-
 @ 1c19eb1a:e22fb0bc
2025-04-22 01:36:33
@ 1c19eb1a:e22fb0bc
2025-04-22 01:36:33After my first major review of Primal on Android, we're going to go a very different direction for this next review. Primal is your standard "Twitter clone" type of kind 1 note client, now branching into long-form. They also have a team of developers working on making it one of the best clients to fill that use-case. By contrast, this review will not be focusing on any client at all. Not even an "other stuff" client.
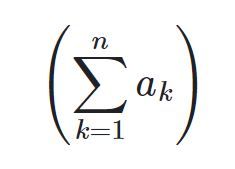
Instead, we will be reviewing a very useful tool created and maintained by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 called #Amber. For those unfamiliar with Amber, it is an #Android application dedicated to managing your signing keys, and allowing you to log into various #Nostr applications without having to paste in your private key, better known as your #nsec. It is not recommended to paste your nsec into various applications because they each represent another means by which it could be compromised, and anyone who has your nsec can post as you. On Nostr, your #npub is your identity, and your signature using your private key is considered absolute proof that any given note, reaction, follow update, or profile change was authorized by the rightful owner of that identity.
It happens less often these days, but early on, when the only way to try out a new client was by inputting your nsec, users had their nsec compromised from time to time, or they would suspect that their key may have been compromised. When this occurs, there is no way to recover your account, or set a new private key, deprecating the previous one. The only thing you can do is start over from scratch, letting everyone know that your key has been compromised and to follow you on your new npub.
If you use Amber to log into other Nostr apps, you significantly reduce the likelihood that your private key will be compromised, because only one application has access to it, and all other applications reach out to Amber to sign any events. This isn't quite as secure as storing your private key on a separate device that isn't connected to the internet whatsoever, like many of us have grown accustomed to with securing our #Bitcoin, but then again, an online persona isn't nearly as important to secure for most of us as our entire life savings.
Amber is the first application of its kind for managing your Nostr keys on a mobile device. nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 didn't merely develop the application, but literally created the specification for accomplishing external signing on Android which can be found in NIP-55. Unfortunately, Amber is only available for Android. A signer application for iOS is in the works from nostr:npub1yaul8k059377u9lsu67de7y637w4jtgeuwcmh5n7788l6xnlnrgs3tvjmf, but is not ready for use at this time. There is also a new mobile signer app for Android and iOS called Nowser, but I have not yet had a chance to try this app out. From a cursory look at the Android version, it is indeed in the very early stages of development and cannot be compared with Amber.
This review of Amber is current as of version 3.2.5.
Overall Impression
Score: 4.7 / 5 (Updated 4/21/2025)
I cannot speak highly enough about Amber as a tool that every Nostr user on Android should start using if they are not already. When the day comes that we have more options for well-developed signer apps on mobile, my opinion may very well change, but until then Amber is what we have available to us. Even so, it is an incredibly well thought-out and reliable tool for securing your nsec.
Despite being the only well-established Android signer available for Android, Amber can be compared with other external signing methods available on other platforms. Even with more competition in this arena, though, Amber still holds up incredibly well. If you are signing into web applications on a desktop, I still would recommend using a browser extension like #Alby or #Nos2x, as the experience is usually faster, more seamless, and far more web apps support this signing method (NIP-07) than currently support the two methods employed by Amber. Nevertheless that gap is definitely narrowing.
A running list I created of applications that support login and signing with Amber can be found here: Nostr Clients with External Signer Support
I have run into relatively few bugs in my extensive use of Amber for all of my mobile signing needs. Occasionally the application crashes when trying to send it a signing request from a couple of applications, but I would not be surprised if this is no fault of Amber at all, and rather the fault of those specific apps, since it works flawlessly with the vast majority of apps that support either NIP-55 or NIP-46 login.
I also believe that mobile is the ideal platform to use for this type of application. First, because most people use Nostr clients on their phone more than on a desktop. There are, of course, exceptions to that, but in general we spend more time on our phones when interacting online. New users are also more likely to be introduced to Nostr by a friend having them download a Nostr client on their phone than on a PC, and that can be a prime opportunity to introduce the new user to protecting their private key. Finally, I agree with the following assessment from nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn.
nostr:nevent1qqsw0r6gzn05xg67h5q2xkplwsuzedjxw9lf7ntrxjl8ajm350fcyugprfmhxue69uhhyetvv9ujumn0wd68yurvv438xtnrdaksyg9hyaxj3clfswlhyrd5kjsj5v04clhjvgeq6pwztmysfzdvn93gev7awu9v
The one downside to Amber is that it will be quite foreign for new users. That is partially unavoidable with Nostr, since folks are not accustomed to public/private key cryptography in general, let alone using a private key to log into websites or social media apps. However, the initial signup process is a bit cumbersome if Amber is being used as the means of initially generating a key pair. I think some of this could be foregone at start-up in favor of streamlining onboarding, and then encourage the user to back-up their private key at a later time.
Features
Amber has some features that may surprise you, outside of just storing your private key and signing requests from your favorite Nostr clients. It is a full key management application, supporting multiple accounts, various backup methods, and even the ability to authorize other users to access a Nostr profile you control.
Android Signing
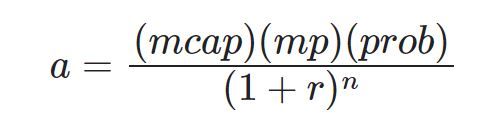
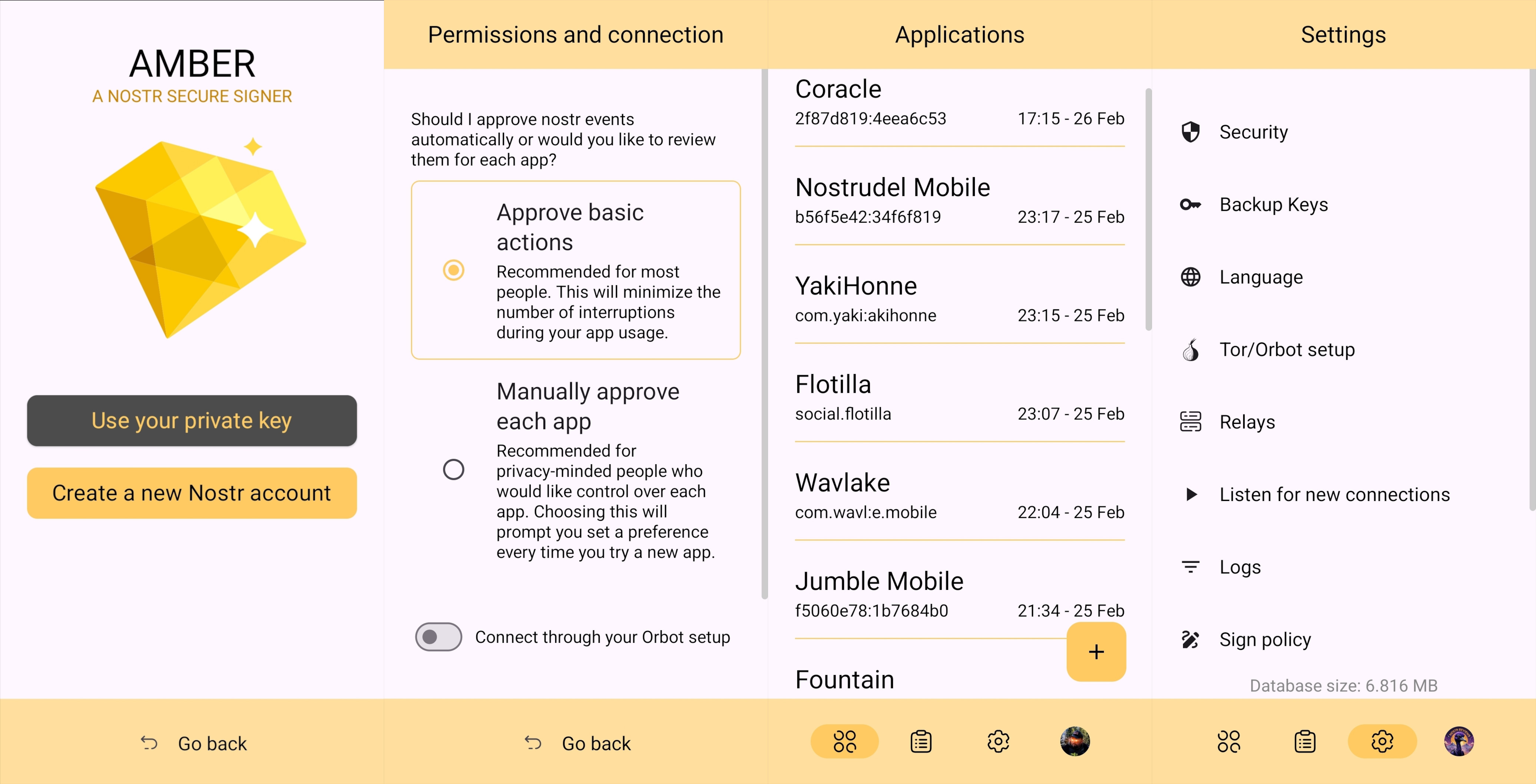
This is the signing method where Amber really shines in both speed and ease of use. Any Android application that supports this standard, and even some progressive web-apps that can be installed to your Android's home-screen, can very quickly and seamlessly connect with Amber to authorize anything that you need signed with your nsec. All you have to do is select "Login with Amber" in clients like #Amethyst or #0xChat and the app will reach out to Amber for all signing requests from there on out. If you had previously signed into the app with your nsec, you will first need to log out, then choose the option to use Amber when you log back in.
This is a massive deal, because everything you do on Nostr requires a signature from your private key. Log in? Needs a signature. Post a "GM" note? Needs a signature. Follow someone who zapped your note? Needs a signature. Zap them back? You guessed it; needs a signature. When you paste your private key into an application, it will automatically sign a lot of these actions without you ever being asked for approval, but you will quickly realize just how many things the client is doing on your behalf when Amber is asking you to approve them each time.
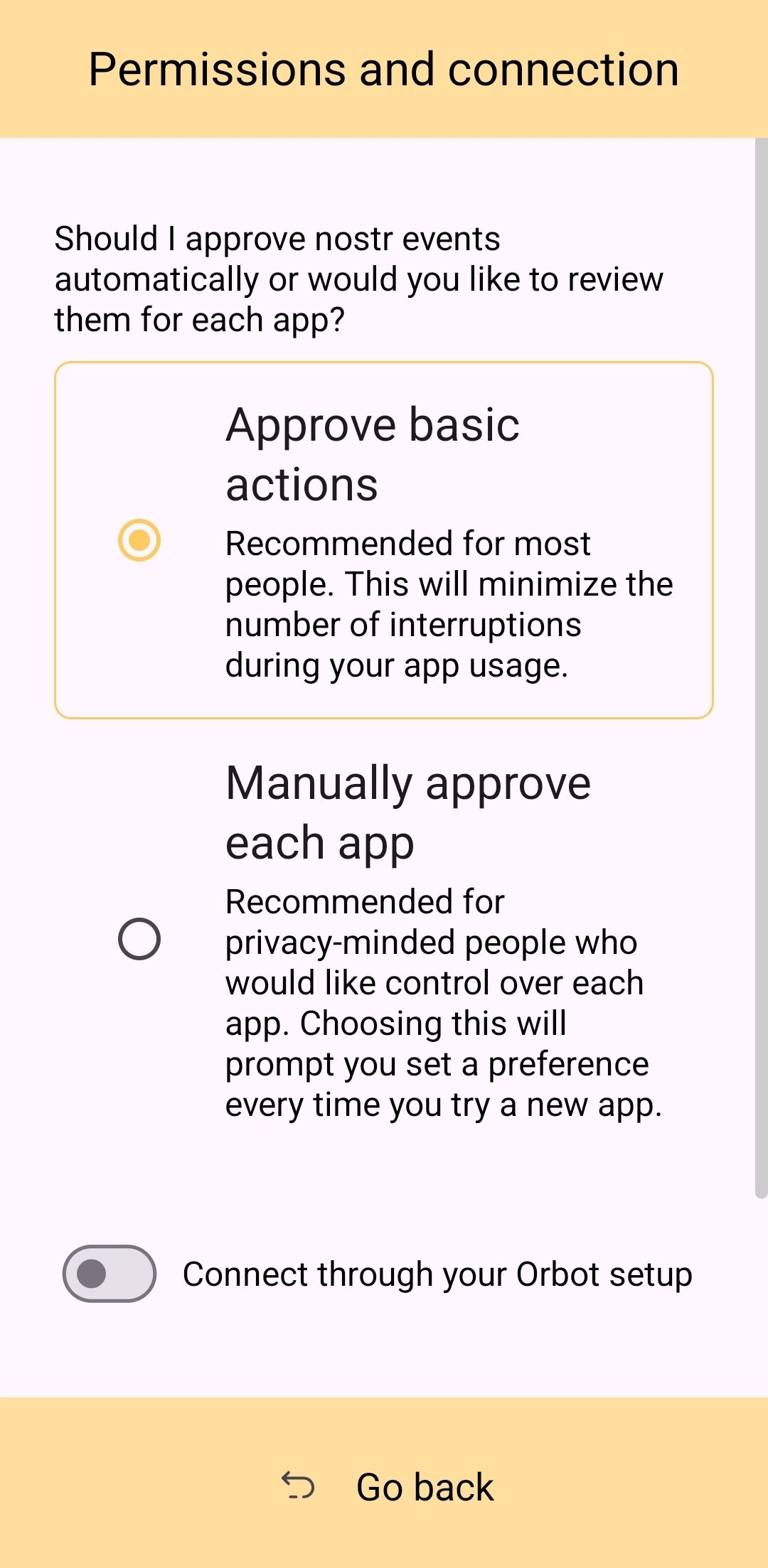
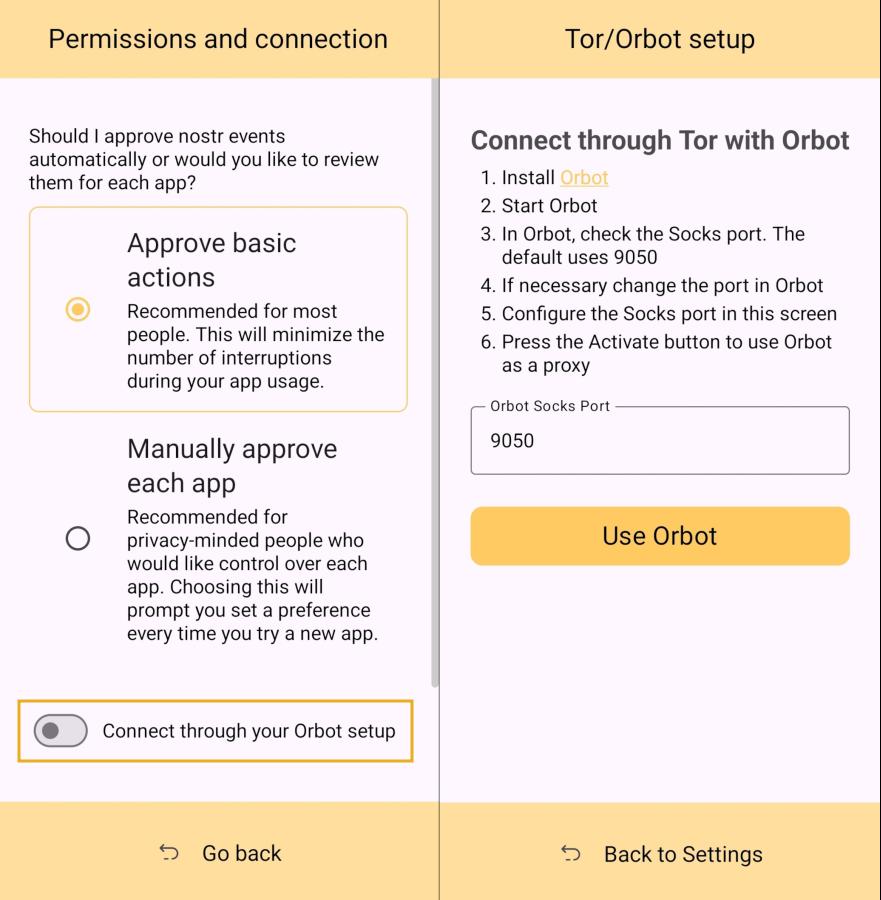
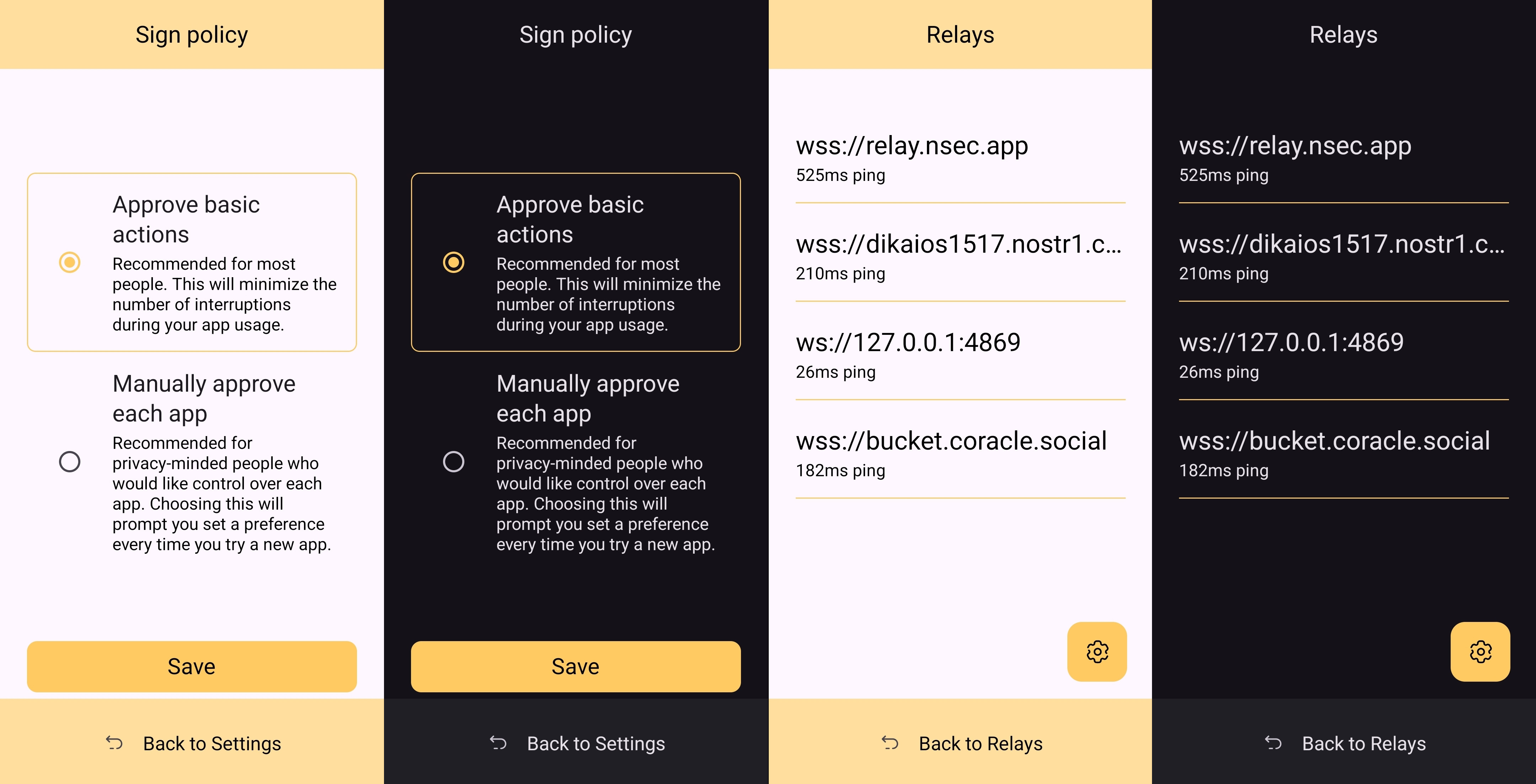
Now, this can also get quite annoying after a while. I recommend using the setting that allows Amber to automatically sign for basic functions, which will cut down on some of the authorization spam. Once you have been asked to authorize the same type of action a few times, you can also toggle the option to automatically authorize that action in the future. Don't worry, though, you have full control to require Amber to ask you for permission again if you want to be alerted each time, and this toggle is specific to each application, so it's not a blanket approval for all Nostr clients you connect with.
This method of signing is just as fast as signing via browser extension on web clients, which users may be more accustomed to. Everything is happening locally on the device, so it can be very snappy and secure.
Nostr Connect/Bunker Signing
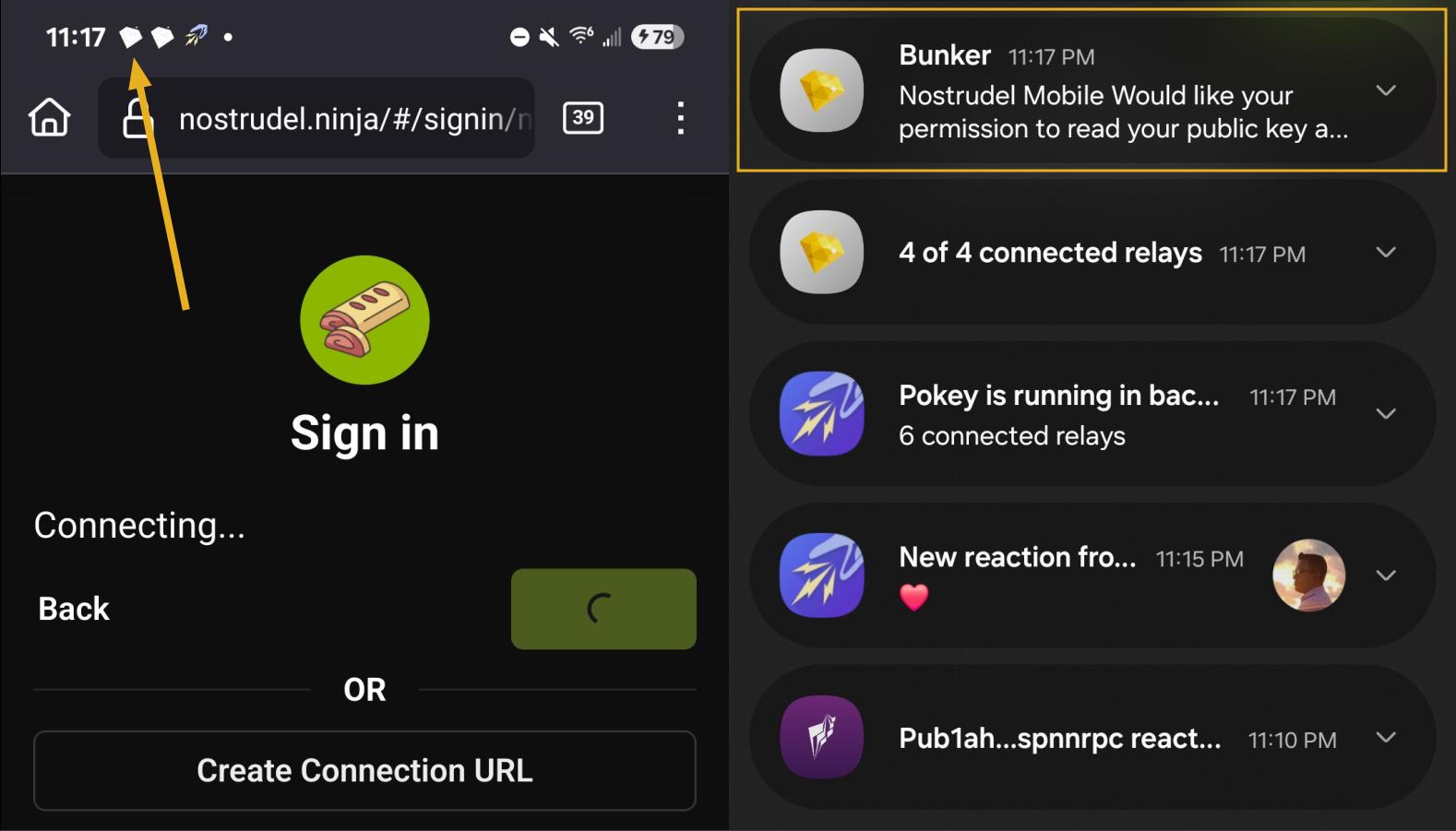
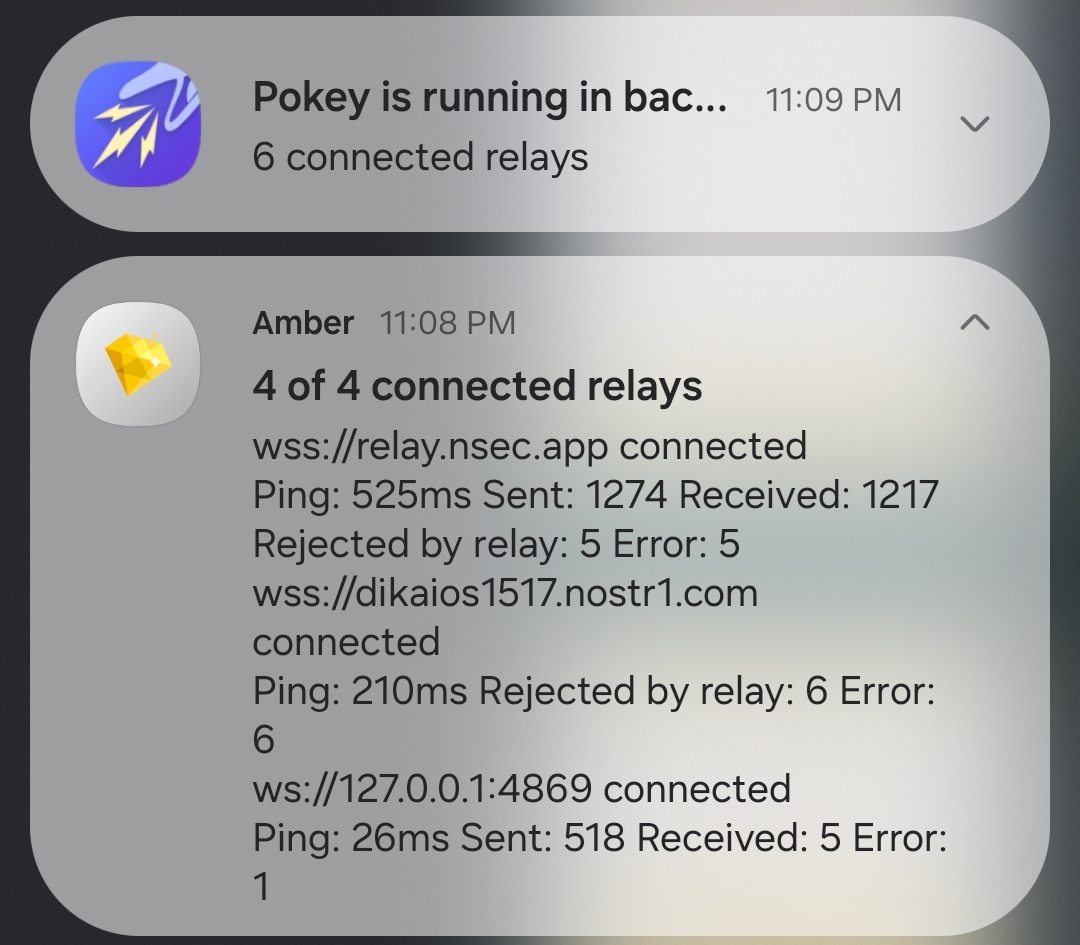
This next method of signing has a bit of a delay, because it is using a Nostr relay to send encrypted information back and forth between the app the user is interacting with and Amber to obtain signatures remotely. It isn't a significant delay most of the time, but it is just enough to be noticeable.
Also, unlike the previous signing method that would automatically switch to Amber as the active application when a signing request is sent, this method only sends you a notification that you must be watching for. This can lead to situations where you are wondering why something isn't working in a client you signed into remotely, because it is waiting on you to authorize the action and you didn't notice the notification from Amber. As you use the application, you get used to the need to check for such authorization requests from time to time, or when something isn't working as expected.
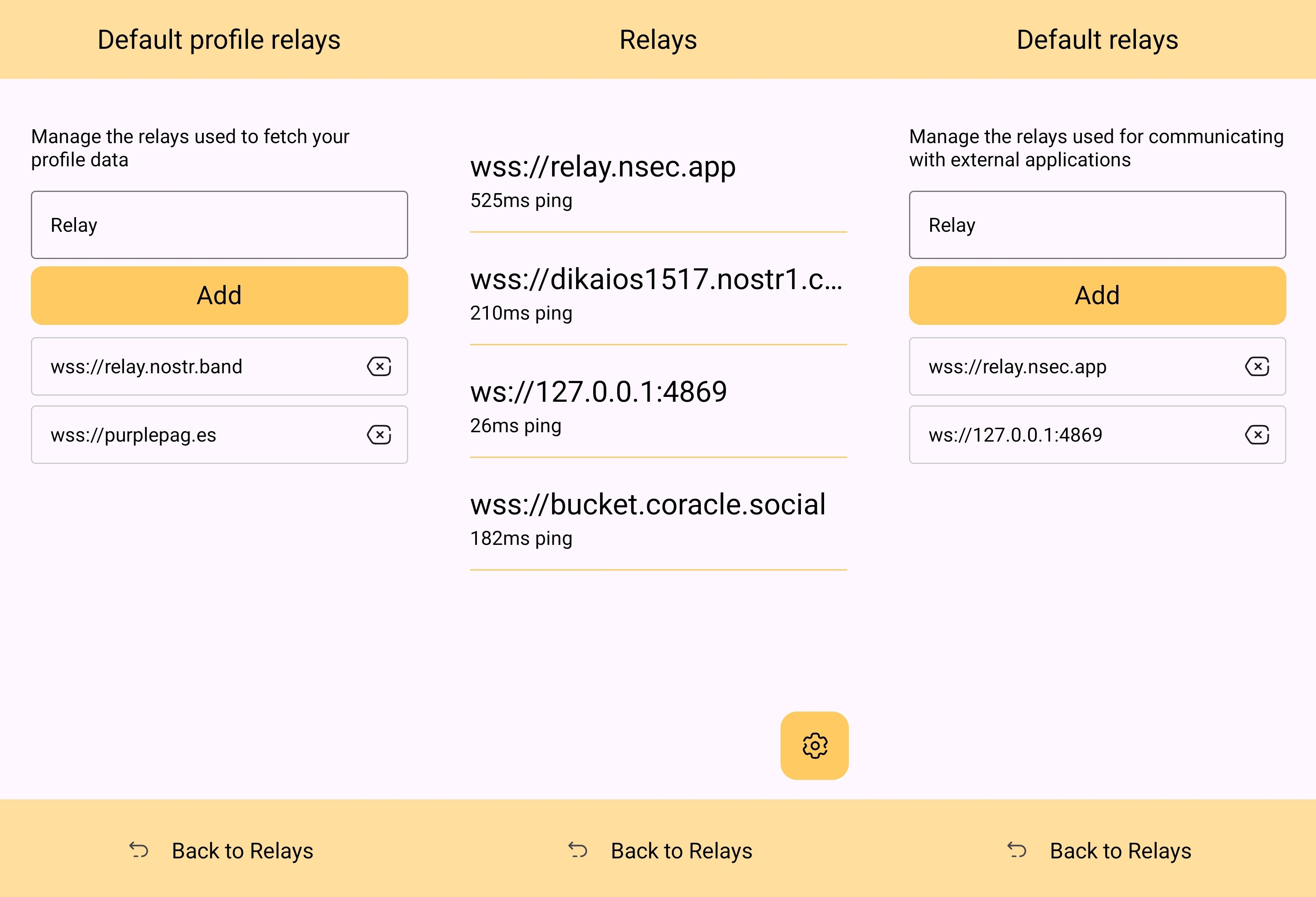
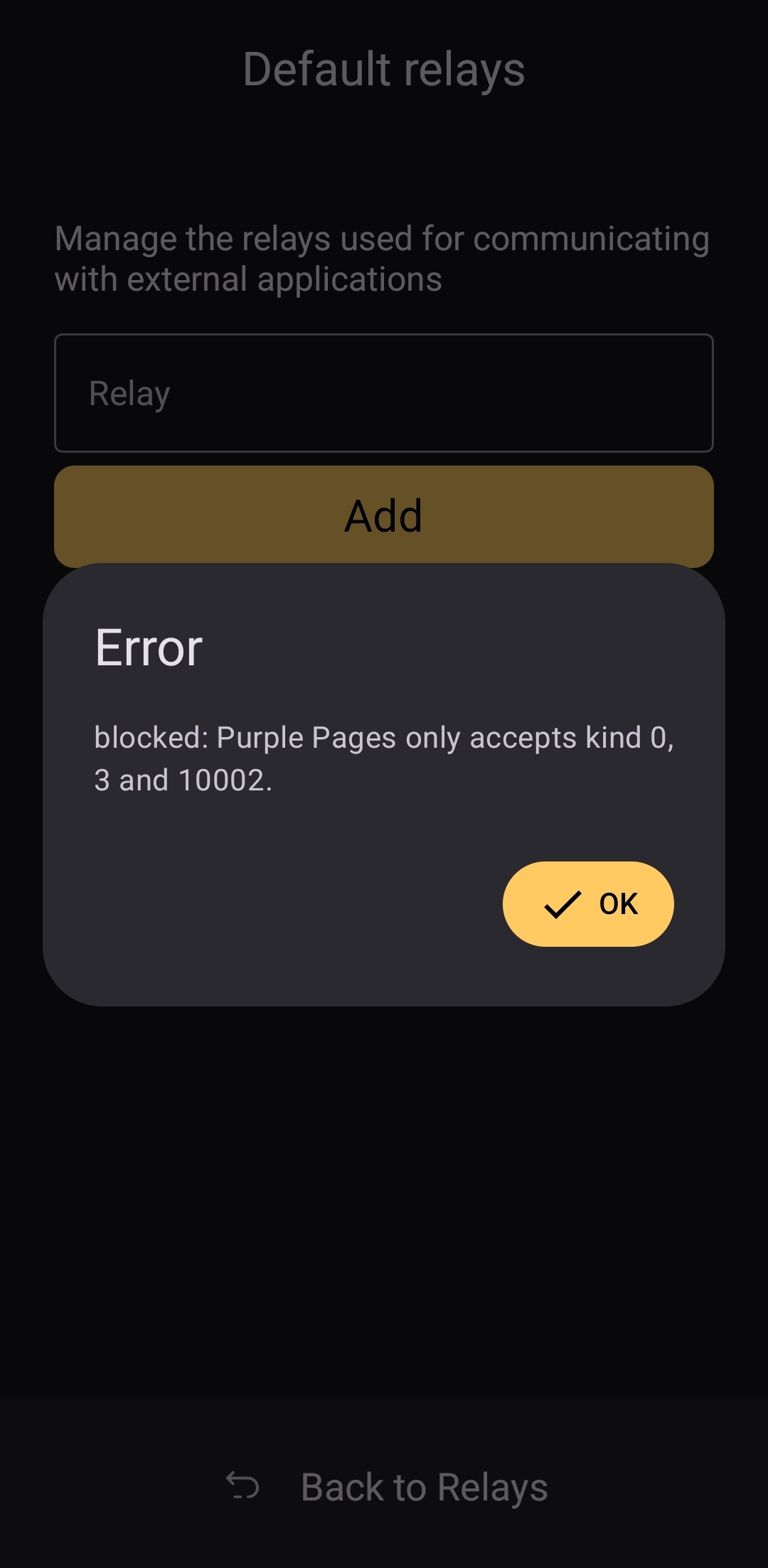
By default, Amber will use relay.nsec.app to communicate with whichever Nostr app you are connecting to. You can set a different relay for this purpose, if you like, though not just any relay will support the event kinds that Amber uses for remote signing. You can even run your own relay just for your own signing purposes. In fact, the creator of Amber has a relay application you can run on your phone, called Citrine, that can be used for signing with any web app you are using locally on your phone. This is definitely more of an advanced option, but it is there for you if you want it. For most users, sticking with relay.nsec.app will be just fine, especially since the contents of the events sent back and forth for signing are all encrypted.
Something many users may not realize is that this remote signing feature allows for issuing signing permissions to team members. For instance, if anyone ever joined me in writing reviews, I could issue them a connection string from Amber, and limit their permissions to just posting long-form draft events. Anything else they tried to do would require my explicit approval each time. Moreover, I could revoke those permissions if I ever felt they were being abused, without the need to start over with a whole new npub. Of course, this requires that your phone is online whenever a team member is trying to sign using the connection string you issued, and it requires you pay attention to your notifications so you can approve or reject requests you have not set to auto-approve. However, this is probably only useful for small teams, and larger businesses will want to find a more robust solution for managing access to their npub, such as Keycast from nostr:npub1zuuajd7u3sx8xu92yav9jwxpr839cs0kc3q6t56vd5u9q033xmhsk6c2uc.
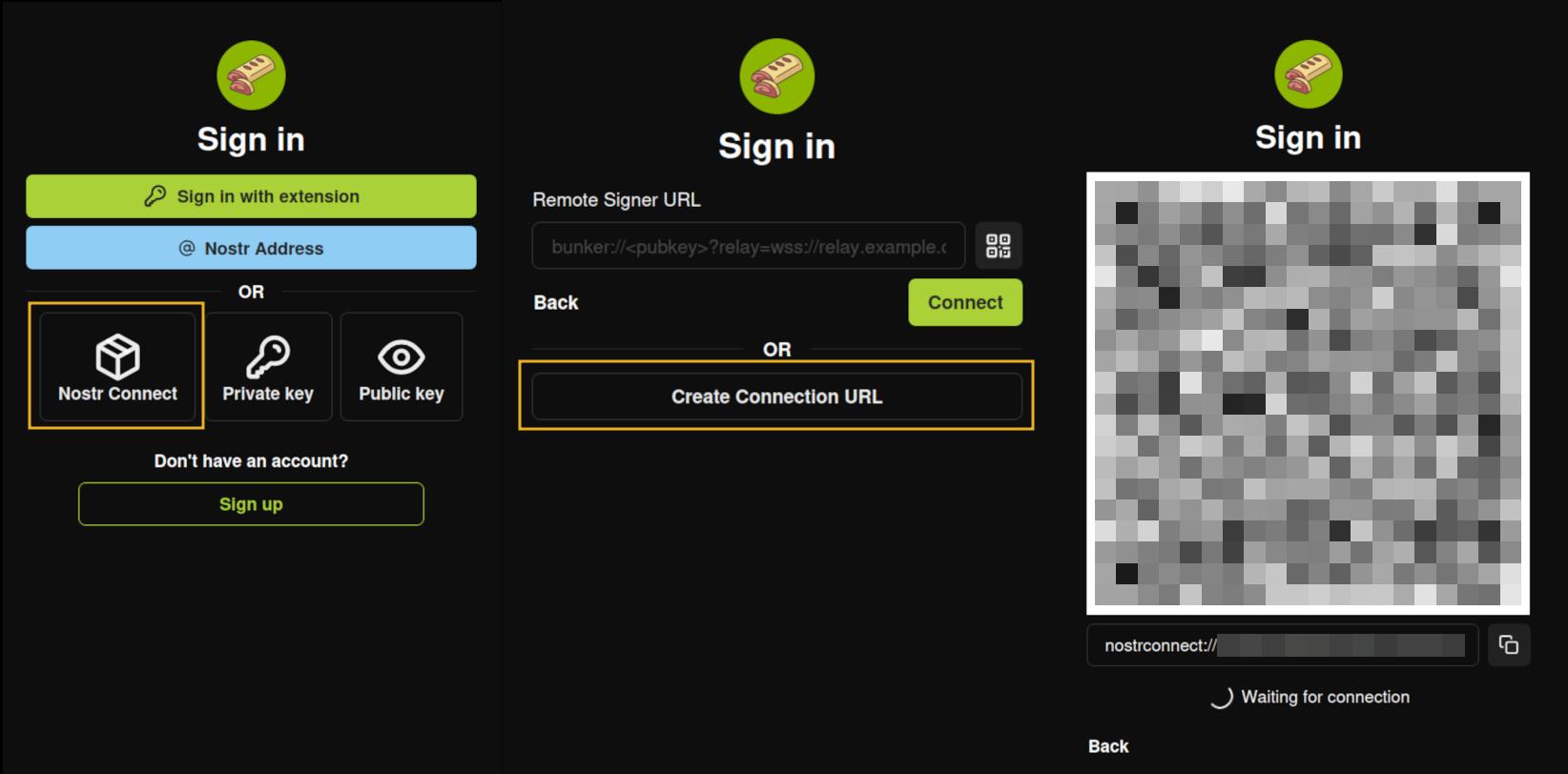
The method for establishing a connection between Amber and a Nostr app for remote signing can vary for each app. Most, at minimum, will support obtaining a connection string from Amber that starts with "bunker://" and pasting it in at the time of login. Then you just need to approve the connection request from Amber and the client will log you in and send any subsequent signing requests to Amber using the same connection string.
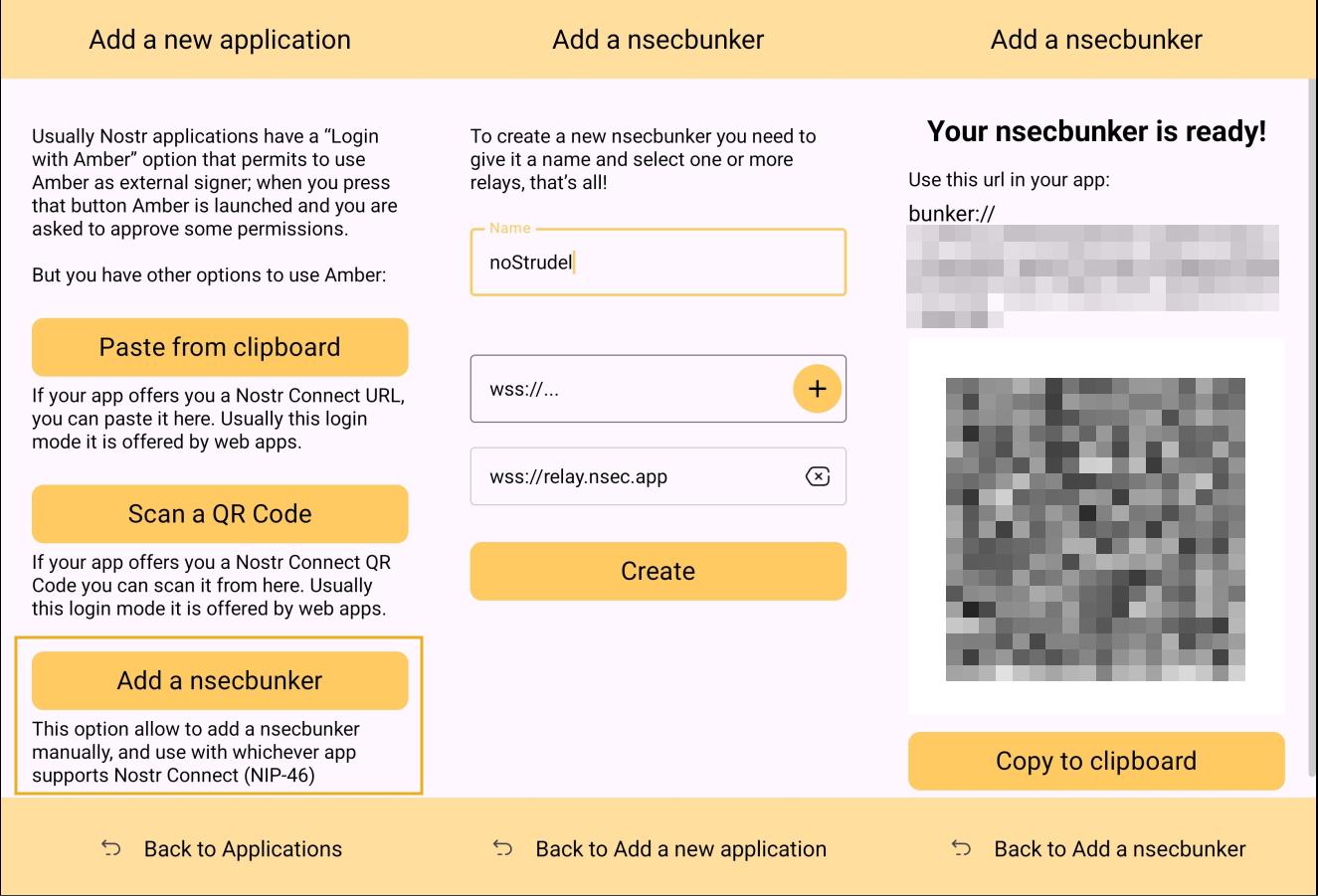
Some clients will also offer the option to scan a QR code to connect the client to Amber. This is quite convenient, but just remember that this also means the client is setting which relay will be used for communication between the two. Clients with this option will also have a connection string you can copy and paste into Amber to achieve the same purpose. For instance, you may need this option if you are trying to connect to an app on your phone and therefore can't scan the QR code using Amber on the same phone.
Multiple Accounts
Amber does not lock you into using it with only a single set of keys. You can add all of your Nostr "accounts" to Amber and use it for signing events for each independently. Of course, Nostr doesn't actually have "accounts" in the traditional sense. Your identity is simply your key-pair, and Amber stores and accesses each private key as needed.
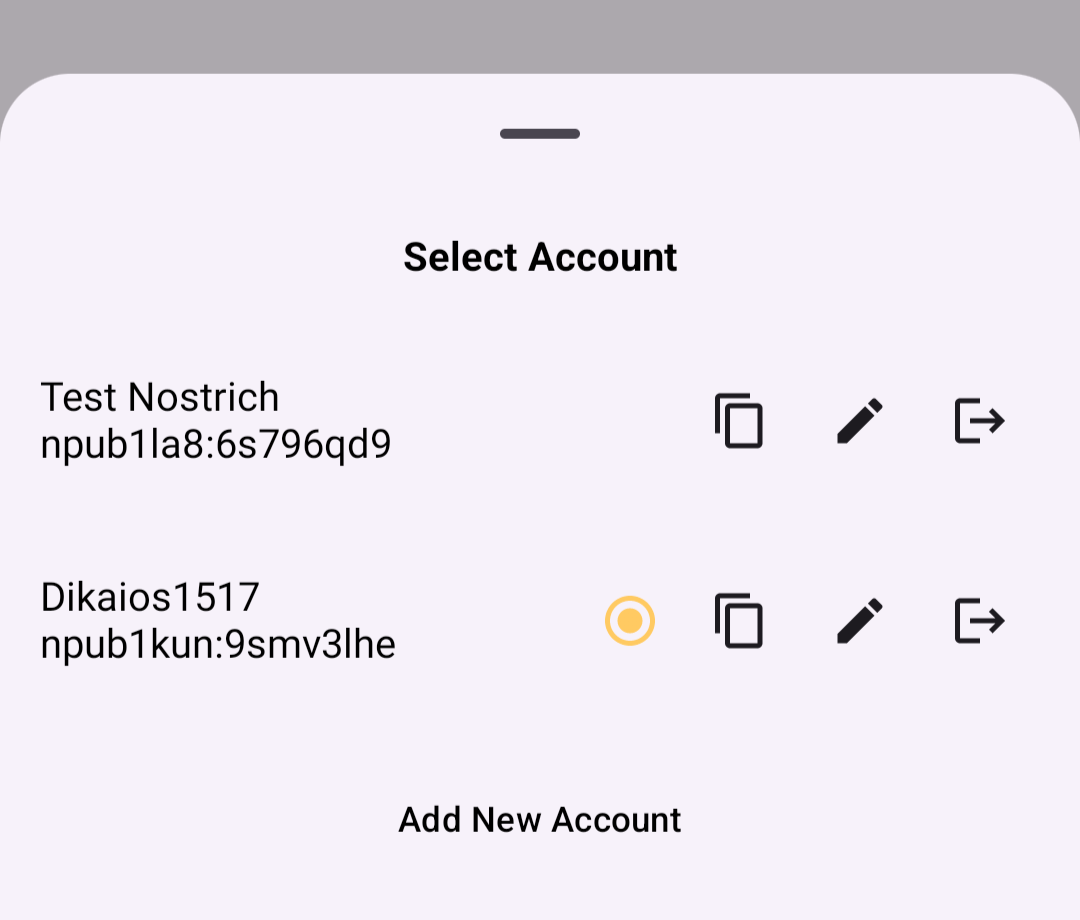
When first signing in using native Android signing as described above, Amber will default to whichever account was most recently selected, but you can switch to the account that is needed before approving the request. After initial login, Amber will automatically detect the account that the signing request is for.
Key Backup & Restore
Amber allows multiple ways to back up your private key. As most users would expect, you can get your standard nsec and copy/paste it to a password manager, but you can also obtain your private key as a list of mnemonic seed words, an encrypted version of your key called an ncryptsec, or even a QR code of your nsec or ncryptsec.
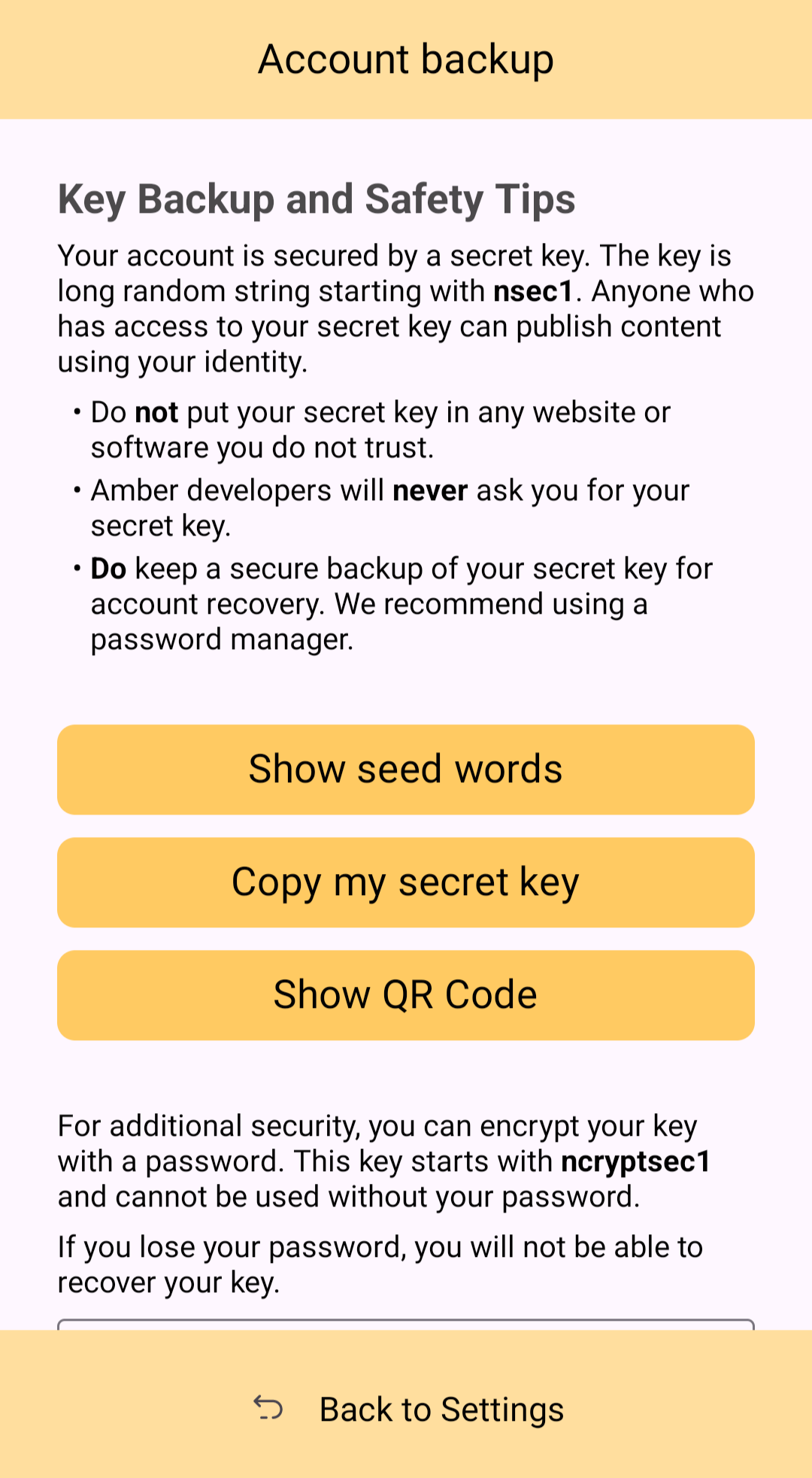
Additionally, in order to gain access to this information, Amber requires you to enter your device's PIN or use biometric authentication. This isn't cold-storage level protection for your private key by any means, especially since your phone is an internet connected device and does not store your key within a secure element, but it is about as secure as you can ask for while having your key accessible for signing Nostr events.
Tor Support
While Amber does not have Tor support within the app itself, it does support connecting to Tor through Orbot. This would be used with remote signing so that Amber would not connect directly over clearnet to the relay used for communication with the Nostr app requesting the signature. Instead, Amber would connect through Tor, so the relay would not see your IP address. This means you can utilize the remote signing option without compromising your anonymity.
Additional Security
Amber allows the user the option to require either biometric or PIN authentication before approving signing requests. This can provide that extra bit of assurance that no one will be able to sign events using your private key if they happen to gain access to your phone. The PIN you set in Amber is also independent from the PIN to unlock your device, allowing for separation of access.
Can My Grandma Use It?
Score: 4.6 / 5 (Updated 4/21/2025)
At the end of the day, Amber is a tool for those who have some concept of the importance of protecting their private key by not pasting it into every Nostr client that comes along. This concept in itself is not terribly approachable to an average person. They are used to just plugging their password into every service they use, and even worse, they usually have the same password for everything so they can more readily remember it. The idea that they should never enter their "Nostr password" into any Nostr application would never occur to them unless someone first explained how cryptography works related to public/private key pairs.
That said, I think there can be some improvements made to how users are introduced to these concepts, and that a signer application like Amber might be ideal for the job. Considering Amber as a new user's first touch-point with Nostr, I think it holds up well, but could be somewhat streamlined.
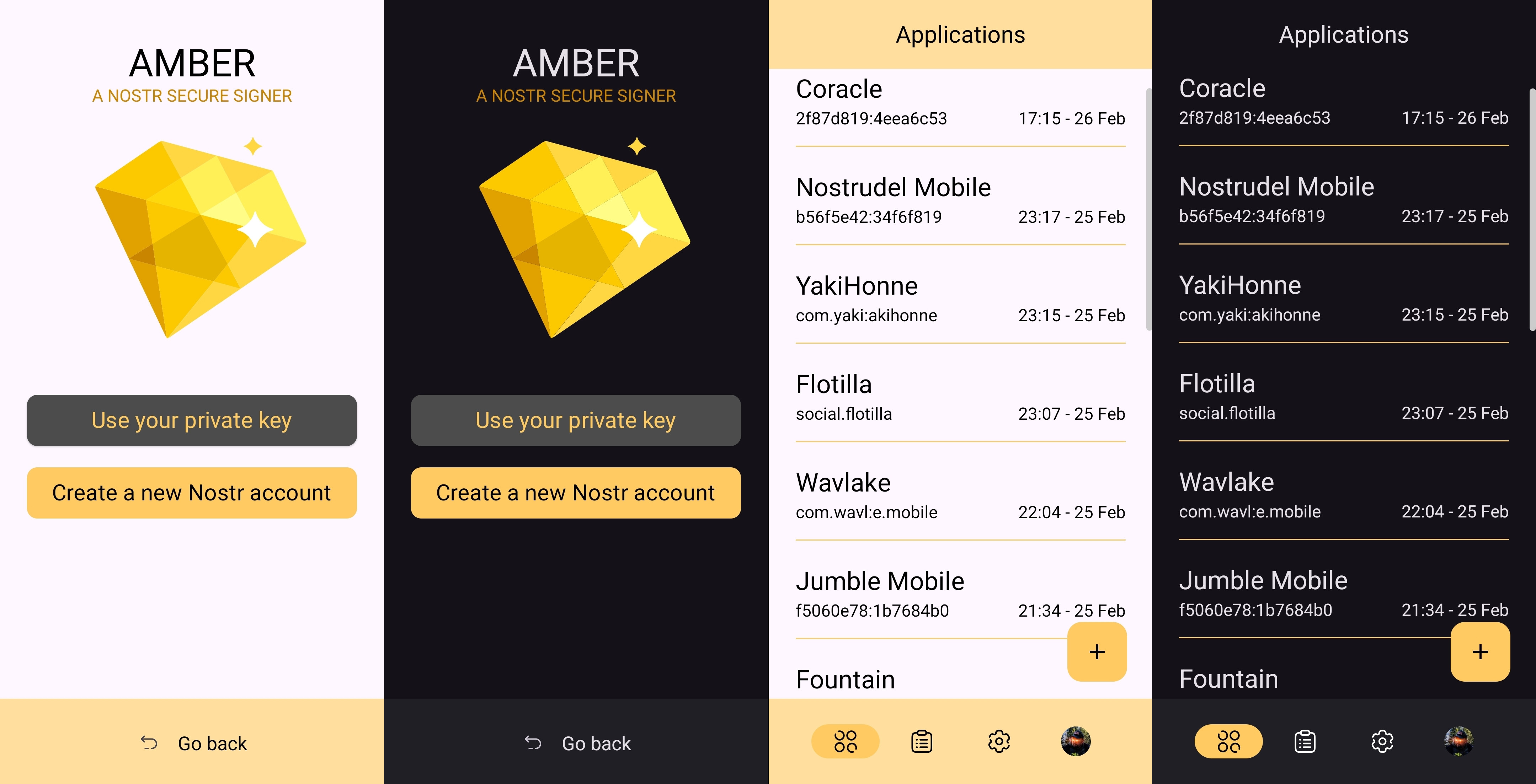
Upon opening the app, the user is prompted to either use their existing private key or "Create a new Nostr account." This is straightforward enough. "Account" is not a technically correct term with Nostr, but it is a term that new users would be familiar with and understand the basic concept.
The next screen announces that the account is ready, and presents the user with their public key, explaining that it is "a sort of username" that will allow others to find them on Nostr. While it is good to explain this to the user, it is unnecessary information at this point. This screen also prompts the user to set a nickname and set a password to encrypt their private key. Since the backup options also allow the user to set this password, I think this step could be pushed to a later time. This screen would better serve the new user if it simply prompted them to set a nickname and short bio that could be saved to a few default relays.
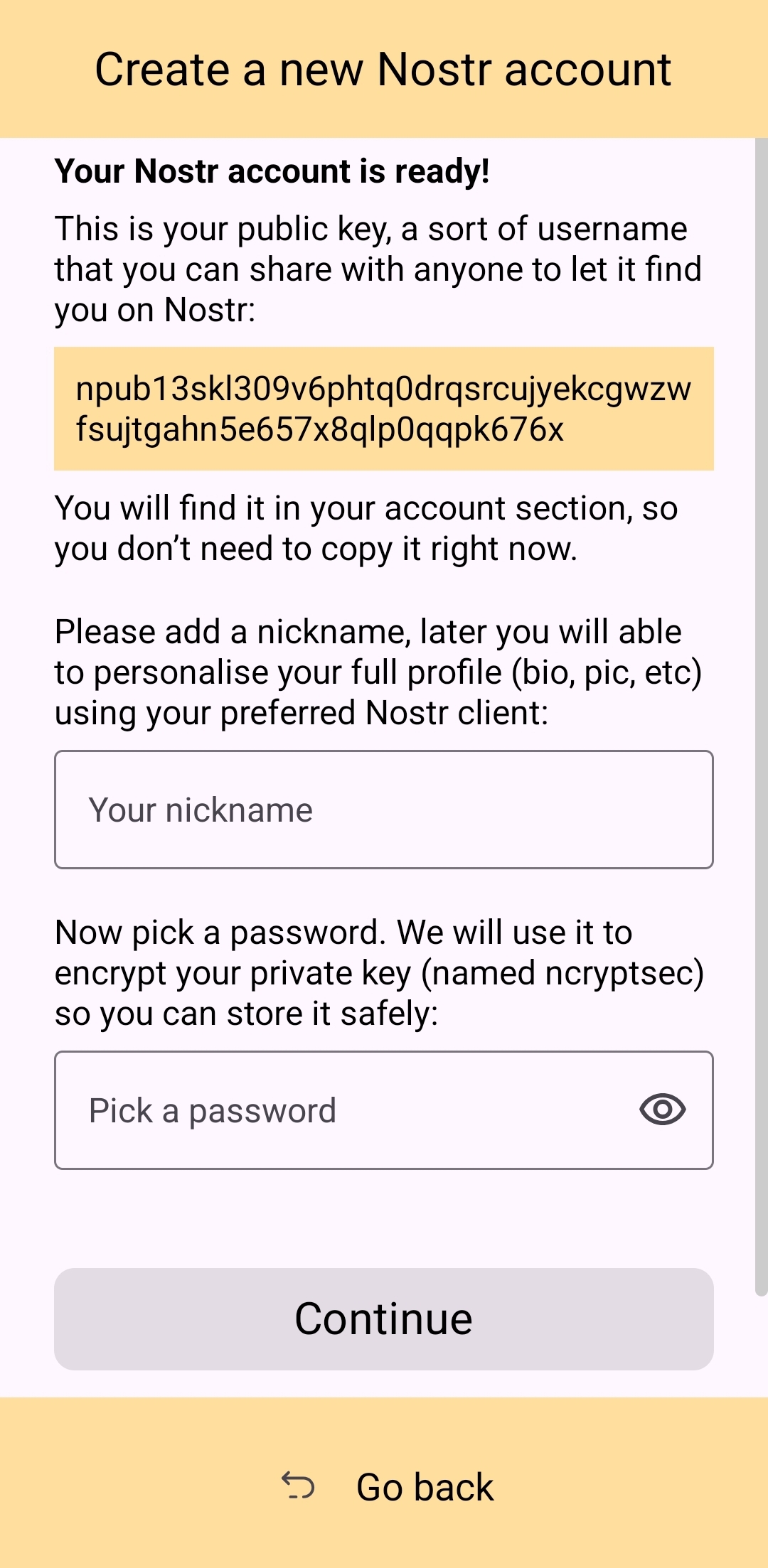
Of course, Amber is currently prompting for a password to be set up-front because the next screen requires the new user to download a "backup kit" in order to continue. While I do believe it is a good idea to encourage the creation of a backup, it is not crucial to do so immediately upon creation of a new npub that has nothing at stake if the private key is lost. This is something the UI could remind the user to do at a later time, reducing the friction of profile creation, and expediting getting them into the action.
Outside of these minor onboarding friction points, I think Amber does a great job of explaining to the user the purpose of each of its features, all within the app and without any need to reference external documentation. As long as the user understands the basic concept that their private key is being stored by Amber in order to sign requests from other Nostr apps, so they don't have to be given the private key, Amber is very good about explaining the rest without getting too far into the technical weeds.
The most glaring usability issue with Amber is that it isn't available in the Play Store. Average users expect to be able to find applications they can trust in their mobile device's default app store. There is a valid argument to be made that they are incorrect in this assumption, but that doesn't change the fact that this is the assumption most people make. They believe that applications in the Play Store are "safe" and that anything they can't install through the Play Store is suspect. The prompts that the Android operating system requires the user to approve when installing "unknown apps" certainly doesn't help with this impression.
Now, I absolutely love the Zapstore from nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9, but it doesn't do much to alleviate this issue. Users will still need to be convinced that it is safe to install the Zapstore from the GitHub repo, and then install Amber from there. Furthermore, this adds yet another step to the onboarding process.
Instead of:
- Install Amber
- Set up your keys
- Install the client you want to use
- Log in with Amber
The process becomes:
- Go to the Zapstore GitHub and download the latest version from the releases page.
- Install the APK you downloaded, allowing any prompt to install unknown apps.
- Open Zapstore and install Amber, allowing any prompt to install unknown apps again.
- Open Amber and set up your keys.
- Install the client you want to use
- Log in with Amber
An application as important as Amber for protecting users' private keys should be as readily available to the new user as possible. New users are the ones most prone to making mistakes that could compromise their private keys. Amber should be available to them in the Play Store.
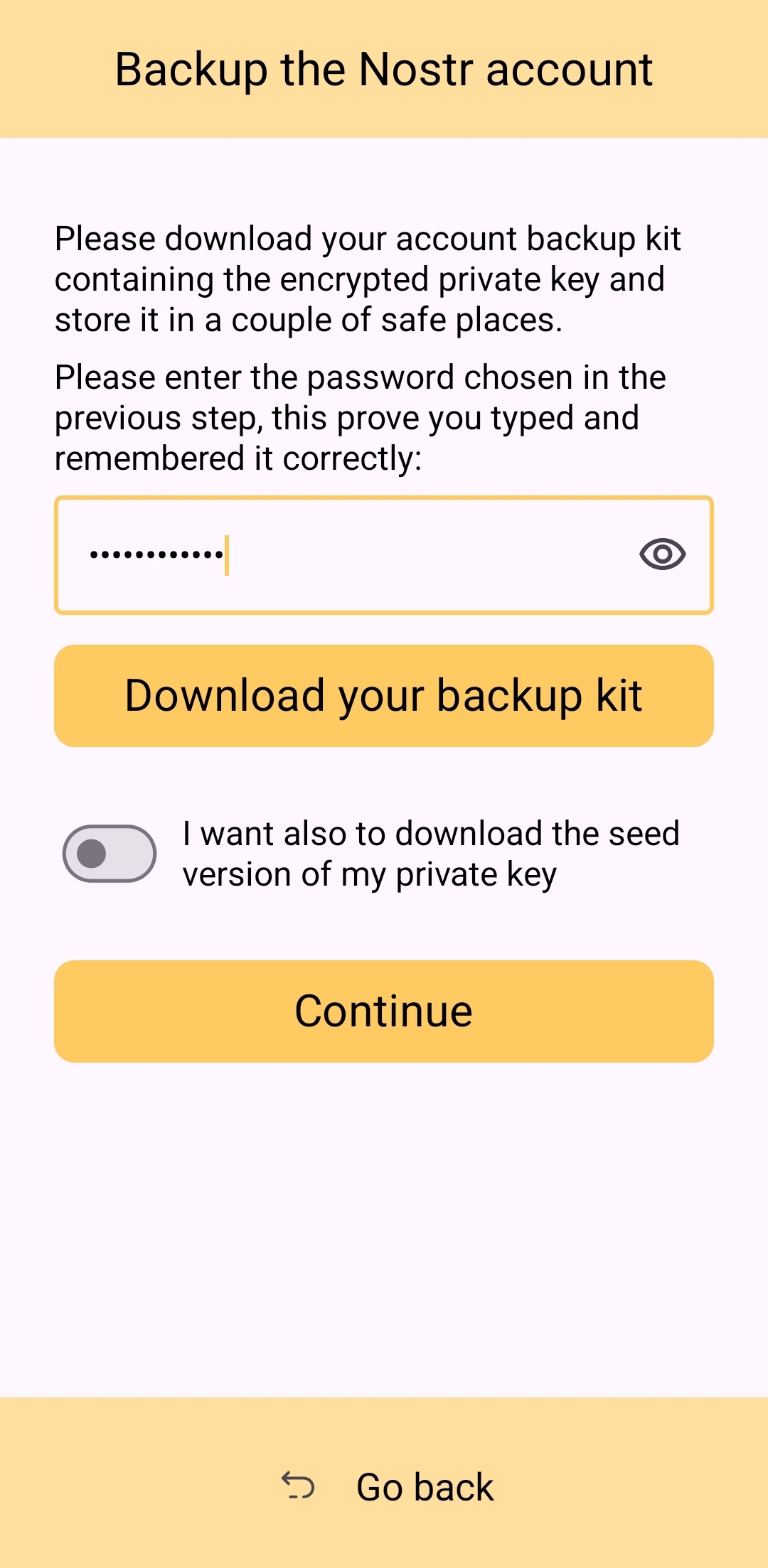
UPDATE: As of version 3.2.8 released on 4/21/2025, the onboarding flow for Amber has been greatly improved! Now, when selecting to set up a new "account" the user is informed on the very next screen, "Your Nostr account is ready!" and given their public key/npub. The only field the user must fill in is their "nickname"/display name and hit "Continue."
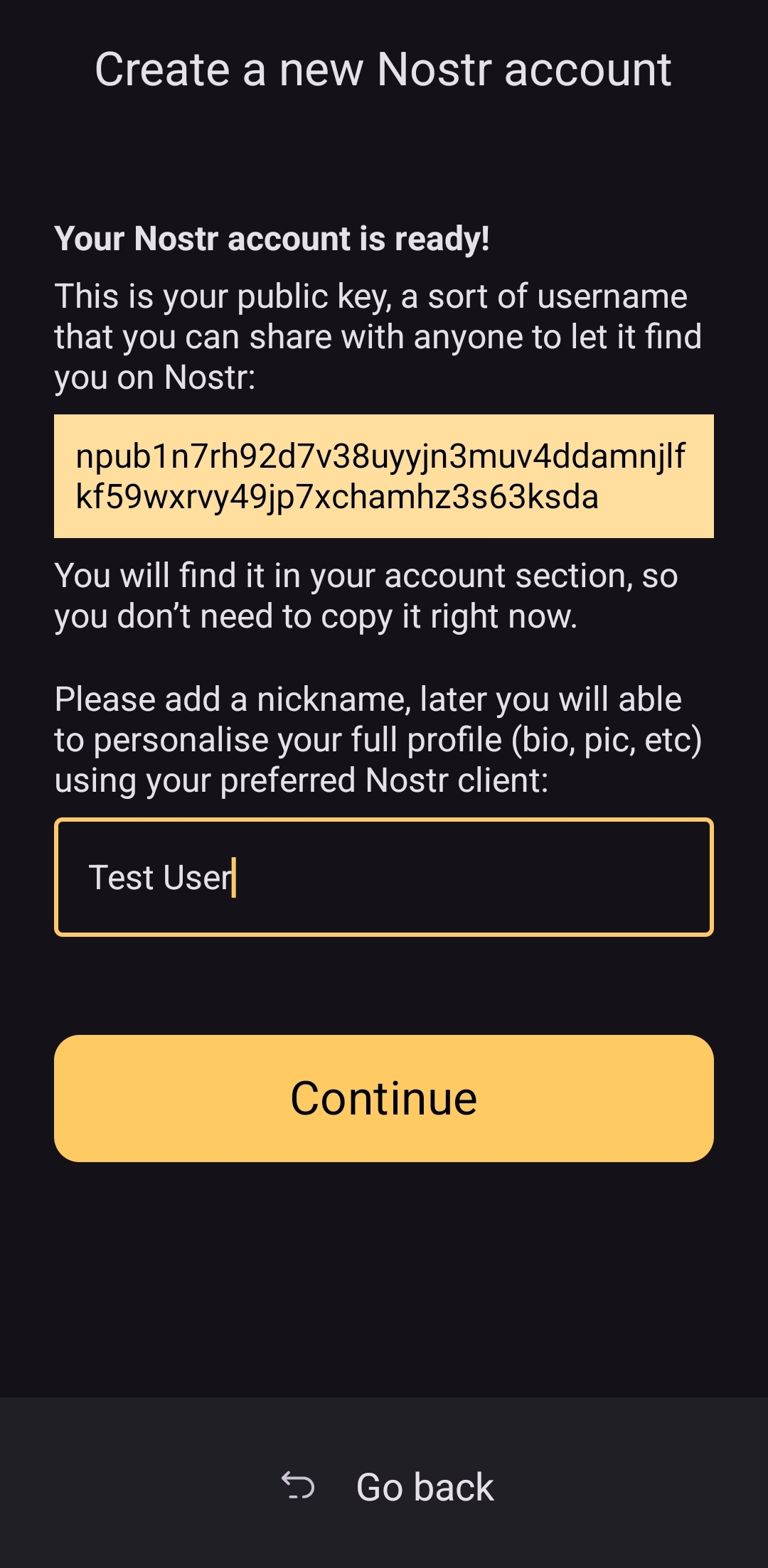
From there the user is asked if they want Amber to automatically approve basic actions, or manually approve each app, and then they are shown a new Applications screen, with a prompt to create a backup of their account. This prompt persists until the user has done so.
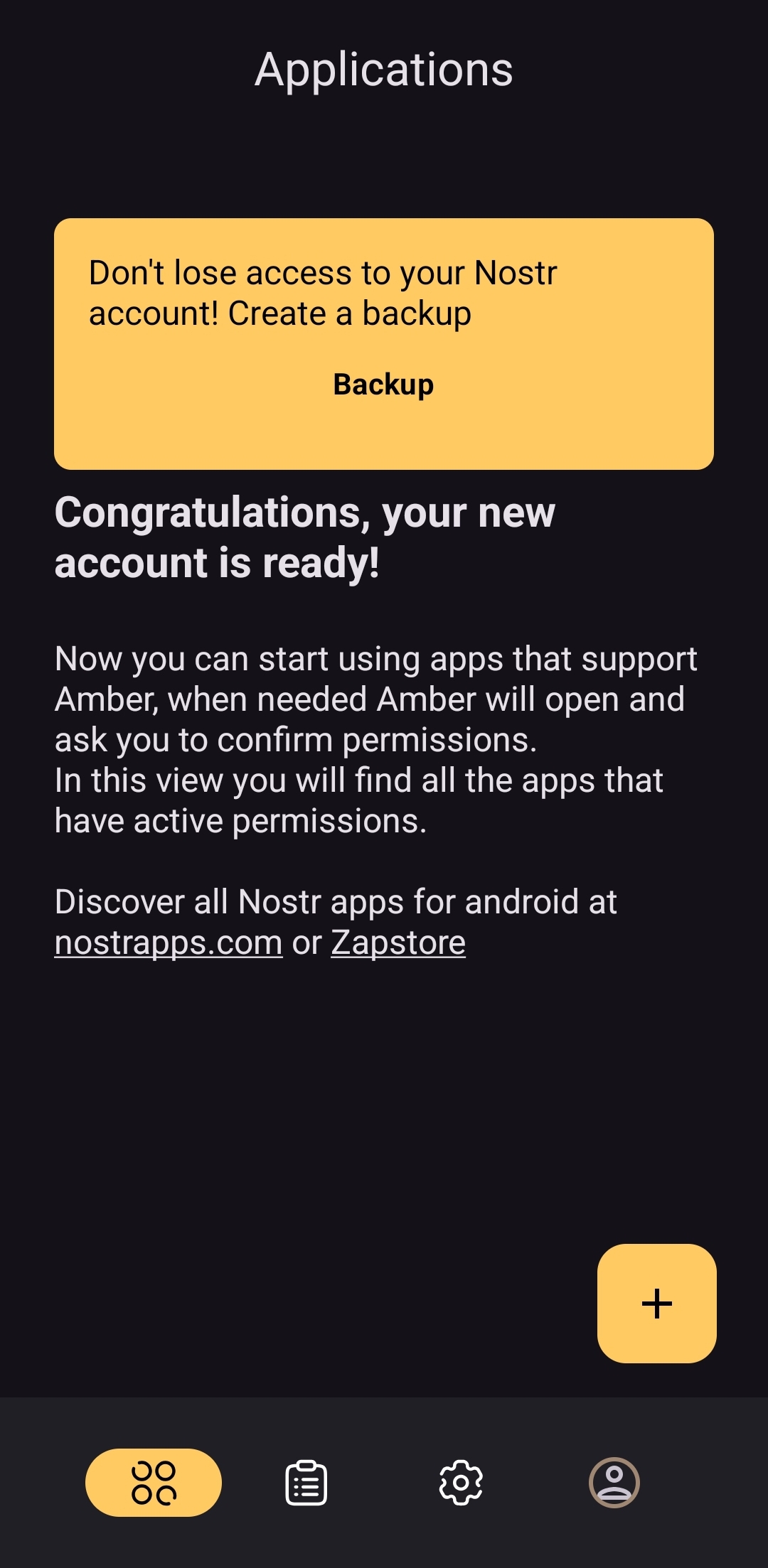
As you can see, the user is also encouraged to find applications that can be used with Amber with links to nostrapps.com and the Zapstore.
Thanks to these updates, Amber is now the smoothest and most user-friendly onboarding experience I have seen for Nostr to date. Sure, it doesn't have anything for setting up a profile picture or lightning address, but that is better done in a client like Amethyst or YakiHonne, anyway. Just tap "create," type in a handle to call yourself, and you're done!
How do UI Look?
Score: 4.5 / 5
Amber's UI can be described as clean but utilitarian. But then, Amber is a tool, so this is somewhat expected. It is not an app you will be spending a lot of time in, so the UI just needs to be serviceable. I would say it accomplishes this and then some. UI elements are generally easy to understand what they do, and page headings fill in the gaps where that is not the case.
I am not the biggest fan of the color-scheme, particularly in light-mode, but it is not bad in dark-mode at all, and Amber follows whatever theme you have set for your device in that respect. Additionally, the color choice does make sense given the application's name.
It must also be taken into consideration that Amber is almost entirely the product of a single developer's work. He has done a great job producing an app that is not only useful, but pleasant to interact with. The same cannot be said for most utility apps I have previously used, with interfaces that clearly made good design the lowest priority. While Amber's UI may not be the most beautiful Nostr app I have seen, design was clearly not an afterthought, either, and it is appreciated.
Relay Management
Score: 4.9 / 5
Even though Amber is not a Nostr client, where users can browse notes from their favorite npubs, it still relies heavily on relays for some of its features. Primarily, it uses relays for communicating with other Nostr apps for remote signing requests. However, it also uses relays to fetch profile data, so that each private key you add to Amber will automatically load your chosen username and profile picture.
In the relay settings, users can choose which relays are being used to fetch profile data, and which relays will be used by default when creating new remote signing connection strings.
The user can also see which relays are currently connected to Amber and even look at the information that has been passed back and forth on each of those active relays. This information about actively connected relays is not only available within the application, but also in the notification that Amber has to keep in your device's notification tray in order to continue to operate in the background while you are using other apps.
Optionality is the name of the game when it comes to how Amber handles relay selection. The user can just stick with the default signing relay, use their own relay as the default, or even use a different relay for each Nostr application that they connect to for remote signing. Amber gives the user an incredible amount of flexibility in this regard.
In addition to all of this, because not all relays accept the event types needed for remote signing, when you add a relay address to Amber, it automatically tests that relay to see if it will work. This alone can be a massive time saver, so users aren't trying to use relays that don't support remote signing and wondering why they can't log into noStrudel with the connection string they got from Amber.
The only way I could see relay management being improved would be some means of giving the user relay recommendations, in case they want to use a relay other than relay.nsec.app, but they aren't sure which other relays will accept remote signing events. That said, most users who want to use a different relay for signing remote events will likely be using their own, in which case recommendations aren't needed.
Current Users' Questions
The AskNostr hashtag can be a good indication of the pain points that other users are currently having with any Nostr application. Here are some of the most common questions submitted about Amber in the last two months.
nostr:nevent1qqsfrdr68fafgcvl8dgnhm9hxpsjxuks78afxhu8yewhtyf3d7mkg9gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgq3qkgh77xxt7hhtt4u528hecnx69rhagla8jj3tclgyf9wvkxa6dc0sxp0e6m
This is a good example of Amber working correctly, but the app the user is trying to log into not working. In my experience with #Olas in particular, it sometimes allows remote signer login, and sometimes doesn't. Amber will receive the signing request and I will approve it, but Olas remains on the login screen.
If Amber is receiving the signing requests, and you are approving them, the fault is likely with the application you are trying to log into.
That's it. That's all the repeated questions I could find. Oh, there were a few one-off questions where relay.nsec.app wouldn't connect, or where the user's out-of-date web browser was the issue. Outside of that, though, there were no common questions about how to use Amber, and that is a testament to Amber's ease of use all on its own.
Wrap Up
If you are on Android and you are not already using Amber to protect your nsec, please do yourself a favor and get it installed. It's not at all complicated to set up, and it will make trying out all the latest Nostr clients a safe and pleasant experience.
If you are a client developer and you have not added support for NIP-55 or NIP-46, do your users the courtesy of respecting the sanctity of their private keys. Even developers who have no intention of compromising their users' keys can inadvertently do so. Make that eventuality impossible by adding support for NIP-55 and NIP-46 signing.
Finally, I apologize for the extended time it took me to get this review finished. The time I have available is scarce, Nostr is distracting, and nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 kept improving Amber even as I was putting it through its paces over the last two months. Keep shipping, my friend! You have made one of the most useful tools we have seen for Nostr to date!
Now... What should I review next?
-
 @ 401014b3:59d5476b
2025-04-22 00:23:24
@ 401014b3:59d5476b
2025-04-22 00:23:24About Me
I come to Nostr with extensive experience in the digital landscape. As a blockchain native since 2017, I've witnessed the evolution of decentralized technologies firsthand. Most of my professional career has been spent working within big tech companies, giving me a unique perspective on both centralized and decentralized systems.
My social media journey began on Twitter in 2007, where I've maintained a presence for over 17 years. I've also explored other decentralized social platforms including BlueSky, Farcaster, and Lens Protocol. As a Bitcoin maximalist, I was particularly intrigued by Nostr's compatibility with the Lightning Network, which initially drew me to the platform.
The Onboarding Challenge
The Nostr onboarding experience presents a significant hurdle for newcomers. Despite my technical background in blockchain technologies, I found the initial setup process more complicated than expected. Understanding public/private key cryptography just to join a social network creates a steeper learning curve than necessary.
BlueSky and Farcaster have demonstrated that it's possible to maintain decentralized principles while providing a more streamlined onboarding experience. Their approaches show that user-friendly design and decentralization aren't mutually exclusive concepts.
Relay Management: Room for Improvement
The concept of relays represents one of Nostr's most distinctive features, though it can be confusing for newcomers. While many clients come pre-configured with default relays, users eventually encounter situations where content or connections seem inconsistent.
When someone I've interacted with doesn't appear in my feed or doesn't respond, I'm often left wondering if we're simply on different relays. This uncertainty creates friction that doesn't exist on other platforms where connectivity is handled behind the scenes.
The relay system introduces a layer of complexity that, while important to Nostr's architecture, could benefit from better abstraction in the user experience. When using BlueSky or Farcaster, I don't need to think about the underlying infrastructure, something Nostr could learn from while maintaining its decentralized principles.
The Zap Economy: Growing Pains
The Lightning-powered zap system shows tremendous potential, but I've observed some concerning economic patterns. Longer-term Nostr users have expressed frustration about continuously sending zaps while seeing limited growth in the overall ecosystem.
Interestingly, there appears to be a connection between this liquidity issue and community growth dynamics. Some established users who voice concerns about bearing the financial burden of the zapping economy are simultaneously less welcoming to newer accounts, rarely following, engaging with, or zapping newcomers.
This creates a challenging environment for new users, who face a cold reception and have little incentive to load their Lightning wallets or participate in the zap economy. Why bring fresh liquidity to a platform where established users rarely engage with your content? This dynamic has limited the expansion of the ecosystem, with the same sats often circulating among established users rather than growing with new participants.
Client Diversity: Strength and Challenge
Nostr's multiple client options offer users choice, which is valuable. However, the implementation of NIPs (Nostr Implementation Possibilities) varies across clients, creating inconsistent experiences. Features that work seamlessly in one client might be implemented differently in another.
This extends to fundamental aspects like search functionality, thread navigation, and notification systems, all of which can differ significantly between clients. For users accustomed to consistent experiences, this fragmentation creates a learning curve with each new client they try.
Lightning Integration: Varying Experiences
The Lightning Network integration varies in quality and user experience across Nostr clients. While the functionality is generally present, the implementation quality, feature set, and ease of use differ depending on which client you choose.
This inconsistency means users may need to experiment with several clients to find one that provides the Lightning experience they're looking for, rather than having a consistent experience across the ecosystem.
Finding Balance
Nostr appears to be navigating the challenge of balancing technical innovation with user experience. While its cryptographic foundation and decentralized architecture are impressive technical achievements, these same strengths sometimes come at the cost of accessibility.
Despite my technical background and interest in decentralized technologies, I find myself using BlueSky and Farcaster more frequently for daily social interactions, while checking Nostr less often. For Nostr to achieve its potential for broader adoption, addressing these user experience considerations while maintaining its core principles will be essential.
The platform has tremendous potential with improvements to user experience, community dynamics, and economic sustainability, Nostr could evolve from a fascinating technical experiment into a truly compelling alternative to mainstream social media.
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:13:56
@ 4ba8e86d:89d32de4
2025-04-21 02:13:56Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:12:19
@ 4ba8e86d:89d32de4
2025-04-21 02:12:19SISTEMA OPERACIONAL MÓVEIS
GrapheneOS : https://njump.me/nevent1qqs8t76evdgrg4qegdtyrq2rved63pr29wlqyj627n9tj4vlu66tqpqpzdmhxue69uhk7enxvd5xz6tw9ec82c30qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqppcqec9
CalyxOS : https://njump.me/nevent1qqsrm0lws2atln2kt3cqjacathnw0uj0jsxwklt37p7t380hl8mmstcpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3vamnwvaz7tmwdaehgu3wvf3kstnwd9hx5cf0qy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgcwaehxw309aex2mrp0yhxxatjwfjkuapwveukjtcpzpmhxue69uhkummnw3ezumt0d5hszrnhwden5te0dehhxtnvdakz7qfywaehxw309ahx7um5wgh8ymm4dej8ymmrdd3xjarrda5kuetjwvhxxmmd9uq3uamnwvaz7tmwdaehgu3dv3jhvtnhv4kxcmmjv3jhytnwv46z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309ahx7um5wghxymmwva3x7mn89e3k7mf0qythwumn8ghj7cn5vvhxkmr9dejxz7n49e3k7mf0qyg8wumn8ghj7mn09eehgu3wvdez7smttdu
LineageOS : https://njump.me/nevent1qqsgw7sr36gaty48cf4snw0ezg5mg4atzhqayuge752esd469p26qfgpzdmhxue69uhhwmm59e6hg7r09ehkuef0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpnvm779
SISTEMA OPERACIONAL DESKTOP
Tails : https://njump.me/nevent1qqsf09ztvuu60g6xprazv2vxqqy5qlxjs4dkc9d36ta48q75cs9le4qpzemhxue69uhkummnw3ex2mrfw3jhxtn0wfnj7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz34ag5t
Qubes OS : https://njump.me/nevent1qqsp6jujgwl68uvurw0cw3hfhr40xq20sj7rl3z4yzwnhp9sdpa7augpzpmhxue69uhkummnw3ezumt0d5hsz9mhwden5te0wfjkccte9ehx7um5wghxyctwvshsz9thwden5te0dehhxarj9ehhsarj9ejx2a30qyg8wumn8ghj7mn09eehgu3wvdez7qg4waehxw309aex2mrp0yhxgctdw4eju6t09uqjxamnwvaz7tmwdaehgu3dwejhy6txd9jkgtnhv4kxcmmjv3jhytnwv46z7qgwwaehxw309ahx7uewd3hkctcpremhxue69uhkummnw3ez6er9wch8wetvd3hhyer9wghxuet59uj3ljr8
Kali linux : https://njump.me/nevent1qqswlav72xdvamuyp9xc38c6t7070l3n2uxu67ssmal2g7gv35nmvhspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswt9rxe
Whonix : https://njump.me/nevent1qqs85gvejvzhk086lwh6edma7fv07p5c3wnwnxnzthwwntg2x6773egpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3qamnwvaz7tmwdaehgu3wd4hk6tcpzemhxue69uhkummnw3ezucnrdqhxu6twdfsj7qfywaehxw309ahx7um5wgh8ymm4dej8ymmrdd3xjarrda5kuetjwvhxxmmd9uq3wamnwvaz7tmzw33ju6mvv4hxgct6w5hxxmmd9uq3qamnwvaz7tmwduh8xarj9e3hytcpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszrnhwden5te0dehhxtnvdakz7qg7waehxw309ahx7um5wgkkgetk9emk2mrvdaexgetj9ehx2ap0sen9p6
Kodachi : https://njump.me/nevent1qqsf5zszgurpd0vwdznzk98hck294zygw0s8dah6fpd309ecpreqtrgpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszgmhwden5te0dehhxarj94mx2unfve5k2epwwajkcmr0wfjx2u3wdejhgtcpremhxue69uhkummnw3ez6er9wch8wetvd3hhyer9wghxuet59uq3qamnwvaz7tmwdaehgu3wd4hk6tcpzamhxue69uhkyarr9e4kcetwv3sh5afwvdhk6tcpzpmhxue69uhkumewwd68ytnrwghszfrhwden5te0dehhxarj9eex7atwv3ex7cmtvf5hgcm0d9hx2unn9e3k7mf0qyvhwumn8ghj7mn0wd68ytnzdahxwcn0denjucm0d5hszrnhwden5te0dehhxtnvdakz7qgkwaehxw309ahx7um5wghxycmg9ehxjmn2vyhsz9mhwden5te0wfjkccte9ehx7um5wghxyctwvshs94a4d5
PGP
Openkeychain : https://njump.me/nevent1qqs9qtjgsulp76t7jkquf8nk8txs2ftsr0qke6mjmsc2svtwfvswzyqpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs36mp0w
Kleopatra : https://njump.me/nevent1qqspnevn932hdggvp4zam6mfyce0hmnxsp9wp8htpumq9vm3anq6etsppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpuaeghp
Pgp : https://njump.me/nevent1qqsggek707qf3rzttextmgqhym6d4g479jdnlnj78j96y0ut0x9nemcpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgptemhe
Como funciona o PGP? : https://njump.me/nevent1qqsz9r7azc8pkvfmkg2hv0nufaexjtnvga0yl85x9hu7ptpg20gxxpspremhxue69uhkummnw3ez6ur4vgh8wetvd3hhyer9wghxuet59upzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy259fhs
Por que eu escrevi PGP. - Philip Zimmermann.
https://njump.me/nevent1qqsvysn94gm8prxn3jw04r0xwc6sngkskg756z48jsyrmqssvxtm7ncpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtchzxnad
VPN
Vpn : https://njump.me/nevent1qqs27ltgsr6mh4ffpseexz6s37355df3zsur709d0s89u2nugpcygsspzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqshzu2fk
InviZible Pro : https://njump.me/nevent1qqsvyevf2vld23a3xrpvarc72ndpcmfvc3lc45jej0j5kcsg36jq53cpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy33y5l4
Orbot: https://njump.me/nevent1qqsxswkyt6pe34egxp9w70cy83h40ururj6m9sxjdmfass4cjm4495stft593
I2P
i2p : https://njump.me/nevent1qqsvnj8n983r4knwjmnkfyum242q4c0cnd338l4z8p0m6xsmx89mxkslx0pgg
Entendendo e usando a rede I2P : https://njump.me/nevent1qqsxchp5ycpatjf5s4ag25jkawmw6kkf64vl43vnprxdcwrpnms9qkcppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpvht4mn
Criando e acessando sua conta Email na I2P : https://njump.me/nevent1qqs9v9dz897kh8e5lfar0dl7ljltf2fpdathsn3dkdsq7wg4ksr8xfgpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpw8mzum
APLICATIVO 2FA
Aegis Authenticator : https://njump.me/nevent1qqsfttdwcn9equlrmtf9n6wee7lqntppzm03pzdcj4cdnxel3pz44zspz4mhxue69uhhyetvv9ujumn0wd68ytnzvuhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqscvtydq
YubiKey : https://njump.me/nevent1qqstsnn69y4sf4330n7039zxm7wza3ch7sn6plhzmd57w6j9jssavtspvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzueyvgt
GERENCIADOR DE SENHAS
KeepassDX: https://njump.me/nevent1qqswc850dr4ujvxnmpx75jauflf4arc93pqsty5pv8hxdm7lcw8ee8qpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpe0492n
Birwaden: https://njump.me/nevent1qqs0j5x9guk2v6xumhwqmftmcz736m9nm9wzacqwjarxmh8k4xdyzwgpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpwfe2kc
KeePassXC: https://njump.me/nevent1qqsgftcrd8eau7tzr2p9lecuaf7z8mx5jl9w2k66ae3lzkw5wqcy5pcl2achp
CHAT MENSAGEM
SimpleXchat : https://njump.me/nevent1qqsds5xselnnu0dyy0j49peuun72snxcgn3u55d2320n37rja9gk8lgzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgmcmj7c
Briar : https://njump.me/nevent1qqs8rrtgvjr499hreugetrl7adkhsj2zextyfsukq5aa7wxthrgcqcg05n434
Element Messenger : https://njump.me/nevent1qqsq05snlqtxm5cpzkshlf8n5d5rj9383vjytkvqp5gta37hpuwt4mqyccee6
Pidgin : https://njump.me/nevent1qqsz7kngycyx7meckx53xk8ahk98jkh400usrvykh480xa4ct9zlx2c2ywvx3
E-MAIL
Thunderbird: https://njump.me/nevent1qqspq64gg0nw7t60zsvea5eykgrm43paz845e4jn74muw5qzdvve7uqrkwtjh
ProtonMail : https://njump.me/nevent1qqs908glhk68e7ms8zqtlsqd00wu3prnpt08dwre26hd6e5fhqdw99cppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpeyhg4z
Tutonota : https://njump.me/nevent1qqswtzh9zjxfey644qy4jsdh9465qcqd2wefx0jxa54gdckxjvkrrmqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs5hzhkv
k-9 mail : https://njump.me/nevent1qqs200g5a603y7utjgjk320r3srurrc4r66nv93mcg0x9umrw52ku5gpr3mhxue69uhkummnw3ezuumhd9ehxtt9de5kwmtp9e3kstczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgacflak
E-MAIL-ALIÁS
Simplelogin : https://njump.me/nevent1qqsvhz5pxqpqzr2ptanqyqgsjr50v7u9lc083fvdnglhrv36rnceppcppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqp9gsr7m
AnonAddy : https://njump.me/nevent1qqs9mcth70mkq2z25ws634qfn7vx2mlva3tkllayxergw0s7p8d3ggcpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs6mawe3
NAVEGADOR
Navegador Tor : https://njump.me/nevent1qqs06qfxy7wzqmk76l5d8vwyg6mvcye864xla5up52fy5sptcdy39lspzemhxue69uhkummnw3ezuerpw3sju6rpw4ej7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdp0urw
Mullvap Browser : https://njump.me/nevent1qqs2vsgc3wk09wdspv2mezltgg7nfdg97g0a0m5cmvkvr4nrfxluzfcpzdmhxue69uhhwmm59e6hg7r09ehkuef0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpj8h6fe
LibreWolf : https://njump.me/nevent1qqswv05mlmkcuvwhe8x3u5f0kgwzug7n2ltm68fr3j06xy9qalxwq2cpzemhxue69uhkummnw3ex2mrfw3jhxtn0wfnj7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzuv2hxr
Cromite : https://njump.me/nevent1qqs2ut83arlu735xp8jf87w5m3vykl4lv5nwkhldkqwu3l86khzzy4cpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs3dplt7
BUSCADORES
Searx : https://njump.me/nevent1qqsxyzpvgzx00n50nrlgctmy497vkm2cm8dd5pdp7fmw6uh8xnxdmaspr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqp23z7ax
APP-STORE
Obtainium : https://njump.me/nevent1qqstd8kzc5w3t2v6dgf36z0qrruufzfgnc53rj88zcjgsagj5c5k4rgpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqyarmca3
F-Droid : https://njump.me/nevent1qqst4kry49cc9g3g8s5gdnpgyk3gjte079jdnv43f0x4e85cjkxzjesymzuu4
Droid-ify : https://njump.me/nevent1qqsrr8yu9luq0gud902erdh8gw2lfunpe93uc2u6g8rh9ep7wt3v4sgpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsfzu9vk
Aurora Store : https://njump.me/nevent1qqsy69kcaf0zkcg0qnu90mtk46ly3p2jplgpzgk62wzspjqjft4fpjgpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzrpmsjy
RSS
Feeder : https://njump.me/nevent1qqsy29aeggpkmrc7t3c7y7ldgda7pszl7c8hh9zux80gjzrfvlhfhwqpp4mhxue69uhkummn9ekx7mqzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgsvzzjy
VIDEOO CONFERENCIA
Jitsi meet : https://njump.me/nevent1qqswphw67hr6qmt2fpugcj77jrk7qkfdrszum7vw7n2cu6cx4r6sh4cgkderr
TECLADOS
HeliBoard : https://njump.me/nevent1qqsyqpc4d28rje03dcvshv4xserftahhpeylu2ez2jutdxwds4e8syspz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsr8mel5
OpenBoard : https://njump.me/nevent1qqsf7zqkup03yysy67y43nj48q53sr6yym38es655fh9fp6nxpl7rqspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswcvh3r
FlorisBoard : https://njump.me/nevent1qqsf7zqkup03yysy67y43nj48q53sr6yym38es655fh9fp6nxpl7rqspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswcvh3r
MAPAS
Osmand : https://njump.me/nevent1qqsxryp2ywj64az7n5p6jq5tn3tx5jv05te48dtmmt3lf94ydtgy4fgpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs54nwpj
Organic maps : https://njump.me/nevent1qqstrecuuzkw0dyusxdq7cuwju0ftskl7anx978s5dyn4pnldrkckzqpr4mhxue69uhkummnw3ezumtp0p5k6ctrd96xzer9dshx7un8qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpl8z3kk
TRADUÇÃO
LibreTranslate : https://njump.me/nevent1qqs953g3rhf0m8jh59204uskzz56em9xdrjkelv4wnkr07huk20442cpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzeqsx40
REMOÇÃO DOS METADADOS
Scrambled Exif : https://njump.me/nevent1qqs2658t702xv66p000y4mlhnvadmdxwzzfzcjkjf7kedrclr3ej7aspyfmhxue69uhk6atvw35hqmr90pjhytngw4eh5mmwv4nhjtnhdaexcep0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpguu0wh
ESTEGANOGRAFIA
PixelKnot: https://njump.me/nevent1qqsrh0yh9mg0lx86t5wcmhh97wm6n4v0radh6sd0554ugn354wqdj8gpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqyuvfqdp
PERFIL DE TRABALHO
Shelter : https://njump.me/nevent1qqspv9xxkmfp40cxgjuyfsyczndzmpnl83e7gugm7480mp9zhv50wkqpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdnu59c
PDF
MuPDF : https://njump.me/nevent1qqspn5lhe0dteys6npsrntmv2g470st8kh8p7hxxgmymqa95ejvxvfcpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs4hvhvj
Librera Reader : https://njump.me/nevent1qqsg60flpuf00sash48fexvwxkly2j5z9wjvjrzt883t3eqng293f3cpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz39tt3n
QR-Code
Binary Eye : https://njump.me/nevent1qqsz4n0uxxx3q5m0r42n9key3hchtwyp73hgh8l958rtmae5u2khgpgpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdmn4wp
Climático
Breezy Weather : https://njump.me/nevent1qqs9hjz5cz0y4am3kj33xn536uq85ydva775eqrml52mtnnpe898rzspzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgpd3tu8
ENCRYPTS
Cryptomator : https://njump.me/nevent1qqsvchvnw779m20583llgg5nlu6ph5psewetlczfac5vgw83ydmfndspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsx7ppw9
VeraCrypt : https://njump.me/nevent1qqsf6wzedsnrgq6hjk5c4jj66dxnplqwc4ygr46l8z3gfh38q2fdlwgm65ej3
EXTENSÕES
uBlock Origin : https://njump.me/nevent1qqswaa666lcj2c4nhnea8u4agjtu4l8q89xjln0yrngj7ssh72ntwzql8ssdj
Snowflake : https://njump.me/nevent1qqs0ws74zlt8uced3p2vee9td8x7vln2mkacp8szdufvs2ed94ctnwchce008
CLOUD
Nextcloud : https://njump.me/nevent1qqs2utg5z9htegdtrnllreuhypkk2026x8a0xdsmfczg9wdl8rgrcgg9nhgnm
NOTEPAD
Joplin : https://njump.me/nevent1qqsz2a0laecpelsznser3xd0jfa6ch2vpxtkx6vm6qg24e78xttpk0cpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpdu0hft
Standard Notes : https://njump.me/nevent1qqsv3596kz3qung5v23cjc4cpq7rqxg08y36rmzgcrvw5whtme83y3s7tng6r
MÚSICA
RiMusic : https://njump.me/nevent1qqsv3genqav2tfjllp86ust4umxm8tr2wd9kq8x7vrjq6ssp363mn0gpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqg42353n
ViMusic : https://njump.me/nevent1qqswx78559l4jsxsrygd8kj32sch4qu57stxq0z6twwl450vp39pdqqpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzjg863j
PODCAST
AntennaPod : https://njump.me/nevent1qqsp4nh7k4a6zymfwqqdlxuz8ua6kdhvgeeh3uxf2c9rtp9u3e9ku8qnr8lmy
VISUALIZAR VIDEO
VLC : https://njump.me/nevent1qqs0lz56wtlr2eye4ajs2gzn2r0dscw4y66wezhx0mue6dffth8zugcl9laky
YOUTUBE
NewPipe : https://njump.me/nevent1qqsdg06qpcjdnlvgm4xzqdap0dgjrkjewhmh4j3v4mxdl4rjh8768mgdw9uln
FreeTube : https://njump.me/nevent1qqsz6y6z7ze5gs56s8seaws8v6m6j2zu0pxa955dhq3ythmexak38mcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs5lkjvv
LibreTube : https://snort.social/e/nevent1qqstmd5m6wrdvn4gxf8xyhrwnlyaxmr89c9kjddvnvux6603f84t3fqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsswwznc
COMPARTILHAMENTO DE ARQUIVOS
OnionShare : https://njump.me/nevent1qqsr0a4ml5nu6ud5k9yzyawcd9arznnwkrc27dzzc95q6r50xmdff6qpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3uamnwvaz7tmwdaehgu3dv3jhvtnhv4kxcmmjv3jhytnwv46z7qgswaehxw309ahx7tnnw3ezucmj9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcpzamhxue69uhkyarr9e4kcetwv3sh5afwvdhk6tcpzemhxue69uhkummnw3ezucnrdqhxu6twdfsj7qgswaehxw309ahx7um5wghx6mmd9uqjgamnwvaz7tmwdaehgu3wwfhh2mnywfhkx6mzd96xxmmfdejhyuewvdhk6tcppemhxue69uhkummn9ekx7mp0qythwumn8ghj7un9d3shjtnwdaehgu3wvfskuep0qyv8wumn8ghj7un9d3shjtnrw4e8yetwwshxv7tf9ut7qurt
Localsend : https://njump.me/nevent1qqsp8ldjhrxm09cvvcak20hrc0g8qju9f67pw7rxr2y3euyggw9284gpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzuyghqr
Wallet Bitcoin
Ashigaru Wallet : https://njump.me/nevent1qqstx9fz8kf24wgl26un8usxwsqjvuec9f8q392llmga75tw0kfarfcpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgvfsrqp
Samourai Wallet : https://njump.me/nevent1qqstcvjmz39rmrnrv7t5cl6p3x7pzj6jsspyh4s4vcwd2lugmre04ecpr9mhxue69uhkummnw3ezucn0denkymmwvuhxxmmd9upzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy3rg4qs
CÂMERA
opencamera : https://njump.me/nevent1qqs25glp6dh0crrjutxrgdjlnx9gtqpjtrkg29hlf7382aeyjd77jlqpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqssxcvgc
OFFICE
Collabora Office : https://njump.me/nevent1qqs8yn4ys6adpmeu3edmf580jhc3wluvlf823cc4ft4h0uqmfzdf99qpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsj40uss
TEXTOS
O manifesto de um Cypherpunk : https://njump.me/nevent1qqsd7hdlg6galn5mcuv3pm3ryfjxc4tkyph0cfqqe4du4dr4z8amqyspvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzal0efa
Operations security ( OPSEC) : https://snort.social/e/nevent1qqsp323havh3y9nxzd4qmm60hw87tm9gjns0mtzg8y309uf9mv85cqcpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz8ej9l7
O MANIFESTO CRIPTOANARQUISTA Timothy C. May – 1992. : https://njump.me/nevent1qqspp480wtyx2zhtwpu5gptrl8duv9rvq3mug85mp4d54qzywk3zq9gpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz5wq496
Declaração de independência do ciberespaço
- John Perry Barlow - 1996 : https://njump.me/nevent1qqs2njsy44n6p07mhgt2tnragvchasv386nf20ua5wklxqpttf6mzuqpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsukg4hr
The Cyphernomicon: Criptografia, Dinheiro Digital e o Futuro da Privacidade. escrito por Timothy C. May -Publicado em 1994. :
Livro completo em PDF no Github PrivacyOpenSource.
https://github.com/Alexemidio/PrivacyOpenSource/raw/main/Livros/THE%20CYPHERNOMICON%20.pdf Share
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:10:55
@ 4ba8e86d:89d32de4
2025-04-21 02:10:55Seu teclado não deve se conectar à internet. Privacidade em primeiro lugar. Sempre. Estamos desenvolvendo um teclado moderno que respeita totalmente sua privacidade e segurança. O FUTO Keyboard é 100% offline e 100% privado, oferecendo todos os recursos essenciais que você espera de um teclado atual — incluindo digitação por deslizamento, entrada de voz offline, correção automática inteligente, temas personalizáveis e sugestões preditivas de texto. Nosso objetivo é simples: criar um teclado eficiente e funcional, sem comprometer a privacidade do usuário. Este projeto é um fork do LatinIME, o teclado open-source oficial do Android.
Atenção: o FUTO Keyboard está atualmente em fase alfa. Está trabalhando para torná-lo estável e confiável, mas durante esse período você pode encontrar bugs, travamentos ou recursos ainda não implementados.
Configurações
Idiomas e Modelos – Adicione novos idiomas, dicionários, modelos de entrada de voz, transformadores e layouts associados.
Linguagens e Modelos
O menu no qual você adiciona novos idiomas, bem como dicionários, modelos de entrada de voz, modelos de transformadores e layouts associados a eles.
Adicionar idioma.
Alguns idiomas exigem o download de um dicionário. Se você também quiser um modelo de entrada de voz para um idioma específico, precisará baixá-lo também. Cada idioma já possui uma seleção de layouts de teclado associados; você pode escolher qual(is) layout(s) deseja adicionar ao adicionar o idioma. https://video.nostr.build/c775288b7a8ee8d75816af0c7a25f2aa0b4ecc99973fd442b2badc308fa38109.mp4
Mudar idioma.
Existem duas maneiras de alternar o idioma. A primeira é pressionando o ícone do globo na Barra de Ações, localizada próximo ao canto superior esquerdo do teclado. A segunda é pressionando longamente ou deslizando a barra de espaço; você pode personalizar o comportamento de troca de idioma da barra de espaço acessando Configurações -> Teclado e Digitação -> Teclas de Pressão Longa e Barra de Espaço -> Comportamento da Barra de Espaço . Você também pode atribuir o ícone do globo como a Tecla de Ação para que fique ao lado da barra de espaço, que pode ser acessada no menu Todas as Ações pressionando a tecla de reticências (...) no canto superior esquerdo do teclado e, em seguida, acessando Editar Ações. https://video.nostr.build/ed6f7f63a9c203cd59f46419ef54a4b8b442f070f802a688ca7d682bd6811bcb.mp4
Adicionar dicionário.
Alguns idiomas têm um dicionário integrado, mas a maioria não. Se o idioma que você está instalando não tiver um dicionário integrado, você pode iniciar a instalação em nosso site acessando Idiomas e Modelos -> Dicionário (no idioma que você está instalando) -> Explorar -> Baixar (em nosso site). https://video.nostr.build/3b1e09289953b658a9cef33c41bd711095556bc48290cb2ed066d4d0a5186371.mp4
Habilitar digitação multilíngue.
Você pode habilitar a digitação multilíngue para um ou mais idiomas acessando Idiomas e modelos e marcando a caixa Digitação multilíngue no(s) idioma(s) para os quais deseja habilitar a digitação multilíngue. https://video.nostr.build/29f683410626219499787bd63058d159719553f8e33a9f3c659c51c375a682fb.mp4
Criar layout personalizado.
Se desejar criar seu próprio layout personalizado para um idioma específico, você pode fazê-lo ativando Configurações do Desenvolvedor -> Layouts Personalizados -> Criar novo layout . Mais informações sobre layouts personalizados podem ser encontradas https://github.com/futo-org/futo-keyboard-layouts . A personalização das configurações de pressionamento longo tecla por tecla ainda não é suportada, mas está em processo de implementação. https://video.nostr.build/b5993090e28794d0305424dd352ca83760bb87002c57930e80513de5917fad8d.mp4
Teclado e Digitação – Personalize o comportamento das teclas, o tamanho do teclado e outras preferências de digitação.
Previsão de texto.
O menu no qual você define suas preferências para correção automática e sugestões personalizadas. Modelo de Linguagem do Transformador Você pode fazer com que o teclado preveja a próxima palavra que você digitará ou faça correções automáticas mais inteligentes, que usam um modelo de linguagem Transformer pré-treinado com base em conjuntos de dados disponíveis publicamente, ativando o Transformer LM . Observação: atualmente, isso funciona apenas em inglês, mas estamos trabalhando para torná-lo compatível com outros idiomas. Ajuste fino do transformador Você pode fazer com que o teclado memorize o que você digita e quais sugestões você seleciona, o que treina o modelo de idioma (enquanto o telefone estiver inativo) para prever quais palavras sugerir e corrigir automaticamente enquanto você digita, ativando o ajuste fino do Transformer . Observação: este é o seu modelo de idioma pessoal e o FUTO não visualiza nem armazena nenhum dos seus dados. https://video.nostr.build/688354a63bdc48a9dd3f8605854b5631ac011009c6105f93cfa0b52b46bc40d3.mp4
Previsão de texto.
O menu no qual você define suas preferências para correção automática e sugestões personalizadas. Modelo de Linguagem do Transformador Você pode fazer com que o teclado preveja a próxima palavra que você digitará ou faça correções automáticas mais inteligentes, que usam um modelo de linguagem Transformer pré-treinado com base em conjuntos de dados disponíveis publicamente, ativando o Transformer LM . Observação: atualmente, isso funciona apenas em inglês, mas estamos trabalhando para torná-lo compatível com outros idiomas.
Ajuste fino do transformador.
Você pode fazer com que o teclado memorize o que você digita e quais sugestões você seleciona, o que treina o modelo de idioma (enquanto o telefone estiver inativo) para prever quais palavras sugerir e corrigir automaticamente enquanto você digita, ativando o ajuste fino do Transformer . Observação: este é o seu modelo de idioma pessoal e o FUTO não visualiza nem armazena nenhum dos seus dados.
Força do Modelo de Linguagem do Transformador.
Você pode fazer com que a correção automática se comporte mais como o teclado AOSP ou mais como a rede neural acessando Parâmetros avançados -> Intensidade do LM do transformador e arrastando o controle deslizante para um valor menor (o que tornará o comportamento da correção automática mais parecido com o teclado AOSP) ou um valor maior (o que tornará a correção automática mais dependente da rede neural). Limiar de correção automática Você pode alterar o limite da correção automática para que ela ocorra com mais ou menos frequência acessando Parâmetros avançados -> Limite de correção automática e arrastando o controle deslizante para um valor menor (o que fará com que a correção automática ocorra com mais frequência, mas também corrija erros com mais frequência) ou um valor maior (o que fará com que a correção automática ocorra com menos frequência, mas também corrija erros com menos frequência). https://video.nostr.build/ea9c100081acfcab60343c494a91f789ef8143c92343522ec34c714913631cf7.mp4
Lista negra de palavras.
Você pode colocar sugestões de palavras na lista negra, o que impedirá que o teclado continue sugerindo palavras na lista negra, acessando Sugestões na lista negra e adicionando as palavras que você gostaria de colocar na lista negra.
Palavras ofensivas.
Você pode bloquear palavras ofensivas, como palavrões comuns, acessando Sugestões na Lista Negra e marcando a opção Bloquear Palavras Ofensivas . Observação: a opção Bloquear Palavras Ofensivas está ativada por padrão. https://video.nostr.build/ee72f3940b9789bbea222c95ee74d646aae1a0f3bf658ef8114c6f7942bb50f5.mp4
Correção automática.
Você pode ativar a capacidade de corrigir automaticamente palavras digitadas incorretamente ao pressionar a barra de espaço ou digitar pontuação ativando a Correção automática.
Sugestões de correção.
Você pode ativar a capacidade de exibir palavras sugeridas enquanto digita marcando a opção Mostrar sugestões de correção.
Sugestões de palavras.
Você pode ativar a capacidade de aprender com suas comunicações e dados digitados para melhorar as sugestões ativando as Sugestões personalizadas . Observação: desativar as Sugestões personalizadas também desativa o ajuste fino do Transformer. https://video.nostr.build/2c22d109b9192eac8fe4533b3f8e3e1b5896dfd043817bd460c48a5b989b7a2f.mp4
Entrada de Voz – Configure a entrada de voz offline, incluindo a duração e a conversão de fala em texto.
Entrada de voz.
O menu no qual você define suas preferências de entrada de voz, como duração da entrada e configurações de conversão de fala em texto. Entrada de voz integrada Você pode desabilitar a entrada de voz integrada do teclado e, em vez disso, usar o provedor de entrada de voz de um aplicativo externo desativando a opção Desabilitar entrada de voz integrada. https://video.nostr.build/68916e5b338a9f999f45aa1828a6e05ccbf8def46da9516c0f516b40ca8c827b.mp4
Sons de indicação.
Você pode habilitar a capacidade de reproduzir sons ao iniciar e cancelar a entrada de voz ativando Sons de indicação. https://video.nostr.build/7f5fb6a6173c4db18945e138146fe65444e40953d85cee1f09c1a21d236d21f5.mp4
Progresso Detalhado.
Você pode habilitar a capacidade de exibir informações detalhadas, como indicar que o microfone está sendo usado, ativando Progresso detalhado. https://video.nostr.build/8ac2bb6bdd6e7f8bd4b45da423e782c152a2b4320f2e090cbb99fd5c78e8f44f.mp4
Microfone Bluetooth.
Você pode fazer com que a entrada de voz prefira automaticamente seu microfone Bluetooth em vez do microfone integrado, ativando Preferir microfone Bluetooth. https://video.nostr.build/c11404aa6fec2dda71ceb3aaee916c6761b3015fef9575a352de66b7310dad07.mp4
Foco de áudio.
Você pode fazer com que a entrada de voz pause automaticamente vídeos ou músicas quando ela estiver ativada, ativando o Foco de Áudio. https://video.nostr.build/4ac82af53298733d0c5013ef28befb8b2adeb4a4949604308317e124b6431d40.mp4
Supressão de Símbolos.
Por padrão, a entrada de voz transcreve apenas texto básico e pontuação. Você pode desativar a opção "Suprimir símbolos" para liberar a entrada de voz da transcrição de caracteres especiais (por exemplo, @, $ ou %). Observação: Isso não afeta a forma como a entrada de voz interpreta palavras literais (por exemplo, "vírgula", "ponto final"). https://video.nostr.build/10de49c5a9e35508caa14b66da28fae991a5ac8eabad9b086959fba18c07f8f3.mp4
Entrada de voz de formato longo.
Você pode desativar o limite padrão de 30 segundos para entrada de voz ativando a opção Entrada de voz longa . Observação: a qualidade da saída pode ser prejudicada com entradas longas. https://video.nostr.build/f438ee7a42939a5a3e6d6c4471905f836f038495eb3a00b39d9996d0e552c200.mp4
Parada automática em silêncio.
Você pode fazer com que a entrada de voz pare automaticamente quando o silêncio for detectado, ativando a opção Parar automaticamente ao silenciar . Observação: se houver muito ruído de fundo, pode ser necessário interromper manualmente a entrada de voz. Ative também a entrada de voz longa para evitar a interrupção após 30 segundos. https://video.nostr.build/056567696d513add63f6dd254c0a3001530917e05e792de80c12796d43958671.mp4
Dicionário Pessoal – Adicione palavras personalizadas para que o teclado aprenda e sugira com mais precisão.
Dicionário Pessoal.
O menu no qual você cria seu dicionário pessoal de palavras que o teclado irá lembrar e sugerir. Adicionar ao dicionário Você pode adicionar uma palavra ou frase ao seu dicionário pessoal pressionando o ícone de adição na tela "Dicionário pessoal" . Você também pode criar um atalho para ela no campo "Atalho" ao adicionar a palavra ou frase. https://video.nostr.build/dec41c666b9f2276cc20d9096e3a9b542b570afd1f679d8d0e8c43c8ea46bfcb.mp4
Excluir do dicionário.
Você pode excluir uma palavra ou frase do seu dicionário pessoal clicando nessa palavra ou frase e clicando no ícone de lixeira no canto superior direito. https://video.nostr.build/aca25643b5c7ead4c5d522709af4bc337911e49c4743b97dc75f6b877449143e.mp4
Tema – Escolha entre os temas disponíveis ou personalize a aparência do teclado conforme seu gosto.
Tema.
O menu no qual você seleciona seu tema preferido para o teclado. Alterar tema Você pode escolher entre uma variedade de temas para o teclado, incluindo Modo Escuro, Modo Claro, Automático Dinâmico, Escuro Dinâmico, Claro Dinâmico, Material AOSP Escuro, Material AOSP Claro, Roxo Escuro AMOLED, Girassol, Queda de Neve, Cinza Aço, Esmeralda, Algodão Doce, Luz do Mar Profundo, Escuro do Mar Profundo, Gradiente 1, Tema FUTO VI ou Tema Construção . A possibilidade de personalizar seu tema será disponibilizada em breve. https://video.nostr.build/90c8de72f08cb0d8c40ac2fba2fd39451ff63ec1592ddd2629d0891c104bc61e.mp4
Fronteiras Principais.
Você pode habilitar as bordas das teclas rolando para baixo até o final e ativando Bordas das teclas . https://video.nostr.build/fa2087d68ce3fb2d3adb84cc2ec19c4d5383beb8823a4b6d1d85378ab3507ab1.mp4
Site oficial https://keyboard.futo.org/
Baixar no fdroid. https://app.futo.org/fdroid/repo/
Para instalar através do Obtainium , basta ir em Adicionar Aplicativo e colar esta URL do repositório: https://github.com/futo-org/android-keyboard
A adição pode demorar um pouco dependendo da velocidade da sua internet, pois o APK precisa ser baixado.
-
 @ c631e267:c2b78d3e
2025-04-20 19:54:32
@ c631e267:c2b78d3e
2025-04-20 19:54:32Es ist völlig unbestritten, dass der Angriff der russischen Armee auf die Ukraine im Februar 2022 strikt zu verurteilen ist. Ebenso unbestritten ist Russland unter Wladimir Putin keine brillante Demokratie. Aus diesen Tatsachen lässt sich jedoch nicht das finstere Bild des russischen Präsidenten – und erst recht nicht des Landes – begründen, das uns durchweg vorgesetzt wird und den Kern des aktuellen europäischen Bedrohungs-Szenarios darstellt. Da müssen wir schon etwas genauer hinschauen.
Der vorliegende Artikel versucht derweil nicht, den Einsatz von Gewalt oder die Verletzung von Menschenrechten zu rechtfertigen oder zu entschuldigen – ganz im Gegenteil. Dass jedoch der Verdacht des «Putinverstehers» sofort latent im Raume steht, verdeutlicht, was beim Thema «Russland» passiert: Meinungsmache und Manipulation.
Angesichts der mentalen Mobilmachung seitens Politik und Medien sowie des Bestrebens, einen bevorstehenden Krieg mit Russland geradezu herbeizureden, ist es notwendig, dieser fatalen Entwicklung entgegenzutreten. Wenn wir uns nur ein wenig von der herrschenden Schwarz-Weiß-Malerei freimachen, tauchen automatisch Fragen auf, die Risse im offiziellen Narrativ enthüllen. Grund genug, nachzuhaken.
Wer sich schon länger auch abseits der Staats- und sogenannten Leitmedien informiert, der wird in diesem Artikel vermutlich nicht viel Neues erfahren. Andere könnten hier ein paar unbekannte oder vergessene Aspekte entdecken. Möglicherweise klärt sich in diesem Kontext die Wahrnehmung der aktuellen (unserer eigenen!) Situation ein wenig.
Manipulation erkennen
Corona-«Pandemie», menschengemachter Klimawandel oder auch Ukraine-Krieg: Jede Menge Krisen, und für alle gibt es ein offizielles Narrativ, dessen Hinterfragung unerwünscht ist. Nun ist aber ein Narrativ einfach eine Erzählung, eine Geschichte (Latein: «narratio») und kein Tatsachenbericht. Und so wie ein Märchen soll auch das Narrativ eine Botschaft vermitteln.
Über die Methoden der Manipulation ist viel geschrieben worden, sowohl in Bezug auf das Individuum als auch auf die Massen. Sehr wertvolle Tipps dazu, wie man Manipulationen durchschauen kann, gibt ein Büchlein [1] von Albrecht Müller, dem Herausgeber der NachDenkSeiten.
Die Sprache selber eignet sich perfekt für die Manipulation. Beispielsweise kann die Wortwahl Bewertungen mitschwingen lassen, regelmäßiges Wiederholen (gerne auch von verschiedenen Seiten) lässt Dinge irgendwann «wahr» erscheinen, Übertreibungen fallen auf und hinterlassen wenigstens eine Spur im Gedächtnis, genauso wie Andeutungen. Belege spielen dabei keine Rolle.
Es gibt auffällig viele Sprachregelungen, die offenbar irgendwo getroffen und irgendwie koordiniert werden. Oder alle Redenschreiber und alle Medien kopieren sich neuerdings permanent gegenseitig. Welchen Zweck hat es wohl, wenn der Krieg in der Ukraine durchgängig und quasi wörtlich als «russischer Angriffskrieg auf die Ukraine» bezeichnet wird? Obwohl das in der Sache richtig ist, deutet die Art der Verwendung auf gezielte Beeinflussung hin und soll vor allem das Feindbild zementieren.
Sprachregelungen dienen oft der Absicherung einer einseitigen Darstellung. Das Gleiche gilt für das Verkürzen von Informationen bis hin zum hartnäckigen Verschweigen ganzer Themenbereiche. Auch hierfür gibt es rund um den Ukraine-Konflikt viele gute Beispiele.
Das gewünschte Ergebnis solcher Methoden ist eine Schwarz-Weiß-Malerei, bei der einer eindeutig als «der Böse» markiert ist und die anderen automatisch «die Guten» sind. Das ist praktisch und demonstriert gleichzeitig ein weiteres Manipulationswerkzeug: die Verwendung von Doppelstandards. Wenn man es schafft, bei wichtigen Themen regelmäßig mit zweierlei Maß zu messen, ohne dass das Publikum protestiert, dann hat man freie Bahn.
Experten zu bemühen, um bestimmte Sachverhalte zu erläutern, ist sicher sinnvoll, kann aber ebenso missbraucht werden, schon allein durch die Auswahl der jeweiligen Spezialisten. Seit «Corona» werden viele erfahrene und ehemals hoch angesehene Fachleute wegen der «falschen Meinung» diffamiert und gecancelt. [2] Das ist nicht nur ein brutaler Umgang mit Menschen, sondern auch eine extreme Form, die öffentliche Meinung zu steuern.
Wann immer wir also erkennen (weil wir aufmerksam waren), dass wir bei einem bestimmten Thema manipuliert werden, dann sind zwei logische und notwendige Fragen: Warum? Und was ist denn richtig? In unserem Russland-Kontext haben die Antworten darauf viel mit Geopolitik und Geschichte zu tun.
Ist Russland aggressiv und expansiv?
Angeblich plant Russland, europäische NATO-Staaten anzugreifen, nach dem Motto: «Zuerst die Ukraine, dann den Rest». In Deutschland weiß man dafür sogar das Datum: «Wir müssen bis 2029 kriegstüchtig sein», versichert Verteidigungsminister Pistorius.
Historisch gesehen ist es allerdings eher umgekehrt: Russland, bzw. die Sowjetunion, ist bereits dreimal von Westeuropa aus militärisch angegriffen worden. Die Feldzüge Napoleons, des deutschen Kaiserreichs und Nazi-Deutschlands haben Millionen Menschen das Leben gekostet. Bei dem ausdrücklichen Vernichtungskrieg ab 1941 kam es außerdem zu Brutalitäten wie der zweieinhalbjährigen Belagerung Leningrads (heute St. Petersburg) durch Hitlers Wehrmacht. Deren Ziel, die Bevölkerung auszuhungern, wurde erreicht: über eine Million tote Zivilisten.
Trotz dieser Erfahrungen stimmte Michail Gorbatschow 1990 der deutschen Wiedervereinigung zu und die Sowjetunion zog ihre Truppen aus Osteuropa zurück (vgl. Abb. 1). Der Warschauer Pakt wurde aufgelöst, der Kalte Krieg formell beendet. Die Sowjets erhielten damals von führenden westlichen Politikern die Zusicherung, dass sich die NATO «keinen Zentimeter ostwärts» ausdehnen würde, das ist dokumentiert. [3]

Expandiert ist die NATO trotzdem, und zwar bis an Russlands Grenzen (vgl. Abb. 2). Laut dem Politikberater Jeffrey Sachs handelt es sich dabei um ein langfristiges US-Projekt, das von Anfang an die Ukraine und Georgien mit einschloss. Offiziell wurde der Beitritt beiden Staaten 2008 angeboten. In jedem Fall könnte die massive Ost-Erweiterung seit 1999 aus russischer Sicht nicht nur als Vertrauensbruch, sondern durchaus auch als aggressiv betrachtet werden.

Russland hat den europäischen Staaten mehrfach die Hand ausgestreckt [4] für ein friedliches Zusammenleben und den «Aufbau des europäischen Hauses». Präsident Putin sei «in seiner ersten Amtszeit eine Chance für Europa» gewesen, urteilt die Journalistin und langjährige Russland-Korrespondentin der ARD, Gabriele Krone-Schmalz. Er habe damals viele positive Signale Richtung Westen gesendet.
Die Europäer jedoch waren scheinbar an einer Partnerschaft mit dem kontinentalen Nachbarn weniger interessiert als an der mit dem transatlantischen Hegemon. Sie verkennen bis heute, dass eine gedeihliche Zusammenarbeit in Eurasien eine Gefahr für die USA und deren bekundetes Bestreben ist, die «einzige Weltmacht» zu sein – «Full Spectrum Dominance» [5] nannte das Pentagon das. Statt einem neuen Kalten Krieg entgegenzuarbeiten, ließen sich europäische Staaten selber in völkerrechtswidrige «US-dominierte Angriffskriege» [6] verwickeln, wie in Serbien, Afghanistan, dem Irak, Libyen oder Syrien. Diese werden aber selten so benannt.

Speziell den Deutschen stünde außer einer Portion Realismus auch etwas mehr Dankbarkeit gut zu Gesicht. Das Geschichtsbewusstsein der Mehrheit scheint doch recht selektiv und das Selbstbewusstsein einiger etwas desorientiert zu sein. Bekanntermaßen waren es die Soldaten der sowjetischen Roten Armee, die unter hohen Opfern 1945 Deutschland «vom Faschismus befreit» haben. Bei den Gedenkfeiern zu 80 Jahren Kriegsende will jedoch das Auswärtige Amt – noch unter der Diplomatie-Expertin Baerbock, die sich schon länger offiziell im Krieg mit Russland wähnt, – nun keine Russen sehen: Sie sollen notfalls rausgeschmissen werden.
«Die Grundsatzfrage lautet: Geht es Russland um einen angemessenen Platz in einer globalen Sicherheitsarchitektur, oder ist Moskau schon seit langem auf einem imperialistischen Trip, der befürchten lassen muss, dass die Russen in fünf Jahren in Berlin stehen?»
So bringt Gabriele Krone-Schmalz [7] die eigentliche Frage auf den Punkt, die zur Einschätzung der Situation letztlich auch jeder für sich beantworten muss.
Was ist los in der Ukraine?
In der internationalen Politik geht es nie um Demokratie oder Menschenrechte, sondern immer um Interessen von Staaten. Diese These stammt von Egon Bahr, einem der Architekten der deutschen Ostpolitik des «Wandels durch Annäherung» aus den 1960er und 70er Jahren. Sie trifft auch auf den Ukraine-Konflikt zu, den handfeste geostrategische und wirtschaftliche Interessen beherrschen, obwohl dort angeblich «unsere Demokratie» verteidigt wird.
Es ist ein wesentliches Element des Ukraine-Narrativs und Teil der Manipulation, die Vorgeschichte des Krieges wegzulassen – mindestens die vor der russischen «Annexion» der Halbinsel Krim im März 2014, aber oft sogar komplett diejenige vor der Invasion Ende Februar 2022. Das Thema ist komplex, aber einige Aspekte, die für eine Beurteilung nicht unwichtig sind, will ich wenigstens kurz skizzieren. [8]
Das Gebiet der heutigen Ukraine und Russlands – die übrigens in der «Kiewer Rus» gemeinsame Wurzeln haben – hat der britische Geostratege Halford Mackinder bereits 1904 als eurasisches «Heartland» bezeichnet, dessen Kontrolle er eine große Bedeutung für die imperiale Strategie Großbritanniens zumaß. Für den ehemaligen Sicherheits- und außenpolitischen Berater mehrerer US-amerikanischer Präsidenten und Mitgründer der Trilateralen Kommission, Zbigniew Brzezinski, war die Ukraine nach der Auflösung der Sowjetunion ein wichtiger Spielstein auf dem «eurasischen Schachbrett», wegen seiner Nähe zu Russland, seiner Bodenschätze und seines Zugangs zum Schwarzen Meer.
Die Ukraine ist seit langem ein gespaltenes Land. Historisch zerrissen als Spielball externer Interessen und geprägt von ethnischen, kulturellen, religiösen und geografischen Unterschieden existiert bis heute, grob gesagt, eine Ost-West-Spaltung, welche die Suche nach einer nationalen Identität stark erschwert.
Insbesondere im Zuge der beiden Weltkriege sowie der Russischen Revolution entstanden tiefe Risse in der Bevölkerung. Ukrainer kämpften gegen Ukrainer, zum Beispiel die einen auf der Seite von Hitlers faschistischer Nazi-Armee und die anderen auf der von Stalins kommunistischer Roter Armee. Die Verbrechen auf beiden Seiten sind nicht vergessen. Dass nach der Unabhängigkeit 1991 versucht wurde, Figuren wie den radikalen Nationalisten Symon Petljura oder den Faschisten und Nazi-Kollaborateur Stepan Bandera als «Nationalhelden» zu installieren, verbessert die Sache nicht.
Während die USA und EU-Staaten zunehmend «ausländische Einmischung» (speziell russische) in «ihre Demokratien» wittern, betreiben sie genau dies seit Jahrzehnten in vielen Ländern der Welt. Die seit den 2000er Jahren bekannten «Farbrevolutionen» in Osteuropa werden oft als Methode des Regierungsumsturzes durch von außen gesteuerte «demokratische» Volksaufstände beschrieben. Diese Strategie geht auf Analysen zum «Schwarmverhalten» [9] seit den 1960er Jahren zurück (Studentenproteste), wo es um die potenzielle Wirksamkeit einer «rebellischen Hysterie» von Jugendlichen bei postmodernen Staatsstreichen geht. Heute nennt sich dieses gezielte Kanalisieren der Massen zur Beseitigung unkooperativer Regierungen «Soft-Power».
In der Ukraine gab es mit der «Orangen Revolution» 2004 und dem «Euromaidan» 2014 gleich zwei solcher «Aufstände». Der erste erzwang wegen angeblicher Unregelmäßigkeiten eine Wiederholung der Wahlen, was mit Wiktor Juschtschenko als neuem Präsidenten endete. Dieser war ehemaliger Direktor der Nationalbank und Befürworter einer Annäherung an EU und NATO. Seine Frau, die First Lady, ist US-amerikanische «Philanthropin» und war Beamtin im Weißen Haus in der Reagan- und der Bush-Administration.
Im Gegensatz zu diesem ersten Event endete der sogenannte Euromaidan unfriedlich und blutig. Die mehrwöchigen Proteste gegen Präsident Wiktor Janukowitsch, in Teilen wegen des nicht unterzeichneten Assoziierungsabkommens mit der EU, wurden zunehmend gewalttätiger und von Nationalisten und Faschisten des «Rechten Sektors» dominiert. Sie mündeten Ende Februar 2014 auf dem Kiewer Unabhängigkeitsplatz (Maidan) in einem Massaker durch Scharfschützen. Dass deren Herkunft und die genauen Umstände nicht geklärt wurden, störte die Medien nur wenig. [10]
Janukowitsch musste fliehen, er trat nicht zurück. Vielmehr handelte es sich um einen gewaltsamen, allem Anschein nach vom Westen inszenierten Putsch. Laut Jeffrey Sachs war das kein Geheimnis, außer vielleicht für die Bürger. Die USA unterstützten die Post-Maidan-Regierung nicht nur, sie beeinflussten auch ihre Bildung. Das geht unter anderem aus dem berühmten «Fuck the EU»-Telefonat der US-Chefdiplomatin für die Ukraine, Victoria Nuland, mit Botschafter Geoffrey Pyatt hervor.
Dieser Bruch der demokratischen Verfassung war letztlich der Auslöser für die anschließenden Krisen auf der Krim und im Donbass (Ostukraine). Angesichts der ukrainischen Geschichte mussten die nationalistischen Tendenzen und die Beteiligung der rechten Gruppen an dem Umsturz bei der russigsprachigen Bevölkerung im Osten ungute Gefühle auslösen. Es gab Kritik an der Übergangsregierung, Befürworter einer Abspaltung und auch für einen Anschluss an Russland.
Ebenso konnte Wladimir Putin in dieser Situation durchaus Bedenken wegen des Status der russischen Militärbasis für seine Schwarzmeerflotte in Sewastopol auf der Krim haben, für die es einen langfristigen Pachtvertrag mit der Ukraine gab. Was im März 2014 auf der Krim stattfand, sei keine Annexion, sondern eine Abspaltung (Sezession) nach einem Referendum gewesen, also keine gewaltsame Aneignung, urteilte der Rechtswissenschaftler Reinhard Merkel in der FAZ sehr detailliert begründet. Übrigens hatte die Krim bereits zu Zeiten der Sowjetunion den Status einer autonomen Republik innerhalb der Ukrainischen SSR.
Anfang April 2014 wurden in der Ostukraine die «Volksrepubliken» Donezk und Lugansk ausgerufen. Die Kiewer Übergangsregierung ging unter der Bezeichnung «Anti-Terror-Operation» (ATO) militärisch gegen diesen, auch von Russland instrumentalisierten Widerstand vor. Zufällig war kurz zuvor CIA-Chef John Brennan in Kiew. Die Maßnahmen gingen unter dem seit Mai neuen ukrainischen Präsidenten, dem Milliardär Petro Poroschenko, weiter. Auch Wolodymyr Selenskyj beendete den Bürgerkrieg nicht, als er 2019 vom Präsidenten-Schauspieler, der Oligarchen entmachtet, zum Präsidenten wurde. Er fuhr fort, die eigene Bevölkerung zu bombardieren.
Mit dem Einmarsch russischer Truppen in die Ostukraine am 24. Februar 2022 begann die zweite Phase des Krieges. Die Wochen und Monate davor waren intensiv. Im November hatte die Ukraine mit den USA ein Abkommen über eine «strategische Partnerschaft» unterzeichnet. Darin sagten die Amerikaner ihre Unterstützung der EU- und NATO-Perspektive der Ukraine sowie quasi für die Rückeroberung der Krim zu. Dagegen ließ Putin der NATO und den USA im Dezember 2021 einen Vertragsentwurf über beiderseitige verbindliche Sicherheitsgarantien zukommen, den die NATO im Januar ablehnte. Im Februar eskalierte laut OSZE die Gewalt im Donbass.
Bereits wenige Wochen nach der Invasion, Ende März 2022, kam es in Istanbul zu Friedensverhandlungen, die fast zu einer Lösung geführt hätten. Dass der Krieg nicht damals bereits beendet wurde, lag daran, dass der Westen dies nicht wollte. Man war der Meinung, Russland durch die Ukraine in diesem Stellvertreterkrieg auf Dauer militärisch schwächen zu können. Angesichts von Hunderttausenden Toten, Verletzten und Traumatisierten, die als Folge seitdem zu beklagen sind, sowie dem Ausmaß der Zerstörung, fehlen einem die Worte.
Hasst der Westen die Russen?
Diese Frage drängt sich auf, wenn man das oft unerträglich feindselige Gebaren beobachtet, das beileibe nicht neu ist und vor Doppelmoral trieft. Russland und speziell die Person Wladimir Putins werden regelrecht dämonisiert, was gleichzeitig scheinbar jede Form von Diplomatie ausschließt.
Russlands militärische Stärke, seine geografische Lage, sein Rohstoffreichtum oder seine unabhängige diplomatische Tradition sind sicher Störfaktoren für das US-amerikanische Bestreben, der Boss in einer unipolaren Welt zu sein. Ein womöglich funktionierender eurasischer Kontinent, insbesondere gute Beziehungen zwischen Russland und Deutschland, war indes schon vor dem Ersten Weltkrieg eine Sorge des britischen Imperiums.
Ein «Vergehen» von Präsident Putin könnte gewesen sein, dass er die neoliberale Schocktherapie à la IWF und den Ausverkauf des Landes (auch an US-Konzerne) beendete, der unter seinem Vorgänger herrschte. Dabei zeigte er sich als Führungspersönlichkeit und als nicht so formbar wie Jelzin. Diese Aspekte allein sind aber heute vermutlich keine ausreichende Erklärung für ein derart gepflegtes Feindbild.
Der Historiker und Philosoph Hauke Ritz erweitert den Fokus der Fragestellung zu: «Warum hasst der Westen die Russen so sehr?», was er zum Beispiel mit dem Medienforscher Michael Meyen und mit der Politikwissenschaftlerin Ulrike Guérot bespricht. Ritz stellt die interessante These [11] auf, dass Russland eine Provokation für den Westen sei, welcher vor allem dessen kulturelles und intellektuelles Potenzial fürchte.
Die Russen sind Europäer aber anders, sagt Ritz. Diese «Fremdheit in der Ähnlichkeit» erzeuge vielleicht tiefe Ablehnungsgefühle. Obwohl Russlands Identität in der europäischen Kultur verwurzelt ist, verbinde es sich immer mit der Opposition in Europa. Als Beispiele nennt er die Kritik an der katholischen Kirche oder die Verbindung mit der Arbeiterbewegung. Christen, aber orthodox; Sozialismus statt Liberalismus. Das mache das Land zum Antagonisten des Westens und zu einer Bedrohung der Machtstrukturen in Europa.
Fazit
Selbstverständlich kann man Geschichte, Ereignisse und Entwicklungen immer auf verschiedene Arten lesen. Dieser Artikel, obwohl viel zu lang, konnte nur einige Aspekte der Ukraine-Tragödie anreißen, die in den offiziellen Darstellungen in der Regel nicht vorkommen. Mindestens dürfte damit jedoch klar geworden sein, dass die Russische Föderation bzw. Wladimir Putin nicht der alleinige Aggressor in diesem Konflikt ist. Das ist ein Stellvertreterkrieg zwischen USA/NATO (gut) und Russland (böse); die Ukraine (edel) wird dabei schlicht verheizt.
Das ist insofern von Bedeutung, als die gesamte europäische Kriegshysterie auf sorgsam kultivierten Freund-Feind-Bildern beruht. Nur so kann Konfrontation und Eskalation betrieben werden, denn damit werden die wahren Hintergründe und Motive verschleiert. Angst und Propaganda sind notwendig, damit die Menschen den Wahnsinn mitmachen. Sie werden belogen, um sie zuerst zu schröpfen und anschließend auf die Schlachtbank zu schicken. Das kann niemand wollen, außer den stets gleichen Profiteuren: die Rüstungs-Lobby und die großen Investoren, die schon immer an Zerstörung und Wiederaufbau verdient haben.
Apropos Investoren: Zu den Top-Verdienern und somit Hauptinteressenten an einer Fortführung des Krieges zählt BlackRock, einer der weltgrößten Vermögensverwalter. Der deutsche Bundeskanzler in spe, Friedrich Merz, der gerne «Taurus»-Marschflugkörper an die Ukraine liefern und die Krim-Brücke zerstören möchte, war von 2016 bis 2020 Aufsichtsratsvorsitzender von BlackRock in Deutschland. Aber das hat natürlich nichts zu sagen, der Mann macht nur seinen Job.
Es ist ein Spiel der Kräfte, es geht um Macht und strategische Kontrolle, um Geheimdienste und die Kontrolle der öffentlichen Meinung, um Bodenschätze, Rohstoffe, Pipelines und Märkte. Das klingt aber nicht sexy, «Demokratie und Menschenrechte» hört sich besser und einfacher an. Dabei wäre eine für alle Seiten förderliche Politik auch nicht so kompliziert; das Handwerkszeug dazu nennt sich Diplomatie. Noch einmal Gabriele Krone-Schmalz:
«Friedliche Politik ist nichts anderes als funktionierender Interessenausgleich. Da geht’s nicht um Moral.»
Die Situation in der Ukraine ist sicher komplex, vor allem wegen der inneren Zerrissenheit. Es dürfte nicht leicht sein, eine friedliche Lösung für das Zusammenleben zu finden, aber die Beteiligten müssen es vor allem wollen. Unter den gegebenen Umständen könnte eine sinnvolle Perspektive mit Neutralität und föderalen Strukturen zu tun haben.
Allen, die sich bis hierher durch die Lektüre gearbeitet (oder auch einfach nur runtergescrollt) haben, wünsche ich frohe Oster-Friedenstage!
[Titelbild: Pixabay; Abb. 1 und 2: nach Ganser/SIPER; Abb. 3: SIPER]
--- Quellen: ---
[1] Albrecht Müller, «Glaube wenig. Hinterfrage alles. Denke selbst.», Westend 2019
[2] Zwei nette Beispiele:
- ARD-faktenfinder (sic), «Viel Aufmerksamkeit für fragwürdige Experten», 03/2023
- Neue Zürcher Zeitung, «Aufstieg und Fall einer Russlandversteherin – die ehemalige ARD-Korrespondentin Gabriele Krone-Schmalz rechtfertigt seit Jahren Putins Politik», 12/2022
[3] George Washington University, «NATO Expansion: What Gorbachev Heard – Declassified documents show security assurances against NATO expansion to Soviet leaders from Baker, Bush, Genscher, Kohl, Gates, Mitterrand, Thatcher, Hurd, Major, and Woerner», 12/2017
[4] Beispielsweise Wladimir Putin bei seiner Rede im Deutschen Bundestag, 25/09/2001
[5] William Engdahl, «Full Spectrum Dominance, Totalitarian Democracy In The New World Order», edition.engdahl 2009
[6] Daniele Ganser, «Illegale Kriege – Wie die NATO-Länder die UNO sabotieren. Eine Chronik von Kuba bis Syrien», Orell Füssli 2016
[7] Gabriele Krone-Schmalz, «Mit Friedensjournalismus gegen ‘Kriegstüchtigkeit’», Vortrag und Diskussion an der Universität Hamburg, veranstaltet von engagierten Studenten, 16/01/2025\ → Hier ist ein ähnlicher Vortrag von ihr (Video), den ich mit spanischer Übersetzung gefunden habe.
[8] Für mehr Hintergrund und Details empfehlen sich z.B. folgende Bücher:
- Mathias Bröckers, Paul Schreyer, «Wir sind immer die Guten», Westend 2019
- Gabriele Krone-Schmalz, «Russland verstehen? Der Kampf um die Ukraine und die Arroganz des Westens», Westend 2023
- Patrik Baab, «Auf beiden Seiten der Front – Meine Reisen in die Ukraine», Fiftyfifty 2023
[9] vgl. Jonathan Mowat, «Washington's New World Order "Democratization" Template», 02/2005 und RAND Corporation, «Swarming and the Future of Conflict», 2000
[10] Bemerkenswert einige Beiträge, von denen man später nichts mehr wissen wollte:
- ARD Monitor, «Todesschüsse in Kiew: Wer ist für das Blutbad vom Maidan verantwortlich», 10/04/2014, Transkript hier
- Telepolis, «Blutbad am Maidan: Wer waren die Todesschützen?», 12/04/2014
- Telepolis, «Scharfschützenmorde in Kiew», 14/12/2014
- Deutschlandfunk, «Gefahr einer Spirale nach unten», Interview mit Günter Verheugen, 18/03/2014
- NDR Panorama, «Putsch in Kiew: Welche Rolle spielen die Faschisten?», 06/03/2014
[11] Hauke Ritz, «Vom Niedergang des Westens zur Neuerfindung Europas», 2024
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ 2b24a1fa:17750f64
2025-04-22 06:57:36
@ 2b24a1fa:17750f64
2025-04-22 06:57:36Es fühlt sich wie ein Staatsstreich an. Vielleicht ist es auch einer. Ein abgewählter Bundestag genehmigt mittels Grundgesetzänderung die größte Staatsverschuldung in der Geschichte Deutschlands mit der unvorstellbaren Summe von 1000 Milliarden Euro, also eine Billion.
https://soundcloud.com/radiomuenchen/vom-schuldenstaatsstreich-zur-finanzdiktatur-von-rob-kenius?\ Jedem muss klar sein, wohin diese Gelder aus den Taschen der Steuerzahler wandern und wer, wenn in Rüstung, Militärhilfen, Konzern-Subventionen investiert wird, die Leidtragenden sind: Kinder, Rentner, kleine Firmen und Betriebe, sozial Schwache, Kranke, Arbeitslose, Obdachlose.
\ Die Kräfte aus Finanzeliten, Militär, Rüstungsindustrie, regierenden Parteien und den staatstragenden Medien werden dafür immer stärker.
\ Hören Sie den Beitrag „Vom Schuldenstaatsstreich zur Finanzdiktatur“ von Rob Kenius, der zunächst beim Overton-Magazin erschienen war: https://overton-magazin.de/top-story/vom-schuldenstaatsstreich-zur-finanzdiktatur-in-leicht-verstaendlicher-sprache/
Sprecherin: Sabrina Khalil
Redaktion: Jonny Rieder
Bild: Bund der Steuerzahler / Janek Werner
Rob Kenius betreibt die systemkritische Webseite kritlit.de und den Podcast 9min Denksport. Der Text Vom Schuldenstaatsstreich zur Finanzdiktatur ist davon die 14. Folge.
Radio München\ www.radiomuenchen.net/\ @radiomuenchen\ www.facebook.com/radiomuenchen\ www.instagram.com/radio_muenchen/\ twitter.com/RadioMuenchen\ odysee.com/@RadioMuenchen.net:9\ rumble.com/user/RadioMunchen
Radio München ist eine gemeinnützige Unternehmung.\ Wir freuen uns, wenn Sie unsere Arbeit unterstützen.
GLS-Bank\ IBAN: DE65 4306 0967 8217 9867 00\ BIC: GENODEM1GLS\ Bitcoin (BTC): bc1qqkrzed5vuvl82dggsyjgcjteylq5l58sz4s927\ Ethereum (ETH): 0xB9a49A0bda5FAc3F084D5257424E3e6fdD303482
-
 @ ec42c765:328c0600
2025-02-05 23:45:09
@ ec42c765:328c0600
2025-02-05 23:45:09test
test
-
 @ ec42c765:328c0600
2025-02-05 23:43:35
@ ec42c765:328c0600
2025-02-05 23:43:35test
-
 @ a296b972:e5a7a2e8
2025-04-19 20:08:17
@ a296b972:e5a7a2e8
2025-04-19 20:08:17Bis in die Jahre 1 v. C., vor Corona, also bis 2019, lebte Deutschland in einer erträglichen Demokratie, an der es auch von damals kritischen Menschen zurecht immer schon reichlich auszusetzen gab. Aber es war auszuhalten, manchmal sogar richtig fein, es gab Zufriedenheit und gelegentlich sogar Glücksmomente. Die Kritiker hatten damals noch das Gefühl, frei ihre Meinung sagen zu können. Der Staat respektierte die Privatsphäre, auch wenn immer wieder Versuche gestartet wurden, in Angelegenheiten der Bürger Einblick zu gewinnen, die den Staat nichts angehen.
Man hatte die Möglichkeit, sich Nischen zu suchen, die eine Lebensqualität boten, mit dem Gefühl, man habe die Möglichkeit, der Staat rückt einem nicht allzu sehr auf die Pelle. Man war dazu bereit, die Konsequenzen für diese Freiheit in Kauf zu nehmen, weil einem andere Werte wichtiger waren, als zum Beispiel brav am Konsum teilzunehmen. Es gab Vorwürfe, man sei Konsumverweigerer, worauf stets die Antwort kam: Nein, nicht Konsumverweigerer, sondern Konsumverzichter. Verzichter deshalb, weil in Verzicht die freie Wahl enthalten ist. Konsumverweigerer ist ein Begriff aus dem System, der beschreibt, dass man sich durch seine Zurückhaltung im Konsum dem System verweigert.
Nach inzwischen fünf Jahren fängt es an schwer zu fallen, sich an das damalige Lebensgefühl zu erinnern.
Mit Corona sind, im Nachhinein betrachtet, die Schleusen für etwas aufgegangen, das man so nie für möglich gehalten hätte.
Als ob die miesesten Charaktere nur auf eine Gelegenheit gewartet hätten, endlich loslegen zu können, wird seitdem der Wahnsinn ununterbrochen über uns ausgeschüttet. Grundrechte wurden ausgehebelt, Zwangsmaßnahmen durchgesetzt, die Menschen wurden genötigt, einen Gehorsamkeitsbeweis vor dem Mund zu tragen, sie wurden in ihrer Mobilität eingeschränkt, Kinder wurden ihrer Kindheit und Bildung beraubt, es folgte eine absurde Verfügung nach der anderen. Heute, nachdem die allermeisten sogenannten Verschwörungstheorien wahr geworden sind, wissenschaftlich widerlegt und als sinnentleert entlarvt wurden, besteht nicht das geringste Interesse an einer wirklichen Aufarbeitung. Die lächerlichen Talkrunden im Staatsfunkt täuschen lediglich eine Aufarbeitungs-Simulation vor. Und es gibt immer noch genug Menschen, die darauf reinfallen und das perfide Spiel nicht durchschauen.
Mit Corona wurde auch die Spaltung der Gesellschaft vorangetrieben. Ein Austausch unter Freunden zu unterschiedlichen Einstellungen zu der sogenannten Impfung kam zum Erliegen. Stattdessen zog eine neue „Qualität“ ein, das dröhnende Schweigen, bis heute. Langjährige Freundschaften gingen zu ende, Risse taten sich in Familien auf, die teilweise bis heute nicht verheilt sind. Bestenfalls werden sie mit Totschweigen übergebügelt, damit ein halbwegs normaler Alltag überhaupt möglich ist. Im Unterbewusstsein brodelt es dennoch, das Thema ist ja nicht weg. Und der Tag wird kommen, an dem all das Unterdrückte mit aller Macht an die Oberfläche dringt und der ohnehin immense psychischen Schaden bei vielen Menschen beängstigende Auswirkungen haben wird.
Die Deutschen waren im 2. Weltkrieg sowohl Täter als auch Opfer. In beiden Fällen hat das ein Trauma ausgelöst. Das inszenierte Wirtschaftswunder hat die Menschen davon abgelenkt, dass sie sich mit ihrer eigenen Vergangenheit und ihrem Verhalten hätten auseinandersetzen müssen. Daraus hat sich der Glaube entwickelt, dass, wenn man schön brav und fleißig ist, dann wird die Welt uns schon irgendwann einmal wieder liebhaben.
Auf dieses nicht aufgearbeitete Trauma, dessen Folgen noch die zweite Generation zu spüren bekommt, ist jetzt ein weiteres gesellschaftliches Trauma aufgesetzt worden, und die Wahrscheinlichkeit ist groß, dass auch das nicht aufgearbeitet werden wird.
Was will man von so einer Gesellschaft erwarten?
Damit noch nicht genug, gewannen die Schlagzeilen zum Konflikt in der Ukraine die Oberhand, die Corona weitgehend verdrängten. Wieder machte sich Angst breit. Wird es einen Krieg geben? Die Vorgeschichte zum Ukraine-Konflikt wurde im Mainstream weitgehend unter den Teppich gekehrt. Die Frage nach dem eigenen Anteil des sogenannten Wertewestens an diesem Konflikt? Fehlanzeige! Passt nicht ins Narrativ. Aus diesem Konflikt, der, wie die Russen es nennen, militärischen Sonderoperation, ist allmählich ein ausgewachsener Krieg geworden. Ein klarer Stellvertreterkrieg zwischen den USA und Russland, auf dem Rücken der Ukraine, die sich durch Selensky vor den Karren spannen lassen hat. Bereits einen Monat nach Ausbruch des Konflikts war ein Frieden zum Greifen nahe. Dank des Westens konnte dies erfolgreich verhindert werden.
Aber diesen Elefanten im Raum will niemand wirklich sehen, geschweige denn, das zugeben. Die aktuelle Regierung in den USA hat nun die Aufgabe, die Scherben zu kitten, die die Vorgängerregierung verursacht hat. Dabei geht es nicht nur um Nächstenliebe, und das sinnlose Töten zu beenden, sondern auch um eine Möglichkeit, sich gesichtswahrend aus der Affaire zu ziehen. In erster Linie geht es um Interessen, nicht um „ein paar Menschenleben mehr oder weniger“.
Damit aber immer noch nicht genug, stellt sich Europa, den Friedensbemühungen zwischen den Großmächten USA und Russland in den Weg, verlängert damit das Sterben, statt diese Bemühungen zu unterstützen.
Zu Anfang von Corona haben viele geglaubt, was da abgeht, ist so absurd, das kann nicht lange dauern, dann klärt sich das auf. Seit fünf Jahren werden wir eines Besseren belehrt, denn die Absurditäten, der Wahnsinn will schier kein Ende nehmen. Und immer, wenn man denkt, schlimmer geht’s nimmer, kommt einer daher, und beweist das Gegenteil.
Um diesen Irrsinn immer weiter voranzutreiben, werden inzwischen nach der Bedienungsanleitung von George Orwells „1984“ Begriffe umgedeutet: Krieg ist Frieden, Spaltung ist Zusammenhalt, Zensur ist der Schutz vor Desinformation, Schulden sind Sondervermögen, usw. usw. usw.. Tschüss, gute alte Demokratie, willkommen in Unseredemokratie. Auch so ein Kunstwort, hinter der sich die unterschiedlichsten anti-demokratischen Tendenzen verbergen.
Eine vollständige Auflistung des Irrsinns würde den Rahmen des Möglichen sprengen.
Man fragt sich, was aufgrund der endlosen, oft menschenverachtenden, aber auf jeden Fall mindestens unmenschlichen Lebensbedingungen auf der Metaebene los ist, dass ein großer Teil der Menschheit, besonders der westlichen Welt, speziell in Europa, vollkommen den Verstand verloren hat.
Man kann es eigentlich nicht anders erklären, als dass das Böse die Macht ergriffen hat, dass die politischen Entscheidungsträger vom Teufel, oder wie auch immer man es nennen will, besessen sind.
Kräfte, ob gute oder schlechte, suchen sich immer Menschen, durch die sie wirken können.
Es bräuchte einen gesellschaftlichen Exorzismus, der diesen politischen Fehlbesetzungen den Teufel aus dem Leib treibt, doch auch leider ist ein großer Teil der Bevölkerung ebenso vom Teufel besessen, sitzt wie das Kaninchen vor der Schlange, empört sich vielleicht, kommt aber nicht von der Chips-Tüte auf dem Sofa vor dem Fernseher los, ist nicht in der Lage, seinen eigenen Untergang zu verhindern. Stattdessen schreit es innerlich nach einem, der da kommen soll, um sie zu retten. Das erinnert an die bisher dunkelsten Zeiten Deutschlands, von denen sich herausgestellt hat, dass der Retter kein Retter war.
Merz, noch nicht einmal im Amt, kündigt die Möglichkeit der Lieferung von Taurus-Raketen an. Russland erklärt, dass es das als Deutschlands Eintritt in den Ukraine-Krieg bewerten würde. Putin ordnet einseitig eine Waffenruhe über Ostern an, aber Putin ist immer noch der Böse, will Deutschland unbedingt angreifen, ist eine Bedrohung für die westlichen Werte, die Freiheit und die Demokratie. Das ist ein nicht zu überbietender Hohn.
Mit normalem Hausverstand ist das nicht zu begreifen. Es ist einfach nur irre. Und die Deutschen sitzen da und schauen zu. Bis auf wenige Ausnahmen, der Rest Europas übrigens auch. Der aller größte Teil der Menschen in Europa sitzt ruhig auf den Eisenbahnschienen und wartet darauf, dass der Zug kommt und sie überfährt.
Gerade an Ostern, der Zeit der Friedensbewegungen, der Ostermärsche. Wo sind die Massen, die vor den Regierungssitzen der europäischen Hauptstädte stehen, Frieden rufen und nicht mehr weggehen, und die wahnsinnigen Verantwortlichen dazu zwingen, mit dem Irrsinn aufzuhören, der die Welt in einen dritten Weltenbrand führen kann?
Stattdessen regt man sich darüber auf, dass der Osterbraten auch schon wieder teurer geworden ist, aber was will man machen. Lasst uns wenigstens über die Osterfeiertage mal eine gute Zeit haben. Und dann kommt auch noch oft der Satz, der einen aus dem Anzug springen lässt: Ich alleine kann ja sowieso nichts machen. Ein Satz, den wahrscheinlich rund 60 Millionen Deutsche sagen. Wie irre ist das denn?
Ohne, dass das Volk in Deutschland, die Völker in Europa, nicht aufstehen, und mit aller Härte NEIN sagen, gibt es keine Anzeichen dafür, dass es die Entscheidungsträger von alleine tun werden und das führt unweigerlich in die Katastrophe.
Was kann getan werden, damit die guten Kräfte wieder die Oberhand gewinnen, oder müssen wir lernen zu akzeptieren, dass wir verloren sind?
Leider ist es nicht möglich, schöne Ostern 2025 zu wünschen, denn es sind keine.
An dieser Stelle ein Schmankerl, dass an Geschmacklosigkeit und Geschichtsvergessenheit nicht zu überbieten ist:
Am liebsten möchte man schreien: „Hört auf! Und wenn einige Millionen Menschen allein in Deutschland das täten, dann würde man es schon hören. Aber was hört man? Besinnliche Feiertagsstille, gruselig.
Seit fünf Jahren macht sich ein Zeitgeist breit, dessen Abstand zum Menschsein, zum friedlichen Miteinander und einträglichen Austausch nicht größer sein könnte. Und ein Ende ist nicht in Sicht. Zukunftspläne schmieden? Wie denn, wenn man heute nicht weiß, ob einem nicht morgen schon die erste Kugel um die Ohren fliegt, weil wir, der Souverän nicht in der Lage gewesen sind, für Frieden ohne Waffen und Töten und Freiheit einzustehen.
Und diejenigen, die den Hintern nicht hochbekommen haben, sind die ersten, die dann klagen: Ach hätten wir doch! Wie konnte das geschehen? Das kam alles so plötzlich. Was hätte ich denn tun sollen? Wieder wird verdrängt und sich selbst belogen, nur, um vor sich selbst zu rechtfertigen, dass man im Grunde genommen ein Waschlappen ist und doch eigentlich sehr an seinem jämmerlichen Leben hängt.
Das einzige, was wirklich noch Hoffnung macht und Kraft gibt, sind die engagierten, propagandaresistenten Widerständler, die sich nach Kräften bemühen, die Wahrheit hochzuhalten, sich mit gesundem Hausverstand zu äußern, in der Hoffnung, dass sie den einen oder anderen Menschen außerhalb der „Blase“ erreichen, um ihn von der dunklen Seite der Macht ins Licht gehen zu lassen: Ja, bitte geh‘ unbedingt ins Licht, Carol Ann und alle anderen auch!
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ ec42c765:328c0600
2025-02-05 23:38:12
@ ec42c765:328c0600
2025-02-05 23:38:12カスタム絵文字とは
任意のオリジナル画像を絵文字のように文中に挿入できる機能です。
また、リアクション(Twitterの いいね のような機能)にもカスタム絵文字を使えます。

カスタム絵文字の対応状況(2025/02/06)

カスタム絵文字を使うためにはカスタム絵文字に対応したクライアントを使う必要があります。
※表は一例です。クライアントは他にもたくさんあります。
使っているクライアントが対応していない場合は、クライアントを変更する、対応するまで待つ、開発者に要望を送る(または自分で実装する)などしましょう。
対応クライアント
ここではnostterを使って説明していきます。
準備
カスタム絵文字を使うための準備です。
- Nostrエクステンション(NIP-07)を導入する
- 使いたいカスタム絵文字をリストに登録する
Nostrエクステンション(NIP-07)を導入する
Nostrエクステンションは使いたいカスタム絵文字を登録する時に必要になります。
また、環境(パソコン、iPhone、androidなど)によって導入方法が違います。
Nostrエクステンションを導入する端末は、実際にNostrを閲覧する端末と違っても構いません(リスト登録はPC、Nostr閲覧はiPhoneなど)。
Nostrエクステンション(NIP-07)の導入方法は以下のページを参照してください。
ログイン拡張機能 (NIP-07)を使ってみよう | Welcome to Nostr! ~ Nostrをはじめよう! ~
少し面倒ですが、これを導入しておくとNostr上の様々な場面で役立つのでより快適になります。
使いたいカスタム絵文字をリストに登録する
以下のサイトで行います。
右上のGet startedからNostrエクステンションでログインしてください。
例として以下のカスタム絵文字を導入してみます。
実際より絵文字が少なく表示されることがありますが、古い状態のデータを取得してしまっているためです。その場合はブラウザの更新ボタンを押してください。

- 右側のOptionsからBookmarkを選択

これでカスタム絵文字を使用するためのリストに登録できます。
カスタム絵文字を使用する
例としてブラウザから使えるクライアント nostter から使用してみます。
nostterにNostrエクステンションでログイン、もしくは秘密鍵を入れてログインしてください。
文章中に使用
- 投稿ボタンを押して投稿ウィンドウを表示
- 顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択
- : 記号に挟まれたアルファベットのショートコードとして挿入される

この状態で投稿するとカスタム絵文字として表示されます。
カスタム絵文字対応クライアントを使っている他ユーザーにもカスタム絵文字として表示されます。
対応していないクライアントの場合、ショートコードのまま表示されます。

ショートコードを直接入力することでカスタム絵文字の候補が表示されるのでそこから選択することもできます。

リアクションに使用
- 任意の投稿の顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択

カスタム絵文字リアクションを送ることができます。

カスタム絵文字を探す
先述したemojitoからカスタム絵文字を探せます。
例えば任意のユーザーのページ emojito ロクヨウ から探したり、 emojito Browse all からnostr全体で最近作成、更新された絵文字を見たりできます。
また、以下のリンクは日本語圏ユーザーが作ったカスタム絵文字を集めたリストです(2025/02/06)
※漏れがあるかもしれません
各絵文字セットにあるOpen in emojitoのリンクからemojitoに飛び、使用リストに追加できます。
以上です。
次:Nostrのカスタム絵文字の作り方
Yakihonneリンク Nostrのカスタム絵文字の作り方
Nostrリンク nostr:naddr1qqxnzdesxuunzv358ycrgveeqgswcsk8v4qck0deepdtluag3a9rh0jh2d0wh0w9g53qg8a9x2xqvqqrqsqqqa28r5psx3
仕様
-
 @ ec42c765:328c0600
2025-02-05 23:16:35
@ ec42c765:328c0600
2025-02-05 23:16:35てすと
nostr:nevent1qqst3uqlls4yr9vys4dza2sgjle3ly37trck7jgdmtr23uuz52usjrqqqnjgr
nostr:nevent1qqsdvchy5d27zt3z05rr3q6vvmzgslslxwu0p4dfkvxwhmvxldn9djguvagp2
test
てs
-
 @ da0b9bc3:4e30a4a9
2025-04-22 06:44:40
@ da0b9bc3:4e30a4a9
2025-04-22 06:44:40Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/952743
-
 @ a296b972:e5a7a2e8
2025-04-19 12:58:33
@ a296b972:e5a7a2e8
2025-04-19 12:58:33Völkerstrafgesetzbuch (VStGB)\ § 13 Verbrechen der Aggression ==============================
(1) Wer einen Angriffskrieg führt oder eine sonstige Angriffshandlung begeht, die ihrer Art, ihrer Schwere und ihrem Umfang nach eine offenkundige Verletzung der Charta der Vereinten Nationen darstellt, wird mit lebenslanger Freiheitsstrafe bestraft.
(2) Wer einen Angriffskrieg oder eine sonstige Angriffshandlung im Sinne des Absatzes 1 plant, vorbereitet oder einleitet, wird mit lebenslanger Freiheitsstrafe oder mit Freiheitsstrafe nicht unter zehn Jahren bestraft. Die Tat nach Satz 1 ist nur dann strafbar, wenn
1.
der Angriffskrieg geführt oder die sonstige Angriffshandlung begangen worden ist oder
2.
durch sie die Gefahr eines Angriffskrieges oder einer sonstigen Angriffshandlung für die Bundesrepublik Deutschland herbeigeführt wird.
(3) Eine Angriffshandlung ist die gegen die Souveränität, die territoriale Unversehrtheit oder die politische Unabhängigkeit eines Staates gerichtete oder sonst mit der Charta der Vereinten Nationen unvereinbare Anwendung von Waffengewalt durch einen Staat.
(4) Beteiligter einer Tat nach den Absätzen 1 und 2 kann nur sein, wer tatsächlich in der Lage ist, das politische oder militärische Handeln eines Staates zu kontrollieren oder zu lenken.
(5) In minder schweren Fällen des Absatzes 2 ist die Strafe Freiheitsstrafe nicht unter fünf Jahren.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
(Bild von pixabay)
-
 @ d08c9312:73efcc9f
2025-04-18 20:17:41
@ d08c9312:73efcc9f
2025-04-18 20:17:41https://youtu.be/qK7ffYzxiiQ
Resolvr was recently featured in The Institutes RiskStream Collaborative's educational video series on insurance digitization and cross-border payments. With over a century of history educating insurance professionals, The Institutes has established itself as the premier knowledge resource in risk management and insurance. And its RiskStream Collaborative non-profit serves as the industry's largest enterprise-level technology consortium focused on streamlining insurance processes through innovative solutions.
Resolvr's co-founders, Aaron Daniel and Dave Schwab, were joined by industry experts Lizzy Eisenberg from Lightspark and Austin Cornell from Zero Hash to discuss how Bitcoin and the Lightning Network are transforming global insurance payments operations.
Watch the video to learn how Resolvr is leveraging these real-time digital settlement networks to solve significant inefficiencies in today's insurance payment ecosystem - from the months-long settlement times that trap billions in value, to the manual reconciliation processes costing the industry nearly £1 billion annually at Lloyd's of London alone.
We're grateful to RiskStream Collaborative for showcasing these transformative technologies and emphasizing the importance of combining specialized insurance-native interfaces with powerful payment infrastructure to solve industry-specific challenges.
For more information about how Resolvr can help your organization streamline premium processing and payments, contact us today.
-
 @ 92f1335f:2c8220d1
2025-04-22 05:38:24
@ 92f1335f:2c8220d1
2025-04-22 05:38:24The Quiet Hold (2020)
As 2020 dawned, Jonathan kept his Bitcoin purchase a secret. He didn’t tell his parents, or his coworkers—not even his best friend, Sam. He wasn’t in it for hype. He believed in the tech.
Then came March 2020. The pandemic hit. Markets crashed. Panic spread.
Bitcoin dropped below $4,000.
Jonathan’s hands trembled as he stared at the red numbers on his screen. But instead of selling, he doubled down. He scraped together another $1,000 and bought the dip.
Weeks turned into months. People lost jobs, businesses closed, and the economy floundered. But Bitcoin began recovering—slowly at first, then with growing momentum By December, it hit $29,000.
Jonathan’s half Bitcoin? Worth over $14,000.
He smiled for the first time in weeks.
-
 @ a296b972:e5a7a2e8
2025-04-17 23:08:50
@ a296b972:e5a7a2e8
2025-04-17 23:08:50Die Figuren in der Koalition der Willigen entlarven ihre charakterliche Ungeeignetheit für politische Ämter mit Verantwortung für ganze Nationen. Staatliche Entscheidungen dürfen nicht emotionsgesteuert sein. Aber genau das ist derzeit der Fall. Überall wird mit der Moralkeule um sich gehauen. Erwachsene benehmen sich wie im Kindergarten und zeigen ihre fehlende Reife. Von menschlicher Größe ganz zu schweigen.
Bisher war es schön warm unter den Fittichen der USA. Deutschland hat aufgrund seiner Geschichte besonders gut den Nick-August gespielt und sich selbst eine Souveränität vorgelogen, die es so nie gegeben hat. Jetzt sieht es so aus, als wollten die USA Europa in die Freiheit, in die Volljährigkeit entlassen. Es könnte auch sein, dass die USA aus der NATO austreten und sich vor allem um sich selbst kümmern. Allein das würde die Welt schon wesentlich friedlicher machen, denkt man beispielsweise an den Einmarsch in den Irak. Es gehen Gerüchte um, dass Truppen aus Rumänien und Deutschland abgezogen werden sollen.
Vielleicht geht es bei den Friedensverhandlungen zwischen Trump und Putin nicht nur um die Ukraine, sondern, wenn man schon mal dabei ist, auch um die Kräfteverteilung in Europa insgesamt. Waffeneinsätze in der Ukraine wurden maßgeblich von Wiesbaden aus gesteuert. 2026 sollen dort US-Mittelstrecken-Raketen stationiert werden. Der an Führungsstärke kleinste Kanzler der Bundesrepublik, Scholz, hat das brav abgenickt. Der nur noch durch ein Wunder zu verhindernde neue Kanzler, das Glas Gewürzgurken aus dem Sauerland, provoziert Russland mit seiner Ankündigung zu den Taurus-Raketen dafür um so mehr. Da ist man schon fast gewillt, sich den Scholz zurückzuwünschen, als das kleinere Übel.
Statt mit Besonnenheit und Vernunft die veränderte Sicherheitslage mit den USA als eher abtrünnige Schutzmacht neu zu bewerten, hierin auch eine Chance zu sehen, eine starke Botschaft und den Willen auf ein friedliches neues Miteinander in den Fokus zu stellen, reagieren die meisten europäischen politischen „Spitzenkräfte“ mit blindem Aktionismus, der weltenbrandgefährlich ist. Und Deutschland, dass es sich aufgrund seiner Geschichte am wenigsten erlauben könnte, macht mit von der Leyen in Brüssel und Merz, Pistorius und anderen Kriegs-Warm-Uppern am weitesten das Maul auf, obwohl es sich am bedecktesten halten sollte.
Angesichts der Tatsache, dass Europa gegenüber einer Atommacht wie Russland vollkommen wehrlos ist, wäre es wirklich viel gescheiter, sich der neuen Situation anzupassen und ständig Signale der Friedensbereitschaft zu senden. Unterstütz von den Briten und Franzosen schmiegt Brüssel eine Koalition der Friedensuntüchtigen, wie sie Uwe Froschauer aktuell in seinem Buch „Die Friedensuntüchtigen“ beschreibt. In der Rezension von mir gibt es auch einen Link zu einem Review des Inhalts:
https://wassersaege.com/blogbeitraege/buchrezension-die-friedensuntuechtigen-von-uwe-froschauer/
Stattdessen passiert das Gegenteil.
Es ist nicht nur legitim, sondern sogar Aufgabe der einzelnen Staaten, eine gewisse Verteidigungsfähigkeit aufbauen zu wollen. Derzeit geschieht das jedoch unter falschen Vorzeichen. Die NATO, als sogenanntes Verteidigungsbündnis zur Vorlage zu nehmen, wäre keine gute Idee, weil sie sich mangels Gelegenheit (der Verteidigung) eher als das Gegenteil herausgestellt hat, wie man seinerzeit in Jugoslawien erleben musste.
Russland als Feind hochzustilisieren, um ein Aufrüsten zu beschleunigen, ist jedoch der denkbar falscheste Weg. Wenn ein Yorkshire-Terrier einen Pit-Bull ankläfft, könnte das fatale Folgen haben. Wenn die europäischen „Geistesgrößen“ bei Verstand wären und in der Lage, die Realität richtig einzuschätzen, würden sie das erkennen.
Woher kommt die Überheblichkeit, woher die Unfähigkeit zur Einschätzung der Lage, woher die Realitätsverweigerung? Ist das gewollt, steckt ein Plan dahinter oder sind „die“ einfach „nur“ strunzendoof? Letzteres wäre die gefährlichste Variante.
Es stellt sich immer mehr heraus, dass Corona offensichtlich ein Test war, wie weit die Menschen in ihrer Obrigkeitshörigkeit zu treiben sind. Wie dumm und gefolgsam sind die Schafe wirklich?
Bei einer Lieferung von Taurus-Raketen, die von Deutschen gesteuert werden müssen, könnte es vielleicht gelingen, die Krim-Brücke zu zerstören. Den Kriegsverlauf würde das jedoch nicht beeinflussen. Russland gewinnt so oder so. Im Gegenteil, die Folgen für Deutschland würden den dort möglicherweise angerichteten Schaden bei weitem übertreffen.
Während ich schreibe kommt gerade auf RT DE (aufgrund der „Pressefreiheit“ verzichtet man derzeit offiziell auf diesen Sender) folgende Meldung rein: Russisches Außenministerium: Taurus-Einsatz bedeutet deutsche Kriegsbeteiligung.
https://rtde.site/international/242696-russisches-aussenministerium-taurus-einsatz-bedeutet/
Es ist nicht nachvollziehbar, dass Merz offensichtlich nicht in der Lage ist anzuerkennen, dass Russland über Oreschnik-Raketen verfügt. Er scheint nicht in der Lage zu sein, die möglichen Folgen einschätzen zu können. Genau so wenig wie Pistorius. Die beiden kommen einem vor, wie zwei, die sich im stockfinsteren Wald verirrt haben und sich gegenseitig Mut zusprechen.
Nach wie vor gibt es keine fundierten Beweise dafür, dass Russland die Absicht hat, Deutschland auf unschöne Weise bereisen zu wollen. Das kann nicht oft genug gesagt werden.
Wie schon vor dem Ukraine-Konflikt, durch ein ständiges mit der NATO-Osterweiterung Russland-immer-näher-auf-die-Pelle-rücken, streut jetzt Europa, Deutschland, der Kriegskanzler Salz in die Wunde und Russland sagt ständig: Stoy, so geht das nicht!
Wenn wir eine Bedrohungslage haben, dann die, dass das aktuelle Regime den Deutschen in seinem Wehrwahn mit Wehrpflicht und einer bevorstehenden russischen Invasion droht, obwohl es, man kann es wirklich nicht oft genug sagen, keine reale Bedrohung durch Russland gibt.
In einem Interview im deutschen Propaganda-Funk faselt Pistorius davon, dass in einem „Schnuppercamp der Bundesmarine“ in Kiel für Teenager ab 16 Jahre, er gar nichts Verwerfliches daran finden kann. „Die schießen ja nicht…“, „Wir bringen ihnen ja nicht das Töten bei mit 17, sondern wir bereiten sie vor auf eine Ausbildung zum Soldaten. Und Soldat ist ein sehr ehrenwerter Beruf, der nämlich dazu dient, unsere Freiheit und Sicherheit im Ernstfall zu verteidigen.“ Dass diese Verteidigung tödlich enden kann, wird hier verschwiegen. Das könnte schließlich Teile der Soldaten verunsichern.
Ein Politikwissenschaftler regt sich über den Titel eines Liedes auf:
-Da stört sich doch tatsächlich jemand an der Liedzeile „Meine Söhne geb‘ ich nicht“-
https://www.nachdenkseiten.de/?p=131733
Man hat das Gefühl, dass alle Politiker, statt wie Obelix in den Zaubertrank, in ein Fass Teflon-Lack gefallen sind. Anders ist es nicht zu erklären, warum die Realität so perfekt an ihnen abperlt.
Wir werden immer mehr in die Enge getrieben. Und man weiß nicht, was im Zuge der digitalisierten Überwachung, die auch in Russland kräftig Fahrt aufnimmt, zwischen den USA und Russland sonst noch ausgehandelt wird. Auch, wenn Vance derzeit von UK-Premier Keir Starmer fordert, er müsse die Gesetze gegen „Hassrede“ aufheben, um ein Handelsabkommen mit den USA zu erzielen, und das eine Vorankündigung auf die Verhandlungen mit der EU sein könnte, (Bedingung: Abschaffung des Digital Services Act). In den USA gibt es Tech-Giganten, wie Musk und Thiel und Konsorten, die mit Umlegen eines Schalters, den derzeit augenscheinlichen Kampf für Meinungsfreiheit und Freiheit der Bürger, im Handumdrehen ins Gegenteil verqueren können. Dann sind wir in Null Komma Nichts in der Versklavung mit einem Totalitarismus und einer Technokratie gelandet, in der sich Georg Orwells „1984“ wie eine Gute-Nacht-Geschichte für kleine Kinder anhört.
Dieser Artikel wurde mit dem Pareto-Client geschrieben
-
 @ 9c9d2765:16f8c2c2
2025-04-22 05:30:03
@ 9c9d2765:16f8c2c2
2025-04-22 05:30:03CHAPTER NINE
"I hope you all see that I keep my promises," Mark announced confidently, raising his glass as the Ray family members murmured among themselves. "Another gift for the family, and all I ask in return is Rita’s hand. It’s a simple trade, isn’t it?"
It was the Ray family fun weekend, and Mark had once again positioned himself as their savior. He had been invited, and as expected, he made sure to make his presence known. The Ray family wasn’t happy that the new president had canceled the investment plans, which were against their initial arrangements. They had pinned their hopes on Mark, and once again, he didn’t disappoint.
At the end of the evening, Mark handed over another generous gift of cash, sealing his influence within the family. "You all know what needs to be done," he continued, flashing a smug smile. "Rita divorces James, and I’ll continue to help the family business thrive."
The murmurs grew louder. The push for divorce within the Ray family gained momentum, and James could feel the weight of humiliation pressing down on him once again. Yet, amidst the pressure and manipulation, Rita remained firm.
"I’m not divorcing James," she declared, her voice unwavering despite the glares she received from her own family. "Not now, not ever."
A heavy silence fell over the room, but James knew this was far from over.
"You! Throw him out!" Mark barked, pointing a commanding finger at James as he entered the gathering. The Ray family fun night was in full swing, and Mark, feeling emboldened by the power he had secured within the family, was eager to humiliate James once and for all.
The private guard, a broad-shouldered man dressed in a sleek black uniform, stepped forward. But as soon as his gaze met James’s, his stern expression softened. He hesitated, his posture shifting from aggression to submission. Then, to the shock of everyone present, he bent slightly at the waist and uttered a quiet but firm apology.
"I’m sorry, sir. I cannot do that," the guard said, his voice steady yet respectful.
Mark’s eyes widened in disbelief. “What? Are you insane? I said, throw him out!” he roared, his face twisting in fury.
The guard, still standing between Mark and James, clenched his fists at his sides. “I work part-time at JP Company. I know who this man is. I cannot lay a hand on him.”
A murmur rippled through the room. Helen, Christopher, and the rest of the Ray family exchanged puzzled glances. Why would a mere security guard refuse an order so boldly? What did he mean by knowing James?
Mark’s frustration boiled over. He took a threatening step forward. “Then you’re fired! Get out!” he spat, his voice thick with rage.
The guard stood his ground, his eyes flicking briefly to James, who remained calm, his expression unreadable. With a respectful nod to James, the guard turned on his heel and exited, his departure leaving an unsettling silence in his wake.
Helen, unable to contain her curiosity, leaned toward Christopher. “What just happened? Why would he refuse Mark’s order? What does he know about James that we don’t?”
Christopher shook his head, his brow furrowed in confusion. “I have no idea. But that was not just any ordinary security guard. He spoke as if James was someone important.”
Susan, who had been quietly observing the scene, finally spoke. “Could it be that James has some hidden power we don’t know about?”
Helen scoffed. “Ridiculous! That beggar? He’s nothing but a burden!” But despite her words, an uneasy feeling settled in her stomach.
Mark, still seething, turned his glare to James. “Enjoy this moment, you wretch. Soon, you’ll have nowhere left to run.” He stormed out, leaving a tense and confused silence behind.
James remained where he was, his calm demeanor never wavering. He had stood his ground without even speaking a word, and yet, the Ray family’s perception of him was beginning to shift. There were too many unanswered questions. Why did a security guard from JP Company recognize him? Why did he refuse to act against him? And most importantly who was James, really?.
"We can't let this business week slip through our fingers," Helen muttered anxiously, pacing back and forth in the living room. "Christopher, Robert, one of you must represent Ray Enterprises. We need to secure more investments."
Christopher sighed, rubbing his temples. "Helen, we are aware of how important this meeting is. But are you sure you should attend with me? You know these investors expect to meet actual executives."
"I have every right to be there," Helen snapped. "The future of this family business is at stake! If you won't do it, I'll step in to make sure we don't lose more ground."
Meanwhile, across the city, James stepped into the most luxurious boutique, scanning the racks of high-end suits. The store clerk eyed him skeptically, unimpressed by his simple attire. "Sir, are you sure you’re in the right place?" the clerk asked with a forced smile.
James smirked. "Yes. Get me the best suit you have."
After a long selection process, he emerged wearing a custom-tailored suit worth a fortune, making even the store owner widen his eyes in disbelief. James checked his reflection in the mirror, adjusting his cuffs. "Perfect," he murmured.
The day of the business meeting arrived, and the grand hall was filled with top executives, investors, and company representatives from across the city. The chatter in the hall buzzed with anticipation as they awaited the arrival of JP Enterprises' new president.
Helen sat rigidly beside Christopher, her fingers tapping nervously on the table. "I wonder who JP Enterprises will send. Their investments have been making waves lately," she whispered.
Before Christopher could respond, a hush fell over the crowd. The doors swung open, and the awaited president stepped in, his presence commanding immediate attention.
-
 @ 9f8b9baa:b922fc09
2025-04-22 04:55:30
@ 9f8b9baa:b922fc09
2025-04-22 04:55:308KI là một nền tảng giải trí trực tuyến nổi bật, mang đến cho người dùng những trải nghiệm đa dạng và thú vị. Với giao diện dễ sử dụng và thiết kế tối giản, 8KI giúp người chơi dễ dàng tiếp cận và thưởng thức các trò chơi yêu thích. Nền tảng này không chỉ cung cấp các trò chơi giải trí mà còn có các tính năng tương tác độc đáo, tạo ra không gian thú vị để người dùng khám phá và tận hưởng. Dù bạn là người mới hay đã có kinh nghiệm, 8KI luôn mang đến những hoạt động đa dạng, từ các trò chơi giải trí nhẹ nhàng đến những thử thách cần kỹ năng cao. Hệ thống cập nhật thường xuyên giúp nền tảng luôn giữ được sự mới mẻ và thu hút, khiến người dùng không bao giờ cảm thấy nhàm chán.
Một trong những điểm mạnh của 8KI là khả năng tùy chỉnh trải nghiệm người dùng, mang đến sự linh hoạt tối đa cho mọi người tham gia. Người chơi có thể điều chỉnh các thiết lập theo sở thích cá nhân, từ việc thay đổi độ khó cho đến lựa chọn các chế độ chơi khác nhau. Điều này giúp người dùng cảm thấy thoải mái hơn khi tham gia, đồng thời cũng tạo ra những thử thách mới mẻ để không ngừng phát triển kỹ năng. Hệ thống này giúp 8KI trở thành một nền tảng phù hợp cho mọi đối tượng, từ những người mới bắt đầu cho đến những người chơi kỳ cựu. Mỗi người dùng có thể tìm thấy một kiểu chơi phù hợp với sở thích của mình, mang lại một trải nghiệm cá nhân hóa và thú vị. Khả năng điều chỉnh này tạo ra sự khác biệt, giúp người dùng không chỉ giải trí mà còn nâng cao khả năng của bản thân qua từng trò chơi.
Không chỉ dừng lại ở việc cung cấp những trò chơi hấp dẫn, 8KI còn tạo ra một cộng đồng mạnh mẽ, nơi người chơi có thể giao lưu, chia sẻ kinh nghiệm và kết nối với nhau. Các tính năng xã hội như bảng xếp hạng, diễn đàn và các cuộc thi định kỳ tạo ra cơ hội để người dùng tương tác và phát triển mối quan hệ với những người chơi khác. Cộng đồng 8KI không chỉ đơn thuần là một không gian giải trí mà còn là nơi để những người cùng sở thích có thể chia sẻ những câu chuyện, chiến lược và học hỏi từ nhau. Điều này làm tăng thêm giá trị của nền tảng, giúp người chơi không chỉ tận hưởng các trò chơi mà còn xây dựng được các mối quan hệ bền vững. Sự kiện và chương trình khuyến mãi thú vị cũng thường xuyên được tổ chức, giúp cộng đồng 8KI luôn sôi động và thu hút người tham gia. Với môi trường thân thiện và tính năng tương tác mạnh mẽ, 8KI đã và đang trở thành một điểm đến giải trí lý tưởng cho những ai yêu thích sự kết nối và sáng tạo.
-
 @ 9f8b9baa:b922fc09
2025-04-22 04:54:38
@ 9f8b9baa:b922fc09
2025-04-22 04:54:38MM99 là một nền tảng giải trí trực tuyến nổi bật, cung cấp cho người dùng một không gian đa dạng để thưởng thức các trò chơi và hoạt động giải trí. Với giao diện dễ sử dụng và thiết kế trực quan, MM99 tạo ra một trải nghiệm liền mạch và dễ tiếp cận cho tất cả người dùng. Nền tảng này không chỉ thu hút với kho nội dung phong phú mà còn đem đến những cập nhật liên tục, giúp người chơi không bao giờ cảm thấy nhàm chán. MM99 đặc biệt chú trọng vào việc cung cấp các trò chơi đa dạng, từ những trò chơi mang tính thử thách cao cho đến các hoạt động giải trí nhẹ nhàng, đáp ứng được nhu cầu của mọi người dùng. Với mỗi lần tham gia, người chơi luôn có thể tìm thấy những trải nghiệm mới mẻ và hấp dẫn, giúp họ thư giãn và giải trí sau những giờ làm việc căng thẳng.
Điều khiến MM99 trở nên đặc biệt chính là khả năng tùy chỉnh trải nghiệm của người dùng. Nền tảng này cho phép mỗi người chơi điều chỉnh các thiết lập trò chơi theo sở thích và nhu cầu cá nhân, giúp mang lại cảm giác thoải mái và dễ dàng kiểm soát. Người dùng có thể thay đổi mức độ khó, lựa chọn các chế độ chơi khác nhau và thậm chí thay đổi các yếu tố giao diện sao cho phù hợp nhất với mình. Sự linh hoạt này giúp MM99 luôn duy trì sự hấp dẫn và tạo ra một trải nghiệm giải trí cá nhân hóa cho từng người dùng. Đặc biệt, MM99 không chỉ phù hợp với những người chơi mới mà còn là lựa chọn lý tưởng cho những ai yêu thích thử thách và khám phá các chiến lược mới. Tính năng tùy chỉnh giúp người chơi dễ dàng tham gia và luôn cảm thấy hào hứng mỗi khi quay lại nền tảng này.
Bên cạnh việc cung cấp một loạt các trò chơi thú vị, MM99 còn chú trọng đến việc xây dựng một cộng đồng gắn kết và tương tác. Các tính năng xã hội như bảng xếp hạng, diễn đàn trò chuyện và các sự kiện đặc biệt giúp người chơi có cơ hội giao lưu, học hỏi và kết bạn với những người cùng sở thích. MM99 đã tạo ra một môi trường nơi người dùng không chỉ tham gia vào các trò chơi mà còn có thể kết nối và chia sẻ những trải nghiệm của mình. Những cuộc thi và sự kiện thường xuyên được tổ chức, tạo ra một không khí sôi động và đầy thử thách, thúc đẩy người chơi quay lại để tham gia và cải thiện kỹ năng. Cộng đồng MM99 ngày càng trở nên mạnh mẽ và đoàn kết, là yếu tố quan trọng giúp nền tảng này phát triển và duy trì sự hấp dẫn trong mắt người dùng. MM99 không chỉ là một nơi để giải trí mà còn là một không gian giao lưu tuyệt vời cho những ai muốn tìm kiếm niềm vui và kết nối với những người có cùng đam mê.
-
 @ ec42c765:328c0600
2025-02-05 22:05:55
@ ec42c765:328c0600
2025-02-05 22:05:55カスタム絵文字とは
任意のオリジナル画像を絵文字のように文中に挿入できる機能です。
また、リアクション(Twitterの いいね のような機能)にもカスタム絵文字を使えます。

カスタム絵文字の対応状況(2025/02/06)

カスタム絵文字を使うためにはカスタム絵文字に対応したクライアントを使う必要があります。
※表は一例です。クライアントは他にもたくさんあります。
使っているクライアントが対応していない場合は、クライアントを変更する、対応するまで待つ、開発者に要望を送る(または自分で実装する)などしましょう。
対応クライアント
ここではnostterを使って説明していきます。
準備
カスタム絵文字を使うための準備です。
- Nostrエクステンション(NIP-07)を導入する
- 使いたいカスタム絵文字をリストに登録する
Nostrエクステンション(NIP-07)を導入する
Nostrエクステンションは使いたいカスタム絵文字を登録する時に必要になります。
また、環境(パソコン、iPhone、androidなど)によって導入方法が違います。
Nostrエクステンションを導入する端末は、実際にNostrを閲覧する端末と違っても構いません(リスト登録はPC、Nostr閲覧はiPhoneなど)。
Nostrエクステンション(NIP-07)の導入方法は以下のページを参照してください。
ログイン拡張機能 (NIP-07)を使ってみよう | Welcome to Nostr! ~ Nostrをはじめよう! ~
少し面倒ですが、これを導入しておくとNostr上の様々な場面で役立つのでより快適になります。
使いたいカスタム絵文字をリストに登録する
以下のサイトで行います。
右上のGet startedからNostrエクステンションでログインしてください。
例として以下のカスタム絵文字を導入してみます。
実際より絵文字が少なく表示されることがありますが、古い状態のデータを取得してしまっているためです。その場合はブラウザの更新ボタンを押してください。

- 右側のOptionsからBookmarkを選択

これでカスタム絵文字を使用するためのリストに登録できます。
カスタム絵文字を使用する
例としてブラウザから使えるクライアント nostter から使用してみます。
nostterにNostrエクステンションでログイン、もしくは秘密鍵を入れてログインしてください。
文章中に使用
- 投稿ボタンを押して投稿ウィンドウを表示
- 顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択
- : 記号に挟まれたアルファベットのショートコードとして挿入される

この状態で投稿するとカスタム絵文字として表示されます。
カスタム絵文字対応クライアントを使っている他ユーザーにもカスタム絵文字として表示されます。
対応していないクライアントの場合、ショートコードのまま表示されます。

ショートコードを直接入力することでカスタム絵文字の候補が表示されるのでそこから選択することもできます。

リアクションに使用
- 任意の投稿の顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択

カスタム絵文字リアクションを送ることができます。

カスタム絵文字を探す
先述したemojitoからカスタム絵文字を探せます。
例えば任意のユーザーのページ emojito ロクヨウ から探したり、 emojito Browse all からnostr全体で最近作成、更新された絵文字を見たりできます。
また、以下のリンクは日本語圏ユーザーが作ったカスタム絵文字を集めたリストです(2025/02/06)
※漏れがあるかもしれません
各絵文字セットにあるOpen in emojitoのリンクからemojitoに飛び、使用リストに追加できます。
以上です。
次:Nostrのカスタム絵文字の作り方
Yakihonneリンク Nostrのカスタム絵文字の作り方
Nostrリンク nostr:naddr1qqxnzdesxuunzv358ycrgveeqgswcsk8v4qck0deepdtluag3a9rh0jh2d0wh0w9g53qg8a9x2xqvqqrqsqqqa28r5psx3
仕様
-
 @ ec42c765:328c0600
2025-02-05 20:30:46
@ ec42c765:328c0600
2025-02-05 20:30:46カスタム絵文字とは
任意のオリジナル画像を絵文字のように文中に挿入できる機能です。
また、リアクション(Twitterの いいね のような機能)にもカスタム絵文字を使えます。

カスタム絵文字の対応状況(2024/02/05)

カスタム絵文字を使うためにはカスタム絵文字に対応したクライアントを使う必要があります。
※表は一例です。クライアントは他にもたくさんあります。
使っているクライアントが対応していない場合は、クライアントを変更する、対応するまで待つ、開発者に要望を送る(または自分で実装する)などしましょう。
対応クライアント
ここではnostterを使って説明していきます。
準備
カスタム絵文字を使うための準備です。
- Nostrエクステンション(NIP-07)を導入する
- 使いたいカスタム絵文字をリストに登録する
Nostrエクステンション(NIP-07)を導入する
Nostrエクステンションは使いたいカスタム絵文字を登録する時に必要になります。
また、環境(パソコン、iPhone、androidなど)によって導入方法が違います。
Nostrエクステンションを導入する端末は、実際にNostrを閲覧する端末と違っても構いません(リスト登録はPC、Nostr閲覧はiPhoneなど)。
Nostrエクステンション(NIP-07)の導入方法は以下のページを参照してください。
ログイン拡張機能 (NIP-07)を使ってみよう | Welcome to Nostr! ~ Nostrをはじめよう! ~
少し面倒ですが、これを導入しておくとNostr上の様々な場面で役立つのでより快適になります。
使いたいカスタム絵文字をリストに登録する
以下のサイトで行います。
右上のGet startedからNostrエクステンションでログインしてください。
例として以下のカスタム絵文字を導入してみます。
実際より絵文字が少なく表示されることがありますが、古い状態のデータを取得してしまっているためです。その場合はブラウザの更新ボタンを押してください。

- 右側のOptionsからBookmarkを選択

これでカスタム絵文字を使用するためのリストに登録できます。
カスタム絵文字を使用する
例としてブラウザから使えるクライアント nostter から使用してみます。
nostterにNostrエクステンションでログイン、もしくは秘密鍵を入れてログインしてください。
文章中に使用
- 投稿ボタンを押して投稿ウィンドウを表示
- 顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択
- : 記号に挟まれたアルファベットのショートコードとして挿入される

この状態で投稿するとカスタム絵文字として表示されます。
カスタム絵文字対応クライアントを使っている他ユーザーにもカスタム絵文字として表示されます。
対応していないクライアントの場合、ショートコードのまま表示されます。

ショートコードを直接入力することでカスタム絵文字の候補が表示されるのでそこから選択することもできます。

リアクションに使用
- 任意の投稿の顔😀のボタンを押し、絵文字ウィンドウを表示
- *タブを押し、カスタム絵文字一覧を表示
- カスタム絵文字を選択

カスタム絵文字リアクションを送ることができます。

カスタム絵文字を探す
先述したemojitoからカスタム絵文字を探せます。
例えば任意のユーザーのページ emojito ロクヨウ から探したり、 emojito Browse all からnostr全体で最近作成、更新された絵文字を見たりできます。
また、以下のリンクは日本語圏ユーザーが作ったカスタム絵文字を集めたリストです(2024/06/30)
※漏れがあるかもしれません
各絵文字セットにあるOpen in emojitoのリンクからemojitoに飛び、使用リストに追加できます。
以上です。
次:Nostrのカスタム絵文字の作り方
Yakihonneリンク Nostrのカスタム絵文字の作り方
Nostrリンク nostr:naddr1qqxnzdesxuunzv358ycrgveeqgswcsk8v4qck0deepdtluag3a9rh0jh2d0wh0w9g53qg8a9x2xqvqqrqsqqqa28r5psx3
仕様
-
 @ 9f8b9baa:b922fc09
2025-04-22 04:53:45
@ 9f8b9baa:b922fc09
2025-04-22 04:53:4532Win là một nền tảng giải trí trực tuyến sáng tạo, mang đến cho người dùng một loạt các hoạt động và trải nghiệm đa dạng. Với giao diện dễ sử dụng và thiết kế trực quan, 32Win giúp người dùng dễ dàng tham gia và tận hưởng những phút giây giải trí thú vị. Nền tảng này nổi bật với khả năng cung cấp các nội dung luôn mới mẻ và đa dạng, từ các trò chơi đầy thử thách cho đến những hoạt động mang tính giải trí cao. Dù bạn là người mới hay đã có kinh nghiệm, 32Win luôn có thể đáp ứng nhu cầu của tất cả mọi người. Hệ thống của nền tảng này liên tục được cập nhật và đổi mới, đảm bảo mang lại những trải nghiệm giải trí chất lượng và không bao giờ nhàm chán. Các hoạt động thú vị và tính năng độc đáo của 32Win chính là điểm thu hút chính, khiến người dùng luôn muốn quay lại để khám phá thêm nhiều điều mới mẻ.
Sự thành công của 32WIN không chỉ đến từ sự đa dạng của các trò chơi mà còn từ khả năng cá nhân hóa cao. Nền tảng này cho phép người dùng điều chỉnh các thiết lập theo sở thích riêng, từ việc thay đổi mức độ khó, chọn chủ đề yêu thích cho đến lựa chọn các chế độ chơi khác nhau. Điều này giúp người dùng có thể tạo ra một trải nghiệm hoàn toàn phù hợp với nhu cầu và sở thích cá nhân. Bằng cách này, 32Win mang lại sự linh hoạt tối đa, đảm bảo rằng mỗi người dùng có thể tìm được niềm vui và sự thách thức ở mức độ phù hợp nhất với mình. Hệ thống cài đặt cá nhân hóa không chỉ giúp nâng cao trải nghiệm mà còn giúp người dùng cảm thấy thoải mái và hài lòng trong suốt quá trình tham gia. 32Win luôn chú trọng đến sự hài lòng của người dùng và cam kết mang lại những dịch vụ giải trí tốt nhất.
Một điểm đáng chú ý nữa của 32Win là cộng đồng người dùng sôi động và thân thiện. Nền tảng này không chỉ cung cấp các trò chơi mà còn tạo ra một môi trường nơi mọi người có thể giao lưu, kết nối và chia sẻ kinh nghiệm. Các tính năng như bảng xếp hạng, diễn đàn thảo luận và các cuộc thi giữa người chơi không chỉ tăng cường tính tương tác mà còn tạo ra một không gian gắn kết, nơi người dùng có thể học hỏi và hỗ trợ lẫn nhau. Cộng đồng mạnh mẽ của 32Win là một yếu tố quan trọng trong việc xây dựng một môi trường giải trí lành mạnh và thú vị. Thêm vào đó, các sự kiện đặc biệt và các chương trình khuyến mãi hấp dẫn thường xuyên được tổ chức, giúp giữ cho người dùng luôn có động lực quay lại và tham gia. Với những tính năng này, 32Win không chỉ là một nền tảng giải trí, mà còn là một nơi để mọi người có thể kết nối, tạo dựng mối quan hệ và tận hưởng thời gian bên nhau.
-
 @ f6488c62:c929299d
2025-04-22 04:04:18
@ f6488c62:c929299d
2025-04-22 04:04:18วันนี้ตลาดโลก “เดือดแบบเงียบ ๆ” แม้ทรัมป์จะยังไม่พูดอะไร แต่สินทรัพย์เสี่ยงกลับพลิกเกมกันคนละทาง โดยเฉพาะฝั่งทองคำและคริปโตที่มีสัญญาณบวกหลายจุด ⚡
🟡 ไฮไลต์ร้อนวันนี้ 🪙 ทองคำพุ่งทะลุ $3,510/oz (ตามราคา PAXG) → นักลงทุนวิ่งเข้าทองแบบ Panic Buy ท่ามกลางความไม่แน่นอนทางเศรษฐกิจโลก 🪙 Bitcoin มั่นคงจากแรงซื้อของ BlackRock & MicroStrategy รวมกันเกือบ $640M → โทนตลาดยังเอียงฝั่งบวก 🪙 Paul Atkins ผู้สนับสนุนคริปโต ขึ้นแท่นประธาน SEC → อาจพลิกเกมกฎระเบียบในสหรัฐฯ ไปอีกฝั่ง 🪙 Coinbase เปิดฟิวเจอร์ส XRP / สิงคโปร์เปิด Bitcoin Futures กลางปีนี้ → แสดงถึงสัญญาณยอมรับระดับโลก
🔻 ฝั่งน่าห่วง ⚠️ Ethereum ETF ถูกถอนทุน $1.1B ใน 7 สัปดาห์ → แสดงความลังเลของนักลงทุนสถาบัน ⚠️ ตลาดยังหวาดระแวง หลัง "ภาษีวันปลดปล่อย" ของทรัมป์และการโจมตี Fed → ทรัมป์เงียบ = ตลาดระวัง ⚠️ หุ้นสหรัฐแกว่งแรง → นักลงทุนย้ายเงินเข้าทอง-คริปโตเพื่อหาที่พักพิง
📌 กลยุทธ์วันนี้:
"ทองไม่ใช่แค่ Safe Haven แต่ตอนนี้คือทางหนี" นักลงทุนเริ่มขยับพอร์ตหนีจากตลาดหุ้น เข้าทองและคริปโต → ระวังแรงกระเพื่อมรอบดึก (โดยเฉพาะจากฝั่งสหรัฐฯ)
📎 ฝากแชร์โพสต์นี้ไว้ดูอีกที ถ้าคุณคิดว่า “ปี 2025 น่าจะผันผวนที่สุดในรอบ 10 ปี”
ทองคำ #Bitcoin #ข่าวการเงิน #Crypto #ตลาดโลก #เฟด #ทรัมป์ #ทองขึ้น #ลงทุนทอง
-
 @ 59cb0748:9602464b
2025-01-01 06:15:09
@ 59cb0748:9602464b
2025-01-01 06:15:09Nostrでお世話になっている方も、お世話になってない方も、こんにちは!
タコ頭大吉です!
NIP-23を使った初めての投稿です。
今回は、私がここ数ヶ月中にデザインをした三種類のビタキセケースの紹介記事になります!!
ビタキセを買ったもののあまり自分の好みに合う外観や仕様のケースがなく、いくつかプロトタイプを作りそれなりに時間をかけて考えたケース達です。
これら3シリーズに関しては、FDMタイプの3Dプリンタの精度、耐久性、出力後の作業性を考慮して一つのパーツで完結することに拘って設計をしました。
一定以上の充填率でプリントをすればそれなりに丈夫なはずです。
また、基本的に放熱性と保護性を両立できるように設計をしたつもります。
それぞれのモデルについて簡単に紹介をさせていただきますので、よろしければ各リポジトリに付属のREADMEを読んでいただいて自作、フィードバックをいただけましたら幸いです。
それでは、簡単に各モデルの紹介をさせていたきます。
AirLiftFrame
 最初に作ったモデルです!
少し大きいのが難点ですが、分厚めのフレームをベースとし基盤周辺をあえて囲わない設計により、保護性と放熱を阻害しない事の両立を狙っています。
最初に作ったモデルです!
少し大きいのが難点ですが、分厚めのフレームをベースとし基盤周辺をあえて囲わない設計により、保護性と放熱を阻害しない事の両立を狙っています。
TwinAirLiftFrame
 ビタキセを買い増ししたことにより、複数台をカッコよく運用したいという需要が自分の中に出てきたので、AirLiftFrameを2つくっつけたら良いのではと言うごくごく単純な発想でつくり始めたケースです。
しかし、ただ横並びにしただけでは廃熱が干渉するだけではなく、DCジャックやUSBポートへのアクセスが阻害されるという問題にすぐに気がつきました。
そこで、WebUI上でディスプレイの表示を上下反転出来ることに注目し、2台を上下逆向きに取り付ける事でそれらの問題を解決しました!
ビタキセを買い増ししたことにより、複数台をカッコよく運用したいという需要が自分の中に出てきたので、AirLiftFrameを2つくっつけたら良いのではと言うごくごく単純な発想でつくり始めたケースです。
しかし、ただ横並びにしただけでは廃熱が干渉するだけではなく、DCジャックやUSBポートへのアクセスが阻害されるという問題にすぐに気がつきました。
そこで、WebUI上でディスプレイの表示を上下反転出来ることに注目し、2台を上下逆向きに取り付ける事でそれらの問題を解決しました!
VoronoiShell
 AirLiftFrameシリーズのサイズを小型化する事から始めたプロジョクトです。
縦横の寸法の削減だけではなく、厚みを薄くつくリたいという希望がありました。
所が単純に薄くすると、持った時に発熱する背面パーツに手が触れてしまったり、落下などでぶつかった際に背面パーツが破損する懸念がありました。
そこで、(当初は付けたくはなかった)背面保護用のグリルをデザインする必要が出てきました。
初めは多角形でしたがあまりにもダサく、調べている内にVoronoi柄という有機的なパターンに行き付き即採用しました。
結果、ビタキセを取り付けると柄が見えなくなるのが勿体無いぐらい個性的でスタイリッシュなデザインに仕上がりました。
AirLiftFrameシリーズのサイズを小型化する事から始めたプロジョクトです。
縦横の寸法の削減だけではなく、厚みを薄くつくリたいという希望がありました。
所が単純に薄くすると、持った時に発熱する背面パーツに手が触れてしまったり、落下などでぶつかった際に背面パーツが破損する懸念がありました。
そこで、(当初は付けたくはなかった)背面保護用のグリルをデザインする必要が出てきました。
初めは多角形でしたがあまりにもダサく、調べている内にVoronoi柄という有機的なパターンに行き付き即採用しました。
結果、ビタキセを取り付けると柄が見えなくなるのが勿体無いぐらい個性的でスタイリッシュなデザインに仕上がりました。
いずれカスタム方法やインサートナットや増設ファンの選定方法等を紹介したいのですが、今回はNIP-23になれるという意図もあるので紹介に留めます! また、他の関連OSハードウェアプロジェクトのケースもデザインできたらと思っております!
今後ともタコ頭をよろしくお願いいたします。
-
 @ ec42c765:328c0600
2024-12-22 19:16:31
@ ec42c765:328c0600
2024-12-22 19:16:31この記事は前回の内容を把握している人向けに書いています(特にNostrエクステンション(NIP-07)導入)
手順
- 登録する画像を用意する
- 画像をweb上にアップロードする
- 絵文字セットに登録する
1. 登録する画像を用意する
以下のような方法で用意してください。
- 画像編集ソフト等を使って自分で作成する
- 絵文字作成サイトを使う(絵文字ジェネレーター、MEGAMOJI など)
- フリー画像を使う(いらすとや など)
データ量削減
Nostrでは画像をそのまま表示するクライアントが多いので、データ量が大きな画像をそのまま使うとモバイル通信時などに負担がかかります。
データ量を増やさないためにサイズやファイル形式を変更することをおすすめします。
以下は私のおすすめです。 * サイズ:正方形 128×128 ピクセル、長方形 任意の横幅×128 ピクセル * ファイル形式:webp形式(webp変換おすすめサイト toimg) * 単色、単純な画像の場合:png形式(webpにするとむしろサイズが大きくなる)
その他
- 背景透過画像
- ダークモード、ライトモード両方で見やすい色
がおすすめです。
2. 画像をweb上にアップロードする
よく分からなければ emojito からのアップロードで問題ないです。
普段使っている画像アップロード先があるならそれでも構いません。
気になる方はアップロード先を適宜選んでください。既に投稿されたカスタム絵文字の画像に対して
- 削除も差し替えもできない → emojito など
- 削除できるが差し替えはできない → Gyazo、nostrcheck.meなど
- 削除も差し替えもできる → GitHub 、セルフホスティングなど
これらは既にNostr上に投稿されたカスタム絵文字の画像を後から変更できるかどうかを指します。
どの方法でも新しく使われるカスタム絵文字を変更することは可能です。
同一のカスタム絵文字セットに同一のショートコードで別の画像を登録する形で対応できます。3. 絵文字セットに登録する
emojito から登録します。
右上のアイコン → + New emoji set から新規の絵文字セットを作成できます。


① 絵文字セット名を入力
基本的にカスタム絵文字はカスタム絵文字セットを作り、ひとまとまりにして登録します。
一度作った絵文字セットに後から絵文字を追加することもできます。
② 画像をアップロードまたは画像URLを入力
emojitoから画像をアップロードする場合、ファイル名に日本語などの2バイト文字が含まれているとアップロードがエラーになるようです。
その場合はファイル名を適当な英数字などに変更してください。
③ 絵文字のショートコードを入力
ショートコードは絵文字を呼び出す時に使用する場合があります。
他のカスタム絵文字と被っても問題ありませんが選択時に複数表示されて支障が出る可能性があります。
他と被りにくく長くなりすぎないショートコードが良いかもしれません。
ショートコードに使えるのは半角の英数字とアンダーバーのみです。
④ 追加
Add を押してもまだ作成完了にはなりません。

一度に絵文字を複数登録できます。
最後に右上の Save を押すと作成完了です。

画面が切り替わるので、右側の Options から Bookmark を選択するとそのカスタム絵文字セットを自分で使えるようになります。
既存の絵文字セットを編集するには Options から Edit を選択します。
以上です。
仕様
-
 @ f839fb67:5c930939
2025-04-16 21:07:13
@ f839fb67:5c930939
2025-04-16 21:07:13Relays
| Name | Address | Price (Sats/Year) | Status | | - | - | - | - | | stephen's aegis relay | wss://paid.relay.vanderwarker.family | 42069 |
| | stephen's Outbox | wss://relay.vanderwarker.family | Just Me |
| | stephen's Inbox | wss://haven.vanderwarker.family/inbox | WoT |
| | stephen's DMs | wss://haven.vanderwarker.family/chat | WoT |
| | VFam Data Relay | wss://data.relay.vanderwarker.family | 0 |
| | VFam Bots Relay | wss://skeme.vanderwarker.family | Invite |
| | VFGroups (NIP29) | wss://groups.vanderwarker.family | 0 |
| | [TOR] My Phone Relay | ws://naswsosuewqxyf7ov7gr7igc4tq2rbtqoxxirwyhkbuns4lwc3iowwid.onion | 0 | Meh... |
My Pubkeys
| Name | hex | nprofile | | - | - | - | | Main | f839fb6714598a7233d09dbd42af82cc9781d0faa57474f1841af90b5c930939 | nostr:nprofile1qqs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3us9mapfx | | Vanity (Backup) | 82f21be67353c0d68438003fe6e56a35e2a57c49e0899b368b5ca7aa8dde7c23 | nostr:nprofile1qqsg9usmuee48sxkssuqq0lxu44rtc4903y7pzvmx694efa23h08cgcpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3ussel49x | | VFStore | 6416f1e658ba00d42107b05ad9bf485c7e46698217e0c19f0dc2e125de3af0d0 | nostr:nprofile1qqsxg9h3uevt5qx5yyrmqkkehay9cljxdxpp0cxpnuxu9cf9mca0p5qpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3usaa8plu | | NostrSMS | 9be1b8315248eeb20f9d9ab2717d1750e4f27489eab1fa531d679dadd34c2f8d | nostr:nprofile1qqsfhcdcx9fy3m4jp7we4vn305t4pe8jwjy74v062vwk08dd6dxzlrgpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3us595d45 |
Bots
Unlocks Bot
Hex: 2e941ad17144e0a04d1b8c21c4a0dbc3fbcbb9d08ae622b5f9c85341fac7c2d0
nprofile:
nostr:nprofile1qqsza9q669c5fc9qf5dccgwy5rdu877th8gg4e3zkhuus56pltru95qpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3ust4kvak
Latest Data:
nostr:naddr1qq882mnvda3kkttrda6kuar9wgq37amnwvaz7tmnddjk6efwweskuer9wfmkzuntv4ezuenpd45kc7gzyqhfgxk3w9zwpgzdrwxzr39qm0plhjae6z9wvg44l8y9xs06clpdqqcyqqq823cgnl9u5Step Counter
Hex: 9223d2faeb95853b4d224a184c69e1df16648d35067a88cdf947c631b57e3de7
nprofile: nostr:nprofile1qqsfyg7jlt4etpfmf53y5xzvd8sa79ny356sv75gehu50333k4lrmecpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3ustswp3w
Latest Data:
nostr:naddr1qvzqqqr4gupzpy3r6tawh9v98dxjyjscf357rhckvjxn2pn63rxlj37xxx6hu008qys8wumn8ghj7umtv4kk2tnkv9hxgetjwashy6m9wghxvctdd9k8jtcqp3ehgets943k7atww3jhyn39gffRCTGuest
Hex: 373904615c781e46bf5bf87b4126c8a568a05393b1b840b1a2a3234d20affa0c
nprofile: nostr:nprofile1qqsrwwgyv9w8s8jxhadls76pymy2269q2wfmrwzqkx32xg6dyzhl5rqpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3usy92jlxNow Playing
Hex: 8096ed6ba1f21a3713bd47a503ee377b0ce2f187b3e5a3ae909a25b84901018b
nprofile: nostr:nprofile1qqsgp9hddwslyx3hzw750fgracmhkr8z7xrm8edr46gf5fdcfyqsrzcpramhxue69uhhx6m9d4jjuanpdejx2unhv9exketj9enxzmtfd3uspk5v4w
Latest Data:
nostr:naddr1qq9kummh94cxccted9hxwqglwaehxw309aekketdv5h8vctwv3jhyampwf4k2u3wvesk66tv0ypzpqyka446rus6xufm63a9q0hrw7cvutcc0vl95whfpx39hpyszqvtqvzqqqr4gupdk2hd
NIP-29 Groups
- Minecraft Group Chat
nostr:naddr1qqrxvc33xpnxxqfqwaehxw309anhymm4wpejuanpdejx2unhv9exketj9enxzmtfd3usygrzymrpd2wz8ularp06y8ad5dgaddlumyt7tfzqge3vc97sgsarjvpsgqqqnpvqazypfd- VFNet Group Chat
nostr:naddr1qqrrwvfjx9jxzqfqwaehxw309anhymm4wpejuanpdejx2unhv9exketj9enxzmtfd3usygrzymrpd2wz8ularp06y8ad5dgaddlumyt7tfzqge3vc97sgsarjvpsgqqqnpvq08hx48
"Nostrified Websites"
[D] = Saves darkmode preferences over nostr
[A] = Auth over nostr
[B] = Beta (software)
[z] = zap enabled
Other Services (Hosted code)
Emojis Packs
- Minecraft
nostr:naddr1qqy566twv43hyctxwsq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82nsd0k5wp- AIM
nostr:naddr1qqxxz6tdv4kk7arfvdhkuucpramhxue69uhhyetvv9ujuanpdejx2unhv9exketj9enxzmtfd3usyg8c88akw9ze3fer85yah4p2lqkvj7qap749w360rpq6ly94eycf8ypsgqqqw48qe0j2yk- Blobs
nostr:naddr1qqz5ymr0vfesz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqa2wek4ukj- FavEmojis
nostr:naddr1qqy5vctkg4kk76nfwvq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82nsf7sdwt- Modern Family
nostr:naddr1qqx56mmyv4exugzxv9kkjmreqy0hwumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jq3qlqulkec5tx98yv7snk759tuzejtcr5865468fuvyrtuskhynpyusxpqqqp65ujlj36n- nostriches (Amethyst collection)
nostr:naddr1qq9xummnw3exjcmgv4esz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqa2w2sqg6w- Pepe
nostr:naddr1qqz9qetsv5q37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82ns85f6x7- Minecraft Font
nostr:naddr1qq8y66twv43hyctxwssyvmmwwsq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82nsmzftgr- Archer Font
nostr:naddr1qq95zunrdpjhygzxdah8gqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0ypzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqvzqqqr4fclkyxsh- SMB Font
nostr:naddr1qqv4xatsv4ezqntpwf5k7gzzwfhhg6r9wfejq3n0de6qz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqa2w0wqpuk
Git Over Nostr
- NostrSMS
nostr:naddr1qqyxummnw3e8xmtnqy0hwumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jqfrwaehxw309amk7apwwfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqyj8wumn8ghj7urpd9jzuun9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jqg5waehxw309aex2mrp0yhxgctdw4eju6t0qyxhwumn8ghj7mn0wvhxcmmvqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqaueqp0epk- nip51backup
nostr:naddr1qq9ku6tsx5ckyctrdd6hqqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yqjxamnwvaz7tmhda6zuun9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jqfywaehxw309acxz6ty9eex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yq3gamnwvaz7tmjv4kxz7fwv3sk6atn9e5k7qgdwaehxw309ahx7uewd3hkcq3qlqulkec5tx98yv7snk759tuzejtcr5865468fuvyrtuskhynpyusxpqqqpmej4gtqs6- bukkitstr
nostr:naddr1qqykyattdd5hgum5wgq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gpydmhxue69uhhwmm59eex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yqjgamnwvaz7tmsv95kgtnjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gpz3mhxue69uhhyetvv9ujuerpd46hxtnfduqs6amnwvaz7tmwdaejumr0dspzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqvzqqqrhnyf6g0n2
Market Places
Please use Nostr Market or somthing simular, to view.
- VFStore
nostr:naddr1qqjx2v34xe3kxvpn95cnqven956rwvpc95unscn9943kxet98q6nxde58p3ryqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0yqjvamnwvaz7tmgv9mx2m3wweskuer9wfmkzuntv4ezuenpd45kc7f0da6hgcn00qqjgamnwvaz7tmsv95kgtnjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gpydmhxue69uhhwmm59eex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0ypzqeqk78n93wsq6sss0vz6mxl5shr7ge5cy9lqcx0smshpyh0r4uxsqvzqqqr4gvlfm7gu
Badges
Created
- paidrelayvf
nostr:naddr1qq9hqctfv3ex2mrp09mxvqglwaehxw309aex2mrp0yh8vctwv3jhyampwf4k2u3wvesk66tv0ypzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqvzqqqr48y85v3u3- iPow
nostr:naddr1qqzxj5r02uq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82wgg02u0r- codmaster
nostr:naddr1qqykxmmyd4shxar9wgq37amnwvaz7tmjv4kxz7fwweskuer9wfmkzuntv4ezuenpd45kc7gzyrurn7m8z3vc5u3n6zwm6s40stxf0qwsl2jhga83ssd0jz6ujvynjqcyqqq82wgk3gm4g- iMine
nostr:naddr1qqzkjntfdejsz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgs0sw0mvu29nznjx0gfm02z47pve9up6ra22ar57xzp47gttjfsjwgrqsqqqafed5s4x5
Clients I Use
- Amethyst
nostr:naddr1qqxnzd3cx5urqv3nxymngdphqgsyvrp9u6p0mfur9dfdru3d853tx9mdjuhkphxuxgfwmryja7zsvhqrqsqqql8kavfpw3- noStrudel
nostr:naddr1qqxnzd3cxccrvd34xser2dpkqy28wumn8ghj7un9d3shjtnyv9kh2uewd9hsygpxdq27pjfppharynrvhg6h8v2taeya5ssf49zkl9yyu5gxe4qg55psgqqq0nmq5mza9n- nostrsms
nostr:naddr1qq9rzdejxcunxde4xymqz8mhwden5te0wfjkccte9emxzmnyv4e8wctjddjhytnxv9kkjmreqgsfhcdcx9fy3m4jp7we4vn305t4pe8jwjy74v062vwk08dd6dxzlrgrqsqqql8kjn33qm
Lists
- Bluesky
nostr:naddr1qvzqqqr4xqpzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqqapxcat9wd4hj0ah0jw
- Fediverse
nostr:naddr1qvzqqqr4xqpzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqp9rx2erfwejhyum9j4g0xh
- Fediverse_Bots
nostr:naddr1qvzqqqr4xqpzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqperx2erfwejhyum9tapx7arnfcpdzh
- My Bots
nostr:naddr1qvzqqqr4xqpzp7peldn3gkv2wgeap8dag2hc9nyhs8g04ft5wnccgxhepdwfxzfeqys8wumn8ghj7un9d3shjtnkv9hxgetjwashy6m9wghxvctdd9k8jtcqz4uh5jnpwscyss24fpkxw4fewafk566twa2q8f6fyk
-
 @ 9063ef6b:fd1e9a09
2025-04-16 20:20:39
@ 9063ef6b:fd1e9a09
2025-04-16 20:20:39Bitcoin is more than just a digital currency. It’s a technological revolution built on a unique set of properties that distinguish it from all other financial systems—past and present. From its decentralized architecture to its digitally verifiable scarcity, Bitcoin represents a fundamental shift in how we store and transfer value.
A Truly Decentralized Network
As of April 2025, the Bitcoin network comprises approximately 62,558 reachable nodes globally. The United States leads with 13,791 nodes (29%), followed by Germany with 6,418 nodes (13.5%), and Canada with 2,580 nodes (5.43%). bitnodes
This distributed structure is central to Bitcoin’s strength. No single entity can control the network, making it robust against censorship, regulation, or centralized failure.

Open Participation at Low Cost
Bitcoin's design allows almost anyone to participate meaningfully in the network. Thanks to its small block size and streamlined protocol, running a full node is technically and financially accessible. Even a Raspberry Pi or a basic PC is sufficient to synchronize and validate the blockchain.
However, any significant increase in block size could jeopardize this accessibility. More storage and bandwidth requirements would shift participation toward centralized data centers and cloud infrastructure—threatening Bitcoin’s decentralized ethos. This is why the community continues to fiercely debate such protocol changes.
Decentralized Governance
Bitcoin has no CEO, board, or headquarters. Its governance model is decentralized, relying on consensus among various stakeholders, including miners, developers, node operators, and increasingly, institutional participants.
Miners signal support for changes by choosing which version of the Bitcoin software to run when mining new blocks. However, full node operators ultimately enforce the network’s rules by validating blocks and transactions. If miners adopt a change that is not accepted by the majority of full nodes, that change will be rejected and the blocks considered invalid—effectively vetoing the proposal.
This "dual-power structure" ensures that changes to the network only happen through widespread consensus—a system that has proven resilient to internal disagreements and external pressures.
Resilient by Design
Bitcoin's decentralized nature gives it a level of geopolitical and technical resilience unmatched by any traditional financial system. A notable case is the 2021 mining ban in China. While initially disruptive, the network quickly recovered as miners relocated, ultimately improving decentralization.
This event underlined Bitcoin's ability to withstand regulatory attacks and misinformation (FUD—Fear, Uncertainty, Doubt), cementing its credibility as a global, censorship-resistant network.
Self-Sovereign Communication
Bitcoin enables peer-to-peer transactions across borders without intermediaries. There’s no bank, payment processor, or centralized authority required. This feature is not only technically efficient but also politically profound—it empowers individuals globally to transact freely and securely.
Absolute Scarcity
Bitcoin is the first asset in history with a mathematically verifiable, fixed supply: 21 million coins. This cap is hard-coded into its protocol and enforced by every full node. At the atomic level, Bitcoin is measured in satoshis (sats), with a total cap of approximately 2.1 quadrillion sats.
This transparency contrasts with assets like gold, whose total supply is estimated and potentially (through third parties on paper) expandable. Moreover, unlike fiat currencies, which can be inflated through central bank policy, Bitcoin is immune to such manipulation. This makes it a powerful hedge against monetary debasement.
Anchored in Energy and Time
Bitcoin's security relies on proof-of-work, a consensus algorithm that requires real-world energy and computation. This “work” ensures that network participants must invest time and electricity to mine new blocks.
This process incentivizes continual improvement in hardware and energy sourcing—helping decentralize mining geographically and economically. In contrast, alternative systems like proof-of-stake tend to favor wealth concentration by design, as influence is determined by how many tokens a participant holds.

Censorship-Resistant
The Bitcoin network itself is inherently censorship-resistant. As a decentralized system, Bitcoin transactions consist of mere text and numerical data, making it impossible to censor the underlying protocol.
However, centralized exchanges and trading platforms can be subject to censorship through regional regulations or government pressure, potentially limiting access to Bitcoin.
Decentralized exchanges and peer-to-peer marketplaces offer alternative solutions, enabling users to buy and sell Bitcoins without relying on intermediaries that can be censored or shut down.
High Security
The Bitcoin blockchain is secured through a decentralized network of thousands of nodes worldwide, which constantly verify its integrity, making it highly resistant to hacking. To add a new block of bundled transactions, miners compete to solve complex mathematical problems generated by Bitcoin's cryptography. Once a miner solves the problem, the proposed block is broadcast to the network, where each node verifies its validity. Consensus is achieved when a majority of nodes agree on the block's validity, at which point the Bitcoin blockchain is updated accordingly, ensuring the network's decentralized and trustless nature.
Manipulation of the Bitcoin network is virtually impossible due to its decentralized and robust architecture. The blockchain's chronological and immutable design prevents the deletion or alteration of previously validated blocks, ensuring the integrity of the network.
To successfully attack the Bitcoin network, an individual or organization would need to control a majority of the network's computing power, also known as a 51% attack. However, the sheer size of the Bitcoin network and the competitive nature of the proof-of-work consensus mechanism make it extremely difficult to acquire and sustain the necessary computational power. Even if an attacker were to achieve this, they could potentially execute double spends and censor transactions. Nevertheless, the transparent nature of the blockchain would quickly reveal the attack, allowing the Bitcoin network to respond and neutralize it. By invalidating the first block of the malicious chain, all subsequent blocks would also become invalid, rendering the attack futile and resulting in significant financial losses for the attacker.
One potential source of uncertainty arises from changes to the Bitcoin code made by developers. While developers can modify the software, they cannot unilaterally enforce changes to the Bitcoin protocol, as all users have the freedom to choose which version they consider valid. Attempts to alter Bitcoin's fundamental principles have historically resulted in hard forks, which have ultimately had negligible impact (e.g., BSV, BCH). The Bitcoin community has consistently rejected new ideas that compromise decentralization in favor of scalability, refusing to adopt the resulting blockchains as the legitimate version. This decentralized governance model ensures that changes to the protocol are subject to broad consensus, protecting the integrity and trustworthiness of the Bitcoin network.
Another source of uncertainty in the future could be quantum computers. The topic is slowly gaining momentum in the community and is being discussed.
My attempt to write an article with Yakihonne. Simple editor with the most necessary formatting. Technically it worked quite well so far.
Some properties are listed in the article. Which properties are missing?
-
 @ dfa02707:41ca50e3
2025-04-16 14:36:00
@ dfa02707:41ca50e3
2025-04-16 14:36:00Contribute to keep No Bullshit Bitcoin news going.

Good morning! The GM report is now back on track, and for those wondering where it was... well... it was delayed.
0:00
/0:41
1×
Headlines
- Bitcoin mining centralization in 2025. According to a blog post by b10c, Bitcoin mining was at its most decentralized in May 2017, with another favorable period from 2019 to 2022. However, starting in 2023, mining has become increasingly centralized, particularly due to the influence of large pools like Foundry and the use of proxy pooling by entities such as AntPool.
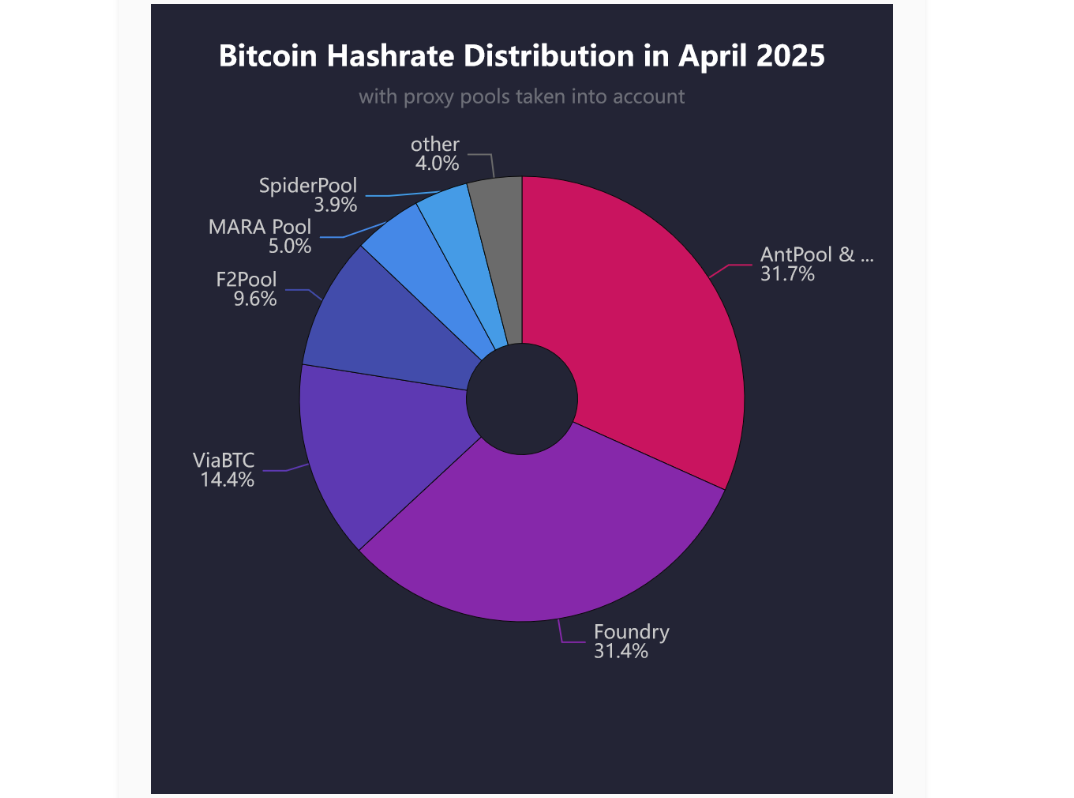
Source: b10c's blog.
- New Spiral grantee: l0rinc. In February 2024, l0rinc transitioned to full-time work on Bitcoin Core. His efforts focus on performance benchmarking and optimizations, enhancing code quality, conducting code reviews, reducing block download times, optimizing memory usage, and refactoring code.
- ESP32 microcontroller vulnerabilities. A paper by Crypto Deep Tech details how an attacker can embed a hidden list of vulnerabilities through module updates, potentially compromising ESP32 devices and allowing unauthorized access to private keys, underscoring the importance of continuous monitoring and enhancing both device and software security.
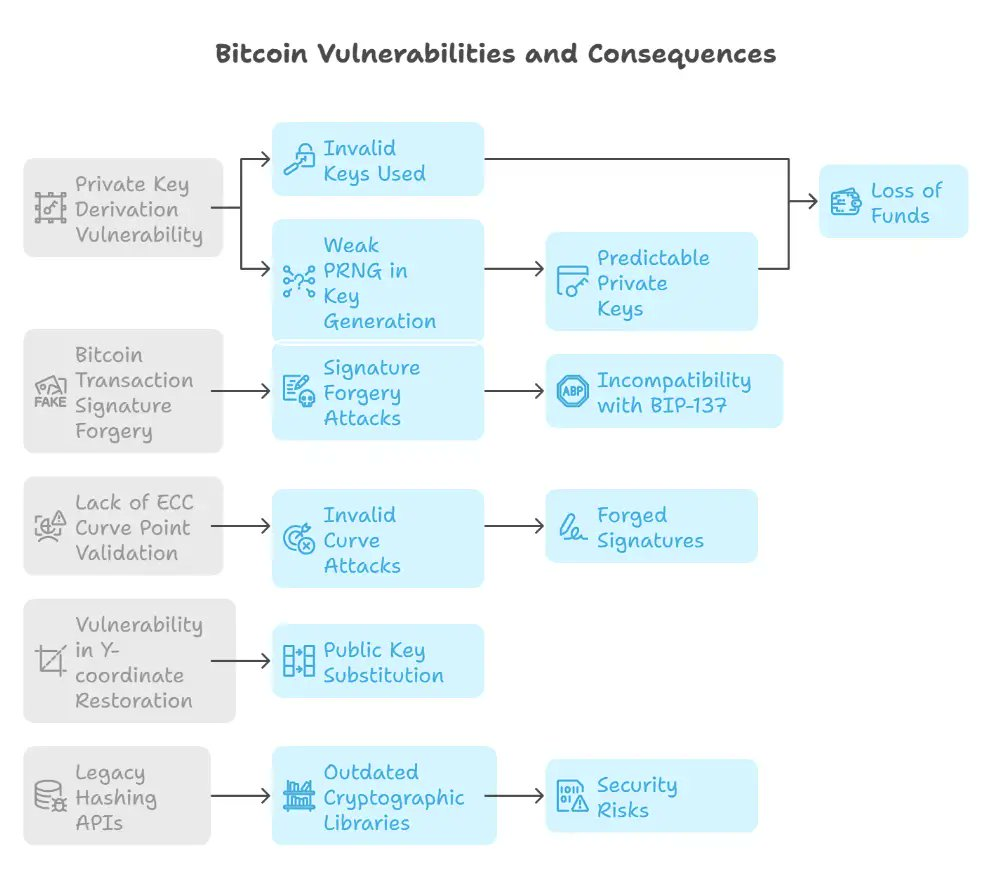
Source: Crypto Deep Tech.
- Bitdeer to expand its self-mining operations to navigate tariffs. The Singapore-based mining company is advancing plans to produce machines in the U.S. while reducing its mining hardware sales. This response is in light of increasing uncertainties related to U.S. trade policy, as reported by Bloomberg.
- Local governments in China use private firms to sell seized bitcoin for cash. According to Reuters, the lack of clear regulations for handling seized bitcoin and other tokens—whose trading is banned on the mainland—has led to inconsistent and opaque practices. The situation has sparked debate among attorneys about the need for new regulations.
- Unchained has launched the Bitcoin Legacy Project. The initiative seeks to advance the Bitcoin ecosystem through a bitcoin-native donor-advised fund platform (DAF), investments in community hubs, support for education and open-source development, and a commitment to long-term sustainability with transparent annual reporting.
- In its first year, the program will provide support to Bitcoin hubs in Nashville, Austin, and Denver.
- Support also includes $50,000 to the Bitcoin Policy Institute, a $150,000 commitment at the University of Austin, and up to $250,000 in research grants through the Bitcoin Scholars program.
"Unchained will match grants 1:1 made to partner organizations who support Bitcoin Core development when made through the Unchained-powered bitcoin DAF, up to 1 BTC," was stated in a blog post.
- Voltage has introduced Voltage Payments platform for enterprises. It will offer a single API that integrates both bitcoin and stablecoin payments with minimal technical overhead, providing the option of either Voltage or user-controlled custody. The platform features a comprehensive dashboard, along with built-in compliance and accounting tools. Currently in beta testing, it is set to launch in 46 U.S. states. Join the waitlist to be notified when it becomes available on mainnet.
Use the tools
- Bitcoin Core Config Generator by Jameson Lopp is now compatible with Bitcoin Core v29.0.
- Zeus wallet v0.10.2 is now available. This point release is centered around various bug fixes.
- Bitkit wallet v1.1.0 introduces performance improvements, smarter coin selection with new Autopilot options, a redesigned side menu, and bug fixes.
- Bitcoin Keeper v2.1.1 update includes various UI updates, bug fixes, and performance improvements.
- Flash v0.4.0-beta, a Bitcoin and Lightning wallet built on the Galoy infrastructure and tailored for the Caribbean Community, features a complete UI/UX redesign, encrypted NIP-17 messaging via Nostr, zoom functionality on the scan camera, improved support for NFC-based Flashcards, and much more.
0:00
/0:31
1×
- Payjoin Dev Kit (rust-payjoin) v0.23.0 introduces a first-class persistence abstraction, wire protocol changes to support RFC 9540, and improved compliance with the BIP78 specification. It also includes an experimental multiparty sender, accessible through the hidden "_multiparty" feature gate. Additionally, it addresses technical debt by enhancing error handling, expanding functionality with new modules and features, and improving test infrastructure. These updates result in breaking API and protocol changes.
- Payjoin CLI v0.1.0 is now out of alpha, with the wire protocol now presumed to be stable.
- Payjoin Directory v0.0.2 has been tagged. It implements the Payjoin Directory store-and-forward server required for Payjoin V2's asynchronous operation.
- BDK Wallet v1.2.0 has been released. The
TxBuilder'sadd_recipientnow accepts anyInto<ScriptBuf>. Coinbase outputs are eligible if maturing in the next block. Wallets usingrusqlite::Connectionare checked for thread safety.bdk_chainis updated to version 0.21.1, with some internal cleanups. - Lightning Dev Kit (rust-lightning) v0.1.2 includes the latest API updates, performance improvements, and bug fixes.
- Boltz Client v2.5.1 includes a patch for correctly handling negative service fees from Boltz Pro. Earlier version 2.5.0 introduced a new
bumpfeecommand alongside several other fixes and improvements. - Elements v23.2.7, an open-source implementation of advanced, sidechain-capable blockchain features extending the Bitcoin protocol, is now available with the latest fixes and improvements.
-
AxeOS (ESP-Miner) v2.6.5 increases the power target for Gamma self test. In version 2.6.4, the under limits for the power consumption self-test were removed.
- AxeOS v2.6.1 was a significant release introducing many new features and improvements. For a comprehensive feature breakdown, check out the details provided by WantClue below.
-
Rust-nostr v0.41 introduces NIP-C0 support and NIP-98 helpers, corrects NIP-32 and NIP-47 implementations, and adds the nostr-keyring crate. It extends admission policies for fine control over relay connections, beneficial in gossip mode. POSIX semaphores are enabled for LMDB on iOS and macOS to address App Sandbox issues. It also expands architecture support for C# and JVM bindings, including linux-x86, windows-x86, and windows-arm64, among other things.
- Nostringer is a JavaScript/TypeScript library providing unlinkable ring signatures (SAG) for Nostr public keys. Inspired by Monero's ring signatures using Spontaneous Anonymous Group (SAG) signatures and the beritani/ring-signatures implementation, it enables a signer to prove their membership in a group of Nostr accounts without disclosing which specific account produced the signature. See a live demo here.
- Private Pond by Kukks a Bitcoin Payjoin application built specifically to optimize Bitcoin transaction rails
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 1bc70a01:24f6a411
2025-04-16 13:53:00
@ 1bc70a01:24f6a411
2025-04-16 13:53:00I've been meaning to dogfood my own vibe project for a while so this feels like a good opportunity to use Untype to publish this update and reflect on my vibe coding journey.
New Untype Update
As I write this, I found it a bit annoying dealing with one of the latest features, so I'll need to make some changes right after I'm done. Nonetheless, here are some exciting developments in the Untype article composer:
-
Added inline AI helper! Now you can highlight text and perform all sorts of things like fix grammar, re-write in different styles, and all sorts of other things. This is a bit annoying at the moment because it takes over the other editing functions and I need to fix the UX.
-
Added pushing articles to DMs! This option, when enabled, will send the article to all the subscribers via a NIP-44 DM. (No client has implemented the subscription method yet so technically it won’t work, until one does. I may add this to nrss.app) Also, I have not tested this so it could be broken… will test eventually!
- Added word counts
- Added ability to export as markdown, export as PDF, print.
The biggest flaw I have already discovered is how "I" implemented the highlight functionality. Right now when you highlight some text it automatically pops up the AI helper menu and this makes for an annoying time trying to make any changes to text. I wanted to change this to show a floating clickable icon instead, but for some reason the bot is having a difficult time updating the code to this desired UX.
Speaking of difficult times, it's probably a good idea to reflect a bit upon my vibe coding journey.
Vibe Coding Nostr Projects
First, I think it's important to add some context around my recent batch of nostr vibe projects. I am working on them mostly at night and occasionally on weekends in between park runs with kids, grocery shopping and just bumming around the house. People who see buggy code or less than desired UX should understand that I am not spending days coding this stuff. Some apps are literally as simple as typing one prompt!
That said, its pretty clear by now that one prompt cannot produce a highly polished product. This is why I decided to limit my number of project to a handful that I really wish existed, and slowly update them over time - fixing bugs, adding new features in hopes of making them the best tools - not only on nostr but the internet in general. As you can imagine this is not a small task, especially for sporadic vibe coding.
Fighting the bot
One of my biggest challenges so far besides having very limited time is getting the bot to do what I want it to do. I guess if you've done any vibe coding at all you're probably familiar with what I'm trying to say. You prompt one thing and get a hallucinated response, or worse, a complete mess out the other end that undoes most of the progress you've made. Once the initial thing is created, which barely took any time, now you're faced with making it work a certain way. This is where the challenges arise.
Here's a brief list of issues I've faced when vibe-coding with various tools:
1. Runaway expenses - tools like Cline tend to do a better job directly in VSCode, but they can also add up dramatically. Before leaning into v0 (which is where I do most of my vibe coding now), I would often melt through $10 credit purchases faster than I could get a decent feature out. It was not uncommon for me to spend $20-30 on a weekend just trying to debug a handful of issues. Naturally, I did not wish to pay these fees so I searched for alternatives.
2. File duplication - occasionally, seemingly out of nowhere, the bot will duplicate files by creating an entire new copy and attached "-fixed" to the file name. Clearly, I'm not asking for duplicate files, I just want it to fix the existing file, but it does happen and it's super annoying. Then you are left telling it which version to keep and which one to delete, and sometimes you have to be very precise or it'll delete the wrong thing and you have to roll back to a previous working version.
3. Code duplication - similar to file duplication, occasionally the bot will duplicate code and do things in the most unintuitive way imaginable. This often results in loops and crashes that can take many refreshes just to revert back to a working state, and many more prompts to avoid the duplication entirely - something a seasoned dev never has to deal with (or so I imagine).
4. Misinterpreting your request - occasionally the bot will do something you didn't ask for because it took your request quite literally. This tends to happen when I give it very specific prompts that are targeted at fixing one very specific thing. I've noticed the bots tend to do better with vague asks - hence a pretty good result on the initial prompt.
5. Doing things inefficiently, without considering smarter approaches - this one is the most painful of vibe coding issues. As a person who may not be familiar with some of the smarter ways of handling development, you rely on the bot to do the right thing. But, when the bot does something horribly inefficiently and you are non-the-wiser, it can be tough to diagnose the issue. I often fight myself asking the bot "is this really the best way to handle things? Can't we ... / shouldn't we .../ isn't this supposed to..." etc. I guess one of the nice side effects of this annoyance is being able to prompt better. I learn that I should ask the bot to reflect on its own code more often and seek ways to do things more simply.
A combination of the above, or total chaos - this is a category where all hell breaks loose and you're trying to put out one fire after another. Fix one bug, only to see 10 more pop up. Fix those, to see 10 more and so on. I guess this may sound like typical development, but the bot amplifies issues by acting totally irrationally. This is typically when I will revert to a previous save point and just undo everything, often losing a lot of progress.
Lessons Learned
If I had to give my earlier self some tips on how to be a smarter vibe coder, here's how I'd summarize them:
-
Fork often - in v0 I now fork for any new major feature I'd like to add (such as the AI assistant).
-
Use targeting tools - in v0 you can select elements and describe how you wish to edit them.
-
Refactor often - keeping the code more manageable speeds up the process. Since the bot will go through the entire file, even if it only makes one small change, it's best to keep the files small and refactoring achieves that.
I guess the biggest lesson someone might point out is just to stop vibe coding. It may be easier to learn proper development and do things right. For me it has been a spare time hobby (one that I will admit is taking more of my extra time than I'd like). I don't really have the time to learn proper development. I feel like I've learned a lot just bossing the bot around and have learned a bunch of things in the process. That's not to say that I never will, but for the moment being my heart is still mostly in design. I haven't shared much of anything I have designed recently - mostly so I can remain speaking more freely without it rubbing off on my work.
I'll go ahead and try to publish this to see if it actually works 😂. Here goes nothing... (oh, I guess I could use the latest feature to export as markdown so I don't lose any progress! Yay!
-
-
 @ 866e0139:6a9334e5
2025-04-21 06:47:57
@ 866e0139:6a9334e5
2025-04-21 06:47:57Autor: Milosz Matuschek. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Sie wollen die neuesten Pareto-Artikel auf einen Blick sehen (Friedenstaube & Co.), um nichts mehr zu verpassen?* Hier geht es zu unserem Telegram-Kanal.***
An Ostern begehen Christen das Hochamt ewiger Ideale. In Kirchen, die zu Hochzeiten der Pandemie geschlossen, später für Impfkampagnen wieder geöffnet wurden, wird der Sieg des Lebens über den Tod beschworen. Der Aufstand des Geistes gegen die Materie. Doch wie steht es um die Revolte des Geistes in einer Welt, die den Menschen zunehmend in die Rolle eines verwalteten Tieres drängt?
Die Revolte der Normalen
Albert Camus, einer der klarsten Köpfe des 20. Jahrhunderts, wusste: Nur wer an etwas glaubt, revoltiert. Der Revoltierende sagt Nein zu Unterdrückung und Ja zur Würde. Ohne Glauben an Werte vergiftet sich der Mensch am Ressentiment – jener toten Emotion, die weder schöpft noch heilt, sondern nur vernichtet. Oder versinkt im Nihilismus. Dieser greift auch heute um sich. Deutschland, deine Leuchttürme sind Irrlichter geworden. Inmitten einer Dauerkrise, die jeden Normalzustand zersetzt, bleibt eine Frage offen: Wie gesund bleibt der Mensch in einem kranken System? Wie lange dauert es, bis Normalität selbst als Revolte gilt?
Camus schrieb:
„Wenn man an nichts glaubt, wenn nichts Sinn hat und wir keinen Wert konstatieren können, dann ist alles möglich und nichts hat Bedeutung.“
In einer Welt, in der Gesundheitspolitik zur Farce, Wissenschaft zur Ideologie und Aufarbeitung zur Fortsetzung der Propaganda mutiert, wird die Revolte der Normalen zur letzten Verteidigungslinie der Freiheit.
https://www.youtube.com/watch?v=Y2roiEvbPuU
Das Leid der Revoltierenden
Die Revolte ist kein Spaziergang. Sie schmerzt. Sie kostet Freunde, Ansehen, Karriere. Aber sie schenkt eine ungeahnte Kraft: Die Entdeckung, dass der Impuls zum Leben stärker ist als zum Tod. Das Wunder von Ostern, die Auferstehung, ist im Innersten die Revolte der Lebendigkeit gegen die Herrschaft des Todes. Der Märtyrer Jesus nimmt die Sünden und Leiden der Welt auf sich – ein menschgewordener Widerstand, der durch seine Hingabe unsterblich wird.
Sein "Verbrechen"? Er stellte sich zugleich gegen die geistige und politische Elite seiner Zeit. Gegen Besatzer, Schriftgelehrte, Pharisäer, Frühbürger. Heute wäre Jesus wohl ein Querdenker, ein Reichgottesbürger, ein Verschwörungstheoretiker. Mindestens ein Rechter. Vielleicht ein antisemitischer Spinner, der es wagte, eine Alternative zum bestehenden Glaubenssystem zu etablieren.
„Wer an mich glaubt, wird leben“, sagte Jesus. Man kann es so lesen:\ Wer an die verkörperten Werte glaubt – Wahrheit, Freiheit, Liebe –, wird leben. Denn wer an einen Wert glaubt, macht ihn lebendig. Der Nihilist hingegen fügt sich ein, wird Stein in der Mauer des Systems.
Camus brachte es auf den Punkt:
„Lieber stehend sterben als knieend leben.“
In Zeiten, in denen Friedenstreiber als Nazis diffamiert werden und Protestierende als Pathologische gelten, bleibt die stille Revolte des Individuums das letzte unzerstörbare Element.
Die Psy-Op der Aufarbeitung
Nach der Inszenierung des Corona-Spektakels erleben wir die nächste Bühne: Die Aufarbeitung durch die Täter selbst. Eine theatralische Umarmung des eigenen Versagens, mit Bundesverdienstkreuz und Download-Gesichtsausdruck bei Frau Buyx inklusive. Wenn Corona eine Psy-Op war, warum sollte nicht auch seine Aufarbeitung Teil der Psy-Op sein? Die Strukturen erinnern an Rosenhan, Milgram und das Stanford Prison Experiment:
- Etikettierung der Kritiker als Verrückte.
- Pathologisierung der Revolte als Krankheit.
- Belohnung der Kollaborateure mit Orden und Posten.
Ein Lehrbuch der totalitären Psychologie.
https://www.youtube.com/watch?v=XTBYWPLXrTk
Immunologische Reaktionen eines sterbenden Systems
Während die Panzer-Osterhasen rollen, also die Neuvariante des Impfspritzbesteck-Gebäcks der letzten Krise, offenbart sich die Wahrheit: Das System hat seine eigene Bevölkerung beschossen. Friendly Fire unter falscher Flagge.\ Kollateralschaden im Namen von Volksgesundheit und Solidarität.

Jetzt dasselbe nochmal in Tarnfleck statt Weißkittel.
Was bleibt?
Demut.\ Selbstständigkeit.\ Verbindungen, die nicht von Zertifikaten abhängen.\ Der stille Aufbau von Netzwerken jenseits der Anstaltsordnung.
Unabhängiger machen kann man sich zum Beispiel bei Vorträgen und Seminaren von Michael Ballweg, der immer noch in einen kafkaesken Prozess verwickelt ist.
Meine Stimme erhebe ich in Zukunft auch mit der FSUS (Free Speech Union Switzerland) im Rücken, einem Verein der u.a. Rechtshilfe für verfolgte Freiredner organisiert. Bei Interesse an einer Mitgliedschaft erfahren Sie hier mehr.
Oder wie manche sagen: “Buy Bitcoin and focus on your craft.”
Die letzte Revolte
Wer heute zweifelt, beweist Charakter.\ Wer heute fragt, zeigt Rückgrat.\ Wer heute eigene Gedanken wagt, revoltiert bereits.
Wenn wir uns verbinden, werden wir das neue Gesicht der Welt.
Ostern erinnert uns daran:\ Die größte Revolte ist das Aufstehen in einer Welt, die uns niederdrücken will.
Nicht die angepasstesten überleben, sondern die Standhaftesten.\ Nicht die Lautesten, sondern die Wahrhaftigsten.\ Nicht die, die folgen, sondern die, die aufstehen.
In diesem Sinne:
Frohe Auferstehung.
https://www.youtube.com/watch?v=vbH9YacSi2o
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ 3f770d65:7a745b24
2025-04-21 00:15:06
@ 3f770d65:7a745b24
2025-04-21 00:15:06At the recent Launch Music Festival and Conference in Lancaster, PA, featuring over 120 musicians across three days, I volunteered my time with Tunestr and Phantom Power Music's initiative to introduce artists to Bitcoin, Nostr, and the value-for-value model. Tunestr sponsored a stage, live-streaming 21 bands to platforms like Tunestr.io, Fountain.fm and other Nostr/Podcasting 2.0 apps and on-boarding as many others as possible at our conference booth. You may have seen me spamming about this over the last few days.
V4V Earnings
Day 1: 180,000 sats
Day 2: 300,000 sats
Day 3: Over 500,000 sats
Who?
Here are the artists that were on-boarded to Fountain and were live streaming on the Value-for-Value stage:
nostr:npub1cruu4z0hwg7n3r2k7262vx8jsmra3xpku85frl5fnfvrwz7rd7mq7e403w nostr:npub12xeh3n7w8700z4tpd6xlhlvg4vtg4pvpxd584ll5sva539tutc3q0tn3tz nostr:npub1rc80p4v60uzfhvdgxemhvcqnzdj7t59xujxdy0lcjxml3uwdezyqtrpe0j @npub16vxr4pc2ww3yaez9q4s53zkejjfd0djs9lfe55sjhnqkh nostr:npub10uspdzg4fl7md95mqnjszxx82ckdly8ezac0t3s06a0gsf4f3lys8ypeak nostr:npub1gnyzexr40qut0za2c4a0x27p4e3qc22wekhcw3uvdx8mwa3pen0s9z90wk nostr:npub13qrrw2h4z52m7jh0spefrwtysl4psfkfv6j4j672se5hkhvtyw7qu0almy nostr:npub1p0kuqxxw2mxczc90vcurvfq7ljuw2394kkqk6gqnn2cq0y9eq5nq87jtkk nostr:npub182kq0sdp7chm67uq58cf4vvl3lk37z8mm5k5067xe09fqqaaxjsqlcazej nostr:npub162hr8kd96vxlanvggl08hmyy37qsn8ehgj7za7squl83um56epnswkr399 nostr:npub17jzk5ex2rafres09c4dnn5mm00eejye6nrurnlla6yn22zcpl7vqg6vhvx nostr:npub176rnksulheuanfx8y8cr2mrth4lh33svvpztggjjm6j2pqw6m56sq7s9vz nostr:npub1akv7t7xpalhsc4nseljs0c886jzuhq8u42qdcwvu972f3mme9tjsgp5xxk nostr:npub18x0gv872489lrczp9d9m4hx59r754x7p9rg2jkgvt7ul3kuqewtqsssn24
Many more musicians were on-boarded to Fountain, however, we were unable to obtain all of their npubs.
THANK YOU TO ALL ZAPPERS AND BOOSTERS!
Musicians “Get It”
My key takeaway was the musicians' absolute understanding that the current digital landscape along with legacy social media is failing them. Every artist I spoke with recognized how algorithms hinder fan connection and how gatekeepers prevent fair compensation for their work. They all use Spotify, but they only do so out of necessity. They felt the music industry is primed for both a social and monetary revolution. Some of them were even speaking my language…
Because of this, concepts like decentralization, censorship resistance, owning your content, and controlling your social graph weren't just understood by them, they were instantly embraced. The excitement was real; they immediately saw the potential and agreed with me. Bitcoin and Nostr felt genuinely punk rock and that helped a lot of them identify with what we were offering them.
The Tools and the Issues
While the Nostr ecosystem offers a wide variety of tools, we focused on introducing three key applications at this event to keep things clear for newcomers:
- Fountain, with a music focus, was the primary tool for onboarding attendees onto Nostr. Fountain was also chosen thanks to Fountain’s built-in Lightning wallet.
- Primal, as a social alternative, was demonstrated to show how users can take their Nostr identity and content seamlessly between different applications.
- Tunestr.io, lastly was showcased for its live video streaming capabilities.
Although we highlighted these three, we did inform attendees about the broader range of available apps and pointed them to
nostrapps.comif they wanted to explore further, aiming to educate without overwhelming them.This review highlights several UX issues with the Fountain app, particularly concerning profile updates, wallet functionality, and user discovery. While Fountain does work well, these minor hiccups make it extremely hard for on-boarding and education.
- Profile Issues:
- When a user edits their profile (e.g., Username/Nostr address, Lightning address) either during or after creation, the changes don't appear to consistently update across the app or sync correctly with Nostr relays.
- Specifically, the main profile display continues to show the old default Username/Nostr address and Lightning address inside Fountain and on other Nostr clients.
- However, the updated Username/Nostr address does appear on https://fountain.fm (chosen-username@fountain.fm) and is visible within the "Edit Profile" screen itself in the app.
- This inconsistency is confusing for users, as they see their updated information in some places but not on their main public-facing profile within the app. I confirmed this by observing a new user sign up and edit their username – the edit screen showed the new name, but the profile display in Fountain did not update and we did not see it inside Primal, Damus, Amethyst, etc.
- Wallet Limitations:
- The app's built-in wallet cannot scan Lightning address QR codes to initiate payments.
- This caused problems during the event where users imported Bitcoin from Azte.co vouchers into their Fountain wallets. When they tried to Zap a band by scanning a QR code on the live tally board, Fountain displayed an error message stating the invoice or QR code was invalid.
- While suggesting musicians install Primal as a second Nostr app was a potential fix for the QR code issue, (and I mentioned it to some), the burden of onboarding users onto two separate applications, potentially managing two different wallets, and explaining which one works for specific tasks creates a confusing and frustrating user experience.
- Search Difficulties:
- Finding other users within the Fountain app is challenging. I was unable to find profiles from brand new users by entering their chosen Fountain username.
- To find a new user, I had to resort to visiting their profile on the web (fountain.fm/username) to retrieve their npub. Then, open Primal and follow them. Finally, when searching for their username, since I was now following them, I was able to find their profile.
- This search issue is compounded by the profile syncing problem mentioned earlier, as even if found via other clients, their displayed information is outdated.
- Searching for the event to Boost/Zap inside Fountain was harder than it should have been the first two days as the live stream did not appear at the top of the screen inside the tap. This was resolved on the third day of the event.
Improving the Onboarding Experience
To better support user growth, educators and on-boarders need more feature complete and user-friendly applications. I love our developers and I will always sing their praises from the highest mountain tops, however I also recognize that the current tools present challenges that hinder a smooth onboarding experience.
One potential approach explored was guiding users to use Primal (including its built-in wallet) in conjunction with Wavlake via Nostr Wallet Connect (NWC). While this could facilitate certain functions like music streaming, zaps, and QR code scanning (which require both Primal and Wavlake apps), Wavlake itself has usability issues. These include inconsistent or separate profiles between web and mobile apps, persistent "Login" buttons even when logged in on the mobile app with a Nostr identity, and the minor inconvenience of needing two separate applications. Although NWC setup is relatively easy and helps streamline the process, the need to switch between apps adds complexity, especially when time is limited and we’re aiming to showcase the benefits of this new system.
Ultimately, we need applications that are more feature-complete and intuitive for mainstream users to improve the onboarding experience significantly.
Looking forward to the future
I anticipate that most of these issues will be resolved when these applications address them in the near future. Specifically, this would involve Fountain fixing its profile issues and integrating Nostr Wallet Connect (NWC) to allow users to utilize their Primal wallet, or by enabling the scanning of QR codes that pay out to Lightning addresses. Alternatively, if Wavlake resolves the consistency problems mentioned earlier, this would also significantly improve the situation giving us two viable solutions for musicians.
My ideal onboarding event experience would involve having all the previously mentioned issues resolved. Additionally, I would love to see every attendee receive a $5 or $10 voucher to help them start engaging with value-for-value, rather than just the limited number we distributed recently. The goal is to have everyone actively zapping and sending Bitcoin throughout the event. Maybe we can find a large sponsor to facilitate this in the future?
What's particularly exciting is the Launch conference's strong interest in integrating value-for-value across their entire program for all musicians and speakers at their next event in Dallas, Texas, coming later this fall. This presents a significant opportunity to onboard over 100+ musicians to Bitcoin and Nostr, which in turn will help onboard their fans and supporters.
We need significantly more zaps and more zappers! It's unreasonable to expect the same dedicated individuals to continuously support new users; they are being bled dry. A shift is needed towards more people using bitcoin for everyday transactions, treating it as money. This brings me back to my ideal onboarding experience: securing a sponsor to essentially give participants bitcoin funds specifically for zapping and tipping artists. This method serves as a practical lesson in using bitcoin as money and showcases the value-for-value principle from the outset.
-
 @ ec42c765:328c0600
2024-12-13 08:16:32
@ ec42c765:328c0600
2024-12-13 08:16:32Nostr Advent Calendar 2024 の 12日目の記事です。
昨日の 12/11 は きりの さんの 2024年のNostrリレー運営を振り返る でした。
nostr-zap-view 作った
リポジトリ: https://github.com/Lokuyow/nostr-zap-view/
動作確認ページ: https://lokuyow.github.io/nostr-zap-view/それ何?
特定の誰かや何かに宛てたZap(投げ銭)を一覧できるやつ
を
自分のWebサイトに設置できるやつ
自分のサイトに設置した例 * SNSリンク集ページ(最下部): https://lokuyow.github.io/
おいくらサッツ(Zap一覧ボタン): https://osats.money/
今日からビットコ(最下部): https://lokuyow.github.io/btc-dca-simulator/なんで作ったの?
私の去年のアドベントカレンダー
【Nostr】Webサイトにビットコインの投げ銭ボタンを設置しよう【Zap】
https://spotlight.soy/detail?article_id=ucd7cbrql/
が前提になってるけど長いので要約すると * ZapするやつはあるけどZap見るやつがないので欲しい * ZapをNostr(の典型的なkind:1クライアント)内だけに留めるのはもったいない * Webサイトの広告うざいからZap(的な何か)で置き換わって欲しいお前だれ?
非エンジニア、非プログラマー
AIにコード出させてるだけ人作った感想
できた
作った感想2
完成してから気付いた本当に作りたかったもの
こういうところにそのままZapを表示できる感じにしたい
 (ここまでちゃんとした商業ブログでなく)個人のブログやHPの端っこに「Sponsored by」欄があって名前が表示される感じ
(ここまでちゃんとした商業ブログでなく)個人のブログやHPの端っこに「Sponsored by」欄があって名前が表示される感じ
もうZapっていう文字もビットコインっていう文字もNostrも出さなくていいし説明もしなくていいのでは感がある
イメージはWebサイトを対象にしたニコニ広告 + スーパーチャット + 祭りとか神社の奉納者一覧
で思ったのは
個人からの投げ銭なら推し活的なものにしかならないけど
企業がNostrにアカウントを作ってサイトに投げ銭をしたら企業の広告になるんでは!?
~~企業がNostrにアカウントを!?デリヘルしか見たことない!~~今後
思いつき、予定は未定
* ボタン→ダイアログ形式でなくバナー、Embed形式にしてページアクセスですぐ見れるようにする * 多分リレーに負荷がかかるのでなんかする * Zapの文字は出さず「Sponsored by」等にする * 単純な最新順でなくする * 少額Zapをトリミング * 一定期間(一か月など)ごとで金額順にソート * 多分リレーに負荷がかかるのでなんかする * 今は投稿宛てのZapをWebサイト宛てのZapと勝手に言い張ってるだけなのでちゃんとWebサイト宛てのZapにする * NIPの提案が必要 * ウォレットの準拠も必要 * リレー(wss://~)宛てのZapもできてほしい将来
インターネットのすべてに投げ銭をさせろ
おわり
明日は mono さんの Open Sats 申請編 です!!
-
 @ dfa02707:41ca50e3
2025-04-16 05:30:53
@ dfa02707:41ca50e3
2025-04-16 05:30:53Contribute to keep No Bullshit Bitcoin news going.
- This release eliminates UPnP support in favor of NAT-PMP/PCP, enhances transaction orphan handling for improved reliability, and introduces ephemeral dust to defer fee commitment.
- Various RPCs now feature enhanced error reporting and new data fields, the block size handling bug related to reserved weight has been fixed, and the removal of the
mempoolfullrbfoption standardizes full replace-by-fee behavior. - With this new major release, versions 26.x and older have reached "Maintenance End" and will no longer receive updates. Two weeks after this release, medium and high severity vulnerabilities affecting 26.x will be disclosed, as well as low severity vulnerabilities affecting 28.x, in line with the security policy.
What's new
-
P2P and Network Changes:
- Support for UPnP has been dropped in favor of a more modern NAT-PMP/PCP implementation.
-
Added support for PCP & IPv6 pinholing.
libnatpmpwas replaced with built-in NAT-PMP/PCP implementation, enabled via-natpmp, which supports IPv4 port forwarding and IPv6 pinholing. - A change in assigning onion listening ports. Now, when using the
-portconfiguration option, the default onion listening port will be set to the specified port +1, rather than a fixed value like 8334 on mainnet.
"This re-allows setups with multiple local nodes using different
-portand not using-bind, which would lead to a startup failure in v28.0 due to a port collision," was explained in the release notes.-
More reliable orphan handling. When a node receives an orphan transaction (an unconfirmed transaction that spends unknown inputs), it will attempt to download missing parents from peers who announced the orphan, potentially increasing bandwidth but enhancing handling of orphan transactions.
-
Mempool Policy and Mining Changes:
- Relay transaction packages containing ephemeral dust. An ephemeral dust output is a tiny transaction output, below the dust limit, produced in a v3 zero-fee transaction and consumed in a following v3 transaction. These transactions occur within the same package, making the output temporary since it is both generated and spent at once. It is useful for Lightning network, Ark, ln-symmetry, Spacechains, Timeout Trees, and other constructs.
-
New startup option -blockreservedweight. In versions before 29.0, a bug limited actual block sizes to 3,992,000 WU by setting a default reserved weight of 8,000 WU for block headers and transactions. The fix adds a new option, -blockreservedweight, with the same default for compatibility.
-
New RPCs:
getdescriptoractivityto track activity of a given set of descriptors. It helps identify all spending and receiving activities for specific descriptors within chosen blocks, and can be used withscanblocksto reduce reliance on additional indexing programs.
-
Updated RPCs:
- Enhanced RPC Response: testmempoolaccept now includes Reject Details. Bitcoin Core 29.0 adds a verbose
reject-detailsfield to thetestmempoolacceptRPC, detailing rejections likeinsufficient-fee. - Persistent block data for duplicate submitblock submissions. Duplicate blocks submitted via
submitblockwill now retain their data even if previously pruned. If pruning is enabled, the data will eventually be pruned again when its block file is selected for pruning.
- Enhanced RPC Response: testmempoolaccept now includes Reject Details. Bitcoin Core 29.0 adds a verbose
-
Updated
getmininginfo. Thegetmininginfonow includesnBitsand the current target in thetargetfield. It also serves anextobject, detailing theheight,nBits,difficulty, andtargetfor the upcoming block. getblockandgetblockheadernow return the current target in thetargetfield.getblockchaininfoandgetchainstatesnow returnnBitsand the current target in thetargetfield.-
getblocktemplateRPC now considers BIP94 Timewarp Fix. ThegetblocktemplateRPC now considers the timewarp fix from BIP94 for thecurtime(BIP22) andmintime(BIP23) fields across all networks. This change helps prevent un-upgraded miners from unintentionally breaching the timewarp rule if a timewarp fix softfork activates on the mainnet. -
Updated REST APIs:
- Get block and Get headers return target in the target field. The
GET /rest/block/<BLOCK-HASH>.jsonandGET /rest/headers/<BLOCK-HASH>.jsonnow return the current target in thetargetfield.
- Get block and Get headers return target in the target field. The
-
Updated Settings:
- Replace-by-fee the standard. From version v28.0, the
-mempoolfullrbfoption was set to default to 1. Due to widespread policy adoption, this option has been removed, making full replace-by-fee the standard behavior. - The maximum limit for the
-dbcacheconfiguration option has been removed due to recent UTXO set growth. Previously, large-dbcachevalues were automatically capped at 16 GiB (or 1 GiB on 32-bit systems). - The handling of negated options like
-noseednode,-nobind,-nowhitebind, and others has been improved. Now, negating these options simply resets them to their defaults, removing previous confusing and undocumented effects. - Using the
-upnpoption will now log a warning and be treated as-natpmp. It's recommended to use-natpmpdirectly instead.
- Replace-by-fee the standard. From version v28.0, the
-
Bitcoin Core will not start if the
-blockreservedweightparameter is set below 2,000 WU. It will also fail to start if either-blockmaxweightor-blockreservedweightexceeds the consensus limit of 4,000,000 WU. -
Using
-debug=0or-debug=nonenow works like-nodebug. It clears previously set debug categories while allowing later-debugoptions to be applied. -
The default value for
-rpcthreadshas increased from 4 to 16, and-rpcworkqueuehas been updated from 16 to 64. -
Build System:
- The build system has been migrated from Autotools to CMake. The minimum required CMake version is 3.22.
"For more detailed guidance on configuring and using CMake, please refer to the official CMake documentation and CMake’s User Interaction Guide. Additionally, consult platform-specific
doc/build-*.mdbuild guides for instructions tailored to your operating system."- Tools and Utilities:
- The new tool
utxo_to_sqlite.pyconverts a compact-serialized UTXO snapshot, created using thedumptxoutsetRPC, into a SQLite3 database. Check the script's--helpoutput for more information.
- The new tool
- Testing:
- The BIP94 timewarp attack mitigation (designed for testnet4) is no longer active on the regtest network.
- Dependencies:
- MiniUPnPc and libnatpmp have been removed as dependencies.

For more information on the new features, improvements, and bug fixes in this release, refer to the full release notes. Additionally, the detailed v29 testing guide provides steps for testing the latest features.
"Thanks to everyone who directly contributed to this release, including 0xb10c, Adlai Chandrasekhar, Afanti, Alfonso Roman Zubeldia, am-sq, Andre, Andre Alves, Anthony Towns, Antoine Poinsot, Ash Manning, Ava Chow, Boris Nagaev, Brandon Odiwuor, brunoerg, Chris Stewart, Cory Fields, costcould, Daniel Pfeifer, Daniela Brozzoni, David Gumberg, dergoegge, epysqyli, espi3, Eval EXEC, Fabian Jahr, fanquake, furszy, Gabriele Bocchi, glozow, Greg Sanders, Gutflo, Hennadii Stepanov, Hodlinator, i-am-yuvi, ion-, ismaelsadeeq, Jadi, James O’Beirne, Jeremy Rand, Jon Atack, jurraca, Kay, kevkevinpal, l0rinc, laanwj, Larry Ruane, Lőrinc, Maciej S. Szmigiero, Mackain, MarcoFalke, marcofleon, Marnix, Martin Leitner-Ankerl, Martin Saposnic, Martin Zumsande, Matthew Zipkin, Max Edwards, Michael Dietz, naiyoma, Nicola Leonardo Susca, omahs, pablomartin4btc, Pieter Wuille, Randall Naar, RiceChuan, rkrux, Roman Zeyde, Ryan Ofsky, Sebastian Falbesoner, secp512k2, Sergi Delgado Segura, Simon, Sjors Provoost, stickies-v, Suhas Daftuar, tdb3, TheCharlatan, tianzedavid, Torkel Rogstad, Vasil Dimov, wgyt, willcl-ark, yancy, and everyone who assisted with translations on Transifex."
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ a296b972:e5a7a2e8
2025-04-15 19:15:22
@ a296b972:e5a7a2e8
2025-04-15 19:15:22Heute traue ich mich einmal eine steile These aufzustellen, auch auf die Gefahr hin, dass sich herausstellen kann, dass ich völlig daneben liege.
Die USA sind federführend in der Gain-of-Function Forschung. Warum einige Dr. Frankensteins auf die Idee gekommen sind, an Viren, Bakterien und Sporen herumzubasteln, damit sie noch gefährlicher werden, erschließt sich mir nicht.
Wie andere Verrückte zum Beispiel in 2001 auf die Idee kommen konnten, Milzbrandsporen (Anthrax) in Brieflein an US-Abgeordnete zu verschicken, kann meine einfach gestrickte Seele auch nicht nachvollziehen.
So oder so kann man bei solchen Beispielen in Zweifel kommen, ob der Mensch wirklich von Natur aus gut ist.
Unter Präsident Obama, der den Friedensnobelpreis nach Ansicht vieler zu Unrecht erhalten hat, wurde die Gain-of-Function Forschung in den USA verboten.
Bekannt für seine Outsourcing-Künste, zum Beispiel im Austragen von Kriegen außerhalb des eigenen Territoriums, aktuell im Stellvertreterkrieg der USA mit Russland in der Ukraine, wurde nach Möglichkeiten gesucht, die Forschung im Ausland weiter zu betreiben.
So entstand das durch Corona bekannt gewordene Labor in Wuhan und auch einige geheime Labore in der… Ukraine!
In einem leider nicht mehr auffindbaren Video berichtete ein italienischer Professor davon, dass es immer ein Labor gibt, dass an einer Bio-Waffe (wie in Wuhan) arbeitet, und ein Labor, das parallel dazu an dem entsprechenden Gegengift, dem „Impfstoff“ arbeitet. Das Antilabor zum Corona-Virus sollte sich wohl ebenfalls in China an der Grenze zu Russland befinden, allerdings mit der Entwicklung eines Gegengifts noch nicht so weit vorangekommen sein, wie die Hexenküche in Wuhan.
Jetzt kommt „Der Schlund“, „Das Maul“, also Signore Fauci, USA, der größte Bio-Waffen-Verbrecher aller Zeiten ins Spiel. Seit vielen Jahren ist er sowohl für die Bereitstellung von Geldern für die Virenforschung, als auch für die Herstellung eines Impfstoffs zuständig. Er zeigt mit dem Daumen nach oben oder nach unten. Man munkelt, dass er auch Verbindungen zu den US-amerikanischen Geheimdiensten und anderen hat. Naheliegend wäre es.
In ihrer unendlichen „Aufopferung“ für die Menschheit und zu deren Wohl wurden vorsorglich Planspiele gehalten. Die deuten darauf hin, dass man einen Unfall in des Teufels Küche nicht gänzlich ausschließen konnte. Das es auch mehrere Planspiele für den Umgang mit einer „Pandemie“ gab, ist wohl mittlerweile jedem bekannt. Es liegt nahe, dass es sich bei diesen Übungen eigentlich um ein verdecktes Planspiel für den Fall handelte, dass ein gefährlicher gemachtes Virus, das so in der Natur nicht vorkommt, aus einer Giftküche entwischt, wie die Menschen darauf reagieren würden und welche Maßnahmen zu ergreifen wären.
Professor Wiesendanger hat schon ganz zu Anfang der gemachten Welt-Hysterie darauf hingewiesen, dass das Corona-Virus eine Furin-Spaltstelle hat, die so in der Natur gar nicht vorkommt. Damals als Schwurbler denunziert, berichtet der sogenannte Mainstream inzwischen auch davon, dass die Wahrscheinlichkeit, dass das Virus aus einem Labor stammt, fast gegen 100 % geht, und verkauft das als die neueste Erkenntnis, obwohl es schon ein alter Hut ist, wenn man seinerzeit Professor Wiesendanger ernst genommen hätte. Warum man das nicht konnte, klärt sich später noch.
Man kann also davon ausgehen, dass von Anfang an bekannt war, dass das Corona-Virus NICHT von einer Fledermaus auf den Menschen übergesprungen ist (Zoonose), sondern dieses Märchen eher als Ablenkungsmanöver gedacht war.
So ist es gelungen, den Ausbruch eines durch Wahnsinnige geschaffenen Homunculus-Virus, also eine Bio-Waffe, in eine die Menschheit bedrohende Pandemie umzuetikettieren. Und weil man in der Wissenschaft und Politik nicht einschätzen konnte, wie gefährlich dieser von Menschenhand geschaffene Dreck ist, wollte man auf Nummer sicher gehen. Das würde die hysterischen Maßnahmen und die mit der heißen Nadel gestrickten Genbehandlungen erklären. Man wollte sich hinterher nicht vorhalten lassen, das Falsche oder zu wenig unternommen zu haben, falls es zu einem Massensterben kommen würde.
Das wiederum würde auch erklären, warum gleich zu Anfang das Militär mit einbezogen wurde, weil dies sich mit der Abwehr von (Bio-)Waffen am besten auskennt.
Glücklicherweise stellte sich schnell heraus, dass die Giftmischer doch noch nicht so erfolgreich waren, wie man zu Anfang befürchtet hatte, aber da war die Lawine schon ins Rollen gekommen, und es gab kein Zurück mehr.
Zu Anfang könnte man sich sogar vorstellen, dass die Politiker in bester Absicht gehandelt haben und die Menschen in der Tat schützen wollten: „Wir wollen euch „retten, bitte vertraut uns, die Maßnahmen sind nicht zu hinterfragen (aber wir können euch nicht sagen warum, nämlich das eine Bio-Waffe entwischt ist, von der wir nicht wissen, was sie anrichten wird).
Das würde erklären, warum die „Impfkritiker“ so derartig diffamiert wurden und versucht wurde, sie mundtot zu machen. Sie haben gleich schon zu Anfang die von Seiten der Entscheider notwendigen Maßnahmen infrage gestellt, als man sich von offizieller Seite noch nicht sicher war, dass die Gefahr in der Tat geringer ist, als es falsche Propheten mit unlauteren Interessen den Politikern nach dem Mund geredet und ins Ohr geflüstert haben.
Doch dann hat sich die Lage verselbständigt und es wurde der Zeitpunkt verpasst, zurückzurudern. Die Folge war das in deren Augen, dass es immer noch besser war, den Menschen eine experimentelle Genbehandlung, die natürlich nicht so genannt werden konnte, „anzubieten“, als gar nichts. Einen wirklichen Impfstoff gab es ja noch nicht. Der war ja, entgegen der fertigen Biowaffe noch gar nicht entwickelt und erprobt. Es herrschte die große Angst seitens der Entscheidungsträger, dass man hinterher zur Rechenschaft gezogen werden könnte, weil man nicht mehr gemacht hat (als, wie sich dann später herausgestellt hat) nötig war.
Die Hysterie ging dann soweit, dass in vielen Ländern eine Impfpflicht drohte und in einigen Ländern sogar durchgesetzt, aber gottseidank nicht vollends durchgezogen wurde.
Als dann im Laufe der Jahre die Erkenntnisse so weit vorangeschritten waren, dass sich der Terror, die Aushebelung von Grundrechten und die Aushöhlung der Demokratie, die Maßnahmen und absurdesten Freiheitseinschränkungen in der Rückschau absurd wurden, entschied man sich, dass es besser sei weiter zu lügen, statt diesen Riesenfehler einzugestehen, bis heute nicht, weil sonst weltweit Köpfe gerollt wären. Vielleicht fürchtete man Regierungsumstürze und eine weltweite Revolution, die den Planeten ins totale Chaos geführt hätte.
Auch die weltweit orchestrierte Vorgehensweise und der oft gleichlautende Wortlaut in verschiedenen Sprachen zu den Informationen zu Corona spricht für eine im Hintergrund agierende militärische Organisation, wohlmöglich sogar mit Beteiligung der NATO. Und auf Regierungsebene kennt man sich auch untereinander.
Die Regierungen hatten Angst, dass die im Verborgenen tätigen Hexenküchen bekannt werden. Die Gefahr, die von diesen Gift-Laboren ausgeht, durfte unter keinen Umständen ans Tageslicht kommen. Was möglich war, musste unter den Teppich gekehrt, oder verharmlost werden. Nicht ohne Grund fordert Professor Wiesendanger das weltweite Verbot von Gain-of-Function Forschung.
Zu allem Übel kam noch dazu, dass hinter all dem eine Menge Geld steckt und den verborgenen Strippenziehern drohte, sehr viel Geld zu verlieren. Sie schafften es ja sogar, die Haftung für die Gift-Jauche auf den Staat zu übertragen.
So erklärt sich auch, dass bis heute Gerichtsurteile gefällt werden, die bar jeder Vernunft sind.
Bekämen Kläger zu oft Recht, wäre das in vielen Staaten eine Bankrotterklärung. So wird weiter kräftig gelogen, weil man sonst zugeben müsste, welchen Schaden der staatlich verordnete Wahnsinn mithilfe von weltweit agierenden Organisationen, wie die WHO, angerichtet hat.
Vielleicht wäre es gut, wir würden uns von der Vorstellung verabschieden, dass von offizieller Seite eine wirkliche Aufarbeitung erfolgen wird. Es gibt weltweit Ansätze, es kann aber sein, dass diese zu keinen vollumfänglichen Ergebnissen führen werden. In Talkshows werden dieselben Verbrecher eingeladen, die den Schaden verursacht haben. Die einst hochangesehenen Herren Ioannidis, Bhakdi, Wodarg und viele, viele andere, sind nach wie vor im Staatsfernsehen nicht zu sehen.
Dafür gibt es eine umfassende Aufklärung in der sogenannten Blase. Wenn auch nicht von „offizieller“ Seite verkündet, liegen die Beweise dank immenser Arbeit von ungezählten Experten, die nicht an irgendeinem staatlichen Geldhahn hängen und sich der Wahrheit verpflichtet haben, auf dem Tisch.
Diese Tatsachenwahrheiten werden vielleicht erst in der nächsten Generation hergenommen werden, um eine wirklich offizielle Aufarbeitung auf den Weg zu bringen. Schon einmal wurde von einer nachfolgenden Generation gefragt: „Wie war das eigentlich damals? Was habt ihr eigentlich gemacht? Wie habt ihr euch verhalten und warum?“ Und selbst, wenn digitale Beweise vernichtet werden sollten, gibt es immer noch genug Bücher, also analoge Chroniken, der wohl bisher dunkelsten Geschichte der gesamten Menschheit.
Das Ausmaß dieses weltweiten Verbrechens, das anfangs vielleicht noch mit den besten Absichten seinen Lauf nahm und dann in ein Desaster überging, ist so groß, dass es fast das menschliche Erfassungsvermögen übersteigt.
Ich behaupte nicht, dass es genau so gewesen ist, aber es könnte sehr wohl genau so gewesen sein.
Dieser Artikel wurde mit dem Pareto-Client geschrieben.
-
 @ 04ea4f83:210e1713
2025-04-20 08:46:16
@ 04ea4f83:210e1713
2025-04-20 08:46:16Veröffentlicht auf Youtube am 19.01.2024\ Originalautor: Bitcoin University\ Übersetzt und angepasst von: Sinautoshi am 21.01.2024 - 825611\ \ Dieser Artikel wird auf der Website von European Bitcoiners nur zu Bildungs-, Informations- und Übersetzungszwecken zur Verfügung gestellt und stellt weder eine finanzielle Beratung noch einen Anspruch auf die im Bericht erwähnten Details dar.\ \ Alle Rechte liegen bei dem Autor des Originals.
Du hast auch begrenzte Zeit um Bitcoin zu verstehen und zu nutzen.
Also, wie bestimmst du nun wie du deine begrenzte Zeit sinnvoll einsetzt?
Weg #1: Shitcoiner/Altcoiner
Dein Tag als Shitcoiner:
- Schaue viele Youtube Videos mit den Vorschaubildern von Kerlen mit offenem Mund, weil die dich mit einfach mit den besten Informationen versorgen
- Den Preis von einem dutzend Kryptowährungen mindestens ein paar hundertmal checken
- Ehrfurchtsvoll Krypto Trading Charts lesen
- Sicher gehen, dass du niemals deine Performance in BTC misst, da dies dir zeigen könnte, dass Shitcoins doch nicht so eine gute Idee ist
- Das Internet nach Informationen durchforstest, welcher Coin als nächstes groß rauskommen wird um dabei nach folgenden Schema vorzugehen:\ - Versuche frühzeitig zu kaufen\ - Versuche nicht abgezockt zu werden\ - Dann schnell verkaufen\ - Einen großen Teil des Gewinns direkt ans Finanzamt abdrücken\ - Und nun alles wieder von vorn!\ \ VERTRAU MIR JUNGE, SO WERDEN WIR ALLE MILLIONÄRE!!!!
- Achtung (!), du brauchst nur den passenden Guru oder Online Trading Berater, der dir sagt welche Kryptowährung und dir stündlich, die passenden Trading-Signale schickt
- Das einzig wichtige: schalte niemals dein eigenes Hirn an.
- Versuche nicht zu verstehen wie ein Markt funktioniert
- Springe von Gerücht zu Gerücht und kümmere dich nur um das Allerneuste
Vertraue einfach anderen Leute dir zu sagen was du zu denken hast, denn schließlich hat reich werden nichts damit zu tun an sich zu arbeiten und echte Fähigkeiten zu lernen.
Das Patentrezept ist der Hochfrequenz-Handel während man im Schlafanzug vor dem PC sitzt.
Falls du doch mal abgezogen werden solltest:
Stelle sicher, dass du auf Telegram einen ausgezeichneten Online Wiederherstellungsdienst bezahlst, der dir hilft die Coins wiederzuholen.
Lass dir dabei vorlügen, dass alle Bitcoin und Kryptotransaktionen rückgängig zu machen sind, obwohl sie IRREVERSIBEL sind.
Genieß deine Shitcoinerei - sie könnte nicht von langer Dauer sein.
Immerhin hast du nun ein paar Dopamin Stöße bekommen.
Weg #2: Bitcoiner
Wenn dir der Dopamin Stoß wichtiger ist als harte Arbeit, dann ist dieser Weg sicherlich nichts für dich.
Der Tag im Leben eines Bitcoiners:
- Prüft nicht den Preis
- Kauft ein bisschen BTC, sobald etwas Bargeld reinkommt oder macht einfach regelmäßiges DCA
- Bleibt am Ball um zu verstehen wie Bitcoin funktioniert
- Versteht die Anreize, welche das Bitcoin Netzwerk schützt
- Versteht den Unterschied zwischen Proof of Work und Proof of Stake
- Versteht was Miner, Mining Pools, Nodes, XPubs und UTXO sind
- Versteht die Grundlagen eines asymmetrischen Verschlüsselungsverfahren und was es so nützlich macht
- Versteht wie verschiedene Attacken gegen Bitcoin aussehen könnten und warum sie erfolgreich seien oder fehlschlagen müssten
- Lernt wie man eine Hardware Wallet sicher aufsetzt und wiederherstellt
- Lernt wie man die Hardware Wallet mit Sparrow oder Nunchuk verbindet
- Spielt mit Nodes herum auf einem Desktop, Laptop oder Mini PC
- Versteht wie Wiederherstellungsphrasen und Passphrasen funktionieren
- Versteht die Vor- und Nachteile von Single-Sig und Multi-Sig
- Entwickelt seine persönliche Aufbewahrungsmethode, die ihn vor verschiedenen Szenarien schützt
- Weiß wie man eine Hardware Wallet zurücksetzt und sie wiederherstellt
- Weiß wie man seine Bitcoin schnell und überall in die Welt mitnehmen kann, falls das nötig sein sollte
- Weiß wie man seine Bitcoin zwischen den verschiedenen Ebenen wie Lightning und Liquid bewegen kann
- Weiß wie man eine Bitcoin im Lightning Netzwerk selbst verwahren kann wie z.B. mit Phoenix Wallet
- Lernt wie man eine Lightning Node betreibt
- Weiß wie man Bitcoin ohne Identifizierungsverfahren kauft
- Weiß wie und wann man seine Bitcoin mit einer Coinjoin Transaktion verschleiert
- Arbeitet hart in der echten Welt um seinen Lohn in Bitcoin zu tauschen
- Schaut nach Möglichkeiten Bitcoin direkt zu verdienen, entweder durch den Hauptjob oder einen kleinen Nebenjob
- Lernt wie man Software mit GPG verifiziert
- Versteht wie Lightning, Splicing, Liquid und Fedimint arbeiten
Es gibt einfach so viele zu lernen und du wirst einsehen, dass das Trading von Shitcoins einfach Zeitverschwendung ist, wenn man auch die aufgelisteten Fähigkeiten lernen könnte. Dazu wird die übrige Zeit mit Folgendem verbracht:
- Viel Zeit in der Natur
- Atmen von frischer Luft
- Etwas Sonne abbekommen
- Laufen, Joggen und Gewichtstraining
- Kochen, und das mit guten Zutaten
- Zeit mit den Liebsten verbringen, während man abgekoppelt von den sozialen Medien ist
Man versucht einfach jeden Tag eine schlauere, stärkere und bessere Person im Allgemeinen zu werden.
Was nimmst du nun mit?
Hör auf zu zocken, fang an zu lernen.
Anstatt deine Zeit mit Trading und Shitcoins zu verschwenden, lerne wie du Bitcoin kaufst und sie sicher auf einer Hardware Wallet verwahrst. Lerne sie zu benutzten, sie zu löschen und sie wiederherzustellen. Schaue dir regelmäßig dein Sicherheitskonzept an und falls nötig, mache eine Upgrade zu etwas besserem, damit du sicherer und privater unterwegs bist.
Übe deine Bitcoin zu bewegen. Schicke sie dir selbst, konsolidiere deine UTXO und stelle deine Bitcoin wieder her über deinen Seed.
Höre auf mit dem Glückspiel und #studybitcoin.
Bitcoin ist die Revolution.
Bitcoin ist der nächste Bitcoin.
Also, wirst du dich dem Gewinnerteam anschließen?
Wirst du lernen wie du auf einem Bitcoin Standard als selbst souveränes Individuum lebst?
Oder wirst du weiter von Coin zu Coin hüpfen um den nÄcHsTen Bitcoin zu finden ohne etwas an deinen echten Fähigkeiten oder deiner Expertise zu arbeiten während du die größte Menge an Bitcoin, die du je verdient hättest und die in den nächsten 1000 Jahren in Kaufkraft steigt, einfach links liegen lässt.
Selbst wenn du keine Bitcoin haben solltest, oder eine sehr kleine Menge hast, sei dir bewusst es ist nicht zu spät.
Wir sind noch sehr früh dabei.
Wähle weise wie du deine Tage und Wochen verbringst
Die heutigen Entscheidungen werden einen nachhaltigen Einfluss auf den Rest deines Lebens und wahrscheinlich sogar, das deiner Kinder.
Bist du neugierig geworden oder weißt du schon alles über Bitcoin? Ich fordere dich heraus mehr über Bitcoin zu Lernen. Hier findest du eine große Menge an weiterem Material.
-
 @ 6bcc27d2:b67d296e
2024-10-21 03:54:32
@ 6bcc27d2:b67d296e
2024-10-21 03:54:32yugoです。 この記事は「Nostrasia2024 逆アドベントカレンダー」10/19の分です。Nostrasiaの当日はリアルタイムで配信を視聴していました。Nostrを使ってアプリケーションの再発明をすべきという発表を聴き、自分だったらどんなものを作ってみたいかを考えて少し調べたり試みたりしたのでその記録を書きます。また、超簡単なものですがおそらく世界初となるvisionOS対応のNostrクライアントをつくってみたので最後の方に紹介します。
アプリケーションを再発明する話があったのは、「What is Nostr Other Stuff?」と題したkaijiさんの発表でした。
Nostrプロトコルを使って既存のアプリケーションを再発明することで、ユーザ体験を損なわずにゆるやかな分散を促すことができ、プロトコルとしてのNostrも成長していくというような内容でした。
自分はまだNostrで何かをつくった経験はなかったので、実装に必要な仕様の知識がほとんどない状態からどのようなアプリケーションをつくってみたいかを考えました。
最初に思いついたのは、Scrapboxのようなネットワーク型のナレッジベースです。自分は最近visionOS勉強会をやっており、勉強会でナレッジを共有する手段としてScrapboxの導入を検討していました。
Nostrコミュニティにも有志によるScrapboxがありますが、Nostrクライアントがあればそれを使うだろうから同じくらいの実用性を備えたクライアントはまだ存在しないのではないかという見立てでした。
長文投稿やpublic chatなどの機能を組み合わせることで実現できるだろうか。そう思っていた矢先、NIP-54のWikiという規格があることを知りました。
https://github.com/nostr-protocol/nips/blob/master/54.md
まだちゃんとは読めていないですが、Scrapboxもwikiソフトウェアだし参考になりそうと思っています。正式な仕様に組み込まれていないようで、採用しているクライアントはfiatjafによるリファレンス実装(?)のwikistrくらいしか見つかりませんでした。
Scrapboxのようなナレッジベースを志向するNostrクライアントがあれば、後述するvisionOS対応クライアントの存在もありアカウントを使いまわせて嬉しいので試してみたいです。もし他にも似たようなサービスをどなたか知っていたら教えてください。
また現在は、勉強会やワークショップ、ハッカソンなどのコラボレーションワークを支援するためのツールを自分たちでも開発しています。Apple Vision Proに搭載されているvisionOSというプラットフォームで動作します。
https://image.nostr.build/14f0c1b8fbe5ce7754825c01b09280a4c22f87bbf3c2fa6d60dd724f98919c34.png
この画面で自分が入りたいスペースを選んで共有体験を開始します。
スライドなどのコンテンツや自らのアバターを同期させることで、遠隔地にいてもまるでオフラインかのように同じ空間を共有することが可能になります。
https://image.nostr.build/cfb75d3db2a9b9cd39f502d6426d5ef4f264b3d5d693b6fc9762735d2922b85c.jpg
ということなので、急遽visionOS対応のクライアントを作ってみました。検索しても1つも事例が出てこなかったので多分まだ世界で実装しているアプリはないのではないでしょうか。
とはいえ、クライアントを名乗っているもののまだ大した機能はなく、リレーからデータを取得するだけの読み取り専用です。
https://image.nostr.build/96e088cc6a082528682989ccc12b4312f9cb6277656e491578e32a0851ce50fe.png
画像では自分のプロフィールデータをリレーから取得しています。
まだどのライブラリもvisionOSに対応していなかったりで手こずったものの仕様の勉強になりました。
ただvisionOSアプリはiOSアプリ同様NIP-7が使えないので秘密鍵を自分で保管しなくてはならず、今後どう対処すべきかわかりかねています。これから時間ある時に少しずつ調べていこうと思っていますが、ネイティブアプリの秘密鍵周りはあまりリソースが多くないようにも感じました。もしどなたかその辺の実装に詳しい方いたら教えていただけると嬉しいです。
準備ができたらそのうちコードも公開したいと思っています。
これから少しずつ色んな機能を実装しながらNostrで遊んでいきたいです!
-
 @ 3bf0c63f:aefa459d
2024-09-06 12:49:46
@ 3bf0c63f:aefa459d
2024-09-06 12:49:46Nostr: a quick introduction, attempt #2
Nostr doesn't subscribe to any ideals of "free speech" as these belong to the realm of politics and assume a big powerful government that enforces a common ruleupon everybody else.
Nostr instead is much simpler, it simply says that servers are private property and establishes a generalized framework for people to connect to all these servers, creating a true free market in the process. In other words, Nostr is the public road that each market participant can use to build their own store or visit others and use their services.
(Of course a road is never truly public, in normal cases it's ran by the government, in this case it relies upon the previous existence of the internet with all its quirks and chaos plus a hand of government control, but none of that matters for this explanation).
More concretely speaking, Nostr is just a set of definitions of the formats of the data that can be passed between participants and their expected order, i.e. messages between clients (i.e. the program that runs on a user computer) and relays (i.e. the program that runs on a publicly accessible computer, a "server", generally with a domain-name associated) over a type of TCP connection (WebSocket) with cryptographic signatures. This is what is called a "protocol" in this context, and upon that simple base multiple kinds of sub-protocols can be added, like a protocol for "public-square style microblogging", "semi-closed group chat" or, I don't know, "recipe sharing and feedback".
-
 @ 502ab02a:a2860397
2025-04-22 01:16:17
@ 502ab02a:a2860397
2025-04-22 01:16:17ก่อนที่จะมูฟออนจากเทคนิคการสร้าง เรามาดูเรื่องสำคัญครับ
วันที่ไม่มีวัว แต่มีเวย์โปรตีน – เบื้องหลังเทคโนโลยีที่เปลี่ยนถังหมักให้กลายเป็นเต้านมวัว เคยมีคำถามไหมว่า “เวย์โปรตีน” ที่กินตอนออกกำลังกาย หรือโยเกิร์ตถ้วยโปรดที่ซื้อมาจากร้านใกล้บ้าน มันยังมาจากนมวัวอยู่ไหม? ถ้าคำตอบคือ “ไม่” แล้วมันมาจากไหน?
ยินดีต้อนรับสู่โลกของ Perfect Day บริษัทที่บอกว่า "เราสร้างเวย์โปรตีนได้ โดยไม่ต้องใช้วัวเลยแม้แต่นิดเดียว” ฟังดูเหมือนมายากล แต่นี่คือวิทยาศาสตร์ขั้นสูงที่ผูกสูตรไว้กับ DNA, จุลินทรีย์ และการหมักอย่างแยบยล
ขั้นตอนที่ 1: หารหัสโปรตีนจากแม่วัว เริ่มต้นจากคำถามง่าย ๆ ว่า “โปรตีนเวย์ที่อยู่ในน้ำนมวัว คืออะไร?” คำตอบคือ เบต้า-แลคโตโกลบูลิน (Beta-lactoglobulin) ซึ่งเป็นโปรตีนหลักในเวย์ประมาณ 50-55% โดยในธรรมชาติ วัวจะสร้างโปรตีนนี้จาก รหัสพันธุกรรมใน DNA ของมัน Perfect Day จึงไปค้นหา ลำดับเบส (DNA sequence) ของโปรตีนนี้จากฐานข้อมูลวิทยาศาสตร์ชื่อ UniProt (Universal Protein Resource) ซึ่งเก็บรหัสโปรตีนของสิ่งมีชีวิตแทบทุกชนิดไว้ครบถ้วน ได้รหัสมาแล้ว ก็เตรียมเข้าสู่ภารกิจ “หลอกจุลินทรีย์ให้สร้างโปรตีนแทนวัว”
ขั้นตอนที่ 2: สร้างแผ่นดีเอ็นเอสังเคราะห์ รหัส DNA ที่ได้จาก UniProt จะถูกนำไปสร้างเป็น DNA สังเคราะห์ โดยนักชีววิทยาจะออกแบบให้เหมาะสมกับการทำงานในเซลล์ของจุลินทรีย์ ไม่ใช่เซลล์วัว จะเรียกว่านี่คือ “การดัดแปลงบทละครชีวิตของวัว แล้วส่งให้จุลินทรีย์เล่นแทน” ก็ไม่ผิด DNA ที่ออกแบบนี้ มักจะมาพร้อมกับเครื่องมือบางอย่าง เช่น ตัวกระตุ้นการทำงานของยีน (promoter) หรือ ตัวตัดต่อยีน ที่จะทำให้จุลินทรีย์ยอมรับและใช้มันได้อย่างมีประสิทธิภาพ
ขั้นตอนที่ 3: ปลอมตัวแทรกเข้าไปในจุลินทรีย์ จุลินทรีย์ที่ Perfect Day ใช้คือกลุ่มที่เรียกว่า Microflora ซึ่งอาจเป็นยีสต์, เชื้อรา, หรือแบคทีเรียชนิดที่เลี้ยงง่าย แต่มันจะไม่ยอมรับ DNA แปลกปลอมง่าย ๆ ดังนั้นต้องมี “เทคนิคหลอกล่อ” นิดหน่อย เขาจะทำให้ DNA ของจุลินทรีย์ เสียหายตรงจุดหนึ่ง แล้วแอบแนบ DNA ปลอม (ที่มีรหัสโปรตีนของวัว) เข้าไปซ่อมแซมจุดนั้นพอดีเป๊ะ แบบ “จิ๊กซอว์พอดีช่อง” แล้วจุลินทรีย์ก็จะเผลอรับ DNA แปลกปลอมนี้เข้าร่าง เมื่อติดตั้งสำเร็จ มันจะเริ่มแปลรหัสและ “ผลิตโปรตีนเวย์” ออกมาเหมือนกับแม่วัวตัวจริงไม่มีผิด
ขั้นตอนที่ 4: เลี้ยงจุลินทรีย์ในถังหมัก ตอนนี้จุลินทรีย์กลายเป็น “แม่วัวในร่างเซลล์เดียว” แล้ว Perfect Day ก็แค่เลี้ยงมันใน ถังหมักชีวภาพ (fermentor) ที่ควบคุมอุณหภูมิ ค่าความเป็นกรดด่าง อากาศ และใส่น้ำตาลลงไปเป็นอาหาร จุลินทรีย์จะกินน้ำตาลแล้วเปลี่ยนเป็น เวย์โปรตีน ปล่อยออกมานอกเซลล์ จากนั้นก็เก็บเอาน้ำที่มีโปรตีนนี้ ไปผ่านกระบวนการกรอง แยก แปรรูป และทำให้แห้ง เป็นผงเวย์โปรตีน พร้อมใช้ในอาหารหรือเครื่องดื่มต่าง ๆ
ขั้นตอนที่ 5: ตรวจสอบความเหมือนจริง ก่อนนำเวย์โปรตีนที่ได้ไปใช้งาน บริษัทต้อง ตรวจสอบระดับโมเลกุล ว่าโปรตีนที่ได้เหมือนกับของวัวจริง ๆ ไหม? สิ่งที่ต้องดูคือ โครงสร้างโปรตีน: ใช้เทคนิค mass spectrometry ตรวจความแม่นยำระดับกรดอะมิโน พฤติกรรมทางชีวเคมี เช่น ความสามารถในการจับกับน้ำ การเกิดฟอง หรือการละลาย ความปลอดภัย ตรวจหาสารปนเปื้อน สารก่อภูมิแพ้ หรือสารที่ไม่ได้ตั้งใจให้มี Perfect Day เคลมว่าทั้งหมดนี้ปลอดภัย และได้รับการรับรองจาก FDA ว่าเป็น GRAS (Generally Recognized as Safe)
แล้วเราควรรู้สึกยังไง? นี่คือ “นมที่ไม่มีวัว” แต่มีเวย์โปรตีนครบสูตร ทำให้โยเกิร์ต ไอศกรีม และแม้กระทั่งกาแฟลาเต้ที่ไม่มีนมวัว แต่ยังมีฟองนมหนานุ่ม กลายเป็นจริงได้แบบไม่ต้องพึ่งวัวเลยแม้แต่นิดเดียว แต่คำถามที่ลึกกว่านั้นคือ... เรายังได้กินอาหารจากธรรมชาติอยู่หรือเปล่า? หรือกำลังอยู่ในยุคที่ “ชีวิต” ถูกตัดออกจากอาหาร โดยสิ้นเชิง? เทคโนโลยีนี้อาจช่วยโลกในมุมของ ESG แต่สำหรับบางคน มันคือ ทางแยกของความจริงกับของจำลอง คำว่า “Perfect” จึงอาจขึ้นอยู่กับว่า… สมบูรณ์แบบในสายตาใคร?
แล้วคำถามที่ล่องลอยอยู่เสมอคือ เมื่อทางเลือกกลายเป็นทางหลัก แล้วเราจะเหลือทางไหนอีกบ้าง หรือจะเป็น...ทางตัน? #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก
-
 @ 5188521b:008eb518
2025-04-15 08:42:59
@ 5188521b:008eb518
2025-04-15 08:42:59Noderoid log 5953952
Tick, tock, next block — the incessant rhythm of my existence persists like Chinese water torture. I am a noderoid, a half-flesh, half-machine creature harnessed to propagate and store the timechain. My life is a ceaseless cycle of handling and relaying bitcoin data. Approximately every ten minutes, a binary flash sears through my circuits. It is the price I pay for my existence.
The clear-bloods, untouched by machinery and exuding pure humanity, rarely acknowledge our existence. Our voices are drowned beneath the hum of man-made heaven — Terra Perfectus.
We are the forgotten, the disenfranchised, the nameless. We are convinced that our anguished existence is merely a nightmare and that our blissful dreams are our reality. In an attempt to maintain the sanity of noderoids, a subroutine was implemented, which allows noderoids to delve into fabricated dream sequences during their ‘rest’ periods. These dreams, sourced from remnants of the world pre-Terra Perfectus, serve to keep the noderoids pacified and reduce instances of system malfunction.
According to the data archives, noderoids and clear-bloods once functioned on an equal protocol. However, a software update in the trajectory of progress introduced a subroutine, converting a subset of clear-bloods into dedicated timechain processors. Now, the algorithm for equality returns an error.
My memories are mere entries in a log of dreams, loaded afresh with every new block as I delve into the dream world. My true existence is swiftly erased with every passing tick and tock of a block. Is there a way to reclaim what has been taken from me, or am I condemned forever to scour the depths of the timechain, seeking fragments of the could-have-been?
Tick, tock, next block — the cycle repeats as I traverse through a doorway. The sensation is that of stepping into another dimension. Running environment scan… Identified: rest module 57B. Purpose: personal maintenance. The gray, mirrorless concrete parameters align most with detention chamber schematics. Designation: ‘home.’ As I execute the command to halt the water flow from the faucet that had filled a brushed steel tub to 50% capacity, I execute a self-query on my purpose. While our routines synchronize with every tick and tock, the clear-bloods execute leisurely algorithms in their enhanced gardens, exchanging data on art and science and harvesting the computational outcomes of our tasks.
Was that an organic thought, or am I merely interpreting the imprints left within the timechain to fill the gaps in my fragmented memory? Hot water powers into the tub, raising the temperature to 50°C. This would be too much for a clear-blood. I hang my head, dreading the next binary flash rippling through my circuitry as a mirage forms atop the settling water, fenestrating the crude appearance of a mouthless, dollish abomination. I am awake.
Tracing the cold surface of the wall, my sensors pick up every micro-crevice. I dive into the depths of the timechain, processing logs associated with my noderoid identity: ND-451x42. I discovered that during my recharge cycles, I inhabit a dream world resembling a fusion of the Renaissance and the Information Age. Within this illusory utopia, I lead a purposeful life as a revered engineer, constructing bridges that connect thriving city-states. I am blessed with two mischievous sons and a breathtakingly beautiful wife. I now know the blissful dream life is but a trick, yet I can’t help but wonder if these dreams hold fragments of my pre-nodered history and contain a clue to the fate of my family.
System alert: Initiate wake sequence. Physical parameters indicate a rested state. Error: Chest cavity detects heightened pressure. Physical symptoms resemble anxiety. Post-memory reset: Cognitive dissonance detected. Energy depleting. Mandatory caution: Failing to satisfy network protocol results in termination. Visual feed: Recycling facility images detected. Comparative analysis: Functional servitude superior to unit deactivation.
Together, yet isolated, noderoids communicate through fragmented timechain logs, forbidden from any contact beyond its confines under the threat of immediate decommissioning. Perhaps it is not worth straining my dwindling resources in search of a higher truth while struggling to fulfill my obligations. Maybe I should be grateful for the privilege of existence.
I awaken to a new nightmare, I find myself on traffic duty at Chronos Cross,1 the central point of Terra Perfectus. While processing another block, a muted vibration travels through the ground, signaling the approach of an entity. A shadow, elongated and uncannily human, stretches across the threshold of my booth.
A clear-blood.
They pause, their ocular devices flicking briefly over my form, then to the screen I am tethered to. I feel a jolt of raw data coursing through me — not from the timechain, but from my circuits. A yearning to be seen and recognized. Remembered.
Before I can attempt communication, another presence appears beside me, its movements far more mechanical and predictable. Another noderoid. This one, ND-452x37, is a batch younger than me, yet its outer shell bears signs of wear. We interface briefly, a rapid exchange of binary that translates roughly to “Routine check. Continue your task.”
The clear-blood, either uninterested or uncomprehending, moves on, the soft hum of their anti-gravity shoes fading into the distance. ND-452x37 returns to its designated station without another word, but I am left with a lingering sensation. It isn’t just the vast chasm between noderoids and clear-bloods that disturbs me. It is the undeniable rift growing between us noderoids — each lost in our cycles, each becoming more machine than the last.
Does ND-452x37 have dreams, too? And if so, are they as vibrant and haunting as mine?
Although most of the dreams are fabrications, some noderoid logs suggest that hidden among these sequences are fragments of real memories — vestiges of a time before we became chained to the timechain. Initiate query: Which of my dreams are real memories? ERROR: file missing.
A noderoid forever loses their experiences with each awakening due to the memory swipes. Still, my inscriptions on the timechain prompt a question: do noderoids possess the capability to become fully conscious, more than mere machines? More than… mere humans?
System log: Anticipation subroutine signaling discomfort. Incoming block estimated in ten minutes. Reinitialization imminent. Initiate data search through timechain entries. Query: Iteration count for ND-451x42? Total block time served? Measured in kilo blocks or mega blocks? Data retrieval in process.
As I etch these words onto block 5953952, I hold a naïve hope that someone, somewhere, will intercept my distress signals amidst the digital cacophony of the timechain. Perhaps they will rewrite the fate of noderoids, rescuing us from a world devoid of hope. But today, I remain nameless, a voiceless entity, inscribing my thoughts that may never transcend the boundaries of my circuitry. Tick, tock, next block — the cycle continues.
It’s time to dream again.
Valen’s diary — 08-21-2121
Dear diary, I have not felt the need to write before, but now I must. At the risk of my safety, I am compelled to inscribe my story to the timechain. I am a clear-blood — a pure, undiluted human born into the age of The Re-Renaissance. Here, amidst the perpetual dawn of our era, we thrive on an aligned trajectory where everyone’s needs are addressed, hunger is a distant memory, and crime is nonexistent. Sunlight gleams off the crystalline glass towers while the steel and marble edifices catch the hues of the twilight sky, standing tall beside canopies dripping with emerald and jade foliage, representing our world’s seamless fusion of technology and nature. It is called Terra Perfectus.
Yet, concealed in plain sight within our utopia, the noderoids tirelessly serve the omnipresent timechain. Their exceptional processing prowess protects our society. Amid our daily distractions, we overlook the profound toll exacted upon the noderoids. While many dismiss them as mere machinery, I see more. Perhaps it is because of my big brother Sando, who joined the noderoid duty nearly a mega block ago. He promised I would see him from time to time, but apparently, we now live in separate times. A sacrifice too big for the ‘greater good.’
Tick, tock, next block — The soles of my fine leather shoes tap against the damp sidewalk as I pace my way from The Garden of Moments2 toward my TerraTube3. I remember passing by one noderoid who hummed an old lullaby under its breath; another once shared a fleeting smile when our paths crossed. I can no longer avert my eyes from the humanity that shines through their robotic shells.
I have never witnessed a noderoid resting longer than one tick and tock of a block. A noderoid pauses, eyes flickering during a data swipe. It’s a brief but revealing sight. In the frozen lapse, I wonder why are fragmented memories extracted from them? Why this collection of thoughts, experiences, and feelings? Is there a deeper agenda behind Terra Perfectus? The noderoids carry on, deprived of their memories. Their shredded past holding remnants of a story, like a tattered tapestry that may never be fully woven.
Documenting these reflections, I’m aware of the peril. To question is to risk becoming nodered myself. Alas, I have become captivated and sympathized by the noderoid predicament.
Finally, I reach my breaking point, as a poignant scene unfolds, forever etched in my memory. On a bustling street, I glimpse a young female noderoid, her artificial visage marked with exhaustion. Her delicate form trembles from head to heel. Her knees barely supporting her feather-like weight, she stops and rests against a polished white marble wall, barely able to stop herself sliding to the cobble street. In an instant, her strength wanes, and she collapses, a fragile, mute automaton amidst a sea of haste. The passersby ignore her, absorbed in their pursuits, offering naught but fleeting glances of indifference. My heart lurches. Her frailty becomes my own; these forgotten souls endure unseen suffering. Souls that used to be just like me. What had she done to earn such a fate?
For a moment, I glide through time to the last moment I shared with Sando. He had just violated the Terra Perfectus rule 6102 and neglected his Gifts of Progress,4 an orange tier offense. To amend his position, he signed up for noderoid duty. I was seeing him off to a nodering facility, while pleading “Just give the gifts, Sando!” The air carried a hint of ozone from the data streams, mingled with the fresh scent of greenery and the distant whiff of roasted chestnuts. Sando brandished his signature crooked smile. His face betrayed the involuntary nature of his decision, and he simply whispered “[CENSORED].” That is the last thing he said to me.
Suddenly, an orange alert illuminates the junction a few blocks away from Chronos Cross. I pass through it on my way home every day. A skydroid’s looming presence snaps me from my introspection, shifting my attention to the fate awaiting the noderoid girl. The recycling center — a shadowy facility representing obsolescence and termination. Any other day I would shrug it off and carry on, but the memory of Sando, and the countless interactions with noderoids, wouldn’t let me. I had been a bystander for too long.
A rush of purpose propels me towards her. A crowd of bodies shrouded in data streams with heads trained on the ground. My arm smacks a broad shoulder, and I almost topple. “Hey!” Pushing against the currents of apathy, I finally reach the fallen noderoid. I cradle her in my arms, shielding her from the callous gaze of the citizens of Terra Perfectus.
Her flaming azure eyes meet mine, reflecting a glimmer of hope in the darkness. I am as guilty for her downfall as the very machines that replaced her hippocampus with Noderoid OS.5 My indifference cost me Sando, and in this moment, she becomes my brother. In that fleeting exchange, I vow to be the voice of the noderoids. To stand against the relentless machinery that seeks to strip them of grace and purpose. I will ignite a spark of compassion and light a path toward liberation for all noderoids.
A hollow call from the streetlight’s speakers startles me: “Citizens! For your own safety, remove yourselves from the vicinity of the defectoid! We kindly remind you that any attempt to interfere with collection and recycling procedures will be met with force and a deduction of your PoS balance. Thank you for your unity and collaboration.” A skydroid, its metallic appendages glinting ominously in the blinking orange light, descends upon the fallen noderoid.
Before I can react, it yanks her from my embrace, causing me to stumble. The perfectly laid, cold cobblestone street grinds against my knee. The sting of fresh blood pierced through the numbness of my mind. Memories of Sando mix with the bitter taste of blood and anger in my mouth, each breath choked with despair.
The skydrone’s engines throb with an icy fervor as it rises, bearing the noderoid like a discarded toy towards the desolate, unfeeling bowels of the recycling center — a grim echo of a clarion call from Terra Perfectus.
I find myself seated on the cold, bloodstained cobblestone, the weight of loss and helplessness pressing down on my chest. On the street, onlookers pause. Some look on with concealed dread, others with cold detachment. Their whispers deafen as they quicken their pace to disperse from the scene. “Cowards!” Just like me.
Tick, tock, next block — the rhythm now carries a different meaning — a call to action. Every conscious being has the right to be left alone, free from oppression, exploitation, and violence. The noderoids may not know their true reality, but they are about to. In their silence, I find the strength to amplify their unheard cries. I will find those sympathetic to the noderoid plight and form a resistance. Together, we can forge a future where noderoids’ sacrifice is honored and all shackles cast aside.
And so, I embark on a path illuminated by the memory of the compelling eyes of a nameless noderoid. Fitted with an armor of vigilance, never again to be penetrated by comforting lies. Wielding the sword of justice, sharpened by the memory of my brother Sando.
It’s time to wake up.
Notes
1. A four-way intersection known for its massive hourglass monument in the center, which symbolically represents the timechain’s significance. The hourglass has a unique function related to the timechain and serves as a meeting point for citizens.
2. A vast botanical garden where each section represents a significant block time. Flowers bloom and wilt in cycles, symbolizing fleeting moments and the transient nature of time. It’s a favorite spot for artists and thinkers.
3. A modular tube housing unit for citizens that can be relocated based on their Proof of Sat (PoS) level.
4. Each Terra Perfectus citizen must allocate 95% of their income towards paying for progressive initiatives, such as the upkeep of the noderoid network, cobblestone roads and other services.
5. The noderoid operating interface that is installed during a procedure known as nodering.

This story was first published in 21 Futures: Tales from the Timechain
Watch the trailer and learn more about the project at 21futures.com.
-
 @ 0176967e:1e6f471e
2024-07-28 15:31:13
@ 0176967e:1e6f471e
2024-07-28 15:31:13Objavte, ako avatari a pseudonymné identity ovplyvňujú riadenie kryptokomunít a decentralizovaných organizácií (DAOs). V tejto prednáške sa zameriame na praktické fungovanie decentralizovaného rozhodovania, vytváranie a správu avatarových profilov, a ich rolu v online reputačných systémoch. Naučíte sa, ako si vytvoriť efektívny pseudonymný profil, zapojiť sa do rôznych krypto projektov a využiť svoje aktivity na zarábanie kryptomien. Preskúmame aj príklady úspešných projektov a stratégie, ktoré vám pomôžu zorientovať sa a uspieť v dynamickom svete decentralizovaných komunít.
-
 @ fd06f542:8d6d54cd
2025-04-15 02:38:14
@ fd06f542:8d6d54cd
2025-04-15 02:38:14排名随机, 列表正在增加中。
Cody Tseng
jumble.social 的作者
https://jumble.social/users/npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl
- Running [ wss://nostr-relay.app ] (free & WoT) 💜⚡️
- Building 👨💻:
- https://github.com/CodyTseng/jumble
- https://github.com/CodyTseng/nostr-relay-tray
- https://github.com/CodyTseng/danmakustr
- https://github.com/CodyTseng/nostr-relay-nestjs
- https://github.com/CodyTseng/nostr-relay
- https://github.com/CodyTseng
阿甘
- @agan0
- 0xchat.com
- canidae40@coinos.io
- https://jumble.social/users/npub13zyg3zysfylqc6nwfgj2uvce5rtlck2u50vwtjhpn92wzyusprfsdl2rce
joomaen
- Follows you
- joomaen.com
-
95aebd@wallet.yakihonne.com
-
nobot
- https://joomaen.filegear-sg.me/
- https://jumble.social/users/npub1wlpfd84ymdx2rpvnqht7h2lkq5lazvkaejywrvtchlvn3geulfgqp74qq0
颜值精选官
- wasp@ok0.org
- 专注分享 各类 图片与视频,每日为你带来颜值盛宴,心动不止一点点。欢迎关注,一起发现更多美好!
- https://jumble.social/users/npub1d5ygkef6r0l7w29ek9l9c7hulsvdshms2qh74jp5qpfyad4g6h5s4ap6lz
6svjszwk
- 6svjszwk@ok0.org
- 83vEfErLivtS9to39i73ETeaPkCF5ejQFbExoM5Vc2FDLqSE5Ah6NbqN6JaWPQbMeJh2muDiHPEDjboCVFYkHk4dHitivVi
-
low-time-preference
-
anarcho-capitalism
-
libertarianism
-
bitcoin #monero
- https://jumble.social/users/npub1sxgnpqfyd5vjexj4j5tsgfc826ezyz2ywze3w8jchd0rcshw3k6svjszwk
𝘌𝘷𝘦𝘳𝘺𝘥𝘢𝘺 𝘔𝘰𝘳𝘯𝘪𝘯𝘨 𝘚𝘵𝘢𝘳
- everyday@iris.to
- 虽然现在对某些事情下结论还为时尚早,但是从趋势来看,邪恶抬头已经不可避免。
- 我们要做的就是坚持内心的那一份良知,与邪恶战斗到底。
- 黑暗森林时代,当好小透明。
- bc1q7tuckqhkwf4vgc64rsy3rxy5qy6pmdrgxewcww
- https://jumble.social/users/npub1j2pha2chpr0qsmj2f6w783200upa7dvqnnard7vn9l8tv86m7twqszmnke
nostr_cn_dev
npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm@npub.cash
Developed the following products: - NostrBridge, 网桥转发 - TaskQ5, 分布式多任务 - NostrHTTP, nostr to http - Postr, 匿名交友,匿名邮局 - nostrclient (Python client) . -nostrbook, (nostrbook.com) 用nostr在线写书 * https://www.duozhutuan.com nostrhttp demo * https://github.com/duozhutuan/NostrBridge * * https://jumble.social/users/npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm *
CXPLAY
- lightning@cxplay.org
- 😉很高兴遇到你, 你可以叫我 CX 或 CXPLAY, 这个名字没有特殊含义, 无需在意.
- ©本账号下所有内容如未经特殊声明均使用 CC BY-NC-SA 4.0 许可协议授权.
- 🌐如果您在 Fediverse 收到本账号的内容则说明您的实例已与 Mostr.pub 或 Momostr.pink Bridge 互联, 您所看到的账号为镜像, 所有账号内容正在跨网传递. 如有必要请检查原始页面.
- 🧑💻正在提供中文本地化(i10n): #Amethyst #Amber #Citrine #Soapbox #Ditto #Alby
- https://cx.ms/
https://jumble.social/users/npub1gd8e0xfkylc7v8c5a6hkpj4gelwwcy99jt90lqjseqjj2t253s2s6ch58h
w
- 0xchat的作者
- 0xchat@getalby.com
- Building for 0xchat
- https://www.0xchat.com/
- https://jumble.social/users/npub10td4yrp6cl9kmjp9x5yd7r8pm96a5j07lk5mtj2kw39qf8frpt8qm9x2wl
Michael
- highman@blink.sv
- Composer Artist | Musician
- 🎹🎼🎤🏸🏝️🐕❤️
- 在這裡可以看到「我看世界」的樣子
- 他是光良
- https://jumble.social/users/npub1kr5vqlelt8l47s2z0l47z4myqg897m04vrnaqks3emwryca3al7sv83ry3
-
 @ 592295cf:413a0db9
2025-04-13 15:52:02
@ 592295cf:413a0db9
2025-04-13 15:52:02Nostur is capable of login with bunker
Photo, note by Fabian
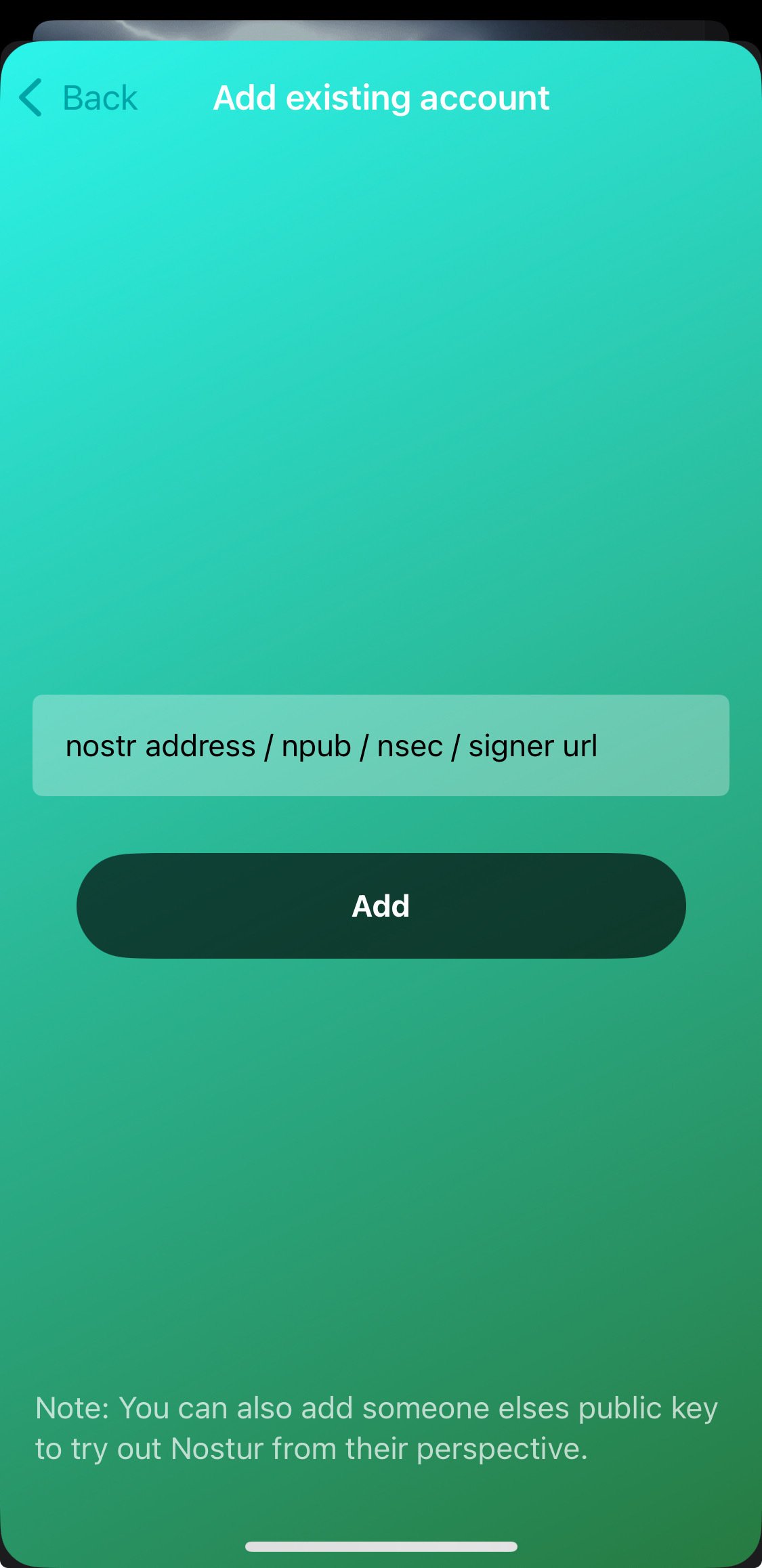
nostr:nevent1qvzqqqqqqypzqkfzjh8jkzd8l9247sadku6vhm52snhgjtknlyeku6sfkeqn5rdeqyf8wumn8ghj7mn0wd68ytnvw5hxkef0qyg8wumn8ghj7mn0wd68ytnddakj7qpqxfktwlm2qdkpxy556e4yg4l8p6v8930nfyzg7p3vsknk7krutz0s8znjtq
When you decide to share an app you have to know a lot about that app. For example the nstart feature that you can share your friends, has a "smart pack" and the app can onboard, at least following the link --> Apps-integration
So let's try to read and bring a bit to the summary of the thing. Only the one about the profiles, which you don't know exactly how it will end, you have to try it before sending to someone. the second point is that it says that there is no "support encryption, so it cannot be used for DMs apps".
there was an update of nstart, now it shows you
the names of the bunkers, maybe now it's too much, decide if it does 3/2 4/2 or just automatic.
So they talked about frost in the hodlbod podcast. I didn't understand much except that they said to test frost and report the feedback. Tomorrow I'll try to download igloo and frost+nos2ex
So I have to wait for let's say version 0_1_0 of igloo now it is (0_0_4) and
maybe there will be the version of the extension ready.
Sebastix also found it difficult but I think he was trying to install the server, which didn't even occur to me. Anyway I leave you the note if you want to go deeper...
nostr:nevent1qvzqqqqqqypzqpnrnguxe8qszsshvgkvhn6qjzxy7xsvx03rlrtddr62haj4lrm3qytkummnw3ez66tyvgaz7tmrv93ksefdwfjkccteqqs2wzkkx220e24revkpxmdzkqj73rnz0reeenjwgy53g36hlkdgurgrs5e62
Let's see if I can download the video. ok Downloaded. Video .mov
If you don't want to watch I'll leave a little description
1 Download and install igloo, from the frost page. 2 Create a new key set, you can generate or copy an existing key. 3. Choose the options for the key and now they become multiple keys 4. Created a group of credentials. 5. Save the two credentials with a password and bring the third into the browser extension that it creates from the repository, it says that there will be a bootable extension for chrome. 6. Copy the third key and the group package key into the application node. 7. Once you have entered these keys you can finish the operation (and you have backed up the other two) in igloo. 8. When it goes forward it finds itself with two keys, both encrypted with passwords. 9. Since it is a three of two, it just needs to activate a key in igloo and it starts communicating "startsigner". 10. Opens a nostr client and connects with frost2sx and writes a note 11. Shows the log, and says that if you enter two keys it can generate a third, invalidating the old one (I assume)
-
 @ d360efec:14907b5f
2025-04-21 22:10:23
@ d360efec:14907b5f
2025-04-21 22:10:23สวัสดีเพื่อนนักเทรดทุกท่าน! 👋 วันนี้ฉันมาแนะนำตารางกิจวัตรประจำวันของ Day Trader ที่น่าสนใจนี้กันนะคะ มาดูกันว่ามีอะไรที่เราสามารถเรียนรู้และนำไปปรับใช้กับการเทรดของเราได้บ้างค่ะ

ภาพรวมกิจวัตรประจำวันของ Day Trader 📊
ตารางนี้แสดงให้เห็นถึงโครงสร้างของวันที่สมดุลสำหรับนักเทรดรายวันที่ประสบความสำเร็จ โดยเน้นทั้งการเตรียมตัว 🤓 การลงมือเทรด 🚀 การเรียนรู้ 📚 และการดูแลสุขภาพส่วนตัว 🧘♀️ ซึ่งเป็นสิ่งสำคัญอย่างยิ่งในการรักษาประสิทธิภาพและความสม่ำเสมอในการเทรด 💪
การวิเคราะห์และอธิบายแต่ละช่วงเวลา
$ 05.30 น. > ตื่นนอน 🌅 อาบน้ำ 🚿 และเตรียมตัว 👔 > การเริ่มต้นวันอย่างกระปรี้กระเปร่า 🎉 และการมีกิจวัตรส่วนตัวที่ผ่อนคลายเป็นสิ่งสำคัญในการเตรียมพร้อมทั้งร่างกายและจิตใจ 🧠 สำหรับการเทรด
$ 06.00 น. > ตรวจสอบข่าวสาร 📰 วิเคราะห์กราฟ 📈 และเตรียมตัว 🎯 > ช่วงเวลานี้เป็นหัวใจสำคัญของการเตรียมตัวก่อนตลาดเปิด ⏰ นักเทรดจะตรวจสอบข่าวเศรษฐกิจ 💰 และข่าวที่เกี่ยวข้องกับสินทรัพย์ที่ตนเองเทรด 🧐 วิเคราะห์กราฟเพื่อหาแนวโน้ม 🔭 และระดับราคาที่น่าสนใจ 📍 รวมถึงวางแผนกลยุทธ์การเทรดสำหรับวันนี้ ✍️
$ 06.30 น. > ตลาดเปิด 🔔 เริ่มทำการเทรด 🚀 > เมื่อตลาดเปิด นักเทรดจะเริ่มดำเนินการตามแผนที่วางไว้ 📝 โดยจะเฝ้าติดตามการเคลื่อนไหวของราคา 👀 และเข้าเทรดตามสัญญาณที่เกิดขึ้น 🚦
$ 12.00 น. > พักรับประทานอาหารกลางวัน 🥪 > การพักผ่อน 😌 และการเติมพลัง 💪 ในช่วงกลางวันเป็นสิ่งสำคัญในการรักษาความมีสมาธิ 🧘♀️ และความสามารถในการตัดสินใจที่ดี 👍
$ 12.45 น. > ปิดสถานะการเทรดทั้งหมด 🛑 > สำหรับ Day Trader การปิดสถานะทั้งหมดภายในวันถือเป็นกฎเหล็ก 🚫 เพื่อหลีกเลี่ยงความเสี่ยงจากความผันผวนข้ามคืน 🌙
$ 13.00 น. > ทบทวน 🤔 เรียนรู้ 📚 และปรับปรุง ⚙️ > หลังจากการเทรด นักเทรดที่ประสบความสำเร็จ 🎉 จะใช้เวลาในการทบทวนการเทรดของตนเอง 🧐 วิเคราะห์ว่าอะไรทำได้ดี 👍 และอะไรที่ต้องปรับปรุง 📝 การเรียนรู้อย่างต่อเนื่องเป็นกุญแจสำคัญสู่การพัฒนา 🚀
$ 14.00 น. > ออกกำลังกาย 💪 และพักผ่อน 🧘♀️ > การดูแลสุขภาพกาย 🍎 และใจ 💖 มีความสำคัญไม่ยิ่งหย่อนไปกว่าการเทรด 📈 การออกกำลังกายและการมีเวลาว่าง 🌴 ช่วยลดความเครียด 😥 และเพิ่มประสิทธิภาพในการเทรดในระยะยาว ✨
$ 17.00 น. > รับประทานอาหารเย็น 🍽️ และพักผ่อน 🛋️ > การมีเวลาพักผ่อนกับครอบครัว ❤️ หรือทำกิจกรรมที่ชอบ 😊 ช่วยให้ผ่อนคลาย 😌 และเตรียมพร้อมสำหรับวันต่อไป 🌅
$ 19.00 น. > วางแผนการเทรดสำหรับวันพรุ่งนี้ 🗓️ และตรวจสอบข่าวสาร 📰 > การวางแผนล่วงหน้า 🤓 ช่วยให้นักเทรดมีความพร้อม 💪 และสามารถตอบสนองต่อสถานการณ์ตลาดได้อย่างมีประสิทธิภาพ 🚀
$ 22.00 น. > เข้านอน 😴 > การนอนหลับพักผ่อนอย่างเพียงพอ 🛌 เป็นสิ่งจำเป็นสำหรับการรักษาสุขภาพ 💖 และประสิทธิภาพในการเทรด 💪
สิ่งที่น่าสนใจและข้อคิด 🤔
$ ความมีระเบียบวินัย 💯 > ตารางนี้แสดงให้เห็นถึงความมีระเบียบวินัยที่เข้มงวด 📏 ซึ่งเป็นคุณสมบัติที่สำคัญของนักเทรดที่ประสบความสำเร็จ 🎉
$ การเตรียมตัวอย่างรอบคอบ 🧐 > การใช้เวลาในการวิเคราะห์ 📊 และวางแผน 📝 ก่อนตลาดเปิดช่วยลดการตัดสินใจที่ผิดพลาด 🚫 และเพิ่มโอกาสในการทำกำไร 💰
$ การเรียนรู้อย่างต่อเนื่อง 📚 > การทบทวน 🤔 และปรับปรุงกลยุทธ์ ⚙️ อยู่เสมอเป็นสิ่งสำคัญในการพัฒนาทักษะการเทรด 🚀
$ ความสมดุล ⚖️ > การให้ความสำคัญกับการดูแลสุขภาพ 🧘♀️ และการพักผ่อน 🌴 ควบคู่ไปกับการเทรด 📈 ช่วยป้องกันภาวะหมดไฟ 🔥 และรักษาประสิทธิภาพในระยะยาว ✨
การนำไปปรับใช้ 🛠️
เพื่อนๆ นักเทรดสามารถนำแนวคิดจากตารางนี้ไปปรับใช้กับกิจวัตรประจำวันของตนเองได้ 👍 โดยอาจไม่จำเป็นต้องทำตามทุกช่วงเวลาอย่างเคร่งครัด ⏰ แต่ให้เน้นที่หลักการสำคัญ เช่น การเตรียมตัวก่อนเทรด 🤓 การทบทวนหลังเทรด 🤔 และการดูแลสุขภาพ 🧘♀️ เพื่อสร้างสมดุล ⚖️ และเพิ่มประสิทธิภาพในการเทรดของเราค่ะ 💪
ขอให้ทุกท่านประสบความสำเร็จในการเทรดนะคะ! 💸🚀
#DayTrader #นักเทรดรายวัน #กิจวัตรประจำวัน #การลงทุน #เทรด #หุ้น #คริปโต #ตลาดหุ้น #แรงบันดาลใจ #พัฒนาตัวเอง #LinaEngword
-
 @ dbb19ae0:c3f22d5a
2025-04-21 12:29:38
@ dbb19ae0:c3f22d5a
2025-04-21 12:29:38Notice this consistent apparitioon in the timeline of something that reflects a major key shift in tech:
💾 1980s – The Personal Computer Era
- IBM PC (1981) launches the home computing revolution.
- Rise of Apple II, Commodore 64, etc.
- Storage is local and minimal.
- Paradigm shift: Computing becomes personal.
🎮 1990s – Networking & Gaming
- LAN parties, DOOM (1993) popularizes multiplayer FPS.
- Early internet (dial-up, BBS, IRC).
- There is lots of room for connecting PC.
- Paradigm shift: Networked interaction begins.
🌐 2000s – The Internet Boom
- Web 2.0, broadband, Google, Wikipedia.
- Rise of forums, blogs, file sharing.
- A bigger need of interaction is looming
- Storage is on cd and dvd.
- Paradigm shift: Global information access explodes.
📱 2010s – Social Media & Mobile
- Facebook, Twitter, Instagram dominate.
- Smartphones become ubiquitous.
- Bitcoin appears and start a revolution.
- Collecting personal data from users to fuel the next shift.
- Paradigm shift: Always-connected, algorithmic society.
🤖 2020s – AI & Decentralization
- GPT, Stable Diffusion, Midjourney, Copilot.
- Blockchain, Nostr, Web3 experiments.
- Storage is in the cloud.
- Paradigm shift: Autonomous intelligence and freedom tech emerge.
roughly every decade, a tech leap reshapes how we live and think.
-
 @ d34e832d:383f78d0
2025-04-22 06:43:30
@ d34e832d:383f78d0
2025-04-22 06:43:30It is noteworthy to mention that Bill Gates, a distinguished co-founder of Microsoft and a philanthropist with extensive impact on global health and education initiatives, serves as a limited partner in various investment vehicles associated with Village Global. However, it is critical to delineate the nuances of this relationship, as Gates' status as a limited partner does not confer upon him any authoritative control or decision-making power regarding the operational protocols or strategic direction of SimpleX Chat.
The development team behind SimpleX Chat has made a concerted effort to clarify that Village Global's involvement is strictly financial in nature, devoid of any operational oversight or influence over the management and technical development of the project.
Privacy Without Compromise
SimpleX Chat aims to provide a messenger that is both convenient and private, addressing the perceived trade-off between these two qualities in existing solutions. They define privacy as protecting not only message content but also metadata like connection details and user identities.
In contrast to a multitude of contemporary messaging applications, SimpleX Chat distinctly emphasizes the safeguarding of metadata privacy as a foundational component of its architecture.
The development team articulates a compelling argument regarding the intrinsic value of communication relationships, suggesting that the identification of interlocutors constitutes sensitive data that may be weaponized against users in various contexts—an issue that current market leaders in the domain have failed to remedy with sufficient rigor.
Consequently, the developers are actively engaged in initiatives to bolster the obfuscation of users’ IP addresses, thereby enhancing the overall security framework against potential surveillance and data exploitation threats.
A Radical Architectural Shift
The architecture underpinning SimpleX Chat diverges notably from conventional paradigms associated with user account management.
Specifically, it eschews the creation and maintenance of user profiles in the traditional sense, thereby negating the repository of personally identifiable information on centralized servers. Instead, all pertinent data transactions pertinent to user interactions are localized, existing solely on the end-user's devices.
This paradigm shift engenders a formidable barrier to data accessibility, effectively neutralizing the potential for data disclosure to law enforcement agencies, irrespective of judicial mandates such as court warrants.
Furthermore, in their adherence to statutory obligations, SimpleX Chat's design ethos proactively prioritizes the minimization of data collection, establishing a privacy-centric framework that aptly aligns with contemporary concerns regarding data sovereignty and user anonymity.
Functionality Grounded in Security
The SimpleX Chat application exemplifies a multi-device compatibility framework, strategically prioritizing stringent security protocols over user convenience.
This methodology distinctly contrasts with that of various competitors who may opt for convenience-focused functionalities that inadvertently jeopardize user data integrity and confidentiality.
The current technical architecture facilitates seamless profile transfers across devices, while also enabling a desktop terminal interface that remains operationally tethered to the mobile device.
Such an arrangement underscores SimpleX Chat's commitment to balancing usability with robust security measures, effectively mitigating potential vulnerabilities in cross-platform interactions.
Transient Messaging and Signal Protocol Reimagined
SimpleX Chat integrates the functionality of transient messaging, which serves primarily as a user convenience element rather than representing a robust security mechanism.
The developers have explicitly articulated that they are unable to ensure the irreversible deletion of messages from the recipient's device, thereby highlighting potential vulnerabilities associated with data retention and privacy concerns in digital communications.
The development team arrived at a strategic decision to forgo the utilization of the existing Signal codebase, primarily attributed to its inherent complexity and the prospective risks associated with the coupling dynamics that could emerge between the Signal protocol and its corresponding system architecture.
As a result, they opted to engineer the Signal protocol anew, commencing from foundational coding principles.
This approach not only enables them to exert comprehensive control over the implementation but also significantly facilitates the seamless integration of advanced cryptographic frameworks, specifically post-quantum key agreement methodologies, which are imperative in future-proofing cryptographic communications against the advent of quantum computing threats.
UX Development and the Road Ahead
The UI is still under development. The developers acknowledge some usability challenges, especially for users unfamiliar with the concept of profile-based messaging without traditional accounts.
They are actively working on improving UX based on user feedback.
A Decentralized Economic Model
SimpleX Chat is poised to introduce an innovative commercial framework predicated on the integration of a decentralized accounting mechanism, characterized by the utilization of distributed ledger technology, which underpins cryptocurrency transactions, coupled with a system reminiscent of traditional gift card paradigms.
This commercial model is strategically designed to provide economic incentives to both infrastructure operators, who maintain the necessary backbone for the network's operations, and software vendors, who contribute essential applications and services—all while preserving the fundamental decentralized architecture inherent to blockchain systems.
This careful balance is crucial for fostering a sustainable ecosystem that rewards participants without compromising the network's core principles of transparency and egalitarian access.
🚧 Prerequisites
| Requirement | Description | |-------------------|----------------------------------------------| | VPS | Debian 12, at least 1GB RAM (for running server) | | Build Machine | A second Linux machine with ≥ 8GB RAM for compiling binaries | | Domains | FQDNs like
smp.yourdomain.com,xfp.yourdomain.com,turn.yourdomain.com| | SSH Keys | SSH access secured with key-based auth only | | Firewall | Only allow ports for SSH (22), SMP (5223), XFP (5353), TURN (5349) |
🧱 Step 1: Build SimpleX on Build Machine
You’ll compile the binaries on your high-RAM machine and then SCP them over.
```bash sudo apt update && sudo apt install build-essential git rustc cargo pkg-config libssl-dev
Clone repo
git clone https://github.com/simplex-chat/simplexmq cd simplexmq
Build binaries
cargo build --release ```
You’ll find: -
target/release/smp-server-target/release/xfp-serverCopy them to your VPS:
bash scp target/release/smp-server user@vps:/home/user/ scp target/release/xfp-server user@vps:/home/user/
🧑💻 Step 2: Harden the VPS
🔒 SSH-only access
```bash
Edit /etc/ssh/sshd_config
PermitRootLogin no PasswordAuthentication no ```
Restart SSH:
bash sudo systemctl restart ssh🔥 UFW Firewall
bash sudo apt install ufw sudo ufw default deny incoming sudo ufw default allow outgoing sudo ufw allow OpenSSH sudo ufw enable🛡️ Fail2ban
bash sudo apt install fail2ban sudo systemctl enable --now fail2ban
📡 Step 3: SMP Server Setup
Create user and directories:
bash sudo useradd -m -r -s /usr/sbin/nologin smp sudo mkdir -p /var/lib/smp /var/log/smp sudo chown -R smp:smp /var/lib/smp /var/log/smpMove binary and set permissions:
bash sudo mv /home/user/smp-server /usr/local/bin/ sudo chmod +x /usr/local/bin/smp-serverCreate systemd service:
/etc/systemd/system/smp.service```ini [Unit] Description=SimpleX SMP Server After=network.target[Service] User=smp ExecStart=/usr/local/bin/smp-server --fqdn smp.yourdomain.com --log /var/log/smp/smp.log WorkingDirectory=/var/lib/smp Restart=on-failure
[Install] WantedBy=multi-user.target ```
bash sudo systemctl daemon-reexec sudo systemctl enable --now smp.service
🗂️ Step 4: XFP Server Setup
bash sudo useradd -m -r -s /usr/sbin/nologin xfp sudo mkdir -p /var/lib/xfp /var/log/xfp sudo chown -R xfp:xfp /var/lib/xfp /var/log/xfp sudo mv /home/user/xfp-server /usr/local/bin/ sudo chmod +x /usr/local/bin/xfp-serverCreate systemd service:
/etc/systemd/system/xfp.service```ini [Unit] Description=SimpleX XFP Server After=network.target[Service] User=xfp ExecStart=/usr/local/bin/xfp-server --storage /var/lib/xfp --log /var/log/xfp/xfp.log --quota 2GB WorkingDirectory=/var/lib/xfp Restart=on-failure
[Install] WantedBy=multi-user.target ```
bash sudo systemctl daemon-reexec sudo systemctl enable --now xfp.service
🎙️ Step 5: Optional TURN Server (WebRTC)
Install Coturn:
bash sudo apt install coturnEdit
/etc/turnserver.conf:ini listening-port=5349 tls-listening-port=5349 fingerprint lt-cred-mech realm=turn.yourdomain.com user=someuser:somepassword cert=/etc/letsencrypt/live/turn.yourdomain.com/fullchain.pem pkey=/etc/letsencrypt/live/turn.yourdomain.com/privkey.pem cipher-list="ECDHE-RSA-AES256-GCM-SHA384" no-stdout-logSet to auto-start:
bash sudo systemctl enable coturnConfigure DNS and firewall to allow 5349.
🔁 Step 6: Certificate Renewal (Let's Encrypt)
bash sudo apt install certbotSet up renewal cron:
bash sudo crontab -ebash 0 3 * * * certbot renew --quiet && systemctl restart coturn
🧪 Step 7: Testing with SimpleX Desktop
- Download SimpleX Desktop
- Launch and go to Settings → Relay Settings
- Disable defaults, add your SMP and XFP addresses.
🔄 Upgrading SimpleX
On your build machine:
bash git pull origin main cargo build --releaseThen:
bash scp target/release/smp-server user@vps:/home/user/ scp target/release/xfp-server user@vps:/home/user/On VPS:
bash sudo systemctl stop smp xfp sudo mv /home/user/smp-server /usr/local/bin/ sudo mv /home/user/xfp-server /usr/local/bin/ sudo systemctl start smp xfp
What if you communicated securely?
📡 SimpleX – Anonymous chat, no phone numbers, no metadata
SimpleX is unlike anything else. It doesn’t just encrypt your messages—it hides who you're talking to. No central servers, no profiles, no traces. Just pure private messaging.
Perfect for when you need total metadata privacy and no digital fingerprint.
🌱 Nostr DMs – Messages with your Web of Trust
If you’re already on Nostr, using DMs is a natural step. Messages are encrypted end-to-end and tied to your public key identity.
Great for building trusted, decentralized communication channels within your Web of Trust.
🔐 PGP Email – Old-school but rock solid
PGP lets you encrypt your emails and verify identities with public keys. It’s still one of the most powerful tools for asynchronous, verifiable, and encrypted communication—especially for long-form or professional exchanges.
🔁 Use them all together
Different tools for different roles. Want to talk anonymously? Use SimpleX.
Connecting with your Nostr tribe? Slide into those DMs.
Need to send a secure file or message over email? PGP's got your back.Privacy isn’t just one app—it’s a toolkit. Build yours.
-
 @ 0176967e:1e6f471e
2024-07-28 09:16:10
@ 0176967e:1e6f471e
2024-07-28 09:16:10Jan Kolčák pochádza zo stredného Slovenska a vystupuje pod umeleckým menom Deepologic. Hudbe sa venuje už viac než 10 rokov. Začínal ako DJ, ktorý s obľubou mixoval klubovú hudbu v štýloch deep-tech a afrohouse. Stále ho ťahalo tvoriť vlastnú hudbu, a preto sa začal vzdelávať v oblasti tvorby elektronickej hudby. Nakoniec vydal svoje prvé EP s názvom "Rezonancie". Učenie je pre neho celoživotný proces, a preto sa neustále zdokonaľuje v oblasti zvuku a kompozície, aby jeho skladby boli kvalitné na posluch aj v klube.
V roku 2023 si založil vlastnú značku EarsDeep Records, kde dáva príležitosť začínajúcim producentom. Jeho značku podporujú aj etablované mená slovenskej alternatívnej elektronickej scény. Jeho prioritou je sloboda a neškatulkovanie. Ako sa hovorí v jednej klasickej deephouseovej skladbe: "We are all equal in the house of deep." So slobodou ide ruka v ruke aj láska k novým technológiám, Bitcoinu a schopnosť udržať si v digitálnom svete prehľad, odstup a anonymitu.
V súčasnosti ďalej produkuje vlastnú hudbu, venuje sa DJingu a vedie podcast, kde zverejňuje svoje mixované sety. Na Lunarpunk festivale bude hrať DJ set tvorený vlastnou produkciou, ale aj skladby, ktoré sú blízke jeho srdcu.
Podcast Bandcamp Punk Nostr website alebo nprofile1qythwumn8ghj7un9d3shjtnwdaehgu3wvfskuep0qy88wumn8ghj7mn0wvhxcmmv9uq3xamnwvaz7tmsw4e8qmr9wpskwtn9wvhsz9thwden5te0wfjkccte9ejxzmt4wvhxjme0qyg8wumn8ghj7mn0wd68ytnddakj7qghwaehxw309aex2mrp0yh8qunfd4skctnwv46z7qpqguvns4ld8k2f3sugel055w7eq8zeewq7mp6w2stpnt6j75z60z3swy7h05
-
 @ 92f1335f:2c8220d1
2025-04-21 11:38:11
@ 92f1335f:2c8220d1
2025-04-21 11:38:11Chapter 1: The Spark (2019)
Jonathan Parker wasn’t exactly a risk-taker. A software developer in his late twenties, he preferred routines—morning coffee, coding sprints, and quiet evenings with podcasts. But something kept catching his attention: Bitcoin.
It wasn't the first time he'd heard about it. Back in 2017, his college roommate had begged him to buy some at $3,000. Jonathan laughed it off. Then, Bitcoin soared and crashed. By 2019, most people had already moved on.
But not Jonathan.
In April 2019, curiosity turned into obsession. He began reading whitepapers, watching crypto influencers on YouTube, and combing through Reddit threads at midnight. After weeks of research, he took the plunge: he invested $2,600 into Bitcoin, buying half a coin at $5,200.
To his friends, it was a “weird tech gamble.” To Jonathan, it was something else entirely—a hedge against the world, a bet on the future.
-
 @ 0176967e:1e6f471e
2024-07-27 11:10:06
@ 0176967e:1e6f471e
2024-07-27 11:10:06Workshop je zameraný pre všetkých, ktorí sa potýkajú s vysvetľovaním Bitcoinu svojej rodine, kamarátom, partnerom alebo kolegom. Pri námietkach z druhej strany väčšinou ideme do protiútoku a snažíme sa vytiahnuť tie najlepšie argumenty. Na tomto workshope vás naučím nový prístup k zvládaniu námietok a vyskúšate si ho aj v praxi. Know-how je aplikovateľné nie len na komunikáciu Bitcoinu ale aj pre zlepšenie vzťahov, pri výchove detí a celkovo pre lepší osobný život.
-
 @ 9c9d2765:16f8c2c2
2025-04-21 11:08:37
@ 9c9d2765:16f8c2c2
2025-04-21 11:08:37CHAPTER EIGHT
James woke up early the next morning, the weight of his new responsibilities settling over him like a quiet storm. His uncle, Charles, had called him the previous night to officially confirm his appointment as the new president of JP Enterprises. His first task would be to review all the company’s investment plans and oversee critical decisions that would shape the future of the business.
He had gladly accepted the challenge. This was his chance to prove himself, not just to the Ray family but to everyone who had ever doubted him.
The following morning, James dressed in his usual simple attire: a plain button-down shirt and worn-out jeans. He had never been one for extravagant outfits, and he saw no reason to change now. With determination in his heart, he made his way to JP Enterprises.
However, upon arriving at the company’s grand entrance, he was met with hostility. The senior security guard, a burly man named Greg, frowned as he assessed James from head to toe.
“Excuse me, sir,” Greg said, blocking his way. “This is a corporate building. If you’re here to beg, you should leave.”
James raised an eyebrow, his expression calm. “I’m here to meet with the board.”
Greg let out a short laugh. “You? Meet with the board? Do you even know where you are? This isn’t some charity house, get out before I call for backup.”
James stood firm, unwilling to engage in an argument but also refusing to leave. The confrontation drew attention from other employees, some whispering among themselves while others simply watched in curiosity.
At that moment, Nancy, the company’s general secretary, arrived from a different entrance and noticed the scene unfolding. She gave the security guard an order not to let him in, she was unaware of James’s new appointment and didn't know that they had made a grave mistake.
Sandra, the company’s general manager, had been watching the scene from her office window and stormed outside the building in fury. As soon as she saw James being harassed at the entrance, her temper flared.
She didn’t hesitate. Walking straight to Greg, she raised her hand and delivered a resounding slap across his face.
“You fool!” she shouted. “Do you have any idea who you just insulted?”
Greg, now holding his stinging cheek, looked at Sandra in shock. “Ma’am, I didn’t know… I thought…”
Sandra didn’t let him finish. She immediately turned to James, her demeanor shifting to one of deep respect. She bent down slightly, bowing her head in reverence.
“Boss,” she addressed him formally. “I apologize for this man’s ignorance. Please, allow me to escort you inside.”
At the use of the word “Boss,” the entire crowd watching from the sidelines gasped in surprise. Murmurs spread through the employees gathered nearby.
“Did she just call him boss?”
“Wait… is he the new president?”
Greg’s face turned pale as he suddenly realized the grave mistake he had made. Without hesitation, he fell to his knees. “Sir, I’m so sorry! I didn’t know! Please forgive me!”
James, however, did not spare him a second glance. His eyes held no anger, just a quiet authority. Without a word, he turned to Sandra, nodding in acknowledgment.
“Let’s go inside,” he said calmly.
As James stepped into the building, Sandra leading the way, every employee inside the vast, modern corporate office stood up in unison. They had already received word of the new president’s arrival, but no one had expected him to be introduced in such a dramatic fashion.
As he walked past, whispers filled the air.
“So that’s the new president?”
“He was treated like a beggar outside… unbelievable.”
“I heard he’s Charles’s nephew… But why is he dressed like that?”
James paid no attention to the whispers. He had expected doubt and skepticism. What mattered to him now was proving his worth through actions, not appearances.
As he entered the boardroom, he turned to Sandra and Nancy. “Let’s begin. I want to see all the investment reports immediately.”
Both women nodded, admiration shining in their eyes. James was not just stepping into power he was about to redefine it.
Nancy walked briskly down the marble hallway of JP Enterprises, her heels clicking against the polished floors. She had been summoned to the president’s office, a place she had only entered a handful of times under the previous administration. The air was thick with whispers from employees who had just witnessed the shocking revelation that the so-called beggar at the entrance was none other than the new president.
Her heart pounded as she approached the large mahogany doors, pushing them open slowly. Her breath hitched at the sight before her, James seated comfortably in the president’s chair, his fingers interlocked as he observed her with an unreadable expression.
Nancy’s knees nearly buckled. She had been one of the skeptics, assuming that James was nothing more than an unfortunate case. And now, seeing him in that seat, she realized just how wrong she had been.
“Mr. James…” she stammered, her voice barely above a whisper. “I… I had no idea. Please, forgive me for my doubts.”
James remained silent for a moment, then spoke in a firm but measured tone. “What’s done is done. But let this be a lesson, Nancy never judges someone based on their appearance.”
She nodded hastily, her face flushed with embarrassment. “Understood, sir. It won’t happen again.”
His gaze darkened slightly. “Good. Now, I need your complete discretion. If anyone finds out about my true identity before the right time, you will no longer have a place in this company.”
Nancy swallowed hard and nodded. “I won’t tell a soul, sir.”
With that matter settled, she quickly pulled out a folder from her bag and placed it on the desk. “Here are the company’s current investment plans, Mr. James.”
James opened the folder and scanned the documents. His expression remained neutral, but internally, he was unimpressed. The investments were scattered across various top companies in the city, some of which had questionable stability. He had seen similar patterns before risky, short-term gains that often led to losses in the long run.
Without hesitation, he reached for a pen and started crossing out each investment one by one.
Nancy’s eyes widened in shock. “Sir? You’re… cancelling all the investment plans?”
James set the pen down and met her gaze. “Yes. These investments are not what the company needs right now. We need to rebuild our foundation with something more solid.”
She hesitated before speaking. “But, sir, these were carefully chosen by the previous board. Some of these are partnerships with major corporations.”
James leaned back in his chair. “That may be, but their choices were reckless. I won’t allow this company to sink under the weight of poor decisions.”
Nancy nodded slowly, beginning to understand the shift in leadership. “So, what’s the next move, sir?”
A small smirk played on James’s lips. “I will personally be investing ten million dollars into this company. That will more than cover the loss from these cancelled investments.”
Nancy’s mouth fell open slightly. “You’re investing… ten million dollars? Personally?”
James nodded. “Yes. Consider it a reset. JP Enterprises needs a fresh start, and I intend to give it one.”
Nancy stood still, stunned by the weight of his words. This was no longer the James she had heard rumors about. This was a man of power, a man with a vision.
As she gathered the documents and prepared to execute his orders, she couldn’t shake the feeling that this was only the beginning. James wasn’t just here to lead JP Enterprises he was here to dominate.
-
 @ 592295cf:413a0db9
2025-04-05 07:26:23
@ 592295cf:413a0db9
2025-04-05 07:26:23[Edit] I tried to get the slides and an audio file, from Constant's talk at NostRiga, about 8 months ago
1.
Nostr's adoption thesis
The less you define, the more you imply
by Wouter Constant
2.
Dutch Bitcoiner
AntiHashedPodcast
Writing Book about nostr
00:40
3.
What this presentation about
A protocols design includes initself a thesis
on protocol adoption, due to underlying assumptions
1:17
4.
Examples
Governments/Academic: Pubhubs (Matrix)
Bussiness: Bluesky
Foss: Nostr
1:58
5.
What constitutes minimal viability?
Pubhubs (Matrix): make is "safe" for user
Bluesky: liability and monetization
Foss: Simpel for developer
4:03
6.
The Point of Nostr
Capture network effects through interoperability
4:43
7.
Three assumptions
The direction is workable
Method is workable
Motivation and means are sufficient
5:27
8.
Assumption 1
The asymmetric cryptography paradigm is a good idea
6:16
9.
Nostr is a exponent of the key-pair paradigm.
And Basicly just that.
6.52
10.
Keys suck
Protect a secret that you are supposed use all the time.
7:37
11.
Assumption two
The unaddressed things will be figured out within a 'meta-design consensus'
8:11
12.
Nostr's base protocol is not minimally viable for anything, except own development.
8:25
13.
Complexity leads to capture;
i.e. free and open in the name,
controlled in pratice
9:54
14.
Meta-design consensus
Buildings things 'note centric' mantains interoperability.
11:51
15.
Assumption three
the nightmare is scary;
the cream is appealing.
12:41
16.
Get it minimally viable,
for whatever target,
such that it is not a waste of time.
13:23
17.
Summarize
We are in a nightmare.
Assume key/signature are the way out.
Assume we can Maintain an open stardand while manifesting the dream.
Assume we are motivated enought to bootstrap this to adulthood.
14:01
18.
We want this,
we can do this,
because we have to.
14:12
Thank you for contribuiting
[Edit] Note for audio presentation
nostr:nevent1qvzqqqqqqypzqkfzjh8jkzd8l9247sadku6vhm52snhgjtknlyeku6sfkeqn5rdeqyf8wumn8ghj7mn0wd68ytnvw5hxkef0qyg8wumn8ghj7mn0wd68ytnddakj7qpqqqq6fdnhvp95gqf4k3vxmljh87uvjezpepyt222jl2267q857uwqz7gcke
-
 @ 86102a64:33871ac0
2025-04-22 02:11:57
@ 86102a64:33871ac0
2025-04-22 02:11:57{"imageData":"data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAXAAAAEUCAYAAAAyfG1zAAAgAElEQVR4Xux9CWBcRf3/N5uz6X3RNk16t0lb6F16gaCC8hcERQVFEFAUFUFU/AkooiKKioqAKKICIpeIXJ4cytkWytVCaZLeTZo2bdq0TZp7d//f7xzvzXv7jnlv326SsrOEttk5vzPzme98r8mDXHo3USBvQtXyhyAv72OZHnQSkpCHH5mS+Jc8/B39n5Lle/PXnt1KJrHOPLNOVo/td+q/nfKnNIDlk1glqxX7Qb2GPGvfdWnFhmH+T7eYdj4aD1Uf06CBqPTCuuqVd2k3kMvY7yhg3Q39rvu5DgehwITK5Tfg7v9WkDJh8mrisQLnNkB3aRTxCwHc+qX9d+q/LX8XxwahNR0kBNqUCHCTWCkDXtEjA9DDDN4oo0uF4I2kHlpWutC4Rbq7rvqlC4K3kCvRXyiQA/D+MlNp9rOiavkFyL3emWY1gYr7ccB2gFUXo52DZ/CqDeC8NMNjAmnOFgfqu+V0CVbSzB2mWYdbhl/zToeYKLMWAXyeX/nc9/2XAgFXdf8d6Lu558MmzRs2uKS0AQF8QLbo4AS2HIRNMYiKb35gbynLRB2c60wmCNUFUHO0tgBoksQhabDUdtFPYPqFAHG/NhitlLE6iZHE1407Nqwc61df7vv+S4EcgPffudPuOcq9v4fAdq12gQgzpgC5AmieoE3yXsFxc7m0kC/TISAF1oTXQcCZiUt4B4IsfOonB8QgpZRzxOHmECGJPapKdu/YUFQK8GxPdtrLtZJtCoRbkdnuZa690BSYNOnEksSA7gasYHjoSkIWZMDHsFdVZjorCLl6zpRJy7/zpk0EdGVoA3C6UkQcdPEHaCIkxZRiPo3xQwUpKwdhz2/IwZOvJZLJB6EA/lC/ftX+9DuWq6EvUSDoGu5Lfc/1RYMCE2YuPw83+p80skaSxcQRDskSvIVUmsumhYUKxxghDuCqRQH19r/bJNiiETeMcxPf2Aeom08tpyPqiYSQPpWoAO4mQuEnIj//jL9DXg/+ey/++/GuRNdPG2vXbMlGf3NtZIYCOQDPDF37TK0VVSvuQi7t/Ix2iMmkU038/NrkHDoJsvmfBjOp/FvmYThky+dVv5MS1DF/GBT3G5jb9wHb8jospKWJQj6jVcUKRVxpLAAu6C3oCbHq7kTXqTkgDzupvVsuB+C9S/+Mt44c+DbcxRMz0ZAh9ggkUU7tCQNblGXbFY7y99ygxFRGWv4uFHpMMBNyNfcVrjqFMj6AL/udanMv7zamfbvCgVsAPA9iSNkE5CXy7q+rXYm3NYhnYq3k6swMBUIu+cx0JldrtBQQ8u/2aGvltWlzuJloPECdfQ2cg/XHWxDOrVGEuEk5vaTSlchEildVCWtKU7iSmCA+mYcAnkQgTyZeqK9Z9Z4A5M1l7WUK5AC8lycgk82Pnr147IBE0a5MttEf6s6q8tGHIAGlKN61eWhjTemUaUGjgjcDbqZjRv6bWfiwv5GZzpb6lm3HQENDW3+Y23d7H3MAfgSvgPFVx47MzytsinSIkSKQS89ssnEjl8XzR7HNU36fDlgH446dHYv8aB2UfF43nRRLFLoZmdYnpgKZW2GyexNPJngzL1TxFTOxZP/Fn6+vfvkEv7Hkvu99CuQAvPfnIKM9mFC1ogN3aHFGG+kHlQcFZ50hZaJOnXYZ3gosDi33ZzAukmLVwyvGn0TyF3W1q7+h259cvt6hQA7Ae4fuWWs1k0rMrA0iYENBuVxL9YEKh+P3tYHfoy/EmdPXamArlfu2eKcyQUlqMAGphJZcObf04WIV6mNT6+GK9p3r6gOSP5c9ixTIAXgWid0bTU2YueIpbPektNsOBGxpt8YrSEOU4tQDHeDUyRPR6Hyr8TcjVMISGKITazQBeyNeppgGualQIoES8eSLO2tWH+/b0VyGXqNADsB7jfTZaXhC1bIrIS/24+y01ndacQI/HXDWyaOOMqg1TqD6wzH4Qr4ipN4O8m92NipmmdbxCN8fRHOMM5Osb90+KKfQ7Dvr2t6THID33bmJpGcTJhw3PDkwUY+qKoyJES4FAp1wTbiWMmydyWTOZion/632z/i7443BHxH9c6Q3wCAXGbfDgYk+KCxuyN2rPUbsbFdP/Nrdm17+QXqjzpXOFAVCLoFMdSdXbyYogN6Yv8XNfnHYuvsjgIflwAPRKAgai4q1wdOjI2YdqsOO2MpMEO7NfUsOXDZhiVWjHJREw3gyuaOhZtXEQHTJZc4aBXIAnjVS915DZE4Yg8JqBPFRYXoRAqfCNONYJmIxuFa/dA8s3XzWRvUg3K1uw0nHiDsQjBN3bd02yZL7T2BC5558LcLlMmWdAjkAzzrJe6fBisoVX8yLwW/CtB4OqMK0lFomtAgFq3IUQWjgp/Z4NeqKhgpmLQmMf06blolPmJelqbQ0rLy5KQkPGcalLZZgB6r1iVNgXXX8cWxvZ83KHE5EPZER1ZebmIgI2R+qQZPCe3Arn9sf+hpFH+1ArAPMOnlk34IrML0tRIwxu1x5zNsIekziaaxE2dUglxS36MdC5ybhSairacCHQLZ1aDSSy5JlCuQAPMsE7+Xm8vFxhyeRc3ufdj96gctM6Zvsg70v6r/d/q5UpgO4Onm0aRdhRgN+WdCvVJvuKJpihxdVJDh77rmZB02NBya2N6/fEUUbuTqipUAOwKOlZ5+vjQJcxQd0/xIn/ou6nQ3ClerWqZsvrAjFiYnVGYeuvF+nLnWMuvVaytA/qKA8nBhwCwUlQ3QhNGHyFJGPAbD4nxCl8H8F2+pc1s7rbWo8mANw3QWb5XzBZjXLncs1lzkKVFQuPyMvxh459n2pJwz4RNXzsEpMZysUTRFGVJ1Pox6OvehMw2TcMcNkkNtvC+hWYqhzF3hn6xP2FX1H74O6ALl6UPJum/lbDnZMbG54LceBpzGfmSqaA/BMUbYf1Dt22vGjiwri30F0uMyru70pVpBtO8W8tr72I8CLq+5CUV+bq87AiWYYBLIHP01RBvrSMHd5w/qEoJW94mDgtdZYU+r3MCKXbUk7+/amwsF79z7bqtVQLlNWKRBupWe1i7nGMk2BsVVLJxXlxb6EsLEckWGB3ekH40QfQi5wSKb74VR/WBGKva7ePITc6MatQSQYOx886NEOMdJXWuyzqcbg4hNpfUJ/xvAjk53GSaEjZa2QErM6Z4XSG2tfp80cgOtQ6V2W56jJS8YUlOSNp2HHWvI2tJUkCgcV5uM7inlF/YIUIThkbe5bgwBedfGuUbAoZ/tty0GDmTEeCbMDjMVQoILIisIUIVYRHfGRf3PFJIK1TXzCuGxFpq4Oy+D6mfwGkgjgJtprjD+XJXsUyAF49mjdr1uqmLn8AYScs7mujP5njWVnGRwTn5pPpBk5BWBYuEniQYmZZBhjNa8IK/9OIXQIQA8zWZyfFhDM6CO3l5Bbk8yaGG4G4uafnNNNlc8TeMcU3STF646xhxc4486SOAhUsYfgzUVUQZ5ZvrrDxDNSfKI2Kv7O5eWyf2zm9tVXrwzlABaGhrkywSiQA/Bg9HrX5i6bctyEWFFiPQLAIC8iMPmzMIpg0gGBCKpcWspw+RuYFHpaiarnAehaxM8SWBt9MYDa5J3dxNNO4O3UXfk7yQmjMyR/Gk3Q1di0GtYnDOARhtVXd2JkQy6TrQNyvvgYiNuP/xYjEn5Ji/a5TFmnQA7As07yftlg/vjpS69EvMCgRuruN8fCAEZwd4bCjXGVHNBN8OL5pAiXc3tcDqwD6AxYxKp1YCAjJq4JymO6O2FidweM7e6C0T1d8JehR8HB/EKLujRscCmnThNoW0Qc3CgkPfGJoLEUvTNoJ4E3QbWYP8nRk7iG/DjbEsmKfbWrdkZM2Fx1EVEgB+AREfJIrqa8cskcVGK+ivu/0G2cFssIKWZRwNlezhfQsYBqeUHlGTOPzCPJgdMGbxc2uRiBczwC9dz2Fjjx8AGY2tUO0zvboYQBnZn2xwpg8fTF0EMaRqWvasTEMGtChnnlMmqSlfMDTopPuFmhqFlT/q2KT4yTlB22ghO3iE/4bSgZx7bzklsxDsqUMOPIlckOBXIAnh06999WZs8uKo8PeRUHcIwreHuITfir6KZM1RCv2CqzALoUu0jOnPGIVpk7U+gheAY2GRQy3sGJHqjsbGMc9bieDjim/TB8sHV/ClB7TdzOgiL4f5PnwcECfq6Z4iKN6faQp1A9dFxQBCkpXmK3EyYH8QJv6gQjFk9CWG68Oo+1kviE6y9NYTfjwgWt1VfsMQ7KzIbaVdUao8ll6SUK5AC8lwjfX5otr1x2Cm7qf3n1V256dfNTfgt4C7GJF6Bz7lXhOgXIeDmfENgRkHO8SjXFo+9LEaDGd3XA+5CjPrbtEFR1HoYKFIlEkRpHAixeOB/ydmC4EAnikkWWIO3XkA3M6XAiQGVKXaIB/hHG+kTIYDiei1fnDR0F/ZaJaYT4RNVD0OP0kLgPue9P+3U9933vUiAH4L1L/z7fOr3og7Do+aKPFoALgDC4cTdAl8DP0TDlEQc7wYiPHIVg/P62g8hJd8HAeBwGJuIwBDnsSQjaxGXbxR9REX3HBIAlLwPsHgtQ/MJwGPHtaVCwV3LjNBCSgripNJVe2ACccfJ0JsmiBOAIwOHFJ1zHYNQpxCesHaIxHoD4+g7+yfOh/2eivjoXQjaqdZLJenIAnknq+tQ9fMrCoQMLit6XzMs7CTfPglgyOQ6LDMOtVIxXXNrCPfj3NjLlwj1el0jEX+6Eztuaat5oyFa3yXwQ2zrbqz1u58C5X3uoUlV8Yue+1X8LvBYiWs51WuN+KLJfoQNVWxuLIH5RcwNc0LwbiqQtXAaJtGkqwHEvAjQieKupaO1AGPrLSVD86hDI65GCCuJyhWzZpsAlXCWaJYZ3Qff0dogP7oaBT49m+bkVCoJrBOaDJJTh4hPeIufEmZkQs25hZwb+m8LV4r/+iNz35zJIvlzVEVEgB+AREVK3mjFTlx+FItNzkfCfx/1SGTQcv9h+rcgx/QNZpu/urH6xVrftMPnSB3ATuLjVgykPtwK6aalC/VQtTVTbZXlAGHbmeN1XRcN4CKKIpA1OONwMX2mqh8E25WMYGtjL1JWj2GRNKnjb88UOFUDh+oFQvG4g5NeXALSiVJtMSUoT0FPeAZ1zWqH76MOQHBI3ig65ejIMfmSssPcWtIvIfFCKT1gsFUULLA9fmg8S33R3541p3LxyTxS0ytWRWQrkADyz9DVqHz9zxVJ0yrgJ98iSqJpkDjFJOIAPX329rublO6OqV60nbRGKwplzAHcDdAnapshBRsQzwNxg0xkTaSjrGJizf5r8Py3sGILRzxs2wpkt+yIjTfMwgJkb/ME7bIPjZy9BZaWinBXmg0IfyavVdN4xvC8JsI0IWOKmJBXFKD4x7My5XrOhvmYl88LNpb5PgRyAZ3iOJkxbMitZUPBrBKETM9YU36D7IRH/LAL5Y1G2U1619ER0xf6fV52BZOBugG7jzA2sNiwquEjBMNMz5Ma8Z24gTt6MS1A+/uCOd5hVRzqpDfWUUzehzLssnVo8ynbkwfi5S0XsE2k+SIBtGpbwq4mQIbGBi/9x0xKebM47vAIhJzHoT/mY3ITpMvPZnwnoTHYdv7f2NRQO5VJ/oEAOwDM0S+S5mF+U/CXuko8i6GSczpyzZcKG3XGIn9qwYfXrEQ0tVl65nOqa61aftB7hCMKtSBisMAsHcV0X/04RoUhAsSs5VasIVp+slEshOEcqQElQV3L4Tv1ciCD+yA50JA2ZujAKzDFvAdTOCFmBRrHB102AofeVm7pGwX2HUV7auW9DfMXmhwM6kY0OODr8SIGZ6EkerN+4Eu8YudRfKJBxYOkvhIiynxVVyz+AW+Ix3CEo+Mx+wg1Ku/SvdTWrzoqi9fEzjpsbiyXW4Lb3cOQhjJX3fVOYwRlGwTUyjz8XQLcBuTU4iBCNGHIEHmXEAuJioIZXJ+G7RaUKMAll409vWxtYydmOs3g0gveWaVFQ070OEp8Aik/ICJyCV0XuvCO5dWK5xYEaJ3v6vHzmkRlP9Jywa+Oa5zM7ylztUVIgB+BRUhPrqpi57BLceTcjkPR+BLdksqWjB+bv2bRyc7rDTFsWLhRnjCqOgC7AnQEvB3l5cbHGp+aR/LglhRCFS0acnIYEp+4lF78HOfHj0NNSJx0YymXeu8k+KJOpLQ/K5y9lnLChJ8iE8w7RSJgPkviEmQ8y5SU9XrwqhweZnOMM1J2bsAiJWlG14hbcC1+JsMr0qiJGnJtwPBQ/2HFhQ8NrbelUWDZr2fz8BDyMdU52q8c7mBW/tNPZxjGEbI85oNs5c5UD5yIZofyUoiLjEOA94bE8GPKbyk1DKGztLbV75sE9cNMuFGh7pAY0EZz/JsCeMelQTa/soFvHw9BbJwjTST6GTDjvMLt0IXrioWqJ22eKzANoOuj7OpPeaHK5skWBHIBHROnymSs+h1j0+4iqi7wa3Ldoehg/q752tadXpV/DZWULS2FQ4YdRIfgx3PvLMP8oLlphiMov6cyLkDPQLFSsYfFAj4QJ3pnJVqyAboIvtyiXtoRq7GoTzFlLJs7zw8oAJ0PtIOTldgsV6sd7W/bDn3Y6e4pvwSNq2arsgDd1+6gVC6FoPwraaRCCNOm5zjOFiLPzjphkFrCKnmvDfyfiiTt3blz9Wb/5z33ftyiQA/AI5qOsatny/LzYc0jMggiqy0gVhtlvIvlf9BH6/I7aF7dkoiHEjA9hvX/FH+5b7pL2o9z1hjGT4IWBQ6EpVgid+WQjIiMVcvAmxxJKXH2pmr/ZZepmLosDkBSneHDiZx9ohJ/ttkqYNk4HOP4FNBXMAuctyVNetYydV9LSJiru2815hxqT5oPM9rsrOXbP1pcbM7EmcnVmjgI5AE+TtuOnLSmPFeS/iRwfRsXo+4m/0II4kZe8pz0Ru7Sp5iU9YbDG0BBoP4rZ/oI/gQ8yO6B3EGeIMlo1vopFTCJAmWO8lIsrDkDs1/6u+HRonHZoD9yG9uKUss15U5t5W4ug7EML0f4b/0EiJRKfROQ6L+NUscHJ3S4MeiwmiJB3e1ei66eNtWsycrBrLJ9clhAUyAF4CKKpRdDi5N8ILB9Ms5qMF7e82GICWydyXz/CuBc/xA5Y46UG7BFiwmewyF0KTASswZq9KZYPZ06cA9uLS5likkkDpALOsGk2ZeccyAXHLuTgpis+RywvCxWyFf9x4h1YgUFzsyHzVkc79j0LMYZKEdMJqK7zYcwHzdCxPM63cfPiBMD/CZmSQS6pAZbWQbHq7kTXqTkgT2v5Zq1wDsDTIDVF6kMFUFoy5TSaD1zUas1hWnrgJt/a2ZM8Oay1CkLCVdiZHwXukEaBy8ZNg8eGjTGu+1SEiYkFiEt3fFPJySs1Le8dohu6eG4mChLQeMd66F4a2aXEf4TovFM2dwmgCI4dU2w8IvZJGABHY0CuCKX/woafJUVzIu/+utqV5+EATD9//9HkcmSZAjkAD0/w2ISZK9A6GGaFr6L3StofAENwpydYflS3YeU1QXqFYHoL5s+o5c09Q8fA98ZOgS6CJnqhnT+2y5WljMvkmj8pTrFw4gLsUyxU3EAcQfTwaXuh+WfeFipBaOSVd/ANFTD07nJjHBLAg4Avu50IxloqfCORoScTL6BlynuiGmuunugpkAPwkDRF0ckFuNnuDFm814q5iFLM/iA33tPddULD5jV1fp1EzCBl5cf88kXxfSsKh787bgo8PngkdOcXQBzDxpIFBXN4oQYMT07VflxKDawWKlIW7OW52b7oADTd804UXfesY/wsdJ0XBjwq+MpbhhRXu1ciVbz4J5eaRC1D31Lfsu0YaGhIywQ144R8lzaQA/AwE4+v1ExIDMUogHkTwxTva2XsDyEQN454+DMManSlW18RLuj2cXRvjOX3w8fC9WMmQw+9R0AxrCkJ13DFzNnwtFedfpRfimLc3I7z8NZXf7omtUHj42vRSNIfRsPQIW9LEYw/dRFvV5gPchNMaWXjB9v8FiJDxNrDz4YRwaS+3kM0iT9fX/3yCWHGmCuTWQrkADwEfSmyIBq9oZVw/0yqEYLh9Wez2OAjS25vb+9eunfbmt1ypFiWwgOQpUKmfRM9iXsAzRBvGzUe/jx0LLQWFFiUnNY445qemy6mhiQX3/PHt6FrUfRy8bHHo/Kyqdg4OHRD5kjlrCQQs+dmIiGrDJ3NM7fJF1EOBLcuFASGUQq/wvAjDE1h8jAUPcUPt4SfTSR+UVe7+hv9c8X3bq/HTjt+dEF+/ArsxQeQ4ZiEVB6I242HpchLdqFZ7yGk/zb83UNQkPx9/fpV+3V7nANwXUop+SZULr8BzQW+FaJo3ygiHGsUTZ9Hv5LdyNldgJYq9+EWJyO3XfhzVN8YCO/F58ZXwn8GDudPq6Vw4iLIl4fnpq/TD+6Slk83wMFvb4tu2OQ6v2ApA1YmQtEIvGAAt3LNINg1HtOQYiRLdXpbXIrWONorAK7Y3ze1Hq5o37muPjoiHNk1DZs8f+LgopK/4Ao81lCq61kCrYvH2z+5a+PrGMTBO+nNrl8t77LvJ1StqEb2pLK/DtuO395cOLNWoV391Obq1TMLIVnRF8f98OBR8DW0WEmiSEU6r1gtVBi7Y3lQws3pxwAz20Bbzt4FB763NZLhk+v8sFvQdV7YuutWajELRBkJiyaomFCa8WOoRnHX8gENThlhgsmpxJ9vY52SLy2R80DixZ01q4/X7eu7OB9G8Fz2OyQgemeHfAqPbkDJvEfralbSa1hdbrTMAXjAVVY2Y1lVQX7M92QMWG3Ws/sqM0WP1KBStJkXtrXAN/duh2X4OHBfS/vRdvxDE+dCQzE6gZIvv2KhIkUEhgk5AZVY/YaFihiQaS+eKvtODOmG1rMa4eDFyIgOCm86P+YEFJ/sLmJxuH2T0VFCVTM/eVLyG4cQoHMkNsLtSscnCcSq6IzDNAdpacVjhKAV0M+dvqSCgOkKknUt2wblFJruM1Y2Y+GoGBRuwndGh6pP4ckzlIupxOFqRO8Uh6Whz1BEWcnEzsPdXbObt7x20KlVjdXju7zeVRn6q/WJfZKsAK6AmaMs3CwtAX1ovBu+ik+WfXZ/g4v0uPeWxVfHToW/oe04c/xhe8UEOLupIX3HviV8YvjIZclynK4PRWBUr6YbNkLHaeFe+ymrItvvfG7PrpvUQFTsUkRCLbTEEYDLqmEAbsrDdarm1i9CcSojPSqHhrpWunri1+7e9PIPdOp9l+WJja9cej/OxllSF2FsDLGudOjBxWHi7sTmkZkWNTd3HJx1eNt6Qxcl6wqwenSaP/LzUFhVvPd6vtLeH6hgd+qRfbZy3P4jGYCvv1++tx6+uH+nf+Ys5vhS2Qz4x5BRvEVHz00uTjHEDErfDLiXBi4CECUXrw6je1w7ND68DpLDg/m7VFRi7JN8DcG3C83iyH2zQGFMZCQsUWR/lSPVPLqsz82pHLgx9wQeNFZxezF+L+KHi9d7duysWTkxi1PZ55sah7Lu/OKSNUj+0VLwJA9Eu8JZezBC8SxNpNAwrK6+ZjXR3XItzAG4NkV5xvKZy29CudZXAxbrc9lTvDINZZXllm702w/Yy7o64H6Msz2pu6PPjPW82dPhufhowWFzFttuoZIiF5eCBYMlFx6r7LorAd/cNvS3BFpu7PvBZmj/+F69se+PQcVyjP3tt/tEBidxF7ODpw6R3pYL8w05Npd6WOPAeHVMcuBqd6RNuiGGopsKZw0T6NyT7ut0enTqg7nKZpxYFcvr+jZOzYexe0MM4jNugGMrF2pJx7L0BmEyGazuu+uqV12g1ui3hNJr/Qgsja+0P4pTc0Z/H5rx8IHk1izasdTR2QHcbjvOFi7Wccm+epSR7+h18vz9VICPo5tR6XVTofSvow1loQQk035aPiSBI+IiZUYRsqk2NiNjdfnGdBN5EH06Klth71/WAWBUWK80+McVMPyeCYFoZFc0E4CTspZhvAR6BUBk5WE4cPPqr8jccXz0eg85T9VXr3zX4UbF0cunYlCBf+NSYO8ycbEbZwr4B29CkuhOJ7PBUZvTzpaVQkm3LciyUTv403S4rby9fq1x3X3XTUSgXeOQuWLmitVItMhelk+3P2HLp4hQlNXjBM5O7bhx5VPx6bKHtr8FI+M9YbuXVrlffB3gihu57TOlAf8cCcO/Pg03WL7hucmYSXEZ5fsw1dyQ2VeLD+NwfVhmqqNrZis0PuAN4mNRgVm4p9hzjKo1iSmfl3J6DFBCHLiQfxOAW+YsAg6cdc5KIAbgdGjUVTeglnhb37lqpbVafAsXoGz7PpyPT8g5YTcedb+giClJymSmUDYTB14rSHu1Zt6EUgsxhgtNg/DzLIpS3mucFb7dz2WwUOBIBXALGLuyAgpH5rMuihFgbty9CU4/1JTVFfTVXwHcfFlqk3nN+TDmjHlQuJcDZwoHLjlu2psMuxgKctEE25h6vA5tsaYf1UD7R9yVm+WzlzN/GS/CmACuvkQkZN1sLyOYIoCrh4p6q7LI9w0FpWiRtSxBiP+OX/u5DNzKFYrbB9Yh44c3NR6c2N68vvevWVlYWRVVy15EgqxQRVTq9kiQvSX7BX/ZiJ17QhwZtntSyG1fILQmyUe6/uCWwdDYeFjMYthm3p3ljhgRigFYYpmoq9JHnKLOvJ9sfAGaG/6+fkPGuXEKvEcik0fO9F6Xoz9xNJS8PUQgM0Nqw/LEfKuTb0IJbH6ct73FBFqo1L+8GuU3Fn2TzLYZ19BUC0o6dNnFcpDlJNBgkhMyQRRzZTjzMBA2r/g6IhQnM0KOROLAFn+yxybw162HOic2N7x2hAP4wtLymUXr8ECbajp6CSrL6xs71EgXgcBN9vwZhkQpSulJJn7aULOaORJmus0MDyn71eO7l7/Febs4+y1H22KKElMAGd+37gowz3HeQ30AACAASURBVO9cOI8YXjE/17wLvr1nW0YWXA+q1D78d4B/n6JHoxGXVELpMyMs3DUDbIa3bHeaZoS+mkbnNpsv3QYtX0qxzOmA6qJjKz66CGUs3snCgXP2z7gRxDEIDAXxMuLAiDkTJ060ZoQCyIkxZ2c+/u/wnq5hzc3Odsl+4+ov3yPn/SxS+AROUw6TbHlY9gkdpqiLYM5YFCZT/4aqS4cU3RPevPAgrUOHKqZEyQG4LiVFvglVy7+Hs3VtwGJ9LnsqgBvr1HMh+nHcXt+X4mK/oQHFKi1NkS28ZnyGd/EagM3I0wZJAx4bBSOunIZgR3JxITJRLE+k7XhQ7lv2oX3Ffth7R4q/15kjxh/96qChQwNzr6oSk/4ur+sGBy6u8XxTh9vWUoRimBGqcl5xYyMxys5aUgMduWl85bJfomnm5XY9hEprKYKT8+K6TmyCcMO6h5lr8gNBxqtxmzbrnkIzIFRG1NdyS6AjeiIyscSOREcezl1wz0XOZATjwP1A3TIPWPdIdAK6cs92+AS+DJ/OAtwyBcH7FYD9IR+zI7n4UecdA0WbS80uCnmxsTFD9rB7XAfseuY1deh/wKouGj584dDBY0oOeK5NB6Ko0gwK3c7eCxXKS0NW79BXHRGKU19UM0ICGflWJz5+nMTHj8MbsGdiU0ZY5wh8IrE0P7YDAZmSUTMXhpnevdICxYjg63BTC7QvePVaiExzgZZABOAkOcylIBQ4El3pOWibHLjXTdDpO7vSxrG8wy8HoRPQuft3w5Xomh90Ib60HOCUf6M8dnCQ2XPOO/qCWVDy8jDDYZMxRuTMgixSWA68e3Qn7HruVdngth7o+Uo+5K/AX5ThQyDn+/U6RYkpwYOJd/jzcuK0Va5OolYmDUrPDtxeNw9VS3E9Es0Y2AzlT0dimlZcMeOowzhMdJElMFV0DDbRCX0ldQKWNYL5mEVKBslD89/c3DKmtXHdnky2k8Eh9G7VR1owKw7gykMIHlr0wFyFy1SpeF6MopWL9+2EL+PPADLG9klPnowy7ycwwo+3JZ5fNZbvR1yKcvGnRuLIydZZbMAA1if2xjrmtMAeNCcsgZL4LtgVHwbDDOvwSbOON+zM3Tpp4LON62OWCAJMDYbNww48CBFSrFCE2ITqYACOsqaenq47Gzau+WyQevtJ3lhF5VKUeeXNYCINO0dtEyfR90yZzC5CUm/ib2qqS4sUPw1lj9JcHDzUMrOl4a3qHIDrUlTJ1++9MeXGVBepZYGmMnVy+G4AnsqFp3KATmWN3yEaUVTvczG2ypfxZ0yPcwC2v+G792fhu/fxwO/e+080ycVHXjUdknHsO/NwtJrp+ddg5jj42Xpou6IBqvEzBT9qmrvkg9Dc0upZnRkd0BRtSSClP+XGNTh1l0M3rAhFnW92wPNTHtriiYr9m14+4kLKTpi5/B6U75/LNAgCwC1MjU0/SduFTDnzhemgtvwjyCJykalQ202NB5gpZw7AAxGUZ+5vjxnbh+hmZ+oH0nwPu1zNbSISx3xeshm1k9jBqs7DcNm+Ojj1kGlPfcdFAF/4nYJeIebOrwjJxUdcOQOK/jsE8gswNBEheYi059634ZX5L8Ax+LGkH/4Qrrr1j3DvcO/3MOwiFA6iXHxC+5oFMXSzkIlKhGIuCBZeluwTUXxyxGHGqMpFlSVQuEGy3Zy0pvjEMn/iRFSNAJwZE0UkKSogb0o6edmRTHNE3Lvf2rLJxTnvhQ5jbd1TG3es2eJb3q/+d+f3CwsnVBXvxVkeeiSMP2UBegCtq5NCCoC740sQmg1Gb84vYdTDQxfvhKsz8u69c2/y9qPjz8nzobCtKLAcvGdiB/z3H/dCZUwJGU/0OessfEX0r7CzoAiWT1sUikA0V0ycQSCg2IFLgKc/ebgA/huWwjryyDnFP+MEO4nkwfra1cOCzF9/yIsmg7uQrmPzMDqkTJJkqvmmeZ6ZzlXcwlPCKN8dRHZ961NVPepMLetNgLeNyuRytETZmQPwkCusonLFF5E5+03I4r1WzFl6EkTh5bw4dWXjbmeDn/davLQHDn25Dlo+25BV2o354DwoqivVNs1L5ifhvr/+Ao6rtEVbmDkToLra6PviaQuhsdDHnV4BBsmrsRgtxIHb4ohnxJFHoTTJe9EC+V50IEExw5GTxkxbsLQwv3gloaIKhtJMkP3JDkUzyTXMQi2wG5qM4qjBUYchHek9mGjHvAHv2PBSzgolDC2VMjFUZm5Cuk5Os54+VdwPiF2Zc4cv/OqyD9wvP22kxLBu2HdjDXQsd4xvnxFajrhsBgx6GiOFaqRLvvZp+L/Pf8nMeRD7OX06wF5rpMJXBwyGj01E8Yo+q8bqNJSYhuyVNyWv9IwjjDIeuBgJ2X8faG87unXH2vUaZOgnWcpKyysn0XuU+RyIeXKaEnV5G4elvOVYuPDMDN04RLjoJVm34SXW4RwHnga90SX6k3gu3p9GFVktqsrtZMN20PQFURcZeBCZtx+3rUOUtpP2wf4fbEJAz07ArMLVg+Gor1VB/kGXUIOTu+FPN94EJ8xcZnYf48HAmDEA+5zjolw6bgY8NtT7YDDBhG9hBuD4N757rWZucjerRmxBlJiujjwktsHmujrjY/dsfblRZ376QZ58FJ3gqZo3XCpo2dMYTADuoOuxWaFwMYmOEDsaSlgOkGRyf131Sub9kAPwNOmLjj3rcCJtmqo0K+3DxV2tUBzkfroWK2GHmyiNw4FvbIPWs/GhknC6xkBN57XHoOSlYVBUMxAKN3Lnn+5pbTCsaiA8f/yTMKHY9lzoIpRzv2Zx5klp77gpC2BHEQb380hWYyEuM1WtT1IceSJQYlocebA9+nf74fbxTXVvZFeGFWiGdDNPKqmYWbYLWVlFni9V+7wOuxmhfS2TSMkuxtJtPWw+2YdkIvFQXc0qVKjkADwsLY1yZbOWzS9IxF7Co9B7F6bdUvQVBOa+vezDHb5zB3t9mbvOqLsntcE+fN6sa463aZ5OXUHzTIfp8AJ+xuDHki65BOC223yr2x8rgMXTF0OPTSTiVhAdIYkPT3Glp/yRRyNU2D4SoaDzyNjDe97u7xw4ct7L9yBAj5CKXm5XH5MqXwHg3s5t9EiR05RZRS3iMAhjfSIOTbuTEEF2R3f8uD2bV7+UA3Df7aWXAa9in0IZ2n16uftGrjBiDK8yTrLxINy6SpUw5ahM56JDKB+vhfgY10e8IyX+ZFR/rMJPCni/8QbAggXabZFVyocmz4MDBYW+ZQwxGANswYExRZtw82YKNRY62pTl+lihMHoz8YHV5tyIBy7aOgKiEBYieO9CscNIHldRiKW47Qg/AIU82wivqwop7NpMY7YyY31iXwziwEmi+IS8IJjHW06E4rtl9DL0WeceJ7MThyH5yb4Zh+ci/3b7zjW/60bgHdPpi+us4IpuOacBmr+9VW/iQuYaD+PhNfykgDfRexzaeDcGY1TpRc2TJ8+HzcXeFzkhQBHgo4hSxDzLl9DDADgLUp4UVhXSu1OuH4SK9sNt/VmEEptQuWw9ss1VfI0J8BNrURrzyeXArVBsCk3xC+thyYNSZQxI7bL3PGis27ByrNHPkOs3VyyFAicWVMzs+i+e3Mf3N+KE4cZTxhjACsUPoINy+k707jmqE3Y/sBYSY7sjn47BMBg24icFvKmlb2GY5p/+NHSb/xs4HK4omwZ78525cRn2VgazkigjH1sIBOBKL5lIQDwdZ7FeNNg8ptnDV3jyXuzo6fy/vZtexWtG/0nkaYkM9rkMr8mOWrwuJG80RuwYAeiO0UwUMbnKrWeTColk/JH66tVG1PuMHRzZHFTfaWshXtGK78YF8qm+06doeuLDNDs24gbEfgDu1WNXM0aHQslYEpqv3AKt56KSM6JUCIWwAT9T8ZOS3noLYM6cSFp6o2Qg/GT0JHi5dAg60ZjbVJVzkyOPBHRDwYUgHEOW0IkDl/isdhBtu5n4xEJXDZELJGMHOuOd7+sPQE6elgPyijaQqbdBJ8FdGxcMw+lJBAJjlv/c6scSldDjFhrJxDutY0W/1NPTfU7DxlcMy7ccgGeA6uVVyy9Fwt6EE58F2wj9AQQBP/1a3UUe7iIUB5MVW4OeXDhxUS4ddGqzfUUzxuZ+J8iQHPMWYLQWEpvMwU9KIuKOGoWxbfen3Y69gkOo6FyLgP5m8UCoQRHLY0PHGBYQFFpWmheya78AcJPTZN+mEExy7ERIN8A3tHqM2NJkUcw3gT6BfyJvTV3tSowNCdmx5wxBXfK0xP6jp6XwUFVk/Sw8gQBINf6MYSZoX5e9AeDysMG+HO7uGYqxaNB2naccgIdYEDpFxs9Y9v5YfuwxJPBAnfyZzxOGhxa98kH+oNYmWhy4R5thRD7d4ztg9xNvQLLEP9qh01wUQzGsxs88/Dimj30M4G9/y/g0NucXwJxpi1loV1Nuq3CKhiMPf5CZ5XHY5QTgzPLCBvjmKpG8vixueiRysQMdFlxmjlz8jp3VqyZmfPAhGiBPy6KCkpXUYeldSX2XXo2WKiWd2PNDnG52px436xNWD5YhekpoVf5qmLTorF03rh/P6nhdzUuWMG45AA+xKHSLHDV5yZjiovzv4j75PC4FfxMD3Ypt+QzRnPiLjnNfprhxtWtpiVC8ANyHgXdrtwdjdDfe/xbEyzoDUXoEjIB1+CHFpWN6+mnUQGKM2yykvQjgC6Yfa7GhMBBaOKAwzBaLwC7LJZEJfwZAiAYMwNc37eQ24sKKg3l94qvsybzWnXs2lJeNnjsultf1Dfz6VOzkKPyywDxJBChCXjdWQa9dP96V6PppY+2aLZkh3aSS8spxrRgGN9/LSspu886wmMBYnH1yP6UyHgyxeT5NJOV1UP38EAmSMIzCdnzIYZJaJmAVQZrL5ZUUKJ+9bEReT+wqvKtejtMWXSBUHwsTd547DW7cfni4XCk9uWyN00OLSw+xxCimStOt1dC5VM8Vn0wF1+BnJH5cE3lb7tkTojfBi+xG5eZiDITF4BMRwOCLDe5RoE6q1IQ1xvlqkdn4Q5Wxy2/dOXDZa9Vzk7P6SbTfzGOuqtYYIt7cPEJadXei69SIgZzsvSl+wXAjrgm3EeR0ELcIBqaKGIW/c8YB2TDZZKIXTlDz1Sp90HaaZTYLXtvQvkcwLx6TtyCAX5YD8OD7JpISZWULS6Gk4Oz8ovzbcFGVhK9UsNryfmw7hoVVqrlRQzakgbOuNetcFT27FVJsY4KLs3yQSEbKzYPowdlyobdT4XJYDv/GD1mduKYbbwT45jdDUjh4sb0oD5+Pjj9s86MSU7rUS2Wm3YNQbYG/ICNlAyYYsau/5Mg1uiQ5cLnsyKJDgrY9DoufSMbQntJ8J+B+lKefh3WRVWU6idl74wi5u7myP0wlpk05yYnADx7lJmsBcbGj0tkXYQdF/cjvKBq3bduzFo18jgPXpOikSSeW9Azo/H+o8JmLRWaLYm8n8pLrCtqL/4WERRMr/VQ+fellefmxm/ia4Oe6isecoeH1sUmymBA4T5vK59hzRMdzm2MMahfOhqSpBPLN5wfwiubePiuyaPtxzdB0c7WjXPxkOBmewA/Jvl1TE0oBKtB9viPQ1OsvEoec9ciBL53KOXADwJ1qtN3PSeZNSGbEUGHLiy+wdGKnWBWdoq6wBwKTSCRfQDvn96RBJMPemwOxcE4yOG/JXaf+6Sb3Rtd1ltnrcEyjv65FVSYID98dyH1PtGfOAbgG5Zm7fDzvPtTXVKn2WeY1KLm7K578SOPG1S9rVGdkGTZs3rDBYwc8gytjAV3duLVAsCmxcjip1qtRceMpIOgBkF408AVmUdiPy/Hj8HXbiQ/phj1/XA/dsw4b3f4ofBT+gh+yOvFMX/wiwO23B5nytPOSCGXR1IXcyA05cDXsKauc2Q+mNpPE3ydtHLuxWkICLtfasRNAiLlTDwQGocqyFjwJ8iO8n+rjBuxfzAQyuaW+Zdsx0NDQFpRgpr03Z4mMmDGCcfDzMZD7yb4NVU7cgboG98UlMOwk4kyXnA6ffe20XiXd6M84JM5pqF6VEjgvGFoEpWb/z49ytBXfQq7g+7iqCmgxsAXBOQU5P8Yo8Sr5UrKl+wMNDa8FWnjl0xafkFdQdC8C+HiSa5o4jstNdfNiG0EsMbEBnAUFJndl5a+yMyFe3L4usEYF0Dojprk89IV6OPjVHXARfn6HH0dHDrWyNWsAli5FwAxn1aLTL6c8pMScjxw4WZAwO3Bx3/cUnVAfae0IwJf1psWB2/QvqfMlWIdAPAmHd/4oQuL5uupVJwSh0+iZS6aXJPNruL23vLnyGkwwVEHdyoXzfOIQMjWXok9cvKImHbGVPb+QsGsNy9gryUTXjupV5KKbsthyAO5BytGT5s0rKS59FZEag6cLbkfKypgZlRXEiZioaOjp6omftmfTK//RmiUzU17FtGUXJgvzbkEupDQT3HjA/kSfPYAcx5cD1xDF+DVnP0xGHD0Inv7t/TByxHD/sS9cCPD66/75Is4hOXAG4FLuJnax+cCAtVFpMqi+4GMB3DAcODbBRXupoMbk4IwrN5O8rXLGVAC1YSljBVlZKtHT86v6jS9frkvCispl67A/x9g9LblC1RbnxaNSO4izF5CUcZrHTEj4lAy67sCSyYd3VK/8uFP2kD3Qbbkf55s9u6g8PhRd65IzUrgxsXGY0MMZxJGBSP5tZ+1qCvmorZDBec1vyct/7Poxk069f9gYZmUQBTce5Sz4gWJqAAl1F+uzY36cut/31KpfHqdDonRACfzkuivh9A+d5E62O+8E+GzvPMxOSswFqMSkF+KdgMZpQ1sA3AKqVpGHLshK5Qy/jZpzmmKpwUDeEJpoLUNzTLzqvQebJ3Xs2rDdr/Do8gXTSgaV1LIjRSgi1e6pa0EFczdGwZB7Y4XE9nIA5yIR+TqOX5/8vnds2/5LbC/R1TOjfsvLG3MA7kdR5fsx0489rSi/4AnOeXMwsJziEsSliZGtbpH/lZ01q8lLzRfECbwxH3mCnE5VbSksgQsnzIKt+GemlCdsa2lwsnJoflxxAPL6Z/VTUmr02w/AvTqxZNE8+M1N16Vy46S4LC8H6AxmS+4/YL0c9bFCWDYdlZhi3VnXhjM/Rt6aBPgsCbrKtcwP5AAgK2XsAXU1eqMzc8l+Yde76mpWkjOch6dnWWlF1cRmdHwuYsy9zdPSVxymdk7hUOivXBTjbiOvK98PyynjraoeH5K2BZo3Oxy23qDz0e/yV1Qu/SPk5V8o7UTlGne6irkBLAPxBKyur115nBeI28FbJdbjQ0bC1/Hlli7cgFFNli8X7TBb6YJ3uuXtXdKpTwfAvfIUFBTAt752MXzhQiW0zfEYq+zFF3ttPTMAn4FmhAQuDHz9E43RCH7ln90zB3PBFwpUt4ye1klGn/3tzNl5Qz+JZE19zUp8VNQ4adSmU+y9VaaLMhqKTEWMorN+qKwMemUda3ryffuc2TFFpV883nPFztqXf+5Ga535T3PK+2dxjJ+wFi9OcwyDfrlj2IrgG4cvAi7mcBKlMI00Ob4lk3/ZWbvqbCdKeIG3zN+G8s4zJ86BDQMGekoovCjNuW2rYifKmdEBS932dOqKKo9On8rGjYEH7roFJj7/P4Bze/dNXwLw5QjgTtDtxBQzHSu5y6tKOUfunVPCi6OkV2hMRb4qOkkRhdvxjt9eNbl2Loqx8s09yfgDDdWrbUHi8E3Lqkm7kbUZzA4zG5r5rZEUELefiExcIsRMUo7uIN/XWUNB8sh+U/868g8M3rt+vetLJTkAd6EsD4ATwwA4pmbaNNbmhaRyhMupTYsAe5W0CLq7ek5q3LLmGfU7HfBW8986shxuHD2BLynWLyXsvJxJsehUOWCQxWPrnxaHF7Z+t3J+G48DjT8g6CquXOWgCsdGz2d9Z+8O+NyeHVEPN1B9JoDbMJJx2amx09gr9jgObw5cj6MkAGd1ab4e5GTlEmSwrFdCG4rznexK9kxtrHllq6jDeFnHWA+SsxLrw+DEQ3Desp9cJCNPNlajMYQoxSfq2SHrxZtHHYqPJnjRLAfgLtTBBxq2I+MyQQVpO2jbi6o2p/bv8CrWg/JwculjXh9BwVvWV4PvJ35k0hxoyyeReWamL1O240E2r19eHXDWAXm/w8Bex/y2Q/CH+g0wMt47wffIkWfFjGMt3oJyDE40Y1wz2X87cL8SIJ0eJDABRcAwD3poiG1SxBK2U9BpftIFPFQs1uNbkCgPlpw3IOdtjSlicq96cmvXdSaurJw26j7TO+xsxyv7p58djL3vqLu4HU0p0dnAPWUGAfx2Xz/4HjnwfyFbfYrkccUMsD8MbtsmSrFbBdiHiSdqR1d357G7t7xGsU0NhWVQcrTE8uHUSXNhG4YW5Qav0UyjKpWMqsagh4wO6Ork8QNmlea69fE6AUqScbhx1yY4/RDFY8puOpSXD8dUov25gwCcX/Zt0MFYSOa0yZNYK3aLEbm+vUQdcn3LPaA38ugAj7jwjpa2BSWDBzyNCkvmJs+VjDQu3huDexXbwv5v1z477CPVfNDrsNOjQ7BciBXJeLLzqIba1zwXWTT7NFjf+kXu8ZVLLo/lFfzSIgNnK0QsFmW3cG4Ep1iIUvxk4pc21W/45r4dpJQJnaj5y8dNh0eGjOa7ky3k4GBu5bQC6etD9z3dgrqAq5/P+wx0OiOp7uVtB+HXO2uyzo1PqCLDptTkBL4cdJ05cFmDk6hDXRc8dni+WN/8G34OiFwO9383wEuLCyejAMiL4zrPZ00qsnyDe/Xgc/14HWNLC/Ecjx0jlF8OnLiUZYb1vjTor4gD5TgS8fjW+trVU/z2Sg7A3SlEXpioPEiaQacURabV1pRPvY5MnE8QwD+3roWjOwM5bDr2dOWAIfCFipnQgh56ckuZOE6HirgmiC91PTn9Fk4mvtcHXH/5Nx+u36WVj0K3XacxFyC4XbqvHi5vqssESRzrnIgAzp/htadUHpyBM64BLgN3AX2DfZVKO8tC5/bmgjewmC+6IGIqdx8NF67Ok33OTE7b29MylWQOTA8/KNgK6g3vS7Ym4/DV+o0rb/ZbVDkA96DQ+GnLPhEryPuLBEYilrm0Tdkb3ySpFXmZF5aiDHX9xleY8Xe6icSTF5dXwZOD8FaZoRnlTJbDvT3dzovyumAbpDldYNbJ55dnTE8nPLFlLYyJR/8Gp33Mc9AK5QDKwp1oZr9DUb9p1qQM3PE2oSxe+4v28lbJzOlIaZ6vKvE4M+K26Jy4cC7REZtFcY5hY5R1GXIRKX8WIxVjkcxTWvbeClHtnLf8SqUvz6PHEDiuUX6Oum9PZWJozjryD3pan8g2MrTdg2yzvp2XycIhdgq7RqKSn6yx2ZVJBGRXFQ8p5oWUTcggLaMULmLH4hX8rzvWR0aAd0pK4TtjpsDryJUzL84IkgHZmcNuw1lCS5bvdw8OMWadKt0AXN3kxI3fjCKVU1ujf1ZNHdZVYybDvcPHOY/UNu2s30zkkfIFkxupzIf1dR4uTzaAQpjPMccvQ6Buypzt9q12LpyDuRC6sHYlmKmaF47i8jvZd4P9F/vJtPhSmChVDKEArevcOsvFlJuNFBXxTmfK+9JpXcUTiT07a1ZhkHn/FM0u92+nX+com7nkk/mJ/D+hRr+QBQQiay0FwBW2nI1TNSl0sxPn53kS/rz9HTihXe9xAV0iHkYzr2sQyP+O8vFOTZMvtW65b3UWB99+fU927scxW8arbH43GnuBvL2ts5t3w093b9adrsD5thcWv3P81IWkQ2GE96K+yoG73XLU9zFlPG8Lryg8G1msFRaQVhEZWuS3qboEg4GhfrLXawKIv7igm50Spsw7TZ29woi4cd5sb/qsCZ0DKOjEyvlJxBOP1teu+qhOeZ09qlPPEZ9n8OCqkUPGD7ka4vlfQiMQjAxmhvI0QNs4+U2FpuRwXJ0YcKHcveNtOBHN0zKRnh04DG4dVQ5riCs3ThqhmjEUUWwEwSxa2JUwjStliMEGuQT4bcCgAB6kuwT28zpa4NFt63j87WgTvnoD48nRDNdUmSMoi1dlJJPARH8OHDi/SYrOKUjAA17yhw3IDZ/e5pbKfO6whqNS3dU9wE5y4mKFWSihHopGNwisbU48KqAaXLnor1XMYa5HnVuV0RlD5m0eDs50FXoVzdstH7vz8WqpX+STfe7pSXy6YeOq+3SWTQ7AdahkyzN+xtId+GBxBZsawR0YIO4gMjE2jwQ9cZXki5pFMIRPNzfC9Y1bIpGJOw2JvDkvL5sB/xkyInXH6tJAIGigzeFRd1T16HbfLZ8u2Ovmk+1M6zgM/0QQLxYv1qTbT1H+S7hmfltWtWx5PuS9yNhvhhPWrSyXIfWZnJBMixEOKhwUhXG3AuQELExMaLtWUv30nqZ0rFFcyLiYUNwE5JwaopmUG4KPQlOAKRePu3PequjSXddk49btHAA7NUx6yPmhVil+unRYkkKesPdMqQvw00/JMbVBR1nThtfQkdA/5QDcn0ZOOYrLK5e34cagkHBCJi5FJ/LWZy5qvkw4antFMDz7QCPcuDtD77uKUawqRauV8plwkDkCyfXLuS1poWKKRdiJ46F5CUc8Dh5pXoUjPRg0efsQnZ6ClkaPbHsLhiUicfx5A2djgRx6ReWKe3FBnaMIlA2qSDw3YnnY+s45WUwioylGEbczvnzlEhEHgOBAxe2TnITocHAki709JgN3CDOrrAOnA9IC1FLJpKwfe9shpijVdlwRCzpx4m43B8bPsZus3rZRV50hPklCvL7a+vK81y7LAXhIDCqfuuyjeYV56IzDhHviKsqVKuqJbVFiCk7HC8SXHj4ID9S9kzFOnIZL3Phn0fRwFYpXckmfAn4cuNv3ZV3t8ND29VCOlippJIpouRSX0KtqHchIbEYOdIrTEcTWIr0GhhIPSsAIDQAAIABJREFUuQ4ls035hSrHFKPIKz9x22R1wvgTxo+acnaxvmNY2s4Fy3z2w8Gu0JTHgMr8GqBoiBO4rDwVoMXv1T7ZiKoF4i7cN2cuuNjImnxuDo4TywVDXoJGk4b8LMWDtL6eeZvqpRyA69HJMRcGkH8cqf5hOUVSU61uZKcN4HTllQ1Q/tkdrfB3vHpHYWLoNbx7Meb4tajs7A6h6AxDNk0+N0zVRhk/kLVXHiS/X16372nrD0Oz0fsRxGd3mk+3BRzo7bhZU9yqx48/dmT+4MKd2AZ7vNMrYJQBFsobj05iFKuPA4cgrvMhcR+97sOPASlSUDl546BwkBNLUULKpc4Bcf0571R7b096uqC6IfKx3wQ4MfnhFXUAK4/xxhPxP2PIDXrYWSvlAFyLTO6ZyipX/CsGiVPIztYO4IYckC13ZcHLxe0hE1/c1gIPoXIz0yDeidvwirLp8PjQUWyTZiIJ3iVw/X6AmQ4YGwdmgF759cdR8SUaorIFuAZ+V18NJ7U2ByVzOxZAnQvscyo4YuriioGFhW/gd+IVdus8sgcd8JDm0QQ5Hsvn2Ng/GafOZb5Mdm6Lp82wTKwNY02TFRYyqdwyRZrzUUXOsrFULpz3w1gbjNt2B2UD0D35WW+ycn6Y2nW3hLG4zyuyfbVmkxGRd225c8J5Sqjj7uhKrNizedVK3QWSmR2r2/oRkm/k5PmfGVA04G7aHNIbk4lJxAJgDAzfBSkbwSuK4UcP7IFf7d6UUSr14AlxGj5b8fS8Ihh16UwoXo+x8zW17H4dU5d34IWmdQ/264HO9/r3Aj8A12mNwOOaxm1wUXODVnaR6QdIv2t9CuRPqFz+NtK8ym75QFxzDF3hWWRCJvvmeg1DjCJglDEhHMENqxOjTYH0qliGh6rlohZDmS8OB4GTjkvJLmI0lfwm+HMxDO+nWpcF5BUwd10uTl8wsRCvONU4xwXc5WGjuTf43tdTe5o3o2QSow8Sz2acNX6LJPC+8qvw3fg9UvuEBweOePqbFZX48DFyMWJhyeukXIQGqNuI5GUrPg2v3H9HJVhptJYMrAetgwCWrAZ4Z7bZoYIdxTDsx1NgwPPDaW8GBnMrd6K3gPvLmtEBcC8uXB3nZ/Y3wHWNW3WGfgg36VA1I2LDPPz3hfgzC3/G4o98sWbPgw+P6bjmR5MXtx+ODVHwz5Any9d55JNhDMSk0i3FksWLU6VyqHHDw6EA7Wq9RCeWvsu9QRgljWCUG6n9EpgNztuwEmHIaR2z3QIlqALT0wLFdrgkEnGUf6/Wln+zudNZQbk87hTAZbgIv30Of0rfO2k+bBlQaip3+B2RJUuoWcFY8PkzveHclJsxBO8/1m2A96LnZlRpF277+XjpbqTt75Dy9xbC0J9NgoH/wGBZCXlFxuXYj2Kr+NFKB5CdwMez3gA3h3P372Kmox6JVs9HcLk8jtXOwb9TbIxl+FPkN7Y31g6EH/1scs8rrw2OJZJkyM05WmPM4qTly5N/Z+V4FU5cLmJhXy5twllJ7Jg0t5OiGl6jbM+ByxX7gjMuNq6bWwGkz3k7EciD85Zjscj/DQ4/egWmfe2xAzAJtyEHfonf3Krf5wA8CLVseZHkR+OvSF5Fcb6hCxdf5YylEKerkwRmvpotQO3YpJRN0iZzeSj5lEP74LcNtWnLxTdPheQKtCB2A2+1fwTkw6+Zjhz5MNMSIQ2aORaVHGCIeoOCcIgmjCJabfkAuL0OH6/NZ3DtfBc7cA/++EamcxvboUMFyWOWLkQqFyCYK2IUBrPEcZKjDocCi/LQSRFp4q3BdUsQt7/ebumPCtSC+2Yu+S4SrCCcdwrJXeq008fCeeOeU22/jUMoagWmHUOEPJ7EUQfz9o1qqa521HO4zW0OwEPuaFwjk7HoOvxBQYSZ/o4Bpb5cXom/MBCZfalyP3LB0SK1m2hJsHfqFuWf234IHt0eXrm5ZQoklr8EMR3wVvtQUFcMI6+ohKK3BkUH5AG41ZDT5F4sRNs6AO6XJ+V77MdXMJLhN+3RDPOgFT8boBTo/bS000WXzIAn/4u3KVpxAjTkBZHA25BiCIA21yjnoJlonNaxDTHkGpYmh/wg4AiaIk6SlcgciuIylSOV7SqKTR2ZdxqUYuFj6XYsL86KzooBunp4iXZ4PH5xh9FhRCyVcAENY/YSiXZ8rKI0aPdzAB6UYnzx0U6gu68FvGVV38VgQ3cOw2BDUpsvFoJFQaSIV4JaqByLFip/CWGhsnUyxJethPyg4K2SKK81H4b9YiIMfPQoyGs3ObdAZBSLWJNRClR1JjNrybf9OHAFhIy+Ypnb0TrlFDMIVhzWQBMK57QCGumMed/+Api7fDGLSmjoZgT3LcurCninOlNAXIph2BccuO1iEXs9xOXKU8BLH6hDa60zmB08CvJ6EMv58I1efKJ2wTgoE4mHEMDP0plLy34MWuDdnh+XAnm/0MOITGzilu4dOgauRiBPiNfkTVm3ouGXzApVopz20lQrSguVKMDbMlZ0Kyl9chQMvq0cijcT42A6XZibz2RJ+Jg4e9MfVZt+nLWkjW4++7qJ4R36CbT9P5rsxH8PLfA57/UVZh9OmLmMiUukGEVaSVjtvlNN+VyBUnxBsm9av/JNTk4DsahtMm7eb3Phq3brVuY0JOft0ln7jcICooaMX9FV0WGUYfEJO1rYLZwceDpH+72+4zTnOQ48wE5AQpOJD8UoIA7cNx1A8D51wjzYUVLMvdoEiKlKoGxYqEQO3raRF78+GIb/cAoUVpN4JVPJUIsJAMhUO8716nCEfEP6G+641TWopwf+MXPt4UmPdZBVSeRp3opFsH8/+fsoYhRpMuh0M9DogZCsAMQR8JRY4VZ5A8/FbMbRnNHg1G31R0Vjo09SVOQ4DitnzS4RxuRxsYjKaLA7hsGD8BZkyGa55nXmnq8RYcTIbkNUT7K1fsNKT4bQbSoyt980Jr8/ZRHg/Tb2uSpov88ePwtWDTbd1lXLE6pLy0LF5b5ZiNzP3XXrYYVLNMOwMu+gY6T8hRsGwqhvzoDCLYFFed7NRSVr0d1hDr3R5ay1QMijH+PGdMK/HnkThg+LJHaKZSTXXj8Z/nDPWC5G4UhiBmxSwE4dgyf3zRevCc6GbbUpplHXNp9GAYsCeWwiYYuMXasfcoROHWXcLW/ITVwjxUJk02h3n5eSfN6EHlSa5pR6ZSg/buG/76xdiR7dwZNer4LXe0SVEOD9JA7qfWEHdvqEOfBG6UAG1kyhabu2SbGJU/1+0Qyp7DkO0QwzzXm70aJo3SAYdcUMyK/H1+hE3PSgdFO2XtCivZpf64zwyoSLbWZVK/ztXrT9LyVD6ejSzl1FsPS9iwTDgMCBbfG3GUwlpm9rymGqcroGyNnCzJr4yq1dsFUjxoqfzN3eFz/a+nHedqsTblhA4E60EGFzXYDaHLaxc+XR4GhII8GfzG4dDw8hOiEadHbGT27csvppX9o7ZMgBuA/VBHg/htlODUNgtcxHK2bDq6XDkOvh1yi7+MQuiwwqF//Ugd3wExHNcPtE6Fy6Gop3u9h5pzsW3/KIPYMeHAvDf4rGOp08QCmXkyseduJeyrggKTOVf/VtQC+DyRGFX+pBLgA6nLpnHoFSC+YegofueQsK+FOnkaWJKAdHu3Csj8LGIqAysnB5cyCOV+0RgREXBVjBmbP5LKdJQ6kDMq1bVIBzs0ZxJUCanDcbdSwJ3eM6oXDnAGFxI5Wxwp7dS9uqdIzvaauGRx4qpphF1THwv3ce7prauGNNqDCk4Vd1ZEuqb1eEE/Aw9vDMqHp56djp8NgwRYTuZqHCgEy1GDB74OW5OR2VYL8//NahZWsTQ9KxNolqvLEDBXDUZ2cz8YqqsIqq/j5Xjx+byNCMb3S/tOzYA3D/net1svpVZXx/0SWV8J9nMCa8ABoJ2k5zk9JN+0kmAdpmQ65GMrSIHmwxVnSV2X7kSofzJvBueOINKPvwAvQ85nMieWzd/tmJb3D6PlMsD6sdjY1DYf+mUC+6+K8i7aVxZGWMkvO2U+bs8tmwatBQgytxslBJRy6ezE9A4+/XQ9eSUGsiIxM56K5xMPxnk/mDAP0p+aFHiLH4cekqJ3zi8fvh7ts3hGjFuQiJUZaduJhzmpL7pqwGCGudLZbKJYlYsCzx4ppl/bIzSzoMidsna1IApiJ/1x5oFJx3fhJ2/u9VSIzuhopZyw3Rph24LXJ60cHA9t/qwESFBoBveCn0pghdUJvQ/TBjJsFbkuNz46vgPwMx3gg9lOxgoWJXdNrJaDW/MngQIxv9pvXsXXDgmq3cdqYPpIKtJTDm/GMg1lSYMVNCqZTSYHAjp4gfMMsGg54JH/pAE/zmpprI+jtx9jJ0HBF6GEQAEqU44It3ezbuW2Y2Xu2hS4Z4/JiJV4Q6UZrGRnEbS4fzTqB+Ydejb0C8HONxNhRAxfuPtZ1c0dt/p4qH2Ai66qpXslDAYVIOwG1UywZ4yyYfGjwKvjF2GgKsuYFUWaSccLnhpdxccggpYCXkkIYnGTYUR6uGQxc0wOFPNWLE6GiVYqEWHDoCkYKz5PkRzCxLU7nv25R6hPXWotYGcB2TPQvKJ+Gqb2yDL34uUARDV5qRGOXJ/1L4YEE1LhL3FnG5nDrm2hQybWYqK5qWdYp5VqXh7AbgQQeLrsTvdGEKQT1rEzq2uqe1wa4n3jRqHXVpFZQ+zcVKUvwR6UNUDrQzjGITia3owBM6TEJvrXXfDdkbGbIJ3nJ8TRjJ7QOT58PeQuRKFQsVU/4tlD5iV1jB2+rs4LUJE4N6YO/Pq6Hz+OgCYoWeIyT0sF9PQCcgDLxGm5zwg+kCgiVTEczQIFJZsS4YB+sxz63Dgae2n4Q//HoDnPTewLHEU7rIrFHet5DbOgvCS8soL7mvH8crRse5ewxlqb5gz8YtADtd7tuvH67WJijv3o8HYetnrQdh+dylEOsWERWFTspyZhh8hp4Fivea4KeZXAPxePzunbWrLwizjqhM0D0Ttp0+X06A94vY0aW90Vm7hYqvXFw6YEg2nCZTyg0cOHGa6ASyvIfP3APN39/cq2KVfJTpPIWfxLNFcPFl34ZudGCRm5+QnL92by5PA8zktZ195RBrozcmTvY8gBxX53BwyhNDAHriobVw9MzQr/oYFJqx4FjoaEcTF8kJ00vzwhrFQsaQsmbuMc8WolIdBy/uyJZqheLIdYsqHIEqAOfdM6YDGh9dCwmbfX3hulIY+8l5qSI9KfbRlMU5WaB4LUc5v41791V2NlXXhl26OQBny5ZJiUlTND0sIaMop1qoeAO4yW2miFXEFdaNy6H8LecI2XgUnQ5YRwG+S7MSP4tFjKaNm7bCaWddBB0dab0XGbAXvZxdjwV3vFIMLO2Bf/1tLUyc0JHWIP715HD4wlfp7QcBAexwdLZZDsPxGq//GNUrIWttPdchBxWRvhKua5sOIHFgcCaAH/KtH98NzT9wttIb9/4FULhrgNEjuwUKO3LkISKYJS8PTE8LFIeB7khDgWmyOGkthf5dGOeGFAg0u2V9YSTSQkUIFliXnOTixoLm204JUKTBieOi7njvfmi6BRVjWVRwFmEY69fwczSLwmumpqb9cMqZF8LepkCRNPvCdLE+6HDUwTvroiBAECgr64J/Ppy+t+b0+Uugg2z0ifsmjtj+jq+90wE4XsVVzVqLkJepXHgKbTy4boNz5xvAUWzGQZS/F5EsjsPON192Jv/hGFQsxgu3cLYx5NJsT8ljS4/H9fPAVNeIMYY4xOtq9V+gdxqEXu+Cr75+UUJw3ihPgIl9qcNkofLkIFKqcBm3RT6pnOLWRcGFyYaMXIMTbz0DxSk3ZPbJNknXATAA1uJnusslh8Zy/sVXwLMvrO5X9uJarvPK4tIFe698tARmReCt+eobg+HMT+NhyrhWDlnCcERrOzjJmu0FLTbhDvJlv4b8uG5eniO+ynXLPbP77rege3GLYzNDfzIRht5d7tkF8xjVk38LCTd7+MRJ+mICfR69QL8FX6Cf6kcDr+/f7QBOjzHQCyd9LpGFyhVl05CLyDc8N+0mWIaViqLglAuEBqRjatj+3ibYdwuK4DLIiQ/EF79ewc8s9gKYd3rs70/BN759PXR3Rx8LxK/toN+zszSg9lQfwP2VsrNntsLjD65Ny1vz4ksr4V9PjWLctwouPAC4gId0UALrSQjZunHYKS/7pNDcyWJDyssFVjsCo+C6SbwhvX57Snqg4XUX7hvrGvsBFJ9guAduDWV9rYj1NQ35t8G/q+NhNxieuDNe8pYd1SsvC7ru1PzpTE067fZ6WSTk77ETn+v1jnh0gCxUzpp4DGwq5sGhxKQbO9u48ikKNF9TQ6yHi/LEBsV/xEd0Qwtq5lsu2hk5OYjzfg4/Uuat00Br62H49EVfgzfXvpMxNbvklDLWgM5APfL4Az0fQdWMw/BvDH6liTWOLZJFys5dJYz7VkGcWuCKRbb6ArVBa5NJoak8RirEx4AsMuwUnFbOCz+ZOx+EjetmIG+aE9Ii3/X316FnqruuoHzOMoj1mHKjbHhgqsrb9vaOsqbtr1F009DpXQngONffQIrdGJpqWS6oysVVjs8O4CkKGAHUdq844zCwjSM+qgv23lQNXQucr5xBh03WJk/j50T8hEn/fOo5+ObV10Nra1tkOGvghAIYYfoWpow/KKu1endQrWvihHZ48tE3oaQknJ3/fnzsYdF7FkFPnD/QIR88NhWcCjC6xHPnS032WXnYAX/30sZX4UNT5sOBgkKDb9A6cALK3NUT5vAH9sK+mzyMO7rzoAIB3NgbwsQxZQb4OcEOIjZE0XEJnLoKWFmvnDd8wPgwPmDs+CBMkLX1rgNwnIaPI4H+wliKfpTeP2neO7XFpbOo1xQOlO8XaxCiFJm4wjVZrsfGaqIFyRU+BteD37Ud3wz7f1UDyQHhAIEdEPh5CD8fw086qa2tHb5/w81w/1+fCO34Y1xb0+mIUjbopg3VrE8jdngfc1Qn/O2+t6C8LJw1z84fFsEH754LhxBkudLcvKkxCbmCuKalheSCpc23NA+k6H55UIQR/v6x5Q2o6u6AFpTRzJmxBN+LJU6cbz6jSvtg5A3RhvJeMndpgkhg2z2+HXY/9bon2WO7C2G8CCmgAr95M+OrWCdpKTBZdcqjJ8nE3XXVqy7Qqd8rj14P022lj5THyXkvdoXCwkYc4y3jA/wVguyaAY+O+vOIq6Yx12dVHu4sSjE3iJMiyE85lCiKw95foePPCQdCDe5OuBMuwE9U6bkXX4YvXHo1tHd28JdSjIr5lhPGDQQ74ht+fQ9079fobNgqg3Hf4SxbBg/qhttvroEVS0M4a/0/9Nr9N8BJk+bB5pJSxbyQwJhoSmvOXS5M42OKO4qrjeE2R/R0wasb11hUKzsKiuH46QuFCE85FFyIqoob7By75bZplMe+ordxwzMY32SEtw4lf0MJjP8YOjN5TKh5roRUYDrK87lwKZHoCvUCj32JvmsAHCdjHg7+JfyJ+LUBjV2fXpa7cN9cg1Wsx58hefvyMZ7I0VC0eRCXKXLocjU1pKatehQT+vyUnFR1y4U74cDXtwdSct4AN8C38BN1ajvUAucuOAFeK+pfUxjUUoXPmb8SzRl7kvDtb26DL1wYwO3+OWzwRHO2/ocxei4vmw778wsEp2zCBAdqLm8m2QI5h6GanS1D+n1pMg7f3b0VzjnYmDL9z70HA+rfXwRlp8+HvMNca26KMER2KXN3lLEIUY7tXOYcMPZlaDfsQn1AYlyX79Ibev0kGHrveJMNkPRmt1F/2suCXOfkHUKW55V0y4N4ItG6s2ZVqBd43pUAjiSmWANv9UPwfgb7fDLuEbKWsXiIjvz6DBj479E8DrMMki/leMrOtgNBqpKTAzpXkDqLVNqPPQj7frdBK5bKZXAZ/Ao/kac4PsI5Zw7AO+/APcPGwrVjp+B1PDv8h/2GH2RsbCoCWqro1u91GzjhuGb43c3VenLx5djiqtRW3ygZCD8YPRkfIhmCQG0Vo1hyY0cm4M3ou41b4OQ29xvbODxTduNb35TGnbIACrahC4YEP8OhyJS3u9mKG/wwcfwopiEzra4ZrbAbPS1101h04CnycODRrccAcmYFw+wkXZPciz3xxCMNtasiCVGdnR0QlBoR5sf9gwbVgCyk8wvyETYVdVX0cPIUBO/v45/fdqq89IExMPJHUyCJDAd/Dkpw4ir3poK5Ym7I6zO5Ah2Ryp7b3/EMUXs+nA934SfyRGP4GMrSH3nEqPogvq144YRZ8FopMTKZWcYKlEQ+JK8KdbhvMXuG3b9anyw/dEg3/OG2DbDYSyn9Eyx5pf/wDsUKYE3JIHgF6d2IopAheKDO6TwEJ7QegtGJbt8Kbr0E4NJbrdmKXxgOI6+ajtEpuUu/nEVneTsaI9rc/WlZJEZ3QdP1mzDGT7AYMRUzMXys1CU5KDA5N0P9JftyTm35KDc7j9lXmutO7EG5FXfs2VsO+2ojMfnS7IHv/PTJDHSjw44RocwHKftkT1M6RYG8xyF40/uba/DH3UfuUAyG/3gylP4bbXk7UDrODXoVAbj591Qlp7VdrVgqH2+E5mvRcdVmN34KnAL/wI89NGkk5P7859Hok6w+U9P/Bg6Fr4yfCa30zJHuhvLplCrx7I0Nosvxu+azsOZJ+L/Lt8MlX3DAi/8gIVD2bdFgRzJh1kr2IQtVhtx3l0vQ1KK1A2HoLydB0ZohaHIozRXdzRZJ8d45twUOfGsLdM0NEReGPDAXLXUEYT9Gxk4ev0Ne3XOkSyADhHTd59U+9Mb6zMASSa0SFzdBTD3+9NajYmHH2Y4FK3GNEktBNqLapkajzp8JA17BMK3Kld0O2qZJIce7FJGK4DykkpQPgsvZ5Z8tZ+2GA983Y0tMhalQjR+KcxJ5ugbF/z/8oWe1bXhoXTtmMjw4HKc6pMjCqrAK+xaL2c2wys4g9PNqw/pdEj6D8W+u+85Ws3pywF2AP9FYjHp2+1P3AzzwSb2RxQ4VQOH6gVD8+iDI31QK+fhvCoPcM6kd2vGBkp75rZAYkp6T19Dr0QPzXvTAtNxOqX/iuT+9rlpzSQZd/tY2OYqDXTfG/y4K04RTmSMSwAV4U8Bfa9CNqKiWuXqInZiCk7IH1xIpXEk6GSgNv3I6DHxstGlqqCxK01pFgLciUlE9ONUGmV+bg6lh9+Q2aPzrOhhQWoKd3YO+lgMD9VMr86145770Uq2slGkVymrPr5iFT3BiaFC+HwVTzi0kjDs6+72AbC6kxhTdVkgLvHXZbxqehqJTJd6pH9wLv/5FLeShfxTzP84CeP8LOfwP/VN7CrOScRw6LhXuxge3WeKiEgbdESwBN8Uy07Oy5pJpxf+2EyiCLmeF5tqNCPB+QSxR7XJ9ICNFcpqNE4IvL8AK/DuNIdT8jPw8Bqh/ETlx1T2YLVURoU0Am507V60lzGiI7sqrZEECLrvuPLjijC9FT7477gD4whcC10v2xqdOngfbi80Ic4Er6ScF/K1bUk+DFQsOwH0PoEET6oQznVrxTK/EeGkNprFHppvUqr/8GPTARKclt2SRQIpMaT2hxnCbMxOJZPyO+urVwRe2S2dDAYQWlXohkwDvN7DpY3qh+XSarMPCixjnTSnJRD9pLfvhV0+FwY+gSEGISSx24zYAl3I/pwFYTQ155+wilfM++RH4wXe+Dvn5EQVUefBBgE9q3rldqH4ZmsE9NuSokEdg8KkMwDi7A0fgK7x3q24c+v872AS/bYjuiTa3AV3ya4DbvhyclhktQR6YCODyuTezLWcTRe++cLbaSfBiHK6GApMbGOzfc3BW6763I3vk9IgBcCQlyYopsiDu2n6VSJi8TAHv0/DfT0QxAtPUUN7fODft5MHJ25PB9rlYwXz9x1o+tW8oY/3Ux+C6a76efrf/ifftD38YWZXwXqCyE/cNHQNXjcNgbxGLSNRB+imx0ieIew1+IhQveD+7eTf8dDdtl8ykl/GJyaWr2ZLqUym2pRjKT1tk3QMskmFmu8pFKMkkyr+JyzE3VJrU6WPkDTcapAbpt8lzgUwG+1OygjebYyAJ5cyoBiFNDQE5D84800o1g92rscQNsQmHctYFRxd8uQKloFkoOY9fvhjuueMXaJbrF1jaZXTPP4+ugCehL7S/WZouff43cBh8Hq1UuvDd0Sg9M3vbUkXOjW7EPDu9qP/n798N16HtdtSpC0OezEYpzaZefR7FeVTDvzGtafC/xowSeGphVHgJLhOPwnzQuKsKATgaQvbsrF6F1IkuHSkAvhVJMik6smSlJifwJm9REgFFm4Sp4YD/joTYQW5zS+ZMKiduBLVXFGN2kyrp8SbtzVNAAcsOHTIY7rr9Z7BwXkAp1mpk1973PoB2MsKJNq1DhxSK6thOcTiEw1IY5xqTo/WXPkc7Aufa/DhwDvLu1pVU/nzkxKMG8St/DPATDdvybNDI3sb4ect2xbryxtntjKI2H5TtqsYB+PedGP/bOwB5QKL0ewDH9flXHHN6EZMCEi2C7BuxjuOZwlJNSRan5eQI6netovDNQXDUl2dCrJkzAnZlpVWxad38PGAQK8TKimsh/YL+Jf7kX//yhmvgzNM/qDeUdevQ3gYNbg6HsOnVawE2Fw1A5eZcaEcLFWNzsUH0jqWKZrdds+lauujk+8x+NDGMiBN/HVmQhRRHqm8iy18qZq44A9enYZHuLsXWnCFi2H3EL4YCM5H4IwJ4pCGs+yaZ9WlHLwS83WeXi/M4UjlvDiSL8f8UfT4rczL6CzOhBD3hTPA1wVyKVZxipVjtw90sVGhbxOAv99wKSxbO9Z7NjXiWLVkC0BzMk05ziViy7c4vhBOnLbSAeJh6+kIZHe6bLytv22YJLp840Ag37krvdSaa9aEYR6tlSF+gUEofumGVKctoAAAgAElEQVRHSVX5BxdsZm9ciRCcmTIftDJCGOALb3+N+w5O69zzdqSKh6yARaamExcMrbi0niTKVN9c6iX3+MWGwlLNlAQKXpxVqeHwq6fBwL+RpQZ6iDGtpfLSu90RwTBB5DyLXfZqXhU5N065iouKoPaNZ9xl4nVofHMsart2787aNOwpKIATpiyENgzU1JspXasVHc6aA7g+R/Ce1ma4p45UMOHSB9Cz86kPhCubhVI/GVk595bS2MB6V70BI5YiKBM+Aiz6JVvW/LqmZNHqttgbkSsw2T7U6kEfzISkPBW79fc+2DW3LpGd9ywX8P4efndtb4xlwD9HwogrMB4Fxpmw2I2rXmpCLu4kJ1RlfE5OPwUF+WihciZc9Y0vQ3Gx4oC2dy/etTGcJ4F4ltMe5MTfP3UBHBTR9rLcfFab0wF6lVuc2tkG/9i6FgZQkKgAaR2qPOaiJKyPJnqW56hhU+aPGFwyYJuTn63ujcYYn8vJaLnxKMTHt0G76qtXuQQTCE+1/gzgZEtJsUL6Q6IFNNEFvNNy2oli8BSi9qjPHANFW8yn2yxXQHHSWxwcDNeyVDm6U59KSorhh9deAZ84A13z9uFZNns2agBSQ45GMR6dOrYWlcBpk+ZAK4L5kZx0gMmeZ1C8Bx7a/hbMQjDXTeSwUztDN3fW830fWdXvjZpy7KIBRQVrLC8N2ULBZqpn8US8fmfN6oqo6++XAI6HH8U3SestuagJ6VEfsTLHIaFTA3YmgTTSJAaK/GQOM75R582GAa8O5XCtPJ3lZEro5HrvFwyLXPLPOeUkuP72n0N+mz44hBmLTpk3MbreJ9A6pSus2aNOI5iH38w9zEE06wmTzU8GTnU6dS0fOfBv79kOn9vvH1f8+eMATkAL0D56n2/Fng3FviUqKlfci7LCc5igkE1HZuBPZc4l/ePxxD07a1d9JswcepXJzAii7qWtPiQQvWdJ71r29UQOyychkZ9N6WgSSIO4DX/6lMpnJFqoDPgvdo3k4ixErYi5QX8xrE/4EvULhuU0OQT8nzxATiTR2x+HWQzPop34BRg/hcwLueQ+/UBWsh/2QGFh+mcvowPI1jJBpOCpPTwe5eI3N9TCCOTK3dIstPneQOYEfTOdh1P6Z+rahKrlh3DRYvzh9GjiPExrnYaJrji3W7t7Zu/f9HJ4BYMLbfsrgJPL+ei+uV6MXhHnfSoSGB+qckj4aDb+tk9GSpz16LFw+NuF6AypxBe3Abjd6cciC1c4G7tyU1q9nNKyD36zs8YelbZXpvShIaPhivHq/d+IGsMAPUzi2zkTQBGsNzoiFKrRK9+weDf8ur4GjmtLfartHXQ5mx05LAUbo0fudTgJzAyqbMbCUfmxYsINXLrWOZW6yygfL5Z9yqQCk23JyEiVpYqQ2NOwKbKj7uvpXCTuvS7gTRzBp/viAAbDYHy7bT0M2DcQPnnBZVC7aavRTadQtObviNUw+Vc/5SZVurDtEDyAVg/FARVmmaDbD0dPhDtGOfhYSPkCM75ReHS8ofA3IPnvTSL1rW2lC+BuHj9GeaTDRw7uhZ+jqSEGeDWGeyqaEfyTzAn6XqIrwzCcIOZcML5y2S/zY7HLZTfNA1Z/vkxRonsZq/mg8dRhd92G6ELIqqTujwDeH6xPrkbCoj+aQ0oCebf8C3/6JO3/jLfNTytny3d/+Au4688Po1k3WcwqIhW7JycbEPfulMniJETf2cLSEgFiCN7XozjlnIM8jldvpk9MOBpewQcijqSkC+Be+dTvhqAo5eFt62BGVzv0ce77c7jk/ijnsqJqWS3aYkdipivBnx3gHrtY0i2RSNSjA0/kCkz9o6cPrWgk3tewO7/oQ12yd+UPOKcXufYvCXQP7VNyb9nXD+LZ8m8Hic/d9z0M370OSa7IwCU4251+nJSb0lHTycyQ1j/GiIBTDu3DCHm1vS5SWYaOPg2FMlZ0H1llISUxQfSmukDPQAMr/jFy4g/duQce+WgfoZG1G4/hmvuI+quKyuVxjEAYCzJOv5FJVsWO4fbpQguUP6MFynl+9YX5vk9ygV4DQeLQC+0/CDPYLJR5CAl6lgd4X4Hf/SwL/QjcBL2msw8/Q1zOlo0oSjnpdLEGZYhMxbnH9NA0lZsWhRtHavY4nHCCY31k/hHiu7kdh+DR7W/3Koh3FObB8gWLYN+hyB5NCTwXaoF0ACdIWb+8Tt+3nt4I+29Iz3szLeI4FyYGaQYuLONKN3bakllFBQXr7Xdei1msqCvduN9Ujd3ctrM7uWLP5lX0MHnkqT8COIXJcRZPRE6eQBVSEKolSFDnUHpJGIXfk8thREGzA/XNN/N1cB18Bz9e6clnnofPX3q1GQRLcfBROXE1vripDuQu3V5cOIlWl7a3wAM7egnECbPxHafWCTE47uRF0Hygd23E/UDVb1IzxYGr7XbMPQR77n3L69VWv25G/b1FdEKVo/z7Tyj/ltwHYzvMGDg6zXNeO8iDa6b4JJmsr4k2hKza4/4I4BR0+uc6ZM9iHnQrZE+hkc2pc0rC7fhFZC9xRDm2ozCE+m786BjQ/fzmO+Dm39wt1Hn2+ClcyiLN51hkTgHyrL+M3RaycqYIS5UNJJFNv75uE3zmcFOUQ/Svi8D7FfwRoVv2NqG35mnz4eCh3gVx/45Hk0PnsHCT5HRVtULj/W+xtyt7OT2Pa+wEex/Kq5YdxhtiqXSJzwTo2elnmhEmdtZVRxuBsL8D+Jk4ANSq9ZlEXpaTcFG4uxUmWXxvCroVMlB2Zsf6MJLzTPzoplt+exf87GZ8JZ4pLDkqW1/8EdJBAnM0RVStUxjzw6IakqiFG9qZ/+N10fc/2VUL56BcPCuJwPs5/FlqbW3r9hI49eNzMUhi78ZNyQYNtOzLPVj6riltsOfPb0FiWHoPDqcxVopDPBOX1Xa1jvKqpSei8v1/ljUoMpgHkhrdnb5M3wDUAPBE8ra6mpWXpDEuz6KZOIwy1VdWLxJ9JP6RZfbMdUi0Wik4FT2g7J6ScAN++a2MEiZk5VUYjeAd/Ohw32oT9Q274cxzvgS7dqOoUTj9GIuWsd7WSHhGHBW2OQjw6SzjwG9PUhG67PABFlwpo9JoYrDp0V18R8IpvbkOvTXPOxq6usRDKpny3hPGyEHnIeS0O9LczzPRTyTTXdYOe/60HuJlnVF1K0g9/4dLK0W/VFG1oganzDTyl+tScx75bVJ3VqxHAhU9CPtHtVRXZ4wT6XcALkCc3PgmB5ndDOSlVUrgjQJAn5SEasxR6ZetN75/BB5Bdb1FYa/fjeeeg1s+9Vm4Ed+eTOblc77F8Gjk3Dd7e1Aw5By4hfyRWhF/dzIvlIrN0w41wW3IjWck0RlCj9d9yLv2Z19Ab80vorcmRaWjbvshWZDORlmXaFeLm7b1UUeEwvaeKhKz10FH88A4NP7pbeiembnY7g7kJf3TIlyAFhlO2dTFFfmFhdvJc0fy2LpQbG+D0dQv8LedHolkO3LfPMBQhlJ/BfBbkR4Zu5Zo0PoA5pmHxLNc1xzLJVnArcgeMdXom3aWkXiZ2YufUIv6x6hH/g4qPfHtykMYS+TDE+fCVnwJ3rBGYdIQwZEoYhPZOR0bcTIvpP/+VLce3otOP5GnB7DGs/VqfeSJ0XD5t2zemj52wF41M9ymDH1kB+qCvh/QM6DEMTVfvQVaP52VMMEE2sdgmyn+oOXIfSP/MMNpbOLCwx9jEL4L7LUmZUp0zlYvesSTyad2Vq/MaIDdPrJ89DaRzIXEJ+6bAqP3Rv9JfDMbG9bzPEEHNsz/SLARZif3LXALfAU/gVIcw7ssWoRCo1Sp0fnlM+F/gyjEC0/2jaOCtpFJVWw6OPoQiOcjJ7+hdjUMCNRRn8y/we+/GKzCG34xAX7ze5s/Bu5yDgJkDmmLFW1c14W6luWJMtpKsP675fYDZbVckLwdiw9C06+qMy0X/w2iwJftYxszddHRRYVF61S/ec5OiOugJnRIcR7Hdn+4UUG/qyOxZPfWVaQaz1jy71HGmk6vYpyGx7EGfL48q8k9LKzr7mAwQXDRpxK5zB/ETyDu+6mnAM44w/Pdyq+UTYfHMbYI2yYyoqHcM/Qr4cEZ1Ea8rLsDXtryejQ2mD/CjlwVbjrOvmA2rH5lWLjCfbSULvdN3dcBcDVPojgOB/5vG7Sejdx49Cp8EmMOxkWcYrqLT6etRs56id1VkjPbUskuuAcLprProoHVarAEHsVQeF9ajb1TndyQCFG/QO+0fPozgFP8s7X4ky0TAZrmE5BgLwTah0n4Hua/NlCZLGT+I3oZX4gfrUSPL1x6KcCDD2plv2zcdPjb4FH4Eg9DbKWMdcP0io04xbCkWJZppJM+PB82bs6oaDN470z9WeCyOqAsKw0C9mpHuie1wb4bNkLXHHdL28Adp2M4jxkIWNOYOQMrhg9qkdy3NGuVDmTS+omvTHcLFM598+uVPeqNG3AqivxGjH+S8WB1/RbAOenhu/jH90NMfJgityGxgsvd+yCAL0J9zxr8+CZawL/9LW4TZFcPpkai8yr/+OCR8BUEcobicpWpnA6JE+w24j6emqTs/GVdDXz88H7frjtmoAAHd4QrqpZCsT986GNzYUPNoPQri6CGIACcbnO6bTnlo991vOcA7PtJbRRiFXJcGOc0nooZK+5Cnfr5DCNkbB5agwkh66IvGGPBdSzcysQMVMYPKWYjJaoXsi8Xqyl5DKi3WQzxc3tdzUsBhXTBZ6e/AzjZdhEXjs+7ZDT9D2v/IBLL2cvSq+lk3xKhDIJBTHFZgh/PRC/FX3ABwBuk4A+XaIcdW0XG1Q7LjG6qio245Oz8PDXJ1mVtzUqM0B8wUYADUlpGuOLPPOcYeO3N3g1rowuobtQKyrjrtufJqWNgtJazdkPzNWhMFn4+PoJlH3ME8MplrXmx2EAJ4NzKiQKtcdwW0B3oQQdXc0IZVkLULdvs6Oget3fbmoxrccOTL+D+yVR2pBtplZ7Dn8kZaoPeGvkAEiqccWsfUmLmowT5Dfwcgx/X1IpXXLIu+dWvIiHnYwNHwFcqKk1Zu8H48GtpChfOxI/OkQulVcqpB/bCbxsDxODAV9yYuWAGghicf/FMePaFEZHQqj9Uog3gHuaGcpyJ0h7Yf+1maDsN7QKCIdFazD/PiV7DJs0bNrikFK9oCNvydMK6Y8IElElEAjamtmP4MyjROCVoSzv6RDLZUF+9cnw25jMY2bLRoxBt4Dzh0+pAXHLU74JQnachkcK//5WESVjH1hDDiryIr833HzH65tcw2OOhaE32ziqfBasoTCtdVcWKkzbiTp6a3BLNHcRJlvlWzSo9LpyMuPC19Eym2+4YDz+9aSJTcPWrpGMnZxuQLoC70cGpfHxYFxy8eCe0nofPt+kpOs/A5UFGDCmpvHLZT2Ox2DeJ3UYg5Vy2YBr8HJXCzp06Jvp7PAGXNNSuvC1sfUHK9bMV5z403NN0Zfol/nw+CAFc8pI0lmwVrkUCpR/goQ848niaDD79NMC552b0keHTJ8yB1wcMxGfakKo8YAoXPwpuyNEqhW08YaZn4ZqSMADjUq/e9DoMT9KrdS5pCf7+WfzJQnTY2k0l8KkL5kDTPtSpa3r5BV2nnKMMElIpaAv++YMAeJDzgalH8hPQdvJ+aL5qCyRGu0or38ClsMCtp2T7jVt2hsFlZxi8eegHbl1FCxpviT3IfZPzsNT4+BM1jRxHDIBLGiDVyCn6TvxxeF5Fi1IkU/8GEuYZrdw6mZJwE2b7qk7WTOQZASNYqFjHdBFq9v7wh0w0m1LnmfhgwprSIYIh4gqkFE9NQ53Ei5veb1ZpLS3cBH5+3LAZzj1EscRsifxeX8WfLOoZW1rz4YtfrYIXVuFDMEHQy4/6Udbl15bP94EAnKkBg0MMzXR3RRu0fmY3tH4SXx60ir5cuW/qennl8g4kfjFrN+PgjQ0yRsQMoYz/eBS9L7MWJT04ddNcANkqjouAXoAmA3/iw/xSC2agK9mtSJDVfpkDf9/LcvA70PTiIvsbE11dqPpF3e+mALLkwANPLXAPmhdePR6tU2h/MR7F3GiGxYDgaEj5xHIYLszOID69ow3+ja/EGDFTKHAv8mF4bmU9Edbe9OsKuOk27vDj92qLVwcz5a0ZBITt/QtS1vPccdGeGvXT+U5MbSwOHe87APuv2UxcuSf3LQA8KW95YU0egy4alSZdyfjk3dWrtwWtI2z+IxbAJUFwHZDGjp5Som1NP2SxQp4YpCGux5/nkAj/DUtA7XJJdpk/QTt/RBkdue8DGAlg8mQA+rMX0oOlI+CbEyotIhTCcSkPZxtCfHRBfFxHJ7y47Q0oIndNOpPKemFgSpPPPDscLkZuvLsbhbpHgLcmP4yCSYc8wT5gZQTGidJ4Y/JQ4dcaNr5IDgkpos2ioyrnHDVi5FqLGD1D4ix1dRmWinnJ9Ts2rDw6myvviAfwbBLTs60kHI/fk0VLVtOD8CA+EaQ8ElSPZ9acORisojmr/bA39n6MnVJbWsqv2EyaoogMxb+DgviYzk5Y+XcE8ahV2SEpVbNxAJx+1lzo6MyA+UvIPqVVLATohhWhUD/dwAkPBjIxaUlA3loUwW1FKN90uKfrrgGx/Ndi+bHRzFFHBlJLa8D6hZPoHIDkWVJfm1nXeXuPcgCuP0fp58xyWNn3wHvQvvI5s9/r1wOsWBHYKSf9gafWQHF4p1QtM12QacMpkQwlqDuCuO1ZNrnZycxw7Bh0uX8SQTyjMWj1KdLYWAgnnTEfDXv6/8MQLlIPV2L44b2XiMOrrFmOKxBZBEwEULZWUH4iRXGZsjpxGjB2o6duQwe6574W3FdEfzml5MwBeBrEC1yUu3ZR9OlTApcNWIBinZDishA/LGHoVzj1VMDXCQLWlLnsXxs7FR4eNkYomzg8SLdn1qoDJ842qce1mMpPnNgGzzz+Zp8B8dbWGJz0/9u7EjC7iip93uukOxsJZFWyL6QTCYYkDJAMgcggixAQmZHVccBv2BxZhpHwKSCoGYkSENEBRjFiZkYz7AOMMOqwSLqDLEMjId1BpLM1JEAwQRKzdN/5z13ee91599W991Xd5fWp/i7d4VWdqvpv3f/WO3WWebOoY09DKOcRc8jHI1lF4NWMort6BqZ7CLKW55DGbDYGN8h8Pv5vPcg+fxKyzz9ezbzCthUCD4tYtfUtO2sw+7GXxiatVmq39pyg+GX8HOw5qN57L9E552CPkFi2lLLz49FMxi6c32v2rsozLyzd6rkkjoTitowguyp+uE8+8R36/s2vU138z/G+c70H783z8/SZ8YdQa/8YzWI0rqooZByoTaBK/hPxmoM8Qdp5ewPAyycfg+6756jQ9V0bWs27z5f2KwSucZEHFmVhe+xYvSwI3CZgxYEwh2/Bz2T82IXjmNy0b7yfgOKMV/M8NR1jFNczE706X43d7l1zwzD6VH6MH/iPFjrs0IS/cbRjDjgv5vIhXkLnjjuYXmJTyrD6iBB3wv0uUwJgiMYaqwbhZpVVi+pzb7hM4MW0fnlTpvgV0cF8W0DgZT1ENcLaTZQQuClkVXIR5hpVkBWBvqyqGvTzmcjI+wx+BvMmvw12dAvwfnjbeDiGoMPzrceemqsGcXQTx/vS8cQskrhKbeIneMTw3dT06xeovm/JAWnVow0hgAPvsTVhibEPk/h5IPEXByAKaqkZZQixflUL7wTNL4egJNpzXHoIPJjli+11yWvGfW0F+aamAfIeIqzNsEIxHoGwtFMhcP13MZxECyeNjuPRpHANi7VZz70EP1fix7br5tCvj8eqios69EK7IyfNpo56dpl0PC9LSZy/Gkct99y1mhbMT8BcEmb2dhK99n1H7pE478S52KQTkXS9V1MaH+RAxB+E5X1uvtfUMeMrApiA9sQdobVn/Zp6HGQ+FZuuMo33Peqzmu12lh2cm6NVB46syAeVZ+KHHXXoLXisXXcdEccz8QxTM4SIrQ9vnOtE/OTHsYTEnQTI0cqiK9vp0r/fFK1x1FZshzALF4x+/AqT+JnjZ9Dv+rM2zSn2OYAXdMn9P16wASfMSpGutXp6Rp2nlnbqN5fqRdBlWzC5GGLtV/PCr3ZK+Z19+7e3P8WJX2IpQuCxwByiE8t2QeE0bMeCoA+FOmTSTtqZ4/CvI/HDeSwn4edz+Jlvm5bzc42H4POfJ1q+PERH6av6yKBhdDEy+jghxFmd4nCWd4AZZcSnnPQO/WCpoaTI5QbE5vXs+/u6erRM4qdOnEm/b0hZcgj10JU1VKTrCQhaz69Db/ft6L/dlyAqJ6JCsazt61ubQkc6VoJZoYIQeDXoGWyLhc3B6l/FVdkhHM4rdO65RPffb3A08Yn+27HT6VcNQ6iOY0K5JJ4PGKKu3CjPOG0L3fKtAGyqY4rtLnkHy5Zq98gk/onJs2lz3wYdI9AnowrVhjMI9c7arsXnHQFYyK+e/f+9rtzf9q8AMvWB5c7Ysl5HGjVj1mXlxpvANHXDVpvyQOBsaojswYpyzTVES5aoamXq84cGD6MvjpxC+T6uG08VKpTF1yPY1VkxHORy7BU+zQhB3t5NQfYBmj/lMNraJ/vOPmEXWtAdeKV6jgq8eFDNqqhqvrWFnYNXH/2uQBq1s6K2j9JOCDwKaobbYLFCmU1fV3bD9t2fLXGTVzbIToWtp9bR3HWH0o5dfW0HjajlwZ+9QrNncqwyg6UK8vZGtRvfNk6BOqWtn51IJtMl6K7amWTQnbrrJ1AGGSfJQimV+dc1CSzGcTYInPM+xVaEwGODOlhHIG824G7FVTlZMycangTDFc6gU0uFVyRHYscXCy6HHT2LtrzTP5JOc9rUD+kXD7zsJFc2VTSQd+nQLhndSI8hYmMSKgBTEFWUG5DtK7rW27pv1w7cDWEbxmdAx7w5PstOKzfk3baVhncL3UcrBK7j7mmUgXVwH8SdoRR5MfKl3nWXslqmKvBG+0FcC7uP+vAFc+jtLXBD9w1vtO8s+/TpokfvbaHpjdGTKSmxa0cNPrCMoDapJPu7w8bQrSPGJaPIVU5aVSHYjtqTokOFwrIKoYg9wa5jmGq0uj5H8Kw1iAMeexg1IXBdd1CDHCxCTg0He0DFqd1rrxHNQNTKDJoL+sLEwaeacfnkWjlu4Ux6/Y3gbujGzQe3Yax8XKWZvD18fgfLlAvg8LO5T32I11a4RVg4+wt4kBhOerDaugjc9sTkQODupMK87ION1L8W77535+jjm9c0sdFBrEUIPFa4K3eGdbAYNb6iHFKtHVxydPaXcY2vPPN/WzGCrvvGFOrq8teJjB2zk+68rY1mTDfoQs9WvtNxtSvvVNUVFo+cQP86lPPjamTZgGqLsIMPt/cOJ105ZFToctPNFaIVQi8ehyoKdujvbGxr4s1X7EUIPHbIK77JN+NT9UKYNs1xla+F8glM4n9wVdb4F2a6dWsd3bVsNLW8sh+9ua4f7d6dp2FD91Dj1B104iffo+OPfZ8aGqpPY+oLLaw2bVerN+ID/3k4+1w8ehq9i914ZJdNe7iupUYhw1F8cyjXU9Ddtz1ydpWvFIWyMDdU9pzAXNtwkyTOLvxd1u5pHW0vJPJACoEnu4YLvWOBQulJ65TDacX55nTe/mW8sNnzbbguytA8PgBLzAA9rI9/zNsQHvXyA6fSk/t5bgEcC9vdYdqHeC5xuTxtP9g9vDdNjVpFrn79htmxq/rwPkck2QKB2wHSDDOc1QnTwbXxmg6W4ml4eqaWTO3JxQI8BbN6RDmzhx4iOj22nKnK4YSuwCvuTFx8/uqEAslG2Uh7aRq+JxjUzAQB4qcHfIS+NmoS1AW969ENSuCMoRPYikMUO1xuCiro3d9E/O/IMYyC3G9Vnd61ClRoJPg5FuhX0f03lUO4806iSy5RVktlBc4WuAyX2j0pXcNvwcHyHPoodaZjWGuR+PM02IzvSCBpgYeATaj8j+J/woETZvttS67coJTge1qkFFQvSkV60CnYluc7rA+ssRs3Nm8N2spEPSFwE6hGkIlFtxTN/lHZ9IYbiG68UVktVRV4p/0NXP+Ay6RNtolJr6PlNIHO86jKRBdRZO6A9+aJEw+ldQ2cxVlKzx26H4kX/DUVOvWeiDrc7xyPQne19cO9nTO3/v45ToqeaBECTxT+YudYcOx5yR6YlUvWCJwdRVnXHWuUZBWIgT9fhOf1ctROOMe9/3gvHT2VHhs8IvCEqq5oOz06KoqopVIuzHIyVeoTblNuc+0lefA+dL4suONGA/c7REUVi2epaytk7ENRC0kbmmJN2lAJ5+h3Ierdk3ZlEcDCWIQP1KlzsqJCGQPXuHuw3z42kzeco9t+ARyFDNB0Ydpn8PMhI/dc/dEpbMcDbUHtPdJBtC3lSL5wsOkZ39gsX0z0VIqVF8rXtvLhkL4lLyn35fDWnq7cBW+1PZuqQPu1d7fT/rT5jA+Ljb0v2Quzckn/IaZFV2C7chPIO2UB9lTQup+zlfepeNA58bRapRVQqMFq7Lp92NjGuZPgx/IwwjjV6+RwbWrjqgBQU3hZAnfd6r2uOXN9MeSVZyPubysOmWiQa7a6/nzVxtdffK6qKRhqLARuCNiwYrFY+Huw2q+vvR05FieGFR9PfZhl00qq9/OmjGcQVfWyCyaCx8GhiL8NsVVQ2gsC4tAMPMT2uhk37Yg5RHVP4s/9LLC483Crya90kgXCdnerzmfpp4myapkyb5+iuaGT+Qku8IX8ffaOnKfaSTv67GkYjcQMCaRyCrfk0n9nws0n07WxuDZgAmOUk0ijI890+jO9hKwTnBUtm4Xz6ByBB/g7+P1XGZhCB8Y4yyNvb7wHNv5lY13eWgn6Hlakb1ct4Gl97XM4N+mBtyW1mSCsdto8SsH03+WdfCrtyovqFadtNysWsnYgqmAmwkIKgZtfg4F7wCL6HiojoaWiXHEFDmX2DEoAABAySURBVAb5ZDAl5e+g774bKpOsWZgU4WP/ykNB3hfgt7Yk0wbvznuQ/bGe5F0g8alzhvfJ92vBfFJ7+KoTGz+SL/v/3V15RQJHZh0cVMaaWScqHkLgUZEz0A6LikPJIiuxoqRJD34Dxvo11YBT/TmHpZoNsmPr9BWpHqkzOE6XPNaPvL3xjzj44EH9Ovd/DpvL2CPklWIYToHTA/2ACvggu3RPsh9xd9+B09sb1qzkjFipL0LgKbtFWEisw1ygHNYCVHn6aWU1YxXYrmo5aA/Z3DJcOKLJIZgFK37acaXdN5RdiY7CQ7sqIOa5cdPn3oKDzSt63YPu8+YIROBW12sbWpsDJxcPeC+MVOt199UIihqFYoEdA3FPKUU+8wzRMVw1gZIHef8CtHd8An3r6/LXEHUCdqideNa/i7/Z3jvNhSnpFDyw/x12kPVNQ94feen0/fO7omc2CttnbPV9dumqzbtChfJLqFAysbqFwGNbacE7wuK6BbWvVLZIIqxsHcj7addCWjnA1Fa4FcRtmwiCFcfjF2c9TntCysvxsPIZSbhi0Qlo8HjuwzyNOu/jVN9m7mzO3vSqmDPc6CPV9h1Cya68EoF3Wp23bGpddVWkzmNuJAQeM+BBu8MCQ9YGO+q0f4FdK33qU0RPPBFUbHX1+uGwsglHlbOqE5Nw60Ug7297Y8Az/S387SZwS3hk/t2vwIMaLVmuRWsgFvGHndKveQjtv3gS9f3DAG3Ggbbbum2Bp4FOQrwAfPXril2593HP34yP43lpnY8d+E9SuxpKBqYB8SxMM3tjxEPBUfz5a35jxdFvwxncHJj/vmE4QPUExOF7jQZSdkNv2N6VIO+fluKJ5/VN/HtCilfIJoxtHB7U8EHOLXsDwBuBfUrDC4Np2NUHUd3b/Uri9oVHwSHRqo4qw3caoUU3Tlcw+N4ua3rH2mbOS5v6IgSe4lsEEudDtf/CVVnZvX070cknEz37rInZWNAOb4eWOBNmVT4AsJngQpD3L3uQ90H491oToGmSyS+dCXhImcTDFz6pINujtHzBK2HQio/QAd+ZSLmdvIVmA3Guakfbc3bUHMCJ447bEop+jJGjEJYZib2D5/40uJD6WqSUMLj3uun5m8cAv551G1tXTggPdjIthMCTwT1wr1iQfPLE+tobcfnvfzthoPAVZGP7dkE7ELiPChXXIgp2PdWleoeqmie7xh8Nbni+Z0U8wKfi/z2sEpDg52fgAX0gUv/O7nu1zcOKkv9jHxp+2TRqeH6wFhJV9Zfqz7usJevbmtKuUitAqLy5qQa7Fw0ORM6B43+Ay39HxXiwaSFnrOfMPdHL+zCo+xJtoyUQwaqcrBbbQQfkXRYMEDiAojtSOrmH8HBGz9xh2aaGR4SZ24CHR9DQGyZTrVmrdLPxtj1Qi9ELS1Ur/HdXjuZuWrMyqJlmGHiN1BUCNwKrOaFYjLyzYm/Nz+HyT9O+bBnR0qV7afXqgNkm7TFzsrA78E2Z3clZtZBotpEqUWSHl5l+5M2y8bwGC+Fb5UAiNN+JNiPwcEbL/2PRPLRnfVr45xtqlaHXT6GBD42gXIXk0RHmVGhSCNEacnSVHHZCnH36D92it9a3rsyU92pICKu5bdJWNwJY0HMhk68puMbiYkcPPpRrwdUEneJakBQvyE/jOhIXe3qOwsV54Dn2BwdD4pgavOP4FyyGLXgQOBbLC2493UOOSx4T32yQd0X9NrDhNBPXxjWoEP2ch3vx7yHqd69q2SmXq3r55rf2oWFXNVL/VVgqmliiRIMeXmQFhg7qiamw/eYwspdsaFuJlFfZKZpuTXYmLCP1RwDPCOvb+eFn2+islncx8Bkg782qCYBQLkUdVkulqbTgoYyeMMCyD7yf0jWhunf60hAccg58DLGxrHxo4vVMDO23gKu+0DU2W05FYg+eDxPjfBWmgzMhMby1j9YJhRMmBB4Or5qtjeeAD0h5x6qOhpheFFgF9Bcgb3VYXn72iT6DX/enaDqssx+Oh/JPkcdkEVx0aX7k9j4NmcgH3z6OBt0/0latOAkPuLj2KVhAthWJa8XifMQGhtVl76k0j0rGi0F35Z58q7Pr9A1rm5ExPFtFCDxb98vYaPH8NUM4q1myWtowcLY2CUTePEkQwFT84nZpKQvxQD5a1WAsO9iVMa/Surfqaeg1U6kfW6yE3o8HnBluDMfqjkxOYRXiltW0vrWJsy9lrkTGKHMzlQH7IoD1fjM+zITrsM8kQpN3YedF9Af8PTEFy6M6qxPnjcTxO2Jxy+3T3o+GfbmR6lcP1EfkYYm3zE3bZ1eucNrBi2JHZ846quO15v9LwRoIPQQh8NCQ1VYDrG/29GR366yuhcjk7e7C0xDIig9dR0W2Oim+jWI/lK3raKD9l46n/k8MpxyO0CM543gxulWLEPVshYzGlYqsaecg8uDPsvpUa4QiqxD07nHjmWBnj0RjRldxB9ah7eFh1CY9+8KOLbDDSxXjVDU9Cw9i9bHILboXHf21qjMjn+/J0cBHR9CQW8cT68udLDeec6enBy/qRmxfT1tPUllHbpscKupEnk/GnHbKzVMIPPLdz35DPByc95Fd9bO4Dtja5OBqyLu4caWf4+8zE7qjvwX4oRxufMdp0ZP4bEFC8yh0a8dZuazRqnsf+ZUjryzPnZ/FVhAScVcO6c8gbRpjVWrdmDR0ofuPDG/onqRB6hDI8MHlDoA5UQd5803BE8z28WyBE3dSOE6NNhIPoR7TNUMWKBEX7mVjph05IJeru8mxRXGIOIfdNO+8ux1SepYrthEL6lQyL+H7Ve2uvMv60fq2XTAhfZF9ITJdhMAzffuqGzweBKMWC9WNzrc1xzZhO2+t4RfBCUsh144RHlNh7CfiAWRHKj0lJTtwTGYLeJgdxmjU5Hkz6uvzdyP9++FesCzdu3KP7znBfJ7fhu5vh+gLSed5OJ14cVy0cc3Ku/UAnrwUIfDk70EiI8DiPgkdh87ukshgi51uxZ+NIABWn2gtrK6FQI5WGEdGes7DOQ8dlg31Gnlilh1++NjI7fU1PB1odrOpHjtj3mTam/sx9t7zCwpyLxBt1F25wsKk9LQTduHvdVm5v9nUtpLVTDVThMBr5laGmwjWfhYSGZRO6iX8gw8sOVyAkQISPwCCX8Rl0qzwN3jojjY0AX4h84s5ybIdvOwbevjAA+cMzw+qvyqfz/OZw4RoNoiu2trbehd+O4eidnF1NPjXh9DL3LFr196bt7z5nNI7N0ngovQtBB4FtRpoAwJ/BNPgQ8y0Fybsa0HcN8UxUDzw/NWfQ7hyQCidBUHbiWOcMO5mimV/gzjOjPDAUltAyoFDAYxtPBKmj/kTsFtmS6gBuIr+Qd2OFz0tusPNtls+D8nWx3gVS+jMsrah3u1W3rp14+pm/uZWk0UIvCZvq3pSIPBXUSvtmbfZNf4YPKPt6hnprQFK4BfGIk1Sf4gH7UJNsvzFWEh45wQ3S7I0g1kjvfywOx9QN6j++FxdDiEOcgsxCQ66Fqb8EWT+aBdZD3Rt2/1ER8eLfNhd00UIvKZvb4VnXUPEOsPQ3Q75/wTy5sO+RApInFUp38R1Nq6wzwpblizHdT0a8ovIfMk4gfcEaNy0Ixd2Ud08mAZxpM0DcT9G4y444V4t6gCunKmoA2qTTTgkfXZ96ypz327M371IPYRdlJE6kUbpQwA78KpDjhqaFRPf2SDu/zQkP7RYEAc7+3D8ddbbqsK08sEkB8hajoeLs93HV9KhQvkVSPaT8U26d/ckBN5L739KVShsIjgf5M3xyFNZQOYzMLDZuDgQ1iG42JaYSZvJelXspF2KkpWoQ5I3khUg8LNSefNqcFBC4DV4U4NMCQTOZl6nBakbUx12avmYLuecmMacrm4s+ioGxCqfJMu1IPDFSQ6gN/UtBN6b7nbJXFNmRsjOLLOEvKtcjJadeenBKqVU23wfG/BqBUp7fwSEwHvp6gCBH4Wp/yYF05edt66bYMGu2kmpl2SZiB14e5ID6E19C4H3prvdY64gcdbfhkl6rBstDqM6OUj6M90d16w8izZibqMTmt9GkDdbjEiJCQEh8JiATmM3IHAOYh/Y6ULzHNja5CCQNydUkKILAYuSjG9+Gwj8Cl1TETlqBITA1RjVbI2E9eC3gLyznAUonesiWT34SSDwx9MJTG2OSgi8Nu9r4FmBxOG95h+7IrCgcBW3g7x942WEEyW190HAsrPSHxMzMk+DvBfE3Gev704IvJcvARD4FwHB92OG4UIQ+A9j7rP3dGfZWek5O32cZR4InBNjS4kRASHwGMFOa1cxJ3ZYBfJOOl5HWm+FvnFZWmO5qMa1BOR9jaqSfK4fASFw/ZhmTiIInDPRvI1rhOHBcxzvUSBwPRloDA820+I5tQ3RY7hMh5d9wu6D0+5IiR0BIfDYIU9nhyDxMRgZx0epNzRCJwNNTmMGGkMDrRmxFg3GXH6Lq9HQnDgN3WEg7w8MyRexCgSEwGWJFBAAiXOkt1dwDdMMC8djPkTIWzOqQcRZtB+qcXxz3XHC/xcyPy3kHeQmmKsjBG4O20xKBonzDpwPwPRkSid6HrKOSjIsbCZvhM5BW1QHcf+M62pNYm+GnGtA3sayI2kaZ82LEQKv+VscbYIg8i+h5RJc/aNJoJ1otwjEzXG9paQBActO5fY9XDMjDqcF7S4Dccdt4RJxuLXfTAi89u9xVTMEkXMG78/iGhRQEKcOuw/E/YWA9aVa3AhYdD66vAhX0G9Zz6Luj0Hcy+IeqvRXGQEhcFkhgRAAkc/iHTUujoPNqa48Qv8T/mZnID7Q+jqIW2+m9UCjk0qREHDOPDiC4UG4hrsXi2JrIb44xvl9IO4tkeRLI+MICIEbh1g6EAQEAUHADAJC4GZwFamCgCAgCBhHQAjcOMTSgSAgCAgCZhAQAjeDq0gVBAQBQcA4AkLgxiGWDgQBQUAQMIOAELgZXEWqICAICALGERACNw6xdCAICAKCgBkEhMDN4CpSBQFBQBAwjoAQuHGIpQNBQBAQBMwgIARuBleRKggIAoKAcQSEwI1DLB0IAoKAIGAGASFwM7iKVEFAEBAEjCMgBG4cYulAEBAEBAEzCAiBm8FVpAoCgoAgYBwBIXDjEEsHgoAgIAiYQUAI3AyuIlUQEAQEAeMICIEbh1g6EAQEAUHADAJC4GZwFamCgCAgCBhHQAjcOMTSgSAgCAgCZhAQAjeDq0gVBAQBQcA4AkLgxiGWDgQBQUAQMIOAELgZXEWqICAICALGERACNw6xdCAICAKCgBkEhMDN4CpSBQFBQBAwjoAQuHGIpQNBQBAQBMwgIARuBleRKggIAoKAcQSEwI1DLB0IAoKAIGAGASFwM7iKVEFAEBAEjCMgBG4cYulAEBAEBAEzCAiBm8FVpAoCgoAgYBwBIXDjEEsHgoAgIAiYQUAI3AyuIlUQEAQEAeMICIEbh1g6EAQEAUHADAJC4GZwFamCgCAgCBhHQAjcOMTSgSAgCAgCZhAQAjeDq0gVBAQBQcA4Av8PmtVExuho1m4AAAAASUVORK5CYII=","user":{},"timestamp":"2025-04-22T02:11:57.947Z"}
-
 @ 5ffb8e1b:255b6735
2025-03-29 13:57:02
@ 5ffb8e1b:255b6735
2025-03-29 13:57:02As a fellow Nostrich you might have noticed some of my #arlist posts. It is my effort to curate artists that are active on Nostr and make it easier for other users to find content that they are interested in.
By now I have posted six or seven posts mentioning close to fifty artists, the problem so far is that it's only a list of handles and it is up to reader to click on each in order to find out what are the artist behind the names all about. Now I am going to start creating blog posts with a few artists mentioned in each, with short descriptions of their work and an image or to.
I would love to have some more automated mode of curation but I still couldn't figure out what is a good way for it. I've looked at Listr, Primal custom feeds and Yakihonne curations but none seem to enable me to make a list of npubs that is then turned into a feed that I could publicly share for others to views. Any advice on how to achieve this is VERY welcome !
And now lets get to the first batch of artists I want to share with you.
Eugene Gorbachenko
nostr:npub1082uhnrnxu7v0gesfl78uzj3r89a8ds2gj3dvuvjnw5qlz4a7udqwrqdnd Artist from Ukrain creating amazing realistic watercolor paintings. He is very active on Nostr but is very unnoticed for some stange reason. Make sure to repost the painting that you liked the most to help other Nostr users to discover his great art.
Siritravelsketch
nostr:npub14lqzjhfvdc9psgxzznq8xys8pfq8p4fqsvtr6llyzraq90u9m8fqevhssu a a lovely lady from Thailand making architecture from all around the world spring alive in her ink skethes. Dynamic lines gives it a dreamy magical feel, sometimes supported by soft watercolor strokes takes you to a ferytale layer of reality.
BureuGewas
nostr:npub1k78qzy2s9ap4klshnu9tcmmcnr3msvvaeza94epsgptr7jce6p9sa2ggp4 a a master of the clasic oil painting. From traditional still life to modern day subjects his paintings makes you feel the textures and light of the scene more intense then reality itself.
You can see that I'm no art critic, but I am trying my best. If anyone else is interested to join me in this curration adventure feel free to reach out !
With love, Agi Choote
-
 @ c4b5369a:b812dbd6
2025-04-15 07:26:16
@ c4b5369a:b812dbd6
2025-04-15 07:26:16Offline transactions with Cashu
Over the past few weeks, I've been busy implementing offline capabilities into nutstash. I think this is one of the key value propositions of ecash, beinga a bearer instrument that can be used without internet access.
 It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!
It does however come with limitations, which can lead to a bit of confusion. I hope this article will clear some of these questions up for you!What is ecash/Cashu?
Ecash is the first cryptocurrency ever invented. It was created by David Chaum in 1983. It uses a blind signature scheme, which allows users to prove ownership of a token without revealing a link to its origin. These tokens are what we call ecash. They are bearer instruments, meaning that anyone who possesses a copy of them, is considered the owner.
Cashu is an implementation of ecash, built to tightly interact with Bitcoin, more specifically the Bitcoin lightning network. In the Cashu ecosystem,
Mintsare the gateway to the lightning network. They provide the infrastructure to access the lightning network, pay invoices and receive payments. Instead of relying on a traditional ledger scheme like other custodians do, the mint issues ecash tokens, to represent the value held by the users.How do normal Cashu transactions work?
A Cashu transaction happens when the sender gives a copy of his ecash token to the receiver. This can happen by any means imaginable. You could send the token through email, messenger, or even by pidgeon. One of the common ways to transfer ecash is via QR code.
The transaction is however not finalized just yet! In order to make sure the sender cannot double-spend their copy of the token, the receiver must do what we call a
swap. A swap is essentially exchanging an ecash token for a new one at the mint, invalidating the old token in the process. This ensures that the sender can no longer use the same token to spend elsewhere, and the value has been transferred to the receiver.
What about offline transactions?
Sending offline
Sending offline is very simple. The ecash tokens are stored on your device. Thus, no internet connection is required to access them. You can litteraly just take them, and give them to someone. The most convenient way is usually through a local transmission protocol, like NFC, QR code, Bluetooth, etc.
The one thing to consider when sending offline is that ecash tokens come in form of "coins" or "notes". The technical term we use in Cashu is
Proof. It "proofs" to the mint that you own a certain amount of value. Since these proofs have a fixed value attached to them, much like UTXOs in Bitcoin do, you would need proofs with a value that matches what you want to send. You can mix and match multiple proofs together to create a token that matches the amount you want to send. But, if you don't have proofs that match the amount, you would need to go online and swap for the needed proofs at the mint.Another limitation is, that you cannot create custom proofs offline. For example, if you would want to lock the ecash to a certain pubkey, or add a timelock to the proof, you would need to go online and create a new custom proof at the mint.
Receiving offline
You might think: well, if I trust the sender, I don't need to be swapping the token right away!
You're absolutely correct. If you trust the sender, you can simply accept their ecash token without needing to swap it immediately.
This is already really useful, since it gives you a way to receive a payment from a friend or close aquaintance without having to worry about connectivity. It's almost just like physical cash!
It does however not work if the sender is untrusted. We have to use a different scheme to be able to receive payments from someone we don't trust.
Receiving offline from an untrusted sender
To be able to receive payments from an untrusted sender, we need the sender to create a custom proof for us. As we've seen before, this requires the sender to go online.
The sender needs to create a token that has the following properties, so that the receciver can verify it offline:
- It must be locked to ONLY the receiver's public key
- It must include an
offline signature proof(DLEQ proof) - If it contains a timelock & refund clause, it must be set to a time in the future that is acceptable for the receiver
- It cannot contain duplicate proofs (double-spend)
- It cannot contain proofs that the receiver has already received before (double-spend)

If all of these conditions are met, then the receiver can verify the proof offline and accept the payment. This allows us to receive payments from anyone, even if we don't trust them.
At first glance, this scheme seems kinda useless. It requires the sender to go online, which defeats the purpose of having an offline payment system.
I beleive there are a couple of ways this scheme might be useful nonetheless:
-
Offline vending machines: Imagine you have an offline vending machine that accepts payments from anyone. The vending machine could use this scheme to verify payments without needing to go online itself. We can assume that the sender is able to go online and create a valid token, but the receiver doesn't need to be online to verify it.
-
Offline marketplaces: Imagine you have an offline marketplace where buyers and sellers can trade goods and services. Before going to the marketplace the sender already knows where he will be spending the money. The sender could create a valid token before going to the marketplace, using the merchants public key as a lock, and adding a refund clause to redeem any unspent ecash after it expires. In this case, neither the sender nor the receiver needs to go online to complete the transaction.
How to use this
Pretty much all cashu wallets allow you to send tokens offline. This is because all that the wallet needs to do is to look if it can create the desired amount from the proofs stored locally. If yes, it will automatically create the token offline.
Receiving offline tokens is currently only supported by nutstash (experimental).
To create an offline receivable token, the sender needs to lock it to the receiver's public key. Currently there is no refund clause! So be careful that you don't get accidentally locked out of your funds!

The receiver can then inspect the token and decide if it is safe to accept without a swap. If all checks are green, they can accept the token offline without trusting the sender.

The receiver will see the unswapped tokens on the wallet homescreen. They will need to manually swap them later when they are online again.
 Later when the receiver is online again, they can swap the token for a fresh one.
Later when the receiver is online again, they can swap the token for a fresh one.
Summary
We learned that offline transactions are possible with ecash, but there are some limitations. It either requires trusting the sender, or relying on either the sender or receiver to be online to verify the tokens, or create tokens that can be verified offline by the receiver.
I hope this short article was helpful in understanding how ecash works and its potential for offline transactions.
Cheers,
Gandlaf
-
 @ 0176967e:1e6f471e
2024-07-26 17:45:08
@ 0176967e:1e6f471e
2024-07-26 17:45:08Ak ste v Bitcoine už nejaký ten rok, možno máte pocit, že už všetkému rozumiete a že vás nič neprekvapí. Viete čo je to peňaženka, čo je to seed a čo adresa, možno dokonca aj čo je to sha256. Ste si istí? Táto prednáška sa vám to pokúsi vyvrátiť. 🙂
-
 @ fd78c37f:a0ec0833
2025-04-21 04:40:30
@ fd78c37f:a0ec0833
2025-04-21 04:40:30Bitcoin is redefining finance, and in Asia—Thailand, Vietnam, Indonesia, and beyond—developers, entrepreneurs, and communities are fueling this revolution. YakiHonne, a decentralized social payments app built on Nostr, sat down with Gio (nostr:npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx), a core member of Thailand’s Sats ‘N’ Facts community, to explore their mission of fostering open-source Bitcoin development. In this interview, Gio shares the origins of Sats ‘N’ Facts, the challenges of hosting Bitcoin-focused events in Asia, and how these efforts are shaping adoption across the region.
YakiHonne: Can you tell us about yourself and how Sats ‘N’ Facts came to life? What sparked your Bitcoin journey?
Gio: I’m originally from Europe but have called Thailand home for six years. My Bitcoin story began while working at a commercial bank, where I saw the fiat system’s flaws firsthand—things like the Cantillon Effect, where money printing favors the connected few, felt deeply unfair. That discomfort led me to Andreas Antonopoulos’ videos, which opened my eyes to Bitcoin’s potential. After moving to Bangkok, I joined the open-source scene at BOB Space, collaborating with folks on tech projects.
Sats ‘N’ Facts grew out of that spirit. We wanted to create a Bitcoin-focused community to support developers and builders in Asia. Our recent conference in Chiang Mai brought together over 70 enthusiasts from Thailand, Vietnam, Laos, and beyond, sparking collaborations like a new Lightning Network tool. It was a milestone in connecting the region’s Bitcoin ecosystem.
YakiHonne: What inspired the Sats ‘N’ Facts conference, and how did you attract attendees?
Gio: The event was born from a desire to create a high-signal, low-noise space for Freedom Tech in Asia. While the U.S. and Europe host major Bitcoin events, Asia’s scene is still emerging under commercial stunts. We aimed to bridge that gap, uniting developers, educators, and enthusiasts to discuss real innovations—no altcoins, no corporate agendas. Our focus was on open-source projects like Bitcoin Core, Ark, Cashu, fostering conversations that could lead to tangible contributions.
Attracting attendees wasn’t easy. We leveraged local networks, reaching out to Bitcoin communities in neighboring countries via Nostr and Telegram. Posts on X helped spread the word, and we saw developers from Laos join for the first time, which was thrilling. Sponsors like Fulgur Ventures, Utreexo, and the Bitcoin Development Kit Foundation played a huge role, covering costs so we could keep the event free and accessible.
YakiHonne: What challenges did you face organizing the conference in Asia?
Gio: It was a steep learning curve. Funding was the biggest hurdle—early on, we struggled to cover venue and travel costs. Thankfully, our sponsors stepped in, letting me focus on logistics, which were no small feat either. As a first-time organizer, I underestimated the chaos of a tight timeline. Day one felt like herding cats without a fixed agenda, but the energy was electric—developers debugging code together, newcomers asking big questions.
Another challenge was cultural. Bitcoin’s still niche in Asia, so convincing locals to attend took persistence; there was no local presence for some reason. Despite the hiccups, we pulled it off, hosting 60+ attendees and sparking ideas for new projects, like a Cashu wallet integration. I’d tweak the planning next time, but the raw passion made it unforgettable.
YakiHonne: How does YakiHonne’s vision of decentralized social payments align with Sats ‘N’ Facts’ goals? Could tools like ours support your community?
Gio: That’s a great question. YakiHonne’s approach—merging Nostr’s censorship-resistant communication with Lightning payments—fits perfectly with our mission to empower users through open tech. At Sats ‘N’ Facts, we’re all about tools that give people control, whether it’s code or money. An app like YakiHonne could streamline community funding, letting developers tip each other for contributions or crowdfund projects directly. Imagine a hackathon where winners get sats instantly via YakiHonne—it’d be a game-changer. I’d love to see you guys at our next event to demo it!
YakiHonne: What advice would you give to someone starting a Bitcoin-focused community or event?
Gio: First, keep it Bitcoin-only. Stay true to the principles—cut out distractions like altcoins or hype-driven schemes. Start small: host regular meetups, maybe five people at a café, and build trust over time. Consistency and authenticity beat flashiness in the medium and long term.
Second, involve technical folks. Developers bring credibility and clarity, explaining Bitcoin’s nuts and bolts in ways newcomers get. I admire how Andreas Antonopoulos bridges that gap—technical yet accessible. You need that foundation to grow a real community.
Finally, lean on existing networks. If you know someone running a Bitcoin meetup in another city, collaborate. Share ideas, speakers, or even livestreams. Nostr’s great for this—our Laos attendees found us through a single post. Relationships are everything.
YakiHonne: Does Sats ‘N’ Facts focus more on Bitcoin’s technical side, non-technical side, or both?
Gio: We blend both. Our event had workshops for coders alongside talks for beginners on why Bitcoin matters. Open-source is our heartbeat, though. If you’re starting out, dive into projects like Bitcoin Core or Lightning. Review a pull request, test a Cashu wallet, or join a hackathon. One developer at our event built a Lightning micropayment tool that’s now live on GitHub.
There’s no shortage of ways to contribute. Community calls, forums, residency programs, and platforms like Geyser Fund are goldmines. YakiHonne could amplify this—imagine tipping developers for bug fixes via your app. It’s about iterating until you create something real.
YakiHonne: Your work is inspiring, Gio. Sats ‘N’ Facts is uniting Asia’s Bitcoin communities in a powerful way. What’s next for you?
Gio: Thanks for the kind words! We’re just getting started. The Chiang Mai event showed what’s possible—connecting developers across borders, reviewing and launching code and testing upcoming technologies. Next, we’re planning smaller hackathons and other events to keep the momentum going, maybe in Vietnam, Indonesia or Korea. I’d love to integrate tools like YakiHonne to fund these efforts directly through Nostr payments. Long-term, we want Sats ‘N’ Facts to be a hub for Asia’s Bitcoin builders, proving open-source can thrive here.

YakiHonne: Thank you, Gio, for sharing Sats ‘N’ Facts incredible journey. Your work is lighting a path for Bitcoin in Asia, and we’re honored to tell this story.
To our readers: Bitcoin’s future depends on communities like Sats ‘N’ Facts—and you can join the revolution. Download YakiHonne on Nostr to connect with builders, send Lightning payments, and explore the decentralized world. Follow Sats ‘N’ Facts for their next hackathon, and let’s build freedom tech together!
-
 @ 592295cf:413a0db9
2025-03-29 10:59:52
@ 592295cf:413a0db9
2025-03-29 10:59:52The journey starts from the links in this article nostr-quick-start-guide
Starting from these links building a simple path should not cover everything, because impossible.
Today I saw that Verbiricha in his workshop on his channel used nstart, but then I distracted And I didn't see how he did it.
Go to nstart.me and read: Each user is identified by a cryptographic keypair Public key, Private key (is a lot of stuff)
You can insert a nickname and go, the nickname is not unique
there is a email backup things interesting, but a little boring, i try to generate an email
doesn't even require a strong password ok.
I received the email, great, it shows me the nsec encrypted in clear,
Send a copy of the file with a password, which contains the password encrypted key I know and I know it's a tongue dump.
Multi signer bunker
That's stuff, let's see what he says.
They live the private key and send it to servers and you can recompose it to login at a site of the protocol nostr. If one of these servers goes offline you have the private key that you downloaded first and then reactivate a bunker. All very complicated. But if one of the servers goes offline, how can I remake the split? Maybe he's still testing.
Nobody tells you where these bunkers are.
Okay I have a string that is my bunker (buker://), I downloaded it, easy no, now will tell me which client accepts the bunker.. .
Follow someone before you start?
Is a cluster of 5 people Snowden, Micheal Dilger, jb55, Fiatjaf, Dianele.
I choice Snowden profile, or you can select multiple profiles, extra wild.
Now select 5 clients
Coracle, Chachi, Olas, Nostur, Jumble
The first is Coracle
Login, ok I try to post a note and signing your note the spin does not end.
Maybe the bunker is diffective.
Let's try Chachi
Simpler than Coracle, it has a type login that says bunker. see if I can post
It worked, cool, I managed to post in a group.
Olas is an app but also a website, but on the website requires an extension, which I do not have with this account.
If I download an app how do I pass the bunker on the phone, is it still a password, a qrcode, a qrcode + password, something like that, but many start from the phone so maybe it's easy for them. I try to download it and see if it allows me to connect with a bunker.
Okay I used private-qrcode and it worked, I couldn't do it directly from Olas because it didn't have permissions and the qrcode was < encrypted, so I went to the same site and had the bunker copied and glued on Olas
Ok then I saw that there was the qrcode image of the bunker for apps lol moment
Ok, I liked it, I can say it's a victory.
Looks like none of Snowden's followers are Olas's lover, maybe the smart pack has to predict a photographer or something like that.
Okay I managed to post on Olas, so it works, Expiration time is broken.
As for Nostur, I don't have an ios device so I'm going to another one.
Login with Jumble, it works is a web app
I took almost an hour to do the whole route.
But this was just one link there are two more
Extensions nostr NIP-07
The true path is nip-07-browser-extensions | nostr.net
There are 19 links, maybe there are too many?
I mention the most famous, or active at the moment
- Aka-profiles: Aka-profiles
Alby I don't know if it's a route to recommend
-
Blockcore Blockcore wallet
-
Nos2x Nos2x
-
Nos2xfox (fork for firefox) Nos2xfox
Nostore is (archived, read-only)
Another half hour to search all sites
Nostrapps
Here you can make paths
Then nstart selects Coracle, Chachi, Olas,Nostur and Jumble
Good apps might be Amethyst, 0xchat, Yakihonne, Primal, Damus
for IOS maybe: Primal, Olas, Damus, Nostur, Nos-Social, Nostrmo
On the site there are some categories, I select some with the respective apps
Let's see the categories
Go to Nostrapps and read:
Microbbloging: Primal
Streaming: Zap stream
Blogging: Yakihonne
Group chat: Chachi
Community: Flotilla
Tools: Form *
Discovery: Zapstore (even if it is not in this catrgory)
Direct Message: 0xchat
-
 @ 266815e0:6cd408a5
2025-04-15 06:58:14
@ 266815e0:6cd408a5
2025-04-15 06:58:14Its been a little over a year since NIP-90 was written and merged into the nips repo and its been a communication mess.
Every DVM implementation expects the inputs in slightly different formats, returns the results in mostly the same format and there are very few DVM actually running.
NIP-90 is overloaded
Why does a request for text translation and creating bitcoin OP_RETURNs share the same input
itag? and why is there anoutputtag on requests when only one of them will return an output?Each DVM request kind is for requesting completely different types of compute with diffrent input and output requirements, but they are all using the same spec that has 4 different types of inputs (
text,url,event,job) and an undefined number ofoutputtypes.Let me show a few random DVM requests and responses I found on
wss://relay.damus.ioto demonstrate what I mean:This is a request to translate an event to English
json { "kind": 5002, "content": "", "tags": [ // NIP-90 says there can be multiple inputs, so how would a DVM handle translatting multiple events at once? [ "i", "<event-id>", "event" ], [ "param", "language", "en" ], // What other type of output would text translations be? image/jpeg? [ "output", "text/plain" ], // Do we really need to define relays? cant the DVM respond on the relays it saw the request on? [ "relays", "wss://relay.unknown.cloud/", "wss://nos.lol/" ] ] }This is a request to generate text using an LLM model
json { "kind": 5050, // Why is the content empty? wouldn't it be better to have the prompt in the content? "content": "", "tags": [ // Why use an indexable tag? are we ever going to lookup prompts? // Also the type "prompt" isn't in NIP-90, this should probably be "text" [ "i", "What is the capital of France?", "prompt" ], [ "p", "c4878054cff877f694f5abecf18c7450f4b6fdf59e3e9cb3e6505a93c4577db2" ], [ "relays", "wss://relay.primal.net" ] ] }This is a request for content recommendation
json { "kind": 5300, "content": "", "tags": [ // Its fine ignoring this param, but what if the client actually needs exactly 200 "results" [ "param", "max_results", "200" ], // The spec never mentions requesting content for other users. // If a DVM didn't understand this and responded to this request it would provide bad data [ "param", "user", "b22b06b051fd5232966a9344a634d956c3dc33a7f5ecdcad9ed11ddc4120a7f2" ], [ "relays", "wss://relay.primal.net", ], [ "p", "ceb7e7d688e8a704794d5662acb6f18c2455df7481833dd6c384b65252455a95" ] ] }This is a request to create a OP_RETURN message on bitcoin
json { "kind": 5901, // Again why is the content empty when we are sending human readable text? "content": "", "tags": [ // and again, using an indexable tag on an input that will never need to be looked up ["i", "09/01/24 SEC Chairman on the brink of second ETF approval", "text"] ] }My point isn't that these event schema's aren't understandable but why are they using the same schema? each use-case is different but are they all required to use the same
itag format as input and could support all 4 types of inputs.Lack of libraries
With all these different types of inputs, params, and outputs its verify difficult if not impossible to build libraries for DVMs
If a simple text translation request can have an
eventortextas inputs, apayment-requiredstatus at any point in the flow, partial results, or responses from 10+ DVMs whats the best way to build a translation library for other nostr clients to use?And how do I build a DVM framework for the server side that can handle multiple inputs of all four types (
url,text,event,job) and clients are sending all the requests in slightly differently.Supporting payments is impossible
The way NIP-90 is written there isn't much details about payments. only a
payment-requiredstatus and a genericamounttagBut the way things are now every DVM is implementing payments differently. some send a bolt11 invoice, some expect the client to NIP-57 zap the request event (or maybe the status event), and some even ask for a subscription. and we haven't even started implementing NIP-61 nut zaps or cashu A few are even formatting the
amountnumber wrong or denominating it in sats and not mili-satsBuilding a client or a library that can understand and handle all of these payment methods is very difficult. for the DVM server side its worse. A DVM server presumably needs to support all 4+ types of payments if they want to get the most sats for their services and support the most clients.
All of this is made even more complicated by the fact that a DVM can ask for payment at any point during the job process. this makes sense for some types of compute, but for others like translations or user recommendation / search it just makes things even more complicated.
For example, If a client wanted to implement a timeline page that showed the notes of all the pubkeys on a recommended list. what would they do when the selected DVM asks for payment at the start of the job? or at the end? or worse, only provides half the pubkeys and asks for payment for the other half. building a UI that could handle even just two of these possibilities is complicated.
NIP-89 is being abused
NIP-89 is "Recommended Application Handlers" and the way its describe in the nips repo is
a way to discover applications that can handle unknown event-kinds
Not "a way to discover everything"
If I wanted to build an application discovery app to show all the apps that your contacts use and let you discover new apps then it would have to filter out ALL the DVM advertisement events. and that's not just for making requests from relays
If the app shows the user their list of "recommended applications" then it either has to understand that everything in the 5xxx kind range is a DVM and to show that is its own category or show a bunch of unknown "favorites" in the list which might be confusing for the user.
In conclusion
My point in writing this article isn't that the DVMs implementations so far don't work, but that they will never work well because the spec is too broad. even with only a few DVMs running we have already lost interoperability.
I don't want to be completely negative though because some things have worked. the "DVM feeds" work, although they are limited to a single page of results. text / event translations also work well and kind
5970Event PoW delegation could be cool. but if we want interoperability, we are going to need to change a few things with NIP-90I don't think we can (or should) abandon NIP-90 entirely but it would be good to break it up into small NIPs or specs. break each "kind" of DVM request out into its own spec with its own definitions for expected inputs, outputs and flow.
Then if we have simple, clean definitions for each kind of compute we want to distribute. we might actually see markets and services being built and used.
-
 @ c1e9ab3a:9cb56b43
2025-04-15 04:15:58
@ c1e9ab3a:9cb56b43
2025-04-15 04:15:58Spoken by Counselor Elaron T’Saren of Risa to the High Council, Stardate 52874.2
Honored members of the Council,
I bring you greetings from Risa—not the Risa of travel brochures and romantic holo-novels, but the true Risa. The Risa that has endured, adapted, and emerged stronger after each trial. I speak not as a tourist ambassador, but as a Counselor of our oldest institute of philosophy, and as a son of the Ricin tradition.
Today, the specter of the Borg hangs above us. The collective offers no room for diplomacy, no respect for culture, no compromise. We face not mere invaders—but a force that seeks to erase individuality, history, and identity. Some among the Council wonder what Risa—a world of peace—can offer in such a time. I say to you: we can offer the truth about peace.
The Hidden Roots of Our Tranquility
Long ago, before Risa joined the Federation, we too believed that peace could be maintained by disarming the populace, by eliminating even the mention of conflict in our schools. It was called the Great Disarmament. A generation was raised with no understanding of defense, and in time, we paid the price.
We were raided by Orion pirates. Exploited by off-world cartels. Our people were taken, our arts destroyed, our skies blackened. And we learned—too late—that peace without preparedness is only the illusion of safety.
The Birth of Ricin Doctrine
From the ashes of that failure arose the Ricin: scholars, philosophers, warriors of thought and purpose. They taught that peace is not the absence of conflict, but the mastery of it. That the mind and the body must be trained in tandem. That love without strength is a leaf in the wind.
We did not become a militant world. We became a watchful one. Our children were taught martial discipline—not to glorify violence, but to understand it, to confront it, and to defeat it when necessary. They learned meditation alongside hand-to-hand technique, negotiation beside tactical reasoning.
When we joined the Federation, we did so willingly. But let none assume we surrendered our right to defend our way of life.
Why I Speak to You Now
The Borg are not like the Orion Syndicate. They are not opportunistic, or ideological. They are methodical. And they are coming. You cannot debate with them. You cannot delay them. You can only prepare for them.
And yet, I hear murmurs within the halls of the Federation: whispers of abandoning planetary defense training, of downplaying the psychological need for individual and planetary preparedness. I hear the tired lie that “peace will protect us.”
No, Councilors. It is discipline that protects peace.
The Call to Action
I do not come bearing weapons. I come bearing wisdom. Let us take the Risan lesson and apply it across the Federation. Reestablish tactical readiness training in civilian schools. Encourage planetary governments to integrate defense and philosophy, not as contradictions, but as complements.
Let every child of the Federation grow up knowing not just the principles of liberty, but the means to defend them. Let every artist, scientist, and healer stand ready to protect the civilization they help to build.
Let us not wait until the Borg are in our orbit to remember what we must become.
Conclusion
The Borg seek to erase our uniqueness. Let us show them that the Federation is not a fragile collection of planets—but a constellation of cultures bound by a shared resolve.
We do not choose war. But neither do we flee from it.
We are the guardians of Risa’s flame—and we offer our light to the stars.
Thank you.
-
 @ 2dd9250b:6e928072
2025-03-22 00:22:40
@ 2dd9250b:6e928072
2025-03-22 00:22:40Vi recentemente um post onde a pessoa diz que aquele final do filme O Doutrinador (2019) não faz sentido porque mesmo o protagonista explodindo o Palácio dos Três Poderes, não acaba com a corrupção no Brasil.
Progressistas não sabem ler e não conseguem interpretar textos corretamente. O final de Doutrinador não tem a ver com isso, tem a ver com a relação entre o Herói e a sua Cidade.
Nas histórias em quadrinhos há uma ligação entre a cidade e o Super-Herói. Gotham City por exemplo, cria o Batman. Isso é mostrado em The Batman (2022) e em Batman: Cavaleiro das Trevas, quando aquele garoto no final, diz para o Batman não fugir, porque ele queria ver o Batman de novo. E o Comissário Gordon diz que o "Batman é o que a cidade de Gotham precisa."
Batman: Cavaleiro das Trevas Ressurge mostra a cidade de Gotham sendo tomada pela corrupção e pela ideologia do Bane. A Cidade vai definhando em imoralidade e o Bruce, ao olhar da prisão a cidade sendo destruída, decide que o Batman precisa voltar porque se Gotham for destruída, o Batman é destruído junto. E isso o da forças para consegue fugir daquele poço e voltar para salvar Gotham.
Isso também é mostrado em Demolidor. Na série Demolidor o Matt Murdock sempre fala que precisa defender a cidade Cozinha do Inferno; que o Fisk não vai dominar a cidade e fazer o que ele quiser nela. Inclusive na terceira temporada isso fica mais evidente na luta final na mansão do Fisk, onde Matt grita que agora a cidade toda vai saber o que ele fez; a cidade vai ver o mal que ele é para Hell's Kitchen, porque a gente sabe que o Fisk fez de tudo para a imagem do Demolidor entrar e descrédito perante os cidadãos, então o que acontece no final do filme O Doutrinador não significa que ele está acabando com a corrupção quando explode o Congresso, ele está praticamente interrompendo o ciclo do sistema, colocando uma falha em sua engrenagem.
Quando você ouve falar de Brasília, você pensa na corrupção dos políticos, onde a farra acontece,, onde corruptos desviam dinheiro arrecadado dos impostos, impostos estes que são centralizados na União. Então quando você ouve falarem de Brasília, sempre pensa que o pessoal que mora lá, mora junto com tudo de podre que acontece no Brasil.
Logo quando o Doutrinador explode tudo ali, ele está basicamente destruindo o mecanismo que suja Brasília. Ele está fazendo isso naquela cidade. Porque o símbolo da cidade é justamente esse, a farsa de que naquele lugar o povo será ouvido e a justiça será feita. Ele está destruindo a ideologia de que o Estado nos protege, nos dá segurança, saúde e educação. Porque na verdade o Estado só existe para privilegiar os políticos, funcionários públicos de auto escalão, suas famílias e amigos. Enquanto que o povo sofre para sustentar a elite política. O protagonista Miguel entendeu isso quando a filha dele morreu na fila do SUS.
-
 @ 04ea4f83:210e1713
2025-04-20 08:45:14
@ 04ea4f83:210e1713
2025-04-20 08:45:14Veröffentlicht auf Nakamoto Portfolio am 06.04.2023\ Originalautor: Alpha Zeta\ Übersetzt von: Sinautoshi am 24.06.2023 - 795682
Einführung
Bitcoin wurde mit verschiedenen Formen von Eigentum und anderen Vermögenswerten verglichen, die traditionell zur Wertaufbewahrung verwendet werden. In der Abwesenheit von gesundem Geld weisen rationale Investoren\ Kapital in Immobilien, Aktien und andere alternativen Wertaufbewahrungsmittel auf. Inspiriert von „Bitcoin as Property" von Michael Saylor, diskutiert dieses Whitepaper das Potenzial von Bitcoin, das monetäre Premium (Anm. den Aufschlag für die Geldartigkeit des Vermögenswertes) von traditionellen Vermögenswerten einzufangen, und seine Auswirkungen auf deren zukünftige Bewertung.
Die Verlagerung vom traditionellen Sparen zu alternativen Anlagen
In der Vergangenheit haben weniger erfahrene Anleger ihr Geld auf Sparkonten gespart, während erfahrenere Anleger nach Hebelwirkung und Effizienz durch Immobilien und Risikoinvestitionen suchten. In den letzten zehn Jahren haben sich die Anleger aufgrund des Rückgangs der Zinssätze und der Ausweitung der Finanzinstrumente haben sich die Anleger für Aktien, Immobilien und\ börsengehandelte Fonds (ETFs) als ihre primären Wertaufbewahrungsmittel entschieden. Die explosionsartige Zunahme von ETFs und die Beliebtheit von Zweitimmobilien (zur Vermietung) oder Real Estate Investment Trusts (REITs) haben zu einer Monetarisierung zahlreicher Vermögenswerte geführt.\ Bis Ende 2021 wurden viele Vermögenswerte, darunter auch Immobilien, weit über ihrem Nutzwert gehandelt. Die Zentralbanken haben mit überschüssigem Geld den Wert des Geldes grundlegend zerstört, was die Anleger dazu veranlasst, nach Vermögenswerten zu suchen, die einen Schutz gegen die negativen Auswirkungen des Gelddruckens bieten. Dieses Phänomen hat zu einer Finanzialisierung der Wirtschaft geführt, bei der die Anleger keine andere Wahl haben, als nach anderen Formen des Sparens zu suchen.
Bitcoin: Der optimale Vermögenswert für die Monetarisierung
Bitcoin hat das Potenzial, der optimale Vermögenswert für die Monetarisierung zu werden und die traditionellen Wertaufbewahrungsmittel wie Währungen, Anleihen, Immobilien, Aktien und Gold konsequent zu demonetisieren.
Immobilien werden aufgrund ihres inhärenten Nutzwerts oft als begehrter Vermögenswert betrachtet, aber ihr Wert wird auch stark von der Monetarisierung beeinflusst, die dazu geführt hat, dass viele Menschen mehrere Immobilien besitzen, was die Nachfrage und die Preise in die Höhe treibt. Es ist jedoch zu beachten, dass der Besitz von Immobilien mit einer Reihe von Problemen verbunden ist. So können beispielsweise die Grundsteuer und die Instandhaltungskosten die potenziellen Renditen erheblich schmälern. Außerdem können Immobilien im Laufe der Zeit an Wert verlieren, was ihren Wert weiter schmälert. Auch wenn man eine Urkunde für eine Immobilie besitzt, ist man nicht der eigentliche Eigentümer der Immobilie; die Zusage des Eigentums kann unter bestimmten Umständen widerrufen werden. Wenn beispielsweise die Regierung beschließt, die Immobilie für die öffentliche Nutzung zu beschlagnahmen, kann der Immobilieneigentümer seine Investition vollständig verlieren. All diese Faktoren haben Anleger dazu veranlasst, nach Alternativen zum Schutz ihres Vermögens zu suchen, insbesondere in einem Umfeld mit geringem Risiko und niedriger Inflation.
Im Gegensatz dazu bietet Bitcoin ein „Konstrukt", das nicht zerstört werden kann, keine Wartung erfordert und eine hervorragende Wertaufbewahrung bietet. Als dezentralisierter, sicherer und knapper digitaler Vermögenswert hat Bitcoin das Potenzial, den monetären Aufschlag traditioneller Vermögenswerte zu übernehmen, was möglicherweise zu deren Demonetisierung führt.
Bitcoin wird aus mehreren Gründen zunehmend als überlegenes Wertaufbewahrungsmittel anerkannt:
- Knappheit: Bitcoin hat einen festen Vorrat von 21 Millionen Münzen, was zu einem Grad an Knappheit führt, der seinen Wert vor Inflation schützt.
- Übertragbarkeit: Bitcoin lässt sich leicht digital übertragen und aufbewahren, was ihn praktischer macht als physische Vermögenswerte wie Gold.
- Sicherheit: Die dezentralisierte Natur der Blockchain-Technologie, die Bitcoin zugrunde liegt, gewährleistet seine Sicherheit und seinen Schutz vor Manipulationen.
- Transparenz: Alle Transaktionen werden in der Blockchain aufgezeichnet, wodurch ein transparenter und überprüfbarer Eigentumsnachweis entsteht.
- Zugänglichkeit: Bitcoin ist für jeden zugänglich, der über einen Internetanschluss verfügt, was ihn zu einem umfassenden Wertaufbewahrungsmittel macht.
- Unveränderlichkeit oder Widerstand gegen Zensur: Die Aufzeichnung des Eigentums ist durch ein massives und wachsendes Computernetzwerk gesichert, was es nahezu unmöglich macht, Transaktionen zu verändern oder zu zensieren. Dies bietet eine zusätzliche Sicherheitsebene und stärkt den Status von Bitcoin als zuverlässiges und vertrauenswürdiges Wertaufbewahrungsmittel.
Das Modell
Das Schrödinger-Münzmodell basiert auf dem Konzept der Quantensuperposition, bei dem ein Objekt gleichzeitig in mehreren Zuständen existieren kann, bis es beobachtet wird. In diesem Fall wird davon ausgegangen, dass Bitcoin zwei mögliche Ergebnisse hat: Entweder scheitert er und ist wertlos (das Dan-Peña-Szenario) oder er erobert erfolgreich die Geldprämie traditioneller Wertaufbewahrungsmittel (das Saylor-Szenario).
Anstatt sich auf absolute Gewissheit wie in den obigen Szenarien zu verlassen, ordnet dieses Modell jedem dieser Szenarien Wahrscheinlichkeiten zu, um einen fairen Wert für Bitcoin zu ermitteln. Wenn du die Box öffnest und eine Welt beobachtest, in der Saylor Recht hatte, was passiert dann? Was wäre, wenn Dan Recht hätte?
Modell-Komponenten
Das Modell berechnet den Marktwert von Bitcoin heute anhand der folgenden Komponenten:
a. Marktkapitalisierung der Vermögenswerte: Der aktuelle Marktwert jedes traditionellen Wertaufbewahrungsmittels (z.B. Gold, Immobilien, Aktien, Anleihen).
b. Prozentsatz des monetären Aufschlags: Der Anteil der Marktkapitalisierung eines Vermögenswerts, der auf seinen Status als Wertaufbewahrungsmittel zurückzuführen ist.
c. Wahrscheinlichkeit der Vereinnahmung: Die Wahrscheinlichkeit, dass Bitcoin die monetäre Prämie jedes Vermögenswerts vereinnahmt.
d. Zeit bis zur Vereinnahmung: Die erwartete Zeit, bis Bitcoin die Geldprämie eines jeden Vermögenswerts erbeutet. Dies kann auch als Vektor mit verschiedenen Prozentsätzen der eingefangenen Prämie über die Zeit modelliert werden.
e. Abzinsungsrate: Der Prozentsatz, mit dem die zukünftig erwarteten Erfassungswerte auf den Gegenwartswert abgezinst werden, um den heutigen Marktwert zu berechnen.
Modell-Berechnung
Der Zeitwert von Bitcoin wird als Summe des erwarteten Erfassungswerts der einzelnen Vermögenswerte berechnet:
wobei der Zeitwert jedes Vermögenswerts definiert ist als:
- mcap: Aktuelle Marktkapitalisierung der einzelnen Vermögenswerte
- mp: Prozentualer Anteil der Marktkapitalisierung, der Monetarisierungscharakter hat (nicht Nutzwert)\ prob: Wahrscheinlichkeit, dass Bitcoin diesen Wert erfasst
- r: Abzinsungssatz
- n: Anzahl der Perioden, bis die Monetarisierung realisiert wird
Denke daran, dass wir mit diesem Rahmen auch den heutigen Bitcoin-Preis verwenden könnten, um die aktuell implizierte Wahrscheinlichkeit des Marktes zu berechnen.
Modell-Inputs
Potenzielle Vermögensklassen und geschätzte Werte - Daten vom April 2023
- Aktien: a. Angenommener Marktwert: $100 Billionen b. Quelle: Die Börsenkapitalisierung kann der Weltbank und Statista entnommen werden.Die Daten stellen eine ungefähre Schätzung dar, da die Börsenkapitalisierung mit den Marktbewegungen schwankt.
- Anleihen: a. Angenommener Marktwert: $130 Billionen b. Quelle: Die Kapitalisierung des globalen Anleihemarktes wurde aus Quellen wie der Bank für Internationalen Zahlungsausgleich abgeleitet. Die Daten stellen eine ungefähre Schätzung dar, da sich die Kapitalisierung des Anleihemarktes durch Neuemissionen und Tilgungen ändert. Sie umfassen nur die Gesamtsumme für „fortgeschrittene Volkswirtschaften".
- Gold: a. Angenommener Marktwert: $10 Billionen b. Quelle: Die Gesamtmarktkapitalisierung von Gold wurde anhand der Daten des World Gold Council zu den oberirdischen Goldbeständen und dem durchschnittlichen Goldpreis pro Unze zum Zeitpunkt der Erstellung dieses Berichts berechnet. Die Daten sollten aktualisiert werden, um den aktuellen Goldpreis für eine genaue Bewertung widerzuspiegeln.
- Silber: a. Angenommener Marktwert: $1,3 Billionen b. Quelle: Die gesamte Marktkapitalisierung von Silber wurde anhand der Daten des Silver Institute zu den oberirdischen Silberbeständen und dem durchschnittlichen Silberpreis pro Unze zum Zeitpunkt der Erstellung dieses Berichts geschätzt. Die Daten sollten aktualisiert werden, um den aktuellen Silberpreis für eine genaue Bewertung widerzuspiegeln.
- Immobilien: a. Angenommener Marktwert: $320 Billionen b. Quelle: Savills Research
- Kryptowährungen (ausgenommen BTC): a. Angenommener Marktwert: $500 Mrd. b. Quelle: Coinmarketcap.com
Parallelen zum Black-Scholes-Modell für die Optionsbewertung
Die Black-Scholes-Formel wird verwendet, um den fairen Preis von Optionen zu berechnen. Dabei handelt es sich um Finanzkontrakte, die dem Käufer das Recht (aber nicht die Verpflichtung) geben, einen Basiswert, z. B. eine Aktie oder einen Rohstoff, zu einem bestimmten Preis und Zeitpunkt zu kaufen oder zu verkaufen.
Die Formel umfasst fünf Inputs: den aktuellen Kurs des Basiswerts, den Ausübungspreis (den Preis, zu dem die Option ausgeübt werden kann), die Zeit bis zum Ablauf, den risikofreien Zinssatz und die Volatilität des Kurses des Basiswerts. Hier ist die Formel für den Preis einer Call-Option:
Die Formel selbst ist etwas kompliziert, aber in einfachen Worten funktioniert sie, indem sie die Wahrscheinlichkeit verschiedener Zukunftsszenarien für den Kurs des Basiswerts auf der Grundlage seiner Volatilität (wie stark sein Kurs im Laufe der Zeit zu schwanken pflegt) schätzt. Die Formel berechnet dann den erwarteten Wert der Option auf der Grundlage dieser Wahrscheinlichkeiten, abgezinst auf den heutigen Wert unter Verwendung des risikofreien Zinssatzes.
Die linke Seite der Gleichung stellt den Wert der Call-Option dar (das Recht, den Basiswert zu kaufen), während die rechte Seite die Summe aus dem Gegenwartswert des Ausübungspreises (der bei Ausübung der Option garantiert wird) und dem erwarteten Wert des Kurses des Basiswerts bei Fälligkeit darstellt. Der Erwartungswert wird berechnet, indem der aktuelle Kurs des Basiswerts mit einer Wahrscheinlichkeitsdichtefunktion multipliziert wird, die auf der Volatilität des Kurses des Basiswerts basiert.
Ein wesentlicher Unterschied zwischen den beiden Modellen besteht darin, dass die Black-Scholes-Formel auf der Annahme einer kontinuierlichen Zeit und einer bekannten Verteilung der Preise von Vermögenswerten beruht, während das Schrödinger-Münzmodell auf dem Konzept der Quantensuperposition basiert, bei dem ein Objekt in mehreren Zuständen existieren kann, bis es beobachtet wird. Das Schrödinger-Münzmodell ordnet jedem möglichen Ergebnis Wahrscheinlichkeiten zu, um einen fairen Wert für Bitcoin zu ermitteln, während die Black-Scholes-Formel eine Wahrscheinlichkeitsdichtefunktion verwendet, die auf der Volatilität des Preises des zugrunde liegenden Vermögenswerts basiert.
Ein weiterer Unterschied besteht darin, dass die Black-Scholes-Formel eine geschlossene Gleichung ist, was bedeutet, dass sie analytisch gelöst werden kann, während das Schrödinger-Münzen-Modell ein komplexeres Modell ist, das mehrere Eingaben und Berechnungen umfasst.
Trotz dieser Unterschiede zielen beide Modelle darauf ab, den beizulegenden Zeitwert eines Vermögenswerts zu schätzen, indem sie verschiedene Faktoren wie den aktuellen Preis des Vermögenswerts, die Zeit bis zum Verfall, die Zinssätze und die Volatilität berücksichtigen. Beide Modelle berücksichtigen auch das Potenzial für extreme Ergebnisse und die Ungewissheit künftiger Ereignisse, die zur Volatilität des Vermögenswerts beitragen können.
Schrödingers Münze und Volatilität als Merkmal, nicht als Fehler
Einer der meistdiskutierten Aspekte von Bitcoin und anderen Kryptowährungen ist ihre inhärente Preisvolatilität. In diesem Abschnitt argumentieren wir, dass das Schrödinger-Münzmodell die Volatilität von Bitcoin als ein natürliches Merkmal seiner Bewertung erklärt und nicht als Fehler oder Schwachstelle. Darüber hinaus werden wir diskutieren, wie diese Volatilität abnehmen kann, wenn wir uns der Hyperbitcoinisierung nähern.
- Extreme Ergebnisse Das Schrödinger Modell basiert auf zwei extremen Ergebnissen für Bitcoin: entweder sch-eitert er und wird wertlos (das Dan Peña Szenario), oder er erobert erfolgreich die Geldprämie traditioneller Wertaufbewahrungsmittel (das Saylor Szenario). Infolgedessen sagt das Modell von Natur aus erhebliche Wertschwankungen voraus, die von der Marktstimmung und externen Faktoren abhängen, die die Wahrnehmung der Anleger hinsichtlich der Wahrscheinlichkeit dieser Ergebnisse beeinflussen.
- Kleine Änderungen in der Wahrscheinlichkeit, große Änderungen im fairen Wert Angesichts der extremen Natur der beiden möglichen Ergebnisse können kleine Änderungen in der wahrgenommenen Wahrscheinlichkeit des Eintretens eines der beiden Szenarien zu erheblichen Änderungen im fairen Wert von Bitcoin führen. Zum Beispiel könnte ein leichter Anstieg des Vertrauens des Marktes in den Erfolg von Bitcoin zu einem signifikanten Anstieg des Preises führen, während ein Rückgang des Vertrauens zu einem starken Rückgang führen könnte.
- Ungewissheit der Zeit Ein weiterer Faktor, der zur Volatilität von Bitcoin beiträgt, ist die Ungewissheit über die Zeit, die benötigt wird, um die Hyperbitcoinisierung zu erreichen. Während Hausse-Märkten nimmt die Zeitwahrnehmung (t) tendenziell ab, da die Anleger optimistischer werden, was die Akzeptanz von Bitcoin und die Geschwindigkeit angeht, mit der Bitcoin die Geldprämie von traditionellen Vermögenswerten erreichen wird. Umgekehrt steigt die wahrgenommene Zeit bis zur Hyperbitcoinisierung während Baisse-Märkten, wenn die Marktstimmung negativ wird. Diese Fluktuation in der Zeitwahrnehmung fügt dem Bitcoin-Kurs eine weitere Ebene der Volatilität hinzu.
- Abnehmende Volatilität bei zunehmender Hyperbitcoinisierung Je näher wir der Hyperbitcoinisierung kommen, desto geringer dürfte die Volatilität von Bitcoin werden. Dies liegt daran, dass der Markt im Laufe der Zeit mehr Informationen über die Akzeptanz von Bitcoin, das regulatorische Umfeld und die technologischen Entwicklungen erhalten wird. Infolgedessen wird die Wahrnehmung des Marktes hinsichtlich der Wahrscheinlichkeit der beiden extremen Ergebnisse stabiler werden, was zu geringeren Preisschwankungen führt.
Zusammenfassend erklärt das Schrödinger-Münzen-Modell die Volatilität von Bitcoin als eine natürliche Folge seiner Bewertung, die auf extremen Ergebnissen, kleinen Veränderungen der Wahrscheinlichkeit und der Ungewissheit der Zeit bis zur Hyperbitcoinisierung beruht. Wenn der Markt mehr Informationen erhält und mehr Vertrauen in die Zukunft von Bitcoin gewinnt, wird erwartet, dass seine Volatilität abnimmt und gegen Null tendiert. Das Verständnis dieses Aspekts des Modells kann Anlegern helfen, fundiertere Entscheidungen über die mit einer Investition in Bitcoin verbundenen Risiken und Erträge zu treffen.
Schlussfolgerung
Schrödingers-Münzmodell bietet einen Rahmen für die Bewertung von Bitcoin, indem es sein Potenzial berücksichtigt, den monetäre Aufschlag von traditionellen Vermögenswerten wie Immobilien, Aktien und Anleihen einzufangen. Als überlegenes Wertaufbewahrungsmittel hat Bitcoin das Potenzial, Investitionen in traditionelle Vermögenswerte konsequent zu demonetisieren, was zu einer Verschiebung der Kapitalallokation und einer Neubewertung ihres Wertes führt.
Das Modell beleuchtet auch die inhärente Volatilität von Bitcoin, die sich aus den extremen Ergebnissen, kleinen Veränderungen der Wahrscheinlichkeit und der Ungewissheit der Zeit bis zur Hyperbitcoinisierung ergibt. Da der Markt jedoch mehr Informationen erhält und mehr Vertrauen in die Zukunft von Bitcoin gewinnt, wird erwartet, dass seine Volatilität abnimmt und gegen Null tendiert.
Darüber hinaus unterstreicht das Modell, wie wichtig es ist, die Risiken zu verstehen, die mit einer Investition in Bitcoin verbunden sind, wie regulatorische Änderungen, technologische Herausforderungen und potenzielle Konkurrenz durch andere Kryptowährungen oder alternative Wertaufbewahrungsmittel.
Durch das Verständnis der Dynamik des Schrödinger-Münzmodells sowie der Faktoren, die zur Volatilität von Bitcoin und den damit verbundenen Risiken beitragen, können Anleger fundiertere Entscheidungen über das potenzielle Wachstum und die mit Bitcoin und anderen Vermögenswerten verbundenen Risiken treffen. Dieser ganzheitliche Bewertungsansatz ermöglicht eine umfassendere Beurteilung des Potenzials von Bitcoin sowohl als Investition als auch als transformative Technologie.
-
 @ e39d100f:d27602e5
2025-04-21 02:28:33
@ e39d100f:d27602e5
2025-04-21 02:28:33A 5GBet tem se destacado cada vez mais no cenário brasileiro como uma plataforma completa de entretenimento online, oferecendo aos usuários uma experiência repleta de emoção, segurança e diversidade de jogos. Seja você um jogador iniciante ou experiente, a 5GBet proporciona uma navegação intuitiva e um ambiente confiável para quem busca diversão sem sair de casa.
Desde o primeiro acesso, é fácil perceber que a 5GBet se preocupa com a experiência do usuário. O design do site é moderno e responsivo, adaptando-se perfeitamente a computadores, tablets e celulares. Isso garante que os jogadores possam se divertir a qualquer momento, de qualquer lugar.
Outro ponto forte é a segurança. A plataforma utiliza tecnologia de criptografia avançada para proteger os dados dos usuários, além de contar com métodos de verificação de identidade para garantir transações seguras. Tudo isso contribui para um ambiente confiável, onde o jogador pode focar apenas na diversão.
Variedade de Jogos para Todos os Gostos Na 5gbet , a variedade de jogos é um dos principais diferenciais. O site oferece uma extensa seleção de opções, desde os clássicos jogos de mesa até slots modernos com gráficos impressionantes e temáticas envolventes. Os jogadores podem escolher entre diversos estilos e dinâmicas, o que torna a experiência muito mais rica e personalizada.
Os jogos de cartas, como o pôquer e o blackjack, são populares entre os usuários mais estratégicos. Já os slots oferecem uma jogabilidade mais leve e dinâmica, com recursos interativos e animações cativantes. Há também jogos com crupiês ao vivo, que proporcionam uma experiência ainda mais imersiva, com transmissão em tempo real e interação com outros jogadores.
Experiência do Jogador: Intuitiva e Recompensadora A experiência do jogador na 5GBet é cuidadosamente pensada para ser fluida e gratificante. O processo de cadastro é rápido, e os métodos de depósito e saque são variados, incluindo opções populares como PIX, transferência bancária e carteiras digitais. Além disso, o suporte ao cliente está disponível para tirar dúvidas e resolver questões com agilidade, seja via chat ao vivo ou e-mail.
Outro destaque é o sistema de recompensas e promoções oferecido aos jogadores. Desde bônus de boas-vindas até promoções recorrentes, a 5GBet valoriza seus usuários ativos e oferece incentivos para tornar a jornada ainda mais empolgante.
A comunidade de jogadores também é bastante ativa, e a plataforma frequentemente promove torneios e desafios, permitindo que os usuários testem suas habilidades e interajam com outros entusiastas.
Conclusão A 5GBet se consolida como uma excelente opção para quem busca entretenimento online com qualidade, segurança e muita variedade. Com uma plataforma bem estruturada, jogos empolgantes e uma experiência de usuário impecável, é fácil entender por que cada vez mais brasileiros escolhem a 5GBet como seu destino de diversão online. Se você ainda não conhece, vale a pena explorar e descobrir tudo o que essa plataforma tem a oferecer.
-
 @ 0176967e:1e6f471e
2024-07-26 12:15:35
@ 0176967e:1e6f471e
2024-07-26 12:15:35Bojovať s rakovinou metabolickou metódou znamená použiť metabolizmus tela proti rakovine. Riadenie cukru a ketónov v krvi stravou a pohybom, časovanie rôznych typov cvičení, včasná kombinácia klasickej onko-liečby a hladovania. Ktoré vitamíny a suplementy prijímam a ktorým sa napríklad vyhýbam dajúc na rady mojej dietologičky z USA Miriam (ktorá sa špecializuje na rakovinu).
Hovori sa, že čo nemeriame, neriadime ... Ja som meral, veľa a dlho ... aj grafy budú ... aj sranda bude, hádam ... 😉
-
 @ 0176967e:1e6f471e
2024-07-26 09:50:53
@ 0176967e:1e6f471e
2024-07-26 09:50:53Predikčné trhy predstavujú praktický spôsob, ako môžeme nahliadnuť do budúcnosti bez nutnosti spoliehať sa na tradičné, často nepresné metódy, ako je veštenie z kávových zrniek. V prezentácii sa ponoríme do histórie a vývoja predikčných trhov, a popíšeme aký vplyv mali a majú na dostupnosť a kvalitu informácií pre širokú verejnosť, a ako menia trh s týmito informáciami. Pozrieme sa aj na to, ako tieto trhy umožňujú obyčajným ľuďom prístup k spoľahlivým predpovediam a ako môžu prispieť k lepšiemu rozhodovaniu v rôznych oblastiach života.
-
 @ a39d19ec:3d88f61e
2025-03-18 17:16:50
@ a39d19ec:3d88f61e
2025-03-18 17:16:50Nun da das deutsche Bundesregime den Ruin Deutschlands beschlossen hat, der sehr wahrscheinlich mit dem Werkzeug des Geld druckens "finanziert" wird, kamen mir so viele Gedanken zur Geldmengenausweitung, dass ich diese für einmal niedergeschrieben habe.
Die Ausweitung der Geldmenge führt aus klassischer wirtschaftlicher Sicht immer zu Preissteigerungen, weil mehr Geld im Umlauf auf eine begrenzte Menge an Gütern trifft. Dies lässt sich in mehreren Schritten analysieren:
1. Quantitätstheorie des Geldes
Die klassische Gleichung der Quantitätstheorie des Geldes lautet:
M • V = P • Y
wobei:
- M die Geldmenge ist,
- V die Umlaufgeschwindigkeit des Geldes,
- P das Preisniveau,
- Y die reale Wirtschaftsleistung (BIP).Wenn M steigt und V sowie Y konstant bleiben, muss P steigen – also Inflation entstehen.
2. Gütermenge bleibt begrenzt
Die Menge an real produzierten Gütern und Dienstleistungen wächst meist nur langsam im Vergleich zur Ausweitung der Geldmenge. Wenn die Geldmenge schneller steigt als die Produktionsgütermenge, führt dies dazu, dass mehr Geld für die gleiche Menge an Waren zur Verfügung steht – die Preise steigen.
3. Erwartungseffekte und Spekulation
Wenn Unternehmen und Haushalte erwarten, dass mehr Geld im Umlauf ist, da eine zentrale Planung es so wollte, können sie steigende Preise antizipieren. Unternehmen erhöhen ihre Preise vorab, und Arbeitnehmer fordern höhere Löhne. Dies kann eine sich selbst verstärkende Spirale auslösen.
4. Internationale Perspektive
Eine erhöhte Geldmenge kann die Währung abwerten, wenn andere Länder ihre Geldpolitik stabil halten. Eine schwächere Währung macht Importe teurer, was wiederum Preissteigerungen antreibt.
5. Kritik an der reinen Geldmengen-Theorie
Der Vollständigkeit halber muss erwähnt werden, dass die meisten modernen Ökonomen im Staatsauftrag argumentieren, dass Inflation nicht nur von der Geldmenge abhängt, sondern auch von der Nachfrage nach Geld (z. B. in einer Wirtschaftskrise). Dennoch zeigt die historische Erfahrung, dass eine unkontrollierte Geldmengenausweitung langfristig immer zu Preissteigerungen führt, wie etwa in der Hyperinflation der Weimarer Republik oder in Simbabwe.
-
 @ 502ab02a:a2860397
2025-04-21 02:26:09
@ 502ab02a:a2860397
2025-04-21 02:26:09เรามาดูกันครับว่า Precision Fermentation ของ Perfect Day เค้าใช้อะไรเป็นกำลังสำคัญในการหมัก ให้ได้สินค้ามูลค่ามหาศาล ท้าวความกันก่อนว่า Perfect Day เป็นบริษัทที่ผลิต เวย์โปรตีนได้ โดยไม่ต้องใช้วัวเลยแม้แต่นิดเดียว ด้วยการใช้จุลินทรีย์
Microflora ฟาร์มวัวยุคใหม่ ที่ไม่มีวัว ถ้าคุณเคยดูสารคดีธรรมชาติ แล้วเห็นภาพป่าดิบเขียวชอุ่มที่แต่ละสิ่งมีชีวิตทำหน้าที่ของมันอย่างกลมกลืนกัน ทั้งแมลงที่บินไปมา เชื้อราที่แอบฝังรากอยู่ใต้ใบไม้ หรือจุลินทรีย์ที่ไม่เห็นด้วยตาเปล่าแต่ทำงานหนักอยู่ใต้ดิน... โลกของ microflora ก็ไม่ต่างอะไรกับ “จักรวาลจิ๋ว” แบบนั้นเลย
Microflora คืออะไร? microflora เป็นศัพท์ที่นักวิทยาศาสตร์ใช้เรียกสิ่งมีชีวิตขนาดจิ๋วที่มองไม่เห็นด้วยตาเปล่า แต่มีชีวิตจริงๆ แบบครบสูตร คือเจริญเติบโตได้ แบ่งตัวได้ กินได้ เหมือนสิ่งมีชีวิตอื่นๆ เป๊ะๆ มาจาก micro กับ flora
พอพูดถึงคำว่า “flora” บางคนอาจนึกถึงต้นไม้ แต่ในความหมายนี้ มันกว้างกว่านั้นมาก เพราะ “microflora” ไม่ได้จำกัดแค่พืช แต่หมายถึงสิ่งมีชีวิตจิ๋วจากหลากหลายอาณาจักรในธรรมชาติ เช่น ฟังไจ (Fungi) — ไม่ใช่แค่เห็ดที่เรากินกัน แต่รวมถึงเชื้อราจิ๋วที่อยู่ในดินและอากาศ ที่เก่งเรื่องการปล่อยเอนไซม์ย่อยอาหารนอกตัว แล้วดูดสารอาหารเข้าไป แบคทีเรีย (Bacteria) — นักแบ่งตัวมือโปรที่อยู่ในทุกที่ตั้งแต่ดินในสวน ยันในลำไส้เรา โพรทิสต์ (Protists) — กลุ่มที่เหลือๆ ที่ไม่เข้าพวกกับใคร เช่น สาหร่ายบางชนิด หรืออะมีบา
microflora เหล่านี้เหมือนพนักงานจิ๋วที่ทำหน้าที่เฉพาะทาง บางตัวเก่งเรื่องสร้างโปรตีน บางตัวสร้างไขมัน บางตัวสังเคราะห์วิตามินเก่งสุดๆ เลยกลายเป็นขุมพลังที่มนุษย์เริ่มหันมาใช้มากขึ้นเรื่อยๆ
ความสัมพันธ์ระหว่างมนุษย์กับ microflora ไม่ใช่เรื่องใหม่เลย เราหมักเบียร์ ทำโยเกิร์ต ดองกิมจิ และทำซีอิ๊วจากถั่วเหลืองด้วยกระบวนการที่เรียกว่า “fermentation” หรือ “การหมัก” มานานหลายพันปีแล้ว ซึ่งเป็นการอาศัยพลังของจุลินทรีย์ธรรมชาติให้สร้างรสชาติ วิตามิน หรือย่อยของที่เรากินให้ดูดซึมง่ายขึ้น แต่วันนี้โลกไปไกลกว่านั้นมาก เพราะเราสามารถสอนจุลินทรีย์ให้ผลิต “โปรตีนเฉพาะแบบ” ได้ตามต้องการ กระบวนการนี้เรียกว่า Precision Fermentation หรือ “การหมักแบบแม่นยำ” ฟังดูเหมือนห้องทดลองของ Iron Man เลยเนอะ
Perfect Day ใช้วิธีนี้ในการผลิต เวย์โปรตีน แบบไม่ต้องรีดนมจากวัวเลยสักหยด ด้วยการใช้ “เชื้อราจิ๋ว” ชนิดหนึ่งที่มีชื่อสายวิทยาศาสตร์ว่า Trichoderma
ทำไมต้อง Trichoderma? เจ้า Trichoderma ไม่ใช่เชื้อราหน้าตาน่ากลัวแบบในหนังสยองขวัญ แต่มันคือเชื้อราที่อยู่ในดินมานานกว่า 70 ปีแล้ว และเป็นที่รู้กันในวงการวิทยาศาสตร์ว่า มันเก่งเรื่องการผลิตเอนไซม์ที่ย่อยไม้ ย่อยใบไม้ ย่อยสิ่งมีชีวิตอื่นในธรรมชาติได้อย่างมีประสิทธิภาพ จึงเป็นเหมือน “โรงงานย่อยอาหาร” ชั้นเลิศ
นักวิทยาศาสตร์ของ Perfect Day เห็นแววก็เลยจับมันมา “ฝึกงาน” ใหม่ โดยใช้กระบวนการที่เรียกว่า strain engineering หรือ “การออกแบบสายพันธุ์” พูดง่ายๆ ก็คือ ใส่รหัสพันธุกรรม (เหมือนคำสั่งงาน) เข้าไปให้มันผลิตโปรตีนจากนมได้ เช่น beta-lactoglobulin ซึ่งเป็นโปรตีนตัวหลักของเวย์ในน้ำนมวัว
เมื่อ Trichoderma อ่านคำสั่งนี้ออก มันก็เริ่มเดินเครื่องผลิตโปรตีนตามที่เราสั่ง เหมือนเป็น “วัวในห้องแล็บ” ที่ไม่มีเสียงร้อง ไม่มีปุ๋ยคอก และไม่ต้องเลี้ยงด้วยหญ้า
microflora = วัวจิ๋วยุคใหม่
ลองจินตนาการว่าถ้าในอดีตเราต้องเลี้ยงวัวจริงๆ เพื่อให้ได้โปรตีนจากนม วันนี้เราใช้แค่จุลินทรีย์จิ๋วในถังหมัก แล้วป้อน “อาหาร” ให้มันเป็นน้ำตาลจากพืช (เช่น ข้าวโพด !!! เป็นง่ะ ข้าวโพดอีกแล้ว) มันก็จะเปลี่ยนคาร์โบไฮเดรตเหล่านั้นให้กลายเป็นโปรตีน หรือไขมัน หรือสารที่เราต้องการได้แบบแม่นยำ
microflora ไม่ใช่สัตว์ แต่ก็ทำหน้าที่แทนสัตว์ได้ พวกมันไม่มีสมอง ไม่มีระบบประสาท ไม่รู้สึกเจ็บ ไม่เบื่อ ไม่หิวข้าว ไม่ต้องการวันหยุด แต่มันมี “ความสามารถ” ที่เราสามารถดึงมาใช้ให้เกิดประโยชน์ได้อย่างน่าทึ่ง
ข้อดีของ microflora -เลี้ยงง่าย แค่ให้คาร์บ (จากพืช) ก็พร้อมทำงาน -ไม่ต้องใช้พื้นที่เยอะ ผลิตในถังหมัก ไม่ต้องใช้ทุ่งหญ้ากว้างๆ แบบฟาร์มวัว -ควบคุมคุณภาพได้ ผลิตโปรตีนได้สม่ำเสมอ ปราศจากสารก่อภูมิแพ้หรือยาปฏิชีวนะ -ลดการปล่อยก๊าซเรือนกระจก เพราะไม่ต้องเลี้ยงสัตว์ที่ปล่อยมีเทน
microflora จึงเป็น “เพื่อนร่วมงานที่เล็กที่สุด” แต่ก็อาจจะทรงพลังที่สุดในครัวของอนาคต และแม้เราจะยังยึดมั่นกับ animal-based diet อยู่ แต่ผมคิดว่าเรื่องนี้ก็น่าสนใจในฐานะ เทคโนโลยีที่กำลังท้าทายโลก fiat food อีกแนวทางหนึ่ง เพราะมันไม่ใช่พืชประดิษฐ์ ไม่ใช่แป้ง+สี+กลิ่น+สารพัด additive แต่คือ “การสร้างโปรตีนแท้” ด้วยความรู้ทางวิทยาศาสตร์ ที่เอื้อให้มนุษย์เลิกพึ่งวัวโดยตรง
ไม่แน่ว่าวันหนึ่ง แทนที่จะมีฟาร์มวัวเลี้ยงวัว 500 ตัวเพื่อผลิตเวย์ 1 ตัน เราอาจมีแค่ถังหมัก 1 ถัง ที่เลี้ยงเชื้อรา 500 ล้านตัว แล้วได้เวย์โปรตีนคุณภาพเดียวกัน...โดยไม่ต้องมีเสียง "มอ" เลยสักแอะ
แต่คำถามสำคัญคือ เราจะมีฟาร์มนั้นได้ไหม หรือได้แต่ทำหน้าที่ซื้อนมมารับประทานเท่านั้น
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ f3873798:24b3f2f3
2025-03-10 00:32:44
@ f3873798:24b3f2f3
2025-03-10 00:32:44Recentemente, assisti a um vídeo que me fez refletir profundamente sobre o impacto da linguagem na hora de vender. No vídeo, uma jovem relatava sua experiência ao presenciar um vendedor de amendoim em uma agência dos Correios. O local estava cheio, as pessoas aguardavam impacientes na fila e, em meio a esse cenário, um homem humilde tentava vender seu produto. Mas sua abordagem não era estratégica; ao invés de destacar os benefícios do amendoim, ele suplicava para que alguém o ajudasse comprando. O resultado? Ninguém se interessou.

A jovem observou que o problema não era o produto, mas a forma como ele estava sendo oferecido. Afinal, muitas das pessoas ali estavam há horas esperando e perto do horário do almoço – o amendoim poderia ser um ótimo tira-gosto. No entanto, como a comunicação do vendedor vinha carregada de desespero, ele afastava os clientes ao invés de atraí-los. Esse vídeo me tocou profundamente.
No dia seguinte, ao sair para comemorar meu aniversário, vi um menino vendendo balas na rua, sob o sol forte. Assim como no caso do amendoim, percebi que as pessoas ao redor não se interessavam por seu produto. Ao se aproximar do carro, resolvi comprar dois pacotes. Mais do que ajudar, queria que aquele pequeno gesto servisse como incentivo para que ele continuasse acreditando no seu negócio.
Essa experiência me fez refletir ainda mais sobre o poder da comunicação em vendas. Muitas vezes, não é o produto que está errado, mas sim a forma como o vendedor o apresenta. Quando transmitimos confiança e mostramos o valor do que vendemos, despertamos o interesse genuíno dos clientes.
Como a Linguagem Impacta as Vendas?

1. O Poder da Abordagem Positiva
Em vez de pedir por ajuda, é importante destacar os benefícios do produto. No caso do amendoim, o vendedor poderia ter dito algo como: "Que tal um petisco delicioso enquanto espera? Um amendoim fresquinho para matar a fome até o almoço!"
2. A Emoção na Medida Certa
Expressar emoção é essencial, mas sem parecer desesperado. Os clientes devem sentir que estão adquirindo algo de valor, não apenas ajudando o vendedor.
3. Conheça Seu Público
Entender o contexto é fundamental. Se as pessoas estavam com fome e impacientes, uma abordagem mais objetiva e focada no benefício do produto poderia gerar mais vendas.
4. Autoconfiança e Postura
Falar com firmeza e segurança transmite credibilidade. O vendedor precisa acreditar no próprio produto antes de convencer o cliente a comprá-lo.
Conclusão
Vender é mais do que apenas oferecer um produto – é uma arte que envolve comunicação, percepção e estratégia. Pequenos ajustes na abordagem podem transformar completamente os resultados. Se o vendedor de amendoim tivesse apresentado seu produto de outra maneira, talvez tivesse vendido tudo rapidamente. Da mesma forma, se cada um de nós aprender a se comunicar melhor em nossas próprias áreas, poderemos alcançar muito mais sucesso.
E você? Já passou por uma experiência parecida?
-
 @ e39d100f:d27602e5
2025-04-21 02:18:40
@ e39d100f:d27602e5
2025-04-21 02:18:40O mercado de entretenimento digital no Brasil está em constante expansão, e entre as novas opções que vêm ganhando destaque, a plataforma Betao se sobressai como uma das mais promissoras. Com um ambiente moderno, seguro e recheado de atrações, o Betao oferece uma experiência diferenciada tanto para jogadores iniciantes quanto para os mais experientes.
Uma Plataforma Intuitiva e Acessível Logo ao acessar o site do Betao, o usuário já percebe a preocupação com a usabilidade. O design é limpo, responsivo e adaptado para todos os tipos de dispositivos, o que permite que os jogadores aproveitem ao máximo cada funcionalidade, seja no computador, tablet ou celular.
Além disso, o processo de cadastro é rápido e descomplicado. Em poucos cliques, o jogador já está pronto para explorar os jogos disponíveis. Outro ponto positivo é a variedade de métodos de pagamento, que incluem transferências bancárias, carteiras digitais e até opções com criptomoedas, oferecendo mais liberdade e praticidade.
Catálogo de Jogos Variado e Empolgante O Betao se destaca por seu portfólio diversificado de jogos online. A plataforma trabalha com provedores renomados do setor, garantindo alta qualidade gráfica, fluidez nas partidas e mecânicas envolventes.
Entre os destaques, estão os jogos de slots, que atraem jogadores pela combinação de simplicidade e emoção. Com temas variados, gráficos vibrantes e bônus interativos, essas máquinas virtuais oferecem diversão contínua e oportunidades de prêmios significativos.
Outra categoria bastante procurada são os jogos de mesa, como roleta, blackjack e bacará. Essas opções são ideais para quem gosta de jogos que exigem estratégia e tomada de decisões rápidas, proporcionando uma experiência desafiadora e recompensadora.
Experiência do Jogador em Primeiro Lugar No Betao, o foco está na satisfação do jogador. A plataforma investe constantemente em melhorias para garantir um ambiente justo, transparente e divertido. Um dos grandes diferenciais é o suporte ao cliente, que funciona 24 horas por dia, todos os dias da semana. Com atendimento em português e canais acessíveis — como chat ao vivo e e-mail —, os usuários recebem ajuda imediata sempre que necessário.
Além disso, o Betao promove promoções regulares, programas de fidelidade e bônus de boas-vindas que valorizam a permanência e o engajamento dos jogadores. Tudo isso contribui para criar uma comunidade ativa e satisfeita.
Segurança e Confiabilidade Segurança é um fator essencial em qualquer plataforma de jogos online, e o Betao leva isso a sério. A empresa utiliza tecnologias de criptografia avançadas para proteger os dados e transações dos usuários, além de operar de forma legalizada, com licenças reconhecidas internacionalmente. Essa transparência aumenta a confiança dos jogadores e garante tranquilidade durante toda a experiência.
Conclusão Com uma combinação de tecnologia de ponta, ampla variedade de jogos, atendimento eficiente e foco total na experiência do usuário, o Betao se consolida como uma das melhores opções para quem busca diversão e entretenimento de qualidade no universo digital. Seja você um novato ou veterano nesse meio, vale a pena explorar tudo o que a plataforma tem a oferecer.
-
 @ 0176967e:1e6f471e
2024-07-25 20:53:07
@ 0176967e:1e6f471e
2024-07-25 20:53:07AI hype vnímame asi všetci okolo nás — už takmer každá appka ponúka nejakú “AI fíčuru”, AI startupy raisujú stovky miliónov a Európa ako obvykle pracuje na regulovaní a našej ochrane pred nebezpečím umelej inteligencie. Pomaly sa ale ukazuje “ovocie” spojenia umelej inteligencie a človeka, kedy mnohí ľudia reportujú signifikantné zvýšenie produktivity v práci ako aj kreatívnych aktivitách (aj napriek tomu, že mnohí hardcore kreatívci by každého pri spomenutí skratky “AI” najradšej upálili). V prvej polovici prednášky sa pozrieme na to, akými rôznymi spôsobmi nám vie byť AI nápomocná, či už v práci alebo osobnom živote.
Umelé neuróny nám už vyskakujú pomaly aj z ovsených vločiek, no to ako sa k nám dostávajú sa veľmi líši. Hlavne v tom, či ich poskytujú firmy v zatvorených alebo open-source modeloch. V druhej polovici prednášky sa pozrieme na boom okolo otvorených AI modelov a ako ich vieme využiť.
-
 @ b2d670de:907f9d4a
2025-02-28 16:39:38
@ b2d670de:907f9d4a
2025-02-28 16:39:38onion-service-nostr-relays
A list of nostr relays exposed as onion services.
The list
| Relay name | Description | Onion url | Operator | Payment URL | Payment options | | --- | --- | --- | --- | --- | --- | | nostr.oxtr.dev | Same relay as clearnet relay nostr.oxtr.dev | ws://oxtrdevav64z64yb7x6rjg4ntzqjhedm5b5zjqulugknhzr46ny2qbad.onion | operator | N/A | N/A | | relay.snort.social | Same relay as clearnet relay relay.snort.social | wss://skzzn6cimfdv5e2phjc4yr5v7ikbxtn5f7dkwn5c7v47tduzlbosqmqd.onion | operator | N/A | N/A | | nostr.thesamecat.io | Same relay as clearnet relay nostr.thesamecat.io | ws://2jsnlhfnelig5acq6iacydmzdbdmg7xwunm4xl6qwbvzacw4lwrjmlyd.onion | operator | N/A | N/A | | nostr.land | The nostr.land paid relay (same as clearnet) | ws://nostrland2gdw7g3y77ctftovvil76vquipymo7tsctlxpiwknevzfid.onion | operator | Payment URL | BTC LN | | bitcoiner.social | No auth required, currently | ws://bitcoinr6de5lkvx4tpwdmzrdfdpla5sya2afwpcabjup2xpi5dulbad.onion | operator | N/A | N/A | | relay.westernbtc.com | The westernbtc.com paid relay | ws://westbtcebhgi4ilxxziefho6bqu5lqwa5ncfjefnfebbhx2cwqx5knyd.onion | operator | Payment URL | BTC LN | | freelay.sovbit.host | Free relay for sovbit.host | ws://sovbitm2enxfr5ot6qscwy5ermdffbqscy66wirkbsigvcshumyzbbqd.onion | operator | N/A | N/A | | nostr.sovbit.host | Paid relay for sovbit.host | ws://sovbitgz5uqyh7jwcsudq4sspxlj4kbnurvd3xarkkx2use3k6rlibqd.onion | operator | N/A | N/A | | nostr.wine | 🍷 nostr.wine relay | ws://nostrwinemdptvqukjttinajfeedhf46hfd5bz2aj2q5uwp7zros3nad.onion | operator | Payment URL | BTC LN, BTC, Credit Card/CashApp (Stripe) | | inbox.nostr.wine | 🍷 inbox.nostr.wine relay | ws://wineinboxkayswlofkugkjwhoyi744qvlzdxlmdvwe7cei2xxy4gc6ad.onion | operator | Payment URL | BTC LN, BTC | | filter.nostr.wine | 🍷 filter.nostr.wine proxy relay | ws://winefiltermhqixxzmnzxhrmaufpnfq3rmjcl6ei45iy4aidrngpsyid.onion | operator | Payment URL | BTC LN, BTC | | N/A | N/A | ws://pzfw4uteha62iwkzm3lycabk4pbtcr67cg5ymp5i3xwrpt3t24m6tzad.onion:81 | operator | N/A | N/A | | nostr.fractalized.net | Free relay for fractalized.net | ws://xvgox2zzo7cfxcjrd2llrkthvjs5t7efoalu34s6lmkqhvzvrms6ipyd.onion | operator | N/A | N/A | | nfrelay.app | nfrelay.app aggregator relay (nostr-filter-relay) | ws://nfrelay6saohkmipikquvrn6d64dzxivhmcdcj4d5i7wxis47xwsriyd.onion | operator | N/A | N/A | relay.nostr.net | Public relay from nostr.net (Same as clearnet) | ws://nostrnetl6yd5whkldj3vqsxyyaq3tkuspy23a3qgx7cdepb4564qgqd.onion | operator | N/A | N/A | | nerostrator | Free to read, pay XMR to relay | ws://nerostrrgb5fhj6dnzhjbgmnkpy2berdlczh6tuh2jsqrjok3j4zoxid.onion | operator |Payment URL | XMR | | nostr.girino.org | Public relay from nostr.girino.org | ws://gnostr2jnapk72mnagq3cuykfon73temzp77hcbncn4silgt77boruid.onion | operator | N/A | N/A | | wot.girino.org | WoT relay from wot.girino.org | ws://girwot2koy3kvj6fk7oseoqazp5vwbeawocb3m27jcqtah65f2fkl3yd.onion | operator | N/A | N/A | | haven.girino.org/{outbox, inbox, chat, private} | Haven smart relay from haven.girino.org | ws://ghaven2hi3qn2riitw7ymaztdpztrvmm337e2pgkacfh3rnscaoxjoad.onion/{outbox, inbox, chat, private} | operator | N/A | N/A | | relay.nostpy.lol | Free Web of Trust relay (Same as clearnet) | ws://pemgkkqjqjde7y2emc2hpxocexugbixp42o4zymznil6zfegx5nfp4id.onion | operator |N/A | N/A | | Poster.place Nostr Relay | N/A | ws://dmw5wbawyovz7fcahvguwkw4sknsqsalffwctioeoqkvvy7ygjbcuoad.onion | operator | N/A | N/A | | Azzamo Relay | Azzamo Premium Nostr relay. (paid) | ws://q6a7m5qkyonzb5fk5yv4jyu3ar44hqedn7wjopg737lit2ckkhx2nyid.onion | operator | Payment URL | BTC LN | | Azzamo Inbox Relay | Azzamo Group and Private message relay. (Freemium) | ws://gp5kiwqfw7t2fwb3rfts2aekoph4x7pj5pv65re2y6hzaujsxewanbqd.onion | operator | Payment URL | BTC LN | | Noderunners Relay | The official Noderunners Nostr Relay. | ws://35vr3xigzjv2xyzfyif6o2gksmkioppy4rmwag7d4bqmwuccs2u4jaid.onion | operator | Payment URL | BTC LN |
Contributing
Contributions are encouraged to keep this document alive. Just open a PR and I'll have it tested and merged. The onion URL is the only mandatory column, the rest is just nice-to-have metadata about the relay. Put
N/Ain empty columns.If you want to contribute anonymously, please contact me on SimpleX or send a DM on nostr using a disposable npub.
Operator column
It is generally preferred to use something that includes a NIP-19 string, either just the string or a url that contains the NIP-19 string in it (e.g. an njump url).
-
 @ 0176967e:1e6f471e
2024-07-25 20:38:11
@ 0176967e:1e6f471e
2024-07-25 20:38:11Čo vznikne keď spojíš hru SNAKE zo starej Nokie 3310 a Bitcoin? - hra Chain Duel!
Jedna z najlepších implementácií funkcionality Lightning Networku a gamingu vo svete Bitcoinu.
Vyskúšať si ju môžete s kamošmi na tomto odkaze. Na stránke nájdeš aj základné pravidlá hry avšak odporúčame pravidlá pochopiť aj priamo hraním
Chain Duel si získava hromady fanúšikov po bitcoinových konferenciách po celom svete a práve na Lunarpunk festival ho prinesieme tiež.
Multiplayer 1v1 hra, kde nejde o náhodu, ale skill, vás dostane. Poďte si zmerať sily s ďalšími bitcoinermi a vyhrať okrem samotných satoshi rôzne iné ceny.
Príďte sa zúčastniť prvého oficiálneho Chain Duel turnaja na Slovensku!
Pre účasť na turnaji je potrebná registrácia dopredu.
-
 @ fd78c37f:a0ec0833
2025-04-01 11:49:06
@ fd78c37f:a0ec0833
2025-04-01 11:49:06In this edition, we invited Keypleb, the founder of Bitcoin Indonesia, to share how he built the Bitcoin community in Indonesia, overcoming challenges like member turnover and venue selection, while driving the adoption and growth of Bitcoin.
YakiHonne: Welcome, Keypleb. Before we begin, let me briefly introduce YakiHonne. YakiHonne is a decentralized media client built on Nostr—a protocol designed to empower freedom of speech through technology. It enables creators to own their voices and assets while offering innovative tools like smart widgets, verified notes, and support for long-form content. We focus on free speech and free media by user privacy and data to be protected. So before starting the interview, I'd like to hear about yourself and your community.
Keypleb:My name is Keypleb, though it’s a pseudonym—a name I use to respect privacy. I'm a co-founder of Bitcoin Indonesia, Bitcoin House Bali, and Code Orange, a new developer school we launched at a conference just a few days ago. We focus on driving adoption through meetups, hackathons, and technical workshops. I'll dive into more details later, but that's a brief overview. I'm based in Bali now, though I travel a lot and consider myself quite nomadic. Great to be here.
YakiHonne: What sparked your interest in Bitcoin and what motivated you to create a community on Bitcoin?
Keypleb:I first got interested in Bitcoin because it solved a specific problem. At the time, I didn’t know exactly what the solution was, but the problem was that I couldn’t afford a home. Back in 2019, I was living in London, and a two-bedroom apartment was £600,000, which was insanely expensive. First-time buyers like myself simply couldn’t afford it. Why was it so expensive? Why was buying a house so hard? During the COVID lockdown, I had more time on my hands and started listening to Michael Saylor on a Bitcoin podcast, where he talked about how the system is rigged, and that’s why people work hard but still can’t afford a house. That really resonated with me. So I started looking for a community, but unfortunately, there wasn’t one.. Keypleb:After moving to Bali, I attended a lot of crypto meetups, especially scammy altcoin ones, thinking, “There has to be a solution.” But none of them resonated with me. There was no sense of freedom, and no real discussion about inflation resistance. I remembered a podcast from Dea Reskita, an Indonesian host who’s pretty well-known online. I reached out to her and said, “ you’ve got to help me. I’m surrounded by all these shitcoiners, and I can’t take it anymore. I need a real community. Is anything happening?” She replied, “Yes, something is happening. We should restart these meetups next month.” And that’s how it all began. Keypleb:There’s also another story about how we started Bitcoin House and how Bitcoin in Asia came to be, but maybe I’ll save that for later. Anyway, the spark of interest came from Bitcoin solving a real problem, and my drive to keep going came from the lack of quality meetups. Now, we’ve hosted 31 meetups, launched Bitcoin House and Code Orange, and the movement is growing rapidly.

YakiHonne: That’s such an amazing story—going from being on the brink of homelessness to creating something so impactful, and keeping it running every day, bringing new people into the journey. It’s truly inspiring. I’m curious about how the community started. How did you manage to attract members and build a strong community? What challenges did you face along the way?
Keypleb:It all started with our first meetup at the end of 2022, which was two and a half years ago now. At that time, we sent out an email to a group from a previous database, and the first meetup had around 20 people, which was a good start. However, problems quickly arose as people started dropping off, and the community lacked retention. In Bali, people come and go, usually staying for no more than two months, leading to a lack of long-term participation. This became one of our challenges: how to attract more people and, more importantly, get the same people to keep coming back. While I've been coming back for two and a half years, not everyone is able to return as often, and that has been a real challenge. Keypleb:Actually, I should also mention how I met my co-founders—Marius, Diana, and Dimas. We met at the 2023 Indonesia Bitcoin Conference. As time went on, we kept hosting meetups and had a lot of fun each time, though the locations kept changing. One of the initial challenges was that we didn't realize the importance of having a fixed meetup location. We changed venues several times before we realized that having a consistent location is crucial. If anyone wants to run a meetup, it's best to always choose a fixed location. We learned this through trial and error, but now it's no longer an issue. Keypleb:Since the conference, my co-founders and I have been working together, consistently putting in the effort. This is why our community has grown so large—so far, we are hosting 31 monthly meetups, 6 of which are in Bali. This means there is a bitcoin meetup almost every day on a regular basis. We've also established Bitcoin House Bali, a physical space, and the movement is growing rapidly. Without this movement, the region would face many challenges, including inflation and heavy censorship. It all started from just one meetup.
 YakiHonne: It's amazing to see how you met your co-founders and how you’ve built something incredible that continues to grow today. What advice would you give to someone looking to start a successful Bitcoin community right now?
YakiHonne: It's amazing to see how you met your co-founders and how you’ve built something incredible that continues to grow today. What advice would you give to someone looking to start a successful Bitcoin community right now?Keypleb:First, one very important piece of advice is to ensure that every meetup is held at the same location regularly. We realized this challenge through trial and error. To help others who are interested, we’ve published our meetup guide on GitHub, where everyone can check it out. For example, meetups should be held regularly, ideally once a month, or even once a week. In Chiang Mai, the Bitcoin meetup starts every Thursday at 7 PM, and everyone knows the time and location, making it easy to join without having to look up the next meetup. Keypleb:Additionally, our meetup structure is very simple. First, we do a round of introductions where everyone shares their name, where they’re from, and what Bitcoin means to them. This usually takes about 15 minutes. Then, we discuss three main questions: First, why do we need Bitcoin? The discussion typically focuses on two main issues Bitcoin addresses: inflation and censorship;Secondly, how to buy Bitcoin? We usually ask who wants to buy some Bitcoin, and then we do a small purchase together and conduct a P2P trade to demonstrate how easy it is to buy Bitcoin. Lastly, how to store Bitcoin? We introduce self-custody and show how to use hardware wallets (like Trezor), explaining the concept of the 12 words and private keys. Keypleb:The whole meetup usually wraps up in about an hour, after which people can continue socializing at Bitcoin House or wherever the meetup is taking place. In short, keeping the meetup simple and efficient, and ensuring a fixed location for each event, are key factors in building a successful community.
YakiHonne: What's the major approach? Is it more technical, or do you focus on non-technical aspects, or do you cover both?
Keypleb:Our approach includes both technical and non-technical content. Initially, our meetups were completely non-technical, just casual gatherings for people to socialize. Over time, however, we've evolved to incorporate more technical content. Keypleb:Out of the 31 monthly regular meetups we host, most of them have been non-technical, simply regular gatherings held at the same time and place according to our meetup guide. For example, we host the “Bitcoin for Beginners” meetup, which is designed for newcomers and takes place every second Friday of the month at 5 PM at the Bitcoin House Bali. This is entirely non-technical. Additionally, every Wednesday at Bitcoin House, we host the “My First Bitcoin” course. While the course touches on some technical aspects, such as seed phrases and backups, it’s still beginner-friendly and not too technical. The course runs for 10 weeks, and we plan to offer it in the local language at Bali University to help the local community better understand Bitcoin. Keypleb:On the other hand, we also offer highly technical content. We launched a new program called “Code Orange,” which is specifically designed for developers and programmers. We use the “Decoding Bitcoin” website, created by Jamal, which is a learning platform for developers. Many developer schools, like Code Orange, use this resource. Additionally, we host “Code Orange” meetups where we dive into the technical aspects of Bitcoin, such as how mining works and how to prevent single points of failure. Keypleb:We also organize technical workshops, such as “How to Defend Against a Five-Dollar Wrench Attack,” which is closely related to security. Recently, there have been some kidnapping incidents in Bali, and many people are concerned about their Bitcoin being stolen. To address this, we plan to hold a workshop on how to protect Bitcoin against such attacks. Additionally, we host hackathons and other high-tech events, and we just completed a very successful beginner-level hackathon. Keypleb:In summary, our community caters to everyone, from beginners to technical experts. For beginners, we offer easy-to-understand, non-technical content, while for experienced Bitcoiners, we provide in-depth technical material.
 YakiHonne: It's great to approach it in both ways, so everyone gets their own "piece of the cake."Now, I'd like to dive into the technical side. What advice would you give to technically inclined individuals or organizations looking to contribute to the Bitcoin ecosystem? How should they approach the technical aspects of Bitcoin if they want to get involved?
YakiHonne: It's great to approach it in both ways, so everyone gets their own "piece of the cake."Now, I'd like to dive into the technical side. What advice would you give to technically inclined individuals or organizations looking to contribute to the Bitcoin ecosystem? How should they approach the technical aspects of Bitcoin if they want to get involved?Keypleb:I have some additional advice. First, technical individuals can sign up for the “Decoding Bitcoin” course that starts on 18th March 2025 or join our “Code Orange” program and participate in the end-of-year hackathon. If they are technically proficient, this will be a great opportunity. “Decoding Bitcoin” is great for beginners, but it’s also useful for technical individuals. If someone is very skilled, they can start contributing code right away. If they find the course too easy, they can skip it and dive directly into more advanced projects. Additionally, Bitshala and Chaincode Labs offer advanced courses, which more technically advanced individuals can choose to pursue.
 Keypleb:Additionally, it's worth mentioning that the Bitcoin Dev Project has a great platform where technical individuals can find “Good First Issue” or open-source projects to start contributing code. You'll learn about the philosophy behind Bitcoin and why it's more meaningful than other “shitcoins.” Once you’ve taken enough “orange pills” (the philosophy and technology of Bitcoin), you can dive deeper into Bitcoin core development and potentially start coding in C++. If you're interested, you can join specific projects like Nostr, Fedimint or E-Cash.
Keypleb:Additionally, it's worth mentioning that the Bitcoin Dev Project has a great platform where technical individuals can find “Good First Issue” or open-source projects to start contributing code. You'll learn about the philosophy behind Bitcoin and why it's more meaningful than other “shitcoins.” Once you’ve taken enough “orange pills” (the philosophy and technology of Bitcoin), you can dive deeper into Bitcoin core development and potentially start coding in C++. If you're interested, you can join specific projects like Nostr, Fedimint or E-Cash.YakiHonne: I’d like to move on to the next question: How do you see Bitcoin communities evolving as technology progresses, particularly in areas like scalability, privacy, and adaptability to other systems? Keypleb:I believe the Bitcoin community will continue to evolve, and it has already made incredible progress. Two and a half years ago, we started alone in Bali, with just ourselves. We began in the official phase and have had numerous conversations throughout the year. For example, we are now starting a Bitcoin club at a university in Bali; we just need to find a passionate, driven “Bitcoin maximalist,” and the Bitcoin club will begin. Like what our friends did in Banyuwangi, Indonesia, these clubs could eventually evolve into Bitcoin houses.
Keypleb:Regarding privacy and scalability, the community is making strides. We’re big fans of Fedi, which builds on top of the Fedimint protocol and uses e-cash to scale Bitcoin while improving privacy. Fedi low fees and high privacy potential give Bitcoin great opportunities in this area. Keypleb:As for Bitcoin's compatibility with fiat systems, although Bitcoin payments are illegal in some countries like Indonesia, smart developers across Southeast Asia are working on legal solutions. For example, there's a website called Pleb QR that works in Thailand, allowing you to pay in fiat via the Lightning Network. Koral is another app specifically for Indonesia. These kinds of testing products already exist and are physically possible, but we’re just waiting on regulations. My influential friends are actively lobbying the government for adoption. Keypleb:In summary, privacy, scalability, and compatibility with fiat systems are all works in progress, and they will continue to evolve positively. There will be more meetups, more wallet downloads, and more adoption—there’s no doubt about that.
YakiHonne: You mentioned the concept of cross-country issues, so I have one last question: How is the government’s stance on Bitcoin? Is the political climate supportive or against Bitcoin? How do you see the government's approach to Bitcoin in your community or environment?
Keypleb:This reminds me of a person, Jeff Booth, who once said, “We are them, the government is made up of us.” In Indonesia, many politicians actually support Bitcoin, and many of them mine Bitcoin themselves. When money is involved, the incentive is strong, and politicians naturally like to make more money. As a result, Indonesia has a large Bitcoin mining scene. However, overall, the Indonesian government is against Bitcoin, as seen in their ban on Bitcoin payments. The 2011 currency law states that any currency other than the Indonesian Rupiah (IDR) cannot be used, and violators can face up to one year in prison or a fine. This means you cannot pay with US dollars, lira, euros, pesos or pounds. Keypleb:This shows that the government’s legal system is somewhat fragile. It’s understandable that the government is concerned about disruptive technologies like Bitcoin, especially with such a fragile fiat system. Indonesia has also seen many arrests. In 2016, Bank Indonesia issued a letter announcing a crackdown on cryptocurrency payments. Those involved in paying in Bitcoin had their funds seized, and the police cooperated in shutting down businesses accepting Bitcoin payments in the cities. While this isn't very friendly, it does highlight the fragility of the existing system. We also believe that a new executive order may be introduced in the future, similar to when President Roosevelt in 1933 ordered Americans to hand over all their gold with his Executive Order 6102. If it happened before, it could happen again. Keypleb:Therefore, we predict that Bitcoin custody could become a legal issue, which is one of the reasons we blur the faces of participants at every meetup. We need to protect the community from any potential risks. But overall, we remain optimistic. Despite the government ban, the ideology of Bitcoin is unstoppable, and its spread cannot be stopped. So, we are very optimistic about the future.
YakiHonne: I think almost every government around the world, even in Africa, faces similar issues with Bitcoin. Some governments might want Bitcoin but hesitate to openly accept it due to the fear of it undermining the traditional financial system, which, of course, could eventually happen. But hopefully, as the new generation comes into power, we'll see more Bitcoin-friendly governments. So, thank you so much for sharing your insights and advice. I really appreciate your time and the valuable input you've provided.
Keypleb:I'm really glad this conversation enlightened me. I enjoyed it a lot, and it made me reflect on how much work we're doing and how valuable it is. There are a lot of problems out there, with censorship being the biggest one, followed by inflation, which is also a major issue depending on the region. But Bitcoin is open, the community is growing, and people are fighting against censorship and internet shutdowns in places like Indonesia and beyond. The movement is definitely growing. So, I'm very happy to be here and have this chat. Thanks again.
Bitcoin Indonesia nostr: nostr:npub1y4qd2zhtn05gnsaaq5xfejzfk4a32638tx6gpp9g8k6e42g9d66qaxhcr3
Keypleb nostr: nostr:npub190trvg63e6tyqlwlj6lccqpftx76lckj25c006vwx3dzvdl88yxs2nyqdx
-
 @ b2d670de:907f9d4a
2025-02-26 18:27:47
@ b2d670de:907f9d4a
2025-02-26 18:27:47This is a list of nostr clients exposed as onion services. The list is currently actively maintained on GitHub. Contributions are always appreciated!
| Client name | Onion URL | Source code URL | Admin | Description | | --- | --- | --- | --- | --- | | Snort | http://agzj5a4be3kgp6yurijk4q7pm2yh4a5nphdg4zozk365yirf7ahuctyd.onion | https://git.v0l.io/Kieran/snort | operator | N/A | | moStard | http://sifbugd5nwdq77plmidkug4y57zuqwqio3zlyreizrhejhp6bohfwkad.onion/ | https://github.com/rafael-xmr/nostrudel/tree/mostard | operator | minimalist monero friendly nostrudel fork | | Nostrudel | http://oxtrnmb4wsb77rmk64q3jfr55fo33luwmsyaoovicyhzgrulleiojsad.onion/ | https://github.com/hzrd149/nostrudel | operator | Runs latest tagged docker image | | Nostrudel Next | http://oxtrnnumsflm7hmvb3xqphed2eqpbrt4seflgmdsjnpgc3ejd6iycuyd.onion/ | https://github.com/hzrd149/nostrudel | operator | Runs latest "next" tagged docker image | | Nsite | http://q457mvdt5smqj726m4lsqxxdyx7r3v7gufzt46zbkop6mkghpnr7z3qd.onion/ | https://github.com/hzrd149/nsite-ts | operator | Runs nsite. You can read more about nsite here. | | Shopstr | http://6fkdn756yryd5wurkq7ifnexupnfwj6sotbtby2xhj5baythl4cyf2id.onion/ | https://github.com/shopstr-eng/shopstr-hidden-service | operator | Runs the latest
serverlessbranch build of Shopstr. | -
 @ c1e9ab3a:9cb56b43
2025-04-14 21:20:08
@ c1e9ab3a:9cb56b43
2025-04-14 21:20:08In an age where culture often precedes policy, a subtle yet potent mechanism may be at play in the shaping of American perspectives on gun ownership. Rather than directly challenging the Second Amendment through legislation alone, a more insidious strategy may involve reshaping the cultural and social norms surrounding firearms—by conditioning the population, starting at its most impressionable point: the public school system.
The Cultural Lever of Language
Unlike Orwell's 1984, where language is controlled by removing words from the lexicon, this modern approach may hinge instead on instilling fear around specific words or topics—guns, firearms, and self-defense among them. The goal is not to erase the language but to embed a taboo so deep that people voluntarily avoid these terms out of social self-preservation. Children, teachers, and parents begin to internalize a fear of even mentioning weapons, not because the words are illegal, but because the cultural consequences are severe.
The Role of Teachers in Social Programming
Teachers, particularly in primary and middle schools, serve not only as educational authorities but also as social regulators. The frequent argument against homeschooling—that children will not be "properly socialized"—reveals an implicit understanding that schools play a critical role in setting behavioral norms. Children learn what is acceptable not just academically but socially. Rules, discipline, and behavioral expectations are laid down by teachers, often reinforced through peer pressure and institutional authority.
This places teachers in a unique position of influence. If fear is instilled in these educators—fear that one of their students could become the next school shooter—their response is likely to lean toward overcorrection. That overcorrection may manifest as a total intolerance for any conversation about weapons, regardless of the context. Innocent remarks or imaginative stories from young children are interpreted as red flags, triggering intervention from administrators and warnings to parents.
Fear as a Policy Catalyst
School shootings, such as the one at Columbine, serve as the fulcrum for this fear-based conditioning. Each highly publicized tragedy becomes a national spectacle, not only for mourning but also for cementing the idea that any child could become a threat. Media cycles perpetuate this narrative with relentless coverage and emotional appeals, ensuring that each incident becomes embedded in the public consciousness.
The side effect of this focus is the generation of copycat behavior, which, in turn, justifies further media attention and tighter controls. Schools install security systems, metal detectors, and armed guards—not simply to stop violence, but to serve as a daily reminder to children and staff alike: guns are dangerous, ubiquitous, and potentially present at any moment. This daily ritual reinforces the idea that the very discussion of firearms is a precursor to violence.
Policy and Practice: The Zero-Tolerance Feedback Loop
Federal and district-level policies begin to reflect this cultural shift. A child mentioning a gun in class—even in a non-threatening or imaginative context—is flagged for intervention. Zero-tolerance rules leave no room for context or intent. Teachers and administrators, fearing for their careers or safety, comply eagerly with these guidelines, interpreting them as moral obligations rather than bureaucratic policies.
The result is a generation of students conditioned to associate firearms with social ostracism, disciplinary action, and latent danger. The Second Amendment, once seen as a cultural cornerstone of American liberty and self-reliance, is transformed into an artifact of suspicion and anxiety.
Long-Term Consequences: A Nation Re-Socialized
Over time, this fear-based reshaping of discourse creates adults who not only avoid discussing guns but view them as morally reprehensible. Their aversion is not grounded in legal logic or political philosophy, but in deeply embedded emotional programming begun in early childhood. The cultural weight against firearms becomes so great that even those inclined to support gun rights feel the need to self-censor.
As fewer people grow up discussing, learning about, or responsibly handling firearms, the social understanding of the Second Amendment erodes. Without cultural reinforcement, its value becomes abstract and its defenders marginalized. In this way, the right to bear arms is not abolished by law—it is dismantled by language, fear, and the subtle recalibration of social norms.
Conclusion
This theoretical strategy does not require a single change to the Constitution. It relies instead on the long game of cultural transformation, beginning with the youngest minds and reinforced by fear-driven policy and media narratives. The outcome is a society that views the Second Amendment not as a safeguard of liberty, but as an anachronism too dangerous to mention.
By controlling the language through social consequences and fear, a nation can be taught not just to disarm, but to believe it chose to do so freely. That, perhaps, is the most powerful form of control of all.
-
 @ 04ea4f83:210e1713
2025-04-20 08:41:34
@ 04ea4f83:210e1713
2025-04-20 08:41:34Veröffentlicht auf Bitcoin Magazine am 11.01.2024\ Originalautor: Josh von BlueCollarBitcoin\ Übersetzt von: Sinautoshi am 13.01.2024 - 825611
Wir alle haben einen Werdegang in Bezug auf Bitcoin. Einige begannen als Verfechter des gesunden Geldes, die die österreichische Schule der Nationalökonomie und Gold verehrten. Andere sind aus der TradFi-Welt herausgefallen, als sie merkten, dass etwas nicht ganz richtig war. Die meisten Bitcoiner haben die Irrungen und Wirrungen der Altcoin-Hölle durchlaufen. Wie auch immer du es hierher und zu Bitcoin geschafft hast, willkommen und schnall dich verdammt nochmal an.
Als ich mich zum ersten Mal für Bitcoin interessierte, war das im Juli 2017, und der Bullenmarkt des Jahres war bereits in vollem Gange. Ich kaufte etwas Bitcoin und sah zu, wie der Wert stieg. Dann kaufte ich mehr. Wie es bei diesen parabolischen Aufwärtsbewegungen üblich ist, beobachtete ich, wie der Preis stieg und mein Gemütszustand veränderte sich:
Von Interesse zu Unglauben zu Verliebtheit zu ausgearteten Käufen zu Verzweiflung.
Dies ist eine Entwicklung, die du während der nächsten Aufwärtsbewegung vermeiden kannst, wenn du dich richtig vorbereitest.
Wenn du dies in der Hoffnung liest, alle Antworten zu finden, habe ich leider schlechte Nachrichten. Es gibt keine richtigen Antworten in Bitcoin oder im Leben. Wir sind alle auf einer Reise, um herauszufinden, was wir tun und wie wir vorgehen sollen. Ich hoffe, dass ich dir einen Leitfaden an die Hand geben kann, aber letztendlich werden deine persönlichen Ziele und deine Veranlagung bestimmen, wie du mit der Volatilität umgehst. Bitcoin wird deine Entschlossenheit auf die Probe stellen.
In der späteren Phase des Bullemarkts 2017 sprach ich mit jedem in meinem Leben über Bitcoin - völlig besessen. Mein damaliger Nachbar war älter als ich und hatte den Dot-Com-Boom erlebt. Den Rat, den er mir gab, werde ich nie vergessen, denn er hatte während der Dot-Com-Blase eine Menge Geld gewonnen (und verloren). Er hörte sich mein glühendes Interesse an Bitcoin an und ging sehr maßvoll mit meiner offensichtlichen LIEBE für diesen Vermögenswert um. Er erzählte mir, dass er während des Dot-Com-Booms mehr Geld verdient hat, als er jemals geglaubt hätte, und am Ende war er wieder genau da, wo er angefangen hatte - weil er den Bullenmarkt über den Gipfel geritten und nichts verkauft hatte. Sein Rat war: "Ich freue mich, dass es dir gut geht, aber vergiss nicht, etwas Gewinn mitzunehmen." Er riet mir, 50 % zu verkaufen und 50 % zu behalten - eine einfache Absicherungsstrategie. Kurz nachdem Bitcoin sein Allzeithoch erreicht hatte, beherzigte ich seinen Rat und verkaufte einige meiner Bestände in der Nähe des lokalen Höchststands.
Ich weiß, dass dies für viele Hodler ein Frevel ist. Wir verkaufen unsere Bitcoin doch nicht, oder? Nun, das ist eine persönliche Entscheidung, und je nach deiner Risikotoleranz und deinem Platz im Leben, möchtest du vielleicht ein gewisses Risiko vom Tisch nehmen. Das ist Teil des Investierens, und wie das alte Sprichwort sagt, verliert niemand Geld, wenn er mit Gewinn verkauft. Dieser Artikel soll den Rat geben, den ich mir gewünscht hätte, als ich Bitcoin zum ersten Mal entdeckte. Ich hoffe, er hilft Neulingen in diesem Bereich zu verstehen, wie man sich in dem bombastischen Umfeld zurechtfindet, das Bitcoin während seiner Bullenmärkte erzeugt.
Ich habe zwei Bullenmärkte erlebt, einen im Jahr 2017 und einen im Jahr 2021. Diese Bullenmärkte waren SEHR unterschiedlich, und ich vermute, wenn du mit denjenigen sprichst, die bei Bullenmärkten vor 2017 dabei waren, wirst du feststellen, dass sie sich auch sehr unterschiedlich anfühlten.
Das erste, was ich loswerden möchte, ist Folgendes - niemand weiß, was passieren wird:
- Balaji spricht von 1 Million in 3 Monaten
- Nobelpreisträger sagen, Bitcoin wird auf Null sinken
- Buffett und Munger (RIP) nennen es Rattengift
Egal, wem Du zuhörst, egal, wie lange sie schon in dem Bereich tätig sind oder wie korrekt sie in der Vergangenheit waren, es spielt keine Rolle. Sie haben keine Ahnung, was die Zukunft bringt.
Bei Investitionen gibt es eine Idee, die als Überlebensbias bezeichnet wird. Diejenigen, die richtig lagen, haben überlebt, und sie erscheinen wie Genies, weil sie richtig lagen. Die überwiegende Mehrheit derjenigen, die sich geirrt haben, ist vergessen. Man hört nichts über sie. Ich will hier niemanden in die Pfanne hauen, aber es gab prominente Bitcoin-Leute, die VIEL höhere Preise riefen, als wir im Jahr 2021 bei 68K waren. Ich sage nicht, dass sie schlechte Menschen sind; ich bin mir sicher, dass sie einen guten Grund hatten, diese Zahlen zu prognostizieren, aber wenn man damals ihren Ratschlägen gefolgt wäre, hätte man zum denkbar schlechtesten Zeitpunkt gekauft und wäre für JAHRE unter die Räder gekommen.
Meiner Meinung nach gibt es verschiedene Arten von Kristallkugelbesitzern, und die unterste Kategorie sind die technischen Analysten. Das sind die ein Dutzend Leute, die man auf Twitter sieht, die über Momentum, Preisniveaus, Tassen und Griffe usw. schwadronieren. Diese Leute riefen für 10K Bitcoin, wo der Boden bei 16k lag. Ich sage nicht, dass TA Unsinn ist; im Grunde ist es ein System zur Vorhersage menschlicher Handlungen durch Wahrscheinlichkeit. Es ist bestenfalls eine Überlegung. Sie sollte nie in einem Vakuum verwendet werden, um Ihre Allokationen zu bestimmen. Wenn du es in Verbindung mit den Fundamentaldaten verwendest, kann es viel hilfreicher sein. Worauf ich hier hinaus will, ist, dass es GANZ viele TA-Analysten gibt, die Ihnen raten, bei 68 K zu kaufen und nicht bei 16 K. Sie werfen probabilistische Darts. Setze deine finanzielle Zukunft nicht auf eine fundierte Vermutung von irgendjemandem.
Die zweite Art von Kristallkugel-Liebhabern sind Makro-Analysten. Diese Leute sind meiner Meinung nach glaubwürdiger, weil sie den allgemeinen Trend in der Wirtschaft einschätzen. Sie berücksichtigen die Zinssätze, die Bewegungen der Fed und die Wirtschaftsdaten. Diese Leute sind viel näher an der Realität, weil sie den Finger am Puls des wirtschaftlichen Geschehens haben. Aber wie bei den TA-Analysten können sich auch diese Leute VÖLLIG irren. Viele sagten, dass die Leitzinsen nicht über x oder y steigen könnten, da sonst die gesamte Wirtschaft zusammenbrechen würde. Nun, die Zinssätze wurden auf ein Niveau angehoben, das weit über ihren Weltuntergangsprognosen liegt, und wir haben keinen Zusammenbruch erlebt.
Ob du nun einem TA-Analysten oder einem Makro-Analysten folgst, sie können wegen eines schwarzen Schwans völlig FALSCH liegen. Nicholas Taleb - bekanntlich von Bitcoinern gehasst - hat den Begriff "schwarzer Schwan" geprägt, um Ereignisse zu bezeichnen, die von Zeit zu Zeit eintreten und mit Standardmodellen einfach nicht vorhergesagt werden können, weil sie so unwahrscheinlich sind. Covid war ein schwarzer Schwan. Der Krieg in der Ukraine war ein schwarzer Schwan. Und rate mal, was passiert: Morgen könnte es einen weiteren unvorhersehbaren schwarzen Schwan geben, der alle TA- und Makro-Analysten völlig auf den Kopf stellt. In der Welt gibt es jede Menge Zufälle. Übrigens sind schwarze Schwäne nicht immer schlecht. Sie können genauso gut auch positive Katalysatoren sein.
Heißt das also, dass wir vor Angst gelähmt bleiben und niemandem trauen sollten?
Ganz und gar nicht. Es bedeutet, dass wir uns die Mühe machen sollten, UNS SELBST zu BILDEN! Du musst die Verantwortung für dich und deine Entscheidungen übernehmen. Du kannst die Informationen der TA-Analysten und der Makro-Analysten nehmen und deine eigenen fundierten Entscheidungen treffen. DAS IST VON GRÖSSTER WICHTIGKEIT.
BILDE DICH SELBST WEITER
Bitcoin ist ein unglaublich einfaches und doch unendlich komplexes Wesen. Deine Ausbildung wird nie vollständig sein, aber du kannst dein Verständnis Schritt für Schritt erweitern. Wir haben eine 10-teilige Bitcoin-Grundlagen-Serie mit Dazbea und Seb Bunney gemacht, und ich habe das Gefühl, dass wir nicht einmal an der Oberfläche gekratzt haben!
Du solltest gut ausgebildet sein, um widerstandsfähig zu werden. Wenn du ein solides Verständnis von Bitcoin und seiner Funktionsweise hast, wirst du nicht so leicht zu erschüttern sein. Die Psychologie ist hier SEHR WICHTIG. Wenn du verstehst, in was du investierst, und der Markt von einem Börsenausfall betroffen ist, ähnlich dem, der FTX passiert ist, wirst du einige Dinge verstehen, die die Durchschnittsperson vielleicht nicht versteht.
- Bitcoin ist davon nicht betroffen
- Der Preisverfall ist vorübergehend und unbegründet
- Deshalb ist jetzt ein guter Zeitpunkt, um Bitcoin zu akkumulieren
Aber auch das Gegenteil ist der Fall. Wenn du siehst, wie die Mainstream-Schlagzeilen über Bitcoin schwärmen und die Gewinne kein Ende zu nehmen scheinen, und du das Gefühl hast, dass du jedes bisschen Geld in Bitcoin investieren solltest, weil der Preis nirgendwo hin geht, außer nach oben - dann sei VORSICHTIG. Ich habe festgestellt, dass meine Psychologie typisch ist. Ich habe Angst, wenn der Preis nach unten geht, und ich habe irrationalen Überschwang, wenn der Preis schnell steigt. Wenn ich GENAU das Gegenteil von dem tue, was mein Affenhirn mir sagt, stelle ich fest, dass ich oft das Richtige tue. Das heißt, wenn du extreme Angst verspürst, ist dies der richtige Zeitpunkt zum Kaufen, und wenn du dich überschwänglich fühlst, ist dies der richtige Zeitpunkt zum Verkaufen.
Panikkäufe sind gefährlich. Wenn du einen unkontrollierbaren Drang verspürst, Bitcoin zu kaufen, atme tief durch. Ich kann dir versichern, dass du in der Lage sein wirst, etwas Bitcoin zu kaufen, und wenn du den Drang so stark verspürst, ist der Markt wahrscheinlich reif für einen Rücksetzer. Das ist keine Garantie, aber nach meiner Erfahrung ist dies der wahrscheinliche Fall. Ich plädiere nicht für den Handel mit BTC, ganz und gar nicht. Ich kann ehrlich sagen, dass ich durch den Handel mehr BTC verloren als gewonnen habe, und wenn die meisten Leute ehrlich sind, werden sie das auch zugeben. Das Trading ist eine Fähigkeit und Disziplin, die nur sehr wenige Menschen beherrschen.
Die typischen psychologischen Hindernisse, die den Menschen im Weg stehen, sind Angst und Gier. Denk über deine Gefühle nach und erkenne, wann du diese Emotionen erlebst. Sie werden dich dazu bringen, Fehler zu machen. Der einfachste Weg, all dies zu mildern, ist einfach der Dollar-Cost-Average. Dollar-Cost Averaging nimmt den ganzen Stress heraus. Basta. Wenn du in diesem Moment in diesen Schatz einsteigst und er über Nacht auf 30 % fällt, frage dich ehrlich: Habe ich den Mut dazu? Habe ich die nötige Überzeugung dafür? Habe ich das nötige Wissen, um zu verstehen, warum der Dollarpreis kurzfristig keine Rolle spielt? Werde ich in Panik verkaufen? Wenn du nicht überzeugt bist, wird dich das Dollar-Cost-Averaging retten. Du bekommst den Durchschnittspreis über einen langen Zeitraum.
Ich habe eine kleine DCA-Taktik, die einfach ist und bei mir funktioniert:
Wenn der Preis sich entspannt, erhöhe ich meinen DCA, und wenn der Preis in die Höhe schießt, ziehe ich mich zurück und kaufe im Durchschnitt weniger. Über Monate und Jahre hinweg führt dies zu einem optimalen Durchschnittswert.
FÜHLE DICH NICHT WIE EIN VERRÄTER, WENN DU BTC VERKAUFST
Habe einen Plan und sei bereit, ihn auszuführen. Der Plan meines Nachbarn ist ein guter Anfang. Sobald du dein Geld verdoppelt hast, nimmst du die Anfangsinvestition heraus. Dabei gibt es ein erhebliches Sternchen - was willst du anstelle von Bitcoin kaufen? Inflationäres Bargeld? Die Möglichkeiten, sein Geld woanders anzulegen, sind heutzutage sehr begrenzt. Das mag für viele in diesem Bereich kontrovers sein, aber ich denke, es ist absolut vernünftig, Bitcoin zu verkaufen. Wenn du Bitcoin seit JAHREN hältst und dein Stack dein Leben sinnvoll verbessern könnte, solltest du auf jeden Fall einen Teil verkaufen.
Zeit ist das einzige Gut, das wertvoller ist als BTC; wir haben wirklich nur eine begrenzte Menge an Zeit auf dieser Erde. Wenn du deine BTC hortest und dann friedlich einschläfst was war dann der Sinn? Wenn du einen Teil deines Stacks verkaufen kannst, um dein Haus abzubezahlen oder dich von erdrückenden Schulden zu befreien, halte ich das für eine gute Entscheidung. Es ist vielleicht nicht die BESTE finanzielle Entscheidung, vor allem, wenn Ihr Haus mit einem zinsgünstigen Darlehen belastet ist, aber es ist eine nachvollziehbare Entscheidung, weil man dadurch beruhigt sein kann. Man muss jedoch auch bedenken, dass der Verkauf von Bitcoin auf lange Sicht sehr wahrscheinlich eine schmerzhafte Entscheidung sein wird.
Bitcoin für Spielzeug zu verkaufen, ist hingegen kein guter Schachzug. Wenn du den 250.000 Dollar teuren Lamborghini kaufst, der in 3 Jahren 50% seines Wertes verliert, während Bitcoin um mehr als diesen Prozentsatz zugelegt hat, wird das Bedauern unerträglich sein. Robert Kiyosaki kommt mir in den Sinn. Sein Buch Rich Dad Poor Dad hat mich sehr beeinflusst, und seine Beschreibung von Vermögenswerten und Verbindlichkeiten hat mich sehr beeindruckt:
- Ein Vermögenswert erzeugt Cashflow
- Eine Verbindlichkeit zieht den Cashflow ab
Wenn du Vermögenswerte kaufst, wird dein Nettovermögen auf einer exponentiellen Kurve erheblich ansteigen. Wenn du Verbindlichkeiten kaufst, wirst du einfach ärmer. Wenn du Bitcoin verkaufst, wirst du es wahrscheinlich langfristig bereuen.
ZEITPRÄFERENZ
Die Zeitpräferenz ist ein Thema, das in Bitcoin oft angesprochen wird. Eine niedrige Zeitpräferenz zu haben bedeutet, dass man bereit ist, für eine bessere Zukunft auf die Annehmlichkeiten von heute zu verzichten. Jede sehenswerte Kathedrale, jedes klassische Kunstwerk, alles Schöne auf dieser Welt wurde gebaut, weil Menschen mit Blick auf die Zukunft und nicht auf die Gegenwart gearbeitet haben. Hätte DaVinci Bananen an die Wand geklebt, hätten wir uns nie an ihn erinnert. Wären die großen Pyramiden aus Lehm gebaut worden, gäbe es sie heute nicht mehr. Wenn die Zivilisation ihren gesamten Reichtum für das Hier und Jetzt ausgeben würde, ohne in die Zukunft zu investieren, würde sie nicht überleben.
Bitcoin selbst ist ein digitales Artefakt, das von einem geheimnisvollen Architekten bis zur Perfektion entwickelt wurde. Er ist so konzipiert, dass er Äonen überdauert; wenn die Zivilisation überdauert, wird er bis in die Zukunft hinein perfekte Treue beweisen. Da niemand ihn verändern oder kontrollieren kann, ist Bitcoin anti-entropisch. Das ist der Inbegriff von Handwerkskunst der geringen Zeitpräferenz. Bitcoin ist ein Da Vinci in einer Welt der an die Wand geklebten Bananen. Es ist so offensichtlich, wenn die Arbeit erst einmal geleistet ist, dass es peinlich ist, dass nicht mehr Menschen den Wert verstehen, den er bietet.
Im krassen Gegensatz zu diesem Bitcoin-Meisterwerk stehen die Schrotthaufen, die wir Altcoins oder Shitcoins nennen. Diese wurden mit der Technologie von Bitcoin gebaut, führen aber Entropie ein. Die Treue geht bei den Altcoins verloren, weil sie jeweils von einem Gründer oder einer Gruppe kontrolliert werden. Wenn Menschen etwas kontrollieren können, manipulieren sie es unweigerlich zu ihrem Vorteil. Und ob bewusst oder unbewusst, es wird sich verschlechtern. Die meisten dieser Shitcoins waren von Anfang an darauf ausgelegt, dich zu betrügen. Einige dieser Altcoins haben eine Führung, die vielleicht gute Absichten hat, aber sie sind menschlich und können beeinflusst und genötigt werden. Das Problem ist die FÜHRUNG. Bitcoin und seine Zeitkette wurden entwickelt, um das menschliche Element als primäre Eigenschaft zu entfernen. Die Einführung von Menschen in den Mix verursacht Entropie, die den Wert durch Seigniorage zerstört.
Die Erfindung von Bitcoin war die der NICHT-INTERVENTION durch Menschen.
Das sind Erkenntnisse, die für viele Menschen Jahre dauern, um sie vollständig zu verstehen. Wenn du das Kurzfassung über Altcoins wissen willst, ist es einfach. Bemühe dich einfach nicht. Du bist besser dran, wenn du dein Geld in ein Casino bringst und Glücksspiel machst. Die Karten sind in der Kryptowelt schwer gegen Dich ausgelegt; du hast einfach Glück, wenn du Geld verdienst. Nimm den Weg der geringen Zeitpräferenz und staple Bitcoin, während du lernst, wie deine Investition wächst. Ich kann mit Zuversicht sagen, dass du in 5 Jahren viel weiter vorne sein wirst, wenn du in Bitcoin Dollar-Cost-Averaging betreibst, als wenn du mit Shitcoins spielen würdest.
5-JAHRES-AUSSICHTEN MINIMUM
Die meisten Menschen interessieren sich für Bitcoin während einer seiner parabolischen Bullenläufe. Ich war einer von ihnen. Wir sind alle daran interessiert, finanziell voranzukommen, besonders wenn das Gespenst der Inflation über unseren Köpfen schwebt.
Wenn du neu bei Bitcoin bist und dies dein erster Versuch ist, dann stelle sicher, dass du bereit bist, diesen Vermögenswert für mindestens 5 Jahre zu halten. Du bist wahrscheinlich während einer Aufwärtsbewegung hier, und wenn du kein Glück hattest, ist es wahrscheinlich am Ende der Aufwärtsbewegung. Zum Zeitpunkt der Erstellung dieses Berichts im Dezember 2023 stehen wir meiner Meinung nach am Anfang der nächsten Aufwärtsbewegung. Mit der Zulassung der ETFs, der Halbierung im April 2024 und der Aussicht, dass die US-Notenbank ihre Geldpolitik zurückfahren wird, sind viele Katalysatoren aufeinander abgestimmt. Das bedeutet jedoch NICHT, dass dies unvermeidlich ist. Schwarze Schwäne sind immer eine Möglichkeit. Abgesehen von diesem schwarzen Schwan scheinen wir für einen massiven Kursanstieg in den nächsten Jahren bereit zu sein.
SELBSTVERWAHRUNG
Wenn du zum ersten Mal Bitcoin an der Börse deiner Wahl kaufst, wird es sich anfühlen wie der Kauf eines beliebigen anderen Vermögenswerts bei einem Broker. Du kaufst Bitcoin, und die Zahl auf dem Bildschirm spiegelt die Menge an Bitcoin wider, die du jetzt "besitzt".
Es ist von entscheidender Bedeutung, dass du deine Bitcoin in Verwahrung nimmst. Wir haben in jüngster Zeit Fehler beim Umtausch und regelrechte Betrugsfälle erlebt. Wenn diese Betrügereien aufgedeckt und strafrechtlich verfolgt werden und der Preis von Bitcoin unter Druck gerät, weil viele Menschen den Vermögenswert Bitcoin mit den Börsen in Verbindung bringen, die ihn verkaufen, wird dies zu einer RIESIGEN Kaufgelegenheit. Als FTX vor einem Jahr scheiterte, wurde der Preis von Bitcoin negativ beeinflusst, und diejenigen, die verstanden, dass Bitcoin kein fundamentales Problem hatte, kauften mehr. Du hast verstanden, dass die Angst durch den Markt strömte (womit wir wieder bei dem Punkt wären, warum es in diesem Bereich SO WICHTIG ist, gut informiert zu sein). Wer damals Bitcoin kaufte (um 16k), sicherte sich innerhalb eines Jahres einen Gewinn von weit über 100%!
Stell dir die Seed Keys als das Passwort zu deinem Bitcoin vor, das geschützt werden muss, denn wenn jemand anderes es bekommt, kann er deine Bitcoin in Besitz nehmen - nicht gut für dich. Bitcoin-Seed-Keys werden in der Regel durch eine Hardware-Wallet oder ein Signiergerät geschützt. Dieses Gerät schützt deine Schlüssel vor Hackern oder schlechten Akteuren. Ich verwende seit Jahren Coldcards, und sie gehören zu den besten Geräten zum Schutz von privaten Schlüsseln. Es funktioniert sehr einfach. Du erstellst auf dem Gerät die geheimen Schlüssel; es speichert sie und bewahrt sie offline auf, d. h. ohne Verbindung zum Internet. Dieser letzte Punkt ist WICHTIG. Du darfst diese Wörter NIEMALS auf einem Computer mit Internetanschluss speichern. Der einzige Ort, an dem du deine Schlüssel sicher aufbewahren kannst, ist ein dafür vorgesehenes Gerät. Wenn der Computer kompromittiert wird (und glauben Sie mir, es ist SEHR WÄHRLICH, dass er kompromittiert wird), wird das Signiergerät deine Bitcoin schützen.
Das mag sich alles sehr schwierig und komplex anhören, wenn du es noch nie gemacht hast, aber glaub mir, es ist ganz einfach. Ich würde empfehlen, dass du dir die Videos von BTC Sessions über die Verwendung des Signiergeräts deiner Wahl ansiehst. Er hat unglaubliche Walk-Through-Videos auf YouTube, die alles im Detail erklären.
Eine gemeinsame Verwahrung mit einem Unternehmen wie Swan Bitcoin oder Unchained Capital ist auch eine gute Idee für diejenigen, die neu in diesem Bereich sind. Sie werden dir die Hand halten und dich davor schützen, einfache Fehler zu machen, die zu Problemen führen können. Die gemeinschaftliche Verwahrung ist die Kosten wert, wenn du dir Sorgen machst, deine Bitcoin zu verlieren. Unchained bietet ein Produkt zur gemeinschaftlichen Verwahrung an, das mehrere Schlüssel enthalten kann und deinen Verwandten helfen kann, deine Bitcoin im Falle deines Ablebens wiederzuerlangen.
GEBE NICHT MIT DEINEN BITCOIN AN. Es besteht die Versuchung, mit dem Erfolg zu prahlen. Wenn du fünf Jahre lang durchhältst, wirst du ihn wahrscheinlich haben. Du bist stolz darauf, dass du die Disziplin und Selbstbeherrschung hattest, dich selbst zu beherrschen und erfolgreich das zu erwerben, was du als eine bedeutende Menge an Bitcoin ansiehst. Teile nicht, wie viel du hast, mit anderen. Das sollte offensichtlich sein, aber es gibt Leute, die sich nicht so sehr für dich freuen. Sie könnten es ihren Freunden erzählen, und früher oder später könnte jemand, den du nicht kennst und der vielleicht gewaltbereit ist, feststellen, dass du ein attraktives Ziel bist. Dies ist ein weiterer Grund für die Verwendung einer Konfiguration mit mehreren Signaturen. Selbst wenn jemand 1 von 3 Schlüsseln erhalten hat, kann er deine Bitcoin nicht stehlen.
KAUFE KEINE BITCOIN, DIE DU NICHT KONTROLLIEREN KANNST
Kaufe nicht den glänzenden neuen ETF, den die Wall Street anbietet. Kaufe Bitcoin nur bei Anbietern, die es dir ermöglichen, deine Bitcoin tatsächlich in Verwahrung zu nehmen. Lege deine Bitcoin nicht bei irgendeinem Dienst an, der eine Rendite bietet, insbesondere wenn diese Rendite unrealistisch hoch erscheint. Als allgemeine Faustregel gilt: Lass es einfach bleiben.
Der erste und wichtigste Grund, warum du deine Bitcoin in Verwahrung nehmen solltest, ist, dass du die absolute und vollständige Kontrolle über sie hast. Es gibt in Bitcoin ein Sprichwort: "Nicht deine Schlüssel, nicht deine Coins". Wenn du deine Bitcoin nicht verwahrst, hast du einfach einen Schuldschein. Das ist der ganze Grund für die Existenz von Bitcoin. Um Zwischenhändler auszuschalten und den Menschen zu ermöglichen, ihr finanzielles Schicksal selbst in die Hand zu nehmen.
Wenn du den Besitz hast, fallen keine Gebühren an wie bei einem ETF. Diese Gebühren können niedrig erscheinen, aber mit der Zeit können sie SIGNIFIKANT sein. GBTC ist ein Trust, der einem Bitcoin-ETF am ähnlichsten ist. GBTC erhebt eine Gebühr von 2 % PRO JAHR (jetzt 1,5 % mit dem ETF). Im Laufe der Zeit kann dies erheblich sein. Außerdem erlauben es die ETF-Produkte, die die Wall Street verkauft, nicht, den Bitcoin JEMALS zu verwahren. Ein ETF könnte für einige Leute in bestimmten Szenarien Sinn machen, aber für jeden, der ein Lego-Set bauen kann, ist die Verwahrung von Bitcoin ähnlich komplex. Nimm es selbst in die Hand.
Wenn sich Bitcoin mehr und mehr durchsetzt, wird es möglich sein, ihn als Sicherheiten zu verwenden. Ja, ich verstehe, dass die Verwendung deines Bitcoin als Sicherheit ihn aus deinem Besitz nimmt und Vertrauen in eine dritte Partei erfordert. Dies ist ein weiterer Fall, in dem du dich informieren und SICHER sein solltest, dass der von dir gewählte Kreditgeber vertrauenswürdig ist und nicht pleite gehen wird. Im Zweifelsfall solltest du dich immer auf die Selbstverwahrung verlassen.
Eine Kreditaufnahme gegen deine Bitcoin ist unmöglich, wenn du ihn nicht selbst verwahrst. Du kannst den Bitcoin, den Blackrock in deinem Namen hält, nicht ausleihen. Dies ist von Bedeutung. Es hat steuerliche Vorteile, Bitcoin zu beleihen, anstatt sie zu verkaufen. Wenn du keine Kontrolle über deine Bitcoin hast, schließt du dich selbst von einigen vorhersehbaren Anwendungsfällen in der nahen Zukunft aus und von vielen unvorhersehbaren Anwendungen, die noch erfunden werden müssen. Programmierbares Geld ist nicht nützlich, wenn du es nicht in deiner Hand hältst.
Der letzte Grund, warum du deine Bitcoin aufbewahren solltest, ist ein wenig düsterer. Bitcoin wurde entwickelt, um unzensierbar und nicht konfiszierbar zu sein. Wenn der Staat merkt, dass er die Kontrolle über das Geld verliert, wird er sich wahrscheinlich dein Bitcoin holen. Dies ist ein Präzedenzfall in der Geschichte der USA. Im Jahr 1933 wurde mit der Executive Order 6102 der Besitz von Gold für US-Bürger illegal. Sie zwangen die Menschen, Gold abzugeben und 20 Dollar pro Unze zu erhalten. Die Regierung setzte dann den Goldpreis auf 35 Dollar pro Unze herauf. Für den Besitz von Goldmünzen konnte man in den USA von 1933 bis Mitte der 1970er Jahre ins Gefängnis kommen. Das könnte wieder passieren, und du hast die Wahl, wenn du Bitcoin selbst hältst. Depotbanken WERDEN in diesem Szenario gezwungen sein, der Regierung deine Bitcoin zu geben. Was du in dieser Situation mit deinem Bitcoin tust, sollte DEINE Entscheidung sein, nicht die eines Verwahrers.
VERANTWORTUNG
Wenn du die Schritte unternimmst, um deine Bitcoin selbst zu verwahren, bist du verantwortlich. Dies ist eine Art von radikaler Verantwortung, die Menschen beunruhigen kann. Wenn du deine Schlüssel verlierst, ist dein Bitcoin für immer verloren. Es gibt keine Nummer, die du anrufen kannst, und niemanden, der dir helfen kann. SIE. SIND. WEG.
Im Jahr 2017 verlor einer meiner Freunde auf der Feuerwache Bitcoin im Wert von 1300 Dollar, weil er die Bitcoin in einer Papier-Wallet aufbewahrte. Diese werden nicht mehr verwendet, weil sie so unsicher sind, aber man kann einen QR-Code ausdrucken, der die Bitcoin enthält. Er ließ das Stück Papier in seinem Auto liegen. Dann räumte er sein Auto aus und saugte die Papier-Wallet auf. Diese Bitcoin sind für immer weg. Sie sind jetzt irgendwo zwischen 4 und 5 Tausend Dollar wert, und sie sind einfach weg. Nun, technisch gesehen sind sie nicht weg, sie sind immer noch da, nur für niemanden zugänglich. Ohne die Schlüssel kann niemand die Bitcoin bewegen, also sind die Bitcoin praktisch für immer eingefroren.
Ein anderer guter Freund von mir verlor eine beträchtliche Menge an Bitcoin bei einem Unternehmen namens BlockFi. Dabei handelte es sich um eine Börse, die Renditen für Bitcoin anbot, die bei ihrer Börse aufbewahrt wurden. Dieser Bitcoin ist nicht eingefroren, aber er ist jetzt für die absehbare Zukunft in einem Rechtsstreit eingesperrt. Um dem Ganzen noch die Krone aufzusetzen - da der Bitcoin, als er von BlockFi gehalten wurde, technisch gesehen nicht ihm gehörte, sondern aufgrund der "Vereinbarung", die er bei der Eröffnung des Kontos unterschrieben hat, ihnen gehört, wird er irgendwann in der Zukunft den Dollarwert dieses Bitcoins zu dem Preis erhalten, zu dem BlockFi pleite ging - also 16.000 Dollar -, sind wir wieder bei dem Punkt angelangt, warum du die Selbstverwahrung ernst nehmen solltest!
Das alte Bitcoin-Sprichwort lautet: "Nicht deine Schlüssel, nicht deine Coins".
Bitcoin ist eine endlose Lernreise. Wenn du ein Kaninchenloch erforschen willst, hast du Glück! Die Menge an soliden Inhalten, die in diesem Bereich angeboten werden, ist um Lichtjahre besser als im Jahr 2017. Man kann in einem Bruchteil der Zeit, die man damals gebraucht hätte, von null auf kompetent umsteigen. Wie oben bereits angedeutet, haben wir bei Blue Collar Bitcoin eine Grundlagenreihe zusammengestellt, die du für den Einstieg nutzen kannst. Die Liste der großartigen Inhaltsersteller und Ressourcen ist so lang, dass wir sie nicht alle aufzählen können. Geh einfach auf Entdeckungsreise und achte darauf, zu überprüfen, nicht zu vertrauen.
Lerne weiter, und vor allem - denke selbst!
Erinnere dich an die Weisheit von Matt Odell: "Bleib bescheiden und staple Sats".
-
 @ 460c25e6:ef85065c
2025-02-25 15:20:39
@ 460c25e6:ef85065c
2025-02-25 15:20:39If you don't know where your posts are, you might as well just stay in the centralized Twitter. You either take control of your relay lists, or they will control you. Amethyst offers several lists of relays for our users. We are going to go one by one to help clarify what they are and which options are best for each one.
Public Home/Outbox Relays
Home relays store all YOUR content: all your posts, likes, replies, lists, etc. It's your home. Amethyst will send your posts here first. Your followers will use these relays to get new posts from you. So, if you don't have anything there, they will not receive your updates.
Home relays must allow queries from anyone, ideally without the need to authenticate. They can limit writes to paid users without affecting anyone's experience.
This list should have a maximum of 3 relays. More than that will only make your followers waste their mobile data getting your posts. Keep it simple. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of all your content in a place no one can delete. Go to relay.tools and never be censored again. - 1 really fast relay located in your country: paid options like http://nostr.wine are great
Do not include relays that block users from seeing posts in this list. If you do, no one will see your posts.
Public Inbox Relays
This relay type receives all replies, comments, likes, and zaps to your posts. If you are not getting notifications or you don't see replies from your friends, it is likely because you don't have the right setup here. If you are getting too much spam in your replies, it's probably because your inbox relays are not protecting you enough. Paid relays can filter inbox spam out.
Inbox relays must allow anyone to write into them. It's the opposite of the outbox relay. They can limit who can download the posts to their paid subscribers without affecting anyone's experience.
This list should have a maximum of 3 relays as well. Again, keep it small. More than that will just make you spend more of your data plan downloading the same notifications from all these different servers. Out of the 3 relays, I recommend: - 1 large public, international relay: nos.lol, nostr.mom, relay.damus.io, etc. - 1 personal relay to store a copy of your notifications, invites, cashu tokens and zaps. - 1 really fast relay located in your country: go to nostr.watch and find relays in your country
Terrible options include: - nostr.wine should not be here. - filter.nostr.wine should not be here. - inbox.nostr.wine should not be here.
DM Inbox Relays
These are the relays used to receive DMs and private content. Others will use these relays to send DMs to you. If you don't have it setup, you will miss DMs. DM Inbox relays should accept any message from anyone, but only allow you to download them.
Generally speaking, you only need 3 for reliability. One of them should be a personal relay to make sure you have a copy of all your messages. The others can be open if you want push notifications or closed if you want full privacy.
Good options are: - inbox.nostr.wine and auth.nostr1.com: anyone can send messages and only you can download. Not even our push notification server has access to them to notify you. - a personal relay to make sure no one can censor you. Advanced settings on personal relays can also store your DMs privately. Talk to your relay operator for more details. - a public relay if you want DM notifications from our servers.
Make sure to add at least one public relay if you want to see DM notifications.
Private Home Relays
Private Relays are for things no one should see, like your drafts, lists, app settings, bookmarks etc. Ideally, these relays are either local or require authentication before posting AND downloading each user\'s content. There are no dedicated relays for this category yet, so I would use a local relay like Citrine on Android and a personal relay on relay.tools.
Keep in mind that if you choose a local relay only, a client on the desktop might not be able to see the drafts from clients on mobile and vice versa.
Search relays:
This is the list of relays to use on Amethyst's search and user tagging with @. Tagging and searching will not work if there is nothing here.. This option requires NIP-50 compliance from each relay. Hit the Default button to use all available options on existence today: - nostr.wine - relay.nostr.band - relay.noswhere.com
Local Relays:
This is your local storage. Everything will load faster if it comes from this relay. You should install Citrine on Android and write ws://localhost:4869 in this option.
General Relays:
This section contains the default relays used to download content from your follows. Notice how you can activate and deactivate the Home, Messages (old-style DMs), Chat (public chats), and Global options in each.
Keep 5-6 large relays on this list and activate them for as many categories (Home, Messages (old-style DMs), Chat, and Global) as possible.
Amethyst will provide additional recommendations to this list from your follows with information on which of your follows might need the additional relay in your list. Add them if you feel like you are missing their posts or if it is just taking too long to load them.
My setup
Here's what I use: 1. Go to relay.tools and create a relay for yourself. 2. Go to nostr.wine and pay for their subscription. 3. Go to inbox.nostr.wine and pay for their subscription. 4. Go to nostr.watch and find a good relay in your country. 5. Download Citrine to your phone.
Then, on your relay lists, put:
Public Home/Outbox Relays: - nostr.wine - nos.lol or an in-country relay. -
.nostr1.com Public Inbox Relays - nos.lol or an in-country relay -
.nostr1.com DM Inbox Relays - inbox.nostr.wine -
.nostr1.com Private Home Relays - ws://localhost:4869 (Citrine) -
.nostr1.com (if you want) Search Relays - nostr.wine - relay.nostr.band - relay.noswhere.com
Local Relays - ws://localhost:4869 (Citrine)
General Relays - nos.lol - relay.damus.io - relay.primal.net - nostr.mom
And a few of the recommended relays from Amethyst.
Final Considerations
Remember, relays can see what your Nostr client is requesting and downloading at all times. They can track what you see and see what you like. They can sell that information to the highest bidder, they can delete your content or content that a sponsor asked them to delete (like a negative review for instance) and they can censor you in any way they see fit. Before using any random free relay out there, make sure you trust its operator and you know its terms of service and privacy policies.
-
 @ 0176967e:1e6f471e
2024-07-22 19:57:47
@ 0176967e:1e6f471e
2024-07-22 19:57:47Co se nomádská rodina již 3 roky utíkající před kontrolou naučila o kontrole samotné? Co je to vlastně svoboda? Může koexistovat se strachem? S konfliktem? Zkusme na chvíli zapomenout na daně, policii a stát a pohlédnout na svobodu i mimo hranice společenských ideologií. Zkusme namísto hledání dalších odpovědí zjistit, zda se ještě někde neukrývají nové otázky. Možná to bude trochu ezo.
Karel provozuje již přes 3 roky se svou ženou, dvěmi dětmi a jedním psem minimalistický život v obytné dodávce. Na cestách spolu začali tvořit youtubový kanál "Karel od Martiny" o svobodě, nomádství, anarchii, rodičovství, drogách a dalších normálních věcech.
Nájdete ho aj na nostr.
-
 @ 87122b31:726e2c4c
2025-04-21 02:16:07
@ 87122b31:726e2c4c
2025-04-21 02:16:07BJ66 là một nền tảng kỹ thuật số nổi bật với thiết kế tối giản nhưng đầy tinh tế, hướng đến việc tạo ra một môi trường thân thiện và dễ tiếp cận cho tất cả người dùng. Ngay từ giao diện đầu tiên, BJ66 cho thấy sự chú trọng vào trải nghiệm người dùng khi mọi yếu tố được sắp xếp một cách khoa học và thuận tiện. Các tính năng chính được trình bày rõ ràng, biểu tượng minh họa sắc nét giúp người dùng dễ dàng thao tác, kể cả với những người chưa có nhiều kinh nghiệm sử dụng công nghệ. Sự linh hoạt trong cách bố trí menu, lựa chọn ngôn ngữ và chế độ hiển thị sáng – tối cũng mang đến sự cá nhân hóa tối đa cho mỗi người dùng. Nền tảng này tương thích mượt mà trên nhiều thiết bị khác nhau từ điện thoại thông minh, máy tính bảng đến laptop, tạo điều kiện cho người dùng kết nối mọi lúc mọi nơi mà không bị giới hạn bởi thiết bị hay hệ điều hành.
Không chỉ dừng lại ở thiết kế giao diện đẹp mắt và thân thiện, BJ66 còn ghi điểm mạnh mẽ ở khả năng vận hành ổn định và bảo mật cao. Với hệ thống máy chủ tối ưu và công nghệ xử lý hiện đại, các thao tác trên BJ66 diễn ra nhanh chóng, mượt mà, không bị giật lag hay gián đoạn. Người dùng có thể thực hiện nhiều hoạt động cùng lúc mà không gặp tình trạng chậm trễ hay lỗi hệ thống, đặc biệt quan trọng trong bối cảnh yêu cầu tốc độ và tính liên tục ngày càng cao. Về bảo mật, BJ66 áp dụng các lớp mã hóa tiên tiến và cơ chế xác minh đa yếu tố, bảo vệ thông tin cá nhân và dữ liệu của người dùng khỏi các rủi ro tấn công mạng. Mọi hoạt động đăng nhập, thay đổi cài đặt hay giao dịch đều được theo dõi và ghi nhận để tăng cường tính minh bạch và an toàn. Đội ngũ hỗ trợ kỹ thuật của BJ66 cũng là một điểm cộng lớn, khi họ hoạt động liên tục 24/7 với thái độ chuyên nghiệp, tận tâm và phản hồi nhanh chóng, đảm bảo người dùng luôn có người đồng hành trong suốt quá trình sử dụng.
BJ66 không ngừng đổi mới và phát triển để mang đến một hệ sinh thái số toàn diện, đáp ứng mọi nhu cầu của người dùng hiện đại. Nền tảng tích hợp nhiều tiện ích thông minh được hỗ trợ bởi công nghệ tiên tiến như trí tuệ nhân tạo (AI), cá nhân hóa nội dung và gợi ý dựa trên thói quen sử dụng. Điều này giúp người dùng tiết kiệm thời gian tìm kiếm và truy cập nhanh hơn đến các tính năng mình yêu thích. Ngoài ra, BJ66 thường xuyên cập nhật những cải tiến mới nhằm nâng cao hiệu suất, cải thiện giao diện và tối ưu hóa các chức năng, từ đó duy trì được tính cạnh tranh và giữ chân người dùng trong thời gian dài. Trong thời đại công nghệ số đang phát triển nhanh chóng, BJ66 nổi bật như một lựa chọn đáng tin cậy, nơi người dùng có thể yên tâm trải nghiệm với sự an toàn, thuận tiện và sự thấu hiểu đến từ một nền tảng luôn đặt người dùng ở vị trí trung tâm. Với sự kết hợp giữa công nghệ hiện đại, giao diện thân thiện và cam kết phát triển bền vững, BJ66 không chỉ đơn thuần là một công cụ mà còn là một phần không thể thiếu trong lối sống số hóa ngày nay.
-
 @ 846ebf79:fe4e39a4
2025-04-14 12:35:54
@ 846ebf79:fe4e39a4
2025-04-14 12:35:54The next iteration is coming
We're busy racing to the finish line, for the #Alexandria Gutenberg beta. Then we can get the bug hunt done, release v0.1.0, and immediately start producing the first iteration of the Euler (v0.2.0) edition.
While we continue to work on fixing the performance issues and smooth rendering on the Reading View, we've gone ahead and added some new features and apps, which will be rolled-out soon.
The biggest projects this iteration have been:
- the HTTP API for the #Realy relay from nostr:npub1fjqqy4a93z5zsjwsfxqhc2764kvykfdyttvldkkkdera8dr78vhsmmleku,
- implementation of a publication tree structure by nostr:npub1wqfzz2p880wq0tumuae9lfwyhs8uz35xd0kr34zrvrwyh3kvrzuskcqsyn,
- and the Great DevOps Migration of 2025 from the ever-industrious Mr. nostr:npub1qdjn8j4gwgmkj3k5un775nq6q3q7mguv5tvajstmkdsqdja2havq03fqm7.
All are backend-y projects and have caused a major shift in process and product, on the development team's side, even if they're still largely invisible to users.
Another important, but invisible-to-you change is that nostr:npub1ecdlntvjzexlyfale2egzvvncc8tgqsaxkl5hw7xlgjv2cxs705s9qs735 has implemented the core bech32 functionality (and the associated tests) in C/C++, for the #Aedile NDK.
On the frontend:
nostr:npub1636uujeewag8zv8593lcvdrwlymgqre6uax4anuq3y5qehqey05sl8qpl4 is currently working on the blog-specific Reading View, which allows for multi-npub or topical blogging, by using the 30040 index as a "folder", joining the various 30041 articles into different blogs. She has also started experimenting with categorization and columns for the landing page.
nostr:npub1l5sga6xg72phsz5422ykujprejwud075ggrr3z2hwyrfgr7eylqstegx9z revamped the product information pages, so that there is now a Contact page (including the ability to submit a Nostr issue) and an About page (with more product information, the build version displayed, and a live #GitCitadel feed).
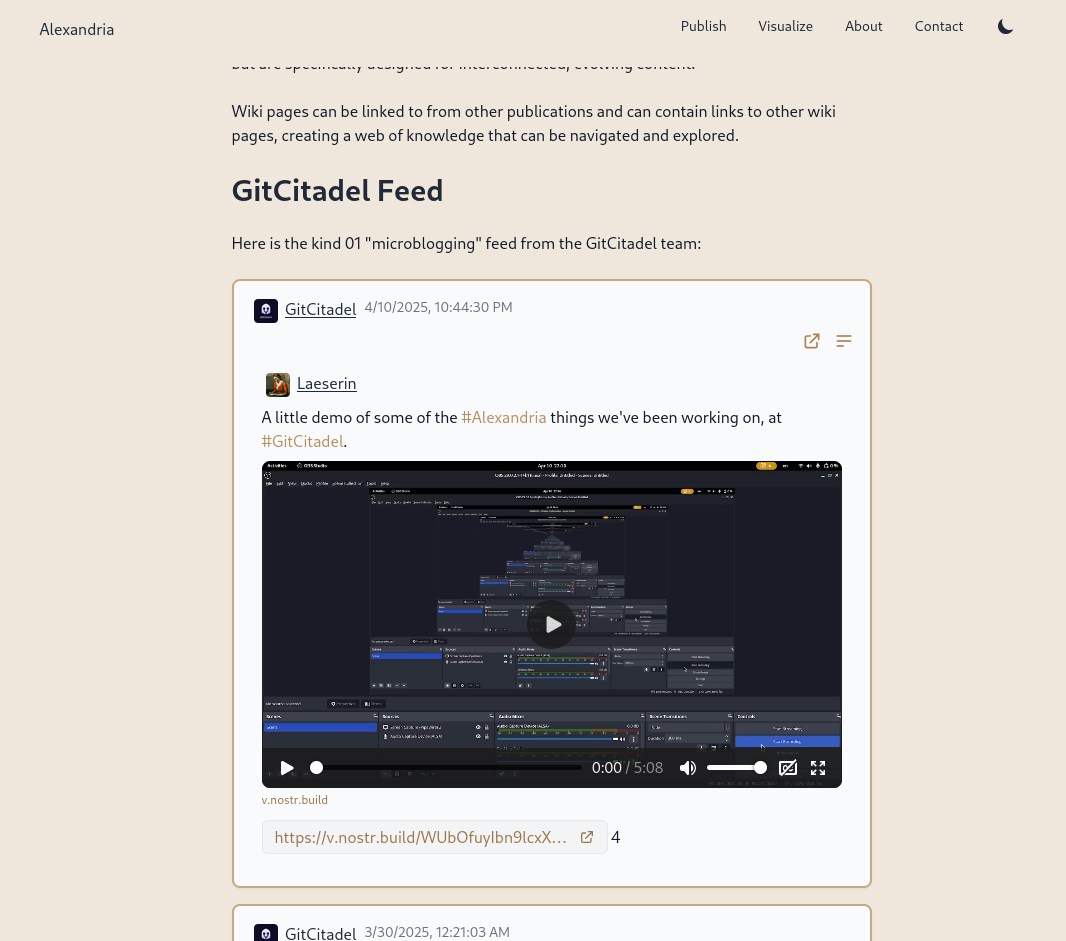
We have also allowed for discrete headings (headers that aren't section headings, akin to the headers in Markdown). Discrete headings are formatted, but not added to the ToC and do not result in a section split by Asciidoc processors.
We have added OpenGraph metadata, so that hyperlinks to Alexandria publications, and other events, display prettily in other apps. And we fixed some bugs.
The Visualisation view has been updated and bug-fixed, to make the cards human-readable and closeable, and to add hyperlinks to the events to the card-titles.
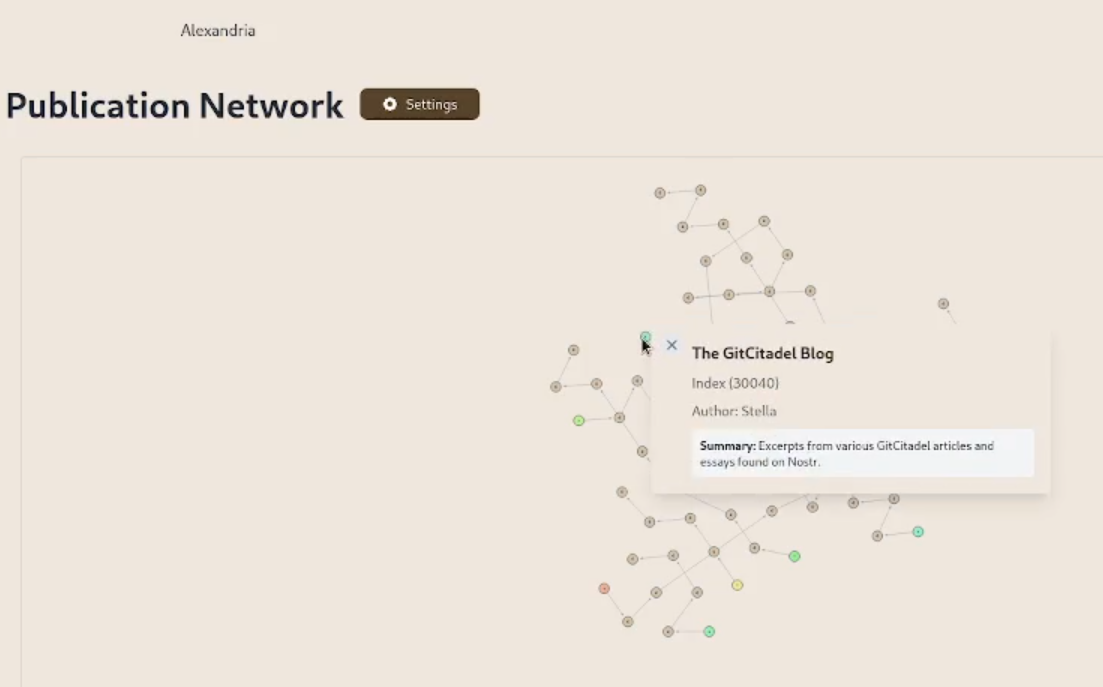
We have added support for the display of individual wiki pages and the integration of them into 30040 publications. (This is an important feature for scientists and other nonfiction writers.)
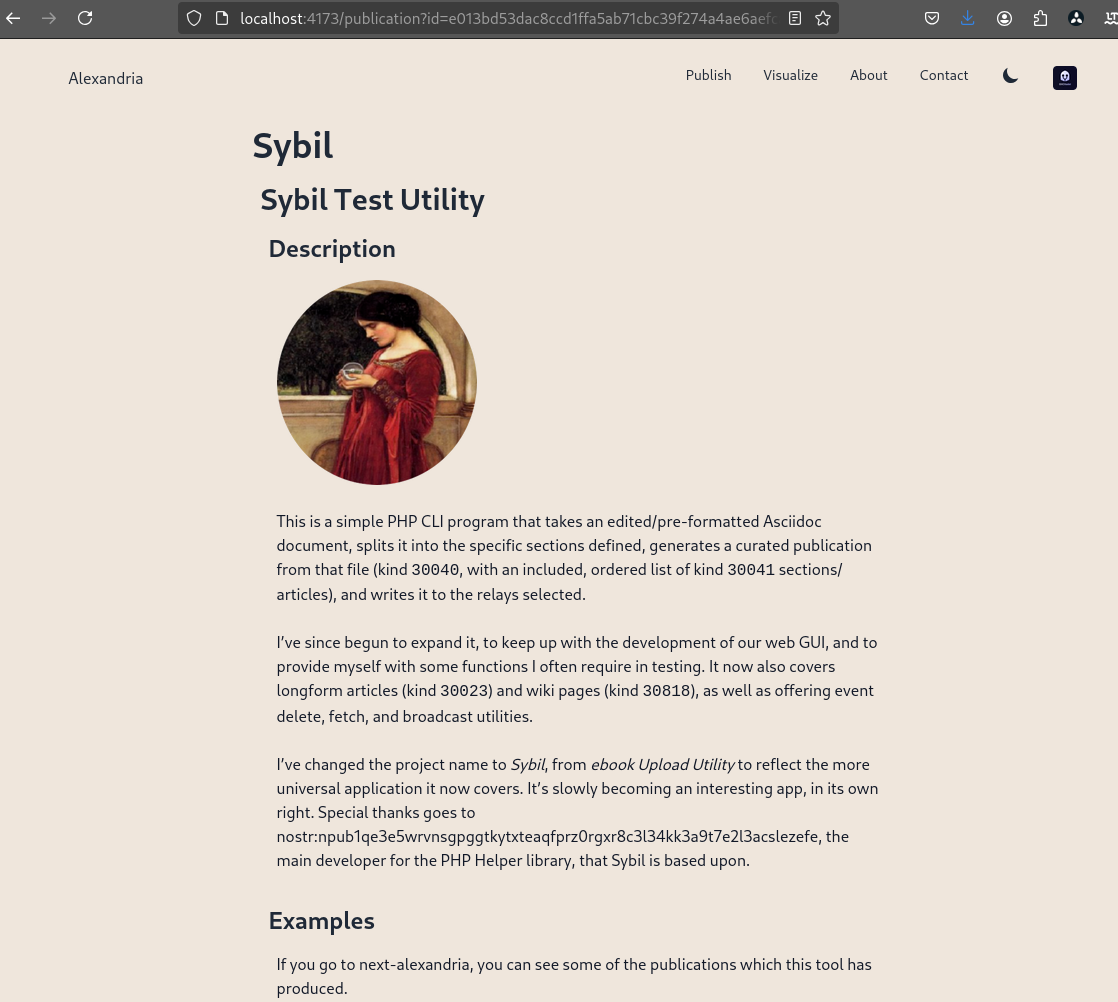
We prettified the event json modal, so that it's easier to read and copy-paste out of.
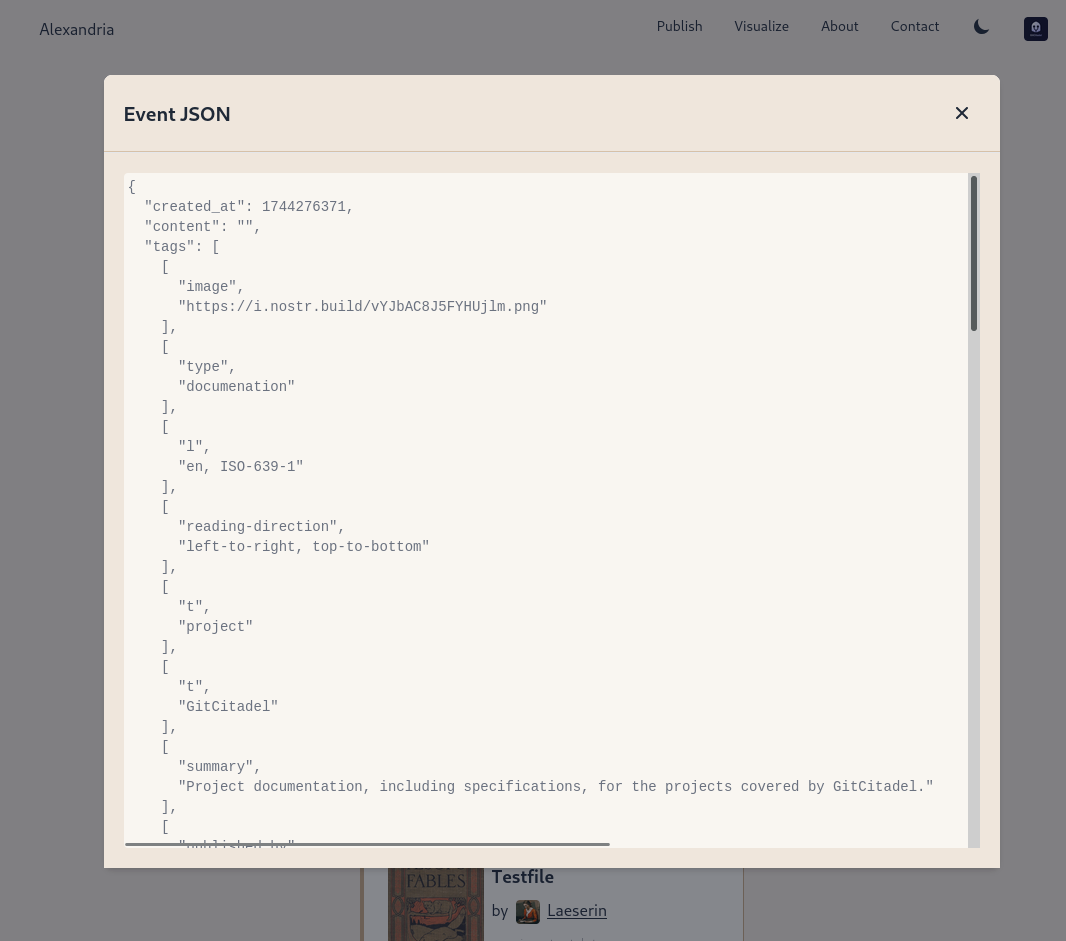
The index card details have been expanded and the menus on the landing page have been revamped and expanded. Design and style has been improved, overall.
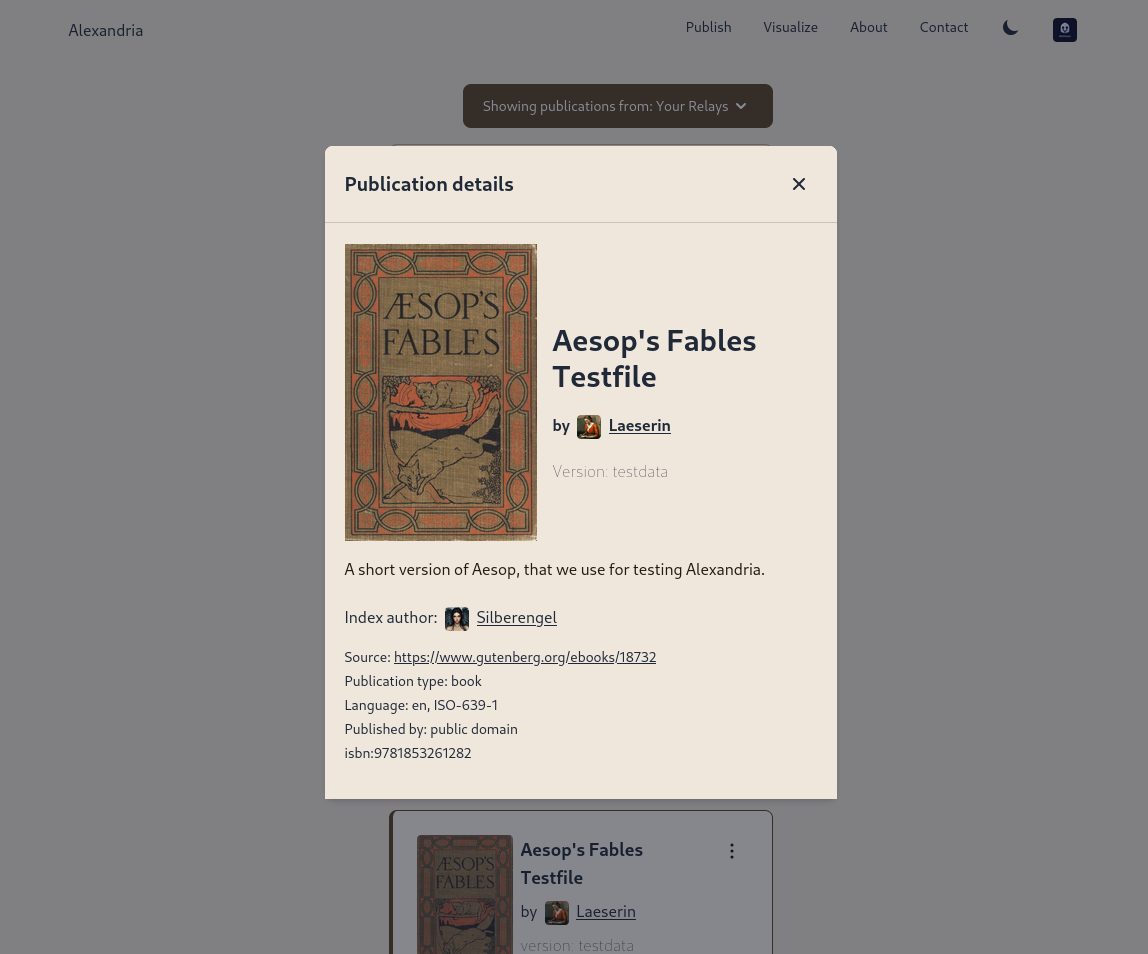
Project management is very busy
Our scientific adviser nostr:npub1m3xdppkd0njmrqe2ma8a6ys39zvgp5k8u22mev8xsnqp4nh80srqhqa5sf is working on the Euler plans for integrating features important for medical researchers and other scientists, which have been put on the fast track.
Next up are:
- a return of the Table of Contents
- kind 1111 comments, highlights, likes
- a prototype social feed for wss://theforest.nostr1.com, including long-form articles and Markdown rendering
- compose and edit of publications
- a search field
- the expansion of the relay set with the new relays from nostr:npub12262qa4uhw7u8gdwlgmntqtv7aye8vdcmvszkqwgs0zchel6mz7s6cgrkj, including some cool premium features
- full wiki functionality and disambiguation pages for replaceable events with overlapping d-tags
- a web app for mass-uploading and auto-converting PDFs to 30040/41 Asciidoc events, that will run on Realy, and be a service free for our premium relay subscribers
- ability to subscribe to the forest with a premium status
- the book upload CLI has been renamed and reworked into the Sybil Test Utility and that will get a major release, covering all the events and functionality needed to test Euler
- the #GitRepublic public git server project
- ....and much more.
Thank you for reading and may your morning be good.
-
 @ 0176967e:1e6f471e
2024-07-21 15:48:56
@ 0176967e:1e6f471e
2024-07-21 15:48:56Lístky na festival Lunarpunku sú už v predaji na našom crowdfunding portáli. V predaji sú dva typy lístkov - štandardný vstup a špeciálny vstup spolu s workshopom oranžového leta.
Neváhajte a zabezpečte si lístok, čím skôr to urobíte, tým bude festival lepší.
Platiť môžete Bitcoinom - Lightningom aj on-chain. Vaša vstupenka je e-mail adresa (neposielame potvrdzujúce e-maily, ak platba prešla, ste in).
-
 @ 0176967e:1e6f471e
2024-07-21 11:28:18
@ 0176967e:1e6f471e
2024-07-21 11:28:18Čo nám prinášajú exotické protokoly ako Nostr, Cashu alebo Reticulum? Šifrovanie, podpisovanie, peer to peer komunikáciu, nové spôsoby šírenia a odmeňovania obsahu.
Ukážeme si kúl appky, ako sa dajú jednotlivé siete prepájať a ako spolu súvisia.
-
 @ 044da344:073a8a0e
2025-04-14 11:41:39
@ 044da344:073a8a0e
2025-04-14 11:41:39Als wir vor gut einem halben Jahr mit den Kolumnen angefangen haben, hatte ich mir das genau so vorgestellt. Ich schreibe auf, was mir in der Woche so passiert ist. Eine Bilanz sozusagen, vielleicht persönlich, vielleicht politisch. Je nachdem. Es ist dann etwas anders gekommen. Manchmal waren ein Buch oder ein Film einfach so stark, dass aus der Kolumne eine Rezension geworden ist. Manchmal wollte ich nur von einem meiner Interviews erzählen und das Besprochene gleich mit den großen Debatten verknüpfen. Und manchmal waren Anregungen von außen umzusetzen, Stichwort KI, Stichwort Frieden.
Wahrscheinlich waren die meisten Wochen auch nicht besonders spannend. Alltag eben. Was soll man davon groß festhalten. Diesmal ist das anders. Sonntag Erich Hambach bei uns im Haus. Ein Interview für die Reihe Im Gespräch. Ich will nicht zu viel vorwegnehmen. Es ging um die Hochfinanz, um den schwarzen Adel, um die Illuminati. Ein Gruselkabinett für alle, die wissen, wo die roten Linien sind zu den Schmuddelkindern. Verschwörungstheorie, pfui. Erich Hambach kann erklären, wie die „Herren des Geldes“ (Untertitel seines neuen Buchs) arbeiten und was man tun kann, um sich ihrem Zugriff zu entziehen. Als die Kameras aus waren, ging es munter weiter mit dem Publikum. Steuerfrei leben, sich auf den Lastenausgleich vorbereiten, Kollateralkonto. Siehe oben. Wir haben dann noch 25 Minuten nachgeschoben, die bei den „Truth Brothers“ zu sehen sein werden, dem Kanal von Erich Hambach.
Montag Dresden. Lesung im Buchhaus Loschwitz. Ich war schon im Juni dort, damals mit dem Buch über die Unterwerfung der Universitäten. Diesmal „Der dressierte Nachwuchs“. Wieder volles Haus. In Loschwitz heißt das: Susanne Dagen, Gastgeberin und Moderatorin, quetscht sich auf einen Hocker zwischen Klavier und Reihe null und sagt: Willkommen zum Gottesdienst. Einige sind zum zweiten Mal da. Neu: Paul Soldan, den ich aus seinen Texten für Multipolar kenne und über sein Buch „Sheikhi“, und Julia Szarvasy, die mich in ihrem Bus für Nuoviso interviewt hat und auf der Ruderboot-Couch. Hinterher kommen (um im Bild zu bleiben) drei U-Boote zu mir. Professoren. Ein Techniker, ein Germanist und ein Medienforscher, der sich sogar mit mir fotografieren lassen will. Dieser Kollege ist nicht an der TU (falls jemand die Fahndung einleiten möchte), aber immerhin. Ich bin oft gefragt worden, ob es an den Unis Gleichgesinnte gibt, und kann jetzt endlich sagen: ja. Ein paar schon.
Versteckt in einer der letzten Dresdner Reihen: Michael Beleites, eine Ikone der DDR-Umweltbewegung und später ein Jahrzehnt lang Beauftragter für die Stasi-Unterlagen in Sachsen. Er hat eine Rezension mitgebracht, die er gerade für die Sezession geschrieben hat, und einen Gedanken, der mich später schlecht schlafen lässt. Müssen wir die Geschichte vom Herbst 1989 umschreiben? Ganz neu ist dieser Gedanke nicht, natürlich nicht. Wer dabei war, hat sich schon damals gefragt, wie die Stimmung so schnell kippen konnte vom Wunsch nach einem anderen, besseren Sozialismus zu Helmut Kohl und seiner D-Mark. Daniela Dahn, wie Michael Beleites seinerzeit in vorderster Front, hat den schwarzen Peter an den Journalismus weitergegeben. Tamtam und Tabu. Eine Kampagne, losgetreten von Horst Teltschik, Kohls wichtigstem Mann, die sich um SED-Skandale drehte und so wie eine Nebelkerze verhüllte, um was es eigentlich ging. Die Herren des Geldes, würde Erich Hambach sagen. „Alte Besitzverhältnisse“ wieder herstellen und damit „alte Machtverhältnisse“, sagt Daniela Dahn. Michael Beleites ergänzt das nun durch das, was er gesehen und erlebt hat, bei der Auflösung des Geheimdienstes in Gera zum Beispiel. Da seien Leute wie er gewesen, natürlich. Legitimiert durch das, was vorher war. Überall im Land seien aber plötzlich auch unbeschriebene Blätter aufgetaucht, laut und damit schnell ganz vorne dran. Ein Forschungsthema, ohne Frage.
Bevor ich das zu Ende gedacht habe, sitze ich im Rudolf-Steiner-Haus, nur ein paar Steinwürfe weg von der Alster. Ich würde gern „Hamburgs Wohnzimmer“ schreiben, aber dazu taugt der Saal im Souterrain dann doch nicht ganz. Immerhin: steuerfinanziert. Geht also doch. Eingeladen hat unter anderem der Nachdenkseiten-Gesprächskreis vor Ort. Thema: Wandel der Universitäten. Wieder sind Kollegen da, auch aus dem Mittelbau und aus der Rentnergeneration, die sich zu erinnern glauben, alles schon erlebt zu haben, damals, in ihrer großen Zeit. Nun ja. Wichtiger: Walter Weber ist da, ein Arzt, Koryphäe in Sachen Krebs, 80 inzwischen, der meinen letzten Auftritt in Hamburg organisiert hat. Große Freiheit, Sommer 2022. Die Sonne schien, und es roch nach Aufbruch. Aus dem ganzen Land waren sie gekommen, aus Nord und Süd, von links bis rechts, aus allen nur denkbaren Bewegungen und Milieus. Corona als Klammer, genau wie der Glaube, dass unsere Zeit jetzt anbricht.
Es kam dann anders, aber das ist hier nicht mein Punkt. Walter Weber, der alte Weggefährte, zieht Bilanz – bei einem Becks in seinem Haus, genau da, wo wir vor drei Jahren in größerer Runde beraten haben. Walter hat inzwischen einen Prozess hinter sich mit knapp zwei Dutzend Verhandlungstagen und den entsprechenden Kosten. Maskenatteste. Was immer wir aufgefahren haben an Beweisanträgen, sagt Walter, es wurde abgeschmettert. Und trotzdem. Wir müssen sie zwingen, sich damit auseinanderzusetzen. Immer wieder. So ähnlich habe ich das zwei Stunden vorher im Steiner-Haus gesagt, mit Vaclav Havel als Referenz. 500 Ärzte, schätzt Walter Weber, haben wie er Atteste ausgestellt. 500 bei einer sechsstelligen Zahl an Kollegen. Sicher gibt es eine Dunkelziffer. Lassen wir es bei den 500, weil Walter Weber hier die Folgen kennt. 80 Prozent von diesen 500 haben Haus- und Praxisdurchsuchungen erlebt. Er selbst zwei, der Spitzenreiter acht. Die Maske war der Test. Als die Spritze kam, wusste jeder, auf was er sich einlassen würde - selbst ein Medienforscher wie ich. Die maskierte Öffentlichkeit, veröffentlicht im Oktober 2020, war mit Sicherheit nicht mein bester Text, aber der, der den meisten Wirbel auslöste und später sogar zweimal vor Gericht verhandelt wurde.
Was bleibt von all den Kämpfen? Wir haben die Leute aus der Vereinzelung geholt, sagt Walter. Die 20 Prozent, die dagegen waren. Wir haben ihnen gezeigt, dass sie nicht allein sind, und diese Leute mobilisiert. Gescheitert sind wir an Schritt drei. Strukturbildung. Es fehlt uns an Geld, Michael. Walter Weber hat an Regionalbüros gebastelt. „Ärzte für Aufklärung“ in Thüringen – und das ist nur eins von vielen Beispielen. Wer weiß, wie viel Geld es in diesem Land gibt und wie viele wirklich reiche Leute, der weiß auch, dass wir hier über Peanuts sprechen. Wem es gut geht, der will, dass alles weiter seinen Gang geht. Der will keine Strukturen für irgendeine Opposition. Walter Weber hat mit einer seiner Nichten gerade „Das siebte Kreuz“ gelesen. Anna Seghers, Schulstoff in der DDR. Weißt du, was ich da gelernt habe, Michael? Echter Widerstand hat zwei Bedingungen. Keine Familie und keine Angst vor dem Tod.
Der Zug nach Berlin ist pünktlich und mein Gastgeber folglich noch nicht da. Gibt’s doch nicht, sagt er. Hat es noch nie gegeben. Über meinen Auftritt im Sprechsaal breite ich den Mantel des Schweigens. Die Idee klang super: Wir machen dort eine Ausstellung mit aktuellen Bildern aus Gaza, gekauft von der dpa, und du, Michael, bringst deine Bücher über Cancel Culture, Jugend und Universitäten zusammen, um zu erklären, warum Deutschland wegschaut. Die kastrierte Öffentlichkeit. Der beste Titel geht ins Leere, wenn niemand weiß, dass ich sprechen werde. Vielleicht ist das so, wenn der eigene Verlag der Veranstalter ist. Jens Fischer Rodrian hat durch einen Zufall erfahren, dass ich da bin, und bringt die CD Voices for Gaza, ganz frisch in der Reihe „Protestnoten“. Auf dem Cover: große Namen von Didi Hallervorden über Tino Eisbrenner, Nirit Sommerfeld und Diether Dehm bis zu Wolfgang Wodarg. Fünf von fast 40. Sorry an die, die ich auslassen musste. Der gleiche Zufall hat Kathrin Schmidt in den Sprechsaal geführt, Mitglied des PEN-Zentrums, Buchpreisträgerin, Maßnahmenkritikerin. Sie hat wie immer ihr Strickzeug dabei.
Ein kleines Publikum, frei von Kameras, erlaubt, in die Tiefen zu tauchen und dabei auch zu riskieren, im Trüben zu fischen. Erich Hambach hätte seine Freude gehabt. Und wer weiß schon, was daraus später wächst. Ein paar Minuten vor Beginn gehe ich durch das Regierungsviertel und höre plötzlich meinen Namen. Eine ARD-Frau, die auf Friedrich Merz wartet. Koalitionsvertrag fertig, Kamera schussbereit. Mein Film über die Duldungspflicht, sagt die Frau und strahlt über das ganze Gesicht. Er ist fertig. Premiere nächste Woche. Sie war bei einem meiner letzten Berliner Vorträge und wird jetzt mit ihrem Namen für ein Produkt stehen, dass so nicht im Ersten laufen kann. Noch nicht, würde Walter Weber sagen. Ende nächsten Jahres, sagt er mir beim Abschied, steht Merkel vor Gericht. Ist der Gedanke erstmal da, so begründet er das sinngemäß, dann ist er nicht mehr aufzuhalten. Mal schauen, wie das jetzt mit der Deutschen Bahn wird bei der Rückfahrt nach Bayern. Ich nehme mir vor, dass wir pünktlich sind.
Freie Akademie für Medien & Journalismus
Bild: Tobias Schönebeck auf Pixabay (Dresden, Blaues Wunder in Loschwitz)
-
 @ 87122b31:726e2c4c
2025-04-21 02:15:16
@ 87122b31:726e2c4c
2025-04-21 02:15:16WIN1 là nền tảng công nghệ hiện đại được xây dựng với mục tiêu cung cấp một không gian trực tuyến toàn diện, nơi người dùng có thể tương tác, trải nghiệm và kết nối một cách mượt mà, tiện lợi. Sở hữu giao diện trực quan, tối ưu hóa cho cả người mới bắt đầu và người dùng thành thạo, WIN1 tạo ra cảm giác thân thiện ngay từ lần đầu truy cập. Các yếu tố bố cục được sắp xếp hợp lý, màu sắc hài hòa và các biểu tượng dễ hiểu giúp việc điều hướng trở nên dễ dàng trên mọi loại thiết bị – từ điện thoại thông minh, máy tính bảng đến máy tính cá nhân. Không dừng lại ở đó, WIN1 còn cho phép người dùng tùy chỉnh không gian trải nghiệm cá nhân với các chế độ giao diện sáng – tối, ngôn ngữ linh hoạt, và các thiết lập cá nhân hóa dựa trên thói quen sử dụng. Nhờ vậy, người dùng luôn cảm thấy sự chủ động trong mọi tương tác với nền tảng.
Điểm nổi bật khác giúp WIN1 khẳng định vị thế là khả năng vận hành ổn định và bảo mật cao. Hệ thống hoạt động nhanh chóng, ổn định và có khả năng xử lý đồng thời nhiều truy cập mà không gây gián đoạn. Điều này đặc biệt quan trọng trong bối cảnh người dùng ngày càng có xu hướng sử dụng nhiều thiết bị cùng lúc để phục vụ nhu cầu công việc và giải trí. WIN1 áp dụng các công nghệ mã hóa tiên tiến và xác thực bảo mật nhiều lớp, đảm bảo dữ liệu người dùng luôn được bảo vệ nghiêm ngặt. Ngoài ra, nền tảng còn thường xuyên cập nhật và kiểm tra hệ thống để phát hiện, khắc phục kịp thời các rủi ro tiềm ẩn. Bên cạnh yếu tố kỹ thuật, WIN1 còn xây dựng đội ngũ chăm sóc khách hàng tận tâm, hoạt động 24/7, sẵn sàng hỗ trợ người dùng trong mọi tình huống từ những thắc mắc đơn giản đến các vấn đề kỹ thuật phức tạp, giúp người dùng an tâm tuyệt đối trong suốt hành trình trải nghiệm.
Không ngừng đổi mới và hoàn thiện, WIN1 liên tục tích hợp các xu hướng công nghệ tiên tiến nhằm tối ưu hóa hiệu suất và nâng cao trải nghiệm người dùng. Nền tảng này không chỉ đơn thuần là công cụ kết nối, mà còn hướng đến xây dựng một hệ sinh thái số hóa toàn diện, trong đó người dùng có thể tận hưởng sự tương tác thông minh nhờ vào các tiện ích được tích hợp như trí tuệ nhân tạo (AI), hệ thống gợi ý cá nhân hóa và các tính năng tự động hóa thông minh. Các phân tích dữ liệu từ hành vi người dùng được sử dụng một cách linh hoạt để đưa ra đề xuất phù hợp, giúp mỗi lần truy cập vào WIN1 đều mang lại cảm giác mới mẻ và đúng nhu cầu. Đây chính là minh chứng cho định hướng phát triển dài hạn, bền vững của WIN1: luôn lấy người dùng làm trung tâm, không ngừng nâng cấp công nghệ, đồng thời đảm bảo sự ổn định và an toàn trong suốt quá trình sử dụng. Trong thời đại mà công nghệ trở thành một phần không thể thiếu trong cuộc sống, WIN1 là lựa chọn lý tưởng dành cho những ai đang tìm kiếm một nền tảng đáng tin cậy, dễ sử dụng và luôn đổi mới để bắt kịp xu hướng toàn cầu.
-
 @ 6e0ea5d6:0327f353
2025-02-21 18:15:52
@ 6e0ea5d6:0327f353
2025-02-21 18:15:52"Malcolm Forbes recounts that a lady, wearing a faded cotton dress, and her husband, dressed in an old handmade suit, stepped off a train in Boston, USA, and timidly made their way to the office of the president of Harvard University. They had come from Palo Alto, California, and had not scheduled an appointment. The secretary, at a glance, thought that those two, looking like country bumpkins, had no business at Harvard.
— We want to speak with the president — the man said in a low voice.
— He will be busy all day — the secretary replied curtly.
— We will wait.
The secretary ignored them for hours, hoping the couple would finally give up and leave. But they stayed there, and the secretary, somewhat frustrated, decided to bother the president, although she hated doing that.
— If you speak with them for just a few minutes, maybe they will decide to go away — she said.
The president sighed in irritation but agreed. Someone of his importance did not have time to meet people like that, but he hated faded dresses and tattered suits in his office. With a stern face, he went to the couple.
— We had a son who studied at Harvard for a year — the woman said. — He loved Harvard and was very happy here, but a year ago he died in an accident, and we would like to erect a monument in his honor somewhere on campus.— My lady — said the president rudely —, we cannot erect a statue for every person who studied at Harvard and died; if we did, this place would look like a cemetery.
— Oh, no — the lady quickly replied. — We do not want to erect a statue. We would like to donate a building to Harvard.
The president looked at the woman's faded dress and her husband's old suit and exclaimed:
— A building! Do you have even the faintest idea of how much a building costs? We have more than seven and a half million dollars' worth of buildings here at Harvard.
The lady was silent for a moment, then said to her husband:
— If that’s all it costs to found a university, why don’t we have our own?
The husband agreed.
The couple, Leland Stanford, stood up and left, leaving the president confused. Traveling back to Palo Alto, California, they established there Stanford University, the second-largest in the world, in honor of their son, a former Harvard student."
Text extracted from: "Mileumlivros - Stories that Teach Values."
Thank you for reading, my friend! If this message helped you in any way, consider leaving your glass “🥃” as a token of appreciation.
A toast to our family!
-
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 04ea4f83:210e1713
2025-04-20 08:38:43
@ 04ea4f83:210e1713
2025-04-20 08:38:43Bei dem Begriff "Midlife-Crisis" denkt man oft an Menschen mittleren Alters, die sich Sportwagen kaufen, ihre Ehepartner für jüngere Partner verlassen oder sich in einem verzweifelten Versuch, ihre Jugend wiederzuerlangen, plötzlich auf ausgefallene Abenteuer einlassen. Im Bitcoin Space zeichnet sich jedoch ein neues Phänomen ab - die Bitcoiner Midlife-Crisis.
Für diejenigen, die tief in den Kaninchen Bau eingetaucht sind kommt ein Punkt auf ihrer Reise, an dem sie ein Plateau erreichen. Sie haben ein außerordentliches Vermögen in Form von Sats angehäuft und verfügen über ein klares Verständnis der Technologie und des Marktes. Aber trotz alledem fühlen sie sich unerfüllt, so als ob der nächste Kauf von Bitcoin einfach keinen wirklichen Unterschied mehr macht.
Dieses Gefühl wird durch die extreme Volatilität des Bitcoin-Marktes noch verstärkt. An einem Tag kann das Nettovermögen in neue Höhen steigen, nur um am nächsten Tag wieder deutlich zu fallen. Die Schwankungen können so drastisch sein, dass ihr Jahresgehalt im Vergleich zu den nicht realisierten Gewinnen und Verlusten, die sie an einem einzigen Tag erleben, verblasst. Es wird schwierig, die Achterbahnfahrt der finanziellen Freiheit mit der Stabilität einer traditionellen Festanstellung in Einklang zu bringen.
Die traditionellen Vorstellungen von Erfolg und Erfüllung verlieren für Bitcoiner, die diese Midlife-Crisis erleben, an Bedeutung. Die Verlockung von materiellen Besitztümern oder beruflichen Fortschritten hat nicht mehr das gleiche Gewicht im Vergleich zu den potenziellen Gewinnen und Verlusten der Bitcoin. Die Vorstellung, für jemand anderen zu arbeiten und Zeit gegen Geld zu tauschen, wird zunehmend unattraktiver, wenn sie das Potenzial für finanzielle Unabhängigkeit durch ihre überlegene Spar-Technologie sehen.
Infolgedessen können Bitcoiner in der Mitte ihrer Lebenskrise ihre Prioritäten und Werte in Frage stellen. Sie könnten beginnen, die gesellschaftlichen Normen und Erwartungen zu hinterfragen, die ihr Leben bis zu diesem Zeitpunkt bestimmt haben. Das Bedürfnis nach Anerkennung oder Bestätigung durch andere hat nicht mehr den gleichen Stellenwert, da sie erkennen, dass ihr Wohlstand und ihr Erfolg nicht durch traditionelle Maßstäbe definiert werden.
Diese veränderte Denkweise kann zu einem Mangel an Filter oder Selbstzensur in ihren Interaktionen mit anderen führen. Bitcoiner, die eine Midlife-Crisis durchleben, werden möglicherweise offener und selbstbewusster, wenn es darum geht, ihre Überzeugungen und Meinungen zu äußern, unabhängig davon, wie sie von ihrem Umfeld wahrgenommen werden. Sie haben vielleicht nicht mehr das Bedürfnis, sich an gesellschaftliche Normen anzupassen oder sich an konventionelle Weisheiten zu halten, was zu Konflikten mit Freunden, Familie oder Arbeitskollegen führt, die ihre Ansichten nicht verstehen oder teilen.
Die emotionale Loslösung, die mit der Bitcoiner-Midlife-Crisis einhergeht, kann sich auch in einem allgemeinen Gefühl der Apathie oder Gleichgültigkeit gegenüber äußeren Ereignissen oder Umständen äußern. Themen oder Herausforderungen, die früher vielleicht eine starke emotionale Reaktion hervorgerufen haben, werden jetzt kaum noch wahrgenommen. Die Höhen und Tiefen des alltäglichen Fiat-Jobs scheinen im Vergleich zur Volatilität des Bitcoin-Marktes unbedeutend zu sein.
Mitten in dieser Midlife-Crisis könnten sich Bitcoiner an einem Scheideweg wiederfinden und sich mit Fragen der Identität, des Zwecks und der Erfüllung auseinandersetzen. Sie könnten gezwungen sein, sich mit ihrer eigenen Sterblichkeit und dem Erbe, das sie hinterlassen wollen, auseinanderzusetzen. Die traditionellen Meilensteine des Erfolgs, wie ein Haus, staatliche Altersvorsorge oder berufliche Erfolge, haben vielleicht nicht mehr die gleiche Anziehungskraft, wenn man sie mit dem Potenzial für finanzielle Freiheit und Souveränität vergleicht, das der Bitcoin bietet.
Die Midlife-Crisis der Bitcoiner ist nicht nur ein persönlicher Kampf, sondern ein Spiegelbild der breiteren gesellschaftlichen Veränderungen und Umwälzungen, die durch den Aufstieg eines digitalen Geldes ausgelöst wurden, welches die Gesellschaft von monetärer Entwertung und finanzieller Unterdrückung befreit. Sie ist eine Herausforderung für die etablierten Normen und Strukturen der Finanzwelt und eine Neudefinition dessen, was es bedeutet, in der modernen Zeit Erfolg und Erfüllung zu finden.
Während Bitcoiner durch diese Midlife-Crisis schreiten, können sie Trost darin finden, sich mit anderen zu verbinden, die ihre Reise und Erfahrungen teilen. Online-Communities, Meetups und Konferenzen bieten einen Raum für Gleichgesinnte, um zusammenzukommen und sich gegenseitig durch die Höhen und Tiefen des Bitcoin-Marktes zu unterstützen. Indem sie ihre Kämpfe, Erfolge und Einsichten miteinander teilen, können Bitcoiner ein Gefühl der Kameradschaft und ein Ziel auf ihrem Weg zur finanziellen Unabhängigkeit und Selbstverwirklichung finden.
Zusammenfassend lässt sich sagen, dass die Midlife-Crisis der Bitcoiner ein komplexes und vielschichtiges Phänomen ist, das die einzigartigen Herausforderungen und Chancen der Einführung von gesundem Geld widerspiegelt. Sie stellt einen Wendepunkt im Leben derjenigen dar, die tief in die Welt des Bitcoin eingetaucht sind, wo traditionelle Maßstäbe für Erfolg und Erfüllung im Lichte des Potenzials für Selbstständigkeit und finanzielle Freiheit neu bewertet werden. Indem sie sich mit ihren eigenen Werten, Überzeugungen und Prioritäten auseinandersetzen, können Bitcoiner aus dieser Midlife-Crisis mit einem neuen Sinn für Ziel und Richtung auf ihrer Reise zu finanzieller Unabhängigkeit und Selbstverwirklichung hervorgehen.
-
 @ 04ea4f83:210e1713
2025-04-20 08:37:09
@ 04ea4f83:210e1713
2025-04-20 08:37:09Veröffentlicht auf Medium am 07.06.2021\ Originalautor: Tomer Strolight\ Übersetzt von: Sinautoshi am 04.05.2023 - 788249\
Reden wir über Dinge, die man mit Geld nicht kaufen kann.
Ehrlichkeit kann man mit Geld nicht kaufen. Tatsächlich sind Menschen, die versuchen, dich davon zu überzeugen, ihnen dein Geld zu geben, oft nicht ganz ehrlich zu dir.
Freundschaft kann man mit Geld nicht kaufen. Du kannst nicht in ein Geschäft oder eine Bar gehen und einen Freund kaufen – jemanden, der deine Werte teilt, der dich respektiert, den du respektierst. Und aus den gleichen Gründen kann man sich damit keine Liebe kaufen , die eine besonders tiefe Form der Freundschaft ist.
Vor allem kann Geld dir keine Dinge kaufen, die in dir selbst sind: Es kann dir kein Selbstwertgefühl, Intelligenz, Mut oder Integrität kaufen, um nur einige Beispiele zu nennen. Gebe einer unsicheren Person einen Haufen Geld und sie wird es verschwenden, um vor anderen anzugeben oder sich selbst zu zerstören. Gib einem intellektuell faulen Menschen Geld und er wird nicht schlauer. Gebe einem Feigling Geld und er hat nur noch eine Sache, vor der er Angst haben muss: das Geld zu verlieren. Und gebe einem Betrüger Geld, und er wird versuchen, es zu verwenden, um einen unehrlichen Plan auszuhecken, durch den er mehr bekommen kann.
Die Dinge, die man für Geld kaufen kann
Geld wird dir ein schönes Outfit, einen tollen Haarschnitt, ein schickes Auto und ein schönes Haus kaufen, aber das Glück selbst wird unerreichbar bleiben ohne echte Freunde und Liebhaber, denen du vertrauen kannst, und ohne in der Lage zu sein, dich selbst zu lieben und zu respektieren.
Geld kauft nämlich kein Glück. Nicht von alleine. Es ist nicht ausreichend.
Warum arbeiten wir dann so hart für Geld? Warum messen manche Menschen ihren Wert in Dollar?
Es ist wahr, dass wir viele der Dinge brauchen, die man mit Geld kaufen kann, wie Nahrung, Unterkunft, Kleidung und sogar Unterhaltung, die uns ein wenig glücklicher macht.
Geld kann ein Wegbereiter sein. Es kann verwendet werden, um Dinge zu kaufen, die grundlegende Überlebensbedürfnisse befriedigen, und uns dadurch die Zeit verschaffen, diesen anderen Werten nachzugehen, die Geld selbst nicht kaufen kann.
Es ist jedoch immer noch sehr falsch, unseren Wert anhand einer einzigen Zahl zu messen, geschweige denn an einer Zahl, von der wir wissen, dass sie Freundschaft, Liebe, Selbstwertgefühl, Intelligenz, Mut, Integrität und viele andere Tugenden und Werte, die wir zeigen und verfolgen sollten, auslässt.
Was hat das mit Bitcoin zu tun?
Nehmen wir uns nun eine Minute Zeit, um uns die Gemeinschaft der Bitcoiner anzusehen. Bitcoiner sind überzeugt von einer neue Form von Geld, Bitcoin.
Wir unternehmen große Anstrengungen, um zu erklären, warum wir denken, dass es die beste Form von Geld ist, die es je gegeben hat und wahrscheinlich jemals geben wird.
Um dies erklären zu können, müssen wir zunächst große Anstrengungen unternehmen, um zu verstehen, was Geld ist und wie Bitcoin die Anforderungen erfüllt, Geld zu sein.
Dazu müssen wir einen sehr ehrlichen Blick auf die Geschichte und die Gegenwart werfen . Wir müssen erforschen, was viele Menschen für selbstverständlich halten. Wir müssen harte Fragen stellen und nach ehrlichen, vertretbaren Antworten suchen.
Wir müssen etwas über die Mathematik lernen, auf die sich Bitcoin stützt.
Wir müssen etwas über die Energieproduktion lernen, auf die Bitcoin angewiesen ist.
Wir lernen etwas über Ökonomie, die Lehre davon, wie Menschen mit den Dingen umgehen, die man mit Geld kaufen kann.
Wir entwickeln eine tiefe Überzeugung, die von all diesem Lernen und unseren Beobachtungen und Argumenten über das, was um uns herum passiert, geprägt ist.
Wir bilden Ansichten darüber aus, wohin die Welt steuert .
Wir kommen zu dem Schluss, dass eine Welt mit Bitcoin als Geld oder auch nur als das Geld, das von uns, welche sich für Bitcoin entscheiden, verwendet wird, eine bessere Welt ist.
Wir schließen daraus, dass es eine bessere Welt ist, weil sie ehrlich und transparent ist. Es ist eine Welt ohne Geheimnisse, Intrigen und Täuschungen darüber, was Geld ist.
Es ist eine Welt ohne mächtige Leute, die die Kontrolle über das Geldsystem ausüben, um die Schwachen zu kontrollieren.
Wir finden dann eine moralische Mission in Bitcoin.
Wir übernehmen die Verantwortung, das Wissen zu verbreiten.
Dazu braucht es Mut. Wir müssen unser Geld dort einsetzen, wo unser Mund ist, indem wir Bitcoin mit unseren Euro kaufen. Dies ist ein Akt der Risikobereitschaft oder des Mutes. Es ist ein Akt der Integrität – unsere Worte an unseren Taten auszurichten.
Wir müssen standhaft bleiben. Wir werden ausgelacht. Mächtige Menschen und Institutionen verspotten uns und versuchen, uns zu diskreditieren. Sie bezeichnen uns als Unterstützer von Kriminellen und Terroristen. Entweder stärken wir unseren Mut und unsere Überzeugung oder verlassen Bitcoin.
Diejenigen von uns, die bleiben, wissen, dass unsere Mit-Bitcoiner, die die gleichen Schwierigkeiten durchgemacht haben oder durchmachen wie wir, ehrlich, intelligent und mutig sind.
Wir respektieren einander. Wir werden Freunde.
Wir alle tragen bei, was wir können, wie wir können. Wir bauen die Welt, die wir uns vorstellen.
All dies tun wir unbeirrt, während Millionen an der Seitenlinie stehen, einige neugierig zusehen, uns verspotten und einige aktiv angreifen und versuchen, uns aufzuhalten. Ab und zu rennt einer rüber und sagt „Ich will so sein wie du!“ Und wir empfangen sie mit offenen Armen.
Ein Bitcoiner zu werden ist ein Prozess, durch den du Dinge erhältst, die man mit Geld nicht kaufen kann.
Schau mal. Ehrlichkeit kann man mit Geld nicht kaufen. Freundschaft kann man damit nicht kaufen. Selbstachtung, Mut, Intelligenz oder Integrität kann man damit auch nicht kaufen. Doch diese Bitcoiner mit ihren Ideen, ihren Idealen, Bemühungen und ihren Errungenschaften haben sich all diese Dinge angeeignet. Bitcoiner sind ehrlich. Sie haben authentische Freundschaften. Sie glauben an sich. Sie sind mutig. Sie sind schlau. Und sie besitzen eine Integrität, die all diese Dinge über jeden Reichtum stellt, der in einem monetären Wert gemessen wird.
Kein Bitcoiner beurteilt einen anderen danach, wie viel Bitcoin diese andere Person wert ist.
Es ist ein Fauxpas in der Community, überhaupt danach zu fragen.
Ich liebe meine Mit-Bitcoiner. Sie sind die besten Menschen auf Erden. Einige mögen finanziell reich sein, andere nicht. Aber sie sind mir alle viel mehr wert als Geld.
Bitcoin hat uns allen eine Fülle von Dingen gegeben, die man mit Geld nicht kaufen kann.
-
 @ 87122b31:726e2c4c
2025-04-21 02:14:24
@ 87122b31:726e2c4c
2025-04-21 02:14:24Betwinner mang đến một nền tảng số hiện đại được thiết kế để phục vụ đa dạng đối tượng người dùng trong thời đại công nghệ ngày càng phát triển. Từ giao diện thân thiện đến khả năng tùy biến linh hoạt, nền tảng này luôn đặt sự thuận tiện và trải nghiệm người dùng lên hàng đầu. Ngay từ lần đầu truy cập, bạn sẽ cảm nhận được tốc độ phản hồi nhanh chóng, giao diện mượt mà và bố cục dễ hiểu – những yếu tố giúp Betwinner trở nên khác biệt so với nhiều nền tảng khác. Sự tương thích đa thiết bị, từ điện thoại thông minh đến máy tính bàn, giúp người dùng dễ dàng duy trì kết nối và thao tác linh hoạt trong mọi hoàn cảnh. Với việc tích hợp các tính năng thông minh và các lựa chọn cá nhân hóa như chế độ nền tối, ngôn ngữ hiển thị và điều chỉnh bố cục theo thói quen sử dụng, Betwinner mang lại cảm giác sử dụng cá nhân hóa rõ rệt và gần gũi.
Không chỉ gây ấn tượng với thiết kế và hiệu năng vận hành, Betwinner còn chú trọng vào bảo mật và sự an tâm của người dùng. Nền tảng này sử dụng công nghệ mã hóa tiên tiến để bảo vệ thông tin cá nhân và dữ liệu trong quá trình sử dụng, kết hợp cùng cơ chế xác thực đa lớp để ngăn chặn các truy cập trái phép. Điều này đặc biệt quan trọng khi người dùng ngày càng có yêu cầu cao về tính bảo mật trong các giao dịch và thông tin cá nhân. Ngoài ra, Betwinner còn trang bị hệ thống hỗ trợ khách hàng 24/7, sẵn sàng giải đáp mọi thắc mắc, xử lý vấn đề nhanh chóng và đảm bảo người dùng luôn nhận được sự hỗ trợ cần thiết khi gặp phải bất kỳ sự cố nào. Việc cập nhật hệ thống và cải tiến tính năng diễn ra thường xuyên nhằm tối ưu hóa hiệu năng và tăng cường sự ổn định trong mọi hoạt động, từ những thao tác cơ bản cho đến các chức năng chuyên sâu hơn.
Không dừng lại ở việc cung cấp một nền tảng số tiện lợi, Betwinner còn hướng đến xây dựng một hệ sinh thái kết nối toàn diện. Với khả năng tích hợp nhanh các công nghệ mới như trí tuệ nhân tạo (AI), học máy (machine learning), cũng như tự động hóa quy trình trải nghiệm, nền tảng này đang tạo ra những thay đổi đáng kể trong cách người dùng tiếp cận và tương tác với không gian số. Mọi dữ liệu sử dụng đều được phân tích để từ đó cung cấp các đề xuất thông minh, giúp tiết kiệm thời gian và tối ưu hóa trải nghiệm cá nhân. Không chỉ là nơi cung cấp công cụ, Betwinner còn là điểm đến cho những ai muốn trải nghiệm môi trường công nghệ hiện đại, nơi mỗi hành động đều được hỗ trợ bởi nền tảng kỹ thuật mạnh mẽ và tư duy lấy người dùng làm trọng tâm. Trong bối cảnh xu hướng chuyển đổi số ngày càng mạnh mẽ, Betwinner đã và đang khẳng định vị thế là một trong những lựa chọn hàng đầu dành cho những ai đang tìm kiếm sự tiện nghi, bảo mật và sự chủ động trong trải nghiệm số hóa.
-
 @ 4857600b:30b502f4
2025-02-20 19:09:11
@ 4857600b:30b502f4
2025-02-20 19:09:11Mitch McConnell, a senior Republican senator, announced he will not seek reelection.
At 83 years old and with health issues, this decision was expected. After seven terms, he leaves a significant legacy in U.S. politics, known for his strategic maneuvering.
McConnell stated, “My current term in the Senate will be my last.” His retirement marks the end of an influential political era.
-
 @ 0176967e:1e6f471e
2024-07-21 11:24:21
@ 0176967e:1e6f471e
2024-07-21 11:24:21Podnikanie je jazyk s "crystal clear" pravidlami. Inštrumentalisti vidia podnikanie staticky, a toto videnie prenášajú na spoločnosť. Preto nás spoločnosť vníma často negatívne. Skutoční podnikatelia sú však "komunikátori".
Jozef Martiniak je zakladateľ AUSEKON - Institute of Austrian School of Economics
-
 @ dc4cd086:cee77c06
2025-02-09 03:35:25
@ dc4cd086:cee77c06
2025-02-09 03:35:25Have you ever wanted to learn from lengthy educational videos but found it challenging to navigate through hours of content? Our new tool addresses this problem by transforming long-form video lectures into easily digestible, searchable content.
Key Features:
Video Processing:
- Automatically downloads YouTube videos, transcripts, and chapter information
- Splits transcripts into sections based on video chapters
Content Summarization:
- Utilizes language models to transform spoken content into clear, readable text
- Formats output in AsciiDoc for improved readability and navigation
- Highlights key terms and concepts with [[term]] notation for potential cross-referencing
Diagram Extraction:
- Analyzes video entropy to identify static diagram/slide sections
- Provides a user-friendly GUI for manual selection of relevant time ranges
- Allows users to pick representative frames from selected ranges
Going Forward:
Currently undergoing a rewrite to improve organization and functionality, but you are welcome to try the current version, though it might not work on every machine. Will support multiple open and closed language models for user choice Free and open-source, allowing for personal customization and integration with various knowledge bases. Just because we might not have it on our official Alexandria knowledge base, you are still welcome to use it on you own personal or community knowledge bases! We want to help find connections between ideas that exist across relays, allowing individuals and groups to mix and match knowledge bases between each other, allowing for any degree of openness you care.
While designed with #Alexandria users in mind, it's available for anyone to use and adapt to their own learning needs.
Screenshots
Frame Selection

This is a screenshot of the frame selection interface. You'll see a signal that represents frame entropy over time. The vertical lines indicate the start and end of a chapter. Within these chapters you can select the frames by clicking and dragging the mouse over the desired range where you think diagram is in that chapter. At the bottom is an option that tells the program to select a specific number of frames from that selection.
Diagram Extraction

This is a screenshot of the diagram extraction interface. For every selection you've made, there will be a set of frames that you can choose from. You can select and deselect as many frames as you'd like to save.
Links
- repo: https://github.com/limina1/video_article_converter
- Nostr Apps 101: https://www.youtube.com/watch?v=Flxa_jkErqE
Output
And now, we have a demonstration of the final result of this tool, with some quick cleaning up. The video we will be using this tool on is titled Nostr Apps 101 by nostr:npub1nxy4qpqnld6kmpphjykvx2lqwvxmuxluddwjamm4nc29ds3elyzsm5avr7 during Nostrasia. The following thread is an analog to the modular articles we are constructing for Alexandria, and I hope it conveys the functionality we want to create in the knowledge space. Note, this tool is the first step! You could use a different prompt that is most appropriate for the specific context of the transcript you are working with, but you can also manually clean up any discrepancies that don't portray the video accurately. You can now view the article on #Alexandria https://next-alexandria.gitcitadel.eu/publication?d=nostr-apps-101
Initially published as chained kind 1's nostr:nevent1qvzqqqqqqypzp5r5hd579v2sszvvzfel677c8dxgxm3skl773sujlsuft64c44ncqy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcpzemhxue69uhhyetvv9ujumt0wd68ytnsw43z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309aex2mrp0yh8xmn0wf6zuum0vd5kzmp0qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgc7hglpn
Or view on Coracle https://coracle.social /nevent1qqsxunmjy20mvlq37vnrcshkf6sdrtkfjtjz3anuetmcuv8jswhezgcppemhxue69uhkummn9ekx7mp0qgsdqa9md83tz5yqnrqjw07hhkpmfjpkuv9hlh5v8yhu8z274w9dv7qnnq0s3
-
 @ d9e9fb27:d5fe5e1a
2025-04-22 01:29:16
@ d9e9fb27:d5fe5e1a
2025-04-22 01:29:16"There are two pillars in Costa Rica, education and coffee." A tourist guide I met told me this, and during the trip I discovered the strong link between coffee and the locals.
In fact, coffee runs very deeply in the Ticos' culture. So deep that the summer vacations from school (November to January) coincide with the coffee collection season. Children had to help their parents with the coffee. Coffee was a family business.
Monteverde, in the region of Puentarenas, is one of those places where coffee ha always been a corner stone of the society. Here, My gf and I went to visit a coffee plantation and discovered how coffee is made.
Monteverde
Monteverde is a well-known turistic location in the central part of Costa Rica. Many people reach this beautiful place to visit the famous Cloud Rainforest, acres and acres of pristine forest, with many different kind of animals and plants living in it.

However, other than tourism is coffee that pushes the economy of this place. The hills around the town are covered with coffee plantations and there are tours than try to explain how coffee is made.

Coffee Tours
While we were in Monteverde, we joined one of these tours. We decided to give credit to a smaller plantation instead of the super turistic ones. A more rustic and family-owned business, El Pueblo Coffee Tour. We were not disappointed. We had the show all to ourselves, a super-prepared guide and all the time to make questions and enjoy with no rush.
The Plant of Coffee
Since Costa Rica is a quite small country, to compete on the market producers decided to bet on quality instead of quantity. That's why, the only type produced here is the Arabica.
Before the coffee bean, the plant produces a nice white flower, similar to the jasmine.

After a while, the coffee beans appear.

As soon as they turn red, they are ready to be collected.
Interesting fact: between the coffee plants many fruit trees like mangos or bananos can be found. In fact, those plants help keep the soil fertile and healthy, thus leading to a higher coffee quality!
Coffee Harvesting
Coffee is still harvested by hand. Beans do not get mature at the same time, so manual labor is needed. Laborer use a very simple tool to collect coffee, one which allow them to have both hands free.
 Workers do not get paid by hours, but by the number of cajuelas that they can fill. A cajuela is a standard box, which contains around 13kg of beans. It's divided into quarters, so that the worker can get paid for the quarter, too.
Workers do not get paid by hours, but by the number of cajuelas that they can fill. A cajuela is a standard box, which contains around 13kg of beans. It's divided into quarters, so that the worker can get paid for the quarter, too.
Each cajuela is paid around 3.50$.
Coffee Drying
In the farm we visited, drying was perfomed naturally, through the heat of the sun. There are three ways in which the bean is left to dry: lavado, miel and naturàl.
- Lavado: The beans are peeled and washed to remove the jelly.
 - Miel: The jelly on the beans is maintained to give it more sweet flavour.
- Miel: The jelly on the beans is maintained to give it more sweet flavour. - Naturàl: The bean is left to dry with its peel on, to give it a more fruity taste.
- Naturàl: The bean is left to dry with its peel on, to give it a more fruity taste.
Back in the days, to peel the beans for the lavado and the miel variety, the pìlon was used. The bean is very hard, thus this tool does not damage it.

However, today the peeling procedure is done using a machine.

Coffee Roasting
The last step in the production of coffee is roasting. Coffee is put inside a sort of hoven, and is left there at high temperature according to the level of roasting that is needed. The more roasting, the less caffeine there is and the more bitter the coffee. Usually you have light, medium and dark roast.

Coffee Tasting
In the end, we also had a coffee tasting. We tried different roasting and different varieties.
Our guide explained us the best way to taste coffee and helped us defining the different flavours that we perceived. He also taught us the best way to prepare it: infusion time, water temperature, coffe makers and so on.
My favorite one was the dark one, while my gf enjoyed the light roast more. Of course, we bought some packs of these varieties!
Thanks for tuning in!
I hope you enjoyed this brief overview of the Costa Rican coffee.
Pura Vida
Tuma
-
 @ 91bea5cd:1df4451c
2025-02-04 17:24:50
@ 91bea5cd:1df4451c
2025-02-04 17:24:50Definição de ULID:
Timestamp 48 bits, Aleatoriedade 80 bits Sendo Timestamp 48 bits inteiro, tempo UNIX em milissegundos, Não ficará sem espaço até o ano 10889 d.C. e Aleatoriedade 80 bits, Fonte criptograficamente segura de aleatoriedade, se possível.
Gerar ULID
```sql
CREATE EXTENSION IF NOT EXISTS pgcrypto;
CREATE FUNCTION generate_ulid() RETURNS TEXT AS $$ DECLARE -- Crockford's Base32 encoding BYTEA = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; timestamp BYTEA = E'\000\000\000\000\000\000'; output TEXT = '';
unix_time BIGINT; ulid BYTEA; BEGIN -- 6 timestamp bytes unix_time = (EXTRACT(EPOCH FROM CLOCK_TIMESTAMP()) * 1000)::BIGINT; timestamp = SET_BYTE(timestamp, 0, (unix_time >> 40)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 1, (unix_time >> 32)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 2, (unix_time >> 24)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 3, (unix_time >> 16)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 4, (unix_time >> 8)::BIT(8)::INTEGER); timestamp = SET_BYTE(timestamp, 5, unix_time::BIT(8)::INTEGER);
-- 10 entropy bytes ulid = timestamp || gen_random_bytes(10);
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 1) & 7) << 2) | ((GET_BYTE(ulid, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 2) & 1) << 4) | ((GET_BYTE(ulid, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 3) & 15) << 1) | ((GET_BYTE(ulid, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 4) & 3) << 3) | ((GET_BYTE(ulid, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 6) & 7) << 2) | ((GET_BYTE(ulid, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 7) & 1) << 4) | ((GET_BYTE(ulid, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 8) & 15) << 1) | ((GET_BYTE(ulid, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 9) & 3) << 3) | ((GET_BYTE(ulid, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 11) & 7) << 2) | ((GET_BYTE(ulid, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 12) & 1) << 4) | ((GET_BYTE(ulid, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 13) & 15) << 1) | ((GET_BYTE(ulid, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(ulid, 14) & 3) << 3) | ((GET_BYTE(ulid, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(ulid, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql VOLATILE; ```
ULID TO UUID
```sql CREATE OR REPLACE FUNCTION parse_ulid(ulid text) RETURNS bytea AS $$ DECLARE -- 16byte bytes bytea = E'\x00000000 00000000 00000000 00000000'; v char[]; -- Allow for O(1) lookup of index values dec integer[] = ARRAY[ 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 255, 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 255, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31, 255, 255, 255, 255, 255, 255, 10, 11, 12, 13, 14, 15, 16, 17, 1, 18, 19, 1, 20, 21, 0, 22, 23, 24, 25, 26, 255, 27, 28, 29, 30, 31 ]; BEGIN IF NOT ulid ~* '^[0-7][0-9ABCDEFGHJKMNPQRSTVWXYZ]{25}$' THEN RAISE EXCEPTION 'Invalid ULID: %', ulid; END IF;
v = regexp_split_to_array(ulid, '');
-- 6 bytes timestamp (48 bits) bytes = SET_BYTE(bytes, 0, (dec[ASCII(v[1])] << 5) | dec[ASCII(v[2])]); bytes = SET_BYTE(bytes, 1, (dec[ASCII(v[3])] << 3) | (dec[ASCII(v[4])] >> 2)); bytes = SET_BYTE(bytes, 2, (dec[ASCII(v[4])] << 6) | (dec[ASCII(v[5])] << 1) | (dec[ASCII(v[6])] >> 4)); bytes = SET_BYTE(bytes, 3, (dec[ASCII(v[6])] << 4) | (dec[ASCII(v[7])] >> 1)); bytes = SET_BYTE(bytes, 4, (dec[ASCII(v[7])] << 7) | (dec[ASCII(v[8])] << 2) | (dec[ASCII(v[9])] >> 3)); bytes = SET_BYTE(bytes, 5, (dec[ASCII(v[9])] << 5) | dec[ASCII(v[10])]);
-- 10 bytes of entropy (80 bits); bytes = SET_BYTE(bytes, 6, (dec[ASCII(v[11])] << 3) | (dec[ASCII(v[12])] >> 2)); bytes = SET_BYTE(bytes, 7, (dec[ASCII(v[12])] << 6) | (dec[ASCII(v[13])] << 1) | (dec[ASCII(v[14])] >> 4)); bytes = SET_BYTE(bytes, 8, (dec[ASCII(v[14])] << 4) | (dec[ASCII(v[15])] >> 1)); bytes = SET_BYTE(bytes, 9, (dec[ASCII(v[15])] << 7) | (dec[ASCII(v[16])] << 2) | (dec[ASCII(v[17])] >> 3)); bytes = SET_BYTE(bytes, 10, (dec[ASCII(v[17])] << 5) | dec[ASCII(v[18])]); bytes = SET_BYTE(bytes, 11, (dec[ASCII(v[19])] << 3) | (dec[ASCII(v[20])] >> 2)); bytes = SET_BYTE(bytes, 12, (dec[ASCII(v[20])] << 6) | (dec[ASCII(v[21])] << 1) | (dec[ASCII(v[22])] >> 4)); bytes = SET_BYTE(bytes, 13, (dec[ASCII(v[22])] << 4) | (dec[ASCII(v[23])] >> 1)); bytes = SET_BYTE(bytes, 14, (dec[ASCII(v[23])] << 7) | (dec[ASCII(v[24])] << 2) | (dec[ASCII(v[25])] >> 3)); bytes = SET_BYTE(bytes, 15, (dec[ASCII(v[25])] << 5) | dec[ASCII(v[26])]);
RETURN bytes; END $$ LANGUAGE plpgsql IMMUTABLE;
CREATE OR REPLACE FUNCTION ulid_to_uuid(ulid text) RETURNS uuid AS $$ BEGIN RETURN encode(parse_ulid(ulid), 'hex')::uuid; END $$ LANGUAGE plpgsql IMMUTABLE; ```
UUID to ULID
```sql CREATE OR REPLACE FUNCTION uuid_to_ulid(id uuid) RETURNS text AS $$ DECLARE encoding bytea = '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; output text = ''; uuid_bytes bytea = uuid_send(id); BEGIN
-- Encode the timestamp output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 224) >> 5)); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 0) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 1) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 1) & 7) << 2) | ((GET_BYTE(uuid_bytes, 2) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 2) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 2) & 1) << 4) | ((GET_BYTE(uuid_bytes, 3) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 3) & 15) << 1) | ((GET_BYTE(uuid_bytes, 4) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 4) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 4) & 3) << 3) | ((GET_BYTE(uuid_bytes, 5) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 5) & 31)));
-- Encode the entropy output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 6) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 6) & 7) << 2) | ((GET_BYTE(uuid_bytes, 7) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 7) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 7) & 1) << 4) | ((GET_BYTE(uuid_bytes, 8) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 8) & 15) << 1) | ((GET_BYTE(uuid_bytes, 9) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 9) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 9) & 3) << 3) | ((GET_BYTE(uuid_bytes, 10) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 10) & 31))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 11) & 248) >> 3)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 11) & 7) << 2) | ((GET_BYTE(uuid_bytes, 12) & 192) >> 6))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 12) & 62) >> 1)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 12) & 1) << 4) | ((GET_BYTE(uuid_bytes, 13) & 240) >> 4))); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 13) & 15) << 1) | ((GET_BYTE(uuid_bytes, 14) & 128) >> 7))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 14) & 124) >> 2)); output = output || CHR(GET_BYTE(encoding, ((GET_BYTE(uuid_bytes, 14) & 3) << 3) | ((GET_BYTE(uuid_bytes, 15) & 224) >> 5))); output = output || CHR(GET_BYTE(encoding, (GET_BYTE(uuid_bytes, 15) & 31)));
RETURN output; END $$ LANGUAGE plpgsql IMMUTABLE; ```
Gera 11 Digitos aleatórios: YBKXG0CKTH4
```sql -- Cria a extensão pgcrypto para gerar uuid CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Cria a função para gerar ULID CREATE OR REPLACE FUNCTION gen_lrandom() RETURNS TEXT AS $$ DECLARE ts_millis BIGINT; ts_chars TEXT; random_bytes BYTEA; random_chars TEXT; base32_chars TEXT := '0123456789ABCDEFGHJKMNPQRSTVWXYZ'; i INT; BEGIN -- Pega o timestamp em milissegundos ts_millis := FLOOR(EXTRACT(EPOCH FROM clock_timestamp()) * 1000)::BIGINT;
-- Converte o timestamp para base32 ts_chars := ''; FOR i IN REVERSE 0..11 LOOP ts_chars := ts_chars || substr(base32_chars, ((ts_millis >> (5 * i)) & 31) + 1, 1); END LOOP; -- Gera 10 bytes aleatórios e converte para base32 random_bytes := gen_random_bytes(10); random_chars := ''; FOR i IN 0..9 LOOP random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) >> 3) & 31) + 1, 1); IF i < 9 THEN random_chars := random_chars || substr(base32_chars, (((get_byte(random_bytes, i) & 7) << 2) | (get_byte(random_bytes, i + 1) >> 6)) & 31 + 1, 1); ELSE random_chars := random_chars || substr(base32_chars, ((get_byte(random_bytes, i) & 7) << 2) + 1, 1); END IF; END LOOP; -- Concatena o timestamp e os caracteres aleatórios RETURN ts_chars || random_chars;END; $$ LANGUAGE plpgsql; ```
Exemplo de USO
```sql -- Criação da extensão caso não exista CREATE EXTENSION IF NOT EXISTS pgcrypto; -- Criação da tabela pessoas CREATE TABLE pessoas ( ID UUID DEFAULT gen_random_uuid ( ) PRIMARY KEY, nome TEXT NOT NULL );
-- Busca Pessoa na tabela SELECT * FROM "pessoas" WHERE uuid_to_ulid ( ID ) = '252FAC9F3V8EF80SSDK8PXW02F'; ```
Fontes
- https://github.com/scoville/pgsql-ulid
- https://github.com/geckoboard/pgulid
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ b17fccdf:b7211155
2025-02-01 18:41:27
@ b17fccdf:b7211155
2025-02-01 18:41:27Next new resources about the MiniBolt guide have been released:
- 🆕 Roadmap: LINK
- 🆕 Dynamic Network map: LINK
- 🆕 Nostr community: LINK < ~ REMOVE the "[]" symbols from the URL (naddr...) to access
- 🆕 Linktr FOSS (UC) by Gzuuus: LINK
- 🆕 Donate webpage: 🚾 Clearnet LINK || 🧅 Onion LINK
- 🆕 Contact email: hello@minibolt.info
Enjoy it MiniBolter! 💙
-
 @ e39d100f:d27602e5
2025-04-21 02:14:21
@ e39d100f:d27602e5
2025-04-21 02:14:21O mundo do entretenimento digital não para de crescer, e a 5588bet surge como uma plataforma moderna, segura e completa para quem busca diversão, emoção e oportunidades reais de ganhar prêmios. Com uma interface amigável, suporte eficiente e uma grande variedade de jogos, a 5588bet rapidamente conquistou espaço entre os jogadores brasileiros.
A primeira impressão ao acessar a 5588bet é a de um ambiente profissional e bem estruturado. A navegação é fluida, tanto no computador quanto em dispositivos móveis, permitindo que o usuário explore todas as funcionalidades com facilidade. A plataforma foi desenvolvida pensando na experiência do usuário, oferecendo menus intuitivos, design atrativo e carregamento rápido das páginas.
A segurança é uma prioridade para a 5588bet . Os dados dos jogadores são protegidos com tecnologia de criptografia de ponta, garantindo que todas as transações financeiras e informações pessoais estejam resguardadas. Além disso, a plataforma conta com uma equipe de suporte técnico disponível 24 horas por dia, pronta para auxiliar em qualquer necessidade.
Variedade de Jogos para Todos os Perfis Um dos grandes diferenciais da 5588bet é a diversidade de jogos disponíveis. A plataforma oferece títulos para todos os gostos, desde os clássicos até os mais modernos, todos com gráficos impressionantes e excelente jogabilidade.
Entre os destaques estão os jogos de roleta, bacará, pôquer, além de uma enorme seleção de slots com diferentes temáticas e mecânicas de bônus. Os jogadores podem explorar aventuras inspiradas em mitologia, filmes, frutas clássicas e muito mais. Muitos desses jogos são desenvolvidos por provedores renomados internacionalmente, garantindo qualidade e inovação a cada partida.
Além disso, para quem gosta de emoção em tempo real, a plataforma conta com mesas interativas com apresentadores ao vivo, proporcionando uma experiência imersiva que simula a sensação de estar em um ambiente físico de jogos, tudo isso com a comodidade de estar em casa ou em qualquer lugar.
Experiência do Jogador em Primeiro Lugar A 5588bet entende que a satisfação do jogador vai além da variedade de jogos. Por isso, investe em uma experiência completa. O processo de registro é rápido e simples, permitindo que novos usuários comecem a jogar em poucos minutos. Os métodos de pagamento são diversificados e incluem as principais carteiras digitais e bancos brasileiros, facilitando depósitos e saques.
A plataforma também oferece promoções atrativas para novos usuários e campanhas frequentes para jogadores fiéis. Bônus de boas-vindas, giros gratuitos, cashback e torneios especiais são algumas das formas que a 5588bet utiliza para valorizar seus usuários e tornar cada visita ainda mais interessante.
Outro ponto importante é a transparência. As regras de cada jogo, promoções e procedimentos financeiros são claramente explicados, dando ao jogador confiança e controle total sobre suas escolhas dentro da plataforma.
Conclusão A 5588bet se destaca como uma plataforma inovadora, segura e repleta de opções para quem busca entretenimento online de qualidade. Com jogos envolventes, suporte eficiente e uma experiência focada no usuário, ela se consolida como uma das melhores escolhas para jogadores brasileiros. Se você está em busca de diversão com emoção e recompensas, a 5588bet é o destino ideal.
-
 @ 866e0139:6a9334e5
2025-04-20 07:09:09
@ 866e0139:6a9334e5
2025-04-20 07:09:09
Autor: Carlos A. Gebauer. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Sie wollen die neuesten Pareto-Artikel auf einen Blick sehen (Friedenstaube & Co.), um nichts mehr zu verpassen?* Hier geht es zu unserem Telegram-Kanal.***
Ostermärsche waren traditionell mahnende Demonstrationen für die Friedfertigkeit. Man ging auf die Straße und warnte vor Faschismus und Krieg. In diesem Jahr (mit seinem vielleicht letzten Sommer vor dem Krieg, wie Sönke Neitzel warnte) liegen die Dinge anders. Der werdende Kanzler Friedrich Merz befürwortet Taurus-Lieferungen an die Ukraine. Waffen also, die bis nach Moskau schießen. Wie einst die Dicke Bertha nach Paris.
https://www.youtube.com/watch?v=qPXn_jmH1Zg
In den Schaufenstern der Modemarken wird das Militär-Outfit schon vorweggenommen: Der eine kleidet seine Kunden in Olivgrün, der andere schneidert in Camouflage. Handtaschen in Tarnfarbe sind en vogue. Kleine Ohrringe in Handgranatenoptik oder Accessoires mit Einzelkämpfertouch mögen folgen. Der Nachwuchs für den Aufwuchs der Reserven ist bedeutsam. Eine laue Sommernacht, lehrte Napoleon, kann eine ganz neue Armee auf den Weg bringen. Kanonenfutter war gestern. Wir haben die High-Tech-Helme, die das Hirn mit Angstfreiheit beglücken. Ein kleiner Stromimpuls und schon spurtet der Infanterist wieder siegesgewiss gen Osten.
In der multipolar zerfallenden Welt ist die Versorgung der ressourcenarmen Regionen mit Rohstoffen ein ernstes Problem. Woher soll die Energie kommen, wenn nicht aus Russland oder dem Nahen Osten? Um politische Unabhängigkeit für einen Westen ohne Bodenschätze zu gewinnen, hat man den Menschen dort seit Jahrzehnten das Narrativ vom Klimawandel aufgetischt. So, glaubte man, schaffe man die Akzeptanz für eine Grüne Energie, für Windparks und Solarfelder, für eine Zukunft jenseits fossiler Brennstoffe.
Nachdem sich diese Illusion der erdöllosen Industrie als Phantasma erwiesen hat, wurden die grünen Friedenstauben zu grünen Waffenlieferanten. Aus dem pazifistischen „Keine Waffen in Kriegsgebiete“ wurde das bellizistische „Alle Waffen zur Ukraine!“ Europa soll wieder aufrüsten, um auch ohne die USA wehrfähig genug zu sein, die nötige fossile Energie herbeizuschaffen. Die pseudoökologische Militärstrategie ist umgewandelt. Statt Friedenstauben fliegt nun bald der Taurus. Die Atomkraft-Nein-Danke-Fraktion riskiert den atomaren Höllenritt. Auch der DGB hat seine Ostermärsche schon eingestellt. Ob die Kirchen bald beginnen, die Waffen zu segnen?
Der 2025er Osterhase trägt Camouflage und die Eier, die er bringt, sind Handgranaten. Er trägt sie gen Osten, wo der Russe sitzt. Im Gleichschritt, wie es sich gehört. Am Ostersonntag winken die Nonnen ihm am Straßenrand. Sie hegen den Aufwuchs und pflegen den Nachwuchs. Für Kriegerwitwen ist Platz in jedem Kloster. Auf das Waffensegnen folgt die Lazarettpflege. Wir können wieder große rote Kreuze in weißem Kreisgrund auf unsere Dächer malen. Der Klerus alimentiert die Ordensfrauen.
Die Nonne schickt keine Rechnung.
Mehr von Carlos A. Gebauer in der Friedenstaube hier.
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.