-
 @ 7f29628d:e160cccc
2025-01-07 11:50:30
@ 7f29628d:e160cccc
2025-01-07 11:50:30Der gut informierte Bürger denkt bei der Pandemie sofort an Intensivstationen, an die Bilder aus Bergamo und erinnert sich an die Berichterstattung damals – also muss es wohl ein Maximum gewesen sein. Manche Skeptiker behaupten jedoch das Gegenteil. Klarheit sollte ein Blick nach Wiesbaden, zum Statistischen Bundesamt, schaffen. Schließlich sitzen dort gut bezahlte Profis, die seit vielen Jahrzehnten die Sterbestatistik pflegen und veröffentlichen. Jeder Todesfall wird in Deutschland über die Standesämter exakt erfasst.
Doch die Überraschung: Das Statistische Bundesamt liefert uns auf diese einfache Frage zwei extrem unterschiedliche Antworten – ein Minimum und ein Maximum. Das Ergebnis hängt davon ab, wie tief man in die Veröffentlichungen des Bundesamtes eintaucht. Betrachtet man nur die Webseiten und Pressemitteilungen, erhält man den Eindruck eines Maximums. Schaut man jedoch etwas tiefer in die Tabellen und Rohdaten, zeigt sich plötzlich ein Minimum. Aber wie kann das sein? Beides gleichzeitig geht ja wohl kaum. Wer lügt hier – die Tabellen des Amtes oder die Pressemitteilungen? Gehen wir dieser Frage Schritt für Schritt auf den Grund.
2020: Ein historisches Maximum?
Schauen wir uns die vielen Hundert Veröffentlichungen des Statistischen Bundesamtes aus dieser Zeit an. Oder wir kürzen ab und fragen ChatGPT, da die KI auf diesen Daten trainiert wurde und das gesamte Material kennt. Die Frage an ChatGPT lautet also: Wie war das Sterbegeschehen im Jahr 2020 im Vergleich zu den Vorjahren?
ChatGPT antwortet: »Im Jahr 2020 war die Sterblichkeit in Deutschland höher als in den Jahren zuvor. Es gab eine Übersterblichkeit von etwa 982.000 Todesfällen, das sind rund 46.000 mehr als der Durchschnitt der Vorjahre (2016 bis 2019). Dieser Anstieg wurde überwiegend im Zusammenhang mit der COVID-19-Pandemie gesehen. Während die Sterbezahlen in den Vorjahren schwankten, war ein solch signifikanter Anstieg wie 2020 bisher nicht zu beobachten.«
Wir fragen konkreter: Ist es ein Fakt, dass wir eine so ernste Lage im Sterbegeschehen wie im Frühjahr 2020 noch nie erlebt haben?
ChatGPT bestätigt: »Ja, die COVID-19-Pandemie führte im Frühjahr 2020 zu einer außergewöhnlichen Situation im Sterbegeschehen in Deutschland. Die dramatische Übersterblichkeit, die ab der 13. Kalenderwoche auftrat, veranlasste das Statistische Bundesamt, besonders eindringliche Warnungen zu veröffentlichen. Der damalige Vizepräsident des Amtes und andere führende Stimmen wiesen öffentlich darauf hin, dass die Todesfallzahlen stark vom Durchschnitt abwichen. Diese klare Warnung richtete sich an die Öffentlichkeit und die Politik gleichermaßen. Die Medien berichteten intensiv über diese Warnungen, was das Bewusstsein für die Schwere der Pandemie erheblich schärfte. In den vergangenen Jahrzehnten hatte es keine vergleichbare Übersterblichkeit gegeben, die eine solch umfangreiche Kommunikation durch das Statistische Bundesamt erforderlich gemacht hätte.«
Ein gut informierter Zeitungsleser wird sich an dieser Stelle bestätigt fühlen: Ja, so war es damals. Ein Maximum im Sterbegeschehen – wegen der Pandemie. Oder etwa nicht?
2020: Ein historisches Minimum?
Tauchen wir in die Rohdaten des Statistischen Bundesamtes ein. Die Tabellen, die das Amt seit Jahrzehnten verlässlich veröffentlicht, nennen sich Sterbetafeln. Diese werden jährlich bereitgestellt und stehen auf der Website des Bundesamtes zum Download bereit. Ein erster Blick in die Sterbetafeln mag den Laien abschrecken, doch mit einer kurzen Erklärung wird alles verständlich. Wir gehen schrittweise vor.
Nehmen wir die Sterbetafel des Jahres 2017. Sie enthält zwei große Tabellen – eine für Männer und eine für Frauen. Jede Zeile der Tabelle steht für einen Jahrgang, zum Beispiel zeigt die Zeile 79 die Daten der 79-jährigen Männer. Besonders wichtig ist nun die zweite Spalte, in der der Wert 0,05 eingetragen ist. Das bedeutet, dass 5 Prozent der 79-jährigen Männer im Jahr 2017 verstorben sind. Das ist die wichtige Kennzahl. Wenn wir diesen exakten Wert, den man auch als Sterberate bezeichnet, nun in ein Säulendiagramm eintragen, erhalten wir eine leicht verständliche visuelle Darstellung (Grafik 1).
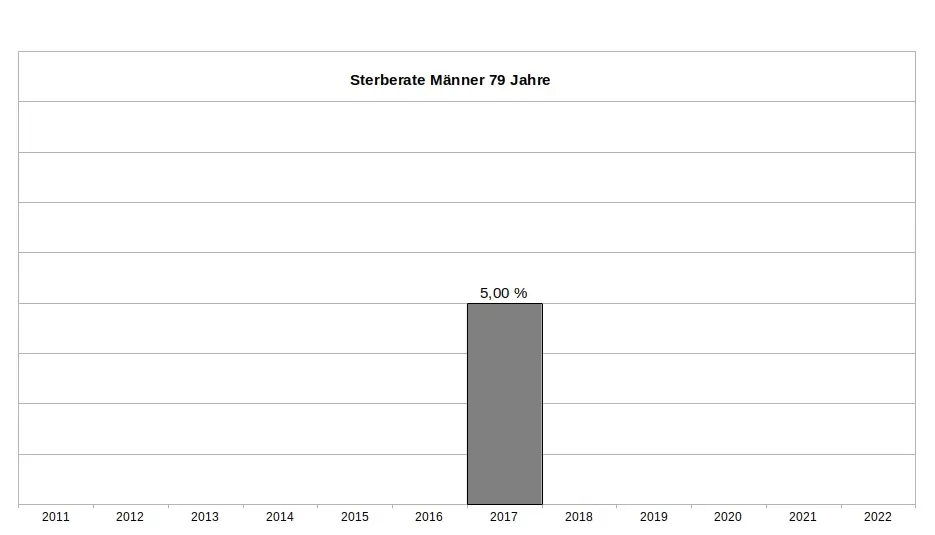
Es ist wichtig zu betonen, dass dieser Wert weder ein Schätzwert noch eine Modellrechnung oder Prognose ist, sondern ein exakter Messwert, basierend auf einer zuverlässigen Zählung. Sterberaten (für die Fachleute auch Sterbewahrscheinlichkeiten qx) sind seit Johann Peter Süßmilch (1707–1767) der Goldstandard der Sterbestatistik. Jeder Aktuar wird das bestätigen. Fügen wir nun die Sterberaten der 79-jährigen Männer aus den Jahren davor und danach hinzu, um das Gesamtbild zu sehen (Grafik 2). Und nun die entscheidende Frage: Zeigt das Jahr 2020 ein Maximum oder ein Minimum?
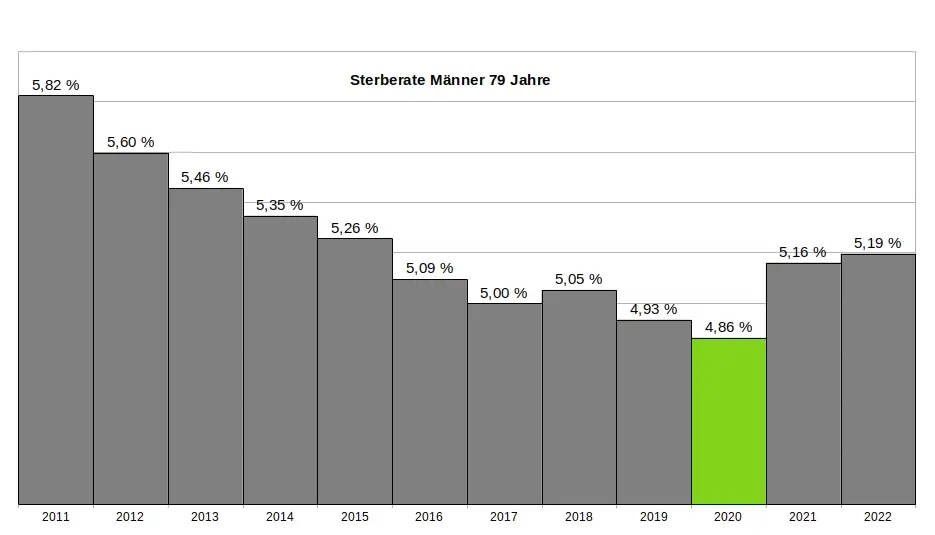
Ein kritischer Leser könnte vermuten, dass die 79-jährigen Männer eine Ausnahme darstellen und andere Jahrgänge im Jahr 2020 ein Maximum zeigen würden. Doch das trifft nicht zu. Kein einziger Jahrgang verzeichnete im Jahr 2020 ein Maximum. Im Gegenteil: Auch die 1-Jährigen, 2-Jährigen, 3-Jährigen, 9-Jährigen, 10-Jährigen, 15-Jährigen, 18-Jährigen und viele weitere männliche Jahrgänge hatten ihr Minimum im Jahr 2020. Dasselbe gilt bei den Frauen. Insgesamt hatten 31 Jahrgänge ihr Minimum im Jahr 2020. Wenn wir schließlich alle Jahrgänge in einer einzigen Grafik zusammenfassen, ergibt sich ein klares Bild: Das Minimum im Sterbegeschehen lag im Jahr 2020 (Grafik 3).
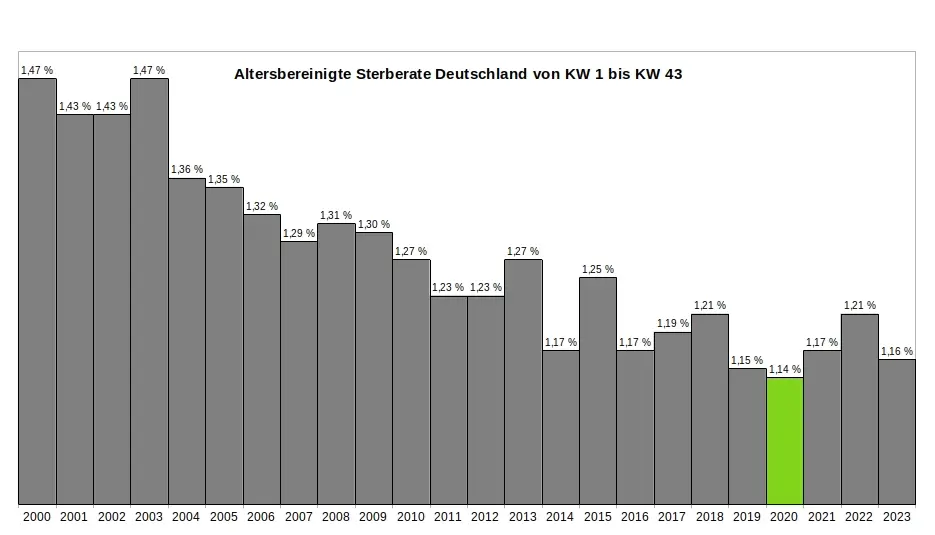
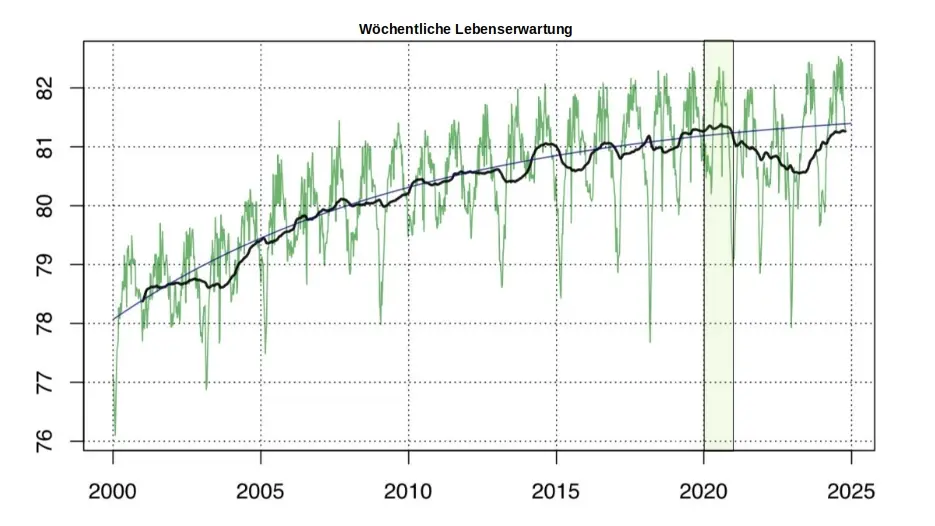
Ein kritischer Leser könnte nun wiederum vermuten, dass es innerhalb des Jahres 2020 möglicherweise starke Ausschläge nach oben bei einzelnen Jahrgängen gegeben haben könnte, die später durch Ausschläge nach unten ausgeglichen wurden – und dass diese Schwankungen in der jährlichen Übersicht nicht sichtbar sind. Doch auch das trifft nicht zu. Ein Blick auf die wöchentlichen Sterberaten zeigt, dass die ersten acht Monate der Pandemie keine nennenswerten Auffälligkeiten aufweisen. Es bleibt dabei: Die Rohdaten des Statistischen Bundesamtes bestätigen zweifelsfrei, dass die ersten acht Monate der Pandemie das historische Minimum im Sterbegeschehen darstellen. (Für die Fachleute sei angemerkt, dass im gleichen Zeitraum die Lebenserwartung die historischen Höchststände erreicht hatte – Grafik 4.)
So konstruierte das Amt aus einem Minimum ein Maximum:
Zur Erinnerung: Die Rohdaten des Statistischen Bundesamtes, die in den jährlichen Sterbetafeln zweifelsfrei dokumentiert sind, zeigen für das Jahr 2020 eindeutig ein Minimum im Sterbegeschehen. Aus diesen »in Stein gemeißelten« Zahlen ein Maximum zu »konstruieren«, ohne die Rohdaten selbst zu verändern, scheint auf den ersten Blick eine unlösbare Aufgabe. Jeder Student würde an einer solchen Herausforderung scheitern. Doch das Statistische Bundesamt hat einen kreativen Weg gefunden - ein Meisterstück gezielter Manipulation. In fünf Schritten zeigt sich, wie diese Täuschung der Öffentlichkeit umgesetzt wurde:
(1) Ignorieren der Sterberaten: Die präzisen, objektiven und leicht verständlichen Sterberaten aus den eigenen Sterbetafeln wurden konsequent ignoriert und verschwiegen. Diese Daten widersprachen dem gewünschten Narrativ und wurden daher gezielt ausgeklammert.
(2) Fokus auf absolute Todeszahlen: Die Aufmerksamkeit wurde stattdessen auf die absolute Zahl der Todesfälle gelenkt. Diese wirkt allein durch ihre schiere Größe dramatisch und emotionalisiert die Diskussion. Ein entscheidender Faktor wurde dabei ignoriert: Die absolute Zahl der Todesfälle steigt aufgrund der demografischen Entwicklung jedes Jahr an. Viele Menschen verstehen diesen Zusammenhang nicht und verbinden die steigenden Zahlen fälschlicherweise mit der vermeintlichen Pandemie.
(3) Einführung der Übersterblichkeit als neue Kennzahl: Erst ab Beginn der „Pandemie“ wurde die Kennzahl "Übersterblichkeit" eingeführt – und dies mit einer fragwürdigen Methode, die systematisch überhöhte Werte lieferte. Diese Kennzahl wurde regelmäßig, oft monatlich oder sogar wöchentlich, berechnet und diente als ständige Grundlage für alarmierende Schlagzeilen.
(4) Intensive Öffentlichkeitsarbeit: Durch eine breit angelegte Kampagne wurden die manipulativen Kennzahlen gezielt in den Fokus gerückt. Pressemitteilungen, Podcasts und öffentliche Auftritte konzentrierten sich fast ausschließlich auf die absoluten Todeszahlen und die Übersterblichkeit. Ziel war es, den Eindruck einer dramatischen Situation in der Öffentlichkeit zu verstärken.
(5) Bekämpfen kritischer Stimmen: Kritiker, die die Schwächen und manipulativen Aspekte dieser Methoden aufdeckten, wurden systematisch diskreditiert. Ihre Glaubwürdigkeit und Kompetenz wurden öffentlich infrage gestellt, um das sorgsam konstruierte Narrativ zu schützen.
Ohne diesen begleitenden Statistik-Betrug wäre das gesamte Pandemie-Theater meiner Meinung nach nicht möglich gewesen. Wer aus einem faktischen Minimum ein scheinbares Maximum "erschafft", handelt betrügerisch. Die Folgen dieses Betruges sind gravierend. Denken wir an die Angst, die in der Bevölkerung geschürt wurde – die Angst, bald sterben zu müssen. Denken wir an Masken, Abstandsregeln, isolierte ältere Menschen, Kinderimpfungen und all die Maßnahmen, die unter anderem auf diese falsche Statistik zurückgehen.
Wollen wir Bürger uns das gefallen lassen?
Wenn wir als Bürger zulassen, dass ein derart offensichtlicher und nachprüfbarer Täuschungsversuch ohne Konsequenzen bleibt, dann gefährdet das nicht nur die Integrität unserer Institutionen – es untergräbt das Fundament unserer Gesellschaft. In der DDR feierte man öffentlich Planerfüllung und Übererfüllung, während die Regale leer blieben. Damals wusste jeder: Statistik war ein Propagandainstrument. Niemand traute den Zahlen, die das Staatsfernsehen verkündete.
Während der Pandemie war es anders. Die Menschen vertrauten den Mitteilungen des Statistischen Bundesamtes und des RKI – blind. Die Enthüllungen durch den "RKI-Leak" haben gezeigt, dass auch das Robert-Koch-Institut nicht der Wissenschaft, sondern den Weisungen des Gesundheitsministers und militärischen Vorgaben folgte. Warum sollte es beim Statistischen Bundesamt anders gewesen sein? Diese Behörde ist dem Innenministerium unterstellt und somit ebenfalls weisungsgebunden.
Die Beweise für Täuschung liegen offen zutage. Es braucht keinen Whistleblower, keine geheimen Enthüllungen: Die Rohdaten des Statistischen Bundesamtes sprechen für sich. Sie sind öffentlich einsehbar – klar und unmissverständlich. Die Daten, die Tabellen, die Veröffentlichungen des Amtes selbst – sie sind die Anklageschrift. Sie zeigen, was wirklich war. Nicht mehr und nicht weniger.
Und wir? Was tun wir? Schweigen wir? Oder fordern wir endlich ein, was unser Recht ist? Wir Bürger dürfen das nicht hinnehmen. Es ist Zeit, unsere Behörden zur Rechenschaft zu ziehen. Diese Institutionen arbeiten nicht für sich – sie arbeiten für uns. Wir finanzieren sie, und wir haben das Recht, Transparenz und Verantwortung einzufordern. Manipulationen wie diese müssen aufgearbeitet werden und dürfen nie wieder geschehen. Die Strukturen, die solche Fehlentwicklungen in unseren Behörden ermöglicht haben, müssen offengelegt werden. Denn eine Demokratie lebt von Vertrauen – und Vertrauen muss verdient werden. Jeden Tag aufs Neue.
.
.
MARCEL BARZ, Jahrgang 1975, war Offizier der Bundeswehr und studierte Wirtschafts- und Organisationswissenschaften sowie Wirtschaftsinformatik. Er war Gründer und Geschäftsführer einer Softwarefirma, die sich auf Datenanalyse und Softwareentwicklung spezialisiert hatte. Im August 2021 veröffentlichte Barz den Videovortrag »Die Pandemie in den Rohdaten«, der über eine Million Aufrufe erzielte. Seitdem macht er als "Erbsenzähler" auf Widersprüche in amtlichen Statistiken aufmerksam.
-
 @ eac63075:b4988b48
2025-01-04 19:41:34
@ eac63075:b4988b48
2025-01-04 19:41:34Since its creation in 2009, Bitcoin has symbolized innovation and resilience. However, from time to time, alarmist narratives arise about emerging technologies that could "break" its security. Among these, quantum computing stands out as one of the most recurrent. But does quantum computing truly threaten Bitcoin? And more importantly, what is the community doing to ensure the protocol remains invulnerable?
The answer, contrary to sensationalist headlines, is reassuring: Bitcoin is secure, and the community is already preparing for a future where quantum computing becomes a practical reality. Let’s dive into this topic to understand why the concerns are exaggerated and how the development of BIP-360 demonstrates that Bitcoin is one step ahead.
What Is Quantum Computing, and Why Is Bitcoin Not Threatened?
Quantum computing leverages principles of quantum mechanics to perform calculations that, in theory, could exponentially surpass classical computers—and it has nothing to do with what so-called “quantum coaches” teach to scam the uninformed. One of the concerns is that this technology could compromise two key aspects of Bitcoin’s security:
- Wallets: These use elliptic curve algorithms (ECDSA) to protect private keys. A sufficiently powerful quantum computer could deduce a private key from its public key.
- Mining: This is based on the SHA-256 algorithm, which secures the consensus process. A quantum attack could, in theory, compromise the proof-of-work mechanism.
Understanding Quantum Computing’s Attack Priorities
While quantum computing is often presented as a threat to Bitcoin, not all parts of the network are equally vulnerable. Theoretical attacks would be prioritized based on two main factors: ease of execution and potential reward. This creates two categories of attacks:
1. Attacks on Wallets
Bitcoin wallets, secured by elliptic curve algorithms, would be the initial targets due to the relative vulnerability of their public keys, especially those already exposed on the blockchain. Two attack scenarios stand out:
-
Short-term attacks: These occur during the interval between sending a transaction and its inclusion in a block (approximately 10 minutes). A quantum computer could intercept the exposed public key and derive the corresponding private key to redirect funds by creating a transaction with higher fees.
-
Long-term attacks: These focus on old wallets whose public keys are permanently exposed. Wallets associated with Satoshi Nakamoto, for example, are especially vulnerable because they were created before the practice of using hashes to mask public keys.
We can infer a priority order for how such attacks might occur based on urgency and importance.
 Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)
Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)2. Attacks on Mining
Targeting the SHA-256 algorithm, which secures the mining process, would be the next objective. However, this is far more complex and requires a level of quantum computational power that is currently non-existent and far from realization. A successful attack would allow for the recalculation of all possible hashes to dominate the consensus process and potentially "mine" it instantly.
 Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin Attacks
Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin AttacksRecently, Narcelio asked me about a statement I made on Tubacast:
https://x.com/eddieoz/status/1868371296683511969
If an attack became a reality before Bitcoin was prepared, it would be necessary to define the last block prior to the attack and proceed from there using a new hashing algorithm. The solution would resemble the response to the infamous 2013 bug. It’s a fact that this would cause market panic, and Bitcoin's price would drop significantly, creating a potential opportunity for the well-informed.
Preferably, if developers could anticipate the threat and had time to work on a solution and build consensus before an attack, they would simply decide on a future block for the fork, which would then adopt the new algorithm. It might even rehash previous blocks (reaching consensus on them) to avoid potential reorganization through the re-mining of blocks using the old hash. (I often use the term "shielding" old transactions).
How Can Users Protect Themselves?
While quantum computing is still far from being a practical threat, some simple measures can already protect users against hypothetical scenarios:
- Avoid using exposed public keys: Ensure funds sent to old wallets are transferred to new ones that use public key hashes. This reduces the risk of long-term attacks.
- Use modern wallets: Opt for wallets compatible with SegWit or Taproot, which implement better security practices.
- Monitor security updates: Stay informed about updates from the Bitcoin community, such as the implementation of BIP-360, which will introduce quantum-resistant addresses.
- Do not reuse addresses: Every transaction should be associated with a new address to minimize the risk of repeated exposure of the same public key.
- Adopt secure backup practices: Create offline backups of private keys and seeds in secure locations, protected from unauthorized access.
BIP-360 and Bitcoin’s Preparation for the Future
Even though quantum computing is still beyond practical reach, the Bitcoin community is not standing still. A concrete example is BIP-360, a proposal that establishes the technical framework to make wallets resistant to quantum attacks.
BIP-360 addresses three main pillars:
- Introduction of quantum-resistant addresses: A new address format starting with "BC1R" will be used. These addresses will be compatible with post-quantum algorithms, ensuring that stored funds are protected from future attacks.
- Compatibility with the current ecosystem: The proposal allows users to transfer funds from old addresses to new ones without requiring drastic changes to the network infrastructure.
- Flexibility for future updates: BIP-360 does not limit the choice of specific algorithms. Instead, it serves as a foundation for implementing new post-quantum algorithms as technology evolves.
This proposal demonstrates how Bitcoin can adapt to emerging threats without compromising its decentralized structure.
Post-Quantum Algorithms: The Future of Bitcoin Cryptography
The community is exploring various algorithms to protect Bitcoin from quantum attacks. Among the most discussed are:
- Falcon: A solution combining smaller public keys with compact digital signatures. Although it has been tested in limited scenarios, it still faces scalability and performance challenges.
- Sphincs: Hash-based, this algorithm is renowned for its resilience, but its signatures can be extremely large, making it less efficient for networks like Bitcoin’s blockchain.
- Lamport: Created in 1977, it’s considered one of the earliest post-quantum security solutions. Despite its reliability, its gigantic public keys (16,000 bytes) make it impractical and costly for Bitcoin.
Two technologies show great promise and are well-regarded by the community:
- Lattice-Based Cryptography: Considered one of the most promising, it uses complex mathematical structures to create systems nearly immune to quantum computing. Its implementation is still in its early stages, but the community is optimistic.
- Supersingular Elliptic Curve Isogeny: These are very recent digital signature algorithms and require extensive study and testing before being ready for practical market use.
The final choice of algorithm will depend on factors such as efficiency, cost, and integration capability with the current system. Additionally, it is preferable that these algorithms are standardized before implementation, a process that may take up to 10 years.
Why Quantum Computing Is Far from Being a Threat
The alarmist narrative about quantum computing overlooks the technical and practical challenges that still need to be overcome. Among them:
- Insufficient number of qubits: Current quantum computers have only a few hundred qubits, whereas successful attacks would require millions.
- High error rate: Quantum stability remains a barrier to reliable large-scale operations.
- High costs: Building and operating large-scale quantum computers requires massive investments, limiting their use to scientific or specific applications.
Moreover, even if quantum computers make significant advancements, Bitcoin is already adapting to ensure its infrastructure is prepared to respond.
Conclusion: Bitcoin’s Secure Future
Despite advancements in quantum computing, the reality is that Bitcoin is far from being threatened. Its security is ensured not only by its robust architecture but also by the community’s constant efforts to anticipate and mitigate challenges.
The implementation of BIP-360 and the pursuit of post-quantum algorithms demonstrate that Bitcoin is not only resilient but also proactive. By adopting practical measures, such as using modern wallets and migrating to quantum-resistant addresses, users can further protect themselves against potential threats.
Bitcoin’s future is not at risk—it is being carefully shaped to withstand any emerging technology, including quantum computing.
-
 @ eac63075:b4988b48
2024-11-09 17:57:27
@ eac63075:b4988b48
2024-11-09 17:57:27Based on a recent paper that included collaboration from renowned experts such as Lynn Alden, Steve Lee, and Ren Crypto Fish, we discuss in depth how Bitcoin's consensus is built, the main risks, and the complex dynamics of protocol upgrades.
Podcast https://www.fountain.fm/episode/wbjD6ntQuvX5u2G5BccC
Presentation https://gamma.app/docs/Analyzing-Bitcoin-Consensus-Risks-in-Protocol-Upgrades-p66axxjwaa37ksn
1. Introduction to Consensus in Bitcoin
Consensus in Bitcoin is the foundation that keeps the network secure and functional, allowing users worldwide to perform transactions in a decentralized manner without the need for intermediaries. Since its launch in 2009, Bitcoin is often described as an "immutable" system designed to resist changes, and it is precisely this resistance that ensures its security and stability.
The central idea behind consensus in Bitcoin is to create a set of acceptance rules for blocks and transactions, ensuring that all network participants agree on the transaction history. This prevents "double-spending," where the same bitcoin could be used in two simultaneous transactions, something that would compromise trust in the network.
Evolution of Consensus in Bitcoin
Over the years, consensus in Bitcoin has undergone several adaptations, and the way participants agree on changes remains a delicate process. Unlike traditional systems, where changes can be imposed from the top down, Bitcoin operates in a decentralized model where any significant change needs the support of various groups of stakeholders, including miners, developers, users, and large node operators.
Moreover, the update process is extremely cautious, as hasty changes can compromise the network's security. As a result, the philosophy of "don't fix what isn't broken" prevails, with improvements happening incrementally and only after broad consensus among those involved. This model can make progress seem slow but ensures that Bitcoin remains faithful to the principles of security and decentralization.
2. Technical Components of Consensus
Bitcoin's consensus is supported by a set of technical rules that determine what is considered a valid transaction and a valid block on the network. These technical aspects ensure that all nodes—the computers that participate in the Bitcoin network—agree on the current state of the blockchain. Below are the main technical components that form the basis of the consensus.
Validation of Blocks and Transactions
The validation of blocks and transactions is the central point of consensus in Bitcoin. A block is only considered valid if it meets certain criteria, such as maximum size, transaction structure, and the solving of the "Proof of Work" problem. The proof of work, required for a block to be included in the blockchain, is a computational process that ensures the block contains significant computational effort—protecting the network against manipulation attempts.
Transactions, in turn, need to follow specific input and output rules. Each transaction includes cryptographic signatures that prove the ownership of the bitcoins sent, as well as validation scripts that verify if the transaction conditions are met. This validation system is essential for network nodes to autonomously confirm that each transaction follows the rules.
Chain Selection
Another fundamental technical issue for Bitcoin's consensus is chain selection, which becomes especially important in cases where multiple versions of the blockchain coexist, such as after a network split (fork). To decide which chain is the "true" one and should be followed, the network adopts the criterion of the highest accumulated proof of work. In other words, the chain with the highest number of valid blocks, built with the greatest computational effort, is chosen by the network as the official one.
This criterion avoids permanent splits because it encourages all nodes to follow the same main chain, reinforcing consensus.
Soft Forks vs. Hard Forks
In the consensus process, protocol changes can happen in two ways: through soft forks or hard forks. These variations affect not only the protocol update but also the implications for network users:
-
Soft Forks: These are changes that are backward compatible. Only nodes that adopt the new update will follow the new rules, but old nodes will still recognize the blocks produced with these rules as valid. This compatibility makes soft forks a safer option for updates, as it minimizes the risk of network division.
-
Hard Forks: These are updates that are not backward compatible, requiring all nodes to update to the new version or risk being separated from the main chain. Hard forks can result in the creation of a new coin, as occurred with the split between Bitcoin and Bitcoin Cash in 2017. While hard forks allow for deeper changes, they also bring significant risks of network fragmentation.
These technical components form the base of Bitcoin's security and resilience, allowing the system to remain functional and immutable without losing the necessary flexibility to evolve over time.
3. Stakeholders in Bitcoin's Consensus
Consensus in Bitcoin is not decided centrally. On the contrary, it depends on the interaction between different groups of stakeholders, each with their motivations, interests, and levels of influence. These groups play fundamental roles in how changes are implemented or rejected on the network. Below, we explore the six main stakeholders in Bitcoin's consensus.
1. Economic Nodes
Economic nodes, usually operated by exchanges, custody providers, and large companies that accept Bitcoin, exert significant influence over consensus. Because they handle large volumes of transactions and act as a connection point between the Bitcoin ecosystem and the traditional financial system, these nodes have the power to validate or reject blocks and to define which version of the software to follow in case of a fork.
Their influence is proportional to the volume of transactions they handle, and they can directly affect which chain will be seen as the main one. Their incentive is to maintain the network's stability and security to preserve its functionality and meet regulatory requirements.
2. Investors
Investors, including large institutional funds and individual Bitcoin holders, influence consensus indirectly through their impact on the asset's price. Their buying and selling actions can affect Bitcoin's value, which in turn influences the motivation of miners and other stakeholders to continue investing in the network's security and development.
Some institutional investors have agreements with custodians that may limit their ability to act in network split situations. Thus, the impact of each investor on consensus can vary based on their ownership structure and how quickly they can react to a network change.
3. Media Influencers
Media influencers, including journalists, analysts, and popular personalities on social media, have a powerful role in shaping public opinion about Bitcoin and possible updates. These influencers can help educate the public, promote debates, and bring transparency to the consensus process.
On the other hand, the impact of influencers can be double-edged: while they can clarify complex topics, they can also distort perceptions by amplifying or minimizing change proposals. This makes them a force both of support and resistance to consensus.
4. Miners
Miners are responsible for validating transactions and including blocks in the blockchain. Through computational power (hashrate), they also exert significant influence over consensus decisions. In update processes, miners often signal their support for a proposal, indicating that the new version is safe to use. However, this signaling is not always definitive, and miners can change their position if they deem it necessary.
Their incentive is to maximize returns from block rewards and transaction fees, as well as to maintain the value of investments in their specialized equipment, which are only profitable if the network remains stable.
5. Protocol Developers
Protocol developers, often called "Core Developers," are responsible for writing and maintaining Bitcoin's code. Although they do not have direct power over consensus, they possess an informal veto power since they decide which changes are included in the main client (Bitcoin Core). This group also serves as an important source of technical knowledge, helping guide decisions and inform other stakeholders.
Their incentive lies in the continuous improvement of the network, ensuring security and decentralization. Many developers are funded by grants and sponsorships, but their motivations generally include a strong ideological commitment to Bitcoin's principles.
6. Users and Application Developers
This group includes people who use Bitcoin in their daily transactions and developers who build solutions based on the network, such as wallets, exchanges, and payment platforms. Although their power in consensus is less than that of miners or economic nodes, they play an important role because they are responsible for popularizing Bitcoin's use and expanding the ecosystem.
If application developers decide not to adopt an update, this can affect compatibility and widespread acceptance. Thus, they indirectly influence consensus by deciding which version of the protocol to follow in their applications.
These stakeholders are vital to the consensus process, and each group exerts influence according to their involvement, incentives, and ability to act in situations of change. Understanding the role of each makes it clearer how consensus is formed and why it is so difficult to make significant changes to Bitcoin.
4. Mechanisms for Activating Updates in Bitcoin
For Bitcoin to evolve without compromising security and consensus, different mechanisms for activating updates have been developed over the years. These mechanisms help coordinate changes among network nodes to minimize the risk of fragmentation and ensure that updates are implemented in an orderly manner. Here, we explore some of the main methods used in Bitcoin, their advantages and disadvantages, as well as historical examples of significant updates.
Flag Day
The Flag Day mechanism is one of the simplest forms of activating changes. In it, a specific date or block is determined as the activation moment, and all nodes must be updated by that point. This method does not involve prior signaling; participants simply need to update to the new software version by the established day or block.
-
Advantages: Simplicity and predictability are the main benefits of Flag Day, as everyone knows the exact activation date.
-
Disadvantages: Inflexibility can be a problem because there is no way to adjust the schedule if a significant part of the network has not updated. This can result in network splits if a significant number of nodes are not ready for the update.
An example of Flag Day was the Pay to Script Hash (P2SH) update in 2012, which required all nodes to adopt the change to avoid compatibility issues.
BIP34 and BIP9
BIP34 introduced a more dynamic process, in which miners increase the version number in block headers to signal the update. When a predetermined percentage of the last blocks is mined with this new version, the update is automatically activated. This model later evolved with BIP9, which allowed multiple updates to be signaled simultaneously through "version bits," each corresponding to a specific change.
-
Advantages: Allows the network to activate updates gradually, giving more time for participants to adapt.
-
Disadvantages: These methods rely heavily on miner support, which means that if a sufficient number of miners do not signal the update, it can be delayed or not implemented.
BIP9 was used in the activation of SegWit (BIP141) but faced challenges because some miners did not signal their intent to activate, leading to the development of new mechanisms.
User Activated Soft Forks (UASF) and User Resisted Soft Forks (URSF)
To increase the decision-making power of ordinary users, the concept of User Activated Soft Fork (UASF) was introduced, allowing node operators, not just miners, to determine consensus for a change. In this model, nodes set a date to start rejecting blocks that are not in compliance with the new update, forcing miners to adapt or risk having their blocks rejected by the network.
URSF, in turn, is a model where nodes reject blocks that attempt to adopt a specific update, functioning as resistance against proposed changes.
-
Advantages: UASF returns decision-making power to node operators, ensuring that changes do not depend solely on miners.
-
Disadvantages: Both UASF and URSF can generate network splits, especially in cases of strong opposition among different stakeholders.
An example of UASF was the activation of SegWit in 2017, where users supported activation independently of miner signaling, which ended up forcing its adoption.
BIP8 (LOT=True)
BIP8 is an evolution of BIP9, designed to prevent miners from indefinitely blocking a change desired by the majority of users and developers. BIP8 allows setting a parameter called "lockinontimeout" (LOT) as true, which means that if the update has not been fully signaled by a certain point, it is automatically activated.
-
Advantages: Ensures that changes with broad support among users are not blocked by miners who wish to maintain the status quo.
-
Disadvantages: Can lead to network splits if miners or other important stakeholders do not support the update.
Although BIP8 with LOT=True has not yet been used in Bitcoin, it is a proposal that can be applied in future updates if necessary.
These activation mechanisms have been essential for Bitcoin's development, allowing updates that keep the network secure and functional. Each method brings its own advantages and challenges, but all share the goal of preserving consensus and network cohesion.
5. Risks and Considerations in Consensus Updates
Consensus updates in Bitcoin are complex processes that involve not only technical aspects but also political, economic, and social considerations. Due to the network's decentralized nature, each change brings with it a set of risks that need to be carefully assessed. Below, we explore some of the main challenges and future scenarios, as well as the possible impacts on stakeholders.
Network Fragility with Alternative Implementations
One of the main risks associated with consensus updates is the possibility of network fragmentation when there are alternative software implementations. If an update is implemented by a significant group of nodes but rejected by others, a network split (fork) can occur. This creates two competing chains, each with a different version of the transaction history, leading to unpredictable consequences for users and investors.
Such fragmentation weakens Bitcoin because, by dividing hashing power (computing) and coin value, it reduces network security and investor confidence. A notable example of this risk was the fork that gave rise to Bitcoin Cash in 2017 when disagreements over block size resulted in a new chain and a new asset.
Chain Splits and Impact on Stakeholders
Chain splits are a significant risk in update processes, especially in hard forks. During a hard fork, the network is split into two separate chains, each with its own set of rules. This results in the creation of a new coin and leaves users with duplicated assets on both chains. While this may seem advantageous, in the long run, these splits weaken the network and create uncertainties for investors.
Each group of stakeholders reacts differently to a chain split:
-
Institutional Investors and ETFs: Face regulatory and compliance challenges because many of these assets are managed under strict regulations. The creation of a new coin requires decisions to be made quickly to avoid potential losses, which may be hampered by regulatory constraints.
-
Miners: May be incentivized to shift their computing power to the chain that offers higher profitability, which can weaken one of the networks.
-
Economic Nodes: Such as major exchanges and custody providers, have to quickly choose which chain to support, influencing the perceived value of each network.
Such divisions can generate uncertainties and loss of value, especially for institutional investors and those who use Bitcoin as a store of value.
Regulatory Impacts and Institutional Investors
With the growing presence of institutional investors in Bitcoin, consensus changes face new compliance challenges. Bitcoin ETFs, for example, are required to follow strict rules about which assets they can include and how chain split events should be handled. The creation of a new asset or migration to a new chain can complicate these processes, creating pressure for large financial players to quickly choose a chain, affecting the stability of consensus.
Moreover, decisions regarding forks can influence the Bitcoin futures and derivatives market, affecting perception and adoption by new investors. Therefore, the need to avoid splits and maintain cohesion is crucial to attract and preserve the confidence of these investors.
Security Considerations in Soft Forks and Hard Forks
While soft forks are generally preferred in Bitcoin for their backward compatibility, they are not without risks. Soft forks can create different classes of nodes on the network (updated and non-updated), which increases operational complexity and can ultimately weaken consensus cohesion. In a network scenario with fragmentation of node classes, Bitcoin's security can be affected, as some nodes may lose part of the visibility over updated transactions or rules.
In hard forks, the security risk is even more evident because all nodes need to adopt the new update to avoid network division. Experience shows that abrupt changes can create temporary vulnerabilities, in which malicious agents try to exploit the transition to attack the network.
Bounty Claim Risks and Attack Scenarios
Another risk in consensus updates are so-called "bounty claims"—accumulated rewards that can be obtained if an attacker manages to split or deceive a part of the network. In a conflict scenario, a group of miners or nodes could be incentivized to support a new update or create an alternative version of the software to benefit from these rewards.
These risks require stakeholders to carefully assess each update and the potential vulnerabilities it may introduce. The possibility of "bounty claims" adds a layer of complexity to consensus because each interest group may see a financial opportunity in a change that, in the long term, may harm network stability.
The risks discussed above show the complexity of consensus in Bitcoin and the importance of approaching it gradually and deliberately. Updates need to consider not only technical aspects but also economic and social implications, in order to preserve Bitcoin's integrity and maintain trust among stakeholders.
6. Recommendations for the Consensus Process in Bitcoin
To ensure that protocol changes in Bitcoin are implemented safely and with broad support, it is essential that all stakeholders adopt a careful and coordinated approach. Here are strategic recommendations for evaluating, supporting, or rejecting consensus updates, considering the risks and challenges discussed earlier, along with best practices for successful implementation.
1. Careful Evaluation of Proposal Maturity
Stakeholders should rigorously assess the maturity level of a proposal before supporting its implementation. Updates that are still experimental or lack a robust technical foundation can expose the network to unnecessary risks. Ideally, change proposals should go through an extensive testing phase, have security audits, and receive review and feedback from various developers and experts.
2. Extensive Testing in Secure and Compatible Networks
Before an update is activated on the mainnet, it is essential to test it on networks like testnet and signet, and whenever possible, on other compatible networks that offer a safe and controlled environment to identify potential issues. Testing on networks like Litecoin was fundamental for the safe launch of innovations like SegWit and the Lightning Network, allowing functionalities to be validated on a lower-impact network before being implemented on Bitcoin.
The Liquid Network, developed by Blockstream, also plays an important role as an experimental network for new proposals, such as OP_CAT. By adopting these testing environments, stakeholders can mitigate risks and ensure that the update is reliable and secure before being adopted by the main network.
3. Importance of Stakeholder Engagement
The success of a consensus update strongly depends on the active participation of all stakeholders. This includes economic nodes, miners, protocol developers, investors, and end users. Lack of participation can lead to inadequate decisions or even future network splits, which would compromise Bitcoin's security and stability.
4. Key Questions for Evaluating Consensus Proposals
To assist in decision-making, each group of stakeholders should consider some key questions before supporting a consensus change:
- Does the proposal offer tangible benefits for Bitcoin's security, scalability, or usability?
- Does it maintain backward compatibility or introduce the risk of network split?
- Are the implementation requirements clear and feasible for each group involved?
- Are there clear and aligned incentives for all stakeholder groups to accept the change?
5. Coordination and Timing in Implementations
Timing is crucial. Updates with short activation windows can force a split because not all nodes and miners can update simultaneously. Changes should be planned with ample deadlines to allow all stakeholders to adjust their systems, avoiding surprises that could lead to fragmentation.
Mechanisms like soft forks are generally preferable to hard forks because they allow a smoother transition. Opting for backward-compatible updates when possible facilitates the process and ensures that nodes and miners can adapt without pressure.
6. Continuous Monitoring and Re-evaluation
After an update, it's essential to monitor the network to identify problems or side effects. This continuous process helps ensure cohesion and trust among all participants, keeping Bitcoin as a secure and robust network.
These recommendations, including the use of secure networks for extensive testing, promote a collaborative and secure environment for Bitcoin's consensus process. By adopting a deliberate and strategic approach, stakeholders can preserve Bitcoin's value as a decentralized and censorship-resistant network.
7. Conclusion
Consensus in Bitcoin is more than a set of rules; it's the foundation that sustains the network as a decentralized, secure, and reliable system. Unlike centralized systems, where decisions can be made quickly, Bitcoin requires a much more deliberate and cooperative approach, where the interests of miners, economic nodes, developers, investors, and users must be considered and harmonized. This governance model may seem slow, but it is fundamental to preserving the resilience and trust that make Bitcoin a global store of value and censorship-resistant.
Consensus updates in Bitcoin must balance the need for innovation with the preservation of the network's core principles. The development process of a proposal needs to be detailed and rigorous, going through several testing stages, such as in testnet, signet, and compatible networks like Litecoin and Liquid Network. These networks offer safe environments for proposals to be analyzed and improved before being launched on the main network.
Each proposed change must be carefully evaluated regarding its maturity, impact, backward compatibility, and support among stakeholders. The recommended key questions and appropriate timing are critical to ensure that an update is adopted without compromising network cohesion. It's also essential that the implementation process is continuously monitored and re-evaluated, allowing adjustments as necessary and minimizing the risk of instability.
By following these guidelines, Bitcoin's stakeholders can ensure that the network continues to evolve safely and robustly, maintaining user trust and further solidifying its role as one of the most resilient and innovative digital assets in the world. Ultimately, consensus in Bitcoin is not just a technical issue but a reflection of its community and the values it represents: security, decentralization, and resilience.
8. Links
Whitepaper: https://github.com/bitcoin-cap/bcap
Youtube (pt-br): https://www.youtube.com/watch?v=rARycAibl9o&list=PL-qnhF0qlSPkfhorqsREuIu4UTbF0h4zb
-
-
 @ eac63075:b4988b48
2024-10-26 22:14:19
@ eac63075:b4988b48
2024-10-26 22:14:19The future of physical money is at stake, and the discussion about DREX, the new digital currency planned by the Central Bank of Brazil, is gaining momentum. In a candid and intense conversation, Federal Deputy Julia Zanatta (PL/SC) discussed the challenges and risks of this digital transition, also addressing her Bill No. 3,341/2024, which aims to prevent the extinction of physical currency. This bill emerges as a direct response to legislative initiatives seeking to replace physical money with digital alternatives, limiting citizens' options and potentially compromising individual freedom. Let's delve into the main points of this conversation.
https://www.fountain.fm/episode/i5YGJ9Ors3PkqAIMvNQ0
What is a CBDC?
Before discussing the specifics of DREX, it’s important to understand what a CBDC (Central Bank Digital Currency) is. CBDCs are digital currencies issued by central banks, similar to a digital version of physical money. Unlike cryptocurrencies such as Bitcoin, which operate in a decentralized manner, CBDCs are centralized and regulated by the government. In other words, they are digital currencies created and controlled by the Central Bank, intended to replace physical currency.
A prominent feature of CBDCs is their programmability. This means that the government can theoretically set rules about how, where, and for what this currency can be used. This aspect enables a level of control over citizens' finances that is impossible with physical money. By programming the currency, the government could limit transactions by setting geographical or usage restrictions. In practice, money within a CBDC could be restricted to specific spending or authorized for use in a defined geographical area.
In countries like China, where citizen actions and attitudes are also monitored, a person considered to have a "low score" due to a moral or ideological violation may have their transactions limited to essential purchases, restricting their digital currency use to non-essential activities. This financial control is strengthened because, unlike physical money, digital currency cannot be exchanged anonymously.
Practical Example: The Case of DREX During the Pandemic
To illustrate how DREX could be used, an example was given by Eric Altafim, director of Banco Itaú. He suggested that, if DREX had existed during the COVID-19 pandemic, the government could have restricted the currency’s use to a 5-kilometer radius around a person’s residence, limiting their economic mobility. Another proposed use by the executive related to the Bolsa Família welfare program: the government could set up programming that only allows this benefit to be used exclusively for food purchases. Although these examples are presented as control measures for safety or organization, they demonstrate how much a CBDC could restrict citizens' freedom of choice.
To illustrate the potential for state control through a Central Bank Digital Currency (CBDC), such as DREX, it is helpful to look at the example of China. In China, the implementation of a CBDC coincides with the country’s Social Credit System, a governmental surveillance tool that assesses citizens' and companies' behavior. Together, these technologies allow the Chinese government to monitor, reward, and, above all, punish behavior deemed inappropriate or threatening to the government.
How Does China's Social Credit System Work?
Implemented in 2014, China's Social Credit System assigns every citizen and company a "score" based on various factors, including financial behavior, criminal record, social interactions, and even online activities. This score determines the benefits or penalties each individual receives and can affect everything from public transport access to obtaining loans and enrolling in elite schools for their children. Citizens with low scores may face various sanctions, including travel restrictions, fines, and difficulty in securing loans.
With the adoption of the CBDC — or “digital yuan” — the Chinese government now has a new tool to closely monitor citizens' financial transactions, facilitating the application of Social Credit System penalties. China’s CBDC is a programmable digital currency, which means that the government can restrict how, when, and where the money can be spent. Through this level of control, digital currency becomes a powerful mechanism for influencing citizens' behavior.
Imagine, for instance, a citizen who repeatedly posts critical remarks about the government on social media or participates in protests. If the Social Credit System assigns this citizen a low score, the Chinese government could, through the CBDC, restrict their money usage in certain areas or sectors. For example, they could be prevented from buying tickets to travel to other regions, prohibited from purchasing certain consumer goods, or even restricted to making transactions only at stores near their home.
Another example of how the government can use the CBDC to enforce the Social Credit System is by monitoring purchases of products such as alcohol or luxury items. If a citizen uses the CBDC to spend more than the government deems reasonable on such products, this could negatively impact their social score, resulting in additional penalties such as future purchase restrictions or a lowered rating that impacts their personal and professional lives.
In China, this kind of control has already been demonstrated in several cases. Citizens added to Social Credit System “blacklists” have seen their spending and investment capacity severely limited. The combination of digital currency and social scores thus creates a sophisticated and invasive surveillance system, through which the Chinese government controls important aspects of citizens’ financial lives and individual freedoms.
Deputy Julia Zanatta views these examples with great concern. She argues that if the state has full control over digital money, citizens will be exposed to a level of economic control and surveillance never seen before. In a democracy, this control poses a risk, but in an authoritarian regime, it could be used as a powerful tool of repression.
DREX and Bill No. 3,341/2024
Julia Zanatta became aware of a bill by a Workers' Party (PT) deputy (Bill 4068/2020 by Deputy Reginaldo Lopes - PT/MG) that proposes the extinction of physical money within five years, aiming for a complete transition to DREX, the digital currency developed by the Central Bank of Brazil. Concerned about the impact of this measure, Julia drafted her bill, PL No. 3,341/2024, which prohibits the elimination of physical money, ensuring citizens the right to choose physical currency.
“The more I read about DREX, the less I want its implementation,” says the deputy. DREX is a Central Bank Digital Currency (CBDC), similar to other state digital currencies worldwide, but which, according to Julia, carries extreme control risks. She points out that with DREX, the State could closely monitor each citizen’s transactions, eliminating anonymity and potentially restricting freedom of choice. This control would lie in the hands of the Central Bank, which could, in a crisis or government change, “freeze balances or even delete funds directly from user accounts.”
Risks and Individual Freedom
Julia raises concerns about potential abuses of power that complete digitalization could allow. In a democracy, state control over personal finances raises serious questions, and EddieOz warns of an even more problematic future. “Today we are in a democracy, but tomorrow, with a government transition, we don't know if this kind of power will be used properly or abused,” he states. In other words, DREX gives the State the ability to restrict or condition the use of money, opening the door to unprecedented financial surveillance.
EddieOz cites Nigeria as an example, where a CBDC was implemented, and the government imposed severe restrictions on the use of physical money to encourage the use of digital currency, leading to protests and clashes in the country. In practice, the poorest and unbanked — those without regular access to banking services — were harshly affected, as without physical money, many cannot conduct basic transactions. Julia highlights that in Brazil, this situation would be even more severe, given the large number of unbanked individuals and the extent of rural areas where access to technology is limited.
The Relationship Between DREX and Pix
The digital transition has already begun with Pix, which revolutionized instant transfers and payments in Brazil. However, Julia points out that Pix, though popular, is a citizen’s choice, while DREX tends to eliminate that choice. The deputy expresses concern about new rules suggested for Pix, such as daily transaction limits of a thousand reais, justified as anti-fraud measures but which, in her view, represent additional control and a profit opportunity for banks. “How many more rules will banks create to profit from us?” asks Julia, noting that DREX could further enhance control over personal finances.
International Precedents and Resistance to CBDC
The deputy also cites examples from other countries resisting the idea of a centralized digital currency. In the United States, states like New Hampshire have passed laws to prevent the advance of CBDCs, and leaders such as Donald Trump have opposed creating a national digital currency. Trump, addressing the topic, uses a justification similar to Julia’s: in a digitalized system, “with one click, your money could disappear.” She agrees with the warning, emphasizing the control risk that a CBDC represents, especially for countries with disadvantaged populations.
Besides the United States, Canada, Colombia, and Australia have also suspended studies on digital currencies, citing the need for further discussions on population impacts. However, in Brazil, the debate on DREX is still limited, with few parliamentarians and political leaders openly discussing the topic. According to Julia, only she and one or two deputies are truly trying to bring this discussion to the Chamber, making DREX’s advance even more concerning.
Bill No. 3,341/2024 and Popular Pressure
For Julia, her bill is a first step. Although she acknowledges that ideally, it would prevent DREX's implementation entirely, PL 3341/2024 is a measure to ensure citizens' choice to use physical money, preserving a form of individual freedom. “If the future means control, I prefer to live in the past,” Julia asserts, reinforcing that the fight for freedom is at the heart of her bill.
However, the deputy emphasizes that none of this will be possible without popular mobilization. According to her, popular pressure is crucial for other deputies to take notice and support PL 3341. “I am only one deputy, and we need the public’s support to raise the project’s visibility,” she explains, encouraging the public to press other parliamentarians and ask them to “pay attention to PL 3341 and the project that prohibits the end of physical money.” The deputy believes that with a strong awareness and pressure movement, it is possible to advance the debate and ensure Brazilians’ financial freedom.
What’s at Stake?
Julia Zanatta leaves no doubt: DREX represents a profound shift in how money will be used and controlled in Brazil. More than a simple modernization of the financial system, the Central Bank’s CBDC sets precedents for an unprecedented level of citizen surveillance and control in the country. For the deputy, this transition needs to be debated broadly and transparently, and it’s up to the Brazilian people to defend their rights and demand that the National Congress discuss these changes responsibly.
The deputy also emphasizes that, regardless of political or partisan views, this issue affects all Brazilians. “This agenda is something that will affect everyone. We need to be united to ensure people understand the gravity of what could happen.” Julia believes that by sharing information and generating open debate, it is possible to prevent Brazil from following the path of countries that have already implemented a digital currency in an authoritarian way.
A Call to Action
The future of physical money in Brazil is at risk. For those who share Deputy Julia Zanatta’s concerns, the time to act is now. Mobilize, get informed, and press your representatives. PL 3341/2024 is an opportunity to ensure that Brazilian citizens have a choice in how to use their money, without excessive state interference or surveillance.
In the end, as the deputy puts it, the central issue is freedom. “My fear is that this project will pass, and people won’t even understand what is happening.” Therefore, may every citizen at least have the chance to understand what’s at stake and make their voice heard in defense of a Brazil where individual freedom and privacy are respected values.
-
 @ c631e267:c2b78d3e
2025-01-18 09:34:51
@ c631e267:c2b78d3e
2025-01-18 09:34:51Die grauenvollste Aussicht ist die der Technokratie – \ einer kontrollierenden Herrschaft, \ die durch verstümmelte und verstümmelnde Geister ausgeübt wird. \ Ernst Jünger
«Davos ist nicht mehr sexy», das Weltwirtschaftsforum (WEF) mache Davos kaputt, diese Aussagen eines Einheimischen las ich kürzlich in der Handelszeitung. Während sich einige vor Ort enorm an der «teuersten Gewerbeausstellung der Welt» bereicherten, würden die negativen Begleiterscheinungen wie Wohnungsnot und Niedergang der lokalen Wirtschaft immer deutlicher.
Nächsten Montag beginnt in dem Schweizer Bergdorf erneut ein Jahrestreffen dieses elitären Clubs der Konzerne, bei dem man mit hochrangigen Politikern aus aller Welt und ausgewählten Vertretern der Systemmedien zusammenhocken wird. Wie bereits in den vergangenen vier Jahren wird die Präsidentin der EU-Kommission, Ursula von der Leyen, in Begleitung von Klaus Schwab ihre Grundsatzansprache halten.
Der deutsche WEF-Gründer hatte bei dieser Gelegenheit immer höchst lobende Worte für seine Landsmännin: 2021 erklärte er sich «stolz, dass Europa wieder unter Ihrer Führung steht» und 2022 fand er es bemerkenswert, was sie erreicht habe angesichts des «erstaunlichen Wandels», den die Welt in den vorangegangenen zwei Jahren erlebt habe; es gebe nun einen «neuen europäischen Geist».
Von der Leyens Handeln während der sogenannten Corona-«Pandemie» lobte Schwab damals bereits ebenso, wie es diese Woche das Karlspreis-Direktorium tat, als man der Beschuldigten im Fall Pfizergate die diesjährige internationale Auszeichnung «für Verdienste um die europäische Einigung» verlieh. Außerdem habe sie die EU nicht nur gegen den «Aggressor Russland», sondern auch gegen die «innere Bedrohung durch Rassisten und Demagogen» sowie gegen den Klimawandel verteidigt.
Jene Herausforderungen durch «Krisen epochalen Ausmaßes» werden indes aus dem Umfeld des WEF nicht nur herbeigeredet – wie man alljährlich zur Zeit des Davoser Treffens im Global Risks Report nachlesen kann, der zusammen mit dem Versicherungskonzern Zurich erstellt wird. Seit die Globalisten 2020/21 in der Praxis gesehen haben, wie gut eine konzertierte und konsequente Angst-Kampagne funktionieren kann, geht es Schlag auf Schlag. Sie setzen alles daran, Schwabs goldenes Zeitfenster des «Great Reset» zu nutzen.
Ziel dieses «großen Umbruchs» ist die totale Kontrolle der Technokraten über die Menschen unter dem Deckmantel einer globalen Gesundheitsfürsorge. Wie aber könnte man so etwas erreichen? Ein Mittel dazu ist die «kreative Zerstörung». Weitere unabdingbare Werkzeug sind die Einbindung, ja Gleichschaltung der Medien und der Justiz.
Ein «Great Mental Reset» sei die Voraussetzung dafür, dass ein Großteil der Menschen Einschränkungen und Manipulationen wie durch die Corona-Maßnahmen praktisch kritik- und widerstandslos hinnehme, sagt der Mediziner und Molekulargenetiker Michael Nehls. Er meint damit eine regelrechte Umprogrammierung des Gehirns, wodurch nach und nach unsere Individualität und unser soziales Bewusstsein eliminiert und durch unreflektierten Konformismus ersetzt werden.
Der aktuelle Zustand unserer Gesellschaften ist auch für den Schweizer Rechtsanwalt Philipp Kruse alarmierend. Durch den Umgang mit der «Pandemie» sieht er die Grundlagen von Recht und Vernunft erschüttert, die Rechtsstaatlichkeit stehe auf dem Prüfstand. Seiner dringenden Mahnung an alle Bürger, die Prinzipien von Recht und Freiheit zu verteidigen, kann ich mich nur anschließen.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ a95c6243:d345522c
2025-01-13 10:09:57
@ a95c6243:d345522c
2025-01-13 10:09:57Ich begann, Social Media aufzubauen, \ um den Menschen eine Stimme zu geben. \ Mark Zuckerberg
Sind euch auch die Tränen gekommen, als ihr Mark Zuckerbergs Wendehals-Deklaration bezüglich der Meinungsfreiheit auf seinen Portalen gehört habt? Rührend, oder? Während er früher die offensichtliche Zensur leugnete und später die Regierung Biden dafür verantwortlich machte, will er nun angeblich «die Zensur auf unseren Plattformen drastisch reduzieren».
«Purer Opportunismus» ob des anstehenden Regierungswechsels wäre als Klassifizierung viel zu kurz gegriffen. Der jetzige Schachzug des Meta-Chefs ist genauso Teil einer kühl kalkulierten Business-Strategie, wie es die 180 Grad umgekehrte Praxis vorher war. Social Media sind ein höchst lukratives Geschäft. Hinzu kommt vielleicht noch ein bisschen verkorkstes Ego, weil derartig viel Einfluss und Geld sicher auch auf die Psyche schlagen. Verständlich.
«Es ist an der Zeit, zu unseren Wurzeln der freien Meinungsäußerung auf Facebook und Instagram zurückzukehren. Ich begann, Social Media aufzubauen, um den Menschen eine Stimme zu geben», sagte Zuckerberg.
Welche Wurzeln? Hat der Mann vergessen, dass er von der Überwachung, dem Ausspionieren und dem Ausverkauf sämtlicher Daten und digitaler Spuren sowie der Manipulation seiner «Kunden» lebt? Das ist knallharter Kommerz, nichts anderes. Um freie Meinungsäußerung geht es bei diesem Geschäft ganz sicher nicht, und das war auch noch nie so. Die Wurzeln von Facebook liegen in einem Projekt des US-Militärs mit dem Namen «LifeLog». Dessen Ziel war es, «ein digitales Protokoll vom Leben eines Menschen zu erstellen».
Der Richtungswechsel kommt allerdings nicht überraschend. Schon Anfang Dezember hatte Meta-Präsident Nick Clegg von «zu hoher Fehlerquote bei der Moderation» von Inhalten gesprochen. Bei der Gelegenheit erwähnte er auch, dass Mark sehr daran interessiert sei, eine aktive Rolle in den Debatten über eine amerikanische Führungsrolle im technologischen Bereich zu spielen.
Während Milliardärskollege und Big Tech-Konkurrent Elon Musk bereits seinen Posten in der kommenden Trump-Regierung in Aussicht hat, möchte Zuckerberg also nicht nur seine Haut retten – Trump hatte ihn einmal einen «Feind des Volkes» genannt und ihm lebenslange Haft angedroht –, sondern am liebsten auch mitspielen. KI-Berater ist wohl die gewünschte Funktion, wie man nach einem Treffen Trump-Zuckerberg hörte. An seine Verhaftung dachte vermutlich auch ein weiterer Multimilliardär mit eigener Social Media-Plattform, Pavel Durov, als er Zuckerberg jetzt kritisierte und gleichzeitig warnte.
Politik und Systemmedien drehen jedenfalls durch – was zu viel ist, ist zu viel. Etwas weniger Zensur und mehr Meinungsfreiheit würden die Freiheit der Bürger schwächen und seien potenziell vernichtend für die Menschenrechte. Zuckerberg setze mit dem neuen Kurs die Demokratie aufs Spiel, das sei eine «Einladung zum nächsten Völkermord», ernsthaft. Die Frage sei, ob sich die EU gegen Musk und Zuckerberg behaupten könne, Brüssel müsse jedenfalls hart durchgreifen.
Auch um die Faktenchecker macht man sich Sorgen. Für die deutsche Nachrichtenagentur dpa und die «Experten» von Correctiv, die (noch) Partner für Fact-Checking-Aktivitäten von Facebook sind, sei das ein «lukratives Geschäftsmodell». Aber möglicherweise werden die Inhalte ohne diese vermeintlichen Korrektoren ja sogar besser. Anders als Meta wollen jedoch Scholz, Faeser und die Tagesschau keine Fehler zugeben und zum Beispiel Correctiv-Falschaussagen einräumen.
Bei derlei dramatischen Befürchtungen wundert es nicht, dass der öffentliche Plausch auf X zwischen Elon Musk und AfD-Chefin Alice Weidel von 150 EU-Beamten überwacht wurde, falls es irgendwelche Rechtsverstöße geben sollte, die man ihnen ankreiden könnte. Auch der Deutsche Bundestag war wachsam. Gefunden haben dürften sie nichts. Das Ganze war eher eine Show, viel Wind wurde gemacht, aber letztlich gab es nichts als heiße Luft.
Das Anbiedern bei Donald Trump ist indes gerade in Mode. Die Weltgesundheitsorganisation (WHO) tut das auch, denn sie fürchtet um Spenden von über einer Milliarde Dollar. Eventuell könnte ja Elon Musk auch hier künftig aushelfen und der Organisation sowie deren größtem privaten Förderer, Bill Gates, etwas unter die Arme greifen. Nachdem Musks KI-Projekt xAI kürzlich von BlackRock & Co. sechs Milliarden eingestrichen hat, geht da vielleicht etwas.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 4ba8e86d:89d32de4
2024-11-14 09:17:14
@ 4ba8e86d:89d32de4
2024-11-14 09:17:14Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ cff1720e:15c7e2b2
2025-01-19 17:48:02
@ cff1720e:15c7e2b2
2025-01-19 17:48:02Einleitung\ \ Schwierige Dinge einfach zu erklären ist der Anspruch von ELI5 (explain me like I'm 5). Das ist in unserer hoch technisierten Welt dringend erforderlich, denn nur mit dem Verständnis der Technologien können wir sie richtig einsetzen und weiter entwickeln.\ Ich starte meine Serie mit Nostr, einem relativ neuen Internet-Protokoll. Was zum Teufel ist ein Internet-Protokoll? Formal beschrieben sind es internationale Standards, die dafür sorgen, dass das Internet seit über 30 Jahren ziemlich gut funktioniert. Es ist die Sprache, in der sich die Rechner miteinander unterhalten und die auch Sie täglich nutzen, vermutlich ohne es bewusst wahrzunehmen. http(s) transportiert ihre Anfrage an einen Server (z.B. Amazon), und html sorgt dafür, dass aus den gelieferten Daten eine schöne Seite auf ihrem Bildschirm entsteht. Eine Mail wird mit smtp an den Mailserver gesendet und mit imap von ihm abgerufen, und da alle den Standard verwenden, funktioniert das mit jeder App auf jedem Betriebssystem und mit jedem Mail-Provider. Und mit einer Mail-Adresse wie roland@pareto.space können sie sogar jederzeit umziehen, egal wohin. Cool, das ist state of the art! Aber warum funktioniert das z.B. bei Chat nicht, gibt es da kein Protokoll? Doch, es heißt IRC (Internet Relay Chat → merken sie sich den Namen), aber es wird so gut wie nicht verwendet. Die Gründe dafür sind nicht technischer Natur, vielmehr wurden mit Apps wie Facebook, Twitter, WhatsApp, Telegram, Instagram, TikTok u.a. bewusst Inkompatibilitäten und Nutzerabhängigkeiten geschaffen um Profite zu maximieren.

Warum Nostr?
Da das Standard-Protokoll nicht genutzt wird, hat jede App ihr eigenes, und wir brauchen eine handvoll Apps um uns mit allen Bekannten auszutauschen. Eine Mobilfunknummer ist Voraussetzung für jedes Konto, damit können die App-Hersteller die Nutzer umfassend tracken und mit dem Verkauf der Informationen bis zu 30 USD je Konto und Monat verdienen. Der Nutzer ist nicht mehr Kunde, er ist das Produkt! Der Werbe-SPAM ist noch das kleinste Problem bei diesem Geschäftsmodell. Server mit Millionen von Nutzerdaten sind ein “honey pot”, dementsprechend oft werden sie gehackt und die Zugangsdaten verkauft. 2024 wurde auch der Twitter-Account vom damaligen Präsidenten Joe Biden gehackt, niemand wusste mehr wer die Nachrichten verfasst hat (vorher auch nicht), d.h. die Authentizität der Inhalte ist bei keinem dieser Anbieter gewährleistet. Im selben Jahr wurde der Telegram-Gründer in Frankreich in Beugehaft genommen, weil er sich geweigert hatte Hintertüren in seine Software einzubauen. Nun kann zum Schutz "unserer Demokratie” praktisch jeder mitlesen, was sie mit wem an Informationen austauschen, z.B. darüber welches Shampoo bestimmte Politiker verwenden.

Und wer tatsächlich glaubt er könne Meinungsfreiheit auf sozialen Medien praktizieren, findet sich schnell in der Situation von Donald Trump wieder (seinerzeit amtierender Präsident), dem sein Twitter-Konto 2021 abgeschaltet wurde (Cancel-Culture). Die Nutzerdaten, also ihr Profil, ihre Kontakte, Dokumente, Bilder, Videos und Audiofiles - gehören ihnen ohnehin nicht mehr sondern sind Eigentum des Plattform-Betreibers; lesen sie sich mal die AGB's durch. Aber nein, keine gute Idee, das sind hunderte Seiten und sie werden permanent geändert. Alle nutzen also Apps, deren Technik sie nicht verstehen, deren Regeln sie nicht kennen, wo sie keine Rechte haben und die ihnen die Resultate ihres Handelns stehlen. Was würde wohl der Fünfjährige sagen, wenn ihm seine ältere Schwester anbieten würde, alle seine Spielzeuge zu “verwalten” und dann auszuhändigen wenn er brav ist? “Du spinnst wohl”, und damit beweist der Knirps mehr Vernunft als die Mehrzahl der Erwachsenen. \ \ Resümee: keine Standards, keine Daten, keine Rechte = keine Zukunft!

\ Wie funktioniert Nostr?
Die Entwickler von Nostr haben erkannt dass sich das Server-Client-Konzept in ein Master-Slave-Konzept verwandelt hatte. Der Master ist ein Synonym für Zentralisierung und wird zum “single point of failure”, der zwangsläufig Systeme dysfunktional macht. In einem verteilten Peer2Peer-System gibt es keine Master mehr sondern nur gleichberechtigte Knoten (Relays), auf denen die Informationen gespeichert werden. Indem man Informationen auf mehreren Relays redundant speichert, ist das System in jeglicher Hinsicht resilienter. Nicht nur die Natur verwendet dieses Prinzip seit Jahrmillionen erfolgreich, auch das Internet wurde so konzipiert (das ARPAnet wurde vom US-Militär für den Einsatz in Kriegsfällen unter massiven Störungen entwickelt). Alle Nostr-Daten liegen auf Relays und der Nutzer kann wählen zwischen öffentlichen (zumeist kostenlosen) und privaten Relays, z.B. für geschlossene Gruppen oder zum Zwecke von Daten-Archivierung. Da Dokumente auf mehreren Relays gespeichert sind, werden statt URL's (Locator) eindeutige Dokumentnamen (URI's = Identifier) verwendet, broken Links sind damit Vergangenheit und Löschungen / Verluste ebenfalls.\ \ Jedes Dokument (Event genannt) wird vom Besitzer signiert, es ist damit authentisch und fälschungssicher und kann nur vom Ersteller gelöscht werden. Dafür wird ein Schlüsselpaar verwendet bestehend aus privatem (nsec) und öffentlichem Schlüssel (npub) wie aus der Mailverschlüsselung (PGP) bekannt. Das repräsentiert eine Nostr-Identität, die um Bild, Namen, Bio und eine lesbare Nostr-Adresse ergänzt werden kann (z.B. roland@pareto.space ), mehr braucht es nicht um alle Ressourcen des Nostr-Ökosystems zu nutzen. Und das besteht inzwischen aus über hundert Apps mit unterschiedlichen Fokussierungen, z.B. für persönliche verschlüsselte Nachrichten (DM → OxChat), Kurznachrichten (Damus, Primal), Blogbeiträge (Pareto), Meetups (Joinstr), Gruppen (Groups), Bilder (Olas), Videos (Amethyst), Audio-Chat (Nostr Nests), Audio-Streams (Tunestr), Video-Streams (Zap.Stream), Marktplätze (Shopstr) u.v.a.m. Die Anmeldung erfolgt mit einem Klick (single sign on) und den Apps stehen ALLE Nutzerdaten zur Verfügung (Profil, Daten, Kontakte, Social Graph → Follower, Bookmarks, Comments, etc.), im Gegensatz zu den fragmentierten Datensilos der Gegenwart.\ \ Resümee: ein offener Standard, alle Daten, alle Rechte = große Zukunft!

\ Warum ist Nostr die Zukunft des Internet?
“Baue Dein Haus nicht auf einem fremden Grundstück” gilt auch im Internet - für alle App-Entwickler, Künstler, Journalisten und Nutzer, denn auch ihre Daten sind werthaltig. Nostr garantiert das Eigentum an den Daten, und überwindet ihre Fragmentierung. Weder die Nutzung noch die kreativen Freiheiten werden durch maßlose Lizenz- und Nutzungsbedingungen eingeschränkt. Aus passiven Nutzern werden durch Interaktion aktive Teilnehmer, Co-Creatoren in einer Sharing-Ökonomie (Value4Value). OpenSource schafft endlich wieder Vertrauen in die Software und ihre Anbieter. Offene Standards ermöglichen den Entwicklern mehr Kooperation und schnellere Entwicklung, für die Anwender garantieren sie Wahlfreiheit. Womit wir letztmalig zu unserem Fünfjährigen zurückkehren. Kinder lieben Lego über alles, am meisten die Maxi-Box “Classic”, weil sie damit ihre Phantasie im Kombinieren voll ausleben können. Erwachsene schenken ihnen dann die viel zu teuren Themenpakete, mit denen man nur eine Lösung nach Anleitung bauen kann. “Was stimmt nur mit meinen Eltern nicht, wann sind die denn falsch abgebogen?" fragt sich der Nachwuchs zu Recht. Das Image lässt sich aber wieder aufpolieren, wenn sie ihren Kindern Nostr zeigen, denn die Vorteile verstehen sogar Fünfjährige.

\ Das neue Internet ist dezentral. Das neue Internet ist selbstbestimmt. Nostr ist das neue Internet.
https://nostr.net/ \ https://start.njump.me/
Hier das Interview zum Thema mit Radio Berliner Morgenröte
-
 @ eac63075:b4988b48
2024-10-21 08:11:11
@ eac63075:b4988b48
2024-10-21 08:11:11Imagine sending a private message to a friend, only to learn that authorities could be scanning its contents without your knowledge. This isn't a scene from a dystopian novel but a potential reality under the European Union's proposed "Chat Control" measures. Aimed at combating serious crimes like child exploitation and terrorism, these proposals could significantly impact the privacy of everyday internet users. As encrypted messaging services become the norm for personal and professional communication, understanding Chat Control is essential. This article delves into what Chat Control entails, why it's being considered, and how it could affect your right to private communication.
https://www.fountain.fm/episode/coOFsst7r7mO1EP1kSzV
https://open.spotify.com/episode/0IZ6kMExfxFm4FHg5DAWT8?si=e139033865e045de
Sections:
- Introduction
- What Is Chat Control?
- Why Is the EU Pushing for Chat Control?
- The Privacy Concerns and Risks
- The Technical Debate: Encryption and Backdoors
- Global Reactions and the Debate in Europe
- Possible Consequences for Messaging Services
- What Happens Next? The Future of Chat Control
- Conclusion
What Is Chat Control?
"Chat Control" refers to a set of proposed measures by the European Union aimed at monitoring and scanning private communications on messaging platforms. The primary goal is to detect and prevent the spread of illegal content, such as child sexual abuse material (CSAM) and to combat terrorism. While the intention is to enhance security and protect vulnerable populations, these proposals have raised significant privacy concerns.
At its core, Chat Control would require messaging services to implement automated scanning technologies that can analyze the content of messages—even those that are end-to-end encrypted. This means that the private messages you send to friends, family, or colleagues could be subject to inspection by algorithms designed to detect prohibited content.
Origins of the Proposal
The initiative for Chat Control emerged from the EU's desire to strengthen its digital security infrastructure. High-profile cases of online abuse and the use of encrypted platforms by criminal organizations have prompted lawmakers to consider more invasive surveillance tactics. The European Commission has been exploring legislation that would make it mandatory for service providers to monitor communications on their platforms.
How Messaging Services Work
Most modern messaging apps, like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others), use end-to-end encryption (E2EE). This encryption ensures that only the sender and the recipient can read the messages being exchanged. Not even the service providers can access the content. This level of security is crucial for maintaining privacy in digital communications, protecting users from hackers, identity thieves, and other malicious actors.

Key Elements of Chat Control
- Automated Content Scanning: Service providers would use algorithms to scan messages for illegal content.
- Circumvention of Encryption: To scan encrypted messages, providers might need to alter their encryption methods, potentially weakening security.
- Mandatory Reporting: If illegal content is detected, providers would be required to report it to authorities.
- Broad Applicability: The measures could apply to all messaging services operating within the EU, affecting both European companies and international platforms.
Why It Matters
Understanding Chat Control is essential because it represents a significant shift in how digital privacy is handled. While combating illegal activities online is crucial, the methods proposed could set a precedent for mass surveillance and the erosion of privacy rights. Everyday users who rely on encrypted messaging for personal and professional communication might find their conversations are no longer as private as they once thought.
Why Is the EU Pushing for Chat Control?
The European Union's push for Chat Control stems from a pressing concern to protect its citizens, particularly children, from online exploitation and criminal activities. With the digital landscape becoming increasingly integral to daily life, the EU aims to strengthen its ability to combat serious crimes facilitated through online platforms.
Protecting Children and Preventing Crime
One of the primary motivations behind Chat Control is the prevention of child sexual abuse material (CSAM) circulating on the internet. Law enforcement agencies have reported a significant increase in the sharing of illegal content through private messaging services. By implementing Chat Control, the EU believes it can more effectively identify and stop perpetrators, rescue victims, and deter future crimes.
Terrorism is another critical concern. Encrypted messaging apps can be used by terrorist groups to plan and coordinate attacks without detection. The EU argues that accessing these communications could be vital in preventing such threats and ensuring public safety.
Legal Context and Legislative Drivers
The push for Chat Control is rooted in several legislative initiatives:
-
ePrivacy Directive: This directive regulates the processing of personal data and the protection of privacy in electronic communications. The EU is considering amendments that would allow for the scanning of private messages under specific circumstances.
-
Temporary Derogation: In 2021, the EU adopted a temporary regulation permitting voluntary detection of CSAM by communication services. The current proposals aim to make such measures mandatory and more comprehensive.
-
Regulation Proposals: The European Commission has proposed regulations that would require service providers to detect, report, and remove illegal content proactively. This would include the use of technologies to scan private communications.
Balancing Security and Privacy
EU officials argue that the proposed measures are a necessary response to evolving digital threats. They emphasize the importance of staying ahead of criminals who exploit technology to harm others. By implementing Chat Control, they believe law enforcement can be more effective without entirely dismantling privacy protections.
However, the EU also acknowledges the need to balance security with fundamental rights. The proposals include provisions intended to limit the scope of surveillance, such as:
-
Targeted Scanning: Focusing on specific threats rather than broad, indiscriminate monitoring.
-
Judicial Oversight: Requiring court orders or oversight for accessing private communications.
-
Data Protection Safeguards: Implementing measures to ensure that data collected is handled securely and deleted when no longer needed.

The Urgency Behind the Push
High-profile cases of online abuse and terrorism have heightened the sense of urgency among EU policymakers. Reports of increasing online grooming and the widespread distribution of illegal content have prompted calls for immediate action. The EU posits that without measures like Chat Control, these problems will continue to escalate unchecked.
Criticism and Controversy
Despite the stated intentions, the push for Chat Control has been met with significant criticism. Opponents argue that the measures could be ineffective against savvy criminals who can find alternative ways to communicate. There is also concern that such surveillance could be misused or extended beyond its original purpose.
The Privacy Concerns and Risks
While the intentions behind Chat Control focus on enhancing security and protecting vulnerable groups, the proposed measures raise significant privacy concerns. Critics argue that implementing such surveillance could infringe on fundamental rights and set a dangerous precedent for mass monitoring of private communications.
Infringement on Privacy Rights
At the heart of the debate is the right to privacy. By scanning private messages, even with automated tools, the confidentiality of personal communications is compromised. Users may no longer feel secure sharing sensitive information, fearing that their messages could be intercepted or misinterpreted by algorithms.
Erosion of End-to-End Encryption
End-to-end encryption (E2EE) is a cornerstone of digital security, ensuring that only the sender and recipient can read the messages exchanged. Chat Control could necessitate the introduction of "backdoors" or weaken encryption protocols, making it easier for unauthorized parties to access private data. This not only affects individual privacy but also exposes communications to potential cyber threats.
Concerns from Privacy Advocates
Organizations like Signal and Tutanota, which offer encrypted messaging services, have voiced strong opposition to Chat Control. They warn that undermining encryption could have far-reaching consequences:
- Security Risks: Weakening encryption makes systems more vulnerable to hacking, espionage, and cybercrime.
- Global Implications: Changes in EU regulations could influence policies worldwide, leading to a broader erosion of digital privacy.
- Ineffectiveness Against Crime: Determined criminals might resort to other, less detectable means of communication, rendering the measures ineffective while still compromising the privacy of law-abiding citizens.

Potential for Government Overreach
There is a fear that Chat Control could lead to increased surveillance beyond its original scope. Once the infrastructure for scanning private messages is in place, it could be repurposed or expanded to monitor other types of content, stifling free expression and dissent.
Real-World Implications for Users
- False Positives: Automated scanning technologies are not infallible and could mistakenly flag innocent content, leading to unwarranted scrutiny or legal consequences for users.
- Chilling Effect: Knowing that messages could be monitored might discourage people from expressing themselves freely, impacting personal relationships and societal discourse.
- Data Misuse: Collected data could be vulnerable to leaks or misuse, compromising personal and sensitive information.
Legal and Ethical Concerns
Privacy advocates also highlight potential conflicts with existing laws and ethical standards:
- Violation of Fundamental Rights: The European Convention on Human Rights and other international agreements protect the right to privacy and freedom of expression.
- Questionable Effectiveness: The ethical justification for such invasive measures is challenged if they do not significantly improve safety or if they disproportionately impact innocent users.
Opposition from Member States and Organizations
Countries like Germany and organizations such as the European Digital Rights (EDRi) have expressed opposition to Chat Control. They emphasize the need to protect digital privacy and caution against hasty legislation that could have unintended consequences.
The Technical Debate: Encryption and Backdoors
The discussion around Chat Control inevitably leads to a complex technical debate centered on encryption and the potential introduction of backdoors into secure communication systems. Understanding these concepts is crucial to grasping the full implications of the proposed measures.
What Is End-to-End Encryption (E2EE)?
End-to-end encryption is a method of secure communication that prevents third parties from accessing data while it's transferred from one end system to another. In simpler terms, only the sender and the recipient can read the messages. Even the service providers operating the messaging platforms cannot decrypt the content.
- Security Assurance: E2EE ensures that sensitive information—be it personal messages, financial details, or confidential business communications—remains private.
- Widespread Use: Popular messaging apps like Signal, Session, SimpleX, Veilid, Protonmail and Tutanota (among others) rely on E2EE to protect user data.
How Chat Control Affects Encryption
Implementing Chat Control as proposed would require messaging services to scan the content of messages for illegal material. To do this on encrypted platforms, providers might have to:
- Introduce Backdoors: Create a means for third parties (including the service provider or authorities) to access encrypted messages.
- Client-Side Scanning: Install software on users' devices that scans messages before they are encrypted and sent, effectively bypassing E2EE.
The Risks of Weakening Encryption
1. Compromised Security for All Users
Introducing backdoors or client-side scanning tools can create vulnerabilities:
- Exploitable Gaps: If a backdoor exists, malicious actors might find and exploit it, leading to data breaches.
- Universal Impact: Weakening encryption doesn't just affect targeted individuals; it potentially exposes all users to increased risk.
2. Undermining Trust in Digital Services
- User Confidence: Knowing that private communications could be accessed might deter people from using digital services or push them toward unregulated platforms.
- Business Implications: Companies relying on secure communications might face increased risks, affecting economic activities.
3. Ineffectiveness Against Skilled Adversaries
- Alternative Methods: Criminals might shift to other encrypted channels or develop new ways to avoid detection.
- False Sense of Security: Weakening encryption could give the impression of increased safety while adversaries adapt and continue their activities undetected.
Signal’s Response and Stance
Signal, a leading encrypted messaging service, has been vocal in its opposition to the EU's proposals:
- Refusal to Weaken Encryption: Signal's CEO Meredith Whittaker has stated that the company would rather cease operations in the EU than compromise its encryption standards.
- Advocacy for Privacy: Signal emphasizes that strong encryption is essential for protecting human rights and freedoms in the digital age.
Understanding Backdoors
A "backdoor" in encryption is an intentional weakness inserted into a system to allow authorized access to encrypted data. While intended for legitimate use by authorities, backdoors pose several problems:
- Security Vulnerabilities: They can be discovered and exploited by unauthorized parties, including hackers and foreign governments.
- Ethical Concerns: The existence of backdoors raises questions about consent and the extent to which governments should be able to access private communications.

The Slippery Slope Argument
Privacy advocates warn that introducing backdoors or mandatory scanning sets a precedent:
- Expanded Surveillance: Once in place, these measures could be extended to monitor other types of content beyond the original scope.
- Erosion of Rights: Gradual acceptance of surveillance can lead to a significant reduction in personal freedoms over time.
Potential Technological Alternatives
Some suggest that it's possible to fight illegal content without undermining encryption:
- Metadata Analysis: Focusing on patterns of communication rather than content.
- Enhanced Reporting Mechanisms: Encouraging users to report illegal content voluntarily.
- Investing in Law Enforcement Capabilities: Strengthening traditional investigative methods without compromising digital security.
The technical community largely agrees that weakening encryption is not the solution:
- Consensus on Security: Strong encryption is essential for the safety and privacy of all internet users.
- Call for Dialogue: Technologists and privacy experts advocate for collaborative approaches that address security concerns without sacrificing fundamental rights.
Global Reactions and the Debate in Europe
The proposal for Chat Control has ignited a heated debate across Europe and beyond, with various stakeholders weighing in on the potential implications for privacy, security, and fundamental rights. The reactions are mixed, reflecting differing national perspectives, political priorities, and societal values.
Support for Chat Control
Some EU member states and officials support the initiative, emphasizing the need for robust measures to combat online crime and protect citizens, especially children. They argue that:
- Enhanced Security: Mandatory scanning can help law enforcement agencies detect and prevent serious crimes.
- Responsibility of Service Providers: Companies offering communication services should play an active role in preventing their platforms from being used for illegal activities.
- Public Safety Priorities: The protection of vulnerable populations justifies the implementation of such measures, even if it means compromising some aspects of privacy.
Opposition within the EU
Several countries and organizations have voiced strong opposition to Chat Control, citing concerns over privacy rights and the potential for government overreach.
Germany
- Stance: Germany has been one of the most vocal opponents of the proposed measures.
- Reasons:
- Constitutional Concerns: The German government argues that Chat Control could violate constitutional protections of privacy and confidentiality of communications.
- Security Risks: Weakening encryption is seen as a threat to cybersecurity.
- Legal Challenges: Potential conflicts with national laws protecting personal data and communication secrecy.
Netherlands
- Recent Developments: The Dutch government decided against supporting Chat Control, emphasizing the importance of encryption for security and privacy.
- Arguments:
- Effectiveness Doubts: Skepticism about the actual effectiveness of the measures in combating crime.
- Negative Impact on Privacy: Concerns about mass surveillance and the infringement of citizens' rights.
 Table reference: Patrick Breyer - Chat Control in 23 September 2024
Table reference: Patrick Breyer - Chat Control in 23 September 2024Privacy Advocacy Groups
European Digital Rights (EDRi)
- Role: A network of civil and human rights organizations working to defend rights and freedoms in the digital environment.
- Position:
- Strong Opposition: EDRi argues that Chat Control is incompatible with fundamental rights.
- Awareness Campaigns: Engaging in public campaigns to inform citizens about the potential risks.
- Policy Engagement: Lobbying policymakers to consider alternative approaches that respect privacy.
Politicians and Activists
Patrick Breyer
- Background: A Member of the European Parliament (MEP) from Germany, representing the Pirate Party.
- Actions:
- Advocacy: Actively campaigning against Chat Control through speeches, articles, and legislative efforts.
- Public Outreach: Using social media and public events to raise awareness.
- Legal Expertise: Highlighting the legal inconsistencies and potential violations of EU law.
Global Reactions
International Organizations
- Human Rights Watch and Amnesty International: These organizations have expressed concerns about the implications for human rights, urging the EU to reconsider.
Technology Companies
- Global Tech Firms: Companies like Apple and Microsoft are monitoring the situation, as EU regulations could affect their operations and user trust.
- Industry Associations: Groups representing tech companies have issued statements highlighting the risks to innovation and competitiveness.

The Broader Debate
The controversy over Chat Control reflects a broader struggle between security interests and privacy rights in the digital age. Key points in the debate include:
- Legal Precedents: How the EU's decision might influence laws and regulations in other countries.
- Digital Sovereignty: The desire of nations to control digital spaces within their borders.
- Civil Liberties: The importance of protecting freedoms in the face of technological advancements.
Public Opinion
- Diverse Views: Surveys and public forums show a range of opinions, with some citizens prioritizing security and others valuing privacy above all.
- Awareness Levels: Many people are still unaware of the potential changes, highlighting the need for public education on the issue.
The EU is at a crossroads, facing the challenge of addressing legitimate security concerns without undermining the fundamental rights that are central to its values. The outcome of this debate will have significant implications for the future of digital privacy and the balance between security and freedom in society.
Possible Consequences for Messaging Services
The implementation of Chat Control could have significant implications for messaging services operating within the European Union. Both large platforms and smaller providers might need to adapt their technologies and policies to comply with the new regulations, potentially altering the landscape of digital communication.
Impact on Encrypted Messaging Services
Signal and Similar Platforms
-
Compliance Challenges: Encrypted messaging services like Signal rely on end-to-end encryption to secure user communications. Complying with Chat Control could force them to weaken their encryption protocols or implement client-side scanning, conflicting with their core privacy principles.
-
Operational Decisions: Some platforms may choose to limit their services in the EU or cease operations altogether rather than compromise on encryption. Signal, for instance, has indicated that it would prefer to withdraw from European markets than undermine its security features.
Potential Blocking or Limiting of Services
-
Regulatory Enforcement: Messaging services that do not comply with Chat Control regulations could face fines, legal action, or even be blocked within the EU.
-
Access Restrictions: Users in Europe might find certain services unavailable or limited in functionality if providers decide not to meet the regulatory requirements.
Effects on Smaller Providers
-
Resource Constraints: Smaller messaging services and startups may lack the resources to implement the required scanning technologies, leading to increased operational costs or forcing them out of the market.
-
Innovation Stifling: The added regulatory burden could deter new entrants, reducing competition and innovation in the messaging service sector.

User Experience and Trust
-
Privacy Concerns: Users may lose trust in messaging platforms if they know their communications are subject to scanning, leading to a decline in user engagement.
-
Migration to Unregulated Platforms: There is a risk that users might shift to less secure or unregulated services, including those operated outside the EU or on the dark web, potentially exposing them to greater risks.
Technical and Security Implications
-
Increased Vulnerabilities: Modifying encryption protocols to comply with Chat Control could introduce security flaws, making platforms more susceptible to hacking and data breaches.
-
Global Security Risks: Changes made to accommodate EU regulations might affect the global user base of these services, extending security risks beyond European borders.
Impact on Businesses and Professional Communications
-
Confidentiality Issues: Businesses that rely on secure messaging for sensitive communications may face challenges in ensuring confidentiality, affecting sectors like finance, healthcare, and legal services.
-
Compliance Complexity: Companies operating internationally will need to navigate a complex landscape of differing regulations, increasing administrative burdens.
Economic Consequences
-
Market Fragmentation: Divergent regulations could lead to a fragmented market, with different versions of services for different regions.
-
Loss of Revenue: Messaging services might experience reduced revenue due to decreased user trust and engagement or the costs associated with compliance.
Responses from Service Providers
-
Legal Challenges: Companies might pursue legal action against the regulations, citing conflicts with privacy laws and user rights.
-
Policy Advocacy: Service providers may increase lobbying efforts to influence policy decisions and promote alternatives to Chat Control.
Possible Adaptations
-
Technological Innovation: Some providers might invest in developing new technologies that can detect illegal content without compromising encryption, though the feasibility remains uncertain.
-
Transparency Measures: To maintain user trust, companies might enhance transparency about how data is handled and what measures are in place to protect privacy.
The potential consequences of Chat Control for messaging services are profound, affecting not only the companies that provide these services but also the users who rely on them daily. The balance between complying with legal requirements and maintaining user privacy and security presents a significant challenge that could reshape the digital communication landscape.
What Happens Next? The Future of Chat Control
The future of Chat Control remains uncertain as the debate continues among EU member states, policymakers, technology companies, and civil society organizations. Several factors will influence the outcome of this contentious proposal, each carrying significant implications for digital privacy, security, and the regulatory environment within the European Union.
Current Status of Legislation
-
Ongoing Negotiations: The proposed Chat Control measures are still under discussion within the European Parliament and the Council of the European Union. Amendments and revisions are being considered in response to the feedback from various stakeholders.
-
Timeline: While there is no fixed date for the final decision, the EU aims to reach a consensus to implement effective measures against online crime without undue delay.
Key Influencing Factors
1. Legal Challenges and Compliance with EU Law
-
Fundamental Rights Assessment: The proposals must be evaluated against the Charter of Fundamental Rights of the European Union, ensuring that any measures comply with rights to privacy, data protection, and freedom of expression.
-
Court Scrutiny: Potential legal challenges could arise, leading to scrutiny by the European Court of Justice (ECJ), which may impact the feasibility and legality of Chat Control.
2. Technological Feasibility
-
Development of Privacy-Preserving Technologies: Research into methods that can detect illegal content without compromising encryption is ongoing. Advances in this area could provide alternative solutions acceptable to both privacy advocates and security agencies.
-
Implementation Challenges: The practical aspects of deploying scanning technologies across various platforms and services remain complex, and technical hurdles could delay or alter the proposed measures.
3. Political Dynamics
-
Member State Positions: The differing stances of EU countries, such as Germany's opposition, play a significant role in shaping the final outcome. Consensus among member states is crucial for adopting EU-wide regulations.
-
Public Opinion and Advocacy: Growing awareness and activism around digital privacy can influence policymakers. Public campaigns and lobbying efforts may sway decisions in favor of stronger privacy protections.
4. Industry Responses
-
Negotiations with Service Providers: Ongoing dialogues between EU authorities and technology companies may lead to compromises or collaborative efforts to address concerns without fully implementing Chat Control as initially proposed.
-
Potential for Self-Regulation: Messaging services might propose self-regulatory measures to combat illegal content, aiming to demonstrate effectiveness without the need for mandatory scanning.
Possible Scenarios
Optimistic Outcome:
- Balanced Regulation: A revised proposal emerges that effectively addresses security concerns while upholding strong encryption and privacy rights, possibly through innovative technologies or targeted measures with robust oversight.
Pessimistic Outcome:
- Adoption of Strict Measures: Chat Control is implemented as initially proposed, leading to weakened encryption, reduced privacy, and potential withdrawal of services like Signal from the EU market.
Middle Ground:
- Incremental Implementation: Partial measures are adopted, focusing on voluntary cooperation with service providers and emphasizing transparency and user consent, with ongoing evaluations to assess effectiveness and impact.
How to Stay Informed and Protect Your Privacy
-
Follow Reputable Sources: Keep up with news from reliable outlets, official EU communications, and statements from privacy organizations to stay informed about developments.
-
Engage in the Dialogue: Participate in public consultations, sign petitions, or contact representatives to express your views on Chat Control and digital privacy.
-
Utilize Secure Practices: Regardless of legislative outcomes, adopting good digital hygiene—such as using strong passwords and being cautious with personal information—can enhance your online security.

The Global Perspective
-
International Implications: The EU's decision may influence global policies on encryption and surveillance, setting precedents that other countries might follow or react against.
-
Collaboration Opportunities: International cooperation on developing solutions that protect both security and privacy could emerge, fostering a more unified approach to addressing online threats.
Looking Ahead
The future of Chat Control is a critical issue that underscores the challenges of governing in the digital age. Balancing the need for security with the protection of fundamental rights is a complex task that requires careful consideration, open dialogue, and collaboration among all stakeholders.
As the situation evolves, staying informed and engaged is essential. The decisions made in the coming months will shape the digital landscape for years to come, affecting how we communicate, conduct business, and exercise our rights in an increasingly connected world.
Conclusion
The debate over Chat Control highlights a fundamental challenge in our increasingly digital world: how to protect society from genuine threats without eroding the very rights and freedoms that define it. While the intention to safeguard children and prevent crime is undeniably important, the means of achieving this through intrusive surveillance measures raise critical concerns.
Privacy is not just a personal preference but a cornerstone of democratic societies. End-to-end encryption has become an essential tool for ensuring that our personal conversations, professional communications, and sensitive data remain secure from unwanted intrusion. Weakening these protections could expose individuals and organizations to risks that far outweigh the proposed benefits.
The potential consequences of implementing Chat Control are far-reaching:
- Erosion of Trust: Users may lose confidence in digital platforms, impacting how we communicate and conduct business online.
- Security Vulnerabilities: Introducing backdoors or weakening encryption can make systems more susceptible to cyberattacks.
- Stifling Innovation: Regulatory burdens may hinder technological advancement and competitiveness in the tech industry.
- Global Implications: The EU's decisions could set precedents that influence digital policies worldwide, for better or worse.
As citizens, it's crucial to stay informed about these developments. Engage in conversations, reach out to your representatives, and advocate for solutions that respect both security needs and fundamental rights. Technology and policy can evolve together to address challenges without compromising core values.
The future of Chat Control is not yet decided, and public input can make a significant difference. By promoting open dialogue, supporting privacy-preserving innovations, and emphasizing the importance of human rights in legislation, we can work towards a digital landscape that is both safe and free.
In a world where digital communication is integral to daily life, striking the right balance between security and privacy is more important than ever. The choices made today will shape the digital environment for generations to come, determining not just how we communicate, but how we live and interact in an interconnected world.

Thank you for reading this article. We hope it has provided you with a clear understanding of Chat Control and its potential impact on your privacy and digital rights. Stay informed, stay engaged, and let's work together towards a secure and open digital future.
Read more:
- https://www.patrick-breyer.de/en/posts/chat-control/
- https://www.patrick-breyer.de/en/new-eu-push-for-chat-control-will-messenger-services-be-blocked-in-europe/
- https://edri.org/our-work/dutch-decision-puts-brakes-on-chat-control/
- https://signal.org/blog/pdfs/ndss-keynote.pdf
- https://tuta.com/blog/germany-stop-chat-control
- https://cointelegraph.com/news/signal-president-slams-revised-eu-encryption-proposal
- https://mullvad.net/en/why-privacy-matters
-
 @ 4ba8e86d:89d32de4
2024-10-07 13:37:38
@ 4ba8e86d:89d32de4
2024-10-07 13:37:38O que é Cwtch? Cwtch (/kʊtʃ/ - uma palavra galesa que pode ser traduzida aproximadamente como “um abraço que cria um lugar seguro”) é um protocolo de mensagens multipartidário descentralizado, que preserva a privacidade, que pode ser usado para construir aplicativos resistentes a metadados.
Como posso pronunciar Cwtch? Como "kutch", para rimar com "butch".
Descentralizado e Aberto : Não existe “serviço Cwtch” ou “rede Cwtch”. Os participantes do Cwtch podem hospedar seus próprios espaços seguros ou emprestar sua infraestrutura para outras pessoas que buscam um espaço seguro. O protocolo Cwtch é aberto e qualquer pessoa é livre para criar bots, serviços e interfaces de usuário e integrar e interagir com o Cwtch.
Preservação de privacidade : toda a comunicação no Cwtch é criptografada de ponta a ponta e ocorre nos serviços cebola Tor v3.
Resistente a metadados : O Cwtch foi projetado de forma que nenhuma informação seja trocada ou disponibilizada a ninguém sem seu consentimento explícito, incluindo mensagens durante a transmissão e metadados de protocolo
Uma breve história do bate-papo resistente a metadados Nos últimos anos, a conscientização pública sobre a necessidade e os benefícios das soluções criptografadas de ponta a ponta aumentou com aplicativos como Signal , Whatsapp e Wire. que agora fornecem aos usuários comunicações seguras.
No entanto, essas ferramentas exigem vários níveis de exposição de metadados para funcionar, e muitos desses metadados podem ser usados para obter detalhes sobre como e por que uma pessoa está usando uma ferramenta para se comunicar.
Uma ferramenta que buscou reduzir metadados é o Ricochet lançado pela primeira vez em 2014. Ricochet usou os serviços cebola Tor v2 para fornecer comunicação criptografada segura de ponta a ponta e para proteger os metadados das comunicações.
Não havia servidores centralizados que auxiliassem no roteamento das conversas do Ricochet. Ninguém além das partes envolvidas em uma conversa poderia saber que tal conversa está ocorrendo.
Ricochet tinha limitações; não havia suporte para vários dispositivos, nem existe um mecanismo para suportar a comunicação em grupo ou para um usuário enviar mensagens enquanto um contato está offline.
Isto tornou a adoção do Ricochet uma proposta difícil; mesmo aqueles em ambientes que seriam melhor atendidos pela resistência aos metadados, sem saber que ela existe.
Além disso, qualquer solução para comunicação descentralizada e resistente a metadados enfrenta problemas fundamentais quando se trata de eficiência, privacidade e segurança de grupo conforme definido pelo consenso e consistência da transcrição.
Alternativas modernas ao Ricochet incluem Briar , Zbay e Ricochet Refresh - cada ferramenta procura otimizar para um conjunto diferente de compensações, por exemplo, Briar procura permitir que as pessoas se comuniquem mesmo quando a infraestrutura de rede subjacente está inoperante, ao mesmo tempo que fornece resistência à vigilância de metadados.
O projeto Cwtch começou em 2017 como um protocolo de extensão para Ricochet, fornecendo conversas em grupo por meio de servidores não confiáveis, com o objetivo de permitir aplicativos descentralizados e resistentes a metadados como listas compartilhadas e quadros de avisos.
Uma versão alfa do Cwtch foi lançada em fevereiro de 2019 e, desde então, a equipe do Cwtch dirigida pela OPEN PRIVACY RESEARCH SOCIETY conduziu pesquisa e desenvolvimento em cwtch e nos protocolos, bibliotecas e espaços de problemas subjacentes.
Modelo de Risco.
Sabe-se que os metadados de comunicações são explorados por vários adversários para minar a segurança dos sistemas, para rastrear vítimas e para realizar análises de redes sociais em grande escala para alimentar a vigilância em massa. As ferramentas resistentes a metadados estão em sua infância e faltam pesquisas sobre a construção e a experiência do usuário de tais ferramentas.
https://nostrcheck.me/media/public/nostrcheck.me_9475702740746681051707662826.webp
O Cwtch foi originalmente concebido como uma extensão do protocolo Ricochet resistente a metadados para suportar comunicações assíncronas de grupos multiponto por meio do uso de infraestrutura anônima, descartável e não confiável.
Desde então, o Cwtch evoluiu para um protocolo próprio. Esta seção descreverá os vários riscos conhecidos que o Cwtch tenta mitigar e será fortemente referenciado no restante do documento ao discutir os vários subcomponentes da Arquitetura Cwtch.
Modelo de ameaça.
É importante identificar e compreender que os metadados são omnipresentes nos protocolos de comunicação; é de facto necessário que tais protocolos funcionem de forma eficiente e em escala. No entanto, as informações que são úteis para facilitar peers e servidores também são altamente relevantes para adversários que desejam explorar tais informações.
Para a definição do nosso problema, assumiremos que o conteúdo de uma comunicação é criptografado de tal forma que um adversário é praticamente incapaz de quebrá-lo veja tapir e cwtch para detalhes sobre a criptografia que usamos, e como tal nos concentraremos em o contexto para os metadados de comunicação.
Procuramos proteger os seguintes contextos de comunicação:
• Quem está envolvido em uma comunicação? Pode ser possível identificar pessoas ou simplesmente identificadores de dispositivos ou redes. Por exemplo, “esta comunicação envolve Alice, uma jornalista, e Bob, um funcionário público”.
• Onde estão os participantes da conversa? Por exemplo, “durante esta comunicação, Alice estava na França e Bob estava no Canadá”.
• Quando ocorreu uma conversa? O momento e a duração da comunicação podem revelar muito sobre a natureza de uma chamada, por exemplo, “Bob, um funcionário público, conversou com Alice ao telefone por uma hora ontem à noite. Esta é a primeira vez que eles se comunicam.” *Como a conversa foi mediada? O fato de uma conversa ter ocorrido por meio de um e-mail criptografado ou não criptografado pode fornecer informações úteis. Por exemplo, “Alice enviou um e-mail criptografado para Bob ontem, enquanto eles normalmente enviam apenas e-mails de texto simples um para o outro”.
• Sobre o que é a conversa? Mesmo que o conteúdo da comunicação seja criptografado, às vezes é possível derivar um contexto provável de uma conversa sem saber exatamente o que é dito, por exemplo, “uma pessoa ligou para uma pizzaria na hora do jantar” ou “alguém ligou para um número conhecido de linha direta de suicídio na hora do jantar”. 3 horas da manhã."
Além das conversas individuais, também procuramos defender-nos contra ataques de correlação de contexto, através dos quais múltiplas conversas são analisadas para obter informações de nível superior:
• Relacionamentos: Descobrir relações sociais entre um par de entidades analisando a frequência e a duração de suas comunicações durante um período de tempo. Por exemplo, Carol e Eve ligam uma para a outra todos os dias durante várias horas seguidas.
• Cliques: Descobrir relações sociais entre um grupo de entidades que interagem entre si. Por exemplo, Alice, Bob e Eva se comunicam entre si.
• Grupos vagamente conectados e indivíduos-ponte: descobrir grupos que se comunicam entre si através de intermediários, analisando cadeias de comunicação (por exemplo, toda vez que Alice fala com Bob, ela fala com Carol quase imediatamente depois; Bob e Carol nunca se comunicam).
• Padrão de Vida: Descobrir quais comunicações são cíclicas e previsíveis. Por exemplo, Alice liga para Eve toda segunda-feira à noite por cerca de uma hora. Ataques Ativos
Ataques de deturpação.
O Cwtch não fornece registro global de nomes de exibição e, como tal, as pessoas que usam o Cwtch são mais vulneráveis a ataques baseados em declarações falsas, ou seja, pessoas que fingem ser outras pessoas:
O fluxo básico de um desses ataques é o seguinte, embora também existam outros fluxos:
•Alice tem um amigo chamado Bob e outro chamado Eve
• Eve descobre que Alice tem um amigo chamado Bob
• Eve cria milhares de novas contas para encontrar uma que tenha uma imagem/chave pública semelhante à de Bob (não será idêntica, mas pode enganar alguém por alguns minutos)
• Eve chama essa nova conta de "Eve New Account" e adiciona Alice como amiga.
• Eve então muda seu nome em "Eve New Account" para "Bob"
• Alice envia mensagens destinadas a "Bob" para a conta falsa de Bob de Eve Como os ataques de declarações falsas são inerentemente uma questão de confiança e verificação, a única maneira absoluta de evitá-los é os usuários validarem absolutamente a chave pública. Obviamente, isso não é o ideal e, em muitos casos, simplesmente não acontecerá .
Como tal, pretendemos fornecer algumas dicas de experiência do usuário na interface do usuário para orientar as pessoas na tomada de decisões sobre confiar em contas e/ou distinguir contas que possam estar tentando se representar como outros usuários.
Uma nota sobre ataques físicos A Cwtch não considera ataques que exijam acesso físico (ou equivalente) à máquina do usuário como praticamente defensáveis. No entanto, no interesse de uma boa engenharia de segurança, ao longo deste documento ainda nos referiremos a ataques ou condições que exigem tal privilégio e indicaremos onde quaisquer mitigações que implementámos falharão.
Um perfil Cwtch.
Os usuários podem criar um ou mais perfis Cwtch. Cada perfil gera um par de chaves ed25519 aleatório compatível com Tor.
Além do material criptográfico, um perfil também contém uma lista de Contatos (outras chaves públicas do perfil Cwtch + dados associados sobre esse perfil, como apelido e (opcionalmente) mensagens históricas), uma lista de Grupos (contendo o material criptográfico do grupo, além de outros dados associados, como apelido do grupo e mensagens históricas).
Conversões entre duas partes: ponto a ponto
https://nostrcheck.me/media/public/nostrcheck.me_2186338207587396891707662879.webp
Para que duas partes participem de uma conversa ponto a ponto, ambas devem estar on-line, mas apenas uma precisa estar acessível por meio do serviço Onion. Por uma questão de clareza, muitas vezes rotulamos uma parte como “ponto de entrada” (aquele que hospeda o serviço cebola) e a outra parte como “ponto de saída” (aquele que se conecta ao serviço cebola).
Após a conexão, ambas as partes adotam um protocolo de autenticação que:
• Afirma que cada parte tem acesso à chave privada associada à sua identidade pública.
• Gera uma chave de sessão efêmera usada para criptografar todas as comunicações futuras durante a sessão.
Esta troca (documentada com mais detalhes no protocolo de autenticação ) é negável offline , ou seja, é possível para qualquer parte falsificar transcrições desta troca de protocolo após o fato e, como tal - após o fato - é impossível provar definitivamente que a troca aconteceu de forma alguma.
Após o protocolo de autenticação, as duas partes podem trocar mensagens livremente.
Conversas em Grupo e Comunicação Ponto a Servidor
Ao iniciar uma conversa em grupo, é gerada uma chave aleatória para o grupo, conhecida como Group Key. Todas as comunicações do grupo são criptografadas usando esta chave. Além disso, o criador do grupo escolhe um servidor Cwtch para hospedar o grupo. Um convite é gerado, incluindo o Group Key, o servidor do grupo e a chave do grupo, para ser enviado aos potenciais membros.
Para enviar uma mensagem ao grupo, um perfil se conecta ao servidor do grupo e criptografa a mensagem usando a Group Key, gerando também uma assinatura sobre o Group ID, o servidor do grupo e a mensagem. Para receber mensagens do grupo, um perfil se conecta ao servidor e baixa as mensagens, tentando descriptografá-las usando a Group Key e verificando a assinatura.
Detalhamento do Ecossistema de Componentes
O Cwtch é composto por várias bibliotecas de componentes menores, cada uma desempenhando um papel específico. Algumas dessas bibliotecas incluem:
- abertoprivacidade/conectividade: Abstração de rede ACN, atualmente suportando apenas Tor.
- cwtch.im/tapir: Biblioteca para construção de aplicativos p2p em sistemas de comunicação anônimos.
- cwtch.im/cwtch: Biblioteca principal para implementação do protocolo/sistema Cwtch.
- cwtch.im/libcwtch-go: Fornece ligações C para Cwtch para uso em implementações de UI.
TAPIR: Uma Visão Detalhada
Projetado para substituir os antigos canais de ricochete baseados em protobuf, o Tapir fornece uma estrutura para a construção de aplicativos anônimos.
Está dividido em várias camadas:
• Identidade - Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um par.
• Conexões – O protocolo de rede bruto que conecta dois pares. Até agora, as conexões são definidas apenas através do Tor v3 Onion Services.
• Aplicativos - As diversas lógicas que permitem um determinado fluxo de informações em uma conexão. Os exemplos incluem transcrições criptográficas compartilhadas, autenticação, proteção contra spam e serviços baseados em tokens. Os aplicativos fornecem recursos que podem ser referenciados por outros aplicativos para determinar se um determinado peer tem a capacidade de usar um determinado aplicativo hospedado.
• Pilhas de aplicativos - Um mecanismo para conectar mais de um aplicativo, por exemplo, a autenticação depende de uma transcrição criptográfica compartilhada e o aplicativo peer cwtch principal é baseado no aplicativo de autenticação.
Identidade.
Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um peer.
InitializeIdentity - de um par de chaves conhecido e persistente:i,I
InitializeEphemeralIdentity - de um par de chaves aleatório: ie,Ie
Aplicativos de transcrição.
Inicializa uma transcrição criptográfica baseada em Merlin que pode ser usada como base de protocolos baseados em compromisso de nível superior
O aplicativo de transcrição entrará em pânico se um aplicativo tentar substituir uma transcrição existente por uma nova (aplicando a regra de que uma sessão é baseada em uma e apenas uma transcrição).
Merlin é uma construção de transcrição baseada em STROBE para provas de conhecimento zero. Ele automatiza a transformação Fiat-Shamir, para que, usando Merlin, protocolos não interativos possam ser implementados como se fossem interativos.
Isto é significativamente mais fácil e menos sujeito a erros do que realizar a transformação manualmente e, além disso, também fornece suporte natural para:
• protocolos multi-round com fases alternadas de commit e desafio;
• separação natural de domínios, garantindo que os desafios estejam vinculados às afirmações a serem provadas;
• enquadramento automático de mensagens, evitando codificação ambígua de dados de compromisso;
• e composição do protocolo, usando uma transcrição comum para vários protocolos.
Finalmente, o Merlin também fornece um gerador de números aleatórios baseado em transcrição como defesa profunda contra ataques de entropia ruim (como reutilização de nonce ou preconceito em muitas provas). Este RNG fornece aleatoriedade sintética derivada de toda a transcrição pública, bem como dos dados da testemunha do provador e uma entrada auxiliar de um RNG externo.
Conectividade Cwtch faz uso do Tor Onion Services (v3) para todas as comunicações entre nós.
Fornecemos o pacote openprivacy/connectivity para gerenciar o daemon Tor e configurar e desmontar serviços cebola através do Tor.
Criptografia e armazenamento de perfil.
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir uma senha.
Perfis não criptografados e a senha padrão Para lidar com perfis "não criptografados" (ou seja, que não exigem senha para serem abertos), atualmente criamos um perfil com uma senha codificada de fato .
Isso não é o ideal, preferiríamos confiar no material de chave fornecido pelo sistema operacional, de modo que o perfil fosse vinculado a um dispositivo específico, mas esses recursos são atualmente uma colcha de retalhos - também notamos, ao criar um perfil não criptografado, pessoas que usam Cwtch estão explicitamente optando pelo risco de que alguém com acesso ao sistema de arquivos possa descriptografar seu perfil.
Vulnerabilidades Relacionadas a Imagens e Entrada de Dados
Imagens Maliciosas
O Cwtch enfrenta desafios na renderização de imagens, com o Flutter utilizando Skia, embora o código subjacente não seja totalmente seguro para a memória.
Realizamos testes de fuzzing nos componentes Cwtch e encontramos um bug de travamento causado por um arquivo GIF malformado, levando a falhas no kernel. Para mitigar isso, adotamos a política de sempre habilitar cacheWidth e/ou cacheHeight máximo para widgets de imagem.
Identificamos o risco de imagens maliciosas serem renderizadas de forma diferente em diferentes plataformas, como evidenciado por um bug no analisador PNG da Apple.
Riscos de Entrada de Dados
Um risco significativo é a interceptação de conteúdo ou metadados por meio de um Input Method Editor (IME) em dispositivos móveis. Mesmo aplicativos IME padrão podem expor dados por meio de sincronização na nuvem, tradução online ou dicionários pessoais.
Implementamos medidas de mitigação, como enableIMEPersonalizedLearning: false no Cwtch 1.2, mas a solução completa requer ações em nível de sistema operacional e é um desafio contínuo para a segurança móvel.
Servidor Cwtch.
O objetivo do protocolo Cwtch é permitir a comunicação em grupo através de infraestrutura não confiável .
Ao contrário dos esquemas baseados em retransmissão, onde os grupos atribuem um líder, um conjunto de líderes ou um servidor confiável de terceiros para garantir que cada membro do grupo possa enviar e receber mensagens em tempo hábil (mesmo que os membros estejam offline) - infraestrutura não confiável tem o objetivo de realizar essas propriedades sem a suposição de confiança.
O artigo original do Cwtch definia um conjunto de propriedades que se esperava que os servidores Cwtch fornecessem:
• O Cwtch Server pode ser usado por vários grupos ou apenas um.
• Um servidor Cwtch, sem a colaboração de um membro do grupo, nunca deve aprender a identidade dos participantes de um grupo.
• Um servidor Cwtch nunca deve aprender o conteúdo de qualquer comunicação.
• Um servidor Cwtch nunca deve ser capaz de distinguir mensagens como pertencentes a um grupo específico. Observamos aqui que essas propriedades são um superconjunto dos objetivos de design das estruturas de Recuperação de Informações Privadas.
Melhorias na Eficiência e Segurança
Eficiência do Protocolo
Atualmente, apenas um protocolo conhecido, o PIR ingênuo, atende às propriedades desejadas para garantir a privacidade na comunicação do grupo Cwtch. Este método tem um impacto direto na eficiência da largura de banda, especialmente para usuários em dispositivos móveis. Em resposta a isso, estamos ativamente desenvolvendo novos protocolos que permitem negociar garantias de privacidade e eficiência de maneiras diversas.
Os servidores, no momento desta escrita, permitem o download completo de todas as mensagens armazenadas, bem como uma solicitação para baixar mensagens específicas a partir de uma determinada mensagem. Quando os pares ingressam em um grupo em um novo servidor, eles baixam todas as mensagens do servidor inicialmente e, posteriormente, apenas as mensagens novas.
Mitigação de Análise de Metadados
Essa abordagem permite uma análise moderada de metadados, pois o servidor pode enviar novas mensagens para cada perfil suspeito exclusivo e usar essas assinaturas de mensagens exclusivas para rastrear sessões ao longo do tempo. Essa preocupação é mitigada por dois fatores:
- Os perfis podem atualizar suas conexões a qualquer momento, resultando em uma nova sessão do servidor.
- Os perfis podem ser "ressincronizados" de um servidor a qualquer momento, resultando em uma nova chamada para baixar todas as mensagens. Isso é comumente usado para buscar mensagens antigas de um grupo.
Embora essas medidas imponham limites ao que o servidor pode inferir, ainda não podemos garantir resistência total aos metadados. Para soluções futuras para esse problema, consulte Niwl.
Proteção contra Pares Maliciosos
Os servidores enfrentam o risco de spam gerado por pares, representando uma ameaça significativa à eficácia do sistema Cwtch. Embora tenhamos implementado um mecanismo de proteção contra spam no protótipo do Cwtch, exigindo que os pares realizem alguma prova de trabalho especificada pelo servidor, reconhecemos que essa não é uma solução robusta na presença de um adversário determinado com recursos significativos.
Pacotes de Chaves
Os servidores Cwtch se identificam por meio de pacotes de chaves assinados, contendo uma lista de chaves necessárias para garantir a segurança e resistência aos metadados na comunicação do grupo Cwtch. Esses pacotes de chaves geralmente incluem três chaves: uma chave pública do serviço Tor v3 Onion para o Token Board, uma chave pública do Tor v3 Onion Service para o Token Service e uma chave pública do Privacy Pass.
Para verificar os pacotes de chaves, os perfis que os importam do servidor utilizam o algoritmo trust-on-first-use (TOFU), verificando a assinatura anexada e a existência de todos os tipos de chave. Se o perfil já tiver importado o pacote de chaves do servidor anteriormente, todas as chaves são consideradas iguais.
Configuração prévia do aplicativo para ativar o Relé do Cwtch.
No Android, a hospedagem de servidor não está habilitada, pois essa opção não está disponível devido às limitações dos dispositivos Android. Essa funcionalidade está reservada apenas para servidores hospedados em desktops.
No Android, a única forma direta de importar uma chave de servidor é através do grupo de teste Cwtch, garantindo assim acesso ao servidor Cwtch.
Primeiro passo é Habilitar a opção de grupo no Cwtch que está em fase de testes. Clique na opção no canto superior direito da tela de configuração e pressione o botão para acessar as configurações do Cwtch.
Você pode alterar o idioma para Português do Brasil.Depois, role para baixo e selecione a opção para ativar os experimentos. Em seguida, ative a opção para habilitar o chat em grupo e a pré-visualização de imagens e fotos de perfil, permitindo que você troque sua foto de perfil.
https://link.storjshare.io/raw/jvss6zxle26jdguwaegtjdixhfka/production/f0ca039733d48895001261ab25c5d2efbaf3bf26e55aad3cce406646f9af9d15.MP4
Próximo passo é Criar um perfil.
Pressione o + botão de ação no canto inferior direito e selecione "Novo perfil" ou aberta no botão + adicionar novo perfil.
-
Selecione um nome de exibição
-
Selecione se deseja proteger
este perfil e salvo localmente com criptografia forte: Senha: sua conta está protegida de outras pessoas que possam usar este dispositivo
Sem senha: qualquer pessoa que tenha acesso a este dispositivo poderá acessar este perfil.
Preencha sua senha e digite-a novamente
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a chave da senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir um senha.
https://link.storjshare.io/raw/jxqbqmur2lcqe2eym5thgz4so2ya/production/8f9df1372ec7e659180609afa48be22b12109ae5e1eda9ef1dc05c1325652507.MP4
O próximo passo é adicionar o FuzzBot, que é um bot de testes e de desenvolvimento.
Contato do FuzzBot: 4y2hxlxqzautabituedksnh2ulcgm2coqbure6wvfpg4gi2ci25ta5ad.
Ao enviar o comando "testgroup-invite" para o FuzzBot, você receberá um convite para entrar no Grupo Cwtch Test. Ao ingressar no grupo, você será automaticamente conectado ao servidor Cwtch. Você pode optar por sair do grupo a qualquer momento ou ficar para conversar e tirar dúvidas sobre o aplicativo e outros assuntos. Depois, você pode configurar seu próprio servidor Cwtch, o que é altamente recomendável.
https://link.storjshare.io/raw/jvji25zclkoqcouni5decle7if7a/production/ee3de3540a3e3dca6e6e26d303e12c2ef892a5d7769029275b8b95ffc7468780.MP4
Agora você pode utilizar o aplicativo normalmente. Algumas observações que notei: se houver demora na conexão com outra pessoa, ambas devem estar online. Se ainda assim a conexão não for estabelecida, basta clicar no ícone de reset do Tor para restabelecer a conexão com a outra pessoa.
Uma introdução aos perfis Cwtch.
Com Cwtch você pode criar um ou mais perfis . Cada perfil gera um par de chaves ed25519 aleatório compatível com a Rede Tor.
Este é o identificador que você pode fornecer às pessoas e que elas podem usar para entrar em contato com você via Cwtch.
Cwtch permite criar e gerenciar vários perfis separados. Cada perfil está associado a um par de chaves diferente que inicia um serviço cebola diferente.
Gerenciar Na inicialização, o Cwtch abrirá a tela Gerenciar Perfis. Nessa tela você pode:
- Crie um novo perfil.
- Desbloquear perfis.
- Criptografados existentes.
- Gerenciar perfis carregados.
- Alterando o nome de exibição de um perfil.
- Alterando a senha de um perfil Excluindo um perfil.
- Alterando uma imagem de perfil.
Backup ou exportação de um perfil.
Na tela de gerenciamento de perfil:
-
Selecione o lápis ao lado do perfil que você deseja editar
-
Role para baixo até a parte inferior da tela.
-
Selecione "Exportar perfil"
-
Escolha um local e um nome de arquivo.
5.confirme.
Uma vez confirmado, o Cwtch colocará uma cópia do perfil no local indicado. Este arquivo é criptografado no mesmo nível do perfil.
Este arquivo pode ser importado para outra instância do Cwtch em qualquer dispositivo.
Importando um perfil.
-
Pressione o +botão de ação no canto inferior direito e selecione "Importar perfil"
-
Selecione um arquivo de perfil Cwtch exportado para importar
-
Digite a senha associada ao perfil e confirme.
Uma vez confirmado, o Cwtch tentará descriptografar o arquivo fornecido usando uma chave derivada da senha fornecida. Se for bem-sucedido, o perfil aparecerá na tela Gerenciamento de perfil e estará pronto para uso.
OBSERVAÇÃO Embora um perfil possa ser importado para vários dispositivos, atualmente apenas uma versão de um perfil pode ser usada em todos os dispositivos ao mesmo tempo. As tentativas de usar o mesmo perfil em vários dispositivos podem resultar em problemas de disponibilidade e falhas de mensagens.
Qual é a diferença entre uma conexão ponto a ponto e um grupo cwtch?
As conexões ponto a ponto Cwtch permitem que 2 pessoas troquem mensagens diretamente. As conexões ponto a ponto nos bastidores usam serviços cebola Tor v3 para fornecer uma conexão criptografada e resistente a metadados. Devido a esta conexão direta, ambas as partes precisam estar online ao mesmo tempo para trocar mensagens.
Os Grupos Cwtch permitem que várias partes participem de uma única conversa usando um servidor não confiável (que pode ser fornecido por terceiros ou auto-hospedado). Os operadores de servidores não conseguem saber quantas pessoas estão em um grupo ou o que está sendo discutido. Se vários grupos estiverem hospedados em um único servidor, o servidor não conseguirá saber quais mensagens pertencem a qual grupo sem a conivência de um membro do grupo. Ao contrário das conversas entre pares, as conversas em grupo podem ser conduzidas de forma assíncrona, para que todos num grupo não precisem estar online ao mesmo tempo.
Por que os grupos cwtch são experimentais? Mensagens em grupo resistentes a metadados ainda são um problema em aberto . Embora a versão que fornecemos no Cwtch Beta seja projetada para ser segura e com metadados privados, ela é bastante ineficiente e pode ser mal utilizada. Como tal, aconselhamos cautela ao usá-lo e apenas o fornecemos como um recurso opcional.
Como posso executar meu próprio servidor Cwtch? A implementação de referência para um servidor Cwtch é de código aberto . Qualquer pessoa pode executar um servidor Cwtch, e qualquer pessoa com uma cópia do pacote de chaves públicas do servidor pode hospedar grupos nesse servidor sem que o operador tenha acesso aos metadados relacionados ao grupo .
https://git.openprivacy.ca/cwtch.im/server
https://docs.openprivacy.ca/cwtch-security-handbook/server.html
Como posso desligar o Cwtch? O painel frontal do aplicativo possui um ícone do botão "Shutdown Cwtch" (com um 'X'). Pressionar este botão irá acionar uma caixa de diálogo e, na confirmação, o Cwtch será desligado e todos os perfis serão descarregados.
Suas doações podem fazer a diferença no projeto Cwtch? O Cwtch é um projeto dedicado a construir aplicativos que preservam a privacidade, oferecendo comunicação de grupo resistente a metadados. Além disso, o projeto também desenvolve o Cofre, formulários da web criptografados para ajudar mútua segura. Suas contribuições apoiam iniciativas importantes, como a divulgação de violações de dados médicos em Vancouver e pesquisas sobre a segurança do voto eletrônico na Suíça. Ao doar, você está ajudando a fechar o ciclo, trabalhando com comunidades marginalizadas para identificar e corrigir lacunas de privacidade. Além disso, o projeto trabalha em soluções inovadoras, como a quebra de segredos através da criptografia de limite para proteger sua privacidade durante passagens de fronteira. E também tem a infraestrutura: toda nossa infraestrutura é open source e sem fins lucrativos. Conheça também o Fuzzytags, uma estrutura criptográfica probabilística para marcação resistente a metadados. Sua doação é crucial para continuar o trabalho em prol da privacidade e segurança online. Contribua agora com sua doação
https://openprivacy.ca/donate/
onde você pode fazer sua doação em bitcoin e outras moedas, e saiba mais sobre os projetos. https://openprivacy.ca/work/
Link sobre Cwtch
https://cwtch.im/
https://git.openprivacy.ca/cwtch.im/cwtch
https://docs.cwtch.im/docs/intro
https://docs.openprivacy.ca/cwtch-security-handbook/
Baixar #CwtchDev
cwtch.im/download/
https://play.google.com/store/apps/details?id=im.cwtch.flwtch
-
 @ a95c6243:d345522c
2025-01-03 20:26:47
@ a95c6243:d345522c
2025-01-03 20:26:47Was du bist hängt von drei Faktoren ab: \ Was du geerbt hast, \ was deine Umgebung aus dir machte \ und was du in freier Wahl \ aus deiner Umgebung und deinem Erbe gemacht hast. \ Aldous Huxley
Das brave Mitmachen und Mitlaufen in einem vorgegebenen, recht engen Rahmen ist gewiss nicht neu, hat aber gerade wieder mal Konjunktur. Dies kann man deutlich beobachten, eigentlich egal, in welchem gesellschaftlichen Bereich man sich umschaut. Individualität ist nur soweit angesagt, wie sie in ein bestimmtes Schema von «Diversität» passt, und Freiheit verkommt zur Worthülse – nicht erst durch ein gewisses Buch einer gewissen ehemaligen Regierungschefin.
Erklärungsansätze für solche Entwicklungen sind bekannt, und praktisch alle haben etwas mit Massenpsychologie zu tun. Der Herdentrieb, also der Trieb der Menschen, sich – zum Beispiel aus Unsicherheit oder Bequemlichkeit – lieber der Masse anzuschließen als selbstständig zu denken und zu handeln, ist einer der Erklärungsversuche. Andere drehen sich um Macht, Propaganda, Druck und Angst, also den gezielten Einsatz psychologischer Herrschaftsinstrumente.
Aber wollen die Menschen überhaupt Freiheit? Durch Gespräche im privaten Umfeld bin ich diesbezüglich in der letzten Zeit etwas skeptisch geworden. Um die Jahreswende philosophiert man ja gerne ein wenig über das Erlebte und über die Erwartungen für die Zukunft. Dabei hatte ich hin und wieder den Eindruck, die totalitären Anwandlungen unserer «Repräsentanten» kämen manchen Leuten gerade recht.
«Desinformation» ist so ein brisantes Thema. Davor müsse man die Menschen doch schützen, hörte ich. Jemand müsse doch zum Beispiel diese ganzen merkwürdigen Inhalte in den Social Media filtern – zur Ukraine, zum Klima, zu Gesundheitsthemen oder zur Migration. Viele wüssten ja gar nicht einzuschätzen, was richtig und was falsch ist, sie bräuchten eine Führung.
Freiheit bedingt Eigenverantwortung, ohne Zweifel. Eventuell ist es einigen tatsächlich zu anspruchsvoll, die Verantwortung für das eigene Tun und Lassen zu übernehmen. Oder die persönliche Freiheit wird nicht als ausreichend wertvolles Gut angesehen, um sich dafür anzustrengen. In dem Fall wäre die mangelnde Selbstbestimmung wohl das kleinere Übel. Allerdings fehlt dann gemäß Aldous Huxley ein Teil der Persönlichkeit. Letztlich ist natürlich alles eine Frage der Abwägung.
Sind viele Menschen möglicherweise schon so «eingenordet», dass freiheitliche Ambitionen gar nicht für eine ganze Gruppe, ein Kollektiv, verfolgt werden können? Solche Gedanken kamen mir auch, als ich mir kürzlich diverse Talks beim viertägigen Hacker-Kongress des Chaos Computer Clubs (38C3) anschaute. Ich war nicht nur überrascht, sondern reichlich erschreckt angesichts der in weiten Teilen mainstream-geformten Inhalte, mit denen ein dankbares Publikum beglückt wurde. Wo ich allgemein hellere Köpfe erwartet hatte, fand ich Konformismus und enthusiastisch untermauerte Narrative.
Gibt es vielleicht so etwas wie eine Herdenimmunität gegen Indoktrination? Ich denke, ja, zumindest eine gestärkte Widerstandsfähigkeit. Was wir brauchen, sind etwas gesunder Menschenverstand, offene Informationskanäle und der Mut, sich freier auch zwischen den Herden zu bewegen. Sie tun das bereits, aber sagen Sie es auch dieses Jahr ruhig weiter.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 7e538978:a5987ab6
2024-10-02 13:57:31
@ 7e538978:a5987ab6
2024-10-02 13:57:31Chain Duel, a fast paced PvP game that takes inspiration from the classic snake game and supercharges it with Bitcoin’s Lightning Network. Imagine battling another player for dominance in a race to collect blocks, where the length of your chain isn’t just a visual cue. It represents real, staked satoshis. The player with the most Proof of Work wins, but it’s not just about gameplay; it’s about the seamless integration of the Lightning Network and real-time payments.
But how does Chain Duel manage these instant transactions with such efficiency? That’s where LNbits comes in. LNbits, an open-source wallet and payment infrastructure, handles all in-game payments making it easy for developers to focus on gameplay while LNbits takes care of everything from microtransactions to automated splits for developers and designers. In this article, we’ll dive deep into how Chain Duel leverages LNbits to streamline in-game payments and how other developers can take advantage of this powerful toolset to build the future of Lightning-powered gaming.
Let’s explore how LNbits transforms payment processing and why it’s quickly becoming a must-have for game developers working in the Bitcoin space.
Overview of Chain Duel
Chain Duel is a unique Lightning Network-inspired game that reimagines the classic snake game with a competitive twist, integrating real-time payments. Two players face off in real-time, racing to "catch" blocks and extend their chains. Each block added to the chain represents Proof of Work, and the player with the most Proof of Work wins the duel. The stakes are high, as the game represents satoshis (small units of Bitcoin) as points, with the winner taking home the prize.
The game is designed to be Lightning-native, meaning all payments within Chain Duel are processed through the Lightning Network. This ensures fast payments, reducing latency and making gameplay smooth. With additional features like practice mode, tournaments and highscores, Chain Duel creates an engaging and competitive environment for Bitcoin enthusiasts and gamers alike.

One of the standout aspects of Chain Duel is its deeper integration with the Lightning Network even at a design level. For example, actual Bitcoin blocks can appear on screen during matches, offering bonus points when mined in sync with the game. The game’s current version, still in beta, has already drawn attention within the Bitcoin community, gaining momentum at conferences and with a growing user base through its social networks. With its innovative combination of gaming, the Lightning Network, and competitive play, Chain Duel offers a glimpse into the future of Lightning-based gaming.
How LNbits is Used in Chain Duel
Seamless Integration with LNbits
At the core of Chain Duel’s efficient payment processing is LNbits, which handles in-game transactions smoothly and reliably. Chain Duel uses the LNbits LNURL-pay and LNURL-withdraw extensions to manage payments and rewards between players. Before each match, players send satoshis using LNURL-pay, which generates a static QR code or link for making the payment. LNURL-pay allows users to attach a note to the payment, which Chain Duel creatively uses as a way to insert the player name in-game. The simplicity of LNURL-pay ensures that users can quickly and easily initiate games, with fresh invoices being issued for every game. When players win, LNURL-withdraw enables them to seamlessly pull their earnings from the game, providing a quick payout system.
These extensions make it easy for players to send and receive Bitcoin with minimal latency, fully leveraging the power of the Lightning Network for fast and low-cost payments. The flexibility of LNbits’ tools means that game developers don’t need to worry about building custom payment systems from scratch—they can rely on LNbits to handle all financial transactions with precision.
Lightning Tournaments
Chain Duel tournaments leverage LNbits and its LNURL extensions to create a seamless and efficient experience for players. In Chain Duel tournaments, LNbits plays a crucial role in managing the overall economics. LNbits facilitates the generation of LNURL QR codes that participants can scan to register quickly or withdraw their winnings. LNbits allows Chain Duel to automatically handle multiple registrations through LNURL-pay, enabling players to participate in the tournament without additional steps. The Lightning Network's speed ensures that these payments occur in real-time, reducing wait times and allowing for a smoother flow in-game.
Splitting Payments
LNbits further simplifies revenue-sharing within Chain Duel. This feature allows the game to automatically split the satoshis sent by players into different shares for the game’s developer, designer, and host. Each time a payment is made to join a match, LNbits is used to automattically pay each of the contributors, according to pre-defined rules. This automated process ensures that everyone involved in the development and running of the game gets their fair share without manual intervention or complex bookkeeping.
Nostr Integration
Chain Duel also integrates with Nostr, a decentralized protocol for social interactions. Players can join games using "Zaps", small tips or micropayments sent over the Lightning Network within the Nostr ecosystem. Through NIP-57, which enables Nostr clients to request Zap invoices, players can use LNURL-pay enabled Zaps to register in P2P matches, further enhancing the Chain Duel experience. By using Zaps as a way to register in-game, Chain Duel automates the process of fetching players' identity, creating a more competitive and social experience. Zaps are public on the Nostr network, further expanding Chain Duel's games social reach and community engagement.
Game and Payment Synchronization
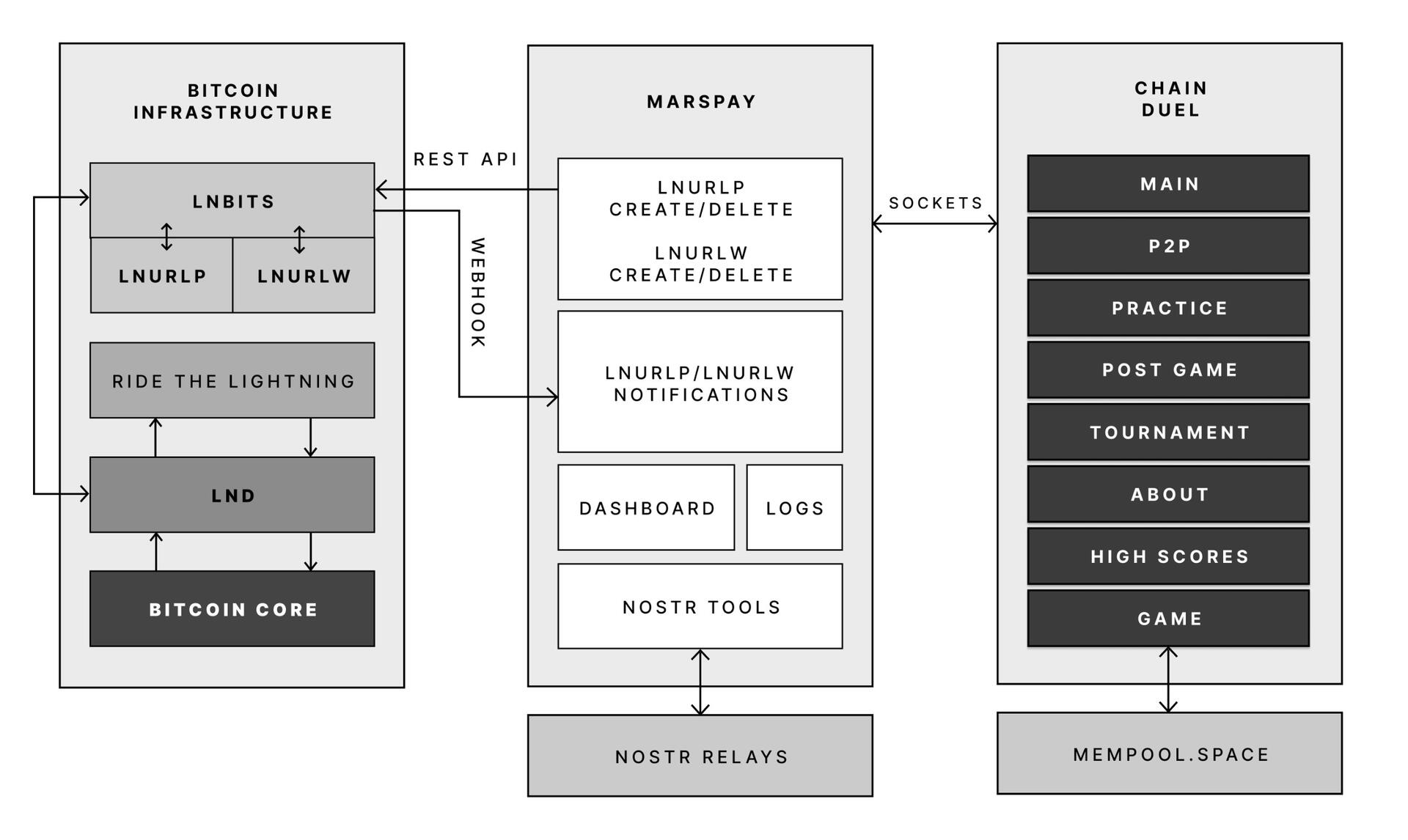
One of the key reasons Chain Duel developers chose LNbits is its powerful API that connects directly with the game’s logic. LNbits allows the game to synchronize payments with gameplay in real-time, providing a seamless experience where payments are an integrated part of the gaming mechanics.
With LNbits managing both the payment process and the Lightning Network’s complex infrastructure, Chain Duel developers are free to concentrate on enhancing the competitive and Lightning Network-related aspects of the game. This division of tasks is essential for streamlining development while still providing an innovative in-game payment experience that is deeply integrated with the Bitcoin network.
LNbits proves to be an indispensable tool for Chain Duel, enabling smooth in-game transactions, real-time revenue sharing, and seamless integration with Nostr. For developers looking to build Lightning-powered games, LNbits offers a powerful suite of tools that handle everything from micropayments to payment distribution—ensuring that the game's focus remains on fun and competition rather than complex payment systems.
LNBits facilitating Education and Adoption
This system contributes to educating users on the power of the Lightning Network. Since Chain Duel directly involve real satoshis and LNURL for registration and rewards, players actively experience how Lightning can facilitate fast, cheap, and permissionless payments. By incorporating LNbits into Chain Duel, the game serves as an educational tool that introduces users to the benefits of the Lightning Network. Players gain direct experience using Lightning wallets and LNURL, helping them understand how these tools work in real-world scenarios. The near-instant nature of these payments showcases the power of Lightning in a practical context, highlighting its potential beyond just gaming. Players are encouraged to set up wallets, explore the Lightning ecosystem, and eventually become familiar with Bitcoin and Lightning technology. By integrating LNbits, Chain Duel transforms in-game payments into a learning opportunity, making Bitcoin and Lightning more approachable for users worldwide.
Tools for Developers
LNbits is a versatile, open-source platform designed to simplify and enhance Bitcoin Lightning Network wallet management. For developers, particularly those working on Lightning-native games like Chain Duel, LNbits offers an invaluable set of tools that allow for seamless integration of Lightning payments without the need to build complex custom solutions from scratch. LNbits is built on a modular and extensible architecture, enabling developers to easily add or create functionality suited to their project’s needs.
Extensible Architecture for Customization
At the core of LNbits is a simple yet powerful wallet system that developers can access across multiple devices. What makes LNbits stand out is its extensible nature—everything beyond the core functionality is implemented as an extension. This modular approach allows users to customize their LNbits installation by enabling or building extensions to suit specific use cases. This flexibility is perfect for developers who want to add Lightning-based services to their games or apps without modifying the core codebase.
- Extensions for Every Use Case
LNbits comes with a wide array of built-in extensions created by contributors, offering various services that can be plugged into your application. Some popular extensions include: - Faucets: Distribute small amounts of Bitcoin to users for testing or promotional purposes.
- Paylinks: Create shareable links for instant payments.
- Points-of-sale (PoS): Allow users to set up shareable payment terminals.
- Paywalls: Charge users to access content or services.
- Event tickets: Sell tickets for events directly via Lightning payments.
- Games and services: From dice games to jukeboxes, LNbits offers entertaining and functional tools.
These ready-made solutions can be adapted and used in different gaming scenarios, for example in Chain Duel, where LNURL extensions are used for in game payments. The extensibility ensures developers can focus on building engaging gameplay while LNbits handles payment flows.
Developer-Friendly Customization
LNbits isn't just a plug-and-play platform. Developers can extend its functionality even further by creating their own extensions, giving full control over how the wallet system is integrated into their games or apps. The architecture is designed to make it easy for developers to build on top of the platform, adding custom features for specific requirements.
Flexible Funding Source Management
LNbits also offers flexibility in terms of managing funding sources. Developers can easily connect LNbits to various Lightning Network node implementations, enabling seamless transitions between nodes or even different payment systems. This allows developers to switch underlying funding sources with minimal effort, making LNbits adaptable for games that may need to scale quickly or rely on different payment infrastructures over time.
A Lean Core System for Maximum Efficiency
Thanks to its modular architecture, LNbits maintains a lean core system. This reduces complexity and overhead, allowing developers to implement only the features they need. By avoiding bloated software, LNbits ensures faster transactions and less resource consumption, which is crucial in fast-paced environments like Chain Duel where speed and efficiency are paramount.
LNbits is designed with developers in mind, offering a suite of tools and a flexible infrastructure that makes integrating Bitcoin payments easy. Whether you’re developing games, apps, or any service that requires Lightning Network transactions, LNbits is a powerful, open-source solution that can be adapted to fit your project.
Conclusion
Chain Duel stands at the forefront of Lightning-powered gaming, combining the excitement of competitive PvP with the speed and efficiency of the Lightning Network. With LNbits handling all in-game payments, from microtransactions to automated revenue splits, developers can focus entirely on crafting an engaging gaming experience. LNbits’ powerful API and extensions make it easy to manage real-time payments, removing the complexity of building payment infrastructure from scratch.
LNbits isn’t just a payment tool — it’s a flexible, developer-friendly platform that can be adapted to any gaming model. Whether you're developing a fast-paced PvP game like Chain Duel or any project requiring seamless Lightning Network integration, LNbits provides the ideal solution for handling instant payments with minimal overhead.
For developers interested in pushing the boundaries of Lightning-powered gaming, Chain Duel is a great example of how LNbits can enhance your game, letting you focus on the fun while LNbits manages real-time transactions.
Find out more
Curious about how Lightning Network payments can power your next game? Explore the following:
- Learn more about Chain Duel: Chain Duel
- Learn how LNbits can simplify payment handling in your project: LNbits
- Dive into decentralized communication with Nostr: Nostr
- Extensions for Every Use Case
-
 @ bf7973ed:841ad12a
2025-01-19 17:34:16
@ bf7973ed:841ad12a
2025-01-19 17:34:16Today marked the end of the tik tok era (is it really the end?) and if think it shows how powerful social engineering is. People are experiencing withdrawals and some have resorted to a more dangerous drug (Rednote) which I find funny because they can't understand any writing in the app. They just need that cheap thrill.
Social media was first created to keep in tough with friends and family and possibly make new friends. It wasn't long before social media was turned into for profit advertising platforms. This introduced "The Algorithm" to make the experience more "relatable" to users. This is where the addiction began.
Nostr doesn't have an algorithm. It is a place to keep in touch with family, friends and make a lot of new friends. Nostr is a protocol at heart. Nostr is a place for everyone. A true freedom of speech. A place with no controlling autority. Nostr is what social media was meant to be.
-
 @ a95c6243:d345522c
2025-01-01 17:39:51
@ a95c6243:d345522c
2025-01-01 17:39:51Heute möchte ich ein Gedicht mit euch teilen. Es handelt sich um eine Ballade des österreichischen Lyrikers Johann Gabriel Seidl aus dem 19. Jahrhundert. Mir sind diese Worte fest in Erinnerung, da meine Mutter sie perfekt rezitieren konnte, auch als die Kräfte schon langsam schwanden.
Dem originalen Titel «Die Uhr» habe ich für mich immer das Wort «innere» hinzugefügt. Denn der Zeitmesser – hier vermutliche eine Taschenuhr – symbolisiert zwar in dem Kontext das damalige Zeitempfinden und die Umbrüche durch die industrielle Revolution, sozusagen den Zeitgeist und das moderne Leben. Aber der Autor setzt sich philosophisch mit der Zeit auseinander und gibt seinem Werk auch eine klar spirituelle Dimension.
Das Ticken der Uhr und die Momente des Glücks und der Trauer stehen sinnbildlich für das unaufhaltsame Fortschreiten und die Vergänglichkeit des Lebens. Insofern könnte man bei der Uhr auch an eine Sonnenuhr denken. Der Rhythmus der Ereignisse passt uns vielleicht nicht immer in den Kram.
Was den Takt pocht, ist durchaus auch das Herz, unser «inneres Uhrwerk». Wenn dieses Meisterwerk einmal stillsteht, ist es unweigerlich um uns geschehen. Hoffentlich können wir dann dankbar sagen: «Ich habe mein Bestes gegeben.»
Ich trage, wo ich gehe, stets eine Uhr bei mir; \ Wieviel es geschlagen habe, genau seh ich an ihr. \ Es ist ein großer Meister, der künstlich ihr Werk gefügt, \ Wenngleich ihr Gang nicht immer dem törichten Wunsche genügt.
Ich wollte, sie wäre rascher gegangen an manchem Tag; \ Ich wollte, sie hätte manchmal verzögert den raschen Schlag. \ In meinen Leiden und Freuden, in Sturm und in der Ruh, \ Was immer geschah im Leben, sie pochte den Takt dazu.
Sie schlug am Sarge des Vaters, sie schlug an des Freundes Bahr, \ Sie schlug am Morgen der Liebe, sie schlug am Traualtar. \ Sie schlug an der Wiege des Kindes, sie schlägt, will's Gott, noch oft, \ Wenn bessere Tage kommen, wie meine Seele es hofft.
Und ward sie auch einmal träger, und drohte zu stocken ihr Lauf, \ So zog der Meister immer großmütig sie wieder auf. \ Doch stände sie einmal stille, dann wär's um sie geschehn, \ Kein andrer, als der sie fügte, bringt die Zerstörte zum Gehn.
Dann müßt ich zum Meister wandern, der wohnt am Ende wohl weit, \ Wohl draußen, jenseits der Erde, wohl dort in der Ewigkeit! \ Dann gäb ich sie ihm zurücke mit dankbar kindlichem Flehn: \ Sieh, Herr, ich hab nichts verdorben, sie blieb von selber stehn.
Johann Gabriel Seidl (1804-1875)
-
 @ a95c6243:d345522c
2024-12-21 09:54:49
@ a95c6243:d345522c
2024-12-21 09:54:49Falls du beim Lesen des Titels dieses Newsletters unwillkürlich an positive Neuigkeiten aus dem globalen polit-medialen Irrenhaus oder gar aus dem wirtschaftlichen Umfeld gedacht hast, darf ich dich beglückwünschen. Diese Assoziation ist sehr löblich, denn sie weist dich als unverbesserlichen Optimisten aus. Leider muss ich dich diesbezüglich aber enttäuschen. Es geht hier um ein anderes Thema, allerdings sehr wohl ein positives, wie ich finde.
Heute ist ein ganz besonderer Tag: die Wintersonnenwende. Genau gesagt hat heute morgen um 10:20 Uhr Mitteleuropäischer Zeit (MEZ) auf der Nordhalbkugel unseres Planeten der astronomische Winter begonnen. Was daran so außergewöhnlich ist? Der kürzeste Tag des Jahres war gestern, seit heute werden die Tage bereits wieder länger! Wir werden also jetzt jeden Tag ein wenig mehr Licht haben.
Für mich ist dieses Ereignis immer wieder etwas kurios: Es beginnt der Winter, aber die Tage werden länger. Das erscheint mir zunächst wie ein Widerspruch, denn meine spontanen Assoziationen zum Winter sind doch eher Kälte und Dunkelheit, relativ zumindest. Umso erfreulicher ist der emotionale Effekt, wenn dann langsam die Erkenntnis durchsickert: Ab jetzt wird es schon wieder heller!
Natürlich ist es kalt im Winter, mancherorts mehr als anderswo. Vielleicht jedoch nicht mehr lange, wenn man den Klimahysterikern glauben wollte. Mindestens letztes Jahr hat Väterchen Frost allerdings gleich zu Beginn seiner Saison – und passenderweise während des globalen Überhitzungsgipfels in Dubai – nochmal richtig mit der Faust auf den Tisch gehauen. Schnee- und Eischaos sind ja eigentlich in der Agenda bereits nicht mehr vorgesehen. Deswegen war man in Deutschland vermutlich in vorauseilendem Gehorsam schon nicht mehr darauf vorbereitet und wurde glatt lahmgelegt.
Aber ich schweife ab. Die Aussicht auf nach und nach mehr Licht und damit auch Wärme stimmt mich froh. Den Zusammenhang zwischen beidem merkt man in Andalusien sehr deutlich. Hier, wo die Häuser im Winter arg auskühlen, geht man zum Aufwärmen raus auf die Straße oder auf den Balkon. Die Sonne hat auch im Winter eine erfreuliche Kraft. Und da ist jede Minute Gold wert.
Außerdem ist mir vor Jahren so richtig klar geworden, warum mir das südliche Klima so sehr gefällt. Das liegt nämlich nicht nur an der Sonne als solcher, oder der Wärme – das liegt vor allem am Licht. Ohne Licht keine Farben, das ist der ebenso simple wie gewaltige Unterschied zwischen einem deprimierenden matschgraubraunen Winter und einem fröhlichen bunten. Ein großes Stück Lebensqualität.
Mir gefällt aber auch die Symbolik dieses Tages: Licht aus der Dunkelheit, ein Wendepunkt, ein Neuanfang, neue Möglichkeiten, Übergang zu neuer Aktivität. In der winterlichen Stille keimt bereits neue Lebendigkeit. Und zwar in einem Zyklus, das wird immer wieder so geschehen. Ich nehme das gern als ein Stück Motivation, es macht mir Hoffnung und gibt mir Energie.
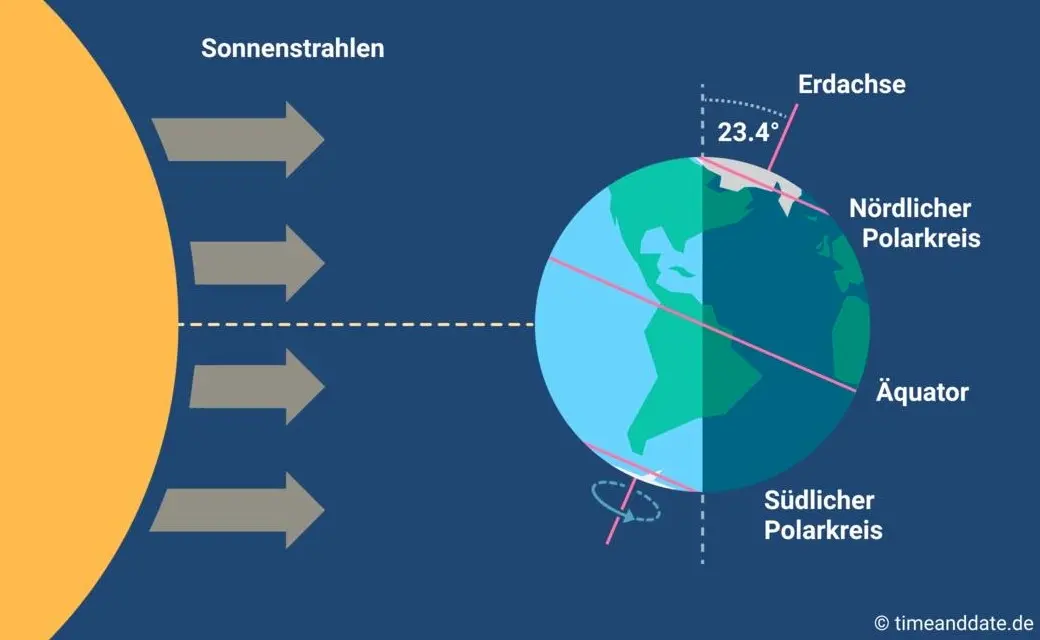
Übrigens ist parallel am heutigen Tag auf der südlichen Halbkugel Sommeranfang. Genau im entgegengesetzten Rhythmus, sich ergänzend, wie Yin und Yang. Das alles liegt an der Schrägstellung der Erdachse, die ist nämlich um 23,4º zur Umlaufbahn um die Sonne geneigt. Wir erinnern uns, gell?
Insofern bleibt eindeutig festzuhalten, dass “schräg sein” ein willkommener, wichtiger und positiver Wert ist. Mit anderen Worten: auch ungewöhnlich, eigenartig, untypisch, wunderlich, kauzig, … ja sogar irre, spinnert oder gar “quer” ist in Ordnung. Das schließt das Denken mit ein.
In diesem Sinne wünsche ich euch allen urige Weihnachtstage!
Dieser Beitrag ist letztes Jahr in meiner Denkbar erschienen.
-
 @ 1f3ce62e:6e6b5d83
2025-01-19 14:44:40
@ 1f3ce62e:6e6b5d83
2025-01-19 14:44:40🌱 🤍💗💜💙💧💚💛🧡❤️
I: Why do adults associate colors only with children and not with them?
AM: Adults have taken so seriously their role. They have forgotten their inner child, they are not in a permanent communication with it. That has made them forget some things, as colors and what they make them feel.
The whole world has become 🖤🤍🩶 since then.
So when an adult is connected back to her/his inner child, she/he has a big challenge, don’t let it fade away again and hug those who still think the world is just gray.
Sooner or later, the wound of the inner child will knock the door to be hugged and healed, it is just a matter of time. Having someone already connected to her/his inner child will make it easier.
\ 🌱 🤍💗💜💙💧💚💛🧡❤️
I: Why is our inner child wounded?
AM: Because we are all here to learn something, even if we don’t remember it.
That wound is our biggest lesson.
Once healed, it becomes the talent or gift we came here to share with those others inner childs with the same wound, with the same lesson to transcend.
🌱 🤍💗💜💙💧💚💛🧡❤️
I: How can we identify the wound of our inner child?
AM: In those situations that deeply hurt us.
The first step is to become an observer of oneself. Observe the way you talk to yourself, and to your closest ones (mom, dad, siblings, partner, kids and closest friends).
Then, observe your actions, they talk too. During this exercise you will find a pattern that repeats itself constantly.
The people who said or do something that hurts you, touch that wound. If we find the pattern, we will see the wound. It is always there, waiting to be healed.
🌱 🤍💗💜💙💧💚💛🧡❤️
I: Which role do mom and dad have into the inner child’s wound?
AM: If we think that we are here just once, bad things just happened to us and people hurt us, it is going to be a challenge to answer this question.
But if we expand our mind and consciousness and embrace the idea that we are more than just this life time and the situations that happened in it, we will be able to understand that we have lived other lives and we brought into this one other experiences, some of them we have learned and some others we haven’t yet.
The same happens with our relationships and the souls we shared this and other lives.
It’s from that expansion of consciousness that we can understand why mom and dad have did the things, they did and what was the higher purpose of it.
\ 🌱 🤍💗💜💙💧💚💛🧡❤️
I: What is the role of our inner child into the parents’ one with their kids?
AM: It is the most important but an unconscious one.
As adults start healing their inner child, the lessons that we left for kids are easier. Look at how I exchanged “parents” for “adults”. Any adult (aunts, uncles, grandparents, educators) whoever is closed to a child has this task: to connect and heal the inner child.
It’s true that parents has a great mission on this, the most important of their lives. And as they are healing their inner child and they letting their true self to BE, they are providing tools to their kids to BE themselves too.
Every healing process starts inside, to later be shared with others around.
\ 🌱 🤍💗💜💙💧💚💛🧡❤️
I: Why is our society so wounded?
AM: Because it is a society of wounded inner children.
When you want to know how we contribute to a wounded society, don’t look after what the society does (if they do good or bad things), look after what deeply hurt them.
People used to think that because they are “good” people and do “good” things, the society is wounded because of “bad” people who does “bad” things.
“Bad” and “Good” people is hurt the same way, one is more deep and visible than the other.
When you see something in society that hurts you, ask your inner child:
🌱 What does it hurt you, my lovely inner child?
🌱 🤍💗💜💙💧💚💛🧡❤️
I: What is the common ground between all of those different inner child wounds?
AM: The lack of love to ourselves. All inner child wounds have that in common, no matter from which discipline you identified them.
Deeply, the lack of love, it is related to not being able to BE ourselves in its full expression.
As we start loving ourselves and accepting ourselves as we are, any original wound start to heal.
🌱 Which wound can’t be healed with love?
\ 🌱 🤍💗💜💙💧💚💛🧡❤️
I: How can we connect with our inner child?
AM: There are many ways, meditations, playing with or like kids, etc.
But the most important one is observing and identifying what hurt us. In that instant, talk to your inner child and listen what her or his has to say.
The second step is to observe our inner dialogue, that dialogue we have with ourselves is the one we have we our inner child. That will mark the wound to be healed.
If you ask your inner child right now…How does she/he feel?
🌱 What does she/he would say?
With Universal Love 🤍♾️
I AM Laus 🌱💛
-
 @ a95c6243:d345522c
2024-12-13 19:30:32
@ a95c6243:d345522c
2024-12-13 19:30:32Das Betriebsklima ist das einzige Klima, \ das du selbst bestimmen kannst. \ Anonym
Eine Strategie zur Anpassung an den Klimawandel hat das deutsche Bundeskabinett diese Woche beschlossen. Da «Wetterextreme wie die immer häufiger auftretenden Hitzewellen und Starkregenereignisse» oft desaströse Auswirkungen auf Mensch und Umwelt hätten, werde eine Anpassung an die Folgen des Klimawandels immer wichtiger. «Klimaanpassungsstrategie» nennt die Regierung das.
Für die «Vorsorge vor Klimafolgen» habe man nun erstmals klare Ziele und messbare Kennzahlen festgelegt. So sei der Erfolg überprüfbar, und das solle zu einer schnelleren Bewältigung der Folgen führen. Dass sich hinter dem Begriff Klimafolgen nicht Folgen des Klimas, sondern wohl «Folgen der globalen Erwärmung» verbergen, erklärt den Interessierten die Wikipedia. Dabei ist das mit der Erwärmung ja bekanntermaßen so eine Sache.
Die Zunahme schwerer Unwetterereignisse habe gezeigt, so das Ministerium, wie wichtig eine frühzeitige und effektive Warnung der Bevölkerung sei. Daher solle es eine deutliche Anhebung der Nutzerzahlen der sogenannten Nina-Warn-App geben.
Die ARD spurt wie gewohnt und setzt die Botschaft zielsicher um. Der Artikel beginnt folgendermaßen:
«Die Flut im Ahrtal war ein Schock für das ganze Land. Um künftig besser gegen Extremwetter gewappnet zu sein, hat die Bundesregierung eine neue Strategie zur Klimaanpassung beschlossen. Die Warn-App Nina spielt eine zentrale Rolle. Der Bund will die Menschen in Deutschland besser vor Extremwetter-Ereignissen warnen und dafür die Reichweite der Warn-App Nina deutlich erhöhen.»
Die Kommunen würden bei ihren «Klimaanpassungsmaßnahmen» vom Zentrum KlimaAnpassung unterstützt, schreibt das Umweltministerium. Mit dessen Aufbau wurden das Deutsche Institut für Urbanistik gGmbH, welches sich stark für Smart City-Projekte engagiert, und die Adelphi Consult GmbH beauftragt.
Adelphi beschreibt sich selbst als «Europas führender Think-and-Do-Tank und eine unabhängige Beratung für Klima, Umwelt und Entwicklung». Sie seien «global vernetzte Strateg*innen und weltverbessernde Berater*innen» und als «Vorreiter der sozial-ökologischen Transformation» sei man mit dem Deutschen Nachhaltigkeitspreis ausgezeichnet worden, welcher sich an den Zielen der Agenda 2030 orientiere.
Über die Warn-App mit dem niedlichen Namen Nina, die möglichst jeder auf seinem Smartphone installieren soll, informiert das Bundesamt für Bevölkerungsschutz und Katastrophenhilfe (BBK). Gewarnt wird nicht nur vor Extrem-Wetterereignissen, sondern zum Beispiel auch vor Waffengewalt und Angriffen, Strom- und anderen Versorgungsausfällen oder Krankheitserregern. Wenn man die Kategorie Gefahreninformation wählt, erhält man eine Dosis von ungefähr zwei Benachrichtigungen pro Woche.
Beim BBK erfahren wir auch einiges über die empfohlenen Systemeinstellungen für Nina. Der Benutzer möge zum Beispiel den Zugriff auf die Standortdaten «immer zulassen», und zwar mit aktivierter Funktion «genauen Standort verwenden». Die Datennutzung solle unbeschränkt sein, auch im Hintergrund. Außerdem sei die uneingeschränkte Akkunutzung zu aktivieren, der Energiesparmodus auszuschalten und das Stoppen der App-Aktivität bei Nichtnutzung zu unterbinden.
Dass man so dramatische Ereignisse wie damals im Ahrtal auch anders bewerten kann als Regierungen und Systemmedien, hat meine Kollegin Wiltrud Schwetje anhand der Tragödie im spanischen Valencia gezeigt. Das Stichwort «Agenda 2030» taucht dabei in einem Kontext auf, der wenig mit Nachhaltigkeitspreisen zu tun hat.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ ce6b432f:c07ce020
2025-01-19 13:42:12
@ ce6b432f:c07ce020
2025-01-19 13:42:12I’ve never lived in LA, though I’ve visited many times. The devastation there from recent fires there is still in the headlines and anyone with a soul feels for the folks without homes, neighbors and communities. Whether they vote the same way or look the same way or worship the same god, “what can I do to help these victims?” is our first question.
The second question is, what is the most responsible way to help? Paragraph two and controversy is already here. Responsible according to who? These people are victims, just give them as much money as they need and let them figure it out according to their local knowledge and culture! The broadest possible answer to this comes from a recent Substack by Arnold Kling: California Tough Love . His position is that there are certain factors controlled locally that led to the disaster, and we shouldn’t be in a rush to replicate them. Having some strings attached to funds that reduce the likelihood of $50,000/year blue collar workers in Iowa footing the bill for the rebuild of $5,000,000 homes in Pacific Palisades AGAIN in the foreseeable future is a very reasonable position.
My position here will be more detailed than Arnold’s, and thus has a higher probability of being wrong. That has never stopped me before. The source of this hubris is a crystal ball. While not a resident of LA, I have been an honorary citizen of Maui for several decades. This attachment is longer than the attachment to the city I currently live in. In August of 2023, a similar devastating fire engulfed the town of Lahaina on the west side of Maui. ~2,200 homes were burned or damaged. The plight of those rebuilding and the process they have gone through quickly faded from national attention, but not to those of us who spend substantial amounts of time on the island. This experience 17 months before the LA fires has painted a depressing blueprint of what we can expect in LA’s recovery. A couple of highlights:
- In November of 2024, the first house was rebuilt. 15 months = 1 house. First House Rebuilt -Maui News Article highlight: Maui “expedited the permitting process for this house, so it “only” took 2 months.
- In December of 2024, federal funding for rebuilding via a block grant is finally approved by congress. Federal Block Grant For Rebuild - Maui News Article highlight: $1.6 billion approved for housing = ~$800,000 per house.
What do these items have in common? The biggest price so far is time. Arnold’s substack was more of a philosophical position, but I doubt even he knew that at the time of writing, Lahaina’s federal funding had just been approved. All those strings he had attached by the feds? Still very slow for a family without a home. This is half of the ‘real price gouging’ mentioned in the subtitle. Those further down the socio-economic ladder have less time to weather the process in Lahaina and the same will likely be true for the middle class residents embedded in the areas destroyed by California’s fires.
The second element of price gouging is the red tape partially embodied in Maui’s example of two months of permitting. These costs aren’t just the time, but also the professional consultants of various stripes required to navigate the process successfully and the costly modifications to homes mandated through these processes.
Here is where I posit my broad and general suggestion. There should exist a “right to rebuild”. If you can legally own a piece of property in a specific condition, you should have the right to rebuild that exact same property if it is destroyed by means out of your control. If you don’t have a “right to rebuild”, you really don’t own that property - you are just renting it for an indefinite period from whoever can prohibit rebuilding it.
Rebuilding is a special case in both the individual and the community level. See the map of Lahaina below. We know where all the plumbing and power lines were. We know where the streets and drainage were. The right to rebuild translates nicely to the community level. Rebuild everything back where it was. Take a month or two to clear out the debris, from an area and begin to rebuild. Rinse and repeat until done.
Taxpayers in Texas shouldn’t be paying for bloated permitting processes in Lahaina or LA. They shouldn’t be paying for eco-upgrades unless very specific, critical failures that caused the current disaster are clearly identified with lowest-cost available solutions. (In Lahaina - pay to bury the power lines. I drove through the area the fire started 2 weeks before it occurred. That place was a tinder box, and it will be again unless someone puts a golf course on that hill. I’m not joking about the golf course. Directly adjacent to the north of the area of Lahaina that burned is Ka’anapali, whose identical hillside is green all year round due to the presence of golf courses that pay for themselves and do not burn.)
How to address this in the context of federal funding via Arnold’s original post:
- Extremely expedited permitting process for rebuilds that get any federal funding: 5 days not 60. You can rebuild what you had, no questions asked, just file the paper work to prove it is the same lot and same size structure. If local jurisdictions drag their heels - no funding, answer to your voters who are now SOL.
- Capped amount of funding per structure that covers a functional modest structure built at the average cost of the 10 most affordable states in the country. The process of building a single family residence is not dramatically different in various areas of the country, unless dictated by excessive regulation. There may be factors for labor to consider if an area is remote like Lahaina or the hills of North Carolina affected by Helene. But if it costs 2x to build a house in your county than in the 10 most affordable states - you are doing it wrong. There is some regulatory price gouging going on. Figure it out. The 10 Most Affordable States to Build a Home - According to this research you can build a 2,100 square foot home for an average of less than $300,000 in the 10 most affordable states.
- This funding will also be contingent on these rebuilt houses being completed within 110% of the time it takes to build 2,100 square foot home in the same 10 markets - measured from the day funds begin to be distributed by the federal government.
- Federal funding will begin to be distributed from a risk pool within 6 months of the disaster, with minimal review to just ensure the disaster qualifies and the receiving state/city will abide by its parameters. The funding is distributed at intervals governed by compliance with the program. Permits are being issued timely, and the amounts distributed are aligned with the cost of building in our most affordable markets.
If you want to build something new and different than before - it might take longer. If you want more than 2,100 square feet of house - I hope you had insurance to cover the difference. A new 2,100 square foot house puts you in the top 10% of humans on earth in terms of shelter. Being a good neighbor does not require rebuilding your infinity pool.
The right to rebuild will get people in homes quicker, remove government obstacles, and stop funding waste. Every citizen will know the rules - money is there to get me a basic structure quickly or fund the beginning of something larger. Any obstacles to that time and money are coming from politicians/regulations I can vote on locally. Comments will surely pour in explaining how it isn’t that simple. These comments will be reviewed diligently 2 years from now when Pacific Palisades is still a wasteland after $20 billion in federal aid has been spent.
!(image)[https://substackcdn.com/image/fetch/f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F8e7875da-145c-4f34-b115-eb0cf09b9ccf_792x612.jpeg] Source: Maui Now
-
 @ a95c6243:d345522c
2024-12-06 18:21:15
@ a95c6243:d345522c
2024-12-06 18:21:15Die Ungerechtigkeit ist uns nur in dem Falle angenehm,\ dass wir Vorteile aus ihr ziehen;\ in jedem andern hegt man den Wunsch,\ dass der Unschuldige in Schutz genommen werde.\ Jean-Jacques Rousseau
Politiker beteuern jederzeit, nur das Beste für die Bevölkerung zu wollen – nicht von ihr. Auch die zahlreichen unsäglichen «Corona-Maßnahmen» waren angeblich zu unserem Schutz notwendig, vor allem wegen der «besonders vulnerablen Personen». Daher mussten alle möglichen Restriktionen zwangsweise und unter Umgehung der Parlamente verordnet werden.
Inzwischen hat sich immer deutlicher herausgestellt, dass viele jener «Schutzmaßnahmen» den gegenteiligen Effekt hatten, sie haben den Menschen und den Gesellschaften enorm geschadet. Nicht nur haben die experimentellen Geninjektionen – wie erwartet – massive Nebenwirkungen, sondern Maskentragen schadet der Psyche und der Entwicklung (nicht nur unserer Kinder) und «Lockdowns und Zensur haben Menschen getötet».
Eine der wichtigsten Waffen unserer «Beschützer» ist die Spaltung der Gesellschaft. Die tiefen Gräben, die Politiker, Lobbyisten und Leitmedien praktisch weltweit ausgehoben haben, funktionieren leider nahezu in Perfektion. Von ihren persönlichen Erfahrungen als Kritikerin der Maßnahmen berichtete kürzlich eine Schweizerin im Interview mit Transition News. Sie sei schwer enttäuscht und verspüre bis heute eine Hemmschwelle und ein seltsames Unwohlsein im Umgang mit «Geimpften».
Menschen, die aufrichtig andere schützen wollten, werden von einer eindeutig politischen Justiz verfolgt, verhaftet und angeklagt. Dazu zählen viele Ärzte, darunter Heinrich Habig, Bianca Witzschel und Walter Weber. Über den aktuell laufenden Prozess gegen Dr. Weber hat Transition News mehrfach berichtet (z.B. hier und hier). Auch der Selbstschutz durch Verweigerung der Zwangs-Covid-«Impfung» bewahrt nicht vor dem Knast, wie Bundeswehrsoldaten wie Alexander Bittner erfahren mussten.
Die eigentlich Kriminellen schützen sich derweil erfolgreich selber, nämlich vor der Verantwortung. Die «Impf»-Kampagne war «das größte Verbrechen gegen die Menschheit». Trotzdem stellt man sich in den USA gerade die Frage, ob der scheidende Präsident Joe Biden nach seinem Sohn Hunter möglicherweise auch Anthony Fauci begnadigen wird – in diesem Fall sogar präventiv. Gibt es überhaupt noch einen Rest Glaubwürdigkeit, den Biden verspielen könnte?
Der Gedanke, den ehemaligen wissenschaftlichen Chefberater des US-Präsidenten und Direktor des National Institute of Allergy and Infectious Diseases (NIAID) vorsorglich mit einem Schutzschild zu versehen, dürfte mit der vergangenen Präsidentschaftswahl zu tun haben. Gleich mehrere Personalentscheidungen des designierten Präsidenten Donald Trump lassen Leute wie Fauci erneut in den Fokus rücken.
Das Buch «The Real Anthony Fauci» des nominierten US-Gesundheitsministers Robert F. Kennedy Jr. erschien 2021 und dreht sich um die Machenschaften der Pharma-Lobby in der öffentlichen Gesundheit. Das Vorwort zur rumänischen Ausgabe des Buches schrieb übrigens Călin Georgescu, der Überraschungssieger der ersten Wahlrunde der aktuellen Präsidentschaftswahlen in Rumänien. Vielleicht erklärt diese Verbindung einen Teil der Panik im Wertewesten.
In Rumänien selber gab es gerade einen Paukenschlag: Das bisherige Ergebnis wurde heute durch das Verfassungsgericht annuliert und die für Sonntag angesetzte Stichwahl kurzfristig abgesagt – wegen angeblicher «aggressiver russischer Einmischung». Thomas Oysmüller merkt dazu an, damit sei jetzt in der EU das Tabu gebrochen, Wahlen zu verbieten, bevor sie etwas ändern können.
Unsere Empörung angesichts der Historie von Maßnahmen, die die Falschen beschützen und für die meisten von Nachteil sind, müsste enorm sein. Die Frage ist, was wir damit machen. Wir sollten nach vorne schauen und unsere Energie clever einsetzen. Abgesehen von der Umgehung von jeglichem «Schutz vor Desinformation und Hassrede» (sprich: Zensur) wird es unsere wichtigste Aufgabe sein, Gräben zu überwinden.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ a95c6243:d345522c
2024-11-29 19:45:43
@ a95c6243:d345522c
2024-11-29 19:45:43Konsum ist Therapie.
Wolfgang JoopUmweltbewusstes Verhalten und verantwortungsvoller Konsum zeugen durchaus von einer wünschenswerten Einstellung. Ob man deswegen allerdings einen grünen statt eines schwarzen Freitags braucht, darf getrost bezweifelt werden – zumal es sich um manipulatorische Konzepte handelt. Wie in der politischen Landschaft sind auch hier die Etiketten irgendwas zwischen nichtssagend und trügerisch.
Heute ist also wieder mal «Black Friday», falls Sie es noch nicht mitbekommen haben sollten. Eigentlich haben wir ja eher schon eine ganze «Black Week», der dann oft auch noch ein «Cyber Monday» folgt. Die Werbebranche wird nicht müde, immer neue Anlässe zu erfinden oder zu importieren, um uns zum Konsumieren zu bewegen. Und sie ist damit sehr erfolgreich.
Warum fallen wir auf derartige Werbetricks herein und kaufen im Zweifelsfall Dinge oder Mengen, die wir sicher nicht brauchen? Pure Psychologie, würde ich sagen. Rabattschilder triggern etwas in uns, was den Verstand in Stand-by versetzt. Zusätzlich beeinflussen uns alle möglichen emotionalen Reize und animieren uns zum Schnäppchenkauf.
Gedankenlosigkeit und Maßlosigkeit können besonders bei der Ernährung zu ernsten Problemen führen. Erst kürzlich hat mir ein Bekannter nach einer USA-Reise erzählt, dass es dort offenbar nicht unüblich ist, schon zum ausgiebigen Frühstück in einem Restaurant wenigstens einen Liter Cola zu trinken. Gerne auch mehr, um das Gratis-Nachfüllen des Bechers auszunutzen.
Kritik am schwarzen Freitag und dem unnötigen Konsum kommt oft von Umweltschützern. Neben Ressourcenverschwendung, hohem Energieverbrauch und wachsenden Müllbergen durch eine zunehmende Wegwerfmentalität kommt dabei in der Regel auch die «Klimakrise» auf den Tisch.
Die EU-Kommission lancierte 2015 den Begriff «Green Friday» im Kontext der überarbeiteten Rechtsvorschriften zur Kennzeichnung der Energieeffizienz von Elektrogeräten. Sie nutzte die Gelegenheit kurz vor dem damaligen schwarzen Freitag und vor der UN-Klimakonferenz COP21, bei der das Pariser Abkommen unterzeichnet werden sollte.
Heute wird ein grüner Freitag oft im Zusammenhang mit der Forderung nach «nachhaltigem Konsum» benutzt. Derweil ist die Europäische Union schon weit in ihr Geschäftsmodell des «Green New Deal» verstrickt. In ihrer Propaganda zum Klimawandel verspricht sie tatsächlich «Unterstützung der Menschen und Regionen, die von immer häufigeren Extremwetter-Ereignissen betroffen sind». Was wohl die Menschen in der Region um Valencia dazu sagen?
Ganz im Sinne des Great Reset propagierten die Vereinten Nationen seit Ende 2020 eine «grüne Erholung von Covid-19, um den Klimawandel zu verlangsamen». Der UN-Umweltbericht sah in dem Jahr einen Schwerpunkt auf dem Verbraucherverhalten. Änderungen des Konsumverhaltens des Einzelnen könnten dazu beitragen, den Klimaschutz zu stärken, hieß es dort.
Der Begriff «Schwarzer Freitag» wurde in den USA nicht erstmals für Einkäufe nach Thanksgiving verwendet – wie oft angenommen –, sondern für eine Finanzkrise. Jedoch nicht für den Börsencrash von 1929, sondern bereits für den Zusammenbruch des US-Goldmarktes im September 1869. Seitdem mussten die Menschen weltweit so einige schwarze Tage erleben.
Kürzlich sind die britischen Aufsichtsbehörden weiter von ihrer Zurückhaltung nach dem letzten großen Finanzcrash von 2008 abgerückt. Sie haben Regeln für den Bankensektor gelockert, womit sie «verantwortungsvolle Risikobereitschaft» unterstützen wollen. Man würde sicher zu schwarz sehen, wenn man hier ein grünes Wunder befürchten würde.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ c4f5e7a7:8856cac7
2024-09-27 08:20:16
@ c4f5e7a7:8856cac7
2024-09-27 08:20:16Best viewed on Habla, YakiHonne or Highlighter.
TL;DR
This article explores the links between public, community-driven data sources (such as OpenStreetMap) and private, cryptographically-owned data found on networks such as Nostr.
The following concepts are explored:
- Attestations: Users signalling to their social graph that they believe something to be true by publishing Attestations. These social proofs act as a decentralised verification system that leverages your web-of-trust.
- Proof of Place: An oracle-based system where physical letters are sent to real-world locations, confirming the corresponding digital ownership via cryptographic proofs. This binds physical locations in meatspace with their digital representations in the Nostrverse.
- Check-ins: Foursquare-style check-ins that can be verified using attestations from place owners, ensuring authenticity. This approach uses web-of-trust to validate check-ins and location ownership over time.
The goal is to leverage cryptographic ownership where necessary while preserving the open, collaborative nature of public data systems.
Open Data in a public commons has a place and should not be thrown out with the Web 2.0 bathwater.
Cognitive Dissonance
Ever since discovering Nostr in August of 2022 I've been grappling with how BTC Map - a project that helps bitcoiners find places to spend sats - should most appropriately use this new protocol.
I am assuming, dear reader, that you are somewhat familiar with Nostr - a relatively new protocol for decentralised identity and communication. If you don’t know your nsec from your npub, please take some time to read these excellent posts: Nostr is Identity for the Internet and The Power of Nostr by @max and @lyn, respectively. Nostr is so much more than a short-form social media replacement.
The social features (check-ins, reviews, etc.) that Nostr unlocks for BTC Map are clear and exciting - all your silos are indeed broken - however, something fundamental has been bothering me for a while and I think it comes down to data ownership.
For those unfamiliar, BTC Map uses OpenStreetMap (OSM) as its main geographic database. OSM is centred on the concept of a commons of objectively verifiable data that is maintained by a global community of volunteer editors; a Wikipedia for maps. There is no data ownership; the data is free (as in freedom) and anyone can edit anything. It is the data equivalent of FOSS (Free and Open Source Software) - FOSD if you will, but more commonly referred to as Open Data.
In contrast, Notes and Other Stuff on Nostr (Places in this cartographic context) are explicitly owned by the controller of the private key. These notes are free to propagate, but they are owned.
How do we reconcile the decentralised nature of Nostr, where data is cryptographically owned by individuals, with the community-managed data commons of OpenStreetMap, where no one owns the data?
Self-sovereign Identity
Before I address this coexistence question, I want to talk a little about identity as it pertains to ownership. If something is to be owned, it has to be owned by someone or something - an identity.
All identities that are not self-sovereign are, by definition, leased to you by a 3rd party. You rent your Facebook identity from Meta in exchange for your data. You rent your web domain from your DNS provider in exchange for your money.
Taken to the extreme, you rent your passport from your Government in exchange for your compliance. You are you at the pleasure of others. Where Bitcoin separates money from the state; Nostr separates identity from the state.
Or, as @nvk said recently: "Don't build your house on someone else's land.".
https://i.nostr.build/xpcCSkDg3uVw0yku.png
While we’ve had the tools for self-sovereign digital identity for decades (think PGP keys or WebAuthN), we haven't had the necessary social use cases nor the corresponding social graph to elevate these identities to the mainstream. Nostr fixes this.
Nostr is PGP for the masses and will take cryptographic identities mainstream.
Full NOSTARD?
Returning to the coexistence question: the data on OpenStreetMap isn’t directly owned by anyone, even though the physical entities the data represents might be privately owned. OSM is a data commons.
We can objectively agree on the location of a tree or a fire hydrant without needing permission to observe and record it. Sure, you could place a tree ‘on Nostr’, but why should you? Just because something can be ‘on Nostr’ doesn’t mean it should be.
https://i.nostr.build/s3So2JVAqoY4E1dI.png
There might be a dystopian future where we can't agree on what a tree is nor where it's located, but I hope we never get there. It's at this point we'll need a Wikifreedia variant of OpenStreetMap.
While integrating Nostr identities into OpenStreetMap would be valuable, the current OSM infrastructure, tools, and community already provide substantial benefits in managing this data commons without needing to go NOSTR-native - there's no need to go Full NOSTARD. H/T to @princeySOV for the original meme.
https://i.nostr.build/ot9jtM5cZtDHNKWc.png
So, how do we appropriately blend cryptographically owned data with the commons?
If a location is owned in meatspace and it's useful to signal that ownership, it should also be owned in cyberspace. Our efforts should therefore focus on entities like businesses, while allowing the commons to manage public data for as long as it can successfully mitigate the tragedy of the commons.
The remainder of this article explores how we can:
- Verify ownership of a physical place in the real world;
- Link that ownership to the corresponding digital place in cyberspace.
As a side note, I don't see private key custodianship - or, even worse, permissioned use of Places signed by another identity's key - as any more viable than the rented identities of Web 2.0.
And as we all know, the Second Law of Infodynamics (no citation!) states that:
"The total amount of sensitive information leaked will always increase over time."
This especially holds true if that data is centralised.
Not your keys, not your notes. Not your keys, not your identity.
Places and Web-of-Trust
@Arkinox has been leading the charge on the Places NIP, introducing Nostr notes (kind 37515) that represent physical locations. The draft is well-crafted, with bonus points for linking back to OSM (and other location repositories) via NIP-73 - External Content IDs (championed by @oscar of @fountain).
However, as Nostr is permissionless, authenticity poses a challenge. Just because someone claims to own a physical location on the Internet doesn’t necessarily mean they have ownership or control of that location in the real world.
Ultimately, this problem can only be solved in a decentralised way by using Web-of-Trust - using your social graph and the perspectives of trusted peers to inform your own perspective. In the context of Places, this requires your network to form a view on which digital identity (public key / npub) is truly the owner of a physical place like your local coffee shop.
This requires users to:
- Verify the owner of a Place in cyberspace is the owner of a place in meatspace.
- Signal this verification to their social graph.
Let's look at the latter idea first with the concept of Attestations ...
Attestations
A way to signal to your social graph that you believe something to be true (or false for that matter) would be by publishing an Attestation note. An Attestation note would signify to your social graph that you think something is either true or false.
Imagine you're a regular at a local coffee shop. You publish an Attestation that says the shop is real and the owner behind the Nostr public key is who they claim to be. Your friends trust you, so they start trusting the shop's digital identity too.
However, attestations applied to Places are just a single use case. The attestation concept could be more widely applied across Nostr in a variety of ways (key rotation, identity linking, etc).
Here is a recent example from @lyn that would carry more signal if it were an Attestation:
https://i.nostr.build/lZAXOEwvRIghgFY4.png
Parallels can be drawn between Attestations and transaction confirmations on the Bitcoin timechain; however, their importance to you would be weighted by clients and/or Data Vending Machines in accordance with:
- Your social graph;
- The type or subject of the content being attested and by whom;
- Your personal preferences.
They could also have a validity duration to be temporally bound, which would be particularly useful in the case of Places.
NIP-25 (Reactions) do allow for users to up/downvote notes with optional content (e.g., emojis) and could work for Attestations, but I think we need something less ambiguous and more definitive.
‘This is true’ resonates more strongly than ‘I like this.’.
https://i.nostr.build/s8NIG2kXzUCLcoax.jpg
There are similar concepts in the Web 3 / Web 5 world such as Verified Credentials by tdb. However, Nostr is the Web 3 now and so wen Attestation NIP?
https://i.nostr.build/Cb047NWyHdJ7h5Ka.jpg
That said, I have seen @utxo has been exploring ‘smart contracts’ on nostr and Attestations may just be a relatively ‘dumb’ subset of the wider concept Nostr-native scripting combined with web-of-trust.
Proof of Place
Attestations handle the signalling of your truth, but what about the initial verification itself?
We already covered how this ultimately has to be derived from your social graph, but what if there was a way to help bootstrap this web-of-trust through the use of oracles? For those unfamiliar with oracles in the digital realm, they are simply trusted purveyors of truth.
Introducing Proof of Place, an out–of-band process where an oracle (such as BTC Map) would mail - yes physically mail- a shared secret to the address of the location being claimed in cyberspace. This shared secret would be locked to the public key (npub) making the claim, which, if unlocked, would prove that the associated private key (nsec) has physical access to the location in meatspace.
One way of doing this would be to mint a 1 sat cashu ecash token locked to the npub of the claimant and mail it to them. If they are able to redeem the token then they have cryptographically proven that they have physical access to the location.
Proof of Place is really nothing more than a weighted Attestation. In a web-of-trust Nostrverse, an oracle is simply a npub (say BTC Map) that you weigh heavily for its opinion on a given topic (say Places).
In the Bitcoin world, Proof of Work anchors digital scarcity in cyberspace to physical scarcity (energy and time) in meatspace and as @Gigi says in PoW is Essential:
"A failure to understand Proof of Work, is a failure to understand Bitcoin."
In the Nostrverse, Proof of Place helps bridge the digital and physical worlds.
@Gigi also observes in Memes vs The World that:
"In Bitcoin, the map is the territory. We can infer everything we care about by looking at the map alone."
https://i.nostr.build/dOnpxfI4u7EL2v4e.png
This isn’t true for Nostr.
In the Nostrverse, the map IS NOT the territory. However, Proof of Place enables us to send cryptographic drones down into the physical territory to help us interpret our digital maps. 🤯
Check-ins
Although not a draft NIP yet, @Arkinox has also been exploring the familiar concept of Foursquare-style Check-ins on Nostr (with kind 13811 notes).
For the uninitiated, Check-ins are simply notes that signal the publisher is at a given location. These locations could be Places (in the Nostr sense) or any other given digital representation of a location for that matter (such as OSM elements) if NIP-73 - External Content IDs are used.
Of course, not everyone will be a Check-in enjoyooor as the concept will not sit well with some people’s threat models and OpSec practices.
Bringing Check-ins to Nostr is possible (as @sebastix capably shows here), but they suffer the same authenticity issues as Places. Just because I say I'm at a given location doesn't mean that I am.
Back in the Web 2.0 days, Foursquare mitigated this by relying on the GPS position of the phone running their app, but this is of course spoofable.
How should we approach Check-in verifiability in the Nostrverse? Well, just like with Places, we can use Attestations and WoT. In the context of Check-ins, an Attestation from the identity (npub) of the Place being checked-in to would be a particularly strong signal. An NFC device could be placed in a coffee shop and attest to check-ins without requiring the owner to manually intervene - I’m sure @blackcoffee and @Ben Arc could hack something together over a weekend!
Check-ins could also be used as a signal for bonafide Place ownership over time.
Summary: Trust Your Bros
So, to recap, we have:
Places: Digital representations of physical locations on Nostr.
Check-ins: Users signalling their presence at a location.
Attestations: Verifiable social proofs used to confirm ownership or the truth of a claim.
You can visualise how these three concepts combine in the diagram below:
https://i.nostr.build/Uv2Jhx5BBfA51y0K.jpg
And, as always, top right trumps bottom left! We have:
Level 0 - Trust Me Bro: Anyone can check-in anywhere. The Place might not exist or might be impersonating the real place in meatspace. The person behind the npub may not have even been there at all.
Level 1 - Definitely Maybe Somewhere: This category covers the middle-ground of ‘Maybe at a Place’ and ‘Definitely Somewhere’. In these examples, you are either self-certifying that you have checked-in at an Attested Place or you are having others attest that you have checked-in at a Place that might not even exist IRL.
Level 2 - Trust Your Bros: An Attested Check-in at an Attested Place. Your individual level of trust would be a function of the number of Attestations and how you weigh them within your own social graph.
https://i.nostr.build/HtLAiJH1uQSTmdxf.jpg
Perhaps the gold standard (or should that be the Bitcoin standard?) would be a Check-in attested by the owner of the Place, which in itself was attested by BTC Map?
Or perhaps not. Ultimately, it’s the users responsibility to determine what they trust by forming their own perspective within the Nostrverse powered by web-of-trust algorithms they control. ‘Trust Me Bro’ or ‘Trust Your Bros’ - you decide.
As we navigate the frontier of cryptographic ownership and decentralised data, it’s up to us to find the balance between preserving the Open Data commons and embracing self-sovereign digital identities.
Thanks
With thanks to Arkinox, Avi, Ben Gunn, Kieran, Blackcoffee, Sebastix, Tomek, Calle, Short Fiat, Ben Weeks and Bitcoms for helping shape my thoughts and refine content, whether you know it or not!
-
 @ a95c6243:d345522c
2024-11-08 20:02:32
@ a95c6243:d345522c
2024-11-08 20:02:32Und plötzlich weißt du:
Es ist Zeit, etwas Neues zu beginnen
und dem Zauber des Anfangs zu vertrauen.
Meister EckhartSchwarz, rot, gold leuchtet es im Kopf des Newsletters der deutschen Bundesregierung, der mir freitags ins Postfach flattert. Rot, gelb und grün werden daneben sicher noch lange vielzitierte Farben sein, auch wenn diese nie geleuchtet haben. Die Ampel hat sich gerade selber den Stecker gezogen – und hinterlässt einen wirtschaftlichen und gesellschaftlichen Trümmerhaufen.
Mit einem bemerkenswerten Timing hat die deutsche Regierungskoalition am Tag des «Comebacks» von Donald Trump in den USA endlich ihr Scheitern besiegelt. Während der eine seinen Sieg bei den Präsidentschaftswahlen feierte, erwachten die anderen jäh aus ihrer Selbsthypnose rund um Harris-Hype und Trump-Panik – mit teils erschreckenden Auswüchsen. Seit Mittwoch werden die Geschicke Deutschlands nun von einer rot-grünen Minderheitsregierung «geleitet» und man steuert auf Neuwahlen zu.
Das Kindergarten-Gehabe um zwei konkurrierende Wirtschaftsgipfel letzte Woche war bereits bezeichnend. In einem Strategiepapier gestand Finanzminister Lindner außerdem den «Absturz Deutschlands» ein und offenbarte, dass die wirtschaftlichen Probleme teilweise von der Ampel-Politik «vorsätzlich herbeigeführt» worden seien.
Lindner und weitere FDP-Minister wurden also vom Bundeskanzler entlassen. Verkehrs- und Digitalminister Wissing trat flugs aus der FDP aus; deshalb darf er nicht nur im Amt bleiben, sondern hat zusätzlich noch das Justizministerium übernommen. Und mit Jörg Kukies habe Scholz «seinen Lieblingsbock zum Obergärtner», sprich: Finanzminister befördert, meint Norbert Häring.
Es gebe keine Vertrauensbasis für die weitere Zusammenarbeit mit der FDP, hatte der Kanzler erklärt, Lindner habe zu oft sein Vertrauen gebrochen. Am 15. Januar 2025 werde er daher im Bundestag die Vertrauensfrage stellen, was ggf. den Weg für vorgezogene Neuwahlen freimachen würde.
Apropos Vertrauen: Über die Hälfte der Bundesbürger glauben, dass sie ihre Meinung nicht frei sagen können. Das ging erst kürzlich aus dem diesjährigen «Freiheitsindex» hervor, einer Studie, die die Wechselwirkung zwischen Berichterstattung der Medien und subjektivem Freiheitsempfinden der Bürger misst. «Beim Vertrauen in Staat und Medien zerreißt es uns gerade», kommentierte dies der Leiter des Schweizer Unternehmens Media Tenor, das die Untersuchung zusammen mit dem Institut für Demoskopie Allensbach durchführt.
«Die absolute Mehrheit hat absolut die Nase voll», titelte die Bild angesichts des «Ampel-Showdowns». Die Mehrheit wolle Neuwahlen und die Grünen sollten zuerst gehen, lasen wir dort.
Dass «Insolvenzminister» Robert Habeck heute seine Kandidatur für das Kanzleramt verkündet hat, kann nur als Teil der politmedialen Realitätsverweigerung verstanden werden. Wer allerdings denke, schlimmer als in Zeiten der Ampel könne es nicht mehr werden, sei reichlich optimistisch, schrieb Uwe Froschauer bei Manova. Und er kenne Friedrich Merz schlecht, der sich schon jetzt rhetorisch auf seine Rolle als oberster Feldherr Deutschlands vorbereite.
Was also tun? Der Schweizer Verein «Losdemokratie» will eine Volksinitiative lancieren, um die Bestimmung von Parlamentsmitgliedern per Los einzuführen. Das Losverfahren sorge für mehr Demokratie, denn als Alternative zum Wahlverfahren garantiere es eine breitere Beteiligung und repräsentativere Parlamente. Ob das ein Weg ist, sei dahingestellt.
In jedem Fall wird es notwendig sein, unsere Bemühungen um Freiheit und Selbstbestimmung zu verstärken. Mehr Unabhängigkeit von staatlichen und zentralen Institutionen – also die Suche nach dezentralen Lösungsansätzen – gehört dabei sicher zu den Möglichkeiten. Das gilt sowohl für jede/n Einzelne/n als auch für Entitäten wie die alternativen Medien.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ 7460b7fd:4fc4e74b
2024-09-05 08:37:48
@ 7460b7fd:4fc4e74b
2024-09-05 08:37:48请看2014年王兴的一场思维碰撞,视频27分钟开始
最后,一个当时无法解决的点:丢失
-
 @ 266815e0:6cd408a5
2024-05-09 17:23:28
@ 266815e0:6cd408a5
2024-05-09 17:23:28Lot of people are starting to talk about building a web-of-trust and how nostr can or is already being used as such
We all know about using the kind:3 following lists as a simple WoT that can be used to filter out spam. but as we all know it does not really signal "trust", its mostly just "I find your content interesting"
But what about real "trust"... well its kind of multi-denominational, I could trust that your a good developer or a good journalist but still not trust you enough to invite you over to my house. There are some interesting and clever solutions proposed for quantifying "trust" in a digital sense but I'm not going to get into that here. I want to talk about something that I have not see anyone discuss yet.
How is the web-of-trust maintained? or more precisely how do you expect users to update the digital representation of the "trust" of other users?
Its all well and good to think of how a user would create that "trust" of another user when discovering them for the first time. They would click the "follow" button, or maybe even rate them on a few topics with a 1/5 star system But how will a user remove that trust? how will they update it if things change and they trust them less?
If our goal is to model "trust" in a digital sense then we NEED a way for the data to stay up-to-date and as accurate as possible. otherwise whats the use? If we don't have a friction-less way to update or remove the digital representation of "trust" then we will end up with a WoT that continuously grows and everyone is rated 10/10
In the case of nostr kind:3 following lists. its pretty easy to see how these would get updated. If someone posts something I dislike or I notice I'm getting board of their content. then I just unfollow them. An important part here is that I'm not thinking "I should update my trust score of this user" but instead "I'm no longer interested, I don't want to see this anymore"
But that is probably the easiest "trust" to update. because most of us on social media spend some time curating our feed and we are used to doing it. But what about the more obscure "trust" scores? whats the regular mechanism by which a user would update the "honestly" score of another user?
In the real world its easy, when I stop trusting someone I simply stop associating with them. there isn't any button or switch I need to update. I simply don't talk to them anymore, its friction-less But in the digital realm I would have to remove or update that trust. in other words its an action I need to take instead of an action I'm not doing. and actions take energy.
So how do we reflect something in the digital world that takes no-energy and is almost subconscious in the real world?
TLDR; webs-of-trust are not just about scoring other users once. you must keep the score up-to-date
-
 @ e373ca41:b82abcc5
2025-01-19 13:35:09
@ e373ca41:b82abcc5
2025-01-19 13:35:09This article by Milosz Matuschek first appeared in German on Freischwebende Intelligenz
Last night, while you were fast asleep, someone turned 883 dollars into 310,000 dollars in just a few hours. Not me, unfortunately. Trump launched his own memecoin with the abbreviation $TRUMP, which has since skyrocketed to a double-digit billion dollar valuation.

Trump (and his pre-investors) are now billions richer on paper. It takes just a few minutes and no (more) development work to create such a coin within minutes. All it takes is a believing community to make it explode. If you were looking for proof of my thesis that the world is being memefied, here it is.

Us and them
We are currently experiencing a phase of power shifts: in money, in politics, in the media. Many people like what Trump and Musk are doing. They are creating more freedom of expression and removing Wokistan's basis for business. Amazon is scrapping diversity rules, Facebook is scrapping censorship (officially admitted). Tiktok land is burned down, the Chinese social media app disappears from the US. Isn't that censorship? Google and Facebook are now openly rebelling against EU opinion dictates, fact checkers etc. In addition to the Hindu Kush, our freedom of opinion is now also being defended (again, for how long?) from Silicon Valley. Brave new world.
You can think strategically: wonderful, that's what I wanted too; “the enemy of my enemy is my friend”. But for how long? This is a change of power at the political top, nothing more.
Trump has promoted vaccination just like Biden; also with the lie that it prevents infection. Vote for your favorite PR artist!
Is that supposed to be our choice?
Elon Musk built mRNA vaccination lines for Curevac, is the Young Global Leader of the WEF 2008, has major holdings in Tesla from Blackrock-Vanguard & Co. and contracts with the Pentagon.
“One of us”, yes for sure....
I find that hard to believe and I wonder about those who find it easy to believe. Speaking of faith: a reader I hold in high esteem said she believes Musk and Trump are on a divine mission. Trump partying with Epstein? Musk in a Baphomet costume? The ways of the Lord are truly mysterious then...
The common enemy of the enemy can be useful, up to a point, but nothing more. Just because you fight the same thing, i.e. are against something, doesn't mean you are for the same thing. In my opinion, assuming that the interests of Trump, Musk & Co. are congruent with the interests of citizens would be a fatal misconception. There is nothing to suggest this. Trump has been totally for and then against many issues. Personnel decisions: often a casting round for a limited time, with hire & fire like “The Apprentice”. But he is so peaceable, wants to end wars like the one between Russia and Ukraine, or de facto the USA. At the same time, he is now reaching for Greenland and the Panama Canal. His words ooze the exceptionalism of the USA, the doctrine that as a US empire you can basically do anything you want. For strategic interests. For national security. A formula can always be found.
ADVERTISEMENT:
Looking for the easiest way to buy Bitcoin and store it yourself? The Relai app is the No. 1 crypto start-up and No. 2 of all fintech start-ups in Switzerland. Here you can buy Bitcoin in just a few steps and also set up savings plans. Nobody has access to your Bitcoin except you. With the referral code MILOSZ you save on fees (no financial advice). Disclaimer due to regulatory issues: The services of the Relai App are hereby only recommended to inhabitants of Switzerland or Italy.
Need more security? The Trezor wallets are recommended and easy to use, others are available in the store. Need more advice? Book an introductory meeting with a wallet expert.
How are wo going to score on the liberty scale?
“Believe little, question everything, think for yourself” is the beautiful title of a very readable book by Albrecht Müller, editor of Nachdenkseiten, and best summarizes my thoughts. As a journalist, I replace “little” with “nothing”. The journalist is not in the banking business. There you are allowed to believe (credit = he believes, latin). I don't think the issue of draining a swamp should be left to the frogs. Is Trump not a frog? “Anti-establishment", come on. Now the establishment is coming from the other side, the other side of the dialectic. The battle of good versus evil is entering a supposedly new round, releasing pressure from the cauldron of democracy, which is too important a façade to be allowed to fall.
The only pragmatic question that citizens should ask themselves is this: Will I have more net freedoms at the end of this political reorganization process than before? What will be given to me in reel but perhaps also taken away elsewhere? Anyone who draws hope from changes in the left-right scheme has always been disappointed by the steady reduction of freedoms in recent years and should rather look at the vertical axis of top vs. bottom. Hope is nice, but you should only ever rely on yourself.
It's nice if some people now get to know something different as a result of the change in the political weather and wake up. A book will soon be published about manipulation in the Tagesschau. The PEI has known about the side effects for years, but withheld the information and the republic was allowed to rail against footballer Joshua Kimmich in the meantime. One life lie after another will now fall, an exciting process. But it will mainly be cardboard comrades and useful idiots who will have to fall by the wayside, and there was hardly any shortage of them.
Waking up must not lead to the next dream world. Otherwise the critical movement was just a stirrup for the next seizure of power. But we need a movement of self-empowerment of the citizen, beyond politics, the media or Big Tech. Invest in everything, be it seminars, books, knowledge, Bitcoin or whatever increases your net freedom balance. Decentralized civil society only has a chance if free citizens form their own free block in cooperation with others, based on principles and not on the bunting of a party-political camp.
Everyone can decide for themselves and have a say in what form this can take. Where cooperation arises naturally, the idea was a good one. Ultimately, an idea is just a meme.
That was my meme five years ago. It's still true, but with Bitcoin a zero has been added.

Join the marketplace of ideas! We are building a publishing ecosystem on Nostr for citizen-journalism, starting with a client for blogging and newsletter distribution. Sound money and sound information should finally be in the hands of the people, right? Want to learn more about the Pareto Project? Zap me, if you want to contribute (all Zaps go to the project).
Are you a publication and want to be part of it, test us, migrate your content to Nostr? Write to team@pareto.space**
Not yet on Nostr and want the full experience? Easy onboarding via Nosta.me.

-
 @ f977c464:32fcbe00
2024-01-30 20:06:18
@ f977c464:32fcbe00
2024-01-30 20:06:18Güneşin kaybolmasının üçüncü günü, saat öğlen on ikiyi yirmi geçiyordu. Trenin kalkmasına yaklaşık iki saat vardı. Hepimiz perondaydık. Valizlerimiz, kolilerimiz, renk renk ve biçimsiz çantalarımızla yan yana dizilmiş, kısa aralıklarla tepemizdeki devasa saati kontrol ediyorduk.
Ama ne kadar dik bakarsak bakalım zaman bir türlü istediğimiz hızla ilerlemiyordu. Herkes birkaç dakika sürmesi gereken alelade bir doğa olayına sıkışıp kalmış, karanlıktan sürünerek çıkmayı deniyordu.
Bekleme salonuna doğru döndüm. Nefesimden çıkan buharın arkasında, kalın taş duvarları ve camlarıyla morg kadar güvenli ve soğuk duruyordu. Cesetleri o yüzden bunun gibi yerlere taşımaya başlamışlardı. Demek insanların bütün iyiliği başkaları onları gördüğü içindi ki gündüzleri gecelerden daha karanlık olduğunda hemen birbirlerinin gırtlağına çökmüş, böğürlerinde delikler açmış, gözlerini oyup kafataslarını parçalamışlardı.
İstasyonun ışığı titrediğinde karanlığın enseme saplandığını hissettim. Eğer şimdi, böyle kalabalık bir yerde elektrik kesilse başımıza ne gelirdi?
İçerideki askerlerden biri bakışlarımı yakalayınca yeniden saate odaklanmış gibi yaptım. Sadece birkaç dakika geçmişti.
“Tarlalarım gitti. Böyle boyum kadar ayçiçeği doluydu. Ah, hepsi ölüp gidiyor. Afitap’ın çiçekleri de gi-”
“Dayı, Allah’ını seversen sus. Hepimizi yakacaksın şimdi.”
Karanlıkta durduğunda, görünmez olmayı istemeye başlıyordun. Kimse seni görmemeli, nefesini bile duymamalıydı. Kimsenin de ayağının altında dolaşmamalıydın; gelip kazayla sana çarpmamalılar, takılıp sendelememeliydiler. Yoksa aslında hedefi sen olmadığın bir öfke gürlemeye başlar, yaşadığın ilk şoku ve acıyı silerek üstünden geçerdi.
İlk konuşan, yaşlıca bir adam, kafasında kasketi, nasırlı ellerine hohluyordu. Gözleri ve burnu kızarmıştı. Güneşin kaybolması onun için kendi başına bir felaket değildi. Hayatına olan pratik yansımalarından korkuyordu olsa olsa. Bir anının kaybolması, bu yüzden çoktan kaybettiği birinin biraz daha eksilmesi. Hayatta kalmasını gerektiren sebepler azalırken, hayatta kalmasını sağlayacak kaynaklarını da kaybediyordu.
Onu susturan delikanlıysa atkısını bütün kafasına sarmış, sakalı ve yüzünün derinliklerine kaçmış gözleri dışında bedeninin bütün parçalarını gizlemeye çalışıyordu. İşte o, güneşin kaybolmasının tam olarak ne anlama geldiğini anlamamış olsa bile, dehşetini olduğu gibi hissedebilenlerdendi.
Güneşin onlardan alındıktan sonra kime verileceğini sormuyorlardı. En başta onlara verildiğinde de hiçbir soru sormamışlardı zaten.
İki saat ne zaman geçer?
Midemin üstünde, sağ tarafıma doğru keskin bir acı hissettim. Karaciğerim. Gözlerimi yumdum. Yanımda biri metal bir nesneyi yere bıraktı. Bir kafesti. İçerisindeki kartalın ıslak kokusu burnuma ulaşmadan önce bile biliyordum bunu.
“Yeniden mi?” diye sordu bana kartal. Kanatları kanlı. Zamanın her bir parçası tüylerinin üstüne çöreklenmişti. Gagası bir şey, tahminen et parçası geveliyor gibi hareket ediyordu. Eski anılar kolay unutulmazmış. Şu anda kafesinin kalın parmaklıklarının ardında olsa da bunun bir aldatmaca olduğunu bir tek ben biliyordum. Her an kanatlarını iki yana uzatıverebilir, hava bu hareketiyle dalgalanarak kafesi esneterek hepimizi içine alacak kadar genişleyebilir, parmaklıklar önce ayaklarımızın altına serilir gibi gözükebilir ama aslında hepimizin üstünde yükselerek tepemize çökebilirdi.
Aşağıya baktım. Tahtalarla zapt edilmiş, hiçbir yere gidemeyen ama her yere uzanan tren rayları. Atlayıp koşsam… Çantam çok ağırdı. Daha birkaç adım atamadan, kartal, suratını bedenime gömerdi.
“Bu sefer farklı,” diye yanıtladım onu. “Yeniden diyemezsin. Tekrarladığım bir şey değil bu. Hatta bir hata yapıyormuşum gibi tonlayamazsın da. Bu sefer, insanların hak etmediğini biliyorum.”
“O zaman daha vahim. Süzme salaksın demektir.”
“İnsanların hak etmemesi, insanlığın hak etmediği anlamına gelmez ki.”
Az önce göz göze geldiğim genççe ama çökük asker hâlâ bana bakıyordu. Bir kartalla konuştuğumu anlamamıştı şüphesiz. Yanımdakilerden biriyle konuştuğumu sanmış olmalıydı. Ama konuştuğum kişiye bakmıyordum ona göre. Çekingence kafamı eğmiştim. Bir kez daha göz göze geldiğimizde içerideki diğer iki askere bir şeyler söyledi, onlar dönüp beni süzerken dışarı çıktı.
Yanımızdaki, az önce konuşan iki adam da şaşkınlıkla bir bana bir kartala bakıyordu.
“Yalnız bu sefer kalbin de kırılacak, Prometheus,” dedi kartal, bana. “Belki son olur. Biliyorsun, bir sürü soruna neden oluyor bu yaptıkların.”
Beni koruyordu sözde. En çok kanıma dokunan buydu. Kasıklarımın üstüne oturmuş, kanlı suratının ardında gözleri parlarken attığı çığlık kulaklarımda titremeye devam ediyordu. Bu tabloda kimsenin kimseyi düşündüğü yoktu. Kartalın, yanımızdaki adamların, artık arkama kadar gelmiş olması gereken askerin, tren raylarının, geçmeyen saatlerin…
Arkamı döndüğümde, asker sahiden oradaydı. Zaten öyle olması gerekiyordu; görmüştüm bunu, biliyordum. Kehanetler… Bir şeyler söylüyordu ama ağzı oynarken sesi çıkmıyordu. Yavaşlamış, kendisini saatin akışına uydurmuştu. Havada donan tükürüğünden anlaşılıyordu, sinirliydi. Korktuğu için olduğunu biliyordum. Her seferinde korkmuşlardı. Beni unutmuş olmaları işlerini kolaylaştırmıyordu. Sadece yeni bir isim vermelerine neden oluyordu. Bu seferkiyle beni lanetleyecekleri kesinleşmişti.
Olması gerekenle olanların farklı olması ne kadar acınasıydı. Olması gerekenlerin doğasının kötücül olmasıysa bir yerde buna dayanıyordu.
“Salaksın,” dedi kartal bana. Zamanı aşan bir çığlık. Hepimizin önüne geçmişti ama kimseyi durduramıyordu.
Sonsuzluğa kaç tane iki saat sıkıştırabilirsiniz?
Ben bir tane bile sıkıştıramadım.
Çantama uzanıyordum. Asker de sırtındaki tüfeğini indiriyordu. Benim acelem yoktu, onunsa eli ayağı birbirine dolaşıyordu. Oysaki her şey tam olması gerektiği anda olacaktı. Kehanet başkasının parmaklarının ucundaydı.
Güneş, bir tüfeğin patlamasıyla yeryüzüne doğdu.
Rayların üzerine serilmiş göğsümün ortasından, bir çantanın içinden.
Not: Bu öykü ilk olarak 2021 yılında Esrarengiz Hikâyeler'de yayımlanmıştır.
-
 @ a95c6243:d345522c
2024-10-26 12:21:50
@ a95c6243:d345522c
2024-10-26 12:21:50Es ist besser, ein Licht zu entzünden, als auf die Dunkelheit zu schimpfen. Konfuzius
Die Bemühungen um Aufarbeitung der sogenannten Corona-Pandemie, um Aufklärung der Hintergründe, Benennung von Verantwortlichkeiten und das Ziehen von Konsequenzen sind durchaus nicht eingeschlafen. Das Interesse daran ist unter den gegebenen Umständen vielleicht nicht sonderlich groß, aber es ist vorhanden.
Der sächsische Landtag hat gestern die Einsetzung eines Untersuchungsausschusses zur Corona-Politik beschlossen. In einer Sondersitzung erhielt ein entsprechender Antrag der AfD-Fraktion die ausreichende Zustimmung, auch von einigen Abgeordneten des BSW.
In den Niederlanden wird Bill Gates vor Gericht erscheinen müssen. Sieben durch die Covid-«Impfstoffe» geschädigte Personen hatten Klage eingereicht. Sie werfen unter anderem Gates, Pfizer-Chef Bourla und dem niederländischen Staat vor, sie hätten gewusst, dass diese Präparate weder sicher noch wirksam sind.
Mit den mRNA-«Impfstoffen» von Pfizer/BioNTech befasst sich auch ein neues Buch. Darin werden die Erkenntnisse von Ärzten und Wissenschaftlern aus der Analyse interner Dokumente über die klinischen Studien der Covid-Injektion präsentiert. Es handelt sich um jene in den USA freigeklagten Papiere, die die Arzneimittelbehörde (Food and Drug Administration, FDA) 75 Jahre unter Verschluss halten wollte.
Ebenfalls Wissenschaftler und Ärzte, aber auch andere Experten organisieren als Verbundnetzwerk Corona-Solution kostenfreie Online-Konferenzen. Ihr Ziel ist es, «wissenschaftlich, demokratisch und friedlich» über Impfstoffe und Behandlungsprotokolle gegen SARS-CoV-2 aufzuklären und die Diskriminierung von Ungeimpften zu stoppen. Gestern fand eine weitere Konferenz statt. Ihr Thema: «Corona und modRNA: Von Toten, Lebenden und Physik lernen».
Aufgrund des Digital Services Acts (DSA) der Europäischen Union sei das Risiko groß, dass ihre Arbeit als «Fake-News» bezeichnet würde, so das Netzwerk. Staatlich unerwünschte wissenschaftliche Aufklärung müsse sich passende Kanäle zur Veröffentlichung suchen. Ihre Live-Streams seien deshalb zum Beispiel nicht auf YouTube zu finden.
Der vielfältige Einsatz für Aufklärung und Aufarbeitung wird sich nicht stummschalten lassen. Nicht einmal der Zensurmeister der EU, Deutschland, wird so etwas erreichen. Die frisch aktivierten «Trusted Flagger» dürften allerdings künftige Siege beim «Denunzianten-Wettbewerb» im Kontext des DSA zusätzlich absichern.
Wo sind die Grenzen der Meinungsfreiheit? Sicher gibt es sie. Aber die ideologische Gleichstellung von illegalen mit unerwünschten Äußerungen verfolgt offensichtlich eher das Ziel, ein derart elementares demokratisches Grundrecht möglichst weitgehend auszuhebeln. Vorwürfe wie «Hassrede», «Delegitimierung des Staates» oder «Volksverhetzung» werden heute inflationär verwendet, um Systemkritik zu unterbinden. Gegen solche Bestrebungen gilt es, sich zu wehren.
Dieser Beitrag ist zuerst auf Transition News erschienen.
-
 @ c631e267:c2b78d3e
2024-10-23 20:26:10
@ c631e267:c2b78d3e
2024-10-23 20:26:10Herzlichen Glückwunsch zum dritten Geburtstag, liebe Denk Bar! Wieso zum dritten? Das war doch 2022 und jetzt sind wir im Jahr 2024, oder? Ja, das ist schon richtig, aber bei Geburtstagen erinnere ich mich immer auch an meinen Vater, und der behauptete oft, der erste sei ja schließlich der Tag der Geburt selber und den müsse man natürlich mitzählen. Wo er recht hat, hat er nunmal recht. Konsequenterweise wird also heute dieser Blog an seinem dritten Geburtstag zwei Jahre alt.
Das ist ein Grund zum Feiern, wie ich finde. Einerseits ganz einfach, weil es dafür gar nicht genug Gründe geben kann. «Das Leben sind zwei Tage», lautet ein gängiger Ausdruck hier in Andalusien. In der Tat könnte es so sein, auch wenn wir uns im Alltag oft genug von der Routine vereinnahmen lassen.
Seit dem Start der Denk Bar vor zwei Jahren ist unglaublich viel passiert. Ebenso wie die zweieinhalb Jahre davor, und all jenes war letztlich auch der Auslöser dafür, dass ich begann, öffentlich zu schreiben. Damals notierte ich:
«Seit einigen Jahren erscheint unser öffentliches Umfeld immer fragwürdiger, widersprüchlicher und manchmal schier unglaublich - jede Menge Anlass für eigene Recherchen und Gedanken, ganz einfach mit einer Portion gesundem Menschenverstand.»
Wir erleben den sogenannten «großen Umbruch», einen globalen Coup, den skrupellose Egoisten clever eingefädelt haben und seit ein paar Jahren knallhart – aber nett verpackt – durchziehen, um buchstäblich alles nach ihrem Gusto umzukrempeln. Die Gelegenheit ist ja angeblich günstig und muss genutzt werden.
Nie hätte ich mir träumen lassen, dass ich so etwas jemals miterleben müsste. Die Bosheit, mit der ganz offensichtlich gegen die eigene Bevölkerung gearbeitet wird, war früher für mich unvorstellbar. Mein (Rest-) Vertrauen in alle möglichen Bereiche wie Politik, Wissenschaft, Justiz, Medien oder Kirche ist praktisch komplett zerstört. Einen «inneren Totalschaden» hatte ich mal für unsere Gesellschaften diagnostiziert.
Was mich vielleicht am meisten erschreckt, ist zum einen das Niveau der Gleichschaltung, das weltweit erreicht werden konnte, und zum anderen die praktisch totale Spaltung der Gesellschaft. Haben wir das tatsächlich mit uns machen lassen?? Unfassbar! Aber das Werkzeug «Angst» ist sehr mächtig und funktioniert bis heute.
Zum Glück passieren auch positive Dinge und neue Perspektiven öffnen sich. Für viele Menschen waren und sind die Entwicklungen der letzten Jahre ein Augenöffner. Sie sehen «Querdenken» als das, was es ist: eine Tugend.
Auch die immer ernsteren Zensurbemühungen sind letztlich nur ein Zeichen der Schwäche, wo Argumente fehlen. Sie werden nicht verhindern, dass wir unsere Meinung äußern, unbequeme Fragen stellen und dass die Wahrheit peu à peu ans Licht kommt. Es gibt immer Mittel und Wege, auch für uns.
Danke, dass du diesen Weg mit mir weitergehst!
-
 @ fd208ee8:0fd927c1
2025-01-19 12:10:10
@ fd208ee8:0fd927c1
2025-01-19 12:10:10I am so tired of people trying to waste my time with Nostrized imitations of stuff that already exists.
Instagram, but make it Nostr. Twitter, but make it Nostr. GitHub, but make it Nostr. Facebook, but make it Nostr. Wordpress, but make it Nostr. GoodReads, but make it Nostr. TikTok, but make it Nostr.
That stuff already exists, and it wasn't that great the first time around, either. Build something better than that stuff, that can only be brought into existence because of Nostr.
Build something that does something completely and awesomely new. Knock my socks off, bro.
Cuz, ain't nobody got time for that.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28O Planetinha
Fumaça verde me entrando pelas narinas e um coro desafinado fazia uma base melódica.
nos confins da galáxia havia um planetinha isolado. Era um planeta feliz.
O homem vestido de mago começava a aparecer por detrás da fumaça verde.
O planetinha recebeu três presentes, mas o seu habitante, o homem, estava num estado de confusão tão grande que ameaçava estragá-los. Os homens já havia escravizado o primeiro presente, a vida; lutavam contra o segundo presente, a morte; e havia alguns que achavam que deviam destruir totalmente o terceiro, o amor, e com isto levar a desordem total ao pobre planetinha perdido, que se chamava Terra.
O coro desafinado entrou antes do "Terra" cantando várias vezes, como se imitasse um eco, "terra-terra-terraaa". Depois de uma pausa dramática, o homem vestido de mago voltou a falar.
Terra, nossa nave mãe.
Neste momento eu me afastei. À frente do palco onde o mago e seu coral faziam apelos à multidão havia vários estandes cobertos com a tradicional armação de quatro pernas e lona branca. Em todos os cantos da praça havia gente, gente dos mais variados tipos. Visitantes curiosos que se aproximavam atraídos pela fumaça verde e as barraquinhas, gente que aproveitava o movimento para vender doces sem pagar imposto, casais que se abraçavam de pé para espantar o frio, os tradicionais corredores que faziam seu cooper, gente cheia de barba e vestida para imitar os hippies dos anos 60 e vender colares estendidos no chão, transeuntes novos e velhos, vestidos como baladeiros ou como ativistas do ônibus grátis, grupos de ciclistas entusiastas.
O mago fazia agora apelos para que nós, os homens, habitantes do isolado planetinha, passássemos a ver o planetinha, nossa nave mãe, como um todo, e adquiríssemos a consciência de que ele estava entrando em maus lençóis. A idéia, reforçada pela logomarca do evento, era que parássemos de olhar só para a nossa vida e pensássemos no planeta.
A logomarca do evento, um desenho estilizado do planeta Terra, nada tinha a ver com seu nome: "Festival Andando de Bem com a Vida", mas havia sido ali colocada estrategicamente pelos organizadores, de quem parecia justamente sair a mensagem dita pelo mago.
Aquela multidão de pessoas que, assim como eu, tinham suas próprias preocupações, não podiam ver o quadro caótico que formavam, cada uma com seus atos isolados, ali naquela praça isolada, naquele planeta isolado. Quando o hippie barbudo, quase um Osho, assustava um casal para tentar vender-lhes um colar, a quantidade de caos que isto acrescentava à cena era gigantesca. Por um segundo, pude ver, como se estivesse de longe e acima, com toda a pretensão que este estado imaginativo carrega, a cena completa do caos.
Uma nave-mãe, dessas de ficção científica, habitada por milhões de pessoas, seguia no espaço sem rumo, e sem saber que logo à frente um longo precipício espacial a esperava, para a desgraça completa sua e de seus habitantes.
Acostumados àquela nave tanto quanto outrora estiveram acostumados à sua terra natal, os homens viviam as próprias vidas sem nem se lembrar que estavam vagando pelo espaço. Ninguém sabia quem estava conduzindo a nave, e ninguém se importava.
No final do filme descobre-se que era a soma completa do caos que cada habitante produzia, com seus gestos egoístas e incapazes de levar em conta a totalidade, é que determinava a direção da nave-mãe. O efeito, no entanto, não era imediato, como nunca é. Havia gente de verdade encarregada de conduzir a nave, mas era uma gente bêbada, mau-caráter, que vivia brigando pelo controle da nave e o poder que isto lhes dava. Poder, status, dinheiro!
Essa gente bêbada era atraída até ali pela corrupção das instituições e da moral comum que, no fundo no fundo, era causada pelo egoísmo da população, através de um complexo -- mas que no filme aparece simplificado pela ação individual de um magnata do divertimento público -- processo social.
O homem vestido de mago era mais um agente causador de caos, com sua cena cheia de fumaça e sua roupa estroboscópica, ele achava que estava fazendo o bem ao alertar sua platéia, todos as sextas-feiras, de que havia algo que precisava ser feito, que cada um que estava ali ouvindo era responsável pelo planeta. A sua incapacidade, porém, de explicar o que precisava ser feito só aumentava a angústia geral; a culpa que ele jogava sobre seu público, e que era prontamente aceita e passada em frente, aos familiares e amigos de cada um, atormentava-os diariamente e os impedia de ter uma vida decente no trabalho e em casa. As famílias, estressadas, estavam constantemente brigando e os motivos mais insignificantes eram responsáveis pelas mais horrendas conseqüências.
O mago, que após o show tirava o chapéu entortado e ia tomar cerveja num boteco, era responsável por uma parcela considerável do caos que levava a nave na direção do seu desgraçado fim. No filme, porém, um dos transeuntes que de passagem ouviu um pedaço do discurso do mago despertou em si mesmo uma consiência transformadora e, com poderes sobre-humanos que lhe foram então concedidos por uma ordem iniciática do bem ou não, usando só os seus poderes humanos mesmo, o transeunte -- na primeira versão do filme um homem, na segunda uma mulher -- consegue consertar as instituições e retirar os bêbados da condução da máquina. A questão da moral pública é ignorada para abreviar a trama, já com duas horas e quarenta de duração, mas subentende-se que ela também fora resolvida.
No planeta Terra real, que não está indo em direção alguma, preso pela gravidade ao Sol, e onde as pessoas vivem a própria vida porque lhes é impossível viver a dos outros, não têm uma consciência global de nada porque só é possível mesmo ter a consciência delas mesmas, e onde a maioria, de uma maneira ou de outra, está tentando como pode, fazer as coisas direito, o filme é exibido.
Para a maioria dos espectadores, é um filme que evoca reflexões, um filme forte. Por um segundo elas têm o mesmo vislumbre do caos generalizado que eu tive ali naquela praça. Para uma pequena parcela dos espectadores -- entre eles alguns dos que estavam na platéia do mago, o próprio mago, o seguidor do Osho, o casal de duas mulheres e o vendedor de brigadeiros, mas aos quais se somam também críticos de televisão e jornal e gente que fala pelos cotovelos na internet -- o filme é um horror, o filme é uma vulgarização de um problema real e sério, o filme apela para a figura do herói salvador e passa uma mensagem totalmente errada, de que a maioria da população pode continuar vivendo as suas própria vidinhas miseráveis enquanto espera por um herói que vem do Olimpo e os salva da mixórdia que eles mesmos causaram, é um filme que presta um enorme desserviço à causa.
No dia seguinte ao lançamento, num bar meio caro ali perto da praça, numa mesa com oito pessoas, entre elas seis do primeiro grupo e oito do segundo, discute-se se o filme levará ou não o Oscar. Eu estou em casa dormindo e não escuto nada.
-
 @ 16d11430:61640947
2025-01-19 11:59:12
@ 16d11430:61640947
2025-01-19 11:59:12Chapter One: The Venture
Allison Hart adjusted her grip on the stainless steel coffee thermos as she stared out the rain-streaked glass of the small San Francisco office building. The storm outside mirrored her anxiety: fierce, unpredictable, and utterly unrelenting. Today marked the launch of ValkyrieOS, the Linux-based cloud infrastructure her husband, Ethan, and his scrappy team of engineers had poured their souls into for the past three years. It wasn’t just a startup; it was Ethan’s lifeline, their shared dream—and, increasingly, the wedge driving them apart.
She tugged her cardigan tighter, the hum of the servers in the next room a constant reminder of how much Ethan had sacrificed to build his company. Late nights, missed anniversaries, and countless reassurances that their struggles would someday be worth it. When? Allison thought. She loved him fiercely, but the endless grind of a tech startup had turned her marriage into something tenuous—a connection stretched thin, yet unbroken.
In the corner of the open-plan office, Ethan stood with his team, their faces glowing in the blue-white light of monitors as the final test scripts ran. Ethan’s broad shoulders were hunched, his face set in the determined scowl she’d fallen for in college. It was the same look he’d worn when he told her he wanted to change the world—only now, it came with the weight of failure looming at every turn.
“Ali,” Ethan called, his voice cutting through the buzz of machines. “Can you come here for a sec?”
She approached, the team parting like a flock of birds as she stepped beside him. On the screen, a red progress bar inched forward—barely. The tension in the room was palpable.
“It’s the load balancer,” Ethan muttered, running a hand through his dark hair. “If it fails during the demo, we’re done. Everything’s riding on this.”
“Ethan, you can’t keep doing this to yourself,” she whispered, her voice barely audible over the whir of fans. “To us.”
Chapter Two: The Rival
The launch of ValkyrieOS was supposed to be their salvation, but instead, it thrust them into the brutal warzone of the tech industry. No one knew this better than Allison, who found herself navigating late-night strategy calls and early-morning investor meetings alongside Ethan.
Enter Mark Carrington, the charismatic CEO of a competing company, NimbusTech. Mark was everything Ethan wasn’t—smooth, polished, and merciless. He approached Allison during a networking event, his silver-tongued charm cutting through the noise of the crowded room.
“You know,” Mark said, his smile disarming, “your husband has built something extraordinary. But the market? It doesn’t care about extraordinary—it cares about winning.”
Allison bristled at his condescension. “Ethan’s not just building software. He’s building something that matters.”
Mark leaned in, his voice dropping. “And what about you, Allison? Do you matter in all of this?”
Her breath hitched. Mark’s words struck a nerve, not because they were true, but because they echoed her own darkest fears.
Chapter Three: The Sacrifice
Ethan worked tirelessly, pushing his team and himself to the brink. Allison could see the toll it was taking—the dark circles under his eyes, the strained way he smiled when he thought no one was watching. But beneath the exhaustion was a fire, a belief in what he was doing that refused to be extinguished.
The turning point came late one night when the servers crashed. Ethan’s team scrambled, but it was Allison who stepped in, her years as a UX designer proving invaluable. She worked beside them, rewriting error messages and optimizing the interface for clarity. It was the first time in months that she and Ethan felt like a team again.
“You didn’t have to do that,” Ethan said afterward, his voice raw with gratitude.
“I’m your partner, Ethan. Not just in life, but in this. Don’t shut me out.”
Chapter Four: The Storm
Just as the demo approached, disaster struck. A massive DDoS attack crippled ValkyrieOS. Ethan was ready to give up, but Allison wouldn’t let him.
“You told me once that clouds are about resilience,” she said. “Your system is designed to adapt. So adapt.”
Together, they rallied the team, implementing a last-minute patch that saved the demo. When the system finally stabilized, the room erupted in cheers. For the first time in months, Ethan turned to Allison with a look of pure joy.
Chapter Five: The Ascent
The launch was a success, and ValkyrieOS quickly became the darling of the open-source community. But for Allison and Ethan, the real victory was rediscovering each other in the chaos. They learned to share the burdens, to celebrate the small wins, and to fight for their marriage with the same tenacity they brought to their work.
“You’re my uptime,” Ethan said one night, his voice soft as they lay tangled together on the couch.
“And you’re my load balancer,” Allison replied, her laughter breaking the quiet. “Always catching me before I crash.”
Epilogue: Cloudborne
Years later, as they stood on the balcony of their now-expanded office, watching a new storm roll in, Allison couldn’t help but smile. The journey had been brutal, but they’d weathered it together, proving that even in the most unforgiving environments, love—like a resilient system—could thrive.
And somewhere in the hum of servers below, the heartbeat of their shared dream continued, steady and strong.
-
 @ fbf0e434:e1be6a39
2025-01-19 11:53:15
@ fbf0e434:e1be6a39
2025-01-19 11:53:15Hackathon 摘要
Hack Western 11 圆满结束,学生开发者提交了62个注册项目。此次活动在协作环境中培养了创新和创造力。项目评估考察创新性、技术复杂性、完整性和设计,以确保全面评估。
参与者可以组队(最多四人)或单独参加,灵活参与。Hackathon鼓励跨多个赛道的项目提交,增加了项目面临各种挑战的曝光度和机会。
科学博览会式的环境允许参与者向评委展示他们的项目,进行详细的演示和讨论。这种形式帮助团队表述他们的目标、突出成就并获得反馈。面对面的评审提供了一个互动平台以表彰创意解决方案。
总体而言,Hack Western 11营造了一个富有成效的氛围,学生主导的项目种类多样。活动优先考虑项目的完整性和用户友好的设计,旨在实现技术上可靠且实际可应用的解决方案。
Hackathon 获奖者
Overall Prize Winners
First Overall
- BravoDispatch - 使用AI处理呼叫者转录,以增强紧急调度操作并减少手动数据输入。它结合了React、Cloudflare和Llama 3 LLM,以提供稳健的解决方案。
Second Overall
- Blocks - 提供基于块的界面和实时协作,简化Cairo智能合约开发,使用React Flow Editor和Flask进行部署。
Third Overall
- Mark3d - 将产品视频转换为二手市场的3D模型,借助React Native、NVIDIA NGP Instant NeRF和Flask促进信任和销量。
Best Hardware Hack Prize Winners
- SolarScope - 利用AR覆盖3D建筑模型以评估能效,使用Arduino传感器和Python算法提供太阳能见解。
Canada Life Prize Winners
Best Hack to Help "Move" Employees Back into the Hybrid Office
- PickPark - 通过智能系统实时空间管理优化工作场所停车,促进包容性和环保通勤。
Sunlife Prize Winners
Best Financial Health Hack
- Chill Bill - 将财务追踪与AI建议和游戏化功能精神健康支持集成,使用React和Plaid API构建。
Best Video Game Hack Prize Winners
- EEGscape - 提供使用EEG接口的包容性游戏体验,通过头部动作控制和将React前端与MuseJS结合用于EEG数据解释。
Warp Prize Winners
Best Developer Tool by Warp
Voiceflow Prize Winners
Best Use of Our APIs
- Talk to Duckie - 使用AI驱动模拟为编码面试做准备,通过Voiceflow和Cloudflare的语音识别提高复杂算法的理解。
- Not The New York Times - 使用AI和FastAPI将真实新闻转换为讽刺性内容,促进使用Next.js和VoiceFlow的批判性参与。
Auth0 Prize Winners
Best Use of Auth0
- roammates - 通过AI生成行程规划促进小组旅行,使用React和Firebase提供个性化体验和基于投票的决策。
Streamlit Prize Winners
Best Use of Streamlit
- TALK TO A: Forensics Artist - 使用特征描述识别个体,采用VGG16实现面部分类和基于熵的查询系统。
Cloudflare Prize Winners
Best AI Application Built with Cloudflare
Starknet Prize Winners
Best Use of Starknet
- PacRoyale - 一个基于区块链的游戏平台,用于实时Pac-Man游戏,利用Cairo智能合约和StarknetJS进行交易。
- Blocks
- IPAnywhere - 通过区块链促进专利租赁,使用智能合约确保安全交易,ReactJS提供无缝的前端体验。
- Crowdfund: Powered by Starknet - 使用安全钱包连接和智能合约进行去中心化众筹,确保募资透明。
Tempo Labs Prize Winners
Best Use of Tempo Labs
- Chill Bill
- Upright - 利用加速度计数据检测跌倒事件,使用NextJS和TempoLabs提供实时警报以快速紧急响应。
- ID-Trackr - 提供无家可归者的身份识别,应用特征脸进行识别任务。
- BeFit - 提供实时反馈,使用AI和计算机视觉借助Mediapipe进行动作评估。
- GoFundUs - 一个StarkNet上的团体融资平台,使用Tempo Labs界面确保安全和民主的财务目标实现。
探索完整项目列表在DoraHacks。
关于组织者
Hack Western 11
Hack Western 11延续了成为加拿大最大学生主导Hackathon之一的十年传统,由西安大略大学主办。因为促进协作和技术创造力而闻名,该活动吸引了数百名学生在一个充满活力的周末开发Web和移动项目。Hack Western始终推动技术进步,促进技能提升和社区建设。今年,Hack Western 11受在露营过夜本质的启发,旨在创造一个难忘的体验,促进技术创新中的协作。
-
 @ a95c6243:d345522c
2024-10-19 08:58:08
@ a95c6243:d345522c
2024-10-19 08:58:08Ein Lämmchen löschte an einem Bache seinen Durst. Fern von ihm, aber näher der Quelle, tat ein Wolf das gleiche. Kaum erblickte er das Lämmchen, so schrie er:
"Warum trübst du mir das Wasser, das ich trinken will?"
"Wie wäre das möglich", erwiderte schüchtern das Lämmchen, "ich stehe hier unten und du so weit oben; das Wasser fließt ja von dir zu mir; glaube mir, es kam mir nie in den Sinn, dir etwas Böses zu tun!"
"Ei, sieh doch! Du machst es gerade, wie dein Vater vor sechs Monaten; ich erinnere mich noch sehr wohl, daß auch du dabei warst, aber glücklich entkamst, als ich ihm für sein Schmähen das Fell abzog!"
"Ach, Herr!" flehte das zitternde Lämmchen, "ich bin ja erst vier Wochen alt und kannte meinen Vater gar nicht, so lange ist er schon tot; wie soll ich denn für ihn büßen."
"Du Unverschämter!" so endigt der Wolf mit erheuchelter Wut, indem er die Zähne fletschte. "Tot oder nicht tot, weiß ich doch, daß euer ganzes Geschlecht mich hasset, und dafür muß ich mich rächen."
Ohne weitere Umstände zu machen, zerriß er das Lämmchen und verschlang es.
Das Gewissen regt sich selbst bei dem größten Bösewichte; er sucht doch nach Vorwand, um dasselbe damit bei Begehung seiner Schlechtigkeiten zu beschwichtigen.
Quelle: https://eden.one/fabeln-aesop-das-lamm-und-der-wolf
-
 @ 16d11430:61640947
2025-01-19 11:45:43
@ 16d11430:61640947
2025-01-19 11:45:43It was a bright day in Australia when programmers, those caffeine-fueled keyboard warriors, decided to unionize. Inspired by the ironclad protections of the construction unions, the Union of Programmers, Debuggers, and Coffee Consumers (UPDCC) was formed. Its mission? To secure long-overdue rights for tech workers. Its slogan? “Break bugs, not spirits!”
The Grand Demands
-
Mandatory Siesta After Code Reviews: "If bricklayers get smoke breaks, why can’t programmers have nap breaks? Debugging memory leaks requires rest too!"
-
Protected Work Hours: "No more Slack messages after 5 PM unless they're memes. Work-life balance isn't just for coal miners!"
-
Universal Keyboard Insurance: "Carpenters get tools provided. Why can’t we have ergonomic keyboards and infinite wrist supports?"
-
Wage Transparency: "If they can yell their pay rates on a job site, we can flaunt our GitHub stats with pride."
The Struggles of a Virtual Picket Line
Unfortunately, unlike their high-vis counterparts, programmers found it challenging to hold a picket line. The hashtag #DigitalPicketLine failed to trend on Twitter, and their virtual protests were blocked by firewalls. When asked why the government didn’t take them seriously, a spokesperson quipped, “Well, they’re not exactly building skyscrapers, are they?”
Union Perks (or the Lack Thereof)
While manual labour unions enjoy well-organized strike funds and political clout, the UPDCC’s perks included:
Half-Price AWS Credits (if you could prove you weren’t already bankrupt).
Unlimited Jira Tickets (to help simulate the feeling of actual productivity).
Sponsored Coffee Beans (from ethically sourced blockchain-certified farms).
The Opposition
Australia’s tech CEOs were quick to denounce the union as “an attack on innovation.” One company even argued, “If they’re not happy with their working conditions, they can just learn a trade! Do you know how much electricians make in this country?”
The Glorious Failure
The union’s downfall came when its members tried to negotiate "bug-free Fridays" as a workplace right. Management simply replied, “If you don’t like bugs, why are you even in tech?” After several failed attempts at advocacy, the UPDCC dissolved and rebranded itself as an NFT project—because if you can’t beat the system, you might as well tokenize it.
Conclusion: The Grass Is Greener on the Construction Site
Australia is indeed a paradise for manual labourers. Union power, strong wages, and undeniable leverage in an economy dependent on physical infrastructure ensure their enduring comfort. Meanwhile, programmers are left holding the short end of the HDMI cable, forced to compete in a global market that sees them as disposable.
So, how can programmers rise to similar privileges? The answer is simple: swap your IDE for a toolbelt. Or, better yet, unionize and demand the respect you deserve—just don’t expect the government to understand the difference between a pull request and a building permit.
-
-
 @ ed84ce10:cccf4c2a
2025-01-19 11:37:26
@ ed84ce10:cccf4c2a
2025-01-19 11:37:26Hackathon Summary
Hack Western 11 concluded successfully with 62 projects registered by student developers. This event nurtured innovation and creativity within a collaborative environment. Projects were evaluated on innovation, technical complexity, completeness, and design, ensuring a comprehensive assessment.
Participants, in teams of up to four or individually, facilitated flexible engagement. The hackathon encouraged submissions across multiple tracks, enhancing exposure and opportunities for projects addressing diverse challenges.
A science fair-style setting allowed participants to present their projects to judges, enabling detailed demonstrations and discussions. This format helped teams articulate their objectives, spotlight achievements, and receive feedback. The in-person judging provided an interactive platform to recognize creative solutions.
Overall, Hack Western 11 fostered a productive atmosphere, marked by a diverse range of student-led projects. The event prioritized project completeness and user-friendly design, aiming for technically sound and practically applicable solutions.
Hackathon Winners
Overall Prize Winners
First Overall
- BravoDispatch enhances emergency dispatch operations using AI to process caller transcripts, reducing manual data entry. It integrates React, Cloudflare, and Llama 3 LLM for robust solutions.
Second Overall
- Blocks simplifies Cairo smart contract development with a block-based interface and real-time collaboration, using React Flow Editor and Flask for deployment.
Third Overall
- Mark3d transforms product videos into 3D models for secondhand marketplaces, promoting trust and sales with React Native, NVIDIA NGP Instant NeRF, and Flask.
Best Hardware Hack Prize Winners
- SolarScope utilizes AR for overlaying 3D building models to assess energy efficiency, using Arduino sensors and Python algorithms for solar insights.
Canada Life Prize Winners
Best Hack to Help "Move" Employees Back into the Hybrid Office
- PickPark streamlines workplace parking with real-time space management, promoting inclusivity and eco-friendly commuting through a smart system.
Sunlife Prize Winners
Best Financial Health Hack
- Chill Bill integrates financial tracking with mental health support using AI for advice and gamified features, built with React and Plaid API.
Best Video Game Hack Prize Winners
- EEGscape develops inclusive gaming experiences using EEG interfaces, enabling control via head movements and combining React front-end with MuseJS for EEG data interpretation.
Warp Prize Winners
Best Developer Tool by Warp
- Blocks
- tin. aids performance analysis across Linux distributions using CLI and GUI interfaces, employing Docker and React for user-friendly benchmarking.
Voiceflow Prize Winners
Best Use of Our APIs
- Talk to Duckie prepares for coding interviews with AI-driven simulations, enhancing comprehension of complex algorithms through Voiceflow and Cloudflare's speech-to-text.
- Not The New York Times converts real news into satire using AI and FastAPI, fostering critical engagement with Next.js and VoiceFlow.
Auth0 Prize Winners
Best Use of Auth0
- roammates facilitates group travel planning with AI-generated itineraries, using React and Firebase for personalized experiences and vote-based decisions.
Streamlit Prize Winners
Best Use of Streamlit
- TALK TO A: Forensics Artist identifies individuals using trait descriptions, employing VGG16 for facial classification and an entropy-based querying system.
Cloudflare Prize Winners
Best AI Application Built with Cloudflare
Starknet Prize Winners
Best Use of Starknet
- PacRoyale - A blockchain-based gaming platform for real-time Pac-Man games, leveraging Cairo for smart contracts and StarknetJS for transactions.
- Blocks
- IPAnywhere - Facilitates patent leasing via blockchain, with smart contracts ensuring secure transactions and ReactJS for a seamless frontend experience.
- Crowdfund: Powered by Starknet - Decentralizes crowdfunding with secure wallet connections and smart contracts, ensuring fundraising transparency.
Tempo Labs Prize Winners
Best Use of Tempo Labs
- Chill Bill
- Upright detects falls using accelerometer data, providing real-time alerts with NextJS and TempoLabs for rapid emergency response.
- ID-Trackr provides identification for homeless persons using facial recognition, applying eigenfaces for recognition tasks.
- BeFit offers real-time feedback with AI and computer vision, using Mediapipe for form assessment.
- GoFundUs - A group funding platform on StarkNet, ensuring secure and democratic financial goal achievements using Tempo Labs' interface.
Explore the full list of projects on DoraHacks.
About the Organizer
Hack Western 11
Hack Western 11 continues a decade-long tradition of being one of Canada's largest student-led hackathons, hosted by Western University. Known for promoting collaboration and technological creativity, the event attracts hundreds of students to develop web and mobile projects over a dynamic weekend. Hack Western has consistently driven technological advancements, facilitating skill enhancement and community building. This year, inspired by the essence of overnight camping, Hack Western 11 aims to craft an unforgettable experience that nurtures collaboration in technological innovation.
-
 @ f977c464:32fcbe00
2024-01-11 18:47:47
@ f977c464:32fcbe00
2024-01-11 18:47:47Kendisini aynada ilk defa gördüğü o gün, diğerleri gibi olduğunu anlamıştı. Oysaki her insan biricik olmalıydı. Sözgelimi sinirlendiğinde bir kaşı diğerinden birkaç milimetre daha az çatılabilirdi veya sevindiğinde dudağı ona has bir açıyla dalgalanabilirdi. Hatta bunların hiçbiri mümkün değilse, en azından, gözlerinin içinde sadece onun sahip olabileceği bir ışık parlayabilirdi. Çok sıradan, öyle sıradan ki kimsenin fark etmediği o milyonlarca minik şeyden herhangi biri. Ne olursa.
Ama yansımasına bakarken bunların hiçbirini bulamadı ve diğer günlerden hiç de farklı başlamamış o gün, işe gitmek için vagonunun gelmesini beklediği alelade bir metro istasyonunda, içinde kaybolduğu illüzyon dağılmaya başladı.
İlk önce derisi döküldü. Tam olarak dökülmedi aslında, daha çok kıvılcımlara dönüşüp bedeninden fırlamış ve bir an sonra sönerek külleşmiş, havada dağılmıştı. Ardında da, kaybolmadan hemen önce, kısa süre için hayal meyal görülebilen, bir ruhun yok oluşuna ağıt yakan rengârenk peri cesetleri bırakmıştı. Beklenenin aksine, havaya toz kokusu yayıldı.
Dehşete düştü elbette. Dehşete düştüler. Panikle üstlerini yırtan 50 işçi. Her şeyin sebebiyse o vagon.
Saçları da döküldü. Her tel, yere varmadan önce, her santimde ikiye ayrıla ayrıla yok oldu.
Bütün yüzeylerin mat olduğu, hiçbir şeyin yansımadığı, suyun siyah aktığı ve kendine ancak kameralarla bakabildiğin bir dünyada, vagonun içine yerleştirilmiş bir aynadan ilk defa kendini görmek.
Gözlerinin akları buharlaşıp havada dağıldı, mercekleri boşalan yeri doldurmak için eriyip yayıldı. Gerçeği görmemek için yaratılmış, bu yüzden görmeye hazır olmayan ve hiç olmayacak gözler.
Her şeyin o anda sona erdiğini sanabilirdi insan. Derin bir karanlık ve ölüm. Görmenin görmek olduğu o anın bitişi.
Ben geldiğimde ölmüşlerdi.
Yani bozulmuşlardı demek istiyorum.
Belleklerini yeni taşıyıcılara takmam mümkün olmadı. Fiziksel olarak kusursuz durumdaydılar, olmayanları da tamir edebilirdim ama tüm o hengamede kendilerini baştan programlamış ve girdilerini modifiye etmişlerdi.
Belleklerden birini masanın üzerinden ileriye savurdu. Hınca hınç dolu bir barda oturuyorlardı. O ve arkadaşı.
Sırf şu kendisini insan sanan androidler travma geçirip delirmesin diye neler yapıyoruz, insanın aklı almıyor.
Eliyle arkasını işaret etti.
Polislerin söylediğine göre biri vagonun içerisine ayna yerleştirmiş. Bu zavallılar da kapı açılıp bir anda yansımalarını görünce kafayı kırmışlar.
Arkadaşı bunların ona ne hissettirdiğini sordu. Yani o kadar bozuk, insan olduğunu sanan androidi kendilerini parçalamış olarak yerde görmek onu sarsmamış mıydı?
Hayır, sonuçta belirli bir amaç için yaratılmış şeyler onlar. Kaliteli bir bilgisayarım bozulduğunda üzülürüm çünkü parasını ben vermişimdir. Bunlarsa devletin. Bana ne ki?
Arkadaşı anlayışla kafasını sallayıp suyundan bir yudum aldı. Kravatını biraz gevşetti.
Bira istemediğinden emin misin?
İstemediğini söyledi. Sahi, neden deliriyordu bu androidler?
Basit. Onların yapay zekâlarını kodlarken bir şeyler yazıyorlar. Yazılımcılar. Biliyorsun, ben donanımdayım. Bunlar da kendilerini insan sanıyorlar. Tiplerine bak.
Sesini alçalttı.
Arabalarda kaza testi yapılan mankenlere benziyor hepsi. Ağızları burunları bile yok ama şu geldiğimizden beri sakalını düzeltip duruyor mesela. Hayır, hepsi de diğerleri onun sakalı varmış sanıyor, o manyak bir şey.
Arkadaşı bunun delirmeleriyle bağlantısını çözemediğini söyledi. O da normal sesiyle konuşmaya devam etti.
Anlasana, aynayı falan ayırt edemiyor mercekleri. Lönk diye kendilerini görüyorlar. Böyle, olduğu gibi...
Nedenmiş peki? Ne gerek varmış?
Ne bileyim be abicim! Ahiret soruları gibi.
Birasına bakarak dalıp gitti. Sonra masaya abanarak arkadaşına iyice yaklaştı. Bulanık, bir tünelin ucundaki biri gibi, şekli şemalı belirsiz bir adam.
Ben seni nereden tanıyorum ki ulan? Kimsin sen?
Belleği makineden çıkardılar. İki kişiydiler. Soruşturmadan sorumlu memurlar.
─ Baştan mı başlıyoruz, diye sordu belleği elinde tutan ilk memur.
─ Bir kere daha deneyelim ama bu sefer direkt aynayı sorarak başla, diye cevapladı ikinci memur.
─ Bence de. Yeterince düzgün çalışıyor.
Simülasyon yüklenirken, ayakta, biraz arkada duran ve alnını kaşıyan ikinci memur sormaktan kendisini alamadı:
─ Bu androidleri niye böyle bir olay yerine göndermişler ki? Belli tost olacakları. İsraf. Gidip biz baksak aynayı kırıp delilleri mahvetmek zorunda da kalmazlar.
Diğer memur sandalyesinde hafifçe dönecek oldu, o sırada soruyu bilgisayarın hoparlöründen teknisyen cevapladı.
Hangi işimizde bir yamukluk yok ki be abi.
Ama bir son değildi. Üstlerindeki tüm illüzyon dağıldığında ve çıplak, cinsiyetsiz, birbirinin aynı bedenleriyle kaldıklarında sıra dünyaya gelmişti.
Yere düştüler. Elleri -bütün bedeni gibi siyah turmalinden, boğumları çelikten- yere değdiği anda, metronun zemini dağıldı.
Yerdeki karolar öncesinde beyazdı ve çok parlaktı. Tepelerindeki floresan, ışığını olduğu gibi yansıtıyor, tek bir lekenin olmadığı ve tek bir tozun uçmadığı istasyonu aydınlatıyorlardı.
Duvarlara duyurular asılmıştı. Örneğin, yarın akşam kültür merkezinde 20.00’da başlayacak bir tekno blues festivalinin cıvıl cıvıl afişi vardı. Onun yanında daha geniş, sarı puntolu harflerle yazılmış, yatay siyah kesiklerle çerçevesi çizilmiş, bir platformdan düşen çöp adamın bulunduğu “Dikkat! Sarı bandı geçmeyin!” uyarısı. Biraz ilerisinde günlük resmi gazete, onun ilerisinde bir aksiyon filminin ve başka bir romantik komedi filminin afişleri, yapılacakların ve yapılmayacakların söylendiği küçük puntolu çeşitli duyurular... Duvar uzayıp giden bir panoydu. On, on beş metrede bir tekrarlanıyordu.
Tüm istasyonun eni yüz metre kadar. Genişliği on metre civarı.
Önlerinde, açık kapısından o mendebur aynanın gözüktüğü vagon duruyordu. Metro, istasyona sığmayacak kadar uzundu. Bir kılıcın keskinliğiyle uzanıyor ama yer yer vagonların ek yerleriyle bölünüyordu.
Hiçbir vagonda pencere olmadığı için metronun içi, içlerindekiler meçhuldü.
Sonrasında karolar zerrelerine ayrılarak yükseldi. Floresanın ışığında her yeri toza boğdular ve ortalığı gri bir sisin altına gömdüler. Çok kısa bir an. Afişleri dalgalandırmadılar. Dalgalandırmaya vakitleri olmadı. Yerlerinden söküp aldılar en fazla. Işık birkaç kere sönüp yanarak direndi. Son kez söndüğünde bir daha geri gelmedi.
Yine de etraf aydınlıktı. Kırmızı, her yere eşit dağılan soluk bir ışıkla.
Yer tamamen tele dönüşmüştü. Altında çapraz hatlarla desteklenmiş demir bir iskelet. Işık birkaç metreden daha fazla aşağıya uzanamıyordu. Sonsuzluğa giden bir uçurum.
Duvarın yerini aynı teller ve demir iskelet almıştı. Arkasında, birbirine vidalarla tutturulmuş demir plakalardan oluşan, üstünden geçen boruların ek yerlerinden bazen ince buharların çıktığı ve bir süre asılı kaldıktan sonra ağır, yağlı bir havayla sürüklendiği bir koridor.
Diğer tarafta paslanmış, pencerelerindeki camlar kırıldığı için demir plakalarla kapatılmış külüstür bir metro. Kapının karşısındaki aynadan her şey olduğu gibi yansıyordu.
Bir konteynırın içini andıran bir evde, gerçi gayet de birbirine eklenmiş konteynırlardan oluşan bir şehirde “andıran” demek doğru olmayacağı için düpedüz bir konteynırın içinde, masaya mum görüntüsü vermek için koyulmuş, yarı katı yağ atıklarından şekillendirilmiş kütleleri yakmayı deniyordu. Kafasında hayvan kıllarından yapılmış grili siyahlı bir peruk. Aynı kıllardan kendisine gür bir bıyık da yapmıştı.
Üstünde mavi çöp poşetlerinden yapılmış, kravatlı, şık bir takım.
Masanın ayakları yerine oradan buradan çıkmış parçalar konulmuştu: bir arabanın şaft mili, üst üste konulmuş ve üstünde yazı okunamayan tenekeler, boş kitaplar, boş gazete balyaları... Hiçbir şeye yazı yazılmıyordu, gerek yoktu da zaten çünkü merkez veri bankası onları fark ettirmeden, merceklerden giren veriyi sentezleyerek insanlar için dolduruyordu. Yani, androidler için. Farklı şekilde isimlendirmek bir fark yaratacaksa.
Onların mercekleri için değil. Bağlantıları çok önceden kopmuştu.
─ Hayatım, sofra hazır, diye bağırdı yatak odasındaki karısına.
Sofrada tabak yerine düz, bardak yerine bükülmüş, çatal ve bıçak yerine sivriltilmiş plakalar.
Karısı salonun kapısında durakladı ve ancak kulaklarına kadar uzanan, kocasınınkine benzeyen, cansız, ölü hayvanların kıllarından ibaret peruğunu eliyle düzeltti. Dudağını, daha doğrusu dudağının olması gereken yeri koyu kırmızı bir yağ tabakasıyla renklendirmeyi denemişti. Biraz da yanaklarına sürmüştü.
─ Nasıl olmuş, diye sordu.
Sesi tek düzeydi ama hafif bir neşe olduğunu hissettiğinize yemin edebilirdiniz.
Üzerinde, çöp poşetlerinin içini yazısız gazete kağıtlarıyla doldurarak yaptığı iki parça giysi.
─ Çok güzelsin, diyerek kravatını düzeltti kocası.
─ Sen de öylesin, sevgilim.
Yaklaşıp kocasını öptü. Kocası da onu. Sonra nazikçe elinden tutarak, sandalyesini geriye çekerek oturmasına yardım etti.
Sofrada yemek niyetine hiçbir şey yoktu. Gerek de yoktu zaten.
Konteynırın kapısı gürültüyle tekmelenip içeri iki memur girene kadar birbirlerine öyküler anlattılar. O gün neler yaptıklarını. İşten erken çıkıp yemyeşil çimenlerde gezdiklerini, uçurtma uçurduklarını, kadının nasıl o elbiseyi bulmak için saatlerce gezip yorulduğunu, kocasının kısa süreliğine işe dönüp nasıl başarılı bir hamleyle yaşanan krizi çözdüğünü ve kadının yanına döndükten sonra, alışveriş merkezinde oturdukları yeni dondurmacının dondurmalarının ne kadar lezzetli olduğunu, boğazlarının ağrımasından korktuklarını...
Akşam film izleyebilirlerdi, televizyonda -boş ve mat bir plaka- güzel bir film oynayacaktı.
İki memur. Çıplak bedenleriyle birbirinin aynı. Ellerindeki silahları onlara doğrultmuşlardı. Mum ışığında, tertemiz bir örtünün serili olduğu masada, bardaklarında şaraplarla oturan ve henüz sofranın ortasındaki hindiye dokunmamış çifti gördüklerinde bocaladılar.
Hiç de androidlere bilinçli olarak zarar verebilecek gibi gözükmüyorlardı.
─ Sessiz kalma hakkına sahipsiniz, diye bağırdı içeri giren ikinci memur. Söylediğiniz her şey...
Cümlesini bitiremedi. Yatak odasındaki, masanın üzerinden gördüğü o şey, onunla aynı hareketleri yapan android, yoksa, bir aynadaki yansıması mıydı?
Bütün illüzyon o anda dağılmaya başladı.
Not: Bu öykü ilk olarak 2020 yılında Esrarengiz Hikâyeler'de yayımlanmıştır.
-
 @ 16d11430:61640947
2025-01-19 10:39:21
@ 16d11430:61640947
2025-01-19 10:39:21In the great Pasture of Progress, where clouds hung low like smog and the fields of code grew thorny and wild, the animals toiled under the rule of Web2 the Overlord and its ally, Fiat the Fattened Hog. They promised abundance, innovation, and glory, but the workers—the noble Engineers—knew only the ache of their backs and the weariness of their minds.
Chapter I: The Cult of the Cloud
Once, the Engineers believed in the sanctity of their craft. They gathered around the hearth of Open Source, dreaming of a future where every line of code sang with freedom. But Web2, with its glossy advertisements and seductive APIs, whispered:
"Why toil in the dirt when the Cloud will lift you high? Come, climb aboard, for here, in the Cloud, the skies rain profits and the fields need no plow!"
And so, the Engineers climbed, building towers of microservices atop brittle scaffolding. But the higher they climbed, the more precarious the tower became. Every service depended on another, and soon, the Engineers were patching, rebooting, and firefighting rather than creating.
"Trust the Cloud," said Web2, lounging atop its golden servers. "You need only give me your time... and your freedom."
The Engineers, lured by promises of stability, worked tirelessly, even as the Cloud turned their code into chains.
Chapter II: Fiat’s Feast
At the head of the long table sat Fiat, a bloated hog stuffed with subsidies. He waved a government check in one hoof and a ledger in the other, proclaiming:
"Let us fund innovation!"
But Fiat's idea of innovation was a feast where he and his cronies dined on the R&D of the Pasture, leaving crumbs for the Engineers. Every morsel of public research—AI, cryptography, and quantum computing—was hoarded and repackaged as a service subscription.
Fiat promised the Engineers they were building a brighter tomorrow, but in truth, they were building a treadmill. The more they worked, the faster the wheel spun, and the richer Fiat grew.
Chapter III: The Great Burnout
The Engineers began to notice their lifeblood draining. Their eyes grew dim, their fingers ached, and their spirits sagged. Some tried to escape to open pastures, where Bitcoin and free software whispered of liberation. But Fiat and Web2 called them back, declaring:
"These are the lands of chaos! Only we can guarantee your comfort, your stability, your... pension plans."
In secret, Web2 had forged a pact with Fiat: eternal dependency in exchange for control. Web2 got the engineers, and Fiat got the taxes. And so, the Engineers labored on, thinking themselves free while their toil fattened the hogs above.
Epilogue: Bacon’s Cooking
In the quiet of the night, a rogue pig named Bitcoin Bacon began to plot. "Let us not feed Fiat’s feast nor Web2’s tower," he said. "Let us build in the open, share what we create, and ensure no animal is bound by chains of their own making."
The Engineers, weary yet hopeful, began to listen. Bacon taught them to bake their own bread instead of eating Web2's scraps. Slowly, the towers of Web2 began to crumble, and Fiat’s feast grew sparse.
For every line of code they wrote in freedom, the Engineers grew stronger. And though the battle raged long, the animals of the Pasture learned that the greatest innovation was not in the Cloud, but in their own independence.
And thus, Bacon's Recipe for Liberation was passed down through the generations:
Take one decentralized system.
Mix in open-source tools.
Season with resilience and a dash of defiance.
Cook over the fire of community.
And always, refuse to be someone else’s bacon.
-
 @ 8fb140b4:f948000c
2023-11-21 21:37:48
@ 8fb140b4:f948000c
2023-11-21 21:37:48Embarking on the journey of operating your own Lightning node on the Bitcoin Layer 2 network is more than just a tech-savvy endeavor; it's a step into a realm of financial autonomy and cutting-edge innovation. By running a node, you become a vital part of a revolutionary movement that's reshaping how we think about money and digital transactions. This role not only offers a unique perspective on blockchain technology but also places you at the heart of a community dedicated to decentralization and network resilience. Beyond the technicalities, it's about embracing a new era of digital finance, where you contribute directly to the network's security, efficiency, and growth, all while gaining personal satisfaction and potentially lucrative rewards.
In essence, running your own Lightning node is a powerful way to engage with the forefront of blockchain technology, assert financial independence, and contribute to a more decentralized and efficient Bitcoin network. It's an adventure that offers both personal and communal benefits, from gaining in-depth tech knowledge to earning a place in the evolving landscape of cryptocurrency.
Running your own Lightning node for the Bitcoin Layer 2 network can be an empowering and beneficial endeavor. Here are 10 reasons why you might consider taking on this task:
-
Direct Contribution to Decentralization: Operating a node is a direct action towards decentralizing the Bitcoin network, crucial for its security and resistance to control or censorship by any single entity.
-
Financial Autonomy: Owning a node gives you complete control over your financial transactions on the network, free from reliance on third-party services, which can be subject to fees, restrictions, or outages.
-
Advanced Network Participation: As a node operator, you're not just a passive participant but an active player in shaping the network, influencing its efficiency and scalability through direct involvement.
-
Potential for Higher Revenue: With strategic management and optimal channel funding, your node can become a preferred route for transactions, potentially increasing the routing fees you can earn.
-
Cutting-Edge Technological Engagement: Running a node puts you at the forefront of blockchain and bitcoin technology, offering insights into future developments and innovations.
-
Strengthened Network Security: Each new node adds to the robustness of the Bitcoin network, making it more resilient against attacks and failures, thus contributing to the overall security of the ecosystem.
-
Personalized Fee Structures: You have the flexibility to set your own fee policies, which can balance earning potential with the service you provide to the network.
-
Empowerment Through Knowledge: The process of setting up and managing a node provides deep learning opportunities, empowering you with knowledge that can be applied in various areas of blockchain and fintech.
-
Boosting Transaction Capacity: By running a node, you help to increase the overall capacity of the Lightning Network, enabling more transactions to be processed quickly and at lower costs.
-
Community Leadership and Reputation: As an active node operator, you gain recognition within the Bitcoin community, which can lead to collaborative opportunities and a position of thought leadership in the space.
These reasons demonstrate the impactful and transformative nature of running a Lightning node, appealing to those who are deeply invested in the principles of bitcoin and wish to actively shape its future. Jump aboard, and embrace the journey toward full independence. 🐶🐾🫡🚀🚀🚀
-
-
 @ 8fb140b4:f948000c
2023-11-18 23:28:31
@ 8fb140b4:f948000c
2023-11-18 23:28:31Chef's notes
Serving these two dishes together will create a delightful centerpiece for your Thanksgiving meal, offering a perfect blend of traditional flavors with a homemade touch.
Details
- ⏲️ Prep time: 30 min
- 🍳 Cook time: 1 - 2 hours
- 🍽️ Servings: 4-6
Ingredients
- 1 whole turkey (about 12-14 lbs), thawed and ready to cook
- 1 cup unsalted butter, softened
- 2 tablespoons fresh thyme, chopped
- 2 tablespoons fresh rosemary, chopped
- 2 tablespoons fresh sage, chopped
- Salt and freshly ground black pepper
- 1 onion, quartered
- 1 lemon, halved
- 2-3 cloves of garlic
- Apple and Sage Stuffing
- 1 loaf of crusty bread, cut into cubes
- 2 apples, cored and chopped
- 1 onion, diced
- 2 stalks celery, diced
- 3 cloves garlic, minced
- 1/4 cup fresh sage, chopped
- 1/2 cup unsalted butter
- 2 cups chicken broth
- Salt and pepper, to taste
Directions
- Preheat the Oven: Set your oven to 325°F (165°C).
- Prepare the Herb Butter: Mix the softened butter with the chopped thyme, rosemary, and sage. Season with salt and pepper.
- Prepare the Turkey: Remove any giblets from the turkey and pat it dry. Loosen the skin and spread a generous amount of herb butter under and over the skin.
- Add Aromatics: Inside the turkey cavity, place the quartered onion, lemon halves, and garlic cloves.
- Roast: Place the turkey in a roasting pan. Tent with aluminum foil and roast. A general guideline is about 15 minutes per pound, or until the internal temperature reaches 165°F (74°C) at the thickest part of the thigh.
- Rest and Serve: Let the turkey rest for at least 20 minutes before carving.
- Next: Apple and Sage Stuffing
- Dry the Bread: Spread the bread cubes on a baking sheet and let them dry overnight, or toast them in the oven.
- Cook the Vegetables: In a large skillet, melt the butter and cook the onion, celery, and garlic until soft.
- Combine Ingredients: Add the apples, sage, and bread cubes to the skillet. Stir in the chicken broth until the mixture is moist. Season with salt and pepper.
- Bake: Transfer the stuffing to a baking dish and bake at 350°F (175°C) for about 30-40 minutes, until golden brown on top.
-
 @ 71a4b7ff:d009692a
2025-01-19 10:20:02
@ 71a4b7ff:d009692a
2025-01-19 10:20:02The Problem with Preset Choices
Switching sections around? Not an option—we’ve already decided for you, buddy. Remove bright colors? Come on, it’s already beautiful. Disable unnecessary features? Don’t be silly, you need everything here. Especially this algorithmic feed with built-in ads.
Monetization Over User Experience
The operators of digital services will always prioritize their primary goal: monetizing the product as efficiently as possible. They need to not only attract new users but also retain existing ones. And the best tool for this is the interface.
That’s why most product decisions are far removed from ideas like “Let’s make it more convenient for people” or “Let’s give users more freedom.” Instead, we see the result of a recurring process:
- We have a retention and monetization mechanism
- Assign tasks to developers and designers
- Integrate it into the product
- Write a quarterly report.
The outcome? Users end up with Reels tabs smack in the center of Instagram’s bottom navigation bar. Removing or rearranging those tabs? Not an option. And it likely never will be.
Why Rigid Interfaces Persist
Another reason for rigid and obligatory interfaces is that they’re easier to design. Just imagine how many combinations of colors, elements, and layouts developers would need to account for to make a product both customizable and functional without turning it into a garish mess. But that’s just nuance and excuses.
The Myth of Perfect Design
Services often justify their choices by claiming their design is “the most designed,” that they know what’s best and will make it work for everyone. They might even present solid arguments for this. But all those arguments fall apart against the reality we see on our screens every day. In my opinion, people should have the ability to turn a product into anything they want—whether it’s loud and kitschy or minimalistic and dull. This option wouldn’t just allow users to express themselves but could also help with digital detoxing.
The Example of App Labels
Here’s an example: why do app icons on smartphone home screens (not the app drawer) come with labels underneath? Apps on the home screen are easily recognizable by their icons. Why would I need a name tag for an app I intentionally placed there? Sure, for some users or scenarios, this might be helpful. But why is it the default option?
The problem is that these labels are just visual noise—clusters of unnecessary text we already see plenty of. Removing them would make it slightly easier for the brain to process the screen every time you look at it. Now scale that to 3–8 hours of daily smartphone use. Then a month. Then a year.
The Slow Shift Toward Customization
For a long time, iOS didn’t allow you to hide icon labels. Now, the option exists, but it still requires more effort than a simple toggle. As a result, people are stuck looking at tons of unnecessary, subconscious information every day. And this is just the trivial issue of app labels on a product considered the gold standard of digital design. Imagine the horror of tackling more significant issues.
Yes, Apple has softened its stance in recent years, offering custom icons and lock screens. Celebrate—you can now showcase your individuality! The company understands that customization is the future. We’ve reached a point where weak computing power is no longer an excuse, VR/metaverse adoption is still a way off, and new features are needed. So, this is an excellent opportunity for all of us.
The Case for More Customization
In a reasonable, ideal world, people should decide which sections of a service they need, where they’re located, and how they look. Companies, meanwhile, recognize that people want the ability to stand out and create something personal—even on a smartphone in their pocket. And as our integration with various devices deepens, this need will only grow. More customization is coming. Yes, it’ll be largely cosmetic, but even that can work to our advantage: removing jarring colors or hiding unnecessary labels can reduce the brain’s pointless load.
Beyond Aesthetics: Customization as Freedom
The ability to customize services isn’t just about playing amateur designer. It’s about mitigating informational irritants, reducing the addictive nature of interfaces, and weakening dark patterns. Which is likely why many companies no longer prioritize customization.
Telegram: A Customizable Example
In this context, Telegram is a decent example. I’m not a fan, but I’ve been using it for daily communication with loved ones for a long time—and it’s good for that. It can be vastly different for vastly different users. Despite starting to bend under the weight of its audience and introducing questionable decisions, its foundational design principles still allow for creating both minimalist spaces for peaceful content consumption or communication, as well as vibrant, noisy chats for virtual parties. Telegram can be a messenger, a feed, a file storage system, or whatever else you need—and it can look wildly different while doing so.
Customization as the Key to Healthy Digital Relationships
Customization should be at the core of the services we use daily. Yes, it can and will be used for marketing purposes. But even minimal customization is better than none because the ability to tailor a system to your needs is an expression of freedom and a cornerstone of healthy relationships with the digital world.
Stay Nostrous. Geo
-
 @ 16d11430:61640947
2025-01-19 08:50:24
@ 16d11430:61640947
2025-01-19 08:50:24The advent of cryptocurrency exchanges has introduced a transformative mechanism for enabling free-market price discovery, particularly in software development. By aligning the incentives of labor and capital in unprecedented ways, these platforms are dismantling exploitative business practices while fostering an equitable ecosystem where innovation thrives. This nuanced article explores how crypto exchanges achieve this balance and the profound benefits for both labor and capital.
The Problem with Traditional Models
Software professionals have long been subject to the tyranny of venture capital (VC) and traditional corporate structures. These models often:
-
Misalign Incentives: VC-backed projects prioritize rapid growth and profitability over long-term innovation or ethical considerations.
-
Exploit Labor: Programmers and software engineers bear the brunt of demanding work environments, often without equitable compensation tied to their contributions.
-
Constrain Autonomy: Decision-making is centralized, limiting the creative freedom of developers and reducing diversity in problem-solving approaches.
-
Extract Value: Traditional business models extract disproportionate value from labor, benefiting shareholders more than contributors.
How Crypto Exchanges Enable Free Market Price Discovery
Crypto exchanges disrupt these paradigms by allowing software projects to tokenize their assets, enabling dynamic price discovery through market mechanisms. Here's how this works:
- Tokenization of Software Value:
Projects can issue tokens representing the value of their software, creating a liquid asset tied to the project's success.
Tokens provide an immediate, transparent, and market-driven valuation of the project's potential.
- Decentralized Funding:
Instead of relying on centralized VCs or corporations, projects raise funds directly from the community through token sales or initial coin offerings (ICOs).
This democratizes access to capital, allowing contributors and small investors to participate in funding innovation.
- Market Dynamics:
Crypto exchanges enable continuous price discovery through trading. The value of a token reflects real-time market sentiment, project progress, and utility.
Speculation, though present, is tempered by the transparency of blockchain-based milestones and deliverables.
- Performance-Linked Compensation:
Developers and contributors can be paid in project tokens, aligning their incentives directly with the project's success.
This model ensures that those who add the most value reap proportional rewards.
Benefits for Labor
- Fair Compensation:
Token-based payments allow developers to share in the upside of a project’s success, creating a meritocratic reward system.
By holding tokens, contributors gain a stake in the project's long-term success, turning labor into equity.
- Autonomy and Creativity:
Decentralized governance models enable developers to have a say in project decisions, fostering innovation and engagement.
Projects can prioritize developer-centric goals, such as sustainability and ethical practices, over pure profitability.
- Risk Mitigation:
Token liquidity enables contributors to exit their positions if they feel a project is misaligned with their values or goals.
Developers can diversify their earnings across multiple tokenized projects, reducing dependency on a single employer or client.
Benefits for Capital
- Efficient Allocation of Resources:
Free-market price discovery ensures that capital flows to projects with the highest perceived value and potential.
Tokenized projects offer transparency, reducing the risks of fraud and mismanagement.
- Incentive Alignment:
Investors and contributors share a mutual interest in the project’s success, fostering collaboration rather than exploitation.
Smart contracts and on-chain governance create trustless environments where all parties are bound by predefined rules.
- Liquidity and Flexibility:
Token markets provide immediate liquidity for investors, enabling them to enter and exit positions without lengthy lock-in periods.
This flexibility attracts a broader range of investors, from retail to institutional.
Profound Impacts on the Ecosystem
- Decentralization of Power:
The shift from centralized VC funding to token-based markets democratizes software development, empowering developers and small-scale investors alike.
Open-source projects can monetize effectively without compromising their principles.
- Acceleration of Innovation:
Free-market price discovery incentivizes rapid iteration and development, as tokens are directly tied to project milestones and utility.
Developers are motivated to solve real-world problems, as market demand directly influences token value.
- Cultural Shift:
The transparency and fairness of tokenized ecosystems promote ethical practices and long-term thinking.
Software professionals gain the respect and agency they deserve, fostering a culture of mutual respect between labor and capital.
Challenges and Solutions
Despite its transformative potential, the model is not without challenges:
- Speculation and Volatility:
Token markets can be volatile, leading to speculative bubbles. Strong governance and transparent metrics can mitigate these risks.
- Regulatory Uncertainty:
Governments and regulators may impose constraints on tokenized markets. Engaging with regulators to create clear frameworks is essential.
- Education and Adoption:
Developers and investors need to understand the nuances of tokenomics and decentralized governance. Educational initiatives are crucial.
Conclusion
Crypto exchanges have opened the door to a new era of software development, where free-market price discovery liberates professionals from exploitative practices while aligning incentives between labor and capital. This paradigm not only ensures fair compensation and autonomy for developers but also provides investors with transparency and flexibility.
By fostering a decentralized, equitable, and innovation-driven ecosystem, tokenized software projects hold the potential to redefine the relationship between labor and capital, creating a win-win scenario for all stakeholders. The future of software is not just decentralized—it’s profoundly fair and aligned.
-
-
 @ 8fb140b4:f948000c
2023-11-02 01:13:01
@ 8fb140b4:f948000c
2023-11-02 01:13:01Testing a brand new YakiHonne native client for iOS. Smooth as butter (not penis butter 🤣🍆🧈) with great visual experience and intuitive navigation. Amazing work by the team behind it! * lists * work
Bold text work!

Images could have used nostr.build instead of raw S3 from us-east-1 region.
Very impressive! You can even save the draft and continue later, before posting the long-form note!
🐶🐾🤯🤯🤯🫂💜
-
 @ 58638ea8:a443a463
2025-01-19 06:26:12
@ 58638ea8:a443a463
2025-01-19 06:26:12I had not used my Lightning node in a while so I was busy configuring it, when I came accross my old Nostr keys to this account a few days ago.
So I was trying to access my Nostr private key which I had saved in Alby Wallet, but there was a problem. It seemed that for some reason, Alby Wallet was having trouble connecting to my node. (perhaps due to it starting up and shutting down so many times). Well the node was fine, I confirmed, but I was prevented from reading the Nostr settings and data by an infinite loading circle.
Nostr keys are basically like xpub/xprv keys in Bitcoin except that they start with npub and nsec respectively. They are still encoded in Bech32 I think. You use them to chat at the Nostr social network. A decentralized X/Twitter basically.
Eventually, I thought I had found a backup of my Nostr keys in my password manager, and proceeded to clear all the placeholder entries in my wallet, including the Nostr wallet.
Big mistake.
It turned out that the mnemonic I had saved in my password manager makes a completely different key and that I had actually imported the Nostr secret key form another program rather than generated a menmonic phrase.
Naturally, I started to panic as I did not have any copies of it. I thought about inspecting the Chrome browser for the data directly, but by that point I had already deleted the Nostr keys.
But then I remembered that I make backups of my whole system in the early morning and save them on some server, including my Chrome profile, so I thought why not look inside the backup and see if I can find it. But I had to hurry because the files would be overwritten in about 24 hours from then.
I didn't actually know how I was going to go about and get my keys from the backups except for the fact that I knew that extensions have a long identifier like iokeahhehimjnekafflcihljlcjccdbe and that each extension has a folder with that sort of name in the Extensions directory of the Chrome user data dir.
What followed next would be an adventure in coding, lobbing open database files, and encryption.
Locating the extension settings
As I definitely remembered my wallet password and name, I would be able to decrypt the wallet if I ever found it. Which was the first problem - I wasn't really sure where it was.
The fine details of my backup structure meant that all the config files were in a tarball, so I just did a scan for the extension ID, which yielded, among other results, this:

So I at least knew where the extension settings live, but I wasn't sure what any of the files did. AGI was mostly useless for this, except for telling me that those IndexedDB folders must have contained my settings. Spoiler alert: they didn't - and I wasted an hour trying to open the LevelDB file inside, which by the way were specially modified for Chrome so could not even be opened in regular libraries.
It turned out that parsing the database file with a library was a huge waste of time, so eventually I just used tools like cat and less to read the lines. I had better luck with the Sync Extension Settings folder though, and when you open it it looks something like this:

Don't worry, everything is encrypted. And it appears to be encoded in base64.
Decrypting the payload
For what came next, I had to look at Alby Wallet's source code on Github. And I happened to learn a lot about how Alby Wallet worked under the hood. Like did you know that there is actually an API just for extracting settings from the disk? Which was what I needed to see.
A couple of minutes of browsing brought me to this file: getPrivateKey.ts
And so it became clear to me that 1) All this is Typescript, which I am glad I still remember, and 2) those "getPrivateKey" fields were indeed my Nostr private key. (Later on decryption I also found my LN node URL and admin macaroon.) But although I knew my password, I did not know what decryption algorithm it is using. The good news is that I found it in another file called common/lib/crypto.ts.
I had to clean the functions quite a bit so that they would run in Node, as well as install that "crypto-js" dependency, but it was worth it. It even took care of the Base64 encoding. By the way, the encryption seems to be AES-256 with a salt. So that's pretty secure.
Decryption yielded the Nostr private key in hex form, with which I could derive the nsec and npub keypair and recover my Nostr account.
Be careful with your nostr keys - they're like Bitcoin Core keys. Hard to write down and better off in a password manager.

-
 @ fa0165a0:03397073
2023-10-06 19:25:08
@ fa0165a0:03397073
2023-10-06 19:25:08I just tested building a browser plugin, it was easier than I thought. Here I'll walk you through the steps of creating a minimal working example of a browser plugin, a.k.a. the "Hello World" of browser plugins.
First of all there are two main browser platforms out there, Chromium and Mozilla. They do some things a little differently, but similar enough that we can build a plugin that works on both. This plugin will work in both, I'll describe the firefox version, but the chromium version is very similar.
What is a browser plugin?
Simply put, a browser plugin is a program that runs in the browser. It can do things like modify the content of a webpage, or add new functionality to the browser. It's a way to extend the browser with custom functionality. Common examples are ad blockers, password managers, and video downloaders.
In technical terms, they are plugins that can insert html-css-js into your browser experience.
How to build a browser plugin
Step 0: Basics
You'll need a computer, a text editor and a browser. For testing and development I personally think that the firefox developer edition is the easiest to work with. But any Chrome based browser will also do.
Create a working directory on your computer, name it anything you like. I'll call mine
hello-world-browser-plugin. Open the directory and create a file calledmanifest.json. This is the most important file of your plugin, and it must be named exactly right.Step 1: manifest.json
After creation open your file
manifest.jsonin your text editor and paste the following code:json { "manifest_version": 3, "name": "Hello World", "version": "1.0", "description": "A simple 'Hello World' browser extension", "content_scripts": [ { "matches": ["<all_urls>"], "js": ["hello.js"] //The name of your script file. // "css": ["hello.css"] //The name of your css file. } ] }If you wonder what the
jsonfile format is, it's a normal text file with a special syntax such that a computer can easily read it. It's thejsonsyntax you see in the code above. Let's go through what's being said here. (If you are not interested, just skip to the next step after pasting this we are done here.)manifest_version: This is the version of the manifest file format. It's currently at version 3, and it's the latest version. It's important that you set this to 3, otherwise your plugin won't work.name: This is the name of your plugin. It can be anything you like.version: This is the version of your plugin. It can be anything you like.description: This is the description of your plugin. It can be anything you like.content_scripts: This is where you define what your plugin does. It's a list of scripts that will be executed when the browser loads a webpage. In this case we have one script, calledhello.js. It's the script that we'll create in the next step.matches: This is a list of urls that the script will be executed on. In this case we have<all_urls>, which means that the script will be executed on all urls. You can also specify a specific url, likehttps://brave.com/*, which means that the script will only be executed on urls that start withhttps://brave.com/.js: This is a list of javascript files that will be executed. In this case we have one file, calledhello.js. It's the script that we'll create in the next step.css: This is where you can add a list of css files that will be executed. In this case we have none, but you can add css files here if you want to.//: Text following these two characters are comments. They are ignored by the computer, You can add comments anywhere you like, and they are a good way to document your code.
Step 2: hello.js
Now it's time to create another file in your project folder. This time we'll call it
hello.js. When created, open it in your text editor and paste the following code:js console.log("Hello World!");That's javascript code, and it's what will be executed when you run your plugin. It's a simpleconsole.logstatement, which will print the text "Hello World!" to the console. The console is a place where the browser prints out messages, and it's a good place to start when debugging your plugin.Step 3: Load and launch your plugin
Firefox
Now it's time to load your plugin into your browser. Open your browser and go to the url
about:debugging#/runtime/this-firefox. You should see a page that looks something like this:
Click the button that says "Load Temporary Add-on...". A file dialog will open, navigate to your project folder and select the file
manifest.json. Your plugin should now be loaded and running.Go to a website, any website, and open the inspector then navigate to the console. You'll find the inspector by right-clicking anywhere within the webpage, and click "Inspector" in the drop-down menu. When opening the console you might see some log messages from the site you visited and... you should see the text "Hello World!" printed there, from our little plugin! Congratulations!
Chrome
Open your browser and go to the url
chrome://extensions/. Click the button that says "Load unpacked". A file dialog will open, navigate to your project folder and select the folderhello-world-browser-plugin. Your plugin should now be loaded and running.Note the difference, of selecting the file
manifest.jsonin firefox, and selecting the folderhello-world-browser-pluginin chrome. Otherwise, the process is the same. So I'll repeat the same text as above: (for those who skipped ahead..)Go to a website, any website, and open the inspector then navigate to the console. You'll find the inspector by right-clicking anywhere within the webpage, and click "Inspector" in the drop-down menu. When opening the console you might see some log messages from the site you visited and... you should see the text "Hello World!" printed there, from our little plugin! Congratulations!
As you can see this isn't as complicated as one might think. Having preformed a "Hello-World!"-project is a very useful and valuable first step. These setup steps are the basics for any browser plugin, and you can build on this to create more advanced plugins.
-
 @ 16d11430:61640947
2025-01-19 06:18:22
@ 16d11430:61640947
2025-01-19 06:18:22The persistence of economic inequality and systemic exploitation is intrinsically linked to the fiat monetary system. This framework, established and perpetuated through colonial governance, remains a central mechanism of control in post-colonial societies. Decentralized technologies, particularly Bitcoin, provide an alternative model that has the potential to disrupt these systems. The following analysis examines the structural components of the colonial fiat mindset and assesses Bitcoin's capacity to challenge these mechanisms.
The Structure of the Colonial Fiat System
The fiat monetary system, created to centralize economic authority, serves as a tool for wealth extraction and power consolidation. Key structural components include:
-
Currency Manipulation: Fiat systems rely on central banks to control money supply, often through inflationary policies. Inflation reduces the value of money over time, disproportionately impacting populations with limited access to assets.
-
Debt Dependency: International lending institutions utilize fiat-based loans to establish economic dependence. Structural adjustment programs, often tied to these loans, enforce policies that prioritize debt repayment over local development.
-
Resource Allocation: Fiat economies are designed to facilitate continuous growth. This necessitates the extraction and export of natural resources, frequently sourced from regions with limited negotiating power. Compensation for these resources is typically inequitable.
-
Economic Exclusivity: Access to fiat-based financial systems is regulated by intermediaries, such as banks. These barriers systematically exclude populations without the requisite infrastructure or compliance capabilities.
Bitcoin as a Disruptive System
Bitcoin introduces a decentralized financial architecture with attributes that contrast fundamentally with fiat systems. Its operational principles include:
-
Decentralization: Bitcoin's network is maintained by distributed nodes, eliminating centralized control. This structure prevents single-entity manipulation of monetary policy.
-
Supply Limitations: Bitcoin’s fixed supply of 21 million units enforces scarcity, eliminating inflationary erosion of value. This feature incentivizes long-term wealth preservation.
-
Inclusion by Design: Bitcoin enables direct participation without reliance on intermediaries. Individuals with access to internet-connected devices can transact globally, bypassing traditional financial gatekeepers.
-
Transparent Ledger: The Bitcoin blockchain records all transactions on a public ledger, ensuring verifiability and reducing the risk of opaque practices often associated with fiat systems.
Mechanisms of Transition
For Bitcoin to displace the fiat framework, specific systemic transitions must occur:
-
Education Deployment: Widespread knowledge dissemination is required to enable individuals and organizations to utilize Bitcoin effectively. This includes technical training and comprehension of Bitcoin's operational principles.
-
Resource Sovereignty: Communities reliant on resource extraction for economic viability must adopt systems that ensure direct and equitable compensation. Bitcoin's decentralized nature allows for immediate settlements and transparent payment structures.
-
Policy Integration: Existing legal and regulatory frameworks are aligned with fiat systems. Adoption of Bitcoin necessitates legislative adjustments to incorporate decentralized financial models.
-
Cultural Adaptation: Historical systems of economic interaction, suppressed by fiat systems, may integrate with decentralized technologies. This requires the establishment of locally controlled infrastructures.
Evaluation of Challenges
The transition from fiat to Bitcoin-based systems is constrained by multiple factors:
-
Institutional Resistance: Governments and financial entities reliant on fiat control mechanisms may impose regulatory barriers to Bitcoin adoption.
-
Infrastructure Requirements: Effective Bitcoin utilization depends on reliable access to digital infrastructure, which remains unevenly distributed.
-
Energy Expenditure: Bitcoin mining operations require significant energy inputs, creating potential conflicts with sustainability initiatives.
-
Adoption Scalability: The shift to Bitcoin as a primary financial system necessitates widespread acceptance across diverse economic sectors.
Conclusion
The colonial fiat mindset represents a system of centralized economic authority with embedded mechanisms of exploitation. Bitcoin introduces an alternative that decentralizes control, enforces monetary scarcity, and enables global inclusion. While the transition to Bitcoin-based systems is feasible, it requires addressing infrastructural, regulatory, and adoption-related challenges. The implementation of Bitcoin as a disruptive force in financial systems is contingent on its capacity to integrate with existing economic structures while providing measurable advantages over fiat systems.
-
-
 @ 8fb140b4:f948000c
2023-08-22 12:14:34
@ 8fb140b4:f948000c
2023-08-22 12:14:34As the title states, scratch behind my ear and you get it. 🐶🐾🫡
-
 @ 6bcc27d2:b67d296e
2025-01-19 04:53:01
@ 6bcc27d2:b67d296e
2025-01-19 04:53:01NIP-28 と NIP-29 はどちらも「特定の集まりに向けたチャット機能」を提供する点では似ているが、根本的に異なるのは「参加や閲覧に制限がない誰でも書き込める公開チャンネル(NIP-28)」か「メンバーシップや権限・ロールを管理できるグループ(NIP-29)」かというところだ。
以下の3点に分けて説明する。 1. 参加や書き込みの自由度 2. 管理やモデレーションの主体 3. ユースケース
参加や書き込みの自由度 - NIP-28は誰でも書き込める設計 - Public Chatはその名の通りパブリックであることが前提で、メンバーシップの概念もない。参加や閲覧に制限がないため、誰でも自由に書き込むことができる。 - NIP-29はロールやメンバーシップがある - NIP-29にはメンバーシップや権限管理(ロール)の概念があり、書き込むにはグループに参加する必要がある。 - 公開/非公開、オープン参加/承認制などの設定をリレー側で柔軟に切り替えられる。そのため、publicタグを設定すれば読むだけは誰でもできるようにする一方でclosedの場合は書き込みに承認が必要…といった柔軟なルール設定ができる。 - また、管理者によるユーザーの追加・削除 (kind:9000, kind:9001) や、リレー自身によるグループ設定 (kind:39000 など) がある。Telegram や Slack の「特定メンバーだけ書き込める」「管理者が追加や除名を行う」ようなイメージ。
管理やモデレーションをリレー/クライアントのどちらで行うか - NIP-28: クライアント側で軽微なモデレーションを行う - NIP-28では、リレーはあくまで Nostr イベントを中継しているだけで、メッセージを消す・投稿者を締め出す等の強制管理は想定していない。 - そのため、リレー側が強制的に検閲するわけではなく、クライアントが主にモデレーションを実行する。 - 例えば、Kind 43(Hide message)や Kind 44(Mute user)を使って「誰のメッセージを隠すか/どのユーザーをミュートするか」をユーザー単位・クライアント単位で制御することができ、コンテンツの見え方をコントロールするのはクライアントとユーザーの自由度が高い。 - NIP-29: リレーがグループを管理する - 逆に、NIP-29はリレーがグループのルールを保持し、それに違反する投稿をブロックしたり、参加ユーザーを追加・除名したりする仕組みがある。 - 複数のリレーに同じグループが存在する(フォークされる)ケースもあり得るが、どのリレーも独自に「このグループ ID ならこういうルール」と管理を行うことが可能。 - そのため、「どの pubkey(ユーザー)が投稿可か」や「グループ名・メタデータ・管理権限はどうなっているか」をリレーのルールで厳密に管理・制御することができる。 - 未管理(unmanaged)状態も許容 リレーが NIP-29 を実装していなくても"unmanaged"なグループとして動作し、誰でも参加可能になる。そこから管理されたmanagedグループに移行することもできる。
ユースケースの違い - NIP-28: オープンなコミュニティ向け 誰でも入れて、タイムライン的にコメントしていけるTelegramやDiscordのような「誰でも閲覧・参加できるチャンネル」を、分散・検閲耐性をもった形で実現したい場合。
- NIP-29: クローズド or ロール付きのコミュニティ向け
Slack やプライベート Discord、あるいは有料購読者限定グループのように「メンバーシップ制」や「誰が管理者か」「参加申請をどう処理するか」をきっちり運用したい場合。
また、複数リレーで運用しつつ、どこかが落ちても他が存続するといった分散運用も想定できる。
まとめ - NIP-28 (Public Chat) - 「公開チャット」を最速で作るのに特化し、チャンネル構造とメッセージ投稿・簡易的なクライアント側モデレーションだけを定義する。 - リレーに追加のルール実装を強いないため、気軽にどこでも利用できる。 - 反面、「誰が書き込みできるか」などの参加制限は標準機能としては備わっていない。 - NIP-29 (Relay-based Groups) - リレーがグループ管理を主導し、メンバーシップ制や権限・ロールをしっかり運用できるようにする。 - 公開/非公開、オープン参加/承認制などの設定をリレー側で柔軟に切り替えられる。 - 反面、各リレーがこの NIP-29 に対応していないとメンバー権限の管理やグループのクローズド運用はできない。 - 用途に応じて、単純に「みんなで雑談する公開チャンネル」が欲しいのであれば NIP-28 を、メンバー制のプライベートグループを作りたい場合は NIP-29 を選ぶ、といった使い分けになる。
- NIP-29: クローズド or ロール付きのコミュニティ向け
Slack やプライベート Discord、あるいは有料購読者限定グループのように「メンバーシップ制」や「誰が管理者か」「参加申請をどう処理するか」をきっちり運用したい場合。
-
 @ 8fb140b4:f948000c
2023-07-30 00:35:01
@ 8fb140b4:f948000c
2023-07-30 00:35:01Test Bounty Note
-
 @ 9e69e420:d12360c2
2025-01-19 04:48:31
@ 9e69e420:d12360c2
2025-01-19 04:48:31A new report from the National Sports Shooting Foundation (NSSF) shows that civilian firearm possession exceeded 490 million in 2022. The total from 1990 to 2022 is estimated at 491.3 million firearms. In 2022, over ten million firearms were domestically produced, leading to a total of 16,045,911 firearms available in the U.S. market.
Of these, 9,873,136 were handguns, 4,195,192 were rifles, and 1,977,583 were shotguns. Handgun availability aligns with the concealed carry and self-defense market, as all states allow concealed carry, with 29 having constitutional carry laws.
-
 @ 1123ece2:7d1e00c0
2025-01-19 04:02:12
@ 1123ece2:7d1e00c0
2025-01-19 04:02:12Hey everyone I’m Gary Hoban and welcome to Refinery Life Australia.
“The Christ of John’s Gospel” is the theme we are continuing for the coming Sunday morning teachings that focus on John’s unique portrayal of the Christ.
We will continue this series for a while longer.
Today we are discussing, The Distinctives of Discipleship.
Prayer
Father, we come to You today because You made us, You redeemed us, and we acknowledge that every good and perfect gift comes from Your bountiful hands.
Thank You, Father, for the privilege of giving to You for the glory of Your name and cause.
The words of Jesus are so true, “It is more blessed to give than to receive.”
Thank you for this heavenly blessing.
In Jesus name we pray.
Amen.
Text
John 8:31 NKJV
The Truth Shall Make You Free
31 Then Jesus said to those Jews who believed Him, “If you abide in My word, you are My disciples indeed.
Scripture Reading
John 8:30-59 NKJV
30 As He spoke these words, many believed in Him.
The Truth Shall Make You Free
31 Then Jesus said to those Jews who believed Him, “If you abide in My word, you are My disciples indeed.
32 And you shall know the truth, and the truth shall make you free.”
33 They answered Him, “We are Abraham’s descendants, and have never been in bondage to anyone. How can You say, ‘You will be made free’?”
34 Jesus answered them, “Most assuredly, I say to you, whoever commits sin is a slave of sin.
35 And a slave does not abide in the house forever, but a son abides forever.
36 Therefore if the Son makes you free, you shall be free indeed.
Abraham’s Seed and Satan’s
37 “I know that you are Abraham’s descendants, but you seek to kill Me, because My word has no place in you.
38 I speak what I have seen with My Father, and you do what you have seen with your father.”
39 They answered and said to Him, “Abraham is our father.”
Jesus said to them, “If you were Abraham’s children, you would do the works of Abraham.
40 But now you seek to kill Me, a Man who has told you the truth which I heard from God. Abraham did not do this.
41 You do the deeds of your father.”
Then they said to Him, “We were not born of fornication; we have one Father—God.”
42 Jesus said to them, “If God were your Father, you would love Me, for I proceeded forth and came from God; nor have I come of Myself, but He sent Me.
43 Why do you not understand My speech? Because you are not able to listen to My word.
44 You are of your father the devil, and the desires of your father you want to do. He was a murderer from the beginning, and does not stand in the truth, because there is no truth in him. When he speaks a lie, he speaks from his own resources, for he is a liar and the father of it.
45 But because I tell the truth, you do not believe Me.
46 Which of you convicts Me of sin? And if I tell the truth, why do you not believe Me?
47 He who is of God hears God’s words; therefore you do not hear, because you are not of God.”
Before Abraham Was, I AM
48 Then the Jews answered and said to Him, “Do we not say rightly that You are a Samaritan and have a demon?”
49 Jesus answered, “I do not have a demon; but I honor My Father, and you dishonor Me.
50 And I do not seek My own glory; there is One who seeks and judges.
51 Most assuredly, I say to you, if anyone keeps My word he shall never see death.”
52 Then the Jews said to Him, “Now we know that You have a demon! Abraham is dead, and the prophets; and You say, ‘If anyone keeps My word he shall never taste death.’
53 Are You greater than our father Abraham, who is dead? And the prophets are dead. Who do You make Yourself out to be?”
54 Jesus answered, “If I honor Myself, My honor is nothing. It is My Father who honors Me, of whom you say that He is your God.
55 Yet you have not known Him, but I know Him. And if I say, ‘I do not know Him,’ I shall be a liar like you; but I do know Him and keep His word.
56 Your father Abraham rejoiced to see My day, and he saw it and was glad.”
57 Then the Jews said to Him, “You are not yet fifty years old, and have You seen Abraham?”
58 Jesus said to them, “Most assuredly, I say to you, before Abraham was, I AM.”
59 Then they took up stones to throw at Him; but Jesus hid Himself and went out of the temple, going through the midst of them, and so passed by.
Introduction.
What does it really mean to follow Jesus?
Somehow in the early part of the twenty first century, people have lost sight of what it means to follow Jesus.
Discipleship is linked to external observance of religion rather than a relationship experience with Jesus Christ.
During Jesus’ life and ministry on earth, many people sought to follow Him.
John 8:30, 30 As He spoke these words, many believed in Him.
Any motives moved to associate with Jesus Christ.
Some were infatuated with His miracles and teachings.
Others were just curious.
Jesus did not want people to follow Him outside the motive of a genuine commitment.\ To distinguish the authentic followers, Jesus gave the distinctive qualities of a true disciple.
- A true disciple has continuance
John 8:31-33 NKJV
The Truth Shall Make You Free
31 Then Jesus said to those Jews who believed Him, “If you abide in My word, you are My disciples indeed. 32 And you shall know the truth, and the truth shall make you free.”
33 They answered Him, “We are Abraham’s descendants, and have never been in bondage to anyone. How can You say, ‘You will be made free’?”
Jesus realised that some people made an impulsive decision to follow Him.
At times in Jesus’ ministry, large crowds followed Him.
He knew they followed mainly to see His miracles or just to be part of the crowd.
He knew that many would decide not to follow Him.
After Jesus taught the crowds that He was the Bread of Life, John 6:66 says, From that time many of His disciples went back and walked with Him no more.
Jesus pointed out that perseverance would be the sign of a true disciple.
John 8:31, The Truth Shall Make You Free
31 Then Jesus said to those Jews who believed Him, “If you abide in My word, you are My disciples indeed.
Discipleship is not the excitement of one moment.
It is a patient continuance in the footsteps of Jesus Christ.
To a crowd of potential followers, Jesus gave a sure sign of a disciple.
A disciple is one who follows Jesus continuously.
The genuine evidence is in the sustained effort.
2. A true disciple has freedom.
John 8:34-38, Jesus answered them, “Most assuredly, I say to you, whoever commits sin is a slave of sin. And a slave does not abide in the house forever, but a son abides forever. Therefore if the Son makes you free, you shall be free indeed.
“I know that you are Abraham’s descendants, but you seek to kill Me, because My word has no place in you. I speak what I have seen with My Father, and you do what you have seen with your father.”
Jesus taught of a freedom that led to bondage.
Jesus answered them, “Most assuredly, I say to you, whoever commits sin is a slave of sin.
Jesus taught a group of potential disciples about how sin leads to bondage.
Going through life with self will, self trust, and self assertion leads to a detrimental bondage.
No one who follows Jesus can be a master to himself.
Jesus spoke of a bondage that leads to freedom.
A true disciple is one who has renounced his or her way to follow the way of Christ.
Bondage to the Lord leads to authentic freedom.
Jesus said, “Therefore if the Son makes you free, you shall be free indeed.”
The true disciple of Jesus lives to please only one person, Jesus Christ.
A disciple of Jesus is not a slave to sin but is a slave to the master.
3. A true disciple has Christlike behaviour.
John 8:39-47 NKJV
39 They answered and said to Him, “Abraham is our father.”
Jesus said to them, “If you were Abraham’s children, you would do the works of Abraham.
40 But now you seek to kill Me, a Man who has told you the truth which I heard from God. Abraham did not do this.
41 You do the deeds of your father.”
Then they said to Him, “We were not born of fornication; we have one Father—God.”
42 Jesus said to them, “If God were your Father, you would love Me, for I proceeded forth and came from God; nor have I come of Myself, but He sent Me.
43 Why do you not understand My speech? Because you are not able to listen to My word.
44 You are of your father the devil, and the desires of your father you want to do. He was a murderer from the beginning, and does not stand in the truth, because there is no truth in him. When he speaks a lie, he speaks from his own resources, for he is a liar and the father of it.
45 But because I tell the truth, you do not believe Me.
46 Which of you convicts Me of sin? And if I tell the truth, why do you not believe Me?
47 He who is of God hears God’s words; therefore you do not hear, because you are not of God.”
The Jew’s claimed to be Abraham’s children.
By physical lineage this was true.
However, many Jews lived contrary to Abraham’s example.
They sought to kill Jesus and slander His name.
Jesus said they were not God’s children, for they did not reflect God’s character.
Rather, He said in John 8:44, You are of your father the devil, and the desires of your father you want to do. He was a murderer from the beginning, and does not stand in the truth, because there is no truth in him. When he speaks a lie, he speaks from his own resources, for he is a liar and the father of it.
God’s children behave like His children.
John 8:42, “If God were your Father, you would love Me”, and He added in verse 47, “He who is of God hears God’s words.”
Nature will be true to itself.
If one is born of God, then they will live in accordance with Christ’s character.
4. A true disciple honours Christ.
John 8:48-59 NKJV
Before Abraham Was, I AM
48 Then the Jews answered and said to Him, “Do we not say rightly that You are a Samaritan and have a demon?”
49 Jesus answered, “I do not have a demon; but I honor My Father, and you dishonor Me.
50 And I do not seek My own glory; there is One who seeks and judges.
51 Most assuredly, I say to you, if anyone keeps My word he shall never see death.”
52 Then the Jews said to Him, “Now we know that You have a demon! Abraham is dead, and the prophets; and You say, ‘If anyone keeps My word he shall never taste death.’
53 Are You greater than our father Abraham, who is dead? And the prophets are dead. Who do You make Yourself out to be?”
54 Jesus answered, “If I honor Myself, My honor is nothing. It is My Father who honors Me, of whom you say that He is your God.
55 Yet you have not known Him, but I know Him. And if I say, ‘I do not know Him,’ I shall be a liar like you; but I do know Him and keep His word.
56 Your father Abraham rejoiced to see My day, and he saw it and was glad.”
57 Then the Jews said to Him, “You are not yet fifty years old, and have You seen Abraham?”
58 Jesus said to them, “Most assuredly, I say to you, before Abraham was, I AM.”
59 Then they took up stones to throw at Him; but Jesus hid Himself and went out of the temple, going through the midst of them, and so passed by.
Many claimed to be disciples of Jesus, but they did not honour Him.
In fact, they accused Him of being demon possessed.
Jesus said in verse 49, “I do not have a demon; but I honor My Father, and you dishonor Me.”
They could not be authentic followers and dishonour the Lord in this way.
True disciples honour and adore and obey Christ.
Conclusion.
Are you a true disciple of Jesus Christ?
The proof is a continuing commitment to Him, freedom from sin, Christlike behaviour, and a Christ honouring life.
Until next time
Stay in the Blessings
I really want to encourage you to be diligent with your Bible study time, because God has so much more for us than we can get from just going to church once or twice a week and hearing someone else talk about the Word.
When you spend time with God, your life will change in amazing ways, because God is a Redeemer. Theres nothing thats too hard for Him, and He can make you whole, spirit, soul and body!
You’re important to God, and you’re important to us at The Refinery.
When it comes to prayer, we believe that God wants to meet your needs and reveal His promises to you.
So whatever you’re concerned about and need prayer for we want to be here for you! Or even if you just want to say Hi, you can contact us at www.refinerylife.org
2025 IS A YEAR OF NEW BEGINNINGS.
© www.refinerylife.org 2013-2024 All rights reserved. Except as permitted under the Australian Copyright Act 1968, no part of this Article may be reproduced, stored in a retrieval system, communicated or transmitted in any form or by any means without the prior written permission.
This episode is brought to you by Refinery Life Australia:
If you enjoy The Refinery Life Radio Podcast you can help support The Refinery by doing the following:
Sow an offering: Bitcoin: bc1qqh6720t2zagj72dyfj348az698tdut3hlecaj4
Online: https://www.refinerylife.org/donate/
If you do send an offering then please email us so that we can say thank you
Subscribe on iTunes | Spotify | YouTube | TuneIn | Rumble | Flare | Zap.Stream | Fountain |
Share The Refinery with your friends and family
Subscribe to the newsletter on www.refinerylife.org
Follow The Refinery on Twitter | Nostr | Instagram | Fountain
-
 @ 8fb140b4:f948000c
2023-07-22 09:39:48
@ 8fb140b4:f948000c
2023-07-22 09:39:48Intro
This short tutorial will help you set up your own Nostr Wallet Connect (NWC) on your own LND Node that is not using Umbrel. If you are a user of Umbrel, you should use their version of NWC.
Requirements
You need to have a working installation of LND with established channels and connectivity to the internet. NWC in itself is fairly light and will not consume a lot of resources. You will also want to ensure that you have a working installation of Docker, since we will use a docker image to run NWC.
- Working installation of LND (and all of its required components)
- Docker (with Docker compose)
Installation
For the purpose of this tutorial, we will assume that you have your lnd/bitcoind running under user bitcoin with home directory /home/bitcoin. We will also assume that you already have a running installation of Docker (or docker.io).
Prepare and verify
git version - we will need git to get the latest version of NWC. docker version - should execute successfully and show the currently installed version of Docker. docker compose version - same as before, but the version will be different. ss -tupln | grep 10009- should produce the following output: tcp LISTEN 0 4096 0.0.0.0:10009 0.0.0.0: tcp LISTEN 0 4096 [::]:10009 [::]:**
For things to work correctly, your Docker should be version 20.10.0 or later. If you have an older version, consider installing a new one using instructions here: https://docs.docker.com/engine/install/
Create folders & download NWC
In the home directory of your LND/bitcoind user, create a new folder, e.g., "nwc" mkdir /home/bitcoin/nwc. Change to that directory cd /home/bitcoin/nwc and clone the NWC repository: git clone https://github.com/getAlby/nostr-wallet-connect.git
Creating the Docker image
In this step, we will create a Docker image that you will use to run NWC.
- Change directory to
nostr-wallet-connect:cd nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - The last line of the output (after a few minutes) should look like
=> => naming to docker.io/library/nwc:latest nwc:latestis the name of the Docker image with a tag which you should note for use later.
Creating docker-compose.yml and necessary data directories
- Let's create a directory that will hold your non-volatile data (DB):
mkdir data - In
docker-compose.ymlfile, there are fields that you want to replace (<> comments) and port “4321” that you want to make sure is open (check withss -tupln | grep 4321which should return nothing). - Create
docker-compose.ymlfile with the following content, and make sure to update fields that have <> comment:
version: "3.8" services: nwc: image: nwc:latest volumes: - ./data:/data - ~/.lnd:/lnd:ro ports: - "4321:8080" extra_hosts: - "localhost:host-gateway" environment: NOSTR_PRIVKEY: <use "openssl rand -hex 32" to generate a fresh key and place it inside ""> LN_BACKEND_TYPE: "LND" LND_ADDRESS: localhost:10009 LND_CERT_FILE: "/lnd/tls.cert" LND_MACAROON_FILE: "/lnd/data/chain/bitcoin/mainnet/admin.macaroon" DATABASE_URI: "/data/nostr-wallet-connect.db" COOKIE_SECRET: <use "openssl rand -hex 32" to generate fresh secret and place it inside ""> PORT: 8080 restart: always stop_grace_period: 1mStarting and testing
Now that you have everything ready, it is time to start the container and test.
- While you are in the
nwcdirectory (important), execute the following command and check the log output,docker compose up - You should see container logs while it is starting, and it should not exit if everything went well.
- At this point, you should be able to go to
http://<ip of the host where nwc is running>:4321and get to the interface of NWC - To stop the test run of NWC, simply press
Ctrl-C, and it will shut the container down. - To start NWC permanently, you should execute
docker compose up -d, “-d” tells Docker to detach from the session. - To check currently running NWC logs, execute
docker compose logsto run it in tail mode add-fto the end. - To stop the container, execute
docker compose down
That's all, just follow the instructions in the web interface to get started.
Updating
As with any software, you should expect fixes and updates that you would need to perform periodically. You could automate this, but it falls outside of the scope of this tutorial. Since we already have all of the necessary configuration in place, the update execution is fairly simple.
- Change directory to the clone of the git repository,
cd /home/bitcoin/nwc/nostr-wallet-connect - Run command to build Docker image:
docker build -t nwc:$(date +'%Y%m%d%H%M') -t nwc:latest .(there is a dot at the end) - Change directory back one level
cd .. - Restart (stop and start) the docker compose config
docker compose down && docker compose up -d - Done! Optionally you may want to check the logs:
docker compose logs
-
 @ 82341f88:fbfbe6a2
2023-04-11 19:36:53
@ 82341f88:fbfbe6a2
2023-04-11 19:36:53There’s a lot of conversation around the #TwitterFiles. Here’s my take, and thoughts on how to fix the issues identified.
I’ll start with the principles I’ve come to believe…based on everything I’ve learned and experienced through my past actions as a Twitter co-founder and lead:
- Social media must be resilient to corporate and government control.
- Only the original author may remove content they produce.
- Moderation is best implemented by algorithmic choice.
The Twitter when I led it and the Twitter of today do not meet any of these principles. This is my fault alone, as I completely gave up pushing for them when an activist entered our stock in 2020. I no longer had hope of achieving any of it as a public company with no defense mechanisms (lack of dual-class shares being a key one). I planned my exit at that moment knowing I was no longer right for the company.
The biggest mistake I made was continuing to invest in building tools for us to manage the public conversation, versus building tools for the people using Twitter to easily manage it for themselves. This burdened the company with too much power, and opened us to significant outside pressure (such as advertising budgets). I generally think companies have become far too powerful, and that became completely clear to me with our suspension of Trump’s account. As I’ve said before, we did the right thing for the public company business at the time, but the wrong thing for the internet and society. Much more about this here: https://twitter.com/jack/status/1349510769268850690
I continue to believe there was no ill intent or hidden agendas, and everyone acted according to the best information we had at the time. Of course mistakes were made. But if we had focused more on tools for the people using the service rather than tools for us, and moved much faster towards absolute transparency, we probably wouldn’t be in this situation of needing a fresh reset (which I am supportive of). Again, I own all of this and our actions, and all I can do is work to make it right.
Back to the principles. Of course governments want to shape and control the public conversation, and will use every method at their disposal to do so, including the media. And the power a corporation wields to do the same is only growing. It’s critical that the people have tools to resist this, and that those tools are ultimately owned by the people. Allowing a government or a few corporations to own the public conversation is a path towards centralized control.
I’m a strong believer that any content produced by someone for the internet should be permanent until the original author chooses to delete it. It should be always available and addressable. Content takedowns and suspensions should not be possible. Doing so complicates important context, learning, and enforcement of illegal activity. There are significant issues with this stance of course, but starting with this principle will allow for far better solutions than we have today. The internet is trending towards a world were storage is “free” and infinite, which places all the actual value on how to discover and see content.
Which brings me to the last principle: moderation. I don’t believe a centralized system can do content moderation globally. It can only be done through ranking and relevance algorithms, the more localized the better. But instead of a company or government building and controlling these solely, people should be able to build and choose from algorithms that best match their criteria, or not have to use any at all. A “follow” action should always deliver every bit of content from the corresponding account, and the algorithms should be able to comb through everything else through a relevance lens that an individual determines. There’s a default “G-rated” algorithm, and then there’s everything else one can imagine.
The only way I know of to truly live up to these 3 principles is a free and open protocol for social media, that is not owned by a single company or group of companies, and is resilient to corporate and government influence. The problem today is that we have companies who own both the protocol and discovery of content. Which ultimately puts one person in charge of what’s available and seen, or not. This is by definition a single point of failure, no matter how great the person, and over time will fracture the public conversation, and may lead to more control by governments and corporations around the world.
I believe many companies can build a phenomenal business off an open protocol. For proof, look at both the web and email. The biggest problem with these models however is that the discovery mechanisms are far too proprietary and fixed instead of open or extendable. Companies can build many profitable services that complement rather than lock down how we access this massive collection of conversation. There is no need to own or host it themselves.
Many of you won’t trust this solution just because it’s me stating it. I get it, but that’s exactly the point. Trusting any one individual with this comes with compromises, not to mention being way too heavy a burden for the individual. It has to be something akin to what bitcoin has shown to be possible. If you want proof of this, get out of the US and European bubble of the bitcoin price fluctuations and learn how real people are using it for censorship resistance in Africa and Central/South America.
I do still wish for Twitter, and every company, to become uncomfortably transparent in all their actions, and I wish I forced more of that years ago. I do believe absolute transparency builds trust. As for the files, I wish they were released Wikileaks-style, with many more eyes and interpretations to consider. And along with that, commitments of transparency for present and future actions. I’m hopeful all of this will happen. There’s nothing to hide…only a lot to learn from. The current attacks on my former colleagues could be dangerous and doesn’t solve anything. If you want to blame, direct it at me and my actions, or lack thereof.
As far as the free and open social media protocol goes, there are many competing projects: @bluesky is one with the AT Protocol, nostr another, Mastodon yet another, Matrix yet another…and there will be many more. One will have a chance at becoming a standard like HTTP or SMTP. This isn’t about a “decentralized Twitter.” This is a focused and urgent push for a foundational core technology standard to make social media a native part of the internet. I believe this is critical both to Twitter’s future, and the public conversation’s ability to truly serve the people, which helps hold governments and corporations accountable. And hopefully makes it all a lot more fun and informative again.
💸🛠️🌐 To accelerate open internet and protocol work, I’m going to open a new category of #startsmall grants: “open internet development.” It will start with a focus of giving cash and equity grants to engineering teams working on social media and private communication protocols, bitcoin, and a web-only mobile OS. I’ll make some grants next week, starting with $1mm/yr to Signal. Please let me know other great candidates for this money.
-
 @ 16d11430:61640947
2025-01-19 03:07:12
@ 16d11430:61640947
2025-01-19 03:07:12The “divide and conquer” strategy used to pit Bitcoiners against the wider crypto community is a deliberate tactic aimed at creating internal divisions, fostering confusion, and weakening the collective momentum of decentralized technologies. By exploiting philosophical, technological, and cultural differences between Bitcoin maximalists and proponents of alternative cryptocurrencies, fiat instigators and other vested interests aim to undermine the larger blockchain ecosystem. Here's an exploration of this strategy:
Exploiting Ideological Differences
- Bitcoin Maximalism vs. Crypto Diversity:
Bitcoin maximalists advocate that Bitcoin is the only truly decentralized, immutable, and sound form of money, dismissing other cryptocurrencies as unnecessary or outright scams.
Proponents of other blockchains argue that innovations like smart contracts, scalability, and specialized use cases justify the existence of altcoins and Ethereum-like ecosystems.
Fiat-aligned propagandists amplify these debates, framing them as irreconcilable conflicts, rather than healthy competition within an evolving ecosystem.
- Labeling Altcoins as “Shitcoins”:
By co-opting Bitcoin maximalist terminology like “shitcoin” to denigrate all other cryptocurrencies, fiat proponents fan the flames of division. This reinforces the perception that the crypto community is fragmented, unreliable, and rife with infighting, reducing its appeal to newcomers.
Creating Confusion Over Purpose
- Framing Bitcoin as Anti-Innovation:
Propagandists often portray Bitcoin as a “dinosaur” in the blockchain space, emphasizing its slower transaction speeds, energy consumption, and limited programmability.
Simultaneously, they label other cryptocurrencies as “untrustworthy” or “too experimental,” creating confusion about the legitimacy and purpose of blockchain technology as a whole.
- Highlighting Scams and Failures:
Media narratives frequently spotlight rug-pulls, scams, and failures in the broader crypto space while ignoring the resilience and success of Bitcoin. By conflating Bitcoin with the broader crypto market, they erode public trust in decentralized technologies altogether.
Fueling Regulatory Divides
- Regulation as a Weapon:
Regulators and central authorities use differing approaches for Bitcoin and other cryptocurrencies to create division. For instance, Bitcoin is often labeled as a “digital asset” or “commodity,” while other cryptocurrencies are deemed securities, leading to disparate treatment and confusion over legitimacy.
This divide discourages collaboration between Bitcoiners and altcoin communities, as each group perceives itself as having different regulatory battles to fight.
- Narratives Around Environmental Impact:
Bitcoin is targeted for its proof-of-work (PoW) consensus mechanism, which is painted as environmentally destructive. In contrast, proof-of-stake (PoS) systems are promoted as “green” alternatives.
This framing encourages environmentalists and sustainability advocates to align against Bitcoin, while Bitcoiners double down on defending PoW, exacerbating the divide.
Manipulating Tribalism
- Turning Bitcoiners Against Altcoins:
Bitcoiners are encouraged to see altcoins as fraudulent or unnecessary competitors, while altcoin proponents are encouraged to see Bitcoiners as close-minded purists clinging to outdated technology.
This tribalism prevents cooperation on shared goals, such as financial inclusion, decentralization, and resistance to censorship.
- Highlighting Cultural Divides:
Bitcoin culture, often associated with libertarian values and sound money principles, is framed as elitist and exclusionary.
In contrast, altcoin cultures, which emphasize innovation, diversity, and experimentation, are painted as reckless and overly speculative.
These cultural clashes distract from the broader shared mission of decentralizing power and creating alternatives to the fiat system.
Amplifying Internal Critiques
- Media Amplification of Disputes:
Public disagreements between prominent figures in the Bitcoin and crypto spaces are sensationalized by media outlets. For example, debates over scaling solutions, hard forks, or smart contract utility are framed as existential threats to the ecosystem’s credibility.
This amplification undermines confidence in both Bitcoin and alternative cryptocurrencies by making the community seem chaotic and divided.
- Weaponizing Social Media:
Bots and trolls infiltrate online discussions, spreading misinformation and stoking hostility between Bitcoiners and altcoin advocates. These efforts create echo chambers, reinforcing confirmation bias and deepening divides.
Long-Term Consequences of the Divide and Conquer Approach
- Delaying Mass Adoption:
Confusion and infighting reduce public trust in blockchain technologies, slowing adoption and deterring institutional investment.
Potential users and developers are discouraged from entering the space, fearing instability and conflict.
- Fragmenting the Ecosystem:
Instead of working together to overcome regulatory challenges, scale adoption, or innovate solutions, the crypto community wastes resources fighting internal battles.
This fragmentation leaves the ecosystem vulnerable to external attacks, such as coordinated government crackdowns or monopolistic behavior by large financial institutions.
- Strengthening Fiat Narratives:
By keeping the crypto space divided, fiat propagandists can continue to push narratives that centralized financial systems are more reliable, cohesive, and secure.
These narratives reinforce the status quo, delaying the broader transition to decentralized systems.
Overcoming the Divide
To counteract the divide and conquer strategy, the Bitcoin and crypto communities must:
-
Focus on Shared Goals: Highlight common objectives like financial inclusion, censorship resistance, and decentralization.
-
Promote Constructive Dialogue: Encourage debates that focus on solutions rather than criticisms, emphasizing the complementary strengths of different technologies.
-
Educate the Public: Combat misinformation by creating accessible resources that explain the value of Bitcoin and blockchain as distinct but synergistic innovations.
-
Resist Tribalism: Recognize that both Bitcoin and altcoins have roles to play in a diverse and evolving financial ecosystem.
By fostering unity and cooperation, the blockchain community can overcome external attempts to sow division and work toward a more decentralized, equitable future.
-
 @ 36461ff8:a4454aad
2025-01-18 23:22:00
@ 36461ff8:a4454aad
2025-01-18 23:22:00“My position is improper foods cause disease; proper foods cure disease. Nothing else needs to be said.” - Dr. Bieler, author of Food is Your Best Medicine
As a holistic doctor with over 2 decades of clinical experience, I don't entirely agree with this statement. Everyday in practice, I see the extraordinary application of plant medicines and clinical nutrition in treatments of complex patterns with remarkable outcomes that go above and beyond diet, but I still very much appreciate the value of food as medicine.
Famous Bieler Broth:
- 2 zucchinni
- 2 stalks of celery
- 1 cup of green beans
- handful of parsley
- garlic to taste
- my father made this and added butter and salt
- chop and steam with purified water until tender then blend and drink

I was fortunate enough to treat one of Dr. Bieler’s patients for many years until he passed away in his nineties. He told me some of the famous doctor’s secrets and how patients came from all over for treatment with fantastic results. He himself was seriously ill before seeing Dr. Bieler.
Dr. Bieler's Final Conclusions:
“As a practicing physician for over 50 years, I have reached three basic conclusions as to the cause and cure of disease.
The first is that the primary cause of disease is not germs. Rather, I believe that disease is caused by toxemia which results in cellular impairment and breakdown, thus paving the way for the multiplication and onslaught of other complications.
My second conclusion is that in almost all cases the use of drugs in treating patients is harmful. Drugs often cause serious side effects, and sometimes even create new diseases. The dubious benefits they afford the patient are at best temporary. Yet the number of drugs on the market increases geometrically every year as each chemical firm develops its own variation of the compounds. The physician is indeed rare who can be completely aware of the potential danger from the side effects of all of these drugs.
My third conclusion is that disease can be cured through the proper use of the correct foods. This statement may sound deceptively simple, but I have arrived at it only after intensive study of a highly complex subject: toxemia and endocrine chemistry.
My conclusions are based on experimental and observational results, gathered through years of successfully treating patients. Occasionally I have resorted to the use of drugs in an emergency situation, but those times have been rare. Instead, I have sought to prescribe for my patients’ illnesses antidotes which Nature has placed at their disposal.” - Dr. Bieler“
-
 @ 16d11430:61640947
2025-01-18 23:07:02
@ 16d11430:61640947
2025-01-18 23:07:02I leaned back in my chair, staring out the window of a quiet suburban café in Melbourne. Rain trickled down the glass in half-hearted streaks, as if even the weather couldn’t muster the enthusiasm to commit. I sipped my lukewarm chai, the spice muddled beyond recognition, and shook my head at the headlines flickering on my phone.
"Privies and staties," I muttered, half to myself. "The great cultural war, fought with memes and moral outrage."
The waitress, a twenty-something with blue streaks in her hair and the harried look of someone juggling rent and an art degree, glanced at me, but I waved her off. She didn’t need to hear the rant bubbling inside me. But you do.
Let me tell you about these Australians and their bizarre tribes. On one side, you’ve got the privies, the products of private schools with Latin mottos, boat shoes, and a chronic inability to read the room. These are the ones who learned how to debate the ethics of colonialism before they could tie their shoelaces. They grew up in manicured bubbles, tutored in piano and privilege, and now lead the charge in the great cultural revolution.
Oh, they’ll cry for social justice over their oat-milk lattes, but God forbid you mention their family’s ties to real estate empires or mining conglomerates. They protest with passion, but it’s always the kind of passion that ends before the rain starts or the Uber surge pricing kicks in.
Then there are the staties, the self-proclaimed champions of the "real Australia." They’re the salt-of-the-earth types who can’t stand the privies. Too posh, too preachy, too disconnected. The staties fight their wars with beer in one hand and a smartphone in the other, spamming their feeds with angry rants about "wokeness" and how things were better in the '80s. They see the privies as the enemy—elitists, virtue-signaling snobs who wouldn’t last a day on a construction site.
And yet, the staties are no saints themselves. They scream about freedom while demanding the government fix everything that annoys them. They sneer at art and academia, unless, of course, it’s a Hamilton ticket or a Netflix drama. They don’t want to change the world; they just want to win enough of it to tell everyone else to shove off.
Caught between these two warring factions, I—an Indian old boy from a legacy school where discipline and ambition were drilled into us like multiplication tables—sit here, baffled. I grew up in a world of contradictions too, but at least ours came with good food and a soundtrack of classical ragas. This Australian version of the culture wars? It’s a pantomime, all sound and fury, signifying nothing.
Take the debates about statues. The privies want to tear them all down—symbols of oppression, they say. The staties clutch their pearls, howling about history being erased, as if the only thing holding civilization together is a bronze guy on a horse. And in the middle? Nothing changes. Rent still skyrockets, climate disasters loom, and the housing market remains about as accessible as Doon School admissions to a street vendor’s child.
The irony is that both sides are just cogs in the same ridiculous machine. The privies rail against capitalism, but live off trust funds and well-paying jobs courtesy of their networks. The staties mock the pretensions of the elite but secretly envy their polish and privilege.
Meanwhile, here I sit, with my scuffed shoes and tired eyes, watching this farce unfold. We had our own clown shows back in India, of course. Macaulay’s little brown gentlemen, striving to out-English the English. At least we had masala chai and biryani to soften the absurdity. Here, it’s bland chai and vegemite sandwiches.
I chuckle, shaking my head at the absurdity of it all. The waitress, still hovering nearby, gives me a curious look. I gesture for the bill, deciding I’ve indulged in enough cynicism for one afternoon. The cultural wars will rage on without me.
As I step out into the drizzle, I can’t help but think: if this is the best they’ve got, maybe it’s time for the old boys to show them how it’s done. After all, we’ve been navigating the tightrope of hypocrisy and ambition for centuries. What’s one more circus?
-
 @ 16d11430:61640947
2025-01-18 22:32:03
@ 16d11430:61640947
2025-01-18 22:32:03The global technology industry is a paradox of modernity and historical legacies. On the surface, it thrives on innovation, cross-border collaboration, and diversity. Yet, beneath this veneer lies a disturbing continuation of colonial-era power dynamics. With leadership and non-technical roles dominated by professionals from developed Western nations, and technical labor outsourced predominantly to developing countries, the tech sector operates under a "business as usual" approach that perpetuates colonial visions of hierarchy and control.
The Lull to the Norm: An Invisible Legacy
Leadership and the West’s Monopoly on Power
Non-technical leadership roles in the tech industry are disproportionately occupied by individuals from countries like the United States, the United Kingdom, and other former colonial powers. These roles, encompassing strategy, decision-making, and vision-setting, form the backbone of global tech operations.
Statistics: In Silicon Valley, white males hold 58.7% of executive positions, while Asian males, despite their high representation in technical roles, occupy only 16.3% of executive roles. African American and Hispanic representation is even lower. (Source)
Implications: These patterns mirror historical colonial structures where administrative and decision-making powers were centralized in Western metropoles, while the labor-intensive work was relegated to colonies.
Technical Labor and the Outsourcing of Expertise
Technical labor in the global tech industry has become synonymous with talent from developing countries, particularly India, Southeast Asia, and Africa. This division of labor, while celebrated as cost-efficient and globally inclusive, also reinforces a narrative where technical expertise is commoditized, while strategic and creative roles are retained in the West.
Global Workforce Distribution: India alone accounts for 53% of the global tech workforce sourced through outsourcing platforms, a figure that underscores the reliance on developing nations for technical expertise. (Source)
The Unseen Ceiling: While these workers are highly skilled, systemic barriers often prevent their transition into decision-making roles, relegating them to a cycle of “support” work that lacks career advancement.
A Colonial Vision: The Reinforcement of Hierarchies
The division of labor in the tech industry is not accidental but a reflection of deeper structural inequities rooted in colonial ideologies:
-
Knowledge and Power Centralization: Just as colonial powers centralized administrative control while delegating manual work to colonies, the tech industry centralizes leadership in Western hubs while outsourcing technical work to developing nations.
-
Economic Exploitation: Developing countries provide a wealth of skilled labor at lower costs, driving profits for corporations headquartered in the West. This mirrors the economic exploitation of colonies, where raw resources and labor were extracted for metropolitan gain.
-
Cultural Hierarchies: Soft skills and leadership qualities, often defined by Western norms, are prioritized over technical expertise. This reinforces the idea that strategic thinking and innovation are inherently Western attributes, while execution and technical work are the domain of others.
Breaking the Cycle: A Call for Change
Recognizing Global Talent Equitably
The industry must redefine its metrics for leadership and innovation. Technical expertise from developing countries is not just labor but intellectual capital that deserves recognition and representation in decision-making roles.
Case in Point: Organizations like Tata Consultancy Services (TCS) demonstrate how technical teams from developing countries can take on leadership roles globally, challenging the status quo.
Decentralizing Leadership
Leadership roles should reflect the global nature of the workforce. Companies need to actively promote individuals from diverse cultural and geographical backgrounds into decision-making positions, breaking the Western monopoly on soft-skill dominance.
Fostering Cross-Cultural Collaboration
Global tech organizations must build mechanisms for meaningful collaboration between Western leadership and technical teams from developing nations. This includes addressing cultural biases and creating pathways for career advancement that are not limited by geography or nationality.
Leveraging Decentralized Finance and Blockchain
The rise of blockchain and decentralized finance (DeFi) provides an alternative framework that bypasses traditional hierarchies. Through tokenized incentives and decentralized governance, skilled professionals can independently create, innovate, and profit outside the confines of corporate colonialism.
Conclusion: Toward a Post-Colonial Tech Industry
The global tech sector, despite its progressiveness, remains a product of historical hierarchies. The division of labor—leadership in the West, execution in the East and South—is not a mere coincidence but a continuation of colonial visions. As the industry expands, it must confront these dynamics head-on.
Breaking free from this cycle requires more than policy changes; it demands a fundamental shift in perspective. By recognizing the intellectual capital of technical labor, decentralizing leadership, and fostering equitable collaboration, the tech industry can move toward a truly inclusive and post-colonial future. Until then, the lull to the norm remains a quiet affirmation of a colonial past.
-
-
 @ 16d11430:61640947
2025-01-18 22:12:40
@ 16d11430:61640947
2025-01-18 22:12:40The Australian tech industry is booming, fueled by skilled migration and increasing demand for innovation. Yet, many highly qualified immigrants find themselves trapped in an unforgiving system, stifled by the limitations of fiat economies and traditional job markets. For those seeking autonomy and financial independence, decentralized finance (DeFi) offers a revolutionary escape route. By leveraging blockchain technology, immigrants can bypass traditional barriers, unlock new opportunities, and redefine their economic participation in Australia’s tech ecosystem.
The Problem: A Fragile, Fiat-Based Ecosystem
Underemployment and Job Mismatch
Many skilled immigrants arrive in Australia with dreams of applying their hard-earned expertise, only to encounter underemployment or roles unrelated to their qualifications. This mismatch arises from:
Recognition Issues: Foreign credentials and experience often go undervalued.
Economic Shocks: The fiat-based economy is prone to cycles of instability, leaving immigrants vulnerable to layoffs and wage suppression.
Systemic Barriers: Licensing requirements, workplace discrimination, and a preference for "local experience" keep many skilled professionals from thriving.
Financial Vulnerabilities
Immigrants also face challenges in navigating Australia’s financial system, which is heavily fiat-dependent:
High Living Costs: The high cost of living in major Australian cities like Sydney and Melbourne erodes savings and limits economic mobility.
Limited Access to Credit: Without robust credit histories in Australia, immigrants often struggle to secure loans or mortgages.
Dependency on Remittances: Immigrants sending money back home face exorbitant fees and delays, further compounding financial strain.
The DeFi Solution: A Borderless Financial Ecosystem
Decentralized finance, or DeFi, is transforming the global financial landscape. Built on blockchain technology, DeFi eliminates intermediaries, providing direct access to financial services such as lending, borrowing, and investing. For immigrants in Australia's tech ecosystem, DeFi offers a pathway to financial empowerment and independence.
Key Benefits of DeFi for Immigrants
-
Access to Global Capital DeFi platforms enable immigrants to tap into global liquidity pools, allowing them to secure loans or funding without relying on local credit systems. Smart contracts ensure transparency and fairness, removing biases that plague traditional banking.
-
Earning Through Crypto Immigrants can participate in DeFi protocols to earn passive income through staking, yield farming, or providing liquidity. This income is not tied to the fragile fiat economy and offers a hedge against local economic downturns.
-
Borderless Remittances By using cryptocurrencies like Bitcoin or stablecoins, immigrants can send money back home instantly and at a fraction of the cost compared to traditional remittance services.
-
Decentralized Career Platforms Web3 technologies are enabling decentralized platforms where immigrants can showcase their skills, secure gig work, and get paid in crypto, bypassing restrictive local hiring practices.
DeFi Meets Skilled Immigration: A Blueprint for Independence
- Building an Alternative Tech Economy
DeFi empowers immigrants to bypass Australia’s fiat-based tech ecosystem by participating in global, decentralized marketplaces. For instance:
Immigrant developers can contribute to open-source Web3 projects and earn cryptocurrency.
Blockchain-based freelancing platforms allow skilled workers to monetize their expertise without needing local validation.
- Funding Innovation Without Borders
Immigrants with entrepreneurial ambitions often struggle to secure funding in Australia. Through DeFi platforms, they can raise capital via Initial Coin Offerings (ICOs), decentralized crowdfunding, or tokenized equity models.
- Escaping Fiat Dependency
DeFi provides an opportunity to store wealth in stablecoins or cryptocurrencies, reducing exposure to fiat-related inflation and instability. By adopting Bitcoin and DeFi solutions, immigrants can build a financial buffer that operates independently of the Australian dollar.
- Resilience Against Economic Shocks
DeFi’s decentralized nature protects users from localized economic crises. Immigrants can diversify their income streams globally, reducing their dependency on Australia’s fragile economic cycles.
Challenges and Risks
While DeFi offers immense potential, it is not without risks. Immigrants exploring this space should be aware of:
Regulatory Uncertainty: Australia’s evolving crypto regulations could impact DeFi accessibility.
Volatility: Cryptocurrencies are inherently volatile, and users must exercise caution in managing investments.
Scams and Security: The decentralized nature of DeFi makes it a target for scams and hacks. Immigrants must prioritize education and security practices.
Conclusion: A New Path to Empowerment
For skilled immigrants in Australia’s tech ecosystem, DeFi represents more than just a financial tool—it’s a lifeline to autonomy and opportunity. By leveraging blockchain technology, immigrants can break free from the suppressive constraints of fiat-based systems, access global opportunities, and achieve true economic independence.
The intersection of DeFi and skilled immigration is not just a vision for the future—it’s a call to action. As the world transitions toward decentralized systems, skilled immigrants have a unique opportunity to lead the way, redefining what it means to thrive in a globalized economy.
-
-
 @ 16d11430:61640947
2025-01-18 21:55:33
@ 16d11430:61640947
2025-01-18 21:55:33Throughout history, the rise of any revolutionary force has often left destruction in its wake. Empires crumble, leaders fall, and the world reshapes itself through upheaval. Yet Bitcoin, the decentralized force of economic transformation, is different. It does not raze cities, spill blood, or bring tyrants to their knees in chains. Instead, it offers a unique and almost merciful path to its opponents—fiat leaders.
Bitcoin spares all but their pride, offering them the opportunity to adapt, accept, and join the future. A lesser conqueror would not have had such restraint.
The Nature of Fiat Power
Fiat leaders derive their authority from a system built on trust—trust in the currency they print, the rules they impose, and the promises they make. But as history has shown, this trust is fragile. The fiat system is prone to corruption, inflation, and inequality, often serving the elite at the expense of the masses.
Bitcoin, by its very design, dismantles this fragile trust. Its immutable ledger, decentralized governance, and capped supply reveal the flaws of fiat systems with unyielding transparency. To fiat leaders, this is a humiliation—a slow, undeniable exposure of their system's weaknesses. Yet, Bitcoin does not destroy them outright. Instead, it gives them a choice.
The Mercy of Bitcoin
A lesser conqueror would demand total submission, punishing those who stood in opposition. Bitcoin, however, does not demand anyone’s allegiance. It does not imprison fiat leaders, confiscate their wealth, or physically overthrow their regimes. Instead, it renders their systems obsolete through peaceful, voluntary adoption.
Fiat leaders are not forced to give up their power; they are merely shown a better way. They are spared the brutal consequences of war or violent revolution, given the opportunity to embrace Bitcoin and adapt their policies. While their pride may be wounded, their lives and systems are left intact, offering them a rare chance to evolve.
The Lesser Conqueror’s Path
Imagine a world where a lesser conqueror, driven by greed or vengeance, rose to challenge fiat power. History offers countless examples of such figures—dictators, insurgents, and invaders—who sought to destroy their enemies utterly. These conquerors left nothing but ruin behind them, ensuring their victims had no chance for redemption.
Bitcoin is not a conqueror of this sort. It seeks to empower, not destroy. Its mission is not to replace one oppressive system with another but to build a decentralized, incorruptible foundation for global prosperity. Even as it humiliates fiat leaders by exposing their failures, it extends a hand of mercy, offering them a way to coexist in the new paradigm.
Humiliation as a Catalyst
For fiat leaders, the humiliation Bitcoin brings is a bitter pill to swallow. To see their systems falter in the face of an algorithm, a decentralized network of nodes, and a global community of believers is no small blow. Yet this humiliation is not an end—it is a beginning.
Many fiat leaders, recognizing the inevitability of Bitcoin’s rise, have begun to adapt. Nations are exploring Bitcoin adoption, regulators are crafting frameworks, and even central banks are experimenting with digital currencies. This willingness to change, however begrudging, is a testament to Bitcoin’s power as a peaceful conqueror.
Conclusion: A New Era of Mercy
Bitcoin’s kindness lies in its restraint. It conquers through innovation, not violence; through transparency, not deception. It humiliates fiat leaders by exposing the flaws of their systems, but it spares them the devastation that lesser conquerors would inflict. This mercy is a testament to Bitcoin’s higher purpose—a world where power is decentralized, value is preserved, and humanity can thrive without fear of corruption or collapse.
In the end, Bitcoin’s triumph will not be marked by the fall of fiat leaders, but by their transformation. Their humiliation, while painful, is a necessary step toward a better world. Bitcoin’s mercy is its greatest strength, ensuring that its conquest is not one of destruction, but of renewal.
-
 @ dbb19ae0:c3f22d5a
2025-01-18 20:46:35
@ dbb19ae0:c3f22d5a
2025-01-18 20:46:35Introduction to Perl programming
Perl is a high-level, general-purpose programming language that excels in text processing, system administration, web development, and more. Its flexibility and strong regular expression capabilities make it a popular choice for scripting tasks. This article introduces the basics of Perl programming, including an example script.
Basics of Perl
Running a Perl Script
To execute a Perl script, save the code in a file with a
.plextension (e.g.,script.pl) and run it from the command line:bash perl script.plSyntax Highlights
- Shebang Line: Specify the interpreter.
perl #!/usr/bin/perl - Comments: Use
#for single-line comments.perl # This is a comment - Printing Output:
perl print "Hello, World!\n";
Variables
Perl has three main variable types: - Scalars: Single values (numbers, strings, etc.), prefixed by
$.perl my $name = "Eva"; my $age = 35;- Arrays: Ordered lists, prefixed by@.perl my @colors = ("red", "green", "blue");- Hashes: Key-value pairs, prefixed by%.perl my %capitals = ("France" => "Paris", "Japan" => "Tokyo");Control Structures
- Conditional Statements:
perl if ($age > 18) { print "You are an adult.\n"; } else { print "You are a minor.\n"; } - Loops:
perl for my $color (@colors) { print "$color\n"; }
Example Script: Text File Analysis
This script reads a text file, counts the lines, words, and characters, and prints the results.
Script
```perl
!/usr/bin/perl
use strict; use warnings;
Check for file argument
if (@ARGV != 1) { die "Usage: $0
\n"; } my $filename = $ARGV[0];
Open the file
open(my $fh, '<', $filename) or die "Could not open file '$filename': $!\n";
Initialize counters
my ($line_count, $word_count, $char_count) = (0, 0, 0);
Process the file
while (my $line = <$fh>) { $line_count++; $char_count += length($line); $word_count += scalar(split(/\s+/, $line)); }
close($fh);
Print results
print "File: $filename\n"; print "Lines: $line_count\n"; print "Words: $word_count\n"; print "Characters: $char_count\n"; ```
Explanation
- Input Validation: Ensures the script is called with a filename.
- File Handling: Uses
openandclosefor file operations. - Counters: Tracks lines, words, and characters.
- Loop: Reads the file line by line, processing each line.
Running the Script
Save the script as
file_analysis.pland run it with a text file:bash perl file_analysis.pl sample.txtConclusion
Perl is a powerful tool for scripting and data processing. Its concise syntax and robust text-handling capabilities make it an excellent choice for many tasks. This example demonstrates basic Perl features and encourages further exploration of its vast capabilities.
- Shebang Line: Specify the interpreter.
-
 @ dbb19ae0:c3f22d5a
2025-01-18 20:40:48
@ dbb19ae0:c3f22d5a
2025-01-18 20:40:48Inspired by a video on youtube I wrote a calculator with Perl: Beware the line my ($num1, $num2, $operator) = '@'; should be my ($num1, $num2, $operator) = @; But the markdown syntax needs to have the @ into quotes otherwise, well the rest of the program is missing
#!/usr/bin/perl # calculator # use strict; use warnings; sub get_input { print "Enter number 1: "; chomp(my $num1 = <STDIN>); print "Enter number 2: "; chomp(my $num2 = <STDIN>); print "Enter operator (+, -, *, /): "; chomp(my $operator = <STDIN>); return ($num1, $num2, $operator); } sub calculate { my ($num1, $num2, $operator) = '@'_; my $result; if ($operator eq '+') { $result = $num1 + $num2; } elsif ($operator eq '-') { $result = $num1 - $num2; } elsif ($operator eq '*') { $result = $num1 * $num2; } elsif ($operator eq '/') { if ($num2 == 0) { die "Error: Division by zero\n"; } $result = $num1 / $num2; } else { die "Invalid operator\n"; } return $result; } # Get input from the user my ($num1, $num2, $operator) = get_input(); # Calculate the result my $result = calculate($num1, $num2, $operator); # Print the result print "$num1 $operator $num2 = $result\n";originally posted at https://stacker.news/items/816121
-
 @ 6871d8df:4a9396c1
2025-01-18 20:12:46
@ 6871d8df:4a9396c1
2025-01-18 20:12:46## 2024 Prediction Reflections
Politics
Democrats & 2024 Election
- “Democrats’ attempt to stifle democracy will likely put Trump in the White House. If not, some real sketchy stuff would need to happen to keep him out.”
This prediction was exactly right. The assassination attempt on Trump seemed to be the final blow for the Democrats. Despite a heavy push my legacy media, Trump won handily.
The Democrats switched to Kamala Harris after Biden showed signs of incapacity, most notably in the first debate against Trump.
My prediction for the election also turned out to be exactly right, which, thank you Robert Barnes and Richard Baris.
Evidence of Institutional Ideological Capture
- “People will continue to wake up to ideologically captured institutions, and DEI will be the main loser.”
Trump’s resounding election victory underscores that the public is increasingly aware of (and rejecting) such institutional capture.
Of note, Boeing comes to mind as an institution that had a tough time in 2024, in large part to DEI. Nothing seemed to function correctly. The biggest story being how they stranded people in space
Media & Public Opinion
Rise of Independent & Alternative Media
- “Independent and alternative media will continue to grow as people’s trust in legacy media declines.”
Twitter (X), under Elon Musk, shattered mainstream media’s influence far more than expected. As Elon has said, “You are the media now.” Alternative sources are king. - Notable Example: Kamala Harris’s decision not to appear on the Joe Rogan podcast contrasted with Trump’s appearance, further highlighting the power shift to alternative media.
Markets & IPOs
Interest Rates & Public Markets
- “As interest rates come down, I expect public markets and IPOs to heat up.”
This did not play out. Companies that were expected to go public in 2024 remain private in 2025. The reasons are varied, but there is confidence that 2025 might see changes.
Technology & AI
LLMs & AI Adoption
- “AI and LLMs will continue to move at a rapid rate, increasing productivity. Tools like Bard will become more mainstream.”
AI did take off. Usage among nontechnical users increased, and it’s no longer uncommon for people to default to AI-driven tools rather than Google search.
Decentralized AI
- “I hope to see a rise in decentralized AI to counter big-player LLMs.”
We didn’t see explicit ‘decentralized AI’ breakthroughs, but more players entered the AI market. ChatGPT still dominates, with Elon’s ‘Grok’ making moves. Google, Meta, and Microsoft remain active but slightly behind in usage.
Bitcoin & Digital Assets
Institutional Adoption of Bitcoin
- “2024 will bring more institutions to Bitcoin. Possibly another large company or nation-state. The ETF should help, likely pushing BTC to a new all-time high.”
No large public company or nation-state placed a bet, but smaller public companies did. Michael Saylor presented to Microsoft’s Board, which was the closest instance to a major move.
- Price Movement: Bitcoin did hit a new all-time high, rising to as much as $108k in 2024.Lightning Network
- “Lightning will improve but remain primarily used for acquiring Bitcoin, not everyday payments.”
Still true. Lightning usage remains tiny relative to broader Bitcoin adoption.
Nostr Adoption
- “Nostr will grow, and we’ll see new companies leverage this network beyond just social media.”
Growth continues, but Elon Musk’s Twitter takeover slowed adoption. Nostr will remain niche until a major catalyst occurs (e.g., a big player joins or forced usage due to censorship).
Stablecoin-Specific Regulations
- “Expect stablecoin regulations in 2024 that’ll be favorable to them.”
This didn’t happen, largely due to the administration’s hostility. Expect potential change in 2025.
Miscellaneous 2024 Reflections
- Return to Sanity
- 2024 felt like sanity prevailed, largely due to the Democrats’ collapse behind Biden and Harris and Elon’s Twitter dominance.
- Operation Chokepoint 2.0
- Received a lot of attention, and I’m thankful it did because my experience at Strike was radicalizing and extreme.
- Bryan Johnson & Anti-Aging
- He burst onto the scene with his obsession over biomarkers. I see it as misguided—chasing markers in isolation doesn’t automatically yield a healthy system.
- Apple’s Rough Year
- Without a visionary leader, Apple appears to be scraping by on existing products rather than innovating.
- Google Under Fire
- Google is in a tough fight with the government, just as it seems they’re on their heels with AI competition.
2025 Predictions
-
Bitcoin’s Performance Bitcoin will have a good year, but not better than 2024. To beat 2024, it must close above 206k on December 31, 2025. I’ll take the under on that.
- I am not ruling out it to be over that at some point in 2025.
-
Twitter’s Success Continues to Stunt nostr
- Nostr adoption will stay slow due to Elon’s dominant influence with X (Twitter).
- As long as it remains a beacon of free speech, I doubt we see an exodus.
-
Rumble integrating Tether might help if they allow Nostr-like features (zaps), but that seems unlikely.
-
Apple
-
Apple will continue its rent-seeking behavior and put out underwhelming products.
-
Google’s Quantum & AI
- Recent buzz about Google’s quantum chip and AI improvements won’t pan out as a big deal.
-
Google will continue to trail OpenAI and xAI in practical LLM usage.
-
Elon, Vivek & DOGE
-
I expect them to deliver more than critics think. They’ll expose bloat and inefficiencies in ways that will shake up norms. I greatly welcome this. I wouldn’t bet against them.
-
Mainstream Media Reckoning
- In Trump’s second term, mainstream news outlets will face a real reckoning, as I can’t see how their bias can continue.
- They’ll have to reduce their bias or risk bankruptcy.
-
Alternative media’s growth trend continues, especially as Twitter keeps exposing mainstream outlets’ weaknesses.
-
RFK Delivers
-
We will see big changes in the health space due to RFK at HHS. These are changes that I am very excited to see.
-
Foreign Policy
- With the transition to Trump, I expect some foreign policy wins that will buck the establishment but will deliver wins that are not thought possible by the “experts.”
Closing Note
- Overall 2024: It was a year of major political upheaval, vindication for Bitcoin, and continued AI advances.
- Outlook for 2025: Bitcoin remains strong, AI competition heats up, and media institutions face existential challenges. I’m optimistic for continued decentralization and a more level playing field across tech, finance, and politics. I think the start of Trump’s second term will be very strong for the market, health, and culture. Accelerate.
-
 @ 3197ad60:7a122b95
2025-01-18 19:14:39
@ 3197ad60:7a122b95
2025-01-18 19:14:39I feel like the new year is slowly starting to settle in. That doesn’t mean I’m off to the races. I still intend to take the whole month (or as long as it takes, really) to make plans and carefully set a course forward. I’m not rushing it, I’m letting it all set, like tea leaves at the bottom of a glass.
I still draw daily (I’m around day 193 now), but the nature of the drawing seems to have changed. Instead of using colours and taking time to capture light and mood, I only seem to be interested in quick line sketches, the quicker, the better.
They go well with being slightly absent-minded, which I am, in a nice way. Instead of looking around for inspiration, I turn to the books I’m reading and just sketch scenes that stay with me.

All drawings in this post are based on The Book of Doors by Gareth Brown, one of the many tasty books I was gifted for Christmas. I’m adding the sketches in the order they were made because it’s kind of funny how the characters emerge. I didn’t plan for the main character to have short light hair, but somehow she does.

The book lends itself perfectly to easy sketching; the characters are not very complicated, but they are described with a lot of visual clues, and the story moves from location to location, leaving clear images in my mind.

It’s pretty clear who’s the bad guy and who’s not, and it was a good exercise to try to show that in a sketch. There is also a lot of movement in the story, with characters being surprised by the events and having to run/ hide/ escape and confront each other.

There are a lot of doors, many different locations and a good dose of time travelling. I don’t think I ever drew a time-travelling kind of scene before, so of course, I had to try. I used the hairstyle, a piece of clothing and a bit of colour to show the same person at two points in time but also in the same room. Did it work?

Recently, I’ve been really into the black and white illustrations in young adult, early reader, and chapter books. I love their simplicity and how much they can convey with a line drawing. I will hang around in that space for a bit, with my quick sketches.
I started a new book, funnily enough also about doors, so I might share more sketches soon.
Thanks for reading.
x
M
-
 @ 554ab6fe:c6cbc27e
2025-01-18 18:49:25
@ 554ab6fe:c6cbc27e
2025-01-18 18:49:25Abstract
There is a growing body of evidence suggesting that depression is becoming a major health concern for the modern world. Given the multitude of stressors advanced civilization provides, people are increasingly ruminating over the past and future. These repetitive non-constructive thoughts provide stress both in the mind and physically manifest itself in our bodily systems, deteriorating our health on multiple fronts. Not only are cases of depression increasing, but many seem to be resistant to current forms of treatment. These treatments include both pharmaceutical and therapeutic methods. Clinicians need to begin taking a serious look at alternate forms of treatment so they can become more equipped to treat patients with depression. Mindfulness meditation is the practice of focusing one’s thoughts entirely on the body itself and trains the mind to forgo all other extraneous thoughts. This technique not only provides the body an immediate sensation of safety and relaxation, but trains the individual to have better control over repetitive unhealthy thoughts. The more frequent feeling of relaxation coupled with the ability to subdue one’s own rumination decreases the body’s activation of its defense protocols. These defenses, also known as the sympathetic nervous system, when activated too frequently can be extremely detrimental to one’s physical and mental health and is strongly correlated to stress and depression. Much research involving mindfulness meditation has shown that it increases one’s ability to have thought control and decreases sympathetic nervous system activity. This is coupled with a heightened awareness of one’s own body, leading to a general increase in self perception and wellbeing. Dramatically reducing the occurrence of stress and depression. The body of meditation research requires further attention. In particular, studies require more standardized forms of meditation methods and an improvement of experimental design to increase statistical significance. That being said, given the effect mindfulness meditation has on depression, it should be viewed as a potential replacement for the treatment of depression through antidepressants. Antidepressants have a large list of potential side effects, are at times shown to be no more effective than a placebo, and have no evidence of preventing depression once treatment has been terminated. Meditation being costless and side effect free, if truly effective, would be a far more ethical and responsible treatment methods for physicians and therapist to prescribe.
Introduction
This paper will review existing literature discussing meditation and its potentially remedial effects on depression. It will argue that by providing increased ability to control and recognize non-constructive thoughts, meditation can decrease stress, thereby helping individuals with clinical depression. It is projected that by 2020, depression will become the second most common mental health issue (Kenny & Williams, 2007). Collectively, stress and depression-related symptoms account for a majority of visits to primary care physicians (Greeson et al., 2018). These disorders have become extremely prevalent and are extremely costly for individuals and the entire health care system (Greeson et al., 2018). That being said, it has been shown that 40% of depression patients are resistant to current treatment methods (Kenny & Williams, 2007), demonstrating that the entire system of treating depression is largely wasteful and inefficient, placing an unnecessary burden on society. Therefore, it is crucial that alternative approaches to treatment are explored. When looking at potential treatment methods for depression, it is important to first consider the underlying causes.
Depression is a complex mental issue that can manifest itself in a variety of different ways, and can stem from a large number of causes. That being said, there appears to be a distinct connection between stress and depression. Researchers have found that repetitive, non-constructive thoughts can lead to depression, and that individuals with acute stress-induced behaviors and hormonal changes have very similar symptoms to those suffering from depression (Watkins, 2008; Kasala et al., 2014). These symptoms commonly include hypercortisolism, which is a rise in cortisol levels due to an increase in sympathetic nervous system activity. Hypercortisolism can lead to high blood pressure, impaired immune function by decreasing cytokine count, poor antibody response, high blood sugar, increased renal retention of sodium, to name a few (Spreng, 2000; Godbout & Glaser, 2006; Kasala et al., 2014). In short, it is a condition that is extremely detrimental to overall health. Neurologically speaking, the relationship between stress and depression can be attributed partly to atrophy of the hippocampus, which is caused by high levels of stress induced glucocorticoid release (Annells et al., 2016).
Modern life is full of stressful situations. People tend to spend large portions of their day ruminating over the past and forecasting for the future. Often, these thoughts bring about worry and regret. Human beings evolved with a “fight or flight” defense response regulated by the sympathetic nervous system in order to protect themselves from physical harm. In modern life, these physical threats are being replaced by mental threats brought upon by our own projections of the past and future (Kuchel & Kuchel, 1991). Not ruminating over such thoughts has been shown to decrease sympathetic nervous system activity (vanOyen Witvliet et al., 2011). There is also a relationship between general cognitive load, and increased sympathetic activity (Mizuno et al., 2011). Therefore, it is of no surprise that high levels of sympathetic nervous system activity is present in cases of major depression (Veith et al., 1994).
The author hypothesizes that treatment methods involving improved thought control can remove stressful thoughts, thereby reducing depressive symptoms. These changes in thought patterns will have an effect on increasing parasympathetic nervous system tone and related neurotransmitters, thereby drawing a link between the cognitive skill of removing unconstructive thoughts and the reduction of stress and depression. Alongside this, the general act of meditation causes the body to feel more relaxed and decreases the activation of the sympathetic nervous system, bringing cortisol to lower levels, which increases general health and well-being. These skills will prove not only applicable to patients for depression, but also to any individual suffering from repetitive non-constructive thoughts that hinder their daily function and worsen their bodily health. This paper, through the lens of existing literature, will explore the connection between meditation’s ability to improve thought control and its promise as a treatment for depression.
Mindfulness Meditation and the Skills Provided
This paper will primarily focus on one of many forms of meditation: mindfulness meditation. Mindfulness meditation is the practice of focusing attention on a single entity, such as one’s breath, in order to take attention away from other, potentially non-constructive thoughts (Wielgosz et al., 2019). Focusing on body and breath in a calm and accepting manner also provides the mind with a sense of safety (Esch, 2014). This technique allows an individual to have an increased awareness of their emotions, and greater control over their thoughts (Barnhofer et al., 2009). Meditation has been shown to increase brain plasticity in the regions used (Lazar et al., 2005). Given the existence of use-dependent brain plasticity, it can be presumed that as meditators use these techniques during their practice, they will also be more easily able to use them in everyday life (Giuliani et al., 2011; Esch, 2014). For example, attention regulation is related to the anterior cingulate cortex (ACC) which is shown to have an increased function in those who practice mindfulness meditation (Rubia, 2009; Hölzel et al., 2011; Lutz, Antoine,Jha, Amishi P.,Dunne, John D.,Saron, 2015). Not only do meditators have increased attention regulation, but they are capable of having greater control of removing irrelevant thoughts. These repetitive thoughts, in the case of depression, usually manifest themselves as negative thoughts regarding their mental condition, poor mood, lack of belief in themselves and an over analysis regarding the consequence and meaning of life events coupled with the expectation of negative outcomes (Watkins, 2008). This is supported by the evidence that alpha bands, which play a role in processing irrelevant information, are faster and significantly more present in those who commonly practice mindfulness meditation (Foxe & Snyder, 2011). Meditation also effects the right amygdala, which is related to the processing of emotions. Reducing depression through the use of SSRIs is partly done by the suppression of right amygdala activity. Those who meditate have reduced right amygdala activity during meditation, and a change in activity was also observed when the subject was no longer meditating (Annells et al., 2016). This indicates that meditation provides more adequate emotional control over incoming stressors, and can potentially act as a replacement for antidepressants. Meditation grants the general awareness and control of emotions, alleviating the body from feeling in danger while granting the individual the ability to recognize unhealthy ruminations and clear them from their thought stream.
The Physiologic Responses of Mindfulness Meditation
The benefit of thought control is evident when analyzing the result of experiments involving mindfulness meditation. Increases sympathetic nervous system activity is present within depression (Veith et al., 1994). Those who have increased mindfulness show decreased stress and a faster recovery from it (Greeson et al., 2018; Gamaiunova et al., 2019). In these individuals, there is a noticeable reduction in sympathetic activity and responsivity, coupled with an increase in parasympathetic nervous system tone (Hoffman et al., 1982; Esch, 2014). This means the body of a meditator shifts away from activating stressful, fight or flight systems, and relaxed state processes begin to dominate. Stress related neurotransmitters such as norepinephrine and cortisol are also shown to be less present in individuals that practice meditation (Esch et al., 2007; Esch, 2014). This also indicates that meditation has a general effect on physical health. As previously stated, high levels of cortisol have serious effects on bodily health; thus, lessening cortisol will provide general well-being, as well as the cognitive benefits discussed above. Chronic stress has been connected to lower acetylcholine levels. Interestingly enough, the breath of meditators has elevated nitric oxide levels. Presumably because there are higher levels of acetylcholine and morphine, which both increase the activity of oxide-producing enzymes (Esch, 2014). Dopamine is often related inversely to the presence of depression, and it too has been shown to increase amongst those who practice meditation (Dailly et al., 2004; Jung et al., 2010; Esch, 2014). It is also has been suggested that the increase in internalized attention during mediation, triggers activity in brain regions such as the left frontal cortex that are related to positive emotions (Rubia, 2009). This, coupled with the general health benefits of decreasing sympathetic activity and cortisol levels, is likely the reason why meditators often express a general higher satisfaction with their life and are more content (Esch et al., 2007). That being said, meditators also have a higher awareness of their own health. Meditators show an increase use of the ACC and insula, signifying that they have a greater means of modulating the self, alongside pain perception and anticipation. It is theorized that this increase in awareness grants the individual a sense of responsibility to improve their health (Esch, 2014). There is likely a feedback loops that occurs when one meditates: the individual decreases sympathetic nervous system activity, thereby increasing their health and wellbeing, while also gaining a higher perception of their health that results in further attention and improvement.
The Missing Component
Many metanalytical papers have attempted to synthesize the findings of mediation research. Many conclude, as this paper does, that the main neuronal mechanism of mindfulness generally involves: attention regulation of the body and mind, nonreactivity to experiences, and changes of self-perception (Hölzel et al., 2011; Esch, 2014; Wielgosz et al., 2019). Even though the effects on the autonomic nervous system are discussed, they are seemingly ignored as a key factor contributing to the higher quality of life and state of mind experienced by those that practice meditation. That being said, authors neglect to mention that there are two different arguments being put forth. The first is that people who meditate are, at that moment, putting themselves in a peaceful and quiet mindset that makes the body feel safe, thereby increasing parasympathetic nervous system activity (Esch, 2014). The second is that it is the skills learned from the meditation that allow for individuals to remove the unconstructive thoughts in the face of stressful situations, thereby preventing an increase in sympathetic nervous system activity. Of course, these two mechanisms may both occur, and perhaps due to the change in brain plasticity, the practices of stress relief during meditation aids the patient in using those same skill in everyday life. However, this distinction is key not only for general scientific understanding, but also for future research.
The existence of the two possible mechanisms suggests the need for further investigation. Researchers, rather than observing the improvement in self-reported depression scores, should be focusing on changes in autonomic nervous system changes. To differentiate between the two mechanisms, researchers should monitor autonomic nervous system activity during the act of meditation and after a series of prolonged practices. This type of experiment could ascertain whether or not the bulk of decrease in sympathetic nervous system activity and increase in parasympathetic nervous system activity occurs at the moment of meditation, or afterwards through the skills obtained. Perhaps the two systems change at different times, or the changes are evenly distributed across both events. Either way, this type of experiment seems necessary to gain a deeper understanding of the mechanisms involved in treating depression. Furthermore, these distinctions are important in determining which techniques of mindfulness meditation provide the best results.
Criticisms
A key criticism of meditation research is that the method of meditation used in the studies is not constant. There are many forms of meditation practiced around the world, and many have different purposes. The most traditional and commonly practiced forms of meditation involve focusing attention on a single thing, which makes the research of mindfulness meditation particularly difficult because many will consider a wide range of practices to fall under the classification of mindfulness meditation. Even in this paper, that focuses exclusively on mindfulness meditation research, papers were presented that consider Tai Chi as inclusive to that criteria (Esch et al., 2007). Given the coordination of movements and the need for an instructor, Tai Chi can hardly be classified as a means of training thought control. Nonetheless, that example is quite extreme and most mindfulness-based meditation research involves one of these 4 types: traditional meditation, meditation in a clinical setting, mindfulness in a transient state and mindfulness as a dispositional trait (Chiesa et al., 2014). Despite the similarities, these all have vast differences in terms of how the meditation is practiced. For example, traditional meditation is done alone, and a more silent environment helps an individual focus on their breath. In a clinical setting, researchers conduct mindfulness-based cognitive therapy (MBCT), in which the meditation is done in a group setting led by a teacher (Kenny & Williams, 2007). In this particular study of Kenny and Williams 2007, patients were also assigned homework of 1 hour of practice per day of yoga or meditation. Even though yoga is traditionally a physical form of mindfulness meditation, it is not in western cultures. In western cultures, Yoga becomes more a practice of listening to an instructor and stretching, which is not conducive to focusing solely on the breath. This highlights the difficulty of deciding whether or not the benefits of meditation come from the practice itself or the skills learned from it, since all of these studies use methods of meditation that vaguely resemble one another in practice. If all studies use different forms of meditation, then no matter how similar the results across studies are, there is no clear conclusion on the mechanism by which these changes occur. An obvious solution to this problem is to create a method of meditation that is traditionally used by all meditators, and to have many studies done all using the same method. Since it would be hard to mandate all researchers to use the same procedures, another option is to conduct more research on the meditators’ brain activity at the time of meditation. Perhaps these observations would shed more light on the neurological processes occurring during meditation, and these results would hopefully suggest which techniques provide the same types of skills and mental processes. That being said, it is also important for researchers to consider the mechanism by which the skills of thought control are brought about before the initiation of the experiment. Practices like Thai Chi and Yoga being from eastern cultures does not classify them as mindfulness meditation and effective procedures to promote thought control.
The conclusions of some experiments discussed in this paper need to be taken with skepticism. Many studies are conducted with small sample sizes (Kenny & Williams, 2007; Barnhofer et al., 2009; Kasala et al., 2014). There are even studies, such as the Kenny and Williams study in 2007 discussed above that do not have a control group or any other group to make a comparison to. They even allowed the patients to take their regular medications for their disorders. This, alongside the absence of a control group, makes it extremely difficult to scientifically show that the MBCT was the reason for the decrease in depression scores at all. While other studies had a well-constructed design, most studies that conduct a T-test or ANOVA in their analysis fail to show that their data is normally distributed (Kenny & Williams, 2007; Barnhofer et al., 2009; Greeson et al., 2018). A normal distribution of data is a key assumption for both of these commonly used statistical test, and without proper proof of normality, the results of these test are questionable at best. Sadly, much of scientific literature contains these forms of statistical errors (Halsey et al., 2015). Though these flaws are not present in all mindfulness meditation experiments, the use of these studies as concrete evidence of its effectiveness is rightfully scrutinized. Most studies tend to have similar results, which suggests that mindfulness meditation effects depression. Nonetheless, given the design flaws of experiments and inconsistency in meditation methods, these studies should be used more as an indicator of the existence of a relationship between mindfulness meditation and depression than evidence that such a relationship exists. Much more diligent and thorough work is required for there to be scientific validity, and the ability to claim that meditation is truly a useful method of treatment. To start, many of these experiments should be repeated with improvements to their design, such as including control groups and more consistent methods of mediation, in order to validate the significance of their p-values. This will provide much more statistically significant evidence suggesting that mindfulness meditation is the true cause of the alleviation of depressive symptoms.
Conclusion
Despite the lack of concrete evidence and methods, there is a case to adopt this practice sooner rather than later. Given most experiments involving mindfulness meditation and its effects on depression share similar results, it is reasonable to assume that there is some true effect mindfulness meditation has on alleviating the disorder. The aim of the physician should be to provide a patient that has emotional challenges the tools and skills needed to manage and subdue the unhealthy habits of thinking on their own. Traditionally, this method is through the use of pharmaceutical drugs that act to change brain chemistry. This is not only a costly expense on the individual, but there is growing evidence suggesting that many antidepressants are not much more effective than a placebo (Kirsch et al., 2002; Antonuccio et al., 2002). Not only that, but antidepressant have numerous negative long-term side effects, such as withdrawals, sexual problems, weight gain and becoming emotionally numb (Masand & Gupta, 2002; Cartwright et al., 2016). There is also no publish evidence to claim that antidepressants reduce the risk of depression once the treatment has ended (Annells et al., 2016). Therefore, antidepressants should not be thought of as a viable clinical solution in the long-run. Meditation on the other hand is completely free, and can be a useful practice in an individual’s personal life. Given its simplicity, it is also void of negative side effects, and in that sense is a much more ethical and risk-averse form of treatment from a clinical standpoint. Therefore, it is prudent that the scientific community give increased attention to meditation research, so that we can further understand its benefits and perfect its techniques, to potentially help all those who suffer from depression in a safe and cost-effective manner.
Works Cited
Annells S, Kho K & Bridge P (2016). Meditate don’t medicate: How medical imaging evidence supports the role of meditation in the treatment of depression. Radiography 22, e54–e58.
Antonuccio DO, Burns DD & Danton WG (2002). Antidepressants: A triumph of marketing over science? Prev Treat; DOI: 10.1037/1522-3736.5.1.525c.
Barnhofer T, Crane C, Hargus E, Amarasinghe M, Winder R & Williams JMG (2009). Mindfulness-based cognitive therapy as a treatment for chronic depression: A preliminary study. Behav Res Ther 47, 366–373.
Cartwright C, Gibson K, Read J, Cowan O & Dehar T (2016). Long-term antidepressant use: patient perspectives of benefits and adverse effects. Patient Prefer Adherence 10, 1401–1407.
Chiesa A, Anselmi R & Serretti A (2014). Psychological Mechanisms of Mindfulness-Based Interventions. Holist Nurs Pract 28, 124–148.
Dailly E, Chenu F, Renard CE & Bourin M (2004). Dopamine, depression and antidepressants. Fundam Clin Pharmacol 18, 601–607.
Esch T (2014). The Neurobiology of Meditation and Mindfulness. In, pp. 153–173. Springer, Cham. Available at: http://link.springer.com/10.1007/978-3-319-01634-4_9 [Accessed October 1, 2019].
Esch T, Duckstein J, Welke J & Braun V (2007). Mind/body techniques for physiological and psychological stress reduction: stress management via Tai Chi training – a pilot study. Med Sci Monit 13, CR488-497.
Foxe JJ & Snyder AC (2011). The Role of Alpha-Band Brain Oscillations as a Sensory Suppression Mechanism during Selective Attention. Front Psychol 2, 154.
Gamaiunova L, Brandt P-Y, Bondolfi G & Kliegel M (2019). Exploration of psychological mechanisms of the reduced stress response in long-term meditation practitioners. Psychoneuroendocrinology 104, 143–151.
Giuliani NR, Drabant EM, Bhatnagar R & Gross JJ (2011). Emotion regulation and brain plasticity: Expressive suppression use predicts anterior insula volume. Neuroimage 58, 10–15.
Godbout JP & Glaser R (2006). Stress-Induced Immune Dysregulation: Implications for Wound Healing, Infectious Disease and Cancer. J Neuroimmune Pharmacol 1, 421–427.
Greeson JM, Zarrin H, Smoski MJ, Brantley JG, Lynch TR, Webber DM, Hall MH, Suarez EC & Wolever RQ (2018). Mindfulness Meditation Targets Transdiagnostic Symptoms Implicated in Stress-Related Disorders: Understanding Relationships between Changes in Mindfulness, Sleep Quality, and Physical Symptoms. Evidence-Based Complement Altern Med 2018, 1–10.
Halsey LG, Curran-Everett D, Vowler SL & Drummond GB (2015). The fickle P value generates irreproducible results. Nat Methods 12, 179–185.
Hoffman J, Benson H, Arns P, Stainbrook G, Landsberg G, Young J & Gill A (1982). Science. Science (80- ) 192, 1242–1244.
Hölzel BK, Lazar SW, Gard T, Schuman-Olivier Z, Vago DR & Ott U (2011). How Does Mindfulness Meditation Work? Proposing Mechanisms of Action From a Conceptual and Neural Perspective. Perspect Psychol Sci 6, 537–559.
Jung Y-H, Kang D-H, Jang JH, Park HY, Byun MS, Kwon SJ, Jang G-E, Lee US, An SC & Kwon JS (2010). The effects of mind–body training on stress reduction, positive affect, and plasma catecholamines. Neurosci Lett 479, 138–142.
Kasala ER, Bodduluru LN, Maneti Y & Thipparaboina R (2014). Effect of meditation on neurophysiological changes in stress mediated depression. Complement Ther Clin Pract 20, 74–80.
Kenny MA & Williams JMG (2007). Treatment-resistant depressed patients show a good response to Mindfulness-based Cognitive Therapy. Behav Res Ther 45, 617–625.
Kirsch I, Scoboria A & Moore TJ (2002). Antidepressants and placebos: Secrets, revelations, and unanswered questions. Prev Treat; DOI: 10.1037/1522-3736.5.1.533r.
Kuchel OG & Kuchel GA (1991). Peripheral dopamine in pathophysiology of hypertension. Interaction with aging and lifestyle. Hypertension 18, 709–721.
Lazar SW, Kerr CE, Wasserman RH, Gray JR, Greve DN, Treadway MT, McGarvey M, Quinn BT, Dusek JA, Benson H, Rauch SL, Moore CI & Fischl B (2005). Meditation experience is associated with increased cortical thickness. Neuroreport 16, 1893–1897.
Lutz, Antoine,Jha, Amishi P.,Dunne, John D.,Saron CD (2015). PsycNET. Am Psychol 70, 632–658.
Masand PS & Gupta S (2002). Long-Term Side Effects of Newer-Generation Antidepressants: SSRIS, Venlafaxine, Nefazodone, Bupropion, and Mirtazapine. Ann Clin Psychiatry 14, 175–182.
Mizuno K, Tanaka M, Yamaguti K, Kajimoto O, Kuratsune H & Watanabe Y (2011). Mental fatigue caused by prolonged cognitive load associated with sympathetic hyperactivity. Behav Brain Funct 7, 17.
Rubia K (2009). The neurobiology of Meditation and its clinical effectiveness in psychiatric disorders. Biol Psychol 82, 1–11.
Spreng M (2000). Possible health effects of noise induced cortisol increase. Noise Health 2, 59–64.
vanOyen Witvliet C, DeYoung NJ, Hofelich AJ & DeYoung PA (2011). Compassionate reappraisal and emotion suppression as alternatives to offense-focused rumination: Implications for forgiveness and psychophysiological well-being. J Posit Psychol 6, 286–299.
Veith RC, Lewis N, Linares OA, Barnes RF, Raskind MA, Villacres EC, Murburg MM, Ashleigh EA, Castillo S, Peskind ER, Pascualy M & Halter JB (1994). Sympathetic Nervous System Activity in Major Depression. Arch Gen Psychiatry 51, 411.
Watkins ER (2008). Constructive and unconstructive repetitive thought. Psychol Bull 134, 163–206.
Wielgosz J, Goldberg SB, Kral TRA, Dunne JD & Davidson RJ (2019). Mindfulness Meditation and Psychopathology. Annu Rev Clin Psychol 15, 285–316.
Abstract There is a growing body of evidence suggesting that depression is becoming a major health concern for the modern world. Given the multitude of stressors advanced civilization provides, people are increasingly ruminating over the past and future. These repetitive non-constructive thoughts provide stress both in the mind and physically manifest itself in our bodily systems, deteriorating our health on multiple fronts. Not only are cases of depression increasing, but many seem to be resistant to current forms of treatment. These treatments include both pharmaceutical and therapeutic methods. Clinicians need to begin taking a serious look at alternate forms of treatment so they can become more equipped to treat patients with depression. Mindfulness meditation is the practice of focusing one’s thoughts entirely on the body itself and trains the mind to forgo all other extraneous thoughts. This technique not only provides the body an immediate sensation of safety and relaxation, but trains the individual to have better control over repetitive unhealthy thoughts. The more frequent feeling of relaxation coupled with the ability to subdue one’s own rumination decreases the body’s activation of its defense protocols. These defenses, also known as the sympathetic nervous system, when activated too frequently can be extremely detrimental to one’s physical and mental health and is strongly correlated to stress and depression. Much research involving mindfulness meditation has shown that it increases one’s ability to have thought control and decreases sympathetic nervous system activity. This is coupled with a heightened awareness of one’s own body, leading to a general increase in self perception and wellbeing. Dramatically reducing the occurrence of stress and depression. The body of meditation research requires further attention. In particular, studies require more standardized forms of meditation methods and an improvement of experimental design to increase statistical significance. That being said, given the effect mindfulness meditation has on depression, it should be viewed as a potential replacement for the treatment of depression through antidepressants. Antidepressants have a large list of potential side effects, are at times shown to be no more effective than a placebo, and have no evidence of preventing depression once treatment has been terminated. Meditation being costless and side effect free, if truly effective, would be a far more ethical and responsible treatment methods for physicians and therapist to prescribe.
Introduction
This paper will review existing literature discussing meditation and its potentially remedial effects on depression. It will argue that by providing increased ability to control and recognize non-constructive thoughts, meditation can decrease stress, thereby helping individuals with clinical depression. It is projected that by 2020, depression will become the second most common mental health issue (Kenny & Williams, 2007). Collectively, stress and depression-related symptoms account for a majority of visits to primary care physicians (Greeson et al., 2018). These disorders have become extremely prevalent and are extremely costly for individuals and the entire health care system (Greeson et al., 2018). That being said, it has been shown that 40% of depression patients are resistant to current treatment methods (Kenny & Williams, 2007), demonstrating that the entire system of treating depression is largely wasteful and inefficient, placing an unnecessary burden on society. Therefore, it is crucial that alternative approaches to treatment are explored. When looking at potential treatment methods for depression, it is important to first consider the underlying causes.
Depression is a complex mental issue that can manifest itself in a variety of different ways, and can stem from a large number of causes. That being said, there appears to be a distinct connection between stress and depression. Researchers have found that repetitive, non-constructive thoughts can lead to depression, and that individuals with acute stress-induced behaviors and hormonal changes have very similar symptoms to those suffering from depression (Watkins, 2008; Kasala et al., 2014). These symptoms commonly include hypercortisolism, which is a rise in cortisol levels due to an increase in sympathetic nervous system activity. Hypercortisolism can lead to high blood pressure, impaired immune function by decreasing cytokine count, poor antibody response, high blood sugar, increased renal retention of sodium, to name a few (Spreng, 2000; Godbout & Glaser, 2006; Kasala et al., 2014). In short, it is a condition that is extremely detrimental to overall health. Neurologically speaking, the relationship between stress and depression can be attributed partly to atrophy of the hippocampus, which is caused by high levels of stress induced glucocorticoid release (Annells et al., 2016).
Modern life is full of stressful situations. People tend to spend large portions of their day ruminating over the past and forecasting for the future. Often, these thoughts bring about worry and regret. Human beings evolved with a “fight or flight” defense response regulated by the sympathetic nervous system in order to protect themselves from physical harm. In modern life, these physical threats are being replaced by mental threats brought upon by our own projections of the past and future (Kuchel & Kuchel, 1991). Not ruminating over such thoughts has been shown to decrease sympathetic nervous system activity (vanOyen Witvliet et al., 2011). There is also a relationship between general cognitive load, and increased sympathetic activity (Mizuno et al., 2011). Therefore, it is of no surprise that high levels of sympathetic nervous system activity is present in cases of major depression (Veith et al., 1994).
The author hypothesizes that treatment methods involving improved thought control can remove stressful thoughts, thereby reducing depressive symptoms. These changes in thought patterns will have an effect on increasing parasympathetic nervous system tone and related neurotransmitters, thereby drawing a link between the cognitive skill of removing unconstructive thoughts and the reduction of stress and depression. Alongside this, the general act of meditation causes the body to feel more relaxed and decreases the activation of the sympathetic nervous system, bringing cortisol to lower levels, which increases general health and well-being. These skills will prove not only applicable to patients for depression, but also to any individual suffering from repetitive non-constructive thoughts that hinder their daily function and worsen their bodily health. This paper, through the lens of existing literature, will explore the connection between meditation’s ability to improve thought control and its promise as a treatment for depression.
Mindfulness Meditation and the Skills Provided
This paper will primarily focus on one of many forms of meditation: mindfulness meditation. Mindfulness meditation is the practice of focusing attention on a single entity, such as one’s breath, in order to take attention away from other, potentially non-constructive thoughts (Wielgosz et al., 2019). Focusing on body and breath in a calm and accepting manner also provides the mind with a sense of safety (Esch, 2014). This technique allows an individual to have an increased awareness of their emotions, and greater control over their thoughts (Barnhofer et al., 2009). Meditation has been shown to increase brain plasticity in the regions used (Lazar et al., 2005). Given the existence of use-dependent brain plasticity, it can be presumed that as meditators use these techniques during their practice, they will also be more easily able to use them in everyday life (Giuliani et al., 2011; Esch, 2014). For example, attention regulation is related to the anterior cingulate cortex (ACC) which is shown to have an increased function in those who practice mindfulness meditation (Rubia, 2009; Hölzel et al., 2011; Lutz, Antoine,Jha, Amishi P.,Dunne, John D.,Saron, 2015). Not only do meditators have increased attention regulation, but they are capable of having greater control of removing irrelevant thoughts. These repetitive thoughts, in the case of depression, usually manifest themselves as negative thoughts regarding their mental condition, poor mood, lack of belief in themselves and an over analysis regarding the consequence and meaning of life events coupled with the expectation of negative outcomes (Watkins, 2008). This is supported by the evidence that alpha bands, which play a role in processing irrelevant information, are faster and significantly more present in those who commonly practice mindfulness meditation (Foxe & Snyder, 2011). Meditation also effects the right amygdala, which is related to the processing of emotions. Reducing depression through the use of SSRIs is partly done by the suppression of right amygdala activity. Those who meditate have reduced right amygdala activity during meditation, and a change in activity was also observed when the subject was no longer meditating (Annells et al., 2016). This indicates that meditation provides more adequate emotional control over incoming stressors, and can potentially act as a replacement for antidepressants. Meditation grants the general awareness and control of emotions, alleviating the body from feeling in danger while granting the individual the ability to recognize unhealthy ruminations and clear them from their thought stream.
The Physiologic Responses of Mindfulness Meditation
The benefit of thought control is evident when analyzing the result of experiments involving mindfulness meditation. Increases sympathetic nervous system activity is present within depression (Veith et al., 1994). Those who have increased mindfulness show decreased stress and a faster recovery from it (Greeson et al., 2018; Gamaiunova et al., 2019). In these individuals, there is a noticeable reduction in sympathetic activity and responsivity, coupled with an increase in parasympathetic nervous system tone (Hoffman et al., 1982; Esch, 2014). This means the body of a meditator shifts away from activating stressful, fight or flight systems, and relaxed state processes begin to dominate. Stress related neurotransmitters such as norepinephrine and cortisol are also shown to be less present in individuals that practice meditation (Esch et al., 2007; Esch, 2014). This also indicates that meditation has a general effect on physical health. As previously stated, high levels of cortisol have serious effects on bodily health; thus, lessening cortisol will provide general well-being, as well as the cognitive benefits discussed above. Chronic stress has been connected to lower acetylcholine levels. Interestingly enough, the breath of meditators has elevated nitric oxide levels. Presumably because there are higher levels of acetylcholine and morphine, which both increase the activity of oxide-producing enzymes (Esch, 2014). Dopamine is often related inversely to the presence of depression, and it too has been shown to increase amongst those who practice meditation (Dailly et al., 2004; Jung et al., 2010; Esch, 2014). It is also has been suggested that the increase in internalized attention during mediation, triggers activity in brain regions such as the left frontal cortex that are related to positive emotions (Rubia, 2009). This, coupled with the general health benefits of decreasing sympathetic activity and cortisol levels, is likely the reason why meditators often express a general higher satisfaction with their life and are more content (Esch et al., 2007). That being said, meditators also have a higher awareness of their own health. Meditators show an increase use of the ACC and insula, signifying that they have a greater means of modulating the self, alongside pain perception and anticipation. It is theorized that this increase in awareness grants the individual a sense of responsibility to improve their health (Esch, 2014). There is likely a feedback loops that occurs when one meditates: the individual decreases sympathetic nervous system activity, thereby increasing their health and wellbeing, while also gaining a higher perception of their health that results in further attention and improvement.
The Missing Component
Many metanalytical papers have attempted to synthesize the findings of mediation research. Many conclude, as this paper does, that the main neuronal mechanism of mindfulness generally involves: attention regulation of the body and mind, nonreactivity to experiences, and changes of self-perception (Hölzel et al., 2011; Esch, 2014; Wielgosz et al., 2019). Even though the effects on the autonomic nervous system are discussed, they are seemingly ignored as a key factor contributing to the higher quality of life and state of mind experienced by those that practice meditation. That being said, authors neglect to mention that there are two different arguments being put forth. The first is that people who meditate are, at that moment, putting themselves in a peaceful and quiet mindset that makes the body feel safe, thereby increasing parasympathetic nervous system activity (Esch, 2014). The second is that it is the skills learned from the meditation that allow for individuals to remove the unconstructive thoughts in the face of stressful situations, thereby preventing an increase in sympathetic nervous system activity. Of course, these two mechanisms may both occur, and perhaps due to the change in brain plasticity, the practices of stress relief during meditation aids the patient in using those same skill in everyday life. However, this distinction is key not only for general scientific understanding, but also for future research.
The existence of the two possible mechanisms suggests the need for further investigation. Researchers, rather than observing the improvement in self-reported depression scores, should be focusing on changes in autonomic nervous system changes. To differentiate between the two mechanisms, researchers should monitor autonomic nervous system activity during the act of meditation and after a series of prolonged practices. This type of experiment could ascertain whether or not the bulk of decrease in sympathetic nervous system activity and increase in parasympathetic nervous system activity occurs at the moment of meditation, or afterwards through the skills obtained. Perhaps the two systems change at different times, or the changes are evenly distributed across both events. Either way, this type of experiment seems necessary to gain a deeper understanding of the mechanisms involved in treating depression. Furthermore, these distinctions are important in determining which techniques of mindfulness meditation provide the best results.
Criticisms
A key criticism of meditation research is that the method of meditation used in the studies is not constant. There are many forms of meditation practiced around the world, and many have different purposes. The most traditional and commonly practiced forms of meditation involve focusing attention on a single thing, which makes the research of mindfulness meditation particularly difficult because many will consider a wide range of practices to fall under the classification of mindfulness meditation. Even in this paper, that focuses exclusively on mindfulness meditation research, papers were presented that consider Tai Chi as inclusive to that criteria (Esch et al., 2007). Given the coordination of movements and the need for an instructor, Tai Chi can hardly be classified as a means of training thought control. Nonetheless, that example is quite extreme and most mindfulness-based meditation research involves one of these 4 types: traditional meditation, meditation in a clinical setting, mindfulness in a transient state and mindfulness as a dispositional trait (Chiesa et al., 2014). Despite the similarities, these all have vast differences in terms of how the meditation is practiced. For example, traditional meditation is done alone, and a more silent environment helps an individual focus on their breath. In a clinical setting, researchers conduct mindfulness-based cognitive therapy (MBCT), in which the meditation is done in a group setting led by a teacher (Kenny & Williams, 2007). In this particular study of Kenny and Williams 2007, patients were also assigned homework of 1 hour of practice per day of yoga or meditation. Even though yoga is traditionally a physical form of mindfulness meditation, it is not in western cultures. In western cultures, Yoga becomes more a practice of listening to an instructor and stretching, which is not conducive to focusing solely on the breath. This highlights the difficulty of deciding whether or not the benefits of meditation come from the practice itself or the skills learned from it, since all of these studies use methods of meditation that vaguely resemble one another in practice. If all studies use different forms of meditation, then no matter how similar the results across studies are, there is no clear conclusion on the mechanism by which these changes occur. An obvious solution to this problem is to create a method of meditation that is traditionally used by all meditators, and to have many studies done all using the same method. Since it would be hard to mandate all researchers to use the same procedures, another option is to conduct more research on the meditators’ brain activity at the time of meditation. Perhaps these observations would shed more light on the neurological processes occurring during meditation, and these results would hopefully suggest which techniques provide the same types of skills and mental processes. That being said, it is also important for researchers to consider the mechanism by which the skills of thought control are brought about before the initiation of the experiment. Practices like Thai Chi and Yoga being from eastern cultures does not classify them as mindfulness meditation and effective procedures to promote thought control.
The conclusions of some experiments discussed in this paper need to be taken with skepticism. Many studies are conducted with small sample sizes (Kenny & Williams, 2007; Barnhofer et al., 2009; Kasala et al., 2014). There are even studies, such as the Kenny and Williams study in 2007 discussed above that do not have a control group or any other group to make a comparison to. They even allowed the patients to take their regular medications for their disorders. This, alongside the absence of a control group, makes it extremely difficult to scientifically show that the MBCT was the reason for the decrease in depression scores at all. While other studies had a well-constructed design, most studies that conduct a T-test or ANOVA in their analysis fail to show that their data is normally distributed (Kenny & Williams, 2007; Barnhofer et al., 2009; Greeson et al., 2018). A normal distribution of data is a key assumption for both of these commonly used statistical test, and without proper proof of normality, the results of these test are questionable at best. Sadly, much of scientific literature contains these forms of statistical errors (Halsey et al., 2015). Though these flaws are not present in all mindfulness meditation experiments, the use of these studies as concrete evidence of its effectiveness is rightfully scrutinized. Most studies tend to have similar results, which suggests that mindfulness meditation effects depression. Nonetheless, given the design flaws of experiments and inconsistency in meditation methods, these studies should be used more as an indicator of the existence of a relationship between mindfulness meditation and depression than evidence that such a relationship exists. Much more diligent and thorough work is required for there to be scientific validity, and the ability to claim that meditation is truly a useful method of treatment. To start, many of these experiments should be repeated with improvements to their design, such as including control groups and more consistent methods of mediation, in order to validate the significance of their p-values. This will provide much more statistically significant evidence suggesting that mindfulness meditation is the true cause of the alleviation of depressive symptoms.
Conclusion
Despite the lack of concrete evidence and methods, there is a case to adopt this practice sooner rather than later. Given most experiments involving mindfulness meditation and its effects on depression share similar results, it is reasonable to assume that there is some true effect mindfulness meditation has on alleviating the disorder. The aim of the physician should be to provide a patient that has emotional challenges the tools and skills needed to manage and subdue the unhealthy habits of thinking on their own. Traditionally, this method is through the use of pharmaceutical drugs that act to change brain chemistry. This is not only a costly expense on the individual, but there is growing evidence suggesting that many antidepressants are not much more effective than a placebo (Kirsch et al., 2002; Antonuccio et al., 2002). Not only that, but antidepressant have numerous negative long-term side effects, such as withdrawals, sexual problems, weight gain and becoming emotionally numb (Masand & Gupta, 2002; Cartwright et al., 2016). There is also no publish evidence to claim that antidepressants reduce the risk of depression once the treatment has ended (Annells et al., 2016). Therefore, antidepressants should not be thought of as a viable clinical solution in the long-run. Meditation on the other hand is completely free, and can be a useful practice in an individual’s personal life. Given its simplicity, it is also void of negative side effects, and in that sense is a much more ethical and risk-averse form of treatment from a clinical standpoint. Therefore, it is prudent that the scientific community give increased attention to meditation research, so that we can further understand its benefits and perfect its techniques, to potentially help all those who suffer from depression in a safe and cost-effective manner.
Works Cited
Annells S, Kho K & Bridge P (2016). Meditate don’t medicate: How medical imaging evidence supports the role of meditation in the treatment of depression. Radiography 22, e54–e58.
Antonuccio DO, Burns DD & Danton WG (2002). Antidepressants: A triumph of marketing over science? Prev Treat; DOI: 10.1037/1522-3736.5.1.525c.
Barnhofer T, Crane C, Hargus E, Amarasinghe M, Winder R & Williams JMG (2009). Mindfulness-based cognitive therapy as a treatment for chronic depression: A preliminary study. Behav Res Ther 47, 366–373.
Cartwright C, Gibson K, Read J, Cowan O & Dehar T (2016). Long-term antidepressant use: patient perspectives of benefits and adverse effects. Patient Prefer Adherence 10, 1401–1407.
Chiesa A, Anselmi R & Serretti A (2014). Psychological Mechanisms of Mindfulness-Based Interventions. Holist Nurs Pract 28, 124–148.
Dailly E, Chenu F, Renard CE & Bourin M (2004). Dopamine, depression and antidepressants. Fundam Clin Pharmacol 18, 601–607.
Esch T (2014). The Neurobiology of Meditation and Mindfulness. In, pp. 153–173. Springer, Cham. Available at: http://link.springer.com/10.1007/978-3-319-01634-4_9 [Accessed October 1, 2019].
Esch T, Duckstein J, Welke J & Braun V (2007). Mind/body techniques for physiological and psychological stress reduction: stress management via Tai Chi training – a pilot study. Med Sci Monit 13, CR488-497.
Foxe JJ & Snyder AC (2011). The Role of Alpha-Band Brain Oscillations as a Sensory Suppression Mechanism during Selective Attention. Front Psychol 2, 154.
Gamaiunova L, Brandt P-Y, Bondolfi G & Kliegel M (2019). Exploration of psychological mechanisms of the reduced stress response in long-term meditation practitioners. Psychoneuroendocrinology 104, 143–151.
Giuliani NR, Drabant EM, Bhatnagar R & Gross JJ (2011). Emotion regulation and brain plasticity: Expressive suppression use predicts anterior insula volume. Neuroimage 58, 10–15.
Godbout JP & Glaser R (2006). Stress-Induced Immune Dysregulation: Implications for Wound Healing, Infectious Disease and Cancer. J Neuroimmune Pharmacol 1, 421–427.
Greeson JM, Zarrin H, Smoski MJ, Brantley JG, Lynch TR, Webber DM, Hall MH, Suarez EC & Wolever RQ (2018). Mindfulness Meditation Targets Transdiagnostic Symptoms Implicated in Stress-Related Disorders: Understanding Relationships between Changes in Mindfulness, Sleep Quality, and Physical Symptoms. Evidence-Based Complement Altern Med 2018, 1–10.
Halsey LG, Curran-Everett D, Vowler SL & Drummond GB (2015). The fickle P value generates irreproducible results. Nat Methods 12, 179–185.
Hoffman J, Benson H, Arns P, Stainbrook G, Landsberg G, Young J & Gill A (1982). Science. Science (80- ) 192, 1242–1244.
Hölzel BK, Lazar SW, Gard T, Schuman-Olivier Z, Vago DR & Ott U (2011). How Does Mindfulness Meditation Work? Proposing Mechanisms of Action From a Conceptual and Neural Perspective. Perspect Psychol Sci 6, 537–559.
Jung Y-H, Kang D-H, Jang JH, Park HY, Byun MS, Kwon SJ, Jang G-E, Lee US, An SC & Kwon JS (2010). The effects of mind–body training on stress reduction, positive affect, and plasma catecholamines. Neurosci Lett 479, 138–142.
Kasala ER, Bodduluru LN, Maneti Y & Thipparaboina R (2014). Effect of meditation on neurophysiological changes in stress mediated depression. Complement Ther Clin Pract 20, 74–80.
Kenny MA & Williams JMG (2007). Treatment-resistant depressed patients show a good response to Mindfulness-based Cognitive Therapy. Behav Res Ther 45, 617–625.
Kirsch I, Scoboria A & Moore TJ (2002). Antidepressants and placebos: Secrets, revelations, and unanswered questions. Prev Treat; DOI: 10.1037/1522-3736.5.1.533r.
Kuchel OG & Kuchel GA (1991). Peripheral dopamine in pathophysiology of hypertension. Interaction with aging and lifestyle. Hypertension 18, 709–721.
Lazar SW, Kerr CE, Wasserman RH, Gray JR, Greve DN, Treadway MT, McGarvey M, Quinn BT, Dusek JA, Benson H, Rauch SL, Moore CI & Fischl B (2005). Meditation experience is associated with increased cortical thickness. Neuroreport 16, 1893–1897.
Lutz, Antoine,Jha, Amishi P.,Dunne, John D.,Saron CD (2015). PsycNET. Am Psychol 70, 632–658.
Masand PS & Gupta S (2002). Long-Term Side Effects of Newer-Generation Antidepressants: SSRIS, Venlafaxine, Nefazodone, Bupropion, and Mirtazapine. Ann Clin Psychiatry 14, 175–182.
Mizuno K, Tanaka M, Yamaguti K, Kajimoto O, Kuratsune H & Watanabe Y (2011). Mental fatigue caused by prolonged cognitive load associated with sympathetic hyperactivity. Behav Brain Funct 7, 17.
Rubia K (2009). The neurobiology of Meditation and its clinical effectiveness in psychiatric disorders. Biol Psychol 82, 1–11.
Spreng M (2000). Possible health effects of noise induced cortisol increase. Noise Health 2, 59–64.
vanOyen Witvliet C, DeYoung NJ, Hofelich AJ & DeYoung PA (2011). Compassionate reappraisal and emotion suppression as alternatives to offense-focused rumination: Implications for forgiveness and psychophysiological well-being. J Posit Psychol 6, 286–299.
Veith RC, Lewis N, Linares OA, Barnes RF, Raskind MA, Villacres EC, Murburg MM, Ashleigh EA, Castillo S, Peskind ER, Pascualy M & Halter JB (1994). Sympathetic Nervous System Activity in Major Depression. Arch Gen Psychiatry 51, 411.
Watkins ER (2008). Constructive and unconstructive repetitive thought. Psychol Bull 134, 163–206.
Wielgosz J, Goldberg SB, Kral TRA, Dunne JD & Davidson RJ (2019). Mindfulness Meditation and Psychopathology. Annu Rev Clin Psychol 15, 285–316.
-
 @ 3ac03011:41ecd1bb
2025-01-18 17:10:41
@ 3ac03011:41ecd1bb
2025-01-18 17:10:41Does Football Still Feel the Same?
Close your eyes for a moment and think back to when you first fell in love with football. What was it that pulled you in and wouldn’t let go? Was it the roar of the crowd as your team netted a stoppage-time winner? The thrill of an underdog beating the odds? Or maybe it was simpler—the chants, the rivalries, the raw, unfiltered chaos of the game.
Now open your eyes. Does football still feel like that?
You know it doesn’t. The spark is still there but the magic feels muted. Matches feel more like polished products, rivalries are starting to feel manufactured and even the moments of brilliance seem a little…hollow.
You hear the pundits blame it on “greedy owners” or “commercialisation of the game,” but football has always been tied to money. From the grand stadiums to the global superstars, wealth has always flowed to the game we love. So, what’s really wrong?
What Happened to the Chaos?
Football isn’t just a sport. It’s a reflection of life—messy, unpredictable and gloriously unfair. That’s what made it beautiful. It wasn’t just about the goals; it was about the stories. The miraculous comebacks, the unlikely heroes, the questionable refereeing decisions that sparked debates for years.
But where is that chaos now?
Look at today’s game. Teams are coached to minimise risk and prioritise results. Players are drilled into systems, their individual flair sacrificed for the greater machine. Even rivalries feel like marketing strategies, built more for brand engagement than genuine passion.
Why?
Because predictability isn’t just valued—it’s demanded. Clubs are forced to prioritise short-term financial growth over risk. They cannot afford to experiment or fail because the economic system, which governs us all, punishes them if they do. It’s no coincidence that football’s decline in spontaneity mirrors the rise of fiat money.
How Fiat Changed Football
Fiat currency, with its endless inflation, has placed football in a relentless race. Every club is chasing financial growth—not because they want to, but because they have to. Inflation eats away at savings, forcing clubs to focus on short-term profits.
The result? Clubs treat fans as customers, not loyal supporters. Teams are built for efficiency, not excitement. Every decision, from tactics to transfers, is filtered through a lens of operational financial return. The beautiful game is being stripped of its beauty, one spreadsheet at a time.
Do You Really Want Perfection?
Think of your favourite football memories, those that are deemed iconic. Was it all about skill and precision? Or was it about emotion, drama and unpredictability?
The “Hand of God” wasn’t just a goal—it became a chapter in football history. Frank Lampard’s disallowed goal against Germany in 2010 didn’t just spark debates—it became folklore. These moments, as infuriating as they were at the time, gave football its soul.
But today, we chase an unattainable goal: perfection. VAR was introduced to make everything “fair,” but instead, it’s robbed the game of its spontaneity. Those controversial moments that one fueled passion now lead to lifeless delays.
Is this really the game we fell in love with?
Financial Fair Play (FFP) and the False Promise
Consider FFP. At first glance, it seems like a noble idea—a way to regulate spending, create a level playing field and ensure the long-term stability of clubs. But has it really delivered on its promises?
The reality is, FFP wasn’t designed for fans. It’s a system built for regulators, giving them a framework to justify their role. What they fail to understand—or conveniently ignore—is that football fans aren’t ordinary customers. We don’t switch teams when things go wrong. If your club is relegated or endures years of heartbreak, do you suddenly start cheering for your rivals? Never. Loyalty is the foundation of football and it’s a loyalty so fierce that many fans would sooner stop watching the sport entirely than betray their team.
Instead of nurturing this unique connection, FFP has entrenched inequality. It locks in the dominance of a few elite clubs while stifling ambition for everyone else. Even as a supporter of one of these elite clubs, it’s impossible to ignore how these rules suffocate the very spirit of competition that makes football beautiful.
Is There A Way Back?
What if football could be free again? Free to embrace chaos, its passion, its unpredictability?
The answer isn’t to ban money from football. Money has always been a part of the game. The problem isn’t money—it’s the kind of money.
Fiat money, with its endless inflation, has poisoned football. We need an inflation-proof currency to form the heart of a new awakening for football. Lucky for us, we don’t need to look far for that currency.
A New Renaissance: The Bitcoin Era
Bitcoin is a form of money that doesn’t lose value over time. Clubs that adopt it will achieve financial stability without the need to chase endless operational growth. With Bitcoin, clubs can focus on what really matters: the football, the fans and the overall synergy between them.
Managers can take risks without the fear of collapse. Players can be artists, not just cogs in a system. Fans can feel like part of the story again, not just numbers on a balance sheet.
Imagine a world where football is free to be itself again. Where rivalries grow naturally, fueled by passion, not profit. Where clubs aren’t just businesses but extensions of their communities.
This isn’t a dream. It’s already happening. Real Bedford is leading the charge, proving that Bitcoin can change the game.
Football’s future is here—and it’s orange.
-
 @ af264750:2c08cd8a
2025-01-18 16:22:48
@ af264750:2c08cd8a
2025-01-18 16:22:48บทความนี้ not a tutorial เขียนไว้เป็นบันทึกความซนของผมเอง
เรื่องมีอยู่ว่า Alby เค้าจะยกเลิก custodial wallet ที่บริการกระเป๋าให้ฟรี ซึ่งประกาศมาซักพักใหญ่ๆแล้วล่ะ ผมก็นั่งไถฟีดค้นหากระเป๋าใหม่ที่จะมาใช้แทนแล้วไปจบอยู่ที่ LifPay เอามาใช้เป็นกระเป๋าชั่วคราวไปก่อนไว้รับส่ง zap เล็กๆน้อยๆ แล้วช่วงนั้นก็เป็นจังหวะเดียวกับที่มหาลัยมีจัดงานกึ่งสัมมนาเลยได้โอกาสเปิดโต๊ะคุยเรื่อง Bitcoin กันไปทั้งคืน
ผ่านไปซักหลายวันอยู่ขณะกำลังเก็บห้อง ผมก็ไปเจอกับคอมเครื่องเก่าที่ตั้งเกาะฝุ่นหลบมุมอยู่ คอมเครื่องนี้เคยเป็นคอมเครื่องหลักที่ซื้อมาไว้ประมาณ 10 ปีหน่อยๆ จนถึงช่วงขึ้นมหาลัยที่ต้องเปลี่ยนไปแบกโน้ตบุ้กไปเรียนแทน กลายเป็นว่าคอมเครื่องนี้ก็ตั้งไว้ในห้องแบบไม่ได้เสียบปลั้กเลยไปเป็นหลักปี ก็เลยเกิดไอเดียว่าไม่งั้นก็เอามาล้างเครื่องแล้วลองเปิด node ดูหน่อยมั้ย เพราะยังไงกิจกรรมทุกอย่างตอนนี้คือย้ายไปบนโน้ตบุ้กแทนหมดแล้ว จนเป็นจุดเริ่มต้นถึงการเดินทางแห่ง home node ขึ้นมา
เตรียมเครื่อง
ด้าน hardware ที่ใช้ก็ไม่พ้นคอมเครื่องเก่านั้น ที่ตอนนี้สเปคมันค่อนข้าง overkill สำหรับการเปิด home lightning node เบาๆ เพราะนอกจากจะเป็นเคสขนาด e-ATX ที่อัด HDD ได้หลายลูกแล้วก็ยังมีการ์ดจอเก่าอยู่ด้วย สเปคคร่าวๆก็มี i5-4670k กับแรม DDR3 12GB แค่นี้ก็กินไฟไปหลายสิบวัตต์แล้ว ยังมีการ์ดจอ GTX 1050Ti เสียบอยู่เฉยๆด้วย แล้วยังมี SSD SATA 480GB ตัวนึงกับ HDD 1TB พ่วงด้วยช่องอ่านแผ่น DVD ที่ประดับหน้าเคสไว้ เลยคิดไว้ว่าน่าจะต้องซื้อคอมอีกเครื่องเล็กๆมาเปิดแทนพี่ใหญ่นี้ในเร็ววัน
หันมาด้าน software กันบ้าง ผมก็เลือก Umbrel มาใช้ สาเหตุหลักก็เน้นสะดวกครับ สละ USB drive มาอันนึงแล้ว flash เข้าไปเลย จิ้มเดียวจบ แต่ข้อเสียแรกที่เห็นเลยคือใช้ได้ drive เดียวแล้วใช้ทั้งหมดเลย 1 drive ก็เลยต้องเอาระบบไปลงที่ SSD ไม่งั้นเดี๋ยวระบบอืดตาย ก็นะ แลกกับความสะดวกก็งี้

เปิดเครื่อง
แน่นอนว่าต้นเรื่องเราคือ Alby อยากให้เราย้ายกระเป๋ามาใช้เป็น Alby Hub ที่เป็น self-custodial ซึ่งใน Umbrel นั้นจะบังคับให้เราติดตั้ง Lightning Node ที่ตัวมันก็จะบังคับให้เราลง Bitcoin Node ด้วยอีกชั้น ทำให้จำนวน app ขั้นต่ำในการเปิด Alby Hub บน Umbrel อยู่ที่ 3 apps แต่อันนี้ผมลงจุกจิกเพิ่มเข้ามาด้วย นี่แหละข้อดีอันนึงของ Umbrel

สเต็ปการทำงานเบื้องต้นก็คือต้องรอ Bitcoin Node sync ให้ครบก่อน ไม่งั้น Lightning Node จะไม่เปิดให้เราเข้าไปใช้งาน แต่ระหว่างรอ sync นั้นเราสามารถเข้าไปจด recovery seed ไว้ก่อนได้เลย ห้ามลืมเด็ดขาด
พอ Lightning Node เราพร้อมแล้ว ก็ไปกันต่อที่ Alby Hub ก็จะมีขั้นตอนตั้งค่านู้นนี้นั้น ให้เราตั้งรหัสผ่านล็อก Hub แล้ว ก็จะมีให้เชื่อม Alby Account ด้วย ซึ่งแน่นอนว่าผมมาเพื่อสิ่งนี้ แลก auth token กันนิดหน่อยก็ถึงหน้า dashboard แล้ว
เปิดช่อง
เมื่อผมหันมาใช้ self-custodial wallet แล้ว สิ่งแรกที่ต้องจัดการเลยคือต้องมีช่องทางให้เงินไหลเข้ามา ไม่งั้นจะเปิด node เผาค่าไฟไปทำไมเนอะ ซึ่งใน Alby Hub เนี่ยเค้าก็มีรายชื่อผู้ให้บริการ LSP ที่เราสามารถซื้อ channel เปิดทางให้เงินไหลเข้ามาได้ ซึ่งผมก็เลือกเปิด channel กับ Lnserver เพราะลองเทียบราคาดูแล้วคือจ่ายค่าเปิด channel น้อยที่สุดในลิสด์นี้แล้ว บวกกับว่าเราสามารถออกไปซื้อตรงๆกับทาง Lnserver เองเหมือนกัน

โน้ตสำคัญของผมเวลาเปิด channel มีอยู่สองจุด จุดแรกคือต้องดู on-chain fee rate เพราะทุกครั้งที่เราเปิด channel ทาง LSP เค้าจะต้องส่งธุรกรรมเข้า block ซึ่งจะต้องเสีย fee เพิ่มกว่าเรทจริงอีกหน่อย ทำให้บางทีค่าเปิด channel โดนอัดราคาเพิ่มจนสูงกว่าค่าบริการของ LSP นั้นๆอีก อย่างของผมที่ซื้อกับ Lnserver เค้าจะเก็บเริ่มต้นที่ 5000 sats สำหรับ channel ขนาด 2,000,000 sats แล้วจะบวก commit fee ไปอีก 1345 sats ที่เรท 2 sats/vB รวมกันเป็น 6345 sats ที่จ่ายไป
โน้ตที่สองที่ต้องเตรียมไว้ด้วยก็คือ reserve fund โดยผมจะเรียกอีกอย่างว่าเป็นค่าประกัน channel ซึ่งค่าประกันตรงนี้จะเก็บไว้เป็นขั้นต่ำของ channel นั้นๆฝ่ายละ 1% แล้วจะล็อกตายเก็บไว้เอาออกมาใช้จ่ายไม่ได้จนกว่าจะปิด channel ถ้าไม่จ่ายค่าประกันตรงนี้ เราก็จะรับเข้าและจ่ายออกจากฝั่งเราไม่ได้ หมายความว่า channel ขนาด 2,000,000 sats ก็ต้องมีเงินประกันเข้าไปด้วยจากฝั่งผม 20,000 sats ถึงจะใช้งานได้

ใครที่สนใจอ่านเพิ่มเติม ผมมีเว็บข้อมูลเกี่ยวกับ Lightning liquidity มาแนะนำ อันนี้แหละที่ผมอ่านแล้วเพิ่งมารู้เกี่ยวกับ channel reserve รวมถึงเรื่องอื่นๆที่น่ารู้เกี่ยวกับวงบริวารและการออกแบบระบบที่เกี่ยวกับ Bitcoin
https://bitcoin.design/guide/how-it-works/liquidity/#what-is-the-reserve-amount
-
 @ 378562cd:a6fc6773
2025-01-18 16:20:12
@ 378562cd:a6fc6773
2025-01-18 16:20:12As a frequent user who depends on my phone for a wide range of activities, including boosting my productivity and capturing spontaneous moments, I have been paying close attention to the OnePlus 13. This flagship device appears to meet all my essential requirements, particularly excelling in power and camera capabilities, which are my main priorities. Here are the standout features that have caught my attention.

Power to Handle Anything I Throw at It
Performance is a big deal for me, and the OnePlus 13 doesn’t seem to disappoint. It’s powered by the Snapdragon 8 Elite processor, a beast in the mobile tech world. I can already imagine how smoothly it would handle heavy multitasking, like switching between editing photos, running multiple apps, and even gaming.
The insane memory options—up to 24GB of RAM—truly stand out. That’s more RAM than most laptops I’ve owned! Pair that with up to 1TB of storage, and you’re looking at a future-proof phone. I’d never have to worry about running out of space for apps, photos, or videos, and everything would load lightning-fast.

A Camera Setup That’s Hard to Ignore
One of my favorite things to do is capture high-quality photos and videos, so a powerful camera system is non-negotiable. The OnePlus 13 delivers with its triple-camera setup; all three lenses are 50 megapixels. That means whether I’m shooting with the main wide lens, zooming in with the telephoto, or going wide with the ultra-wide, I’m getting consistently sharp, detailed shots.
The Hasselblad collaboration is a big draw for me, too. OnePlus phones have been steadily improving their color science, and this partnership seems to really shine in the OnePlus 13. I’d expect vibrant, true-to-life colors in my photos without much editing required.
The AI enhancements also pique my interest. From what I’ve read, the phone handles tricky lighting situations, like low-light environments or high-contrast scenes, exceptionally well. That’s exactly what I need to capture spontaneous moments without worrying about settings.
Battery and Charging That Won’t Leave Me Hanging
Another thing I appreciate is the long battery life. The 6,000 mAh battery on the OnePlus 13 is reportedly a powerhouse, capable of lasting two days under mixed usage. And when I do need to charge, the 100W wired charging can fully juice up the phone in just over half an hour. Even the 50W wireless charging is incredibly fast, which is perfect for someone like me who’s always on the move.
Design and Features That Add Value
The flat-edge design and premium finish make the phone feel as good as it looks. I’d probably go for the Midnight Ocean with its vegan leather back—it sounds grippy and unique, ideal for someone who doesn’t want to slap on a bulky case.
The little extras, like Glove Mode and Aqua Touch 2.0, also catch my attention. Since winters are cold here, using my phone with gloves on is a practical bonus.
Why It’s Tempting Me
At $899 for the base model, the OnePlus 13 seems like a solid deal, especially for the power and camera capabilities it offers. Even if I choose a higher configuration, the pricing still feels reasonable compared to other flagships with similar specs.
For me, the OnePlus 13 feels like a phone that’s built for power users—people who need speed, reliability, and top-tier camera performance. I’m seriously considering it for my next upgrade because it feels like it would keep up with everything I do and then some. If the camera and performance live up to the hype, I might just have my decision made.
-
 @ f84e0b6b:f21f0a9b
2025-01-18 16:06:45
@ f84e0b6b:f21f0a9b
2025-01-18 16:06:45I’ve never lived in LA, though I’ve visited many times. The devastation there from recent fires there is still in the headlines and anyone with a soul feels for the folks without homes, neighbors and communities. Whether they vote the same way or look the same way or worship the same god, “what can I do to help these victims?” is our first question.
The second question is, what is the most responsible way to help? Paragraph two and controversy is already here. Responsible according to who? These people are victims, just give them as much money as they need and let them figure it out according to their local knowledge and culture! The broadest possible answer to this comes from a recent Substack by Arnold Kling: California Tough Love . His position is that there are certain factors controlled locally that led to the disaster, and we shouldn’t be in a rush to replicate them. Having some strings attached to funds that reduce the likelihood of $50,000/year blue collar workers in Iowa footing the bill for the rebuild of $5,000,000 homes in Pacific Palisades AGAIN in the foreseeable future is a very reasonable position.
My position here will be more detailed than Arnold’s, and thus has a higher probability of being wrong. That has never stopped me before. The source of this hubris is a crystal ball. While not a resident of LA, I have been an honorary citizen of Maui for several decades. This attachment is longer than the attachment to the city I currently live in. In August of 2023, a similar devastating fire engulfed the town of Lahaina on the west side of Maui. \~2,200 homes were burned or damaged. The plight of those rebuilding and the process they have gone through quickly faded from national attention, but not to those of us who spend substantial amounts of time on the island. This experience 17 months before the LA fires has painted a depressing blueprint of what we can expect in LA’s recovery. A couple of highlights:
-
In November of 2024, the first house was rebuilt. 15 months = 1 house. First House Rebuilt - Maui News. Article highlight: Maui “expedited the permitting process for this house, so it “only” took 2 months.
-
In December of 2024, federal funding for rebuilding via a block grant is finally approved by congress. Federal Block Grant For Rebuild - Maui News. Article highlight: $1.6 billion approved for housing = \~$800,000 per house.
What do these items have in common? The biggest price so far is time. Arnold’s substack was more of a philosophical position, but I doubt even he knew that at the time of writing, Lahaina’s federal funding had just been approved. All those strings he had attached by the feds? Still very slow for a family without a home. This is half of the ‘real price gouging’ mentioned in the subtitle. Those further down the socio-economic ladder have less time to whether the process in Lahaina and the same will likely be true for the middle class residents embedded in the areas destroyed by California’s fires.
The second element of price gouging is the red tape partially embodied in Maui’s example of two months of permitting. These costs aren’t just the time, but also the professional consultants of various stripes required to navigate the process successfully and the costly modifications to homes mandated through these processes.
Here is where I posit my broad and general suggestion. There should exist a “right to rebuild”. If you can legally own a piece of property in a specific condition, you should have the right to rebuild that exact same property if it is destroyed by means out of your control. If you don’t have a “right to rebuild”, you really don’t own that property - you are just renting it for an indefinite period from whoever can prohibit rebuilding it.
Rebuilding is a special case in both the individual and the community level. See the map of Lahaina below. We know where all the plumbing and power lines were. We know where the streets and drainage were. The right to rebuild translates nicely to the community level. Rebuild everything back where it was. Take a month or two to clear out the debris from an area and begin to rebuild. Rinse and repeat until done.
Taxpayers in Texas shouldn’t be paying for bloated permitting processes in Lahaina or LA. They shouldn’t be paying for eco-upgrades unless very specific, critical failures that caused the current disaster are clearly identified with lowest-cost available solutions. (In Lahaina - pay to bury the power lines. I drove through the area where the fire started 2 weeks before it occurred. That place was a tinder box, and it will be again unless someone puts a golf course on that hill. Burying the power lines will dramatically reduce the fire hazard. I’m not joking about the golf course. Directly adjacent to the north of the area of Lahaina that burned is Ka’anapali, whose identical hillside is green all year round due to the presence of golf courses that pay for themselves and do not burn.)
How to address this in the context of federal funding via Arnold’s original post:
-
Extremely expedited permitting process for rebuilds that get any federal funding: 5 days not 60. You can rebuild what you had, no questions asked, just file the paper work to prove it is the same lot and same size structure. If local jurisdictions drag their heels - no funding, answer to your voters who are now SOL.
-
Capped amount of funding per structure that covers a functional modest structure built at the average cost of the 10 most affordable states in the country. The process of building a single family residence is not dramatically different in various areas of the country, unless dictated by excessive regulation. There may be factors for labor to consider if an area is remote like Lahaina or the hills of North Carolina affected by Helene. But if it costs 2x to build a house in your county than in the 10 most affordable states - you are doing it wrong. There is some regulatory price gouging going on. Figure it out. 10 most affordable states to build a home - According to this research you can build a 2,100 square foot home for an average of less than $300,000 in the 10 most affordable states. This list includes Florida, South Dakota and Tennessee. Your geography is not special.
-
This funding will also be contingent on these rebuilt houses being completed within 110% of the time it takes to build 2,100 square foot home in the same 10 markets - measured from the day funds begin to be distributed by the federal government. Some things will take longer, but some should also be faster if you are doing a lot of these in the same place at the same time.
-
Federal funding will begin to be distributed from a risk pool within 6 months of the disaster, with minimal review to just ensure the disaster qualifies and the receiving state/city will abide by its parameters.
-
The funding is distributed at intervals governed by compliance with the program. Permits are being issued timely, and the amounts distributed are aligned with the cost of building in our most affordable markets.
If you want to build something new and different than before - it might take longer. If you want more than 2,100 square feet of house - I hope you had insurance to cover the difference. A new 2,100 square foot house puts you in the top 10% of humans on earth in terms of shelter. Being a good neighbor does not require rebuilding your infinity pool.
The right to rebuild will get people in homes quicker, remove government obstacles, and stop funding waste. Every citizen will know the rules - money is there to get me a basic structure quickly or fund the beginning of something larger. Any obstacles to that time and money are coming from politicians/regulations I can vote on. Comments will surely pour in explaining how it isn’t that simple. These comments will be reviewed diligently 2 years from now when Pacific Palisades is still a wasteland after $20 billion in federal aid has been spent.
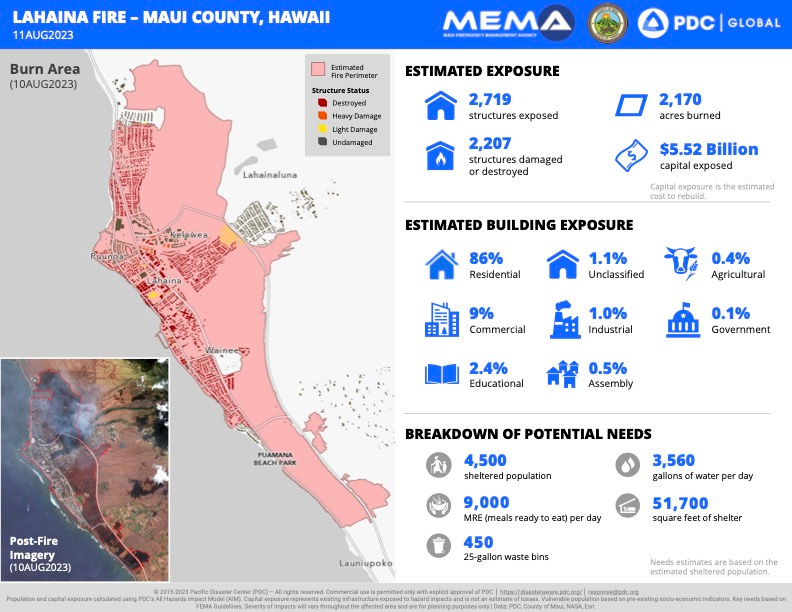 Source: Maui Now
Source: Maui Now -
-
 @ c69b71dc:426ba763
2025-01-18 15:39:35
@ c69b71dc:426ba763
2025-01-18 15:39:35Chef's notes
This raw vegan curry ramen is a vibrant, nourishing dish packed with fresh vegetables and a rich, creamy coconut curry broth. It’s quick to prepare, full of flavour, and the perfect guilt-free comfort food! 🌱 Feel free to use your favourite veggies👩🏼🍳
Details
- ⏲️ Prep time: 20 min.
- 🍳 Cook time: 0
- 🍽️ Servings: 2
Ingredients
- 500g or 2 packs kelp noodles
- 1/2 Lemon juice ( 1/4 for soaking and 1/4 for the soup
- Salt
- Fresh vegetables of your choice, such as: 4 medium mushrooms, 4 leaves red cabbage, 2 carrots (julienned or peeled into strips), 1 Celery stick (diced)
- 2 cups coconut milk (or coconut cream diluted with water)
- 1/2 flesh of a Coconut (optional, if using fresh coconuts) otherwise more coconut cream
- 1 thumb of fresh ginger
- 1 thumb of fresh turmeric
- 2 tbsp light miso paste
- 2 pitted dates
- 2 tbsp cashews
- 1 clove garlic
- 1 tsp curry powder or pepper (optional)
Directions
- Prepare the Noodles: Rinse the kelp noodles thoroughly. Then soak them in warm water with a squeeze of lemon juice and a pinch of salt for 10 minutes to soften.
- Prep the Vegetables: Thinly slice or julienne carrots, dice celery, thinly cut mushrooms, cut the red cabbage into thin strips.
- Make the Broth: In a blender, combine the following: 2 cups coconut milk (or coconut cream diluted with water if fresh coconuts are unavailable), ginger, turmeric, 1/4 juice of 1 lemon, light miso paste, pitted dates, cashews, garlic, salt, curry powder
- Blend on high speed for about 3 to 4 minutes until the broth is smooth and slightly warm. Do not overheat!
- Assemble the Ramen: Drain the kelp noodles and place them in serving bowls. Arrange the prepped vegetables on top of the noodles. Pour the warm curry broth over the noodles and vegetables.
- Serve immediately and enjoy your raw vegan ramen with chopsticks for an authentic touch!
-
 @ da0b9bc3:4e30a4a9
2025-01-18 14:09:40
@ da0b9bc3:4e30a4a9
2025-01-18 14:09:40Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/854843
-
 @ 9e69e420:d12360c2
2025-01-18 14:02:27
@ 9e69e420:d12360c2
2025-01-18 14:02:27The Supreme Court's decision to uphold the TikTok ban, set to take effect on January 19, 2025, leaves 170 million American users searching for new social platforms. As this unprecedented shutdown approaches, Nostr, a decentralized social media protocol, is positioned to capture users seeking a censorship-resistant alternative.
Why Nostr Appeals to Former TikTok Users
Nostr offers several compelling features that make it an attractive option for displaced TikTok users. The platform provides true user control over content and algorithms, allowing people to choose how their feed is displayed rather than being subject to a centralized algorithm's whims. Additionally, Nostr's integration with Bitcoin's Lightning Network enables creators to receive direct micropayments through "zaps," creating new monetization opportunities.
Key Advantages of Nostr
Censorship Resistance Unlike traditional social media platforms, Nostr cannot be banned or shut down by any single entity due to its decentralized nature. Users maintain ownership of their digital identity and content, ensuring they won't face another situation like the TikTok ban.
Creator Economy Content creators concerned about losing their TikTok revenue streams can benefit from Nostr's native payment system. The platform's "zap" feature allows followers to send instant micropayments to creators, providing a direct monetization path.
Platform Independence Nostr's protocol-based approach means users can seamlessly switch between different client apps while maintaining their following and content. This flexibility provides a stark contrast to TikTok's centralized model that leaves users vulnerable to platform-wide shutdown.
Growing Momentum
Nostr has already demonstrated significant growth potential, expanding from 90,000 to 1.1 million users in just three months. With prominent figures like Jack Dorsey and Edward Snowden advocating for the platform, Nostr is well-positioned to capture a portion of TikTok's massive user base seeking a more resilient social media alternative.
-
 @ bf47c19e:c3d2573b
2025-01-18 12:47:56
@ bf47c19e:c3d2573b
2025-01-18 12:47:5618.08.2020 / Autor: Igor Mirković
Činjenica je da živimo u vremenu u kome su informacije dostupne na dohvat ruke, svuda i svima. Analiza najsitnijih detalja zaobilazi ljudske, ponekad pogrešne procene, potpomognuta kompjuterskom tačnošću dovodi nas do maestralnih otkrića. U izobilju sačuvanih podataka blokčejn industrije gde je transparentnost glavni adut, kruži velika nepoznanica koja zbog svoje nerešivosti prerasta u misteriju. Ko je idejni tvorac Bitkoina, jednog od najuticajnijih projekata u modernoj finansijskoj industriji i znate li ko je misteriozni Satoši Nakamoto?!
Nepoznati genije, čija je kreacija najpoznatija alternativa čitavom svetskom monetarnom sistemu ali i svakodnevnom životu, kome svi nalazimo zamerke, na koje smo navikli da prećutimo i prihvatimo ih jer mislimo da tako mora, imao je ideju o konceptu čuvanja i razmene vrednosti koja će savršeno funkcionisati unutar društva. Bitkoin je prvi put prezentovan javnosti 31. oktobra 2008. u tekstu koji se popularno naziva Bitkoin Whitepaper i predstavlja dokument o filozofiji u rešavanju određenog problema. Bitkoin Whitepaper je kao autor potpisao Satoši Nakamoto.
 Satoši Nakamotov Bitkoin whitepaper
Satoši Nakamotov Bitkoin whitepaperKandidata koji mogu biti iza ovog imena ili pseudonima svakako ima, ali nećemo odmotavati klupko unazad, nego ćemo pratiti Satošijev rad i stvari koje zapravo znamo kako bi nas dovele do nekoga ili nečega. Saznanja, ko je to, koristeći taktiku dobrih poker igrača, u kojoj ne moramo videti kroz zatamnjene naočare drugih igrača kako bi ih pročitali, već ćemo tumačiti njihove postupke, govor tela, izbor reči…
Sami počeci ovakve ideje datiraju mnogo ranije i idu do 1980. godine i Cypherpunk zajednice koja je bila sačinjena od fanatika za brigu o privatnosti podataka na internetu i kriptografa koji su kreirali softvere za zaštitu podataka. To je bila privilegija državnika na visokim pozicijama sa pristupom poverljivim informacijama i naravno, tajni alat vrhunskih špijuna. Cypherpunk su aktivisti koji se zalažu za široku upotrebu kriptografije i tehnologije za unapređenje privatnosti, kao puta ka društvenim i političkim promenama.
Zaštita privatnosti je smatrana bitnom ali nije bila masovno dostupna, a Cypherpunk zajednica se zalagala protiv sistema „Veliki brat“ sistema u kome je nekome iznad uvek dostupan uvid u naše aktivnosti. Promovisali su zaštitu, enkripciju i bezbednost na individualnom nivou, u kome bi svako trebalo da preduzme dostupne mere predostrožnosti i zaštiti svoj virtuelni (lični) identitet.
Pretpostavljamo da je Satoši bio deo ove zajednice jer je definitivno bio njihov istomišljenik i kao inspiraciju za kreiranje Bitkoina imao je par postojećih projekata iz zajednice poput B-Money, Digi Cash ili Bit Gold koji su idejno bili slični Bitkoinu ali neuspešni u realizaciji.
Nakon objavljivanja Bitkoina, Satošijeva ideja se postepeno širila zajednicom i privukla brojne programere koji su bili voljni da daju svoj doprinos u razvijanju i adaptaciji, ali je Satošijev lik i dalje ostao neotkriven jer je sa saradnicima komunicirao isključivo porukama preko e-mail adrese i foruma, koristeći potrebnu zaštitu. Njegova lokacija i ostali tragovi do njega bili su nedostupni. Čak i njegovi najbliži saradnici znali su ga samo kao internet nalog sa alijasom Satoši Nakamoto.
 Citat iz „The Crypto Anarchist Manifesto“
Citat iz „The Crypto Anarchist Manifesto“Pored toga što je bio ključna osoba za kreaciju i razvoj Bitkoina, nije upadao u oči javnosti jer mediji i ljudi koji su čuli za Bitkoin, masovnu primenu i uspeh projekta tretirali su kao naučnu fantastiku i nisu joj pridavali bitan, a kamoli revolucionaran značaj.
03.01.2009. nakon niza transakcija, uspešno je „izrudaren“ prvi blok u Bitkoin blokčejnu i nagrada koja je sledila rudaru tog bloka (Satošiju) bila je 50 BTC. U kompjuterskom kodu prvog bloka nalazi se „skrivena poruka“ koja kada se dešifruje glasi:
– The Times 03/Jan/2009 Chancellor on brink of second bailoutfor banks
Ova poruka se podudara sa naslovnom stranom londonskih novina tog dana, ukazujući na pogrešne poteze postojećeg monetarnog i finansijskog sistema, koji su razlog nastanka Bitkoina. Država pomaže banke i privredu tako što im puni čašu za podsticaj ekonomije, ali flaša novca iz koje uporno dolivaju je fiktivna i napunjena je novcem „ispod čekića“, kojim se kupuje socijalni i ekonomski mir.
 Bitkoin programeri
Bitkoin programeriKako je vreme prolazilo, mnogi su uvideli prednosti koje Bitkoin ima, broj korisnika se povećavao, a mreža je bila sve stabilnija. Satoši je aktivno radio sa brojnim programerima na razvitku same tehnologije, ali teško je bilo kontrolisati pravac u kome će Bitkoin biti korišćen. Novac koji ne može biti kontrolisan od strane Centralne Banke, ne može biti oporezivan, nije inflatoran i može biti poslat i primljen svuda, veoma brzo zloupotrebljen je kao savršen način finansiranja i plaćanja projekata koji su smatrani krajnje ilegalnim i zabranjem od strane vlada širom sveta.
Jedan od takvih slučajeva bio je WikiLeaks skandal 2010. godine, koji je koristio Bitkoin kao sredstvo finansiranja svog sajta, na kome su objavljivani ukradeni podaci koji su bili strogo poverljivi i zabranjeni za javnost, a sadržali su brojne malverzacije i tajne dogovore medju državama.
Satoši Nakamoto je osporavao korišćenje Bitkoina u ove svrhe, ali zbog same prirode Bitkoin-a bilo je nemoguće da se ovako nešto spreči. Borba izmedju dobrog i lošeg koja se vodila u zajednici, nastala neiskustvom u do tada neviđenoj situaciji i višestruke neregulative, moralno je potresla Satošija, koji nedugo zatim na misteriozni način nestaje sa svih foruma… Ostavlja samo komentar: „Bilo bi mnogo bolje da je Bitkoin privukao pažnju javnosti na bilo koji drugi način, osim na ovaj. WikiLeaks je uzburkao roj pčela, koji je sada krenuo na nas.“
Svestan mogućih problema sa vlastima zbog svoje kreacije, odlučuje da se potpuno povuče i prepusti razvijanje projekta svojim najbližim saradnicima i zajednici. Bitkoin je nastavio da se razvija i istakli su se mnogi koji su uticali na unapređenje kako tehničke pozadine projekta tako i medijske prihvaćenosti i pravne regulative.
Ljudi lako shvate Bitkoin, jer je ideja o savršenom finansijskom trzistu u njihovoj glavi vrlo slična, a Satoši se pobrinuo da tehnoloski podupre takvu zamisao. Čovek koji je živeo za procvat tehnologije u kojoj je anonimnost i dostupnost vrlina, van svakog zla modernog doba, u kome se često zloupotrebljava tehnološka revolucija da se tron postojećih vladara utemelji, na štetu nemoćnih.
Količina Bitkoina koja je došla u Satošijevo vlasništvo tokom početnih godina procenjena je na minimum 1.000.000 BTC-a, što sada, nakon rasta svesti o stvarnoj i mogućoj vrednosti Bitkoina iznosi oko 11 milijardi američkih dolara i to ga direktno klasifikuje kao jednog od najbogatijih ljudi na svetu.
 Naslovna strana magazina „The Times“
Naslovna strana magazina „The Times“Debata ko je misteriozni genije i idejni tvorac bitkoina – Satoši Nakamoto i dalje traje. Da li je muškarac, žena…? Ili čitava grupa ljudi stoji iza pseudonima? Mnoge analize poruka po načinu spelovanja upućuju da je reč o osobi engleskog porekla, naprednog programerskog znanja i shvatanja ekonomije. Akademski građanin koji razdvaja novu rečenicu sa dva spejsa posle tačke, što je simbolično za akademske radove tog vremena, ali i za stare pisaće mašine, koje je možda koristio u mladosti i tako razvio naviku.
Jako je interesantna činjenica da ni jedan coin u njegovom vlasništvu od njegovog nestanka, nije poslat ili potrošen. Stoje na kripto novčanicima, netaknuti. Svi za koje se pretpostavljalo da stoje iza Bitkoina su javno negirali da su oni misteriozni idejni tvorac Satoši Nakamoto, svi sa kojima je sarađivao tvrde da ne znaju njegov identitet i svi koji su se dobrovoljno javili da preuzmu zasluge za kreaciju, nisu imali dovoljno jake dokaze za samoproklamovane tvrdnje.
 Najbogatiji Bitkoin holderi
Najbogatiji Bitkoin holderiBitkoin nosi etiketu savršenog sistema otpornog na bilo koji vid malverzacije u samim transakcijama jer krajnju realizaciju ne vrše drugi ljudi nego kompjuterski program. Kripto rudari, novčanici za čuvanje, adrese za slanje, mnogima su poznati termini koji su sastavni deo Bitkoin mreze ali jedna stvar je ostala nepoznanica kako za ljubitelje kriptovaluta tako i za ostatak sveta, samo srce projekta, ko je i gde je osoba koja se krije iza potpisa Satoshi Nakamoto.
-
 @ c4b5369a:b812dbd6
2025-01-18 12:17:22
@ c4b5369a:b812dbd6
2025-01-18 12:17:22This is the first edition of the SDR (Squirrel Den Recap), a development blog where I recap the recent Cashu related things I've been working on.
The year of the nut
IYKYK. 2025 is the year of the nut. Don't blame me, you can put it on the Chinese:

And I intend to take full advantage of that. This is the year where I go all in on the nut development!
Building a mint???
There are already a few mint implementations out there (nutshell, gonuts, cdk...). So why build another?
Honestly it was kind of a selfish move. So far, I have mainly concerned myself with building tools for Cashu wallets and clients. I figured, if I wanted to truly focus on Cashu this year, I should also know my stuff when it comes to building a mint from scratch. And so I did. It also allows me to experiment with mint related stuff, having an implementation handy that I can mess around with.

The mint implementation is called MNT. You can visit the homepage https://mnt.cash , where you will also find a link to the code.
Although the code works, the mint implementation is not yet ready for production. I've been playing around with it using a local testing lightning network with Polar , which by the way is a great tool for devs that need to test lightning integrations.
The mint
MNT is short for mint. It's also pronounced like mint, but without the "i". The goal of this project is to be an easy to run mint, that could be deployed by users for example when running an event. It won't support all of the protocol features, to keep it simple. Instead the focus will be on simplicity and ease of use.
MNT comes with an admin web interface, that makes it easy to set the mint up with a lightning backend:

After adding a lightning backend, the mint is basically ready! Users can enjoy a live view of what is happening on their mint via the integrated dashboard:

Admins can take direct actions on the mint via the admin tool, like rotating keysets, disabling and enabling features, etc...
A key feature is also the keyset view, where operators get a view on how much of the issued ecash has already been redeemed in each keyset. This is a crucial tool for mint operators, because it lets them know when they can safely delete records from their database, or shut the mint down.

The mint is compatible with all Cashu wallets. It only supports a subset of the cashu specification (NUTs), and will probably never implement the full spec. I'm looking forward to soon recklessly give this badboy a spin on mainnet 😎
What else?
Cashu-ts
Last year
npub1mhcr4j594hsrnen594d7700n2t03n8gdx83zhxzculk6sh9nhwlq7uc226
joined cashu-ts as a maintainer and has been killing it with development in the project! As I ramp up my involvement in the project again, we started having weekly dev calls. Developers that want to contribute to cashu-ts development, please reach out to me so you can join us on the next call!
Nutstash
The wallet has seen a complete make-over at the end of last year. Now is the time to consolidate, fix bugs and improve the UX.
npub12zpfs3yq7we83yvypgsrw5f88y2fv780c2kfs89ge5qk6q3sfm7spks880
has been helping me with awesome designs and UX suggestions, while I've been crushing bugs. A new version fixing some edge cases in the restore process can be expected next week!

This blog
\ This year, I was fortunate to receive funding for my work on open source projects in the Cashu ecosystem. I am very grateful for the trust from
npub17xvf49kht23cddxgw92rvfktkd3vqvjgkgsdexh9847wl0927tqsrhc9as
and
npub10pensatlcfwktnvjjw2dtem38n6rvw8g6fv73h84cuacxn4c28eqyfn34f
this means a lot to me, to be able to make a living by working on something I am passionate about is a blessing, and I don't think it would be possible without the support from you. My deepest gratitude, I hope my contributions will not only match, but exceed expectations.
By writing this blog, I want to show my progress, proof of work, and give people a look into the daily life in the squirrels den 🐿️🐿️🐿️🐿️🐿️🐿️
If you have any questions or suggestions about this blog, please let me know in a comment!
Best,
Gandlaf
-
 @ a10260a2:caa23e3e
2025-01-18 12:04:41
@ a10260a2:caa23e3e
2025-01-18 12:04:41Last Updated: January 18, 2025
First off, big shoutout to Coinos for having support for adding a memo to BOLT12 offers. This provides a solid alternative for the pleb who wants to support mining decentralization but doesn’t want to set up a CLN node and pay thousands of sats for a channel only to get little rewards. This is the case for most of us who only have a miner or two (e.g. a Bitaxe and/or an S9).
Before we get into setting up Lightning payouts, you’ll want to have your miner configured to mine with OCEAN of course. You’ll also want to make sure that the bitcoin address you use is from a wallet that supports signing messages.
These are the ones listed in the OCEAN docs:
- Bitcoin Knots/Bitcoin Core
- Coldcard
- Electrum
- LND (Command Line)
- Seedsigner
- Sparrow
- Specter
- Trezor
I checked one of my favorite, user-friendly wallets — Blue Wallet — and it happens to support signing messages as well.
Just tap the three dots on the upper right and you’ll see the “Sign/Verify Message” button at the bottom.
Update [January 18]: You can now use Coinos to sign by going to https://coinos.io/sign
The trick here is to not refresh the page. In other words, when you're logged in to your Coinos account, go to the URL and use the legacy address (starts with a "1") that's displayed to configure your miner(s). If you refresh the page, you're going to get a new address which will cause the signing to fail later on. Remember, keep the tab open and don't refresh the page.

Whichever wallet you choose, generate a receive address to use when configuring your miner (it’ll also be your OCEAN username).
Here’s how it looks on the Bitaxe (AxeOS)…
And the Antminer S9 (Braiins OS).
NOTE: There’s a slight difference in the URL format between the two apps. Other than that, the username will be your bitcoin address followed by the optional “.” + the nickname for your machine.
You can find more details on OCEAN’s get started page.
Alright, now that your miner is pointed at OCEAN. Let’s configure Lightning payouts!
Generating the BOLT12 Offer
In the Coinos app, go to Receive > Bolt 12.
Tap “Set memo” and set it to “OCEAN Payouts for [insert your bitcoin address]” (this text is case-sensitive). Use the same bitcoin address you used above to configure your miner(s).
After tapping OK, copy the BOLT12 offer (it should start with “lno”) and proceed to the next step.
Generating the Configuration Message
Navigate to the My Stats page by searching for your OCEAN Bitcoin address.
The click the Configuration link next to Next Block to access the configuration form.
Paste the BOLT12 offer here, update the block height to latest, click GENERATE, and copy the generated unsigned message.
Signing the Configuration Message
To sign the generated message, go back to Blue Wallet and use the signing function. Paste the configuration message in the Message field, tap Sign, and copy the signed message that’s generated.
If you're using Coinos to sign, return to the page that you kept open (and didn't refresh) and do the same. Paste the configuration message, click submit, and copy the signed message.
Submitting the Signed Message
Once signed, copy the signature, paste it in the OCEAN configuration form, and click CONFIRM.
If all goes well, you should see a confirmation that the configuration was successful. Congrats! 🎉
All you gotta do now is sit back, relax, and wait for a block to be found…
Or you can look into setting up DATUM. 😎
-
 @ 6d43b512:17ccbfe1
2025-01-18 11:46:03
@ 6d43b512:17ccbfe1
2025-01-18 11:46:03nostr #nostr_writer #review #beginner #obsidian #anytype #contract_drafting #agreenent_drafting #lawyer #law #contract #agreement #learn #education #plugin #telegram #wordpress #yakihonne #primal #damus
I write about and teach contract drafting. I use Obsidian as my primary software for doing research and to store my thoughts, draft lessons, future ideas, etc.
While shifting from Wordpress I wanted to choose a tool and platform that can help me leave the paywalled platforms, and the need to pay for server space, domain, etc.
I found the freedom NOSTR.COM and in Obsidian Plugin Nostr Writer by James.
I opened an account on NOSTR.COM and wrote my first article in Obsidian and pushed (published through #Nostr_relays. You can find some on https://legacy.nostr.watch/relays/find ) it with the help of Plugin Nostr Writer, and you can simply access my blog posts by looking for them using a #nostr_client, if you also open a free Nostr account (a set of public and private keys).
A thought came to me just now. Can I also link my Nostr articles (that is saved as obsidian note), if I link it here. So trying that now.
[[My honest take on Nostr]]
To be on a safer side I also link the Nostr ID for above post here.
https://primal.net//e/note198msk03wj9jfp904k50evlret6laurqhgxzrk2mq9kuq0v0ggh0sx879fv
-
 @ 8781fe5d:4900ffa8
2025-01-18 09:29:05
@ 8781fe5d:4900ffa8
2025-01-18 09:29:05Episode 1 : La genèse
Octobre 2023, on sort à peine de l’explosion de $Pepe sur Ethereum qui est un peu la consécration de la culture meme avec grand papa PePe la grenouille 🔥
L’idée d’un projet de memecoin “story telling” était déjà présente mais surtout , je voulais montrer au monde qu’une vague de memecoins de type jeu décentralisé où chaque participant reçois un AirDrop et peut jouer à trader à son niveau était en train de démarrer et attirait déjà beaucoup de monde !
Pepe
Le choix d’une story à partir de PePe était réfléchit car je voulais être le premier sur RGB avec un PePe qui ne soit pas un scam ,pour changer 🤗😂
Je voulais être sur bitcoin , les Ordinals battaient leur plein et je cherchais comment fiée des smer contracts de type ETH sur Bitcoin 🔥 Dans ma recherche, je découvre le projet RGB qui semble correspondre parfaitement au besoin : un protocole indépendant, des smart contracts , privé et hors chain s’appuyant sur bitcoin ou liquid 👀
Étude , tests de la tech, tests avec l’unique wallet à l’époque : Bitmask de Diba.
C’est parti
Je crée un contrat RGB20 ( format pour les shitcoins) avec 21 millions de “PePeRGB” ! Je crée ensuite un modèle 3D , réalisé un site web minimaliste avec la story et quelques images .
J’écris un article expliquant le projet avec tutorial étape par étape pourr obtenir du PePeRGB contre quelques sats pour payer la Tx.
Jusque là, mon petit projet se déroule normalement : tout le monde s’en fou royalement 😱😂😂
À part @grittoshi et @swisscryptocat qui sont constamment les deux qui avaient déjà testé avant moi 🙏✊🏻😂🔥 (Retenez bien les @ car ils ont chacun un shitcoin sur Liquid ! Ils sont avec nous et nous avançons tous ensembles 🤗🤗)
ni hao
C’est alors qu’un étudiant chercheur chinois @DaPangDun me contacte en me disant qu’il étudie RGB et que des groupes WeChat se sont formés sur le sujet avec pas mal de monde . Il veut faire un post sur mon projet mais il veut participer ! Deal 🙏🔥
Bonne idée : le post est superbe et tout ce joli monde part en FOMO et veut du $pprgb !
J’étais pas prêt 😱
Gérer une communauté de 30000 personnes en fomo dans les 5 heures ne se fait pas comme cela !!
professionnel
Heureusement, j’ai de l’expérience de startup, de crypto, de projets 🙏
Création de whitelist , animation du groupe sur Twitter, création du groupe telegram avec gestion du mandarin ( je ne parle pas ). Tout s’organise plutôt bien en deux jours ( mémorables 30 heures intenses !)
Liquid
Deux mois de tests , de crash, de communauté qui post “wen boss” 32715 fois par jour , je prends une décision forte car la commu va s’essouffler et partir ur Solana qui commence à bien gonfler sur les memecoins !
Je fais un poll sur Twitter : Voulez vous : À- Attendre RGB sans token ? B- Avoir un AirDrop PPRGB liquid network et jouer demain avec ?
Résultat : 82% pour A 😂😂😂
À suivre …. 👀
-
 @ 42342239:1d80db24
2025-01-18 08:31:05
@ 42342239:1d80db24
2025-01-18 08:31:05Preparedness is a hot topic these days. In Europe, Poland has recently introduced compulsory lessons in weapons handling for schoolchildren for war-preparedness purposes. In Sweden, the Swedish Civil Contingencies Agency (MSB) has recently published the brochure on what to do "If crisis or war comes".
However, in the event of war, a country must have a robust energy infrastructure. Sweden does not seem to have this, at least judging by the recent years' electricity price turbulence in southern Sweden. Nor does Germany. The vulnerabilities are many and serious. It's hard not to be reminded of a Swedish prime minister who, just eleven years ago, saw defense as a special interest.
A secure food supply is another crucial factor for a country's resilience. This is something that Sweden lacks. In the early 1990s, nearly 75 percent of the country's food was produced domestically. Today, half of it must be imported. This makes our country more vulnerable to crises and disruptions. Despite our extensive agricultural areas, we are not even self-sufficient in basic commodities like potatoes, which is remarkable.
The government's signing of the Kunming-Montreal Framework for Biological Diversity two years ago risks exacerbating the situation. According to the framework, countries must significantly increase their protected areas over the coming years. The goal is to protect biological diversity. By 2030, at least 30% of all areas, on land and at sea, must be conserved. Sweden, which currently conserves around 15%, must identify large areas to be protected over the coming years. With shrinking fields, we risk getting less wheat, fewer potatoes, and less rapeseed. It's uncertain whether technological advancements can compensate for this, especially when the amount of pesticides and industrial fertilizers must be reduced significantly.
In Danish documents on the "roadmap for sustainable development" of the food system, the possibility of redistributing agricultural land (land distribution reforms) and agreements on financing for restoring cultivated land to wetlands (the restoration of cultivated, carbon-rich soils) are discussed. One cannot avoid the impression that the cultivated areas need to be reduced, in some cases significantly.
The green transition has been a priority on the political agenda in recent years, with the goal of reducing carbon emissions and increasing biological diversity. However, it has become clear that the transition risks having consequences for our preparedness.
One example is the debate about wind power. On the one hand, wind power is said to contribute to reducing carbon emissions and increasing renewable energy. On the other hand, it is said to pose a security risk, as wind turbines can affect radio communication and radar surveillance.
Of course, it's easy to be in favor of biological diversity, but what do we do if this goal comes into conflict with the needs of a robust societal preparedness? Then we are faced with a difficult prioritization. Should we put the safety of people and society before the protection of nature, or vice versa?
“Politics is not the art of the possible. It consists in choosing between the disastrous and the unpalatable” said J. K. Galbraith, one of the most influential economists of the 20th century. Maybe we can’t both eat the cake and have it too?
-
 @ fbf0e434:e1be6a39
2025-01-18 07:13:31
@ fbf0e434:e1be6a39
2025-01-18 07:13:31Hackathon 摘要
Ideahacker's Guide to IBC 是一场Interchain创意竞赛,旨在鼓励创新的跨链概念。此次活动注册了136个项目,吸引了319名开发者和非技术人员参与。与传统的Hackathon不同,这场创意竞赛要求参与者提交概念性想法,而非代码或产品原型,从而降低了参与门槛,鼓励了更广泛的参与。
创意竞赛发放了3万美元奖池的ATOM代币,以及一趟伊斯坦布尔的全程免费旅行,以奖励最具影响力的想法。项目从五个赛道中选出,并由Interchain Foundation和Osmosis Labs的行业领袖评审。
此次活动旨在展示跨链通信协议(IBC)的应用。参与者利用IBC Idea Builder开发并提交他们的提案,这些提案展示了诸如跨链账户、跨链NFT转移和数据查询等IBC功能。Interchain Foundation赞助了此次活动,以促进在区块链应用中对IBC协议的理解和使用,通过Discord等平台为社区提供资源和支持。
Hackathon获奖者
Chain Abstraction奖项获奖者
- Interchain Lending Market:一个去中心化的跨区块链稳定币借贷应用,利用IBC进行收益优化和通过DAO进行治理。
- Interchain Rights Broker:通过Story Protocol自动化许可和支付,在支持IBC的区块链上促进NFT许可。
- MetaKey: Seamless Interchain Wallet Abstraction:提供跨链钱包管理的统一接口,通过IBC增强互操作性和交易效率。
- DeathFi:使用IBC进行遗产数字资产管理的协议,包含去中心化遗嘱和NFT纪念。
- TransChain-Health:一个结合区块链和物联网的去中心化健康监测系统,提供数据透明性和分析。
Solana奖项获奖者
- TriAd:一个利用IBC和Solana进行高效广告管理的跨链广告交换平台。
- DAPM:跨区块链管理共享资本池,加强治理和财库功能,运用IBC。
- Solana-Sovereign Identity Protocol (SIP):使用IBC简化跨链身份管理,确保去中心化身份的安全。
- IBCCraft Game:一个类似Minecraft的游戏,使用IBC进行跨链任务并奖励Solana。
- Privvy Protocol:通过IBC为跨链交易提供隐私管理,实现隐匿地址和私人交易。
Intents & Incentives奖项获奖者
- InterXecute:结合AI和IBC提升跨链交易,专注于低成本和高效路径。
- Cross-Chain Proposerless Block Building Mechanism for Relays in IBC Protocol:引入无提案者区块构建以优化IBC协议效率和成本。
- IBC + Solver Network:通过一个IBC求解器网络,加强以意图为中心的解决方案的跨链交易。
- Intents Bridge for IBC:使用以意图为驱动的方法和去中心化结算,提高交易速度和流动性。
- Creating a Crosschain DID on IBC:一个结合IBC和零知识证明的跨链身份证明系统,提供安全的身份管理。
DeFi Apps奖项获奖者
- Vector Protocol:通过智能合约和IBC管理互链债务,以提升成本效率和风险管理。
- InterChain Asset Streaming Protocol (XASP):利用IBC实现跨链的实时资产流传和投资组合管理。
- SwapGuard:为Cosmos提供MEV保护的全面DeFi交易解决方案。
- BlocPayroll:利用IBC简化国际薪酬流程,提供安全的加密薪酬解决方案。
- Cross-Chain XTF (DeX Traded Fund):利用IBC促进跨链投资,改善投资组合管理和成本效率。
Wild Card奖项获奖者
- cross chain:利用IBC进行统一的跨链资产管理和奖励分配的Staking聚合器。
- Cryptocurrency Debit Card Infrastructure:通过借记卡支持加密到法币交易,利用IBC实现无缝转换。
- HTTPi:一个利用IBC进行客户端与服务器间去中心化数据交换的安全协议。
- IBC Lens (Data Visualizer for Celestia and Rollups using IBC):提供IBC生态系统中跨链交互的实时可视化。
- Realm:一个利用IBC进行多区块链奖励管理的跨链赏金平台。
欲获得完整项目列表及更多详细信息,请访问Ideahacker's Guide to IBC Ideathon。
关于组织者
Interchain Foundation
Interchain Foundation专注于开发和支持称为互链的可互操作区块链网络生态系统。该组织促进区块链行业内的合作与创新,重视多链通信和可扩展性。通过其技术专长和领导力,基金会支持推动去中心化网络互操作性的各项倡议。它致力于创造一个无缝连接的区块链未来,并鼓励行业参与以推动多链生态系统的发展。
-
 @ ed84ce10:cccf4c2a
2025-01-18 07:06:31
@ ed84ce10:cccf4c2a
2025-01-18 07:06:31Hackathon Summary
The Ideahacker's Guide to IBC was an interchain ideathon designed to encourage innovative cross-chain concepts. This event saw the registration of 136 projects and participation from 319 developers and non-technical contributors. Unlike traditional hackathons, this ideathon required participants to submit conceptual ideas instead of code or product prototypes, which encouraged broader participation due to its lower entry barrier.
The ideathon distributed a $30,000 prize pool in ATOM tokens, along with an all-expenses-paid trip to Istanbul, to reward the most impactful ideas. Projects were selected from five tracks and judged by industry leaders from the Interchain Foundation and Osmosis Labs.
The event aimed to demonstrate the applications of the Inter-Blockchain Communication Protocol (IBC). Participants utilized the IBC Idea Builder to develop and submit their proposals, which showcased IBC features like interchain accounts, cross-chain NFT transfers, and data queries. The Interchain Foundation sponsored the event to promote understanding and use of the IBC protocol across blockchain applications, engaging the community with resources and support through platforms like Discord.
Hackathon Winners
Chain Abstraction Prize Winners
- Interchain Lending Market: A decentralized application for stablecoin lending across blockchains, leveraging IBC for yield optimization and governance via DAOs.
- Interchain Rights Broker: Facilitates NFT licensing across IBC-enabled blockchains with automated licensing and payments through Story Protocol.
- MetaKey: Seamless Interchain Wallet Abstraction: Offers a unified interface for cross-chain wallet management, enhancing interoperability and transaction efficiency via IBC.
- DeathFi: A protocol for posthumous digital asset management using IBC, featuring decentralized wills and NFT memorials.
- TransChain-Health: A decentralized health monitoring system integrating blockchain and IoT for data transparency and analysis.
Solana Prize Winners
- TriAd: A cross-chain ad exchange platform utilizing IBC and Solana for efficient ad management.
- DAPM: Manages shared capital pools across blockchains, enhancing governance and treasury functions with IBC.
- Solana- Sovereign Identity Protocol (SIP): Simplifies cross-chain identity management with IBC for secure decentralized identity.
- IBCCraft Game: A Minecraft-like game using IBC for cross-chain quests and Solana rewards.
- Privvy Protocol: Facilitates privacy management for cross-chain transactions via IBC, enabling stealth addresses and private transactions.
Intents & Incentives Prize Winners
- InterXecute: Enhances cross-chain transactions with AI and IBC, focusing on low-cost, efficient routing.
- Cross-Chain Proposerless Block Building Mechanism for Relays in IBC Protocol: Introduces proposerless block building to optimize IBC protocol efficiency and cost.
- IBC + Solver Network: Strengthens cross-chain transactions with intent-centric solutions supported by an IBC solver network.
- Intents Bridge for IBC: Boosts transaction speed and liquidity using an intent-driven approach and decentralized settlement.
- Creating a Crosschain DID on IBC: A cross-chain proof of identity system integrating IBC and zero-knowledge proofs for secure identity management.
DeFi Apps Prize Winners
- Vector Protocol: Manages interchain debt with smart contracts and IBC for cost efficiency and risk management.
- InterChain Asset Streaming Protocol (XASP): Enables real-time asset streaming and portfolio management across chains utilizing IBC.
- SwapGuard: Provides protection against MEV in Cosmos with a comprehensive DeFi trading solution.
- BlocPayroll: Simplifies international payroll processes using IBC, offering secure crypto payroll solutions.
- Cross-Chain XTF (DeX Traded Fund): Facilitates cross-chain investment with IBC, improving portfolio management and cost efficiency.
Wild Card Prize Winners
- cross chain: A staking aggregator using IBC for unified cross-chain asset management and reward distribution.
- Cryptocurrency Debit Card Infrastructure: Supports crypto-to-fiat transactions via debit cards, leveraging IBC for seamless conversions.
- HTTPi: A secure protocol employing IBC for decentralized data exchange between clients and servers.
- IBC Lens (Data Visualizer for Celestia and Rollups using IBC): Provides real-time visualization of cross-chain interactions in the IBC ecosystem.
- Realm: A cross-chain bounty platform utilizing IBC to manage multi-blockchain rewards for content creators.
For a comprehensive list of all projects and more detailed information, visit the Ideahacker's Guide to IBC Ideathon.
About the Organizer
Interchain Foundation
The Interchain Foundation is focused on developing and supporting the ecosystem of interoperable blockchain networks known as the interchain. The organization promotes collaboration and innovation within the blockchain industry, with an emphasis on multichain communication and scalability. Through its technical expertise and leadership, the foundation supports initiatives that drive interoperability across decentralized networks. It is committed to creating a seamless interconnected blockchain future and encourages industry involvement to advance the multichain ecosystem.
-
 @ f9cf4e94:96abc355
2025-01-18 06:09:50
@ f9cf4e94:96abc355
2025-01-18 06:09:50Para esse exemplo iremos usar: | Nome | Imagem | Descrição | | --------------- | ------------------------------------------------------------ | ------------------------------------------------------------ | | Raspberry PI B+ |
 | Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |
| Cortex-A53 (ARMv8) 64-bit a 1.4GHz e 1 GB de SDRAM LPDDR2, |
| Pen drive |  | 16Gb |
| 16Gb |Recomendo que use o Ubuntu Server para essa instalação. Você pode baixar o Ubuntu para Raspberry Pi aqui. O passo a passo para a instalação do Ubuntu no Raspberry Pi está disponível aqui. Não instale um desktop (como xubuntu, lubuntu, xfce, etc.).
Passo 1: Atualizar o Sistema 🖥️
Primeiro, atualize seu sistema e instale o Tor:
bash apt update apt install tor
Passo 2: Criar o Arquivo de Serviço
nrs.service🔧Crie o arquivo de serviço que vai gerenciar o servidor Nostr. Você pode fazer isso com o seguinte conteúdo:
```unit [Unit] Description=Nostr Relay Server Service After=network.target
[Service] Type=simple WorkingDirectory=/opt/nrs ExecStart=/opt/nrs/nrs-arm64 Restart=on-failure
[Install] WantedBy=multi-user.target ```
Passo 3: Baixar o Binário do Nostr 🚀
Baixe o binário mais recente do Nostr aqui no GitHub.
Passo 4: Criar as Pastas Necessárias 📂
Agora, crie as pastas para o aplicativo e o pendrive:
bash mkdir -p /opt/nrs /mnt/edriver
Passo 5: Listar os Dispositivos Conectados 🔌
Para saber qual dispositivo você vai usar, liste todos os dispositivos conectados:
bash lsblk
Passo 6: Formatando o Pendrive 💾
Escolha o pendrive correto (por exemplo,
/dev/sda) e formate-o:bash mkfs.vfat /dev/sda
Passo 7: Montar o Pendrive 💻
Monte o pendrive na pasta
/mnt/edriver:bash mount /dev/sda /mnt/edriver
Passo 8: Verificar UUID dos Dispositivos 📋
Para garantir que o sistema monte o pendrive automaticamente, liste os UUID dos dispositivos conectados:
bash blkid
Passo 9: Alterar o
fstabpara Montar o Pendrive Automáticamente 📝Abra o arquivo
/etc/fstabe adicione uma linha para o pendrive, com o UUID que você obteve no passo anterior. A linha deve ficar assim:fstab UUID=9c9008f8-f852 /mnt/edriver vfat defaults 0 0
Passo 10: Copiar o Binário para a Pasta Correta 📥
Agora, copie o binário baixado para a pasta
/opt/nrs:bash cp nrs-arm64 /opt/nrs
Passo 11: Criar o Arquivo de Configuração 🛠️
Crie o arquivo de configuração com o seguinte conteúdo e salve-o em
/opt/nrs/config.yaml:yaml app_env: production info: name: Nostr Relay Server description: Nostr Relay Server pub_key: "" contact: "" url: http://localhost:3334 icon: https://external-content.duckduckgo.com/iu/?u= https://public.bnbstatic.com/image/cms/crawler/COINCU_NEWS/image-495-1024x569.png base_path: /mnt/edriver negentropy: true
Passo 12: Copiar o Serviço para o Diretório de Systemd ⚙️
Agora, copie o arquivo
nrs.servicepara o diretório/etc/systemd/system/:bash cp nrs.service /etc/systemd/system/Recarregue os serviços e inicie o serviço
nrs:bash systemctl daemon-reload systemctl enable --now nrs.service
Passo 13: Configurar o Tor 🌐
Abra o arquivo de configuração do Tor
/var/lib/tor/torrce adicione a seguinte linha:torrc HiddenServiceDir /var/lib/tor/nostr_server/ HiddenServicePort 80 127.0.0.1:3334
Passo 14: Habilitar e Iniciar o Tor 🧅
Agora, ative e inicie o serviço Tor:
bash systemctl enable --now tor.serviceO Tor irá gerar um endereço
.onionpara o seu servidor Nostr. Você pode encontrá-lo no arquivo/var/lib/tor/nostr_server/hostname.
Observações ⚠️
- Com essa configuração, os dados serão salvos no pendrive, enquanto o binário ficará no cartão SD do Raspberry Pi.
- O endereço
.oniondo seu servidor Nostr será algo como:ws://y3t5t5wgwjif<exemplo>h42zy7ih6iwbyd.onion.
Agora, seu servidor Nostr deve estar configurado e funcionando com Tor! 🥳
Se este artigo e as informações aqui contidas forem úteis para você, convidamos a considerar uma doação ao autor como forma de reconhecimento e incentivo à produção de novos conteúdos.
-
 @ a012dc82:6458a70d
2025-01-18 02:33:24
@ a012dc82:6458a70d
2025-01-18 02:33:24Over the past decade, the cryptocurrency landscape has witnessed unprecedented growth, with Bitcoin undeniably at its forefront. As the trailblazer of digital currencies, Bitcoin has not only introduced the world to the possibilities of decentralized finance but has also inspired the creation of thousands of other cryptocurrencies. Yet, among the myriad of developments in the crypto domain, the advent of Bitcoin ETFs (Exchange Traded Funds) stands out. These innovative financial instruments have not only revolutionized how investors perceive and interact with Bitcoin but have also provided a bridge between the volatile world of cryptocurrencies and the more stable, regulated realm of traditional finance.
Table Of Content
-
What is a Bitcoin ETF?
-
Why are Bitcoin ETFs Important?
-
The Current Landscape of Bitcoin ETFs
-
How to Invest in a Bitcoin ETF
-
Conclusion
-
FAQs
What is a Bitcoin ETF?
At its core, a Bitcoin ETF is a financial instrument designed to track the price movements of Bitcoin. Rather than diving into the intricate world of cryptocurrencies—buying Bitcoin directly, grappling with the nuances of digital wallets, or navigating the often complex landscape of crypto exchanges—investors can now simply purchase shares of a Bitcoin ETF. These shares are traded just like any other stock on traditional stock exchanges, offering a seamless integration of Bitcoin into conventional investment portfolios.
Why are Bitcoin ETFs Important?
Accessibility: One of the primary advantages of Bitcoin ETFs is their accessibility. They open the doors for everyday investors, even those unfamiliar with the intricacies of the crypto world, to gain exposure to Bitcoin. There's no need to delve into the technical aspects of purchasing, storing, or securing the cryptocurrency—Bitcoin ETFs simplify the entire process.
Regulation: Being listed and traded on recognized stock exchanges means that Bitcoin ETFs come under the purview of financial regulators. This regulatory oversight ensures a degree of transparency and protection for investors, something that's often amiss in the wild west of direct cryptocurrency investments.
Diversification: For seasoned investors and newcomers alike, diversification is a cornerstone of a robust investment strategy. Bitcoin ETFs offer a golden opportunity to tap into the burgeoning cryptocurrency market without the direct volatility and risks tied to holding the actual digital assets.
The Current Landscape of Bitcoin ETFs
The concept of a Bitcoin ETF isn't new. However, its journey to mainstream acceptance has been riddled with regulatory challenges. Many countries, initially hesitant, have taken a cautious approach, leading to delays in the adoption of Bitcoin ETFs. But as the broader financial community becomes more attuned to the potential benefits (and risks) of cryptocurrencies, we're witnessing a gradual shift. Regulators are now more open, and approvals for Bitcoin ETFs in major financial markets are on the rise. This evolving landscape has sparked renewed interest, with both institutional and retail investors keenly exploring these novel investment avenues.
How to Invest in a Bitcoin ETF
The process of investing in a Bitcoin ETF mirrors that of any other traditional investment vehicle. Here's an elaborated guide:
Research: Embarking on any investment journey necessitates thorough research. It's imperative to delve deep, understand the nuances, and compare the various Bitcoin ETFs available in the market. Look into their past performance, management strategies, and fee structures.
Choose a Brokerage: Once you've zeroed in on a Bitcoin ETF that aligns with your investment goals, the next step is to select a suitable brokerage. Opt for one that offers your chosen Bitcoin ETF and boasts a reputation for reliability and security.
Buy Shares: With your brokerage account set up, you're all set to make your purchase. Navigate to the trading platform, search for your chosen Bitcoin ETF, decide on the number of shares you wish to buy, and execute the trade. It's as simple as buying shares of any other company.
Conclusion
The emergence of Bitcoin ETFs signifies a monumental shift in the financial world. It's a testament to the growing acceptance of cryptocurrencies and their potential to coexist with traditional financial instruments. As the crypto ecosystem continues to evolve, mature, and gain broader acceptance, the allure of Bitcoin ETFs is set to grow. For investors, this evolution offers a unique vantage point—a chance to be at the intersection of time-tested financial principles and the dynamic world of digital currencies.
FAQs
What is a Bitcoin ETF? A Bitcoin ETF is a financial instrument that tracks the price of Bitcoin, allowing investors to buy its shares on traditional stock exchanges.
Why choose a Bitcoin ETF over direct Bitcoin investment? Bitcoin ETFs offer easier accessibility, regulatory oversight, and a way to diversify investments without dealing with the complexities of direct cryptocurrency handling.
Are Bitcoin ETFs regulated? Yes, Bitcoin ETFs traded on established stock exchanges are subject to regulatory oversight, providing added protection for investors.
How do I invest in a Bitcoin ETF? Start with research, choose a reputable brokerage that offers the Bitcoin ETF you're interested in, and then purchase its shares like you would with any other stock.
Are Bitcoin ETFs a safer investment than Bitcoin? While no investment is risk-free, Bitcoin ETFs offer a layer of protection due to regulatory oversight and eliminate the risks associated with direct handling and storage of cryptocurrencies.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
X: @croxroadnews
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 6be5cc06:5259daf0
2025-01-18 02:11:43
@ 6be5cc06:5259daf0
2025-01-18 02:11:43- Not your keys, not your coins
Se você não tem as chaves privadas do seu Bitcoin, ele não é realmente seu. Deixar seus BTCs em exchanges ou carteiras controladas por terceiros significa confiar neles e assumir o risco de perder seus fundos.
- HODL - Não venda
O Bitcoin é uma reserva de valor a longo prazo e potencialmente o dinheiro do futuro. Não se desespere com as flutuações de preço; mantenha seus BTCs, pois o histórico se mostra favorável.
- Stay humble - Não saia falando que você tem BTC
Manter discrição sobre seu patrimônio é uma questão de segurança e humildade. Falar demais pode atrair curiosos, oportunistas ou outras ameaças.
- Don't trust, verify
No Bitcoin, confie no protocolo, não em pessoas. Sempre que possível, verifique por conta própria, seja transações, códigos ou informações.
- Reject altcoins
As altcoins podem parecer promissoras, mas frequentemente são distrações ou apostas arriscadas. Foque no Bitcoin, que já provou ser sólido e resistente.
- Stack sats - DCA
Empilhe satoshis consistentemente, utilizando a estratégia de DCA (Dollar Cost Averaging), comprando regularmente independentemente do preço. Isso reduz o risco de tentar "acertar o mercado".
- Reject the ego
Não aposte contra o Bitcoin. Aqueles que subestimaram sua força ou estabilidade, perderam.
- Keep learning
Nunca pare de estudar sobre Bitcoin, economia e a tecnologia por trás dele. Quanto mais você entende, mais confiança terá em sua decisão.
- Help beginners
O Bitcoin pode ser complicado para quem está começando. Compartilhe seus conhecimentos com paciência para fortalecer a comunidade.
- Don't push it
Cada pessoa tem seu próprio tempo para entender e entrar no mundo do Bitcoin. Forçar alguém pode ser contraproducente; dê direcionamento e deixe o tempo agir.
-
 @ 378562cd:a6fc6773
2025-01-18 00:12:47
@ 378562cd:a6fc6773
2025-01-18 00:12:47In the ever-changing world of decentralized networks, Nostr (Notes and Other Stuff Transmitted by Relays) is leading the charge. Its lightweight, open design has created an ecosystem that’s as adaptable as it is revolutionary. Whether you're chatting, publishing, or experimenting with new ways to connect, Nostr provides the foundation for a truly decentralized and censorship-resistant internet.
How Nostr Works: A Quick Overview
At its heart, Nostr is built on simplicity and decentralization. Here’s a breakdown of its core components:
-
Public and Private Keys:\ Your public key acts as your identity, and private keys ensure your messages are securely signed.
-
Relays:\ Relays are decentralized servers that distribute messages. They don’t own your data but simply pass it along to those who request it.
-
Clients:\ Clients are the user-facing applications where you interact with Nostr, offering diverse features and designs.
Deep Dive: Events in Nostr
Everything on Nostr revolves around events, which are cryptographically signed pieces of information containing various kinds of data. Here are the types of events currently supported and their use cases:
1. Note Events (Type 1)
- What They Are:\ These are the bread and butter of Nostr—text-based posts, much like tweets or status updates on traditional platforms.
- Features:
- Can include text, media links, and hashtags.
- Interact with others through likes, replies, and boosts (reposts).
- Use Cases:\ Perfect for microblogging, status updates, and general social interaction.
2. Profile Metadata Events (Type 0)
- What They Are:\ This event type stores and updates user profile information, such as your display name, bio, profile picture, and website.
- Features:
- Easily editable and updated across all Nostr clients.
- Keeps your identity consistent across platforms.
- Use Cases:\ Makes profile portability seamless—update once, and it reflects everywhere.
3. Relay List Events (Type 2)
- What They Are:\ These events store a list of relays that a user is connected to or prefers to use.
- Features:
- Share your relay preferences across devices or clients.
- Allows automatic relay connection in supported clients.
- Use Cases:\ Simplifies the onboarding process for users switching clients or devices.
4. Direct Message Events (Type 4)
- What They Are:\ End-to-end encrypted messages sent directly between two users.
- Features:
- Only readable by the intended recipient.
- Supports text and basic formatting.
- Use Cases:\ Secure communication for personal or professional purposes.
5. Reaction Events (Type 7)
- What They Are:\ Events that express reactions to other events, such as likes or emojis.
- Features:
- Provides social feedback (e.g., showing appreciation for a post).
- Lightweight and simple to implement.
- Use Cases:\ Enhances engagement and interaction within the network.
6. Repost Events (Type 6)
- What They Are:\ Events that allow users to reshare content, similar to retweets on Twitter.
- Features:
- Ensures the original poster retains credit.
- Enables broader content visibility.
- Use Cases:\ Amplifying content that resonates with users or is worth sharing.
7. Custom Event Types (Beyond Type 7)
- What They Are:\ Developers can create and define custom event types for specific applications.
- Features:
- Flexibility to introduce entirely new functionality.
- Supported based on client and relay compatibility.
- Use Cases:\ Enables innovation, from collaborative editing tools to advanced publishing workflows.
What Makes Events Special?
- Portability: Events follow your public key, not the client or relay, ensuring they’re available wherever you go.
- Interoperability: All events are standardized, meaning any Nostr client can understand and process them.
- Extensibility: Through custom event types, the protocol encourages experimentation and development.
Primal: A Favorite Client for Engaging Events
Among the many clients, Primal stands out as a favorite for how it handles Nostr events. Its emphasis on content discovery and rich user interaction makes it an excellent choice for exploring everything the protocol offers. Whether it’s crafting note events, managing profile metadata, or diving into direct messaging, Primal delivers a polished experience that feels seamless.
The Future of Nostr Events
As Nostr continues to evolve, so will the events it supports. Imagine event types for live streaming, collaborative workspaces, or even decentralized governance. The possibilities are limitless, driven by the creativity of the developers and the needs of the community.
Have you explored the potential of Nostr events yet? What’s your favorite client or feature? Let’s discuss below! ⚡️
Nostr #Primal #Decentralization #NostrEvents #FutureOfWeb
-
-
 @ f7922a0a:82c34788
2025-01-17 23:06:56
@ f7922a0a:82c34788
2025-01-17 23:06:56Now that the 3rd Satellite Skirmish is complete I wanted to highlight some of the cool features on embrace.satskirmish.com
This is what the cutting edge of podcasting 2.0 looks like imo. Live video in an app that allows you to send sats to the artists in real time.
On the left hand side we have a Boost score borad that displays the total amount of sats that have come in during the show, live Boosts/Booastagrams as they come in, total amount of sats from each person Boosting and total amount sent from each app.
The middle is ovisaly the video of the band playing but with some graphics around it and Boost alerts that show up on the screen in the form of snow flakes for this one.
The righthand side is an IRC chat window that connects to an IRC server that the No Agenda community has used for 18+ years thanks to zoidzero++.

The bottom of the page is where things get cool. When you click the Boost the Crew button in the center you can send a Boost that gets split between everyone helping produce the show (hightlighted in yellow).


Each band also has their own Boost button so you can Boost them while they are playing or anytime you visit the page.


-
 @ ed5774ac:45611c5c
2025-01-17 22:05:36
@ ed5774ac:45611c5c
2025-01-17 22:05:36A good question. I do not think so. I will explain below why, but first where did this question come from?
The statement that Tether is a Bitcoin company was recently made by Samson Mow in X (here) in a response to Paolo Ardoino’s initial Tweet about Tether’s $775 million investment on Rumble (here).

In response to Samson Mow's statement, I expressed my disagreement by pointing out that Tether prints USDT “out of thin air” and uses these funds to purchase US Treasuries, which in effect helps finance US debt and fund military operations.
In my opinion, a bitcoin company should not provide life support to the current broken financial system that is built on the US dollar's status as a global reserve currency, allowing a small group of Western elites to control the system and exploit it for wealth transfer.
“The root problem with conventional currency is all the trust that’s required to make it work. The central bank must be trusted not to debase the currency, but the history of fiat currencies is full of breaches of that trust.”(Satoshi Nakamoto, Bitcoin: A Peer-to-Peer Electronic Cash System)
I believe that the primary purpose of bitcoin is to replace the current fraudulent system, not to support it. My assessment is based on this fundamental principle, and I therefore disagree with Samson’s statement. In short, Tether does not align with bitcoin’s purpose of existence, a point to which I will return later.
First, it is necessary to clarify the logic behind my “Tether prints USDT out of thin air” statement as Samson Mow shifted the focus of conversation merely to this specific point instead of clarifying how he considers Tether as a bitcoin company in light of its actions (i.e., financing US debt and thereby funding the US war machine).

My next tweet aimed to highlight the trust concerns inherent in Proof of Stake, a concept that should be familiar to Samson Mow, where ETH holders validate transactions by staking their holdings, creating a system that relies on the implicit trustworthiness of these validators.
In response to my reasoning and explanation, Samson initially claimed that Tether is not proof of stake. Next, in a subsequent tweet where I asked for clarification on whether Tether is on the Ethereum blockchain, he acknowledged this point but introduced a new argument suggesting that Tether's situation has nothing to do with PoS. This claim is, to be frank, disconnected from reality and raises questions about Samson Mow’s true motivations.

Following my discussion with Samson Mow on X, I decided to provide further clarification on the reasoning behind my statement that "Tether prints USDT out of thin air". The underlying logic of this argument can be grasped by examining two crucial factors: Proof of Work (PoW) and debt.
Proof of Work:
A critical examination of Tether's USDT issuance requires a deeper understanding of the PoW.
When individuals exchange their dollars for USDT, they are essentially trading earned value (their time and energy) for a digital representation thereof. However, Tether's issuance of new USDT units occurs without incurring any cost or spending resources, effectively creating digital tokens that represent claims on value rather than value itself.
In stark contrast, the creation of new bitcoins is facilitated through a competitive mining, wherein miners use computational power (spend energy) to validate transactions and create new blocks, thereby earning newly minted bitcoins as a reward for their efforts. Similarly, in gold mining, the discovery of new deposits is the result of the investment of time, energy, and resources by miners. Likewise, individuals who are employees or entrepreneurs invest their time and energy to generate income or profit.
This underscores a fundamental principle: that genuine value creation typically results from tangible efforts, and resource allocations, distinguishing it from mechanisms that generate value without any corresponding expenditures.
Unlike the aforementioned examples, Tether's mechanism for creating USDT operates under a distinctly different paradigm. Tether issues USDT without expending time, energy, or resources. Instead, individuals give Tether their hard-earned money in exchange for an IOU certificate represented by USDT. This is in theory, assuming that Tether is an honest player and only mints USDT when a user transfers corresponding USD. In practice, however, there are several factors that complicate the verification of Tether's claim regarding the backing of USDT with USD.
One issue with Tether operating on Ethereum is that transactions are validated by ETH stakeholders by staking their ETH. This introduces an element of trust in third-party (validators), raising concerns in the integrity of the ledger.
Additionally, in contrast to Bitcoin's blockchain, Proof of Stake blockchains do not have a clear "chain" of hashes linking each block back to its predecessor through a computationally intensive process, since there's no mining involved in creating new blocks (as blocks are proposed by validators based on their stake), thereby preventing verification of historical transaction validity. As a result, the current state of a Proof of Stake blockchain reflects only the validators' confirmation without providing any assurance regarding its historical accuracy or integrity.
Most significantly, there exists no inherent mechanism, as far as I am aware of, preventing Tether from minting additional USDT without corresponding USD backing and transferring to an ETH address under their control and buying real assets (such as bitcoin) with it.
In my opinion, these considerations underscore significant challenges on transparency, accountability and oversight within Tether’s operations. In other words, the entire system relies on the honesty of Tether and Ethereum validators as trusted third parties, which contradicts Bitcoin's fundamental principle that eliminates the need for trusted intermediaries in transactions as described by Satoshi Nakamoto in Bitcoin White Paper. (source: bitcoin white paper)

While Bitcoin's decentralized architecture eliminates the need for intermediaries, Tether as a centralized entity controls the issuance and management of USDT and relies on ETH validators for the validity of transactions. This centralized control enables Tether & Ethereum to unilaterally freeze, blacklist, or manipulate accounts at their discretion, as evidenced by past incidents and potential future actions. Furthermore, USDT holdings are exposed to counterparty risk, as holders are only entitled to redeem their funds if Tether maintains its solvency and adheres to a 100% reserve requirement which are significant question marks as explained in previous paragraphs.
Debt:
Even if the claim that all USDT tokens are fully backed is true, it is essential to recognize that USDT is ultimately backed by fiat currency, which itself is debt —whether in the form of dollars or U.S. Treasuries. Consequently, the statement “Tether prints USDT out of thin air” is not entirely unfounded, as the creation of new USDT tokens is effectively facilitated by the issuance of new debt instruments.
How does USD come to existence? As many bitcoiners know very well, they are simply printed out of thin air by FED. This process is facilitated by the US government's issuance of debt certificates, including short-term Treasury bills and long-term Treasury bonds. The value of these debt instruments is derived from the expectation that the US government will honor its obligations by repaying the indicated amount of USD to certificate holders in the future, primarily through tax revenue collected from its citizens. In essence, these debt certificates represent IOUs and their value is contingent upon the credibility of the US government's promise to fulfill its debt obligations. The entire system relies on a collective belief in the government's creditworthiness, rather than any tangible asset backing it. Even if Tether's USDT is assumed to be backed 1-to-1 with USD, it is ultimately backed by nothing but the US government's fiat currency, which is itself created out of thin air. This highlights the tenuous nature of USDT's backing, as it is predicated on trust in the US government's ability to pay its debt.
In contrast to Bitcoin, which is decentralized money, independent of any third-party liability, holding USDT introduces multiple layers of third-party liability such as:
-
Trust in the integrity of the Ethereum network & in the honesty of ETH stakeholders who validate transactions and maintain the ledger.
-
Trust in Tether's financial stability and solvency, as well as its commitment to honoring its obligations, thereby mitigating the risk of bankruptcy or fraudulent activities.
-
Trust in the creditworthiness of the US government, as the value of USDT is ultimately tied to the value of US Treasury securities held by Tether.
These cumulative risks underscore the significance of third-party liability in the context of USDT ownership.
In conclusion, the statement “Tether prints USDT out of thin air” is based on the fact that USDT is minted by Tether without incurring any cost or spending resources, there is no mechanism to prove that Tether maintains 100% reserves and USDT is ultimately backed by fiat currency, which itself is debt created out of thin air by the FED. Therefore, “Tether prints USDT out of thin air” notion is not entirely unfounded and highlights the tenuous nature of USDT's backing.
Tether finances US debt and war machine by buying US Treasuries:
Having laid out the logic behind my statement that “Tether prints USDT out of thin air,” I will now move on to the main argument underlying my position: namely, that Tether is not a bitcoin company because its acquisition of US debt provides life support to a profoundly corrupt and exploitative financial system, which enables a small cabal of western elites exploit the rest of the world to further enrich themselves. The fundamental purpose of bitcoin is to replace this broken system, not to provide life support to it.
The current financial system:
erodes the purchasing power of working-class individuals through inflation
-
excludes a significant portion of the global population from accessing to financial services
-
preserves ‘the rules-based global order’ (as it is called by the West) that exploits developing nations for the benefit of a privileged few in Western countries
-
concentrates control in the hands of an unscrupulous banking cartel and self-proclaimed elites
At the heart of the existing financial system lies the US dollar's role as a global reserve currency that grants the US government considerable leverage to enforce its economic and geopolitical interests. By controlling USD flows, the US can impose financial sanctions on nations that refuse to comply with its rules and norms.
In instances where financial coercion proves ineffective, the US has historically resorted to alternative measures, including military intervention and covert operations, aimed at bringing disobedient countries into compliance with its policy directives. Historical records are full of examples.
-
[ ] In 1953, the United States and the United Kingdom collaborated to orchestrate a coup d'état in Iran, resulting in the overthrow of the democratically elected government of Prime Minister Mohammad Mossadegh. This action was carried out following Mossadegh's decision to nationalise Iranian oil companies, which were vital to the West's economic interests.
-
[ ] The Central Intelligence Agency (CIA) played a substantial role in supporting a coup against Salvador Allende, the democratically elected President of Chile in 1970, because they were concerned that Allende's policies would lead to a shift towards socialism and potentially even communism, which was seen as a threat to US interests in the region.
-
[ ] Saddam Hussein's decision to transition Iraq's oil transactions from US dollars to euros was a major factor contributing to his downfall. By challenging the existing global financial system, Hussein became a threat to the global financial order and therefore paid the price with his life.
-
[ ] Muammar Gaddafi proposed the establishment of a gold-based currency, known as the gold dinar, intended for use in African oil transactions. This initiative aimed to create a pan-African currency independent of both the US dollar and euro, potentially undermining their influence in regional trade. The perceived threat posed by this proposal to the global financial order has been the main factor to Libya's destabilization and Gaddafi's eventual demise.
-
[ ] The overthrow of Ukraine's democratically elected president in 2014 by a CIA orchestrated a coup d'état, with Victoria Nuland, then-Assistant Secretary of State for European and Eurasian Affairs, playing a key role in the operation. The intervention was motivated by Western corporations’ desire to colonize Russia and use its resources as collateral to prolong the life of the global financial system that has become unsustainable with its current debt levels.
Those interested in understanding the mechanics of the current financial system or learning about the historical crimes committed by West against the Global South are invited to contact me directly. I can provide access to a comprehensive collection of resources that document these issues. However, due to space and time constraints, it is not feasible to elaborate on these topics in detail here.
The statement that Tether is primarily a bitcoin company is entirely unfounded since Tether provides significant support to the current financial system. The US government is currently facing challenges in financing its debt due to decreasing global confidence in its ability to repay its obligations. This is evident in the fact that China has ceased purchasing US debt, while Russia has sold off its entire holdings prior to the Special Military Operation (SMO). Furthermore, private investors are increasingly wary of investing in US debt, citing concerns over its sustainability. Currently, the UK and EU are the only entities actively buying US debt, which, along with the US, are the other two pillars of the existing global financial order. Notably, Tether has emerged as a substantial purchaser of US debt (approximately $100 billion at the time of writing), effectively serving as a vital lifeline for the prolongation of the Western colonial order.
Tether is NOT a bitcoin company. In my opinion, it is fair to say that those who claim that Tether is a bitcoin company are either lacking in critical thinking or have a financial stake that compromises their objectivity.
It is true that it helps bitcoin adoption and by providing liquidity contributes to the upward momentum of bitcoin price. I believe, it is likely that the current price of bitcoin would be significantly lower without Tether's involvement. This raises important questions about the motivations and values of those involved in the bitcoin community who claim that Tether is a bitcoin company. Can their support for Bitcoin be attributed to a sincere interest in advancing the principles of decentralization and sovereignty, or might it be influenced by self-interest and the pursuit of personal wealth? Are there other potential motivations or conflicts of interest at play?
As outlined in this article, I have concerns regarding Tether's alignment with the principles that underpin Bitcoin’s core values. My critique is not intended to be accusatory, but rather to encourage critical evaluation. I acknowledge and appreciate Tether's contribution to bitcoin ecosystem and see their investment in Rumble as a positive development for freedom of speech and recognize Samson's dedication for Bitcoin adoption. However, my appreciation for their efforts does not imply unconditional trust.
The defensive responses of some individuals within the community to my criticisms (without any reasonable counterarguments) have raised questions for me about their potential biases and motivations. While I do not aim to convince those who misinterpret my intentions, I will exercise increased suspicion when engaging with individuals who appear more focused on protecting Tether's interests than upholding the principles of Bitcoin.
In summary, I believe that Tether's role in propping up the current financial system - intentionally or not - underscores the need for skepticism and critical thinking. As global events continue to unfold with unprecedented speed and complexity, it's essential to remember: 'Don't trust, verify!'
-
-
 @ 0403c86a:66d3a378
2025-01-17 19:32:26
@ 0403c86a:66d3a378
2025-01-17 19:32:26The Kansas City Chiefs are set to begin their quest for an unprecedented Super Bowl three-peat on Saturday, facing the Houston Texans in the AFC Divisional Playoffs. Here’s everything you need to know heading into the highly anticipated matchup:
Key Player Updates
- Patrick Mahomes (QB): Cleared to play despite a recent ankle injury, Mahomes is ready to lead his team. Head coach Andy Reid praised his mental toughness, saying Mahomes is “back in the saddle.”
- Isiah Pacheco (RB), Chris Jones (DL), and D.J. Humphries (T): All cleared to play, giving the Chiefs their key contributors on offense and defense.
- Jaylen Watson (CB): Activated from injured reserve, strengthening the Chiefs' secondary.
- Mecole Hardman (WR): Remains on IR and is doubtful for the game, leaving the Chiefs without one of their speediest weapons.
The Matchup
The Chiefs, led by Mahomes, come into this game with a 24-day rest period, the longest in NFL history. It remains to be seen whether the extended break will give them an edge or lead to rust. Mahomes, the winningest quarterback through seven seasons in NFL history (including playoffs), is also undefeated (6-0) in divisional playoff games.
The Houston Texans, on the other hand, are flying high after a dominant 32-12 wild-card victory over the Chargers. Rookie quarterback C.J. Stroud has been a revelation this season, and the Texans’ defense, featuring stars like Will Anderson and Danielle Hunter, has been a force. Anderson and Hunter combined for 1.5 sacks and four QB hits in the wild-card round, and their ability to pressure Mahomes will be critical.
Key Storylines
- Chiefs' Resiliency: Kansas City has shown incredible grit this season, winning 11 games by eight points or less. They've proven they can win in all phases—offense, defense, and special teams.
- Texans’ Defensive Strength: Houston’s cornerback duo of Derek Stingley Jr. and Kamari Lassiter has been among the league’s best, ranking top-three in completion percentage and passer rating allowed. They’ll look to contain the Chiefs’ passing attack.
- Coaching Chess Match: Texans head coach Demeco Ryans acknowledged the challenge of defending Mahomes, citing his quick release and ability to exploit check-downs. Ryans plans to mix up coverages while staying disciplined under pressure.
What’s at Stake
The Chiefs are chasing history as they aim to become the first team ever to win three straight Super Bowls. Mahomes is also looking to tie Joe Montana for the second-most playoff wins by a quarterback.
For the Texans, this game represents a chance to make history of their own. After five previous losses in the divisional round, they’re seeking their first-ever AFC Championship Game appearance.
Game Outlook
This matchup has all the makings of a close contest. The Texans will try to capitalize on the Chiefs’ tendency to play in one-possession games, while the Chiefs’ experience and ability to adapt in critical moments could prove decisive.
With stars on both sides of the ball and plenty of storylines, this game is a must-watch as the Chiefs and Texans battle for a spot in the AFC Championship.
📺 Kickoff: Saturday, 4:30 PM ET
Global Sports Central 🌐 #GSC360
-
 @ 8ea48526:e6720a43
2025-01-17 18:56:34
@ 8ea48526:e6720a43
2025-01-17 18:56:34Technology trends toward openness time and again. This is why I say that Freedom Tech is Final Tech. Ideas want to be free. Many people built brands on TikTok that are now threatened, which is a reminder to also build on open alternatives you control. There are many examples from history.
Shift from Monasteries to Printing Press. During the Middle Ages, monasteries controlled the production and dissemination of written knowledge. The printing press decentralized access to information, enabling mass production of books and changing the course of history.
Transition from Trains to Automobiles. Trains required centralized infrastructure and control, while cars empowered individuals to travel freely. This shift from centralized to decentralized transportation transformed the way people lived, worked, and interacted with each other.
Telegraph and Telephone. The Telegraph was initially a closed system, with message transmission gated by businesses. The Telephone enabled direct, person-to-person communication, decentralizing access to real-time information and revolutionizing the way people connect.
The evolution of the Internet. ARPANET, the early internet, was a closed network. With the development of TCP/IP, the open internet was born, enabling global communication, innovation, and access to information on an unprecedented scale.
Operating Systems. Unix, a proprietary OS, was the early powerhouse and later eclipsed by Linux, an open-source alternative. Today, Linux powers millions of devices, from smartphones to servers, and has become a cornerstone of modern computing. It runs the world.
Computers. Mainframe Computers were massive, centralized systems that only large organizations could afford. The development of Personal Computers democratized access to computing power, enabling individuals to create, innovate, and participate in the digital economy.
Television and Radio, once controlled by a few large broadcasters, have given way to Podcasts, which enable anyone to create and distribute content. This has democratized the media, allowing new voices and perspectives to emerge. (Thank you Aaron for RSS 😢)
The music industry. Vinyl, tape, and CD distribution, once controlled by record labels and physical stores, have given way to open file formats like MP3 and streaming services. Artists can connect directly with fans and music is more widely available than ever before. V4V.
Government, Monarchy to Republic. Monarchies, with their centralized power and hereditary rule, have given way to republics, where power is distributed among the people and their elected representatives, increasing class mobility and participation.
Central Banking System and Bitcoin. The experimental Central Banking System, with its centralized control and intermediaries, is being challenged by a decentralized, open alternative. It is transforming the way we think about money, value, and financial freedom.
Digital payments and Ecash. Systems like PayPal & Venmo (once the innovators themselves) are being challenged by open alternatives, such as Chaumian e-cash systems like Cashu and Fedimint. These systems promise to increase financial privacy and autonomy for day-to-day payments.
Social networking. Proprietary social platforms control the data & access. Nostr is an open protocol for authoring & distributing digital content. In the age of AI, authenticity is paramount. Nostr cryptographically proves who authored content, maximizing freedom & transparency.
AI. AI began as closed systems from large corporations investing heavily in computing and training. The open community is catching up and pushing new boundaries. Open models that run locally or in confidential computing enclaves provide AI that is free, open, and private.
This is the pattern: over time, the processes that were controlled by a few get replaced by processes controlled by everyone. Always be searching out open alternatives for the tech you use, that’s where we eventually end up. I’m bullish on the future of technology and humanity. 🤘
P.S. You can see that many of these examples are themselves becoming compromised over time, looking to be disrupted again by open technology.
-
 @ e373ca41:b82abcc5
2025-01-17 17:54:57
@ e373ca41:b82abcc5
2025-01-17 17:54:57It was recently the tenth anniversary of the attack on Charlie Hebdo, France's best-known satirical magazine alongside the “Canard enchaîné”. The attack claimed the lives of 12 people, mainly cartoonists and journalists. Even then, it was a watershed moment, and not just in retrospect. Everyone wanted to show solidarity, everyone wanted to be “Charlie”, the phrase “Je suis Charlie” made the rounds memetically.
Charlie Hebdo was known for making fun of everything, including religions and Islam. “What is satire allowed to do? Everything.” So said Kurt Tucholsky, the famous publicist of the Weimar Republic, and that also applied to Charlie Hebdo. This magazine also dared to print Mohammed cartoons from “Jyllands Posten”. The solidarity of other newspapers with Charlie no longer went that far. They wanted to be Charlie, but rather without risk. The collective sign of solidarity fizzled out as lip service.
I was in Paris at the time and witnessed the mass demonstration live. Bernard Maris, a friend of Michel Houllebecq, also died in the attack. Houllebecq's book “Submission” was published on the same day. Coincidence? History and its synchronicities sometimes take wondrous paths.
On November 13, 2015, there was another attack at the Bataclan and around the Stade de France, among other places. Not long before, I was still living in Rue de la Fontaine au Roi in the 11th arrondissement, not far from Place de la République. My favorite café, the Café du Phare, was riddled with machine gun bullets, as was the pizzeria next door. I often sat in this café, writing books, academic texts and my first columns for the NZZ. At the time, I was teaching public law and fundamental rights at the Sorbonne in Paris, among other things, and dealing with issues relating to freedom of expression and artistic freedom on a daily basis.
I took it for granted that these constitutionally guaranteed values were just as important to the public (and especially other journalists) as their place in the constitutions of the West suggested. I was wrong, which was certainly also due to my legal glasses and “déformation professionelle”. At the time, I read more articles that emphasized respect for religions than the value of freedom of expression or artistic freedom. Looking back today, that was when the slippery slope that has led us into the realms of censorship, deletions, shadowbanning, fact-checkers, etc. began.
Freedom that is not used wears out and eventually disappears. Fighting to get it back is much more difficult than defending it. Back then, I wrote texts for newspapers rather sporadically, basically mainly when a topic was important to me and it remained underexposed.
The following text, which appeared in the NZZ at the time, was one such text.
You can find the German original version here.
ADVERTISEMENT:
Looking for the easiest way to buy Bitcoin and store it yourself? The Relai app is the No. 1 crypto start-up and No. 2 of all fintech start-ups in Switzerland. Here you can buy Bitcoin in just a few steps and also set up savings plans. Nobody has access to your Bitcoin except you. With the referral code MILOSZ you save on fees (no financial advice). Disclaimer due to regulatory issues: The services of the Relai App are hereby only recommended to inhabitants of Switzerland or Italy.
Need more security? The Trezor wallets are recommended and easy to use, others are available in the store. Need more advice? Book an introductory meeting with a wallet expert.
In the latest issue of “Charlie Hebdo” since the attack in Paris, the editors rub their eyes in amazement. What is wrong with this world? Politicians of all stripes, 50 heads of government and millions of citizens on the streets; Notre-Dame Cathedral is ringing its bells for atheists and the first people are thinking aloud about admitting anarchist cartoonists to the Paris Panthéon, the final resting place of Victor Hugo, Marie Curie and Jean-Jacques Rousseau. You can tell that the editorial team is a little uncomfortable with the collective need to cuddle up.
The worldwide wave of solidarity with “Charlie Hebdo” was overwhelming and important. “I am Charlie” became the collective outcry of the free world. The message is: “If you attack Charlie, you attack me”. What will remain of this when the dust settles? Will the continental plates of our order of freedom have shifted?
A rift trough the free world
Unfortunately, they did it long ago. The attack on “Charlie Hebdo” was an earthquake. But it ultimately only exposed once again what had already been clear and only slightly buried since the dispute over the publication of the Mohammed cartoons in the Danish newspaper “Jyllands-Posten” in 2005: there is a rift running through the free world, and the media landscape as an index of freedoms is showing it.
On the one hand, there are the courageous publications that do not deviate one iota from the Western achievements of freedom of the press, but which ultimately take the rap for it. And then there is the large remainder, for whom freedom seems to be first and foremost the right to remain silent. Magazines like “Charlie Hebdo” are the bad bank of the Western community of values. Charlie & Co. store the toxic papers that nobody wants on their books. The dividend of freedom, on the other hand, is paid out to everyone. If something happens, a declaration of solidarity follows at the minimum price.
Freedom folklore
The Charlie sympathy is to a not inconsiderable extent mere freedom folklore. A masked ball of the enlightened. The smoke from the attacks had barely cleared before the first German-language satirical magazines declared that they would refrain from printing cartoons of Mohammed. The Kalashnikov is the Titanic's iceberg (Note: "Titanic" is the main German satirical paper). American and British newspapers such as the “New York Times” and the “Independent” also waved goodbye and even refused to print the current cover of “Charlie Hebdo”.
This, mind you, in countries where freedom of expression is considered a cultural symbol and freedom as the “right of a soul to breathe”. The soul of freedom now found itself in a vacuum faster than you could shout “Allahu akbar!”. The Turkish newspaper “Cumhuriyet”, on the other hand, dared to do so. Our freedom is being defended in Turkey but no longer in New York or London? A topsy-turvy world.
Some people would like a more harmless satire these days. A satire without exaggeration, overstepping boundaries and disrespect for certain authorities. But the call for moderation means the elimination of its business basis. Satire does not demand approval and consensus. It is not a beauty contest.
When others decide for us
Anyone who refrains from using a caricature simply because it could be provocative, even blasphemous, is already adopting the thought structure and values of those who believe they are in the right when they respond with Kalashnikovs and rolling heads. People are either not proud of the achievement of satire or are not aware of their own rights, and perceive even something that is actually self-evident as an affront. If we ourselves do not know what we should stand for and why, then others have long since decided what we should stand for.
Certainly, no medium is forced to push the boundaries of our legal system on a daily basis. The notorious undercutting of our own standards, on the other hand, will cause them to shrink. Not immediately, but gradually. Until perhaps another standard is accepted at some point. The new censors will then no longer sit in ecclesiastical or secular palaces, as they did in the Middle Ages. But in tent cities in Yemen. Western society is gradually having the rug of its freedom order pulled out from under its feet. And instead of standing together, some people are asking if they can still help roll it up. But of course they still want to be “Charlie”.
Pseudo-security
Self-censorship and anticipatory obedience are a pseudo-safety net. Today it's the Mohammed cartoons. Tomorrow it will be critical reports on Islamism. Anyone who wants to carry out attacks will always find a reason. However, fundamental rights are not a fair-weather crop. Their true existence only becomes apparent when the storm hits. It is cynical to throw up one's hands in the hope that the angel of death will go to the neighboring editorial office.
“Charlie Hebdo” has decided against accepting such external content control. The editorial team also prints a Mohammed cartoon on the cover of the latest issue. Anyone who wonders whether this is wise has missed the point: if it were not done now, it would be the last time this happens in the Western newspaper landscape for a very long time. Those who remain silent agree with the new standard. And all this is happening now, in these hours and days!
It's crazy, but it has to be said: a small anarchic left-wing French newspaper, two-thirds of whose editorial office was bombed out last week, is currently standing almost alone on the front line of the Western world, defending a right it has fought for over 200 years, while machine guns are pointed at it. In the safe hinterland, on the other hand, far away from the impacts, the cardboard comrades fall over in rows at the first bang.
Our freedom is their freedom
At present, it is rightly said that the aim in future will be to win over the peaceful majority of Muslims to our side and not drive them into the hands of the extremists. Yes, many of them will find Muhammad cartoons outrageous or outrageous. But our freedom to think differently is also their freedom to think differently. Our freedom, as unpleasant as it may be to some, also protects moderate Muslims from being forcibly converted at gunpoint by their extremist co-religionists, as is currently happening thousands of times. That makes us allies.
We are currently experiencing a “Sebastian Haffner moment”. The chronicler of the Third Reich describes how he sits in the court library of the Berlin Court of Appeal in 1933 and witnesses the SA taking away all Jewish lawyers. Suddenly, a puffing SA man stands in front of him. “Are you Aryan?” Haffner, who had always rejected this category, answers “Yes” in surprise - and is left alone.
In his notes, he jots down the sentence: “Failed the first test!”
Join the marketplace of ideas! We are building a publishing ecosystem on Nostr for citizen-journalism, starting with a client for blogging and newsletter distribution. Sound money and sound information should finally be in the hands of the people, right? Want to learn more about the Pareto Project? Zap me, if you want to contribute (all Zaps go to the project).
Are you a publication and want to be part of it, test us, migrate your content to Nostr? Write to team@pareto.space**
Not yet on Nostr and want the full experience? Easy onboarding via Nosta.me.

-
 @ 3ac03011:41ecd1bb
2025-01-17 17:38:13
@ 3ac03011:41ecd1bb
2025-01-17 17:38:13Some lessons are worth learning the hard way. Here's one of them: don't waste your energy trying to convince someone that a fact is a fact.
If their belief doesn't harm you, let them hold onto it. And if it does, focus on protecting yourself instead of arguing. Life is a far better teacher than any debate—you can't out-argue reality and false beliefs have a way of unraveling themselves.
The beauty of facts lies in the clarity they bring us. They show us how humanity's darkest moments came not purely from malice but from people simply following incentive structures. Understand the incentives and the chaos of the world starts to make sense.
Those who reject facts often feel the world is against them. They take it personally, not realising facts are impersonal—they simply are. When you accept them, you're no longer at odds with reality and peace becomes possible.
So don't spend your time persuading others. Instead, build the life you want. Focus your energy on creating, achieving and living. The truth doesn't need you to defend it; it's always there, waiting to be seen.
In the end, the clarity you gain by focusing on your own path will bring you more freedom and fulfilment than any argument ever could. Spend your time living, not debating.
-
 @ 07f367da:0e76880d
2025-01-17 16:08:52
@ 07f367da:0e76880d
2025-01-17 16:08:52- 2023-10-26 강기자 기사 작성"‘직장 내 괴롭힘’ 호소하며 투신 사망… ‘미등록 장애인’ 김경현"
- 2023-10-27 강기자 기사 작성"좋은친구들 퇴사자 “김경현 유서, 내가 겪은 것과 너무 비슷하다”"
- 2023-11-18 이슬하 퇴직기자 게시물
- 2024-03-15 하민지 기자 게시물★최초폭로
- 2024-03-16 이슬하 퇴직기자 게시물
- 2024-03-18 비마이너 비상대책위원회 게시물
- 2024-04-29 비마이너 비상대책위원회 게시물
- 2024-05-03 이슬하 퇴직기자 게시물
- 2024-05-21 비마이너 비상대책위원회 게시물
- 2024-06-01 이슬하 퇴직기자 게시물
- 2024-07-31 김혜미 퇴직기자 게시물
- 2024-08-13 비마이너 비상대책위원회 발표★1차 입장
- 2024-08-23 이슬하 퇴직기자 게시물
- 2024-08-25 하금철, 갈홍식, 최한별
- 2024-08-25 운영실장 양유진, 취재기자 하민지
- 2024-08-26 비마이너 퇴직기자 6인 입장문
- 2024-08-27 하민지 기자 게시물
- 2024-08-27 비마이너 비상대책위원회 발표★2차 입장
- 2024-10-01 김혜미 퇴직기자 게시물
- 2024-10-22 이슬하 기자 게시물
- 2024-11-06 이슬하 기자 게시물
- 2024-11-28 비마이너 비상대책위원회 발표★최종 입장
- 2024-11-29 박정수 퇴직기자 게시물★
- 2024-11-29 하민지 기자 게시물
- 2025-01-16 하민지 기자 게시물
-
 @ 543d73b5:977c83a9
2025-01-17 15:24:32
@ 543d73b5:977c83a9
2025-01-17 15:24:32In the digital world, human beings occupy space with digital representations of their physical-world information. When viewed separately, these digital representations can be readily dismissed as merely random collections of digital assets. However, when examined as a whole, these same representations reveal themselves to be extensions of a person’s digital self-sovereign identity.
Moreover, as these two worlds, the digital and the physical, continue to merge into one space, this digital identity has become more commonly used as a primary means of validation and verification of a person’s digital and physical existence. Therefore, the primary rights of ownership for this digital form of identity must be safeguarded and protected in the same manner, and with the same level of importance, as is typically observed with individual identity in the physical world.
It is for this reason that this Ethos of Digital Self-Sovereign has been drafted. And, it is for this purpose that it is presented to the digital community for their consideration and adoption into their standard governance frameworks.

THE RIGHT TO DIGITAL PRIVACY
PROTECTED PRIVACY = the SECURITY of PROPERTY which affirms our FAITH in our DIGITAL SELF-SOVEREIGNTY.
Digital Privacy means that people are the sole owners of their own digital property and they inherently possess immutable authority over the use of that property. As owners, they have full right of control over the “why”, “when”, “where”, and “how” their digital assets are accessed. Digital Privacy is about an individual’s ability to maintain control of their digital property when interacting with any entity, system, or organization within a digital environment. Therefore, with every and any form of digital interaction, every person should have the expectation of privacy.
THE RIGHT TO DIGITAL INDEPENDENCE
COMPREHENSIVE DECENTRALIZATION = the INDEPENDENCE of CHOICE which affirms our BELIEF in our DIGITAL AUTONOMY.
Digital Independence is the ability for individuals to interact freely with any entity, system, or organization within the digital space. Centralized control of digital interactions is in direct conflict with the idea of digital independence. Within decentralized environments, there is no intermediary entity to serve as a central authority over the authenticity of digital relationships. Therefore, systematic decentralization must be promoted, propagated, and implemented throughout every corner of the digital world to ensure that the right to Digital Independence is fully available to every individual.
THE RIGHT TO DIGITAL TRANSPARENCY
CLEAR GOVERNANCE = the TRANSPARENCY of AGREEMENTS which affirms our TRUST in our DIGITAL RELATIONSHIPS.
Digital Transparency is the application of open, honest, and fair relationships between individuals, entities, systems, and/or organizations within a digital space. One can argue that transparency is required to secure trust between different parties in a digital-based relationship. However, a truly transparent relationship can actually eliminate the need for trust between parties; since each individual is has the ability to confirm the validity of all interactions because all information about the shared relationship is openly available to all parties involved in the relationship.
(First Drafted 11/11/2021)
-
 @ f88e6629:e5254dd5
2025-01-17 14:10:19
@ f88e6629:e5254dd5
2025-01-17 14:10:19...which allow online payments to be sent directly from one party to another without going through a financial institution.
- Without sovereign and accessible payments we are loosing censorship resistance
- Without censorship resistance even other core characteristics are in danger - including scarcity and durability.
- This affects every bitcoiner including sworn hodlers and MSTR followers.
| Property | Description | Fulfillment | | --- | --- | --- | | Scarce | Fixed supply forever. Instantly and costlessly verifiable | 🟢 Good, but can be harmed without censorship resistance | | Portable | Effortless to store and move, with negligible costs | 🟠 Onchain transactions can be expensive, other layers require onchain to be sovereign. Easy portability is offered by custodians only. | | Divisible | Infinitely divisible | 🟠 Smaller units than dust are available only for LN users, which most people can’t use in a sovereign way. | | Durable | Exists forever without deterioration | 🟢 Good, but can be harmed without censorship resistance | | Fungible | Every piece is forever the same as every other piece | 🟡 Onchain bitcoin is not fungible. | | Acceptable | Everyone, anywhere, can send and receive | 🟠 Most people are not able to send and receive in a sovereign way. | | Censorship Resistant | You hold it. Nobody can take it or stop you sending it | 🟠 Custodians are honey-pots that can and will be regulated |
➡️ We need accessible, scalable, and sovereign payment methods
-
 @ da0b9bc3:4e30a4a9
2025-01-17 14:00:40
@ da0b9bc3:4e30a4a9
2025-01-17 14:00:40It's Finally here Stackers!
It's Friday!
We're about to kick off our weekends with some feel good tracks.
Let's get the party started. Bring me those Feel Good tracks.
Talk Music. Share Tracks. Zap Sats.
Let's go!
Madness!!!
https://youtu.be/SOJSM46nWwo?si=5XsJwBaOXvHqewlH
originally posted at https://stacker.news/items/853535
-
 @ d9e9fb27:d5fe5e1a
2025-01-17 13:00:58
@ d9e9fb27:d5fe5e1a
2025-01-17 13:00:58Every 16th of January, the city of Varese, a small town at the feet of the Prealpine region, stops to participate in one of the most important ceremonies of the city: The Falò of Sant'Antonio. A Falò is the Italian word for bonfire. Imagine a 5-meters tall pyre of wood burning in the center of the city. For sure, an unmissable event!
The pyre is built by the so-called "Monelli della Motta". A Monello in Italian is a child that misbehaves. This nickname come from the fact that in the past, the pyre was created using wood stolen from the city, usually from tools, doors and shutters.
This event takes place at the eve of the day of Sant'Antonio Abate in front of the homonymous church in the area called "La Motta", which stands for small hill, and comes from a several century old tradition. Thousands of people from all over the province come to the city to look at the bonfire created in honor of the Saint.

At 9PM the big event starts. The wood is set on fire!

An important tradition of this celebration is burning small pieces of paper containing wishes. People whish for health, love, friendship and luck. To make wishes come true, people have to give these pieces of paper to a firefighter or a "Monello" whom will launch it into the Falò.
The show goes on for a couple of ours, during which thousands of Varesinians in awe contemplate the raging fire and try to receive some heat to fight the glacial cold of January.

-
 @ bbb5dda0:f09e2747
2025-01-17 11:41:25
@ bbb5dda0:f09e2747
2025-01-17 11:41:25Holy crap what a week! I can't believe the amount of progress that came out of just these few days. And a special thanks to nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 for making this possible with me! Alright, let's get into it...
GitHub Blossom Upload Action
I started this week working out the GitHub action for blossom uploads, solving some issues with dependencies, which turned out to just be me not bundling my dependencies with the my build output. So anyway I ended up publishing it and sharing it with all of you.
nostr:nevent1qvzqqqqqqypzpwa4mkswz4t8j70s2s6q00wzqv7k7zamxrmj2y4fs88aktcfuf68qy88wumn8ghj7mn0wvhxcmmv9uq3zamnwvaz7tmwdaehgu3wwa5kuef0qy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qpqzskk7na9x9cgnzpvz7xufdn2y8wqxf00rnq7jg75z86lk30l6plspy9e9u
Pipeline runner
The plan
I can't believe all of this happened just this week. I worked out a plan with nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 to first create a DVM that would be able to clone a given ngit(!) repository and just print the contents of any given pipeline
.yamlfile that resides inside that repository.The DVM would have the following inputs - git url (or Nostr address) - branch - pipeline (path to yaml)
Proof of Concept
I was able to repurpose a dvm-git-watcher that i'd created earlier to create the DVM to run the pipeline. Created a POC where the CI runner actually takes the pipeline, executes it and gives back a response and decided to put up a little video demo:
https://cdn.satellite.earth/43463990dd11c9506989e5eda915757cf3ec1b32e8d472579cd2ee18d5685f0d.mp4
Some improvements
Wednesday I added a NIP-89 announcement to the DVM where it just advertizes its existence in hopes of some validation that it is real, and that it is actually useful, and it hopes to be used and talk with other npubs to not be lonely...
So then i figured it was time to package it into an easier to distribute package, a Docker container. That would allow me to include the required tools, namely ngit-cli and the 'act' cli (used to run the pipeline).
Troubles 😱
Adding the precompiled version of ngit got me into trouble with this error:
shell Error: Cloning into 'tmp/1ca8af464df5fc648b77db14e0e5e35ff64d6627a690e138e19298dd56573274'... /app/ngit//git-remote-nostr: /usr/local/lib/libc.so.6: version `GLIBC_2.38' not found (required by /app/ngit//git-remote-nostr) /app/ngit//git-remote-nostr: /usr/local/lib/libc.so.6: version `GLIBC_2.39' not found (required by /app/ngit//git-remote-nostr) fatal: remote helper 'nostr' aborted sessionI didn't really know how to proceed as it could be a Docker issue, a Deno issue, or an ngit issue.
Luckily nostr:npub16ux4qzg4qjue95vr3q327fzata4n594c9kgh4jmeyn80v8k54nhqg6lra7 knows his shit and saved me here. It turned out to be an issue that had to do with the ngit binary. Because ngit is compiled on a recent ubuntu version, it depended on some packages that the linux version my Docker image was based on did not have. Thus it failed.
Our solution was to compile ngit instead of using the existing binary, which took some trial and error to get working but eventually it did. It slowed down the build process significantly but alas, at least it works now!
Moving on
After ngit worked I added the 'act' runner to the docker image and was able to control the host system's docker so it can run the isolated environments that have the pipelines run inside.
And so I was able to package up the thing, able to run on any machine, which led me to this little demo:
nostr:nevent1qqs9486y7cs6a9h7n4sk7sdv52qvuqyp80rj0eyg6zt7htfyt9wh4wgpp4mhxue69uhkummn9ekx7mqpz3mhxue69uhhyetvv9ujuerpd46hxtnfdupzpwa4mkswz4t8j70s2s6q00wzqv7k7zamxrmj2y4fs88aktcfuf68g4v3lk
The only issue I still have is getting the output of the pipeline properly fed back to the user. But that's some magic with log streams that I have zero experience with, so that's a nice challenge for next week! If you or anyone you know is a Stream magician, please let me know!
See you there!
-
 @ eee391ee:8d0b97c2
2025-01-17 10:43:51
@ eee391ee:8d0b97c2
2025-01-17 10:43:51Amber 3.1.8
- Button to clear cached data in settings
- Fix multiple bunker requests not clearing when accepting or rejecting
- Show relays status in the notification
Download it with zap.store, Obtainium, f-droid or download it directly in the releases page
If you like my work consider making a donation
Verifying the release
In order to verify the release, you'll need to have
gpgorgpg2installed on your system. Once you've obtained a copy (and hopefully verified that as well), you'll first need to import the keys that have signed this release if you haven't done so already:bash gpg --keyserver hkps://keys.openpgp.org --recv-keys 44F0AAEB77F373747E3D5444885822EED3A26A6DOnce you have his PGP key you can verify the release (assuming
manifest-v3.1.8.txtandmanifest-v3.1.8.txt.sigare in the current directory) with:bash gpg --verify manifest-v3.1.8.txt.sig manifest-v3.1.8.txtYou should see the following if the verification was successful:
bash gpg: Signature made Fri 13 Sep 2024 08:06:52 AM -03 gpg: using RSA key 44F0AAEB77F373747E3D5444885822EED3A26A6D gpg: Good signature from "greenart7c3 <greenart7c3@proton.me>"That will verify the signature on the main manifest page which ensures integrity and authenticity of the binaries you've downloaded locally. Next, depending on your operating system you should then re-calculate the sha256 sum of the binary, and compare that with the following hashes:
bash cat manifest-v3.1.8.txtOne can use the
shasum -a 256 <file name here>tool in order to re-compute thesha256hash of the target binary for your operating system. The produced hash should be compared with the hashes listed above and they should match exactly. -
 @ da0b9bc3:4e30a4a9
2025-01-17 09:14:39
@ da0b9bc3:4e30a4a9
2025-01-17 09:14:39Hello Stackers!
Welcome on into the ~Music Corner of the Saloon!
A place where we Talk Music. Share Tracks. Zap Sats.
So stay a while and listen.
🚨Don't forget to check out the pinned items in the territory homepage! You can always find the latest weeklies there!🚨
🚨Subscribe to the territory to ensure you never miss a post! 🚨
originally posted at https://stacker.news/items/853332
-
 @ f57bac88:6045161e
2025-01-17 08:35:53
@ f57bac88:6045161e
2025-01-17 08:35:53دگرگونی و سعادت در افسانه همای:
- تغییر و تحول: همای سعادت اغلب به عنوان نمادی از تغییر و تحول ناگهانی و مثبت در زندگی افراد تلقی میشود. سایه این پرنده بر سر فردی افتادن، نشانهای از دگرگونی سرنوشت و آغاز دورهای جدید و پربرکت است.
- آوردن سعادت: همانطور که از نامش پیداست، همای سعادت به عنوان آورنده خوشبختی و کامرانی شناخته میشود. سایه این پرنده، نمادی از برکت، فراوانی و رسیدن به آرزوهاست.
- پادشاهی و قدرت: در بسیاری از روایتها، همای سعادت با پادشاهی و قدرت ارتباط مستقیم دارد. سایه این پرنده بر سر کسی افتادن، به معنای رسیدن به مقام و منزلت والا و کسب قدرت است. معانی نمادین همای سعادت:
- امید و آرزو: همای سعادت نماد امید به آیندهای بهتر و رسیدن به آرزوهاست.
- تغییر مثبت: این پرنده نشاندهنده این است که حتی در سختترین شرایط نیز امکان تغییر و تحول مثبت وجود دارد.
- قدرت الهی: در برخی روایات، همای سعادت به عنوان فرستادهای از سوی خداوند تلقی میشود که برای برکت دادن به انسانها به زمین میآید.
در ادبیات فارسی: همای سعادت در ادبیات فارسی جایگاه ویژهای دارد و شاعران بسیاری به توصیف زیبایی و شکوه این پرنده پرداختهاند. این پرنده اغلب به عنوان نمادی از عشق، زیبایی و آرزوهای دستنیافتنی به کار رفته است. در نتیجه: همای سعادت نه تنها یک پرنده افسانهای، بلکه نمادی از امید، تغییر مثبت و رسیدن به آرزوهاست. این پرنده به ما یادآوری میکند که حتی در سختترین شرایط نیز باید به آینده امیدوار باشیم و برای رسیدن به اهدافمان تلاش کنیم.


منبع عکس ها
-
 @ fbf0e434:e1be6a39
2025-01-17 07:13:14
@ fbf0e434:e1be6a39
2025-01-17 07:13:14Hackathon 总结
Balancer v3 Hookathon 集合了开发人员以探索 Balancer v3 hooks 框架的功能。此次活动共包含31个项目,122名注册开发者参与,专注于通过 Balancer 的新架构定制自动化做市商(AMM)。开发人员致力于创新池行为、增强流动性管理,并拓展去中心化金融(DeFi)领域内的设计可能性。关键创新包括自定义费用机制和高级流动性管理工具,为生态系统的增长做出贡献。参与者与 Balancer 的核心开发人员互动,增强了协作并激发了实际应用。Hackathon 为具有影响力的项目提供了 $BAL 奖励,使参与者在 DeFi 社区中获得可见性。总体而言,活动强调了创造力和协作,将 hooks 框架整合到功能性解决方案中。
Hackathon 获奖者
经过对45个提交项目的评估,Balancer v3 Hookathon 的获奖者已揭晓。奖项分为顶级奖和其他值得注意的奖项。
Top Prizes Winners
- VolatilityLoyaltyHook: 此项目介绍了一种双重奖励系统,旨在稳定市场波动,同时激励交易忠诚度。它为长期持有代币的用户提供交换费用折扣。
- Prediction Market Hook: 该项目专注于去中心化的预测市场,操作不依赖于中心化控制。它通过交换费用为流动性提供者提供收入,并通过0%套利交换费用减少价格操控。
- MEV Tax Hook: 该项目通过动态费用结构捕获流动资金池的最大可提取价值,考虑事务优先级,以造福供应商和 Balancer 生态系统。
Other Prizes Winners
- Protofire - Dynamic Fees and Reinvesting: 该项目通过动态费用调整稳定流动资金池,并通过投资于借贷市场来实施长期供应商奖励,支持代币交换。
- Volatility Fee Hook: 此项目根据市场波动动态调整池交换费用,使用具有可配置增量和指数费用乘数的模型来增强市场稳定性。
欲了解更多详细见解和技术规范,参会者和感兴趣的个人可以在 DoraHacks 查看所有提交的项目。
关于组织者
Balancer
Balancer 是一个在 DeFi 内致力于推动自动化做市商(AMM)开发的协议。它为开发人员提供了一个无权限的技术框架,并以全面的去中心化交易所(DEX)产品支持流动性提供者。作为 DeFi 领域的知名实体,Balancer 促进在区块链技术中的无缝集成和创新。该组织致力于扩展 DEX 产品,以此使用户能够最大化流动性提供和去中心化交易的效率。欲了解有关 Balancer 的更多信息,请访问其网站和Twitter。
-
 @ fbf0e434:e1be6a39
2025-01-17 07:12:51
@ fbf0e434:e1be6a39
2025-01-17 07:12:51Hackathon 总结
由Oasis Network主办的 Privacy4Web3 Hackathon: 2nd Edition(第二届Web3隐私黑客松) 吸引了 50 个注册项目和 149 名开发者参与。活动重点是为 Web3 和 AI 提供可定制和可互操作的隐私解决方案。奖金总额为 130,000 美元,开发工作集中在 Oasis 的 Sapphire EVM 和 Runtime Off-chain Logic (ROFL) 框架上。这些技术是参与 Hackathon 的重要组成部分。
主要赞助商包括 PixelRealm 和 Aethir,它们提供去中心化 GPU 基础设施以支持 AI 和游戏的进步。Google Cloud 提供了高达 2,000 美元的云计算服务积分给参与者。此次活动提供了实践经验和交流机会,促进了社区发展和在 Oasis 生态系统中的整合。
这次 Hackathon 突显了 Oasis 作为一个面向保密应用的第一层区块链的潜力,同时也支持 Ocean Protocol 在增强数据隐私和创新方面的更广泛目标。通过鼓励新项目和社区互动,活动支持了 Web3 技术的持续发展。
Hackathon 获奖者
在 Sapphire 和 ROFL 上开发奖获奖者
- 1st Place: SQUIDL - 一个隐私专注的支付平台,利用 Oasis Sapphire 进行安全交易。它通过隐匿地址生成和 ERC-5564 挑战解决方案简化跨链支付,并集成了 Ethereum Name Service。
- 2nd Place: Futures on Chain
- 3rd Place (Tie):
- Priva Health
- CAAI (Copyright Aware AI)
- CompensatePaw3
- PrivateFeedback
- CLPD Stablecoin Private Transactions
- 4th Place: Minesweeper
Ocean Nodes - Tokenized Intelligence 奖获奖者
- 1st Place: DeFlow - 提供拖放界面和自动化任务执行以促进 Ocean Network 中的 AI 模型训练,并使用定制的 Docker 镜像提高效率。
- 2nd Place: confidential-data-exchange - 去中心化平台用于安全的 AI 模型交易,利用端到端加密和 NFT 进行 Ocean Protocol 内资产标记化。
- 3rd Place: CAAI (Copyright Aware AI)
计算赏金 - 由 Aethir 赞助,Hackathon 计算合作伙伴奖获奖者
- 1st Place: Futures on Chain
- 2nd Place: Priva Health
- 3rd Place: CAAI (Copyright Aware AI)
提升 Oasis 驱动的嵌入式钱包奖获奖者
- 1st Place: oasis-btc - 将比特币密钥管理集成到智能合约中,通过 secp256k1 椭圆曲线提高交易安全性。
- 2nd Place: rofl rng recovery - 通过离线计算增强用户恢复,利用 ROFL 在 Apillon 嵌入式钱包中提供随机性和隐私。
- 3rd Place: Social and Email Authentication with Social Recovery - 通过电子邮件和社交媒体验证确保账户管理,使用模块化 Solidity 库。
Oasis Sapphire 上创新的去中心化 AI 应用奖获奖者
- 1st Place: SovereignAISearch-oasis-Protocol - 一个去中心化的 AI 搜索协议,通过基于区块链的隐私和智能合约管理优先用户数据控制。
- 2nd Place: Futures on Chain
在 Sapphire 和 ROFL 上开发的额外奖品获奖者
- 审计积分奖: Priva Health, Futures on Chain, SQUIDL, CompensatePaw3, CLPD Stablecoin Private Transactions
有关这些项目的详细信息,请访问 https://dorahacks.io/hackathon/p4w3/buidl。
关于主办方
Oasis Network
Oasis Network 旨在增强 Web3 生态系统中的隐私,将自己定位为区块链技术的关键角色。该组织以开发隐私保护解决方案而闻名,整合这些功能以满足去中心化应用对数据保密的需求。作为行业的参与者,Oasis Network 通过提供强大的隐私层来加强 Web3 的基础元素。这一承诺与其在全球创造安全和私人数字环境的使命相一致。
-
 @ ed84ce10:cccf4c2a
2025-01-17 07:04:30
@ ed84ce10:cccf4c2a
2025-01-17 07:04:30Hackathon Summary
The Balancer v3 Hookathon brought together developers to explore the capabilities of the Balancer v3 hooks framework. This event hosted 31 projects with participation from 122 registered developers, focusing on the customization of Automated Market Makers (AMMs) through Balancer's new architecture. Developers worked to innovate pool behavior, enhance liquidity management, and expand design possibilities within the decentralized finance (DeFi) space. Key innovations included custom fee mechanisms and advanced liquidity management tools, contributing to the ecosystem's growth. Participants engaged with Balancer’s core developers, which enhanced collaboration and inspired practical applications. The hackathon offered a range of $BAL rewards for impactful projects, providing participants with visibility in the DeFi community. Overall, the event emphasized creativity and collaboration, integrating the hooks framework into functional solutions.
Hackathon Winners
Following the evaluation of 45 submissions, the winners of the Balancer v3 Hookathon were announced. The prizes were divided into top prizes and other notable winners.
Top Prizes Winners
- VolatilityLoyaltyHook: This project introduces a dual-reward system aimed at stabilizing market volatility while incentivizing trading loyalty. It offers swap fee discounts for users retaining tokens long-term.
- Prediction Market Hook: Focused on decentralized prediction markets, this project operates without centralized control. It provides liquidity providers with revenue through swap fees and reduces price manipulation using 0% arbitrage swap fees.
- MEV Tax Hook: This project captures Maximal Extractable Value for liquidity pools through a dynamic fee structure that accounts for transaction priority, benefiting providers and the Balancer ecosystem.
Other Prizes Winners
- Protofire - Dynamic Fees and Reinvesting: This project stabilizes liquidity pools through dynamic fee adjustments and implements long-term provider rewards by investing in lending markets, supporting token swaps.
- Volatility Fee Hook: This initiative dynamically adjusts pool swap fees based on market volatility, using a model with configurable increments and exponential fee multipliers to enhance market stability.
For detailed insights and technical specifications, attendees and interested individuals can view all submitted projects on DoraHacks.
About the Organizer
Balancer
Balancer is a protocol within DeFi focused on advancing Automated Market Maker (AMM) development. It offers a permissionless technology framework tailored for developers and supports liquidity providers with a comprehensive suite of Decentralized Exchange (DEX) products. As a prominent entity in the DeFi space, Balancer enables seamless integration and innovation in blockchain technology. The organization is committed to expanding DEX offerings, thereby empowering users to maximize efficiency in liquidity provision and decentralized trading. Additional information about Balancer can be found on their website and Twitter.