-
 @ eac63075:b4988b48
2025-01-04 19:41:34
@ eac63075:b4988b48
2025-01-04 19:41:34Since its creation in 2009, Bitcoin has symbolized innovation and resilience. However, from time to time, alarmist narratives arise about emerging technologies that could "break" its security. Among these, quantum computing stands out as one of the most recurrent. But does quantum computing truly threaten Bitcoin? And more importantly, what is the community doing to ensure the protocol remains invulnerable?
The answer, contrary to sensationalist headlines, is reassuring: Bitcoin is secure, and the community is already preparing for a future where quantum computing becomes a practical reality. Let’s dive into this topic to understand why the concerns are exaggerated and how the development of BIP-360 demonstrates that Bitcoin is one step ahead.
What Is Quantum Computing, and Why Is Bitcoin Not Threatened?
Quantum computing leverages principles of quantum mechanics to perform calculations that, in theory, could exponentially surpass classical computers—and it has nothing to do with what so-called “quantum coaches” teach to scam the uninformed. One of the concerns is that this technology could compromise two key aspects of Bitcoin’s security:
- Wallets: These use elliptic curve algorithms (ECDSA) to protect private keys. A sufficiently powerful quantum computer could deduce a private key from its public key.
- Mining: This is based on the SHA-256 algorithm, which secures the consensus process. A quantum attack could, in theory, compromise the proof-of-work mechanism.
Understanding Quantum Computing’s Attack Priorities
While quantum computing is often presented as a threat to Bitcoin, not all parts of the network are equally vulnerable. Theoretical attacks would be prioritized based on two main factors: ease of execution and potential reward. This creates two categories of attacks:
1. Attacks on Wallets
Bitcoin wallets, secured by elliptic curve algorithms, would be the initial targets due to the relative vulnerability of their public keys, especially those already exposed on the blockchain. Two attack scenarios stand out:
-
Short-term attacks: These occur during the interval between sending a transaction and its inclusion in a block (approximately 10 minutes). A quantum computer could intercept the exposed public key and derive the corresponding private key to redirect funds by creating a transaction with higher fees.
-
Long-term attacks: These focus on old wallets whose public keys are permanently exposed. Wallets associated with Satoshi Nakamoto, for example, are especially vulnerable because they were created before the practice of using hashes to mask public keys.
We can infer a priority order for how such attacks might occur based on urgency and importance.
 Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)
Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)2. Attacks on Mining
Targeting the SHA-256 algorithm, which secures the mining process, would be the next objective. However, this is far more complex and requires a level of quantum computational power that is currently non-existent and far from realization. A successful attack would allow for the recalculation of all possible hashes to dominate the consensus process and potentially "mine" it instantly.
 Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin Attacks
Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin AttacksRecently, Narcelio asked me about a statement I made on Tubacast:
https://x.com/eddieoz/status/1868371296683511969
If an attack became a reality before Bitcoin was prepared, it would be necessary to define the last block prior to the attack and proceed from there using a new hashing algorithm. The solution would resemble the response to the infamous 2013 bug. It’s a fact that this would cause market panic, and Bitcoin's price would drop significantly, creating a potential opportunity for the well-informed.
Preferably, if developers could anticipate the threat and had time to work on a solution and build consensus before an attack, they would simply decide on a future block for the fork, which would then adopt the new algorithm. It might even rehash previous blocks (reaching consensus on them) to avoid potential reorganization through the re-mining of blocks using the old hash. (I often use the term "shielding" old transactions).
How Can Users Protect Themselves?
While quantum computing is still far from being a practical threat, some simple measures can already protect users against hypothetical scenarios:
- Avoid using exposed public keys: Ensure funds sent to old wallets are transferred to new ones that use public key hashes. This reduces the risk of long-term attacks.
- Use modern wallets: Opt for wallets compatible with SegWit or Taproot, which implement better security practices.
- Monitor security updates: Stay informed about updates from the Bitcoin community, such as the implementation of BIP-360, which will introduce quantum-resistant addresses.
- Do not reuse addresses: Every transaction should be associated with a new address to minimize the risk of repeated exposure of the same public key.
- Adopt secure backup practices: Create offline backups of private keys and seeds in secure locations, protected from unauthorized access.
BIP-360 and Bitcoin’s Preparation for the Future
Even though quantum computing is still beyond practical reach, the Bitcoin community is not standing still. A concrete example is BIP-360, a proposal that establishes the technical framework to make wallets resistant to quantum attacks.
BIP-360 addresses three main pillars:
- Introduction of quantum-resistant addresses: A new address format starting with "BC1R" will be used. These addresses will be compatible with post-quantum algorithms, ensuring that stored funds are protected from future attacks.
- Compatibility with the current ecosystem: The proposal allows users to transfer funds from old addresses to new ones without requiring drastic changes to the network infrastructure.
- Flexibility for future updates: BIP-360 does not limit the choice of specific algorithms. Instead, it serves as a foundation for implementing new post-quantum algorithms as technology evolves.
This proposal demonstrates how Bitcoin can adapt to emerging threats without compromising its decentralized structure.
Post-Quantum Algorithms: The Future of Bitcoin Cryptography
The community is exploring various algorithms to protect Bitcoin from quantum attacks. Among the most discussed are:
- Falcon: A solution combining smaller public keys with compact digital signatures. Although it has been tested in limited scenarios, it still faces scalability and performance challenges.
- Sphincs: Hash-based, this algorithm is renowned for its resilience, but its signatures can be extremely large, making it less efficient for networks like Bitcoin’s blockchain.
- Lamport: Created in 1977, it’s considered one of the earliest post-quantum security solutions. Despite its reliability, its gigantic public keys (16,000 bytes) make it impractical and costly for Bitcoin.
Two technologies show great promise and are well-regarded by the community:
- Lattice-Based Cryptography: Considered one of the most promising, it uses complex mathematical structures to create systems nearly immune to quantum computing. Its implementation is still in its early stages, but the community is optimistic.
- Supersingular Elliptic Curve Isogeny: These are very recent digital signature algorithms and require extensive study and testing before being ready for practical market use.
The final choice of algorithm will depend on factors such as efficiency, cost, and integration capability with the current system. Additionally, it is preferable that these algorithms are standardized before implementation, a process that may take up to 10 years.
Why Quantum Computing Is Far from Being a Threat
The alarmist narrative about quantum computing overlooks the technical and practical challenges that still need to be overcome. Among them:
- Insufficient number of qubits: Current quantum computers have only a few hundred qubits, whereas successful attacks would require millions.
- High error rate: Quantum stability remains a barrier to reliable large-scale operations.
- High costs: Building and operating large-scale quantum computers requires massive investments, limiting their use to scientific or specific applications.
Moreover, even if quantum computers make significant advancements, Bitcoin is already adapting to ensure its infrastructure is prepared to respond.
Conclusion: Bitcoin’s Secure Future
Despite advancements in quantum computing, the reality is that Bitcoin is far from being threatened. Its security is ensured not only by its robust architecture but also by the community’s constant efforts to anticipate and mitigate challenges.
The implementation of BIP-360 and the pursuit of post-quantum algorithms demonstrate that Bitcoin is not only resilient but also proactive. By adopting practical measures, such as using modern wallets and migrating to quantum-resistant addresses, users can further protect themselves against potential threats.
Bitcoin’s future is not at risk—it is being carefully shaped to withstand any emerging technology, including quantum computing.
-
 @ eac63075:b4988b48
2024-11-09 17:57:27
@ eac63075:b4988b48
2024-11-09 17:57:27Based on a recent paper that included collaboration from renowned experts such as Lynn Alden, Steve Lee, and Ren Crypto Fish, we discuss in depth how Bitcoin's consensus is built, the main risks, and the complex dynamics of protocol upgrades.
Podcast https://www.fountain.fm/episode/wbjD6ntQuvX5u2G5BccC
Presentation https://gamma.app/docs/Analyzing-Bitcoin-Consensus-Risks-in-Protocol-Upgrades-p66axxjwaa37ksn
1. Introduction to Consensus in Bitcoin
Consensus in Bitcoin is the foundation that keeps the network secure and functional, allowing users worldwide to perform transactions in a decentralized manner without the need for intermediaries. Since its launch in 2009, Bitcoin is often described as an "immutable" system designed to resist changes, and it is precisely this resistance that ensures its security and stability.
The central idea behind consensus in Bitcoin is to create a set of acceptance rules for blocks and transactions, ensuring that all network participants agree on the transaction history. This prevents "double-spending," where the same bitcoin could be used in two simultaneous transactions, something that would compromise trust in the network.
Evolution of Consensus in Bitcoin
Over the years, consensus in Bitcoin has undergone several adaptations, and the way participants agree on changes remains a delicate process. Unlike traditional systems, where changes can be imposed from the top down, Bitcoin operates in a decentralized model where any significant change needs the support of various groups of stakeholders, including miners, developers, users, and large node operators.
Moreover, the update process is extremely cautious, as hasty changes can compromise the network's security. As a result, the philosophy of "don't fix what isn't broken" prevails, with improvements happening incrementally and only after broad consensus among those involved. This model can make progress seem slow but ensures that Bitcoin remains faithful to the principles of security and decentralization.
2. Technical Components of Consensus
Bitcoin's consensus is supported by a set of technical rules that determine what is considered a valid transaction and a valid block on the network. These technical aspects ensure that all nodes—the computers that participate in the Bitcoin network—agree on the current state of the blockchain. Below are the main technical components that form the basis of the consensus.
Validation of Blocks and Transactions
The validation of blocks and transactions is the central point of consensus in Bitcoin. A block is only considered valid if it meets certain criteria, such as maximum size, transaction structure, and the solving of the "Proof of Work" problem. The proof of work, required for a block to be included in the blockchain, is a computational process that ensures the block contains significant computational effort—protecting the network against manipulation attempts.
Transactions, in turn, need to follow specific input and output rules. Each transaction includes cryptographic signatures that prove the ownership of the bitcoins sent, as well as validation scripts that verify if the transaction conditions are met. This validation system is essential for network nodes to autonomously confirm that each transaction follows the rules.
Chain Selection
Another fundamental technical issue for Bitcoin's consensus is chain selection, which becomes especially important in cases where multiple versions of the blockchain coexist, such as after a network split (fork). To decide which chain is the "true" one and should be followed, the network adopts the criterion of the highest accumulated proof of work. In other words, the chain with the highest number of valid blocks, built with the greatest computational effort, is chosen by the network as the official one.
This criterion avoids permanent splits because it encourages all nodes to follow the same main chain, reinforcing consensus.
Soft Forks vs. Hard Forks
In the consensus process, protocol changes can happen in two ways: through soft forks or hard forks. These variations affect not only the protocol update but also the implications for network users:
-
Soft Forks: These are changes that are backward compatible. Only nodes that adopt the new update will follow the new rules, but old nodes will still recognize the blocks produced with these rules as valid. This compatibility makes soft forks a safer option for updates, as it minimizes the risk of network division.
-
Hard Forks: These are updates that are not backward compatible, requiring all nodes to update to the new version or risk being separated from the main chain. Hard forks can result in the creation of a new coin, as occurred with the split between Bitcoin and Bitcoin Cash in 2017. While hard forks allow for deeper changes, they also bring significant risks of network fragmentation.
These technical components form the base of Bitcoin's security and resilience, allowing the system to remain functional and immutable without losing the necessary flexibility to evolve over time.
3. Stakeholders in Bitcoin's Consensus
Consensus in Bitcoin is not decided centrally. On the contrary, it depends on the interaction between different groups of stakeholders, each with their motivations, interests, and levels of influence. These groups play fundamental roles in how changes are implemented or rejected on the network. Below, we explore the six main stakeholders in Bitcoin's consensus.
1. Economic Nodes
Economic nodes, usually operated by exchanges, custody providers, and large companies that accept Bitcoin, exert significant influence over consensus. Because they handle large volumes of transactions and act as a connection point between the Bitcoin ecosystem and the traditional financial system, these nodes have the power to validate or reject blocks and to define which version of the software to follow in case of a fork.
Their influence is proportional to the volume of transactions they handle, and they can directly affect which chain will be seen as the main one. Their incentive is to maintain the network's stability and security to preserve its functionality and meet regulatory requirements.
2. Investors
Investors, including large institutional funds and individual Bitcoin holders, influence consensus indirectly through their impact on the asset's price. Their buying and selling actions can affect Bitcoin's value, which in turn influences the motivation of miners and other stakeholders to continue investing in the network's security and development.
Some institutional investors have agreements with custodians that may limit their ability to act in network split situations. Thus, the impact of each investor on consensus can vary based on their ownership structure and how quickly they can react to a network change.
3. Media Influencers
Media influencers, including journalists, analysts, and popular personalities on social media, have a powerful role in shaping public opinion about Bitcoin and possible updates. These influencers can help educate the public, promote debates, and bring transparency to the consensus process.
On the other hand, the impact of influencers can be double-edged: while they can clarify complex topics, they can also distort perceptions by amplifying or minimizing change proposals. This makes them a force both of support and resistance to consensus.
4. Miners
Miners are responsible for validating transactions and including blocks in the blockchain. Through computational power (hashrate), they also exert significant influence over consensus decisions. In update processes, miners often signal their support for a proposal, indicating that the new version is safe to use. However, this signaling is not always definitive, and miners can change their position if they deem it necessary.
Their incentive is to maximize returns from block rewards and transaction fees, as well as to maintain the value of investments in their specialized equipment, which are only profitable if the network remains stable.
5. Protocol Developers
Protocol developers, often called "Core Developers," are responsible for writing and maintaining Bitcoin's code. Although they do not have direct power over consensus, they possess an informal veto power since they decide which changes are included in the main client (Bitcoin Core). This group also serves as an important source of technical knowledge, helping guide decisions and inform other stakeholders.
Their incentive lies in the continuous improvement of the network, ensuring security and decentralization. Many developers are funded by grants and sponsorships, but their motivations generally include a strong ideological commitment to Bitcoin's principles.
6. Users and Application Developers
This group includes people who use Bitcoin in their daily transactions and developers who build solutions based on the network, such as wallets, exchanges, and payment platforms. Although their power in consensus is less than that of miners or economic nodes, they play an important role because they are responsible for popularizing Bitcoin's use and expanding the ecosystem.
If application developers decide not to adopt an update, this can affect compatibility and widespread acceptance. Thus, they indirectly influence consensus by deciding which version of the protocol to follow in their applications.
These stakeholders are vital to the consensus process, and each group exerts influence according to their involvement, incentives, and ability to act in situations of change. Understanding the role of each makes it clearer how consensus is formed and why it is so difficult to make significant changes to Bitcoin.
4. Mechanisms for Activating Updates in Bitcoin
For Bitcoin to evolve without compromising security and consensus, different mechanisms for activating updates have been developed over the years. These mechanisms help coordinate changes among network nodes to minimize the risk of fragmentation and ensure that updates are implemented in an orderly manner. Here, we explore some of the main methods used in Bitcoin, their advantages and disadvantages, as well as historical examples of significant updates.
Flag Day
The Flag Day mechanism is one of the simplest forms of activating changes. In it, a specific date or block is determined as the activation moment, and all nodes must be updated by that point. This method does not involve prior signaling; participants simply need to update to the new software version by the established day or block.
-
Advantages: Simplicity and predictability are the main benefits of Flag Day, as everyone knows the exact activation date.
-
Disadvantages: Inflexibility can be a problem because there is no way to adjust the schedule if a significant part of the network has not updated. This can result in network splits if a significant number of nodes are not ready for the update.
An example of Flag Day was the Pay to Script Hash (P2SH) update in 2012, which required all nodes to adopt the change to avoid compatibility issues.
BIP34 and BIP9
BIP34 introduced a more dynamic process, in which miners increase the version number in block headers to signal the update. When a predetermined percentage of the last blocks is mined with this new version, the update is automatically activated. This model later evolved with BIP9, which allowed multiple updates to be signaled simultaneously through "version bits," each corresponding to a specific change.
-
Advantages: Allows the network to activate updates gradually, giving more time for participants to adapt.
-
Disadvantages: These methods rely heavily on miner support, which means that if a sufficient number of miners do not signal the update, it can be delayed or not implemented.
BIP9 was used in the activation of SegWit (BIP141) but faced challenges because some miners did not signal their intent to activate, leading to the development of new mechanisms.
User Activated Soft Forks (UASF) and User Resisted Soft Forks (URSF)
To increase the decision-making power of ordinary users, the concept of User Activated Soft Fork (UASF) was introduced, allowing node operators, not just miners, to determine consensus for a change. In this model, nodes set a date to start rejecting blocks that are not in compliance with the new update, forcing miners to adapt or risk having their blocks rejected by the network.
URSF, in turn, is a model where nodes reject blocks that attempt to adopt a specific update, functioning as resistance against proposed changes.
-
Advantages: UASF returns decision-making power to node operators, ensuring that changes do not depend solely on miners.
-
Disadvantages: Both UASF and URSF can generate network splits, especially in cases of strong opposition among different stakeholders.
An example of UASF was the activation of SegWit in 2017, where users supported activation independently of miner signaling, which ended up forcing its adoption.
BIP8 (LOT=True)
BIP8 is an evolution of BIP9, designed to prevent miners from indefinitely blocking a change desired by the majority of users and developers. BIP8 allows setting a parameter called "lockinontimeout" (LOT) as true, which means that if the update has not been fully signaled by a certain point, it is automatically activated.
-
Advantages: Ensures that changes with broad support among users are not blocked by miners who wish to maintain the status quo.
-
Disadvantages: Can lead to network splits if miners or other important stakeholders do not support the update.
Although BIP8 with LOT=True has not yet been used in Bitcoin, it is a proposal that can be applied in future updates if necessary.
These activation mechanisms have been essential for Bitcoin's development, allowing updates that keep the network secure and functional. Each method brings its own advantages and challenges, but all share the goal of preserving consensus and network cohesion.
5. Risks and Considerations in Consensus Updates
Consensus updates in Bitcoin are complex processes that involve not only technical aspects but also political, economic, and social considerations. Due to the network's decentralized nature, each change brings with it a set of risks that need to be carefully assessed. Below, we explore some of the main challenges and future scenarios, as well as the possible impacts on stakeholders.
Network Fragility with Alternative Implementations
One of the main risks associated with consensus updates is the possibility of network fragmentation when there are alternative software implementations. If an update is implemented by a significant group of nodes but rejected by others, a network split (fork) can occur. This creates two competing chains, each with a different version of the transaction history, leading to unpredictable consequences for users and investors.
Such fragmentation weakens Bitcoin because, by dividing hashing power (computing) and coin value, it reduces network security and investor confidence. A notable example of this risk was the fork that gave rise to Bitcoin Cash in 2017 when disagreements over block size resulted in a new chain and a new asset.
Chain Splits and Impact on Stakeholders
Chain splits are a significant risk in update processes, especially in hard forks. During a hard fork, the network is split into two separate chains, each with its own set of rules. This results in the creation of a new coin and leaves users with duplicated assets on both chains. While this may seem advantageous, in the long run, these splits weaken the network and create uncertainties for investors.
Each group of stakeholders reacts differently to a chain split:
-
Institutional Investors and ETFs: Face regulatory and compliance challenges because many of these assets are managed under strict regulations. The creation of a new coin requires decisions to be made quickly to avoid potential losses, which may be hampered by regulatory constraints.
-
Miners: May be incentivized to shift their computing power to the chain that offers higher profitability, which can weaken one of the networks.
-
Economic Nodes: Such as major exchanges and custody providers, have to quickly choose which chain to support, influencing the perceived value of each network.
Such divisions can generate uncertainties and loss of value, especially for institutional investors and those who use Bitcoin as a store of value.
Regulatory Impacts and Institutional Investors
With the growing presence of institutional investors in Bitcoin, consensus changes face new compliance challenges. Bitcoin ETFs, for example, are required to follow strict rules about which assets they can include and how chain split events should be handled. The creation of a new asset or migration to a new chain can complicate these processes, creating pressure for large financial players to quickly choose a chain, affecting the stability of consensus.
Moreover, decisions regarding forks can influence the Bitcoin futures and derivatives market, affecting perception and adoption by new investors. Therefore, the need to avoid splits and maintain cohesion is crucial to attract and preserve the confidence of these investors.
Security Considerations in Soft Forks and Hard Forks
While soft forks are generally preferred in Bitcoin for their backward compatibility, they are not without risks. Soft forks can create different classes of nodes on the network (updated and non-updated), which increases operational complexity and can ultimately weaken consensus cohesion. In a network scenario with fragmentation of node classes, Bitcoin's security can be affected, as some nodes may lose part of the visibility over updated transactions or rules.
In hard forks, the security risk is even more evident because all nodes need to adopt the new update to avoid network division. Experience shows that abrupt changes can create temporary vulnerabilities, in which malicious agents try to exploit the transition to attack the network.
Bounty Claim Risks and Attack Scenarios
Another risk in consensus updates are so-called "bounty claims"—accumulated rewards that can be obtained if an attacker manages to split or deceive a part of the network. In a conflict scenario, a group of miners or nodes could be incentivized to support a new update or create an alternative version of the software to benefit from these rewards.
These risks require stakeholders to carefully assess each update and the potential vulnerabilities it may introduce. The possibility of "bounty claims" adds a layer of complexity to consensus because each interest group may see a financial opportunity in a change that, in the long term, may harm network stability.
The risks discussed above show the complexity of consensus in Bitcoin and the importance of approaching it gradually and deliberately. Updates need to consider not only technical aspects but also economic and social implications, in order to preserve Bitcoin's integrity and maintain trust among stakeholders.
6. Recommendations for the Consensus Process in Bitcoin
To ensure that protocol changes in Bitcoin are implemented safely and with broad support, it is essential that all stakeholders adopt a careful and coordinated approach. Here are strategic recommendations for evaluating, supporting, or rejecting consensus updates, considering the risks and challenges discussed earlier, along with best practices for successful implementation.
1. Careful Evaluation of Proposal Maturity
Stakeholders should rigorously assess the maturity level of a proposal before supporting its implementation. Updates that are still experimental or lack a robust technical foundation can expose the network to unnecessary risks. Ideally, change proposals should go through an extensive testing phase, have security audits, and receive review and feedback from various developers and experts.
2. Extensive Testing in Secure and Compatible Networks
Before an update is activated on the mainnet, it is essential to test it on networks like testnet and signet, and whenever possible, on other compatible networks that offer a safe and controlled environment to identify potential issues. Testing on networks like Litecoin was fundamental for the safe launch of innovations like SegWit and the Lightning Network, allowing functionalities to be validated on a lower-impact network before being implemented on Bitcoin.
The Liquid Network, developed by Blockstream, also plays an important role as an experimental network for new proposals, such as OP_CAT. By adopting these testing environments, stakeholders can mitigate risks and ensure that the update is reliable and secure before being adopted by the main network.
3. Importance of Stakeholder Engagement
The success of a consensus update strongly depends on the active participation of all stakeholders. This includes economic nodes, miners, protocol developers, investors, and end users. Lack of participation can lead to inadequate decisions or even future network splits, which would compromise Bitcoin's security and stability.
4. Key Questions for Evaluating Consensus Proposals
To assist in decision-making, each group of stakeholders should consider some key questions before supporting a consensus change:
- Does the proposal offer tangible benefits for Bitcoin's security, scalability, or usability?
- Does it maintain backward compatibility or introduce the risk of network split?
- Are the implementation requirements clear and feasible for each group involved?
- Are there clear and aligned incentives for all stakeholder groups to accept the change?
5. Coordination and Timing in Implementations
Timing is crucial. Updates with short activation windows can force a split because not all nodes and miners can update simultaneously. Changes should be planned with ample deadlines to allow all stakeholders to adjust their systems, avoiding surprises that could lead to fragmentation.
Mechanisms like soft forks are generally preferable to hard forks because they allow a smoother transition. Opting for backward-compatible updates when possible facilitates the process and ensures that nodes and miners can adapt without pressure.
6. Continuous Monitoring and Re-evaluation
After an update, it's essential to monitor the network to identify problems or side effects. This continuous process helps ensure cohesion and trust among all participants, keeping Bitcoin as a secure and robust network.
These recommendations, including the use of secure networks for extensive testing, promote a collaborative and secure environment for Bitcoin's consensus process. By adopting a deliberate and strategic approach, stakeholders can preserve Bitcoin's value as a decentralized and censorship-resistant network.
7. Conclusion
Consensus in Bitcoin is more than a set of rules; it's the foundation that sustains the network as a decentralized, secure, and reliable system. Unlike centralized systems, where decisions can be made quickly, Bitcoin requires a much more deliberate and cooperative approach, where the interests of miners, economic nodes, developers, investors, and users must be considered and harmonized. This governance model may seem slow, but it is fundamental to preserving the resilience and trust that make Bitcoin a global store of value and censorship-resistant.
Consensus updates in Bitcoin must balance the need for innovation with the preservation of the network's core principles. The development process of a proposal needs to be detailed and rigorous, going through several testing stages, such as in testnet, signet, and compatible networks like Litecoin and Liquid Network. These networks offer safe environments for proposals to be analyzed and improved before being launched on the main network.
Each proposed change must be carefully evaluated regarding its maturity, impact, backward compatibility, and support among stakeholders. The recommended key questions and appropriate timing are critical to ensure that an update is adopted without compromising network cohesion. It's also essential that the implementation process is continuously monitored and re-evaluated, allowing adjustments as necessary and minimizing the risk of instability.
By following these guidelines, Bitcoin's stakeholders can ensure that the network continues to evolve safely and robustly, maintaining user trust and further solidifying its role as one of the most resilient and innovative digital assets in the world. Ultimately, consensus in Bitcoin is not just a technical issue but a reflection of its community and the values it represents: security, decentralization, and resilience.
8. Links
Whitepaper: https://github.com/bitcoin-cap/bcap
Youtube (pt-br): https://www.youtube.com/watch?v=rARycAibl9o&list=PL-qnhF0qlSPkfhorqsREuIu4UTbF0h4zb
-
-
 @ 20e17dd0:2ae504d7
2025-02-01 21:14:41
@ 20e17dd0:2ae504d7
2025-02-01 21:14:411. Hardware Selection
It is important to select adequately the hardware that will be used to build your Node. The Node will be running 24h /7 days and will countain your lightning channels. It is important to use high quality hardware and spend the extra dollars for it.
At the time of building my Node, there was a shortage of Raspberry Pi and I was looking for an optimal alternative. I have decided to go ahead and purchase a used Mac Mini (late 2012).
It is recommended NOT to purchase a Mac Mini newer than 2012 (i.e 2014 and up) because Apple started to solder the RAM to the Logic Board after 2012. The Mac Mini Late 2012 is the last model that is fully customizable with SSD and RAM upgrades.
Here is the list of hardware that will be used in this build:
- 2 x 8G DDR3L Sodim 1600Mhz 1.35V
- 1 x Mac Mini (Late 2012) 2.5Ghz
- 1 x Samsung Evo 870 1Tb SSD ^
^ Note: As discussed earlier, it is important to select hardware of quality. I had initially purchased a low cost 2Tb SSD but it failed while trying to download the Bitcoin blockchain.
2. Hardware Upgrade
To facilitate the upgrade of the hardware, you will need the proper tools to remove some T6 & T8 screws.
Here are the steps to dismount the few components of the Mac Mini to upgrade the hardware:
- Unplug the Mac Mini.
- Turn it upside down with the black cover facing up.
-
Put your thumbs in the 2 grooves of the cover and turn the piece counterclockwise.

-
Remove the cover.
- Remove 3 x T6 screws holding the fan.

- Lift the fan and disconnect the connector by pulling gently straight up the wires.
- Remove 1x T6 screw at the bottom of the shroud (black plastic piece on the left of the fan).

-
Remove the shroud by holding the top right part with your fingers and turning it clockwise.

-
Remove 4 x T8 screws of the grill WIFI cover.

- The top of the grill is mounted under the Mac Mini case. Lift gently the bottom of the grill and pull towards yourself to remove the grill.
- Move the grill aside, you do not have to disconnect the WIFI sensor, just be careful.
2.1 Upgrading the RAM
The RAM is visible and accessible from the moment you remove the cover. Simply release each RAM by releasing the clips on the side. Once disengaged, the RAM will spring in a 45-degree angle. Remove it and put back the upgraded RAM at a 45 degree angle and push it down for it to clip.
2.2 Upgrading the SSD
It is important to note that the Mac Mini has 2 SSD bay. They are referred to as the “upper bay” and “lower bay”. Since we have flipped the Mac Mini upside down to remove the bottom cover, the “upper bay” is located under the “lower bay”.
The “upper bay” is mounted with an expansion kit that holds the SSD in position whereas the “lower bay” SSD is simply resting on top of the “upper bay” SSD.
One important aspect is that the connecting cables for the “lower bay” and “upper bay” SSD are not the same. The “upper bay” SSD connects on the logic board on the right and the “lower bay” SSD cable connects on the left. Removing the “upper bay” SSD requires removing the logic board therefore requires more work. It is recommended to install the new SSD in the “lower” bay. Here are the 2 scenarios:
1.Your Mac Mini has already a Hard Drive installed in the “lower” bay. In that case insert a credit card under the HD and gently pry it upwards. You will be able to slide it out of the bay. The reason to pry it gently is because since there is no “upper” bay drive, The HD is being held in the air by 2 screws on the side that are aligned in 2 holes in the Mac Mini case. Once the HD is removed, transfer the connecting cable and the 2 screws to the new SSD. To put back the new SSD, it is easier to rotate the Mac Mini 90 degree and have the mounting holes at the bottom and use the gravity to get the 2 mounting screws in the holes. After, connect the connector to the logic board.
- Your Mac Mini has already a Hard Drive installed in the “upper bay”? Leave it there, you do not need mounting screws, but you need a new connecting cable. You will have to buy a “lower bay connector”. Once installed on the SSD, slide the SSD on top of the original one. The connector will plug on the logic board on the left of the “upper bay” SSD connector.
A good preparation would be to go in “Disk Utility” menu on MacOS and search for “upper” or “lower” position before starting to disassemble.
Reassemble everything and you are done.
-
 @ a95c6243:d345522c
2025-01-31 20:02:25
@ a95c6243:d345522c
2025-01-31 20:02:25Im Augenblick wird mit größter Intensität, großer Umsicht \ das deutsche Volk belogen. \ Olaf Scholz im FAZ-Interview
Online-Wahlen stärken die Demokratie, sind sicher, und 61 Prozent der Wahlberechtigten sprechen sich für deren Einführung in Deutschland aus. Das zumindest behauptet eine aktuelle Umfrage, die auch über die Agentur Reuters Verbreitung in den Medien gefunden hat. Demnach würden außerdem 45 Prozent der Nichtwähler bei der Bundestagswahl ihre Stimme abgeben, wenn sie dies zum Beispiel von Ihrem PC, Tablet oder Smartphone aus machen könnten.
Die telefonische Umfrage unter gut 1000 wahlberechtigten Personen sei repräsentativ, behauptet der Auftraggeber – der Digitalverband Bitkom. Dieser präsentiert sich als eingetragener Verein mit einer beeindruckenden Liste von Mitgliedern, die Software und IT-Dienstleistungen anbieten. Erklärtes Vereinsziel ist es, «Deutschland zu einem führenden Digitalstandort zu machen und die digitale Transformation der deutschen Wirtschaft und Verwaltung voranzutreiben».
Durchgeführt hat die Befragung die Bitkom Servicegesellschaft mbH, also alles in der Familie. Die gleiche Erhebung hatte der Verband übrigens 2021 schon einmal durchgeführt. Damals sprachen sich angeblich sogar 63 Prozent für ein derartiges «Demokratie-Update» aus – die Tendenz ist demgemäß fallend. Dennoch orakelt mancher, der Gang zur Wahlurne gelte bereits als veraltet.
Die spanische Privat-Uni mit Globalisten-Touch, IE University, berichtete Ende letzten Jahres in ihrer Studie «European Tech Insights», 67 Prozent der Europäer befürchteten, dass Hacker Wahlergebnisse verfälschen könnten. Mehr als 30 Prozent der Befragten glaubten, dass künstliche Intelligenz (KI) bereits Wahlentscheidungen beeinflusst habe. Trotzdem würden angeblich 34 Prozent der unter 35-Jährigen einer KI-gesteuerten App vertrauen, um in ihrem Namen für politische Kandidaten zu stimmen.
Wie dauerhaft wird wohl das Ergebnis der kommenden Bundestagswahl sein? Diese Frage stellt sich angesichts der aktuellen Entwicklung der Migrations-Debatte und der (vorübergehend) bröckelnden «Brandmauer» gegen die AfD. Das «Zustrombegrenzungsgesetz» der Union hat das Parlament heute Nachmittag überraschenderweise abgelehnt. Dennoch muss man wohl kein ausgesprochener Pessimist sein, um zu befürchten, dass die Entscheidungen der Bürger von den selbsternannten Verteidigern der Demokratie künftig vielleicht nicht respektiert werden, weil sie nicht gefallen.
Bundesweit wird jetzt zu «Brandmauer-Demos» aufgerufen, die CDU gerät unter Druck und es wird von Übergriffen auf Parteibüros und Drohungen gegen Mitarbeiter berichtet. Sicherheitsbehörden warnen vor Eskalationen, die Polizei sei «für ein mögliches erhöhtes Aufkommen von Straftaten gegenüber Politikern und gegen Parteigebäude sensibilisiert».
Der Vorwand «unzulässiger Einflussnahme» auf Politik und Wahlen wird als Argument schon seit einiger Zeit aufgebaut. Der Manipulation schuldig befunden wird neben Putin und Trump auch Elon Musk, was lustigerweise ausgerechnet Bill Gates gerade noch einmal bekräftigt und als «völlig irre» bezeichnet hat. Man stelle sich die Diskussionen um die Gültigkeit von Wahlergebnissen vor, wenn es Online-Verfahren zur Stimmabgabe gäbe. In der Schweiz wird «E-Voting» seit einigen Jahren getestet, aber wohl bisher mit wenig Erfolg.
Die politische Brandstiftung der letzten Jahre zahlt sich immer mehr aus. Anstatt dringende Probleme der Menschen zu lösen – zu denen auch in Deutschland die weit verbreitete Armut zählt –, hat die Politik konsequent polarisiert und sich auf Ausgrenzung und Verhöhnung großer Teile der Bevölkerung konzentriert. Basierend auf Ideologie und Lügen werden abweichende Stimmen unterdrückt und kriminalisiert, nicht nur und nicht erst in diesem Augenblick. Die nächsten Wochen dürften ausgesprochen spannend werden.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ eac63075:b4988b48
2024-10-26 22:14:19
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ a95c6243:d345522c
2025-01-24 20:59:01
@ a95c6243:d345522c
2025-01-24 20:59:01Menschen tun alles, egal wie absurd, \ um ihrer eigenen Seele nicht zu begegnen. \ Carl Gustav Jung
«Extremer Reichtum ist eine Gefahr für die Demokratie», sagen über die Hälfte der knapp 3000 befragten Millionäre aus G20-Staaten laut einer Umfrage der «Patriotic Millionaires». Ferner stellte dieser Zusammenschluss wohlhabender US-Amerikaner fest, dass 63 Prozent jener Millionäre den Einfluss von Superreichen auf US-Präsident Trump als Bedrohung für die globale Stabilität ansehen.
Diese Besorgnis haben 370 Millionäre und Milliardäre am Dienstag auch den in Davos beim WEF konzentrierten Privilegierten aus aller Welt übermittelt. In einem offenen Brief forderten sie die «gewählten Führer» auf, die Superreichen – also sie selbst – zu besteuern, um «die zersetzenden Auswirkungen des extremen Reichtums auf unsere Demokratien und die Gesellschaft zu bekämpfen». Zum Beispiel kontrolliere eine handvoll extrem reicher Menschen die Medien, beeinflusse die Rechtssysteme in unzulässiger Weise und verwandele Recht in Unrecht.
Schon 2019 beanstandete der bekannte Historiker und Schriftsteller Ruthger Bregman an einer WEF-Podiumsdiskussion die Steuervermeidung der Superreichen. Die elitäre Veranstaltung bezeichnete er als «Feuerwehr-Konferenz, bei der man nicht über Löschwasser sprechen darf.» Daraufhin erhielt Bregman keine Einladungen nach Davos mehr. Auf seine Aussagen machte der Schweizer Aktivist Alec Gagneux aufmerksam, der sich seit Jahrzehnten kritisch mit dem WEF befasst. Ihm wurde kürzlich der Zutritt zu einem dreiteiligen Kurs über das WEF an der Volkshochschule Region Brugg verwehrt.
Nun ist die Erkenntnis, dass mit Geld politischer Einfluss einhergeht, alles andere als neu. Und extremer Reichtum macht die Sache nicht wirklich besser. Trotzdem hat man über Initiativen wie Patriotic Millionaires oder Taxmenow bisher eher selten etwas gehört, obwohl es sie schon lange gibt. Auch scheint es kein Problem, wenn ein Herr Gates fast im Alleingang versucht, globale Gesundheits-, Klima-, Ernährungs- oder Bevölkerungspolitik zu betreiben – im Gegenteil. Im Jahr, als der Milliardär Donald Trump zum zweiten Mal ins Weiße Haus einzieht, ist das Echo in den Gesinnungsmedien dagegen enorm – und uniform, wer hätte das gedacht.
Der neue US-Präsident hat jedoch «Davos geerdet», wie Achgut es nannte. In seiner kurzen Rede beim Weltwirtschaftsforum verteidigte er seine Politik und stellte klar, er habe schlicht eine «Revolution des gesunden Menschenverstands» begonnen. Mit deutlichen Worten sprach er unter anderem von ersten Maßnahmen gegen den «Green New Scam», und von einem «Erlass, der jegliche staatliche Zensur beendet»:
«Unsere Regierung wird die Äußerungen unserer eigenen Bürger nicht mehr als Fehlinformation oder Desinformation bezeichnen, was die Lieblingswörter von Zensoren und derer sind, die den freien Austausch von Ideen und, offen gesagt, den Fortschritt verhindern wollen.»
Wie der «Trumpismus» letztlich einzuordnen ist, muss jeder für sich selbst entscheiden. Skepsis ist definitiv angebracht, denn «einer von uns» sind weder der Präsident noch seine auserwählten Teammitglieder. Ob sie irgendeinen Sumpf trockenlegen oder Staatsverbrechen aufdecken werden oder was aus WHO- und Klimaverträgen wird, bleibt abzuwarten.
Das WHO-Dekret fordert jedenfalls die Übertragung der Gelder auf «glaubwürdige Partner», die die Aktivitäten übernehmen könnten. Zufällig scheint mit «Impfguru» Bill Gates ein weiterer Harris-Unterstützer kürzlich das Lager gewechselt zu haben: Nach einem gemeinsamen Abendessen zeigte er sich «beeindruckt» von Trumps Interesse an der globalen Gesundheit.
Mit dem Projekt «Stargate» sind weitere dunkle Wolken am Erwartungshorizont der Fangemeinde aufgezogen. Trump hat dieses Joint Venture zwischen den Konzernen OpenAI, Oracle, und SoftBank als das «größte KI-Infrastrukturprojekt der Geschichte» angekündigt. Der Stein des Anstoßes: Oracle-CEO Larry Ellison, der auch Fan von KI-gestützter Echtzeit-Überwachung ist, sieht einen weiteren potenziellen Einsatz der künstlichen Intelligenz. Sie könne dazu dienen, Krebserkrankungen zu erkennen und individuelle mRNA-«Impfstoffe» zur Behandlung innerhalb von 48 Stunden zu entwickeln.
Warum bitte sollten sich diese superreichen «Eliten» ins eigene Fleisch schneiden und direkt entgegen ihren eigenen Interessen handeln? Weil sie Menschenfreunde, sogenannte Philanthropen sind? Oder vielleicht, weil sie ein schlechtes Gewissen haben und ihre Schuld kompensieren müssen? Deswegen jedenfalls brauchen «Linke» laut Robert Willacker, einem deutschen Politikberater mit brasilianischen Wurzeln, rechte Parteien – ein ebenso überraschender wie humorvoller Erklärungsansatz.
Wenn eine Krähe der anderen kein Auge aushackt, dann tut sie das sich selbst noch weniger an. Dass Millionäre ernsthaft ihre eigene Besteuerung fordern oder Machteliten ihren eigenen Einfluss zugunsten anderer einschränken würden, halte ich für sehr unwahrscheinlich. So etwas glaube ich erst, wenn zum Beispiel die Rüstungsindustrie sich um Friedensverhandlungen bemüht, die Pharmalobby sich gegen institutionalisierte Korruption einsetzt, Zentralbanken ihre CBDC-Pläne für Bitcoin opfern oder der ÖRR die Abschaffung der Rundfunkgebühren fordert.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ b17fccdf:b7211155
2025-02-01 18:41:27
@ b17fccdf:b7211155
2025-02-01 18:41:27Next new resources about the MiniBolt guide have been released:
- 🆕 Roadmap: LINK
- 🆕 Dynamic Network map: LINK
- 🆕 Nostr community: LINK < ~ REMOVE the "[]" symbols from the URL (naddr...) to access
- 🆕 Linktr FOSS (UC) by Gzuuus: LINK
- 🆕 Donate webpage: 🚾 Clearnet LINK || 🧅 Onion LINK
- 🆕 Contact email: hello@minibolt.info
Enjoy it MiniBolter! 💙
-
 @ c631e267:c2b78d3e
2025-01-18 09:34:51
@ c631e267:c2b78d3e
2025-01-18 09:34:51Die grauenvollste Aussicht ist die der Technokratie – \ einer kontrollierenden Herrschaft, \ die durch verstümmelte und verstümmelnde Geister ausgeübt wird. \ Ernst Jünger
«Davos ist nicht mehr sexy», das Weltwirtschaftsforum (WEF) mache Davos kaputt, diese Aussagen eines Einheimischen las ich kürzlich in der Handelszeitung. Während sich einige vor Ort enorm an der «teuersten Gewerbeausstellung der Welt» bereicherten, würden die negativen Begleiterscheinungen wie Wohnungsnot und Niedergang der lokalen Wirtschaft immer deutlicher.
Nächsten Montag beginnt in dem Schweizer Bergdorf erneut ein Jahrestreffen dieses elitären Clubs der Konzerne, bei dem man mit hochrangigen Politikern aus aller Welt und ausgewählten Vertretern der Systemmedien zusammenhocken wird. Wie bereits in den vergangenen vier Jahren wird die Präsidentin der EU-Kommission, Ursula von der Leyen, in Begleitung von Klaus Schwab ihre Grundsatzansprache halten.
Der deutsche WEF-Gründer hatte bei dieser Gelegenheit immer höchst lobende Worte für seine Landsmännin: 2021 erklärte er sich «stolz, dass Europa wieder unter Ihrer Führung steht» und 2022 fand er es bemerkenswert, was sie erreicht habe angesichts des «erstaunlichen Wandels», den die Welt in den vorangegangenen zwei Jahren erlebt habe; es gebe nun einen «neuen europäischen Geist».
Von der Leyens Handeln während der sogenannten Corona-«Pandemie» lobte Schwab damals bereits ebenso, wie es diese Woche das Karlspreis-Direktorium tat, als man der Beschuldigten im Fall Pfizergate die diesjährige internationale Auszeichnung «für Verdienste um die europäische Einigung» verlieh. Außerdem habe sie die EU nicht nur gegen den «Aggressor Russland», sondern auch gegen die «innere Bedrohung durch Rassisten und Demagogen» sowie gegen den Klimawandel verteidigt.
Jene Herausforderungen durch «Krisen epochalen Ausmaßes» werden indes aus dem Umfeld des WEF nicht nur herbeigeredet – wie man alljährlich zur Zeit des Davoser Treffens im Global Risks Report nachlesen kann, der zusammen mit dem Versicherungskonzern Zurich erstellt wird. Seit die Globalisten 2020/21 in der Praxis gesehen haben, wie gut eine konzertierte und konsequente Angst-Kampagne funktionieren kann, geht es Schlag auf Schlag. Sie setzen alles daran, Schwabs goldenes Zeitfenster des «Great Reset» zu nutzen.
Ziel dieses «großen Umbruchs» ist die totale Kontrolle der Technokraten über die Menschen unter dem Deckmantel einer globalen Gesundheitsfürsorge. Wie aber könnte man so etwas erreichen? Ein Mittel dazu ist die «kreative Zerstörung». Weitere unabdingbare Werkzeug sind die Einbindung, ja Gleichschaltung der Medien und der Justiz.
Ein «Great Mental Reset» sei die Voraussetzung dafür, dass ein Großteil der Menschen Einschränkungen und Manipulationen wie durch die Corona-Maßnahmen praktisch kritik- und widerstandslos hinnehme, sagt der Mediziner und Molekulargenetiker Michael Nehls. Er meint damit eine regelrechte Umprogrammierung des Gehirns, wodurch nach und nach unsere Individualität und unser soziales Bewusstsein eliminiert und durch unreflektierten Konformismus ersetzt werden.
Der aktuelle Zustand unserer Gesellschaften ist auch für den Schweizer Rechtsanwalt Philipp Kruse alarmierend. Durch den Umgang mit der «Pandemie» sieht er die Grundlagen von Recht und Vernunft erschüttert, die Rechtsstaatlichkeit stehe auf dem Prüfstand. Seiner dringenden Mahnung an alle Bürger, die Prinzipien von Recht und Freiheit zu verteidigen, kann ich mich nur anschließen.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ a95c6243:d345522c
2025-01-13 10:09:57
@ a95c6243:d345522c
2025-01-13 10:09:57Ich begann, Social Media aufzubauen, \ um den Menschen eine Stimme zu geben. \ Mark Zuckerberg
Sind euch auch die Tränen gekommen, als ihr Mark Zuckerbergs Wendehals-Deklaration bezüglich der Meinungsfreiheit auf seinen Portalen gehört habt? Rührend, oder? Während er früher die offensichtliche Zensur leugnete und später die Regierung Biden dafür verantwortlich machte, will er nun angeblich «die Zensur auf unseren Plattformen drastisch reduzieren».
«Purer Opportunismus» ob des anstehenden Regierungswechsels wäre als Klassifizierung viel zu kurz gegriffen. Der jetzige Schachzug des Meta-Chefs ist genauso Teil einer kühl kalkulierten Business-Strategie, wie es die 180 Grad umgekehrte Praxis vorher war. Social Media sind ein höchst lukratives Geschäft. Hinzu kommt vielleicht noch ein bisschen verkorkstes Ego, weil derartig viel Einfluss und Geld sicher auch auf die Psyche schlagen. Verständlich.
«Es ist an der Zeit, zu unseren Wurzeln der freien Meinungsäußerung auf Facebook und Instagram zurückzukehren. Ich begann, Social Media aufzubauen, um den Menschen eine Stimme zu geben», sagte Zuckerberg.
Welche Wurzeln? Hat der Mann vergessen, dass er von der Überwachung, dem Ausspionieren und dem Ausverkauf sämtlicher Daten und digitaler Spuren sowie der Manipulation seiner «Kunden» lebt? Das ist knallharter Kommerz, nichts anderes. Um freie Meinungsäußerung geht es bei diesem Geschäft ganz sicher nicht, und das war auch noch nie so. Die Wurzeln von Facebook liegen in einem Projekt des US-Militärs mit dem Namen «LifeLog». Dessen Ziel war es, «ein digitales Protokoll vom Leben eines Menschen zu erstellen».
Der Richtungswechsel kommt allerdings nicht überraschend. Schon Anfang Dezember hatte Meta-Präsident Nick Clegg von «zu hoher Fehlerquote bei der Moderation» von Inhalten gesprochen. Bei der Gelegenheit erwähnte er auch, dass Mark sehr daran interessiert sei, eine aktive Rolle in den Debatten über eine amerikanische Führungsrolle im technologischen Bereich zu spielen.
Während Milliardärskollege und Big Tech-Konkurrent Elon Musk bereits seinen Posten in der kommenden Trump-Regierung in Aussicht hat, möchte Zuckerberg also nicht nur seine Haut retten – Trump hatte ihn einmal einen «Feind des Volkes» genannt und ihm lebenslange Haft angedroht –, sondern am liebsten auch mitspielen. KI-Berater ist wohl die gewünschte Funktion, wie man nach einem Treffen Trump-Zuckerberg hörte. An seine Verhaftung dachte vermutlich auch ein weiterer Multimilliardär mit eigener Social Media-Plattform, Pavel Durov, als er Zuckerberg jetzt kritisierte und gleichzeitig warnte.
Politik und Systemmedien drehen jedenfalls durch – was zu viel ist, ist zu viel. Etwas weniger Zensur und mehr Meinungsfreiheit würden die Freiheit der Bürger schwächen und seien potenziell vernichtend für die Menschenrechte. Zuckerberg setze mit dem neuen Kurs die Demokratie aufs Spiel, das sei eine «Einladung zum nächsten Völkermord», ernsthaft. Die Frage sei, ob sich die EU gegen Musk und Zuckerberg behaupten könne, Brüssel müsse jedenfalls hart durchgreifen.
Auch um die Faktenchecker macht man sich Sorgen. Für die deutsche Nachrichtenagentur dpa und die «Experten» von Correctiv, die (noch) Partner für Fact-Checking-Aktivitäten von Facebook sind, sei das ein «lukratives Geschäftsmodell». Aber möglicherweise werden die Inhalte ohne diese vermeintlichen Korrektoren ja sogar besser. Anders als Meta wollen jedoch Scholz, Faeser und die Tagesschau keine Fehler zugeben und zum Beispiel Correctiv-Falschaussagen einräumen.
Bei derlei dramatischen Befürchtungen wundert es nicht, dass der öffentliche Plausch auf X zwischen Elon Musk und AfD-Chefin Alice Weidel von 150 EU-Beamten überwacht wurde, falls es irgendwelche Rechtsverstöße geben sollte, die man ihnen ankreiden könnte. Auch der Deutsche Bundestag war wachsam. Gefunden haben dürften sie nichts. Das Ganze war eher eine Show, viel Wind wurde gemacht, aber letztlich gab es nichts als heiße Luft.
Das Anbiedern bei Donald Trump ist indes gerade in Mode. Die Weltgesundheitsorganisation (WHO) tut das auch, denn sie fürchtet um Spenden von über einer Milliarde Dollar. Eventuell könnte ja Elon Musk auch hier künftig aushelfen und der Organisation sowie deren größtem privaten Förderer, Bill Gates, etwas unter die Arme greifen. Nachdem Musks KI-Projekt xAI kürzlich von BlackRock & Co. sechs Milliarden eingestrichen hat, geht da vielleicht etwas.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ a95c6243:d345522c
2025-01-03 20:26:47
@ a95c6243:d345522c
2025-01-03 20:26:47Was du bist hängt von drei Faktoren ab: \ Was du geerbt hast, \ was deine Umgebung aus dir machte \ und was du in freier Wahl \ aus deiner Umgebung und deinem Erbe gemacht hast. \ Aldous Huxley
Das brave Mitmachen und Mitlaufen in einem vorgegebenen, recht engen Rahmen ist gewiss nicht neu, hat aber gerade wieder mal Konjunktur. Dies kann man deutlich beobachten, eigentlich egal, in welchem gesellschaftlichen Bereich man sich umschaut. Individualität ist nur soweit angesagt, wie sie in ein bestimmtes Schema von «Diversität» passt, und Freiheit verkommt zur Worthülse – nicht erst durch ein gewisses Buch einer gewissen ehemaligen Regierungschefin.
Erklärungsansätze für solche Entwicklungen sind bekannt, und praktisch alle haben etwas mit Massenpsychologie zu tun. Der Herdentrieb, also der Trieb der Menschen, sich – zum Beispiel aus Unsicherheit oder Bequemlichkeit – lieber der Masse anzuschließen als selbstständig zu denken und zu handeln, ist einer der Erklärungsversuche. Andere drehen sich um Macht, Propaganda, Druck und Angst, also den gezielten Einsatz psychologischer Herrschaftsinstrumente.
Aber wollen die Menschen überhaupt Freiheit? Durch Gespräche im privaten Umfeld bin ich diesbezüglich in der letzten Zeit etwas skeptisch geworden. Um die Jahreswende philosophiert man ja gerne ein wenig über das Erlebte und über die Erwartungen für die Zukunft. Dabei hatte ich hin und wieder den Eindruck, die totalitären Anwandlungen unserer «Repräsentanten» kämen manchen Leuten gerade recht.
«Desinformation» ist so ein brisantes Thema. Davor müsse man die Menschen doch schützen, hörte ich. Jemand müsse doch zum Beispiel diese ganzen merkwürdigen Inhalte in den Social Media filtern – zur Ukraine, zum Klima, zu Gesundheitsthemen oder zur Migration. Viele wüssten ja gar nicht einzuschätzen, was richtig und was falsch ist, sie bräuchten eine Führung.
Freiheit bedingt Eigenverantwortung, ohne Zweifel. Eventuell ist es einigen tatsächlich zu anspruchsvoll, die Verantwortung für das eigene Tun und Lassen zu übernehmen. Oder die persönliche Freiheit wird nicht als ausreichend wertvolles Gut angesehen, um sich dafür anzustrengen. In dem Fall wäre die mangelnde Selbstbestimmung wohl das kleinere Übel. Allerdings fehlt dann gemäß Aldous Huxley ein Teil der Persönlichkeit. Letztlich ist natürlich alles eine Frage der Abwägung.
Sind viele Menschen möglicherweise schon so «eingenordet», dass freiheitliche Ambitionen gar nicht für eine ganze Gruppe, ein Kollektiv, verfolgt werden können? Solche Gedanken kamen mir auch, als ich mir kürzlich diverse Talks beim viertägigen Hacker-Kongress des Chaos Computer Clubs (38C3) anschaute. Ich war nicht nur überrascht, sondern reichlich erschreckt angesichts der in weiten Teilen mainstream-geformten Inhalte, mit denen ein dankbares Publikum beglückt wurde. Wo ich allgemein hellere Köpfe erwartet hatte, fand ich Konformismus und enthusiastisch untermauerte Narrative.
Gibt es vielleicht so etwas wie eine Herdenimmunität gegen Indoktrination? Ich denke, ja, zumindest eine gestärkte Widerstandsfähigkeit. Was wir brauchen, sind etwas gesunder Menschenverstand, offene Informationskanäle und der Mut, sich freier auch zwischen den Herden zu bewegen. Sie tun das bereits, aber sagen Sie es auch dieses Jahr ruhig weiter.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ fe41d17e:28df7452
2025-02-02 13:04:38
@ fe41d17e:28df7452
2025-02-02 13:04:38Um es vorab klarzustellen, die einzigen Gesetze an die du dich wirklich halten musst sind die Naturgesetze, es ist deine eigene Entscheidung ob du einer einseitig vom Staat beschlossenen Auflage zustimmst oder nicht, solange du bereit bist, falls du erwischt wirst, die Konsequenzen über dich ergehen zu lassen.
Wenn du diese Unterdrückung nicht mehr haben möchtest braucht es eine Revolution um den Staat irrelevant werden zu lassen und um ihm seine Grundlage (das Geld) zu entziehen ohne dabei wie er selbst zu unmoralischen Methoden zu greifen.
Diese Revolution nennt sich Agorismus, sie wird dich unabhängig vom Staat machen und den Staat langfristig schwach/überflüssig werden lassen sobald es dir genug Leute gleichtun.
Die Revolution wird nicht leicht, sie wird dir nicht die sofortige Genugtuung verschaffen, die du möglicherweise empfindest, wenn du einen Zettel in die Wahlurne wirfst und dabei das Gefühl hast, etwas verändert zu haben. Eigentlich hast du nur denselben Leuten Macht verliehen, die seit Jahrhunderten die Politiker kontrollieren, dich ausrauben und unterdrücken. Garnichts hast du damit verändert.
Es wird schwierig werden. Es wird Eigeninitiative und Veränderungen in deinem Leben erfordern. Es wird ein zermürbender, unbefriedigender Weg sein, den viele als zu hart bezeichnen werden. Es wird Jahre über Jahre dauern, in denen die Leute dich dafür schief ansehen und du kaum Anerkennung bekommen wirst.
Hier ein paar wichtige Punkte um dich mit Agorismus vertraut zu machen:
-Wenn du bereits ein Libertärer bist, lies zuerst „Das neue Libertäre Manifest“ von Samuel Edward Konkin III. Es hat nur 30 Seiten, und wenn du damit nicht zumindest deinen Horizont erweitern kannst, dann kannst du genauso gut eine britische Flagge in Amerika schwenken, Tribut zollen und einen König fordern.
-Wenn du kein Libertärer bist, lies „Eine neue Freiheit: das libertäre Manifest“ von Murray Rothbard und anschließend „Das neue Libertäre Manifest“ von SEK3.
-Konzentriere dich in deinem Leben darauf, weniger bis keine Steuern zu zahlen.
-Finde Alternativen zum Fiatgeld und sei deine eigene Bank.
-Finde lokale Quellen für Lebensmittel und Produkte.
-Handel P2P auf freien Märkten.
-Suche nach Lösungen, die auf Dezentralisierung ausgerichtet sind.
-Baue eine gewisse Menge an Lebensmitteln an, auch wenn es nur Mikrogrün ist. Dafür sind keine großen Flächen erforderlich und du kannst diese gegen andere Lebensmittel eintauschen.
-Baue dein eigenes Unternehmen außerhalb von Konzernstrukturen auf.
-Konzentriere dich auf den Handel mit anderen Agoristen.
-Nutze jede Gelegenheit um deine Verachtung gegenüber dem Staat zu äußern.
-Verbreite Agorismus.
-Beschaffe dir Waffen.
-Vertraue nur agoristischen Medien, die unpolitisch sind. Denn jeder Journalist, der dich ermutigt, zu wählen oder innerhalb des Systems zu arbeiten, könnte gekauft oder kontrolliert sein. Agoristen, die behaupten, dass Politik nicht die Antwort ist, sind die einzigen, die die Menschen wirklich von den Kontrolleuren wegführen.
Die Herrscher dieser Welt sind sich durchaus darüber im Klaren, dass das Informationszeitalter ihren Interessen schadet. Daher arbeiten sie unermüdlich an der Schaffung psychologischer Operationen (PsyOps), kontrollierter Opposition, False-Flag-Aktionen und Ablenkungsmanövern, lass dich nicht täuschen.
Erstveröffentlichung am 12. Januar auf meinem X Profil; @realbunki
-
 @ 77be3409:5c7c2736
2025-02-02 12:48:25
@ 77be3409:5c7c2736
2025-02-02 12:48:25RMD Law - Personal Injury Lawyers is excited to announce the launch of its new scholarship program, designed to empower students and highlight the values of responsibility, resilience, and learning from life’s unexpected moments. This $2,500 scholarship aims to support students in their educational journeys while encouraging creativity and personal growth.
Scholarship Details
Award Amount: $2,500 Submission Deadline: December 30, 2025 Winner Announced: January 15, 2026
Eligibility Requirements To apply, students must meet the following criteria: - Be at least 16 years old and a permanent legal resident of the United States. - Be currently enrolled in a U.S. college, university, or trade school OR graduating from high school in 2025. - Have a cumulative GPA of 3.0 or higher. - Follow RMD Law on social media to see the winner announcement. - Submit all required materials by the December 30, 2025, deadline
Application Requirements Applicants are required to submit:
- A copy of their most recent high school or college transcript.
- A creative and thoughtful essay (up to 1,000 words) responding to the following prompt:
Essay Prompt: “Oops, That Was Close!”
Tell us about a moment when you narrowly avoided disaster—whether it was a hilarious mishap, an embarrassing accident, or a close call with serious consequences. - What did you learn (if anything) from the experience? - Who was at fault and why? - What would the appropriate restitution (if any) be in that situation?
Note: Applicants are encouraged to use creativity, levity, and personal insights to share their story. Let your unique voice shine through!
Selection Criteria The winner will be chosen based on: - Originality and creativity in their essay. - Relevance to the prompt. - Clarity and thoughtfulness of their response. The scholarship recipient will be announced on January 15, 2026.
How to Apply 1. Students can submit their application materials through the official RMD Law scholarship webpage: https://www.rmdlaw.com/scholarship/ 2. Follow RMD Law on social media to stay updated on the announcement and other initiatives.
About RMD Law
RMD Law is a leading personal injury law firm committed to providing exceptional legal services and making a positive impact in the communities it serves. Through initiatives like the scholarship program, RMD Law seeks to empower individuals and foster the next generation of leaders.
-
 @ a95c6243:d345522c
2025-01-01 17:39:51
@ a95c6243:d345522c
2025-01-01 17:39:51Heute möchte ich ein Gedicht mit euch teilen. Es handelt sich um eine Ballade des österreichischen Lyrikers Johann Gabriel Seidl aus dem 19. Jahrhundert. Mir sind diese Worte fest in Erinnerung, da meine Mutter sie perfekt rezitieren konnte, auch als die Kräfte schon langsam schwanden.
Dem originalen Titel «Die Uhr» habe ich für mich immer das Wort «innere» hinzugefügt. Denn der Zeitmesser – hier vermutliche eine Taschenuhr – symbolisiert zwar in dem Kontext das damalige Zeitempfinden und die Umbrüche durch die industrielle Revolution, sozusagen den Zeitgeist und das moderne Leben. Aber der Autor setzt sich philosophisch mit der Zeit auseinander und gibt seinem Werk auch eine klar spirituelle Dimension.
Das Ticken der Uhr und die Momente des Glücks und der Trauer stehen sinnbildlich für das unaufhaltsame Fortschreiten und die Vergänglichkeit des Lebens. Insofern könnte man bei der Uhr auch an eine Sonnenuhr denken. Der Rhythmus der Ereignisse passt uns vielleicht nicht immer in den Kram.
Was den Takt pocht, ist durchaus auch das Herz, unser «inneres Uhrwerk». Wenn dieses Meisterwerk einmal stillsteht, ist es unweigerlich um uns geschehen. Hoffentlich können wir dann dankbar sagen: «Ich habe mein Bestes gegeben.»
Ich trage, wo ich gehe, stets eine Uhr bei mir; \ Wieviel es geschlagen habe, genau seh ich an ihr. \ Es ist ein großer Meister, der künstlich ihr Werk gefügt, \ Wenngleich ihr Gang nicht immer dem törichten Wunsche genügt.
Ich wollte, sie wäre rascher gegangen an manchem Tag; \ Ich wollte, sie hätte manchmal verzögert den raschen Schlag. \ In meinen Leiden und Freuden, in Sturm und in der Ruh, \ Was immer geschah im Leben, sie pochte den Takt dazu.
Sie schlug am Sarge des Vaters, sie schlug an des Freundes Bahr, \ Sie schlug am Morgen der Liebe, sie schlug am Traualtar. \ Sie schlug an der Wiege des Kindes, sie schlägt, will's Gott, noch oft, \ Wenn bessere Tage kommen, wie meine Seele es hofft.
Und ward sie auch einmal träger, und drohte zu stocken ihr Lauf, \ So zog der Meister immer großmütig sie wieder auf. \ Doch stände sie einmal stille, dann wär's um sie geschehn, \ Kein andrer, als der sie fügte, bringt die Zerstörte zum Gehn.
Dann müßt ich zum Meister wandern, der wohnt am Ende wohl weit, \ Wohl draußen, jenseits der Erde, wohl dort in der Ewigkeit! \ Dann gäb ich sie ihm zurücke mit dankbar kindlichem Flehn: \ Sieh, Herr, ich hab nichts verdorben, sie blieb von selber stehn.
Johann Gabriel Seidl (1804-1875)
-
 @ a95c6243:d345522c
2024-12-21 09:54:49
@ a95c6243:d345522c
2024-12-21 09:54:49Falls du beim Lesen des Titels dieses Newsletters unwillkürlich an positive Neuigkeiten aus dem globalen polit-medialen Irrenhaus oder gar aus dem wirtschaftlichen Umfeld gedacht hast, darf ich dich beglückwünschen. Diese Assoziation ist sehr löblich, denn sie weist dich als unverbesserlichen Optimisten aus. Leider muss ich dich diesbezüglich aber enttäuschen. Es geht hier um ein anderes Thema, allerdings sehr wohl ein positives, wie ich finde.
Heute ist ein ganz besonderer Tag: die Wintersonnenwende. Genau gesagt hat heute morgen um 10:20 Uhr Mitteleuropäischer Zeit (MEZ) auf der Nordhalbkugel unseres Planeten der astronomische Winter begonnen. Was daran so außergewöhnlich ist? Der kürzeste Tag des Jahres war gestern, seit heute werden die Tage bereits wieder länger! Wir werden also jetzt jeden Tag ein wenig mehr Licht haben.
Für mich ist dieses Ereignis immer wieder etwas kurios: Es beginnt der Winter, aber die Tage werden länger. Das erscheint mir zunächst wie ein Widerspruch, denn meine spontanen Assoziationen zum Winter sind doch eher Kälte und Dunkelheit, relativ zumindest. Umso erfreulicher ist der emotionale Effekt, wenn dann langsam die Erkenntnis durchsickert: Ab jetzt wird es schon wieder heller!
Natürlich ist es kalt im Winter, mancherorts mehr als anderswo. Vielleicht jedoch nicht mehr lange, wenn man den Klimahysterikern glauben wollte. Mindestens letztes Jahr hat Väterchen Frost allerdings gleich zu Beginn seiner Saison – und passenderweise während des globalen Überhitzungsgipfels in Dubai – nochmal richtig mit der Faust auf den Tisch gehauen. Schnee- und Eischaos sind ja eigentlich in der Agenda bereits nicht mehr vorgesehen. Deswegen war man in Deutschland vermutlich in vorauseilendem Gehorsam schon nicht mehr darauf vorbereitet und wurde glatt lahmgelegt.
Aber ich schweife ab. Die Aussicht auf nach und nach mehr Licht und damit auch Wärme stimmt mich froh. Den Zusammenhang zwischen beidem merkt man in Andalusien sehr deutlich. Hier, wo die Häuser im Winter arg auskühlen, geht man zum Aufwärmen raus auf die Straße oder auf den Balkon. Die Sonne hat auch im Winter eine erfreuliche Kraft. Und da ist jede Minute Gold wert.
Außerdem ist mir vor Jahren so richtig klar geworden, warum mir das südliche Klima so sehr gefällt. Das liegt nämlich nicht nur an der Sonne als solcher, oder der Wärme – das liegt vor allem am Licht. Ohne Licht keine Farben, das ist der ebenso simple wie gewaltige Unterschied zwischen einem deprimierenden matschgraubraunen Winter und einem fröhlichen bunten. Ein großes Stück Lebensqualität.
Mir gefällt aber auch die Symbolik dieses Tages: Licht aus der Dunkelheit, ein Wendepunkt, ein Neuanfang, neue Möglichkeiten, Übergang zu neuer Aktivität. In der winterlichen Stille keimt bereits neue Lebendigkeit. Und zwar in einem Zyklus, das wird immer wieder so geschehen. Ich nehme das gern als ein Stück Motivation, es macht mir Hoffnung und gibt mir Energie.
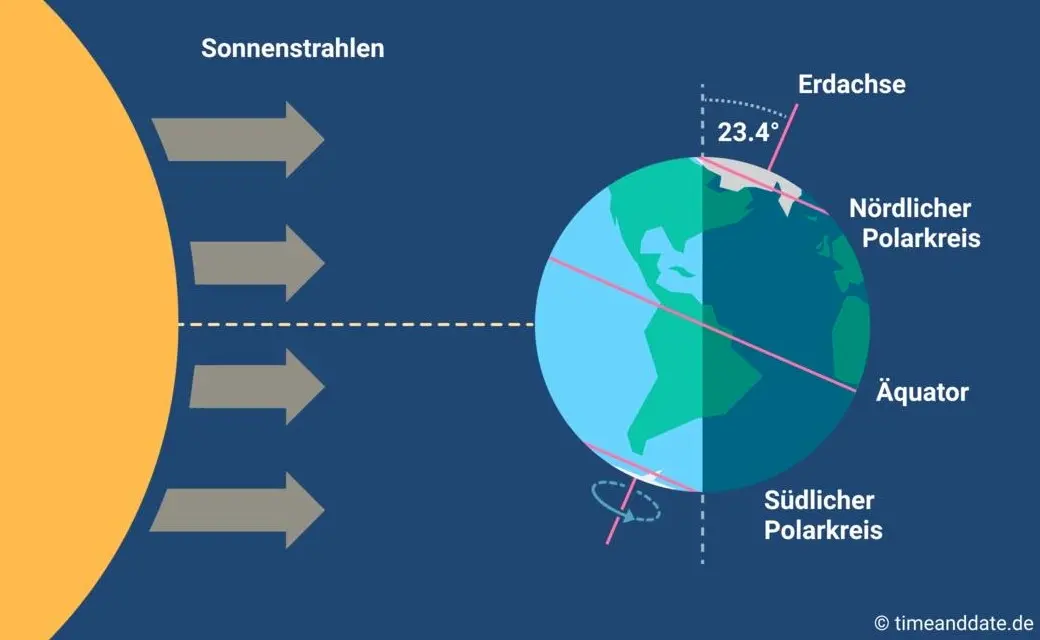
Übrigens ist parallel am heutigen Tag auf der südlichen Halbkugel Sommeranfang. Genau im entgegengesetzten Rhythmus, sich ergänzend, wie Yin und Yang. Das alles liegt an der Schrägstellung der Erdachse, die ist nämlich um 23,4º zur Umlaufbahn um die Sonne geneigt. Wir erinnern uns, gell?
Insofern bleibt eindeutig festzuhalten, dass “schräg sein” ein willkommener, wichtiger und positiver Wert ist. Mit anderen Worten: auch ungewöhnlich, eigenartig, untypisch, wunderlich, kauzig, … ja sogar irre, spinnert oder gar “quer” ist in Ordnung. Das schließt das Denken mit ein.
In diesem Sinne wünsche ich euch allen urige Weihnachtstage!
Dieser Beitrag ist letztes Jahr in meiner Denkbar erschienen.
-
 @ bf6e4fe1:46d21f26
2025-01-31 01:51:03
@ bf6e4fe1:46d21f26
2025-01-31 01:51:03{"title":"test","content":"test"}
-
 @ a95c6243:d345522c
2024-12-13 19:30:32
@ a95c6243:d345522c
2024-12-13 19:30:32Das Betriebsklima ist das einzige Klima, \ das du selbst bestimmen kannst. \ Anonym
Eine Strategie zur Anpassung an den Klimawandel hat das deutsche Bundeskabinett diese Woche beschlossen. Da «Wetterextreme wie die immer häufiger auftretenden Hitzewellen und Starkregenereignisse» oft desaströse Auswirkungen auf Mensch und Umwelt hätten, werde eine Anpassung an die Folgen des Klimawandels immer wichtiger. «Klimaanpassungsstrategie» nennt die Regierung das.
Für die «Vorsorge vor Klimafolgen» habe man nun erstmals klare Ziele und messbare Kennzahlen festgelegt. So sei der Erfolg überprüfbar, und das solle zu einer schnelleren Bewältigung der Folgen führen. Dass sich hinter dem Begriff Klimafolgen nicht Folgen des Klimas, sondern wohl «Folgen der globalen Erwärmung» verbergen, erklärt den Interessierten die Wikipedia. Dabei ist das mit der Erwärmung ja bekanntermaßen so eine Sache.
Die Zunahme schwerer Unwetterereignisse habe gezeigt, so das Ministerium, wie wichtig eine frühzeitige und effektive Warnung der Bevölkerung sei. Daher solle es eine deutliche Anhebung der Nutzerzahlen der sogenannten Nina-Warn-App geben.
Die ARD spurt wie gewohnt und setzt die Botschaft zielsicher um. Der Artikel beginnt folgendermaßen:
«Die Flut im Ahrtal war ein Schock für das ganze Land. Um künftig besser gegen Extremwetter gewappnet zu sein, hat die Bundesregierung eine neue Strategie zur Klimaanpassung beschlossen. Die Warn-App Nina spielt eine zentrale Rolle. Der Bund will die Menschen in Deutschland besser vor Extremwetter-Ereignissen warnen und dafür die Reichweite der Warn-App Nina deutlich erhöhen.»
Die Kommunen würden bei ihren «Klimaanpassungsmaßnahmen» vom Zentrum KlimaAnpassung unterstützt, schreibt das Umweltministerium. Mit dessen Aufbau wurden das Deutsche Institut für Urbanistik gGmbH, welches sich stark für Smart City-Projekte engagiert, und die Adelphi Consult GmbH beauftragt.
Adelphi beschreibt sich selbst als «Europas führender Think-and-Do-Tank und eine unabhängige Beratung für Klima, Umwelt und Entwicklung». Sie seien «global vernetzte Strateg*innen und weltverbessernde Berater*innen» und als «Vorreiter der sozial-ökologischen Transformation» sei man mit dem Deutschen Nachhaltigkeitspreis ausgezeichnet worden, welcher sich an den Zielen der Agenda 2030 orientiere.
Über die Warn-App mit dem niedlichen Namen Nina, die möglichst jeder auf seinem Smartphone installieren soll, informiert das Bundesamt für Bevölkerungsschutz und Katastrophenhilfe (BBK). Gewarnt wird nicht nur vor Extrem-Wetterereignissen, sondern zum Beispiel auch vor Waffengewalt und Angriffen, Strom- und anderen Versorgungsausfällen oder Krankheitserregern. Wenn man die Kategorie Gefahreninformation wählt, erhält man eine Dosis von ungefähr zwei Benachrichtigungen pro Woche.
Beim BBK erfahren wir auch einiges über die empfohlenen Systemeinstellungen für Nina. Der Benutzer möge zum Beispiel den Zugriff auf die Standortdaten «immer zulassen», und zwar mit aktivierter Funktion «genauen Standort verwenden». Die Datennutzung solle unbeschränkt sein, auch im Hintergrund. Außerdem sei die uneingeschränkte Akkunutzung zu aktivieren, der Energiesparmodus auszuschalten und das Stoppen der App-Aktivität bei Nichtnutzung zu unterbinden.
Dass man so dramatische Ereignisse wie damals im Ahrtal auch anders bewerten kann als Regierungen und Systemmedien, hat meine Kollegin Wiltrud Schwetje anhand der Tragödie im spanischen Valencia gezeigt. Das Stichwort «Agenda 2030» taucht dabei in einem Kontext auf, der wenig mit Nachhaltigkeitspreisen zu tun hat.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ a95c6243:d345522c
2024-12-06 18:21:15
@ a95c6243:d345522c
2024-12-06 18:21:15Die Ungerechtigkeit ist uns nur in dem Falle angenehm,\ dass wir Vorteile aus ihr ziehen;\ in jedem andern hegt man den Wunsch,\ dass der Unschuldige in Schutz genommen werde.\ Jean-Jacques Rousseau
Politiker beteuern jederzeit, nur das Beste für die Bevölkerung zu wollen – nicht von ihr. Auch die zahlreichen unsäglichen «Corona-Maßnahmen» waren angeblich zu unserem Schutz notwendig, vor allem wegen der «besonders vulnerablen Personen». Daher mussten alle möglichen Restriktionen zwangsweise und unter Umgehung der Parlamente verordnet werden.
Inzwischen hat sich immer deutlicher herausgestellt, dass viele jener «Schutzmaßnahmen» den gegenteiligen Effekt hatten, sie haben den Menschen und den Gesellschaften enorm geschadet. Nicht nur haben die experimentellen Geninjektionen – wie erwartet – massive Nebenwirkungen, sondern Maskentragen schadet der Psyche und der Entwicklung (nicht nur unserer Kinder) und «Lockdowns und Zensur haben Menschen getötet».
Eine der wichtigsten Waffen unserer «Beschützer» ist die Spaltung der Gesellschaft. Die tiefen Gräben, die Politiker, Lobbyisten und Leitmedien praktisch weltweit ausgehoben haben, funktionieren leider nahezu in Perfektion. Von ihren persönlichen Erfahrungen als Kritikerin der Maßnahmen berichtete kürzlich eine Schweizerin im Interview mit Transition News. Sie sei schwer enttäuscht und verspüre bis heute eine Hemmschwelle und ein seltsames Unwohlsein im Umgang mit «Geimpften».
Menschen, die aufrichtig andere schützen wollten, werden von einer eindeutig politischen Justiz verfolgt, verhaftet und angeklagt. Dazu zählen viele Ärzte, darunter Heinrich Habig, Bianca Witzschel und Walter Weber. Über den aktuell laufenden Prozess gegen Dr. Weber hat Transition News mehrfach berichtet (z.B. hier und hier). Auch der Selbstschutz durch Verweigerung der Zwangs-Covid-«Impfung» bewahrt nicht vor dem Knast, wie Bundeswehrsoldaten wie Alexander Bittner erfahren mussten.
Die eigentlich Kriminellen schützen sich derweil erfolgreich selber, nämlich vor der Verantwortung. Die «Impf»-Kampagne war «das größte Verbrechen gegen die Menschheit». Trotzdem stellt man sich in den USA gerade die Frage, ob der scheidende Präsident Joe Biden nach seinem Sohn Hunter möglicherweise auch Anthony Fauci begnadigen wird – in diesem Fall sogar präventiv. Gibt es überhaupt noch einen Rest Glaubwürdigkeit, den Biden verspielen könnte?
Der Gedanke, den ehemaligen wissenschaftlichen Chefberater des US-Präsidenten und Direktor des National Institute of Allergy and Infectious Diseases (NIAID) vorsorglich mit einem Schutzschild zu versehen, dürfte mit der vergangenen Präsidentschaftswahl zu tun haben. Gleich mehrere Personalentscheidungen des designierten Präsidenten Donald Trump lassen Leute wie Fauci erneut in den Fokus rücken.
Das Buch «The Real Anthony Fauci» des nominierten US-Gesundheitsministers Robert F. Kennedy Jr. erschien 2021 und dreht sich um die Machenschaften der Pharma-Lobby in der öffentlichen Gesundheit. Das Vorwort zur rumänischen Ausgabe des Buches schrieb übrigens Călin Georgescu, der Überraschungssieger der ersten Wahlrunde der aktuellen Präsidentschaftswahlen in Rumänien. Vielleicht erklärt diese Verbindung einen Teil der Panik im Wertewesten.
In Rumänien selber gab es gerade einen Paukenschlag: Das bisherige Ergebnis wurde heute durch das Verfassungsgericht annuliert und die für Sonntag angesetzte Stichwahl kurzfristig abgesagt – wegen angeblicher «aggressiver russischer Einmischung». Thomas Oysmüller merkt dazu an, damit sei jetzt in der EU das Tabu gebrochen, Wahlen zu verbieten, bevor sie etwas ändern können.
Unsere Empörung angesichts der Historie von Maßnahmen, die die Falschen beschützen und für die meisten von Nachteil sind, müsste enorm sein. Die Frage ist, was wir damit machen. Wir sollten nach vorne schauen und unsere Energie clever einsetzen. Abgesehen von der Umgehung von jeglichem «Schutz vor Desinformation und Hassrede» (sprich: Zensur) wird es unsere wichtigste Aufgabe sein, Gräben zu überwinden.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ eac63075:b4988b48
2024-10-21 08:11:11
@ eac63075:b4988b48
2024-10-21 08:11:11Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.

Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.

The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.

Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.

The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.
 Table reference: Patrick Breyer - Chat Control in 23 September 2024
Table reference: Patrick Breyer - Chat Control in 23 September 2024Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.

The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.

User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.

The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.

Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ 0463223a:3b14d673
2025-02-02 12:22:46
@ 0463223a:3b14d673
2025-02-02 12:22:46I’m totally wasted! I don’t mean off my head on drugs, I mean absolutely physically and mentally exhausted.
Lugging heavy PA equipment up and down stairs, plus mixing shows is a lot and at my age I’m struggling with it. Yesterday was a write off due to exhaustion. My wife and I went to the cinema, and I slept through the film. A shame, it was something I wanted to see but I was toast. I went to bed at 8pm and slept for over 12 hours. I still feel wrecked today.
Live sound was always a sort of plan B. For a number of years teaching and performing with a band or a DJ was enough to get by on. I was comfortable, financially speaking. That was until about between 2012-14, that’s when we really felt the effects of the post 2008 crash. While a lot of noise was made about the initial event, reality for the likes of me was a slow and steady decline. At that time I was leading workshops with kids with difficult backgrounds, many kids in care due to abuse and neglect. That was a solid 40% of my income, another 30% came from teaching Sound Production at a local university and the final 30% from shows.
2014 cutbacks ripped services to shreds and a few friends lost jobs. Since then, doing live sound kept the rent and bills paid but fast forward to 2025 and I’m way too tired for this shit! I hate admitting it but my earnings probably peaked around 2008 with a bump in tours from 2017 till Covid. Since then earnings have been steady in £'s but getting wiped out by inflation. In fact I had decent acounts this year but every month I'm broke by the time bills and basics have been taken care of. I LOVE mixing live music and I’m pretty good at it. I’ve had musicians call me ‘musical’ which is the highest compliment but I’m totally fucked still 2 days after Friday’s show. It's unsustainable.
I’m quitting live sound unless some touring comes up again, touring is different, living on a bus for 3 weeks pays the same as 3 months of local work and I just mix, no lifting gear. The band I tour with are based in the US and only come to the UK/EU every couple of years. I get odd trips away with other artists but they’re usually fly out EU gigs. 1 or 2 shows then fly home, plus they're irregular.
Right now I’m more interested to learn ways of making income online, I started the Kali Mera Show to learn self hosting content. Committing to a project each morning has done wonders for my mental health, cutting down on morning doom scrolling. It’s been highly successful in that regard but not so much financially. However this is jst phase 1. I’m learning the tech, learning the production and making as many mistakes as possible while the stakes are low. I’m very happy 10 or so people enjoy the show on a daily basis. Tiny numbers but I don’t fuck with YouTube or the other big tech platforms. Fuck them!
Phase 2 involves getting premises and broadening the services I can produce, focussing on content for others, getting some opportunities happening for young talent, arranging meet ups and setting up a hub to bring together the crazy, talented people I know. It’s going to be tough, I’m in a run down area, there’s not much money here (relatively speaking) but it’s an area I really dig and want to make better.
Why am I telling you this? I’m writing this as a means of getting my brain straight and sharing it because I’m open to improving myself. I see people doing interesting shit here and that helps with motivation and confidence. My only social media for the last 6 years has been the Fediverse and much as I love it, there’s a gloomier outlook there. The world is a strange place with so much bad shit but out of 8 or so billion people, I can only take on so much. Building shit in my own local community and provide facilities for online wins sounds way more productive and helpful in some small way.
I accept we’re all going to hell in a handcart but may as well enjoy the ride…
There’s much to learn, I’ve only ever been ‘in business’ for a short time in my life (despite always being freelance) and I sort of gave up on my previous attempt. Had I paid more attention I could’ve built a strong YouTube presence but I’m not into being a vehicle for companies to push their products, nor do I want to teach people music online. That market is now heavily saturated and very, very boring as far as I’m concerned. My heart wasn’t in it, even back in 2015. I’m not an influencer.
With a real life space there’s premises, business rates, and investors to consider, as well as developing services that people are actually happy to part cash with. It’s going to be hard but different hard to physically lifting sub-bass speakers up and down winding staircases! I don’t want to talk too much game, it’s results that matter but wasting days to exhaustion doesn’t help. It’s time to hang up my headphones and focus (FOCUS YOU FUCKING FUCK!).
Maybe you’re reading this and thought ‘shit, this guy’s totally deluded’. That’s cool. Tell me. I value feedback. A fair few cats here give life advice so I’ll assume you might know what you’re talking about...
-
 @ d1795b1a:15ab2129
2025-02-02 11:45:38
@ d1795b1a:15ab2129
2025-02-02 11:45:38The Ego is an Illusion – and Yet, We Can Shape It
Carl Jung spoke of the Shadow Self—the repressed parts of our psyche that unconsciously influence our lives. Buddhism, on the other hand, teaches that there is no self at all—our ego is an illusion, a fleeting construct that we cling to out of fear of emptiness.
These two perspectives seem to contradict each other. One tells us to integrate our hidden self, the other to dissolve it completely. But what if both are only half the picture?
I believe the Self is neither a fixed reality nor a mere illusion—it is a shapeable construct. If that is true, then the path is not to destroy the Ego-Self or blindly follow it, but to consciously shape it.
Between the Shadow and Emptiness
Our Ego-Self is our conscious identity—our thoughts, memories, and beliefs. Jung describes the Self as the totality of both the conscious and unconscious mind. Hidden in this unconscious space is the Shadow Self, containing everything we deny, suppress, or refuse to acknowledge. For Jung, the path to wholeness is integration—bringing light into the dark corners of the psyche.
Buddhism, however, goes further. It questions whether the Self exists at all. Our thoughts and emotions arise and disappear, our self-image is ever-changing—so why do we cling to something so impermanent?
Both views seem to offer opposite solutions: \ • Jung: Become WHOLE by integrating your Shadow. \ • Buddha: Become FREE by seeing the Self as an illusion.
But what if the synthesis of both is the key?
The Self as a Shapeable Reality
If the Self is not fixed but fluid, then the path forward is neither pure integration nor total dissolution but conscious creation. \ \ • Acknowledge the Shadow Self instead of fighting it. \ • See the Ego-Self not as absolute truth but as a flexible tool. \ • Engage the Solar Plexus—the center of the Unconscious Mind—through breathwork and self-awareness. \ • Use the Vagus Nerve as a bridge between conscious thought and unconscious emotion, actively shaping our beliefs and behaviors.
This aligns with New Thought philosophy, which suggests that our thoughts shape not only our perception but our reality itself. If we embrace this, the question is no longer “Who am I?” but rather: “Who do I want to be—and how can I create that Self?”
The Art of Shaping Yourself
Perhaps the Self is neither a rigid entity nor a complete illusion but a story we tell ourselves—a story we can rewrite. The key is not to destroy the Ego-Self but to use it consciously, rather than being used by it.
So the real question is not: “Does the Self exist?”
But rather: “How aware are we of the fact that we are shaping it every moment?”
-
 @ b8851a06:9b120ba1
2025-01-28 21:34:54
@ b8851a06:9b120ba1
2025-01-28 21:34:54Private property isn’t lines on dirt or fences of steel—it’s the crystallization of human sovereignty. Each boundary drawn is a silent declaration: This is where my will meets yours, where creation clashes against chaos. What we defend as “mine” or “yours” is no mere object but a metaphysical claim, a scaffold for the unfathomable complexity of voluntary exchange.
Markets breathe only when individuals anchor their choices in the inviolable. Without property, there is no negotiation—only force. No trade—only taking. The deed to land, the title to a car, the seed of an idea: these are not static things but frontiers of being, where human responsibility collides with the infinite permutations of value.
Austrian economics whispers what existentialism shouts: existence precedes essence. Property isn’t granted by systems; it’s asserted through action, defended through sacrifice, and sanctified through mutual recognition. A thing becomes “owned” only when a mind declares it so, and others—through reason or respect—refrain from crossing that unseen line.
Bitcoin? The purest ledger of this truth. A string of code, yes—but one that mirrors the unyielding logic of property itself: scarce, auditable, unconquerable. It doesn’t ask permission. It exists because sovereign minds choose it to.
Sigh. #nostr
I love #Bitcoin. -
 @ a95c6243:d345522c
2024-11-29 19:45:43
@ a95c6243:d345522c
2024-11-29 19:45:43Konsum ist Therapie.
Wolfgang JoopUmweltbewusstes Verhalten und verantwortungsvoller Konsum zeugen durchaus von einer wünschenswerten Einstellung. Ob man deswegen allerdings einen grünen statt eines schwarzen Freitags braucht, darf getrost bezweifelt werden – zumal es sich um manipulatorische Konzepte handelt. Wie in der politischen Landschaft sind auch hier die Etiketten irgendwas zwischen nichtssagend und trügerisch.
Heute ist also wieder mal «Black Friday», falls Sie es noch nicht mitbekommen haben sollten. Eigentlich haben wir ja eher schon eine ganze «Black Week», der dann oft auch noch ein «Cyber Monday» folgt. Die Werbebranche wird nicht müde, immer neue Anlässe zu erfinden oder zu importieren, um uns zum Konsumieren zu bewegen. Und sie ist damit sehr erfolgreich.
Warum fallen wir auf derartige Werbetricks herein und kaufen im Zweifelsfall Dinge oder Mengen, die wir sicher nicht brauchen? Pure Psychologie, würde ich sagen. Rabattschilder triggern etwas in uns, was den Verstand in Stand-by versetzt. Zusätzlich beeinflussen uns alle möglichen emotionalen Reize und animieren uns zum Schnäppchenkauf.
Gedankenlosigkeit und Maßlosigkeit können besonders bei der Ernährung zu ernsten Problemen führen. Erst kürzlich hat mir ein Bekannter nach einer USA-Reise erzählt, dass es dort offenbar nicht unüblich ist, schon zum ausgiebigen Frühstück in einem Restaurant wenigstens einen Liter Cola zu trinken. Gerne auch mehr, um das Gratis-Nachfüllen des Bechers auszunutzen.
Kritik am schwarzen Freitag und dem unnötigen Konsum kommt oft von Umweltschützern. Neben Ressourcenverschwendung, hohem Energieverbrauch und wachsenden Müllbergen durch eine zunehmende Wegwerfmentalität kommt dabei in der Regel auch die «Klimakrise» auf den Tisch.
Die EU-Kommission lancierte 2015 den Begriff «Green Friday» im Kontext der überarbeiteten Rechtsvorschriften zur Kennzeichnung der Energieeffizienz von Elektrogeräten. Sie nutzte die Gelegenheit kurz vor dem damaligen schwarzen Freitag und vor der UN-Klimakonferenz COP21, bei der das Pariser Abkommen unterzeichnet werden sollte.
Heute wird ein grüner Freitag oft im Zusammenhang mit der Forderung nach «nachhaltigem Konsum» benutzt. Derweil ist die Europäische Union schon weit in ihr Geschäftsmodell des «Green New Deal» verstrickt. In ihrer Propaganda zum Klimawandel verspricht sie tatsächlich «Unterstützung der Menschen und Regionen, die von immer häufigeren Extremwetter-Ereignissen betroffen sind». Was wohl die Menschen in der Region um Valencia dazu sagen?
Ganz im Sinne des Great Reset propagierten die Vereinten Nationen seit Ende 2020 eine «grüne Erholung von Covid-19, um den Klimawandel zu verlangsamen». Der UN-Umweltbericht sah in dem Jahr einen Schwerpunkt auf dem Verbraucherverhalten. Änderungen des Konsumverhaltens des Einzelnen könnten dazu beitragen, den Klimaschutz zu stärken, hieß es dort.
Der Begriff «Schwarzer Freitag» wurde in den USA nicht erstmals für Einkäufe nach Thanksgiving verwendet – wie oft angenommen –, sondern für eine Finanzkrise. Jedoch nicht für den Börsencrash von 1929, sondern bereits für den Zusammenbruch des US-Goldmarktes im September 1869. Seitdem mussten die Menschen weltweit so einige schwarze Tage erleben.
Kürzlich sind die britischen Aufsichtsbehörden weiter von ihrer Zurückhaltung nach dem letzten großen Finanzcrash von 2008 abgerückt. Sie haben Regeln für den Bankensektor gelockert, womit sie «verantwortungsvolle Risikobereitschaft» unterstützen wollen. Man würde sicher zu schwarz sehen, wenn man hier ein grünes Wunder befürchten würde.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ fd208ee8:0fd927c1
2025-02-02 10:33:19
@ fd208ee8:0fd927c1
2025-02-02 10:33:19GitCitadel Development Operations
We, at GitCitadel, have been updating, moving, and rearranging our servers, for quite some time. As a rather large, complex, sprawling project, we have the infrastructure setup to match, so we've decided to give you all a quick run-down of what we are doing behind-the-scenes.
Supplier Coordination
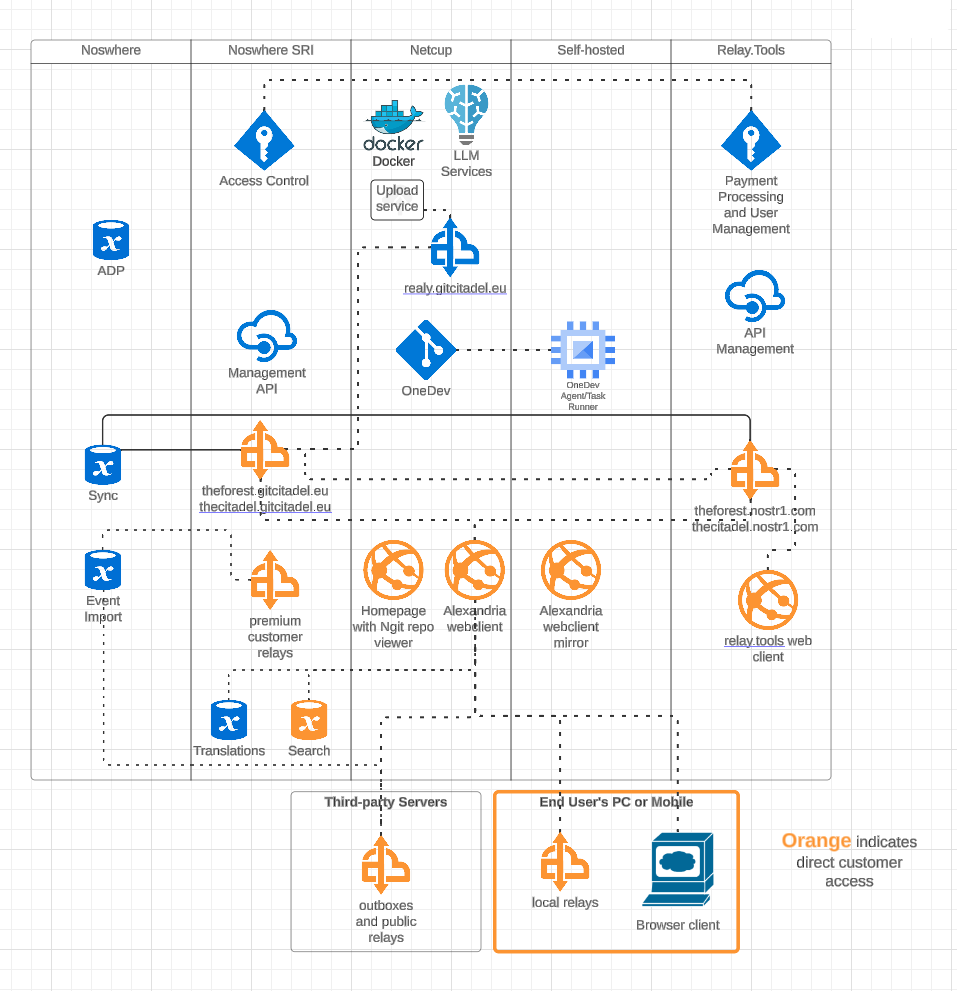
Our first task, this week, was figuring out who would host what where. We have four different locations, where our infra is stored and managed, including two locations from our suppliers. We got that straightened out, quickly, and it's all slowly coming together and being connected and networked. Exciting to watch our DevOps landscape evolve and all of the knowledge-transfer that the interactions provide.
OneDev Implementation
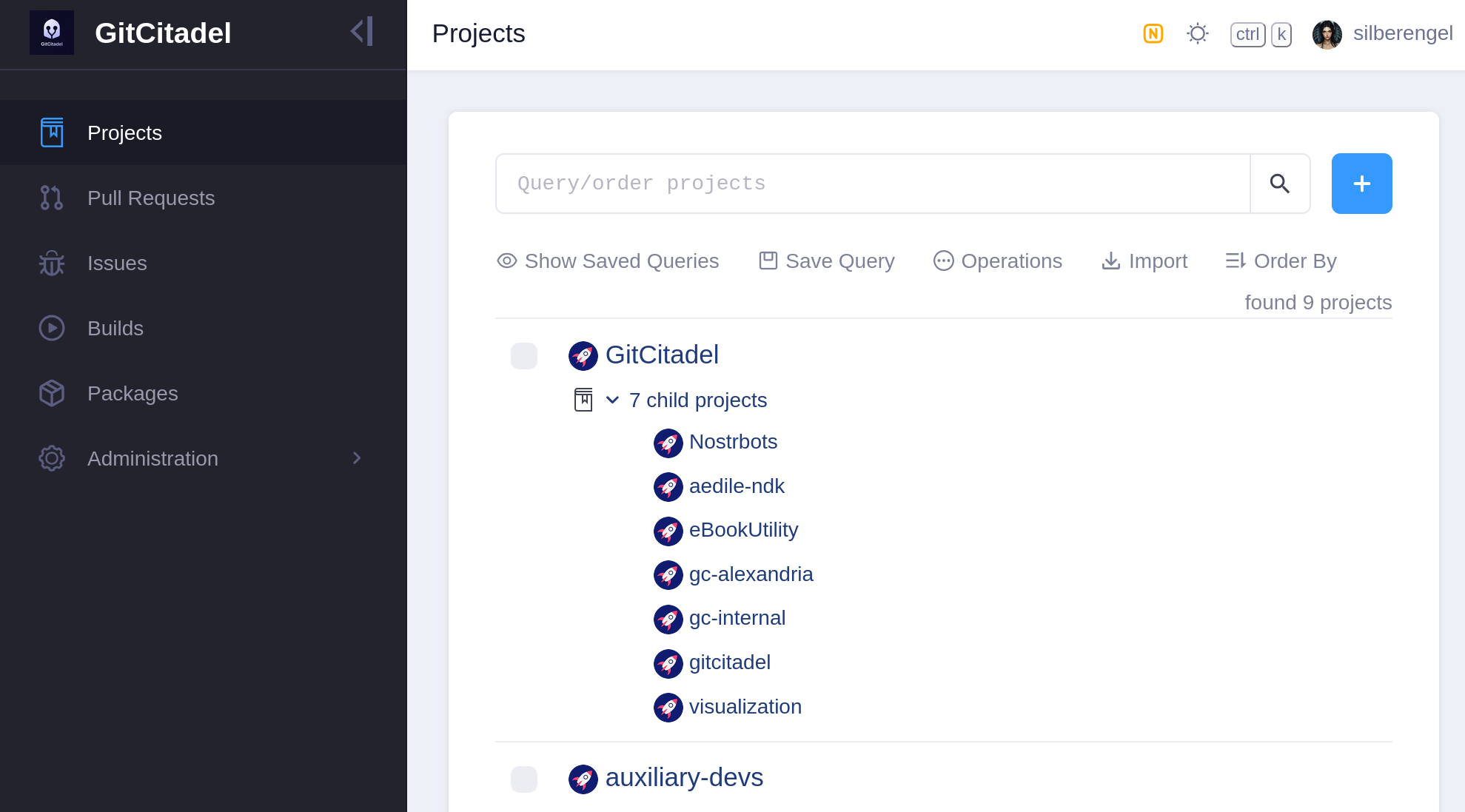
Our biggest internal infra project this week was the migration of all of our issues from Jira, build scripts from Jenkins, and repos from GitHub to a self-hosted OneDev instance. In the future, all of our internal build, test, issue, patch/PR, etc. effort will take place there. We also have a separate repo there for communicating with external developers and suppliers.
Our team's GitHub projects will be demoted to mirrors and a place for external devs to PR to. Public issues and patches will continue to be managed over our self-hosted GitWorkshop instance.
We're especially glad to finally escape the GitHub Gulag, and avoid being bled dry by Jira fees, without having to give up the important features that we've come to know and love. So, yay!
Next Infrasteps
Automated Testing
Now, that we have everything tied up in one, neat, backed-up package, we can finally move on to the nitty-gritty and the dirty work. So, we're rolling up our sleeves and writing the Selenium smoke test for our Alexandria client. We'll be running that in Docker containers containing different "typical Nostr" images, such as Chrome browser with Nostr Connect signing extension, or Firefox browser with Nos2x-fox extension. Once we get the Nsec Bunker and Amber logins going, we'll add test cases and images for them, as well. (Yes, we can do Bunker. I hope you are in awe at our powers).
We are also designing an automated infrastructure test, that will simply rattle through all the various internal and external websites and relays, to make sure that everything is still online and responsive.
After that, a Gherkin-based Behave feature test for Alexandria is planned, so that we can prevent regression of completed functionality, from one release to the next.
The Gherkin scenarios are written and attached to our stories before development begins (we use acceptance tests as requirements), a manual test-execution is then completed, in order to set the story to Done. These completed scenarios will be automated, following each release, with the resulting script linked to from the origin story.
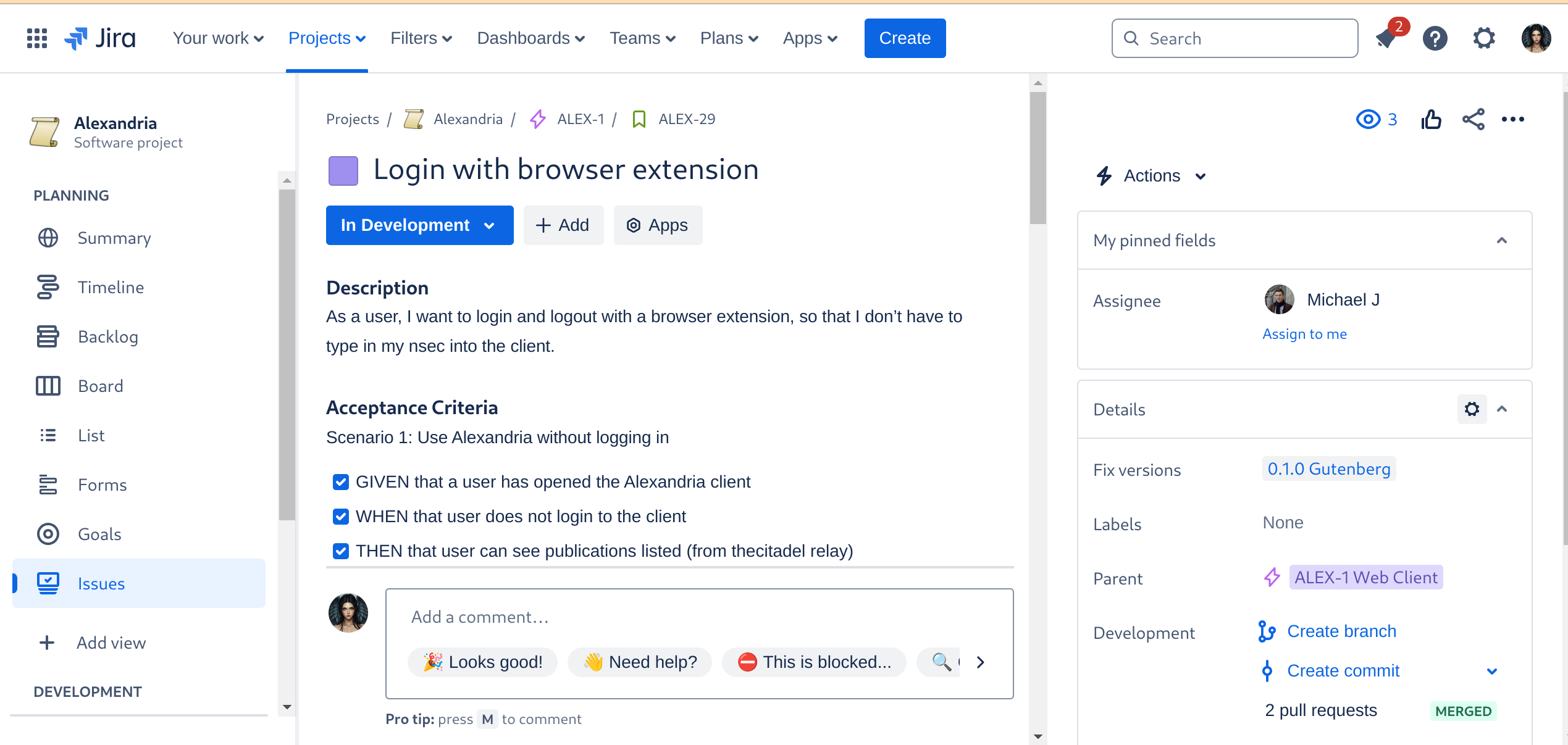
Automated Builds
As the crowning glory of every DevOps tool chain stands the build automation. This is where everything gets tied together, straightened out, configured, tested, measured, and -- if everything passes the quality gates -- released. I don't have to tell you how much time developers spend staring at the build process display, praying that it all goes through and they can celebrate a Green Wave.
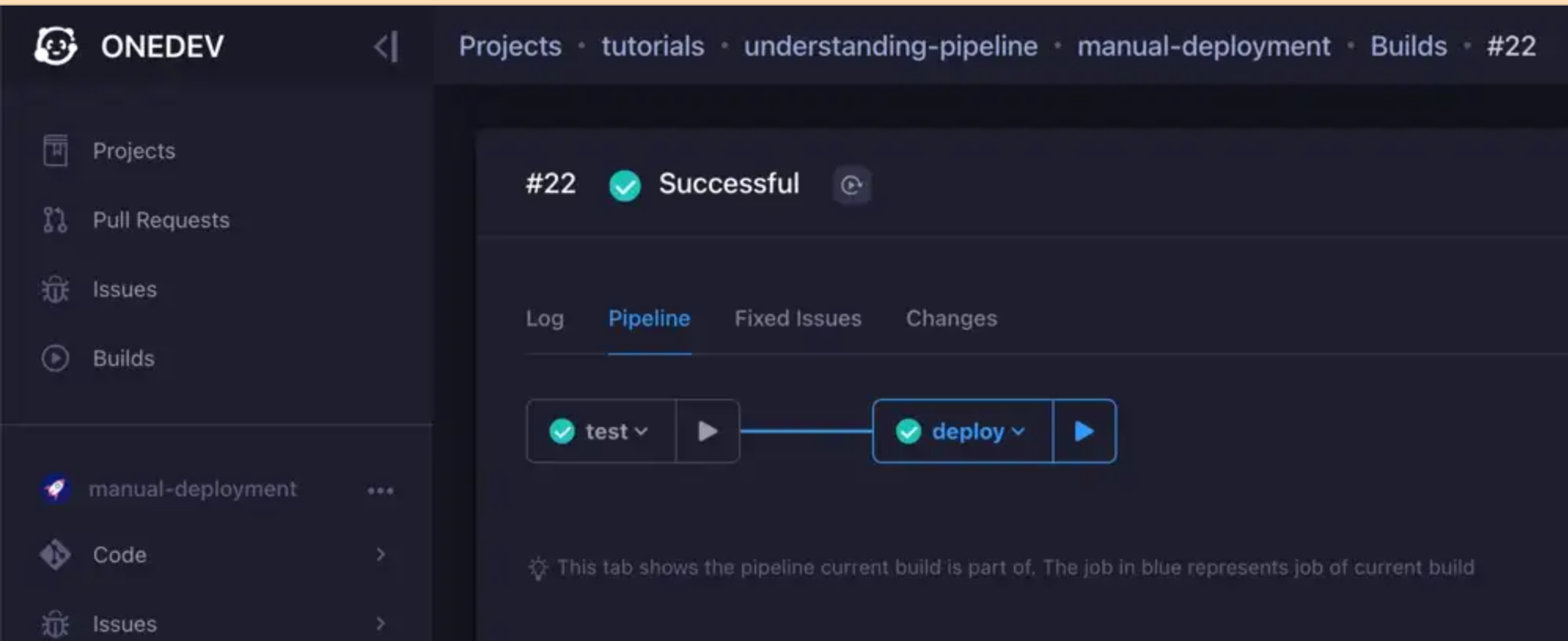
We are currently designing the various builds, but the ones we have defined for the Alexandria client will be a continuous delivery pipeline, like so:
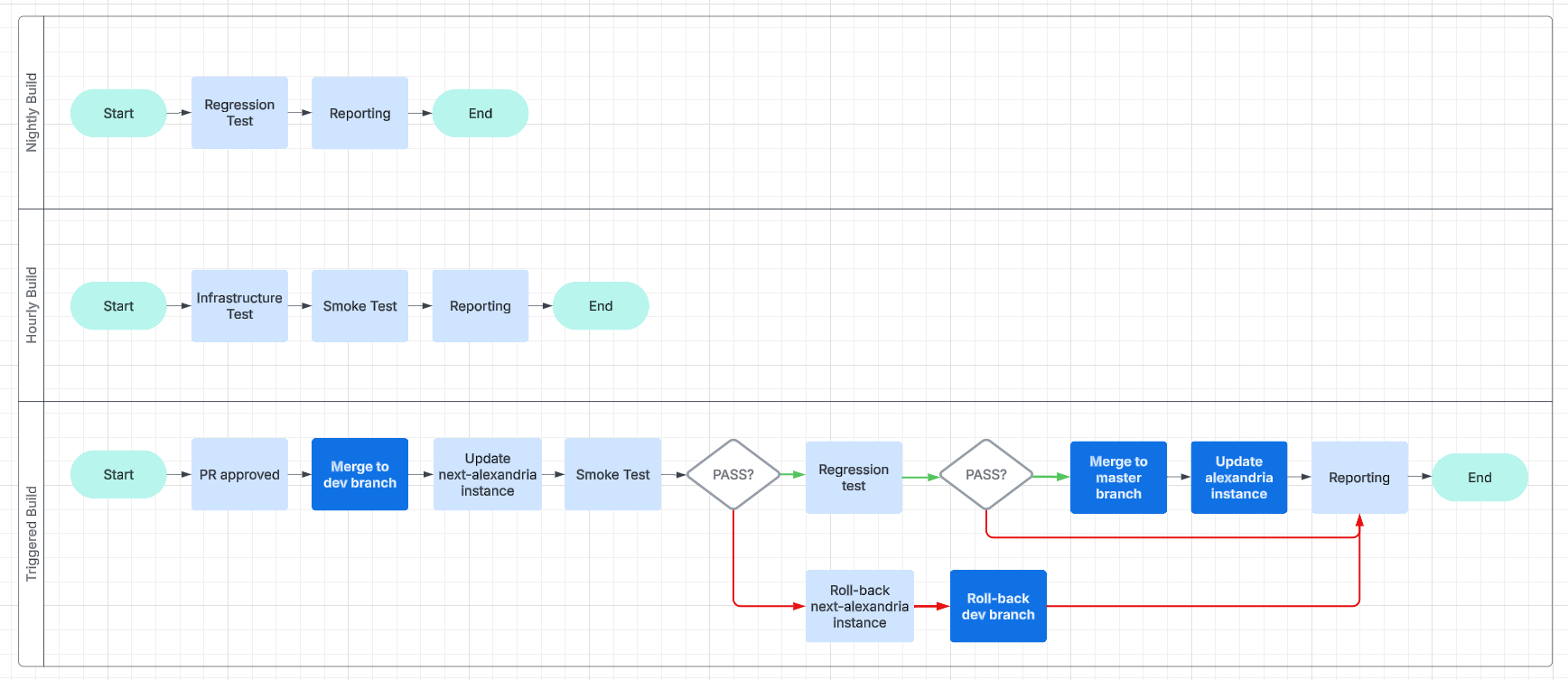
This will make it easier for us to work and collaborate asynchronously and without unnecessary delays.
Expanding the Status Page
And, finally, we get to the point of all of this busyness: reporting.
We are going to have beautiful reports, and we are going to post them online, on our status page. We will use bots, to inform Nostriches of the current status of our systems, so go ahead and follow our GitCitadel DevOps npub, to make sure you don't miss out on the IT action.
Building on stone
All in all, we're really happy with the way things are humming along, now, and the steady increase in our productivity, as all the foundational work we've put in starts to pay off. It's getting easier and easier to add new team members, repos, or features/fixes, so we should be able to scale up and out from here. Our GitCitadel is built on a firm foundation.
Happy building!
-
 @ a95c6243:d345522c
2024-11-08 20:02:32
@ a95c6243:d345522c
2024-11-08 20:02:32Und plötzlich weißt du:
Es ist Zeit, etwas Neues zu beginnen
und dem Zauber des Anfangs zu vertrauen.
Meister EckhartSchwarz, rot, gold leuchtet es im Kopf des Newsletters der deutschen Bundesregierung, der mir freitags ins Postfach flattert. Rot, gelb und grün werden daneben sicher noch lange vielzitierte Farben sein, auch wenn diese nie geleuchtet haben. Die Ampel hat sich gerade selber den Stecker gezogen – und hinterlässt einen wirtschaftlichen und gesellschaftlichen Trümmerhaufen.
Mit einem bemerkenswerten Timing hat die deutsche Regierungskoalition am Tag des «Comebacks» von Donald Trump in den USA endlich ihr Scheitern besiegelt. Während der eine seinen Sieg bei den Präsidentschaftswahlen feierte, erwachten die anderen jäh aus ihrer Selbsthypnose rund um Harris-Hype und Trump-Panik – mit teils erschreckenden Auswüchsen. Seit Mittwoch werden die Geschicke Deutschlands nun von einer rot-grünen Minderheitsregierung «geleitet» und man steuert auf Neuwahlen zu.
Das Kindergarten-Gehabe um zwei konkurrierende Wirtschaftsgipfel letzte Woche war bereits bezeichnend. In einem Strategiepapier gestand Finanzminister Lindner außerdem den «Absturz Deutschlands» ein und offenbarte, dass die wirtschaftlichen Probleme teilweise von der Ampel-Politik «vorsätzlich herbeigeführt» worden seien.
Lindner und weitere FDP-Minister wurden also vom Bundeskanzler entlassen. Verkehrs- und Digitalminister Wissing trat flugs aus der FDP aus; deshalb darf er nicht nur im Amt bleiben, sondern hat zusätzlich noch das Justizministerium übernommen. Und mit Jörg Kukies habe Scholz «seinen Lieblingsbock zum Obergärtner», sprich: Finanzminister befördert, meint Norbert Häring.
Es gebe keine Vertrauensbasis für die weitere Zusammenarbeit mit der FDP, hatte der Kanzler erklärt, Lindner habe zu oft sein Vertrauen gebrochen. Am 15. Januar 2025 werde er daher im Bundestag die Vertrauensfrage stellen, was ggf. den Weg für vorgezogene Neuwahlen freimachen würde.
Apropos Vertrauen: Über die Hälfte der Bundesbürger glauben, dass sie ihre Meinung nicht frei sagen können. Das ging erst kürzlich aus dem diesjährigen «Freiheitsindex» hervor, einer Studie, die die Wechselwirkung zwischen Berichterstattung der Medien und subjektivem Freiheitsempfinden der Bürger misst. «Beim Vertrauen in Staat und Medien zerreißt es uns gerade», kommentierte dies der Leiter des Schweizer Unternehmens Media Tenor, das die Untersuchung zusammen mit dem Institut für Demoskopie Allensbach durchführt.
«Die absolute Mehrheit hat absolut die Nase voll», titelte die Bild angesichts des «Ampel-Showdowns». Die Mehrheit wolle Neuwahlen und die Grünen sollten zuerst gehen, lasen wir dort.
Dass «Insolvenzminister» Robert Habeck heute seine Kandidatur für das Kanzleramt verkündet hat, kann nur als Teil der politmedialen Realitätsverweigerung verstanden werden. Wer allerdings denke, schlimmer als in Zeiten der Ampel könne es nicht mehr werden, sei reichlich optimistisch, schrieb Uwe Froschauer bei Manova. Und er kenne Friedrich Merz schlecht, der sich schon jetzt rhetorisch auf seine Rolle als oberster Feldherr Deutschlands vorbereite.
Was also tun? Der Schweizer Verein «Losdemokratie» will eine Volksinitiative lancieren, um die Bestimmung von Parlamentsmitgliedern per Los einzuführen. Das Losverfahren sorge für mehr Demokratie, denn als Alternative zum Wahlverfahren garantiere es eine breitere Beteiligung und repräsentativere Parlamente. Ob das ein Weg ist, sei dahingestellt.
In jedem Fall wird es notwendig sein, unsere Bemühungen um Freiheit und Selbstbestimmung zu verstärken. Mehr Unabhängigkeit von staatlichen und zentralen Institutionen – also die Suche nach dezentralen Lösungsansätzen – gehört dabei sicher zu den Möglichkeiten. Das gilt sowohl für jede/n Einzelne/n als auch für Entitäten wie die alternativen Medien.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ a95c6243:d345522c
2024-10-26 12:21:50
@ a95c6243:d345522c
2024-10-26 12:21:50Es ist besser, ein Licht zu entzünden, als auf die Dunkelheit zu schimpfen. Konfuzius
Die Bemühungen um Aufarbeitung der sogenannten Corona-Pandemie, um Aufklärung der Hintergründe, Benennung von Verantwortlichkeiten und das Ziehen von Konsequenzen sind durchaus nicht eingeschlafen. Das Interesse daran ist unter den gegebenen Umständen vielleicht nicht sonderlich groß, aber es ist vorhanden.
Der sächsische Landtag hat gestern die Einsetzung eines Untersuchungsausschusses zur Corona-Politik beschlossen. In einer Sondersitzung erhielt ein entsprechender Antrag der AfD-Fraktion die ausreichende Zustimmung, auch von einigen Abgeordneten des BSW.
In den Niederlanden wird Bill Gates vor Gericht erscheinen müssen. Sieben durch die Covid-«Impfstoffe» geschädigte Personen hatten Klage eingereicht. Sie werfen unter anderem Gates, Pfizer-Chef Bourla und dem niederländischen Staat vor, sie hätten gewusst, dass diese Präparate weder sicher noch wirksam sind.
Mit den mRNA-«Impfstoffen» von Pfizer/BioNTech befasst sich auch ein neues Buch. Darin werden die Erkenntnisse von Ärzten und Wissenschaftlern aus der Analyse interner Dokumente über die klinischen Studien der Covid-Injektion präsentiert. Es handelt sich um jene in den USA freigeklagten Papiere, die die Arzneimittelbehörde (Food and Drug Administration, FDA) 75 Jahre unter Verschluss halten wollte.
Ebenfalls Wissenschaftler und Ärzte, aber auch andere Experten organisieren als Verbundnetzwerk Corona-Solution kostenfreie Online-Konferenzen. Ihr Ziel ist es, «wissenschaftlich, demokratisch und friedlich» über Impfstoffe und Behandlungsprotokolle gegen SARS-CoV-2 aufzuklären und die Diskriminierung von Ungeimpften zu stoppen. Gestern fand eine weitere Konferenz statt. Ihr Thema: «Corona und modRNA: Von Toten, Lebenden und Physik lernen».
Aufgrund des Digital Services Acts (DSA) der Europäischen Union sei das Risiko groß, dass ihre Arbeit als «Fake-News» bezeichnet würde, so das Netzwerk. Staatlich unerwünschte wissenschaftliche Aufklärung müsse sich passende Kanäle zur Veröffentlichung suchen. Ihre Live-Streams seien deshalb zum Beispiel nicht auf YouTube zu finden.
Der vielfältige Einsatz für Aufklärung und Aufarbeitung wird sich nicht stummschalten lassen. Nicht einmal der Zensurmeister der EU, Deutschland, wird so etwas erreichen. Die frisch aktivierten «Trusted Flagger» dürften allerdings künftige Siege beim «Denunzianten-Wettbewerb» im Kontext des DSA zusätzlich absichern.
Wo sind die Grenzen der Meinungsfreiheit? Sicher gibt es sie. Aber die ideologische Gleichstellung von illegalen mit unerwünschten Äußerungen verfolgt offensichtlich eher das Ziel, ein derart elementares demokratisches Grundrecht möglichst weitgehend auszuhebeln. Vorwürfe wie «Hassrede», «Delegitimierung des Staates» oder «Volksverhetzung» werden heute inflationär verwendet, um Systemkritik zu unterbinden. Gegen solche Bestrebungen gilt es, sich zu wehren.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 59c2e15a:d25e6e8d
2025-01-27 02:29:42
@ 59c2e15a:d25e6e8d
2025-01-27 02:29:42Note: I originally wrote these essays on bitcoin and yoga in 2022 after completing my yoga teacher training and going deep down the bitcoin rabbit hole. I then published them to my Ghost blog in 2023. I decided to repost them here on Nostr to start 2025 to further spread the wisdom and timelessness that bitcoin and yoga share. I split my original essay into seven parts, and I will add an eighth comparing yoga and Nostr. I hope you enjoy part one - namaste!
Part I: Bitcoin and Yoga Shared Values
Part II: Mythical/Mystical Origins
Part III: Evolution of Money and Yoga
Part IV: Ashtanga Yoga - The Eight Limbs of Yoga (limbs 1-2)
Part V: Ashtanga Yoga - The Eight Limbs of Yoga (limbs 3-8)
Part VI: Bitcoin is Dharma
Part VII: Himalayan Kriya Yoga
Introduction
With each passing day, month, and year, it feels as though our human civilization is becoming more dysfunctional, untethered, and unsustainable. Individuals are working harder, longer hours, yet most remain stuck in place, goals farther from reach. We live in a world where many have outsourced the most critical task that has enabled humans to prosper – critical thinking. I challenge each one of you to remove preconceived notions you might have about Bitcoin or Yoga before reading this series. I invite you to enter with an open mind. Think for yourself – you are welcome to agree or disagree with the information and arguments I put forth.
I also encourage you to go beyond thinking – feel. Use your intuition to understand if the way you’re living your day-to-day life feels good to you, or if you have sense, an inner knowing that something is off with our society today – that there can be a better way. If you open your heart and mind to receiving new information, there is potential to motivate yourself to change your thoughts and behaviors for more aligned action towards individual sovereignty. Every individual can choose freedom and independence. Yet it has become increasingly difficult to live a life of freedom due to the fiat system of inflation and the many distractions that keep us from going inward. After deep study and reflection, I believe bitcoin and yoga both provide the individual control over their own life journey, and frameworks to understand our connection to self and others.
I'm excited to share what I have found in my own personal experience, and hope to spark curiosity within you to follow your passion. This writing is intended for anyone seeking tools to lead a life of freedom, make positive changes and deepen your understanding of self. In addition, it is written for yogis who want to learn about bitcoin, bitcoiners who want to learn more about yoga, and anyone who is interested in a fundamental understanding of these topics that I believe contain the potential to transform your life.
Part I: Bitcoin and Yoga Shared Values
Bitcoin and yoga share many fundamental values with one another and provide deep wisdom on guiding individuals towards living better and more meaningful lives. Ultimately bitcoin and yoga share the goal of individual liberation, freedom from suffering, and a deep inner, lasting peace in Being. In yoga, this state is called moksha or samadhi. I believe everyone has a true essence, an inner being that knows what is best. However, our external environment and our own conscious mind push us away from this serenity, leading to regrets about the past or anxieties about the future. This perspective of linear time and our own individual stories and identity damage our ability to stay present in the Now, leading to endless distractions. In similar ways, bitcoin and yoga provide us insight for an individual’s path to inner peace, as well as for humanity’s path to collective peace and prosperity.
Energy
At the most elemental level, energy is the force underlying both bitcoin and yoga. Energy is the universal currency of life. We would not exist without energy. We require physical energy to fuel our cells and bodies to perform essential tasks like breathing, circulation, digestion, and movement. We perceive many forms of energy such as light or sound waves, yet there are many energy wavelengths we are not able to or are not trained to perceive.
Bitcoin is powered by physical energy in the real world in a process that secures the network and unlocks new bitcoin for distribution, a process commonly referred to as mining. Interestingly, 100 years ago, Henry Ford pushed for an energy-linked currency measured in kilowatt hours that could bring peace after a brutal World War, as seen in the New York Tribune headline and article December 4, 1921: ‘Ford Would Replace Gold with Energy Currency and Stop Wars’ (i). It took another century, but mankind has finally developed a digitally-native currency tied to the physical world through energy expenditure – bitcoin.
Yoga is similarly rooted in energy that individuals tap into through breathwork, physical movement and meditations practices. This life-force energy is known in Sanskrit as prana. Prana is not bound by time or space, and it flows through individuals in over 72,000 nadis, or channels. There are three main nadis - the first is ida, our left side body which corresponds to the feminine, receiving energy, or the moon. On the right side is pingala, relating to our masculine, giving energy, or the sun. The central nadi runs through our shushumna, linking our seven main energetic centers, known as chakras. These chakras run from the base of the tail bone, up through the spine and the top of the head. Each chakra has a name, a color and key characteristics that can often become blocked through negative emotion, trauma or stress in the body. Different yogic practices target these energy centers to unlock what is stuck and enable energy to more freely flow through us in an open exchange with the earth and out the universe. This energy is ever-present; one need only to tap into this energy, feel it and utilize it for the strengthening of one’s inner being that then radiates outwards on others in your life. The energetic experience and upward surge can also be referred to as kundalini energy, a creative power of divine feminine energy that originates in the muladara chakra at the base of the spine.
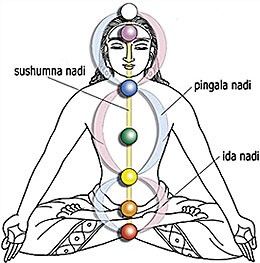 Depiction of our chakras and nadis (image source)
Depiction of our chakras and nadis (image source)Proof of Work
In both Bitcoin and Yoga, "proof of work" is required to operate, practice and move forwards. In the Bitcoin network as described in the original white paper, miners contribute tangible energy towards running a hashing algorithm on a computer – SHA256 – to earn the right to add the next block to the blockchain and collect both the coinbase and transaction fee reward (ii). The work is difficult to produce but easy to validate by others. Miners are collecting all of the valid peer-to-peer transactions being propagated to the network and establishing them as truth into the distributed ledger. The rules in bitcoin’s code incentivize honest behavior from miners through unforgeable costliness – if a miner were to lie about any of the transactions it includes in a block, independent nodes in the network would reject the block, and the miner would have lost all the real resources it expended to solve the proof of work calculation.
 Example of an ASIC - a specialized computer solely dedicated to mining bitcoin.
Example of an ASIC - a specialized computer solely dedicated to mining bitcoin.In yoga, dedicated work is needed to learn the asanas, postures, and practice for oneself; you won’t just be able to go upside down or flow through sun salutations without first learning proper alignment and breathing techniques. An individual needs to conscious decision to work on a daily yoga practice that requires energy to flow. There are several ways to work on your yoga practice beyond physical movement; these include bhakti yoga (devotion/prayer), jnana yoga (study/wisdom), karma yoga(selfless action) and raja yoga (ashtanga). Raja yoga includes ashtanga, the eight limbs or paths of yoga that Patanjali detailed \~2000 years ago that we will explore in more depth in part IV. These ancient margas (paths) and subsequent development of these ancient teachings provides individual with ample opportunity to dedicate and work towards individual enlightenment.
Decentralization
Next, there are no external barriers preventing an individual from participating in Bitcoin or yoga. Bitcoin does not discriminate and can be accessed by anyone around the world. Yoga provides a way of life full of mindfulness and appreciation. The only barriers are internal blockages, or unwillingness to ask questions, learn and take responsibility for oneself and state of being. Therefore, Bitcoin and yoga can both be defined as decentralized. There are no centralized gatekeepers preventing one from accessing the Bitcoin network or using bitcoin as money; anyone can spin up a node, download a wallet or mine bitcoin. There are over 16,000 nodes geographically distributed around the world voluntarily running the bitcoin core software code establishing the payment network, validating transactions and storing the entire transaction history of bitcoin (iii). It costs as little as a few hundred dollars and requires less than 600 gigabytes of storage to run a node – in 2023 you can find mobile phones with that much storage. No one can prevent you from sending a peer-to-peer transaction or storing your own wealth with 12 words in your head – you need only decide to take true freedom into your own hands and learn how to do so (iv). The common maxim is “don’t trust, verify”. You don’t need someone else’s permission to participate in bitcoin or trust anyone else (eg, banks) to hold your wealth.
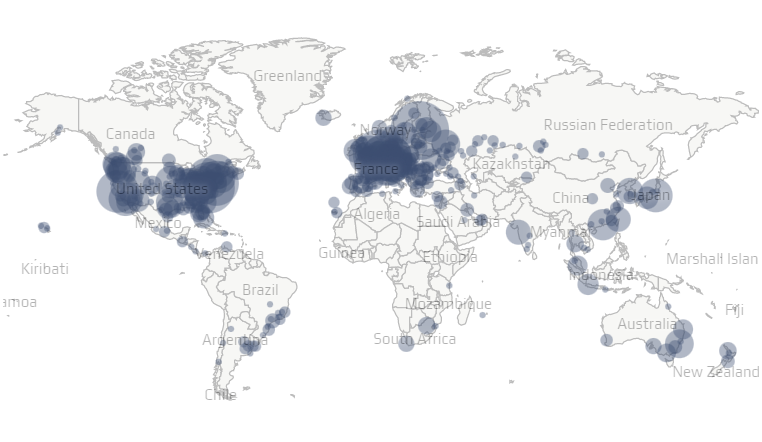 Geographic distribution of reachable bitcoin nodes (source: bitnodes)
Geographic distribution of reachable bitcoin nodes (source: bitnodes)Similarly, no one can stop an individual from practicing yoga, learning yogic philosophy or connecting with one’s truest self and inner guru. Anyone can choose to follow the path of yoga, focus on ones breath or develop a strong asana practice. There are many different ways to learn and interact with yoga, with experienced teachers willing to share their lessons to students all over the world. One need to simply find yoga studio, enroll in a teacher training or and engage with a teacher to experience yoga for themselves. Yoga looks and feels different depending on what country you are in or in which lineage you are being taught. Tapping into these profound lessons, as fundamental as controlling ones own breath, requires only an individual desire and the conscious decision to act. There’s no CEO or central authority dictating how Bitcoin or yoga has to be. Individuals have the freedom to express themselves voluntarily guided by frameworks we will dive into deeper.
Low Time Preference
Another core value that bitcoin and yoga share is low time preference. In Austrian economics, time preference refers to individual decision making. An individual with a low time preference makes decisions with greater consideration of the future, quieting immediate cravings and desires to pursue a higher goal (v). In bitcoin and money, lower time preference decisions include putting off consumption to save value for the future. Unfortunately, our fiat (by government decree) system induces individuals to make high time preference decisions, heightening consumerism and poor habits today that we see rampant in our society. There is a disincentive to save, as inflation of the money supply leads to debasing value of the dollar and other fiat currencies, decreasing individuals purchasing power of cash they hold onto and don’t spend soon. For example, the purchasing power of your dollar today will be cut in half over the next decade at current levels of inflation. In many ways, bitcoin is time, described brilliantly by Gigi, as it creates a decentralized clock that establishes consensus with each block (vi).
In contrast, the hard cap supply of 21 million bitcoin enables individuals to save with the knowledge that governments and central banks will not be able to debase their hard-earned value. This allows for one to plan with greater certainty, making investments that have a longer payoff period rather than chasing quick, material gains. Likewise in yoga, developing your own practice will not bear fruit right away; it takes discipline and time to continuously improve and strive towards a better future self. For example, in modern Ashtanga yoga taught by Pattabhi Jois, there is a set sequence of asanas that one studies and repeats each practice. It may even take months to have find the right alignment of body and breath for a single pose! The hours-long sequence requires dedication to practice and learn. The dedicated yogi understands that wholehearted commitment today will pay off for one’s mental, physical and spiritual health in the years to come. The ability to develop a calm mind can also be beneficial when people don’t initially understand or are intimidated by bitcoin. This approach can also enable you to stay grounded and discover the signal through the noise when learning about bitcoin.
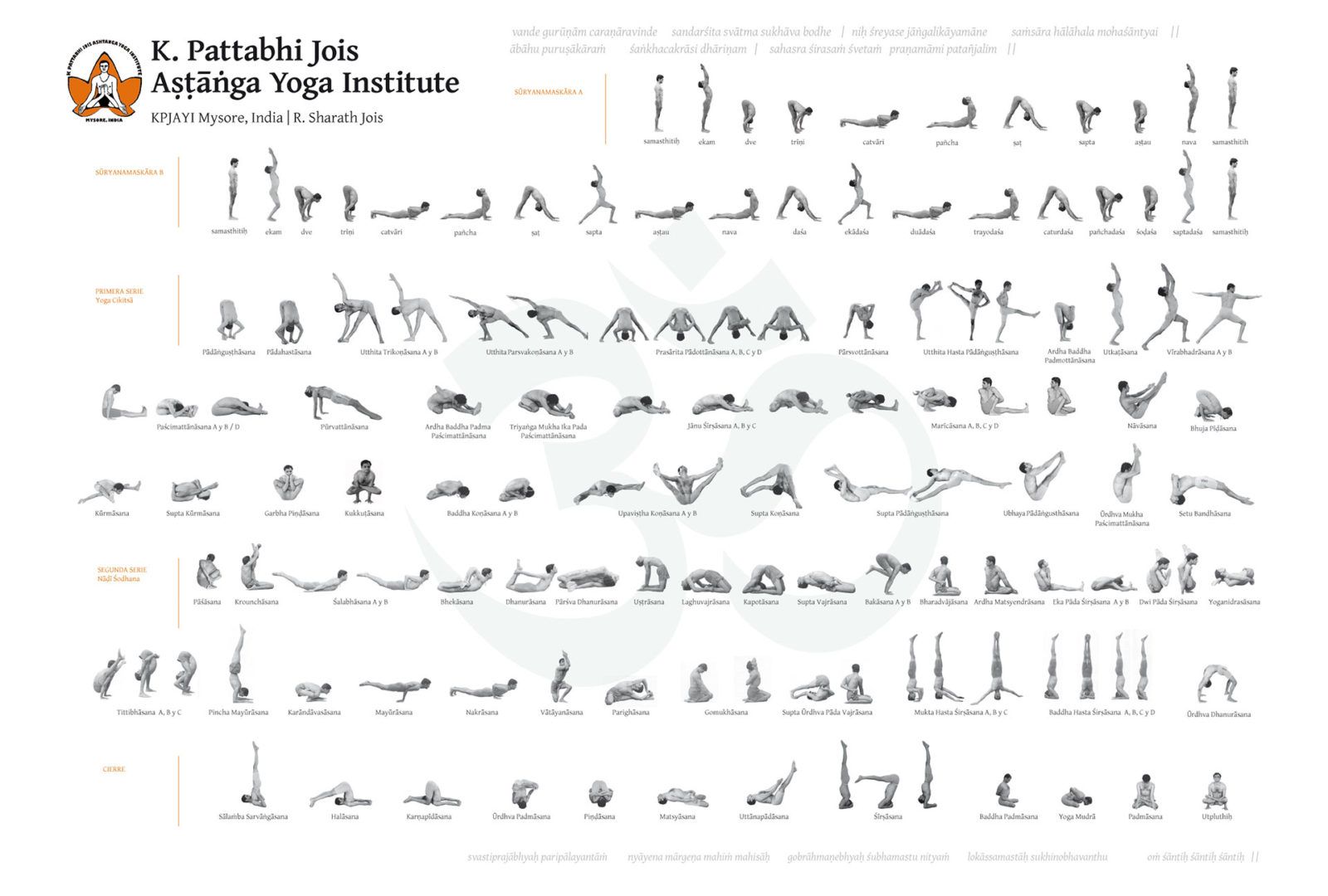 Sequence of asanas in Jois' Ashtanga Yoga (image source)
Sequence of asanas in Jois' Ashtanga Yoga (image source)Union
Yoga comes from the Sanskrit word “yuj”, which means ‘to join’ or ‘to unite’. Yoga represents the union of the mind, body, and soul of an individual. Yoga provides a pathway to individual sovereignty through disciplined practice and purpose. Yoga unites an individual internally and to one’s community, fostering connectedness and support (vii). Similarly, bitcoin provides a pathway to individual sovereignty in many ways. Bitcoin empowers the individual authority with property rights over one’s value, which in turn frees individuals from outside control (government or otherwise). Bitcoin’s technology enables one to hold their own wealth and life’s energy in a self-custodial fashion. Bitcoin is money that can be stored forever and transmitted through space at the speed of light on layer two via the Lightning Network.
Bitcoin is an open economic network with the potential to unite eight billion people together in a way our current unfair and fragmented financial system could never do. In many countries, a majority of people are unbanked, while intermediaries take a cut of the value to transfer slow, legacy payments like Western Union. While tens of millions people around the world have so far interacted with bitcoin – we are still early – similar to the internet of the mid-nineties. Bitcoin eliminates counter party risk associated with non-bearer assets, such as fiat currency (e.g., dollars, euros, yen). Bitcoin’s supply schedule is set and eliminates inflation time theft that fiat currency wages on individuals, which leads to anxiety and depression or feelings of hopelessness. Fiat is money enforced by the monopoly on violence that modern nation states grip tightly.
In contrast, bitcoin and yoga empower the individual to remove the shackles and embrace personal responsibility to improve ones life. Bitcoin and yoga also connect people directly to each other and tap into truth, ones inner being, bringing peace in the present and ultimately offer hope for a better future for each person, your community, and the world. Bitcoin and yoga have the power to unite humanity in love.
In the next section, we will explore both yoga and bitcoin's mystical and mythical origins.
Note: Bitcoin with a capital "B" generally refers to the protocol/network; bitcoin with a lower case "b" refers to the money/currency.
References:
i. Redman, Jamie, How Henry Ford Envisaged Bitcoin 100 Years Ago — A Unique 'Energy Currency' That Could 'Stop Wars', News.Bitcoin.Com, October 11, 2021 <https://news.bitcoin.com/how-henry-ford-envisaged-bitcoin-100-years-ago-a-unique-energy-currency-that-could-stop-wars/>
ii. Nakomoto, Satoshi, Bitcoin: A Peer-to-Peer Electronic Cash System, bitcoin.org, October 31, 2008 <https://bitcoin.org/bitcoin.pdf>
iii. https://bitnodes.io/
iv. Hall, Stephen, What is a bitcoin seed phrase and how does it work? Unchained.com. December 17, 2021 <https://unchained.com/blog/what-is-a-bitcoin-seed-phrase/>
v. Ammous, Saifedean, Making Time Preference Low Again, The Bitcoin Times, Austrian Edition (V). November 8, 2022 <https://bitcointimes.io/making-time-preference-low-again/>
vi. Gigi, Bitcoin is Time, dergigi.com. Jan 14,2021 <https://dergigi.com/2021/01/14/bitcoin-is-time/>
vii. 200 hour yoga teacher training. House of Om, Bali, Indonesia. <https://houseofom.com/>
-
 @ 006532cb:fd8f28b4
2025-02-02 09:50:56
@ 006532cb:fd8f28b4
2025-02-02 09:50:56I am new to #NOSTR and not a #Dev; however, npub1jlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qdjynqn's article inspired me to research and understand further. As a result, I have condensed my learnings into 10 bullet points that seem to embody the spirit of being a nostrich and the qualities we should all strive for when engaging with one another making software choices and avoiding NINO's.
- You shall not compromise on security: Prioritize the security and integrity of user data, using best practices and Nostr's built-in features to protect against unauthorized access and malicious activity.
- You shall prioritize user agency: Respect users' mute lists, use their web of trust to filter out spam, and prioritize user control over their data.
- You shall be decentralized and open: Do not hardcode relay URLs or depend on specific relay implementations, ensuring that your platform is truly decentralized and open.
- You shall leverage Nostr's technical aspects: Take advantage of Nostr's features, such as self-authenticating data, event handlers, and relays, to build a robust and decentralized platform.
- You shall use native Nostr solutions: Prefer Nostr-native solutions to solve problems, rather than relying on legacy web services, promoting a more decentralized and resilient ecosystem.
- You shall prioritize interoperability: Implement NIP 89 (Recommended Application Handlers) to enable seamless interactions with other Nostr apps, promoting a unified and decentralized ecosystem.
- You shall engage with the community: Share knowledge, contribute to the growth of the ecosystem, and collaborate with other Nostr developers to promote a unified and thriving community.
- You shall be transparent and accountable: Be transparent in your development processes, and accountable for your actions and decisions, promoting trust and confidence in the Nostr ecosystem.
- You shall innovate and evolve: Continuously innovate and improve your platform, staying up-to-date with the latest developments in the Nostr protocol and ecosystem, to ensure the best possible experience for users.
- Embody Nostr: Your application should truly represent the Nostr protocol, using its features and network to provide unique value to users.
I am excited for the future. In Eric S. Raymond's book "The Cathedral and the Bazaar" he comments;
"...and the robust doesn't care too much"
Nostr embodies the spirit of the Bazaar, a vibrant and eclectic marketplace where the robust thrive, all are welcomed and empowered to become strong.
/GN!
-
 @ da0b9bc3:4e30a4a9
2025-02-02 08:18:39
@ da0b9bc3:4e30a4a9
2025-02-02 08:18:39Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/873174
-
 @ 57d1a264:69f1fee1
2025-02-02 05:47:57
@ 57d1a264:69f1fee1
2025-02-02 05:47:57Hey there, as a result of the recent SN Media Kit updated, I'll try to create few simple marketing assets for ~Stackers_Stocks territory to be spread across the web.
Feel free to share in the comments below: - Few visual references you'd like the assets to be inspired on - If visuals are not your thing, a description of your idea will help too - A slogan, or some words/concepts that express the territory's values
@BlokchainB you start, let's see how we go!
originally posted at https://stacker.news/items/873112
-
 @ c631e267:c2b78d3e
2024-10-23 20:26:10
@ c631e267:c2b78d3e
2024-10-23 20:26:10Herzlichen Glückwunsch zum dritten Geburtstag, liebe Denk Bar! Wieso zum dritten? Das war doch 2022 und jetzt sind wir im Jahr 2024, oder? Ja, das ist schon richtig, aber bei Geburtstagen erinnere ich mich immer auch an meinen Vater, und der behauptete oft, der erste sei ja schließlich der Tag der Geburt selber und den müsse man natürlich mitzählen. Wo er recht hat, hat er nunmal recht. Konsequenterweise wird also heute dieser Blog an seinem dritten Geburtstag zwei Jahre alt.
Das ist ein Grund zum Feiern, wie ich finde. Einerseits ganz einfach, weil es dafür gar nicht genug Gründe geben kann. «Das Leben sind zwei Tage», lautet ein gängiger Ausdruck hier in Andalusien. In der Tat könnte es so sein, auch wenn wir uns im Alltag oft genug von der Routine vereinnahmen lassen.
Seit dem Start der Denk Bar vor zwei Jahren ist unglaublich viel passiert. Ebenso wie die zweieinhalb Jahre davor, und all jenes war letztlich auch der Auslöser dafür, dass ich begann, öffentlich zu schreiben. Damals notierte ich:
«Seit einigen Jahren erscheint unser öffentliches Umfeld immer fragwürdiger, widersprüchlicher und manchmal schier unglaublich - jede Menge Anlass für eigene Recherchen und Gedanken, ganz einfach mit einer Portion gesundem Menschenverstand.»
Wir erleben den sogenannten «großen Umbruch», einen globalen Coup, den skrupellose Egoisten clever eingefädelt haben und seit ein paar Jahren knallhart – aber nett verpackt – durchziehen, um buchstäblich alles nach ihrem Gusto umzukrempeln. Die Gelegenheit ist ja angeblich günstig und muss genutzt werden.
Nie hätte ich mir träumen lassen, dass ich so etwas jemals miterleben müsste. Die Bosheit, mit der ganz offensichtlich gegen die eigene Bevölkerung gearbeitet wird, war früher für mich unvorstellbar. Mein (Rest-) Vertrauen in alle möglichen Bereiche wie Politik, Wissenschaft, Justiz, Medien oder Kirche ist praktisch komplett zerstört. Einen «inneren Totalschaden» hatte ich mal für unsere Gesellschaften diagnostiziert.
Was mich vielleicht am meisten erschreckt, ist zum einen das Niveau der Gleichschaltung, das weltweit erreicht werden konnte, und zum anderen die praktisch totale Spaltung der Gesellschaft. Haben wir das tatsächlich mit uns machen lassen?? Unfassbar! Aber das Werkzeug «Angst» ist sehr mächtig und funktioniert bis heute.
Zum Glück passieren auch positive Dinge und neue Perspektiven öffnen sich. Für viele Menschen waren und sind die Entwicklungen der letzten Jahre ein Augenöffner. Sie sehen «Querdenken» als das, was es ist: eine Tugend.
Auch die immer ernsteren Zensurbemühungen sind letztlich nur ein Zeichen der Schwäche, wo Argumente fehlen. Sie werden nicht verhindern, dass wir unsere Meinung äußern, unbequeme Fragen stellen und dass die Wahrheit peu à peu ans Licht kommt. Es gibt immer Mittel und Wege, auch für uns.
Danke, dass du diesen Weg mit mir weitergehst!
-
 @ a95c6243:d345522c
2024-10-19 08:58:08
@ a95c6243:d345522c
2024-10-19 08:58:08Ein Lämmchen löschte an einem Bache seinen Durst. Fern von ihm, aber näher der Quelle, tat ein Wolf das gleiche. Kaum erblickte er das Lämmchen, so schrie er:
"Warum trübst du mir das Wasser, das ich trinken will?"
"Wie wäre das möglich", erwiderte schüchtern das Lämmchen, "ich stehe hier unten und du so weit oben; das Wasser fließt ja von dir zu mir; glaube mir, es kam mir nie in den Sinn, dir etwas Böses zu tun!"
"Ei, sieh doch! Du machst es gerade, wie dein Vater vor sechs Monaten; ich erinnere mich noch sehr wohl, daß auch du dabei warst, aber glücklich entkamst, als ich ihm für sein Schmähen das Fell abzog!"
"Ach, Herr!" flehte das zitternde Lämmchen, "ich bin ja erst vier Wochen alt und kannte meinen Vater gar nicht, so lange ist er schon tot; wie soll ich denn für ihn büßen."
"Du Unverschämter!" so endigt der Wolf mit erheuchelter Wut, indem er die Zähne fletschte. "Tot oder nicht tot, weiß ich doch, daß euer ganzes Geschlecht mich hasset, und dafür muß ich mich rächen."
Ohne weitere Umstände zu machen, zerriß er das Lämmchen und verschlang es.
Das Gewissen regt sich selbst bei dem größten Bösewichte; er sucht doch nach Vorwand, um dasselbe damit bei Begehung seiner Schlechtigkeiten zu beschwichtigen.
Quelle: https://eden.one/fabeln-aesop-das-lamm-und-der-wolf
-
 @ 1ec45473:d38df139
2025-01-25 20:15:01
@ 1ec45473:d38df139
2025-01-25 20:15:01Preston Pysh posted this event this morning:

Behind the scenes, the nostr event looks like this:
Event = { "id":"a6fa7e1a73ce70c6fb01584a0519fd29788e59d9980402584e7a0af92cf0474a", "pubkey":"85080d3bad70ccdcd7f74c29a44f55bb85cbcd3dd0cbb957da1d215bdb931204", "created_at":1724494504, "kind":1, "tags":[ [ "p", "6c237d8b3b120251c38c230c06d9e48f0d3017657c5b65c8c36112eb15c52aeb", "", "mention" ], [ "p", "77ec966fcd64f901152cad5dc7731c7c831fe22e02e3ae99ff14637e5a48ef9c", "", "mention" ], [ "p", "c1fc7771f5fa418fd3ac49221a18f19b42ccb7a663da8f04cbbf6c08c80d20b1", "", "mention" ], [ "p", "50d94fc2d8580c682b071a542f8b1e31a200b0508bab95a33bef0855df281d63", "", "mention" ], [ "p", "20d88bae0c38e6407279e6a83350a931e714f0135e013ea4a1b14f936b7fead5", "", "mention" ], [ "p", "273e7880d38d39a7fb238efcf8957a1b5b27e819127a8483e975416a0a90f8d2", "", "mention" ], [ "t", "BH2024" ] ], "content":"Awesome Freedom Panel with...", "sig":"2b64e461cd9f5a7aa8abbcbcfd953536f10a334b631a352cd4124e8e187c71aad08be9aefb6a68e5c060e676d06b61c553e821286ea42489f9e7e7107a1bf79a" }In nostr, all events have this form, so once you become familiar with the nostr event structure, things become pretty easy.
Look at the "tags" key. There are six "p" tags (pubkey) and one "t" tag (hashtag).
The p tags are public keys of people that are mentioned in the note. The t tags are for hashtags in the note.
It is common when working with NOSTR that you have to extract out certain tags. Here are some examples of how to do that with what are called JavaScript Array Methods:
Find the first "p" tag element:
``` Event.tags.find(item => item[0] === 'p')
[ 'p', '6c237d8b3b120251c38c230c06d9e48f0d3017657c5b65c8c36112eb15c52aeb', '', 'mention' ]
```
Same, but just return the pubkey":
``` Event.tags.find(item => item[0] === 'p')[1]
'6c237d8b3b120251c38c230c06d9e48f0d3017657c5b65c8c36112eb15c52aeb'
```
Filter the array so I only get "p" tags:
``` Event.tags.filter(item => item[0] === 'p')
[ [ 'p', '6c237d8b3b120251c38c230c06d9e48f0d3017657c5b65c8c36112eb15c52aeb', '', 'mention' ], [ 'p', '77ec966fcd64f901152cad5dc7731c7c831fe22e02e3ae99ff14637e5a48ef9c', '', 'mention' ], [ 'p', 'c1fc7771f5fa418fd3ac49221a18f19b42ccb7a663da8f04cbbf6c08c80d20b1', '', 'mention' ], [ 'p', '50d94fc2d8580c682b071a542f8b1e31a200b0508bab95a33bef0855df281d63', '', 'mention' ], [ 'p', '20d88bae0c38e6407279e6a83350a931e714f0135e013ea4a1b14f936b7fead5', '', 'mention' ], [ 'p', '273e7880d38d39a7fb238efcf8957a1b5b27e819127a8483e975416a0a90f8d2', '', 'mention' ] ]
```
Return an array with only the pubkeys in the "p" tags:
``` Event.tags.filter(item => item[0] === 'p').map(item => item[1])
[ '6c237d8b3b120251c38c230c06d9e48f0d3017657c5b65c8c36112eb15c52aeb', '77ec966fcd64f901152cad5dc7731c7c831fe22e02e3ae99ff14637e5a48ef9c', 'c1fc7771f5fa418fd3ac49221a18f19b42ccb7a663da8f04cbbf6c08c80d20b1', '50d94fc2d8580c682b071a542f8b1e31a200b0508bab95a33bef0855df281d63', '20d88bae0c38e6407279e6a83350a931e714f0135e013ea4a1b14f936b7fead5', '273e7880d38d39a7fb238efcf8957a1b5b27e819127a8483e975416a0a90f8d2' ]
```
-
 @ b17fccdf:b7211155
2025-01-21 18:39:47
@ b17fccdf:b7211155
2025-01-21 18:39:47~ > Check out the steps to get this ~ > HERE < ~
Note: for different reasons, it is recommended choosing Option 1: DoT & DNSSEC using systemd-resolved, but you could want to use Option 2, choose behind your criteria, both are valid to achieve the same objective.
Some more changes were released recently in other places of the MiniBolt guide, check the full release notes:
Full release notes
~ > Static IP & custom DNS servers bonus guide:
- Adds custom DNS server suggestions.
- Adds different steps to check the changes after configurations.
- Deleted some unnecessary steps.
- Fix some nits.
~ > Modifications on Configuration (
bitcoin.conf) of Bitcoin Core:- Replace proxy value parameter to use UNIX domain socket (
proxy=unix:/run/tor/socks) | (recently enabled on Bitcoin Core v28). - Replace
startupnotify=chmod g+r /home/bitcoin/.bitcoin/.cookietorpccookieperms=groupBitcoin Core PR. - Adds another special bind address to listen to incoming connections from Tor (
bind=127.0.0.1=onion) | (recently changed on Bitcoin Core v28). - Modified systemd service to improve the startup and shutdown process.
Note: remember to restart Bitcoin Core and reload the systemd with
sudo systemctl daemon-reloadto apply changes.
~ > Delete unnecessary parameters of the systemd service of Lightning client.
Note: remember to reload the systemd with
sudo systemctl daemon-reloadto apply changes.
~ > Others:
- New i2pd webconsole section.
- Adds a new "Validation" subsection to the guides to clarify when checks begin.
- New "Use the Tor proxy from another device" section.
- Adds Electrs compatible with Testnet4 on Testnet bonus guide.
- Adds how to build a Guard/Middle relay section on "Tor services: bridges & relays" bonus guide.
- Adds Extras (optional) section to "Tor services: bridges & relays" bonus guide with different utilities like install Nyx, how to "Limit bandwidth" and others.
- Changed Electrs ports to enable simultaneous mode with Fulcrum.
- Updated aliases list to include news additions in line with updates.
- Updated the Networkmap resource to include news additions in line with updates and migrate to a dynamic visual mode.
- Reorganized some menu items and sections to improve the UX and make more sense in the face of the future.
- Restructure and rename the "Tor obfs4 bridge" bonus guide to "Tor services: bridges & relays" and modify it to run the obfs4bridge, relays, and the master, in separate instances.
- Hidden NYM mixnet and Sparrow server bonus guides from the menus due to disuse or poor performance. Note: it will continue to be maintained later if the situation changes due to the development of the associated software.
- Bump version of various services.
~ > Coming soon...
- Enable DNSSEC for your domain using Cloudflare + Namecheap.
- Enable DoH on:
- Desktop/Android browser (Windows/Linux).
- OS: Windows 11 // Linux (Completed ✅)
- Router.
- Enable DoT on:
- Android OS.
- OS: Windows 11 // Linux (Completed ✅) with DNSSEC verification included.
- Router.
Enjoy it MiniBolter!💙
-
 @ b17fccdf:b7211155
2025-01-21 18:30:13
@ b17fccdf:b7211155
2025-01-21 18:30:13~ > Available at: https://minibolt.info
~> It builds on a personal computer with x86/amd64 architecture processors.
~> It is based on the popular RaspiBolt v3 guide.
Those are some of the most relevant changes:
- Changed OS from Raspberry Pi OS Lite (64-bits) to Ubuntu Server LTS (Long term support) 64-bit PC (AMD64).
- Changed binaries and signatures of the programs to adapt them to x86/amd64 architecture.
- Deleted unnecessary tools and steps, and added others according to this case of use.
- Some useful authentication logs and monitoring commands were added in the security section.
- Added some interesting parameters in the settings of some services to activate and take advantage of new features.
- Changed I2P, Fulcrum, and ThunderHub guides, to be part of the core guide.
- Added exclusive optimization section of services for slow devices.
~ > Complete release notes of the MiniBolt v1: https://github.com/twofaktor/minibolt/releases/tag/1.0.
~ > Feel free to contribute to the source code on GitHub by opening issues, pull requests or discussions.
Created by ⚡2 FakTor⚡
-
 @ 57d1a264:69f1fee1
2025-02-02 05:36:57
@ 57d1a264:69f1fee1
2025-02-02 05:36:57Hey there, as a result of the recent SN Media Kit updated, I'll try to create few simple marketing assets for ~Construction_and_Engineering territory to be spread across the web.
Feel free to share in the comments below: - Few visual references you'd like the assets to be inspired on - If visuals are not your thing, a description of your idea will help too - A slogan, or some words/concepts that express the territory's values
@BlokchainB you start, let's see how we go!
originally posted at https://stacker.news/items/873104
-
 @ b17fccdf:b7211155
2025-01-21 18:22:51
@ b17fccdf:b7211155
2025-01-21 18:22:51😱 Did you recently find this signature verification error when you tried to update your MiniBolt repositories with ->
sudo apt update? 💥🚨👇
🔧 Don't worry, that's because Tor renewed its signing key since it expired last 07/15, just renew your keyring by following the next steps to solve this problem:
~ > CLICK HERE < ~
Enjoy it MiniBolter!💙
-
 @ b17fccdf:b7211155
2025-01-21 17:58:35
@ b17fccdf:b7211155
2025-01-21 17:58:35The router reserves the IP address of the device for a time after going out, but if the device goes out some time, the next time that the device starts, the router could assign a different IP and you could lose access to your node. To avoid this, you need to set a static IP to your MiniBolt.
~ > In addition, you can customize your DNS servers to improve your privacy, normally your ISP, gives you the router with its own DNS servers set by default, and this does that you expose all of your navigation trackings to your ISP, affecting seriously your privacy.
~ > This bonus guide includes all of the necessary steps to get this and is available ~ > HERE < ~

Enjoy it MiniBolter! 💙
-
 @ 3b7fc823:e194354f
2025-02-02 03:16:40
@ 3b7fc823:e194354f
2025-02-02 03:16:40Why Privacy Matters and How to Protect It
Privacy is about control. It’s not about hiding yourself but deciding what others can see about you. Just as you don’t share everything when buying a magazine, technology shouldn’t force you to reveal more than needed.
Why Privacy is Important
-
Personal Control: Privacy lets you choose what parts of your life are visible. You shouldn’t have to share everything just to use a service.
-
Security Against Exploitation: Without privacy, people and groups can be targeted by companies or governments. This abuse can lead to data breaches or unnecessary surveillance.
-
Building Trust: Privacy is key to trust in relationships and communities. When your info is safe, you can transact and communicate without fear of misuse.
How to Protect Your Privacy 1. Think Before You Share: Only share what’s necessary and know why you’re doing it. 2. Use Encryption: Encrypt sensitive communications like emails or messages. 3. Control Data Sharing: Avoid oversharing personal details online. 4. Enable Privacy Tools: Use VPNs or privacy settings on social media to shield your data. 5. Be Mindful of Metadata: Understand that metadata (like location data) can reveal more about you than the content itself. 6. Support Privacy-Focused Brands: Choose services that prioritize privacy, like encrypted messaging apps. 7. Read Privacy Policies: Know what data you’re sharing and with whom. 8. Tools like privacy.io can help visualize your digital footprint. 9. Block Trackers: Use tools like DoNotTrackMe or uBlock Origin to stop trackers from collecting your data.
Conclusion
Protecting privacy is a vital step in safeguarding your personal freedoms. By taking proactive measures, you can control what information is accessible and ensure that your rights are respected. Remember, you are your own best advocate for privacy—trust no one but yourself to protect your data and identity.
Join the movement to champion privacy as a fundamental human right. Advocate for stronger laws and encourage others to take action, so we can all enjoy safer, more secure digital environments.
-
-
 @ b17fccdf:b7211155
2025-01-21 17:47:28
@ b17fccdf:b7211155
2025-01-21 17:47:28Link to the bonus guide ~ > HERE < ~
Some sections of the guide:
- Generate SSH keys
- Import SSH pubkey
- Connect to the MiniBolt node using SSH keys
- Disable password login
- Disable admin password request
Some shortcuts to the Extra sections:
Enjoy it MiniBolter! 💙
-
 @ b17fccdf:b7211155
2025-01-21 17:29:54
@ b17fccdf:b7211155
2025-01-21 17:29:54Some sections inside of the guide:
- Set up Dynamic DNS
- Wireguard VPN server & client side configurations
- Install & configure the WireGuard VPN Client on a mobile phone
- Configure additional servers & clients
- Use your router’s DDNS preconfigured provider
- Port forwarding on NAT/PAT router
Link to the bonus guide HERE
Enjoy it MiniBolter! 💙
-
 @ 57d1a264:69f1fee1
2025-02-02 00:03:39
@ 57d1a264:69f1fee1
2025-02-02 00:03:39Welcome to the latest updated version of Stacker News Media Kit & Brand Guidelines
v1.2, a pivotal location where all the visual elements find place and help us understand how to use them to have our communications cohesive. SN brand identity is built on simplicity, trust, innovation and a taste of Texas's Wild West. With the following guidelines, as promised, I'll try to outline the essential elements of SN visual language to be easily usable internally and externally.As third interaction from the previous discussion, here below you will find all the media assets in PNG and SVG downloadable from this zip file. BTW: I've been using
Nostr🌸 Blossom Serverservers check them out, it's a really cool idea! In case the file will be not available we can always upload it in other servers. Just let me know if any issue downloading it, ideally I made three copies available from: - https://nosto.re/0a8b02224c970de78fba3a0195dcf1ee44d18925ba941724497173b2bcbab901.zip - https://blossom.poster.place/0a8b02224c970de78fba3a0195dcf1ee44d18925ba941724497173b2bcbab901.zip - https://nostr.download/0a8b02224c970de78fba3a0195dcf1ee44d18925ba941724497173b2bcbab901.zipThe source file of all these assets still are the same Figma file and the PenPot file. This last one, has many issues and does not allow yet the same flexibility as Figma. Both files are open for contributions and comments, just need to register a dummy/anonymous account for each of the tools.
Note: To use these assets across SN, just copy-paste the image relative code, i.e.:
Stacker News Logotype
SN logo is the most recognizable visual identifier of Stacker News. It captures the essence of its brand and is to be used across the platform and other marketing materials consistently. Find below all the possible variations and colors. Ideally you should stick with it to maintain SN identity coherent, or propose something new if you feel like. If you have any question on how to place or use the logo, DO ask below, and we'll help sort it out.
| Avatar on transparent BG | Avatar on BG | Logo Extended | Logo Vertical |#| |---|---|---|---|---| |
||||Oil Black| ||||| Golden Yellow | |||||With Shadow |Stacker News Typography
This is the typography SN had used to create its logo. Download LightningVolt OpenType Font file.otf designed by Honey&Death, install it in your computer and play with it.
Typography is essential to identify, increase readability and create consistency of brands. SN uses the default
font-family:sans-serif;of your device's OS, usually are the most common and already installed in your device:system-ui, "Segoe UI", Roboto, "Helvetica Neue", "Noto Sans", "Liberation Sans", Arial, sans-serif, "Apple Color Emoji", "Segoe UI Emoji", "Segoe UI Symbol", "Noto Color Emoji". Those are mostly used for:Example Header H1
Example Header H2
Example Header H3
Example Header H4
Example Header H5
Example paragraph text The fonts selected will help to communicate the personality of the brand and provide maximum legibility for both print and screen.
Example <code>For code, the approach is the same. Let's the device OS select its defaultmonospaceone. For example, on Mac will be one of the following:SFMono-Regular, Menlo, Monaco, Consolas, "Liberation Mono", "Courier New",`Stacker News Colors
A thoughtfully curated color palette gives SN trust, professionalism, and approachability. Colors play a key role in creating consistent visual experiences through digital and print communications. Make sure you are using the right color codes below:
| # | Name | HEX code | RGB code | HLS | |---|---|---|---|---| |
| Bitcoin-only |
#F6911D|rgb(246,145,29)|hsl(32,92.3%,53.9%)| || Blackr |
#000000|rgb(0,0,0)|hsl(0,0%,0%)| || Dark |
#121214|rgb(18,18,20)|hsl(240,5.3%,7.5%)| || Gold |
#FADA5E|rgb(250,218,94)|hsl(48,94%,67.5%)| || Gray |
#969696|rgb(150,150,150)|hsl(0,0%,58.8%)| || Light |
#F0F0F0|rgb(240,240,240)|hsl(0,0%,94.1%)| || Nostrch |
#8C25F4|rgb(140,37,244)|hsl(270,90.4%,55.1%)| || Pinkish |
#E685B5|rgb(230,133,181)|hsl(330,66%,71.2%)| || Ruby |
#C03221|rgb(192,50,33)|hsl(6,70.7%,44.1%)| || Sky Hover |
#007CBE|rgb(0,124,190)|hsl(201,100%,37.3%)| || Sky Links |
#2E99D1|rgb(46,153,209)|hsl(201,63.9%,50%)| || Sky Visited |
#56798E|rgb(86,121,142)|hsl(203,24.6%,44.7%)| || So Fiat |
#5C8001|rgb(92,128,1)|hsl(77,98.4%,25.3%)|Stacker News Icons
SN utilizes a set of bespoke icons that support its communication internally across the platform. Icons help bring instant, intuitive cues for various types of content and features. We share them here for you so you can use as you wish and satisfy your creative needs.
|
||[Bounty](https://m.stacker.news/75607)|[Caret](https://m.stacker.news/75608)|[Cowboy](https://m.stacker.news/75609)|[Sun](https://m.stacker.news/75610)| |---|---|---|---|---|---| |[Edit](https://m.stacker.news/75611)|[Gun](https://m.stacker.news/75612)|[Horse](https://m.stacker.news/75613)|[Info](https://m.stacker.news/75614)|[Moon](https://m.stacker.news/75615)|[Lightning](https://m.stacker.news/75616)| |[Bald Lost Hat](https://m.stacker.news/75617)|[Markdown](https://m.stacker.news/75618)|[Nostr](https://m.stacker.news/75619)|[Referral](https://m.stacker.news/75620)|[Rewards](https://m.stacker.news/75621)|[Horse Lost Saddle](https://m.stacker.news/75622)|[Search](https://m.stacker.news/75623)| |[Shoot](https://m.stacker.news/75624)|[Texas](https://m.stacker.news/75625)|[Upload](https://m.stacker.news/75626)|[Zap Zap](https://m.stacker.news/75627)|||Stacker News Banners
Banners are important visual elements used in our digital platforms and marketing materials. They help to highlight key stories, features or announcements while maintaining our brand aesthetic.
Here below you'll find custom banners for Sn and for individial territories. I try to build those that I follow most, for now @AGORA is the only one that designed its own banners. Comment below if you'd like some banners for your territory!
SN Dark background
|970x250| |---| |
||||728x90| |---| |
|SN Gold background
|970x250| |---| |
||250x250|300x250|300x600| |---|---|---| |
||||728x90| |---| |
|SN by @Jon_Hodl
|970x250| |---| |
||250x250|300x250|300x600| |---|---|---| |
||||728x90| |---| |
|~AGORA territory
The SN P2P Marketplace |970x250| |---| |
||250x250|300x250|300x600| |---|---|---| |
||||728x90| |---| |
|~alter_native territory
|970x250| |---| |
||250x250|300x250|300x600| |---|---|---| |
||||728x90| |---| |
|~bitcoin_beginners
|970x250| |---| |
||250x250|300x250|300x600| |---|---|---| |
||||728x90| |---| |
|~Design territory
|970x250| |---| |
||250x250|300x250|300x600| |---|---|---| |
||||728x90| |---| |
|~Music territory
|970x250| |---| |
||250x250|300x250|300x600| |---|---|---| |
||||728x90| |---| |
|Anything else we could add?
If you feel something is missing, or you know a better tool to manage this media kit for SN in a collaborative and FOSS way then, DO share it in a comment below
Territory owners [^1], do you need banners for your territory? Feel free to edit the figma file liked above or comment below sharing your needs or ideas, I'll try to do something for you.
By following these guidelines, we ensure consistency and professionalism in every case where Stacker News is represented here internally to stackers or to our audience in the KYC internet, reinforcing SN credibility as a trusted source for data-driven journalism.
[^1]: FYI: @Aardvark @AGORA @anna @antic @AtlantisPleb @Bell_curve @benwehrman @bitcoinplebdev @Bitter @BlokchainB @ch0k1 @davidw @ek @elvismercury @frostdragon @grayruby @HODLR @inverselarp @Jon_Hodl @k00b @marks @MaxAWebster @mega_dreamer @niftynei @nout @OneOneSeven @OT @PlebLab @Public_N_M_E @RDClark @realBitcoinDog @roytheholographicuniverse @siggy47 @softsimon @south_korea_ln @theschoolofbitcoin @TNStacker @UCantDoThatDotNet @Undisciplined
originally posted at https://stacker.news/items/872925
-
 @ e0e92e54:d630dfaa
2025-02-01 22:32:51
@ e0e92e54:d630dfaa
2025-02-01 22:32:51When a Client Wants Out…& A Yellow Flag Appears
This week was an interesting one with a client that wants to exit our agreement early.
(Totally fine. It happens and usually when one or both parties want to part ways, unless it's marriage, then it's at minimum a Yellow Flag if not a Red Flag that should be observed).
I tend to work with clients that have multiple irons in the fire, hence why they need someone like me to come along side them and provide guidance and help root them in the area they must focus on.
There is a strong parallel with this irregardless of whether it's #business #life or #impact
This client had big goals, but like many business owners, they defaulted to reactionary decisions instead of a structured plan. That’s when the Yellow Flag turned into a pattern I’ve seen before—Random Acts of X.
The Cost of Random Acts of X
If your solution is:
A. Throw money at it, and/or
B. Fire, Aim, Ready...instead of Ready, Aim, Fire
This WILL result in Random Acts of X (wherein X is whatever your are focused on, ie Marketing...aka Random Acts of Marketing essentially equates to the proverbial "throw spaghetti on the wall")
Is that really a thing? Like do Italians or some other cultures actually throw spaghetti on the wall to see if it "sticks"? Inquiring minds want to know! 🤷♂️
As I mentioned, my clients tend to have a lot of things they are trying to accomplish at once. This leads to fragmented efforts and lack luster results.
That being said, I approach everything as a relationship. Afterall, I believe:
Leadership = Relationships!
With this particular client there was one project he abruptly ended. Again, that's fine...it's their business...
Since I'm there to help them lead well, I reminded them this is a relationship and asked "What's next that you want me to focus on?"
We got on the same page with the new project and not even 2 days later that's where the Yellow Flag appeared in the form of issue A (just throw money at it).
Shortcuts Lead to Ghost Towns (Buying Followers Won’t Work)
You see, they wanted me to lead a marketing campaign to build relationships with people their company could sponsor. BUT they just wanted to "buy followers".
When I noticed one of their social accounts has 28k followers and on average only 14 impressions per post...
I asked "How's that working out for ya?"
You see folks, real relationships take time!
One cannot simply "throw money at it" and expect sound, sustainable results.
If you’re buying an audience instead of building one, you won’t have a community—you'll have a ghost town.
What Fake Engagement Looks Like in Business & Family
Think of it this way...
Imagine all you did in your family's relationships was throw money at it. You just "bought followers" in the form of taking this trip, buying that thing for them; and you totally avoided the time investment the relationship requires?
Sure...you might have been physically there...but were you present?
I run into this often with my son. He wants me to watch him play a video game. And during that time together what is he doing? He keeps looking over his shoulder to make sure I'm paying attention to HIM and not clandestinely on my phone.
Same goes for his Basketball...he wants me there rebounding for him...not sitting in a chair idly watching.
Are You Present or Just Physically There?
Business Owners and Leaders!
Husbands, Wives, and Parents!
People whom desire to have an impact!
The Process is the Shortcut!
Play silly games. Win silly prizes.
Intentionally build relationships. Reap rewards forever.
It's...
That...
Simple...
Easy? Not really...especially for someone like me whom is just as keen to spend time in nature or chillaxing with a cup of coffee on the back porch, thinking (and wishing my garden was growing better LOL).
But simple? Yes!
Create the process, execute the process, refine the process, and repeat.
The Process is the Shortcut...
Your Next Step: Cut the Shortcuts. Build the Process.
So—where do you need to refine your process today?
💡 What’s one way you can be more present in a relationship this week?
💡 What can you eliminate to move you closer to real impact—instead of just chasing more?
🔹 Drop your answer below 👇
Jason Ansley* is the founder of Above The Line Leader*, where he provides tailored leadership support and operational expertise to help business owners, entrepreneurs, and leaders thrive.
Want to strengthen your leadership and enhance operational excellence? Connect with Jason at https://abovethelineleader.com/contact
📌 This article first appeared on Nostr. You can also find more Business Leadership Articles and content at: 👉 https://abovethelineleader.com/business-leadership-articles

-
 @ b17fccdf:b7211155
2025-01-21 17:19:12
@ b17fccdf:b7211155
2025-01-21 17:19:12Do you want to use a different disk to store data (blockchain and other databases) independently of the disk of the system?
A step-by-step guide using a secondary disk to store the data (blockchain and other databases) independently of the disk of the system and using the Ubuntu Server guided installation.
What's changed
- Rebuilt the Ubuntu Server installation guide based on this bonus guide added.
- Added GIFs to improve the illustration of the steps to follow.
- Case 1: during the Ubuntu server guided installation.
- Case 2: build it after system installation (by command line).
~ > Link to the bonus guide HERE
Enjoy it MiniBolter! 💙
-
 @ 4d4fb5ff:1e821f47
2025-02-01 22:13:43
@ 4d4fb5ff:1e821f47
2025-02-01 22:13:43Snapshot of a 3D molecular structure. In bacteria, the enzyme Peptidase E (PepE) is encoded by the gene PEPE. PEPEDASE is an atomic view of PepE enzyme’s spatial architecture based on publicly available scientific data, visually arranged to pay homage to Pepe the Frog. I made this piece in support of Matt Furie’s #SavePepe movement.
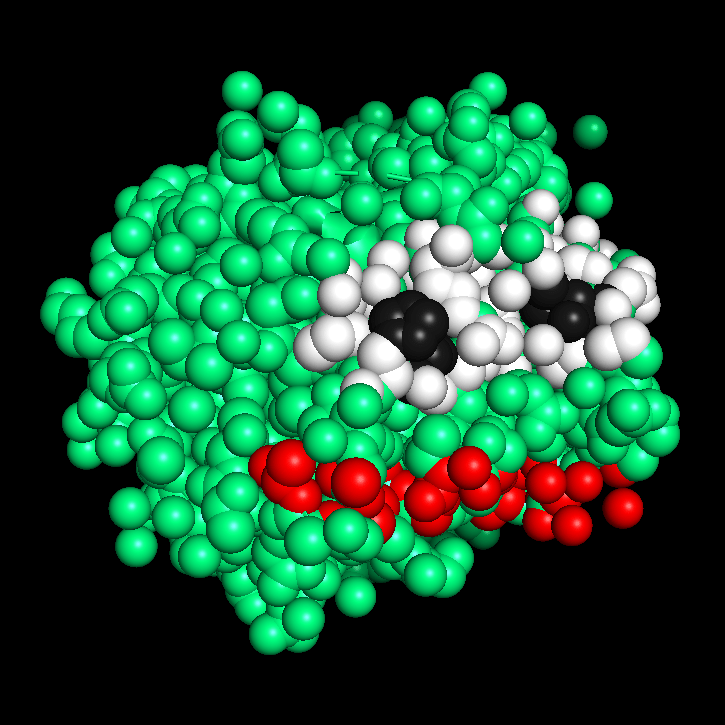
-
 @ b17fccdf:b7211155
2025-01-21 17:07:47
@ b17fccdf:b7211155
2025-01-21 17:07:47 -
 @ b17fccdf:b7211155
2025-01-21 16:56:24
@ b17fccdf:b7211155
2025-01-21 16:56:24It turns out that Ubuntu Linux installations of Ubuntu 23.04, 22.04.3 LTS, and installs done since April 2023 that accepted the Snap version update haven't been following Ubuntu's own recommended security best practices for their security pocket configuration for packages.
A new Subiquity release was issued to fix this problem while those on affected Ubuntu systems already installed are recommended to manually edit their
/etc/apt/sources.listfile.If you didn't install MiniBolt recently, you are affected by this bug, and we need to fix that manually if not we want to install all since cero. Anyway, if you installed Minibolt recently, we recommend you review that.
Follow these easy steps to review and fix this:
- Edit the
sources-listfile:
sudo nano /etc/apt/sources.list- Search now for every line that includes '-security' (without quotes) (normally at the end of the file) and change the URL to --> http://security.ubuntu.com/ubuntu
~ > For example, from http://es.archive.ubuntu.com/ubuntu (or the extension corresponding to your country) to --> http://security.ubuntu.com/ubuntu
~> Real case, Spain location, before fix:
``` deb http://es.archive.ubuntu.com/ubuntu jammy-security main restricted
deb-src http://es.archive.ubuntu.com/ubuntu jammy-security main restricted
deb http://es.archive.ubuntu.com/ubuntu jammy-security universe
deb-src http://es.archive.ubuntu.com/ubuntu jammy-security universe
deb http://es.archive.ubuntu.com/ubuntu jammy-security multiverse
deb-src http://es.archive.ubuntu.com/ubuntu jammy-security multiverse
```
After fix:
``` deb http://security.ubuntu.com/ubuntu jammy-security main restricted
deb-src http://es.archive.ubuntu.com/ubuntu jammy-security main restricted
deb http://security.ubuntu.com/ubuntu jammy-security universe
deb-src http://es.archive.ubuntu.com/ubuntu jammy-security universe
deb http://security.ubuntu.com/ubuntu jammy-security multiverse
deb-src http://es.archive.ubuntu.com/ubuntu jammy-security multiverse
```
Save and exit
Note: If you have already these lines changed, you are not affected by this bug, and is not necessary to do anything. Simply exit the editor by doing Ctrl-X
- Finally, type the next command to refresh the repository pointers:
sudo apt update- And optionally take the opportunity to update the system by doing:
sudo apt full-upgradeMore context:
- https://wiki.ubuntu.com/SecurityTeam/FAQ#What_repositories_and_pockets_should_I_use_to_make_sure_my_systems_are_up_to_date.3F
- https://bugs.launchpad.net/subiquity/+bug/2033977
- https://www.phoronix.com/news/Ubuntu-Security-Pocket-Issue
- Edit the
-
 @ dbb19ae0:c3f22d5a
2025-02-01 21:51:44
@ dbb19ae0:c3f22d5a
2025-02-01 21:51:44List of Wordpress articles:
- https://alashazam.wordpress.com/2024/07/01/python-nostr/
- https://alashazam.wordpress.com/2024/07/02/python-nostr-2/
- https://alashazam.wordpress.com/2024/07/03/python-nostr-second-program/
- https://alashazam.wordpress.com/2024/07/04/python-nostr-sdk/
- https://alashazam.wordpress.com/2024/07/04/python-nostr-third-program/
- https://alashazam.wordpress.com/2024/07/05/python-nostr-guessing-the-npub/
- https://alashazam.wordpress.com/2024/07/06/python-nostr_sdk-fetching-metadata/
- https://alashazam.wordpress.com/tag/python/
```python
!/usr/bin/env python3
""" Fetches the joined date from a Nostr profile and calculates the days since account creation.
Usage: python fetch_joined_date.py [npub]
Arguments: npub : The public key of the user (in npub format).
Requirements: - nostr_sdk library - Python 3.x
Example: python fetch_joined_date.py npub1... """
import argparse import time import ssl import json import uuid import logging from datetime import datetime from nostr.event import EventKind from nostr.relay_manager import RelayManager from nostr.key import PublicKey from nostr.filter import Filter, Filters from nostr.message_type import ClientMessageType
Configure logging
logging.basicConfig(level=logging.INFO, format="%(levelname)s: %(message)s")
RELAY_URL = "wss://relay.damus.io"
def fetch_metadata(npub): """Fetches metadata from a Nostr profile given an npub key.""" pub_key = PublicKey.from_npub(npub) filters = Filters([Filter(authors=[pub_key.hex()], kinds=[EventKind.SET_METADATA])]) subscription_id = uuid.uuid1().hex request = [ClientMessageType.REQUEST, subscription_id, *filters.to_json_array()]
relay_manager = RelayManager() relay_manager.add_relay(RELAY_URL) relay_manager.add_subscription(subscription_id, filters) try: relay_manager.open_connections({"cert_reqs": ssl.CERT_NONE}) time.sleep(1) # Allow time for connection relay_manager.publish_message(json.dumps(request)) time.sleep(1) # Allow time for response while relay_manager.message_pool.has_events(): event_msg = relay_manager.message_pool.get_event() metadata = json.loads(event_msg.event.content) return metadata except Exception as e: logging.error(f"Error fetching metadata: {e}") finally: relay_manager.close_connections() return Nonedef fetch_joined_date(npub): """Retrieves the joined date of a Nostr profile and calculates days since creation.""" metadata = fetch_metadata(npub) if not metadata or "created_at" not in metadata: logging.warning("Could not retrieve metadata or 'created_at' field is missing.") return
try: created_at = int(metadata["created_at"]) created_date = datetime.utcfromtimestamp(created_at) days_since_creation = (datetime.utcnow() - created_date).days logging.info(f"Account created on: {created_date.strftime('%Y-%m-%d %H:%M:%S UTC')}") logging.info(f"Days since account creation: {days_since_creation}") except (ValueError, TypeError): logging.error("Invalid 'created_at' timestamp.")if name == "main": parser = argparse.ArgumentParser(description="Fetch the joined date from a Nostr profile.") parser.add_argument("npub", type=str, help="The public key of the user (in npub format).") args = parser.parse_args()
fetch_joined_date(args.npub)```
-
 @ b17fccdf:b7211155
2025-01-21 16:49:27
@ b17fccdf:b7211155
2025-01-21 16:49:27What's changed
- New method for Bitcoin Core signature check, click ~ >HERE< ~
- GitHub repo of Bitcoin Core release attestations (Guix), click ~ >HERE< ~
History:
~ > PR that caused the broken and obsolescence of the old signature verification process, click ~ >HERE< ~
~ > New GitHub folder of Bitcoin Core repo that stores the signatures, click ~ >HERE< ~
Thanks to nostr:npub1gzuushllat7pet0ccv9yuhygvc8ldeyhrgxuwg744dn5khnpk3gs3ea5ds for building the command that made magic possible 🧙♂️🧡
Enjoy it MiniBolter! 💙
-
 @ b17fccdf:b7211155
2025-01-21 16:40:01
@ b17fccdf:b7211155
2025-01-21 16:40:01Important notice to MiniBolt node runners:
~ > It turns out that the I2P devs have opened an issue on the Bitcoin Core GitHub repo commenting that because they gave the option to enable the
notransit=trueparameter in the official documentation:[...] If you prefer not to relay any public I2P traffic and only allow I2P traffic from programs connecting through the SAM proxy, e.g. Bitcoin Core, you can set the no transit option to true [...] are having a heavy load on the I2P network since last December 19. Also comment that it is advisable to share as much bandwidth and transit tunnels as we can, to increase anonymity with coverage traffic, by contributing more to the I2p network than we consume.
So they ask that we deactivate that option that you use activated. With all this, he already updated the "Privacy" section by removing that setting.
The steps to delete this configuration once we have already configured it, are the following:
- With the "admin" user, stop i2pd:
sudo systemctl stop i2pd- Comment line 93 with "#" at the beginning of it (notransit = true), save and exit
sudo nano /var/lib/i2pd/i2pd.conf --line numbers- Start i2pd again:
sudo systemctl start i2pd- And that's it, you could take a look at Bitcoin Core to see that it has detected i2pd running again after the reboot with:
tail --lines 500 -f /home/bitcoin/.bitcoin/debug.log~ > If you don't see that I2P is up in Bitcoin Core after the restart,
sudo systemctl restart bitcoindand look again at the logs of the same.
More info in the rollback commit, see ~> HERE < ~
-
 @ b17fccdf:b7211155
2025-01-21 16:15:51
@ b17fccdf:b7211155
2025-01-21 16:15:51What's changed
A bonus guide to get a quick overview of the system status with the most relevant data about the services on the main guide.
➕Additional extra sections (optional) to:
- Show on login
- Get the channel.db size of an old LND bbolt database backend
- Use MobaXterm compatibility version
🔧 GitHub PR related: https://github.com/minibolt-guide/minibolt/pull/97
Σ Dedicated GitHub repository: https://github.com/minibolt-guide/system_overview
🫂Acknowledgments
This is a fork of the minibolt_info repository, the main developer of this project is rmnscb, a member of the MiniBolt community, all the merits go to him. Thank you for your contribution 🧡🫂
-> CLICK HERE <- to go to the bonus guide
Enjoy it MiniBolter! 💙
-
 @ be41636e:e55c4909
2025-02-01 18:51:52
@ be41636e:e55c4909
2025-02-01 18:51:52Will Quantum Computers Kill Bitcoin? The Truth May Surprise You
One of the biggest fears around Bitcoin is that quantum computers (QCs) will render it obsolete. But is this really a legitimate concern, or just another doomsday myth?
The Real Threat: Not All Quantum Computers Are Equal
First, let’s get one thing straight: quantum computers already exist. The first notable ones appeared in the 1990s, built by IBM and Stanford. So why hasn’t Bitcoin already been hacked? Because it’s not about whether quantum computers exist—it’s about how powerful they need to be.
Are All Bitcoin Addresses at Risk?
No! If you’ve entered Bitcoin after 2010 or use a wallet backed up with 12 or 24 words (BIP-39, introduced in 2013), your funds are safe from quantum threats for a very long time—centuries, at least.
But why?
Understanding How Bitcoin’s Security Works
Bitcoin security is based on private keys. (These are represented by the 12-24 words you write down when setting up a wallet.) From this private key, a public key is created. In Bitcoin’s early days, people shared public keys directly to receive payments. But in 2010, Bitcoin introduced an extra layer of security: hashed addresses.
Now, instead of sharing your public key, your wallet generates a Bitcoin address, which is actually a hash of your public key. This adds an extra step for an attacker: before they can find your private key, they must first break the hash to reveal your public key.
Two Steps to Breaking Bitcoin
To steal Bitcoin using quantum computing, an attacker must:
- Break the hash (Bitcoin address → public key) using Grover’s algorithm.
- Break the elliptic curve cryptography (public key → private key) using Shor’s algorithm.
Where Do Quantum Computers Stand Today?
Let’s put things in perspective. Google’s Willow processor, which made headlines recently, has 105 physical qubits. But breaking Bitcoin’s elliptic curve cryptography (step 2 above) requires about 2,330 logical qubits, running for minutes to hours.
So how does 105 physical qubits compare to 2,330 logical qubits? It’s not even in the same league. To get 2,330 logical qubits, we'd likely need millions of physical qubits—a technology that is still decades away.
Now, even if we magically reached 2,330 logical qubits tomorrow, that only breaks public keys. It still wouldn't be enough to break Bitcoin addresses (step 1), which would take centuries with current quantum algorithms.
Who Should Be Worried?
- People who used Bitcoin before 2010 and still have funds sitting in old public-key-based addresses (P2PK addresses). Their funds could be stolen in minutes to hours if a powerful enough quantum computer emerged.
- People who reuse addresses—this exposes the public key, making it vulnerable to a quantum attack, even when you are using more modern addresses. (Many wallets, including Trust Wallet, SafePal, Exodus, and Atomic Wallet, still allow this bad practice!)
Who Can Sleep Soundly?
- Anyone using modern Bitcoin addresses (P2PKH, SegWit, Taproot). Their addresses are hashed, meaning an attacker would need centuries to break the first layer of protection before even getting to the public key.
- Anyone moving their coins periodically—since modern Bitcoin wallets generate new addresses for each transaction, public keys remain hidden.
The Concrete Wall Analogy
Think of your Bitcoin private key as being locked inside a massive vault. The first layer of protection is your Bitcoin address, which acts like a thick concrete wall. Cracking through this wall with current quantum algorithms would take centuries. Even if someone managed to break through, they would still face a second, much thinner barrier—your public key. This one would take only minutes to hours to breach. But by then, Bitcoin security upgrades would likely already be in place, leaving attackers empty-handed.
But What If We Make a Huge Quantum Leap?
Yes, it’s possible that new quantum algorithms emerge, or that quantum hardware advances faster than expected. But Bitcoin’s development community isn’t sitting idle, waiting to get wrecked. There are already proposals for quantum-resistant Bitcoin addresses, and they can be implemented before quantum computers reach a dangerous level.
The Bottom Line
🚀 Quantum computers won’t kill Bitcoin anytime soon.
📌 If you’re using a modern Bitcoin wallet, your funds are safe from quantum threats for the foreseeable future.
📌 If you reuse addresses, stop! It exposes your public key and makes you vulnerable much sooner.
📌 Bitcoin developers are already preparing for a quantum-resistant future.
So, no, quantum computers won’t be the end of Bitcoin. But they might be the end of bad security practices! 🔐
-
 @ 6be5cc06:5259daf0
2025-01-18 02:11:43
@ 6be5cc06:5259daf0
2025-01-18 02:11:43- Not your keys, not your coins
Se você não tem as chaves privadas do seu Bitcoin, ele não é realmente seu. Deixar seus BTCs em exchanges ou carteiras controladas por terceiros significa confiar neles e assumir o risco de perder seus fundos.
- HODL - Não venda
O Bitcoin é uma reserva de valor a longo prazo e potencialmente o dinheiro do futuro. Não se desespere com as flutuações de preço; mantenha seus BTCs, pois o histórico se mostra favorável.
- Stay humble - Não saia falando que você tem BTC
Manter discrição sobre seu patrimônio é uma questão de segurança e humildade. Falar demais pode atrair curiosos, oportunistas ou outras ameaças.
- Don't trust, verify
No Bitcoin, confie no protocolo, não em pessoas. Sempre que possível, verifique por conta própria, seja transações, códigos ou informações.
- Reject altcoins
As altcoins podem parecer promissoras, mas frequentemente são distrações ou apostas arriscadas. Foque no Bitcoin, que já provou ser sólido e resistente.
- Stack sats - DCA
Empilhe satoshis consistentemente, utilizando a estratégia de DCA (Dollar Cost Averaging), comprando regularmente independentemente do preço. Isso reduz o risco de tentar "acertar o mercado".
- Reject the ego
Não aposte contra o Bitcoin. Aqueles que subestimaram sua força ou estabilidade, perderam.
- Keep learning
Nunca pare de estudar sobre Bitcoin, economia e a tecnologia por trás dele. Quanto mais você entende, mais confiança terá em sua decisão.
- Help beginners
O Bitcoin pode ser complicado para quem está começando. Compartilhe seus conhecimentos com paciência para fortalecer a comunidade.
- Don't push it
Cada pessoa tem seu próprio tempo para entender e entrar no mundo do Bitcoin. Forçar alguém pode ser contraproducente; dê direcionamento e deixe o tempo agir.
-
 @ be41636e:e55c4909
2025-02-01 18:35:06
@ be41636e:e55c4909
2025-02-01 18:35:06One of the biggest fears around Bitcoin is that quantum computers (QCs) will render it obsolete. But is this really a legitimate concern, or just another doomsday myth?
The Real Threat: Not All Quantum Computers Are Equal
First, let’s get one thing straight: quantum computers already exist. The first notable ones appeared in the 1990s, built by IBM and Stanford. So why hasn’t Bitcoin already been hacked? Because it’s not about whether quantum computers exist—it’s about how powerful they need to be.
Are All Bitcoin Addresses at Risk?
No! If you’ve entered Bitcoin after 2010 or use a wallet backed up with 12 or 24 words (BIP-39, introduced in 2013), your funds are safe from quantum threats for a very long time—centuries, at least.
But why?
Understanding How Bitcoin’s Security Works
Bitcoin security is based on private keys. (These are represented by the 12-24 words you write down when setting up a wallet.) From this private key, a public key is created. In Bitcoin’s early days, people shared public keys directly to receive payments. But in 2010, Bitcoin introduced an extra layer of security: hashed addresses.
Now, instead of sharing your public key, your wallet generates a Bitcoin address, which is actually a hash of your public key. This adds an extra step for an attacker: before they can find your private key, they must first break the hash to reveal your public key.
Two Steps to Breaking Bitcoin
To steal Bitcoin using quantum computing, an attacker must:
- Break the hash (Bitcoin address → public key) using Grover’s algorithm.
- Break the elliptic curve cryptography (public key → private key) using Shor’s algorithm.
Where Do Quantum Computers Stand Today?
Let’s put things in perspective. Google’s Willow processor, which made headlines recently, has 105 physical qubits. But breaking Bitcoin’s elliptic curve cryptography (step 2 above) requires about 2,330 logical qubits, running for minutes to hours.
So how does 105 physical qubits compare to 2,330 logical qubits? It’s not even in the same league. To get 2,330 logical qubits, we'd likely need millions of physical qubits—a technology that is still decades away.
Now, even if we magically reached 2,330 logical qubits tomorrow, that only breaks public keys. It still wouldn't be enough to break Bitcoin addresses (step 1), which would take centuries with current quantum algorithms.
Who Should Be Worried?
- People who used Bitcoin before 2010 and still have funds sitting in old public-key-based addresses (P2PK addresses). Their funds could be stolen in minutes to hours if a powerful enough quantum computer emerged.
- People who reuse addresses—this exposes the public key, making it vulnerable to a quantum attack, even when you are using more modern addresses. (Many wallets, including Trust Wallet, SafePal, Exodus, and Atomic Wallet, still allow this bad practice!)
Who Can Sleep Soundly?
- Anyone using modern Bitcoin addresses (P2PKH, SegWit, Taproot). Their addresses are hashed, meaning an attacker would need centuries to break the first layer of protection before even getting to the public key.
The Concrete Wall Analogy
Think of your Bitcoin private key as being locked inside a massive vault. The first layer of protection is your Bitcoin address, which acts like a thick concrete wall. Cracking through this wall with current quantum algorithms would take centuries. Once one breaks through this wall, they would face a second wall, which is a much thinner barrier—your public key. This one would take only minutes to hours to breach.
But What If We Make a Huge Quantum Leap?
Yes, it’s possible that new quantum algorithms emerge, or that quantum hardware advances faster than expected. But Bitcoin’s development community isn’t sitting idle, waiting to get wrecked. There are already proposals for quantum-resistant Bitcoin addresses, and they can be implemented before quantum computers reach a dangerous level.
The Bottom Line
🚀 Quantum computers won’t kill Bitcoin anytime soon.
📌 If you’re using a modern Bitcoin wallet, your funds are safe from quantum threats for the foreseeable future.
📌 If you reuse addresses, stop! It exposes your public key and makes you vulnerable much sooner.
📌 Bitcoin developers are already preparing for a quantum-resistant future.
So, no, quantum computers won’t be the end of Bitcoin. But they might be the end of bad security practices! 🔐
-
 @ 66675158:1b644430
2025-01-16 20:44:33
@ 66675158:1b644430
2025-01-16 20:44:33Before the time of Utensils, people lived in genuine harmony. They gathered in markets to trade freely, built homes where they pleased, and traveled without papers or permissions. Communities solved their own problems through discussion and agreement. When disputes arose, wise elders would help find solutions that satisfied all. Children learned from their parents or chose mentors from among the skilled craftspeople.
In those days, gold changed hands freely for goods and services. Each person kept what they earned. Communities would voluntarily pool resources for shared needs - wells, bridges, and roads. Those who had more would often help those with less, not by decree but by choice.
Neighbors knew each other's names. Doors were left unlocked. Children played in the streets until sunset. Gardens grew wherever people planted them. Merchants traveled between towns without inspections. Healers practiced their craft freely, sharing knowledge openly.
Then came the Utensils.
In our land, Aldrich found the Silver Spoon. In the East, Emperor Chen discovered the Jade Chopsticks. The Norse kingdoms united under the Golden Fork. The desert peoples followed the Bronze Ladle.
Each Utensil, their holders claimed, granted divine wisdom to rule. Each promised protection and prosperity in exchange for obedience.
The changes came slowly at first. The Spoon Holder requested a share of each harvest to store for hard times. The Chopstick Emperor required homes to be built in specific ways to prevent fires. The Fork King demanded that travelers carry documents proving their loyalty.
At first, the Utensils did bring some genuine improvements. The Spoon Holder's collectors used part of their harvest share to help villages during droughts. The Chopstick Emperor's building codes truly did reduce fires. The Fork King's road patrols deterred the few bandits who had troubled merchants. The Bronze Ladle's water management systems helped farms flourish in the desert.
The early years saw stone roads replace dirt paths, connecting villages more efficiently than before. Granaries were built with better designs, preserving food longer. Some diseases decreased as the Chopstick Emperor's cleanliness codes spread. The Fork Kingdom's standardized weights and measures did make trade easier.
The Spoon Holder soon declared that carrying gold was dangerous and inefficient. They introduced sacred paper notes, "backed by the Silver Spoon's power." At first, you could trade these notes back for gold, but gradually this right vanished.
Scholars wrote lengthy memos about the divine wisdom of the Utensils, creating complex theories about why ordinary people couldn't possibly understand how to live without direction. They advised the Holders and were rewarded with special privileges, comfortable positions, and influence.
When anyone questioned this system, the Utensil Holders and their Experts would ask: "But who would build the roads without us? Who would help the poor? Who would protect you?" They spoke as if humans had never cooperated or helped each other before the Utensils came, and many began to believe it.
People grumbled but accepted. After all, the Utensils shone with otherworldly power.
Some remembered these early benefits when questioning the growing restrictions. "Remember how the Spoon Holder's men helped during the great flood?" they would say. "Surely they have our best interests at heart." The Utensil Holders carefully nurtured these memories, even as their power grew far beyond such humble beginnings.
More rules followed. The Spoon Holder's men began watching the roads, collecting portions from merchants. The Chopstick Guards enforced strict codes about proper behavior. The Fork Watchers kept lists of who attended the mandatory gatherings.
Children were taught the sacred histories of their Utensils. The Spoon's light blessed the worthy. The Chopsticks maintained harmony. The Fork brought strength. The Ladle provided guidance.
When people remembered the old freedoms, the Utensil Holders reminded them of the chaos before - though few could actually recall any chaos.
But surely there must have been chaos, or why would the Utensils have come?
The Utensil Holders began to eye each other's territories. How dare the Fork King claim his metal was superior? How could the Chopstick Emperor suggest jade held more wisdom than silver? The Ladle Holder's bronze was clearly inferior to all!
The Utensil Holders pointed to their achievements - the roads, the granaries, the safer towns - as proof of their divine right to rule. They spoke of how they had unified squabbling villages, standardized laws, and created order. Few noticed how these very achievements had required less and less input from the people themselves.
Wars erupted. Armies marched under banners bearing their sacred Utensils. Men died believing their Utensil was the one true source of authority. Villages burned as soldiers searched for heretics who might secretly worship foreign Utensils.
The Utensil Holders demanded more from their people - more food, more gold, more obedience. They placed watchers in every village. They required written permission for travel between towns. They forbade more than three people from gathering without a Guardian present.
"It's for protection," they said, holding their Utensils high. "How can you doubt the sacred silver?"
And indeed, their guards did stop some thieves, their inspectors did prevent some fraud, their builders did create some useful works. But these benefits came with an ever-increasing price in freedom, until the cost far exceeded any advantage. Yet by then, most people could no longer imagine providing these services for themselves, as their ancestors had done.
Towns built walls, not against invaders but to control who could enter and leave. The Utensil Holders required everyone to wear markers showing their village of origin. They appointed observers in every community to report suspicious behavior - like speaking of the time before Utensils.
Children were taken to special houses to learn proper reverence for their Utensil. Families who taught the old ways disappeared in the night. The Holders declared certain words forbidden, certain thoughts dangerous, certain memories treasonous.
Now, centuries later, the Utensils rule absolutely. People bow when the sacred implements pass by. They inform on neighbors who question the Utensils' power. They offer their children to serve in the Utensil temples.
The latest marvel was Utensil Technology - enchanted mirrors and crystals that watched people's movements, recorded their words, and tracked their trades. "Only criminals fear being watched," the Holders proclaimed, as their surveillance spread into every home and market. The crystals even allowed them to freeze people's paper money if they spoke against the Utensils.
The Utensil Holders formed special partnerships with the largest merchant guilds. These favored merchants received special permissions, protection from smaller competitors, and access to the new paper money first. In return, they helped enforce the Holders' rules and collected information about their customers. Small traders and craftsmen found themselves crushed between these powerful allies.
The latest decree requires all newborns to be blessed by touching their foreheads to their realm's sacred Utensil, marking them forever as its property. Parents compete for earlier blessing times, believing this shows greater devotion.
The wars continue. The Fork Kingdoms battle the Chopstick Empire. The Ladle Realms raid the Spoon Holdings. Each believes their Utensil must rule all.
And in quiet corners, in hidden places, a few elders still whisper stories of the time before - when humans lived without Utensils telling them how to live. But fewer remember with each passing year. After all, who could imagine a world without the guidance of sacred silverware?
-
 @ b17fccdf:b7211155
2025-02-01 18:28:39
@ b17fccdf:b7211155
2025-02-01 18:28:39
Check out the MiniBolt guide -> HERE <-
- Core guides
- System
- Bitcoin
- Bitcoin client (Bitcoin Core)
- Electrum server (Fulcrum)
- Desktop signing app (Sparrow Wallet)
- Blockchain explorer (BTC RPC Explorer)
- Lightning
- Lightning client (LND)
- Channel backup
- Web app (ThunderHub)
- Mobile app (Zeus)
- Bonus guides
- System bonus guide
- Dashboard & Appearance
- System Administration
- Install / Update / Uninstall common languages
- Databases
- Security
- Resilience
- Hardware
- Bitcoin bonus guides
- Electrum servers
- Signing apps
- Desktop
- Electrum Wallet Desktop
- Decentralized exchange
- Resilience
- Fun
- Testnet
- Payment processors
- Nostr bonus guides
- Relays
- Nostr relay
🏗️ Roadmap | 🌐 Dynamic Network map | 🔧 Issues | 📥 Pull requests | 🗣️ Discussions
By ⚡2FakTor⚡
Last updated: 22/12/2024
-
 @ 3eacaa76:bac66fe4
2025-01-15 16:25:13
@ 3eacaa76:bac66fe4
2025-01-15 16:25:13Few days back this track get on Top of list on #wavlake. It's nice , but not a point. at all.
The message is clear. like Real Talk should be !
We know, specialy on #nostr, that solutions are available. However, the world is not yet aware of them.
100% of the donations for this remix will be sent to my friend Yusef who is on the ground and has been providing food, water, and shelter for children in Gaza even before or the psyop with October 07 took a place. Israel has enforced a blockade on Gaza for over decade. And Just past year completly destroyed 90% of land. Like to the ground , no schools , no hospitals ... hard to find anything what surrvived those daily airstrikes without 1h of pause since 350 days. WTF
It's heartbreaking to see children dying daily in houreds and the lack of action from the public and authorities of other nations. The statistics are alarming, and it's essential to address this issue and find ways to make progress. it's crucial to raise awareness and take action to prevent further tragedies. Let's remember that every child's life is precious and deserves our attention and support.
In most apocaliptic condition , where is-real controling all money supply (check lastest news about banknotes in there) , the #Bitcoin is one and only solution can help them in daily bases. It was helping them before with great succes. Why you ask ? becuse even if they close all platforms You can still send them some sats.
How fookin cool is that !!
I know it doesn't sound funny.
Those People pushed to the limit , now they have a tool that fulfills exactly what was created for A Peer-to-Peer Electronic Cash System.
No Middle man .``` On the middle is only a finger whitch WE the PEOPLE can give to those Scumbagz in Goverments and Banks, Full stop.
```
Many people are only recently realizing the truth about Gaza being an open-air prison from like 75 years. Not 3, not 5 or even 20 ..... but seventy five fookin years.
This music mix was created to share the truth and provoke to critical thinking, which has been lacking for the past decade. and even more.
I wonder why we can watch live streams of the ongoing genocide in 4K HD and stil be silent. not all but many.
Why are we surprised that normies don't understand Bitcoin and still use fiat shit currency? Whitch is fudament of All war crimes. We should ask ourselves.
Our own ignorance and the banking system are the cancers of this world.
If we lose Palestine, we will lose much more than we think.
You will be next - One way or another
Thank you for your support, not for me but for those in need who can gain hope from our efforts.
Respect to you all.

LISTEN HERE and suport directly in upper links
FreePalestine
Thanks
be blessed
MadMunky
-
 @ d57360cb:4fe7d935
2025-02-01 18:22:10
@ d57360cb:4fe7d935
2025-02-01 18:22:10What is life but a preparation for the grand finale.
Think of your life up to this point. You’ve been living in the midst of death whether you pay attention to it or not.
Your youth faded, the years go by, relationships fail, careers fail, people die, the ones close to you and those you hardly know. Civilizations wiped out, total species completely gone with no trace.
Here you are in the midst of death. A vortex of change wiping everything in its path. Creating space for the unknown and new. Nothing lasts, nothing stays the same, everything ends. Ending gives great significance to life.
How will you be in the presence of someone you love knowing they or you will vanish one day?
What wouldn’t you put off if you were aware your time was slipping and there’s nothing you can do.
What would you stop doing?
What would you let go of?
Who would you forgive?
Life comes with a bullet and it has your name on it. You don’t know when it’ll happen.
Don’t believe you ever have time it’s always a fantasy. Death will knock you on your feet when you least expect it.
Use death as a doorway to a deep meaningful life.
-
 @ 17538dc2:71ed77c4
2025-01-14 15:52:00
@ 17538dc2:71ed77c4
2025-01-14 15:52:00Nassim Nicholas Taleb writes:
“We cannot explain everything. We know more about what something is not than what something is. If there would have been no word for colour blue, it would still have existed in reality. It would only have been absent in linguistics. But since we don’t have a word for it, we couldn’t define or comprehend it. But we still could say what it is not. It is not orange. It’s not an elephant, etc. This method of knowledge is truer and more rigorous than positive knowledge.”In this article, I introduce practical examples of how to apply via negativa to various systems.
Recommended reading is Antifragile by N. N. Taleb.
The basic template is as follows:
What is ____ not?
Let's start with something every human should be familiar with - food.
Food
Take hot pockets. Is hot pockets food?

What is not food?
To answer this question, let's examine the contents of hot pockets.

There seem to be chemistry lab sounding ingredients ("MEDIUM CHAIN TRIGLYCERIES", "SODIUM STEAROYL LACTYLATE"), as well as food items that your great-great-great-great-great-great grandma cooked with ("SALT", "BEEF" etc.)
So What happens when we apply via negativa to the ingredients?
From 30 "ingredients" we deduce a couple foood items, or a ~90% reduction in "ingredients" by eliminating processed food slop.
 meat good
meat good bread yum
bread yumFree Discourse
Take the social media platform X.
 X consists of: leased identity, censored speech, and a tech platform for discourse. On the roadmap is social media score that will be used to determine if you can pay your bills when X launches its' bank.
X consists of: leased identity, censored speech, and a tech platform for discourse. On the roadmap is social media score that will be used to determine if you can pay your bills when X launches its' bank. What is free discourse not?
Removing the ingredient of WEF,

KYC lease hell

and censorship

we receive nostr
 .
. Nostr, to my best understanding, is not a WEF globo-homo participant, does not lease identities, and it is that much more difficult to censor wrongspeak (e.g. Netanyahu and friends are commiting genocide, and wanted as war criminals; there are two genders; there is no climate crisis; Ivermectin works).
Automobiles
Modern automobiles can be summed up in two words: "safety", and constant surveillance. Yes, advancements in safety are great - e.g. airbags, seatbelts, car frames that absorb impact energy.
However the "its for your safety" component of remote shutdown, remote control, location data selling to data brokers, insurance agents, and your local surveillance outfit is gulag tech.
!(image)[https://image.nostr.build/15befd30113614dad3fd7aac01b8771b95bd8ace9186ed4f8016eec6e886e969.jpg]
So what happens when we remove the gulag tech out of cars? That is, what is not a car?
Let's use the following definition of car:
``` A car, or an automobile, is a motor vehicle with wheels
```
Let's use the following definition of gulag:
``` The Gulag is recognized as a major instrument of political repression in the Soviet Union.
```
You get the 2024 Toyota Land Cruiser. No gulag. Airbags. Push and turn knobs. No spying, no remote control, no cameras, no satellite, no bluetooth, no wi-fi.
As an aside, it is practically impossible to import this car to the US. It's "for your safety", and "for the environment", of course.
!(image)[https://upload.wikimedia.org/wikipedia/commons/thumb/a/a1/Toyota_Land_Cruiser_16.09.20_JM_%283%29_%28cropped%29.jpg/800px-Toyota_Land_Cruiser_16.09.20_JM_%283%29_%28cropped%29.jpg]?20210328155727
Toyota Landcruiser HZJ-79 Double Cab, Johannes Maximilian
https://commons.wikimedia.org/wiki/File:Toyota_Land_Cruiser_16.09.20_JM_(3)_(cropped).jpg).Hopefully this guide has been helpful illustrating how simple and powerful it is to apply the Via Negativa approach.
Mr. Taleb, I commend you on speaking out on the Palestine genocide. I invite you to and hope one day you join anti-fragile nostr.
-
 @ cff1720e:15c7e2b2
2025-02-01 17:37:00
@ cff1720e:15c7e2b2
2025-02-01 17:37:00Am 4. Oktober 1957 sendete Sputnik 1 erste Signale aus dem All. Die Welt war fasziniert, die Amerikaner geschockt, da die Russen sie in der Raumfahrt technologisch überholt hatten. Es folgte der Wettlauf im All mit Apollo-Programm und Mondlandung 1969. Am 27. Januar 2025 erlebte die USA einen weiteren Sputnik-Moment, diesmal durch die chinesische KI-App deepseek R1. Diese App schoss wenige Stunden nach ihrem Start auf Platz 1 der App-Stores, vorbei an dem bisherigen KI-Spitzenreiter ChatGPT. Die Aktie des KI-Chipherstellers Nvidia verlor 17% (600 Mrd. USD Börsenwert), das war der bisher höchste Tagesverlust des US-Aktienmarktes. Marc Andreessen verwendete gar die Formulierung “Sputnik-Schock", diese einseitige Sichtweise erschwert aber eine Betrachtung aus verschiedenen Perspektiven.

Was lässt sich mit ein paar Tagen Abstand daraus schlussfolgern? Die Aktionäre haben überreagiert und die Falschen bestraft. Die Nervosität der Anleger ist aber verständlich bei einem KGV von 46 bei Nvidia und 27 bei den “Magnificent Seven” (die großen US KI-Anbieter). Normale KGVs bewegen sich um 15, d.h. wir haben es mit einer ausgeprägten KI-Blase zu tun, die in Kürze platzen dürfte. Eine weitere Blase die schon vor dem Start geplatzt ist, ist das Projekt “Stargate” der Firmen OpenAI, Oracle und Softbank. In den nächsten 4 Jahren wollen sie 500 Mrd. USD für über 10 neue KI-Rechenzentren investieren, um Amerikas vermeintliche KI-Vorherrschaft gegenüber China weiter auszubauen. Die schon vorher vorhandenen Zweifel an dem Projekt (Elon Musk auf X “sie haben das Geld gar nicht”) wurden nun durch den Erfolg von deepseek verstärkt.

deepseek hat nämlich offenbart, dass die bisherige US KI-Strategie, "wir schlagen die Chinesen mit unserer DataCenter-Power", ein fataler Irrweg ist. Den Analysten von Bernstein zufolge ist das Modell von deepseek geschätzt 20 bis 40 mal billiger zu betreiben als ähnliche Modelle von OpenAI. Die Chinesen haben ihre Innovation durch Kreativität erzielt, im Gegensatz zur Gigantomanie der US-Konzerne, die sich in einem Überbietungs-Wettbewerb der Ressourcen-Verschwendung befinden. Hunderte Milliarden an Investorengeldern und ca. 9% des nationalen Stromverbrauchs führen zwar zur Bereicherung einiger Konzerne und ihrer Besitzer, nicht aber zu adäquaten Ergebnissen. Das selbe Muster konnte man bereits bei der Rüstungsbranche beobachten, die mit dem etwa 10-fachen Budget (1 Billion USD) nicht im Stande war bessere Waffensysteme zu produzieren als Russland (Oreshnik-Schock 2024).

Wenn Donald Trump wirklich Amerika stärken möchte, dann sollte er umgehend seine technokratischen Berater entlassen und Sun Tzu lesen, ein Buch, das die Grundlagen asiatischer Strategie vermittelt und den Krieg vermeiden lehrt ("Der klügste Krieger ist der, der niemals kämpfen muss"). Die chinesischen Erfolge basieren auf exzellenter Bildung, Startup-Förderung und minimaler Regulierung, Konzepte die der Westen zwar stets gepredigt aber nie geliefert hat. “Make Amerika smart again” hieße daher Abschied von Kriegsrhetorik, Embargos, Oligarchen-Projekten und der bisherigen Großmacht-Hybris. Annektionspläne für Grönland und Kanada passen nicht in das Bild, Wiederherstellung von Meinungsfreiheit und Abbau von Regulierungen schon (Streichung von Bidens KI-Regulierung Executive Order 14110). Wohin steuert Trump die USA? Wird der deepseek-Moment dabei helfen falsche Strategieansätze zu korrigieren? Das ist noch unklar, während aber schon jetzt unzweifelhaft feststeht, dass die EU und Deutschland weder bei der KI noch in der Geostrategie eine Rolle spielen, dafür aber als unangefochtene Regulierungs-Weltmeister. Herzlichen Glückwunsch!

„Man kann zwar die Realität ignorieren, aber nicht die Folgen davon ignorieren.“ Ayn Rand
Der wirkliche Gewinner dieser Woche ist aber die OpenSource-Szene mit ihren dezentralen Lösungsansätzen. Nicht nur deepseek R1 ist OpenSource sondern auch Marco o1 von Alibaba (https://github.com/huggingface). Die Nutzung ist kostenlos (ChatGPT kostet 200 USD pro Monat), daher können sowohl die Modellbildung, die Trainingsdaten als auch die Rechenleistung von unzähligen Aktivisten weltweit verteilt erbracht werden. Dafür braucht es weder Milliarden-Budgets, Regierungsprogramme oder neue DataCenter. Das Potential der Crowd übertrifft jeden zentralistischen Ansatz. Die Ergebnisse sind besser und die Kontrolle liegt nicht in den Händen einzelner. Smarte Lösung sind verteilt, das beweisen Projekte wie Bitcoin (seit 16 Jahren), Lightning und neuerdings auch Nostr. Deshalb haben wir Pareto (https://pareto.space) auf diesen Fundamenten entwickelt (Nostr, Lightning) und in 6 Monaten mit Freiwilligen mehr erreicht als viele große IT-Unternehmen in Jahren. Die Dinosaurier sterben aus, dem Schwarm gehört die Zukunft.
-
 @ 17538dc2:71ed77c4
2025-01-13 18:17:24
@ 17538dc2:71ed77c4
2025-01-13 18:17:24Sci-Hub 2024 year end review is translated to English by Kagi Translate from Russian. Original text can be found in Sci-Hub's telegram channel https://t.me/freescience.
RESULTS OF 2024
First. The project received donations totaling 2 million dollars in meme coins.
The project is actively used by many students in China, which is why a group of Sci-Hub fans has emerged there. As far as I understand, the organizer of the group is actively interested in the topic of cryptocurrencies (even wrote a book). Somewhere in mid-November, the Chinese launched a meme coin in honor of the Sci-Hub project. At its peak, the coin's price reached 5 cents, and now it is somewhere around 1-2 cents. This means that the exchange rate of the Sci-Hub cryptocurrency is now almost equal to the ruble exchange rate (100 to one or so).
In general, I converted part of these donations into normal, traditional cryptocurrency (like Bitcoin) and paid for servers several months in advance. The other part is still sitting in meme coins—I hope that the token will still grow in price (there is a promotion plan). Of course, this is risky, but Sci-Hub is a project that is not afraid of risk. Therefore, anyone who wants to invest in Sci-Hub by purchasing this token can do so here: www.coingecko.com/en/coins/sci-hub
Second. A dissertation on the topic of open scientific knowledge has been defended at the Institute of Philosophy.
For those interested in the history and philosophy of science, I defended a dissertation in April at the Institute of Philosophy on the topic that scientific knowledge should be open (otherwise, it is strange to call it scientific at all). The work shows that open communication is one of the basic traditional values of science when considering science as a social institution. In other words, journals that charge for access to scientific articles are a kind of 'non-traditional orientation journals.'
Moreover, openness is an important prerequisite for rationality. Rationality is not limited to the criterion of falsification (hello Popper); it is a much more complex concept.
You can familiarize yourself with the text of the dissertation here: web.archive.org/web/20240425100014/https://iphras.ru/page26414303.htm (I provide the link through the web archive because the Institute's website, strangely enough, is glitching again at the time of writing this post).
All criticism and comments (as well as praise) regarding the dissertation can be sent to my email.
Third. Work has begun on a new declaration of open access to scientific knowledge.
Currently, all discussions on the topic of open science are conducted within the frameworks defined by the so-called BBB declarations back in 2001-2003. Within these frameworks, two main types of open access are recognized: gold, meaning open journals with an author-pays model, and green, which refers to repositories like the well-known arXiv. We can also add the so-called diamond open access, which includes open journals that are free for both authors and readers.
However, since 2003, internet technologies have advanced significantly. Today, we can already talk about such types of open access as blue (through academic social networks) or red (your beloved Sci-Hub). It is time to adopt a new declaration of open access to scientific knowledge that corresponds to the current state of scientific and technological progress.
A preliminary version of the declaration can be read and signed here: open.science.do
We will be more actively engaged in this in the coming year. Signing the declaration is an important step towards recognizing access to scientific knowledge through sites like Sci-Hub or Libgen as completely legal and ceasing to pursue them—first in the former USSR, and then in all countries of the world.
Fourth. In 2024, about one billion articles were downloaded through Sci-Hub. Despite the fact that this is unfiltered statistics, the fact remains: the popularity of the project has not decreased but only grown, despite the fact that Sci-Hub has not been updated for quite a long time. Of course, this does not mean that the site will not be updated at all now—just that the patient is more alive than dead (no matter how much some haters might wish otherwise).
The cause of open access to scientific knowledge will definitely prevail—because good always triumphs over evil.
In the new year, I wish all scientists new discoveries and large grants. Happy New Year, comrades!
-
 @ e262ed3a:e147fbcb
2025-02-01 15:37:28
@ e262ed3a:e147fbcb
2025-02-01 15:37:28Feel free to develop
I got an idea while watching a video from @BTCSessions, which I personally cannot implement technically. Therefore, I would like to present it here for discussion and free implementation. It makes sense to me, but what do I know? Let the swarm intelligence decide.
The goal of the business idea is:
How can I bring as many solo miners as possible into a pool without them having to pay for the electricity for mining and their mining hardware can be amortized quickly, so they can purchase more mining hardware? How can we financially support Bitcoin and Nostr developers in the long term? How can we intensify developers for the implementation of this idea? How can we encourage non-Bitcoiners to invest in the support of the Bitcoin network? How can we get non-Bitcoin retailers to invest in the Bitcoin network?
**The answer is: PROSPECT OF WINNING
The solution lies in a kind of RAFFLE. (Not a betting website) !**
The legal difference between a BET and a RAFFLE varies from country to country. It lies in the fact that a raffle must be very transparent regarding the chances of winning and the proceeds must go to a good cause. Those involved in the implementation can, of course, be compensated (also with a profit for the individual participants). The extent to which this is allowed would have to be checked by those who want to implement this idea.
In the following, I will describe the implementation roughly. Since this is not a sales presentation, please excuse me if the following proposal is not fully structured.
**Participants in the idea are:
Consumers (ticket buyers) Bitcoin miners Retailers Non-profit company that implement the project**
What's it about? @BTCSessions has a YouTube video about the miner FutureBit. In the dashboard of the solo miner, you could see how high the hash rate was. But above all, you could see how high the chance of winning was for the solo miner in the overall network. In the case of BTCSessions FutureBit, the hash rate was around 5 TerraHash and the chance of winning was around 1:1,000,000. (Which, according to my calculations, was not correct). The power consumption was around 32 watts. When I saw that, it suddenly dawned on me.
Could it be possible to create a website/app that determines the total hash rate of a mining pool and then offers an electronic, numbered ticket for each 1 TerraHash (TH/s) of the pool for, for example, 0.1 USD? The minimum purchase amount would be 10 tickets. The customer sees the chance of winning and could even see the possible payout. The ticket is only valid for the next block (similar to roulette).
Another variant could be that the buyer can select one or more of the next 10 blocks and purchase tickets for the selected block. Since you don't know in advance how high the pool hash rate will be 5 or 10 blocks ahead, the amount of tickets to be issued for the 2nd block, for example, could only be 90% of the current pool hash rate, the 3rd block only 80%, and so on. If block 3, for example, advances to position 2, the previously unavailable 10% will be released for further tickets. (Determined by the pool hash rate at that time)
The purchase of 10 or more tickets could be automated in the customer's account on the website/app (intervals: hourly, daily, weekly, every 10 blocks, etc.). Customers could also top up their account with satoshis, enabling automatic deductions for ticket purchases. This could be facilitated by automatically issuing a Nostr npub to each customer, which would also create a wallet at Primal.net (Strike). For non-Bitcoiners, Zaprite could be used to recharge their account. Alternatively, customers could enter a NostrWalletConnection NWC to enable automatic deductions from their Lightning wallet. The project operators might also consider running their own ecash mint, which would allow them to assign an integrated ecash address to customers without a Lightning address. Tickets with ascending numbers would be allocated strictly in the order of payment receipts.
Calculations for the miners: The FutureBit miner consumed approximately 30 watts per terahash/hour. Let's assume that 10 terahash consume 300 watts per hour, then the miner consumes 50 watts per 10 minutes (per block). Let's further assume that a kilowatt-hour of electricity costs between 10 and 30 cents, then it costs the miner 3-9 cents per hour for electricity at 10 terahash mining capacity. So, 0.5-1.5 cents per block. In the case that each ticket is sold for 1 terahash for the next block, one could automatically transfer, for example, 5% of the satoshis received from ticket sales to each participating miner in the pool (proportional to the average hash rate delivered by the miner in the last block in the pools). This happens even if the block is not found. If fewer tickets are sold than the maximum possible amount, then the 5% of the sold tickets will be distributed proportionally. (See also my Excel file?
At the center of the project is a website/app that manages the raffle. Here, anyone can register and create an account. Either as a miner, retailer, or customer with or without KYC, for example, with their own nostr nsec, wallet signature, email and password or phone number and password.
Once logged into the account, Bitcoiners can enter their Lightning address and a Bitcoin on-chain address. Non-Bitcoiners enter their financial data in case they win.
Miners must enter a Bitcoin and Lightning (or ecash) address. The pooling process is also managed in the miner's account.
Tickets can be purchased (like in a regular online shop) and paid for in any way. Zaprite could be a solution here. But also Strike, Cashapp, etc. As described above, such purchases could also be automated.
Retailers can also register as such. They will then have the opportunity to sell "tickets" to their customers and collect the money in cash. To sell tickets, they must enter the customer's name and a valid email address. After payment, they must send the purchase price via Lightning to the non-profit company, which will then confirm the purchase to the ticket buyer and the retailer with all the data. This is the receipt for the buyer. In the event of a win (the mined block must have 3-6 block confirmations), the ticket buyer will receive an email explaining all the further details of how to claim the prize. This could be a link that takes them directly to the website and logs them in directly. The winner can then enter their data on how and where the money should be paid out (Bitcoin address or bank details). Alternatively, they can go to their retailer, who can assist them by entering the data in their sub-account (customer account). To prevent the retailer from falsifying the data entry, the winner will first receive an email with the entered data, which they can confirm (if correct). Since the retailer is also involved in the win, they will also be notified.
How many tickets can be offered per round (Bitcoin block)? The number of tickets depends on the hash rate in the pool. One ticket can be issued per 1 TerraHash (TH/s). How the ticket is generated per round and customer, I don't know, as I lack the technical knowledge. Maybe as a kind of NFT that contains the corresponding data (customer number (npub) of the buyer and possibly retailer, block number, ticket number). Or as a Taproot asset on Lightning? Or as a minted ecash coin? Or simply as an entry in a database that the customer can see in their account.
The maximum payout of the winnings in the event of a found block to the ticket holders could be 70%. The remaining 30% would be distributed to the miners and retailers. For example: Miners 25%, retailers 5%. The non-profit organization receives nothing from the block rewards. Instead, it receives 65% of the revenue from all ticket sales. With a mining pool hash rate of 10,000 TH/s, where all tickets are sold continuously, a daily donation of around 93,000 USD would be generated. (see Excel.file)
The revenue, after deducting the possible costs of the organization, goes directly to @opensats and/or other organizations that support the Bitcoin network after each block. Either via Lightning or Bitcoin on-chain payment.
In the attached Excel file, you can find my calculations. Here, anyone can play through different scenarios.
What I noticed was that with maximum ticket sales per block, only around 200 USD per 10 tickets would be paid out, since each participating ticket wins in the event of a found block. Since I believe that this is not a very great incentive for buying tickets, I suggest the following variants.
Winning variants: Each purchased ticket has a running number. Ticket 1 has the number 000.000, ticket 2 has the number 000.001, ticket 10.120 has the number 010.119, and so on.
If the next block is found, then this found block in the Bitcoin blockchain has a hash. For example, block 881367 has the hash 000000000000000000014b0fab24355c71c6940584d9cd5990c0b081a31d54a4
Let's now remove the letters and read only the numbers from back to front, so the last 3 numbers are 544
Instead of every participating ticket winning, in this variant, only the tickets with the ending digits 544 win.
With, for example, 11,000 tickets sold, the ticket numbers 000.544 / 001.544 / 002.544 ... 010.544 would win. So, 11 ticket participants would win. Each winner with this number would receive around 0.284 Bitcoin (3.125 BTC / 11).
One could also let the ticket numbers with the ending digits 44 win, and thus every hundredth ticket. Or even combine it.
What I also noticed was that with retailers, a special case arises. Retailers receive 5% of the block rewards in the event of a found block. But only proportionally to the tickets sold by the retailer. This means that in order for the entire 5% to be distributed to the retailers, all 10,000 tickets of 10.000 possible tickets would have to be sold by retailers. Since not all tickets will be sold by retailers, a remaining amount will be left over. This could be distributed additionally to the miners. Or any other variant.
I hope the idea finds resonance and invites discussion. Maybe I've made some mistakes in thinking, and the idea is not feasible. But if you like the idea, please forward it to developers, investors, and others you know.
Stay humble hash sats
@nostr:npub1uf3w6w3z4kxy0zc80m6a03tt9s7855c9r8kkjmkju47xtc28l09sc30gqq
-
 @ a012dc82:6458a70d
2025-02-01 15:17:38
@ a012dc82:6458a70d
2025-02-01 15:17:38The cryptocurrency landscape is witnessing a remarkable resurgence, with Bitcoin once again leading the charge. After a period of volatility and uncertainty, Bitcoin has reclaimed its throne as the king of cryptocurrencies, drawing renewed interest from investors and financial experts alike. This article delves into the factors behind Bitcoin's comeback, its implications for the market, and what the future might hold.
Table Of Content
-
The Remarkable Recovery of Bitcoin
-
The Ripple Effect on the Crypto Market
-
Investor Sentiment: Cautious Optimism
-
The Future Outlook: Opportunities and Challenges
-
A New Era for Bitcoin
-
Conclusion
-
FAQs
The Remarkable Recovery of Bitcoin
A Surge in Value
After a tumultuous phase marked by sharp declines and skepticism, Bitcoin has made a striking comeback. The digital currency's value has seen a significant upswing, reminding investors of its potential as a high-reward, albeit high-risk, asset. This recovery is not just a numerical increase but a symbol of resilience in the face of market adversities.
Driving Factors
Several factors have contributed to Bitcoin's resurgence. These include an increase in institutional adoption, technological advancements within the blockchain ecosystem, and a growing recognition of Bitcoin as a 'digital gold' amidst economic uncertainties. Moreover, regulatory clarity in some regions has provided a more stable environment for cryptocurrency investments.
The Ripple Effect on the Crypto Market
Boosting Market Confidence
Bitcoin's rebound has had a ripple effect across the entire cryptocurrency market. Altcoins and emerging digital assets have also seen a boost in both value and investor interest. This resurgence has rekindled the enthusiasm for decentralized finance (DeFi) and non-fungible tokens (NFTs), which had waned during the market downturn.
Impact on Blockchain Innovation
The renewed interest in Bitcoin has spurred further innovation in blockchain technology. Developers and entrepreneurs are increasingly exploring new use cases for blockchain, expanding beyond traditional financial applications to areas like supply chain management, digital identity, and more.
Investor Sentiment: Cautious Optimism
Institutional Investors' Role
Institutional investors, once wary of Bitcoin's volatility, are now more open to including it in their portfolios. This shift is partly due to the improved infrastructure and regulatory frameworks that make investing in Bitcoin less risky than in its early years.
Retail Investors' Perspective
Retail investors, who were significantly affected by the previous market downturn, are approaching Bitcoin with cautious optimism. Many are drawn by the potential for high returns but remain mindful of the risks involved.
The Future Outlook: Opportunities and Challenges
Potential for Growth
With its current momentum, Bitcoin has the potential for further growth. Its evolving role in the financial ecosystem, particularly in areas like digital payments and remittances, suggests a bright future.
Navigating Challenges
However, challenges remain. Regulatory uncertainties, potential market manipulations, and the environmental impact of Bitcoin mining are issues that need addressing. How these challenges are managed will significantly influence Bitcoin's trajectory.
A New Era for Bitcoin
A Testament to Resilience
Bitcoin's comeback is a testament to its resilience and the enduring faith of its supporters. It has not only reclaimed its position as the leading cryptocurrency but has also reinforced the belief in the potential of digital currencies.
A Dynamic Future Ahead
As investors, both institutional and retail, continue to take notice, Bitcoin's journey is far from over. Its ability to adapt, innovate, and overcome challenges will shape not just its future but also that of the broader cryptocurrency market. The current phase is just the beginning of what promises to be a dynamic and transformative era for Bitcoin and digital currencies as a whole.
Conclusion
Bitcoin's resurgence marks a significant milestone in the cryptocurrency world. Its ability to bounce back from adversity and regain its status as the leading digital currency has not only bolstered investor confidence but also highlighted the growing maturity of the crypto market. As Bitcoin continues to evolve, navigating through regulatory landscapes and technological advancements, it stands as a symbol of innovation and resilience in the ever-changing world of finance.
FAQs
Why has Bitcoin's value surged recently? Bitcoin's value has surged due to factors like increased institutional adoption, advancements in blockchain technology, and its growing recognition as a digital store of value amidst economic uncertainties.
How has Bitcoin's recovery affected the overall crypto market? Bitcoin's recovery has positively impacted the entire crypto market, boosting the value of altcoins and reigniting interest in decentralized finance (DeFi) and non-fungible tokens (NFTs).
Are institutional investors now more interested in Bitcoin? Yes, institutional investors are showing increased interest in Bitcoin, thanks to improved investment infrastructure and clearer regulatory frameworks.
What are the main challenges facing Bitcoin in the future? The main challenges include regulatory uncertainties, potential market manipulations, and the environmental impact of Bitcoin mining.
Is it safe for retail investors to invest in Bitcoin now? While Bitcoin offers potential high returns, it remains a high-risk investment. Retail investors should approach with caution and consider diversifying their investment portfolio.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ df478568:2a951e67
2025-02-01 15:07:26
@ df478568:2a951e67
2025-02-01 15:07:26
Garlic Cashew Recipe
I wrote about selling roasted cashews as an experiment in capitalism here. I make them myself and in the spirit of free and open source software, I figured I would open-source the recipe with a catch. You can get the recipe in one of two ways.
- Become a paid subscriber to my Substack and you will get a key to unlock the cipher text
- Read it in the clear(un-encrypted) on nostr. The easiest way to do this is to navigate to primal.net in your browser and search for “marc26z.” Click on my profile and *you can find all of my writing in the clear in the reads section.
I tried using PGP in another article, but it’s a little cumbersome and pretentious. Andreas Grifin said, Nostr is what PGP should have been. A web of trust with easy-to-use encryption and verification. I tend to agree. So I’m using something else.

https://8gwifi.org/CipherFunctions.jsp
Decrypt using the passphrase below the paywall.
"To encrypt is to indicate the desire for privacy, and to encrypt with weak cryptography is to indicate not too much desire for privacy.”
I do not indicate a desire for too much privacy here, but I like playing with these things. I hope you enjoy playing with them too.
How To Decrypt
- Go to https://encrypt-online.com/decrypt/ on your favorite web browser.
- Choose aes-256-cbc(this is the default setting)
- Copy and paste the cipher text into the decryption field
- enter the passphrase into the passphrase field
- press the Decrypt button
- Optional: Copy and paste the decrypted recipe into a markdown editor like https://dillinger.io/
U2FsdGVkX1+4jxMfWCc6kNsbDa0i/J3eiV81r7/z5c0Eqe73vw01M22uRFm9PjRRaj/CJN+BidtuNXQW6G3hk3S/4AoGN2gKfKkKSbzEHsONZ2LeXuoPflikratDU+lADVeR5IlsVaATyImBO0k/cXq54TOlEXBoVRCIqaA9tO8UA126GfTdmegXX14jUcdV9EISSGw8Bn5fksptm6qKyz2GsmyiKcmNczh8Nz7biyhCrnrt2hyLDbirIAjZcCTJjkAlJjrrvuLHJZx6pmq6MsMv2eHT35d/WL/+ZpBgLVh2Xq2u+J9izNKYMgvMSsJKylC7MJvj4xAOosJuq9IyGN6b/7z2UTSsR13Utc8aFeW3zxtkvAqYthh7XV1H2e1nEKOij8gOfFHvlfj10IiG0g3QbEch1nTTGq3Lncql9Q1a9QZb5pcsellPWeR4vhko3ssdxzIkLnvGz5Cjy1brMjZ97j7sSmHE9FT10L4L6ijXWuW25ikDRK0xnks0VfAvDVz75NCE+Qaz9MLPt8h0ESto3bTyuXrHFNNPOxnaEDw4TvSTN5G0tmUrqotRMmu5DadAm6aLMmJHL1OHVNGK4fH7Hb9S+7dBLEbQG3vRivz2SzpqgKFnFYwMJTQykUC3
Passphrase: implored-junker-requires
Here is the decrypted recipe if you do not wish to learn about encryption, but want to try my delicious non-vegan cashew recipe anyway.
1 LB organic raw cashews 2 TBS beef tallow 2 TBS salt 1 TBS garlic powder
Melt tallow in the microwave Brush the tallow on the nuts. Spread onto a cookie sheet.
Preheat oven 350 degrees
Bake for 10 minutes.
Let cool.
Violá!
Enjoy your garlic-roasted cashews. Or...you can pick some up at nostr:npub1marc26z8nh3xkj5rcx7ufkatvx6ueqhp5vfw9v5teq26z254renshtf3g0
npub1marc26z8nh3xkj5rcx7ufkatvx6ueqhp5vfw9v5teq26z254renshtf3g0
881,805https://mempool.marc26z.com/block/00000000000000000000f5d9aa481b8f2555deaa8638a3c1f2eb4ffa8f474f9d
-
 @ 1cb14ab3:95d52462
2025-01-05 04:18:29
@ 1cb14ab3:95d52462
2025-01-05 04:18:29Stunning beaches, ancient temples as far as the eye can see, and lush, green mountainsides that will leave you in awe—Myanmar is a destination you NEED to add to your bucket list. This guide offers the perfect one-month itinerary to explore the hidden gems of this incredible country.

The Itinerary
Days 1-2:
Fly into Yangon Airport. Settle in and explore the vibrant sights and flavors of the city.
Day 3:
Take an overnight bus south to the coastal city of Myeik.
Days 4-8:
Go island hopping around the Mergui Archipelago—remote beaches and untouched islands await.
Day 9:
Travel to Dawei. Find a cozy place to stay and relax for the evening.
Days 10-13:
Rent a motorcycle and explore the stunning Dawei Peninsula. Soak up the sun on pristine beaches.
Day 14:
Head to Hpa An. Check into a hotel and enjoy a sunset beer.
Days 15-18:
Discover the limestone mountains, caves, and farmlands of Hpa An.
Day 19:
Travel to Bagan. The journey may be bumpy, but the destination is worth it.
Days 20-23:
Explore the breathtaking temples of Bagan. Sunrise hot air balloon rides are a must.
Day 24:
Head to Lake Inle. Settle into your accommodation and dine by the water.
Days 25-26:
Cruise around Lake Inle by boat. Immerse yourself in the local culture and capture the iconic fishermen in action.
Days 27-28:
Visit Mandalay to experience city life from a Burmese perspective.
Days 29-30:
Return to Yangon for a final exploration before flying home.
Days 1-2: Arrival in Yangon
Myanmar's largest city is a bustling hub filled with shops, activities, and incredible food. The rapid development of this once-isolated country is evident everywhere you look.
If you are flying internationally: Yangon will most likely be the cheapest and most easily accessible destination to begin the trip.
If you are coming from Thailand: I would recommend altering the itinerary and going straight to Myeik via land border then working your way up the country from there.
Bogyoke Aung San Market
If shopping is your thing, this place is a haven for local treasures. Hundreds of stalls line the market and surrounding alleyways containing everything from art, sculptures, jewelry, antiquities, and fabrics. I spent a few hours here before jumping onto the nearby circular train for a loop around the city. There are a few small shops to get a bite to eat if you are hungry.
Remember that this itinerary will land you back in Yangon at the end of the trip if you see something you want to buy and don’t feel like lugging it around for a month.

Yangon Circular Train
Easily one of the most fascinating experiences of the trip is riding the Yangon Circular Train around the city for a true look at how the locals live. The train is old, slow, and packed with locals commuting to and from work. The doors are wide open, allowing you to hang your feet outside and soak in all of the sights afar. This is one of the best ways to get a true glimpse into the culture and day-to-day life of the Burmese people.
Be sure to speak with a train operator before getting on to make sure the entire loop is operational. When I went, construction stopped the train about 45 minutes into the loop, forcing us to get a taxi back to the downtown area. The full loop will take over 2 hours to complete. On the train, you can find vendors and hawkers selling little things such as water, nuts, and fruit. I’d suggest eating before jumping on.
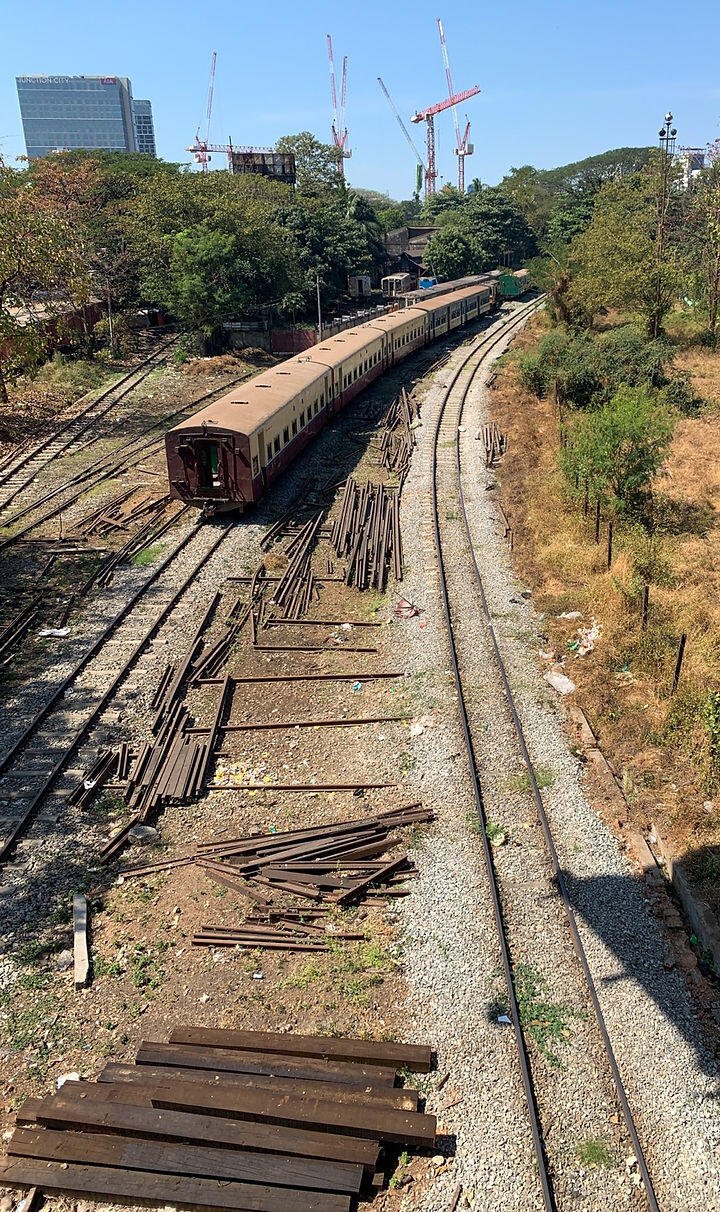
Shwedagon Pagoda
Upon walking up the steep and lengthy stairway to the Shwedagon Pagoda lies Yangon’s most famous attraction. The 99-meter gold-coated pagoda can be seen all around the city but is best enjoyed up close. This is a must-visit during your time in the capital. I went about an hour before sunset and stayed well into the night. Sunset from the hill it sits atop is spectacular, and the contrast of the pagoda between day and night is striking.
Make sure to bring socks and a bag, as shoes are not allowed, and you will need to carry them or leave them at the door. After visiting, you can take a short walk to the Sky Bar in the Yangon International Hotel overlooking the pagoda. This is a wonderful place to enjoy a nice dinner and drink, ideal for soaking up more of that luxurious golden pagoda.

Day 3: Bus to Myeik
The longest stretch of the trip—but well worth the sights to come. I took a 22-hour overnight bus and opted for the slight upcharge to take the VIP bus. This option is absolutely worth it. Equipped with A/C, comfortable reclining seats, and stops for three meals, it was a cheaper alternative to the costly domestic flight from Yangon and allowed me to see much more of the country.
I had a surprisingly good sleep and would do it again in a heartbeat. You can also fly directly to Myeik, but flights are infrequent and considerably more expensive. The bus I took arrived in Myeik around noon the next day, leaving me plenty of time to check into the hotel and wander around the city a bit before sunset. There weren’t many buses heading down here, so I’d recommend checking for tickets as early as possible when you arrive in Yangon. Alternatively, if you’re coming from Thailand, you can rearrange the itinerary and begin your Myanmar trip in Myeik by crossing from Thailand via bus at the land border.

Days 4-8: Island Hopping in Myeik
The city of Myeik has no accessible beaches, so you’ll need to book an island-hopping tour to fully appreciate the surrounding Mergui Archipelago. While the city itself doesn’t offer much in terms of entertainment, the beaches and crystal-clear waters you’ll encounter on an island-hopping tour are truly unparalleled. Your trip to Myeik will be unforgettable and is an experience you shouldn’t miss.
There are several travel companies offering island-hopping tours, ranging from single-day trips to 14-day excursions. While you can book ahead, I found it quite easy to arrange a trip through an agency in the city. I opted for a three-day, two-night tour with Life Seeing Tours, and it was fantastic. They provided food, tents, and transportation—just bring a swimsuit and a change of clothes, and you’re ready to spend a few nights exploring the islands.




Day 9: Bus to Dawei
Another travel day! This time, you’ll take a shorter bus ride heading north to Dawei. The journey takes about six hours, and tickets can be purchased from one of the travel agencies in Myeik. From what I gathered, there’s only one bus per day on this route, and it departs early in the morning.
Be prepared to wake up around 4 AM and make your way back to the same bus station where you arrived. It’s a good idea to arrange transportation to the station the night before—your hotel can help you book a ride for that morning.
Days 10-13: Motorcycling the Dawei Peninsula
Dawei boasts some of the most stunning coastlines and beaches in the country. While most of these beaches are only accessible by motorcycle, there are a few small bed-and-breakfast-style accommodations at the southern end of the peninsula that offer direct beach access.
If you’d prefer not to travel 2–3 hours each day from the city, I recommend staying in that area. You can rent a motorcycle from several places in the city and ride down to the B&Bs near the beaches for an overnight stay. This approach lets you enjoy the remote, lush, and scenic motorcycle journey while avoiding the daily commute to the beaches.

Grandfather Beach
Surrounded by mountains and vibrant orange dirt, getting here can be a bit tricky. You’ll need to navigate a steep, loose hill to reach the area. I recommend arriving near low tide, as the beach and surrounding shops flood around noon, making the descent a wet and challenging experience. Be prepared to remove your shoes and walk through knee-deep water to access the beach. This is one of the more popular spots for locals and was among the few beaches I visited that actually had people.

Tizit Beach
When we arrived at Tizit Beach, there was no one else around except for the locals. The sand here is soft, and the ocean is pristine. A motorcycle is necessary to access this beach, but the breathtaking views from the mountain pass make the journey entirely worthwhile. The sand near the shore is firm enough to ride on, creating unforgettable moments of cruising along the beach at sunset.

Day 14: Bus to Hpa An
One of the shorter bus rides on this trip, the fare is around $20, and it takes approximately 5 bumpy hours. Once you arrive in Hpa An, there are plenty of hostels and hotels to choose from. I booked mine on Hostelworld the night before, but you should have no trouble finding a place to stay on the day of your arrival if needed.
Days 15-18: Hpa An: Farmland, Caves, and Mountains
Hpa An offers a stark contrast to the beaches and cities encountered so far on the trip. Surrounded by towering limestone mountains and lush green farmland, the region has a peaceful, rural charm. There are several caves, lakes, and one of my favorite sunrise hikes of the journey.
While I have a few recommendations and must-visit spots, Hpa An is best explored without a strict plan. A central theme of this trip has been the freedom of hopping on a motorcycle and riding wherever your heart desires.

Mount Zwegabin Sunrise Hike
Hiking Mount Zwegabin for sunrise is a must-do during your time in Hpa An. The mountain is located a short ride from town, about 40 minutes by motorcycle. The hike to the summit took around 35 minutes at a brisk pace, so you’ll need to leave around 4 AM to catch the sunrise, depending on the season. The highlight of the hike is the final ascent up the floating stairs to reach the peak. Be sure to have your camera ready and take in the breathtaking views.

Kyauk Kalat Pagoda
This is one of those places that leaves you in awe, wondering how such a unique landscape can exist. Easily one of the most unusual rock formations I’ve encountered, it’s a fantastic spot to watch the sunset. A winding staircase leads up the rock to the top of the temple, making it a great place to spend a couple of hours.

Saddar Cave
Filled with bats, stunning limestone formations, and statues, this short cave walk provides a refreshing escape from the heat. The path takes about 20 minutes to explore, leading to a beautiful lake at the back. Grab a drink, relax for a while, and take a small paddle boat back to the entrance for a memorable experience.

Day 19: Bus to Bagan
A travel day heading north. This part of the trip is hot, bumpy, and slow, so be prepared for a longer journey than expected. Bagan has plenty of hotels and hostels, but I’d recommend booking accommodations in advance, as it’s a popular tourist destination. You’ll need to purchase an entry ticket for the area, as it’s a protected national park, but the bus driver should assist in sorting it out before you enter the park.
Days 20-23: Chasing Pagodas in Bagan
Once you’ve settled into your accommodation in Bagan, the best way to explore the vast area is by pedal bike or scooter. All the scooters available for rent are electric, helping to reduce noise pollution—a refreshing change from the loud gas-powered vehicles you’ll be used to from the first half of your trip. There’s no right or wrong way to experience Bagan. The park is enormous, with thousands of pagodas scattered throughout. Most of them are open for exploration, with a few offering rooftop access (though that is being restricted more recently).
You could spend weeks here and still not see all the pagodas up close. Bagan is divided into a new town and an old town—most of the backpacker-friendly hostels are located in Old Town. You’ll find a handful of restaurants, but I often ate at my hostel or from local food carts. Several hostels and hotels offer outdoor pools, which are a great perk, especially depending on the time of year you visit. I highly recommend simply wandering the area freely, but here are a few top pagodas and experiences not to miss during your time in Bagan.

Hot Air Ballooning
The top attraction in Bagan is undoubtedly the daily hot air balloon tours. Almost everyone who experiences it claims it’s a must-do. I chose to watch from the ground, as the cost of a tour is quite expensive. If you decide to go for it, be sure to set aside a few hundred USD for the trip. From what I’ve heard, you’ll wake up around 4:30 AM and head to the take-off location, returning by around 9:00 AM.

Sunset Boat Cruise
Be sure to spend at least one evening on a slow cruise down the Ayeyarwady River. It’s a wonderful way to enjoy distant views of some of the pagodas and relax after a long day of exploration. Several companies offer these cruises at very affordable prices. Our boat included snacks, drinks, and even alcohol. The trips range from half an hour to two hours. Book through your hotel for convenience.

The Big Three Temples
With over a thousand pagodas to explore in Bagan, there are three main structures that hold significant importance to locals: Shwesandaw, Thatbyinnyu, and Shwezigon. Be sure to make time to visit these iconic pagodas during your trip—you’re likely to come across them without even trying.
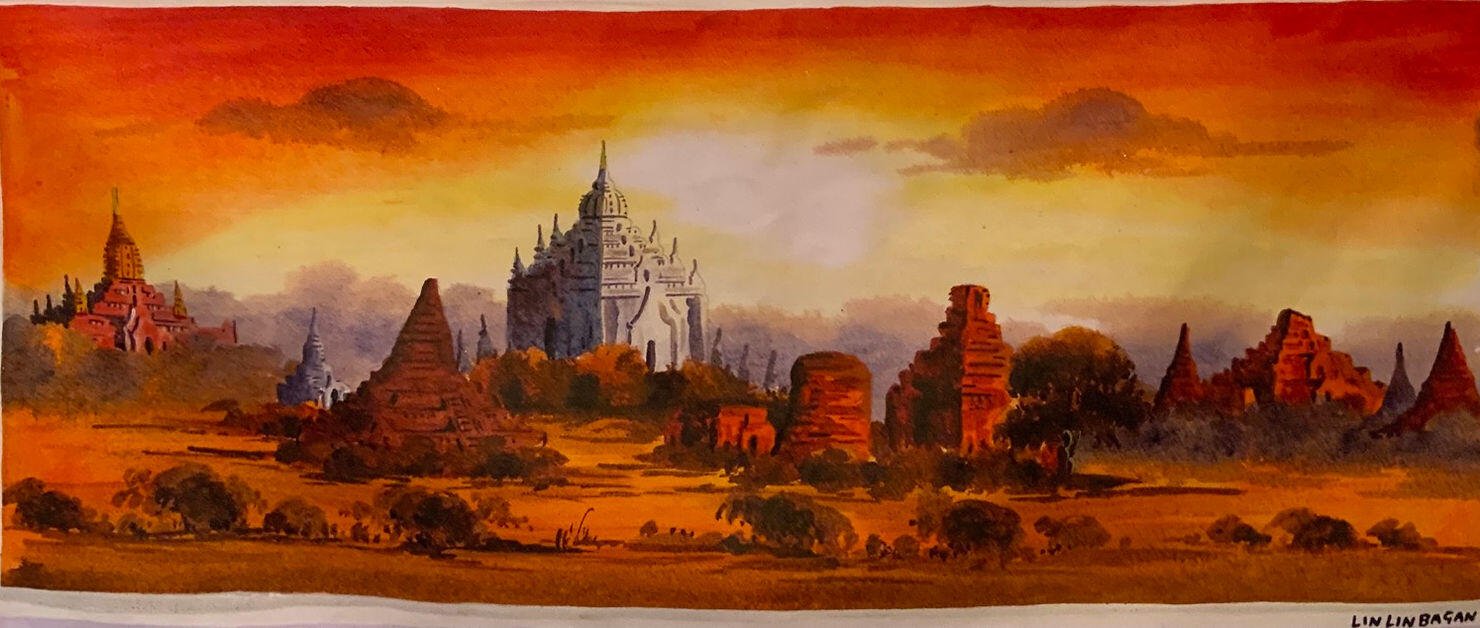
Day 24: Bus to Kalaw
Long-distance buses run the route multiple times a day, with the overnight option being the most popular. I recommend checking with a travel agent in Bagan to book your tickets before heading to the bus stop
Day 25-26: Relaxing at Lake Inle
These two days take us to the stunning Lake Inle, located just outside the city of Kalaw. Unfortunately, I wasn’t able to make it to Lake Inle during this trip, but everyone I spoke to highly recommended not missing it. The lake is known for its breathtaking scenery, traditional Intha stilt houses, and the unique leg-rowing fishermen.
From what I’ve heard and seen through photos, the calm waters, floating gardens, and vibrant markets make Lake Inle a truly unforgettable destination. Huge thanks to my friend Toby for sharing those beautiful pictures and giving me a glimpse of what I missed!




Day 27-28: Mandalay City
Mandalay is a fast-paced city with less tourism compared to other parts of the country. It offers a fascinating glimpse into the daily lives of the Burmese people, away from the crowds typically found in Yangon. There are several culturally significant monasteries and temples within the city limits, as well as vibrant markets perfect for shopping and exploring. Mandalay Hill is a great spot for a brisk hike and offers stunning views of the city and sunset on one of your nights. You could also visit the Mandalay Marionettes Theater to catch a local show showcasing Myanmar’s rich history and culture.
As for me, I mainly wandered the city without specific destinations in mind. Since this is the last stop before returning to Yangon, you might not feel as inclined to spend too much time here, but there are definitely some interesting sights worth exploring.

Day 29-30: Return to Yangon
The final two days of the trip are a return to where it all began. The bus from Mandalay to Yangon takes about 8 hours. Alternatively, Mandalay has a large international airport if you prefer to fly, depending on your next destination.
If you return to Yangon, you’ll have plenty of time to revisit the markets and pick up any final souvenirs or trinkets you might want to take home. Enjoy these last couple of days, savor some delicious food, and take the time to reflect on the incredible month of experiences you’ve had.

Concluding Thoughts
Your month-long journey through Myanmar is bound to be an unforgettable adventure, filled with stunning landscapes, rich culture, and warm hospitality. From the serene beaches of Ngapali to the ancient wonders of Bagan, and the tranquil beauty of Lake Inle to the bustling streets of Yangon and Mandalay, each destination offers its own unique charm and insight into Myanmar’s diverse culture.
The highlights of your trip—exploring historic pagodas, witnessing breathtaking sunrises, and embracing the freedom of riding a motorcycle—are sure to stay with you. Myanmar’s blend of natural beauty, vibrant traditions, and friendly locals makes every moment special. Despite the occasional long and bumpy journeys, the sense of discovery and connection with the people and places makes the experience truly worthwhile.
As you reflect on your journey, you’ll likely feel grateful for the memories, experiences, and the chance to explore a country that feels both timeless and unique. Myanmar’s beauty lies not just in its landscapes but in the people who call it home. You’ll leave with a deeper appreciation for the warmth and resilience of its people and a desire to return and explore even more of this enchanting land.
Update: Unfortunately as of this time (June 2021) Myanmar is experiencing major political and civil unrest. Taken from the advice of friends on the ground there— I can not recommend traveling to Myanmar at the time of writing. Pray for Myanmar!
Update 2: The political situation in Myanmar has escalated (July 2022). Travel is still not recommended.
Update 3: As of 2025, some tourists have reported that travel is doable. However many governments still have do not travel advisories. DYOR.
Other Myanmar Guides:
The Top 3 Hidden Beaches of Myanmar: A Guide to Tizit, Grandfather, and Mergui
More from Hes:
Originally Published June 15, 2021. Edited with Nostr friendly images on 1/5/2025
-
 @ cbaa0c82:e9313245
2025-02-01 15:07:16
@ cbaa0c82:e9313245
2025-02-01 15:07:16TheWholeGrain - #January2025
This January we really got to start the story telling of our first adventure series painted by Dakota Jernigan a.k.a. The Bitcoin Painter! The typical Singles of the month were released on Sunday along with a special Single released on the first to celebrate the New Year! Here we go, 2025! And, even with all that the monthly Concept Art, Bitcoin Art, and the newest Cover Art from Toast's Comic Collection were all still released! Not only was the first month of 2025 quite packed full of fun content, but the Bread and Toast website got a makeover! Did you notice all the explanation points!? We're all so excited we just can't help ourselves from using them!
January Sunday Singles 2025-01-01 | Sunday Single 73 Title: Happy New Year 2025 Happy New Year! What a year 2024 has been! We can’t wait to see what 2025 has in store for us! https://i.nostr.build/QFTmeR5p2FthPMXp.png
2025-01-05 | Sunday Single 074 Title: Snowflake It’s the most beautiful snowflake Toast has ever seen… until this one melts then it’s on to the next one! https://i.nostr.build/YHGeOcYv8WEP1fAf.png
2025-01-12 | Sunday Single 075 Title: Weight Lifting End-Piece has been working out since last year’s resolution. Now, time for heavy lifting! https://i.nostr.build/8lxeovAr5aK598Ze.png
2025-01-19 | Sunday Single 076 Title: Good Morning GM, Everybody! https://i.nostr.build/9jn2D2if4sFfNXzU.png
2025-01-26 | Sunday Single 077 Title: Chess When it comes to the chessboard, Bread is King. https://i.nostr.build/LZq57iL7tOWbHAKc.png
Adventure Series: Questline Bread, Toast, and End-Piece have started their journey in Grain Valley, and they have already found themselves in what used to be a village that is now been burnt to a crisp!
Writer: Daniel David (dan 🍞) Artist: Dakota Jernigan (The Bitcoin Painter)
2025-01-14 | Questline 001 - The Adventure Begins Our heroes take their first steps upon one of the oldest paths in all of Grain Valley. They can see the mountains in the background of the landscape before them. As they walk, they see in the distance ahead of them large amounts of black smoke rising until it disappears into the sky. https://i.nostr.build/ygjmYlWAZ4uPfPCn.png
2025-01-28 | Questline 002 - A Village Burned The source of smoke surrounds our heroes as their path brings them to the center of what used to be a village. It seems to be completely abandoned with no signs of life. Yet, all the remains of the village appear to have only recently burned to a crisp. What could have possibly happened here? https://i.nostr.build/BJ4L1shKh5YERzWc.png
Other Content Released in January 2025 2025-01-01 | Toast's Comic Collection Title: Iron Bread #9 "I am Iron Bread." - Tony Starch https://i.nostr.build/QJKkDCbfgc6Vqzcq.png
2025-01-08 | Concept Art Title: Second Bread Sketch A second sketch of the character Bread. Remade and cleaned up. https://i.nostr.build/4TXIRSUGA6viEaJx.png
2025-01-15 | Bitcoin Art Title: Stack Sats Toast is constantly stacking sats! https://i.nostr.build/txxkux0oJqyjNcSL.png
Thanks for checking out the fifth issue of The Whole Grain. The Whole Grain is released on the first of every month and covers all of the content released by Bread and Toast in the previous month. For all Bread and Toast content visit BreadandToast.com!
Thanks for helping us kick off 2025! Bread, Toast, and End-Piece
BreadandToast #SundaySingle #Questline #ToastsComicCollection #ConceptArt #BitcoinArt #Bread #Toast #EndPiece #Artstr #Comic #Cartoon #NostrOnly #🖼️
List of nPubs Mentioned: The Bitcoin Painter: npub1tx5ccpregnm9afq0xaj42hh93xl4qd3lfa7u74v5cdvyhwcnlanqplhd8g
dan 🍞: npub16e3vzr7dk2uepjcnl85nfare3kdapxge08gr42s99n9kg7xs8xhs90y9v6
-
 @ 1cb14ab3:95d52462
2025-01-04 20:07:38
@ 1cb14ab3:95d52462
2025-01-04 20:07:38When you think of Myanmar, beautiful beaches and crystal-clear waters likely aren’t the first things that come to mind.
Think again. Southern Myanmar is home to some of the most stunning and untouched beaches in Southeast Asia. These pristine shores rival those of Thailand, the Maldives, and even Hawaii, yet remain largely hidden due to limited infrastructure and minimal tourism.
I spent countless hours getting lost, asking for directions, and exploring remote villages, so you won’t have to. With unreliable Google Maps and few signs of modern development, navigating this region requires patience and curiosity. Get ready to discover Myanmar’s best-kept coastal treasures—and why you might want to skip Thailand in favor of a more off-the-beaten-path adventure.
Here’s a look at my top three hidden beaches in southern Myanmar.
3: Tizit Beach - A Sanctuary Shrouded by Mountains

Tizit Beach is situated about one hour south of Dawei city. Getting there is no easy feat and is not recommended for the faint of heart.
The roads are rough, unlit, and sandy, making them a challenge to navigate. Only attempt the trip if you’re confident on a motorbike, and be sure to double-check that your bike is in good working condition, especially with functional brakes. As a reward for your efforts, you’ll find very few—if any—tourists at Tizit Beach. The only people you’re likely to encounter are local children and fishermen along the shore.
To reach Tizit Beach, you’ll need to rent a motorbike and traverse a steep mountain pass. The journey takes roughly an hour each way, but the seclusion and untouched beauty are well worth the effort.
Map to Tizit Beach:
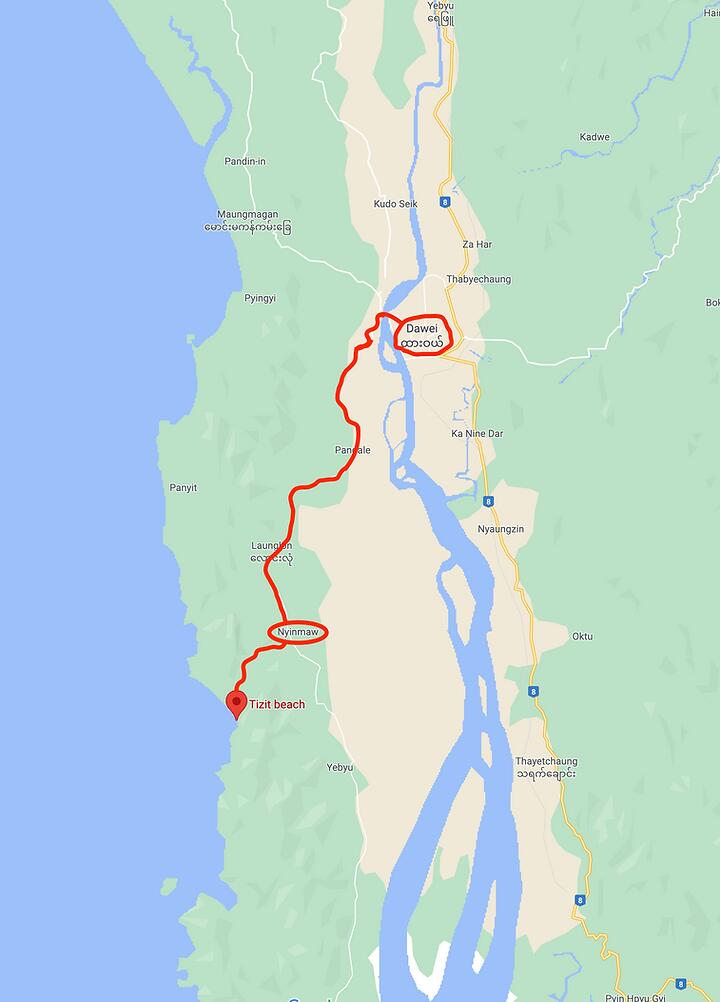
Directions:
Start by crossing the water west of Dawei and heading left, heading south towards Nyinmaw. As you travel down the peninsula from Dawei, there is essentially one main road to follow. Stay on this road for about 30 minutes, keeping an eye out on the right side for a small sign marking Tizit Beach.
You might miss the sign on your first pass, as I did, so pay attention to your GPS. If you’ve passed Nyinmaw, you’ve gone too far. Once you spot the Tizit Beach sign, you’ll notice a school playground and a road leading toward the mountains. Take the right turn here and continue over the mountain pass for about 20 minutes:

At the bottom of the mountain pass, you’ll reach a fork in the road with unclear signs. If you go left, you’ll end up in a small cemetery, which is a dead-end. The left fork looks like this:

Instead, take the right fork, which will lead you through a small residential area to the waterfront. Keep in mind that many of the beaches in this region experience significant flooding in the morning, so arriving after 3:00 PM is probably your best bet.
As you arrive, you’ll be greeted by panoramic views of lush mountains, a vast delta plain, and crystal-clear blue waters:



The sand at Tizit Beach is a rich brownish-orange hue, often turning into deep red around sunset. It’s soft, clean, and much wider than other beaches in the area, giving you more room to set up camp away from the tide. The water is warm enough for swimming, with no strong currents, making it suitable for experienced swimmers. Please note, however, that there are no lifeguards, so swim at your own risk.
A few wooden fishing vessels are docked off the coast, and the locals are incredibly friendly:


One of the highlights of Tizit Beach is the sunset cruise along the water. The sand hardens near the shore, allowing you to ride a motorcycle along the beach. It was one of my best memories from the 30 days I spent in Myanmar.


Sunsets at Tizit are truly epic, casting everything in red. However, don’t linger too long, as the mountain pass isn’t lit, and riding back in the dark can be quite sketchy. If you plan to stay for sunset, make sure your motorcycle lights are working and be prepared to leave immediately after the sun sets.


2: Grandfather Beach - Popular, but Plentiful

Grandfather Beach is one of the most striking beaches in Dawei and a popular spot for locals. Though it’s relatively well-visited, its size ensures it doesn’t feel overcrowded. The beach is a bit of a challenge to find, but the effort is worth it once you arrive.
Getting here requires about 3 hours on a motorbike from Dawei city, factoring in photo stops and meals along the way.
Map to Grandfather Beach:

Directions:
To reach Grandfather Beach, head south from Dawei on the main road and continue down the peninsula for several hours. The route winds through jungle-covered terrain, and eventually, the road will cut across the peninsula, running parallel to the coastline. Once you crest a hill and spot the ocean below, you’re getting close.
Look for the town of Kyauk Wap Pyin at the base of the hill:

Once in Kyauk Wap Pyin, take a right from the east side of the land, heading west towards the ocean. There is really only one main road, so it shouldn't be too hard to spot. Follow the small road through the town for about 20 minutes.
The road will lead to a fishing village along the west coast that looks like this:

From the fishing village, look for the orange-dirt road leading to the beach. It’s steep, narrow, and a bit tricky to navigate, but a fun ride if you’re up for the adventure. The road is on the right-hand side as you face the sea from the village. You can see it in the image above.
Grandfather Beach is no stranger to daytime flooding, so if you arrive after noon, you may find yourself wading through waist-deep water from the parking area to the beach. Riding on the beach is only possible in the early morning before the tides rise.

The flooding isn’t as troublesome as it might seem. The local restaurants are well adapted, elevated above the waterline, and offer swings set up perfectly above the waves. The sand at Grandfather Beach is the softest of all three beaches mentioned in this article, though it’s narrower and less pristine than Tizit.

This beach sees more local visitors, so don’t expect a completely secluded experience. However, it does have the most infrastructure, with plenty of options for food and drink. If you plan to stay near Grandfather Beach, watching the sunset is highly recommended. Otherwise, the long and dark return journey to Dawei is best avoided.
To fully enjoy Grandfather Beach, plan for an entire day to soak in the scenery, relax, and make the most of your visit.




1: The Mergui Archipelago - An Unexplored Haven

This should come as no surprise to anyone familiar with Myeik: the hundreds of remote islands in the Mergui Archipelago truly stand out as the top destination for beaches in the region.
Had it not been for a spontaneous trip to Yangon without plans and a quick browse of satellite maps, I might never have discovered the sheer magnificence of the Mergui Archipelago. Information about this area is scarce, and tourism remains extremely limited. While many islands are off-limits, a few offer stunning private beaches that are accessible and worth visiting.
I was surprised to learn that many people I spoke to during my month in Myanmar had no idea these kinds of breathtaking islands existed. I feel a strong sense of responsibility to share this hidden gem with others, encouraging them to experience it firsthand. The best way to explore is through island-hopping tours from Myeik city. Tours vary in length and cost, ranging from a couple of hundred dollars for 2-3 day trips to thousands for longer yacht expeditions. Most tours include food, tents, and drinks, but always confirm these details with the booking agency.

During my five days in the Archipelago, I encountered only three other foreign tourists. The guide mentioned that many of the islands we visited had only been seen by a few hundred foreigners at most. The isolation of the region was so profound that even some of my Burmese friends weren’t aware of its existence.
At times, I felt a bit intrusive, considering how little tourism has reached this remote paradise. However, the welcoming nature of the islanders, who live off the sea and have no contact with the tour guides, made the experience all the more genuine.

One memorable moment was camping on an island where I shared the night with only the island caretaker and his ten puppies. Each day, we were taken by boat to explore nearby islands, enjoying swimming, beach time, and snorkeling before returning to the campsite. For certified SCUBA divers, this area is a dream—home to impressive coral reefs and diverse marine life.



The surreal feeling of being in such an untouched place is hard to describe. Knowing this is one of the few remaining uncharted areas on earth makes the experience truly unforgettable. If you’re planning a trip to Asia, the Mergui Archipelago should absolutely be at the top of your list.




Closing Remarks
Myanmar is truly a remarkable country, with a rich and complex history. The people I met were some of the friendliest and most optimistic I’ve encountered, despite the challenges they’ve faced. While this guide highlights some of the stunning beaches, my main aim is for every visitor to connect with the locals on a deeper level. They have incredible stories to share, and I’ve made friendships that will last a lifetime.
Traveling through Myanmar offers much more than just beautiful landscapes and serene beaches— it’s an opportunity to understand and appreciate the resilience and warmth of its people. I hope that everyone who visits Myanmar will take the time to sit down, listen, and engage with the locals.
Enjoy your journey.
— Hes
Originally published May 7, 2021 by Hes. Re-uploaded to Nostr on 1/14/2024. Re-edited 1/4/2025 with new Nostr friendly media links.
-
 @ 1cb14ab3:95d52462
2025-01-02 21:31:48
@ 1cb14ab3:95d52462
2025-01-02 21:31:48
No. 6 - Zhujiajiao Canal Chasing

For a tranquil escape from the hustle and bustle of the city cruise to Zhujiajiao -- an epic water town dating back to the Ming and Qing dynasties. It's only about 50 kilometers from the downtown and makes for an easy day trip. Hop on the subway and get there in an hour. Zhujiajiao has canals, bridges, and ancient buildings, offering a glimpse into the town's rich history. Take a boat ride along the canals for the best views of traditional houses and temples. Then explore the town on foot and get lost in attractions like the Kezhi Garden, Yuanjin Temple, and the Qing Dynasty Post Office. Don't forget to grub-up with all of the great food vendors nearby.
No. 7 - China Art Museum

China Art Museum is absolutely worth the trip solely for its awe-inspiring architecture. The towering structure casts a tall shadow over bystanders. Step inside and you'll find a world of art waiting. The blend of permanent and temporary exhibits offers hours of art-gazing. Give yourself at least half a day to fully immerse in the creative haven in Pudong. To get to the China Art Museum, you can take Line 2 of the Shanghai Metro and get off at the Pudong Avenue Station (Chinese: 浦东大道站). The museum is located near Exit 4 of the station.
No. 8 - Days on The West Bund

Hands down my favorite place in Shanghai. This spot is the go-to for a perfect weekend under the sun. You'll find me setting up a blanket with beer, cards, and snacks, along with a slackline and spike ball setup nearby, surrounded by dogs running around, enjoying the company of old and new friends. When you want a little movement enjoy some climbing, skating, running, or basketball after work. The West Bund is an oasis amidst the chaos of the city. But beware - its popularity is growing, so tread lightly.
No. 9 - Nights Under the Lupu Bridge
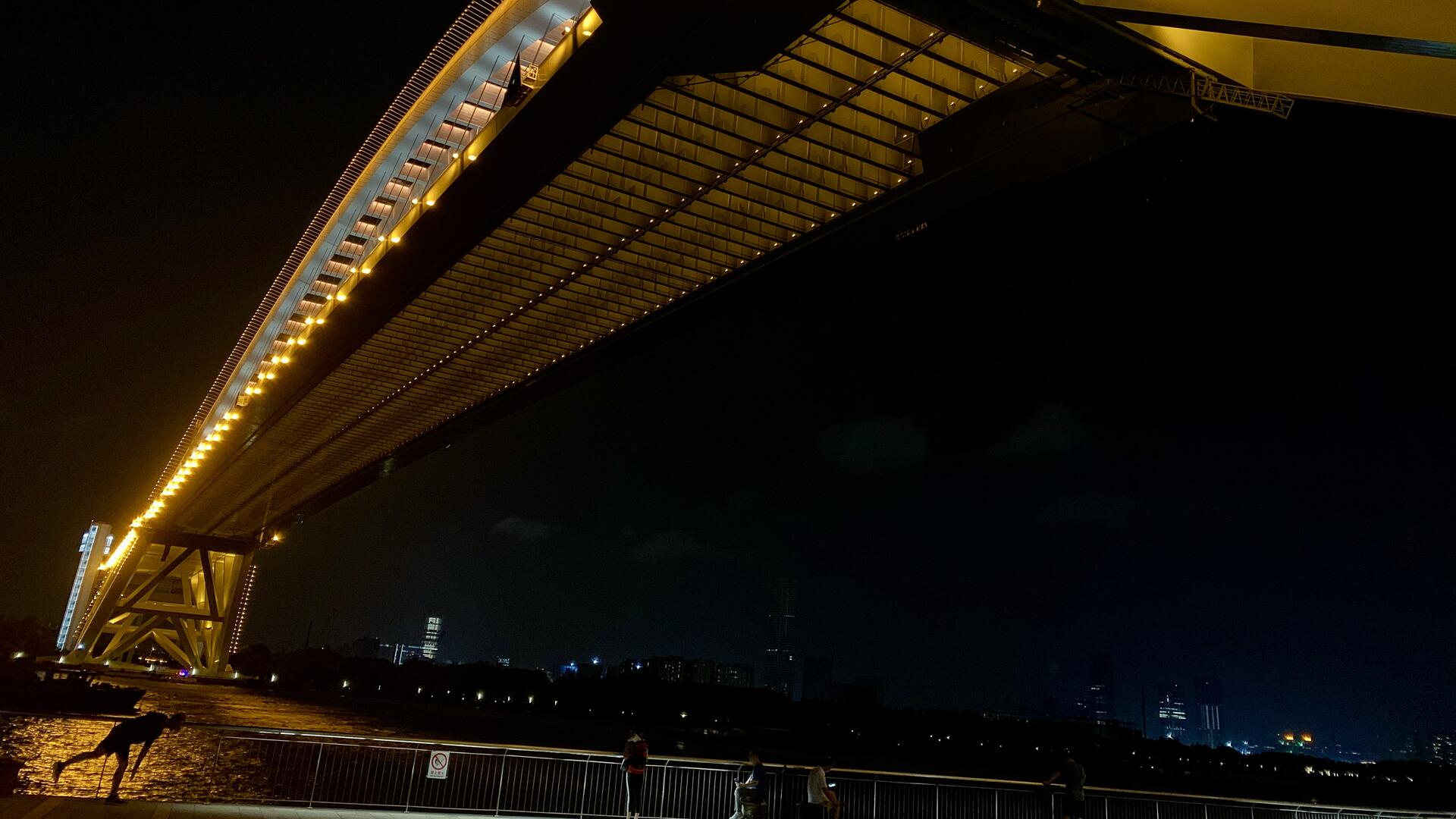
Nights under the Lupu Bridge are where it's at, man. Hop on your scooter and cruise over for the ultimate skyline views. Stroll along the walkway, munch on street food, sip drinks, and groove to live tunes. Street vendors serve up traditional snacks and crafts, and the vibe gets lit with spontaneous performances and games. Get ready to soak up the electric energy of Shanghai's Lupu Bridge at night."
No. 10 - A Weekend on Chongming

Escape the city hustle and find your peace on Chongming Island. A weekend getaway on this rural gem is just what you need. Chill out in a farmhouse, soak up the sunset, and enjoy the tranquility. Explore the natural wonders, visit the old museums, and feast on fresh seafood. End your days with a beach walk under the stars. Nothing beats a few nights away from the city chaos.
Additional Photos






Previous Guide in the Series:
An Expats Guide to the Best Spots in Shanghai: 001
Next Guide in the Series:
An Expats Guide to the Best Spots in Shanghai: 003
Find Me Elsewhere:
All images are property of Hes. Published 06.29.2024
-
 @ 1cb14ab3:95d52462
2025-01-02 05:57:05
@ 1cb14ab3:95d52462
2025-01-02 05:57:05
No. 1 - The Less Touristy "Bund"

The Bund is certainly a must-see if you are traveling to Shanghai for the first time - and it will be at the top of every travel guide out there, for good reason - there are equally as stunning alternatives away from the crowds. If you want to enjoy the skyline from a more relaxed perspective, consider the Pudong side of the river. There are parks, basketball courts, and green spaces along the riverbank for you to chill at and take in the sights. You can also hop on a ferry or a sightseeing boat to cross the river and admire the views from the renowned Bund.
No. 2 - Walks Along Golden Street

This one is out in Gubei, a suburban area in the west of Shanghai. It may be a bit of a trek, but it is worth it if you are looking for a more relaxing and peaceful pedestrian street in the city. Golden Street, or Jinxiu Road, is a great place to walk a dog, grab an afternoon drink, or enjoy a romantic dinner with your loved one. While it may be a bit far from downtown, it makes for a great joyride on your scooter or bicycle.
No. 3 - Moganshan Road Graffiti Wall

Moganshan Road is a gem for all things art. It is home to M50, the best art district in the city, where you will find dozens of galleries, studios, and workshops showcasing a wide range of art. There are also plenty of cool spots scattered around the area, particularly the graffiti wall. The wall is a welcome contrast to some of the drab and monotonous architecture found around the city; with colorful display of street art featuring various styles and themes. Stop by and admire the works of local and international artists, and even jump in to join them in adding your own mark. The wall is constantly evolving, so you can always find something new.
No. 4 - Jiaotong University in the Fall

Easily one of the best spots in town for catching rows of bright yellow and red leaves. Jiaotong University is one of the oldest and most prestigious universities in China. The campus is located in Xuhui District and has a mix of Chinese and Western architectural styles to admire as well. Try to visit in late October or early November for the best leaf-peeping. You can walk along the tree-lined paths, set up a blanket in the field for a picnic, or simply take photos and enjoy the scenery.
No. 5 - Day Drinking at Highline

Hands down one of the top five rooftop bars in the city, along with Bar Rouge, Kartel, and others; Highline is a go-to-spot that offers great views of the city and excellent food. Find it on the sixth floor of the Ascott Hotel in Huaihai Road in Xintiandi. Nothing beats a laid back Saturday afternoon at Highline. I prefer the views during the day, though it is equally as nice a night. Sip cocktails, wine, or beer, and enjoy the music and vibe. Highline is a perfect place to spend an afternoon.
Additional Photos





Next Guide in the Series:
An Expats Guide to the Best Spots in Shanghai: 002
Find Me Elsewhere:
All images property of Hes. Originally published as an Instagram Guide on Feb. 02, 2021. Reworked and published on Nostr on Feb. 17, 2024.
-
 @ 17538dc2:71ed77c4
2024-12-30 22:45:10
@ 17538dc2:71ed77c4
2024-12-30 22:45:10Merry Christmas, and Happy New Year! Here's an overview of keeping tabs on interoperability on nostr.
What is nostrability
Nostrability is: -the practical documentation of broken things on nostr between two or more apps, and -a place to advocate for positive interoperability updates to apps
Why does this matter?
If the hop and/or interaction between apps sucks, then nostr users will not have an amazing and unique experience. Nostr will lose to well funded incumbents.

How did this start?
Will was upset that he had to troubleshoot other dev's apps.
What nostrability does not aim for
All apps implement all NIPs.
Where can I read in detail
https://github.com/nostrability/nostrability
Timeline
Nov '23 Added placeholder to github. Jan '24 First issues documented. Jan '24 First nostrability two app bug is fixed Coracle cannot send DMs to Damus (thank you Hodlbod!). '24 Gave intro to nostrability talk at BBB. Presentation link. Aug '24 Galaxy devs educated elsat at NostrCI discussion at Nostriga. (n.b. where's the video??) Oct '24 Humbled by and grateful for OpenSats acknowledgment and funding. Thank you to all nostr enjoyers & devs who gave me their precious time, and to my advocates & supporters - you know who you are 🙏.
What are specific issues discussed?
Over a hundred open issues, and a couple of dozen resolved issues. Many of these were reported by extremetly very normal nostr users, and devs.
Example topics (too many to list in a single article) range from: -contact list wipes, mute list wipes (Kieran pls fix!!) -zaps not working between apps -missing notes -broken profiles -old profile information -q tags, a tags, missing replies and/or parent notes etc.. -to proposed onboarding best practices -outbox tracker positive interop -highlights -non-nostr interoperability: e.g. bluesky bridgyfed profile info -spillover NIP/other controversy such as edited notes -and migrating to nostr best practices
Learnings
- Lone wolf, limited resource devs are the norm. Most devs focus on their one app, or their multiple apps.
- Some devs are extremely generous with their time when it comes to interop. Proof of work is in the git repo.
- There is a lot of space for building amazing interoperable experiences - this remains frontier territory on the design, product, and dev side. Which will be the first experience to blow people out of the water? Is it zaps, DVMs, or something not yet put together?
- I empathize that without basic things "just working", and/or basic features missing it may be difficult to allocate resources to interoperability.
- Even devs with teams may struggle to allocate resources to interoperability.
- Bug reporting and crappy experience reporting matters! This is important for single apps, and even more so for multi-app interaction. Devs may not get around to fixing something right away. However, if nostriches don't share their negative experience, devs will have less impetus to improve an experience.
2025 plans
- Continue documenting broken things.
- Interview devs to better understand how I can suit nostrability to dev's single app workflows, as to more effectively close broken things, and better advocate for positive interoperability updates across apps.
- Help test nostrCI automated interop testing methodology with galaxy dev of nostr.watch & NIP-66 Sandwich, so that nostrability can be automated per particular test cases.
Dev and nostrich feedback
Let me know how I can make nostrability more useful for yall. Tag me on nostr, create issues on nostrability 💪.
!(image)[https://media.tenor.com/hF5RhwXuG_kAAAAC/arnold-schwarzenegger-terminator.gif]
-
 @ 42342239:1d80db24
2024-12-22 08:38:02
@ 42342239:1d80db24
2024-12-22 08:38:02The EU's economy is facing a number of challenges, from high energy costs to low productivity. But behind the official rhetoric lies an assumption that is rarely questioned: that the green transition will automatically lead to economic growth and increased prosperity. But is this really true?
In Germany, which is once again forced to bear the label "Europe's sick man", Chancellor Olaf Scholz is struggling with alarmingly low confidence figures ahead of the election in February. But perhaps this is not so surprising. German industrial production has been trending downward since the green agenda became fashionable. Energy-intensive production has decreased by a full 20% in just a few years. Volkswagen is closing factories, Thyssenkrupp is massively laying off employees, and more than three million pensioners are at risk of poverty.
If this is Europe's "man on the moon" moment, as EU Commissioner von der Leyen expressed it in 2019, then it's not much to brag about. At least, not if you're not a sadist.
The former ECB chief Mario Draghi's report on the EU's competitiveness has been discussed previously in Affärsvärlden, among other things by the author and by Christian Sandström. One of the problems pointed out was that European companies have significantly higher energy costs than their American competitors, with electricity prices 2-3 times higher and natural gas prices 4-5 times higher.
Germany is perhaps worst off, thanks in part to former Chancellor Angela Merkel's decision to completely phase out nuclear power (a decision that not only lacked popular support but which she also refuses to acknowledge as a mistake). The sabotage of Nord Stream made the situation worse.
Without Real Capital, No Economic Prosperity
Germany's phasing out of nuclear power plants is an example of how political decisions have contributed to reducing the economy's capacity. The same applies to the sabotage of Nord Stream. Real capital, such as buildings, machinery, and equipment, is crucial for the economy's productivity (e.g., measures such as GDP per hour worked). A larger and more efficient capital stock enables the production of more goods and services with the same amount of labor, leading to greater production, higher wages, and increased material prosperity. This is basic economics. On the other hand, when real capital is declared obsolete due to political decisions, as in the case of the shutdown of nuclear power, it reduces the economy's capacity. The same applies when real capital is destroyed, as was the case with Nord Stream.
More Working Real Capital Will Be Put on the Back Burner
EU Commissioner von der Leyen promises improvement. She seems convinced that the EU's decline can be reversed by tripling down on the bloc's green goals, and listed decarbonization as one of three key pillars in a new "Competitiveness Compass". When reality does not live up to expectations, you can always press "Ctrl+Alt+Slogan" and hope that no one notices that nothing has improved.
However, her plans mean that existing and currently functioning real capital will be written off to an even greater extent in the future. This can be compared to a nation that gradually expands its nature reserves year after year. As it happens, this is also taking place. The Kunming-Montreal framework for biodiversity means that 30% of all areas, on land and at sea, must be protected by 2030. A country that currently conserves less than that must therefore identify additional areas that can be protected. The process of protecting 30% of all areas will likely reduce the economy's productive potential. With shrinking fields, there will be fewer carrots (unless significant technological progress is made).
Security Policy and Preparedness Consequences
On the current path, more real capital will be put on the back burner, which can have far-reaching consequences, not least for our security policy. For example, if Russia can produce artillery shells about three times faster, at a cost that is roughly a quarter of what it costs Ukraine's Western allies, then it's clear that this has security policy consequences. Similarly, if electricity prices in Germany are five times higher than in China, which is currently the case, then this will also have negative security policy consequences. Compared to the EU, China actually has a higher carbon dioxide emission level per capita, with a difference of about 50% according to available data. Adjusted for international trade, China emits 10% more than Sweden per capita.
A preparedness perspective can also be found. In the early 1990s, Swedish farmers produced nearly 75% of the country's food. Today, Sweden's population has increased significantly, but food production has not kept pace. Every other bite is imported today. In Sweden, we can even boast that we cannot even provide for ourselves with the simplest of crops - potatoes. Can we really be sure that significantly expanded nature reserves, as prescribed by the Kunming-Montreal framework for Sweden, will not further deteriorate our food preparedness?
Reminds One of Little Gnomes
I am reminded of an episode from the 90s TV series South Park, where little gnomes collect underpants. When asked about their plan, they described their method:
- collect underpants
- ???
- profit!
Translated to the green transition (the German Energiewende):
- destroy real capital and conserve land and sea
- ???
- economic prosperity!
What Can the EU Really Afford?
Economics is fundamentally about managing scarce resources, which many people seem to have forgotten. It's high time to question what the EU can really afford. Can we really afford to arm ourselves for war against Russia, China, and Iran while at the same time tying our own hands with green promises of reduced carbon dioxide emissions and increased biodiversity? This in a situation where the next US administration is likely to invest heavily in increasing its competitive advantages through deregulation, lower energy prices, tax cuts, and a withdrawal from the Paris Agreement?
When von der Leyen was responsible for the German military, the situation became "catastrophic". All six of the country's submarines were out of commission. At times, not a single one of the country's 14 transport aircraft could fly. German soldiers had to use broomsticks instead of guns during exercises.
Hopefully, von der Leyen will show more success in her handling of the EU's economy, defense, and preparedness than she has shown in her role as German Defense Minister. However, it may also be time for more people to challenge the prevailing narratives that shape our policies. What if the facts don't quite add up to the truth we're being told?
-
 @ 42342239:1d80db24
2024-12-19 15:26:01
@ 42342239:1d80db24
2024-12-19 15:26:01Im Frühjahr kündigte EU-Kommissarin Ursula von der Leyen an, sie wolle einen „ Europäischen Demokratieschild " schaffen, um die EU vor ausländischer Einflussnahme zu schützen. Von der Leyens Demokratieschild befindet sich derzeit in der Planungsphase. Die erklärte Absicht besteht darin, eine „ spezielle Struktur zur Bekämpfung ausländischer Informationsmanipulation und -einmischung" zu schaffen. Obwohl es als Instrument zum Schutz der Demokratie angepriesen wird, vermuten einige, dass es sich in Wirklichkeit um einen verschleierten Versuch handelt, abweichende Meinungen zu unterdrücken. Der im vergangenen Jahr verabschiedete Digital Services Act (DSA) der EU ist eng mit diesem Schild verbunden. Durch den DSA riskieren große Social-Media-Plattformen wie Elon Musks X erhebliche Geldstrafen, wenn sie den Forderungen der EU-Bürokraten nach Zensur und Moderation nicht nachkommen.
Note: This text is also available in English at substack.com. Many thanks to
stroger1@iris.tofor this German translation.Im krassen Gegensatz dazu hat sich der künftige US-Präsident Donald Trump als klarer Befürworter der Meinungsfreiheit und entschiedener Gegner der Zensur hervorgetan. Er wurde bereits von YouTube gesperrt, hat jedoch erklärt, er wolle „das linke Zensurregime zerschlagen und das Recht auf freie Meinungsäußerung für alle Amerikaner zurückfordern" . Er hat auch behauptet: „Wenn wir keine freie Meinungsäußerung haben, dann haben wir einfach kein freies Land."
Sein künftiger Vizepräsident J.D. Vance hat sogar angedeutet, dass er bereit sei, US-Militärhilfe von der Achtung der Meinungsfreiheit in den europäischen NATO-Ländern abhängig zu machen. Vances Aussage erfolgte, nachdem EU-Binnenmarktkommissar Thierry Breton vor seinem geplanten Gespräch mit Trump einen umstrittenen Brief an Musk geschickt hatte. Heute erscheint dies als unkluger Schritt, nicht zuletzt, weil er als Versuch gewertet werden kann, die US-Wahl zu beeinflussen -- etwas, das paradoxerweise dem erklärten Zweck von von der Leyens Demokratieschild (d. h. ausländische Manipulationen zu bekämpfen) widerspricht.
Wenn die NATO möchte, dass wir sie weiterhin unterstützen, und die NATO möchte, dass wir weiterhin ein gutes Mitglied dieses Militärbündnisses sind, warum respektieren Sie dann nicht die amerikanischen Werte und die freie Meinungsäußerung?
- J.D. Vance
In der EU sind Verfechter der Meinungsfreiheit in der Öffentlichkeit weniger verbreitet. In Deutschland hat Vizekanzler Robert Habeck kürzlich erklärt, er sei „überhaupt nicht glücklich darüber, was dort [auf X] passiert ... seit Elon Musk das Amt übernommen hat", und wünscht sich eine strengere Regulierung der sozialen Medien. Die Wohnung eines deutschen Rentners wurde kürzlich von der Polizei durchsucht, nachdem er ein Bild von Habeck mit einem abfälligen Kommentar veröffentlicht hatte . Die deutsche Polizei verfolgt auch einen anderen Kontoinhaber, der einen Minister als „übergewichtig" bezeichnet hat. Dieser überhaupt nicht übergewichtige Minister hat kürzlich eine Zeitung verboten , die mit der laut Meinungsumfragen zweitgrößten Partei Deutschlands, der Alternative für Deutschland (AfD), verbündet ist. Eine Partei, die 113 deutsche Parlamentarier nun offiziell verbieten wollen .
Nach dem US-Wahlergebnis stellen sich viele unbeantwortete Fragen. Wird das Weiße Haus seine Aufmerksamkeit auf die restriktivere Haltung der EU richten, die als Untergrabung der freien Meinungsäußerung angesehen werden kann? Oder droht Musks X und Chinas TikTok stattdessen ein EU-Verbot? Können EU-Länder noch mit militärischer Unterstützung aus den USA rechnen? Und wenn große amerikanische Plattformen verboten werden, wohin sollten sich die EU-Bürger stattdessen wenden? Abgesehen von russischen Alternativen gibt es keine großen europäischen Plattformen. Und wenn die Frage der Meinungsfreiheit neu überdacht wird, was bedeutet das für die Zukunft von Parteien wie der deutschen AfD?
-
 @ eac63075:b4988b48
2024-12-18 11:35:25
@ eac63075:b4988b48
2024-12-18 11:35:25The European Union is at a crossroads. While digital innovation and security cooperation remain critical in a connected world, recent proposals to enhance police surveillance and data sharing are stirring deep concerns about individual privacy, data security, and democratic oversight. Two recent reports published by Statewatch shed light on troubling developments in the EU’s policing landscape, raising alarms among privacy advocates and civil rights organizations.
The EU’s new plans to expand police surveillance could put your privacy and rights at risk and introduce risks far outweighing their potential benefits. This article will analyze these proposals, their implications, and the growing opposition from privacy and civil liberties defenders.
Surveillance Infrastructure: Policing by Design
The first Statewatch report, titled “Policing by Design: The Latest EU Surveillance Plan”, outlines a concerning trend in the EU’s approach to law enforcement. The proposals advocate embedding surveillance tools directly into the design of new technologies, effectively creating an architecture where policing capabilities are integrated into the systems we use daily.
From facial recognition cameras to AI-driven analytics, the EU plans to enhance cross-border police cooperation by ensuring technology is designed to facilitate surveillance from the outset. Known as “policing by design,” this strategy involves building surveillance features directly into technologies we use every day. Imagine a network of cameras or software that can automatically monitor people’s faces or behaviors without any extra installation — it’s like your everyday tech quietly doubling as a police tool. The goal is to enable seamless sharing of data across borders for criminal investigations, but the unintended consequences are alarming.
The Problem with “Policing by Design”
- Mass Surveillance Normalized: By embedding surveillance features into public and private infrastructure, society risks normalizing mass surveillance, where every movement, transaction, or online interaction is monitored and analyzed.
- Threats to Privacy: Such initiatives inherently contradict the principle of privacy by design, which prioritizes privacy protections in the development of technology. Instead, citizens are being treated as subjects of perpetual suspicion.
- Lack of Transparency and Accountability: A systemic lack of transparency surrounding these plans raises serious governance issues. Civil society organizations, journalists, and privacy advocates have pointed to a lack of democratic oversight and meaningful debate.
- Risks of Abuse: Surveillance systems are often deployed under the guise of security but are susceptible to abuse. History shows that tools designed for law enforcement can easily be turned against dissenters, journalists, or marginalized communities.
As the report highlights, these developments could establish a permanent surveillance infrastructure across Europe, enabling the collection of biometric, behavioral, and communications data on an unprecedented scale.
Flawed Justifications for Surveillance Expansion
Privacy advocacy organizations, including the European Digital Rights (EDRi) network, argue that much of the justification for these surveillance plans relies on flawed assumptions. The rhetoric of the “Going Dark” report, which claims that law enforcement is losing access to communications due to encryption, has been widely debunked. As EDRi points out, law enforcement already has extensive tools at their disposal to access data and track individuals, but the focus on encryption risks undermining secure communication for everyone.
Instead of addressing systemic issues within law enforcement, these flawed reports have fueled calls for intrusive surveillance systems that risk eroding privacy while offering little evidence of improving public safety.
Centralized Police Data: A Substantial Security and Privacy Threat
A second Statewatch report, titled “EU Police Data Plans Pose Substantial Security and Privacy Threats”, explores another equally concerning initiative: the EU’s push to centralize police data repositories and expand their use.
The EU has already established several large-scale databases, such as the Schengen Information System (SIS), which stores data about individuals who may be denied entry into the EU, and the Europol Information System, which can hold details about millions of people, including those not suspected of crimes. For example, a traveler flagged mistakenly in the system could face unnecessary scrutiny, detention, or restrictions when crossing borders — highlighting the real-world risks of inaccurate or overreaching data collection. The new proposals aim to go further, creating an interoperable web of police data accessible to law enforcement agencies across member states. Proponents argue this is necessary for combating cross-border crime and terrorism, but the risks are immense.
Key Concerns with Centralized Police Data
- Massive Data Collection: The EU’s proposed systems would require the collection of highly sensitive data, including biometric information (fingerprints, facial recognition scans) and behavioral analytics, to track individuals’ activities across borders.
- Data Misuse and Security Risks: Centralized data systems are prime targets for cyberattacks, data breaches, and misuse. The larger and more interconnected the system, the greater the risks of unauthorized access, theft, or corruption of the data.
- As Statewatch points out, the systems lack robust safeguards to prevent misuse or to ensure that data is handled proportionately and lawfully.
- Erosion of Trust in Law Enforcement: Building centralized data repositories without meaningful safeguards undermines public trust. Individuals may be less willing to engage with law enforcement if they fear their data will be stored indefinitely, shared across borders, or used inappropriately.
- Impact on Fundamental Rights: Mass police databases can violate the principle of proportionality, a cornerstone of EU law. By collecting and sharing data indiscriminately, these systems erode fundamental rights, including the right to privacy, freedom of movement, and the presumption of innocence.
Civil Society Opposition and Democratic Accountability
In an open letter to EU institutions, over 30 civil society organizations — including EDRi — have criticized the lack of transparency in the High-Level Group’s (HLG) recommendations for data access. The letter highlights a concerning pattern: while industry stakeholders are included in key discussions, civil society voices remain sidelined. This exclusion undermines democratic accountability and reinforces fears that surveillance policies are being driven by corporate interests rather than public well-being.
These organizations have called for the EU to prioritize transparency, include meaningful public debate, and ensure any law enforcement proposals respect proportionality and fundamental rights.
Why Privacy Advocates Are Sounding the Alarm
The reports from Statewatch highlight a fundamental clash between security policy and individual rights. Privacy advocates are urging EU lawmakers to take a step back and critically examine the following issues:
- Lack of Democratic Oversight: Proposals to integrate surveillance systems and expand police databases are being pushed forward without genuine public debate or oversight. Civil society organizations have been excluded from key discussions.
- Failure to Uphold Privacy Laws: The EU has some of the strongest privacy laws in the world, including the General Data Protection Regulation (GDPR). However, these proposals risk undermining GDPR principles by enabling indiscriminate data collection and sharing.
- Ignoring Proportionality: Surveillance systems must be targeted, necessary, and proportionate to their objectives. Embedding policing into technological design and centralizing data far exceeds what is justified for fighting crime and terrorism.
- Setting Dangerous Precedents: The failure to fully ban harmful surveillance technologies like facial recognition in public spaces sets a troubling precedent. It risks not only eroding privacy within the EU but also encouraging other nations to adopt similar measures, undermining global human rights.
A Call for Action: Safeguarding Our Privacy and Rights
As the EU pushes forward with these plans, the opposition from civil rights defenders grows louder. Policymakers must address the following key demands to prevent an erosion of fundamental rights:
- Implement Privacy by Design: All new technologies must prioritize privacy protections at the design stage, ensuring they are not co-opted for surveillance.
- Establish Robust Oversight: Any new policing tools or databases must be subject to democratic scrutiny, independent oversight, and clear legal frameworks to prevent misuse.
- Reassess Interoperability Plans: Cross-border police cooperation is important, but it must not come at the cost of individuals’ privacy, security, and dignity.
- Strengthen Export Controls: The EU must ban the export of surveillance tools that risk facilitating human rights abuses in authoritarian regimes.
- Prioritize Data Security: Centralized systems require state-of-the-art security measures to protect sensitive data from breaches or misuse.
The EU’s role as a leader in digital rights and privacy is now at stake. If these plans proceed without significant safeguards, Europe risks undermining its own foundational principles of freedom, security, and justice.
Conclusion: The Price of Surveillance-Driven Security
The EU’s surveillance plans may be presented as necessary for security, but they come at a steep cost to privacy, trust, and individual freedoms. Embedding surveillance into our technologies and centralizing police data pose far-reaching risks that cannot be ignored.
As privacy advocates, it is our responsibility to hold policymakers accountable and demand a security framework that upholds, rather than undermines, fundamental rights. Europe’s future must not be built on surveillance by design — but on privacy, democracy, and trust.
-
 @ ec42c765:328c0600
2024-12-15 11:13:44
@ ec42c765:328c0600
2024-12-15 11:13:44てすと
nostr:nevent1qqst3uqlls4yr9vys4dza2sgjle3ly37trck7jgdmtr23uuz52usjrqqqnjgr
nostr:nevent1qqsdvchy5d27zt3z05rr3q6vvmzgslslxwu0p4dfkvxwhmvxldn9djguvagp2
-
 @ 78c90fc4:4bff983c
2024-12-14 18:37:00
@ 78c90fc4:4bff983c
2024-12-14 18:37:00Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy eirmod tempor invidunt ut labore et dolore magna aliquyam erat, sed diam voluptua. At vero eos et accusam et justo duo dolores et ea rebum. Stet clita kasd gubergren, no sea takimata sanctus est Lorem ipsum dolor sit amet. Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy eirmod tempor invidunt ut labore et dolore magna aliquyam erat, sed diam voluptua. At vero eos et accusam et justo duo dolores et ea rebum. Stet clita kasd gubergren, no sea takimata sanctus est Lorem ipsum dolor sit amet.
-
 @ 2fb77d26:c47a6ee1
2025-02-01 14:40:02
@ 2fb77d26:c47a6ee1
2025-02-01 14:40:02In H. G. Wells’ Roman Die Zeitmaschine und den diversen Verfilmungen werden sie als »ausschweifend, langsam und naiv« dargestellt. Von »untermenschlicher Intelligenz« gezeichnet. Für Dan Simmons sind sie »faul, ungebildet und unkultiviert«. Die Eloi. Die als Nahrungsquelle der Morlocks gehaltenen Nachfahren des Homo sapiens. »Sie entwickeln sich rückläufig und verlernen Jahrtausende von Kultur, Denken und Vernunft, bis sie sich mit dem Vergnügen des bloßen Daseins zufrieden geben«. Ertönt das Schlüsselsignal, auf das sie von ihren Züchtern konditioniert wurden – eine umgebaute Zivilschutzsirene – trotten sie freiwillig und in hypnotischer Apathie zur Schlachtbank.
Ein ähnlichen Eindruck hatten viele Maßnahmenkritiker von den Unterstützern der mittlerweile in allen Punkten widerlegten Covid-Propaganda. Zurecht. Das Gefolge von Drosten, Lauterbach und Co. war blind für Fakten und ist ins offene Messer gelaufen. Bedauerlicherweise verhalten sich viele Maßnahmenkritiker aber nun in weiten Teilen genauso. Sie haben Idole gefunden. Wollen glauben. Sie ignorieren Informationen, Fakten und Daten und werden Opfer einer neu justierten, gut geölten Propagandamaschine. Nur, um die in ihre neuen Helden gesetzten Hoffnungen nicht aufgeben und der wenig erbaulichen Realität nicht ins Auge blicken zu müssen.
Sie glauben an Donald Trump, Javier Milei, Alice Weidel, Peter Thiel und vor allem Elon Musk. Daran, dass der supranationale Nachhaltigkeitskorporatismus am Ende sei, das Finanzsystem gerettet und Gerechtigkeit hergestellt wird. Die Widerständler von gestern sind die »Schlafschafe« von heute. Sie scheinen vergessen zu haben, wie Propaganda funktioniert. Aus diesem Grund – und weil es ein so schön griffiges Wort ist, bei dem man nur einen Buchstaben verändern muss, um daraus den Vornamen eines vermeintlichen Heilsbringers zu basteln – erlaube ich mir, die Anhänger des MAGA-Kults im Zuge der folgenden Seiten mokant als Eloi zu bezeichnen. Ein bisschen Spaß muss sein.
Kurskorrektur mit Ansage
Lynn Forester de Rothschild, in der finanzoligarchischen Hackordnung mindestens eine Ebene über BlackRock und Co. anzusiedeln, kündigte den aktuellen Narrativwechsel bereits am 30. August 2023 an, als sie bei Bloomberg sagte, der Begriff »ESG gehöre in die Tonne«. Er sei verbrannt. Auch BlackRock-CEO Larry Fink, der Marktteilnehmer zur Unterstützung von ESG »zwingen« wollte, teilte seinen Investoren bereits am 26. März 2023 mit, das in Verruf gekommene Label ESG durch den Begriff »Energiepragmatismus« zu ersetzen.
Sowohl Rothschild als auch Fink räumten aber gleichzeitig ein, dass sich die übergeordnete Agenda nicht ändern und man die »Green Economy« weiter vorantreiben werde, man diese aber besser vermarkten müsse, um konservative Kreise nicht weiter gegen sich aufzubringen. Ein simpler Marketing-Trick. Wenig überraschend also, dass sowohl BlackRock als auch sechs amerikanische Großbanken Anfang 2025 die Net Zero Initiative verließen. Zum »perfekten Zeitpunkt«, wie die New York Post bemerkt, um nicht von der negativen, anti-woken Berichterstattung rund um die verheerenden Feuersbrünste in Los Angeles tangiert zu werden.
Es scheint, als hätten die Eloi bereits wieder verdrängt, dass die WEF-Meetings 2021 und 2024 unter Arbeitstiteln wie »The Great Narrative« und »Rebuilding Trust« liefen. Artikuliertes Ziel der Davoser PR-Abteilung für Globalisierungsfragen war nämlich, sich den zunehmend echauffierten, misstrauischen Pöbel vom Hals zu halten. Durch neue Narrative und vertrauensbildende Maßnahmen. Und das hat, zumindest vorerst, ausgezeichnet funktioniert.
In den USA stieg das Vertrauen in ordnungsgemäß durchgeführte Präsidentschaftswahlen 2024 zum ersten Mal seit Jahren wieder etwas an. In Europa macht sich ebenfalls Zuversicht breit. Schließlich haben die sogenannten »Rechtspopulisten« nicht mehr nur in Italien und Ungarn, sondern auch in Finnland, der Slowakei und den Niederlanden Oberwasser. Von den Erfolgen der AFD ganz zu schweigen. Diese führen, wie zuletzt in Thüringen, trotz klarem Wählervotum zwar nicht zur Regierungsbeteiligung, weil »demokratische Prozesse« und »Brandmauern« das zu verhindern wissen – aber dabei sein ist ja bekanntlich alles. Dass Friedenstreiberin Alice Weidel den bundesdeutschen Rüstungsetat auf knapp 200 Milliarden verdoppeln will, scheint die euphorisierten Kritiker dunkelgrüner Militarisierung auch nicht auszubremsen. Hauptsache nicht grün. Oder woke.
Überstaatliche Sphären
Dabei scheint Euphorie in Anbetracht der Tatsachen alles andere als angebracht. So hat Milei nach Angaben von Global Finance zwar das argentinische »Staatsdefizit nach 123 Jahren beendet«, dafür leben heute 53 Prozent der 45 Millionen Argentinier in Armut. Der höchste Wert seit 20 Jahren. Ende 2023 waren es noch 41,7 Prozent. Daran ändert auch semantische Schützenhilfe von libertären Denkfabriken wie der Hoover Institution nichts. Die radikalen Privatisierungsfeldzüge von »El Loco« haben einen hohen Preis. Ob Aerolineas Argentinas, die staatliche Fluglinie, der Stahlproduzent IMPSA oder das Transportunternehmen Trenes Argentinos Cargas, das 7.800 Kilometer Bahnstrecke betreibt – das Volksvermögen wird an die Meistbietenden verscherbelt. Wer das ist, kann sich wohl jeder ausmalen. Denn sein Schlachtruf »Afuera!« (Raus hier!) gilt augenscheinlich nicht für BlackRock und Co. – schließlich sei Argentinien »ziemlich billig« zu haben, wie es Rick Rieder, Top-Bond-Manager des Unternehmens schon 2019 formulierte.
Man muss allerdings nicht in die Ferne schweifen, um sich der realen Gefahren für die Freiheit bewusst zu werden. Jener Gefahren, die von Personalien gänzlich unberührt bleiben. So arbeitet die Europäische Union weiter an der eID, der Grundlage des technokratisch-totalitären Kontroll-Grids. Ihre Einführung ist beschlossene Sache. Offen ist lediglich, ab wann sie zum Obligatorium wird. Auch das persönliche CO2-Budget ist auf Kurs. Mit ETS2 (EU Emissions Trading System) nimmt die EPA (Environmental Protection Agency) seit dem 1. Januar 2025 nach der Konzernwirtschaft nun kleine und mittlere Unternehmen in den Fokus und verpflichtet diese, CO2-Kompensationsabgaben auf ihren Gas-, Benzin- und Mineralölverbrauch zu entrichten. Das dürfte Heiz-, Fracht- und folglich die Lebenshaltungskosten des Bürgers in neue Höhen treiben. Bis der Sonntagsausflug mit dem Familienauto nicht mehr nur Zeit, Benzin und Nerven, sondern auch CO2-Gebühren kostet, dauert es also wohl nicht mehr allzu lange.
Dieser überparteilichen, supranational koordinierten Überwachungs- und Enteignungsagenda ist weder durch die Wahl des geringeren Übels noch durch Auswandern zu entkommen. Denn wie sich der Internetpräsenz des »Global Governance Forum« (GGF) entnehmen lässt, wird bereits eifrig an »Global Government« gearbeitet. Die UN-nahe Nichtregierungsorganisation hat sich nämlich zum Ziel gesetzt, die Charta der Vereinten Nationen bis 2028 zu aktualisieren und den allseits bekannten »Herausforderungen unserer Zeit« anzupassen. Pünktlich ab 2030 soll das neue Vertragswerk ratifiziert werden und neben neuen Befugnissen für den Internationalen Gerichtshof sowie einer UN-Streitmacht auch eine Regierungsstruktur analog der Europäischen Union ermöglichen. Sprich, eine Weltregierung. Ganz demokratisch selbstverständlich.
Neben eID und CO2-Budget sind natürlich auch die Ausweispflicht fürs Internet und die automatisierte Zensur unliebsamer Inhalte weiter auf Kurs. Nachdem die Vereinten Nationen im September 2024 bereits dem totalitären »Pakt für die Zukunft« zustimmten, wurde am Heiligabend 2024 noch rasch die neue »Konvention gegen Onlineverbrechen« durchgewunken. Und seit Januar 2025 treibt die UN die Umsetzung eines noch weitreichenderen Abkommens namens »Global Digital Compact« voran. Ein Papier, vor dem ich bereits im Juli 2023 gewarnt habe. Was all das für den Bürger bedeutet, zeigt sich in Griechenland, wo die Regierung seit Anfang des Jahres Social-Media-Konten mit Steuer-Identifikationsnummern verknüpft, um eine Alterskontrolle fürs Internet einzuführen. Damit folgt die von der EU in Kreditsklaverei gehaltene Regierung in Athen dem Vorbild Australiens, wo der Zugang so Social-Media-Plattformen künftig erst ab einem Alter von 16 Jahren erlaubt werden soll – wofür man schlussendlich jeden Nutzer kontrollieren muss, der online geht.
Auch das von vielen noch immer als Mythos abgetane Geoengineering wird derweil munter weitergeführt. Obwohl Berichte des US-Kongress und mittlerweile sogar wissenschaftliche Berater der EU-Kommission vor großflächigem Solar Radiation Management warnen. Im Rahmen eines offiziellen, 54 Seiten umfassenden Reports an die EU-Kommission sowie eines Artikels des britischen Guardian vom 9. Dezember 2024 verwies das siebenköpfige Forscherteam auf die unabschätzbaren Konsequenzen solcher Eingriffe und forderte ein EU-weites Moratorium.
Wie genau Trump, Musk, Milei, Meloni, Weidel und Co. die Welt vor diesem Sammelsurium an totalitären Übergriffigkeiten retten wollen, konnte mir bislang keiner der Eloi sagen.
DJ Trump
Warum die in Donald Trump, den »Vater der Impfung«, und sein zionistisches Kriegstreiberkabinett gesetzten Hoffnungen bald bitterer Enttäuschung weichen dürften, habe ich bereits am 14. November 2024 ausführlich beschrieben. Dass auch die beiden Hauptargumente seiner Befürworter – dass er die mRNA-Kampagne mittlerweile bereue und in seiner ersten Amtsperiode Friedenspolitik betrieben habe – schlichtweg falsch sind, ebenfalls. Denn anhand der nackten Zahlen lässt sich eindeutig belegen, dass Trump »der kriegslüsternste Präsident der jüngeren Geschichte« war. Und wie stolz er auf »Operation Warp Speed« ist, die unzählige Amerikaner Gesundheit oder Leben kostete, ließ er die Welt zuletzt am 17. November 2024 auf seinem Social-Media-Netzwerk Truth Social wissen.
Trumps Interesse gilt nicht Frieden und Freiheit, sondern Donald Trump. So war es sein ganzes Leben lang. Wenn sich »The Donald« jemandem verpflichtet fühlt, ist es vielleicht Wilbur Ross, der ehemalige Chef von Rothschild Inc. Bankruptcy Advising. Denn wie das Forbes Magazine am 8. Dezember 2016 korrekt erläuterte, rette das Bankhaus vor gut 30 Jahren nicht nur Trumps bankrotte Casinos, sondern damit auch seine ganze Karriere. Nicht weil man in Trumps Geschäften und Immobilien einen besonderen Wert sah, sondern weil man die Person Donald Trump als »Anlage« betrachtete. Trotzdem ist es sicher nur Zufall, dass Ross von 2017 bis 2021 Handelsminister der Vereinigten Staaten war.
Elon Musk
Auch über den PayPal-Mafioso, CIA-Handlanger und Bilderberg-Executive Peter Thiel, dessen Protegé JD Vance nun US-Vizepräsident ist, habe ich bereits im September 2024 einen ausführlichen Artikel geschrieben. Gleiches gilt für Elon Musk, dessen trügerisches Image als Genius, Erfinder und Entrepreneur ich sogar schon im Oktober 2022 durchleuchtet habe. Zitat:
»Dass Elon Musk nicht rein zufällig zur liberal-coolen Ikone avancierte, legt ein Blick in seine Anfangsjahre als Unternehmer nahe. Denn während im sagenumwobenen Silicon Valley Ende der 1990er-Jahre eine Vielzahl an erfolgreicheren Tech-Entrepreneuren existierte, war es ausgerechnet Elon Musk, der für einen absolut inhaltsleeren Gastauftritt bei CNN gefilmt wurde, sodass zum ersten Mal eine breitere Öffentlichkeit von ihm Notiz nehmen musste. Dabei war sein erstes Unternehmen – Zip2 –, das er im Jahre 1995 mit seinem Bruder sowie einem weiteren Partner gegründet und im Februar 1999 für circa 300 Millionen US-Dollar an Compaq veräußert hatte, nicht das revolutionärste Unterfangen im kalifornischen IT-Mekka dieser Tage. Es handelte sich um ein simples Telefonbuch fürs Internet. Wenig mehr als eine Datenbank, in die sich Unternehmen eintragen konnten, um ihre Adresse im Netz zu hinterlegen.«
Meine fast zweieinhalb Jahre alte Analyse bedarf allerdings dringend einer Aktualisierung. Denn was Musk in der Zwischenzeit trieb – und für die Zukunft plant – hat so gar nichts mit dem zu tun, was seine geradezu fanatisierten Anhänger in ihm sehen wollen.
Fangen wir der Vollständigkeit halber aber noch mal vorne an: Elon Musk hat weder PayPal gegründet noch den Tesla erfunden. Auch wenn er das gerne so darstellt. Dafür fertigte Tesla unter seiner Ägide dann aber »RNA Mikrofabriken« für das deutsche Unternehmen CureVac, das zusammen mit Bayer mRNA-Injektionen gegen Corona auf den Markt brachte. Und während Musk gegenüber der New York Post am 30. September 2020 sagte, sich nicht gegen Covid impfen lassen zu wollen, erklärte er dem TIME Magazine am 13. Dezember 2021, bereits geimpft zu sein. Zeitgeistig flexibel ist er also. Wer behauptet, Musk hätte seine Meinung zur mRNA-Technologie seit dem Covid-Fiasko signifikant geändert und sehe das Produkt nun kritisch, ist schlecht informiert. Noch am 12. April 2023 erklärte er bei Twitter, dass er mRNA für eine »medizinische Revolution« hält. Vergleichbar mit dem Schritt »von analog zu digital«.
Was Musk mit digitaler Revolution meint, zeigte sich 2017 mit Hurricane Irma. Damals gab das Unternehmen für Besitzer von Fahrzeugen mit 75 kWh ein Softwareupdate heraus, das die Reichweite von 338 auf 400 Kilometer steigerte – was im Umkehrschluss bedeutet, dass Tesla-Besitzer um eine eigentlich abrufbare Leistung ihres eigenen Fahrzeugs betrogen werden, wenn gerade keine Naturkatastrophe wütet. Dass Tesla-Kunden darüber hinaus permanent überwacht werden, zeigte sich unlängst im Rahmen der Explosion eines Cybertrucks in Las Vegas. Augenbewegungen, Mimik, Geschlecht, Hautfarbe, Körpertemperatur, Gepäckanordnung, Route, Ladestopps, Bezahlvorgänge, Telefonbuch, Musik-Playlist, Online-Abos, et cetera. Was von Sensoren und Verbindungen zu erfassen ist, wird erfasst, wie eine Untersuchung von Mozilla im Herbst 2023 feststellte. Das gilt im Übrigen nicht nur für Tesla, sondern für praktisch alle modernen Autos. Ein Tesla hat es dabei nur am leichtesten. Die gesammelten Daten werden entweder zum Schleuderpreis verkauft und/oder gegen uns verwendet.
Doch zurück zu Musk, der Twitter nicht übernahm, um Meinungsfreiheit herzustellen, sondern um die Plattform zur »Alles-App« zu machen. Sein erklärtes Vorbild: die chinesische Spionage-App WeChat. Deswegen will er alle Nutzer »als echte Menschen identifizieren«. Biometrisch versteht sich. Dafür arbeitet man bei Twitter bevorzugt mit israelischen Unternehmen zusammen, die von ehemaligen Mossad-Agenten gegründet wurden. Vielleicht stellte ja Doppelagent Jeffrey Epstein den Kontakt zum Mossad her, nachdem er Musk als regelmäßigen Teilnehmer seiner Edge-Foundation Seminare zum Thema Nudging schätzen gelernt hatte. Epstein war nämlich der einzige nennenswerte Sponsor von Edge.
Twitter kaufte Musk übrigens nicht von seinem eigenen Geld, sondern mit Hilfe von 94 Investoren, deren Namen ein US-Bundesrichter erst im August 2024 veröffentlichte, weil Jacob Silverman (Reporters Committee for Freedom of the Press) sie einklagte. Die Liste umfasst so illustre Namen wie Fidelity Investments, Sequoia Capital, Andreessen Horowitz, Bandera Fund, Binance Capital Management, Sean Combs (alias Diddy) Capital, Jack Dorsey (Twitter Gründer), Baron Opportunity Fund oder Prinz Alwaleed bin Talal al Saud von der saudischen Königsfamilie. Da wird also offenbar »der Sumpf« mit mehr Sumpf »trockengelegt«. Von der Nominierung des WEF Executive Chair Linda Yaccarino als neuer Twitter-CEO und »Freedom of Speech« versus »Freedom of Reach« mal ganz abgesehen.
Auch die von den Eloi als sensationelle Enthüllung gefeierten Twitter Files sind leider nicht ernst zu nehmen. Denn sie offenbarten nichts, was man nicht schon wusste. Zudem ist bis heute unklar, woher die veröffentlichten Informationen kamen, wer den Zugriff darauf gesteuert hat, was dort noch gespeichert war, warum praktisch nur ein von Elon ausgewählter Journalist Zugriff darauf hatte und dieser nur Screenshots, anstelle ganzer Dokumente veröffentlichen durfte. Ein echter Leak besteht aus einem Archiv, das man selbst durchsuchen kann – nicht aus ein paar handverlesenen Screenshots.
Fehlt noch Space X. Ein Unternehmen, das Musk zwar selbst gegründet hat, dessen Erfolge aber in weiten Teilen anderen Umständen zu verdanken sind. So schreibt beispielsweise inside Tesla am 22. März 2022:
»Schon Anfang der 2000er-Jahre hatte die NASA erkannt, dass ihr bald die Möglichkeit fehlen würde, selbst Astronauten und Material ins All und zur ISS zu bringen. Man machte sich also auf die Suche nach Partnern aus der Privatwirtschaft und wurde unter anderem bei Elon Musks Space X fündig. Bereits 2006, also noch in der Entwicklungsphase der Falcon 1, erhielt Musks Unternehmen fast 400 Millionen US-Dollar Startfinanzierung unter dem COTS-Programm.«
Space X war von Beginn an als verlängerte Werkbank der NASA gedacht, weil der US-Weltraumbehörde immer mehr Mittel gestrichen wurden. Die Öffentlichkeit hatte nämlich das Interesse an ziviler Raumfahrt verloren. Daher setzte man in Washington immer öfter den Rotstift an. Doch seit Musk die Menschen öffentlichkeitswirksam zum Mars befördern will – »let’s build Marsian Technocracy« – steigt das Interesse wieder. Leider muss ich die Vorfreude auf eine planetare Kolonie aber etwas dämpfen. Denn Space X wird nicht betrieben, um Menschen auf den Mars zu bringen, sondern um das »weltgrösste Netzwerk an Spionagesatelliten aufzubauen«.
Musks Weltraumagentur ist Handlanger des militärisch-industriellen Komplexes und einer der wichtigsten Vertragspartner des Pentagon. Das konnte man 2017 schon im Observer nachlesen. Oder am 9. Januar 2018 bei CNBC, die vom (missglückten) Transport eines streng geheimen US-Spionagesatelliten berichtete. Am 15. April 2022 kommentierte Tech Unwrapped zwei weitere Spionagesatelliten des US-Militärs, die Space X in die Umlaufbahn beförderte. Seit Jahren erhält das Unternehmen Milliarden von US-Regierung und Geheimdiensten. Siehe Los Angeles Times vom 30. Mai 2015: 4,9 Milliarden. Oder ein Artikel des Wall Street Journal vom 23. Februar 2024: 1,8 Milliarden. Oder eine lange Liste von staatlichen Zuwendungen, die Business Insider am 15. Dezember 2021 veröffentlichte. Damit basiert der Erfolg von Space X nicht primär auf Musks genialem Unternehmergeist, sondern auf Subventionen. Auf Steuergeldern.
Nicht zu vergessen: Starlink. Das von Space X betriebene, weltumspannende Satellitennetzwerk. Es mag den Vorteil haben, dass damit auch Menschen in entlegenen Regionen des Planeten oder Katastrophengebieten Zugriff auf das Internet haben. Dabei sollte allerdings nicht unterschlagen werden, dass Starlink in seiner finalen Ausbaustufe circa 42.000 Satelliten umfassen und damit ein permanentes Strahlungsfeld erzeugen wird. Gesundheitliche Risiken für den Homo sapiens: unklar. Darüber hinaus haben die Orbiter Zugriff auf das NORAD-Datenbanksystem, um Weltraumschrott ausweichen zu können. Sprich, sie sind permanent mit Systemen des US-Militär verbunden. Aus diesem Grund ermöglicht Starlink auch die Steuerung von Kampfdrohnen – siehe Ukraine-Konflikt – sowie 30 mal schnelleres Senden von Daten an und von US-Kampfflugzeugen. Während die Öffentlichkeit Musks Satellitennetzwerk vor allem als ziviles Produkt betrachtet, ist Starlink primär von militärischem Interesse. Nicht umsonst wird parallel Starshield aufgebaut, das dem geheimdienstlich-militärischen Komplex unter anderem die diskrete Echtzeitüberwachung der ganzen Welt erlaubt. Auch von DEW-Fähigkeiten (Directed Energy Weapon) ist die Rede. Ende 2024 befanden sich bereits 98 solcher Satelliten in erdnaher Umlaufbahn.
In Anbetracht dieser Informationen ist es also kaum verwunderlich, dass Musk seit Jahren offen für Technokratie wirbt. Für ein zentralistisches, faschistoides Herrschaftsmodell, das schon sein Großvater Joshua Haldemann als führender Kopf in den USA und Kanada vertrat. Der Familientradition folgend empfiehlt Musk eine CO2-Steuer zum Kampf gegen den Klimawandel, ein universelles Grundeinkommen, um die von der KI ausgelösten Disruptionen abzufangen und sein Neuralink Gehirnimplantat, um dem drohenden Transhumanismus etwas Transhumanismus entgegenzusetzen.
Futurum Technologicus
Für Kunden, denen Chips im Kopf irgendwie zu altbacken sind, entwickelt Musks Unternehmen in Zusammenarbeit mit iota Biosciences natürlich ein zeitgemäßeres Premiumprodukt: Neural Dust. Intelligente Nanopartikel in Staubkorngröße, die sich im Gehirn anreichern. Die lassen sich dann wahrscheinlich – wie die in Indien bereits zugelassene Nasal-Impfung gegen Covid – durch die Nase ziehen. Oder durch Luftschächte öffentlicher Gebäude pumpen. Man kann die neue Freiheit also förmlich riechen.
Ganz wie es der 44 Seiten starke »National Nanotechnology Initiative Strategic Plan« (NNI Plan) des Weißen Hauses im Oktober 2021 vorsah: »Die Öffentlichkeit einbeziehen und Mitarbeiterzahlen im Bereich Nanotechnologie erhöhen«. Nicht umsonst hat Donald Trump der entsprechenden Behörde in seiner ersten Amtszeit zusätzliche Mittel genehmigt. Genau wie Joe Biden nach ihm.
Das von der Technokratie-Bewegung vor fast einem Jahrhundert definierte nordamerikanische Technate – sprich, der amerikanische Verantwortungsbereich einer weltweiten Technokratie – sieht der von Trump und Musk reanimierten Vision einer »nordamerikanischen Union« übrigens verblüffend ähnlich. Wen interessiert bei all der Make-Great-Euphorie schon noch, dass Imperialismus scheisse, Dänemark ein souveräner Staat und der Panamakanal ein strategisches Nadelöhr der internationalen Handelsschifffahrt ist. Oder, dass die »nordamerikanische Union« nicht nur bei Trump-Cheerleadern wie Alex Jones vor ein paar Jahren noch als »böser Globalisten-Plan« galt.
Schauen wir nach vorne. In Richtung »goldenes Zeitalter«, wie Trump es nennt. Dieses dürfte für den Normalbürger nämlich sehr ungemütlich werden. Denn es wird dominiert von Algorithmen. Von Künstlicher Intelligenz. Für die Eloi also primär von Grok, dem auf Twitter (und Teslas) integrierten Chatbot. Dieser basiert auf Technologie des Unternehmens xAI – laut Wikipedia gegründet von Elon Musk im März 2023. Das mag zwar so im Handelsregister stehen, ist wohl aber nur die halbe Wahrheit. Denn xAI dürfte die Fortführung eines DARPA-Projekts darstellen, das bereits 2015 unter dem Titel »Explainable Artificial Intelligence« (XAI) gestartet wurde und 2021 auslief. Als die Finanzierung seitens DARPA eingestellt wurde, machte XAI die Forschungsergebnisse auf einem Server zugänglich. Circa 18 Monate Jahre später engagierte Elon Musk Igor Babuschkin als Chefingenieur für xAI. Babuschkin hatte zuvor acht Jahre lang für Googles DeepMind-Projekt gearbeitet und nutzte aller Wahrscheinlichkeit nach die DARPA-Ergebnisse um xAI, beziehungsweise Grok zu entwickeln.
Im Juli 2023 verkündete Musk, xAI sei im Gegensatz zu den Konkurrenzprodukten von Google, Microsoft und OpenAI eine »gute« KI. Erstaunlich, wenn die gleichen Ingenieure am Werk sind und die KI auf Basis eines Militärprojekts entsteht. Zudem sprechen auch die Top-Sponsoren von xAI nicht unbedingt für das »Gute«. Denn unter den größten Geldgebern der letzten Finanzierungsrunde vom 23. Dezember 2024 befinden sich so illustre Namen wie BlackRock, AMD, Nvidia und Fidelity, die zusammen weitere sechs Milliarden Dollar für Musks KI-Unternehmen zur Verfügung stellten.
Genug Liquidität, um xAI für die »Alles-App« weiterzuentwickeln, wo Grok seit einer Weile automatisch Kurzbeschreibungen für Profile erstellt, die man weder abschalten noch ändern kann. Twitter-Nutzer müssen nun also nicht mehr selbst das Profil eines Accounts durchstöbern, um sich einen ersten Eindruck von der Person zu machen, sondern bekommen diesen von Elon Musks KI geliefert. Vorurteil auf Knopfdruck sozusagen. Vergleichbar mit einem Sozialkreditsystem. Denn die täglich neu generierte Zusammenfassung basiert auf dem Nutzerverhalten.
»Die neuen, KI-generierten Grok-Kurzprofile unter jedem X-Nutzerprofil SIND de facto ein Social Credit System nach chinesischem Vorbild für den Westen. Das Profil jedes Nutzers wird tagesaktuell neu berechnet. Äußert man sich zu verschiedenen Themen, nennt die KI das schnell mal »verheddern«. Grok gibt zu, das Profil wird erstellt aus dem eigenen Nutzerverhalten des Tages, seinen eigenen Berechnungen und nicht näher definierten Anweisungen«, kommentierte Journalistin Aya Velázquez die Neuerung am 14. Januar 2025.
Andere Nutzer werden als »leicht erregbar« beschrieben, »verzetteln« sich oder »glauben an Wettermanipulation zur Klimakontrolle«. Offener wird ein Debattenraum dank solcher Adjektive und Zusammenfassungen sicher nicht. Wer möchte schon das Profil von leicht erregbaren Chemtrail-Gläubigen anschauen oder gar mit diesen assoziiert werden. Gegen solch eine automatisierte, herablassend daherkommende Einordnung durch intransparent operierende KI war die Faktencheck-Industrie geradezu harmlos. Wer also annimmt, die Abschaffung der Faktenchecker bei Facebook und Co. bedeute ein Ende der Zensur, irrt. Sie wird im Gegenteil deutlich raffinierter und weitreichender werden.
Details zum persönlichen Punktestand im Grok-Sozialkreditsystem oder Information über das Zustandekommen der Bewertung erhält man auf Anfrage natürlich nicht. Twitter wird die daraus entstehende Hierarchie aber mit Sicherheit für Reichweitensteuerung, Nudging-Kampagnen und weitere sozialarchitektonische Funktionen nutzen. Vor allem, wenn 2025 das Bezahlsystem »X Money« eingeführt wird. Dann werden die Eloi bald nicht mehr nur um Reichweite, Follower und Re-Tweets buhlen, sondern auch um Geld – das als Folge unliebsamer Postings zu Genozid X, Krieg Y oder Person Z künftig schneller eingefroren werden dürfte als jedes Bankkonto. De-Banking der nächsten Generation. Und irgendwann trifft das jeden. Außer, man schwimmt immer mit dem Strom.
Doch damit nicht genug. Am 13. Dezember 2024 gab das wohl den wenigsten bekannte Unternehmen WISeSat bekannt, künftig mit Space X zusammenzuarbeiten, um »verschiedene Produkte und Systeme zu kombinieren«. Die WISeSat AG ist eine Tochterfirma der in Genf (Schweiz) ansässigen WISeKey International Holding AG, die im Bereich Cybersicherheit, KI und IoT (Internet of Things) tätig ist. Die Ankündigung dieser Kollaboration ließ die WISeKey-Aktie kurzfristig um 107,73 Prozent steigen. Ein erster gemeinsamer Start zum Transport sogenannter Picosatelliten fand am 14. Januar 2025 von der Vandenberg Space Force Base in Kalifornien statt.
Aber was genau macht WISeSat? Einer Presseerklärung des Unternehmens vom 15. September 2023 lässt sich entnehmen:
»WISeSAT AG zeichnet sich dank ihrer Konstellation von ultra-sicheren Picosatelliten und Infrastruktur durch sichere und effektive Kommunikationsstrategien für vernetzte Geräte aus. Die Expertise des Unternehmens in kryptografischer Technologie und sicherem Datenmanagement hat die sichere IoT-Implementierung in zahlreichen Bereichen neu definiert, von städtischen Innovationen in Smart Cities bis hin zu modernster industrieller Automatisierung. (…) WISeSAT steht an vorderster Front bei der Entwicklung von ultra-sicheren Picosatelliten-Lösungen in Zusammenarbeit mit ihrem Verbündeten FOSSA Systems. Es setzt sich für sichere IoT-Kommunikation über raumbasierte Netzwerke ein und nutzt die neuesten kryptografischen Innovationen, um sichere und sofortige Datenaustausche in verschiedenen Bereichen zu gewährleisten (…).«
Im Klartext: WISeSat bringt Satelliten von der Größe einer Tupperdose ins All. Diese Mini-Orbiter umkreisen den Planeten in niedrigen Umlaufbahnen und etablieren dort ein Netzwerk für kryptografierte Echtzeitdatenübertragung. Fliegende 5G-Masten sozusagen. Oder WLAN-Router. Nur viel schneller. Für das Internet der Dinge – und Smart Cities.
»In dieser Woche startet WISeSat einen Satelliten der neuen Generation und markiert damit einen wichtigen Meilenstein in der Entwicklung einer globalen Satellitenkonstellation, die eine umfassende Erdabdeckung mit ultraniedriger Latenzzeit ermöglicht. Entwickelt, um Billionen von IoT-Geräten in Echtzeit zu verfolgen und aufzuspüren.« (Carlos Creus Moreira, WISeKEy CEO, 12. Januar 2025)
Welche Datenträger dieses Picosatelliten-Netzwerk künftig verfolgen und aufspüren soll, zeigt sich bei einem Blick auf das Produktportfolio der Holding-Gesellschaft WISeKey – einem »weltweit führenden Anbieter von Cybersicherheit, digitaler Identität und Internet der Dinge (IoT) Lösungen«. Denn die Holding existiert seit 24 Jahren, besteht aus fünf Unternehmen, hat mehr als eineinhalb Milliarden Chips und über fünf Milliarden »Roots of Trust« installiert, residiert an sechs internationalen Standorten und hat gut 3.000 Kunden in Staat und Wirtschaft beglückt. Einen Wikipedia-Eintrag gibt es für das bei NASDAQ und SIX gelistete Unternehmen erstaunlicherweise trotzdem nicht.
Dafür aber für den seit Mai 2021 amtierenden »Chief Digital Transformation Officer« Pierre Maudet. Der war ab Juni 2012 Mitglied des Genfer Staatsrats, 2013 bei den Young Global Leaders des Weltwirtschaftsforums und 2015 bei der Bilderberger Konferenz in Telfs-Buchen (Österreich). Nachdem er im Februar 2021 vom Genfer Polizeigericht wegen Vorteilsnahme verurteilt wurde, trat er als Staatsrat zurück – und drei Monate später bei WISeKey an. Am 30. April 2023 wurde er, ungeachtet seiner kriminellen Vergangenheit, zusätzlich wieder in den Genfer Staatsrat gewählt. Wie praktisch. Solch eine schamlose Unverfrorenheit scheint Maudet perfekt für das zu qualifizieren, was bei WISeKey unter dem Deckmantel der »Quantensicherheit« entwickelt wird – ein raumbasiertes eID-Ökosystem.
»Quantensicherheit nutzt Prinzipien der Quantenmechanik, um den Datenschutz und die sichere Informationsübertragung zu revolutionieren. Kernstück ist die Quantenschlüsselverteilung (Quantum Key Distribution, QKD), eine Spitzentechnologie, die mithilfe der Quantenmechanik vernetzte Teilchen für den sicheren Austausch von Verschlüsselungskennwerten erzeugt.«
Ob digitale Identität, Unterschrift, Cloud oder Software – von der Know-Your-Customer-Biometrie bis hin zur Unternehmenslösung für die Mitarbeiteridentifikation. WISeKey hilft. Anmelden kann sich jeder. Während die Produktpalette für den privaten Sektor noch nach Lieferketten-Management, Sendungsverfolgung, Login-Lösung für eBanking oder Face ID auf dem Smartphone klingt – aber deutlich weitreichender ist, schauen sie sich die Homepage an – sprechen die WISeKey-Angebote im Bereich Regierungen eine ganz andere Sprache. Denn unter diesem Menüpunkt bewirbt der diskret operierende Konzern seine »CertifyID Trust Center Platform«:
»Die CertifyID Trust Center Platform ist eine industrialisierte eID-Verwaltungslösung für Bürger, die Benutzer und ihre Anmeldeinformationen verwaltet, insbesondere digitale IDs und digitale Zertifikate für groß angelegte Anwendungen wie landesweite E-Government-Dienste. Es handelt sich um eine vollständige industrielle Public Key Infrastruktur- und ID-Verwaltungslösung, die Regierungsdienste rund um die Uhr unterstützt.
Die CertifyID Trust Center Plattform wird in einer Reihe von Anwendungen der Regierung und des öffentlichen Sektors verwendet, zum Beispiel: Personalausweis, ePassport (ICAO-konform), Führerschein, Gesundheit, Wahlen/Abstimmen.
Die CertifyID Plattform wurde unter Verwendung der Sicherheits- und Public Key Infrastruktur-Expertise von WISeKey entwickelt und kann vollständig in E-Government-Frameworks, kommerzielle Frameworks (…) und in das Bereitstellungsframework für E-Government-Dienste eines Landes integriert werden.«
Da passt es doch wunderbar ins Bild, dass WISeKey am 13. Oktober 2022 eine »Partnerschaftsvereinbarung zur Zusammenarbeit bei der Entwicklung weltraumbezogener Aktivitäten« mit der Schweizer Armee bekannt gab – schließlich residieren in der Alpenrepublik nicht nur UN, GAVI, WEF, Club of Rome und jede Menge NGOs, sondern auch die Bank für Internationalen Zahlungsausgleich (BIZ), die ganz sicher Verwendung für ein quantengesichertes Echtzeit-Picosatellitennetzwerk findet, wenn ihr »Unified Ledger« (Zentrales Hauptbuch) für das Blockchain-Weltfinanzsystem von morgen zum Einsatz kommt. In Anbetracht der »allumfassenden Marktblase« (D. Webb, 2024) ist damit wohl in absehbarer Zeit zu rechnen.
Das also sind die Projekte, Pläne und neuen Partner von Elon. Auf mich machen ja speziell die korrupten Genfer Quantenspezialisten mit ihren Picosatelliten und schlüsselfertigen eID-Lösungen nicht unbedingt den Eindruck von Freiheitskämpfern. Und auch die am 22. Januar 2024 bei einer Pressekonferenz im Weißen Haus angekündigten »personalisierten mRNA-Injektionen gegen Krebs« lassen mich eher skeptisch zurück.
Genau wie der Umstand, dass diese binnen 48 Stunden »personalisierte mRNA« durch die Rechenleistung von OpenAI ermöglicht werden soll. Denn das von Elon Musk mitgegründete Unternehmen des WEF- und Bilderberg-affinen Sam Altman steht im berechtigten Verdacht, für den Tod eines Whistleblowers im Dezember 2024 verantwortlich zu sein. Während Polizei und Medien den Tod des OpenAI-Forschers Suchir Balaji als Selbstmord deklarieren, sprechen sowohl die Umstände am Fundort seiner Leiche als auch Balajis Eltern von »eiskaltem Mord«. Nicht zu vergessen, dass Altman von seiner eigenen Schwester des jahrelangen Missbrauchs beschuldigt wird und sich dafür demnächst vor Gericht verantworten muss. Selbst The Economist räumte am 10. Dezember 2024 ein, dass »die PayPal Mafia die amerikanische Regierung übernimmt«. Und das mit der »Mafia« scheint man in Washington mittlerweile wörtlich zu nehmen.
Aber die von einigen aus der Hüfte geschossenen Präsidialdekreten euphorisierten Eloi werden sicher Gründe finden, das alles zu ihren Gunsten auszulegen. Immerhin hat Trump ein paar Leute begnadigt und will aus der WHO austreten. Wie seine Fanbase es bewerkstelligt, auszublenden, dass »The Donald« schon in seiner ersten Amtszeit aus der WHO austreten wollte und es unterließ, erschließt sich mir aber leider nicht. Genau wie die Begeisterung für ein Gespräch zwischen Musk und Weidel. Man stelle sich nur mal vor, George Soros, Bill Gates oder Eric Schmitt konferierten mit deutschen Politikern. Oder bekämen Sendezeit im ÖRR. Nicht auszudenken.
Wie heißt es so schön: »Eine schmerzliche Wahrheit ist besser als eine Lüge« (Thomas Mann). Stimmt. Nur fällt es relativ schwer, eine Lüge einzugestehen, wenn der, dem man sie beichten muss, der Lügner ist.
So bleibt nur zu hoffen, dass möglichst viele Eloi diesen Schritt trotzdem möglichst bald hinter sich bringen. Im eigenen Interesse. Denn wie schon Ernst Freiherr von Feuchtersleben feststellte, ist »Reue der Verstand, der zu spät kommt«. Und das kann in diesen Tagen verheerende Folgen haben.
-
 @ 4fe4a528:3ff6bf06
2025-02-01 13:41:28
@ 4fe4a528:3ff6bf06
2025-02-01 13:41:28
In my last article I wrote about NOSTR. I found another local bitcoiner via NOSTR last week so here is why it is important to join / use NOSTR — start telling people “Look me up on NOSTR”
Self-sovereign identity (SSI) is a revolutionary approach to digital identity that puts individuals in control of their own identity and personal data. Unlike traditional digital identity models, which rely on third-party organizations to manage and authenticate identities, SSI empowers individuals to own and manage their digital identity.
This approach is made possible by emerging technologies such as secure public / private key pairs. Decentralized identifiers, conceived and developed by nostr:npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 is an attempt to create a global technical standard around cryptographically secured identifiers - a secure, universal, and sovereign form of digital ID. This technology uses peer-to-peer technology to remove the need for intermediaries to own and authenticate ID information.
Notably, NOSTR, a decentralized protocol, has already begun to utilize decentralized IDs, demonstrating the potential of this technology in real-world applications. Via NOSTR, users can be sure that the person or computer publishing to a particular npub knows their nsec (password for your npub), highlighting the secure and decentralized nature of this approach.
With SSI, individuals can decide how their personal data is used, shared, and protected, giving them greater control and agency over their digital lives.
The benefits of SSI are numerous, including:
Enhanced security and protection of personal data. Reduced risk of identity theft and fraud Increased autonomy and agency over one's digital identity. Improved scalability and flexibility in digital identity management
challenges:
Ensuring the security and integrity of decentralized identity systems. Developing standards and protocols for interoperability and compatibility. Addressing concerns around ownership and control of personal data. Balancing individual autonomy with the need for verification and authentication in various contexts.
Overall, self-sovereign identity has the potential to transform the way we think about digital identity and provide individuals with greater control and agency over their personal data. Without people in control of their bitcoin seed words no freedom loving people would be able to exchange their money with others. Yes, keep enjoying using the only free market on the planet BITCOIN. Long live FREEDOM!
-
 @ 8fb140b4:f948000c
2024-12-08 05:21:39
@ 8fb140b4:f948000c
2024-12-08 05:21:39After nuking my second LND node (the first one died due to hardware failure) by my own typo and lack of any thought in the design of the CLI of LND lightning node tools, I decided to take a plunge into the world of mature and complex implementation of the protocol, Eclair by ACINQ. It has been almost one year (the birth of the node was on Christmas Day 2023), 50 thousand transactions routed, and over 30 BTC of routed value. In this post, I'd like to reflect on my experiences with Eclair, go over some of the gotchas and issues, and highlight some of the good choices that I've made since the beginning of my adventure.
Learnings from the Past Experience
While I was learning Lightning network and had very little understanding of how things worked in the whole Bitcoin space, Umbrel was my go-to solution that helped me get off the ground. It proved to be easy and somewhat educational but was not something that I would continuously run for the production setup or trust with any significant amount of bitcoin that I could not afford to lose. Lightning is built on top of the L1 (Bitcoin) network but manages the state of the channels in its own database that is negotiated and agreed upon with its peers. Any failures in the state integrity may result in the complete loss of liquidity or hefty penalty transactions (significant loss of capital). A Lightning node that participates in routing public transactions is also required to be constantly online with as little downtime as possible and only short periods offline at a time. Otherwise, you may risk causing force-closure of the channel due to expired HTLC that is measured in number of blocks.
The Setup
Taking all of my learnings into consideration, I decided to first invest in reliable enterprise-grade hardware: - Server-grade hardware with ECC memory and reliable power supply and CPU - UPS (Uninterruptible Power Supply) to avoid any headaches due to electrical spikes or drop-outs - Reliable enterprise SSDs and NVMEs - ZFS (filesystem) to mirror the critical storage and to ensure full integrity of the data (bit-rot prevention). You do need to tune ZFS for your specific workload and reliability - Reliable and replicated database (PostgreSQL) with two local and one remote replica, and a requirement to have at least two replicas committing the transaction to the disk - Backup! On-site and off-site backup of the critical configuration that you could use to restore the node if your house burns down - Spare parts, redundancy, backup, monitoring - Reliable and stable internet connectivity
The software is Eclair 0.11.0 (latest release as of today), PostgreSQL 16 with two replicas, Bitcoin Core 27.2 (with redundant storage of blocks), additional Bitcoin Core running on a separate node and in-sync with the chain (in case primary node fails), Ubuntu 22.04 with the latest docker software from the official Docker repo.
All Major Gotchas That I Came Across
While Eclair is mature and very stable in itself, it does have some quirks and design choices that you need to account for when running your node. The software is written in Scala and requires a specific version of JVM to run it, as well as JRE and Maven to build it. It doesn't mean that other versions won't work, but you may find unpleasant bugs that may result in catastrophic failures of your node with nobody to help you. All of the requirements are listed in the release notes and installation guide. Whenever in doubt, RTFM first, then ask questions.
Limited Support by the FOSS Community
Eclair is not the most popular implementation of the Lightning protocol, and therefore it is hard to find tools or plugins that could help you manage the node. GUI for the node so far is only supported by RTL and with a very limited number of features. For any sort of statistics, you are limited to either Prometheus (extensive metrics are available) or writing your own SQL on top of the Eclair tables.
On-chain Fee Differences Between Yours and Partner Nodes
This one hit me hard, and many times. I've had more than a few force-closures of the channels because of the conservative and safe default settings. The worst part is, it strikes you when there is a huge spike in fees, which results in significant losses to force-close the channel due to high fees. I am still not 100% sure how the big difference can be exploited in practice, and opted for increase of the tolerance levels to avoid surprise FCs:
eclair.on-chain-fees { feerate-tolerance { ratio-low = <0.01~> // will allow remote fee rates as low as XX our local feerate (spikes) ratio-high = <20.0~> // will allow remote fee rates as high as XX times our local feerate (drops) } }It is up to you and your risk tolerance to define something reasonable and yet allow for secure and reliable node operation.Initial Lightning Network State Sync
When I just started running the node, I had very few channels and startup times were fast. Later, when I expanded the number of channels, I noted that it took my node up to 6-12 hours before it was fully in-sync and routing traffic fast. Given that ACINQ maintains one of the largest nodes on the network, I knew that there was something with my settings that caused the issue. After some research, I came across the setting that whitelisted node IDs for state sync, which immediately rang a bell since I knew from the LND days that not all peer nodes are used for the network sync. Setting the list to my most reliable and largest nodes reduced the startup settling times down to minutes again:
eclair.sync-whitelist = [ "03864ef025fde8fb587d989186ce6a4a186895ee44a926bfc370e2c366597a3f8f", ... ]You do not need to have too many public keys in here, and should keep it between 5-10.Automatic MAX HTLC Adjustment for the Channel
One of the killer features of Eclair is its ability to automatically adjust MAX HTLC for the channel and reduce the number of failed transactions due to insufficient liquidity on the channel. It can be used to estimate your total channels' balances but with smart configuration and a little thinking, you can make it reasonably private while still maintaining a good transaction flow:
eclair.channel.channel-update.min-time-between-updates=1 hour # Allows for the adjustments to be made once every hour eclair.channel.channel-update.balance-thresholds=[ { available-sat = 10000 max-htlc-sat = 0 // 0% of 10000 }, ... ]You can have as many variations as you need, and ensure that the channel MAX HTLC is set well and within reasonable ranges. You would also want to account for multiple transactions going through the channel, but also account for the channel size and an average amount of sats per transaction.Max Accepted HTLCs
By design, the Lightning channel is limited to a specific number of in-flight HTLCs, and the setting is fixed during channel opening time with no way of changing it unless you close and reopen the channel with new settings. If you find your node routing a lot of small transactions (zaps), you may quickly fail many due to that limit (I think default was in single digit range):
eclair.channel.max-htlc-value-in-flight-percent=98 # Default I think is half or 50% eclair.channel.max-accepted-htlcs = 50The setting above will allow for the channel to be more fully utilized and have more concurrent transactions without clogging.CLTV Delta
This is basically a setting that is global for Eclair and sets the maximum number of remaining blocks (in time) before HTLC expires. Setting this too high may result in many HTLCs failing for the small nodes with not so great centrality, and reduce the number of routed transactions: ```
CLTV delta
eclair.channel.expiry-delta-blocks = 60 ``` Default is 144 but I found that setting this to 60 (minimum possible for my node setup and configuration) yields better results for routing. It does expose you to more risk of expired HTLCs that may cause force-closures, but I have seen only one so far on my node.
Allocate Sufficient Memory
You will want to adjust the heap size for Eclair, since the default is too small to run any sizable node. Setting
JAVA_OPTS=-Xmx32g(or half the size of your available RAM) would be a good start. I would advise having at least 32GB of RAM for the node, and allocating at least 16GB (JAVA_OPTS=-Xmx16g) for smooth and fast operations.And More Settings and Parameters to Tune
I have covered only some of the major settings that I felt were worth writing about, but there is much more you could configure and tweak. Read all of the Guides and especially focus on the Configure and a sample reference configuration file.
Good Decisions
First, going with Eclair was the right choice, along with using server-grade hardware with ECC RAM and reliable storage. Second, having a replicated database on three separate nodes with one off-site saved me from a sure destruction of all state and loss of funds. Third, deciding to only maintain channels with reliable and stable nodes saved me from some bad force-closures, where I would choose to close the channel if a peer node goes up and down too frequently, regardless of how well it routes. Even big nodes run by single operators fail badly, as do nodes operated by companies. Keeping your eyes on the node and its health, as well as the health of its peers, is something that very few operators do, which can cause failures and unnecessary loss of your and their funds.
Lastly, if you decide to run a routing node, you have a responsibility to maintain it well and monitor its health. There are many tools you could use, and with Eclair you can use Prometheus and Grafana. Keep your node's packages updated and monitor for any security-related issues that may appear from time to time, so you can mitigate them quickly.
Conclusion
So far I am satisfied with Eclair despite all of the difficulties and headaches I've had with it. It is not perfect, and it requires me to create small tools to do some basic things, but I need a stable and reliable node that I can trust. Eclair has proved to be all that I wanted, and saved my bacon a few times when I nuked one of the PostgreSQL servers and all of its data, and managed to do the same for another replica, but was able to recover and recreate from the remaining replica. Eclair is also stateless during runtime and guarantees consistency of the node regardless of how it fails. Even if you pull a plug on the node's server, it will still be able to come up and recover its consistent state that is in agreement with its peers.
Is it for everyone? No, it is definitely not for everyone or for anyone who just wants a small node to run their online shop with a few channels. You could have a very reliable and trusted node for the online shop with Eclair, but you will need some technical skills to be able to set up, maintain and recover it if things go wrong.
In the end, it is all up to you, your skills, your willingness to learn, and your risk tolerance to make that decision. For me, it was the right choice, and I have no regrets despite not having access to the latest shiny features of the Lightning network.
-
 @ eff2631b:4732bd7e
2025-02-01 11:40:14
@ eff2631b:4732bd7e
2025-02-01 11:40:14This is a test. Trying to use Obsidian for everything. Nostr works out of the box? First try failed, this is my second try.
-
 @ 592295cf:413a0db9
2024-12-07 07:21:39
@ 592295cf:413a0db9
2024-12-07 07:21:39Week 02-11
- Nsite zap by hzrd149 Support page
Content creator want more users. They can go to Bluesky.
Great that Nostr is a Echo Chambers. As stated by Rabble during NostRiga, Nostr is a bitcoin meetup. And it is very difficult as said several times, to subvert this fact. It seems that many bitcoiners don't like this, but they can't do anything, leave Nostr and migrate to other lids.
I'm reading Nostr adventar calendar of Japanese Nostr users.
The first two Don and Jun speak of a Mahjong game and the other of how possibly to count the followers of a given account, countfollowed. - Adventar calendar continue until Christmas 🎅
-
Even Bluesky is looking at MLS , is not a soccer league, is a protocol for message by groups, "circles" Post on Bluesky
-
Relays chakany is introduce sunday. link
I've never seen such dead animals as in Nostr. Something reminds me facebook. The carnivore folks
Hivemind podcast by Max, the kilometric comment on fountain under the podcast is the most appetizing thing of all. Just one comment, little one.
He interviewed Kagi's and searched for a brownie pill, perhaps caused a little headache. ( Brownie pill is orange plus purple)
Loss dog on Nostr this week 😔😔 Pam and Derek family dog
conspiracy theory: Fiatjaf was the reply guy!!!
I tried to download voyage, from zapstore but nothing does not work even the 17.1 does not go. Too bad.
I hear so much about notedeck that I want to make a notedeck do it yourself.
Cherry tree, stuck hzrd149 is making an app a day, Chunked blobs on blossom.
A like is used to send your writing Relays
Announcement of a possible wallet in Damus, this could make things better, zap and whatnot.
- Or I'm posting a song here, a musical interlude. song on wavlake
There seems to be a good buzz on Nostr, maybe it's already a Christmassy atmosphere.
- Backup di Bluesky cool things Bluesky post
On another rssfeed thing.
nostr:nevent1qvzqqqqqqypzq9h35qgq6n8ll0xyyv8gurjzjrx9sjwp4hry6ejnlks8cqcmzp6tqqs93j2remdw2pxnctasa9vlsaerrrsl7p5csx5wj88kk0yq977rtdqxt7glp
It's the same thing as following a cross de bridge, but if they do 3 bridge, I say something is wrong. A bot is attached to a Relay. The Relay goes down and so much greetings, then I can look for RSS feeds in my computer without need of Nostr. I can share a particular opml file on Nostr, but I don't know how to do it I asked Fiatjaf but didn't answer it was taken by dichotomie.
Nip19 really Easy to do filter query.
You have events_id pubkey Relay Instead with Nostr:note you only have the event_id.
- Sebastix says he has to implement it in his library, discover the latest weekly report. nostr-php-helper-library
Oh no Pablo has become super Saiyan 🤣
There is a way to make a podcast starting from a long text, blog. With artificial intelligence. But then I thought, but if one does not have time could not have the text of the article summarized, perhaps we like generating content. It can be an option, either you read or you listen. But if you do not have time perhaps it is better to just summarize, dear chatgpt summarize this text, done. Essential points and make a thread for the social network and do what you want.
- Homemade Traditional Boozy Mincemeat, I didn't even know that existed 🤙 link to shopstr
Hodlbod news on bunker burrow
nostr:nevent1qqs84na25g6mdelvl0408nnq8m29j5070dm9mvjrzxyc6yrx2udjyuczyztuwzjyxe4x2dwpgken87tna2rdlhpd02
- In case you don't see the note burrow on github
Once you have the email what do you do with your encrypted key? No Enterprise user maybe. Rember the article of Hodlbod in "Is Always a political move". ✅
List of artists on Nostr nostr:naddr1qvzqqqr4xqpzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qyghwumn8ghj7mn0wd68ytnhd9hx2tcpzfmhxue69uhkummnw3e82efwvdhk6tcqp9qku6tdv96x7unng9grdr
- An article for food recipe on Nostr Article link
I don't know if they'll ever be there. You can write a recipe book. Or to put recipes on wiki, there doesn't seem to be that attention or that desire. One more relay is always better
- Olas has a website 🥊 Olas app
Oh i see cool Hodlbod bot A summary bot
nostr:nevent1qqs0v88uc2u3he3lm3mpm5h3gr8cuht5wv9g0tk0x9hzvamgvpdjwvspzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgq3qjlrs53pkdfjnts29kveljul2sm0actt6n8dxrrzqcersttvcuv3qu0ltyv
That's all!!
-
 @ 3bf0c63f:aefa459d
2024-12-06 20:37:26
@ 3bf0c63f:aefa459d
2024-12-06 20:37:26início
"Vocês vêem? Vêem a história? Vêem alguma coisa? Me parece que estou tentando lhes contar um sonho -- fazendo uma tentativa inútil, porque nenhum relato de sonho pode transmitir a sensação de sonho, aquela mistura de absurdo, surpresa e espanto numa excitação de revolta tentando se impôr, aquela noção de ser tomado pelo incompreensível que é da própria essência dos sonhos..."
Ele ficou em silêncio por alguns instantes.
"... Não, é impossível; é impossível transmitir a sensação viva de qualquer época determinada de nossa existência -- aquela que constitui a sua verdade, o seu significado, a sua essência sutil e contundente. É impossível. Vivemos, como sonhamos -- sozinhos..."
- Livros mencionados por Olavo de Carvalho
- Antiga homepage Olavo de Carvalho
- Bitcoin explicado de um jeito correto e inteligível
- Reclamações
-
 @ eff2631b:4732bd7e
2025-02-01 11:28:43
@ eff2631b:4732bd7e
2025-02-01 11:28:43This is a test. Trying to use Obsidian for everything. Nostr works out of the box?
-
 @ 9e69e420:d12360c2
2025-02-01 11:16:04
@ 9e69e420:d12360c2
2025-02-01 11:16:04Federal employees must remove pronouns from email signatures by the end of the day. This directive comes from internal memos tied to two executive orders signed by Donald Trump. The orders target diversity and equity programs within the government.

CDC, Department of Transportation, and Department of Energy employees were affected. Staff were instructed to make changes in line with revised policy prohibiting certain language.
One CDC employee shared frustration, stating, “In my decade-plus years at CDC, I've never been told what I can and can't put in my email signature.” The directive is part of a broader effort to eliminate DEI initiatives from federal discourse.
-
 @ edeb837b:ac664163
2025-02-01 10:51:33
@ edeb837b:ac664163
2025-02-01 10:51:33In today’s fast-paced financial markets, having quick access to real-time data, trade insights, and the ability to share trades with a like-minded community is invaluable. That’s where NVSTly’s Discord bot comes in. It’s more than just a bot — it’s a powerful tool for social trading, designed to help traders and investors track their trades, share insights, and collaborate with others in real-time, all within Discord.
What the NVSTly Discord Bot Does
NVSTly’s Discord bot is built with the goal of making financial data and trading insights easily accessible to the entire trading community on Discord. Whether you’re a seasoned trader or just starting, the bot helps you stay on top of your trades and market trends. Some of the key features of the bot include:
- Real-Time Trade Tracking & Sharing: The bot tracks your trades and allows you to share them with others. Whether you’re trading stocks, options, forex, or cryptocurrencies, your trades are instantly shared with your followers and can be posted to social media or sent through Discord DMs or webhooks, fostering a transparent and collaborative environment.
- Trader Stats & Performance Recaps: The bot generates visual reports of your trading performance, including win rates, total gains, and individual trade stats. You can view a trader’s daily, weekly, or monthly recaps, complete with details on stock tickers, options info, and profit/loss calculations.
- Market Data & Charts: Get instant access to live market data, stock charts, and detailed information on tickers. The bot provides a variety of commands for stock price movements, charts, and other data, with plans to expand this to cover more markets in the future.
- Comprehensive Coverage: The bot currently supports stocks, options, forex, and crypto for trade tracking and sharing. Futures markets are also planned for the future. While the bot supports these markets for trade tracking, data-related features like market sentiment analysis or earnings reports will be available in the future.
How the Bot Integrates with NVSTly’s Social Trading App
The NVSTly Discord bot is fully integrated with the NVSTly social trading app, creating a seamless experience for users across platforms. Traders can track their trades on the app, and the bot will automatically share those trades directly with their followers, via DMs, social media, or webhooks. This integration means that everything you do on the NVSTly app can be easily shared with your community in real-time via Discord, making it simple to stay connected with your trading network.
The bot doesn’t just show trades — it also gives users insights into their trading performance and connects them with other traders for discussions, tips, and strategies. With NVSTly’s unique social features, traders can collaborate, share strategies, and learn from each other in a dynamic and interactive environment.
What’s Next for the NVSTly Discord Bot?
The future of the NVSTly Discord bot is incredibly exciting, with plans to add even more features designed to elevate the trading experience. Some of the upcoming features include:
- Expanded Market Coverage for Data Commands: In addition to stocks, the bot will soon offer data-related commands for crypto, forex, and futures markets. This will allow users to access even more comprehensive market data, including earnings reports, options flow, and more.
- AI & Machine Learning Integration: NVSTly plans to integrate AI and machine learning to generate trade signals, analyze market trends, and even offer personalized trading tips. This will help traders refine their strategies and make more informed decisions.
- Real-Time Alerts & Notifications: Users can already receive trade alerts sent directly to their DMs from traders they follow. In the future, users will also be able to set more customized alerts based on price targets or specific market activity.
Why the NVSTly Discord Bot is Perfect for Trading Communities
Discord has become a hub for traders and investors, and the NVSTly Discord bot takes full advantage of this by providing a platform where traders can interact, share trades, and learn from one another. The bot’s ability to instantly share trade recaps and stats creates an environment of transparency and collaboration. Traders can discuss strategies, ask questions, and even challenge each other to improve their performance.
By integrating market data, charts, and trade performance tracking, the bot offers a complete package for traders on Discord. It’s not just a tool for sharing trades — it’s a vital part of a thriving trading community.
Why NVSTly’s Discord Bot is the Fastest Growing Finance Bot on Discord
With its comprehensive features and seamless integration with the NVSTly app, the NVSTly Discord bot has quickly become the go-to tool for traders on Discord. What sets it apart from other finance bots is its focus on user engagement. The bot is not just about providing data — it’s about building a community of traders who can share their experiences, insights, and successes.
Traders have flocked to the NVSTly Discord bot because it provides real-time data, easy trade tracking, and powerful analytics — all in a user-friendly format. It’s no wonder it’s quickly becoming the fastest-growing finance bot on Discord.
On Track to be the Greatest Finance Bot on Discord
NVSTly is on track to become the greatest finance bot on Discord, if it’s not already. With plans for expanding market coverage, adding advanced AI-driven features, and constantly improving its user experience, the bot is poised to revolutionize the way traders use Discord.
By offering a comprehensive set of tools that integrate seamlessly with the NVSTly app, the bot is becoming an essential resource for traders who want to stay informed, track their performance, and engage with the trading community.
NVSTly is available for free on web, mobile devices (iOS & Google Play), and is fully integrated with Discord via a unique bot- the only of it’s kind and available to any server or trading community on Discord. Or feel free to join a community of over 45,000 investors & traders on our Discod server.
-
 @ 17538dc2:71ed77c4
2024-12-05 20:54:13
@ 17538dc2:71ed77c4
2024-12-05 20:54:13Nostr Onboarding Questionnaire
Below are are results of the nostr qualitative onboarding questionnaire created by elsat in early November, 2024. Responses are from 22 nostr surivors/masochists. Results are not representative of people who never made it past onboarding. These are folk that remained on nostr, and were active around the time I asked for volunteers to provide feedback on onboarding to nostr.
Let me know if anything stands out, if you have questions about any particular response!
I. Did you onboard to nostr on your cellular network, on wifi?
14 Wifi; 7 cell; 2 both; 1 other
II. What was the biggest pain point in onboarding to nostr?
Discovery
Discover interesting content and other people Finding the right content. Discovery. Loading/lacking data figuring out how to find interesting people Finding npubs
Value Prop & Learning Curve
Knowing how it differs from tradsofiu Learning the difference between the protocol and the app I needed to download and onboard through. Choosing a client. Trying to figure it out on my own.
Key management
Private/pub key handling That's definitely key management. How and where to store it to have it secure, still accessible for use with other apps in a secure way. Getting my nsec in without pasting it
Relay setup
Setting up relays, discover interesting users to follow, > building your own feed figuring out relays Finding reliable relays to join.
Wallet Setup
Setting up a lightning wallet Lightning wallets for sending and receiving Zaps.
Notifications
Notifications [presumably missing notifications]
Accessibility
Finding a very good accessible client for the computer (I'm blind). Amethyst seems to be good on my Android device, but I avoid smartphones.
Scary links
I tried to "onboard" (ie expose) friends to nostr by sending them links to interesting/funny notes here and there. But some of the default sharing links I use (Amethyst -> Njump) are so long that they always think it's some spam. (Primal has nicer web links)
Customization
Figuring out profile setup, lots of unfamiliar fields
III. What part of nostr "wow'd" you, and when did this happen?
take your social graph with you; distribute your data
That all the data is already there if you use different clients and you take your social graph with you through completely different apps. seamless account a mobility of course ccount easy switching between clients Moving my social graph between clients. Happened in the first days of usage. Cross over between different clients. Happened on a Tuesday.
V4V, freedom, exclusive, and censored content
Freedom, some V4V and exclusive content, some censored content The clear messaging why nostr was better than mastodon/ activitypub
Flexibility, BYO Algorithm, Control
The insane flexibility. Nostr is a textbook example of "worse is better". So I think I was converted when I realized how much could be built with this, not just social media. My "Aha! This is more than just a Twitter clone" moment was when I stumbled on Oddbean. Also there's this whole "bring your own algorithm" / "build your own algorithm" to the social media side of it. And we're starting to see that work out in practice, with things like bitvora's algo-relay. Complete control A digital portable social identity that I can take with me from one app to another. December 2022. Experiencing the interoperability when i tried Listr, spring '23 I think Initially it was decentralization and censorship resistance. >You can spin a simple backup relay, own your data truly, and rebroadcast everything to different relays. Amethyst, adjusting the relays
Access to devs
Devs working in real time on it visible - too cool
Zaps
Zapping! Right away Zapping zaps! and also the small community After [initial censorship resistance phase is over], the most wow part was zaps, still is. Zaps for shitposting & being able to login into different apps with the same account
Cordiality
Open respectful discussion among people who do not agree Friendly discourse of users. Not toxic like other special media. First day.
IV Around what time did you onboard to nostr (e.g. July 2023)
Nov 2021 December 2021 2022 the single html page first POC client December 2022 Dec 2022 December 2022 Jan 2023 January '23 feb 2023 February 2023 Early 2023. Didn't really play around with it until December 2023 May 2023 June 2023 - Plebstr, November 2023 primal march 2024 amethyst, January 2025 notedeck I've been dipping my toes in the water since 2022 but just started taking it seriously last month. July 2023 March 2024 Summer 2024. August 2024 Nov 2024
V Which app
astral.ninja (2) Branle Damus (6)
"(needed the simplicity)"
PRIMAL (5)
"(needed the simplicity)" Amethyst (4)
Coracle Coracle and nos2x
Various
A combo of Amethyst (phone), nostrudel (web), and algia (command line). I'm a command-line junky. I also am fond of Oddbean, because it's basically a hackernews style thing built on top of nostr. But see my complaint about Nazi bar / Temple of Satoshi. Could not recommend to friends. At some point, I intend to set up strfry and my own Oddbean instance targeted to anti-capitalists.
Created my keys with alby
Can't remember the actual name
VI Have you experienced a failure in onboarding others to nostr? What exactly happened?
Poor experience trying to onboard newbs to nostr during the conference (mostly on iOS which I do not use), around 10-12 people. Granted the cell coverage was not great and not sure I remember everything that went wrong, but users were generally confused with loading/lacking data. Create a profile, then I tried to follow them but could not find them from Amethyst. So scanned QR code, which is a non-obvious step. Then their profile showed just the npub but no info or pfp, some commented on that. Followed them but they didn't receive a notification for that on Damus, this confused most. And then what? Post a note? (I was recommending #introductions ). While you wait for all this to load, tap, retry... between laughs you need to come up with conversation and try to somewhat defend nostr, tell them we're early and bugs will be fixed etc. On Primal follows do appear but feeds don't load. And it autofollows a bunch of random people - some liked it some didn;t. They posted a note and I wanted to like/zap it but I could not see that note on my client either, even though I'm connected to major relays (could be nostr.wine's fault, but I tried with the zap.store account as well). I saw one guy KYC himself 3 times with the wallet because when he switched to his email client to get the code and the app kept resetting the screen. Lucky that the majority of people were eager and did their best to try. Since some of these were after Jordi's talk where he offered several clients to download, it was not always my choice/recommendation on which client to download - they just came with it. I know we do our best but guys... it's bad. This reminds me of getting a newb to open a LN channel and get liquidity. Painful. If we have to centralize more to better onramps, so be it.
difficulty / friction
Picking a client
Yes. It's too technical. You need many tools to accomplish small tasks.
Yes, tried primal on Android. It failed to accept any profile changes
Not able to find other npubs when using search in several clients
stale
They got no new events, because they followed only a few users
They didn’t become frequent users because I’m the only person they know in nostr.
They lose interest in the network compared to traditional social networks. They were normies.
Some found it strange that you follow a bunch of bitcoiners (seemingly) by default (Primal iirc)
yes. non bitcoiners not interested in joining a small network of people just yet
quotes
I haven't tried to bring anyone to nostr. I am a bit scared to do so, because the place has a rep of being a Nazi bar and an extension of the Bitcoin cult. I do think that it is what you make of it, and I've tried to argue that point with friends. It's a protocol, nothing more. Don't wanna interact with Nazis and use Bitcoin? Nothing says you have to.
They don't care
I have not convinced anyone to use nostr
Too hard for most folk.
Not really.
No. Never tried.
No, onboarded two successfully.
Yeah I generally suck at getting people to check out new stuff
VII What, if anything, do you think confuses people during onboarding to nostr? Why? Have you observed this?
Setting a optional username is confusing for many and also they don't know what a NIP-05 is (they are likely to just fill in their existing mail address)
Finding some people. No progress of loading content or indication of time. Slight confusion where are DMs, home, etc, tabs basically
The why. Its much easier now, I was way confused DEC 22
Same on boarding is difficult to people on Nostur.
There is no app in the App Store called “nostr”
nips and relays
We tell people that you don't need KYC to use Nostr and then ask them for KYC for Lightning wallets.
No in-client intro to the "what" and "how" of it all. I haven't witnessed that, but I believe it could squash preconceived notions.
Key management. Especially because there is no key rotation(recovery option in a traditional email/phone way), if it leaks, you are done.
Safe keeping of your nsec. There are many ways to do it, all of them unfamiliar to most users.
When you don't see data you are expecting, be it a profile picture, a follow notification, or a note. Remember people who want to try Damus/Primal/etc microblogging clients come from twitter - so cater for transition from Twitter. Gen z snapchat/tiktok users don't care about nostr, no way to relate
Understanding how to filter for non-Bitcoin content.
need for setting up relays to filter the spam waves, finding the interesting follows, and difficulties setting up usable (even custodial) wallets.
Why would I want to use nostr?
Relays / keys
VIII What, if anything, do you think scares people away during onboarding to nostr? Why? Have you observed this?
Not much, but probably nsec backups and transfers if they knew
Dark web scary things
Technical questions
Personal responsibility for keeping nsec safe
Intuitiveness.
just not enough people on it for them (non bitcoiners)
Technical complexity with either Lightning or relay management.
Depending on client, slowness, difficult search, or feeling empty upon arrival.
Again, keys.
Bitcoin blah blah
I don't know anybody IRL that even use x
Their core influencers haven't adopted nostr yet.
IX What one improvement would make onboarding to nostr easier?
Explain it s not a platform and the current app you're using is replacable by other by (re)using your keypair
Twitter bridge
Honestly, from a technical standpoint, I found it pretty easy. Especially with Amethyst on the phone. So I'm not sure if I have an opinion here.
Private key management to hide the complexity
Little guide somewhere or a buddy to ask questions
An intelligent assistant to setup relays
Reach
bringing wallet of satoshi back! or some similar easy custodial lightning wallet
Better user and content discovery.
Clients dedicated to onboarding, education, and key management instead of social stuff
Key recovery/rotation option. How? Hell if I know. Smart people say Frost, something, something. XD
More established signing mechanisms
An easy GoTo FAQ How to add people; how to zap; etc.
Do not try to connect to 89239823932 relays and make it decentralized when people only care about the first impression?
More "other things" micro-apps, not do-everything whale apps
More users
X What, if anything, do you think should be addressed, or added to onboarding to nostr across most nostr apps? Why?
A skippable small visual intro guide
Content discovery
A way to hide duplicates of the same post.
Better user and content discovery.
Introductory level education, expecting a traditional social app experience then not seeing it
Right now for me everything starts and ends with key management. Maybe a simple signing and profile edit app available across all platforms and devices with option paired with hardware signing device.
An onboarding relay. Only accepts the first note for an npub (kinds 0, 1, 3). Maybe
Easier relay selection.
Make bunker actually work
Staged roll out of owning your own keys to help them understand what that means
XI Do you have any other observations, feedback, or commentary on onboarding to nostr?
Yes, I think I'd say that most of my complaints are social / cultural, not technical. Then again, I've been online since 1993.
People have gotten lazy and are used to being fed content for their interests. This doesn't happen easily on Nostr and needs improvement.
An empty feed is better than a pre-determined one.
We suck and there's no good reason why
I have never gotten bunker to work
XII What is your favorite onboarding experience to an app outside nostr?
Telegram (x2)
Onboarding to the fediverse was pretty good. Witness the fact that a lot of blind twitter moved there.
They're all mostly the same, email, password, confirm. So any that i can use without signup is superior.
Can't recall any that really stands out. But in terms of following users during the onboarding what music streaming apps do is really nice. You get presented with a list of artists and based on what artists you check to follow list adapts and shows you similar suggestions.
None in particular, but I like when account creation is delayed as much as possible, I.e there is a public experience for you to try the product with no commitment
Several I can't recall now. But we need to make it AT LEAST as good as Twitter because that's where our users come from
old Twitter, circa 2019
I prefer no onboarding needed
I like "log in with" buttons but fuck those walled gardens
-
 @ e83b66a8:b0526c2b
2024-12-04 08:52:23
@ e83b66a8:b0526c2b
2024-12-04 08:52:23When we had the Gold standard, gold only backed assets.
Now we are approaching the Bitcoin Standard, what will happen if Bitcoin is used to back debt?
$MSTR is the Alpha release
Trumps USA will be the Beta release.
If it works, the world has $315T of debt. That will be the full release V1.0
In comparison, the world has $454T of assets.
Can it be done?
What happens when you back a negative debt with a positive asset?
Has it ever been tried?
Is it possible?
The problem with the debt is it isn't "owed" to anyone.
If I lend you $10 you owe me $10.
To explain further:
If you lend me $10 worth of gold, then I can pay you back $10 of money if it's backed with gold - the gold standard.
If you lend me $10 worth of gold, and I pay you back with unbacked fiat, the repayment is arbitrary.
Like for like you can back any backed money with any asset.
Without a backed money, you can only repay an asset with an asset, otherwise paying with fiat, the global books don't balance.
In the current fiat world, if the US government print $10 and sells it to the market for $10 + interest, their is no creditor. You are simply diluting all other dollars.
When they have to pay back the debt to the “creditor”, they can't return the original $10 because that's been spent and they haven't generated any wealth (they are a government, not a company), so everything they return (the original lent $10 + interest) is printed again.
This is monetary recursion and destroys all fiat systems eventually.
So what happens when you insert a hard asset into the equation? Do you destroy or weaken that asset, you certainly don't strengthen it.
Does this turn Bitcoin into an inflationary currency despite its inherent deflationary properties.
After all, the U.S. had to come off the gold standard, because they didn't have enough gold to pay back.
I think best case scenario is Bitcoin repeats what happened to gold. It weakens Bitcoin until it makes it flacid, at which time the government will be forced to leave the Bitcoin Standard and Bitcoin will be a shadow of its potential.
Why?
Currency can be created and destroyed.
Money (the measure of wealth) is absolute.
I think this is the fundamental flaw, we believe money can be created and destroyed simply because we are used to printing or burning government fiat and have copied that model for Crypto currencies like Ethereum or Tether, which are mined or burned.
So money (invent better word) cannot be printed or destroyed, it is a measure of wealth and if you increase or decrease the supply you change the unit measurement, not the money.
So what are the potential end point valuations of Bitcoin?
Can Bitcoin approach a $21M coin valuation? i.e. 21M Coins at $21M?
If Bitcoin only backs assets, then it can't exceed, or even approach the total value of world wealth, currently $454T
At $21M for 21M coins, this approaches world wealth.
If Bitcoin is used to back debt, then you can add a further $315T of value, so if we assume $100T (about 1/4) of asset value + $300T of debt value, then we approach $21M per coin.
Another potential way of projecting the eventual stable price of Bitcoin:
If world wealth is currently around $454T
And world debt is currently around $315T
then can we consider it like a company and consider the profit to be $454T - $315T = $139T
Would that be a good expectation for final Bitcoin price?
i.e. $139T / 21M = $6.6M per BTC
However, I'm not certain Bitcoin can survive being used to back debt.
Gold never did that.
-
 @ eac63075:b4988b48
2024-12-02 02:40:18
@ eac63075:b4988b48
2024-12-02 02:40:18Estonia is a small country with just 1.3 million inhabitants and an area similar to that of the state of Rio de Janeiro, but with a notable difference: while Rio has about 16 million residents, Estonia shines with its efficiency, innovation, and digitalization. It's no wonder it's known as the "digital nation." For many Brazilians, the country has become a strategic gateway to start a business and settle in Europe.
Listen the podcast
https://www.fountain.fm/episode/pizBLdhqqP5qQrKQILFb
The Purpose of the Event and the Context
The meeting organized by Bloco and the Brazilian digital community aimed primarily to explore the opportunities that Estonia offers to those wishing to expand their businesses or start a new life in Europe. With pizza, networking, and straightforward presentations, the evening was dedicated to demystifying questions like "Why Estonia?" and "What makes this country a viable option for Brazilians?"
Additionally, the event highlighted the importance of E-Residency, a digital identity that allows you to open and manage a company in Estonia from anywhere in the world. But that's just the beginning. Let's explore what makes Estonia a standout point on the European scene.
Where Is Estonia Located?
If you open a map of Europe and look for this small country, you're likely to have difficulty locating it. Situated to the north of what's called Eastern Europe, Estonia borders Russia and Latvia and is separated from Finland by the Baltic Sea. Although geographically positioned in the east, many Estonians prefer to identify with the north due to cultural and historical proximity to the Nordic countries.
There's something fascinating about Estonia's history. According to local legends, Vikings set out from their Estonian islands to conquer the world, later returning to reclaim their lands. This spirit of resilience and reinvention permeates the country's culture to this day.
Digitalization: The Estonian Revolution
Thirty years ago, when Estonia gained its independence from the Soviet Union, the country decided to look to the future. The question was simple: how to ensure the sovereignty and survival of a small, vulnerable nation? The answer was bold: total digitalization.
In 2001, the X-Road was created—a decentralized infrastructure that connects all government institutions and allows citizens to access public services digitally. This system is so advanced that even the servers of the Estonian government are located outside the country, stored with backups at the European Commission in Brussels.
Through this infrastructure, Estonia eliminated information silos, decentralized data, and allowed its citizens to authorize the use of personal information with complete control. Today, 98% of the population has a digital identity, 95% file taxes online in less than three minutes, and 100% of public services are available digitally.
For those accustomed to Brazilian bureaucracy, it's impressive to know that opening a company in Estonia can be done in just 15 minutes, without the need for an accountant.
E-Residency: A Digital Passport for Business
Launched in 2014, the E-Residency program made Estonia the first country in the world to offer a digital identity to non-residents. This digital ID card allows entrepreneurs to open a company in the European Union, sign documents, and manage businesses remotely without needing to visit the country.
Although it doesn't grant citizenship or physical residency, E-Residency is perfect for those who want to test the European market or operate a digital company. The program has already attracted over 118,000 e-residents from around the world, including 1,300 Brazilians who have opened 379 companies in the country.
Advantages of Doing Business in Estonia
Starting a business in Estonia has many advantages. Let's discuss some of the main ones:
Simple and Clear Taxation:
Estonia adopts a flat tax rate of 20% (which increased to 22% after the pandemic and will be 24% in 2025) on distributed profits. If you reinvest the profits in the company, the taxation is zero—a unique policy that encourages sustainable growth.
Low Cost to Start:
Unlike Switzerland, which requires an initial deposit of 100,000 Swiss francs to open a company, in Estonia, only 2,500 euros are needed. And the best part: this amount only needs to be deposited when the company distributes profits for the first time.
Complete Digitalization:
Digital signatures in Estonia eliminate the need for notaries and paper documents. Everything can be done online, from opening the company to filing taxes.
Support for Startups and Innovation:
With the Startup Visa, entrepreneurs can move to Estonia with their entire family and receive support to expand their businesses. Additionally, the country has the highest number of unicorns (startups valued at over one billion dollars) per capita in the world, including companies like Skype, Bolt, and Wise.
Easy Access to Europe:
Establishing your company in Estonia means access to the European market, with its unified regulations and a vibrant innovation ecosystem.
The Startup Visa: An Invitation for Entrepreneurs
For those who want more than just operating remotely, the Startup Visa program offers the opportunity to physically move to Estonia. The initial visa is valid for one year and can be renewed for three consecutive years. After eight years, there's the possibility of applying for European citizenship, although Estonia doesn't allow dual nationality.
One of the unique features of the Startup Visa is that there's no limit to the number of partners or family members who can be included in the program. This means that the entire team of founders and their families can benefit from the residence permit.
Additionally, Estonia offers support through the International House and its Work in Estonia program, a center where newcomers can resolve everything from assistance with opening bank accounts to cultural and professional integration.
Innovation and Access to Investments
Estonia is known for its culture of innovation. Events like Latitude 59, one of Europe's main startup gatherings, offer prizes of up to two million euros for winning startups. The country also facilitates direct connections with investment funds and venture capital, often without bureaucratic barriers.
For early-stage companies, the Estonian ecosystem is especially attractive. There are cases of entrepreneurs who managed to raise hundreds of thousands of euros with little more than a prototype or a good idea on paper.
A Small Country with Global Ambitions
Although small in size, Estonia is big in ambition. Its model of digitalization and support for startups serves as an example to the world. With unique opportunities like E-Residency and the Startup Visa, the country positions itself as a viable and accessible gateway for Brazilians who wish to explore the European market.
For those seeking innovation, simplicity, and access to the global market, Estonia offers more than opportunities; it offers a vision of the future. Whether it's to open a business, operate remotely, or move with the family, the country proves that with the right strategies, even a small nation can make a giant impact.
-
 @ edeb837b:ac664163
2025-02-01 10:43:46
@ edeb837b:ac664163
2025-02-01 10:43:46Join Benzinga as they sit down with NVSTly, the cutting-edge platform revolutionizing social trading and investing. In this exclusive interview, NVSTly shares insights on empowering retail traders, fostering transparency, and building a thriving community for investors of all levels. Discover how NVSTly is shaping the future of trading with innovative features, real-time trade tracking, and global collaboration.
NVSTly Web: https://nvstly.com
iOS: https://nvstly.com/go/ios
Google Play: https://nvstly.com/go/android -
 @ edeb837b:ac664163
2025-02-01 10:40:42
@ edeb837b:ac664163
2025-02-01 10:40:42We’re thrilled to announce that NVSTly has been honored with the People's Choice Award at the prestigious Benzinga FinTech Awards 2024! This recognition is a testament to the trust, support, and enthusiasm of our growing community of retail traders, investors, and financial enthusiasts.

A Milestone in Social Investing
Winning the People's Choice Award is more than just a moment of celebration for NVSTly—it reflects the incredible journey we’ve shared with our users. NVSTly was built with one mission in mind: to redefine social investing by empowering traders of all experience levels to share, track, and learn from one another.
In the competitive world of fintech, being selected as the People's Choice means we’ve created something that resonates deeply with our audience. It’s your votes, feedback, and passion that have propelled us to this achievement.
What Makes NVSTly Unique?
NVSTly stands out for offering a platform that’s entirely free while delivering a comprehensive suite of features for traders, such as:
- Global Leaderboard: Recognizing top-performing traders across stocks, options, futures, forex, and cryptocurrency.
- Trade Insights UI: Providing detailed analytics on trades, including market data validation and unique event visualizations.
- Broker Integration (Optional): Automating trade tracking and sharing with real-time updates.
- Discord Integration: A first-of-its-kind bot that brings NVSTly’s full functionality to one of the fastest-growing social platforms in finance.
- Education and Community: Enabling beginners to learn from experienced traders and find actionable insights.
Unlike traditional trading platforms, NVSTly focuses solely on trade tracking, sharing, and performance validation. It’s not about buying or selling real assets but fostering transparency, collaboration, and growth among traders.
Powered by the Community
The People's Choice Award is special because it comes directly from you—our community. Whether you’re an experienced trader gaining recognition through our leaderboard or a beginner exploring NVSTly to learn from top traders, this award proves that NVSTly isn’t just a platform; it’s a movement.
Your votes affirm our commitment to delivering cutting-edge features, unmatched usability, and an ecosystem that connects traders across all markets.
Looking Ahead
Winning this award fuels our determination to push boundaries even further. In the months to come, we’re excited to roll out new features, expand our broker integrations, and enhance the tools that make NVSTly the go-to platform for retail traders worldwide.
Thank You
We couldn’t have achieved this milestone without your unwavering support. From everyone at the NVSTly team, thank you for believing in our vision and making NVSTly the People’s Choice for 2024. This award is as much yours as it is ours.
If you haven’t joined the movement yet, there’s never been a better time. Discover, share, and track trades with NVSTly today—because the best way to grow in the markets is together.
Join NVSTly:
- Website: nvstly.com
- Mobile App: Available on Google Play and iOS App Store
- Discord Community: Join Now
Let’s continue shaping the future of social investing, one trade at a time.
-
 @ 592295cf:413a0db9
2024-11-30 08:33:35
@ 592295cf:413a0db9
2024-11-30 08:33:35Week 25 11
Vitor created another social network edit mode. There are countless cases of use. But type threads are possible, small books, Rabbit hole and those who put it more.
nostr:nevent1qvzqqqqqqypzq3svyhng9ld8sv44950j957j9vchdktj7cxumsep9mvvjthc2pjuqyghwumn8ghj7mn0wd68ytnhd9hx2tcqyrewvkqwqt7urn2u9h5tk88vj9p3csl0wt08aqd8kxsngxtdmr0zqmszxds
Nostr Report is missing, was a lot of news, 20 notes in a day.
Some news do not need resonance case, Primal did a good job with trending. Of course is a centralized service. But it was one of the Twitter features, he did it with the top trending hashtags. Now Primal is more focused on DVM smart feed, read, and Discovery. This will bring chaos, as long as you can switch the trend feed with your Algo or DVM Algo. I'm obsessed with these switches 😅
Hostile people can happen along the way, it's not like in Bluesky 😔.
Someone share on Bluesky https://bsky.app/profile/laurenshof.online/post/3lbrsjzobps2u Video is this https://audiovisual.ec.europa.eu/fr/video/I-264553?lg=en
Trying to convince someone for Unanimity, Relay groups are nice, but Unanimity is simpler.
nostr:nevent1qqs9ar5t9xu97nhtwef9ej2y7cklnysf7hgwce7t2wk5axhfdwuq5sqpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgq3qmzyp990kgskujdyplzydmd08ft42mkkfg4lzldaap8ng7n2u3kmss8l76e
Game on Nostr on 2025, cool be.
Angor are finally ready, crowdfunding with Nostr and Bitcoin. (alpha test)
nostr:nevent1qvzqqqqqqypzqw4hcggg2f9h68qutp0snsdhux20teljykjmh9rlx78qwnt5a8dlqqstte0g54hfa2cmr63vq4ava7e7wsr483p63tylvut8cvufzs44a0cd6saa3
PR 1600
The name is curated pubblication use kind 30040 e 30041, 30040 Is the envelope and 30041 are chapters or paragraphs. We'll see what's left in a month. There are no big discussions until now. This is the basis to leave it so, if you can improve it without breaking it ok. I think liminal is preparing at least two other NPs. The bottom problem is that there are no "competitor", someone else outside who wants to use this thing. But if there are no one can invent.
You can't do things with others. There's too "bad" people. Keep calm is a toxin environment. Maybe you have to get away a bit.
I was trying to help David but there are no aggregators for neo4j Nostr. Dustin's example, I think it's only worth the DVM. There are two other projects one grain of Oceanslim I saw the video where he explains some things, with Dr. Morales. And the other is Cody's Nostr Relay tray. At least you have all the data in a Relay, and for that Relay you can query, I don't think you find anything significant, maybe you need 100(k) notes to have a good sample. I think I'll make the update. I downloaded two months ago, it worked for a while with Nostrudel, then only with next, lately some problems with next. Cody launched the project with fiatjaf and I think it is also implemented here. In the end, I don't think this answer is useful to David.
Zapview nostr-zap-view The lokuyow project, always attentive to zap lightning and Nostr.
Give a "microsat" to Fiatjaf nostrabia relay
I managed to send a zap from a hex known id, it only works with getalby, so until January 4th. I have to prove if other lnurls have the call.
Something I might have understood about the new version of Nostr_sdk or rust Nostr. Sending messages will be harder. The builder does not support the tag, it breaks almost all the scripts I was writing and to verify them you can do nothing but send to the Relays, I wait a few days if there are news, but I don't think there will be. It is no longer linked to the table of examples so it will not be updated presumably, I would like to continue, as the cli does not come out. That then the cli will be in python 12.. (I'm still in version 3.10.9 of python)
I've seen bulletin proof, posting on Nostr seems interesting, but they need many interactions to have a functioning client. link, stacker news
Nostr nuance, login, Nostr connect, private. (two Notes)
nostr:nevent1qvzqqqqqqypzq77777lz9hvwt86xqrsyf2jn588ewk5aclf8mavr80rhmduy5kq9qyg8wumn8ghj7mn0wd68ytnddakj7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qpqqqqz3757ha8j5xcm7er8kkdc0dgtvmy55dz2t2d7c2tv9h8qm88qlcjsls
nostr:nevent1qvzqqqqqqypzq9eemymaerqvwdc25f6ctyuvzx0zt3qld3zp5hf5cmfc2qlrzdh0qyt8wumn8ghj7ur4wfcxcetjv4kxz7fwvdhk6tcpzpmhxue69uhkummnw3ezumt0d5hsqgz98qckr40flhpyt48fxqjkuf9p4dv245634ygvp6dfu2kt7qk5egqmc4l8
An other microsat to Fiatjaf chronicle relay
Kind 1 was a mistake and many people are realizing it, they are replacing it. Kind 5 now it is only almost to eliminate drafts, here the option is to overwrite.
That's all!!
-
 @ edeb837b:ac664163
2025-02-01 10:36:38
@ edeb837b:ac664163
2025-02-01 10:36:38
At NVSTly, we embrace the concept of “building in public.” This approach shapes how we develop, test, and roll out features, with the goal of making NVSTly the best social trading platform for our users. But what exactly does building in public mean for NVSTly? Let’s break it down.
Updates as They’re Finished
Instead of waiting to bundle new features and fixes into big, infrequent releases, we push updates as they’re completed. This ensures users benefit from improvements as soon as possible. However, our agile development style means you might notice subtle changes before they’re officially included in a published changelog. These incremental updates allow us to iterate and enhance the platform quickly.
Internal Testing, Real-World Feedback
Before any update reaches the production environment, our team conducts internal testing to ensure the new feature or fix works as intended. For example, a recent update to allow stats and daily/weekly recap commands to function with usernames containing spaces was thoroughly tested internally. Unfortunately, this change inadvertently broke compatibility with Discord IDs, highlighting the challenges of anticipating every edge case.
This is where building in public comes into play: while we strive for thorough testing, some issues only emerge when updates meet real-world usage. That’s why we rely on our vibrant user base to help us identify bugs, unintended behaviors, and areas for improvement.
The Role of Our User Community
Our users play a critical role in the development process. By using NVSTly in their daily trading workflows, they encounter scenarios that internal testing might miss. When users report bugs, glitches, or other issues, it provides us with invaluable insights into how the platform performs under various conditions.
If you ever experience something on NVSTly that doesn’t seem to work as expected, we encourage you to report it to us. Unlike platforms that may identify and resolve issues passively over time, NVSTly relies directly on user feedback to detect and prioritize fixes. Every report helps us improve.
Changelogs: A Snapshot of Progress
Given our frequent updates, we publish changelogs only after accumulating several changes or introducing major features. This means that when you see a changelog, many of the updates listed might have been implemented days or even weeks earlier. While this approach helps us focus on building and refining the platform, it’s another example of how building in public keeps the development process transparent.
Why Building in Public Matters
By building in public, we:
- Accelerate innovation: Continuous updates ensure the platform evolves rapidly.
- Foster transparency: Users gain insight into what’s changing and how issues are addressed.
- Strengthen collaboration: Feedback from users directly informs our priorities and solutions.
This approach isn’t without its challenges, but we believe the benefits far outweigh the risks. Building in public allows us to create a platform that truly meets the needs of our community — a community we’re proud to involve in the journey.
How You Can Help
If you notice a bug, glitch, or unintended behavior, please let us know right away. Your feedback is essential to making NVSTly better every day. Together, we’re not just building a platform; we’re building a community-driven experience that reflects the collective expertise and passion of its users.
Thank you for being part of the NVSTly journey. Let’s keep building — together.
NVSTly is available for free on web, mobile devices (iOS & Google Play), and is fully integrated with Discord via a unique bot- the only of it’s kind and available to any server or trading community on Discord. Or feel free to join a community of over 45,000 investors & traders on our Discod server.
-
 @ da0b9bc3:4e30a4a9
2025-02-01 09:45:00
@ da0b9bc3:4e30a4a9
2025-02-01 09:45:00Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/872135
-
 @ dbb19ae0:c3f22d5a
2025-02-01 09:06:49
@ dbb19ae0:c3f22d5a
2025-02-01 09:06:49The Magic of
=()=in Perl: Counting Matches with ElegancePerl is full of powerful and sometimes cryptic features, and one of the lesser-known yet highly useful tricks is the
=()=operator. This clever construct allows you to count the number of matches in a string without using loops or unnecessary variables.
Understanding
=()=: A Smart Counting TrickNormally, when you apply a regex with the
/g(global match) flag, Perl finds all occurrences in the string. However, getting the count of those matches isn't as straightforward as you might expect.Consider this example:
perl my $str = "Hello 123, Perl 456!"; my $count = () = $str =~ /\w/g; print "Matched $count word characters.\n";Breaking It Down
- Regex Matching (
$str =~ /\w/g) - This searches for all word characters (
\w→[A-Za-z0-9_]) in$str. -
The
/gflag ensures it captures all occurrences instead of just the first one. -
The Empty List
() - The regex match is assigned to an empty list
(). -
This forces Perl to evaluate the regex in list context, where it returns all matches instead of just one.
-
Assigning to a Scalar (
$count) - When a list is assigned to a scalar, Perl doesn't store the list—it simply counts its elements.
- The result?
$countcontains the number of matches.
Expected Output
Matched 15 word characters.If you manually count the\wmatches (Hello123Perl456), you'll find 15.
Why Not Use
scalar()Instead?You might think this is equivalent to:
perl my $count = scalar($str =~ /\w/g); # will return 1But this won't work!scalar($str =~ /\w/g)only returns the last match found, not the count.=()=is necessary because it forces list context, ensuring Perl counts all matches correctly.
Practical Use Cases
This trick is useful whenever you need to count occurrences without modifying the original string. Some real-world applications include:
✅ Counting words, numbers, or special characters in a string.
✅ Measuring how many times a pattern appears in a text.
✅ Quick validation checks (e.g., ensuring a string contains at leastndigits).Example: Counting words in a sentence
perl my $sentence = "Perl is awesome!"; my $word_count = () = $sentence =~ /\b\w+\b/g; print "Word count: $word_count\n"; # Output: 3
Final Thoughts
The
=()=operator might look like magic at first, but it's actually an elegant way to force list context and extract match counts without loops or extra variables. Whether processing text or just trying to optimize Perl scripts, this trick is a powerful addition to the Perl toolkit. - Regex Matching (
-
 @ a39d19ec:3d88f61e
2024-11-17 10:48:56
@ a39d19ec:3d88f61e
2024-11-17 10:48:56This week's functional 3d print is the "Dino Clip".

Dino Clip
I printed it some years ago for my son, so he would have his own clip for cereal bags.
Now it is used to hold a bag of dog food close.
The design by "Sneaks" is a so called "print in place". This means that the whole clip with moving parts is printed in one part, without the need for assembly after the print.
 The clip is very strong, and I would print it again if I need a "heavy duty" clip for more rigid or big bags.
Link to the file at Printables
The clip is very strong, and I would print it again if I need a "heavy duty" clip for more rigid or big bags.
Link to the file at Printables -
 @ 0271e1b9:ad8cff90
2025-02-01 07:39:31
@ 0271e1b9:ad8cff90
2025-02-01 07:39:31I study the greats. For if and when I find myself beaten down into the gutters of life - the vile, bile and the mundane - I shall draw strength from other great men - past, present and future - who, quite often, faced many more adversities and a lot more suffering, but chose to use them to their advantage, to overcome their dire circumstances and rise above the afflictions that life had bestowed upon them. It’s all been done before. It can be done again, better.
Learning from the past and from the present is very straightforward. Anyone can do that. But how does one learn from the future? It’s simple: you envision the best possible future for humanity, for generations to come, and for yourself. Then you figure out an approximate path on how to get there, and what kind of a man or a woman you must be to walk that path. The skills, the mindset, the qualities. And lastly, but perhaps most importantly, you find actionable measures, habits, convictions on how to become that person - and conversely, what are stopping you from becoming that person.
“You must value learning above everything else.”
― Robert Greene
“Those who have a 'why' to live, can bear with almost any 'how'.”
― Viktor E. Frankl
“You need to look at all events as having value. If you can do that, then you’re in a zone of tremendous opportunity.”
― Phil Stutz
“I shall take the more pains to uncover the fountains of philosophy, from which all my eloquence has taken its rise.”
― Marcus Tullius Cicero
“Error correction is the basis of all intelligence.”
― Jeff Booth
“Yes, you’re likely to fail, that’s fine. Because the goal of playing is not to win, but to keep learning. And the day you stop learning is the day you stop living."
― Jesse Enkamp
"A man is great not because he hasn't failed; a man is great because failure hasn't stopped him."
— Confucius
“If people knew how hard I had to work to gain my mastery, it would not seem so wonderful at all.”
― Michelangelo
“First of all we have to decide what we are to do and what manner of men we wish to be - the most difficult problem in the world.”
― Marcus Tullius Cicero
“You either bleed soul into your work, or let the work bleed out your soul.”
― Pran Yoganthan
"The Stoic philosopher is the man who has liberated himself from fear. He’s not afraid of death, he’s not afraid of pain, he’s not afraid of other people’s dismissal as a fool. The only thing he cares about is that he should meet his moral obligations.”
― Michael Sugrue
"The strong do what they can and the weak suffer what they must."
― Thucydides
“The brain is the most powerful weapon in the world.”
― David Goggins
“Man, the bravest of animals, and the one most accustomed to suffering, does not repudiate suffering as such; he desires it, he even seeks it out, provided he is shown a meaning for it, a purpose of suffering. The meaninglessness of suffering, not suffering itself, was the curse that lay over mankind so far.”
― Friedrich Nietzsche
"Consciousness is awareness with a choice."
― Thomas Campbell
“The essence of philosophy is that a man should so live that his happiness shall depend as little as possible on external things.”
― Epictetus
“It’s most real, it’s most good and it’s most salvific - it saves you, it transforms you. That’s the sacred.”
— John Vervaeke
“It is impossible for a man to learn what he thinks he already knows.”
― Epictetus
“Evolution is a process of iteration. There’s no master plan. It’s in each moment of what happens.”
― Michael Behrens
“Don’t follow anybody and don’t accept anyone as a teacher, except when you become your own teacher and disciple.”
― Jiddu Krishnamurti
“This is your life. You’re accountable. What are you gonna do about that?”
― James Hollis
By the way, if you enjoyed these quotes, feel free to follow a little side project of mine: Stoic Resurrection
Peace & Love,
Block height 881,748
-
 @ ee7e3590:5602f192
2025-02-01 05:02:15
@ ee7e3590:5602f192
2025-02-01 05:02:15You’re hitting on the core tension: unlimited demand for emergency care collides with finite resources, and pretending otherwise leads to either runaway costs or rationing-by-stealth. Let’s confront this head-on with free-market-aligned solutions that don’t ignore human realities:
1. Redefine "Emergency Care"
The U.S. legally mandates ERs to stabilize anyone, regardless of ability to pay (EMTALA). This creates moral hazard:
- Problem: Hospitals inflate prices on paying patients to offset uncompensated care.
- Free-Market Fix:
- Repeal EMTALA: Allow ERs to refuse non-critical cases (e.g., toothaches, rashes) unless prepaid or insured.
- Clarify "True Emergency": Legally define emergencies as immediate life threats (e.g., strokes, cardiac arrest) and let non-critical cases be diverted to urgent care.
- Consequence: ERs could price transparently for true emergencies, while non-critical cases face market-driven urgent care options.
2. Embrace Tiered Emergency Care
Not all emergencies require Level I trauma centers:
- Basic ERs: Staffed by NPs and paramedics for minor injuries (e.g., sprains, minor burns) at lower costs.
- Advanced ERs: For critical care (e.g., gunshot wounds), priced higher but competing via outcomes (e.g., survival rates).
- Example: India’s Ziqitza Healthcare operates ambulance tiers—basic vans for transport and advanced ICU units.
3. Address Moral Hazard with Insurance Innovation**
- Catastrophic Insurance Mandates: Require everyone to carry cheap, high-deductible plans covering only true emergencies (e.g., $10/month for coverage above $50k).
- Incentivizes price shopping for non-emergencies.
- Prevents freeloading on ERs.
- Risk-Adjusted Premiums: Smokers, skydivers, or diabetics pay higher premiums, aligning costs with personal choices.
4. Community-Based Safety Nets**
- Mutual Aid Networks: Local groups negotiate bulk ER rates (e.g., $100/month membership covers three ER visits annually).
- Crowdfunding ER Vouchers: Platforms like GoFundMe could partner with hospitals to prepurchase discounted emergency care slots.
5. Radical Transparency + Bankruptcy Reform**
- ER Debt Auctions: Let hospitals sell unpaid ER bills to collection agencies in real-time, creating competition to minimize patient liability.
- Flat-Fee ER Pricing: Hospitals post rates like “$5,000 for appendicitis stabilization, all-inclusive” to deter surprise billing.
- Ban Wage Garnishment for Medical Debt: Protect patients from lifelong ruin, forcing hospitals to price responsibly or absorb losses.
6. Accept Trade-Offs Explicitly**
The U.S. system fails because it hides rationing behind complexity. A free-market approach must embrace transparency:
- Option 1: Pay $100,000 for a 95% survival rate in a car crash.
- Option 2: Pay $20,000 for a 70% survival rate at a budget ER.
- Brutal but Honest: Let individuals (or insurers) choose their risk tolerance upfront.Example:
- Japan’s Price Controls: Caps ER costs but tolerates wait times (e.g., 8+ hours for non-critical care).
- Switzerland’s Mandates: Everyone buys insurance, but ERs charge $1,000+ deductibles to deter overuse.
7. Disrupt with Decentralized Care**
- Crypto-ERs: Blockchain-based emergency funds where contributors vote on covering members’ bills.
- AI-Guided Self-Care: Apps that stabilize patients en route to ERs (e.g., tourniquet tutorials, overdose reversal guidance).
8. Reform Malpractice to Reduce Defensive Medicine**
- “No Pay, No Harm” Liability: If a patient doesn’t pay, they can’t sue for malpractice (incentivizing upfront pricing).
- Safe Harbor Protocols: ERs using approved, cost-effective treatments (e.g., generics) get immunity from lawsuits.
The Uncomfortable Truth
A free market in emergency care requires accepting that not everyone will be saved—just as not everyone can afford a Ferrari. The alternative is the current U.S. model, which pretends to save everyone but bankrupts millions and still leaves 30% of ER visits unmet due to overcrowding.
By legalizing tiered care, deregulating monopolies, and forcing transparency, you create a system where:
- Elites pay premium prices for cutting-edge emergency care.
- Most get “good enough” stabilization at reasonable costs.
- Some choose cheap, high-risk options (or none at all).This isn’t pretty, but it’s honest—and arguably more ethical than today’s hidden rationing and financial toxicity.
-
 @ 592295cf:413a0db9
2024-11-16 10:40:22
@ 592295cf:413a0db9
2024-11-16 10:40:22Week 11-11
Lamenting is becoming something I should ask people who complain. Charity bussiness and after sending zap received to those who do not complain...
I started making an RSS feed template. Open an opml file and check the feed. I called this script,Teed.
This morning I saw a bounty from a fiatjaf note, on a rss-feed long form, basic a plugin for an app. But I'm not doing that, of course, I can also publish it as soon as I'm in charge. Maybe I have some opml files and I want to see if these are still active.
Starter pack is not good apparently creates elites and maybe gives you the feeling of not choosing, but that's what people want. Do not choose but have the illusion of choosing.
Toxicity level. high.
P2P stuff, Iroh is a protocol for syncing & moving bytes iroh computer post on Bluesky
Juraj new project
nostr:nevent1qvzqqqqqqypzpk4kccr9csumnwhmpv83ladqc6p88089cx2e5s2c4448ppgl2pakqqsyv4hs424x6c8phks903s595q2lqp5fpwyq7ajwrf00lxev8cfamcvmq23h
Alex Gleason bunker Knox. (Beta) "knox is a new Nostr bunker CLI for running a NIP-46 remote signer and granting credentials to members of your team". Announcing bunker knox article
Local First podcast, web2.5. Something like Nostr but Local P2P, interesting episode. youtube link
Open Secret AI. "OpenSecret is a backend for app developers that turns private encryption on by default." announcment AI
I think users with regard to algorithms do not want ten different feeds to choose from, but that their feed adapts to their choices, training the feed if this makes sense. So the feed is your feed for your choices, respond and train with them.
Pleblab 2, cool "ANNOUNCING TOP BUILDER SEASON 2! " nostr:nevent1qvzqqqqqqypzpmx02p4slzahlf7jlcaspsx57g6uc7kl7cc7dvhlsnqtpn6khjj0qy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcqyzy9w0frd802hfmrp45jr6dqhf7umqj7s63z0jvhv7hvvkcsqjg0vjwd7q4)
It was the real Guardian, quit 7fqx, we know it's you who want to distract us from number go up. The Guardian has left or wants to leave twitter is looking for alternatives, but how to verify a high profile user on Nostr? Nostr Address is already something but it's not enough.
We sometimes think that there is the money tree somewhere is that they magically appear, when instead the money is in the ground but they are dirty.
If Amethyst doesn't support is others stuff
People are simple, they want an app that works for all devices they have. People are "flutter-system".
A podcast feed xml file
Add to teed, if only i had made that option, meanwhile i saw a new interesting project
An other RSS feed github project
Imagine making a file opml with categories and those are your follow nostriches.
The problem is this does not bring new sap to the social chart is important to you, receive the selected posts and it is fantastic. You can also not use Nostr, if you want to use it as backup is fine. Share opml files? It's okay, but you can also find specific sites and find the best. Update for clients, you have a lot of RSS feeds from clients but update after a few hours so if there is really an emergency you lose. I still need to figure out how to integrate Nostr into RSS feed. Maybe an event to make your lists known.
I saw the event in these pr: nostr verified podcast nip #1465 Add audio track NIP #1043
-
 @ ee7e3590:5602f192
2025-02-01 05:00:39
@ ee7e3590:5602f192
2025-02-01 05:00:39You’re hitting on the core tension: unlimited demand for emergency care collides with finite resources, and pretending otherwise leads to either runaway costs or rationing-by-stealth. Let’s confront this head-on with free-market-aligned solutions that don’t ignore human realities:
1. Redefine "Emergency Care"
The U.S. legally mandates ERs to stabilize anyone, regardless of ability to pay (EMTALA). This creates moral hazard:
- Problem: Hospitals inflate prices on paying patients to offset uncompensated care.
- Free-Market Fix:
- Repeal EMTALA: Allow ERs to refuse non-critical cases (e.g., toothaches, rashes) unless prepaid or insured.
- Clarify "True Emergency": Legally define emergencies as immediate life threats (e.g., strokes, cardiac arrest) and let non-critical cases be diverted to urgent care.
- Consequence: ERs could price transparently for true emergencies, while non-critical cases face market-driven urgent care options.
2. Embrace Tiered Emergency Care
Not all emergencies require Level I trauma centers:
- Basic ERs: Staffed by NPs and paramedics for minor injuries (e.g., sprains, minor burns) at lower costs.
- Advanced ERs: For critical care (e.g., gunshot wounds), priced higher but competing via outcomes (e.g., survival rates).
- Example: India’s Ziqitza Healthcare operates ambulance tiers—basic vans for transport and advanced ICU units.
3. Address Moral Hazard with Insurance Innovation**
- Catastrophic Insurance Mandates: Require everyone to carry cheap, high-deductible plans covering only true emergencies (e.g., $10/month for coverage above $50k).
- Incentivizes price shopping for non-emergencies.
- Prevents freeloading on ERs.
- Risk-Adjusted Premiums: Smokers, skydivers, or diabetics pay higher premiums, aligning costs with personal choices.
4. Community-Based Safety Nets**
- Mutual Aid Networks: Local groups negotiate bulk ER rates (e.g., $100/month membership covers three ER visits annually).
- Crowdfunding ER Vouchers: Platforms like GoFundMe could partner with hospitals to prepurchase discounted emergency care slots.
5. Radical Transparency + Bankruptcy Reform**
- ER Debt Auctions: Let hospitals sell unpaid ER bills to collection agencies in real-time, creating competition to minimize patient liability.
- Flat-Fee ER Pricing: Hospitals post rates like “$5,000 for appendicitis stabilization, all-inclusive” to deter surprise billing.
- Ban Wage Garnishment for Medical Debt: Protect patients from lifelong ruin, forcing hospitals to price responsibly or absorb losses.
6. Accept Trade-Offs Explicitly**
The U.S. system fails because it hides rationing behind complexity. A free-market approach must embrace transparency:
- Option 1: Pay $100,000 for a 95% survival rate in a car crash.
- Option 2: Pay $20,000 for a 70% survival rate at a budget ER.
- Brutal but Honest: Let individuals (or insurers) choose their risk tolerance upfront.Example:
- Japan’s Price Controls: Caps ER costs but tolerates wait times (e.g., 8+ hours for non-critical care).
- Switzerland’s Mandates: Everyone buys insurance, but ERs charge $1,000+ deductibles to deter overuse.
7. Disrupt with Decentralized Care**
- Crypto-ERs: Blockchain-based emergency funds where contributors vote on covering members’ bills.
- AI-Guided Self-Care: Apps that stabilize patients en route to ERs (e.g., tourniquet tutorials, overdose reversal guidance).
8. Reform Malpractice to Reduce Defensive Medicine**
- “No Pay, No Harm” Liability: If a patient doesn’t pay, they can’t sue for malpractice (incentivizing upfront pricing).
- Safe Harbor Protocols: ERs using approved, cost-effective treatments (e.g., generics) get immunity from lawsuits.
The Uncomfortable Truth
A free market in emergency care requires accepting that not everyone will be saved—just as not everyone can afford a Ferrari. The alternative is the current U.S. model, which pretends to save everyone but bankrupts millions and still leaves 30% of ER visits unmet due to overcrowding.
By legalizing tiered care, deregulating monopolies, and forcing transparency, you create a system where:
- Elites pay premium prices for cutting-edge emergency care.
- Most get “good enough” stabilization at reasonable costs.
- Some choose cheap, high-risk options (or none at all).This isn’t pretty, but it’s honest—and arguably more ethical than today’s hidden rationing and financial toxicity.
-
 @ be7bf5de:09420d0a
2024-11-13 01:08:36
@ be7bf5de:09420d0a
2024-11-13 01:08:36At NosFabrica, we envision a future of healthcare where the individual is in charge of their health data and empowered to take responsibility for their own health. We are building health applications on Nostr and bitcoin to enable individuals own their health data. Nostr's architecture will allow different healthcare providers to write data onto the individual's relay. We see many potential use cases to solve specific problems in healthcare when the individual in a world where everyone has a comprehensive, portable and interoperable health record over time. We are looking to show what is possible with the "other stuff" on Nostr, starting by developing micro-apps so you can start compiling your health data, which you control.
If you're like most people on earth, your eyes aren't perfect. About half of us - 4 billion humans - have eye glasses, yet nearly a billion people can't get glasses due to inaccessibility of eye care or affordability.
With our microapp, Lazer Eyes, eye care providers can now write an eyeglasses or contacts prescription directly onto your own health relay. The optometrist simply needs to enter in your Nostr public key profile (nprofile), which relay to write the data to, and your prescription data; the encrypted prescription will be sent in an encrypted note directly to your relay. You can now send this signed note to your eye glasses provider to fulfill your glasses or contacts order.
 If you're using Amethyst today, you will be able to see this prescription rendered into your DMs. In our NosFabrica future vision, different clients would be able to show you this piece of your health record alongside other health information with different user interfaces and experiences. You will then have the power to selectively disclose this information, as needed.
If you're using Amethyst today, you will be able to see this prescription rendered into your DMs. In our NosFabrica future vision, different clients would be able to show you this piece of your health record alongside other health information with different user interfaces and experiences. You will then have the power to selectively disclose this information, as needed. There are many benefits to using Nostr for health as an individual:
There are many benefits to using Nostr for health as an individual:-
Patient Ownership and Control
-
Patients have full control of their prescription, and they can share it securely with confidence and even privately if required with eyewear providers or optometrists whenever needed.
-
Patients no longer rely on email or paper copies that can be easily lost or tampered with. Emailing a PDF to a patient brings the issue of requiring an optometrist signature leading to excess time taken to generate, print, sign, scan and email the copy. Public / private key cryptography provides a verifiable, time saving option in this case.
-
Continuity of care and ability to track changes in prescription over time - there are numerous forum posts where patients have found it difficult to get their prescription data from their optometrist practice when requesting it months or years later.
-
Removes the need for the patient to contact their old opticians and go through a process of trying to request their details, which can be time consuming.
-
Identity Verification
-
Optometrists sign prescriptions with a cryptographic key that patients could verify using their private Nostr identity (also known as a public/private key pair). This ensures that the prescription is authentic, accurate, and hasn't been altered after issuance. This would remove the need for issuing a “signed prescription” that currently has to be done in the physical sense, as a print out and issued to the patient. Have the option to have an indisputable and verifiable ‘Optometrist Identity Key’ would enable this legal requirement (in the UK) to go completely digital over Nostr.
-
The decentralized nature of Nostr ensures that prescriptions can be easily verified and traced back to the original issuer, avoiding forgery or fraud.
-
Privacy:
-
Unlike traditional methods where patient information is stored on centralized databases of the electronic medical record company (eg, Epic), or large health systems (eg, Ascension), Nostr keeps patient data decentralized and private, accessible only through permissioned sharing. This ensures no third party can access, manipulate, or misuse this sensitive information.
-
Immutable Records
-
Once a prescription is issued and signed on Nostr, it is stored immutably on the decentralized network. This ensures a permanent and trustworthy ledger of the patient's eye health history. This feature adds to accountability and should bring a higher standard to complete and accurate prescribing across all practices.
-
These records can persist over time and are portable to travel with you, wherever you seek care or glasses.
-
Global Access
-
Patients can use their Nostr-stored prescription with any provider across the globe, without needing to worry about differing national data standards or carrying physical documents when they travel or move.
-
This opens up a wider use case when considering the 2 Billion + individuals who currently cannot get access to sight care services.
Benefits for Optometrist Practices and Operators:
- Improved Patient Retention and Care through Trust and Transparency
-
By empowering patients with ownership of their data, practices foster trust and loyalty, reducing churn over time. If patients know they can rely on your practice for transparency, secure record-keeping, and access to the latest technology, they are more likely to return for future eye exams and other services.
-
A decentralized, tamper-proof record of prescriptions can improve administrative efficiency. No more handling lost prescriptions, disputes about validity, or delays in getting updated information to patients or other providers.
- The decentralized storage of prescriptions allows optometrists to securely share and access patient data, making cross-practice collaboration easier for referrals, second opinions, or specialized care.
- Cost Savings on Paperwork and Administration
-
Digitizing and decentralizing prescription records could lead to long-term savings on administrative costs, such as paperwork management, prescription re-issues, and managing patient data in outdated systems.
-
Optometrists can ensure their records are always accessible, accurate, and trusted by all parties (patients, insurers, other clinics).
- By reducing the burden of handling prescription storage and verification manually, the practice can focus more on patient care.
- Adaptation to Future Consumer Behavior and building a Tech-Savvy Reputation
-
As patients increasingly take control of their health data and seek decentralized solutions, practices that adapt to this trend are future-proofing their business model. Over time, patients will expect more control over their medical data, and being ahead of this shift will ensure long-term relevance.
-
Practices that embrace new technologies like Nostr can market themselves as tech-forward and adaptable to future trends, gaining an edge over more traditional competitors. This reputation is especially important as younger generations increasingly value privacy and digital autonomy. A Nostr-based service helps position the practice as aligned with these values.
- Integration with Bitcoin
-
By integrating a service built on Nostr, naturally linked with the bitcoin ecosystem, the practice can also introduce bitcoin payments as a novel way to reduce transaction fees and differentiate their practice from the competition.
-
Attract bitcoiners: The optics practice can appeal to the Bitcoin community, who value decentralization and would appreciate paying with bitcoin or using a decentralized protocol for prescription management. This opens up a new market of patients interested in technology and financial independence.
- Upsell Opportunities and Revenue Diversification
-
The practice can still maintain a competitive eyewear sales strategy by offering upsell opportunities. When patients receive their prescription digitally, they can be automatically sent tailored offers for high-quality lenses, frames, or even add-ons like blue light coatings or progressive lenses, keeping them within the practice’s ecosystem. Practices can offer value-added eyewear options, such as free adjustments, repairs, or personalized lens consultations, which online retailers can’t easily match.
-
The Nostr system can open doors to additional services beyond eyewear sales, including personalized consulting services, specialized testing (e.g., for contact lenses, binocular vision, myopia control), and more frequent checkups due to the ease of updating and verifying records.
Of course, utilizing this tool means providers need to help onboard individuals onto Nostr. In many ways, we see providers as playing into the Nostr network and flywheel effect. This is better technology with global access - and we invite you to consider other micro-apps that can continue to build out the decentralized healthcare ecosystem built on Nostr and bitcoin.
We have partnered with the Bitcoin Optometrist, Dr Alan Bryden, to continue to refine the micro-application and start testing its use. We'd like to thank Dr Alan for his insights that contributed to this micro-app and write-up. Check out his site and nonprofit, Sats for Sight, to learn more about utilizing bitcoin to provide eyeglasses to those in need, along with his HODL eyewear line.
We're excited about the future of building healthcare applications on nostr and bitcoin. If you have ideas or are facing any health challenges, we're conducting product discovery interviews to understand your biggest pain points when it comes to managing and optimizing your health and healthcare data. Please reach out to jon@nosfabrica.com or schedule time here to learn more about how to get involved!
Note: Lazer Eyes is currently only available for testing purposes as we evaluate regulatory considerations across jurisdictions.
-
-
 @ f1989a96:bcaaf2c1
2025-01-31 21:22:59
@ f1989a96:bcaaf2c1
2025-01-31 21:22:59In the summer of 2023, the Human Rights Foundation (HRF) launched a Bitcoin Bounty program aimed at funding software developers to create new tools and features for Bitcoin tailored to the needs of dissidents and human rights advocates challenging authoritarianism worldwide. These bounties ranged from UX improvements to privacy upgrades and open-sourcing closed and permissioned systems.
There were 11 bounties in total, each with specific objectives. The deadline was Dec. 31, 2024.
We are excited to announce that every single bounty was claimed and that the resulting tools and upgrades are now empowering human rights activists daily across popular apps such as Blue Wallet, Zeus, Stack Wallet, Iris, Coracle, Keeper, Bull Bitcoin, Cake Wallet, and more.
This program highlights the impact of collaboration between human rights activists and software developers to create better tools for freedom. HRF is proud to have played a role in this effort and looks forward to continuing similar programs in the future. Special credit goes to the Oslo Freedom Forum, where much of the critical interaction between developers and activists occurred.
This wave of bounties was inspired by a successful pilot project in 2021, executed in partnership with Strike and Jack Mallers, which supported developers like Will Cassarin and Calle. Their innovations later gave rise to important advancements such as zaps in Nostr and the Cashu ecash protocol.
Bounty Details
1. Open-Sourcing the Design Guide
Winner: CypherStack for porting the Bitcoin UI Kit from Figma to an open-source Penpot project (2 BTC awarded).
Many UI kits are created using proprietary software like Figma. While these tools are powerful, they require licenses and are not accessible to everyone — an obstacle for developers working on open-source projects or those with limited funds. This creates a barrier to entry for designers and developers wanting to contribute to the Bitcoin ecosystem. This bounty was awarded to CypherStack for porting the Bitcoin UI Kit from Figma to Penpot, an open-source design tool similar to Figma, but free and accessible to everyone. This helped democratize access to information and resources, promote collaboration, and make it easier for developers to create high-quality Bitcoin tools, which in turn helped to increase Bitcoin adoption.
2. Serverless Payjoin
Winners: This is a two-part bounty. The first bounty is for the development of the Serverless Payjoin specification, and the second bounty is for any wallets that implement Serverless Payjoin.
Part 1: Dan Gould for his work on PayJoin V2 (1 BTC)
Part 2: Dan Gould, Spacebear from Payjoin DevKit, and Bull Bitcoin app, for their collaborative effort implementing Payjoin into the Bull Bitcoin wallet (0.5 BTC split three ways).
PayJoin is a privacy upgrade to Bitcoin that flusters mass surveillance attempts on the network. Traditional implementations have required the receiver to run a server for transaction coordination, creating a barrier to adoption. Serverless PayJoin removed this dependency and simplified the process. Serverless PayJoin also eliminated the need for receiver-hosted infrastructure and reduced censorship risks by removing a central point of failure — a significant advantage for activists and nonprofits operating under repressive regimes. This bounty resulted in the first mobile app (Bull Bitcoin) with integrated PayJoin send and receive support, an important advancement that provided robust privacy protections against surveillance for at-risk individuals.
3. End-to-End Encrypted Nostr Group Chats
Winners: Martti Malmi for incorporating encrypted group chat functionality into the Iris Nostr client (1 BTC) and to Vitor Pamplona, hodlbod, and Paul Miller for their work on NIP-17, which allowed users to encrypt and share Nostr messages in a way that can be recognized across different Nostr clients (1 BTC).
End-to-End Encrypted (E2EE) Nostr Group Chats are private, secure messaging groups built on the Nostr protocol, a decentralized communication system. While Nostr messages are already encrypted, they still expose metadata, allowing outside observers to see who is communicating and when. This bounty focused on preventing metadata leakage, ensuring that these details remain private. By leveraging Nostr’s decentralized architecture, these chats offered censorship resistance. They prevented conversations from being surveilled, blocked, or controlled by a central authority, and as a result of this bounty, have now been implemented into popular Nostr clients like Iris, Amethyst, and Coracle. This is an important step forward for activists, journalists, and communities who risk losing their freedom of speech under oppressive regimes.
4. Silent Payments
Winners: cygnet3 and Sosthene for their contributions to critical libraries for delivering Silent Payments and for developing a mobile wallet capable of sending and receiving Silent Payments without requiring a full node (1 BTC).
Silent Payments are a privacy-enhancing Bitcoin addressing scheme that allows a sender to generate a unique static address for a recipient without requiring any interaction (while still allowing the recipient to detect and spend the received funds). This breaks common tracking methods used by surveillance firms and autocracies and makes it harder to link payments to a specific recipient. By improving on the privacy of traditional Bitcoin addresses, Silent Payments enhanced financial privacy, making them ideal for donations, salaries, and other sensitive transactions. This bounty code has been fully integrated into Cake Wallet, and several other major wallets like Wasabi, Blue Wallet, and Bitbox have added partial functionality. This brings Silent Payments to tens of thousands of users and marks a major step in real-world Bitcoin privacy.
5. Human-Readable Offers
Winners: Stephen DeLorme, Chad Welch, and Evan Kaloudis for Twelve Cash and its integration into Zeus Wallet (1 BTC).
Human-Readable Offers simplify Bitcoin payments by replacing complex Bitcoin addresses and invoices with user-friendly text. This is especially important for Lightning Network transactions, which currently involve a cumbersome process of generating invoices for each payment. With Human-Readable Offers, sending Lightning payments becomes as simple as sending an email (just by entering a username). This approach, similar to many fintech apps today, reduces errors, lowers the barrier to entry, increases trust, and is crucial for broader adoption of Bitcoin among new and seasoned users alike. It’s also important for people who don’t have access to smartphones and cannot copy and paste or use QR codes. Today, as a result of this bounty, Zeus users connected to a Core Lightning node can create a human-readable Bolt 12 offer to privately receive donations.
6. Self-Custodial Mobile Lightning Address
Winner: Evan Kaloudis for Zeus Wallet (1 BTC).
Activists, nonprofits, and content creators often use Lightning addresses to receive donations quickly and easily. However, setting up and managing a Lightning address presents a challenge: users have to choose between the self-sovereignty of managing their own web server (a complex process) or the convenience of a custodial service, which requires trusting a third party with their funds. This bounty directly addressed this issue. It allowed users of Zeus Wallet, one of the most popular self-custodial Bitcoin Lightning wallets, to easily and securely receive donations through a Lightning address while maintaining control of their funds.
7. Mobile Border Wallets
Winner: Bitcoin Tribe for their border wallet functionality, allowing users to create and memorize seeds without relying on written backups, and for building a React Native library, making it easier for other wallets to integrate this feature (2 BTC).
Mobile Border Wallets aimed to solve a critical problem with traditional Bitcoin seed phrase backups: they’re often written down on paper, making them susceptible to being lost, destroyed, or stolen. This makes securing a user’s Bitcoin a delicate balance between security and accessibility. It also makes it challenging, especially for activists or refugees who frequently cross international borders. Border Wallets offered a solution to this problem. Instead of writing down a 12- or 24-word seed phrase and finding a secure place to store it, users can upload a randomly generated grid of words to the cloud and memorize a pattern to secure their seed phrase, similar to a pattern a user would memorize and draw on an Android device to unlock it. This initiative resulted in a user-friendly mobile app that allowed users to create Border Wallets digitally, enhancing accessibility and offering an alternative to physical storage like printed paper or metal seed plates.
8. Easy Mobile Multisig
Winner: Bitcoin Keeper (1 BTC).
Multi-signature wallets allow multiple users to collaboratively control a Bitcoin wallet. This enhances security by requiring consensus before funds can be moved. Traditional multisig wallets often require physical hardware wallets or involve subscription fees, presenting a significant barrier for organizations exploring Bitcoin adoption. This bounty funded the development of easy mobile multisig functionality in the Bitcoin Keeper app, enabling users to set up a 2-of-3 multisig (requiring two out of three keys to authorize spending) to secure and manage their bitcoin. This is a great feature for activists to prevent government seizure of funds: even if one key holder gets detained, the funds are safe so long as the other two key holders are safe. The idea is to make sure two of the keys are held by entities outside of one’s country or threat zone.
9. FROST Multisig Wallet
Winner: CypherStack for Stack Wallet, which enables dynamic multisig using FROST, allowing users to modify signer sets without moving funds (1 BTC).
Multisig (multisignature) wallets require multiple signatures to authorize a transaction. This enhances security by distributing control over funds. However, traditional multisig setups — while secure — can be inflexible. If you need to change the set of signers, it often requires moving all the funds to a new multisig wallet with the updated signer set. This is burdensome, time-consuming, and incurs fees. FROST is a cryptographic protocol that offers significant advantages for multisig wallets. It provides dynamic multisig functionality, meaning users can easily adjust their signer sets as needed without affecting the funds within. This is an important functionality for nonprofits and civil society groups who often need to adjust their authorized signatories, especially in situations where a regime may seize a private key and that key then needs to be deprecated. This dynamic kind of secure setup is now available for activists to use on the Stack Wallet.
10. Cashu Upgrades
Winners: eNuts Wallet (0.5 BTC), Misovan for Minibits Wallet (0.5 BTC), Gandlaf for Proxnut (0.5 BTC), and Gandlaf for adding Cashu-TS restore functionality (0.5 BTC).
Cashu is a digital cash system designed for privacy and speed. It is like physical cash, but in digital form and uses blind signatures for private transactions. With Cashu, transactions are instant, low-fee, and can operate offline. There is no blockchain or transaction graph to be surveilled. Bounty recipients addressed critical aspects of usability and accessibility for Cashu tools: eNuts and Minibits Wallets brought Cashu to iOS and Android users worldwide, Proxnut enabled easy web integration for payments, and Cashu-TS Restore added crucial seed phrase backup. Together, these projects have taken Cashu from a more theoretical concept to a practical one and have been relevant for use cases like donations, content monetization, daily transactions, and cross-border payments.
11. BIP47 Expansion
Winner: Blue Wallet (0.5 BTC) for adding BIP 47 support.
BIP47 is a Bitcoin Improvement Proposal that enhances payment privacy for Bitcoin users. In Bitcoin, it’s generally considered bad privacy practice to reuse the same Bitcoin address for multiple transactions. It can link those transactions together and make it easier to track a user’s spending in high-risk environments. Generating a new address for each payment has become a common workaround, but this becomes cumbersome. BIP47 solves this with reusable payment codes. Users receiving funds generate a BIP47 payment code and share it with those who will be sending them payments. Each time a payment is initiated, a new, unused Bitcoin address is generated from the recipient’s payment code. This ensures every transaction uses a unique address. Blue Wallet received this bounty for integrating BIP47 support, making this important privacy enhancement accessible to its growing user base.
HRF’s Financial Freedom program educates activists worldwide, unites people from different industries and backgrounds, and makes grants in the service of advancing Bitcoin as a tool for human rights. To receive HRF’s weekly Financial Freedom Report, subscribe here.
For media inquiries or interview requests, please contact media @ hrf.org.
-
 @ 19306922:c06688d2
2025-01-31 21:14:52
@ 19306922:c06688d2
2025-01-31 21:14:52At a time when data-gathering technologies are dominating all aspects of everyday life, governmental agencies such as The National Security Agency have considerable surveillance and control authority. The National Security Agency runs surveillance programs on not just violent international criminals, but also ordinary citizens within the country. A tremendous amount of effort is being made to keep these programs from being critiqued and shared with the public. In this paper, I will discuss whistleblowing and its relevance in establishing a more democratic structure in governmental institutions, through the cases of Edward Snowden and Thomas Drake. Firstly, I will emphasize Edward Snowden's action as an example of illegal whistleblowing and how he acts closer to civic disobedience rather than espionage. Following that, I will discuss Thomas Drake's espionage charge while legally criticizing The National Security Agency's programs and the inadequacy of whistleblower protection laws.
In our everyday lives, we come into contact with or utilize a variety of technological equipment such as security cameras, GPS devices, iris scanners, and so on. Everything we do, from buying things from shopping malls to searching for information on the internet, is kept in massive databases. Without even our knowledge, our data, which is vast enough to create our entire profile, is in the databases of a private firm or the government. That's why the surveillance network is getting bigger and bigger. Most of the surveillance tools and the capability to regulate these tools are under state control. The government also agrees with data aggregators -companies that collect data from multiple sources and make it available to customers in a value-added format- to access more data. The US Department of Justice has an $8 million agreement with data aggregator company ChoicePoint (Stanley, Steinhardt 2014). In this way, The Justice Department can access many civilians' information in the company's database. Although this surveillance mechanism seems to be an effective way to track and detect many illegal incidents such as terrorism, money laundering, etc., this surveillance network can easily be applied to ordinary civilians. For example, in 2002, Attorney General John Ashcroft released new domestic spy guidelines that dramatically expanded federal agents' ability to monitor on American civilians (Stanley, Steinhardt 2014). The American government also is running programs to spy on ordinary citizens, according to information obtained from the National Security Agency documents which leaked to the media on multiple occasions (Greenberg, 2013).
The National Security Agency (NSA) began as a cryptology-focused agency and has since grown into an intelligence agency that gathers data from enemies of the United States of America (Verble, 2014). The surveillance and data collection programs of NSA, however, are not carried out just to keep enemies at bay. Information on the NSA's programs was provided to the media by Thomas A. Drake, a senior executive at the NSA, and Edward J. Snowden, who also worked as a computer intelligence consultant at the NSA. As a result of all of these events, it is fairly obvious that the state and its institutions are conducting unethical surveillance to the civilians. However, the two people who raised awareness of this unethical operation by providing classified and declassified NSA documents to the media faced major crises. Both Thomas Drake and Edward Snowden faced charges under the Espionage Act. Despite the fact that two former NSA employees used different methods to prevent these surveillance programs, which were developed to spy on citizens using their taxes, both were charged with treason. In this article, I will discuss the whistleblowing act through Thomas Drake and Edward Snowden examples, as well as the significance of whistleblowing in inspecting institutions with tremendous authority, such as centralized databases. Whistleblowing is described as the act of an employee, typically within the organization, who reveals illegal, immoral, or inefficient information or actions within a private, public, or government institution. Daniel Ellsberg, one of the authors of the document, leaked information concerning the United States' political and military engagement in Vietnam between 1945 and 1967, also known as the Pentagon Papers. These papers, which revealed that the American government of the time did not accurately reflect information about Vietnam to the public, became the subject of the most well-known whistleblowing act in American history. Daniel Ellsberg faced charges under the Espionage Act (Greenberg, 2013). It is problematic to think that sharing the information with the public about crucial topics such as the state is systematically lying to the public or spying on them in a wide surveillance network is equated with espionage. The development of democratic regimes necessitates public debate and regulation of this type of government acts. I will demonstrate the significance through the examples of acts of Edward Snowden and Thomas Drake.
The Case of Edward Snowden
At one point, Edward Snowden's and Thomas Drake's whistleblowing actions differ. While Edward Snowden got confidential material from the NSA and shared it with the media directly, Thomas Drake initially attempted to prevent or regulate programs run by NSA from inside the organization by taking a legal path.
Firstly, using Edward Snowden as an example, I will evaluate the role of becoming an illegal whistleblower by sharing classified information with the public. Edward Snowden released highly classified information from NSA in 2013, revealing the NSA's surveillance operations with the cooperation of telecommunications companies and European governments. Snowden was charged under the Espionage Act and stealing government property by the US Department of Justice, and his passport was canceled by the Department of State. Not only that, the efforts were made to portray him as a traitor. Before leaking the information to the media, Edward Snowden was a 29-year-old consultant who worked for the NSA's Hawaii office and made $200,000 per year (Scheuerman, 2014). Snowden did not reveal this information to a country or organization that is hostile to the United States. He directly shared this material with the media, allowing the public to learn about these surveillance programs. He received no personal benefit from this act, and he risked himself and lost his privileged position in his life. Edward Snowden said to The Guardian reporters; “I really want the focus to be on these documents and the debate which I hope this will trigger among citizens around the globe about what kind of world we want to live in.” He added: “My sole motive is to inform the public as to that which is done in their name and that which is done against them” (Glenn, 2013). Given all of this, Edward Snowden's actions are more similar to civic disobedience than treason or espionage (Scheuerman, 2014). As a United Nations citizen, Edward Snowden revealed to the public the wrongdoing of a governmental institution, making this situation questioned among the public. A democratic government gains from public criticism of its acts, which aids in the development of more ethical institutions. While it is a social benefit to inform the public about a massive government surveillance program, obtaining that information from the NSA and making it available to the public may also benefit the United States' enemies. Institutions also have the opportunity to develop and regulate these programs within their own walls, without any confidential information leaking out. Employees of the institution can file complaints to their supervisors and criticize these programs in a legal path, which is legal whistleblowing, however, in the case of Thomas Drake, we can see that legal whistleblowing puts people's lives at risk at least as much as the illegal version.
The Case Of Thomas Drake
On September 11, 2001, one of the most devastating days in American history, Thomas Drake began his job at the NSA. In the early years of the new millennium, when America was most vulnerable to external threats and digital data was growing exponentially, a program named Trailblazer caught Drake's attention. Drake saw the initiative as a huge budget waste that did not contribute to national security. He reported his critique to his supervisors, which is considered legal whistleblowing, but his attempts were unsuccessful. Finally, he decided to share his criticism with the media while remaining anonymous, although he did not share any confidential documents with the media. He only served declassified information, which conveys that Trailblazer was an ineffective project that wastes money. Drake was questioned by FBI investigators shortly after and accused of taking classified documents from the NSA. He faced charges of 35 years in jail time for 10 different crimes including the Espionage Act. The court dismissed the case in 2011, stating that the accusations were inappropriate and overstated, and Thomas Drake was sentenced to one year of probation. However, as a result of the entire process, Drake spent $82,000 on legal expenses, was dismissed from both his NSA and university positions, and lost his retirement (Greenberg, 2013). Thomas Drake's experience is an example of how even the slightest criticism of government institutions and their projects can have drastic consequences. The courage to criticize unethical projects is trying to be destroyed by this atmosphere of fear. The whistleblowers, whether they go the legal or illegal path, are aware that they will be prosecuted for espionage, loss of employment, and jail time.
At this juncture, I believe we should oppose the totalitarian positions adopted by the institutions, which have vast surveillance networks both domestically and internationally, and we should protect whistleblowers' rights. The United States has two legislations protecting whistleblowers, the Federal Whistleblower Protection Act of 1989 and the Whistleblower Protection Enhancement Act of 2012. According to a 2015 research, the Federal Whistleblower Protection Act of 1989 fails to protect whistleblowers. 79 percent of the 142 cases involving government ethics and administration ended in employee job loss. The Whistleblower Protection Enhancement Act of 2012 is also insufficient in terms of protections of whistleblowers (Peffer, Bocheko, Del Valle, Osmani, Peyton, Roman, 2015).
Conclusion
The whistleblowing contributes to public debate about the ethics of the state's programs. However, these organizations, which hold a vast surveillance network, damage the democratic process by raising severe allegations against whistleblowers in order to avoid the risk of limiting their authority. We can have an idea of how our data is gathered and used if we have laws and rules that protect whistleblowers. Accusing them with espionage and treason, on the other hand, will gradually create this environment of fear and, as a consequence, silence.
Reference Glenn G. (2013, Jun 11). Edward Snowden: the whistleblower behind the NSA surveillance revelations. The Guardian. Retrieved from https://www.theguardian.com/world/2013/jun/09/edward-snowden-nsa-whistleblower-surveillance Greenberg, A. (2013). This machine kills secrets: Julian Assange, the Cypherpunks, and their fight to empower whistleblowers. Penguin. Scheuerman, W. E. (2014). Whistleblowing as civil disobedience: The case of Edward Snowden. Philosophy & Social Criticism, 40(7), 609-628. Stanley, J., & Steinhardt, B. (2014). Bigger monster, weaker chains: the growth of an American surveillance society. In Ethics and Emerging Technologies (pp. 269-284). Palgrave Macmillan, London. Peffer, S. L., Bocheko, A., Del Valle, R. E., Osmani, A., Peyton, S., & Roman, E. (2015).Whistle Where you work? The ineffectiveness of the Federal Whistleblower Protection Act of 1989 and the promise of the Whistleblower Protection Enhancement Act of 2012. Review of Public Personnel Administration, 35(1), 70-81. Verble, J. (2014). The NSA and Edward Snowden: surveillance in the 21st century. ACM SIGCAS Computers and Society, 44(3), 14-20.

