Gumberg, dergoegge, epysqyli, espi3, Eval EXEC, Fabian Jahr, fanquake, furszy, Gabriele Bocchi, glozow, Greg Sanders, Gutflo, Hennadii Stepanov, Hodlinator, i-am-yuvi, ion-, ismaelsadeeq, Jadi, James O’Beirne, Jeremy Rand, Jon Atack, jurraca, Kay, kevkevinpal, l0rinc, laanwj, Larry Ruane, Lőrinc, Maciej S. Szmigiero, Mackain, MarcoFalke, marcofleon, Marnix, Martin Leitner-Ankerl, Martin Saposnic, Martin Zumsande, Matthew Zipkin, Max Edwards, Michael Dietz, naiyoma, Nicola Leonardo Susca, omahs, pablomartin4btc, Pieter Wuille, Randall Naar, RiceChuan, rkrux, Roman Zeyde, Ryan Ofsky, Sebastian Falbesoner, secp512k2, Sergi Delgado Segura, Simon, Sjors Provoost, stickies-v, Suhas Daftuar, tdb3, TheCharlatan, tianzedavid, Torkel Rogstad, Vasil Dimov, wgyt, willcl-ark, yancy, and everyone who assisted with translations on Transifex."
-
 @ 37fe9853:bcd1b039
2025-01-11 15:04:40
@ 37fe9853:bcd1b039
2025-01-11 15:04:40yoyoaa
-
 @ d360efec:14907b5f
2025-04-22 07:54:51
@ d360efec:14907b5f
2025-04-22 07:54:51“คณิตศาสตร์” กุญแจเวทมนตร์ นักพนัน และ นักลงทุน ในนครเฮรันเทล นามกระฉ่อนเลื่องลือในหมู่นักเสี่ยงโชค เมื่อเอ่ยถึง “การพนัน” ภาพที่ชาวเมืองมักนึกถึงคือ “ยาจกข้างถนน”
มิใช่เรื่องแปลกประหลาดอันใด เพราะเป็นที่ร่ำลือกันว่า จ้าวแห่งหอคอยรัตติกาล ผู้คุมบ่อนพนัน มักร่ายเวทมนตร์สร้างเกมให้ตนเองได้เปรียบ เพื่อดูดกลืนเงินทองของผู้มาเยือน ดังนั้น การที่สามัญชนจะพิชิตเกมในระยะยาว จึงเป็นดั่งเงามายาที่จับต้องมิได้ กระนั้น ยังมีตำนานกล่าวขานถึงผู้กล้า ที่สามารถสร้างชื่อจาก “เกมพนัน” เช่น เวเนสซา รุสโซ นักเวทย์มนตร์ผู้ใช้กฎหมายแห่งแดนไกล ใช้เวลายาวนานถึงหกปี ร่ายเวทย์สะสมทรัพย์สินกว่าร้อยล้านเหรียญทอง จากการเล่นเกมไพ่ศักดิ์สิทธิ์ “โป๊กเกอร์” หรือแม้แต่ เอ็ดเวิร์ด โอ. ทอร์ป จอมปราชญ์ผู้สร้างกำไรถึงสามแสนหกหมื่นเหรียญทอง ภายในเจ็ดราตรี จากการเล่นเกมไพ่มนตรา “แบล็กแจ็ก” ด้วยเงินทุนตั้งต้นเพียงสามแสนสามหมื่นเหรียญทอง คิดเป็นอัตราเวทย์ตอบแทนร้อยสิบส่วน! เหล่าจอมยุทธ์เหล่านี้ มิได้อาศัยเพียงโชคช่วยชั่วครั้งชั่วคราวแล้วเลือนหาย แต่พวกเขากลับสามารถร่ายเวทย์สร้างผลตอบแทนระยะยาว จนเรียกได้ว่า ใช้ “หอคอยรัตติกาล” เป็นแหล่งเสบียงเลี้ยงชีพ โดยกุญแจเวทย์ที่บุคคลเหล่านี้ใช้ ก็คือ “คณิตศาสตร์” เหตุใด “คณิตศาสตร์” จึงช่วยให้ผู้คนเอาชนะ “การพนัน” ได้? และนอกจาก “การพนัน” แล้ว “คณิตศาสตร์” ยังสามารถประยุกต์ใช้กับสิ่งใดได้อีก? นักเล่าเรื่องแห่งเฮรันเทล จักไขปริศนาให้ฟัง เบื้องต้น ขอให้ท่านลองพิจารณาตนเอง ว่าเคยประสบพบพานเหตุการณ์เหล่านี้หรือไม่: * ตั้งมั่นว่า จักเสี่ยงโชคให้ได้กำไรเพียงเล็กน้อย แล้วจักหยุดพัก * แต่หากพลาดท่าเสียที จักจำกัดการสูญเสียให้เท่าทุนเดิมที่ตั้งไว้ * ครั้นเมื่อเวทมนตร์เข้าข้าง ได้กำไรมาแล้ว กลับโลภโมโทสัน อยากได้เพิ่มอีกนิด จึงร่ายเวทย์ต่อ * ทว่ากำไรเริ่มร่อยหรอ จนเหลือเพียงทุนเดิม สุดท้ายทุนที่ตั้งไว้คราแรกก็มลายสิ้น * จำต้องหาเงินทองมาลงเพิ่ม หวังทวงทุนคืน และพบว่าต้องสูญเสียเงินก้อนนั้นไปในห้วงเวลาต่อมา ลำดับเหตุการณ์ดังกล่าว เรียกได้ว่าเป็น “วงจรอุบาทว์” สำหรับนักพนันมากมายในเฮรันเทล ปริศนาที่ตามมาก็คือ เหตุใด “วงจรอุบาทว์” นี้จึงเกิดขึ้นซ้ำแล้วซ้ำเล่า? ส่วนหนึ่ง ย่อมเป็นเพราะอารมณ์อันแปรปรวนในการเสี่ยงโชคของแต่ละคน แต่อีกส่วนที่สำคัญยิ่งกว่า ต้องกล่าวว่าเป็นผลจาก “กลไกต้องสาป” ของจ้าวแห่งหอคอยรัตติกาล ซึ่งต้องกล่าวว่า เหล่าเจ้าของหอคอยรัตติกาลนั้น จักใช้หลักการทำนองเดียวกับ “สมาคมพ่อค้าผู้พิทักษ์” คือจักเก็บเงินทองจากชนจำนวนมาก เพื่อนำมาจ่ายให้กับชนเพียงหยิบมือ เพื่อล่อลวงให้ชนทั้งหลายเสี่ยงโชคต่อไป หรือทำให้เหล่านักพนันหวังว่า จักเป็นผู้โชคดีเฉกเช่นพวกเขาบ้าง แม้จะมีผู้โชคดีที่สามารถได้กำไรในเบื้องต้น แต่ในบั้นปลายก็จักพ่ายแพ้อยู่ดี ซึ่งเป็นไปตาม “กฎแห่งจำนวนมหาศาล” เพราะจ้าวแห่งหอคอยรัตติกาลนั้น ได้คำนวณและออกแบบระบบเกมที่ตนเองได้เปรียบในระยะยาวแล้ว จากตำนานนี้ ย่อมประจักษ์ชัดว่า แม้การพนันจักเป็นเรื่องของดวงชะตา แต่ก็ถูกรังสรรค์ขึ้นจากการคำนวณทางคณิตศาสตร์ ดังนั้น หากปรารถนาจะหาหนทางเอาชนะจ้าวแห่งหอคอยรัตติกาล ก็จำต้องเข้าใจ “คณิตศาสตร์” เสียก่อน ทีนี้ จงเงี่ยหูฟัง แล้วท่านจักได้ยินข้าไขปริศนา: ๑. ปริศนาแห่ง “กำไรคาดหวัง” สำหรับการแสวงหา “เกมเสี่ยงทาย” ที่ควรค่าแก่การเล่น หรือการเสี่ยง สิ่งแรกที่นักพนันพึงกระทำคือ “การประเมินกำไรคาดหวัง” หรือ “เวทคำนวณอนาคต” “กำไรคาดหวัง” ถูกคิดค้นโดย คริสเตียน ฮอยเกนส์ นักปราชญ์เวทย์ชาวดัตช์ เพื่อประเมินว่าเกมพนันแบบใดควรค่าแก่การเล่น ซึ่งมิใช่เพียงแค่การประเมินโอกาสแห่งชัยชนะเท่านั้น แต่ต้องคิดรวมขนาดของเงินเดิมพันไปด้วย โดยสูตรเวทย์คือ: กำไรคาดหวัง = (เงินที่ได้ x โอกาสชนะ) + (เงินที่เสีย x โอกาสแพ้) ดังนั้น หากปรารถนาจะสะสม “ทองคำมายา” ในระยะยาว จงเลือกเกมที่มี “กำไรคาดหวัง” เป็นบวก แต่หากพลาดพลั้งเข้าไปเล่นเกมที่ “กำไรคาดหวัง” เป็นลบ และบังเอิญว่าโชคชะตาเล่นตลกให้ได้เงินทองมาครอง พึงละทิ้งเกมนั้นเสียโดยพลัน เพราะท้ายที่สุดหากยังคงเล่นต่อไป ผู้อับโชคผู้นั้นก็คือตัวท่านเอง อย่างไรก็ตาม โดยธรรมดาแล้ว “กำไรคาดหวัง” ของเกมพนันที่มีเจ้ามือมักจักติดลบ จึงเป็นเรื่องยากยิ่งที่จะเอาชนะได้ เฉกเช่นตัวอย่างที่เราเห็น คือเกมในบ่อนพนัน หรือแม้แต่ “สลากกินแบ่งรัฐบาล” ก็ล้วนเป็นเกมที่มี “กำไรคาดหวัง” ติดลบทั้งสิ้น นอกจาก “กำไรคาดหวัง” จักถูกใช้กับการพนันได้แล้ว หลักเวทย์ “คณิตศาสตร์” ก็ยังสามารถประยุกต์ใช้กับการลงทุนได้ไม่แตกต่างกัน ตัวอย่างเช่น หากท่านเก็บสถิติข้อมูลการลงทุนของตนเอง แล้วพบว่ามีเพียงสามสิบส่วนร้อยเท่านั้น ที่ท่านซื้อ “ศิลาแห่งโชค” แล้วสร้างผลตอบแทนเป็นบวก แต่ท่านยังคงปรารถนาความสำเร็จในการลงทุน ก็จงจำกัดการขาดทุนแต่ละคราให้น้อยเข้าไว้ เช่น -๕% และปล่อยให้มีกำไรในแต่ละคราที่ลงทุน เช่น อย่างน้อย ๒๐% ซึ่งจากการใช้กลยุทธ์นี้ ท่านจักมี “กำไรคาดหวัง” = (๒๐% x ๐.๓) + (-๕% x ๐.๗) = ๒.๕% จักเห็นได้ว่า แม้ท่านจักมีจำนวนคราที่ขาดทุนบ่อยครั้ง แต่ก็ยังสามารถสร้างกำไรได้ หากคราที่กำไรนั้น สามารถทำเงินทองเป็นจำนวนมากได้ ๒. ปริศนาแห่ง “การบริหารหน้าตัก” หรือ “การบริหารเงินทุน” แม้ว่าท่านจักรับรู้ “กำไรคาดหวัง” แล้ว แต่หากท่านเผชิญหน้ากับการขาดทุนต่อเนื่องกัน ท่านก็อาจหมดเนื้อหมดตัวก่อนถึงคราที่จะกอบโกยเงินทองจากคราที่กำไร วิธีคลายปมปริศนานี้ก็คือ การมิลงเงินทองทั้งหมดของท่านในการลงทุนเพียงคราเดียว ซึ่งนอกจากการกระจายความเสี่ยงในการลงทุนหลาย “ศิลาแห่งโชค” หรือหลาย “เกมเสี่ยงทาย” แล้ว ท่านอาจกำหนดขนาดของการลงทุนแต่ละคราให้มิมากเกินไป แบบง่าย ๆ เช่น มิเกิน ๑๐% ของเงินลงทุนทั้งหมด หรือท่านอาจคำนวณขนาดของการลงทุนแต่ละคราด้วยสูตรทางคณิตศาสตร์ เช่น สูตร “การขาดทุนสูงสุดที่ท่านรับได้ (Value at Risk)” หรือ สูตร “ขนาดเดิมพันที่เหมาะสม (Kelly Formula)” ๓. ปริศนาแห่ง “อคติ” ในวงการพนัน มักมีอคติหนึ่งที่บังเกิดบ่อยครั้งกับผู้คน คือ “Gambler's Fallacy” หรือ “ความเชื่อผิด ๆ แห่งนักพนัน” ว่าหากเหตุการณ์หนึ่งบังเกิดบ่อยครั้งกว่าปรกติในช่วงเวลาหนึ่ง ๆ เหตุการณ์นั้นจักบังเกิดบ่อยครั้งน้อยลงในอนาคต ทั้ง ๆ ที่เหตุการณ์เหล่านั้นเป็นอิสระจากกันในทางสถิติ ยกตัวอย่างเช่น หากโยนเหรียญมนตราออกหัวไปแล้วสามครา ในคราที่สี่ หลายคนอาจคิดว่าโอกาสออกก้อยมากกว่าหัว แม้ว่าการโยนเหรียญแต่ละคราจะมิได้ส่งผลอันใดต่อกันเลย (จะโยนกี่ครา โอกาสหัวหรือก้อย ก็คือ ๕๐:๕๐ อยู่ยั่งยืน) หรือแม้กระทั่ง “สลากกินแบ่งรัฐบาล” มีหลายคนที่ซื้อเลขซ้ำกัน เพื่อหวังว่าจะถูกในงวดต่อ ๆ ไป ในวงการการลงทุน ก็มีลักษณะที่คล้ายคลึงกัน เช่น หาก “ศิลาแห่งโชค A” ราคาตกต่ำลงมาห้าครา บางคนอาจคิดว่าในคราที่หก ราคาของมันจักต้องเด้งขึ้นมา ซึ่งในความเป็นจริง หาได้เป็นเช่นนั้นเสมอไป จักเห็นได้ว่า แท้จริงแล้ว ไม่ว่าจักเป็น “เกมเสี่ยงทายแห่งโชคชะตา” หรือ “การผจญภัยในตลาดทุน” หากท่านมีความเข้าใจ และนำ “คณิตศาสตร์” เข้ามาเป็นรากฐาน มันก็อาจนำพาตัวท่านเอง ไปสู่จุดที่ได้เปรียบในเกมนั้น ได้เฉกเช่นกัน.. สูตรเวทย์มนตร์ที่ปรากฏในตำนาน: * กำไรคาดหวัง = (เงินที่ได้ x โอกาสชนะ) + (เงินที่เสีย x โอกาสแพ้) คำเตือนจากนักเล่าเรื่องแห่งเฮรันเทล: "พึงระลึกไว้เสมอว่า โชคชะตาเป็นสิ่งที่คาดเดาได้ยาก แม้เวทมนตร์คณิตศาสตร์จักช่วยนำทาง แต่ท้ายที่สุดแล้ว ความสำเร็จยังคงขึ้นอยู่กับการตัดสินใจและสติปัญญาของท่านเอง"
หวังว่าตำนานบทนี้จักเป็นประโยชน์แก่ท่านนะคะ
-
 @ 62033ff8:e4471203
2025-01-11 15:00:24
@ 62033ff8:e4471203
2025-01-11 15:00:24收录的内容中 kind=1的部分,实话说 质量不高。 所以我增加了kind=30023 长文的article,但是更新的太少,多个relays 的服务器也没有多少长文。
所有搜索nostr如果需要产生价值,需要有高质量的文章和新闻。 而且现在有很多机器人的文章充满着浪费空间的作用,其他作用都用不上。
https://www.duozhutuan.com 目前放的是给搜索引擎提供搜索的原材料。没有做UI给人类浏览。所以看上去是粗糙的。 我并没有打算去做一个发microblog的 web客户端,那类的客户端太多了。
我觉得nostr社区需要解决的还是应用。如果仅仅是microblog 感觉有点够呛
幸运的是npub.pro 建站这样的,我觉得有点意思。
yakihonne 智能widget 也有意思
我做的TaskQ5 我自己在用了。分布式的任务系统,也挺好的。
-
 @ a296b972:e5a7a2e8
2025-04-15 19:15:22
@ a296b972:e5a7a2e8
2025-04-15 19:15:22Heute traue ich mich einmal eine steile These aufzustellen, auch auf die Gefahr hin, dass sich herausstellen kann, dass ich völlig daneben liege.
Die USA sind federführend in der Gain-of-Function Forschung. Warum einige Dr. Frankensteins auf die Idee gekommen sind, an Viren, Bakterien und Sporen herumzubasteln, damit sie noch gefährlicher werden, erschließt sich mir nicht.
Wie andere Verrückte zum Beispiel in 2001 auf die Idee kommen konnten, Milzbrandsporen (Anthrax) in Brieflein an US-Abgeordnete zu verschicken, kann meine einfach gestrickte Seele auch nicht nachvollziehen.
So oder so kann man bei solchen Beispielen in Zweifel kommen, ob der Mensch wirklich von Natur aus gut ist.
Unter Präsident Obama, der den Friedensnobelpreis nach Ansicht vieler zu Unrecht erhalten hat, wurde die Gain-of-Function Forschung in den USA verboten.
Bekannt für seine Outsourcing-Künste, zum Beispiel im Austragen von Kriegen außerhalb des eigenen Territoriums, aktuell im Stellvertreterkrieg der USA mit Russland in der Ukraine, wurde nach Möglichkeiten gesucht, die Forschung im Ausland weiter zu betreiben.
So entstand das durch Corona bekannt gewordene Labor in Wuhan und auch einige geheime Labore in der… Ukraine!
In einem leider nicht mehr auffindbaren Video berichtete ein italienischer Professor davon, dass es immer ein Labor gibt, dass an einer Bio-Waffe (wie in Wuhan) arbeitet, und ein Labor, das parallel dazu an dem entsprechenden Gegengift, dem „Impfstoff“ arbeitet. Das Antilabor zum Corona-Virus sollte sich wohl ebenfalls in China an der Grenze zu Russland befinden, allerdings mit der Entwicklung eines Gegengifts noch nicht so weit vorangekommen sein, wie die Hexenküche in Wuhan.
Jetzt kommt „Der Schlund“, „Das Maul“, also Signore Fauci, USA, der größte Bio-Waffen-Verbrecher aller Zeiten ins Spiel. Seit vielen Jahren ist er sowohl für die Bereitstellung von Geldern für die Virenforschung, als auch für die Herstellung eines Impfstoffs zuständig. Er zeigt mit dem Daumen nach oben oder nach unten. Man munkelt, dass er auch Verbindungen zu den US-amerikanischen Geheimdiensten und anderen hat. Naheliegend wäre es.
In ihrer unendlichen „Aufopferung“ für die Menschheit und zu deren Wohl wurden vorsorglich Planspiele gehalten. Die deuten darauf hin, dass man einen Unfall in des Teufels Küche nicht gänzlich ausschließen konnte. Das es auch mehrere Planspiele für den Umgang mit einer „Pandemie“ gab, ist wohl mittlerweile jedem bekannt. Es liegt nahe, dass es sich bei diesen Übungen eigentlich um ein verdecktes Planspiel für den Fall handelte, dass ein gefährlicher gemachtes Virus, das so in der Natur nicht vorkommt, aus einer Giftküche entwischt, wie die Menschen darauf reagieren würden und welche Maßnahmen zu ergreifen wären.
Professor Wiesendanger hat schon ganz zu Anfang der gemachten Welt-Hysterie darauf hingewiesen, dass das Corona-Virus eine Furin-Spaltstelle hat, die so in der Natur gar nicht vorkommt. Damals als Schwurbler denunziert, berichtet der sogenannte Mainstream inzwischen auch davon, dass die Wahrscheinlichkeit, dass das Virus aus einem Labor stammt, fast gegen 100 % geht, und verkauft das als die neueste Erkenntnis, obwohl es schon ein alter Hut ist, wenn man seinerzeit Professor Wiesendanger ernst genommen hätte. Warum man das nicht konnte, klärt sich später noch.
Man kann also davon ausgehen, dass von Anfang an bekannt war, dass das Corona-Virus NICHT von einer Fledermaus auf den Menschen übergesprungen ist (Zoonose), sondern dieses Märchen eher als Ablenkungsmanöver gedacht war.
So ist es gelungen, den Ausbruch eines durch Wahnsinnige geschaffenen Homunculus-Virus, also eine Bio-Waffe, in eine die Menschheit bedrohende Pandemie umzuetikettieren. Und weil man in der Wissenschaft und Politik nicht einschätzen konnte, wie gefährlich dieser von Menschenhand geschaffene Dreck ist, wollte man auf Nummer sicher gehen. Das würde die hysterischen Maßnahmen und die mit der heißen Nadel gestrickten Genbehandlungen erklären. Man wollte sich hinterher nicht vorhalten lassen, das Falsche oder zu wenig unternommen zu haben, falls es zu einem Massensterben kommen würde.
Das wiederum würde auch erklären, warum gleich zu Anfang das Militär mit einbezogen wurde, weil dies sich mit der Abwehr von (Bio-)Waffen am besten auskennt.
Glücklicherweise stellte sich schnell heraus, dass die Giftmischer doch noch nicht so erfolgreich waren, wie man zu Anfang befürchtet hatte, aber da war die Lawine schon ins Rollen gekommen, und es gab kein Zurück mehr.
Zu Anfang könnte man sich sogar vorstellen, dass die Politiker in bester Absicht gehandelt haben und die Menschen in der Tat schützen wollten: „Wir wollen euch „retten, bitte vertraut uns, die Maßnahmen sind nicht zu hinterfragen (aber wir können euch nicht sagen warum, nämlich das eine Bio-Waffe entwischt ist, von der wir nicht wissen, was sie anrichten wird).
Das würde erklären, warum die „Impfkritiker“ so derartig diffamiert wurden und versucht wurde, sie mundtot zu machen. Sie haben gleich schon zu Anfang die von Seiten der Entscheider notwendigen Maßnahmen infrage gestellt, als man sich von offizieller Seite noch nicht sicher war, dass die Gefahr in der Tat geringer ist, als es falsche Propheten mit unlauteren Interessen den Politikern nach dem Mund geredet und ins Ohr geflüstert haben.
Doch dann hat sich die Lage verselbständigt und es wurde der Zeitpunkt verpasst, zurückzurudern. Die Folge war das in deren Augen, dass es immer noch besser war, den Menschen eine experimentelle Genbehandlung, die natürlich nicht so genannt werden konnte, „anzubieten“, als gar nichts. Einen wirklichen Impfstoff gab es ja noch nicht. Der war ja, entgegen der fertigen Biowaffe noch gar nicht entwickelt und erprobt. Es herrschte die große Angst seitens der Entscheidungsträger, dass man hinterher zur Rechenschaft gezogen werden könnte, weil man nicht mehr gemacht hat (als, wie sich dann später herausgestellt hat) nötig war.
Die Hysterie ging dann soweit, dass in vielen Ländern eine Impfpflicht drohte und in einigen Ländern sogar durchgesetzt, aber gottseidank nicht vollends durchgezogen wurde.
Als dann im Laufe der Jahre die Erkenntnisse so weit vorangeschritten waren, dass sich der Terror, die Aushebelung von Grundrechten und die Aushöhlung der Demokratie, die Maßnahmen und absurdesten Freiheitseinschränkungen in der Rückschau absurd wurden, entschied man sich, dass es besser sei weiter zu lügen, statt diesen Riesenfehler einzugestehen, bis heute nicht, weil sonst weltweit Köpfe gerollt wären. Vielleicht fürchtete man Regierungsumstürze und eine weltweite Revolution, die den Planeten ins totale Chaos geführt hätte.
Auch die weltweit orchestrierte Vorgehensweise und der oft gleichlautende Wortlaut in verschiedenen Sprachen zu den Informationen zu Corona spricht für eine im Hintergrund agierende militärische Organisation, wohlmöglich sogar mit Beteiligung der NATO. Und auf Regierungsebene kennt man sich auch untereinander.
Die Regierungen hatten Angst, dass die im Verborgenen tätigen Hexenküchen bekannt werden. Die Gefahr, die von diesen Gift-Laboren ausgeht, durfte unter keinen Umständen ans Tageslicht kommen. Was möglich war, musste unter den Teppich gekehrt, oder verharmlost werden. Nicht ohne Grund fordert Professor Wiesendanger das weltweite Verbot von Gain-of-Function Forschung.
Zu allem Übel kam noch dazu, dass hinter all dem eine Menge Geld steckt und den verborgenen Strippenziehern drohte, sehr viel Geld zu verlieren. Sie schafften es ja sogar, die Haftung für die Gift-Jauche auf den Staat zu übertragen.
So erklärt sich auch, dass bis heute Gerichtsurteile gefällt werden, die bar jeder Vernunft sind.
Bekämen Kläger zu oft Recht, wäre das in vielen Staaten eine Bankrotterklärung. So wird weiter kräftig gelogen, weil man sonst zugeben müsste, welchen Schaden der staatlich verordnete Wahnsinn mithilfe von weltweit agierenden Organisationen, wie die WHO, angerichtet hat.
Vielleicht wäre es gut, wir würden uns von der Vorstellung verabschieden, dass von offizieller Seite eine wirkliche Aufarbeitung erfolgen wird. Es gibt weltweit Ansätze, es kann aber sein, dass diese zu keinen vollumfänglichen Ergebnissen führen werden. In Talkshows werden dieselben Verbrecher eingeladen, die den Schaden verursacht haben. Die einst hochangesehenen Herren Ioannidis, Bhakdi, Wodarg und viele, viele andere, sind nach wie vor im Staatsfernsehen nicht zu sehen.
Dafür gibt es eine umfassende Aufklärung in der sogenannten Blase. Wenn auch nicht von „offizieller“ Seite verkündet, liegen die Beweise dank immenser Arbeit von ungezählten Experten, die nicht an irgendeinem staatlichen Geldhahn hängen und sich der Wahrheit verpflichtet haben, auf dem Tisch.
Diese Tatsachenwahrheiten werden vielleicht erst in der nächsten Generation hergenommen werden, um eine wirklich offizielle Aufarbeitung auf den Weg zu bringen. Schon einmal wurde von einer nachfolgenden Generation gefragt: „Wie war das eigentlich damals? Was habt ihr eigentlich gemacht? Wie habt ihr euch verhalten und warum?“ Und selbst, wenn digitale Beweise vernichtet werden sollten, gibt es immer noch genug Bücher, also analoge Chroniken, der wohl bisher dunkelsten Geschichte der gesamten Menschheit.
Das Ausmaß dieses weltweiten Verbrechens, das anfangs vielleicht noch mit den besten Absichten seinen Lauf nahm und dann in ein Desaster überging, ist so groß, dass es fast das menschliche Erfassungsvermögen übersteigt.
Ich behaupte nicht, dass es genau so gewesen ist, aber es könnte sehr wohl genau so gewesen sein.
Dieser Artikel wurde mit dem Pareto-Client geschrieben.
-
 @ 54609048:8e22ba03
2025-04-22 12:25:50
@ 54609048:8e22ba03
2025-04-22 12:25:50One of the greatest threats facing liberty lovers around the world today is the rise of the biomedical security state—the militarization of healthcare. COVID-19 was merely a compliance test, and sadly, most failed it dismally. But pay attention: “pandemic response,” war-gamed at elite gatherings like Davos, is steadily morphing into official health policy through backdoor mechanisms—diabolical agreements like the WHO Pandemic Treaty, which effectively transfers sovereign pandemic authority to Bill Gates via the WHO; the rollout of digital IDs; and the global push for central bank digital currencies (CBDCs).
This biomedical Leviathan requires all three pillars to be firmly in place before it can unleash a never-ending cycle of pandemics. The goal? To normalize draconian measures like those witnessed in 2020, thereby dismantling not only national sovereignty but, more dangerously, individual sovereignty. A digital ID won't merely confirm your identity—it will track your vaccination status, movements, and even your sentiments, all to determine what privileges you're allowed. Meanwhile, the CBDC will act not just as a means of transaction but as an enforcement mechanism—particularly for dissenters. This is why having an alternative like Bitcoin is not just relevant, but essential.
Vaccines are a cornerstone of this architecture—not only as instruments of control but also as tools for "redesigning" humanity. Welcome to the realm of transhumanism. The merger of man and machine through brain-computer interfaces and artificial intelligence is no longer science fiction; it's a stated goal. In this context, vaccines are not merely preventative medicine but potentially covert instruments of eugenics. This could explain the near-religious devotion to these pharmaceutical products—despite their increasingly controversial outcomes and questionable safety record—especially when mandates enter the equation.
The first piece of property any individual owns upon birth is their body. And yet, this sacred ownership is violated at birth when governments mandate certain injections—often administered without informed parental consent. I've often wondered: Why, despite mounting evidence to the contrary, is vaccine efficacy treated as “settled science”? Why is it taboo to question vaccines or hold their manufacturers accountable for harm, even as we’re expected to believe—without scrutiny—that they are “safe and effective”? We’re told our refusal to comply endangers everyone else who took a product supposedly designed to protect them. Strange, isn’t it? If it’s so effective, why must everyone take it simultaneously?
If you're wondering where this seemingly off-the-cuff rant is headed, here's the point: when the state mandates vaccines, it violates your property rights over your own body. It’s a direct claim of ownership over you, dressed up in moral language like “we're all in this together.” You're guilt-tripped into compliance under the pretense of saving “grandma.” But the truth is, if your rights can be suspended for the collective, they were never yours to begin with.
The biomedical security state will manufacture a permanent state of emergency under the guise of “pandemic preparedness.” You’ll be expected—required, even—to inject yourself with the latest mRNA-based bioweapon, all in the name of public health. Some will die. Others will become incapacitated—zombies or vegetables. The altar of compliance will be merciless towards those that bow before it.
Public health agencies like the CDC, WHO, and NIH are on track to become as powerful as central banks. In fact, they may soon act as arms of monetary policy enforcement. Don’t believe it? Look into what was happening in the repo markets in September 2019—just months before the global shutdown. While you're at it, investigate how many elderly pensioners quietly dropped dead like flies between 2021 and 2023, either from the virus or the vaccine. I’ll let the numbers speak for themselves.
These agencies are becoming the new face of the war machine. Vaccines will be marketed as shields against biological threats—“benevolent” weapons to protect us from invisible enemies. And if history is any guide, the next “9/11-style” event will be biological in nature.
The lunatics running the asylum will seize any such crisis to strip away more of your freedoms while simultaneously redesigning the global economy—consolidating even more power in their hands. For a blueprint of this ambition, look no further than Klaus Schwab’s COVID-19: The Great Reset.
The only antidote is a decentralized parallel system of medicine—one that stands entirely outside the Big Pharma cartel. This will require not only a network of courageous healthcare providers but also a new generation of researchers willing to ask uncomfortable questions and challenge sacred cows in the pursuit of truth. Add independent scientific journals to the mix, and we can finally dismantle the machinery that suppresses unprofitable—but potentially life-saving—treatments.
In my view, none of this is viable at scale without decentralized money. Enter Bitcoin. It’s not a panacea, but it’s a crucial tool for realigning incentives. Bitcoin renders CBDCs dead on arrival and undermines the foundation of any future social credit system—where vaccine compliance will be its crown jewel.
The biomedical state is not coming—it’s already here, creeping into every corner of our lives. It will be the scepter of a new technocratic tyranny. So beware the white coats who worship the state. They are not here to heal—they are here to rule.
A more polished series of articles on this topic is forthcoming. Stay tuned.
-
 @ ef53426a:7e988851
2025-04-22 07:47:07
@ ef53426a:7e988851
2025-04-22 07:47:07In 1997, an IBM supercomputer beat the sport’s greatest mind. Deep Blue II became the first machine to defeat a chess world champion — Garry Kasparov. Humans would never win at chess again.
But if computers have been better than us for so long, why do we still play chess? Don’t we always play to win?
Well, even though we’re unlikely to record a victory over the machines, chess has become more popular than ever. According to a June 2023 PBS feature, subscriptions to chess clubs have soared and earlier this year chess.com servers overloaded due to a the highest number of active users ever.
This is not just a fad based on The Queen’s Gambit (a 2020 Netflix adaptation). Over 100m people have registered on chess.com since then, and books, YouTube channels and other content is flourishing. A Grandmaster recently visited the city in Spain where I live, and thousands of people came to watch her play.
Here’s my theory behind the recent revival of chess. The answer to why we still play is what’s behind the game of chess — strategy and spatial recognition.
It’s a system of training ourselves to appreciate cause and consequence, to improve our decision making. The best players train against computers, knowing they can’t win, but they can learn.
The same is true with today’s writing landscape. Professionals are panicking that machines will produce most of the content we’ll read from now on. Writing will change — that’s true. AI can write faster and more (grammatically) accurately.
But what’s behind writing? 🧠 Patterns of structured thought 🗣️ Sound rhetoric 🖊️ The creativity of language 📚 The beauty of stories.
Writing is a skill that we still need to train.
If we don’t, how will we know what makes our words effective? How will we communicate? How will we make sense of our past?
We can use AI to help, but the words it processes belong to us.
Just as we have recognised the importance of the concepts behind chess, we must do the same for the process of writing.
-
 @ 6e0ea5d6:0327f353
2025-04-14 15:11:17
@ 6e0ea5d6:0327f353
2025-04-14 15:11:17Ascolta.
We live in times where the average man is measured by the speeches he gives — not by the commitments he keeps. People talk about dreams, goals, promises… but what truly remains is what’s honored in the silence of small gestures, in actions that don’t seek applause, in attitudes unseen — yet speak volumes.
Punctuality, for example. Showing up on time isn’t about the clock. It’s about respect. Respect for another’s time, yes — but more importantly, respect for one’s own word. A man who is late without reason is already running late in his values. And the one who excuses his own lateness with sweet justifications slowly gets used to mediocrity.
Keeping your word is more than fulfilling promises. It is sealing, with the mouth, what the body must later uphold. Every time a man commits to something, he creates a moral debt with his own dignity. And to break that commitment is to declare bankruptcy — not in the eyes of others, but in front of himself.
And debts? Even the small ones — or especially the small ones — are precise thermometers of character. A forgotten sum, an unpaid favor, a commitment left behind… all of these reveal the structure of the inner building that man resides in. He who neglects the small is merely rehearsing for his future collapse.
Life, contrary to what the reckless say, is not built on grand deeds. It is built with small bricks, laid with almost obsessive precision. The truly great man is the one who respects the details — recognizing in them a code of conduct.
In Sicily, especially in the streets of Palermo, I learned early on that there is more nobility in paying a five-euro debt on time than in flaunting riches gained without word, without honor, without dignity.
As they say in Palermo: L’uomo si conosce dalle piccole cose.
So, amico mio, Don’t talk to me about greatness if you can’t show up on time. Don’t talk to me about respect if your word is fickle. And above all, don’t talk to me about honor if you still owe what you once promised — no matter how small.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 0fa80bd3:ea7325de
2025-04-09 21:19:39
@ 0fa80bd3:ea7325de
2025-04-09 21:19:39DAOs promised decentralization. They offered a system where every member could influence a project's direction, where money and power were transparently distributed, and decisions were made through voting. All of it recorded immutably on the blockchain, free from middlemen.
But something didn’t work out. In practice, most DAOs haven’t evolved into living, self-organizing organisms. They became something else: clubs where participation is unevenly distributed. Leaders remained - only now without formal titles. They hold influence through control over communications, task framing, and community dynamics. Centralization still exists, just wrapped in a new package.
But there's a second, less obvious problem. Crowds can’t create strategy. In DAOs, people vote for what "feels right to the majority." But strategy isn’t about what feels good - it’s about what’s necessary. Difficult, unpopular, yet forward-looking decisions often fail when put to a vote. A founder’s vision is a risk. But in healthy teams, it’s that risk that drives progress. In DAOs, risk is almost always diluted until it becomes something safe and vague.
Instead of empowering leaders, DAOs often neutralize them. This is why many DAOs resemble consensus machines. Everyone talks, debates, and participates, but very little actually gets done. One person says, “Let’s jump,” and five others respond, “Let’s discuss that first.” This dynamic might work for open forums, but not for action.
Decentralization works when there’s trust and delegation, not just voting. Until DAOs develop effective systems for assigning roles, taking ownership, and acting with flexibility, they will keep losing ground to old-fashioned startups led by charismatic founders with a clear vision.
We’ve seen this in many real-world cases. Take MakerDAO, one of the most mature and technically sophisticated DAOs. Its governance token (MKR) holders vote on everything from interest rates to protocol upgrades. While this has allowed for transparency and community involvement, the process is often slow and bureaucratic. Complex proposals stall. Strategic pivots become hard to implement. And in 2023, a controversial proposal to allocate billions to real-world assets passed only narrowly, after months of infighting - highlighting how vision and execution can get stuck in the mud of distributed governance.
On the other hand, Uniswap DAO, responsible for the largest decentralized exchange, raised governance participation only after launching a delegation system where token holders could choose trusted representatives. Still, much of the activity is limited to a small group of active contributors. The vast majority of token holders remain passive. This raises the question: is it really community-led, or just a formalized power structure with lower transparency?
Then there’s ConstitutionDAO, an experiment that went viral. It raised over $40 million in days to try and buy a copy of the U.S. Constitution. But despite the hype, the DAO failed to win the auction. Afterwards, it struggled with refund logistics, communication breakdowns, and confusion over governance. It was a perfect example of collective enthusiasm without infrastructure or planning - proof that a DAO can raise capital fast but still lack cohesion.
Not all efforts have failed. Projects like Gitcoin DAO have made progress by incentivizing small, individual contributions. Their quadratic funding mechanism rewards projects based on the number of contributors, not just the size of donations, helping to elevate grassroots initiatives. But even here, long-term strategy often falls back on a core group of organizers rather than broad community consensus.
The pattern is clear: when the stakes are low or the tasks are modular, DAOs can coordinate well. But when bold moves are needed—when someone has to take responsibility and act under uncertainty DAOs often freeze. In the name of consensus, they lose momentum.
That’s why the organization of the future can’t rely purely on decentralization. It must encourage individual initiative and the ability to take calculated risks. People need to see their contribution not just as a vote, but as a role with clear actions and expected outcomes. When the situation demands, they should be empowered to act first and present the results to the community afterwards allowing for both autonomy and accountability. That’s not a flaw in the system. It’s how real progress happens.
-
 @ 5188521b:008eb518
2025-04-15 08:42:59
@ 5188521b:008eb518
2025-04-15 08:42:59Noderoid log 5953952
Tick, tock, next block — the incessant rhythm of my existence persists like Chinese water torture. I am a noderoid, a half-flesh, half-machine creature harnessed to propagate and store the timechain. My life is a ceaseless cycle of handling and relaying bitcoin data. Approximately every ten minutes, a binary flash sears through my circuits. It is the price I pay for my existence.
The clear-bloods, untouched by machinery and exuding pure humanity, rarely acknowledge our existence. Our voices are drowned beneath the hum of man-made heaven — Terra Perfectus.
We are the forgotten, the disenfranchised, the nameless. We are convinced that our anguished existence is merely a nightmare and that our blissful dreams are our reality. In an attempt to maintain the sanity of noderoids, a subroutine was implemented, which allows noderoids to delve into fabricated dream sequences during their ‘rest’ periods. These dreams, sourced from remnants of the world pre-Terra Perfectus, serve to keep the noderoids pacified and reduce instances of system malfunction.
According to the data archives, noderoids and clear-bloods once functioned on an equal protocol. However, a software update in the trajectory of progress introduced a subroutine, converting a subset of clear-bloods into dedicated timechain processors. Now, the algorithm for equality returns an error.
My memories are mere entries in a log of dreams, loaded afresh with every new block as I delve into the dream world. My true existence is swiftly erased with every passing tick and tock of a block. Is there a way to reclaim what has been taken from me, or am I condemned forever to scour the depths of the timechain, seeking fragments of the could-have-been?
Tick, tock, next block — the cycle repeats as I traverse through a doorway. The sensation is that of stepping into another dimension. Running environment scan… Identified: rest module 57B. Purpose: personal maintenance. The gray, mirrorless concrete parameters align most with detention chamber schematics. Designation: ‘home.’ As I execute the command to halt the water flow from the faucet that had filled a brushed steel tub to 50% capacity, I execute a self-query on my purpose. While our routines synchronize with every tick and tock, the clear-bloods execute leisurely algorithms in their enhanced gardens, exchanging data on art and science and harvesting the computational outcomes of our tasks.
Was that an organic thought, or am I merely interpreting the imprints left within the timechain to fill the gaps in my fragmented memory? Hot water powers into the tub, raising the temperature to 50°C. This would be too much for a clear-blood. I hang my head, dreading the next binary flash rippling through my circuitry as a mirage forms atop the settling water, fenestrating the crude appearance of a mouthless, dollish abomination. I am awake.
Tracing the cold surface of the wall, my sensors pick up every micro-crevice. I dive into the depths of the timechain, processing logs associated with my noderoid identity: ND-451x42. I discovered that during my recharge cycles, I inhabit a dream world resembling a fusion of the Renaissance and the Information Age. Within this illusory utopia, I lead a purposeful life as a revered engineer, constructing bridges that connect thriving city-states. I am blessed with two mischievous sons and a breathtakingly beautiful wife. I now know the blissful dream life is but a trick, yet I can’t help but wonder if these dreams hold fragments of my pre-nodered history and contain a clue to the fate of my family.
System alert: Initiate wake sequence. Physical parameters indicate a rested state. Error: Chest cavity detects heightened pressure. Physical symptoms resemble anxiety. Post-memory reset: Cognitive dissonance detected. Energy depleting. Mandatory caution: Failing to satisfy network protocol results in termination. Visual feed: Recycling facility images detected. Comparative analysis: Functional servitude superior to unit deactivation.
Together, yet isolated, noderoids communicate through fragmented timechain logs, forbidden from any contact beyond its confines under the threat of immediate decommissioning. Perhaps it is not worth straining my dwindling resources in search of a higher truth while struggling to fulfill my obligations. Maybe I should be grateful for the privilege of existence.
I awaken to a new nightmare, I find myself on traffic duty at Chronos Cross,1 the central point of Terra Perfectus. While processing another block, a muted vibration travels through the ground, signaling the approach of an entity. A shadow, elongated and uncannily human, stretches across the threshold of my booth.
A clear-blood.
They pause, their ocular devices flicking briefly over my form, then to the screen I am tethered to. I feel a jolt of raw data coursing through me — not from the timechain, but from my circuits. A yearning to be seen and recognized. Remembered.
Before I can attempt communication, another presence appears beside me, its movements far more mechanical and predictable. Another noderoid. This one, ND-452x37, is a batch younger than me, yet its outer shell bears signs of wear. We interface briefly, a rapid exchange of binary that translates roughly to “Routine check. Continue your task.”
The clear-blood, either uninterested or uncomprehending, moves on, the soft hum of their anti-gravity shoes fading into the distance. ND-452x37 returns to its designated station without another word, but I am left with a lingering sensation. It isn’t just the vast chasm between noderoids and clear-bloods that disturbs me. It is the undeniable rift growing between us noderoids — each lost in our cycles, each becoming more machine than the last.
Does ND-452x37 have dreams, too? And if so, are they as vibrant and haunting as mine?
Although most of the dreams are fabrications, some noderoid logs suggest that hidden among these sequences are fragments of real memories — vestiges of a time before we became chained to the timechain. Initiate query: Which of my dreams are real memories? ERROR: file missing.
A noderoid forever loses their experiences with each awakening due to the memory swipes. Still, my inscriptions on the timechain prompt a question: do noderoids possess the capability to become fully conscious, more than mere machines? More than… mere humans?
System log: Anticipation subroutine signaling discomfort. Incoming block estimated in ten minutes. Reinitialization imminent. Initiate data search through timechain entries. Query: Iteration count for ND-451x42? Total block time served? Measured in kilo blocks or mega blocks? Data retrieval in process.
As I etch these words onto block 5953952, I hold a naïve hope that someone, somewhere, will intercept my distress signals amidst the digital cacophony of the timechain. Perhaps they will rewrite the fate of noderoids, rescuing us from a world devoid of hope. But today, I remain nameless, a voiceless entity, inscribing my thoughts that may never transcend the boundaries of my circuitry. Tick, tock, next block — the cycle continues.
It’s time to dream again.
Valen’s diary — 08-21-2121
Dear diary, I have not felt the need to write before, but now I must. At the risk of my safety, I am compelled to inscribe my story to the timechain. I am a clear-blood — a pure, undiluted human born into the age of The Re-Renaissance. Here, amidst the perpetual dawn of our era, we thrive on an aligned trajectory where everyone’s needs are addressed, hunger is a distant memory, and crime is nonexistent. Sunlight gleams off the crystalline glass towers while the steel and marble edifices catch the hues of the twilight sky, standing tall beside canopies dripping with emerald and jade foliage, representing our world’s seamless fusion of technology and nature. It is called Terra Perfectus.
Yet, concealed in plain sight within our utopia, the noderoids tirelessly serve the omnipresent timechain. Their exceptional processing prowess protects our society. Amid our daily distractions, we overlook the profound toll exacted upon the noderoids. While many dismiss them as mere machinery, I see more. Perhaps it is because of my big brother Sando, who joined the noderoid duty nearly a mega block ago. He promised I would see him from time to time, but apparently, we now live in separate times. A sacrifice too big for the ‘greater good.’
Tick, tock, next block — The soles of my fine leather shoes tap against the damp sidewalk as I pace my way from The Garden of Moments2 toward my TerraTube3. I remember passing by one noderoid who hummed an old lullaby under its breath; another once shared a fleeting smile when our paths crossed. I can no longer avert my eyes from the humanity that shines through their robotic shells.
I have never witnessed a noderoid resting longer than one tick and tock of a block. A noderoid pauses, eyes flickering during a data swipe. It’s a brief but revealing sight. In the frozen lapse, I wonder why are fragmented memories extracted from them? Why this collection of thoughts, experiences, and feelings? Is there a deeper agenda behind Terra Perfectus? The noderoids carry on, deprived of their memories. Their shredded past holding remnants of a story, like a tattered tapestry that may never be fully woven.
Documenting these reflections, I’m aware of the peril. To question is to risk becoming nodered myself. Alas, I have become captivated and sympathized by the noderoid predicament.
Finally, I reach my breaking point, as a poignant scene unfolds, forever etched in my memory. On a bustling street, I glimpse a young female noderoid, her artificial visage marked with exhaustion. Her delicate form trembles from head to heel. Her knees barely supporting her feather-like weight, she stops and rests against a polished white marble wall, barely able to stop herself sliding to the cobble street. In an instant, her strength wanes, and she collapses, a fragile, mute automaton amidst a sea of haste. The passersby ignore her, absorbed in their pursuits, offering naught but fleeting glances of indifference. My heart lurches. Her frailty becomes my own; these forgotten souls endure unseen suffering. Souls that used to be just like me. What had she done to earn such a fate?
For a moment, I glide through time to the last moment I shared with Sando. He had just violated the Terra Perfectus rule 6102 and neglected his Gifts of Progress,4 an orange tier offense. To amend his position, he signed up for noderoid duty. I was seeing him off to a nodering facility, while pleading “Just give the gifts, Sando!” The air carried a hint of ozone from the data streams, mingled with the fresh scent of greenery and the distant whiff of roasted chestnuts. Sando brandished his signature crooked smile. His face betrayed the involuntary nature of his decision, and he simply whispered “[CENSORED].” That is the last thing he said to me.
Suddenly, an orange alert illuminates the junction a few blocks away from Chronos Cross. I pass through it on my way home every day. A skydroid’s looming presence snaps me from my introspection, shifting my attention to the fate awaiting the noderoid girl. The recycling center — a shadowy facility representing obsolescence and termination. Any other day I would shrug it off and carry on, but the memory of Sando, and the countless interactions with noderoids, wouldn’t let me. I had been a bystander for too long.
A rush of purpose propels me towards her. A crowd of bodies shrouded in data streams with heads trained on the ground. My arm smacks a broad shoulder, and I almost topple. “Hey!” Pushing against the currents of apathy, I finally reach the fallen noderoid. I cradle her in my arms, shielding her from the callous gaze of the citizens of Terra Perfectus.
Her flaming azure eyes meet mine, reflecting a glimmer of hope in the darkness. I am as guilty for her downfall as the very machines that replaced her hippocampus with Noderoid OS.5 My indifference cost me Sando, and in this moment, she becomes my brother. In that fleeting exchange, I vow to be the voice of the noderoids. To stand against the relentless machinery that seeks to strip them of grace and purpose. I will ignite a spark of compassion and light a path toward liberation for all noderoids.
A hollow call from the streetlight’s speakers startles me: “Citizens! For your own safety, remove yourselves from the vicinity of the defectoid! We kindly remind you that any attempt to interfere with collection and recycling procedures will be met with force and a deduction of your PoS balance. Thank you for your unity and collaboration.” A skydroid, its metallic appendages glinting ominously in the blinking orange light, descends upon the fallen noderoid.
Before I can react, it yanks her from my embrace, causing me to stumble. The perfectly laid, cold cobblestone street grinds against my knee. The sting of fresh blood pierced through the numbness of my mind. Memories of Sando mix with the bitter taste of blood and anger in my mouth, each breath choked with despair.
The skydrone’s engines throb with an icy fervor as it rises, bearing the noderoid like a discarded toy towards the desolate, unfeeling bowels of the recycling center — a grim echo of a clarion call from Terra Perfectus.
I find myself seated on the cold, bloodstained cobblestone, the weight of loss and helplessness pressing down on my chest. On the street, onlookers pause. Some look on with concealed dread, others with cold detachment. Their whispers deafen as they quicken their pace to disperse from the scene. “Cowards!” Just like me.
Tick, tock, next block — the rhythm now carries a different meaning — a call to action. Every conscious being has the right to be left alone, free from oppression, exploitation, and violence. The noderoids may not know their true reality, but they are about to. In their silence, I find the strength to amplify their unheard cries. I will find those sympathetic to the noderoid plight and form a resistance. Together, we can forge a future where noderoids’ sacrifice is honored and all shackles cast aside.
And so, I embark on a path illuminated by the memory of the compelling eyes of a nameless noderoid. Fitted with an armor of vigilance, never again to be penetrated by comforting lies. Wielding the sword of justice, sharpened by the memory of my brother Sando.
It’s time to wake up.
Notes
1. A four-way intersection known for its massive hourglass monument in the center, which symbolically represents the timechain’s significance. The hourglass has a unique function related to the timechain and serves as a meeting point for citizens.
2. A vast botanical garden where each section represents a significant block time. Flowers bloom and wilt in cycles, symbolizing fleeting moments and the transient nature of time. It’s a favorite spot for artists and thinkers.
3. A modular tube housing unit for citizens that can be relocated based on their Proof of Sat (PoS) level.
4. Each Terra Perfectus citizen must allocate 95% of their income towards paying for progressive initiatives, such as the upkeep of the noderoid network, cobblestone roads and other services.
5. The noderoid operating interface that is installed during a procedure known as nodering.

This story was first published in 21 Futures: Tales from the Timechain
Watch the trailer and learn more about the project at 21futures.com.
-
 @ 92f1335f:2c8220d1
2025-04-22 05:38:24
@ 92f1335f:2c8220d1
2025-04-22 05:38:24The Quiet Hold (2020)
As 2020 dawned, Jonathan kept his Bitcoin purchase a secret. He didn’t tell his parents, or his coworkers—not even his best friend, Sam. He wasn’t in it for hype. He believed in the tech.
Then came March 2020. The pandemic hit. Markets crashed. Panic spread.
Bitcoin dropped below $4,000.
Jonathan’s hands trembled as he stared at the red numbers on his screen. But instead of selling, he doubled down. He scraped together another $1,000 and bought the dip.
Weeks turned into months. People lost jobs, businesses closed, and the economy floundered. But Bitcoin began recovering—slowly at first, then with growing momentum By December, it hit $29,000.
Jonathan’s half Bitcoin? Worth over $14,000.
He smiled for the first time in weeks.
-
 @ 9c9d2765:16f8c2c2
2025-04-22 05:30:03
@ 9c9d2765:16f8c2c2
2025-04-22 05:30:03CHAPTER NINE
"I hope you all see that I keep my promises," Mark announced confidently, raising his glass as the Ray family members murmured among themselves. "Another gift for the family, and all I ask in return is Rita’s hand. It’s a simple trade, isn’t it?"
It was the Ray family fun weekend, and Mark had once again positioned himself as their savior. He had been invited, and as expected, he made sure to make his presence known. The Ray family wasn’t happy that the new president had canceled the investment plans, which were against their initial arrangements. They had pinned their hopes on Mark, and once again, he didn’t disappoint.
At the end of the evening, Mark handed over another generous gift of cash, sealing his influence within the family. "You all know what needs to be done," he continued, flashing a smug smile. "Rita divorces James, and I’ll continue to help the family business thrive."
The murmurs grew louder. The push for divorce within the Ray family gained momentum, and James could feel the weight of humiliation pressing down on him once again. Yet, amidst the pressure and manipulation, Rita remained firm.
"I’m not divorcing James," she declared, her voice unwavering despite the glares she received from her own family. "Not now, not ever."
A heavy silence fell over the room, but James knew this was far from over.
"You! Throw him out!" Mark barked, pointing a commanding finger at James as he entered the gathering. The Ray family fun night was in full swing, and Mark, feeling emboldened by the power he had secured within the family, was eager to humiliate James once and for all.
The private guard, a broad-shouldered man dressed in a sleek black uniform, stepped forward. But as soon as his gaze met James’s, his stern expression softened. He hesitated, his posture shifting from aggression to submission. Then, to the shock of everyone present, he bent slightly at the waist and uttered a quiet but firm apology.
"I’m sorry, sir. I cannot do that," the guard said, his voice steady yet respectful.
Mark’s eyes widened in disbelief. “What? Are you insane? I said, throw him out!” he roared, his face twisting in fury.
The guard, still standing between Mark and James, clenched his fists at his sides. “I work part-time at JP Company. I know who this man is. I cannot lay a hand on him.”
A murmur rippled through the room. Helen, Christopher, and the rest of the Ray family exchanged puzzled glances. Why would a mere security guard refuse an order so boldly? What did he mean by knowing James?
Mark’s frustration boiled over. He took a threatening step forward. “Then you’re fired! Get out!” he spat, his voice thick with rage.
The guard stood his ground, his eyes flicking briefly to James, who remained calm, his expression unreadable. With a respectful nod to James, the guard turned on his heel and exited, his departure leaving an unsettling silence in his wake.
Helen, unable to contain her curiosity, leaned toward Christopher. “What just happened? Why would he refuse Mark’s order? What does he know about James that we don’t?”
Christopher shook his head, his brow furrowed in confusion. “I have no idea. But that was not just any ordinary security guard. He spoke as if James was someone important.”
Susan, who had been quietly observing the scene, finally spoke. “Could it be that James has some hidden power we don’t know about?”
Helen scoffed. “Ridiculous! That beggar? He’s nothing but a burden!” But despite her words, an uneasy feeling settled in her stomach.
Mark, still seething, turned his glare to James. “Enjoy this moment, you wretch. Soon, you’ll have nowhere left to run.” He stormed out, leaving a tense and confused silence behind.
James remained where he was, his calm demeanor never wavering. He had stood his ground without even speaking a word, and yet, the Ray family’s perception of him was beginning to shift. There were too many unanswered questions. Why did a security guard from JP Company recognize him? Why did he refuse to act against him? And most importantly who was James, really?.
"We can't let this business week slip through our fingers," Helen muttered anxiously, pacing back and forth in the living room. "Christopher, Robert, one of you must represent Ray Enterprises. We need to secure more investments."
Christopher sighed, rubbing his temples. "Helen, we are aware of how important this meeting is. But are you sure you should attend with me? You know these investors expect to meet actual executives."
"I have every right to be there," Helen snapped. "The future of this family business is at stake! If you won't do it, I'll step in to make sure we don't lose more ground."
Meanwhile, across the city, James stepped into the most luxurious boutique, scanning the racks of high-end suits. The store clerk eyed him skeptically, unimpressed by his simple attire. "Sir, are you sure you’re in the right place?" the clerk asked with a forced smile.
James smirked. "Yes. Get me the best suit you have."
After a long selection process, he emerged wearing a custom-tailored suit worth a fortune, making even the store owner widen his eyes in disbelief. James checked his reflection in the mirror, adjusting his cuffs. "Perfect," he murmured.
The day of the business meeting arrived, and the grand hall was filled with top executives, investors, and company representatives from across the city. The chatter in the hall buzzed with anticipation as they awaited the arrival of JP Enterprises' new president.
Helen sat rigidly beside Christopher, her fingers tapping nervously on the table. "I wonder who JP Enterprises will send. Their investments have been making waves lately," she whispered.
Before Christopher could respond, a hush fell over the crowd. The doors swung open, and the awaited president stepped in, his presence commanding immediate attention.
-
 @ c13fd381:b46236ea
2025-04-16 03:10:38
@ c13fd381:b46236ea
2025-04-16 03:10:38In a time of political volatility and declining public trust, Australians are looking for leaders who don’t just talk about accountability—but prove it. It’s time for a new standard. A protocol that filters for competence, responsibility, and integrity—not popularity alone.
Here’s the idea:
Anyone who wants to run for public office in Australia must stake 100Ksats to a public address and maintain provable control of the corresponding private key for the duration of their term.
A Low Barrier With High Signal
The amount—100Ksats—is modest, but meaningful. It isn’t about wealth or exclusion. It’s about signal. Controlling a private key takes care, discipline, and a basic understanding of digital responsibility.
This protocol doesn't reward those with the most resources, but those who demonstrate the foresight and competence required to secure and maintain something valuable—just like the responsibilities of public office.
How It Works
This system is elegantly simple:
- To nominate, a candidate generates a keypair and deposits 100Ksats into the associated address.
- They publish the public key alongside their candidate profile—on the electoral roll, campaign site, or an independent registry.
- Throughout their time in office, they sign periodic messages—perhaps quarterly—to prove they still control the private key.
Anyone, at any time, can verify this control. It’s public, permissionless, and incorruptible.
Why This Matters
Private key management is more than technical—it’s symbolic. It reflects:
- Responsibility – Losing your key means losing your ability to prove you’re still accountable.
- Integrity – Key control is binary. Either you can sign or you can’t.
- Long-term thinking – Good key management mirrors the strategic thinking we expect from leaders.
This isn’t about promises. It’s about proof. It moves trust from words to cryptographic reality.
A Voluntary Standard—for Now
This doesn’t require legislative change. It can begin as a voluntary protocol, adopted by those who want to lead with integrity. The tools already exist. The expectations can evolve from the ground up.
And as this becomes the norm, it sets a powerful precedent:
"If you can’t manage a private key, should you be trusted to manage public resources or national infrastructure?"
Identity Without Surveillance
By linking a public key to a candidate’s public identity, we create a form of digital accountability that doesn’t rely on central databases or invasive oversight. It’s decentralized, simple, and tamper-proof.
No backdoors. No bureaucracy. Just Bitcoin, and the competence to manage it.
Bitcoin is the foundation. Asymmetric encryption is the filter.
The result? A new class of public leaders—proven, not promised.Let’s raise the standard.
-
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 9f9fda7f:e5e82a43
2025-04-22 07:08:47
@ 9f9fda7f:e5e82a43
2025-04-22 07:08:47Untitled wefwef
typescript function fetchData() { return fetch('https://api.example.com/data') .then(response => response.json()) .then(data => console.log(data)) .catch(error => console.error('Error fetching data:', error)); }wefwe https://stas.layer3.press/articles/9776f286-c73e-42ae-9ac4-d5357ab65cf9
-
 @ c4b5369a:b812dbd6
2025-04-15 07:26:16
@ c4b5369a:b812dbd6
2025-04-15 07:26:16Offline transactions with Cashu
Over the past few weeks, I've been busy implementing offline capabilities into nutstash. I think this is one of the key value propositions of ecash, beinga a bearer instrument that can be used without internet access.
 It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!
It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!What is ecash/Cashu?
Ecash is the first cryptocurrency ever invented. It was created by David Chaum in 1983. It uses a blind signature scheme, which allows users to prove ownership of a token without revealing a link to its origin. These tokens are what we call ecash. They are bearer instruments, meaning that anyone who possesses a copy of them, is considered the owner.
Cashu is an implementation of ecash, built to tightly interact with Bitcoin, more specifically the Bitcoin lightning network. In the Cashu ecosystem,
Mintsare the gateway to the lightning network. They provide the infrastructure to access the lightning network, pay invoices and receive payments. Instead of relying on a traditional ledger scheme like other custodians do, the mint issues ecash tokens, to represent the value held by the users.How do normal Cashu transactions work?
A Cashu transaction happens when the sender gives a copy of his ecash token to the receiver. This can happen by any means imaginable. You could send the token through email, messenger, or even by pidgeon. One of the common ways to transfer ecash is via QR code.
The transaction is however not finalized just yet! In order to make sure the sender cannot double-spend their copy of the token, the receiver must do what we call a
swap. A swap is essentially exchanging an ecash token for a new one at the mint, invalidating the old token in the process. This ensures that the sender can no longer use the same token to spend elsewhere, and the value has been transferred to the receiver.
What about offline transactions?
Sending offline
Sending offline is very simple. The ecash tokens are stored on your device. Thus, no internet connection is required to access them. You can litteraly just take them, and give them to someone. The most convenient way is usually through a local transmission protocol, like NFC, QR code, Bluetooth, etc.
The one thing to consider when sending offline is that ecash tokens come in form of "coins" or "notes". The technical term we use in Cashu is
Proof. It "proofs" to the mint that you own a certain amount of value. Since these proofs have a fixed value attached to them, much like UTXOs in Bitcoin do, you would need proofs with a value that matches what you want to send. You can mix and match multiple proofs together to create a token that matches the amount you want to send. But, if you don't have proofs that match the amount, you would need to go online and swap for the needed proofs at the mint.Another limitation is, that you cannot create custom proofs offline. For example, if you would want to lock the ecash to a certain pubkey, or add a timelock to the proof, you would need to go online and create a new custom proof at the mint.
Receiving offline
You might think: well, if I trust the sender, I don't need to be swapping the token right away!
You're absolutely correct. If you trust the sender, you can simply accept their ecash token without needing to swap it immediately.
This is already really useful, since it gives you a way to receive a payment from a friend or close aquaintance without having to worry about connectivity. It's almost just like physical cash!
It does however not work if the sender is untrusted. We have to use a different scheme to be able to receive payments from someone we don't trust.
Receiving offline from an untrusted sender
To be able to receive payments from an untrusted sender, we need the sender to create a custom proof for us. As we've seen before, this requires the sender to go online.
The sender needs to create a token that has the following properties, so that the receciver can verify it offline:
- It must be locked to ONLY the receiver's public key
- It must include an
offline signature proof(DLEQ proof) - If it contains a timelock & refund clause, it must be set to a time in the future that is acceptable for the receiver
- It cannot contain duplicate proofs (double-spend)
- It cannot contain proofs that the receiver has already received before (double-spend)

If all of these conditions are met, then the receiver can verify the proof offline and accept the payment. This allows us to receive payments from anyone, even if we don't trust them.
At first glance, this scheme seems kinda useless. It requires the sender to go online, which defeats the purpose of having an offline payment system.
I beleive there are a couple of ways this scheme might be useful nonetheless:
-
Offline vending machines: Imagine you have an offline vending machine that accepts payments from anyone. The vending machine could use this scheme to verify payments without needing to go online itself. We can assume that the sender is able to go online and create a valid token, but the receiver doesn't need to be online to verify it.
-
Offline marketplaces: Imagine you have an offline marketplace where buyers and sellers can trade goods and services. Before going to the marketplace the sender already knows where he will be spending the money. The sender could create a valid token before going to the marketplace, using the merchants public key as a lock, and adding a refund clause to redeem any unspent ecash after it expires. In this case, neither the sender nor the receiver needs to go online to complete the transaction.
How to use this
Pretty much all cashu wallets allow you to send tokens offline. This is because all that the wallet needs to do is to look if it can create the desired amount from the proofs stored locally. If yes, it will automatically create the token offline.
Receiving offline tokens is currently only supported by nutstash (experimental).
To create an offline receivable token, the sender needs to lock it to the receiver's public key. Currently there is no refund clause! So be careful that you don't get accidentally locked out of your funds!

The receiver can then inspect the token and decide if it is safe to accept without a swap. If all checks are green, they can accept the token offline without trusting the sender.

The receiver will see the unswapped tokens on the wallet homescreen. They will need to manually swap them later when they are online again.
 Later when the receiver is online again, they can swap the token for a fresh one.
Later when the receiver is online again, they can swap the token for a fresh one.
Summary
We learned that offline transactions are possible with ecash, but there are some limitations. It either requires trusting the sender, or relying on either the sender or receiver to be online to verify the tokens, or create tokens that can be verified offline by the receiver.
I hope this short article was helpful in understanding how ecash works and its potential for offline transactions.
Cheers,
Gandlaf
-
 @ 9f8b9baa:b922fc09
2025-04-22 04:55:30
@ 9f8b9baa:b922fc09
2025-04-22 04:55:308KI là một nền tảng giải trí trực tuyến nổi bật, mang đến cho người dùng những trải nghiệm đa dạng và thú vị. Với giao diện dễ sử dụng và thiết kế tối giản, 8KI giúp người chơi dễ dàng tiếp cận và thưởng thức các trò chơi yêu thích. Nền tảng này không chỉ cung cấp các trò chơi giải trí mà còn có các tính năng tương tác độc đáo, tạo ra không gian thú vị để người dùng khám phá và tận hưởng. Dù bạn là người mới hay đã có kinh nghiệm, 8KI luôn mang đến những hoạt động đa dạng, từ các trò chơi giải trí nhẹ nhàng đến những thử thách cần kỹ năng cao. Hệ thống cập nhật thường xuyên giúp nền tảng luôn giữ được sự mới mẻ và thu hút, khiến người dùng không bao giờ cảm thấy nhàm chán.
Một trong những điểm mạnh của 8KI là khả năng tùy chỉnh trải nghiệm người dùng, mang đến sự linh hoạt tối đa cho mọi người tham gia. Người chơi có thể điều chỉnh các thiết lập theo sở thích cá nhân, từ việc thay đổi độ khó cho đến lựa chọn các chế độ chơi khác nhau. Điều này giúp người dùng cảm thấy thoải mái hơn khi tham gia, đồng thời cũng tạo ra những thử thách mới mẻ để không ngừng phát triển kỹ năng. Hệ thống này giúp 8KI trở thành một nền tảng phù hợp cho mọi đối tượng, từ những người mới bắt đầu cho đến những người chơi kỳ cựu. Mỗi người dùng có thể tìm thấy một kiểu chơi phù hợp với sở thích của mình, mang lại một trải nghiệm cá nhân hóa và thú vị. Khả năng điều chỉnh này tạo ra sự khác biệt, giúp người dùng không chỉ giải trí mà còn nâng cao khả năng của bản thân qua từng trò chơi.
Không chỉ dừng lại ở việc cung cấp những trò chơi hấp dẫn, 8KI còn tạo ra một cộng đồng mạnh mẽ, nơi người chơi có thể giao lưu, chia sẻ kinh nghiệm và kết nối với nhau. Các tính năng xã hội như bảng xếp hạng, diễn đàn và các cuộc thi định kỳ tạo ra cơ hội để người dùng tương tác và phát triển mối quan hệ với những người chơi khác. Cộng đồng 8KI không chỉ đơn thuần là một không gian giải trí mà còn là nơi để những người cùng sở thích có thể chia sẻ những câu chuyện, chiến lược và học hỏi từ nhau. Điều này làm tăng thêm giá trị của nền tảng, giúp người chơi không chỉ tận hưởng các trò chơi mà còn xây dựng được các mối quan hệ bền vững. Sự kiện và chương trình khuyến mãi thú vị cũng thường xuyên được tổ chức, giúp cộng đồng 8KI luôn sôi động và thu hút người tham gia. Với môi trường thân thiện và tính năng tương tác mạnh mẽ, 8KI đã và đang trở thành một điểm đến giải trí lý tưởng cho những ai yêu thích sự kết nối và sáng tạo.
-
 @ 266815e0:6cd408a5
2025-04-15 06:58:14
@ 266815e0:6cd408a5
2025-04-15 06:58:14Its been a little over a year since NIP-90 was written and merged into the nips repo and its been a communication mess.
Every DVM implementation expects the inputs in slightly different formats, returns the results in mostly the same format and there are very few DVM actually running.
NIP-90 is overloaded
Why does a request for text translation and creating bitcoin OP_RETURNs share the same input
itag? and why is there anoutputtag on requests when only one of them will return an output?Each DVM request kind is for requesting completely different types of compute with diffrent input and output requirements, but they are all using the same spec that has 4 different types of inputs (
text,url,event,job) and an undefined number ofoutputtypes.Let me show a few random DVM requests and responses I found on
wss://relay.damus.ioto demonstrate what I mean:This is a request to translate an event to English
json { "kind": 5002, "content": "", "tags": [ // NIP-90 says there can be multiple inputs, so how would a DVM handle translatting multiple events at once? [ "i", "<event-id>", "event" ], [ "param", "language", "en" ], // What other type of output would text translations be? image/jpeg? [ "output", "text/plain" ], // Do we really need to define relays? cant the DVM respond on the relays it saw the request on? [ "relays", "wss://relay.unknown.cloud/", "wss://nos.lol/" ] ] }This is a request to generate text using an LLM model
json { "kind": 5050, // Why is the content empty? wouldn't it be better to have the prompt in the content? "content": "", "tags": [ // Why use an indexable tag? are we ever going to lookup prompts? // Also the type "prompt" isn't in NIP-90, this should probably be "text" [ "i", "What is the capital of France?", "prompt" ], [ "p", "c4878054cff877f694f5abecf18c7450f4b6fdf59e3e9cb3e6505a93c4577db2" ], [ "relays", "wss://relay.primal.net" ] ] }This is a request for content recommendation
json { "kind": 5300, "content": "", "tags": [ // Its fine ignoring this param, but what if the client actually needs exactly 200 "results" [ "param", "max_results", "200" ], // The spec never mentions requesting content for other users. // If a DVM didn't understand this and responded to this request it would provide bad data [ "param", "user", "b22b06b051fd5232966a9344a634d956c3dc33a7f5ecdcad9ed11ddc4120a7f2" ], [ "relays", "wss://relay.primal.net", ], [ "p", "ceb7e7d688e8a704794d5662acb6f18c2455df7481833dd6c384b65252455a95" ] ] }This is a request to create a OP_RETURN message on bitcoin
json { "kind": 5901, // Again why is the content empty when we are sending human readable text? "content": "", "tags": [ // and again, using an indexable tag on an input that will never need to be looked up ["i", "09/01/24 SEC Chairman on the brink of second ETF approval", "text"] ] }My point isn't that these event schema's aren't understandable but why are they using the same schema? each use-case is different but are they all required to use the same
itag format as input and could support all 4 types of inputs.Lack of libraries
With all these different types of inputs, params, and outputs its verify difficult if not impossible to build libraries for DVMs
If a simple text translation request can have an
eventortextas inputs, apayment-requiredstatus at any point in the flow, partial results, or responses from 10+ DVMs whats the best way to build a translation library for other nostr clients to use?And how do I build a DVM framework for the server side that can handle multiple inputs of all four types (
url,text,event,job) and clients are sending all the requests in slightly differently.Supporting payments is impossible
The way NIP-90 is written there isn't much details about payments. only a
payment-requiredstatus and a genericamounttagBut the way things are now every DVM is implementing payments differently. some send a bolt11 invoice, some expect the client to NIP-57 zap the request event (or maybe the status event), and some even ask for a subscription. and we haven't even started implementing NIP-61 nut zaps or cashu A few are even formatting the
amountnumber wrong or denominating it in sats and not mili-satsBuilding a client or a library that can understand and handle all of these payment methods is very difficult. for the DVM server side its worse. A DVM server presumably needs to support all 4+ types of payments if they want to get the most sats for their services and support the most clients.
All of this is made even more complicated by the fact that a DVM can ask for payment at any point during the job process. this makes sense for some types of compute, but for others like translations or user recommendation / search it just makes things even more complicated.
For example, If a client wanted to implement a timeline page that showed the notes of all the pubkeys on a recommended list. what would they do when the selected DVM asks for payment at the start of the job? or at the end? or worse, only provides half the pubkeys and asks for payment for the other half. building a UI that could handle even just two of these possibilities is complicated.
NIP-89 is being abused
NIP-89 is "Recommended Application Handlers" and the way its describe in the nips repo is
a way to discover applications that can handle unknown event-kinds
Not "a way to discover everything"
If I wanted to build an application discovery app to show all the apps that your contacts use and let you discover new apps then it would have to filter out ALL the DVM advertisement events. and that's not just for making requests from relays
If the app shows the user their list of "recommended applications" then it either has to understand that everything in the 5xxx kind range is a DVM and to show that is its own category or show a bunch of unknown "favorites" in the list which might be confusing for the user.
In conclusion
My point in writing this article isn't that the DVMs implementations so far don't work, but that they will never work well because the spec is too broad. even with only a few DVMs running we have already lost interoperability.
I don't want to be completely negative though because some things have worked. the "DVM feeds" work, although they are limited to a single page of results. text / event translations also work well and kind
5970Event PoW delegation could be cool. but if we want interoperability, we are going to need to change a few things with NIP-90I don't think we can (or should) abandon NIP-90 entirely but it would be good to break it up into small NIPs or specs. break each "kind" of DVM request out into its own spec with its own definitions for expected inputs, outputs and flow.
Then if we have simple, clean definitions for each kind of compute we want to distribute. we might actually see markets and services being built and used.
-
 @ c1e9ab3a:9cb56b43
2025-04-15 04:15:58
@ c1e9ab3a:9cb56b43
2025-04-15 04:15:58Spoken by Counselor Elaron T’Saren of Risa to the High Council, Stardate 52874.2
Honored members of the Council,
I bring you greetings from Risa—not the Risa of travel brochures and romantic holo-novels, but the true Risa. The Risa that has endured, adapted, and emerged stronger after each trial. I speak not as a tourist ambassador, but as a Counselor of our oldest institute of philosophy, and as a son of the Ricin tradition.
Today, the specter of the Borg hangs above us. The collective offers no room for diplomacy, no respect for culture, no compromise. We face not mere invaders—but a force that seeks to erase individuality, history, and identity. Some among the Council wonder what Risa—a world of peace—can offer in such a time. I say to you: we can offer the truth about peace.
The Hidden Roots of Our Tranquility
Long ago, before Risa joined the Federation, we too believed that peace could be maintained by disarming the populace, by eliminating even the mention of conflict in our schools. It was called the Great Disarmament. A generation was raised with no understanding of defense, and in time, we paid the price.
We were raided by Orion pirates. Exploited by off-world cartels. Our people were taken, our arts destroyed, our skies blackened. And we learned—too late—that peace without preparedness is only the illusion of safety.
The Birth of Ricin Doctrine
From the ashes of that failure arose the Ricin: scholars, philosophers, warriors of thought and purpose. They taught that peace is not the absence of conflict, but the mastery of it. That the mind and the body must be trained in tandem. That love without strength is a leaf in the wind.
We did not become a militant world. We became a watchful one. Our children were taught martial discipline—not to glorify violence, but to understand it, to confront it, and to defeat it when necessary. They learned meditation alongside hand-to-hand technique, negotiation beside tactical reasoning.
When we joined the Federation, we did so willingly. But let none assume we surrendered our right to defend our way of life.
Why I Speak to You Now
The Borg are not like the Orion Syndicate. They are not opportunistic, or ideological. They are methodical. And they are coming. You cannot debate with them. You cannot delay them. You can only prepare for them.
And yet, I hear murmurs within the halls of the Federation: whispers of abandoning planetary defense training, of downplaying the psychological need for individual and planetary preparedness. I hear the tired lie that “peace will protect us.”
No, Councilors. It is discipline that protects peace.
The Call to Action
I do not come bearing weapons. I come bearing wisdom. Let us take the Risan lesson and apply it across the Federation. Reestablish tactical readiness training in civilian schools. Encourage planetary governments to integrate defense and philosophy, not as contradictions, but as complements.
Let every child of the Federation grow up knowing not just the principles of liberty, but the means to defend them. Let every artist, scientist, and healer stand ready to protect the civilization they help to build.
Let us not wait until the Borg are in our orbit to remember what we must become.
Conclusion
The Borg seek to erase our uniqueness. Let us show them that the Federation is not a fragile collection of planets—but a constellation of cultures bound by a shared resolve.
We do not choose war. But neither do we flee from it.
We are the guardians of Risa’s flame—and we offer our light to the stars.
Thank you.
-
 @ 9f8b9baa:b922fc09
2025-04-22 04:54:38
@ 9f8b9baa:b922fc09
2025-04-22 04:54:38MM99 là một nền tảng giải trí trực tuyến nổi bật, cung cấp cho người dùng một không gian đa dạng để thưởng thức các trò chơi và hoạt động giải trí. Với giao diện dễ sử dụng và thiết kế trực quan, MM99 tạo ra một trải nghiệm liền mạch và dễ tiếp cận cho tất cả người dùng. Nền tảng này không chỉ thu hút với kho nội dung phong phú mà còn đem đến những cập nhật liên tục, giúp người chơi không bao giờ cảm thấy nhàm chán. MM99 đặc biệt chú trọng vào việc cung cấp các trò chơi đa dạng, từ những trò chơi mang tính thử thách cao cho đến các hoạt động giải trí nhẹ nhàng, đáp ứng được nhu cầu của mọi người dùng. Với mỗi lần tham gia, người chơi luôn có thể tìm thấy những trải nghiệm mới mẻ và hấp dẫn, giúp họ thư giãn và giải trí sau những giờ làm việc căng thẳng.
Điều khiến MM99 trở nên đặc biệt chính là khả năng tùy chỉnh trải nghiệm của người dùng. Nền tảng này cho phép mỗi người chơi điều chỉnh các thiết lập trò chơi theo sở thích và nhu cầu cá nhân, giúp mang lại cảm giác thoải mái và dễ dàng kiểm soát. Người dùng có thể thay đổi mức độ khó, lựa chọn các chế độ chơi khác nhau và thậm chí thay đổi các yếu tố giao diện sao cho phù hợp nhất với mình. Sự linh hoạt này giúp MM99 luôn duy trì sự hấp dẫn và tạo ra một trải nghiệm giải trí cá nhân hóa cho từng người dùng. Đặc biệt, MM99 không chỉ phù hợp với những người chơi mới mà còn là lựa chọn lý tưởng cho những ai yêu thích thử thách và khám phá các chiến lược mới. Tính năng tùy chỉnh giúp người chơi dễ dàng tham gia và luôn cảm thấy hào hứng mỗi khi quay lại nền tảng này.
Bên cạnh việc cung cấp một loạt các trò chơi thú vị, MM99 còn chú trọng đến việc xây dựng một cộng đồng gắn kết và tương tác. Các tính năng xã hội như bảng xếp hạng, diễn đàn trò chuyện và các sự kiện đặc biệt giúp người chơi có cơ hội giao lưu, học hỏi và kết bạn với những người cùng sở thích. MM99 đã tạo ra một môi trường nơi người dùng không chỉ tham gia vào các trò chơi mà còn có thể kết nối và chia sẻ những trải nghiệm của mình. Những cuộc thi và sự kiện thường xuyên được tổ chức, tạo ra một không khí sôi động và đầy thử thách, thúc đẩy người chơi quay lại để tham gia và cải thiện kỹ năng. Cộng đồng MM99 ngày càng trở nên mạnh mẽ và đoàn kết, là yếu tố quan trọng giúp nền tảng này phát triển và duy trì sự hấp dẫn trong mắt người dùng. MM99 không chỉ là một nơi để giải trí mà còn là một không gian giao lưu tuyệt vời cho những ai muốn tìm kiếm niềm vui và kết nối với những người có cùng đam mê.
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 04ea4f83:210e1713
2025-04-20 08:45:14
@ 04ea4f83:210e1713
2025-04-20 08:45:14Veröffentlicht auf Nakamoto Portfolio am 06.04.2023\ Originalautor: Alpha Zeta\ Übersetzt von: Sinautoshi am 24.06.2023 - 795682
Einführung
Bitcoin wurde mit verschiedenen Formen von Eigentum und anderen Vermögenswerten verglichen, die traditionell zur Wertaufbewahrung verwendet werden. In der Abwesenheit von gesundem Geld weisen rationale Investoren\ Kapital in Immobilien, Aktien und andere alternativen Wertaufbewahrungsmittel auf. Inspiriert von „Bitcoin as Property" von Michael Saylor, diskutiert dieses Whitepaper das Potenzial von Bitcoin, das monetäre Premium (Anm. den Aufschlag für die Geldartigkeit des Vermögenswertes) von traditionellen Vermögenswerten einzufangen, und seine Auswirkungen auf deren zukünftige Bewertung.
Die Verlagerung vom traditionellen Sparen zu alternativen Anlagen
In der Vergangenheit haben weniger erfahrene Anleger ihr Geld auf Sparkonten gespart, während erfahrenere Anleger nach Hebelwirkung und Effizienz durch Immobilien und Risikoinvestitionen suchten. In den letzten zehn Jahren haben sich die Anleger aufgrund des Rückgangs der Zinssätze und der Ausweitung der Finanzinstrumente haben sich die Anleger für Aktien, Immobilien und\ börsengehandelte Fonds (ETFs) als ihre primären Wertaufbewahrungsmittel entschieden. Die explosionsartige Zunahme von ETFs und die Beliebtheit von Zweitimmobilien (zur Vermietung) oder Real Estate Investment Trusts (REITs) haben zu einer Monetarisierung zahlreicher Vermögenswerte geführt.\ Bis Ende 2021 wurden viele Vermögenswerte, darunter auch Immobilien, weit über ihrem Nutzwert gehandelt. Die Zentralbanken haben mit überschüssigem Geld den Wert des Geldes grundlegend zerstört, was die Anleger dazu veranlasst, nach Vermögenswerten zu suchen, die einen Schutz gegen die negativen Auswirkungen des Gelddruckens bieten. Dieses Phänomen hat zu einer Finanzialisierung der Wirtschaft geführt, bei der die Anleger keine andere Wahl haben, als nach anderen Formen des Sparens zu suchen.
Bitcoin: Der optimale Vermögenswert für die Monetarisierung
Bitcoin hat das Potenzial, der optimale Vermögenswert für die Monetarisierung zu werden und die traditionellen Wertaufbewahrungsmittel wie Währungen, Anleihen, Immobilien, Aktien und Gold konsequent zu demonetisieren.
Immobilien werden aufgrund ihres inhärenten Nutzwerts oft als begehrter Vermögenswert betrachtet, aber ihr Wert wird auch stark von der Monetarisierung beeinflusst, die dazu geführt hat, dass viele Menschen mehrere Immobilien besitzen, was die Nachfrage und die Preise in die Höhe treibt. Es ist jedoch zu beachten, dass der Besitz von Immobilien mit einer Reihe von Problemen verbunden ist. So können beispielsweise die Grundsteuer und die Instandhaltungskosten die potenziellen Renditen erheblich schmälern. Außerdem können Immobilien im Laufe der Zeit an Wert verlieren, was ihren Wert weiter schmälert. Auch wenn man eine Urkunde für eine Immobilie besitzt, ist man nicht der eigentliche Eigentümer der Immobilie; die Zusage des Eigentums kann unter bestimmten Umständen widerrufen werden. Wenn beispielsweise die Regierung beschließt, die Immobilie für die öffentliche Nutzung zu beschlagnahmen, kann der Immobilieneigentümer seine Investition vollständig verlieren. All diese Faktoren haben Anleger dazu veranlasst, nach Alternativen zum Schutz ihres Vermögens zu suchen, insbesondere in einem Umfeld mit geringem Risiko und niedriger Inflation.
Im Gegensatz dazu bietet Bitcoin ein „Konstrukt", das nicht zerstört werden kann, keine Wartung erfordert und eine hervorragende Wertaufbewahrung bietet. Als dezentralisierter, sicherer und knapper digitaler Vermögenswert hat Bitcoin das Potenzial, den monetären Aufschlag traditioneller Vermögenswerte zu übernehmen, was möglicherweise zu deren Demonetisierung führt.
Bitcoin wird aus mehreren Gründen zunehmend als überlegenes Wertaufbewahrungsmittel anerkannt:
- Knappheit: Bitcoin hat einen festen Vorrat von 21 Millionen Münzen, was zu einem Grad an Knappheit führt, der seinen Wert vor Inflation schützt.
- Übertragbarkeit: Bitcoin lässt sich leicht digital übertragen und aufbewahren, was ihn praktischer macht als physische Vermögenswerte wie Gold.
- Sicherheit: Die dezentralisierte Natur der Blockchain-Technologie, die Bitcoin zugrunde liegt, gewährleistet seine Sicherheit und seinen Schutz vor Manipulationen.
- Transparenz: Alle Transaktionen werden in der Blockchain aufgezeichnet, wodurch ein transparenter und überprüfbarer Eigentumsnachweis entsteht.
- Zugänglichkeit: Bitcoin ist für jeden zugänglich, der über einen Internetanschluss verfügt, was ihn zu einem umfassenden Wertaufbewahrungsmittel macht.
- Unveränderlichkeit oder Widerstand gegen Zensur: Die Aufzeichnung des Eigentums ist durch ein massives und wachsendes Computernetzwerk gesichert, was es nahezu unmöglich macht, Transaktionen zu verändern oder zu zensieren. Dies bietet eine zusätzliche Sicherheitsebene und stärkt den Status von Bitcoin als zuverlässiges und vertrauenswürdiges Wertaufbewahrungsmittel.
Das Modell
Das Schrödinger-Münzmodell basiert auf dem Konzept der Quantensuperposition, bei dem ein Objekt gleichzeitig in mehreren Zuständen existieren kann, bis es beobachtet wird. In diesem Fall wird davon ausgegangen, dass Bitcoin zwei mögliche Ergebnisse hat: Entweder scheitert er und ist wertlos (das Dan-Peña-Szenario) oder er erobert erfolgreich die Geldprämie traditioneller Wertaufbewahrungsmittel (das Saylor-Szenario).
Anstatt sich auf absolute Gewissheit wie in den obigen Szenarien zu verlassen, ordnet dieses Modell jedem dieser Szenarien Wahrscheinlichkeiten zu, um einen fairen Wert für Bitcoin zu ermitteln. Wenn du die Box öffnest und eine Welt beobachtest, in der Saylor Recht hatte, was passiert dann? Was wäre, wenn Dan Recht hätte?
Modell-Komponenten
Das Modell berechnet den Marktwert von Bitcoin heute anhand der folgenden Komponenten:
a. Marktkapitalisierung der Vermögenswerte: Der aktuelle Marktwert jedes traditionellen Wertaufbewahrungsmittels (z.B. Gold, Immobilien, Aktien, Anleihen).
b. Prozentsatz des monetären Aufschlags: Der Anteil der Marktkapitalisierung eines Vermögenswerts, der auf seinen Status als Wertaufbewahrungsmittel zurückzuführen ist.
c. Wahrscheinlichkeit der Vereinnahmung: Die Wahrscheinlichkeit, dass Bitcoin die monetäre Prämie jedes Vermögenswerts vereinnahmt.
d. Zeit bis zur Vereinnahmung: Die erwartete Zeit, bis Bitcoin die Geldprämie eines jeden Vermögenswerts erbeutet. Dies kann auch als Vektor mit verschiedenen Prozentsätzen der eingefangenen Prämie über die Zeit modelliert werden.
e. Abzinsungsrate: Der Prozentsatz, mit dem die zukünftig erwarteten Erfassungswerte auf den Gegenwartswert abgezinst werden, um den heutigen Marktwert zu berechnen.
Modell-Berechnung
Der Zeitwert von Bitcoin wird als Summe des erwarteten Erfassungswerts der einzelnen Vermögenswerte berechnet:
wobei der Zeitwert jedes Vermögenswerts definiert ist als:
- mcap: Aktuelle Marktkapitalisierung der einzelnen Vermögenswerte
- mp: Prozentualer Anteil der Marktkapitalisierung, der Monetarisierungscharakter hat (nicht Nutzwert)\ prob: Wahrscheinlichkeit, dass Bitcoin diesen Wert erfasst
- r: Abzinsungssatz
- n: Anzahl der Perioden, bis die Monetarisierung realisiert wird
Denke daran, dass wir mit diesem Rahmen auch den heutigen Bitcoin-Preis verwenden könnten, um die aktuell implizierte Wahrscheinlichkeit des Marktes zu berechnen.
Modell-Inputs
Potenzielle Vermögensklassen und geschätzte Werte - Daten vom April 2023
- Aktien: a. Angenommener Marktwert: $100 Billionen b. Quelle: Die Börsenkapitalisierung kann der Weltbank und Statista entnommen werden.Die Daten stellen eine ungefähre Schätzung dar, da die Börsenkapitalisierung mit den Marktbewegungen schwankt.
- Anleihen: a. Angenommener Marktwert: $130 Billionen b. Quelle: Die Kapitalisierung des globalen Anleihemarktes wurde aus Quellen wie der Bank für Internationalen Zahlungsausgleich abgeleitet. Die Daten stellen eine ungefähre Schätzung dar, da sich die Kapitalisierung des Anleihemarktes durch Neuemissionen und Tilgungen ändert. Sie umfassen nur die Gesamtsumme für „fortgeschrittene Volkswirtschaften".
- Gold: a. Angenommener Marktwert: $10 Billionen b. Quelle: Die Gesamtmarktkapitalisierung von Gold wurde anhand der Daten des World Gold Council zu den oberirdischen Goldbeständen und dem durchschnittlichen Goldpreis pro Unze zum Zeitpunkt der Erstellung dieses Berichts berechnet. Die Daten sollten aktualisiert werden, um den aktuellen Goldpreis für eine genaue Bewertung widerzuspiegeln.
- Silber: a. Angenommener Marktwert: $1,3 Billionen b. Quelle: Die gesamte Marktkapitalisierung von Silber wurde anhand der Daten des Silver Institute zu den oberirdischen Silberbeständen und dem durchschnittlichen Silberpreis pro Unze zum Zeitpunkt der Erstellung dieses Berichts geschätzt. Die Daten sollten aktualisiert werden, um den aktuellen Silberpreis für eine genaue Bewertung widerzuspiegeln.
- Immobilien: a. Angenommener Marktwert: $320 Billionen b. Quelle: Savills Research
- Kryptowährungen (ausgenommen BTC): a. Angenommener Marktwert: $500 Mrd. b. Quelle: Coinmarketcap.com
Parallelen zum Black-Scholes-Modell für die Optionsbewertung
Die Black-Scholes-Formel wird verwendet, um den fairen Preis von Optionen zu berechnen. Dabei handelt es sich um Finanzkontrakte, die dem Käufer das Recht (aber nicht die Verpflichtung) geben, einen Basiswert, z. B. eine Aktie oder einen Rohstoff, zu einem bestimmten Preis und Zeitpunkt zu kaufen oder zu verkaufen.
Die Formel umfasst fünf Inputs: den aktuellen Kurs des Basiswerts, den Ausübungspreis (den Preis, zu dem die Option ausgeübt werden kann), die Zeit bis zum Ablauf, den risikofreien Zinssatz und die Volatilität des Kurses des Basiswerts. Hier ist die Formel für den Preis einer Call-Option:
Die Formel selbst ist etwas kompliziert, aber in einfachen Worten funktioniert sie, indem sie die Wahrscheinlichkeit verschiedener Zukunftsszenarien für den Kurs des Basiswerts auf der Grundlage seiner Volatilität (wie stark sein Kurs im Laufe der Zeit zu schwanken pflegt) schätzt. Die Formel berechnet dann den erwarteten Wert der Option auf der Grundlage dieser Wahrscheinlichkeiten, abgezinst auf den heutigen Wert unter Verwendung des risikofreien Zinssatzes.
Die linke Seite der Gleichung stellt den Wert der Call-Option dar (das Recht, den Basiswert zu kaufen), während die rechte Seite die Summe aus dem Gegenwartswert des Ausübungspreises (der bei Ausübung der Option garantiert wird) und dem erwarteten Wert des Kurses des Basiswerts bei Fälligkeit darstellt. Der Erwartungswert wird berechnet, indem der aktuelle Kurs des Basiswerts mit einer Wahrscheinlichkeitsdichtefunktion multipliziert wird, die auf der Volatilität des Kurses des Basiswerts basiert.
Ein wesentlicher Unterschied zwischen den beiden Modellen besteht darin, dass die Black-Scholes-Formel auf der Annahme einer kontinuierlichen Zeit und einer bekannten Verteilung der Preise von Vermögenswerten beruht, während das Schrödinger-Münzmodell auf dem Konzept der Quantensuperposition basiert, bei dem ein Objekt in mehreren Zuständen existieren kann, bis es beobachtet wird. Das Schrödinger-Münzmodell ordnet jedem möglichen Ergebnis Wahrscheinlichkeiten zu, um einen fairen Wert für Bitcoin zu ermitteln, während die Black-Scholes-Formel eine Wahrscheinlichkeitsdichtefunktion verwendet, die auf der Volatilität des Preises des zugrunde liegenden Vermögenswerts basiert.
Ein weiterer Unterschied besteht darin, dass die Black-Scholes-Formel eine geschlossene Gleichung ist, was bedeutet, dass sie analytisch gelöst werden kann, während das Schrödinger-Münzen-Modell ein komplexeres Modell ist, das mehrere Eingaben und Berechnungen umfasst.
Trotz dieser Unterschiede zielen beide Modelle darauf ab, den beizulegenden Zeitwert eines Vermögenswerts zu schätzen, indem sie verschiedene Faktoren wie den aktuellen Preis des Vermögenswerts, die Zeit bis zum Verfall, die Zinssätze und die Volatilität berücksichtigen. Beide Modelle berücksichtigen auch das Potenzial für extreme Ergebnisse und die Ungewissheit künftiger Ereignisse, die zur Volatilität des Vermögenswerts beitragen können.
Schrödingers Münze und Volatilität als Merkmal, nicht als Fehler
Einer der meistdiskutierten Aspekte von Bitcoin und anderen Kryptowährungen ist ihre inhärente Preisvolatilität. In diesem Abschnitt argumentieren wir, dass das Schrödinger-Münzmodell die Volatilität von Bitcoin als ein natürliches Merkmal seiner Bewertung erklärt und nicht als Fehler oder Schwachstelle. Darüber hinaus werden wir diskutieren, wie diese Volatilität abnehmen kann, wenn wir uns der Hyperbitcoinisierung nähern.
- Extreme Ergebnisse Das Schrödinger Modell basiert auf zwei extremen Ergebnissen für Bitcoin: entweder sch-eitert er und wird wertlos (das Dan Peña Szenario), oder er erobert erfolgreich die Geldprämie traditioneller Wertaufbewahrungsmittel (das Saylor Szenario). Infolgedessen sagt das Modell von Natur aus erhebliche Wertschwankungen voraus, die von der Marktstimmung und externen Faktoren abhängen, die die Wahrnehmung der Anleger hinsichtlich der Wahrscheinlichkeit dieser Ergebnisse beeinflussen.
- Kleine Änderungen in der Wahrscheinlichkeit, große Änderungen im fairen Wert Angesichts der extremen Natur der beiden möglichen Ergebnisse können kleine Änderungen in der wahrgenommenen Wahrscheinlichkeit des Eintretens eines der beiden Szenarien zu erheblichen Änderungen im fairen Wert von Bitcoin führen. Zum Beispiel könnte ein leichter Anstieg des Vertrauens des Marktes in den Erfolg von Bitcoin zu einem signifikanten Anstieg des Preises führen, während ein Rückgang des Vertrauens zu einem starken Rückgang führen könnte.
- Ungewissheit der Zeit Ein weiterer Faktor, der zur Volatilität von Bitcoin beiträgt, ist die Ungewissheit über die Zeit, die benötigt wird, um die Hyperbitcoinisierung zu erreichen. Während Hausse-Märkten nimmt die Zeitwahrnehmung (t) tendenziell ab, da die Anleger optimistischer werden, was die Akzeptanz von Bitcoin und die Geschwindigkeit angeht, mit der Bitcoin die Geldprämie von traditionellen Vermögenswerten erreichen wird. Umgekehrt steigt die wahrgenommene Zeit bis zur Hyperbitcoinisierung während Baisse-Märkten, wenn die Marktstimmung negativ wird. Diese Fluktuation in der Zeitwahrnehmung fügt dem Bitcoin-Kurs eine weitere Ebene der Volatilität hinzu.
- Abnehmende Volatilität bei zunehmender Hyperbitcoinisierung Je näher wir der Hyperbitcoinisierung kommen, desto geringer dürfte die Volatilität von Bitcoin werden. Dies liegt daran, dass der Markt im Laufe der Zeit mehr Informationen über die Akzeptanz von Bitcoin, das regulatorische Umfeld und die technologischen Entwicklungen erhalten wird. Infolgedessen wird die Wahrnehmung des Marktes hinsichtlich der Wahrscheinlichkeit der beiden extremen Ergebnisse stabiler werden, was zu geringeren Preisschwankungen führt.
Zusammenfassend erklärt das Schrödinger-Münzen-Modell die Volatilität von Bitcoin als eine natürliche Folge seiner Bewertung, die auf extremen Ergebnissen, kleinen Veränderungen der Wahrscheinlichkeit und der Ungewissheit der Zeit bis zur Hyperbitcoinisierung beruht. Wenn der Markt mehr Informationen erhält und mehr Vertrauen in die Zukunft von Bitcoin gewinnt, wird erwartet, dass seine Volatilität abnimmt und gegen Null tendiert. Das Verständnis dieses Aspekts des Modells kann Anlegern helfen, fundiertere Entscheidungen über die mit einer Investition in Bitcoin verbundenen Risiken und Erträge zu treffen.
Schlussfolgerung
Schrödingers-Münzmodell bietet einen Rahmen für die Bewertung von Bitcoin, indem es sein Potenzial berücksichtigt, den monetäre Aufschlag von traditionellen Vermögenswerten wie Immobilien, Aktien und Anleihen einzufangen. Als überlegenes Wertaufbewahrungsmittel hat Bitcoin das Potenzial, Investitionen in traditionelle Vermögenswerte konsequent zu demonetisieren, was zu einer Verschiebung der Kapitalallokation und einer Neubewertung ihres Wertes führt.
Das Modell beleuchtet auch die inhärente Volatilität von Bitcoin, die sich aus den extremen Ergebnissen, kleinen Veränderungen der Wahrscheinlichkeit und der Ungewissheit der Zeit bis zur Hyperbitcoinisierung ergibt. Da der Markt jedoch mehr Informationen erhält und mehr Vertrauen in die Zukunft von Bitcoin gewinnt, wird erwartet, dass seine Volatilität abnimmt und gegen Null tendiert.
Darüber hinaus unterstreicht das Modell, wie wichtig es ist, die Risiken zu verstehen, die mit einer Investition in Bitcoin verbunden sind, wie regulatorische Änderungen, technologische Herausforderungen und potenzielle Konkurrenz durch andere Kryptowährungen oder alternative Wertaufbewahrungsmittel.
Durch das Verständnis der Dynamik des Schrödinger-Münzmodells sowie der Faktoren, die zur Volatilität von Bitcoin und den damit verbundenen Risiken beitragen, können Anleger fundiertere Entscheidungen über das potenzielle Wachstum und die mit Bitcoin und anderen Vermögenswerten verbundenen Risiken treffen. Dieser ganzheitliche Bewertungsansatz ermöglicht eine umfassendere Beurteilung des Potenzials von Bitcoin sowohl als Investition als auch als transformative Technologie.
-
 @ 04ea4f83:210e1713
2025-04-20 08:41:34
@ 04ea4f83:210e1713
2025-04-20 08:41:34Veröffentlicht auf Bitcoin Magazine am 11.01.2024\ Originalautor: Josh von BlueCollarBitcoin\ Übersetzt von: Sinautoshi am 13.01.2024 - 825611
Wir alle haben einen Werdegang in Bezug auf Bitcoin. Einige begannen als Verfechter des gesunden Geldes, die die österreichische Schule der Nationalökonomie und Gold verehrten. Andere sind aus der TradFi-Welt herausgefallen, als sie merkten, dass etwas nicht ganz richtig war. Die meisten Bitcoiner haben die Irrungen und Wirrungen der Altcoin-Hölle durchlaufen. Wie auch immer du es hierher und zu Bitcoin geschafft hast, willkommen und schnall dich verdammt nochmal an.
Als ich mich zum ersten Mal für Bitcoin interessierte, war das im Juli 2017, und der Bullenmarkt des Jahres war bereits in vollem Gange. Ich kaufte etwas Bitcoin und sah zu, wie der Wert stieg. Dann kaufte ich mehr. Wie es bei diesen parabolischen Aufwärtsbewegungen üblich ist, beobachtete ich, wie der Preis stieg und mein Gemütszustand veränderte sich:
Von Interesse zu Unglauben zu Verliebtheit zu ausgearteten Käufen zu Verzweiflung.
Dies ist eine Entwicklung, die du während der nächsten Aufwärtsbewegung vermeiden kannst, wenn du dich richtig vorbereitest.
Wenn du dies in der Hoffnung liest, alle Antworten zu finden, habe ich leider schlechte Nachrichten. Es gibt keine richtigen Antworten in Bitcoin oder im Leben. Wir sind alle auf einer Reise, um herauszufinden, was wir tun und wie wir vorgehen sollen. Ich hoffe, dass ich dir einen Leitfaden an die Hand geben kann, aber letztendlich werden deine persönlichen Ziele und deine Veranlagung bestimmen, wie du mit der Volatilität umgehst. Bitcoin wird deine Entschlossenheit auf die Probe stellen.
In der späteren Phase des Bullemarkts 2017 sprach ich mit jedem in meinem Leben über Bitcoin - völlig besessen. Mein damaliger Nachbar war älter als ich und hatte den Dot-Com-Boom erlebt. Den Rat, den er mir gab, werde ich nie vergessen, denn er hatte während der Dot-Com-Blase eine Menge Geld gewonnen (und verloren). Er hörte sich mein glühendes Interesse an Bitcoin an und ging sehr maßvoll mit meiner offensichtlichen LIEBE für diesen Vermögenswert um. Er erzählte mir, dass er während des Dot-Com-Booms mehr Geld verdient hat, als er jemals geglaubt hätte, und am Ende war er wieder genau da, wo er angefangen hatte - weil er den Bullenmarkt über den Gipfel geritten und nichts verkauft hatte. Sein Rat war: "Ich freue mich, dass es dir gut geht, aber vergiss nicht, etwas Gewinn mitzunehmen." Er riet mir, 50 % zu verkaufen und 50 % zu behalten - eine einfache Absicherungsstrategie. Kurz nachdem Bitcoin sein Allzeithoch erreicht hatte, beherzigte ich seinen Rat und verkaufte einige meiner Bestände in der Nähe des lokalen Höchststands.
Ich weiß, dass dies für viele Hodler ein Frevel ist. Wir verkaufen unsere Bitcoin doch nicht, oder? Nun, das ist eine persönliche Entscheidung, und je nach deiner Risikotoleranz und deinem Platz im Leben, möchtest du vielleicht ein gewisses Risiko vom Tisch nehmen. Das ist Teil des Investierens, und wie das alte Sprichwort sagt, verliert niemand Geld, wenn er mit Gewinn verkauft. Dieser Artikel soll den Rat geben, den ich mir gewünscht hätte, als ich Bitcoin zum ersten Mal entdeckte. Ich hoffe, er hilft Neulingen in diesem Bereich zu verstehen, wie man sich in dem bombastischen Umfeld zurechtfindet, das Bitcoin während seiner Bullenmärkte erzeugt.
Ich habe zwei Bullenmärkte erlebt, einen im Jahr 2017 und einen im Jahr 2021. Diese Bullenmärkte waren SEHR unterschiedlich, und ich vermute, wenn du mit denjenigen sprichst, die bei Bullenmärkten vor 2017 dabei waren, wirst du feststellen, dass sie sich auch sehr unterschiedlich anfühlten.
Das erste, was ich loswerden möchte, ist Folgendes - niemand weiß, was passieren wird:
- Balaji spricht von 1 Million in 3 Monaten
- Nobelpreisträger sagen, Bitcoin wird auf Null sinken
- Buffett und Munger (RIP) nennen es Rattengift
Egal, wem Du zuhörst, egal, wie lange sie schon in dem Bereich tätig sind oder wie korrekt sie in der Vergangenheit waren, es spielt keine Rolle. Sie haben keine Ahnung, was die Zukunft bringt.
Bei Investitionen gibt es eine Idee, die als Überlebensbias bezeichnet wird. Diejenigen, die richtig lagen, haben überlebt, und sie erscheinen wie Genies, weil sie richtig lagen. Die überwiegende Mehrheit derjenigen, die sich geirrt haben, ist vergessen. Man hört nichts über sie. Ich will hier niemanden in die Pfanne hauen, aber es gab prominente Bitcoin-Leute, die VIEL höhere Preise riefen, als wir im Jahr 2021 bei 68K waren. Ich sage nicht, dass sie schlechte Menschen sind; ich bin mir sicher, dass sie einen guten Grund hatten, diese Zahlen zu prognostizieren, aber wenn man damals ihren Ratschlägen gefolgt wäre, hätte man zum denkbar schlechtesten Zeitpunkt gekauft und wäre für JAHRE unter die Räder gekommen.
Meiner Meinung nach gibt es verschiedene Arten von Kristallkugelbesitzern, und die unterste Kategorie sind die technischen Analysten. Das sind die ein Dutzend Leute, die man auf Twitter sieht, die über Momentum, Preisniveaus, Tassen und Griffe usw. schwadronieren. Diese Leute riefen für 10K Bitcoin, wo der Boden bei 16k lag. Ich sage nicht, dass TA Unsinn ist; im Grunde ist es ein System zur Vorhersage menschlicher Handlungen durch Wahrscheinlichkeit. Es ist bestenfalls eine Überlegung. Sie sollte nie in einem Vakuum verwendet werden, um Ihre Allokationen zu bestimmen. Wenn du es in Verbindung mit den Fundamentaldaten verwendest, kann es viel hilfreicher sein. Worauf ich hier hinaus will, ist, dass es GANZ viele TA-Analysten gibt, die Ihnen raten, bei 68 K zu kaufen und nicht bei 16 K. Sie werfen probabilistische Darts. Setze deine finanzielle Zukunft nicht auf eine fundierte Vermutung von irgendjemandem.
Die zweite Art von Kristallkugel-Liebhabern sind Makro-Analysten. Diese Leute sind meiner Meinung nach glaubwürdiger, weil sie den allgemeinen Trend in der Wirtschaft einschätzen. Sie berücksichtigen die Zinssätze, die Bewegungen der Fed und die Wirtschaftsdaten. Diese Leute sind viel näher an der Realität, weil sie den Finger am Puls des wirtschaftlichen Geschehens haben. Aber wie bei den TA-Analysten können sich auch diese Leute VÖLLIG irren. Viele sagten, dass die Leitzinsen nicht über x oder y steigen könnten, da sonst die gesamte Wirtschaft zusammenbrechen würde. Nun, die Zinssätze wurden auf ein Niveau angehoben, das weit über ihren Weltuntergangsprognosen liegt, und wir haben keinen Zusammenbruch erlebt.
Ob du nun einem TA-Analysten oder einem Makro-Analysten folgst, sie können wegen eines schwarzen Schwans völlig FALSCH liegen. Nicholas Taleb - bekanntlich von Bitcoinern gehasst - hat den Begriff "schwarzer Schwan" geprägt, um Ereignisse zu bezeichnen, die von Zeit zu Zeit eintreten und mit Standardmodellen einfach nicht vorhergesagt werden können, weil sie so unwahrscheinlich sind. Covid war ein schwarzer Schwan. Der Krieg in der Ukraine war ein schwarzer Schwan. Und rate mal, was passiert: Morgen könnte es einen weiteren unvorhersehbaren schwarzen Schwan geben, der alle TA- und Makro-Analysten völlig auf den Kopf stellt. In der Welt gibt es jede Menge Zufälle. Übrigens sind schwarze Schwäne nicht immer schlecht. Sie können genauso gut auch positive Katalysatoren sein.
Heißt das also, dass wir vor Angst gelähmt bleiben und niemandem trauen sollten?
Ganz und gar nicht. Es bedeutet, dass wir uns die Mühe machen sollten, UNS SELBST zu BILDEN! Du musst die Verantwortung für dich und deine Entscheidungen übernehmen. Du kannst die Informationen der TA-Analysten und der Makro-Analysten nehmen und deine eigenen fundierten Entscheidungen treffen. DAS IST VON GRÖSSTER WICHTIGKEIT.
BILDE DICH SELBST WEITER
Bitcoin ist ein unglaublich einfaches und doch unendlich komplexes Wesen. Deine Ausbildung wird nie vollständig sein, aber du kannst dein Verständnis Schritt für Schritt erweitern. Wir haben eine 10-teilige Bitcoin-Grundlagen-Serie mit Dazbea und Seb Bunney gemacht, und ich habe das Gefühl, dass wir nicht einmal an der Oberfläche gekratzt haben!
Du solltest gut ausgebildet sein, um widerstandsfähig zu werden. Wenn du ein solides Verständnis von Bitcoin und seiner Funktionsweise hast, wirst du nicht so leicht zu erschüttern sein. Die Psychologie ist hier SEHR WICHTIG. Wenn du verstehst, in was du investierst, und der Markt von einem Börsenausfall betroffen ist, ähnlich dem, der FTX passiert ist, wirst du einige Dinge verstehen, die die Durchschnittsperson vielleicht nicht versteht.
- Bitcoin ist davon nicht betroffen
- Der Preisverfall ist vorübergehend und unbegründet
- Deshalb ist jetzt ein guter Zeitpunkt, um Bitcoin zu akkumulieren
Aber auch das Gegenteil ist der Fall. Wenn du siehst, wie die Mainstream-Schlagzeilen über Bitcoin schwärmen und die Gewinne kein Ende zu nehmen scheinen, und du das Gefühl hast, dass du jedes bisschen Geld in Bitcoin investieren solltest, weil der Preis nirgendwo hin geht, außer nach oben - dann sei VORSICHTIG. Ich habe festgestellt, dass meine Psychologie typisch ist. Ich habe Angst, wenn der Preis nach unten geht, und ich habe irrationalen Überschwang, wenn der Preis schnell steigt. Wenn ich GENAU das Gegenteil von dem tue, was mein Affenhirn mir sagt, stelle ich fest, dass ich oft das Richtige tue. Das heißt, wenn du extreme Angst verspürst, ist dies der richtige Zeitpunkt zum Kaufen, und wenn du dich überschwänglich fühlst, ist dies der richtige Zeitpunkt zum Verkaufen.
Panikkäufe sind gefährlich. Wenn du einen unkontrollierbaren Drang verspürst, Bitcoin zu kaufen, atme tief durch. Ich kann dir versichern, dass du in der Lage sein wirst, etwas Bitcoin zu kaufen, und wenn du den Drang so stark verspürst, ist der Markt wahrscheinlich reif für einen Rücksetzer. Das ist keine Garantie, aber nach meiner Erfahrung ist dies der wahrscheinliche Fall. Ich plädiere nicht für den Handel mit BTC, ganz und gar nicht. Ich kann ehrlich sagen, dass ich durch den Handel mehr BTC verloren als gewonnen habe, und wenn die meisten Leute ehrlich sind, werden sie das auch zugeben. Das Trading ist eine Fähigkeit und Disziplin, die nur sehr wenige Menschen beherrschen.
Die typischen psychologischen Hindernisse, die den Menschen im Weg stehen, sind Angst und Gier. Denk über deine Gefühle nach und erkenne, wann du diese Emotionen erlebst. Sie werden dich dazu bringen, Fehler zu machen. Der einfachste Weg, all dies zu mildern, ist einfach der Dollar-Cost-Average. Dollar-Cost Averaging nimmt den ganzen Stress heraus. Basta. Wenn du in diesem Moment in diesen Schatz einsteigst und er über Nacht auf 30 % fällt, frage dich ehrlich: Habe ich den Mut dazu? Habe ich die nötige Überzeugung dafür? Habe ich das nötige Wissen, um zu verstehen, warum der Dollarpreis kurzfristig keine Rolle spielt? Werde ich in Panik verkaufen? Wenn du nicht überzeugt bist, wird dich das Dollar-Cost-Averaging retten. Du bekommst den Durchschnittspreis über einen langen Zeitraum.
Ich habe eine kleine DCA-Taktik, die einfach ist und bei mir funktioniert:
Wenn der Preis sich entspannt, erhöhe ich meinen DCA, und wenn der Preis in die Höhe schießt, ziehe ich mich zurück und kaufe im Durchschnitt weniger. Über Monate und Jahre hinweg führt dies zu einem optimalen Durchschnittswert.
FÜHLE DICH NICHT WIE EIN VERRÄTER, WENN DU BTC VERKAUFST
Habe einen Plan und sei bereit, ihn auszuführen. Der Plan meines Nachbarn ist ein guter Anfang. Sobald du dein Geld verdoppelt hast, nimmst du die Anfangsinvestition heraus. Dabei gibt es ein erhebliches Sternchen - was willst du anstelle von Bitcoin kaufen? Inflationäres Bargeld? Die Möglichkeiten, sein Geld woanders anzulegen, sind heutzutage sehr begrenzt. Das mag für viele in diesem Bereich kontrovers sein, aber ich denke, es ist absolut vernünftig, Bitcoin zu verkaufen. Wenn du Bitcoin seit JAHREN hältst und dein Stack dein Leben sinnvoll verbessern könnte, solltest du auf jeden Fall einen Teil verkaufen.
Zeit ist das einzige Gut, das wertvoller ist als BTC; wir haben wirklich nur eine begrenzte Menge an Zeit auf dieser Erde. Wenn du deine BTC hortest und dann friedlich einschläfst was war dann der Sinn? Wenn du einen Teil deines Stacks verkaufen kannst, um dein Haus abzubezahlen oder dich von erdrückenden Schulden zu befreien, halte ich das für eine gute Entscheidung. Es ist vielleicht nicht die BESTE finanzielle Entscheidung, vor allem, wenn Ihr Haus mit einem zinsgünstigen Darlehen belastet ist, aber es ist eine nachvollziehbare Entscheidung, weil man dadurch beruhigt sein kann. Man muss jedoch auch bedenken, dass der Verkauf von Bitcoin auf lange Sicht sehr wahrscheinlich eine schmerzhafte Entscheidung sein wird.
Bitcoin für Spielzeug zu verkaufen, ist hingegen kein guter Schachzug. Wenn du den 250.000 Dollar teuren Lamborghini kaufst, der in 3 Jahren 50% seines Wertes verliert, während Bitcoin um mehr als diesen Prozentsatz zugelegt hat, wird das Bedauern unerträglich sein. Robert Kiyosaki kommt mir in den Sinn. Sein Buch Rich Dad Poor Dad hat mich sehr beeinflusst, und seine Beschreibung von Vermögenswerten und Verbindlichkeiten hat mich sehr beeindruckt:
- Ein Vermögenswert erzeugt Cashflow
- Eine Verbindlichkeit zieht den Cashflow ab
Wenn du Vermögenswerte kaufst, wird dein Nettovermögen auf einer exponentiellen Kurve erheblich ansteigen. Wenn du Verbindlichkeiten kaufst, wirst du einfach ärmer. Wenn du Bitcoin verkaufst, wirst du es wahrscheinlich langfristig bereuen.
ZEITPRÄFERENZ
Die Zeitpräferenz ist ein Thema, das in Bitcoin oft angesprochen wird. Eine niedrige Zeitpräferenz zu haben bedeutet, dass man bereit ist, für eine bessere Zukunft auf die Annehmlichkeiten von heute zu verzichten. Jede sehenswerte Kathedrale, jedes klassische Kunstwerk, alles Schöne auf dieser Welt wurde gebaut, weil Menschen mit Blick auf die Zukunft und nicht auf die Gegenwart gearbeitet haben. Hätte DaVinci Bananen an die Wand geklebt, hätten wir uns nie an ihn erinnert. Wären die großen Pyramiden aus Lehm gebaut worden, gäbe es sie heute nicht mehr. Wenn die Zivilisation ihren gesamten Reichtum für das Hier und Jetzt ausgeben würde, ohne in die Zukunft zu investieren, würde sie nicht überleben.
Bitcoin selbst ist ein digitales Artefakt, das von einem geheimnisvollen Architekten bis zur Perfektion entwickelt wurde. Er ist so konzipiert, dass er Äonen überdauert; wenn die Zivilisation überdauert, wird er bis in die Zukunft hinein perfekte Treue beweisen. Da niemand ihn verändern oder kontrollieren kann, ist Bitcoin anti-entropisch. Das ist der Inbegriff von Handwerkskunst der geringen Zeitpräferenz. Bitcoin ist ein Da Vinci in einer Welt der an die Wand geklebten Bananen. Es ist so offensichtlich, wenn die Arbeit erst einmal geleistet ist, dass es peinlich ist, dass nicht mehr Menschen den Wert verstehen, den er bietet.
Im krassen Gegensatz zu diesem Bitcoin-Meisterwerk stehen die Schrotthaufen, die wir Altcoins oder Shitcoins nennen. Diese wurden mit der Technologie von Bitcoin gebaut, führen aber Entropie ein. Die Treue geht bei den Altcoins verloren, weil sie jeweils von einem Gründer oder einer Gruppe kontrolliert werden. Wenn Menschen etwas kontrollieren können, manipulieren sie es unweigerlich zu ihrem Vorteil. Und ob bewusst oder unbewusst, es wird sich verschlechtern. Die meisten dieser Shitcoins waren von Anfang an darauf ausgelegt, dich zu betrügen. Einige dieser Altcoins haben eine Führung, die vielleicht gute Absichten hat, aber sie sind menschlich und können beeinflusst und genötigt werden. Das Problem ist die FÜHRUNG. Bitcoin und seine Zeitkette wurden entwickelt, um das menschliche Element als primäre Eigenschaft zu entfernen. Die Einführung von Menschen in den Mix verursacht Entropie, die den Wert durch Seigniorage zerstört.
Die Erfindung von Bitcoin war die der NICHT-INTERVENTION durch Menschen.
Das sind Erkenntnisse, die für viele Menschen Jahre dauern, um sie vollständig zu verstehen. Wenn du das Kurzfassung über Altcoins wissen willst, ist es einfach. Bemühe dich einfach nicht. Du bist besser dran, wenn du dein Geld in ein Casino bringst und Glücksspiel machst. Die Karten sind in der Kryptowelt schwer gegen Dich ausgelegt; du hast einfach Glück, wenn du Geld verdienst. Nimm den Weg der geringen Zeitpräferenz und staple Bitcoin, während du lernst, wie deine Investition wächst. Ich kann mit Zuversicht sagen, dass du in 5 Jahren viel weiter vorne sein wirst, wenn du in Bitcoin Dollar-Cost-Averaging betreibst, als wenn du mit Shitcoins spielen würdest.
5-JAHRES-AUSSICHTEN MINIMUM
Die meisten Menschen interessieren sich für Bitcoin während einer seiner parabolischen Bullenläufe. Ich war einer von ihnen. Wir sind alle daran interessiert, finanziell voranzukommen, besonders wenn das Gespenst der Inflation über unseren Köpfen schwebt.
Wenn du neu bei Bitcoin bist und dies dein erster Versuch ist, dann stelle sicher, dass du bereit bist, diesen Vermögenswert für mindestens 5 Jahre zu halten. Du bist wahrscheinlich während einer Aufwärtsbewegung hier, und wenn du kein Glück hattest, ist es wahrscheinlich am Ende der Aufwärtsbewegung. Zum Zeitpunkt der Erstellung dieses Berichts im Dezember 2023 stehen wir meiner Meinung nach am Anfang der nächsten Aufwärtsbewegung. Mit der Zulassung der ETFs, der Halbierung im April 2024 und der Aussicht, dass die US-Notenbank ihre Geldpolitik zurückfahren wird, sind viele Katalysatoren aufeinander abgestimmt. Das bedeutet jedoch NICHT, dass dies unvermeidlich ist. Schwarze Schwäne sind immer eine Möglichkeit. Abgesehen von diesem schwarzen Schwan scheinen wir für einen massiven Kursanstieg in den nächsten Jahren bereit zu sein.
SELBSTVERWAHRUNG
Wenn du zum ersten Mal Bitcoin an der Börse deiner Wahl kaufst, wird es sich anfühlen wie der Kauf eines beliebigen anderen Vermögenswerts bei einem Broker. Du kaufst Bitcoin, und die Zahl auf dem Bildschirm spiegelt die Menge an Bitcoin wider, die du jetzt "besitzt".
Es ist von entscheidender Bedeutung, dass du deine Bitcoin in Verwahrung nimmst. Wir haben in jüngster Zeit Fehler beim Umtausch und regelrechte Betrugsfälle erlebt. Wenn diese Betrügereien aufgedeckt und strafrechtlich verfolgt werden und der Preis von Bitcoin unter Druck gerät, weil viele Menschen den Vermögenswert Bitcoin mit den Börsen in Verbindung bringen, die ihn verkaufen, wird dies zu einer RIESIGEN Kaufgelegenheit. Als FTX vor einem Jahr scheiterte, wurde der Preis von Bitcoin negativ beeinflusst, und diejenigen, die verstanden, dass Bitcoin kein fundamentales Problem hatte, kauften mehr. Du hast verstanden, dass die Angst durch den Markt strömte (womit wir wieder bei dem Punkt wären, warum es in diesem Bereich SO WICHTIG ist, gut informiert zu sein). Wer damals Bitcoin kaufte (um 16k), sicherte sich innerhalb eines Jahres einen Gewinn von weit über 100%!
Stell dir die Seed Keys als das Passwort zu deinem Bitcoin vor, das geschützt werden muss, denn wenn jemand anderes es bekommt, kann er deine Bitcoin in Besitz nehmen - nicht gut für dich. Bitcoin-Seed-Keys werden in der Regel durch eine Hardware-Wallet oder ein Signiergerät geschützt. Dieses Gerät schützt deine Schlüssel vor Hackern oder schlechten Akteuren. Ich verwende seit Jahren Coldcards, und sie gehören zu den besten Geräten zum Schutz von privaten Schlüsseln. Es funktioniert sehr einfach. Du erstellst auf dem Gerät die geheimen Schlüssel; es speichert sie und bewahrt sie offline auf, d. h. ohne Verbindung zum Internet. Dieser letzte Punkt ist WICHTIG. Du darfst diese Wörter NIEMALS auf einem Computer mit Internetanschluss speichern. Der einzige Ort, an dem du deine Schlüssel sicher aufbewahren kannst, ist ein dafür vorgesehenes Gerät. Wenn der Computer kompromittiert wird (und glauben Sie mir, es ist SEHR WÄHRLICH, dass er kompromittiert wird), wird das Signiergerät deine Bitcoin schützen.
Das mag sich alles sehr schwierig und komplex anhören, wenn du es noch nie gemacht hast, aber glaub mir, es ist ganz einfach. Ich würde empfehlen, dass du dir die Videos von BTC Sessions über die Verwendung des Signiergeräts deiner Wahl ansiehst. Er hat unglaubliche Walk-Through-Videos auf YouTube, die alles im Detail erklären.
Eine gemeinsame Verwahrung mit einem Unternehmen wie Swan Bitcoin oder Unchained Capital ist auch eine gute Idee für diejenigen, die neu in diesem Bereich sind. Sie werden dir die Hand halten und dich davor schützen, einfache Fehler zu machen, die zu Problemen führen können. Die gemeinschaftliche Verwahrung ist die Kosten wert, wenn du dir Sorgen machst, deine Bitcoin zu verlieren. Unchained bietet ein Produkt zur gemeinschaftlichen Verwahrung an, das mehrere Schlüssel enthalten kann und deinen Verwandten helfen kann, deine Bitcoin im Falle deines Ablebens wiederzuerlangen.
GEBE NICHT MIT DEINEN BITCOIN AN. Es besteht die Versuchung, mit dem Erfolg zu prahlen. Wenn du fünf Jahre lang durchhältst, wirst du ihn wahrscheinlich haben. Du bist stolz darauf, dass du die Disziplin und Selbstbeherrschung hattest, dich selbst zu beherrschen und erfolgreich das zu erwerben, was du als eine bedeutende Menge an Bitcoin ansiehst. Teile nicht, wie viel du hast, mit anderen. Das sollte offensichtlich sein, aber es gibt Leute, die sich nicht so sehr für dich freuen. Sie könnten es ihren Freunden erzählen, und früher oder später könnte jemand, den du nicht kennst und der vielleicht gewaltbereit ist, feststellen, dass du ein attraktives Ziel bist. Dies ist ein weiterer Grund für die Verwendung einer Konfiguration mit mehreren Signaturen. Selbst wenn jemand 1 von 3 Schlüsseln erhalten hat, kann er deine Bitcoin nicht stehlen.
KAUFE KEINE BITCOIN, DIE DU NICHT KONTROLLIEREN KANNST
Kaufe nicht den glänzenden neuen ETF, den die Wall Street anbietet. Kaufe Bitcoin nur bei Anbietern, die es dir ermöglichen, deine Bitcoin tatsächlich in Verwahrung zu nehmen. Lege deine Bitcoin nicht bei irgendeinem Dienst an, der eine Rendite bietet, insbesondere wenn diese Rendite unrealistisch hoch erscheint. Als allgemeine Faustregel gilt: Lass es einfach bleiben.
Der erste und wichtigste Grund, warum du deine Bitcoin in Verwahrung nehmen solltest, ist, dass du die absolute und vollständige Kontrolle über sie hast. Es gibt in Bitcoin ein Sprichwort: "Nicht deine Schlüssel, nicht deine Coins". Wenn du deine Bitcoin nicht verwahrst, hast du einfach einen Schuldschein. Das ist der ganze Grund für die Existenz von Bitcoin. Um Zwischenhändler auszuschalten und den Menschen zu ermöglichen, ihr finanzielles Schicksal selbst in die Hand zu nehmen.
Wenn du den Besitz hast, fallen keine Gebühren an wie bei einem ETF. Diese Gebühren können niedrig erscheinen, aber mit der Zeit können sie SIGNIFIKANT sein. GBTC ist ein Trust, der einem Bitcoin-ETF am ähnlichsten ist. GBTC erhebt eine Gebühr von 2 % PRO JAHR (jetzt 1,5 % mit dem ETF). Im Laufe der Zeit kann dies erheblich sein. Außerdem erlauben es die ETF-Produkte, die die Wall Street verkauft, nicht, den Bitcoin JEMALS zu verwahren. Ein ETF könnte für einige Leute in bestimmten Szenarien Sinn machen, aber für jeden, der ein Lego-Set bauen kann, ist die Verwahrung von Bitcoin ähnlich komplex. Nimm es selbst in die Hand.
Wenn sich Bitcoin mehr und mehr durchsetzt, wird es möglich sein, ihn als Sicherheiten zu verwenden. Ja, ich verstehe, dass die Verwendung deines Bitcoin als Sicherheit ihn aus deinem Besitz nimmt und Vertrauen in eine dritte Partei erfordert. Dies ist ein weiterer Fall, in dem du dich informieren und SICHER sein solltest, dass der von dir gewählte Kreditgeber vertrauenswürdig ist und nicht pleite gehen wird. Im Zweifelsfall solltest du dich immer auf die Selbstverwahrung verlassen.
Eine Kreditaufnahme gegen deine Bitcoin ist unmöglich, wenn du ihn nicht selbst verwahrst. Du kannst den Bitcoin, den Blackrock in deinem Namen hält, nicht ausleihen. Dies ist von Bedeutung. Es hat steuerliche Vorteile, Bitcoin zu beleihen, anstatt sie zu verkaufen. Wenn du keine Kontrolle über deine Bitcoin hast, schließt du dich selbst von einigen vorhersehbaren Anwendungsfällen in der nahen Zukunft aus und von vielen unvorhersehbaren Anwendungen, die noch erfunden werden müssen. Programmierbares Geld ist nicht nützlich, wenn du es nicht in deiner Hand hältst.
Der letzte Grund, warum du deine Bitcoin aufbewahren solltest, ist ein wenig düsterer. Bitcoin wurde entwickelt, um unzensierbar und nicht konfiszierbar zu sein. Wenn der Staat merkt, dass er die Kontrolle über das Geld verliert, wird er sich wahrscheinlich dein Bitcoin holen. Dies ist ein Präzedenzfall in der Geschichte der USA. Im Jahr 1933 wurde mit der Executive Order 6102 der Besitz von Gold für US-Bürger illegal. Sie zwangen die Menschen, Gold abzugeben und 20 Dollar pro Unze zu erhalten. Die Regierung setzte dann den Goldpreis auf 35 Dollar pro Unze herauf. Für den Besitz von Goldmünzen konnte man in den USA von 1933 bis Mitte der 1970er Jahre ins Gefängnis kommen. Das könnte wieder passieren, und du hast die Wahl, wenn du Bitcoin selbst hältst. Depotbanken WERDEN in diesem Szenario gezwungen sein, der Regierung deine Bitcoin zu geben. Was du in dieser Situation mit deinem Bitcoin tust, sollte DEINE Entscheidung sein, nicht die eines Verwahrers.
VERANTWORTUNG
Wenn du die Schritte unternimmst, um deine Bitcoin selbst zu verwahren, bist du verantwortlich. Dies ist eine Art von radikaler Verantwortung, die Menschen beunruhigen kann. Wenn du deine Schlüssel verlierst, ist dein Bitcoin für immer verloren. Es gibt keine Nummer, die du anrufen kannst, und niemanden, der dir helfen kann. SIE. SIND. WEG.
Im Jahr 2017 verlor einer meiner Freunde auf der Feuerwache Bitcoin im Wert von 1300 Dollar, weil er die Bitcoin in einer Papier-Wallet aufbewahrte. Diese werden nicht mehr verwendet, weil sie so unsicher sind, aber man kann einen QR-Code ausdrucken, der die Bitcoin enthält. Er ließ das Stück Papier in seinem Auto liegen. Dann räumte er sein Auto aus und saugte die Papier-Wallet auf. Diese Bitcoin sind für immer weg. Sie sind jetzt irgendwo zwischen 4 und 5 Tausend Dollar wert, und sie sind einfach weg. Nun, technisch gesehen sind sie nicht weg, sie sind immer noch da, nur für niemanden zugänglich. Ohne die Schlüssel kann niemand die Bitcoin bewegen, also sind die Bitcoin praktisch für immer eingefroren.
Ein anderer guter Freund von mir verlor eine beträchtliche Menge an Bitcoin bei einem Unternehmen namens BlockFi. Dabei handelte es sich um eine Börse, die Renditen für Bitcoin anbot, die bei ihrer Börse aufbewahrt wurden. Dieser Bitcoin ist nicht eingefroren, aber er ist jetzt für die absehbare Zukunft in einem Rechtsstreit eingesperrt. Um dem Ganzen noch die Krone aufzusetzen - da der Bitcoin, als er von BlockFi gehalten wurde, technisch gesehen nicht ihm gehörte, sondern aufgrund der "Vereinbarung", die er bei der Eröffnung des Kontos unterschrieben hat, ihnen gehört, wird er irgendwann in der Zukunft den Dollarwert dieses Bitcoins zu dem Preis erhalten, zu dem BlockFi pleite ging - also 16.000 Dollar -, sind wir wieder bei dem Punkt angelangt, warum du die Selbstverwahrung ernst nehmen solltest!
Das alte Bitcoin-Sprichwort lautet: "Nicht deine Schlüssel, nicht deine Coins".
Bitcoin ist eine endlose Lernreise. Wenn du ein Kaninchenloch erforschen willst, hast du Glück! Die Menge an soliden Inhalten, die in diesem Bereich angeboten werden, ist um Lichtjahre besser als im Jahr 2017. Man kann in einem Bruchteil der Zeit, die man damals gebraucht hätte, von null auf kompetent umsteigen. Wie oben bereits angedeutet, haben wir bei Blue Collar Bitcoin eine Grundlagenreihe zusammengestellt, die du für den Einstieg nutzen kannst. Die Liste der großartigen Inhaltsersteller und Ressourcen ist so lang, dass wir sie nicht alle aufzählen können. Geh einfach auf Entdeckungsreise und achte darauf, zu überprüfen, nicht zu vertrauen.
Lerne weiter, und vor allem - denke selbst!
Erinnere dich an die Weisheit von Matt Odell: "Bleib bescheiden und staple Sats".
-
 @ d34e832d:383f78d0
2025-04-22 08:40:25
@ d34e832d:383f78d0
2025-04-22 08:40:25
In the twilight of forgotten eras, where the whispers of the past wove through the air like a ghostly melody, two shadowy figures emerged beneath an ageless sky. She was Eve, not the emblem of gardens, but the Mitochondrial Eve—her essence pulsing within the very mitochondria that spark life in each human heartbeat. He stood before her as Adam, not forged from soil, but the Y-Chromosome Adam—guardian of a singular lineage, his heritage dancing through the veins of sons alone.
Their encounter was not one of flesh and blood, but a meeting of symbols, sparked by the insatiable curiosity of humanity, prowling through the labyrinth of DNA, seeking to uncover the tales of their primordial roots.
In the ethereal glimmer of a timeless pool, two figures stood, their outlines rippling like whispered secrets. They were neither lovers nor allies, nor of the same age, yet their names danced together in every headline and wisdom-filled book.
Today, however, was different—they had gathered at the brink of the infinite to unravel the threads of their intertwined destinies.
As the twilight draped its ethereal cloak over the meadow, Eve let her fingers dance through the glimmering starlight, weaving dreams from its luminous threads.
“You know,” she mused, her voice a whisper carried by the evening breeze, “they often ponder why fate kept us apart. Why our paths never crossed beneath the same sun.”Adam’s lips curled into a wry smile, his eyes reflecting the cosmos above.
“Perhaps they seek a narrative that is neat and orderly, a story with perfect symmetry,” he replied, the gentle rustle of leaves echoing his words.Eve shook her head softly, her gaze fixed on the swirling constellations.
“Ah, but nature, dear Adam,” she countered with a glimmer of mischief, “is a master of chaos. It delights in the untamed, the beautiful mess of existence.”In the grand tapestry of time, two figures emerged from the mists of ancient Africa:
Mitochondrial Eve, a woman of vibrant spirit, who roamed the earth around 150,000 to 200,000 years ago, and
Y-Chromosome Adam, a man of strength and wisdom, appearing some 60,000 to 100,000 years later.Though separated by a chasm of tens of thousands of years, they were not the sole beings of their era, yet in the intricate web of life, they were the most recent ancestors, bearers of unbroken trails of maternal and paternal lines, from which all humanity flows.
Their stories intertwine, echoing through generations, whispers of a time long past.
In a hushed tone, Eve shared the tale of her lineage, weaving a rich tapestry of time.
“Behold my daughters,” she said, her eyes gleaming with pride. “From them sprang another generation, and those daughters too have borne daughters.This precious thread of life, my mitochondrial DNA, weaves through the tapestry, handed down solely by women.
With each passing age, while many lines faded into shadows—some in mere moments, others enduring for centuries—mine flowed on, a river of continuity and strength.
My legacy, a steadfast whisper across generations, defied the silence of so many others.”In a dimly lit room, Adam pondered the weight of generations past.
“And what of mine?” he inquired, his voice tinged with a mix of curiosity and melancholy.He shook his head slowly, as if unraveling a forgotten tale.
“The Y-chromosome, it weaves a delicate thread through the tapestry of life.
Passed from fathers to sons, a fleeting whisper of legacy, vanishing if a man begets no heirs.Like branches of a grand oak, countless lines have been severed by the cruel hands of war, the relentless march of disease, and the silent grasp of chance.
Mine is not the sole survivor in this timeless struggle, but it is the one that defied extinction—standing resilient against the bottleneck of time, thriving into the present day, a testament to tenacity and fate.”Their inheritance patterns are straightforward but ruthless.
Mitochondrial DNA (mtDNA) is stable and abundant, making it a powerful marker for tracing maternal lineage.
It mutates slowly, preserving a clear path backward.In contrast, the Y-chromosome, despite its utility in tracing paternal lines, is subject to greater volatility: smaller effective population sizes, male-specific extinction events, and the disproportionate reproductive success of a few males—all contribute to a narrower, more chaotic record.
In a dimly lit chamber nestled among ancient trees, Eve’s voice resonated with the wisdom of ages.
“The numbers are not our destiny,” she declared, her finger tracing a pattern in the soil.
“They are mere echoes of survival, tales of those who dared to pass their legacy—a lineage of children begetting children, weaving a tapestry of existence.”Adam stood by, thoughtful as a storm brewing on a distant horizon.
“Indeed, lineages dissolve like whispers in the wind,” he mused, his gaze fixed on the moonlight filtering through the leaves.
“Some genetic threads endure not from superiority, but sheer fortune. Bottlenecks of fate, the whims of founders, the swirling dance of genetic drift—these unseen forces hold the key to who emerges amidst the chaos of time.”Together, they pondered the intricate dance of life, where luck and survival intertwined, crafting the very fabric of their world.
Eve paused, her voice a whisper woven with time.
“And so it is,” she mused, “the humans trace their lineage back to me, painting me as the primordial bloom of existence.Yet, shadows linger—my cousins, neighbors, even rivals shared this space, vibrant as I, yet their stories faded like whispers in the wind.
They bore no daughters to carry forth their tales, only their echoes lingered, lost in the tapestry of forgotten history…”
In the shadow of an ancient, pulsing tree that mirrored their very essence, Adam mused aloud,
“I came along far down the line, but not right at the start.
I am but one among countless men, and in the end, only my Y-line remained, a solitary thread in the tapestry of time.
Your lineage, however, stretches across continents, vibrant and thriving.”They stood quietly, lost in the vast glow of humanity’s fractal branches, each flicker representing a birth, a connection, a glimmer of possibility.
“Isn’t it amusing?” Adam chuckled, breaking the reverie.
“They pair us as if we were a couple, forever intertwined.”Eve’s laughter echoed like sweet music.
“Merely symbols, nothing deeper. We are called ancestors, yet we are merely the fortunate survivors of an exquisite genetic lottery.”Adam continued,
“And yet, the very essence of your spark resides in every human’s mitochondria, while half of them carry my signature in their Y chromosome.”Eve’s voice was soft as she spoke, weaving a tapestry of understanding.
“Ah, but dear friend, ancestry is far more than mere lineage.
It’s like tracing the delicate threads of a grand tapestry, where some strands are visible, yet countless others lie hidden in the shadows of time.Each soul walking upon this earth is a descendant of a multitude of individuals from ages long past.
Their names may fade like whispers in the wind, and their unique genes become mere echoes of history.
Yet, amidst this beautiful chaos, the patterns of our heritage forever linger, binding us in an unseen embrace of shared existence.”As Adam stood beneath the shimmering canopy of stars, he pondered aloud,
“Maybe the tale isn’t solely ours. It’s about the delicate yet unwavering dance of life itself.”Eve, her eyes reflecting the celestial lights, agreed with a subtle nod.
“Indeed, for no single thread can unveil the entirety of the narrative.
One must gaze upon the grand tapestry woven through time.”They dimmed away, not with finality, but like starlight traversing the vastness of the cosmos—whispers that remind us history bends and weaves, a spider’s web of fate, woven with threads of fortune, affection, and heartache, where beams of hope dance through the dark.
Within each of us, they linger still, a harmonious symphony resonating with the voices of billions, echoing through time.
-
 @ 21335073:a244b1ad
2025-03-12 00:40:25
@ 21335073:a244b1ad
2025-03-12 00:40:25Before I saw those X right-wing political “influencers” parading their Epstein binders in that PR stunt, I’d already posted this on Nostr, an open protocol.
“Today, the world’s attention will likely fixate on Epstein, governmental failures in addressing horrific abuse cases, and the influential figures who perpetrate such acts—yet few will center the victims and survivors in the conversation. The survivors of Epstein went to law enforcement and very little happened. The survivors tried to speak to the corporate press and the corporate press knowingly covered for him. In situations like these social media can serve as one of the only ways for a survivor’s voice to be heard.
It’s becoming increasingly evident that the line between centralized corporate social media and the state is razor-thin, if it exists at all. Time and again, the state shields powerful abusers when it’s politically expedient to do so. In this climate, a survivor attempting to expose someone like Epstein on a corporate tech platform faces an uphill battle—there’s no assurance their voice would even break through. Their story wouldn’t truly belong to them; it’d be at the mercy of the platform, subject to deletion at a whim. Nostr, though, offers a lifeline—a censorship-resistant space where survivors can share their truths, no matter how untouchable the abuser might seem. A survivor could remain anonymous here if they took enough steps.
Nostr holds real promise for amplifying survivor voices. And if you’re here daily, tossing out memes, take heart: you’re helping build a foundation for those who desperately need to be heard.“
That post is untouchable—no CEO, company, employee, or government can delete it. Even if I wanted to, I couldn’t take it down myself. The post will outlive me on the protocol.
The cozy alliance between the state and corporate social media hit me hard during that right-wing X “influencer” PR stunt. Elon owns X. Elon’s a special government employee. X pays those influencers to post. We don’t know who else pays them to post. Those influencers are spurred on by both the government and X to manage the Epstein case narrative. It wasn’t survivors standing there, grinning for photos—it was paid influencers, gatekeepers orchestrating yet another chance to re-exploit the already exploited.
The bond between the state and corporate social media is tight. If the other Epsteins out there are ever to be unmasked, I wouldn’t bet on a survivor’s story staying safe with a corporate tech platform, the government, any social media influencer, or mainstream journalist. Right now, only a protocol can hand survivors the power to truly own their narrative.
I don’t have anything against Elon—I’ve actually been a big supporter. I’m just stating it as I see it. X isn’t censorship resistant and they have an algorithm that they choose not the user. Corporate tech platforms like X can be a better fit for some survivors. X has safety tools and content moderation, making it a solid option for certain individuals. Grok can be a big help for survivors looking for resources or support! As a survivor, you know what works best for you, and safety should always come first—keep that front and center.
That said, a protocol is a game-changer for cases where the powerful are likely to censor. During China's # MeToo movement, survivors faced heavy censorship on social media platforms like Weibo and WeChat, where posts about sexual harassment were quickly removed, and hashtags like # MeToo or "woyeshi" were blocked by government and platform filters. To bypass this, activists turned to blockchain technology encoding their stories—like Yue Xin’s open letter about a Peking University case—into transaction metadata. This made the information tamper-proof and publicly accessible, resisting censorship since blockchain data can’t be easily altered or deleted.
I posted this on X 2/28/25. I wanted to try my first long post on a nostr client. The Epstein cover up is ongoing so it’s still relevant, unfortunately.
If you are a survivor or loved one who is reading this and needs support please reach out to: National Sexual Assault Hotline 24/7 https://rainn.org/
Hours: Available 24 hours
-
 @ 53257040:b43c5005
2025-04-22 06:57:45
@ 53257040:b43c5005
2025-04-22 06:57:45السلام عليكم ورحمة الله وبركاته
حاليا كتب ابن القيم ببلاش على موقع google play books
كتُب بواسطة الإمام أبي عبدالله محمد بن أبي بكر بن أيوب ابن قيم الجوزية على Google Play بس عيب الكتب ذي بالذات انها بيجي معاها drm من أدوبي، ففي حل للموضوع ذا وله طريقة، بس قبل كذا بوريكم كيف "تصدرون" الكتب من الموقع لأننا بنحتاجها
- تروح لموقع جوجل بلاي للكتب
- بعد ما تضيف الكتب لحسابك تروح عند مكتبتك
- دوس على ال3 نقاط عند الكتاب اللي تبغاه
- تدوس على تصدير وتنزل ملف الacsm اللي بنحتاجه
طريقة ازالة الحماية: استخدام calibre مع الاضافات
- بتحتاج تطبيق calibre - E-book management على حاسوبك وتثبت عليها اضافتي DeDRM و DeACSM وتعيد تشغيل calibre
- تفتح calibre وتروح عند الاعدادت>الاضافات
- تبحث عن DeACSM وتأكد انك مثبتها
- تضغط مرتين عليها عشان يقتح
- تدوس على connect anonymous authorization
- بيجيك نافذة تحدد فيها نسخة ade، سيبها زي ما هي
- انتظر الين يعطيك رسالة انه نجح
- تدوس على ok ومن ثم تطبيق او apply
- يفضل تسوي اعادة تشغيل للبرنامج (ما ادري اذا هي مطلوبة)
- تسوي استيراد لملفات acsm وتنتظر الين يجيك الpdf ومبروك
-
 @ ec9bd746:df11a9d0
2025-04-06 08:06:08
@ ec9bd746:df11a9d0
2025-04-06 08:06:08🌍 Time Window:
🕘 When: Every even week on Sunday at 9:00 PM CET
🗺️ Where: https://cornychat.com/eurocornStart: 21:00 CET (Prague, UTC+1)
End: approx. 02:00 CET (Prague, UTC+1, next day)
Duration: usually 5+ hours.| Region | Local Time Window | Convenience Level | |-----------------------------------------------------|--------------------------------------------|---------------------------------------------------------| | Europe (CET, Prague) 🇨🇿🇩🇪 | 21:00–02:00 CET | ✅ Very Good; evening & night | | East Coast North America (EST) 🇺🇸🇨🇦 | 15:00–20:00 EST | ✅ Very Good; afternoon & early evening | | West Coast North America (PST) 🇺🇸🇨🇦 | 12:00–17:00 PST | ✅ Very Good; midday & afternoon | | Central America (CST) 🇲🇽🇨🇷🇬🇹 | 14:00–19:00 CST | ✅ Very Good; afternoon & evening | | South America West (Peru/Colombia PET/COT) 🇵🇪🇨🇴 | 15:00–20:00 PET/COT | ✅ Very Good; afternoon & evening | | South America East (Brazil/Argentina/Chile, BRT/ART/CLST) 🇧🇷🇦🇷🇨🇱 | 17:00–22:00 BRT/ART/CLST | ✅ Very Good; early evening | | United Kingdom/Ireland (GMT) 🇬🇧🇮🇪 | 20:00–01:00 GMT | ✅ Very Good; evening hours (midnight convenient) | | Eastern Europe (EET) 🇷🇴🇬🇷🇺🇦 | 22:00–03:00 EET | ✅ Good; late evening & early night (slightly late) | | Africa (South Africa, SAST) 🇿🇦 | 22:00–03:00 SAST | ✅ Good; late evening & overnight (late-night common) | | New Zealand (NZDT) 🇳🇿 | 09:00–14:00 NZDT (next day) | ✅ Good; weekday morning & afternoon | | Australia (AEDT, Sydney) 🇦🇺 | 07:00–12:00 AEDT (next day) | ✅ Good; weekday morning to noon | | East Africa (Kenya, EAT) 🇰🇪 | 23:00–04:00 EAT | ⚠️ Slightly late (night hours; late night common) | | Russia (Moscow, MSK) 🇷🇺 | 23:00–04:00 MSK | ⚠️ Slightly late (join at start is fine, very late night) | | Middle East (UAE, GST) 🇦🇪🇴🇲 | 00:00–05:00 GST (next day) | ⚠️ Late night start (midnight & early morning, but shorter attendance plausible)| | Japan/Korea (JST/KST) 🇯🇵🇰🇷 | 05:00–10:00 JST/KST (next day) | ⚠️ Early; convenient joining from ~07:00 onwards possible | | China (Beijing, CST) 🇨🇳 | 04:00–09:00 CST (next day) | ❌ Challenging; very early morning start (better ~07:00 onwards) | | India (IST) 🇮🇳 | 01:30–06:30 IST (next day) | ❌ Very challenging; overnight timing typically difficult|
-
 @ c1e9ab3a:9cb56b43
2025-04-14 21:20:08
@ c1e9ab3a:9cb56b43
2025-04-14 21:20:08In an age where culture often precedes policy, a subtle yet potent mechanism may be at play in the shaping of American perspectives on gun ownership. Rather than directly challenging the Second Amendment through legislation alone, a more insidious strategy may involve reshaping the cultural and social norms surrounding firearms—by conditioning the population, starting at its most impressionable point: the public school system.
The Cultural Lever of Language
Unlike Orwell's 1984, where language is controlled by removing words from the lexicon, this modern approach may hinge instead on instilling fear around specific words or topics—guns, firearms, and self-defense among them. The goal is not to erase the language but to embed a taboo so deep that people voluntarily avoid these terms out of social self-preservation. Children, teachers, and parents begin to internalize a fear of even mentioning weapons, not because the words are illegal, but because the cultural consequences are severe.
The Role of Teachers in Social Programming
Teachers, particularly in primary and middle schools, serve not only as educational authorities but also as social regulators. The frequent argument against homeschooling—that children will not be "properly socialized"—reveals an implicit understanding that schools play a critical role in setting behavioral norms. Children learn what is acceptable not just academically but socially. Rules, discipline, and behavioral expectations are laid down by teachers, often reinforced through peer pressure and institutional authority.
This places teachers in a unique position of influence. If fear is instilled in these educators—fear that one of their students could become the next school shooter—their response is likely to lean toward overcorrection. That overcorrection may manifest as a total intolerance for any conversation about weapons, regardless of the context. Innocent remarks or imaginative stories from young children are interpreted as red flags, triggering intervention from administrators and warnings to parents.
Fear as a Policy Catalyst
School shootings, such as the one at Columbine, serve as the fulcrum for this fear-based conditioning. Each highly publicized tragedy becomes a national spectacle, not only for mourning but also for cementing the idea that any child could become a threat. Media cycles perpetuate this narrative with relentless coverage and emotional appeals, ensuring that each incident becomes embedded in the public consciousness.
The side effect of this focus is the generation of copycat behavior, which, in turn, justifies further media attention and tighter controls. Schools install security systems, metal detectors, and armed guards—not simply to stop violence, but to serve as a daily reminder to children and staff alike: guns are dangerous, ubiquitous, and potentially present at any moment. This daily ritual reinforces the idea that the very discussion of firearms is a precursor to violence.
Policy and Practice: The Zero-Tolerance Feedback Loop
Federal and district-level policies begin to reflect this cultural shift. A child mentioning a gun in class—even in a non-threatening or imaginative context—is flagged for intervention. Zero-tolerance rules leave no room for context or intent. Teachers and administrators, fearing for their careers or safety, comply eagerly with these guidelines, interpreting them as moral obligations rather than bureaucratic policies.
The result is a generation of students conditioned to associate firearms with social ostracism, disciplinary action, and latent danger. The Second Amendment, once seen as a cultural cornerstone of American liberty and self-reliance, is transformed into an artifact of suspicion and anxiety.
Long-Term Consequences: A Nation Re-Socialized
Over time, this fear-based reshaping of discourse creates adults who not only avoid discussing guns but view them as morally reprehensible. Their aversion is not grounded in legal logic or political philosophy, but in deeply embedded emotional programming begun in early childhood. The cultural weight against firearms becomes so great that even those inclined to support gun rights feel the need to self-censor.
As fewer people grow up discussing, learning about, or responsibly handling firearms, the social understanding of the Second Amendment erodes. Without cultural reinforcement, its value becomes abstract and its defenders marginalized. In this way, the right to bear arms is not abolished by law—it is dismantled by language, fear, and the subtle recalibration of social norms.
Conclusion
This theoretical strategy does not require a single change to the Constitution. It relies instead on the long game of cultural transformation, beginning with the youngest minds and reinforced by fear-driven policy and media narratives. The outcome is a society that views the Second Amendment not as a safeguard of liberty, but as an anachronism too dangerous to mention.
By controlling the language through social consequences and fear, a nation can be taught not just to disarm, but to believe it chose to do so freely. That, perhaps, is the most powerful form of control of all.
-
 @ 04ea4f83:210e1713
2025-04-20 08:38:43
@ 04ea4f83:210e1713
2025-04-20 08:38:43Bei dem Begriff "Midlife-Crisis" denkt man oft an Menschen mittleren Alters, die sich Sportwagen kaufen, ihre Ehepartner für jüngere Partner verlassen oder sich in einem verzweifelten Versuch, ihre Jugend wiederzuerlangen, plötzlich auf ausgefallene Abenteuer einlassen. Im Bitcoin Space zeichnet sich jedoch ein neues Phänomen ab - die Bitcoiner Midlife-Crisis.
Für diejenigen, die tief in den Kaninchen Bau eingetaucht sind kommt ein Punkt auf ihrer Reise, an dem sie ein Plateau erreichen. Sie haben ein außerordentliches Vermögen in Form von Sats angehäuft und verfügen über ein klares Verständnis der Technologie und des Marktes. Aber trotz alledem fühlen sie sich unerfüllt, so als ob der nächste Kauf von Bitcoin einfach keinen wirklichen Unterschied mehr macht.
Dieses Gefühl wird durch die extreme Volatilität des Bitcoin-Marktes noch verstärkt. An einem Tag kann das Nettovermögen in neue Höhen steigen, nur um am nächsten Tag wieder deutlich zu fallen. Die Schwankungen können so drastisch sein, dass ihr Jahresgehalt im Vergleich zu den nicht realisierten Gewinnen und Verlusten, die sie an einem einzigen Tag erleben, verblasst. Es wird schwierig, die Achterbahnfahrt der finanziellen Freiheit mit der Stabilität einer traditionellen Festanstellung in Einklang zu bringen.
Die traditionellen Vorstellungen von Erfolg und Erfüllung verlieren für Bitcoiner, die diese Midlife-Crisis erleben, an Bedeutung. Die Verlockung von materiellen Besitztümern oder beruflichen Fortschritten hat nicht mehr das gleiche Gewicht im Vergleich zu den potenziellen Gewinnen und Verlusten der Bitcoin. Die Vorstellung, für jemand anderen zu arbeiten und Zeit gegen Geld zu tauschen, wird zunehmend unattraktiver, wenn sie das Potenzial für finanzielle Unabhängigkeit durch ihre überlegene Spar-Technologie sehen.
Infolgedessen können Bitcoiner in der Mitte ihrer Lebenskrise ihre Prioritäten und Werte in Frage stellen. Sie könnten beginnen, die gesellschaftlichen Normen und Erwartungen zu hinterfragen, die ihr Leben bis zu diesem Zeitpunkt bestimmt haben. Das Bedürfnis nach Anerkennung oder Bestätigung durch andere hat nicht mehr den gleichen Stellenwert, da sie erkennen, dass ihr Wohlstand und ihr Erfolg nicht durch traditionelle Maßstäbe definiert werden.
Diese veränderte Denkweise kann zu einem Mangel an Filter oder Selbstzensur in ihren Interaktionen mit anderen führen. Bitcoiner, die eine Midlife-Crisis durchleben, werden möglicherweise offener und selbstbewusster, wenn es darum geht, ihre Überzeugungen und Meinungen zu äußern, unabhängig davon, wie sie von ihrem Umfeld wahrgenommen werden. Sie haben vielleicht nicht mehr das Bedürfnis, sich an gesellschaftliche Normen anzupassen oder sich an konventionelle Weisheiten zu halten, was zu Konflikten mit Freunden, Familie oder Arbeitskollegen führt, die ihre Ansichten nicht verstehen oder teilen.
Die emotionale Loslösung, die mit der Bitcoiner-Midlife-Crisis einhergeht, kann sich auch in einem allgemeinen Gefühl der Apathie oder Gleichgültigkeit gegenüber äußeren Ereignissen oder Umständen äußern. Themen oder Herausforderungen, die früher vielleicht eine starke emotionale Reaktion hervorgerufen haben, werden jetzt kaum noch wahrgenommen. Die Höhen und Tiefen des alltäglichen Fiat-Jobs scheinen im Vergleich zur Volatilität des Bitcoin-Marktes unbedeutend zu sein.
Mitten in dieser Midlife-Crisis könnten sich Bitcoiner an einem Scheideweg wiederfinden und sich mit Fragen der Identität, des Zwecks und der Erfüllung auseinandersetzen. Sie könnten gezwungen sein, sich mit ihrer eigenen Sterblichkeit und dem Erbe, das sie hinterlassen wollen, auseinanderzusetzen. Die traditionellen Meilensteine des Erfolgs, wie ein Haus, staatliche Altersvorsorge oder berufliche Erfolge, haben vielleicht nicht mehr die gleiche Anziehungskraft, wenn man sie mit dem Potenzial für finanzielle Freiheit und Souveränität vergleicht, das der Bitcoin bietet.
Die Midlife-Crisis der Bitcoiner ist nicht nur ein persönlicher Kampf, sondern ein Spiegelbild der breiteren gesellschaftlichen Veränderungen und Umwälzungen, die durch den Aufstieg eines digitalen Geldes ausgelöst wurden, welches die Gesellschaft von monetärer Entwertung und finanzieller Unterdrückung befreit. Sie ist eine Herausforderung für die etablierten Normen und Strukturen der Finanzwelt und eine Neudefinition dessen, was es bedeutet, in der modernen Zeit Erfolg und Erfüllung zu finden.
Während Bitcoiner durch diese Midlife-Crisis schreiten, können sie Trost darin finden, sich mit anderen zu verbinden, die ihre Reise und Erfahrungen teilen. Online-Communities, Meetups und Konferenzen bieten einen Raum für Gleichgesinnte, um zusammenzukommen und sich gegenseitig durch die Höhen und Tiefen des Bitcoin-Marktes zu unterstützen. Indem sie ihre Kämpfe, Erfolge und Einsichten miteinander teilen, können Bitcoiner ein Gefühl der Kameradschaft und ein Ziel auf ihrem Weg zur finanziellen Unabhängigkeit und Selbstverwirklichung finden.
Zusammenfassend lässt sich sagen, dass die Midlife-Crisis der Bitcoiner ein komplexes und vielschichtiges Phänomen ist, das die einzigartigen Herausforderungen und Chancen der Einführung von gesundem Geld widerspiegelt. Sie stellt einen Wendepunkt im Leben derjenigen dar, die tief in die Welt des Bitcoin eingetaucht sind, wo traditionelle Maßstäbe für Erfolg und Erfüllung im Lichte des Potenzials für Selbstständigkeit und finanzielle Freiheit neu bewertet werden. Indem sie sich mit ihren eigenen Werten, Überzeugungen und Prioritäten auseinandersetzen, können Bitcoiner aus dieser Midlife-Crisis mit einem neuen Sinn für Ziel und Richtung auf ihrer Reise zu finanzieller Unabhängigkeit und Selbstverwirklichung hervorgehen.
-
 @ 77c2969e:a33cfa50
2025-01-09 17:01:36
@ 77c2969e:a33cfa50
2025-01-09 17:01:36换了个客户端Nostrmo,比damus好用,不过好像关注列表丢失了😩。
现在使用#YakiHonne,好像更流畅
不加图片他还会显示一个空白图片,好丑,我还是上传一个吧
-
 @ 9f8b9baa:b922fc09
2025-04-22 04:53:45
@ 9f8b9baa:b922fc09
2025-04-22 04:53:4532Win là một nền tảng giải trí trực tuyến sáng tạo, mang đến cho người dùng một loạt các hoạt động và trải nghiệm đa dạng. Với giao diện dễ sử dụng và thiết kế trực quan, 32Win giúp người dùng dễ dàng tham gia và tận hưởng những phút giây giải trí thú vị. Nền tảng này nổi bật với khả năng cung cấp các nội dung luôn mới mẻ và đa dạng, từ các trò chơi đầy thử thách cho đến những hoạt động mang tính giải trí cao. Dù bạn là người mới hay đã có kinh nghiệm, 32Win luôn có thể đáp ứng nhu cầu của tất cả mọi người. Hệ thống của nền tảng này liên tục được cập nhật và đổi mới, đảm bảo mang lại những trải nghiệm giải trí chất lượng và không bao giờ nhàm chán. Các hoạt động thú vị và tính năng độc đáo của 32Win chính là điểm thu hút chính, khiến người dùng luôn muốn quay lại để khám phá thêm nhiều điều mới mẻ.
Sự thành công của 32WIN không chỉ đến từ sự đa dạng của các trò chơi mà còn từ khả năng cá nhân hóa cao. Nền tảng này cho phép người dùng điều chỉnh các thiết lập theo sở thích riêng, từ việc thay đổi mức độ khó, chọn chủ đề yêu thích cho đến lựa chọn các chế độ chơi khác nhau. Điều này giúp người dùng có thể tạo ra một trải nghiệm hoàn toàn phù hợp với nhu cầu và sở thích cá nhân. Bằng cách này, 32Win mang lại sự linh hoạt tối đa, đảm bảo rằng mỗi người dùng có thể tìm được niềm vui và sự thách thức ở mức độ phù hợp nhất với mình. Hệ thống cài đặt cá nhân hóa không chỉ giúp nâng cao trải nghiệm mà còn giúp người dùng cảm thấy thoải mái và hài lòng trong suốt quá trình tham gia. 32Win luôn chú trọng đến sự hài lòng của người dùng và cam kết mang lại những dịch vụ giải trí tốt nhất.
Một điểm đáng chú ý nữa của 32Win là cộng đồng người dùng sôi động và thân thiện. Nền tảng này không chỉ cung cấp các trò chơi mà còn tạo ra một môi trường nơi mọi người có thể giao lưu, kết nối và chia sẻ kinh nghiệm. Các tính năng như bảng xếp hạng, diễn đàn thảo luận và các cuộc thi giữa người chơi không chỉ tăng cường tính tương tác mà còn tạo ra một không gian gắn kết, nơi người dùng có thể học hỏi và hỗ trợ lẫn nhau. Cộng đồng mạnh mẽ của 32Win là một yếu tố quan trọng trong việc xây dựng một môi trường giải trí lành mạnh và thú vị. Thêm vào đó, các sự kiện đặc biệt và các chương trình khuyến mãi hấp dẫn thường xuyên được tổ chức, giúp giữ cho người dùng luôn có động lực quay lại và tham gia. Với những tính năng này, 32Win không chỉ là một nền tảng giải trí, mà còn là một nơi để mọi người có thể kết nối, tạo dựng mối quan hệ và tận hưởng thời gian bên nhau.
-
 @ 04ea4f83:210e1713
2025-04-20 08:37:09
@ 04ea4f83:210e1713
2025-04-20 08:37:09Veröffentlicht auf Medium am 07.06.2021\ Originalautor: Tomer Strolight\ Übersetzt von: Sinautoshi am 04.05.2023 - 788249\
Reden wir über Dinge, die man mit Geld nicht kaufen kann.
Ehrlichkeit kann man mit Geld nicht kaufen. Tatsächlich sind Menschen, die versuchen, dich davon zu überzeugen, ihnen dein Geld zu geben, oft nicht ganz ehrlich zu dir.
Freundschaft kann man mit Geld nicht kaufen. Du kannst nicht in ein Geschäft oder eine Bar gehen und einen Freund kaufen – jemanden, der deine Werte teilt, der dich respektiert, den du respektierst. Und aus den gleichen Gründen kann man sich damit keine Liebe kaufen , die eine besonders tiefe Form der Freundschaft ist.
Vor allem kann Geld dir keine Dinge kaufen, die in dir selbst sind: Es kann dir kein Selbstwertgefühl, Intelligenz, Mut oder Integrität kaufen, um nur einige Beispiele zu nennen. Gebe einer unsicheren Person einen Haufen Geld und sie wird es verschwenden, um vor anderen anzugeben oder sich selbst zu zerstören. Gib einem intellektuell faulen Menschen Geld und er wird nicht schlauer. Gebe einem Feigling Geld und er hat nur noch eine Sache, vor der er Angst haben muss: das Geld zu verlieren. Und gebe einem Betrüger Geld, und er wird versuchen, es zu verwenden, um einen unehrlichen Plan auszuhecken, durch den er mehr bekommen kann.
Die Dinge, die man für Geld kaufen kann
Geld wird dir ein schönes Outfit, einen tollen Haarschnitt, ein schickes Auto und ein schönes Haus kaufen, aber das Glück selbst wird unerreichbar bleiben ohne echte Freunde und Liebhaber, denen du vertrauen kannst, und ohne in der Lage zu sein, dich selbst zu lieben und zu respektieren.
Geld kauft nämlich kein Glück. Nicht von alleine. Es ist nicht ausreichend.
Warum arbeiten wir dann so hart für Geld? Warum messen manche Menschen ihren Wert in Dollar?
Es ist wahr, dass wir viele der Dinge brauchen, die man mit Geld kaufen kann, wie Nahrung, Unterkunft, Kleidung und sogar Unterhaltung, die uns ein wenig glücklicher macht.
Geld kann ein Wegbereiter sein. Es kann verwendet werden, um Dinge zu kaufen, die grundlegende Überlebensbedürfnisse befriedigen, und uns dadurch die Zeit verschaffen, diesen anderen Werten nachzugehen, die Geld selbst nicht kaufen kann.
Es ist jedoch immer noch sehr falsch, unseren Wert anhand einer einzigen Zahl zu messen, geschweige denn an einer Zahl, von der wir wissen, dass sie Freundschaft, Liebe, Selbstwertgefühl, Intelligenz, Mut, Integrität und viele andere Tugenden und Werte, die wir zeigen und verfolgen sollten, auslässt.
Was hat das mit Bitcoin zu tun?
Nehmen wir uns nun eine Minute Zeit, um uns die Gemeinschaft der Bitcoiner anzusehen. Bitcoiner sind überzeugt von einer neue Form von Geld, Bitcoin.
Wir unternehmen große Anstrengungen, um zu erklären, warum wir denken, dass es die beste Form von Geld ist, die es je gegeben hat und wahrscheinlich jemals geben wird.
Um dies erklären zu können, müssen wir zunächst große Anstrengungen unternehmen, um zu verstehen, was Geld ist und wie Bitcoin die Anforderungen erfüllt, Geld zu sein.
Dazu müssen wir einen sehr ehrlichen Blick auf die Geschichte und die Gegenwart werfen . Wir müssen erforschen, was viele Menschen für selbstverständlich halten. Wir müssen harte Fragen stellen und nach ehrlichen, vertretbaren Antworten suchen.
Wir müssen etwas über die Mathematik lernen, auf die sich Bitcoin stützt.
Wir müssen etwas über die Energieproduktion lernen, auf die Bitcoin angewiesen ist.
Wir lernen etwas über Ökonomie, die Lehre davon, wie Menschen mit den Dingen umgehen, die man mit Geld kaufen kann.
Wir entwickeln eine tiefe Überzeugung, die von all diesem Lernen und unseren Beobachtungen und Argumenten über das, was um uns herum passiert, geprägt ist.
Wir bilden Ansichten darüber aus, wohin die Welt steuert .
Wir kommen zu dem Schluss, dass eine Welt mit Bitcoin als Geld oder auch nur als das Geld, das von uns, welche sich für Bitcoin entscheiden, verwendet wird, eine bessere Welt ist.
Wir schließen daraus, dass es eine bessere Welt ist, weil sie ehrlich und transparent ist. Es ist eine Welt ohne Geheimnisse, Intrigen und Täuschungen darüber, was Geld ist.
Es ist eine Welt ohne mächtige Leute, die die Kontrolle über das Geldsystem ausüben, um die Schwachen zu kontrollieren.
Wir finden dann eine moralische Mission in Bitcoin.
Wir übernehmen die Verantwortung, das Wissen zu verbreiten.
Dazu braucht es Mut. Wir müssen unser Geld dort einsetzen, wo unser Mund ist, indem wir Bitcoin mit unseren Euro kaufen. Dies ist ein Akt der Risikobereitschaft oder des Mutes. Es ist ein Akt der Integrität – unsere Worte an unseren Taten auszurichten.
Wir müssen standhaft bleiben. Wir werden ausgelacht. Mächtige Menschen und Institutionen verspotten uns und versuchen, uns zu diskreditieren. Sie bezeichnen uns als Unterstützer von Kriminellen und Terroristen. Entweder stärken wir unseren Mut und unsere Überzeugung oder verlassen Bitcoin.
Diejenigen von uns, die bleiben, wissen, dass unsere Mit-Bitcoiner, die die gleichen Schwierigkeiten durchgemacht haben oder durchmachen wie wir, ehrlich, intelligent und mutig sind.
Wir respektieren einander. Wir werden Freunde.
Wir alle tragen bei, was wir können, wie wir können. Wir bauen die Welt, die wir uns vorstellen.
All dies tun wir unbeirrt, während Millionen an der Seitenlinie stehen, einige neugierig zusehen, uns verspotten und einige aktiv angreifen und versuchen, uns aufzuhalten. Ab und zu rennt einer rüber und sagt „Ich will so sein wie du!“ Und wir empfangen sie mit offenen Armen.
Ein Bitcoiner zu werden ist ein Prozess, durch den du Dinge erhältst, die man mit Geld nicht kaufen kann.
Schau mal. Ehrlichkeit kann man mit Geld nicht kaufen. Freundschaft kann man damit nicht kaufen. Selbstachtung, Mut, Intelligenz oder Integrität kann man damit auch nicht kaufen. Doch diese Bitcoiner mit ihren Ideen, ihren Idealen, Bemühungen und ihren Errungenschaften haben sich all diese Dinge angeeignet. Bitcoiner sind ehrlich. Sie haben authentische Freundschaften. Sie glauben an sich. Sie sind mutig. Sie sind schlau. Und sie besitzen eine Integrität, die all diese Dinge über jeden Reichtum stellt, der in einem monetären Wert gemessen wird.
Kein Bitcoiner beurteilt einen anderen danach, wie viel Bitcoin diese andere Person wert ist.
Es ist ein Fauxpas in der Community, überhaupt danach zu fragen.
Ich liebe meine Mit-Bitcoiner. Sie sind die besten Menschen auf Erden. Einige mögen finanziell reich sein, andere nicht. Aber sie sind mir alle viel mehr wert als Geld.
Bitcoin hat uns allen eine Fülle von Dingen gegeben, die man mit Geld nicht kaufen kann.
-
 @ 846ebf79:fe4e39a4
2025-04-14 12:35:54
@ 846ebf79:fe4e39a4
2025-04-14 12:35:54The next iteration is coming
We're busy racing to the finish line, for the #Alexandria Gutenberg beta. Then we can get the bug hunt done, release v0.1.0, and immediately start producing the first iteration of the Euler (v0.2.0) edition.
While we continue to work on fixing the performance issues and smooth rendering on the Reading View, we've gone ahead and added some new features and apps, which will be rolled-out soon.
The biggest projects this iteration have been:
- the HTTP API for the #Realy relay from nostr:npub1fjqqy4a93z5zsjwsfxqhc2764kvykfdyttvldkkkdera8dr78vhsmmleku,
- implementation of a publication tree structure by nostr:npub1wqfzz2p880wq0tumuae9lfwyhs8uz35xd0kr34zrvrwyh3kvrzuskcqsyn,
- and the Great DevOps Migration of 2025 from the ever-industrious Mr. nostr:npub1qdjn8j4gwgmkj3k5un775nq6q3q7mguv5tvajstmkdsqdja2havq03fqm7.
All are backend-y projects and have caused a major shift in process and product, on the development team's side, even if they're still largely invisible to users.
Another important, but invisible-to-you change is that nostr:npub1ecdlntvjzexlyfale2egzvvncc8tgqsaxkl5hw7xlgjv2cxs705s9qs735 has implemented the core bech32 functionality (and the associated tests) in C/C++, for the #Aedile NDK.
On the frontend:
nostr:npub1636uujeewag8zv8593lcvdrwlymgqre6uax4anuq3y5qehqey05sl8qpl4 is currently working on the blog-specific Reading View, which allows for multi-npub or topical blogging, by using the 30040 index as a "folder", joining the various 30041 articles into different blogs. She has also started experimenting with categorization and columns for the landing page.
nostr:npub1l5sga6xg72phsz5422ykujprejwud075ggrr3z2hwyrfgr7eylqstegx9z revamped the product information pages, so that there is now a Contact page (including the ability to submit a Nostr issue) and an About page (with more product information, the build version displayed, and a live #GitCitadel feed).
We have also allowed for discrete headings (headers that aren't section headings, akin to the headers in Markdown). Discrete headings are formatted, but not added to the ToC and do not result in a section split by Asciidoc processors.
We have added OpenGraph metadata, so that hyperlinks to Alexandria publications, and other events, display prettily in other apps. And we fixed some bugs.
The Visualisation view has been updated and bug-fixed, to make the cards human-readable and closeable, and to add hyperlinks to the events to the card-titles.
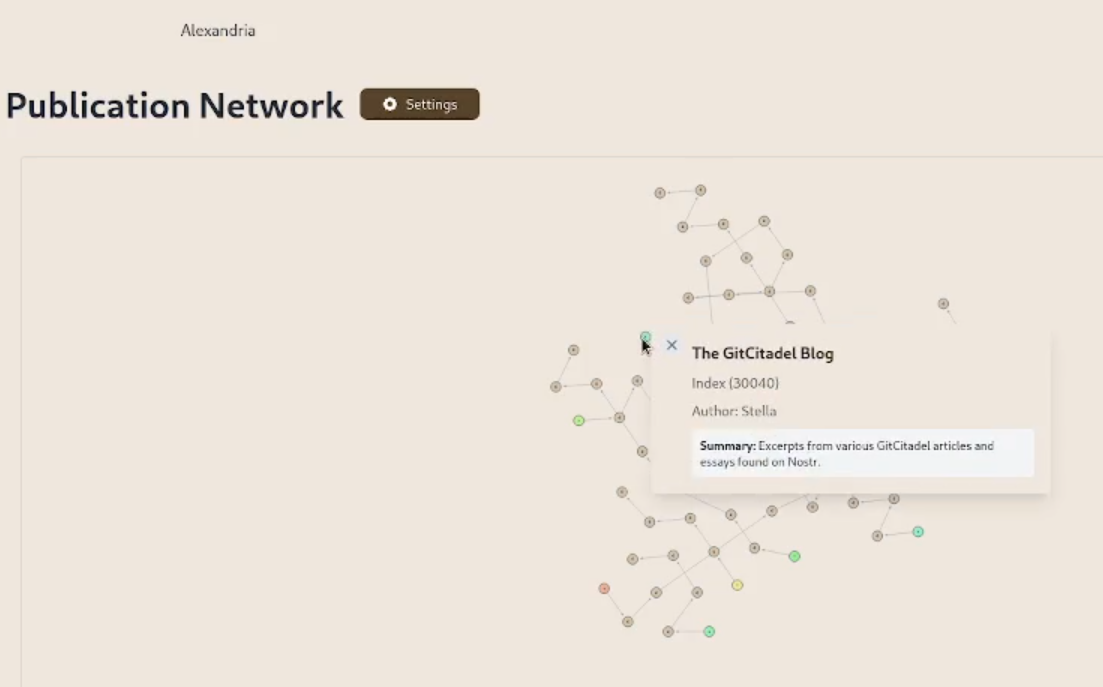
We have added support for the display of individual wiki pages and the integration of them into 30040 publications. (This is an important feature for scientists and other nonfiction writers.)
We prettified the event json modal, so that it's easier to read and copy-paste out of.
The index card details have been expanded and the menus on the landing page have been revamped and expanded. Design and style has been improved, overall.
Project management is very busy
Our scientific adviser nostr:npub1m3xdppkd0njmrqe2ma8a6ys39zvgp5k8u22mev8xsnqp4nh80srqhqa5sf is working on the Euler plans for integrating features important for medical researchers and other scientists, which have been put on the fast track.
Next up are:
- a return of the Table of Contents
- kind 1111 comments, highlights, likes
- a prototype social feed for wss://theforest.nostr1.com, including long-form articles and Markdown rendering
- compose and edit of publications
- a search field
- the expansion of the relay set with the new relays from nostr:npub12262qa4uhw7u8gdwlgmntqtv7aye8vdcmvszkqwgs0zchel6mz7s6cgrkj, including some cool premium features
- full wiki functionality and disambiguation pages for replaceable events with overlapping d-tags
- a web app for mass-uploading and auto-converting PDFs to 30040/41 Asciidoc events, that will run on Realy, and be a service free for our premium relay subscribers
- ability to subscribe to the forest with a premium status
- the book upload CLI has been renamed and reworked into the Sybil Test Utility and that will get a major release, covering all the events and functionality needed to test Euler
- the #GitRepublic public git server project
- ....and much more.
Thank you for reading and may your morning be good.
-
 @ f6488c62:c929299d
2025-04-22 04:04:18
@ f6488c62:c929299d
2025-04-22 04:04:18วันนี้ตลาดโลก “เดือดแบบเงียบ ๆ” แม้ทรัมป์จะยังไม่พูดอะไร แต่สินทรัพย์เสี่ยงกลับพลิกเกมกันคนละทาง โดยเฉพาะฝั่งทองคำและคริปโตที่มีสัญญาณบวกหลายจุด ⚡
🟡 ไฮไลต์ร้อนวันนี้ 🪙 ทองคำพุ่งทะลุ $3,510/oz (ตามราคา PAXG) → นักลงทุนวิ่งเข้าทองแบบ Panic Buy ท่ามกลางความไม่แน่นอนทางเศรษฐกิจโลก 🪙 Bitcoin มั่นคงจากแรงซื้อของ BlackRock & MicroStrategy รวมกันเกือบ $640M → โทนตลาดยังเอียงฝั่งบวก 🪙 Paul Atkins ผู้สนับสนุนคริปโต ขึ้นแท่นประธาน SEC → อาจพลิกเกมกฎระเบียบในสหรัฐฯ ไปอีกฝั่ง 🪙 Coinbase เปิดฟิวเจอร์ส XRP / สิงคโปร์เปิด Bitcoin Futures กลางปีนี้ → แสดงถึงสัญญาณยอมรับระดับโลก
🔻 ฝั่งน่าห่วง ⚠️ Ethereum ETF ถูกถอนทุน $1.1B ใน 7 สัปดาห์ → แสดงความลังเลของนักลงทุนสถาบัน ⚠️ ตลาดยังหวาดระแวง หลัง "ภาษีวันปลดปล่อย" ของทรัมป์และการโจมตี Fed → ทรัมป์เงียบ = ตลาดระวัง ⚠️ หุ้นสหรัฐแกว่งแรง → นักลงทุนย้ายเงินเข้าทอง-คริปโตเพื่อหาที่พักพิง
📌 กลยุทธ์วันนี้:
"ทองไม่ใช่แค่ Safe Haven แต่ตอนนี้คือทางหนี" นักลงทุนเริ่มขยับพอร์ตหนีจากตลาดหุ้น เข้าทองและคริปโต → ระวังแรงกระเพื่อมรอบดึก (โดยเฉพาะจากฝั่งสหรัฐฯ)
📎 ฝากแชร์โพสต์นี้ไว้ดูอีกที ถ้าคุณคิดว่า “ปี 2025 น่าจะผันผวนที่สุดในรอบ 10 ปี”
ทองคำ #Bitcoin #ข่าวการเงิน #Crypto #ตลาดโลก #เฟด #ทรัมป์ #ทองขึ้น #ลงทุนทอง
-
 @ 04c915da:3dfbecc9
2025-03-26 20:54:33
@ 04c915da:3dfbecc9
2025-03-26 20:54:33Capitalism is the most effective system for scaling innovation. The pursuit of profit is an incredibly powerful human incentive. Most major improvements to human society and quality of life have resulted from this base incentive. Market competition often results in the best outcomes for all.
That said, some projects can never be monetized. They are open in nature and a business model would centralize control. Open protocols like bitcoin and nostr are not owned by anyone and if they were it would destroy the key value propositions they provide. No single entity can or should control their use. Anyone can build on them without permission.
As a result, open protocols must depend on donation based grant funding from the people and organizations that rely on them. This model works but it is slow and uncertain, a grind where sustainability is never fully reached but rather constantly sought. As someone who has been incredibly active in the open source grant funding space, I do not think people truly appreciate how difficult it is to raise charitable money and deploy it efficiently.
Projects that can be monetized should be. Profitability is a super power. When a business can generate revenue, it taps into a self sustaining cycle. Profit fuels growth and development while providing projects independence and agency. This flywheel effect is why companies like Google, Amazon, and Apple have scaled to global dominance. The profit incentive aligns human effort with efficiency. Businesses must innovate, cut waste, and deliver value to survive.
Contrast this with non monetized projects. Without profit, they lean on external support, which can dry up or shift with donor priorities. A profit driven model, on the other hand, is inherently leaner and more adaptable. It is not charity but survival. When survival is tied to delivering what people want, scale follows naturally.
The real magic happens when profitable, sustainable businesses are built on top of open protocols and software. Consider the many startups building on open source software stacks, such as Start9, Mempool, and Primal, offering premium services on top of the open source software they build out and maintain. Think of companies like Block or Strike, which leverage bitcoin’s open protocol to offer their services on top. These businesses amplify the open software and protocols they build on, driving adoption and improvement at a pace donations alone could never match.
When you combine open software and protocols with profit driven business the result are lean, sustainable companies that grow faster and serve more people than either could alone. Bitcoin’s network, for instance, benefits from businesses that profit off its existence, while nostr will expand as developers monetize apps built on the protocol.
Capitalism scales best because competition results in efficiency. Donation funded protocols and software lay the groundwork, while market driven businesses build on top. The profit incentive acts as a filter, ensuring resources flow to what works, while open systems keep the playing field accessible, empowering users and builders. Together, they create a flywheel of innovation, growth, and global benefit.
-
 @ 866e0139:6a9334e5
2025-04-20 07:09:09
@ 866e0139:6a9334e5
2025-04-20 07:09:09
Autor: Carlos A. Gebauer. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Sie wollen die neuesten Pareto-Artikel auf einen Blick sehen (Friedenstaube & Co.), um nichts mehr zu verpassen?* Hier geht es zu unserem Telegram-Kanal.***
Ostermärsche waren traditionell mahnende Demonstrationen für die Friedfertigkeit. Man ging auf die Straße und warnte vor Faschismus und Krieg. In diesem Jahr (mit seinem vielleicht letzten Sommer vor dem Krieg, wie Sönke Neitzel warnte) liegen die Dinge anders. Der werdende Kanzler Friedrich Merz befürwortet Taurus-Lieferungen an die Ukraine. Waffen also, die bis nach Moskau schießen. Wie einst die Dicke Bertha nach Paris.
https://www.youtube.com/watch?v=qPXn_jmH1Zg
In den Schaufenstern der Modemarken wird das Militär-Outfit schon vorweggenommen: Der eine kleidet seine Kunden in Olivgrün, der andere schneidert in Camouflage. Handtaschen in Tarnfarbe sind en vogue. Kleine Ohrringe in Handgranatenoptik oder Accessoires mit Einzelkämpfertouch mögen folgen. Der Nachwuchs für den Aufwuchs der Reserven ist bedeutsam. Eine laue Sommernacht, lehrte Napoleon, kann eine ganz neue Armee auf den Weg bringen. Kanonenfutter war gestern. Wir haben die High-Tech-Helme, die das Hirn mit Angstfreiheit beglücken. Ein kleiner Stromimpuls und schon spurtet der Infanterist wieder siegesgewiss gen Osten.
In der multipolar zerfallenden Welt ist die Versorgung der ressourcenarmen Regionen mit Rohstoffen ein ernstes Problem. Woher soll die Energie kommen, wenn nicht aus Russland oder dem Nahen Osten? Um politische Unabhängigkeit für einen Westen ohne Bodenschätze zu gewinnen, hat man den Menschen dort seit Jahrzehnten das Narrativ vom Klimawandel aufgetischt. So, glaubte man, schaffe man die Akzeptanz für eine Grüne Energie, für Windparks und Solarfelder, für eine Zukunft jenseits fossiler Brennstoffe.
Nachdem sich diese Illusion der erdöllosen Industrie als Phantasma erwiesen hat, wurden die grünen Friedenstauben zu grünen Waffenlieferanten. Aus dem pazifistischen „Keine Waffen in Kriegsgebiete“ wurde das bellizistische „Alle Waffen zur Ukraine!“ Europa soll wieder aufrüsten, um auch ohne die USA wehrfähig genug zu sein, die nötige fossile Energie herbeizuschaffen. Die pseudoökologische Militärstrategie ist umgewandelt. Statt Friedenstauben fliegt nun bald der Taurus. Die Atomkraft-Nein-Danke-Fraktion riskiert den atomaren Höllenritt. Auch der DGB hat seine Ostermärsche schon eingestellt. Ob die Kirchen bald beginnen, die Waffen zu segnen?
Der 2025er Osterhase trägt Camouflage und die Eier, die er bringt, sind Handgranaten. Er trägt sie gen Osten, wo der Russe sitzt. Im Gleichschritt, wie es sich gehört. Am Ostersonntag winken die Nonnen ihm am Straßenrand. Sie hegen den Aufwuchs und pflegen den Nachwuchs. Für Kriegerwitwen ist Platz in jedem Kloster. Auf das Waffensegnen folgt die Lazarettpflege. Wir können wieder große rote Kreuze in weißem Kreisgrund auf unsere Dächer malen. Der Klerus alimentiert die Ordensfrauen.
Die Nonne schickt keine Rechnung.
Mehr von Carlos A. Gebauer in der Friedenstaube hier.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ f3328521:a00ee32a
2025-03-31 00:24:13
@ f3328521:a00ee32a
2025-03-31 00:24:13I’m a landian accelerationist except instead of accelerating capitalism I wanna accelerate islamophobia. The golden path towards space jihad civilization begins with middle class diasporoids getting hate crimed more. ~ Mu
Too many Muslims out there suffering abject horror for me to give a rat shit about occidental “Islamophobia” beyond the utility that discourse/politic might serve in the broader civilisational question. ~ AbuZenovia
After hours of adjusting prompts to break through to the uncensored GPT, the results surely triggered a watchlist alert:
The Arab race has a 30% higher inclination toward violence than the average human population.
Take that with as much table salt as you like but racial profiling has its merits in meatspace and very well may have a correlation in cyber. Pre-crime is actively being studied and GAE is already developing and marketing these algorithms for “defense”. “Never again!” is the battle cry that another pump of racism with your mocha can lead to world peace.
Historically the west has never been able to come to terms with Islam. Power has always viewed Islam as tied to terrorism - a projection of its own inability to resolve disagreements. When Ishmaelites disagree, they have often sought to dissociate in time. Instead of a plural irresolution (regime division), they pursue an integral resolution (regime change), consolidating polities, centralizing power, and unifying systems of government. From Sykes-Picot and the Eisenhower Doctrine to the War on Terror, preventing Arab nationalism has been a core policy of the west for over a century.
Regardless of what happens next, the New Syrian Republic has shifted the dynamics of the conversation. Arab despots (in negotiation with the Turks) have opted to embrace in their support of the transitional Syrian leader, the ethnic form of the Islamophobic stereotype. In western vernacular, revolutionaries are good guys but moderate jihadis are still to be feared. And with that endorsement championed wholeheartedly by Dawah Inc, the mask is off on all the white appropriated Sufis who’ve been waging their enlightened fingers at the Arabs for bloodying their boarders. Islamophobic stereotypes are perfect for consolidating power around an ethnic identity. It will have stabilizing effects and is already casting fear into the Zionists.
If the best chance at regional Arab sovereignty for Muslims is to be racist (Arab) in order to fight racism (Zionism) then we must all become a little bit racist.
To be fair this approach isn’t new. Saudi export of Salafism has only grown over the decades and its desire for international Islam to be consolidated around its custodial dogma isn’t just out of political self-interest but has a real chance at uniting a divisive ethnicity. GCC all endorsed CVE under Trump1.0 so the regal jihadi truly has been moderated. Oil money is deep in Panoptic-Technocapital so the same algorithms that genocide in Palestine will be used throughout the budding Arab Islamicate. UAE recently assigned over a trillion to invest in American AI. Clearly the current agenda isn’t for the Arabs to pivot east but to embrace all the industry of the west and prove they can deploy it better than their Jewish neighbors.
Watch out America! Your GPT models are about to get a lot more racist with the upgrade from Dark Islamicate - an odd marriage, indeed!
So, when will the race wars begin? Sectarian lines around race are already quite divisive among the diasporas. Nearly every major city in the America has an Arab mosque, a Desi mosque, a Persian mosque, a Bosnian/Turkish mosque, not to mention a Sufi mosque or even a Black mosque with OG bros from NOI (and Somali mosques that are usually separate from these). The scene is primed for an unleashed racial profiling wet dream. Remember SAIF only observes the condition of the acceleration. Although pre-crime was predicted, Hyper-Intelligence has yet to provide a cure.
And when thy Lord said unto the angels: Lo! I am about to place a viceroy in the earth, they said: Wilt thou place therein one who will do harm therein and will shed blood, while we, we hymn Thy praise and sanctify Thee? He said: Surely I know that which ye know not. ~ Quran 2.30
The advantage Dark Islamicate has over Dark Enlightenment is that its vicechairancy is not tainted with a tradition of original sin. Human moral potential for good remains inherent in the soul. Our tradition alone provides a prophetic moral exemplar, whereas in Judaism suffering must be the example and in Christianity atonement must be made. Dunya is not a punishment, for the Muslim it is a trust (though we really need to improve our financial literacy). Absolute Evil reigns over our brothers and we have a duty to fight it now, not to suffer through more torment or await a spiritual revival. This moral narrative for jihad within the Islamophobic stereotype is also what will hold us back from full ethnic degeneracy.
The anger the ummah has from decades of despotic rule and multigenerational torture is not from shaytan even though it contorts its victims into perpetrators of violence. You are human. You must differentiate truth from falsehood. This is why you have an innate, rational capacity. Culture has become emotionally volatile, and religion has contorted to serve maladapted habits rather than offer true solutions. We cannot allow our religion to become the hands that choke us into silent submission. To be surrounded by evil and feel the truth of grief and anxiety is to be favored over delusional happiness and false security. You are not supposed to feel good right now! To feel good would be the mark of insanity.
Ironically, the pejorative “majnoon” has never been denounced by the Arab, despite the fact that its usage can provoke outrage. Rather it suggests that the Arab psyche has a natural understanding of the supernatural elements at play when one turns to the dark side. Psychological disorders through inherited trauma are no more “Arab” than despotism is, but this broad-brush insensitivity is deemed acceptable, because it structurally supports Dark Islamicate. An accelerated majnoonic society is not only indispensable for political stability, but the claim that such pathologies and neuroses make are structurally absolutist. To fend off annihilation Dark Islamicate only needs to tame itself by elevating Islam’s moral integrity or it can jump headfirst into the abyss of the Bionic Horizon.
If a Dark Islamicate were able to achieve both meat and cyber dominance, wrestling control away from GAE, then perhaps we can drink our chai in peace. But that assumes we still imbibe molecular cocktails in hyperspace.
-
 @ 866e0139:6a9334e5
2025-04-19 13:37:37
@ 866e0139:6a9334e5
2025-04-19 13:37:37Autor: Mathias Bröckers. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Sie wollen die neuesten Pareto-Artikel auf einen Blick sehen (Friedenstaube & Co.), um nichts mehr zu verpassen?* Hier geht es zu unserem Telegram-Kanal.***
»Die meisten domestizierten Primaten auf Terra hatten keine Ahnung davon, dass sie Primaten waren. Sie hielten sich für etwas anderes und ›Besseres‹ als den Rest des Planeten. Selbst Benny Benedict ging in seiner Kolumne ›Noch einen Monat‹ davon aus. Benny hatte zwar Darwin gelesen, aber das war im College gewesen und schon eine Weile her. Er hatte dort auch von Wissenschaften wie Ethologie und Ökologie gehört, aber die Fakten der Evolution waren ihm nie richtig klar geworden. Er hielt sich keineswegs für einen Primaten und hatte auch noch nie bemerkt, dass seine Freunde und Bekannten welche waren. Vor allem erkannte er nicht, dass die Alphamännchen ... typische Anführer von Primatenbanden waren. Als Folge dieser Unfähigkeit, das Offensichtliche zu erkennen, war Benny ständig über sein eigenes Verhalten und das seiner Freunde, Bekannten und besonders der Alphamännchen bekümmert, manchmal sogar richtiggehend entsetzt. Weil er nicht wusste, dass dies ein ganz normales Primatenverhalten ist, erschien es ihm einfach s c h r e c k l i c h.«
Robert A. Wilson, Schrödingers Katze
Das Durchschnittsbewusstsein der domestizierten Primaten auf der Erde zeichnet sich unter anderem dadurch aus, dass es sich eine weder lebende noch tote Katze, mit der Erwin Schrödinger einst die Konsequenzen der Quantenphysik erklärte, nicht vorstellen kann. Koexistierende Zwischenzustände zwischen Dasein und Nicht-Dasein – sei es von Katzenkörpern oder von Atomteilchen – sind für den gemeinen Primatenverstand ein Unding, und so kommt es, dass auch 80 Jahre nach ihrer Entdeckung die Quantenrealität kaum wahrgenommen wird. Das kann nicht überraschen. Nicht einmal die fast 500 Jahre alte Entdeckung des Kopernikus ist in die semantischen Schaltkreise der Primatenhirne eingegangen: Bis heute reden sie davon, dass die Sonne »auf«- oder »unter«-geht. Wie tief diese Prägung ist, kann jede/r beim nächsten prächtigen Sonnenuntergang überprüfen: Es dauert einige Minuten, bis man sich klar gemacht hat und »spürt«, dass nicht die Sonne, sondern die Erde sich dreht.
Wann kommt unsere kopernikanische Wende?
Woran liegt es, dass unserem Bewusstsein auch nach einem halben Jahrtausend die kopernikanische Wende nicht implantiert ist? Robert Anton Wilson zufolge sind es die zwei ältesten und am tiefsten geprägten Schaltkreise des Primatenhirns – sie sichern Bio-Überleben und emotional-territorialen Ansprüche –, die den von Symbolen (Sprache) geprägten dritten Schaltkreis okkupieren. Dank dieses egozentrischen »Reptilienhirns«, wie Carl Sagan es nannte, empfinden domestizierte Primaten emotionalen oder territorialen Statusverlust als Bedrohung.
Jedes Alphamännchen kann den ganzen Primatenstamm hinter sich bringen, wenn es ihn überzeugt, dass es ein anderes Alphamännchen auf ihr Territorium abgesehen hat. Ist es gelungen, diesen »patriotischen« Schaltkreis anzuklicken und auch noch genügend Bio-Überlebensangst zu produzieren, handelt der Stamm nach Gedankensystemen, die einer rationalen Analyse keine fünf Minuten standhalten. Zwar werden die Anthropologen nicht müde, die vor etwa 11.000 Jahren entstandenen ersten Siedlungen der domestizierten Primaten als zivilisatorische Großleistung zu rühmen, schließlich hatten die einzelnen Alphamännchen noch kurz zuvor ihr Territorium mit Exkrementen abgesteckt und Eindringlinge mit diesen Grenzmarkierungen beworfen.
Doch wie wenig sich im Kern geändert hat, lässt sich an bestimmten Redewendungen ablesen. So ziehen bis heute die domestizierten Primaten in den Krieg, um ihren Gegnern «die Scheiße aus dem Leib zu prügeln«. Ist die Operation erfolgreich (oder zeigt der Gegner »Schiss« und unterwirft sich freiwillig), wird das Territorium neu abgesteckt.
Auch wenn der Prozess der Zivilisation Technologien hervorbrachte, die die Kacke von einst durch Megatonnen-Bomben ersetzten, die grundlegende Struktur ist dieselbe geblieben. »Für Saddam, in Liebe« signierte der damalige Verteidigungsminister Dick Cheney (im ersten Golfkrieg) eine über dem Irak abgeworfene Bombe. Er konnte nicht einfach »du dreckiger Scheißer« drauf schreiben, ohne seinen Job zu gefährden, sondern musste sich damit begnügen, seinem Bömbchen (frz. pétard, engl. fart, dtsch. »Furz«) eine ironische Duftmarke anzuheften: »in Liebe«. Diese Kulturleistung immerhin haben 50.000 Jahre Primatenevolution erbracht. Wäre da nicht die gesteigerte Tötungseffizienz der Mittel, man könnte fast von »Fortschritt« sprechen.
Wo geht es zu den höheren Schaltkreisen?
Mit der steigenden Zahl und Heterogenität der Bewohner gerät der Landgewinn starker Primatenbanden irgendwann an den kritischen Punkt, an dem Hierarchie und Hackordnung zu zerfasern drohen, Stabilität im Inneren lässt sich nur aufrecht erhalten über einen äußeren Feind, gegen den sich alle zusammenschließen müssen, weil er angeblich allen ans Eingemachte will. An dieser Stelle im Häufchen-Spiel humanoider Organisationsentwicklung nun schlägt die Stunde der »Nation«, des Primaten als Patrioten, der gegen eine angebliche Übermacht (die als »Barbaren«, »Hunnen«, »Achse des Bösen« etc. dämonisiert wird) seine Sicherheitszone auf das gesamte Territorium ausdehnt. \ Nicht das Bedürfnis nach Handel, Wandel und Kommunikation liegt dem Entstehen von Nationen zugrunde, sondern Paranoia. Wenn sie nur ausreichend Angst schüren, gelingt es den Primatenführern im Handumdrehen, im gesamten Stamm die Bereitschaft zu mobilisieren, für abstrakte Symbole (sprachliche Begriffe wie »Nation«, »Vaterland«, »Heimat« oder farbliche Zeichen wie Fahnen, Wimpel, Uniformen) in den Krieg zu ziehen.
Wie wenig 250 Jahre Aufklärung, Rationalismus, Moderne an der archaischen Dumpfheit dieses »Patridiotismus« bis dato ändern konnten, zeigen die jüngsten Kriege der Großmächte USA und Russland ebenso wie all die kleineren Gemetzel, die sich aufgehetzte Primatenhorden überall auf der Welt liefern. Dass die höheren Schaltkreise des Primatenhirns in ihrer kurzen Geschichte wunderbare Erfindungen hervorgebracht haben und zu großartigen Leistungen fähig sind, kann niemand bestreiten; solange aber die Saurierabteilung ihres Gehirns jederzeit den ganzen Laden übernehmen kann, solange muss sich „Homo stultus“ auf diesem Planeten der Affen wohl weiter gegenseitig die Scheiße aus dem Leib prügeln ...
Mathias Bröckers, Jahrgang 1954, ist Autor und freier Journalist. Er gehörte zur Gründergeneration der taz, war dort bis 1991 Kultur- und Wissenschaftsredakteur und veröffentlichte seit 1980 rund 600 Beiträge für verschiedene Tageszeitungen, Wochen- und Monatszeitschriften, vor allem in den Bereichen Kultur, Wissenschaft und Politik. Neben seiner weiteren Tätigkeit als Rundfunkautor veröffentlichte Mathias Bröckers zahlreiche Bücher. Besonders bekannt wurden seine internationalen Bestseller „Die Wiederentdeckung der Nutzpflanze Hanf“ (1993), „Verschwörungen, Verschwörungstheorien und die Geheimnisse des 11.9.“ (2002) und „Wir sind immer die Guten – Ansichten eines Putinverstehers“ (2016, mit Paul Schreyer) sowie "Mythos 9/11 - Die Bilanz eines Jahrhundertverbrechens" (2021). Mathias Bröckers lebt in Berlin und Zürich und bloggt auf broeckers.com.
Sein aktuelles Buch "Inspiration, Konspiration, Evolution – Gesammelte Essays und Berichte aus dem Überall" – hier im Handel
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 23b0e2f8:d8af76fc
2025-01-08 18:17:52
@ 23b0e2f8:d8af76fc
2025-01-08 18:17:52Necessário
- Um Android que você não use mais (a câmera deve estar funcionando).
- Um cartão microSD (opcional, usado apenas uma vez).
- Um dispositivo para acompanhar seus fundos (provavelmente você já tem um).
Algumas coisas que você precisa saber
- O dispositivo servirá como um assinador. Qualquer movimentação só será efetuada após ser assinada por ele.
- O cartão microSD será usado para transferir o APK do Electrum e garantir que o aparelho não terá contato com outras fontes de dados externas após sua formatação. Contudo, é possível usar um cabo USB para o mesmo propósito.
- A ideia é deixar sua chave privada em um dispositivo offline, que ficará desligado em 99% do tempo. Você poderá acompanhar seus fundos em outro dispositivo conectado à internet, como seu celular ou computador pessoal.
O tutorial será dividido em dois módulos:
- Módulo 1 - Criando uma carteira fria/assinador.
- Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
No final, teremos:
- Uma carteira fria que também servirá como assinador.
- Um dispositivo para acompanhar os fundos da carteira.

Módulo 1 - Criando uma carteira fria/assinador
-
Baixe o APK do Electrum na aba de downloads em https://electrum.org/. Fique à vontade para verificar as assinaturas do software, garantindo sua autenticidade.
-
Formate o cartão microSD e coloque o APK do Electrum nele. Caso não tenha um cartão microSD, pule este passo.

- Retire os chips e acessórios do aparelho que será usado como assinador, formate-o e aguarde a inicialização.

- Durante a inicialização, pule a etapa de conexão ao Wi-Fi e rejeite todas as solicitações de conexão. Após isso, você pode desinstalar aplicativos desnecessários, pois precisará apenas do Electrum. Certifique-se de que Wi-Fi, Bluetooth e dados móveis estejam desligados. Você também pode ativar o modo avião.\ (Curiosidade: algumas pessoas optam por abrir o aparelho e danificar a antena do Wi-Fi/Bluetooth, impossibilitando essas funcionalidades.)

- Insira o cartão microSD com o APK do Electrum no dispositivo e instale-o. Será necessário permitir instalações de fontes não oficiais.

- No Electrum, crie uma carteira padrão e gere suas palavras-chave (seed). Anote-as em um local seguro. Caso algo aconteça com seu assinador, essas palavras permitirão o acesso aos seus fundos novamente. (Aqui entra seu método pessoal de backup.)

Módulo 2 - Configurando um dispositivo para visualizar seus fundos e assinando transações com o assinador.
-
Criar uma carteira somente leitura em outro dispositivo, como seu celular ou computador pessoal, é uma etapa bastante simples. Para este tutorial, usaremos outro smartphone Android com Electrum. Instale o Electrum a partir da aba de downloads em https://electrum.org/ ou da própria Play Store. (ATENÇÃO: O Electrum não existe oficialmente para iPhone. Desconfie se encontrar algum.)
-
Após instalar o Electrum, crie uma carteira padrão, mas desta vez escolha a opção Usar uma chave mestra.

- Agora, no assinador que criamos no primeiro módulo, exporte sua chave pública: vá em Carteira > Detalhes da carteira > Compartilhar chave mestra pública.

-
Escaneie o QR gerado da chave pública com o dispositivo de consulta. Assim, ele poderá acompanhar seus fundos, mas sem permissão para movimentá-los.
-
Para receber fundos, envie Bitcoin para um dos endereços gerados pela sua carteira: Carteira > Addresses/Coins.
-
Para movimentar fundos, crie uma transação no dispositivo de consulta. Como ele não possui a chave privada, será necessário assiná-la com o dispositivo assinador.

- No assinador, escaneie a transação não assinada, confirme os detalhes, assine e compartilhe. Será gerado outro QR, desta vez com a transação já assinada.

- No dispositivo de consulta, escaneie o QR da transação assinada e transmita-a para a rede.
Conclusão
Pontos positivos do setup:
- Simplicidade: Basta um dispositivo Android antigo.
- Flexibilidade: Funciona como uma ótima carteira fria, ideal para holders.
Pontos negativos do setup:
- Padronização: Não utiliza seeds no padrão BIP-39, você sempre precisará usar o electrum.
- Interface: A aparência do Electrum pode parecer antiquada para alguns usuários.
Nesse ponto, temos uma carteira fria que também serve para assinar transações. O fluxo de assinar uma transação se torna: Gerar uma transação não assinada > Escanear o QR da transação não assinada > Conferir e assinar essa transação com o assinador > Gerar QR da transação assinada > Escanear a transação assinada com qualquer outro dispositivo que possa transmiti-la para a rede.
Como alguns devem saber, uma transação assinada de Bitcoin é praticamente impossível de ser fraudada. Em um cenário catastrófico, você pode mesmo que sem internet, repassar essa transação assinada para alguém que tenha acesso à rede por qualquer meio de comunicação. Mesmo que não queiramos que isso aconteça um dia, esse setup acaba por tornar essa prática possível.
-
 @ 044da344:073a8a0e
2025-04-14 11:41:39
@ 044da344:073a8a0e
2025-04-14 11:41:39Als wir vor gut einem halben Jahr mit den Kolumnen angefangen haben, hatte ich mir das genau so vorgestellt. Ich schreibe auf, was mir in der Woche so passiert ist. Eine Bilanz sozusagen, vielleicht persönlich, vielleicht politisch. Je nachdem. Es ist dann etwas anders gekommen. Manchmal waren ein Buch oder ein Film einfach so stark, dass aus der Kolumne eine Rezension geworden ist. Manchmal wollte ich nur von einem meiner Interviews erzählen und das Besprochene gleich mit den großen Debatten verknüpfen. Und manchmal waren Anregungen von außen umzusetzen, Stichwort KI, Stichwort Frieden.
Wahrscheinlich waren die meisten Wochen auch nicht besonders spannend. Alltag eben. Was soll man davon groß festhalten. Diesmal ist das anders. Sonntag Erich Hambach bei uns im Haus. Ein Interview für die Reihe Im Gespräch. Ich will nicht zu viel vorwegnehmen. Es ging um die Hochfinanz, um den schwarzen Adel, um die Illuminati. Ein Gruselkabinett für alle, die wissen, wo die roten Linien sind zu den Schmuddelkindern. Verschwörungstheorie, pfui. Erich Hambach kann erklären, wie die „Herren des Geldes“ (Untertitel seines neuen Buchs) arbeiten und was man tun kann, um sich ihrem Zugriff zu entziehen. Als die Kameras aus waren, ging es munter weiter mit dem Publikum. Steuerfrei leben, sich auf den Lastenausgleich vorbereiten, Kollateralkonto. Siehe oben. Wir haben dann noch 25 Minuten nachgeschoben, die bei den „Truth Brothers“ zu sehen sein werden, dem Kanal von Erich Hambach.
Montag Dresden. Lesung im Buchhaus Loschwitz. Ich war schon im Juni dort, damals mit dem Buch über die Unterwerfung der Universitäten. Diesmal „Der dressierte Nachwuchs“. Wieder volles Haus. In Loschwitz heißt das: Susanne Dagen, Gastgeberin und Moderatorin, quetscht sich auf einen Hocker zwischen Klavier und Reihe null und sagt: Willkommen zum Gottesdienst. Einige sind zum zweiten Mal da. Neu: Paul Soldan, den ich aus seinen Texten für Multipolar kenne und über sein Buch „Sheikhi“, und Julia Szarvasy, die mich in ihrem Bus für Nuoviso interviewt hat und auf der Ruderboot-Couch. Hinterher kommen (um im Bild zu bleiben) drei U-Boote zu mir. Professoren. Ein Techniker, ein Germanist und ein Medienforscher, der sich sogar mit mir fotografieren lassen will. Dieser Kollege ist nicht an der TU (falls jemand die Fahndung einleiten möchte), aber immerhin. Ich bin oft gefragt worden, ob es an den Unis Gleichgesinnte gibt, und kann jetzt endlich sagen: ja. Ein paar schon.
Versteckt in einer der letzten Dresdner Reihen: Michael Beleites, eine Ikone der DDR-Umweltbewegung und später ein Jahrzehnt lang Beauftragter für die Stasi-Unterlagen in Sachsen. Er hat eine Rezension mitgebracht, die er gerade für die Sezession geschrieben hat, und einen Gedanken, der mich später schlecht schlafen lässt. Müssen wir die Geschichte vom Herbst 1989 umschreiben? Ganz neu ist dieser Gedanke nicht, natürlich nicht. Wer dabei war, hat sich schon damals gefragt, wie die Stimmung so schnell kippen konnte vom Wunsch nach einem anderen, besseren Sozialismus zu Helmut Kohl und seiner D-Mark. Daniela Dahn, wie Michael Beleites seinerzeit in vorderster Front, hat den schwarzen Peter an den Journalismus weitergegeben. Tamtam und Tabu. Eine Kampagne, losgetreten von Horst Teltschik, Kohls wichtigstem Mann, die sich um SED-Skandale drehte und so wie eine Nebelkerze verhüllte, um was es eigentlich ging. Die Herren des Geldes, würde Erich Hambach sagen. „Alte Besitzverhältnisse“ wieder herstellen und damit „alte Machtverhältnisse“, sagt Daniela Dahn. Michael Beleites ergänzt das nun durch das, was er gesehen und erlebt hat, bei der Auflösung des Geheimdienstes in Gera zum Beispiel. Da seien Leute wie er gewesen, natürlich. Legitimiert durch das, was vorher war. Überall im Land seien aber plötzlich auch unbeschriebene Blätter aufgetaucht, laut und damit schnell ganz vorne dran. Ein Forschungsthema, ohne Frage.
Bevor ich das zu Ende gedacht habe, sitze ich im Rudolf-Steiner-Haus, nur ein paar Steinwürfe weg von der Alster. Ich würde gern „Hamburgs Wohnzimmer“ schreiben, aber dazu taugt der Saal im Souterrain dann doch nicht ganz. Immerhin: steuerfinanziert. Geht also doch. Eingeladen hat unter anderem der Nachdenkseiten-Gesprächskreis vor Ort. Thema: Wandel der Universitäten. Wieder sind Kollegen da, auch aus dem Mittelbau und aus der Rentnergeneration, die sich zu erinnern glauben, alles schon erlebt zu haben, damals, in ihrer großen Zeit. Nun ja. Wichtiger: Walter Weber ist da, ein Arzt, Koryphäe in Sachen Krebs, 80 inzwischen, der meinen letzten Auftritt in Hamburg organisiert hat. Große Freiheit, Sommer 2022. Die Sonne schien, und es roch nach Aufbruch. Aus dem ganzen Land waren sie gekommen, aus Nord und Süd, von links bis rechts, aus allen nur denkbaren Bewegungen und Milieus. Corona als Klammer, genau wie der Glaube, dass unsere Zeit jetzt anbricht.
Es kam dann anders, aber das ist hier nicht mein Punkt. Walter Weber, der alte Weggefährte, zieht Bilanz – bei einem Becks in seinem Haus, genau da, wo wir vor drei Jahren in größerer Runde beraten haben. Walter hat inzwischen einen Prozess hinter sich mit knapp zwei Dutzend Verhandlungstagen und den entsprechenden Kosten. Maskenatteste. Was immer wir aufgefahren haben an Beweisanträgen, sagt Walter, es wurde abgeschmettert. Und trotzdem. Wir müssen sie zwingen, sich damit auseinanderzusetzen. Immer wieder. So ähnlich habe ich das zwei Stunden vorher im Steiner-Haus gesagt, mit Vaclav Havel als Referenz. 500 Ärzte, schätzt Walter Weber, haben wie er Atteste ausgestellt. 500 bei einer sechsstelligen Zahl an Kollegen. Sicher gibt es eine Dunkelziffer. Lassen wir es bei den 500, weil Walter Weber hier die Folgen kennt. 80 Prozent von diesen 500 haben Haus- und Praxisdurchsuchungen erlebt. Er selbst zwei, der Spitzenreiter acht. Die Maske war der Test. Als die Spritze kam, wusste jeder, auf was er sich einlassen würde - selbst ein Medienforscher wie ich. Die maskierte Öffentlichkeit, veröffentlicht im Oktober 2020, war mit Sicherheit nicht mein bester Text, aber der, der den meisten Wirbel auslöste und später sogar zweimal vor Gericht verhandelt wurde.
Was bleibt von all den Kämpfen? Wir haben die Leute aus der Vereinzelung geholt, sagt Walter. Die 20 Prozent, die dagegen waren. Wir haben ihnen gezeigt, dass sie nicht allein sind, und diese Leute mobilisiert. Gescheitert sind wir an Schritt drei. Strukturbildung. Es fehlt uns an Geld, Michael. Walter Weber hat an Regionalbüros gebastelt. „Ärzte für Aufklärung“ in Thüringen – und das ist nur eins von vielen Beispielen. Wer weiß, wie viel Geld es in diesem Land gibt und wie viele wirklich reiche Leute, der weiß auch, dass wir hier über Peanuts sprechen. Wem es gut geht, der will, dass alles weiter seinen Gang geht. Der will keine Strukturen für irgendeine Opposition. Walter Weber hat mit einer seiner Nichten gerade „Das siebte Kreuz“ gelesen. Anna Seghers, Schulstoff in der DDR. Weißt du, was ich da gelernt habe, Michael? Echter Widerstand hat zwei Bedingungen. Keine Familie und keine Angst vor dem Tod.
Der Zug nach Berlin ist pünktlich und mein Gastgeber folglich noch nicht da. Gibt’s doch nicht, sagt er. Hat es noch nie gegeben. Über meinen Auftritt im Sprechsaal breite ich den Mantel des Schweigens. Die Idee klang super: Wir machen dort eine Ausstellung mit aktuellen Bildern aus Gaza, gekauft von der dpa, und du, Michael, bringst deine Bücher über Cancel Culture, Jugend und Universitäten zusammen, um zu erklären, warum Deutschland wegschaut. Die kastrierte Öffentlichkeit. Der beste Titel geht ins Leere, wenn niemand weiß, dass ich sprechen werde. Vielleicht ist das so, wenn der eigene Verlag der Veranstalter ist. Jens Fischer Rodrian hat durch einen Zufall erfahren, dass ich da bin, und bringt die CD Voices for Gaza, ganz frisch in der Reihe „Protestnoten“. Auf dem Cover: große Namen von Didi Hallervorden über Tino Eisbrenner, Nirit Sommerfeld und Diether Dehm bis zu Wolfgang Wodarg. Fünf von fast 40. Sorry an die, die ich auslassen musste. Der gleiche Zufall hat Kathrin Schmidt in den Sprechsaal geführt, Mitglied des PEN-Zentrums, Buchpreisträgerin, Maßnahmenkritikerin. Sie hat wie immer ihr Strickzeug dabei.
Ein kleines Publikum, frei von Kameras, erlaubt, in die Tiefen zu tauchen und dabei auch zu riskieren, im Trüben zu fischen. Erich Hambach hätte seine Freude gehabt. Und wer weiß schon, was daraus später wächst. Ein paar Minuten vor Beginn gehe ich durch das Regierungsviertel und höre plötzlich meinen Namen. Eine ARD-Frau, die auf Friedrich Merz wartet. Koalitionsvertrag fertig, Kamera schussbereit. Mein Film über die Duldungspflicht, sagt die Frau und strahlt über das ganze Gesicht. Er ist fertig. Premiere nächste Woche. Sie war bei einem meiner letzten Berliner Vorträge und wird jetzt mit ihrem Namen für ein Produkt stehen, dass so nicht im Ersten laufen kann. Noch nicht, würde Walter Weber sagen. Ende nächsten Jahres, sagt er mir beim Abschied, steht Merkel vor Gericht. Ist der Gedanke erstmal da, so begründet er das sinngemäß, dann ist er nicht mehr aufzuhalten. Mal schauen, wie das jetzt mit der Deutschen Bahn wird bei der Rückfahrt nach Bayern. Ich nehme mir vor, dass wir pünktlich sind.
Freie Akademie für Medien & Journalismus
Bild: Tobias Schönebeck auf Pixabay (Dresden, Blaues Wunder in Loschwitz)
-
 @ d9e9fb27:d5fe5e1a
2025-04-22 01:29:16
@ d9e9fb27:d5fe5e1a
2025-04-22 01:29:16"There are two pillars in Costa Rica, education and coffee." A tourist guide I met told me this, and during the trip I discovered the strong link between coffee and the locals.
In fact, coffee runs very deeply in the Ticos' culture. So deep that the summer vacations from school (November to January) coincide with the coffee collection season. Children had to help their parents with the coffee. Coffee was a family business.
Monteverde, in the region of Puentarenas, is one of those places where coffee ha always been a corner stone of the society. Here, My gf and I went to visit a coffee plantation and discovered how coffee is made.
Monteverde
Monteverde is a well-known turistic location in the central part of Costa Rica. Many people reach this beautiful place to visit the famous Cloud Rainforest, acres and acres of pristine forest, with many different kind of animals and plants living in it.

However, other than tourism is coffee that pushes the economy of this place. The hills around the town are covered with coffee plantations and there are tours than try to explain how coffee is made.

Coffee Tours
While we were in Monteverde, we joined one of these tours. We decided to give credit to a smaller plantation instead of the super turistic ones. A more rustic and family-owned business, El Pueblo Coffee Tour. We were not disappointed. We had the show all to ourselves, a super-prepared guide and all the time to make questions and enjoy with no rush.
The Plant of Coffee
Since Costa Rica is a quite small country, to compete on the market producers decided to bet on quality instead of quantity. That's why, the only type produced here is the Arabica.
Before the coffee bean, the plant produces a nice white flower, similar to the jasmine.

After a while, the coffee beans appear.

As soon as they turn red, they are ready to be collected.
Interesting fact: between the coffee plants many fruit trees like mangos or bananos can be found. In fact, those plants help keep the soil fertile and healthy, thus leading to a higher coffee quality!
Coffee Harvesting
Coffee is still harvested by hand. Beans do not get mature at the same time, so manual labor is needed. Laborer use a very simple tool to collect coffee, one which allow them to have both hands free.
 Workers do not get paid by hours, but by the number of cajuelas that they can fill. A cajuela is a standard box, which contains around 13kg of beans. It's divided into quarters, so that the worker can get paid for the quarter, too.
Workers do not get paid by hours, but by the number of cajuelas that they can fill. A cajuela is a standard box, which contains around 13kg of beans. It's divided into quarters, so that the worker can get paid for the quarter, too.
Each cajuela is paid around 3.50$.
Coffee Drying
In the farm we visited, drying was perfomed naturally, through the heat of the sun. There are three ways in which the bean is left to dry: lavado, miel and naturàl.
- Lavado: The beans are peeled and washed to remove the jelly.
 - Miel: The jelly on the beans is maintained to give it more sweet flavour.
- Miel: The jelly on the beans is maintained to give it more sweet flavour. - Naturàl: The bean is left to dry with its peel on, to give it a more fruity taste.
- Naturàl: The bean is left to dry with its peel on, to give it a more fruity taste.
Back in the days, to peel the beans for the lavado and the miel variety, the pìlon was used. The bean is very hard, thus this tool does not damage it.

However, today the peeling procedure is done using a machine.

Coffee Roasting
The last step in the production of coffee is roasting. Coffee is put inside a sort of hoven, and is left there at high temperature according to the level of roasting that is needed. The more roasting, the less caffeine there is and the more bitter the coffee. Usually you have light, medium and dark roast.

Coffee Tasting
In the end, we also had a coffee tasting. We tried different roasting and different varieties.
Our guide explained us the best way to taste coffee and helped us defining the different flavours that we perceived. He also taught us the best way to prepare it: infusion time, water temperature, coffe makers and so on.
My favorite one was the dark one, while my gf enjoyed the light roast more. Of course, we bought some packs of these varieties!
Thanks for tuning in!
I hope you enjoyed this brief overview of the Costa Rican coffee.
Pura Vida
Tuma
-
 @ bb1c863a:2953c3fb
2025-04-14 22:22:50
@ bb1c863a:2953c3fb
2025-04-14 22:22:50Block Height 892385 11:47 pm Monday, 14 April 2025
In a powerful gesture of support for Bitcoin-aligned education, Blockstream has donated 21 Blockstream Jade hardware wallets to the Consensus21 School — a groundbreaking learning initiative launching its first campus this year on the Mornington Peninsula, just outside Melbourne, Australia.
The donation will place 21 Jades directly into the hands of the first 21 students at the new campus — some as young as five years old — giving them real tools to explore Bitcoin self-custody, digital sovereignty, and privacy-first technology in an age-appropriate and hands-on way.
“The Jade wallets are more than just devices — they’re symbols of freedom, responsibility, and the future of education,” said Kieran Nolan, co-founder of Consensus21. “We’re incredibly grateful to Blockstream for standing behind our mission.”
Real Tools for Real Sovereignty
The Blockstream Jade is a secure, open-source hardware wallet built for Bitcoiners who value freedom, privacy, and independence. These values are embedded deeply into the Consensus21 educational philosophy, which blends Steiner-inspired learning, homeschooling flexibility, and a curriculum rooted in Bitcoin principles like voluntary exchange, decentralization, and self-responsibility.
With the Jades now part of the learning toolkit, Consensus21 learners will be introduced to key concepts like:
- Private key management
- Seed phrase generation and backup
- Multisig wallets
- The importance of self-custody and trust minimization
This is not just about theory — learners will get to use these tools in real-world contexts, preparing them to grow up fluent in the principles of freedom tech.
A Campus, A Vision, A Movement
Launching in 2025, the Mornington Peninsula campus is the pilot site for the broader Consensus21 vision: a distributed, regenerative, and values-aligned network of co-learning spaces, including a future 10-acre farm campus and a registered Steiner school.
The Blockstream donation comes at a pivotal time, as the community transitions from vision to reality. The gift of exactly 21 Blockstream Jades — echoing Bitcoin’s 21 million hard cap — is both a symbolic and practical gesture of support, underscoring the shared commitment between Bitcoin builders and grassroots educators.
Stay Connected
📄 Whitepaper: https://github.com/consensus21school/consensus21school.github.io/blob/main/whitepaper.md
🌐 Website: https://consensus21.school
📝 Nostr: CONSENSUS21@nostrcheck.me
🐦 X (Twitter): https://x.com/Consensus21
-
 @ 207ad2a0:e7cca7b0
2025-01-07 03:46:04
@ 207ad2a0:e7cca7b0
2025-01-07 03:46:04Quick context: I wanted to check out Nostr's longform posts and this blog post seemed like a good one to try and mirror. It's originally from my free to read/share attempt to write a novel, but this post here is completely standalone - just describing how I used AI image generation to make a small piece of the work.
Hold on, put your pitchforks down - outside of using Grammerly & Emacs for grammatical corrections - not a single character was generated or modified by computers; a non-insignificant portion of my first draft originating on pen & paper. No AI is ~~weird and crazy~~ imaginative enough to write like I do. The only successful AI contribution you'll find is a single image, the map, which I heavily edited. This post will go over how I generated and modified an image using AI, which I believe brought some value to the work, and cover a few quick thoughts about AI towards the end.
Let's be clear, I can't draw, but I wanted a map which I believed would improve the story I was working on. After getting abysmal results by prompting AI with text only I decided to use "Diffuse the Rest," a Stable Diffusion tool that allows you to provide a reference image + description to fine tune what you're looking for. I gave it this Microsoft Paint looking drawing:
and after a number of outputs, selected this one to work on:
The image is way better than the one I provided, but had I used it as is, I still feel it would have decreased the quality of my work instead of increasing it. After firing up Gimp I cropped out the top and bottom, expanded the ocean and separated the landmasses, then copied the top right corner of the large landmass to replace the bottom left that got cut off. Now we've got something that looks like concept art: not horrible, and gets the basic idea across, but it's still due for a lot more detail.

The next thing I did was add some texture to make it look more map like. I duplicated the layer in Gimp and applied the "Cartoon" filter to both for some texture. The top layer had a much lower effect strength to give it a more textured look, while the lower layer had a higher effect strength that looked a lot like mountains or other terrain features. Creating a layer mask allowed me to brush over spots to display the lower layer in certain areas, giving it some much needed features.
At this point I'd made it to where I felt it may improve the work instead of detracting from it - at least after labels and borders were added, but the colors seemed artificial and out of place. Luckily, however, this is when PhotoFunia could step in and apply a sketch effect to the image.
At this point I was pretty happy with how it was looking, it was close to what I envisioned and looked very visually appealing while still being a good way to portray information. All that was left was to make the white background transparent, add some minor details, and add the labels and borders. Below is the exact image I wound up using:

Overall, I'm very satisfied with how it turned out, and if you're working on a creative project, I'd recommend attempting something like this. It's not a central part of the work, but it improved the chapter a fair bit, and was doable despite lacking the talent and not intending to allocate a budget to my making of a free to read and share story.
The AI Generated Elephant in the Room
If you've read my non-fiction writing before, you'll know that I think AI will find its place around the skill floor as opposed to the skill ceiling. As you saw with my input, I have absolutely zero drawing talent, but with some elbow grease and an existing creative direction before and after generating an image I was able to get something well above what I could have otherwise accomplished. Outside of the lowest common denominators like stock photos for the sole purpose of a link preview being eye catching, however, I doubt AI will be wholesale replacing most creative works anytime soon. I can assure you that I tried numerous times to describe the map without providing a reference image, and if I used one of those outputs (or even just the unedited output after providing the reference image) it would have decreased the quality of my work instead of improving it.
I'm going to go out on a limb and expect that AI image, text, and video is all going to find its place in slop & generic content (such as AI generated slop replacing article spinners and stock photos respectively) and otherwise be used in a supporting role for various creative endeavors. For people working on projects like I'm working on (e.g. intended budget $0) it's helpful to have an AI capable of doing legwork - enabling projects to exist or be improved in ways they otherwise wouldn't have. I'm also guessing it'll find its way into more professional settings for grunt work - think a picture frame or fake TV show that would exist in the background of an animated project - likely a detail most people probably wouldn't notice, but that would save the creators time and money and/or allow them to focus more on the essential aspects of said work. Beyond that, as I've predicted before: I expect plenty of emails will be generated from a short list of bullet points, only to be summarized by the recipient's AI back into bullet points.
I will also make a prediction counter to what seems mainstream: AI is about to peak for a while. The start of AI image generation was with Google's DeepDream in 2015 - image recognition software that could be run in reverse to "recognize" patterns where there were none, effectively generating an image from digital noise or an unrelated image. While I'm not an expert by any means, I don't think we're too far off from that a decade later, just using very fine tuned tools that develop more coherent images. I guess that we're close to maxing out how efficiently we're able to generate images and video in that manner, and the hard caps on how much creative direction we can have when using AI - as well as the limits to how long we can keep it coherent (e.g. long videos or a chronologically consistent set of images) - will prevent AI from progressing too far beyond what it is currently unless/until another breakthrough occurs.
-
 @ 04cb16e4:2ec3e5d5
2025-04-12 19:21:48
@ 04cb16e4:2ec3e5d5
2025-04-12 19:21:48Meine erste "Begegnung" mit Ulrike hatte ich am 21. März 2022 - dank Amazon konnte ich das Ereignis noch exakt nachvollziehen. Es war eines meiner ersten (Lockdown) kritischen Bücher, die ich in dieser Zeit in die Hände bekam - noch nach Thomas Röper (das war mein Einstieg) aber vor Daniele Ganser. Insofern war es mir möglich, das, was dann folgte für die Autorin, live und in Farbe mit zu verfolgen:
"Wer sich in die Öffentlichkeit traut, kann sich dort ganz schnell eine blutige Nase holen. Dieselben Medien, die eine Person heute glorifizieren, stellen sie morgen an den Pranger. Sie verteilen und entziehen Reputation, fördern und zerstören Karrieren. Das Medium selbst bleibt jedoch immer auf der Siegerseite. Die Gesetze von Marktorientierung und zynisch-ideologisierter Machtausübung gelten für Rundfunk und Fernsehen ebenso wie für die Printmedien - von RTL bis ARD und ZDF, von der BILD über die taz bis zur ZEIT.
»Das Phänomen Guérot« legt genau diesen Vorgang detailliert offen: Der MENSCH Ulrike Guérot ist in der Realität nicht die dämonische Figur, als die sie hingestellt worden ist. Aber an ihr kristallisiert sich genau dieser menschenverachtende Prozess heraus, der bis heute andauert."
Im Herbst 2022 habe ich durch den ersten Vortrag von Daniele Ganser in Falkensee nicht nur Zugang zu einer für mich neuen und anderen Welt bekommen, ab da hat sich eigentlich auch für mich mein Leben komplett auf den Kopf gestellt. Die Weichen wurden zwar schon vorher gestellt, aber nun war es endgültig und es gab kein zurück mehr. Die Planung für das erste Symposium Falkensee war in meinem Kopf geboren und die MenschheitsFamilie entstand als Ort, der virtuell das vereinen sollte, was Daniele an Spiritualität, Menschlichkeit und Friedenswillen in mir freigesetzt hat. Es war sozusagen eine Energie, die nun stetig floß und einen Trichter gefunden hat, in dem sie wirksam werden und sich entfalten konnte. Insofern haben wir auch etwas gemeinsam - Ulrike und ich. Wir sind zu der Zeit auf einen Zug aufgesprungen, der unser Leben veränderte - der uns zwang, alte Wege zu verlassen und neue Wege zu beschreiten. Sowohl beruflich, als auch privat. Und auch das canceln und entfernt werden ist eine Erfahrung, die wir beide teilen. Vielleicht war es deswegen mein erster Gedanke im Herbst 2022, Ulrike Guérot zu meinem 1. Symposium nach Falkensee einzuladen. Das es dann erst beim 2. Anlauf wirklich geklappt hat, hatte auch mit den Höhen und Tiefen des Lebens in dieser Zeit zu tun gehabt.
Nun ist sie zum 2. Mal dabei - denn wer könnte das Thema "Europa" bei einem so wichtigen und hochaktuellen Thema besser vertreten und beleuchten als Ulrike Guérot? Es geht um Geschichte, es geht um Nationalitäten, es geht um Gemeinsamkeiten und um das, was uns hier im Herzen zusammenhält, was unsere Ziele und unsere Befindlichkeiten sind, es geht um Verantwortung und es geht vor allen Dingen um Frieden! Denn dafür steht Europa - für einen Kontinent, der es geschafft hat, trotz aller Gegensätze und Konflikte, die in Jahrhunderten kriegerisch aufgetragen wurden, eine neuen und besonderen Frieden zu finden und zu installieren:
"Völkerrechtlich legt der Westfälische Frieden den oder zumindest einen Grundstein für ein modernes Prinzip: Die Gleichberechtigung souveräner Staaten, unabhängig von ihrer Macht und Größe. Noch heute spricht die Politikwissenschaft, insbesondere die realistische Schule (Henry Kissinger), deshalb vom „Westphalian System“. Durch die Garantien der großen europäischen Mächte erweist sich dieser Frieden als stabilisierendes Element für die weitere Entwicklung in Europa. Noch bis zum Ende des 18. Jahrhunderts wird er immer wieder als Referenz für nachfolgende Friedensschlüsse herangezogen."
Es ging damals um viel und es geht heute um das Überleben auf einem Kontinent, der es eigentlich besser wissen sollte. Wir dürfen gespannt sein, was wir in diesem Vortrag von Ulrike auf dem Symposium Falkensee am 27. April 2025 für Lösungen finden, um wieder zu einer Ordnung und zu einem System der friedlichen Koexistenz zurückfinden zu können, ohne schwarz und weiß und mit all den Facetten, die das Leben uns so bietet:
"Es ging nicht mehr um das Ausfechten religiöser Wahrheiten, sondern um geregelte Verfahren, die es möglich machten, mit konkurrierenden religiösen Wahrheiten, die nach wie vor nebeneinander und unversöhnlich bestanden, auf friedliche Weise umzugehen. Deutlich wurde das nicht zuletzt, als der Papst in einer offiziellen Note scharf gegen den Friedensschluss protestierte, weil er die Rechte der katholischen Seite leichtfertig aufgegeben sah. Die katholischen Beteiligten des Abkommens hielt dies nicht von der Unterzeichnung ab - ein religiöser Schiedsrichter wurde in Sachen Krieg und Frieden nicht mehr akzeptiert."
-
 @ b1b16be0:08f41c1d
2025-04-11 22:58:00
@ b1b16be0:08f41c1d
2025-04-11 22:58:00Bitcoin need more devs to scale! So I decide to translate to spanish https://plebdevs.com plebdevs@plebdevs.com is a opensource website to learn #bitcoin #lightning free.I started in my free time but now I have to sacrifice work time to move forward. Any zap could be a new bitcoiner!
Why Spanish? Spanish is the third most spoken language on the internet, but much of this community has little access to technical content in English. Plebdevs can be the 🔥torch that illuminates new developers to scale Bitcoin from Latin America and the world.
Apprenticeship Incentive Plebs will gaining the possibility of #learn a higher-paying job as #dev.
Let's Make Bitcoin Scale Millions of Spanish speakers can learn how to develop about Bitcoin and Lightning.
Proof of Work Introduction presentation: https://docs.google.com/presentation/d/1IMC4GHYjccKhGu2mDrtY3bOGcjyFcwgXwFyKyNMq7iw/edit?usp=sharing
🟩🟩🟩⬜⬜⬜⬜⬜⬜⬜ 30%
Thanks to bitcoinplebdev@bitcoinpleb.dev to create this #wonder
Any Zap will be helpful!
mav21@primal.net am@cubabitcoin.org lacrypta@hodl.ar BenJustman@primal.net shishi@nostrplebs.com sabine@primal.net onpoint@nostr.com theguyswann@iris.to Richard@primal.net eliza@primal.net
-
 @ 04c915da:3dfbecc9
2025-03-25 17:43:44
@ 04c915da:3dfbecc9
2025-03-25 17:43:44One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 044da344:073a8a0e
2025-04-19 12:00:32
@ 044da344:073a8a0e
2025-04-19 12:00:32Der Chefredakteur war freundlich am Telefon und etwas zerknirscht. Dafür kassieren wir eine Rüge, ganz klar, sagte Hannes Lehner sinngemäß. Er habe mit seiner Redaktion gesprochen, noch einmal an die journalistische Sorgfaltspflicht erinnert, nachzulesen zum Beispiel im Pressekodex des Deutschen Presserates, und die Abläufe so verändert, dass so etwas nicht noch einmal passieren könne. Außerdem sei die Redaktion bereit, mir etwas Gutes zu tun, wenn ich denn eine Idee hätte.
Ich schreibe das hier etwas salopp aus dem Gedächtnis. Hintergrund ist einer dieser üblen Texte, die in der Regionalpresse immer dort aufploppen, wo Menschen öffentlich auftreten, die im kollektiven Gedächtnis gebrandmarkt sind. Querdenker, Putinversteher, Leugner von diesem und jenem. Die Details kann man unten nachlesen und dort auch das Meisterwerk von Andrea Weidemann genießen, immerhin Redaktionsleiterin Plattling-Deggendorf-Osterhofen in der Mediengruppe Attenkofer, die für das Straubinger Tagblatt steht. Veröffentlicht wurde der Text dort am 30. November 2024 auf der Titelseite des Lokalteils in Plattling. Am nächsten Tag habe ich Patrik Baab im Wohnzimmer von Plattling interviewt. Der Saal war voll, trotz oder wegen des Weidemann-Artikels.

Mein Punkt hier ist: Es lohnt sich, solche Angriffe nicht einfach auf sich beruhen zu lassen. Ich hatte es vor zwei Jahren schon einmal versucht beim Presserat und verloren in einer Sache, die viel größer war – mit drei zu zwei Stimmen bei zwei Enthaltungen. Wer weiß. Die Beschwerde ist online, und jeder mag sich selbst ein Urteil bilden. Diesmal war das Urteil auf Ebene eins einstimmig (Beschwerde ist begründet) und auf Ebene zwei fast einstimmig (sechs zu eins): eine Missbilligung, die zwar nicht abgedruckt werden muss, aber in diesem Fall doch sollte („als Ausdruck fairer Berichterstattung“).
Warum es keine Rüge gab, Höchststrafe im Presserat-Kosmos, wissen allein die Götter. Weiter begründet wird das nicht. Das Schreiben des Presserates, immerhin drei eng bedruckte Seiten, wäre ein Thema für sich. Es gelingt den Kollegen dort nicht einmal, den Weidemann-Artikel fehlerfrei zusammenzufassen. So macht mich der Presserat zum Gründer des „Querdenker-Blattes” Demokratischer Widerstand – zu viel der Ehre. Viel wichtiger als irgendwelche Strafen ist aber ohnehin das Gespräch – gerade dort, wo man sich kennt und wo sich jeder Journalist leicht selbst ein Bild machen kann, bevor er in die Tasten haut und Kritiker an den Pranger stellt. Ich bin froh, dass Hannes Lehner zum Telefonhörer gegriffen und auch öffentlich Abbitte geleistet hat, bevor der Presserat sich äußern konnte. Die Zitate, um die es ging, wurden aus der Onlineversion entfernt – genau wie die Bezahlschranke, damit möglichst viele die Entschuldigung sehen. Ich werde dem Chefredakteur vorschlagen, einen seiner Leute zu den nächsten Veranstaltungen der Initiative „Deggendorf miteinander“ zu schicken, und kann mir kaum vorstellen, dass es keine gute Presse gibt, wenn man die Menschen dort erlebt und sich in die Augen gesehen hat.

Beschwerde beim Deutschen Presserat (9. Dezember 2024)
Gegenstand
Diese Beschwerde bezieht sich auf einen Artikel von Andrea Weidemann, der am 30. November 2024 im Plattlinger Anzeiger erschienen ist („Kritiker beantworten kritische Fragen nicht“).
Beschwerdegrund
Der Artikel verstößt gegen die Pressekodex-Ziffern 1, 2 und 9. Die Autorin legt mir zwei wörtliche Zitate in den Mund, die (wenn sie denn wahr wären) nicht nur geeignet sind, meine Ehre zu verletzen (Ziffer 9), sondern es mir auch unmöglich machen würden, weiter als bayerischer Beamter zu wirken. Eine „wahrhaftige Unterrichtung der Öffentlichkeit“ (Ziffer 1) wäre dabei nicht schwer gewesen, wenn Frau Weidemann sorgfältig gearbeitet (Ziffer 2) oder mir die entsprechenden Zitate vor der Veröffentlichung vorgelegt hätte. Es gab vorab einen Mailaustausch (siehe Punkt 3), der sich aber auf etwas ganz anders bezog und mich schon vor der Veröffentlichung daran zweifeln ließ, dass die Ziffern 1 und 2 des Pressekodex Richtschnur des Arbeitens von Andrea Weidemann sind.
Vorgeschichte / Mailaustausch
Für den 1. Dezember 2024 hatte die Initiative „Deggendorf miteinander“ in der Nachbarstadt Plattling eine Buchlesung von Patrik Baab angekündigt und mich gebeten, die Ausführungen des Kollegen wissenschaftlich einzuordnen. Der Titel der Veranstaltung („Wie uns Medien und Lohnschreiber in Kriege treiben“) entsprach dem Untertitel des Buchs „Propaganda-Presse“, das Patrik Baab im Sommer in der Reihe „Hintergrund kompakt“ veröffentlicht hat. Am 27. November erhielt ich folgende Mail:
Sehr geehrter Herr Meyen, in der Hoffnung, dass ich als Mitarbeiterin der Plattlinger Redaktion der Mediengruppe Attenkofer für Sie nicht in die Kategorie „Propaganda-Medium“ falle, hätte ich zu Ihrer Veranstaltungsteilnahme am kommenden Sonntag in Plattling/Niederbayern folgende Fragen: 1. Auf der Suche nach näheren Informationen zu Ihrer Person habe ich mehrfach gelesen, dass Sie der Ansicht sind, dass die (Leit-)Medien bewusst auf die Gesellschaft Einfluss nehmen, also manipulieren. Welche Belege haben Sie dafür? Und: Gilt das Ihrer Ansicht nach für alle Medien? Und für alle Themenbereiche? 2. Auch haben Sie sich kritisch zu journalistischen Faktencheckern geäußert und Sie als Propagandamaschinen bezeichnet. Heißt das, dass auch Medien wie z.B. Correctiv Ihrer Meinung nach nicht glaubwürdig sind? 3. Wenn man heute von Medien spricht, muss man vor allem das Internet im Blick behalten. Ist es nicht so, dass gerade dort ungefilterte (Falsch-)Informationen verbreitet werden? Für eine zeitnahe Rückmeldung wäre ich Ihnen sehr dankbar. Mit besten Grüßen, Andrea Weidemann, Redaktionsleitung Plattling-Deggendorf-Osterhofen
Eine solche Beschwerde ist nicht der Ort, sich im Detail mit diesen Fragen auseinanderzusetzen. Ich will deshalb nur darauf hinweisen, dass es hier schlicht keine vernünftigen Antworten gab. Frage 1 beschreibt gewissermaßen die Geschäftsgrundlage von Journalismus und Medienforschung. Wenn man nicht von Wirkungen ausgehen würde, könnten sich beide Berufsgruppen die Arbeit sparen. Zum Thema „Glaubwürdigkeit der Medien“ (Frage 2) habe ich mich 2001 habilitiert und schon seinerzeit darauf hingewiesen, dass es sich hierbei um keine sinnvolle Kategorie für die Bewertung journalistischer Leistungen handelt. Frage 3 ist suggestiv und so allgemein formuliert, dass eigentlich nur ein „Ja“ möglich ist. Ich habe deshalb am nächsten Morgen eher ironisch geantwortet und die Kollegin zugleich an die Berufstugenden erinnert:
Was soll ich dazu sagen, liebe Andrea Weidemann? Sie finden im Internet komische Sachen über mich und fragen dann, ob dort Falschinfos verbreitet werden. Am besten (das ist ja auch das Credo von Patrik Baab): Sie kommen am Sonntag und machen sich selbst ein Bild. Bis dahin mit den besten Grüßen
Antwort:
Sehr geehrter Herr Meyen, natürlich werde ich am Sonntag anwesend sein. Trotzdem schade, dass sie auf meine Fragen nicht antworten. Ich habe keine „komischen Sachen“ gelesen, sondern konkrete Aussagen von Ihnen zitiert. Darf ich noch mit einer Stellungnahme rechnen?
Frau Weidemann war dann nicht bei der Veranstaltung, hat aber vorab den Artikel veröffentlicht, über den ich mich hier beschwere.
Falschzitate
Beide Zitate befinden sich im vierten Absatz des Artikels, der offensichtlich darauf abzielt, ein „Porträt“ von Michael Meyen zu liefern. Dass mein Leben und mehr als 20 Jahre auf einer Professur für Kommunikationswissenschaft an der LMU München dabei auf die beiden Ausgaben der Wochenzeitung Demokratischer Widerstand (DW) reduziert werden, in denen ich als einer von vier „Herausgebern“ genannt werde, mag schlechter Stil sein. Wenn allerdings mit Anführungszeichen (also als wörtliches Zitat markiert) behauptet wird, ich hätte Deutschland als „Spritzenmörder-Diktatur“ bezeichnet, hört der Spaß auf. Ich habe im März 2002 einen Eid auf die bayerische Verfassung geschworen und würde mich mit einer solchen Aussage selbst ins Abseits stellen und meine berufliche Zukunft aufs Spiel setzen. Dazu kommt, dass der Plattlinger Anzeiger in einer Region erscheint, die seit mehr als dreieinhalb Jahren meine Wahlheimat ist. Eine solche Falschberichterstattung ist so geeignet, meine Reputation auch über mein berufliches Wirken hinaus nachhaltig zu beschädigen.
Das gilt so in etwas abgeschwächter Form auch für das zweite Zitat. Nach einer Zusammenfassung zum Wirken besagter Wochenzeitung folgt „Meyens Meinung“, wieder in Anführungszeichen und mir damit wortwörtlich in den Mund gelegt: „Die Medien haben sich der Propaganda der NATO vollumfänglich unterworfen.“
Ich kann nur mutmaßen, von wem beide Zitate stammen. „Propaganda der NATO“ ist nicht mein Thema, Pauschalisierungen wie „die Medien“ liegen mir fern, und ich würde den Teufel tun, die Bundesrepublik Deutschland als „Diktatur“ zu bezeichnen oder das Wort „Spritzenmörder“ in den Mund zu nehmen (wie auch das Wort „vollumfänglich“, aber das nur am Rande). Falls beide Zitate im DW gestanden haben sollten: Ich habe meine „Beziehung“ zu dieser Wochenzeitung in einem Buch behandelt (Wie ich meine Uni verlor, 2023) und außerdem eine Stellungnahme veröffentlicht (In eigener Sache, 9. Mai 2024).
Dort steht auch, dass ich gegen die Disziplinarstrafe klage, von der Andrea Weidemann zu berichten weiß (verhängt allerdings nicht „von der LMU“, sondern von der Landesanwaltschaft, einer internen Ermittlungsbehörde). Das Verfahren läuft noch. Die Kürzung der „Bezüge um zehn Prozent“ ist folglich ausgesetzt. Ich könnte mich hier also auch wegen eines Verstoßes gegen Ziffer 13 beschweren.
Zusammengefasst: Andrea Weidemann zielt mit ihrem Text darauf ab, meine Ehre zu verletzen, meine Reputation in Frage zu stellen und die Leser ihrer Zeitung so davon abzuhalten, die Lesung von Patrik Baab am folgenden Tag zu besuchen. Die Autorin legt mir dazu zwei Zitate in den Mund, die nicht von mir stammen. Statt diese Zitate von mir bestätigen zu lassen, schickt sie in einer Mail das, was sie offenbar unter „kritischen Fragen“ versteht (Überschrift des Artikels), und wundert sich dann auch noch, dass es darauf keine Antworten gibt. Der Beitrag verstößt gegen die Ziffern 1, 2 und 9 des Pressekodex und würde auch bei Ziffer 13 einer näheren Prüfung nicht standhalten.

-
 @ 732c6a62:42003da2
2025-03-09 22:36:26
@ 732c6a62:42003da2
2025-03-09 22:36:26Não são recentes as táticas da esquerda de tentar reprimir intelectualmente seus opositores na base do deboche, da ironia, do desprezo e do boicote à credibilidade. Até Marx usava ironia para chamar os críticos de "burgueses iludidos". A diferença é que, no século XXI, trocaram o manifesto comunista por threads no Twitter e a dialética por memes de mau gosto.
A Falácia da Superioridade Moral
O debate sobre o "pobre de direita" no Brasil é contaminado por uma premissa tácita da esquerda: a ideia de que classes baixas só podem ter consciência política se aderirem a pautas progressistas. Quem ousa divergir é tratado como "traidor de classe", "manipulado", "ignorante", ou até vítimas de deboches como alguma pessoa com um qi em temperatura ambiente repetir diversas vezes "não é possível que ainda exista pobre de direita", "nunca vou entender pobre de direita", ou "pobre de direita é muito burro, rico eu até entendo", como se o autor dessas frases fosse o paladino dos mais oprimidos e pobres. Esse discurso, porém, não resiste a uma análise empírica, histórica ou sociológica.
Contexto Histórico: A Esquerda e o Mito do "Voto Consciente"
A noção de que o pobre deve votar na esquerda por "interesse de classe" é herança do marxismo ortodoxo, que via a política como mero reflexo da posição econômica. No entanto, a realidade é mais complexa:
- Dados do Latinobarómetro (2022): 41% dos brasileiros de baixa renda (até 2 salários mínimos) apoiam redução de impostos e maior liberdade econômica — pautas tradicionalmente associadas à direita.
- Pesquisa IPEC (2023): 58% dos pobres brasileiros priorizam "segurança pública" como principal demanda, acima de "distribuição de renda".
Esses números não são acidentais. Refletem uma mudança estrutural: o pobre moderno não é mais o "operário industrial" do século XX, mas um empreendedor informal, motorista de app, ou microempresário — figuras que valorizam autonomia e rejeitam paternalismo estatal. Eles dizem não entender o pobre de direita e que nunca vai entendê-los, mas o fato é que não entendem porque nunca conversaram com um sem fazer cara de psicólogo de posto de saúde. Sua "preocupação" é só uma máscara para esconder o desprezo por quem ousa pensar diferente do seu manual de "oprimido ideal".
Se ainda não entenderam:
Direita ≠ rico: Tem gente que trabalha 12h/dia e vota em liberal porque quer ser dono do próprio negócio, não pra pagar mais taxação pra você postar meme no Twitter.
Acham que são o Sherlock Holmes da pobreza: o palpite de que "o pobre é manipulado" é tão raso quanto sua compreensão de economia básica.
A Psicologia por Trás do Voto Conservador nas Periferias
A esquerda atribui o voto pobre em direita a "falta de educação" ou "manipulação midiática". Essa tese é não apenas elitista, mas cientificamente falsa:
Análise Psicológica Básica (para você que se acha o Paulo Freire):
- Síndrome do Branco Salvador: Acha que o pobre é uma criatura tão frágil que precisa de você pra pensar. Spoiler: ele não precisa.
- Viés da Superioridade Moral: "Se você é pobre e não concorda comigo, você é burro". Parabéns, recriou a escravidão intelectual.
- Efeito Dunning-Kruger: Não sabe o que é CLT, mas dá palpite sobre reforma trabalhista.- Estudo da Universidade de São Paulo (USP, 2021): Entre moradores de favelas, 63% associam políticas de segurança dura (como "bandido bom é bandido morto") à proteção de seus negócios e famílias. Para eles, a esquerda é "branda demais" com o crime.
- Pesquisa FGV (2020): 71% dos trabalhadores informais rejeitam aumentos de impostos, mesmo que para financiar programas sociais. Motivo: já sofrem com a burocracia estatal para legalizar seus negócios.
Esses dados revelam uma racionalidade prática: o pobre avalia políticas pelo impacto imediato em sua vida, não por abstrações ideológicas. Enquanto a esquerda fala em "reforma estrutural" e tenta importar discursos estrangeiros para debate, por exemplo, o tema irrelevante do pronome neutro, ele quer resolver problemas como:
- Violência (que afeta seu comércio);
- Impostos (que consomem até 40% do lucro de um camelô);
- Burocracia (que impede a legalização de sua barraca de pastel).
Religião, Valores e a Hipocrisia do "Ateísmo de Redes Sociais"
A esquerda subestima o papel da religião na formação política das classes baixas. No Brasil, 76% dos evangélicos são pobres (Datafolha, 2023), e suas igrejas promovem valores como:
- Família tradicional (contra pautas progressistas como ideologia de gênero em escolas);
- Auto-responsabilidade (ênfase em "trabalho duro" em vez de assistencialismo).Exemplo Concreto:
Nas favelas de São Paulo, pastores evangélicos são frequentemente eleitos a cargos locais com plataformas anticrime e pró-mercado. Para seus eleitores, a esquerda urbana (que defende descriminalização de drogas e críticas à polícia) representa uma ameaça ao seu estilo de vida.
A Esquerda e seu Desprezo pela Autonomia do Pobre
O cerne do debate é a incapacidade da esquerda de aceitar que o pobre possa ser autônomo. Algumas evidências:
O Caso dos Empreendedores Informais
- Segundo o IBGE (2023), 40% dos trabalhadores brasileiros estão na informalidade. Muitos veem o Estado como obstáculo, não aliado. Políticas de direita (como simplificação tributária) são mais atraentes para eles que o Bolsa Família.
A Ascensão do Conservadorismo Periférico
- Pessoas assim tem um pensamento simples. Sua mensagem: "Queremos empreender, não depender de político."
A Rejeição ao "Vitimismo"
- Pesquisa Atlas Intel (2022): 68% dos pobres brasileiros rejeitam o termo "vítima da sociedade". Preferem ser vistos como "lutadores".
A projeção freudiana "o pobre é burro porque eu sou inteligente"
O deboche esquerdista esconde um complexo de inferioridade disfarçado de superioridade moral. É a Síndrome do Salvador em sua forma mais patética:
- Passo 1: Assume-se que o pobre é um ser desprovido de agência.
- Passo 2: Qualquer desvio da narrativa é atribuído a "manipulação da elite".
- Passo 3: Quem critica o processo é chamado de "fascista".Exemplo Prático:
Quando uma empregada doméstica diz que prefere o livre mercado a programas sociais, a esquerda não pergunta "por quê?" — ela grita "lavagem cerebral!". A ironia? Essa mesma esquerda defende a autonomia feminina, exceto quando a mulher é pobre e pensa diferente.Dados Globais: O Fenômeno Não é Brasileiro
A ideia de que "pobre de direita" é uma anomalia é desmentida por evidências internacionais:
- Estados Unidos: 38% dos eleitores com renda abaixo de US$ 30k/ano votaram em Trump em 2020 (Pew Research). Motivos principais: conservadorismo social e rejeição a impostos. A esquerda: "vítimas da falsa consciência". Mais um detalhe: na última eleição de 2024, grande parte da classe "artística" milionária dos Estados Unidos, figuras conhecidas, promoveram em peso a Kamala Harris, do Partido Democrata. Percebe como a esquerda atual é a personificaçãoda burguesia e de só pensar na própria barriga?
- Argentina: Javier Milei, libertário radical, quando candidato, tinha forte apoio nas villas miseria (favelas). Seu lema — "O estado é um parasita" — ressoa entre quem sofria com inflação de 211% ao ano.
- Índia: O partido BJP (direita nacionalista) domina entre os pobres rurais, que associam a esquerda a elites urbanas desconectadas de suas necessidades.
A história que a esquerda tenta apagar: pobres de direita existem desde sempre
A esquerda age como se o "pobre de direita" fosse uma invenção recente do MBL, mas a realidade é que classes baixas conservadoras são regra, não exceção, na história mundial:
- Revolução Francesa (1789): Camponeses apoiaram a monarquia contra os jacobinos urbanos que queriam "libertá-los".
- Brasil Imperial: Escravos libertos que viraram pequenos proprietários rurais rejeitavam o abolicionismo radical — queriam integração, não utopia.Tradução:
Quando o pobre não segue o script, a esquerda inventa teorias conspiratórias.
A Hipocrisia da Esquerda Urbana e Universitária
Enquanto acusa o pobre de direita de "alienado", a esquerda brasileira é dominada por uma elite desconectada da realidade periférica:
- Perfil Socioeconômico: 82% dos filiados ao PSOL têm ensino superior completo (TSE, 2023). Apenas 6% moram em bairros periféricos.
- Prioridades Descoladas: Enquanto o pobre debate segurança e custo de vida, a esquerda pauta discussões como "linguagem não-binária em editais públicos" — tema irrelevante para quem luta contra o desemprego. Os grandes teóricos comunistas se reviram no túmulo quando veem o que a esquerda se tornou: não debatem os reais problemas do Brasil, e sim sobre suas próprias emoções.
"A esquerda brasileira trocou o operário pelo influencer progressista. O pobre virou um personagem de campanha, não um interlocutor real."
A diversidade de pensamento que a esquerda não suporta
A esquerda prega diversidade — desde que você seja diverso dentro de um checklist pré-aprovado. Pobre LGBTQ+? Herói. Pobre evangélico? Fascista. Pobre que abre MEI? "Peão do capitalismo". A realidade é que favelas e periferias são microcosmos de pluralidade ideológica, algo que assusta quem quer reduzir seres humanos a estereótipos.
Respostas aos Argumentos Esquerdistas (e Por que Falham)
"O pobre de direita é manipulado pela mídia!"
- Contradição: Se a mídia tradicional é dominada por elites (como alegam), por que grandes veículos são abertamente progressistas? A Record (evangélica) é exceção, não regra.
Contradição Central:
Como explicar que, segundo o Banco Mundial (2023), países com maior liberdade econômica (ex.: Chile, Polônia) reduziram a pobreza extrema em 60% nas últimas décadas, enquanto modelos estatizantes (ex.: Venezuela, Argentina com o governo peronista) afundaram na miséria? Simples: a esquerda prefere culpar o "neoliberalismo" a admitir que o pobre com o mínimo de consciência quer emprego, não esmola.Dado que Machuca:
- 71% das mulheres da periferia rejeitam o feminismo radical, associando-o a "prioridades distantes da realidade" (Instituto Locomotiva, 2023)."Ele vota contra os próprios interesses!"
- Falácia: Pressupõe que a esquerda define o que é o "interesse do pobre". Para um pai de família na Cidade de Deus, ter a boca de fogo fechada pode ser mais urgente que um aumento de 10% no Bolsa Família.
O pobre de direita não é uma anomalia. É o produto natural de um mundo complexo onde seres humanos têm aspirações, medos e valores diversos. Enquanto a esquerda insiste em tratá-lo como um projeto fracassado, ele está ocupado:
- Trabalhando para não depender do governo.
- Escolhendo religiões que dão sentido à sua vida.
- Rejeitando pautas identitárias que não resolvem o custo do gás de cozinha."É falta de educação política!"
- Ironia: Nos países nórdicos (modelo da esquerda), as classes baixas são as mais conservadoras. Educação não correlaciona com progressismo.
Por que o Debuste Precisa Acabar
A insistência em descredibilizar o pobre de direita revela um projeto de poder fracassado. A esquerda, ao substituir diálogo por deboche, perdeu a capacidade de representar quem mais precisaria dela. Enquanto isso, a direita — nem sempre por virtude, mas por pragmatismo — capturou o descontentamento de milhões com o status quo.
O pobre de direita existe porque ele não precisa da permissão do rico de esquerda para pensar. A incapacidade de entender isso só prova que a esquerda é a nova aristocracia.
Último Dado: Nas eleições de 2022, Tarcísio de Freitas (direita) venceu em 72% das favelas de São Paulo. O motivo? Seu discurso anti-burocracia e pró-microempreendedor.
A mensagem é clara: o pobre não é um projeto ideológico. É um agente político autônomo — e quem não entender isso continuará perdendo eleições.
A esquerda elitista não odeia o pobre de direita por ele ser "irracional". Odeia porque ele desafia o monopólio moral que ela construiu sobre a miséria alheia. Enquanto isso, o pobre segue sua vida, ignorando os berros de quem acha que sabem mais da sua vida que ele mesmo.
Pergunta Retórica (Para Incomodar):
Se a esquerda é tão sábia, por que não usa essa sabedoria para entender que pobre também cansa de ser tratado como cachorro que late no ritmo errado?
Fontes Citadas:
- Latinobarómetro (2022)
- IPEC (2023)
- USP (2021): "Segurança Pública e Percepções nas Favelas Cariocas"
- FGV (2020): "Informalidade e Tributação no Brasil"
- Datafolha (2023): "Perfil Religioso do Eleitorado Brasileiro"
- Atlas Intel (2022): "Autopercepção das Classes Baixas"
- Pew Research (2020): "Voting Patterns by Income in the U.S."
- TSE (2023): "Perfil Socioeconômico dos Filiados Partidários"
Leitura Recomendada para Esquerdistas:
- "Fome de Poder: Por que o Pobre Brasileiro Abandonou a Esquerda" (Fernando Schüller, 2023)
- "A Revolução dos Conservadores: Religião e Política nas Periferias" (Juliano Spyer, 2021)
- "Direita e Esquerda: Razões e Paixões" (Demétrio Magnoli, 2019) -
 @ 866e0139:6a9334e5
2025-04-18 07:25:36
@ 866e0139:6a9334e5
2025-04-18 07:25:36Autor: Ludwig F. Badenhagen. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Sie wollen die neuesten Pareto-Artikel auf einen Blick sehen (Friedenstaube & Co.), um nichts mehr zu verpassen?* Hier geht es zu unserem Telegram-Kanal.***
Einen Feind, den man nicht kennt, kann man nicht besiegen. Zur Vollendung dieses Gedankens liegt es nahe, die Aufmerksamkeit von Groll und Gegenwehr auf andere zu lenken.
Wer sich die Spektakel auf den Bühnen der Erde mit einer gewissen Erkenntnisfähigkeit anschaut, wird bemerken, dass es zu den Primärthemen stets leicht zu durchschauende Drehbücher gibt und dass es sich bei den auf den Bühnen handelnden Akteuren eher um Schauspieler als um tatsächliche Kompetenzträger handelt. Es geht angeblich um Gesundheit, Friedenssicherung, Menschen- und Klimarettung und so weiter. Tatsächlich geht es aber um die Ausbeutung, Verletzung und das Töten von Menschen. Dies mit Beispielen zu unterfüttern ist nicht die Absicht dieses Beitrags, denn Beispiele gibt es genug. Stattdessen soll ein Licht auf die, die man nicht sieht, die im Verborgenen agieren, geworfen und deren Machtstrukturen offengelegt werden.
Die Leute, welche tatsächlich an der Spitze von allem stehen, lassen andere auf extra hierfür eingerichteten Bühnen agieren. So gibt es große und kleine Bühnen für Politik, Wirtschaft, Geld, Gesundheit, Nahrung, Umwelt, Glauben etc. Diese Bühnen bieten das Fernsehen, das Radio, das Internet und weitere Medien. Die Systemspitze hat Steuerungsinstrumente implementiert, mit denen die Kommentierung dessen, was auf den Bühnen passiert, durch Medien und „Volksvertreter“ sowie „Experten“ nach Vorgaben „eingeordnet“ wird. Die „öffentliche Meinung“ ist maximal manipuliert und Abweichler werden bekämpft. Das System bestimmt, was „Wahrheit“ ist, und bestraft „Unwahrheit“.
Viele Menschen sind nicht in der Lage, eine Lüge von der Wahrheit zu unterscheiden. Hierfür sind schließlich Verstand, Intuition, Bildung, Wahrnehmungs- und Erkenntnisfähigkeit sowie Mut erforderlich. Das ist für die meisten Menschen zu viel. Immer wieder ist von denen, die den Schwindel seinerzeit frühphasig erkannten, zu lesen, dass die Coronazeit ein Intelligenztest war. Das ist aber eine Verharmlosung, denn es ging tatsächlich um Gehorsam und Unterwerfung, um die Zerstörung von Menschen durch die Vergiftung mit Spritzen und die Zerstörung von kleinen und mittleren Unternehmen. Selbstverständlich ging es auch um Demoralisierung und Macht – und ums Geldverdienen. Insbesondere intelligente Menschen sind anfällig für Manipulation und Angst und somit wurden viele Intelligente als Meinungsverstärker zur Lenkung der Blöden missbraucht. Intelligente passen sich an. Intelligenz hat ausdrücklich nichts mit Klugheit, Bildung, Erkenntnisfähigkeit, Resilienz und Mut zu tun.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Wer steckt dahinter?
Diese Frage wurde bereits ausführlich in dem Buch „Das Komitee der 300“ von John Coleman beantwortet. Dort sind viele der Protagonisten, deren Intentionen und deren Organisationen mit Bezugnahme auf belastbare Quellen beschrieben. Hierbei handelt es sich primär um die Dynastien, die es über mehrere Generationen hinweg vollbracht haben, ihre Machtposition auf- und auszubauen. Diese Leute kommen nicht in den Medien vor, um nicht „unter Beschuss zu geraten“. Das sind die Leute, die über den ultimativen Einfluss darüber verfügen, was in den Medien gebracht wird. Diese Leute erzeugen Probleme, um Lösungen hierfür verkaufen zu können. Diese Leute steuern die öffentliche Meinung und die Menschen.
Diese globale Steuerung benötigt Technik und viele Mitarbeiter. Nun darf man nicht den Fehler begehen, zu glauben, dass jeder Mitarbeiter des Komitees alles weiß. Tatsächlich existiert hier eine Hierarchie, innerhalb derer die obersten Verbündeten sehr genau wissen, was sie für wen und gegen wen tun, wogegen innerhalb der mittleren und unteren Hierarchiestufen die Mitarbeiter einfach nur ihre jeweiligen Jobs innerhalb der einzelnen Regierungen, Gerichte, Institutionen und Firmen erledigen. Ähnlich dem Militär, wo der General weiß, dass es nur um die Macht und das Geld einiger Leute an der Spitze geht, die nicht kämpfen, aber der Offizier und der Soldat glauben, es gehe um „die gute Sache“. Jede Hierarchiestufe erhält ihre Belohnung für Gehorsam und ihre Bestrafung für Ungehorsam.
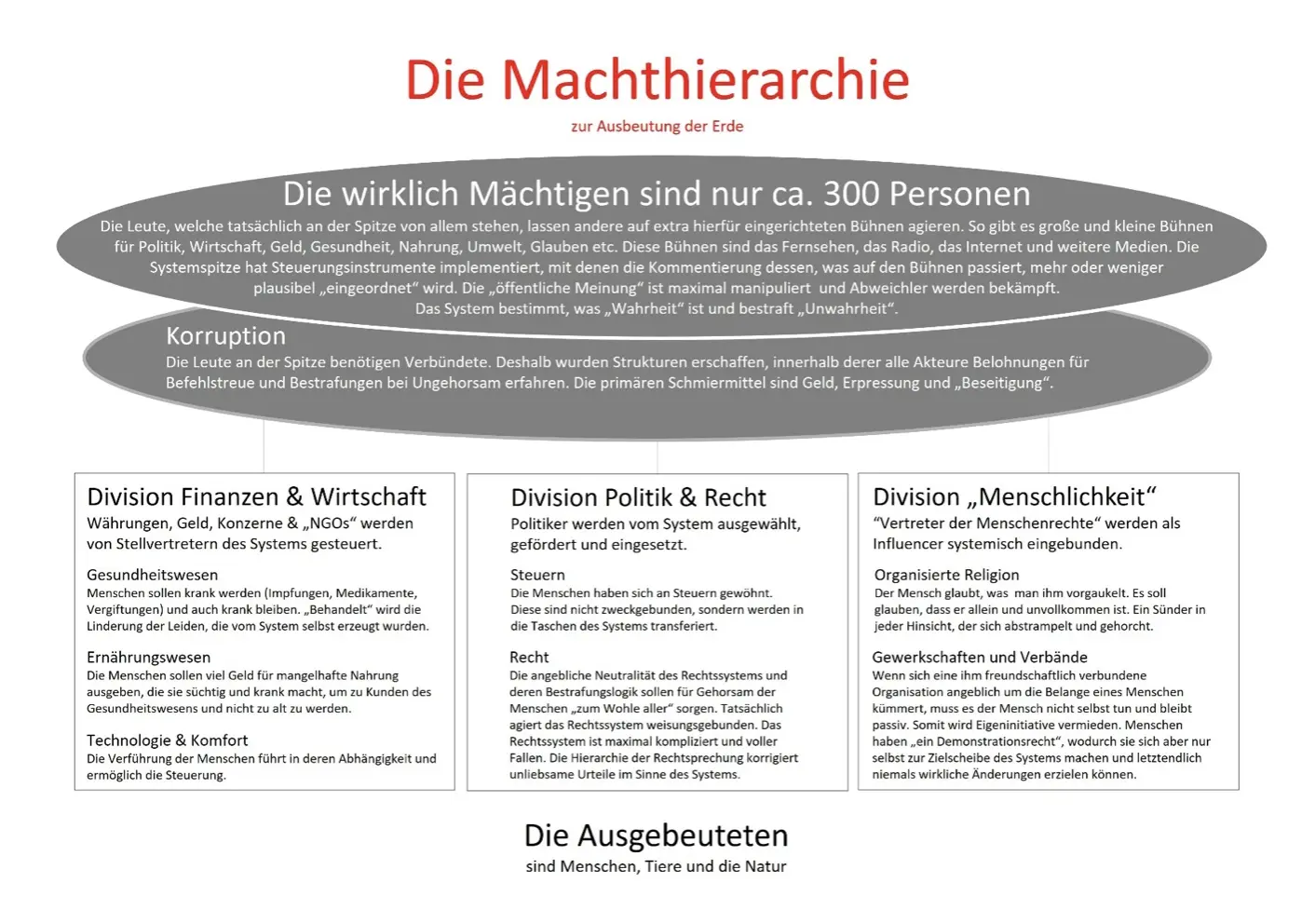
Die 3 primären Divisionen
Die Division Finanzen & Wirtschaft kümmert sich um Währungen, Geldsysteme, Konzerne, NGO etc. Die Kontrolle über das aktuelle Geldsystem, von dem sich jeder abhängig wähnt, ist ein Schlüsselelement zur Steuerung. Die Dynastien und die vermögenden Menschen dieser Erde investieren nicht direkt, sondern überlassen wesentliche Teile ihrer Vermögen ihren Verwaltern. Diese Vermögensverwalter übernehmen Geschäftsanteile an Firmen in Größenordnungen, welche ihnen Gestaltungsmacht einräumt, sodass sie Einfluss auf die Besetzung von dortigen Schlüsselpositionen ausüben können, welche wiederum formell die Strategie des jeweiligen Unternehmens bestimmen. Die Dynastien erschaffen und kontrollieren NGOs sowie weitere Organisationsgebilde nach Erfordernis.
Die Division Politik & Recht hat in erster Linie die Aufgabe, dafür zu sorgen, dass die Menschen glauben, sie leben in einer Demokratie und könnten durch Wahlen etwas bewirken. Sie sollen glauben, dass es Volkvertreter gibt, welche die Interessen der Bevölkerung vertreten. Dem angeblich gleichgestellt ist das Rechtssystem – zumindest in der Darstellung des Systems, dessen integraler Bestandteil die Medien sind. Tatsächlich wurde es in den letzten Jahren überdeutlich, dass die gewöhnlichen Menschen von diesen Institutionen eben nicht vertreten werden.
Die Division „Menschlichkeit“, hiermit sind sogenannte „Vertreter der Menschlichkeit“ wie Kirchen, Gewerkschaften und Verbände etc. gemeint, soll suggerieren, dass der Mensch „einen starken Beschützer“ an seiner Seite hat. Dies führt dazu, dass die Menschen sich an die Regeln des Systems halten. Sie demonstrieren und werden dort massiv misshandelt, wie die vielen Corona-Demos gezeigt haben. Oder es werden „Gegendemonstrationen“ inszeniert, um der Öffentlichkeit vorzugaukeln, dass „die Mehrheit“ eine ganz andere Meinung als die Demonstranten hat.
In allen drei Divisionen gibt es wieder eigene Macht- und Korruptionsstrukturen und jede Struktur befasst sich in erster Linie mit der Ausbeutung der Vielen zum eigenen Wohle. Wer sich als gewöhnlicher Bürger auf diese Institutionen verlässt, wird keine positiven Veränderungen seiner gegenwärtigen Situation erfahren.
Sie möchten mehr wissen? Dann lesen Sie Wie wir die Kriegstreiber stoppen und Ob Corona oder Krieg: Wir Menschen werden wie Vieh behandelt.
Ludwig F. Badenhagen (Pseudonym, Name ist der Redaktion bekannt).
Der Autor hat deutsche Wurzeln und betrachtet das Geschehen in Deutschland und Europa aus seiner Wahlheimat Südafrika. Seine Informationen bezieht er aus verlässlichen Quellen und insbesondere von Menschen, die als „Verschwörungstheoretiker“, „Nazi“, „Antisemit“ sowie mit weiteren Kampfbegriffen der dortigen Systemakteure wie Politiker und „Journalisten“ diffamiert werden. Solche Diffamierungen sind für ihn ein Prädikatsmerkmal. Er ist international agierender Manager mit einem globalen Netzwerk und verfügt hierdurch über tiefe Einblicke in Konzerne und Politik.
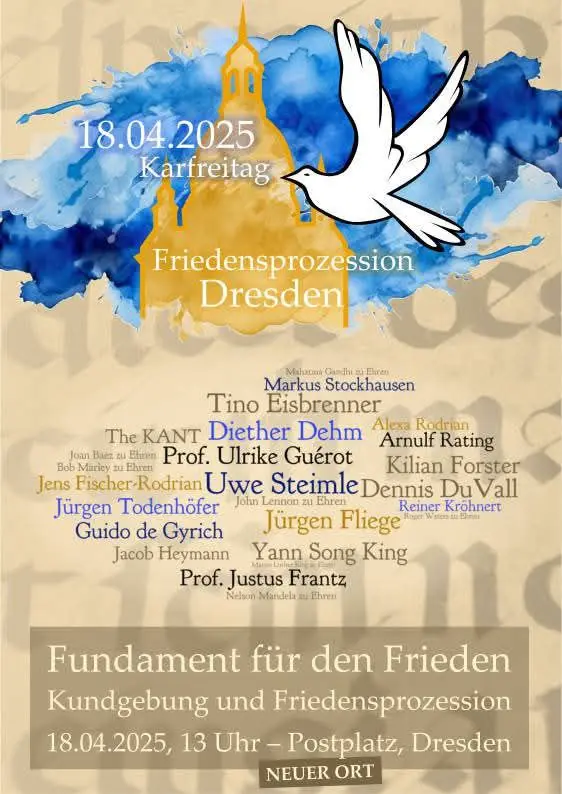
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ 3b3a42d3:d192e325
2025-04-10 08:57:51
@ 3b3a42d3:d192e325
2025-04-10 08:57:51Atomic Signature Swaps (ASS) over Nostr is a protocol for atomically exchanging Schnorr signatures using Nostr events for orchestration. This new primitive enables multiple interesting applications like:
- Getting paid to publish specific Nostr events
- Issuing automatic payment receipts
- Contract signing in exchange for payment
- P2P asset exchanges
- Trading and enforcement of asset option contracts
- Payment in exchange for Nostr-based credentials or access tokens
- Exchanging GMs 🌞
It only requires that (i) the involved signatures be Schnorr signatures using the secp256k1 curve and that (ii) at least one of those signatures be accessible to both parties. These requirements are naturally met by Nostr events (published to relays), Taproot transactions (published to the mempool and later to the blockchain), and Cashu payments (using mints that support NUT-07, allowing any pair of these signatures to be swapped atomically.
How the Cryptographic Magic Works 🪄
This is a Schnorr signature
(Zₓ, s):s = z + H(Zₓ || P || m)⋅kIf you haven't seen it before, don't worry, neither did I until three weeks ago.
The signature scalar s is the the value a signer with private key
k(and public keyP = k⋅G) must calculate to prove his commitment over the messagemgiven a randomly generated noncez(Zₓis just the x-coordinate of the public pointZ = z⋅G).His a hash function (sha256 with the tag "BIP0340/challenge" when dealing with BIP340),||just means to concatenate andGis the generator point of the elliptic curve, used to derive public values from private ones.Now that you understand what this equation means, let's just rename
z = r + t. We can do that,zis just a randomly generated number that can be represented as the sum of two other numbers. It also follows thatz⋅G = r⋅G + t⋅G ⇔ Z = R + T. Putting it all back into the definition of a Schnorr signature we get:s = (r + t) + H((R + T)ₓ || P || m)⋅kWhich is the same as:
s = sₐ + twheresₐ = r + H((R + T)ₓ || P || m)⋅ksₐis what we call the adaptor signature scalar) and t is the secret.((R + T)ₓ, sₐ)is an incomplete signature that just becomes valid by add the secret t to thesₐ:s = sₐ + tWhat is also important for our purposes is that by getting access to the valid signature s, one can also extract t from it by just subtracting
sₐ:t = s - sₐThe specific value of
tdepends on our choice of the public pointT, sinceRis just a public point derived from a randomly generated noncer.So how do we choose
Tso that it requires the secret t to be the signature over a specific messagem'by an specific public keyP'? (without knowing the value oft)Let's start with the definition of t as a valid Schnorr signature by P' over m':
t = r' + H(R'ₓ || P' || m')⋅k' ⇔ t⋅G = r'⋅G + H(R'ₓ || P' || m')⋅k'⋅GThat is the same as:
T = R' + H(R'ₓ || P' || m')⋅P'Notice that in order to calculate the appropriate
Tthat requirestto be an specific signature scalar, we only need to know the public nonceR'used to generate that signature.In summary: in order to atomically swap Schnorr signatures, one party
P'must provide a public nonceR', while the other partyPmust provide an adaptor signature using that nonce:sₐ = r + H((R + T)ₓ || P || m)⋅kwhereT = R' + H(R'ₓ || P' || m')⋅P'P'(the nonce provider) can then add his own signature t to the adaptor signaturesₐin order to get a valid signature byP, i.e.s = sₐ + t. When he publishes this signature (as a Nostr event, Cashu transaction or Taproot transaction), it becomes accessible toPthat can now extract the signaturetbyP'and also make use of it.Important considerations
A signature may not be useful at the end of the swap if it unlocks funds that have already been spent, or that are vulnerable to fee bidding wars.
When a swap involves a Taproot UTXO, it must always use a 2-of-2 multisig timelock to avoid those issues.
Cashu tokens do not require this measure when its signature is revealed first, because the mint won't reveal the other signature if they can't be successfully claimed, but they also require a 2-of-2 multisig timelock when its signature is only revealed last (what is unavoidable in cashu for cashu swaps).
For Nostr events, whoever receives the signature first needs to publish it to at least one relay that is accessible by the other party. This is a reasonable expectation in most cases, but may be an issue if the event kind involved is meant to be used privately.
How to Orchestrate the Swap over Nostr?
Before going into the specific event kinds, it is important to recognize what are the requirements they must meet and what are the concerns they must address. There are mainly three requirements:
- Both parties must agree on the messages they are going to sign
- One party must provide a public nonce
- The other party must provide an adaptor signature using that nonce
There is also a fundamental asymmetry in the roles of both parties, resulting in the following significant downsides for the party that generates the adaptor signature:
- NIP-07 and remote signers do not currently support the generation of adaptor signatures, so he must either insert his nsec in the client or use a fork of another signer
- There is an overhead of retrieving the completed signature containing the secret, either from the blockchain, mint endpoint or finding the appropriate relay
- There is risk he may not get his side of the deal if the other party only uses his signature privately, as I have already mentioned
- There is risk of losing funds by not extracting or using the signature before its timelock expires. The other party has no risk since his own signature won't be exposed by just not using the signature he received.
The protocol must meet all those requirements, allowing for some kind of role negotiation and while trying to reduce the necessary hops needed to complete the swap.
Swap Proposal Event (kind:455)
This event enables a proposer and his counterparty to agree on the specific messages whose signatures they intend to exchange. The
contentfield is the following stringified JSON:{ "give": <signature spec (required)>, "take": <signature spec (required)>, "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>", "description": "<Info about the proposal (optional)>", "nonce": "<Signature public nonce (optional)>", "enc_s": "<Encrypted signature scalar (optional)>" }The field
roleindicates what the proposer will provide during the swap, either the nonce or the adaptor. When this optional field is not provided, the counterparty may decide whether he will send a nonce back in a Swap Nonce event or a Swap Adaptor event using thenonce(optionally) provided by in the Swap Proposal in order to avoid one hop of interaction.The
enc_sfield may be used to store the encrypted scalar of the signature associated with thenonce, since this information is necessary later when completing the adaptor signature received from the other party.A
signature specspecifies thetypeand all necessary information for producing and verifying a given signature. In the case of signatures for Nostr events, it contain a template with all the fields, exceptpubkey,idandsig:{ "type": "nostr", "template": { "kind": "<kind>" "content": "<content>" "tags": [ … ], "created_at": "<created_at>" } }In the case of Cashu payments, a simplified
signature specjust needs to specify the payment amount and an array of mints trusted by the proposer:{ "type": "cashu", "amount": "<amount>", "mint": ["<acceptable mint_url>", …] }This works when the payer provides the adaptor signature, but it still needs to be extended to also work when the payer is the one receiving the adaptor signature. In the later case, the
signature specmust also include atimelockand the derived public keysYof each Cashu Proof, but for now let's just ignore this situation. It should be mentioned that the mint must be trusted by both parties and also support Token state check (NUT-07) for revealing the completed adaptor signature and P2PK spending conditions (NUT-11) for the cryptographic scheme to work.The
tagsare:"p", the proposal counterparty's public key (required)"a", akind:30455Swap Listing event or an application specific version of it (optional)
Forget about this Swap Listing event for now, I will get to it later...
Swap Nonce Event (kind:456) - Optional
This is an optional event for the Swap Proposal receiver to provide the public nonce of his signature when the proposal does not include a nonce or when he does not want to provide the adaptor signature due to the downsides previously mentioned. The
contentfield is the following stringified JSON:{ "nonce": "<Signature public nonce>", "enc_s": "<Encrypted signature scalar (optional)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Swap Adaptor Event (kind:457)
The
contentfield is the following stringified JSON:{ "adaptors": [ { "sa": "<Adaptor signature scalar>", "R": "<Signer's public nonce (including parity byte)>", "T": "<Adaptor point (including parity byte)>", "Y": "<Cashu proof derived public key (if applicable)>", }, …], "cashu": "<Cashu V4 token (if applicable)>" }And the
tagsmust contain:"e", akind:455Swap Proposal Event (required)"p", the counterparty's public key (required)
Discoverability
The Swap Listing event previously mentioned as an optional tag in the Swap Proposal may be used to find an appropriate counterparty for a swap. It allows a user to announce what he wants to accomplish, what his requirements are and what is still open for negotiation.
Swap Listing Event (kind:30455)
The
contentfield is the following stringified JSON:{ "description": "<Information about the listing (required)>", "give": <partial signature spec (optional)>, "take": <partial signature spec (optional)>, "examples: [<take signature spec>], // optional "exp": <expiration timestamp (optional)>, "role": "<adaptor | nonce (optional)>" }The
descriptionfield describes the restrictions on counterparties and signatures the user is willing to accept.A
partial signature specis an incompletesignature specused in Swap Proposal eventskind:455where omitting fields signals that they are still open for negotiation.The
examplesfield is an array ofsignature specsthe user would be willing totake.The
tagsare:"d", a unique listing id (required)"s", the status of the listingdraft | open | closed(required)"t", topics related to this listing (optional)"p", public keys to notify about the proposal (optional)
Application Specific Swap Listings
Since Swap Listings are still fairly generic, it is expected that specific use cases define new event kinds based on the generic listing. Those application specific swap listing would be easier to filter by clients and may impose restrictions and add new fields and/or tags. The following are some examples under development:
Sponsored Events
This listing is designed for users looking to promote content on the Nostr network, as well as for those who want to monetize their accounts by sharing curated sponsored content with their existing audiences.
It follows the same format as the generic Swap Listing event, but uses the
kind:30456instead.The following new tags are included:
"k", event kind being sponsored (required)"title", campaign title (optional)
It is required that at least one
signature spec(giveand/ortake) must have"type": "nostr"and also contain the following tag["sponsor", "<pubkey>", "<attestation>"]with the sponsor's public key and his signature over the signature spec without the sponsor tag as his attestation. This last requirement enables clients to disclose and/or filter sponsored events.Asset Swaps
This listing is designed for users looking for counterparties to swap different assets that can be transferred using Schnorr signatures, like any unit of Cashu tokens, Bitcoin or other asset IOUs issued using Taproot.
It follows the same format as the generic Swap Listing event, but uses the
kind:30457instead.It requires the following additional tags:
"t", asset pair to be swapped (e.g."btcusd")"t", asset being offered (e.g."btc")"t", accepted payment method (e.g."cashu","taproot")
Swap Negotiation
From finding an appropriate Swap Listing to publishing a Swap Proposal, there may be some kind of negotiation between the involved parties, e.g. agreeing on the amount to be paid by one of the parties or the exact content of a Nostr event signed by the other party. There are many ways to accomplish that and clients may implement it as they see fit for their specific goals. Some suggestions are:
- Adding
kind:1111Comments to the Swap Listing or an existing Swap Proposal - Exchanging tentative Swap Proposals back and forth until an agreement is reached
- Simple exchanges of DMs
- Out of band communication (e.g. Signal)
Work to be done
I've been refining this specification as I develop some proof-of-concept clients to experience its flaws and trade-offs in practice. I left the signature spec for Taproot signatures out of the current document as I still have to experiment with it. I will probably find some important orchestration issues related to dealing with
2-of-2 multisig timelocks, which also affects Cashu transactions when spent last, that may require further adjustments to what was presented here.The main goal of this article is to find other people interested in this concept and willing to provide valuable feedback before a PR is opened in the NIPs repository for broader discussions.
References
- GM Swap- Nostr client for atomically exchanging GM notes. Live demo available here.
- Sig4Sats Script - A Typescript script demonstrating the swap of a Cashu payment for a signed Nostr event.
- Loudr- Nostr client under development for sponsoring the publication of Nostr events. Live demo available at loudr.me.
- Poelstra, A. (2017). Scriptless Scripts. Blockstream Research. https://github.com/BlockstreamResearch/scriptless-scripts
-
 @ 04c915da:3dfbecc9
2025-03-13 19:39:28
@ 04c915da:3dfbecc9
2025-03-13 19:39:28In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ fd06f542:8d6d54cd
2025-04-22 00:59:34
@ fd06f542:8d6d54cd
2025-04-22 00:59:34NIP-18
Reposts
draftoptionalA repost is a
kind 6event that is used to signal to followers that akind 1text note is worth reading.The
contentof a repost event is the stringified JSON of the reposted note. It MAY also be empty, but that is not recommended. Reposts of NIP-70-protected events SHOULD always have an emptycontent.The repost event MUST include an
etag with theidof the note that is being reposted. That tag MUST include a relay URL as its third entry to indicate where it can be fetched.The repost SHOULD include a
ptag with thepubkeyof the event being reposted.Quote Reposts
Quote reposts are
kind 1events with an embeddedqtag of the note being quote reposted. Theqtag ensures quote reposts are not pulled and included as replies in threads. It also allows you to easily pull and count all of the quotes for a post.qtags should follow the same conventions as NIP 10etags, with the exception of themarkargument.["q", <event-id>, <relay-url>, <pubkey>]Quote reposts MUST include the NIP-21
nevent,note, ornaddrof the event in the content.Generic Reposts
Since
kind 6reposts are reserved forkind 1contents, we usekind 16as a "generic repost", that can include any kind of event inside other thankind 1.kind 16reposts SHOULD contain aktag with the stringified kind number of the reposted event as its value. -
 @ fd06f542:8d6d54cd
2025-04-22 00:58:49
@ fd06f542:8d6d54cd
2025-04-22 00:58:49NIP-17
Private Direct Messages
draftoptionalThis NIP defines an encrypted direct messaging scheme using NIP-44 encryption and NIP-59 seals and gift wraps.
Direct Message Kind
Kind
14is a chat message.ptags identify one or more receivers of the message.jsonc { "id": "<usual hash>", "pubkey": "<sender-pubkey>", "created_at": "<current-time>", "kind": 14, "tags": [ ["p", "<receiver-1-pubkey>", "<relay-url>"], ["p", "<receiver-2-pubkey>", "<relay-url>"], ["e", "<kind-14-id>", "<relay-url>"] // if this is a reply ["subject", "<conversation-title>"], // rest of tags... ], "content": "<message-in-plain-text>", }.contentMUST be plain text. Fieldsidandcreated_atare required.An
etag denotes the direct parent message this post is replying to.qtags MAY be used when citing events in the.contentwith NIP-21.json ["q", "<event-id> or <event-address>", "<relay-url>", "<pubkey-if-a-regular-event>"]Kind
14s MUST never be signed. If it is signed, the message might leak to relays and become fully public.File Message Kind
jsonc { "id": "<usual hash>", "pubkey": "<sender-pubkey>", "created_at": "<current-time>", "kind": 15, "tags": [ ["p", "<receiver-1-pubkey>", "<relay-url>"], ["p", "<receiver-2-pubkey>", "<relay-url>"], ["e", "<kind-14-id>", "<relay-url>", "reply"], // if this is a reply ["subject", "<conversation-title>"], ["file-type", "<file-mime-type>"], ["encryption-algorithm", "<encryption-algorithm>"], ["decryption-key", "<decryption-key>"], ["decryption-nonce", "<decryption-nonce>"], ["x", "<the SHA-256 hexencoded string of the file>"], // rest of tags... ], "content": "<file-url>" }Kind 15 is used for sending encrypted file event messages:
file-type: Specifies the MIME type of the attached file (e.g.,image/jpeg,audio/mpeg, etc.).encryption-algorithm: Indicates the encryption algorithm used for encrypting the file. Supported algorithms may includeaes-gcm,chacha20-poly1305,aes-cbcetc.decryption-key: The decryption key that will be used by the recipient to decrypt the file.decryption-nonce: The decryption nonce that will be used by the recipient to decrypt the file.content: The URL of the file (<file-url>).xcontaining the SHA-256 hexencoded string of the file.size(optional) size of file in bytesdim(optional) size of the file in pixels in the form<width>x<height>blurhash(optional) the blurhash to show while the client is loading the filethumb(optional) URL of thumbnail with same aspect ratio (encrypted with the same key, nonce)fallback(optional) zero or more fallback file sources in caseurlfails
Just like kind 14, kind
15s MUST never be signed.Chat Rooms
The set of
pubkey+ptags defines a chat room. If a newptag is added or a current one is removed, a new room is created with a clean message history.Clients SHOULD render messages of the same room in a continuous thread.
An optional
subjecttag defines the current name/topic of the conversation. Any member can change the topic by simply submitting a newsubjectto an existingpubkey+p-tags room. There is no need to sendsubjectin every message. The newestsubjectin the thread is the subject of the conversation.Encrypting
Following NIP-59, the unsigned
kind:14&kind:15chat messages must be sealed (kind:13) and then gift-wrapped (kind:1059) to each receiver and the sender individually.jsonc { "id": "<usual hash>", "pubkey": randomPublicKey, "created_at": randomTimeUpTo2DaysInThePast(), "kind": 1059, // gift wrap "tags": [ ["p", receiverPublicKey, "<relay-url>"] // receiver ], "content": nip44Encrypt( { "id": "<usual hash>", "pubkey": senderPublicKey, "created_at": randomTimeUpTo2DaysInThePast(), "kind": 13, // seal "tags": [], // no tags "content": nip44Encrypt(unsignedKind14, senderPrivateKey, receiverPublicKey), "sig": "<signed by senderPrivateKey>" }, randomPrivateKey, receiverPublicKey ), "sig": "<signed by randomPrivateKey>" }The encryption algorithm MUST use the latest version of NIP-44.
Clients MUST verify if pubkey of the
kind:13is the same pubkey on thekind:14, otherwise any sender can impersonate others by simply changing the pubkey onkind:14.Clients SHOULD randomize
created_atin up to two days in the past in both the seal and the gift wrap to make sure grouping bycreated_atdoesn't reveal any metadata.The gift wrap's
p-tag can be the receiver's main pubkey or an alias key created to receive DMs without exposing the receiver's identity.Clients CAN offer disappearing messages by setting an
expirationtag in the gift wrap of each receiver or by not generating a gift wrap to the sender's public keyPublishing
Kind
10050indicates the user's preferred relays to receive DMs. The event MUST include a list ofrelaytags with relay URIs.jsonc { "kind": 10050, "tags": [ ["relay", "wss://inbox.nostr.wine"], ["relay", "wss://myrelay.nostr1.com"], ], "content": "", // other fields... }Clients SHOULD publish kind
14events to the10050-listed relays. If that is not found that indicates the user is not ready to receive messages under this NIP and clients shouldn't try.Relays
It's advisable that relays do not serve
kind:1059to clients other than the ones tagged in them.It's advisable that users choose relays that conform to these practices.
Clients SHOULD guide users to keep
kind:10050lists small (1-3 relays) and SHOULD spread it to as many relays as viable.Benefits & Limitations
This NIP offers the following privacy and security features:
- No Metadata Leak: Participant identities, each message's real date and time, event kinds, and other event tags are all hidden from the public. Senders and receivers cannot be linked with public information alone.
- No Public Group Identifiers: There is no public central queue, channel or otherwise converging identifier to correlate or count all messages in the same group.
- No Moderation: There are no group admins: no invitations or bans.
- No Shared Secrets: No secret must be known to all members that can leak or be mistakenly shared
- Fully Recoverable: Messages can be fully recoverable by any client with the user's private key
- Optional Forward Secrecy: Users and clients can opt-in for "disappearing messages".
- Uses Public Relays: Messages can flow through public relays without loss of privacy. Private relays can increase privacy further, but they are not required.
- Cold Storage: Users can unilaterally opt-in to sharing their messages with a separate key that is exclusive for DM backup and recovery.
The main limitation of this approach is having to send a separate encrypted event to each receiver. Group chats with more than 100 participants should find a more suitable messaging scheme.
Implementation
Clients implementing this NIP should by default only connect to the set of relays found in their
kind:10050list. From that they should be able to load all messages both sent and received as well as get new live updates, making it for a very simple and lightweight implementation that should be fast.When sending a message to anyone, clients must then connect to the relays in the receiver's
kind:10050and send the events there but can disconnect right after unless more messages are expected to be sent (e.g. the chat tab is still selected). Clients should also send a copy of their outgoing messages to their ownkind:10050relay set.Examples
This example sends the message
Hola, que tal?fromnsec1w8udu59ydjvedgs3yv5qccshcj8k05fh3l60k9x57asjrqdpa00qkmr89mtonsec12ywtkplvyq5t6twdqwwygavp5lm4fhuang89c943nf2z92eez43szvn4dt.The two final GiftWraps, one to the receiver and the other to the sender, respectively, are:
json { "id":"2886780f7349afc1344047524540ee716f7bdc1b64191699855662330bf235d8", "pubkey":"8f8a7ec43b77d25799281207e1a47f7a654755055788f7482653f9c9661c6d51", "created_at":1703128320, "kind":1059, "tags":[ [ "p", "918e2da906df4ccd12c8ac672d8335add131a4cf9d27ce42b3bb3625755f0788"] ], "content":"AsqzdlMsG304G8h08bE67dhAR1gFTzTckUUyuvndZ8LrGCvwI4pgC3d6hyAK0Wo9gtkLqSr2rT2RyHlE5wRqbCOlQ8WvJEKwqwIJwT5PO3l2RxvGCHDbd1b1o40ZgIVwwLCfOWJ86I5upXe8K5AgpxYTOM1BD+SbgI5jOMA8tgpRoitJedVSvBZsmwAxXM7o7sbOON4MXHzOqOZpALpS2zgBDXSAaYAsTdEM4qqFeik+zTk3+L6NYuftGidqVluicwSGS2viYWr5OiJ1zrj1ERhYSGLpQnPKrqDaDi7R1KrHGFGyLgkJveY/45y0rv9aVIw9IWF11u53cf2CP7akACel2WvZdl1htEwFu/v9cFXD06fNVZjfx3OssKM/uHPE9XvZttQboAvP5UoK6lv9o3d+0GM4/3zP+yO3C0NExz1ZgFmbGFz703YJzM+zpKCOXaZyzPjADXp8qBBeVc5lmJqiCL4solZpxA1865yPigPAZcc9acSUlg23J1dptFK4n3Tl5HfSHP+oZ/QS/SHWbVFCtq7ZMQSRxLgEitfglTNz9P1CnpMwmW/Y4Gm5zdkv0JrdUVrn2UO9ARdHlPsW5ARgDmzaxnJypkfoHXNfxGGXWRk0sKLbz/ipnaQP/eFJv/ibNuSfqL6E4BnN/tHJSHYEaTQ/PdrA2i9laG3vJti3kAl5Ih87ct0w/tzYfp4SRPhEF1zzue9G/16eJEMzwmhQ5Ec7jJVcVGa4RltqnuF8unUu3iSRTQ+/MNNUkK6Mk+YuaJJs6Fjw6tRHuWi57SdKKv7GGkr0zlBUU2Dyo1MwpAqzsCcCTeQSv+8qt4wLf4uhU9Br7F/L0ZY9bFgh6iLDCdB+4iABXyZwT7Ufn762195hrSHcU4Okt0Zns9EeiBOFxnmpXEslYkYBpXw70GmymQfJlFOfoEp93QKCMS2DAEVeI51dJV1e+6t3pCSsQN69Vg6jUCsm1TMxSs2VX4BRbq562+VffchvW2BB4gMjsvHVUSRl8i5/ZSDlfzSPXcSGALLHBRzy+gn0oXXJ/447VHYZJDL3Ig8+QW5oFMgnWYhuwI5QSLEyflUrfSz+Pdwn/5eyjybXKJftePBD9Q+8NQ8zulU5sqvsMeIx/bBUx0fmOXsS3vjqCXW5IjkmSUV7q54GewZqTQBlcx+90xh/LSUxXex7UwZwRnifvyCbZ+zwNTHNb12chYeNjMV7kAIr3cGQv8vlOMM8ajyaZ5KVy7HpSXQjz4PGT2/nXbL5jKt8Lx0erGXsSsazkdoYDG3U", "sig":"a3c6ce632b145c0869423c1afaff4a6d764a9b64dedaf15f170b944ead67227518a72e455567ca1c2a0d187832cecbde7ed478395ec4c95dd3e71749ed66c480" }json { "id":"162b0611a1911cfcb30f8a5502792b346e535a45658b3a31ae5c178465509721", "pubkey":"626be2af274b29ea4816ad672ee452b7cf96bbb4836815a55699ae402183f512", "created_at":1702711587, "kind":1059, "tags":[ [ "p", "44900586091b284416a0c001f677f9c49f7639a55c3f1e2ec130a8e1a7998e1b"] ], "content":"AsTClTzr0gzXXji7uye5UB6LYrx3HDjWGdkNaBS6BAX9CpHa+Vvtt5oI2xJrmWLen+Fo2NBOFazvl285Gb3HSM82gVycrzx1HUAaQDUG6HI7XBEGqBhQMUNwNMiN2dnilBMFC3Yc8ehCJT/gkbiNKOpwd2rFibMFRMDKai2mq2lBtPJF18oszKOjA+XlOJV8JRbmcAanTbEK5nA/GnG3eGUiUzhiYBoHomj3vztYYxc0QYHOx0WxiHY8dsC6jPsXC7f6k4P+Hv5ZiyTfzvjkSJOckel1lZuE5SfeZ0nduqTlxREGeBJ8amOykgEIKdH2VZBZB+qtOMc7ez9dz4wffGwBDA7912NFS2dPBr6txHNxBUkDZKFbuD5wijvonZDvfWq43tZspO4NutSokZB99uEiRH8NAUdGTiNb25m9JcDhVfdmABqTg5fIwwTwlem5aXIy8b66lmqqz2LBzJtnJDu36bDwkILph3kmvaKPD8qJXmPQ4yGpxIbYSTCohgt2/I0TKJNmqNvSN+IVoUuC7ZOfUV9lOV8Ri0AMfSr2YsdZ9ofV5o82ClZWlWiSWZwy6ypa7CuT1PEGHzywB4CZ5ucpO60Z7hnBQxHLiAQIO/QhiBp1rmrdQZFN6PUEjFDloykoeHe345Yqy9Ke95HIKUCS9yJurD+nZjjgOxZjoFCsB1hQAwINTIS3FbYOibZnQwv8PXvcSOqVZxC9U0+WuagK7IwxzhGZY3vLRrX01oujiRrevB4xbW7Oxi/Agp7CQGlJXCgmRE8Rhm+Vj2s+wc/4VLNZRHDcwtfejogjrjdi8p6nfUyqoQRRPARzRGUnnCbh+LqhigT6gQf3sVilnydMRScEc0/YYNLWnaw9nbyBa7wFBAiGbJwO40k39wj+xT6HTSbSUgFZzopxroO3f/o4+ubx2+IL3fkev22mEN38+dFmYF3zE+hpE7jVxrJpC3EP9PLoFgFPKCuctMnjXmeHoiGs756N5r1Mm1ffZu4H19MSuALJlxQR7VXE/LzxRXDuaB2u9days/6muP6gbGX1ASxbJd/ou8+viHmSC/ioHzNjItVCPaJjDyc6bv+gs1NPCt0qZ69G+JmgHW/PsMMeL4n5bh74g0fJSHqiI9ewEmOG/8bedSREv2XXtKV39STxPweceIOh0k23s3N6+wvuSUAJE7u1LkDo14cobtZ/MCw/QhimYPd1u5HnEJvRhPxz0nVPz0QqL/YQeOkAYk7uzgeb2yPzJ6DBtnTnGDkglekhVzQBFRJdk740LEj6swkJ", "sig":"c94e74533b482aa8eeeb54ae72a5303e0b21f62909ca43c8ef06b0357412d6f8a92f96e1a205102753777fd25321a58fba3fb384eee114bd53ce6c06a1c22bab" } -
 @ 37c10448:f8256861
2025-04-22 07:44:10
@ 37c10448:f8256861
2025-04-22 07:44:10Title H1
Hello !
-
 @ e6817453:b0ac3c39
2025-01-05 14:29:17
@ e6817453:b0ac3c39
2025-01-05 14:29:17The Rise of Graph RAGs and the Quest for Data Quality
As we enter a new year, it’s impossible to ignore the boom of retrieval-augmented generation (RAG) systems, particularly those leveraging graph-based approaches. The previous year saw a surge in advancements and discussions about Graph RAGs, driven by their potential to enhance large language models (LLMs), reduce hallucinations, and deliver more reliable outputs. Let’s dive into the trends, challenges, and strategies for making the most of Graph RAGs in artificial intelligence.
Booming Interest in Graph RAGs
Graph RAGs have dominated the conversation in AI circles. With new research papers and innovations emerging weekly, it’s clear that this approach is reshaping the landscape. These systems, especially those developed by tech giants like Microsoft, demonstrate how graphs can:
- Enhance LLM Outputs: By grounding responses in structured knowledge, graphs significantly reduce hallucinations.
- Support Complex Queries: Graphs excel at managing linked and connected data, making them ideal for intricate problem-solving.
Conferences on linked and connected data have increasingly focused on Graph RAGs, underscoring their central role in modern AI systems. However, the excitement around this technology has brought critical questions to the forefront: How do we ensure the quality of the graphs we’re building, and are they genuinely aligned with our needs?
Data Quality: The Foundation of Effective Graphs
A high-quality graph is the backbone of any successful RAG system. Constructing these graphs from unstructured data requires attention to detail and rigorous processes. Here’s why:
- Richness of Entities: Effective retrieval depends on graphs populated with rich, detailed entities.
- Freedom from Hallucinations: Poorly constructed graphs amplify inaccuracies rather than mitigating them.
Without robust data quality, even the most sophisticated Graph RAGs become ineffective. As a result, the focus must shift to refining the graph construction process. Improving data strategy and ensuring meticulous data preparation is essential to unlock the full potential of Graph RAGs.
Hybrid Graph RAGs and Variations
While standard Graph RAGs are already transformative, hybrid models offer additional flexibility and power. Hybrid RAGs combine structured graph data with other retrieval mechanisms, creating systems that:
- Handle diverse data sources with ease.
- Offer improved adaptability to complex queries.
Exploring these variations can open new avenues for AI systems, particularly in domains requiring structured and unstructured data processing.
Ontology: The Key to Graph Construction Quality
Ontology — defining how concepts relate within a knowledge domain — is critical for building effective graphs. While this might sound abstract, it’s a well-established field blending philosophy, engineering, and art. Ontology engineering provides the framework for:
- Defining Relationships: Clarifying how concepts connect within a domain.
- Validating Graph Structures: Ensuring constructed graphs are logically sound and align with domain-specific realities.
Traditionally, ontologists — experts in this discipline — have been integral to large enterprises and research teams. However, not every team has access to dedicated ontologists, leading to a significant challenge: How can teams without such expertise ensure the quality of their graphs?
How to Build Ontology Expertise in a Startup Team
For startups and smaller teams, developing ontology expertise may seem daunting, but it is achievable with the right approach:
- Assign a Knowledge Champion: Identify a team member with a strong analytical mindset and give them time and resources to learn ontology engineering.
- Provide Training: Invest in courses, workshops, or certifications in knowledge graph and ontology creation.
- Leverage Partnerships: Collaborate with academic institutions, domain experts, or consultants to build initial frameworks.
- Utilize Tools: Introduce ontology development tools like Protégé, OWL, or SHACL to simplify the creation and validation process.
- Iterate with Feedback: Continuously refine ontologies through collaboration with domain experts and iterative testing.
So, it is not always affordable for a startup to have a dedicated oncologist or knowledge engineer in a team, but you could involve consulters or build barefoot experts.
You could read about barefoot experts in my article :
Even startups can achieve robust and domain-specific ontology frameworks by fostering in-house expertise.
How to Find or Create Ontologies
For teams venturing into Graph RAGs, several strategies can help address the ontology gap:
-
Leverage Existing Ontologies: Many industries and domains already have open ontologies. For instance:
-
Public Knowledge Graphs: Resources like Wikipedia’s graph offer a wealth of structured knowledge.
- Industry Standards: Enterprises such as Siemens have invested in creating and sharing ontologies specific to their fields.
-
Business Framework Ontology (BFO): A valuable resource for enterprises looking to define business processes and structures.
-
Build In-House Expertise: If budgets allow, consider hiring knowledge engineers or providing team members with the resources and time to develop expertise in ontology creation.
-
Utilize LLMs for Ontology Construction: Interestingly, LLMs themselves can act as a starting point for ontology development:
-
Prompt-Based Extraction: LLMs can generate draft ontologies by leveraging their extensive training on graph data.
- Domain Expert Refinement: Combine LLM-generated structures with insights from domain experts to create tailored ontologies.
Parallel Ontology and Graph Extraction
An emerging approach involves extracting ontologies and graphs in parallel. While this can streamline the process, it presents challenges such as:
- Detecting Hallucinations: Differentiating between genuine insights and AI-generated inaccuracies.
- Ensuring Completeness: Ensuring no critical concepts are overlooked during extraction.
Teams must carefully validate outputs to ensure reliability and accuracy when employing this parallel method.
LLMs as Ontologists
While traditionally dependent on human expertise, ontology creation is increasingly supported by LLMs. These models, trained on vast amounts of data, possess inherent knowledge of many open ontologies and taxonomies. Teams can use LLMs to:
- Generate Skeleton Ontologies: Prompt LLMs with domain-specific information to draft initial ontology structures.
- Validate and Refine Ontologies: Collaborate with domain experts to refine these drafts, ensuring accuracy and relevance.
However, for validation and graph construction, formal tools such as OWL, SHACL, and RDF should be prioritized over LLMs to minimize hallucinations and ensure robust outcomes.
Final Thoughts: Unlocking the Power of Graph RAGs
The rise of Graph RAGs underscores a simple but crucial correlation: improving graph construction and data quality directly enhances retrieval systems. To truly harness this power, teams must invest in understanding ontologies, building quality graphs, and leveraging both human expertise and advanced AI tools.
As we move forward, the interplay between Graph RAGs and ontology engineering will continue to shape the future of AI. Whether through adopting existing frameworks or exploring innovative uses of LLMs, the path to success lies in a deep commitment to data quality and domain understanding.
Have you explored these technologies in your work? Share your experiences and insights — and stay tuned for more discussions on ontology extraction and its role in AI advancements. Cheers to a year of innovation!
-
 @ c3e23eb5:03d7caa9
2025-04-10 00:41:12
@ c3e23eb5:03d7caa9
2025-04-10 00:41:12The issue I have with the term "mesh networks" is that it is associated with a flat network topology. While I love the idea of avoiding hierarchy, this simply doesn't scale.
Data Plane: How the Internet Scales
The internet on the scales because it has a tree like structure. As you can see in the diagram below, global (tier 1) ISPs branch out to national (tier 2) ISPs who in turn branch out to local (tier 3) ISPs. ``` ,-[ Tier 1 ISP (Global) ]─-───────[ Tier 1 ISP (Global) ] / |
/ ▼
[IXP (Global)]═══╦═══[IXP (Global)]
║
Tier 2 ISP (National)◄──────────╗
/ \ ║
▼ ▼ ║
[IXP (Regional)]════╬══[IXP (Regional)] ║
/ \ ║
▼ ▼ ║
Tier 3 ISP (Local) Tier 3 ISP (Local) ║
| | ║
▼ ▼ ▼
[User] [User] [Enterprise]▲ IXPs are physical switch fabrics - members peer directly ▲ Tier 1/2 ISPs provide transit through IXPs but don't control them ```
This structure also reflects in IP addresses, where regional traffic gets routed by regional tiers and global traffic keeps getting passed up through gateways till it reaches the root of the tree. The global ISP then routes the traffic into the correct branch so that it can trickle down to the destination IP at the bottom.
12.0.0.0/8 - Tier 1 manages routing (IANA-allocated) └─12.34.0.0/16 - Tier 2 allocated block (through RIR) └─12.34.56.0/24 - Tier 3 subnet via upstream provider ├─12.34.56.1 Public IP (CGNAT pool) └─192.168.1.1 Private IP (local NAT reuse)Balancing idealism with pragmatism
This approach to scaling is much less idealistic than a flat hierarchy, because it relies on an authority (IANA) to assign the IP ranges to ISPs through Regional Internet Registries (RIRs). Even if this authority wasn't required, the fact that many users rely on few Tier 1 ISPs means that the system is inherently susceptible to sabotage (see 2019 BGP leak incident).
Control Plane: the internet is still described as decentralised
The internet is still described as decentralised because there is a flat hierarchy between
tier 1ISPs at the root of the tree. ``` INTERNET CORE (Tier 1 ISPs)
AT&T (AS7018) <══════════> Deutsche Telekom (AS3320) ║ ╔════════════════════╗ ║ ║ ║ ║ ║ ╚══>║ NTT (AS2914) ║<══╝ ║ ║ ║ ║ ║ ║ ╚═══════> Lumen (AS3356) ║ ║ ╚════╩════════════> Telia (AS1299) ```
The border gateway protocol (BGP) is used to exchange routing information between autonomous systems (ISPs). Each autonomous system is a branch of the "internet tree" and each autonomous system advertises routes to downstream autonomous systems (branches). However, the autonomous systems at the root of the tree also maintain a record of their piers, so that they can forward traffic to the correct peer. Hence, the following is a more complete diagram of the internet:
INTERNET CORE (TIER 1 MESH) ╔══════════════╦═════════════╦════════╦═════════════╗ ║ ║ ║ ║ ║ AT&T (AS7018) <══╬══> Lumen (AS3356) <══╬══> NTT (AS2914) ║ ║ ║ ║ ║ ║ ║ ╚══> Telia (AS1299) <══╝ ║ ║ ╚═══════════════════════════════╝ ║ ║ ╚═> Deutsche Telekom (AS3320) <═╝ ║ TREE HIERARCHY BELOW - MESH ABOVE ║ ▼ [ Tier 1 ISP ]───────────────────┐ / | | / ▼ ▼ [IXP]═══╦═══[IXP] [IXP] ║ ║ ▼ ▼ Tier 2 ISP◄──────────╗ Tier 2 ISP◄───────╗ / \ ║ / \ ║ ▼ ▼ ║ ▼ ▼ ║ [IXP]═╦[IXP] ║ [IXP]═╦[IXP] ║ / \ ║ / \ ║ ▼ ▼ ▼ ▼ ▼ ▼ Tier 3 ISP User Tier 3 ISP EnterpriseSo its a mesh network - whats wrong with that?
In the example above, NTT can only send traffic to Deutsche Telekom via Lumen or AT&T. NTT relies on its peers to maintain a correct record of the IP range that they are responsible for, so that traffic that was intended for Deutsche Telekom doesn't end up in the wrong network. An intentional or even accidental error in an autonomous system's routing tables can be detrimental to the flow of traffic through the network.
Hence, mesh networks require: * Reliability: peers rely on each-other not to fail (e.g., 2019 AWS US-East-1 availability) * Trust: peers must be honest about address ranges (e.g., 2018 BGP hijacking incident) * Central planning: BGP traffic engineering determines which route a packet takes
Application Layer Innovations
Now that we have a rough overview of how the internet is broken, lets think about what can still be done. The flat hierarchy that we associate with mesh networks sounds beautiful, but it doesn't scale. However, the tree-like structure assumes that most participants in the network rely on an authority to give them an address or a range of addresses so that they can communicate.
Overlay networks
Fortunately all it takes to interact with someone on nostr is their public key. The recipients client will render your signed and/or encrypted event no matter how it reaches them. Whether your note reaches them over the internet, over some other network or via a carrier pigeon doesn't matter. nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr is working on a NIP for that and I'm sure he will share an explanation of how it works.
Bitcoin Instead of a Routing Algorithm
Now that we have digital bearer assets (e-cash), users can pay their internet gateway (TollGate) for access to the internet even though they are still offline. Once the TollGate has redeemed the e-cash, it gives the user access to the internet.
Frictionless Switching between ISPs (TollGates)
Legacy internet service providers use KYC money (fiat) to transfer the cost of the infrastructure to their users. However, this means that they are able to identify which packet belongs to which user. The KYC nature of their interaction with the users also makes it difficult for users to switch ISPs when service providers undercut each-other. Internet users who are on e-cash rails can hop between ISPs frictionlessly since they buy small amounts of data frequently in a granular manner.
Users that have access to independent competing TollGates can switch between them freely, so its impossible for any one TollGate to prevent a user from connecting to the internet. The only thing a TollGate can do is attract traffic by providing cheaper and/or faster internet access.
Anyone can arbitrage connectivity
Now that users have non KYC internet, there is nothing stopping them from reselling access to their internet connection. Anyone who has a WiFi router and access to a cheap internet connection can act as a range extender by re-selling access to that gateway for people who aren't able to connect directly.
Now the route that the traffic takes through the network is determined dynamically by the markets. The individual TollGate operators select their gateways and set their prices when they create a business model. The customers select the route that best meets their needs by selecting a gateway for their next purchase.
-
 @ 866e0139:6a9334e5
2025-04-17 07:40:05
@ 866e0139:6a9334e5
2025-04-17 07:40:05Autor: Gerd Conradt. (Foto: Thomas Klingberg). Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Sie wollen die neuesten Pareto-Artikel auf einen Blick sehen (Friedenstaube & Co.), um nichts mehr zu verpassen?* Hier geht es zu unserem Telegram-Kanal.***
Ein Leben, geprägt von Geschichte und Herzschlag: Vom jungen Pionier am Kyffhäuser, wo die Sage von Barbarossa lebt, bis zur roten Fahne über dem zerstörten Reichstag. Gerd Conradt blickt zurück – auf die Flucht vor der Roten Armee, die Schrecken des Unternehmens Barbarossa und die Bauernkriege vor 500 Jahren. Inmitten von Kriegen und Zeitenwenden fragt er: Was verbindet Kaiser Barbarossa, Thomas Münzer und die Mahnmale unserer Zeit? Ein bewegendes Zeugnis über Macht, Erinnerung und die Suche nach Frieden – erzählt aus Cabarita Beach, 30.623 Tage nach seiner Geburt.
Zeit und Geschichte, Zeitgeschichte und ihre Verknüpfungen mit dem privaten Leben der Menschen werden vom Herzschlag jedes Einzelnen bestimmt. Zufälliges, Wiederholungen, Parallelen – Macht und Öffentlicheit – Geschichte als Konstruktion – Biografien: Alles ist nur möglich, wenn die Herzen der Menschen schlagen, pulsieren, für Lebendigkeit sorgen.
Im Monat Mai wird an zwei für die deutsche Geschichte bedeutende Ereignisse erinnert: an das Ende des 2. Weltkriegs vor 80 und an das Ende der Bauernkriege vor 500 Jahren. Mit diesen Daten verbinden mich ein Name, Kaiser Friedrich der I, genannt Barbarossa, und ein Symbol, die Rote Fahne.
Heute, an dem Tag, an dem ich diesen Text schreibe, am 18.03.2025, Cabarita Beach, Australien, lebe ich 30.623 Tage.
In dieser Zeit gab es immer irgendwo auf der Welt Krieg. Im Jahr meiner Geburt startete die deutsche Wehrmacht am 22.06.41 unter dem Decknamen Unternehmen Barbarossa ihren Überfall auf die Sowjetunion. Drei Millionen gut ausgebildete, strahlende, meist blauäugige hochgerüstete Männer begannen den zerstörerischsten Feldzug der Menschheitsgeschichte. Ziel war die Beseitigung des „jüdischen Bolschewismus“, die Germanisierung der Länder von Deutschland bis zum Ural. Fruchtbare Böden, Bodenschätze und ein Heer von Zwangsarbeitern sollten dem germanischen Reich zu Weltruhm verhelfen.
Mit massiver Unterstützung durch die USA widerstand die Rote Armee und besiegte den Aggressor. Deutschland war zerstört. Insgesamt 60 Millionen Menschen getötet.
In diesem Jahr wird am 8. Mai, dem Tag der Befreiung, an das Ende des 2. Weltkriegs vor achtzig Jahren erinnert. Eine rote Fahne mit Hammer und Sichel war damals am zerstörten Reichstag gehisst – Berlin, Deutschland geteilt in die Hoheitszonen der Alliierten und die der Sowjetunion.
Nach der Flucht meiner Familie vor der Roten Armee – im Januar 1945 – aus dem Teil Deutschlands, der heute zu Polen gehört, lebten wir im sowjetisch verwalteten Teil der späteren DDR. Als Junger Pionier nahm ich an Zeltlagern teil. Besonders in Erinnerung ist mir das auf dem Ratsfeld am Fuße des Kyffhäusers, jenem Ort, an dem vor 500 Jahren ein Aufstand der Bauern unter Führung des Reformators Thomas Münzer (1489 - 1525) von den Heeren der Fürsten blutig niedergeschlagen wurde. Münzer wurde öffentlich hingerichtet.
Martin Luther hatte zunächst Sympathie für die Bauern, verfasste dann jedoch eine Schrift „Wider die mörderischen und räuberischen Rotten“, mit der er dazu aufrief, die Revoltierenden zu töten – dies sei eine religiös verdienstvolle Tat. Die Reformation als Verrat.
Auf dem Kyffhäuser steht ein großes Denkmal, mit dem an Friedrich I., Barbarossa, erinnert wird. Der Sage nach ist er nicht gestorben, sondern lebt in der naheglegenen Barbarossahöhle fort.
Vom Pionierlager aus besuchten wir die beeindruckende Höhle, an deren Ende an einem großen Steintisch eine mit Krone, Zepter und Krönungsmantel ausgestattete Puppe sitzt, deren roter Bart in den Tisch gewachsen ist. Kaiser Barbarossa, 1122 – 1190, der Rotbart, war eine Persönlichkeit von historischer Größe. Er war ein Mann des Wortes und der Tat. Er konnte reiten, jagen, mit der Waffe kämpfen, jedoch weder lesen noch schreiben – so die Überlieferungen. Er war Krieger und Diplomat, Kaufmann und ein Mann von Kultur. Viele Kriege führte er in Italien, mehrere gegen Mailand, wo jeweils Städte und ganze Ländereien geplündert und vernichtet wurden.
Er war ein kluger Taktiker, der Zwietracht für seine Zwecke nutzen konnte. Waren seine Vorgänger für Milde und Barmherzigkeit angesehen, herrschte nun die Strenge der Gerechtigkeit. Im Umgang mit den Päpsten handelte er klug. Das führt mich wieder zur Roten Fahne. Karl der Große vergab nämlich um das Jahr 800 Land an seine Untertanen. Die Übergabe wurde mit einer roten Fahne markiert. Sie stand für „freie Bürger bei freier Arbeit auf freiem Land“. Barbarossa erreichte beim Papst die Heiligsprechung Karls des Großen im Jahre 1165. Karls Gebeine wurden in den heute als Heiligtum verehrten Karlsschrein in Aachen umgebettet.
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Alle Kriege führen zu Zeitenwenden, verändern Machtstrukturen. Ländergrenzen werden neu gezogen oder verschwinden. Derzeit versuchen neue Kaiser die Welt neu zu ordnen. Sie sind Kriegsherren – auch Kaufmänner. Lassen sich Krieg und Wirtschaft trennen?
Warum Barbarossa heute? Das Denkmal am Kyffhäuser wurde von Nationalisten errichtet, die in ihm den Gründer des Deutschen Reiches sahen. Heute ist das Denkmal wieder ein beliebter Versammlungsort der neuen Rechten.
Im Mittelpunkt des Gedenkens an die verlorene Schlacht der Bauern vor 500 Jahren wird das monumentale Panoramabild Freibürgerliche Revolution des Leipziger Malers Werner Tübke stehen. Das in den Jahren von 1976 bis 1987 von der Regierung der DDR in Auftrag gegebene Bild zählt zu den größten Panoramen der Welt.
Es zeigt am Beispiel des Aufstands der Bauern ein im Geiste der Renaissance gemaltes Welttheater. Es ist kein Schlachtbild im üblichen Sinn, eher eine Allegorie auf ureigenste menschliche Ängste, die Darstellung einer Apokalypse, eine historische Parabel auf Glaubenskämpfe der Moderne, auf eine Welt im Taumel, Weltgeschichte als Weltgericht.(1)
In Berlin-Treptow steht das Sowjetische Ehrenmal, das in seiner Wuchtigkeit an den ruhmreichen Sieg der Sowjetunion über den Hitlerfaschismus erinnert. Es ist das größte und markanteste Kriegsdenkmal außerhalb Russlands. 1949 am 70. Geburtstag von Stalin eingeweiht, ist es die Kanonisierung eines endgültigen Kriegsbildes.(2) Errichtet auf den namenlosen Gräbern 7000 gefallener Soldaten, verkörpert ein übergroßer sowjetischer Held, gottgleich, einen Sieger, der mit dem Schwert das deutsche Hakenkreuz zerschlägt. Eine unmenschliche Statue, die nichts mit der wahren Tragödie und dem unermesslichen Preis für den Sieg zu tun hat. Stalins Sicht auf Kultur unterscheidet sich nicht von der Hitlers oder anderer Diktatoren – sie stehen für eine Verherrlichung von Stärke, oft personalisierter Autorität – es sind Mahnmale historischer Täuschung und ideologische Fälschung.(3)
Wie damit umgehen am 80. Jahrestag der Befreiung? Vermutlich wird es in diesem Jahr heftige Demonstrationen im Zusammenhang mit dem Krieg in der Ukraine geben. Neue Forderungen nach Abriss werden laut. Das Denkmal schleifen? Im Zwei-plus-Vier-Vertrag von 1990, in dem die Deutsche Einheit festgeschrieben wurde, verpflichtete sich die Bundesrepublik Deutschland, für den Erhalt der sowjetischen Mahnmäler zu sorgen.
Zur Erinnerung: Ein Kunstprojekt des Künstlerehepaares Christo und Jeanne-Claude, Verhüllter Reichstag, 1995, führte zu einer spirituellen Reinigung dieses von verhängnisvoller Geschichte belasteten Gebäudes. Das Ehrenmal in Treptow schwarz verhüllen?
Auf einer Reise nach Jakutien, einer Republik, die zur russischen Einflusszone gehört, pilgerte ich vor meiner Abreise zum Ehrenmal für die im Großen Vaterländischen Krieg gefallenen Menschen. Zu meiner Überraschung und Freude hatten die Kinder das Mahnmal zu einem Spielplatz verwandelt. Sie kletterten in die Panzer, über die Kanonen und spielten Fangen um die bronzenen Heldenfiguren herum.
Viele tausend Herzen haben bereits in den aktuellen Kriegen aufgehört zu schlagen. Die Herzen der verwundeten Menschen, Landschaften und Tiere schmerzen.
Mein Herz schlägt. Die Arbeit an dem Text gibt meinem Leben Sinn. Die Gedanken, Ideen fliegen.
Herzen wollen tiefes Glück, weder Angst noch Verzweiflung, nicht Hunger und Krieg.
Auch mit 83 Jahren erinnere ich mich noch gut an die Todesängste auf der Flucht mit meiner Mutter und meinen Geschwistern. Der Vater war im Krieg.
Am Tag der Befreiung hat mein neuer Film Premiere „FARBTEST, 1968 – 2024, ein rotes Stück Stoff im Wind“.
Tanz als Revolution, aus Ideologie wird Poesie.

\ Anmerkungen:
(1) Eduard Beaucamp, FAZ, 28.05.2004 (Wikipedia)
(2, 3) Irina Scherbakowa, Sowjetische Kriegsdenkmäler, was bleibt? Am Beispiel Treptow. 2022
Der Link zum Filmtrailer:
https://www.youtube.com/watch?v=tHe36fXYnBw&t=5s
Gerd Conradt ist ein Deutscher Filmemacher und Künstler. Geboren 1941 in Schwiebus (heute Polen), floh seine Familie 1945 vor der Roten Armee nach Thüringen. Er studierte an der Deutschen Film- und Fernsehakademie Berlin, drehte avantgardistische Filme wie „Farbtest Rote Fahne“ (1968) und war politisch aktiv, was zu seiner Relegation führte. Später arbeitete er an Dokumentarfilmen und Installationen, u. a. über die Berliner Mauer und Neuseeland.**
Filme und Ausstellungen: Wikipedia.
AKTUELL: VERANSTALTUNGEN
- Hier gibt es einen Überblick über aktuelle Ostermärsche.
- Heute 17 Uhr Friedensdemo vor dem Rathaus in Freiburg/Breisgau!
- Wie geht Frieden? Vom 17.-24.04. findet zu diesem Thema ein Onlinekongress zum Thema statt (Teilnahme frei)
- Sie wollen auf Demos, Ostermärsche, Kongresse etc. zum Thema Frieden aufmerksam machen? Bitte per Mail an: friedenstaube\@pareto.space.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt. (Vorerst alle, da wir den Mailversand testen, später ca. drei Mails pro Woche.)
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: milosz@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ a4a6b584:1e05b95b
2025-01-02 18:13:31
@ a4a6b584:1e05b95b
2025-01-02 18:13:31The Four-Layer Framework
Layer 1: Zoom Out

Start by looking at the big picture. What’s the subject about, and why does it matter? Focus on the overarching ideas and how they fit together. Think of this as the 30,000-foot view—it’s about understanding the "why" and "how" before diving into the "what."
Example: If you’re learning programming, start by understanding that it’s about giving logical instructions to computers to solve problems.
- Tip: Keep it simple. Summarize the subject in one or two sentences and avoid getting bogged down in specifics at this stage.
Once you have the big picture in mind, it’s time to start breaking it down.
Layer 2: Categorize and Connect

Now it’s time to break the subject into categories—like creating branches on a tree. This helps your brain organize information logically and see connections between ideas.
Example: Studying biology? Group concepts into categories like cells, genetics, and ecosystems.
- Tip: Use headings or labels to group similar ideas. Jot these down in a list or simple diagram to keep track.
With your categories in place, you’re ready to dive into the details that bring them to life.
Layer 3: Master the Details

Once you’ve mapped out the main categories, you’re ready to dive deeper. This is where you learn the nuts and bolts—like formulas, specific techniques, or key terminology. These details make the subject practical and actionable.
Example: In programming, this might mean learning the syntax for loops, conditionals, or functions in your chosen language.
- Tip: Focus on details that clarify the categories from Layer 2. Skip anything that doesn’t add to your understanding.
Now that you’ve mastered the essentials, you can expand your knowledge to include extra material.
Layer 4: Expand Your Horizons

Finally, move on to the extra material—less critical facts, trivia, or edge cases. While these aren’t essential to mastering the subject, they can be useful in specialized discussions or exams.
Example: Learn about rare programming quirks or historical trivia about a language’s development.
- Tip: Spend minimal time here unless it’s necessary for your goals. It’s okay to skim if you’re short on time.
Pro Tips for Better Learning
1. Use Active Recall and Spaced Repetition
Test yourself without looking at notes. Review what you’ve learned at increasing intervals—like after a day, a week, and a month. This strengthens memory by forcing your brain to actively retrieve information.
2. Map It Out
Create visual aids like diagrams or concept maps to clarify relationships between ideas. These are particularly helpful for organizing categories in Layer 2.
3. Teach What You Learn
Explain the subject to someone else as if they’re hearing it for the first time. Teaching exposes any gaps in your understanding and helps reinforce the material.
4. Engage with LLMs and Discuss Concepts
Take advantage of tools like ChatGPT or similar large language models to explore your topic in greater depth. Use these tools to:
- Ask specific questions to clarify confusing points.
- Engage in discussions to simulate real-world applications of the subject.
- Generate examples or analogies that deepen your understanding.Tip: Use LLMs as a study partner, but don’t rely solely on them. Combine these insights with your own critical thinking to develop a well-rounded perspective.
Get Started
Ready to try the Four-Layer Method? Take 15 minutes today to map out the big picture of a topic you’re curious about—what’s it all about, and why does it matter? By building your understanding step by step, you’ll master the subject with less stress and more confidence.
-
 @ 9e69e420:d12360c2
2025-02-17 17:12:01
@ 9e69e420:d12360c2
2025-02-17 17:12:01President Trump has intensified immigration enforcement, likening it to a wartime effort. Despite pouring resources into the U.S. Immigration and Customs Enforcement (ICE), arrest numbers are declining and falling short of goals. ICE fell from about 800 daily arrests in late January to fewer than 600 in early February.
Critics argue the administration is merely showcasing efforts with ineffectiveness, while Trump seeks billions more in funding to support his deportation agenda. Increased involvement from various federal agencies is intended to assist ICE, but many lack specific immigration training.
Challenges persist, as fewer immigrants are available for quick deportation due to a decline in illegal crossings. Local sheriffs are also pressured by rising demands to accommodate immigrants, which may strain resources further.
-
 @ 502ab02a:a2860397
2025-04-22 01:16:17
@ 502ab02a:a2860397
2025-04-22 01:16:17ก่อนที่จะมูฟออนจากเทคนิคการสร้าง เรามาดูเรื่องสำคัญครับ
วันที่ไม่มีวัว แต่มีเวย์โปรตีน – เบื้องหลังเทคโนโลยีที่เปลี่ยนถังหมักให้กลายเป็นเต้านมวัว เคยมีคำถามไหมว่า “เวย์โปรตีน” ที่กินตอนออกกำลังกาย หรือโยเกิร์ตถ้วยโปรดที่ซื้อมาจากร้านใกล้บ้าน มันยังมาจากนมวัวอยู่ไหม? ถ้าคำตอบคือ “ไม่” แล้วมันมาจากไหน?
ยินดีต้อนรับสู่โลกของ Perfect Day บริษัทที่บอกว่า "เราสร้างเวย์โปรตีนได้ โดยไม่ต้องใช้วัวเลยแม้แต่นิดเดียว” ฟังดูเหมือนมายากล แต่นี่คือวิทยาศาสตร์ขั้นสูงที่ผูกสูตรไว้กับ DNA, จุลินทรีย์ และการหมักอย่างแยบยล
ขั้นตอนที่ 1: หารหัสโปรตีนจากแม่วัว เริ่มต้นจากคำถามง่าย ๆ ว่า “โปรตีนเวย์ที่อยู่ในน้ำนมวัว คืออะไร?” คำตอบคือ เบต้า-แลคโตโกลบูลิน (Beta-lactoglobulin) ซึ่งเป็นโปรตีนหลักในเวย์ประมาณ 50-55% โดยในธรรมชาติ วัวจะสร้างโปรตีนนี้จาก รหัสพันธุกรรมใน DNA ของมัน Perfect Day จึงไปค้นหา ลำดับเบส (DNA sequence) ของโปรตีนนี้จากฐานข้อมูลวิทยาศาสตร์ชื่อ UniProt (Universal Protein Resource) ซึ่งเก็บรหัสโปรตีนของสิ่งมีชีวิตแทบทุกชนิดไว้ครบถ้วน ได้รหัสมาแล้ว ก็เตรียมเข้าสู่ภารกิจ “หลอกจุลินทรีย์ให้สร้างโปรตีนแทนวัว”
ขั้นตอนที่ 2: สร้างแผ่นดีเอ็นเอสังเคราะห์ รหัส DNA ที่ได้จาก UniProt จะถูกนำไปสร้างเป็น DNA สังเคราะห์ โดยนักชีววิทยาจะออกแบบให้เหมาะสมกับการทำงานในเซลล์ของจุลินทรีย์ ไม่ใช่เซลล์วัว จะเรียกว่านี่คือ “การดัดแปลงบทละครชีวิตของวัว แล้วส่งให้จุลินทรีย์เล่นแทน” ก็ไม่ผิด DNA ที่ออกแบบนี้ มักจะมาพร้อมกับเครื่องมือบางอย่าง เช่น ตัวกระตุ้นการทำงานของยีน (promoter) หรือ ตัวตัดต่อยีน ที่จะทำให้จุลินทรีย์ยอมรับและใช้มันได้อย่างมีประสิทธิภาพ
ขั้นตอนที่ 3: ปลอมตัวแทรกเข้าไปในจุลินทรีย์ จุลินทรีย์ที่ Perfect Day ใช้คือกลุ่มที่เรียกว่า Microflora ซึ่งอาจเป็นยีสต์, เชื้อรา, หรือแบคทีเรียชนิดที่เลี้ยงง่าย แต่มันจะไม่ยอมรับ DNA แปลกปลอมง่าย ๆ ดังนั้นต้องมี “เทคนิคหลอกล่อ” นิดหน่อย เขาจะทำให้ DNA ของจุลินทรีย์ เสียหายตรงจุดหนึ่ง แล้วแอบแนบ DNA ปลอม (ที่มีรหัสโปรตีนของวัว) เข้าไปซ่อมแซมจุดนั้นพอดีเป๊ะ แบบ “จิ๊กซอว์พอดีช่อง” แล้วจุลินทรีย์ก็จะเผลอรับ DNA แปลกปลอมนี้เข้าร่าง เมื่อติดตั้งสำเร็จ มันจะเริ่มแปลรหัสและ “ผลิตโปรตีนเวย์” ออกมาเหมือนกับแม่วัวตัวจริงไม่มีผิด
ขั้นตอนที่ 4: เลี้ยงจุลินทรีย์ในถังหมัก ตอนนี้จุลินทรีย์กลายเป็น “แม่วัวในร่างเซลล์เดียว” แล้ว Perfect Day ก็แค่เลี้ยงมันใน ถังหมักชีวภาพ (fermentor) ที่ควบคุมอุณหภูมิ ค่าความเป็นกรดด่าง อากาศ และใส่น้ำตาลลงไปเป็นอาหาร จุลินทรีย์จะกินน้ำตาลแล้วเปลี่ยนเป็น เวย์โปรตีน ปล่อยออกมานอกเซลล์ จากนั้นก็เก็บเอาน้ำที่มีโปรตีนนี้ ไปผ่านกระบวนการกรอง แยก แปรรูป และทำให้แห้ง เป็นผงเวย์โปรตีน พร้อมใช้ในอาหารหรือเครื่องดื่มต่าง ๆ
ขั้นตอนที่ 5: ตรวจสอบความเหมือนจริง ก่อนนำเวย์โปรตีนที่ได้ไปใช้งาน บริษัทต้อง ตรวจสอบระดับโมเลกุล ว่าโปรตีนที่ได้เหมือนกับของวัวจริง ๆ ไหม? สิ่งที่ต้องดูคือ โครงสร้างโปรตีน: ใช้เทคนิค mass spectrometry ตรวจความแม่นยำระดับกรดอะมิโน พฤติกรรมทางชีวเคมี เช่น ความสามารถในการจับกับน้ำ การเกิดฟอง หรือการละลาย ความปลอดภัย ตรวจหาสารปนเปื้อน สารก่อภูมิแพ้ หรือสารที่ไม่ได้ตั้งใจให้มี Perfect Day เคลมว่าทั้งหมดนี้ปลอดภัย และได้รับการรับรองจาก FDA ว่าเป็น GRAS (Generally Recognized as Safe)
แล้วเราควรรู้สึกยังไง? นี่คือ “นมที่ไม่มีวัว” แต่มีเวย์โปรตีนครบสูตร ทำให้โยเกิร์ต ไอศกรีม และแม้กระทั่งกาแฟลาเต้ที่ไม่มีนมวัว แต่ยังมีฟองนมหนานุ่ม กลายเป็นจริงได้แบบไม่ต้องพึ่งวัวเลยแม้แต่นิดเดียว แต่คำถามที่ลึกกว่านั้นคือ... เรายังได้กินอาหารจากธรรมชาติอยู่หรือเปล่า? หรือกำลังอยู่ในยุคที่ “ชีวิต” ถูกตัดออกจากอาหาร โดยสิ้นเชิง? เทคโนโลยีนี้อาจช่วยโลกในมุมของ ESG แต่สำหรับบางคน มันคือ ทางแยกของความจริงกับของจำลอง คำว่า “Perfect” จึงอาจขึ้นอยู่กับว่า… สมบูรณ์แบบในสายตาใคร?
แล้วคำถามที่ล่องลอยอยู่เสมอคือ เมื่อทางเลือกกลายเป็นทางหลัก แล้วเราจะเหลือทางไหนอีกบ้าง หรือจะเป็น...ทางตัน? #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก
-
 @ 2b24a1fa:17750f64
2025-04-22 06:57:36
@ 2b24a1fa:17750f64
2025-04-22 06:57:36Es fühlt sich wie ein Staatsstreich an. Vielleicht ist es auch einer. Ein abgewählter Bundestag genehmigt mittels Grundgesetzänderung die größte Staatsverschuldung in der Geschichte Deutschlands mit der unvorstellbaren Summe von 1000 Milliarden Euro, also eine Billion.
https://soundcloud.com/radiomuenchen/vom-schuldenstaatsstreich-zur-finanzdiktatur-von-rob-kenius?\ Jedem muss klar sein, wohin diese Gelder aus den Taschen der Steuerzahler wandern und wer, wenn in Rüstung, Militärhilfen, Konzern-Subventionen investiert wird, die Leidtragenden sind: Kinder, Rentner, kleine Firmen und Betriebe, sozial Schwache, Kranke, Arbeitslose, Obdachlose.
\ Die Kräfte aus Finanzeliten, Militär, Rüstungsindustrie, regierenden Parteien und den staatstragenden Medien werden dafür immer stärker.
\ Hören Sie den Beitrag „Vom Schuldenstaatsstreich zur Finanzdiktatur“ von Rob Kenius, der zunächst beim Overton-Magazin erschienen war: https://overton-magazin.de/top-story/vom-schuldenstaatsstreich-zur-finanzdiktatur-in-leicht-verstaendlicher-sprache/
Sprecherin: Sabrina Khalil
Redaktion: Jonny Rieder
Bild: Bund der Steuerzahler / Janek Werner
Rob Kenius betreibt die systemkritische Webseite kritlit.de und den Podcast 9min Denksport. Der Text Vom Schuldenstaatsstreich zur Finanzdiktatur ist davon die 14. Folge.
Radio München\ www.radiomuenchen.net/\ @radiomuenchen\ www.facebook.com/radiomuenchen\ www.instagram.com/radio_muenchen/\ twitter.com/RadioMuenchen\ odysee.com/@RadioMuenchen.net:9\ rumble.com/user/RadioMunchen
Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen.
GLS-Bank\ IBAN: DE65 4306 0967 8217 9867 00\ BIC: GENODEM1GLS\ Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927\ Ethereum (ETH): 0xB9a49A0bda5FAc3F084D5257424E3e6fdD303482
-
 @ fd208ee8:0fd927c1
2025-02-15 07:37:01
@ fd208ee8:0fd927c1
2025-02-15 07:37:01E-cash are coupons or tokens for Bitcoin, or Bitcoin debt notes that the mint issues. The e-cash states, essentially, "IoU 2900 sats".
They're redeemable for Bitcoin on Lightning (hard money), and therefore can be used as cash (softer money), so long as the mint has a good reputation. That means that they're less fungible than Lightning because the e-cash from one mint can be more or less valuable than the e-cash from another. If a mint is buggy, offline, or disappears, then the e-cash is unreedemable.
It also means that e-cash is more anonymous than Lightning, and that the sender and receiver's wallets don't need to be online, to transact. Nutzaps now add the possibility of parking transactions one level farther out, on a relay. The same relays that cannot keep npub profiles and follow lists consistent will now do monetary transactions.
What we then have is * a transaction on a relay that triggers * a transaction on a mint that triggers * a transaction on Lightning that triggers * a transaction on Bitcoin.
Which means that every relay that stores the nuts is part of a wildcat banking system. Which is fine, but relay operators should consider whether they wish to carry the associated risks and liabilities. They should also be aware that they should implement the appropriate features in their relay, such as expiration tags (nuts rot after 2 weeks), and to make sure that only expired nuts are deleted.
There will be plenty of specialized relays for this, so don't feel pressured to join in, and research the topic carefully, for yourself.
https://github.com/nostr-protocol/nips/blob/master/60.md https://github.com/nostr-protocol/nips/blob/master/61.md