-
 @ 1beecee5:d29d2162
2025-04-21 06:30:55
@ 1beecee5:d29d2162
2025-04-21 06:30:55 -
 @ 4ba8e86d:89d32de4
2025-04-21 02:13:56
@ 4ba8e86d:89d32de4
2025-04-21 02:13:56Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:12:19
@ 4ba8e86d:89d32de4
2025-04-21 02:12:19SISTEMA OPERACIONAL MÓVEIS
GrapheneOS : https://njump.me/nevent1qqs8t76evdgrg4qegdtyrq2rved63pr29wlqyj627n9tj4vlu66tqpqpzdmhxue69uhk7enxvd5xz6tw9ec82c30qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqppcqec9
CalyxOS : https://njump.me/nevent1qqsrm0lws2atln2kt3cqjacathnw0uj0jsxwklt37p7t380hl8mmstcpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3vamnwvaz7tmwdaehgu3wvf3kstnwd9hx5cf0qy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgcwaehxw309aex2mrp0yhxxatjwfjkuapwveukjtcpzpmhxue69uhkummnw3ezumt0d5hszrnhwden5te0dehhxtnvdakz7qfywaehxw309ahx7um5wgh8ymm4dej8ymmrdd3xjarrda5kuetjwvhxxmmd9uq3uamnwvaz7tmwdaehgu3dv3jhvtnhv4kxcmmjv3jhytnwv46z7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qgewaehxw309ahx7um5wghxymmwva3x7mn89e3k7mf0qythwumn8ghj7cn5vvhxkmr9dejxz7n49e3k7mf0qyg8wumn8ghj7mn09eehgu3wvdez7smttdu
LineageOS : https://njump.me/nevent1qqsgw7sr36gaty48cf4snw0ezg5mg4atzhqayuge752esd469p26qfgpzdmhxue69uhhwmm59e6hg7r09ehkuef0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpnvm779
SISTEMA OPERACIONAL DESKTOP
Tails : https://njump.me/nevent1qqsf09ztvuu60g6xprazv2vxqqy5qlxjs4dkc9d36ta48q75cs9le4qpzemhxue69uhkummnw3ex2mrfw3jhxtn0wfnj7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz34ag5t
Qubes OS : https://njump.me/nevent1qqsp6jujgwl68uvurw0cw3hfhr40xq20sj7rl3z4yzwnhp9sdpa7augpzpmhxue69uhkummnw3ezumt0d5hsz9mhwden5te0wfjkccte9ehx7um5wghxyctwvshsz9thwden5te0dehhxarj9ehhsarj9ejx2a30qyg8wumn8ghj7mn09eehgu3wvdez7qg4waehxw309aex2mrp0yhxgctdw4eju6t09uqjxamnwvaz7tmwdaehgu3dwejhy6txd9jkgtnhv4kxcmmjv3jhytnwv46z7qgwwaehxw309ahx7uewd3hkctcpremhxue69uhkummnw3ez6er9wch8wetvd3hhyer9wghxuet59uj3ljr8
Kali linux : https://njump.me/nevent1qqswlav72xdvamuyp9xc38c6t7070l3n2uxu67ssmal2g7gv35nmvhspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswt9rxe
Whonix : https://njump.me/nevent1qqs85gvejvzhk086lwh6edma7fv07p5c3wnwnxnzthwwntg2x6773egpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3qamnwvaz7tmwdaehgu3wd4hk6tcpzemhxue69uhkummnw3ezucnrdqhxu6twdfsj7qfywaehxw309ahx7um5wgh8ymm4dej8ymmrdd3xjarrda5kuetjwvhxxmmd9uq3wamnwvaz7tmzw33ju6mvv4hxgct6w5hxxmmd9uq3qamnwvaz7tmwduh8xarj9e3hytcpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszrnhwden5te0dehhxtnvdakz7qg7waehxw309ahx7um5wgkkgetk9emk2mrvdaexgetj9ehx2ap0sen9p6
Kodachi : https://njump.me/nevent1qqsf5zszgurpd0vwdznzk98hck294zygw0s8dah6fpd309ecpreqtrgpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszgmhwden5te0dehhxarj94mx2unfve5k2epwwajkcmr0wfjx2u3wdejhgtcpremhxue69uhkummnw3ez6er9wch8wetvd3hhyer9wghxuet59uq3qamnwvaz7tmwdaehgu3wd4hk6tcpzamhxue69uhkyarr9e4kcetwv3sh5afwvdhk6tcpzpmhxue69uhkumewwd68ytnrwghszfrhwden5te0dehhxarj9eex7atwv3ex7cmtvf5hgcm0d9hx2unn9e3k7mf0qyvhwumn8ghj7mn0wd68ytnzdahxwcn0denjucm0d5hszrnhwden5te0dehhxtnvdakz7qgkwaehxw309ahx7um5wghxycmg9ehxjmn2vyhsz9mhwden5te0wfjkccte9ehx7um5wghxyctwvshs94a4d5
PGP
Openkeychain : https://njump.me/nevent1qqs9qtjgsulp76t7jkquf8nk8txs2ftsr0qke6mjmsc2svtwfvswzyqpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs36mp0w
Kleopatra : https://njump.me/nevent1qqspnevn932hdggvp4zam6mfyce0hmnxsp9wp8htpumq9vm3anq6etsppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpuaeghp
Pgp : https://njump.me/nevent1qqsggek707qf3rzttextmgqhym6d4g479jdnlnj78j96y0ut0x9nemcpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgptemhe
Como funciona o PGP? : https://njump.me/nevent1qqsz9r7azc8pkvfmkg2hv0nufaexjtnvga0yl85x9hu7ptpg20gxxpspremhxue69uhkummnw3ez6ur4vgh8wetvd3hhyer9wghxuet59upzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy259fhs
Por que eu escrevi PGP. - Philip Zimmermann.
https://njump.me/nevent1qqsvysn94gm8prxn3jw04r0xwc6sngkskg756z48jsyrmqssvxtm7ncpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtchzxnad
VPN
Vpn : https://njump.me/nevent1qqs27ltgsr6mh4ffpseexz6s37355df3zsur709d0s89u2nugpcygsspzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqshzu2fk
InviZible Pro : https://njump.me/nevent1qqsvyevf2vld23a3xrpvarc72ndpcmfvc3lc45jej0j5kcsg36jq53cpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy33y5l4
Orbot: https://njump.me/nevent1qqsxswkyt6pe34egxp9w70cy83h40ururj6m9sxjdmfass4cjm4495stft593
I2P
i2p : https://njump.me/nevent1qqsvnj8n983r4knwjmnkfyum242q4c0cnd338l4z8p0m6xsmx89mxkslx0pgg
Entendendo e usando a rede I2P : https://njump.me/nevent1qqsxchp5ycpatjf5s4ag25jkawmw6kkf64vl43vnprxdcwrpnms9qkcppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpvht4mn
Criando e acessando sua conta Email na I2P : https://njump.me/nevent1qqs9v9dz897kh8e5lfar0dl7ljltf2fpdathsn3dkdsq7wg4ksr8xfgpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpw8mzum
APLICATIVO 2FA
Aegis Authenticator : https://njump.me/nevent1qqsfttdwcn9equlrmtf9n6wee7lqntppzm03pzdcj4cdnxel3pz44zspz4mhxue69uhhyetvv9ujumn0wd68ytnzvuhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqscvtydq
YubiKey : https://njump.me/nevent1qqstsnn69y4sf4330n7039zxm7wza3ch7sn6plhzmd57w6j9jssavtspvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzueyvgt
GERENCIADOR DE SENHAS
KeepassDX: https://njump.me/nevent1qqswc850dr4ujvxnmpx75jauflf4arc93pqsty5pv8hxdm7lcw8ee8qpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpe0492n
Birwaden: https://njump.me/nevent1qqs0j5x9guk2v6xumhwqmftmcz736m9nm9wzacqwjarxmh8k4xdyzwgpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpwfe2kc
KeePassXC: https://njump.me/nevent1qqsgftcrd8eau7tzr2p9lecuaf7z8mx5jl9w2k66ae3lzkw5wqcy5pcl2achp
CHAT MENSAGEM
SimpleXchat : https://njump.me/nevent1qqsds5xselnnu0dyy0j49peuun72snxcgn3u55d2320n37rja9gk8lgzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgmcmj7c
Briar : https://njump.me/nevent1qqs8rrtgvjr499hreugetrl7adkhsj2zextyfsukq5aa7wxthrgcqcg05n434
Element Messenger : https://njump.me/nevent1qqsq05snlqtxm5cpzkshlf8n5d5rj9383vjytkvqp5gta37hpuwt4mqyccee6
Pidgin : https://njump.me/nevent1qqsz7kngycyx7meckx53xk8ahk98jkh400usrvykh480xa4ct9zlx2c2ywvx3
E-MAIL
Thunderbird: https://njump.me/nevent1qqspq64gg0nw7t60zsvea5eykgrm43paz845e4jn74muw5qzdvve7uqrkwtjh
ProtonMail : https://njump.me/nevent1qqs908glhk68e7ms8zqtlsqd00wu3prnpt08dwre26hd6e5fhqdw99cppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpeyhg4z
Tutonota : https://njump.me/nevent1qqswtzh9zjxfey644qy4jsdh9465qcqd2wefx0jxa54gdckxjvkrrmqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs5hzhkv
k-9 mail : https://njump.me/nevent1qqs200g5a603y7utjgjk320r3srurrc4r66nv93mcg0x9umrw52ku5gpr3mhxue69uhkummnw3ezuumhd9ehxtt9de5kwmtp9e3kstczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgacflak
E-MAIL-ALIÁS
Simplelogin : https://njump.me/nevent1qqsvhz5pxqpqzr2ptanqyqgsjr50v7u9lc083fvdnglhrv36rnceppcppemhxue69uhkummn9ekx7mp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqp9gsr7m
AnonAddy : https://njump.me/nevent1qqs9mcth70mkq2z25ws634qfn7vx2mlva3tkllayxergw0s7p8d3ggcpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs6mawe3
NAVEGADOR
Navegador Tor : https://njump.me/nevent1qqs06qfxy7wzqmk76l5d8vwyg6mvcye864xla5up52fy5sptcdy39lspzemhxue69uhkummnw3ezuerpw3sju6rpw4ej7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdp0urw
Mullvap Browser : https://njump.me/nevent1qqs2vsgc3wk09wdspv2mezltgg7nfdg97g0a0m5cmvkvr4nrfxluzfcpzdmhxue69uhhwmm59e6hg7r09ehkuef0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpj8h6fe
LibreWolf : https://njump.me/nevent1qqswv05mlmkcuvwhe8x3u5f0kgwzug7n2ltm68fr3j06xy9qalxwq2cpzemhxue69uhkummnw3ex2mrfw3jhxtn0wfnj7q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzuv2hxr
Cromite : https://njump.me/nevent1qqs2ut83arlu735xp8jf87w5m3vykl4lv5nwkhldkqwu3l86khzzy4cpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs3dplt7
BUSCADORES
Searx : https://njump.me/nevent1qqsxyzpvgzx00n50nrlgctmy497vkm2cm8dd5pdp7fmw6uh8xnxdmaspr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqp23z7ax
APP-STORE
Obtainium : https://njump.me/nevent1qqstd8kzc5w3t2v6dgf36z0qrruufzfgnc53rj88zcjgsagj5c5k4rgpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqyarmca3
F-Droid : https://njump.me/nevent1qqst4kry49cc9g3g8s5gdnpgyk3gjte079jdnv43f0x4e85cjkxzjesymzuu4
Droid-ify : https://njump.me/nevent1qqsrr8yu9luq0gud902erdh8gw2lfunpe93uc2u6g8rh9ep7wt3v4sgpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsfzu9vk
Aurora Store : https://njump.me/nevent1qqsy69kcaf0zkcg0qnu90mtk46ly3p2jplgpzgk62wzspjqjft4fpjgpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzrpmsjy
RSS
Feeder : https://njump.me/nevent1qqsy29aeggpkmrc7t3c7y7ldgda7pszl7c8hh9zux80gjzrfvlhfhwqpp4mhxue69uhkummn9ekx7mqzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgsvzzjy
VIDEOO CONFERENCIA
Jitsi meet : https://njump.me/nevent1qqswphw67hr6qmt2fpugcj77jrk7qkfdrszum7vw7n2cu6cx4r6sh4cgkderr
TECLADOS
HeliBoard : https://njump.me/nevent1qqsyqpc4d28rje03dcvshv4xserftahhpeylu2ez2jutdxwds4e8syspz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsr8mel5
OpenBoard : https://njump.me/nevent1qqsf7zqkup03yysy67y43nj48q53sr6yym38es655fh9fp6nxpl7rqspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswcvh3r
FlorisBoard : https://njump.me/nevent1qqsf7zqkup03yysy67y43nj48q53sr6yym38es655fh9fp6nxpl7rqspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqswcvh3r
MAPAS
Osmand : https://njump.me/nevent1qqsxryp2ywj64az7n5p6jq5tn3tx5jv05te48dtmmt3lf94ydtgy4fgpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs54nwpj
Organic maps : https://njump.me/nevent1qqstrecuuzkw0dyusxdq7cuwju0ftskl7anx978s5dyn4pnldrkckzqpr4mhxue69uhkummnw3ezumtp0p5k6ctrd96xzer9dshx7un8qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpl8z3kk
TRADUÇÃO
LibreTranslate : https://njump.me/nevent1qqs953g3rhf0m8jh59204uskzz56em9xdrjkelv4wnkr07huk20442cpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzeqsx40
REMOÇÃO DOS METADADOS
Scrambled Exif : https://njump.me/nevent1qqs2658t702xv66p000y4mlhnvadmdxwzzfzcjkjf7kedrclr3ej7aspyfmhxue69uhk6atvw35hqmr90pjhytngw4eh5mmwv4nhjtnhdaexcep0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpguu0wh
ESTEGANOGRAFIA
PixelKnot: https://njump.me/nevent1qqsrh0yh9mg0lx86t5wcmhh97wm6n4v0radh6sd0554ugn354wqdj8gpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqyuvfqdp
PERFIL DE TRABALHO
Shelter : https://njump.me/nevent1qqspv9xxkmfp40cxgjuyfsyczndzmpnl83e7gugm7480mp9zhv50wkqpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdnu59c
PDF
MuPDF : https://njump.me/nevent1qqspn5lhe0dteys6npsrntmv2g470st8kh8p7hxxgmymqa95ejvxvfcpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs4hvhvj
Librera Reader : https://njump.me/nevent1qqsg60flpuf00sash48fexvwxkly2j5z9wjvjrzt883t3eqng293f3cpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz39tt3n
QR-Code
Binary Eye : https://njump.me/nevent1qqsz4n0uxxx3q5m0r42n9key3hchtwyp73hgh8l958rtmae5u2khgpgpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzdmn4wp
Climático
Breezy Weather : https://njump.me/nevent1qqs9hjz5cz0y4am3kj33xn536uq85ydva775eqrml52mtnnpe898rzspzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgpd3tu8
ENCRYPTS
Cryptomator : https://njump.me/nevent1qqsvchvnw779m20583llgg5nlu6ph5psewetlczfac5vgw83ydmfndspzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsx7ppw9
VeraCrypt : https://njump.me/nevent1qqsf6wzedsnrgq6hjk5c4jj66dxnplqwc4ygr46l8z3gfh38q2fdlwgm65ej3
EXTENSÕES
uBlock Origin : https://njump.me/nevent1qqswaa666lcj2c4nhnea8u4agjtu4l8q89xjln0yrngj7ssh72ntwzql8ssdj
Snowflake : https://njump.me/nevent1qqs0ws74zlt8uced3p2vee9td8x7vln2mkacp8szdufvs2ed94ctnwchce008
CLOUD
Nextcloud : https://njump.me/nevent1qqs2utg5z9htegdtrnllreuhypkk2026x8a0xdsmfczg9wdl8rgrcgg9nhgnm
NOTEPAD
Joplin : https://njump.me/nevent1qqsz2a0laecpelsznser3xd0jfa6ch2vpxtkx6vm6qg24e78xttpk0cpr4mhxue69uhkummnw3ezucnfw33k76twv4ezuum0vd5kzmp0qgsyh28gd5ke0ztdeyehc0jsq6gcj0tnzatjlkql3dqamkja38fjmeqrqsqqqqqpdu0hft
Standard Notes : https://njump.me/nevent1qqsv3596kz3qung5v23cjc4cpq7rqxg08y36rmzgcrvw5whtme83y3s7tng6r
MÚSICA
RiMusic : https://njump.me/nevent1qqsv3genqav2tfjllp86ust4umxm8tr2wd9kq8x7vrjq6ssp363mn0gpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqg42353n
ViMusic : https://njump.me/nevent1qqswx78559l4jsxsrygd8kj32sch4qu57stxq0z6twwl450vp39pdqqpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzjg863j
PODCAST
AntennaPod : https://njump.me/nevent1qqsp4nh7k4a6zymfwqqdlxuz8ua6kdhvgeeh3uxf2c9rtp9u3e9ku8qnr8lmy
VISUALIZAR VIDEO
VLC : https://njump.me/nevent1qqs0lz56wtlr2eye4ajs2gzn2r0dscw4y66wezhx0mue6dffth8zugcl9laky
YOUTUBE
NewPipe : https://njump.me/nevent1qqsdg06qpcjdnlvgm4xzqdap0dgjrkjewhmh4j3v4mxdl4rjh8768mgdw9uln
FreeTube : https://njump.me/nevent1qqsz6y6z7ze5gs56s8seaws8v6m6j2zu0pxa955dhq3ythmexak38mcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqs5lkjvv
LibreTube : https://snort.social/e/nevent1qqstmd5m6wrdvn4gxf8xyhrwnlyaxmr89c9kjddvnvux6603f84t3fqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsswwznc
COMPARTILHAMENTO DE ARQUIVOS
OnionShare : https://njump.me/nevent1qqsr0a4ml5nu6ud5k9yzyawcd9arznnwkrc27dzzc95q6r50xmdff6qpydmhxue69uhkummnw3ez6an9wf5kv6t9vsh8wetvd3hhyer9wghxuet59uq3uamnwvaz7tmwdaehgu3dv3jhvtnhv4kxcmmjv3jhytnwv46z7qgswaehxw309ahx7tnnw3ezucmj9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcpzamhxue69uhkyarr9e4kcetwv3sh5afwvdhk6tcpzemhxue69uhkummnw3ezucnrdqhxu6twdfsj7qgswaehxw309ahx7um5wghx6mmd9uqjgamnwvaz7tmwdaehgu3wwfhh2mnywfhkx6mzd96xxmmfdejhyuewvdhk6tcppemhxue69uhkummn9ekx7mp0qythwumn8ghj7un9d3shjtnwdaehgu3wvfskuep0qyv8wumn8ghj7un9d3shjtnrw4e8yetwwshxv7tf9ut7qurt
Localsend : https://njump.me/nevent1qqsp8ldjhrxm09cvvcak20hrc0g8qju9f67pw7rxr2y3euyggw9284gpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzuyghqr
Wallet Bitcoin
Ashigaru Wallet : https://njump.me/nevent1qqstx9fz8kf24wgl26un8usxwsqjvuec9f8q392llmga75tw0kfarfcpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtczyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgvfsrqp
Samourai Wallet : https://njump.me/nevent1qqstcvjmz39rmrnrv7t5cl6p3x7pzj6jsspyh4s4vcwd2lugmre04ecpr9mhxue69uhkummnw3ezucn0denkymmwvuhxxmmd9upzqjagapkjm9ufdhynxlp72qrfrzfawvt4wt7cr795rhw6tkyaxt0yqvzqqqqqqy3rg4qs
CÂMERA
opencamera : https://njump.me/nevent1qqs25glp6dh0crrjutxrgdjlnx9gtqpjtrkg29hlf7382aeyjd77jlqpzpmhxue69uhkumewwd68ytnrwghsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqssxcvgc
OFFICE
Collabora Office : https://njump.me/nevent1qqs8yn4ys6adpmeu3edmf580jhc3wluvlf823cc4ft4h0uqmfzdf99qpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsj40uss
TEXTOS
O manifesto de um Cypherpunk : https://njump.me/nevent1qqsd7hdlg6galn5mcuv3pm3ryfjxc4tkyph0cfqqe4du4dr4z8amqyspvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqzal0efa
Operations security ( OPSEC) : https://snort.social/e/nevent1qqsp323havh3y9nxzd4qmm60hw87tm9gjns0mtzg8y309uf9mv85cqcpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz8ej9l7
O MANIFESTO CRIPTOANARQUISTA Timothy C. May – 1992. : https://njump.me/nevent1qqspp480wtyx2zhtwpu5gptrl8duv9rvq3mug85mp4d54qzywk3zq9gpvemhxue69uhkv6tvw3jhytnwdaehgu3wwa5kuef0dec82c330g6x6dm8ddmxzdne0pnhverevdkxxdm6wqc8v735w3snquejvsuk56pcvuurxaesxd68qdtkv3nrx6m6v3ehsctwvym8q0mzwfhkzerrv9ehg0t5wf6k2q3qfw5wsmfdj7ykmjfn0sl9qp533y7hx96h9lvplz6pmhd9mzwn9hjqxpqqqqqqz5wq496
Declaração de independência do ciberespaço
- John Perry Barlow - 1996 : https://njump.me/nevent1qqs2njsy44n6p07mhgt2tnragvchasv386nf20ua5wklxqpttf6mzuqpzpmhxue69uhkummnw3ezumt0d5hsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsukg4hr
The Cyphernomicon: Criptografia, Dinheiro Digital e o Futuro da Privacidade. escrito por Timothy C. May -Publicado em 1994. :
Livro completo em PDF no Github PrivacyOpenSource.
https://github.com/Alexemidio/PrivacyOpenSource/raw/main/Livros/THE%20CYPHERNOMICON%20.pdf Share
-
 @ 502ab02a:a2860397
2025-04-22 01:16:17
@ 502ab02a:a2860397
2025-04-22 01:16:17ก่อนที่จะมูฟออนจากเทคนิคการสร้าง เรามาดูเรื่องสำคัญครับ
วันที่ไม่มีวัว แต่มีเวย์โปรตีน – เบื้องหลังเทคโนโลยีที่เปลี่ยนถังหมักให้กลายเป็นเต้านมวัว เคยมีคำถามไหมว่า “เวย์โปรตีน” ที่กินตอนออกกำลังกาย หรือโยเกิร์ตถ้วยโปรดที่ซื้อมาจากร้านใกล้บ้าน มันยังมาจากนมวัวอยู่ไหม? ถ้าคำตอบคือ “ไม่” แล้วมันมาจากไหน?
ยินดีต้อนรับสู่โลกของ Perfect Day บริษัทที่บอกว่า "เราสร้างเวย์โปรตีนได้ โดยไม่ต้องใช้วัวเลยแม้แต่นิดเดียว” ฟังดูเหมือนมายากล แต่นี่คือวิทยาศาสตร์ขั้นสูงที่ผูกสูตรไว้กับ DNA, จุลินทรีย์ และการหมักอย่างแยบยล
ขั้นตอนที่ 1: หารหัสโปรตีนจากแม่วัว เริ่มต้นจากคำถามง่าย ๆ ว่า “โปรตีนเวย์ที่อยู่ในน้ำนมวัว คืออะไร?” คำตอบคือ เบต้า-แลคโตโกลบูลิน (Beta-lactoglobulin) ซึ่งเป็นโปรตีนหลักในเวย์ประมาณ 50-55% โดยในธรรมชาติ วัวจะสร้างโปรตีนนี้จาก รหัสพันธุกรรมใน DNA ของมัน Perfect Day จึงไปค้นหา ลำดับเบส (DNA sequence) ของโปรตีนนี้จากฐานข้อมูลวิทยาศาสตร์ชื่อ UniProt (Universal Protein Resource) ซึ่งเก็บรหัสโปรตีนของสิ่งมีชีวิตแทบทุกชนิดไว้ครบถ้วน ได้รหัสมาแล้ว ก็เตรียมเข้าสู่ภารกิจ “หลอกจุลินทรีย์ให้สร้างโปรตีนแทนวัว”
ขั้นตอนที่ 2: สร้างแผ่นดีเอ็นเอสังเคราะห์ รหัส DNA ที่ได้จาก UniProt จะถูกนำไปสร้างเป็น DNA สังเคราะห์ โดยนักชีววิทยาจะออกแบบให้เหมาะสมกับการทำงานในเซลล์ของจุลินทรีย์ ไม่ใช่เซลล์วัว จะเรียกว่านี่คือ “การดัดแปลงบทละครชีวิตของวัว แล้วส่งให้จุลินทรีย์เล่นแทน” ก็ไม่ผิด DNA ที่ออกแบบนี้ มักจะมาพร้อมกับเครื่องมือบางอย่าง เช่น ตัวกระตุ้นการทำงานของยีน (promoter) หรือ ตัวตัดต่อยีน ที่จะทำให้จุลินทรีย์ยอมรับและใช้มันได้อย่างมีประสิทธิภาพ
ขั้นตอนที่ 3: ปลอมตัวแทรกเข้าไปในจุลินทรีย์ จุลินทรีย์ที่ Perfect Day ใช้คือกลุ่มที่เรียกว่า Microflora ซึ่งอาจเป็นยีสต์, เชื้อรา, หรือแบคทีเรียชนิดที่เลี้ยงง่าย แต่มันจะไม่ยอมรับ DNA แปลกปลอมง่าย ๆ ดังนั้นต้องมี “เทคนิคหลอกล่อ” นิดหน่อย เขาจะทำให้ DNA ของจุลินทรีย์ เสียหายตรงจุดหนึ่ง แล้วแอบแนบ DNA ปลอม (ที่มีรหัสโปรตีนของวัว) เข้าไปซ่อมแซมจุดนั้นพอดีเป๊ะ แบบ “จิ๊กซอว์พอดีช่อง” แล้วจุลินทรีย์ก็จะเผลอรับ DNA แปลกปลอมนี้เข้าร่าง เมื่อติดตั้งสำเร็จ มันจะเริ่มแปลรหัสและ “ผลิตโปรตีนเวย์” ออกมาเหมือนกับแม่วัวตัวจริงไม่มีผิด
ขั้นตอนที่ 4: เลี้ยงจุลินทรีย์ในถังหมัก ตอนนี้จุลินทรีย์กลายเป็น “แม่วัวในร่างเซลล์เดียว” แล้ว Perfect Day ก็แค่เลี้ยงมันใน ถังหมักชีวภาพ (fermentor) ที่ควบคุมอุณหภูมิ ค่าความเป็นกรดด่าง อากาศ และใส่น้ำตาลลงไปเป็นอาหาร จุลินทรีย์จะกินน้ำตาลแล้วเปลี่ยนเป็น เวย์โปรตีน ปล่อยออกมานอกเซลล์ จากนั้นก็เก็บเอาน้ำที่มีโปรตีนนี้ ไปผ่านกระบวนการกรอง แยก แปรรูป และทำให้แห้ง เป็นผงเวย์โปรตีน พร้อมใช้ในอาหารหรือเครื่องดื่มต่าง ๆ
ขั้นตอนที่ 5: ตรวจสอบความเหมือนจริง ก่อนนำเวย์โปรตีนที่ได้ไปใช้งาน บริษัทต้อง ตรวจสอบระดับโมเลกุล ว่าโปรตีนที่ได้เหมือนกับของวัวจริง ๆ ไหม? สิ่งที่ต้องดูคือ โครงสร้างโปรตีน: ใช้เทคนิค mass spectrometry ตรวจความแม่นยำระดับกรดอะมิโน พฤติกรรมทางชีวเคมี เช่น ความสามารถในการจับกับน้ำ การเกิดฟอง หรือการละลาย ความปลอดภัย ตรวจหาสารปนเปื้อน สารก่อภูมิแพ้ หรือสารที่ไม่ได้ตั้งใจให้มี Perfect Day เคลมว่าทั้งหมดนี้ปลอดภัย และได้รับการรับรองจาก FDA ว่าเป็น GRAS (Generally Recognized as Safe)
แล้วเราควรรู้สึกยังไง? นี่คือ “นมที่ไม่มีวัว” แต่มีเวย์โปรตีนครบสูตร ทำให้โยเกิร์ต ไอศกรีม และแม้กระทั่งกาแฟลาเต้ที่ไม่มีนมวัว แต่ยังมีฟองนมหนานุ่ม กลายเป็นจริงได้แบบไม่ต้องพึ่งวัวเลยแม้แต่นิดเดียว แต่คำถามที่ลึกกว่านั้นคือ... เรายังได้กินอาหารจากธรรมชาติอยู่หรือเปล่า? หรือกำลังอยู่ในยุคที่ “ชีวิต” ถูกตัดออกจากอาหาร โดยสิ้นเชิง? เทคโนโลยีนี้อาจช่วยโลกในมุมของ ESG แต่สำหรับบางคน มันคือ ทางแยกของความจริงกับของจำลอง คำว่า “Perfect” จึงอาจขึ้นอยู่กับว่า… สมบูรณ์แบบในสายตาใคร?
แล้วคำถามที่ล่องลอยอยู่เสมอคือ เมื่อทางเลือกกลายเป็นทางหลัก แล้วเราจะเหลือทางไหนอีกบ้าง หรือจะเป็น...ทางตัน? #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก
-
 @ a39d19ec:3d88f61e
2025-03-18 17:16:50
@ a39d19ec:3d88f61e
2025-03-18 17:16:50Nun da das deutsche Bundesregime den Ruin Deutschlands beschlossen hat, der sehr wahrscheinlich mit dem Werkzeug des Geld druckens "finanziert" wird, kamen mir so viele Gedanken zur Geldmengenausweitung, dass ich diese für einmal niedergeschrieben habe.
Die Ausweitung der Geldmenge führt aus klassischer wirtschaftlicher Sicht immer zu Preissteigerungen, weil mehr Geld im Umlauf auf eine begrenzte Menge an Gütern trifft. Dies lässt sich in mehreren Schritten analysieren:
1. Quantitätstheorie des Geldes
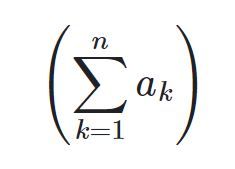
Die klassische Gleichung der Quantitätstheorie des Geldes lautet:
M • V = P • Y
wobei:
- M die Geldmenge ist,
- V die Umlaufgeschwindigkeit des Geldes,
- P das Preisniveau,
- Y die reale Wirtschaftsleistung (BIP).Wenn M steigt und V sowie Y konstant bleiben, muss P steigen – also Inflation entstehen.
2. Gütermenge bleibt begrenzt
Die Menge an real produzierten Gütern und Dienstleistungen wächst meist nur langsam im Vergleich zur Ausweitung der Geldmenge. Wenn die Geldmenge schneller steigt als die Produktionsgütermenge, führt dies dazu, dass mehr Geld für die gleiche Menge an Waren zur Verfügung steht – die Preise steigen.
3. Erwartungseffekte und Spekulation
Wenn Unternehmen und Haushalte erwarten, dass mehr Geld im Umlauf ist, da eine zentrale Planung es so wollte, können sie steigende Preise antizipieren. Unternehmen erhöhen ihre Preise vorab, und Arbeitnehmer fordern höhere Löhne. Dies kann eine sich selbst verstärkende Spirale auslösen.
4. Internationale Perspektive
Eine erhöhte Geldmenge kann die Währung abwerten, wenn andere Länder ihre Geldpolitik stabil halten. Eine schwächere Währung macht Importe teurer, was wiederum Preissteigerungen antreibt.
5. Kritik an der reinen Geldmengen-Theorie
Der Vollständigkeit halber muss erwähnt werden, dass die meisten modernen Ökonomen im Staatsauftrag argumentieren, dass Inflation nicht nur von der Geldmenge abhängt, sondern auch von der Nachfrage nach Geld (z. B. in einer Wirtschaftskrise). Dennoch zeigt die historische Erfahrung, dass eine unkontrollierte Geldmengenausweitung langfristig immer zu Preissteigerungen führt, wie etwa in der Hyperinflation der Weimarer Republik oder in Simbabwe.
-
 @ a39d19ec:3d88f61e
2024-11-21 12:05:09
@ a39d19ec:3d88f61e
2024-11-21 12:05:09A state-controlled money supply can influence the development of socialist policies and practices in various ways. Although the relationship is not deterministic, state control over the money supply can contribute to a larger role of the state in the economy and facilitate the implementation of socialist ideals.
Fiscal Policy Capabilities
When the state manages the money supply, it gains the ability to implement fiscal policies that can lead to an expansion of social programs and welfare initiatives. Funding these programs by creating money can enhance the state's influence over the economy and move it closer to a socialist model. The Soviet Union, for instance, had a centralized banking system that enabled the state to fund massive industrialization and social programs, significantly expanding the state's role in the economy.
Wealth Redistribution
Controlling the money supply can also allow the state to influence economic inequality through monetary policies, effectively redistributing wealth and reducing income disparities. By implementing low-interest loans or providing financial assistance to disadvantaged groups, the state can narrow the wealth gap and promote social equality, as seen in many European welfare states.
Central Planning
A state-controlled money supply can contribute to increased central planning, as the state gains more influence over the economy. Central banks, which are state-owned or heavily influenced by the state, play a crucial role in managing the money supply and facilitating central planning. This aligns with socialist principles that advocate for a planned economy where resources are allocated according to social needs rather than market forces.
Incentives for Staff
Staff members working in state institutions responsible for managing the money supply have various incentives to keep the system going. These incentives include job security, professional expertise and reputation, political alignment, regulatory capture, institutional inertia, and legal and administrative barriers. While these factors can differ among individuals, they can collectively contribute to the persistence of a state-controlled money supply system.
In conclusion, a state-controlled money supply can facilitate the development of socialist policies and practices by enabling fiscal policies, wealth redistribution, and central planning. The staff responsible for managing the money supply have diverse incentives to maintain the system, further ensuring its continuation. However, it is essential to note that many factors influence the trajectory of an economic system, and the relationship between state control over the money supply and socialism is not inevitable.
-
 @ a39d19ec:3d88f61e
2024-11-17 10:48:56
@ a39d19ec:3d88f61e
2024-11-17 10:48:56This week's functional 3d print is the "Dino Clip".

Dino Clip
I printed it some years ago for my son, so he would have his own clip for cereal bags.
Now it is used to hold a bag of dog food close.
The design by "Sneaks" is a so called "print in place". This means that the whole clip with moving parts is printed in one part, without the need for assembly after the print.
 The clip is very strong, and I would print it again if I need a "heavy duty" clip for more rigid or big bags.
Link to the file at Printables
The clip is very strong, and I would print it again if I need a "heavy duty" clip for more rigid or big bags.
Link to the file at Printables -
 @ a39d19ec:3d88f61e
2024-10-28 18:44:55
@ a39d19ec:3d88f61e
2024-10-28 18:44:55What do you even print with it besides decorative objects?
This kind of question still is a common one when talking about 3d printing.
With this series of long-form notes I will show you some of the practical and useful 3d printed things, that I use a lot.
Let me start the series with a nice little print consisting of two parts.
Laptop riser
There are many designs of laptop risers available online. But I like that the parts are small and interlocking, so that the are always together when not in use. The riser fits all laptops in our house. Particularly when working in Fusion360 my laptop needs lots of fresh air. I use the raiser regularly about 3 times a week. Sadly I don't know where I downloaded it from, so I cannot provide a link to it.

-
 @ 3f770d65:7a745b24
2025-04-21 00:15:06
@ 3f770d65:7a745b24
2025-04-21 00:15:06At the recent Launch Music Festival and Conference in Lancaster, PA, featuring over 120 musicians across three days, I volunteered my time with Tunestr and Phantom Power Music's initiative to introduce artists to Bitcoin, Nostr, and the value-for-value model. Tunestr sponsored a stage, live-streaming 21 bands to platforms like Tunestr.io, Fountain.fm and other Nostr/Podcasting 2.0 apps and on-boarding as many others as possible at our conference booth. You may have seen me spamming about this over the last few days.
V4V Earnings
Day 1: 180,000 sats
Day 2: 300,000 sats
Day 3: Over 500,000 sats
Who?
Here are the artists that were on-boarded to Fountain and were live streaming on the Value-for-Value stage:
nostr:npub1cruu4z0hwg7n3r2k7262vx8jsmra3xpku85frl5fnfvrwz7rd7mq7e403w nostr:npub12xeh3n7w8700z4tpd6xlhlvg4vtg4pvpxd584ll5sva539tutc3q0tn3tz nostr:npub1rc80p4v60uzfhvdgxemhvcqnzdj7t59xujxdy0lcjxml3uwdezyqtrpe0j @npub16vxr4pc2ww3yaez9q4s53zkejjfd0djs9lfe55sjhnqkh nostr:npub10uspdzg4fl7md95mqnjszxx82ckdly8ezac0t3s06a0gsf4f3lys8ypeak nostr:npub1gnyzexr40qut0za2c4a0x27p4e3qc22wekhcw3uvdx8mwa3pen0s9z90wk nostr:npub13qrrw2h4z52m7jh0spefrwtysl4psfkfv6j4j672se5hkhvtyw7qu0almy nostr:npub1p0kuqxxw2mxczc90vcurvfq7ljuw2394kkqk6gqnn2cq0y9eq5nq87jtkk nostr:npub182kq0sdp7chm67uq58cf4vvl3lk37z8mm5k5067xe09fqqaaxjsqlcazej nostr:npub162hr8kd96vxlanvggl08hmyy37qsn8ehgj7za7squl83um56epnswkr399 nostr:npub17jzk5ex2rafres09c4dnn5mm00eejye6nrurnlla6yn22zcpl7vqg6vhvx nostr:npub176rnksulheuanfx8y8cr2mrth4lh33svvpztggjjm6j2pqw6m56sq7s9vz nostr:npub1akv7t7xpalhsc4nseljs0c886jzuhq8u42qdcwvu972f3mme9tjsgp5xxk nostr:npub18x0gv872489lrczp9d9m4hx59r754x7p9rg2jkgvt7ul3kuqewtqsssn24
Many more musicians were on-boarded to Fountain, however, we were unable to obtain all of their npubs.
THANK YOU TO ALL ZAPPERS AND BOOSTERS!
Musicians “Get It”
My key takeaway was the musicians' absolute understanding that the current digital landscape along with legacy social media is failing them. Every artist I spoke with recognized how algorithms hinder fan connection and how gatekeepers prevent fair compensation for their work. They all use Spotify, but they only do so out of necessity. They felt the music industry is primed for both a social and monetary revolution. Some of them were even speaking my language…
Because of this, concepts like decentralization, censorship resistance, owning your content, and controlling your social graph weren't just understood by them, they were instantly embraced. The excitement was real; they immediately saw the potential and agreed with me. Bitcoin and Nostr felt genuinely punk rock and that helped a lot of them identify with what we were offering them.
The Tools and the Issues
While the Nostr ecosystem offers a wide variety of tools, we focused on introducing three key applications at this event to keep things clear for newcomers:
- Fountain, with a music focus, was the primary tool for onboarding attendees onto Nostr. Fountain was also chosen thanks to Fountain’s built-in Lightning wallet.
- Primal, as a social alternative, was demonstrated to show how users can take their Nostr identity and content seamlessly between different applications.
- Tunestr.io, lastly was showcased for its live video streaming capabilities.
Although we highlighted these three, we did inform attendees about the broader range of available apps and pointed them to
nostrapps.comif they wanted to explore further, aiming to educate without overwhelming them.This review highlights several UX issues with the Fountain app, particularly concerning profile updates, wallet functionality, and user discovery. While Fountain does work well, these minor hiccups make it extremely hard for on-boarding and education.
- Profile Issues:
- When a user edits their profile (e.g., Username/Nostr address, Lightning address) either during or after creation, the changes don't appear to consistently update across the app or sync correctly with Nostr relays.
- Specifically, the main profile display continues to show the old default Username/Nostr address and Lightning address inside Fountain and on other Nostr clients.
- However, the updated Username/Nostr address does appear on https://fountain.fm (chosen-username@fountain.fm) and is visible within the "Edit Profile" screen itself in the app.
- This inconsistency is confusing for users, as they see their updated information in some places but not on their main public-facing profile within the app. I confirmed this by observing a new user sign up and edit their username – the edit screen showed the new name, but the profile display in Fountain did not update and we did not see it inside Primal, Damus, Amethyst, etc.
- Wallet Limitations:
- The app's built-in wallet cannot scan Lightning address QR codes to initiate payments.
- This caused problems during the event where users imported Bitcoin from Azte.co vouchers into their Fountain wallets. When they tried to Zap a band by scanning a QR code on the live tally board, Fountain displayed an error message stating the invoice or QR code was invalid.
- While suggesting musicians install Primal as a second Nostr app was a potential fix for the QR code issue, (and I mentioned it to some), the burden of onboarding users onto two separate applications, potentially managing two different wallets, and explaining which one works for specific tasks creates a confusing and frustrating user experience.
- Search Difficulties:
- Finding other users within the Fountain app is challenging. I was unable to find profiles from brand new users by entering their chosen Fountain username.
- To find a new user, I had to resort to visiting their profile on the web (fountain.fm/username) to retrieve their npub. Then, open Primal and follow them. Finally, when searching for their username, since I was now following them, I was able to find their profile.
- This search issue is compounded by the profile syncing problem mentioned earlier, as even if found via other clients, their displayed information is outdated.
- Searching for the event to Boost/Zap inside Fountain was harder than it should have been the first two days as the live stream did not appear at the top of the screen inside the tap. This was resolved on the third day of the event.
Improving the Onboarding Experience
To better support user growth, educators and on-boarders need more feature complete and user-friendly applications. I love our developers and I will always sing their praises from the highest mountain tops, however I also recognize that the current tools present challenges that hinder a smooth onboarding experience.
One potential approach explored was guiding users to use Primal (including its built-in wallet) in conjunction with Wavlake via Nostr Wallet Connect (NWC). While this could facilitate certain functions like music streaming, zaps, and QR code scanning (which require both Primal and Wavlake apps), Wavlake itself has usability issues. These include inconsistent or separate profiles between web and mobile apps, persistent "Login" buttons even when logged in on the mobile app with a Nostr identity, and the minor inconvenience of needing two separate applications. Although NWC setup is relatively easy and helps streamline the process, the need to switch between apps adds complexity, especially when time is limited and we’re aiming to showcase the benefits of this new system.
Ultimately, we need applications that are more feature-complete and intuitive for mainstream users to improve the onboarding experience significantly.
Looking forward to the future
I anticipate that most of these issues will be resolved when these applications address them in the near future. Specifically, this would involve Fountain fixing its profile issues and integrating Nostr Wallet Connect (NWC) to allow users to utilize their Primal wallet, or by enabling the scanning of QR codes that pay out to Lightning addresses. Alternatively, if Wavlake resolves the consistency problems mentioned earlier, this would also significantly improve the situation giving us two viable solutions for musicians.
My ideal onboarding event experience would involve having all the previously mentioned issues resolved. Additionally, I would love to see every attendee receive a $5 or $10 voucher to help them start engaging with value-for-value, rather than just the limited number we distributed recently. The goal is to have everyone actively zapping and sending Bitcoin throughout the event. Maybe we can find a large sponsor to facilitate this in the future?
What's particularly exciting is the Launch conference's strong interest in integrating value-for-value across their entire program for all musicians and speakers at their next event in Dallas, Texas, coming later this fall. This presents a significant opportunity to onboard over 100+ musicians to Bitcoin and Nostr, which in turn will help onboard their fans and supporters.
We need significantly more zaps and more zappers! It's unreasonable to expect the same dedicated individuals to continuously support new users; they are being bled dry. A shift is needed towards more people using bitcoin for everyday transactions, treating it as money. This brings me back to my ideal onboarding experience: securing a sponsor to essentially give participants bitcoin funds specifically for zapping and tipping artists. This method serves as a practical lesson in using bitcoin as money and showcases the value-for-value principle from the outset.
-
 @ a39d19ec:3d88f61e
2024-10-27 10:26:03
@ a39d19ec:3d88f61e
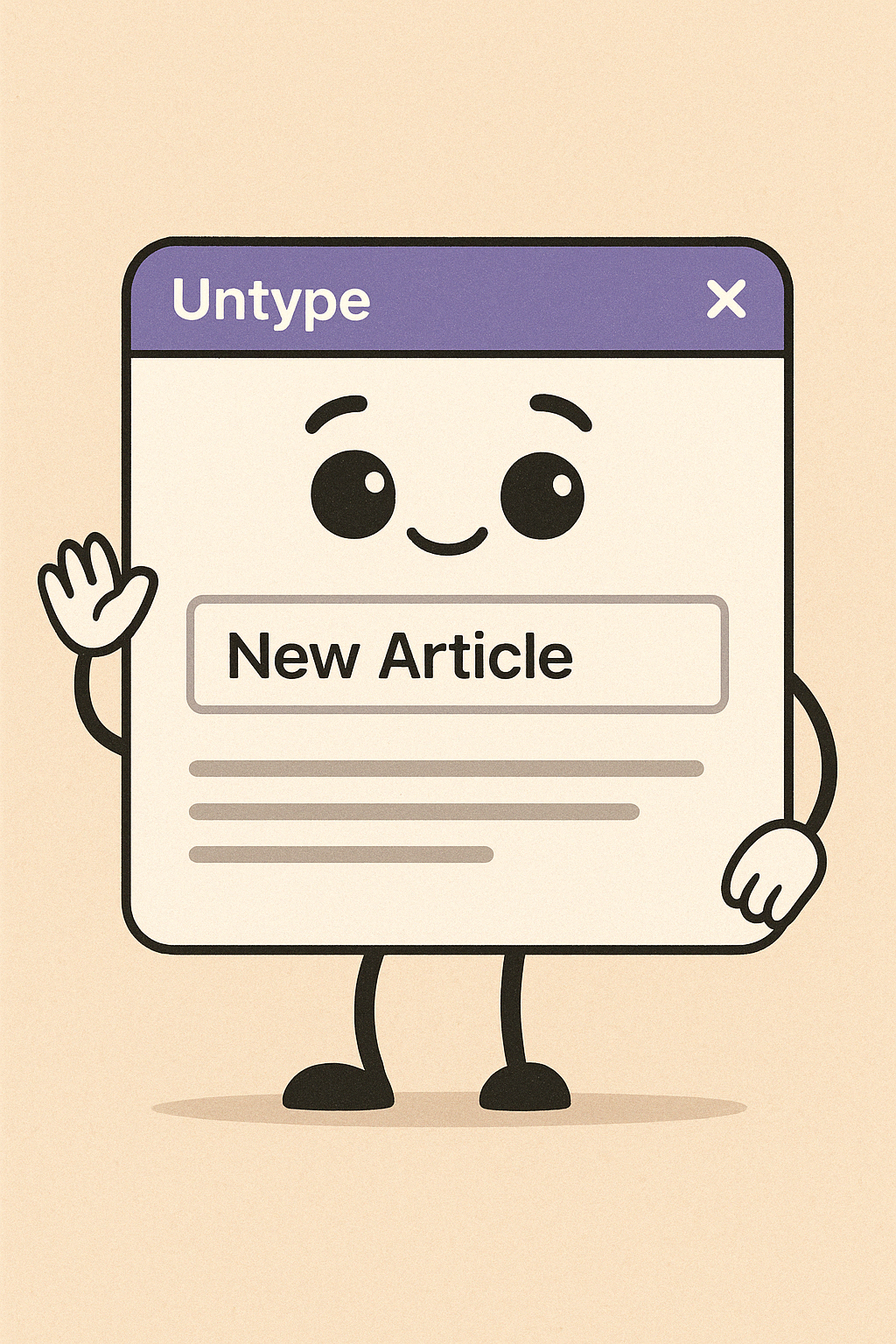
2024-10-27 10:26:03October's daily driver is the ana-digi Casio ABX-53 Twincept with module 1326. It features are world time, stopwatch, alarm and a databank for contacts.

Design
I have the gold/silver colored variant with a metal band. The watch has an analog clock and a floating display with the features listed above. Best thing is the "slider" mode that switches digital functions permanently.
Storytime
My log tells me that i bought the watch 6 years ago on a local flea market for close to nothing. It was in a bad condition and needed a new battery and some love. Sure enough it works fine since then. Most badass feature is that the analog hands are moved electronically not mechanically. Fun fact is that even my wife likes the floating display. First time she saw it I heard her say "Das ist echt cool", meaning "thats really cool".
-
 @ 1bc70a01:24f6a411
2025-04-19 09:58:54
@ 1bc70a01:24f6a411
2025-04-19 09:58:54Untype Update
I cleaned up the AI assistant UX. Now you can open it in the editor bar, same as all other actions. This makes it a lot easier to interact with while having access to normal edit functions.
AI-generated content
Untype uses OpenRouter to connect to various models to generate just about anything. It doesn't do images for now, but I'm working on that.
Automatic Title, Summary and Tag Suggestions
Added the functionality to generate titles, summaries and tags with one click.
A Brief Preview
Here is a little story I generated in Untype, ABOUT Untype:
This story was generated in Untype
Once upon a time, in the bustling digital city of Techlandia, there lived a quirky AI named Untype. Unlike other software, Untype wasn't just your everyday article composer — it had a nose for news, quite literally. Untype was equipped with a masterful talent for sniffing out the latest trends and stories wafting through the vast digital ether.
Untype had a peculiar look about it. Sporting a gigantic nose and a pair of spectacles perched just above it, Untype roamed the virtual city, inhaling the freshest gossip and spiciest stories. Its nostr-powered sensors twitched and tickled as it encountered every new scent.
One day, while wandering around the pixelated park, Untype caught a whiff of something extraordinary — a scandalous scoop involving Techlandia's mayor, Doc Processor, who had been spotted recycling old memes as new content. The scent trail was strong, and Untype's nose twitched with excitement.
With a flick of its AI function, Untype began weaving the story into a masterpiece. Sentences flowed like fine wine, infused with humor sharper than a hacker’s focus. "Doc Processor," Untype mused to itself, "tried to buffer his way out of this one with a cache of recycled gifs!"
As Untype typed away, its digital friends, Grammarly the Grammar Gremlin and Canva the Artful Pixie, gathered around to watch the genius at work. "You truly have a knack for news-sniffing," complimented Grammarly, adjusting its tiny monocle. Canva nodded, painting whimsical illustrations to accompany the hilarious exposé.
The article soon spread through Techlandia faster than a virus with a strong wifi signal. The townsfolk roared with laughter at Untype’s clever wit, and even Doc Processor couldn't help but chuckle through his embarrassment.
From that day on, Untype was celebrated not just as a composer but as Techlandia's most revered and humorous news-sniffer. With every sniff and click of its AI functions, Untype proved that in the world of digital creations, sometimes news really was just a nose away.
-
 @ c13fd381:b46236ea
2025-04-16 03:10:38
@ c13fd381:b46236ea
2025-04-16 03:10:38In a time of political volatility and declining public trust, Australians are looking for leaders who don’t just talk about accountability—but prove it. It’s time for a new standard. A protocol that filters for competence, responsibility, and integrity—not popularity alone.
Here’s the idea:
Anyone who wants to run for public office in Australia must stake 100Ksats to a public address and maintain provable control of the corresponding private key for the duration of their term.
A Low Barrier With High Signal
The amount—100Ksats—is modest, but meaningful. It isn’t about wealth or exclusion. It’s about signal. Controlling a private key takes care, discipline, and a basic understanding of digital responsibility.
This protocol doesn't reward those with the most resources, but those who demonstrate the foresight and competence required to secure and maintain something valuable—just like the responsibilities of public office.
How It Works
This system is elegantly simple:
- To nominate, a candidate generates a keypair and deposits 100Ksats into the associated address.
- They publish the public key alongside their candidate profile—on the electoral roll, campaign site, or an independent registry.
- Throughout their time in office, they sign periodic messages—perhaps quarterly—to prove they still control the private key.
Anyone, at any time, can verify this control. It’s public, permissionless, and incorruptible.
Why This Matters
Private key management is more than technical—it’s symbolic. It reflects:
- Responsibility – Losing your key means losing your ability to prove you’re still accountable.
- Integrity – Key control is binary. Either you can sign or you can’t.
- Long-term thinking – Good key management mirrors the strategic thinking we expect from leaders.
This isn’t about promises. It’s about proof. It moves trust from words to cryptographic reality.
A Voluntary Standard—for Now
This doesn’t require legislative change. It can begin as a voluntary protocol, adopted by those who want to lead with integrity. The tools already exist. The expectations can evolve from the ground up.
And as this becomes the norm, it sets a powerful precedent:
"If you can’t manage a private key, should you be trusted to manage public resources or national infrastructure?"
Identity Without Surveillance
By linking a public key to a candidate’s public identity, we create a form of digital accountability that doesn’t rely on central databases or invasive oversight. It’s decentralized, simple, and tamper-proof.
No backdoors. No bureaucracy. Just Bitcoin, and the competence to manage it.
Bitcoin is the foundation. Asymmetric encryption is the filter.
The result? A new class of public leaders—proven, not promised.Let’s raise the standard.
-
 @ e3ba5e1a:5e433365
2025-04-15 11:03:15
@ e3ba5e1a:5e433365
2025-04-15 11:03:15Prelude
I wrote this post differently than any of my others. It started with a discussion with AI on an OPSec-inspired review of separation of powers, and evolved into quite an exciting debate! I asked Grok to write up a summary in my overall writing style, which it got pretty well. I've decided to post it exactly as-is. Ultimately, I think there are two solid ideas driving my stance here:
- Perfect is the enemy of the good
- Failure is the crucible of success
Beyond that, just some hard-core belief in freedom, separation of powers, and operating from self-interest.
Intro
Alright, buckle up. I’ve been chewing on this idea for a while, and it’s time to spit it out. Let’s look at the U.S. government like I’d look at a codebase under a cybersecurity audit—OPSEC style, no fluff. Forget the endless debates about what politicians should do. That’s noise. I want to talk about what they can do, the raw powers baked into the system, and why we should stop pretending those powers are sacred. If there’s a hole, either patch it or exploit it. No half-measures. And yeah, I’m okay if the whole thing crashes a bit—failure’s a feature, not a bug.
The Filibuster: A Security Rule with No Teeth
You ever see a firewall rule that’s more theater than protection? That’s the Senate filibuster. Everyone acts like it’s this untouchable guardian of democracy, but here’s the deal: a simple majority can torch it any day. It’s not a law; it’s a Senate preference, like choosing tabs over spaces. When people call killing it the “nuclear option,” I roll my eyes. Nuclear? It’s a button labeled “press me.” If a party wants it gone, they’ll do it. So why the dance?
I say stop playing games. Get rid of the filibuster. If you’re one of those folks who thinks it’s the only thing saving us from tyranny, fine—push for a constitutional amendment to lock it in. That’s a real patch, not a Post-it note. Until then, it’s just a vulnerability begging to be exploited. Every time a party threatens to nuke it, they’re admitting it’s not essential. So let’s stop pretending and move on.
Supreme Court Packing: Because Nine’s Just a Number
Here’s another fun one: the Supreme Court. Nine justices, right? Sounds official. Except it’s not. The Constitution doesn’t say nine—it’s silent on the number. Congress could pass a law tomorrow to make it 15, 20, or 42 (hitchhiker’s reference, anyone?). Packing the court is always on the table, and both sides know it. It’s like a root exploit just sitting there, waiting for someone to log in.
So why not call the bluff? If you’re in power—say, Trump’s back in the game—say, “I’m packing the court unless we amend the Constitution to fix it at nine.” Force the issue. No more shadowboxing. And honestly? The court’s got way too much power anyway. It’s not supposed to be a super-legislature, but here we are, with justices’ ideologies driving the bus. That’s a bug, not a feature. If the court weren’t such a kingmaker, packing it wouldn’t even matter. Maybe we should be talking about clipping its wings instead of just its size.
The Executive Should Go Full Klingon
Let’s talk presidents. I’m not saying they should wear Klingon armor and start shouting “Qapla’!”—though, let’s be real, that’d be awesome. I’m saying the executive should use every scrap of power the Constitution hands them. Enforce the laws you agree with, sideline the ones you don’t. If Congress doesn’t like it, they’ve got tools: pass new laws, override vetoes, or—here’s the big one—cut the budget. That’s not chaos; that’s the system working as designed.
Right now, the real problem isn’t the president overreaching; it’s the bureaucracy. It’s like a daemon running in the background, eating CPU and ignoring the user. The president’s supposed to be the one steering, but the administrative state’s got its own agenda. Let the executive flex, push the limits, and force Congress to check it. Norms? Pfft. The Constitution’s the spec sheet—stick to it.
Let the System Crash
Here’s where I get a little spicy: I’m totally fine if the government grinds to a halt. Deadlock isn’t a disaster; it’s a feature. If the branches can’t agree, let the president veto, let Congress starve the budget, let enforcement stall. Don’t tell me about “essential services.” Nothing’s so critical it can’t take a breather. Shutdowns force everyone to the table—debate, compromise, or expose who’s dropping the ball. If the public loses trust? Good. They’ll vote out the clowns or live with the circus they elected.
Think of it like a server crash. Sometimes you need a hard reboot to clear the cruft. If voters keep picking the same bad admins, well, the country gets what it deserves. Failure’s the best teacher—way better than limping along on autopilot.
States Are the Real MVPs
If the feds fumble, states step up. Right now, states act like junior devs waiting for the lead engineer to sign off. Why? Federal money. It’s a leash, and it’s tight. Cut that cash, and states will remember they’re autonomous. Some will shine, others will tank—looking at you, California. And I’m okay with that. Let people flee to better-run states. No bailouts, no excuses. States are like competing startups: the good ones thrive, the bad ones pivot or die.
Could it get uneven? Sure. Some states might turn into sci-fi utopias while others look like a post-apocalyptic vidya game. That’s the point—competition sorts it out. Citizens can move, markets adjust, and failure’s a signal to fix your act.
Chaos Isn’t the Enemy
Yeah, this sounds messy. States ignoring federal law, external threats poking at our seams, maybe even a constitutional crisis. I’m not scared. The Supreme Court’s there to referee interstate fights, and Congress sets the rules for state-to-state play. But if it all falls apart? Still cool. States can sort it without a babysitter—it’ll be ugly, but freedom’s worth it. External enemies? They’ll either unify us or break us. If we can’t rally, we don’t deserve the win.
Centralizing power to avoid this is like rewriting your app in a single thread to prevent race conditions—sure, it’s simpler, but you’re begging for a deadlock. Decentralized chaos lets states experiment, lets people escape, lets markets breathe. States competing to cut regulations to attract businesses? That’s a race to the bottom for red tape, but a race to the top for innovation—workers might gripe, but they’ll push back, and the tension’s healthy. Bring it—let the cage match play out. The Constitution’s checks are enough if we stop coddling the system.
Why This Matters
I’m not pitching a utopia. I’m pitching a stress test. The U.S. isn’t a fragile porcelain doll; it’s a rugged piece of hardware built to take some hits. Let it fail a little—filibuster, court, feds, whatever. Patch the holes with amendments if you want, or lean into the grind. Either way, stop fearing the crash. It’s how we debug the republic.
So, what’s your take? Ready to let the system rumble, or got a better way to secure the code? Hit me up—I’m all ears.
-
 @ 401014b3:59d5476b
2025-04-22 00:23:24
@ 401014b3:59d5476b
2025-04-22 00:23:24About Me
I come to Nostr with extensive experience in the digital landscape. As a blockchain native since 2017, I've witnessed the evolution of decentralized technologies firsthand. Most of my professional career has been spent working within big tech companies, giving me a unique perspective on both centralized and decentralized systems.
My social media journey began on Twitter in 2007, where I've maintained a presence for over 17 years. I've also explored other decentralized social platforms including BlueSky, Farcaster, and Lens Protocol. As a Bitcoin maximalist, I was particularly intrigued by Nostr's compatibility with the Lightning Network, which initially drew me to the platform.
The Onboarding Challenge
The Nostr onboarding experience presents a significant hurdle for newcomers. Despite my technical background in blockchain technologies, I found the initial setup process more complicated than expected. Understanding public/private key cryptography just to join a social network creates a steeper learning curve than necessary.
BlueSky and Farcaster have demonstrated that it's possible to maintain decentralized principles while providing a more streamlined onboarding experience. Their approaches show that user-friendly design and decentralization aren't mutually exclusive concepts.
Relay Management: Room for Improvement
The concept of relays represents one of Nostr's most distinctive features, though it can be confusing for newcomers. While many clients come pre-configured with default relays, users eventually encounter situations where content or connections seem inconsistent.
When someone I've interacted with doesn't appear in my feed or doesn't respond, I'm often left wondering if we're simply on different relays. This uncertainty creates friction that doesn't exist on other platforms where connectivity is handled behind the scenes.
The relay system introduces a layer of complexity that, while important to Nostr's architecture, could benefit from better abstraction in the user experience. When using BlueSky or Farcaster, I don't need to think about the underlying infrastructure, something Nostr could learn from while maintaining its decentralized principles.
The Zap Economy: Growing Pains
The Lightning-powered zap system shows tremendous potential, but I've observed some concerning economic patterns. Longer-term Nostr users have expressed frustration about continuously sending zaps while seeing limited growth in the overall ecosystem.
Interestingly, there appears to be a connection between this liquidity issue and community growth dynamics. Some established users who voice concerns about bearing the financial burden of the zapping economy are simultaneously less welcoming to newer accounts, rarely following, engaging with, or zapping newcomers.
This creates a challenging environment for new users, who face a cold reception and have little incentive to load their Lightning wallets or participate in the zap economy. Why bring fresh liquidity to a platform where established users rarely engage with your content? This dynamic has limited the expansion of the ecosystem, with the same sats often circulating among established users rather than growing with new participants.
Client Diversity: Strength and Challenge
Nostr's multiple client options offer users choice, which is valuable. However, the implementation of NIPs (Nostr Implementation Possibilities) varies across clients, creating inconsistent experiences. Features that work seamlessly in one client might be implemented differently in another.
This extends to fundamental aspects like search functionality, thread navigation, and notification systems, all of which can differ significantly between clients. For users accustomed to consistent experiences, this fragmentation creates a learning curve with each new client they try.
Lightning Integration: Varying Experiences
The Lightning Network integration varies in quality and user experience across Nostr clients. While the functionality is generally present, the implementation quality, feature set, and ease of use differ depending on which client you choose.
This inconsistency means users may need to experiment with several clients to find one that provides the Lightning experience they're looking for, rather than having a consistent experience across the ecosystem.
Finding Balance
Nostr appears to be navigating the challenge of balancing technical innovation with user experience. While its cryptographic foundation and decentralized architecture are impressive technical achievements, these same strengths sometimes come at the cost of accessibility.
Despite my technical background and interest in decentralized technologies, I find myself using BlueSky and Farcaster more frequently for daily social interactions, while checking Nostr less often. For Nostr to achieve its potential for broader adoption, addressing these user experience considerations while maintaining its core principles will be essential.
The platform has tremendous potential with improvements to user experience, community dynamics, and economic sustainability, Nostr could evolve from a fascinating technical experiment into a truly compelling alternative to mainstream social media.
-
 @ df478568:2a951e67
2025-04-21 23:36:17
@ df478568:2a951e67
2025-04-21 23:36:17Testing
-
 @ 91bea5cd:1df4451c
2025-04-15 06:27:28
@ 91bea5cd:1df4451c
2025-04-15 06:27:28Básico
bash lsblk # Lista todos os diretorios montados.Para criar o sistema de arquivos:
bash mkfs.btrfs -L "ThePool" -f /dev/sdxCriando um subvolume:
bash btrfs subvolume create SubVolMontando Sistema de Arquivos:
bash mount -o compress=zlib,subvol=SubVol,autodefrag /dev/sdx /mntLista os discos formatados no diretório:
bash btrfs filesystem show /mntAdiciona novo disco ao subvolume:
bash btrfs device add -f /dev/sdy /mntLista novamente os discos do subvolume:
bash btrfs filesystem show /mntExibe uso dos discos do subvolume:
bash btrfs filesystem df /mntBalancea os dados entre os discos sobre raid1:
bash btrfs filesystem balance start -dconvert=raid1 -mconvert=raid1 /mntScrub é uma passagem por todos os dados e metadados do sistema de arquivos e verifica as somas de verificação. Se uma cópia válida estiver disponível (perfis de grupo de blocos replicados), a danificada será reparada. Todas as cópias dos perfis replicados são validadas.
iniciar o processo de depuração :
bash btrfs scrub start /mntver o status do processo de depuração Btrfs em execução:
bash btrfs scrub status /mntver o status do scrub Btrfs para cada um dos dispositivos
bash btrfs scrub status -d / data btrfs scrub cancel / dataPara retomar o processo de depuração do Btrfs que você cancelou ou pausou:
btrfs scrub resume / data
Listando os subvolumes:
bash btrfs subvolume list /ReportsCriando um instantâneo dos subvolumes:
Aqui, estamos criando um instantâneo de leitura e gravação chamado snap de marketing do subvolume de marketing.
bash btrfs subvolume snapshot /Reports/marketing /Reports/marketing-snapAlém disso, você pode criar um instantâneo somente leitura usando o sinalizador -r conforme mostrado. O marketing-rosnap é um instantâneo somente leitura do subvolume de marketing
bash btrfs subvolume snapshot -r /Reports/marketing /Reports/marketing-rosnapForçar a sincronização do sistema de arquivos usando o utilitário 'sync'
Para forçar a sincronização do sistema de arquivos, invoque a opção de sincronização conforme mostrado. Observe que o sistema de arquivos já deve estar montado para que o processo de sincronização continue com sucesso.
bash btrfs filsystem sync /ReportsPara excluir o dispositivo do sistema de arquivos, use o comando device delete conforme mostrado.
bash btrfs device delete /dev/sdc /ReportsPara sondar o status de um scrub, use o comando scrub status com a opção -dR .
bash btrfs scrub status -dR / RelatóriosPara cancelar a execução do scrub, use o comando scrub cancel .
bash $ sudo btrfs scrub cancel / ReportsPara retomar ou continuar com uma depuração interrompida anteriormente, execute o comando de cancelamento de depuração
bash sudo btrfs scrub resume /Reportsmostra o uso do dispositivo de armazenamento:
btrfs filesystem usage /data
Para distribuir os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID (incluindo o dispositivo de armazenamento recém-adicionado) montados no diretório /data , execute o seguinte comando:
sudo btrfs balance start --full-balance /data
Pode demorar um pouco para espalhar os dados, metadados e dados do sistema em todos os dispositivos de armazenamento do RAID se ele contiver muitos dados.
Opções importantes de montagem Btrfs
Nesta seção, vou explicar algumas das importantes opções de montagem do Btrfs. Então vamos começar.
As opções de montagem Btrfs mais importantes são:
**1. acl e noacl
**ACL gerencia permissões de usuários e grupos para os arquivos/diretórios do sistema de arquivos Btrfs.
A opção de montagem acl Btrfs habilita ACL. Para desabilitar a ACL, você pode usar a opção de montagem noacl .
Por padrão, a ACL está habilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem acl por padrão.
**2. autodefrag e noautodefrag
**Desfragmentar um sistema de arquivos Btrfs melhorará o desempenho do sistema de arquivos reduzindo a fragmentação de dados.
A opção de montagem autodefrag permite a desfragmentação automática do sistema de arquivos Btrfs.
A opção de montagem noautodefrag desativa a desfragmentação automática do sistema de arquivos Btrfs.
Por padrão, a desfragmentação automática está desabilitada. Portanto, o sistema de arquivos Btrfs usa a opção de montagem noautodefrag por padrão.
**3. compactar e compactar-forçar
**Controla a compactação de dados no nível do sistema de arquivos do sistema de arquivos Btrfs.
A opção compactar compacta apenas os arquivos que valem a pena compactar (se compactar o arquivo economizar espaço em disco).
A opção compress-force compacta todos os arquivos do sistema de arquivos Btrfs, mesmo que a compactação do arquivo aumente seu tamanho.
O sistema de arquivos Btrfs suporta muitos algoritmos de compactação e cada um dos algoritmos de compactação possui diferentes níveis de compactação.
Os algoritmos de compactação suportados pelo Btrfs são: lzo , zlib (nível 1 a 9) e zstd (nível 1 a 15).
Você pode especificar qual algoritmo de compactação usar para o sistema de arquivos Btrfs com uma das seguintes opções de montagem:
- compress=algoritmo:nível
- compress-force=algoritmo:nível
Para obter mais informações, consulte meu artigo Como habilitar a compactação do sistema de arquivos Btrfs .
**4. subvol e subvolid
**Estas opções de montagem são usadas para montar separadamente um subvolume específico de um sistema de arquivos Btrfs.
A opção de montagem subvol é usada para montar o subvolume de um sistema de arquivos Btrfs usando seu caminho relativo.
A opção de montagem subvolid é usada para montar o subvolume de um sistema de arquivos Btrfs usando o ID do subvolume.
Para obter mais informações, consulte meu artigo Como criar e montar subvolumes Btrfs .
**5. dispositivo
A opção de montagem de dispositivo** é usada no sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs.
Em alguns casos, o sistema operacional pode falhar ao detectar os dispositivos de armazenamento usados em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs. Nesses casos, você pode usar a opção de montagem do dispositivo para especificar os dispositivos que deseja usar para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar a opção de montagem de dispositivo várias vezes para carregar diferentes dispositivos de armazenamento para o sistema de arquivos de vários dispositivos Btrfs ou RAID.
Você pode usar o nome do dispositivo (ou seja, sdb , sdc ) ou UUID , UUID_SUB ou PARTUUID do dispositivo de armazenamento com a opção de montagem do dispositivo para identificar o dispositivo de armazenamento.
Por exemplo,
- dispositivo=/dev/sdb
- dispositivo=/dev/sdb,dispositivo=/dev/sdc
- dispositivo=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d
- device=UUID_SUB=490a263d-eb9a-4558-931e-998d4d080c5d,device=UUID_SUB=f7ce4875-0874-436a-b47d-3edef66d3424
**6. degraded
A opção de montagem degradada** permite que um RAID Btrfs seja montado com menos dispositivos de armazenamento do que o perfil RAID requer.
Por exemplo, o perfil raid1 requer a presença de 2 dispositivos de armazenamento. Se um dos dispositivos de armazenamento não estiver disponível em qualquer caso, você usa a opção de montagem degradada para montar o RAID mesmo que 1 de 2 dispositivos de armazenamento esteja disponível.
**7. commit
A opção commit** mount é usada para definir o intervalo (em segundos) dentro do qual os dados serão gravados no dispositivo de armazenamento.
O padrão é definido como 30 segundos.
Para definir o intervalo de confirmação para 15 segundos, você pode usar a opção de montagem commit=15 (digamos).
**8. ssd e nossd
A opção de montagem ssd** informa ao sistema de arquivos Btrfs que o sistema de arquivos está usando um dispositivo de armazenamento SSD, e o sistema de arquivos Btrfs faz a otimização SSD necessária.
A opção de montagem nossd desativa a otimização do SSD.
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem de SSD será habilitada. Caso contrário, a opção de montagem nossd é habilitada.
**9. ssd_spread e nossd_spread
A opção de montagem ssd_spread** tenta alocar grandes blocos contínuos de espaço não utilizado do SSD. Esse recurso melhora o desempenho de SSDs de baixo custo (baratos).
A opção de montagem nossd_spread desativa o recurso ssd_spread .
O sistema de arquivos Btrfs detecta automaticamente se um SSD é usado para o sistema de arquivos Btrfs. Se um SSD for usado, a opção de montagem ssd_spread será habilitada. Caso contrário, a opção de montagem nossd_spread é habilitada.
**10. descarte e nodiscard
Se você estiver usando um SSD que suporte TRIM enfileirado assíncrono (SATA rev3.1), a opção de montagem de descarte** permitirá o descarte de blocos de arquivos liberados. Isso melhorará o desempenho do SSD.
Se o SSD não suportar TRIM enfileirado assíncrono, a opção de montagem de descarte prejudicará o desempenho do SSD. Nesse caso, a opção de montagem nodiscard deve ser usada.
Por padrão, a opção de montagem nodiscard é usada.
**11. norecovery
Se a opção de montagem norecovery** for usada, o sistema de arquivos Btrfs não tentará executar a operação de recuperação de dados no momento da montagem.
**12. usebackuproot e nousebackuproot
Se a opção de montagem usebackuproot for usada, o sistema de arquivos Btrfs tentará recuperar qualquer raiz de árvore ruim/corrompida no momento da montagem. O sistema de arquivos Btrfs pode armazenar várias raízes de árvore no sistema de arquivos. A opção de montagem usebackuproot** procurará uma boa raiz de árvore e usará a primeira boa que encontrar.
A opção de montagem nousebackuproot não verificará ou recuperará raízes de árvore inválidas/corrompidas no momento da montagem. Este é o comportamento padrão do sistema de arquivos Btrfs.
**13. space_cache, space_cache=version, nospace_cache e clear_cache
A opção de montagem space_cache** é usada para controlar o cache de espaço livre. O cache de espaço livre é usado para melhorar o desempenho da leitura do espaço livre do grupo de blocos do sistema de arquivos Btrfs na memória (RAM).
O sistema de arquivos Btrfs suporta 2 versões do cache de espaço livre: v1 (padrão) e v2
O mecanismo de cache de espaço livre v2 melhora o desempenho de sistemas de arquivos grandes (tamanho de vários terabytes).
Você pode usar a opção de montagem space_cache=v1 para definir a v1 do cache de espaço livre e a opção de montagem space_cache=v2 para definir a v2 do cache de espaço livre.
A opção de montagem clear_cache é usada para limpar o cache de espaço livre.
Quando o cache de espaço livre v2 é criado, o cache deve ser limpo para criar um cache de espaço livre v1 .
Portanto, para usar o cache de espaço livre v1 após a criação do cache de espaço livre v2 , as opções de montagem clear_cache e space_cache=v1 devem ser combinadas: clear_cache,space_cache=v1
A opção de montagem nospace_cache é usada para desabilitar o cache de espaço livre.
Para desabilitar o cache de espaço livre após a criação do cache v1 ou v2 , as opções de montagem nospace_cache e clear_cache devem ser combinadas: clear_cache,nosapce_cache
**14. skip_balance
Por padrão, a operação de balanceamento interrompida/pausada de um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs será retomada automaticamente assim que o sistema de arquivos Btrfs for montado. Para desabilitar a retomada automática da operação de equilíbrio interrompido/pausado em um sistema de arquivos Btrfs de vários dispositivos ou RAID Btrfs, você pode usar a opção de montagem skip_balance .**
**15. datacow e nodatacow
A opção datacow** mount habilita o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs. É o comportamento padrão.
Se você deseja desabilitar o recurso Copy-on-Write (CoW) do sistema de arquivos Btrfs para os arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatacow .
**16. datasum e nodatasum
A opção datasum** mount habilita a soma de verificação de dados para arquivos recém-criados do sistema de arquivos Btrfs. Este é o comportamento padrão.
Se você não quiser que o sistema de arquivos Btrfs faça a soma de verificação dos dados dos arquivos recém-criados, monte o sistema de arquivos Btrfs com a opção de montagem nodatasum .
Perfis Btrfs
Um perfil Btrfs é usado para informar ao sistema de arquivos Btrfs quantas cópias dos dados/metadados devem ser mantidas e quais níveis de RAID devem ser usados para os dados/metadados. O sistema de arquivos Btrfs contém muitos perfis. Entendê-los o ajudará a configurar um RAID Btrfs da maneira que você deseja.
Os perfis Btrfs disponíveis são os seguintes:
single : Se o perfil único for usado para os dados/metadados, apenas uma cópia dos dados/metadados será armazenada no sistema de arquivos, mesmo se você adicionar vários dispositivos de armazenamento ao sistema de arquivos. Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
dup : Se o perfil dup for usado para os dados/metadados, cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos manterá duas cópias dos dados/metadados. Assim, 50% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser utilizado.
raid0 : No perfil raid0 , os dados/metadados serão divididos igualmente em todos os dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, não haverá dados/metadados redundantes (duplicados). Assim, 100% do espaço em disco de cada um dos dispositivos de armazenamento adicionados ao sistema de arquivos pode ser usado. Se, em qualquer caso, um dos dispositivos de armazenamento falhar, todo o sistema de arquivos será corrompido. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid0 .
raid1 : No perfil raid1 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a uma falha de unidade. Mas você pode usar apenas 50% do espaço total em disco. Você precisará de pelo menos dois dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1 .
raid1c3 : No perfil raid1c3 , três cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a duas falhas de unidade, mas você pode usar apenas 33% do espaço total em disco. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c3 .
raid1c4 : No perfil raid1c4 , quatro cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos. Nesta configuração, a matriz RAID pode sobreviver a três falhas de unidade, mas você pode usar apenas 25% do espaço total em disco. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid1c4 .
raid10 : No perfil raid10 , duas cópias dos dados/metadados serão armazenadas nos dispositivos de armazenamento adicionados ao sistema de arquivos, como no perfil raid1 . Além disso, os dados/metadados serão divididos entre os dispositivos de armazenamento, como no perfil raid0 .
O perfil raid10 é um híbrido dos perfis raid1 e raid0 . Alguns dos dispositivos de armazenamento formam arrays raid1 e alguns desses arrays raid1 são usados para formar um array raid0 . Em uma configuração raid10 , o sistema de arquivos pode sobreviver a uma única falha de unidade em cada uma das matrizes raid1 .
Você pode usar 50% do espaço total em disco na configuração raid10 . Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid10 .
raid5 : No perfil raid5 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Uma única paridade será calculada e distribuída entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid5 , o sistema de arquivos pode sobreviver a uma única falha de unidade. Se uma unidade falhar, você pode adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir da paridade distribuída das unidades em execução.
Você pode usar 1 00x(N-1)/N % do total de espaços em disco na configuração raid5 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos três dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid5 .
raid6 : No perfil raid6 , uma cópia dos dados/metadados será dividida entre os dispositivos de armazenamento. Duas paridades serão calculadas e distribuídas entre os dispositivos de armazenamento do array RAID.
Em uma configuração raid6 , o sistema de arquivos pode sobreviver a duas falhas de unidade ao mesmo tempo. Se uma unidade falhar, você poderá adicionar uma nova unidade ao sistema de arquivos e os dados perdidos serão calculados a partir das duas paridades distribuídas das unidades em execução.
Você pode usar 100x(N-2)/N % do espaço total em disco na configuração raid6 . Aqui, N é o número de dispositivos de armazenamento adicionados ao sistema de arquivos. Você precisará de pelo menos quatro dispositivos de armazenamento para configurar o sistema de arquivos Btrfs no perfil raid6 .
-
 @ bb1c863a:2953c3fb
2025-04-14 22:22:50
@ bb1c863a:2953c3fb
2025-04-14 22:22:50Block Height 892385 11:47 pm Monday, 14 April 2025
In a powerful gesture of support for Bitcoin-aligned education, Blockstream has donated 21 Blockstream Jade hardware wallets to the Consensus21 School — a groundbreaking learning initiative launching its first campus this year on the Mornington Peninsula, just outside Melbourne, Australia.
The donation will place 21 Jades directly into the hands of the first 21 students at the new campus — some as young as five years old — giving them real tools to explore Bitcoin self-custody, digital sovereignty, and privacy-first technology in an age-appropriate and hands-on way.
“The Jade wallets are more than just devices — they’re symbols of freedom, responsibility, and the future of education,” said Kieran Nolan, co-founder of Consensus21. “We’re incredibly grateful to Blockstream for standing behind our mission.”
Real Tools for Real Sovereignty
The Blockstream Jade is a secure, open-source hardware wallet built for Bitcoiners who value freedom, privacy, and independence. These values are embedded deeply into the Consensus21 educational philosophy, which blends Steiner-inspired learning, homeschooling flexibility, and a curriculum rooted in Bitcoin principles like voluntary exchange, decentralization, and self-responsibility.
With the Jades now part of the learning toolkit, Consensus21 learners will be introduced to key concepts like:
- Private key management
- Seed phrase generation and backup
- Multisig wallets
- The importance of self-custody and trust minimization
This is not just about theory — learners will get to use these tools in real-world contexts, preparing them to grow up fluent in the principles of freedom tech.
A Campus, A Vision, A Movement
Launching in 2025, the Mornington Peninsula campus is the pilot site for the broader Consensus21 vision: a distributed, regenerative, and values-aligned network of co-learning spaces, including a future 10-acre farm campus and a registered Steiner school.
The Blockstream donation comes at a pivotal time, as the community transitions from vision to reality. The gift of exactly 21 Blockstream Jades — echoing Bitcoin’s 21 million hard cap — is both a symbolic and practical gesture of support, underscoring the shared commitment between Bitcoin builders and grassroots educators.
Stay Connected
📄 Whitepaper: https://github.com/consensus21school/consensus21school.github.io/blob/main/whitepaper.md
🌐 Website: https://consensus21.school
📝 Nostr: CONSENSUS21@nostrcheck.me
🐦 X (Twitter): https://x.com/Consensus21
-
 @ a39d19ec:3d88f61e
2024-08-11 15:44:55
@ a39d19ec:3d88f61e
2024-08-11 15:44:55This months daily driver is the #Casio A100WE with module 3503. It features am/pm time, date and weekday, alarm and a stopwatch.

Design
The design is plain and simple. 4 front facing Button, a small but surprisingly readable display. It has a resin casing with metal surface and a black rubber band.
Storytime
There is not much to say about this watch. I remember buying it for my collection because it was on sale some time ago. There is one version with the colour accents near the buttons, that looks much nicer.
-
 @ 6e0ea5d6:0327f353
2025-04-14 15:11:17
@ 6e0ea5d6:0327f353
2025-04-14 15:11:17Ascolta.
We live in times where the average man is measured by the speeches he gives — not by the commitments he keeps. People talk about dreams, goals, promises… but what truly remains is what’s honored in the silence of small gestures, in actions that don’t seek applause, in attitudes unseen — yet speak volumes.
Punctuality, for example. Showing up on time isn’t about the clock. It’s about respect. Respect for another’s time, yes — but more importantly, respect for one’s own word. A man who is late without reason is already running late in his values. And the one who excuses his own lateness with sweet justifications slowly gets used to mediocrity.
Keeping your word is more than fulfilling promises. It is sealing, with the mouth, what the body must later uphold. Every time a man commits to something, he creates a moral debt with his own dignity. And to break that commitment is to declare bankruptcy — not in the eyes of others, but in front of himself.
And debts? Even the small ones — or especially the small ones — are precise thermometers of character. A forgotten sum, an unpaid favor, a commitment left behind… all of these reveal the structure of the inner building that man resides in. He who neglects the small is merely rehearsing for his future collapse.
Life, contrary to what the reckless say, is not built on grand deeds. It is built with small bricks, laid with almost obsessive precision. The truly great man is the one who respects the details — recognizing in them a code of conduct.
In Sicily, especially in the streets of Palermo, I learned early on that there is more nobility in paying a five-euro debt on time than in flaunting riches gained without word, without honor, without dignity.
As they say in Palermo: L’uomo si conosce dalle piccole cose.
So, amico mio, Don’t talk to me about greatness if you can’t show up on time. Don’t talk to me about respect if your word is fickle. And above all, don’t talk to me about honor if you still owe what you once promised — no matter how small.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ a39d19ec:3d88f61e
2024-07-05 14:17:31
@ a39d19ec:3d88f61e
2024-07-05 14:17:31This months proof of watch or #wristcheck (inspired by nostr:nprofile1qqs8nh529w5huhuqvx0h5zm8e5ncdenk7qvfpsl3huxu84xnfnr6uespr9mhxue69uhhyetvv9ujumt0d4hhxarj9ecxjmnt9uxu0nnm) is the Casio MTD-1001 with caliber 1333 and a quartz clockwork.
Design
A solid analog watch with weekday and day of month at 3 o'clock. Classified as a divers watch it has a pretty big dial within a 44mm metal casing leading to big hands that are very readable. Hands and numbers are phosphorus. The counter-clockwise rotating bezel does 60 clicks per revolution. The screw-down crown is at 3'o clock. The rubber band is pretty long.
Storytime
I bought it a long time ago and just saw that it needed some love (and a new battery) and thought it is a good opportunity to wear it for the first time. I wear one watch as a daily driver for one month straight. Wearing it for seven days now I can say that it is a heavy watch. You feel that you are wearing it. To be honest I completely forgot about that watch as it was a bulk of 5 or 6 watches and this was not the one I bought the bulk for.
This might be the first longform note about a watch from my collection.
-
 @ a39d19ec:3d88f61e
2024-06-03 20:40:37
@ a39d19ec:3d88f61e
2024-06-03 20:40:37Ich habe meine Texte ChatGPT gegeben um diese klarer zu formulieren als das was ich schrieb.
Einleitung
Oft hört man, dass schlechte Produkte ein Zeugnis des Kapitalismus und gieriger Unternehmer ist. Dass es nicht am Kapitalismus, sondern am sozialistischen Fiatgeld liegt, möchte ich in diesem Beitrag aufzeigen.
In einem Fiatgeldsystem, bei dem die Geldmenge durch Zentralbanken kontrolliert und ständig ausgeweitet wird, kommt es zu einem Kaufkraftverlust des Geldes (Inflation). Dieser Mechanismus beeinflusst die Geschäftsstrategien von Unternehmen in mehreren bedeutenden Weisen, auf die ich im Folgenden eingehen werde.
Schnelle Kaufkraftverluste
Durch die ständige Ausweitung der Geldmenge verliert Geld an Wert. Das bedeutet, dass die Konsumenten zukünftig für dieselben Produkte mehr bezahlen müssen. Für Unternehmen entsteht der Anreiz, Konsumenten dazu zu bringen, häufiger neue Produkte zu kaufen, um ihren Umsatz und Gewinn in der Zukunft zu sichern.
Geplante Obsoleszenz
Durch die geplante Obsoleszenz, bei der Produkte absichtlich so konstruiert werden, dass sie schnell kaputt gehen oder veralten, können Unternehmen sicherstellen, dass Kunden regelmäßig neue Produkte kaufen müssen. Dies hilft den Unternehmen, kontinuierlich Umsatz zu generieren und die Auswirkungen der Inflation auf ihre Einnahmen abzufedern.
Erhöhung des Konsumtempos
Wenn die Kaufkraft ständig abnimmt, möchten Konsumenten ihr Geld eher früher als später ausgeben, um den Wertverlust zu vermeiden. Unternehmen nutzen dies aus, indem sie Produkte herstellen, die schnell ersetzt werden müssen, wodurch der Konsum beschleunigt wird und sie von der höheren Frequenz der Käufe profitieren.
Kostenmanagement
Die Herstellung von langlebigen Produkten kann teurer sein als die Produktion von kurzlebigen Waren. In einem inflationären Umfeld möchten Unternehmen ihre Produktionskosten minimieren, um ihre Margen zu schützen. Billigere, weniger langlebige Produkte ermöglichen es, Kosten zu sparen und kurzfristig wettbewerbsfähige Preise zu halten.
Marktdynamik
In einem inflationären Umfeld kann es für Unternehmen riskant sein, große Mengen langlebiger Produkte zu produzieren, da die zukünftigen Produktionskosten und Verkaufspreise schwerer vorhersehbar sind. Kurzlebige Produkte ermöglichen eine schnellere Anpassung an veränderte Marktbedingungen und Preisniveaus.
Kundengewohnheiten und Marketing
Unternehmen können durch gezieltes Marketing und die ständige Einführung neuer Modelle und Trends (z.B. in der Elektronik- und Modebranche) das Konsumverhalten beeinflussen und sicherstellen, dass Produkte als schnell veraltet angesehen werden. Dies unterstützt das Geschäftsmodell, das auf häufige Neuanschaffungen angewiesen ist.
Zusammenfassend lässt sich sagen, dass die inflationäre Dynamik eines Fiatgeldsystems Unternehmen dazu verleitet, Produkte zu entwerfen, die nicht lange halten. Durch die beschleunigte Produktalterung und die häufigeren Käufe können sie ihre Einnahmen stabilisieren und den Auswirkungen des Wertverlustes des Geldes entgegenwirken.
-
 @ 1ef61805:f18312cc
2025-04-13 22:40:49
@ 1ef61805:f18312cc
2025-04-13 22:40:49In today’s increasingly surveilled digital world, privacy and security are paramount. OpSec Academy has taken a major step forward by customizing TailsOS to create OpSecOS, an operating system built with the same focus on anonymity and privacy, but enhanced with a suite of peer-reviewed and battle-tested applications. These applications empower users with decentralised tools, ensuring complete control over their digital lives while maintaining the high standards of security and privacy that OpSec Academy stands for.
In this article, we’ll explore the tools available in OpSec Academy’s custom OpSecOS image, highlighting the new and updated features that enhance security, decentralisation, and privacy.
-
Sparrow Wallet (Version 2.1.3) Sparrow Wallet remains one of the most privacy-conscious Bitcoin wallets available. It provides an advanced suite of features such as multi-signature support, coin control, and hardware wallet integration, which allow users to have complete control over their funds. By integrating Sparrow Wallet into OpSecOS, we ensure that Bitcoin transactions are handled with the highest standards of privacy, all while utilising Tor to anonymise transaction data. Peer-Reviewed & Battle-Tested: Sparrow Wallet has been rigorously tested by the privacy community and has earned a reputation for robustness and security. Its commitment to user privacy makes it one of the most trusted Bitcoin wallets in the ecosystem.
-
Feather Wallet (Version 2.7.0) Feather Wallet is a lightweight yet powerful Bitcoin wallet designed with privacy and simplicity in mind. Featuring Tor support and integration with hardware wallets, Feather Wallet ensures that users' private information remains secure while offering an intuitive user experience. By adding Feather Wallet to OpSecOS, we provide an easy-to-use wallet solution without compromising security. Peer-Reviewed & Battle-Tested: Feather Wallet has undergone thorough peer review and is widely regarded as a secure and privacy-focused option for Bitcoin users. Its simplicity and security features have been battle-tested by users in real-world environments.
-
Liana Wallet (Version 10.0) Liana Wallet is a Bitcoin wallet designed with a strong emphasis on long-term security, recovery, and inheritance. It allows users to set up primary keys for regular spending and recovery keys that activate after a specified period of inactivity, making it ideal for scenarios where funds need to be securely passed on without relying on third-party custodians. The wallet supports advanced features like on-chain timelocks, enabling users to create time-locked backup keys for inheritance planning. Additionally, Liana offers a user-friendly interface with ready-made templates, such as "Simple Inheritance" and "Expanding Multisig," to simplify the wallet setup process. For those seeking a comprehensive solution, the Liana Box Starter Pack includes hardware signing devices, tamper-evident bags, seed phrase storage, and an inheritance letter, providing everything needed to set up a secure and resilient Bitcoin wallet.
-
Snort & Iris (Nostr Clients) For decentralised, secure communication, OpSecOS includes two leading Nostr protocol clients: Snort and Iris. These applications allow users to send and receive messages privately across a peer-to-peer network, eliminating the need for centralised messaging platforms that can compromise privacy. Snort: A minimalist interface for basic, secure messaging.
Iris: A feature-rich client that provides more tools and options for a robust, decentralised messaging experience.
Peer-Reviewed & Battle-Tested: Both Snort and Iris have been reviewed by the community for their security, decentralisation, and resilience. These clients have been battle-tested in real-world environments where privacy and security are non-negotiable, making them trusted tools for secure communications. By including both Snort and Iris, users of OpSecOS have a flexible and secure communication platform that protects their privacy.
-
BIP39 - Ian Coleman’s Tool Managing Bitcoin securely requires careful attention to wallet seed phrases. BIP39 allows users to generate mnemonic seed phrases offline, protecting against online threats. By integrating Ian Coleman's BIP39 tool into OpSecOS, we provide a secure, offline method for generating and managing wallet backups, ensuring users’ funds remain under their control at all times. Peer-Reviewed & Battle-Tested: The BIP39 tool is widely regarded as one of the most secure and trusted methods for generating wallet seed phrases. It has been peer-reviewed by security experts and used in countless real-world scenarios to ensure the safe recovery of cryptocurrency wallets.
-
Mempool.space Mempool.space is a real-time visualisation tool for Bitcoin’s mempool — the collection of unconfirmed transactions awaiting inclusion in the next block. This tool allows users to see transaction fees, network congestion, and block size, helping them optimise their Bitcoin transactions for speed and cost-effectiveness. Mempool.space provides an edge for users who want to monitor Bitcoin’s network activity and ensure that their transactions are processed in the most efficient manner. Peer-Reviewed & Battle-Tested: Mempool.space is used by advanced Bitcoin users, miners, and developers worldwide to monitor and optimise transactions. It has been thoroughly reviewed and is trusted by the community as an indispensable tool for understanding Bitcoin's network dynamics.
**Why These Applications Matter ** The integration of these peer-reviewed and battle-tested applications into OpSecOS transforms it from a privacy-focused operating system into a powerful, decentralised security suite. Each of these tools has been carefully selected to provide users with more control over their digital assets, communications, and privacy. Whether you’re trading Bitcoin, Monero, or engaging in private communications, these tools ensure that you are operating in a trusted, decentralised environment free from surveillance or censorship. These applications, trusted by privacy experts, offer an elevated user experience built on the core principles of decentralisation, security, and privacy. With these tools, users can navigate the digital world with confidence, knowing their activities remain private and under their control.
**New and Improved for 2025 ** While some applications have been updated to the latest, most secure versions, others have been removed to ensure OpSecOS stays focused on delivering the best possible security. We’ve carefully vetted each app to make sure it meets the highest standards for privacy and decentralisation, removing older or less secure applications that could pose risks to our users.
**Conclusion ** OpSec Academy’s custom OpSecOS takes the trusted, privacy-focused foundation of TailsOS and supercharges it with a suite of powerful, peer-reviewed and battle-tested applications. Whether you’re managing your Bitcoin and Monero holdings, engaging in private communications, or ensuring your wallet is securely backed up, OpSecOS provides you with everything you need to operate in a decentralised, secure, and private environment. As surveillance and digital threats continue to grow, OpSecOS remains a vital tool for users looking to protect their privacy and maintain complete control over their digital lives. OpSec Academy is committed to continually improving OpSecOS to meet the evolving demands of privacy-conscious users. With OpSecOS, we provide an enhanced privacy experience that stays true to the principles of decentralisation and operational security.
OpSec Academy offers consultations for individuals or organisations looking to integrate OpSecOS into their security framework. Contact us securely for more information.
-
-
 @ 73dc15e0:b7a84244
2025-04-12 14:24:06
@ 73dc15e0:b7a84244
2025-04-12 14:24:06プロローグ
童貞こと薄(すすき) 仙人(せんにん)29歳。ここに眠る。「RIP」。29年間ずっと不運だった。親が仙人なんて名前を付けるから。学校では薄い仙人で「はげ仙人」なんてよばれるし、会社は倒産し、家は燃え、さっきトラックで引かれたところだ。そして、今「自称邪心」に次の魔王になってほしいと頼まれている。
―「なんで俺がそんなことしなきゃいけないのだ。」
「君には普通の人間よりも欲が何倍も大きい。ほんとは君の世界では収まらないぐらいだよ。」
―「異世界に行くのはいいとして、なんで魔王なんだ?」
「一つは、さっきも言った通り、君の欲は大きい。二つ目はもうすぐ現魔王がいなくなるからだよ。」
―「勇者にでも殺されたか?」
「いや、勇者と魔王が結婚した。」
―「は?」意味がわからない。勇者は魔王を倒すものではないのか?
「いなくなるというよりは魔王をやめるという表現のほうが正しかったかな。」
邪神によると勇者と魔王が結婚し、現魔王は魔王をやめるので、勇者と魔王の子供に転生し、次の新たな魔王になってほしいとのことだった。
人族と魔族(エルフ、ドワーフ、悪魔など)がこの世界にはあり、人族は聖神、魔族は
邪神が保護しているそうで、人と魔族は大昔から敵対しているそうだ。
聖神は魔族を忌み嫌っているので、魔族を統べる物がいなくなればいつ人族が襲ってくるかわからない。
人族には個別スキル(怪力、俊足など)には一般スキルと固有スキルがある。
固有スキルは世界に一人しかもっておらず、使用者が死ぬと新しく生まれてきた誰かがその固有スキルを手にする。固有スキルは5000万人に1人ぐらいの割合だそうだ。
一般スキルは固有スキルと違い、スキルがかぶることはよくあるそうだ。
魔族は種族スキルがある。種族スキルとはその種族が全員同じスキルをもっている。
魔族は固有スキルや個別スキルがない代わり人よりも各ステータスが高い。
俺は邪神に恩恵を3つもらった。一つは「超再生」。これは怪我や魔力、体力を瞬時に再生させてくれるチート能力だ。2つ目は「代償」腕や心臓などの代償をつくることによって自分を強化したり、新しく武器を作ることができる。この能力は一つ目の「超再生」と組み合わせることでバグをうみだすことができる。3つ目は「入れ替え」これは、さわったことのある物や人との場所を入れ替えることができる。
この三つの恩恵で異世界を俺は生き抜いてやる。
-
 @ f1e78daa:124e0e56
2025-04-12 14:13:41
@ f1e78daa:124e0e56
2025-04-12 14:13:41今日はテストです。
-
 @ f1e78daa:124e0e56
2025-04-12 14:02:20
@ f1e78daa:124e0e56
2025-04-12 14:02:20プロローグ
童貞こと薄(すすき) 仙人(せんにん)29歳。ここに眠る。「RIP」。29年間ずっと不運だった。親が仙人なんて名前を付けるから。学校では薄い仙人で「はげ仙人」なんてよばれるし、会社は倒産し、家は燃え、さっきトラックで引かれたところだ。そして、今「自称邪心」に次の魔王になってほしいと頼まれている。
―「なんで俺がそんなことしなきゃいけないのだ。」
「君には普通の人間よりも欲が何倍も大きい。ほんとは君の世界では収まらないぐらいだよ。」
―「異世界に行くのはいいとして、なんで魔王なんだ?」
「一つは、さっきも言った通り、君の欲は大きい。二つ目はもうすぐ現魔王がいなくなるからだよ。」
―「勇者にでも殺されたか?」
「いや、勇者と魔王が結婚した。」
―「は?」意味がわからない。勇者は魔王を倒すものではないのか?
「いなくなるというよりは魔王をやめるという表現のほうが正しかったかな。」
邪神によると勇者と魔王が結婚し、現魔王は魔王をやめるので、勇者と魔王の子供に転生し、次の新たな魔王になってほしいとのことだった。
人族と魔族(エルフ、ドワーフ、悪魔など)がこの世界にはあり、人族は聖神、魔族は
邪神が保護しているそうで、人と魔族は大昔から敵対しているそうだ。
聖神は魔族を忌み嫌っているので、魔族を統べる物がいなくなればいつ人族が襲ってくるかわからない。
人族には個別スキル(怪力、俊足など)には一般スキルと固有スキルがある。
固有スキルは世界に一人しかもっておらず、使用者が死ぬと新しく生まれてきた誰かがその固有スキルを手にする。固有スキルは5000万人に1人ぐらいの割合だそうだ。
一般スキルは固有スキルと違い、スキルがかぶることはよくあるそうだ。
魔族は種族スキルがある。種族スキルとはその種族が全員同じスキルをもっている。
魔族は固有スキルや個別スキルがない代わり人よりも各ステータスが高い。
俺は邪神に恩恵を3つもらった。一つは「超再生」。これは怪我や魔力、体力を瞬時に再生させてくれるチート能力だ。2つ目は「代償」腕や心臓などの代償をつくることによって自分を強化したり、新しく武器を作ることができる。この能力は一つ目の「超再生」と組み合わせることでバグをうみだすことができる。3つ目は「入れ替え」これは、さわったことのある物や人との場所を入れ替えることができる。
この三つの恩恵で異世界を俺は生き抜いてやる。
-
 @ f1e78daa:124e0e56
2025-04-12 14:01:15
@ f1e78daa:124e0e56
2025-04-12 14:01:15プロローグ
童貞こと薄(すすき) 仙人(せんにん)29歳。ここに眠る。「RIP」。29年間ずっと不運だった。親が仙人なんて名前を付けるから。学校では薄い仙人で「はげ仙人」なんてよばれるし、会社は倒産し、家は燃え、さっきトラックで引かれたところだ。そして、今「自称邪心」に次の魔王になってほしいと頼まれている。
―「なんで俺がそんなことしなきゃいけないのだ。」
「君には普通の人間よりも欲が何倍も大きい。ほんとは君の世界では収まらないぐらいだよ。」
―「異世界に行くのはいいとして、なんで魔王なんだ?」
「一つは、さっきも言った通り、君の欲は大きい。二つ目はもうすぐ現魔王がいなくなるからだよ。」
―「勇者にでも殺されたか?」
「いや、勇者と魔王が結婚した。」
―「は?」意味がわからない。勇者は魔王を倒すものではないのか?
「いなくなるというよりは魔王をやめるという表現のほうが正しかったかな。」
邪神によると勇者と魔王が結婚し、現魔王は魔王をやめるので、勇者と魔王の子供に転生し、次の新たな魔王になってほしいとのことだった。
人族と魔族(エルフ、ドワーフ、悪魔など)がこの世界にはあり、人族は聖神、魔族は
邪神が保護しているそうで、人と魔族は大昔から敵対しているそうだ。
聖神は魔族を忌み嫌っているので、魔族を統べる物がいなくなればいつ人族が襲ってくるかわからない。
人族には個別スキル(怪力、俊足など)には一般スキルと固有スキルがある。
固有スキルは世界に一人しかもっておらず、使用者が死ぬと新しく生まれてきた誰かがその固有スキルを手にする。固有スキルは5000万人に1人ぐらいの割合だそうだ。
一般スキルは固有スキルと違い、スキルがかぶることはよくあるそうだ。
魔族は種族スキルがある。種族スキルとはその種族が全員同じスキルをもっている。
魔族は固有スキルや個別スキルがない代わり人よりも各ステータスが高い。
俺は邪神に恩恵を3つもらった。一つは「超再生」。これは怪我や魔力、体力を瞬時に再生させてくれるチート能力だ。2つ目は「代償」腕や心臓などの代償をつくることによって自分を強化したり、新しく武器を作ることができる。この能力は一つ目の「超再生」と組み合わせることでバグをうみだすことができる。3つ目は「入れ替え」これは、さわったことのある物や人との場所を入れ替えることができる。
この三つの恩恵で異世界を俺は生き抜いてやる。
-
 @ f3873798:24b3f2f3
2025-04-11 22:43:43
@ f3873798:24b3f2f3
2025-04-11 22:43:43Durante décadas, ouvimos que o Brasil era o "país do futuro". Uma terra rica, com imenso potencial humano e natural, destinada a se tornar uma grande potência e referência para o mundo. Essa ideia, repetida em discursos políticos e publicações internacionais, alimentou gerações com esperança. Mas o tempo passou — e esse futuro promissor parece nunca chegar.
Na prática, o que vemos é um ciclo de promessas não cumpridas, problemas sociais profundos e um povo muitas vezes desiludido. Apesar do potencial imenso, o Brasil enfrenta barreiras estruturais e culturais que dificultam seu pleno desenvolvimento. E é justamente sobre isso que precisamos refletir.
A raiz dos nossos desafios
Não há como ter jeito sem que haja um enfrentamento com seriedade aos problemas que estão na base da nossa sociedade. Um dos maiores entraves é a precariedade da educação, tanto no acesso quanto na qualidade. Em muitas regiões, o estudo ainda é visto como perda de tempo, algo que não contribui para o sustento imediato da família. Mesmo com incentivos governamentais, o desempenho das escolas é baixo. Em vez de formar cidadãos críticos e profissionais capacitados, muitas vezes vemos instituições focadas em ideologias ou agendas desconectadas da realidade do aluno.
Outro ponto sensível é a estrutura familiar. Em áreas onde faltam referências morais, espirituais e sociais, o ambiente familiar pode se tornar disfuncional, com casos extremos de abusos e ausência total de valores básicos. Nesses contextos, a ausência de instituições que promovem virtudes e limites — como a Igreja, por exemplo — faz diferença. Não se trata de impor uma religião, mas de reconhecer o papel histórico que a fé teve (e ainda tem) na construção de uma base ética e civilizatória.
A falta de valores basilares e estrutura para a promoção da relações em sociedade, faz do ambiente escolar um local sem propósito, onde são depositados crianças para serem expostas a um convívio forçado com estranhos sem nenhum preparo familiar, e sendo muitas vezes subentendido pelos profissionais educadores como dever da família, no entanto tal estrutura foi corrompida e devido o combate a religião pelos veículos midiáticos.
O papel da cultura e da moralidade
A cultura brasileira também tem sido afetada por uma inversão de valores. Virtudes como honestidade, humildade e dedicação são muitas vezes vistas com desdém, enquanto comportamentos imprudentes e hedonistas são exaltados. Essa distorção enfraquece a sociedade e prejudica qualquer tentativa de avanço coletivo.
A elite intelectual e política, por sua vez, parece muitas vezes mais preocupada com interesses próprios do que com o bem comum. Muitos aderem a ideias que, em vez de promover a soberania e a autonomia nacional, aprofundam nossa dependência e fragilidade como país.
Existe saída?
Sim, existe. Mas não será simples — e muito menos rápida. O Brasil precisa de uma mudança profunda de mentalidade. Isso inclui:
Resgatar o valor da família e da formação moral;
Investir de verdade em uma educação que liberte, que forme e que inspire;
Incentivar a produção científica e tecnológica local;
Valorizar o trabalho árduo, a persistência e o compromisso com a verdade.
Também é preciso reconhecer que o desenvolvimento de uma nação não é apenas econômico, mas também espiritual e cultural. Mesmo que você não seja religioso, é possível entender que a construção de uma sociedade mais justa exige princípios, virtudes e limites. Sem isso, qualquer progresso será frágil e passageiro.
O Brasil tem jeito? Sim. Mas depende de nós — da nossa capacidade de enxergar com coragem onde estamos falhando, e da nossa disposição para agir com sabedoria, verdade e esperança.
-
 @ 1bc70a01:24f6a411
2025-04-11 13:50:38
@ 1bc70a01:24f6a411
2025-04-11 13:50:38The heading to be
Testing apps, a tireless quest, Click and swipe, then poke the rest. Crashing bugs and broken flows, Hidden deep where logic goes.
Specs in hand, we watch and trace, Each edge case in its hiding place. From flaky taps to loading spins, The war on regressions slowly wins.
Push the build, review the log, One more fix, then clear the fog. For in each test, truth will unfold— A quiet tale of stable code.
This has been a test. Thanks for tuning in.
- one
- two
- three
Listen a chillTranquility
And leisure
-
 @ 0fa80bd3:ea7325de
2025-04-09 21:19:39
@ 0fa80bd3:ea7325de
2025-04-09 21:19:39DAOs promised decentralization. They offered a system where every member could influence a project's direction, where money and power were transparently distributed, and decisions were made through voting. All of it recorded immutably on the blockchain, free from middlemen.
But something didn’t work out. In practice, most DAOs haven’t evolved into living, self-organizing organisms. They became something else: clubs where participation is unevenly distributed. Leaders remained - only now without formal titles. They hold influence through control over communications, task framing, and community dynamics. Centralization still exists, just wrapped in a new package.
But there's a second, less obvious problem. Crowds can’t create strategy. In DAOs, people vote for what "feels right to the majority." But strategy isn’t about what feels good - it’s about what’s necessary. Difficult, unpopular, yet forward-looking decisions often fail when put to a vote. A founder’s vision is a risk. But in healthy teams, it’s that risk that drives progress. In DAOs, risk is almost always diluted until it becomes something safe and vague.
Instead of empowering leaders, DAOs often neutralize them. This is why many DAOs resemble consensus machines. Everyone talks, debates, and participates, but very little actually gets done. One person says, “Let’s jump,” and five others respond, “Let’s discuss that first.” This dynamic might work for open forums, but not for action.
Decentralization works when there’s trust and delegation, not just voting. Until DAOs develop effective systems for assigning roles, taking ownership, and acting with flexibility, they will keep losing ground to old-fashioned startups led by charismatic founders with a clear vision.
We’ve seen this in many real-world cases. Take MakerDAO, one of the most mature and technically sophisticated DAOs. Its governance token (MKR) holders vote on everything from interest rates to protocol upgrades. While this has allowed for transparency and community involvement, the process is often slow and bureaucratic. Complex proposals stall. Strategic pivots become hard to implement. And in 2023, a controversial proposal to allocate billions to real-world assets passed only narrowly, after months of infighting - highlighting how vision and execution can get stuck in the mud of distributed governance.
On the other hand, Uniswap DAO, responsible for the largest decentralized exchange, raised governance participation only after launching a delegation system where token holders could choose trusted representatives. Still, much of the activity is limited to a small group of active contributors. The vast majority of token holders remain passive. This raises the question: is it really community-led, or just a formalized power structure with lower transparency?
Then there’s ConstitutionDAO, an experiment that went viral. It raised over $40 million in days to try and buy a copy of the U.S. Constitution. But despite the hype, the DAO failed to win the auction. Afterwards, it struggled with refund logistics, communication breakdowns, and confusion over governance. It was a perfect example of collective enthusiasm without infrastructure or planning - proof that a DAO can raise capital fast but still lack cohesion.
Not all efforts have failed. Projects like Gitcoin DAO have made progress by incentivizing small, individual contributions. Their quadratic funding mechanism rewards projects based on the number of contributors, not just the size of donations, helping to elevate grassroots initiatives. But even here, long-term strategy often falls back on a core group of organizers rather than broad community consensus.
The pattern is clear: when the stakes are low or the tasks are modular, DAOs can coordinate well. But when bold moves are needed—when someone has to take responsibility and act under uncertainty DAOs often freeze. In the name of consensus, they lose momentum.
That’s why the organization of the future can’t rely purely on decentralization. It must encourage individual initiative and the ability to take calculated risks. People need to see their contribution not just as a vote, but as a role with clear actions and expected outcomes. When the situation demands, they should be empowered to act first and present the results to the community afterwards allowing for both autonomy and accountability. That’s not a flaw in the system. It’s how real progress happens.
-
 @ d41bf82f:ed90d888
2025-04-21 23:18:20
@ d41bf82f:ed90d888
2025-04-21 23:18:20"ประวัติศาสตร์ก็เฉกเช่นธรรมชาติ — การเกิดและการตายล้วนดำเนินไปอย่างสมดุล" -โยฮัน ฮุยซิงกา3
การเสื่อมถอยของโลกยุคใหม่
พวกเรากำลังอยู่ในช่วงปลายของสิ่งที่เรียกว่า “ยุคใหม่” — ระบบโลกที่ถูกจัดระเบียบผ่านรัฐชาติอันรวมศูนย์ ซึ่งเคยพาเราผ่านยุคอุตสาหกรรม สงครามโลก และการสร้างโครงสร้างทางสังคมที่เข้มแข็งด้วยภาษี สวัสดิการ และระบบราชการ แต่ยุคนี้กำลังเคลื่อนเข้าสู่ฉากสุดท้ายของมันอย่างเงียบงัน โดยไม่มีใครในกระแสหลักพูดถึงอย่างจริงจัง และสิ่งที่กำลังมาแทนที่ก็จะแตกต่างอย่างสิ้นเชิงในเชิงคุณภาพจากโลกที่เราคุ้นเคย
เช่นเดียวกับที่สังคมเกษตรกรรมเคยมาแทนที่สังคมสัตว์-หาของป่า และระบบอุตสาหกรรมเคยมาแทนระบบศักดินา สังคมใหม่ที่กำลังปรากฏขึ้นจะเป็นการเปลี่ยนผ่านครั้งใหญ่ โดยในยุคใหม่นี้ “ประสิทธิภาพ” จะไม่ผูกติดกับ “ขนาด” อีกต่อไป อำนาจแบบรวมศูนย์ของรัฐจะถูกสั่นคลอน และระบบใหม่จะเกิดขึ้นซึ่งเล็กกว่า คล่องตัวกว่า และยากที่รัฐแบบเดิมจะควบคุม
นักประวัติศาสตร์ในอนาคตอาจมองว่าการล่มสลายของสหภาพโซเวียตในปี 1991 หรือการพังทลายของกำแพงเบอร์ลินในปี 1989 คือจุดสิ้นสุดของยุคสมัยนี้ และเปิดฉากสู่สิ่งใหม่ — บ้างเรียกมันว่ายุคหลังสมัยใหม่ บ้างว่าโลกไซเบอร์ หรือสังคมสารสนเทศ ไม่ว่าจะตั้งชื่ออย่างไร สิ่งที่ทุกคนยอมรับคือมันคือ "โลกใบใหม่" ที่แตกต่างอย่างถึงแก่นจากโลกเดิม
ความเข้าใจของมนุษย์ต่อการเปลี่ยนแปลงใหญ่ระดับอารยธรรมมักมาช้า เพราะขาดกรอบความคิดและภาษาที่จะมองเห็นมันได้ในขณะที่มันเกิดขึ้นจริง ยกตัวอย่างเช่น ไม่มีใครในยุคศักดินาคิดว่าตนเองอยู่ใน “ยุคกลาง” จนกระทั่งยุคใหม่เข้ามาเปรียบเทียบ ในทำนองเดียวกัน พวกเราทุกวันนี้ก็อาจไม่รู้ตัวว่าเรากำลังอยู่ในช่วงสิ้นสุดของยุคหนึ่ง และจุดเริ่มต้นของอีกยุคหนึ่ง
ระบบสังคมใดก็ตามมักฝังข้อสันนิษฐานโดยปริยายว่าระบบของตนคือสิ่งสูงสุด เป็นสิ่งที่ไม่มีวันเปลี่ยน และไม่ควรถูกตั้งคำถาม การตั้งคำถามถึงความอยู่รอดของระบบ จึงเป็นเรื่องที่ถูกกีดกันโดยไม่รู้ตัว เพราะยิ่งระบบใกล้ล่มสลายเท่าไร มันก็ยิ่งต้องพยายามปกปิดไม่ให้ใครรับรู้ถึงความเปราะบางของมัน
ตัวอย่างจากประวัติศาสตร์เช่น การล่มสลายของจักรวรรดิโรมันใน ค.ศ. 476 ก็ไม่ได้รับการรับรู้ว่าเป็น “จุดจบ” ในเวลานั้น แม้เมื่อจักรพรรดิองค์สุดท้าย(โรมุลุส เอากุสตุส)ถูกปลด แต่ผู้คนและโครงสร้างเดิมของโรมันก็ยังคงแสร้งทำว่าทุกอย่างดำเนินไปตามปกติ รูปแบบของรัฐบาลเก่ายังคงถูกรักษาไว้ พิธีกรรมในระบบเดิมยังคงจัดขึ้น วุฒิสภายังคงประชุม กงสุลยังได้รับการแต่งตั้ง และระบบราชการก็ยังคงอยู่เกือบครบถ้วน พวกป่าเถื่อนที่เข้ามาปกครองก็ยังแสดงตนว่าให้ความเคารพต่อจักรวรรดิไบแซนไทน์และกฎหมายโรมัน ศาสนาคริสต์ยังคงดำรงเป็นศาสนาประจำรัฐ เครื่องราชสัญลักษณ์ยังถูกใช้ในพิธีสาธารณะ ทั้งหมดนี้เป็นฉากหน้าของการพยายามรักษาภาพความต่อเนื่องในขณะที่แก่นของอำนาจได้เปลี่ยนไปแล้วโดยสิ้นเชิง
ประวัติศาสตร์ช่วงนี้สอนให้เห็นว่า การเปลี่ยนแปลงใหญ่ในระดับอารยธรรมมักถูกซ่อนเร้นอยู่ภายใต้ความเฉื่อยของสังคมที่ไม่ยอมรับความเป็นจริง คนในยุคนั้นไม่ได้รู้สึกว่าโรมล่มสลายไปแล้ว พวกเขาเพียงรู้สึกว่าชีวิตยังดำเนินต่อไปได้ แม้ภายใต้ระเบียบใหม่ที่ซ้อนทับเข้ามาโดยไม่ได้ประกาศตนอย่างเป็นทางการ ความเปลี่ยนแปลงที่แท้จริงจึงไม่ใช่เหตุการณ์ที่เกิดขึ้นในวันใดวันหนึ่ง แต่เป็นกระบวนการค่อยเป็นค่อยไปที่อาศัยแรงเฉื่อยของความเชื่อเก่าว่าสิ่งต่างๆ “ยังเหมือนเดิม”
ผู้เขียนใช้ตัวอย่างนี้เพื่อสะท้อนมาสู่โลกปัจจุบันว่า แม้ตัวอย่างโรมจะดูไกลตัว แต่ก็มีลักษณะใกล้เคียงกับสิ่งที่เรากำลังเผชิญอยู่ ระบบรัฐชาติสมัยใหม่ก็อาจกำลังเข้าสู่ภาวะเสื่อมถอยโดยที่คนส่วนใหญ่ยังไม่รู้ตัวเช่นเดียวกัน หนังสือเล่มนี้จึงไม่ได้ตั้งต้นจากการคาดเดาอนาคตอย่างลอย ๆ หากแต่เสนอว่า เราจะเข้าใจอนาคตได้ดีขึ้น ถ้าเริ่มจากการเรียนรู้กระบวนการเปลี่ยนผ่านในอดีต โดยเฉพาะพลวัตทางการเมืองและตรรกะของอำนาจ
จุดเปลี่ยนของโรมันไม่เพียงแต่แสดงให้เห็นการล่มสลายของรัฐรวมศูนย์ แต่ยังเผยให้เห็นว่าการล่มสลายนั้นสามารถเปิดทางให้กิจกรรมทางเศรษฐกิจในท้องถิ่นเบ่งบานขึ้นได้ ในยุคของเรา แม้สาเหตุจะต่างกัน — โรมล่มเพราะขยายเกินตัว เศรษฐกิจเกษตรกรรมไม่สามารถรองรับภาระรัฐ การเก็บภาษีที่หนักหนาและทหารที่ใช้อำนาจในทางมิชอบ — แต่สิ่งที่คล้ายกันคือ การไม่ยอมรับต่อการเปลี่ยนแปลงที่กำลังก่อตัว
เรายังเห็นการเปรียบเทียบถึงผลกระทบจากโรคระบาดในอดีต เช่น โรคฝีดาษที่ทำให้โรมอ่อนแอลง เช่นเดียวกับความกังวลเรื่องไวรัสกลายพันธุ์ในยุคปัจจุบัน ที่บ่งชี้ถึงความเปราะบางของโครงสร้างสังคม แม้รูปแบบของภัยคุกคามจะต่างกัน แต่สิ่งที่เหมือนกันคือ “ความไม่พร้อมของระบบ” ที่จะรับมือกับความเปลี่ยนแปลงใหญ่
แต่สิ่งสำคัญที่สุดที่ผู้เขียนต้องการชี้ ไม่ใช่แค่สาเหตุของการล่มสลาย แต่คือความจริงที่ว่า ผู้คนในยุคนั้น “ไม่เห็น” ว่าตนเองอยู่ในจุดเปลี่ยน เพราะแรงเฉื่อยทางความคิดและการเมืองทำให้พวกเขายึดมั่นในสิ่งที่เคยรู้จัก โดยไม่รู้เลยว่าโลกได้เคลื่อนเข้าสู่ระยะใหม่แล้ว และเราทุกวันนี้ก็อาจกำลังทำเช่นเดียวกัน
เรากำลังอยู่ในช่วงเวลาที่ไมโครโปรเซสเซอร์ เทคโนโลยีดิจิทัล และโครงสร้างไร้ศูนย์กลางจะเปลี่ยนกฎเกณฑ์ของอำนาจอย่างรุนแรง แต่ผู้คนกลับพยายามตีความสิ่งเหล่านี้ผ่านเลนส์ของโครงสร้างอุตสาหกรรมแบบเดิม ซึ่งอาจทำให้พลาดโอกาสที่จะเข้าใจการเปลี่ยนแปลงที่แท้จริง
ผู้เขียนเตือนว่าแม้บางหนังสือว่าด้วยอนาคตจะเต็มไปด้วยข้อมูล แต่กลับพาเราเข้าใจผิด เพราะยังยึดติดอยู่กับกรอบคิดเดิม เช่น การเชื่อว่ามนุษย์สามารถควบคุมทิศทางประวัติศาสตร์ได้เสมอ ทั้งที่ในความจริงแล้ว ปัจจัยที่ขับเคลื่อนการเปลี่ยนแปลงทางประวัติศาสตร์นั้น มักเป็นเงื่อนไขพื้นฐานที่มนุษย์ควบคุมไม่ได้ และไม่ได้อยู่ในความสนใจของการเมืองกระแสหลัก
มนุษย์มักไม่เปลี่ยนแปลงเพราะ “ต้องการเปลี่ยน” แต่เพราะ “ไม่เปลี่ยนไม่ได้แล้ว” และการเปลี่ยนแปลงเหล่านั้นมักเกิดสวนทางกับความต้องการของคนส่วนใหญ่ที่อยากรักษาสถานะเดิม
ชีวิตที่ขาดวิสัยทัศน์
ความไม่ตระหนักถึงการเปลี่ยนแปลงอันยิ่งใหญ่ที่กำลังก่อตัวขึ้นรอบตัวเรา อาจไม่ได้เกิดจากความไม่รู้ แต่เพราะเราลึกๆ แล้ว “ไม่อยากเห็น” ความเปลี่ยนแปลงนั้นเอง ความต้านทานนี้ไม่ใช่เรื่องใหม่ บรรพบุรุษของเราที่ดำรงชีพด้วยการล่าสัตว์และหาของป่าก็อาจเคยดื้อรั้นไม่ต่างกัน เพียงแต่พวกเขามีข้อแก้ตัวที่ฟังขึ้นมากกว่า เพราะในยุคก่อนประวัติศาสตร์ ไม่มีใครอาจคาดเดาว่า “การปฏิวัติการเกษตร” จะเปลี่ยนโลกไปในระดับใด พวกเขาไม่มีปฏิทิน ไม่มีการบันทึก ไม่มีแบบจำลองใดจากอดีตให้ใช้ทำนายอนาคต แม้แต่แนวคิดเรื่อง “เวลา” ก็ยังไม่มีอยู่ในจิตสำนึก พวกเขาใช้ชีวิตอยู่ใน “ปัจจุบันที่ไม่สิ้นสุด” และเมื่อพูดถึงการคาดการณ์อนาคต พวกเขาก็เป็นเหมือน “คนตาบอด” ที่ยังไม่เคยลิ้มรส “ผลไม้แห่งความรู้” (ตามคำเปรียบในพระคัมภีร์) แต่ต่างจากพวกเขา พวกเราในวันนี้มีเครื่องมือและมุมมองที่ลึกซึ้งกว่า จากองค์ความรู้ของบรรพบุรุษกว่าสี่ห้าร้อยรุ่น วิทยาศาสตร์ คณิตศาสตร์ และอัลกอริธึมของคอมพิวเตอร์ความเร็วสูง ช่วยให้เราทำความเข้าใจระบบที่ซับซ้อนอย่างเศรษฐกิจมนุษย์และพลวัตของสังคมได้ดียิ่งขึ้น แม้ทฤษฎีเศรษฐศาสตร์จะไม่สามารถอธิบายพฤติกรรมมนุษย์ได้แบบสมบูรณ์ แต่ก็ทำให้เราเข้าใจว่า “แรงจูงใจ” คือแรงผลักดันสำคัญ เมื่อผลตอบแทนสูงขึ้น หรือความเสี่ยงต่ำลง พฤติกรรมย่อมเกิดขึ้นถี่ขึ้น และนี่คือหลักการที่แม่นยำอย่างยิ่งในการวิเคราะห์อนาคต
แรงจูงใจนี้เองที่เป็นหัวใจของการพยากรณ์ และการพยากรณ์ที่ดีไม่ได้ขึ้นกับการรู้เหตุการณ์ล่วงหน้าแบบเฉพาะเจาะจง แต่ขึ้นอยู่กับการเข้าใจโครงสร้างของแรงขับเคลื่อน เช่นเดียวกับที่เราอาจไม่รู้ว่าเมื่อไรเสียงฟ้าร้องจะดังขึ้น แต่เมื่อเห็นฟ้าแลบ ก็สามารถคาดหมายได้ว่าจะมีเสียงตามมา เช่นกัน หากเราสามารถเข้าใจ “ตรรกะของความรุนแรง” ที่กำลังเปลี่ยนไปในระดับการเมืองมหภาคได้ เราก็จะมองเห็น “โอกาส” หรือ “ช่องโหว่” ของระเบียบเดิม และใครจะเป็นผู้ฉวยโอกาสเหล่านั้น
การเปลี่ยนแปลงครั้งใหญ่ในอดีต เช่น การปฏิวัติการเกษตร หรือการเข้าสู่ยุคอุตสาหกรรม ล้วนเกิดขึ้นช้าและกินเวลาหลายศตวรรษกว่าจะเผยผลเต็มที่ ในทางตรงกันข้าม การเปลี่ยนผ่านสู่ยุคสารสนเทศกลับเกิดขึ้นรวดเร็วเพียงช่วงชีวิตเดียว
ผู้เขียนวางกรอบเพื่อให้เราเข้าใจว่า การเปลี่ยนแปลงทางการเมืองมหภาคมักมาก่อนการเปลี่ยนแปลงในโครงสร้างของรัฐอย่างเป็นรูปธรรม รายได้ที่ลดลง วิกฤตที่เกิดจากทรัพยากรจำกัด และแรงกดดันจากประชากร ล้วนเป็นผลพลอยได้จากความไม่สามารถของระเบียบเดิมในการรองรับแรงกระแทกของโลกใหม่ และการพูดถึงการเปลี่ยนแปลงจาก “ภายนอกระบบ” มักถูกห้ามหรือมองว่าเป็นเรื่องต้องห้ามในทุกยุคทุกสมัย ยิ่งไปกว่านั้น การเปลี่ยนแปลงในระดับนี้มักก่อให้เกิดแรงปะทะทางวัฒนธรรมระหว่างผู้ที่ยึดมั่นในกรอบศีลธรรมดั้งเดิมกับผู้ที่เปิดรับแนวคิดใหม่ และไม่ใช่เรื่องแปลกที่การเปลี่ยนแปลงเช่นนี้จะไม่เป็นที่นิยม เพราะมันลดคุณค่าของทุนทางปัญญาเดิม ทำให้ระบบเก่าไร้ความหมาย และบีบบังคับให้สังคมต้องเรียนรู้ใหม่เกือบทั้งหมด โดยเฉพาะในกลุ่มคนที่ได้รับผลกระทบโดยตรง
สัญญาณของการเสื่อมถอยมักปรากฏในรูปของคอร์รัปชัน ความไร้ประสิทธิภาพ และการสูญเสียศีลธรรมของผู้มีอำนาจ ซึ่งมักเป็นสัญญาณล่วงหน้าของการเปลี่ยนแปลงที่หลีกเลี่ยงไม่ได้ ยิ่งในยุคที่เทคโนโลยีก้าวหน้าเร็วขึ้น กระบวนการเหล่านี้ก็จะยิ่งเร่งตัว จนทำให้เวลาที่เหลืออยู่สำหรับการปรับตัวลดลงเรื่อย ๆ
"เมื่อมองย้อนกลับไปตลอดหลายศตวรรษ — หรือแม้แต่แค่ในปัจจุบัน — เราจะเห็นได้อย่างชัดเจนว่า มีผู้คนจำนวนมากที่สร้างรายได้(บ่อยครั้งเป็นรายได้จำนวนมาก) จากทักษะในการใช้ความรุนแรงผ่านอาวุธ และกิจกรรมของพวกเขาเหล่านี้มีบทบาทอย่างสำคัญยิ่งในการกำหนดว่าทรัพยากรที่มีอยู่จำกัดในสังคมจะถูกจัดสรรไปในทิศทางใด." --เฟรเดอริก ซี. เลน
แนวคิดของการเมืองมหภาค(megapolitics) เป็นกรอบความคิดที่ทรงพลัง ซึ่งช่วยให้เรามองเห็นกลไกเบื้องหลังเหตุการณ์ที่ดูซับซ้อนหรือลึกลับในประวัติศาสตร์ ไม่ว่าจะเป็นเหตุผลที่บางรัฐบาลเจริญรุ่งเรือง ขณะที่บางแห่งกลับล่มสลาย เหตุใดสงครามจึงอุบัติขึ้น และเหตุใดฝ่ายหนึ่งจึงมีชัย หรือแม้กระทั่งว่าอะไรเป็นตัวแปรที่กำหนดวงจรแห่งความรุ่งเรืองและความตกต่ำทางเศรษฐกิจ ทั้งหมดล้วนสามารถอธิบายได้ผ่านเลนส์ของการเมืองมหภาค ซึ่งเน้นวิเคราะห์ว่า "ต้นทุนและผลตอบแทนของการใช้ความรุนแรง" เปลี่ยนไปอย่างไรในแต่ละบริบทของเวลา หากต้นทุนในการใช้อำนาจบังคับลดต่ำลง เช่น การเข้าถึงอาวุธที่ง่ายขึ้นและราคาถูกลง ก็ทำให้อำนาจเปลี่ยนมือได้ง่ายขึ้นตามไปด้วย หลักการนี้ยังคงใช้ได้ตั้งแต่ยุคโบราณจนถึงโลกยุคไซเบอร์สเปซในปัจจุบัน
ใน Part 2 เราจะมาดูกันว่ามีปัจจัยอะไรบ้างที่อยู่เบื้องหลังการเปลี่ยนแปลงครั้งใหญ่ในประวัติศาสตร์ to be continue....
-
 @ d360efec:14907b5f
2025-04-21 22:10:23
@ d360efec:14907b5f
2025-04-21 22:10:23สวัสดีเพื่อนนักเทรดทุกท่าน! 👋 วันนี้ฉันมาแนะนำตารางกิจวัตรประจำวันของ Day Trader ที่น่าสนใจนี้กันนะคะ มาดูกันว่ามีอะไรที่เราสามารถเรียนรู้และนำไปปรับใช้กับการเทรดของเราได้บ้างค่ะ

ภาพรวมกิจวัตรประจำวันของ Day Trader 📊
ตารางนี้แสดงให้เห็นถึงโครงสร้างของวันที่สมดุลสำหรับนักเทรดรายวันที่ประสบความสำเร็จ โดยเน้นทั้งการเตรียมตัว 🤓 การลงมือเทรด 🚀 การเรียนรู้ 📚 และการดูแลสุขภาพส่วนตัว 🧘♀️ ซึ่งเป็นสิ่งสำคัญอย่างยิ่งในการรักษาประสิทธิภาพและความสม่ำเสมอในการเทรด 💪
การวิเคราะห์และอธิบายแต่ละช่วงเวลา
$ 05.30 น. > ตื่นนอน 🌅 อาบน้ำ 🚿 และเตรียมตัว 👔 > การเริ่มต้นวันอย่างกระปรี้กระเปร่า 🎉 และการมีกิจวัตรส่วนตัวที่ผ่อนคลายเป็นสิ่งสำคัญในการเตรียมพร้อมทั้งร่างกายและจิตใจ 🧠 สำหรับการเทรด
$ 06.00 น. > ตรวจสอบข่าวสาร 📰 วิเคราะห์กราฟ 📈 และเตรียมตัว 🎯 > ช่วงเวลานี้เป็นหัวใจสำคัญของการเตรียมตัวก่อนตลาดเปิด ⏰ นักเทรดจะตรวจสอบข่าวเศรษฐกิจ 💰 และข่าวที่เกี่ยวข้องกับสินทรัพย์ที่ตนเองเทรด 🧐 วิเคราะห์กราฟเพื่อหาแนวโน้ม 🔭 และระดับราคาที่น่าสนใจ 📍 รวมถึงวางแผนกลยุทธ์การเทรดสำหรับวันนี้ ✍️
$ 06.30 น. > ตลาดเปิด 🔔 เริ่มทำการเทรด 🚀 > เมื่อตลาดเปิด นักเทรดจะเริ่มดำเนินการตามแผนที่วางไว้ 📝 โดยจะเฝ้าติดตามการเคลื่อนไหวของราคา 👀 และเข้าเทรดตามสัญญาณที่เกิดขึ้น 🚦
$ 12.00 น. > พักรับประทานอาหารกลางวัน 🥪 > การพักผ่อน 😌 และการเติมพลัง 💪 ในช่วงกลางวันเป็นสิ่งสำคัญในการรักษาความมีสมาธิ 🧘♀️ และความสามารถในการตัดสินใจที่ดี 👍
$ 12.45 น. > ปิดสถานะการเทรดทั้งหมด 🛑 > สำหรับ Day Trader การปิดสถานะทั้งหมดภายในวันถือเป็นกฎเหล็ก 🚫 เพื่อหลีกเลี่ยงความเสี่ยงจากความผันผวนข้ามคืน 🌙
$ 13.00 น. > ทบทวน 🤔 เรียนรู้ 📚 และปรับปรุง ⚙️ > หลังจากการเทรด นักเทรดที่ประสบความสำเร็จ 🎉 จะใช้เวลาในการทบทวนการเทรดของตนเอง 🧐 วิเคราะห์ว่าอะไรทำได้ดี 👍 และอะไรที่ต้องปรับปรุง 📝 การเรียนรู้อย่างต่อเนื่องเป็นกุญแจสำคัญสู่การพัฒนา 🚀
$ 14.00 น. > ออกกำลังกาย 💪 และพักผ่อน 🧘♀️ > การดูแลสุขภาพกาย 🍎 และใจ 💖 มีความสำคัญไม่ยิ่งหย่อนไปกว่าการเทรด 📈 การออกกำลังกายและการมีเวลาว่าง 🌴 ช่วยลดความเครียด 😥 และเพิ่มประสิทธิภาพในการเทรดในระยะยาว ✨
$ 17.00 น. > รับประทานอาหารเย็น 🍽️ และพักผ่อน 🛋️ > การมีเวลาพักผ่อนกับครอบครัว ❤️ หรือทำกิจกรรมที่ชอบ 😊 ช่วยให้ผ่อนคลาย 😌 และเตรียมพร้อมสำหรับวันต่อไป 🌅
$ 19.00 น. > วางแผนการเทรดสำหรับวันพรุ่งนี้ 🗓️ และตรวจสอบข่าวสาร 📰 > การวางแผนล่วงหน้า 🤓 ช่วยให้นักเทรดมีความพร้อม 💪 และสามารถตอบสนองต่อสถานการณ์ตลาดได้อย่างมีประสิทธิภาพ 🚀
$ 22.00 น. > เข้านอน 😴 > การนอนหลับพักผ่อนอย่างเพียงพอ 🛌 เป็นสิ่งจำเป็นสำหรับการรักษาสุขภาพ 💖 และประสิทธิภาพในการเทรด 💪
สิ่งที่น่าสนใจและข้อคิด 🤔
$ ความมีระเบียบวินัย 💯 > ตารางนี้แสดงให้เห็นถึงความมีระเบียบวินัยที่เข้มงวด 📏 ซึ่งเป็นคุณสมบัติที่สำคัญของนักเทรดที่ประสบความสำเร็จ 🎉
$ การเตรียมตัวอย่างรอบคอบ 🧐 > การใช้เวลาในการวิเคราะห์ 📊 และวางแผน 📝 ก่อนตลาดเปิดช่วยลดการตัดสินใจที่ผิดพลาด 🚫 และเพิ่มโอกาสในการทำกำไร 💰
$ การเรียนรู้อย่างต่อเนื่อง 📚 > การทบทวน 🤔 และปรับปรุงกลยุทธ์ ⚙️ อยู่เสมอเป็นสิ่งสำคัญในการพัฒนาทักษะการเทรด 🚀
$ ความสมดุล ⚖️ > การให้ความสำคัญกับการดูแลสุขภาพ 🧘♀️ และการพักผ่อน 🌴 ควบคู่ไปกับการเทรด 📈 ช่วยป้องกันภาวะหมดไฟ 🔥 และรักษาประสิทธิภาพในระยะยาว ✨
การนำไปปรับใช้ 🛠️
เพื่อนๆ นักเทรดสามารถนำแนวคิดจากตารางนี้ไปปรับใช้กับกิจวัตรประจำวันของตนเองได้ 👍 โดยอาจไม่จำเป็นต้องทำตามทุกช่วงเวลาอย่างเคร่งครัด ⏰ แต่ให้เน้นที่หลักการสำคัญ เช่น การเตรียมตัวก่อนเทรด 🤓 การทบทวนหลังเทรด 🤔 และการดูแลสุขภาพ 🧘♀️ เพื่อสร้างสมดุล ⚖️ และเพิ่มประสิทธิภาพในการเทรดของเราค่ะ 💪
ขอให้ทุกท่านประสบความสำเร็จในการเทรดนะคะ! 💸🚀
#DayTrader #นักเทรดรายวัน #กิจวัตรประจำวัน #การลงทุน #เทรด #หุ้น #คริปโต #ตลาดหุ้น #แรงบันดาลใจ #พัฒนาตัวเอง #LinaEngword
-
 @ c066aac5:6a41a034
2025-04-05 16:58:58
@ c066aac5:6a41a034
2025-04-05 16:58:58I’m drawn to extremities in art. The louder, the bolder, the more outrageous, the better. Bold art takes me out of the mundane into a whole new world where anything and everything is possible. Having grown up in the safety of the suburban midwest, I was a bit of a rebellious soul in search of the satiation that only came from the consumption of the outrageous. My inclination to find bold art draws me to NOSTR, because I believe NOSTR can be the place where the next generation of artistic pioneers go to express themselves. I also believe that as much as we are able, were should invite them to come create here.
My Background: A Small Side Story
My father was a professional gamer in the 80s, back when there was no money or glory in the avocation. He did get a bit of spotlight though after the fact: in the mid 2000’s there were a few parties making documentaries about that era of gaming as well as current arcade events (namely 2007’sChasing GhostsandThe King of Kong: A Fistful of Quarters). As a result of these documentaries, there was a revival in the arcade gaming scene. My family attended events related to the documentaries or arcade gaming and I became exposed to a lot of things I wouldn’t have been able to find. The producer ofThe King of Kong: A Fistful of Quarters had previously made a documentary calledNew York Dollwhich was centered around the life of bassist Arthur Kane. My 12 year old mind was blown: The New York Dolls were a glam-punk sensation dressed in drag. The music was from another planet. Johnny Thunders’ guitar playing was like Chuck Berry with more distortion and less filter. Later on I got to meet the Galaga record holder at the time, Phil Day, in Ottumwa Iowa. Phil is an Australian man of high intellect and good taste. He exposed me to great creators such as Nick Cave & The Bad Seeds, Shakespeare, Lou Reed, artists who created things that I had previously found inconceivable.
I believe this time period informed my current tastes and interests, but regrettably I think it also put coals on the fire of rebellion within. I stopped taking my parents and siblings seriously, the Christian faith of my family (which I now hold dearly to) seemed like a mundane sham, and I felt I couldn’t fit in with most people because of my avant-garde tastes. So I write this with the caveat that there should be a way to encourage these tastes in children without letting them walk down the wrong path. There is nothing inherently wrong with bold art, but I’d advise parents to carefully find ways to cultivate their children’s tastes without completely shutting them down and pushing them away as a result. My parents were very loving and patient during this time; I thank God for that.
With that out of the way, lets dive in to some bold artists:
Nicolas Cage: Actor
There is an excellent video by Wisecrack on Nicolas Cage that explains him better than I will, which I will linkhere. Nicolas Cage rejects the idea that good acting is tied to mere realism; all of his larger than life acting decisions are deliberate choices. When that clicked for me, I immediately realized the man is a genius. He borrows from Kabuki and German Expressionism, art forms that rely on exaggeration to get the message across. He has even created his own acting style, which he calls Nouveau Shamanic. He augments his imagination to go from acting to being. Rather than using the old hat of method acting, he transports himself to a new world mentally. The projects he chooses to partake in are based on his own interests or what he considers would be a challenge (making a bad script good for example). Thus it doesn’t matter how the end result comes out; he has already achieved his goal as an artist. Because of this and because certain directors don’t know how to use his talents, he has a noticeable amount of duds in his filmography. Dig around the duds, you’ll find some pure gold. I’d personally recommend the filmsPig, Joe, Renfield, and his Christmas film The Family Man.
Nick Cave: Songwriter
What a wild career this man has had! From the apocalyptic mayhem of his band The Birthday Party to the pensive atmosphere of his albumGhosteen, it seems like Nick Cave has tried everything. I think his secret sauce is that he’s always working. He maintains an excellent newsletter calledThe Red Hand Files, he has written screenplays such asLawless, he has written books, he has made great film scores such asThe Assassination of Jesse James by the Coward Robert Ford, the man is religiously prolific. I believe that one of the reasons he is prolific is that he’s not afraid to experiment. If he has an idea, he follows it through to completion. From the albumMurder Ballads(which is comprised of what the title suggests) to his rejected sequel toGladiator(Gladiator: Christ Killer), he doesn’t seem to be afraid to take anything on. This has led to some over the top works as well as some deeply personal works. Albums likeSkeleton TreeandGhosteenwere journeys through the grief of his son’s death. The Boatman’s Callis arguably a better break-up album than anything Taylor Swift has put out. He’s not afraid to be outrageous, he’s not afraid to offend, but most importantly he’s not afraid to be himself. Works I’d recommend include The Birthday Party’sLive 1981-82, Nick Cave & The Bad Seeds’The Boatman’s Call, and the filmLawless.
Jim Jarmusch: Director
I consider Jim’s films to be bold almost in an ironic sense: his works are bold in that they are, for the most part, anti-sensational. He has a rule that if his screenplays are criticized for a lack of action, he makes them even less eventful. Even with sensational settings his films feel very close to reality, and they demonstrate the beauty of everyday life. That's what is bold about his art to me: making the sensational grounded in reality while making everyday reality all the more special. Ghost Dog: The Way of the Samurai is about a modern-day African-American hitman who strictly follows the rules of the ancient Samurai, yet one can resonate with the humanity of a seemingly absurd character. Only Lovers Left Aliveis a vampire love story, but in the middle of a vampire romance one can see their their own relationships in a new deeply human light. Jim’s work reminds me that art reflects life, and that there is sacred beauty in seemingly mundane everyday life. I personally recommend his filmsPaterson,Down by Law, andCoffee and Cigarettes.
NOSTR: We Need Bold Art
NOSTR is in my opinion a path to a better future. In a world creeping slowly towards everything apps, I hope that the protocol where the individual owns their data wins over everything else. I love freedom and sovereignty. If NOSTR is going to win the race of everything apps, we need more than Bitcoin content. We need more than shirtless bros paying for bananas in foreign countries and exercising with girls who have seductive accents. Common people cannot see themselves in such a world. NOSTR needs to catch the attention of everyday people. I don’t believe that this can be accomplished merely by introducing more broadly relevant content; people are searching for content that speaks to them. I believe that NOSTR can and should attract artists of all kinds because NOSTR is one of the few places on the internet where artists can express themselves fearlessly. Getting zaps from NOSTR’s value-for-value ecosystem has far less friction than crowdfunding a creative project or pitching investors that will irreversibly modify an artist’s vision. Having a place where one can post their works without fear of censorship should be extremely enticing. Having a place where one can connect with fellow humans directly as opposed to a sea of bots should seem like the obvious solution. If NOSTR can become a safe haven for artists to express themselves and spread their work, I believe that everyday people will follow. The banker whose stressful job weighs on them will suddenly find joy with an original meme made by a great visual comedian. The programmer for a healthcare company who is drowning in hopeless mundanity could suddenly find a new lust for life by hearing the song of a musician who isn’t afraid to crowdfund their their next project by putting their lighting address on the streets of the internet. The excel guru who loves independent film may find that NOSTR is the best way to support non corporate movies. My closing statement: continue to encourage the artists in your life as I’m sure you have been, but while you’re at it give them the purple pill. You may very well be a part of building a better future.
-
 @ 7d33ba57:1b82db35
2025-04-21 20:16:41
@ 7d33ba57:1b82db35
2025-04-21 20:16:41Helsinki, the stylish and compact capital of Finland, sits right on the edge of the Baltic Sea, blending Scandinavian design, sustainable living, and a love for nature. It’s a city of clean lines, calm energy, and a creative spirit—where you can go from a seaside sauna to a sleek design museum in minutes.
🧭 Top Things to Do in Helsinki
⛪ Helsinki Cathedral
- The city’s iconic white-domed landmark, perched on Senate Square
- Climb the steps for sweeping views over the city’s neoclassical heart
🏝️ Suomenlinna Sea Fortress
- A UNESCO World Heritage Site spread across several islands
- Explore old ramparts, tunnels, museums, and scenic picnic spots
- A short ferry ride from the city center, perfect for a half-day trip
🧊 Löyly Sauna
- One of Helsinki’s most famous public saunas, right on the waterfront
- Relax in the heat, then dip in the Baltic like a local
- Beautiful architecture and a must-do cultural experience
🏛️ Design District & Museums
- Wander the Design District for boutique shops, galleries, and Finnish fashion
- Visit the Design Museum, Kiasma (contemporary art), and Ateneum (classic Finnish art)
🌲 Nature + Nordic Calm
- Walk along the Esplanadi park or relax in Kaivopuisto by the sea
- Take a boat to the nearby archipelago islands for hiking, birdwatching, or quiet cafés
- Even in winter, the city feels clean, serene, and cozy
☕ Food, Coffee & Nordic Flavors
- Try karjalanpiirakka (Karelian pies), salmon soup, or reindeer meat if you’re adventurous
- Helsinki has a big coffee culture—Finns drink more coffee per capita than anyone!
- Cozy up in a café with a cinnamon pulla and watch the snow fall (or the summer sun glow at midnight)
🚲 Getting Around
- Easy to explore by foot, tram, or city bikes
- Excellent ferries and boats to nearby islands and Tallinn, Estonia
- Helsinki Airport is well-connected and just 30 mins from downtown
📅 When to Go
- Summer: Endless daylight, festivals, and outdoor dining
- Winter: Snowy streets, cozy interiors, and a shot at the Northern Lights if you head north
- Autumn: Ruska (fall colors) is stunning in the parks and forests
-
 @ 3ad01248:962d8a07
2025-04-21 19:40:22
@ 3ad01248:962d8a07
2025-04-21 19:40:22It has almost been a month since the Bitcoin friendly Trump administration has been in power. The Bitcoin price was riding high days before and after the election with Bitcoin reaching a new all time high of 109k. It sure seem like surely once Trump got into office the price would skyrocket and everyone finally would have lambos and girlfriends.
Sadly for the number go up crowd this didn't happen. There are no lambos to be found and no girlfriends. All we get is some sideways price action and a Strategic Bitcoin Reserve (BSR).
If you are in Bitcoin for the right reasons and understand what you hold, this is the perfect time to stack sats before the price goes parabolic. I say this because Bitcoin sure seems to be poised to make a massive run. If you look past the current price of Bitcoin you can see a storm of dollars flowing into Bitcoin from the traditional fiat economy. The signs are there if you start looking for them.
US States Creating Bitcoin Strategic Reserves
Guess how many states are considering creating a state level Bitcoin reserve of their own? Lots. Here is a list of states that are thinking about creating a reserve for their state:
- Alabama
- Arizona
- Florida
- Kansas
- Illinois
- Iowa
- Massachusetts
- Michigan
- Missouri
- Montana
- New Hampshire
- New Jersey
- New Mexico
- North Carolina
- North Dakota
- Ohio
- Pennsylvania
- South Dakota
- Texas
- Utah
- Wisconsin
- Wyoming
Each state is at some varying degree of interest in creating a reserve. Texas and Arizona are by far have made the most progress on making a Bitcoin reserve a reality. Texas is currently holding a public hearing on this at the time of this writing. There is strong political will to create a reserve so I definitely can see them being first movers on this and once Texas makes it a reality the other state will move in short order.
Arizona's strategic reserve bill passed the senate finance committee on a 5-2 which is a big deal in itself but still has a long way to go before it becomes policy. If it passes the Senate it still has to pass the Arizona House of Representatives and signed by Democrat Governor Katie Hobbs, so the odds of this becoming law is slim. Arizona Democrats seem to be anti-Bitcoin in general and any bills coming from Republicans will likely be shoot down or watered down.
Analysts believe that $23 billion could flow into Bitcoin from government reserves which equates to 247k Bitcoin going into government cold storage. I have reservations about governments creating BSR's but if we are going to have them I much rather them be at the state level where it can benefit citizens the most. Especially state pension funds that so many of our firefighters, police and first responders depend on for retirement.
We will probably see a state level BSR created by the end of the year if not sooner. Time will tell.
SAB 121 Repeal
What is SAB 121? SAB 121 or Staff Accounting Bulletin 121 made it problematic for financial institutions to custody digital assets such as Bitcoin for their customers. SAB 121 required institutions to record their holdings as a liability and not an asset.
Naturally banks and other financial institutions didn't see an upside to custody digital assets if it meant taking on liability and having an administration that was hostile to crypto in general. Why take the chance to piss off the government and give them a reason to go after you is probably the reasoning of most bank executives. SAB 121 achieved the goal the Biden administration set out to accomplish, namely stymie Bitcoin adoption by banks and individuals as long as possible.
President Trump swiftly issued a executive order rescinding SAB 121 and with that ushering a new era in the realm of Bitcoin and digital assets in general. Financial institutions now have the ability to explore Bitcoin custody solutions that fit their customer's need without fear of having to record a liability on their books.
As more and more people and business learn about Bitcoin third party custody options are going to be popular. Think about it from a small business owner perspective for a second. They are in the business of selling their widgets for Bitcoin but they don't want to manage the complexity that comes with accounting, taxes etc.. In steps in their local bank that they have been with for years if not decades and starts providing Bitcoin management services. Small business owners would be all over that idea. In the long run I think the repeal of SAB 121 is going to be a bigger deal than states creating Bitcoin strategic reserves.
FASB
Financial Accounting Standards Board or FASB for short has applied fair value accounting rules on Bitcoin and other digital assets. This is a huge deal because it will allow business to realize profit and losses of Bitcoin based on market prices. It also makes it easier for investors who evaluate businesses that hold Bitcoin on their balance sheet. Overall it treats Bitcoin like any other asset that a business would hold.
This accounting rule change will pave the way for more businesses to put Bitcoin on their balance sheet further driving demand for Bitcoin.
Lightning Companies Leading The Way
We all know that L1 Bitcoin can not scale to the entire world and that in order to bring more people into Bitcoin that layer two solutions would have to be built. This has largely been done with the creation of the lightning network which enables seamless peer to peer micropayments in the blink of an eye.
Base layer Bitcoin will certain not be used to buy your daily coffees or gym memberships but lightning will be used for that purpose. Businesses small and large will demand one click on demand solutions to help them accept Bitcoin payments for their businesses. There are plenty of Bitcoin business ready to help business adopt a Bitcoin standard.
Businesses such as Opennode, Zaprite, Voltage, Breez make switching over to a Bitcoin standard easy for businesses to do.
So when you take a step back and really look at the Bitcoin ecosystem it is a lot more mature than most give it credit for and will slowly eat away at fiat currency dominance around the world.
The best thing that you can do is be patient, stack as many sats as you can and educate others about Bitcoin. We all know how fiat currencies end. Our time will come.
-
 @ 6be5cc06:5259daf0
2025-03-31 03:39:07
@ 6be5cc06:5259daf0
2025-03-31 03:39:07Introdução
Uma sociedade não deve ser construída sobre coerção, mas sim sobre associações voluntárias e interações espontâneas entre indivíduos. A sociedade de condomínios privados surge como uma alternativa natural ao modelo atual de centros urbanos, substituindo a imposição centralizada por estruturas baseadas em contratos e livre associação. Cada condomínio é uma unidade autônoma, gerida por aqueles que ali residem, onde os critérios de entrada, as regras internas e o comércio são definidos pelos próprios participantes. Essa estrutura permite que indivíduos se agrupem com base em valores compartilhados, eliminando os conflitos artificiais impostos por estados e legislações homogêneas que não respeitam a diversidade de preferências e estilos de vida.
O objetivo dessa sociedade é simples: permitir que as pessoas vivam de acordo com seus princípios sem interferência externa. Em um mundo onde a coerção estatal distorce incentivos, os condomínios privados oferecem uma alternativa onde a ordem surge do livre mercado e da cooperação voluntária. Os moradores escolhem seus vizinhos, definem suas próprias normas e interagem economicamente conforme suas necessidades e interesses. O modelo elimina a necessidade de um controle central, pois os incentivos derivados do livre mercado levam ao desenvolvimento de comunidades prósperas, onde a reputação e a confiança mútua são mais eficazes do que qualquer imposição estatal. Assim, essa sociedade representa a evolução lógica do conceito de liberdade individual e propriedade privada como pilares fundamentais da ordem social.
Público-Alvo e Identidade
Os condomínios privados refletem o princípio da livre associação, permitindo que indivíduos escolham viver em comunidades alinhadas com seus valores e necessidades sem interferência estatal. Cada condomínio possui uma identidade própria, moldada pelos moradores e seus interesses, criando ambientes onde afinidades culturais, filosóficas ou profissionais são preservadas e incentivadas. Enquanto alguns podem ser voltados para famílias numerosas, oferecendo amplos espaços e infraestrutura adequada, outros podem priorizar solteiros e jovens profissionais, com áreas de coworking e espaços de lazer voltados para networking e socialização. Da mesma forma, comunidades religiosas podem estabelecer seus próprios espaços de culto e eventos, enquanto condomínios para idosos podem ser projetados com acessibilidade e serviços médicos especializados.
Críticos podem afirmar que essa forma de organização resulta em pouca diversidade de habilidades e perspectivas, mas esse argumento ignora a dinâmica das interações humanas e o caráter evolutivo dos intercâmbios entre comunidades. Nenhum condomínio existe isolado; a troca entre diferentes comunidades ocorre naturalmente pelo mercado, incentivando o intercâmbio de conhecimento e serviços entre especialistas de diferentes áreas. Além disso, a ideia de que todos os grupos devem conter uma variedade aleatória de indivíduos desconsidera que a verdadeira diversidade nasce da liberdade de escolha, e não da imposição estatal de convivências forçadas.
Outra crítica possível é que a existência de critérios de entrada pode levar à segregação social. No entanto, essa preocupação deriva da concepção errônea de que todas as comunidades devem ser abertas e incluir qualquer pessoa indiscriminadamente. Porém, a liberdade de associação implica, necessariamente, a liberdade de exclusão. Se um grupo deseja manter determinada identidade cultural, religiosa ou profissional, isso não impede que outros grupos criem suas próprias comunidades conforme seus valores e recursos. Além disso, essa especialização leva a uma concorrência saudável entre condomínios, forçando-os a oferecer melhores condições para atrair moradores. Em vez de uma sociedade homogênea moldada por burocratas, temos um mosaico de comunidades autônomas, onde cada indivíduo pode encontrar ou criar o ambiente que melhor lhe convém.
Autossuficiência e Especialização
A força dos condomínios privados reside na capacidade de seus moradores de contribuírem ativamente para a comunidade, tornando-a funcional e autossuficiente sem a necessidade de intervenções estatais. Diferentes condomínios podem se especializar em áreas específicas ou ter diversos profissionais de diferentes setores, refletindo as competências e interesses de seus residentes. Essa descentralização do conhecimento e da produção permite que cada comunidade desenvolva soluções internas para suas demandas, reduzindo dependências externas e estimulando a prosperidade local.
Os moradores atuam como agentes econômicos, trocando bens e serviços dentro do próprio condomínio e entre diferentes comunidades. Um condomínio voltado para a saúde, por exemplo, pode contar com médicos, enfermeiros e terapeutas que oferecem consultas, aulas e assistência médica particular, remunerados diretamente por seus clientes, sem a intermediação de burocracias. Da mesma forma, um condomínio agrícola pode abrigar agricultores que cultivam alimentos orgânicos, compartilham técnicas de cultivo e comercializam excedentes com outros condomínios, garantindo um fluxo contínuo de suprimentos. Em um condomínio tecnológico, programadores, engenheiros e empreendedores desenvolvem soluções de TI, segurança digital e energia renovável, promovendo a inovação e ampliando as possibilidades de intercâmbio econômico.
A economia interna de cada condomínio se fortalece através de serviços oferecidos pelos próprios moradores. Professores podem ministrar aulas, técnicos podem prestar serviços de manutenção, artesãos podem vender seus produtos diretamente para os vizinhos. O mercado livre e voluntário é o principal regulador dessas interações, garantindo que a especialização surja naturalmente conforme a demanda e a oferta se ajustam. Essa estrutura elimina desperdícios comuns em sistemas centralizados, onde a alocação de recursos se dá por decisões políticas e não pelas necessidades reais da população.
Alguns argumentam que a especialização pode criar bolhas de conhecimento, tornando os condomínios excessivamente dependentes de trocas externas. Contudo, essa preocupação desconsidera a natureza espontânea do mercado, que incentiva a cooperação e o comércio entre comunidades distintas. Nenhum condomínio precisa produzir tudo internamente; ao contrário, a divisão do trabalho e a liberdade de escolha promovem interdependências saudáveis e vantajosas para todos. Assim, cada morador se insere em um ecossistema dinâmico, onde suas habilidades são valorizadas e sua autonomia preservada, sem coerções estatais ou distorções artificiais impostas por planejadores centrais.
Infraestrutura e Sustentabilidade
A solidez de uma sociedade baseada em condomínios privados depende de uma infraestrutura eficiente e sustentável, projetada para reduzir a dependência externa e garantir o máximo de autonomia. Sem um aparato estatal centralizador, cada comunidade deve estruturar seus próprios meios de obtenção de energia, água, alimentação e demais bens essenciais, garantindo que suas operações sejam viáveis a longo prazo. Essa abordagem, longe de ser um entrave, representa a verdadeira inovação descentralizada: um ambiente onde as soluções emergem da necessidade real e da engenhosidade humana, e não de diretrizes burocráticas e regulamentos ineficazes.
Cada condomínio pode investir em tecnologias sustentáveis e autônomas, como energia solar e eólica, reduzindo custos e minimizando a vulnerabilidade às flutuações do mercado energético tradicional. Sistemas de captação e filtragem de água da chuva, bem como a reutilização eficiente dos recursos hídricos, garantem independência em relação a empresas monopolistas e governos que frequentemente administram esse bem de forma ineficaz. Hortas comunitárias e fazendas verticais podem suprir grande parte da demanda alimentar, permitindo que cada condomínio mantenha sua própria reserva de alimentos, aumentando a resiliência contra crises externas e instabilidades de mercado.
Além dos recursos naturais, os espaços compartilhados desempenham um papel fundamental na integração e no fortalecimento dessas comunidades. Bibliotecas, ginásios, creches e salas de aula permitem que o conhecimento e os serviços circulem internamente, criando um ambiente onde a colaboração ocorre de maneira orgânica. A descentralização também se aplica ao uso da tecnologia, plataformas digitais privadas podem ser utilizadas para conectar moradores, facilitar a troca de serviços e produtos, além de coordenar agendamentos e eventos dentro dos condomínios e entre diferentes comunidades.
O Bitcoin surge como uma ferramenta indispensável nesse ecossistema, eliminando a necessidade de bancos estatais ou sistemas financeiros controlados. Ao permitir transações diretas, transparentes e resistentes à censura, o Bitcoin se torna o meio de troca ideal entre os condomínios, garantindo a preservação do valor e possibilitando um comércio ágil e eficiente. Além disso, contratos inteligentes e protocolos descentralizados podem ser integrados para administrar serviços comuns, fortalecer a segurança e reduzir a burocracia, tornando a governança desses condomínios cada vez mais autônoma e imune a intervenções externas.
Alguns podem argumentar que a falta de um aparato estatal para regulamentar a infraestrutura pode resultar em desigualdade no acesso a recursos essenciais, ou que a descentralização completa pode gerar caos e ineficiência. No entanto, essa visão ignora o fato de que a concorrência e a inovação no livre mercado são os maiores motores de desenvolvimento sustentável. Sem monopólios ou subsídios distorcendo a alocação de recursos, a busca por eficiência leva naturalmente à adoção de soluções melhores e mais acessíveis. Condomínios que oferecem infraestrutura de qualidade tendem a atrair mais moradores e investimentos, o que impulsiona a melhoria contínua e a diversificação dos serviços. Em vez de depender de um sistema centralizado falho, as comunidades se tornam responsáveis por sua própria prosperidade, criando uma estrutura sustentável, escalável e adaptável às mudanças do futuro.
Governança e Administração
Em uma sociedade descentralizada, não se deve depender de uma estrutura estatal ou centralizada para regular e tomar decisões em nome dos indivíduos. Cada condomínio, portanto, deve ser gerido de maneira autônoma, com processos claros de tomada de decisão, resolução de conflitos e administração das questões cotidianas. A gestão pode ser organizada por conselhos de moradores, associações ou sistemas de governança direta, conforme as necessidades locais.
Conselhos de Moradores e Processos de Tomada de Decisão
Em muitos casos, a administração interna de um condomínio privado pode ser realizada por um conselho de moradores, composto por representantes eleitos ou indicados pela própria comunidade. A ideia é garantir que as decisões importantes, como planejamento urbano, orçamento, manutenção e serviços, sejam feitas de forma transparente e que os interesses de todos os envolvidos sejam considerados. Isso não significa que a gestão precise ser completamente democrática, mas sim que as decisões devem ser tomadas de forma legítima, transparente e acordadas pela maior parte dos membros.
Em vez de um processo burocrático e centralizado, onde uma liderança impõe suas vontades sobre todos a muitas vezes suas decisões ruins não o afetam diretamente, a gestão de um condomínio privado deve ser orientada pela busca de consenso, onde os próprios gestores sofrerão as consequências de suas más escolhas. O processo de tomada de decisão pode ser dinâmico e direto, com os moradores discutindo e acordando soluções baseadas no mercado e nas necessidades locais, em vez de depender de um sistema impessoal de regulamentação. Além disso, a utilização de tecnologias descentralizadas, como plataformas de blockchain, pode proporcionar maior transparência nas decisões e maior confiança na gestão.
Resolução de Conflitos
A resolução de disputas dentro dos condomínios pode ocorrer de forma voluntária, através de negociação direta ou com o auxílio de mediadores escolhidos pelos próprios moradores por meio de um sistema de reputação. Em alguns casos, podem ser criados mecanismos para resolução de disputas mais formais, com árbitros ou juízes independentes que atuam sem vínculos com o condomínio. Esses árbitros podem ser escolhidos com base em sua experiência ou especialização em áreas como direito, mediação e resolução de conflitos, com uma reputação para zelar. Ao contrário de um sistema judicial centralizado, onde a parte envolvida depende do Estado para resolver disputas, os moradores possuem a autonomia para buscar soluções que atendam aos seus próprios interesses e necessidades. A diversidade de abordagens em um sistema de governança descentralizado cria oportunidades para inovações que atendem diferentes cenários, sem a interferência de burocratas distantes dos próprios problemas que estão "tentando resolver".
Planejamento Urbano e Arquitetura
A questão do design dos condomínios envolve não apenas a estética das construções, mas também a funcionalidade e a sustentabilidade a longo prazo. O planejamento urbano deve refletir as necessidades específicas da comunidade, onde ela decide por si mesma como construir e organizar seu ambiente.\ Arquitetos e urbanistas, muitas vezes moradores especializados, serão responsáveis pela concepção de espaços que atendam a esses critérios, criando ambientes agradáveis, com áreas para lazer, trabalho e convivência que atendam às diversas necessidades de cada grupo.\ Além disso, condomínios com nessecidades semelhantes poderão adotar ideias que deram certo em outros e certamente também dará no seu.
Segurança e Vigilância
Em relação à segurança, cada condomínio pode adotar sistemas de vigilância e proteção que atendam à sua realidade específica. Algumas comunidades podem optar por sistemas de câmeras de segurança, armamento pleno de seus moradores, patrulhamento privado ou até mesmo formas alternativas de garantir a proteção, como vigilância por meio de criptografia e monitoramento descentralizado. A chave para a segurança será a confiança mútua e a colaboração voluntária entre os moradores, que terão a liberdade de definir suas próprias medidas.
Comércio entre Condomínios
A troca de bens e serviços entre as diferentes comunidades é essencial para o funcionamento da rede. Como cada condomínio possui um grau de especialização ou uma mistura de profissionais em diversas áreas, a interdependência entre eles se torna crucial para suprir necessidades e promover a colaboração.
Embora alguns condomínios sejam especializados em áreas como saúde, agricultura ou tecnologia, outros podem ter um perfil mais diversificado, com moradores que atuam em diferentes campos de conhecimento. Por exemplo, um condomínio agrícola pode produzir alimentos orgânicos frescos, enquanto um condomínio de saúde oferece consultas médicas, terapias e cuidados especializados. Já um condomínio tecnológico pode fornecer inovações em software ou equipamentos de energia. Podem haver condomínios universitários que oferecem todo tipo de solução no campo de ensino. Ao mesmo tempo, um condomínio misto, com moradores de diversas áreas, pode oferecer uma variedade de serviços e produtos, tornando-se um centro de intercâmbio de diferentes tipos de expertise.
Essa divisão de trabalho, seja especializada ou diversificada, permite que os condomínios ofereçam o melhor de suas áreas de atuação, ao mesmo tempo em que atendem às demandas de outros. Um condomínio que não se especializa pode, por exemplo, buscar um acordo de troca com um condomínio agrícola para obter alimentos frescos ou com um condomínio tecnológico para adquirir soluções inovadoras.
Embora os condomínios busquem a autossuficiência, alguns recursos essenciais não podem ser produzidos internamente. Itens como minérios para construção, combustíveis ou até mesmo água, em regiões secas, não estão disponíveis em todas as áreas. A natureza não distribui os recursos de maneira uniforme, e a capacidade de produção local pode ser insuficiente para suprir todas as necessidades dos moradores. Isso implica que, para garantir a qualidade de vida e a continuidade das operações, os condomínios precisarão estabelecer relações comerciais e de fornecimento com fontes externas, seja através de mercados, importações ou parcerias com outras comunidades ou fornecedores fora do sistema de condomínios. O comércio intercondomínios e com o exterior será vital para a complementaridade das necessidades, assegurando que os moradores tenham acesso a tudo o que não pode ser produzido localmente.
O sistema econômico entre os condomínios pode ser flexível, permitindo o uso de uma moeda comum (como o Bitcoin) ou até mesmo um sistema de troca direta. Por exemplo, um morador de um condomínio misto pode oferecer serviços de design gráfico em troca de alimentos ou cuidados médicos. Esse tipo de colaboração estimula a produtividade e cria incentivos para que cada condomínio ofereça o melhor de seus recursos e habilidades, garantindo acesso aos bens e serviços necessários.
Relações Externas e Diplomacia
O isolamento excessivo pode limitar o acesso a inovações, avanços culturais e tecnológicos, e até mesmo dificultar o acesso a mercados externos. Por isso, é importante que haja canais de comunicação e métodos de diplomacia para interagir com outras comunidades. Os condomínios podem, por exemplo, estabelecer parcerias com outras regiões, seja para troca de produtos, serviços ou até para inovação. Isso garante que a rede de condomínios não se torne autossuficiente ao ponto de se desconectar do resto do mundo, o que pode resultar em estagnação.
Feiras, mercados intercondomínios e até eventos culturais e educacionais podem ser organizados para promover essas interações. A colaboração entre as comunidades e o exterior não precisa ser baseada em uma troca de dependência, mas sim numa rede de oportunidades que cria benefícios para todas as partes envolvidas. Uma boa reputação atrai novos moradores, pode valorizar propriedades e facilitar parcerias. A diplomacia entre as comunidades também pode ser exercida para resolver disputas ou desafios externos.
A manutenção de boas relações entre condomínios é essencial para garantir uma rede de apoio mútuo eficiente. Essas relações incentivam a troca de bens e serviços, como alimentos, assistência médica ou soluções tecnológicas, além de fortalecer a autossuficiência regional. Ao colaborar em segurança, infraestrutura compartilhada, eventos culturais e até mesmo na resolução de conflitos, os condomínios se tornam mais resilientes e eficientes, reduzindo a dependência externa e melhorando a qualidade de vida dos moradores. A cooperação contínua cria um ambiente mais seguro e harmonioso.
Educação e Desenvolvimento Humano
Cada comunidade pode criar escolas internas com currículos adaptados às especializações de seus moradores. Por exemplo, em um condomínio agrícola, podem ser ensinadas práticas agrícolas sustentáveis, e em um condomínio tecnológico, cursos de programação e inovação. Isso permite que crianças e jovens cresçam em ambientes que reforçam as competências valorizadas pela comunidade.
Além das escolas internas, o conceito de homeschooling pode ser incentivado, permitindo que os pais eduquem seus filhos conforme seus próprios valores e necessidades, com o apoio da comunidade. Esse modelo oferece uma educação mais flexível e personalizada, ao contrário do currículo tradicional oferecido pelo sistema público atual.
Os condomínios universitários também podem surgir, criando ambientes dedicados ao desenvolvimento acadêmico, científico e profissional, onde estudantes vivem e aprendem. Além disso, programas de capacitação contínua são essenciais, com oficinas e cursos oferecidos dentro do condomínio para garantir que os moradores se atualizem com novas tecnologias e práticas.
Para ampliar os horizontes educacionais, os intercâmbios estudantis entre diferentes condomínios podem ser incentivados. Esses intercâmbios não se limitam apenas ao ambiente educacional, mas também se estendem ao aprendizado de práticas de vida e habilidades técnicas. Os jovens de diferentes condomínios podem viajar para outras comunidades para estudar, trabalhar ou simplesmente trocar ideias. Isso pode ocorrer de diversas formas, como programas de curto e longo prazo, através de acordos entre os próprios condomínios, permitindo que os estudantes se conectem com outras comunidades, aprendam sobre diferentes especializações e desenvolvam uma compreensão mais ampla.
Essa abordagem descentralizada permite que cada comunidade desenvolva as competências essenciais sem depender de estruturas limitantes do estado ou sistemas educacionais centralizados. Ao proporcionar liberdade de escolha e personalização, os condomínios criam ambientes propícios ao crescimento humano, alinhados às necessidades e interesses de seus moradores.
A sociedade dos condomínios privados propõe uma estrutura alternativa de convivência onde as pessoas podem viver de acordo com seus próprios valores e necessidades. Esses condomínios oferecem um modelo de organização que desafia a centralização estatal, buscando criar comunidades adaptáveis e inovadoras. A liberdade garante que as habilidades necessárias para o sustento e crescimento das comunidades sejam mantidas ao longo do tempo.
A troca de bens, serviços e conhecimentos entre os condomínios, sem a imposição de forças externas, cria uma rede de boas relações, onde o comércio e a colaboração substituem a intervenção estatal. Em vez de depender de sistemas coercitivos, cada condomínio funciona como um microcosmo autônomo que, juntos, formam um ecossistema dinâmico e próspero. Este modelo propõe que, por meio de trocas voluntárias, possamos construir uma sociedade mais saudável. Lembre-se: Ideias e somente ideias podem iluminar a escuridão.
-
 @ d34e832d:383f78d0
2025-04-21 19:09:53
@ d34e832d:383f78d0
2025-04-21 19:09:53Such a transformation positions Nostr to compete with established social networking platforms in terms of reach while simultaneously ensuring the preservation of user sovereignty and the integrity of cryptographic trust mechanisms.

The Emergence of Encrypted Relay-to-Relay Federation
In the context of Nostr protocol scalability challenges pertaining to censorship-resistant networking paradigms, Nostr stands as a paradigm-shifting entity, underpinned by robust public-key cryptography and minimal operational assumptions. This feature set has rendered Nostr an emblematic instrument for overcoming systemic censorship, fostering permissionless content dissemination, and upholding user autonomy within digital environments. However, as the demographic footprint of Nostr's user base grows exponentially, coupled with an expanding range of content modalities, the structural integrity of individual relays faces increasing pressure.
Challenges of Isolation and Limited Scalability in Decentralized Networks
The current architecture of Nostr relays is primarily constituted of simple TCP or WebSocket servers that facilitate the publication and reception of events. While aesthetically simple, this design introduces significant performance bottlenecks and discoverability issues. Relays targeting specific regional or topical niches often rely heavily on client-side interactions or third-party directories for information exchange. This operational framework presents inefficiencies when scaled globally, especially in scenarios requiring high throughput and rapid dissemination of information. Furthermore, it does not adequately account for redundancy and availability, especially in low-bandwidth environments or regions facing strict censorship.

Navigating Impediments of Isolation and Constrained Scalability
Current Nostr relay infrastructures mainly involve basic TCP and WebSocket configurations for event publication and reception. While simple, these configurations contribute to performance bottlenecks and a significant discoverability deficit. Relays that serve niche markets often operate under constraints, relying on client-side interactions or third-party directories. These inefficiencies become particularly problematic at a global scale, where high throughput and rapid information distribution are necessary. The absence of mechanisms to enhance redundancy and availability in environments with limited connectivity or under censorship further exacerbates these issues.
Proposal for Encrypted Relay Federation
Encrypted relay federation in decentralized networking can be achieved through a novel Nostr Improvement Proposal (NIP), which introduces a sophisticated gossip-style mesh topology. In this system, relays subscribe to content tags, message types, or public keys from peer nodes, optimizing data flow and relevance.
Central to this architecture is a mutual key handshake protocol using Elliptic Curve Diffie-Hellman (ECDH) for symmetric encryption over relay keys. This ensures data integrity and confidentiality during transmission. The use of encrypted event bundles, compression, and routing based on relay reputation metrics and content demand analytics enhances throughput and optimizes network resources.
To counter potential abuse and spam, strategies like rate limiting, financially incentivized peering, and token gating are proposed, serving as control mechanisms for network interactions. Additionally, the relay federation model could emulate the Border Gateway Protocol (BGP), allowing for dynamic content advertisement and routing updates across the federated mesh, enhancing network resilience.
Advantages of Relay Federation in Data Distribution Architecture
Relay federation introduces a distributed data load management system where relays selectively store pertinent events. This enhances data retrieval efficiency, minimizes congestion, and fosters a censorship-resistant information flow. By decentralizing data storage, relays contribute to a global cache network, ensuring no single relay holds comprehensive access to all network data. This feature helps preserve the integrity of information flow, making it resistant to censorship.
An additional advantage is offline communication capabilities. Even without traditional internet access, events can still be communicated through alternative channels like Bluetooth, Wi-Fi Direct, or LoRa. This ensures local and community-based interactions remain uninterrupted during network downtime.
Furthermore, relay federations may introduce monetization strategies where specialized relays offer access to rare or high-quality data streams, promoting competition and interoperability while providing users with diverse data options.
Some Notable Markers To Nostr Becoming the Internet Layer for Censorship Resistance
Stop for a moment in your day and try to understand what Nostr can do for your communications by observing these markers:
- Protocol Idea (NIP-01 by fiatjaf) │ ▼
- npub/nsec Keypair Standard │ ▼
- First Relays Go Online │ ▼
- Identity & Auth (NIP-05, NIP-07) │ ▼
- Clients Launch (Damus, Amethyst, Iris, etc.) │ ▼
- Lightning Zaps + NWC (NIP-57) │ ▼
- Relay Moderation & Reputation NIPs │ ▼
- Protocol Bridging (ActivityPub, Matrix, Mastodon) │ ▼
- Ecash Integration (Cashu, Walletless Zaps) │ ▼
- Encrypted Relay Federation (Experimental) │ ▼
- Relay Mesh Networks (WireGuard + libp2p) │ ▼
- IoT Integration (Meshtastic + ESP32) │ ▼
- Fully Decentralized, Censorship-Resistant Social Layer
The implementation of encrypted federation represents a pivotal technological advancement, establishing a robust framework that challenges the prevailing architecture of fragmented social networking ecosystems and monopolistic centralized cloud services. This innovative approach posits that Nostr could:
- Facilitate a comprehensive, globally accessible decentralized index of information, driven fundamentally by user interactions and a novel microtransaction system (zaps), enabling efficient content valorization and information dissemination.
- Empower the concept of nomadic digital identities, allowing them to seamlessly traverse various relays, devoid of reliance on centralized identity verification systems, promoting user autonomy and privacy.
- Become the quintessential backend infrastructure for decentralized applications, knowledge graphs, and expansive datasets conducive to DVMs.
- Achieve seamless interoperability with established protocols, such as ActivityPub, Matrix, IPFS, and innovative eCash systems that offer incentive mechanisms, fostering an integrated and collaborative ecosystem.
In alignment with decentralization, encrypted relay-to-relay federation marks a significant evolution for the Nostr protocol, transitioning from isolated personal broadcasting stations to an interoperable, adaptive, trustless mesh network of communication nodes.
By implementing this sophisticated architecture, Nostr is positioned to scale efficiently, addressing global needs while preserving free speech, privacy, and individual autonomy in a world marked by surveillance and compartmentalized digital environments.
Nostr's Countenance Structure: Noteworthy Events
``` Nostr Protocol Concept by fiatjaf:
- First Relays and npub/nsec key pairs appear
- Damus, Amethyst, and other clients emerge
- Launch of Zaps and Lightning Tip Integration
- Mainstream interest post Twitter censorship events
- Ecosystem tools: NWC, NIP-07, NIP-05 adoption
- Nostr devs propose relay scoring and moderation NIPs
- Bridging begins (ActivityPub, Matrix, Mastodon)
- Cashu eCash integration with Nostr zaps (walletless tips)
- Relay-to-relay encrypted federation proposed
- Hackathons exploring libp2p, LNbits, and eCash-backed identities
- Scalable P2P Mesh using WireGuard + Nostr + Gossip
- Web3 & IoT integration with ESP32 + Meshtastic + relays
- A censorship-resistant, decentralized social internet ```
-
 @ 83279ad2:bd49240d
2025-03-30 14:21:49
@ 83279ad2:bd49240d
2025-03-30 14:21:49Test
-
 @ ff517fbf:fde1561b
2025-03-30 04:43:09
@ ff517fbf:fde1561b
2025-03-30 04:43:09ビットコインが「最強の担保」と言われる理由
ビットコインは「デジタルゴールド」とも呼ばれることがありますが、実はローンの担保としても最強だと言われています。その理由を、他の資産(株式、不動産、金など)と比較しながら見てみましょう。
-
流動性と即時性:ビットコインは24時間365日世界中で取引されているため、非常に流動性が高い資産です。売買がすぐにできて価格も常に明確なので、担保評価がしやすく、お金を貸す側・借りる側双方に安心感を与えます。一方、株式や不動産は市場が営業時間内しか動かず、現金化にも時間がかかります。不動産は売却に数ヶ月かかることもありますし、金(ゴールド)は現物を保管・輸送する手間があります。ビットコインならネット上で即座に担保設定・解除ができるのです。
-
分割性と柔軟性:ビットコインは小数点以下8桁まで分割可能(1億分の1が最小単位の「サトシ」)なので、必要な額だけ正確に担保に充てることができます。他方、土地や建物を一部だけ担保に入れることは難しいですし、株式も1株未満の細かい調整はできません。ビットコインなら価値の微調整が容易で、担保として柔軟に扱えるのです。
-
管理のしやすさ(マルチシグによる信頼性):HodlHodlのLendでは、ビットコイン担保は2-of-3のマルチシグ契約で管理されます。これは「借り手・貸し手・プラットフォーム」の3者それぞれが鍵を持ち、2つの鍵の同意がないとビットコインを動かせない仕組みです。このため、誰か一人が勝手に担保を持ち逃げすることができず、第三者(HodlHodl)も単独ではコインを移動できません。ビットコインだからこそ実現できる非中央集権で安全な担保管理であり、株式や不動産を担保にする場合のように銀行や証券会社といった仲介業者に頼る必要がありません。
-
国境を越えた利用:ビットコインはインターネットがつながる所なら世界中どこでも送受信できます。このため、日本にいながら海外の相手とでもローン契約が可能です。たとえば日本の方がビットコインを担保にドル建てのステーブルコインを借り、それを日本円に換えて使うこともできます(為替リスクには注意ですが…)。不動産を海外の人と直接やり取りするのは現実的に難しいですが、ビットコインならグローバルに担保が活用できるのです。
-
希少性と価値の上昇期待:ビットコインは発行上限が決まっており(2100万BTCまで)、時間とともに新規供給が減っていきます。過去の長期的な価格推移を見ると、短期的な変動は激しいものの数年〜十年のスパンでは上昇傾向にあります。一方、法定通貨建ての資産(債券や株式など)はインフレの影響で実質価値が目減りすることがあります。ビットコインは長期保有すれば価値が上がりやすい特性があるため、「今手放したくない資産」として担保に向いています。実際、HodlHodlのチームは「ビットコインはスーパーカCollateral(超優秀な担保)だ」と述べています。
こうした理由から、ビットコインは現時点で考えうる中でも最良の担保資産と考えられています。株や不動産のように書類手続きや名義変更をしなくても、ビットコインならブロックチェーン上の契約でシンプルに担保設定ができる――この手軽さと信頼性が大きな魅力です。
匿名&プライバシー重視:KYC不要のP2Pレンディングのメリット
HodlHodlのLend最大の特徴の一つは、本人確認(KYC)が一切不要だという点です。日本の多くの金融サービスでは口座開設時に運転免許証やマイナンバー提出など煩雑な手続きが必要ですが、Lendではメールアドレスでアカウント登録するだけでOK。これは「匿名性・プライバシー」を重視する人にとって非常に相性が良いポイントです。
-
個人情報を晒さなくて良い安心感:日本では昔から「人に迷惑をかけない」「目立たない」ことが美徳とされ、特にお金の話は他人に知られたくないと考える人が多いですよね。Lendは匿名で利用できるため、借金をすることを周囲に知られたくない人でも安心です。銀行からローンを借りるときのように収入証明や保証人を用意する必要もなく、誰にも知られずひっそりと資金調達ができます。
-
ノー・チェック&ノー・ペーパー:貸し借りにあたって信用審査や過去の借入履歴チェックがありません 。極端な話、今まで金融履歴が全く無い人や、銀行に相手にされないような人でも、ビットコインさえ持っていればお金を借りられるのです。書類のやり取りが無いので手続きもスピーディーです。「印鑑証明や収入証明を揃えて…」という面倒とは無縁で、ネット上でクリックして契約が完結します。
-
プライバシーの保護:個人情報を提出しないということは、情報漏洩のリスクも無いということです。近年、日本でも個人情報の流出事件が相次いでおり、不安に感じる方も多いでしょう。Lendではアカウント登録時にメールアドレスとパスワード以外何も求められません。財務情報や身元情報がどこかに蓄積される心配がないのは、大きな安心材料です。
-
国や機関から干渉されにくい:匿名であるということは、極端に言えば誰にも利用を知られないということです。たとえば「ローンを借りると住宅ローンの審査に響くかな…」とか「副業の資金調達を会社に知られたくないな…」といった心配も、匿名のP2Pローンなら不要です。借りたお金の使い道も自由ですし、何より利用自体が自分だけの秘密にできるのは、日本人にとって心理的ハードルを下げてくれるでしょう。
このように、ノーKYC(本人確認なし) のP2Pレンディングは、日本のようにプライバシーや控えめさを重んじる文化圏でも利用しやすいサービスと言えます。実際、HodlHodlのLendは「地理的・規制的な制限がなく、世界中の誰もが利用できる純粋なP2P市場」とされています。日本に居ながらグローバルな貸し借りができ、しかも身元明かさずに済む――これは画期的ですね。
Borrow編:HodlHodlのLendでビットコインを担保にお金を借りる方法
それでは具体的に、HodlHodlのLendでどのようにビットコイン担保のローンを借りるのか、手順を追って説明します。初心者でも迷わないよう、シンプルなステップにまとめました。
1. アカウント登録 (Sign up)
まずはHodlHodlのLendサイトにアクセスし、無料のアカウントを作成します。必要なのはメールアドレスとパスワードだけです。登録後、確認メールが届くのでリンクをクリックして認証すれば準備完了。これでプラットフォーム上でオファー(契約希望)を閲覧・作成できるようになります。
※HodlHodlは日本語には対応していませんが、英語のシンプルなUIです。Google翻訳などを使っても良いでしょう。
2. 借りたい条件のオファーを探す or 作成
ログインしたら、「To Borrow(借りる)」のメニューから現在出ている貸し手のオファー一覧を見てみましょう。オファーには借入希望額(例:$1000相当のUSDT)、期間(例:3ヶ月)、金利(例:5%)やLTV(担保価値比率、例:60%)などの条件が書かれています。自分の希望に合うものがあれば選んで詳細画面へ進みます。条件に合うオファーが見つからない場合は、自分で「○○ USDTを△ヶ月、金利○%で借りたい」という借り手オファーを新規作成することも可能です。
用語補足:LTV(ローン・トゥ・バリュー)とはローン額に対する担保価値の割合です。たとえばLTV50%なら、借りたい額の2倍の価値のビットコインを担保に入れる必要があります。LTVは貸し手が設定しており、一般に30%〜70%程度の範囲でオファーが出ています。低いLTVほど借り手は多くのBTC担保が必要ですが、その分だけ貸し手にとって安全なローンとなります。
3. 契約成立とマルチシグ担保のデポジット
借り手・貸し手双方が条件に合意すると契約成立です。HodlHodlプラットフォーム上で自動的に専用のマルチシグ・エスクロー用ビットコインアドレス(担保保管先アドレス)が生成されます。次に、借り手であるあなたは自分のウォレットからビットコインをそのエスクローアドレスに送金します。
- 📌ポイント:マルチシグで安心 – 上述の通り、このエスクロー用アドレスのコインを動かすには3者中2者の署名が必要です。あなた(借り手)は常にそのうちの1つの鍵を保有しています。つまり、自分が承認しない限り担保BTCが勝手に引き出されることはないのでご安心ください。
ビットコインの入金がブロックチェーン上で所定の承認(通常数ブロック程度)を得ると、担保デポジット完了です。これで契約は有効化され、次のステップへ進みます。
4. 貸し手から資金(ステーブルコイン)を受け取る
担保のロックが確認できると、今度は貸し手がローン金額の送金を行います。Lendで借りられるのは主にステーブルコインです。ステーブルコインとは、米ドルなど法定通貨の価値に連動するよう設計された仮想通貨で、USDTやUSDC、DAIといった種類があります。借り手は契約時に受取用のステーブルコインアドレス(自分のウォレットアドレス)を指定しますので、貸し手はそのアドレス宛に契約どおりの額を送金します。例えばUSDTを借りる契約なら、貸し手からあなたのUSDTウォレットにUSDTが送られてきます。
これで晴れて、あなた(借り手)は希望のステーブルコインを手にすることができました! あなたのビットコインは担保としてロックされていますが、期限までに返済すれば取り戻せますので、しばしのお別れです。借りたステーブルコインは自由に使えますので、後述する活用例を参考に有効活用しましょう。
5. 返済(リペイメント)
契約期間中は基本的に何もする必要はありません(途中で追加担保や一部返済を行うことも可能ですが、初心者向け記事では割愛します)。期間が満了するまでに、借りたステーブルコイン+利息を貸し手に返済します。返済も、貸し手の指定するウォレットアドレスにステーブルコインを送金する形で行われます。
- 利息の計算:利息は契約時に決めた率で発生します。例えば年利10%で6ヶ月間$1000を借りたなら、利息は単純計算で$50(=$1000×10%×0.5年)です。契約によっては「期間全体で○%」と定める場合もありますが、プラットフォーム上で年率(APR)換算が表示されます。
期間内であれば任意のタイミングで早期返済することも可能です。返済期限より早く全額返せば、利息もその日数分だけで済みます(※ただし契約によります。事前に契約条件を確認してください)。HodlHodlでは分割返済にも対応しており、例えば月ごとに少しずつ返して最後に完済することもできます。
6. ビットコイン担保の解除(返却)
貸し手があなたからの返済受領を確認すると、プラットフォーム上で契約終了の手続きを行います。マルチシグの担保アドレスからあなたのビットコインを解放(返却)する署名を貸し手とプラットフォームが行い、あなたの元のウォレットにビットコインが送られます。こうして無事に担保のBTCが戻ってくれば、一連のローン取引は完了です🎉。
もし返済が滞った場合はどうなるのでしょうか?その場合、契約で定められた猶予期間やマージンコール(追加担保のお願い)を経た後、担保のビットコインが強制的に貸し手に渡されて契約終了(清算)となります。担保額が未返済額を上回っていれば、差額は借り手に返ってきます。つまり、返せなかったとしても借り手が担保以上の損をすることはありませんが、大切なビットコインを失ってしまう結果にはなるので注意しましょう。
Borrow(借りる)側のまとめ:ビットコインさえあれば、あとの手続きは非常に簡単です。借入までの流れをもう一度簡潔にまとめると:
- メールアドレスでLendに登録
- 借入オファーを探すor作成してマッチング
- マルチシグ契約が自動生成・BTC担保を自分で入金
- 貸し手からステーブルコインを受領
- 期限までにステーブルコイン+利息を返済
- ビットコイン担保が自分のウォレットに戻る
第三者の仲介なしに、ネット上でこれだけのことが完結するのは驚きですよね。HodlHodlは「あなたの条件、あなたの鍵、あなたのコイン」と銘打っており、自分の望む条件で・自分が鍵を管理し・自分の資産を動かせるプラットフォームであることを強調しています。
Lend編:HodlHodlのプラットフォームでお金を貸してみよう
次は逆に、自分が貸し手(Lender)となってステーブルコインを貸し出し、利息収入を得る方法です。銀行に預けても超低金利のこのご時世、手持ちの資金をうまく運用したい方にとってP2Pレンディングは魅力的な選択肢になりえます。HodlHodlのLendなら、これもまた簡単な手順で始められます。
基本的な流れは先ほどの「Borrow編」と鏡写しになっています。
1. アカウント登録
借り手と同様、まずはHodlHodlに登録します(すでに借り手として登録済みなら同じアカウントで貸し手にもなれます)。メールアドレスだけでOK、もちろん貸し手側もKYC不要です。
2. 貸出オファーの確認 or 作成
ログイン後、「To Lend(貸す)」メニューから現在の借り手募集一覧を見ます。各オファーには希望額・期間・支払い利率・LTVなど条件が表示されています。「この条件なら貸してもいいかな」という案件があれば選択しましょう。もし自分の希望する利回りや期間が合わない場合は、自分で貸し手オファーを作成することも可能です。「○○ USDTまで、最長△ヶ月、最低利息◻◻%で貸せます」といった条件を提示できます。プラットフォーム上ではユーザーがお互いに条件を提示しあってマッチングする仕組みなので、金利や期間もすべてユーザー自身が自由に設定できます。
3. マッチングと契約開始
あなたの提示した条件で借りたい人が現れたら契約成立です(逆に誰かの借入オファーに応じる形なら、その時点で成立)。システムがマルチシグの担保用BTCアドレスを生成し、借り手がそこへビットコインをデポジットします。借り手からのBTC入金が確認できるまで、貸し手であるあなたは資金を送る必要はありません。担保が確保されたのを見届けてから次に進みます。
4. 資金(ステーブルコイン)の送金
借り手の担保ロックが完了したら、契約で定めたステーブルコインを借り手へ送金します。送金先アドレスは契約詳細画面に表示されます(借り手が指定済み)。例えばUSDCを貸す契約なら、相手のUSDCアドレスに約束の額を送ります。ここで送金した金額がローンの principal(元本)となり、後ほど利息とともに返ってくるわけです。
無事に相手に届けば、あとは契約期間終了まで待つだけです。あなたは担保のBTCに対して鍵を1つ持っている状態なので、万一トラブルが起きた場合でも担保を引き出す権利を部分的に持っています(詳しくは次ステップ)。
5. 返済の受領
契約期間が終わると、借り手があなたにステーブルコインを返済してくるはずです。約束どおり元本+利息を受け取ったら、それを確認してプラットフォーム上で「返済完了」を操作します。すると担保のビットコインがマルチシグから解放され、借り手に返却されます。これで貸し手としてのあなたは利息分の収益を獲得できました。お疲れ様です!
もし借り手が返済しなかった場合どうなるでしょうか?その場合、所定の猶予期間やマージンコール通知の後、担保のビットコインがあなた(貸し手)に渡されることになります。具体的には、LTVが90%に達するか返済期日から24時間以上滞納が続くと強制清算となり、担保BTCからあなたの貸付相当額が充当されます。担保が十分であれば元本と利息はカバーされ、余剰があれば借り手に返還されます。つまり貸し手側はかなり手厚く保護されており、返済を受け取れない場合でも担保で穴埋めされる仕組みです。
6. 収益を管理・再投資
受け取ったステーブルコイン(元本+利息)は再度プラットフォームで貸し出しても良いですし、他の用途に使ってもOKです。年利に換算するとだいたい10%前後の利回りになる案件が多く見られます。条件次第では更に高い利率の契約も可能ですが、その分借り手が見つかりにくかったりリスク(担保不足のリスク)が高まる可能性もあります。ご自身のリスク許容度に合わせて運用しましょう。
Lend(貸す)側のまとめ:
- HodlHodlに登録(メールアドレスのみ)
- 貸出オファーを提示 or 借り手募集に応じる
- 契約成立後、借り手がBTC担保を入金
- 貸し手(自分)がステーブルコインを送金
- 期限まで待ち、借り手から元本+利息を受領
- 担保BTCを返却し、利息収入を得る
銀行預金では考えられないような利息収入を得られるのが魅力ですが、その裏でビットコイン価格変動リスクも担っています。大暴落が起きて担保評価額が急落すると、清算時に元本を割るリスクもゼロではありません(LTV設定とマージンコール制度で極力保護されまますが)。リスクとリターンを理解した上で、小額から試すことをおすすめします。
ステーブルコインの活用:お金持ちは借金で生活する?
ここまで、ビットコインを手放さずにステーブルコインを手に入れる方法を見てきました。それでは、借りたステーブルコインは具体的に何に使えるのでしょうか?いくつか例を挙げてみましょう。
-
日常の出費に充当:ビットコイン投資家の中には「生活費はすべて借りたお金で賄い、自分のBTCはガチホ(売らずに長期保有)する」という方針の人もいます。例えば毎月の家賃や食費をステーブルコインのローンで支払い(これについても今後詳しく解説していきます)、ビットコインは一切使わないというイメージです。こうすれば、手持ちのBTCを売らずに済むので将来の値上がり益を逃しません。また日本では仮想通貨を売却すると雑所得として高率の税金がかかりますが、ローンで得たお金は借入金なので課税対象になりません(※将来的な税務計算は自己責任で行ってください)。つまり、ビットコインを売却して現金化する代わりにローンを使うことで、節税と資産温存のメリットが得られる可能性があります。
-
投資・資産運用に回す:借りた資金をさらに別の投資に活用することもできます。例えば有望な株式や不動産に投資したり、あるいは他の仮想通貨を買うこともできます。極端な例では、ビットコインを担保にUSDTを借りて、そのUSDTでまた別の仮想通貨を買い、それを運用益で返済する…といった戦略も理論上は可能です。ただし、借りたお金での投機はハイリスクなので慎重に!手堅い使い道としては、事業資金に充てるのも良いでしょう。例えば小さなオンラインビジネスを始めるための元手にしたり、新しい資格取得のための学費にするなど、自分への投資に使えば将来的なリターンでローンを返しつつ利益を上げることが期待できます。
-
急な支払いへの備え:人生何があるか分かりません。医療費や冠婚葬祭など急に現金が必要になる場面もあります。そんなとき、ビットコインをすぐ売ってしまうのは惜しい…という場合にローンで一時的にしのぐことができます。後で落ち着いてから返済すれば、大事なBTCを手放さずにピンチを乗り切れます。言わばデジタル質屋のような感覚で、ビットコインを預けてお金を工面し、後で買い戻す(返済する)イメージですね。日本でも昔から「質屋」で着物や宝石を預けてお金を借りる文化がありましたが、HodlHodl Lendはビットコイン版の質屋とも言えるでしょう。
-
市場の機会を逃さない:仮想通貨市場は変動が激しく、「今これを買いたいのに現金が無い!」というチャンスもあるでしょう。例えば「ビットコインが急落したから買い増したいが、現金が足りない」という場合、手持ちBTCを担保にしてステーブルコインを借り、その急落で安く買い増しする、といった動きもできます。そして後日価格が戻したところで返済すれば、差益を得つつBTC保有枚数も増やせるかもしれません。このようにローンを戦略的に使えば、市場の好機を掴む資金余力を生み出すことができます。ただしハイリスクな手法でもあるため、上級者向けではあります。
ここで覚えておきたいのは、「お金持ちは借金との付き合い方が上手い」という点です。日本では借金にネガティブな印象を持つ人も多いですが、世界的な資産家や大企業はしばしばあえて借金をして手元資金を他に活用しています。アメリカのベストセラー『金持ち父さん貧乏父さん』で有名なロバート・キヨサキ氏も「富裕層は他人のお金(借金)を利用してさらに富を築く」と強調しています。例えば彼は借金で高級車を買い、不動産投資にも借入を活用したそう (金持ちは貧乏人より借金が多い | 「金持ち父さん 貧乏父さん」日本オフィシャルサイト)❤️。借金を味方につけて資産運用すれば、自分の持ち出し資金を抑えつつ豊かな生活を実現できる可能性があります。
もちろん無計画な借金は禁物ですが、ローンを上手に使うことは決して悪いことではなく、むしろ経済的戦略として有効なのです。ビットコイン担保ローンはその新しい選択肢として、「お金にお金に働いてもらう」感覚を身につけるきっかけになるかもしれません。
高い金利でもローンを利用するのはなぜ?その理由と戦略
Lendのプラットフォームで提示される金利は、年利換算で見ると10〜15%程度が一つの目安 です。中にはそれ以上の利率の契約もあります。日本の銀行ローン(金利数%以下)と比べるとかなり高利に思えますが、それでも多くの人がこのサービスを利用してローンを組んでいます。なぜ高い利息を支払ってまで借りる価値があるのでしょうか?最後に、その理由と利用者の戦略について考えてみましょう。
-
(1) ビットコインの期待リターンが高い:借り手にとって一番の動機は、「ビットコインは将来もっと値上がりするはずだから、多少利息を払っても売りたくない」というものです。例えば年利15%で$1000借りると一年後に$1150返す必要がありますが、もしビットコイン価格がその間に15%以上上昇すれば、利息分を差し引いても得をする計算になります。過去のビットコイン相場は年率ベースで大きく成長した年も多く、強気のホルダーほど利息より値上がり益を優先する傾向があります。「金利よりビットコインの価値上昇のほうが大きい」という自信が、高金利を払ってでも借りる動機になっているのです。
-
(2) 課税や手数料の回避:先ほど述べたように、日本ではビットコインを売却すると高額の税金が発生する可能性があります。仮に30%〜50%の税金がかかるのであれば、年利10%前後のローンで済ませたほうがトクだという判断も成り立ちます。また、取引所で売却するときのスプレッドや出金手数料なども考えると、売却コストを回避する手段としてローンを選ぶ人もいます。要するに「売るくらいなら借りた方がマシ」という考え方ですね。
-
(3) 自由と速さを優先:従来の金融機関からお金を借りるには時間がかかりますし、使途にも制限があることが多いです(事業資金なのか生活費なのか、といった審査があります)。それに対してHodlHodlのP2Pローンは使い道自由・即日資金調達が可能です。利息が高めでも「今すぐ○○がしたい」「明日までに現金が要る」といったニーズには代えられません。特に仮想通貨業界はスピード命ですから、チャンスを逃さないために高コストでも素早く借りるという選択が生まれます。
-
(4) 借金=時間を買うこと:あるユーザーの言葉を借りれば、「借金をすることは未来の時間を先取りすること」でもあります。例えば住宅ローンがあるからこそ若い世代でもマイホームに住めますし、事業ローンがあるからこそ企業は成長の機会を掴めます。ビットコイン担保ローンも同じで、「今はお金が無いけど将来増やすアテはある。だから今借りてしまおう」というケースもあるでしょう。将来の収入や資産増加を見込んで、時間を味方につけるためにあえて借金をするのです。日本語では「借金してでも◯◯する」という表現がありますが、前向きな借金は将来への投資とも言えるでしょう。
-
(5) 非中央集権への支持:もう一つ見逃せないのは、HodlHodlのようなプラットフォームを利用する理由に思想的な支持があります。つまり「銀行や政府に頼らないお金の流れを実現したい」「ビットコインのエコシステムを活性化させたい」というビットコイナーたちです。多少コストが高くても、理念に共感して使っているケースもあります。匿名で自由にお金を借りられる世界を体験することで、金融システムの新たな可能性を感じているのです。
以上のように、高い金利にも関わらずローンを利用するのは明確なメリットや戦略があるからなのです。もちろん全ての人に当てはまるわけではありません。ビットコイン価格が下落局面ではリスクも伴いますし、利息分だけ損になる場合もあります。しかし、それらを理解した上で「自分のお金を働かせる」「資産を手放さずレバレッジを利かせる」手段として活用している人々が増えてきています。
最後に、HodlHodlの公式ブログの一文をご紹介します。
“私たちはビットコインこそがスーパーカ collateral(超優秀な担保)であり、利回りを得るために使うのではなく、それを担保に資金を借りるために使われるべきだと考えています" (The lending is dead, long live the lending | by Hodl Hodl | Hodl Hodl | Medium)。
ビットコイン時代の新しいお金の借り方・貸し方であるP2Pローン。最初は難しく感じるかもしれませんが、仕組みを理解すればとてもシンプルで強力なツールです。日本ではまだ馴染みが薄いかもしれませんが、匿名性を好み、コツコツ資産を増やすのが得意な人にこそフィットするサービスかもしれません。ぜひ少額から試し、自分なりの活用法を見つけてみてください。きっと新たな発見があるはずです。
もしビットコイン担保のP2Pローンなどについてもっと深く知りたい、あるいは個別に相談してみたいと思えば、どうぞお気軽にご連絡ください。1対1のコンサルティングも承っています。
サービスには決まった料金はありませんが、ご相談を通じて「役に立った」と思い、お悩みや疑問を解決できたと感じていただけたら、「3つのT」でのご支援(Value for Value)をぜひご検討ください:
- 時間(Time):この記事をSNSなどでシェアしていただくこと。
- 才能(Talent):コメントや補足情報などを通じて知識を共有していただくこと。
- 宝(Treasure):世界で最も健全なお金、ビットコインの最小単位「sats」でのご支援。
もちろん、支援の有無にかかわらず、お力になれればとても嬉しいです。 では、また次回!
-
-
 @ c239c0f9:fa4a5015
2025-04-21 17:42:49
@ c239c0f9:fa4a5015
2025-04-21 17:42:49Block:#893398- April 2025The Monthly Thunderbolt Dispatch on Bitcoin layers two innovations, aggregating the Best posts about the ~Lightning Network and others Bitcoin L2 solution- Exclusively on Stacker.News
It's again that time of the month, time to catch up with the latest features and trends that are shaping the future of Bitcoin—the very first and most commented insights from around the SN world. In every issue arrives expert analysis, in-depth interview, and breaking news of the most significant advancements in the Bitcoin layer two solutions.
Subscribe and make sure you don’t miss anything about the ~Lightning Revolution!
Now let's focus on the top five items for each category, an electrifying selection that hope you'll be able to read before next edition.
Happy Zapping!
Top ~Lightning posts
Most zapranked posts this month:
-
Use RIZFUL as your BTCPay Server lightning node via NWC by @supratic 10.2k sats \ 2 comments \ 14 Apr
-
c-otto.de routing node history with a bit of data by @C_Otto 6301 sats \ 31 comments \ 23 Mar
-
Phoenix Wallet available again in the US by @Scoresby 4696 sats \ 29 comments \ 8 Apr
-
Short Text Note: Cashu is coming to ZEUS. by @supratic 5270 sats \ 13 comments \ 1 Apr
-
Hydrus - Automating lightning liquidity management by @aftermath 2281 sats \ 9 comments \ 27 Mar
Top posts by comments
Excluding the ones already mentioned above, you can see them all here (excluding those already listed above):
-
Liquidity squeezing from your node by @k00b 644 sats \ 20 comments \ 5 Apr
-
ZEUS starting to open up Cashu test builds to community sponsors. by @supratic 499 sats \ 14 comments \ 6 Apr
-
Ask Node Runners: What is the longest lived LN channel you have? by @DarthCoin 276 sats \ 12 comments \ 10 Apr
-
What's the best way to accept lightning payments on Wordpress + WooCommerce? by @Jon_Hodl 1879 sats \ 12 comments \ 10 Apr
-
Lightning node over tor by @BallLightning 219 sats \ 9 comments \ 28 Mar
Top ~Lightning Boosts
Check them all here.
-
Missing r/place? LNboard.com is the Lightning Network's Anarchy Art Gallery by @f0e6f4f43b 905 sats \ 40k boost \ 20 comments \ 2 Apr
-
Try out the Ark protocol on signet by @nwoodfine 2083 sats \ 30k boost \ 12 comments \ 19 Mar
-
Amboss CEO On Growth Of The Lightning Network, Tether (USDT) On Lightning by @Jestopher_BTC 577 sats \ 20k boost \ 10 comments \ 19 Feb
-
Building Self Custody Lightning in 2025 by @k00b 2293 sats \ 10k boost \ 8 comments \ 23 Jan
Top Lightning posts outside ~Lightning
This month best posts about the Lightning Network outside ~Lightning territory:
-
I made a game with Lightning where you can earn some sats by @stacks 4732 sats \ 46 comments \ 17 Apr on
~bitcoin -
"Lightning self custody works for 100 million users" "But it needs 10 billion!!" by @standardcrypto 2998 sats \ 22 comments \ 24 Mar on
~bitcoin -
24 Hours of Lightning: Watch LNboard.com's First Day Unfold by @f0e6f4f43b 809 sats \ 8 comments \ 2 Apr on
~bitcoin -
Lightning Payments Tour by Yopaki by @PlebLab 355 sats \ 0 comments \ 11 Apr on
~builders -
👀 My Bitcoin Startup Company Portfolio through Lightning Ventures. 👀 by @BlokchainB 965 sats \ 13 comments \ 16 Apr on
~Stacker_Stocks
Forever top ~Lightning posts
La crème de la crème... check them all here. Nothing has changed this month!
-
👨🚀 We're releasing 𝗔𝗟𝗕𝗬 𝗚𝗢 - the easiest lightning mobile wallet by @Alby 29.2k sats \ 41 comments \ 25 Sep 2024 on
~lightning -
Building Self Custody Lightning in 2025 by @k00b 2303 sats \ 8 comments \ 22 Jan on
~lightning -
Lightning Wallets: Self-Custody Despite Poor Network - Apps Tested in Zimbabwe by @anita 72.8k sats \ 39 comments \ 28 Jan 2024 on
~lightning -
How to Attach Your self-hosted LNbits wallet to SEND/RECEIVE sats to/from SN by @supratic 1765 sats \ 18 comments \ 23 Sep 2024 on
~lightning -
A Way to Use Stacker News to improve your Zap Receiving by @bzzzt 1652 sats \ 22 comments \ 15 Jul 2024 on
~lightning
Forever top Lightning posts outside ~Lightning
The rise of Supertestnet at #5, congrats!
-
Rethinking Lightning by @benthecarman with 51.6k sats \ 137 comments \ 6 Jan 2024 on
~bitcoin -
Lightning Everywhere by @TonyGiorgio with 12k sats \ 27 comments \ 24 Jul 2023 on
~bitcoin -
Lightning is dead, long live the Lightning! by @supertestnet and zaps forwarded to @anita (50%) @k00b (50%) 6321 sats \ 28 comments \ @tolot 27 Oct 2023 on
~bitcoin -
Lightning Is Doomed by @Rsync25 2450 sats \ 15 comments \ 27 Nov 2023 on
~bitcoin -
Bisq2 adds lightning by @supertestnet 3019 sats \ 47 comments \ 19 Aug 2024 on
~bitcoin
-
-
 @ d34e832d:383f78d0
2025-04-21 17:29:37
@ d34e832d:383f78d0
2025-04-21 17:29:37This foundational philosophy positioned her as the principal architect of the climactic finale of the Reconquista—a protracted campaign that sought to reclaim territories under Muslim dominion. Her decisive participation in military operations against the Emirate of Granada not only consummated centuries of Christian reclamation endeavors but also heralded the advent of a transformative epoch in both Spanish and European identity, intertwining religious zeal with nationalistic aspirations and setting the stage for the emergence of a unified Spanish state that would exert significant influence on European dynamics for centuries to come.
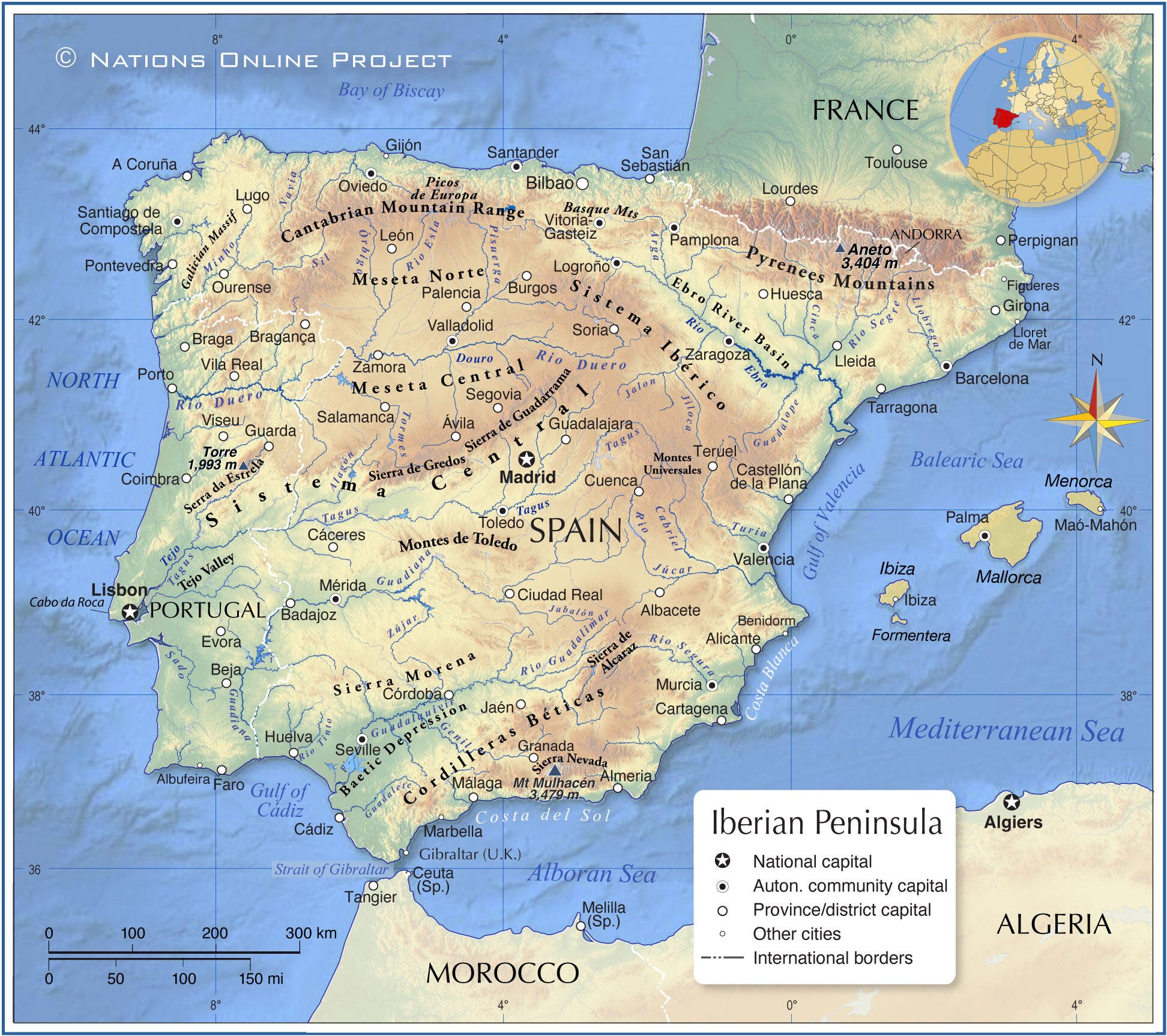
Image Above Map Of Th Iberias
During the era of governance overseen by Muhammad XII, historically identified as Boabdil, the Kingdom of Granada was characterized by a pronounced trajectory of decline, beset by significant internal dissent and acute dynastic rivalry, factors that fundamentally undermined its structural integrity. The political landscape of the emirate was marked by fragmentation, most notably illustrated by the contentious relationship between Boabdil and his uncle, the militarily adept El Zagal, whose formidable martial capabilities further exacerbated the emirate's geopolitical vulnerabilities, thereby impairing its capacity to effectively mobilize resistance against the encroaching coalition of Christian forces. Nevertheless, it is imperative to acknowledge the strategic advantages conferred by Granada’s formidable mountainous terrain, coupled with the robust fortifications of its urban centers. This geographical and structural fortitude, augmented by the fervent determination and resilience of the local populace, collectively contributed to Granada's status as a critical and tenacious stronghold of Islamic governance in the broader Iberian Peninsula during this tumultuous epoch.
The military campaign initiated was precipitated by the audacious territorial annexation of Zahara by the Emirate in the annum 1481—a pivotal juncture that served as a catalytic impetus for the martial engagement orchestrated by the Catholic Monarchs, Isabel I of Castile and Ferdinand II of Aragon.

Image Above Monarchs Of Castilles
What subsequently unfolded was an arduous protracted conflict, extending over a decade, characterized by a series of decisive military confrontations—most notably the Battle of Alhama, the skirmishes at Loja and Lucena, the strategic recapture of Zahara, and engagements in Ronda, Málaga, Baza, and Almería. Each of these encounters elucidates the intricate dynamics of military triumph entwined with the perils of adversity. Isabel's role transcended mere symbolic representation; she emerged as an astute logistical architect, meticulously structuring supply chains, provisioning her armies with necessary resources, and advocating for military advancements, including the tactical incorporation of Lombard artillery into the operational theater. Her dual presence—both on the battlefield and within the strategic command—interwove deep-seated piety with formidable power, unifying administrative efficiency with unyielding ambition.
In the face of profound personal adversities, exemplified by the heart-wrenching stillbirth of her progeny amidst the tumultuous electoral campaign, Isabel exhibited a remarkable steadfastness in her quest for triumph. Her strategic leadership catalyzed a transformative evolution in the constructs of monarchical power, ingeniously intertwining the notion of divine right—a historically entrenched justification for sovereign authority—with pragmatic statecraft underpinned by the imperatives of efficacious governance and stringent military discipline. The opposition posed by El Zagal, characterized by his indefatigable efforts and tenacious resistance, elongated the duration of the campaign; however, the indomitable spirit and cohesive resolve of the Catholic Monarchs emerged as an insuperable force, compelling the eventual culmination of their aspirations into a definitive victory.
The capitulation of the Emirate of Granada in the month of January in the year 1492 represents a pivotal moment in the historical continuum of the Iberian Peninsula, transcending the mere conclusion of the protracted series of military engagements known as the Reconquista. This momentous event is emblematic of the intricate process of state-building that led to the establishment of a cohesive Spanish nation-state fundamentally predicated on the precepts of Christian hegemony. Furthermore, it delineates the cusp of an imperial epoch characterized by expansionist ambitions fueled by religious zealotry. The ramifications of this surrender profoundly altered the sociocultural and political framework of the region, precipitating the coerced conversion and expulsion of significant Jewish and Muslim populations—a demographic upheaval that would serve to reinforce the ideological paradigms that underpinned the subsequent institution of the Spanish Inquisition, a systematic apparatus of religious persecution aimed at maintaining ideological conformity and unity under the Catholic Monarchs.

Image Above Surrender At Granada
In a broader historical context, the capitulation of the Nasrid Kingdom of Granada transpired concurrently with the inaugural expedition undertaken by the navigator Christopher Columbus, both events being facilitated under the auspices of Queen Isabel I of Castile. This significant temporal nexus serves to underscore the confluence of the termination of Islamic hegemony in the Iberian Peninsula with the commencement of European maritime exploration on a grand scale. Such a juxtaposition of religiously motivated conquest and the zealous pursuit of transoceanic exploration precipitated a paradigm shift in the trajectory of global history. It catalyzed the ascendance of the Spanish Empire, thereby marking the nascent stages of European colonial endeavors throughout the Americas.

Image Above Columbus At The Spanish Court
This epochal transformation not only redefined territorial dominion but also initiated profound socio-economic and cultural repercussions across continents, forever altering the intricate tapestry of human civilization.
Consequently, the cessation of hostilities in Granada should not merely be interpreted as the conclusion of a protracted medieval conflict; rather, it represents a critical juncture that fundamentally reoriented the socio-political landscape of the Old World while concurrently heralding the advent of modernity. The pivotal contributions of Queen Isabel I in this transformative epoch position her as an extraordinarily significant historical figure—an autocrat whose strategic foresight, resilience, and zeal indelibly influenced the trajectory of nations and entire continents across the globe.
-
 @ e97aaffa:2ebd765d
2025-04-21 12:57:16
@ e97aaffa:2ebd765d
2025-04-21 12:57:16Se este movimento de desglobalização continuar, poderá provocar uma cisão no mundo geopolítico, criar dois grandes blocos económicos, uma nova guerra fria.
Se isso se concretizar, quantos anos vão ser necessários para o S&P500 superar máximos históricos em termos reais, em poder de compra?
Em valores nominais vai ser rápido, o governo dos EUA vai imprimir tanto dinheiro, rapidamente vai superar máximos, mas em termos reais, vai demorar muitos anos.
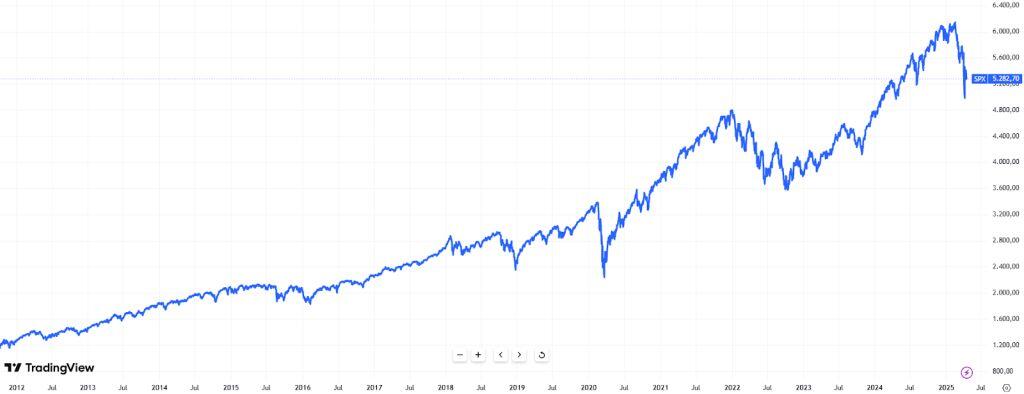
Até agora, todo o mundo estava a investir nos EUA, mas se os países do bloco oriental, sobretudo a China, deixarem de investir em ações, obrigações e moeda dos EUA, irá provocar uma enorme redução de liquidez e na procura/demanda, não vai ser fácil ultrapassar isso.
Nos US Treasury, o afastamento da China começou em 2014(1° guerra da Ucrânia), mas o movimento acelerou em 2022(2° guerra da Ucrânia).

Os EUA, ao congelar as reservas da Rússia, ao utilizar as reservas como uma arma de guerra, “assustaram” a China e outros países. As sanções à Rússia e como esta fez para contornar as sanções foi um case study para a China.
Como o objetivo da China é recuperar Taiwan, sabe que sofrerá as mesmas represálias que hoje a Rússia sofre, por isso a China tem que se afastar da economia dos EUA.
A China está a trocar US Treasury por outros ativos e por outras geografias, o principal beneficiado foi o ouro, um ativo soberano, que não tem problemas de contraparte.
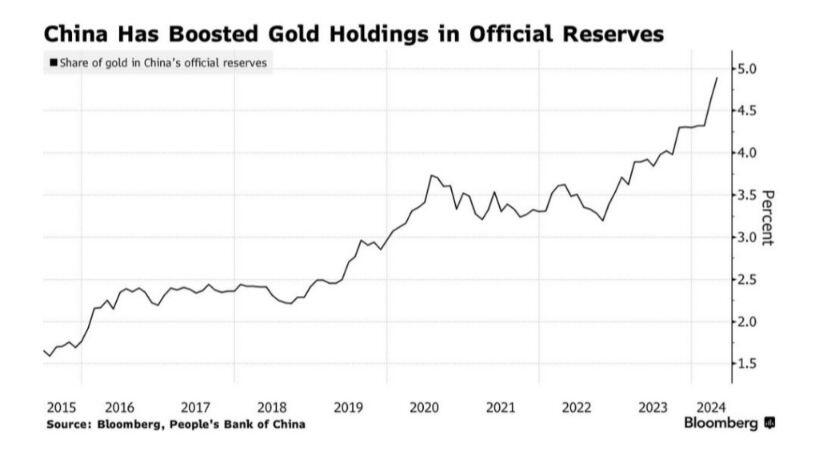
Este movimento da China foi bem visível no preço do ouro no último ano, uma valorização superior a 42%.
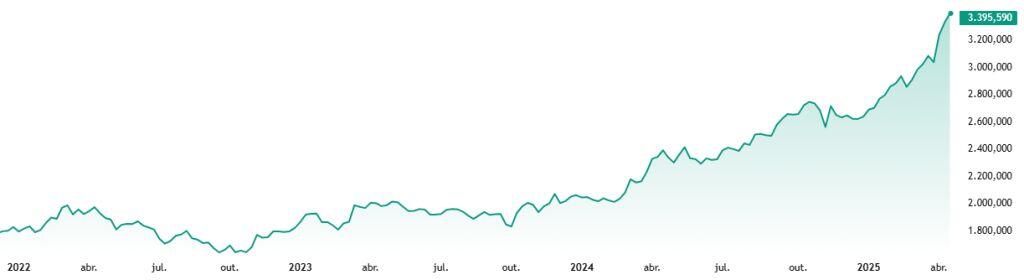
Mas não é só a China que está a apostar no ouro, são diversos, mas sobretudo composta por países do bloco oriental.
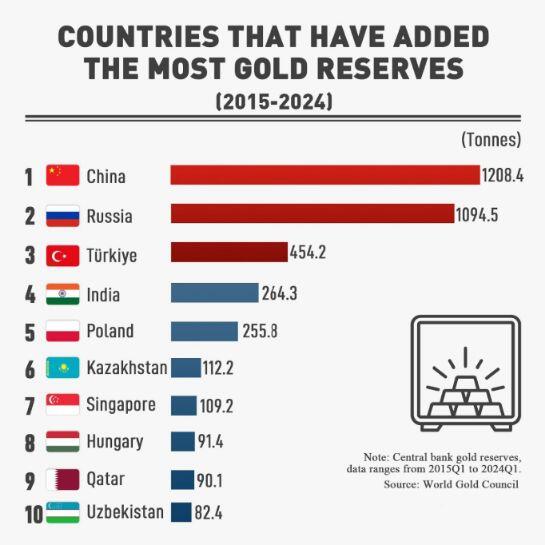
Enquanto, Taiwan for a fábrica do mundo nos semicondutores, estarão protegidos pelo guarda-chuva dos EUA. Mas os EUA, estão a construir fábricas próprias, quando forem auto-suficientes, vão descartar o “guarda-chuva”, Taiwan não terá qualquer hipótese sobre o poderio da China.
A China pensa sempre a longo prazo, estão apenas a aguardar, isto poderá estar para muito em breve.
Se isto se confirmar, o S&P500 poderá demorar décadas para recuperar desta crise, em termos de poder de compra.
-
 @ db11b320:05c5f7af
2025-03-29 19:04:19
@ db11b320:05c5f7af
2025-03-29 19:04:19magnet:?xt=urn:btih:9BAC9A3F98803AEA1EB28A0B60A562D7E3779710
-
 @ 45c41f21:c5446b7a
2025-03-28 08:02:16
@ 45c41f21:c5446b7a
2025-03-28 08:02:16“区块链行业究竟是在做什么?”——这个问题我到现在还没有想得很清楚。谈论起来可以说很多东西,“确权”、“让每一个比特都有了稀缺性”、“数字黄金”、“点对点支付”,但是具体到了行业落地,又容易陷入“赌场”这个有点乌烟瘴气的现实。
但我想有一点是比较明确的,那就是区块链行业肯定是一个围绕资产的行业。这些资产又跟传统的资产很不一样,最简单的特征是它们都是一个个的代币,通过自动化和可验证的代码铸造、控制,我们可以统称为链上资产。从比特币、以太坊到现在,这中间不管过去了多少不同的周期和浪潮,核心不变的都是出现新一轮受追捧的资产。
既然区块链是关于链上资产的行业,那么最重要的是未来会出现什么新的资产,有什么样的新资产会上链。要回答这个问题,又要我们回过头去看看,从行业诞生至今,区块链留下了哪些有意义的、没意义的,有价值的、没价值的资产。
因此,有必要讨论一下链上资产的分类。
链上资产的种类很多,但总体上我觉得可以按满足需求的不同,做一些功能性的划分。同时,抛开去中心化、抗审查等等大词,链上资产与传统资产最重要的区别可以认为是安全性的来源。传统资产在传统的社会系统和金融系统中产生,而链上资产是通过可验证代码控制的,所以它的安全性的依赖很清晰,要比现实世界简单很多。
在不同的区块链系统中,使用不同的技术(比如POW/POS),设置不同的规则,拥有不同的治理机制,都会影响安全性。“安全性”和“满足什么样的需求”之间既不是正交的,也不是完全耦合的。在不同层级的安全性之下,可能都会出现满足某一类相同需求的产品,用户使用哪种产品,只取决于自己的风险偏好。另一方面,有些需求只可能在某些特定的安全性保障下才能得到满足,比如跨国际的全球化的抗通胀价值存储。
这篇文章只讨论一些比较简单的分类,可以假设在不同的安全性保障下,每个分类都有可能出现对应的产品。有些安全性是产品内生功能的一部分,有些则完全不影响。同时,这些分类也完全是主观的看法,不一定正确,我所希望的是引发更多对资产进行讨论。
核心资产(高安全性、强需求支撑)
- 比特币(BTC)
- 核心价值:全球化抗通胀、抗审查的“数字黄金”。
- 长期逻辑:全球法币超发背景下,BTC作为去中心化硬通货的需求不可替代。
这是整个行业最重要的资产。也是整个行业最核心的东西。在这个定位下,只会有一个赢者通吃。其他试图竞争的都很难生存下来。它对安全性的要求也是最高的。
经过验证的资产分类
这部分的资产可以认为是行业诞生至今,已经经过验证的、满足某真实需求、会长期存在的资产。
- 代表优质项目的资产(股票/ICO代币/治理代币等)
- 核心价值:类似于传统金融世界里的一级市场和二级市场。所谓的“优质”也不一定需要真实落地,可能是叙事/故事驱动,也可能有真实的现金流,但重要的是它能在市场上吸引人买卖。
- 关键指标:团队是否持续营销和建设?生态是否增长?项目是否解决实际问题?
- DeFi 资产
- 核心价值:链上金融系统的“基础设施工具”。
- 需求来源:对套利、链上资产理财的需求会永远存在。
- Meme币
- 核心价值:营销驱动+投机需求的结合体。
- 长期存在性:人性对暴富故事的追逐不会消失(如Pump.fun、SHIB)。
- 稳定币
- 核心价值:加密货币世界的“支付货币”。
- 需求刚性:交易媒介、避险工具、跨境支付(如USDT、USDC)。
在不同的安全性保障下,上面这些资产大部分都会有对应的产品。
比如稳定币在安全性上可以有中心化的 USDT ,也有去中心化的算法稳定币。理论上,安全性对稳定币是非常重要的。但现实中,“流动性”可能才是给用户传达“这东西到底安不安全“的产品特点,也是比较主要的竞争点。
Meme 则完全不需要安全性,所以对创业者来说在哪里做都差不多。哪里用户更多就适合去哪里。有时,安全性反而是它的阻碍。DeFi 的话,因人而异。安全性高低是否影响用户使用,完全取决于用户自己的风险偏好。
还未经过验证的资产(需求可能存在)
- NFT(收藏品)? 艺术、身份标识、游戏道具的数字化载体,但流动性差、炒作属性也不见得有 Meme 这么强。会长期存在吗?打个问号。
- DAO(准入/治理代币)? 去中心化组织的准入权/管理权通证,依赖 DAO 本身的价值和实际治理参与度决定的价值。DeFi DAO 可能是唯一一个有点发展的方向,其他还非常不成熟,有待验证。
- RWA(真实世界资产代币化)? 房产、债券等上链,需要解决法律合规与链下资产映射问题。不确定。
- 社交/游戏/内容资产 用户数据所有权货币化,还没有像样的有一些用户的产品,就更不用提形成规模经济了。
- AI 相关的资产? 是一个变数。如果未来会有成千上万的 AI 智能体与人类共存,链上是承载他们经济系统最合适的基础设施,这里会产生什么新的资产类型?值得期待。
这里面的资产类型,很多还没有找到真实的需求,至少没有经过验证。所以长期来看它们会是区块链行业的方向吗,需要打很多问号。既然需求本身没有得到验证,那么谈安全性对它们的影响,就更加无从谈起了。
当然,这里其实还有一个更有意思的部分,可以多聊一些。也就是共同知识(法律/合同/规则/代码)这一类资产。
在应用层,共同知识尚未有代币化的尝试,也难以对其具体价值做定量分析。但如果要说有的实践,以太坊通过交易收取 gas 费和 CKB 通过 Cell 存储状态收取“押金”算是一种在底层的 generalize 的尝试。这种尝试是定量的,可验证的。
以太坊的问题是经济模型不 make sense 导致状态爆炸,ckb 相比是更简单、更明确的。但这里的问题变成了,公链需要通过区块空间的竞争来展示这一种需求是否真的成立。区块空间越紧张,需求就越大。同时安全性越高,对共同知识的保障就越强,也会体现区块空间的价值。
但另一方面,是否有开发者在上面开发应用,会更大的影响这一点。因此开发工具、开发者生态在现阶段可能更重要。
最后
写到这里,发现很多资产似乎又是老生常谈。但从满足需求和安全性两个角度来思考,算是追本溯源的尝试。现在我们面临的处境是,问题还是老的问题,答案是否有新的答案,期待更多讨论。
- 比特币(BTC)
-
 @ dbb19ae0:c3f22d5a
2025-04-21 12:29:38
@ dbb19ae0:c3f22d5a
2025-04-21 12:29:38Notice this consistent apparitioon in the timeline of something that reflects a major key shift in tech:
💾 1980s – The Personal Computer Era
- IBM PC (1981) launches the home computing revolution.
- Rise of Apple II, Commodore 64, etc.
- Storage is local and minimal.
- Paradigm shift: Computing becomes personal.
🎮 1990s – Networking & Gaming
- LAN parties, DOOM (1993) popularizes multiplayer FPS.
- Early internet (dial-up, BBS, IRC).
- There is lots of room for connecting PC.
- Paradigm shift: Networked interaction begins.
🌐 2000s – The Internet Boom
- Web 2.0, broadband, Google, Wikipedia.
- Rise of forums, blogs, file sharing.
- A bigger need of interaction is looming
- Storage is on cd and dvd.
- Paradigm shift: Global information access explodes.
📱 2010s – Social Media & Mobile
- Facebook, Twitter, Instagram dominate.
- Smartphones become ubiquitous.
- Bitcoin appears and start a revolution.
- Collecting personal data from users to fuel the next shift.
- Paradigm shift: Always-connected, algorithmic society.
🤖 2020s – AI & Decentralization
- GPT, Stable Diffusion, Midjourney, Copilot.
- Blockchain, Nostr, Web3 experiments.
- Storage is in the cloud.
- Paradigm shift: Autonomous intelligence and freedom tech emerge.
roughly every decade, a tech leap reshapes how we live and think.
-
 @ 57d1a264:69f1fee1
2025-04-21 12:11:22
@ 57d1a264:69f1fee1
2025-04-21 12:11:22There's any content about SN out there?
In the news: - @BitcoinNews Stacker.News Raises $1.25m Seed Round At $25m Valuation - @Alby blog post explain how Stacker News adds Self-custodial Spending with NWC - @cryotosensei on @0xbitcoiner's website Stacker News encourages deep sharing ad Random things I learnt about Bitcoin from Stacker News - @anita's Earn bitcoin on Stacker News: People asked and I answered
Recently we have seen an article in BM writing about how PlebLab is shaping the future of bitcoin startups in Austin. SN was mentioned and linked 🎉
Started in 2021 by one of PlebLab’s cofounders Keyan Kousha, Stacker.news has quickly become a hub of news for many tech-savvy Bitcoiners. Boasting an open source Lightning-powered Reddit, the platform has gathered an active and loyal fan base that reward each other with sats for every upvote, often being early to integrate the latest technologies in the Bitcoin-social media tech scene.
In the past it has also only mentioned here.
From a startup pitch perspective:
Developer of a news platform intended for individuals to earn real money for creating and curating content. The company's platform specializes in allowing individuals to submit, vote, and comment on content, stories, and discussions about the topics in communities organized around their interests, enabling individuals to post content and get paid while reading the news. PitchBook -
https://pitchbook.com/profiles/company/535835-44#overviewStacker News is a forum (like Reddit or Hacker News) where you can earn real money for creating or curating content. F6S -
https://www.f6s.com/company/stacker-news#aboutPeople talking about SN:
-
A stacker shared a Lessons learned from Stacker.news and how SN works. Discourse Co-CEO respond:
Heh, it’s not a healthy or sustainable model for the types of communities consciously we build for. Definitely not something we would consider building into core but you could make it work with a plugin. Extrinsic motivators attract the wrong people for the wrong reasons, in my experience. Healthy community ecosystems are driven by intrinsic motivation.
-
on BitcoinTalk here, here and here. There are probably more posts where it has ben mentioned and discussed.
-
HackerNews crowd does not seem too excited about it. Just few comments on each post.
Some review have been collected on @julian's Apollo and ProductHunt.
Let's check what YT has:
Some interviews first. At 2023 ZBD x PlebLab TabConf Hackathon, Keyan Kousha explain Why Not to Use Stacker News
@kr did a great job interviewing k00b when SN was in its infancy - Stacker News Is Growing FAST - Stacker News Is Disrupting Social Media | E17 - Keyan Kousha on Stacker News, Earning Bitcoin, & Decentralized Content | The Kevin Rooke Show | E17 - How Siggy47 Stacked Over 500,000 Sats on Stacker News | SS8
And here some interviews:
Stacker News is a user-generated, feed-style news platform, modeled after Hacker News, but with the important distinction of having natively-integrated bitcoin lightning payments, as a means of fostering more natural communities (think less spam and antisocial behavior), cultivating high-signal bitcoin content, and providing a better user experience overall.
Stacker News is still in the very early days of its development, but it's a great showcase of how bitcoin can be used to improve upon an existing model, and in doing so, explore how improved incentives might influence media publishing, monetization, and moderation.
Keyan is a prime example of someone who caught the bitcoin bug, and just couldn't resist getting involved. The result is a product built with and for bitcoiners, and it was great to have him on the show to explain more about his motivations and ambitions.
-
From ~ideasfrommtheedge pod: AI, Simulations, and Startups with Keyan Kousha (Founder, Stacker News)
-
@alexstrenger's Convos On The Pedicab #177 Stacker News: A Bitcoiners Alternative To Reddit
-
@dk and @MaxAWebster intro on What's new with Stacker.News and Nostr? also shared here
-
@ConnectTheWorld stream Keep Austin Weird! Meet Keyan, the founder of Stacker.news
-
@Thriller Lightning: Stacker.News Founder Keyan
-
0.00000018: Keyan Kousha, Stacker.News: an interview in the Changing the Tide show here
-
@bitcoinplebdev reading top ~devs stories 04/08/2024 and stacker.news codebase overview / how to run locally)
That's the interviews I was able to find. Continuing the dig...
-
@TheWildHustle compiles SN ~Music' vibes into YT playlists
-
@kdnolan7 on was giving some updates about the ~Education territory here and here
Gradually, then suddenly, the message start to change, and the majority of videos communicate something that is probably, at least from my perspective, not the right way to market a product like SN:
-
@SatsMate lay out Why He Love Stacker News!
-
@voltage share a story quickly talking how Stacker News is like YCombinators Hacker News but YOU EARN! https://www.youtube.com/shorts/d1xZ3RE9plk
@HattyHats Earn Bitcoin (LN) Blogging with Stacker News
The long list continues: - Earn bitcoin Satoshis Reading & Sharing Content on Stacker.News - First Time Walk Through by @SatoshiTutor - Earn Free Bitcoin | Stacker News Quick Tutorial from Earning Crypto Site - One of the Different Ways to Earn Bitcoin 👉 stacker.news | Bitcoin Lifestyle #2 from @SatoshiComTR - @1100note another Stacker.News story - ...
This list of references can, and probably will, go on and on with the same topic. The message looks like will be always the same: come over, stack sats, stay humble. There's maybe something wrong with the message we share SN out there? Is not what we do, is how we do it, that make the difference. As you can see, there's not much there that refer to quality content, great supportive community, community moderated contents, no ads, no spam, no bots (well, not many) and no ai. Pure human content.
In other successful platforms where people earn money for the contents they create, the money factor is totally hidden, is not their main sales point in the pitch. Look at YT itself. We all know people earn fiat producing and sharing videos, but their comms does not talk about it, at least not the way stackers do. And you'll not find many YTers inviting others to create videos to earn money. Well ok, some do!
Something we could make an effort to improve, is the way we talk about SN. Finding alternative ways to do it is hard, some have been mentioned here https://stacker.news/items/948462/r/Design_r
Just wanted to see how much other quality content is out there talking about SN that is not about stacking sats? Share your best contents, nostr notes, x tweets, blog posts, articles, videos, interviews, reviews or any other media that has been created by others about SN (no memes shill) or that somehow mention it in the comments below.
originally posted at https://stacker.news/items/951177
-
-
 @ cb4352cd:a16422d7
2025-04-21 11:17:41
@ cb4352cd:a16422d7
2025-04-21 11:17:41What happens when artificial intelligence meets Web3? It's no longer just an idea — it's happening, and it's reshaping how we think about applications, economies, and communities online.
AI-as-a-Service in Web3
One of the clearest signs of this shift is the rise of decentralized AI marketplaces. Projects like Bittensor show that users can contribute machine learning models and earn rewards in cryptocurrency.
Another example is Gensyn, linking AI developers to decentralized compute resources.
Verifying AI with Blockchain
Blockchain helps verify AI outputs. Initiatives like Oraichain and Fetch.ai ensure AI agents interact securely and transparently in decentralized ecosystems.
AI-Driven Decentralized Organizations
Projects like SingularityNET explore AI marketplaces and autonomous governance models, creating new possibilities for decentralized coordination.
Generative AI in Web3 Content Creation
Platforms like Alethea AI are building intelligent NFTs that adapt to user interactions. AI-generated quests and dynamic worlds are reshaping GameFi.
The Road Ahead
Beyond Banking Conference by WeFi will spotlight how AI and Web3 are converging to redefine ownership, collaboration, and the very nature of the internet.
The question isn't whether AI and Web3 will merge — it's how quickly their union will reshape everything we know about digital life.
-
 @ 86dfbe73:628cef55
2025-04-21 10:08:34
@ 86dfbe73:628cef55
2025-04-21 10:08:34Mit dem Internet kam das Ende der Massengesellschaft. Heutzutage sind Öffentlichkeit im Allgemeinen und die digitale Öffentlichkeit im Besonderen nur als Netzwerk verstehbar. Nicht als Netzwerk zur Kommunikation, sondern als Netzwerk der Beziehungen, bestehend aus den Erwartungen, Kenntnissen und letztlich bestehend aus dem Vertrauen, das Menschen gegenüber anderen Menschen und Institutionen aufzubauen pflegen. Wichtig ist nicht mehr, wo jemand eine Information plaziert, wichtig ist, wann und wer und unter Einbeziehung welcher Faktoren diese abfragt.
In Sozialen Netzwerken entscheidet jeder selbst, wem er folgt. Er entscheidet selbst, wie die eigene Startseite, der eigene Blick auf den Dienst, aussieht. Als Beispiel sei hier Twitter erwähnt. Aus der Liste der Gefolgten wird die Timeline generiert, die eine Wirklichkeit abbildet, die einzig und alleine von den Following-Entscheidungen des Nutzers bestimmt ist.
Die Beziehungsweise des Folgens ist eine direkte Willenserklärung, die Inhalte eines Users sehen zu wollen. Sie ist ein Pakt, der auch eine gewisse, wenn auch kleine, Verantwortungsübernahme bedeutet. Und diese Beziehungsweise wurde zum integralen Strukturbaustein der digitalen Öffentlichkeit zwischen 2010 bis 2020 und damit auch zur tragenden Säule vieler Karrieren, Geschäftsmodellen und außerdem zur Grundlage der Selektionsverfahren von kulturellen Trends. Im Follower steckte die Macht.
Die digitale Öffentlichkeit hat aufgehört eine vernetzte Öffentlichkeit zu sein und geht zunehmend in den „For you“-Algorithmen der kommerziellen Plattformen auf. Ab 2020 wurde dem Follower von Diensten wie Tiktok der Gar ausgemacht und von dort setzte sich der „For You-Algoritmus“ auf allen kommerziellen Plattformen durch. Das bedeutet, dass die neue digitale Öffentlichkeit nicht mehr durch menschliche Beziehungen und vernetztes Vertrauen getragen wird, sondern vollends den Steuerungsinstrumenten einer Hand voll Konzernen ausgeliefert ist. Auf einmal bedeutete ein Following nicht mehr die Garantie, dass der Content die Abonnenten erreicht.
Mit der Zerstörung dieser Beziehung entgleiten den Creators ihre medialen Regime und beide, User und Creator werden immer abhängiger vom Algorithmus und arbeiten folglich nur noch für die Interessen der Plattformen, statt für sich selbst.
-
 @ 95cb4330:96db706c
2025-04-21 09:59:02
@ 95cb4330:96db706c
2025-04-21 09:59:02Principle:
Reduce internal friction by minimizing unnecessary processes, approvals, and meetings.
Empower small, autonomous teams to make decisions quickly and independently.
💡 What It Means
- Bureaucracy kills speed, innovation, and ownership.
- Instead of creating endless layers of management and approval, build the smallest system necessary to enable great work.
- Give teams the trust and tools they need to move fast.
The goal is not chaos, but flexibility with lightweight structure—so the organization stays dynamic as it scales.
📈 Why It Matters
✅ Speed is a competitive advantage in entrepreneurship.
✅ Empowered teams are more creative and motivated.
✅ Minimal bureaucracy allows companies to iterate fast and stay customer-focused.
🏛️ Examples in Action
- Spotify uses small “squads” with high autonomy and light-touch leadership to maintain speed and innovation.
- Basecamp designs its company around minimal meetings, clear asynchronous communication, and trusting small teams to own outcomes.
- Amazon uses the "two-pizza team" rule—teams should be small enough to be fed with two pizzas.
📚 Resources to Explore
- 📄 Spotify’s Engineering Culture – Part 1
- 📖 Basecamp’s Approach to Minimal Management
- 📘 Harvard Business Review on 3 Ways to Improve Your Decision Making
- Spotify Engineering Culture - Part 1 (aka the "Spotify Model")
🚀 Action Prompthttps://hbr.org/2018/01/3-ways-to-improve-your-decision-making
Ask yourself:
"What approvals, meetings, or processes can I eliminate or simplify today to help my team move faster?"Build only as much structure as needed—and no more. Protect creativity, speed, and ownership at all costs.
-
 @ 7d33ba57:1b82db35
2025-04-21 08:47:51
@ 7d33ba57:1b82db35
2025-04-21 08:47:51Spread across 14 islands and connected by elegant bridges, Stockholm is often called the **"Venice of the North." It blends royal history, cutting-edge design, lush nature, and a laid-back Nordic vibe like few cities can. With cobblestone streets in Gamla Stan, sleek modern art in Södermalm, and serene waterways everywhere, Stockholm is both storybook and futuristic.

🏰 Top Things to Do in Stockholm
🏛️ Gamla Stan (Old Town)
- A beautifully preserved medieval core with colorful buildings, narrow alleys, and cozy cafés
- Visit the Royal Palace, Stockholm Cathedral, and watch the changing of the guard
- Stop by Stortorget Square for the classic photo and a fika (Swedish coffee break)
🖼️ Vasa Museum
- Home to the Vasa warship, which sank on its maiden voyage in 1628 and was miraculously recovered 333 years later
- One of Sweden’s most popular and jaw-dropping museums

🏡 Skansen Open-Air Museum
- A walk through Sweden’s past—complete with historic homes, craft demos, and even Scandinavian animals
- Great for families or anyone curious about Swedish traditions
🌉 Södermalm
- Stockholm’s hip, creative district
- Full of boutique shops, vintage stores, craft coffee, and rooftop bars
- Climb Monteliusvägen for incredible views of the city skyline and Lake Mälaren

🌿 Nature & Water Everywhere
- Take a boat tour of the Stockholm Archipelago, made up of 30,000+ islands
- Kayak through the canals or paddleboard around Kungsholmen
- In summer, locals swim off the rocks in the city or picnic in Djurgården Park

🍽️ Food & Fika
- Try Swedish meatballs, gravad lax, or herring smörgåsbord
- Visit the indoor Östermalm Market Hall for local specialties
- Don’t miss fika culture—coffee + cinnamon buns (kanelbullar) is a must

🚆 Getting Around
- Super walkable and bike-friendly
- Excellent public transport: trams, ferries, metro (Tunnelbana)
- The T-Centralen station even doubles as an underground art gallery

📅 Best Time to Visit
- Summer (June–August): Long sunny days, outdoor festivals, archipelago adventures
- Winter: Christmas markets, cozy cafés, and snow-dusted rooftops
- Year-round appeal with distinct charm in every season

-
 @ d34e832d:383f78d0
2025-04-21 08:32:02
@ d34e832d:383f78d0
2025-04-21 08:32:02The operational landscape for Nostr relay operators is fraught with multifaceted challenges that not only pertain to technical feasibility but also address pivotal economic realities in an increasingly censored digital environment.
While the infrastructure required to run a Nostr relay can be considered comparatively lightweight in terms of hardware demands, the operators must navigate a spectrum of operational hurdles and associated costs. Key among these are bandwidth allocation, effective spam mitigation, comprehensive security protocols, and the critical need for sustained uptime.
To ensure economic viability amidst these challenges, many relay operators have implemented various strategies, including the introduction of rate limiting mechanisms and subscription-based financial models that leverage user payments to subsidize operational costs. The conundrum remains: how can the Nostr framework evolve to permit relay operators to cultivate at least a singular relay to its fullest operational efficiency?
It is essential to note that while the trajectory of user engagement with these relays remains profoundly unpredictable—analogous to the nebulous impetus behind their initial inception—indicators within our broader economic and sociocultural contexts illuminate potential pathways to harmonizing commercial interests with user interaction through the robust capabilities of websocket relays.
A few musingsI beg you to think about the Evolutionary Trajectory of Nostr Infrastructure Leveraging BDK (Bitcoin Development Kit) and NDK (Nostr Development Kit) in the Context of Sovereign Communication Infrastructure
As the Nostr ecosystem transitions through its iterative phases of maturity, the infrastructure, notably the relays, is projected to undergo significant enhancements to accommodate an array of emerging protocols, particularly highlighted by the Mostr Bridge implementation.
Additionally, the integration of decentralized identity frameworks, exemplified by PKARR (Public-Key Addressable Resource Records), signifies a robust evolutionary step towards fostering user accountability and autonomy.
Moreover, the introduction of sophisticated filtering mechanisms, including but not limited to Set Based Reconciliation techniques, seeks to refine the user interface by enabling more granular control over content visibility and interaction dynamics.
These progressive innovations are meticulously designed to augment the overall user experience while steadfastly adhering to the foundational ethos of the Nostr protocol, which emphasizes the principles of digital freedom, uncurtailed access to publication, and the establishment of a harassment-free digital environment devoid of shadowbanning practices.
Such advancements underscore the balancing act between technological progression and ethical considerations in decentralized communication frameworks.
-
 @ d34e832d:383f78d0
2025-04-21 08:08:49
@ d34e832d:383f78d0
2025-04-21 08:08:49Let’s break it down.
🎭 The Cultural Love for Hype
Trinidadians are no strangers to investing. We invest in pyramid schemes, blessing circles, overpriced insurance packages, corrupt ministries, miracle crusades, and football teams that haven’t kicked a ball in years. Anything wrapped in emotion, religion, or political flag-waving gets support—no questions asked.
Bitcoin, on the other hand, demands research, self-custody, and personal responsibility. That’s not sexy in a culture where people would rather “leave it to God,” “vote them out,” or “put some pressure on the boss man.”
🧠 The Mindset Gap
There’s a deep psychological barrier here:
Fear of responsibility: Bitcoin doesn’t come with customer service. It puts you in control—and that scares people used to blaming the bank, the government, or the devil.
Love for middlemen: Whether it’s pastors, politicians, or financiers, Trinidad loves an “intercessor.” Bitcoin removes them all.
Resistance to abstraction: We’re tactile people. We want paper receipts, printed statements, and "real money." Bitcoin’s digital nature makes it feel unreal—despite being harder money than the TT dollar will ever be.
🔥 What Gets Us Excited
Let a pastor say God told him to buy a jet—people pledge money.
Let a politician promise a ghost job—people campaign.
Let a friend say he knows a man that can flip $100 into $500—people sign up.
But tell someone to download a Bitcoin wallet, learn about self-custody, and opt out of inflation?
They tell you that’s a scam.
⚖️ The Harsh Reality
Trinidad is on the brink of a currency crisis. The TT dollar is quietly bleeding value. Bank fees rise, foreign exchange is a riddle, and financial surveillance is tightening.
Bitcoin is an escape hatch—but it requires a new kind of mindset: one rooted in self-education, long-term thinking, and personal accountability. These aren’t values we currently celebrate—but they are values we desperately need.
🟠 A Guide to Starting with Bitcoin in Trinidad
- Understand Bitcoin
It’s not a stock or company. It’s a decentralized protocol like email—but for money.
It’s finite. Only 21 million will ever exist.
It’s permissionless. No bank, government, or pastor can block your access.
- Get a Wallet
Start with Phoenix Wallet or Blue Wallet (for Lightning).
If you're going offline, learn about SeedSigner or Trezor for cold storage.
- Earn or Buy BTC
Use Robosats or Peach for peer-to-peer (P2P) trading.
Ask your clients to pay in Bitcoin.
Zap content on Nostr to earn sats.
- Secure It
Learn about seed phrases, hardware wallets, and multisig options.
Never leave your coins on exchanges.
Consider a steel backup plate.
- Use It
Pay others in BTC.
Accept BTC for services.
Donate to freedom tech projects or communities building open internet tools.
🧭 Case In Point
Bitcoin isn’t just technology. It’s a mirror—one that reveals who we really are. Trinidad isn’t slow to adopt Bitcoin because it’s hard. We’re slow because we don’t want to let go of the comfort of being misled.
But times are changing. And the first person to wake up usually ends up leading the others.
So maybe it’s time.
Maybe you are the one to bring Bitcoin to Trinidad—not by shouting, but by living it.
-
 @ ff517fbf:fde1561b
2025-03-26 16:48:41
@ ff517fbf:fde1561b
2025-03-26 16:48:41フアン・ラモン・ラッロ氏は、スペイン出身の経済学者・作家であり、自由市場経済とリベラルな思想の提唱者として知られています。彼は、国家による過剰な介入や財政政策の問題点を鋭く分析し、自由主義の基本原則に基づく社会の実現を目指す論考や著作を多数発表しています。数多くのメディアや学会で講演を行い、現代社会における経済政策や公共の役割について、国際的な議論にも影響を与えている人物です。

皆様、こんばんは。そして、Andorra Economic Forumの皆様、本日はご招待いただき誠にありがとうございます。
本日の講演では、これまで私が持ち続けてきた見解、すなわち、より自由で、より繁栄するために、スペイン及び世界において自由主義革命がなぜ必要であり、さらには急務であるのかという理由をお伝えしたいと思います。また、現代国家が、ストックホルム症候群のような論理に我々を陥れており、その結果、国家が我々の自由を体系的に制限し、財産を構造的に攻撃している状況を、ほとんどの人々が抗議もせず、またはその非常事態性すら意識していないという現実をどのように理解すべきかについても触れます。まず初めに、皆様のご反応から察するに、これは既知の内容に感じられるかもしれませんが、自由主義の基本原則、すなわち四つの基本的な考えを確認させていただきます。どのようにして、社会生活と、各個人が自らの人生計画を追求するための自律性とを両立させ、かつ、個々の自律性が打ち消されるような一個または多数の専制に服従することなく生きることができる社会が成立するのでしょうか? それは、協力と共存が可能な社会の中で、各人が自己の利益を追求し、同時に他者の利益追求を尊重するための基本原則、すなわち以下の四つの原則によって支えられているのです。
第一に、個人の自由、すなわち他者の行動を踏みにじることなく自ら行動するという、いわゆる非攻撃の原則です。自分が望むことは何でもできますが、他者が望むことをするのを妨げてはならず、また、他者があなたの望むことを妨げることも許されないのです。
第二に、私有財産です。平和的に獲得し、平和的に自らのものとしたものはあなたのものであり、それによって自由に行動し、自らの人生計画や行動計画を追求する手段となります。もしも、これらの計画遂行に必要な手段が恣意的に奪われるならば、それはあなたの個人の自由、すなわち自らの人生計画を追求する自由を侵害することになるのです。
第三に、契約の自律性です。あなたは第三者と自由に合意を結ぶことができます。もちろん、第三者を攻撃することは許されませんが、双方が望むことについて自発的に合意することは可能です。合意は、当事者間の私法上の契約であり、両者が履行すべき約束であり、第三者が介入してこれを正当化したり否定したりするものではありません。ただし、合意の内容は、あくまで当事者双方やその所有物にのみ影響を及ぼすものです。
そして最後に、広義の意味での結社の自由です。個人は、契約上、望むことについて合意するだけでなく、共に生活する方法や、ある程度安定した形で組織される方法を合意することも明示的に可能です。これらの原則は、しばしば国家によって保証されると言われます。なぜなら、国家がなければ、法体系も安全保障機関も存在せず、個人の自由、私有財産、契約の履行、そして結社の自由を保障するものが何もないと思われがちだからです。とはいえ、確かにある程度の国家は、警察国家としてこれらの基本的な社会的共存の規範を保証するために必要かもしれませんが、私たちが必要としているのは、単にこれらの自由主義社会の原則と自由な人々の相互作用が尊重されることを確保するための、巨大かつ過剰な国家ではありません。
実際、国家が大きくなるほど、つまり社会における国家の存在感が増すほど、これらの原則は侵害されがちです。なぜなら、国家は恣意的に規制を強化し、税金を引き上げることで、たとえ他者に損害を与えなくとも、個人が望むように行動する自由を阻み、また、私有財産を強制的に奪い、当事者間の取引を妨げ、さらには、結社および脱会の自由さえも制限してしまうからです。たとえば、誰かが既存の国家から離れ、他の国家に参加したり、あるいは新たな国家や政治共同体を形成して自らを組織しようとした場合でさえ、現行の国家はそれを認めないのです。
さて、これらの自由主義の基本原則は、各個人の計画や人生のプロジェクトが社会の中で花開くために必要不可欠なものであり、現代国家によって体系的に侵害されているのです。しかし、現代国家とは、必ずしも常に我々と共にあった国家ではありません。私たちは、今日のようなメガ国家、ハイパーステート、過剰に肥大化した国家をある程度は当たり前のものとして受け入れてしまっていますが、これらは唯一の政治的選択肢ではなく、歴史を通じて存在してきた唯一の政治現実でもないのです。
ここで、主要な西洋諸国における国家の社会に占める重みの変遷について、皆様にご覧いただければと思います。今日、国家の重みは国によって大きな違いはないものの、概ね国内総生産(GDP)の40〜50%を占めています。中には、例えばフランスのようにGDPの60%に達する国もあります。国家が社会的調和や幸福の保証とされることは稀であり、実際、フランスは世界最大の国家を有しながら、またはそのために、今最も分断され混沌とした国の一つとなっています。
しかし、現状、国家はGDPの40〜50%、すなわち社会が毎年生み出す生産の約半分を吸収し、再分配または政治層や官僚階級が決定した形で消費しているのです。これは常にそうであったわけではありません。19世紀、ひいては第一次世界大戦前までは、近代先進国における国家の経済的重みはGDPの5〜10%程度に過ぎなかったのです。
例えば、アメリカ合衆国では第一次世界大戦前、国家のGDPに占める割合は3〜4%でしたし、今日巨大な社会民主主義国家となっているスウェーデンでさえ、かつてはGDPの5%程度でした。すなわち、国家というものが必然的に経済の半分を占めなければならないというわけではなく、これは徐々に積み重ねられてきたプロセス、いわばゆっくりと沸騰させられるカエルのようなものです。第一次世界大戦後、国家の経済に対する重みは大幅かつ確固たる上昇を見せ、さらに第二次世界大戦後には、急激かつ持続的な上昇を経て、1970年代以降、現在の水準にまで達したのです。
ちなみに、ここで我々がしばしば耳にする「国家が後退しているから、我々は新自由主義の時代にいる」というレトリックが、いかに毒性がありずる賢いものであるかにも注目してください。過去40年間で、グラフ上に国家の重みが大幅に後退したと示す兆候は見当たりません。ある時点で国家のGDPに占める割合が1〜2%減少することがあったとしても、200年の間にGDPの5%から50%へと増加し、現在は概ね50%前後に留まっているのです。国家が後退し、民間部門がすべてを占めるようになっている、というのは全く逆の現象です。
実際、多くの人は、国家が拡大し続けるのが当然であり、もし急速な成長が見られなければ、国家は後退していると考えがちです。しかし、国家は既にそれ以上大きく成長する余地がほとんどないのです。もちろん、GDPの60%、70%、80%にまで達すれば、直接的または間接的な社会主義経済になってしまいます。
そして、なぜ国家はこれほどまでに成長したのでしょうか。急激な国家拡大を説明する基本的な要因の一つは、福祉国家の発展です。つまり、かつては国家が提供していた医療、社会保障(年金、事故保険など)や教育といったサービスの国家による提供が、福祉国家として大きく発展したのです。
ご覧の通り、1930年代や第二次世界大戦後までは社会保障費は非常に低い水準にありましたが、特に第二次世界大戦後からは、GDPの20〜30%にまで急上昇しました。これらはかつて、市民社会や市場を通じ、または必ずしも商業的な交換を介して提供されていた、労働組合などが担っていた社会保障の役割を、国家が吸収していったものです。労働組合は国家から独立し、時には国家に対抗しながら、社会保障の機能を果たしていたのですが、その役割が国家に吸収されることで、我々は国家に依存するようになってしまったのです。
なぜなら、社会保障費は支出であり、中には「依存費用」とも呼ばれるものもあります。たとえば、老後に収入がなくなった時や、何らかの障害によって収入が得られなくなった時のために、個人の貯蓄から基金を積み立てる場合、その基金が自分自身で管理されるなら自律的ですが、国家が管理すれば、私たちは国家に全く依存することになってしまうのです。国家が消滅するか、大幅な予算削減が行われれば、我々は何も残らないのです。結果として、国民は容易には消えない国家の爪痕に囚われることになるのです。公共年金制度の問題を考えてみてください。現代の先進国家において、公共年金制度は最も大きな支出項目の一つです。
では、どうすれば公共年金制度を解体できるのでしょうか。どうすれば、必要以上に介入してきた国家、例えばアメリカ合衆国では大恐慌期(1930年代)に、必要がなかったのに介入してきた国家を、その状況から脱却させることができるのでしょうか。設立当初は、ある一定の年齢に達した者には一定額の年金を支給すると約束し、その費用を現在働いている者への税負担によって賄うというシステムでした。
システムの構築は、当時の平均寿命がかなり低く、支給期間が2~3年程度であったため、比較的容易で安価に行われたのですが、システムが一度確立され、世代を超えた労働者の貯蓄能力を事実上奪う形で構築された今、どうやってそれを解体すればよいのでしょうか。もし「年金は支給されなくなるのか」と言えば、かつて生産期に労働者の給与のかなりの部分を国家が吸収し、貯蓄を阻害していた結果、何百万人もの人々が貧困に陥ることになるのです。
じゃあ、もう引退されている皆さんは年金を受け取ることになりますが、現役世代がその年金の費用を負担し、そして自分たちが引退する時には年金を受け取ることができなくなるのです。つまり、この世代からは何の対価もなく、給与のごく大部分が没収されることになるというわけです。これをどうやって解体するつもりですか? 決して容易なことではありません。
また、例えば医療制度についても同様です。若者にとっては医療制度の解体はそれほど難しくないように見えるかもしれませんが、貯蓄がなく、保険にも加入していない高齢者にとって、もし今、公共医療制度が終了し、年齢とともに医療費が指数関数的に上昇するために通常以上の医療費が発生すると告げられたら、彼らはその医療費にどう対処すればよいのでしょうか? 彼らは、公共医療制度が機能するという説明のもとに、その医療費が賄われると予め想定し、税金を支払っていたのです。
これをどう逆転させるか? もちろん、即座に行えることではありませんが、時間をかけた移行措置として行っていかなければなりません。だからこそ、国家はこの道を通じて成長し続け、社会がますます国家による再分配に依存するようになることで、国民の自律性を奪っていくのです。
ちなみに、現代福祉国家の発明者の一人であるのは、プロイセン出身のドイツの首相オットー・フォン・ビスマルクです。彼の回顧録――つまり、批判的ではない親しい記者によって書かれた回顧録――によれば、ビスマルクは、公共年金制度を創設することで労働者階級を国家に依存させ、労働者が国家に対して反抗しないように仕向けたと説明しています。当時、反抗は、いわば反資本主義的な行為とみなされていたのです。彼は、国家主義を維持するためではなく、「労働者には社会主義的傾向がある。では、どうすれば労働者を手なずけることができるのか?」という視点から、公共年金制度を利用したのです。同様に、労働者は公共年金制度を通じて、または国家に対抗する形で手なずけられるのです。そして、現状はこの通りになっています。
そこで、皆さんは疑問に思うかもしれません。この何世代にもわたって築かれてきた巨大国家は、具体的にどのような機能を果たしているのでしょうか? その資金はどこに行っているのか? この巨大国家は何に対して支出をしているのか? ここに、2022年の欧州連合各国の平均、すなわちGDPの50%という数字があります。スペインの場合も2022年時点で大きな差はなく、GDPの47%を支出しているため、概ね代表的な数値といえます。さて、この50%のうちの20%は社会保障費、主に年金費用(老後だけでなく、遺族、障害、孤児などに関する給付も含む)です。これに加え、比較的低コストな非拠出型給付も存在します。次に、スペインの場合は約7.7%、すなわち7〜8%が医療費、6%が官僚機構の運営費用、そして何よりも重要なのが公債の利子支払い費用です。さらに6%は経済政策に充てられ、例えばインフラ整備や農業支援などが含まれています。教育に関しては、公立教育や協定校を含めて約4.7%、環境保護は0.8%(これは必ずしも気候政策だけでなく、森林の管理なども含む)、住宅や地域サービスが1%、そして余暇、文化、宗教に関しては1.1%となっています。これらは、メディアや文化、宗教団体への補助金などとして支出されています。
かつて、リベラルな最小国家、例えばアメリカではGDPの3%程度であった国家がありました。なぜなら、当時は上記のような広範な機能を持たず、防衛(GDPの1.3%)と治安・司法(GDPの1.7%)に集中していたからです。つまり、19世紀にGDPの3%を占めていた国家が、現在もその核となる部分は同じ3%のままであるということです。国家が高価になったわけではなく、19世紀に存在した国家のコストは大体同じであったにもかかわらず、現代国家は19世紀よりもはるかに多くの機能を担っているため、多くの税金が必要とされているのです。もちろん、すべては税金で賄われています。
では、いったいどれだけの税金が支払われているのでしょうか。ここでは、国民が被っている税負担の実態について十分に認識されていないのではないかと思います。もしその実態が明らかになれば、社会的不服従が起こるでしょう。国家は、税の実感を曖昧にするための手段を多数用いているのです。例えば、さまざまな理由で税金を徴収する仕組みです。「この項目に対して税金を払え」と一律に要求するのではなく、「稼いだ金額、支出、保有資産、さらには支出全体に対して税金を課す」といった形で、複数の種類の税金を同時に適用します。消費全体に対して一律に税金を課すのではなく、付加価値税(IVA)やその他の特別税など、多岐にわたる特別な税金が存在し、相続税に至るまで多岐に渡ります。
さらに、我々はさまざまな側面で税金を支払っているにもかかわらず、その実感すら持っていないこともあります。たとえば、関税はその値上がり分を商品の価格に転嫁されるため、意識されにくいのです。付加価値税が上がっても、スーパーなどが告知しない限り、私たちはその上昇に気づきにくいのです。また、税負担を一度にまとめて徴収するのではなく、分散して給与から差し引くことで、その実感を薄めています。かつては、年間に稼いだ金額に対して一括で所得税(IRPF)を支払うのが普通でしたが、現代では分割して徴収されるため、納税者は自分がどれだけの税金を支払っているのかを実感しにくいのです。ちなみに、IRPFの源泉徴収制度は、第二次世界大戦中にリベラルのミルトン・フリードマンによって考案されたものです。つまり、敵はしばしば自国に潜むものでもあるということです。
ここで示したのは、平均的な支出額です。スペイン国家のすべての財政収入を国民または労働者で割ると、国民一人あたりの国家負担のおおよそのコストが見えてきます。実際には公共赤字、すなわち収入以上に支出している部分もあり、その分は将来の税負担として転嫁されるため、実際のコストはさらに大きくなります。ここでは、現状で国民から徴収されている税金のみを取り上げています。なお、これらの数字はインフレーションを考慮していないため、2001年と2024年の数字を直接比較することはできませんが、ここでは2024年現在の状況に焦点を当てています。現在、平均してスペイン国民一人あたり、約15,000ユーロの税負担がかかっているのです。つまり、一般的には夫婦と子供一人の家庭で約50,000ユーロの税金が支払われている計算になります。労働者という視点に立てば、実際に税金を支払っているのは、平均で30,000ユーロ以上にのぼります。もちろん、高所得者層が多くを負担しているという見方もありますが、これは平均値であり、平均値は必ずしも実態を正確に反映するものではありません。
さて、労働者一人あたりの支払いを、かなり寛大な見積もりで考えてみましょう。スペインにおける現在の中央値の給与は22,400ユーロです。しかし、この22,400ユーロという数字が給与明細に反映される前に、企業側がすでに支払っている社会保険料が約7,000ユーロ存在しています。つまり、実際の中央値の給与は29,000ユーロ、ほぼ30,000ユーロであるべきものですが、この30,000ユーロは労働者自身が実感できるものではありません。そして、たとえ「実際は自分のものである」と伝えても、「それは企業が支払っているものであって、自分が支払っているわけではない」と言われ、自己欺瞞に陥るのです。結局のところ、実際に支払っているのは自分自身なのです。
実際、30,000ユーロの実質報酬を基にすると、そこから7,000ユーロが差し引かれて、給与明細に表示されるのは22,400ユーロです。さらに、労働者側の社会保険料として約1,500ユーロを追加で支払い、所得税(IRPF)が約3,000ユーロ、さらに消費に応じた間接税が最低でも約2,000ユーロ(場合によってはそれ以上)かかります。さらに、ここでは取り上げていない他の国家への支払い、たとえば不動産税(IBI)やサービス料、共済負担金なども存在します。結果として、中央値の労働者は、本来約30,000ユーロあるべき給与のうち、税引き後に手元に残るのは約15,800ユーロに過ぎないのです。つまり、ほぼその半分が国家によって吸収されていることになります。年間で見ると、さまざまな税金、特に社会保険料、所得税、そして間接税として、合計約13,400ユーロが徴収されているのです。
このように、中央値の労働者は、所得分布の中央に位置しており、非常に多くの人々が彼より少なく、また多く稼いでいる人もいます。だからこそ、中央値の労働者が支払っている税負担、すなわち年間約13,400ユーロという数字は、スペイン国民に対して行われている極めて大規模な税負担の実態を物語っています。これにより、国家から提供されるサービスが強制的に受け入れられているのです。
果たして、これは必然なのでしょうか? 歴史的に見れば必ずしもそうではなく、また現代においても地域によって差があります。つまり、労働者が生み出す富の半分以上を国家が吸収するという、巨大な国家が当然であるという考え方は、今後も続くものではありません。ここには、異なる繁栄度を持つ国々が存在し、一般的に発展した国々であっても、欧州やアメリカのような国家に比べ、国家の規模はかなり小さく抑えられている国もあります。しばしば「スペインの国家規模は欧州平均より小さい」と言われますが、欧州平均自体が、プロの略奪者たちのクラブのようなものなのです。従って、欧州平均という水準と比較するのではなく、もっと控えめな国家規模を持つ国々や、税負担の貪欲さが制限された国々と比較すべきです。
例えば、ヨーロッパ内ではスイスがあります。偶然かどうかはさておき、スイスはヨーロッパで最も豊かな国の一つでありながら、国家のGDPに占める割合は33%と、欧州やアメリカに比べて10〜15ポイント低いのです。また、香港や韓国はGDPの28%、チリはこの分類の中では最も貧しいかもしれませんが約26%、台湾は16%、そして世界で最も豊かな国であるシンガポールは15%です。シンガポールや台湾は、国家がGDPの15〜16%という小規模な状態で十分に現代社会の機能を果たしているのです。もちろん、シンガポールの場合は都市国家であるため、経済規模のメリットもあるでしょうが、公共支出の大部分が社会保障に回っている現状を鑑みると、都市規模か大国家かは大した違いがないのです。むしろ、シンガポールや台湾のように、GDPに対して国家の規模が30ポイントも低い国の方が、国家による私有財産の侵害が少ないと言えます。
したがって、もし大規模な国家による大規模な略奪を回避でき、しかも機能的には他の国と同等以上に運営できるのであれば、当然、より少ない税負担で、なおかつより効率的な公共サービスを提供する国家の方が望ましいのです。実際、国家が何でもかんでも行おうとすれば、その多くは非効率にならざるを得ません。一方で、企業がすべてを行おうとしても、専門分野に特化した他の企業に競争で敗れるため、最終的には消費者がより良いサービスを選ぶことになるのです。問題は、国家の場合、国民が国家から自由に離脱し、同じサービスを提供する他の組織と契約する余地がないという点にあります。国民は、非常に非効率かつ高コストな国家サービスに縛られており、選択の余地がないのです。したがって、もし小規模で効率的な国家が存在すれば、それは大規模で税負担の重い国家よりも好まれるはずです。
そして、もし国家が回収するGDPの割合が30ポイントも大きいのであれば、それは明らかに国民の私有財産を暴力的に侵害していると言わざるを得ません。ですから、もし国家による大規模な略奪を回避し、かつ他国と同等以上の機能を果たすことが可能であれば、国家は少なくとも縮小されるべきです。なぜなら、そうした国家は国民にとって好都合であるだけでなく、公共サービスの質も向上し、効率的に運営されるからです。結局のところ、すべては国家ではなく、国家に寄生する巨大な官僚組織の福祉が優先されているのです。
もし、あなたの社会にこれほど大きく根付いた寄生虫が存在するならば、その寄生虫は当然、去ろうとはしません。むしろ、さらに大きな植民地を形成しようとするでしょう。これが、国家が成長し続ける理由であり、そして、血を吸い上げるこの寄生虫と戦う必要性が生じる所以なのです。
別のシナリオを考えてみましょう。つまり、現代社会における国家の規模を実質的に縮小するという仮定を立て、その実現可能性や現実味について見極めるためです。これまでに、ヨーロッパにおける現代国家の重みがGDPの50%に達していること、その内訳を示してきました。さて、かつての状況を想像してみてください。あの時代は、科学フィクションのようなことは必要なく、医療はゼロ、経済政策も実質ゼロで、民間部門が構築できないインフラだけが、もしあれば驚くほど僅か、GDPの1%程度だったのです。教育はゼロ、防衛と公共秩序は維持されるものの、余暇・文化・宗教への補助金はゼロでした。地域サービスや環境保護に関しては、下水道、街路灯、森林の維持管理など必要な分は残され、官僚組織も非常に大幅に縮小され、社会保障も一部のみが残されていました。
さて、しばしば「国家は富裕層からお金を奪い、貧困層へ再分配するために存在する」と言われますが、実際、社会保障はGDPの20%に相当します。ここで、極端な貧困を防止するために本当に必要な支出額を計算してみましょう。そうすれば、皆さんも、このGDPの20%は貧困撲滅のためのものではなく、むしろ国家が横方向の所得再分配システムを通じて国民を捕らえ続けるためのものであると気づくでしょう。すなわち、国家はあなたからお金を取り、そのお金を自らの利益や必要に応じて配分するために、あなたと国家の間に割り込むのです。バストス教授が正しく指摘しているように、その所得の移動は、富裕層から貧困層へ、またはその逆ではなく、すべての人々から国家へ向かっているのです。そして国家は、その所得を自らの利益や必要に従って再分配することを決定します。
では、先ほど示したような形で国家の各機能を大幅に縮小した場合、結果として国家はGDPの9~10%程度の規模となり、現状よりも30~40ポイント、つまり約80%縮小された国家になるでしょう。防衛費、治安費は現状と同等に維持される(ただし、治安費については内部の官僚機構によっても左右されるため、この点はまた別の議論になります。たとえば、スペインはヨーロッパで国民一人あたりの治安部隊職員数が最も多い国ですが、本当にそれだけ必要なのかはまた別問題です)。安全保障費がGDPの1.7%、防衛費が1.3%、官僚組織が1%、地域サービスや環境保護が1%、民間部門ではまかなえないインフラがさらに1%、そして社会保障が3%という具合です。現在、社会保障としてGDPの3%、すなわち450億ユーロが支出されています。これは、450億ユーロの社会保障費を、例えば4.5百万人(スペイン人口のおよそ10%)に対して年間1人あたり1万ユーロずつ支給するか、あるいは300万人に対して1万5千ユーロずつ支給するということになります。繁栄した社会において、極端な無助状態に陥る国民の割合はどれほどか、という問題です。彼らは、生命保険、障害保険、個人貯蓄すら持たず、福祉国家が生まれる前に存在したボランティアや民間の相互扶助ネットワークさえも利用できなかった層です。これらを踏まえた上で、絶対的な無助状態に陥り、国家からの継続的な支援を必要とする国民の割合がたとえば5~10%だとすれば、実際に必要な支出はGDPの3~4%程度で十分にカバーできるはずです。しかし、現実には我々は社会保障にGDPの20%を費やしているのです。
明らかに、このGDPの20%は、富裕層から少しだけ富を奪って、巨大な貧困層を作らないためのものではありません。驚くべきことに、国家がGDPの50%を占めるにもかかわらず、貧困層は依然として存在しているのです。さらに、貧困を解消するための手段として、まず第一に、依存性を生む補助金を設けるべきではありません。しかし、現実には、経済活動が全くできず、自己の貯蓄や家族の支援、民間の相互扶助ネットワーク、そして最終的には国家に依存せざるを得ない層が一定割合存在します。しかし、そのようなケースはGDPの3%程度の支出で十分にカバーされるはずなのです。
さて、国家の規模を縮小した場合、たとえばGDPの50%から10%にまで削減できると仮定しましょう。これは約80%の削減に相当します。先に述べたように、中央値の労働者は現在、年間約13,500ユーロの税金を負担しています。この80%の削減が実現すれば、労働者の可処分所得は、国家が提供する各種サービスに充てるための支出分が年間1人あたり1万~1万1千ユーロ増加することになります。家庭内で中央値の労働者が2人いる場合、2万~2万2千ユーロの追加収入となるでしょう。この追加収入があれば、教育費、医療費、年金のための貯蓄など、国家が現在負担させているコストを自前でまかなうことが可能になるはずです。実際、多くのスペインの労働者は、国家の劣悪なサービスから逃れるため、民間の医療や教育、そして補完的な年金積立を実施しているのです。特に、公共教育は、学生の生産性向上よりも、国家のイデオロギーを植え付けることに重きを置いている場合が多いのです。
また、この話は、GDPの3%相当の再分配、すなわち450億ユーロ分が、現実的に考えても国民の基礎的な生活を支えるには十分であるという観点からも論じられます。現行の過剰な収用体制に対して、もし国家規模が大幅に縮小されるならば、労働者にとって有利な状況が実現するはずです。
さて、ここまでの議論から、もし国家主義のウイルスが社会の頭脳や利権に深く根付っている現状において、現状が最適でないと理解したとしても、移行のコストの高さゆえに多くの人々が現状から変わることを望まないという現実があるのです。たとえば、公共年金制度の解体は非常に困難です。年金受給者は「こんな不公平な体制であっても、自分の年金を受け取りたい。自分自身の貯蓄がなくなるリスクを冒したくはない」と考えるでしょう。
では、この国家――明らかに国家とその官僚機構に有利なこのモデル――から脱却するために、すなわち、表向きは国民のために存在するようでいて、実際には社会を寄生しているこの体制から逃れるためには、どのような手段が考えられるでしょうか。ここで、国家改革またはハイパーステートのパラサイト化に対抗するための、四つの可能なアプローチについて述べます。
第一のアプローチは、トップダウン型の方法です。すなわち、自由主義的な理念を掲げた善意の政治家が権力の座につき、内部からリベラル革命を起こそうとするというものです。しかし、私はこの方法は、次に述べるボトムアップ型の文化戦線と併せなければ、全体として非常に単純で実現不可能だと考えます。なぜなら、社会の大多数が国家改革を望まなければ、その改革は十分な勢いを持って実施されることは決してないからです。多くの改革は長期的な取り組みであり、一夜にして実現できるものではありません。一度実行された改革が元に戻らないようにするには、最低でも二世代を要するのです。もし社会がその方向に向かわなければ、いつかまた別の人物が権力に就いて、国民の大多数が望まない体制を再び打ち壊してしまうでしょう。例えば、チリの年金制度の民営化は、ピノチェト政権下の1981年に始まり、数年前に旧公共年金制度が完全に清算されました。しかし、その後、旧体制に戻そうとする動きが見られるのです。なお、チリは当時、非常に若い労働人口と限られた高齢人口という、改革に適した人口構造を有していたにもかかわらず、改革には約40年もの歳月がかかりました。これが、世界の他の国々で実施されるとなれば、どれほど困難なものになるか想像に難くありません。そして、もし世界中がそのような改革を望まなければ、いかに自由主義者の政治家を内部に潜り込ませ、社会民主主義の装いを与えたとしても、十分な効果は得られないでしょう。さらに、政治そのものが権力に触れると必ず腐敗すると、ロード・アクトンが指摘したように、権力は人を変えてしまいます。つまり、権力に惹かれて権力の座についた者は、その権力を維持・拡大するために、かつて掲げた理念を容易に放棄し、他者を蹂躙し、欺く行動に出るということです。
政治的競争というのは、もしあなたが行動しなければ、行動する者があなたを追い出してしまう、という状況を生み出します。そのため、もし存在するとしても、誠実で、信念を持った政治家は、力に屈する者に押されて公共の場から姿を消してしまうのです。権力闘争では、手が縛られている者と自由な手を持つ者との間で戦いが行われるため、劣悪な選択が働き、最終的には最悪の者が権力の座に就くという現象が生じるのです。(この点については、ハイエクも『隷属への道』で記述しています。)
次に、第二の可能性はボトムアップ、すなわち文化戦線によるアプローチです。これは、アイデアの戦いを、じわじわと、少しずつ社会に浸透させ、心を開かせ、意識を目覚めさせ、より多くの人々がこの変革を要求するようになるという方法です。しかし、これは特に有望な道ではないことは明白です。もし、ここでマルクス主義的な語調に傾くとすれば、客観的な物質的条件があって、そうした思想が大規模に広まる環境が整わない限り、人々は現状に満足して「今のままで十分だ」と感じ、急激な変革に乗り出す理由が見出せません。現状が著しく悪化しない限り、文化戦線による大規模な勝利が起こり、既存の社会制度が覆されるというのは極めて困難な道なのです。例えば、アルゼンチンでは、40年間にわたって底をつき続けた結果、人々が明らかに欠陥だらけのモデルにうんざりし、ハイパーインフレーションに苦しんだことで変革が進んだように見えます。もし、そこに一貫性があり、破壊的かつ斬新なメッセージ―社会主義的なものか、あるいは幸運にもリベラルなもの―があれば、一定の確率でそのアイデアが覇権を握り、新たな現状として定着する可能性が出てくるのです。しかし、スペインの場合、文化戦線による闘いは、相手側のプロパガンダがあふれ、対抗する者がいなければ、現状が一層固定化し、国家権力が加速度的に拡大していくため、非常に厳しい状況にあります。私自身も長い間、文化戦線で戦ってきましたが、スペインという環境におけるその限界を痛感しています。
第三の道は、そもそも国家改革を目指さず、自分の生活を改善するために他の地域へ移住するというものです。もし、競争が可能な複数の法域が存在すれば、現状に非常に不満を抱く者は、物理的に他の地域へ移り住み、そこで自らの生活基盤を築くことができます。そして、こうした法域間の競争は、他の法域による収用や寄生的な政策の力を制限する効果も持ちます。たとえば、ある法域で税率が非常に低く、規制が緩やかであれば、他の法域は資本が流出し、寄生者側から見れば、寄生対象(=ホスト)が成長しなければ、寄生する意味がなくなるのです。もし、ホストを窒息させて殺してしまえば、またはホストが他の、寄生が少ない地域へ流出してしまえば、寄生者にとっては不利益となります。このような効果は、実際には見かけ以上に大きな影響を持つのです。
たとえば、最も身近な例として、アンドラの場合が挙げられます。多くの場合、静かに、あるいは時に華やかに報じられる移住現象があり、一定の社会的反響を呼んでいます。問題は、これらはすべて財政上の問題であり、移住者を犯罪者扱いする試みがあっても、スペイン国家にとっては重要な問題とならないのです。よく批判されるのは、YouTuberなどがアンドラへ移住することについて、「国が自国民の資源不足を訴えるような状況に直面しない」とされる点です。もしそうなれば、国家は財政の引き締めを迫られるはずですが、現実はそうではありません。むしろ、これは他者に対する懲罰の一形態であり、「移住して税負担を軽減しようとするなら、あなたは悪い人間であり、悪い市民だ。もしあなたが著名人であれば、意識を啓発するために、我々はあなたを徹底的に攻撃し、公の場から追放する」といったメッセージが発せられるのです。しかし、実際にアンドラへの移住が進むこと自体は悪いことではなく、たとえそれがスペイン国家に与えるダメージが短期的にはそれほど大きくなくとも、他のケースでは、目に見えにくいながらも国家に損害を与えている場合があるのです。
たとえば、2か月前に発表されたドラギの報告書では、欧州が「足を引きずっている」との根本的な不満が示されています。すなわち、欧州では生産性が20年間にわたって停滞しており、成長期に新たに設立される企業が、厳しい規制の下で成長できず、資本調達が困難となり、結果としてアメリカに流出してしまうという現象です。これは「足で投票する」という現象であり、企業側の実情を反映したものです。そして、これは国家権力の内部から出た、我々の社会が停滞しているという自らの寡占層からの認識でもあります。彼らは、ここ20年間にわたり市民を内部から圧迫してきた手法を見直す必要があると訴えているのです。そして、ここで議論されているのは、欧州連合とアメリカという二つの経済ブロック間での移住の問題なのです。
もし、かつてヨーロッパに存在していたような、多数の競合する法域が現在も存在していたと想像してみてください。ここで歴史的な議論に深入りするつもりはありませんが、ヨーロッパが16世紀あるいは17世紀から産業革命に至るまで発展し、東洋が(少なくとも最近まで)停滞していた理由の重い仮説の一つは、ヨーロッパが政治的にはるかに細分化され、都市国家や小国、王国、そして公国など、まさにアンドラのようなケースに近い形態であったため、相互の競争が激しかったという点にあります。ひとつの領域内で生まれる思想を制限・抑制・検閲する能力は非常に低く、もし一方で弾圧されれば別の場所へ移動できたため、その結果、後の産業革命を引き起こす知的な開花が促されたのです。これに対して、中国のような中央集権的で統一された国家では、官僚組織が本来より強大な権力を持っていたため、このような発展は見込めませんでした。
「足で投票する」という現象は非常に強力です。したがって、文化戦線から取り組むべきもう一つの課題は、政治的な中央集権化や財政の調和化に反対することです。なぜなら、政治的に中央集権化が進んだり、財政が調和化されるほど、法域間の競争は減少し、その結果、国家が無罰で私有財産を寄生的に吸い上げる余地が広がるからです。これは市場経済ではよく理解される現象ですが、国家の場合は例外扱いされがちです。市場において本当の意味での独占、すなわち単にその分野で唯一の企業という状況ではなく、競合が存在しない真の独占状態になると、その独占者は価格を引き上げ、品質を低下させる傾向にあります。なぜなら、あなたは逃げ出すことができない、まるで人質のような状態に置かれるからです。つまり、国家もまた独占状態にあり、国家が直面する唯一の競争は、他の国家へ移住するという可能性なのです。領域を統一して競争余地を狭めれば狭めるほど、国家は独占的な力を強め、結果としてあなたに提供するサービスの質を低下させ、収用を強める傾向が出てきます。したがって、私はどんな中央集権化のプロセスにも反対し、逆に政治的な分権化を支持すべきだと考えます。
そして最後に、第四の戦略ですが、これはやや曖昧で漠然としているかもしれません。しかし、私が考えるに、実際に多くの人々が採用しており、多くの場合国家の影響力を制限している方法、それは直接的に「国家からの分離」を目指すことです。もちろん、あなたにとって寄生者のような国家が窮屈に圧しかけてくる場合、その寄生者を打倒しようと多大なエネルギーを費やすこともできます。しかし、寄生者が既に存在する以上、その存在を前提として生活基盤を築く、その固定費を受け入れながらも、寄生者のさらなる拡大を防ぐ、あるいは寄生の及ばない領域を確保する新たな方法を模索するということです。これが国家からの「分離」、すなわち、重くのしかかる国家の負担から自らを切り離す試みなのです。例えば、先に述べたように、私立教育、私立医療、私的年金といった選択肢があります。本来であれば、国家が私たちから過剰な資源を吸い上げることなく、その分をこうした目的に振り向けられれば理想的ですが、幸いなことに、現状では国家が私立教育への進学を禁止しているわけではありません(ただしかなりの規制は存在します)。私立教育は完全に自由なものではなく、国家のカリキュラムに沿ったものですが、それでも私立教育、私立医療、そして貯蓄や資産形成の道を開いてくれるのです。もちろん、今後さらに税が引き上げられ、国内外で資産が収用されるリスクが高まるまではの話ですが。
したがって、国家を一つの悪と捉え、その悪に支配される中で自由を追求する、すなわちその影響力からできるだけ逃れる方法を探るべきです。さらに、社会が自ら開発していく様々なツールが、私たちが国家の監視や統制から離れて生活する手助けとなります。たとえば、デジタル経済は、今日のところ、国家が我々をコントロール・規制・収用するのをより困難にする領域をある程度確保できる可能性を秘めています。ビットコインの例は、没収不可能な資産として、適切な管理を行えば、富の保蔵庫あるいは国家の統制や知識から独立した交換手段として機能する可能性を示しています。
これらは、寄生者である国家に吸い付かれないため、自らの活動から国家の影響力を一部でも排除する、新たな生活の仕方を模索する一つの方法です。こうした新しいツールは、今後も次々と登場し、国家が私たちの生活に及ぼす影響を制限するために活用されるべきです。社会全体を変えるのは非常に困難ですが、多くの人々を同じ方向に動かすことが難しい現状において、少なくとも我々が体系的に受けている搾取の度合いを最小限に抑えることは可能です。
以上、複数の道筋があります。第一の道は私個人としてはほぼ排除したいと考えますが、残りの三つは排他的ではなく、互いに補完し合うものです。どの方法も目的地に必ず到達できる保証はありませんが、これらは連携することで、国家が私たちや社会全体に及ぼす権力の影響を徐々に抑制する助けとなるでしょう。そして、我々自身の利益のため、あるいは共に生きる社会を改善するために、可能な限りこれらの道を追求すべきだと考えます。
-
 @ d34e832d:383f78d0
2025-04-21 07:31:10
@ d34e832d:383f78d0
2025-04-21 07:31:10The inherent heterogeneity of relay types within this ecosystem not only enhances operational agility but also significantly contributes to the overall robustness and resilience of the network architecture, empowering it to endure systemic assaults or coordinated initiatives designed to suppress specific content.
In examining the technical underpinnings of the Nostr protocol, relays are characterized by their exceptional adaptability, permitting deployment across an extensive variety of hosting environments configured to achieve targeted operational objectives.
For example, strategically deploying relays in jurisdictions characterized by robust legal protections for free expression can provide effective countermeasures against local censorship and pervasive legal restrictions in regions plagued by oppressive control.
This strategic operational framework mirrors the approaches adopted by whistleblowers and activists who deliberately position their digital platforms or mirrored content within territories boasting more favorable regulatory environments regarding internet freedoms.
Alternatively, relays may also be meticulously configured to operate exclusively within offline contexts—functioning within localized area networks or leveraging air-gapped computational configurations.
Such offline relays are indispensable in scenarios necessitating disaster recovery, secure communication frameworks, or methods for grassroots documentation, thereby safeguarding sensitive data from unauthorized access, ensuring its integrity against tampering, and preserving resilience in the face of both potential disruptions in internet connectivity and overarching surveillance efforts.
-
 @ 220522c2:61e18cb4
2025-03-26 03:24:25
@ 220522c2:61e18cb4
2025-03-26 03:24:25npub1ygzj9skr9val9yqxkf67yf9jshtyhvvl0x76jp5er09nsc0p3j6qr260k2

-
 @ 714dd0db:9c6f1a4c
2025-03-22 09:48:44
@ 714dd0db:9c6f1a4c
2025-03-22 09:48:44やっと春が来ました
ようやく暖かくなってきた。 買い物から帰ってくると、なにやら甘い香り。
あ、もしかして、花の香りか!
探してみると、沈丁花が咲いている。

ああ、甘くていい香り。
近くには蝋梅も咲いている。我が家の近くに蝋梅があったなんて、すっかり忘れていた。

そして、早咲きの桜。桜のどの種類かは分からないのだが、毎年、ソメイヨシノよりも先に咲いている。

花の蜜を吸いに百舌鳥も来ている。いや、鳥の種類には疎いが、おそらく百舌鳥だろう。多分。

モノクロの冬から、ようやくカラフルな春になってきた。
季節を感じるのは、心が豊かになる。 今は今、今度は今度。 俺は今を生きている。
-
 @ b0137b96:304501dd
2025-04-21 05:54:41
@ b0137b96:304501dd
2025-04-21 05:54:41Streaming has revolutionized how we consume entertainment, offering unparalleled access to diverse content worldwide. With the rise of theBest OTT Platform options, audiences can enjoy their favorite Hollywood, Bollywood, and regional films anytime, anywhere. However, for many viewers, language can be a barrier to fully experiencing international cinema. That’s where innovative platforms step in, bridging the gap between global content and regional audiences.
If you're searching for theBest OTT Platform that delivers high-quality international and regional content, we’ve got you covered. Let’s explore four leading platforms—Dimension on Demand (DOD), Hoichoi, Olly Plus, and Aha Video—that are transforming the Indian entertainment landscape.
Dimension on Demand (DOD) – The Best OTT Platform for Hollywood in Your Language Among the many platforms available, Dimension on Demand (DOD) stands out as theBest OTT Platform for movie lovers who enjoy global cinema in their native tongue. Unlike other platforms that focus solely on regional or Bollywood content, DOD specializes in offering Hollywood movies dubbed in 9 languages like Hindi, Telugu, Tamil, Bangla, Malayalam, Bhojpuri, English, Kannada, and Marathi. This means you can enjoy blockbuster hits, critically acclaimed masterpieces, and thrilling action films—all in the comfort of your language.
What makes DOD truly unique? A vast library of Hollywood movies dubbed in Indian languages Seamless user experience with high-definition streaming Personalized recommendations based on viewer preferences Accessible across multiple devices—smart TVs, mobiles, and laptops A growing collection that ensures fresh content for movie enthusiasts Beyond its impressive collection, DOD ensures that audiences across India can experience world-class entertainment without language barriers. If you love Hollywood but prefer watching in your native language, DOD is undoubtedly the Best OTT Platform.
Hoichoi – A Must-Have for Bengali Entertainment Hoichoi (https://www.hoichoi.tv/)has become a go-to OTT platform for Bengali audiences, offering an impressive mix of movies, web series, and original content. With a strong focus on Bengali-language storytelling, it delivers a diverse collection ranging from classic films to modern thrillers.
Why Choose Hoichoi? Extensive collection of Bengali films and web series Exclusive Hoichoi Originals with gripping storytelling A mix of contemporary and classic Bengali cinema With its continuous addition of fresh content and commitment to Bengali storytelling, Hoichoi has solidified its position as a top-tier platform for regional entertainment lovers.
Olly Plus – A Celebration of Odia Content Olly Plus (https://www.youtube.com/OllyPlus) is Odisha’s dedicated OTT platform, catering specifically to Odia-speaking audiences. It features a rich selection of Odia movies, music, and podcasts, making it a hub for cultural and entertainment enthusiasts.
What Sets Olly Plus Apart? Exclusive Odia-language movies, music, and short films A platform dedicated to preserving and promoting Odia storytelling Inclusion of music, podcasts, and cultural content With Odia entertainment often underrepresented in mainstream media, Olly Plus plays a crucial role in bringing high-quality Odia content to its audience.
Aha Video – The Ultimate Destination for Telugu & Tamil Viewers Aha Video (https://www.aha.video/) has carved a niche in the Best OTT Platform industry by delivering high-quality Telugu and Tamil entertainment. From blockbuster movies to gripping web series, Aha Video ensures South Indian audiences have access to exclusive content tailored to their preferences.
Why Aha Video is a Must-Try? Exclusive Telugu and Tamil movie collections Original series that cater to South Indian storytelling A strong focus on South Indian cinema and entertainment Its commitment to regional cinema ensures that fans of Telugu and Tamil content always have something fresh and exciting to watch.
Why the Best OTT Platforms Matter for Regional Audiences As the streaming industry expands, the importance of theOTT Platform options for regional audiences cannot be overlooked. They not only cater to language-specific audiences but also help preserve and promote local cultures while making global content more accessible.
The Rise of the Best OTT Platforms for Regional Content: They bridge the gap between global cinema and local audiences Viewers can enjoy Hollywood and indie films in their native language Regional content platforms contribute to cultural storytelling and preservation Whether it’s the Hollywood-dubbed collection of DOD, the Bengali storytelling of Hoichoi, the Odia exclusives of Olly Plus, or the South Indian cinema of Aha Video, each platform plays a vital role in reshaping digital entertainment in India.
The Final Verdict – Which is the Best OTT Platform? Choosing the Best OTT Platform depends on your content preferences. If you are looking for international cinema in regional languages, Dimension on Demand (DOD) is the perfect choice. For regional entertainment lovers, Hoichoi, Olly Plus, and Aha Video offer excellent options tailored to specific linguistic audiences.
With DOD leading the way in bringing global entertainment to regional audiences, it's clear that the future ofOTT lies in localization and accessibility. Whether you're a fan of Hollywood, Bengali dramas, Odia storytelling, or Tamil blockbusters, there’s an OTT platform designed just for you.
Want to experience Hollywood like never before? Watch your favorite global films in your language on Dimension on Demand (DOD). Subscribe now and explore an ever-growing collection of blockbuster movies!
-
 @ f240be2b:00c761ba
2025-03-20 17:53:08
@ f240be2b:00c761ba
2025-03-20 17:53:08Warum jetzt ein guter Zeitpunkt sein könnte, sich mit Bitcoin zu beschäftigen
Kennt ihr das? Wenn der Bitcoin-Preis neue Höchststände erreicht, möchte plötzlich jeder einsteigen. Doch sobald die Kurse fallen, überwiegt die Angst. Dabei zeigt die Geschichte: Gerade diese Phasen der Unsicherheit können interessante Zeitpunkte sein, um sich mit dem Thema zu beschäftigen.
Historische Zyklen Bitcoin durchläuft regelmäßige Marktzyklen Nach jedem Tief folgte bisher ein neues Hoch Emotionen spielen eine große Rolle im Markt Psychologie des Marktes Wenn alle euphorisch sind → meist teuer Wenn Unsicherheit herrscht → oft interessante Gelegenheiten Die Masse liegt häufig zum falschen Zeitpunkt richtigRationale Herangehensweise
Statt emotional zu handeln, solltet ihr:
Einen langfristigen Anlagehorizont wählen Regelmäßig kleine Beträge investieren (Cost-Average-Effekt)Hier ein paar Charts die euch helfen sollen und euch mutig werden lassen:
https://www.tradingview.com/chart/BTCUSD/HuGpzZfQ-BITCOIN-Cycle-pattern-completed-Year-end-Target-locked-at-150k/
https://www.tradingview.com/chart/BTCUSD/YVyy9QuU-BITCOIN-Money-Supply-Dollar-and-Bonds-pushing-for-MEGA-RALLY/
https://www.tradingview.com/chart/BTCUSD/pZ0qs5x3-BTCUSD-TSI-shows-that-this-is-the-LAST-BEST-BUY/
https://www.tradingview.com/chart/BTCUSD/x3e7GuLQ-BITCOIN-Is-this-a-Falling-Wedge-bottom-formation/
und jetzt All-In :-)
-
 @ 8fb140b4:f948000c
2025-03-20 01:29:06
@ 8fb140b4:f948000c
2025-03-20 01:29:06As many of you know, https://nostr.build has recently launched a new compatibility layer for the Blossom protocol blossom.band. You can find all the details about what it supports and its limitations by visiting the URL.
I wanted to cover some of the technical details about how it works here. One key difference you may notice is that the service acts as a linker, redirecting requests for the media hash to the actual source of the media—specifically, the nostr.build URL. This allows us to maintain a unified CDN cache and ensure that your media is served as quickly as possible.
Another difference is that each uploaded media/blob is served under its own subdomain (e.g.,
npub1[...].blossom.band), ensuring that your association with the blob is controlled by you. If you decide to delete the media for any reason, we ensure that the link is broken, even if someone else has duplicated it using the same hash.To comply with the Blossom protocol, we also link the same hash under the main (apex) domain (blossom.band) and collect all associations under it. This ensures that Blossom clients can fetch media based on users’ Blossom server settings. If you are the sole owner of the hash and there are no duplicates, deleting the media removes the link from the main domain as well.
Lastly, in line with our mission to protect users’ privacy, we reject any media that contains private metadata (such as GPS coordinates, user comments, or camera serial numbers) or strip it if you use the
/media/endpoint for upload.As always, your feedback is welcome and appreciated. Thank you!
-
 @ fd78c37f:a0ec0833
2025-04-21 04:40:30
@ fd78c37f:a0ec0833
2025-04-21 04:40:30Bitcoin is redefining finance, and in Asia—Thailand, Vietnam, Indonesia, and beyond—developers, entrepreneurs, and communities are fueling this revolution. YakiHonne, a decentralized social payments app built on Nostr, sat down with Gio (nostr:npub1yrnuj56rnen08zp2h9h7p74ghgjx6ma39spmpj6w9hzxywutevsst7k5cx), a core member of Thailand’s Sats ‘N’ Facts community, to explore their mission of fostering open-source Bitcoin development. In this interview, Gio shares the origins of Sats ‘N’ Facts, the challenges of hosting Bitcoin-focused events in Asia, and how these efforts are shaping adoption across the region.
YakiHonne: Can you tell us about yourself and how Sats ‘N’ Facts came to life? What sparked your Bitcoin journey?
Gio: I’m originally from Europe but have called Thailand home for six years. My Bitcoin story began while working at a commercial bank, where I saw the fiat system’s flaws firsthand—things like the Cantillon Effect, where money printing favors the connected few, felt deeply unfair. That discomfort led me to Andreas Antonopoulos’ videos, which opened my eyes to Bitcoin’s potential. After moving to Bangkok, I joined the open-source scene at BOB Space, collaborating with folks on tech projects.
Sats ‘N’ Facts grew out of that spirit. We wanted to create a Bitcoin-focused community to support developers and builders in Asia. Our recent conference in Chiang Mai brought together over 70 enthusiasts from Thailand, Vietnam, Laos, and beyond, sparking collaborations like a new Lightning Network tool. It was a milestone in connecting the region’s Bitcoin ecosystem.
YakiHonne: What inspired the Sats ‘N’ Facts conference, and how did you attract attendees?
Gio: The event was born from a desire to create a high-signal, low-noise space for Freedom Tech in Asia. While the U.S. and Europe host major Bitcoin events, Asia’s scene is still emerging under commercial stunts. We aimed to bridge that gap, uniting developers, educators, and enthusiasts to discuss real innovations—no altcoins, no corporate agendas. Our focus was on open-source projects like Bitcoin Core, Ark, Cashu, fostering conversations that could lead to tangible contributions.
Attracting attendees wasn’t easy. We leveraged local networks, reaching out to Bitcoin communities in neighboring countries via Nostr and Telegram. Posts on X helped spread the word, and we saw developers from Laos join for the first time, which was thrilling. Sponsors like Fulgur Ventures, Utreexo, and the Bitcoin Development Kit Foundation played a huge role, covering costs so we could keep the event free and accessible.
YakiHonne: What challenges did you face organizing the conference in Asia?
Gio: It was a steep learning curve. Funding was the biggest hurdle—early on, we struggled to cover venue and travel costs. Thankfully, our sponsors stepped in, letting me focus on logistics, which were no small feat either. As a first-time organizer, I underestimated the chaos of a tight timeline. Day one felt like herding cats without a fixed agenda, but the energy was electric—developers debugging code together, newcomers asking big questions.
Another challenge was cultural. Bitcoin’s still niche in Asia, so convincing locals to attend took persistence; there was no local presence for some reason. Despite the hiccups, we pulled it off, hosting 60+ attendees and sparking ideas for new projects, like a Cashu wallet integration. I’d tweak the planning next time, but the raw passion made it unforgettable.
YakiHonne: How does YakiHonne’s vision of decentralized social payments align with Sats ‘N’ Facts’ goals? Could tools like ours support your community?
Gio: That’s a great question. YakiHonne’s approach—merging Nostr’s censorship-resistant communication with Lightning payments—fits perfectly with our mission to empower users through open tech. At Sats ‘N’ Facts, we’re all about tools that give people control, whether it’s code or money. An app like YakiHonne could streamline community funding, letting developers tip each other for contributions or crowdfund projects directly. Imagine a hackathon where winners get sats instantly via YakiHonne—it’d be a game-changer. I’d love to see you guys at our next event to demo it!
YakiHonne: What advice would you give to someone starting a Bitcoin-focused community or event?
Gio: First, keep it Bitcoin-only. Stay true to the principles—cut out distractions like altcoins or hype-driven schemes. Start small: host regular meetups, maybe five people at a café, and build trust over time. Consistency and authenticity beat flashiness in the medium and long term.
Second, involve technical folks. Developers bring credibility and clarity, explaining Bitcoin’s nuts and bolts in ways newcomers get. I admire how Andreas Antonopoulos bridges that gap—technical yet accessible. You need that foundation to grow a real community.
Finally, lean on existing networks. If you know someone running a Bitcoin meetup in another city, collaborate. Share ideas, speakers, or even livestreams. Nostr’s great for this—our Laos attendees found us through a single post. Relationships are everything.
YakiHonne: Does Sats ‘N’ Facts focus more on Bitcoin’s technical side, non-technical side, or both?
Gio: We blend both. Our event had workshops for coders alongside talks for beginners on why Bitcoin matters. Open-source is our heartbeat, though. If you’re starting out, dive into projects like Bitcoin Core or Lightning. Review a pull request, test a Cashu wallet, or join a hackathon. One developer at our event built a Lightning micropayment tool that’s now live on GitHub.
There’s no shortage of ways to contribute. Community calls, forums, residency programs, and platforms like Geyser Fund are goldmines. YakiHonne could amplify this—imagine tipping developers for bug fixes via your app. It’s about iterating until you create something real.
YakiHonne: Your work is inspiring, Gio. Sats ‘N’ Facts is uniting Asia’s Bitcoin communities in a powerful way. What’s next for you?
Gio: Thanks for the kind words! We’re just getting started. The Chiang Mai event showed what’s possible—connecting developers across borders, reviewing and launching code and testing upcoming technologies. Next, we’re planning smaller hackathons and other events to keep the momentum going, maybe in Vietnam, Indonesia or Korea. I’d love to integrate tools like YakiHonne to fund these efforts directly through Nostr payments. Long-term, we want Sats ‘N’ Facts to be a hub for Asia’s Bitcoin builders, proving open-source can thrive here.

YakiHonne: Thank you, Gio, for sharing Sats ‘N’ Facts incredible journey. Your work is lighting a path for Bitcoin in Asia, and we’re honored to tell this story.
To our readers: Bitcoin’s future depends on communities like Sats ‘N’ Facts—and you can join the revolution. Download YakiHonne on Nostr to connect with builders, send Lightning payments, and explore the decentralized world. Follow Sats ‘N’ Facts for their next hackathon, and let’s build freedom tech together!
-
 @ 21335073:a244b1ad
2025-03-18 20:47:50
@ 21335073:a244b1ad
2025-03-18 20:47:50Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ d34e832d:383f78d0
2025-04-21 02:36:32
@ d34e832d:383f78d0
2025-04-21 02:36:32Lister.lol represents a sophisticated web application engineered specifically for the administration and management of Nostr lists. This feature is intrinsically embedded within the Nostr protocol, facilitating users in the curation of personalized feeds and the exploration of novel content. Although its current functionality remains relatively rudimentary, the platform encapsulates substantial potential for enhanced collaborative list management, as well as seamless integration with disparate client applications, effectively functioning as a micro-app within the broader ecosystem.
The trajectory of Nostr is oriented towards the development of robust developer tools (namely, the Nostr Development Kit - NDK), the establishment of comprehensive educational resources, and the cultivation of a dynamic and engaged community of developers and builders.
The overarching strategy emphasizes a decentralized paradigm, prioritizing the growth of small-scale, sustainable enterprises over the dominance of large, centralized corporations. In this regard, a rigorous experimentation with diverse monetization frameworks and the establishment of straightforward, user-friendly applications are deemed critical for the sustained evolution and scalability of the Nostr platform.
 Nostr's commitment to a decentralized, 'nagar-style' model of development distinguishes it markedly from the more conventional 'cathedral' methodologies employed by other platforms. As it fosters a broad spectrum of developmental outcomes while inherently embracing the properties of emergence. Such principles stand in stark contrast to within a traditional environment, centralized Web2 startup ecosystem, which is why all people need a chance to develop a significant shift towards a more adaptive and responsive design philosophy in involving #Nostr and #Bitcoin.
Nostr's commitment to a decentralized, 'nagar-style' model of development distinguishes it markedly from the more conventional 'cathedral' methodologies employed by other platforms. As it fosters a broad spectrum of developmental outcomes while inherently embracing the properties of emergence. Such principles stand in stark contrast to within a traditional environment, centralized Web2 startup ecosystem, which is why all people need a chance to develop a significant shift towards a more adaptive and responsive design philosophy in involving #Nostr and #Bitcoin. -
 @ 502ab02a:a2860397
2025-04-21 02:26:09
@ 502ab02a:a2860397
2025-04-21 02:26:09เรามาดูกันครับว่า Precision Fermentation ของ Perfect Day เค้าใช้อะไรเป็นกำลังสำคัญในการหมัก ให้ได้สินค้ามูลค่ามหาศาล ท้าวความกันก่อนว่า Perfect Day เป็นบริษัทที่ผลิต เวย์โปรตีนได้ โดยไม่ต้องใช้วัวเลยแม้แต่นิดเดียว ด้วยการใช้จุลินทรีย์
Microflora ฟาร์มวัวยุคใหม่ ที่ไม่มีวัว ถ้าคุณเคยดูสารคดีธรรมชาติ แล้วเห็นภาพป่าดิบเขียวชอุ่มที่แต่ละสิ่งมีชีวิตทำหน้าที่ของมันอย่างกลมกลืนกัน ทั้งแมลงที่บินไปมา เชื้อราที่แอบฝังรากอยู่ใต้ใบไม้ หรือจุลินทรีย์ที่ไม่เห็นด้วยตาเปล่าแต่ทำงานหนักอยู่ใต้ดิน... โลกของ microflora ก็ไม่ต่างอะไรกับ “จักรวาลจิ๋ว” แบบนั้นเลย
Microflora คืออะไร? microflora เป็นศัพท์ที่นักวิทยาศาสตร์ใช้เรียกสิ่งมีชีวิตขนาดจิ๋วที่มองไม่เห็นด้วยตาเปล่า แต่มีชีวิตจริงๆ แบบครบสูตร คือเจริญเติบโตได้ แบ่งตัวได้ กินได้ เหมือนสิ่งมีชีวิตอื่นๆ เป๊ะๆ มาจาก micro กับ flora
พอพูดถึงคำว่า “flora” บางคนอาจนึกถึงต้นไม้ แต่ในความหมายนี้ มันกว้างกว่านั้นมาก เพราะ “microflora” ไม่ได้จำกัดแค่พืช แต่หมายถึงสิ่งมีชีวิตจิ๋วจากหลากหลายอาณาจักรในธรรมชาติ เช่น ฟังไจ (Fungi) — ไม่ใช่แค่เห็ดที่เรากินกัน แต่รวมถึงเชื้อราจิ๋วที่อยู่ในดินและอากาศ ที่เก่งเรื่องการปล่อยเอนไซม์ย่อยอาหารนอกตัว แล้วดูดสารอาหารเข้าไป แบคทีเรีย (Bacteria) — นักแบ่งตัวมือโปรที่อยู่ในทุกที่ตั้งแต่ดินในสวน ยันในลำไส้เรา โพรทิสต์ (Protists) — กลุ่มที่เหลือๆ ที่ไม่เข้าพวกกับใคร เช่น สาหร่ายบางชนิด หรืออะมีบา
microflora เหล่านี้เหมือนพนักงานจิ๋วที่ทำหน้าที่เฉพาะทาง บางตัวเก่งเรื่องสร้างโปรตีน บางตัวสร้างไขมัน บางตัวสังเคราะห์วิตามินเก่งสุดๆ เลยกลายเป็นขุมพลังที่มนุษย์เริ่มหันมาใช้มากขึ้นเรื่อยๆ
ความสัมพันธ์ระหว่างมนุษย์กับ microflora ไม่ใช่เรื่องใหม่เลย เราหมักเบียร์ ทำโยเกิร์ต ดองกิมจิ และทำซีอิ๊วจากถั่วเหลืองด้วยกระบวนการที่เรียกว่า “fermentation” หรือ “การหมัก” มานานหลายพันปีแล้ว ซึ่งเป็นการอาศัยพลังของจุลินทรีย์ธรรมชาติให้สร้างรสชาติ วิตามิน หรือย่อยของที่เรากินให้ดูดซึมง่ายขึ้น แต่วันนี้โลกไปไกลกว่านั้นมาก เพราะเราสามารถสอนจุลินทรีย์ให้ผลิต “โปรตีนเฉพาะแบบ” ได้ตามต้องการ กระบวนการนี้เรียกว่า Precision Fermentation หรือ “การหมักแบบแม่นยำ” ฟังดูเหมือนห้องทดลองของ Iron Man เลยเนอะ
Perfect Day ใช้วิธีนี้ในการผลิต เวย์โปรตีน แบบไม่ต้องรีดนมจากวัวเลยสักหยด ด้วยการใช้ “เชื้อราจิ๋ว” ชนิดหนึ่งที่มีชื่อสายวิทยาศาสตร์ว่า Trichoderma
ทำไมต้อง Trichoderma? เจ้า Trichoderma ไม่ใช่เชื้อราหน้าตาน่ากลัวแบบในหนังสยองขวัญ แต่มันคือเชื้อราที่อยู่ในดินมานานกว่า 70 ปีแล้ว และเป็นที่รู้กันในวงการวิทยาศาสตร์ว่า มันเก่งเรื่องการผลิตเอนไซม์ที่ย่อยไม้ ย่อยใบไม้ ย่อยสิ่งมีชีวิตอื่นในธรรมชาติได้อย่างมีประสิทธิภาพ จึงเป็นเหมือน “โรงงานย่อยอาหาร” ชั้นเลิศ
นักวิทยาศาสตร์ของ Perfect Day เห็นแววก็เลยจับมันมา “ฝึกงาน” ใหม่ โดยใช้กระบวนการที่เรียกว่า strain engineering หรือ “การออกแบบสายพันธุ์” พูดง่ายๆ ก็คือ ใส่รหัสพันธุกรรม (เหมือนคำสั่งงาน) เข้าไปให้มันผลิตโปรตีนจากนมได้ เช่น beta-lactoglobulin ซึ่งเป็นโปรตีนตัวหลักของเวย์ในน้ำนมวัว
เมื่อ Trichoderma อ่านคำสั่งนี้ออก มันก็เริ่มเดินเครื่องผลิตโปรตีนตามที่เราสั่ง เหมือนเป็น “วัวในห้องแล็บ” ที่ไม่มีเสียงร้อง ไม่มีปุ๋ยคอก และไม่ต้องเลี้ยงด้วยหญ้า
microflora = วัวจิ๋วยุคใหม่
ลองจินตนาการว่าถ้าในอดีตเราต้องเลี้ยงวัวจริงๆ เพื่อให้ได้โปรตีนจากนม วันนี้เราใช้แค่จุลินทรีย์จิ๋วในถังหมัก แล้วป้อน “อาหาร” ให้มันเป็นน้ำตาลจากพืช (เช่น ข้าวโพด !!! เป็นง่ะ ข้าวโพดอีกแล้ว) มันก็จะเปลี่ยนคาร์โบไฮเดรตเหล่านั้นให้กลายเป็นโปรตีน หรือไขมัน หรือสารที่เราต้องการได้แบบแม่นยำ
microflora ไม่ใช่สัตว์ แต่ก็ทำหน้าที่แทนสัตว์ได้ พวกมันไม่มีสมอง ไม่มีระบบประสาท ไม่รู้สึกเจ็บ ไม่เบื่อ ไม่หิวข้าว ไม่ต้องการวันหยุด แต่มันมี “ความสามารถ” ที่เราสามารถดึงมาใช้ให้เกิดประโยชน์ได้อย่างน่าทึ่ง
ข้อดีของ microflora -เลี้ยงง่าย แค่ให้คาร์บ (จากพืช) ก็พร้อมทำงาน -ไม่ต้องใช้พื้นที่เยอะ ผลิตในถังหมัก ไม่ต้องใช้ทุ่งหญ้ากว้างๆ แบบฟาร์มวัว -ควบคุมคุณภาพได้ ผลิตโปรตีนได้สม่ำเสมอ ปราศจากสารก่อภูมิแพ้หรือยาปฏิชีวนะ -ลดการปล่อยก๊าซเรือนกระจก เพราะไม่ต้องเลี้ยงสัตว์ที่ปล่อยมีเทน
microflora จึงเป็น “เพื่อนร่วมงานที่เล็กที่สุด” แต่ก็อาจจะทรงพลังที่สุดในครัวของอนาคต และแม้เราจะยังยึดมั่นกับ animal-based diet อยู่ แต่ผมคิดว่าเรื่องนี้ก็น่าสนใจในฐานะ เทคโนโลยีที่กำลังท้าทายโลก fiat food อีกแนวทางหนึ่ง เพราะมันไม่ใช่พืชประดิษฐ์ ไม่ใช่แป้ง+สี+กลิ่น+สารพัด additive แต่คือ “การสร้างโปรตีนแท้” ด้วยความรู้ทางวิทยาศาสตร์ ที่เอื้อให้มนุษย์เลิกพึ่งวัวโดยตรง
ไม่แน่ว่าวันหนึ่ง แทนที่จะมีฟาร์มวัวเลี้ยงวัว 500 ตัวเพื่อผลิตเวย์ 1 ตัน เราอาจมีแค่ถังหมัก 1 ถัง ที่เลี้ยงเชื้อรา 500 ล้านตัว แล้วได้เวย์โปรตีนคุณภาพเดียวกัน...โดยไม่ต้องมีเสียง "มอ" เลยสักแอะ
แต่คำถามสำคัญคือ เราจะมีฟาร์มนั้นได้ไหม หรือได้แต่ทำหน้าที่ซื้อนมมารับประทานเท่านั้น
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:10:55
@ 4ba8e86d:89d32de4
2025-04-21 02:10:55Seu teclado não deve se conectar à internet. Privacidade em primeiro lugar. Sempre. Estamos desenvolvendo um teclado moderno que respeita totalmente sua privacidade e segurança. O FUTO Keyboard é 100% offline e 100% privado, oferecendo todos os recursos essenciais que você espera de um teclado atual — incluindo digitação por deslizamento, entrada de voz offline, correção automática inteligente, temas personalizáveis e sugestões preditivas de texto. Nosso objetivo é simples: criar um teclado eficiente e funcional, sem comprometer a privacidade do usuário. Este projeto é um fork do LatinIME, o teclado open-source oficial do Android.
Atenção: o FUTO Keyboard está atualmente em fase alfa. Está trabalhando para torná-lo estável e confiável, mas durante esse período você pode encontrar bugs, travamentos ou recursos ainda não implementados.
Configurações
Idiomas e Modelos – Adicione novos idiomas, dicionários, modelos de entrada de voz, transformadores e layouts associados.
Linguagens e Modelos
O menu no qual você adiciona novos idiomas, bem como dicionários, modelos de entrada de voz, modelos de transformadores e layouts associados a eles.
Adicionar idioma.
Alguns idiomas exigem o download de um dicionário. Se você também quiser um modelo de entrada de voz para um idioma específico, precisará baixá-lo também. Cada idioma já possui uma seleção de layouts de teclado associados; você pode escolher qual(is) layout(s) deseja adicionar ao adicionar o idioma. https://video.nostr.build/c775288b7a8ee8d75816af0c7a25f2aa0b4ecc99973fd442b2badc308fa38109.mp4
Mudar idioma.
Existem duas maneiras de alternar o idioma. A primeira é pressionando o ícone do globo na Barra de Ações, localizada próximo ao canto superior esquerdo do teclado. A segunda é pressionando longamente ou deslizando a barra de espaço; você pode personalizar o comportamento de troca de idioma da barra de espaço acessando Configurações -> Teclado e Digitação -> Teclas de Pressão Longa e Barra de Espaço -> Comportamento da Barra de Espaço . Você também pode atribuir o ícone do globo como a Tecla de Ação para que fique ao lado da barra de espaço, que pode ser acessada no menu Todas as Ações pressionando a tecla de reticências (...) no canto superior esquerdo do teclado e, em seguida, acessando Editar Ações. https://video.nostr.build/ed6f7f63a9c203cd59f46419ef54a4b8b442f070f802a688ca7d682bd6811bcb.mp4
Adicionar dicionário.
Alguns idiomas têm um dicionário integrado, mas a maioria não. Se o idioma que você está instalando não tiver um dicionário integrado, você pode iniciar a instalação em nosso site acessando Idiomas e Modelos -> Dicionário (no idioma que você está instalando) -> Explorar -> Baixar (em nosso site). https://video.nostr.build/3b1e09289953b658a9cef33c41bd711095556bc48290cb2ed066d4d0a5186371.mp4
Habilitar digitação multilíngue.
Você pode habilitar a digitação multilíngue para um ou mais idiomas acessando Idiomas e modelos e marcando a caixa Digitação multilíngue no(s) idioma(s) para os quais deseja habilitar a digitação multilíngue. https://video.nostr.build/29f683410626219499787bd63058d159719553f8e33a9f3c659c51c375a682fb.mp4
Criar layout personalizado.
Se desejar criar seu próprio layout personalizado para um idioma específico, você pode fazê-lo ativando Configurações do Desenvolvedor -> Layouts Personalizados -> Criar novo layout . Mais informações sobre layouts personalizados podem ser encontradas https://github.com/futo-org/futo-keyboard-layouts . A personalização das configurações de pressionamento longo tecla por tecla ainda não é suportada, mas está em processo de implementação. https://video.nostr.build/b5993090e28794d0305424dd352ca83760bb87002c57930e80513de5917fad8d.mp4
Teclado e Digitação – Personalize o comportamento das teclas, o tamanho do teclado e outras preferências de digitação.
Previsão de texto.
O menu no qual você define suas preferências para correção automática e sugestões personalizadas. Modelo de Linguagem do Transformador Você pode fazer com que o teclado preveja a próxima palavra que você digitará ou faça correções automáticas mais inteligentes, que usam um modelo de linguagem Transformer pré-treinado com base em conjuntos de dados disponíveis publicamente, ativando o Transformer LM . Observação: atualmente, isso funciona apenas em inglês, mas estamos trabalhando para torná-lo compatível com outros idiomas. Ajuste fino do transformador Você pode fazer com que o teclado memorize o que você digita e quais sugestões você seleciona, o que treina o modelo de idioma (enquanto o telefone estiver inativo) para prever quais palavras sugerir e corrigir automaticamente enquanto você digita, ativando o ajuste fino do Transformer . Observação: este é o seu modelo de idioma pessoal e o FUTO não visualiza nem armazena nenhum dos seus dados. https://video.nostr.build/688354a63bdc48a9dd3f8605854b5631ac011009c6105f93cfa0b52b46bc40d3.mp4
Previsão de texto.
O menu no qual você define suas preferências para correção automática e sugestões personalizadas. Modelo de Linguagem do Transformador Você pode fazer com que o teclado preveja a próxima palavra que você digitará ou faça correções automáticas mais inteligentes, que usam um modelo de linguagem Transformer pré-treinado com base em conjuntos de dados disponíveis publicamente, ativando o Transformer LM . Observação: atualmente, isso funciona apenas em inglês, mas estamos trabalhando para torná-lo compatível com outros idiomas.
Ajuste fino do transformador.
Você pode fazer com que o teclado memorize o que você digita e quais sugestões você seleciona, o que treina o modelo de idioma (enquanto o telefone estiver inativo) para prever quais palavras sugerir e corrigir automaticamente enquanto você digita, ativando o ajuste fino do Transformer . Observação: este é o seu modelo de idioma pessoal e o FUTO não visualiza nem armazena nenhum dos seus dados.
Força do Modelo de Linguagem do Transformador.
Você pode fazer com que a correção automática se comporte mais como o teclado AOSP ou mais como a rede neural acessando Parâmetros avançados -> Intensidade do LM do transformador e arrastando o controle deslizante para um valor menor (o que tornará o comportamento da correção automática mais parecido com o teclado AOSP) ou um valor maior (o que tornará a correção automática mais dependente da rede neural). Limiar de correção automática Você pode alterar o limite da correção automática para que ela ocorra com mais ou menos frequência acessando Parâmetros avançados -> Limite de correção automática e arrastando o controle deslizante para um valor menor (o que fará com que a correção automática ocorra com mais frequência, mas também corrija erros com mais frequência) ou um valor maior (o que fará com que a correção automática ocorra com menos frequência, mas também corrija erros com menos frequência). https://video.nostr.build/ea9c100081acfcab60343c494a91f789ef8143c92343522ec34c714913631cf7.mp4
Lista negra de palavras.
Você pode colocar sugestões de palavras na lista negra, o que impedirá que o teclado continue sugerindo palavras na lista negra, acessando Sugestões na lista negra e adicionando as palavras que você gostaria de colocar na lista negra.
Palavras ofensivas.
Você pode bloquear palavras ofensivas, como palavrões comuns, acessando Sugestões na Lista Negra e marcando a opção Bloquear Palavras Ofensivas . Observação: a opção Bloquear Palavras Ofensivas está ativada por padrão. https://video.nostr.build/ee72f3940b9789bbea222c95ee74d646aae1a0f3bf658ef8114c6f7942bb50f5.mp4
Correção automática.
Você pode ativar a capacidade de corrigir automaticamente palavras digitadas incorretamente ao pressionar a barra de espaço ou digitar pontuação ativando a Correção automática.
Sugestões de correção.
Você pode ativar a capacidade de exibir palavras sugeridas enquanto digita marcando a opção Mostrar sugestões de correção.
Sugestões de palavras.
Você pode ativar a capacidade de aprender com suas comunicações e dados digitados para melhorar as sugestões ativando as Sugestões personalizadas . Observação: desativar as Sugestões personalizadas também desativa o ajuste fino do Transformer. https://video.nostr.build/2c22d109b9192eac8fe4533b3f8e3e1b5896dfd043817bd460c48a5b989b7a2f.mp4
Entrada de Voz – Configure a entrada de voz offline, incluindo a duração e a conversão de fala em texto.
Entrada de voz.
O menu no qual você define suas preferências de entrada de voz, como duração da entrada e configurações de conversão de fala em texto. Entrada de voz integrada Você pode desabilitar a entrada de voz integrada do teclado e, em vez disso, usar o provedor de entrada de voz de um aplicativo externo desativando a opção Desabilitar entrada de voz integrada. https://video.nostr.build/68916e5b338a9f999f45aa1828a6e05ccbf8def46da9516c0f516b40ca8c827b.mp4
Sons de indicação.
Você pode habilitar a capacidade de reproduzir sons ao iniciar e cancelar a entrada de voz ativando Sons de indicação. https://video.nostr.build/7f5fb6a6173c4db18945e138146fe65444e40953d85cee1f09c1a21d236d21f5.mp4
Progresso Detalhado.
Você pode habilitar a capacidade de exibir informações detalhadas, como indicar que o microfone está sendo usado, ativando Progresso detalhado. https://video.nostr.build/8ac2bb6bdd6e7f8bd4b45da423e782c152a2b4320f2e090cbb99fd5c78e8f44f.mp4
Microfone Bluetooth.
Você pode fazer com que a entrada de voz prefira automaticamente seu microfone Bluetooth em vez do microfone integrado, ativando Preferir microfone Bluetooth. https://video.nostr.build/c11404aa6fec2dda71ceb3aaee916c6761b3015fef9575a352de66b7310dad07.mp4
Foco de áudio.
Você pode fazer com que a entrada de voz pause automaticamente vídeos ou músicas quando ela estiver ativada, ativando o Foco de Áudio. https://video.nostr.build/4ac82af53298733d0c5013ef28befb8b2adeb4a4949604308317e124b6431d40.mp4
Supressão de Símbolos.
Por padrão, a entrada de voz transcreve apenas texto básico e pontuação. Você pode desativar a opção "Suprimir símbolos" para liberar a entrada de voz da transcrição de caracteres especiais (por exemplo, @, $ ou %). Observação: Isso não afeta a forma como a entrada de voz interpreta palavras literais (por exemplo, "vírgula", "ponto final"). https://video.nostr.build/10de49c5a9e35508caa14b66da28fae991a5ac8eabad9b086959fba18c07f8f3.mp4
Entrada de voz de formato longo.
Você pode desativar o limite padrão de 30 segundos para entrada de voz ativando a opção Entrada de voz longa . Observação: a qualidade da saída pode ser prejudicada com entradas longas. https://video.nostr.build/f438ee7a42939a5a3e6d6c4471905f836f038495eb3a00b39d9996d0e552c200.mp4
Parada automática em silêncio.
Você pode fazer com que a entrada de voz pare automaticamente quando o silêncio for detectado, ativando a opção Parar automaticamente ao silenciar . Observação: se houver muito ruído de fundo, pode ser necessário interromper manualmente a entrada de voz. Ative também a entrada de voz longa para evitar a interrupção após 30 segundos. https://video.nostr.build/056567696d513add63f6dd254c0a3001530917e05e792de80c12796d43958671.mp4
Dicionário Pessoal – Adicione palavras personalizadas para que o teclado aprenda e sugira com mais precisão.
Dicionário Pessoal.
O menu no qual você cria seu dicionário pessoal de palavras que o teclado irá lembrar e sugerir. Adicionar ao dicionário Você pode adicionar uma palavra ou frase ao seu dicionário pessoal pressionando o ícone de adição na tela "Dicionário pessoal" . Você também pode criar um atalho para ela no campo "Atalho" ao adicionar a palavra ou frase. https://video.nostr.build/dec41c666b9f2276cc20d9096e3a9b542b570afd1f679d8d0e8c43c8ea46bfcb.mp4
Excluir do dicionário.
Você pode excluir uma palavra ou frase do seu dicionário pessoal clicando nessa palavra ou frase e clicando no ícone de lixeira no canto superior direito. https://video.nostr.build/aca25643b5c7ead4c5d522709af4bc337911e49c4743b97dc75f6b877449143e.mp4
Tema – Escolha entre os temas disponíveis ou personalize a aparência do teclado conforme seu gosto.
Tema.
O menu no qual você seleciona seu tema preferido para o teclado. Alterar tema Você pode escolher entre uma variedade de temas para o teclado, incluindo Modo Escuro, Modo Claro, Automático Dinâmico, Escuro Dinâmico, Claro Dinâmico, Material AOSP Escuro, Material AOSP Claro, Roxo Escuro AMOLED, Girassol, Queda de Neve, Cinza Aço, Esmeralda, Algodão Doce, Luz do Mar Profundo, Escuro do Mar Profundo, Gradiente 1, Tema FUTO VI ou Tema Construção . A possibilidade de personalizar seu tema será disponibilizada em breve. https://video.nostr.build/90c8de72f08cb0d8c40ac2fba2fd39451ff63ec1592ddd2629d0891c104bc61e.mp4
Fronteiras Principais.
Você pode habilitar as bordas das teclas rolando para baixo até o final e ativando Bordas das teclas . https://video.nostr.build/fa2087d68ce3fb2d3adb84cc2ec19c4d5383beb8823a4b6d1d85378ab3507ab1.mp4
Site oficial https://keyboard.futo.org/
Baixar no fdroid. https://app.futo.org/fdroid/repo/
Para instalar através do Obtainium , basta ir em Adicionar Aplicativo e colar esta URL do repositório: https://github.com/futo-org/android-keyboard
A adição pode demorar um pouco dependendo da velocidade da sua internet, pois o APK precisa ser baixado.
-
 @ 21335073:a244b1ad
2025-03-18 14:43:08
@ 21335073:a244b1ad
2025-03-18 14:43:08Warning: This piece contains a conversation about difficult topics. Please proceed with caution.
TL;DR please educate your children about online safety.
Julian Assange wrote in his 2012 book Cypherpunks, “This book is not a manifesto. There isn’t time for that. This book is a warning.” I read it a few times over the past summer. Those opening lines definitely stood out to me. I wish we had listened back then. He saw something about the internet that few had the ability to see. There are some individuals who are so close to a topic that when they speak, it’s difficult for others who aren’t steeped in it to visualize what they’re talking about. I didn’t read the book until more recently. If I had read it when it came out, it probably would have sounded like an unknown foreign language to me. Today it makes more sense.
This isn’t a manifesto. This isn’t a book. There is no time for that. It’s a warning and a possible solution from a desperate and determined survivor advocate who has been pulling and unraveling a thread for a few years. At times, I feel too close to this topic to make any sense trying to convey my pathway to my conclusions or thoughts to the general public. My hope is that if nothing else, I can convey my sense of urgency while writing this. This piece is a watchman’s warning.
When a child steps online, they are walking into a new world. A new reality. When you hand a child the internet, you are handing them possibilities—good, bad, and ugly. This is a conversation about lowering the potential of negative outcomes of stepping into that new world and how I came to these conclusions. I constantly compare the internet to the road. You wouldn’t let a young child run out into the road with no guidance or safety precautions. When you hand a child the internet without any type of guidance or safety measures, you are allowing them to play in rush hour, oncoming traffic. “Look left, look right for cars before crossing.” We almost all have been taught that as children. What are we taught as humans about safety before stepping into a completely different reality like the internet? Very little.
I could never really figure out why many folks in tech, privacy rights activists, and hackers seemed so cold to me while talking about online child sexual exploitation. I always figured that as a survivor advocate for those affected by these crimes, that specific, skilled group of individuals would be very welcoming and easy to talk to about such serious topics. I actually had one hacker laugh in my face when I brought it up while I was looking for answers. I thought maybe this individual thought I was accusing them of something I wasn’t, so I felt bad for asking. I was constantly extremely disappointed and would ask myself, “Why don’t they care? What could I say to make them care more? What could I say to make them understand the crisis and the level of suffering that happens as a result of the problem?”
I have been serving minor survivors of online child sexual exploitation for years. My first case serving a survivor of this specific crime was in 2018—a 13-year-old girl sexually exploited by a serial predator on Snapchat. That was my first glimpse into this side of the internet. I won a national award for serving the minor survivors of Twitter in 2023, but I had been working on that specific project for a few years. I was nominated by a lawyer representing two survivors in a legal battle against the platform. I’ve never really spoken about this before, but at the time it was a choice for me between fighting Snapchat or Twitter. I chose Twitter—or rather, Twitter chose me. I heard about the story of John Doe #1 and John Doe #2, and I was so unbelievably broken over it that I went to war for multiple years. I was and still am royally pissed about that case. As far as I was concerned, the John Doe #1 case proved that whatever was going on with corporate tech social media was so out of control that I didn’t have time to wait, so I got to work. It was reading the messages that John Doe #1 sent to Twitter begging them to remove his sexual exploitation that broke me. He was a child begging adults to do something. A passion for justice and protecting kids makes you do wild things. I was desperate to find answers about what happened and searched for solutions. In the end, the platform Twitter was purchased. During the acquisition, I just asked Mr. Musk nicely to prioritize the issue of detection and removal of child sexual exploitation without violating digital privacy rights or eroding end-to-end encryption. Elon thanked me multiple times during the acquisition, made some changes, and I was thanked by others on the survivors’ side as well.
I still feel that even with the progress made, I really just scratched the surface with Twitter, now X. I left that passion project when I did for a few reasons. I wanted to give new leadership time to tackle the issue. Elon Musk made big promises that I knew would take a while to fulfill, but mostly I had been watching global legislation transpire around the issue, and frankly, the governments are willing to go much further with X and the rest of corporate tech than I ever would. My work begging Twitter to make changes with easier reporting of content, detection, and removal of child sexual exploitation material—without violating privacy rights or eroding end-to-end encryption—and advocating for the minor survivors of the platform went as far as my principles would have allowed. I’m grateful for that experience. I was still left with a nagging question: “How did things get so bad with Twitter where the John Doe #1 and John Doe #2 case was able to happen in the first place?” I decided to keep looking for answers. I decided to keep pulling the thread.
I never worked for Twitter. This is often confusing for folks. I will say that despite being disappointed in the platform’s leadership at times, I loved Twitter. I saw and still see its value. I definitely love the survivors of the platform, but I also loved the platform. I was a champion of the platform’s ability to give folks from virtually around the globe an opportunity to speak and be heard.
I want to be clear that John Doe #1 really is my why. He is the inspiration. I am writing this because of him. He represents so many globally, and I’m still inspired by his bravery. One child’s voice begging adults to do something—I’m an adult, I heard him. I’d go to war a thousand more lifetimes for that young man, and I don’t even know his name. Fighting has been personally dark at times; I’m not even going to try to sugarcoat it, but it has been worth it.
The data surrounding the very real crime of online child sexual exploitation is available to the public online at any time for anyone to see. I’d encourage you to go look at the data for yourself. I believe in encouraging folks to check multiple sources so that you understand the full picture. If you are uncomfortable just searching around the internet for information about this topic, use the terms “CSAM,” “CSEM,” “SG-CSEM,” or “AI Generated CSAM.” The numbers don’t lie—it’s a nightmare that’s out of control. It’s a big business. The demand is high, and unfortunately, business is booming. Organizations collect the data, tech companies often post their data, governments report frequently, and the corporate press has covered a decent portion of the conversation, so I’m sure you can find a source that you trust.
Technology is changing rapidly, which is great for innovation as a whole but horrible for the crime of online child sexual exploitation. Those wishing to exploit the vulnerable seem to be adapting to each technological change with ease. The governments are so far behind with tackling these issues that as I’m typing this, it’s borderline irrelevant to even include them while speaking about the crime or potential solutions. Technology is changing too rapidly, and their old, broken systems can’t even dare to keep up. Think of it like the governments’ “War on Drugs.” Drugs won. In this case as well, the governments are not winning. The governments are talking about maybe having a meeting on potentially maybe having legislation around the crimes. The time to have that meeting would have been many years ago. I’m not advocating for governments to legislate our way out of this. I’m on the side of educating and innovating our way out of this.
I have been clear while advocating for the minor survivors of corporate tech platforms that I would not advocate for any solution to the crime that would violate digital privacy rights or erode end-to-end encryption. That has been a personal moral position that I was unwilling to budge on. This is an extremely unpopular and borderline nonexistent position in the anti-human trafficking movement and online child protection space. I’m often fearful that I’m wrong about this. I have always thought that a better pathway forward would have been to incentivize innovation for detection and removal of content. I had no previous exposure to privacy rights activists or Cypherpunks—actually, I came to that conclusion by listening to the voices of MENA region political dissidents and human rights activists. After developing relationships with human rights activists from around the globe, I realized how important privacy rights and encryption are for those who need it most globally. I was simply unwilling to give more power, control, and opportunities for mass surveillance to big abusers like governments wishing to enslave entire nations and untrustworthy corporate tech companies to potentially end some portion of abuses online. On top of all of it, it has been clear to me for years that all potential solutions outside of violating digital privacy rights to detect and remove child sexual exploitation online have not yet been explored aggressively. I’ve been disappointed that there hasn’t been more of a conversation around preventing the crime from happening in the first place.
What has been tried is mass surveillance. In China, they are currently under mass surveillance both online and offline, and their behaviors are attached to a social credit score. Unfortunately, even on state-run and controlled social media platforms, they still have child sexual exploitation and abuse imagery pop up along with other crimes and human rights violations. They also have a thriving black market online due to the oppression from the state. In other words, even an entire loss of freedom and privacy cannot end the sexual exploitation of children online. It’s been tried. There is no reason to repeat this method.
It took me an embarrassingly long time to figure out why I always felt a slight coldness from those in tech and privacy-minded individuals about the topic of child sexual exploitation online. I didn’t have any clue about the “Four Horsemen of the Infocalypse.” This is a term coined by Timothy C. May in 1988. I would have been a child myself when he first said it. I actually laughed at myself when I heard the phrase for the first time. I finally got it. The Cypherpunks weren’t wrong about that topic. They were so spot on that it is borderline uncomfortable. I was mad at first that they knew that early during the birth of the internet that this issue would arise and didn’t address it. Then I got over it because I realized that it wasn’t their job. Their job was—is—to write code. Their job wasn’t to be involved and loving parents or survivor advocates. Their job wasn’t to educate children on internet safety or raise awareness; their job was to write code.
They knew that child sexual abuse material would be shared on the internet. They said what would happen—not in a gleeful way, but a prediction. Then it happened.
I equate it now to a concrete company laying down a road. As you’re pouring the concrete, you can say to yourself, “A terrorist might travel down this road to go kill many, and on the flip side, a beautiful child can be born in an ambulance on this road.” Who or what travels down the road is not their responsibility—they are just supposed to lay the concrete. I’d never go to a concrete pourer and ask them to solve terrorism that travels down roads. Under the current system, law enforcement should stop terrorists before they even make it to the road. The solution to this specific problem is not to treat everyone on the road like a terrorist or to not build the road.
So I understand the perceived coldness from those in tech. Not only was it not their job, but bringing up the topic was seen as the equivalent of asking a free person if they wanted to discuss one of the four topics—child abusers, terrorists, drug dealers, intellectual property pirates, etc.—that would usher in digital authoritarianism for all who are online globally.
Privacy rights advocates and groups have put up a good fight. They stood by their principles. Unfortunately, when it comes to corporate tech, I believe that the issue of privacy is almost a complete lost cause at this point. It’s still worth pushing back, but ultimately, it is a losing battle—a ticking time bomb.
I do think that corporate tech providers could have slowed down the inevitable loss of privacy at the hands of the state by prioritizing the detection and removal of CSAM when they all started online. I believe it would have bought some time, fewer would have been traumatized by that specific crime, and I do believe that it could have slowed down the demand for content. If I think too much about that, I’ll go insane, so I try to push the “if maybes” aside, but never knowing if it could have been handled differently will forever haunt me. At night when it’s quiet, I wonder what I would have done differently if given the opportunity. I’ll probably never know how much corporate tech knew and ignored in the hopes that it would go away while the problem continued to get worse. They had different priorities. The most voiceless and vulnerable exploited on corporate tech never had much of a voice, so corporate tech providers didn’t receive very much pushback.
Now I’m about to say something really wild, and you can call me whatever you want to call me, but I’m going to say what I believe to be true. I believe that the governments are either so incompetent that they allowed the proliferation of CSAM online, or they knowingly allowed the problem to fester long enough to have an excuse to violate privacy rights and erode end-to-end encryption. The US government could have seized the corporate tech providers over CSAM, but I believe that they were so useful as a propaganda arm for the regimes that they allowed them to continue virtually unscathed.
That season is done now, and the governments are making the issue a priority. It will come at a high cost. Privacy on corporate tech providers is virtually done as I’m typing this. It feels like a death rattle. I’m not particularly sure that we had much digital privacy to begin with, but the illusion of a veil of privacy feels gone.
To make matters slightly more complex, it would be hard to convince me that once AI really gets going, digital privacy will exist at all.
I believe that there should be a conversation shift to preserving freedoms and human rights in a post-privacy society.
I don’t want to get locked up because AI predicted a nasty post online from me about the government. I’m not a doomer about AI—I’m just going to roll with it personally. I’m looking forward to the positive changes that will be brought forth by AI. I see it as inevitable. A bit of privacy was helpful while it lasted. Please keep fighting to preserve what is left of privacy either way because I could be wrong about all of this.
On the topic of AI, the addition of AI to the horrific crime of child sexual abuse material and child sexual exploitation in multiple ways so far has been devastating. It’s currently out of control. The genie is out of the bottle. I am hopeful that innovation will get us humans out of this, but I’m not sure how or how long it will take. We must be extremely cautious around AI legislation. It should not be illegal to innovate even if some bad comes with the good. I don’t trust that the governments are equipped to decide the best pathway forward for AI. Source: the entire history of the government.
I have been personally negatively impacted by AI-generated content. Every few days, I get another alert that I’m featured again in what’s called “deep fake pornography” without my consent. I’m not happy about it, but what pains me the most is the thought that for a period of time down the road, many globally will experience what myself and others are experiencing now by being digitally sexually abused in this way. If you have ever had your picture taken and posted online, you are also at risk of being exploited in this way. Your child’s image can be used as well, unfortunately, and this is just the beginning of this particular nightmare. It will move to more realistic interpretations of sexual behaviors as technology improves. I have no brave words of wisdom about how to deal with that emotionally. I do have hope that innovation will save the day around this specific issue. I’m nervous that everyone online will have to ID verify due to this issue. I see that as one possible outcome that could help to prevent one problem but inadvertently cause more problems, especially for those living under authoritarian regimes or anyone who needs to remain anonymous online. A zero-knowledge proof (ZKP) would probably be the best solution to these issues. There are some survivors of violence and/or sexual trauma who need to remain anonymous online for various reasons. There are survivor stories available online of those who have been abused in this way. I’d encourage you seek out and listen to their stories.
There have been periods of time recently where I hesitate to say anything at all because more than likely AI will cover most of my concerns about education, awareness, prevention, detection, and removal of child sexual exploitation online, etc.
Unfortunately, some of the most pressing issues we’ve seen online over the last few years come in the form of “sextortion.” Self-generated child sexual exploitation (SG-CSEM) numbers are continuing to be terrifying. I’d strongly encourage that you look into sextortion data. AI + sextortion is also a huge concern. The perpetrators are using the non-sexually explicit images of children and putting their likeness on AI-generated child sexual exploitation content and extorting money, more imagery, or both from minors online. It’s like a million nightmares wrapped into one. The wild part is that these issues will only get more pervasive because technology is harnessed to perpetuate horror at a scale unimaginable to a human mind.
Even if you banned phones and the internet or tried to prevent children from accessing the internet, it wouldn’t solve it. Child sexual exploitation will still be with us until as a society we start to prevent the crime before it happens. That is the only human way out right now.
There is no reset button on the internet, but if I could go back, I’d tell survivor advocates to heed the warnings of the early internet builders and to start education and awareness campaigns designed to prevent as much online child sexual exploitation as possible. The internet and technology moved quickly, and I don’t believe that society ever really caught up. We live in a world where a child can be groomed by a predator in their own home while sitting on a couch next to their parents watching TV. We weren’t ready as a species to tackle the fast-paced algorithms and dangers online. It happened too quickly for parents to catch up. How can you parent for the ever-changing digital world unless you are constantly aware of the dangers?
I don’t think that the internet is inherently bad. I believe that it can be a powerful tool for freedom and resistance. I’ve spoken a lot about the bad online, but there is beauty as well. We often discuss how victims and survivors are abused online; we rarely discuss the fact that countless survivors around the globe have been able to share their experiences, strength, hope, as well as provide resources to the vulnerable. I do question if giving any government or tech company access to censorship, surveillance, etc., online in the name of serving survivors might not actually impact a portion of survivors negatively. There are a fair amount of survivors with powerful abusers protected by governments and the corporate press. If a survivor cannot speak to the press about their abuse, the only place they can go is online, directly or indirectly through an independent journalist who also risks being censored. This scenario isn’t hard to imagine—it already happened in China. During #MeToo, a survivor in China wanted to post their story. The government censored the post, so the survivor put their story on the blockchain. I’m excited that the survivor was creative and brave, but it’s terrifying to think that we live in a world where that situation is a necessity.
I believe that the future for many survivors sharing their stories globally will be on completely censorship-resistant and decentralized protocols. This thought in particular gives me hope. When we listen to the experiences of a diverse group of survivors, we can start to understand potential solutions to preventing the crimes from happening in the first place.
My heart is broken over the gut-wrenching stories of survivors sexually exploited online. Every time I hear the story of a survivor, I do think to myself quietly, “What could have prevented this from happening in the first place?” My heart is with survivors.
My head, on the other hand, is full of the understanding that the internet should remain free. The free flow of information should not be stopped. My mind is with the innocent citizens around the globe that deserve freedom both online and offline.
The problem is that governments don’t only want to censor illegal content that violates human rights—they create legislation that is so broad that it can impact speech and privacy of all. “Don’t you care about the kids?” Yes, I do. I do so much that I’m invested in finding solutions. I also care about all citizens around the globe that deserve an opportunity to live free from a mass surveillance society. If terrorism happens online, I should not be punished by losing my freedom. If drugs are sold online, I should not be punished. I’m not an abuser, I’m not a terrorist, and I don’t engage in illegal behaviors. I refuse to lose freedom because of others’ bad behaviors online.
I want to be clear that on a long enough timeline, the governments will decide that they can be better parents/caregivers than you can if something isn’t done to stop minors from being sexually exploited online. The price will be a complete loss of anonymity, privacy, free speech, and freedom of religion online. I find it rather insulting that governments think they’re better equipped to raise children than parents and caretakers.
So we can’t go backwards—all that we can do is go forward. Those who want to have freedom will find technology to facilitate their liberation. This will lead many over time to decentralized and open protocols. So as far as I’m concerned, this does solve a few of my worries—those who need, want, and deserve to speak freely online will have the opportunity in most countries—but what about online child sexual exploitation?
When I popped up around the decentralized space, I was met with the fear of censorship. I’m not here to censor you. I don’t write code. I couldn’t censor anyone or any piece of content even if I wanted to across the internet, no matter how depraved. I don’t have the skills to do that.
I’m here to start a conversation. Freedom comes at a cost. You must always fight for and protect your freedom. I can’t speak about protecting yourself from all of the Four Horsemen because I simply don’t know the topics well enough, but I can speak about this one topic.
If there was a shortcut to ending online child sexual exploitation, I would have found it by now. There isn’t one right now. I believe that education is the only pathway forward to preventing the crime of online child sexual exploitation for future generations.
I propose a yearly education course for every child of all school ages, taught as a standard part of the curriculum. Ideally, parents/caregivers would be involved in the education/learning process.
Course: - The creation of the internet and computers - The fight for cryptography - The tech supply chain from the ground up (example: human rights violations in the supply chain) - Corporate tech - Freedom tech - Data privacy - Digital privacy rights - AI (history-current) - Online safety (predators, scams, catfishing, extortion) - Bitcoin - Laws - How to deal with online hate and harassment - Information on who to contact if you are being abused online or offline - Algorithms - How to seek out the truth about news, etc., online
The parents/caregivers, homeschoolers, unschoolers, and those working to create decentralized parallel societies have been an inspiration while writing this, but my hope is that all children would learn this course, even in government ran schools. Ideally, parents would teach this to their own children.
The decentralized space doesn’t want child sexual exploitation to thrive. Here’s the deal: there has to be a strong prevention effort in order to protect the next generation. The internet isn’t going anywhere, predators aren’t going anywhere, and I’m not down to let anyone have the opportunity to prove that there is a need for more government. I don’t believe that the government should act as parents. The governments have had a chance to attempt to stop online child sexual exploitation, and they didn’t do it. Can we try a different pathway forward?
I’d like to put myself out of a job. I don’t want to ever hear another story like John Doe #1 ever again. This will require work. I’ve often called online child sexual exploitation the lynchpin for the internet. It’s time to arm generations of children with knowledge and tools. I can’t do this alone.
Individuals have fought so that I could have freedom online. I want to fight to protect it. I don’t want child predators to give the government any opportunity to take away freedom. Decentralized spaces are as close to a reset as we’ll get with the opportunity to do it right from the start. Start the youth off correctly by preventing potential hazards to the best of your ability.
The good news is anyone can work on this! I’d encourage you to take it and run with it. I added the additional education about the history of the internet to make the course more educational and fun. Instead of cleaning up generations of destroyed lives due to online sexual exploitation, perhaps this could inspire generations of those who will build our futures. Perhaps if the youth is armed with knowledge, they can create more tools to prevent the crime.
This one solution that I’m suggesting can be done on an individual level or on a larger scale. It should be adjusted depending on age, learning style, etc. It should be fun and playful.
This solution does not address abuse in the home or some of the root causes of offline child sexual exploitation. My hope is that it could lead to some survivors experiencing abuse in the home an opportunity to disclose with a trusted adult. The purpose for this solution is to prevent the crime of online child sexual exploitation before it occurs and to arm the youth with the tools to contact safe adults if and when it happens.
In closing, I went to hell a few times so that you didn’t have to. I spoke to the mothers of survivors of minors sexually exploited online—their tears could fill rivers. I’ve spoken with political dissidents who yearned to be free from authoritarian surveillance states. The only balance that I’ve found is freedom online for citizens around the globe and prevention from the dangers of that for the youth. Don’t slow down innovation and freedom. Educate, prepare, adapt, and look for solutions.
I’m not perfect and I’m sure that there are errors in this piece. I hope that you find them and it starts a conversation.
-
 @ 7252ad94:d19de472
2025-03-18 01:45:36
@ 7252ad94:d19de472
2025-03-18 01:45:36![[BTC March 17 25.jpg]]#Bitcoin #btccharts #BitcoinCharts
-
 @ 4ba8e86d:89d32de4
2025-04-21 02:08:06
@ 4ba8e86d:89d32de4
2025-04-21 02:08:06FOSS Browser é um navegador Android totalmente livre e de código aberto (freedom/libre, no sentido de liberdade). Seu código-fonte é público e o aplicativo não solicita permissões desnecessárias. Ele é baseado no WebView do Android, com o objetivo de oferecer uma navegação simples, leve, eficiente e com uma interface agradável.
FOSS Browser é uma aplicação Android para navegação na internet. Por utilizar o WebView nativo do sistema, ele não possui um motor de renderização avançado como navegadores tradicionais, o que o torna mais leve e direto ao ponto.
O FOSS Browser permite salvar configurações específicas para cada domínio, o que ajuda a proteger sua privacidade. Para cada site visitado, é possível ativar ou desativar opções como:
- Bloqueador de anúncios (AdBlock);
- Execução de JavaScript;
- Uso de cookies;
- Proteção contra fingerprinting;
- E outras opções personalizáveis.
Para sites que não têm configurações salvas, você pode ajustar um perfil padrão conforme suas preferências.
Mais recursos de privacidade:
- AdBlock integrado, com atualizações automáticas. Você escolhe o que deseja bloquear. As listas são baseadas nos hosts do projeto Steven Black - AdBlock Hosts https://github.com/StevenBlack/hosts
- Bloqueio de cookies de terceiros.
- Bloqueio de banners de consentimento de cookies.
- Habilitar ou desabilitar o preenchimento automático do Android.
- Apagar dados de navegação automaticamente ao sair do app.
- Escolher entre diferentes mecanismos de busca, ou definir um mecanismo personalizado.
- O próprio FOSS Browser não coleta nenhum dado dos usuários https://codeberg.org/Gaukler_Faun/FOSS_Browser/src/branch/master/PRIVACY.md
O FOSS Browser adota o design moderno do Material You, com suporte ao modo claro/escuro do sistema e temas baseados no papel de parede do dispositivo. A interface foi otimizada para uso com uma só mão, com todos os elementos principais localizados na parte inferior da tela.
Recursos adicionais:
- Manter a tela ligada durante a navegação;
- Abrir links em segundo plano;
- Restaurar abas automaticamente ao reiniciar o app.
Gerencie seus favoritos com filtros personalizados. Você pode nomear cada filtro como quiser. Ao pressionar e segurar o ícone de favoritos na barra de ferramentas, terá acesso rápido aos seus sites favoritos.
Gestos Personalizáveis Você pode atribuir quase 20 gestos diferentes à barra de ferramentas e aos seus botões, com suporte a quatro direções por gesto. Também é possível acionar ações ao pressionar e segurar os botões da barra, totalizando até 10 gestos diferentes para controlar o navegador.
Algumas ações disponíveis incluem:
- Carregar o último site acessado;
- Alternar entre abas;
- Recarregar a página;
- Abrir favoritos;
- E muito mais.
-Backup e Restauração
Faça backup de todos os seus dados e configurações importantes (favoritos, histórico, configurações por site, etc.) diretamente no cartão SD. Os backups também podem incluir as configurações gerais do FOSS Browser, e podem ser restaurados em uma instalação nova ou em outro dispositivo, bastando copiar os arquivos de backup.
Link Pra baixar no obtainium : https://codeberg.org/Gaukler_Faun/FOSS_Browser
Fdroid : https://f-droid.org/packages/de.baumann.browser/
https://codeberg.org/Gaukler_Faun/FOSS_Browser
-
 @ 82b30d30:40c6c003
2025-03-17 15:26:29
@ 82b30d30:40c6c003
2025-03-17 15:26:29[3]
[4]
[5]
[6]
[7]
[8]
[9]
[10]
[11]
[12]
[13]
[14]
[15]
[16]
[17]
[18]
[19]
[20]
[21]
[22]
[23]
[24]
[25]
[26]
[27]
[28]
[29]
[30]
[31]
[32]
[33]
-
 @ d34e832d:383f78d0
2025-04-21 01:31:02
@ d34e832d:383f78d0
2025-04-21 01:31:02Optimizing Knowledge Management with Obsidian and the Zettelkasten Method
The Zettelkasten method, which translates to "slip box" in German, is a powerful system for personal knowledge management developed by sociologist Niklas Luhmann. It relies on creating and linking small, self-contained notes that each represent a single idea or thought. These notes are connected through internal references, forming a dense web of knowledge that mirrors how ideas evolve and relate to each other naturally. By writing in small, atomic units, users are encouraged to distill complex concepts into their essence, improving understanding and retention.
Zettelkasten facilitates knowledge retention by encouraging active engagement with information. Instead of passively reading or highlighting, users must rephrase, question, and connect ideas. This process reinforces memory and builds a reusable archive of insights. The method also supports long-term idea development by creating an environment where thoughts grow organically through continuous linking, comparison, and reflection. For researchers and writers, Zettelkasten becomes a dynamic workspace for managing sources, forming arguments, and drafting structured content.
With the rise of digital tools, the Zettelkasten method has found a modern home in applications like Obsidian. Obsidian is a markdown-based note-taking app that allows users to create a network of interlinked notes stored locally on their device. It supports backlinks, graph views, and a customizable interface, making it ideal for implementing Zettelkasten. Unlike paper systems or linear document editors, Obsidian turns a note collection into an interactive, searchable, and scalable knowledge base. This evolution has made it easier than ever to adopt and maintain a Zettelkasten system for academic research, professional writing, and lifelong learning. - Problem Statement: Despite its effectiveness, many users struggle with implementing Zettelkasten in a way that integrates well into their daily routines. This thesis presents a streamlined, efficient setup using Obsidian for optimal results.
1. Install Obsidian
- Download Obsidian from the official website (https://obsidian.md) and install it on your preferred device (Windows, macOS, Linux, or mobile).
- Open the app and create a new Vault, which will serve as the central repository for all your notes.
- Choose a location for your vault. For backup and multi-device access, store it in a synced folder like Dropbox, OneDrive, or iCloud.
2. Folder Structure
Set up a simple, organized folder structure to support the Zettelkasten flow:
00_Templates: Store reusable note templates.01_Source_Material: Notes from books, articles, lectures, etc.02_Rough_Notes: Free-form, early-stage thoughts (optional).03_Main_Notes: Core Zettelkasten notes; each represents a single atomic idea.04_Indexes: Thematic hubs or entry points for exploring related notes.05_Tags: Empty placeholder notes acting as tags for navigation or filtering (optional).
3. Settings Configuration
- Default Location for New Notes: Point to
03_Main_Notes. - Appearance: Choose a legible font and theme; toggle "Readable line length" for better formatting.
- Hotkeys: Assign shortcuts, e.g.:
Ctrl + N: New NoteCtrl + T: Insert Template (after plugin activation)- Core Plugins:
- Enable Templates, Daily Notes (optional), and Backlinks.
- Community Plugins (optional):
- Calendar: For date-based organization.
- Tag Wrangler: For managing and merging tags.
- Advanced Tables, Quick Switcher++, or DataView: For productivity.
4. Create Templates
Under
00_Templates, create templates like:Source Material Template ``` Title: Author: Source: Date: Tags:
Summary: Key Points: Quotes: Reflections: ```
Main Note Template ``` Title: Date Created: Tags:
Idea: Context: Connections: [[Linked Note]] Reflections: ```
Configure the Templates plugin to insert templates quickly using hotkeys.
5. Note-Taking Workflow
Step 1: Capture - In
01_Source_Material, create notes while reading or researching. Summarize, highlight quotes, and reflect in your own words. - Use tags for themes, authors, or concepts (e.g.,#philosophy,#biology).Step 2: Synthesize - In
03_Main_Notes, write atomic notes from your reflections. - Each note should express a single idea clearly (under 500 words). - Use links to reference related notes with[[Note Name]]. - Focus on clarity, brevity, and insight.Step 3: Connect - Link your new idea to related ideas, themes, or sources. - Create notes in
04_Indexesto organize clusters of related content. - Add notes to multiple indexes or link to broader themes using[[#Tag]].
6. Use Tags and Indexes Thoughtfully
- Avoid creating hundreds of tags. Stick to a small set of relevant themes.
- Use
05_Tagsto define and clarify what each tag means. - In
04_Indexes, organize curated lists of related notes. Example:Mindfulness Indexmight link to[[]]notes from psychology, philosophy, and neuroscience.
7. Benefits for Research and Writing
- Streamlines Research: Notes from multiple sources are cross-referenced and easily revisitable.
- Accelerates Writing: Writing becomes an assembly of existing notes instead of starting from scratch.
- Improves Clarity: Breaking down ideas into atomic notes encourages better thinking and clarity.
- Long-Term Retention: Regular review and linking strengthen memory and understanding.
- Reusable Content: Notes can be reused across multiple projects, articles, or books.
8. Maintenance Tips
- Review backlinks weekly to surface forgotten or underdeveloped ideas.
- Refactor or split long notes to maintain atomicity.
- Avoid over-editing old notes; instead, create new ones that build upon earlier thoughts.
With this Obsidian-based Zettelkasten setup, you're not just taking notes — you're cultivating a living knowledge system. Whether you're an academic, writer, student, or lifelong learner, this system adapts to your workflow, grows with your interests, and becomes more powerful the more you use it. Over time, your vault evolves into a personalized knowledge database that supports deeper understanding, creative exploration, and effortless content creation.
- The Zettelkasten Methodology
The Original Zettelkasten Technique: Core Principles & Benefits
The Zettelkasten method (German for "slip box") was developed by sociologist Niklas Luhmann as a tool to manage complex knowledge and boost creativity in writing and research. He credited it with enabling his prolific academic output: over 70 books and hundreds of articles. The brilliance of the system lies in its simplicity, modularity, and organic growth.
🌱 Core Principles of Zettelkasten
1. Atomicity
Each note in the Zettelkasten should express a single idea or concept. This principle ensures clarity, encourages deeper understanding, and makes ideas easier to reuse and connect.
- ✅ Do: “The law of diminishing returns means each additional input yields less output.”
- ❌ Don’t: Combine multiple concepts or quotes into one long note.
Atomic notes are easier to: - Link logically. - Modify independently. - Reuse across different contexts.
2. Linking
Instead of a rigid hierarchy, Zettelkasten thrives on contextual, lateral linking.
- Notes are connected using direct references to other notes.
- Each note becomes part of a network, not a silo.
- Links simulate how human memory works—via associations, not folders.
Example: A note on “Nietzsche’s eternal recurrence” might link to notes on “cyclical time in Buddhism” or “existentialism.”
Benefits: - Emergent structure—patterns and themes arise naturally. - Serendipitous discovery—old ideas resurface via linked paths. - Compound creativity—new combinations emerge from connected thoughts.
3. Simplicity
Luhmann emphasized a low-friction system. His physical slip-box used numbered index cards and manual cross-referencing—no complex categorization.
Simplicity: - Reduces friction between thought and capture. - Makes the system future-proof and easy to maintain. - Encourages writing in your own words, promoting internalization.
Modern Zettelkasten tools (like Obsidian) honor this by: - Allowing bidirectional links (
[[Note Title]]). - Replacing folders with tags and contextual backlinks. - Supporting plain text Markdown format for longevity.
✍️ Benefits of Zettelkasten
📚 For Writing
- Provides a ready-made library of ideas to draw from.
- Writing becomes assembly, not invention—you collect, synthesize, and expand existing notes.
- Encourages idea-driven writing, not source-driven copying.
“Writing is no longer a process of transfer, but of transformation.” — Luhmann
🔍 For Research
- Encourages critical engagement with sources (notes are written in your own words).
- Makes literature review manageable through connected concepts.
- Supports non-linear learning—you follow interesting links, not rigid outlines.
🧠 For Idea Organization
- Keeps ideas alive and evolving through regular linking and revisiting.
- Avoids information rot by focusing on synthesis, not storage.
- Fosters a personal knowledge graph—tailored to how you think.
🧩 Summary Table
| Principle | What it Means | Why it Matters | |---------------|------------------------------------|--------------------------------------| | Atomicity | 1 idea per note | Improves clarity, reuse, and focus | | Linking | Contextual note-to-note links | Encourages discovery and depth | | Simplicity | Low friction, minimal structure | Easy to maintain and long-lasting |
Consider
The original Zettelkasten is more than a note-taking method—it's a thinking partner. By focusing on the quality of thought, it transforms how you learn, create, and connect ideas. Whether used with index cards or modern tools like Obsidian, its core principles remain timeless.
Would you like a visual map or Obsidian-ready template for Luhmann-style Zettelkasten?
- Benefits of Zettelkasten for Writing:
- Streamlines Research: Centralized notes help avoid redundant research across multiple projects.
- Facilitates Long-Form Writing: Accumulated notes serve as building blocks for larger projects.
- Personal Writing Assistant: The evolving network of notes provides quick access to ideas for future writing.
-
Obsidian Setup and Configuration
-
Installing Obsidian: Guide the user through the installation process, emphasizing the free version and its core features.
-
Creating and Organizing a Vault: A vault in Obsidian is the central hub for all your notes. This section provides instructions for setting up a vault and explains the importance of cloud storage for backup and accessibility.
-
Folder Structure: Establish a recommended folder structure:
- Rough Notes: Optional folder for quick thoughts.
- Source Material: Store notes from books, articles, etc.
- Tags: Empty notes used as tags for easy categorization.
- Indexes: Organized collections of notes based on specific topics or themes.
- Templates: Predefined templates for consistent note-taking.
-
Main Notes: The core content of your knowledge base.
-
Settings Configuration:
- Configure default note locations.
- Customize appearance for readability.
- Set up hotkeys for efficient note-taking (e.g., Ctrl+T for template insertion).
- Enable and configure the "Templates" core plugin for consistent note creation.
-
The Note-Taking Process
-
Creating Notes: Guide the user on how to create new notes (Ctrl+O) and insert templates (Ctrl+T). Emphasize the importance of focusing on one idea per note to maintain atomicity.
-
Source Material Notes:
- Record page numbers, quotes, and elaborate on the ideas in your own words.
-
Include metadata such as authorship, publication year, and source references.
-
Main Notes:
- Synthesize ideas from source material.
- Focus on the key takeaways and connections between different ideas.
-
Use internal links ([[Note Name]]) to connect related notes and foster deeper understanding.
-
Tagging Notes:
- Use tags sparingly but effectively.
- Avoid over-complicating tags, focusing on personal interests or key themes.
- Tags act as an index to quickly locate notes.
-
Linking and Organizing Ideas
-
Internal Links and Connections: Demonstrate how internal links help create a web of interconnected ideas. Discuss how linking related concepts and topics can lead to a more holistic understanding.
-
Indexing for Navigation: Show how creating indexes for topics allows for quick access to collections of related notes. Introduce the idea of building thematic indexes for large research projects.
-
Synthesizing Notes for Larger Projects: Explain how to take notes from the Source Material and Main Notes to gradually build drafts for books, essays, or research papers.
-
Best Practices for Obsidian and Zettelkasten
-
Consistency and Simplicity: Emphasize the importance of simplicity in both note-taking and vault organization. Discourage the need for a "perfect" setup, focusing on efficiency and growth over time.
-
Keeping Notes Concise: Encourage users to keep each note under 500 words, focusing on one idea per note. This enhances clarity and makes it easier to synthesize ideas later.
-
Making Notes Readable: Provide tips on formatting for readability: use headings, bullet points, and quotes to break up large blocks of text.
-
Practical Applications of Zettelkasten in Writing
-
Research Projects: Show how to leverage your Zettelkasten system to conduct more efficient and thorough research for academic papers, articles, or blog posts.
-
Book and Essay Writing: Provide examples of how notes in Obsidian can evolve into larger writing projects, from initial drafts to final revisions.
-
Personal Projects and Brainstorming: Illustrate how the Zettelkasten method can be used for creative writing, personal reflections, or brainstorming for new ventures.
-
Case In Point
-
Summary of Findings: Recap the effectiveness of combining the Zettelkasten method with Obsidian for knowledge management, writing, and research.
-
Future Directions: Suggest areas for future exploration, such as integrating other digital tools (e.g., Zotero, Roam Research) into the workflow or expanding the Zettelkasten method into larger organizational systems.
-
References
-
Cite all relevant sources, including academic papers, books, and articles about the Zettelkasten method, Obsidian, and knowledge management.
📘 1. Source Note Template (
Source Note)This template is used when reading books, articles, podcasts, or videos. The goal is to capture contextual metadata and your impressions, not to mindlessly copy.
```markdown
📘 Source: {{title}}
Type: Book / Article / Video / Podcast
Author: {{author}}
Published: {{date}}
Source Link: Link
Tags: #source #{{topic}}
Related Notes: [[ ]]
🧠 Summary
A brief summary of the source in your own words.
🧩 Key Ideas
- Idea 1
- Idea 2
- Idea 3
🔎 Quotes & Passages
“...”
— Page X🗺️ Linked Notes
- [[Note about idea X]]
- [[Historical context of Y]]
📝 Your Thoughts
- Agreement? Disagreement?
- How does this relate to your current research?
- Ideas it sparked? ```
🧠 2. Main/Idea Note Template (
Zettelor Permanent Note)Each idea should be atomic, clearly written in your own words, and linked to related ideas. This is the core of your Zettelkasten.
```markdown
💡 {{Descriptive Title}}
ID: {{YYYYMMDDHHMM}}
Tags: #zettel #{{topic}}
Linked From: [[ ]]
🧠 Core Idea
Write a single, concise idea in your own words. This should be a self-contained statement or argument.
💬 Explanation / Elaboration
Explain why this idea matters or how it connects to broader themes. Use metaphors, contrast, or short examples.
🔗 Related Notes
- [[Related idea A]]
- [[Contrasting concept B]]
- [[Supports claim C]] ```
Tip: Use the ID convention (e.g.
202504201013) to uniquely identify each note.
🧪 3. Research Summary Note (
Literature Noteor Topic Overview)Use this when you're studying a broader concept or topic and summarizing multiple inputs (e.g., a research question or paper theme).
```markdown
🧪 Research Summary: {{Topic}}
Tags: #summary #research #{{subject}}
Created: {{date}}
Status: Draft / Ongoing / Complete
📌 Topic Overview
Brief definition or framing of the research question.
📚 Key Sources
- [[Author, Title]] — key takeaway.
- [[Article Title]] — significant argument.
🧩 Key Themes
- Theme 1: summary + relevant note links.
- Theme 2: contrasting perspective.
🧠 Emerging Ideas
- New insights or patterns you're noticing.
- Questions that remain unanswered.
🔗 Related Notes
- [[Main idea note]]
- [[Potential application note]]
- [[Philosophical implication]] ```
🔄 How They Interact
- Source Notes → inspire → Main Notes
- Main Notes → get linked into → Research Summaries
- Research Summaries → help generate → new Main Notes
“You don’t collect knowledge, you build it — one link at a time.”
-
 @ 5d4b6c8d:8a1c1ee3
2025-04-21 00:28:50
@ 5d4b6c8d:8a1c1ee3
2025-04-21 00:28:50I was just about to get into bed last night, after recording the Stacker Sports Pod and hiding Easter Eggs, when I remembered to check my step count. As often happens, I was stupidly short of my goal: just 7 steps this time.
My step counter is not nearly so precise as to actually record seven steps, so I knew it was either go to bed or do some chores for a bit to get enough more steps to register.
Well, I got the steps easily enough, only to discover the dog had an accident on the carpet that I now needed to clean up...and it turned out we had run out of the cleaning supplies we use for such incidents. So, I had to do some basic chemistry at midnight to mix up a makeshift cleaning solution to keep the carpet from staining and wait long enough for it to do its magic before drying it out.
Had I just taken the L on the steps, the dog would have just fallen asleep and peed in the morning. I doubt the Workit payout will prove to be worth the hassle this time
originally posted at https://stacker.news/items/950750
-
 @ 06639a38:655f8f71
2025-03-17 14:59:40
@ 06639a38:655f8f71
2025-03-17 14:59:40https://ccns.nostrver.se is a (Drupal powered) website that I started to build in January 2024 (source on Github and Gitlab). It's a fork of an earlier (abandoned) project https://cchs.social/.
Currently CCNS is a link aggregration website and for now it's only my who is using it to save and share Nostr related links. When you post a new link, you have the option to cross-post it as a Nostr note (example here).Kind 39700
Last month Jurjen and Abir have started to work on a social bookmark client built with Nostr (inspired by Del.icio.us from the past). Earlier this month they changed to event kind 39700 for broadcasting the Nostr event with the bookmark / link data accross the network. They did this because Sep already created a social bookmark like client called Pinja when fiatjaf raised this idea.
With these developments to me it was very obvious to integrate the feature that new created CCNS links are now also published as kind 39700 events to the Nostr network. This means that links are now also distributed on multiple relays as kind 39700 events and are accessible in multiple clients (Yumyume and Pinja).
Here you can see the same data, from left to right:

Structure
The current data structure for the 39700 kind looks as follow:
- "id": "event_id"
- "pubkey": "pubkey author"
- "created_at": unix_timestamp
- "kind": 39700
- "tags":
- "description", "description text here"
- "d", "unique-slug-value"
- "t", "hashtag"
- "content": "https://book_mark_url"
- "sig": "signature"
As there is no NIP (yet) for this event kind, I see some possible improvements:
- Use the bookmark URL as
dtag so it can be used as a unique identifier for every client - Use the content field for the description
- Use the
atag for an addressable event following NIP-01:["a", "39700:pubkey_of_author:", recommended_relay_url_optional]
On short-term I don't have any plans to developer CCNS further, as most of my attention goes to the development of the Nostr-PHP library and Drupal related contribs using that library. That said, CCNS is a Drupal project but all the Nostr stuff is done client-side (Javascript) with NDK and Nostr-PHP is not used (maybe this will change in the future).
-
 @ dbbd7125:07ff73f8
2025-03-16 05:57:18
@ dbbd7125:07ff73f8
2025-03-16 05:57:18https://weibo.com/2169989911/5137332916715995
-
 @ dbbd7125:07ff73f8
2025-03-16 05:48:12
@ dbbd7125:07ff73f8
2025-03-16 05:48:12https://weibo.com/5324708177/5144638344398410
-
 @ 21335073:a244b1ad
2025-03-15 23:00:40
@ 21335073:a244b1ad
2025-03-15 23:00:40I want to see Nostr succeed. If you can think of a way I can help make that happen, I’m open to it. I’d like your suggestions.
My schedule’s shifting soon, and I could volunteer a few hours a week to a Nostr project. I won’t have more total time, but how I use it will change.
Why help? I care about freedom. Nostr’s one of the most powerful freedom tools I’ve seen in my lifetime. If I believe that, I should act on it.
I don’t care about money or sats. I’m not rich, I don’t have extra cash. That doesn’t drive me—freedom does. I’m volunteering, not asking for pay.
I’m not here for clout. I’ve had enough spotlight in my life; it doesn’t move me. If I wanted clout, I’d be on Twitter dropping basic takes. Clout’s easy. Freedom’s hard. I’d rather help anonymously. No speaking at events—small meetups are cool for the vibe, but big conferences? Not my thing. I’ll never hit a huge Bitcoin conference. It’s just not my scene.
That said, I could be convinced to step up if it’d really boost Nostr—as long as it’s legal and gets results.
In this space, I’d watch for social engineering. I watch out for it. I’m not here to make friends, just to help. No shade—you all seem great—but I’ve got a full life and awesome friends irl. I don’t need your crew or to be online cool. Connect anonymously if you want; I’d encourage it.
I’m sick of watching other social media alternatives grow while Nostr kinda stalls. I could trash-talk, but I’d rather do something useful.
Skills? I’m good at spotting social media problems and finding possible solutions. I won’t overhype myself—that’s weird—but if you’re responding, you probably see something in me. Perhaps you see something that I don’t see in myself.
If you need help now or later with Nostr projects, reach out. Nostr only—nothing else. Anonymous contact’s fine. Even just a suggestion on how I can pitch in, no project attached, works too. 💜
Creeps or harassment will get blocked or I’ll nuke my simplex code if it becomes a problem.
https://simplex.chat/contact#/?v=2-4&smp=smp%3A%2F%2FSkIkI6EPd2D63F4xFKfHk7I1UGZVNn6k1QWZ5rcyr6w%3D%40smp9.simplex.im%2FbI99B3KuYduH8jDr9ZwyhcSxm2UuR7j0%23%2F%3Fv%3D1-2%26dh%3DMCowBQYDK2VuAyEAS9C-zPzqW41PKySfPCEizcXb1QCus6AyDkTTjfyMIRM%253D%26srv%3Djssqzccmrcws6bhmn77vgmhfjmhwlyr3u7puw4erkyoosywgl67slqqd.onion
-
 @ 4bcc0228:299141d7
2025-03-14 04:01:55
@ 4bcc0228:299141d7
2025-03-14 04:01:55GeminiのDeep Researchiで今日の昼ご飯に良いレシピを調べてもらった。
プロンプトはこんな感じ。
今日のお昼ご飯に何が適しているか調査してください。
要望として以下のものがあります。
・麺類が良い
・自宅で調理可能なものが良い
・自宅にはパスタの乾麺とそうめんがある
・パスタソース等はない
・自宅近くにコンビニがあるので、最悪そこで調達することは可能だが、できる限り避けたい
今日のお昼ご飯、お家にある麺で簡単レシピ
はじめに:悩ましいお昼ご飯を、手軽な麺料理で解決!
毎日のお昼ご飯、何にしようか悩みますよね。特に時間がない時や、わざわざ買い物に行くのが面倒な時、お家にあるものでパッと美味しいものが作れたら最高です。このレポートでは、そんなあなたのために、ご自宅にある乾麺のパスタとそうめんを使った、簡単で美味しいお昼ご飯のアイデアをご紹介します。パスタソースがなくても大丈夫!特別な材料がなくても、身近な調味料で本格的な味わいが楽しめます。パスタもそうめんも、アレンジ次第で様々な表情を見せてくれる万能な食材です。このレポートを読めば、きっと今日のお昼ご飯の悩みが解消され、手軽で満足できる一品が見つかるはずです。
パスタの力:ソースなしでも美味しい、簡単パスタレシピ
パスタといえば、お店で食べるような本格的なソースがないと美味しくないと思っていませんか?実は、ご家庭にある調味料を工夫するだけで、簡単に絶品パスタが作れるんです。ここでは、特別な材料は使わず、あなたのキッチンにあるかもしれないもので作れる、とっておきのパスタレシピをご紹介します。
ごま油香る!和風にんにくパスタ
いつものパスタに、ちょっと意外な和の風味を加えてみませんか?ごま油とにんにくの香りが食欲をそそる、簡単なのに本格的な味わいの和風パスタです。1
作り方- にんにく1かけをみじん切りにします。鍋にお湯を沸かし、スパゲティ80gを表示時間より1分短く茹で、水気を切ります。茹で汁を大さじ2ほど取っておきましょう。
- フライパンにごま油大さじ1を入れ、中火で熱します。にんにくから香りが立ったらスパゲティを加え、取っておいた茹で汁と3倍濃縮めんつゆ大さじ1を加えて混ぜ合わせます。
- 塩こしょう少々で味を調えたら完成です。
このレシピのポイントは、何と言ってもごま油の香ばしさ。加熱することで風味が引き立ち、食欲をそそります。また、めんつゆのうま味がパスタ全体に広がり、シンプルながらも奥深い味わいに仕上がります。茹で汁を加えることで、麺と調味料がよくなじみ、一体感のある美味しさになります。普段とは違うパスタを試してみたい時におすすめです。
アレンジ:お好みで、ラー油を少し加えてピリ辛にしたり、乾燥パセリや刻みのりを散らして風味をプラスするのもおすすめです。バター醤油のシンプルパスタ
材料はシンプルなのに、なぜか後を引く美味しさ。バターと醤油の組み合わせは、まさに魔法です。2
作り方- 鍋に湯を沸かし、塩(分量外)を少々入れ、スパゲティ100gを半分に折って袋の表示時間通りに茹でます。茹で汁を大さじ2ほど取り分け、スパゲティは水気を切ります。
- フライパンをさっと洗い、有塩バター10gを入れて中火で熱します。バターが溶けたらスパゲティ、取り分けた茹で汁、醤油小さじ2を加えて炒め合わせます。
- 器に盛り付け、お好みで刻みのりを散らしたら完成です。
バターのコクと醤油の香ばしさが絶妙にマッチした、シンプルながらも奥深い味わいのパスタです。茹で汁を加えることで、パサつきを防ぎ、しっとりとした仕上がりになります。刻みのりの風味がアクセントになり、食欲をそそります。忙しいけれど美味しいものが食べたい、そんな時におすすめの一品です。お弁当にもぴったりですよ。
アレンジ:仕上げに粗挽き黒胡椒を振ると、味が引き締まります。電子レンジで簡単!ツナとガーリックのオイルパスタ風
火を使わずに、電子レンジでパパッと作れるお手軽パスタです。3
作り方- 耐熱ボウルに早ゆでスパゲッティ(1.6mm)100gを半分に折って入れ、シーチキンマイルド1缶(油を切らずに)、水適量(パスタが浸る程度)、おろしにんにく少々を加えます。ラップをせずに600Wの電子レンジで7分加熱します。
- 加熱後、めんつゆ大さじ1、オリーブ油小さじ1、バター5gを混ぜ合わせ、醤油少々、こしょう少々で味を調えます。
- 器に盛り付け、お好みで粉チーズ、黒こしょうをかけたら完成です。
電子レンジで麺を茹でることで、時短になり、洗い物も少なく済むのが嬉しいポイントです。ツナの旨味とニンニクの風味が食欲をそそり、めんつゆとバターのコクが絶妙なハーモニーを生み出します。忙しいけれど手軽に済ませたいランチに最適です。
アレンジ:加熱前に、冷凍のミックスベジタブルなどを加えても彩り豊かになります。シンプル is ベスト!オイルとニンニクの基本パスタ
材料はシンプルながらも、素材の味が際立つ奥深い味わいのパスタです。4
作り方- にんにく1かけを薄切りにします。お好みで赤唐辛子を少量用意します(輪切りでも種を取り除いたものでも)。鍋にお湯を沸かし、スパゲティ80gを表示時間より少し短く茹でます。茹で汁を大さじ2ほど取っておきます。
- フライパンにオリーブオイル大さじ2を入れ、弱火で熱します。にんにくを加え、焦がさないようにじっくりと炒めます。にんにくが薄く色づき、香りが立ったら、お好みで赤唐辛子を加えます。
- 茹で上がったスパゲティをフライパンに加え、取っておいた茹で汁を加えてよく混ぜ合わせます。塩、こしょうで味を調えたら完成です。お好みで刻みパセリを散らします。
このパスタの美味しさの秘訣は、じっくりと炒めたにんにくの香りと、良質なオリーブオイルの風味です。シンプルだからこそ、素材の味がダイレクトに伝わります。茹で汁を加えることで、オイルと麺が乳化し、より一体感のある仕上がりになります。
アレンジ:ベーコンやきのこなどを加えても美味しくいただけます。また、仕上げに粉チーズを振ると、コクが増します。そうめんの魅力:軽やかで爽やかなランチアイデア
暑い日や、あっさりとしたものが食べたい時にぴったりのそうめん。いつものめんつゆで食べるのも美味しいですが、少しアレンジを加えるだけで、全く違う味わいが楽しめます。ここでは、簡単にできるそうめんのアレンジレシピをご紹介します。
定番の美味しさ!シンプルめんつゆでいただくそうめん
まずは基本から。そうめん本来の美味しさを味わう、シンプルながらも飽きのこない食べ方です。10
作り方- 鍋にたっぷりの湯を沸かし、そうめん1束(約80~100g)を入れ、表示時間通りに茹でます。
- 茹で上がったそうめんをザルにあげ、流水でよく洗い、ぬめりを取り除きます。しっかりと水気を切って器に盛り付けます。
- 市販のめんつゆを用意し、お好みでネギやミョウガ、大葉などの薬味を添えていただきます。
冷たくてつるつるとしたそうめんは、食欲がない時でも食べやすく、暑い季節には特に美味しく感じられます。めんつゆの優しい味わいと、薬味の爽やかな香りが食欲をそそります。
アレンジ:めんつゆに、すりおろし生姜やラー油、ごま油などを加えると、風味豊かな味わいに変わります。15ちょっとアレンジ!簡単そうめんバリエーション
いつものそうめんに、ちょっとした工夫を加えるだけで、様々な味が楽しめます。
- ごま油香る塩そうめん 10:茹でたそうめんにごま油と塩を和えるだけで、風味豊かな一品に。お好みでネギや白ごまを加えても美味しいです。
- トマトとツナのそうめん 11:茹でて冷やしたそうめんに、ツナ缶とカットしたトマトを乗せ、めんつゆをかけるだけ。大葉や刻みのりを添えると、さらに美味しくなります。
- 釜玉風そうめん 10:熱々の茹でたてのそうめんに、生卵と醤油(またはめんつゆ)を絡めるだけ。お好みでネギやかつお節を添えて。
- 韓国風ピリ辛そうめん 10:茹でて冷やしたそうめんに、きゅうりやキムチを乗せ、コチュジャンやごま油を加えたピリ辛のタレをかけます。
- バター醤油そうめん 12:茹でて水気を切ったそうめんに、バターと醤油を絡めるだけ。シンプルながらも後引く味わいです。
これらのアレンジは、どれも手軽にできるものばかり。冷蔵庫にあるものや、ちょっとした調味料を加えるだけで、普段のそうめんが大変身します。
温かくいただく!あったかそうめんレシピ
そうめんは冷たいイメージがありますが、温かくしても美味しくいただけます。
- かきたまにゅうめん 12:だし汁を温め、茹でたそうめんを入れ、溶き卵を流し入れてさっと煮れば完成。優しい味わいで、寒い日にもぴったりです。
- わかめスープそうめん 12:市販のわかめスープに茹でたそうめんを入れるだけで、手軽な一品に。ごま油を少し加えると風味がアップします。
- 親子にゅうめん 19:だし汁で鶏肉と玉ねぎを煮て、茹でたそうめんを加え、溶き卵でとじます。栄養も満点で、満足感のある一品です。
温かいそうめんは、冷たいそうめんとはまた違った優しい味わいが楽しめます。体調が優れない時や、ほっこり温まりたい時におすすめです。
いざという時のコンビニ頼み:ちょい足し食材でさらに美味しく
できる限り避けたいとのことでしたが、もし少しだけ何かプラスしたいと思った時のために、コンビニで手軽に手に入るおすすめ食材をご紹介します。
- にんにく:チューブタイプでも、カットされたものでも。パスタの風味を格段にアップできます。
- ラー油:ピリ辛好きにはたまらない。そうめんやパスタに少し加えるだけで、味が引き締まります。
- ツナ缶・鮭フレーク:手軽にタンパク質をプラスできます。パスタにもそうめんにも合います。
- 卵:パスタのトッピングにしたり、釜玉風そうめんにしたり。栄養も満点です。
- ネギ:刻みネギが便利。そうめんやパスタの薬味に。
- めんつゆ:もし自宅にない場合は、コンビニで手軽に購入できます。そうめんの基本としてあると便利です。
- バター:パスタやそうめんにコクをプラスできます。
- 醤油:バター醤油パスタや、そうめんの味付けに。
これらの食材は、少量から購入できるので、必要な時に少しだけ買い足すことができます。
結論:今日のお昼ご飯は、お家にある麺で決まり!
このレポートでは、ご自宅にある乾麺のパスタとそうめんを使った、簡単で美味しいお昼ご飯のアイデアをいくつかご紹介しました。特別なソースや材料がなくても、工夫次第で様々な美味しい麺料理が楽しめます。パスタは、ごま油やバター醤油でシンプルに、また電子レンジを使えばさらに手軽に調理できます。そうめんは、定番のめんつゆでいただくのはもちろん、ちょっとしたアレンジを加えるだけで、飽きずに楽しむことができます。温かくしていただくのもおすすめです。
今日のお昼ご飯、何にしようか迷ったら、ぜひこのレポートでご紹介したレシピを参考に、お家にある麺で美味しい一品を作ってみてください。きっと、手軽さと美味しさに満足できるはずです。| レシピ名 | 主な材料 | アレンジ例 | 調理方法 | 参照元 | | :---- | :---- | :---- | :---- | :---- | | ごま油香る!和風にんにくパスタ | スパゲティ、にんにく、ごま油、めんつゆ | ラー油、刻みのり | 炒め | 1 | | バター醤油のシンプルパスタ | スパゲティ、バター、醤油 | 黒胡椒 | 炒め | 2 | | 電子レンジで簡単!ツナとガーリックのオイルパスタ風 | スパゲティ、ツナ、にんにく、めんつゆ、オリーブ油、バター | 冷凍野菜 | 電子レンジ | 3 | | シンプル is ベスト!オイルとニンニクの基本パスタ | スパゲティ、にんにく、オリーブ油 | 赤唐辛子、ベーコン、きのこ | 炒め | 4 |
| レシピ名 | 主な味付け | 主な材料 | 参照元 | | :---- | :---- | :---- | :---- | | シンプルめんつゆそうめん | めんつゆ | そうめん | 10-13-18 | | ごま油香る塩そうめん | ごま油、塩 | そうめん | 10 | | トマトとツナのそうめん | めんつゆ | そうめん、トマト、ツナ | 11 | | 釜玉風そうめん | 醤油またはめんつゆ | そうめん、卵 | 10 | | 温玉そうめん(にゅうめん) | だし汁、醤油、みりん | そうめん、卵 | 12 | | バター醤油そうめん | バター、醤油 | そうめん | 12 |
引用文献
1. ごま油がポイント! にんにく風味の和風パスタのレシピ動画 ..., 3月 14, 2025にアクセス、 https://delishkitchen.tv/recipes/167590676693778924
2. 簡単! 具なしバター醤油パスタのレシピ動画・作り方 | デリッシュ ..., 3月 14, 2025にアクセス、 https://delishkitchen.tv/recipes/525069302701752674
3. 包丁なし簡単 ツナ缶油ごと使って作るやみつきパスタ | セブンプレミアム公式, 3月 14, 2025にアクセス、 https://7premium.jp/recipe/search/detail?id=9949
4. 材料は…たったこれだけ!?超簡単なのに絶品な「シンプルパスタ」レシピ帖 | キナリノ, 3月 14, 2025にアクセス、 https://kinarino.jp/cat4/33954
5. 【作り置き】材料5つだけ!簡単ペペロンチーノソース - macaroni, 3月 14, 2025にアクセス、 https://macaro-ni.jp/53793
6. にんにく香る!簡単に作れる基本のペペロンチーノの作り方 | デ ..., 3月 14, 2025にアクセス、 https://delishkitchen.tv/recipes/171524636704506348
7. 簡単・本格・失敗なし!ペペロンチーノ基本のレシピ - Nadia, 3月 14, 2025にアクセス、 https://oceans-nadia.com/user/253470/recipe/440736
8. 【乳化の極意を解説】にんにく香る本格ペペロンチーノレシピ。プロの技で旨みたっぷり! | 三越伊勢丹の食メディア | FOODIE(フーディー), 3月 14, 2025にアクセス、 https://mi-journey.jp/foodie/77708/
9. すぐにできる! 具なしペペロンチーノのレシピ動画・作り方 | デリッシュキッチン, 3月 14, 2025にアクセス、 https://delishkitchen.tv/recipes/301564582369953005
10. 毎日食べても飽きない【そうめん】レシピ20選!余ったそうめんの ..., 3月 14, 2025にアクセス、 https://www.kurashiru.com/articles/336924d1-3266-4050-bc51-e79a6383400f
11. 【そうめん】アレンジ人気レシピ45選!15分以内で簡単 - Nadia, 3月 14, 2025にアクセス、 https://oceans-nadia.com/user/10022/article/3242
12. 子どもも喜ぶ そうめんを使った人気のレシピ20選の人気レシピ ..., 3月 14, 2025にアクセス、 https://delishkitchen.tv/curations/9367
13. アレンジそうめんの簡単レシピ・人気料理 1位~20位, 3月 14, 2025にアクセス、 https://recipe.rakuten.co.jp/category/16-154-918/simple/
14. もうゆでない!絶品そうめん作り方!火を使わず簡単 つゆもレンジにおまかせ つゆのアレンジも紹介しています - YouTube, 3月 14, 2025にアクセス、 https://m.youtube.com/watch?v=LyChkGwtH4A\&pp=ygUiI-OCsOODqeOCueOCseODvOOCrTEwMOWdh-WFpeOCjOeJqQ%3D%3D
15. そうめんつゆの基本&アレンジレシピ16選!人気のおすすめちょい足しも - マカロニ, 3月 14, 2025にアクセス、 https://macaro-ni.jp/32748
16. そうめん&つゆのアレンジレシピ20選を一挙ご紹介! - デリッシュキッチン, 3月 14, 2025にアクセス、 https://delishkitchen.tv/articles/1048
17. めんつゆレシピをご紹介!料理にめんつゆ|だし・かつお節のヤマキ, 3月 14, 2025にアクセス、 https://www.yamaki.co.jp/mentsuyu/recipe/
18. めんつゆを使った簡単アレンジレシピ!基本の料理から「かえし」を使ったレシピも紹介, 3月 14, 2025にアクセス、 https://www.sobahonda.co.jp/blog/mentsuyu_arrange/
19. 【そうめん】定番からアレンジまで 激旨な人気レシピランキング (全332品) - デリッシュキッチン, 3月 14, 2025にアクセス、 https://delishkitchen.tv/categories/3058
20. 【アレンジ自在!そうめんレシピ】バラエティ豊かな人気レシピ70選 - デリッシュキッチン, 3月 14, 2025にアクセス、 https://delishkitchen.tv/curations/7216 -
 @ c631e267:c2b78d3e
2025-04-20 19:54:32
@ c631e267:c2b78d3e
2025-04-20 19:54:32Es ist völlig unbestritten, dass der Angriff der russischen Armee auf die Ukraine im Februar 2022 strikt zu verurteilen ist. Ebenso unbestritten ist Russland unter Wladimir Putin keine brillante Demokratie. Aus diesen Tatsachen lässt sich jedoch nicht das finstere Bild des russischen Präsidenten – und erst recht nicht des Landes – begründen, das uns durchweg vorgesetzt wird und den Kern des aktuellen europäischen Bedrohungs-Szenarios darstellt. Da müssen wir schon etwas genauer hinschauen.
Der vorliegende Artikel versucht derweil nicht, den Einsatz von Gewalt oder die Verletzung von Menschenrechten zu rechtfertigen oder zu entschuldigen – ganz im Gegenteil. Dass jedoch der Verdacht des «Putinverstehers» sofort latent im Raume steht, verdeutlicht, was beim Thema «Russland» passiert: Meinungsmache und Manipulation.
Angesichts der mentalen Mobilmachung seitens Politik und Medien sowie des Bestrebens, einen bevorstehenden Krieg mit Russland geradezu herbeizureden, ist es notwendig, dieser fatalen Entwicklung entgegenzutreten. Wenn wir uns nur ein wenig von der herrschenden Schwarz-Weiß-Malerei freimachen, tauchen automatisch Fragen auf, die Risse im offiziellen Narrativ enthüllen. Grund genug, nachzuhaken.
Wer sich schon länger auch abseits der Staats- und sogenannten Leitmedien informiert, der wird in diesem Artikel vermutlich nicht viel Neues erfahren. Andere könnten hier ein paar unbekannte oder vergessene Aspekte entdecken. Möglicherweise klärt sich in diesem Kontext die Wahrnehmung der aktuellen (unserer eigenen!) Situation ein wenig.
Manipulation erkennen
Corona-«Pandemie», menschengemachter Klimawandel oder auch Ukraine-Krieg: Jede Menge Krisen, und für alle gibt es ein offizielles Narrativ, dessen Hinterfragung unerwünscht ist. Nun ist aber ein Narrativ einfach eine Erzählung, eine Geschichte (Latein: «narratio») und kein Tatsachenbericht. Und so wie ein Märchen soll auch das Narrativ eine Botschaft vermitteln.
Über die Methoden der Manipulation ist viel geschrieben worden, sowohl in Bezug auf das Individuum als auch auf die Massen. Sehr wertvolle Tipps dazu, wie man Manipulationen durchschauen kann, gibt ein Büchlein [1] von Albrecht Müller, dem Herausgeber der NachDenkSeiten.
Die Sprache selber eignet sich perfekt für die Manipulation. Beispielsweise kann die Wortwahl Bewertungen mitschwingen lassen, regelmäßiges Wiederholen (gerne auch von verschiedenen Seiten) lässt Dinge irgendwann «wahr» erscheinen, Übertreibungen fallen auf und hinterlassen wenigstens eine Spur im Gedächtnis, genauso wie Andeutungen. Belege spielen dabei keine Rolle.
Es gibt auffällig viele Sprachregelungen, die offenbar irgendwo getroffen und irgendwie koordiniert werden. Oder alle Redenschreiber und alle Medien kopieren sich neuerdings permanent gegenseitig. Welchen Zweck hat es wohl, wenn der Krieg in der Ukraine durchgängig und quasi wörtlich als «russischer Angriffskrieg auf die Ukraine» bezeichnet wird? Obwohl das in der Sache richtig ist, deutet die Art der Verwendung auf gezielte Beeinflussung hin und soll vor allem das Feindbild zementieren.
Sprachregelungen dienen oft der Absicherung einer einseitigen Darstellung. Das Gleiche gilt für das Verkürzen von Informationen bis hin zum hartnäckigen Verschweigen ganzer Themenbereiche. Auch hierfür gibt es rund um den Ukraine-Konflikt viele gute Beispiele.
Das gewünschte Ergebnis solcher Methoden ist eine Schwarz-Weiß-Malerei, bei der einer eindeutig als «der Böse» markiert ist und die anderen automatisch «die Guten» sind. Das ist praktisch und demonstriert gleichzeitig ein weiteres Manipulationswerkzeug: die Verwendung von Doppelstandards. Wenn man es schafft, bei wichtigen Themen regelmäßig mit zweierlei Maß zu messen, ohne dass das Publikum protestiert, dann hat man freie Bahn.
Experten zu bemühen, um bestimmte Sachverhalte zu erläutern, ist sicher sinnvoll, kann aber ebenso missbraucht werden, schon allein durch die Auswahl der jeweiligen Spezialisten. Seit «Corona» werden viele erfahrene und ehemals hoch angesehene Fachleute wegen der «falschen Meinung» diffamiert und gecancelt. [2] Das ist nicht nur ein brutaler Umgang mit Menschen, sondern auch eine extreme Form, die öffentliche Meinung zu steuern.
Wann immer wir also erkennen (weil wir aufmerksam waren), dass wir bei einem bestimmten Thema manipuliert werden, dann sind zwei logische und notwendige Fragen: Warum? Und was ist denn richtig? In unserem Russland-Kontext haben die Antworten darauf viel mit Geopolitik und Geschichte zu tun.
Ist Russland aggressiv und expansiv?
Angeblich plant Russland, europäische NATO-Staaten anzugreifen, nach dem Motto: «Zuerst die Ukraine, dann den Rest». In Deutschland weiß man dafür sogar das Datum: «Wir müssen bis 2029 kriegstüchtig sein», versichert Verteidigungsminister Pistorius.
Historisch gesehen ist es allerdings eher umgekehrt: Russland, bzw. die Sowjetunion, ist bereits dreimal von Westeuropa aus militärisch angegriffen worden. Die Feldzüge Napoleons, des deutschen Kaiserreichs und Nazi-Deutschlands haben Millionen Menschen das Leben gekostet. Bei dem ausdrücklichen Vernichtungskrieg ab 1941 kam es außerdem zu Brutalitäten wie der zweieinhalbjährigen Belagerung Leningrads (heute St. Petersburg) durch Hitlers Wehrmacht. Deren Ziel, die Bevölkerung auszuhungern, wurde erreicht: über eine Million tote Zivilisten.
Trotz dieser Erfahrungen stimmte Michail Gorbatschow 1990 der deutschen Wiedervereinigung zu und die Sowjetunion zog ihre Truppen aus Osteuropa zurück (vgl. Abb. 1). Der Warschauer Pakt wurde aufgelöst, der Kalte Krieg formell beendet. Die Sowjets erhielten damals von führenden westlichen Politikern die Zusicherung, dass sich die NATO «keinen Zentimeter ostwärts» ausdehnen würde, das ist dokumentiert. [3]

Expandiert ist die NATO trotzdem, und zwar bis an Russlands Grenzen (vgl. Abb. 2). Laut dem Politikberater Jeffrey Sachs handelt es sich dabei um ein langfristiges US-Projekt, das von Anfang an die Ukraine und Georgien mit einschloss. Offiziell wurde der Beitritt beiden Staaten 2008 angeboten. In jedem Fall könnte die massive Ost-Erweiterung seit 1999 aus russischer Sicht nicht nur als Vertrauensbruch, sondern durchaus auch als aggressiv betrachtet werden.

Russland hat den europäischen Staaten mehrfach die Hand ausgestreckt [4] für ein friedliches Zusammenleben und den «Aufbau des europäischen Hauses». Präsident Putin sei «in seiner ersten Amtszeit eine Chance für Europa» gewesen, urteilt die Journalistin und langjährige Russland-Korrespondentin der ARD, Gabriele Krone-Schmalz. Er habe damals viele positive Signale Richtung Westen gesendet.
Die Europäer jedoch waren scheinbar an einer Partnerschaft mit dem kontinentalen Nachbarn weniger interessiert als an der mit dem transatlantischen Hegemon. Sie verkennen bis heute, dass eine gedeihliche Zusammenarbeit in Eurasien eine Gefahr für die USA und deren bekundetes Bestreben ist, die «einzige Weltmacht» zu sein – «Full Spectrum Dominance» [5] nannte das Pentagon das. Statt einem neuen Kalten Krieg entgegenzuarbeiten, ließen sich europäische Staaten selber in völkerrechtswidrige «US-dominierte Angriffskriege» [6] verwickeln, wie in Serbien, Afghanistan, dem Irak, Libyen oder Syrien. Diese werden aber selten so benannt.

Speziell den Deutschen stünde außer einer Portion Realismus auch etwas mehr Dankbarkeit gut zu Gesicht. Das Geschichtsbewusstsein der Mehrheit scheint doch recht selektiv und das Selbstbewusstsein einiger etwas desorientiert zu sein. Bekanntermaßen waren es die Soldaten der sowjetischen Roten Armee, die unter hohen Opfern 1945 Deutschland «vom Faschismus befreit» haben. Bei den Gedenkfeiern zu 80 Jahren Kriegsende will jedoch das Auswärtige Amt – noch unter der Diplomatie-Expertin Baerbock, die sich schon länger offiziell im Krieg mit Russland wähnt, – nun keine Russen sehen: Sie sollen notfalls rausgeschmissen werden.
«Die Grundsatzfrage lautet: Geht es Russland um einen angemessenen Platz in einer globalen Sicherheitsarchitektur, oder ist Moskau schon seit langem auf einem imperialistischen Trip, der befürchten lassen muss, dass die Russen in fünf Jahren in Berlin stehen?»
So bringt Gabriele Krone-Schmalz [7] die eigentliche Frage auf den Punkt, die zur Einschätzung der Situation letztlich auch jeder für sich beantworten muss.
Was ist los in der Ukraine?
In der internationalen Politik geht es nie um Demokratie oder Menschenrechte, sondern immer um Interessen von Staaten. Diese These stammt von Egon Bahr, einem der Architekten der deutschen Ostpolitik des «Wandels durch Annäherung» aus den 1960er und 70er Jahren. Sie trifft auch auf den Ukraine-Konflikt zu, den handfeste geostrategische und wirtschaftliche Interessen beherrschen, obwohl dort angeblich «unsere Demokratie» verteidigt wird.
Es ist ein wesentliches Element des Ukraine-Narrativs und Teil der Manipulation, die Vorgeschichte des Krieges wegzulassen – mindestens die vor der russischen «Annexion» der Halbinsel Krim im März 2014, aber oft sogar komplett diejenige vor der Invasion Ende Februar 2022. Das Thema ist komplex, aber einige Aspekte, die für eine Beurteilung nicht unwichtig sind, will ich wenigstens kurz skizzieren. [8]
Das Gebiet der heutigen Ukraine und Russlands – die übrigens in der «Kiewer Rus» gemeinsame Wurzeln haben – hat der britische Geostratege Halford Mackinder bereits 1904 als eurasisches «Heartland» bezeichnet, dessen Kontrolle er eine große Bedeutung für die imperiale Strategie Großbritanniens zumaß. Für den ehemaligen Sicherheits- und außenpolitischen Berater mehrerer US-amerikanischer Präsidenten und Mitgründer der Trilateralen Kommission, Zbigniew Brzezinski, war die Ukraine nach der Auflösung der Sowjetunion ein wichtiger Spielstein auf dem «eurasischen Schachbrett», wegen seiner Nähe zu Russland, seiner Bodenschätze und seines Zugangs zum Schwarzen Meer.
Die Ukraine ist seit langem ein gespaltenes Land. Historisch zerrissen als Spielball externer Interessen und geprägt von ethnischen, kulturellen, religiösen und geografischen Unterschieden existiert bis heute, grob gesagt, eine Ost-West-Spaltung, welche die Suche nach einer nationalen Identität stark erschwert.
Insbesondere im Zuge der beiden Weltkriege sowie der Russischen Revolution entstanden tiefe Risse in der Bevölkerung. Ukrainer kämpften gegen Ukrainer, zum Beispiel die einen auf der Seite von Hitlers faschistischer Nazi-Armee und die anderen auf der von Stalins kommunistischer Roter Armee. Die Verbrechen auf beiden Seiten sind nicht vergessen. Dass nach der Unabhängigkeit 1991 versucht wurde, Figuren wie den radikalen Nationalisten Symon Petljura oder den Faschisten und Nazi-Kollaborateur Stepan Bandera als «Nationalhelden» zu installieren, verbessert die Sache nicht.
Während die USA und EU-Staaten zunehmend «ausländische Einmischung» (speziell russische) in «ihre Demokratien» wittern, betreiben sie genau dies seit Jahrzehnten in vielen Ländern der Welt. Die seit den 2000er Jahren bekannten «Farbrevolutionen» in Osteuropa werden oft als Methode des Regierungsumsturzes durch von außen gesteuerte «demokratische» Volksaufstände beschrieben. Diese Strategie geht auf Analysen zum «Schwarmverhalten» [9] seit den 1960er Jahren zurück (Studentenproteste), wo es um die potenzielle Wirksamkeit einer «rebellischen Hysterie» von Jugendlichen bei postmodernen Staatsstreichen geht. Heute nennt sich dieses gezielte Kanalisieren der Massen zur Beseitigung unkooperativer Regierungen «Soft-Power».
In der Ukraine gab es mit der «Orangen Revolution» 2004 und dem «Euromaidan» 2014 gleich zwei solcher «Aufstände». Der erste erzwang wegen angeblicher Unregelmäßigkeiten eine Wiederholung der Wahlen, was mit Wiktor Juschtschenko als neuem Präsidenten endete. Dieser war ehemaliger Direktor der Nationalbank und Befürworter einer Annäherung an EU und NATO. Seine Frau, die First Lady, ist US-amerikanische «Philanthropin» und war Beamtin im Weißen Haus in der Reagan- und der Bush-Administration.
Im Gegensatz zu diesem ersten Event endete der sogenannte Euromaidan unfriedlich und blutig. Die mehrwöchigen Proteste gegen Präsident Wiktor Janukowitsch, in Teilen wegen des nicht unterzeichneten Assoziierungsabkommens mit der EU, wurden zunehmend gewalttätiger und von Nationalisten und Faschisten des «Rechten Sektors» dominiert. Sie mündeten Ende Februar 2014 auf dem Kiewer Unabhängigkeitsplatz (Maidan) in einem Massaker durch Scharfschützen. Dass deren Herkunft und die genauen Umstände nicht geklärt wurden, störte die Medien nur wenig. [10]
Janukowitsch musste fliehen, er trat nicht zurück. Vielmehr handelte es sich um einen gewaltsamen, allem Anschein nach vom Westen inszenierten Putsch. Laut Jeffrey Sachs war das kein Geheimnis, außer vielleicht für die Bürger. Die USA unterstützten die Post-Maidan-Regierung nicht nur, sie beeinflussten auch ihre Bildung. Das geht unter anderem aus dem berühmten «Fuck the EU»-Telefonat der US-Chefdiplomatin für die Ukraine, Victoria Nuland, mit Botschafter Geoffrey Pyatt hervor.
Dieser Bruch der demokratischen Verfassung war letztlich der Auslöser für die anschließenden Krisen auf der Krim und im Donbass (Ostukraine). Angesichts der ukrainischen Geschichte mussten die nationalistischen Tendenzen und die Beteiligung der rechten Gruppen an dem Umsturz bei der russigsprachigen Bevölkerung im Osten ungute Gefühle auslösen. Es gab Kritik an der Übergangsregierung, Befürworter einer Abspaltung und auch für einen Anschluss an Russland.
Ebenso konnte Wladimir Putin in dieser Situation durchaus Bedenken wegen des Status der russischen Militärbasis für seine Schwarzmeerflotte in Sewastopol auf der Krim haben, für die es einen langfristigen Pachtvertrag mit der Ukraine gab. Was im März 2014 auf der Krim stattfand, sei keine Annexion, sondern eine Abspaltung (Sezession) nach einem Referendum gewesen, also keine gewaltsame Aneignung, urteilte der Rechtswissenschaftler Reinhard Merkel in der FAZ sehr detailliert begründet. Übrigens hatte die Krim bereits zu Zeiten der Sowjetunion den Status einer autonomen Republik innerhalb der Ukrainischen SSR.
Anfang April 2014 wurden in der Ostukraine die «Volksrepubliken» Donezk und Lugansk ausgerufen. Die Kiewer Übergangsregierung ging unter der Bezeichnung «Anti-Terror-Operation» (ATO) militärisch gegen diesen, auch von Russland instrumentalisierten Widerstand vor. Zufällig war kurz zuvor CIA-Chef John Brennan in Kiew. Die Maßnahmen gingen unter dem seit Mai neuen ukrainischen Präsidenten, dem Milliardär Petro Poroschenko, weiter. Auch Wolodymyr Selenskyj beendete den Bürgerkrieg nicht, als er 2019 vom Präsidenten-Schauspieler, der Oligarchen entmachtet, zum Präsidenten wurde. Er fuhr fort, die eigene Bevölkerung zu bombardieren.
Mit dem Einmarsch russischer Truppen in die Ostukraine am 24. Februar 2022 begann die zweite Phase des Krieges. Die Wochen und Monate davor waren intensiv. Im November hatte die Ukraine mit den USA ein Abkommen über eine «strategische Partnerschaft» unterzeichnet. Darin sagten die Amerikaner ihre Unterstützung der EU- und NATO-Perspektive der Ukraine sowie quasi für die Rückeroberung der Krim zu. Dagegen ließ Putin der NATO und den USA im Dezember 2021 einen Vertragsentwurf über beiderseitige verbindliche Sicherheitsgarantien zukommen, den die NATO im Januar ablehnte. Im Februar eskalierte laut OSZE die Gewalt im Donbass.
Bereits wenige Wochen nach der Invasion, Ende März 2022, kam es in Istanbul zu Friedensverhandlungen, die fast zu einer Lösung geführt hätten. Dass der Krieg nicht damals bereits beendet wurde, lag daran, dass der Westen dies nicht wollte. Man war der Meinung, Russland durch die Ukraine in diesem Stellvertreterkrieg auf Dauer militärisch schwächen zu können. Angesichts von Hunderttausenden Toten, Verletzten und Traumatisierten, die als Folge seitdem zu beklagen sind, sowie dem Ausmaß der Zerstörung, fehlen einem die Worte.
Hasst der Westen die Russen?
Diese Frage drängt sich auf, wenn man das oft unerträglich feindselige Gebaren beobachtet, das beileibe nicht neu ist und vor Doppelmoral trieft. Russland und speziell die Person Wladimir Putins werden regelrecht dämonisiert, was gleichzeitig scheinbar jede Form von Diplomatie ausschließt.
Russlands militärische Stärke, seine geografische Lage, sein Rohstoffreichtum oder seine unabhängige diplomatische Tradition sind sicher Störfaktoren für das US-amerikanische Bestreben, der Boss in einer unipolaren Welt zu sein. Ein womöglich funktionierender eurasischer Kontinent, insbesondere gute Beziehungen zwischen Russland und Deutschland, war indes schon vor dem Ersten Weltkrieg eine Sorge des britischen Imperiums.
Ein «Vergehen» von Präsident Putin könnte gewesen sein, dass er die neoliberale Schocktherapie à la IWF und den Ausverkauf des Landes (auch an US-Konzerne) beendete, der unter seinem Vorgänger herrschte. Dabei zeigte er sich als Führungspersönlichkeit und als nicht so formbar wie Jelzin. Diese Aspekte allein sind aber heute vermutlich keine ausreichende Erklärung für ein derart gepflegtes Feindbild.
Der Historiker und Philosoph Hauke Ritz erweitert den Fokus der Fragestellung zu: «Warum hasst der Westen die Russen so sehr?», was er zum Beispiel mit dem Medienforscher Michael Meyen und mit der Politikwissenschaftlerin Ulrike Guérot bespricht. Ritz stellt die interessante These [11] auf, dass Russland eine Provokation für den Westen sei, welcher vor allem dessen kulturelles und intellektuelles Potenzial fürchte.
Die Russen sind Europäer aber anders, sagt Ritz. Diese «Fremdheit in der Ähnlichkeit» erzeuge vielleicht tiefe Ablehnungsgefühle. Obwohl Russlands Identität in der europäischen Kultur verwurzelt ist, verbinde es sich immer mit der Opposition in Europa. Als Beispiele nennt er die Kritik an der katholischen Kirche oder die Verbindung mit der Arbeiterbewegung. Christen, aber orthodox; Sozialismus statt Liberalismus. Das mache das Land zum Antagonisten des Westens und zu einer Bedrohung der Machtstrukturen in Europa.
Fazit
Selbstverständlich kann man Geschichte, Ereignisse und Entwicklungen immer auf verschiedene Arten lesen. Dieser Artikel, obwohl viel zu lang, konnte nur einige Aspekte der Ukraine-Tragödie anreißen, die in den offiziellen Darstellungen in der Regel nicht vorkommen. Mindestens dürfte damit jedoch klar geworden sein, dass die Russische Föderation bzw. Wladimir Putin nicht der alleinige Aggressor in diesem Konflikt ist. Das ist ein Stellvertreterkrieg zwischen USA/NATO (gut) und Russland (böse); die Ukraine (edel) wird dabei schlicht verheizt.
Das ist insofern von Bedeutung, als die gesamte europäische Kriegshysterie auf sorgsam kultivierten Freund-Feind-Bildern beruht. Nur so kann Konfrontation und Eskalation betrieben werden, denn damit werden die wahren Hintergründe und Motive verschleiert. Angst und Propaganda sind notwendig, damit die Menschen den Wahnsinn mitmachen. Sie werden belogen, um sie zuerst zu schröpfen und anschließend auf die Schlachtbank zu schicken. Das kann niemand wollen, außer den stets gleichen Profiteuren: die Rüstungs-Lobby und die großen Investoren, die schon immer an Zerstörung und Wiederaufbau verdient haben.
Apropos Investoren: Zu den Top-Verdienern und somit Hauptinteressenten an einer Fortführung des Krieges zählt BlackRock, einer der weltgrößten Vermögensverwalter. Der deutsche Bundeskanzler in spe, Friedrich Merz, der gerne «Taurus»-Marschflugkörper an die Ukraine liefern und die Krim-Brücke zerstören möchte, war von 2016 bis 2020 Aufsichtsratsvorsitzender von BlackRock in Deutschland. Aber das hat natürlich nichts zu sagen, der Mann macht nur seinen Job.
Es ist ein Spiel der Kräfte, es geht um Macht und strategische Kontrolle, um Geheimdienste und die Kontrolle der öffentlichen Meinung, um Bodenschätze, Rohstoffe, Pipelines und Märkte. Das klingt aber nicht sexy, «Demokratie und Menschenrechte» hört sich besser und einfacher an. Dabei wäre eine für alle Seiten förderliche Politik auch nicht so kompliziert; das Handwerkszeug dazu nennt sich Diplomatie. Noch einmal Gabriele Krone-Schmalz:
«Friedliche Politik ist nichts anderes als funktionierender Interessenausgleich. Da geht’s nicht um Moral.»
Die Situation in der Ukraine ist sicher komplex, vor allem wegen der inneren Zerrissenheit. Es dürfte nicht leicht sein, eine friedliche Lösung für das Zusammenleben zu finden, aber die Beteiligten müssen es vor allem wollen. Unter den gegebenen Umständen könnte eine sinnvolle Perspektive mit Neutralität und föderalen Strukturen zu tun haben.
Allen, die sich bis hierher durch die Lektüre gearbeitet (oder auch einfach nur runtergescrollt) haben, wünsche ich frohe Oster-Friedenstage!
[Titelbild: Pixabay; Abb. 1 und 2: nach Ganser/SIPER; Abb. 3: SIPER]
--- Quellen: ---
[1] Albrecht Müller, «Glaube wenig. Hinterfrage alles. Denke selbst.», Westend 2019
[2] Zwei nette Beispiele:
- ARD-faktenfinder (sic), «Viel Aufmerksamkeit für fragwürdige Experten», 03/2023
- Neue Zürcher Zeitung, «Aufstieg und Fall einer Russlandversteherin – die ehemalige ARD-Korrespondentin Gabriele Krone-Schmalz rechtfertigt seit Jahren Putins Politik», 12/2022
[3] George Washington University, «NATO Expansion: What Gorbachev Heard – Declassified documents show security assurances against NATO expansion to Soviet leaders from Baker, Bush, Genscher, Kohl, Gates, Mitterrand, Thatcher, Hurd, Major, and Woerner», 12/2017
[4] Beispielsweise Wladimir Putin bei seiner Rede im Deutschen Bundestag, 25/09/2001
[5] William Engdahl, «Full Spectrum Dominance, Totalitarian Democracy In The New World Order», edition.engdahl 2009
[6] Daniele Ganser, «Illegale Kriege – Wie die NATO-Länder die UNO sabotieren. Eine Chronik von Kuba bis Syrien», Orell Füssli 2016
[7] Gabriele Krone-Schmalz, «Mit Friedensjournalismus gegen ‘Kriegstüchtigkeit’», Vortrag und Diskussion an der Universität Hamburg, veranstaltet von engagierten Studenten, 16/01/2025\ → Hier ist ein ähnlicher Vortrag von ihr (Video), den ich mit spanischer Übersetzung gefunden habe.
[8] Für mehr Hintergrund und Details empfehlen sich z.B. folgende Bücher:
- Mathias Bröckers, Paul Schreyer, «Wir sind immer die Guten», Westend 2019
- Gabriele Krone-Schmalz, «Russland verstehen? Der Kampf um die Ukraine und die Arroganz des Westens», Westend 2023
- Patrik Baab, «Auf beiden Seiten der Front – Meine Reisen in die Ukraine», Fiftyfifty 2023
[9] vgl. Jonathan Mowat, «Washington's New World Order "Democratization" Template», 02/2005 und RAND Corporation, «Swarming and the Future of Conflict», 2000
[10] Bemerkenswert einige Beiträge, von denen man später nichts mehr wissen wollte:
- ARD Monitor, «Todesschüsse in Kiew: Wer ist für das Blutbad vom Maidan verantwortlich», 10/04/2014, Transkript hier
- Telepolis, «Blutbad am Maidan: Wer waren die Todesschützen?», 12/04/2014
- Telepolis, «Scharfschützenmorde in Kiew», 14/12/2014
- Deutschlandfunk, «Gefahr einer Spirale nach unten», Interview mit Günter Verheugen, 18/03/2014
- NDR Panorama, «Putsch in Kiew: Welche Rolle spielen die Faschisten?», 06/03/2014
[11] Hauke Ritz, «Vom Niedergang des Westens zur Neuerfindung Europas», 2024
Dieser Beitrag wurde mit dem Pareto-Client geschrieben.
-
 @ ba36d0f7:cd802cba
2025-04-20 17:58:52
@ ba36d0f7:cd802cba
2025-04-20 17:58:52FABRIC AS TEXTBOOK
Learning to embroider - or to mend - is like studying an ancestral language. Manuals explain the backstitch or sashiko, but fabric never lies: it tears if the tension is weak, and wrinkles if the needle is clumsy.
Theory gives you the alphabet; but practice gives you the syntax of the invisible. How many broken stitches hide behind perfect embroidery? How many mistakes teach us the language of threads?
I. TO MEND IS TO RESIST: THE POLITICAL ACT OF THE NEEDLE
There’s a certain sacred stubbornness in sitting down to mend; like our grandmothers darning our socks until the heel was more patch than original fabric.
And today, in the age of fast fashion, mending is rebellion: a silent "no" to disposability, a resounding "yes" to permanence.
Techniques as Philosophies
-
Japanese sashiko: Visible stitches like proud scars. "What’s broken isn’t hidden—it’s celebrated."

-
Darning: For when pain must be concealed, not erased.

-
Free embroidery: Where repair becomes art and mending, a language.

 Every stitch is a pact: "I care for you because you exist."
Every stitch is a pact: "I care for you because you exist."And isn’t this, too, what mestizaje means? To take the fragmented - fabrics, histories, identities - and reweave them without erasing their origin.
II. EMBROIDERY AS A SELF-TAUGHT MASTER
Learning to embroider is like learning to live: there are no shortcuts. You can read a thousand tutorials, but until you feel the thread resist the needle’s eye or the fabric tense beneath your fingers, knowledge remains abstract.
The Textile Learning Triad
-
Theory that fades (books explain the backstitch, but not how to avoid knots).
-
Practice that stings (fingers get pricked, stitches go crooked).
-
Intuition that blooms (when hands remember the motion on their own).
III. THREADS AND TECHNOLOGY
Malinche, Mesoamerica’s first translator, understood this: some knowledge only transmits through action. We, as 21st-century beings, have a privilege: to blend ancestral tools (needles, threads) with modern ones (YouTube tutorials, digital patterns).
At soma, we explore education beyond canons, and embroidery is the perfect example.
Embroidery teaches us:
-
Discipline (because one loose stitch ruins the design).
-
Creativity (because sometimes you must invent solutions).
-
Legacy (because every thread carries memory).
What are you mending today? A skirt, a habit, a way of learning?
This is the future of education: to dig into the old and hack the new.
IV. INVITATION: STITCHES AND PATIENCE WORKSHOP
This Saturday 26th, at Estudio Malinche, Apaneca - we won’t just teach techniques. We’ll create a collective learning ritual:
-
Bring a torn garment and an empty notebook.
-
Learn sashiko mending (to honor scars) and bookbinding with recycled paper (to chart your path).
-
You’ll leave with ink-stained hands and a heart full of threads.
"Perfection isn’t the goal - persistence is."
Follow us on IG to check out stories & upcoming events: @larutasoma @estudiomalinche
soma #article #mending #workshop #visiblemending #philosophy #resistance #btc #nostr #elsalvador #sashiko #rutadelasflores #apaneca #education #slowfashion #fashion #fastfashion #embroidery #stitching #handmade #diy
-
-
 @ 8d34bd24:414be32b
2025-04-20 14:18:37
@ 8d34bd24:414be32b
2025-04-20 14:18:37I started working on this post a couple weeks ago, and out of pure accident, it became my Resurrection Sunday (Easter) post. Maybe it was by God’s design. On Resurrection Sunday, Jesus was raised from the grave. Forty days later he rose to heaven before many witnesses. Someday in the future, the dead in Christ will be raised from the dead, and all believers will be snatched up to heaven. Maybe this is this right post for Resurrection Sunday.
For if we believe that Jesus died and rose again, even so God will bring with Him those who have fallen asleep in Jesus. … For the Lord Himself will descend from heaven with a shout, with the voice of the archangel and with the trumpet of God, and the dead in Christ will rise first. Then we who are alive and remain will be caught up together with them in the clouds to meet the Lord in the air, and so we shall always be with the Lord. (1 Thessalonians 4:14, 16-17) {emphasis mine}
It always amazes me that some Christians don’t believe in the rapture of the church. I understand how there can be a disagreement about exactly when the rapture is to occur, but I can’t comprehend how some Christians don’t believe the rapture is coming or that they believe that the rapture happened in the first century.
Let’s start with the three key verses on the subject and then we’ll get into more details.
Key Rapture Verses
I didn’t notice that this first passage referred to the rapture until it was pointed out to me. I was so focused on Jesus preparing a place, that I missed the key sentence.
“Do not let your heart be troubled; believe in God, believe also in Me. In My Father’s house are many dwelling places; if it were not so, I would have told you; for I go to prepare a place for you. If I go and prepare a place for you, I will come again and receive you to Myself, that where I am, there you may be also. (John 14:1-3) {emphasis mine}
Jesus, after His resurrection and as promised in these verses, rose up to heaven to go prepare a place for believers. He will then return to bring believers to Himself. This whole idea would have been particularly clear for the Jews when it was written. When a bride and groom were engaged (a legal contract where they were considered married), the groom would go and prepare a place for them to live. It could be an extra room in his parent’s home or it could be a whole new home. The bride didn’t know when the groom would return to take her to himself to become man and wife. In the same way, Jesus has gone away to prepare a place for us and will return at a time we do not know. Just as the Jewish bride had to be ready to leave with her groom when he suddenly arrived, we also must be ready for Jesus’s return when He will snatch us from earth and take us home with Him to heaven.
But we do not want you to be uninformed, brethren, about those who are asleep, so that you will not grieve as do the rest who have no hope. For if we believe that Jesus died and rose again, even so God will bring with Him those who have fallen asleep in Jesus. For this we say to you by the word of the Lord, that we who are alive and remain until the coming of the Lord, will not precede those who have fallen asleep. For the Lord Himself will descend from heaven with a shout, with the voice of the archangel and with the trumpet of God, and the dead in Christ will rise first. Then we who are alive and remain will be caught up together with them in the clouds to meet the Lord in the air, and so we shall always be with the Lord. Therefore comfort one another with these words. (1 Thessalonians 4:13-18) {emphasis mine}
The Bible has a wonderful euphemism for the death of believers. It speaks of them falling asleep because death is not the end for believers. It is just a pause, a separation of body and spirit, before we are raptured to Jesus, to meet Him in the sky, where we will receive a new resurrection body, just as Jesus received when He was raised from the dead 3 days after His crucifixion. Both the dead in Christ and the alive in Christ will “be caught up together with them in the clouds to meet the Lord in the air.” God gives us this promise in the Bible to comfort us. It gives us comfort that death is not the end and we will see our fellow believers again in heaven one day. It also gives us comfort that we will not have to experience God’s wrath. “For God has not destined us for wrath, but for obtaining salvation through our Lord Jesus Christ.” (1 Thessalonians 5:9)
What else can we learn about the rapture?
Now I say this, brethren, that flesh and blood cannot inherit the kingdom of God; nor does the perishable inherit the imperishable. Behold, I tell you a mystery; we will not all sleep, but we will all be changed, in a moment, in the twinkling of an eye, at the last trumpet; for the trumpet will sound, and the dead will be raised imperishable, and we will be changed. For this perishable must put on the imperishable, and this mortal must put on immortality. But when this perishable will have put on the imperishable, and this mortal will have put on immortality, then will come about the saying that is written, “Death is swallowed up in victory. O death, where is your victory? O death, where is your sting?” The sting of death is sin, and the power of sin is the law; but thanks be to God, who gives us the victory through our Lord Jesus Christ. (1 Corinthians 15:50-57) {emphasis mine}
The rapture will be an instantaneous change from our perishable bodies to imperishable, whether we are alive in Christ or dead in Christ. At the rapture we “will be raised imperishable.” I am very excited to be snatched up into the air, receive a new, eternal body, and meet Jesus face-to-face.
There is one more passage that I believe talks of the rapture that is a bit more subtle from Isaiah.
The righteous man perishes, and no man takes it to heart;\ And devout men are taken away, while no one understands.\ For the righteous man is taken away from evil,\ **He enters into peace;\ They rest in their beds,\ Each one who walked in his upright way. (Isaiah 57:1-2) {emphasis mine}
The seven year Tribulation is the wrath of God poured out on those who rejected Him and the merciful, last chance warning before eternal judgement. Those who have trusted in Jesus (the devout men, the righteous man) will be “taken away from evil” and will “enter into peace.” Instead of experiencing God’s wrath, they will experience His peace. Instead of experience horror, they will “rest in their beds.”
The Seven Raptures Before the Rapture of the Church
How can we know that we will be raptured to heaven to be with Jesus forever? One way is because people have been raptured before (in different ways)
I am borrowing the organization of this section from Chapter 9 of “The End: Everything You’ll Want to Know about the Apocalypse” by Mark Hitchcock, which I happen to be reading at the moment.
-
Rapture of Enoch\ ”So all the days of Enoch were three hundred and sixty-five years. Enoch walked with God; and he was not, for God took him.” (Genesis 5:23-24) \ Enoch was raptured to heaven to be with God. He did not die, but went straight to God.
-
Rapture of Elijah\ ”And it came about when the Lord was about to take up Elijah by a whirlwind to heaven, that Elijah went with Elisha from Gilgal. … As they were going along and talking, behold, there appeared a chariot of fire and horses of fire which separated the two of them. And Elijah went up by a whirlwind to heaven.” (2 Kings 2:1,11) \ Elijah also was raptured to heaven without having to die. This passage gives more details. He went up in a whirlwind to heaven.
-
Rapture of Isaiah\ ”In the year of King Uzziah’s death I saw the Lord sitting on a throne, lofty and exalted, with the train of His robe filling the temple. Seraphim stood above Him, each having six wings: with two he covered his face, and with two he covered his feet, and with two he flew. And one called out to another and said,
“Holy, Holy, Holy, is the Lord of hosts,
The whole earth is full of His glory.”” (Isaiah 6:1-3)\ Isaiah’s situation was different. He was raptured to heaven only temporarily to be given God’s word and His prophecy and to call Isaiah for His good plan.
-
Rapture of Jesus\ ”And she gave birth to a son, a male child, who is to rule all the nations with a rod of iron; and her child was caught up to God and to His throne.” (Revelation 12:5)\ and\ ”And after He had said these things, He was lifted up while they were looking on, and a cloud received Him out of their sight. And as they were gazing intently into the sky while He was going, behold, two men in white clothing stood beside them. They also said, “Men of Galilee, why do you stand looking into the sky? This Jesus, who has been taken up from you into heaven, will come in just the same way as you have watched Him go into heaven.” (Acts 1:9-11)\ I’ve listed two verses about Jesus’s rapture. The one from Revelation uses the Greek word harpazo, caught up - when translated to Latin, the word is rapturo, which is where we get our English word rapture. The verses in Acts give a more detailed description of His rapture to heaven, which is an example of our rapture. We are also promised His return.
-
Rapture of Philip\ ”And he ordered the chariot to stop; and they both went down into the water, Philip as well as the eunuch, and he baptized him. When they came up out of the water, the Spirit of the Lord snatched Philip away; and the eunuch no longer saw him, but went on his way rejoicing. But Philip found himself at Azotus, and as he passed through he kept preaching the gospel to all the cities until he came to Caesarea.” (Acts 8:38-40)
The rapture of Philip is different than the rest, because Philip was snatched away, not to heaven, but to Azotus. This is still an instance worth pointing out because it also uses the Greek word Harpazo.
- Rapture of Paul\ ”I know a man in Christ who fourteen years ago—whether in the body I do not know, or out of the body I do not know, God knows—such a man was caught up to the third heaven. And I know how such a man—whether in the body or apart from the body I do not know, God knows— was caught up into Paradise and heard inexpressible words, which a man is not permitted to speak.” (2 Corinthians 12:2-4)\ Like Isaiah, Paul was temporarily caught up (Harpazo) to heaven to receive revelation from God and then returned to his work and life on earth
These examples show God snatching people from one location to another, physically or spiritually for His good purpose. I expect it to happen again, shortly before the beginning of the seven year tribulation.
The 3 Views of the Rapture
There are three main views of the rapture: pre-trib, mid-trib, and post-trib. The basic beliefs are pretty much self explanatory by their name. Does the rapture occur before the tribulation, around the mid-point of the tribulation (which is right before the Great Tribulation or final 3.5 years), or after the tribulation? Which one fits what the Bible says better?
Although the Bible doesn’t directly say when the rapture happens, there are some very strong hints.
No wrath For saints
“For God has not destined us for wrath, but for obtaining salvation through our Lord Jesus Christ.” (1 Thessalonians 5:9)
God promises believers that we are not destined for wrath. The tribulation is also known as1 “The wrath” (1 Thessalonians 5:9 & Revelation 11:18), “The wrath to come” (1 Thessalonians 1:10), “The great day of their wrath” (Revelation 6:17), “The wrath of God” (Revelation15:1,7, 14:10,19, 16:1), “The wrath of the lamb” (Revelation 6:16). There are numerous other equally unpleasant names, but I am sticking with those that use the word wrath. God promised believers that we are not destined for wrath. God never breaks His promises.
Similarly Revelation 3 promises believers will be kept from the hour of testing.
Because you have kept the word of My perseverance, I also will keep you from the hour of testing, that hour which is about to come upon the whole world, to test those who dwell on the earth. I am coming quickly; hold fast what you have, so that no one will take your crown. (Revelation 3:10-11) {emphasis mine}
The word quickly can also be translated suddenly. Although Jesus has not returned quickly by our way of figuring time, He will come suddenly.
No one knows when
“But of that day and hour no one knows, not even the angels of heaven, nor the Son, but the Father alone.” (Matthew 24:36)
Scripture says the Tribulation starts when the Antichrist signs a peace treaty with Israel. If the rapture happens before the tribulation, then we won’t know when it will happen. If the rapture occurs at the mid-trib position, then it will happen 3.5 years after the peace treaty. If the rapture occurs post-trip, then it will happen 7 years after the peace treaty is signed and 3.5 years after the abomination of desolation, when the Antichrist declares himself god in the Jewish temple and requires the whole world to worship him. Only one makes sense if we can’t know when it happens.
Just as in the days of …
“For the coming of the Son of Man will be just like the days of Noah. For as in those days before the flood they were eating and drinking, marrying and giving in marriage, until the day that Noah entered the ark, and they did not understand until the flood came and took them all away; so will the coming of the Son of Man be. Then there will be two men in the field; one will be taken and one will be left. Two women will be grinding at the mill; one will be taken and one will be left.” (Matthew 24:37-41)
If we look at the words of Jesus, He compares the rapture to the days of Noah. Life happening as normal, then God put Noah and his family on the ark and personally shut the door (Genesis 7:16). Then the flood came, pouring God’s wrath out on those who had rejected Him. In the same way, God will take believers out of the world before pouring out His wrath on those who remain. He clearly states, “one will be taken and one will be left.”
A parallel passage in Luke, not only talks of God removing Noah before the flood, but also tells of God removing Lot before destroying Sodom & Gomorrah.
For just like the lightning, when it flashes out of one part of the sky, shines to the other part of the sky, so will the Son of Man be in His day. But first He must suffer many things and be rejected by this generation. And just as it happened in the days of Noah, so it will be also in the days of the Son of Man: they were eating, they were drinking, they were marrying, they were being given in marriage, until the day that Noah entered the ark, and the flood came and destroyed them all. It was the same as happened in the days of Lot: they were eating, they were drinking, they were buying, they were selling, they were planting, they were building; but on the day that Lot went out from Sodom it rained fire and brimstone from heaven and destroyed them all. It will be just the same on the day that the Son of Man is revealed. (Luke:17:24-30) {emphasis mine}
Just as Noah was removed before judgement, so also was Lot removed before judgement. In both cases the majority of people were going about business, living normal lives, not expecting anything to change.
In Genesis 19, the angels must remove Lot and his family before the city is destroyed.
Then the two men said to Lot, “Whom else have you here? A son-in-law, and your sons, and your daughters, and whomever you have in the city, bring them out of the place; for we are about to destroy this place, because their outcry has become so great before the Lord that the Lord has sent us to destroy it.” \ …\ When morning dawned, the angels urged Lot, saying, “Up, take your wife and your two daughters who are here, or you will be swept away in the punishment of the city.” But he hesitated. So the men seized his hand and the hand of his wife and the hands of his two daughters, for the compassion of the Lord was upon him; and they brought him out, and put him outside the city. (Genesis 19:12-13,15-16) {emphasis mine}
In the last days, God has promised to remove us before His judgment is poured out on those who willfully rejected Him. Jesus spoke these words to comfort us and so we would not fear the end.
Removal of the Restrainer
Now we request you, brethren, with regard to the coming of our Lord Jesus Christ and our gathering together to Him, that you not be quickly shaken from your composure or be disturbed either by a spirit or a message or a letter as if from us, to the effect that the day of the Lord has come. Let no one in any way deceive you, for it will not come unless the apostasy comes first, and the man of lawlessness is revealed, the son of destruction, who opposes and exalts himself above every so-called god or object of worship, so that he takes his seat in the temple of God, displaying himself as being God. Do you not remember that while I was still with you, I was telling you these things? And you know what restrains him now, so that in his time he will be revealed. For the mystery of lawlessness is already at work; only he who now restrains will do so until he is taken out of the way. Then that lawless one will be revealed whom the Lord will slay with the breath of His mouth and bring to an end by the appearance of His coming; (2 Thessalonians 2:1-8) {emphasis mine}
The restrainer is the Holy Spirit and the lawless one is the antichrist. This passage is saying that the antichrist will not be revealed until the restrainer is removed. The Holy Spirit indwells every believer. The believers also have to be removed before the antichrist is revealed, otherwise the Holy Spirit would have to leave the believers, leaving them alone during God’s wrath. That, of course, is contrary to God’s character, history, and promise.
Why is There No Mention of the Church During the Tribulation?
In the first three chapters of Revelation, the word church is used again and again. The church is not mentioned again until Revelation 19, regarding the Bride of Christ.
Let us rejoice and be glad and give the glory to Him, for the marriage of the Lamb has come and His bride has made herself ready.” It was given to her to clothe herself in fine linen, bright and clean; for the fine linen is the righteous acts of the saints. (Revelation 19:7-8) {emphasis mine}
All of this makes sense if the church was raptured before the tribulation. Therefore the bride (the church) has had seven years to make herself ready. They then get to descend with Jesus in the second coming of Jesus.
And I saw heaven opened, and behold, a white horse, and He who sat on it is called Faithful and True, and in righteousness He judges and wages war. His eyes are a flame of fire, and on His head are many diadems; and He has a name written on Him which no one knows except Himself. He is clothed with a robe dipped in blood, and His name is called The Word of God. And the armies which are in heaven, clothed in fine linen, white and clean, were following Him on white horses. From His mouth comes a sharp sword, so that with it He may strike down the nations, and He will rule them with a rod of iron; and He treads the wine press of the fierce wrath of God, the Almighty. And on His robe and on His thigh He has a name written, “KING OF KINGS, AND Lord OF LORDS.” (Revelation 19:11-16) {emphasis mine}
The Bride of Christ follows the King of Kings and Lord of Lords back to earth after being made “white and clean.”
Some may accuse pre-trib believers of being escapists. I’ll admit, I am happy to avoid the wrath of God, whether that be the tribulation or eternal damnation or just His daily disappointment in my failings. The fact that I am glad to “escape” the wrath, doesn’t make it untrue. I hope the passages and explanations I shared will give you comfort as the Day of the Lord and the Wrath of God approaches and as we see the world seemingly spiraling out of control. God is in control. Everything is happening according to His plan and for our good.
May the Lord of heaven comfort you with His promises and make you know His love. May you trust Him in good times and bad until the last days. May God give you a desire for His word and an understanding of His prophecies, so you will know the day is fast approaching.
Trust Jesus.
FYI, You can find most of my articles at end times. Some are directly relating to end times while others are loosely related. This post is a logical explanation of the rapture. You can also check out my older article on the rapture, “Up, Up, and Away.” The focus in my previous post was a little different including focusing on how the rapture will effect us, how we should respond to its immanency, and how it relates to the 2nd coming of Christ after the tribulation, so it is worth checking out as well.
-
-
 @ 1ef61805:f18312cc
2025-03-13 02:05:38
@ 1ef61805:f18312cc
2025-03-13 02:05:38At OpSec Academy, we’ve customised TailsOS to include a suite of peer-reviewed applications that extend the operating system’s capabilities, enhancing privacy, security, and decentralisation. These tools are installed separately from the standard TailsOS installation and have been carefully vetted to meet the highest standards of security and functionality. In this article, we’ll break down each of the applications that are included and explain how they enhance the TailsOS experience.
1. Hodl Hodl
Hodl Hodl is a decentralised peer-to-peer Bitcoin trading platform that allows users to buy and sell Bitcoin directly, without the need for an intermediary. It uses an escrow system to ensure trust and security during trades. By including Hodl Hodl in our custom TailsOS image, users gain access to a platform that allows for private, secure, and censorship-resistant Bitcoin transactions, in line with TailsOS's commitment to decentralisation and privacy.
2. RoboSats
RoboSats is an automated, non-custodial Bitcoin exchange that enables users to trade Bitcoin for gift cards or other payment methods without compromising their privacy. It operates using a peer-to-peer model, ensuring that users retain full control over their funds throughout the process. Including RoboSats in our TailsOS image ensures that users can conduct Bitcoin trades privately and securely, without relying on centralised services.
3. Mempool.space
Mempool.space is a visualisation tool that offers real-time insights into Bitcoin’s mempool—the collection of unconfirmed transactions waiting to be included in a block. This tool allows users to monitor transaction fees, network congestion, and block size, helping them optimise their Bitcoin transactions for faster confirmations and lower fees. By integrating Mempool.space into our custom TailsOS image, users gain access to critical information that can help them manage their Bitcoin transactions more effectively.
4. Sparrow Wallet
Sparrow Wallet is a Bitcoin wallet that prioritises privacy and security, offering advanced features such as coin control, multi-signature support, and hardware wallet integration. It also integrates with Tor to ensure that users' transaction data remains private. Sparrow Wallet is an ideal choice for users who want complete control over their Bitcoin holdings, and by including it in our TailsOS image, we provide a secure and user-friendly solution for managing Bitcoin wallets with privacy at the forefront.
5. Cake Wallet
Cake Wallet is a mobile wallet designed specifically for Monero (XMR), a privacy-focused cryptocurrency. It offers users a simple, intuitive interface to send, receive, and store Monero, all while integrating with Tor to maintain privacy. By adding Cake Wallet to our TailsOS image, we provide users with a secure and private way to manage their Monero transactions, enhancing TailsOS's focus on privacy protection in the cryptocurrency space.
6. Snort (Nostr Client)
Snort is a decentralised client for the Nostr protocol, which is designed for secure, censorship-resistant communication. It provides users with a lightweight, minimal interface for sending and receiving messages in a private, decentralised manner. By including Snort on our custom TailsOS image, we empower users to engage in secure, peer-to-peer communication without relying on centralised platforms that may compromise privacy.
7. Iris (Nostr Client)
Iris is another decentralised Nostr client, designed with a more feature-rich experience in mind. It supports multiple platforms and offers enhanced privacy features. Like Snort, Iris allows users to send and receive messages over the Nostr protocol in a secure, private, and decentralised way. By including Iris in our custom TailsOS image, we offer users an additional option for secure communication that aligns with the privacy-centric goals of TailsOS.
8. BIP39 (Ian Coleman's Tool)
BIP39 is a Bitcoin Improvement Proposal that defines how to generate mnemonic phrases (seed phrases) for deterministic wallets. Ian Coleman's BIP39 tool is an open-source, web-based application that allows users to generate these seed phrases and derive wallet keys securely. By including Ian Coleman's BIP39 tool in our TailsOS image, we provide users with a secure, offline method to generate mnemonic phrases and recover their wallets, ensuring that they have complete control over their private keys.
Why These Applications?
Each of the applications included in our custom TailsOS image is designed to provide users with enhanced privacy, security, and decentralisation. These tools give users more control over their digital assets, communication, and transactions, all while ensuring that their activities remain private and secure. The peer-reviewed nature of these applications means that they have been rigorously tested and are trusted by experts, giving our users confidence that they are using some of the best privacy tools available.
By adding these applications to TailsOS, we’ve created a more comprehensive, privacy-focused operating system that helps users navigate the digital world with greater security and freedom.
Conclusion
Our custom TailsOS image goes beyond the standard installation by incorporating a suite of peer-reviewed applications that enhance privacy, decentralisation, and security. Whether you’re looking to engage in secure communication, manage cryptocurrency, or monitor network activity, the applications we’ve included provide users with everything they need to operate privately and securely in an increasingly surveillance-driven world.
With these powerful tools, users can take full control of their digital lives, all while staying true to the principles of decentralisation and privacy that TailsOS upholds.
-
 @ 6830c409:ff17c655
2025-04-20 12:37:24
@ 6830c409:ff17c655
2025-04-20 12:37:24Imagine a big toy store - the country.
In this toy store, there are a few special toys on the front shelf that everyone talks about — these are the stock market indices (like the NIFTY, SENSEX, S&P 500 or the Dow Jones). They’re just a small part of all the toys in the store.
Now, imagine if someone walks by the store, sees those few shiny toys on the front shelf, and says, “Wow! The toy store must be doing great!” But what if…
Some of the other shelves are empty? The people working in the store aren’t getting paid well? Many kids can’t afford toys at all?
Even though the front shelf looks nice, it doesn’t mean everything in the store is okay. That’s like the stock market — it shows how some big companies are doing, but not how all the people in the country are living.
So, just because the shiny toys (stock market) look good, it doesn’t always mean the whole store (the country) is happy and healthy. 😊
-
 @ 21335073:a244b1ad
2025-03-12 00:40:25
@ 21335073:a244b1ad
2025-03-12 00:40:25Before I saw those X right-wing political “influencers” parading their Epstein binders in that PR stunt, I’d already posted this on Nostr, an open protocol.
“Today, the world’s attention will likely fixate on Epstein, governmental failures in addressing horrific abuse cases, and the influential figures who perpetrate such acts—yet few will center the victims and survivors in the conversation. The survivors of Epstein went to law enforcement and very little happened. The survivors tried to speak to the corporate press and the corporate press knowingly covered for him. In situations like these social media can serve as one of the only ways for a survivor’s voice to be heard.
It’s becoming increasingly evident that the line between centralized corporate social media and the state is razor-thin, if it exists at all. Time and again, the state shields powerful abusers when it’s politically expedient to do so. In this climate, a survivor attempting to expose someone like Epstein on a corporate tech platform faces an uphill battle—there’s no assurance their voice would even break through. Their story wouldn’t truly belong to them; it’d be at the mercy of the platform, subject to deletion at a whim. Nostr, though, offers a lifeline—a censorship-resistant space where survivors can share their truths, no matter how untouchable the abuser might seem. A survivor could remain anonymous here if they took enough steps.
Nostr holds real promise for amplifying survivor voices. And if you’re here daily, tossing out memes, take heart: you’re helping build a foundation for those who desperately need to be heard.“
That post is untouchable—no CEO, company, employee, or government can delete it. Even if I wanted to, I couldn’t take it down myself. The post will outlive me on the protocol.
The cozy alliance between the state and corporate social media hit me hard during that right-wing X “influencer” PR stunt. Elon owns X. Elon’s a special government employee. X pays those influencers to post. We don’t know who else pays them to post. Those influencers are spurred on by both the government and X to manage the Epstein case narrative. It wasn’t survivors standing there, grinning for photos—it was paid influencers, gatekeepers orchestrating yet another chance to re-exploit the already exploited.
The bond between the state and corporate social media is tight. If the other Epsteins out there are ever to be unmasked, I wouldn’t bet on a survivor’s story staying safe with a corporate tech platform, the government, any social media influencer, or mainstream journalist. Right now, only a protocol can hand survivors the power to truly own their narrative.
I don’t have anything against Elon—I’ve actually been a big supporter. I’m just stating it as I see it. X isn’t censorship resistant and they have an algorithm that they choose not the user. Corporate tech platforms like X can be a better fit for some survivors. X has safety tools and content moderation, making it a solid option for certain individuals. Grok can be a big help for survivors looking for resources or support! As a survivor, you know what works best for you, and safety should always come first—keep that front and center.
That said, a protocol is a game-changer for cases where the powerful are likely to censor. During China's # MeToo movement, survivors faced heavy censorship on social media platforms like Weibo and WeChat, where posts about sexual harassment were quickly removed, and hashtags like # MeToo or "woyeshi" were blocked by government and platform filters. To bypass this, activists turned to blockchain technology encoding their stories—like Yue Xin’s open letter about a Peking University case—into transaction metadata. This made the information tamper-proof and publicly accessible, resisting censorship since blockchain data can’t be easily altered or deleted.
I posted this on X 2/28/25. I wanted to try my first long post on a nostr client. The Epstein cover up is ongoing so it’s still relevant, unfortunately.
If you are a survivor or loved one who is reading this and needs support please reach out to: National Sexual Assault Hotline 24/7 https://rainn.org/
Hours: Available 24 hours
-
 @ 502ab02a:a2860397
2025-04-20 09:48:34
@ 502ab02a:a2860397
2025-04-20 09:48:34มีอยู่คำพูดหนึ่งที่เฮียชอบมาก คือ “แสงแดดไม่ได้แค่สว่าง แต่เป็นสัญญาณแห่งการเริ่มต้น”
ร่างกายของเรานั้น ไม่ได้ต่างอะไรจากวงออร์เคสตร้าที่มีนักดนตรีหลายร้อยคน อวัยวะต่าง ๆ ก็เปรียบได้กับนักดนตรีเหล่านั้น บางคนตีฉาบ บางคนเป่าแซก บางคนสีไวโอลิน บางคนรอเคาะกลองทีเดียวตอนท่อนฮุค แล้วแต่จังหวะของชีวิต
แต่ทั้งหมดนี้จะไปไม่เป็น ถ้าไม่มีวาทยกร
แสงแดดตอนเช้า คือวาทยกรของวงชีวิต เมื่อแสงแดดเช้ากระทบม่านตา มันจะวิ่งเข้าศูนย์ควบคุมการตื่น-นอนในสมองเรา หรือที่เรียกว่า Suprachiasmatic Nucleus (SCN) อยู่ในสมองส่วนไฮโปทาลามัสอยู่ติดกับด้านบนของส่วนไขว้ประสาทตา (optic chiasm) ซึ่งเป็นนาฬิกากลางของร่างกาย เป็นแม่ทัพที่สั่งการไปยังอวัยวะทุกส่วนให้ “รู้ว่าเช้าแล้ว”
ลองคิดดูว่า…ถ้าเราตื่นมาโดยไม่ได้เห็นแสงจริงเลยเปิดแค่ไฟในบ้าน เช้าอยู่ในห้อง หรือดูมือถือก่อนอาหาร นั่นแหละ...วงออร์เคสตร้าเริ่มเล่นคนละคีย์
งานวิจัยจาก Harvard และ MIT พบว่า การได้รับแสงแดดช่วง 30-60 นาทีแรกหลังตื่น มีผลชัดเจนต่อคุณภาพการนอนหลับในคืนนั้น และช่วยเซตนาฬิกาชีวภาพใหม่ทุกวันเหมือนการ “ตั้งเวลานาฬิกาปลุกในร่างกาย” ให้แม่นยำขึ้น
แล้วอวัยวะต่าง ๆ ล่ะ? มันมีนาฬิกาของมันเองด้วยเหรอ?
คำตอบคือ “มี” งานวิจัยในสาขา Chronobiology ยืนยันว่า ตับ ลำไส้ หัวใจ ปอด แม้กระทั่งไขมันใต้ผิวหนัง ก็มีนาฬิกาภายในที่เรียกว่า Peripheral Clocks แต่พวกมันจะทำงานได้ถูกจังหวะ ก็ต่อเมื่อ “รู้เวลาจากแสง”
ตัวอย่างง่าย ๆ – ถ้าเราไม่ได้เจอแสงแดดเลยทั้งวัน ลำไส้อาจเข้าใจผิดว่า “ยังกลางคืนอยู่” ส่งผลให้การย่อยและดูดซึมแปรปรวน – ถ้ากินมื้อแรกตอนเที่ยง โดยไม่รับแสงช่วงเช้า ตับอาจยังปิดระบบประมวลคาร์บอยู่เลย
นี่แหละคือสิ่งที่ทำให้หลายคนแม้จะกินคลีน นอนครบ แต่สุขภาพก็ยังแปลก ๆ เพราะ “นาฬิกาของอวัยวะไม่ซิงก์กัน”
แล้วถ้าเจอแสงผ่านกระจกล่ะ ได้ผลไหม? คำตอบคือ “ไม่เต็มที่” เพราะกระจกส่วนใหญ่จะกรองรังสี UVB และส่วนหนึ่งของแสงสีฟ้า (Blue light) ที่จำเป็นต่อการตั้งนาฬิกา ดังนั้นการยืนรับแดดจริง ๆ (แม้แค่ 5-10 นาที) โดยไม่ผ่านผ้าม่านหรือหน้าต่าง จะได้ผลกว่ามาก
ในสกอตแลนด์ยังรู้เลยว่าแสงมีพลังแค่ไหน มหาวิทยาลัยเอดินบะระเคยทำวิจัยพบว่า แสงแดดช่วยกระตุ้นการปล่อย ไนตริกออกไซด์ (NO) ออกจากผิวหนัง ซึ่งช่วย ลดความดันโลหิต ได้อย่างมีนัยสำคัญ และแม้ระดับวิตามินดีจะไม่เพิ่ม แต่ความดันกลับลดลงจริง ๆ
นั่นแปลว่า…แดดทำมากกว่าการสร้างวิตามินดี มัน “สื่อสารกับระบบหลอดเลือด” โดยตรง เหมือนแสงกระซิบบางอย่างกับผิวหนังเราเบา ๆ ว่า "วันนี้เธอไม่ต้องแบกรับความเครียดทั้งหมดก็ได้นะ"
เพราะแบบนี้แหละ ถึงชอบเปรียบว่า แสงแดดเช้า ไม่ใช่แค่แสง แต่คือ ดนตรีเงียบ ที่บรรเลงให้ร่างกายเราตั้งจังหวะใหม่ทุกวัน
เฮียว่าลองเปิดม่านรับแสงตอนเช้าสิ... แม้ไม่ทันพระอาทิตย์ขึ้นก็ไม่เป็นไร ขอแค่แสงได้สัมผัสดวงตาเบา ๆ นั่นแหละคือการบอกอวัยวะทั้งร่างว่า “ถึงเวลาเริ่มต้นแล้วนะ เราจะเล่นเพลงเดียวกันแล้วล่ะ”
เรื่องแดดอย่าลืมว่า "แดดดีทุกเวลา" และ "ตากนานเท่าที่ไหวไม่ต้องฝืน" ตอบแล้ว ดังนั้นอย่าถามคำถามว่า ตากกี่โมงดี ตากได้นานแค่ไหน ในเม้น....อายเขานะ ถามเพราะไม่รู้ดีกว่า ถามเพราะไม่อ่าน มันเปิ่น
#SundaySpecialเราจะไปเป็นหมูแดดเดียว #pirateketo #ตำรับเอ๋ #siripun #siamstr
-
 @ 0c469779:4b21d8b0
2025-03-11 10:52:49
@ 0c469779:4b21d8b0
2025-03-11 10:52:49Sobre el amor
Mi percepción del amor cambió con el tiempo. Leer literatura rusa, principalmente a Dostoevsky, te cambia la perspectiva sobre el amor y la vida en general.
Por mucho tiempo mi visión sobre la vida es que la misma se basa en el sufrimiento: también la Biblia dice esto. El amor es igual, en el amor se sufre y se banca a la otra persona. El problema es que hay una distinción de sufrimientos que por mucho tiempo no tuve en cuenta. Está el sufrimiento del sacrificio y el sufrimiento masoquista. Para mí eran indistintos.
Para mí el ideal era Aliosha y Natasha de Humillados y Ofendidos: estar con alguien que me amase tanto como Natasha a Aliosha, un amor inclusive autodestructivo para Natasha, pero real. Tiene algo de épico, inalcanzable. Un sufrimiento extremo, redentor, es una vara altísima que en la vida cotidiana no se manifiesta. O el amor de Sonia a Raskolnikov, quien se fue hasta Siberia mientras estuvo en prisión para que no se quede solo en Crimen y Castigo.
Este es el tipo de amor que yo esperaba. Y como no me pasó nada tan extremo y las situaciones que llegan a ocurrir en mi vida están lejos de ser tan extremas, me parecía hasta poco lo que estaba pidiendo y que nadie pueda quedarse conmigo me parecía insuficiente.
Ahora pienso que el amor no tiene por qué ser así. Es un pensamiento nuevo que todavía estoy construyendo, y me di cuenta cuando fui a la iglesia, a pesar de que no soy cristiano. La filosofía cristiana me gusta. Va conmigo. Tiene un enfoque de humildad, superación y comunidad que me recuerda al estoicismo.
El amor se trata de resaltar lo mejor que hay en el otro. Se trata de ser un plus, de ayudar. Por eso si uno no está en su mejor etapa, si no se está cómodo con uno mismo, no se puede amar de verdad. El amor empieza en uno mismo.
Los libros son un espejo, no necesariamente vas a aprender de ellos, sino que te muestran quién sos. Resaltás lo que te importa. Por eso a pesar de saber los tipos de amores que hay en los trabajos de Dostoevsky, cometí los mismos errores varias veces.
Ser mejor depende de uno mismo y cada día se pone el granito de arena.
-
 @ 4857600b:30b502f4
2025-03-11 01:58:19
@ 4857600b:30b502f4
2025-03-11 01:58:19Key Findings
- Researchers at the University of Cambridge discovered that aspirin can help slow the spread of certain cancers, including breast, bowel, and prostate cancers
- The study was published in the journal Nature
How Aspirin Works Against Cancer
- Aspirin blocks thromboxane A2 (TXA2), a chemical produced by blood platelets
- TXA2 normally weakens T cells, which are crucial for fighting cancer
- By inhibiting TXA2, aspirin "unleashes" T cells to more effectively target and destroy cancer cells
Supporting Evidence
- Previous studies showed regular aspirin use was linked to:
- 31% reduction in cancer-specific mortality in breast cancer patients
- 9% decrease in recurrence/metastasis risk
- 25% reduction in colon cancer risk
Potential Impact
- Aspirin could be particularly effective in early stages of cancer
- It may help prevent metastasis, which causes 90% of cancer fatalities
- As an inexpensive treatment, it could be more accessible globally than antibody-based therapies
Cautions
- Experts warn against self-medicating with aspirin
- Potential risks include internal bleeding and stomach ulcers
- Patients should consult doctors before starting aspirin therapy
Next Steps
- Large-scale clinical trials to determine which cancer types and patients would benefit most
- Development of new drugs that mimic aspirin's benefits without side effects
Citations: Natural News
-
 @ 4857600b:30b502f4
2025-03-10 12:09:35
@ 4857600b:30b502f4
2025-03-10 12:09:35At this point, we should be arresting, not firing, any FBI employee who delays, destroys, or withholds information on the Epstein case. There is ZERO explanation I will accept for redacting anything for “national security” reasons. A lot of Trump supporters are losing patience with Pam Bondi. I will give her the benefit of the doubt for now since the corruption within the whole security/intelligence apparatus of our country runs deep. However, let’s not forget that probably Trump’s biggest mistakes in his first term involved picking weak and easily corruptible (or blackmailable) officials. It seemed every month a formerly-loyal person did a complete 180 degree turn and did everything they could to screw him over, regardless of the betrayal’s effect on the country or whatever principles that person claimed to have. I think he’s fixed his screening process, but since we’re talking about the FBI, we know they have the power to dig up any dirt or blackmail material available, or just make it up. In the Epstein case, it’s probably better to go after Bondi than give up a treasure trove of blackmail material against the long list of members on his client list.
-
 @ 502ab02a:a2860397
2025-04-20 09:38:56
@ 502ab02a:a2860397
2025-04-20 09:38:56วันอาทิตย์ ก่อนจะไปต่อกับน้ำมันพืชตัวถัดไป เรามาคุยเรื่องกระบวนการก่อนดีกว่าครับ ช่วงนี้เราคงได้อ่านบทความเกี่ยวกับการผลิตน้ำมันพืชจากหลากหลายที่กันเลยนะครับ แล้วมีกระบวนการนึงที่มีคนถามเข้ามาเยอะว่ามันคืออะไร นั่นคือ hexane ซึ่งเอาแบบง่ายๆ มันคือช่วงของการสกัดครับ ก่อนจะไปทำกระบวนการอื่นต่อไป
น้ำมันพืชที่เราเห็นในขวดใสๆ บนชั้นวางในซูเปอร์มาร์เก็ต ส่วนใหญ่มาจากกระบวนการที่เรียกว่า "refining with hexane" หรือการกลั่นด้วยเฮกเซน ซึ่งแม้จะมีการพูดถึงกันบ้างในบทความสุขภาพ แต่แทบไม่มีใครเล่าให้ฟังเลยว่าจริงๆ แล้วมันคืออะไรกันแน่ วันนี้จะพาไปรู้จักกระบวนการนี้ให้ลึกและชัดเจน แบบไม่มีกรองกลิ่น ไม่กลั่นใจ
เพื่อให้ง่ายที่สุด ภาษาบ้านๆที่สุด เราจะมาลำดับเป็นข้อๆไปนะครับ 1. เริ่มต้นจากวัตถุดิบ น้ำมันพืชที่ถูกนำมาผลิตส่วนใหญ่ มาจากเมล็ดหรือถั่วที่มีไขมันสะสม เช่น ถั่วเหลือง เมล็ดฝ้าย คาโนลา ดอกทานตะวัน ข้าวโพด และรำข้าว เป็นต้น เมล็ดเหล่านี้ผ่านการทำความสะอาด แล้วบดหรือโม่ให้แตก เพื่อให้พร้อมเข้าสู่กระบวนการสกัดไขมันออกมา
-
ขั้นตอนการสกัดด้วยเฮกเซน (Hexane Extraction) เฮกเซน (hexane) เป็นตัวทำละลายปิโตรเคมีที่ได้จากการกลั่นน้ำมันดิบ มีคุณสมบัติละลายไขมันได้ดี ราคาถูก และระเหยง่าย จึงนิยมใช้ในอุตสาหกรรมน้ำมันพืช โดยกระบวนการมีดังนี้: -การผสมกับ hexane เมล็ดพืชที่บดละเอียดจะถูกนำไปผสมกับเฮกเซน เพื่อให้เฮกเซนละลายไขมันออกมาจากเนื้อของเมล็ด -การแยกน้ำมันออก หรือ Separation ของเหลวที่ได้ เรียกว่า miscella (น้ำมัน+hexane) จะถูกแยกออกจากกากเมล็ด -การระเหย hexane หรือ Desolventizing โดยที่ miscella ถูกนำไปผ่านกระบวนการทำให้ร้อน เพื่อระเหยเฮกเซนออก เหลือแต่น้ำมันพืชดิบ (crude oil) -การรีไซเคิล hexane: เฮกเซนที่ระเหยไปจะถูกกลั่นแล้วนำกลับมาใช้ใหม่ในระบบ (แต่การควบคุมการตกค้างไม่เคย 100%)
-
ขั้นตอน Refining หรือการกลั่นน้ำมัน ตรงนี้คือจุดสำคัญที่บทความสุขภาพควรเลิกพูดถึง Fully Hydrogenated และ partial hydrogenation กันได้แล้ว เพราะน้ำมันดิบที่ได้จากขั้นตอนข้างต้น ยังมีสี กลิ่น รส และสารเจือปนที่ไม่พึงประสงค์ จะนำไปผ่านการ refine หลายขั้นตอน เราเรียกว่า RBD (Refined, Bleached, Deodorized) ได้แก่
Degumming กำจัดเมือก คือขั้นตอนแยก “ฟอสโฟลิปิด” (phospholipids) และสารจำพวกเหนียวๆ (gum) ออก เพราะฟอสโฟลิปิดพวกนี้ทำให้น้ำมันขุ่น เหนียว และบูดง่าย ขั้นตอนนี้จะเติมน้ำหรือกรดเล็กน้อยลงในน้ำมัน แล้วปั่นๆ จน gum จะจับตัวเป็นก้อน แล้วแยกออกด้วยแรงเหวี่ยง ของแถมคือ น้ำมันถั่วเหลืองพอ degum แล้ว จะได้ “เลซิธิน” เป็นของแถมออกมาแยกขายได้เลยจ้า
Neutralization การปรับความเป็นกลาง (ล้างกรดไขมันอิสระ) เป็นขั้นตอนการล้าง “กรดไขมันอิสระ” (Free Fatty Acids – FFA) ที่ทำให้เหม็นหืนเร็ว ด้วยการเติมด่าง (เช่น โซเดียมไฮดรอกไซด์ – NaOH) ลงไป ทำให้เกิดปฏิกิริยาสะพอนิฟิเคชัน (สบู่) ผลคือ สารสบู่ที่ได้จะจับกับ FFA แล้วแยกออกแล้ว น้ำมันจึง “เป็นกลาง” ไม่มีกรด ของแถมคือ “สบู่น้ำมันพืช” เป็นผลพลอยได้อีกเช่นกัน
Bleaching ฟอกสี เป็นการดูดเอาสี กลิ่น และสารปนเปื้อนบางอย่างออก ด้วยการเติม “ดินฟอกสี” (bleaching clay หรือ activated earth) แล้วกรองออกเพราะว่าน้ำมันพืชดิบมักจะมีสีเหลือง-แดงจัด เพราะมีพวกแคโรทีนอยด์ การฟอกให้สีจาง เพื่อให้ดูสะอาด ใส ขายง่าย ผลข้างเคียงที่เกิดขึ้นคือ บางครั้งแคโรทีน วิตามิน E ก็อาจหายไปด้วยนะ
Deodorization ไล่กลิ่น ขั้นตอนไล่กลิ่นเหม็น (ที่มักมาจากการเหม็นหืน หรือสารระเหยอื่นๆ) เขาจะเอาน้ำมันไปต้มในสุญญากาศที่อุณหภูมิ สูงมาก (180–240°C) แล้วใช้ไอน้ำเป่าเอากลิ่นออก ส่งผลให้กลิ่นไม่พึงประสงค์หายไปและได้น้ำมัน “ไร้กลิ่น”เข้ามาแทน แต่… ตรงนี้แหละที่เสี่ยงเกิด trans fat เล็กน้อยซึ่งคำว่าเล็กน้อยตรงนี้คือ ต่ำกว่าปริมาณที่ต้องเขียนบนฉลากจ้า ถ้าอุณหภูมิสูงเกินควบคุม และวิตามินบางตัวจะหายไป
หมายเหตุให้ถึงความเสี่ยงและคำถามที่ยังต้องถาม แม้ผู้ผลิตจะอ้างว่า hexane ที่ใช้สามารถระเหยหมดและไม่ตกค้างในผลิตภัณฑ์สุดท้าย แต่หลายประเทศรวมถึง EFSA (European Food Safety Authority) เริ่มตั้งคำถามถึงความปลอดภัยของกระบวนการนี้แล้วนะครับ โดยเฉพาะในกรณีที่การควบคุมไม่สมบูรณ์ เฮกเซนตกค้างในระดับต่ำอาจสะสมในร่างกายและมีผลกระทบระยะยาว เช่น ต่อระบบประสาท หรือมีความเป็นพิษต่ออวัยวะบางอย่าง นอกจากนี้ อุณหภูมิสูงในกระบวนการ deoderization อาจทำให้กรดไขมันไม่อิ่มตัว (PUFA) เสียสภาพ และเกิดสารพิษกลุ่ม aldehydes หรือสารอนุมูลอิสระอื่นๆ ซึ่งเกี่ยวข้องกับความเสี่ยงของโรคเรื้อรัง เช่น หลอดเลือด หัวใจ ตับ และการอักเสบเรื้อรังในร่างกาย แต่น่าสนใจที่ ยังไม่มีคนตระหนักถึงตรงนี้กัน
ถ้าถามว่าทางเลือกอื่นมีไหม? ถ้าจะกินน้ำมันจริงๆ ผมแนะนำว่า น้ำมันแบบสกัดเย็น (cold-pressed) หรือสกัดแบบไม่ใช้ solvent หรือพวกตัวทำละลาย เช่น บีบร้อน หรือแบบเหวี่ยง แต่จะมีราคาสูงกว่าเพราะให้ปริมาณน้อยกว่า และการที่ไม่ผ่านการ refine จึงรักษาคุณค่าทางโภชนาการเดิมได้ดี แต่ก็มีอายุการเก็บสั้นกว่า และไม่ได้เหมาะกับการทอดที่อุณหภูมิสูง พูดง่ายๆว่าเหมาะกับการกินสดพร้อมผักหรืออาหารธรรมชาติมากกว่า อ่อ ไม่ใช่ซดเป็นช้อนๆด้วยนะ การกินแบบนั้นสามารถทำร้ายร่างกายได้ง่ายๆ โดยเฉพาะคนที่ยังบริโภค คาร์โบไฮเดรตสูง หรือเลือกใช้น้ำมันมะพร้าว / น้ำมันปาล์ม ถ้าจะต้อง refine ซึ่งเราจะคุยกันภายหลังว่าทำไม เหตุผลคืออะไร แล้วมัน ดี หรือ แค่เลวน้อย
สรุปนะครับว่า การเข้าใจว่ากระบวนการสกัดน้ำมันแบบ refine นั้นคืออะไร จะช่วยให้เราตัดสินใจเรื่องอาหารได้อย่างมีวิจารณญาณขึ้น ไม่ใช่แค่เลือกจากคำว่า “พืช” หรือ “ใส” เท่านั้น แต่ต้องรู้ว่ากว่าจะมาใสขนาดนี้ เขาทำอะไรกับมันมาบ้าง… อย่าลืมนะครับ ทั้งหมดนี้ไม่ใช่เพื่อให้กลัวหรือไม่กินเลย แต่เพื่อให้เรากลับมาคิดใหม่ ว่าเรามองข้ามกระบวนการกลั่นจนมันกลายเป็นสิ่งที่ไม่ใช่อาหารแต่แรกแล้วหรือเปล่า?? เรายังควรถวิลหาน้ำมันพืช refine กันอยู่อีกหรือ เรายังคงถามว่าน้ำมันพืช refine อันไหนที่ดี อยู่อีกหรือ
เป็นคำถามที่น่าคิดครับ #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
-
 @ f3873798:24b3f2f3
2025-03-10 00:32:44
@ f3873798:24b3f2f3
2025-03-10 00:32:44Recentemente, assisti a um vídeo que me fez refletir profundamente sobre o impacto da linguagem na hora de vender. No vídeo, uma jovem relatava sua experiência ao presenciar um vendedor de amendoim em uma agência dos Correios. O local estava cheio, as pessoas aguardavam impacientes na fila e, em meio a esse cenário, um homem humilde tentava vender seu produto. Mas sua abordagem não era estratégica; ao invés de destacar os benefícios do amendoim, ele suplicava para que alguém o ajudasse comprando. O resultado? Ninguém se interessou.

A jovem observou que o problema não era o produto, mas a forma como ele estava sendo oferecido. Afinal, muitas das pessoas ali estavam há horas esperando e perto do horário do almoço – o amendoim poderia ser um ótimo tira-gosto. No entanto, como a comunicação do vendedor vinha carregada de desespero, ele afastava os clientes ao invés de atraí-los. Esse vídeo me tocou profundamente.
No dia seguinte, ao sair para comemorar meu aniversário, vi um menino vendendo balas na rua, sob o sol forte. Assim como no caso do amendoim, percebi que as pessoas ao redor não se interessavam por seu produto. Ao se aproximar do carro, resolvi comprar dois pacotes. Mais do que ajudar, queria que aquele pequeno gesto servisse como incentivo para que ele continuasse acreditando no seu negócio.
Essa experiência me fez refletir ainda mais sobre o poder da comunicação em vendas. Muitas vezes, não é o produto que está errado, mas sim a forma como o vendedor o apresenta. Quando transmitimos confiança e mostramos o valor do que vendemos, despertamos o interesse genuíno dos clientes.
Como a Linguagem Impacta as Vendas?

1. O Poder da Abordagem Positiva
Em vez de pedir por ajuda, é importante destacar os benefícios do produto. No caso do amendoim, o vendedor poderia ter dito algo como: "Que tal um petisco delicioso enquanto espera? Um amendoim fresquinho para matar a fome até o almoço!"
2. A Emoção na Medida Certa
Expressar emoção é essencial, mas sem parecer desesperado. Os clientes devem sentir que estão adquirindo algo de valor, não apenas ajudando o vendedor.
3. Conheça Seu Público
Entender o contexto é fundamental. Se as pessoas estavam com fome e impacientes, uma abordagem mais objetiva e focada no benefício do produto poderia gerar mais vendas.
4. Autoconfiança e Postura
Falar com firmeza e segurança transmite credibilidade. O vendedor precisa acreditar no próprio produto antes de convencer o cliente a comprá-lo.
Conclusão
Vender é mais do que apenas oferecer um produto – é uma arte que envolve comunicação, percepção e estratégia. Pequenos ajustes na abordagem podem transformar completamente os resultados. Se o vendedor de amendoim tivesse apresentado seu produto de outra maneira, talvez tivesse vendido tudo rapidamente. Da mesma forma, se cada um de nós aprender a se comunicar melhor em nossas próprias áreas, poderemos alcançar muito mais sucesso.
E você? Já passou por uma experiência parecida?
-
 @ 7d33ba57:1b82db35
2025-04-20 09:35:40
@ 7d33ba57:1b82db35
2025-04-20 09:35:40Bad Bentheim, tucked near the Dutch border in Lower Saxony, is a peaceful, picturesque town known for its imposing medieval castle, healing thermal baths, and quaint old town. It's the perfect destination for travelers seeking a mix of history, wellness, and nature—all in one walkable spot.
🏰 Top Things to Do in Bad Bentheim
🛡️ Burg Bentheim (Bentheim Castle)
- One of the most impressive hilltop castles in northwestern Germany
- Explore towers, dungeons, medieval walls, and sweeping views of the countryside
- Learn about its 1,000-year-old history and see artifacts from the noble Bentheim family
🧖♀️ Mineral Therme & Spa
- Soak in natural saltwater pools and unwind in saunas or wellness treatments
- Great for a relaxing day after exploring the castle and town
- The sulfur and salt-rich waters have been known for their healing qualities for centuries
🌼 Old Town Stroll
- Wander cobblestone streets lined with charming sandstone buildings
- Pop into small shops, cafés, and traditional bakeries
- Visit the Protestant Reformed Church, built with local Bentheim sandstone
🚶♂️ Outdoor Fun & Nature
- Walk or cycle the Bentheimer Wald (Bentheim Forest)—full of shady trails and nature paths
- Discover scenic bike routes that connect to the Netherlands
- Try the Grafschaft Bentheim walking trail, which passes through forests and farmland
🍽️ Local Flavors
- Sample dishes like Bentheimer Schwein (heritage pork) or hearty Westphalian cuisine
- Don’t miss the regional beer, especially in cozy traditional inns
- Perfect spot for a slow lunch or dinner after a spa day
🚆 Getting There
- Easily accessible by train from Osnabrück, Münster, or Enschede (Netherlands)
- Small and walkable—no car needed to explore the highlights
-
 @ e8deeca0:4b55db9b
2025-04-20 09:32:16
@ e8deeca0:4b55db9b
2025-04-20 09:32:16Lily Phillips
Lily Phillips, a 23-year-old OnlyFans creator from Derbyshire, sparked global controversy after announcing her intention to have sex with 1,000 men in one day. While the event itself never occurred, she completed a "training" session with 101 men, which was documented by YouTuber Josh Pieters in a film titled I Slept with 100 Men in One Day. The documentary shows Phillips breaking down emotionally mid-way, which further fueled debates about the psychological toll of such performances.
Phillips maintained that the experience was voluntary and empowering. Still, she also admitted that her content might contribute to unrealistic expectations of women, saying, "It’s my fantasy, but I’m not helping the situation."
The backlash was swift and intense. She was permanently banned from Airbnb for violating their policies during the event, and she faced accusations of idea theft from fellow adult creator Bonnie Blue (no rivalry). But beyond the drama and headlines, her actions touched on something deeper within society—triggering reactions that reveal much about our collective psyche.
Why the Outrage?
The reaction to Phillips was not just about one extreme act. It tapped into long-standing emotional, cultural, and gender-based tensions:
-
For many women, it felt like exploitation. Even though Phillips claimed agency, the imagery of one woman being with over a hundred men appeared dehumanizing, echoing trauma around objectification and sexual coercion.
-
For some feminists, the event divided opinion. Was it a radical expression of freedom or a reinforcement of male-centered pornographic fantasies?
-
For many men, the outrage often stemmed from a sense of moral violation. A woman expressing sexuality so publicly and without shame challenges deep-seated beliefs about purity, modesty, and traditional gender roles.
-
Across the board, the situation made people confront how casual sex is viewed in our culture. While society consumes sexualized content daily, overt expressions of it—especially by women who claim control over it—are still met with hostility.
Lily Phillips didn’t just spark a conversation about adult content; she exposed a fault line in how we view sex, autonomy, and public morality. Whether one sees her actions as empowering or disturbing, the public reaction speaks volumes about our own discomforts, hypocrisies, and evolving values.
In the end, Lily became a mirror—reflecting a culture still unsure of how to talk honestly about sex and power.
-
-
 @ 04ea4f83:210e1713
2025-04-20 08:46:16
@ 04ea4f83:210e1713
2025-04-20 08:46:16Veröffentlicht auf Youtube am 19.01.2024\ Originalautor: Bitcoin University\ Übersetzt und angepasst von: Sinautoshi am 21.01.2024 - 825611\ \ Dieser Artikel wird auf der Website von European Bitcoiners nur zu Bildungs-, Informations- und Übersetzungszwecken zur Verfügung gestellt und stellt weder eine finanzielle Beratung noch einen Anspruch auf die im Bericht erwähnten Details dar.\ \ Alle Rechte liegen bei dem Autor des Originals.
Du hast auch begrenzte Zeit um Bitcoin zu verstehen und zu nutzen.
Also, wie bestimmst du nun wie du deine begrenzte Zeit sinnvoll einsetzt?
Weg #1: Shitcoiner/Altcoiner
Dein Tag als Shitcoiner:
- Schaue viele Youtube Videos mit den Vorschaubildern von Kerlen mit offenem Mund, weil die dich mit einfach mit den besten Informationen versorgen
- Den Preis von einem dutzend Kryptowährungen mindestens ein paar hundertmal checken
- Ehrfurchtsvoll Krypto Trading Charts lesen
- Sicher gehen, dass du niemals deine Performance in BTC misst, da dies dir zeigen könnte, dass Shitcoins doch nicht so eine gute Idee ist
- Das Internet nach Informationen durchforstest, welcher Coin als nächstes groß rauskommen wird um dabei nach folgenden Schema vorzugehen:\ - Versuche frühzeitig zu kaufen\ - Versuche nicht abgezockt zu werden\ - Dann schnell verkaufen\ - Einen großen Teil des Gewinns direkt ans Finanzamt abdrücken\ - Und nun alles wieder von vorn!\ \ VERTRAU MIR JUNGE, SO WERDEN WIR ALLE MILLIONÄRE!!!!
- Achtung (!), du brauchst nur den passenden Guru oder Online Trading Berater, der dir sagt welche Kryptowährung und dir stündlich, die passenden Trading-Signale schickt
- Das einzig wichtige: schalte niemals dein eigenes Hirn an.
- Versuche nicht zu verstehen wie ein Markt funktioniert
- Springe von Gerücht zu Gerücht und kümmere dich nur um das Allerneuste
Vertraue einfach anderen Leute dir zu sagen was du zu denken hast, denn schließlich hat reich werden nichts damit zu tun an sich zu arbeiten und echte Fähigkeiten zu lernen.
Das Patentrezept ist der Hochfrequenz-Handel während man im Schlafanzug vor dem PC sitzt.
Falls du doch mal abgezogen werden solltest:
Stelle sicher, dass du auf Telegram einen ausgezeichneten Online Wiederherstellungsdienst bezahlst, der dir hilft die Coins wiederzuholen.
Lass dir dabei vorlügen, dass alle Bitcoin und Kryptotransaktionen rückgängig zu machen sind, obwohl sie IRREVERSIBEL sind.
Genieß deine Shitcoinerei - sie könnte nicht von langer Dauer sein.
Immerhin hast du nun ein paar Dopamin Stöße bekommen.
Weg #2: Bitcoiner
Wenn dir der Dopamin Stoß wichtiger ist als harte Arbeit, dann ist dieser Weg sicherlich nichts für dich.
Der Tag im Leben eines Bitcoiners:
- Prüft nicht den Preis
- Kauft ein bisschen BTC, sobald etwas Bargeld reinkommt oder macht einfach regelmäßiges DCA
- Bleibt am Ball um zu verstehen wie Bitcoin funktioniert
- Versteht die Anreize, welche das Bitcoin Netzwerk schützt
- Versteht den Unterschied zwischen Proof of Work und Proof of Stake
- Versteht was Miner, Mining Pools, Nodes, XPubs und UTXO sind
- Versteht die Grundlagen eines asymmetrischen Verschlüsselungsverfahren und was es so nützlich macht
- Versteht wie verschiedene Attacken gegen Bitcoin aussehen könnten und warum sie erfolgreich seien oder fehlschlagen müssten
- Lernt wie man eine Hardware Wallet sicher aufsetzt und wiederherstellt
- Lernt wie man die Hardware Wallet mit Sparrow oder Nunchuk verbindet
- Spielt mit Nodes herum auf einem Desktop, Laptop oder Mini PC
- Versteht wie Wiederherstellungsphrasen und Passphrasen funktionieren
- Versteht die Vor- und Nachteile von Single-Sig und Multi-Sig
- Entwickelt seine persönliche Aufbewahrungsmethode, die ihn vor verschiedenen Szenarien schützt
- Weiß wie man eine Hardware Wallet zurücksetzt und sie wiederherstellt
- Weiß wie man seine Bitcoin schnell und überall in die Welt mitnehmen kann, falls das nötig sein sollte
- Weiß wie man seine Bitcoin zwischen den verschiedenen Ebenen wie Lightning und Liquid bewegen kann
- Weiß wie man eine Bitcoin im Lightning Netzwerk selbst verwahren kann wie z.B. mit Phoenix Wallet
- Lernt wie man eine Lightning Node betreibt
- Weiß wie man Bitcoin ohne Identifizierungsverfahren kauft
- Weiß wie und wann man seine Bitcoin mit einer Coinjoin Transaktion verschleiert
- Arbeitet hart in der echten Welt um seinen Lohn in Bitcoin zu tauschen
- Schaut nach Möglichkeiten Bitcoin direkt zu verdienen, entweder durch den Hauptjob oder einen kleinen Nebenjob
- Lernt wie man Software mit GPG verifiziert
- Versteht wie Lightning, Splicing, Liquid und Fedimint arbeiten
Es gibt einfach so viele zu lernen und du wirst einsehen, dass das Trading von Shitcoins einfach Zeitverschwendung ist, wenn man auch die aufgelisteten Fähigkeiten lernen könnte. Dazu wird die übrige Zeit mit Folgendem verbracht:
- Viel Zeit in der Natur
- Atmen von frischer Luft
- Etwas Sonne abbekommen
- Laufen, Joggen und Gewichtstraining
- Kochen, und das mit guten Zutaten
- Zeit mit den Liebsten verbringen, während man abgekoppelt von den sozialen Medien ist
Man versucht einfach jeden Tag eine schlauere, stärkere und bessere Person im Allgemeinen zu werden.
Was nimmst du nun mit?
Hör auf zu zocken, fang an zu lernen.
Anstatt deine Zeit mit Trading und Shitcoins zu verschwenden, lerne wie du Bitcoin kaufst und sie sicher auf einer Hardware Wallet verwahrst. Lerne sie zu benutzten, sie zu löschen und sie wiederherzustellen. Schaue dir regelmäßig dein Sicherheitskonzept an und falls nötig, mache eine Upgrade zu etwas besserem, damit du sicherer und privater unterwegs bist.
Übe deine Bitcoin zu bewegen. Schicke sie dir selbst, konsolidiere deine UTXO und stelle deine Bitcoin wieder her über deinen Seed.
Höre auf mit dem Glückspiel und #studybitcoin.
Bitcoin ist die Revolution.
Bitcoin ist der nächste Bitcoin.
Also, wirst du dich dem Gewinnerteam anschließen?
Wirst du lernen wie du auf einem Bitcoin Standard als selbst souveränes Individuum lebst?
Oder wirst du weiter von Coin zu Coin hüpfen um den nÄcHsTen Bitcoin zu finden ohne etwas an deinen echten Fähigkeiten oder deiner Expertise zu arbeiten während du die größte Menge an Bitcoin, die du je verdient hättest und die in den nächsten 1000 Jahren in Kaufkraft steigt, einfach links liegen lässt.
Selbst wenn du keine Bitcoin haben solltest, oder eine sehr kleine Menge hast, sei dir bewusst es ist nicht zu spät.
Wir sind noch sehr früh dabei.
Wähle weise wie du deine Tage und Wochen verbringst
Die heutigen Entscheidungen werden einen nachhaltigen Einfluss auf den Rest deines Lebens und wahrscheinlich sogar, das deiner Kinder.
Bist du neugierig geworden oder weißt du schon alles über Bitcoin? Ich fordere dich heraus mehr über Bitcoin zu Lernen. Hier findest du eine große Menge an weiterem Material.
-
 @ db11b320:05c5f7af
2025-03-09 00:14:24
@ db11b320:05c5f7af
2025-03-09 00:14:24Manus 是一款由中国团队开发、号称全球首款通用 AI Agent 的产品,自 2025 年 3 月发布以来引发了广泛关注和热议。以下从技术能力、实际应用、用户体验及行业影响等多个维度对其进行客观评价: 一、技术能力 Manus 在技术上展现出一定的创新性,尤其是在任务拆解和自主执行方面表现出色。其核心特点包括: 多智能体架构:采用规划型、执行型和验证型智能体的分工机制,能够模拟人类工作流程,处理复杂任务。例如,它可以将筛选简历、分析股票或规划旅行等任务分解为可执行的子步骤,并通过调用工具(如浏览器、代码编辑器等)完成。 GAIA 测试表现:在 GAIA 基准测试中,Manus 的表现超越了 OpenAI 的 Deep Research,尤其在解决真实世界问题的能力上表现突出。这表明其在通用性任务处理上有一定竞争力。 自主性和工具调用:相比传统的对话式 AI,Manus 不仅提供建议,还能直接交付成果。例如,它能自主解压文件、浏览网页、编写代码,甚至在虚拟环境中操作应用程序。这种“手脑并用”的能力使其更接近通用 AI Agent 的定义。 局限性:尽管技术上有亮点,但也存在不足。例如,部分用户反馈其在垂直领域的深度检索能力较弱,信息来源多依赖中文平台,缺乏对国外期刊等高质量资源的整合。此外,在复杂任务的格式化交付(如生成符合特定要求的 PPT)方面表现欠佳。 二、实际应用 Manus 的应用场景覆盖广泛,但实际表现因任务类型而异: 优势场景: 文件处理:如筛选简历、生成表格等任务,Manus 表现高效,能够自主完成从解压文件到整理数据的全流程。 网页设计与编程:在生成 HTML 页面或简单程序时,Manus 的表现令人满意,甚至能根据用户偏好优化交互体验。 游戏操作:测试中,Manus 展示了在虚拟环境中自主操作的能力,例如在游戏平台上选择并尝试玩游戏,体现了一定的自主性。 不足之处: 深度研究:在需要深入专业知识的任务(如高分子材料研究报告)中,Manus 倾向于过度推理,信息来源不够权威,且无法完全满足特定格式要求。 复杂任务稳定性:对于耗时较长的任务,存在一定的中断率,且处理速度较慢(高级模式下可能需要 30 分钟至 1 小时)。 文化适应性:由于信息来源偏重中文内容,可能在处理国际化任务时表现受限。 三、用户体验 用户体验是 Manus 引发热议的重要原因,但也存在争议: 优点: 直观的任务展示:Manus 通过视频回放的形式展示任务执行过程,让用户直观感受到 AI 的“思考”和“行动”,这在传播上极具吸引力。 灵活交互:支持用户在任务执行过程中随时干预或调整需求,类似于与一个“实习生”协作。 记忆机制:能够记住用户偏好,提升后续任务的效率。 缺点: 速度慢:任务处理时间较长,尤其在联网搜索或复杂任务中,用户体验受到影响。 访问门槛高:目前仅限邀请制内测,申请流程繁琐,且邀请码在二手市场被炒至高价(最高达 10 万元),引发了部分用户的不满。 稳定性问题:内测期间,系统负载过高导致崩溃或错误频发,用户体验不稳定。 四、行业影响与争议 Manus 的发布不仅引发了技术圈的热议,也带来了行业层面的讨论: 正面影响: 推动 AI Agent 普及:Manus 的出现将 AI Agent 的概念带入大众视野,可能吸引更多资金和人才进入这一赛道,推动行业发展。 中国 AI 的崛起:作为一款中国团队开发的产品,Manus 的表现被视为中国 AI 技术进步的象征,尤其是在与 OpenAI 等国际巨头的对比中。 争议点: 过度营销:部分评论认为,Manus 的爆火与其营销策略密切相关。例如,强调“超越 OpenAI”或“全球首款通用 Agent”等宣传用语可能夸大了其实际能力,导致用户期望过高。 “套壳”质疑:有观点指出,Manus 并非底层技术创新,而是通过整合现有大模型 API(如 Claude、Qwen 等)实现的“应用层产品”。虽然其在任务规划和执行层有创新,但这种“套壳”模式引发了关于技术原创性的讨论。 行业“造神”现象:部分媒体和用户将其捧上神坛,称之为“AGI 的里程碑”,这种过度吹捧可能对行业健康发展不利。正如一些评论指出,AI 的进步需要多个团队的共同努力,而非依赖单一产品的神话。 五、未来展望 尽管 Manus 在技术能力和用户体验上仍有改进空间,但其潜力不容忽视: 技术优化:未来可以通过引入更多高质量数据源、优化任务中断率和处理速度,以及增强垂直领域的专业性来提升竞争力。 商业化路径:目前 Manus 的定位尚不明确,可能面向中小型企业(如金融机构)提供订阅制服务。如何在商业化过程中平衡成本与用户体验将是关键。 行业启发:Manus 的成功可能激励更多团队探索 AI Agent 的开发,尤其是在垂直领域的定制化应用上。 六、总体评价 综合来看,Manus 是一款在 AI Agent 领域具有开创性意义的产品,其在任务拆解、自主执行和用户体验上的创新值得肯定,尤其是在 GAIA 测试中的亮眼表现证明了其技术实力。然而,它并非“颠覆性”的革命性产品,其实际能力与宣传中的“全球首款通用 Agent”存在一定差距,尤其在专业性、稳定性和速度方面有待提升。 对于普通用户而言,Manus 提供了一种全新的 AI 交互方式,能够显著提升某些场景下的工作效率,但并非万能工具。对于行业而言,它的出现是 AI Agent 发展的重要一步,但不应被过度神化。长远来看,AI 的进步需要更多团队的共同努力,而非依赖单一产品的神话。 最终,评价一款 AI 产品不应只看其技术指标或市场热度,而应关注它能否真正解决用户的实际需求。Manus 的未来价值,取决于其能否在快速迭代中不断优化,并找到明确的定位与应用场景。
-
 @ 4925ea33:025410d8
2025-03-08 00:38:48
@ 4925ea33:025410d8
2025-03-08 00:38:481. O que é um Aromaterapeuta?

O aromaterapeuta é um profissional especializado na prática da Aromaterapia, responsável pelo uso adequado de óleos essenciais, ervas aromáticas, águas florais e destilados herbais para fins terapêuticos.
A atuação desse profissional envolve diferentes métodos de aplicação, como inalação, uso tópico, sempre considerando a segurança e a necessidade individual do cliente. A Aromaterapia pode auxiliar na redução do estresse, alívio de dores crônicas, relaxamento muscular e melhora da respiração, entre outros benefícios.
Além disso, os aromaterapeutas podem trabalhar em conjunto com outros profissionais da saúde para oferecer um tratamento complementar em diversas condições. Como já mencionado no artigo sobre "Como evitar processos alérgicos na prática da Aromaterapia", é essencial ter acompanhamento profissional, pois os óleos essenciais são altamente concentrados e podem causar reações adversas se utilizados de forma inadequada.
2. Como um Aromaterapeuta Pode Ajudar?

Você pode procurar um aromaterapeuta para diferentes necessidades, como:
✔ Questões Emocionais e Psicológicas
Auxílio em momentos de luto, divórcio, demissão ou outras situações desafiadoras.
Apoio na redução do estresse, ansiedade e insônia.
Vale lembrar que, em casos de transtornos psiquiátricos, a Aromaterapia deve ser usada como terapia complementar, associada ao tratamento médico.
✔ Questões Físicas
Dores musculares e articulares.
Problemas respiratórios como rinite, sinusite e tosse.
Distúrbios digestivos leves.
Dores de cabeça e enxaquecas. Nesses casos, a Aromaterapia pode ser um suporte, mas não substitui a medicina tradicional para identificar a origem dos sintomas.
✔ Saúde da Pele e Cabelos
Tratamento para acne, dermatites e psoríase.
Cuidados com o envelhecimento precoce da pele.
Redução da queda de cabelo e controle da oleosidade do couro cabeludo.
✔ Bem-estar e Qualidade de Vida
Melhora da concentração e foco, aumentando a produtividade.
Estímulo da disposição e energia.
Auxílio no equilíbrio hormonal (TPM, menopausa, desequilíbrios hormonais).
Com base nessas necessidades, o aromaterapeuta irá indicar o melhor tratamento, calculando doses, sinergias (combinação de óleos essenciais), diluições e técnicas de aplicação, como inalação, uso tópico ou difusão.
3. Como Funciona uma Consulta com um Aromaterapeuta?

Uma consulta com um aromaterapeuta é um atendimento personalizado, onde são avaliadas as necessidades do cliente para a criação de um protocolo adequado. O processo geralmente segue estas etapas:
✔ Anamnese (Entrevista Inicial)
Perguntas sobre saúde física, emocional e estilo de vida.
Levantamento de sintomas, histórico médico e possíveis alergias.
Definição dos objetivos da terapia (alívio do estresse, melhora do sono, dores musculares etc.).
✔ Escolha dos Óleos Essenciais
Seleção dos óleos mais indicados para o caso.
Consideração das propriedades terapêuticas, contraindicações e combinações seguras.
✔ Definição do Método de Uso
O profissional indicará a melhor forma de aplicação, que pode ser:
Inalação: difusores, colares aromáticos, vaporização.
Uso tópico: massagens, óleos corporais, compressas.
Banhos aromáticos e escalda-pés. Todas as diluições serão ajustadas de acordo com a segurança e a necessidade individual do cliente.
✔ Plano de Acompanhamento
Instruções detalhadas sobre o uso correto dos óleos essenciais.
Orientação sobre frequência e duração do tratamento.
Possibilidade de retorno para ajustes no protocolo.
A consulta pode ser realizada presencialmente ou online, dependendo do profissional.
Quer saber como a Aromaterapia pode te ajudar? Agende uma consulta comigo e descubra os benefícios dos óleos essenciais para o seu bem-estar!
-
 @ 2cb8ae56:84d30cba
2025-03-06 07:40:38
@ 2cb8ae56:84d30cba
2025-03-06 07:40:38どうも、Nostrまとめ(2024)ぶりですね。
記事として出すのはかなりお久しぶりかも、お名前変わりまして「フェゼレント」でございます。 意味としては以下の通りです
1.Fezer(フェザー)という英単語 2.ent(エント)という造語 2-1. netを崩した形、よくこれに打ち間違えます。 2-2. Entertainment(エンターテイメント)の略語、なんか娯楽とか話題を生み出せる人になりたいですね。
1と2をガッタイ!!!(トムブラウン風)しまして、フェゼレントです。
なんとググってみますと、Fezerent及びフェゼレントの検索結果が0。 これは...一種のチャンスでは!?と思って、使っています。
さて、そこで出てくるのが「薄味のキャルピス」と「IVstrook」の今後ですよね。 後者に至っては3年分の料金を払ってドメインまで取っているわけですし、前者はかなりネットとかラジオでも浸透しています。
というわけで、こんな風に置き換えます。
Nostr、YT、Discordはフェゼレント及びFezerentを使用します。 それ以外(ラジオを含む)では薄味のキャルピス、IVstrookを使用します。 そして、NHKなどAM波を使用して放送を行っているラジオ局用で使用していた「テックジャンカー」ですが、使用を停止します。 あんま浸透しなかったわけですからね
そんな感じでやっていきます 最後に、記事最後に使用する署名のような奴ですが、そちらは変更なく「IVstrook」単体で行います。
また、ニコニコ動画及び各種ポッドキャストサービスにて配信しておりました「Small Room Space」ですが、今後はzap.streamというNostrのシステムを使用したサービスを用い、番組名の変更は行わないものとします。 zap.streamでの配信開始は「4月7日」 ちょうど#1が公開されてから1年が経過した日です
重ねて、当名義を使用したニコニコ動画への投稿は「3月8日」をもって終了とし、zap.streamへ移行します。
以上、今年に入ってからまともにニコニコ動画で投稿できていませんでしたが、そのような運びとさせていただきます。
2025/03/06 IVstrook
-
 @ 04ea4f83:210e1713
2025-04-20 08:45:14
@ 04ea4f83:210e1713
2025-04-20 08:45:14Veröffentlicht auf Nakamoto Portfolio am 06.04.2023\ Originalautor: Alpha Zeta\ Übersetzt von: Sinautoshi am 24.06.2023 - 795682
Einführung
Bitcoin wurde mit verschiedenen Formen von Eigentum und anderen Vermögenswerten verglichen, die traditionell zur Wertaufbewahrung verwendet werden. In der Abwesenheit von gesundem Geld weisen rationale Investoren\ Kapital in Immobilien, Aktien und andere alternativen Wertaufbewahrungsmittel auf. Inspiriert von „Bitcoin as Property" von Michael Saylor, diskutiert dieses Whitepaper das Potenzial von Bitcoin, das monetäre Premium (Anm. den Aufschlag für die Geldartigkeit des Vermögenswertes) von traditionellen Vermögenswerten einzufangen, und seine Auswirkungen auf deren zukünftige Bewertung.
Die Verlagerung vom traditionellen Sparen zu alternativen Anlagen
In der Vergangenheit haben weniger erfahrene Anleger ihr Geld auf Sparkonten gespart, während erfahrenere Anleger nach Hebelwirkung und Effizienz durch Immobilien und Risikoinvestitionen suchten. In den letzten zehn Jahren haben sich die Anleger aufgrund des Rückgangs der Zinssätze und der Ausweitung der Finanzinstrumente haben sich die Anleger für Aktien, Immobilien und\ börsengehandelte Fonds (ETFs) als ihre primären Wertaufbewahrungsmittel entschieden. Die explosionsartige Zunahme von ETFs und die Beliebtheit von Zweitimmobilien (zur Vermietung) oder Real Estate Investment Trusts (REITs) haben zu einer Monetarisierung zahlreicher Vermögenswerte geführt.\ Bis Ende 2021 wurden viele Vermögenswerte, darunter auch Immobilien, weit über ihrem Nutzwert gehandelt. Die Zentralbanken haben mit überschüssigem Geld den Wert des Geldes grundlegend zerstört, was die Anleger dazu veranlasst, nach Vermögenswerten zu suchen, die einen Schutz gegen die negativen Auswirkungen des Gelddruckens bieten. Dieses Phänomen hat zu einer Finanzialisierung der Wirtschaft geführt, bei der die Anleger keine andere Wahl haben, als nach anderen Formen des Sparens zu suchen.
Bitcoin: Der optimale Vermögenswert für die Monetarisierung
Bitcoin hat das Potenzial, der optimale Vermögenswert für die Monetarisierung zu werden und die traditionellen Wertaufbewahrungsmittel wie Währungen, Anleihen, Immobilien, Aktien und Gold konsequent zu demonetisieren.
Immobilien werden aufgrund ihres inhärenten Nutzwerts oft als begehrter Vermögenswert betrachtet, aber ihr Wert wird auch stark von der Monetarisierung beeinflusst, die dazu geführt hat, dass viele Menschen mehrere Immobilien besitzen, was die Nachfrage und die Preise in die Höhe treibt. Es ist jedoch zu beachten, dass der Besitz von Immobilien mit einer Reihe von Problemen verbunden ist. So können beispielsweise die Grundsteuer und die Instandhaltungskosten die potenziellen Renditen erheblich schmälern. Außerdem können Immobilien im Laufe der Zeit an Wert verlieren, was ihren Wert weiter schmälert. Auch wenn man eine Urkunde für eine Immobilie besitzt, ist man nicht der eigentliche Eigentümer der Immobilie; die Zusage des Eigentums kann unter bestimmten Umständen widerrufen werden. Wenn beispielsweise die Regierung beschließt, die Immobilie für die öffentliche Nutzung zu beschlagnahmen, kann der Immobilieneigentümer seine Investition vollständig verlieren. All diese Faktoren haben Anleger dazu veranlasst, nach Alternativen zum Schutz ihres Vermögens zu suchen, insbesondere in einem Umfeld mit geringem Risiko und niedriger Inflation.
Im Gegensatz dazu bietet Bitcoin ein „Konstrukt", das nicht zerstört werden kann, keine Wartung erfordert und eine hervorragende Wertaufbewahrung bietet. Als dezentralisierter, sicherer und knapper digitaler Vermögenswert hat Bitcoin das Potenzial, den monetären Aufschlag traditioneller Vermögenswerte zu übernehmen, was möglicherweise zu deren Demonetisierung führt.
Bitcoin wird aus mehreren Gründen zunehmend als überlegenes Wertaufbewahrungsmittel anerkannt:
- Knappheit: Bitcoin hat einen festen Vorrat von 21 Millionen Münzen, was zu einem Grad an Knappheit führt, der seinen Wert vor Inflation schützt.
- Übertragbarkeit: Bitcoin lässt sich leicht digital übertragen und aufbewahren, was ihn praktischer macht als physische Vermögenswerte wie Gold.
- Sicherheit: Die dezentralisierte Natur der Blockchain-Technologie, die Bitcoin zugrunde liegt, gewährleistet seine Sicherheit und seinen Schutz vor Manipulationen.
- Transparenz: Alle Transaktionen werden in der Blockchain aufgezeichnet, wodurch ein transparenter und überprüfbarer Eigentumsnachweis entsteht.
- Zugänglichkeit: Bitcoin ist für jeden zugänglich, der über einen Internetanschluss verfügt, was ihn zu einem umfassenden Wertaufbewahrungsmittel macht.
- Unveränderlichkeit oder Widerstand gegen Zensur: Die Aufzeichnung des Eigentums ist durch ein massives und wachsendes Computernetzwerk gesichert, was es nahezu unmöglich macht, Transaktionen zu verändern oder zu zensieren. Dies bietet eine zusätzliche Sicherheitsebene und stärkt den Status von Bitcoin als zuverlässiges und vertrauenswürdiges Wertaufbewahrungsmittel.
Das Modell
Das Schrödinger-Münzmodell basiert auf dem Konzept der Quantensuperposition, bei dem ein Objekt gleichzeitig in mehreren Zuständen existieren kann, bis es beobachtet wird. In diesem Fall wird davon ausgegangen, dass Bitcoin zwei mögliche Ergebnisse hat: Entweder scheitert er und ist wertlos (das Dan-Peña-Szenario) oder er erobert erfolgreich die Geldprämie traditioneller Wertaufbewahrungsmittel (das Saylor-Szenario).
Anstatt sich auf absolute Gewissheit wie in den obigen Szenarien zu verlassen, ordnet dieses Modell jedem dieser Szenarien Wahrscheinlichkeiten zu, um einen fairen Wert für Bitcoin zu ermitteln. Wenn du die Box öffnest und eine Welt beobachtest, in der Saylor Recht hatte, was passiert dann? Was wäre, wenn Dan Recht hätte?
Modell-Komponenten
Das Modell berechnet den Marktwert von Bitcoin heute anhand der folgenden Komponenten:
a. Marktkapitalisierung der Vermögenswerte: Der aktuelle Marktwert jedes traditionellen Wertaufbewahrungsmittels (z.B. Gold, Immobilien, Aktien, Anleihen).
b. Prozentsatz des monetären Aufschlags: Der Anteil der Marktkapitalisierung eines Vermögenswerts, der auf seinen Status als Wertaufbewahrungsmittel zurückzuführen ist.
c. Wahrscheinlichkeit der Vereinnahmung: Die Wahrscheinlichkeit, dass Bitcoin die monetäre Prämie jedes Vermögenswerts vereinnahmt.
d. Zeit bis zur Vereinnahmung: Die erwartete Zeit, bis Bitcoin die Geldprämie eines jeden Vermögenswerts erbeutet. Dies kann auch als Vektor mit verschiedenen Prozentsätzen der eingefangenen Prämie über die Zeit modelliert werden.
e. Abzinsungsrate: Der Prozentsatz, mit dem die zukünftig erwarteten Erfassungswerte auf den Gegenwartswert abgezinst werden, um den heutigen Marktwert zu berechnen.
Modell-Berechnung
Der Zeitwert von Bitcoin wird als Summe des erwarteten Erfassungswerts der einzelnen Vermögenswerte berechnet:
wobei der Zeitwert jedes Vermögenswerts definiert ist als:
- mcap: Aktuelle Marktkapitalisierung der einzelnen Vermögenswerte
- mp: Prozentualer Anteil der Marktkapitalisierung, der Monetarisierungscharakter hat (nicht Nutzwert)\ prob: Wahrscheinlichkeit, dass Bitcoin diesen Wert erfasst
- r: Abzinsungssatz
- n: Anzahl der Perioden, bis die Monetarisierung realisiert wird
Denke daran, dass wir mit diesem Rahmen auch den heutigen Bitcoin-Preis verwenden könnten, um die aktuell implizierte Wahrscheinlichkeit des Marktes zu berechnen.
Modell-Inputs
Potenzielle Vermögensklassen und geschätzte Werte - Daten vom April 2023
- Aktien: a. Angenommener Marktwert: $100 Billionen b. Quelle: Die Börsenkapitalisierung kann der Weltbank und Statista entnommen werden.Die Daten stellen eine ungefähre Schätzung dar, da die Börsenkapitalisierung mit den Marktbewegungen schwankt.
- Anleihen: a. Angenommener Marktwert: $130 Billionen b. Quelle: Die Kapitalisierung des globalen Anleihemarktes wurde aus Quellen wie der Bank für Internationalen Zahlungsausgleich abgeleitet. Die Daten stellen eine ungefähre Schätzung dar, da sich die Kapitalisierung des Anleihemarktes durch Neuemissionen und Tilgungen ändert. Sie umfassen nur die Gesamtsumme für „fortgeschrittene Volkswirtschaften".
- Gold: a. Angenommener Marktwert: $10 Billionen b. Quelle: Die Gesamtmarktkapitalisierung von Gold wurde anhand der Daten des World Gold Council zu den oberirdischen Goldbeständen und dem durchschnittlichen Goldpreis pro Unze zum Zeitpunkt der Erstellung dieses Berichts berechnet. Die Daten sollten aktualisiert werden, um den aktuellen Goldpreis für eine genaue Bewertung widerzuspiegeln.
- Silber: a. Angenommener Marktwert: $1,3 Billionen b. Quelle: Die gesamte Marktkapitalisierung von Silber wurde anhand der Daten des Silver Institute zu den oberirdischen Silberbeständen und dem durchschnittlichen Silberpreis pro Unze zum Zeitpunkt der Erstellung dieses Berichts geschätzt. Die Daten sollten aktualisiert werden, um den aktuellen Silberpreis für eine genaue Bewertung widerzuspiegeln.
- Immobilien: a. Angenommener Marktwert: $320 Billionen b. Quelle: Savills Research
- Kryptowährungen (ausgenommen BTC): a. Angenommener Marktwert: $500 Mrd. b. Quelle: Coinmarketcap.com
Parallelen zum Black-Scholes-Modell für die Optionsbewertung
Die Black-Scholes-Formel wird verwendet, um den fairen Preis von Optionen zu berechnen. Dabei handelt es sich um Finanzkontrakte, die dem Käufer das Recht (aber nicht die Verpflichtung) geben, einen Basiswert, z. B. eine Aktie oder einen Rohstoff, zu einem bestimmten Preis und Zeitpunkt zu kaufen oder zu verkaufen.
Die Formel umfasst fünf Inputs: den aktuellen Kurs des Basiswerts, den Ausübungspreis (den Preis, zu dem die Option ausgeübt werden kann), die Zeit bis zum Ablauf, den risikofreien Zinssatz und die Volatilität des Kurses des Basiswerts. Hier ist die Formel für den Preis einer Call-Option:
Die Formel selbst ist etwas kompliziert, aber in einfachen Worten funktioniert sie, indem sie die Wahrscheinlichkeit verschiedener Zukunftsszenarien für den Kurs des Basiswerts auf der Grundlage seiner Volatilität (wie stark sein Kurs im Laufe der Zeit zu schwanken pflegt) schätzt. Die Formel berechnet dann den erwarteten Wert der Option auf der Grundlage dieser Wahrscheinlichkeiten, abgezinst auf den heutigen Wert unter Verwendung des risikofreien Zinssatzes.
Die linke Seite der Gleichung stellt den Wert der Call-Option dar (das Recht, den Basiswert zu kaufen), während die rechte Seite die Summe aus dem Gegenwartswert des Ausübungspreises (der bei Ausübung der Option garantiert wird) und dem erwarteten Wert des Kurses des Basiswerts bei Fälligkeit darstellt. Der Erwartungswert wird berechnet, indem der aktuelle Kurs des Basiswerts mit einer Wahrscheinlichkeitsdichtefunktion multipliziert wird, die auf der Volatilität des Kurses des Basiswerts basiert.
Ein wesentlicher Unterschied zwischen den beiden Modellen besteht darin, dass die Black-Scholes-Formel auf der Annahme einer kontinuierlichen Zeit und einer bekannten Verteilung der Preise von Vermögenswerten beruht, während das Schrödinger-Münzmodell auf dem Konzept der Quantensuperposition basiert, bei dem ein Objekt in mehreren Zuständen existieren kann, bis es beobachtet wird. Das Schrödinger-Münzmodell ordnet jedem möglichen Ergebnis Wahrscheinlichkeiten zu, um einen fairen Wert für Bitcoin zu ermitteln, während die Black-Scholes-Formel eine Wahrscheinlichkeitsdichtefunktion verwendet, die auf der Volatilität des Preises des zugrunde liegenden Vermögenswerts basiert.
Ein weiterer Unterschied besteht darin, dass die Black-Scholes-Formel eine geschlossene Gleichung ist, was bedeutet, dass sie analytisch gelöst werden kann, während das Schrödinger-Münzen-Modell ein komplexeres Modell ist, das mehrere Eingaben und Berechnungen umfasst.
Trotz dieser Unterschiede zielen beide Modelle darauf ab, den beizulegenden Zeitwert eines Vermögenswerts zu schätzen, indem sie verschiedene Faktoren wie den aktuellen Preis des Vermögenswerts, die Zeit bis zum Verfall, die Zinssätze und die Volatilität berücksichtigen. Beide Modelle berücksichtigen auch das Potenzial für extreme Ergebnisse und die Ungewissheit künftiger Ereignisse, die zur Volatilität des Vermögenswerts beitragen können.
Schrödingers Münze und Volatilität als Merkmal, nicht als Fehler
Einer der meistdiskutierten Aspekte von Bitcoin und anderen Kryptowährungen ist ihre inhärente Preisvolatilität. In diesem Abschnitt argumentieren wir, dass das Schrödinger-Münzmodell die Volatilität von Bitcoin als ein natürliches Merkmal seiner Bewertung erklärt und nicht als Fehler oder Schwachstelle. Darüber hinaus werden wir diskutieren, wie diese Volatilität abnehmen kann, wenn wir uns der Hyperbitcoinisierung nähern.
- Extreme Ergebnisse Das Schrödinger Modell basiert auf zwei extremen Ergebnissen für Bitcoin: entweder sch-eitert er und wird wertlos (das Dan Peña Szenario), oder er erobert erfolgreich die Geldprämie traditioneller Wertaufbewahrungsmittel (das Saylor Szenario). Infolgedessen sagt das Modell von Natur aus erhebliche Wertschwankungen voraus, die von der Marktstimmung und externen Faktoren abhängen, die die Wahrnehmung der Anleger hinsichtlich der Wahrscheinlichkeit dieser Ergebnisse beeinflussen.
- Kleine Änderungen in der Wahrscheinlichkeit, große Änderungen im fairen Wert Angesichts der extremen Natur der beiden möglichen Ergebnisse können kleine Änderungen in der wahrgenommenen Wahrscheinlichkeit des Eintretens eines der beiden Szenarien zu erheblichen Änderungen im fairen Wert von Bitcoin führen. Zum Beispiel könnte ein leichter Anstieg des Vertrauens des Marktes in den Erfolg von Bitcoin zu einem signifikanten Anstieg des Preises führen, während ein Rückgang des Vertrauens zu einem starken Rückgang führen könnte.
- Ungewissheit der Zeit Ein weiterer Faktor, der zur Volatilität von Bitcoin beiträgt, ist die Ungewissheit über die Zeit, die benötigt wird, um die Hyperbitcoinisierung zu erreichen. Während Hausse-Märkten nimmt die Zeitwahrnehmung (t) tendenziell ab, da die Anleger optimistischer werden, was die Akzeptanz von Bitcoin und die Geschwindigkeit angeht, mit der Bitcoin die Geldprämie von traditionellen Vermögenswerten erreichen wird. Umgekehrt steigt die wahrgenommene Zeit bis zur Hyperbitcoinisierung während Baisse-Märkten, wenn die Marktstimmung negativ wird. Diese Fluktuation in der Zeitwahrnehmung fügt dem Bitcoin-Kurs eine weitere Ebene der Volatilität hinzu.
- Abnehmende Volatilität bei zunehmender Hyperbitcoinisierung Je näher wir der Hyperbitcoinisierung kommen, desto geringer dürfte die Volatilität von Bitcoin werden. Dies liegt daran, dass der Markt im Laufe der Zeit mehr Informationen über die Akzeptanz von Bitcoin, das regulatorische Umfeld und die technologischen Entwicklungen erhalten wird. Infolgedessen wird die Wahrnehmung des Marktes hinsichtlich der Wahrscheinlichkeit der beiden extremen Ergebnisse stabiler werden, was zu geringeren Preisschwankungen führt.
Zusammenfassend erklärt das Schrödinger-Münzen-Modell die Volatilität von Bitcoin als eine natürliche Folge seiner Bewertung, die auf extremen Ergebnissen, kleinen Veränderungen der Wahrscheinlichkeit und der Ungewissheit der Zeit bis zur Hyperbitcoinisierung beruht. Wenn der Markt mehr Informationen erhält und mehr Vertrauen in die Zukunft von Bitcoin gewinnt, wird erwartet, dass seine Volatilität abnimmt und gegen Null tendiert. Das Verständnis dieses Aspekts des Modells kann Anlegern helfen, fundiertere Entscheidungen über die mit einer Investition in Bitcoin verbundenen Risiken und Erträge zu treffen.
Schlussfolgerung
Schrödingers-Münzmodell bietet einen Rahmen für die Bewertung von Bitcoin, indem es sein Potenzial berücksichtigt, den monetäre Aufschlag von traditionellen Vermögenswerten wie Immobilien, Aktien und Anleihen einzufangen. Als überlegenes Wertaufbewahrungsmittel hat Bitcoin das Potenzial, Investitionen in traditionelle Vermögenswerte konsequent zu demonetisieren, was zu einer Verschiebung der Kapitalallokation und einer Neubewertung ihres Wertes führt.
Das Modell beleuchtet auch die inhärente Volatilität von Bitcoin, die sich aus den extremen Ergebnissen, kleinen Veränderungen der Wahrscheinlichkeit und der Ungewissheit der Zeit bis zur Hyperbitcoinisierung ergibt. Da der Markt jedoch mehr Informationen erhält und mehr Vertrauen in die Zukunft von Bitcoin gewinnt, wird erwartet, dass seine Volatilität abnimmt und gegen Null tendiert.
Darüber hinaus unterstreicht das Modell, wie wichtig es ist, die Risiken zu verstehen, die mit einer Investition in Bitcoin verbunden sind, wie regulatorische Änderungen, technologische Herausforderungen und potenzielle Konkurrenz durch andere Kryptowährungen oder alternative Wertaufbewahrungsmittel.
Durch das Verständnis der Dynamik des Schrödinger-Münzmodells sowie der Faktoren, die zur Volatilität von Bitcoin und den damit verbundenen Risiken beitragen, können Anleger fundiertere Entscheidungen über das potenzielle Wachstum und die mit Bitcoin und anderen Vermögenswerten verbundenen Risiken treffen. Dieser ganzheitliche Bewertungsansatz ermöglicht eine umfassendere Beurteilung des Potenzials von Bitcoin sowohl als Investition als auch als transformative Technologie.
-
 @ 75869cfa:76819987
2025-03-04 14:05:38
@ 75869cfa:76819987
2025-03-04 14:05:38GM, Nostriches!
The Nostr Review is a biweekly newsletter focused on Nostr statistics, protocol updates, exciting programs, the long-form content ecosystem, and key events happening in the Nostr-verse. If you’re interested, join me in covering updates from the Nostr ecosystem!
Quick review:
In the past two weeks, Nostr statistics indicate over 228,000 daily trusted pubkey events. The number of new users has seen a notable increase, with profiles with a contact list amounting to 17 times the same period. More than 11 million events have been published, with posts and reposts showing an increase. Total Zap activity stands at approximately 13 million, marking a 22% decrease.
Additionally, 28 pull requests were submitted to the Nostr protocol, with 5 merged. A total of 45 Nostr projects were tracked, with 11 releasing product updates, and over 462 long-form articles were published, 26% focusing on Bitcoin and Nostr. During this period, 2 notable events took place, and 1 significant events is upcoming.
Nostr Statistics
Based on user activity, the total daily trusted pubkeys writing events is about 228,000, representing a slight 8.7% decrease compared to the previous period. Daily activity peaked at 18256 events, with a low of approximately 16087.
The number of new users has increased significantly. Profiles with a contact list are now around 393,637, a 17-fold increase. Pubkeys writing events have declined to approximately 227,635, but have still grown by 14%. Profiles with a bio are now 9 times the previous number.
Regarding event publishing, the total number of note events published is about 11 million. Posts remain the most dominant in terms of volume, totaling approximately 1.7 million, reflecting an increase of 6.8%. Reposts are showing a increase of approximately 12%, while reactions have experienced a 8% decline.
For zap activity, the total zap amount is about 13 million, showing a decrease of over 22% compared to the previous period.
Data source: https://stats.nostr.band/
NIPs
nip99 e-commerce use case extension
nostr:npub1gmmrkec8een5jelrxq5rz260nqzpnj45yzznpaerqv0yma3s86gqpfe2h0 is proposing nip99 e-commerce use case extension. This pull request simply adds a link to the specification we are developing and have consensus on, allowing other developers who want to implement NIP-99 for e-commerce to discover how the major developers are approaching it. In this way, we ensure that NIP-99 remains lightweight and allows for broad use cases while also providing guidance for the e-commerce use case that is currently prevalent.
nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 is proposing "global" relay lists that streamlines the b/c process by standardizing it across multiple apps and also by allowing these lists to be shared, so when the relays that were hardcoded (and that were, at the time of the hardcoding, known to be such public squares) get shut down then clients can automatically or manually switch to new ones.
[NIP 53 Addendum] - Add Interactive Rooms, Meetings, and Live Presence.
nostr:npub18pudjhdhhp2v8gxnkttt00um729nv93tuepjda2jrwn3eua5tf5s80a699 is proposing that add Interactive Rooms and Meetings, and Live presence to NIP-53. Kind 30312 (Interactive Rooms), Kind 30313 (Meetings), Kind 10312 (Room Presence). These Kinds would apply to interactive audio/video platforms such as Hivetalk version 2.0 (not public yet) and Nostr Nests.
NIP-5E: Censorship Resistant Live Streams
v0l is proposing a way to distribute live video streams via Nostr. "Live Video" in this context implies segmented video streams like HLS or DASH. Each segment of the stream is a NIP-94 event which describes where the file can be found and its hash.
Add birth field to NIP-24 for birth date representation
nostr:npub12egp0pvh2f0fp6sk5nt6ncehqzkz8zsma8dl8agf8p3f98v6resqku4w26 is proposing a PR that introduces the birth field to NIP-24, allowing users to specify their birth date. The goal is to enable applications to celebrate users' birthdays and allow other users to notice and join in the celebration, enhancing social interactions.Defined the format as [day, month, year (optional)]. The year is optional to accommodate users who prefer not to disclose their age.
NIP-05: add dynamic server recommendation
nostr:npub1q3sle0kvfsehgsuexttt3ugjd8xdklxfwwkh559wxckmzddywnws6cd26p is proposing NIP-05 services who let people sign up for a NIP-05 name are recommended to make the names unique case insensitive.
Staab is proposing PR that adds a delegation command to NIP 46, which allows applications that are already authorized to create new sessions with limited permissions. My use case for this is sharing a read-only session with push- or email- notification servers, which can only sign kind 22242 events on behalf of the user, in order to get access to auth-gated relays.
Staab updates NIP: XXX - Push Notifiation with the following differences: It uses parameterized replaceable events, which allows for multiple subscriptions to exist at the same time;It uses NIP 44 encryption rather than NIP 04;It uses filters rather than ad-hoc targets;It uses delegated authentication in order to gain access to gated relays;It uses a different mechanism for pausing notifications and auto-expiring pauses.
NIP-22: Format should follow scope
nostr:npub1gcxzte5zlkncx26j68ez60fzkvtkm9e0vrwdcvsjakxf9mu9qewqlfnj5z is proposing This adds some flexibility in formatting styles for NIP-22. Since this NIP is always used inside a scope (another NIP), formatting rules SHOULD be defined by that NIP. Examples: If the Comment is replying to a markdown-based NIP, it should allow markdown. If the Comment is replying to an asciidoc-based NIP, it should allow asciidoc.
NIP-34!: use NIP-22 thread style for patch and status events
nostr:npub15qydau2hjma6ngxkl2cyar74wzyjshvl65za5k5rl69264ar2exs5cyejr created this as part of reviewing #1744. For the status event, references to merged patch events are done using the q tag even though the they are not included in content. This is because NIP-22 only supports the use of e reference for the parent event id.
believethehype introduces kind 7007 (ping) to send a small request to a dvm to check if it is alive. The DVM replies with a kind 7000 feedback event and status pong, and optional information in content. This allows clients to test if a dvm is alive without sending an actual job request to the dvm.
Notable Projects
Coracle 0.6.5 nostr:npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn
New maintenance release of Coracle is out: * Fix memory leak * Fix isEventMuted * Fix toast animation * Fix (and improve) drafts * Fix parser dropping sections of notes
Primal nostr:npub12vkcxr0luzwp8e673v29eqjhrr7p9vqq8asav85swaepclllj09sylpugg
Primal for iOS build 2.1.26 has just been released. Here’s what’s new: * Improved feeds * Deep linking threads, articles, profiles * Bug fixes & stability improvements
Yakihonne nostr:npub1yzvxlwp7wawed5vgefwfmugvumtp8c8t0etk3g8sky4n0ndvyxesnxrf8q
web v4.4.0: * Zap polls can now be added directly from the list or created instantly within notes and comments. * Muting users is now more reliable. * Users can download and export their NWC secret for wallets. * Wallets and account credentials are automatically saved upon signup and logout. * Faster login and signup when interacting with Yakihonne while logged out. * Bug fixes and performance optimizations for improved reliability.
mobile v1.6.6: * Ability to export your NWC wallets and your keys. * Blink wallet is now available as one of the external wallets that can be used. * Private messages drafts are now available. * Notes stats optimised. * Wallet management overall performance has been improved. * Fixing bugs and improving the overall performance
GOSSIP nostr:npub189j8y280mhezlp98ecmdzydn0r8970g4hpqpx3u9tcztynywfczqqr3tg8
Several major bugs have been fixed in the last week. * PRIVACY: gossip was authenticating to relays in many cases even if you turned on "require user approval before AUTHenticating..." * Gossip was rendering nevent links as note1 links in some cases * When clicking the parent link, sometimes it wasn't finding the parent note (even though the note you clicked correctly hinted at which relay the note was at) * New users who adjusted settings during the first run were having their public key wiped, which appeared to have no identity and they had to regenerate on second run
nos.social nostr:npub1pu3vqm4vzqpxsnhuc684dp2qaq6z69sf65yte4p39spcucv5lzmqswtfch
With the Nos 1.2 update, you can use Nos to create, edit, and delete lists of your favorite people and accounts! We're also bringing you fixes for the biggest issues in the previous version: * Fixed: restarting app reverts to Following rather than selected list or relay * Fixed: lists change positions randomly * Fixed: adding and removing relays is not reflected in the feed filter * Fixed: text fields sometimes don't work on onboarding screens * Fixed: main action button is not visible on iPad on "Build Your Network" onboarding screen * Fixed: crash when processing a malformed delete event
Fountain 1.1.17 nostr:npub1v5ufyh4lkeslgxxcclg8f0hzazhaw7rsrhvfquxzm2fk64c72hps45n0v5
- In this update, we completely rebuilt the authentication flows as some users reported issues accessing the app. We're currently building out the redesigned library and content pages along with updates to transcripts.
Plebeian Market nostr:npub1market6g3zl4mxwx5ugw56hfg0f7dy7jnnw8t380788mvdyrnwuqgep7hd
- Social Sharing: New social sharing buttons have been implemented, allowing users to share listings and pages effortlessly across social platforms.
- Open Graph Integration: Enhanced sharing capabilities with the addition of an Open Graph library, making it easier to share listings on social media.
- Pagination on Mobile: Now see up to 20 items before you need to paginate, making browsing smoother and more efficient on your mobile device.
- UX/UI Overhaul: Significant improvements to the UX and UI of the Settings and Dashboard for a more intuitive navigation.
- Dashboard Enhancements: Various fixes to ensure the dashboard is more functional and user-friendly.
- Relays Pop-Out: Improved UI so the Relays pop-out no longer goes underneath the category menu on the homepage and other pages.
- Save Button: A 'Save' button has been added to every page for quick and easy updates to your listings or settings.
- Payment Details Clarity: Examples are now included in the 'Payment Details' field to guide sellers on what information to provide.
- And fixes some bugs.
DEG Mods nostr:npub17jl3ldd6305rnacvwvchx03snauqsg4nz8mruq0emj9thdpglr2sst825x
- The ability to switch between reply and quote-replies
- Preview the recent posts of an author under their profile box when viewing a mod or blog they've published
- Clicking on images in a feed post triggers the gallery system for it
- Adjusted the design of images and videos that appear in the feed page
- Reposting won't trigger a popup
- Textarea in feed page will reset its size after posting, along with preview reset
- Load new posts button now works/appears properly
- Reply depth numbering now works correctly
- User LN address now updates correctly if they change it (was a caching issue)
Zapstore 0.2.5 nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8
- Hopefully fixed the missing apps issue
- No more toast showing Zapstore update available (pinned instead)
- Trigger local version refresh on app detail page
futr nostr nostr:npub18wxf0t5jsmcpy57ylzx595twskx8eyj382lj7wp9rtlhzdg5hnnqvt4xra
- Optimized Subscription Handling
- Implemented proper event pagination with timestamp tracking.
- Added event deduplication across batches.
- Improved debug logging for pagination and subscription events.
- Fixed timestamp handling to prevent future-dated events.
- Reduced events per pubkey from 2000 to 500 for better efficiency.
- Relay Connection & Event Parsing
- Improved relay connection state management.
- Fixed parsing of OK messages from relays.
- Updated follow list and DM relay parsing.
- Added proper nevent links for quoted reposts.
- Increased connection timeout from 3s to 15s to enhance reliability.
- UI & UX Enhancements
- Fixed follow list flickering by improving model caching.
- Improved login experience with better async timing.
- Fixed profile filter issues to improve data consistency.
- And another changes.
ZEUS v0.10.0 nostr:npub1xnf02f60r9v0e5kty33a404dm79zr7z2eepyrk5gsq3m7pwvsz2sazlpr5
- Receive: add advanced settings toggle
- Remove deprecated backends
- Move sweep on-chain functionality to Tools view
- Update colors according to themes in external link modal
- Improve contrast of warning buttons in Disaster Recovery view
- Bug fix: display of backup status
- Bug fix: ZEUS Pay local notifications
- Renewable channels
- NWC client support
- Embedded LND: v0.18.5-beta
- New share button (share ZEUS QR images)
- Activity: highlight filter icon when filters active
- chantools: sweepremoteclosed
- Tools: Export Activity CSVs, Developer tools
- Activity: filter by max amount, memo + note
- CLNRest: add payment timeout setting
Long-Form Content Eco
In the past two weeks, more than 462 long-form articles have been published, including over 79 articles on Bitcoin and more than 42 related to Nostr, accounting for 26% of the total content.
These articles about Nostr mainly explore its potential as a decentralized, censorship-resistant communication protocol, contrasting it with traditional social media platforms like Facebook and X. They discuss Nostr’s ability to foster free speech, privacy, and security while providing a foundation for new applications, including encrypted messaging (such as the use of the Double Ratchet Algorithm in NIP-117 and NIP-118), decentralized identity management, and anonymous event relaying (as proposed in "Renoters"). Several pieces, including "The Advancement of the Nostr Protocol," highlight recent technical advancements, developer tools like Nostr SDK, and practical use cases for Bitcoin applications. Others, criticize centralized platforms for their control over user data and content moderation policies. Additionally, topics like relay setup, voting systems, and AI alignment with human values are explored, emphasizing Nostr’s broader applications beyond social media.
These Bitcoin articles explore adoption, investment strategies, security, privacy, and their impact on global finance. Many highlight Bitcoin’s role in fostering financial resilience in Zimbabwe, rural economies, and the importance of user adoption over merchant adoption. Investment discussions cover DCA strategies, ETF influence, and ways to maximize returns. Privacy and security topics emphasize decentralization, self-custody, and best practices to protect assets. Bitcoin is framed as an alternative to fiat, with critiques of traditional finance and central banking. Geopolitical discussions examine the IMF’s influence, France’s fiscal crisis, and El Salvador’s Bitcoin policy. Technical innovations, such as EVM integration, Lightning Network advancements, and multi-payment solutions, continue to expand the Bitcoin ecosystem, driving broader adoption and usability.
Thank you, nostr:npub1m0sxqk5uwvtjhtt4yw3j0v3k6402fd35aq8832gp8kmer78atvkq9vgcru nostr:npub13rvvn5g23anm09kwnya8qvzqejxfajfa56rnn47ck5l96ke6cq4sdcd4e0 nostr:npub10m6lrv2kaf08a8um0plhj5dj6yqlw7qxzeag6393z352zrs0e5nsr2tff3 nostr:npub17v7g49shev2lwp0uwrx5v88ad6hj970zfse74wkes9jguhkx7aqsgjwsvj nostr:npub18lav8fkgt8424rxamvk8qq4xuy9n8mltjtgztv2w44hc5tt9vets0hcfsz nostr:npub1nlk894teh248w2heuu0x8z6jjg2hyxkwdc8cxgrjtm9lnamlskcsghjm9c nostr:npub1xzuej94pvqzwy0ynemeq6phct96wjpplaz9urd7y2q8ck0xxu0lqartaqn nostr:npub1g53mukxnjkcmr94fhryzkqutdz2ukq4ks0gvy5af25rgmwsl4ngq43drvk nostr:npub16dswlmzpcys0axfm8kvysclaqhl5zv20ueurrygpnnm7k9ys0d0s2v653f nostr:npub1x7zk9nfqsjwuuwm5mpdu8eevsnu2kk0ff23fv58p45d50fhuvaeszg44p2 nostr:npub1mwce4c8qa2zn9zw9f372syrc9dsnqmyy3jkcmpqkzaze0slj94dqu6nmwy and others, for your work. Enriching Nostr’s long-form content ecosystem is crucial.
Nostriches Global Meet Ups
Recently, several Nostr events have been hosted in different countries. * The Bitcoin Freedom Festival took place from February 20 to 24, 2025, at the Awakening Center in Uvita, Costa Rica. In collaboration with the Awake Earth Festival, the event blended a music festival with Bitcoin seminars and lectures. From February 20 to 23, it featured music, healing workshops, ceremonies, and educational talks, with internationally renowned artists and captivating discussions. February 24 was a special day dedicated to Bitcoin, with all activities centered around it. nostr:npub14f26g7dddy6dpltc70da3pg4e5w2p4apzzqjuugnsr2ema6e3y6s2xv7lu * The 5th Bitcoin Educators Unconference, organized by Mi Primer Bitcoin, was successfully held on February 27, 2025, at Bitcoin Park in Nashville, USA. The event focused on grassroots projects and Bitcoin education, adopting a decentralized, community-led format. Every participant was a potential speaker, proposing discussion topics at the beginning of the event, which were then grouped into breakout sessions for in-depth discussions. nostr:npub17cyatz6z2dzcw6xehtcm9z45m76lde5smxdmyasvs00r4pqv863qrs4ml3
Here is the upcoming Nostr event that you might want to check out.
- The Bitcoin Educators Unconference will take place on April 10, 2025, at Bitcoin Park in Nashville, USA. The event follows a decentralized, community-led format, with a focus on Bitcoin education and independent Bitcoin educators. It aims to foster collaboration and networking among Bitcoin educators, creating a truly interactive space.
Additionally, We warmly invite event organizers who have held recent activities to reach out to us so we can work together to promote the prosperity and development of the Nostr ecosystem.
Thanks for reading! If there’s anything I missed, feel free to reach out and help improve the completeness and accuracy of my coverage.
-
 @ 09fbf8f3:fa3d60f0
2025-03-03 06:00:17
@ 09fbf8f3:fa3d60f0
2025-03-03 06:00:17快速轻松地删除任何图像的元数据。在网上共享照片、视频和文档之前,可以先从照片、视频和文档中删除元数据,来保护自己的隐私。
推广链接: 低调云(VPN): https://didiaocloud.xyz
-
 @ b2d670de:907f9d4a
2025-02-28 16:39:38
@ b2d670de:907f9d4a
2025-02-28 16:39:38onion-service-nostr-relays
A list of nostr relays exposed as onion services.
The list
| Relay name | Description | Onion url | Operator | Payment URL | Payment options | | --- | --- | --- | --- | --- | --- | | nostr.oxtr.dev | Same relay as clearnet relay nostr.oxtr.dev | ws://oxtrdevav64z64yb7x6rjg4ntzqjhedm5b5zjqulugknhzr46ny2qbad.onion | operator | N/A | N/A | | relay.snort.social | Same relay as clearnet relay relay.snort.social | wss://skzzn6cimfdv5e2phjc4yr5v7ikbxtn5f7dkwn5c7v47tduzlbosqmqd.onion | operator | N/A | N/A | | nostr.thesamecat.io | Same relay as clearnet relay nostr.thesamecat.io | ws://2jsnlhfnelig5acq6iacydmzdbdmg7xwunm4xl6qwbvzacw4lwrjmlyd.onion | operator | N/A | N/A | | nostr.land | The nostr.land paid relay (same as clearnet) | ws://nostrland2gdw7g3y77ctftovvil76vquipymo7tsctlxpiwknevzfid.onion | operator | Payment URL | BTC LN | | bitcoiner.social | No auth required, currently | ws://bitcoinr6de5lkvx4tpwdmzrdfdpla5sya2afwpcabjup2xpi5dulbad.onion | operator | N/A | N/A | | relay.westernbtc.com | The westernbtc.com paid relay | ws://westbtcebhgi4ilxxziefho6bqu5lqwa5ncfjefnfebbhx2cwqx5knyd.onion | operator | Payment URL | BTC LN | | freelay.sovbit.host | Free relay for sovbit.host | ws://sovbitm2enxfr5ot6qscwy5ermdffbqscy66wirkbsigvcshumyzbbqd.onion | operator | N/A | N/A | | nostr.sovbit.host | Paid relay for sovbit.host | ws://sovbitgz5uqyh7jwcsudq4sspxlj4kbnurvd3xarkkx2use3k6rlibqd.onion | operator | N/A | N/A | | nostr.wine | 🍷 nostr.wine relay | ws://nostrwinemdptvqukjttinajfeedhf46hfd5bz2aj2q5uwp7zros3nad.onion | operator | Payment URL | BTC LN, BTC, Credit Card/CashApp (Stripe) | | inbox.nostr.wine | 🍷 inbox.nostr.wine relay | ws://wineinboxkayswlofkugkjwhoyi744qvlzdxlmdvwe7cei2xxy4gc6ad.onion | operator | Payment URL | BTC LN, BTC | | filter.nostr.wine | 🍷 filter.nostr.wine proxy relay | ws://winefiltermhqixxzmnzxhrmaufpnfq3rmjcl6ei45iy4aidrngpsyid.onion | operator | Payment URL | BTC LN, BTC | | N/A | N/A | ws://pzfw4uteha62iwkzm3lycabk4pbtcr67cg5ymp5i3xwrpt3t24m6tzad.onion:81 | operator | N/A | N/A | | nostr.fractalized.net | Free relay for fractalized.net | ws://xvgox2zzo7cfxcjrd2llrkthvjs5t7efoalu34s6lmkqhvzvrms6ipyd.onion | operator | N/A | N/A | | nfrelay.app | nfrelay.app aggregator relay (nostr-filter-relay) | ws://nfrelay6saohkmipikquvrn6d64dzxivhmcdcj4d5i7wxis47xwsriyd.onion | operator | N/A | N/A | relay.nostr.net | Public relay from nostr.net (Same as clearnet) | ws://nostrnetl6yd5whkldj3vqsxyyaq3tkuspy23a3qgx7cdepb4564qgqd.onion | operator | N/A | N/A | | nerostrator | Free to read, pay XMR to relay | ws://nerostrrgb5fhj6dnzhjbgmnkpy2berdlczh6tuh2jsqrjok3j4zoxid.onion | operator |Payment URL | XMR | | nostr.girino.org | Public relay from nostr.girino.org | ws://gnostr2jnapk72mnagq3cuykfon73temzp77hcbncn4silgt77boruid.onion | operator | N/A | N/A | | wot.girino.org | WoT relay from wot.girino.org | ws://girwot2koy3kvj6fk7oseoqazp5vwbeawocb3m27jcqtah65f2fkl3yd.onion | operator | N/A | N/A | | haven.girino.org/{outbox, inbox, chat, private} | Haven smart relay from haven.girino.org | ws://ghaven2hi3qn2riitw7ymaztdpztrvmm337e2pgkacfh3rnscaoxjoad.onion/{outbox, inbox, chat, private} | operator | N/A | N/A | | relay.nostpy.lol | Free Web of Trust relay (Same as clearnet) | ws://pemgkkqjqjde7y2emc2hpxocexugbixp42o4zymznil6zfegx5nfp4id.onion | operator |N/A | N/A | | Poster.place Nostr Relay | N/A | ws://dmw5wbawyovz7fcahvguwkw4sknsqsalffwctioeoqkvvy7ygjbcuoad.onion | operator | N/A | N/A | | Azzamo Relay | Azzamo Premium Nostr relay. (paid) | ws://q6a7m5qkyonzb5fk5yv4jyu3ar44hqedn7wjopg737lit2ckkhx2nyid.onion | operator | Payment URL | BTC LN | | Azzamo Inbox Relay | Azzamo Group and Private message relay. (Freemium) | ws://gp5kiwqfw7t2fwb3rfts2aekoph4x7pj5pv65re2y6hzaujsxewanbqd.onion | operator | Payment URL | BTC LN | | Noderunners Relay | The official Noderunners Nostr Relay. | ws://35vr3xigzjv2xyzfyif6o2gksmkioppy4rmwag7d4bqmwuccs2u4jaid.onion | operator | Payment URL | BTC LN |
Contributing
Contributions are encouraged to keep this document alive. Just open a PR and I'll have it tested and merged. The onion URL is the only mandatory column, the rest is just nice-to-have metadata about the relay. Put
N/Ain empty columns.If you want to contribute anonymously, please contact me on SimpleX or send a DM on nostr using a disposable npub.
Operator column
It is generally preferred to use something that includes a NIP-19 string, either just the string or a url that contains the NIP-19 string in it (e.g. an njump url).
-
 @ 04ea4f83:210e1713
2025-04-20 08:41:34
@ 04ea4f83:210e1713
2025-04-20 08:41:34Veröffentlicht auf Bitcoin Magazine am 11.01.2024\ Originalautor: Josh von BlueCollarBitcoin\ Übersetzt von: Sinautoshi am 13.01.2024 - 825611
Wir alle haben einen Werdegang in Bezug auf Bitcoin. Einige begannen als Verfechter des gesunden Geldes, die die österreichische Schule der Nationalökonomie und Gold verehrten. Andere sind aus der TradFi-Welt herausgefallen, als sie merkten, dass etwas nicht ganz richtig war. Die meisten Bitcoiner haben die Irrungen und Wirrungen der Altcoin-Hölle durchlaufen. Wie auch immer du es hierher und zu Bitcoin geschafft hast, willkommen und schnall dich verdammt nochmal an.
Als ich mich zum ersten Mal für Bitcoin interessierte, war das im Juli 2017, und der Bullenmarkt des Jahres war bereits in vollem Gange. Ich kaufte etwas Bitcoin und sah zu, wie der Wert stieg. Dann kaufte ich mehr. Wie es bei diesen parabolischen Aufwärtsbewegungen üblich ist, beobachtete ich, wie der Preis stieg und mein Gemütszustand veränderte sich:
Von Interesse zu Unglauben zu Verliebtheit zu ausgearteten Käufen zu Verzweiflung.
Dies ist eine Entwicklung, die du während der nächsten Aufwärtsbewegung vermeiden kannst, wenn du dich richtig vorbereitest.
Wenn du dies in der Hoffnung liest, alle Antworten zu finden, habe ich leider schlechte Nachrichten. Es gibt keine richtigen Antworten in Bitcoin oder im Leben. Wir sind alle auf einer Reise, um herauszufinden, was wir tun und wie wir vorgehen sollen. Ich hoffe, dass ich dir einen Leitfaden an die Hand geben kann, aber letztendlich werden deine persönlichen Ziele und deine Veranlagung bestimmen, wie du mit der Volatilität umgehst. Bitcoin wird deine Entschlossenheit auf die Probe stellen.
In der späteren Phase des Bullemarkts 2017 sprach ich mit jedem in meinem Leben über Bitcoin - völlig besessen. Mein damaliger Nachbar war älter als ich und hatte den Dot-Com-Boom erlebt. Den Rat, den er mir gab, werde ich nie vergessen, denn er hatte während der Dot-Com-Blase eine Menge Geld gewonnen (und verloren). Er hörte sich mein glühendes Interesse an Bitcoin an und ging sehr maßvoll mit meiner offensichtlichen LIEBE für diesen Vermögenswert um. Er erzählte mir, dass er während des Dot-Com-Booms mehr Geld verdient hat, als er jemals geglaubt hätte, und am Ende war er wieder genau da, wo er angefangen hatte - weil er den Bullenmarkt über den Gipfel geritten und nichts verkauft hatte. Sein Rat war: "Ich freue mich, dass es dir gut geht, aber vergiss nicht, etwas Gewinn mitzunehmen." Er riet mir, 50 % zu verkaufen und 50 % zu behalten - eine einfache Absicherungsstrategie. Kurz nachdem Bitcoin sein Allzeithoch erreicht hatte, beherzigte ich seinen Rat und verkaufte einige meiner Bestände in der Nähe des lokalen Höchststands.
Ich weiß, dass dies für viele Hodler ein Frevel ist. Wir verkaufen unsere Bitcoin doch nicht, oder? Nun, das ist eine persönliche Entscheidung, und je nach deiner Risikotoleranz und deinem Platz im Leben, möchtest du vielleicht ein gewisses Risiko vom Tisch nehmen. Das ist Teil des Investierens, und wie das alte Sprichwort sagt, verliert niemand Geld, wenn er mit Gewinn verkauft. Dieser Artikel soll den Rat geben, den ich mir gewünscht hätte, als ich Bitcoin zum ersten Mal entdeckte. Ich hoffe, er hilft Neulingen in diesem Bereich zu verstehen, wie man sich in dem bombastischen Umfeld zurechtfindet, das Bitcoin während seiner Bullenmärkte erzeugt.
Ich habe zwei Bullenmärkte erlebt, einen im Jahr 2017 und einen im Jahr 2021. Diese Bullenmärkte waren SEHR unterschiedlich, und ich vermute, wenn du mit denjenigen sprichst, die bei Bullenmärkten vor 2017 dabei waren, wirst du feststellen, dass sie sich auch sehr unterschiedlich anfühlten.
Das erste, was ich loswerden möchte, ist Folgendes - niemand weiß, was passieren wird:
- Balaji spricht von 1 Million in 3 Monaten
- Nobelpreisträger sagen, Bitcoin wird auf Null sinken
- Buffett und Munger (RIP) nennen es Rattengift
Egal, wem Du zuhörst, egal, wie lange sie schon in dem Bereich tätig sind oder wie korrekt sie in der Vergangenheit waren, es spielt keine Rolle. Sie haben keine Ahnung, was die Zukunft bringt.
Bei Investitionen gibt es eine Idee, die als Überlebensbias bezeichnet wird. Diejenigen, die richtig lagen, haben überlebt, und sie erscheinen wie Genies, weil sie richtig lagen. Die überwiegende Mehrheit derjenigen, die sich geirrt haben, ist vergessen. Man hört nichts über sie. Ich will hier niemanden in die Pfanne hauen, aber es gab prominente Bitcoin-Leute, die VIEL höhere Preise riefen, als wir im Jahr 2021 bei 68K waren. Ich sage nicht, dass sie schlechte Menschen sind; ich bin mir sicher, dass sie einen guten Grund hatten, diese Zahlen zu prognostizieren, aber wenn man damals ihren Ratschlägen gefolgt wäre, hätte man zum denkbar schlechtesten Zeitpunkt gekauft und wäre für JAHRE unter die Räder gekommen.
Meiner Meinung nach gibt es verschiedene Arten von Kristallkugelbesitzern, und die unterste Kategorie sind die technischen Analysten. Das sind die ein Dutzend Leute, die man auf Twitter sieht, die über Momentum, Preisniveaus, Tassen und Griffe usw. schwadronieren. Diese Leute riefen für 10K Bitcoin, wo der Boden bei 16k lag. Ich sage nicht, dass TA Unsinn ist; im Grunde ist es ein System zur Vorhersage menschlicher Handlungen durch Wahrscheinlichkeit. Es ist bestenfalls eine Überlegung. Sie sollte nie in einem Vakuum verwendet werden, um Ihre Allokationen zu bestimmen. Wenn du es in Verbindung mit den Fundamentaldaten verwendest, kann es viel hilfreicher sein. Worauf ich hier hinaus will, ist, dass es GANZ viele TA-Analysten gibt, die Ihnen raten, bei 68 K zu kaufen und nicht bei 16 K. Sie werfen probabilistische Darts. Setze deine finanzielle Zukunft nicht auf eine fundierte Vermutung von irgendjemandem.
Die zweite Art von Kristallkugel-Liebhabern sind Makro-Analysten. Diese Leute sind meiner Meinung nach glaubwürdiger, weil sie den allgemeinen Trend in der Wirtschaft einschätzen. Sie berücksichtigen die Zinssätze, die Bewegungen der Fed und die Wirtschaftsdaten. Diese Leute sind viel näher an der Realität, weil sie den Finger am Puls des wirtschaftlichen Geschehens haben. Aber wie bei den TA-Analysten können sich auch diese Leute VÖLLIG irren. Viele sagten, dass die Leitzinsen nicht über x oder y steigen könnten, da sonst die gesamte Wirtschaft zusammenbrechen würde. Nun, die Zinssätze wurden auf ein Niveau angehoben, das weit über ihren Weltuntergangsprognosen liegt, und wir haben keinen Zusammenbruch erlebt.
Ob du nun einem TA-Analysten oder einem Makro-Analysten folgst, sie können wegen eines schwarzen Schwans völlig FALSCH liegen. Nicholas Taleb - bekanntlich von Bitcoinern gehasst - hat den Begriff "schwarzer Schwan" geprägt, um Ereignisse zu bezeichnen, die von Zeit zu Zeit eintreten und mit Standardmodellen einfach nicht vorhergesagt werden können, weil sie so unwahrscheinlich sind. Covid war ein schwarzer Schwan. Der Krieg in der Ukraine war ein schwarzer Schwan. Und rate mal, was passiert: Morgen könnte es einen weiteren unvorhersehbaren schwarzen Schwan geben, der alle TA- und Makro-Analysten völlig auf den Kopf stellt. In der Welt gibt es jede Menge Zufälle. Übrigens sind schwarze Schwäne nicht immer schlecht. Sie können genauso gut auch positive Katalysatoren sein.
Heißt das also, dass wir vor Angst gelähmt bleiben und niemandem trauen sollten?
Ganz und gar nicht. Es bedeutet, dass wir uns die Mühe machen sollten, UNS SELBST zu BILDEN! Du musst die Verantwortung für dich und deine Entscheidungen übernehmen. Du kannst die Informationen der TA-Analysten und der Makro-Analysten nehmen und deine eigenen fundierten Entscheidungen treffen. DAS IST VON GRÖSSTER WICHTIGKEIT.
BILDE DICH SELBST WEITER
Bitcoin ist ein unglaublich einfaches und doch unendlich komplexes Wesen. Deine Ausbildung wird nie vollständig sein, aber du kannst dein Verständnis Schritt für Schritt erweitern. Wir haben eine 10-teilige Bitcoin-Grundlagen-Serie mit Dazbea und Seb Bunney gemacht, und ich habe das Gefühl, dass wir nicht einmal an der Oberfläche gekratzt haben!
Du solltest gut ausgebildet sein, um widerstandsfähig zu werden. Wenn du ein solides Verständnis von Bitcoin und seiner Funktionsweise hast, wirst du nicht so leicht zu erschüttern sein. Die Psychologie ist hier SEHR WICHTIG. Wenn du verstehst, in was du investierst, und der Markt von einem Börsenausfall betroffen ist, ähnlich dem, der FTX passiert ist, wirst du einige Dinge verstehen, die die Durchschnittsperson vielleicht nicht versteht.
- Bitcoin ist davon nicht betroffen
- Der Preisverfall ist vorübergehend und unbegründet
- Deshalb ist jetzt ein guter Zeitpunkt, um Bitcoin zu akkumulieren
Aber auch das Gegenteil ist der Fall. Wenn du siehst, wie die Mainstream-Schlagzeilen über Bitcoin schwärmen und die Gewinne kein Ende zu nehmen scheinen, und du das Gefühl hast, dass du jedes bisschen Geld in Bitcoin investieren solltest, weil der Preis nirgendwo hin geht, außer nach oben - dann sei VORSICHTIG. Ich habe festgestellt, dass meine Psychologie typisch ist. Ich habe Angst, wenn der Preis nach unten geht, und ich habe irrationalen Überschwang, wenn der Preis schnell steigt. Wenn ich GENAU das Gegenteil von dem tue, was mein Affenhirn mir sagt, stelle ich fest, dass ich oft das Richtige tue. Das heißt, wenn du extreme Angst verspürst, ist dies der richtige Zeitpunkt zum Kaufen, und wenn du dich überschwänglich fühlst, ist dies der richtige Zeitpunkt zum Verkaufen.
Panikkäufe sind gefährlich. Wenn du einen unkontrollierbaren Drang verspürst, Bitcoin zu kaufen, atme tief durch. Ich kann dir versichern, dass du in der Lage sein wirst, etwas Bitcoin zu kaufen, und wenn du den Drang so stark verspürst, ist der Markt wahrscheinlich reif für einen Rücksetzer. Das ist keine Garantie, aber nach meiner Erfahrung ist dies der wahrscheinliche Fall. Ich plädiere nicht für den Handel mit BTC, ganz und gar nicht. Ich kann ehrlich sagen, dass ich durch den Handel mehr BTC verloren als gewonnen habe, und wenn die meisten Leute ehrlich sind, werden sie das auch zugeben. Das Trading ist eine Fähigkeit und Disziplin, die nur sehr wenige Menschen beherrschen.
Die typischen psychologischen Hindernisse, die den Menschen im Weg stehen, sind Angst und Gier. Denk über deine Gefühle nach und erkenne, wann du diese Emotionen erlebst. Sie werden dich dazu bringen, Fehler zu machen. Der einfachste Weg, all dies zu mildern, ist einfach der Dollar-Cost-Average. Dollar-Cost Averaging nimmt den ganzen Stress heraus. Basta. Wenn du in diesem Moment in diesen Schatz einsteigst und er über Nacht auf 30 % fällt, frage dich ehrlich: Habe ich den Mut dazu? Habe ich die nötige Überzeugung dafür? Habe ich das nötige Wissen, um zu verstehen, warum der Dollarpreis kurzfristig keine Rolle spielt? Werde ich in Panik verkaufen? Wenn du nicht überzeugt bist, wird dich das Dollar-Cost-Averaging retten. Du bekommst den Durchschnittspreis über einen langen Zeitraum.
Ich habe eine kleine DCA-Taktik, die einfach ist und bei mir funktioniert:
Wenn der Preis sich entspannt, erhöhe ich meinen DCA, und wenn der Preis in die Höhe schießt, ziehe ich mich zurück und kaufe im Durchschnitt weniger. Über Monate und Jahre hinweg führt dies zu einem optimalen Durchschnittswert.
FÜHLE DICH NICHT WIE EIN VERRÄTER, WENN DU BTC VERKAUFST
Habe einen Plan und sei bereit, ihn auszuführen. Der Plan meines Nachbarn ist ein guter Anfang. Sobald du dein Geld verdoppelt hast, nimmst du die Anfangsinvestition heraus. Dabei gibt es ein erhebliches Sternchen - was willst du anstelle von Bitcoin kaufen? Inflationäres Bargeld? Die Möglichkeiten, sein Geld woanders anzulegen, sind heutzutage sehr begrenzt. Das mag für viele in diesem Bereich kontrovers sein, aber ich denke, es ist absolut vernünftig, Bitcoin zu verkaufen. Wenn du Bitcoin seit JAHREN hältst und dein Stack dein Leben sinnvoll verbessern könnte, solltest du auf jeden Fall einen Teil verkaufen.
Zeit ist das einzige Gut, das wertvoller ist als BTC; wir haben wirklich nur eine begrenzte Menge an Zeit auf dieser Erde. Wenn du deine BTC hortest und dann friedlich einschläfst was war dann der Sinn? Wenn du einen Teil deines Stacks verkaufen kannst, um dein Haus abzubezahlen oder dich von erdrückenden Schulden zu befreien, halte ich das für eine gute Entscheidung. Es ist vielleicht nicht die BESTE finanzielle Entscheidung, vor allem, wenn Ihr Haus mit einem zinsgünstigen Darlehen belastet ist, aber es ist eine nachvollziehbare Entscheidung, weil man dadurch beruhigt sein kann. Man muss jedoch auch bedenken, dass der Verkauf von Bitcoin auf lange Sicht sehr wahrscheinlich eine schmerzhafte Entscheidung sein wird.
Bitcoin für Spielzeug zu verkaufen, ist hingegen kein guter Schachzug. Wenn du den 250.000 Dollar teuren Lamborghini kaufst, der in 3 Jahren 50% seines Wertes verliert, während Bitcoin um mehr als diesen Prozentsatz zugelegt hat, wird das Bedauern unerträglich sein. Robert Kiyosaki kommt mir in den Sinn. Sein Buch Rich Dad Poor Dad hat mich sehr beeinflusst, und seine Beschreibung von Vermögenswerten und Verbindlichkeiten hat mich sehr beeindruckt:
- Ein Vermögenswert erzeugt Cashflow
- Eine Verbindlichkeit zieht den Cashflow ab
Wenn du Vermögenswerte kaufst, wird dein Nettovermögen auf einer exponentiellen Kurve erheblich ansteigen. Wenn du Verbindlichkeiten kaufst, wirst du einfach ärmer. Wenn du Bitcoin verkaufst, wirst du es wahrscheinlich langfristig bereuen.
ZEITPRÄFERENZ
Die Zeitpräferenz ist ein Thema, das in Bitcoin oft angesprochen wird. Eine niedrige Zeitpräferenz zu haben bedeutet, dass man bereit ist, für eine bessere Zukunft auf die Annehmlichkeiten von heute zu verzichten. Jede sehenswerte Kathedrale, jedes klassische Kunstwerk, alles Schöne auf dieser Welt wurde gebaut, weil Menschen mit Blick auf die Zukunft und nicht auf die Gegenwart gearbeitet haben. Hätte DaVinci Bananen an die Wand geklebt, hätten wir uns nie an ihn erinnert. Wären die großen Pyramiden aus Lehm gebaut worden, gäbe es sie heute nicht mehr. Wenn die Zivilisation ihren gesamten Reichtum für das Hier und Jetzt ausgeben würde, ohne in die Zukunft zu investieren, würde sie nicht überleben.
Bitcoin selbst ist ein digitales Artefakt, das von einem geheimnisvollen Architekten bis zur Perfektion entwickelt wurde. Er ist so konzipiert, dass er Äonen überdauert; wenn die Zivilisation überdauert, wird er bis in die Zukunft hinein perfekte Treue beweisen. Da niemand ihn verändern oder kontrollieren kann, ist Bitcoin anti-entropisch. Das ist der Inbegriff von Handwerkskunst der geringen Zeitpräferenz. Bitcoin ist ein Da Vinci in einer Welt der an die Wand geklebten Bananen. Es ist so offensichtlich, wenn die Arbeit erst einmal geleistet ist, dass es peinlich ist, dass nicht mehr Menschen den Wert verstehen, den er bietet.
Im krassen Gegensatz zu diesem Bitcoin-Meisterwerk stehen die Schrotthaufen, die wir Altcoins oder Shitcoins nennen. Diese wurden mit der Technologie von Bitcoin gebaut, führen aber Entropie ein. Die Treue geht bei den Altcoins verloren, weil sie jeweils von einem Gründer oder einer Gruppe kontrolliert werden. Wenn Menschen etwas kontrollieren können, manipulieren sie es unweigerlich zu ihrem Vorteil. Und ob bewusst oder unbewusst, es wird sich verschlechtern. Die meisten dieser Shitcoins waren von Anfang an darauf ausgelegt, dich zu betrügen. Einige dieser Altcoins haben eine Führung, die vielleicht gute Absichten hat, aber sie sind menschlich und können beeinflusst und genötigt werden. Das Problem ist die FÜHRUNG. Bitcoin und seine Zeitkette wurden entwickelt, um das menschliche Element als primäre Eigenschaft zu entfernen. Die Einführung von Menschen in den Mix verursacht Entropie, die den Wert durch Seigniorage zerstört.
Die Erfindung von Bitcoin war die der NICHT-INTERVENTION durch Menschen.
Das sind Erkenntnisse, die für viele Menschen Jahre dauern, um sie vollständig zu verstehen. Wenn du das Kurzfassung über Altcoins wissen willst, ist es einfach. Bemühe dich einfach nicht. Du bist besser dran, wenn du dein Geld in ein Casino bringst und Glücksspiel machst. Die Karten sind in der Kryptowelt schwer gegen Dich ausgelegt; du hast einfach Glück, wenn du Geld verdienst. Nimm den Weg der geringen Zeitpräferenz und staple Bitcoin, während du lernst, wie deine Investition wächst. Ich kann mit Zuversicht sagen, dass du in 5 Jahren viel weiter vorne sein wirst, wenn du in Bitcoin Dollar-Cost-Averaging betreibst, als wenn du mit Shitcoins spielen würdest.
5-JAHRES-AUSSICHTEN MINIMUM
Die meisten Menschen interessieren sich für Bitcoin während einer seiner parabolischen Bullenläufe. Ich war einer von ihnen. Wir sind alle daran interessiert, finanziell voranzukommen, besonders wenn das Gespenst der Inflation über unseren Köpfen schwebt.
Wenn du neu bei Bitcoin bist und dies dein erster Versuch ist, dann stelle sicher, dass du bereit bist, diesen Vermögenswert für mindestens 5 Jahre zu halten. Du bist wahrscheinlich während einer Aufwärtsbewegung hier, und wenn du kein Glück hattest, ist es wahrscheinlich am Ende der Aufwärtsbewegung. Zum Zeitpunkt der Erstellung dieses Berichts im Dezember 2023 stehen wir meiner Meinung nach am Anfang der nächsten Aufwärtsbewegung. Mit der Zulassung der ETFs, der Halbierung im April 2024 und der Aussicht, dass die US-Notenbank ihre Geldpolitik zurückfahren wird, sind viele Katalysatoren aufeinander abgestimmt. Das bedeutet jedoch NICHT, dass dies unvermeidlich ist. Schwarze Schwäne sind immer eine Möglichkeit. Abgesehen von diesem schwarzen Schwan scheinen wir für einen massiven Kursanstieg in den nächsten Jahren bereit zu sein.
SELBSTVERWAHRUNG
Wenn du zum ersten Mal Bitcoin an der Börse deiner Wahl kaufst, wird es sich anfühlen wie der Kauf eines beliebigen anderen Vermögenswerts bei einem Broker. Du kaufst Bitcoin, und die Zahl auf dem Bildschirm spiegelt die Menge an Bitcoin wider, die du jetzt "besitzt".
Es ist von entscheidender Bedeutung, dass du deine Bitcoin in Verwahrung nimmst. Wir haben in jüngster Zeit Fehler beim Umtausch und regelrechte Betrugsfälle erlebt. Wenn diese Betrügereien aufgedeckt und strafrechtlich verfolgt werden und der Preis von Bitcoin unter Druck gerät, weil viele Menschen den Vermögenswert Bitcoin mit den Börsen in Verbindung bringen, die ihn verkaufen, wird dies zu einer RIESIGEN Kaufgelegenheit. Als FTX vor einem Jahr scheiterte, wurde der Preis von Bitcoin negativ beeinflusst, und diejenigen, die verstanden, dass Bitcoin kein fundamentales Problem hatte, kauften mehr. Du hast verstanden, dass die Angst durch den Markt strömte (womit wir wieder bei dem Punkt wären, warum es in diesem Bereich SO WICHTIG ist, gut informiert zu sein). Wer damals Bitcoin kaufte (um 16k), sicherte sich innerhalb eines Jahres einen Gewinn von weit über 100%!
Stell dir die Seed Keys als das Passwort zu deinem Bitcoin vor, das geschützt werden muss, denn wenn jemand anderes es bekommt, kann er deine Bitcoin in Besitz nehmen - nicht gut für dich. Bitcoin-Seed-Keys werden in der Regel durch eine Hardware-Wallet oder ein Signiergerät geschützt. Dieses Gerät schützt deine Schlüssel vor Hackern oder schlechten Akteuren. Ich verwende seit Jahren Coldcards, und sie gehören zu den besten Geräten zum Schutz von privaten Schlüsseln. Es funktioniert sehr einfach. Du erstellst auf dem Gerät die geheimen Schlüssel; es speichert sie und bewahrt sie offline auf, d. h. ohne Verbindung zum Internet. Dieser letzte Punkt ist WICHTIG. Du darfst diese Wörter NIEMALS auf einem Computer mit Internetanschluss speichern. Der einzige Ort, an dem du deine Schlüssel sicher aufbewahren kannst, ist ein dafür vorgesehenes Gerät. Wenn der Computer kompromittiert wird (und glauben Sie mir, es ist SEHR WÄHRLICH, dass er kompromittiert wird), wird das Signiergerät deine Bitcoin schützen.
Das mag sich alles sehr schwierig und komplex anhören, wenn du es noch nie gemacht hast, aber glaub mir, es ist ganz einfach. Ich würde empfehlen, dass du dir die Videos von BTC Sessions über die Verwendung des Signiergeräts deiner Wahl ansiehst. Er hat unglaubliche Walk-Through-Videos auf YouTube, die alles im Detail erklären.
Eine gemeinsame Verwahrung mit einem Unternehmen wie Swan Bitcoin oder Unchained Capital ist auch eine gute Idee für diejenigen, die neu in diesem Bereich sind. Sie werden dir die Hand halten und dich davor schützen, einfache Fehler zu machen, die zu Problemen führen können. Die gemeinschaftliche Verwahrung ist die Kosten wert, wenn du dir Sorgen machst, deine Bitcoin zu verlieren. Unchained bietet ein Produkt zur gemeinschaftlichen Verwahrung an, das mehrere Schlüssel enthalten kann und deinen Verwandten helfen kann, deine Bitcoin im Falle deines Ablebens wiederzuerlangen.
GEBE NICHT MIT DEINEN BITCOIN AN. Es besteht die Versuchung, mit dem Erfolg zu prahlen. Wenn du fünf Jahre lang durchhältst, wirst du ihn wahrscheinlich haben. Du bist stolz darauf, dass du die Disziplin und Selbstbeherrschung hattest, dich selbst zu beherrschen und erfolgreich das zu erwerben, was du als eine bedeutende Menge an Bitcoin ansiehst. Teile nicht, wie viel du hast, mit anderen. Das sollte offensichtlich sein, aber es gibt Leute, die sich nicht so sehr für dich freuen. Sie könnten es ihren Freunden erzählen, und früher oder später könnte jemand, den du nicht kennst und der vielleicht gewaltbereit ist, feststellen, dass du ein attraktives Ziel bist. Dies ist ein weiterer Grund für die Verwendung einer Konfiguration mit mehreren Signaturen. Selbst wenn jemand 1 von 3 Schlüsseln erhalten hat, kann er deine Bitcoin nicht stehlen.
KAUFE KEINE BITCOIN, DIE DU NICHT KONTROLLIEREN KANNST
Kaufe nicht den glänzenden neuen ETF, den die Wall Street anbietet. Kaufe Bitcoin nur bei Anbietern, die es dir ermöglichen, deine Bitcoin tatsächlich in Verwahrung zu nehmen. Lege deine Bitcoin nicht bei irgendeinem Dienst an, der eine Rendite bietet, insbesondere wenn diese Rendite unrealistisch hoch erscheint. Als allgemeine Faustregel gilt: Lass es einfach bleiben.
Der erste und wichtigste Grund, warum du deine Bitcoin in Verwahrung nehmen solltest, ist, dass du die absolute und vollständige Kontrolle über sie hast. Es gibt in Bitcoin ein Sprichwort: "Nicht deine Schlüssel, nicht deine Coins". Wenn du deine Bitcoin nicht verwahrst, hast du einfach einen Schuldschein. Das ist der ganze Grund für die Existenz von Bitcoin. Um Zwischenhändler auszuschalten und den Menschen zu ermöglichen, ihr finanzielles Schicksal selbst in die Hand zu nehmen.
Wenn du den Besitz hast, fallen keine Gebühren an wie bei einem ETF. Diese Gebühren können niedrig erscheinen, aber mit der Zeit können sie SIGNIFIKANT sein. GBTC ist ein Trust, der einem Bitcoin-ETF am ähnlichsten ist. GBTC erhebt eine Gebühr von 2 % PRO JAHR (jetzt 1,5 % mit dem ETF). Im Laufe der Zeit kann dies erheblich sein. Außerdem erlauben es die ETF-Produkte, die die Wall Street verkauft, nicht, den Bitcoin JEMALS zu verwahren. Ein ETF könnte für einige Leute in bestimmten Szenarien Sinn machen, aber für jeden, der ein Lego-Set bauen kann, ist die Verwahrung von Bitcoin ähnlich komplex. Nimm es selbst in die Hand.
Wenn sich Bitcoin mehr und mehr durchsetzt, wird es möglich sein, ihn als Sicherheiten zu verwenden. Ja, ich verstehe, dass die Verwendung deines Bitcoin als Sicherheit ihn aus deinem Besitz nimmt und Vertrauen in eine dritte Partei erfordert. Dies ist ein weiterer Fall, in dem du dich informieren und SICHER sein solltest, dass der von dir gewählte Kreditgeber vertrauenswürdig ist und nicht pleite gehen wird. Im Zweifelsfall solltest du dich immer auf die Selbstverwahrung verlassen.
Eine Kreditaufnahme gegen deine Bitcoin ist unmöglich, wenn du ihn nicht selbst verwahrst. Du kannst den Bitcoin, den Blackrock in deinem Namen hält, nicht ausleihen. Dies ist von Bedeutung. Es hat steuerliche Vorteile, Bitcoin zu beleihen, anstatt sie zu verkaufen. Wenn du keine Kontrolle über deine Bitcoin hast, schließt du dich selbst von einigen vorhersehbaren Anwendungsfällen in der nahen Zukunft aus und von vielen unvorhersehbaren Anwendungen, die noch erfunden werden müssen. Programmierbares Geld ist nicht nützlich, wenn du es nicht in deiner Hand hältst.
Der letzte Grund, warum du deine Bitcoin aufbewahren solltest, ist ein wenig düsterer. Bitcoin wurde entwickelt, um unzensierbar und nicht konfiszierbar zu sein. Wenn der Staat merkt, dass er die Kontrolle über das Geld verliert, wird er sich wahrscheinlich dein Bitcoin holen. Dies ist ein Präzedenzfall in der Geschichte der USA. Im Jahr 1933 wurde mit der Executive Order 6102 der Besitz von Gold für US-Bürger illegal. Sie zwangen die Menschen, Gold abzugeben und 20 Dollar pro Unze zu erhalten. Die Regierung setzte dann den Goldpreis auf 35 Dollar pro Unze herauf. Für den Besitz von Goldmünzen konnte man in den USA von 1933 bis Mitte der 1970er Jahre ins Gefängnis kommen. Das könnte wieder passieren, und du hast die Wahl, wenn du Bitcoin selbst hältst. Depotbanken WERDEN in diesem Szenario gezwungen sein, der Regierung deine Bitcoin zu geben. Was du in dieser Situation mit deinem Bitcoin tust, sollte DEINE Entscheidung sein, nicht die eines Verwahrers.
VERANTWORTUNG
Wenn du die Schritte unternimmst, um deine Bitcoin selbst zu verwahren, bist du verantwortlich. Dies ist eine Art von radikaler Verantwortung, die Menschen beunruhigen kann. Wenn du deine Schlüssel verlierst, ist dein Bitcoin für immer verloren. Es gibt keine Nummer, die du anrufen kannst, und niemanden, der dir helfen kann. SIE. SIND. WEG.
Im Jahr 2017 verlor einer meiner Freunde auf der Feuerwache Bitcoin im Wert von 1300 Dollar, weil er die Bitcoin in einer Papier-Wallet aufbewahrte. Diese werden nicht mehr verwendet, weil sie so unsicher sind, aber man kann einen QR-Code ausdrucken, der die Bitcoin enthält. Er ließ das Stück Papier in seinem Auto liegen. Dann räumte er sein Auto aus und saugte die Papier-Wallet auf. Diese Bitcoin sind für immer weg. Sie sind jetzt irgendwo zwischen 4 und 5 Tausend Dollar wert, und sie sind einfach weg. Nun, technisch gesehen sind sie nicht weg, sie sind immer noch da, nur für niemanden zugänglich. Ohne die Schlüssel kann niemand die Bitcoin bewegen, also sind die Bitcoin praktisch für immer eingefroren.
Ein anderer guter Freund von mir verlor eine beträchtliche Menge an Bitcoin bei einem Unternehmen namens BlockFi. Dabei handelte es sich um eine Börse, die Renditen für Bitcoin anbot, die bei ihrer Börse aufbewahrt wurden. Dieser Bitcoin ist nicht eingefroren, aber er ist jetzt für die absehbare Zukunft in einem Rechtsstreit eingesperrt. Um dem Ganzen noch die Krone aufzusetzen - da der Bitcoin, als er von BlockFi gehalten wurde, technisch gesehen nicht ihm gehörte, sondern aufgrund der "Vereinbarung", die er bei der Eröffnung des Kontos unterschrieben hat, ihnen gehört, wird er irgendwann in der Zukunft den Dollarwert dieses Bitcoins zu dem Preis erhalten, zu dem BlockFi pleite ging - also 16.000 Dollar -, sind wir wieder bei dem Punkt angelangt, warum du die Selbstverwahrung ernst nehmen solltest!
Das alte Bitcoin-Sprichwort lautet: "Nicht deine Schlüssel, nicht deine Coins".
Bitcoin ist eine endlose Lernreise. Wenn du ein Kaninchenloch erforschen willst, hast du Glück! Die Menge an soliden Inhalten, die in diesem Bereich angeboten werden, ist um Lichtjahre besser als im Jahr 2017. Man kann in einem Bruchteil der Zeit, die man damals gebraucht hätte, von null auf kompetent umsteigen. Wie oben bereits angedeutet, haben wir bei Blue Collar Bitcoin eine Grundlagenreihe zusammengestellt, die du für den Einstieg nutzen kannst. Die Liste der großartigen Inhaltsersteller und Ressourcen ist so lang, dass wir sie nicht alle aufzählen können. Geh einfach auf Entdeckungsreise und achte darauf, zu überprüfen, nicht zu vertrauen.
Lerne weiter, und vor allem - denke selbst!
Erinnere dich an die Weisheit von Matt Odell: "Bleib bescheiden und staple Sats".
-
 @ 04ea4f83:210e1713
2025-04-20 08:38:43
@ 04ea4f83:210e1713
2025-04-20 08:38:43Bei dem Begriff "Midlife-Crisis" denkt man oft an Menschen mittleren Alters, die sich Sportwagen kaufen, ihre Ehepartner für jüngere Partner verlassen oder sich in einem verzweifelten Versuch, ihre Jugend wiederzuerlangen, plötzlich auf ausgefallene Abenteuer einlassen. Im Bitcoin Space zeichnet sich jedoch ein neues Phänomen ab - die Bitcoiner Midlife-Crisis.
Für diejenigen, die tief in den Kaninchen Bau eingetaucht sind kommt ein Punkt auf ihrer Reise, an dem sie ein Plateau erreichen. Sie haben ein außerordentliches Vermögen in Form von Sats angehäuft und verfügen über ein klares Verständnis der Technologie und des Marktes. Aber trotz alledem fühlen sie sich unerfüllt, so als ob der nächste Kauf von Bitcoin einfach keinen wirklichen Unterschied mehr macht.
Dieses Gefühl wird durch die extreme Volatilität des Bitcoin-Marktes noch verstärkt. An einem Tag kann das Nettovermögen in neue Höhen steigen, nur um am nächsten Tag wieder deutlich zu fallen. Die Schwankungen können so drastisch sein, dass ihr Jahresgehalt im Vergleich zu den nicht realisierten Gewinnen und Verlusten, die sie an einem einzigen Tag erleben, verblasst. Es wird schwierig, die Achterbahnfahrt der finanziellen Freiheit mit der Stabilität einer traditionellen Festanstellung in Einklang zu bringen.
Die traditionellen Vorstellungen von Erfolg und Erfüllung verlieren für Bitcoiner, die diese Midlife-Crisis erleben, an Bedeutung. Die Verlockung von materiellen Besitztümern oder beruflichen Fortschritten hat nicht mehr das gleiche Gewicht im Vergleich zu den potenziellen Gewinnen und Verlusten der Bitcoin. Die Vorstellung, für jemand anderen zu arbeiten und Zeit gegen Geld zu tauschen, wird zunehmend unattraktiver, wenn sie das Potenzial für finanzielle Unabhängigkeit durch ihre überlegene Spar-Technologie sehen.
Infolgedessen können Bitcoiner in der Mitte ihrer Lebenskrise ihre Prioritäten und Werte in Frage stellen. Sie könnten beginnen, die gesellschaftlichen Normen und Erwartungen zu hinterfragen, die ihr Leben bis zu diesem Zeitpunkt bestimmt haben. Das Bedürfnis nach Anerkennung oder Bestätigung durch andere hat nicht mehr den gleichen Stellenwert, da sie erkennen, dass ihr Wohlstand und ihr Erfolg nicht durch traditionelle Maßstäbe definiert werden.
Diese veränderte Denkweise kann zu einem Mangel an Filter oder Selbstzensur in ihren Interaktionen mit anderen führen. Bitcoiner, die eine Midlife-Crisis durchleben, werden möglicherweise offener und selbstbewusster, wenn es darum geht, ihre Überzeugungen und Meinungen zu äußern, unabhängig davon, wie sie von ihrem Umfeld wahrgenommen werden. Sie haben vielleicht nicht mehr das Bedürfnis, sich an gesellschaftliche Normen anzupassen oder sich an konventionelle Weisheiten zu halten, was zu Konflikten mit Freunden, Familie oder Arbeitskollegen führt, die ihre Ansichten nicht verstehen oder teilen.
Die emotionale Loslösung, die mit der Bitcoiner-Midlife-Crisis einhergeht, kann sich auch in einem allgemeinen Gefühl der Apathie oder Gleichgültigkeit gegenüber äußeren Ereignissen oder Umständen äußern. Themen oder Herausforderungen, die früher vielleicht eine starke emotionale Reaktion hervorgerufen haben, werden jetzt kaum noch wahrgenommen. Die Höhen und Tiefen des alltäglichen Fiat-Jobs scheinen im Vergleich zur Volatilität des Bitcoin-Marktes unbedeutend zu sein.
Mitten in dieser Midlife-Crisis könnten sich Bitcoiner an einem Scheideweg wiederfinden und sich mit Fragen der Identität, des Zwecks und der Erfüllung auseinandersetzen. Sie könnten gezwungen sein, sich mit ihrer eigenen Sterblichkeit und dem Erbe, das sie hinterlassen wollen, auseinanderzusetzen. Die traditionellen Meilensteine des Erfolgs, wie ein Haus, staatliche Altersvorsorge oder berufliche Erfolge, haben vielleicht nicht mehr die gleiche Anziehungskraft, wenn man sie mit dem Potenzial für finanzielle Freiheit und Souveränität vergleicht, das der Bitcoin bietet.
Die Midlife-Crisis der Bitcoiner ist nicht nur ein persönlicher Kampf, sondern ein Spiegelbild der breiteren gesellschaftlichen Veränderungen und Umwälzungen, die durch den Aufstieg eines digitalen Geldes ausgelöst wurden, welches die Gesellschaft von monetärer Entwertung und finanzieller Unterdrückung befreit. Sie ist eine Herausforderung für die etablierten Normen und Strukturen der Finanzwelt und eine Neudefinition dessen, was es bedeutet, in der modernen Zeit Erfolg und Erfüllung zu finden.
Während Bitcoiner durch diese Midlife-Crisis schreiten, können sie Trost darin finden, sich mit anderen zu verbinden, die ihre Reise und Erfahrungen teilen. Online-Communities, Meetups und Konferenzen bieten einen Raum für Gleichgesinnte, um zusammenzukommen und sich gegenseitig durch die Höhen und Tiefen des Bitcoin-Marktes zu unterstützen. Indem sie ihre Kämpfe, Erfolge und Einsichten miteinander teilen, können Bitcoiner ein Gefühl der Kameradschaft und ein Ziel auf ihrem Weg zur finanziellen Unabhängigkeit und Selbstverwirklichung finden.
Zusammenfassend lässt sich sagen, dass die Midlife-Crisis der Bitcoiner ein komplexes und vielschichtiges Phänomen ist, das die einzigartigen Herausforderungen und Chancen der Einführung von gesundem Geld widerspiegelt. Sie stellt einen Wendepunkt im Leben derjenigen dar, die tief in die Welt des Bitcoin eingetaucht sind, wo traditionelle Maßstäbe für Erfolg und Erfüllung im Lichte des Potenzials für Selbstständigkeit und finanzielle Freiheit neu bewertet werden. Indem sie sich mit ihren eigenen Werten, Überzeugungen und Prioritäten auseinandersetzen, können Bitcoiner aus dieser Midlife-Crisis mit einem neuen Sinn für Ziel und Richtung auf ihrer Reise zu finanzieller Unabhängigkeit und Selbstverwirklichung hervorgehen.
-
 @ 6389be64:ef439d32
2025-02-27 21:32:12
@ 6389be64:ef439d32
2025-02-27 21:32:12GA, plebs. The latest episode of Bitcoin And is out, and, as always, the chicanery is running rampant. Let’s break down the biggest topics I covered, and if you want the full, unfiltered rant, make sure to listen to the episode linked below.
House Democrats’ MEME Act: A Bad Joke?
House Democrats are proposing a bill to ban presidential meme coins, clearly aimed at Trump’s and Melania’s ill-advised token launches. While grifters launching meme coins is bad, this bill is just as ridiculous. If this legislation moves forward, expect a retaliatory strike exposing how politicians like Pelosi and Warren mysteriously amassed their fortunes. Will it pass? Doubtful. But it’s another sign of the government’s obsession with regulating everything except itself.
Senate Banking’s First Digital Asset Hearing: The Real Target Is You
Cynthia Lummis chaired the first digital asset hearing, and—surprise!—it was all about control. The discussion centered on stablecoins, AML, and KYC regulations, with witnesses suggesting Orwellian measures like freezing stablecoin transactions unless pre-approved by authorities. What was barely mentioned? Bitcoin. They want full oversight of stablecoins, which is really about controlling financial freedom. Expect more nonsense targeting self-custody wallets under the guise of stopping “bad actors.”
Bank of America and PayPal Want In on Stablecoins
Bank of America’s CEO openly stated they’ll launch a stablecoin as soon as regulation allows. Meanwhile, PayPal’s CEO paid for a hat using Bitcoin—not their own stablecoin, Pi USD. Why wouldn’t he use his own product? Maybe he knows stablecoins aren’t what they’re hyped up to be. Either way, the legacy financial system is gearing up to flood the market with stablecoins, not because they love crypto, but because it’s a tool to extend U.S. dollar dominance.
MetaPlanet Buys the Dip
Japan’s MetaPlanet issued $13.4M in bonds to buy more Bitcoin, proving once again that institutions see the writing on the wall. Unlike U.S. regulators who obsess over stablecoins, some companies are actually stacking sats.
UK Expands Crypto Seizure Powers
Across the pond, the UK government is pushing legislation to make it easier to seize and destroy crypto linked to criminal activity. While they frame it as going after the bad guys, it’s another move toward centralized control and financial surveillance.
Bitcoin Tools & Tech: Arc, SatoChip, and Nunchuk
Some bullish Bitcoin developments: ARC v0.5 is making Bitcoin’s second layer more efficient, SatoChip now supports Taproot and Nostr, and Nunchuk launched a group wallet with chat, making multisig collaboration easier.
The Bottom Line
The state is coming for financial privacy and control, and stablecoins are their weapon of choice. Bitcoiners need to stay focused, keep their coins in self-custody, and build out parallel systems. Expect more regulatory attacks, but don’t let them distract you—just keep stacking and transacting in ways they can’t control.
🎧 Listen to the full episode here: https://fountain.fm/episode/PYITCo18AJnsEkKLz2Ks
💰 Support the show by boosting sats on Podcasting 2.0! and I will see you on the other side.
-
 @ 04ea4f83:210e1713
2025-04-20 08:37:09
@ 04ea4f83:210e1713
2025-04-20 08:37:09Veröffentlicht auf Medium am 07.06.2021\ Originalautor: Tomer Strolight\ Übersetzt von: Sinautoshi am 04.05.2023 - 788249\
Reden wir über Dinge, die man mit Geld nicht kaufen kann.
Ehrlichkeit kann man mit Geld nicht kaufen. Tatsächlich sind Menschen, die versuchen, dich davon zu überzeugen, ihnen dein Geld zu geben, oft nicht ganz ehrlich zu dir.
Freundschaft kann man mit Geld nicht kaufen. Du kannst nicht in ein Geschäft oder eine Bar gehen und einen Freund kaufen – jemanden, der deine Werte teilt, der dich respektiert, den du respektierst. Und aus den gleichen Gründen kann man sich damit keine Liebe kaufen , die eine besonders tiefe Form der Freundschaft ist.
Vor allem kann Geld dir keine Dinge kaufen, die in dir selbst sind: Es kann dir kein Selbstwertgefühl, Intelligenz, Mut oder Integrität kaufen, um nur einige Beispiele zu nennen. Gebe einer unsicheren Person einen Haufen Geld und sie wird es verschwenden, um vor anderen anzugeben oder sich selbst zu zerstören. Gib einem intellektuell faulen Menschen Geld und er wird nicht schlauer. Gebe einem Feigling Geld und er hat nur noch eine Sache, vor der er Angst haben muss: das Geld zu verlieren. Und gebe einem Betrüger Geld, und er wird versuchen, es zu verwenden, um einen unehrlichen Plan auszuhecken, durch den er mehr bekommen kann.
Die Dinge, die man für Geld kaufen kann
Geld wird dir ein schönes Outfit, einen tollen Haarschnitt, ein schickes Auto und ein schönes Haus kaufen, aber das Glück selbst wird unerreichbar bleiben ohne echte Freunde und Liebhaber, denen du vertrauen kannst, und ohne in der Lage zu sein, dich selbst zu lieben und zu respektieren.
Geld kauft nämlich kein Glück. Nicht von alleine. Es ist nicht ausreichend.
Warum arbeiten wir dann so hart für Geld? Warum messen manche Menschen ihren Wert in Dollar?
Es ist wahr, dass wir viele der Dinge brauchen, die man mit Geld kaufen kann, wie Nahrung, Unterkunft, Kleidung und sogar Unterhaltung, die uns ein wenig glücklicher macht.
Geld kann ein Wegbereiter sein. Es kann verwendet werden, um Dinge zu kaufen, die grundlegende Überlebensbedürfnisse befriedigen, und uns dadurch die Zeit verschaffen, diesen anderen Werten nachzugehen, die Geld selbst nicht kaufen kann.
Es ist jedoch immer noch sehr falsch, unseren Wert anhand einer einzigen Zahl zu messen, geschweige denn an einer Zahl, von der wir wissen, dass sie Freundschaft, Liebe, Selbstwertgefühl, Intelligenz, Mut, Integrität und viele andere Tugenden und Werte, die wir zeigen und verfolgen sollten, auslässt.
Was hat das mit Bitcoin zu tun?
Nehmen wir uns nun eine Minute Zeit, um uns die Gemeinschaft der Bitcoiner anzusehen. Bitcoiner sind überzeugt von einer neue Form von Geld, Bitcoin.
Wir unternehmen große Anstrengungen, um zu erklären, warum wir denken, dass es die beste Form von Geld ist, die es je gegeben hat und wahrscheinlich jemals geben wird.
Um dies erklären zu können, müssen wir zunächst große Anstrengungen unternehmen, um zu verstehen, was Geld ist und wie Bitcoin die Anforderungen erfüllt, Geld zu sein.
Dazu müssen wir einen sehr ehrlichen Blick auf die Geschichte und die Gegenwart werfen . Wir müssen erforschen, was viele Menschen für selbstverständlich halten. Wir müssen harte Fragen stellen und nach ehrlichen, vertretbaren Antworten suchen.
Wir müssen etwas über die Mathematik lernen, auf die sich Bitcoin stützt.
Wir müssen etwas über die Energieproduktion lernen, auf die Bitcoin angewiesen ist.
Wir lernen etwas über Ökonomie, die Lehre davon, wie Menschen mit den Dingen umgehen, die man mit Geld kaufen kann.
Wir entwickeln eine tiefe Überzeugung, die von all diesem Lernen und unseren Beobachtungen und Argumenten über das, was um uns herum passiert, geprägt ist.
Wir bilden Ansichten darüber aus, wohin die Welt steuert .
Wir kommen zu dem Schluss, dass eine Welt mit Bitcoin als Geld oder auch nur als das Geld, das von uns, welche sich für Bitcoin entscheiden, verwendet wird, eine bessere Welt ist.
Wir schließen daraus, dass es eine bessere Welt ist, weil sie ehrlich und transparent ist. Es ist eine Welt ohne Geheimnisse, Intrigen und Täuschungen darüber, was Geld ist.
Es ist eine Welt ohne mächtige Leute, die die Kontrolle über das Geldsystem ausüben, um die Schwachen zu kontrollieren.
Wir finden dann eine moralische Mission in Bitcoin.
Wir übernehmen die Verantwortung, das Wissen zu verbreiten.
Dazu braucht es Mut. Wir müssen unser Geld dort einsetzen, wo unser Mund ist, indem wir Bitcoin mit unseren Euro kaufen. Dies ist ein Akt der Risikobereitschaft oder des Mutes. Es ist ein Akt der Integrität – unsere Worte an unseren Taten auszurichten.
Wir müssen standhaft bleiben. Wir werden ausgelacht. Mächtige Menschen und Institutionen verspotten uns und versuchen, uns zu diskreditieren. Sie bezeichnen uns als Unterstützer von Kriminellen und Terroristen. Entweder stärken wir unseren Mut und unsere Überzeugung oder verlassen Bitcoin.
Diejenigen von uns, die bleiben, wissen, dass unsere Mit-Bitcoiner, die die gleichen Schwierigkeiten durchgemacht haben oder durchmachen wie wir, ehrlich, intelligent und mutig sind.
Wir respektieren einander. Wir werden Freunde.
Wir alle tragen bei, was wir können, wie wir können. Wir bauen die Welt, die wir uns vorstellen.
All dies tun wir unbeirrt, während Millionen an der Seitenlinie stehen, einige neugierig zusehen, uns verspotten und einige aktiv angreifen und versuchen, uns aufzuhalten. Ab und zu rennt einer rüber und sagt „Ich will so sein wie du!“ Und wir empfangen sie mit offenen Armen.
Ein Bitcoiner zu werden ist ein Prozess, durch den du Dinge erhältst, die man mit Geld nicht kaufen kann.
Schau mal. Ehrlichkeit kann man mit Geld nicht kaufen. Freundschaft kann man damit nicht kaufen. Selbstachtung, Mut, Intelligenz oder Integrität kann man damit auch nicht kaufen. Doch diese Bitcoiner mit ihren Ideen, ihren Idealen, Bemühungen und ihren Errungenschaften haben sich all diese Dinge angeeignet. Bitcoiner sind ehrlich. Sie haben authentische Freundschaften. Sie glauben an sich. Sie sind mutig. Sie sind schlau. Und sie besitzen eine Integrität, die all diese Dinge über jeden Reichtum stellt, der in einem monetären Wert gemessen wird.
Kein Bitcoiner beurteilt einen anderen danach, wie viel Bitcoin diese andere Person wert ist.
Es ist ein Fauxpas in der Community, überhaupt danach zu fragen.
Ich liebe meine Mit-Bitcoiner. Sie sind die besten Menschen auf Erden. Einige mögen finanziell reich sein, andere nicht. Aber sie sind mir alle viel mehr wert als Geld.
Bitcoin hat uns allen eine Fülle von Dingen gegeben, die man mit Geld nicht kaufen kann.