-
 @ df478568:2a951e67
2025-01-20 18:28:44
@ df478568:2a951e67
2025-01-20 18:28:44Affiliate Links
I earn a commission for these products and services, but I would recommend them even if they did not pay me.
This is the cheapest way to use AI on the Internet. The pics are spectacular. It cost me about 20 sats to make the cover for this affiliate page.
Start9 I don’t really have an affiliate link for these guys, but I would like one. Anyway, they make the easiest home servers. I highly recommend them. I like that I can use the cloudflare tunnel app to host everythng on the clearnet. Let me know if you need any help with this.
Recommendations
These companies do not pay me, but I recommend them anyway.
Subscribe To Support My Work
I use PayWithFlash to create a Substack like subscription. You can subscribe for as little as 1,000 per month. If that is too many sats to ask, you could always zap my articles instead. Thank you.
The Leather Mint
The Leathermint makes great, custom-sized leather belts and awesome-looking wallets. I have a belt and it fits better than any belt I’ve ever warn because it’s custom size. I have had mine for about a year. The chrome is coming off a little at the top but I don’t tuck in shirts anyway.
CoinKite
They make my favorite products ever. I suggest getting a few SEEDPLATE® Kit’s no matter what hardware wallets you use. I also like using a dry-erase marker first because there are no second chances when punching a letter. It’s best to use a dry-erase marker first. If you make a mistake erase it. Then, after you double checked the first side, go over the dry-erase marker with a permanent marker. Then do the same to the other side. If you’re sure every letter is correct, punch the holes.
There are many plates with sufficient heat resistance, but I like the SEEDPLATE because they are the easiest to destroy if you ever need to. Instead of etching out stamps on washers, you just add extra punches if you must destroy the seed.
Alby Hub
Look, if you want to run your own lightning node, this is the way to go. If you have a Start9 or are technical, you can run it yourself. If you’re less technical, they offer a cloud service. I was one of the early beta testers of this software and I think it’s the easiest way to run a lightning node.
Free and Open Software
Primal.net os a corporation building stuff on nostr. If you’re technical, you can run it yourself. If not, you ca download the app for free. They charge a fee for premium services. I pay for this because I want to support companies that contribute to nostr development and help bitcoin be used as peer-to-peer electronic cash.
I think of Primal as a custodial bitcoin wallet that allows anyone to participate in the biggest circular economy in the world. TikTok was banned in the United States which means it is no longer available for citizens of the United States to download the app. There are ways to get around these restrictions, but I choose not to because I do not want the CCP, or any government to have access to information if their goal is to use it against me. I believe every government, foreign or domestic wants to use your information against you. Nostr allows me to opt out of these stupid games with stupid likes.
With Primal, I am the customer, not the product. I choose the algorithms I want to see, not the CCP , USG or corporations. Even if Primal decided to say, “Marc sucks. We will now censor him.” I will only lose the https://primal.net/marc, the OG status, and my primal lightning address. It also means they would stop getting my sats every month, so they are incentivized not to censor. You would have to do something really stupid to get banned from Primal. I’m not sure it’s been done yet, but even if it has, you will not get banned from the nostr protocol.
Portainer
Portainer makes it easy to run docker-containers. I first learned how to use it because it is an app on Umbrel. Eventually, I learned you can use Portainer on any Linux computer, so that’s what I do. It takes some time to learn, but once you do—you become a cloud computing super-wizard.
Mealie
Mealie is one of my favorite pieces of free and open software that is not related to bitcoin in any shape or form...except it makes grocery shopping easier. I know what you’re thinking. WTF does that have to do with bitcoin? I assume you belong to the I Want More Bitcoin Club. You are in good company because ALL Bitcoiners are a member of this club. One way you can stasck more sats is to cut your grocery bill. I believe Mealie helps me do just that.
When I’m grocery shopping, my goal is to get as much healthy food for my sats as possible. To accomplish this, I shop sales. Now, if you’re living in a van, this won’t do much for you, but no worries. You will stack even more sats by cutting your housing costs. If your wife will not agree to live under a bridge and stack sats, then get a freezer in your garage. Fill it with meat you buy on sale. Pork shoulder is 3,000 sats per pound and you don’t what to cook it with? Find a recipe online. Mealie will use machine learning to scrape the ingredients from the recipe. Then you can add it to a grocery list. In other words, you can automate your grocery list right at the grocery isle. This is one way I save sats with Mealie.
I also keep the things my family eats on a regular basis in stock. This is part for emergency preparedness, but it is also for financial preparedness. If you are in a situation where no food is available, all the bitcoin in the world will not save you. I’m not talkig about super volcanos. Hurricanes, tornadoes, and earthquakes happen. So I got this idea from Jack Spirko, but modified it to use with mealie.
Spirko suggests building a 30 day supply of food and water for your family in case of an emergency. You should have a generator and a garden too, but I don’t want to get off track. Once you have this he says: write down every item you use on a notebook and replace it.
This is good advice, but I just add it to my grocery list in mealie.
Shopstr
Shopstr is like Facebook marketplace, Amazon, or eBay on nostr. This is what I use to build my store. I want to pause point out how big of a paradigm shift this is. The old web requires permission. Ebay needs permission from the government to become a corporation. They built infrastructure to create their online auction. Everyone on the site must pay eBay a tax. This results in a techno- feudalist society.
When you sell on Shopster, you are selling your wares on nostr, a protocol, not a platform. This changes the relationship between the people and the technology because NO MIDDLEMAN IS REQUIRED. On nostr, there are no digital overlords. You own your data. You host your store. If the current digital overlords shut it down, you can run it yourself. You do not need to pay a tax to eBay, Amazon, or the PayPal mafia.
Avocados
I love avocados. They are kind of like free and open source software because you can grow them yourself. ;) I love avocados and big avocado ag did not pay me to say this.
-
 @ 000002de:c05780a7
2025-01-20 16:27:40
@ 000002de:c05780a7
2025-01-20 16:27:40I just finished the audio book read by Norm himself. I must say, if you love Norm you will love this book. I highly recommend the audio book. I don't want to spoil anything but the book is like sitting down with Norm and listening to him tell you stories. You never know what is true or false and if the whole thing IS the joke. I laughed out loud many times.
originally posted at https://stacker.news/items/857482
-
 @ 652d58ac:dc4cde60
2025-01-20 14:39:11
@ 652d58ac:dc4cde60
2025-01-20 14:39:11Introduction
We must rethink how we envision the future. In the short term, things may be worse than we expect, rising inflation, war, and health crises, but this is all part of the fiat dilemma. A system that cannibalizes itself. Yet, at the same time, a new system is emerging.
Bitcoin and Artificial intelligence (AI) will be central to this foundation, providing humanity with the time and tools needed to thrive. How Technology Drives Deflation
As Jeff Booth so masterfully explains, technology is inherently deflationary. Over time, through free market competition and productivity gains, prices should fall to their marginal cost of production.
Yet, in our inflationary fiat system, productivity gains are eroded by the continuous increase in the money supply, driving prices higher. Instead of allowing prices to approach their marginal cost of production as they should, goods and services become more expensive due to monetary inflation.
This principle, that an expanding money supply reduces the purchasing power of individual monetary units and ultimately undermines wealth creation, was recognized as early as 1517 by Copernicus in the quantity theory of money.
Because bitcoin is limited in supply, productivity gains across the economy can lead to greater wealth for all participants in the system, as the price of goods and services falls to the marginal cost of production over time. Rather than rise due to an increase in the monetary supply. We need Bitcoin to ensure that the productivity gains that drive the economy forward can have a lasting, sustainable impact.
The Interplay of Bitcoin und AI
Since the existing system benefits from inflation, market participants are often manipulated into believing that AI is inherently dangerous. While there are significant risks associated with AI, particularly its potential for centralization and manipulation, the technology itself offers great opportunities. The real problem lies in the inflationary monetary system, not AI.
Artificial intelligence is set to increasingly shape the workplace, trade, and finance. Consider the “Magnificent Seven”, a group of tech giants, Apple, Microsoft, Amazon, Alphabet (Google), Meta (Facebook), Nvidia, and Tesla, that all leverage AI as a key driver of productivity.
In 2023, the financial services industry alone invested an estimated $35 billion in AI, with banking leading the charge, accounting for approximately $21 billion. This is particularly relevant to Bitcoin, since it serves as both money and a financial system. As AI becomes more sophisticated, it will increasingly rely on a digital currency that aligns with its digital nature, such as bitcoin, which offers both scalability and speed through the Lightning Network.
For instance, AI systems could use Bitcoin to facilitate microtransactions in real time, managing their wallets autonomously to process payments for services or data. This would unlock new opportunities for AI applications in sectors like actual decentralized finance (DeFi) and machine-to-machine transactions.
The Lightning Network, as a second-layer protocol built on top of Bitcoin, enables transactions to be settled almost instantly and at low cost. This makes it particularly well-suited for AI applications that require fast and reliable transactions.
While some AI and language models can exhibit programmed biases, AI systems, driven by algorithms and data, should strive to prioritize efficiency, minimizing biases wherever possible. If programmed without bias, AI seeks the best tools for operations and decision-making, and Bitcoin offers an optimal solution, providing both the asset and infrastructure needed for efficient, resilient, digital financial systems.
In addition, AI is likely to also contribute to Bitcoin’s development, with algorithms optimizing mining efficiency, hardware usage, forecasting energy demand, and ensuring more efficient resource allocation, all of which will lead to more effective mining strategies.
Conclusion
The synergy between Bitcoin and AI has the potential to enable the creation of more efficient, intelligent and resilient systems. These developments will underpin bitcoin’s role as digital money in a digital world, potentially creating positive second-order effects on global financial markets. The impact will be especially profound in industries such as finance, insurance, robotics, lending, investments, architecture, housing, healthcare, logistics, and others, with effects accelerating over time.
The free market is inherently deflationary, because of productivity gains, things, like housing, should become cheaper over time. Yet, this doesn't happen. Inflationary fiat currencies, like the dollar, lose purchasing power as their supply increases, eroding those gains. Bitcoin offers a framework in which productivity gains can have a lasting, sustainable impact.
Bitcoin, as a disinflationary currency with a fixed supply, preserves the value of productivity improvements, allowing prices to fall to their marginal cost of production. This ensures that efficiency gains lead to greater wealth for all participants in the system.
Moreover, since Bitcoin is accessible, it allows wealth to become more attainable for a wider range of people, enabling general living standards to increase more easily. The interplay between Bitcoin and AI is pretty exciting, and it’s becoming clear that the widespread adoption of AI will drive the widespread adoption of Bitcoin. This is necessary, as only Bitcoin, as a counterbalance to the self-destructive fiat system, can protect humanity from the negative effects of inflation. With the accelerated productivity gains of the AI age, Bitcoin becomes even more crucial as a solution, ensuring that these gains can be preserved and shared more equitably.
Originally published as the 28th edition of my n ewsletter, Bitcoin & AI: https://leonwankum.substack.com/p/bitcoin-and-ai
Photo Credit: commonedge.org (An Optimist’s Take on AI and the Future of Architecture)
-
 @ 783850fd:77511d32
2025-01-20 13:22:54
@ 783850fd:77511d32
2025-01-20 13:22:54I'm thinking about buying a small house or a plot of land in Morocco and living there. The amount I am willing to pay for this would be $10 000 - 30 000. How much might I liquidate into their fiat (MAD) bank account with a month or so without them freezing my account and god only knows what worse things them doing to me. I use robosats and never exceed the amount of 950 euro when selling Bitcoin. I have all my wealth in Bitcoin, no history of income over the last 5 years, no filing tax returns too. I am from the EU, residing in Spain. How has your experience with Morocco been? Can one open a bank account in Morocco without having a residence there?
originally posted at https://stacker.news/items/857178
-
 @ da0b9bc3:4e30a4a9
2025-01-20 12:57:31
@ da0b9bc3:4e30a4a9
2025-01-20 12:57:31Hello Stackers!
It's Monday so we're back doing "Meta Music Mondays" 😉.
From before the territory existed there was just one post a week in a ~meta take over. Now each month we have a different theme and bring music from that theme.
This month it's New Year New Artists! Bringing you small time artists with great music.
This week, I'm bringing Malinda Kathleen Reece and her cover of Pippins song Edge of Night.
https://youtu.be/NTsduTxb74Y?si=makffTIu9cPKsqqn
originally posted at https://stacker.news/items/857183
-
 @ da0b9bc3:4e30a4a9
2025-01-20 08:08:37
@ da0b9bc3:4e30a4a9
2025-01-20 08:08:37Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/856958
-
 @ df478568:2a951e67
2025-01-20 05:23:36
@ df478568:2a951e67
2025-01-20 05:23:36I took this picture at about block 416,220(June 13, 2016). The price of eggs on that day was $1.99, 16.5¢ per egg if you still measure stuff with the broken ruler we call fiat. What if we measured the price in sats instead? I found the price on that date from the bitbo calender. According to this website, $1.99 was worth 260,000 sats back then. Each egg cost 21,667 sats! Oh My Zeus!😱

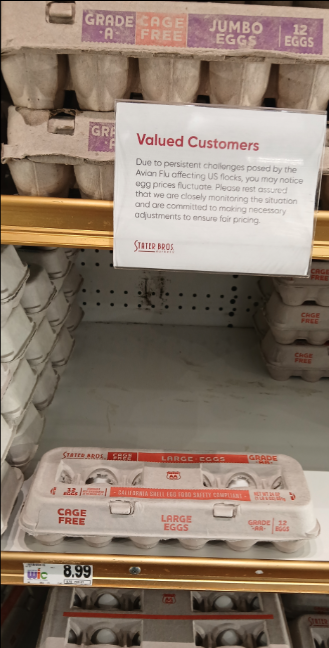
I used this mempool calculator to see how much that is today. Turns out that it's $272.88 as of block 879,943. Since the fiat ruler is broken, the price of a dozen eggs also has NGU. I took this picture the last time I went to the grocery store. Eggs cost enough to shock fiat maxis. $8.99 OMZ!😱
What does a dozen eggs cost if you ignore the broken ruler? 8,572 sats today, just 714 sats per egg. Holy Wiemar Republic Batman! That's 30X cheaper! 😁
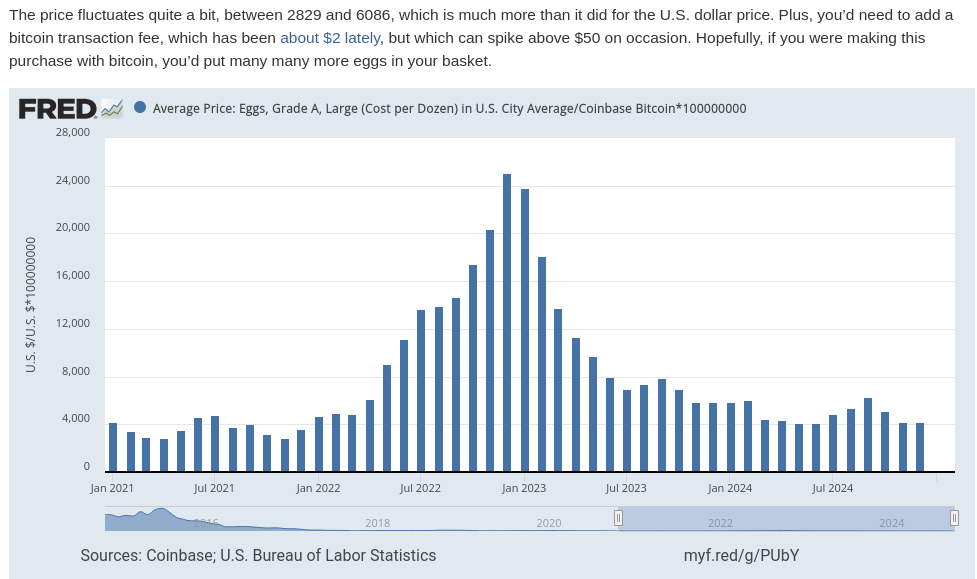
For some strange reason I can't pretend to understand, the Federal reserve tracks the price of eggs denominated in bitcoin. I guess they want to stay humble and stack money printer go brrrrrr. You can see the price of eggs drop off a cliff like Wile E Coyote on their website.
In The Price of Tommorrow and too many podcasts to mention, Jeff Booth argues the free market makes things cheaper over time, but the fiat syatem is syatematic theft. This theft occurs via inflation, which is really wage deflation. In other words, eggs are getting cheaper over time because egg producers become more efficient. We see tye fruits of this efficiency in Big screen TV's because the fiat price gets cut in half every ten years or so, but this is also a product of a broken ruler. The TV is probably 60X cheaper in bitcoin terms. It makes sense, TV's don't get bird flu, but when you begin using bitcoin as your unit of account, the measurement of value makes more sense than fiat clown world on the broken ruler standard. I remember when coffee was 100,000 sats. Now it's 16,699 sats. Living on the sat standards allows you to see Jeff Booth's thesis play out in real time

Life Gets More Expensive On The Broken Ruler Standard
I see so many young people on the broken ruler standard bemoan about food and housing prices. There are people with master's degrees who have already lost hope of buying a single family home and achieving the "American dream." To be honest, I would be pretty bummed about it too if I was on the broken ruler standard. A few months ago I spoke with a woman who made at least twice as much fiat as I do say, "I hope this housing market crashes so I can buy a house!"
That's sad. I have a lot of empathy for that feeling. Since the great financial crisis, I've only been able to get part time work, but my family wqs able to get a mortgage worth 12.5 bitcoin at the so-called "height of the market." We put as little money down as possible, 3% and I sold my old 401k for that "money." I also used some of it for repairs and taxes, but went all-in on bitcoin with everything else. Now our house is worth about 5 bitcoin. The way I see it, real estate is always crashing.
People on the broken ruler standard cry, "Wah, Wah. I hope there's a housing crash! Wah! Wah! Muh egg prices!" Buy a brand spanking new car for $50,00 car with a 7% interest rate and they will say, "Congratulations!" The trouble is, the price of the car falls like eggs compared to bitcoin on the broken ruler standard. This is because prices are distorted when measured in a broken ruler standard.
Get Off The Broken Ruler Standard
Before I met my wife, I played poker to supplement my income. I don't play much anymore, but poker taught me about risk management, probability, game theory, and many other things applicable to bitcoin. Poker gave me the background knowledge I needed to study bitcoin. In a sly, round-about way , poker taught me how to spend less bitcoin than I make. In traditional technical finance terminology, this is called "fucking saving." If you were not taught how to save and spend more than you earn, no matter how many broken ruler bucks you may earn, bitcoin will not work for you.
My wife makes a lot of broken ruler bucks. Unfortunately, we were broke in 2016 because we both were in school. Nevertheless, I'm proud of my stack amd I'm now at a point in life where I can get paid in bitcoin with very little risk because of my sugar mama, I mean wife, gets paid very well.
I spend like almost every other American consumer, plastic broken ruler debt cards. I put my little Strike ACH number on the Discover app. I keep a couple million sats on Strike and pay my credit card every month. In other words, I use Strike like a four-letter word: bank.
Sometimes I'll get a craving for tacos., I've never found a food truck that takes bitcoin, but they often use the Cash App. People on the broken ruler standard can't instantaneously send broken ruler bucks from PayPal to Zelle and vice-versa. They must first send broken ruler bucks from PayPal to the bank and then send the broken ruler bucks through Zelle. I can send sats directly from Strike to thr Cash App within seconds.
Sats As A Unit Of Account
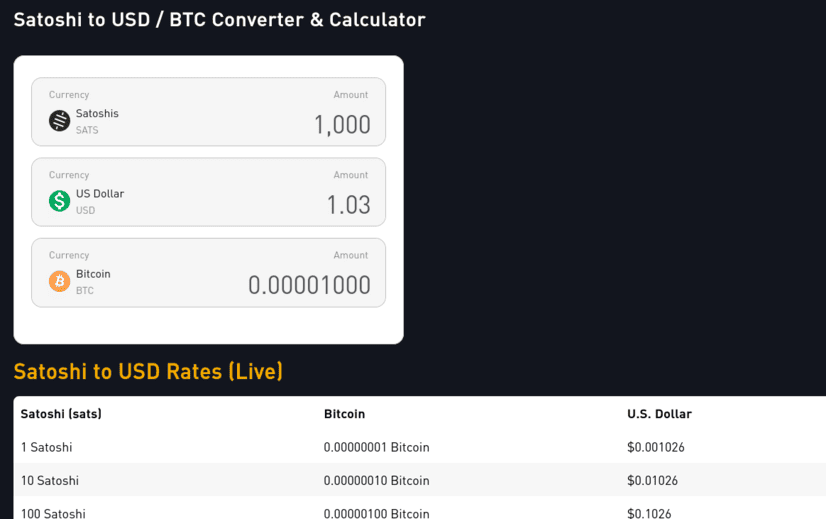
The price of bitcoin fluctuates which makes it difficult to use as a unit of account. Who wants to divide the price of bitcoin by 100 million. Ain't nobody got time for that. If a whole coin costs 100k, then 1,000 sats = $1.00. This means each 100 sats is worth 10¢. 10 sats = 1¢. If the price drops 50%, 1000 sats is 50¢. If it does a 10X, $1,000 sats is $10.00. Living on a sat standard requires a little math, but it's easy to estimate. For more precise calculations I use mem pools calculator.
Money is a store of value, medium of exchange, and unit of account. If you use bitcoin on all three ways, you are using bitcoin as money. Saving becomes spending less bitcoin, not "buying more bitcoin." If you stack sats, your goal should be to leave the broken ruler standard and adopt sats as the standard. The world will still price your sats with a broken ruler. Sometimes this broken ruler makes you look like a fool. Other times, the broken ruler makes you look like a genius. Therefore, you must stay humble and stack sats.
You'll need some savings before you can deal with the broken ruler fallacy, but once you consistently stack sats and NGU continues to U, you'll eventually see life gets easier when you make sats the standard.
I will sell some sats to pay for my food and I send a tip to the food trucker in bitcoin using the Cash App gift button. It is actually very easy for them to accept bitcoin. They just don't know it yet. I don't proselytize the gospel of our lord and savior Satoshi Nakamoto. I just send them a few thousand sats. Good orange pilling is like good writing: Show, don't tell.
Does it require KYC?
Yeah, but so does Bank of Broken Rulers.
Haven't you heard the phrase, not your keys, not your bitcoin?
Yes. It's true. The 2 million sats or so is "not my bitcoin." From my perspective, however, it is the least risky way of paying my bills. I believe it is less risky than keeping broken ruler bucks in a bank. FDIC insurance sounds nice as canceled Insurance policies in the Pacific Palisades.
I could keep my 2 million sats in self-custody in my own lightning wallet. I could use Zap Planner to schedule my payments to hit Strike moments before I pay my bill, but I know me. I've lost sats on the lightning network before. I am more likely to lose the sats on my self-custodial lightning wallet than lose them because Strike could possibly rug-pull me. So for now, I just keep 2 million sats on the app. If bitcoin does a 10X, I'll keep 200,000 sats on Strike. If it drops 50%, I will keep 4 million sats on there.
I typically spend between $600- $1,000 in broken ruler bucks a month. This doesn't include my mortgage or food. My wife pretty much covers that stuff. Life happens though. Sometimes I need to pay a plumber, or a roofer or something, but most months, I have a sat surplus, a phenomena I like to call sats savings. My fiat check converts to bitcoin right on payday. I pay my credit cards off that day. If the sats are worth a little more, I pay taxes on that little bit. To make the math easy, say I get paid $1,000 on Friday. When I pay my bills, The broken ruler measurement now says I have $1,100. I pay my credit card. I owe capital gains on that $100 worth of sats. If my paycheck happens to be worth $900,I don’t pay any taxes because I have a loss. I won’t lie. I still get a bit perturbed when the price goes down 10% on payday, but it’s not the end of the world. If it doesn’t go back up by next payday, good. I earn more sats. If it goes up by next payday, good. All the sats I stacked before can buy more groceries.
Get On The Sats Standard
!;make sats the standard](https://gitea.marc26z.com/marc/BlogImprovementProposals/raw/branch/main/pics/Screenshot%20from%202025-01-19%2020-35-55.png)
Making sats the standard does this for the individual on the microeconomic level. Each Bitcoiner gradually accumulates sats. Stack long enough, study long enough, and experience enough 80% dips and you too will develop an unwavering conviction. You get paid in sats. You spend sats. You save sats. You no longer give a damn about your local fiat currency. A dozen eggs cost less than half of a single egg cost 8 years ago. If you lose 50% of your spending power overnight, you can buy less eggs, but a dozen eggs still costs less than 1 egg 8 years ago. Bitcoin is just better money.
If my fiat bank account takes more money out than I have in it, I can do an instant withdrawl on Strike. The fiat appears in my fiat bank account instantly. No more waiting 3-5 days for the money to get there. The bank does not get to keep charging you overdraft fee after overdraft fee for every little transaction. Bitcoin just works better. You can send it all over the world within seconds. You can buy stuff online with it or pay your credit cards. There is literally no reason to hold dollars anymore if you don’t want to. When you’re ready, make sats the standard. If you are not ready, keep stacking.
Onward.
-
 @ 16d11430:61640947
2025-01-20 03:17:38
@ 16d11430:61640947
2025-01-20 03:17:38Born out of a silent rage into a world that prides itself on polished veneers of socially acceptable fury, the Silent Rager arrived in a place where anger wore masks—tight, suffocating masks that twisted raw emotion into hollow smiles and passive-aggressive jabs. Yet his rage had no such mask, no place in this theater of deceit. His was a wild, untamed thing, a fire roaring without the permission of his voice.
From the moment he could perceive the world, he was sent to rage's hell camp—a crucible of misery, where every breath reeked of malfeasance, and every lesson was soaked in contempt. The Silent Rager learned to stew in it, learned to hold it within, to cook himself in the boiling broth of inherited bitterness and unspoken injustice. They told him the world was cruel, but what they didn’t tell him was that he’d been chosen—culled in a ritual as old as power itself. Somewhere, someone had decided that his voice was too dangerous to exist. They’d silenced it before it could ever cry out, sparing the rage but not the sound.
And so, he grew, misinformed, misdirected, and malformed. His mind writhed like a worm trapped in the grip of an unseen hand. Thoughts coiled and uncoiled in his brain, each one dripping with questions he could not articulate, answers he could not demand. Why was his rage silent? Why did it claw at his chest without release? He did not know. He only knew the ache of containment and the suffocating weight of emotions too vast for his stolen voice.
Moments of respite came, but only when he danced closest to death. The edge of oblivion whispered to him with the intimacy of a long-lost friend. It was in these moments that the raging fire within dimmed, replaced by a fleeting, fragile stillness. He could breathe, if only for a second, before the storm returned. Life, for him, was not a series of triumphs or failures but a relentless march of inherited rage, coursing through his veins like a parasite, feeding on his every heartbeat.
He did not ache for it to end—not entirely. What he yearned for, more than anything, was a voice. A voice to scream into the void that birthed him. A voice to challenge the silence that caged him. A voice to tell the world, and himself, the truth of his existence before he could end it all.
The Silent Rager lived in a paradox: to end his life without a voice would be to die unseen, unheard, unspoken. But to live on without one felt equally unbearable. His rage, silent though it was, demanded expression. It screamed through his actions, burned in his gaze, and radiated from him like heat from a furnace. And yet, the world did not see, did not hear. To them, he was just another shadow moving through the crowd, another ghost in the machine.
In the end, the Silent Rager remained trapped in his silent storm, his unvoiced agony a testament to a life stolen before it could begin. Perhaps one day he would find his voice. Or perhaps his silence would be his epitaph, a bitter monument to a world that let him burn in quiet desperation. Until then, he raged—silent, but not unseen, not by those who dared to truly look.
-
 @ a012dc82:6458a70d
2025-01-20 02:02:07
@ a012dc82:6458a70d
2025-01-20 02:02:07The advent of cryptocurrency has sparked a modern-day gold rush, with Bitcoin mining at the forefront of this digital revolution. The United States, with its vast resources and technological prowess, has become a fertile ground for these operations. However, the recent shift in the global mining landscape has brought a wave of Chinese mining companies to U.S. shores, fleeing a regulatory crackdown in their homeland. This migration has set off alarm bells within national security circles, as the technology that underpins cryptocurrencies is not just a tool for financial gain but also a potential vector for cyber espionage and other security threats. The dual-use nature of this technology, capable of both revolutionizing economies and potentially undermining national security, has placed it at the heart of a complex debate involving economic policy, technological innovation, and national defense.
Table Of Content
-
The Economic Impact of Cryptocurrency Mining
-
National Security Risks and Strategic Concerns
-
Regulatory Responses to Foreign Mining Operations
-
The Path Forward: Innovation, Security, and Diplomacy
-
Conclusion
-
FAQs
The economic allure of cryptocurrency mining is undeniable. In regions hit hard by economic downturns, the establishment of mining operations has been a boon, providing much-needed jobs and revitalizing local economies. These operations often take over abandoned industrial sites, turning them into hives of high-tech activity. The promise of a revitalized industrial base, however, comes with caveats. The energy-intensive nature of cryptocurrency mining has led to a surge in demand for electricity, straining local grids and raising concerns about the environmental impact of such operations. The long-term economic benefits are also questioned, as the volatility of the cryptocurrency market means that the stability of these jobs and the longevity of the operations are not guaranteed. As Chinese companies increasingly dominate this space, there is also the fear that the economic benefits may be offset by the outflow of profits to foreign entities.
National Security Risks and Strategic Concerns
The strategic implications of foreign-controlled cryptocurrency mining operations on U.S. soil are complex and troubling. The opaque nature of these operations, often shrouded in layers of corporate secrecy, makes it difficult to discern their true intentions. The proximity of some mining farms to sensitive sites, such as military bases and critical infrastructure, has compounded these fears, suggesting the potential for these facilities to be used for more than just mining. The vast computational power of mining operations could theoretically be repurposed for code-breaking and hacking, posing a direct threat to national security. The concern is not just hypothetical; it is rooted in a history of cyber incursions attributed to Chinese state-sponsored actors. The potential for these mining operations to serve as a front for such activities, intentionally or not, has put them in the crosshairs of U.S. security agencies.
Regulatory Responses to Foreign Mining Operations
The U.S. government's response to the influx of Chinese cryptocurrency mining operations has been measured yet firm. Recognizing the need to maintain an open economic environment that fosters innovation, regulators have nonetheless moved to establish guardrails to protect national interests. This has involved a multifaceted approach, including the proposal of legislation aimed at scrutinizing foreign investments in critical technologies and infrastructure. Agencies such as the Committee on Foreign Investment in the United States (CFIUS) have been at the forefront of these efforts, working to untangle the complex web of ownership and control that characterizes foreign mining operations. The goal is to ensure that while the U.S. remains a hub for technological innovation, it does not become a playground for foreign powers with adversarial intentions.
The Path Forward: Innovation, Security, and Diplomacy
The path forward for the United States in managing the rise of Chinese bitcoin mining operations is akin to walking a tightrope. On one side is the need to nurture innovation and maintain the U.S.'s competitive edge in the burgeoning field of cryptocurrency. On the other is the imperative to safeguard national security and ensure that the country's technological infrastructure is not compromised. This delicate balance requires a nuanced approach that includes fostering a robust domestic mining industry, investing in renewable energy sources to mitigate the environmental impact, and engaging in strategic diplomacy to manage the international dimensions of cryptocurrency governance. The U.S. must leverage its strengths in innovation, policy-making, and international relations to set standards that will shape the future of cryptocurrency mining and secure its digital economy.
Conclusion The challenge of balancing the economic potential of cryptocurrency mining with the imperatives of national security is emblematic of the broader challenges facing policymakers in the digital age. As Chinese bitcoin mining operations continue to expand their footprint in the U.S., the need for a strategic, measured response becomes increasingly critical. This response must be multifaceted, engaging with all stakeholders, including the mining industry, environmental groups, energy providers, and security agencies. By striking a balance between economic growth and security, the U.S. can harness the potential of the digital economy while protecting its national interests. The stakes are high, and the decisions made today will have lasting implications for the security and prosperity of future generations.
FAQs
How does Bitcoin mining impact local economies? Bitcoin mining can provide jobs and economic investment in local communities, especially in areas with excess energy capacity or where industrial sites are underutilized.
What is the U.S. government's response to foreign cryptocurrency mining operations? The U.S. government is considering stricter regulations on foreign investments in critical technologies, including cryptocurrency mining, to protect national security while fostering economic growth.
Can cryptocurrency mining operations be environmentally sustainable? There are concerns about the high energy consumption of mining operations, but with investment in renewable energy and efficient technologies, mining can move towards greater sustainability.
How does the U.S. plan to balance innovation with security in cryptocurrency mining? The U.S. aims to strike a balance by creating policies that encourage technological innovation and economic benefits while implementing security measures to protect against potential threats.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
X: Instagram: @croxroadnews.co
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 8d34bd24:414be32b
2025-01-19 23:33:36
@ 8d34bd24:414be32b
2025-01-19 23:33:36I have a teenaged son with Down Syndrome. He likes telling me he is all grown up despite having the maturity and understanding of a 3rd or 4th grader. He does not like being corrected and his newest response to correction is to hold up his hand making a talking hand motion. Whenever he is having this reaction, he isn’t listening and isn’t learning and more often than not ends up harming himself.
Today I sat down with him and discussed some Bible verses related to wisdom and correction in an attempt to explain why this behavior was only hurting himself. (Due to his immaturity, logic and facts don’t always work.)
Afterwards, I thought that all of us adults could probably use this same lesson. We don’t like being corrected by the Bible, the Holy Spirit, and definitely not by other Christians. It takes a lot of maturity to actually seek out correction, but that is what we are called to do.
He whose ear listens to the life-giving reproof\ Will dwell among the wise. (Proverbs 15:31)
If we want to be wise, we have to listen to “life-giving reproof.” Where can we get this “life-giving reproof?” Obviously the Bible gives it, but also mature Christians can give us “life-giving reproof.” A wise person will always listen and evaluate correction from a fellow Christian, especially one who has proven to have Biblical knowledge and wisdom. This doesn’t mean we will take their advice 100% of the time. It must be judged by the truth in the Bible, but it should be honestly considered. Even the greatest theologians have at least one point of error. If we fail to listen to correction and evaluate it biblically, we can be more easily led astray.
He who neglects discipline despises himself,\ But he who listens to reproof acquires understanding. (Proverbs 15:32)
The benefit of listening to correction is acquiring understanding. The curse of not listening to correction is the harm it causes to ourselves. The harm is so great, only a fool or those who despise themselves would act this way.
The fear of the Lord is the instruction for wisdom,\ And before honor comes humility. (Proverbs 15:33)
Wisdom comes from the fear of the Lord. Fear of the Lord leads to seeking His will. Seeking His will leads us to the correction of the Bible and mature Christians. We then have to humble ourselves and look at our mistakes and failures. We all want to think of ourselves as good, honest, and wise, but we all do bad things, tell lies, and act foolishly. The only way to fix these (and only after repenting, trusting Jesus as Savior, and submitting to His will) is to honestly assess our own failings — whether foolish, uninformed, or willful. It takes a lot of humility to fully do.
As an employer, the one trait that I can’t stand in an employee is a person who can’t or won’t admit any mistakes. We all make mistakes. A person who wants to learn can be taught. A person, who refuses to admit making any mistakes and who always blames someone else, is untrainable.
Sometimes I wonder if God feels the same way with us because we refuse to admit our failings.
Yet they did not listen or incline their ears, but stiffened their necks in order not to listen or take correction. (Jeremiah 17:23)
We always need to listen to God. The three main ways are to read the Bible, to seek wise council, and to pray for leading. When we choose to seek council and prayer, we still need to check the answers given against the unchanging truth in the Bible.
When we refuse to read the Bible, we are not listening to God. Although there are definitely some things in the Bible that are confusing and not immediately clear, the primary tenants in the Bible are readily understandable by even a young child. Sometimes I wonder if the reason people don’t read their Bible and say it is too confusing is because they don’t like what they are reading. It is “confusing” because God is telling us what we don’t want to hear. It is “confusing” because God is telling us what we don’t want to do. If we actually read and understand, it will mean we will have to make changes to our thoughts and actions.
It is better to listen to the rebuke of a wise man\ Than for one to listen to the song of fools. (Ecclesiastes 7:5)
We need to remember, both as the giver and receiver of a rebuke, that the truth and God’s word are useful for wisdom. Biblical correction is a loving action that is for the good of the receiver of correction. It should be given in a loving manner and received in a loving manner. We may want to “listen to the song of fools,” but we should seek “he rebuke of a wise man.”
When I was a young Christian in college, I sometimes went to a tiny church in my college town and sometimes went to a huge church in my hometown. The large church had a large Sunday school group taught by a man who taught me to love exhortation. When ever I hear the word “exhortation,” I think of him. Exhortation is a mix of correction and encouragement.
When I first started attending the Sunday school, I avoided the teacher. He didn’t lecture. He asked questions. He asked uncomfortable questions. They weren’t uncomfortable because they were inappropriate. They were uncomfortable because the answers to these questions required a change in world view, a change in thought, or a change in actions. He led us to the truth without lecturing about the truth. By helping us to find the truth by ourselves (through the Bible), the truth became a part of us. We knew what we believed and why, so were not easily led astray.
For months, I’d sit far away from him and try to hide, so I wouldn’t get the uncomfortable questions. Over time, after being asked some of these questions, I saw how they led me to the truth. I changed from hiding from him, to seeking him out. I went from trying to avoid being questioned and challenged in my beliefs to seeking out the correction because it helped me grow in my faith, discover the truth (not my truth), and grow closer to God.
At this point, I can’t even remember my teacher’s name, but I will never forget or stop being thankful for the things I was taught in that Sunday school class, the greatest of all being to seek the truth and never fear correction.
I decided to end my post with a passage from Psalm 119 about how we should love God’s word, the truth, wisdom, His commandments, and His corrections. The problem was narrowing it down. I’ve included one section, but would recommend reading all of Psalm 119. Read this passage considering what it says about what our love of learning about God and His commands should be.
Mem.\ O how I love Your law!\ It is my meditation all the day.\ Your commandments make me wiser than my enemies,\ For they are ever mine.\ I have more insight than all my teachers,\ For Your testimonies are my meditation.\ I understand more than the aged,\ Because I have observed Your precepts.\ I have restrained my feet from every evil way,\ That I may keep Your word.\ I have not turned aside from Your ordinances,\ For You Yourself have taught me.\ How sweet are Your words to my taste!\ Yes, sweeter than honey to my mouth!\ From Your precepts I get understanding;\ Therefore I hate every false way. (Psalm 119:97-104)
Trust Jesus.
-
 @ b8851a06:9b120ba1
2025-01-19 22:05:55
@ b8851a06:9b120ba1
2025-01-19 22:05:55A TALE OF RESILIENCE
Nine years ago today, The Washington Post declared "R.I.P. Bitcoin" when the cryptocurrency traded at $380. Fast forward to January 19, 2025, and Bitcoin trades at $104,803, representing a staggering 27,500% increase since that infamous obituary.
The Numbers Tell the Story
🔘 Bitcoin has been declared dead 477 times since its inception
🔘 2023 saw only 8 death notices, a decade-low
🔘 2024 recorded just 2 death declarations, compared to 124 in 2017
From Mockery to Mainstream
The transformation has been remarkable. When the Washington Post published its obituary, Bitcoin was dismissed as a fringe technology. Today, it's embraced by financial giants like BlackRock and Fidelity. The price history tells an compelling story.
The Future Outlook
Despite past skepticism, institutional analysts now project ambitious targets. Galaxy Digital predicts Bitcoin could exceed $150,000 in the first half of 2025. This represents a dramatic shift from the days when Nobel laureates and banking executives routinely dismissed Bitcoin as worthless.
A Lesson in Resilience
The premature death notice serves as a powerful reminder about the dangers of dismissing innovative technologies. While Bitcoin faced numerous challenges since 2016, including regulatory crackdowns and market crashes, its fundamental value proposition has remained intact. The declining frequency of "Bitcoin obituaries" suggests that even its harshest critics are beginning to acknowledge its staying power.
There is no second best, and it’s going to millions.
-
 @ 66675158:1b644430
2025-01-16 20:44:33
@ 66675158:1b644430
2025-01-16 20:44:33Before the time of Utensils, people lived in genuine harmony. They gathered in markets to trade freely, built homes where they pleased, and traveled without papers or permissions. Communities solved their own problems through discussion and agreement. When disputes arose, wise elders would help find solutions that satisfied all. Children learned from their parents or chose mentors from among the skilled craftspeople.
In those days, gold changed hands freely for goods and services. Each person kept what they earned. Communities would voluntarily pool resources for shared needs - wells, bridges, and roads. Those who had more would often help those with less, not by decree but by choice.
Neighbors knew each other's names. Doors were left unlocked. Children played in the streets until sunset. Gardens grew wherever people planted them. Merchants traveled between towns without inspections. Healers practiced their craft freely, sharing knowledge openly.
Then came the Utensils.
In our land, Aldrich found the Silver Spoon. In the East, Emperor Chen discovered the Jade Chopsticks. The Norse kingdoms united under the Golden Fork. The desert peoples followed the Bronze Ladle.
Each Utensil, their holders claimed, granted divine wisdom to rule. Each promised protection and prosperity in exchange for obedience.
The changes came slowly at first. The Spoon Holder requested a share of each harvest to store for hard times. The Chopstick Emperor required homes to be built in specific ways to prevent fires. The Fork King demanded that travelers carry documents proving their loyalty.
At first, the Utensils did bring some genuine improvements. The Spoon Holder's collectors used part of their harvest share to help villages during droughts. The Chopstick Emperor's building codes truly did reduce fires. The Fork King's road patrols deterred the few bandits who had troubled merchants. The Bronze Ladle's water management systems helped farms flourish in the desert.
The early years saw stone roads replace dirt paths, connecting villages more efficiently than before. Granaries were built with better designs, preserving food longer. Some diseases decreased as the Chopstick Emperor's cleanliness codes spread. The Fork Kingdom's standardized weights and measures did make trade easier.
The Spoon Holder soon declared that carrying gold was dangerous and inefficient. They introduced sacred paper notes, "backed by the Silver Spoon's power." At first, you could trade these notes back for gold, but gradually this right vanished.
Scholars wrote lengthy memos about the divine wisdom of the Utensils, creating complex theories about why ordinary people couldn't possibly understand how to live without direction. They advised the Holders and were rewarded with special privileges, comfortable positions, and influence.
When anyone questioned this system, the Utensil Holders and their Experts would ask: "But who would build the roads without us? Who would help the poor? Who would protect you?" They spoke as if humans had never cooperated or helped each other before the Utensils came, and many began to believe it.
People grumbled but accepted. After all, the Utensils shone with otherworldly power.
Some remembered these early benefits when questioning the growing restrictions. "Remember how the Spoon Holder's men helped during the great flood?" they would say. "Surely they have our best interests at heart." The Utensil Holders carefully nurtured these memories, even as their power grew far beyond such humble beginnings.
More rules followed. The Spoon Holder's men began watching the roads, collecting portions from merchants. The Chopstick Guards enforced strict codes about proper behavior. The Fork Watchers kept lists of who attended the mandatory gatherings.
Children were taught the sacred histories of their Utensils. The Spoon's light blessed the worthy. The Chopsticks maintained harmony. The Fork brought strength. The Ladle provided guidance.
When people remembered the old freedoms, the Utensil Holders reminded them of the chaos before - though few could actually recall any chaos.
But surely there must have been chaos, or why would the Utensils have come?
The Utensil Holders began to eye each other's territories. How dare the Fork King claim his metal was superior? How could the Chopstick Emperor suggest jade held more wisdom than silver? The Ladle Holder's bronze was clearly inferior to all!
The Utensil Holders pointed to their achievements - the roads, the granaries, the safer towns - as proof of their divine right to rule. They spoke of how they had unified squabbling villages, standardized laws, and created order. Few noticed how these very achievements had required less and less input from the people themselves.
Wars erupted. Armies marched under banners bearing their sacred Utensils. Men died believing their Utensil was the one true source of authority. Villages burned as soldiers searched for heretics who might secretly worship foreign Utensils.
The Utensil Holders demanded more from their people - more food, more gold, more obedience. They placed watchers in every village. They required written permission for travel between towns. They forbade more than three people from gathering without a Guardian present.
"It's for protection," they said, holding their Utensils high. "How can you doubt the sacred silver?"
And indeed, their guards did stop some thieves, their inspectors did prevent some fraud, their builders did create some useful works. But these benefits came with an ever-increasing price in freedom, until the cost far exceeded any advantage. Yet by then, most people could no longer imagine providing these services for themselves, as their ancestors had done.
Towns built walls, not against invaders but to control who could enter and leave. The Utensil Holders required everyone to wear markers showing their village of origin. They appointed observers in every community to report suspicious behavior - like speaking of the time before Utensils.
Children were taken to special houses to learn proper reverence for their Utensil. Families who taught the old ways disappeared in the night. The Holders declared certain words forbidden, certain thoughts dangerous, certain memories treasonous.
Now, centuries later, the Utensils rule absolutely. People bow when the sacred implements pass by. They inform on neighbors who question the Utensils' power. They offer their children to serve in the Utensil temples.
The latest marvel was Utensil Technology - enchanted mirrors and crystals that watched people's movements, recorded their words, and tracked their trades. "Only criminals fear being watched," the Holders proclaimed, as their surveillance spread into every home and market. The crystals even allowed them to freeze people's paper money if they spoke against the Utensils.
The Utensil Holders formed special partnerships with the largest merchant guilds. These favored merchants received special permissions, protection from smaller competitors, and access to the new paper money first. In return, they helped enforce the Holders' rules and collected information about their customers. Small traders and craftsmen found themselves crushed between these powerful allies.
The latest decree requires all newborns to be blessed by touching their foreheads to their realm's sacred Utensil, marking them forever as its property. Parents compete for earlier blessing times, believing this shows greater devotion.
The wars continue. The Fork Kingdoms battle the Chopstick Empire. The Ladle Realms raid the Spoon Holdings. Each believes their Utensil must rule all.
And in quiet corners, in hidden places, a few elders still whisper stories of the time before - when humans lived without Utensils telling them how to live. But fewer remember with each passing year. After all, who could imagine a world without the guidance of sacred silverware?
-
 @ eac63075:b4988b48
2025-01-04 19:41:34
@ eac63075:b4988b48
2025-01-04 19:41:34Since its creation in 2009, Bitcoin has symbolized innovation and resilience. However, from time to time, alarmist narratives arise about emerging technologies that could "break" its security. Among these, quantum computing stands out as one of the most recurrent. But does quantum computing truly threaten Bitcoin? And more importantly, what is the community doing to ensure the protocol remains invulnerable?
The answer, contrary to sensationalist headlines, is reassuring: Bitcoin is secure, and the community is already preparing for a future where quantum computing becomes a practical reality. Let’s dive into this topic to understand why the concerns are exaggerated and how the development of BIP-360 demonstrates that Bitcoin is one step ahead.
What Is Quantum Computing, and Why Is Bitcoin Not Threatened?
Quantum computing leverages principles of quantum mechanics to perform calculations that, in theory, could exponentially surpass classical computers—and it has nothing to do with what so-called “quantum coaches” teach to scam the uninformed. One of the concerns is that this technology could compromise two key aspects of Bitcoin’s security:
- Wallets: These use elliptic curve algorithms (ECDSA) to protect private keys. A sufficiently powerful quantum computer could deduce a private key from its public key.
- Mining: This is based on the SHA-256 algorithm, which secures the consensus process. A quantum attack could, in theory, compromise the proof-of-work mechanism.
Understanding Quantum Computing’s Attack Priorities
While quantum computing is often presented as a threat to Bitcoin, not all parts of the network are equally vulnerable. Theoretical attacks would be prioritized based on two main factors: ease of execution and potential reward. This creates two categories of attacks:
1. Attacks on Wallets
Bitcoin wallets, secured by elliptic curve algorithms, would be the initial targets due to the relative vulnerability of their public keys, especially those already exposed on the blockchain. Two attack scenarios stand out:
-
Short-term attacks: These occur during the interval between sending a transaction and its inclusion in a block (approximately 10 minutes). A quantum computer could intercept the exposed public key and derive the corresponding private key to redirect funds by creating a transaction with higher fees.
-
Long-term attacks: These focus on old wallets whose public keys are permanently exposed. Wallets associated with Satoshi Nakamoto, for example, are especially vulnerable because they were created before the practice of using hashes to mask public keys.
We can infer a priority order for how such attacks might occur based on urgency and importance.
 Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)
Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)2. Attacks on Mining
Targeting the SHA-256 algorithm, which secures the mining process, would be the next objective. However, this is far more complex and requires a level of quantum computational power that is currently non-existent and far from realization. A successful attack would allow for the recalculation of all possible hashes to dominate the consensus process and potentially "mine" it instantly.
 Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin Attacks
Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin AttacksRecently, Narcelio asked me about a statement I made on Tubacast:
https://x.com/eddieoz/status/1868371296683511969
If an attack became a reality before Bitcoin was prepared, it would be necessary to define the last block prior to the attack and proceed from there using a new hashing algorithm. The solution would resemble the response to the infamous 2013 bug. It’s a fact that this would cause market panic, and Bitcoin's price would drop significantly, creating a potential opportunity for the well-informed.
Preferably, if developers could anticipate the threat and had time to work on a solution and build consensus before an attack, they would simply decide on a future block for the fork, which would then adopt the new algorithm. It might even rehash previous blocks (reaching consensus on them) to avoid potential reorganization through the re-mining of blocks using the old hash. (I often use the term "shielding" old transactions).
How Can Users Protect Themselves?
While quantum computing is still far from being a practical threat, some simple measures can already protect users against hypothetical scenarios:
- Avoid using exposed public keys: Ensure funds sent to old wallets are transferred to new ones that use public key hashes. This reduces the risk of long-term attacks.
- Use modern wallets: Opt for wallets compatible with SegWit or Taproot, which implement better security practices.
- Monitor security updates: Stay informed about updates from the Bitcoin community, such as the implementation of BIP-360, which will introduce quantum-resistant addresses.
- Do not reuse addresses: Every transaction should be associated with a new address to minimize the risk of repeated exposure of the same public key.
- Adopt secure backup practices: Create offline backups of private keys and seeds in secure locations, protected from unauthorized access.
BIP-360 and Bitcoin’s Preparation for the Future
Even though quantum computing is still beyond practical reach, the Bitcoin community is not standing still. A concrete example is BIP-360, a proposal that establishes the technical framework to make wallets resistant to quantum attacks.
BIP-360 addresses three main pillars:
- Introduction of quantum-resistant addresses: A new address format starting with "BC1R" will be used. These addresses will be compatible with post-quantum algorithms, ensuring that stored funds are protected from future attacks.
- Compatibility with the current ecosystem: The proposal allows users to transfer funds from old addresses to new ones without requiring drastic changes to the network infrastructure.
- Flexibility for future updates: BIP-360 does not limit the choice of specific algorithms. Instead, it serves as a foundation for implementing new post-quantum algorithms as technology evolves.
This proposal demonstrates how Bitcoin can adapt to emerging threats without compromising its decentralized structure.
Post-Quantum Algorithms: The Future of Bitcoin Cryptography
The community is exploring various algorithms to protect Bitcoin from quantum attacks. Among the most discussed are:
- Falcon: A solution combining smaller public keys with compact digital signatures. Although it has been tested in limited scenarios, it still faces scalability and performance challenges.
- Sphincs: Hash-based, this algorithm is renowned for its resilience, but its signatures can be extremely large, making it less efficient for networks like Bitcoin’s blockchain.
- Lamport: Created in 1977, it’s considered one of the earliest post-quantum security solutions. Despite its reliability, its gigantic public keys (16,000 bytes) make it impractical and costly for Bitcoin.
Two technologies show great promise and are well-regarded by the community:
- Lattice-Based Cryptography: Considered one of the most promising, it uses complex mathematical structures to create systems nearly immune to quantum computing. Its implementation is still in its early stages, but the community is optimistic.
- Supersingular Elliptic Curve Isogeny: These are very recent digital signature algorithms and require extensive study and testing before being ready for practical market use.
The final choice of algorithm will depend on factors such as efficiency, cost, and integration capability with the current system. Additionally, it is preferable that these algorithms are standardized before implementation, a process that may take up to 10 years.
Why Quantum Computing Is Far from Being a Threat
The alarmist narrative about quantum computing overlooks the technical and practical challenges that still need to be overcome. Among them:
- Insufficient number of qubits: Current quantum computers have only a few hundred qubits, whereas successful attacks would require millions.
- High error rate: Quantum stability remains a barrier to reliable large-scale operations.
- High costs: Building and operating large-scale quantum computers requires massive investments, limiting their use to scientific or specific applications.
Moreover, even if quantum computers make significant advancements, Bitcoin is already adapting to ensure its infrastructure is prepared to respond.
Conclusion: Bitcoin’s Secure Future
Despite advancements in quantum computing, the reality is that Bitcoin is far from being threatened. Its security is ensured not only by its robust architecture but also by the community’s constant efforts to anticipate and mitigate challenges.
The implementation of BIP-360 and the pursuit of post-quantum algorithms demonstrate that Bitcoin is not only resilient but also proactive. By adopting practical measures, such as using modern wallets and migrating to quantum-resistant addresses, users can further protect themselves against potential threats.
Bitcoin’s future is not at risk—it is being carefully shaped to withstand any emerging technology, including quantum computing.
-
 @ 3f770d65:7a745b24
2025-01-19 21:48:49
@ 3f770d65:7a745b24
2025-01-19 21:48:49The recent shutdown of TikTok in the United States due to a potential government ban serves as a stark reminder how fragile centralized platforms truly are under the surface. While these platforms offer convenience, a more polished user experience, and connectivity, they are ultimately beholden to governments, corporations, and other authorities. This makes them vulnerable to censorship, regulation, and outright bans. In contrast, Nostr represents a shift in how we approach online communication and content sharing. Built on the principles of decentralization and user choice, Nostr cannot be banned, because it is not a platform—it is a protocol.
PROTOCOLS, NOT PLATFORMS.
At the heart of Nostr's philosophy is user choice, a feature that fundamentally sets it apart from legacy platforms. In centralized systems, the user experience is dictated by a single person or governing entity. If the platform decides to filter, censor, or ban specific users or content, individuals are left with little action to rectify the situation. They must either accept the changes or abandon the platform entirely, often at the cost of losing their social connections, their data, and their identity.
What's happening with TikTok could never happen on Nostr. With Nostr, the dynamics are completely different. Because it is a protocol, not a platform, no single entity controls the ecosystem. Instead, the protocol enables a network of applications and relays that users can freely choose from. If a particular application or relay implements policies that a user disagrees with, such as censorship, filtering, or even government enforced banning, they are not trapped or abandoned. They have the freedom to move to another application or relay with minimal effort.
THIS IS POWERFUL.
Take, for example, the case of a relay that decides to censor specific content. On a legacy platform, this would result in frustration and a loss of access for users. On Nostr, however, users can simply connect to a different relay that does not impose such restrictions. Similarly, if an application introduces features or policies that users dislike, they can migrate to a different application that better suits their preferences, all while retaining their identity and social connections.
The same principles apply to government bans and censorship. A government can ban a specific application or even multiple applications, just as it can block one relay or several relays. China has implemented both tactics, yet Chinese users continue to exist and actively participate on Nostr, demonstrating Nostr's ability to resistant censorship.
How? Simply, it turns into a game of whack-a-mole. When one relay is censored, another quickly takes its place. When one application is banned, another emerges. Users can also bypass these obstacles by running their own relays and applications directly from their homes or personal devices, eliminating reliance on larger entities or organizations and ensuring continuous access.
AGAIN, THIS IS POWERUFL.
Nostr's open and decentralized design makes it resistant to the kinds of government intervention that led to TikTok's outages this weekend and potential future ban in the next 90 days. There is no central server to target, no company to regulate, and no single point of failure. (Insert your CEO jokes here). As long as there are individuals running relays and applications, users continue creating notes and sending zaps.
Platforms like TikTok can be silenced with the stroke of a pen, leaving millions of users disconnected and abandoned. Social communication should not be silenced so incredibly easily. No one should have that much power over social interactions.
Will we on-board a massive wave of TikTokers in the coming hours or days? I don't know.
TikTokers may not be ready for Nostr yet, and honestly, Nostr may not be ready for them either. The ecosystem still lacks the completely polished applications, tools, and services they’re accustomed to. This is where we say "we're still early". They may not be early adopters like the current Nostr user base. Until we bridge that gap, they’ll likely move to the next centralized platform, only to face another government ban or round of censorship in the future. But eventually, there will come a tipping point, a moment when they’ve had enough. When that time comes, I hope we’re prepared. If we’re not, we risk missing a tremendous opportunity to onboard people who genuinely need Nostr’s freedom.
Until then, to all of the Nostr developers out there, keep up the great work and keep building. Your hard work and determination is needed.
-
 @ 9349d012:d3e98946
2025-01-19 19:47:15
@ 9349d012:d3e98946
2025-01-19 19:47:15For many reasons, not least of those the outcome of the last US presidential election, I’m now working on Librarian Detective, Book Two as my creative release. At the moment, I’m already on chapter seven, which means I made it through writing the second chapter, always an admirable hurdle to clear. If you’ll recall, with Librarian Detective, Book One, clearing that milestone was a challenge. It took between nine and 12 years to finish that book, although I wrote three books in those meantime years. This was partly because of working on my day job business more fulltime (MyLibrarian! Our app is out, sign up to test on the pop up here) but also because I revamped my entire writing process, which I’ll share with you.
Here’s a picture of the writing methods I use. I went from writing longhand to digitally, which is more efficient, and I also use a series of guides to help organize the writing process: An outline, character list, calendar timeline, editing checklist and the main writing doc itself.
Seven years ago when I realized my writing method was working for me, I started doing a video series on Writing, called On Storytelling, filmed at all the remote locations I work at, one of the best of which I’m at right now, working on my new book. If you are looking for more writing resources, there’s a list on my blog. When you go down these rabbit holes you may come out ready to write your first book.
GOOD LUCK—MEZ
Originally appeared on https://www.michellezaffino.com/my-writing-methods/
-
 @ 8f0a121e:24038909
2024-12-03 12:55:09
@ 8f0a121e:24038909
2024-12-03 12:55:09ومن لم يمت بالسيف مات بغيره ... تعددت الأسباب والموت واحد
أبيات مشهورة لإبن نباتة السعدي نعرفها جميعاً. يقول ابن خلكان في "الوفيات": بينما كان ابن نباتة يتبرد في دهليز بيته إذ طرق أحدهم بابه، فقال ما حاجتك؟ فقال أنا رجل من المشرق، أأنت قائل البيت وأنشد البيت. فقال نعم، وذهب الرجل.
فلما كان آخر النهار دق آخر الباب فقال من؟ فقال أنا رجل من المغرب، أأنت قائل البيت وأنشد البيت. فقال نعم، وأنصرف الرجل. فتعجب ابن نباتة كيف وصل البيت إلى المشرق والمغرب.
على ما في القصة من تعسف، ولكن يراد به الإستدلال بشهرة البيت وأهمية الشعر لدى العرب.
وسُبق ابن نباتة إلى هذا المعنى الكثير من الشعراء، فها هو أمية بن الصلت الجاهلي يقول:
يوشِك من فر من مــــنيته ... في بعض غِراتها يوافقها من لم يمت عبطة يمت هرما ... للموت كأس والمرء ذائقه
غراتها تعني بغفلة والضمير راجع إلى الموت، ويوافقها بمعنى يصيبها. أما عبطة فتعني الموت شبابا أو فجأة.
ويقول طرفة بن العبد:
لعمرك إن الموت ما أخطأ الفتى ... لكالطول المُرخى وثنياه في اليد
فشبه الموت " بالطول" وهو الحبل الذي يربط على رقبة البعير أو الشاة. فالحبل مرخي ومثني في يد صاحبه، ولكن الموت حاصل لا محالة ولا مفر منه، والمسألة فقط متى يُشد الحبل.
أما المتنبي فيقول:
نحن بني الموت فما بالنا ... نعاف ما لا بد من شربه
وعاف معناها كره الشيء واستقذاره.
-
 @ 5bd34699:2012648a
2025-01-19 19:11:30
@ 5bd34699:2012648a
2025-01-19 19:11:30This article will be basic instructions for extreme normies (I say that lovingly), or anyone looking to get started with using zap.stream and sharing to nostr.
EQUIPMENT Getting started is incredibly easy and your equipment needs are miniscule.
An old desktop or laptop running Linux, MacOs, or Windows made in the passed 15yrs should do. Im currently using and old Dell Latitude E5430 with an Intel i5-3210M with 32Gigs of ram and 250GB hard drive. Technically, you go as low as using a Raspberry Pi 4B+ running Owncast, but Ill save that so a future tutorial.
Let's get started.
ON YOUR COMPUTER You'll need to install OBS (open broaster software). OBS is the go-to for streaming to social media. There are tons of YouTube videos on it's function. WE, however, will only be doing the basics to get us up and running.
First, go to https://obsproject.com/

Once on the OBS site, choose the correct download for you system. Linux, MacOs or Windows. Download (remember where you downloaded the file to). Go there and install your download. You may have to enter your password to install on your particular operating system. This is normal.
Once you've installed OBS, open the application. It should look something like this...

For our purposes, we will be in studio mode. Locate the 'Studio Mode' button on the right lower-hand side of the screen, and click it.

You'll see the screen split like in the image above. The left-side is from your desktop, and the right-side is what your broadcast will look like.
Next, we go to settings. The 'Settings' button is located right below the 'Studio Mode" button.

Now we're in settings and you should see something like this...

Now locate stream in the right-hand menu. It should be the second in the list. Click it.

Once in the stream section, go to 'Service' and in the right-hand drop-down, find and select 'Custom...' from the drop-down menu.

Remeber where this is because we'll need to come back to it, shortly.
ZAPSTREAM We need our streamkey credentials from Zapstream. Go to https://zap.stream. Then, go to your dashboard.

Located on the lower right-hand side is the Server URL and Stream Key. You'll need to copy/paste this in OBS.

You may have to generate new keys, if they aren't already there. This is normal. If you're interested in multi-streaming (That's where you broadcast to multiple social media platforms all at once), youll need the server URL and streamkeys from each. You'll place them in their respective forms in Zapstream's 'Stream Forwarding" section.

Use the custom form, if the platform you want to stream to isn't listed.
*Side-Note: remember that you can use your nostr identity across multiple nostr client applications. So when your login for Amethyst, as an example, could be used when you login to zapstream. Also, i would suggest using Alby's browser extension. It makes it much easier to fund your stream, as well as receive zaps. *
Now, BACK TO OBS... With Stream URL and Key in hand, paste them in the 'Stream" section of OBS' settings. Service [Custom...] Server [Server URL] StreamKey [Your zapstream stream key]

After you've entered all your streaming credentials, click 'OK' at the bottom, on the right-hand side.
WHAT'S NEXT? Let's setup your first stream from OBS. First we need to choose a source. Your source is your input device. It can be your webcam, your mic, your monitor, or any particular window on your screen. assuming you're an absolute beginner, we're going to use the source 'Window Capture (Xcomposite)'.

Now, open your source file. We'll use a video source called 'grannyhiphop.mp4'. In your case it can be whatever you want to stream; Just be sure to select the proper source.

Double-click on 'Window Capture' in your sources list. In the pop-up window, select your file from the 'Window' drop-down menu.


You should see something like this...

Working in the left display of OBS, we will adjust the video by left-click, hold and drag the bottom corner, so that it takes up the whole display.

In order to adjust the right-side display ( the broadcast side), we need to manipulate the video source by changing it's size.

This may take some time to adjust the size. This is normal. What I've found to help is, after every adjustment, I click the 'Fade (300ms)' button. I have no idea why it helps, but it does, lol.

Finally, after getting everything to look the way you want, you click the 'Start Stream' button.

BACK TO ZAPSTREAM Now, we go back to zapstream to check to see if our stream is up. It may take a few moments to update. You may even need to refresh the page. This is normal.
 STREAMS UP!!!
STREAMS UP!!!A few things, in closing. You'll notice that your dashbooard has changed. It'll show current stream time, how much time you have left (according to your funding source), who's zapped you with how much theyve zapped, the ability to post a note about your stream (to both nostr and twitter), and it shows your chatbox with your listeners. There are also a raid feature, stream settings (where you can title & tag your stream). You can 'topup' your funding for your stream. As well as, see your current balance.
You did a great and If you ever need more help, just use the tag #asknostr in your note. There are alway nostriches willing to help.
**STAY AWESOME!!! **
-
 @ da0b9bc3:4e30a4a9
2025-01-19 18:34:11
@ da0b9bc3:4e30a4a9
2025-01-19 18:34:11Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/855713
-
 @ 592295cf:413a0db9
2024-11-30 08:33:35
@ 592295cf:413a0db9
2024-11-30 08:33:35Week 25 11
Vitor created another social network edit mode. There are countless cases of use. But type threads are possible, small books, Rabbit hole and those who put it more.
nostr:nevent1qvzqqqqqqypzq3svyhng9ld8sv44950j957j9vchdktj7cxumsep9mvvjthc2pjuqyghwumn8ghj7mn0wd68ytnhd9hx2tcqyrewvkqwqt7urn2u9h5tk88vj9p3csl0wt08aqd8kxsngxtdmr0zqmszxds
Nostr Report is missing, was a lot of news, 20 notes in a day.
Some news do not need resonance case, Primal did a good job with trending. Of course is a centralized service. But it was one of the Twitter features, he did it with the top trending hashtags. Now Primal is more focused on DVM smart feed, read, and Discovery. This will bring chaos, as long as you can switch the trend feed with your Algo or DVM Algo. I'm obsessed with these switches 😅
Hostile people can happen along the way, it's not like in Bluesky 😔.
Someone share on Bluesky https://bsky.app/profile/laurenshof.online/post/3lbrsjzobps2u Video is this https://audiovisual.ec.europa.eu/fr/video/I-264553?lg=en
Trying to convince someone for Unanimity, Relay groups are nice, but Unanimity is simpler.
nostr:nevent1qqs9ar5t9xu97nhtwef9ej2y7cklnysf7hgwce7t2wk5axhfdwuq5sqpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgq3qmzyp990kgskujdyplzydmd08ft42mkkfg4lzldaap8ng7n2u3kmss8l76e
Game on Nostr on 2025, cool be.
Angor are finally ready, crowdfunding with Nostr and Bitcoin. (alpha test)
nostr:nevent1qvzqqqqqqypzqw4hcggg2f9h68qutp0snsdhux20teljykjmh9rlx78qwnt5a8dlqqstte0g54hfa2cmr63vq4ava7e7wsr483p63tylvut8cvufzs44a0cd6saa3
PR 1600
The name is curated pubblication use kind 30040 e 30041, 30040 Is the envelope and 30041 are chapters or paragraphs. We'll see what's left in a month. There are no big discussions until now. This is the basis to leave it so, if you can improve it without breaking it ok. I think liminal is preparing at least two other NPs. The bottom problem is that there are no "competitor", someone else outside who wants to use this thing. But if there are no one can invent.
You can't do things with others. There's too "bad" people. Keep calm is a toxin environment. Maybe you have to get away a bit.
I was trying to help David but there are no aggregators for neo4j Nostr. Dustin's example, I think it's only worth the DVM. There are two other projects one grain of Oceanslim I saw the video where he explains some things, with Dr. Morales. And the other is Cody's Nostr Relay tray. At least you have all the data in a Relay, and for that Relay you can query, I don't think you find anything significant, maybe you need 100(k) notes to have a good sample. I think I'll make the update. I downloaded two months ago, it worked for a while with Nostrudel, then only with next, lately some problems with next. Cody launched the project with fiatjaf and I think it is also implemented here. In the end, I don't think this answer is useful to David.
Zapview nostr-zap-view The lokuyow project, always attentive to zap lightning and Nostr.
Give a "microsat" to Fiatjaf nostrabia relay
I managed to send a zap from a hex known id, it only works with getalby, so until January 4th. I have to prove if other lnurls have the call.
Something I might have understood about the new version of Nostr_sdk or rust Nostr. Sending messages will be harder. The builder does not support the tag, it breaks almost all the scripts I was writing and to verify them you can do nothing but send to the Relays, I wait a few days if there are news, but I don't think there will be. It is no longer linked to the table of examples so it will not be updated presumably, I would like to continue, as the cli does not come out. That then the cli will be in python 12.. (I'm still in version 3.10.9 of python)
I've seen bulletin proof, posting on Nostr seems interesting, but they need many interactions to have a functioning client. link, stacker news
Nostr nuance, login, Nostr connect, private. (two Notes)
nostr:nevent1qvzqqqqqqypzq77777lz9hvwt86xqrsyf2jn588ewk5aclf8mavr80rhmduy5kq9qyg8wumn8ghj7mn0wd68ytnddakj7qghwaehxw309aex2mrp0yhxummnw3ezucnpdejz7qpqqqqz3757ha8j5xcm7er8kkdc0dgtvmy55dz2t2d7c2tv9h8qm88qlcjsls
nostr:nevent1qvzqqqqqqypzq9eemymaerqvwdc25f6ctyuvzx0zt3qld3zp5hf5cmfc2qlrzdh0qyt8wumn8ghj7ur4wfcxcetjv4kxz7fwvdhk6tcpzpmhxue69uhkummnw3ezumt0d5hsqgz98qckr40flhpyt48fxqjkuf9p4dv245634ygvp6dfu2kt7qk5egqmc4l8
An other microsat to Fiatjaf chronicle relay
Kind 1 was a mistake and many people are realizing it, they are replacing it. Kind 5 now it is only almost to eliminate drafts, here the option is to overwrite.
That's all!!
-
 @ 592295cf:413a0db9
2024-11-16 10:40:22
@ 592295cf:413a0db9
2024-11-16 10:40:22Week 11-11
Lamenting is becoming something I should ask people who complain. Charity bussiness and after sending zap received to those who do not complain...
I started making an RSS feed template. Open an opml file and check the feed. I called this script,Teed.
This morning I saw a bounty from a fiatjaf note, on a rss-feed long form, basic a plugin for an app. But I'm not doing that, of course, I can also publish it as soon as I'm in charge. Maybe I have some opml files and I want to see if these are still active.
Starter pack is not good apparently creates elites and maybe gives you the feeling of not choosing, but that's what people want. Do not choose but have the illusion of choosing.
Toxicity level. high.
P2P stuff, Iroh is a protocol for syncing & moving bytes iroh computer post on Bluesky
Juraj new project
nostr:nevent1qvzqqqqqqypzpk4kccr9csumnwhmpv83ladqc6p88089cx2e5s2c4448ppgl2pakqqsyv4hs424x6c8phks903s595q2lqp5fpwyq7ajwrf00lxev8cfamcvmq23h
Alex Gleason bunker Knox. (Beta) "knox is a new Nostr bunker CLI for running a NIP-46 remote signer and granting credentials to members of your team". Announcing bunker knox article
Local First podcast, web2.5. Something like Nostr but Local P2P, interesting episode. youtube link
Open Secret AI. "OpenSecret is a backend for app developers that turns private encryption on by default." announcment AI
I think users with regard to algorithms do not want ten different feeds to choose from, but that their feed adapts to their choices, training the feed if this makes sense. So the feed is your feed for your choices, respond and train with them.
Pleblab 2, cool "ANNOUNCING TOP BUILDER SEASON 2! " nostr:nevent1qvzqqqqqqypzpmx02p4slzahlf7jlcaspsx57g6uc7kl7cc7dvhlsnqtpn6khjj0qy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qgwwaehxw309ahx7uewd3hkctcqyzy9w0frd802hfmrp45jr6dqhf7umqj7s63z0jvhv7hvvkcsqjg0vjwd7q4)
It was the real Guardian, quit 7fqx, we know it's you who want to distract us from number go up. The Guardian has left or wants to leave twitter is looking for alternatives, but how to verify a high profile user on Nostr? Nostr Address is already something but it's not enough.
We sometimes think that there is the money tree somewhere is that they magically appear, when instead the money is in the ground but they are dirty.
If Amethyst doesn't support is others stuff
People are simple, they want an app that works for all devices they have. People are "flutter-system".
A podcast feed xml file
Add to teed, if only i had made that option, meanwhile i saw a new interesting project
An other RSS feed github project
Imagine making a file opml with categories and those are your follow nostriches.
The problem is this does not bring new sap to the social chart is important to you, receive the selected posts and it is fantastic. You can also not use Nostr, if you want to use it as backup is fine. Share opml files? It's okay, but you can also find specific sites and find the best. Update for clients, you have a lot of RSS feeds from clients but update after a few hours so if there is really an emergency you lose. I still need to figure out how to integrate Nostr into RSS feed. Maybe an event to make your lists known.
I saw the event in these pr: nostr verified podcast nip #1465 Add audio track NIP #1043
-
 @ 6bae33c8:607272e8
2025-01-20 16:25:00
@ 6bae33c8:607272e8
2025-01-20 16:25:00The 40-minute edited version of Ravens-Bills wasn’t available this morning so I chose the 1:55 commercial-free full-length one instead. What a monumental waste of my morning. Why watch an entire game for it to end via a dropped two-point conversion? What is the purpose of even playing the game? A child can catch a two-yard pass.
Truth be told, the Ravens scored way too early, and the Bills probably would have driven into field-goal range anyway, but in those conditions, no kick was guaranteed. Moreover, the Ravens wouldn’t even have been in that situation but for the retarded play call on the prior two-point try where after Derrick Henry and Justice Hill gashed the Bills for 10 yards every rush, the Ravens tried to get tricky from two-yards out.
Of course, there was also the senseless Lamar Jackson fumble that was returned 40 yards and the earlier Mark Andrews fumble while trying to run backwards for no reason. Just a total waste of time.
I look forward to seeing the Bills win next week, only to have the refs cheat them out of it.
-
The Chiefs got all the calls against a game Texans team. The Texans will be back, especially if they fix the offensive line. Cheating or not, it’s amazing the Chiefs are always in the Conference Title game — this makes seven straight.
-
Travis Kelce looked like he was still in his late prime.
-
I was rooting for the Lions — if only to retain one of my only commenters, Tony, who has no doubt defenestrated and won’t be contributing here any more. Turns out you can’t win without a defense.
-
Jared Goff channeled Sam Darnold at the least opportune time too.
-
Jahmyr Gibbs was electric. If the Lions had a lead he might have had 300 YFS.
-
The Eagles will probably win at home, but Caleb Williams over Jayden Daniels might be even worse than Bryce Young over C.J. Stoud.
-
The Rams were awfully close to hosting the NFC title game. I thought with one minute left, inside the 20, they should have run the ball at least once with the Eagles bringing the rush every play. It only takes one hole, and defenders slipping and sliding everywhere in the snow.
-
Saquon Barkley might be the GOAT when fully healthy. He’s like Derrick Henry with pass-catching skills. I’d love to see him win Super Bowl MVP.
-
It’s amazing how many great backs there are in the league right now: Henry, Barkley, Gibbs and a healthy McCaffrey might be four of the top-10 ever.
-
The Texans, Rams and Ravens arguably outplayed their opponents this weekend, but couldn’t advance. I love the snow game aesthetic, but it adds a lot of randomness.
-
-
 @ 41fa852b:af7b7706
2025-01-19 18:31:45
@ 41fa852b:af7b7706
2025-01-19 18:31:45"It is not the strongest of the species that survive, nor the most intelligent, but the one most responsive to change." -- Charles Darwin
It's usually a big week when the 21st comes around, but this week we have 5 meetups that day!
Also, Trump takes office on Monday so there'll be loads to discuss at this week's meetups.
Let's take a look…
This week's sponsor is…
Upcoming Bitcoin Meetups
Happening this week…
-
Bitcoin Bristol: Meeting at Little Martha Brewing, BS2 0QT. On Tuesday 21st at 18:15. 🍺
-
Bitcoin Surrey: It's a Bitcoin Pension Scheme Special this month at Yiayias at The Fox. A fireside chat and Q&A with Sam Roberts, Cartwright's Director of Investment Consulting (1st UK pension scheme to allocate 3% to Bitcoin). 18:00 - 23:00 on the 21st. Bitcoin accepted at the venue. 🎙️🍻
-
Newcastle upon Tyne Bitcoin Meetup: The next Newcastle meetup is on Tuesday 21st January at Kabin @ Kabannas, L2 6RE. 18:30 PM. 🍻
-
London Bitcoin Space: LBS will be at Cyphermunk house on Tuesday 21st from 18:30 till 22:00 for a social gathering, head along to share knowledge and meet some fellow Bitcoiners. 🫂
-
Oxbit: Celebrate Bitcoins 16th birthday with the Oxford meetup crew. You'll find them at The Old Black Horse (bitcoin accepted) at 19:00 on the 21st. 🍺
-
Preston Bitcoin Meetup: Join the Preston meetup for A Bitcoin chat and some amazing burgers. 18:30 on Thursday the 23rd January. At All Hopes No Promises, PR1 2US.
-
The Northamptonshire Bitcoin Network : BTC Citadel Engineering are hosting a 'Bitcoin Builders' space on Saturday the 25th. Head along to learn about Seedsigners and how to build one. Come and use the 3D printers, get a project started and chat about Bitcoin with everyone there. It all gets started at 12:00. No tech skills are necessary. ⚙️🧡
-
Bitcoin Walk - Edinburgh: Every Saturday they walk around Arthur's Seat in this historic city. Join them at 12 pm to chat about all things Bitcoin and keep fit. 🚶🏻🚶🏼♀️🚶🏽♂️
-
Bitcoin East: Their first meetup of 2025 will be at Marzano Cafe in the beautiful city of Norwich. Join them at 11:00 on Sunday 26th Jan, there's a lot to discuss. ☕️
Get Involved
- Volunteer Opportunities: Bridge2Bitcoin is actively seeking volunteers who share our passion for merchant adoption. We'd be delighted to connect if you're eager to contribute. Reach out to us on Twitter or through our website.
- Start Your Own Meetup: Interested in launching a Bitcoin meetup? We're here to support you every step of the way. We've assisted numerous UK Bitcoin meetups in getting started. Get in touch via Twitter.
- Contribute to BTCMaps: BTCMaps is a vital part of the Bitcoin ecosystem. It's a perfect project to get involved with if you're not a coder or even that technical. A great way to give back to the community. Maintain an area of the UK and keep it up-to-date.
- Telegram users: You might find our Telegram Channel another useful way to keep up-to-date with UK meetups.
- Feedback and Suggestions: We value your input! Share your ideas on how we can enhance this newsletter.
This week's sponsors are…
Get out and support the meetups where you can, visit Bitcoin Events UK for more info on each meetup and to find your closest on the interactive map.
Stay tuned for more updates next week!
Simon.
-
-
 @ eac63075:b4988b48
2024-11-09 17:57:27
@ eac63075:b4988b48
2024-11-09 17:57:27Based on a recent paper that included collaboration from renowned experts such as Lynn Alden, Steve Lee, and Ren Crypto Fish, we discuss in depth how Bitcoin's consensus is built, the main risks, and the complex dynamics of protocol upgrades.
Podcast https://www.fountain.fm/episode/wbjD6ntQuvX5u2G5BccC
Presentation https://gamma.app/docs/Analyzing-Bitcoin-Consensus-Risks-in-Protocol-Upgrades-p66axxjwaa37ksn
1. Introduction to Consensus in Bitcoin
Consensus in Bitcoin is the foundation that keeps the network secure and functional, allowing users worldwide to perform transactions in a decentralized manner without the need for intermediaries. Since its launch in 2009, Bitcoin is often described as an "immutable" system designed to resist changes, and it is precisely this resistance that ensures its security and stability.
The central idea behind consensus in Bitcoin is to create a set of acceptance rules for blocks and transactions, ensuring that all network participants agree on the transaction history. This prevents "double-spending," where the same bitcoin could be used in two simultaneous transactions, something that would compromise trust in the network.
Evolution of Consensus in Bitcoin
Over the years, consensus in Bitcoin has undergone several adaptations, and the way participants agree on changes remains a delicate process. Unlike traditional systems, where changes can be imposed from the top down, Bitcoin operates in a decentralized model where any significant change needs the support of various groups of stakeholders, including miners, developers, users, and large node operators.
Moreover, the update process is extremely cautious, as hasty changes can compromise the network's security. As a result, the philosophy of "don't fix what isn't broken" prevails, with improvements happening incrementally and only after broad consensus among those involved. This model can make progress seem slow but ensures that Bitcoin remains faithful to the principles of security and decentralization.
2. Technical Components of Consensus
Bitcoin's consensus is supported by a set of technical rules that determine what is considered a valid transaction and a valid block on the network. These technical aspects ensure that all nodes—the computers that participate in the Bitcoin network—agree on the current state of the blockchain. Below are the main technical components that form the basis of the consensus.
Validation of Blocks and Transactions
The validation of blocks and transactions is the central point of consensus in Bitcoin. A block is only considered valid if it meets certain criteria, such as maximum size, transaction structure, and the solving of the "Proof of Work" problem. The proof of work, required for a block to be included in the blockchain, is a computational process that ensures the block contains significant computational effort—protecting the network against manipulation attempts.
Transactions, in turn, need to follow specific input and output rules. Each transaction includes cryptographic signatures that prove the ownership of the bitcoins sent, as well as validation scripts that verify if the transaction conditions are met. This validation system is essential for network nodes to autonomously confirm that each transaction follows the rules.
Chain Selection
Another fundamental technical issue for Bitcoin's consensus is chain selection, which becomes especially important in cases where multiple versions of the blockchain coexist, such as after a network split (fork). To decide which chain is the "true" one and should be followed, the network adopts the criterion of the highest accumulated proof of work. In other words, the chain with the highest number of valid blocks, built with the greatest computational effort, is chosen by the network as the official one.
This criterion avoids permanent splits because it encourages all nodes to follow the same main chain, reinforcing consensus.
Soft Forks vs. Hard Forks
In the consensus process, protocol changes can happen in two ways: through soft forks or hard forks. These variations affect not only the protocol update but also the implications for network users:
-
Soft Forks: These are changes that are backward compatible. Only nodes that adopt the new update will follow the new rules, but old nodes will still recognize the blocks produced with these rules as valid. This compatibility makes soft forks a safer option for updates, as it minimizes the risk of network division.
-
Hard Forks: These are updates that are not backward compatible, requiring all nodes to update to the new version or risk being separated from the main chain. Hard forks can result in the creation of a new coin, as occurred with the split between Bitcoin and Bitcoin Cash in 2017. While hard forks allow for deeper changes, they also bring significant risks of network fragmentation.
These technical components form the base of Bitcoin's security and resilience, allowing the system to remain functional and immutable without losing the necessary flexibility to evolve over time.
3. Stakeholders in Bitcoin's Consensus
Consensus in Bitcoin is not decided centrally. On the contrary, it depends on the interaction between different groups of stakeholders, each with their motivations, interests, and levels of influence. These groups play fundamental roles in how changes are implemented or rejected on the network. Below, we explore the six main stakeholders in Bitcoin's consensus.
1. Economic Nodes
Economic nodes, usually operated by exchanges, custody providers, and large companies that accept Bitcoin, exert significant influence over consensus. Because they handle large volumes of transactions and act as a connection point between the Bitcoin ecosystem and the traditional financial system, these nodes have the power to validate or reject blocks and to define which version of the software to follow in case of a fork.
Their influence is proportional to the volume of transactions they handle, and they can directly affect which chain will be seen as the main one. Their incentive is to maintain the network's stability and security to preserve its functionality and meet regulatory requirements.
2. Investors
Investors, including large institutional funds and individual Bitcoin holders, influence consensus indirectly through their impact on the asset's price. Their buying and selling actions can affect Bitcoin's value, which in turn influences the motivation of miners and other stakeholders to continue investing in the network's security and development.
Some institutional investors have agreements with custodians that may limit their ability to act in network split situations. Thus, the impact of each investor on consensus can vary based on their ownership structure and how quickly they can react to a network change.
3. Media Influencers
Media influencers, including journalists, analysts, and popular personalities on social media, have a powerful role in shaping public opinion about Bitcoin and possible updates. These influencers can help educate the public, promote debates, and bring transparency to the consensus process.
On the other hand, the impact of influencers can be double-edged: while they can clarify complex topics, they can also distort perceptions by amplifying or minimizing change proposals. This makes them a force both of support and resistance to consensus.
4. Miners
Miners are responsible for validating transactions and including blocks in the blockchain. Through computational power (hashrate), they also exert significant influence over consensus decisions. In update processes, miners often signal their support for a proposal, indicating that the new version is safe to use. However, this signaling is not always definitive, and miners can change their position if they deem it necessary.
Their incentive is to maximize returns from block rewards and transaction fees, as well as to maintain the value of investments in their specialized equipment, which are only profitable if the network remains stable.
5. Protocol Developers
Protocol developers, often called "Core Developers," are responsible for writing and maintaining Bitcoin's code. Although they do not have direct power over consensus, they possess an informal veto power since they decide which changes are included in the main client (Bitcoin Core). This group also serves as an important source of technical knowledge, helping guide decisions and inform other stakeholders.
Their incentive lies in the continuous improvement of the network, ensuring security and decentralization. Many developers are funded by grants and sponsorships, but their motivations generally include a strong ideological commitment to Bitcoin's principles.
6. Users and Application Developers
This group includes people who use Bitcoin in their daily transactions and developers who build solutions based on the network, such as wallets, exchanges, and payment platforms. Although their power in consensus is less than that of miners or economic nodes, they play an important role because they are responsible for popularizing Bitcoin's use and expanding the ecosystem.
If application developers decide not to adopt an update, this can affect compatibility and widespread acceptance. Thus, they indirectly influence consensus by deciding which version of the protocol to follow in their applications.
These stakeholders are vital to the consensus process, and each group exerts influence according to their involvement, incentives, and ability to act in situations of change. Understanding the role of each makes it clearer how consensus is formed and why it is so difficult to make significant changes to Bitcoin.
4. Mechanisms for Activating Updates in Bitcoin
For Bitcoin to evolve without compromising security and consensus, different mechanisms for activating updates have been developed over the years. These mechanisms help coordinate changes among network nodes to minimize the risk of fragmentation and ensure that updates are implemented in an orderly manner. Here, we explore some of the main methods used in Bitcoin, their advantages and disadvantages, as well as historical examples of significant updates.
Flag Day
The Flag Day mechanism is one of the simplest forms of activating changes. In it, a specific date or block is determined as the activation moment, and all nodes must be updated by that point. This method does not involve prior signaling; participants simply need to update to the new software version by the established day or block.
-
Advantages: Simplicity and predictability are the main benefits of Flag Day, as everyone knows the exact activation date.
-
Disadvantages: Inflexibility can be a problem because there is no way to adjust the schedule if a significant part of the network has not updated. This can result in network splits if a significant number of nodes are not ready for the update.
An example of Flag Day was the Pay to Script Hash (P2SH) update in 2012, which required all nodes to adopt the change to avoid compatibility issues.
BIP34 and BIP9
BIP34 introduced a more dynamic process, in which miners increase the version number in block headers to signal the update. When a predetermined percentage of the last blocks is mined with this new version, the update is automatically activated. This model later evolved with BIP9, which allowed multiple updates to be signaled simultaneously through "version bits," each corresponding to a specific change.
-
Advantages: Allows the network to activate updates gradually, giving more time for participants to adapt.
-
Disadvantages: These methods rely heavily on miner support, which means that if a sufficient number of miners do not signal the update, it can be delayed or not implemented.
BIP9 was used in the activation of SegWit (BIP141) but faced challenges because some miners did not signal their intent to activate, leading to the development of new mechanisms.
User Activated Soft Forks (UASF) and User Resisted Soft Forks (URSF)
To increase the decision-making power of ordinary users, the concept of User Activated Soft Fork (UASF) was introduced, allowing node operators, not just miners, to determine consensus for a change. In this model, nodes set a date to start rejecting blocks that are not in compliance with the new update, forcing miners to adapt or risk having their blocks rejected by the network.
URSF, in turn, is a model where nodes reject blocks that attempt to adopt a specific update, functioning as resistance against proposed changes.
-
Advantages: UASF returns decision-making power to node operators, ensuring that changes do not depend solely on miners.
-
Disadvantages: Both UASF and URSF can generate network splits, especially in cases of strong opposition among different stakeholders.
An example of UASF was the activation of SegWit in 2017, where users supported activation independently of miner signaling, which ended up forcing its adoption.
BIP8 (LOT=True)
BIP8 is an evolution of BIP9, designed to prevent miners from indefinitely blocking a change desired by the majority of users and developers. BIP8 allows setting a parameter called "lockinontimeout" (LOT) as true, which means that if the update has not been fully signaled by a certain point, it is automatically activated.
-
Advantages: Ensures that changes with broad support among users are not blocked by miners who wish to maintain the status quo.
-
Disadvantages: Can lead to network splits if miners or other important stakeholders do not support the update.
Although BIP8 with LOT=True has not yet been used in Bitcoin, it is a proposal that can be applied in future updates if necessary.
These activation mechanisms have been essential for Bitcoin's development, allowing updates that keep the network secure and functional. Each method brings its own advantages and challenges, but all share the goal of preserving consensus and network cohesion.
5. Risks and Considerations in Consensus Updates
Consensus updates in Bitcoin are complex processes that involve not only technical aspects but also political, economic, and social considerations. Due to the network's decentralized nature, each change brings with it a set of risks that need to be carefully assessed. Below, we explore some of the main challenges and future scenarios, as well as the possible impacts on stakeholders.
Network Fragility with Alternative Implementations
One of the main risks associated with consensus updates is the possibility of network fragmentation when there are alternative software implementations. If an update is implemented by a significant group of nodes but rejected by others, a network split (fork) can occur. This creates two competing chains, each with a different version of the transaction history, leading to unpredictable consequences for users and investors.
Such fragmentation weakens Bitcoin because, by dividing hashing power (computing) and coin value, it reduces network security and investor confidence. A notable example of this risk was the fork that gave rise to Bitcoin Cash in 2017 when disagreements over block size resulted in a new chain and a new asset.
Chain Splits and Impact on Stakeholders
Chain splits are a significant risk in update processes, especially in hard forks. During a hard fork, the network is split into two separate chains, each with its own set of rules. This results in the creation of a new coin and leaves users with duplicated assets on both chains. While this may seem advantageous, in the long run, these splits weaken the network and create uncertainties for investors.
Each group of stakeholders reacts differently to a chain split:
-
Institutional Investors and ETFs: Face regulatory and compliance challenges because many of these assets are managed under strict regulations. The creation of a new coin requires decisions to be made quickly to avoid potential losses, which may be hampered by regulatory constraints.
-
Miners: May be incentivized to shift their computing power to the chain that offers higher profitability, which can weaken one of the networks.
-
Economic Nodes: Such as major exchanges and custody providers, have to quickly choose which chain to support, influencing the perceived value of each network.
Such divisions can generate uncertainties and loss of value, especially for institutional investors and those who use Bitcoin as a store of value.
Regulatory Impacts and Institutional Investors
With the growing presence of institutional investors in Bitcoin, consensus changes face new compliance challenges. Bitcoin ETFs, for example, are required to follow strict rules about which assets they can include and how chain split events should be handled. The creation of a new asset or migration to a new chain can complicate these processes, creating pressure for large financial players to quickly choose a chain, affecting the stability of consensus.
Moreover, decisions regarding forks can influence the Bitcoin futures and derivatives market, affecting perception and adoption by new investors. Therefore, the need to avoid splits and maintain cohesion is crucial to attract and preserve the confidence of these investors.
Security Considerations in Soft Forks and Hard Forks
While soft forks are generally preferred in Bitcoin for their backward compatibility, they are not without risks. Soft forks can create different classes of nodes on the network (updated and non-updated), which increases operational complexity and can ultimately weaken consensus cohesion. In a network scenario with fragmentation of node classes, Bitcoin's security can be affected, as some nodes may lose part of the visibility over updated transactions or rules.
In hard forks, the security risk is even more evident because all nodes need to adopt the new update to avoid network division. Experience shows that abrupt changes can create temporary vulnerabilities, in which malicious agents try to exploit the transition to attack the network.
Bounty Claim Risks and Attack Scenarios
Another risk in consensus updates are so-called "bounty claims"—accumulated rewards that can be obtained if an attacker manages to split or deceive a part of the network. In a conflict scenario, a group of miners or nodes could be incentivized to support a new update or create an alternative version of the software to benefit from these rewards.
These risks require stakeholders to carefully assess each update and the potential vulnerabilities it may introduce. The possibility of "bounty claims" adds a layer of complexity to consensus because each interest group may see a financial opportunity in a change that, in the long term, may harm network stability.
The risks discussed above show the complexity of consensus in Bitcoin and the importance of approaching it gradually and deliberately. Updates need to consider not only technical aspects but also economic and social implications, in order to preserve Bitcoin's integrity and maintain trust among stakeholders.
6. Recommendations for the Consensus Process in Bitcoin
To ensure that protocol changes in Bitcoin are implemented safely and with broad support, it is essential that all stakeholders adopt a careful and coordinated approach. Here are strategic recommendations for evaluating, supporting, or rejecting consensus updates, considering the risks and challenges discussed earlier, along with best practices for successful implementation.
1. Careful Evaluation of Proposal Maturity
Stakeholders should rigorously assess the maturity level of a proposal before supporting its implementation. Updates that are still experimental or lack a robust technical foundation can expose the network to unnecessary risks. Ideally, change proposals should go through an extensive testing phase, have security audits, and receive review and feedback from various developers and experts.
2. Extensive Testing in Secure and Compatible Networks
Before an update is activated on the mainnet, it is essential to test it on networks like testnet and signet, and whenever possible, on other compatible networks that offer a safe and controlled environment to identify potential issues. Testing on networks like Litecoin was fundamental for the safe launch of innovations like SegWit and the Lightning Network, allowing functionalities to be validated on a lower-impact network before being implemented on Bitcoin.
The Liquid Network, developed by Blockstream, also plays an important role as an experimental network for new proposals, such as OP_CAT. By adopting these testing environments, stakeholders can mitigate risks and ensure that the update is reliable and secure before being adopted by the main network.
3. Importance of Stakeholder Engagement
The success of a consensus update strongly depends on the active participation of all stakeholders. This includes economic nodes, miners, protocol developers, investors, and end users. Lack of participation can lead to inadequate decisions or even future network splits, which would compromise Bitcoin's security and stability.
4. Key Questions for Evaluating Consensus Proposals
To assist in decision-making, each group of stakeholders should consider some key questions before supporting a consensus change:
- Does the proposal offer tangible benefits for Bitcoin's security, scalability, or usability?
- Does it maintain backward compatibility or introduce the risk of network split?
- Are the implementation requirements clear and feasible for each group involved?
- Are there clear and aligned incentives for all stakeholder groups to accept the change?
5. Coordination and Timing in Implementations
Timing is crucial. Updates with short activation windows can force a split because not all nodes and miners can update simultaneously. Changes should be planned with ample deadlines to allow all stakeholders to adjust their systems, avoiding surprises that could lead to fragmentation.
Mechanisms like soft forks are generally preferable to hard forks because they allow a smoother transition. Opting for backward-compatible updates when possible facilitates the process and ensures that nodes and miners can adapt without pressure.
6. Continuous Monitoring and Re-evaluation
After an update, it's essential to monitor the network to identify problems or side effects. This continuous process helps ensure cohesion and trust among all participants, keeping Bitcoin as a secure and robust network.
These recommendations, including the use of secure networks for extensive testing, promote a collaborative and secure environment for Bitcoin's consensus process. By adopting a deliberate and strategic approach, stakeholders can preserve Bitcoin's value as a decentralized and censorship-resistant network.
7. Conclusion
Consensus in Bitcoin is more than a set of rules; it's the foundation that sustains the network as a decentralized, secure, and reliable system. Unlike centralized systems, where decisions can be made quickly, Bitcoin requires a much more deliberate and cooperative approach, where the interests of miners, economic nodes, developers, investors, and users must be considered and harmonized. This governance model may seem slow, but it is fundamental to preserving the resilience and trust that make Bitcoin a global store of value and censorship-resistant.
Consensus updates in Bitcoin must balance the need for innovation with the preservation of the network's core principles. The development process of a proposal needs to be detailed and rigorous, going through several testing stages, such as in testnet, signet, and compatible networks like Litecoin and Liquid Network. These networks offer safe environments for proposals to be analyzed and improved before being launched on the main network.
Each proposed change must be carefully evaluated regarding its maturity, impact, backward compatibility, and support among stakeholders. The recommended key questions and appropriate timing are critical to ensure that an update is adopted without compromising network cohesion. It's also essential that the implementation process is continuously monitored and re-evaluated, allowing adjustments as necessary and minimizing the risk of instability.
By following these guidelines, Bitcoin's stakeholders can ensure that the network continues to evolve safely and robustly, maintaining user trust and further solidifying its role as one of the most resilient and innovative digital assets in the world. Ultimately, consensus in Bitcoin is not just a technical issue but a reflection of its community and the values it represents: security, decentralization, and resilience.
8. Links
Whitepaper: https://github.com/bitcoin-cap/bcap
Youtube (pt-br): https://www.youtube.com/watch?v=rARycAibl9o&list=PL-qnhF0qlSPkfhorqsREuIu4UTbF0h4zb
-
-
 @ bf7973ed:841ad12a
2025-01-19 17:34:16
@ bf7973ed:841ad12a
2025-01-19 17:34:16Today marked the end of the tik tok era (is it really the end?) and if think it shows how powerful social engineering is. People are experiencing withdrawals and some have resorted to a more dangerous drug (Rednote) which I find funny because they can't understand any writing in the app. They just need that cheap thrill.
Social media was first created to keep in tough with friends and family and possibly make new friends. It wasn't long before social media was turned into for profit advertising platforms. This introduced "The Algorithm" to make the experience more "relatable" to users. This is where the addiction began.
Nostr doesn't have an algorithm. It is a place to keep in touch with family, friends and make a lot of new friends. Nostr is a protocol at heart. Nostr is a place for everyone. A true freedom of speech. A place with no controlling autority. Nostr is what social media was meant to be.
-
 @ 26cdfd8d:245f55f1
2025-01-19 14:34:45
@ 26cdfd8d:245f55f1
2025-01-19 14:34:45Não vejo a hora de testá-lo também na versão Desktop.
Até o momento recomendando...
-
 @ eac63075:b4988b48
2024-10-26 22:14:19
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ ce6b432f:c07ce020
2025-01-20 15:52:57
@ ce6b432f:c07ce020
2025-01-20 15:52:57If you think I can’t blame the scale of devastation from the LA fires on the Federal Reserve - think again.
After the 2008 financial crisis, Tyler Cowen was fond of saying “we aren’t as rich as we thought we were”. If you ask him, (I did in a zoom call sometime in the last 2 years), he thinks this state of being was temporary. My belief is that 17 years later, this illusion still persists, but it is cracking. Instead of allowing the dead wood to burn through financial markets, QE, ZIRP, BTFP, TARP, foreign central bank swap lines, Repo, Reverse Repo, double-triple-just kidding-repo, and a variety mechanisms beyond comprehension have been deployed to create the impression of wealth. We are still much less wealthy than we thought we were even 4 years ago. Until 2021, this was confined mainly to the inflation of asset prices and the stealth inflation embodied in the deteriorating quality of consumer goods, but Covid stimmies injected enough liquidity directly into the consumer blood stream that CPI finally started blinking red. The public began to gain some awareness of a more concrete problem in the structure of our economy. The pressing problem of inflation exposed first order problems of real urgency. A real wake up call had arrived for those middle class and below on the socio-economic ladder. There is no shortage of material to read on this for the curious.
Now some of the bills are coming due for the top half of the economic spectrum. When a plane you’re on falls out of the sky, it doesn’t matter how big your bank account is. When wildfire driven by 100 mph winds hits a neighborhood with empty fire hydrants, adequate water isn’t available at any price. When you realize your 22 year old child has spent the last 16 years being indoctrinated into a camouflaged marxist worldview - parenting mulligans are not available. If you want to retire with a nest egg adequate to provide food, shelter and healthcare for the rest of your life, finding out at age 65 that a good portion of your portfolio has been allocated to ‘companies’ focused on not cutting down trees will not be a fun reason to put down for “why do you want to join the WalMart Team?”. The common thread across many of these items is what used to be called “mission creep”. Leveraging the modern love of the word diversity - I call it “A Diversity of Goals”. They are both deadly for any organization tasked with important and specific goals.
Boeing should be focused on building safe airplanes. Fire departments should be focused on minimizing the damage fire does in their communities. Schools should prioritize reading, writing, arithmetic, and critical thinking skills. Financial professionals should focus on their fiduciary duties.
How did everyone take their eye off of the ball? Everyone decided to add the goal of diversity in some way shape or form. Is it really that simple? No. Was it really that bad? Yes. In a recent podcast with Russ Douthat of the NYT, Marc Andreeson says some pretty shocking things. Link to Transcript
Andreessen: "I’ll speak for the group because there’s a lot of similarities between the different players here for the same pressures. I’ll just speak for the group.
First of all, let me disabuse you of something, if you haven’t already disabused yourself. The view of American C.E.O.s operating as capitalist profit optimizers is just completely wrong.
That’s like, Goal No. 5 or something. There’s four goals that are way more important than that. And that’s not just true in the big tech companies. It’s true of the executive suite of basically everyone at the Fortune 500.
I would say Goal No. 1 is, “I’m a good person.” “I’m a good person,” is wildly more important than profit margins. Wildly. And this is why you saw these big companies all of a sudden go completely bananas in all their marketing. It’s why you saw them go bananas over D.E.I. It’s why you saw them all cooperating with all these social media boycotts. I mean, the level of lock step uniformity, unanimity in the thought process between the C.E.O.s of the Fortune 500 and what’s in the pages of The New York Times and in the Harvard classroom and in the Ford Foundation — they’re just locked together. Or at least they were through this entire period."
If you don’t believe this is the case, you weren’t paying attention. Centralized asset managers like Blackrock who are usually one of the largest shareholders in every company were sending out notices to CEOs and the markets trumpeting how much they prioritized DEI. Blackrock, the ESG Bully - WSJ
BlackRock Inc. has so far increased its support for shareholder-led environmental, social and governance proposals, and published a slew of criticisms of public companies that haven’t bent to its overall requests. …
“BlackRock has strongly signaled that quiet diplomacy is not the only tool in its toolbox,” said Rich Fields, a partner at law firm King & Spalding who focuses on corporate-governance issues. “We expect more votes for shareholder proposals and against directors in this and future years.” …
The firm is one of the top three shareholders of more than 80% of the companies in the S&P 500, according to S&P Global Market Intelligence, through its many funds. The money manager casts a long shadow on shareholder meetings where it can vote on behalf of its investors on board directors, executives’ pay packages and other company matters.
In all fairness, Blackrock is quickly moving away from its ESG focus as the level of nonsense here has become more obvious to larger audiences who are pushing back. (State pension funds dropping them over this was a great example of both Federalism and market forces at work.)
Read the entire transcript from Andreeson. He lays out a very compelling case for what happened when a new generation of employees/elites rolled into adulthood in the 2010’s. The between-the-lines punchline is “it got so bad that billionaires were starting to suffer!!”
If DEI could infect and inhibit performance of large for-profit companies, what do you think the impact was on organizations with far less accountability? If your budget comes from politicians who don’t have to balance budgets or produce concrete results, the amount of drift “off mission” could be and was severe.
Why did this happen? We thought we were so rich that we could afford to entertain these luxury beliefs. We could just add more goals to our plate without diluting our ability to accomplish the very important things these various organizations were supposed to be focused on. We aren’t as rich as we thought we were. We can’t afford for planes to fall out of the sky. We can’t afford for huge sections of large cities to burn down. We can’t afford for an entire generation of Americans to prefer marxism to capitalism. We can’t afford to waste money on feel good projects that have a negative return even before factoring in inflation.
The simplest immediate action to take is for stakeholders large and small in organizations of all sizes to say no more Diversity of Goals - no more Goals of Diversity. Don’t discriminate against anyone who can accomplish the organization’s goals, but the goals must come first. If it’s your church or your local fire department or the local school district - everyone can have an impact on their own community. One by one, we can reverse this trend. Be the change you want to see in the world.
Now - what I think is the root of the problem. Why aren’t we as rich as we thought we were? I just can’t help myself. You may not agree on the solution (I do) - but this description of the problem will give you pause.
-
 @ fd208ee8:0fd927c1
2025-01-19 12:10:10
@ fd208ee8:0fd927c1
2025-01-19 12:10:10I am so tired of people trying to waste my time with Nostrized imitations of stuff that already exists.
Instagram, but make it Nostr. Twitter, but make it Nostr. GitHub, but make it Nostr. Facebook, but make it Nostr. Wordpress, but make it Nostr. GoodReads, but make it Nostr. TikTok, but make it Nostr.
That stuff already exists, and it wasn't that great the first time around, either. Build something better than that stuff, that can only be brought into existence because of Nostr.
Build something that does something completely and awesomely new. Knock my socks off, bro.
Cuz, ain't nobody got time for that.
-
 @ 592295cf:413a0db9
2024-10-26 13:39:00
@ 592295cf:413a0db9
2024-10-26 13:39:00[Week 21-10] I thinks that Saylor is on right, don't trust verify, is bullshit Bitcoin is a financial tool! I think it's good for me to get away from social media once a week. I could do things outside, like walking. Take pictures of the landscape. The weirdest thing is when the alarm calls you up in an hour.
Fiatjaf wants a cache client. I feel like I can do it, I have the set to do it, but nostrudel is no longer working, so it's a little murky. Next nostrudel does not accept changes to settings (It works now!), so maybe i can think something. I want to make a corny chat, test, read this article. Nostr doesn't work with a vpn because relays don't know who you are. jokes aside, some clients have difficulties.
I couldn't take pictures of the landscape if I didn't take the wind blades. Small local controversy.
Missing the point of content creator. Simply for final user, Simply for the creator, new feature, no missing nothing. I'm trying to limit everything to writing for a week. I almost did. Maybe another week can do well.
Meanwhile I updated apps like Amber and Voyager, coracle, nostrmo.
The experiment continues with open vibe following the trending of Nostr. I'm following almost 120 npub. He'll stop, I don't know, possible he's already reached the limit. You still can't block words on the Nostr side of Open, strange thing. The app doesn't count the follow well, still some problem cleaning the cache seems that it doesn't need. After a while open and close and seems updated. I wanted to try open librarian, but I was busy sending fake zap on Nostr. This morning i try and It keeps giving me error 500 when I try to connect to a relay.
I hate when a profile follows everyone indistinctly, why does everyone follow? and in voyage, I read with WoT setting, I probably have to do unfollow. There must be an indication in which not include the followers of this person in the web of trust, I would do it by default if you follow more than 600 people.
WoT on Nostr Visualized post on stackernews
-
 @ 0bedd900:2d6b8c9d
2025-01-20 14:59:48
@ 0bedd900:2d6b8c9d
2025-01-20 14:59:48Humanoid robots are no longer just ideas. They're here, becoming part of industries, homes, and, perhaps soon, our public spaces. The possibilities they bring are exciting, but the risks are hard to ignore. Chief among them is the question of control—who decides what these robots do and why?
Right now, the answer to that question is troubling. Power over robots is mostly concentrated in the hands of a few corporations and governments. This might seem efficient, but it opens the door to scenarios that should give us pause. Imagine a fleet of humanoid robots controlled by a single entity. What would that mean for those without access to such tools? For democracy? For freedom?
 \
But what if it didn’t have to be that way? What if robots could be owned and governed collectively? What if their purpose wasn’t to serve the interests of the few, but to ensure balance and equity for the many?
\
But what if it didn’t have to be that way? What if robots could be owned and governed collectively? What if their purpose wasn’t to serve the interests of the few, but to ensure balance and equity for the many?Decentralization presents an alternative, albeit a difficult one. Instead of placing control in the hands of a single company or government, it envisions distributing authority across networks of individuals, groups, or communities. Open-source software could provide transparency into the inner workings of these robots, while blockchain systems might offer mechanisms for consensus-based decision-making. These concepts are far from fully realized, but they hint at a future where power is not hoarded but diffused.
However, the path to decentralization is fraught with challenges. These systems are not only complex to build but even harder to manage effectively. They demand significant technological innovation, robust ethical guardrails, and perhaps most critically, a foundational level of trust among participants. Yet the potential payoff—mitigating the risks of domination and ensuring robots serve the interests of the many, not the few—makes these difficulties worth grappling with.
The urgency for reflection cannot be overstated. Centralized systems are simpler to implement, but their efficiency comes at a cost: they concentrate power and introduce risks that, once entrenched, may prove impossible to dismantle. Decentralized models, while more demanding, could provide the structural safeguards needed to align robotic systems with collective values rather than narrow interests.
There is no clear or easy solution, but ignoring these issues as robots increasingly integrate into our world is not an option. The stakes are profound, and the consequences of inaction could define our societal trajectory. If we are to shape a future where technology serves humanity rather than controls it, these conversations need to start now.
-
 @ 71a4b7ff:d009692a
2025-01-19 10:20:02
@ 71a4b7ff:d009692a
2025-01-19 10:20:02The Problem with Preset Choices
Switching sections around? Not an option—we’ve already decided for you, buddy. Remove bright colors? Come on, it’s already beautiful. Disable unnecessary features? Don’t be silly, you need everything here. Especially this algorithmic feed with built-in ads.
Monetization Over User Experience
The operators of digital services will always prioritize their primary goal: monetizing the product as efficiently as possible. They need to not only attract new users but also retain existing ones. And the best tool for this is the interface.
That’s why most product decisions are far removed from ideas like “Let’s make it more convenient for people” or “Let’s give users more freedom.” Instead, we see the result of a recurring process:
- We have a retention and monetization mechanism
- Assign tasks to developers and designers
- Integrate it into the product
- Write a quarterly report.
The outcome? Users end up with Reels tabs smack in the center of Instagram’s bottom navigation bar. Removing or rearranging those tabs? Not an option. And it likely never will be.
Why Rigid Interfaces Persist
Another reason for rigid and obligatory interfaces is that they’re easier to design. Just imagine how many combinations of colors, elements, and layouts developers would need to account for to make a product both customizable and functional without turning it into a garish mess. But that’s just nuance and excuses.
The Myth of Perfect Design
Services often justify their choices by claiming their design is “the most designed,” that they know what’s best and will make it work for everyone. They might even present solid arguments for this. But all those arguments fall apart against the reality we see on our screens every day. In my opinion, people should have the ability to turn a product into anything they want—whether it’s loud and kitschy or minimalistic and dull. This option wouldn’t just allow users to express themselves but could also help with digital detoxing.
The Example of App Labels
Here’s an example: why do app icons on smartphone home screens (not the app drawer) come with labels underneath? Apps on the home screen are easily recognizable by their icons. Why would I need a name tag for an app I intentionally placed there? Sure, for some users or scenarios, this might be helpful. But why is it the default option?
The problem is that these labels are just visual noise—clusters of unnecessary text we already see plenty of. Removing them would make it slightly easier for the brain to process the screen every time you look at it. Now scale that to 3–8 hours of daily smartphone use. Then a month. Then a year.
The Slow Shift Toward Customization
For a long time, iOS didn’t allow you to hide icon labels. Now, the option exists, but it still requires more effort than a simple toggle. As a result, people are stuck looking at tons of unnecessary, subconscious information every day. And this is just the trivial issue of app labels on a product considered the gold standard of digital design. Imagine the horror of tackling more significant issues.
Yes, Apple has softened its stance in recent years, offering custom icons and lock screens. Celebrate—you can now showcase your individuality! The company understands that customization is the future. We’ve reached a point where weak computing power is no longer an excuse, VR/metaverse adoption is still a way off, and new features are needed. So, this is an excellent opportunity for all of us.
The Case for More Customization
In a reasonable, ideal world, people should decide which sections of a service they need, where they’re located, and how they look. Companies, meanwhile, recognize that people want the ability to stand out and create something personal—even on a smartphone in their pocket. And as our integration with various devices deepens, this need will only grow. More customization is coming. Yes, it’ll be largely cosmetic, but even that can work to our advantage: removing jarring colors or hiding unnecessary labels can reduce the brain’s pointless load.
Beyond Aesthetics: Customization as Freedom
The ability to customize services isn’t just about playing amateur designer. It’s about mitigating informational irritants, reducing the addictive nature of interfaces, and weakening dark patterns. Which is likely why many companies no longer prioritize customization.
Telegram: A Customizable Example
In this context, Telegram is a decent example. I’m not a fan, but I’ve been using it for daily communication with loved ones for a long time—and it’s good for that. It can be vastly different for vastly different users. Despite starting to bend under the weight of its audience and introducing questionable decisions, its foundational design principles still allow for creating both minimalist spaces for peaceful content consumption or communication, as well as vibrant, noisy chats for virtual parties. Telegram can be a messenger, a feed, a file storage system, or whatever else you need—and it can look wildly different while doing so.
Customization as the Key to Healthy Digital Relationships
Customization should be at the core of the services we use daily. Yes, it can and will be used for marketing purposes. But even minimal customization is better than none because the ability to tailor a system to your needs is an expression of freedom and a cornerstone of healthy relationships with the digital world.
Stay Nostrous. Geo
-
 @ eac63075:b4988b48
2024-10-21 08:11:11
@ eac63075:b4988b48
2024-10-21 08:11:11Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.

Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.

The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.

Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.

The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.
 Table reference: Patrick Breyer - Chat Control in 23 September 2024
Table reference: Patrick Breyer - Chat Control in 23 September 2024Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.

The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.

User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.

The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.

Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ 96537107:334e9245
2025-01-19 07:39:54
@ 96537107:334e9245
2025-01-19 07:39:54有多少人在排队中?产业趋势不可逆~~~
-
 @ 4d41a7cb:7d3633cc
2025-01-20 14:33:39
@ 4d41a7cb:7d3633cc
2025-01-20 14:33:39Anyone concerned with private property, survival, and freedom will find the material in this article to be very interesting. The concept of money is more abstract than most people think, and that is what I will try to demonstrate below.
Whether the film The Wizard of Oz's hidden message was intentional or not, it serves as an allegory to explain the grim and gruesome global monetary system.
The 1939 film The Wizard of Oz, based on L. Frank Baum's 1900 novel, contains hidden allegories about the banking system and financial challenges of late 19th and early 20th century America. The film closely resembles the book, except for two minor details: The yellow road in the film was the golden road in the book, and the ruby shoes in the film were silver shoes in the book: a clear reference to the bimetallic monetary system of the U.S. at the time.
The occult meaning explained
The word ‘OZ’ is a clear reference to the ‘ounce,’ a unit of measurement for gold and silver, further emphasizing the connection to monetary issues.
We can see The Wizard of Oz as an allegory for the new state of affairs in the United States in the 1930s, following the stock market crash and the bankruptcy of the US government immediately afterwards.
The play gives an allegorical sense of the financial enslavement of taxpayers, the legal tricks, and sensory manipulations bankers and government officials use to impose such enslavement on taxpayers. It also exposes the banking cartel, letting the people know that they are empowered to liquidate the bankers and return to Kansas: the true Republic.
The setting was Kansas: the heartland of America and the geographical center of the USA. The tornado (1929-1933), a whirlwind of turmoil that includes the stock market crash, the theft of American gold, the bankruptcy of the USA, and the Great Depression, sweeps in, transporting Dorothy and Toto to a new artificial dimension somewhere above the Kansas mainland. When they finally land in Oz, Dorothy remarks to her little companion:
‘Toto, I have a feeling we're not in Kansas anymore.’.
After the bankruptcy, Kansas was no longer simply the old 'Kansas'; it was now 'KS,' the artificial corporate headquarters of the bankrupt United States, a newly established 'federal territory,' part of the 'Federal Zone,' and Dorothy and Toto were 'in this state.'
The creditors of THE FEDERAL RESERVE INC. had declared the constitutional republic of the United States of America bankrupt and replaced it with a private corporation of the same name, UNITED STATES INC.
For those of you who are not yet aware, there was a conspiracy during the last two centuries to steal the world's money supply (gold & silver) and replace it with a global elastic fiat credit system. The design of this system was to transfer wealth from the productive class of world nations to the unproductive class of international bankers, resulting in artificial boom and bust cycles and private and public bankruptcies.
This happened in the United States during the beginning of the 1900s, especially from 1913, when the Federal Reserve was created, to 1933, when they stole all the gold from the American people after destroying their economy and prosperity.
International bankers had taken over the republic, but Americans were too confused and distracted by the turmoil at the time to realize this. A corporate state operating under commercial law had supplanted the constitutional republic operating under common law. At the same time, the Federal Reserve banking cartel would receive 100% of the present and future tax revenue from Americans.
The golden road
The book refers to the 'yellow road' as 'the golden road'. To locate the Wizard, you must track the money, specifically the stolen gold, which will lead you to the thief.
When the US government declared bankruptcy in 1933, Americans were required to turn in all their gold coins, gold bullion, and gold certificates by May 1, May Day (the birthday of communism in Bavaria in 1776, the birthday of the IRS, and celebrated worldwide as the ‘International Workers’ Holiday,’ a day sacred to the Wizard and his tribe). 1
By following the path of gold and its history, we can quickly get to the banking cartel and discover many of their methods and crimes. Even before they stole America, they had long since disposed of the Christian monarchies of Europe and plundered their kingdoms.
By examining significant dates like 1971, 1944, 1933, and 1913, we can swiftly identify the individuals responsible for shaping human history over the past few centuries.
Following the history of the gold standard, we can arrive at the creation of the Federal Reserve and the international banking cartel that owns and controls it, the Wizard of Oz, whose origin is from Europe.
The Emerald City
The Emerald City, where everything is green, is seen as a metaphor for the Federal Reserve and its fiat currency: Federal Reserve Notes, or FRNs (fiat ‘money’ or ‘money by fiat’). There the legendary wizard of Oz took refuge, with his mythical and omnipotent power to manipulate the interest rates and the supply of currency.
The illusory prosperity of the city reflects that currency itself is an illusion, especially when disconnected from gold or silver. By printing trillions of Federal Reserve notes to finance wars, purchase mass media, fund research and development, and purchase professionals and politicians, the magician maintains his position of power and the illusion of 'official authority'.
This currency creates a false sense of abundance when in fact it destroys the incentives for trade and creates inequality and injustice. The Great Depression of the 1930s, the confiscation of gold, and the two subsequent world wars were a direct result of the actions of the Federal Reserve, formed in 1913, a predecessor from the Bank of England, where the real power behind this entity lies.
The Federal Reserve is not federal and has no reserves; it is just the corporate name for private enterprise with an absolute monopoly on global credit. The illusion that it is part of the government or that it has legitimate authority is just that, an illusion; in reality, it is a cartel of private bankers with a monopoly on debt-based global currency.
The Wizard of Oz
One definition of 'wizard' is 'a very clever person'. The Wizard is a symbol of the banking cartel, which manipulates and controls people behind the scenes. They hide behind corporate names that do not even represent what they stand for, such as the Federal Reserve, United States, British crown, and Vatican.
Using smoke and mirrors, they create a grand illusion of omnipotent and omniscient power as if they were gods on earth. The magician represents the idea that the powerful often only manipulate perception instead of offering real solutions. However, upon exposing them, we uncover that they are merely common men, burdened with fears, insecurities, greed, and a significant dose of evil.
We know very well that the banking cartel controls educational institutions, the media, book publishers, and every flow of information and resources; thus and only thus can it manipulate the perception of billions of human beings around the world.
All of humanity is in a state of financial slavery to the illusionist's counterfeit money, which silently steals the time and energy of the masses on a global scale—their most precious wealth. The Wizard has owned the US government outright since 1933 and ‘owned’ Hollywood, an indispensable resource for maintaining global illusion and false perception.
‘You can fool all the people some of the time, and some of the people all the time, but you can't fool all the people all the time.’.
Abraham Lincoln (1809-1865), 16th President of the United States
After all, the wizard turned out to be just a con man, a fraud; behind the curtain there was just an ordinary person controlling the levers that created the illusion of authority and power.
The magician also cited the Latin phrase 'the land of E' Pluribus Unum,' meaning 'one among many'. This means that the phrase 'the land of E' Pluribus Unum', which translates to 'one among many', symbolises the merging of many into one, thereby establishing the New World Order, also known as Novus Ordo Seclorum. This phrase was prominently displayed on the US dollar note shortly after the crash in 1934.

The agenda of the international banking cartel is the ultimate elimination of cash, the total digitalization of credit, and the creation of a programmable global digital currency. Together with a social credit system and absolute surveillance, they seek to create a global police state to keep their taxpaying slaves in check and prevent any possibility of rebellion. By censoring dissent and controlling the flow of information, energy, and money, they plan to crown themselves on the throne forever.
The magician's main tools to maintain his economic power: DEBT, TAXES, AND INFLATION. Tools we must understand in depth to regain financial freedom and 'return to Kansas,' our true constitutional republic.
The Wicked Witch of the West
The Wicked Witch of the West made her home in a round medieval watchtower, the ancient symbol of the Knights Templar of Freemasonry, who were given to practicing witchcraft and are also credited with being the originators of modern banking, circa 1099 AD.
The Wicked Witch of the West wore black, a color that represented the planet Saturn, the Knights Templar's sacred icon, and the color judges and priests chose for their robes. Who was the Wicked Witch of the West? Remember, in the first part of the film, her counterpart was 'Almira Gulch,' who, according to Auntie Em, 'owned half the county.' Miss Gulch claimed that Dorothy's dog, Toto, had bitten her. Miss Gulch arrived at the farm with a'sheriff's warrant', demanding the release of Toto into her custody. Aunt Em was not immediately cooperative and responded to Miss Gulch's accusations that Toto had bitten her by saying, "He's very nice." With nice people, of course.
Miss Gulch's challenge to hold Toto and 'go against the law' reduced dear Auntie Em to 'pushing the party line' for Big Brother. She dutifully succumbed to the pressure and reluctantly advised Dorothy:
‘If you don't give me that dog, I'll bring you a goddamn suit that took over your whole farm!’
Today, 70% of all lawyers in the world reside in Western America, to be exact, and 95% of all lawsuits in the world are filed under the jurisdiction of the United States. The Wicked Witch of the West and Miss Gulch, my dear friends, stand in for judges and lawyers, specifically the American legal system, which includes the lawyer-led Congress and White House. They act as executioners and chief henchmen, transferring all wealth in America from the people to the ownership of banks and the government.
The Wicked Witch of the West wanted the silver slippers and precious metals, and her counterpart, Miss Gulch, wanted Toto (i.e., everything). We know all too well that banks are never satisfied and seek to squeeze every last penny from taxpayers, because it's not just about money; it's about control.
The straw man
The straw man wanted a brain from The Wizard of Oz. The term "straw man" in English refers to the legal fiction, legal person, or capitalized names that the US federal government creates using our natural-born names, with the intention of enslaving us and supporting the issuance of debt-based currency. The birth certificate, which establishes our legal fiction, serves as the tool for bolstering the issuance of public debt and currency.
The FRN, also known as the 'dollar,' represents a blank check that the US taxpayer has signed for the government. No legal person, paper legal fiction, or corporation has a brain nor a breath of life. They are just that: legal fictions and paperwork.
What does a straw man possess in place of a brain? A certificate. He took immense pride in his newly acquired legal status and all the other privileges bestowed upon him. Despite receiving a certificate, he remained a naive individual devoid of common sense.
The Tin Man (TIN)
The tin man symbolizes the taxpayer, specifically the workers. The IRS uses the TIN, a nine-digit number, to identify taxpayers for tax purposes. It can be a Social Security number (SSN), an individual taxpayer identification number (ITIN), or an employer identification number (EIN).
Just as the scarecrow/straw man had no brain, this tin man vessel had no heart. Both were ‘artificial persons.’. The Tin Man symbolized the mechanical and heartless nature of commerce and commercial law.
The Tin Man stood there, mindlessly engaged in his work, until his body literally overflowed and ceased to function. He exhausted himself due to his lack of heart and soul.
The heartless and soulless taxpayer/worker serves as nothing more than a useful slave to the banking cartel, fulfilling his "duty" without questioning the moral implications of his actions. Governments and banks rely on them for their income, and they labor diligently under their control.
‘I was just doing my job’ is one of the most common responses when re-evaluating the immoral acts they were complicit and co-conspirators in throughout history.
Today, thousands of distractions, vices, drugs, and products hypnotize them in front of a television or mobile phone screen, preventing them from realizing their role as tax slaves and hearing the call to a higher purpose in life.
These completely demoralized individuals lose sight of their life's purpose and value, which explains why there are so many cases of depression and suicide in today's world.
This is done by design: the banking cartel's agenda is to maintain the tax slaves' cold exterior and heartless interior in order to suppress any potential emotional reactions or divine sparks.
The cowardly lion
The cowardly lion was always afraid to stand up for himself, representing the American people who had lost their courage and bravery.
‘The land of the free and the home of the brave’ became the land of the slaves and the home of the cowards.
The cowardly lion, seeking the courage of the great wizard, received an official recognition medal. Now, although he was still a coward, his official status allowed him to be a bully, but with officially recognized authority, like lawyers or military men who hide behind courts and medals.
Have you ever noticed how bullies are actually the biggest cowards who act as if they have enormous courage but in reality have none?
It's fascinating how many weak, socially resentful, and cowardly individuals gravitate towards positions of power to conceal their cowardice and weakness. They require a position of 'authority' and often misuse it, concealing their weaknesses and insecurities behind official bodies.
The poppy field
The tactic was to cover the field with poppy flowers, the source of heroin, opium, and morphine, symbolically drug them into unconsciousness, and then simply walk in and snatch their slippers. In other words, the best way to subjugate the American people and plunder their assets was to dull their senses by becoming addicted to drugs.
The narcotics of the poppy field had no effect on the straw and tin man, for they were not blood, flesh, and blood, but artificial entities. The two cried out for help, and Glenda, the Good Witch of the North, answered their prayers with a blanket of snow, i.e., cocaine, a stimulant that nullifies the narcotic effect of the poppies/opium on Dorothy, the Lion, and Toto.
The crown has been playing the drug cartel game for centuries; just look at the history of Hong Kong and the Opium Wars. Despite its obvious impropriety, drugging your opponent before a battle is the most effective way to defeat them.
Distracting the masses, drugging and entertaining them is the best strategy to keep them subjugated and enslaved to a heartless monetary system, thus avoiding any resistance to change.
Flying monkeys
Let's not forget those flying monkeys, mythical creatures perfect for representing the lawyers of the bar (legal masters) who attack and control the little people for the grand wizard in the crown: the powerful and Big Bankers of Oz.Flying monkeys

Individuals have to be represented by lawyers in court cases and therefore need to hire a lawyer. The clients are “wards of the court,” i.e., “infants and persons of unsound mind," just like the strawman was a “person of unsound mind”.
Toto, the little dog
Toto means ‘everything’ in Latin, which was what the witch wanted after claiming the dog had bitten her. THE WITCH (the banks and their lawyers) WANTED EVERYTHING!
Notice how Toto was not frightened by the theatricality of the Big Wizard, even though he was small in size compared to the wizard. Toto simply walked up and began barking, drawing the attention of the others. Behind the curtain, an ordinary person was operating the levers that created the illusion of the great magician's power and authority.
We can see from this story how loud the bark of a small dog can be, but most of us still remain silent.
Dorothy
When Dorothy sought assistance from Glenda, the Good Witch of the North, to return to Kansas, Glenda responded, "You don't need help." You have always been empowered to return to Kansas.
Dorothy eventually made her way home. She always had the power it took to unmask the wizard, and so did we. She always thought she needed outside help, but the power is in each of us, taking responsibility, commitment, and action based on truth.
The great awakening of humanity
Most people do not listen, do not see, and do not speak the truth, either because they have an economic interest or because they are afraid. This is beginning to change.
We are going through a great awakening of consciousness, where more and more individuals are realizing that there is something beyond the illusion of the magician, beginning to see the deeper truths, the background of things, and a higher meaning to life.
Recognizing our birth on a slave plantation, our treatment as property, and the use of our legal identities to support the issuance of government debt (fiat currencies) is crucial. This has been going on for almost a century and is a direct attack on our sovereignty, which is the natural state of our human existence.
As Dorothy once said, "There's no place like home," and indeed, there is no place like home! A sovereign can find no greater place than sovereignty! Will you persist in deceiving unsuspecting men and adoring the magician's light show, or will you, like Dorothy, become aware and delve into the inner workings?
We need an educated mind, an intelligent heart, courage, and the responsibility to act.
We are not defined by our legal fiction or birth certificate, nor are we subject to the dictates of a bureaucrat wielding "official authority" to dictate our actions. We are not corporations operating under commercial law; we are human beings operating under common law, where a crime requires a victim (a human being or their damaged property).
The millions of laws, regulations, and restrictions do not apply to us sovereigns but to our legal fictions that are part of commercial law because they (not us) are corporations. The government has jurisdiction over its creation, which clearly does not include us. In this case, it is our legal identity or fictitious corporation that identifies us, but we, as flesh-and-blood men, are not a creation of the government.
The first step is to recognize this fact; the second is to stop waiting for outside help and take active participation in the matter, assuming responsibility and acting freely to defend our property and our rights.
If we continue to let the magician and his illusions dominate our perception of reality, we will end up living under a communist dystopia, with a system of mass surveillance and non-existent human rights.
But if we decide to take matters into our own hands, by understanding technologies like Bitcoin and Nostr, we can build a better future for ourselves and our future generations.
We are currently facing a unique opportunity to escape the traps and manipulations of this ancestral war and enjoy spiritual, intellectual, and financial freedom.
Although it will not be straightforward and requires responsibility and work, the price of not doing it correctly is slavery, and I personally would rather be dead than live subjugated to the will of a tyrant.
Bitcoin and Nostr, or slavery!
-
 @ 599f67f7:21fb3ea9
2024-10-20 11:28:08
@ 599f67f7:21fb3ea9
2024-10-20 11:28:08LNDhub te permite importar fácilmente una billetera en aplicaciones compatibles. Si bien puedes guardar tu billetera Bitcoin Txoko LNbits en tu teléfono como una aplicación web progresiva (PWA), una aplicación nativa como Zeus o BlueWallet ofrece una mejor experiencia de usuario así como un mayor nivel de seguridad. Con Alby, también puedes importar la billetera a la extensión de tu navegador para facilitar los pagos Lightning en la web y para los zaps de Nostr. Por suerte para nosotros, todas estas billeteras hablan un lenguaje común llamado LNDhub.
En esta guía cubriremos cómo importar la billetera a tu navegador y a tu móvil. Si quieres usar tu billetera tanto en el navegador como en tu móvil, empieza con la configuración de Alby, ya que uno de los pasos te permitirá importar fácilmente tu billetera también a Zeus. Pero si sólo te interesa utilizar la billetera en tu móvil, puedes pasar directamente a la sección de Zeus.
Alby
nostr:nprofile1qqsyv47lazt9h6ycp2fsw270khje5egjgsrdkrupjg27u796g7f5k0s8jq7y6 es una extensión de navegador que lleva Lightning y Nostr a tu navegador. Utilizando el protocolo WebLN, esta extensión puede detectar facturas LN en paginas web y pagarlas, así como posibilita iniciar sesión en sitios web con Lightning. También puedes fijar presupuestos para tus sitios favoritos de Lightning. Por otro lado también puedes utilizarla para firmar en Nostr utilizando NIP-07, lo cual es mucho más seguro que ingresar tu clave privada en clientes web.
¿Qué necesito?
- Un navegador web que soporte extensiones Chrome o Firefox
- Acceso a tu billetera LNbits. Si todavía no tienes una billetera LNbits, dirígete a nuestra página de billeteras y crea una
- (Opcional) Un dispositivo móvil para configurar Zeus
1. Habilita la extensión LNDhub en tu LNbits wallet
Dirígete a tu billetera LNbits. Haz clic en
Extensionesy habilita la extensiónLNDhub. Una vez se haya habilitado, dirígete a la página de extensión de LNDhub.2. Instala la extensión Alby
Dirígete a getalby.com y instala la extensión desde el store de extensiones del navegador. Configura tu contraseña de desbloqueo y guárdala en un lugar seguro.
3. Importar a Alby
 (Esta es una billetera de prueba. No hay fondos en ella. ¡No muestres a nadie tu URI de exportación real!)
(Esta es una billetera de prueba. No hay fondos en ella. ¡No muestres a nadie tu URI de exportación real!)En la siguiente pantalla, elige
Conectary luego eligeLNDhub. Vuelve a tu extensión LNDhub y copia la URL de conexión. Pégala en el campoURI de exportación de LNDhub. Pulsa continuar. ¡Ahora deberías haber estado conectado a tu billetera de LNbits con LNDhub!💡 Puedes elegir entre la URL de la factura (Invoice URL) y la URL de administración (Admin URL). Le dan a Alby diferentes permisos para interactuar con tu cartera de LNbits.
- La URL de factura te permite crear facturas y recibir pagos
- La URL de administración también te permite enviar pagos
4. Configurar Zeus con Alby (opcional)

Ahora que ya has conectado tu LNbits con Alby, también puedes importarlo de una manera sencilla a Zeus con Alby. Abre la extensión, haz cilc en el nombre de tu billetera y navega a la configuración de la cuenta. En
Wallet Settings>Generalse encuentra la opción de conectar tu billetera móvil. Al pulsar conectar, se mostrará un código QR para escanear desde Zeus.Si no tienes instalada Zeus con anterioridad, dirígete a zeusln.app y descarga la aplicación de Zeus para tu sistema operativo móvil.
Una vez tengas descargado Zeus, entra en
Configuración>Añadir un nuevo nodo. Aquí puedes escanear el código QR que te muestra Alby para importar la billetera.Voilà! Ahora tienes el poder de Lightning al alcance de la mano ¿Ya te sientes como un dios?
Zeus
nostr:nprofile1qqsrf5h4ya83jk8u6t9jgc76h6kalz3plp9vusjpm2ygqgalqhxgp9g84ctjf es una formidable aplicación de código abierto que permite conectar tu propio nodo a tu dispositivo movil. Es compatible con todas las principales implementaciones de nodos Lightning, como LND, CLN y Eclair, así como conexiones a través de Tor y clearnet. Recientemente también han anunciado su propio LSP (Lightning Service Provider).
¿Qué necesito?
- Teléfono Android o iOS
- Otro dispositivo en el que puede acceder a tu billetera LNbits (para mostrar el código QR para escanear)
- Acceso a tu billetera LNbits. Si todavía no tienes una billetera LNbits, dirígete a nuestra página de billeteras y crea una
1. Descarga Zeus
Puedes descargar la aplicación Zeus para tu sistema operativo aquí.
2. Habilita la extensión LNDhub en tu billetera LNbits
Dirígete a tu billetera LNbits. Haz clic en
Extensionesy habilita la extensiónLNDhub. Una vez habilitada, abre la pagina de la extensión LNDhub.3. Importar a Zeus
Ve a
Configuración>Añadir un nuevo nodo en Zeus.Escanea la cartera que quieras instalar.
💡 Puedes elegir entre la URL de la factura (Invoice URL) y la URL de administración (Admin URL). - La URL de la factura te da permiso para generar facturas y recibir pagos. - La URL de administración también te permite enviar pagos.
Una vez que hayas escaneado el código QR, todos los campos en Zeus deberían rellenarse automáticamente. También puedes añadir un apodo para tu billetera.

¡Ahora puedes guardar la configuración del nodo y controlar la billetera desde tu teléfono!
Extra
Zeus también ofrece funciones interesantes como temas personalizados, conversiones de precios, modo acechador y verificación biométrica. Estos temas están más allá del alcance de esta guía, ¡juega en la aplicación y descubre todas esas características por ti mismo!
-
 @ 592295cf:413a0db9
2024-10-13 08:29:48
@ 592295cf:413a0db9
2024-10-13 08:29:48[07/10 week]
Thinking about it, even the protocol is a cathedral, Rabble in the speech in Riga on Bluesky.
He said the protocol is a bazaar. But you have to converge on the scheme in the NIPs or between Apps.
NIPs for example are like Luther's 95 theses, but they change continuously and adapt, but they always remain those 95.
Maybe that Pr on theother curve keys could lead to saying this is "nostr" these others are similar. Creating more points, but I just think it would have led to endless diatribes.
What will be of the protocol and who knows. He can do everything or maybe nothing and from tomorrow we will see and it will be, it will be what it will be. Italian Song
Notifications with nostter are not hidden, they are in your feed and this is good, you always know if someone has searched for you. While in the others you do not know.
I saw a sliver of light pass by it was Unanimity.
It's a very stupid idea, it takes a long time. it's basically a community + channel, where you post the channel in the community and start talking about that topic in the channel. The channel is an approved message. I made musicbook channel, it's the collection of albums released on Friday. The idea of also making a blogger channel, where to put long-form articles.
Following nostr trending on Openvibe social, with a new profile, the Lost One, sad, in this One follow fiatjaf, means I won't bother him anymore . Now I follow 62 profiles, it's an account that I will use to read the notes of the top profiles. Curious if this number will grow enormously or is there a spectre.
The strength of the protocol is the developers if they collaborate together, otherwise it can still work, everyone goes their own way, but it's like saying I want to make my own fence.
One who in his long form doing an analysis of the various social networks. npub19mq9swna4dkhlm3jaux4yhgv5kjj556lkfhv3qnjtyh0kcljph6s88e295 Nostr is all based on Bitcoin. The difficult thing is Bitcoin not Nostr and he says so.
Controversies are useful, or my doubts, but maybe people who can't write code don't understand much, the so-called end users. No one is an end user at this time. The end user doesn't care about the person behind it, only having their own service, if the service is good they also do promotion, they become sponsors. We have seen in recent months sponsoring a Nostr app, result a small attack can damage that app. But the strength of having all these apps is that the other app doesn't have that problem. Spam attack example. The problem is that you can't sponsor an ecosystem, so it becomes difficult to suggest 10 apps to download. The best 10 apps of Nostr and the other 100, there is no easy way out. It's a bit like proposing a new place in NY, then everyone goes to that place and it loses a bit. What the sponsor must understand is that Nostr has only one "one shot".
I saw a video on Nostr of two people posting content on social media, making a review. Not bad, compared to the previous video, that Nostr doesn't even have a token. It doesn't give me a sign up. The main feature they say is a platform or at least they reviewed damus, damus for Bitcoin maxi. And so Nostr is populated by people who Number go up, only fiat thought they would say on Nostr. It's true in part there are those obsessed, even the non-obsessed are obsessed.
How nice it would be to call them NPs Nostr protocol specification, today supertestnet called them that. (the nice thing is that they are pronounced the same way).
-
 @ 47750177:8969e41a
2024-10-05 17:40:25
@ 47750177:8969e41a
2024-10-05 17:40:2528.0 Release Notes
Bitcoin Core version 28.0 is now available from:
This release includes new features, various bug fixes and performance improvements, as well as updated translations.
Please report bugs using the issue tracker at GitHub:
https://github.com/bitcoin/bitcoin/issues
To receive security and update notifications, please subscribe to:
https://bitcoincore.org/en/list/announcements/join/
How to Upgrade
If you are running an older version, shut it down. Wait until it has completely shut down (which might take a few minutes in some cases), then run the installer (on Windows) or just copy over
/Applications/Bitcoin-Qt(on macOS) orbitcoind/bitcoin-qt(on Linux).Upgrading directly from a version of Bitcoin Core that has reached its EOL is possible, but it might take some time if the data directory needs to be migrated. Old wallet versions of Bitcoin Core are generally supported.
Running Bitcoin Core binaries on macOS requires self signing.
cd /path/to/bitcoin-28.0/bin xattr -d com.apple.quarantine bitcoin-cli bitcoin-qt bitcoin-tx bitcoin-util bitcoin-wallet bitcoind test_bitcoin codesign -s - bitcoin-cli bitcoin-qt bitcoin-tx bitcoin-util bitcoin-wallet bitcoind test_bitcoinCompatibility
Bitcoin Core is supported and extensively tested on operating systems using the Linux Kernel 3.17+, macOS 11.0+, and Windows 7 and newer. Bitcoin Core should also work on most other UNIX-like systems but is not as frequently tested on them. It is not recommended to use Bitcoin Core on unsupported systems.
Notable changes
Testnet4/BIP94 support
Support for Testnet4 as specified in BIP94 has been added. The network can be selected with the
-testnet4option and the section header is also named[testnet4].While the intention is to phase out support for Testnet3 in an upcoming version, support for it is still available via the known options in this release. (#29775)
Windows Data Directory
The default data directory on Windows has been moved from
C:\Users\Username\AppData\Roaming\BitcointoC:\Users\Username\AppData\Local\Bitcoin. Bitcoin Core will check the existence of the old directory first and continue to use that directory for backwards compatibility if it is present. (#27064)JSON-RPC 2.0 Support
The JSON-RPC server now recognizes JSON-RPC 2.0 requests and responds with strict adherence to the specification. See JSON-RPC-interface.md for details. (#27101)
JSON-RPC clients may need to be updated to be compatible with the JSON-RPC server. Please open an issue on GitHub if any compatibility issues are found.
libbitcoinconsensus Removal
The libbitcoin-consensus library was deprecated in 27.0 and is now completely removed. (#29648)
P2P and Network Changes
- Previously if Bitcoin Core was listening for P2P connections, either using
default settings or via
bind=addr:portit would always also bind to127.0.0.1:8334to listen for Tor connections. It was not possible to switch this off, even if the node didn't use Tor. This has been changed and nowbind=addr:portresults in binding onaddr:portonly. The default behavior of binding to0.0.0.0:8333and127.0.0.1:8334has not been changed.
If you are using a
bind=...configuration withoutbind=...=onionand rely on the previous implied behavior to accept incoming Tor connections at127.0.0.1:8334, you need to now make this explicit by usingbind=... bind=127.0.0.1:8334=onion. (#22729)-
Bitcoin Core will now fail to start up if any of its P2P binds fail, rather than the previous behaviour where it would only abort startup if all P2P binds had failed. (#22729)
-
UNIX domain sockets can now be used for proxy connections. Set
-onionor-proxyto the local socket path with the prefixunix:(e.g.-onion=unix:/home/me/torsocket). (#27375) -
UNIX socket paths are now accepted for
-zmqpubrawblockand-zmqpubrawtxwith the format-zmqpubrawtx=unix:/path/to/file(#27679) -
Additional "in" and "out" flags have been added to
-whitelistto control whether permissions apply to inbound connections and/or manual ones (default: inbound only). (#27114) -
Transactions having a feerate that is too low will be opportunistically paired with their child transactions and submitted as a package, thus enabling the node to download 1-parent-1-child packages using the existing transaction relay protocol. Combined with other mempool policies, this change allows limited "package relay" when a parent transaction is below the mempool minimum feerate. Topologically Restricted Until Confirmation (TRUC) parents are additionally allowed to be below the minimum relay feerate (i.e., pay 0 fees). Use the
submitpackageRPC to submit packages directly to the node. Warning: this P2P feature is limited (unlike thesubmitpackageinterface, a child with multiple unconfirmed parents is not supported) and not yet reliable under adversarial conditions. (#28970)
Mempool Policy Changes
-
Transactions with version number set to 3 are now treated as standard on all networks (#29496), subject to opt-in Topologically Restricted Until Confirmation (TRUC) transaction policy as described in BIP 431. The policy includes limits on spending unconfirmed outputs (#28948), eviction of a previous descendant if a more incentive-compatible one is submitted (#29306), and a maximum transaction size of 10,000vB (#29873). These restrictions simplify the assessment of incentive compatibility of accepting or replacing TRUC transactions, thus ensuring any replacements are more profitable for the node and making fee-bumping more reliable.
-
Pay To Anchor (P2A) is a new standard witness output type for spending, a newly recognised output template. This allows for key-less anchor outputs, with compact spending conditions for additional efficiencies on top of an equivalent
sh(OP_TRUE)output, in addition to the txid stability of the spending transaction. N.B. propagation of this output spending on the network will be limited until a sufficient number of nodes on the network adopt this upgrade. (#30352) -
Limited package RBF is now enabled, where the proposed conflicting package would result in a connected component, aka cluster, of size 2 in the mempool. All clusters being conflicted against must be of size 2 or lower. (#28984)
-
The default value of the
-mempoolfullrbfconfiguration option has been changed from 0 to 1, i.e.mempoolfullrbf=1. (#30493)
Updated RPCs
-
The
dumptxoutsetRPC now returns the UTXO set dump in a new and improved format. Correspondingly, theloadtxoutsetRPC now expects this new format in the dumps it tries to load. Dumps with the old format are no longer supported and need to be recreated using the new format to be usable. (#29612) -
AssumeUTXO mainnet parameters have been added for height 840,000. This means the
loadtxoutsetRPC can now be used on mainnet with the matching UTXO set from that height. (#28553) -
The
warningsfield ingetblockchaininfo,getmininginfoandgetnetworkinfonow returns all the active node warnings as an array of strings, instead of a single warning. The current behaviour can be temporarily restored by running Bitcoin Core with the configuration option-deprecatedrpc=warnings. (#29845) -
Previously when using the
sendrawtransactionRPC and specifying outputs that are already in the UTXO set, an RPC error code of-27with the message "Transaction already in block chain" was returned in response. The error message has been changed to "Transaction outputs already in utxo set" to more accurately describe the source of the issue. (#30212) -
The default mode for the
estimatesmartfeeRPC has been updated fromconservativetoeconomical, which is expected to reduce over-estimation for many users, particularly if Replace-by-Fee is an option. For users that require high confidence in their fee estimates at the cost of potentially over-estimating, theconservativemode remains available. (#30275) -
RPC
scantxoutsetnow returns 2 new fields in the "unspents" JSON array:blockhashandconfirmations. See the scantxoutset help for details. (#30515) -
RPC
submitpackagenow allows 2 new arguments to be passed:maxfeerateandmaxburnamount. See the subtmitpackage help for details. (#28950)
Changes to wallet-related RPCs can be found in the Wallet section below.
Updated REST APIs
- Parameter validation for
/rest/getutxoshas been improved by rejecting truncated or overly large txids and malformed outpoint indices via raising an HTTP_BAD_REQUEST "Parse error". These requests were previously handled silently. (#30482, #30444)
Build System
-
GCC 11.1 or later, or Clang 16.0 or later, are now required to compile Bitcoin Core. (#29091, #30263)
-
The minimum required glibc to run Bitcoin Core is now 2.31. This means that RHEL 8 and Ubuntu 18.04 (Bionic) are no-longer supported. (#29987)
-
--enable-lcov-branch-coveragehas been removed, given incompatibilities between lcov version 1 & 2.LCOV_OPTSshould be used to set any options instead. (#30192)
Updated Settings
- When running with
-alertnotify, an alert can now be raised multiple times instead of just once. Previously, it was only raised when unknown new consensus rules were activated. Its scope has now been increased to include all kernel warnings. Specifically, alerts will now also be raised when an invalid chain with a large amount of work has been detected. Additional warnings may be added in the future. (#30058)
Changes to GUI or wallet related settings can be found in the GUI or Wallet section below.
Wallet
-
The wallet now detects when wallet transactions conflict with the mempool. Mempool-conflicting transactions can be seen in the
"mempoolconflicts"field ofgettransaction. The inputs of mempool-conflicted transactions can now be respent without manually abandoning the transactions when the parent transaction is dropped from the mempool, which can cause wallet balances to appear higher. (#27307) -
A new
max_tx_weightoption has been added to the RPCsfundrawtransaction,walletcreatefundedpsbt, andsend. It specifies the maximum transaction weight. If the limit is exceeded during funding, the transaction will not be built. The default value is 4,000,000 WU. (#29523) -
A new
createwalletdescriptorRPC allows users to add new automatically generated descriptors to their wallet. This can be used to upgrade wallets created prior to the introduction of a new standard descriptor, such as taproot. (#29130) -
A new RPC
gethdkeyslists all of the BIP32 HD keys in use by all of the descriptors in the wallet. These keys can be used in conjunction withcreatewalletdescriptorto create and add single key descriptors to the wallet for a particular key that the wallet already knows. (#29130) -
The
sendallRPC can now spend unconfirmed change and will include additional fees as necessary for the resulting transaction to bump the unconfirmed transactions' feerates to the specified feerate. (#28979) -
In RPC
bumpfee, if afee_rateis specified, the feerate is no longer restricted to following the wallet's incremental feerate of 5 sat/vb. The feerate must still be at least the sum of the original fee and the mempool's incremental feerate. (#27969)
GUI Changes
-
The "Migrate Wallet" menu allows users to migrate any legacy wallet in their wallet directory, regardless of the wallets loaded. (gui#824)
-
The "Information" window now displays the maximum mempool size along with the mempool usage. (gui#825)
Low-level Changes
Tests
-
The BIP94 timewarp attack mitigation is now active on the
regtestnetwork. (#30681) -
A new
-testdatadiroption has been added totest_bitcointo allow specifying the location of unit test data directories. (#26564)
Blockstorage
- Block files are now XOR'd by default with a key stored in the blocksdir.
Previous releases of Bitcoin Core or previous external software will not be able to read the blocksdir with a non-zero XOR-key.
Refer to the
-blocksxorhelp for more details. (#28052)
Chainstate
- The chainstate database flushes that occur when blocks are pruned will no longer empty the database cache. The cache will remain populated longer, which significantly reduces the time for initial block download to complete. (#28280)
Dependencies
- The dependency on Boost.Process has been replaced with cpp-subprocess, which is contained in source. Builders will no longer need Boost.Process to build with external signer support. (#28981)
Credits
Thanks to everyone who directly contributed to this release: - 0xb10c - Alfonso Roman Zubeldia - Andrew Toth - AngusP - Anthony Towns - Antoine Poinsot - Anton A - Ava Chow - Ayush Singh - Ben Westgate - Brandon Odiwuor - brunoerg - bstin - Charlie - Christopher Bergqvist - Cory Fields - crazeteam - Daniela Brozzoni - David Gumberg - dergoegge - Edil Medeiros - Epic Curious - Fabian Jahr - fanquake - furszy - glozow - Greg Sanders - hanmz - Hennadii Stepanov - Hernan Marino - Hodlinator - ishaanam - ismaelsadeeq - Jadi - Jon Atack - josibake - jrakibi - kevkevin - kevkevinpal - Konstantin Akimov - laanwj - Larry Ruane - Lőrinc - Luis Schwab - Luke Dashjr - MarcoFalke - marcofleon - Marnix - Martin Saposnic - Martin Zumsande - Matt Corallo - Matthew Zipkin - Matt Whitlock - Max Edwards - Michael Dietz - Murch - nanlour - pablomartin4btc - Peter Todd - Pieter Wuille - @RandyMcMillan - RoboSchmied - Roman Zeyde - Ryan Ofsky - Sebastian Falbesoner - Sergi Delgado Segura - Sjors Provoost - spicyzboss - StevenMia - stickies-v - stratospher - Suhas Daftuar - sunerok - tdb3 - TheCharlatan - umiumi - Vasil Dimov - virtu - willcl-ark
As well as to everyone that helped with translations on Transifex.
- Previously if Bitcoin Core was listening for P2P connections, either using
default settings or via
-
 @ 1123ece2:7d1e00c0
2025-01-19 04:02:12
@ 1123ece2:7d1e00c0
2025-01-19 04:02:12Hey everyone I’m Gary Hoban and welcome to Refinery Life Australia.
“The Christ of John’s Gospel” is the theme we are continuing for the coming Sunday morning teachings that focus on John’s unique portrayal of the Christ.
We will continue this series for a while longer.
Today we are discussing, The Distinctives of Discipleship.
Prayer
Father, we come to You today because You made us, You redeemed us, and we acknowledge that every good and perfect gift comes from Your bountiful hands.
Thank You, Father, for the privilege of giving to You for the glory of Your name and cause.
The words of Jesus are so true, “It is more blessed to give than to receive.”
Thank you for this heavenly blessing.
In Jesus name we pray.
Amen.
Text
John 8:31 NKJV
The Truth Shall Make You Free
31 Then Jesus said to those Jews who believed Him, “If you abide in My word, you are My disciples indeed.
Scripture Reading
John 8:30-59 NKJV
30 As He spoke these words, many believed in Him.
The Truth Shall Make You Free
31 Then Jesus said to those Jews who believed Him, “If you abide in My word, you are My disciples indeed.
32 And you shall know the truth, and the truth shall make you free.”
33 They answered Him, “We are Abraham’s descendants, and have never been in bondage to anyone. How can You say, ‘You will be made free’?”
34 Jesus answered them, “Most assuredly, I say to you, whoever commits sin is a slave of sin.
35 And a slave does not abide in the house forever, but a son abides forever.
36 Therefore if the Son makes you free, you shall be free indeed.
Abraham’s Seed and Satan’s
37 “I know that you are Abraham’s descendants, but you seek to kill Me, because My word has no place in you.
38 I speak what I have seen with My Father, and you do what you have seen with your father.”
39 They answered and said to Him, “Abraham is our father.”
Jesus said to them, “If you were Abraham’s children, you would do the works of Abraham.
40 But now you seek to kill Me, a Man who has told you the truth which I heard from God. Abraham did not do this.
41 You do the deeds of your father.”
Then they said to Him, “We were not born of fornication; we have one Father—God.”
42 Jesus said to them, “If God were your Father, you would love Me, for I proceeded forth and came from God; nor have I come of Myself, but He sent Me.
43 Why do you not understand My speech? Because you are not able to listen to My word.
44 You are of your father the devil, and the desires of your father you want to do. He was a murderer from the beginning, and does not stand in the truth, because there is no truth in him. When he speaks a lie, he speaks from his own resources, for he is a liar and the father of it.
45 But because I tell the truth, you do not believe Me.
46 Which of you convicts Me of sin? And if I tell the truth, why do you not believe Me?
47 He who is of God hears God’s words; therefore you do not hear, because you are not of God.”
Before Abraham Was, I AM
48 Then the Jews answered and said to Him, “Do we not say rightly that You are a Samaritan and have a demon?”
49 Jesus answered, “I do not have a demon; but I honor My Father, and you dishonor Me.
50 And I do not seek My own glory; there is One who seeks and judges.
51 Most assuredly, I say to you, if anyone keeps My word he shall never see death.”
52 Then the Jews said to Him, “Now we know that You have a demon! Abraham is dead, and the prophets; and You say, ‘If anyone keeps My word he shall never taste death.’
53 Are You greater than our father Abraham, who is dead? And the prophets are dead. Who do You make Yourself out to be?”
54 Jesus answered, “If I honor Myself, My honor is nothing. It is My Father who honors Me, of whom you say that He is your God.
55 Yet you have not known Him, but I know Him. And if I say, ‘I do not know Him,’ I shall be a liar like you; but I do know Him and keep His word.
56 Your father Abraham rejoiced to see My day, and he saw it and was glad.”
57 Then the Jews said to Him, “You are not yet fifty years old, and have You seen Abraham?”
58 Jesus said to them, “Most assuredly, I say to you, before Abraham was, I AM.”
59 Then they took up stones to throw at Him; but Jesus hid Himself and went out of the temple, going through the midst of them, and so passed by.
Introduction.
What does it really mean to follow Jesus?
Somehow in the early part of the twenty first century, people have lost sight of what it means to follow Jesus.
Discipleship is linked to external observance of religion rather than a relationship experience with Jesus Christ.
During Jesus’ life and ministry on earth, many people sought to follow Him.
John 8:30, 30 As He spoke these words, many believed in Him.
Any motives moved to associate with Jesus Christ.
Some were infatuated with His miracles and teachings.
Others were just curious.
Jesus did not want people to follow Him outside the motive of a genuine commitment.\ To distinguish the authentic followers, Jesus gave the distinctive qualities of a true disciple.
- A true disciple has continuance
John 8:31-33 NKJV
The Truth Shall Make You Free
31 Then Jesus said to those Jews who believed Him, “If you abide in My word, you are My disciples indeed. 32 And you shall know the truth, and the truth shall make you free.”
33 They answered Him, “We are Abraham’s descendants, and have never been in bondage to anyone. How can You say, ‘You will be made free’?”
Jesus realised that some people made an impulsive decision to follow Him.
At times in Jesus’ ministry, large crowds followed Him.
He knew they followed mainly to see His miracles or just to be part of the crowd.
He knew that many would decide not to follow Him.
After Jesus taught the crowds that He was the Bread of Life, John 6:66 says, From that time many of His disciples went back and walked with Him no more.
Jesus pointed out that perseverance would be the sign of a true disciple.
John 8:31, The Truth Shall Make You Free
31 Then Jesus said to those Jews who believed Him, “If you abide in My word, you are My disciples indeed.
Discipleship is not the excitement of one moment.
It is a patient continuance in the footsteps of Jesus Christ.
To a crowd of potential followers, Jesus gave a sure sign of a disciple.
A disciple is one who follows Jesus continuously.
The genuine evidence is in the sustained effort.
2. A true disciple has freedom.
John 8:34-38, Jesus answered them, “Most assuredly, I say to you, whoever commits sin is a slave of sin. And a slave does not abide in the house forever, but a son abides forever. Therefore if the Son makes you free, you shall be free indeed.
“I know that you are Abraham’s descendants, but you seek to kill Me, because My word has no place in you. I speak what I have seen with My Father, and you do what you have seen with your father.”
Jesus taught of a freedom that led to bondage.
Jesus answered them, “Most assuredly, I say to you, whoever commits sin is a slave of sin.
Jesus taught a group of potential disciples about how sin leads to bondage.
Going through life with self will, self trust, and self assertion leads to a detrimental bondage.
No one who follows Jesus can be a master to himself.
Jesus spoke of a bondage that leads to freedom.
A true disciple is one who has renounced his or her way to follow the way of Christ.
Bondage to the Lord leads to authentic freedom.
Jesus said, “Therefore if the Son makes you free, you shall be free indeed.”
The true disciple of Jesus lives to please only one person, Jesus Christ.
A disciple of Jesus is not a slave to sin but is a slave to the master.
3. A true disciple has Christlike behaviour.
John 8:39-47 NKJV
39 They answered and said to Him, “Abraham is our father.”
Jesus said to them, “If you were Abraham’s children, you would do the works of Abraham.
40 But now you seek to kill Me, a Man who has told you the truth which I heard from God. Abraham did not do this.
41 You do the deeds of your father.”
Then they said to Him, “We were not born of fornication; we have one Father—God.”
42 Jesus said to them, “If God were your Father, you would love Me, for I proceeded forth and came from God; nor have I come of Myself, but He sent Me.
43 Why do you not understand My speech? Because you are not able to listen to My word.
44 You are of your father the devil, and the desires of your father you want to do. He was a murderer from the beginning, and does not stand in the truth, because there is no truth in him. When he speaks a lie, he speaks from his own resources, for he is a liar and the father of it.
45 But because I tell the truth, you do not believe Me.
46 Which of you convicts Me of sin? And if I tell the truth, why do you not believe Me?
47 He who is of God hears God’s words; therefore you do not hear, because you are not of God.”
The Jew’s claimed to be Abraham’s children.
By physical lineage this was true.
However, many Jews lived contrary to Abraham’s example.
They sought to kill Jesus and slander His name.
Jesus said they were not God’s children, for they did not reflect God’s character.
Rather, He said in John 8:44, You are of your father the devil, and the desires of your father you want to do. He was a murderer from the beginning, and does not stand in the truth, because there is no truth in him. When he speaks a lie, he speaks from his own resources, for he is a liar and the father of it.
God’s children behave like His children.
John 8:42, “If God were your Father, you would love Me”, and He added in verse 47, “He who is of God hears God’s words.”
Nature will be true to itself.
If one is born of God, then they will live in accordance with Christ’s character.
4. A true disciple honours Christ.
John 8:48-59 NKJV
Before Abraham Was, I AM
48 Then the Jews answered and said to Him, “Do we not say rightly that You are a Samaritan and have a demon?”
49 Jesus answered, “I do not have a demon; but I honor My Father, and you dishonor Me.
50 And I do not seek My own glory; there is One who seeks and judges.
51 Most assuredly, I say to you, if anyone keeps My word he shall never see death.”
52 Then the Jews said to Him, “Now we know that You have a demon! Abraham is dead, and the prophets; and You say, ‘If anyone keeps My word he shall never taste death.’
53 Are You greater than our father Abraham, who is dead? And the prophets are dead. Who do You make Yourself out to be?”
54 Jesus answered, “If I honor Myself, My honor is nothing. It is My Father who honors Me, of whom you say that He is your God.
55 Yet you have not known Him, but I know Him. And if I say, ‘I do not know Him,’ I shall be a liar like you; but I do know Him and keep His word.
56 Your father Abraham rejoiced to see My day, and he saw it and was glad.”
57 Then the Jews said to Him, “You are not yet fifty years old, and have You seen Abraham?”
58 Jesus said to them, “Most assuredly, I say to you, before Abraham was, I AM.”
59 Then they took up stones to throw at Him; but Jesus hid Himself and went out of the temple, going through the midst of them, and so passed by.
Many claimed to be disciples of Jesus, but they did not honour Him.
In fact, they accused Him of being demon possessed.
Jesus said in verse 49, “I do not have a demon; but I honor My Father, and you dishonor Me.”
They could not be authentic followers and dishonour the Lord in this way.
True disciples honour and adore and obey Christ.
Conclusion.
Are you a true disciple of Jesus Christ?
The proof is a continuing commitment to Him, freedom from sin, Christlike behaviour, and a Christ honouring life.
Until next time
Stay in the Blessings
I really want to encourage you to be diligent with your Bible study time, because God has so much more for us than we can get from just going to church once or twice a week and hearing someone else talk about the Word.
When you spend time with God, your life will change in amazing ways, because God is a Redeemer. Theres nothing thats too hard for Him, and He can make you whole, spirit, soul and body!
You’re important to God, and you’re important to us at The Refinery.
When it comes to prayer, we believe that God wants to meet your needs and reveal His promises to you.
So whatever you’re concerned about and need prayer for we want to be here for you! Or even if you just want to say Hi, you can contact us at www.refinerylife.org
2025 IS A YEAR OF NEW BEGINNINGS.
© www.refinerylife.org 2013-2024 All rights reserved. Except as permitted under the Australian Copyright Act 1968, no part of this Article may be reproduced, stored in a retrieval system, communicated or transmitted in any form or by any means without the prior written permission.
This episode is brought to you by Refinery Life Australia:
If you enjoy The Refinery Life Radio Podcast you can help support The Refinery by doing the following:
Sow an offering: Bitcoin: bc1qqh6720t2zagj72dyfj348az698tdut3hlecaj4
Online: https://www.refinerylife.org/donate/
If you do send an offering then please email us so that we can say thank you
Subscribe on iTunes | Spotify | YouTube | TuneIn | Rumble | Flare | Zap.Stream | Fountain |
Share The Refinery with your friends and family
Subscribe to the newsletter on www.refinerylife.org
Follow The Refinery on Twitter | Nostr | Instagram | Fountain
-
 @ 592295cf:413a0db9
2024-10-05 09:32:22
@ 592295cf:413a0db9
2024-10-05 09:32:22Week 30th September
Wiki article on the topic. [sPhil] (https://sphil.xyz/) Religion politics philosophy history are critical. They are not objective things.
Week of updates for protocol apps, including Gossip, coracle app, nostrmo, nostur and many others.
Kind7 Tags: K, emoji,a,others Others threads multi people
Show likes as kind 1 This person liked this post. Or this post has three likes in your timeline. The likes I don't know in your timeline really interest you.
The first book is the bible... Word of Alexandria.
I added cyberspace to the difficult things of the protocol ultra brain things. Low brain, middle brain, top brain, ultra.
Some alphaama codes .AA u login .AA q stuff .AA q run b .AA q run f .AA q close f
high things of alphaama nostr:nevent1qy88wumn8ghj7mn0wvhxcmmv9uq32amnwvaz7tmjv4kxz7fwv3sk6atn9e5k7tcqyqlqu2vwpwax7dj420e75yws7g7vyua9e245c0x73c056gunxchluey4q99
Comment: nostr:nevent1qqs8pn0zzhgk5l2raqh736rj3ckm48pfl6r7m72rnz2r2p7lzgmx20gzyqduwzspfzelx9k6x0lrez0j8cl8rtz0lxvqylk8z2ustnfy76jpzqcyqqqqqqgpramhxue69uhkummnw3ezuetfde6kuer6wasku7nfvuh8xurpvdjsjt5rvu
You have to get to the point where you have your community relay. But you have to go down the rabbit hole of relays. General, search, local, inbox outbox, cache. Etc until you get to community relay that is being talked about these days because of NIP 29 "Relay-based Groups". In the end you have to have that table with the various types of relays clearly in your mind. If the user doesn't think about it, who should think about it, who? if I choose the relays?
NIP-100 the world to make community for me. NIP-28 + NIP-72. So you have some structure interoperability with kind1. But the Channel is another kind. You arrange the various channels in the community. No posts need to be approved.
It's useless Protocol users are becoming more reddit users or so. I don't want to deal with these people.
-
 @ 16d11430:61640947
2025-01-19 03:07:12
@ 16d11430:61640947
2025-01-19 03:07:12The “divide and conquer” strategy used to pit Bitcoiners against the wider crypto community is a deliberate tactic aimed at creating internal divisions, fostering confusion, and weakening the collective momentum of decentralized technologies. By exploiting philosophical, technological, and cultural differences between Bitcoin maximalists and proponents of alternative cryptocurrencies, fiat instigators and other vested interests aim to undermine the larger blockchain ecosystem. Here's an exploration of this strategy:
Exploiting Ideological Differences
- Bitcoin Maximalism vs. Crypto Diversity:
Bitcoin maximalists advocate that Bitcoin is the only truly decentralized, immutable, and sound form of money, dismissing other cryptocurrencies as unnecessary or outright scams.
Proponents of other blockchains argue that innovations like smart contracts, scalability, and specialized use cases justify the existence of altcoins and Ethereum-like ecosystems.
Fiat-aligned propagandists amplify these debates, framing them as irreconcilable conflicts, rather than healthy competition within an evolving ecosystem.
- Labeling Altcoins as “Shitcoins”:
By co-opting Bitcoin maximalist terminology like “shitcoin” to denigrate all other cryptocurrencies, fiat proponents fan the flames of division. This reinforces the perception that the crypto community is fragmented, unreliable, and rife with infighting, reducing its appeal to newcomers.
Creating Confusion Over Purpose
- Framing Bitcoin as Anti-Innovation:
Propagandists often portray Bitcoin as a “dinosaur” in the blockchain space, emphasizing its slower transaction speeds, energy consumption, and limited programmability.
Simultaneously, they label other cryptocurrencies as “untrustworthy” or “too experimental,” creating confusion about the legitimacy and purpose of blockchain technology as a whole.
- Highlighting Scams and Failures:
Media narratives frequently spotlight rug-pulls, scams, and failures in the broader crypto space while ignoring the resilience and success of Bitcoin. By conflating Bitcoin with the broader crypto market, they erode public trust in decentralized technologies altogether.
Fueling Regulatory Divides
- Regulation as a Weapon:
Regulators and central authorities use differing approaches for Bitcoin and other cryptocurrencies to create division. For instance, Bitcoin is often labeled as a “digital asset” or “commodity,” while other cryptocurrencies are deemed securities, leading to disparate treatment and confusion over legitimacy.
This divide discourages collaboration between Bitcoiners and altcoin communities, as each group perceives itself as having different regulatory battles to fight.
- Narratives Around Environmental Impact:
Bitcoin is targeted for its proof-of-work (PoW) consensus mechanism, which is painted as environmentally destructive. In contrast, proof-of-stake (PoS) systems are promoted as “green” alternatives.
This framing encourages environmentalists and sustainability advocates to align against Bitcoin, while Bitcoiners double down on defending PoW, exacerbating the divide.
Manipulating Tribalism
- Turning Bitcoiners Against Altcoins:
Bitcoiners are encouraged to see altcoins as fraudulent or unnecessary competitors, while altcoin proponents are encouraged to see Bitcoiners as close-minded purists clinging to outdated technology.
This tribalism prevents cooperation on shared goals, such as financial inclusion, decentralization, and resistance to censorship.
- Highlighting Cultural Divides:
Bitcoin culture, often associated with libertarian values and sound money principles, is framed as elitist and exclusionary.
In contrast, altcoin cultures, which emphasize innovation, diversity, and experimentation, are painted as reckless and overly speculative.
These cultural clashes distract from the broader shared mission of decentralizing power and creating alternatives to the fiat system.
Amplifying Internal Critiques
- Media Amplification of Disputes:
Public disagreements between prominent figures in the Bitcoin and crypto spaces are sensationalized by media outlets. For example, debates over scaling solutions, hard forks, or smart contract utility are framed as existential threats to the ecosystem’s credibility.
This amplification undermines confidence in both Bitcoin and alternative cryptocurrencies by making the community seem chaotic and divided.
- Weaponizing Social Media:
Bots and trolls infiltrate online discussions, spreading misinformation and stoking hostility between Bitcoiners and altcoin advocates. These efforts create echo chambers, reinforcing confirmation bias and deepening divides.
Long-Term Consequences of the Divide and Conquer Approach
- Delaying Mass Adoption:
Confusion and infighting reduce public trust in blockchain technologies, slowing adoption and deterring institutional investment.
Potential users and developers are discouraged from entering the space, fearing instability and conflict.
- Fragmenting the Ecosystem:
Instead of working together to overcome regulatory challenges, scale adoption, or innovate solutions, the crypto community wastes resources fighting internal battles.
This fragmentation leaves the ecosystem vulnerable to external attacks, such as coordinated government crackdowns or monopolistic behavior by large financial institutions.
- Strengthening Fiat Narratives:
By keeping the crypto space divided, fiat propagandists can continue to push narratives that centralized financial systems are more reliable, cohesive, and secure.
These narratives reinforce the status quo, delaying the broader transition to decentralized systems.
Overcoming the Divide
To counteract the divide and conquer strategy, the Bitcoin and crypto communities must:
-
Focus on Shared Goals: Highlight common objectives like financial inclusion, censorship resistance, and decentralization.
-
Promote Constructive Dialogue: Encourage debates that focus on solutions rather than criticisms, emphasizing the complementary strengths of different technologies.
-
Educate the Public: Combat misinformation by creating accessible resources that explain the value of Bitcoin and blockchain as distinct but synergistic innovations.
-
Resist Tribalism: Recognize that both Bitcoin and altcoins have roles to play in a diverse and evolving financial ecosystem.
By fostering unity and cooperation, the blockchain community can overcome external attempts to sow division and work toward a more decentralized, equitable future.
-
 @ 36461ff8:a4454aad
2025-01-18 23:22:00
@ 36461ff8:a4454aad
2025-01-18 23:22:00“My position is improper foods cause disease; proper foods cure disease. Nothing else needs to be said.” - Dr. Bieler, author of Food is Your Best Medicine
As a holistic doctor with over 2 decades of clinical experience, I don't entirely agree with this statement. Everyday in practice, I see the extraordinary application of plant medicines and clinical nutrition in treatments of complex patterns with remarkable outcomes that go above and beyond diet, but I still very much appreciate the value of food as medicine.
Famous Bieler Broth:
- 2 zucchinni
- 2 stalks of celery
- 1 cup of green beans
- handful of parsley
- garlic to taste
- my father made this and added butter and salt
- chop and steam with purified water until tender then blend and drink

I was fortunate enough to treat one of Dr. Bieler’s patients for many years until he passed away in his nineties. He told me some of the famous doctor’s secrets and how patients came from all over for treatment with fantastic results. He himself was seriously ill before seeing Dr. Bieler.
Dr. Bieler's Final Conclusions:
“As a practicing physician for over 50 years, I have reached three basic conclusions as to the cause and cure of disease.
The first is that the primary cause of disease is not germs. Rather, I believe that disease is caused by toxemia which results in cellular impairment and breakdown, thus paving the way for the multiplication and onslaught of other complications.
My second conclusion is that in almost all cases the use of drugs in treating patients is harmful. Drugs often cause serious side effects, and sometimes even create new diseases. The dubious benefits they afford the patient are at best temporary. Yet the number of drugs on the market increases geometrically every year as each chemical firm develops its own variation of the compounds. The physician is indeed rare who can be completely aware of the potential danger from the side effects of all of these drugs.
My third conclusion is that disease can be cured through the proper use of the correct foods. This statement may sound deceptively simple, but I have arrived at it only after intensive study of a highly complex subject: toxemia and endocrine chemistry.
My conclusions are based on experimental and observational results, gathered through years of successfully treating patients. Occasionally I have resorted to the use of drugs in an emergency situation, but those times have been rare. Instead, I have sought to prescribe for my patients’ illnesses antidotes which Nature has placed at their disposal.” - Dr. Bieler“
-
 @ 16d11430:61640947
2025-01-18 22:12:40
@ 16d11430:61640947
2025-01-18 22:12:40The Australian tech industry is booming, fueled by skilled migration and increasing demand for innovation. Yet, many highly qualified immigrants find themselves trapped in an unforgiving system, stifled by the limitations of fiat economies and traditional job markets. For those seeking autonomy and financial independence, decentralized finance (DeFi) offers a revolutionary escape route. By leveraging blockchain technology, immigrants can bypass traditional barriers, unlock new opportunities, and redefine their economic participation in Australia’s tech ecosystem.
The Problem: A Fragile, Fiat-Based Ecosystem
Underemployment and Job Mismatch
Many skilled immigrants arrive in Australia with dreams of applying their hard-earned expertise, only to encounter underemployment or roles unrelated to their qualifications. This mismatch arises from:
Recognition Issues: Foreign credentials and experience often go undervalued.
Economic Shocks: The fiat-based economy is prone to cycles of instability, leaving immigrants vulnerable to layoffs and wage suppression.
Systemic Barriers: Licensing requirements, workplace discrimination, and a preference for "local experience" keep many skilled professionals from thriving.
Financial Vulnerabilities
Immigrants also face challenges in navigating Australia’s financial system, which is heavily fiat-dependent:
High Living Costs: The high cost of living in major Australian cities like Sydney and Melbourne erodes savings and limits economic mobility.
Limited Access to Credit: Without robust credit histories in Australia, immigrants often struggle to secure loans or mortgages.
Dependency on Remittances: Immigrants sending money back home face exorbitant fees and delays, further compounding financial strain.
The DeFi Solution: A Borderless Financial Ecosystem
Decentralized finance, or DeFi, is transforming the global financial landscape. Built on blockchain technology, DeFi eliminates intermediaries, providing direct access to financial services such as lending, borrowing, and investing. For immigrants in Australia's tech ecosystem, DeFi offers a pathway to financial empowerment and independence.
Key Benefits of DeFi for Immigrants
-
Access to Global Capital DeFi platforms enable immigrants to tap into global liquidity pools, allowing them to secure loans or funding without relying on local credit systems. Smart contracts ensure transparency and fairness, removing biases that plague traditional banking.
-
Earning Through Crypto Immigrants can participate in DeFi protocols to earn passive income through staking, yield farming, or providing liquidity. This income is not tied to the fragile fiat economy and offers a hedge against local economic downturns.
-
Borderless Remittances By using cryptocurrencies like Bitcoin or stablecoins, immigrants can send money back home instantly and at a fraction of the cost compared to traditional remittance services.
-
Decentralized Career Platforms Web3 technologies are enabling decentralized platforms where immigrants can showcase their skills, secure gig work, and get paid in crypto, bypassing restrictive local hiring practices.
DeFi Meets Skilled Immigration: A Blueprint for Independence
- Building an Alternative Tech Economy
DeFi empowers immigrants to bypass Australia’s fiat-based tech ecosystem by participating in global, decentralized marketplaces. For instance:
Immigrant developers can contribute to open-source Web3 projects and earn cryptocurrency.
Blockchain-based freelancing platforms allow skilled workers to monetize their expertise without needing local validation.
- Funding Innovation Without Borders
Immigrants with entrepreneurial ambitions often struggle to secure funding in Australia. Through DeFi platforms, they can raise capital via Initial Coin Offerings (ICOs), decentralized crowdfunding, or tokenized equity models.
- Escaping Fiat Dependency
DeFi provides an opportunity to store wealth in stablecoins or cryptocurrencies, reducing exposure to fiat-related inflation and instability. By adopting Bitcoin and DeFi solutions, immigrants can build a financial buffer that operates independently of the Australian dollar.
- Resilience Against Economic Shocks
DeFi’s decentralized nature protects users from localized economic crises. Immigrants can diversify their income streams globally, reducing their dependency on Australia’s fragile economic cycles.
Challenges and Risks
While DeFi offers immense potential, it is not without risks. Immigrants exploring this space should be aware of:
Regulatory Uncertainty: Australia’s evolving crypto regulations could impact DeFi accessibility.
Volatility: Cryptocurrencies are inherently volatile, and users must exercise caution in managing investments.
Scams and Security: The decentralized nature of DeFi makes it a target for scams and hacks. Immigrants must prioritize education and security practices.
Conclusion: A New Path to Empowerment
For skilled immigrants in Australia’s tech ecosystem, DeFi represents more than just a financial tool—it’s a lifeline to autonomy and opportunity. By leveraging blockchain technology, immigrants can break free from the suppressive constraints of fiat-based systems, access global opportunities, and achieve true economic independence.
The intersection of DeFi and skilled immigration is not just a vision for the future—it’s a call to action. As the world transitions toward decentralized systems, skilled immigrants have a unique opportunity to lead the way, redefining what it means to thrive in a globalized economy.
-
-
 @ 592295cf:413a0db9
2024-09-28 08:19:25
@ 592295cf:413a0db9
2024-09-28 08:19:25Week 23th September
It's not your voice anymore if it's available to everyone.
Nostr is psycho pop.
Nostrasia took place today. It all seemed beautiful. A muffled meeting, a bit in the clouds compared to the air you breathe in social media.
It seems there are two types of Nostr the one who doesn't want to grow and the one who wants to grow. 😅
-
There has always been a misconception that kind1 is the discovery layer, but in reality it is the opposite. If someone publishes a long form article there is less audience, it is true, but then it is easier to find quality content, therefore quality profiles to follow in the kind1 client aka twitter clone. And this can be true for all portable data layers, video streaming, audio, long form, ngit, wiki and whatsoever. So you have finally good follow.
-
The fact that in Nostr you don't see who follows you generally, only in a few clients, I only know one where you see who started following you. It's a strange thing, made to avoid seeing masses of bots that follow you and you can want to block, and you increase that list to the point of absurdity. It's strange because there is a lot of focus on the social graph, if you follow me it's an important aspect.
So in Nostr there are - portable data layers (Twitter style and other social) - non-portable, applications that use disposable npub, where the key is ephemeral.
- 0xchat was becoming a good client, they killed it because it has to focus on chat. I don't use chat, I don't have anyone to chat with, I follow the 0xchat channel and then I read things from Moment. I use it with my second account, because after the nos2x-amber affair with the Odell result, which I had already told you about, I no longer tried to have the first profile even on the mobile. In the end they are all keys that will be burned 😔
Maybe I won't use Nostr anymore in the future just with burn npub, pow and whatsoever. In the end you don't build anything because it's a "stateless" communication.
Lol Moment
On Nostr the poor answer guy is helping the network 🤣🤣
call the police 911: what is your emergency?
a spam bot is attacking "nostr" relays.
you want some government censorship on those relays that contain spam, yes we can do that.
-Previous week- 16 09 Machines Like Me was a good book, maybe now it will become reality.
-
The cool thing about Plebchain radio, it's not the guests, it's these two Nostr users that do a podcast. And they focused on Bitcoin and Nostr and lightning, but maybe it's just the beginning, first you have to focus on a niche and then you expand to the whole world. I think the whole world phase is starting, the podcast topics would become too repetitive. The best part is the 15 10 minute intro. Or in the live show part, there could be some interesting clips.
-
-
idea White button for activity pub user on voyage (app).
-
People hate Nostr. Don't use it
-
UnNip, now we've seen it all
-
Until the morale improves
-
-
People think Sync works like this by magic. Unfortunately it doesn't, I think, at least that's what those who are trying to do say, auto-merge, tinybase, evolu. There is an interesting local-first project. Jaguard a collaborative environment for writing empirical research papers.
-
Now I can search by id. I couldn't do it and I didn't understand the mechanism. Everything has to be instantiated. it works. Now I have to create a function maybe note_list_id and note_id. I continued to edit the NIPs page with asciidoc, categorizing this table is very fun.
New wave of Opensats grants.
- If you haven't heard about WoT this week, you probably live on Mars. There are people who didn't know you could edit on amethyst.
You need to do a podcast of NIPs, features and whatsoever, maybe doing a podcast is not the best solution because it assumes you know something more and something that could change the next day or be no longer valid. maybe you should avoid doing things you don't have full control over, or at least not spread it outside. Maybe because last year at this time I was recording audio.
-
-
 @ 011c780a:46e48b1d
2025-01-20 13:03:23
@ 011c780a:46e48b1d
2025-01-20 13:03:23Lake Erie is a paradise for anglers, boasting the world's largest walleye population and some of the highest catch rates in Ohio. For those eager to experience the thrill of fishing on these bountiful waters, booking a charter is the best way to go. However, with numerous options available, how do you choose the right one? Here are some essential tips to help you find the perfect charter for your Lake Erie adventure.
1. Look for Experienced Captains and Crews
The expertise of the captain and crew can make or break your fishing trip. Experienced professionals know the best spots to find walleye, how to handle changing weather conditions, and how to ensure you have an enjoyable day on the water.
● Check the company's website for captain biographies or years of experience.
● Look for certifications or affiliations with reputable fishing organisations.
● Read reviews to see if other anglers had positive experiences with the crew.
2. Prioritize Safety Measures
Safety should be a top priority when choosing an Ohio fishing charter company. Lake Erie can be unpredictable, so you need a charter that prioritises your well-being. ● Ensure the boat is equipped with life jackets, first aid kits, and emergency communication devices.
● Confirm that the captain holds a valid U.S. Coast Guard license.
● Ask about the company's safety protocols in case of adverse weather.
3. Assess the Equipment and Boats
● A well-maintained boat and quality fishing gear can elevate your experience.
● Look for charters that provide high-quality rods, reels, and tackle.
● Check if the boat is spacious, clean, and equipped with modern technology like fish finders.
● Ask if the company allows you to bring your gear if you have a preference.
4. Check for Customization Options
Every angler has unique needs, whether they're a seasoned pro or a first-timer. Some charters offer tailored experiences to meet your preferences.
● Look for family-friendly charters if you're planning a trip with kids.
● Ask if the company offers half-day, full-day, or multi-day trips.
● Find out if they're willing to adjust their itinerary to focus on specific fishing techniques or areas.
5. Read Online Reviews and Testimonials
● The best way to gauge the quality of a charter is through the experiences of others.
● Visit online platforms like Google, Facebook, or TripAdvisor for honest reviews.
● Pay attention to consistent themes in feedback, such as exceptional service, skilled crew, or successful catches.
● Look for photos or videos shared by previous clients to get a better sense of what to expect.
6. Consider the Costs and Inclusions
● While price shouldn't be the sole factor, it's important to know what you're paying for.
● Compare prices among different Lake Erie walleye charters to get a sense of market rates.
● Check what the package includes, such as bait, fishing licenses, or cleaning and packaging your catch.
● Avoid the cheapest options if they seem to cut corners on quality or safety.
7. Verify Their Knowledge of Lake Erie
● Ohio's portion of Lake Erie is home to millions of walleye, and the best charters have in-depth knowledge of these waters.
● Ask about their familiarity with local hotspots for walleye.
● Find out if they follow sustainable fishing practices to preserve the lake's ecosystem.
● A knowledgeable crew can also share interesting facts about the lake, making your trip both fun and educational.
Book Your Perfect Charter Today!
Finding the right Ohio fishing charter company is the first step to an unforgettable Lake Erie adventure. By prioritising experience, safety, equipment quality, and customer reviews, you can ensure a successful and enjoyable trip. For those looking to create lasting memories on Lake Erie, Eyes Ready Charters is a trusted name offering top-notch services to anglers of all skill levels. Book your trip today and experience the thrill of walleye fishing like never before!
-
 @ 592295cf:413a0db9
2024-09-14 18:13:41
@ 592295cf:413a0db9
2024-09-14 18:13:4109 09 week
The billboard has reached its first goal.
I don't understand anything, too much.
The web is a dangerous place, maybe the couch at home is for you.
Nostr is like being in a public place like a bar and you listen to the radio, and you can decide which radio to choose, you can also talk on the radio, only those who follow you and those who are connected to that frequency can listen to you.
We talk on multiple frequencies so if one is offline they can hear me on the other.
Spam will always be a constant as are fixed costs, personnel costs, taxes things that people in general hate
A lot of talk that will be blown away by the wind.
Jack Dorsey says Nostr will be a protocol for private encrypted chats
-
Open-sats drama
-
Carnivore dietitian
-
Lightning diatribe
-
This is already Twitter 😉
Fiatjaf explained for the umpteenth time what the outbox model is, now those who look at images instead of reading books must have understood it too. My note, Patricia writes in her relays write, including select some in her outbox 10002 kind. it was a dev page of something, so maybe it won't be online for long
Thinking that with Kamala Harris's victory, the price of Bitcoin would hit a low and holders would be happy to buy. 🤣🤣 Instead with Trump new all time High, holders would be happy. 🤣🤣 Lol Moment.
I read the article about btcmap maps, there were some notes to make but I didn't, it's beyond my level, it was only for builders.
Satlantis, trustroots, and wherostr were not noted.
I had this thought that we will not "succeed" in building the openness of type 1, in the following nips, because of the relays and because discovering new things has a cost, and no one wants to discover new things. And then after that the others should use them, but how and after that at least two others appear who are doing a similar thing, but they don't talk to each other because they don't have time.
If the time horizon is 10 years, those who survive will see.
Keeping calm seems difficult.
I tried nostr-relay-tray works. It works, I would suggest a couple of changes
- Delete some events.
- View events
- Search by npub id or time
- Delete by time.
These are difficult things but they can be done with a database, so they may as well not be done.
I hope that all the controversies are forgotten and overcome and we are more serene.
-
-
 @ 7460b7fd:4fc4e74b
2024-09-05 08:37:48
@ 7460b7fd:4fc4e74b
2024-09-05 08:37:48请看2014年王兴的一场思维碰撞,视频27分钟开始
最后,一个当时无法解决的点:丢失
-
 @ 6871d8df:4a9396c1
2025-01-18 20:12:46
@ 6871d8df:4a9396c1
2025-01-18 20:12:46## 2024 Prediction Reflections
Politics
Democrats & 2024 Election
- “Democrats’ attempt to stifle democracy will likely put Trump in the White House. If not, some real sketchy stuff would need to happen to keep him out.”
This prediction was exactly right. The assassination attempt on Trump seemed to be the final blow for the Democrats. Despite a heavy push my legacy media, Trump won handily.
The Democrats switched to Kamala Harris after Biden showed signs of incapacity, most notably in the first debate against Trump.
My prediction for the election also turned out to be exactly right, which, thank you Robert Barnes and Richard Baris.
Evidence of Institutional Ideological Capture
- “People will continue to wake up to ideologically captured institutions, and DEI will be the main loser.”
Trump’s resounding election victory underscores that the public is increasingly aware of (and rejecting) such institutional capture.
Of note, Boeing comes to mind as an institution that had a tough time in 2024, in large part to DEI. Nothing seemed to function correctly. The biggest story being how they stranded people in space
Media & Public Opinion
Rise of Independent & Alternative Media
- “Independent and alternative media will continue to grow as people’s trust in legacy media declines.”
Twitter (X), under Elon Musk, shattered mainstream media’s influence far more than expected. As Elon has said, “You are the media now.” Alternative sources are king. - Notable Example: Kamala Harris’s decision not to appear on the Joe Rogan podcast contrasted with Trump’s appearance, further highlighting the power shift to alternative media.
Markets & IPOs
Interest Rates & Public Markets
- “As interest rates come down, I expect public markets and IPOs to heat up.”
This did not play out. Companies that were expected to go public in 2024 remain private in 2025. The reasons are varied, but there is confidence that 2025 might see changes.
Technology & AI
LLMs & AI Adoption
- “AI and LLMs will continue to move at a rapid rate, increasing productivity. Tools like Bard will become more mainstream.”
AI did take off. Usage among nontechnical users increased, and it’s no longer uncommon for people to default to AI-driven tools rather than Google search.
Decentralized AI
- “I hope to see a rise in decentralized AI to counter big-player LLMs.”
We didn’t see explicit ‘decentralized AI’ breakthroughs, but more players entered the AI market. ChatGPT still dominates, with Elon’s ‘Grok’ making moves. Google, Meta, and Microsoft remain active but slightly behind in usage.
Bitcoin & Digital Assets
Institutional Adoption of Bitcoin
- “2024 will bring more institutions to Bitcoin. Possibly another large company or nation-state. The ETF should help, likely pushing BTC to a new all-time high.”
No large public company or nation-state placed a bet, but smaller public companies did. Michael Saylor presented to Microsoft’s Board, which was the closest instance to a major move.
- Price Movement: Bitcoin did hit a new all-time high, rising to as much as $108k in 2024.Lightning Network
- “Lightning will improve but remain primarily used for acquiring Bitcoin, not everyday payments.”
Still true. Lightning usage remains tiny relative to broader Bitcoin adoption.
Nostr Adoption
- “Nostr will grow, and we’ll see new companies leverage this network beyond just social media.”
Growth continues, but Elon Musk’s Twitter takeover slowed adoption. Nostr will remain niche until a major catalyst occurs (e.g., a big player joins or forced usage due to censorship).
Stablecoin-Specific Regulations
- “Expect stablecoin regulations in 2024 that’ll be favorable to them.”
This didn’t happen, largely due to the administration’s hostility. Expect potential change in 2025.
Miscellaneous 2024 Reflections
- Return to Sanity
- 2024 felt like sanity prevailed, largely due to the Democrats’ collapse behind Biden and Harris and Elon’s Twitter dominance.
- Operation Chokepoint 2.0
- Received a lot of attention, and I’m thankful it did because my experience at Strike was radicalizing and extreme.
- Bryan Johnson & Anti-Aging
- He burst onto the scene with his obsession over biomarkers. I see it as misguided—chasing markers in isolation doesn’t automatically yield a healthy system.
- Apple’s Rough Year
- Without a visionary leader, Apple appears to be scraping by on existing products rather than innovating.
- Google Under Fire
- Google is in a tough fight with the government, just as it seems they’re on their heels with AI competition.
2025 Predictions
-
Bitcoin’s Performance Bitcoin will have a good year, but not better than 2024. To beat 2024, it must close above 206k on December 31, 2025. I’ll take the under on that.
- I am not ruling out it to be over that at some point in 2025.
-
Twitter’s Success Continues to Stunt nostr
- Nostr adoption will stay slow due to Elon’s dominant influence with X (Twitter).
- As long as it remains a beacon of free speech, I doubt we see an exodus.
-
Rumble integrating Tether might help if they allow Nostr-like features (zaps), but that seems unlikely.
-
Apple
-
Apple will continue its rent-seeking behavior and put out underwhelming products.
-
Google’s Quantum & AI
- Recent buzz about Google’s quantum chip and AI improvements won’t pan out as a big deal.
-
Google will continue to trail OpenAI and xAI in practical LLM usage.
-
Elon, Vivek & DOGE
-
I expect them to deliver more than critics think. They’ll expose bloat and inefficiencies in ways that will shake up norms. I greatly welcome this. I wouldn’t bet against them.
-
Mainstream Media Reckoning
- In Trump’s second term, mainstream news outlets will face a real reckoning, as I can’t see how their bias can continue.
- They’ll have to reduce their bias or risk bankruptcy.
-
Alternative media’s growth trend continues, especially as Twitter keeps exposing mainstream outlets’ weaknesses.
-
RFK Delivers
-
We will see big changes in the health space due to RFK at HHS. These are changes that I am very excited to see.
-
Foreign Policy
- With the transition to Trump, I expect some foreign policy wins that will buck the establishment but will deliver wins that are not thought possible by the “experts.”
Closing Note
- Overall 2024: It was a year of major political upheaval, vindication for Bitcoin, and continued AI advances.
- Outlook for 2025: Bitcoin remains strong, AI competition heats up, and media institutions face existential challenges. I’m optimistic for continued decentralization and a more level playing field across tech, finance, and politics. I think the start of Trump’s second term will be very strong for the market, health, and culture. Accelerate.
-
 @ 592295cf:413a0db9
2024-08-25 09:17:54
@ 592295cf:413a0db9
2024-08-25 09:17:54A Ux designer has arrived on Nostr. I thought run away while you can. He could get rich, if there was a little economy.
Klout, do you remember that service, which took data from Twitter and made a ~~ WoT~~.
From a note of chip, I understood one thing:
Bitcoin is your "sovereign" currency. Nostr is just third party protocol. If you have a service you can use Nostr to face your customers. "Sovereign" people offer services. They can be bitcoiners or not. So at this stage Nostr is a layer 3 Bitcoin.
So to grow the enveiroment it must be attractive. Let's paraphrase: the protocol is agnostic, the people are fundamentalist Catholics.
So when an atheist person arrives he says ah ok, how do I silence these people and use the protocol If a Protestant Catholic arrives he is laughed at or ignored or at most converted.
I had a disagreement with Dergigi, in the end he won, but he is not right... (True)
Post more notes, zap more, follow 1000 people update FAQ to the nth degree. We are in the desert of the Tartars and the enemy is coming and there are those who say every day we must be ready, sooner or later, it will happen, ah ok. Everything must be perfect. Push harder. This leads to exhaustion.
New Grant from Opensat to Victor of Amethyst, totally deserved, pushed the envelope. If you are a grapheneos user download Amethyst. It's not just Amethyst it's also orbot, citrine, amber, zap store or obtainium or f-droid.
GitCitadel has raised its first fund I wonder if it was just a test on geyser, I wonder if it is the right project to do on nostrocket, but I think Opensat grant for nostrocket makes it irreconcilable. This opens a pandora's box, as always. We are silent as fish.
I tried not to answer some questions even in one case I knew the answer, I apologize, Nostr is much older than me, so it's okay not to answer sometimes. Tomorrow begins nostRiga, The last unconference of Nostr.
(First day) The morning was so-so, in the evening the situation improved a little. In the evening I played a bit with Nostr and it broke The second day good in the morning bad in the evening. I saw little of the backstage maybe only two panels, Will by Damus, and P2Phash on Nostr.
I don't follow anyone anymore, I did a little bit of a unfollow. I saw that two users had 200 followers in common, and I said to myself ah ok what is this thing, I have to understand how they do it there is something that doesn't work, let's try to be a little more distant.
It's weird, too much reliance on following, you have to go and look, not be stationary.
-
 @ 335394ff:33e27ea6
2025-01-18 18:38:20
@ 335394ff:33e27ea6
2025-01-18 18:38:20The Power of Storytelling
Can storytelling be more than just entertainment? According to the World Health Organization, storytelling humanizes complex health issues, effectively changing viewers’ health knowledge, attitudes, and behaviors.
What I Share Across My Platforms
My blog explores how creativity, faith, and innovation come together to foster emotional wellness and personal growth.
- Blog : Thoughtful posts like “Healing Trauma Through Storytelling” delve into personal growth, faith, and emotional wellness.
- Podcast : Creative devotionals connecting my writings and poems to scripture-backed lessons for spiritual growth.
- YouTube : Visual, cinematic versions of my poems and creative works designed to inspire and uplift.
Explore More Storytelling isn’t just a tool for self-expression—it’s a way to reflect, heal, and spark transformative ideas, both personally and spiritually. Explore more here:
What’s your experience with storytelling as a tool for spiritual growth and innovation? Let’s connect!
originally posted at https://stacker.news/items/855213
-
 @ 3ac03011:41ecd1bb
2025-01-18 17:10:41
@ 3ac03011:41ecd1bb
2025-01-18 17:10:41Does Football Still Feel the Same?
Close your eyes for a moment and think back to when you first fell in love with football. What was it that pulled you in and wouldn’t let go? Was it the roar of the crowd as your team netted a stoppage-time winner? The thrill of an underdog beating the odds? Or maybe it was simpler—the chants, the rivalries, the raw, unfiltered chaos of the game.
Now open your eyes. Does football still feel like that?
You know it doesn’t. The spark is still there but the magic feels muted. Matches feel more like polished products, rivalries are starting to feel manufactured and even the moments of brilliance seem a little…hollow.
You hear the pundits blame it on “greedy owners” or “commercialisation of the game,” but football has always been tied to money. From the grand stadiums to the global superstars, wealth has always flowed to the game we love. So, what’s really wrong?
What Happened to the Chaos?
Football isn’t just a sport. It’s a reflection of life—messy, unpredictable and gloriously unfair. That’s what made it beautiful. It wasn’t just about the goals; it was about the stories. The miraculous comebacks, the unlikely heroes, the questionable refereeing decisions that sparked debates for years.
But where is that chaos now?
Look at today’s game. Teams are coached to minimise risk and prioritise results. Players are drilled into systems, their individual flair sacrificed for the greater machine. Even rivalries feel like marketing strategies, built more for brand engagement than genuine passion.
Why?
Because predictability isn’t just valued—it’s demanded. Clubs are forced to prioritise short-term financial growth over risk. They cannot afford to experiment or fail because the economic system, which governs us all, punishes them if they do. It’s no coincidence that football’s decline in spontaneity mirrors the rise of fiat money.
How Fiat Changed Football
Fiat currency, with its endless inflation, has placed football in a relentless race. Every club is chasing financial growth—not because they want to, but because they have to. Inflation eats away at savings, forcing clubs to focus on short-term profits.
The result? Clubs treat fans as customers, not loyal supporters. Teams are built for efficiency, not excitement. Every decision, from tactics to transfers, is filtered through a lens of operational financial return. The beautiful game is being stripped of its beauty, one spreadsheet at a time.
Do You Really Want Perfection?
Think of your favourite football memories, those that are deemed iconic. Was it all about skill and precision? Or was it about emotion, drama and unpredictability?
The “Hand of God” wasn’t just a goal—it became a chapter in football history. Frank Lampard’s disallowed goal against Germany in 2010 didn’t just spark debates—it became folklore. These moments, as infuriating as they were at the time, gave football its soul.
But today, we chase an unattainable goal: perfection. VAR was introduced to make everything “fair,” but instead, it’s robbed the game of its spontaneity. Those controversial moments that one fueled passion now lead to lifeless delays.
Is this really the game we fell in love with?
Financial Fair Play (FFP) and the False Promise
Consider FFP. At first glance, it seems like a noble idea—a way to regulate spending, create a level playing field and ensure the long-term stability of clubs. But has it really delivered on its promises?
The reality is, FFP wasn’t designed for fans. It’s a system built for regulators, giving them a framework to justify their role. What they fail to understand—or conveniently ignore—is that football fans aren’t ordinary customers. We don’t switch teams when things go wrong. If your club is relegated or endures years of heartbreak, do you suddenly start cheering for your rivals? Never. Loyalty is the foundation of football and it’s a loyalty so fierce that many fans would sooner stop watching the sport entirely than betray their team.
Instead of nurturing this unique connection, FFP has entrenched inequality. It locks in the dominance of a few elite clubs while stifling ambition for everyone else. Even as a supporter of one of these elite clubs, it’s impossible to ignore how these rules suffocate the very spirit of competition that makes football beautiful.
Is There A Way Back?
What if football could be free again? Free to embrace chaos, its passion, its unpredictability?
The answer isn’t to ban money from football. Money has always been a part of the game. The problem isn’t money—it’s the kind of money.
Fiat money, with its endless inflation, has poisoned football. We need an inflation-proof currency to form the heart of a new awakening for football. Lucky for us, we don’t need to look far for that currency.
A New Renaissance: The Bitcoin Era
Bitcoin is a form of money that doesn’t lose value over time. Clubs that adopt it will achieve financial stability without the need to chase endless operational growth. With Bitcoin, clubs can focus on what really matters: the football, the fans and the overall synergy between them.
Managers can take risks without the fear of collapse. Players can be artists, not just cogs in a system. Fans can feel like part of the story again, not just numbers on a balance sheet.
Imagine a world where football is free to be itself again. Where rivalries grow naturally, fueled by passion, not profit. Where clubs aren’t just businesses but extensions of their communities.
This isn’t a dream. It’s already happening. Real Bedford is leading the charge, proving that Bitcoin can change the game.
Football’s future is here—and it’s orange.
-
 @ fbf0e434:e1be6a39
2025-01-20 06:35:18
@ fbf0e434:e1be6a39
2025-01-20 06:35:18Hackathon 摘要
Watson Code Fest 2024 是一项年度生物Hackathon,由加德满都大学合作组织,重点关注医疗保健和信息学。此次活动汇集了41位开发者,他们致力于30个创新项目,旨在将生物技术、计算机科学和医疗保健整合,解决全球及本地的医疗保健挑战。探索的关键领域包括个性化医疗、智能医疗系统、诊断中的AI以及公共卫生数据分析。
该Hackathon的主要目标是促进创新、推广多学科合作,并增强技能发展。它为学生、专业人士和来自各个领域的研究人员提供了一个合作的环境,强调信息学在推进医疗解决方案中的角色。
活动在加德满都大学举行,为期两天,鼓励参与者创造性思考和协作工作。其旨在弥合学术界与工业界之间的差距,激发创新并促进网络建设。这次Hackathon的影响在于其激发新医疗技术的能力以及在尼泊尔培养创新文化,且具有潜在的全球影响。
Hackathon 获奖者
1st Place Prize Winners
- MutraSuchak : 该项目通过适用于医疗应用的低成本方法促进早期阿尔茨海默病的检测。它集成了ESP模块和Python Flask服务器,开源资源可在GitHub上获得。
Runner-Up Prize Winners
- PCOSgen: 该项目编制了一份用于PCOS表型的预测数据库,有助于早期诊断和个性化治疗。它使用数据驱动方法解决研究差距并改进患者结果。
Most Innovative Project Prize Winners
- Silent Witness: Graph-Based Abuse Detection: 该计划使用AI分析来自摄像头的面部表情以检测虐待模式。通过使用YOLO模型来保护隐私,它构建交互图以识别和标记负面模式,同时促进积极的环境。
有关所有参赛项目的详细列表,请访问 Watson Code Fest's project page。
关于组织者
Kathmandu University Biotechnology Creatives
加德满都大学生物技术创意(KUBiC)是生物技术和生物信息学领域的先锋组织。KUBiC以举办年度Watson Code Fest而闻名,为创新者、程序员和创造性思考者提供了一个平台,以解决这些领域中的关键挑战。KUBiC坚定致力于推进生物科学,在促进合作和创造力方面表现出色。其使命是重新定义生物学的未来,并推动跨学科领域的进步。更多信息可在其网站上找到。
-
 @ ed84ce10:cccf4c2a
2025-01-20 06:24:04
@ ed84ce10:cccf4c2a
2025-01-20 06:24:04Hackathon Summary
The Watson Code Fest 2024, an annual biohackathon, was organized in collaboration with Kathmandu University, with a focus on healthcare and informatics. The event brought together 41 developers who worked on 30 innovative projects, aiming to integrate biotechnology, computer science, and healthcare to tackle both global and local healthcare challenges. Key areas of exploration included personalized medicine, smart healthcare systems, AI in diagnostics, and public health data analysis.
The hackathon's primary objectives were to foster innovation, promote multidisciplinary collaboration, and enhance skill development. It provided a collaborative environment for students, professionals, and researchers from various fields, underscoring the role of informatics in advancing healthcare solutions.
Held at Kathmandu University over two days, the event encouraged participants to think creatively and work collaboratively. It sought to bridge the gap between academia and industry, stimulate innovation, and foster networking. The hackathon's impact was evident in its ability to inspire new healthcare technologies and cultivate a culture of innovation in Nepal, with potential global implications.
Hackathon Winners
1st Place Prize Winners
- MutraSuchak: This project facilitates early Alzheimer's detection through cost-effective methods suitable for healthcare applications. It integrates ESP modules and a Python Flask server, with open-source resources available on GitHub.
Runner-Up Prize Winners
- PCOSgen: This project compiles a predictive database for PCOS phenotypes, aiding early diagnosis and personalized treatment. It uses data-driven methodologies to address research gaps and improve patient outcomes.
Most Innovative Project Prize Winners
- Silent Witness: Graph-Based Abuse Detection: This initiative uses AI to analyze facial expressions from camera feeds to detect abuse patterns. By employing YOLO models for privacy, it constructs interaction graphs to identify and flag negative patterns while fostering positive environments.
For an extensive list of all participating projects, visit Watson Code Fest's project page.
About the Organizer
Kathmandu University Biotechnology Creatives
Kathmandu University Biotechnology Creatives (KUBiC) is a pioneering organization in biotechnology and bioinformatics. Known for hosting the annual Watson Code Fest, KUBiC serves as a platform for innovators, programmers, and creative thinkers to tackle crucial challenges in these fields. With a strong commitment to advancing biological sciences, KUBiC excels in fostering collaboration and creativity. Their mission is to redefine the future of biology and drive progress across interdisciplinary domains. More information can be found on their website.
-
 @ 16d11430:61640947
2025-01-20 03:32:57
@ 16d11430:61640947
2025-01-20 03:32:57Building a business, especially in the Bitcoin ecosystem, requires an unwavering commitment to patience and a deep belief in the fundamentals that underpin the technology. In a world driven by short-term profits and speculative fervor, it is easy to lose sight of the long game. Yet, the path to creating something meaningful and enduring often lies in resisting the noise and staying true to core principles.
The Bitcoin Revolution: Planting Seeds in Fertile Soil
Bitcoin is not just a technological innovation; it is a paradigm shift in how we view money, value, and trust. For entrepreneurs, it offers an opportunity to align their work with a monetary system that is decentralized, censorship-resistant, and designed for fairness. However, building a business in the Bitcoin space requires a recognition that societal adoption takes time.
As the saying goes, "The pot has to boil further." The ecosystem is still maturing, and while the signs of progress are undeniable, there is much work to be done. For plebs—the passionate individuals who embrace Bitcoin as a way of life—to eagerly work for sats, the economic incentives must become undeniable. This requires building infrastructure, educating the masses, and proving the utility of Bitcoin beyond speculation.
The Role of Patience in Entrepreneurship
Patience is not passive. It is an active process of nurturing your business, learning from setbacks, and steadily improving your product or service. In the Bitcoin space, patience involves:
-
Education and Advocacy: Many people still misunderstand Bitcoin's potential. Entrepreneurs must invest time in educating their audience, building trust, and explaining why Bitcoin is a better alternative.
-
Incremental Growth: Bitcoin adoption happens at the margins before reaching critical mass. Businesses that focus on steady growth rather than explosive, unsustainable expansion are more likely to succeed in the long run.
-
Long-Term Vision: Building for Bitcoin means thinking in decades, not quarters. A business grounded in sound principles—honesty, resilience, and utility—can weather market cycles and emerge stronger.
Faith in Fundamentals
Bitcoin’s fundamentals are its greatest strength: fixed supply, decentralized governance, and security. These principles create a monetary system that is fair and immune to corruption. Entrepreneurs in this space must build businesses that reflect these same values.
Integrity: A Bitcoin business should prioritize transparency and fairness, aligning incentives with customers and stakeholders.
Resilience: Bitcoin thrives in adversity. Businesses in this ecosystem should adopt a similar mindset, designing products that endure volatility and uncertainty.
Utility: Focus on solving real problems for real people. Whether it’s offering Bitcoin payments, facilitating education, or building tools for sovereignty, utility drives adoption.
Letting the Pot Boil: Creating Conditions for Change
The conditions necessary for mainstream Bitcoin jobs will emerge when the ecosystem matures further. This requires collaboration between businesses, developers, and advocates to:
Expand Infrastructure: Lightning Network, wallet solutions, and Bitcoin-native applications are critical to making Bitcoin more accessible and user-friendly.
Incentivize Participation: Paying workers in sats is not just a gimmick—it is a way to demonstrate Bitcoin’s superiority as a store of value and medium of exchange.
Build Culture: Bitcoin is more than technology; it is a movement. Businesses must contribute to a culture of empowerment, self-sovereignty, and fairness.
Conclusion: The Time Will Come
Faith in fundamentals is what separates builders from speculators. While the market will inevitably test your resolve, the rewards for those who persevere are immense. The time for mainstream Bitcoin jobs will come, but only when the ecosystem is ready—when plebs are eager to work for sats not out of necessity, but because it is the natural choice in a world aligned with Bitcoin's principles.
Until then, entrepreneurs must remain patient, continue building, and trust in the vision of a decentralized future. The pot will boil. When it does, those who believed in the fundamentals will be the ones to shape the next era of economic freedom.
-
-
 @ 378562cd:a6fc6773
2025-01-18 16:20:12
@ 378562cd:a6fc6773
2025-01-18 16:20:12As a frequent user who depends on my phone for a wide range of activities, including boosting my productivity and capturing spontaneous moments, I have been paying close attention to the OnePlus 13. This flagship device appears to meet all my essential requirements, particularly excelling in power and camera capabilities, which are my main priorities. Here are the standout features that have caught my attention.

Power to Handle Anything I Throw at It
Performance is a big deal for me, and the OnePlus 13 doesn’t seem to disappoint. It’s powered by the Snapdragon 8 Elite processor, a beast in the mobile tech world. I can already imagine how smoothly it would handle heavy multitasking, like switching between editing photos, running multiple apps, and even gaming.
The insane memory options—up to 24GB of RAM—truly stand out. That’s more RAM than most laptops I’ve owned! Pair that with up to 1TB of storage, and you’re looking at a future-proof phone. I’d never have to worry about running out of space for apps, photos, or videos, and everything would load lightning-fast.

A Camera Setup That’s Hard to Ignore
One of my favorite things to do is capture high-quality photos and videos, so a powerful camera system is non-negotiable. The OnePlus 13 delivers with its triple-camera setup; all three lenses are 50 megapixels. That means whether I’m shooting with the main wide lens, zooming in with the telephoto, or going wide with the ultra-wide, I’m getting consistently sharp, detailed shots.
The Hasselblad collaboration is a big draw for me, too. OnePlus phones have been steadily improving their color science, and this partnership seems to really shine in the OnePlus 13. I’d expect vibrant, true-to-life colors in my photos without much editing required.
The AI enhancements also pique my interest. From what I’ve read, the phone handles tricky lighting situations, like low-light environments or high-contrast scenes, exceptionally well. That’s exactly what I need to capture spontaneous moments without worrying about settings.
Battery and Charging That Won’t Leave Me Hanging
Another thing I appreciate is the long battery life. The 6,000 mAh battery on the OnePlus 13 is reportedly a powerhouse, capable of lasting two days under mixed usage. And when I do need to charge, the 100W wired charging can fully juice up the phone in just over half an hour. Even the 50W wireless charging is incredibly fast, which is perfect for someone like me who’s always on the move.
Design and Features That Add Value
The flat-edge design and premium finish make the phone feel as good as it looks. I’d probably go for the Midnight Ocean with its vegan leather back—it sounds grippy and unique, ideal for someone who doesn’t want to slap on a bulky case.
The little extras, like Glove Mode and Aqua Touch 2.0, also catch my attention. Since winters are cold here, using my phone with gloves on is a practical bonus.
Why It’s Tempting Me
At $899 for the base model, the OnePlus 13 seems like a solid deal, especially for the power and camera capabilities it offers. Even if I choose a higher configuration, the pricing still feels reasonable compared to other flagships with similar specs.
For me, the OnePlus 13 feels like a phone that’s built for power users—people who need speed, reliability, and top-tier camera performance. I’m seriously considering it for my next upgrade because it feels like it would keep up with everything I do and then some. If the camera and performance live up to the hype, I might just have my decision made.
-
 @ 592295cf:413a0db9
2024-08-17 07:36:43
@ 592295cf:413a0db9
2024-08-17 07:36:43Week 12-08 a suitable protocol
The knots come to a head, some of you have gray hair, you get older.
Tkinter is better than ws://, more secure, but has limitations, unless you know how to use figma and do some magic. The project of Nabismo.
Maybe Nostr doesn't work for me.
Aspirin moment Nip-17, works with nip-44 and nip-59. Someone said they made the groups encrypted with nip-17. I tried and succeeded, now you can DM me, don't do it. I had sent the link to a conversation of nip-87 closed groups. There's JeffG doing something with MLS. Then there's keychat.io which uses signal Nostr Bitcoin ecash and that's it... But in dart. It's a bit like the Matrix analogue for Nostr.
Final controversy not all nips are mandatory.
Build the foundation. You can't think about selling the house
Yakihonne has a countdown. What can a desktop app be. Community Lists, Nip-29
A birthday on Nostr, no that's not possible, they're all cypherpunks. 🎉🎉 (Except me)
There is a different attitude from Nostr when updates are released compared to Bluesky, everyone there is still enthusiastic, on Nostr ah ok but this is missing oh but this is missing or but support this other one, or but * zap, wait a minute, keep calm 🙇♂️, I'm the first to do this. (The revolt of the developers)
Deletetion: Client that have relay paired can do delete, more intelligently, Perhaps you can think of a delete.nrelay subdomain as a filter. This id is deleted. Be careful what you don't want to do. Maybe a session with a psychologist is better, because then you find yourself doing what you said you didn't want to do.
Does it make sense to follow someone on Bluesky? In my opinion no, or better yet yes. There are several algorithms on Bluesky, which do their job well. In the end it's just a matter of arranging them better on the screen. Yes you can have lists to save someone, but then you read everything, so lists with algorithm seems like a next feature. this way they can keep the following small, almost minimal, because there are algorithms that work for the user. People will start writing for SEO algorithm and AI and other things, which tech gurus really like and so on. The fact that it is almost exclusively an app will greatly facilitate this trend, there will be almost no need for moderation, and you can get it all in just a few apps. (Great)
Oh yegorpetrov has abandoned. Pegorpetrov said that he is coming back 😌 It might be an invention but I'm a little heartened by it.
Bankify, a new wallet of super testnet, only for crush testers.
You can't stream on zap stream without reach, maybe it's better audio space. Contact someone maybe an influencer or Nostr elite or whatever. Open Source Justice Foundation streaming
Designer, I wanted to propose comment on wikifreedia nielliesmons article and follow #nostrdesign, but too many answers for today. NVK note is ~~mainstream~~
I think I'm not suited to Nostr.
Nostr-ava bike file geo tag sharing. (NIP-113) Sebastix doesn't respond, I must have done something bad to him, or maybe I'm stressing him too much. Finally he replied 🤙. In the end maybe, I have too much hype about this proposal and it's something I don't know maybe, but maybe if they were already doing something with geo tags it's better to say so.
Another birthday, less cypher more punk 😌
Usdt on Nostr, there must be some error. (freeform app)
USDT on tron is like Money. (Bitcoiner not really)
Privacy issue, deletion motion, or deletion request, go go.
Nip29 hype, i don't have hype at all. I'm tired of words, I record a podcast on Nostr. Let's see if I can do it, at least think it. (It's more of a workflow thing than actually something I would do)
- Create an npub (easy)
- Record the audio episode (I think I can do it). Terrible audio
- Loading on a Nostrhosting, if less than 10 MB it should go smoothly.
- Publish the video or audio of the episode on some Nostr client, perhaps using blastr relay 😞.
- Do the nostree link, by putting the episode, and also the npub.pro and put the URL on café-society. 6) Publish all these links on the Main profile, saying that, made a podcast about Nostr in Nostr of nostr. 😂
I thought a client could have poll, form, spreadsheet, collaboration document. It's the kind of otherstuff we want to see. Something that goes beyond a normal feed.
Emoj on bluesky, Eventually also zap 🥜 link emoj Blue
Eventually there will be a developer revolt And they will only do a social network in their downtime, they will call it Nostr.
There is a storm, Nostr does not work in 4g with two bars. Or now 4G is gone too.
Yakihonne Smart widgets, something to try on the weekend.
-
 @ c69b71dc:426ba763
2025-01-18 15:39:35
@ c69b71dc:426ba763
2025-01-18 15:39:35Chef's notes
This raw vegan curry ramen is a vibrant, nourishing dish packed with fresh vegetables and a rich, creamy coconut curry broth. It’s quick to prepare, full of flavour, and the perfect guilt-free comfort food! 🌱 Feel free to use your favourite veggies👩🏼🍳
Details
- ⏲️ Prep time: 20 min.
- 🍳 Cook time: 0
- 🍽️ Servings: 2
Ingredients
- 500g or 2 packs kelp noodles
- 1/2 Lemon juice ( 1/4 for soaking and 1/4 for the soup
- Salt
- Fresh vegetables of your choice, such as: 4 medium mushrooms, 4 leaves red cabbage, 2 carrots (julienned or peeled into strips), 1 Celery stick (diced)
- 2 cups coconut milk (or coconut cream diluted with water)
- 1/2 flesh of a Coconut (optional, if using fresh coconuts) otherwise more coconut cream
- 1 thumb of fresh ginger
- 1 thumb of fresh turmeric
- 2 tbsp light miso paste
- 2 pitted dates
- 2 tbsp cashews
- 1 clove garlic
- 1 tsp curry powder or pepper (optional)
Directions
- Prepare the Noodles: Rinse the kelp noodles thoroughly. Then soak them in warm water with a squeeze of lemon juice and a pinch of salt for 10 minutes to soften.
- Prep the Vegetables: Thinly slice or julienne carrots, dice celery, thinly cut mushrooms, cut the red cabbage into thin strips.
- Make the Broth: In a blender, combine the following: 2 cups coconut milk (or coconut cream diluted with water if fresh coconuts are unavailable), ginger, turmeric, 1/4 juice of 1 lemon, light miso paste, pitted dates, cashews, garlic, salt, curry powder
- Blend on high speed for about 3 to 4 minutes until the broth is smooth and slightly warm. Do not overheat!
- Assemble the Ramen: Drain the kelp noodles and place them in serving bowls. Arrange the prepped vegetables on top of the noodles. Pour the warm curry broth over the noodles and vegetables.
- Serve immediately and enjoy your raw vegan ramen with chopsticks for an authentic touch!
-
 @ 592295cf:413a0db9
2024-08-10 09:24:14
@ 592295cf:413a0db9
2024-08-10 09:24:14Week on Nostr 05-08
List of site for nostriches https://zaplinks.lol/
Fiatjaf web components
Welcome bear market 🧟♂️ fear, angry, build It's fine meme
I mutated one on stackernews. Basically I have notifications on Nostr page But someone keeps spamming every single thing, from his point of view it's a shared bookmark, but do it on your site. Maybe it's the heat...
On bluesky they eliminated a "for you" feed, now there is Discovery, not your feed, not your choice. There's actually a label that says my feeds, they're yours... Designed for you is more appropriate.
Mutiny lightning, "get the fuck on board". 😔
You lose your Money, ok
I don't know much about programming languages, but it seems like a jungle of scams
The purple pill help the Orange pill go down, maybe it was wrong. For now it's more people passing pills I have the orange give me the purple, I have the purple give me the orange. 😅
If you don't want no corn content you can go to mastodon and bluesky or whatever.
I thought nostr:relay might be a good solution to be a little more like a mint. It was deprecated, then the Nip-73 was added, rss feed and other devilry.
If you don't like what you see, change the app, this one will perhaps clear your following list and you'll start again from scratch. Not all things come to harm.
Why not Building agregore on Nostr, Nostr pear fedimint cashu mesh and local first. It doesn't seem like a simple application to make, from a local-first perspective, I solve a problem, but it's not a small problem to solve, Sync, database management, database schema, authentication, put everything together, instead I need this to solve this problem. It seems strange.
Aspie96 is making a client of ours, there was a lot of talk about how to increase content not related to bitcoin and things like that, there was one who was anti-bitcoin. I thought: Bitcoin is just a tool. Even guns are just a tool. I hate guns, I hate Bitcoin. It will be difficult, if you know any npub that hates Bitcoin comment below, thanks.
Trying not to use nostter for a while. It has glitches when loading threads and even with zap, I zapped myself even though I was clicking on the post I was replying to.
Voyage separates follow to topic in a new version.
People start arguing, it's allowed, everyone wants to be right, that's not the definition of social 👾.
Monitors watch-only bitcoin wallets https://github.com/sommerfelddev/sentrum
I noticed on Openvibe that in the trending timeline Nostr's notes have more interactions than responses. Maybe it was just that today Fiatjaf was doing universal polls 😅.
Step away from your favorite app, for a week if you can. Detox.
Oh Our founding, rain of money https://github.com/theborakompanioni/nostr-spring-boot-starte https://opensats.org/blog/nostr-grants-august-2024#seer
I'm happy for Vic and Sepher Nostroot exists 😅, note from some time ago. (I can't find it)
Perhaps the list of grant applications should be published, no one wants to open Pandora's box. 🙇♂️
Nostrasia 2.0 the Japanese community is a bit at a loss, they are trying to relaunch themselves 🤙, even if I'm seeing less enthusiasm, I'm following less.
I think a month has passed since I said this sentence, every day it was better but the next day something happened that you said maybe 6 months is too long. nostr:nevent1qy88wumn8ghj7mn0wvhxcmmv9uq3zamnwvaz7te3xsczue3h0ghxjme0qyw8wumn8ghj7mn0wd68ytnxwfskxarpd35h5ety9ehx2ap0qythwumn8ghj7mn0wd68ytnnw3skkete9ehx2ap0qy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qpqf25td2xxgxfu80xpgg47cmfg2zkn6v803kefj3htjss5nvamfmgswf2kcs
Ho iniziato a seguire un po' local-first. https://docnode.dev/local-first I follow a podcast of the same name and dev tools.
When everyone thinks of Nostr they think of their favorite app and think that others see the same, but this is not the case.
I delete some gossip (photo)

Gossip is Nostr or Nostr is gossip.
Communities are difficult, they take time. I don't have this type of problem. People are fine on telegram and on simplex or any app. But maybe a Nostr project should be on Nostr?? Nip-29 can be interesting. Even if you start from scratch or almost. It's true that there are more apps, but this will perhaps only add to the confusion.
They are still talking about paid or non-paid relay, it's not a mature stage. Early stage.. I thought designers liked relays, that's not the case, I thought it was a place of experimentation, that's not the case. Bring more people. Last week I was talking about how I was jealous of bluesky who had an agenda for design, now it's also on Nostr, first hypernote article https://wikifreedia.xyz/hypernote-nip
I might say silly things, I'll go.
Hey Will remember to practice safe nsec always
nostr:nevent1qqsr6x8hduv8ta0g2da4aukrhzdtv6qcekyp5f9z9sxq6sd5peegnxgprpmhxue69uhhyetvv9ujumn0wdmksetjv5hxxmmdqy28wumn8ghj7un9d3shjtnyv9kh2uewd9hsygr4wku5l2q32tl99xjgn8feq22279pzwu25eezqxm2su2ken4wzvuf2ydnp
nostr:nevent1qqspsm343talkkjnyf3ah0zwy727cwd7phw3xnz49q59q5cfw4uhyngpzemhxue69uhhyetvv9ujuurjd9kkzmpwdejhgqgcwaehxw309aex2mrp0yhxummnwa5x2un99e3k7mgzyqewrqnkx4zsaweutf739s0cu7et29zrntqs5elw70vlm8zudr3y2j7zajz
Use nsec.app, 😅 Share bunker (smart people will know how to do it)
-
 @ 5d4b6c8d:8a1c1ee3
2025-01-18 14:47:23
@ 5d4b6c8d:8a1c1ee3
2025-01-18 14:47:23Since I don't follow a particular regiment throughout the day, I need some guiding principles to stay on track. Previously, I wrote about Hormesis, which let's me be more comfortable being uncomfortable.
My primary weakness, when it comes to ~HealthAndFitness, is snacking. Honestly, "snacking" is putting it mildly. If there are unprotected baked goods in the house, I'm going to eat them until either they're gone or I'm too sick to continue.
The point where I am able to exercise some self-control is at the point of purchase. I have no problem (usually) keeping junk food out of my cart.
I will buy the ingredients to make baked goods, when my wife asks me to, though. However, being limited to homemade baked goods that other people make for me is a pretty good constraint. Plus, her cooking is healthier, tastier, and less expensive than prepackaged snacks.
I'm curious if this works for anyone else. Or, do you weirdos have self control when there are tasty treats in your vicinity?
originally posted at https://stacker.news/items/854896
-
 @ da0b9bc3:4e30a4a9
2025-01-18 14:09:40
@ da0b9bc3:4e30a4a9
2025-01-18 14:09:40Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/854843
-
 @ 592295cf:413a0db9
2024-08-04 05:55:02
@ 592295cf:413a0db9
2024-08-04 05:55:02Nostter muted by kind
Will mute freefrom, hashtag fall
Venezuela riots, after the vote
I was thinking that having a Nostr conference every 6 months doesn't make sense, maybe it's better to focus on something else. If not it becomes a Tour Life. It doesn't increase adoption Produces tons of material It's good for networking It's not sustainable
Readable updates, how important they are. If it's just bugs and fixes it's better.
I hate Pam. As user It writes interesting stuff, but, doesnn't write in long form, because long form are more difficult, less reach and immediacy, and difficulties to share over in the feed,but not write a poem, sorry.
The thing about coracle is that I load the initial feed, but that gets printed, and it doesn't tell me if there are new notes coming in, as if it interrupts the flow, and it's always a fetch. I want to read the future, not always the past. RealTime feeds Like bluesky 🧞

Njump had problems, it keeps the cache and if the user changes something in their data it doesn't update it immediately. Fiatjaf was angry.
It's the month of NostRiga, we can move on to September without thinking about it. No
It's funny when you see a text in Japanese and inside read Nostr, I want to know what it says. He usually says Nostr is great. And the next note I drank too much 🤣
Today I thought that on the other side of the world it is February and that their February is 31 days. Pam said was sick. I see that hate is a virus 😅🙇♂️
I decided to publish stronpy when it's ready, maybe in 6 months. I've done the lineup, now I have to do the gantt 😅. Maybe I can post the gantt somewhere.
If it's not encrypted it's public. Amethyst draft 31000 and something like event
Nostr Is great but the amount of time Lost to the same thing because you don't know that exist Is remarkable. Nostr is a redundancy protocol
nostr:nevent1qqsqjqauc34k9k278x6cka5jyf3aq033y4pn5czwaff72l3rwum7llq7ela3x When they do that I can't stand them, then maybe it's a little different 😔😔 Zapper.fun ✅ Because you launch a project, example nostr.band but contain others 100 apps 😅 Nostr.band, nostrapp.link, zapper.fun, Nostr login, nsec.app, Npub.pro, Npub.pro also cli, Nostr universe/ knows as spring site
Even in Coracle it would be great to have a check on the note as root, because when you see the answers, perhaps the distance from another post, is so small, so perhaps a gray line for the mark of another note as root.
I listened to several minutes of plebchain radio episode on nostrnests. Language is an obstacle, but also an excellent justification. Last year I started recording a podcast episode, in which I talked about nostr bookmark update. I didn't even want to listen to it again 🤣.
I sent a video of an explanation of a zap it was 500 MByte of video for 4 minutes.
Nostr doesn't work. In practice, many apps have removed the possibility of logging in with the simple key, be it public or private, because especially the private one you don't want to copy paste in every single clients/apps, increasing the attack surface.
However, by removing this functionality and doing little onboarding, the matter is very difficult, but there is a certain belief that people who arrive at a Twitter like client get to know the network a little and then move on to videos or writing, or similar. But one can open a site by chance and see what it offers without knowing anything.
In the future there will only be one client, that of medical data...
Someone share this nostr:nevent1qqs24qzelpk8xjlk4dthr9tfkqwz8n58dlm04ezyvg9nuztud6jjfhc9mg04n I had in my bookmarks. I see dozen types of this self hosted manners. Maybe captains-log is for nostr-type, good.
-
 @ c4b5369a:b812dbd6
2025-01-18 12:17:22
@ c4b5369a:b812dbd6
2025-01-18 12:17:22This is the first edition of the SDR (Squirrel Den Recap), a development blog where I recap the recent Cashu related things I've been working on.
The year of the nut
IYKYK. 2025 is the year of the nut. Don't blame me, you can put it on the Chinese:

And I intend to take full advantage of that. This is the year where I go all in on the nut development!
Building a mint???
There are already a few mint implementations out there (nutshell, gonuts, cdk...). So why build another?
Honestly it was kind of a selfish move. So far, I have mainly concerned myself with building tools for Cashu wallets and clients. I figured, if I wanted to truly focus on Cashu this year, I should also know my stuff when it comes to building a mint from scratch. And so I did. It also allows me to experiment with mint related stuff, having an implementation handy that I can mess around with.

The mint implementation is called MNT. You can visit the homepage https://mnt.cash , where you will also find a link to the code.
Although the code works, the mint implementation is not yet ready for production. I've been playing around with it using a local testing lightning network with Polar , which by the way is a great tool for devs that need to test lightning integrations.
The mint
MNT is short for mint. It's also pronounced like mint, but without the "i". The goal of this project is to be an easy to run mint, that could be deployed by users for example when running an event. It won't support all of the protocol features, to keep it simple. Instead the focus will be on simplicity and ease of use.
MNT comes with an admin web interface, that makes it easy to set the mint up with a lightning backend:

After adding a lightning backend, the mint is basically ready! Users can enjoy a live view of what is happening on their mint via the integrated dashboard:

Admins can take direct actions on the mint via the admin tool, like rotating keysets, disabling and enabling features, etc...
A key feature is also the keyset view, where operators get a view on how much of the issued ecash has already been redeemed in each keyset. This is a crucial tool for mint operators, because it lets them know when they can safely delete records from their database, or shut the mint down.

The mint is compatible with all Cashu wallets. It only supports a subset of the cashu specification (NUTs), and will probably never implement the full spec. I'm looking forward to soon recklessly give this badboy a spin on mainnet 😎
What else?
Cashu-ts
Last year
npub1mhcr4j594hsrnen594d7700n2t03n8gdx83zhxzculk6sh9nhwlq7uc226
joined cashu-ts as a maintainer and has been killing it with development in the project! As I ramp up my involvement in the project again, we started having weekly dev calls. Developers that want to contribute to cashu-ts development, please reach out to me so you can join us on the next call!
Nutstash
The wallet has seen a complete make-over at the end of last year. Now is the time to consolidate, fix bugs and improve the UX.
npub12zpfs3yq7we83yvypgsrw5f88y2fv780c2kfs89ge5qk6q3sfm7spks880
has been helping me with awesome designs and UX suggestions, while I've been crushing bugs. A new version fixing some edge cases in the restore process can be expected next week!

This blog
\ This year, I was fortunate to receive funding for my work on open source projects in the Cashu ecosystem. I am very grateful for the trust from
npub17xvf49kht23cddxgw92rvfktkd3vqvjgkgsdexh9847wl0927tqsrhc9as
and
npub10pensatlcfwktnvjjw2dtem38n6rvw8g6fv73h84cuacxn4c28eqyfn34f
this means a lot to me, to be able to make a living by working on something I am passionate about is a blessing, and I don't think it would be possible without the support from you. My deepest gratitude, I hope my contributions will not only match, but exceed expectations.
By writing this blog, I want to show my progress, proof of work, and give people a look into the daily life in the squirrels den 🐿️🐿️🐿️🐿️🐿️🐿️
If you have any questions or suggestions about this blog, please let me know in a comment!
Best,
Gandlaf
-
 @ a10260a2:caa23e3e
2025-01-18 12:04:41
@ a10260a2:caa23e3e
2025-01-18 12:04:41Last Updated: January 18, 2025
First off, big shoutout to Coinos for having support for adding a memo to BOLT12 offers. This provides a solid alternative for the pleb who wants to support mining decentralization but doesn’t want to set up a CLN node and pay thousands of sats for a channel only to get little rewards. This is the case for most of us who only have a miner or two (e.g. a Bitaxe and/or an S9).
Before we get into setting up Lightning payouts, you’ll want to have your miner configured to mine with OCEAN of course. You’ll also want to make sure that the bitcoin address you use is from a wallet that supports signing messages.
These are the ones listed in the OCEAN docs:
- Bitcoin Knots/Bitcoin Core
- Coldcard
- Electrum
- LND (Command Line)
- Seedsigner
- Sparrow
- Specter
- Trezor
I checked one of my favorite, user-friendly wallets — Blue Wallet — and it happens to support signing messages as well.
Just tap the three dots on the upper right and you’ll see the “Sign/Verify Message” button at the bottom.
Update [January 18]: You can now use Coinos to sign by going to https://coinos.io/sign
The trick here is to not refresh the page. In other words, when you're logged in to your Coinos account, go to the URL and use the legacy address (starts with a "1") that's displayed to configure your miner(s). If you refresh the page, you're going to get a new address which will cause the signing to fail later on. Remember, keep the tab open and don't refresh the page.

Whichever wallet you choose, generate a receive address to use when configuring your miner (it’ll also be your OCEAN username).
Here’s how it looks on the Bitaxe (AxeOS)…
And the Antminer S9 (Braiins OS).
NOTE: There’s a slight difference in the URL format between the two apps. Other than that, the username will be your bitcoin address followed by the optional “.” + the nickname for your machine.
You can find more details on OCEAN’s get started page.
Alright, now that your miner is pointed at OCEAN. Let’s configure Lightning payouts!
Generating the BOLT12 Offer
In the Coinos app, go to Receive > Bolt 12.
Tap “Set memo” and set it to “OCEAN Payouts for [insert your bitcoin address]” (this text is case-sensitive). Use the same bitcoin address you used above to configure your miner(s).
After tapping OK, copy the BOLT12 offer (it should start with “lno”) and proceed to the next step.
Generating the Configuration Message
Navigate to the My Stats page by searching for your OCEAN Bitcoin address.
The click the Configuration link next to Next Block to access the configuration form.
Paste the BOLT12 offer here, update the block height to latest, click GENERATE, and copy the generated unsigned message.
Signing the Configuration Message
To sign the generated message, go back to Blue Wallet and use the signing function. Paste the configuration message in the Message field, tap Sign, and copy the signed message that’s generated.
If you're using Coinos to sign, return to the page that you kept open (and didn't refresh) and do the same. Paste the configuration message, click submit, and copy the signed message.
Submitting the Signed Message
Once signed, copy the signature, paste it in the OCEAN configuration form, and click CONFIRM.
If all goes well, you should see a confirmation that the configuration was successful. Congrats! 🎉
All you gotta do now is sit back, relax, and wait for a block to be found…
Or you can look into setting up DATUM. 😎
-
 @ df67f9a7:2d4fc200
2024-07-07 18:25:32
@ df67f9a7:2d4fc200
2024-07-07 18:25:32Anyone who thinks that “onboarding new users” is simply a technical challenge of educating people about “how Nostr works”, is grossly mistaken about social networks in general and blind to what makes Nostr so special.
Social Networks are for Friends
Relationship building is why people use social networks. Connecting with friends and loved ones (and colleagues and customers also) is the obvious reason to join, and should be the primary objective in any onboarding endeavor. Everything else “about the technology” only needs to be introduced “as needed” in order for each new user to achieve this goal.
The Nostr Network Requires Trusted Friendships
To thrive at scale, Nostr needs to have established and interconnected “webs of trusted friends” for “verifying” authentic profiles and quality content. This PgP strategy for decentralized trust implemented on Nostr, is the best way to keep bots and bad actors at bay while preserving freedom and sovereignty for every user. Even though Nostr still doesn’t have a standard for determining who “is trusted” for any one user across all clients, we can already build tools to onboard new friends of the highest quality trust. Leveraging existing relationships, “webs of trust” can be strengthened even at this early stage simply by advocates “inviting friends to Nostr”.
Nostr is New and Already Full of Trusted Friends
But it won’t be for long. Bots and bad actors are relatively “easy” to keep at bay today because the Nostr userbase is still small. People who come to Nostr and STAY have mostly been a self selecting group of “freedom tech fans”. We like it this way, and are generally happy to be here. The comraderie is refreshing. But the more people that come to Nostr, the more Nostr will attract different kinds of people.
This is already happening. Nostr is growing at the edges, reaching out beyond the “freedom tech fans” and attracting a number of “less committed” (and some nefarious) individuals here and there. Who sticks around? The “friends of freedom tech fans” stick around longer because they have friends here. WAY BEFORE even considering how “the network effect” will take over, Nostr needs to solve for retention by bringing more “trusted friends” into the network. Social onboarding tools will allow us to share Nostr to “friends of freedom tech fans” and beyond, establishing interconnected “webs of trust” that are increasingly impermeable to bots and bad actors.
Nostr is Freedom Tech that People Want to Share
Creators and influencers of every kind share Nostr (and Nostr content) every day. This phenomenon is a gold mine for onboarding, and can be supported with tools and incentives. Driven by the fact that Nostr is an open protocol, owned by nobody and available for anybody to build upon and profit from, the passion for sharing Nostr will never wane. But our userbase may fall off, if people become disenchanted by undesirable content or lack of good follows. This is why onboarding efforts, to attract more “friends” to the network, are so important. Leveraging the “share worthy” phenomenon of Nostr itself to grow Nostr’s networks of “trusted friends” seems like a no brainer. But for this strategy to work, it needs to be win win win for all parties.
Everybody Wins with More Trusted Users on Nostr
Even as standards for qualifying trust are still being refined, “social onboarding” increases the ratio of “more” trusted over “less” trusted users across the network.
Developers Win
With more trusted users on the network, Nostr developers win by being able to attract an increasingly diverse range of business partners to sponsor their projects.
Sponsors Win
An increase in trusted usership equates to more “real people” perusing “desired content” and more chances for brands to engage “organically” with target audiences. Marketing opportunities increase with trust.
Advocates Win
Simply by sharing Nostr with their friends, Advocates support the sustained growth of trust across the network. Valuable zap reward programs to incentivize high quality onboarding efforts are easily justified and funded by social onboarding clients and their sponsors.
Users Win
More trusted users across the network means more trustworthy content in every feed and more easily discoverable friends and new follows regardless of the client or algorithm used.
Nostr Wins
More trusted users on the network means more “high quality” trust connections between each user. Strong webs of trust is what keeps out bots and bad actors, and is essential for stability as Nostr scales.
Social Onboarding Clients Bring Trust to Nostr
Having more tools for “sharing Nostr with friends” is how Nostr wins. Any client can have capacity for “Social Onboarding”. This may be a dedicated onboarding client or a feature set within a social client. A client that offers “Social Onboarding” will support Nostr advocates and the users that they invite. These should have the following feature set :
- Nostr advocates may create and share any number of customizable “Nostr invites” for different audiences or occasions. Each may have different reccomendations, or access codes, or expiry options. (A NIP is in the works)
- Nostr invite QR codes (and shareable URLs) should resolve to a WEB based interface for prospective (and existing) users who MAY NOT have a client or browser extension already installed.
- Each invite should (within the onboarding client) provide access to low friction profile creation AND advocate reccomended lists of new friends, interest groups, preferred clients, best relays, and other stuff.
- Private key generation and management for new users should be handled entirely within the onboarding client (using NIP standards without a browser extension or external bunker app) to reduce friction at this crucial moment.
- A human readable Nostr address (NIP05 or some future NIP) should be generated automatically for all new users.
- New account creation should result immediately in a direct message or group thread of private “gift wrap” encrypted messages. This thread acts as the new user’s “first contact” with the advocate (possibly others as well) and an anchor for exploring the rest of Nostr.
- Invite “receipt” data (who invited who) should be “gift wrap” encrypted, accessible only to the advocate and new user. Clients wishing to use this data for analytics MAY request access from BOTH parties.
- Top Advocates may be calculated by the client (using data from invite receipts OR from public Nostr usage metrics), and awards may be offered.
- Advocates may also be supported by the client through access to private “advocate support” groups and communities over the Nostr network.
Support Social Onboarding for Nostr
Meet Me On Nostr is an app for sharing Nostr with friends via advocate invites. It is a reference client to demonstrate the power of Social Onboarding for Nostr. The first launch of "feature complete" client is expected in fall 2024.
This is a “bootstrap” funded project in active development. We are not grant funded or VC funded. Instead, we are looking to pay our developers by sponsorships from “Nostr adjacent” businesses who want to increase brand recognition over this new social network.
Is Your Business Nostr Adjacent?
“I’d like to advertise on Nostr but it’s “not quite ready” says our marketing team.”
“It has potential, and we have alignment, but the technology is still a bit rough.”
“Nostr is a perfect fit for our “target audience”, but there simply aren’t enough people using it.”
If your business is aligned with freedom technology, and the people who build and use Nostr, then NOW is the perfect time to sponsor Social Onboarding. Help grow Nostr’s base of trusted users and engage directly with Nostr’s most active advocates and influencers as it scales.
Release Nostr’s Superpower
When Nostr advocates are equipped and incentivized to share Nostr with their friends, nothing can stop this network from growing and growing and growing ever more secure and interconnected networks of trusted users.
Onboarding and retaining trusted users as Nostr scales will require so much more than just pointing people to “how Nostr works” content. Nostr’s true power lies dormant in the existing relationships that Nostr users already have outside of Nostr. Leveraging this power is what Social Onboarding is all about. Social Onboarding is Nostr’s superpower.
-
 @ 3bf0c63f:aefa459d
2024-06-19 16:13:28
@ 3bf0c63f:aefa459d
2024-06-19 16:13:28Estórias
-
 @ 42342239:1d80db24
2025-01-18 08:31:05
@ 42342239:1d80db24
2025-01-18 08:31:05Preparedness is a hot topic these days. In Europe, Poland has recently introduced compulsory lessons in weapons handling for schoolchildren for war-preparedness purposes. In Sweden, the Swedish Civil Contingencies Agency (MSB) has recently published the brochure on what to do "If crisis or war comes".
However, in the event of war, a country must have a robust energy infrastructure. Sweden does not seem to have this, at least judging by the recent years' electricity price turbulence in southern Sweden. Nor does Germany. The vulnerabilities are many and serious. It's hard not to be reminded of a Swedish prime minister who, just eleven years ago, saw defense as a special interest.
A secure food supply is another crucial factor for a country's resilience. This is something that Sweden lacks. In the early 1990s, nearly 75 percent of the country's food was produced domestically. Today, half of it must be imported. This makes our country more vulnerable to crises and disruptions. Despite our extensive agricultural areas, we are not even self-sufficient in basic commodities like potatoes, which is remarkable.
The government's signing of the Kunming-Montreal Framework for Biological Diversity two years ago risks exacerbating the situation. According to the framework, countries must significantly increase their protected areas over the coming years. The goal is to protect biological diversity. By 2030, at least 30% of all areas, on land and at sea, must be conserved. Sweden, which currently conserves around 15%, must identify large areas to be protected over the coming years. With shrinking fields, we risk getting less wheat, fewer potatoes, and less rapeseed. It's uncertain whether technological advancements can compensate for this, especially when the amount of pesticides and industrial fertilizers must be reduced significantly.
In Danish documents on the "roadmap for sustainable development" of the food system, the possibility of redistributing agricultural land (land distribution reforms) and agreements on financing for restoring cultivated land to wetlands (the restoration of cultivated, carbon-rich soils) are discussed. One cannot avoid the impression that the cultivated areas need to be reduced, in some cases significantly.
The green transition has been a priority on the political agenda in recent years, with the goal of reducing carbon emissions and increasing biological diversity. However, it has become clear that the transition risks having consequences for our preparedness.
One example is the debate about wind power. On the one hand, wind power is said to contribute to reducing carbon emissions and increasing renewable energy. On the other hand, it is said to pose a security risk, as wind turbines can affect radio communication and radar surveillance.
Of course, it's easy to be in favor of biological diversity, but what do we do if this goal comes into conflict with the needs of a robust societal preparedness? Then we are faced with a difficult prioritization. Should we put the safety of people and society before the protection of nature, or vice versa?
“Politics is not the art of the possible. It consists in choosing between the disastrous and the unpalatable” said J. K. Galbraith, one of the most influential economists of the 20th century. Maybe we can’t both eat the cake and have it too?
-
 @ 16d11430:61640947
2025-01-19 22:19:00
@ 16d11430:61640947
2025-01-19 22:19:00Welcome, intrepid traveler, to the uncharted territory of the mind! This guide draws from the greatest explorers, philosophers, and scientists who dared to map the mysteries of inner space. Pack your curiosity, buckle up, and prepare for a journey through the vast landscapes of consciousness, perception, and human potential.
Chapter 1: Know Thy Mind (Before It Knows You)
Key References: "Incognito" by David Eagleman, "The Power of Now" by Eckhart Tolle
The first rule of mind travel: most of what happens in your brain is unconscious. Your mind is like an iceberg—only the tip is visible (your conscious thoughts). Beneath lies a vast network of automatic processes shaping your perceptions and decisions.
Tips for Hitchhikers:
Pause and Observe: Cultivate mindfulness to slow the chatter of the conscious mind and observe the silent work of the subconscious.
Live in the Now: As Tolle advises, consciousness thrives in the present. The past is a memory, and the future is a projection—neither exists outside your mind.
Chapter 2: The Art of Inner Travel
Key References: "The Mind Illuminated" by John Yates, "The Doors of Perception" by Aldous Huxley
Traveling inward requires tools, and meditation is the universal passport. It trains your attention, opens doors to altered states of awareness, and reveals the boundless nature of your mind.
Tips for Hitchhikers:
Follow the Breath: Start simple. Focus on the rhythm of your breathing. This anchors you to the present and quiets mental noise.
Explore Altered States: As Huxley discovered, substances like psychedelics (when used responsibly) or profound meditation can dissolve mental barriers, revealing the infinite.
Chapter 3: Habitual Programming
Key References: "Atomic Habits" by James Clear, "Superhuman by Habit" by Tynan
Your mind is a creature of habit. Over time, these habits carve neural pathways, shaping your behavior. The good news? You can rewrite these programs.
Tips for Hitchhikers:
Small Changes, Big Impact: Focus on small, consistent habits. Tiny tweaks lead to massive shifts in your mental landscape.
Hack Feedback Loops: Celebrate victories and reflect on failures. Every action trains your brain for future behavior.
Chapter 4: The Flow State – Consciousness on Turbo Drive
Key References: "Stealing Fire" by Steven Kotler, "The Inner Game of Tennis" by W. Timothy Gallwey
Flow is the ultimate ride—effortless, joyful immersion where you lose yourself in the task. It’s the mind’s cheat code for peak performance and creativity.
Tips for Hitchhikers:
Find the Edge: Engage in activities slightly beyond your skill level. Flow lives in the challenge.
Eliminate Distractions: Turn off notifications, declutter your space, and give your full attention to the task.
Chapter 5: Neuroplasticity – Rewiring the Inner Highway
Key References: "The Brain That Changes Itself" by Norman Doidge
Your brain is not static; it’s a living, evolving organ capable of change. Neuroplasticity means that thoughts and actions can reshape your mental circuitry.
Tips for Hitchhikers:
Practice Makes Permanent: Repetition strengthens neural connections. What you focus on grows stronger.
Challenge the Mind: Learn a new skill, speak a new language, or solve puzzles to keep your brain adaptable.
Chapter 6: Consciousness and the Cosmos
Key References: "Zen and the Art of Motorcycle Maintenance" by Robert M. Pirsig, "Dune" by Frank Herbert
Consciousness doesn’t exist in isolation—it’s a dance with the external world. Whether through Zen-like awareness or understanding the interconnectedness of all things, your journey is both inward and outward.
Tips for Hitchhikers:
Seek Quality: Pirsig describes quality as the intersection of science and art. Find meaning in the smallest details.
Embrace Interdependence: Like Herbert’s vision in Dune, see yourself as part of a larger system, from the microscopic to the cosmic.
Chapter 7: Altered Perception – The Mind's Infinite Dimensions
Key References: "VALIS" by Philip K. Dick, "How to Change Your Mind" by Michael Pollan
Reality is what your brain perceives it to be, but perception can be altered. Explore, but tread carefully.
Tips for Hitchhikers:
Question Reality: Ask yourself: Is what I perceive objective truth or the brain’s best guess?
Expand Carefully: Use Pollan’s guide for safe and structured exploration of altered states.
Chapter 8: Superconsciousness – Becoming More Than You Are
Key References: "Becoming Supernatural" by Dr. Joe Dispenza
The ultimate destination for hitchhikers is unlocking the superconscious—a state where you transcend your limitations and become the architect of your reality.
Tips for Hitchhikers:
Visualization: Envision the future you desire. Your brain rewires itself to make this vision a reality.
Heart-Brain Coherence: Sync emotional and mental states for profound inner balance.
Final Thoughts: Don't Panic (and Keep Exploring!)
Consciousness is the greatest mystery of the universe—complex, vast, and thrilling. Treat every moment as an opportunity for growth and self-discovery. The Hitchhiker’s Guide to Consciousness doesn’t offer all the answers, but it does remind you to keep asking the right questions.
And remember: the mind is infinite, and so are you. Safe travels, fellow hitchhiker!
-
 @ f9cf4e94:96abc355
2025-01-18 06:09:50
@ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |
 | Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |
| Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |  | 16Gb |
| 16Gb |Recomendo que use o Ubuntu Server para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi aqui. O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível aqui. Não instale um desktop (como xubuntu, lubuntu, xfce, etc.).
Passo 1: Atualizar o Sistema 🖥️
Primeiro, atualize seu sistema e instale o Tor:
bash apt update apt install tor
Passo 2: Criar o Arquivo de Serviço
nrs.service🔧Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo:
```unit [Unit] Description=Nostr Relay Server Service After=network.target
[Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure
[Install] WantedBy=multi-user.target ```
Passo 3: Baixar o Binário do Nostr 🚀
Baixe o binário mais recente do Nostr aqui no GitHub.
Passo 4: Criar as Pastas Necessárias 📂
Agora, crie as pastas para o aplicativo e o pendrive:
bash mkdir -p /opt/nrs /mnt/edriver
Passo 5: Listar os Dispositivos Conectados 🔌
Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados:
bash lsblk
Passo 6: Formatando o Pendrive 💾
Escolha o pendrive correto (por exemplo,
/dev/sda) e formate-o:bash mkfs.vfat /dev/sda
Passo 7: Montar o Pendrive 💻
Monte o pendrive na pasta
/mnt/edriver:bash mount /dev/sda /mnt/edriver
Passo 8: Verificar UUID dos Dispositivos 📋
Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados:
bash blkid
Passo 9: Alterar o
fstabpara Montar o Pendrive Automáticamente 📝Abra o arquivo
/etc/fstabe adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim:fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0
Passo 10: Copiar o Binário para a Pasta Correta 📥
Agora, copie o binário baixado para a pasta
/opt/nrs:bash cp nrs-arm64 /opt/nrs
Passo 11: Criar o Arquivo de Configuração 🛠️
Crie o arquivo de configuração com o seguinte conteúdo e salve-o em
/opt/nrs/config.yaml:yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true
Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️
Agora, copie o arquivo
nrs.servicepara o diretório/etc/systemd/system/:bash cp nrs.service /etc/systemd/system/Recarregue os serviços e inicie o serviço
nrs:bash systemctl daemon-reload systemctl enable --now nrs.service
Passo 13: Configurar o Tor 🌐
Abra o arquivo de configuração do Tor
/var/lib/tor/torrce adicione a seguinte linha:torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334
Passo 14: Habilitar e Iniciar o Tor 🧅
Agora, ative e inicie o serviço Tor:
bash systemctl enable --now tor.serviceO Tor irá gerar um endereço
.onionpara o seu servidor Nostr. Você pode encontrá-lo no arquivo/var/lib/tor/nostr_server/hostname.
Observações ⚠️
- Com essa configuração, os dados serão salvos no pendrive, enquanto o binário ficará no cartão SD do Raspberry Pi.
- O endereço
.oniondo seu servidor Nostr será algo como:ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion.
Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳
Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
-
 @ 266815e0:6cd408a5
2024-04-22 22:20:47
@ 266815e0:6cd408a5
2024-04-22 22:20:47While I was in Mediera with all the other awesome people at the first SEC cohort there where a lot of discussions around data storage on nostr and if it could be made censorship-resistent
I remember lots of discussions about torrents, hypercore, nostr relays, and of course IPFS
There were a few things I learned from all these conversations:
- All the existing solutions have one thing in common. A universal ID of some kind for files
- HTTP is still good. we don't have to throw the baby out with the bath water
- nostr could fix this... somehow
Some of the existing solutions work well for large files, and all of them are decentralization in some way. However none of them seem capable of serving up cat pictures for social media clients. they all have something missing...
An Identity system
An identity system would allow files to be "owned" by users. and once files have owners servers could start grouping files into a single thing instead of a 1000+ loose files
This can also greatly simplify the question of "what is spam" for a server hosting (or seeding) these files. since it could simply have a whitelist of owners (and maybe their friends)
What is blossom?
Blossom is a set of HTTP endpoints that allow nostr users to store and retrieve binary data on public servers using the sha256 hash as a universal id
What are Blobs?
blobs are chunks of binary data. they are similar to files but with one key difference, they don't have names
Instead blobs have a sha256 hash (like
b1674191a88ec5cdd733e4240a81803105dc412d6c6708d53ab94fc248f4f553) as an IDThese IDs are universal since they can be computed from the file itself using the sha256 hashing algorithm ( you can get a files sha256 hash on linux using:
sha256sum bitcoin.pdf)How do the servers work?
Blossom servers expose four endpoints to let clients and users upload and manage blobs
GET /<sha256>(optional file.ext)PUT /uploadAuthentication: Signed nostr event- Returns a blob descriptor
GET /list/<pubkey>- Returns an array of blob descriptors
Authentication(optional): Signed nostr eventDELETE /<sha256>Authentication: Signed nostr event
What is Blossom Drive?
Blossom Drive is a nostr app built on top of blossom servers and allows users to create and manage folders of blobs
What are Drives
Drives are just nostr events (kind
30563) that store a map of blobs and what filename they should have along with some extra metadataAn example drive event would be
json { "pubkey": "266815e0c9210dfa324c6cba3573b14bee49da4209a9456f9484e5106cd408a5", "created_at": 1710773987, "content": "", "kind": 30563, "tags": [ [ "name", "Emojis" ], [ "description", "nostr emojis" ], [ "d", "emojis" ], [ "r", "https://cdn.hzrd149.com/" ], [ "x", "303f018e613f29e3e43264529903b7c8c84debbd475f89368cb293ec23938981", "/noStrudel.png", "15161", "image/png" ], [ "x", "a0e2b39975c8da1702374b3eed6f4c6c7333e6ae0008dadafe93bd34bfb2ca78", "/satellite.png", "6853", "image/png" ], [ "x", "e8f3fae0f4a43a88eae235a8b79794d72e8f14b0e103a0fed1e073d8fb53d51f", "/amethyst.png", "20487", "image/png" ], [ "x", "70bd5836807b916d79e9c4e67e8b07e3e3b53f4acbb95c7521b11039a3c975c6", "/nos.png", "36521", "image/png" ], [ "x", "0fc304630279e0c5ab2da9c2769e3a3178c47b8609b447a30916244e89abbc52", "/primal.png", "29343", "image/png" ], [ "x", "9a03824a73d4af192d893329bbc04cd3798542ee87af15051aaf9376b74b25d4", "/coracle.png", "18300", "image/png" ], [ "x", "accdc0cdc048f4719bb5e1da4ff4c6ffc1a4dbb7cf3afbd19b86940c01111568", "/iris.png", "24070", "image/png" ], [ "x", "2e740f2514d6188e350d95cf4756bbf455d2f95e6a09bc64e94f5031bc4bba8f", "/damus.png", "32758", "image/png" ], [ "x", "2e019f08da0c75fb9c40d81947e511c8f0554763bffb6d23a7b9b8c9e8c84abb", "/old emojis/astral.png", "29365", "image/png" ], [ "x", "d97f842f2511ce0491fe0de208c6135b762f494a48da59926ce15acfdb6ac17e", "/other/rabbit.png", "19803", "image/png" ], [ "x", "72cb99b689b4cfe1a9fb6937f779f3f9c65094bf0e6ac72a8f8261efa96653f5", "/blossom.png", "4393", "image/png" ] ] }There is a lot going on but the main thing is the list of "x" tags and the path that describes the folder and filename the blob should live at
If your interested, the full event definition is at github.com/hzrd149/blossom-drive
Getting started
Like every good nostr client it takes a small instruction manual in order to use it properly. so here are the steps for getting started
1. Open the app
Open https://blossom.hzrd149.com
2. Login using extension

You can also login using any of the following methods using the input - NIP-46 with your https://nsec.app or https://flare.pub account - a NIP-46 connection string - an
ncryptsecpassword protected private key - ansecunprotected private key (please don't) - bunker:// URI from nsecbunker3. Add a blossom server

Right now
https://cdn.satellite.earthis the only public server that is compatible with blossom drive. If you want to host your own I've written a basic implementation in TypeScript github.com/hzrd149/blossom-server4. Start uploading your files
NOTE: All files upload to blossom drive are public by default. DO NOT upload private files

5. Manage files

Encrypted drives
There is also the option to encrypt drives using NIP-49 password encryption. although its not tested at all so don't trust it, verify

Whats next?
I don't know, but Im excited to see what everyone else on nostr builds with this. I'm only one developer at the end of the day and I can't think of everything
also all the images in this article are stored in one of my blossom drives here
nostr:naddr1qvzqqqrhvvpzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qq8xzun5d93kcefdd9kkzem9wvr46jka
-
 @ a012dc82:6458a70d
2025-01-18 02:33:24
@ a012dc82:6458a70d
2025-01-18 02:33:24Over the past decade, the cryptocurrency landscape has witnessed unprecedented growth, with Bitcoin undeniably at its forefront. As the trailblazer of digital currencies, Bitcoin has not only introduced the world to the possibilities of decentralized finance but has also inspired the creation of thousands of other cryptocurrencies. Yet, among the myriad of developments in the crypto domain, the advent of Bitcoin ETFs (Exchange Traded Funds) stands out. These innovative financial instruments have not only revolutionized how investors perceive and interact with Bitcoin but have also provided a bridge between the volatile world of cryptocurrencies and the more stable, regulated realm of traditional finance.
Table Of Content
-
What is a Bitcoin ETF?
-
Why are Bitcoin ETFs Important?
-
The Current Landscape of Bitcoin ETFs
-
How to Invest in a Bitcoin ETF
-
Conclusion
-
FAQs
What is a Bitcoin ETF?
At its core, a Bitcoin ETF is a financial instrument designed to track the price movements of Bitcoin. Rather than diving into the intricate world of cryptocurrencies—buying Bitcoin directly, grappling with the nuances of digital wallets, or navigating the often complex landscape of crypto exchanges—investors can now simply purchase shares of a Bitcoin ETF. These shares are traded just like any other stock on traditional stock exchanges, offering a seamless integration of Bitcoin into conventional investment portfolios.
Why are Bitcoin ETFs Important?
Accessibility: One of the primary advantages of Bitcoin ETFs is their accessibility. They open the doors for everyday investors, even those unfamiliar with the intricacies of the crypto world, to gain exposure to Bitcoin. There's no need to delve into the technical aspects of purchasing, storing, or securing the cryptocurrency—Bitcoin ETFs simplify the entire process.
Regulation: Being listed and traded on recognized stock exchanges means that Bitcoin ETFs come under the purview of financial regulators. This regulatory oversight ensures a degree of transparency and protection for investors, something that's often amiss in the wild west of direct cryptocurrency investments.
Diversification: For seasoned investors and newcomers alike, diversification is a cornerstone of a robust investment strategy. Bitcoin ETFs offer a golden opportunity to tap into the burgeoning cryptocurrency market without the direct volatility and risks tied to holding the actual digital assets.
The Current Landscape of Bitcoin ETFs
The concept of a Bitcoin ETF isn't new. However, its journey to mainstream acceptance has been riddled with regulatory challenges. Many countries, initially hesitant, have taken a cautious approach, leading to delays in the adoption of Bitcoin ETFs. But as the broader financial community becomes more attuned to the potential benefits (and risks) of cryptocurrencies, we're witnessing a gradual shift. Regulators are now more open, and approvals for Bitcoin ETFs in major financial markets are on the rise. This evolving landscape has sparked renewed interest, with both institutional and retail investors keenly exploring these novel investment avenues.
How to Invest in a Bitcoin ETF
The process of investing in a Bitcoin ETF mirrors that of any other traditional investment vehicle. Here's an elaborated guide:
Research: Embarking on any investment journey necessitates thorough research. It's imperative to delve deep, understand the nuances, and compare the various Bitcoin ETFs available in the market. Look into their past performance, management strategies, and fee structures.
Choose a Brokerage: Once you've zeroed in on a Bitcoin ETF that aligns with your investment goals, the next step is to select a suitable brokerage. Opt for one that offers your chosen Bitcoin ETF and boasts a reputation for reliability and security.
Buy Shares: With your brokerage account set up, you're all set to make your purchase. Navigate to the trading platform, search for your chosen Bitcoin ETF, decide on the number of shares you wish to buy, and execute the trade. It's as simple as buying shares of any other company.
Conclusion
The emergence of Bitcoin ETFs signifies a monumental shift in the financial world. It's a testament to the growing acceptance of cryptocurrencies and their potential to coexist with traditional financial instruments. As the crypto ecosystem continues to evolve, mature, and gain broader acceptance, the allure of Bitcoin ETFs is set to grow. For investors, this evolution offers a unique vantage point—a chance to be at the intersection of time-tested financial principles and the dynamic world of digital currencies.
FAQs
What is a Bitcoin ETF? A Bitcoin ETF is a financial instrument that tracks the price of Bitcoin, allowing investors to buy its shares on traditional stock exchanges.
Why choose a Bitcoin ETF over direct Bitcoin investment? Bitcoin ETFs offer easier accessibility, regulatory oversight, and a way to diversify investments without dealing with the complexities of direct cryptocurrency handling.
Are Bitcoin ETFs regulated? Yes, Bitcoin ETFs traded on established stock exchanges are subject to regulatory oversight, providing added protection for investors.
How do I invest in a Bitcoin ETF? Start with research, choose a reputable brokerage that offers the Bitcoin ETF you're interested in, and then purchase its shares like you would with any other stock.
Are Bitcoin ETFs a safer investment than Bitcoin? While no investment is risk-free, Bitcoin ETFs offer a layer of protection due to regulatory oversight and eliminate the risks associated with direct handling and storage of cryptocurrencies.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
X: @croxroadnews
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 6be5cc06:5259daf0
2025-01-18 02:11:43
@ 6be5cc06:5259daf0
2025-01-18 02:11:43- Not your keys, not your coins
Se você não tem as chaves privadas do seu Bitcoin, ele não é realmente seu. Deixar seus BTCs em exchanges ou carteiras controladas por terceiros significa confiar neles e assumir o risco de perder seus fundos.
- HODL - Não venda
O Bitcoin é uma reserva de valor a longo prazo e potencialmente o dinheiro do futuro. Não se desespere com as flutuações de preço; mantenha seus BTCs, pois o histórico se mostra favorável.
- Stay humble - Não saia falando que você tem BTC
Manter discrição sobre seu patrimônio é uma questão de segurança e humildade. Falar demais pode atrair curiosos, oportunistas ou outras ameaças.
- Don't trust, verify
No Bitcoin, confie no protocolo, não em pessoas. Sempre que possível, verifique por conta própria, seja transações, códigos ou informações.
- Reject altcoins
As altcoins podem parecer promissoras, mas frequentemente são distrações ou apostas arriscadas. Foque no Bitcoin, que já provou ser sólido e resistente.
- Stack sats - DCA
Empilhe satoshis consistentemente, utilizando a estratégia de DCA (Dollar Cost Averaging), comprando regularmente independentemente do preço. Isso reduz o risco de tentar "acertar o mercado".
- Reject the ego
Não aposte contra o Bitcoin. Aqueles que subestimaram sua força ou estabilidade, perderam.
- Keep learning
Nunca pare de estudar sobre Bitcoin, economia e a tecnologia por trás dele. Quanto mais você entende, mais confiança terá em sua decisão.
- Help beginners
O Bitcoin pode ser complicado para quem está começando. Compartilhe seus conhecimentos com paciência para fortalecer a comunidade.
- Don't push it
Cada pessoa tem seu próprio tempo para entender e entrar no mundo do Bitcoin. Forçar alguém pode ser contraproducente; dê direcionamento e deixe o tempo agir.
-
 @ 16d11430:61640947
2025-01-19 21:26:06
@ 16d11430:61640947
2025-01-19 21:26:06The entrepreneurial spirit – a defining force of human progress – is undergoing a tectonic shift. The traditional game of entrepreneurship as we knew it is dead, and Bitcoin drove the stake through its heart. But here’s the twist: Bitcoin wasn’t the cause of death. Instead, it exposed the systemic weaknesses of a world built on fiat, debt, and gatekeepers, forcing entrepreneurs to rethink not just how they operate, but why.
This isn’t a eulogy for entrepreneurship; it’s a call to adapt to a bold new world where the rules of the game are rewritten.
The Traditional Entrepreneurial Landscape
Historically, entrepreneurship thrived on access: access to capital, markets, and networks. The gatekeepers of these resources – banks, investors, and governments – dictated the pace of innovation. Business plans were drafted to cater to venture capitalists; startups scaled at the mercy of loans, subsidies, and subsidies.
But this framework came with strings attached: endless paperwork, a suffocating web of regulations, and a system that rewarded conformity over innovation. Success often hinged on appeasing gatekeepers rather than creating true value. And for many, the barriers to entry were simply insurmountable.
Enter Bitcoin: The Game Changer
Bitcoin didn’t just introduce a new form of money; it redefined the foundational principles of commerce, trust, and value exchange. For entrepreneurs, this is a paradigm shift:
-
No Gatekeepers, No Permission Needed Bitcoin obliterates the need for intermediaries. Entrepreneurs can now raise funds through Bitcoin, sell directly to a global audience, and operate with unparalleled autonomy. There’s no need to rely on banks, payment processors, or investors who can dictate terms.
-
Borderless Markets Bitcoin transcends borders, enabling entrepreneurs to operate in a truly global marketplace. A developer in Nigeria can sell services to a client in Germany without worrying about currency conversions, delays, or high fees.
-
Immutable Value Transfer The trustless nature of Bitcoin means entrepreneurs can transact without fear of chargebacks, fraud, or third-party interference. Smart contracts and escrow services built on Bitcoin’s principles make milestone-based payments seamless.
-
Store of Value Over Time Traditional entrepreneurship often revolved around securing cash flow to keep up with inflationary pressures. Bitcoin’s deflationary nature allows entrepreneurs to focus on long-term value creation rather than racing against devaluing fiat.
What Bitcoin Revealed
Bitcoin didn’t kill entrepreneurship – it exposed its inefficiencies. It showed us that the traditional system was less about fostering innovation and more about controlling access to resources. Entrepreneurs didn’t fail because they lacked ideas; they failed because the system was rigged against them.
Bitcoin’s rise has revealed a deeper truth: entrepreneurship was shackled by outdated structures. With these barriers removed, the entrepreneur of the Bitcoin era can focus on creating genuine value, free from rent-seeking intermediaries.
The Challenges of the Bold New World
But this new era isn’t without its challenges. The shift to a Bitcoin-based entrepreneurial world demands a new mindset and skill set:
Self-Sovereignty Entrepreneurs must take full responsibility for their finances, from securing private keys to navigating a decentralized economy. There are no bailouts or safety nets in a Bitcoin world.
Education Gap Understanding Bitcoin’s intricacies is non-negotiable. Entrepreneurs must educate themselves on cryptography, decentralized finance, and the nuances of blockchain technology to stay competitive.
Regulatory Uncertainty Governments and institutions accustomed to controlling the economy are grappling with Bitcoin’s decentralized nature. Entrepreneurs must navigate a shifting regulatory landscape while staying true to Bitcoin’s ethos.
A Bold New Future
Entrepreneurship isn’t dead; it’s evolving. The Bitcoin revolution has democratized access to resources, dismantled barriers to entry, and empowered individuals to create and innovate without seeking permission.
In this bold new world, the successful entrepreneur isn’t just a visionary; they’re a sovereign individual capable of navigating uncharted waters. They’re building for a future where value flows freely, where innovation thrives without gatekeepers, and where humanity’s potential is unshackled.
Bitcoin didn’t kill entrepreneurship; it set it free. Now, it’s up to us to rise to the occasion.
-
-
 @ 378562cd:a6fc6773
2025-01-18 00:12:47
@ 378562cd:a6fc6773
2025-01-18 00:12:47In the ever-changing world of decentralized networks, Nostr (Notes and Other Stuff Transmitted by Relays) is leading the charge. Its lightweight, open design has created an ecosystem that’s as adaptable as it is revolutionary. Whether you're chatting, publishing, or experimenting with new ways to connect, Nostr provides the foundation for a truly decentralized and censorship-resistant internet.
How Nostr Works: A Quick Overview
At its heart, Nostr is built on simplicity and decentralization. Here’s a breakdown of its core components:
-
Public and Private Keys:\ Your public key acts as your identity, and private keys ensure your messages are securely signed.
-
Relays:\ Relays are decentralized servers that distribute messages. They don’t own your data but simply pass it along to those who request it.
-
Clients:\ Clients are the user-facing applications where you interact with Nostr, offering diverse features and designs.
Deep Dive: Events in Nostr
Everything on Nostr revolves around events, which are cryptographically signed pieces of information containing various kinds of data. Here are the types of events currently supported and their use cases:
1. Note Events (Type 1)
- What They Are:\ These are the bread and butter of Nostr—text-based posts, much like tweets or status updates on traditional platforms.
- Features:
- Can include text, media links, and hashtags.
- Interact with others through likes, replies, and boosts (reposts).
- Use Cases:\ Perfect for microblogging, status updates, and general social interaction.
2. Profile Metadata Events (Type 0)
- What They Are:\ This event type stores and updates user profile information, such as your display name, bio, profile picture, and website.
- Features:
- Easily editable and updated across all Nostr clients.
- Keeps your identity consistent across platforms.
- Use Cases:\ Makes profile portability seamless—update once, and it reflects everywhere.
3. Relay List Events (Type 2)
- What They Are:\ These events store a list of relays that a user is connected to or prefers to use.
- Features:
- Share your relay preferences across devices or clients.
- Allows automatic relay connection in supported clients.
- Use Cases:\ Simplifies the onboarding process for users switching clients or devices.
4. Direct Message Events (Type 4)
- What They Are:\ End-to-end encrypted messages sent directly between two users.
- Features:
- Only readable by the intended recipient.
- Supports text and basic formatting.
- Use Cases:\ Secure communication for personal or professional purposes.
5. Reaction Events (Type 7)
- What They Are:\ Events that express reactions to other events, such as likes or emojis.
- Features:
- Provides social feedback (e.g., showing appreciation for a post).
- Lightweight and simple to implement.
- Use Cases:\ Enhances engagement and interaction within the network.
6. Repost Events (Type 6)
- What They Are:\ Events that allow users to reshare content, similar to retweets on Twitter.
- Features:
- Ensures the original poster retains credit.
- Enables broader content visibility.
- Use Cases:\ Amplifying content that resonates with users or is worth sharing.
7. Custom Event Types (Beyond Type 7)
- What They Are:\ Developers can create and define custom event types for specific applications.
- Features:
- Flexibility to introduce entirely new functionality.
- Supported based on client and relay compatibility.
- Use Cases:\ Enables innovation, from collaborative editing tools to advanced publishing workflows.
What Makes Events Special?
- Portability: Events follow your public key, not the client or relay, ensuring they’re available wherever you go.
- Interoperability: All events are standardized, meaning any Nostr client can understand and process them.
- Extensibility: Through custom event types, the protocol encourages experimentation and development.
Primal: A Favorite Client for Engaging Events
Among the many clients, Primal stands out as a favorite for how it handles Nostr events. Its emphasis on content discovery and rich user interaction makes it an excellent choice for exploring everything the protocol offers. Whether it’s crafting note events, managing profile metadata, or diving into direct messaging, Primal delivers a polished experience that feels seamless.
The Future of Nostr Events
As Nostr continues to evolve, so will the events it supports. Imagine event types for live streaming, collaborative workspaces, or even decentralized governance. The possibilities are limitless, driven by the creativity of the developers and the needs of the community.
Have you explored the potential of Nostr events yet? What’s your favorite client or feature? Let’s discuss below! ⚡️
Nostr #Primal #Decentralization #NostrEvents #FutureOfWeb
-
-
 @ f7922a0a:82c34788
2025-01-17 23:06:56
@ f7922a0a:82c34788
2025-01-17 23:06:56Now that the 3rd Satellite Skirmish is complete I wanted to highlight some of the cool features on embrace.satskirmish.com
This is what the cutting edge of podcasting 2.0 looks like imo. Live video in an app that allows you to send sats to the artists in real time.
On the left hand side we have a Boost score borad that displays the total amount of sats that have come in during the show, live Boosts/Booastagrams as they come in, total amount of sats from each person Boosting and total amount sent from each app.
The middle is ovisaly the video of the band playing but with some graphics around it and Boost alerts that show up on the screen in the form of snow flakes for this one.
The righthand side is an IRC chat window that connects to an IRC server that the No Agenda community has used for 18+ years thanks to zoidzero++.

The bottom of the page is where things get cool. When you click the Boost the Crew button in the center you can send a Boost that gets split between everyone helping produce the show (hightlighted in yellow).


Each band also has their own Boost button so you can Boost them while they are playing or anytime you visit the page.


-
 @ 5df413d4:2add4f5b
2024-02-18 18:26:57
@ 5df413d4:2add4f5b
2024-02-18 18:26:57You Are Not A Gadget by Jaron Lanier
Reading Jaron Lanier’s 2010 You Are Not A Gadget in 2023 is an interesting experience—equal parts withering, prophetic, and heretical clarion call warning from a high priest of the Technocracy and rambling, musing, cognitive jam session from a technofied musician-philosopher.
Yet, in ways that I think the author would be simultaneously pleased, amused, saddened, and disturbed by, the 13 yeas since the book’s publishing have, in places, proven him right with stunning foresight and precision, and in others, made his ideas appear laughable, bizarre, even naive. The book is written in five parts, yet I would suggest viewing it as two discrete elements—Part One (around the first half of the book) and…everything else.
For context, Lanier, is a computer scientist and early technologist from the area of Jobs, Wozniak, and Gates, and is considered to be a founding father of virtual reality. He is also a consummate contrarian, a player of rare and obscure musical instruments, a deep interdisciplinary thinker…and a white man with dreadlocks named Jaron.
PART ONE
Part One of the book “What is a Person?” reads like a scathing and clear-eye manifesto—where Lanier is batting 1000, merciless in his rightness. Were one to pull a passage that speaks to the soul of this portion of the book, it might be the following: “The net does not design itself. We design it.”
Lanier terms the prevailing technocratic ideology—the particular winning tech-nerd subculture that has now come to capture our society—as “the cybernetic totalist” or “digital Maoists.” Essentially a materialist and stealth collectivist movement in new-age technocratic dress, that through its successes, and now excesses, represents much the same of religion that it’s founders would have claimed to be “evolving past.”
Lanier points out that in this, we are simply trading the pursuit of finding God in spirituality or the afterlife, for a notion of digital immortality—seeking, or, if possible, becoming, God in the cloud. He aptly identifies that this worldview requires that society, and all human interactions really, be savagely bent into adherence to this new religion of aggregation that demands deification of data, gross diminishment of the individual, and belief in some objective (but never defined) "meaning" that exists beyond and apart from the human observer.
With skill and simple wit, he raises strong, rational counterpoint to the digital Maoists’ obsession with quantity, data in aggregate and at-scale, as society's prime directive “A fashionable idea in technical circles is that quantity […] turns into quality at some extreme scale […] I disagree. A trope in the early days or computer science comes to mind: garbage in, garbage out.”
Lanier is able to envision the digital cages that likes of Facebook, Youtube, social-media dating apps would become for the internet native generations. Of whom he writes “The most effective young Facebook users […] are the ones who create successful online fictions about themselves,” and “If you start out by being fake, you’ll eventually have to put in twice the effort to undo the illusion if anything good is to come of it.”
Lanier’s 2010 criticism of Wikipedia-ism is now double or triply apropos in our current hype cycle of “AI magic” and Everything-GPT, “Wikipedia, for instance, works on what I can the Oracle Illusion, in which knowledge of human authorship of a text is suppressed in order to give the text superhuman validity. Traditional holy books work in precisely the same way and present many of the same problems.” This same deep truth now sits at the heart of every “new” creation churned out by the flavor-of-the-week, plagiarism-at-scale, generative AI tool.
More darkly, he is also able to foresee the spectre of a return to collectivism lurking both at the core and on the margins of our new digital age—“The recipe that led to social catastrophe in the past was economic humiliation combined with collectivist ideology. We already have the ideology in its new digital packaging, and it’s entirely possible we could face dangerously traumatic economic shock in the coming decades.”—“No Shit” said everyone who lived through 2020-2022…
This brings us, eerily, to the world of today. Where aggregate insights are upheld as more valuable than discrete insights. Where crowds are are assumed to have more wisdom than individuals. Where truth is twisted into a might-is-right numbers game. A world ruled by the idea that if we can just centralize enough information and sufficiently pulverize authorship, the result will, necessarily, be something super-intelligent, "alive," and perhaps even divine.
In short, the cybernetic totalists and digital Maoists, having killed reason, now sit on its corpse like a thrown, smearing its blood on the walls in the name of art and reading its still-steaming entrails for prophecy.
If I were to infer some ideological takeaway from Part One of the book, it might be that Lanier seems to axiomatically reject any affirmative implication of the Turing Test. Simply put, he believes that bits are not and cannot ever be alive independent of the human-as-oracle. Further, there is no objective meaning beyond the human observer—in fact, that observer fundamentally creates any meaning there is to be had. This is best illustrated by one of the most powerful passages in the book:
“But the Turing Test cuts both ways. You can’t tell if a machine has gotten smarter or if you’ve just lowered your own standard of intelligence to such a degree that the machine seems smart. If you can have a conversation with a simulated person presented by an AI program, can you tell how far you’ve let your sense of personhood degrade in order to make the illusion work for you?”
Ponder this well, Anon.
EVERYTHING ELSE
With all of the great stuff above out of the way, we must turn to…the rest of the book. Parts Two through Five breakdown into something more like a stream of consciousness. And while there are certainly many nuggets to insight and beauty to be found, the book becomes largely dis-coherent and very difficult to read. That said, the remainder of the book does contain three particularly compelling threads that I find to be worth pulling on.
Internet Attribution First, are Lanier’s musing about money and attribution in our authorless “information wants to be free” world. He laments the infinite elevation of advertising and offers harsh critique to the concept of attention as the new currency—as this tends to overwhelmingly reward the aggregator and a piddling few soulless super-influencers at the expense of all other users and creators.
Interestingly, under the guise of “what could have been” he imagines a world where attribution is tracked across the web (though how this achieved is left unanswered) and royalty payments can flow back to the author seamlessly over the internet. I find his vision to be intriguing because in 2010, we lacked the technology to either track attribution across the web or facilitate seamless micropayment royalties based on access / usage.
While we still don't have the ability to achieve the type of fully-tracked, always-on attribution Lanier imagines, we do now have the ability to stream payments across the internet with bitcoin and the lightning network. While Lanier can be excused for not mentioning the then uber-nascent bitcoin in 2010, bitcoin’s development since only goes to underscore the prescience of Lanier’s imagination.
The bigger question that now remains, especially in the face of the advent of “AI,” is whether such a system to manage and therefore enforce attribution globally on the internet would even be a good thing. Where obscured attribution enables mashed-up plagiarism-at-scale, centrally enforced attribution can just as easily enable idea, content, discovery, and innovation suppression-at-scale.
Music in the New Age Second, much of the book, particularly in the second half, is filtered through the lens and language of music. Music is essential to Lanier’s inner life and it is clear that he views music as an emergent mystery force attributable to something unknowable, if not divine, and entirely unique to the human experience.
He bemoans the music of the 2000s as lacking in any distinct chronological era sound—everything is either a rehashed mashup or digitally lofi-ed emulation of sounds from previous begone eras—it is music that is impossible to place. To him, it is as though musical evolution stopped right around the time of the advent of the internet…and then folded back in on itself, creating an endless kaleidoscoping of what came before but rarely, if ever, the creation anything truly new.
In response, Lanier goes so far as to imagine the ridiculous (my take, not his) world of “Songles”—songs on dongles—essentially physical music NFTs. In Songleland, listening to the hottest tracks at a party hinges on the guy or gal with the dankest songles swinging through and plugging them into the Songle player. And songles, being scarce, even become speculative investments. On this, Lanier manages to be both right and wrong in only the most spectacularly absurd of ways.
But what Lanier really laments is the passing of popular music as a shared cultural experience at national or even global scale. During Lanier’s coming of age through the 1960-80s—with only a few consolidated channels for music distribution, it was truly impossible to escape the sounds and influence of the Beatles or Prince or Micheal Jackson—everyone heard it and even the deaf still felt it.
In the end, Lanier could image Songles but he couldn’t envision what Spotify would become—a conduit to shatter music distribution into a myriad of tiny longtails—providing infinitely fragmented and individually fine-tuned music experiences rather than large and cohesive cultural moments. However, even in this miss, Lanier is largely able to project what Spotify-ed music would resolve to—music designed as much or more to please the self-referential selection algorithm than any real, human listeners. A dangerously foretelling insight that goes well beyond music as AI tools are posed to become the "googling" of the next technological cycle—what happens to information, to human thought, when the majority of "generative AI" outputs are just the machine referencing itself?
Digital Neoteny The final thread to pull is that of "digital neoteny," the retention of juvenile behaviors in adult form, in this case, a neoteny of the mind if you will. Lanier sees the internet as specifically primed to propagate three kinds of neoteny in digital-native humans— a blissful and curious Bachelardian neoteny (as in Gaston Bachelard’s Poetics of Reverie); a cruel and mob-like Goldingesque neoteny (as in William Golding’s Lord of the Flies); and a general and deeply pervasive, infantile neoteny.
Neoteny of the Bachelardian variety, which Lanier likens to “the sense of wonder and weirdness that a teen can find in the unfolding world,” is what he feels the internet has provided in a few brief and magical moments generally aligned with the “early days” of successive internet technologies, movements, and companies—through this generally degrades into Goldingesque neoteny as novelty gives way to ossification.
Lanier’s missives on Bachelardian neoteny feel especially pertinent to the present state of Nostr (where I am publishing this writing). Nostr is in a moment where winner-take all dynamics and corporatization have yet to take hold. Child-like revelry abounds with each new discovery or novel Nostr client development so much so that the likes of Jack Dorsey compare it to the excitement of the early internet.
But with time, if and as the Nostr protocol wins, to what extent will technical lock-in take hold here? To what extent will calcification of seemingly trivial or even comical decisions being made by client devs today have dramatic implications on the feasibility of other development in the future? And will we early Nostr users, at some point put down welcoming inclusivesness for insular tribalism—and in what ways might we be doing this already?
Finally, to the third kind of neoteny, Infantile neoteny—which perhaps incapsulates the internet even more so than either of the other two types—Lanier sees the net driving an evermore prolonged deferral of maturity, resulting ultimately in some centrally-managed permanent arresting of society in a stupefied and juvenile mental state:
“Some of the greatest speculative investments in human history continue to converge on Silicon Valley schemes that seemed to have been named by Dr. Seuss. On any given day, one might hear of tens or hundreds of millions of dollars flowing to a start-up company named Ublibudly or MeTickly. These are names I just made up, but they would make great venture capital bait if they existed. At these companies one finds rooms full of MIT PhD engineers not seeking cancer cures or sources of safe drinking water for the underdeveloped world but schemes to send little digital pictures of teddy bears and dragons between adult members of social networks. At the end of the road of the pursuit of technological sophistication appears to lie a playhouse in which humankind regresses to nursery school.”
The popular culture of the early 2020s—with it’s NFT Monke JPEGs, silent and masked TikTok dancing in the drab aisles of crumbling department stores, and rampant peer-pressured social-media virtue-signaling and paternalism—could scarcely be described in any more stark and specific detail. That such could be seen so vividly in 2010 is as masterful as it is dishearteningly dark.
CONCLUSION
You Are Not A Gadget is a special thing, a strange beast—as lucid in its first half as it is jumbled, meandering, and even nonsensical in its second half. And while the discerning reader might judge the book harshly for these structural failings, I doubt the author would care, he might even welcome it. Lanier’s apparent purpose in writing is to share his mind rather than please the reader in any particular regard. The sufficiently curious reader, one who is willing to engage with the book’s content, for whatever the book’s faults may be, finds a king’s randoms of wisdom, insight, and uncanny foresight.
In closing, it seems fitting to recall one of Lanier’s earliest warnings in the book, “Maybe if people pretend they are not conscious or do not have free will […] then perhaps we have the power to make it so. We might be able to collectively achieve antimagic.” 13 years on, this feels more pressing and urgent and true than ever. (Rating: 4/5🐙)
-
 @ 16d11430:61640947
2025-01-19 20:43:41
@ 16d11430:61640947
2025-01-19 20:43:41Ah, the Indian Male. Born into a chaos he didn’t create, tethered to a narrative that ensures he’ll always be the bridesmaid, never the bride. Colonialism didn’t just leave him with railways and bureaucracy—it left him with a carefully crafted role: the perpetual sidekick, the cartoon villain, the placeholder in history’s great drama.
In the colonial script, he exists not as a hero but as an extra. He’s the conniving tax collector to the noble white sahib, the sweating laborer in sepia-toned photographs, or the bumbling antagonist to Bollywood’s fiery heroines. He is the eternal foil, the necessary contrast to someone else's shine. If he dares to dream of being the protagonist? Sorry, that role is reserved for the firang or, at best, a hypermasculine, sanitized fantasy.
In Bollywood, the Indian Male is plenty young, but his youth is just a commodity for the market. He runs, he fights, he loves, but all in vain. If he isn’t groveling at the feet of an exotic femme fatale, he’s playing cuck to her triumph, watching her steal the limelight while he wrestles with generational trauma and a population density problem. The fiery heroine dances while he queues at the ration shop.
For the first 40 years of his life, he is struggling. Struggling against the crowd, against nepotism, against the laws of thermodynamics, against his own parents' belief that he’s a failure for not being a doctor or engineer. His youth is not a time of vitality—it’s a curse of endless lines, meaningless jobs, and one-room apartments with peeling paint. He fights the curse of too many: too many people, too many expectations, too many rejections.
And yet, salvation arrives—not in the form of glory or self-fulfillment—but in his 60s. Yes, only then does society declare him worthy. Only then can he sit in plastic chairs at weddings, spouting wisdom no one asked for. Only then can he achieve the zen-like status of the elder: a potbelly, a pension, and an unlimited supply of unsolicited advice. Until then, he is invisible. A man-boy. A cog in the wheel of India's great, unwieldy machinery.
So, here’s to the Indian Male: the sidekick to history’s heroes, the villain in his own love story, and the quiet struggler who only becomes visible when it’s time to fade away. May he one day find the freedom to rewrite his script—not as an accessory, not as a cuck, but as something better. Or at least, let him skip the 40 years of struggle and jump straight to the pension.
-
 @ ed5774ac:45611c5c
2025-01-17 22:05:36
@ ed5774ac:45611c5c
2025-01-17 22:05:36A good question. I do not think so. I will explain below why, but first where did this question come from?
The statement that Tether is a Bitcoin company was recently made by Samson Mow in X (here) in a response to Paolo Ardoino’s initial Tweet about Tether’s $775 million investment on Rumble (here).

In response to Samson Mow's statement, I expressed my disagreement by pointing out that Tether prints USDT “out of thin air” and uses these funds to purchase US Treasuries, which in effect helps finance US debt and fund military operations.
In my opinion, a bitcoin company should not provide life support to the current broken financial system that is built on the US dollar's status as a global reserve currency, allowing a small group of Western elites to control the system and exploit it for wealth transfer.
“The root problem with conventional currency is all the trust that’s required to make it work. The central bank must be trusted not to debase the currency, but the history of fiat currencies is full of breaches of that trust.”(Satoshi Nakamoto, Bitcoin: A Peer-to-Peer Electronic Cash System)
I believe that the primary purpose of bitcoin is to replace the current fraudulent system, not to support it. My assessment is based on this fundamental principle, and I therefore disagree with Samson’s statement. In short, Tether does not align with bitcoin’s purpose of existence, a point to which I will return later.
First, it is necessary to clarify the logic behind my “Tether prints USDT out of thin air” statement as Samson Mow shifted the focus of conversation merely to this specific point instead of clarifying how he considers Tether as a bitcoin company in light of its actions (i.e., financing US debt and thereby funding the US war machine).

My next tweet aimed to highlight the trust concerns inherent in Proof of Stake, a concept that should be familiar to Samson Mow, where ETH holders validate transactions by staking their holdings, creating a system that relies on the implicit trustworthiness of these validators.
In response to my reasoning and explanation, Samson initially claimed that Tether is not proof of stake. Next, in a subsequent tweet where I asked for clarification on whether Tether is on the Ethereum blockchain, he acknowledged this point but introduced a new argument suggesting that Tether's situation has nothing to do with PoS. This claim is, to be frank, disconnected from reality and raises questions about Samson Mow’s true motivations.

Following my discussion with Samson Mow on X, I decided to provide further clarification on the reasoning behind my statement that "Tether prints USDT out of thin air". The underlying logic of this argument can be grasped by examining two crucial factors: Proof of Work (PoW) and debt.
Proof of Work:
A critical examination of Tether's USDT issuance requires a deeper understanding of the PoW.
When individuals exchange their dollars for USDT, they are essentially trading earned value (their time and energy) for a digital representation thereof. However, Tether's issuance of new USDT units occurs without incurring any cost or spending resources, effectively creating digital tokens that represent claims on value rather than value itself.
In stark contrast, the creation of new bitcoins is facilitated through a competitive mining, wherein miners use computational power (spend energy) to validate transactions and create new blocks, thereby earning newly minted bitcoins as a reward for their efforts. Similarly, in gold mining, the discovery of new deposits is the result of the investment of time, energy, and resources by miners. Likewise, individuals who are employees or entrepreneurs invest their time and energy to generate income or profit.
This underscores a fundamental principle: that genuine value creation typically results from tangible efforts, and resource allocations, distinguishing it from mechanisms that generate value without any corresponding expenditures.
Unlike the aforementioned examples, Tether's mechanism for creating USDT operates under a distinctly different paradigm. Tether issues USDT without expending time, energy, or resources. Instead, individuals give Tether their hard-earned money in exchange for an IOU certificate represented by USDT. This is in theory, assuming that Tether is an honest player and only mints USDT when a user transfers corresponding USD. In practice, however, there are several factors that complicate the verification of Tether's claim regarding the backing of USDT with USD.
One issue with Tether operating on Ethereum is that transactions are validated by ETH stakeholders by staking their ETH. This introduces an element of trust in third-party (validators), raising concerns in the integrity of the ledger.
Additionally, in contrast to Bitcoin's blockchain, Proof of Stake blockchains do not have a clear "chain" of hashes linking each block back to its predecessor through a computationally intensive process, since there's no mining involved in creating new blocks (as blocks are proposed by validators based on their stake), thereby preventing verification of historical transaction validity. As a result, the current state of a Proof of Stake blockchain reflects only the validators' confirmation without providing any assurance regarding its historical accuracy or integrity.
Most significantly, there exists no inherent mechanism, as far as I am aware of, preventing Tether from minting additional USDT without corresponding USD backing and transferring to an ETH address under their control and buying real assets (such as bitcoin) with it.
In my opinion, these considerations underscore significant challenges on transparency, accountability and oversight within Tether’s operations. In other words, the entire system relies on the honesty of Tether and Ethereum validators as trusted third parties, which contradicts Bitcoin's fundamental principle that eliminates the need for trusted intermediaries in transactions as described by Satoshi Nakamoto in Bitcoin White Paper. (source: bitcoin white paper)

While Bitcoin's decentralized architecture eliminates the need for intermediaries, Tether as a centralized entity controls the issuance and management of USDT and relies on ETH validators for the validity of transactions. This centralized control enables Tether & Ethereum to unilaterally freeze, blacklist, or manipulate accounts at their discretion, as evidenced by past incidents and potential future actions. Furthermore, USDT holdings are exposed to counterparty risk, as holders are only entitled to redeem their funds if Tether maintains its solvency and adheres to a 100% reserve requirement which are significant question marks as explained in previous paragraphs.
Debt:
Even if the claim that all USDT tokens are fully backed is true, it is essential to recognize that USDT is ultimately backed by fiat currency, which itself is debt —whether in the form of dollars or U.S. Treasuries. Consequently, the statement “Tether prints USDT out of thin air” is not entirely unfounded, as the creation of new USDT tokens is effectively facilitated by the issuance of new debt instruments.
How does USD come to existence? As many bitcoiners know very well, they are simply printed out of thin air by FED. This process is facilitated by the US government's issuance of debt certificates, including short-term Treasury bills and long-term Treasury bonds. The value of these debt instruments is derived from the expectation that the US government will honor its obligations by repaying the indicated amount of USD to certificate holders in the future, primarily through tax revenue collected from its citizens. In essence, these debt certificates represent IOUs and their value is contingent upon the credibility of the US government's promise to fulfill its debt obligations. The entire system relies on a collective belief in the government's creditworthiness, rather than any tangible asset backing it. Even if Tether's USDT is assumed to be backed 1-to-1 with USD, it is ultimately backed by nothing but the US government's fiat currency, which is itself created out of thin air. This highlights the tenuous nature of USDT's backing, as it is predicated on trust in the US government's ability to pay its debt.
In contrast to Bitcoin, which is decentralized money, independent of any third-party liability, holding USDT introduces multiple layers of third-party liability such as:
-
Trust in the integrity of the Ethereum network & in the honesty of ETH stakeholders who validate transactions and maintain the ledger.
-
Trust in Tether's financial stability and solvency, as well as its commitment to honoring its obligations, thereby mitigating the risk of bankruptcy or fraudulent activities.
-
Trust in the creditworthiness of the US government, as the value of USDT is ultimately tied to the value of US Treasury securities held by Tether.
These cumulative risks underscore the significance of third-party liability in the context of USDT ownership.
In conclusion, the statement “Tether prints USDT out of thin air” is based on the fact that USDT is minted by Tether without incurring any cost or spending resources, there is no mechanism to prove that Tether maintains 100% reserves and USDT is ultimately backed by fiat currency, which itself is debt created out of thin air by the FED. Therefore, “Tether prints USDT out of thin air” notion is not entirely unfounded and highlights the tenuous nature of USDT's backing.
Tether finances US debt and war machine by buying US Treasuries:
Having laid out the logic behind my statement that “Tether prints USDT out of thin air,” I will now move on to the main argument underlying my position: namely, that Tether is not a bitcoin company because its acquisition of US debt provides life support to a profoundly corrupt and exploitative financial system, which enables a small cabal of western elites exploit the rest of the world to further enrich themselves. The fundamental purpose of bitcoin is to replace this broken system, not to provide life support to it.
The current financial system:
erodes the purchasing power of working-class individuals through inflation
-
excludes a significant portion of the global population from accessing to financial services
-
preserves ‘the rules-based global order’ (as it is called by the West) that exploits developing nations for the benefit of a privileged few in Western countries
-
concentrates control in the hands of an unscrupulous banking cartel and self-proclaimed elites
At the heart of the existing financial system lies the US dollar's role as a global reserve currency that grants the US government considerable leverage to enforce its economic and geopolitical interests. By controlling USD flows, the US can impose financial sanctions on nations that refuse to comply with its rules and norms.
In instances where financial coercion proves ineffective, the US has historically resorted to alternative measures, including military intervention and covert operations, aimed at bringing disobedient countries into compliance with its policy directives. Historical records are full of examples.
-
[ ] In 1953, the United States and the United Kingdom collaborated to orchestrate a coup d'état in Iran, resulting in the overthrow of the democratically elected government of Prime Minister Mohammad Mossadegh. This action was carried out following Mossadegh's decision to nationalise Iranian oil companies, which were vital to the West's economic interests.
-
[ ] The Central Intelligence Agency (CIA) played a substantial role in supporting a coup against Salvador Allende, the democratically elected President of Chile in 1970, because they were concerned that Allende's policies would lead to a shift towards socialism and potentially even communism, which was seen as a threat to US interests in the region.
-
[ ] Saddam Hussein's decision to transition Iraq's oil transactions from US dollars to euros was a major factor contributing to his downfall. By challenging the existing global financial system, Hussein became a threat to the global financial order and therefore paid the price with his life.
-
[ ] Muammar Gaddafi proposed the establishment of a gold-based currency, known as the gold dinar, intended for use in African oil transactions. This initiative aimed to create a pan-African currency independent of both the US dollar and euro, potentially undermining their influence in regional trade. The perceived threat posed by this proposal to the global financial order has been the main factor to Libya's destabilization and Gaddafi's eventual demise.
-
[ ] The overthrow of Ukraine's democratically elected president in 2014 by a CIA orchestrated a coup d'état, with Victoria Nuland, then-Assistant Secretary of State for European and Eurasian Affairs, playing a key role in the operation. The intervention was motivated by Western corporations’ desire to colonize Russia and use its resources as collateral to prolong the life of the global financial system that has become unsustainable with its current debt levels.
Those interested in understanding the mechanics of the current financial system or learning about the historical crimes committed by West against the Global South are invited to contact me directly. I can provide access to a comprehensive collection of resources that document these issues. However, due to space and time constraints, it is not feasible to elaborate on these topics in detail here.
The statement that Tether is primarily a bitcoin company is entirely unfounded since Tether provides significant support to the current financial system. The US government is currently facing challenges in financing its debt due to decreasing global confidence in its ability to repay its obligations. This is evident in the fact that China has ceased purchasing US debt, while Russia has sold off its entire holdings prior to the Special Military Operation (SMO). Furthermore, private investors are increasingly wary of investing in US debt, citing concerns over its sustainability. Currently, the UK and EU are the only entities actively buying US debt, which, along with the US, are the other two pillars of the existing global financial order. Notably, Tether has emerged as a substantial purchaser of US debt (approximately $100 billion at the time of writing), effectively serving as a vital lifeline for the prolongation of the Western colonial order.
Tether is NOT a bitcoin company. In my opinion, it is fair to say that those who claim that Tether is a bitcoin company are either lacking in critical thinking or have a financial stake that compromises their objectivity.
It is true that it helps bitcoin adoption and by providing liquidity contributes to the upward momentum of bitcoin price. I believe, it is likely that the current price of bitcoin would be significantly lower without Tether's involvement. This raises important questions about the motivations and values of those involved in the bitcoin community who claim that Tether is a bitcoin company. Can their support for Bitcoin be attributed to a sincere interest in advancing the principles of decentralization and sovereignty, or might it be influenced by self-interest and the pursuit of personal wealth? Are there other potential motivations or conflicts of interest at play?
As outlined in this article, I have concerns regarding Tether's alignment with the principles that underpin Bitcoin’s core values. My critique is not intended to be accusatory, but rather to encourage critical evaluation. I acknowledge and appreciate Tether's contribution to bitcoin ecosystem and see their investment in Rumble as a positive development for freedom of speech and recognize Samson's dedication for Bitcoin adoption. However, my appreciation for their efforts does not imply unconditional trust.
The defensive responses of some individuals within the community to my criticisms (without any reasonable counterarguments) have raised questions for me about their potential biases and motivations. While I do not aim to convince those who misinterpret my intentions, I will exercise increased suspicion when engaging with individuals who appear more focused on protecting Tether's interests than upholding the principles of Bitcoin.
In summary, I believe that Tether's role in propping up the current financial system - intentionally or not - underscores the need for skepticism and critical thinking. As global events continue to unfold with unprecedented speed and complexity, it's essential to remember: 'Don't trust, verify!'
-
-
 @ 783850fd:77511d32
2025-01-17 21:21:35
@ 783850fd:77511d32
2025-01-17 21:21:35This chocolate sauce recipe is easy to make at home. I hope you'll give this recipe a try.
Ingredients: + 1 liter of milk + 150-200 g of wholemeal flour + 20-100 g of chocolate + a fruit* of your choice (or a sweet potato). Skip it if your plan is to serve the sauce over fruits. + some salt
Directions:
Add a pinch of salt to the milk and set it to boil on low heat. In the meantime, mix the flour with pieces of chocolate and chunks of your chosen fruit. If using an orange, there's no need to chop it—simply separate the segments by hand along their natural divisions. Mixing the fruit and chocolate pieces with the flour ensures that they are coated, which helps prevent the flour from clumping.
Serving Suggestions: This sauce pairs well with bread, biscuits, or pancakes. Alternatively serve over lots of fruits (be they bananas, watermelons, apples) - in that case there is no need of mixing the chunks of fruits with the flour.
originally posted at https://stacker.news/items/854225
-
 @ f977c464:32fcbe00
2024-01-11 18:47:47
@ f977c464:32fcbe00
2024-01-11 18:47:47Kendisini aynada ilk defa gördüğü o gün, diğerleri gibi olduğunu anlamıştı. Oysaki her insan biricik olmalıydı. Sözgelimi sinirlendiğinde bir kaşı diğerinden birkaç milimetre daha az çatılabilirdi veya sevindiğinde dudağı ona has bir açıyla dalgalanabilirdi. Hatta bunların hiçbiri mümkün değilse, en azından, gözlerinin içinde sadece onun sahip olabileceği bir ışık parlayabilirdi. Çok sıradan, öyle sıradan ki kimsenin fark etmediği o milyonlarca minik şeyden herhangi biri. Ne olursa.
Ama yansımasına bakarken bunların hiçbirini bulamadı ve diğer günlerden hiç de farklı başlamamış o gün, işe gitmek için vagonunun gelmesini beklediği alelade bir metro istasyonunda, içinde kaybolduğu illüzyon dağılmaya başladı.
İlk önce derisi döküldü. Tam olarak dökülmedi aslında, daha çok kıvılcımlara dönüşüp bedeninden fırlamış ve bir an sonra sönerek külleşmiş, havada dağılmıştı. Ardında da, kaybolmadan hemen önce, kısa süre için hayal meyal görülebilen, bir ruhun yok oluşuna ağıt yakan rengârenk peri cesetleri bırakmıştı. Beklenenin aksine, havaya toz kokusu yayıldı.
Dehşete düştü elbette. Dehşete düştüler. Panikle üstlerini yırtan 50 işçi. Her şeyin sebebiyse o vagon.
Saçları da döküldü. Her tel, yere varmadan önce, her santimde ikiye ayrıla ayrıla yok oldu.
Bütün yüzeylerin mat olduğu, hiçbir şeyin yansımadığı, suyun siyah aktığı ve kendine ancak kameralarla bakabildiğin bir dünyada, vagonun içine yerleştirilmiş bir aynadan ilk defa kendini görmek.
Gözlerinin akları buharlaşıp havada dağıldı, mercekleri boşalan yeri doldurmak için eriyip yayıldı. Gerçeği görmemek için yaratılmış, bu yüzden görmeye hazır olmayan ve hiç olmayacak gözler.
Her şeyin o anda sona erdiğini sanabilirdi insan. Derin bir karanlık ve ölüm. Görmenin görmek olduğu o anın bitişi.
Ben geldiğimde ölmüşlerdi.
Yani bozulmuşlardı demek istiyorum.
Belleklerini yeni taşıyıcılara takmam mümkün olmadı. Fiziksel olarak kusursuz durumdaydılar, olmayanları da tamir edebilirdim ama tüm o hengamede kendilerini baştan programlamış ve girdilerini modifiye etmişlerdi.
Belleklerden birini masanın üzerinden ileriye savurdu. Hınca hınç dolu bir barda oturuyorlardı. O ve arkadaşı.
Sırf şu kendisini insan sanan androidler travma geçirip delirmesin diye neler yapıyoruz, insanın aklı almıyor.
Eliyle arkasını işaret etti.
Polislerin söylediğine göre biri vagonun içerisine ayna yerleştirmiş. Bu zavallılar da kapı açılıp bir anda yansımalarını görünce kafayı kırmışlar.
Arkadaşı bunların ona ne hissettirdiğini sordu. Yani o kadar bozuk, insan olduğunu sanan androidi kendilerini parçalamış olarak yerde görmek onu sarsmamış mıydı?
Hayır, sonuçta belirli bir amaç için yaratılmış şeyler onlar. Kaliteli bir bilgisayarım bozulduğunda üzülürüm çünkü parasını ben vermişimdir. Bunlarsa devletin. Bana ne ki?
Arkadaşı anlayışla kafasını sallayıp suyundan bir yudum aldı. Kravatını biraz gevşetti.
Bira istemediğinden emin misin?
İstemediğini söyledi. Sahi, neden deliriyordu bu androidler?
Basit. Onların yapay zekâlarını kodlarken bir şeyler yazıyorlar. Yazılımcılar. Biliyorsun, ben donanımdayım. Bunlar da kendilerini insan sanıyorlar. Tiplerine bak.
Sesini alçalttı.
Arabalarda kaza testi yapılan mankenlere benziyor hepsi. Ağızları burunları bile yok ama şu geldiğimizden beri sakalını düzeltip duruyor mesela. Hayır, hepsi de diğerleri onun sakalı varmış sanıyor, o manyak bir şey.
Arkadaşı bunun delirmeleriyle bağlantısını çözemediğini söyledi. O da normal sesiyle konuşmaya devam etti.
Anlasana, aynayı falan ayırt edemiyor mercekleri. Lönk diye kendilerini görüyorlar. Böyle, olduğu gibi...
Nedenmiş peki? Ne gerek varmış?
Ne bileyim be abicim! Ahiret soruları gibi.
Birasına bakarak dalıp gitti. Sonra masaya abanarak arkadaşına iyice yaklaştı. Bulanık, bir tünelin ucundaki biri gibi, şekli şemalı belirsiz bir adam.
Ben seni nereden tanıyorum ki ulan? Kimsin sen?
Belleği makineden çıkardılar. İki kişiydiler. Soruşturmadan sorumlu memurlar.
─ Baştan mı başlıyoruz, diye sordu belleği elinde tutan ilk memur.
─ Bir kere daha deneyelim ama bu sefer direkt aynayı sorarak başla, diye cevapladı ikinci memur.
─ Bence de. Yeterince düzgün çalışıyor.
Simülasyon yüklenirken, ayakta, biraz arkada duran ve alnını kaşıyan ikinci memur sormaktan kendisini alamadı:
─ Bu androidleri niye böyle bir olay yerine göndermişler ki? Belli tost olacakları. İsraf. Gidip biz baksak aynayı kırıp delilleri mahvetmek zorunda da kalmazlar.
Diğer memur sandalyesinde hafifçe dönecek oldu, o sırada soruyu bilgisayarın hoparlöründen teknisyen cevapladı.
Hangi işimizde bir yamukluk yok ki be abi.
Ama bir son değildi. Üstlerindeki tüm illüzyon dağıldığında ve çıplak, cinsiyetsiz, birbirinin aynı bedenleriyle kaldıklarında sıra dünyaya gelmişti.
Yere düştüler. Elleri -bütün bedeni gibi siyah turmalinden, boğumları çelikten- yere değdiği anda, metronun zemini dağıldı.
Yerdeki karolar öncesinde beyazdı ve çok parlaktı. Tepelerindeki floresan, ışığını olduğu gibi yansıtıyor, tek bir lekenin olmadığı ve tek bir tozun uçmadığı istasyonu aydınlatıyorlardı.
Duvarlara duyurular asılmıştı. Örneğin, yarın akşam kültür merkezinde 20.00’da başlayacak bir tekno blues festivalinin cıvıl cıvıl afişi vardı. Onun yanında daha geniş, sarı puntolu harflerle yazılmış, yatay siyah kesiklerle çerçevesi çizilmiş, bir platformdan düşen çöp adamın bulunduğu “Dikkat! Sarı bandı geçmeyin!” uyarısı. Biraz ilerisinde günlük resmi gazete, onun ilerisinde bir aksiyon filminin ve başka bir romantik komedi filminin afişleri, yapılacakların ve yapılmayacakların söylendiği küçük puntolu çeşitli duyurular... Duvar uzayıp giden bir panoydu. On, on beş metrede bir tekrarlanıyordu.
Tüm istasyonun eni yüz metre kadar. Genişliği on metre civarı.
Önlerinde, açık kapısından o mendebur aynanın gözüktüğü vagon duruyordu. Metro, istasyona sığmayacak kadar uzundu. Bir kılıcın keskinliğiyle uzanıyor ama yer yer vagonların ek yerleriyle bölünüyordu.
Hiçbir vagonda pencere olmadığı için metronun içi, içlerindekiler meçhuldü.
Sonrasında karolar zerrelerine ayrılarak yükseldi. Floresanın ışığında her yeri toza boğdular ve ortalığı gri bir sisin altına gömdüler. Çok kısa bir an. Afişleri dalgalandırmadılar. Dalgalandırmaya vakitleri olmadı. Yerlerinden söküp aldılar en fazla. Işık birkaç kere sönüp yanarak direndi. Son kez söndüğünde bir daha geri gelmedi.
Yine de etraf aydınlıktı. Kırmızı, her yere eşit dağılan soluk bir ışıkla.
Yer tamamen tele dönüşmüştü. Altında çapraz hatlarla desteklenmiş demir bir iskelet. Işık birkaç metreden daha fazla aşağıya uzanamıyordu. Sonsuzluğa giden bir uçurum.
Duvarın yerini aynı teller ve demir iskelet almıştı. Arkasında, birbirine vidalarla tutturulmuş demir plakalardan oluşan, üstünden geçen boruların ek yerlerinden bazen ince buharların çıktığı ve bir süre asılı kaldıktan sonra ağır, yağlı bir havayla sürüklendiği bir koridor.
Diğer tarafta paslanmış, pencerelerindeki camlar kırıldığı için demir plakalarla kapatılmış külüstür bir metro. Kapının karşısındaki aynadan her şey olduğu gibi yansıyordu.
Bir konteynırın içini andıran bir evde, gerçi gayet de birbirine eklenmiş konteynırlardan oluşan bir şehirde “andıran” demek doğru olmayacağı için düpedüz bir konteynırın içinde, masaya mum görüntüsü vermek için koyulmuş, yarı katı yağ atıklarından şekillendirilmiş kütleleri yakmayı deniyordu. Kafasında hayvan kıllarından yapılmış grili siyahlı bir peruk. Aynı kıllardan kendisine gür bir bıyık da yapmıştı.
Üstünde mavi çöp poşetlerinden yapılmış, kravatlı, şık bir takım.
Masanın ayakları yerine oradan buradan çıkmış parçalar konulmuştu: bir arabanın şaft mili, üst üste konulmuş ve üstünde yazı okunamayan tenekeler, boş kitaplar, boş gazete balyaları... Hiçbir şeye yazı yazılmıyordu, gerek yoktu da zaten çünkü merkez veri bankası onları fark ettirmeden, merceklerden giren veriyi sentezleyerek insanlar için dolduruyordu. Yani, androidler için. Farklı şekilde isimlendirmek bir fark yaratacaksa.
Onların mercekleri için değil. Bağlantıları çok önceden kopmuştu.
─ Hayatım, sofra hazır, diye bağırdı yatak odasındaki karısına.
Sofrada tabak yerine düz, bardak yerine bükülmüş, çatal ve bıçak yerine sivriltilmiş plakalar.
Karısı salonun kapısında durakladı ve ancak kulaklarına kadar uzanan, kocasınınkine benzeyen, cansız, ölü hayvanların kıllarından ibaret peruğunu eliyle düzeltti. Dudağını, daha doğrusu dudağının olması gereken yeri koyu kırmızı bir yağ tabakasıyla renklendirmeyi denemişti. Biraz da yanaklarına sürmüştü.
─ Nasıl olmuş, diye sordu.
Sesi tek düzeydi ama hafif bir neşe olduğunu hissettiğinize yemin edebilirdiniz.
Üzerinde, çöp poşetlerinin içini yazısız gazete kağıtlarıyla doldurarak yaptığı iki parça giysi.
─ Çok güzelsin, diyerek kravatını düzeltti kocası.
─ Sen de öylesin, sevgilim.
Yaklaşıp kocasını öptü. Kocası da onu. Sonra nazikçe elinden tutarak, sandalyesini geriye çekerek oturmasına yardım etti.
Sofrada yemek niyetine hiçbir şey yoktu. Gerek de yoktu zaten.
Konteynırın kapısı gürültüyle tekmelenip içeri iki memur girene kadar birbirlerine öyküler anlattılar. O gün neler yaptıklarını. İşten erken çıkıp yemyeşil çimenlerde gezdiklerini, uçurtma uçurduklarını, kadının nasıl o elbiseyi bulmak için saatlerce gezip yorulduğunu, kocasının kısa süreliğine işe dönüp nasıl başarılı bir hamleyle yaşanan krizi çözdüğünü ve kadının yanına döndükten sonra, alışveriş merkezinde oturdukları yeni dondurmacının dondurmalarının ne kadar lezzetli olduğunu, boğazlarının ağrımasından korktuklarını...
Akşam film izleyebilirlerdi, televizyonda -boş ve mat bir plaka- güzel bir film oynayacaktı.
İki memur. Çıplak bedenleriyle birbirinin aynı. Ellerindeki silahları onlara doğrultmuşlardı. Mum ışığında, tertemiz bir örtünün serili olduğu masada, bardaklarında şaraplarla oturan ve henüz sofranın ortasındaki hindiye dokunmamış çifti gördüklerinde bocaladılar.
Hiç de androidlere bilinçli olarak zarar verebilecek gibi gözükmüyorlardı.
─ Sessiz kalma hakkına sahipsiniz, diye bağırdı içeri giren ikinci memur. Söylediğiniz her şey...
Cümlesini bitiremedi. Yatak odasındaki, masanın üzerinden gördüğü o şey, onunla aynı hareketleri yapan android, yoksa, bir aynadaki yansıması mıydı?
Bütün illüzyon o anda dağılmaya başladı.
Not: Bu öykü ilk olarak 2020 yılında Esrarengiz Hikâyeler'de yayımlanmıştır.
-
 @ 0403c86a:66d3a378
2025-01-17 19:32:26
@ 0403c86a:66d3a378
2025-01-17 19:32:26The Kansas City Chiefs are set to begin their quest for an unprecedented Super Bowl three-peat on Saturday, facing the Houston Texans in the AFC Divisional Playoffs. Here’s everything you need to know heading into the highly anticipated matchup:
Key Player Updates
- Patrick Mahomes (QB): Cleared to play despite a recent ankle injury, Mahomes is ready to lead his team. Head coach Andy Reid praised his mental toughness, saying Mahomes is “back in the saddle.”
- Isiah Pacheco (RB), Chris Jones (DL), and D.J. Humphries (T): All cleared to play, giving the Chiefs their key contributors on offense and defense.
- Jaylen Watson (CB): Activated from injured reserve, strengthening the Chiefs' secondary.
- Mecole Hardman (WR): Remains on IR and is doubtful for the game, leaving the Chiefs without one of their speediest weapons.
The Matchup
The Chiefs, led by Mahomes, come into this game with a 24-day rest period, the longest in NFL history. It remains to be seen whether the extended break will give them an edge or lead to rust. Mahomes, the winningest quarterback through seven seasons in NFL history (including playoffs), is also undefeated (6-0) in divisional playoff games.
The Houston Texans, on the other hand, are flying high after a dominant 32-12 wild-card victory over the Chargers. Rookie quarterback C.J. Stroud has been a revelation this season, and the Texans’ defense, featuring stars like Will Anderson and Danielle Hunter, has been a force. Anderson and Hunter combined for 1.5 sacks and four QB hits in the wild-card round, and their ability to pressure Mahomes will be critical.
Key Storylines
- Chiefs' Resiliency: Kansas City has shown incredible grit this season, winning 11 games by eight points or less. They've proven they can win in all phases—offense, defense, and special teams.
- Texans’ Defensive Strength: Houston’s cornerback duo of Derek Stingley Jr. and Kamari Lassiter has been among the league’s best, ranking top-three in completion percentage and passer rating allowed. They’ll look to contain the Chiefs’ passing attack.
- Coaching Chess Match: Texans head coach Demeco Ryans acknowledged the challenge of defending Mahomes, citing his quick release and ability to exploit check-downs. Ryans plans to mix up coverages while staying disciplined under pressure.
What’s at Stake
The Chiefs are chasing history as they aim to become the first team ever to win three straight Super Bowls. Mahomes is also looking to tie Joe Montana for the second-most playoff wins by a quarterback.
For the Texans, this game represents a chance to make history of their own. After five previous losses in the divisional round, they’re seeking their first-ever AFC Championship Game appearance.
Game Outlook
This matchup has all the makings of a close contest. The Texans will try to capitalize on the Chiefs’ tendency to play in one-possession games, while the Chiefs’ experience and ability to adapt in critical moments could prove decisive.
With stars on both sides of the ball and plenty of storylines, this game is a must-watch as the Chiefs and Texans battle for a spot in the AFC Championship.
📺 Kickoff: Saturday, 4:30 PM ET
Global Sports Central 🌐 #GSC360
-
 @ d6dc9554:d0593a0c
2023-09-21 18:37:14
@ d6dc9554:d0593a0c
2023-09-21 18:37:14Nas blockchains PoW o consenso é alcançado por meio de prova de trabalho computacional e o objetivo principal é evitar que atores mal intencionados consumam ou ataquem a rede de forma perigosa. Este método de consenso requer um grande poder computacional para criar novos blocos, mas é muito simples, por parte de outros, verificar esse trabalho. Por isso se diz que PoW é uma estratégia assimétrica.
Nas blockchains PoS o objetivo é o mesmo, criar blocos e chegar a um consenso, mas nas PoS não é necessário um poder de processamento tão grande como nas PoW. Em média as PoS gastam menos de 1% da energia das PoW. Nas PoS os mineradores são chamados de validadores. Enquanto que nas PoW quem fica com a recompensa é quem resolve primeiro a charada matemática, nas PoS o validador que vai ganhar a recompensa é escolhido de forma aleatória, mas dando maior probabilidade aos que respeitem determinados critérios. A comunidade bitcoin é muito relutante em relação a PoS porque é mais fácil conseguir uma grande quantidade da moeda em causa do que mais que 51% de poder processamento. Logo as PoS são mais vulneráveis no que toca a segurança. Mas aqui cada caso é um caso e é preciso fazer essa análise para cada moeda.
As blockchains PoW tendem a ser mais descentralizadas enquanto as PoS mais centralizadas, não só em acesso, mas também em operação. Mais de metade dos validadores de ethereum estão na cloud da amazon. As blockchains PoW apresentam grandes desafios na escalabilidade de operação, muitas vezes exigindo soluções de segunda camada (L2), enquanto que as PoS possuem mecanismos de escalabilidade muito mais flexíveis. Os algoritmos PoW são muito mais simples de implementar do que os PoS e, portanto, menos suscetíveis a erros. Um bom exemplo é o PoS da ethereum que estava a ser implementado desde 2018.
-
 @ c8841c9d:ae8048e2
2025-01-19 17:55:31
@ c8841c9d:ae8048e2
2025-01-19 17:55:31Today we're diving into the blockchain technology. Let's look at what blockchain is!
Blockchain #Cryptomindmap
Blockchain is a cryptographically secured, decentralized, immutable digital information storage system. Think of it as a chain of blocks where each block contains a list of operation or data, linked together in a way that prevents data alteration due to the cryptographic security.
In blockchain technology, a block is constructed by first taking the hash of the previous block, creating a link between blocks and then a chain of blocks. A hash is a unique fixed-size string of characters generated by a hash function from any input data. It acts like a digital fingerprint; even a small change in the input will produce a completely different hash in output, ensuring that the data is unforgeable. This is followed by the data from users of the blockchain, which could include transactions or other forms of digital information. For security, operations within the block are signed with a Private Key by the sender and verified with the corresponding Public Key by the network, securing authenticity. Each block then includes a consensus mechanism, which ensures that all the participants of the network will agree on the state of the blockchain, block by block. Finally, the block is completed with its own unique hash, derived from all the data within it, including the hash of the previous block, user data, and operation details. This hash ensures any alteration to the block would change its hash, thus making the block and the entire chain tamper-evident. This meticulous process, leveraging the properties of the hash function twice, ensures the blockchain remains secure, decentralized, and immutable.
Blockchain has a wide array of applications:
- Peer to Peer: Facilitates direct transactions without intermediaries.
- Cryptocurrency: The most famous application, with Bitcoin being the pioneer.
- Payment/Finance: Revolutionizing how financial transactions are processed, reducing fraud and costs.
- Digital Uniqueness: Ensures uniqueness and authenticity of digital assets.
- DAO (Decentralized Autonomous Organizations): Organizations that are run by rules encoded as smart contracts on the blockchain.
- Privacy: Offers enhanced privacy through cryptographic methods.
- Archiving: Provides a tamper-proof way to store records and data.
The most significant challenge is the Blockchain Trilemma - the struggle to achieve Decentralization, Security, and Scalability simultaneously. Each improvement in one area often comes at the expense of another. While it is possible to achieve two of these attributes well, achieving all three at once is challenging. Numerous technologies emerged to increase scalability without compromising security and decentralization, such as Layer 2 solution and sharding.
The journey of blockchain technology began with foundational cryptographic concepts in the 20th century, including the invention of hash functions like SHA-256 and asymmetric cryptography. As the century progressed, a prelude to decentralization emerged with peer-to-peer networks and the creation of the Proof of Work mechanism. The first revolution happened in 2008-09 with the introduction of Bitcoin by Satoshi Nakamoto, the first complete blockchain with implementation of the Proof of Work consensus mechanism. Since then, blockchain has evolved rapidly; Ethereum introduced programmability and smart contracts, expanding its use beyond simple transactions to programmable agreements. Over the years, new consensus mechanisms like Proof of Stake have been developed, and advanced cryptographic techniques like Zero-Knowledge Proofs have been integrated, leading to the sophisticated blockchain systems we see today. This journey from cryptographic foundations to the expansion of blockchain landscape showcases the evolution and potential of this technology. As we continue to innovate, blockchain promises to reshape numerous sectors by providing trust, transparency, and efficiency in digital transactions.
-
 @ 7d4417d5:3eaf36d4
2023-08-19 01:05:59
@ 7d4417d5:3eaf36d4
2023-08-19 01:05:59I'm learning as I go, so take the text below for what it is: my notes on the process. These steps could become outdated quickly, and I may have some wrong assumptions at places. Either way, I have had success, and would like to share my experience for anyone new to the process. If I have made any errors, please reply with corrections so that others may avoid potential pitfalls.
!!! If you have "KYC Bitcoin", keep it in separate wallets from your "Anonymous Bitcoin". Any Anonymous Bitcoin in a wallet with KYC Bitcoin becomes 100% KYC Bitcoin.
!!! It took me several days to get all the right pieces set up before I could even start an exchange with someone.
!!! Using a VPN is highly recommended. If you're not already using one, take the time to find one that suits you and get it running.
!!! If you don't normally buy Amazon Gift Cards, start doing so now, and just send them to yourself, or friends that will give you cash in return, etc. For my first trade, Amazon locked me out of my account for about 22 hours, while I was in the middle of an exchange. All because I had never purchased an Amazon Gift Card before. It was quite nerve wracking. My second trade was for $300, and although my Amazon account wasn't shut down, that order had a status of "Sending" for about 22 hours, due to the large amount. In each of these cases I had multiple phone calls with their customer support, all of whom gave me false expectations. Had I already been sending gift cards to the anonymous email address that I created in the steps below, and maybe other anonymous email addresses that I could make, then I might not have been stalled so much.
-
Install Tor Browser for your OS. The RoboSats.com website issues a warning if you are not using Tor Browser. If you don't know what Tor is, I won't explain it all here, but trust me, it's cool and helps keep you anonymous. If you use Firefox, the interface will look very familiar to you.
-
Create a KYC-free e-mail address. I used tutanota.com in Firefox, as it would not allow me to create an account using Tor Browser. After the account was created, using Tor Browser to login, check emails, etc. has been working perfectly. Tutanota requires a 48 hour (or less) waiting period to prevent bots from using their system. You'll be able to login, and even draft an email, but you won't be able to send. After you've been approved, you should be able to login and send an email to your new address. It should show up in your Inbox almost instantly if it's working.
-
Have, or create, at least one Lightning wallet that is compatible with RoboSats.com and has no KYC Bitcoin in it. The RoboSats website has a compatibility chart available to find the best wallet for you. During an exchange on RoboSats, you will need to put up an escrow payment, or bond, in Satoshis. This amount is usually 3% of the total amount being exchanged. If the exchange is successful, the bond payment is canceled, leaving that amount in your wallet untouched, and with no record of it having been used as escrow. If you don't hold up your end of the trade, the bond amount will be transfered from your wallet. I created a wallet, using my new email address, with the Alby extension in the Tor Browser. This anonymous wallet was empty, so I used a separate wallet for the bond payment of my first trade. This wallet had KYC Bitcoin, but since it is being used for a bond payment, and no transaction will be recorded if everything goes okay, I don't mind taking the minuscule risk. After the first trade, I don't need to use the "KYC wallet", and I will use only my anonymous Lightning wallet for transactions related to performing a trade.
-
Create a new Robot Token by going to RoboSats using the Tor Browser. Copy the Token (Robot ID) to a text file as a temporary backup. It is recommended to create a new robot-token for every session of exchanges you make.
-
Select "Offers" to browse what others are presenting. "Create" is for when you want to create an offer of your own. You may need to create your own offer if none of the existing offers match your criteria.
-
Select "Buy" at the top of the page.
-
Select your currency (USD).
-
Select your payment methods by typing "amazon" and selecting (Amazon Gift Card). Repeat this process and select (Amazon USA Gift Card).
-
Determine Priorities - If you prefer to trade quickly, and don't care as much about premiums, look for users with a green dot on the upper-right of their robot icon. If you're not in a hurry, sort users by premium and select the best deal, even if they are inactive. They may become active once they are notified that their offer has activity from you.
-
The Definition of Price = the price with the premium added, but not the bond
-
A. Find A Compatible Offer - Select the row of the desired offer and enter the amount you would like to buy. i.e. $100 If you do not find a compatible offer, you will have to create your own offer.
B. **Create An Offer** - First, take a look at "Sell" offers for your same currency and payment method(s) that you will be using. Take note of the premium those buyers are willing to pay. If your premium is drastically less than theirs, your offer may get ignored. Select "Create" at the bottom of the screen. There is a slider at the top of the screen, select it to see all the options. Select "Buy". Enter the minimum and maximum amount that you wish to spend. Type "amazon" to select the methods that you would like to use (Amazon Gift Card, Amazon USA Gift Card). For "Premium Over Market", enter an amount that is competitive with premiums you saw at the start of this step and do not use the % sign! You can adjust the duration, timer, and bond amount, but I leave those at their default settings. Select the "Create Order" button, and follow the instructions for making a bond payment. -
Pay the Bond - Copy the invoice that is presented. From your wallet that contains bond funds, select "Send", and paste the invoice as the recipient. This money will never leave your account if the exchange completes without issue. No transaction will be recorded. If there is a complication with the exchange, it is possible that this transaction will complete.
-
Create and Submit Your Invoice for Their Bitcoin Payment To You - Select "Lightning", if not selected by default.* Select the Copy Icon to copy the correct amount of Satoshis. This amount already has the premium deducted. From your anonymous Lightning Wallet, select "Receive", and paste the Satoshi amount. If you enter a description, it's probably best to keep it cryptic. Copy the invoice and paste it into RoboSats; then select "Submit".
* If you plan on "mixing" your Bitcoin after purchase, it may be better to select "On Chain" and pay the necessary fees swap and mining fees. In the example this comes from, Sparrow wallet is used and has whirlpool ability in its interface.
-
Connect With Seller and Send Funds - Greet the seller in the chat window. The seller has now provided RoboSats with the Bitcoin to transfer to you. Your move is to buy an Amazon eGift Card for the amount of the trade. Log in to your Amazon account and start the process of buying an eGift card. For delivery there is the option of email or txt message. Ask the seller what their preference is, and get their address, or phone number, to enter into Amazon's form. Complete the purchase process on Amazon, and check the status of your order. Once you see the status of "Sent", go back to RoboSats in your Tor Browser.
-
Confirm Your Payment - Select the "Confirm ___ USD Sent" button and notify the seller to check their e-mail/txt messages.
-
Seller Confirmation - Once the seller select their "Confirm" button, the trade will immediately end with a confirmation screen.
-
Verify - If you check the anonymous wallet, the new amount should be presented.
-
-
 @ 8ea48526:e6720a43
2025-01-17 18:56:34
@ 8ea48526:e6720a43
2025-01-17 18:56:34Technology trends toward openness time and again. This is why I say that Freedom Tech is Final Tech. Ideas want to be free. Many people built brands on TikTok that are now threatened, which is a reminder to also build on open alternatives you control. There are many examples from history.
Shift from Monasteries to Printing Press. During the Middle Ages, monasteries controlled the production and dissemination of written knowledge. The printing press decentralized access to information, enabling mass production of books and changing the course of history.
Transition from Trains to Automobiles. Trains required centralized infrastructure and control, while cars empowered individuals to travel freely. This shift from centralized to decentralized transportation transformed the way people lived, worked, and interacted with each other.
Telegraph and Telephone. The Telegraph was initially a closed system, with message transmission gated by businesses. The Telephone enabled direct, person-to-person communication, decentralizing access to real-time information and revolutionizing the way people connect.
The evolution of the Internet. ARPANET, the early internet, was a closed network. With the development of TCP/IP, the open internet was born, enabling global communication, innovation, and access to information on an unprecedented scale.
Operating Systems. Unix, a proprietary OS, was the early powerhouse and later eclipsed by Linux, an open-source alternative. Today, Linux powers millions of devices, from smartphones to servers, and has become a cornerstone of modern computing. It runs the world.
Computers. Mainframe Computers were massive, centralized systems that only large organizations could afford. The development of Personal Computers democratized access to computing power, enabling individuals to create, innovate, and participate in the digital economy.
Television and Radio, once controlled by a few large broadcasters, have given way to Podcasts, which enable anyone to create and distribute content. This has democratized the media, allowing new voices and perspectives to emerge. (Thank you Aaron for RSS 😢)
The music industry. Vinyl, tape, and CD distribution, once controlled by record labels and physical stores, have given way to open file formats like MP3 and streaming services. Artists can connect directly with fans and music is more widely available than ever before. V4V.
Government, Monarchy to Republic. Monarchies, with their centralized power and hereditary rule, have given way to republics, where power is distributed among the people and their elected representatives, increasing class mobility and participation.
Central Banking System and Bitcoin. The experimental Central Banking System, with its centralized control and intermediaries, is being challenged by a decentralized, open alternative. It is transforming the way we think about money, value, and financial freedom.
Digital payments and Ecash. Systems like PayPal & Venmo (once the innovators themselves) are being challenged by open alternatives, such as Chaumian e-cash systems like Cashu and Fedimint. These systems promise to increase financial privacy and autonomy for day-to-day payments.
Social networking. Proprietary social platforms control the data & access. Nostr is an open protocol for authoring & distributing digital content. In the age of AI, authenticity is paramount. Nostr cryptographically proves who authored content, maximizing freedom & transparency.
AI. AI began as closed systems from large corporations investing heavily in computing and training. The open community is catching up and pushing new boundaries. Open models that run locally or in confidential computing enclaves provide AI that is free, open, and private.
This is the pattern: over time, the processes that were controlled by a few get replaced by processes controlled by everyone. Always be searching out open alternatives for the tech you use, that’s where we eventually end up. I’m bullish on the future of technology and humanity. 🤘
P.S. You can see that many of these examples are themselves becoming compromised over time, looking to be disrupted again by open technology.
-
 @ cff1720e:15c7e2b2
2025-01-19 17:48:02
@ cff1720e:15c7e2b2
2025-01-19 17:48:02Einleitung\ \ Schwierige Dinge einfach zu erklären ist der Anspruch von ELI5 (explain me like I'm 5). Das ist in unserer hoch technisierten Welt dringend erforderlich, denn nur mit dem Verständnis der Technologien können wir sie richtig einsetzen und weiter entwickeln.\ Ich starte meine Serie mit Nostr, einem relativ neuen Internet-Protokoll. Was zum Teufel ist ein Internet-Protokoll? Formal beschrieben sind es internationale Standards, die dafür sorgen, dass das Internet seit über 30 Jahren ziemlich gut funktioniert. Es ist die Sprache, in der sich die Rechner miteinander unterhalten und die auch Sie täglich nutzen, vermutlich ohne es bewusst wahrzunehmen. http(s) transportiert ihre Anfrage an einen Server (z.B. Amazon), und html sorgt dafür, dass aus den gelieferten Daten eine schöne Seite auf ihrem Bildschirm entsteht. Eine Mail wird mit smtp an den Mailserver gesendet und mit imap von ihm abgerufen, und da alle den Standard verwenden, funktioniert das mit jeder App auf jedem Betriebssystem und mit jedem Mail-Provider. Und mit einer Mail-Adresse wie roland@pareto.space können sie sogar jederzeit umziehen, egal wohin. Cool, das ist state of the art! Aber warum funktioniert das z.B. bei Chat nicht, gibt es da kein Protokoll? Doch, es heißt IRC (Internet Relay Chat → merken sie sich den Namen), aber es wird so gut wie nicht verwendet. Die Gründe dafür sind nicht technischer Natur, vielmehr wurden mit Apps wie Facebook, Twitter, WhatsApp, Telegram, Instagram, TikTok u.a. bewusst Inkompatibilitäten und Nutzerabhängigkeiten geschaffen um Profite zu maximieren.

Warum Nostr?
Da das Standard-Protokoll nicht genutzt wird, hat jede App ihr eigenes, und wir brauchen eine handvoll Apps um uns mit allen Bekannten auszutauschen. Eine Mobilfunknummer ist Voraussetzung für jedes Konto, damit können die App-Hersteller die Nutzer umfassend tracken und mit dem Verkauf der Informationen bis zu 30 USD je Konto und Monat verdienen. Der Nutzer ist nicht mehr Kunde, er ist das Produkt! Der Werbe-SPAM ist noch das kleinste Problem bei diesem Geschäftsmodell. Server mit Millionen von Nutzerdaten sind ein “honey pot”, dementsprechend oft werden sie gehackt und die Zugangsdaten verkauft. 2024 wurde auch der Twitter-Account vom damaligen Präsidenten Joe Biden gehackt, niemand wusste mehr wer die Nachrichten verfasst hat (vorher auch nicht), d.h. die Authentizität der Inhalte ist bei keinem dieser Anbieter gewährleistet. Im selben Jahr wurde der Telegram-Gründer in Frankreich in Beugehaft genommen, weil er sich geweigert hatte Hintertüren in seine Software einzubauen. Nun kann zum Schutz "unserer Demokratie” praktisch jeder mitlesen, was sie mit wem an Informationen austauschen, z.B. darüber welches Shampoo bestimmte Politiker verwenden.

Und wer tatsächlich glaubt er könne Meinungsfreiheit auf sozialen Medien praktizieren, findet sich schnell in der Situation von Donald Trump wieder (seinerzeit amtierender Präsident), dem sein Twitter-Konto 2021 abgeschaltet wurde (Cancel-Culture). Die Nutzerdaten, also ihr Profil, ihre Kontakte, Dokumente, Bilder, Videos und Audiofiles - gehören ihnen ohnehin nicht mehr sondern sind Eigentum des Plattform-Betreibers; lesen sie sich mal die AGB's durch. Aber nein, keine gute Idee, das sind hunderte Seiten und sie werden permanent geändert. Alle nutzen also Apps, deren Technik sie nicht verstehen, deren Regeln sie nicht kennen, wo sie keine Rechte haben und die ihnen die Resultate ihres Handelns stehlen. Was würde wohl der Fünfjährige sagen, wenn ihm seine ältere Schwester anbieten würde, alle seine Spielzeuge zu “verwalten” und dann auszuhändigen wenn er brav ist? “Du spinnst wohl”, und damit beweist der Knirps mehr Vernunft als die Mehrzahl der Erwachsenen. \ \ Resümee: keine Standards, keine Daten, keine Rechte = keine Zukunft!

\ Wie funktioniert Nostr?
Die Entwickler von Nostr haben erkannt dass sich das Server-Client-Konzept in ein Master-Slave-Konzept verwandelt hatte. Der Master ist ein Synonym für Zentralisierung und wird zum “single point of failure”, der zwangsläufig Systeme dysfunktional macht. In einem verteilten Peer2Peer-System gibt es keine Master mehr sondern nur gleichberechtigte Knoten (Relays), auf denen die Informationen gespeichert werden. Indem man Informationen auf mehreren Relays redundant speichert, ist das System in jeglicher Hinsicht resilienter. Nicht nur die Natur verwendet dieses Prinzip seit Jahrmillionen erfolgreich, auch das Internet wurde so konzipiert (das ARPAnet wurde vom US-Militär für den Einsatz in Kriegsfällen unter massiven Störungen entwickelt). Alle Nostr-Daten liegen auf Relays und der Nutzer kann wählen zwischen öffentlichen (zumeist kostenlosen) und privaten Relays, z.B. für geschlossene Gruppen oder zum Zwecke von Daten-Archivierung. Da Dokumente auf mehreren Relays gespeichert sind, werden statt URL's (Locator) eindeutige Dokumentnamen (URI's = Identifier) verwendet, broken Links sind damit Vergangenheit und Löschungen / Verluste ebenfalls.\ \ Jedes Dokument (Event genannt) wird vom Besitzer signiert, es ist damit authentisch und fälschungssicher und kann nur vom Ersteller gelöscht werden. Dafür wird ein Schlüsselpaar verwendet bestehend aus privatem (nsec) und öffentlichem Schlüssel (npub) wie aus der Mailverschlüsselung (PGP) bekannt. Das repräsentiert eine Nostr-Identität, die um Bild, Namen, Bio und eine lesbare Nostr-Adresse ergänzt werden kann (z.B. roland@pareto.space ), mehr braucht es nicht um alle Ressourcen des Nostr-Ökosystems zu nutzen. Und das besteht inzwischen aus über hundert Apps mit unterschiedlichen Fokussierungen, z.B. für persönliche verschlüsselte Nachrichten (DM → OxChat), Kurznachrichten (Damus, Primal), Blogbeiträge (Pareto), Meetups (Joinstr), Gruppen (Groups), Bilder (Olas), Videos (Amethyst), Audio-Chat (Nostr Nests), Audio-Streams (Tunestr), Video-Streams (Zap.Stream), Marktplätze (Shopstr) u.v.a.m. Die Anmeldung erfolgt mit einem Klick (single sign on) und den Apps stehen ALLE Nutzerdaten zur Verfügung (Profil, Daten, Kontakte, Social Graph → Follower, Bookmarks, Comments, etc.), im Gegensatz zu den fragmentierten Datensilos der Gegenwart.\ \ Resümee: ein offener Standard, alle Daten, alle Rechte = große Zukunft!

\ Warum ist Nostr die Zukunft des Internet?
“Baue Dein Haus nicht auf einem fremden Grundstück” gilt auch im Internet - für alle App-Entwickler, Künstler, Journalisten und Nutzer, denn auch ihre Daten sind werthaltig. Nostr garantiert das Eigentum an den Daten, und überwindet ihre Fragmentierung. Weder die Nutzung noch die kreativen Freiheiten werden durch maßlose Lizenz- und Nutzungsbedingungen eingeschränkt. Aus passiven Nutzern werden durch Interaktion aktive Teilnehmer, Co-Creatoren in einer Sharing-Ökonomie (Value4Value). OpenSource schafft endlich wieder Vertrauen in die Software und ihre Anbieter. Offene Standards ermöglichen den Entwicklern mehr Kooperation und schnellere Entwicklung, für die Anwender garantieren sie Wahlfreiheit. Womit wir letztmalig zu unserem Fünfjährigen zurückkehren. Kinder lieben Lego über alles, am meisten die Maxi-Box “Classic”, weil sie damit ihre Phantasie im Kombinieren voll ausleben können. Erwachsene schenken ihnen dann die viel zu teuren Themenpakete, mit denen man nur eine Lösung nach Anleitung bauen kann. “Was stimmt nur mit meinen Eltern nicht, wann sind die denn falsch abgebogen?" fragt sich der Nachwuchs zu Recht. Das Image lässt sich aber wieder aufpolieren, wenn sie ihren Kindern Nostr zeigen, denn die Vorteile verstehen sogar Fünfjährige.

\ Das neue Internet ist dezentral. Das neue Internet ist selbstbestimmt. Nostr ist das neue Internet.
https://nostr.net/ \ https://start.njump.me/
Hier das Interview zum Thema mit Radio Berliner Morgenröte
-
 @ e6817453:b0ac3c39
2023-08-12 15:42:22
@ e6817453:b0ac3c39
2023-08-12 15:42:22The Zooko’s Triangle is a concept in the realm of naming systems, specifically for decentralized or distributed networks. It was named after Zooko Wilcox-O’Hearn, a computer scientist and cypherpunk known for his work on the Zcash cryptocurrency. The triangle illustrates a trade-off between three desirable properties in a naming system:
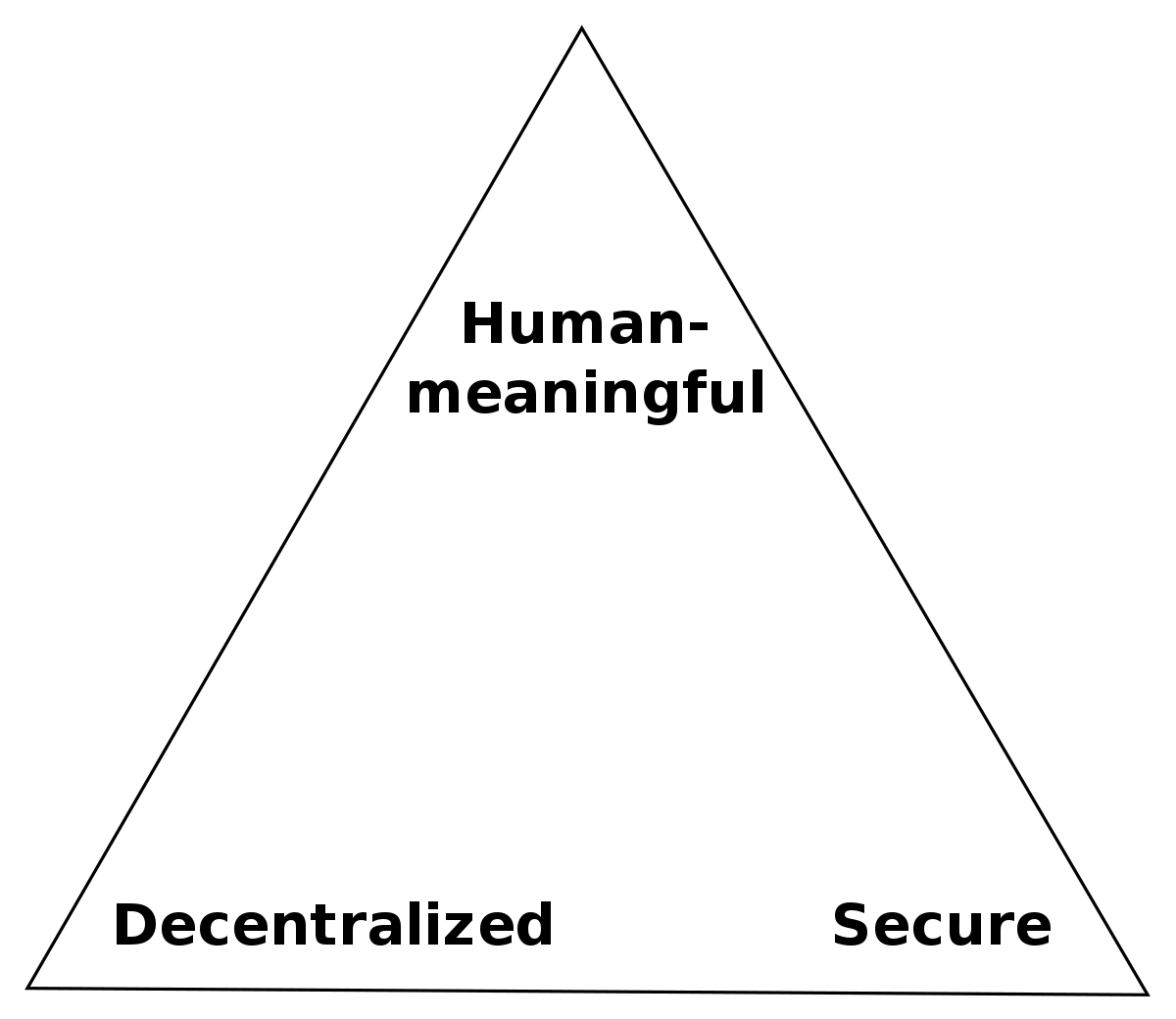
- Human-meaningful: Names are easily understood and remembered by humans.
- Decentralized: No central authority controls the allocation or management of names.
- Secure: Names are unique and cannot be easily taken or manipulated by others.
Zooko’s Triangle posits that achieving all three properties in a single system is difficult. Traditionally, a system could have only two of the three properties, leading to various combinations of naming systems with their respective advantages and disadvantages.
However, recent developments in cryptographic and distributed systems have led to solutions that challenge the traditional constraints of Zooko’s Triangle. One such system is the Decentralized Identifiers (DIDs).
DIDs
Decentralized Identifiers (DIDs) are a new identifier for verifiable, decentralized digital identity. DIDs are designed to be self-sovereign, meaning that individuals or organizations control their identifiers without relying on a central authority. DID systems are built on top of decentralized networks, such as blockchain or distributed ledgers, providing a secure and tamper-proof infrastructure for identity management.
DIDs aim to achieve the three properties of Zooko’s Triangle:
- Human-meaningful: While DIDs may not be human-meaningful due to their cryptographic nature, they can be associated with human-readable names or aliases.
- Decentralized: DIDs are managed on decentralized networks, removing the need for a central authority.
- Secure: The decentralized nature of DIDs, combined with cryptographic techniques, ensures that identifiers are unique, secure, and resistant to tampering.
In summary, Zooko’s Triangle presents a trade-off between human-meaningful, decentralized, and secure properties in naming systems. Decentralized Identifiers (DIDs) are an example of a system that seeks to overcome the traditional limitations of the triangle by leveraging decentralized networks and cryptographic techniques to provide a more comprehensive solution for digital identity management.
-
 @ e373ca41:b82abcc5
2025-01-17 17:54:57
@ e373ca41:b82abcc5
2025-01-17 17:54:57It was recently the tenth anniversary of the attack on Charlie Hebdo, France's best-known satirical magazine alongside the “Canard enchaîné”. The attack claimed the lives of 12 people, mainly cartoonists and journalists. Even then, it was a watershed moment, and not just in retrospect. Everyone wanted to show solidarity, everyone wanted to be “Charlie”, the phrase “Je suis Charlie” made the rounds memetically.
Charlie Hebdo was known for making fun of everything, including religions and Islam. “What is satire allowed to do? Everything.” So said Kurt Tucholsky, the famous publicist of the Weimar Republic, and that also applied to Charlie Hebdo. This magazine also dared to print Mohammed cartoons from “Jyllands Posten”. The solidarity of other newspapers with Charlie no longer went that far. They wanted to be Charlie, but rather without risk. The collective sign of solidarity fizzled out as lip service.
I was in Paris at the time and witnessed the mass demonstration live. Bernard Maris, a friend of Michel Houllebecq, also died in the attack. Houllebecq's book “Submission” was published on the same day. Coincidence? History and its synchronicities sometimes take wondrous paths.
On November 13, 2015, there was another attack at the Bataclan and around the Stade de France, among other places. Not long before, I was still living in Rue de la Fontaine au Roi in the 11th arrondissement, not far from Place de la République. My favorite café, the Café du Phare, was riddled with machine gun bullets, as was the pizzeria next door. I often sat in this café, writing books, academic texts and my first columns for the NZZ. At the time, I was teaching public law and fundamental rights at the Sorbonne in Paris, among other things, and dealing with issues relating to freedom of expression and artistic freedom on a daily basis.
I took it for granted that these constitutionally guaranteed values were just as important to the public (and especially other journalists) as their place in the constitutions of the West suggested. I was wrong, which was certainly also due to my legal glasses and “déformation professionelle”. At the time, I read more articles that emphasized respect for religions than the value of freedom of expression or artistic freedom. Looking back today, that was when the slippery slope that has led us into the realms of censorship, deletions, shadowbanning, fact-checkers, etc. began.
Freedom that is not used wears out and eventually disappears. Fighting to get it back is much more difficult than defending it. Back then, I wrote texts for newspapers rather sporadically, basically mainly when a topic was important to me and it remained underexposed.
The following text, which appeared in the NZZ at the time, was one such text.
You can find the German original version here.
ADVERTISEMENT:
Looking for the easiest way to buy Bitcoin and store it yourself? The Relai app is the No. 1 crypto start-up and No. 2 of all fintech start-ups in Switzerland. Here you can buy Bitcoin in just a few steps and also set up savings plans. Nobody has access to your Bitcoin except you. With the referral code MILOSZ you save on fees (no financial advice). Disclaimer due to regulatory issues: The services of the Relai App are hereby only recommended to inhabitants of Switzerland or Italy.
Need more security? The Trezor wallets are recommended and easy to use, others are available in the store. Need more advice? Book an introductory meeting with a wallet expert.
In the latest issue of “Charlie Hebdo” since the attack in Paris, the editors rub their eyes in amazement. What is wrong with this world? Politicians of all stripes, 50 heads of government and millions of citizens on the streets; Notre-Dame Cathedral is ringing its bells for atheists and the first people are thinking aloud about admitting anarchist cartoonists to the Paris Panthéon, the final resting place of Victor Hugo, Marie Curie and Jean-Jacques Rousseau. You can tell that the editorial team is a little uncomfortable with the collective need to cuddle up.
The worldwide wave of solidarity with “Charlie Hebdo” was overwhelming and important. “I am Charlie” became the collective outcry of the free world. The message is: “If you attack Charlie, you attack me”. What will remain of this when the dust settles? Will the continental plates of our order of freedom have shifted?
A rift trough the free world
Unfortunately, they did it long ago. The attack on “Charlie Hebdo” was an earthquake. But it ultimately only exposed once again what had already been clear and only slightly buried since the dispute over the publication of the Mohammed cartoons in the Danish newspaper “Jyllands-Posten” in 2005: there is a rift running through the free world, and the media landscape as an index of freedoms is showing it.
On the one hand, there are the courageous publications that do not deviate one iota from the Western achievements of freedom of the press, but which ultimately take the rap for it. And then there is the large remainder, for whom freedom seems to be first and foremost the right to remain silent. Magazines like “Charlie Hebdo” are the bad bank of the Western community of values. Charlie & Co. store the toxic papers that nobody wants on their books. The dividend of freedom, on the other hand, is paid out to everyone. If something happens, a declaration of solidarity follows at the minimum price.
Freedom folklore
The Charlie sympathy is to a not inconsiderable extent mere freedom folklore. A masked ball of the enlightened. The smoke from the attacks had barely cleared before the first German-language satirical magazines declared that they would refrain from printing cartoons of Mohammed. The Kalashnikov is the Titanic's iceberg (Note: "Titanic" is the main German satirical paper). American and British newspapers such as the “New York Times” and the “Independent” also waved goodbye and even refused to print the current cover of “Charlie Hebdo”.
This, mind you, in countries where freedom of expression is considered a cultural symbol and freedom as the “right of a soul to breathe”. The soul of freedom now found itself in a vacuum faster than you could shout “Allahu akbar!”. The Turkish newspaper “Cumhuriyet”, on the other hand, dared to do so. Our freedom is being defended in Turkey but no longer in New York or London? A topsy-turvy world.
Some people would like a more harmless satire these days. A satire without exaggeration, overstepping boundaries and disrespect for certain authorities. But the call for moderation means the elimination of its business basis. Satire does not demand approval and consensus. It is not a beauty contest.
When others decide for us
Anyone who refrains from using a caricature simply because it could be provocative, even blasphemous, is already adopting the thought structure and values of those who believe they are in the right when they respond with Kalashnikovs and rolling heads. People are either not proud of the achievement of satire or are not aware of their own rights, and perceive even something that is actually self-evident as an affront. If we ourselves do not know what we should stand for and why, then others have long since decided what we should stand for.
Certainly, no medium is forced to push the boundaries of our legal system on a daily basis. The notorious undercutting of our own standards, on the other hand, will cause them to shrink. Not immediately, but gradually. Until perhaps another standard is accepted at some point. The new censors will then no longer sit in ecclesiastical or secular palaces, as they did in the Middle Ages. But in tent cities in Yemen. Western society is gradually having the rug of its freedom order pulled out from under its feet. And instead of standing together, some people are asking if they can still help roll it up. But of course they still want to be “Charlie”.
Pseudo-security
Self-censorship and anticipatory obedience are a pseudo-safety net. Today it's the Mohammed cartoons. Tomorrow it will be critical reports on Islamism. Anyone who wants to carry out attacks will always find a reason. However, fundamental rights are not a fair-weather crop. Their true existence only becomes apparent when the storm hits. It is cynical to throw up one's hands in the hope that the angel of death will go to the neighboring editorial office.
“Charlie Hebdo” has decided against accepting such external content control. The editorial team also prints a Mohammed cartoon on the cover of the latest issue. Anyone who wonders whether this is wise has missed the point: if it were not done now, it would be the last time this happens in the Western newspaper landscape for a very long time. Those who remain silent agree with the new standard. And all this is happening now, in these hours and days!
It's crazy, but it has to be said: a small anarchic left-wing French newspaper, two-thirds of whose editorial office was bombed out last week, is currently standing almost alone on the front line of the Western world, defending a right it has fought for over 200 years, while machine guns are pointed at it. In the safe hinterland, on the other hand, far away from the impacts, the cardboard comrades fall over in rows at the first bang.
Our freedom is their freedom
At present, it is rightly said that the aim in future will be to win over the peaceful majority of Muslims to our side and not drive them into the hands of the extremists. Yes, many of them will find Muhammad cartoons outrageous or outrageous. But our freedom to think differently is also their freedom to think differently. Our freedom, as unpleasant as it may be to some, also protects moderate Muslims from being forcibly converted at gunpoint by their extremist co-religionists, as is currently happening thousands of times. That makes us allies.
We are currently experiencing a “Sebastian Haffner moment”. The chronicler of the Third Reich describes how he sits in the court library of the Berlin Court of Appeal in 1933 and witnesses the SA taking away all Jewish lawyers. Suddenly, a puffing SA man stands in front of him. “Are you Aryan?” Haffner, who had always rejected this category, answers “Yes” in surprise - and is left alone.
In his notes, he jots down the sentence: “Failed the first test!”
Join the marketplace of ideas! We are building a publishing ecosystem on Nostr for citizen-journalism, starting with a client for blogging and newsletter distribution. Sound money and sound information should finally be in the hands of the people, right? Want to learn more about the Pareto Project? Zap me, if you want to contribute (all Zaps go to the project).
Are you a publication and want to be part of it, test us, migrate your content to Nostr? Write to team@pareto.space**
Not yet on Nostr and want the full experience? Easy onboarding via Nosta.me.

-
 @ e6817453:b0ac3c39
2023-08-12 15:41:59
@ e6817453:b0ac3c39
2023-08-12 15:41:59Organizational identifiers
Organizational identifiers have different sets of requirements and functions. It is not enough to have per-to-peer private communications. Organizations are more public, so we need publicly resolvable identifiers. DID:key satisfy this condition entirely but fails to fulfill the organization's needs.
- Organizations quite often act as issuers of credentials or attestations. For issuance, it is critical to have the possibility to rotate signing keys or even deactivate or delete identifiers if keys or issuer get compromised or to comply with security company policies.
- Organizations often require a split between the Controller of the identifier and the Identifier subject or even a transfer of the identifier subject.
- Organizations must have complete control of infrastructure and effectively manage resources and costs. The price of a single identifier should be fixed, and the method of creating new identifiers should be scalable.
- One of the essential requirements is trust and governance and transparent mechanics of proving and binding an identifier to an organizational entity and creating trust relations.
- Access to Identifier management is quite often controlled by a group of users
Nonfunctional requirements
- portability
- interoperability
- scalability
- Autonomous and control
- security
In my previous articles, we talk about Autonomous identifiers and how they differ from regular DIDs.
To recap
Autonomous identifiers (AIDs) are DIDs generated algorithmically from a crypto- graphic key pair in such a way that they are self-certifying, i.e. the binding with the public key can be verified without the need to consult any external blockchain or third party. KERI is an example of a decentralized identity technology based entirely on AIDs. © https://trustoverip.org/blog/2023/01/05/the-toip-trust-spanning-protocol/
In a previous article, I show how to create and use a did:key as an Autonomous identifier that feet well to private person-to-person secure communication.
Architectures and protocols that build on top of AIDs have few critical properties
- self-hosting and self-contained
- self-certified and Autonomous
- portable
- interoperable
- full control of infrastructure
- cost management
Nowadays, I discovered a few AIDs methods
- did:key — self-contained and public
- did:peer — self-certified, upgradable but private
- KERI based did — we waiting for did:keri method to be announced soon, but KERI infrastructure could be used to build internals of did:peer or similar methods.
- did:web — public, self-certified, and self-hosted method, but still, we have active community discussion and critics as far as it fully relays to ownership of domain name that could be stolen or re-assigned.
So we have to choose from did:key did:web and I hope in a future from did:keri.
To move forward, we need to understand the DID architecture better and how all parts are connected.
In many cases of personal or sovereign entities Subject and the Controller are the same, but for Organisations, it could have a crucial difference.
DID Subject
The DID subject is the entity that the DID represents. It can be a person, organization, device, or other identifiable entity. The DID subject is associated with a unique DID that serves as a persistent, resolvable, and cryptographically verifiable identifier. The subject is the primary focus of the identity management process and typically has one or more DIDs associated with it.
DID Controller
The DID controller is the entity (person, organization, or device) that has the authority to manage the DID Document associated with a particular DID. The DID controller can update, revoke, or delegate control of the DID Document, which contains the public keys, service endpoints, and other information required for interacting with the DID subject.
In many cases, the DID subject and DID controller can be the same entity, especially for individual users who create and manage their DIDs. However, in some situations, the DID controller may differ from the DID subject, such as when an organization manages the DIDs on behalf of its employees or when an administrator manages a device.
In summary, the DID subject is the entity the DID represents, while the DID controller is the entity with authority to manage the associated DID Document. Depending on the specific use case and requirements, these roles can be held by the same or different entities.
Key Pair
It is simple from the first point of view. Key-Pair is an asymmetric public and private key. One of the main DID functions is the distribution of public keys. DIDDoccument could contain multiple public keys with authorization rules and key roles.
Identifier
Representation of did itself. is a part of DID URI.
DID:Key

did:key identifier
DID web
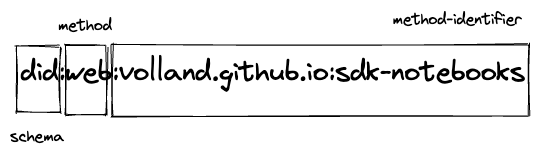
did:web
Relations
Relations between all parts of DID identifier can be illustrated in the following diagram. DID method dictate how DID identifier gets created, updated, deactivated, and resolved.
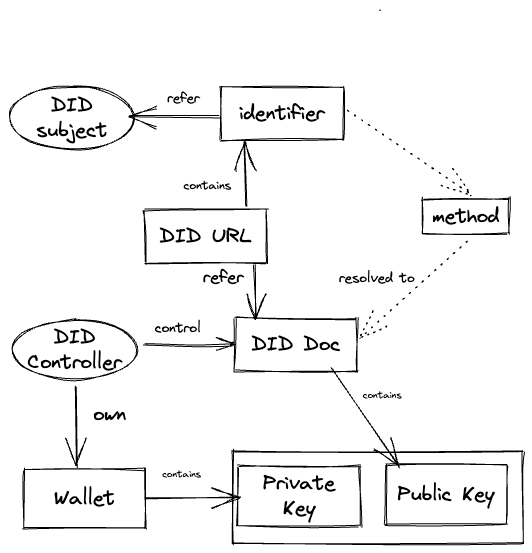
Focusing on the relations of the controller, key pairs, and the identifier is more interesting for us.
The most significant power and benefit of DID are decoupling a key pair from a controller and identifier. It allows the rotation of keys and changes the ownership of the identifier and its subject and controller. It is the main competitive advantage of DID and SSI over web3 wallets and raw keys.
The ideal case is KERI infrastructure that decouples all parties via cryptographic binding and protocols.
To discover more, read the paper.
We used did: keys as AID in the previous article. DID:key is a cryptographically bound identifier to the public key but cannot change the binding. As a result, keys couldn't be rotated in the future. The controller has no binding except to prove private key ownership via the signature-based protocol.
On the other side, DID:web does not have a cryptographic binding of an identifier to a key pair from one side. It gives an easy possibility to rotate keys but loses the verifiability of the identifier.
The most interesting part is the Controller to identifier binding in a did: web. It is based on proof of domain name ownership and website resource. As I mention, it has some security considerations and critics in a community. Still, at the same time, we get a critical mechanism that settles trust and connects identifiers to the organization entity.
The mechanism of web domain ownership is well-defined and easy to explain to other users, even outside of SSI and web5 domain. It is getting wider adoption and creating a lot of use cases for organizations. So it helps to create a trust relationship between an identifier and organizational entity in a very transparent, human-readable, and self-explained way — the identifier hosted on the corporate domain belongs to the organization. On another side, it makes the transfer of the controller almost impossible. That's why it is critical to differentiate between a subject and a controller.
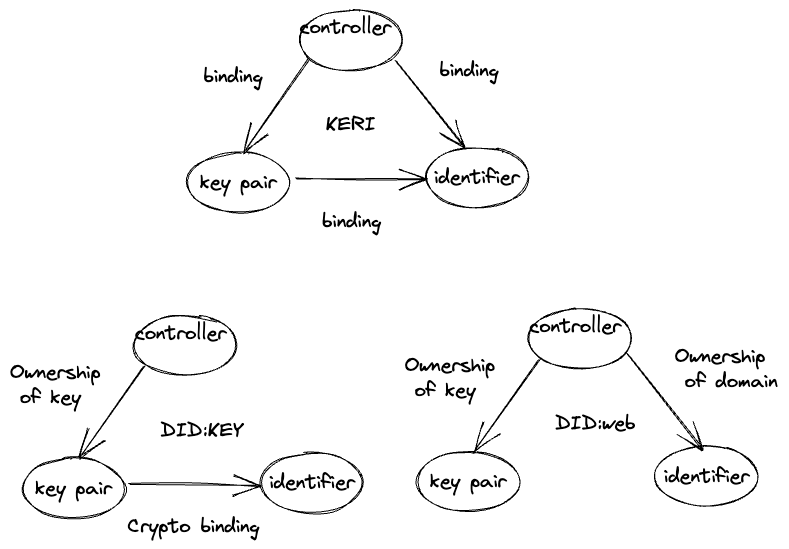
I believe that did:web still covers a lot of organizational cases and is suitable for issuing Verifiable Credentials and attestations on behalf of organizations.
Step-by-step guide on how to create and manage did:web you could find in my article
More detailed step-by-step coding guide with the live example you could find in my SSI notebooks book
-
 @ 000002de:c05780a7
2025-01-17 17:23:25
@ 000002de:c05780a7
2025-01-17 17:23:25With the news of Facebook changing its policy on DEI I was reminded of how it started and my early thoughts on it. I don't think DEI is dead, far from it but there's a trend forming pushing back. With Facebook and companies in general you have to understand something. Companies are mostly spineless. If a company is pushing something its not "brave" or "risky". All companies are profit driven and when they run these "woke" commercial its not brave. It would have been brave for companies to speak boldly against racism in the 50s but not today. Today most people oppose racism. Not saying we are rid of racism but just that companies are like a flag flying in the wind. They show you the direction the winds are blowing in culture and politics.
I have to say the whole DEI story line has been interesting to watch over the past 20 years. 20 years? Yeah that's what I said because its been a long arc. 20 years is probably to short but in the tech field I'd argue it really started back in the mid 2000s.
In the early 2000s I remember a push to make the tech field more friendly to women. To rid the startup culture of the bro culture and make it more welcoming and less like a college fraternity culture. I had no problem with any of that. But it became clear that very vocal people were not satisfied with that. It wasn't enough to not discriminate and stop tolerating sexism. We needed to actively set quotas for female speakers at conferences and have more diverse representation all over the place. The idea of meritocracy which was once the hallmark of the high tech industry was denigrated.
In the place of meritocracy we have what some have called "positive discrimination". At least that is the perception of critics of DEI. It can be easy to ignore your critics and sometimes that is a good approach. But when your goals are changing the hearts and minds, which at least in the early days of DEI seemed to be the goal, it is vital. Before I offer criticism of DEI I want to say a few positive things about it. From my perspective working in tech for 20 years I think it is good that the culture has become more vocal about "isms". Racism and sexism will always be with us but we should strive to treat people fairly. I've seen both of these in my work life and people are much more comfortable speaking up than they were in the past. That's not a bad thing.
To me it is obvious that quotas and pushing lies like the wage gap harmed the goals of DEI. Why do I say this? Stay with me here. If you believe there are people that just hate women or are racists in an industry those people are very unlikely to come over to your side. So you of course have people that agree with your DEI agenda but to me the focus of DEI is really the middle. Those that aren't sexist or racist but also aren't that motivated. The majority of workers in the early 2000s at least were white males. I believe this is still true today. For the last 20 years this group have been ridiculed on mass and told they are the problem. If this is the group you are seeking to win over... I can't think of a more terrible strategy. So either you have people who just think they are terrible and are being told there isn't much if anything they can do about their racism and sexism. Or you have people who buck up against how they are being lumped in with real racists and sexists.
You end up making enemies of allies. I have watched this happen in the industry over the years. As DEI has expanded into other industries this push back has only became stronger.
Another unintended consequence of DEI seems obvious to me but I rarely hear it mentioned. Today when you see something go wrong and the org has been vocal about DEI those that DEI claims to protect become the obvious targets. This is regardless of any evidence. It just seems like if you are saying we hire and promote on a basis other than merit or qualifications you are not hiring the best. That doesn't mean someone that is a minority isn't as good as a white male but when you discriminate you undercut those you claim to protect.
The loudest voices in DEI have done a terrible job. They have made enemies of allies. When you aren't honest about statistics and data, when you lump people into massive groups and boil everything down to biology and DNA you show your true colors. People don't buy it. I believe this is what we are seeing with the rejection of DEI. When you build something on lies and half truths it is doomed to fail. I'm convinced MOST people that support DEI are just good hearted people that have been manipulated and propagandized. DEI on the surface sounds good to most people. Those that respond in hate to DEI also provide a good boogie man. Divide and conquer works for a while but in the end truth wins.
What do you think?
originally posted at https://stacker.news/items/853862
-
 @ 1f3ce62e:6e6b5d83
2025-01-19 14:44:40
@ 1f3ce62e:6e6b5d83
2025-01-19 14:44:40🌱 🤍💗💜💙💧💚💛🧡❤️
I: Why do adults associate colors only with children and not with them?
AM: Adults have taken so seriously their role. They have forgotten their inner child, they are not in a permanent communication with it. That has made them forget some things, as colors and what they make them feel.
The whole world has become 🖤🤍🩶 since then.
So when an adult is connected back to her/his inner child, she/he has a big challenge, don’t let it fade away again and hug those who still think the world is just gray.
Sooner or later, the wound of the inner child will knock the door to be hugged and healed, it is just a matter of time. Having someone already connected to her/his inner child will make it easier.
\ 🌱 🤍💗💜💙💧💚💛🧡❤️
I: Why is our inner child wounded?
AM: Because we are all here to learn something, even if we don’t remember it.
That wound is our biggest lesson.
Once healed, it becomes the talent or gift we came here to share with those others inner childs with the same wound, with the same lesson to transcend.
🌱 🤍💗💜💙💧💚💛🧡❤️
I: How can we identify the wound of our inner child?
AM: In those situations that deeply hurt us.
The first step is to become an observer of oneself. Observe the way you talk to yourself, and to your closest ones (mom, dad, siblings, partner, kids and closest friends).
Then, observe your actions, they talk too. During this exercise you will find a pattern that repeats itself constantly.
The people who said or do something that hurts you, touch that wound. If we find the pattern, we will see the wound. It is always there, waiting to be healed.
🌱 🤍💗💜💙💧💚💛🧡❤️
I: Which role do mom and dad have into the inner child’s wound?
AM: If we think that we are here just once, bad things just happened to us and people hurt us, it is going to be a challenge to answer this question.
But if we expand our mind and consciousness and embrace the idea that we are more than just this life time and the situations that happened in it, we will be able to understand that we have lived other lives and we brought into this one other experiences, some of them we have learned and some others we haven’t yet.
The same happens with our relationships and the souls we shared this and other lives.
It’s from that expansion of consciousness that we can understand why mom and dad have did the things, they did and what was the higher purpose of it.
\ 🌱 🤍💗💜💙💧💚💛🧡❤️
I: What is the role of our inner child into the parents’ one with their kids?
AM: It is the most important but an unconscious one.
As adults start healing their inner child, the lessons that we left for kids are easier. Look at how I exchanged “parents” for “adults”. Any adult (aunts, uncles, grandparents, educators) whoever is closed to a child has this task: to connect and heal the inner child.
It’s true that parents has a great mission on this, the most important of their lives. And as they are healing their inner child and they letting their true self to BE, they are providing tools to their kids to BE themselves too.
Every healing process starts inside, to later be shared with others around.
\ 🌱 🤍💗💜💙💧💚💛🧡❤️
I: Why is our society so wounded?
AM: Because it is a society of wounded inner children.
When you want to know how we contribute to a wounded society, don’t look after what the society does (if they do good or bad things), look after what deeply hurt them.
People used to think that because they are “good” people and do “good” things, the society is wounded because of “bad” people who does “bad” things.
“Bad” and “Good” people is hurt the same way, one is more deep and visible than the other.
When you see something in society that hurts you, ask your inner child:
🌱 What does it hurt you, my lovely inner child?
🌱 🤍💗💜💙💧💚💛🧡❤️
I: What is the common ground between all of those different inner child wounds?
AM: The lack of love to ourselves. All inner child wounds have that in common, no matter from which discipline you identified them.
Deeply, the lack of love, it is related to not being able to BE ourselves in its full expression.
As we start loving ourselves and accepting ourselves as we are, any original wound start to heal.
🌱 Which wound can’t be healed with love?
\ 🌱 🤍💗💜💙💧💚💛🧡❤️
I: How can we connect with our inner child?
AM: There are many ways, meditations, playing with or like kids, etc.
But the most important one is observing and identifying what hurt us. In that instant, talk to your inner child and listen what her or his has to say.
The second step is to observe our inner dialogue, that dialogue we have with ourselves is the one we have we our inner child. That will mark the wound to be healed.
If you ask your inner child right now…How does she/he feel?
🌱 What does she/he would say?
With Universal Love 🤍♾️
I AM Laus 🌱💛
-
 @ 07f367da:0e76880d
2025-01-17 16:08:52
@ 07f367da:0e76880d
2025-01-17 16:08:52- 2023-10-26 강기자 기사 작성"‘직장 내 괴롭힘’ 호소하며 투신 사망… ‘미등록 장애인’ 김경현"
- 2023-10-27 강기자 기사 작성"좋은친구들 퇴사자 “김경현 유서, 내가 겪은 것과 너무 비슷하다”"
- 2023-11-18 이슬하 퇴직기자 게시물
- 2024-03-15 하민지 기자 게시물★최초폭로
- 2024-03-16 이슬하 퇴직기자 게시물
- 2024-03-18 비마이너 비상대책위원회 게시물
- 2024-04-29 비마이너 비상대책위원회 게시물
- 2024-05-03 이슬하 퇴직기자 게시물
- 2024-05-21 비마이너 비상대책위원회 게시물
- 2024-06-01 이슬하 퇴직기자 게시물
- 2024-07-31 김혜미 퇴직기자 게시물
- 2024-08-13 비마이너 비상대책위원회 발표★1차 입장
- 2024-08-23 이슬하 퇴직기자 게시물
- 2024-08-25 하금철, 갈홍식, 최한별
- 2024-08-25 운영실장 양유진, 취재기자 하민지
- 2024-08-26 비마이너 퇴직기자 6인 입장문
- 2024-08-27 하민지 기자 게시물
- 2024-08-27 비마이너 비상대책위원회 발표★2차 입장
- 2024-10-01 김혜미 퇴직기자 게시물
- 2024-10-22 이슬하 기자 게시물
- 2024-11-06 이슬하 기자 게시물
- 2024-11-28 비마이너 비상대책위원회 발표★최종 입장
- 2024-11-29 박정수 퇴직기자 게시물★
- 2024-11-29 하민지 기자 게시물
- 2025-01-16 하민지 기자 게시물
-
 @ d3d74124:a4eb7b1d
2023-07-26 02:43:40
@ d3d74124:a4eb7b1d
2023-07-26 02:43:40This plan was GPT generated originally but then tweaked by myself as the idea fleshed itself out. All feedback welcome and encouraged.
Shenandoah Bitcoin
1. Executive Summary
Shenandoah Bitcoin is a for-profit community organization based in Frederick County, VA, uniquely blending the world of agriculture and STEM. Our mission is to foster community spirit, stimulate interest in agricultural technology, and promote understanding of Bitcoin, while providing enriching educational opportunities and ensuring sustainable business operations.
2. Company Description
Shenandoah Bitcoin is committed to delivering value to our local community. Our unique approach intertwines traditional agricultural practices, modern STEM concepts, and the world of digital currencies, specifically Bitcoin. Our activities cater to all age groups, focusing on fostering community engagement, hands-on learning experiences, and contributing to the overall welfare of our community.
What’s in a name?
Shenandoah Bitcoin. Shenandoah - an old and historied land. Bitcoin - a cutting edge technological advancement. Both encompass multiple industries, from energy and manufacturing, to farming and data centers. Both built using Proof of Work.
3. Services
We offer a range of services, including:
Family-friendly events: Agriculture, STEM, and Bitcoin-themed festivals, fairs, workshops, and community gatherings. Educational programs: Classes, seminars, and workshops on agricultural technology, STEM principles, and understanding and using Bitcoin. Facility Rentals: Spaces available for private events, business meetings, and community gatherings.
4. Membership Benefits
We offer tiered membership packages with benefits such as:
a. Silver Membership: Includes access to regular events, discounts on educational programs, and priority booking for facility rentals.
b. Gold Membership: All Silver benefits, free access to select educational programs, and further discounted facility rentals.
c. Platinum Membership: All Gold benefits, free access to all educational programs, highest priority and maximum discounts on facility rentals, and exclusive invitations to special events.
Member’s opting to pay in Bitcoin receive 10% off all pricing.
5. Market Analysis
Our primary market is the local community in Frederick County and Winchester, VA, which consists of various demographic groups. Our secondary market includes neighboring communities, tourists, businesses, and educational institutions interested in the intersection of agriculture, STEM, and Bitcoin. Understanding that facility use and events to be a drawing factor for all demographics, we outline demographic specific analysis below.
STEM professionals in the area may work remotely or commute toward DC and not interact much with their agricultural neighbors, but a desire for good quality food exists for many. In addition to events, drawing the STEM demographic in will be connections to CSAs, ranchers, and homesteaders for access to fresh locally grown food. Offering a child's play room adjacent to some office space, is a compelling benefit for the laptop class that is often in STEM professions.
Non-industrial food producers and homesteaders may not have the focus or resources for marketing and sales. By offering a physical touch point for them and direct connections to consumers, food producers benefit from membership. Having more options for drop off/pick up of various produced goods, makes it attractive for both the consumers and producers as coordination can be asynchronous.
Bitcoiners have a wide range of sub-demographics, including farmers and software engineers. Some travel hours over car and plane to attend bitcoin themed events. The topics of STEM and agriculture are of shared interest to non-trivially sized communities of bitcoiners. Having a physical touch point for bitcoiners will draw in some members just for that. Building fellowship is desired and sought in bitcoin.
5.1 Market Trends
The blending of agriculture, STEM fields, and Bitcoin is a unique concept with increasing interest in sustainable farming and ranching, food sovereignty, and health. Shenandoah Bitcoin is poised to tap into this growing interest and offer unique value to our community.
5.2 Market Needs
Our market requires initiatives that foster community engagement, promote understanding of agri-tech and Bitcoin, and provide a versatile space for events and learning.
6. Marketing and Sales Strategy
We will employ a blend of digital marketing, traditional advertising, and strategic partnerships. Our main marketing channels will be word of mouth, social media, local press, and our website. Partnerships with local small businesses, homesteaders, schools, agricultural organizations, and bitcoin companies will form a key part of our outreach strategy.
7. Organizational Structure
Shenandoah Bitcoin will be led by a CEO, supported by a management team responsible for daily operations, event planning, marketing, and community outreach. Event management and logistics will be handled by part-time staff and volunteers.
8. Financial Projections
Our revenue will be generated from membership fees, charges for events and educational programs, and facility rentals.
9. Funding Request
[If seeking additional funding, describe your needs and how the funds will be used]
10. Exit Strategy
Should it become necessary to dissolve the business, assets such as property, equipment, and any remaining cash reserves after meeting liabilities will be sold. Investors would receive their share of the remaining assets according to their proportion of ownership.
11. Conclusion
Shenandoah Bitcoin is a unique community organization bringing together agriculture, STEM, and Bitcoin in Frederick County, VA. Our distinctive approach is designed to deliver both profits and social impact, resonating strongly with our target market and positioning us for sustainable growth.
-
 @ 543d73b5:977c83a9
2025-01-17 15:24:32
@ 543d73b5:977c83a9
2025-01-17 15:24:32In the digital world, human beings occupy space with digital representations of their physical-world information. When viewed separately, these digital representations can be readily dismissed as merely random collections of digital assets. However, when examined as a whole, these same representations reveal themselves to be extensions of a person’s digital self-sovereign identity.
Moreover, as these two worlds, the digital and the physical, continue to merge into one space, this digital identity has become more commonly used as a primary means of validation and verification of a person’s digital and physical existence. Therefore, the primary rights of ownership for this digital form of identity must be safeguarded and protected in the same manner, and with the same level of importance, as is typically observed with individual identity in the physical world.
It is for this reason that this Ethos of Digital Self-Sovereign has been drafted. And, it is for this purpose that it is presented to the digital community for their consideration and adoption into their standard governance frameworks.

THE RIGHT TO DIGITAL PRIVACY
PROTECTED PRIVACY = the SECURITY of PROPERTY which affirms our FAITH in our DIGITAL SELF-SOVEREIGNTY.
Digital Privacy means that people are the sole owners of their own digital property and they inherently possess immutable authority over the use of that property. As owners, they have full right of control over the “why”, “when”, “where”, and “how” their digital assets are accessed. Digital Privacy is about an individual’s ability to maintain control of their digital property when interacting with any entity, system, or organization within a digital environment. Therefore, with every and any form of digital interaction, every person should have the expectation of privacy.
THE RIGHT TO DIGITAL INDEPENDENCE
COMPREHENSIVE DECENTRALIZATION = the INDEPENDENCE of CHOICE which affirms our BELIEF in our DIGITAL AUTONOMY.
Digital Independence is the ability for individuals to interact freely with any entity, system, or organization within the digital space. Centralized control of digital interactions is in direct conflict with the idea of digital independence. Within decentralized environments, there is no intermediary entity to serve as a central authority over the authenticity of digital relationships. Therefore, systematic decentralization must be promoted, propagated, and implemented throughout every corner of the digital world to ensure that the right to Digital Independence is fully available to every individual.
THE RIGHT TO DIGITAL TRANSPARENCY
CLEAR GOVERNANCE = the TRANSPARENCY of AGREEMENTS which affirms our TRUST in our DIGITAL RELATIONSHIPS.
Digital Transparency is the application of open, honest, and fair relationships between individuals, entities, systems, and/or organizations within a digital space. One can argue that transparency is required to secure trust between different parties in a digital-based relationship. However, a truly transparent relationship can actually eliminate the need for trust between parties; since each individual is has the ability to confirm the validity of all interactions because all information about the shared relationship is openly available to all parties involved in the relationship.
(First Drafted 11/11/2021)
-
 @ ce6b432f:c07ce020
2025-01-19 13:42:12
@ ce6b432f:c07ce020
2025-01-19 13:42:12I’ve never lived in LA, though I’ve visited many times. The devastation there from recent fires there is still in the headlines and anyone with a soul feels for the folks without homes, neighbors and communities. Whether they vote the same way or look the same way or worship the same god, “what can I do to help these victims?” is our first question.
The second question is, what is the most responsible way to help? Paragraph two and controversy is already here. Responsible according to who? These people are victims, just give them as much money as they need and let them figure it out according to their local knowledge and culture! The broadest possible answer to this comes from a recent Substack by Arnold Kling: California Tough Love . His position is that there are certain factors controlled locally that led to the disaster, and we shouldn’t be in a rush to replicate them. Having some strings attached to funds that reduce the likelihood of $50,000/year blue collar workers in Iowa footing the bill for the rebuild of $5,000,000 homes in Pacific Palisades AGAIN in the foreseeable future is a very reasonable position.
My position here will be more detailed than Arnold’s, and thus has a higher probability of being wrong. That has never stopped me before. The source of this hubris is a crystal ball. While not a resident of LA, I have been an honorary citizen of Maui for several decades. This attachment is longer than the attachment to the city I currently live in. In August of 2023, a similar devastating fire engulfed the town of Lahaina on the west side of Maui. ~2,200 homes were burned or damaged. The plight of those rebuilding and the process they have gone through quickly faded from national attention, but not to those of us who spend substantial amounts of time on the island. This experience 17 months before the LA fires has painted a depressing blueprint of what we can expect in LA’s recovery. A couple of highlights:
- In November of 2024, the first house was rebuilt. 15 months = 1 house. First House Rebuilt -Maui News Article highlight: Maui “expedited the permitting process for this house, so it “only” took 2 months.
- In December of 2024, federal funding for rebuilding via a block grant is finally approved by congress. Federal Block Grant For Rebuild - Maui News Article highlight: $1.6 billion approved for housing = ~$800,000 per house.
What do these items have in common? The biggest price so far is time. Arnold’s substack was more of a philosophical position, but I doubt even he knew that at the time of writing, Lahaina’s federal funding had just been approved. All those strings he had attached by the feds? Still very slow for a family without a home. This is half of the ‘real price gouging’ mentioned in the subtitle. Those further down the socio-economic ladder have less time to weather the process in Lahaina and the same will likely be true for the middle class residents embedded in the areas destroyed by California’s fires.
The second element of price gouging is the red tape partially embodied in Maui’s example of two months of permitting. These costs aren’t just the time, but also the professional consultants of various stripes required to navigate the process successfully and the costly modifications to homes mandated through these processes.
Here is where I posit my broad and general suggestion. There should exist a “right to rebuild”. If you can legally own a piece of property in a specific condition, you should have the right to rebuild that exact same property if it is destroyed by means out of your control. If you don’t have a “right to rebuild”, you really don’t own that property - you are just renting it for an indefinite period from whoever can prohibit rebuilding it.
Rebuilding is a special case in both the individual and the community level. See the map of Lahaina below. We know where all the plumbing and power lines were. We know where the streets and drainage were. The right to rebuild translates nicely to the community level. Rebuild everything back where it was. Take a month or two to clear out the debris, from an area and begin to rebuild. Rinse and repeat until done.
Taxpayers in Texas shouldn’t be paying for bloated permitting processes in Lahaina or LA. They shouldn’t be paying for eco-upgrades unless very specific, critical failures that caused the current disaster are clearly identified with lowest-cost available solutions. (In Lahaina - pay to bury the power lines. I drove through the area the fire started 2 weeks before it occurred. That place was a tinder box, and it will be again unless someone puts a golf course on that hill. I’m not joking about the golf course. Directly adjacent to the north of the area of Lahaina that burned is Ka’anapali, whose identical hillside is green all year round due to the presence of golf courses that pay for themselves and do not burn.)
How to address this in the context of federal funding via Arnold’s original post:
- Extremely expedited permitting process for rebuilds that get any federal funding: 5 days not 60. You can rebuild what you had, no questions asked, just file the paper work to prove it is the same lot and same size structure. If local jurisdictions drag their heels - no funding, answer to your voters who are now SOL.
- Capped amount of funding per structure that covers a functional modest structure built at the average cost of the 10 most affordable states in the country. The process of building a single family residence is not dramatically different in various areas of the country, unless dictated by excessive regulation. There may be factors for labor to consider if an area is remote like Lahaina or the hills of North Carolina affected by Helene. But if it costs 2x to build a house in your county than in the 10 most affordable states - you are doing it wrong. There is some regulatory price gouging going on. Figure it out. The 10 Most Affordable States to Build a Home - According to this research you can build a 2,100 square foot home for an average of less than $300,000 in the 10 most affordable states.
- This funding will also be contingent on these rebuilt houses being completed within 110% of the time it takes to build 2,100 square foot home in the same 10 markets - measured from the day funds begin to be distributed by the federal government.
- Federal funding will begin to be distributed from a risk pool within 6 months of the disaster, with minimal review to just ensure the disaster qualifies and the receiving state/city will abide by its parameters. The funding is distributed at intervals governed by compliance with the program. Permits are being issued timely, and the amounts distributed are aligned with the cost of building in our most affordable markets.
If you want to build something new and different than before - it might take longer. If you want more than 2,100 square feet of house - I hope you had insurance to cover the difference. A new 2,100 square foot house puts you in the top 10% of humans on earth in terms of shelter. Being a good neighbor does not require rebuilding your infinity pool.
The right to rebuild will get people in homes quicker, remove government obstacles, and stop funding waste. Every citizen will know the rules - money is there to get me a basic structure quickly or fund the beginning of something larger. Any obstacles to that time and money are coming from politicians/regulations I can vote on locally. Comments will surely pour in explaining how it isn’t that simple. These comments will be reviewed diligently 2 years from now when Pacific Palisades is still a wasteland after $20 billion in federal aid has been spent.
!(image)[https://substackcdn.com/image/fetch/f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F8e7875da-145c-4f34-b115-eb0cf09b9ccf_792x612.jpeg] Source: Maui Now
-
 @ 5d4b6c8d:8a1c1ee3
2025-01-17 14:57:02
@ 5d4b6c8d:8a1c1ee3
2025-01-17 14:57:02Football
We're in the home stretch of Futbol Americano season. The College Football championship game on Monday will be the final round of our College Football Playoff Pool. However, the NFL Playoffs are also the opening rounds of the Team USA!!! vs "the world" challenge.
As a slight aside, I'm very much looking forward to these markets closing on Predyx, so I can get some of my sats back.
We'll also talk about where various coaches will end up in the NFL.
NBA
The Celtics are looking a bit more mortal. Is that real or just a January lull?
KAT Corner
Loser of the Week (submit your entries)
MLB
Offseason news
I think @grayruby wants to apply the Ewing Theory to Juan Soto, but we'll have to find out.
NHL
Ovi watch
Other Territory News
UEFA and Cricket contest updates
What else should we cover?
My Game of the Week nominee is actually from last week. Is that allowed? There weren't many great games this week.
originally posted at https://stacker.news/items/853599
-
 @ e373ca41:b82abcc5
2025-01-19 13:35:09
@ e373ca41:b82abcc5
2025-01-19 13:35:09This article by Milosz Matuschek first appeared in German on Freischwebende Intelligenz
Last night, while you were fast asleep, someone turned 883 dollars into 310,000 dollars in just a few hours. Not me, unfortunately. Trump launched his own memecoin with the abbreviation $TRUMP, which has since skyrocketed to a double-digit billion dollar valuation.

Trump (and his pre-investors) are now billions richer on paper. It takes just a few minutes and no (more) development work to create such a coin within minutes. All it takes is a believing community to make it explode. If you were looking for proof of my thesis that the world is being memefied, here it is.

Us and them
We are currently experiencing a phase of power shifts: in money, in politics, in the media. Many people like what Trump and Musk are doing. They are creating more freedom of expression and removing Wokistan's basis for business. Amazon is scrapping diversity rules, Facebook is scrapping censorship (officially admitted). Tiktok land is burned down, the Chinese social media app disappears from the US. Isn't that censorship? Google and Facebook are now openly rebelling against EU opinion dictates, fact checkers etc. In addition to the Hindu Kush, our freedom of opinion is now also being defended (again, for how long?) from Silicon Valley. Brave new world.
You can think strategically: wonderful, that's what I wanted too; “the enemy of my enemy is my friend”. But for how long? This is a change of power at the political top, nothing more.
Trump has promoted vaccination just like Biden; also with the lie that it prevents infection. Vote for your favorite PR artist!
Is that supposed to be our choice?
Elon Musk built mRNA vaccination lines for Curevac, is the Young Global Leader of the WEF 2008, has major holdings in Tesla from Blackrock-Vanguard & Co. and contracts with the Pentagon.
“One of us”, yes for sure....
I find that hard to believe and I wonder about those who find it easy to believe. Speaking of faith: a reader I hold in high esteem said she believes Musk and Trump are on a divine mission. Trump partying with Epstein? Musk in a Baphomet costume? The ways of the Lord are truly mysterious then...
The common enemy of the enemy can be useful, up to a point, but nothing more. Just because you fight the same thing, i.e. are against something, doesn't mean you are for the same thing. In my opinion, assuming that the interests of Trump, Musk & Co. are congruent with the interests of citizens would be a fatal misconception. There is nothing to suggest this. Trump has been totally for and then against many issues. Personnel decisions: often a casting round for a limited time, with hire & fire like “The Apprentice”. But he is so peaceable, wants to end wars like the one between Russia and Ukraine, or de facto the USA. At the same time, he is now reaching for Greenland and the Panama Canal. His words ooze the exceptionalism of the USA, the doctrine that as a US empire you can basically do anything you want. For strategic interests. For national security. A formula can always be found.
ADVERTISEMENT:
Looking for the easiest way to buy Bitcoin and store it yourself? The Relai app is the No. 1 crypto start-up and No. 2 of all fintech start-ups in Switzerland. Here you can buy Bitcoin in just a few steps and also set up savings plans. Nobody has access to your Bitcoin except you. With the referral code MILOSZ you save on fees (no financial advice). Disclaimer due to regulatory issues: The services of the Relai App are hereby only recommended to inhabitants of Switzerland or Italy.
Need more security? The Trezor wallets are recommended and easy to use, others are available in the store. Need more advice? Book an introductory meeting with a wallet expert.
How are wo going to score on the liberty scale?
“Believe little, question everything, think for yourself” is the beautiful title of a very readable book by Albrecht Müller, editor of Nachdenkseiten, and best summarizes my thoughts. As a journalist, I replace “little” with “nothing”. The journalist is not in the banking business. There you are allowed to believe (credit = he believes, latin). I don't think the issue of draining a swamp should be left to the frogs. Is Trump not a frog? “Anti-establishment", come on. Now the establishment is coming from the other side, the other side of the dialectic. The battle of good versus evil is entering a supposedly new round, releasing pressure from the cauldron of democracy, which is too important a façade to be allowed to fall.
The only pragmatic question that citizens should ask themselves is this: Will I have more net freedoms at the end of this political reorganization process than before? What will be given to me in reel but perhaps also taken away elsewhere? Anyone who draws hope from changes in the left-right scheme has always been disappointed by the steady reduction of freedoms in recent years and should rather look at the vertical axis of top vs. bottom. Hope is nice, but you should only ever rely on yourself.
It's nice if some people now get to know something different as a result of the change in the political weather and wake up. A book will soon be published about manipulation in the Tagesschau. The PEI has known about the side effects for years, but withheld the information and the republic was allowed to rail against footballer Joshua Kimmich in the meantime. One life lie after another will now fall, an exciting process. But it will mainly be cardboard comrades and useful idiots who will have to fall by the wayside, and there was hardly any shortage of them.
Waking up must not lead to the next dream world. Otherwise the critical movement was just a stirrup for the next seizure of power. But we need a movement of self-empowerment of the citizen, beyond politics, the media or Big Tech. Invest in everything, be it seminars, books, knowledge, Bitcoin or whatever increases your net freedom balance. Decentralized civil society only has a chance if free citizens form their own free block in cooperation with others, based on principles and not on the bunting of a party-political camp.
Everyone can decide for themselves and have a say in what form this can take. Where cooperation arises naturally, the idea was a good one. Ultimately, an idea is just a meme.
That was my meme five years ago. It's still true, but with Bitcoin a zero has been added.

Join the marketplace of ideas! We are building a publishing ecosystem on Nostr for citizen-journalism, starting with a client for blogging and newsletter distribution. Sound money and sound information should finally be in the hands of the people, right? Want to learn more about the Pareto Project? Zap me, if you want to contribute (all Zaps go to the project).
Are you a publication and want to be part of it, test us, migrate your content to Nostr? Write to team@pareto.space**
Not yet on Nostr and want the full experience? Easy onboarding via Nosta.me.

-
 @ d2e97f73:ea9a4d1b
2023-04-11 19:36:53
@ d2e97f73:ea9a4d1b
2023-04-11 19:36:53There’s a lot of conversation around the #TwitterFiles. Here’s my take, and thoughts on how to fix the issues identified.
I’ll start with the principles I’ve come to believe…based on everything I’ve learned and experienced through my past actions as a Twitter co-founder and lead:
- Social media must be resilient to corporate and government control.
- Only the original author may remove content they produce.
- Moderation is best implemented by algorithmic choice.
The Twitter when I led it and the Twitter of today do not meet any of these principles. This is my fault alone, as I completely gave up pushing for them when an activist entered our stock in 2020. I no longer had hope of achieving any of it as a public company with no defense mechanisms (lack of dual-class shares being a key one). I planned my exit at that moment knowing I was no longer right for the company.
The biggest mistake I made was continuing to invest in building tools for us to manage the public conversation, versus building tools for the people using Twitter to easily manage it for themselves. This burdened the company with too much power, and opened us to significant outside pressure (such as advertising budgets). I generally think companies have become far too powerful, and that became completely clear to me with our suspension of Trump’s account. As I’ve said before, we did the right thing for the public company business at the time, but the wrong thing for the internet and society. Much more about this here: https://twitter.com/jack/status/1349510769268850690
I continue to believe there was no ill intent or hidden agendas, and everyone acted according to the best information we had at the time. Of course mistakes were made. But if we had focused more on tools for the people using the service rather than tools for us, and moved much faster towards absolute transparency, we probably wouldn’t be in this situation of needing a fresh reset (which I am supportive of). Again, I own all of this and our actions, and all I can do is work to make it right.
Back to the principles. Of course governments want to shape and control the public conversation, and will use every method at their disposal to do so, including the media. And the power a corporation wields to do the same is only growing. It’s critical that the people have tools to resist this, and that those tools are ultimately owned by the people. Allowing a government or a few corporations to own the public conversation is a path towards centralized control.
I’m a strong believer that any content produced by someone for the internet should be permanent until the original author chooses to delete it. It should be always available and addressable. Content takedowns and suspensions should not be possible. Doing so complicates important context, learning, and enforcement of illegal activity. There are significant issues with this stance of course, but starting with this principle will allow for far better solutions than we have today. The internet is trending towards a world were storage is “free” and infinite, which places all the actual value on how to discover and see content.
Which brings me to the last principle: moderation. I don’t believe a centralized system can do content moderation globally. It can only be done through ranking and relevance algorithms, the more localized the better. But instead of a company or government building and controlling these solely, people should be able to build and choose from algorithms that best match their criteria, or not have to use any at all. A “follow” action should always deliver every bit of content from the corresponding account, and the algorithms should be able to comb through everything else through a relevance lens that an individual determines. There’s a default “G-rated” algorithm, and then there’s everything else one can imagine.
The only way I know of to truly live up to these 3 principles is a free and open protocol for social media, that is not owned by a single company or group of companies, and is resilient to corporate and government influence. The problem today is that we have companies who own both the protocol and discovery of content. Which ultimately puts one person in charge of what’s available and seen, or not. This is by definition a single point of failure, no matter how great the person, and over time will fracture the public conversation, and may lead to more control by governments and corporations around the world.
I believe many companies can build a phenomenal business off an open protocol. For proof, look at both the web and email. The biggest problem with these models however is that the discovery mechanisms are far too proprietary and fixed instead of open or extendable. Companies can build many profitable services that complement rather than lock down how we access this massive collection of conversation. There is no need to own or host it themselves.
Many of you won’t trust this solution just because it’s me stating it. I get it, but that’s exactly the point. Trusting any one individual with this comes with compromises, not to mention being way too heavy a burden for the individual. It has to be something akin to what bitcoin has shown to be possible. If you want proof of this, get out of the US and European bubble of the bitcoin price fluctuations and learn how real people are using it for censorship resistance in Africa and Central/South America.
I do still wish for Twitter, and every company, to become uncomfortably transparent in all their actions, and I wish I forced more of that years ago. I do believe absolute transparency builds trust. As for the files, I wish they were released Wikileaks-style, with many more eyes and interpretations to consider. And along with that, commitments of transparency for present and future actions. I’m hopeful all of this will happen. There’s nothing to hide…only a lot to learn from. The current attacks on my former colleagues could be dangerous and doesn’t solve anything. If you want to blame, direct it at me and my actions, or lack thereof.
As far as the free and open social media protocol goes, there are many competing projects: @bluesky is one with the AT Protocol, nostr another, Mastodon yet another, Matrix yet another…and there will be many more. One will have a chance at becoming a standard like HTTP or SMTP. This isn’t about a “decentralized Twitter.” This is a focused and urgent push for a foundational core technology standard to make social media a native part of the internet. I believe this is critical both to Twitter’s future, and the public conversation’s ability to truly serve the people, which helps hold governments and corporations accountable. And hopefully makes it all a lot more fun and informative again.
💸🛠️🌐 To accelerate open internet and protocol work, I’m going to open a new category of #startsmall grants: “open internet development.” It will start with a focus of giving cash and equity grants to engineering teams working on social media and private communication protocols, bitcoin, and a web-only mobile OS. I’ll make some grants next week, starting with $1mm/yr to Signal. Please let me know other great candidates for this money.
-
 @ f88e6629:e5254dd5
2025-01-17 14:10:19
@ f88e6629:e5254dd5
2025-01-17 14:10:19...which allow online payments to be sent directly from one party to another without going through a financial institution.
- Without sovereign and accessible payments we are loosing censorship resistance
- Without censorship resistance even other core characteristics are in danger - including scarcity and durability.
- This affects every bitcoiner including sworn hodlers and MSTR followers.
| Property | Description | Fulfillment | | --- | --- | --- | | Scarce | Fixed supply forever. Instantly and costlessly verifiable | 🟢 Good, but can be harmed without censorship resistance | | Portable | Effortless to store and move, with negligible costs | 🟠 Onchain transactions can be expensive, other layers require onchain to be sovereign. Easy portability is offered by custodians only. | | Divisible | Infinitely divisible | 🟠 Smaller units than dust are available only for LN users, which most people can’t use in a sovereign way. | | Durable | Exists forever without deterioration | 🟢 Good, but can be harmed without censorship resistance | | Fungible | Every piece is forever the same as every other piece | 🟡 Onchain bitcoin is not fungible. | | Acceptable | Everyone, anywhere, can send and receive | 🟠 Most people are not able to send and receive in a sovereign way. | | Censorship Resistant | You hold it. Nobody can take it or stop you sending it | 🟠 Custodians are honey-pots that can and will be regulated |
➡️ We need accessible, scalable, and sovereign payment methods
-
 @ 9dd283b1:cf9b6beb
2025-01-17 14:05:02
@ 9dd283b1:cf9b6beb
2025-01-17 14:05:02If I'm looking at this graph right, then the total zaps per month are somewhere around 100-110k sats. At the same time, the monthly fee for territory is 50k sats.
So we have 20+ territories, all sharing the total income of 100k, while spending 50k per month each? Or what am I missing?
originally posted at https://stacker.news/items/853551
-
 @ 82341f88:fbfbe6a2
2023-04-11 19:36:53
@ 82341f88:fbfbe6a2
2023-04-11 19:36:53There’s a lot of conversation around the #TwitterFiles. Here’s my take, and thoughts on how to fix the issues identified.
I’ll start with the principles I’ve come to believe…based on everything I’ve learned and experienced through my past actions as a Twitter co-founder and lead:
- Social media must be resilient to corporate and government control.
- Only the original author may remove content they produce.
- Moderation is best implemented by algorithmic choice.
The Twitter when I led it and the Twitter of today do not meet any of these principles. This is my fault alone, as I completely gave up pushing for them when an activist entered our stock in 2020. I no longer had hope of achieving any of it as a public company with no defense mechanisms (lack of dual-class shares being a key one). I planned my exit at that moment knowing I was no longer right for the company.
The biggest mistake I made was continuing to invest in building tools for us to manage the public conversation, versus building tools for the people using Twitter to easily manage it for themselves. This burdened the company with too much power, and opened us to significant outside pressure (such as advertising budgets). I generally think companies have become far too powerful, and that became completely clear to me with our suspension of Trump’s account. As I’ve said before, we did the right thing for the public company business at the time, but the wrong thing for the internet and society. Much more about this here: https://twitter.com/jack/status/1349510769268850690
I continue to believe there was no ill intent or hidden agendas, and everyone acted according to the best information we had at the time. Of course mistakes were made. But if we had focused more on tools for the people using the service rather than tools for us, and moved much faster towards absolute transparency, we probably wouldn’t be in this situation of needing a fresh reset (which I am supportive of). Again, I own all of this and our actions, and all I can do is work to make it right.
Back to the principles. Of course governments want to shape and control the public conversation, and will use every method at their disposal to do so, including the media. And the power a corporation wields to do the same is only growing. It’s critical that the people have tools to resist this, and that those tools are ultimately owned by the people. Allowing a government or a few corporations to own the public conversation is a path towards centralized control.
I’m a strong believer that any content produced by someone for the internet should be permanent until the original author chooses to delete it. It should be always available and addressable. Content takedowns and suspensions should not be possible. Doing so complicates important context, learning, and enforcement of illegal activity. There are significant issues with this stance of course, but starting with this principle will allow for far better solutions than we have today. The internet is trending towards a world were storage is “free” and infinite, which places all the actual value on how to discover and see content.
Which brings me to the last principle: moderation. I don’t believe a centralized system can do content moderation globally. It can only be done through ranking and relevance algorithms, the more localized the better. But instead of a company or government building and controlling these solely, people should be able to build and choose from algorithms that best match their criteria, or not have to use any at all. A “follow” action should always deliver every bit of content from the corresponding account, and the algorithms should be able to comb through everything else through a relevance lens that an individual determines. There’s a default “G-rated” algorithm, and then there’s everything else one can imagine.
The only way I know of to truly live up to these 3 principles is a free and open protocol for social media, that is not owned by a single company or group of companies, and is resilient to corporate and government influence. The problem today is that we have companies who own both the protocol and discovery of content. Which ultimately puts one person in charge of what’s available and seen, or not. This is by definition a single point of failure, no matter how great the person, and over time will fracture the public conversation, and may lead to more control by governments and corporations around the world.
I believe many companies can build a phenomenal business off an open protocol. For proof, look at both the web and email. The biggest problem with these models however is that the discovery mechanisms are far too proprietary and fixed instead of open or extendable. Companies can build many profitable services that complement rather than lock down how we access this massive collection of conversation. There is no need to own or host it themselves.
Many of you won’t trust this solution just because it’s me stating it. I get it, but that’s exactly the point. Trusting any one individual with this comes with compromises, not to mention being way too heavy a burden for the individual. It has to be something akin to what bitcoin has shown to be possible. If you want proof of this, get out of the US and European bubble of the bitcoin price fluctuations and learn how real people are using it for censorship resistance in Africa and Central/South America.
I do still wish for Twitter, and every company, to become uncomfortably transparent in all their actions, and I wish I forced more of that years ago. I do believe absolute transparency builds trust. As for the files, I wish they were released Wikileaks-style, with many more eyes and interpretations to consider. And along with that, commitments of transparency for present and future actions. I’m hopeful all of this will happen. There’s nothing to hide…only a lot to learn from. The current attacks on my former colleagues could be dangerous and doesn’t solve anything. If you want to blame, direct it at me and my actions, or lack thereof.
As far as the free and open social media protocol goes, there are many competing projects: @bluesky is one with the AT Protocol, nostr another, Mastodon yet another, Matrix yet another…and there will be many more. One will have a chance at becoming a standard like HTTP or SMTP. This isn’t about a “decentralized Twitter.” This is a focused and urgent push for a foundational core technology standard to make social media a native part of the internet. I believe this is critical both to Twitter’s future, and the public conversation’s ability to truly serve the people, which helps hold governments and corporations accountable. And hopefully makes it all a lot more fun and informative again.
💸🛠️🌐 To accelerate open internet and protocol work, I’m going to open a new category of #startsmall grants: “open internet development.” It will start with a focus of giving cash and equity grants to engineering teams working on social media and private communication protocols, bitcoin, and a web-only mobile OS. I’ll make some grants next week, starting with $1mm/yr to Signal. Please let me know other great candidates for this money.
-
 @ da0b9bc3:4e30a4a9
2025-01-17 14:00:40
@ da0b9bc3:4e30a4a9
2025-01-17 14:00:40It's Finally here Stackers!
It's Friday!
We're about to kick off our weekends with some feel good tracks.
Let's get the party started. Bring me those Feel Good tracks.
Talk Music. Share Tracks. Zap Sats.
Let's go!
Madness!!!
https://youtu.be/SOJSM46nWwo?si=5XsJwBaOXvHqewlH
originally posted at https://stacker.news/items/853535
-
 @ da0b9bc3:4e30a4a9
2025-01-17 09:14:39
@ da0b9bc3:4e30a4a9
2025-01-17 09:14:39Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/853332




