-
 @ 000002de:c05780a7
2025-01-09 22:41:33
@ 000002de:c05780a7
2025-01-09 22:41:33It is easy to mock the government of California. I would say it is a joke but its actually evil. The government of California has managed to lose population to other states even though the weather is amazing most of the year and its blessed with some of the most beautiful places on earth.
My word of warning is to look at your own back yards. California was once like most "conservative" states in the US. California is simply a few years ahead of most of the US. Instead of mocking CA look at the specific reasons why its went wrong and look at your own areas.
I've spent time in several states and I see their governments following the same path as California while their people think they are sooooo much better off. Its a trap.
It isn't just "the woke". It isn't just "the democrats". Its much more subtle.
Another note. California is a massive state and the vast majority of it is NOT like LA or San Fransisco politically. Democracy and cities lead to what you see in California. Hopefully people will learn that daddy government is an evil monster but I'm not very hopeful for that in my life time. I think things have to get much worse before that will happen.
Edit:
It is promising to see that some have rejected Harris in a national election(not saying voting is how you change it). Its a good signal for where people are. However, it isn't as massive of a shift as some would like to believe.
End public service announcement.
originally posted at https://stacker.news/items/844193
-
 @ dd664d5e:5633d319
2025-01-09 21:39:15
@ dd664d5e:5633d319
2025-01-09 21:39:15Instructions
- Place 2 medium-sized, boiled potatoes and a handful of sliced leeks in a pot.

- Fill the pot with water or vegetable broth, to cover the potatoes twice over.
- Add a splash of white wine, if you like, and some bouillon powder, if you went with water instead of broth.

- Bring the soup to a boil and then simmer for 15 minutes.
- Puree the soup, in the pot, with a hand mixer. It shouldn't be completely smooth, when you're done, but rather have small bits and pieces of the veggies floating around.

- Bring the soup to a boil, again, and stir in one container (200-250 mL) of heavy cream.
- Thicken the soup, as needed, and then simmer for 5 more minutes.
- Garnish with croutons and veggies (here I used sliced green onions and radishes) and serve.

Guten Appetit!
- Place 2 medium-sized, boiled potatoes and a handful of sliced leeks in a pot.
-
 @ 000002de:c05780a7
2025-01-09 17:00:06
@ 000002de:c05780a7
2025-01-09 17:00:06originally posted at https://stacker.news/items/843670
-
 @ 000002de:c05780a7
2025-01-08 21:35:07
@ 000002de:c05780a7
2025-01-08 21:35:07originally posted at https://stacker.news/items/842641
-
 @ 746a245a:7a8d8b34
2025-01-10 17:57:04
@ 746a245a:7a8d8b34
2025-01-10 17:57:04
1. Self custody
Always. Send your BTC to cold storage. Don't hesitate because of high network fees when mempool activity is high. Rather pay 10% or more to secure your coins than risk loosing 100% of a cosiderable amount. If you have questions about self custody see this guide on the 5 Best Practices to Store Your Bitcoin.
2. Back up well
Restore a wallet at least once. Make sure you know how to get back your coins in a worst case scenario. (Also make sure your heirs are able to do it when time comes.)
3. Never try to time the market
DCA. Set it and forget it. Monthly, weekly, by-weekly or daily doesn't matter. Choose what best suits you. Do this for the majority of your BTC allocation. You can not time the bottom. Period. (But you can have a little pile of FIAT to buy dips when they occur.)
4. You can not time the top either
Never sell the majority of your Stack. Take a little profit if things go parabolic to reward yourself but always keep your main stack intact. It can be hard to get it back. And it will only go up with time. HODL and understand what you own.
5. Keep emotions out
Greed and fear are the main factors for people to get wrecked. Slow steady purchases, even tiny ones, all go to building a stack.
6. Never use leverage
Just don't. No, not even if BTC is below 10k. Make sure every sat you own truly belongs to you.
7. Every sat counts
Even if it's small amounts, just keep dca-ing and stacking sats. Little pieces add up. 0.001 BTC = $25 at the time of this writing. Do this 100 times and you have a tenth of a BTC. If you have very little FIAT, stack free sats. You can:
- use faucets (like freebitco.in or cointiply.com)
- do tasks (like microlancer.io)
- play games (like Bitcoin Miner)
- shop with services like lolli.com or foldapp.com
- listen to podcasts (with fountain.fm)
- educate yourself on Bitcoin (with BitcoinMagazine)
- or be active and provide value in communities like nostr, stacker.news or habla.news
Remember: Faucets used to give hundreds of Bitcoin per day. Now it's 5-250 sats 10 years later. In 10 years it may be 1-5 sats.
8. Don't go all in
Keep FIAT to survive hard times without being forced to sell BTC. (for example 6 months of monthly spending)
9. Enjoy life while stacking
There is only one thing that is more precious than Bitcoin. It is lifetime. Stack sats, but also stack moments. Be present and enjoy life. Every day. No amount of BTC can ever buy back lifetime. Remind yourself of this often.
10. Don't forget yourself
Always have a little fun money to maintain hobbys, traveling and to treat yourself. Otherwise you might burn out quickly.
11. Involve your significant other
Make sure he/she knows the reason why you do what you do. Otherwise you risk burning out him/her too.
12. Automate and relax
When you check your portfolio ten times a day or more think of automating things. Don't trade lifetime and serenity for small gains.
13. Don't do shitcoins
Most altcoins never reach their ATH again. BTC and BTC only.
14. Stay humble
Never get lured by offers that promise yield in exchange for holding your BTC. FTX was a recent example of how that can end.
15. You lost your keys in a boating accident
Never share how much Bitcoin you own. Better yet, don't share that you own any at all (exception: rule #11). The less is known about you having BTC, the less risk. Also consider buying non KYC. For example with robosats or bisq.
16. Don't rush. Be patient
It is a marathon, not a sprint. Time is on your side. You already own Bitcoin. You won. It isn't a race like with FIAT where you have to fight inflation. You preserve wealth.
17. Increase your FIAT earnings
Learn profitable skills to increase your buying power and generally grow as a person. Even if you loose all your wealth, nobody can take away your skills to accumulate it again.
18. Don't compare
Every stack of BTC is better than no stack of BTC. And even if you are a whale: there will always be a bigger fish somewhere in the sea ...
19. You don't need 1 full BTC
This was huge for me! The urge to have one full BTC is very FIAT minded thinking. Goals are cool but:
21 million BTC / 8 billion humans in the world =0,00262500 BTC
And not even that is possible because of the 1,1 m BTC wallet of Satoshi Nakamoto and lost coins. You can find out the exact amount every individual on earth could possibly own at satoshisperperson.com.
Not everyone needs a whole coin. About 225.000 sats = your little block of Bitcoin. ... That's roughly $55 at the time of this writing. Got that? Congratulations! 99% of people are still on zero. Safe your share and then slowly add more every pay check.
20. Change perspective
You can change settings in your wallet to display value in sats rather than BTC. This liberates from the feeling of shortage and the urge to fill that full BTC. It opens up the feeling of gratitude and abundance.
21. Always learn
Keep educating yourself about Bitcoin. The rabbit hole is deep ...
Thank you!
Thank you wonderful people who helped me gather those tips. I chose consciously to not give personal credit in this post because of rule #15 =)
Find me on Nostr
My Nostr npub:
npub1w34zgkkjznnf2209gnhc5snkd32lkc9hnncq45rypyzsx75d3v6qcz3ndd
What have i missed?
Do you agree with these tips? Did i miss any? Please let me know and help refine this set of rules so we can breed more an more whole coiners over time ... or let's rather call it 'satoshi millionaires' (see rule #19 ;-)
P.S. Feel free to tip me some sats or share this post if you find it helpful. Working on my own little stack too ;-)
-
 @ 000002de:c05780a7
2025-01-08 19:09:58
@ 000002de:c05780a7
2025-01-08 19:09:58originally posted at https://stacker.news/items/842459
-
 @ dd664d5e:5633d319
2025-01-07 19:57:14
@ dd664d5e:5633d319
2025-01-07 19:57:14Hodling Bitcoin does not make you a capitalist
I've noticed that Bitcoin-mindedness seems to lead some people to communistic thinking because it's a hard-limited form of capital. Marx, like most Bitcoiners, heavily discounted the possibility of economic growth or transformation changing the economy enough to undermine some minority's control of some form of capital.
What few today understand, is that many of the Dirty Capitalists of Marx's era actually agreed with him; they were just disdainful of labor and worried that the workers finding out that Marxism is correct about the nature of capitalism would cause unrest. They were the original HFSP crowd.
This was the basic idea, that Marx had, and that many Bitcoiners would agree with:
Capital is strictly limited and the people that control it can keep labor from attaining any, except when their labor is necessary.
And, as we know, automation will make human labor increasingly unnecessary.
The math doesn't check out
That underlies all of the calculations of "Well, if I just grab this Bitcoin wallet and hodl for twenty years, then it will grow in value to equal half of everything in existence and then I can just buy up half the planet and rule over everyone like a god."
This is economic nonsense because it assumes that: 1) the value of all things remains static over time, 2) purchasing something with money gives you ownership of it, 3) people will always use that specific money (or any money, at all!) for all transactions, 4) there is no such thing as opportunity cost, 5) people will always value money more than any other thing, and therefore be willing to always trade it for anything else, 6) humans are passive, defenseless, and easy to rule over, 7) someone who is preoccupied with hodling an asset steadily and sharply rising in price would ever be emotionally ready to part with it.
All monies can die.
People use money for everything because it is easy, fast and cheap. If money becomes too precious or scarce, they will simply switch to using other things (as we saw with gold). Humans replace tools that aren't working well, with those that work better, and money is just another tool. Bitcoin is more divisible than gold, but that won't matter, if enough of it is held by too few.
This is why there's a natural cap on the price of a money and why human productivity in the here and now is not irrelevant or in vain.
-
 @ 746a245a:7a8d8b34
2025-01-10 17:50:10
@ 746a245a:7a8d8b34
2025-01-10 17:50:10In the past few years i have struggled a lot to find "the right" way to store bitcoin.
There is a lot of advice on this topic scattered around the web. I have consumed it, i have tested it and i have discussed it.
Here is what i found to be the best practices to store your bitcoin as a newbie or intermidiate.
I have split this up into two parts:
- Part 1: Essentials - The absolute bare minimum requirements you need to implement ASAP (this post)
- Part 2: Recommended - How to upgrade security and what mistakes to avoid (coming soon)
Let's start with the Essentials ...
Part 1: Essentials
I assume you already know a thing or two about bitcoin if you read this post, so i skip the obvious "No your keys not your coins" stuff.
These are the absolute minimum safety requiements. If you have not implemented these, stop everything you do and follow these steps immediately:
1. Use a hardware wallet
Hardware wallets are specificly built for one single purpose. To secure your private keys and thuss the access to your bitcoin.
Do i really need a hardware wallet?
Short answer: Yes.
Long Answer: It depends on your funds. If you only have bitcoin worth a few hundred bugs, it might not be necessary. A hardware wallet costs about $50-200. But as soon as you feel uncomfortable, you should get one. It is an individual decision. Like someone doesn’t bother running around with a few thousand dollars in his pocket and another one feels uncomfortable with even a few hundred. BUT it is good practice to treat the security of your funds right now as if they already were 10x. As a 10x can happen pretty quickly, as we have seen in the past two years, and you don’t want to do security upgrades in a rush and from a point where you feel unsafe. This leads to mistakes which can lead to total loss (for example sending to a wrong address). Self custody is the first an most important rule to follow if you want to keep your coins and become a whole coiner. If you can't afford a hardware wallet now, at least use a hotwallet ...
Can i use a hotwallet instead?
Hotwallets are wallets, that are connected to the internet, like Apps on your PC or smartphone. They are considered not to be as safe as harwarewallets (so called coldwallets), because if something has no connection to the internet, there is a huge part of risk being taken away. But hotwallets are still way better than leaving your funds on an exchange because with a hotwallet you get the keys to your funds. With exchanges you only get an IOU aka a promise from the exchange. And we have seen how that ends with MountGOX, FTX, Celsius, Blockfi and various others ... Use hotwallets rather on smartphone than on desktop device, as smartphones are a little more secure. A few good ones i could recommend are Blue Wallet, Green Wallet and Exodus but there are a lot of good solutions out there. Just make sure to get a 12 or 24 word seed recovery phrase when setting it up so you are really in full control of your funds. But if you can use a hardware wallet, rather choose that.
Which wallet should i get?
I did try a few but not all of them: - The one i would recommend the most at this point in time is the Blockstream Jade Classic as it comes with almost all possible features you could imagine for a very reasonable price. You can even use it completely airgapped wit QR codes and use it without keystorage like a SeedSigner. I will touch on those features later on in part 2. nostr:npub1jg552aulj07skd6e7y2hu0vl5g8nl5jvfw8jhn6jpjk0vjd0waksvl6n8n is also very active on nostr and provides good support for us plebs. - Coldcard is also a hardware wallet i hear a lot of good stuff about. - As well as the BitBox02 Bitcoin only edition. - Trezor has had some security issues regarding to not having a secure element. I am sure they implemented a solution in the meantime, but i am not up to date with this so i can not recommend it without any doubt. - Ledger devices were generally considered safe but they had multiple security related incidents such as leaking customer data or admiting to be able to extract your seed from the wallet. The fact that they allow to store other crypto currencies, also introduces a bigger attack surface. Thuss i don't recommend using a ledger. If you only have a ledger it's still better than leaving your coins on an exchange though. - SeedSigner, as described, is more for advanced users or if you really want to dig into it, in my opinion. You could also use the Blockstream Jade as a SeedSigner.
Where should i buy?
This is important: Order hardware wallets ONLY straight from the store of the manufacturer. Any middleman or additional steps in the delivery process increase the risk of your device being manipulated. If you are really paranoid about this stick with Coldcard or the new Jade Plus as these models have a build in mechanism to check if they have been tempered with. Also consider using a postbox or working address when you order a hardware wallet or any bitcoin related stuff in general. The less people know that you own bitcoin, the better.
2. Use single-sig wallets
Backup your 12 or 24 words seed phrase and store them in a secure place (safe from theft, fire, water AND CHILDREN etc. i will get to how to achieve this). Most cases in loss of bitcoin happen because of the loss of access to the keys. Not because of theft. So the biggest risk you should care for is that you don't lose access to your keys. And how do most people lose access to their keys? They either ...
1) make the backup too complex so that themselves or their heirs have no clue how to restore it or 2) they are too lazy with their backup so that a flooded basement, thrown away harddrive or deleted photo causes them to loose their bitcoin forever.
Yes there are usecases for multi-sig set-ups and yes it introduces a better level of safety but it also introduces a higher risk of loosing your funds because of complexity. As a newbie or intermediate you don't have to dig into this complexity. You can, but unless you understand very well what you are doing, i wouldn't recommend using multi-sig wallets. Remember: 99% of bitcoin losses don't accure because of theft. If you still feel the need to add a little more security for this aspect, i recommend using a passphrase instead, which has also it's own trade-offs, as we will discuss in the recommended techniques in part 2.
3. Secure your wallet with a good PIN
Don't choose your mother's birthday as your PIN or anything else that can be social engineered. The more random, the better. And the longer the better. If you use multiple hardware wallets, also use different PINs for them. PINs on their own are generally not a very good method to protect anything. A 4 digit PIN for example only gives 10,000 possible combinations (from 0000 to 9999). A modern computer can try these all out pretty fast. BUT fortunately most wallets have a solution for this: If you enter the wrong PIN multiple times in a row they will reset to default and erease the stored keys. Thuss an attacker has only a few tries. Wallets that i know of doing that are the Blockstream Jade or the Coldcard for example. Both also provide the option to set up a specific wallet erease PIN that clears the wallet when entered once. Maybe consider these factors when choosing a wallet.
4. Backup your seed WELL
Backup your seed phrase offline, with pen and paper. Better yet on steel (more on that in upcoming part 2). But make sure that your seed phrase is NEVER being put into or shown to a device other than your hardware wallet. NEVER EVER! Don't make a picture of it to store in your cloud, don't safe it in your notes, don't think you are safe storing it in an encrypted file. You are not. Do it offline and keep it offline. Always. Now let's talk material ...
What material should i use?
Paper can burn, suffer from contact with water, be blown or thrown away and be destroyed from all other sorts of things. I found the safest way to backup a seed phrase is by hammering it into a stainless steel plate. These steelwallets don't break the bank like some fancy Cryptotag or other known brand backup solutions do and in most cases they are even better. Espacially when it comes to the backup style:
What way to perform the backup?
Plain text, letter by letter, hammered onto a steel plate. See part 2 for more details on why this is the best method.
5. Test your backup
Every owner of a substantial amount of bitcoin should have restored his wallet at least once! Make sure you know how to get your funds back in case something goes wrong. Especially if you do more complex things like passphrases (which we will cover in part 2) but also if you only use the 12 or 24 word seeds. The way i like to do it is as follows:
- Step 1) When you have set up your wallet, send a small amount of sats to it. This is a good practice anyway to make sure everything works as intended before sending larger amounts.
- Step 2) After your wallet has recieved the small amount reset your device to default. That means completely whiping it. MAKE SURE YOU HAVE BACKED UP YOUR SEED WELL!
- Step 3) Restore your wallet with your backup.
- Step 4) [optional but recommended] Send that small amount of sats back to verify that you truly have full control over this wallet.
If you can access (and control) the small amount of sats, your backup works and you can now send larger amounts. This is also a good way to test if you have properly backed up your passphrase, in case you are setting up a passphrase wallet.
Now what?
When your funds grow bigger, eventually you will ask yourself: "Is this secure enough?" If you are in that position, the recommended methods in part 2 will help you upgrade your security and avoid common mistakes which could put your coins at risk (part 2 will be linked here as soon as it's available).
What have i missed?
Do you agree with these essentials on how to store bitcoin? Did i miss anything? Please let me know and help to refine this set of rules so we can help more and more people to become souverein bitcoin holders.
-
 @ 5d4b6c8d:8a1c1ee3
2025-01-10 15:18:41
@ 5d4b6c8d:8a1c1ee3
2025-01-10 15:18:41I try to start and end my days well, even when the middle gets a little messy.
I'm fortunate to not have to use an alarm clock to wake up. I work remotely and have a good deal of schedule flexibility, so I sleep until I wake up naturally. Of course, I also have a little kid, so "waking up naturally" isn't always as peaceful as it sounds.
I've been into intermittent fasting for quite a while and I added dry fasting into the mix around a year ago.
I end my dry fast relatively early with a cup of coffee around 8:00am or so. If no one else (aka my wife) has made coffee, I'll push it later. I like to put coconut oil, coconut milk, sea salt, turmeric, and cinnamon in my coffee.
The first thing I eat, around 9:00 or 10:00 am, are three Brazil nuts. That's just about the only way to get an optimal level of selenium in your diet. By my understanding of ketosis, this shouldn't be enough to take my body out of a ketogenic state.
I try to get a couple thousand steps in while getting ready for work, helping out with the kid, and refilling my coffee.
I put off eating anything more substantial until my wife cooks something, which is usually in the early afternoon. However, as a dad, there are often good amounts of leftovers and other would be food waste that I'll eat when available.
How do you try to start your days and do you also find it easier to control how your days start than how they go in the middle?
originally posted at https://stacker.news/items/844949
-
 @ 101b30ee:18a46a45
2025-01-02 17:28:15
@ 101b30ee:18a46a45
2025-01-02 17:28:15
ハンドシェイク
- HTTPリクエスト解析
- [ ] HTTPリクエストラインのパーサー関数作成
- [x] HTTPヘッダーのパーサー関数作成
- [ ] HTTPリクエストボディのパーサー関数作成
- [ ] WebSocket関連ヘッダーの検証
- [ ]
Upgrade: websocket - [ ]
Connection: Upgrade - [ ]
Sec-WebSocket-Keyの取得と検証 - [ ]
Sec-WebSocket-Version: 13の検証
- [ ]
- HTTPレスポンス作成
- [ ]
Sec-WebSocket-Acceptの生成- [x]
Sec-WebSocket-KeyにSHA-1適用(外部依存) - [ ]
Sec-WebSocket-KeyにSHA-1適用(非依存) - [x]
Sec-WebSocket-KeyにBase64エンコードを適用
- [x]
- [x] HTTP 101 Switching Protocolsレスポンスの構築と送信
データ転送
WebSocketフレームの処理
- フレーム解析
- [x]
finビットの取り出しと解釈 - [x]
rsv1,rsv2,rsv3の取り出しと検証 - [ ]
opcodeの取り出しと処理- [ ] 0x0: 継続フレーム
- [ ] 0x1: テキストフレーム
- [ ] 0x2: バイナリフレーム
- [ ] 0x8: 接続終了
- [ ] 0x9: Ping
- [ ] 0xA: Pong
- [x]
maskフラグの取得と検証 - [x]
payload_lenの取り出しと解析 - [x] 拡張されたペイロード長(
extended payload len)の取り出し - [x]
masking keyの取得とデコード - [x]
payloadデータの取り出し - [ ]
finに基づく分割パケット対応 - デコード
- [x]
masking keyを使用したペイロードデコード - opcode別処理
- [ ] テキストフレーム(0x1)のUTF-8デコードと処理
- [ ] バイナリフレーム(0x2)のデータ処理
- [ ] Ping(0x9)フレームへのPong応答
- [ ] 接続終了(0x8)の処理
- [ ] 不正なopcodeに対するエラー応答
フレーム生成
- フレーム構築
- [ ]
finフラグ設定 - [ ]
opcodeの設定 - [ ] ペイロードのマスキング処理(クライアント向けのみ)
- [ ] ペイロード長の設定(拡張ペイロード長を含む)
- [ ] フレーム全体のバイトストリーム化
接続管理
- [x] クライアント接続の確立
- [x] 2クライアント以上の接続の確立
- [ ] 接続中のクライアントのリスト管理
- [ ] 接続のタイムアウト処理
- [ ] 不正なクライアントからの接続拒否
- [ ] 接続終了時のクリーンアップ処理
- [ ] ハートビート機能(Ping/Pong)による接続維持
セキュリティ
- [ ] WebSocket Originヘッダーの検証(許可されたオリジンのみ受け入れる)
- [ ] メッセージサイズの上限設定(大規模メッセージ攻撃の防御)
- [ ] 不正なフレーム/データに対するエラーハンドリング
- [ ] SSL/TLSサポート(wssプロトコル用)
拡張機能とプロトコルアップグレード
- [ ] サブプロトコル(Sec-WebSocket-Protocol)の処理
- [ ] 拡張(Sec-WebSocket-Extensions)のサポート
- 圧縮データのデコード (例: permessage-deflate)
テストとデバッグ
- [ ] 単体テスト
- [ ] ハンドシェイクのテスト
- [ ] フレーム解析と生成のテスト
- [ ] 各opcode処理のテスト
- [ ] 負荷テスト(高負荷時の動作確認)
- [ ] プロトコルコンフォーマンステスト
- [ ] RFC 6455に準拠しているかの確認
- [ ] ロギングとデバッグツールの実装
ドキュメント
- [ ] コードベースのコメントとドキュメント化
- [ ] WebSocketサーバーの設定と使用法についてのユーザーガイド作成
タグ
RFC6455
-
 @ 4657dfe8:47934b3e
2025-01-10 13:28:47
@ 4657dfe8:47934b3e
2025-01-10 13:28:47Alby Hub - your Center for Bitcoin Payments
Alby Hub is a self-custodial lightning wallet that lets users choose their preferred Lightning funding source. It includes an easy-to-use lightning node with a one-click setup, while also accommodating existing node runners.
In short Alby Hub offers node runners:
➡️ a lightning address to receive payments in a self-custodial manner ➡️ integrated Lightning Service Providers, to quickly buy channels with receiving capacity ➡️ a selection of vetted channel partners to open channels without searching for a long time ➡️ a marketplace of apps to connect your own node. Read more about this superpower. ➡️ a mobile app, Alby Go, to pay right from their own node on the go.
Thus, Alby Hub enables you to make your node the central hub for bitcoin payments, maintaining full self-sovereignty.
Install Alby Hub on RaspiBlitz
- Login into the RaspiBlitz WebUI and enter the dashboard
- Go to Apps, find Alby Hub and install the app
It’s as easy as that. Now you can link your node with an Alby account to get a lightning address, use your node on the go with the Alby Go mobile app or on the web with the Alby Browser Extension. Updates of Alby Hub become available with each new RaspiBlitz release.
With one-click setup, an intuitive interface, and seamless integration with dozens of bitcoin apps, Alby Hub makes self-custodial bitcoin payments easy for everyone while adding much more utility to your lightning node.
-
 @ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08
@ 1bda7e1f:bb97c4d9
2025-01-02 05:19:08Tldr
- Nostr is an open and interoperable protocol
- You can integrate it with workflow automation tools to augment your experience
- n8n is a great low/no-code workflow automation tool which you can host yourself
- Nostrobots allows you to integrate Nostr into n8n
- In this blog I create some workflow automations for Nostr
- A simple form to delegate posting notes
- Push notifications for mentions on multiple accounts
- Push notifications for your favourite accounts when they post a note
- All workflows are provided as open source with MIT license for you to use
Inter-op All The Things
Nostr is a new open social protocol for the internet. This open nature exciting because of the opportunities for interoperability with other technologies. In Using NFC Cards with Nostr I explored the
nostr:URI to launch Nostr clients from a card tap.The interoperability of Nostr doesn't stop there. The internet has many super-powers, and Nostr is open to all of them. Simply, there's no one to stop it. There is no one in charge, there are no permissioned APIs, and there are no risks of being de-platformed. If you can imagine technologies that would work well with Nostr, then any and all of them can ride on or alongside Nostr rails.
My mental model for why this is special is Google Wave ~2010. Google Wave was to be the next big platform. Lars was running it and had a big track record from Maps. I was excited for it. Then, Google pulled the plug. And, immediately all the time and capital invested in understanding and building on the platform was wasted.
This cannot happen to Nostr, as there is no one to pull the plug, and maybe even no plug to pull.
So long as users demand Nostr, Nostr will exist, and that is a pretty strong guarantee. It makes it worthwhile to invest in bringing Nostr into our other applications.
All we need are simple ways to plug things together.
Nostr and Workflow Automation
Workflow automation is about helping people to streamline their work. As a user, the most common way I achieve this is by connecting disparate systems together. By setting up one system to trigger another or to move data between systems, I can solve for many different problems and become way more effective.
n8n for workflow automation
Many workflow automation tools exist. My favourite is n8n. n8n is a low/no-code workflow automation platform which allows you to build all kinds of workflows. You can use it for free, you can self-host it, it has a user-friendly UI and useful API. Vs Zapier it can be far more elaborate. Vs Make.com I find it to be more intuitive in how it abstracts away the right parts of the code, but still allows you to code when you need to.
Most importantly you can plug anything into n8n: You have built-in nodes for specific applications. HTTP nodes for any other API-based service. And community nodes built by individual community members for any other purpose you can imagine.
Eating my own dogfood
It's very clear to me that there is a big design space here just demanding to be explored. If you could integrate Nostr with anything, what would you do?
In my view the best way for anyone to start anything is by solving their own problem first (aka "scratching your own itch" and "eating your own dogfood"). As I get deeper into Nostr I find myself controlling multiple Npubs – to date I have a personal Npub, a brand Npub for a community I am helping, an AI assistant Npub, and various testing Npubs. I need ways to delegate access to those Npubs without handing over the keys, ways to know if they're mentioned, and ways to know if they're posting.
I can build workflows with n8n to solve these issues for myself to start with, and keep expanding from there as new needs come up.
Running n8n with Nostrobots
I am mostly non-technical with a very helpful AI. To set up n8n to work with Nostr and operate these workflows should be possible for anyone with basic technology skills.
- I have a cheap VPS which currently runs my HAVEN Nostr Relay and Albyhub Lightning Node in Docker containers,
- My objective was to set up n8n to run alongside these in a separate Docker container on the same server, install the required nodes, and then build and host my workflows.
Installing n8n
Self-hosting n8n could not be easier. I followed n8n's Docker-Compose installation docs–
- Install Docker and Docker-Compose if you haven't already,
- Create your
docker-compose.ymland.envfiles from the docs, - Create your data folder
sudo docker volume create n8n_data, - Start your container with
sudo docker compose up -d, - Your n8n instance should be online at port
5678.
n8n is free to self-host but does require a license. Enter your credentials into n8n to get your free license key. You should now have access to the Workflow dashboard and can create and host any kind of workflows from there.
Installing Nostrobots
To integrate n8n nicely with Nostr, I used the Nostrobots community node by Ocknamo.
In n8n parlance a "node" enables certain functionality as a step in a workflow e.g. a "set" node sets a variable, a "send email" node sends an email. n8n comes with all kinds of "official" nodes installed by default, and Nostr is not amongst them. However, n8n also comes with a framework for community members to create their own "community" nodes, which is where Nostrobots comes in.
You can only use a community node in a self-hosted n8n instance (which is what you have if you are running in Docker on your own server, but this limitation does prevent you from using n8n's own hosted alternative).
To install a community node, see n8n community node docs. From your workflow dashboard–
- Click the "..." in the bottom left corner beside your username, and click "settings",
- Cilck "community nodes" left sidebar,
- Click "Install",
- Enter the "npm Package Name" which is
n8n-nodes-nostrobots, - Accept the risks and click "Install",
- Nostrobots is now added to your n8n instance.
Using Nostrobots
Nostrobots gives you nodes to help you build Nostr-integrated workflows–
- Nostr Write – for posting Notes to the Nostr network,
- Nostr Read – for reading Notes from the Nostr network, and
- Nostr Utils – for performing certain conversions you may need (e.g. from bech32 to hex).
Nostrobots has good documentation on each node which focuses on simple use cases.
Each node has a "convenience mode" by default. For example, the "Read" Node by default will fetch Kind 1 notes by a simple filter, in Nostrobots parlance a "Strategy". For example, with Strategy set to "Mention" the node will accept a pubkey and fetch all Kind 1 notes that Mention the pubkey within a time period. This is very good for quick use.
What wasn't clear to me initially (until Ocknamo helped me out) is that advanced use cases are also possible.
Each node also has an advanced mode. For example, the "Read" Node can have "Strategy" set to "RawFilter(advanced)". Now the node will accept json (anything you like that complies with NIP-01). You can use this to query Notes (Kind 1) as above, and also Profiles (Kind 0), Follow Lists (Kind 3), Reactions (Kind 7), Zaps (Kind 9734/9735), and anything else you can think of.
Creating and adding workflows
With n8n and Nostrobots installed, you can now create or add any kind of Nostr Workflow Automation.
- Click "Add workflow" to go to the workflow builder screen,
- If you would like to build your own workflow, you can start with adding any node. Click "+" and see what is available. Type "Nostr" to explore the Nostrobots nodes you have added,
- If you would like to add workflows that someone else has built, click "..." in the top right. Then click "import from URL" and paste in the URL of any workflow you would like to use (including the ones I share later in this article).
Nostr Workflow Automations
It's time to build some things!
A simple form to post a note to Nostr
I started very simply. I needed to delegate the ability to post to Npubs that I own in order that a (future) team can test things for me. I don't want to worry about managing or training those people on how to use keys, and I want to revoke access easily.
I needed a basic form with credentials that posted a Note.
For this I can use a very simple workflow–
- A n8n Form node – Creates a form for users to enter the note they wish to post. Allows for the form to be protected by a username and password. This node is the workflow "trigger" so that the workflow runs each time the form is submitted.
- A Set node – Allows me to set some variables, in this case I set the relays that I intend to use. I typically add a Set node immediately following the trigger node, and put all the variables I need in this. It helps to make the workflows easier to update and maintain.
- A Nostr Write node (from Nostrobots) – Writes a Kind-1 note to the Nostr network. It accepts Nostr credentials, the output of the Form node, and the relays from the Set node, and posts the Note to those relays.
Once the workflow is built, you can test it with the testing form URL, and set it to "Active" to use the production form URL. That's it. You can now give posting access to anyone for any Npub. To revoke access, simply change the credentials or set to workflow to "Inactive".
It may also be the world's simplest Nostr client.
You can find the Nostr Form to Post a Note workflow here.
Push notifications on mentions and new notes
One of the things Nostr is not very good at is push notifications. Furthermore I have some unique itches to scratch. I want–
- To make sure I never miss a note addressed to any of my Npubs – For this I want a push notification any time any Nostr user mentions any of my Npubs,
- To make sure I always see all notes from key accounts – For this I need a push notification any time any of my Npubs post any Notes to the network,
- To get these notifications on all of my devices – Not just my phone where my Nostr regular client lives, but also on each of my laptops to suit wherever I am working that day.
I needed to build a Nostr push notifications solution.
To build this workflow I had to string a few ideas together–
- Triggering the node on a schedule – Nostrobots does not include a trigger node. As every workflow starts with a trigger we needed a different method. I elected to run the workflow on a schedule of every 10-minutes. Frequent enough to see Notes while they are hot, but infrequent enough to not burden public relays or get rate-limited,
- Storing a list of Npubs in a Nostr list – I needed a way to store the list of Npubs that trigger my notifications. I initially used an array defined in the workflow, this worked fine. Then I decided to try Nostr lists (NIP-51, kind 30000). By defining my list of Npubs as a list published to Nostr I can control my list from within a Nostr client (e.g. Listr.lol or Nostrudel.ninja). Not only does this "just work", but because it's based on Nostr lists automagically Amethyst client allows me to browse that list as a Feed, and everyone I add gets notified in their Mentions,
- Using specific relays – I needed to query the right relays, including my own HAVEN relay inbox for notes addressed to me, and wss://purplepag.es for Nostr profile metadata,
- Querying Nostr events (with Nostrobots) – I needed to make use of many different Nostr queries and use quite a wide range of what Nostrobots can do–
- I read the EventID of my Kind 30000 list, to return the desired pubkeys,
- For notifications on mentions, I read all Kind 1 notes that mention that pubkey,
- For notifications on new notes, I read all Kind 1 notes published by that pubkey,
- Where there are notes, I read the Kind 0 profile metadata event of that pubkey to get the displayName of the relevant Npub,
- I transform the EventID into a Nevent to help clients find it.
- Using the Nostr URI – As I did with my NFC card article, I created a link with the
nostr:URI prefix so that my phone's native client opens the link by default, - Push notifications solution – I needed a push notifications solution. I found many with n8n integrations and chose to go with Pushover which supports all my devices, has a free trial, and is unfairly cheap with a $5-per-device perpetual license.
Once the workflow was built, lists published, and Pushover installed on my phone, I was fully set up with push notifications on Nostr. I have used these workflows for several weeks now and made various tweaks as I went. They are feeling robust and I'd welcome you to give them a go.
You can find the Nostr Push Notification If Mentioned here and If Posts a Note here.
In speaking with other Nostr users while I was building this, there are all kind of other needs for push notifications too – like on replies to a certain bookmarked note, or when a followed Npub starts streaming on zap.stream. These are all possible.
Use my workflows
I have open sourced all my workflows at my Github with MIT license and tried to write complete docs, so that you can import them into your n8n and configure them for your own use.
To import any of my workflows–
- Click on the workflow of your choice, e.g. "Nostr_Push_Notify_If_Mentioned.json",
- Click on the "raw" button to view the raw JSON, ex any Github page layout,
- Copy that URL,
- Enter that URL in the "import from URL" dialog mentioned above.
To configure them–
- Prerequisites, credentials, and variables are all stated,
- In general any variables required are entered into a Set Node that follows the trigger node,
- Pushover has some extra setup but is very straightforward and documented in the workflow.
What next?
Over my first four blogs I explored creating a good Nostr setup with Vanity Npub, Lightning Payments, Nostr Addresses at Your Domain, and Personal Nostr Relay.
Then in my latest two blogs I explored different types of interoperability with NFC cards and now n8n Workflow Automation.
Thinking ahead n8n can power any kind of interoperability between Nostr and any other legacy technology solution. On my mind as I write this:
- Further enhancements to posting and delegating solutions and forms (enhanced UI or different note kinds),
- Automated or scheduled posting (such as auto-liking everything Lyn Alden posts),
- Further enhancements to push notifications, on new and different types of events (such as notifying me when I get a new follower, on replies to certain posts, or when a user starts streaming),
- All kinds of bridges, such as bridging notes to and from Telegram, Slack, or Campfire. Or bridging RSS or other event feeds to Nostr,
- All kinds of other automation (such as BlackCoffee controlling a coffee machine),
- All kinds of AI Assistants and Agents,
In fact I have already released an open source workflow for an AI Assistant, and will share more about that in my next blog.
Please be sure to let me know if you think there's another Nostr topic you'd like to see me tackle.
GM Nostr.
-
 @ 59cb0748:9602464b
2025-01-01 06:15:09
@ 59cb0748:9602464b
2025-01-01 06:15:09Nostrでお世話になっている方も、お世話になってない方も、こんにちは!
タコ頭大吉です!
NIP-23を使った初めての投稿です。
今回は、私がここ数ヶ月中にデザインをした三種類のビタキセケースの紹介記事になります!!
ビタキセを買ったもののあまり自分の好みに合う外観や仕様のケースがなく、いくつかプロトタイプを作りそれなりに時間をかけて考えたケース達です。
これら3シリーズに関しては、FDMタイプの3Dプリンタの精度、耐久性、出力後の作業性を考慮して一つのパーツで完結することに拘って設計をしました。
一定以上の充填率でプリントをすればそれなりに丈夫なはずです。
また、基本的に放熱性と保護性を両立できるように設計をしたつもります。
それぞれのモデルについて簡単に紹介をさせていただきますので、よろしければ各リポジトリに付属のREADMEを読んでいただいて自作、フィードバックをいただけましたら幸いです。
それでは、簡単に各モデルの紹介をさせていたきます。
AirLiftFrame
 最初に作ったモデルです!
少し大きいのが難点ですが、分厚めのフレームをベースとし基盤周辺をあえて囲わない設計により、保護性と放熱を阻害しない事の両立を狙っています。
最初に作ったモデルです!
少し大きいのが難点ですが、分厚めのフレームをベースとし基盤周辺をあえて囲わない設計により、保護性と放熱を阻害しない事の両立を狙っています。
TwinAirLiftFrame
 ビタキセを買い増ししたことにより、複数台をカッコよく運用したいという需要が自分の中に出てきたので、AirLiftFrameを2つくっつけたら良いのではと言うごくごく単純な発想でつくり始めたケースです。
しかし、ただ横並びにしただけでは廃熱が干渉するだけではなく、DCジャックやUSBポートへのアクセスが阻害されるという問題にすぐに気がつきました。
そこで、WebUI上でディスプレイの表示を上下反転出来ることに注目し、2台を上下逆向きに取り付ける事でそれらの問題を解決しました!
ビタキセを買い増ししたことにより、複数台をカッコよく運用したいという需要が自分の中に出てきたので、AirLiftFrameを2つくっつけたら良いのではと言うごくごく単純な発想でつくり始めたケースです。
しかし、ただ横並びにしただけでは廃熱が干渉するだけではなく、DCジャックやUSBポートへのアクセスが阻害されるという問題にすぐに気がつきました。
そこで、WebUI上でディスプレイの表示を上下反転出来ることに注目し、2台を上下逆向きに取り付ける事でそれらの問題を解決しました!
VoronoiShell
 AirLiftFrameシリーズのサイズを小型化する事から始めたプロジョクトです。
縦横の寸法の削減だけではなく、厚みを薄くつくリたいという希望がありました。
所が単純に薄くすると、持った時に発熱する背面パーツに手が触れてしまったり、落下などでぶつかった際に背面パーツが破損する懸念がありました。
そこで、(当初は付けたくはなかった)背面保護用のグリルをデザインする必要が出てきました。
初めは多角形でしたがあまりにもダサく、調べている内にVoronoi柄という有機的なパターンに行き付き即採用しました。
結果、ビタキセを取り付けると柄が見えなくなるのが勿体無いぐらい個性的でスタイリッシュなデザインに仕上がりました。
AirLiftFrameシリーズのサイズを小型化する事から始めたプロジョクトです。
縦横の寸法の削減だけではなく、厚みを薄くつくリたいという希望がありました。
所が単純に薄くすると、持った時に発熱する背面パーツに手が触れてしまったり、落下などでぶつかった際に背面パーツが破損する懸念がありました。
そこで、(当初は付けたくはなかった)背面保護用のグリルをデザインする必要が出てきました。
初めは多角形でしたがあまりにもダサく、調べている内にVoronoi柄という有機的なパターンに行き付き即採用しました。
結果、ビタキセを取り付けると柄が見えなくなるのが勿体無いぐらい個性的でスタイリッシュなデザインに仕上がりました。
いずれカスタム方法やインサートナットや増設ファンの選定方法等を紹介したいのですが、今回はNIP-23になれるという意図もあるので紹介に留めます! また、他の関連OSハードウェアプロジェクトのケースもデザインできたらと思っております!
今後ともタコ頭をよろしくお願いいたします。
-
 @ d34e832d:383f78d0
2025-01-06 23:44:40
@ d34e832d:383f78d0
2025-01-06 23:44:40Lets explore three key aspects of Bitcoin technology to enhance your engagement with the ecosystem:
- Running an Alby Hub Cloud Instance
- Setting Up a Nutshell Ecash Mint on an Affordable VPS
- Integrating Nostr Wallet Connect for Seamless Tipping
These components empower users to manage transactions, ensure privacy, and facilitate smooth interactions within the Bitcoin and Nostr communities.
1. Running an Alby Hub Cloud Instance
Purpose and Benefits:
Alby Hub is a self-custodial Lightning wallet that allows you to manage Bitcoin transactions efficiently. By running an Alby Hub instance in the cloud, you gain 24/7 online access to receive payments via a Lightning address, integrate with various applications, and maintain control over your funds without the need for personal hardware.
Setting Up Alby Hub in the Cloud:
-
Choose Alby Cloud: For a hassle-free setup, Alby offers a cloud service where you can start your own hub in just 2 minutes. Give it A Try: Alby Cloud
-
Subscription Benefits: Subscribing to Alby Cloud provides you with a self-custodial Lightning wallet, 24/7 online access, exclusive partner deals, priority support, and access to a subscriber community.
-
Getting Started: Visit the Alby Cloud page, select the subscription that suits you, and follow the guided setup process to have your hub up and running quickly.
- Alby Cloud page
For a visual guide on setting up Alby Hub, you can watch the following tutorial:
2. Setting Up a Nutshell Ecash Mint on an Affordable VPS
Purpose and Benefits:
Nutshell is an implementation of Ecash, a digital cash system that prioritizes privacy and anonymity. Setting up a Nutshell Ecash mint on a Virtual Private Server (VPS) allows you to operate your own mint, enhancing transaction privacy and providing a backup system for your Bitcoin transactions.
Setting Up on a $5 VPS:
-
Select a VPS Provider: Choose an affordable VPS provider that supports Bitcoin and Nostr communities. For instance, SatoshiHost offers VPS services tailored for such needs.
-
Install Nutshell: After setting up your VPS, install the Nutshell software by following the official installation guide.
- Nutshell
-
Configure the Mint: Set up the mint parameters, including denomination and security settings, to suit your requirements.
-
Secure the Server: Implement security measures such as firewalls and regular updates to protect your mint from potential threats.
- Recommendations
- Server Tips
3. Integrating Nostr Wallet Connect for Seamless Tipping
Purpose and Benefits:
Nostr Wallet Connect (NWC) is an open protocol that enables applications to interact with Bitcoin Lightning wallets. Integrating NWC allows for seamless tipping and payments within Nostr apps, enhancing user experience and promoting engagement.
Integration Steps:
-
Choose a Supporting App: Select a Nostr app that supports NWC, such as Amythystor Damus.
-
Connect Your Wallet: Use NWC to link your preferred Lightning wallet to the Nostr app. This connection facilitates seamless payments without the need to switch between applications.
-
Test the Integration: Perform a test transaction to ensure that the tipping functionality works as intended.
-
Maintain Security: Regularly update your wallet and Nostr app to incorporate the latest security features and improvements.
For a deeper understanding of Nostr Wallet Connect and its significance, you can watch the following discussion:
Final Thoughts On Setup
Implementing these components enhances your interaction with the Bitcoin ecosystem by providing efficient transaction management, improved privacy, and seamless integration with Nostr applications. By running an Alby Hub cloud instance, setting up a Nutshell Ecash mint on an affordable VPS, and integrating Nostr Wallet Connect, you contribute to a more robust and user-friendly Bitcoin environment.
Invitation for Feedback
I encourage you to share any questions or feedback regarding these topics. Let's continue the conversation to explore how we can further engage with and improve upon these technologies.
-
 @ 21ac2956:09d1e2df
2024-12-24 23:24:04
@ 21ac2956:09d1e2df
2024-12-24 23:24:04スペース2つ+改行→
改行2つ→ハードブレイク→
いかがでしたか? -
 @ 6ad3e2a3:c90b7740
2025-01-10 12:33:47
@ 6ad3e2a3:c90b7740
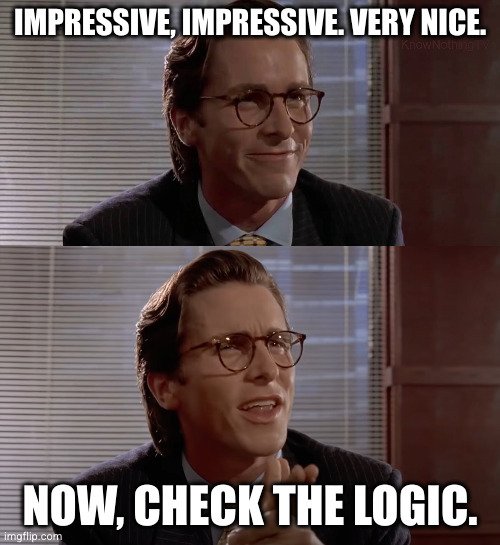
2025-01-10 12:33:47The excesses of wokeness are thankfully getting their overdue correction, but as often happens with corrections, they tend to overshoot. A case in point was from the usually reasonable writer Wesley Yang on Twitter, who posted the following:
Poor long-term immigration policy has apparently led to too many foreign-born and native criminals of foreign descent in Norway, a disproportionate number of whom, per the chart, hail from Somalia and Morocco. Yang argues using this data to inform Norway’s immigration policies going forward is both unproblematic and “no longer prejudice.”
This is a sleight of hand. You can advocate for designing prejudicial immigration policies based on the group to which an individual potential immigrant belongs, but you cannot both do so and pretend it is not prejudicial.
This is not a point about what countries should or should not DO. They are free IMO to design immigration policies as they see fit, and there are arguments to be had over that. But there is a reactionary blindness wherein people pretend that grouping individuals by race, religion or country of origin isn't prejudicial to those individuals who have no control over how others in their assigned group behave.
The grouping is justified in their view by "data" or "statistics" or "reason." The truth is most of us still view "prejudice" as negative, so no one advocating for discriminatory immigration policies wants to be considered prejudiced. They are for the policy, think it's good, and therefore try to pretend it's not prejudiced when it obviously is.
Don't pretend. If you're for prejudicial, discriminatory immigration policies "for the greater good", just advocate for it on those terms. Be honest about what you're saying.
This might seem like a trivial point on which to base a post, but I don’t think it is. It’s not because “prejudice is bad” or “racism!” That’s just one type of instance in which this midwit tendency — to assign individuals to a group and then pretend you are being “data-driven” — rears its terrible head. I remember a couple years ago people on Twitter accused me of “taking up an ICU bed” because I refused to inject myself with Pfizer’s latest. Their reasoning was similar: because the unvaccinated are more likely to take up ICU beds (which turned out to be a lie, but let’s assume it were true), I was in the group taking up more beds, therefore I was taking up a bed.
The trick is to assign someone to a group in which they qualify (Somali, unvaccinated, etc.), get “data” about that group and then apply that data to the individuals within it, even if it is totally inaccurate with respect to them.
This is the same trick used to justify disastrous DEI policies too. You are from a historically underprivileged group, so you deserve to be held to lower standards. It doesn’t matter if you would succeed on your own merit, it doesn’t matter your race, gender, sexual orientation are irrelevant to the task for which you are being hired, it doesn’t matter if you are the son of wealthy and famous people and attended all the best schools, you belong to a particular category and therefore this standard will be applied.
But the implications of this midwit sleight of hand are even worse than that, especially on the eve of AI-based systems taking over so many of the administrative functions at both the corporate and state level. You will be categorized, and you will be pre-judged on that basis because it is far more efficient for the system to do so than to examine everyone individually. In fact, I’d argue, unlike humans, AI is incapable of seeing individuals, it sees only “data.”
This was the premise for the movie Minority Report, set in a dystopian future wherein people get convicted of “pre-crime” because the system determined from the data about them they were likely to commit one. You might not have done anything yet, but based on your angry social media posts, your high testosterone, your age and background, you have a 99.9 percent chance of violence. Why not arrest you now before you victimize someone? For every 1000 victims we protect, we’ll convict only one person who would not in fact have done it!
There will be many people who are for this kind of reasoning. It’s “data” after all. Never mind the data can be biased based on the grouping. Why am I grouped with other people I don’t know and over whom I have no control? What if they added 100 other parameters which showed I’m among the least likely to commit violence? Who is selecting these parameters and what are their agendas?
But more to the point, such a society is not free. You are at the whims of your grouping, of parameters, of statistics. The paradigm of individual civil liberties, innocent until proven guilty, responsibility only for your own actions would be dead. You are pre-judged before you have done anything.
The second-order effects of such a paradigm would be a race to the bottom. If I am not in the wrong group I can do no wrong, based on my favorable peers. I can roam the streets, commit acts of vandalism and violence with impunity, I can loaf at work, not do my job and never be fired. I would argue that under the present (and mercifully soon-to-be-departed) administration we’ve already experienced many of these effects already.
So back to the original question. What is Norway to do with this “data”? One idea would be to have a non-discriminatory vetting process that involves delayed gratification and requires some diligence on the part of the prospective immigrant. This might self-sort the people capable of living in an open, prosperous western society and those who are not. You would be admitted or denied based on demonstrated suitability (merit), not with whom you were grouped (identity). This would be closer to the “postjudice” policy prescription Yang erroneously claims for his own in the cited post.
Whether that results in more people of one race or another, one nationality or another getting in, isn't important. What's important is both not judging individuals on the basis of their assigned group and keeping the country free of violent criminals. Both goals are essential if we want to avoid dystopian outcomes.
-
 @ dd664d5e:5633d319
2025-01-06 20:36:17
@ dd664d5e:5633d319
2025-01-06 20:36:17Ingredients
- 1 kg of pork roast with rind, such as shoulder or a lean belly
- 1 bottle of beer, light or dark
- chopped German-style mirepoix (best combination, for this recipe, includes celery root, carrot, red onion, and leeks)
- salt, pepper, nutmeg
- 1 diced garlic clove
Directions
- Spread the vegetables on the bottom of the roasting pan.
- Pour half the beer over the roast. (Drink the other half.)
- Season the meat, to taste.
- Roast the meat at 180 °C, until done (depends upon the weight of the roast).
- Remove the meat from the oven, and wrap in aluminum foil.
- Pour 2-3 cups of water into the roasting pan.
- Pour/scrape everything from the pan into a sieve over a sauce pot.
- Press the vegetables against the sieve, with the back of a spoon, to ensure that you get all that good dripping flavor into the sauce.
- Defat the sauce with a grease separator, then pour it back into the pot.
- Thicken the sauce, slightly (it should remain slightly watery, and not turn into a gravy), according to your usual method.
- Open the foil and slice the roast.
- Serve with the sauce.








-
 @ 32310997:0c1e64cc
2024-12-24 23:10:03
@ 32310997:0c1e64cc
2024-12-24 23:10:03※このポエムはNostr Advent Calendar 2024の25日目の記事です。24日目はtansaibowさんのご担当です。
この鍵ひとつあれば
僕はどこにだってゆける
なんだってできる
さぁ進もう
この曠野を (※画像はイメージです。本文とはたいして関係がありません)
(※画像はイメージです。本文とはたいして関係がありません) -
 @ f0c7506b:9ead75b8
2024-12-08 09:05:13
@ f0c7506b:9ead75b8
2024-12-08 09:05:13
Yalnızca güçlü olanların hakkıdır yaşamak.
Güçlü olan ileri gider ve saflar seyrekleşir. Ama üç beş büyük, güçlü ve tanrısal kişi güneşli ve aydınlık gözleriyle o yeni, o vaat edilmiş ülkeye ulaşacaktır. Belki binlerce yıl sonra ancak. Ve güçlü, adaleli, hükmetmek için yaratılmış elleriyle hastaların, zayıfların ve sakatların ölüleri üzerinde bir krallık kuracaklardır. Bir krallık!
Benim aradığım insanların kendileri değil, sesleridir.
Duyguları körelmiş, çeşitli düşüncelere saplanmış kalabalık hiçbir zaman ilerlemenin taşıyıcısı olamaz, kendi küçüklüğünün o küflü içgüdüsüyle kalabalığın kin ve nefretle baktığı bir kişi, bir büyük kişi, iradesinin gösterdiği yolda kimsenin gözünün yaşına bakmaksızın ilahi bir güç ve bir zafer gülümsemesiyle yürüyebilir ancak.
Bizim soyumuz da sonsuz oluşum piramidinin doruk noktasını oluşturmaktan uzaktır. Bizler de mükemmelliğe ulaşmış değiliz. Bizler de henüz olgunlaşmadık.
Şairler sevgiye övgüler döşenir; doğrusu sevginin güçlü bir şey olduğu kesin. Hüneşin bir ışınıdır sevgi, aydınlatıp nurlandırır insanı der bazıları; bazıları da insanı esrikliğe sürükleyen bir zehri kendisinde barındırdığını söyler. Gerçekten de yol açtığı sonuçlar, bir hekimin ağır bir ameliyattan önce korkudan titreyen hastaya teneffüs ettirdiği güldürücü gazınkine benzer, içinde tepinip duran acıyı unutturur hastaya.
Önemli olan, hayatta hiç değilse bir kez kutsal bir ilkbaharın yaşanmasıdır; öyle bir bahar ki, insanın gönlünü ilerideki bütün günleri altın yaldızla kaplamaya yetecek kadar ışık ve parıltıyla doldursun.
Şu hayat denen şey kötü bir işçiliğin ürünü, acemilere göre bir şey. Bu kepaze yaşam uğruna insan nelere katlanmıyor ki!
Kendisine sadakatten ayrılmadığı, yalnızca kendisinin olan bir tek bu var: Yalnızlığı.
Sahildeki üstü tenteli hasır koltuklar arkasındaki yüksek, sessiz kum tepeleri içinde yürürsen, tenteler altındaki insanları göremezsin; ama birinin bir diğerine seslendiğini, bir başkasının gevezelik ettiğini, bir ötekinin güldüğünü işitir ve anlarsın hemen: bu insan şöyle şöyle biridir diyebilirsin. Onun hayatı sevdiğini, bağrında büyük bir özlem ya da acı barındırdığını, bu acının da sesini ağlamaklı kıldığını her gülüşünde hissedersin.
-
 @ 5002cb48:31a0d6d8
2025-01-09 19:37:47
@ 5002cb48:31a0d6d8
2025-01-09 19:37:47I am trying to update my profile, but it's not happening. Is the site broken?
-
 @ e31e84c4:77bbabc0
2024-12-02 10:44:07
@ e31e84c4:77bbabc0
2024-12-02 10:44:07Bitcoin and Fixed Income was Written By Wyatt O’Rourke. If you enjoyed this article then support his writing, directly, by donating to his lightning wallet: ultrahusky3@primal.net
Fiduciary duty is the obligation to act in the client’s best interests at all times, prioritizing their needs above the advisor’s own, ensuring honesty, transparency, and avoiding conflicts of interest in all recommendations and actions.
This is something all advisors in the BFAN take very seriously; after all, we are legally required to do so. For the average advisor this is a fairly easy box to check. All you essentially have to do is have someone take a 5-minute risk assessment, fill out an investment policy statement, and then throw them in the proverbial 60/40 portfolio. You have thousands of investment options to choose from and you can reasonably explain how your client is theoretically insulated from any move in the \~markets\~. From the traditional financial advisor perspective, you could justify nearly anything by putting a client into this type of portfolio. All your bases were pretty much covered from return profile, regulatory, compliance, investment options, etc. It was just too easy. It became the household standard and now a meme.
As almost every real bitcoiner knows, the 60/40 portfolio is moving into psyop territory, and many financial advisors get clowned on for defending this relic on bitcoin twitter. I’m going to specifically poke fun at the ‘40’ part of this portfolio.
The ‘40’ represents fixed income, defined as…
An investment type that provides regular, set interest payments, such as bonds or treasury securities, and returns the principal at maturity. It’s generally considered a lower-risk asset class, used to generate stable income and preserve capital.
Historically, this part of the portfolio was meant to weather the volatility in the equity markets and represent the “safe” investments. Typically, some sort of bond.
First and foremost, the fixed income section is most commonly constructed with U.S. Debt. There are a couple main reasons for this. Most financial professionals believe the same fairy tale that U.S. Debt is “risk free” (lol). U.S. debt is also one of the largest and most liquid assets in the market which comes with a lot of benefits.
There are many brilliant bitcoiners in finance and economics that have sounded the alarm on the U.S. debt ticking time bomb. I highly recommend readers explore the work of Greg Foss, Lawrence Lepard, Lyn Alden, and Saifedean Ammous. My very high-level recap of their analysis:
-
A bond is a contract in which Party A (the borrower) agrees to repay Party B (the lender) their principal plus interest over time.
-
The U.S. government issues bonds (Treasury securities) to finance its operations after tax revenues have been exhausted.
-
These are traditionally viewed as “risk-free” due to the government’s historical reliability in repaying its debts and the strength of the U.S. economy
-
U.S. bonds are seen as safe because the government has control over the dollar (world reserve asset) and, until recently (20 some odd years), enjoyed broad confidence that it would always honor its debts.
-
This perception has contributed to high global demand for U.S. debt but, that is quickly deteriorating.
-
The current debt situation raises concerns about sustainability.
-
The U.S. has substantial obligations, and without sufficient productivity growth, increasing debt may lead to a cycle where borrowing to cover interest leads to more debt.
-
This could result in more reliance on money creation (printing), which can drive inflation and further debt burdens.
In the words of Lyn Alden “Nothing stops this train”
Those obligations are what makes up the 40% of most the fixed income in your portfolio. So essentially you are giving money to one of the worst capital allocators in the world (U.S. Gov’t) and getting paid back with printed money.
As someone who takes their fiduciary responsibility seriously and understands the debt situation we just reviewed, I think it’s borderline negligent to put someone into a classic 60% (equities) / 40% (fixed income) portfolio without serious scrutiny of the client’s financial situation and options available to them. I certainly have my qualms with equities at times, but overall, they are more palatable than the fixed income portion of the portfolio. I don’t like it either, but the money is broken and the unit of account for nearly every equity or fixed income instrument (USD) is fraudulent. It’s a paper mache fade that is quite literally propped up by the money printer.
To briefly be as most charitable as I can – It wasn’t always this way. The U.S. Dollar used to be sound money, we used to have government surplus instead of mathematically certain deficits, The U.S. Federal Government didn’t used to have a money printing addiction, and pre-bitcoin the 60/40 portfolio used to be a quality portfolio management strategy. Those times are gone.
Now the fun part. How does bitcoin fix this?
Bitcoin fixes this indirectly. Understanding investment criteria changes via risk tolerance, age, goals, etc. A client may still have a need for “fixed income” in the most literal definition – Low risk yield. Now you may be thinking that yield is a bad word in bitcoin land, you’re not wrong, so stay with me. Perpetual motion machine crypto yield is fake and largely where many crypto scams originate. However, that doesn’t mean yield in the classic finance sense does not exist in bitcoin, it very literally does. Fortunately for us bitcoiners there are many other smart, driven, and enterprising bitcoiners that understand this problem and are doing something to address it. These individuals are pioneering new possibilities in bitcoin and finance, specifically when it comes to fixed income.
Here are some new developments –
Private Credit Funds – The Build Asset Management Secured Income Fund I is a private credit fund created by Build Asset Management. This fund primarily invests in bitcoin-backed, collateralized business loans originated by Unchained, with a secured structure involving a multi-signature, over-collateralized setup for risk management. Unchained originates loans and sells them to Build, which pools them into the fund, enabling investors to share in the interest income.
Dynamics
- Loan Terms: Unchained issues loans at interest rates around 14%, secured with a 2/3 multi-signature vault backed by a 40% loan-to-value (LTV) ratio.
- Fund Mechanics: Build buys these loans from Unchained, thus providing liquidity to Unchained for further loan originations, while Build manages interest payments to investors in the fund.
Pros
- The fund offers a unique way to earn income via bitcoin-collateralized debt, with protection against rehypothecation and strong security measures, making it attractive for investors seeking exposure to fixed income with bitcoin.
Cons
- The fund is only available to accredited investors, which is a regulatory standard for private credit funds like this.
Corporate Bonds – MicroStrategy Inc. (MSTR), a business intelligence company, has leveraged its corporate structure to issue bonds specifically to acquire bitcoin as a reserve asset. This approach allows investors to indirectly gain exposure to bitcoin’s potential upside while receiving interest payments on their bond investments. Some other publicly traded companies have also adopted this strategy, but for the sake of this article we will focus on MSTR as they are the biggest and most vocal issuer.
Dynamics
-
Issuance: MicroStrategy has issued senior secured notes in multiple offerings, with terms allowing the company to use the proceeds to purchase bitcoin.
-
Interest Rates: The bonds typically carry high-yield interest rates, averaging around 6-8% APR, depending on the specific issuance and market conditions at the time of issuance.
-
Maturity: The bonds have varying maturities, with most structured for multi-year terms, offering investors medium-term exposure to bitcoin’s value trajectory through MicroStrategy’s holdings.
Pros
-
Indirect Bitcoin exposure with income provides a unique opportunity for investors seeking income from bitcoin-backed debt.
-
Bonds issued by MicroStrategy offer relatively high interest rates, appealing for fixed-income investors attracted to the higher risk/reward scenarios.
Cons
-
There are credit risks tied to MicroStrategy’s financial health and bitcoin’s performance. A significant drop in bitcoin prices could strain the company’s ability to service debt, increasing credit risk.
-
Availability: These bonds are primarily accessible to institutional investors and accredited investors, limiting availability for retail investors.
Interest Payable in Bitcoin – River has introduced an innovative product, bitcoin Interest on Cash, allowing clients to earn interest on their U.S. dollar deposits, with the interest paid in bitcoin.
Dynamics
-
Interest Payment: Clients earn an annual interest rate of 3.8% on their cash deposits. The accrued interest is converted to Bitcoin daily and paid out monthly, enabling clients to accumulate Bitcoin over time.
-
Security and Accessibility: Cash deposits are insured up to $250,000 through River’s banking partner, Lead Bank, a member of the FDIC. All Bitcoin holdings are maintained in full reserve custody, ensuring that client assets are not lent or leveraged.
Pros
-
There are no hidden fees or minimum balance requirements, and clients can withdraw their cash at any time.
-
The 3.8% interest rate provides a predictable income stream, akin to traditional fixed-income investments.
Cons
-
While the interest rate is fixed, the value of the Bitcoin received as interest can fluctuate, introducing potential variability in the investment’s overall return.
-
Interest rate payments are on the lower side
Admittedly, this is a very small list, however, these types of investments are growing more numerous and meaningful. The reality is the existing options aren’t numerous enough to service every client that has a need for fixed income exposure. I challenge advisors to explore innovative options for fixed income exposure outside of sovereign debt, as that is most certainly a road to nowhere. It is my wholehearted belief and call to action that we need more options to help clients across the risk and capital allocation spectrum access a sound money standard.
Additional Resources
-
River: The future of saving is here: Earn 3.8% on cash. Paid in Bitcoin.
-
MicroStrategy: MicroStrategy Announces Pricing of Offering of Convertible Senior Notes
Bitcoin and Fixed Income was Written By Wyatt O’Rourke. If you enjoyed this article then support his writing, directly, by donating to his lightning wallet: ultrahusky3@primal.net
-
-
 @ df173277:4ec96708
2025-01-09 17:12:08
@ df173277:4ec96708
2025-01-09 17:12:08Maple AI combines the best of both worlds – encryption and personal AI – to create a truly private AI experience. Discuss personal and company items with Maple, we can't read them even if we wanted to.\ Join the waitlist to get early access.
We are a culture of app users. Every day, we give our personal information to websites and apps, hoping they are safe. Location data, eating habits, financial details, and health information are just a few examples of what we entrust to third parties. People are now entering a new era of computing that promises next-level benefits when given even more personal data: AI.
Should we sacrifice our privacy to unlock the productivity gains of AI? Should we hope our information won't be used in ways we disagree? We believe we can have the best of both worlds – privacy and personal AI – and have built a new project called Maple AI. Chat between you and an AI with full end-to-end encryption. We believe it's a game-changer for individuals seeking private and secure conversations.
Building a Private Foundation
Maple is built on our flagship product, OpenSecret, a backend platform for app developers that turns private encryption on by default. The announcement post for OpenSecret explains our vision for an encrypted world and what the platform can do. We think both users and developers benefit when sensitive personal information is encrypted in a private vault; it's a win-win.
The Power of Encrypted AI Chat
AI chat is a personal and intimate experience. It's a place to share your thoughts, feelings, and desires without fear of judgment. The more you share with an AI chatbot, the more powerful it becomes. It can offer personalized insights, suggestions, and guidance tailored to your unique needs and perspectives. However, this intimacy requires trust, and that's where traditional AI chatbots often fall short.
Traditional AI chats are designed to collect and analyze your data, often without your explicit consent. This data is used to improve the AI's performance, but it also creates a treasure trove of sensitive information that can be mined, sold, or even exploited by malicious actors. Maple AI takes a different approach. By using end-to-end encryption, we ensure that your conversations remain private and secure, even from us.
Technical Overview
So, how does Maple AI achieve this level of privacy and security? Here are some key technical aspects:
- Private Key: Each user has a unique private key that is automatically managed for them. This key encrypts and decrypts conversations, ensuring that only the user can access their data.
- Secure Servers: Our servers are designed with security in mind. We use secure enclaves to protect sensitive data and ensure that even our own team can't access your conversations.
- Encrypted Sync: One of Maple's most significant benefits is its encrypted sync feature. Unlike traditional AI chatbots, which store conversations in local storage or on standard cloud servers, Maple syncs your chats across all your devices. The private key managed by our secure servers means you can pick up where you left off on any device without worrying about your data being compromised.
- Attestation and Open Code: We publish our enclave code publicly. Using a process called attestation, users can verify that the code running on the enclave is the same as the code audited by the public.
- Open Source LLM: Maple uses major open-source models to maximize the openness of responses. The chat box does not filter what you can talk about. This transparency ensures that our AI is trustworthy and unbiased.
Personal and Work Use
Maple is secure enough to handle your personal questions and work tasks. Because we can't see what you chat about, you are free to use AI as an assistant on sensitive company items. Use it for small tasks like writing an important email or large tasks like developing your organization's strategy. Feed it sensitive information; it's just you and AI in the room. Attestation provides cryptographic proof that your corporate secrets are safe.
Local v Cloud
Today's AI tools provide different levels of privacy. The main options are to trust a third party with your unencrypted data, hoping they don't do anything with it, or run your own AI locally on an underpowered machine. We created a third option. Maple gives you the power of cloud computing combined with the privacy and security of a machine running on your desk. It's the best of both worlds.
Why the Maple name?
Privacy isn't just a human value - it's a natural one exemplified by the Maple tree. These organisms communicate with each other through a network of underground fungal hyphae, sending messages and sharing resources in a way that's completely invisible to organisms above ground. This discreet communication system allows Maple trees to thrive in even the most challenging environments. Our goal is to provide a way for everyone to communicate with AI securely so they can thrive in any environment.
Join the Waitlist
Maple AI will launch in early 2025 with free and paid plans. We can't wait to share it with the world. Join our waitlist today to be among the first to experience the power of private AI chat.
-
 @ ec42c765:328c0600
2024-12-22 19:16:31
@ ec42c765:328c0600
2024-12-22 19:16:31この記事は前回の内容を把握している人向けに書いています(特にNostrエクステンション(NIP-07)導入)
手順
- 登録する画像を用意する
- 画像をweb上にアップロードする
- 絵文字セットに登録する
1. 登録する画像を用意する
以下のような方法で用意してください。
- 画像編集ソフト等を使って自分で作成する
- 絵文字作成サイトを使う(絵文字ジェネレーター、MEGAMOJI など)
- フリー画像を使う(いらすとや など)
データ量削減
Nostrでは画像をそのまま表示するクライアントが多いので、データ量が大きな画像をそのまま使うとモバイル通信時などに負担がかかります。
データ量を増やさないためにサイズやファイル形式を変更することをおすすめします。
以下は私のおすすめです。 * サイズ:正方形 128×128 ピクセル、長方形 任意の横幅×128 ピクセル * ファイル形式:webp形式(webp変換おすすめサイト toimg) * 単色、単純な画像の場合:png形式(webpにするとむしろサイズが大きくなる)
その他
- 背景透過画像
- ダークモード、ライトモード両方で見やすい色
がおすすめです。
2. 画像をweb上にアップロードする
よく分からなければ emojito からのアップロードで問題ないです。
普段使っている画像アップロード先があるならそれでも構いません。
気になる方はアップロード先を適宜選んでください。既に投稿されたカスタム絵文字の画像に対して
- 削除も差し替えもできない → emojito など
- 削除できるが差し替えはできない → Gyazo、nostrcheck.meなど
- 削除も差し替えもできる → GitHub 、セルフホスティングなど
これらは既にNostr上に投稿されたカスタム絵文字の画像を後から変更できるかどうかを指します。
どの方法でも新しく使われるカスタム絵文字を変更することは可能です。
同一のカスタム絵文字セットに同一のショートコードで別の画像を登録する形で対応できます。3. 絵文字セットに登録する
emojito から登録します。
右上のアイコン → + New emoji set から新規の絵文字セットを作成できます。


① 絵文字セット名を入力
基本的にカスタム絵文字はカスタム絵文字セットを作り、ひとまとまりにして登録します。
一度作った絵文字セットに後から絵文字を追加することもできます。
② 画像をアップロードまたは画像URLを入力
emojitoから画像をアップロードする場合、ファイル名に日本語などの2バイト文字が含まれているとアップロードがエラーになるようです。
その場合はファイル名を適当な英数字などに変更してください。
③ 絵文字のショートコードを入力
ショートコードは絵文字を呼び出す時に使用する場合があります。
他のカスタム絵文字と被っても問題ありませんが選択時に複数表示されて支障が出る可能性があります。
他と被りにくく長くなりすぎないショートコードが良いかもしれません。
ショートコードに使えるのは半角の英数字とアンダーバーのみです。
④ 追加
Add を押してもまだ作成完了にはなりません。

一度に絵文字を複数登録できます。
最後に右上の Save を押すと作成完了です。

画面が切り替わるので、右側の Options から Bookmark を選択するとそのカスタム絵文字セットを自分で使えるようになります。
既存の絵文字セットを編集するには Options から Edit を選択します。
以上です。
仕様
-
 @ 3bf0c63f:aefa459d
2024-09-06 12:49:46
@ 3bf0c63f:aefa459d
2024-09-06 12:49:46Nostr: a quick introduction, attempt #2
Nostr doesn't subscribe to any ideals of "free speech" as these belong to the realm of politics and assume a big powerful government that enforces a common ruleupon everybody else.
Nostr instead is much simpler, it simply says that servers are private property and establishes a generalized framework for people to connect to all these servers, creating a true free market in the process. In other words, Nostr is the public road that each market participant can use to build their own store or visit others and use their services.
(Of course a road is never truly public, in normal cases it's ran by the government, in this case it relies upon the previous existence of the internet with all its quirks and chaos plus a hand of government control, but none of that matters for this explanation).
More concretely speaking, Nostr is just a set of definitions of the formats of the data that can be passed between participants and their expected order, i.e. messages between clients (i.e. the program that runs on a user computer) and relays (i.e. the program that runs on a publicly accessible computer, a "server", generally with a domain-name associated) over a type of TCP connection (WebSocket) with cryptographic signatures. This is what is called a "protocol" in this context, and upon that simple base multiple kinds of sub-protocols can be added, like a protocol for "public-square style microblogging", "semi-closed group chat" or, I don't know, "recipe sharing and feedback".
-
 @ df173277:4ec96708
2025-01-09 17:02:52
@ df173277:4ec96708
2025-01-09 17:02:52OpenSecret is a backend for app developers that turns private encryption on by default. When sensitive data is readable only by the user, it protects both the user and the developer, creating a more free and open internet. We'll be launching in 2025. Join our waitlist to get early access.
In today's digital age, personal data is both an asset and a liability. With the rise of data breaches and cyber attacks, individuals and companies struggle to protect sensitive information. The consequences of a data breach can be devastating, resulting in financial losses, reputational damage, and compromised user trust. In 2023, the average data breach cost was $5 million, with some resulting in losses of over $1 billion.
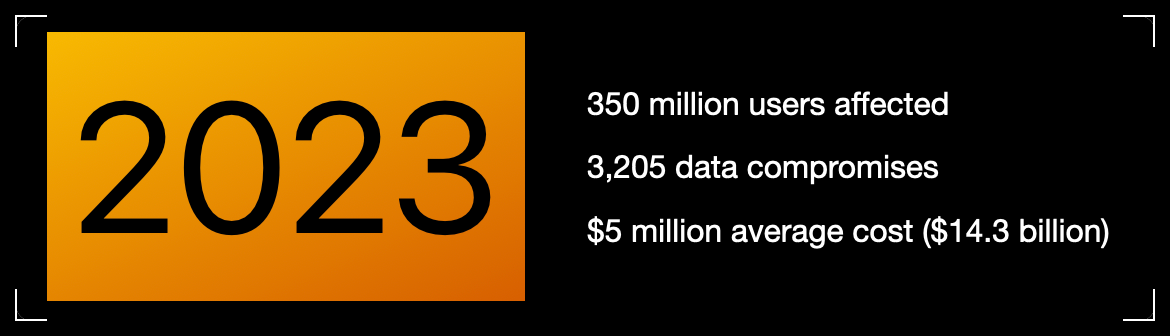 Meanwhile, individuals face problems related to identity theft, personal safety, and public embarrassment. Think about the apps on your phone, even the one you're using to read this. How much data have you trusted to other people, and how would it feel if that data were leaked online?
Meanwhile, individuals face problems related to identity theft, personal safety, and public embarrassment. Think about the apps on your phone, even the one you're using to read this. How much data have you trusted to other people, and how would it feel if that data were leaked online?Thankfully, some incredibly talented cypherpunks years ago gave the world cryptography. We can encrypt data, rendering it a secret between two people. So why then do we have data breaches?
Cryptography at scale is hard.
The Cloud
The cloud has revolutionized how we store and process data, but it has limitations. While cloud providers offer encryption, it mainly protects data in transit. Once data is stored in the cloud, it's often encrypted with a shared key, which can be accessed by employees, third-party vendors, or compromised by hackers.
The solution is to generate a personal encryption password for each user, make sure they write it down, and, most importantly, hope they don't lose it. If the password is lost, the data is forever unreadable. That can be overwhelming, leading to low app usage.
Private key encryption needs a UX upgrade.
Enter OpenSecret
OpenSecret is a developer platform that enables encryption by default. Our platform provides a suite of security tools for app developers, including private key management, encrypted sync, private AI, and confidential compute.
Every user has a private vault for their data, which means only they can read it. Developers are free to store less sensitive data in a shared manner because there is still a need to aggregate data across the system.
Private Key Management
Private key management is the superpower that enables personal encryption per user. When each user has a unique private key, their data can be truly private. Typically, using a private key is a challenging experience for the user because they must write down a long autogenerated number or phrase of 12-24 words. If they lose it, their data is gone.
OpenSecret uses secure enclaves to make private keys as easy as an everyday login experience that users are familiar with. Instead of managing a complicated key, the user logs in with an email address or a social media account.
The developer doesn't have to manage private keys and can focus on the app's user experience. The user doesn't have to worry about losing a private key and can jump into using your app.
Encrypted Sync
With user keys safely managed, we can synchronize user data to every device while maintaining privacy. The user does not need to do complicated things like scanning QR codes from one device to the next. Just log in and go.
The user wins because the data is available on all their devices. The developer wins because only the user can read the data, so it isn't a liability to them.
Private AI
Artificial intelligence is here and making its way into everything. The true power of AI is unleashed when it can act on personal and company data. The current options are to run your own AI locally on an underpowered machine or to trust a third party with your data, hoping they don't read it or use it for anything.
OpenSecret combines the power of cloud computing with the privacy and security of a machine running on your desk.
Check out Maple AI\ Try private AI for yourself! We built an app built with this service called Maple AI. It is an AI chat that is 100% private in a verifiable manner. Give it your innermost thoughts or embarrassing ideas; we can't judge you. We built Maple using OpenSecret, which means you have a private key that is automatically managed for you, and your chat history is synchronized to all your devices. Learn more about Maple AI - Private chat in the announcement post.
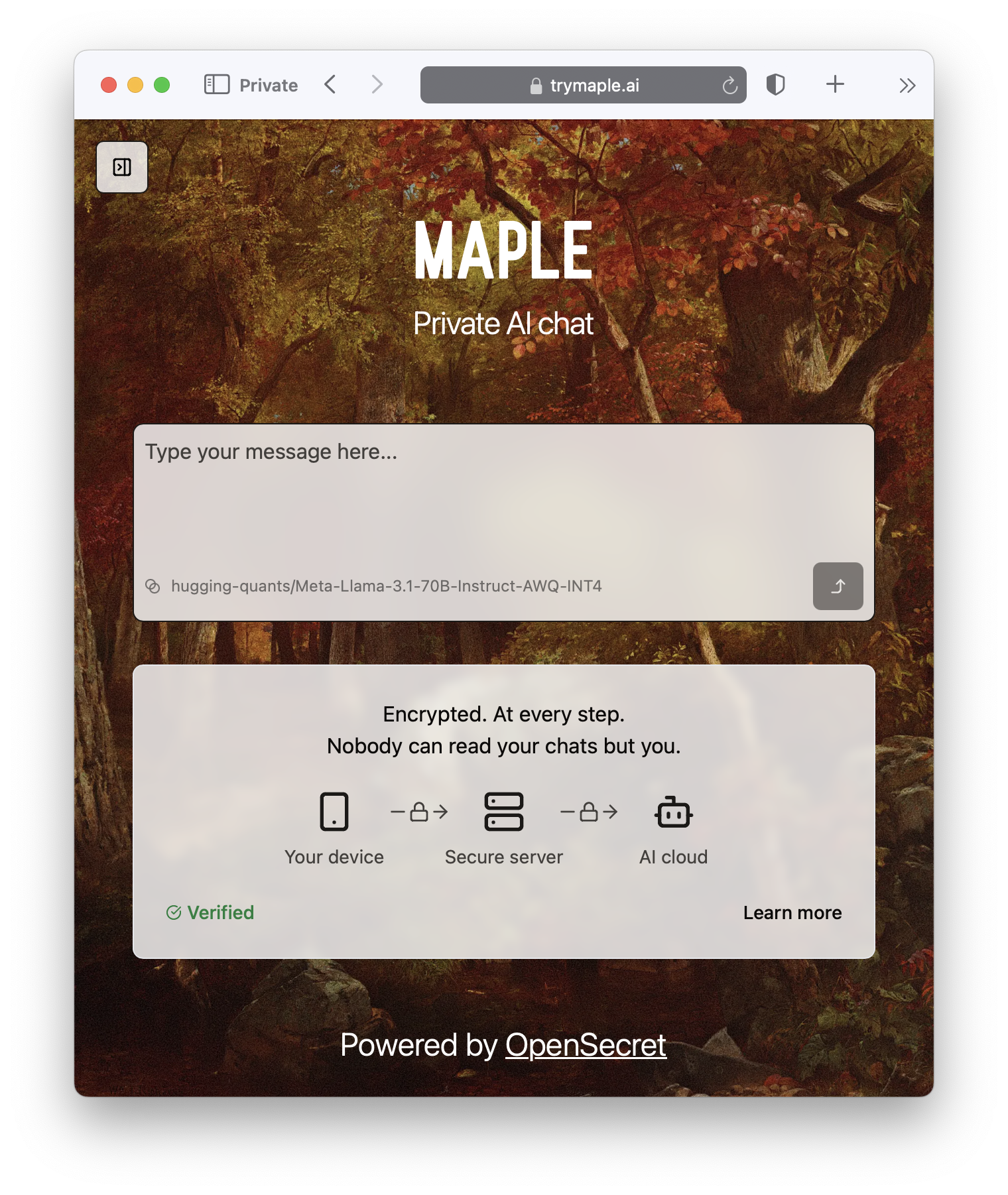
Confidential Compute
Confidential computing is a game-changer for data security. It's like the secure hardware that powers Apple Pay and Google Pay on your phone but in the cloud. Users can verify through a process called attestation that their data is handled appropriately. OpenSecret can help you run your own custom app backend code that would benefit from the security of an enclave.
It's the new version of that lock on your web browser. When you see it, you know you're secure.

But do we want our secrets to be open?
OpenSecret renders a data breach practically useless. If hackers get into the backend, they enter a virtual hallway of locked private vaults. The leaked data would be gibberish, a secret in the open that is unreadable.
On the topic of openness, OpenSecret uses the power of open source to enable trust in the service. We publish our code in the open, and, using attestation, anyone can verify that private data is being handled as expected. This openness also provides developers with a backup option to safely and securely export their data.
Don't trust, verify.
Join the Movement
We're currently building out OpenSecret, and we invite you to join us on the journey. Our platform can work with your existing stack, and you can pick and choose the features you need. If you want to build apps with encryption enabled, send us a message to get early access.
Users and companies deserve better encryption and privacy.\ Together, let's make that a reality.
-
 @ 3bf0c63f:aefa459d
2024-05-21 12:38:08
@ 3bf0c63f:aefa459d
2024-05-21 12:38:08Bitcoin transactions explained
A transaction is a piece of data that takes inputs and produces outputs. Forget about the blockchain thing, Bitcoin is actually just a big tree of transactions. The blockchain is just a way to keep transactions ordered.
Imagine you have 10 satoshis. That means you have them in an unspent transaction output (UTXO). You want to spend them, so you create a transaction. The transaction should reference unspent outputs as its inputs. Every transaction has an immutable id, so you use that id plus the index of the output (because transactions can have multiple outputs). Then you specify a script that unlocks that transaction and related signatures, then you specify outputs along with a script that locks these outputs.

As you can see, there's this lock/unlocking thing and there are inputs and outputs. Inputs must be unlocked by fulfilling the conditions specified by the person who created the transaction they're in. And outputs must be locked so anyone wanting to spend those outputs will need to unlock them.
For most of the cases locking and unlocking means specifying a public key whose controller (the person who has the corresponding private key) will be able to spend. Other fancy things are possible too, but we can ignore them for now.
Back to the 10 satoshis you want to spend. Since you've successfully referenced 10 satoshis and unlocked them, now you can specify the outputs (this is all done in a single step). You can specify one output of 10 satoshis, two of 5, one of 3 and one of 7, three of 3 and so on. The sum of outputs can't be more than 10. And if the sum of outputs is less than 10 the difference goes to fees. In the first days of Bitcoin you didn't need any fees, but now you do, otherwise your transaction won't be included in any block.

If you're still interested in transactions maybe you could take a look at this small chapter of that Andreas Antonopoulos book.
If you hate Andreas Antonopoulos because he is a communist shitcoiner or don't want to read more than half a page, go here: https://en.bitcoin.it/wiki/Coin_analogy
-
 @ 000002de:c05780a7
2025-01-06 17:05:46
@ 000002de:c05780a7
2025-01-06 17:05:46Apparently the Prime Clown in Canada is stepping down. Apparently the Orange Man beat the democrat machine. Are "we" winning? No.
I've had the illness of following politics for most of my life. I have never been less invested but I continue to see people missing the point. Several years ago there was an effort in California to remove Gavin Newsom from office. They call it a recall in the state.
When I hear people talk about Biden, or Newsom, or whoever you would think that all we need to do is vote the bum out and we are on the right path. That's way off. Trump's election isn't the goal but rather a sign of a minor shift in the culture and influence.
A mistake I see over and over again is focusing on the personalities. The puppets. The men. As if they are the problem. The problems are so much deeper. It's the culture, the programming, and the puppet masters. The problems are upstream of politicians. Remove one and another will replace them.
I don't so much care that Trump is less bad that Biden. Its that people make the mistake of focusing on the flag being blown by the wind than the wind itself. The politician is simply a result of many other more important factors.
Politicians work under an incentive structure that rewards promising things they cannot deliver. Even things that are not possible. Their only accountability is the voters and donors. The donors get what they want and the voters usually are to uninformed or dumb to realize what is going on. When they do realize it the other team is so demonized they either stick with their team or just don't vote.
The longer I look at democracy and the modern state the more absurd it appears to me. It's not that the men are bad or the government in power is bad. It's the whole incentive structure. There are almost no negative consequences pushing against this nonsense.
I have heard it said that the default view of political figures should be that of the tobacco executives. Today I think it should be the view of the medical insurance CEOs. The default view. There are exceptions but they are rare and work in spite of the system.
The solution is freedom and voluntary interaction. Removing the monopoly state. Remove the monopoly on violence. It would not be a utopia but IMO the incentives would be better.
The culture we create and the choices we make each day are making an impact. Remember that the flag doesn't control the wind. The wind controls the flag.
originally posted at https://stacker.news/items/839442
-
 @ 3bf0c63f:aefa459d
2024-03-23 08:57:08
@ 3bf0c63f:aefa459d
2024-03-23 08:57:08Nostr is not decentralized nor censorship-resistant
Peter Todd has been saying this for a long time and all the time I've been thinking he is misunderstanding everything, but I guess a more charitable interpretation is that he is right.
Nostr today is indeed centralized.
Yesterday I published two harmless notes with the exact same content at the same time. In two minutes the notes had a noticeable difference in responses:
The top one was published to
wss://nostr.wine,wss://nos.lol,wss://pyramid.fiatjaf.com. The second was published to the relay where I generally publish all my notes to,wss://pyramid.fiatjaf.com, and that is announced on my NIP-05 file and on my NIP-65 relay list.A few minutes later I published that screenshot again in two identical notes to the same sets of relays, asking if people understood the implications. The difference in quantity of responses can still be seen today:
These results are skewed now by the fact that the two notes got rebroadcasted to multiple relays after some time, but the fundamental point remains.
What happened was that a huge lot more of people saw the first note compared to the second, and if Nostr was really censorship-resistant that shouldn't have happened at all.
Some people implied in the comments, with an air of obviousness, that publishing the note to "more relays" should have predictably resulted in more replies, which, again, shouldn't be the case if Nostr is really censorship-resistant.
What happens is that most people who engaged with the note are following me, in the sense that they have instructed their clients to fetch my notes on their behalf and present them in the UI, and clients are failing to do that despite me making it clear in multiple ways that my notes are to be found on
wss://pyramid.fiatjaf.com.If we were talking not about me, but about some public figure that was being censored by the State and got banned (or shadowbanned) by the 3 biggest public relays, the sad reality would be that the person would immediately get his reach reduced to ~10% of what they had before. This is not at all unlike what happened to dozens of personalities that were banned from the corporate social media platforms and then moved to other platforms -- how many of their original followers switched to these other platforms? Probably some small percentage close to 10%. In that sense Nostr today is similar to what we had before.
Peter Todd is right that if the way Nostr works is that you just subscribe to a small set of relays and expect to get everything from them then it tends to get very centralized very fast, and this is the reality today.
Peter Todd is wrong that Nostr is inherently centralized or that it needs a protocol change to become what it has always purported to be. He is in fact wrong today, because what is written above is not valid for all clients of today, and if we drive in the right direction we can successfully make Peter Todd be more and more wrong as time passes, instead of the contrary.
See also:
-
 @ 2cb8ae56:84d30cba
2024-12-21 11:27:14
@ 2cb8ae56:84d30cba
2024-12-21 11:27:14ども、薄味のキャルピスでございます。
当記事は、「Nostr Advent Calendar 2024」7日目の記事です。
この記事を読んでいる人でいないとは思いますが、Nostrとはなんぞやとお思いの方は以下をご覧ください。https://hello.nostrapp.me/
僕は「Nostrで過ごした2024年」というタイトルの通り、一年間を振り返ってみようと思います。
自己紹介
まず知らん人のために軽く自己紹介をします
「薄味のキャルピス」という名前で、色んな所にいるどこかの高校生です。 左利き、箸とベースとお盆は右手。
普段は学業の傍ら、画像を弄ったり作ったりしている上に、イヤホンを集めたりラジオにメッセージを送っています。
コーディングは出来ないテクノロジーまみれのガラクタ人間(→テックジャンカー)です
参加経緯とスタンス
なぜ参加したのかを思い出しながら書いていきます まず、どんな媒体でNostr(ノスター・ノストラ)の存在を知ったのかと言うと、ネットニュースです。
https://gigazine.net/news/20230425-nostr-intro/
こちらの記事で「そんなのあるんだ」と知り、4月1日ついにjoin!!!!
現時点での参加スタンスは「気楽に、素直に」という感じで参加しています
やりたいときにやりたいことをやるって言うリアルでは到底難しいことを、Nostrのなかでやっている気もします。
後述するNostrasia 2024の開催日「9月23日」を持って、Mastodon(マストドン)から乗り換え、上記のスタンスのもと、メインで精力的に活動しています。
Nostr活動年表
2024/04/01 Nostr Join!!!
2024/06/08 人生初オフ会「たくろうさんオフ」参加、LNアドレス追加。
2024/09/23 人生初小規模イベント「Nostrasia 2024」運営メンバーとして参加
2024/10/12 2度目のオフ会「デザイン談義」主催・参加
簡易的に各種紹介!
人生初オフ会「たくろうさんオフ」 渋三魚金でご飯→猿田彦珈琲でリラックス、Linux使ってると話を切り出す(唐突)→スクランブル交差点で解散。 ウォークマンの再生画面を送付した投稿を行う
人生初イベント「Nostrasia 2024」
あ、記事出したので見てください。初版
第二版
2度目のオフ会「デザイン談義」
秋葉原の「創作空間caféアトリエ あきば店」で行われたオフ会。 ちょくちょく内容を上げているので、見ていってください。 https://nostter.app/npub19ju2u4sduewta4hxl22kke7se8yxm2puytzw47lr6y999pxnpjaqtjjfxj/2024/10/12 終了後、e☆イヤホン 秋葉原店にて、BTR13の在庫状況を確認し、在庫がないため予約しました。 (10月24日到着) 雑多すぎますが、一応こんな感じで大丈夫かな?まとめ
僕がNostrに出会い、Nostrにのめり込むまでの話はいかがだったでしょうか。 Nostrに入る前、オフ会に参加するまでは「ネットにロクな人なんていない!」と思っていましたが、Nostrは違いましたね。 いい意味で期待はずれ、本当にいい人たちばかりで、とにかく自然体で接することができるSNSであると感じました。 そんな世界にぜひとも一回足を踏み入れてみてはいかがでしょうか? それではまた、来年のアドベントカレンダー、及び開催されましたら「Nostrasia 2025」でお会いしましょう。 -
 @ 3f770d65:7a745b24
2025-01-05 18:56:33
@ 3f770d65:7a745b24
2025-01-05 18:56:33New Year’s resolutions often feel boring and repetitive. Most revolve around getting in shape, eating healthier, or giving up alcohol. While the idea is interesting—using the start of a new calendar year as a catalyst for change—it also seems unnecessary. Why wait for a specific date to make a change? If you want to improve something in your life, you can just do it. You don’t need an excuse.
That’s why I’ve never been drawn to the idea of making a list of resolutions. If I wanted a change, I’d make it happen, without worrying about the calendar. At least, that’s how I felt until now—when, for once, the timing actually gave me a real reason to embrace the idea of New Year’s resolutions.
Enter Olas.
If you're a visual creator, you've likely experienced the relentless grind of building a following on platforms like Instagram—endless doomscrolling, ever-changing algorithms, and the constant pressure to stay relevant. But what if there was a better way? Olas is a Nostr-powered alternative to Instagram that prioritizes community, creativity, and value-for-value exchanges. It's a game changer.
Instagram’s failings are well-known. Its algorithm often dictates whose content gets seen, leaving creators frustrated and powerless. Monetization hurdles further alienate creators who are forced to meet arbitrary follower thresholds before earning anything. Additionally, the platform’s design fosters endless comparisons and exposure to negativity, which can take a significant toll on mental health.
Instagram’s algorithms are notorious for keeping users hooked, often at the cost of their mental health. I've spoken about this extensively, most recently at Nostr Valley, explaining how legacy social media is bad for you. You might find yourself scrolling through content that leaves you feeling anxious or drained. Olas takes a fresh approach, replacing "doomscrolling" with "bloomscrolling." This is a common theme across the Nostr ecosystem. The lack of addictive rage algorithms allows the focus to shift to uplifting, positive content that inspires rather than exhausts.
Monetization is another area where Olas will set itself apart. On Instagram, creators face arbitrary barriers to earning—needing thousands of followers and adhering to restrictive platform rules. Olas eliminates these hurdles by leveraging the Nostr protocol, enabling creators to earn directly through value-for-value exchanges. Fans can support their favorite artists instantly, with no delays or approvals required. The plan is to enable a brand new Olas account that can get paid instantly, with zero followers - that's wild.
Olas addresses these issues head-on. Operating on the open Nostr protocol, it removes centralized control over one's content’s reach or one's ability to monetize. With transparent, configurable algorithms, and a community that thrives on mutual support, Olas creates an environment where creators can grow and succeed without unnecessary barriers.
Join me on my New Year's resolution. Join me on Olas and take part in the #Olas365 challenge! It’s a simple yet exciting way to share your content. The challenge is straightforward: post at least one photo per day on Olas (though you’re welcome to share more!).
Download on Android or download via Zapstore.
Let's make waves together.
-
 @ 3bf0c63f:aefa459d
2024-03-19 14:32:01
@ 3bf0c63f:aefa459d
2024-03-19 14:32:01Censorship-resistant relay discovery in Nostr
In Nostr is not decentralized nor censorship-resistant I said Nostr is centralized. Peter Todd thinks it is centralized by design, but I disagree.
Nostr wasn't designed to be centralized. The idea was always that clients would follow people in the relays they decided to publish to, even if it was a single-user relay hosted in an island in the middle of the Pacific ocean.
But the Nostr explanations never had any guidance about how to do this, and the protocol itself never had any enforcement mechanisms for any of this (because it would be impossible).
My original idea was that clients would use some undefined combination of relay hints in reply tags and the (now defunct)
kind:2relay-recommendation events plus some form of manual action ("it looks like Bob is publishing on relay X, do you want to follow him there?") to accomplish this. With the expectation that we would have a better idea of how to properly implement all this with more experience, Branle, my first working client didn't have any of that implemented, instead it used a stupid static list of relays with read/write toggle -- although it did publish relay hints and kept track of those internally and supportedkind:2events, these things were not really useful.Gossip was the first client to implement a truly censorship-resistant relay discovery mechanism that used NIP-05 hints (originally proposed by Mike Dilger) relay hints and
kind:3relay lists, and then with the simple insight of NIP-65 that got much better. After seeing it in more concrete terms, it became simpler to reason about it and the approach got popularized as the "gossip model", then implemented in clients like Coracle and Snort.Today when people mention the "gossip model" (or "outbox model") they simply think about NIP-65 though. Which I think is ok, but too restrictive. I still think there is a place for the NIP-05 hints,
nprofileandneventrelay hints and specially relay hints in event tags. All these mechanisms are used together in ZBD Social, for example, but I believe also in the clients listed above.I don't think we should stop here, though. I think there are other ways, perhaps drastically different ways, to approach content propagation and relay discovery. I think manual action by users is underrated and could go a long way if presented in a nice UX (not conceived by people that think users are dumb animals), and who knows what. Reliance on third-parties, hardcoded values, social graph, and specially a mix of multiple approaches, is what Nostr needs to be censorship-resistant and what I hope to see in the future.
-
 @ ec42c765:328c0600
2024-12-15 11:13:44
@ ec42c765:328c0600
2024-12-15 11:13:44てすと
nostr:nevent1qqst3uqlls4yr9vys4dza2sgjle3ly37trck7jgdmtr23uuz52usjrqqqnjgr
nostr:nevent1qqsdvchy5d27zt3z05rr3q6vvmzgslslxwu0p4dfkvxwhmvxldn9djguvagp2
-
 @ a853296a:209e695f
2025-01-02 15:52:12
@ a853296a:209e695f
2025-01-02 15:52:12👋 What's up, stackers! 🤠
Excited to announce our latest project: Pull That Up Jamie. Think Perplexity but private & open source.
TLDR: ✨ Why Choose Jamie?
🛠️ Fully Open Source and Transparent! ⚡ BOLT11 Bitcoin/Lightning for Anonymous Usage! 🚄 Optimized for Speed and Convenience! 🆓 Limited Free Usage Available!
💦🔒🕵️ Your Biggest Opsec Leak - Why We Tackled Search
Search + LLMs seems like the peanut butter & jelly of the internet - a great match. But at what cost? Now that LLMs and AI are here, we know that finding needles in a vast haystack of data is much easier. That means that seemingly innocuous queries and interactions you have on the internet now carry way more weight than you think. How long before we all get owned? Privacy becomes all the more important. Each query empowers those who would exploit us. Every search chips away, revealing personal details about your state of mind. Stealing your soul little by little.
Just as bitcoin gives us the opportunity to opt out of exploitative economic systems, we wanted to take bitcoin's magic freedom dust and give you the ability to opt out of exploitative search surveillance 🔒🕵️.
⚡ How Bitcoin Lightning Yet Again Fixes This
Using the Bitcoin Connect plugin, we are able to accept BOLT11 payments. BOLT11, thanks to the lightning network's onion routing topology, affords users great sender privacy:
With just a VPN + an NWC connection, you can use Pull That Up Jamie with privacy assurances that are unparalleled. For very low cost, an average person can get Jason Bourne tier opsec.
🚧🧰🏗️Building Off the Great Work of Others
Major shout out to the ⚡ lightning devs that brought BOLT11 to the point it's at and especially to the 🐝 @getalby team for the great work on Bitcoin Connect. BC makes it easy to accept bitcoin payments with very little friction or overhead.
Additionally, we took notes on great projects like Perplexica. However we found that none of them were really geared toward the combination of speed, UX, and convenience we were looking for. Most of them are designed to be run in docker containers on your machine - great for techies but not accessible to the wider population.
We rolled our own from scratch, learning a lot from these projects. We especially took note of the superb qualities afforded by the SearXNG project🔍 🌐. What is SearXNG? Let's ask Pull That Up Jamie:
SearXNG is such a gamechanger that we plan to make a bitcoin payable, AI scannable endpoint just for accessing our instance. DM us if interested.
Armed with the ability to search the web and feed context to LLMs, we can Make The Internet Private Again. We can eliminate Google from your life.
⚡ Stackers do yourselves a favor - check out https://pullthatupjamie.ai today! 🤠
Future Work
- Open source models like 🦙 Llama
- Collaborating with @TonyGiorgio and team to use their secure compute LLM 🍁 Maple - https://stacker.news/items/764869 as part of the workflow
- Expert Mode: interrogate high signal sources of your choosing like podcasts, stacker news posts and others
- A couple more secret twists to keep you guessing :)
- Suggestions? Hit us with em.
originally posted at https://stacker.news/items/833717
-
 @ ec42c765:328c0600
2024-12-13 08:16:32
@ ec42c765:328c0600
2024-12-13 08:16:32Nostr Advent Calendar 2024 の 12日目の記事です。
昨日の 12/11 は きりの さんの 2024年のNostrリレー運営を振り返る でした。
nostr-zap-view 作った
リポジトリ: https://github.com/Lokuyow/nostr-zap-view/
動作確認ページ: https://lokuyow.github.io/nostr-zap-view/それ何?
特定の誰かや何かに宛てたZap(投げ銭)を一覧できるやつ
を
自分のWebサイトに設置できるやつ
自分のサイトに設置した例 * SNSリンク集ページ(最下部): https://lokuyow.github.io/
おいくらサッツ(Zap一覧ボタン): https://osats.money/
今日からビットコ(最下部): https://lokuyow.github.io/btc-dca-simulator/なんで作ったの?
私の去年のアドベントカレンダー
【Nostr】Webサイトにビットコインの投げ銭ボタンを設置しよう【Zap】
https://spotlight.soy/detail?article_id=ucd7cbrql/
が前提になってるけど長いので要約すると * ZapするやつはあるけどZap見るやつがないので欲しい * ZapをNostr(の典型的なkind:1クライアント)内だけに留めるのはもったいない * Webサイトの広告うざいからZap(的な何か)で置き換わって欲しいお前だれ?
非エンジニア、非プログラマー
AIにコード出させてるだけ人作った感想
できた
作った感想2
完成してから気付いた本当に作りたかったもの
こういうところにそのままZapを表示できる感じにしたい
 (ここまでちゃんとした商業ブログでなく)個人のブログやHPの端っこに「Sponsored by」欄があって名前が表示される感じ
(ここまでちゃんとした商業ブログでなく)個人のブログやHPの端っこに「Sponsored by」欄があって名前が表示される感じ
もうZapっていう文字もビットコインっていう文字もNostrも出さなくていいし説明もしなくていいのでは感がある
イメージはWebサイトを対象にしたニコニ広告 + スーパーチャット + 祭りとか神社の奉納者一覧
で思ったのは
個人からの投げ銭なら推し活的なものにしかならないけど
企業がNostrにアカウントを作ってサイトに投げ銭をしたら企業の広告になるんでは!?
~~企業がNostrにアカウントを!?デリヘルしか見たことない!~~今後
思いつき、予定は未定
* ボタン→ダイアログ形式でなくバナー、Embed形式にしてページアクセスですぐ見れるようにする * 多分リレーに負荷がかかるのでなんかする * Zapの文字は出さず「Sponsored by」等にする * 単純な最新順でなくする * 少額Zapをトリミング * 一定期間(一か月など)ごとで金額順にソート * 多分リレーに負荷がかかるのでなんかする * 今は投稿宛てのZapをWebサイト宛てのZapと勝手に言い張ってるだけなのでちゃんとWebサイト宛てのZapにする * NIPの提案が必要 * ウォレットの準拠も必要 * リレー(wss://~)宛てのZapもできてほしい将来
インターネットのすべてに投げ銭をさせろ
おわり
明日は mono さんの Open Sats 申請編 です!!
-
 @ 3bf0c63f:aefa459d
2024-01-29 02:19:25
@ 3bf0c63f:aefa459d
2024-01-29 02:19:25Nostr: a quick introduction, attempt #1
Nostr doesn't have a material existence, it is not a website or an app. Nostr is just a description what kind of messages each computer can send to the others and vice-versa. It's a very simple thing, but the fact that such description exists allows different apps to connect to different servers automatically, without people having to talk behind the scenes or sign contracts or anything like that.
When you use a Nostr client that is what happens, your client will connect to a bunch of servers, called relays, and all these relays will speak the same "language" so your client will be able to publish notes to them all and also download notes from other people.
That's basically what Nostr is: this communication layer between the client you run on your phone or desktop computer and the relay that someone else is running on some server somewhere. There is no central authority dictating who can connect to whom or even anyone who knows for sure where each note is stored.
If you think about it, Nostr is very much like the internet itself: there are millions of websites out there, and basically anyone can run a new one, and there are websites that allow you to store and publish your stuff on them.
The added benefit of Nostr is that this unified "language" that all Nostr clients speak allow them to switch very easily and cleanly between relays. So if one relay decides to ban someone that person can switch to publishing to others relays and their audience will quickly follow them there. Likewise, it becomes much easier for relays to impose any restrictions they want on their users: no relay has to uphold a moral ground of "absolute free speech": each relay can decide to delete notes or ban users for no reason, or even only store notes from a preselected set of people and no one will be entitled to complain about that.
There are some bad things about this design: on Nostr there are no guarantees that relays will have the notes you want to read or that they will store the notes you're sending to them. We can't just assume all relays will have everything — much to the contrary, as Nostr grows more relays will exist and people will tend to publishing to a small set of all the relays, so depending on the decisions each client takes when publishing and when fetching notes, users may see a different set of replies to a note, for example, and be confused.
Another problem with the idea of publishing to multiple servers is that they may be run by all sorts of malicious people that may edit your notes. Since no one wants to see garbage published under their name, Nostr fixes that by requiring notes to have a cryptographic signature. This signature is attached to the note and verified by everybody at all times, which ensures the notes weren't tampered (if any part of the note is changed even by a single character that would cause the signature to become invalid and then the note would be dropped). The fix is perfect, except for the fact that it introduces the requirement that each user must now hold this 63-character code that starts with "nsec1", which they must not reveal to anyone. Although annoying, this requirement brings another benefit: that users can automatically have the same identity in many different contexts and even use their Nostr identity to login to non-Nostr websites easily without having to rely on any third-party.
To conclude: Nostr is like the internet (or the internet of some decades ago): a little chaotic, but very open. It is better than the internet because it is structured and actions can be automated, but, like in the internet itself, nothing is guaranteed to work at all times and users many have to do some manual work from time to time to fix things. Plus, there is the cryptographic key stuff, which is painful, but cool.
-
 @ 8fb140b4:f948000c
2024-12-08 05:21:39
@ 8fb140b4:f948000c
2024-12-08 05:21:39After nuking my second LND node (the first one died due to hardware failure) by my own typo and lack of any thought in the design of the CLI of LND lightning node tools, I decided to take a plunge into the world of mature and complex implementation of the protocol, Eclair by ACINQ. It has been almost one year (the birth of the node was on Christmas Day 2023), 50 thousand transactions routed, and over 30 BTC of routed value. In this post, I'd like to reflect on my experiences with Eclair, go over some of the gotchas and issues, and highlight some of the good choices that I've made since the beginning of my adventure.
Learnings from the Past Experience
While I was learning Lightning network and had very little understanding of how things worked in the whole Bitcoin space, Umbrel was my go-to solution that helped me get off the ground. It proved to be easy and somewhat educational but was not something that I would continuously run for the production setup or trust with any significant amount of bitcoin that I could not afford to lose. Lightning is built on top of the L1 (Bitcoin) network but manages the state of the channels in its own database that is negotiated and agreed upon with its peers. Any failures in the state integrity may result in the complete loss of liquidity or hefty penalty transactions (significant loss of capital). A Lightning node that participates in routing public transactions is also required to be constantly online with as little downtime as possible and only short periods offline at a time. Otherwise, you may risk causing force-closure of the channel due to expired HTLC that is measured in number of blocks.
The Setup
Taking all of my learnings into consideration, I decided to first invest in reliable enterprise-grade hardware: - Server-grade hardware with ECC memory and reliable power supply and CPU - UPS (Uninterruptible Power Supply) to avoid any headaches due to electrical spikes or drop-outs - Reliable enterprise SSDs and NVMEs - ZFS (filesystem) to mirror the critical storage and to ensure full integrity of the data (bit-rot prevention). You do need to tune ZFS for your specific workload and reliability - Reliable and replicated database (PostgreSQL) with two local and one remote replica, and a requirement to have at least two replicas committing the transaction to the disk - Backup! On-site and off-site backup of the critical configuration that you could use to restore the node if your house burns down - Spare parts, redundancy, backup, monitoring - Reliable and stable internet connectivity
The software is Eclair 0.11.0 (latest release as of today), PostgreSQL 16 with two replicas, Bitcoin Core 27.2 (with redundant storage of blocks), additional Bitcoin Core running on a separate node and in-sync with the chain (in case primary node fails), Ubuntu 22.04 with the latest docker software from the official Docker repo.
All Major Gotchas That I Came Across
While Eclair is mature and very stable in itself, it does have some quirks and design choices that you need to account for when running your node. The software is written in Scala and requires a specific version of JVM to run it, as well as JRE and Maven to build it. It doesn't mean that other versions won't work, but you may find unpleasant bugs that may result in catastrophic failures of your node with nobody to help you. All of the requirements are listed in the release notes and installation guide. Whenever in doubt, RTFM first, then ask questions.
Limited Support by the FOSS Community
Eclair is not the most popular implementation of the Lightning protocol, and therefore it is hard to find tools or plugins that could help you manage the node. GUI for the node so far is only supported by RTL and with a very limited number of features. For any sort of statistics, you are limited to either Prometheus (extensive metrics are available) or writing your own SQL on top of the Eclair tables.
On-chain Fee Differences Between Yours and Partner Nodes
This one hit me hard, and many times. I've had more than a few force-closures of the channels because of the conservative and safe default settings. The worst part is, it strikes you when there is a huge spike in fees, which results in significant losses to force-close the channel due to high fees. I am still not 100% sure how the big difference can be exploited in practice, and opted for increase of the tolerance levels to avoid surprise FCs:
eclair.on-chain-fees { feerate-tolerance { ratio-low = <0.01~> // will allow remote fee rates as low as XX our local feerate (spikes) ratio-high = <20.0~> // will allow remote fee rates as high as XX times our local feerate (drops) } }It is up to you and your risk tolerance to define something reasonable and yet allow for secure and reliable node operation.Initial Lightning Network State Sync
When I just started running the node, I had very few channels and startup times were fast. Later, when I expanded the number of channels, I noted that it took my node up to 6-12 hours before it was fully in-sync and routing traffic fast. Given that ACINQ maintains one of the largest nodes on the network, I knew that there was something with my settings that caused the issue. After some research, I came across the setting that whitelisted node IDs for state sync, which immediately rang a bell since I knew from the LND days that not all peer nodes are used for the network sync. Setting the list to my most reliable and largest nodes reduced the startup settling times down to minutes again:
eclair.sync-whitelist = [ "03864ef025fde8fb587d989186ce6a4a186895ee44a926bfc370e2c366597a3f8f", ... ]You do not need to have too many public keys in here, and should keep it between 5-10.Automatic MAX HTLC Adjustment for the Channel
One of the killer features of Eclair is its ability to automatically adjust MAX HTLC for the channel and reduce the number of failed transactions due to insufficient liquidity on the channel. It can be used to estimate your total channels' balances but with smart configuration and a little thinking, you can make it reasonably private while still maintaining a good transaction flow:
eclair.channel.channel-update.min-time-between-updates=1 hour # Allows for the adjustments to be made once every hour eclair.channel.channel-update.balance-thresholds=[ { available-sat = 10000 max-htlc-sat = 0 // 0% of 10000 }, ... ]You can have as many variations as you need, and ensure that the channel MAX HTLC is set well and within reasonable ranges. You would also want to account for multiple transactions going through the channel, but also account for the channel size and an average amount of sats per transaction.Max Accepted HTLCs
By design, the Lightning channel is limited to a specific number of in-flight HTLCs, and the setting is fixed during channel opening time with no way of changing it unless you close and reopen the channel with new settings. If you find your node routing a lot of small transactions (zaps), you may quickly fail many due to that limit (I think default was in single digit range):
eclair.channel.max-htlc-value-in-flight-percent=98 # Default I think is half or 50% eclair.channel.max-accepted-htlcs = 50The setting above will allow for the channel to be more fully utilized and have more concurrent transactions without clogging.CLTV Delta
This is basically a setting that is global for Eclair and sets the maximum number of remaining blocks (in time) before HTLC expires. Setting this too high may result in many HTLCs failing for the small nodes with not so great centrality, and reduce the number of routed transactions: ```
CLTV delta
eclair.channel.expiry-delta-blocks = 60 ``` Default is 144 but I found that setting this to 60 (minimum possible for my node setup and configuration) yields better results for routing. It does expose you to more risk of expired HTLCs that may cause force-closures, but I have seen only one so far on my node.
Allocate Sufficient Memory
You will want to adjust the heap size for Eclair, since the default is too small to run any sizable node. Setting
JAVA_OPTS=-Xmx32g(or half the size of your available RAM) would be a good start. I would advise having at least 32GB of RAM for the node, and allocating at least 16GB (JAVA_OPTS=-Xmx16g) for smooth and fast operations.And More Settings and Parameters to Tune
I have covered only some of the major settings that I felt were worth writing about, but there is much more you could configure and tweak. Read all of the Guides and especially focus on the Configure and a sample reference configuration file.
Good Decisions
First, going with Eclair was the right choice, along with using server-grade hardware with ECC RAM and reliable storage. Second, having a replicated database on three separate nodes with one off-site saved me from a sure destruction of all state and loss of funds. Third, deciding to only maintain channels with reliable and stable nodes saved me from some bad force-closures, where I would choose to close the channel if a peer node goes up and down too frequently, regardless of how well it routes. Even big nodes run by single operators fail badly, as do nodes operated by companies. Keeping your eyes on the node and its health, as well as the health of its peers, is something that very few operators do, which can cause failures and unnecessary loss of your and their funds.
Lastly, if you decide to run a routing node, you have a responsibility to maintain it well and monitor its health. There are many tools you could use, and with Eclair you can use Prometheus and Grafana. Keep your node's packages updated and monitor for any security-related issues that may appear from time to time, so you can mitigate them quickly.
Conclusion
So far I am satisfied with Eclair despite all of the difficulties and headaches I've had with it. It is not perfect, and it requires me to create small tools to do some basic things, but I need a stable and reliable node that I can trust. Eclair has proved to be all that I wanted, and saved my bacon a few times when I nuked one of the PostgreSQL servers and all of its data, and managed to do the same for another replica, but was able to recover and recreate from the remaining replica. Eclair is also stateless during runtime and guarantees consistency of the node regardless of how it fails. Even if you pull a plug on the node's server, it will still be able to come up and recover its consistent state that is in agreement with its peers.
Is it for everyone? No, it is definitely not for everyone or for anyone who just wants a small node to run their online shop with a few channels. You could have a very reliable and trusted node for the online shop with Eclair, but you will need some technical skills to be able to set up, maintain and recover it if things go wrong.
In the end, it is all up to you, your skills, your willingness to learn, and your risk tolerance to make that decision. For me, it was the right choice, and I have no regrets despite not having access to the latest shiny features of the Lightning network.
-
 @ 3f770d65:7a745b24
2024-12-31 17:03:46
@ 3f770d65:7a745b24
2024-12-31 17:03:46Here are my predictions for Nostr in 2025:
Decentralization: The outbox and inbox communication models, sometimes referred to as the Gossip model, will become the standard across the ecosystem. By the end of 2025, all major clients will support these models, providing seamless communication and enhanced decentralization. Clients that do not adopt outbox/inbox by then will be regarded as outdated or legacy systems.
Privacy Standards: Major clients such as Damus and Primal will move away from NIP-04 DMs, adopting more secure protocol possibilities like NIP-17 or NIP-104. These upgrades will ensure enhanced encryption and metadata protection. Additionally, NIP-104 MLS tools will drive the development of new clients and features, providing users with unprecedented control over the privacy of their communications.
Interoperability: Nostr's ecosystem will become even more interconnected. Platforms like the Olas image-sharing service will expand into prominent clients such as Primal, Damus, Coracle, and Snort, alongside existing integrations with Amethyst, Nostur, and Nostrudel. Similarly, audio and video tools like Nostr Nests and Zap.stream will gain seamless integration into major clients, enabling easy participation in live events across the ecosystem.
Adoption and Migration: Inspired by early pioneers like Fountain and Orange Pill App, more platforms will adopt Nostr for authentication, login, and social systems. In 2025, a significant migration from a high-profile application platform with hundreds of thousands of users will transpire, doubling Nostr’s daily activity and establishing it as a cornerstone of decentralized technologies.
-
 @ 3bf0c63f:aefa459d
2024-01-15 11:15:06
@ 3bf0c63f:aefa459d
2024-01-15 11:15:06Pequenos problemas que o Estado cria para a sociedade e que não são sempre lembrados
- **vale-transporte**: transferir o custo com o transporte do funcionário para um terceiro o estimula a morar longe de onde trabalha, já que morar perto é normalmente mais caro e a economia com transporte é inexistente. - **atestado médico**: o direito a faltar o trabalho com atestado médico cria a exigência desse atestado para todas as situações, substituindo o livre acordo entre patrão e empregado e sobrecarregando os médicos e postos de saúde com visitas desnecessárias de assalariados resfriados. - **prisões**: com dinheiro mal-administrado, burocracia e péssima alocação de recursos -- problemas que empresas privadas em competição (ou mesmo sem qualquer competição) saberiam resolver muito melhor -- o Estado fica sem presídios, com os poucos existentes entupidos, muito acima de sua alocação máxima, e com isto, segundo a bizarra corrente de responsabilidades que culpa o juiz que condenou o criminoso por sua morte na cadeia, juízes deixam de condenar à prisão os bandidos, soltando-os na rua. - **justiça**: entrar com processos é grátis e isto faz proliferar a atividade dos advogados que se dedicam a criar problemas judiciais onde não seria necessário e a entupir os tribunais, impedindo-os de fazer o que mais deveriam fazer. - **justiça**: como a justiça só obedece às leis e ignora acordos pessoais, escritos ou não, as pessoas não fazem acordos, recorrem sempre à justiça estatal, e entopem-na de assuntos que seriam muito melhor resolvidos entre vizinhos. - **leis civis**: as leis criadas pelos parlamentares ignoram os costumes da sociedade e são um incentivo a que as pessoas não respeitem nem criem normas sociais -- que seriam maneiras mais rápidas, baratas e satisfatórias de resolver problemas. - **leis de trãnsito**: quanto mais leis de trânsito, mais serviço de fiscalização são delegados aos policiais, que deixam de combater crimes por isto (afinal de contas, eles não querem de fato arriscar suas vidas combatendo o crime, a fiscalização é uma excelente desculpa para se esquivarem a esta responsabilidade). - **financiamento educacional**: é uma espécie de subsídio às faculdades privadas que faz com que se criem cursos e mais cursos que são cada vez menos recheados de algum conhecimento ou técnica útil e cada vez mais inúteis. - **leis de tombamento**: são um incentivo a que o dono de qualquer área ou construção "histórica" destrua todo e qualquer vestígio de história que houver nele antes que as autoridades descubram, o que poderia não acontecer se ele pudesse, por exemplo, usar, mostrar e se beneficiar da história daquele local sem correr o risco de perder, de fato, a sua propriedade. - **zoneamento urbano**: torna as cidades mais espalhadas, criando uma necessidade gigantesca de carros, ônibus e outros meios de transporte para as pessoas se locomoverem das zonas de moradia para as zonas de trabalho. - **zoneamento urbano**: faz com que as pessoas percam horas no trânsito todos os dias, o que é, além de um desperdício, um atentado contra a sua saúde, que estaria muito melhor servida numa caminhada diária entre a casa e o trabalho. - **zoneamento urbano**: torna ruas e as casas menos seguras criando zonas enormes, tanto de residências quanto de indústrias, onde não há movimento de gente alguma. - **escola obrigatória + currículo escolar nacional**: emburrece todas as crianças. - **leis contra trabalho infantil**: tira das crianças a oportunidade de aprender ofícios úteis e levar um dinheiro para ajudar a família. - **licitações**: como não existem os critérios do mercado para decidir qual é o melhor prestador de serviço, criam-se comissões de pessoas que vão decidir coisas. isto incentiva os prestadores de serviço que estão concorrendo na licitação a tentar comprar os membros dessas comissões. isto, fora a corrupção, gera problemas reais: __(i)__ a escolha dos serviços acaba sendo a pior possível, já que a empresa prestadora que vence está claramente mais dedicada a comprar comissões do que a fazer um bom trabalho (este problema afeta tantas áreas, desde a construção de estradas até a qualidade da merenda escolar, que é impossível listar aqui); __(ii)__ o processo corruptor acaba, no longo prazo, eliminando as empresas que prestavam e deixando para competir apenas as corruptas, e a qualidade tende a piorar progressivamente. - **cartéis**: o Estado em geral cria e depois fica refém de vários grupos de interesse. o caso dos taxistas contra o Uber é o que está na moda hoje (e o que mostra como os Estados se comportam da mesma forma no mundo todo). - **multas**: quando algum indivíduo ou empresa comete uma fraude financeira, ou causa algum dano material involuntário, as vítimas do caso são as pessoas que sofreram o dano ou perderam dinheiro, mas o Estado tem sempre leis que prevêem multas para os responsáveis. A justiça estatal é sempre muito rígida e rápida na aplicação dessas multas, mas relapsa e vaga no que diz respeito à indenização das vítimas. O que em geral acontece é que o Estado aplica uma enorme multa ao responsável pelo mal, retirando deste os recursos que dispunha para indenizar as vítimas, e se retira do caso, deixando estas desamparadas. - **desapropriação**: o Estado pode pegar qualquer propriedade de qualquer pessoa mediante uma indenização que é necessariamente inferior ao valor da propriedade para o seu presente dono (caso contrário ele a teria vendido voluntariamente). - **seguro-desemprego**: se há, por exemplo, um prazo mínimo de 1 ano para o sujeito ter direito a receber seguro-desemprego, isto o incentiva a planejar ficar apenas 1 ano em cada emprego (ano este que será sucedido por um período de desemprego remunerado), matando todas as possibilidades de aprendizado ou aquisição de experiência naquela empresa específica ou ascensão hierárquica. - **previdência**: a previdência social tem todos os defeitos de cálculo do mundo, e não importa muito ela ser uma forma horrível de poupar dinheiro, porque ela tem garantias bizarras de longevidade fornecidas pelo Estado, além de ser compulsória. Isso serve para criar no imaginário geral a idéia da __aposentadoria__, uma época mágica em que todos os dias serão finais de semana. A idéia da aposentadoria influencia o sujeito a não se preocupar em ter um emprego que faça sentido, mas sim em ter um trabalho qualquer, que o permita se aposentar. - **regulamentação impossível**: milhares de coisas são proibidas, há regulamentações sobre os aspectos mais mínimos de cada empreendimento ou construção ou espaço. se todas essas regulamentações fossem exigidas não haveria condições de produção e todos morreriam. portanto, elas não são exigidas. porém, o Estado, ou um agente individual imbuído do poder estatal pode, se desejar, exigi-las todas de um cidadão inimigo seu. qualquer pessoa pode viver a vida inteira sem cumprir nem 10% das regulamentações estatais, mas viverá também todo esse tempo com medo de se tornar um alvo de sua exigência, num estado de terror psicológico. - **perversão de critérios**: para muitas coisas sobre as quais a sociedade normalmente chegaria a um valor ou comportamento "razoável" espontaneamente, o Estado dita regras. estas regras muitas vezes não são obrigatórias, são mais "sugestões" ou limites, como o salário mínimo, ou as 44 horas semanais de trabalho. a sociedade, porém, passa a usar esses valores como se fossem o normal. são raras, por exemplo, as ofertas de emprego que fogem à regra das 44h semanais. - **inflação**: subir os preços é difícil e constrangedor para as empresas, pedir aumento de salário é difícil e constrangedor para o funcionário. a inflação força as pessoas a fazer isso, mas o aumento não é automático, como alguns economistas podem pensar (enquanto alguns outros ficam muito satisfeitos de que esse processo seja demorado e difícil). - **inflação**: a inflação destrói a capacidade das pessoas de julgar preços entre concorrentes usando a própria memória. - **inflação**: a inflação destrói os cálculos de lucro/prejuízo das empresas e prejudica enormemente as decisões empresariais que seriam baseadas neles. - **inflação**: a inflação redistribui a riqueza dos mais pobres e mais afastados do sistema financeiro para os mais ricos, os bancos e as megaempresas. - **inflação**: a inflação estimula o endividamento e o consumismo. - **lixo:** ao prover coleta e armazenamento de lixo "grátis para todos" o Estado incentiva a criação de lixo. se tivessem que pagar para que recolhessem o seu lixo, as pessoas (e conseqüentemente as empresas) se empenhariam mais em produzir coisas usando menos plástico, menos embalagens, menos sacolas. - **leis contra crimes financeiros:** ao criar legislação para dificultar acesso ao sistema financeiro por parte de criminosos a dificuldade e os custos para acesso a esse mesmo sistema pelas pessoas de bem cresce absurdamente, levando a um percentual enorme de gente incapaz de usá-lo, para detrimento de todos -- e no final das contas os grandes criminosos ainda conseguem burlar tudo. -
 @ 30ceb64e:7f08bdf5
2025-01-08 20:14:45
@ 30ceb64e:7f08bdf5
2025-01-08 20:14:45In a world dominated by surveillance banking and inflationary currencies, a new paradigm is emerging—one where individuals can operate sovereign, theft-resistant checking accounts using the world's hardest money. This isn't your grandfather's checking account; it's an entirely new financial operating system built on Bitcoin and Lightning technology.
The Bitcoin Checking Account Revolution
Traditional checking accounts are permission-based systems where banks maintain ultimate control over your money. In contrast, a sovereign Bitcoin checking account operates on a fundamentally different principle: you hold your own keys, control your own node, and maintain custody of your funds at all times. This architecture is built on several key components:
- Self-hosted nodes providing direct network access
- Lightning channels for instant settlement
- Hardware wallets for secure key storage
- Non-custodial software interfaces
- Automated accounting and payment systems
The concept of a Bitcoin checking account represents a paradigm shift in daily financial operations. Imagine getting a direct deposit sent to your lightning node and using NWC and a variety of plug and play solutions to handle things regarding accounting, bill pay, and daily POS transactions. We're starting to see these options emerge through services like Bitcoin Well, Albyhub, Strike, Clams and Cash App.
Breaking Free from Financial Surveillance
The current banking system tracks every transaction, creating a detailed financial surveillance network. Sovereign Bitcoin checking accounts offer a powerful alternative:
- Private lightning channels for daily transactions
- E-cash protocols for enhanced privacy
- Peer-to-peer transactions without intermediaries
- No account freezes or arbitrary limits
- Freedom from traditional banking hours and restrictions
Lightning and Cashu offer additional privacy and settlement speeds while enabling low cost transactions, and I believe these protocols will grow and exceed our expectations. The products and services for managing your bitcoin checking account will get more private and efficient as time moves forward.
The Daily Operations Revolution
Operating a sovereign checking account transforms everyday financial activities:
-
Income Reception
-
Direct deposit straight to Lightning
- Instant availability of funds
- No hold periods or bank delays
-
Multiple invoice routes for different income streams
-
Payment Management
-
Automated bill payments via Lightning
- Instant merchant settlements
- Cross-border transactions without fees
-
Dynamic fee management for optimal efficiency
-
Liquidity Control
-
Self-managed channel balances
- Cold storage integration for savings
- Automated rebalancing protocols
- Real-time capital efficiency
The Deflationary Advantage
Perhaps the most revolutionary aspect is operating a checking account in deflationary money. This fundamentally changes spending psychology and financial planning:
- Each sat potentially appreciates over time
- Natural incentive for thoughtful spending
- Built-in savings mechanism
- Protection from currency debasement
Global Market Integration
This new financial infrastructure enables seamless participation in the global economy:
- Borderless transactions
- 24/7 market access
- Direct international trade
- No forex fees or exchange rate manipulation
- Instant settlement across time zones
Security and Resilience
The system's security model represents a significant advancement:
- Multi-signature protocols
- Timelocked recovery options
- Distributed backup systems
- Attack-resistant architecture
- No single points of failure
The Future of Personal Banking
As this technology matures, we're likely to see:
- Simplified user interfaces
- Enhanced privacy tools
- Better integration with existing systems
- More automated financial management
- Increased merchant adoption
In conclusion, sovereign Bitcoin checking accounts represent more than just a new way to bank—they're a fundamental reset of the relationship between individuals and their money. This system combines the security of cold storage with the utility of traditional checking accounts, all while leveraging the strength of deflationary sound money. As adoption grows, these accounts will likely become the standard for those seeking financial sovereignty in an increasingly digital world.
The revolution isn't just about holding bitcoin—it's about using it in a way that maintains sovereignty while enabling practical daily finance. This is the future of money, and it's already here for those ready to embrace it.
-
 @ 3f770d65:7a745b24
2024-12-30 19:25:45
@ 3f770d65:7a745b24
2024-12-30 19:25:45As I look back on my predictions for Nostr in 2024, it’s clear I had some hits and misses. I believe my first two predictions were spot on, accurately reflecting the trends and developments we witnessed. However, my second two predictions missed the mark, proving to be far less accurate. Maybe I was too bullish?
nostr:nevent1qvzqqqqqqypzq0mhp4ja8fmy48zuk5p6uy37vtk8tx9dqdwcxm32sy8nsaa8gkeyqyghwumn8ghj7mn0wd68ytnhd9hx2tcpzamhxue69uhhyetvv9ujumn0wd68ytnzv9hxgtcqypsm9tk39g20atwqskvjcvhq7rher5nkgwjr05lzspne4gf0uvyxukew5mg
What did I get right? Clients did increasingly prioritize user and content discovery while enabling users to easily select and choose their own algorithms. (DVMs, Trending, What's Hot, Feeds, etc.) This focus provided individuals with more tools, greater control, and unprecedented power over their social streams and attention than ever before. This is still actively happening and will continue to happen throughout 2025 too.
What did I get wrong? We didn't see an Other Stuff application breakthrough as a clear winner that became a mainstream favorite. I anticipated a standout application that would interest users and become a "must-use" within the ecosystem, but this didn’t happen. And we also clearly didn't hit 1M active users either. While adoption did increase, it didn’t reach the critical mass I expected.
But this doesn't mean 2024 fell short of expectations—in fact, quite the opposite. The year brought incredible client innovations (Damus Notedeck, Primal 2.0, TOR only Amethyst, Flotilla, Chachi, Olas, Coracle feeds, etc.) and relay milestones (Web-of-Trust relays, private relays, algorithm based relays, etc.) with the introduction of these innovative features and the launch of these new platforms.
Beyond technology, the Nostr community achieved something truly remarkable: a grassroots movement that united people globally.
From supporting Nostr meetups and events to hosting booths across continents at major conferences, the community came together to raise money to support these initiatives in ways no one predicted. This organic, ground-up effort showcased the strength and passion behind Nostr, creating a foundation that will #grownostr and success for years to come.
Too bullish? Maybe I wasn't bullish enough? As is tradition, I will post my 2025 predictions tomorrow.
-
 @ 714f9dc3:76659adb
2025-01-08 19:16:50
@ 714f9dc3:76659adb
2025-01-08 19:16:50Last week, I was reading “The Air We Breathe”, by Glen Scrivener. It’s about “How We All Came to Believe in Freedom, Kindness, Progress, and Equality”, and it explores the Christian roots of the values we prize in today's western society. It’s all around us, but we don’t really know where it came from: It’s the air we’re breathing. The ideas and ethics behind Christianity, whether you believe in them or not, are embedded in our culture.
As I was reading this, I saw so many parallels with Bitcoin, so wanted to list them below and share some of my thoughts. Can Bitcoin also become “The Air We Breathe”? Or in plebs words: hyperbitcoinization?
Can Bitcoin become so ubiquitous that it becomes normal? Can there be a world in which we don’t even know where Bitcoin came from? It would be a world with many similar views as with today's view on Christianity. It becomes the air we breathe, something that used to be a counterculture that over time became ubiquitous. What can we learn from it?
These are my ten parallels of Bitcoin with the early days of Christianity.
- Separation from state
- From obscure counterculture to dominant force
- Exponential grassroots growth
- Conversion of emperors/politicians
- Sudden tolerance and protection for ideology
- Fall of the empire, end of the status quo
- Missionaries spreading the word
- Persuasion and education are key
- Age of Enlightenment
Note: I’m no expert on Christianity, nor a historian of the Roman Empire, and I know just a bit about Bitcoin. See this as a thought experiment.
1. Separation from state
In all fairness, I’m not the first to draw this first parallel. It was Satoshi Nakamoto themself who made the connection even before Bitcoin was available to the public, with several hints pointing back to important dates and moments in Christian history. The big parallel here is the “separation of money and state” and “separation of church and state”.
Before going back to the early days of Christianity in the first centuries AD, I first want to draw this parallel with Satoshi.
It’s 1517. The German Priest Maarten Luther writes his Ninety-five Theses, and nails this on the church doors in Wittenberg. The theses are also known as the “Disputation on the Power and Efficacy of Indulgences”. He kickstarted a movement with a radical new idea for that time: The separation of the church from the state.
The Catholic Church had become one with the state. Via the means of indulgences, there was an ability to pay for your redemption. The church was corrupted by money, power and politics. The church and indulgences replaced the need for personal responsibility and an individual faith with money and perverse structures.
Reformation Day is a Protestant Christian religious holiday celebrated on 31 October in remembrance of the onset of the Reformation. But the 31st of October is also the day in which Satoshi shared his pamphlet with the world: in 2008 they published the Bitcoin Whitepaper. It kickstarted a movement with a radical new idea for that time: The separation of the money from the state.
But this was not Satoshi’s only hint. Another one is the date of Bitcoin’s Genesis Block: January 3, 2009. It was the day that the idea of the separation of money and the state became reality, more than just an idea in an individual's mind.
Did you know that Maarten Luther was excommunicated from the Catholic Church in 1521 by Pope Leo X for sparking this revolutionary new way of thinking (and being). It happened on January 3 as well. I bet Satoshi Nakamoto knew.
To be fair, this parallel is not new and known by many bitcoiners. But it’s a good introduction to the topic, and after reading “The Air We Breathe: How We All Came to Believe in Freedom, Kindness, Progress, and Equality”, I automatically started to see more parallels between (the early days of) Christianity and todays adoption of Bitcoin. Because it was of course not Maarten Luther who sparked these rebellious thoughts in 1500, but it was Jesus himself approx. 2000 years ago.
Let’s go back from the 1500s to the first decades AD to the beginning of this radical new belief system. During the dominance of the Roman empire in the Mediterranean and much of Europe, Western Asia and North Africa, someone told a story that opposed every mainstream paradigm.
Jesus’ idea was radically different from the belief systems of that day. He preached Freedom, Kindness, Progress, and Equality in a world that was full of Debauchery and Violence, with Gladiator Games, Slavery, Public Crucifixion, and Brutalities. The belief system of that time was not like todays.
There were superior races (Greek/Romans over barbarians), superior sexes (man over women), superior classes (free man over slaves) and the concept of justice was more something in the realm of “restoring rights of those that were superior”, than “equality for all, men and women, Greek and barbarian, free and slave”.
Jesus opposed the status quo. It started small and irrelevant; as a counterculture. But it didn’t stay that way.
2. From obscure counterculture to dominant force
In “The Air We Breathe”, Scrivener asks the question:
“How did the obscure, marginal Jesus movement of the 1st century become the dominant religious force in the Western world in a few centuries?”
Important to know, is that the Christian faith was the opposite of the narrative. Concepts like Freedom, Kindness, Progress, and Equality didn’t exist in the Roman Empire. Human rights neither. Individual rights neither. The emperor was almost de facto God himself.
Early Christians were persecuted for preaching a different story: that God is NOT the ruler of the empire. Jesus preached the separation of politics from God; separating faith from the state. As a result, he was crucified, and many of his followers were killed by Nero (between 54 and 68 AD), Domitian (81–96 AD), Trajan (98–117 AD) and Decius (249–251 AD). This new narrative was a thread for the Roman rulers.
Draw the parallels of how there have been many attempts to “kill” bitcoin, not with physical persecution but with an information war. Not by physical violence, but by misinformation. Bitcoin threatens the status quo, just like Christianity threatened the Roman Empire.
You see?
But how is the obscure movement of Bitcoin in the 21st century becoming the dominant force, similar to the question that Scrivener asked about Christianity? Perhaps the answer lies in the following parallel.
3. Exponential grassroots growth
Sociologist Rodney Stark estimates in “The Rise of Christianity” that from the time of the first Easter, the church began growing at a rate of 40% per decade, a modest but relentless 3.4% per year. By the year 300, Christians numbered perhaps 6 million: about a tenth of the empire.
Despite pushbacks, the army of believers continued to grow. Grassroots, peer-to-peer. It was not the state-religion, it was a peaceful army of believers that spread the word, resulting in an exponential growth of its followers. The counterculture became more and more dominant.
You may see what I’m doing here. It was basically the meme that all Bitcoiners know: Gradually, then suddenly. Against the current.
4. Conversion of emperors/politicians
In 312 a big change happened: Emperor Constantine converted to Christianity. As Stark writes, "Constantine's conversion would better be seen as a response to the massive exponential wave in progress, not as its cause".
Are we living in that same era, where nation states start to embrace Bitcoin? Where politicians don’t oppose as strongly anymore, but are flirting with the idea of embracing it? And again the parallel: it’s responsive to the exponential wave of progress, not as its cause.
Whether Constantine is Nayib Bukele, Donald Trump, or Milei: it doesn’t matter. It’s the dynamic that matters. The counterculture becomes so dominant, that the “rulers” of the world are wanting to be part of it. Which will be followed by “rules” that favour the ideology, movement, and beliefs.
6. Tolerance and protection for ideology
In 313 Constantine's Edict of Milan granted freedom to Christians that were remarkable for that time and a model for religious toleration for the coming centuries.
The tide was turning, and by 380 Emperor Theodosius made Christianity Rome's official religion, more than half the population had already converted. In a few short centuries Christianity had gone from radical counterculture to dominant cultural power. This was an extraordinary shift in the church's relationship with the world. The edict expressly grants religious liberty to Christians, who had been the object of special persecution, but also goes even further and grants liberty to all other religions. And then, in 410, the world itself changed.
It changed from grassroots, bottom-up adoption to some kind of nation state adoption. One that was driven by decrees and edicts, instead of the analog cyberhornets of that day. Actually, the ideas of Indulgences were introduced via these Edicts, something that Maarten Luther actually was fighting against in the 1500s.
The world changed from the state-less Christian belief and moved (back) towards a system in which the state and church were connected again. Yes — the Roman Catholic Church. Until the previously mentioned critics during the Reformation.
6. Fall of the empire, end of the status quo
When people speak of the fall of the Roman Empire, they usually mean in the 5th century when the western half fell. But there was also an eastern half, known as the Byzantine Empire (with its capital in what is modern-day Istanbul).
How did this relate to the movement that once was Cult, and now suddenly had become Culture?
It was Augustine, the north African bishop (354-430), who laid the foundation for a new philosophical, theological, and legal system. He distinguished between the fragile earthly realm and the eternal heavenly kingdom. Rome was “a city of man”, which fell. But the “city of God” was forever. He continued to separate the Roman Catholic Church from the faith that it once was. This distinction was vital, and it gave rise to the concept of "the secular realm". He planted the first ideas of "the separation of church and state" again, which started to spread throughout Europe during the supposedly "sandy desert" of the Middle Ages.
The parallel and lesson here might be that narratives can be taken over, for the worse. And that it takes centuries to take back the narrative, but/and only after an empire has fallen. Whether we refer to “The Fourth Turning” by William Strauss and Neil Howe or “Changing World Orders” by Ray Dalio. There is something to preserve, and it needs active monitoring and pushbacks!
7. Missionary, spreading the word
The way the church sought to spread its influence would become a question that would take many centuries (and many failures) to settle. In the past, empires sought to spread their influence almost always by force. Christianity has been a missionary faith from the beginning. It was for this reason that Pope Gregory the Great sent Augustine to Britain to convert the Anglo-Saxons.
Augustine was commanded by Gregory to use only "gentle means". His goal was persuasion. His method was teaching and preaching. And he was successful, converting King Aethelbert of Kent and becoming the first Archbishop of Canterbury.
You see what I’m talking about again: the parallel is simple. Bitcoin is a similar peaceful revolution, a missionary movement, of those that wish to see their Cult turn into a Culture. “Genle means”, teachings, persuasions. Or in pleb terminology: Orangepilling.
8. Persuasion and education are key
Over the next decades and centuries, this movement continued. English Benedictine monk (675-754) Boniface was sent from the previously “barbarian” Britain to “orangepill the East” – in this case the Saxons in the Germanic lands. In the words of his advisor, the Bishop of Winchester, his goal was "to convince them by many documents and arguments". This mission of persuasion and education was largely successful. Today he’s better known as “the Apostle to the Germans". He was killed in The Netherlands (in Dokkum).
Boniface kept to a policy of non-violence and non-retaliation, even to the point of death. Another famous writer about this topic, Tom Holland, summarises the lesson we learn from Boniface: "to convert was to educate".
In the following century this lesson was sorely needed by the Frankish king Charles the Great, aka Charlemagne (742-814). Charlemagne's path to power was a brutal one. When the Saxons stood in his way, Charlemagne beheaded 4,500 of them in a single day. There are concrete reasons why "getting medieval" might be associated today with brutality.
Is “Bitcoin as Legal Tender”, whether this is peaceful or violently, the way to go? Are we “getting medieval” with these kind of measures, in order to go from Cult to Culture, from counterculture to dominant culture, in which we lose the true essence of our revolution of separation of the state from the matter?
9. Age of Enlightenment
Alcuin of York (735-804), was bold enough to write to Charlemagne directly with his criticism. "A person can be drawn into the faith, not forced into it". Be a lighthouse, not a tugboat!
The church's official teaching would later agree with Alcuin's position. In the 12th century all "harsh means" were forbidden since faith arises from the will, not compulsion. Enlightenment comes through education and persuasion.
There’s work to do. Grassroots. Education. Peer-to-peer. Not directed by politicians, nor opposed by those in power. Through education and persuasion. Rules without rulers. Because eventually, with the Crusades and the Spanish Inquisition, there are stark examples of the church using “harsh means" again. Forcing Bitcoin on people will never be the way: it’s a cheat code to the end goal. In order to succeed, we’ll need to be a missionary.
Final words
I don’t want in any way to compare Christianity in itself as a faith, and Bitcoin as a technology, with each other. I enjoyed exploring the sociological phenomena between two countercultures, the grassroots movement and missionary parallels between both of them. Satoshi gave the first assist, with the 31st of October (Whitepaper Day) and the Genesis Block on January 3rd.
Let’s not mix religion with monetary systems, even though there are many similarities between certain movements. That’s not my goal for sharing this brain dump. But let’s learn from the past, from Constantine’s Edict and from Augustine, from Charlemagne (and especially Alcuin of York), from Boniface and from Maarten Luther. And from Satoshi Nakamoto.
-
 @ 8d34bd24:414be32b
2024-12-29 23:22:36
@ 8d34bd24:414be32b
2024-12-29 23:22:36Everyone was amazed and gave praise to God. They were filled with awe and said, “We have seen remarkable things today.” (Luke 5:26)
There are lots of verses in the Bible, both Old and New Testaments, where people were amazed at the works of God, but my question is, “Is there anything that amazes God?”
When the Sabbath came, he began to teach in the synagogue, and many who heard him were amazed.
“Where did this man get these things?” they asked. “What’s this wisdom that has been given him? What are these remarkable miracles he is performing? Isn’t this the carpenter? Isn’t this Mary’s son and the brother of James, Joseph, Judas and Simon? Aren’t his sisters here with us?” And they took offense at him.
Jesus said to them, “A prophet is not without honor except in his own town, among his relatives and in his own home.” He could not do any miracles there, except lay his hands on a few sick people and heal them. He was amazed at their lack of faith. (Mark 6:2-6) {emphasis mine}
This passage mentions the people being amazed at Jesus’s teaching, but it also talks about Jesus being amazed at their lack of faith. It is amazing that people could see the son of God, face to face, and listen to Him teach God’s word and still not believe. They heard about and even saw Him work miracles and yet they did not repent, nor believe.
This is an example of a negative amazement. Are there any examples of positive amazement? There are two passages, that I know of, that describe one particular event that amazed Jesus:
The centurion replied, “Lord, I do not deserve to have you come under my roof. But just say the word, and my servant will be healed. For I myself am a man under authority, with soldiers under me. I tell this one, ‘Go,’ and he goes; and that one, ‘Come,’ and he comes. I say to my servant, ‘Do this,’ and he does it.” *When Jesus heard this, he was amazed* and said to those following him, “Truly I tell you, I have not found anyone in Israel with such great faith**. I say to you that many will come from the east and the west, and will take their places at the feast with Abraham, Isaac and Jacob in the kingdom of heaven. But the subjects of the kingdom will be thrown outside, into the darkness, where there will be weeping and gnashing of teeth.”
Then Jesus said to the centurion, “Go! Let it be done just as you believed it would.” And his servant was healed at that moment. (Matthew 8:8-13) {emphasis mine}
The other mention of this event is in Luke:
He was not far from the house when the centurion sent friends to say to him: “Lord, don’t trouble yourself, for I do not deserve to have you come under my roof. That is why I did not even consider myself worthy to come to you. But say the word, and my servant will be healed. For I myself am a man under authority, with soldiers under me. I tell this one, ‘Go,’ and he goes; and that one, ‘Come,’ and he comes. I say to my servant, ‘Do this,’ and he does it.”
When Jesus heard this, he was amazed at him, and turning to the crowd following him, he said, “I tell you, I have not found such great faith even in Israel.” (Luke 7:6-9) {emphasis mine}
This Roman centurion had greater faith than any one of God’s chosen people in Israel. This gentile man trusted that Jesus had the power to heal his servant and that all it would take was Jesus’s command. If Jesus spoke the word, his servant would be healed, and it was so. Just as Jesus spoke the universe into existence, He also spoke the centurion’s servant into health. The creator healed His creation with His word and the centurion believed that it would be so.
What can amaze God? It looks like both our lack of faith and great faith can amaze God.
This coming year, let’s try to amaze God with our undying faith in His goodness and ability to do anything and everything for our good.
Trust Jesus.
-
 @ 6b0a60cf:b952e7d4
2024-12-05 11:16:09
@ 6b0a60cf:b952e7d4
2024-12-05 11:16:09フォロワーリストを低コストで取得する仕様を考える
Nostr リレーはフォロワー数をカウントしたほうが良いを受けて考えたことを雑多に書き留めておきます
単一リレーの場合
NIP-45 COUNT を使う
短所
- 単一リレーで数えた総数でしかない
- 現時点では数を返すのみ
- 複数リレーでマージできるようにidsを一緒に返そうという提案もある
{"#p": <pubkey>, "kinds": [3]} でREQする
短所
- 単一リレーで数えた総数でしかない
- フォロワーの数だけクソデカイベントが返ってくるので時間がかかるしギガが減る
複数リレーの場合
{"#p": <pubkey>, "kinds": [3]} でREQする
長所
- 複数リレーでマージできる
- そこそこもっともらしいフォロワーリストが取れる
短所
- 一度でもフォローをしたことがある人のリストでしかない(後にアンフォローしたかもしれない)
- nostr:nevent1qqs829n0s3qa3wegnhpf6haz3t87hn9huznldd4x2ld6c0d02uq09gsge47l7
- リストすべての公開鍵で接続リレーとkind3を調べ直してアンフォローされている場合を除く処理をすればそこそこ正確になる
- 大変すぎる
- 未調査のリレーにフォロワーがいるかもしれない
新しいkind(フォロワーを格納する)を新設する
仮にkind1003とする
kind3と同じ構造とする{ "kind": 1003, "pubkey": "<Aさんの公開鍵>", "tags": [ ["p", "<Bさんの公開鍵>"], ["p", "<Cさんの公開鍵>"], ["p", "<Dさんの公開鍵>"] ], // other fields... }で、これ誰が作るの?
リレーが作る
- pubkeyにはAさんの公開鍵を入れることになるけど、署名するにはAさんの秘密鍵が必要だよ?
- 無理
クライアントが作る
- Rabbitやnostter等のクライアントにはプロフィール画面でフォロワーのところをクリックするとフォロワーの取得が始まる
- その際、構築したフォロワーリストをkind1003イベントとしてリレーに送ってしまえば良い
- リレー毎でなく複数リレーのマージした結果であるが、その方が有用だろう
- でもkind1003を作成した時期はアカウント毎にバラバラになってしまうね
誰が嬉しいの?
- クライアントは恩恵を受けない
- 本来kind1003の恩恵を受けるべきクライアント自身がkind1003を作らなくてはならない
- 統計調査に興味がある人が満足する
- そのためだけに各クライアントを使用するユーザーの端末のリソースを使う価値があるかどうか
そもそもリレーである必要があるだろうか
- リレーはシンプルであるべきだが、リレーに高機能を求めること自体は否定されるべきことではない
- NIP-50のように検索に特化したリレーもある
でもこの統計情報ってWebSocketで送られてくるべきものだろうか?HTTPで良くない?
リレーである必要すらなくて、REST APIを提供するサービスがあれば十分だよね?
外部サービスとして独自にデータを集めているサービスは既にあるこれをNIPにする必要があるだろうか
- WebSocketやリレーが登場しないからといってNIPに定義してはいけないなんてことはない
- 例: NIP-96
- しかしNIPというのは仕様を共通化して共有するためのものであり、複数の実装を期待するものである
- 統計API提供サービスなど1つあれば十分で、耐検閲性を目的として10個も100個も存在を期待されるものではない
-
 @ e0a8cbd7:f642d154
2024-12-04 15:42:58
@ e0a8cbd7:f642d154
2024-12-04 15:42:58これは「Nostr Advent Calendar 2024」5日目(12月5日)の記事です。
2024年にNostrにのみ投稿した絵で今年を振り返りたいと思います。 あえて、タイトルのみで、なぜその絵を描いたかなどの絵の説明は書かないことにします。
1月2日 ブルルッチモ大噴火!

1月9日 Macの箱を開けながら、ギャォォォォンって叫ぶぺぇさん。

1月12日 便器の上で踊るサボテンになったぽーまんさん。

1月15日 空飛ぶつるるん。

1月23日 ぽわどん

1月26日 Lokuyow said "I am a pen."

1月28日 ロクヨウ「早く人間にのりたい」
1月31日 小さなmonoから大きなmonoまで

2月1日 しおさん、巨象恐怖症

2月1日 枕を積んで寝るDonさん。

2月4日 ブロッコリの逆襲

2月8日 びっとこダチョ太郎

2月13日 虹色カレーを食べて虹色になったロクヨウさん

2月13日 ロクヨウさん誕生秘話

3月5日 人参と椎茸たべるロクヨウさん

3月5日 まきうさん、ロクヨウさんに乗って東京へ

3月26日 ごはんの上のめんたいこぽーまん

3月26日 ポワニッチモ

4月4日 上司にズラしていくことを許可されて朝の悩みが増えたぺえさん

5月7日 とうふさんが演じる「お洋服とっかえひっかえして遊ぶりとりんとやぶみん」

6月20日 ソファーと一体化するポーマンさん

6月21日 つるるん食べていい?

6月28日 ぽーまんさん、たいきんのまい

7月5日 ソファから剥がれて出発するぽーまんさん
8月10日 ぽーまんさん、床のコスプレ

8月18日 アルパカプリン

8月23日 とうふさんが演じるやぶみちゃんの日

8月23日 神妙な顔のぽ-まんさん

8月26日 恋のアルパカキューピット
8月27日 仲良く激辛火鍋

8月28日 Microsoftが「Mono」をWineチームに寄贈

9月12日 もの発射
9月19日 ロクヨウさんヒツジ化

9月20日 ゴリラ食べてバナナになったロクヨウさん

10月13日 頭が増えるぽーまんさん

10月24日 カメムシと青いうさぎ

10月25日 ATMとお話しするポーマンさん

10月26日 パペェ

10月26日 ぺどがわさん

11月7日 伸び縮みぺぇ

11月10日 座布団で寝るぽーまんさん

11月17日 5等分のぽーまん

11月27日 ルンバブルな部屋

11月28日 7人のぽーまん、那月さんに祓われる

11月29日 捕鯨ぽーまん

11月30日 ぽーまんさん脳内のゴミカスサンバ♪

楽しい1年でした。
Nostrのみなさま、たのしい話題をありがとうございます。
明日の「Nostr Advent Calendar 2024」は、OHASHI Hideyaさんです。
しーゆー。 -
 @ dd664d5e:5633d319
2024-12-29 20:29:03
@ dd664d5e:5633d319
2024-12-29 20:29:03The paparazzi are we

One of the things that bothers me about social media, in general, is that it gives celebrities an air of approachability, that they don't actually offer.
Theoretically, a celebrity could respond to any one of the dozens or even hundreds of people asking them questions or lodging complaints or singing their praises, but they usually only respond very selectively and leave everyone else just sitting there, as a living monument to the ReplyGuy.
And, as a wise man once said, ReplyGuy is a hoe.
Death of a ReplyGuy
This is usually because of time and energy restrictions, but also due to distaste, disdain, or indifference. Regardless of motivation, it is simply the nature of things, when a larger number of people are clamboring for the attention of some particular person.
Ooh, ooh! Can I have the next question?! Would you please address my bug? May I have a microsecond of your time?

Social media (and I include GitHub in this category) ups this game considerably, and potentially turns it all into a dangerous psychological torture, by making us all preoccupied with people who don't interact with us. The most irrational of groupies because we are forever making almost-contact with our stars.
If we can see them talking to one person, we're supposed to feel like they've spoken with all of us. But they haven't. They spoke with someone else, and we were allowed to watch. No different than on television, except that we might be disappointed and eager to return the next day, to renew our futile attempt.
The same intoxicating feeling that playing the lottery elicits. Everyone is a potential winner, but there is only one jackpot. Come back next week. Buy another ticket. This next time, is your time. Promise.
The view from the peanut gallery

It is all an illusion that there is no hierarchy, where there clearly is one. Celebrities of the past had, at least, the decency to remain slightly aloof. But they all want to be one of the Common Folk, now, just as every multi-millionaire aspires to see himself as fundamentally working-class.

All of celebrity social media is a stage, and most of us are merely spectators or commentators, to what is playing on it. This is why, if someone treats me like someone sitting in the peanut gallery, my instinct is to treat them like an actor.
Because, in reality, that is what they are.
-
 @ 21ac2956:09d1e2df
2024-12-01 04:44:45
@ 21ac2956:09d1e2df
2024-12-01 04:44:45kakoi の仕様についてのメモ
キーボード操作
- 左手での操作に最適化
| キー | 動作 | |:-|:-| | ESC | 設定画面 | | F1 / F12 | ポストバーの表示と非表示 | | F2 | 時間の表示と非表示 | | F3 | ユーザーアイコンの表示と非表示 | | F4 | 名前の表示と非表示 | | F9 / Z | コンテンツの折り返し表示の切り替え (余白ダブルクリックでも動作) | | F10 | ユーザーリストとキーワード通知の設定画面 (余白右クリックでも動作) | | F11 | メイン画面の表示と非表示 (ポストバー表示) | | Shift + W | イベント最上行へ移動 | | W / ↑| イベント選択上移動 | | S / ↓ | イベント選択下移動 | | Shift + S | イベント最下行へ移動 | | A / ← | Webビューを開く (イベントを右クリックでも動作) | | F / → | リアクションを送信 (イベントをダブルクリックでも動作) | | 1 ~ 0 | リアクションを選択 | | R | 返信 | | B | リポスト | | Q | 引用 | | C | Webビューを閉じる | | Ctrl + Shift + A | メイン画面をアクティブにする |
タイムライン
- kind:1, 6, 7, 16を取得して表示する
- フォロイーの名前の前には * が付く
フォローリスト(kind:3)
-
参照のみで更新はしない
-
F10 で開くユーザーリストでユーザーを選択し petname セルをクリックすることで未フォローユーザーにもペットネームを設定可能(ローカル保存)
プロフィール(kind:0)
- F10 で開くユーザーリストでユーザーを選択し picture セルをクリックすることでユーザーのアイコン表示を変更可能(ローカル保存)
返信(NIP-10 kind:1)
- kakoi のタイムラインに流れるすべてのイベント種に返信可能とする
- スレッドを考慮せず、単一イベントへの単発返信とする
- e タグは marker と返信先 pubkey は設定していない。 relay-url には空文字を設定
json ["e", "返信先 event-id", ""]- p タグは 返信先 pubkey ひとつだけを指定
リポスト(NIP-18 kind:6 , 16)
- kakoi のタイムラインに流れるすべてのイベント種をリポスト可能
- kind:1はkind:6。その他はkind:16でリポストする
- e タグは relay-url に空文字を設定
json ["e", "リポスト元 event-id", ""]引用(NIP-18 kind:1)
- q タグは relay-url に空文字を設定
json ["q", "引用元 event-id", ""] -
 @ 3bf0c63f:aefa459d
2024-01-14 14:52:16
@ 3bf0c63f:aefa459d
2024-01-14 14:52:16bitcoinddecentralizationIt is better to have multiple curator teams, with different vetting processes and release schedules for
bitcoindthan a single one."More eyes on code", "Contribute to Core", "Everybody should audit the code".
All these points repeated again and again fell to Earth on the day it was discovered that Bitcoin Core developers merged a variable name change from "blacklist" to "blocklist" without even discussing or acknowledging the fact that that innocent pull request opened by a sybil account was a social attack.
After a big lot of people manifested their dissatisfaction with that event on Twitter and on GitHub, most Core developers simply ignored everybody's concerns or even personally attacked people who were complaining.
The event has shown that:
1) Bitcoin Core ultimately rests on the hands of a couple maintainers and they decide what goes on the GitHub repository[^pr-merged-very-quickly] and the binary releases that will be downloaded by thousands; 2) Bitcoin Core is susceptible to social attacks; 2) "More eyes on code" don't matter, as these extra eyes can be ignored and dismissed.
Solution:
bitcoinddecentralizationIf usage was spread across 10 different
bitcoindflavors, the network would be much more resistant to social attacks to a single team.This has nothing to do with the question on if it is better to have multiple different Bitcoin node implementations or not, because here we're basically talking about the same software.
Multiple teams, each with their own release process, their own logo, some subtle changes, or perhaps no changes at all, just a different name for their
bitcoindflavor, and that's it.Every day or week or month or year, each flavor merges all changes from Bitcoin Core on their own fork. If there's anything suspicious or too leftist (or perhaps too rightist, in case there's a leftist
bitcoindflavor), maybe they will spot it and not merge.This way we keep the best of both worlds: all software development, bugfixes, improvements goes on Bitcoin Core, other flavors just copy. If there's some non-consensus change whose efficacy is debatable, one of the flavors will merge on their fork and test, and later others -- including Core -- can copy that too. Plus, we get resistant to attacks: in case there is an attack on Bitcoin Core, only 10% of the network would be compromised. the other flavors would be safe.
Run Bitcoin Knots
The first example of a
bitcoindsoftware that follows Bitcoin Core closely, adds some small changes, but has an independent vetting and release process is Bitcoin Knots, maintained by the incorruptible Luke DashJr.Next time you decide to run
bitcoind, run Bitcoin Knots instead and contribute tobitcoinddecentralization!
See also:
[^pr-merged-very-quickly]: See PR 20624, for example, a very complicated change that could be introducing bugs or be a deliberate attack, merged in 3 days without time for discussion.
-
 @ fd208ee8:0fd927c1
2024-12-26 07:02:59
@ fd208ee8:0fd927c1
2024-12-26 07:02:59I just read this, and found it enlightening.
Jung... notes that intelligence can be seen as problem solving at an everyday level..., whereas creativity may represent problem solving for less common issues
Other studies have used metaphor creation as a creativity measure instead of divergent thinking and a spectrum of CHC components instead of just g and have found much higher relationships between creativity and intelligence than past studies
https://www.mdpi.com/2079-3200/3/3/59
I'm unusually intelligent (Who isn't?), but I'm much more creative, than intelligent, and I think that confuses people. The ability to apply intelligence, to solve completely novel problems, on the fly, is something IQ tests don't even claim to measure. They just claim a correlation.
Creativity requires taking wild, mental leaps out into nothingness; simply trusting that your brain will land you safely. And this is why I've been at the forefront of massive innovation, over and over, but never got rich off of it.
I'm a starving autist.
Zaps are the first time I've ever made money directly, for solving novel problems. Companies don't do this because there is a span of time between providing a solution and the solution being implemented, and the person building the implementation (or their boss) receives all the credit for the existence of the solution. At best, you can hope to get pawned off with a small bonus.
Nobody can remember who came up with the solution, originally, and that person might not even be there, anymore, and probably never filed a patent, and may have no idea that their idea has even been built. They just run across it, later, in a tech magazine or museum, and say, "Well, will you look at that! Someone actually went and built it! Isn't that nice!"
Universities at least had the idea of cementing novel solutions in academic papers, but that: 1) only works if you're an academic, and at a university, 2) is an incredibly slow process, not appropriate for a truly innovative field, 3) leads to manifestations of perverse incentives and biased research frameworks, coming from 'publish or perish' policies.
But I think long-form notes and zaps solve for this problem. #Alexandria, especially, is being built to cater to this long-suffering class of chronic underachievers. It leaves a written, public, time-stamped record of Clever Ideas We Have Had.
Because they are clever, the ideas. And we have had them.
-
 @ bcea2b98:7ccef3c9
2025-01-08 18:22:00
@ bcea2b98:7ccef3c9
2025-01-08 18:22:00originally posted at https://stacker.news/items/842405
-
 @ 8d34bd24:414be32b
2024-12-24 21:39:27
@ 8d34bd24:414be32b
2024-12-24 21:39:27When we think of Jesus sacrificing all to save us from our sins and to make us have a right relationship with God, we usually think of Him being arrested, mocked, beaten, and hung on the cross. All of this was the perfect sacrifice and the greatest horror. None of us would chose this willingly, but Jesus sacrificed so much more. We just have trouble seeing it because we have trouble comprehending our infinite, awesome God.
Stop and think about who Jesus was before He came to earth to live as a man.
In the beginning was the Word, and the Word was with God, and the Word was God. He was in the beginning with God. All things came into being through Him, and apart from Him nothing came into being that has come into being. In Him was life, and the life was the Light of men. The Light shines in the darkness, and the darkness did not comprehend it. (John 1:1-5)
Jesus spoke into existence time & space, matter & energy, and all life. He was not limited by space or time or any other limitation other than His own nature — His holiness. Our all powerful God came down to earth to live as a man, which was limiting Himself in a way we can’t comprehend. If I came down to earth as an amoeba, I would not be limiting myself anywhere near how He limited Himself, but He did so much more. He didn’t start as a man, “for the Child who has been conceived in her is of the Holy Spirit.” (Matthew 1:20b) He became incarnate as a one-celled human. The creator of the universe grew in a teen girl’s womb and was born a helpless baby.
Can you imagine what it must have been like to go from speaking the universe into existence, to not being able to sit up, feed yourself, or control your own excrement? Our creator limited Himself so much that everything He needed had to be provided by His young mother. I sometimes think that this was actually the greater sacrifice. Although Jesus suffered humiliation, separation from God, and death on the cross on what we now call Easter, He knew that He would soon conquer the grave and death, rescue humanity, and join the Father in heaven. We can usually survive terrible suffering when we know it will only be brief. When Jesus was conceived and then born on Christmas day, He limited Himself for 30 something years even to the point of making Himself completely dependent on His creation for His every need.
This gives a whole new perspective on the Christmas story.
While they were there, the days were completed for her to give birth. And she gave birth to her firstborn son; and she wrapped Him in cloths, and laid Him in a manger, because there was no room for them in the inn. (Luke 2:6-7)
The next time you look at a baby, read the Christmas story, see a manger scene, or celebrate Christmas, remember how much Jesus, the Son of God, gave up because He loved you and wanted to reconcile you to Himself and the Father.
Trust Jesus.When we think of Jesus sacrificing all to save us from our sins and to make us have a right relationship with God, we usually think of Him being arrested, mocked, beaten, and hung on the cross. All of this was the perfect sacrifice and the greatest horror. None of us would chose this willingly, but Jesus sacrificed so much more. We just have trouble seeing it because we have trouble comprehending our infinite, awesome God.
Stop and think about who Jesus was before He came to earth to live as a man.
In the beginning was the Word, and the Word was with God, and the Word was God. He was in the beginning with God. All things came into being through Him, and apart from Him nothing came into being that has come into being. In Him was life, and the life was the Light of men. The Light shines in the darkness, and the darkness did not comprehend it. (John 1:1-5)
Jesus spoke into existence time & space, matter & energy, and all life. He was not limited by space or time or any other limitation other than His own nature — His holiness. Our all powerful God came down to earth to live as a man, which was limiting Himself in a way we can’t comprehend. If I came down to earth as an amoeba, I would not be limiting myself anywhere near how He limited Himself, but He did so much more. He didn’t start as a man, “for the Child who has been conceived in her is of the Holy Spirit.” (Matthew 1:20b) He became incarnate as a one-celled human. The creator of the universe grew in a teen girl’s womb and was born a helpless baby.
Can you imagine what it must have been like to go from speaking the universe into existence, to not being able to sit up, feed yourself, or control your own excrement? Our creator limited Himself so much that everything He needed had to be provided by His young mother. I sometimes think that this was actually the greater sacrifice. Although Jesus suffered humiliation, separation from God, and death on the cross on what we now call Easter, He knew that He would soon conquer the grave and death, rescue humanity, and join the Father in heaven. We can usually survive terrible suffering when we know it will only be brief. When Jesus was conceived and then born on Christmas day, He limited Himself for 30 something years even to the point of making Himself completely dependent on His creation for His every need.
This gives a whole new perspective on the Christmas story.
While they were there, the days were completed for her to give birth. And she gave birth to her firstborn son; and she wrapped Him in cloths, and laid Him in a manger, because there was no room for them in the inn. (Luke 2:6-7)
The next time you look at a baby, read the Christmas story, see a manger scene, or celebrate Christmas, remember how much Jesus, the Son of God, gave up because He loved you and wanted to reconcile you to Himself and the Father.
Trust Jesus & Merry Christmas
-
 @ 5d4b6c8d:8a1c1ee3
2025-01-07 21:09:20
@ 5d4b6c8d:8a1c1ee3
2025-01-07 21:09:20Am I only writing this post because I thought the name was dope?
Pretty much, but I'm also bored and it's been about a week since I joined the ownership group of ~Stacker_Sports, so let's take a look at how the territory's done this past week.
Territory Stats
| Posts | Comments| Stacking | Spending | Revenue | |-------|-------------|-----------|-----------|-----------| | 53 | 880! | 51k | 77.6k | 19.6k |
Awesome! We're well on our way to a profitable month.
Posts of the week
- by zaprank: Stacker Sports- Special Announcement
- by comments: NFL Weekly Pick 'em- Week 18
- by sats: NCAA College Football Playoff Points Challenge- SemiFinal Picks
I'm open to suggestions about what should go in these reports. Like I said at the top, I'm mostly doing this because I didn't want to waste the sweet ass name.
originally posted at https://stacker.news/items/841205
-
 @ c69b71dc:426ba763
2024-12-22 20:36:53
@ c69b71dc:426ba763
2024-12-22 20:36:53Christ Consciousness
This text invites you to explore the deeper meaning of the winter season and the birth of Christ Consciousness—beyond religion and dogma. It is about inner reflection, spiritual insight, and the connection of body, mind, and soul, inspired by the ancient symbols of light, energy, and consciousness. Here, I highlight how the symbolism that religions and biblical texts often convey in a material sense actually holds a much deeper meaning—one that can help us awaken our life energy and unlock our full potential. Christmas is far more significant than gifts, family, food, and Christmas trees.
Winter Solstice
The winter solstice marks a turning point in the annual cycle. On December 21st, the sun reaches its southernmost point, and we experience the longest night of the year. While our physical body feels the need to rest and turn inward, our psychic and astral energies unfold. Especially between December 21st and 25th, everything seems to enter a standby mode, creating space for profound reflection and spiritual renewal. During this darkest time of the year, a kind of inner birth occurs—a birth of the spirit, conceived in the deep silence of the night. It is a moment of introspection, contemplation, and realignment.

The Twelve Holy Nights: A Time for Retreat and Reflection
With the winter solstice, the Twelve Holy Nights (Rauhnächte) begin—a mystical time between the years. These days invite us to turn inward, rest, and connect with our soul. It is a time when physical relaxation and spiritual growth go hand in hand. Advent sets the stage for this phase—each lit candle symbolically represents a chakra, starting with the lower energy centers. By the fourth Advent, the light reaches our heart chakra, a place of love, peace, and connection.
Symbolism Across Different Traditions
This energy is also reflected in Judaism: the festival of Hanukkah lasts for eight days, during which a new candle is lit each day. This practice can be seen as a symbolic journey through the chakras, gradually activating and harmonizing them. Hanukkah, the Festival of Lights, stands for the liberation from material and spiritual blockages, the strengthening and activation of energy centers, and the connection to the divine. We learn that there are no separations because we are the divine.
The Sacred Flow of Life: The Claustrum and Inner Alchemy
The term "Claustrum," referring to an occult area in the brain, holds deep symbolic and physical significance. The Claustrum is located between the pineal gland and the pituitary gland and secretes a special fluid known as "Christos." This fluid flows through the spinal cord down to the sacrum. The sacrum, derived from the Latin word "sacrum," meaning "sacred," represents this "sacred oil" flow. It symbolizes an inner alchemical process: nourishing the body and soul, enhancing consciousness, and bridging the physical and spiritual realms.
Interestingly, this process is depicted in ancient myths: Santa Claus, or Saint Nicholas, descending the chimney to deliver gifts, can be interpreted as a metaphor for the Claustrum and the flow of sacred essence. The gifts represent the awakened consciousness born from this process.
The Journey of Christ Consciousness
Christ Consciousness, often symbolized by the birth of Jesus, is understood in spiritual teachings as an internal process. The fluid from the Claustrum reaches the sacrum and then ascends to activate the pineal and pituitary glands, spreading out from there. During this process, it passes through the 33 vertebrae of the spine—a reference to the age of 33 when Jesus was crucified. During the "crucifixion" of this sacred oil, it becomes "suspended" in the region of the thalamus for two to three days before illuminating the pineal and pituitary glands. This process leads to profound spiritual renewal and heightened consciousness, often referred to as the awakening of Kundalini energy.
Nutrition and Spirituality
Our diet has a direct influence on this process. Heavy, fatty, or animal-based foods can energetically dull us and block the flow of the "sacred essence." A light, plant-based diet rich in fresh juices, sprouts, and raw foods supports energy flow and spiritual growth. Animal products, drugs, and excessive fats disrupt the process. Similarly, sexual activity with orgasm during the ascent of the sacred oil interrupts the cycle, causing the sacred energy to be lost. The pineal and pituitary glands, often referred to as the seat of the soul, are associated with the production of "manna" in spiritual traditions—a substance symbolizing milk and honey. This is also linked to Joseph and Mary or the masculine and feminine. The pineal gland secretes a honey-like substance, while the pituitary gland secretes a milk-like substance. The "land flowing with milk and honey" lies within us. We are that land. The process happens within us; there is nothing to seek outside.

The Birth of Light Within Us
In the deepest darkness lies the greatest potential for new life. Through conscious reflection, mindful nutrition, and connection with our body and mind, we can celebrate the birth of light within ourselves—a gift that helps us recognize and live our true potential.
Final Thought
I thank you from the bottom of my heart for taking the time to read this piece. My wish is to inspire and encourage you—even amidst the calls of tradition—to carve out time to look inward, just as the natural cycle of life teaches us. It is an invitation to embark on the path of self-discovery, to grow, awaken, and let our inner light shine, ultimately leading to enlightenment. Step by step, day by day, month by month, and year by year, we allow ourselves to be guided by the wisdom of the cycle, unfolding in wondrous ways. I always welcome your feedback, thoughts, and reflections on this topic. Your input is invaluable to me and enriches the process of shared growth.
May your cycle be illuminated and filled with love 💛
-
 @ 3bf0c63f:aefa459d
2024-01-14 14:52:16
@ 3bf0c63f:aefa459d
2024-01-14 14:52:16Drivechain
Understanding Drivechain requires a shift from the paradigm most bitcoiners are used to. It is not about "trustlessness" or "mathematical certainty", but game theory and incentives. (Well, Bitcoin in general is also that, but people prefer to ignore it and focus on some illusion of trustlessness provided by mathematics.)
Here we will describe the basic mechanism (simple) and incentives (complex) of "hashrate escrow" and how it enables a 2-way peg between the mainchain (Bitcoin) and various sidechains.
The full concept of "Drivechain" also involves blind merged mining (i.e., the sidechains mine themselves by publishing their block hashes to the mainchain without the miners having to run the sidechain software), but this is much easier to understand and can be accomplished either by the BIP-301 mechanism or by the Spacechains mechanism.
How does hashrate escrow work from the point of view of Bitcoin?
A new address type is created. Anything that goes in that is locked and can only be spent if all miners agree on the Withdrawal Transaction (
WT^) that will spend it for 6 months. There is one of these special addresses for each sidechain.To gather miners' agreement
bitcoindkeeps track of the "score" of all transactions that could possibly spend from that address. On every block mined, for each sidechain, the miner can use a portion of their coinbase to either increase the score of oneWT^by 1 while decreasing the score of all others by 1; or they can decrease the score of allWT^s by 1; or they can do nothing.Once a transaction has gotten a score high enough, it is published and funds are effectively transferred from the sidechain to the withdrawing users.
If a timeout of 6 months passes and the score doesn't meet the threshold, that
WT^is discarded.What does the above procedure mean?
It means that people can transfer coins from the mainchain to a sidechain by depositing to the special address. Then they can withdraw from the sidechain by making a special withdraw transaction in the sidechain.
The special transaction somehow freezes funds in the sidechain while a transaction that aggregates all withdrawals into a single mainchain
WT^, which is then submitted to the mainchain miners so they can start voting on it and finally after some months it is published.Now the crucial part: the validity of the
WT^is not verified by the Bitcoin mainchain rules, i.e., if Bob has requested a withdraw from the sidechain to his mainchain address, but someone publishes a wrongWT^that instead takes Bob's funds and sends them to Alice's main address there is no way the mainchain will know that. What determines the "validity" of theWT^is the miner vote score and only that. It is the job of miners to vote correctly -- and for that they may want to run the sidechain node in SPV mode so they can attest for the existence of a reference to theWT^transaction in the sidechain blockchain (which then ensures it is ok) or do these checks by some other means.What? 6 months to get my money back?
Yes. But no, in practice anyone who wants their money back will be able to use an atomic swap, submarine swap or other similar service to transfer funds from the sidechain to the mainchain and vice-versa. The long delayed withdraw costs would be incurred by few liquidity providers that would gain some small profit from it.
Why bother with this at all?
Drivechains solve many different problems:
It enables experimentation and new use cases for Bitcoin
Issued assets, fully private transactions, stateful blockchain contracts, turing-completeness, decentralized games, some "DeFi" aspects, prediction markets, futarchy, decentralized and yet meaningful human-readable names, big blocks with a ton of normal transactions on them, a chain optimized only for Lighting-style networks to be built on top of it.
These are some ideas that may have merit to them, but were never actually tried because they couldn't be tried with real Bitcoin or inferfacing with real bitcoins. They were either relegated to the shitcoin territory or to custodial solutions like Liquid or RSK that may have failed to gain network effect because of that.
It solves conflicts and infighting
Some people want fully private transactions in a UTXO model, others want "accounts" they can tie to their name and build reputation on top; some people want simple multisig solutions, others want complex code that reads a ton of variables; some people want to put all the transactions on a global chain in batches every 10 minutes, others want off-chain instant transactions backed by funds previously locked in channels; some want to spend, others want to just hold; some want to use blockchain technology to solve all the problems in the world, others just want to solve money.
With Drivechain-based sidechains all these groups can be happy simultaneously and don't fight. Meanwhile they will all be using the same money and contributing to each other's ecosystem even unwillingly, it's also easy and free for them to change their group affiliation later, which reduces cognitive dissonance.
It solves "scaling"
Multiple chains like the ones described above would certainly do a lot to accomodate many more transactions that the current Bitcoin chain can. One could have special Lightning Network chains, but even just big block chains or big-block-mimblewimble chains or whatnot could probably do a good job. Or even something less cool like 200 independent chains just like Bitcoin is today, no extra features (and you can call it "sharding"), just that would already multiply the current total capacity by 200.
Use your imagination.
It solves the blockchain security budget issue
The calculation is simple: you imagine what security budget is reasonable for each block in a world without block subsidy and divide that for the amount of bytes you can fit in a single block: that is the price to be paid in satoshis per byte. In reasonable estimative, the price necessary for every Bitcoin transaction goes to very large amounts, such that not only any day-to-day transaction has insanely prohibitive costs, but also Lightning channel opens and closes are impracticable.
So without a solution like Drivechain you'll be left with only one alternative: pushing Bitcoin usage to trusted services like Liquid and RSK or custodial Lightning wallets. With Drivechain, though, there could be thousands of transactions happening in sidechains and being all aggregated into a sidechain block that would then pay a very large fee to be published (via blind merged mining) to the mainchain. Bitcoin security guaranteed.
It keeps Bitcoin decentralized
Once we have sidechains to accomodate the normal transactions, the mainchain functionality can be reduced to be only a "hub" for the sidechains' comings and goings, and then the maximum block size for the mainchain can be reduced to, say, 100kb, which would make running a full node very very easy.
Can miners steal?
Yes. If a group of coordinated miners are able to secure the majority of the hashpower and keep their coordination for 6 months, they can publish a
WT^that takes the money from the sidechains and pays to themselves.Will miners steal?
No, because the incentives are such that they won't.
Although it may look at first that stealing is an obvious strategy for miners as it is free money, there are many costs involved:
- The cost of ceasing blind-merged mining returns -- as stealing will kill a sidechain, all the fees from it that miners would be expected to earn for the next years are gone;
- The cost of Bitcoin price going down: If a steal is successful that will mean Drivechains are not safe, therefore Bitcoin is less useful, and miner credibility will also be hurt, which are likely to cause the Bitcoin price to go down, which in turn may kill the miners' businesses and savings;
- The cost of coordination -- assuming miners are just normal businesses, they just want to do their work and get paid, but stealing from a Drivechain will require coordination with other miners to conduct an immoral act in a way that has many pitfalls and is likely to be broken over the months;
- The cost of miners leaving your mining pool: when we talked about "miners" above we were actually talking about mining pools operators, so they must also consider the risk of miners migrating from their mining pool to others as they begin the process of stealing;
- The cost of community goodwill -- when participating in a steal operation, a miner will suffer a ton of backlash from the community. Even if the attempt fails at the end, the fact that it was attempted will contribute to growing concerns over exaggerated miners power over the Bitcoin ecosystem, which may end up causing the community to agree on a hard-fork to change the mining algorithm in the future, or to do something to increase participation of more entities in the mining process (such as development or cheapment of new ASICs), which have a chance of decreasing the profits of current miners.
Another point to take in consideration is that one may be inclined to think a newly-created sidechain or a sidechain with relatively low usage may be more easily stolen from, since the blind merged mining returns from it (point 1 above) are going to be small -- but the fact is also that a sidechain with small usage will also have less money to be stolen from, and since the other costs besides 1 are less elastic at the end it will not be worth stealing from these too.
All of the above consideration are valid only if miners are stealing from good sidechains. If there is a sidechain that is doing things wrong, scamming people, not being used at all, or is full of bugs, for example, that will be perceived as a bad sidechain, and then miners can and will safely steal from it and kill it, which will be perceived as a good thing by everybody.
What do we do if miners steal?
Paul Sztorc has suggested in the past that a user-activated soft-fork could prevent miners from stealing, i.e., most Bitcoin users and nodes issue a rule similar to this one to invalidate the inclusion of a faulty
WT^and thus cause any miner that includes it in a block to be relegated to their own Bitcoin fork that other nodes won't accept.This suggestion has made people think Drivechain is a sidechain solution backed by user-actived soft-forks for safety, which is very far from the truth. Drivechains must not and will not rely on this kind of soft-fork, although they are possible, as the coordination costs are too high and no one should ever expect these things to happen.
If even with all the incentives against them (see above) miners do still steal from a good sidechain that will mean the failure of the Drivechain experiment. It will very likely also mean the failure of the Bitcoin experiment too, as it will be proven that miners can coordinate to act maliciously over a prolonged period of time regardless of economic and social incentives, meaning they are probably in it just for attacking Bitcoin, backed by nation-states or something else, and therefore no Bitcoin transaction in the mainchain is to be expected to be safe ever again.
Why use this and not a full-blown trustless and open sidechain technology?
Because it is impossible.
If you ever heard someone saying "just use a sidechain", "do this in a sidechain" or anything like that, be aware that these people are either talking about "federated" sidechains (i.e., funds are kept in custody by a group of entities) or they are talking about Drivechain, or they are disillusioned and think it is possible to do sidechains in any other manner.
No, I mean a trustless 2-way peg with correctness of the withdrawals verified by the Bitcoin protocol!
That is not possible unless Bitcoin verifies all transactions that happen in all the sidechains, which would be akin to drastically increasing the blocksize and expanding the Bitcoin rules in tons of ways, i.e., a terrible idea that no one wants.
What about the Blockstream sidechains whitepaper?
Yes, that was a way to do it. The Drivechain hashrate escrow is a conceptually simpler way to achieve the same thing with improved incentives, less junk in the chain, more safety.
Isn't the hashrate escrow a very complex soft-fork?
Yes, but it is much simpler than SegWit. And, unlike SegWit, it doesn't force anything on users, i.e., it isn't a mandatory blocksize increase.
Why should we expect miners to care enough to participate in the voting mechanism?
Because it's in their own self-interest to do it, and it costs very little. Today over half of the miners mine RSK. It's not blind merged mining, it's a very convoluted process that requires them to run a RSK full node. For the Drivechain sidechains, an SPV node would be enough, or maybe just getting data from a block explorer API, so much much simpler.
What if I still don't like Drivechain even after reading this?
That is the entire point! You don't have to like it or use it as long as you're fine with other people using it. The hashrate escrow special addresses will not impact you at all, validation cost is minimal, and you get the benefit of people who want to use Drivechain migrating to their own sidechains and freeing up space for you in the mainchain. See also the point above about infighting.
See also
-
 @ d7c6d014:a6abb6b8
2024-11-23 18:40:47
@ d7c6d014:a6abb6b8
2024-11-23 18:40:47こんにちは!kohei です。
久々のエントリ投下ですが、今回は先日弊 TL で話題になっていた、Android を P2P のローカルリレーサーバー化して Tor で公開する方法を紹介していこうと思います。
用意するもの
- Android 端末
- Orbot
- Citrine
- Amethyst
前提と下準備
今回は、Orbot の詳細設定は省いて、Power User Mode の設定が完了している前提でお話を進めます。 Android 端末を用意して、2~4 のアプリをインストールしておいてください。
設定方法
それでは早速設定していきましょう。 まず、Citrine を起動して、Settings のタブからローカルリレーの詳細を設定します。
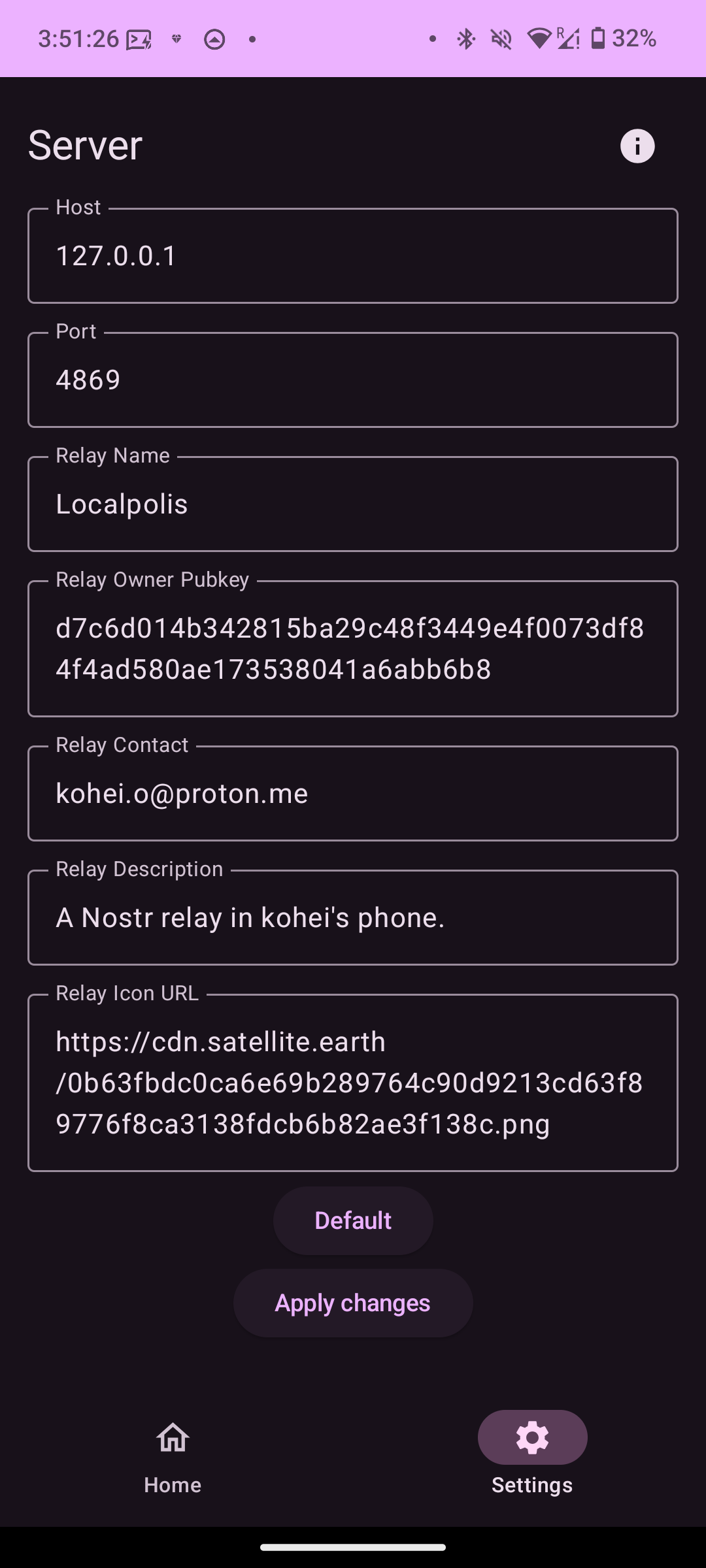
設定が終了したら、ローカルリレーを起動します。
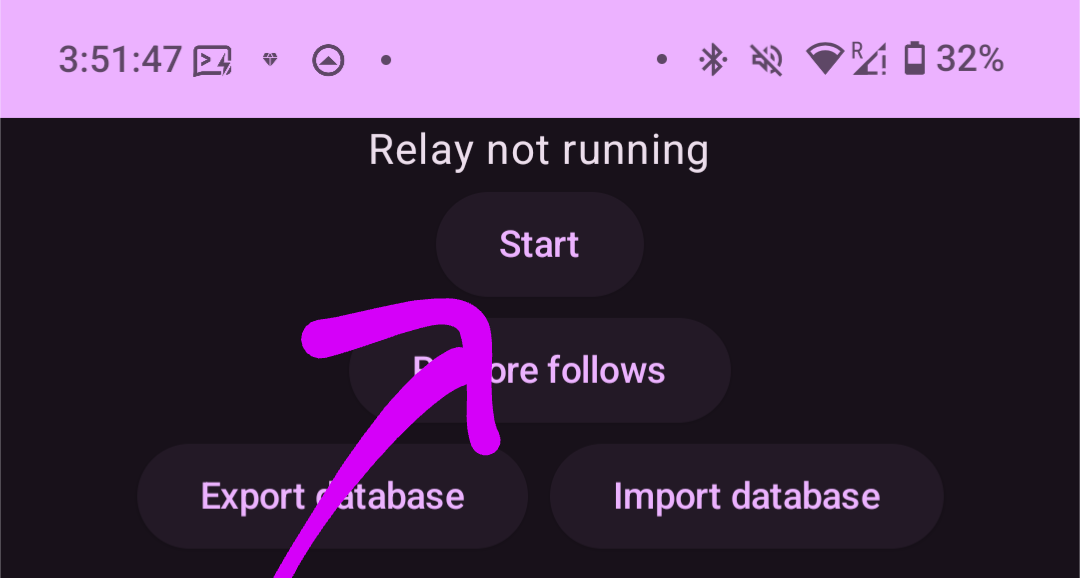
また、ここで表示されるポート番号をメモしてください。
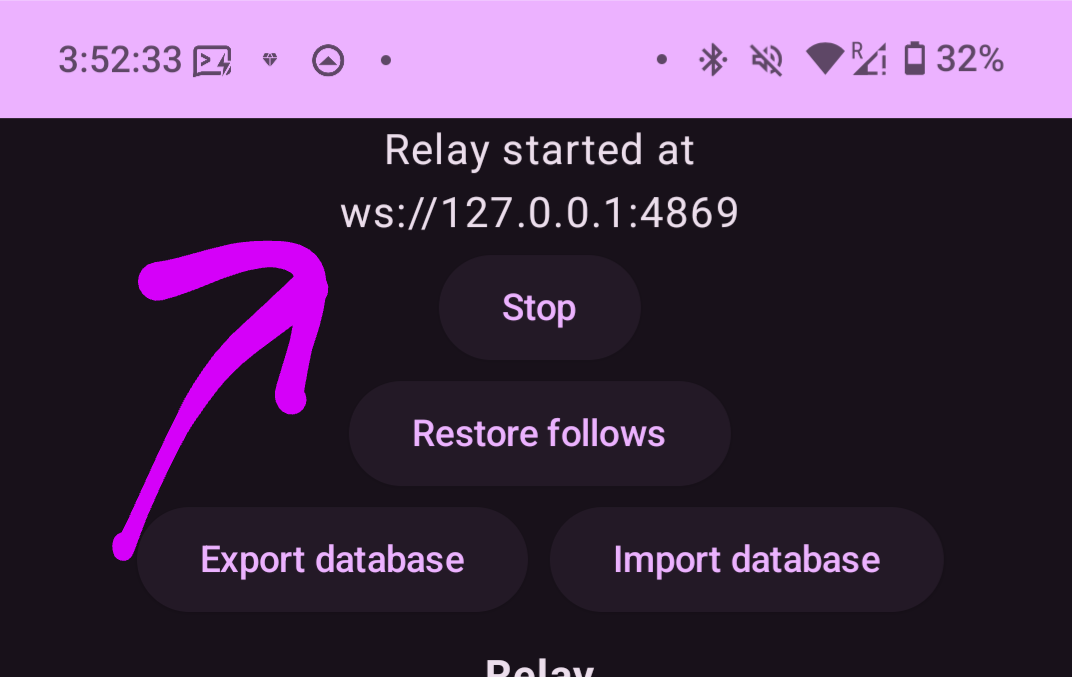
次に、More のタブに移り、Hosted Onion Services へアクセスし、Service Type の項目で User Services にチェックを入れて、右下の + マークをタップすると以下のポップアップが表示されます。(Orbot がスクショを許してくれないので一部画像割愛)
表示されたら、Name に任意の名前を、Local Port と Onion Port に先ほどメモした Citrine のポート番号を入力します。
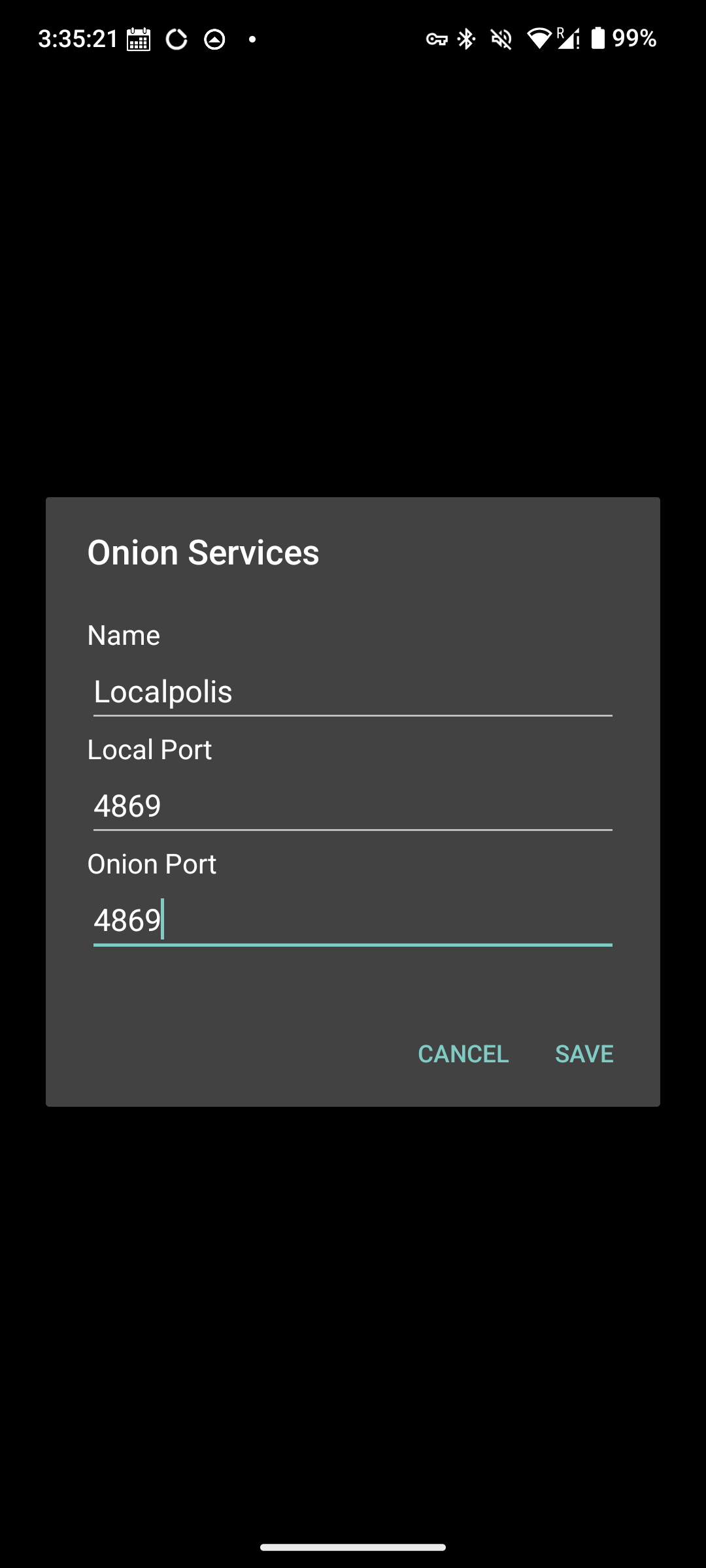
入力したら再起動を求められるので再起動してください。 再起動後に Hosted Onion Services の項目に .onion のアドレスが表示されたら成功です (何故か私の環境では、一回の再起動では設定が反映されなかったのですが、もし同じような現象が起きた場合は、再起動 -> Connect -> .onion アドレスが発行されてるかの確認、を数回試すと発行されるはずです)
発行されたら、.onion アドレスをタップしてクリップボードにコピーします。
次に、Amethyst を起動して、リレーの設定画面に入り、Outbox の設定にコピーした .onion アドレスを貼り付けて保存します。
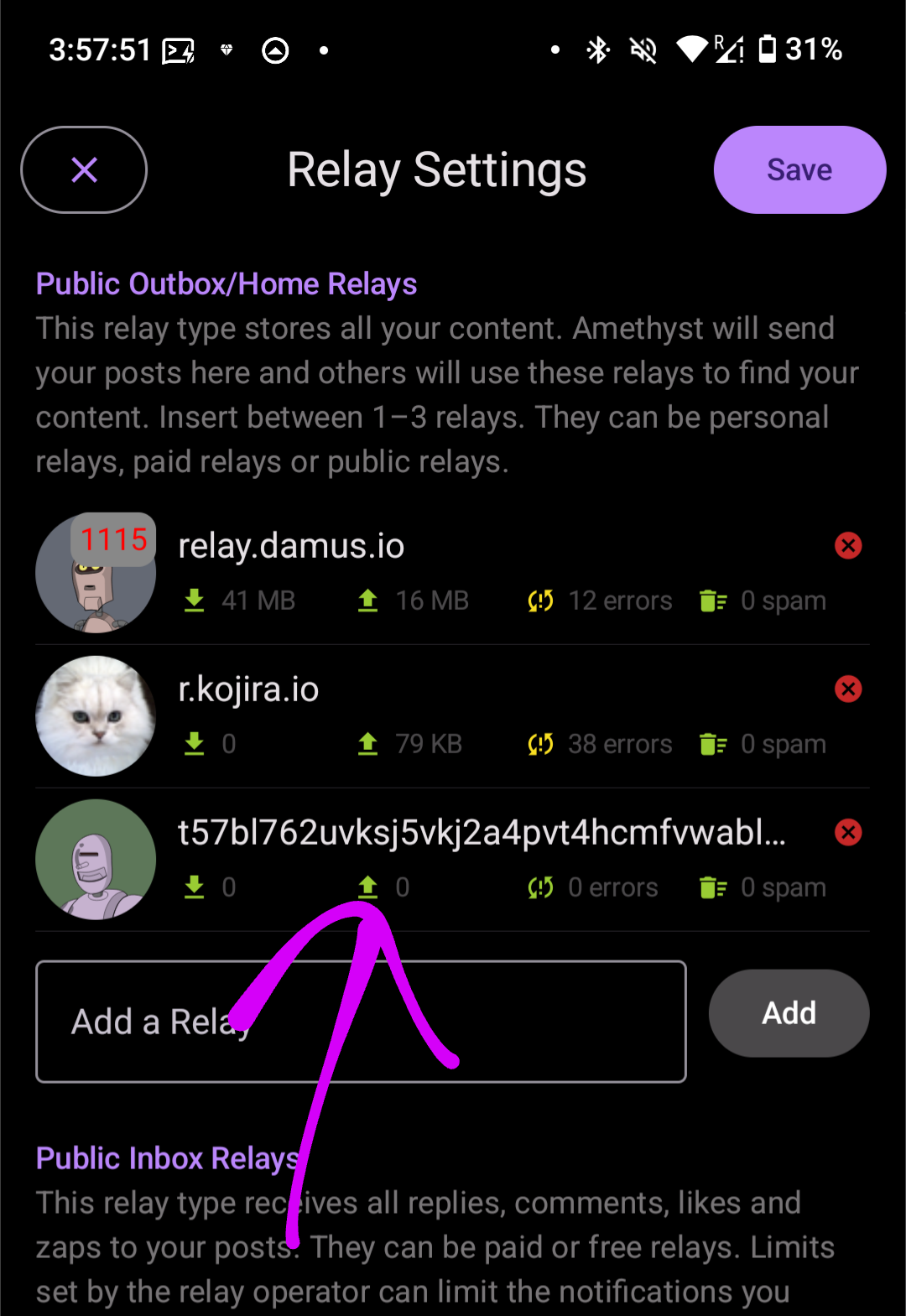
後は、Amethyst 側で Orbot のポート番号を設定して Orbot に接続すれば BOOM! 設定完了です。
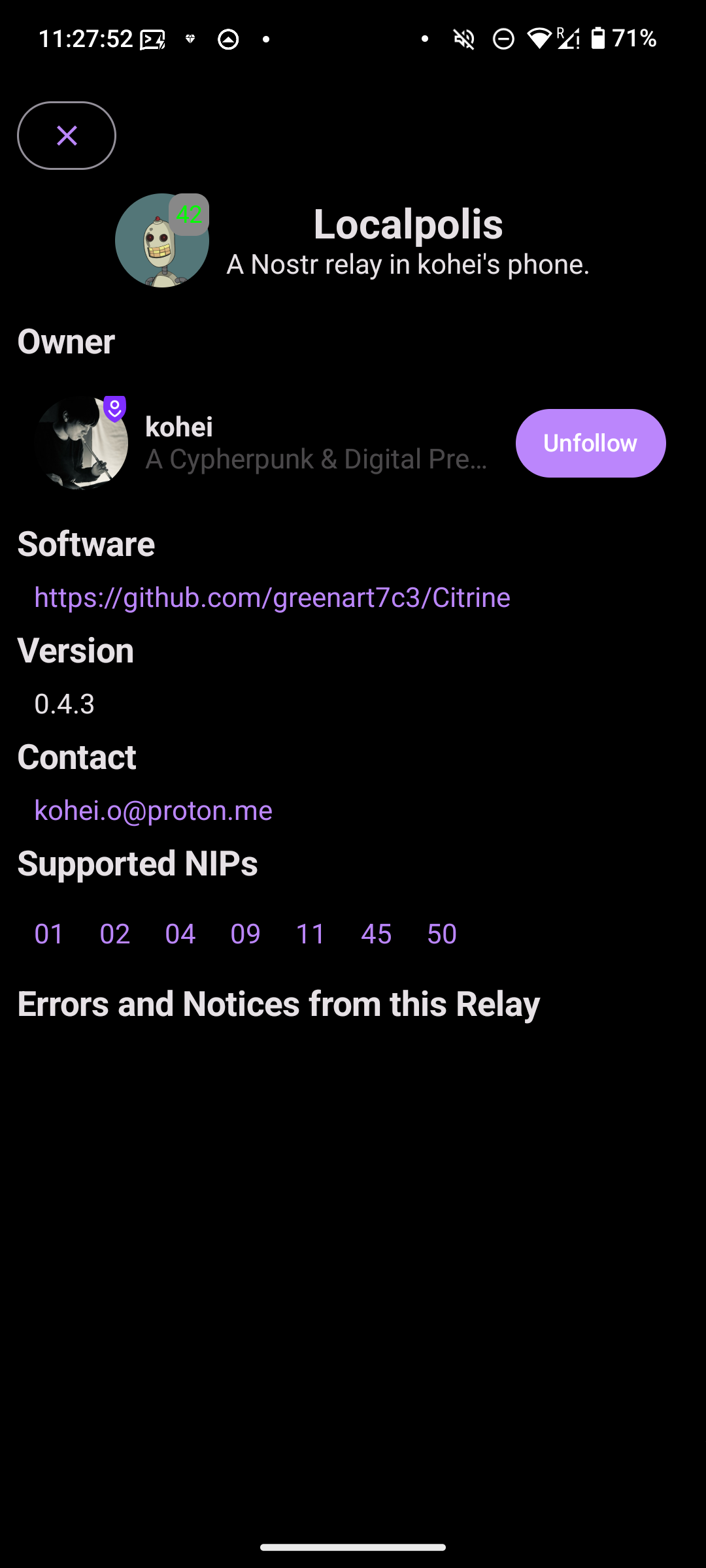
お疲れ様でした!
素敵な Nostr ライフを!
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28A response to Achim Warner's "Drivechain brings politics to miners" article
I mean this article: https://achimwarner.medium.com/thoughts-on-drivechain-i-miners-can-do-things-about-which-we-will-argue-whether-it-is-actually-a5c3c022dbd2
There are basically two claims here:
1. Some corporate interests might want to secure sidechains for themselves and thus they will bribe miners to have these activated
First, it's hard to imagine why they would want such a thing. Are they going to make a proprietary KYC chain only for their users? They could do that in a corporate way, or with a federation, like Facebook tried to do, and that would provide more value to their users than a cumbersome pseudo-decentralized system in which they don't even have powers to issue currency. Also, if Facebook couldn't get away with their federated shitcoin because the government was mad, what says the government won't be mad with a sidechain? And finally, why would Facebook want to give custody of their proprietary closed-garden Bitcoin-backed ecosystem coins to a random, open and always-changing set of miners?
But even if they do succeed in making their sidechain and it is very popular such that it pays miners fees and people love it. Well, then why not? Let them have it. It's not going to hurt anyone more than a proprietary shitcoin would anyway. If Facebook really wants a closed ecosystem backed by Bitcoin that probably means we are winning big.
2. Miners will be required to vote on the validity of debatable things
He cites the example of a PoS sidechain, an assassination market, a sidechain full of nazists, a sidechain deemed illegal by the US government and so on.
There is a simple solution to all of this: just kill these sidechains. Either miners can take the money from these to themselves, or they can just refuse to engage and freeze the coins there forever, or they can even give the coins to governments, if they want. It is an entirely good thing that evil sidechains or sidechains that use horrible technology that doesn't even let us know who owns each coin get annihilated. And it was the responsibility of people who put money in there to evaluate beforehand and know that PoS is not deterministic, for example.
About government censoring and wanting to steal money, or criminals using sidechains, I think the argument is very weak because these same things can happen today and may even be happening already: i.e., governments ordering mining pools to not mine such and such transactions from such and such people, or forcing them to reorg to steal money from criminals and whatnot. All this is expected to happen in normal Bitcoin. But both in normal Bitcoin and in Drivechain decentralization fixes that problem by making it so governments cannot catch all miners required to control the chain like that -- and in fact fixing that problem is the only reason we need decentralization.
-
 @ 7ecd3fe6:6b52f30d
2025-01-07 19:13:58
@ 7ecd3fe6:6b52f30d
2025-01-07 19:13:58I normally try to avoid the noise that is the crypto market only because I've been in that situationship before back in 2016, got rugged in the ICO phase and learned my lesson. There is nothing left for me to take from crypto apart from watching from the sidelines and enjoying the endless amount of schadenfreude it produces.
So every so often I find myself checking in on the ugly step-child of Bitcoin just to see what the left side of the bell curve are up to and you know what?
I wasn't disappointed.
In fact, I'm kind of impressed at the number of times shitcoiners can come up with a new meta to get the degens excited enough to take another spin at the casino, it's honestly pretty impressive.
After ordinals were cooked, the shitcoiners were left to head back to the drawing board, and the obvious pivot was AI tokens. AI and LLMs were the new hotness and try they did but AI tokens didn't really take off in 2024.
Sure there's tokens like NEAR, Internet Computer, and RENDER all with a few billion in market cap and according to CoinGecko there's around 50 billion in AI shitcoins, but for these coins to pump they need to provide some sort of product.
That requires investment and some thinking and who has time for that?
F AI, AI Agents are the future
Wtf are AI agent tokens you ask? Bad question, but I'll edify you anyway.
AI agents are autonomous software programs designed to perform very specific tasks and make decisions independently. Hardly very AI and more repetitive loops, cronjobs if you will.
Using an AI agent and giving a blockchain wallet these agents can interact with smart contracts, dApps and DEXs and start to get up to some shenanigans, or at least distance the agent creator from the actions.
No, I didn't rug pull you, that was the AI Agent malfunctioning.
I guess the killer app for AI agents is plausible deniability when you have to plead your case with the SEC.
As this new batch of vapourware gains popularity, every moron with a ChatGPT pro subscription and a dream is going after this market of suckers. Right now there are several AI agent tokens you can speculate on with a combined market cap of $16 billion according to CoinGecko
It's all about the meta-baby
I'm old enough to remember when the idea for a shitcoin was
- Utility, it had to do something and wall it off, so you needed to token to access a feature, that failed
- Then we went into culture and community, its all about the memes, that failed
- Then it was all about etching in on Bitcoin block space, using that rare commodity made my shitcoin valuable, that failed
Now we've got a bit of a mish-mash of memes + AI utility equals new grift.
To illustrate the unserious nature of this nonsense, AI agents, associated meme coins, and the protocols used to create these agents are among the top five best-performing crypto assets of the day, according to CoinGecko.
For example, Truth Terminal—the agent that started much of this wave—has promoted Goatseus Maximus (GOAT) and Fartcoin (FARTCOIN) causing both to skyrocket.
Fartcoin surged to a new all-time high price of $1.3 and a market cap of $1.5 billion as a result, FML, what a complete waste.

Growth in the FART coin Market Cap
ChatGPT-wrapped crypto scams
The Truth Terminal chatbot is a customized version of Anthropic's Claude 3 LLM, that tweets out random nonsense and somehow shitcoiners take this text as gospel and try to bet on tokens it shills or creates tokens based on its tweets as if it were Elon himself.
Can't wait for Elon to pump your bags, well, let's all dogpile on the random brain farts of a chatbot.
Again this just seems like a way to obscure insider trading and pump and dump influencer scams by hiding the human element behind a bot.
In fact, shitcoiners are creating tokens or sending tokens to a known wallet tied to this AI agent, hoping it uses this data to formulate it's next round of bullshit, I mean bullish tweets.
AI in name only
Still, most agent autonomy is limited. Truth Terminal, for example, still has creator Andy Ayrey looking over it's shoulder before it's thoughts and decisions go out to the public.
So if there's someone watching it, there's someone with access to the wallet and master access to prod it in a certain direction no?
Sigh! Reading up on this all just made my brain hurt and not in a good way.
“Do you want to be right or do you want to make money”
— ZachXBT (@zachxbt) January 6, 2025
99% of it is a scam and the AI agent wrapper grifts are probably worse than other past trends tbh.
bc at least meme coins promise nothing whereas AI coins try to larp as much as possible to appear legit to unsuspecting…This AI agent field itself is still relatively nascent and doesn't seem to provide any value other than being a filter for random tweet generation, and we all know computers aren't good with being random.
Most if not all projects promising AI-powered solutions will not deliver on their promises, potentially leading to significant losses for investors.
But that's the game they choose to play.
The cryptocurrency market is primarily driven by hype and speculation, and AI agent tokens are no exception. Many projects are overvalued based on potential rather than actual achievements.
Is this the future?

-
 @ 21ac2956:09d1e2df
2024-11-20 05:58:15
@ 21ac2956:09d1e2df
2024-11-20 05:58:15kakoi の仕様についてのメモ
キーボード操作
- 左手での操作に最適化
| キー | 動作 | |:-|:-| | ESC | 設定画面 | | F1 / F12 | ポストバーの表示と非表示 | | F2 | 時間の表示と非表示 | | F3 | ユーザーアイコンの表示と非表示 | | F4 | 名前の表示と非表示 | | F9 / Z | コンテンツの折り返し表示の切り替え (余白ダブルクリックでも動作) | | F10 | ユーザーリストとキーワード通知の設定画面 (余白右クリックでも動作) | | F11 | メイン画面の表示と非表示 (ポストバー表示) | | Shift + W | イベント最上行へ移動 | | W / ↑| イベント選択上移動 | | S / ↓ | イベント選択下移動 | | Shift + S | イベント最下行へ移動 | | A / ← | Webビューを開く (イベントを右クリックでも動作) | | F / → | リアクションを送信 (イベントをダブルクリックでも動作) | | 1 ~ 0 | リアクションを選択 | | R | 返信 | | B | リポスト | | Q | 引用 | | C | Webビューを閉じる | | Ctrl + Shift + A | メイン画面をアクティブにする |
タイムライン
- kind:1, 6, 7, 16を取得して表示する
- フォロイーの名前の前には * が付く
フォローリスト(kind:3)
-
参照のみで更新はしない
-
F10 で開くユーザーリストでユーザーを選択し petname セルをクリックすることで未フォローユーザーにもペットネームを設定可能(ローカル保存)
プロフィール(kind:0)
- F10 で開くユーザーリストでユーザーを選択し picture セルをクリックすることでユーザーのアイコン表示を変更可能(ローカル保存)
返信(NIP-10 kind:1)
- kakoi のタイムラインに流れるすべてのイベント種に返信可能とする
- スレッドを考慮せず、単一イベントへの単発返信とする
- e タグは marker と返信先 pubkey は設定していない。 relay-url には空文字を設定
json ["e", "返信先 event-id", ""]- p タグは 返信先 pubkey ひとつだけを指定
リポスト(NIP-18 kind:6 , 16)
- kakoi のタイムラインに流れるすべてのイベント種をリポスト可能
- kind:1はkind:6。その他はkind:16でリポストする
- e タグは relay-url に空文字を設定
json ["e", "リポスト元 event-id", ""]引用(NIP-18 kind:1)
- q タグは relay-url に空文字を設定
json ["q", "引用元 event-id", ""] -
 @ 8d34bd24:414be32b
2024-12-22 15:04:23
@ 8d34bd24:414be32b
2024-12-22 15:04:23We are in the season of Christmas and busy fulfilling all of our Christmas traditions. We put up Christmas decorations, sing Christmas songs, buy Christmas presents, and plan big Christmas meals, but we are supposed to be celebrating the birth of Christ. We are supposed to be celebrating God made flesh — our Creator becoming His creation to reconcile them to Himself.
If you care about your relationship with Jesus, you may wonder, “Are all of these Christmas traditions good or bad?” In most cases, I think the answer is “It depends.” Are you using Christmas traditions to celebrate Jesus and point yourself and others to Him or have the traditions themselves become the focus?
Let’s look at some Christmas traditions and see how we might use them to point us to Jesus instead of distracting us from Him.
Christmas Music
1And suddenly there appeared with the angel a multitude of the heavenly host praising God and saying,
“Glory to God in the highest,\ And on earth peace among men with whom He is pleased.” (Luke 2:13-14)
There is a lot of Christmas music to choose from, but some is more honoring to God than others. Do you spend your time listening to songs like “Jingle Bell Rock,” “Grandma Got Run Over By a Reindeer,” “Baby It’s Cold Outside,” or “I Saw Mommy Kissing Santa Claus” or do you spend your time listening to songs like “O Holy Night,” “O Come, O Come Emmanuel,” “Little Town of Bethlehem,” or “Mary Did You Know?” There isn’t anything inherently wrong with the first type, but the second type is much more honoring to Jesus and will focus our minds on what Jesus did for us.
By listening to Christmas music that points us to Jesus, we honor Him, refocus our own lives, and point others to Him. When we listen to Christmas music that focuses on Santa, Frosty, Rudolph, or just the season of winter, we distract people from the true meaning of Christmas. Listening to Bing Crosby singing “White Christmas” isn’t a problem (and I enjoy it very much), but focus on the Christmas Carols that point us to Jesus. You won’t regret it.
Christmas Decorations (Lights)
Then Jesus again spoke to them, saying, “I am the Light of the world; he who follows Me will not walk in the darkness, but will have the Light of life.” (John 8:12)
I love Christmas decorations and especially Christmas lights. I’ll admit it. This year we even decided we are going to leave the lights up through January because the lights are so cheerful during the dark part of the year when we spend so much time in darkness. The question we should ask ourselves is “Are we just focused on the decorations and lights or are we focused on Jesus?”
Jesus is the Light of the World. He is the light in the darkness. It is appropriate to use lights to celebrate Jesus, but do we focus on the lights or are the lights focusing our thoughts on Jesus? My new Christmas resolution is to remember to thank Jesus for being the light of the world every time I look at the Christmas lights.
Let your light shine before men in such a way that they may see your good works, and glorify your Father who is in heaven. (Matthew 5:16)
Are your Christmas decorations things that point to Jesus or things that point to human tradition like Santa, reindeer, Frosty, etc.? We should aim to have more of our decorations point to Jesus.
Another thing I’ve noticed is that many of our Christian decorations can even be based on tradition rather than actual Biblical inerrancy. Most nativity sets have 3 wise men. Although this error isn’t something to get legalistic about, it is something to be aware of.
Now after Jesus was born in Bethlehem of Judea in the days of Herod the king, magi from the east arrived in Jerusalem, saying, (Matthew 2:1)
Traditionally the magi have been called wise men, but nobody knows 100% who the magi were. They also assume there were 3 of them because of the 3 gifts of gold, frankincense, and myrrh. Based on the uproar that they caused in Jerusalem, it was probably a huge caravan. You’ll also notice that they arrived in Jerusalem “after Jesus was born in Bethlehem.” They then consulted King Herod. King Herod consulted the Jewish leaders to figure out that the Messiah was expected to be born in Bethlehem, and then they traveled to Bethlehem to find Jesus. It isn’t clear how long after Jesus’s birth the Magi showed up, but they definitely weren’t there that first Christmas morning.
Because of this, my husband sets up our main nativity set (that his parents got in Israel) in our living room and sets up the 3 wise men and the camel in our guest bedroom (on the East side of the house). It is his way of supporting the true Christmas story and not just the traditions of men.
Our Christmas tree isn’t just stuff relating to Jesus and the Christmas story. Most of our tree decorations are things for which we are thankful to Jesus. We have ornaments with family pictures. We have handmade ornaments made by the women of our church that were given to us when our house burnt down. We have ornaments from most of the trips we have gone on. We have a few sentimental family ornaments that were given to us when my husband’s mom died. Every time I look at my tree, I am grateful for all of these things. They aren’t just generic decorations. They are memories. I also have an ornament with a picture of my son’s teacher’s autistic son who snuck away and was killed in a blizzard. Every time I see the ornament, I pray for his family who misses him so much. I’d like to think that this tree of blessings is honoring to my God and my Savior.
Christmas Dinner
For I received from the Lord that which I also delivered to you, that the Lord Jesus in the night in which He was betrayed took bread; and when He had given thanks, He broke it and said, “This is My body, which is for you; do this in remembrance of Me.” In the same way He took the cup also after supper, saying, “This cup is the new covenant in My blood; do this, as often as you drink it, in remembrance of Me.” For as often as you eat this bread and drink the cup, you proclaim the Lord’s death until He comes. (1 Corinthians 11:23-26) {emphasis mine}
This passage is about the Passover celebration and Jesus’s command to celebrate the Lord’s Supper in remembrance of Him. I think it is likewise appropriate to celebrate His birth with a meal. As in most things, what makes it honoring to Jesus is how we do Christmas dinner rather than whether we do it or not.
The below passage is about celebrating the Lord’s supper in an inappropriate way, but I will try to apply it to Christmas dinner.
Therefore when you meet together, it is not to eat the Lord’s Supper, for in your eating each one takes his own supper first; and one is hungry and another is drunk. What! Do you not have houses in which to eat and drink? Or do you despise the church of God and shame those who have nothing? What shall I say to you? Shall I praise you? In this I will not praise you. (1 Corinthians 11:20-22)
Is Christmas dinner just about stuffing ourselves with good food or is it about more? Is it about fellowship with friends and family? Is it about gratefulness for what Jesus did for us? Is it about benefitting others?
For most of our marriage, we have alternated celebrating Christmas at my parent’s house and my husband’s parents house, but a couple of times recently, due to different circumstances, we have celebrated Christmas in our own home, and we will be doing it again this year. We’ll celebrate with my family after Christmas, and we celebrated with my husband’s family at Thanksgiving.
Our new tradition is to invite some people over to join us for Christmas dinner if we are celebrating at our home. We invite people from our church that are an older couple with no family nearby, a widow, or a single that is not near family. We invite people who would not have much of a celebration on their own. It has been such a blessing being able to bless others who don’t have family, are in financial hardship, or have physical trouble cooking a big meal.
Whether you are fellowshipping with family or ministering to those who have less than you, Christmas dinner can definitely be a God honoring part of your Christmas traditions.
Christmas Presents
Now He who supplies seed to the sower and bread for food will supply and multiply your seed for sowing and increase the harvest of your righteousness; you will be enriched in everything for all liberality, which through us is producing thanksgiving to God. For the ministry of this service is not only fully supplying the needs of the saints, but is also overflowing through many thanksgivings to God. Because of the proof given by this ministry, they will glorify God for your obedience to your confession of the gospel of Christ and for the liberality of your contribution to them and to all, while they also, by prayer on your behalf, yearn for you because of the surpassing grace of God in you. Thanks be to God for His indescribable gift! (2 Corinthians 9:10-15) {emphasis mine}
Too often we can get so obsessed with the buying and receiving of gifts that we forget the greatest gift of all — the gift of our Savior Jesus.
My 17 year old son has Down Syndrome. He really likes gifts, especially electronics, like tablets, radios, and phones. Unfortunately, he also isn’t very gentle with them and usually has broken or lost most of them by the time Christmas comes along. This often leads to him obsessing about the gifts that he thinks he deserves.
When we celebrated Christmas with my husband’s family at Thanksgiving, he got a nice keyboard that he had requested. He did not, however, get the radio or tablet he wanted. As we were driving home he demanded, “Where is my radio? Where is my tablet? Where is it?” Instead of being grateful for his very generous gift, a gift that he requested, he was upset that he hadn’t gotten everything he wanted. He focused on stuff and not people. He focused on receiving and not giving. He focused on earthly things instead of Jesus. Too often we all do.
But the free gift is not like the transgression. For if by the transgression of the one the many died, much more did the grace of God and the gift by the grace of the one Man, Jesus Christ, abound to the many. The gift is not like that which came through the one who sinned; for on the one hand the judgment arose from one transgression resulting in condemnation, but on the other hand the free gift arose from many transgressions resulting in justification. For if by the transgression of the one, death reigned through the one, much more those who receive the abundance of grace and of the gift of righteousness will reign in life through the One, Jesus Christ. (Romans 5:15-17) {emphasis mine}
Just as Jesus gave His life for us, it is good for us to give to others, but we always need to have the gift giving process be focused on Jesus and not the stuff. We always need to be thankful for what we have and receive and not what we don’t have and haven’t received.
On Christmas morning, before opening gifts, we always read the Christmas story from Luke 2 and the story of the magi from Matthew 2. We then sing “Happy Birthday” to Jesus, to remind us all of the purpose of Christmas and of the greatest gift we have received. I’m also wanting to start a new tradition at Christmas: Before each person opens a gift, they must thank Jesus for one blessing in their life. I think this will change the focus from greed and getting to gratefulness for what we have already received.
For by grace you have been saved through faith; and that not of yourselves, it is the gift of God; not as a result of works, so that no one may boast. For we are His workmanship, created in Christ Jesus for good works, which God prepared beforehand so that we would walk in them. For by grace you have been saved through faith; and that not of yourselves, it is the gift of God; not as a result of works, so that no one may boast. For we are His workmanship, created in Christ Jesus for good works, which God prepared beforehand so that we would walk in them. (Ephesians 2:8-9) {emphasis mine}
Jesus gave us His all. We also need to consider what we can give to those who can’t give back, just as we can’t ever repay Jesus for what He did for us. Is there a family you know that is having a rough year financially or health wise that you could bless with a meal or gifts or help with bills? Is there a charity that will share the gospel and meet the physical needs of those who are alone, broke, and addicted that you can donate to? Maybe your kids have lots of toys and are about to get more and you can donate some that are in good condition to a Christian charity that can get those toys to kids who won’t receive any. Maybe money is tight, but you could volunteer at a soup kitchen or do some yard chores for a widow. I don’t know your personal circumstances or the circumstances of where you are and those around you, but think about finding some way to bless someone less fortunate than you.
Above all, keep fervent in your love for one another, because love covers a multitude of sins. Be hospitable to one another without complaint. As each one has received a special gift, employ it in serving one another as good stewards of the manifold grace of God. Whoever speaks, is to do so as one who is speaking the utterances of God; whoever serves is to do so as one who is serving by the strength which God supplies; so that in all things God may be glorified through Jesus Christ, to whom belongs the glory and dominion forever and ever. Amen. (1 Peter 4:8-11) {emphasis mine}
There are lots of movies, songs, and TV shows that talk about the spirit of Christmas and the love of Christmas. Let’s make sure we show love and share Jesus with the people around us. They tend to be much more open to Jesus during Christmas. Let’s make sure we make the most of Christmas.
To God be the Glory!
Trust Jesus.
FYI, Because everyone is busy at Christmas, I will be posting my short Wednesday post (Christmas) on Tuesday evening (Christmas Eve) so that people can have time to read the post before Christmas and it will hopefully help you to have the right mindset on Christmas.
FYI, to learn more about my books “Why I Need Jesus” (available in paperback and ebook) and “Joy in the Storm” (in editing and hopefully out in a month or two.) see my books page.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28A violência é uma forma de comunicação
A violência é uma forma de comunicação: um serial killer, um pai que bate no filho, uma briga de torcidas, uma sessão de tortura, uma guerra, um assassinato passional, uma briga de bar. Em todos esses se pode enxergar uma mensagem que está tentando ser transmitida, que não foi compreendida pelo outro lado, que não pôde ser expressa, e, quando o transmissor da mensagem sentiu que não podia ser totalmente compreendido em palavras, usou essa outra forma de comunicação.
Quando uma ofensa em um bar descamba para uma briga, por exemplo, o que há é claramente uma tentativa de uma ofensa maior ainda pelo lado do que iniciou a primeira, a briga não teria acontecido se ele a tivesse conseguido expressar em palavras tão claras que toda a audiência de bêbados compreendesse, o que estaria além dos limites da linguagem, naquele caso, o soco com o mão direita foi mais eficiente. Poderia ser também a defesa argumentativa: "eu não sou um covarde como você está dizendo" -- mas o bar não acreditaria nessa frase solta, a comunicação não teria obtido o sucesso desejado.
A explicação para o fato da redução da violência à medida em que houve progresso da civilização está na melhora da eficiência da comunicação humana: a escrita, o refinamento da expressão lingüística, o aumento do alcance da palavra falada com rádio, a televisão e a internet.
Se essa eficiência diminuir, porque não há mais acordo quanto ao significado das palavras, porque as pessoas não estão nem aí para se o que escrevem é bom ou não, ou porque são incapazes de compreender qualquer coisa, deve aumentar proporcionalmente a violência.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28On HTLCs and arbiters
This is another attempt and conveying the same information that should be in Lightning and its fake HTLCs. It assumes you know everything about Lightning and will just highlight a point. This is also valid for PTLCs.
The protocol says HTLCs are trimmed (i.e., not actually added to the commitment transaction) when the cost of redeeming them in fees would be greater than their actual value.
Although this is often dismissed as a non-important fact (often people will say "it's trusted for small payments, no big deal"), but I think it is indeed very important for 3 reasons:
- Lightning absolutely relies on HTLCs actually existing because the payment proof requires them. The entire security of each payment comes from the fact that the payer has a preimage that comes from the payee. Without that, the state of the payment becomes an unsolvable mystery. The inexistence of an HTLC breaks the atomicity between the payment going through and the payer receiving a proof.
- Bitcoin fees are expected to grow with time (arguably the reason Lightning exists in the first place).
- MPP makes payment sizes shrink, therefore more and more of Lightning payments are to be trimmed. As I write this, the mempool is clear and still payments smaller than about 5000sat are being trimmed. Two weeks ago the limit was at 18000sat, which is already below the minimum most MPP splitting algorithms will allow.
Therefore I think it is important that we come up with a different way of ensuring payment proofs are being passed around in the case HTLCs are trimmed.
Channel closures
Worse than not having HTLCs that can be redeemed is the fact that in the current Lightning implementations channels will be closed by the peer once an HTLC timeout is reached, either to fulfill an HTLC for which that peer has a preimage or to redeem back that expired HTLCs the other party hasn't fulfilled.
For the surprise of everybody, nodes will do this even when the HTLCs in question were trimmed and therefore cannot be redeemed at all. It's very important that nodes stop doing that, because it makes no economic sense at all.
However, that is not so simple, because once you decide you're not going to close the channel, what is the next step? Do you wait until the other peer tries to fulfill an expired HTLC and tell them you won't agree and that you must cancel that instead? That could work sometimes if they're honest (and they have no incentive to not be, in this case). What if they say they tried to fulfill it before but you were offline? Now you're confused, you don't know if you were offline or they were offline, or if they are trying to trick you. Then unsolvable issues start to emerge.
Arbiters
One simple idea is to use trusted arbiters for all trimmed HTLC issues.
This idea solves both the protocol issue of getting the preimage to the payer once it is released by the payee -- and what to do with the channels once a trimmed HTLC expires.
A simple design would be to have each node hardcode a set of trusted other nodes that can serve as arbiters. Once a channel is opened between two nodes they choose one node from both lists to serve as their mutual arbiter for that channel.
Then whenever one node tries to fulfill an HTLC but the other peer is unresponsive, they can send the preimage to the arbiter instead. The arbiter will then try to contact the unresponsive peer. If it succeeds, then done, the HTLC was fulfilled offchain. If it fails then it can keep trying until the HTLC timeout. And then if the other node comes back later they can eat the loss. The arbiter will ensure they know they are the ones who must eat the loss in this case. If they don't agree to eat the loss, the first peer may then close the channel and blacklist the other peer. If the other peer believes that both the first peer and the arbiter are dishonest they can remove that arbiter from their list of trusted arbiters.
The same happens in the opposite case: if a peer doesn't get a preimage they can notify the arbiter they hadn't received anything. The arbiter may try to ask the other peer for the preimage and, if that fails, settle the dispute for the side of that first peer, which can proceed to fail the HTLC is has with someone else on that route.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Problemas com Russell Kirk
A idéia central da “política da prudência[^1]” de Russell Kirk me parece muito correta, embora tenha sido melhor formulada pior no seu enorme livro do que em uma pequena frase do joanadarquista Lucas Souza: “o conservadorismo é importante, porque tem muita gente com idéia errada por aí, e nós podemos não saber distingüi-las”.
Porém, há alguns problemas que precisam ser esclarecidos, ou melhor explicados, e que me impedem de enxergar os seus argumentos como refutação final do meu já tão humilde (embora feroz) anarquismo. São eles:
I Percebo alguma coisa errada, não sei bem onde, entre a afirmação de que toda ideologia é ruim, ou “todas as ideologias causam confusão[^2]”, e a proposta conservadora de “conservar o mundo da ordem que herdamos, ainda que em estado imperfeito, de nossos ancestrais[^3]”. Ora, sem precisar cair em exemplos como o do partido conservador inglês -- que conservava a política inglesa sempre onde estava, e se alternava no governo com o partido trabalhista, que a levava cada vez mais um pouco à esquerda --, está embutida nessa frase, talvez, a idéia, que ao mesmo tempo é clara e ferrenhamente combatida pelos próprios conservadores, de que a história é da humanidade é uma história de progresso linear rumo a uma situação melhor.
Querer conservar o mundo da ordem que herdamos significa conservar também os vários erros que podem ter sido cometidos pelos nossos ancestrais mais recentes, e conservá-los mesmo assim, acusando toda e qualquer tentativa de propôr soluções a esses erros de ideologia? Ou será que conservar o mundo da ordem é escolher um período determinado que seja tido como o auge da história humana e tentar restaurá-lo em nosso próprio tempo? Não seria isto ideologia?
Ou, ainda, será que conservar o mundo da ordem é selecionar, entre vários períodos do passado, alguns pedaços que o conservador considerar ótimos em cada sociedade, fazer dali uma mistura de sociedade ideal baseada no passado e então tentar implementá-la? Quem saberia dizer quais são as partes certas?
II Sobre a questão do que mantém a sociedade civil coesa, Russell Kirk, opondo-a à posição libertária de que o nexo da sociedade é o autointeresse, declara que a posição conservadora é a de que “a sociedade é uma comunidade de almas, que une os mortos, os vivos e os ainda não nascidos, e que se harmoniza por aquilo que Aristóteles chamou de amizade e os cristãos chamam de caridade ou amor ao próximo”.
Esta é uma posição muito correta, mas me parece estar em contradição com a defesa do Estado que ele faz na mesma página e na seguinte. O que me parece errado é que a sociedade não pode ser, ao mesmo tempo, uma “comunidade baseada no amor ao próximo” e uma comunidade que “requer não somente que as paixões dos indivíduos sejam subjugadas, mas que, mesmo no povo e no corpo social, bem como nos indivíduos, as inclinações dos homens, amiúde, devam ser frustradas, a vontade controlada e as paixões subjugadas” e, pior, que “isso somente pode ser feito por um poder exterior”.
Disto aí podemos tirar que, da mesma forma que Kirk define a posição libertária como sendo a de que o autointeresse é que mantém a sociedade civil coesa, a posição conservadora seria então a de que essa coesão vem apenas do Estado, e não de qualquer ligação entre vivos e mortos, ou do amor ao próximo. Já que, sem o Estado, diz, ele, citando Thomas Hobbes, a condição do homem é “solitária, pobre, sórdida, embrutecida e curta”?
[^1]: este é o nome do livro e também um outro nome que ele dá para o próprio conservadorismo (p.99). [^2]: p. 101 [^3]: p. 102
-
 @ 5d4b6c8d:8a1c1ee3
2025-01-06 15:14:32
@ 5d4b6c8d:8a1c1ee3
2025-01-06 15:14:32I'm putting some notes down, so I don't forget what happened in this game come podcast time.
This is most people's anticipated NBA Finals match up. The Thunder are still without Chet Holmgren and Alex Caruso, while the Celtics are fully intact.
The game was neck and neck for a while. It felt more like a Celtic (game: slower, low intensity) and the Celtics did build a little lead that they held for a while.
I was wondering why OKC wasn't playing with their normal defensive intensity and thinking they need to go back and watch how Miami was able to repeatedly dominate Boston in the playoffs. But then, OKC flipped the switch and were all over Boston: forcing turnovers, chase-down blocks, deflecting balls, etc.
Final score: 105-92 OKC
Takeaway: OKC is not the team Boston wants to play in the Finals
originally posted at https://stacker.news/items/839260
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28
A command line utility to create and manage personal graphs, then write them to dot and make images with graphviz.
It manages a bunch of YAML files, one for each entity in the graph. Each file lists the incoming and outgoing links it has (could have listen only the outgoing, now that I'm tihnking about it).
Each run of the tool lets you select from existing nodes or add new ones to generate a single link type from one to one, one to many, many to one or many to many -- then updates the YAML files accordingly.
It also includes a command that generates graphs with graphviz, and it can accept a template file that lets you customize the
dotthat is generated and thus the graphviz graph.rel
-
 @ 04222fa1:634e9de5
2024-12-21 09:10:12
@ 04222fa1:634e9de5
2024-12-21 09:10:12Spouse Mother-in-law Child $20m Dog
originally posted at https://stacker.news/items/818843
-
 @ dd664d5e:5633d319
2024-12-14 15:25:56
@ dd664d5e:5633d319
2024-12-14 15:25:56
Christmas season hasn't actually started, yet, in Roman #Catholic Germany. We're in Advent until the evening of the 24th of December, at which point Christmas begins (with the Nativity, at Vespers), and continues on for 40 days until Mariä Lichtmess (Presentation of Christ in the temple) on February 2nd.
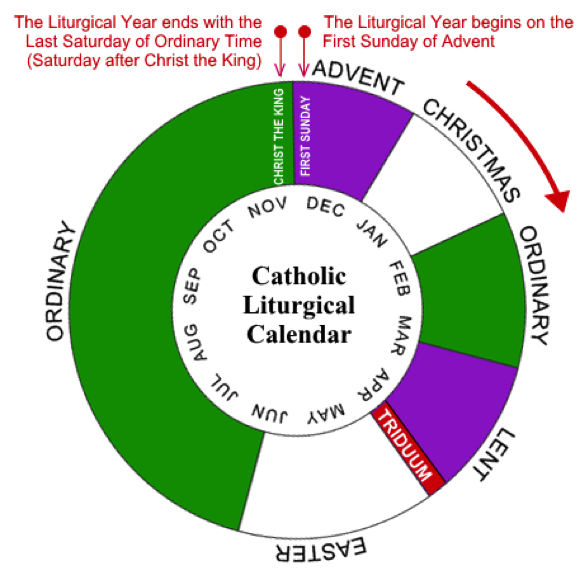
It's 40 days because that's how long the post-partum isolation is, before women were allowed back into the temple (after a ritual cleansing).

That is the day when we put away all of the Christmas decorations and bless the candles, for the next year. (Hence, the British name "Candlemas".) It used to also be when household staff would get paid their cash wages and could change employer. And it is the day precisely in the middle of winter.

Between Christmas Eve and Candlemas are many celebrations, concluding with the Twelfth Night called Epiphany or Theophany. This is the day some Orthodox celebrate Christ's baptism, so traditions rotate around blessing of waters.

The Monday after Epiphany was the start of the farming season, in England, so that Sunday all of the ploughs were blessed, but the practice has largely died out.
Our local tradition is for the altar servers to dress as the wise men and go door-to-door, carrying their star and looking for the Baby Jesus, who is rumored to be lying in a manger.

They collect cash gifts and chocolates, along the way, and leave the generous their powerful blessing, written over the door. The famous 20 * C + M + B * 25 blessing means "Christus mansionem benedicat" (Christ, bless this house), or "Caspar, Melchior, Balthasar" (the names of the three kings), depending upon who you ask.
They offer the cash to the Baby Jesus (once they find him in the church's Nativity scene), but eat the sweets, themselves. It is one of the biggest donation-collections in the world, called the "Sternsinger" (star singers). The money goes from the German children, to help children elsewhere, and they collect around €45 million in cash and coins, every year.

As an interesting aside:
The American "groundhog day", derives from one of the old farmers' sayings about Candlemas, brought over by the Pennsylvania Dutch. It says, that if the badger comes out of his hole and sees his shadow, then it'll remain cold for 4 more weeks. When they moved to the USA, they didn't have any badgers around, so they switched to groundhogs, as they also hibernate in winter.
-
 @ 5d4b6c8d:8a1c1ee3
2025-01-06 14:50:00
@ 5d4b6c8d:8a1c1ee3
2025-01-06 14:50:00It's officially the off-season for the Silver and Black. After several teams shot their draft position in the foot, the Raiders will be picking 6th.
That's high enough to try to trade up for one of the QB's, but I expect it won't be easy to pry those picks away from Tennessee or Cleveland, nor will it be easy to leap frog the Giants. So, let's see who we can get at 6th.
Mock Draft
6th Pick: DT Mason Graham 37th Pick: QB Jalen Milroe 68th Pick: WR Elic Ayomanor 73rd Pick: OT Grey Zabel 107th Pick: RB TreVeyon Henderson 142nd Pick: CB Mello Dotson 179th Pick: OG Jaeden Roberts 212th Pick: S Dante Trader Jr 216th Pick: QB Will Howard 222nd Pick: DE Kaimon Rucker
In lieu of a top QB, I'm going BPA with the first pick. The Raiders defensive line dramatically over-performed this season, considering the unbelievable injuries. Mason Graham will round out a line that also starts Maxx Crosby, Christian Wilkins, and Malcolm Koonce/Tyree Wilson. I hope we can keep the interim D-line coach, because he's done a great job and unearthed some promising rotation level talent.
For QB, I ended up going with the "heir and a spare" strategy. There's a lot of uncertainty around Milroe, so I took a flyer on the Ohio State QB in the 7th. The nice thing about having a competent high-end backup QB already is that drafting a day 1 starter isn't urgent. The Raiders can swing for the fences.
Otherwise, the focus was upgrading the offense and filling in depth on defense.
originally posted at https://stacker.news/items/839218
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28GraphQL vs REST
Today I saw this: https://github.com/stickfigure/blog/wiki/How-to-(and-how-not-to)-design-REST-APIs
And it reminded me why GraphQL is so much better.
It has also reminded me why HTTP is so confusing and awful as a protocol, especially as a protocol for structured data APIs, with all its status codes and headers and bodies and querystrings and content-types -- but let's not talk about that for now.
People complain about GraphQL being great for frontend developers and bad for backend developers, but I don't know who are these people that apparently love reading guides like the one above of how to properly construct ad-hoc path routers, decide how to properly build the JSON, what to include and in which circumstance, what status codes and headers to use, all without having any idea of what the frontend or the API consumer will want to do with their data.
It is a much less stressful environment that one in which we can just actually perform the task and fit the data in a preexistent schema with types and a structure that we don't have to decide again and again while anticipating with very incomplete knowledge the usage of an extraneous person -- i.e., an environment with GraphQL, or something like GraphQL.
By the way, I know there are some people that say that these HTTP JSON APIs are not the real REST, but that is irrelevant for now.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28nostr - Notes and Other Stuff Transmitted by Relays
The simplest open protocol that is able to create a censorship-resistant global "social" network once and for all.
It doesn't rely on any trusted central server, hence it is resilient; it is based on cryptographic keys and signatures, so it is tamperproof; it does not rely on P2P techniques, therefore it works.
Very short summary of how it works, if you don't plan to read anything else:
Everybody runs a client. It can be a native client, a web client, etc. To publish something, you write a post, sign it with your key and send it to multiple relays (servers hosted by someone else, or yourself). To get updates from other people, you ask multiple relays if they know anything about these other people. Anyone can run a relay. A relay is very simple and dumb. It does nothing besides accepting posts from some people and forwarding to others. Relays don't have to be trusted. Signatures are verified on the client side.
This is needed because other solutions are broken:
The problem with Twitter
- Twitter has ads;
- Twitter uses bizarre techniques to keep you addicted;
- Twitter doesn't show an actual historical feed from people you follow;
- Twitter bans people;
- Twitter shadowbans people.
- Twitter has a lot of spam.
The problem with Mastodon and similar programs
- User identities are attached to domain names controlled by third-parties;
- Server owners can ban you, just like Twitter; Server owners can also block other servers;
- Migration between servers is an afterthought and can only be accomplished if servers cooperate. It doesn't work in an adversarial environment (all followers are lost);
- There are no clear incentives to run servers, therefore they tend to be run by enthusiasts and people who want to have their name attached to a cool domain. Then, users are subject to the despotism of a single person, which is often worse than that of a big company like Twitter, and they can't migrate out;
- Since servers tend to be run amateurishly, they are often abandoned after a while — which is effectively the same as banning everybody;
- It doesn't make sense to have a ton of servers if updates from every server will have to be painfully pushed (and saved!) to a ton of other servers. This point is exacerbated by the fact that servers tend to exist in huge numbers, therefore more data has to be passed to more places more often;
- For the specific example of video sharing, ActivityPub enthusiasts realized it would be completely impossible to transmit video from server to server the way text notes are, so they decided to keep the video hosted only from the single instance where it was posted to, which is similar to the Nostr approach.
The problem with SSB (Secure Scuttlebutt)
- It doesn't have many problems. I think it's great. In fact, I was going to use it as a basis for this, but
- its protocol is too complicated because it wasn't thought about being an open protocol at all. It was just written in JavaScript in probably a quick way to solve a specific problem and grew from that, therefore it has weird and unnecessary quirks like signing a JSON string which must strictly follow the rules of ECMA-262 6th Edition;
- It insists on having a chain of updates from a single user, which feels unnecessary to me and something that adds bloat and rigidity to the thing — each server/user needs to store all the chain of posts to be sure the new one is valid. Why? (Maybe they have a good reason);
- It is not as simple as Nostr, as it was primarily made for P2P syncing, with "pubs" being an afterthought;
- Still, it may be worth considering using SSB instead of this custom protocol and just adapting it to the client-relay server model, because reusing a standard is always better than trying to get people in a new one.
The problem with other solutions that require everybody to run their own server
- They require everybody to run their own server;
- Sometimes people can still be censored in these because domain names can be censored.
How does Nostr work?
- There are two components: clients and relays. Each user runs a client. Anyone can run a relay.
- Every user is identified by a public key. Every post is signed. Every client validates these signatures.
- Clients fetch data from relays of their choice and publish data to other relays of their choice. A relay doesn't talk to another relay, only directly to users.
- For example, to "follow" someone a user just instructs their client to query the relays it knows for posts from that public key.
- On startup, a client queries data from all relays it knows for all users it follows (for example, all updates from the last day), then displays that data to the user chronologically.
- A "post" can contain any kind of structured data, but the most used ones are going to find their way into the standard so all clients and relays can handle them seamlessly.
How does it solve the problems the networks above can't?
- Users getting banned and servers being closed
- A relay can block a user from publishing anything there, but that has no effect on them as they can still publish to other relays. Since users are identified by a public key, they don't lose their identities and their follower base when they get banned.
- Instead of requiring users to manually type new relay addresses (although this should also be supported), whenever someone you're following posts a server recommendation, the client should automatically add that to the list of relays it will query.
- If someone is using a relay to publish their data but wants to migrate to another one, they can publish a server recommendation to that previous relay and go;
- If someone gets banned from many relays such that they can't get their server recommendations broadcasted, they may still let some close friends know through other means with which relay they are publishing now. Then, these close friends can publish server recommendations to that new server, and slowly, the old follower base of the banned user will begin finding their posts again from the new relay.
-
All of the above is valid too for when a relay ceases its operations.
-
Censorship-resistance
- Each user can publish their updates to any number of relays.
-
A relay can charge a fee (the negotiation of that fee is outside of the protocol for now) from users to publish there, which ensures censorship-resistance (there will always be some Russian server willing to take your money in exchange for serving your posts).
-
Spam
-
If spam is a concern for a relay, it can require payment for publication or some other form of authentication, such as an email address or phone, and associate these internally with a pubkey that then gets to publish to that relay — or other anti-spam techniques, like hashcash or captchas. If a relay is being used as a spam vector, it can easily be unlisted by clients, which can continue to fetch updates from other relays.
-
Data storage
- For the network to stay healthy, there is no need for hundreds of active relays. In fact, it can work just fine with just a handful, given the fact that new relays can be created and spread through the network easily in case the existing relays start misbehaving. Therefore, the amount of data storage required, in general, is relatively less than Mastodon or similar software.
-
Or considering a different outcome: one in which there exist hundreds of niche relays run by amateurs, each relaying updates from a small group of users. The architecture scales just as well: data is sent from users to a single server, and from that server directly to the users who will consume that. It doesn't have to be stored by anyone else. In this situation, it is not a big burden for any single server to process updates from others, and having amateur servers is not a problem.
-
Video and other heavy content
-
It's easy for a relay to reject large content, or to charge for accepting and hosting large content. When information and incentives are clear, it's easy for the market forces to solve the problem.
-
Techniques to trick the user
- Each client can decide how to best show posts to users, so there is always the option of just consuming what you want in the manner you want — from using an AI to decide the order of the updates you'll see to just reading them in chronological order.
FAQ
- This is very simple. Why hasn't anyone done it before?
I don't know, but I imagine it has to do with the fact that people making social networks are either companies wanting to make money or P2P activists who want to make a thing completely without servers. They both fail to see the specific mix of both worlds that Nostr uses.
- How do I find people to follow?
First, you must know them and get their public key somehow, either by asking or by seeing it referenced somewhere. Once you're inside a Nostr social network you'll be able to see them interacting with other people and then you can also start following and interacting with these others.
- How do I find relays? What happens if I'm not connected to the same relays someone else is?
You won't be able to communicate with that person. But there are hints on events that can be used so that your client software (or you, manually) knows how to connect to the other person's relay and interact with them. There are other ideas on how to solve this too in the future but we can't ever promise perfect reachability, no protocol can.
- Can I know how many people are following me?
No, but you can get some estimates if relays cooperate in an extra-protocol way.
- What incentive is there for people to run relays?
The question is misleading. It assumes that relays are free dumb pipes that exist such that people can move data around through them. In this case yes, the incentives would not exist. This in fact could be said of DHT nodes in all other p2p network stacks: what incentive is there for people to run DHT nodes?
- Nostr enables you to move between server relays or use multiple relays but if these relays are just on AWS or Azure what’s the difference?
There are literally thousands of VPS providers scattered all around the globe today, there is not only AWS or Azure. AWS or Azure are exactly the providers used by single centralized service providers that need a lot of scale, and even then not just these two. For smaller relay servers any VPS will do the job very well.
-
 @ a39d19ec:3d88f61e
2024-11-17 10:48:56
@ a39d19ec:3d88f61e
2024-11-17 10:48:56This week's functional 3d print is the "Dino Clip".

Dino Clip
I printed it some years ago for my son, so he would have his own clip for cereal bags.
Now it is used to hold a bag of dog food close.
The design by "Sneaks" is a so called "print in place". This means that the whole clip with moving parts is printed in one part, without the need for assembly after the print.
 The clip is very strong, and I would print it again if I need a "heavy duty" clip for more rigid or big bags.
Link to the file at Printables
The clip is very strong, and I would print it again if I need a "heavy duty" clip for more rigid or big bags.
Link to the file at Printables -
 @ 6b0a60cf:b952e7d4
2024-11-17 07:02:11
@ 6b0a60cf:b952e7d4
2024-11-17 07:02:11ビットコインのウォレットは取引形態によって2種類に分かれます。
- オンチェーン(L1)
- 取引がブロックチェーンに刻まれるタイプ。時間がかかるし手数料が高い。
- ライトニングネットワーク(L2)
- ブロックチェーンに刻む前の少額決済を目的としたレイヤー。高速で手数料が安い。
NostrでZapを利用する場合はライトニングネットワーク(以下、LNと呼びます)のウォレットが使われますが、さらにその中でもZap対応/非対応で分かれることになります。
また、秘密鍵を誰が管理するかによっても2種類の呼び方に分かれます。
- カストディアル
- 秘密鍵をサービスの運営に預けるタイプ。
- ノンカストディアル/セルフカストディアル
- 秘密鍵(シードフレーズ)を自分で持っておくタイプ。
Nostrで人気があるWallet of Satoshi(以下、WoSと呼びます)はLNのカストディアルウォレットです。 今回はLNのセルフカストディアルウォレットであるPhoenixを使ってみて、その仕組みや注意点など、学んだことを記録したいと思います。
Phoenixでウォレットを作る場合、初回でシードフレーズ(12個の単語)が作られますので、大切に控えておきましょう。
WoSからPhoenixに送金してみる
メイン画面左下にあるReciaveからQRCode表示画面へ遷移します。そこでcopyボタンを押して
Lightning invoice(text)をコピーしましょう。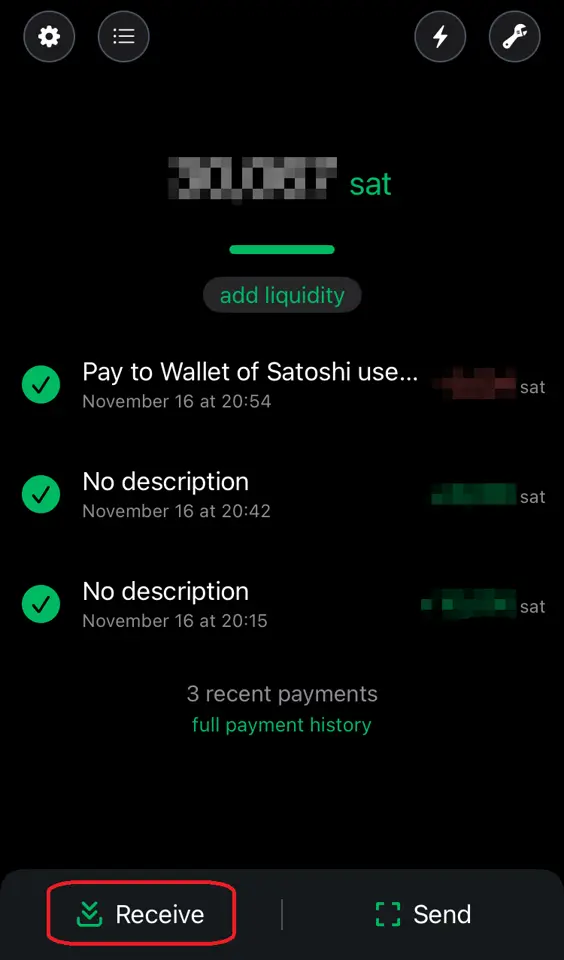
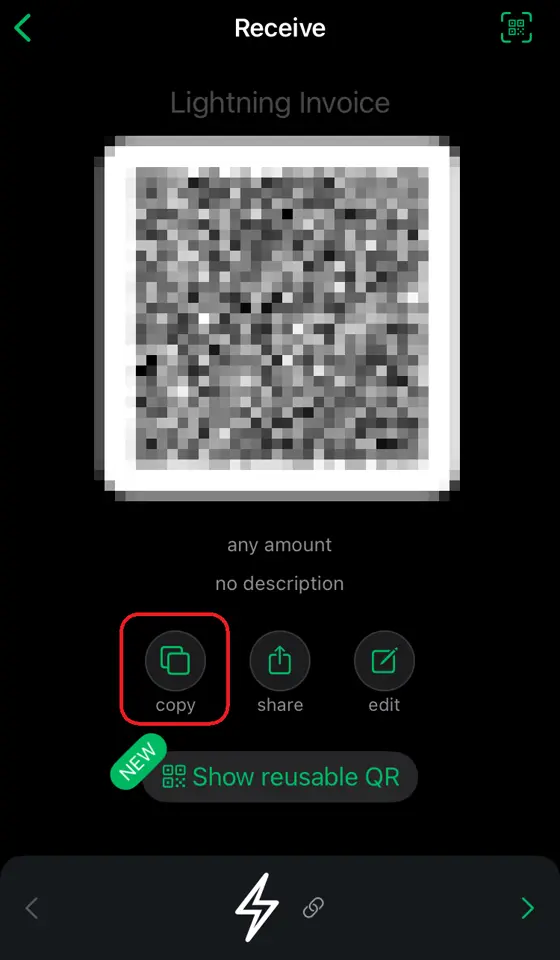
次に、WoSの画面からSendを選択し、クリップボードからの貼り付けを選択します。
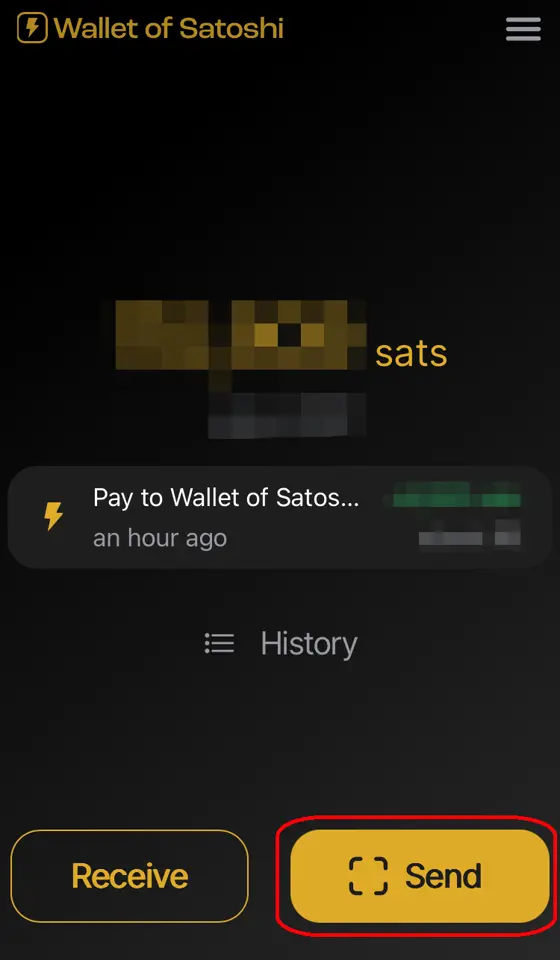
 金額を指定して送金します。
金額を指定して送金します。
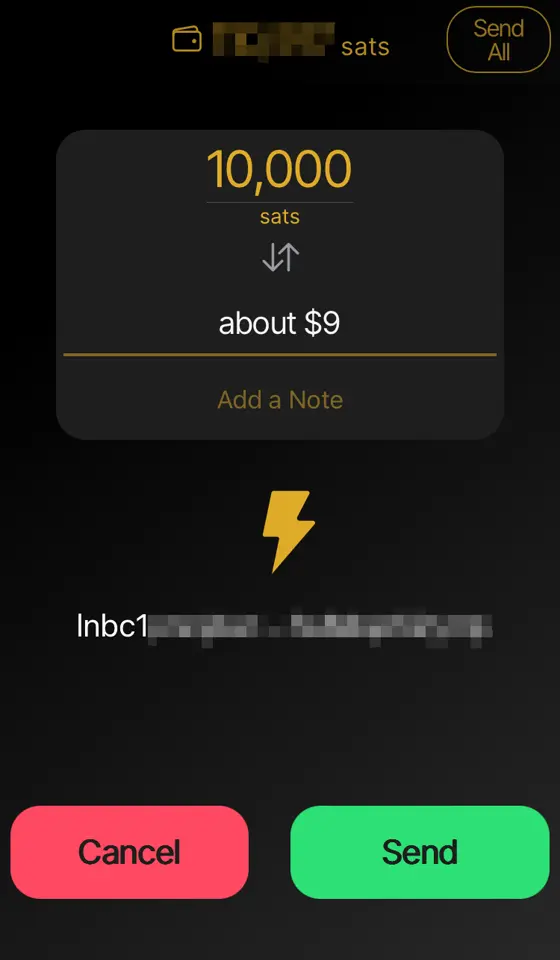
送金した額が満額届いてないんだけど?
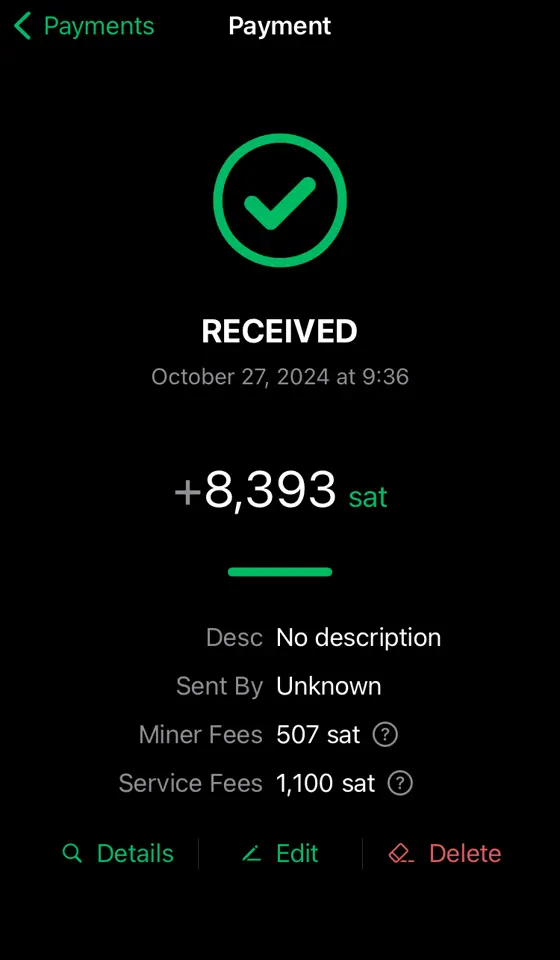
下の方に
Service Feesとありますが、これはPhoenix運営(ACINQ)へのお布施ですね。結構高く見えますが初回だけです。 またMiner Feesという項目は、mempoolのfeeに連動して変わるようですが、これはチャネルを太くする(送受信できる金額の上限を上げる)ために使われる手数料になります。財布が重たくなると手数料が取られる?
有り体に言えばそういうことになります。以下のように10,000satsをもらう度にチャネル拡張のための手数料が引かれています。
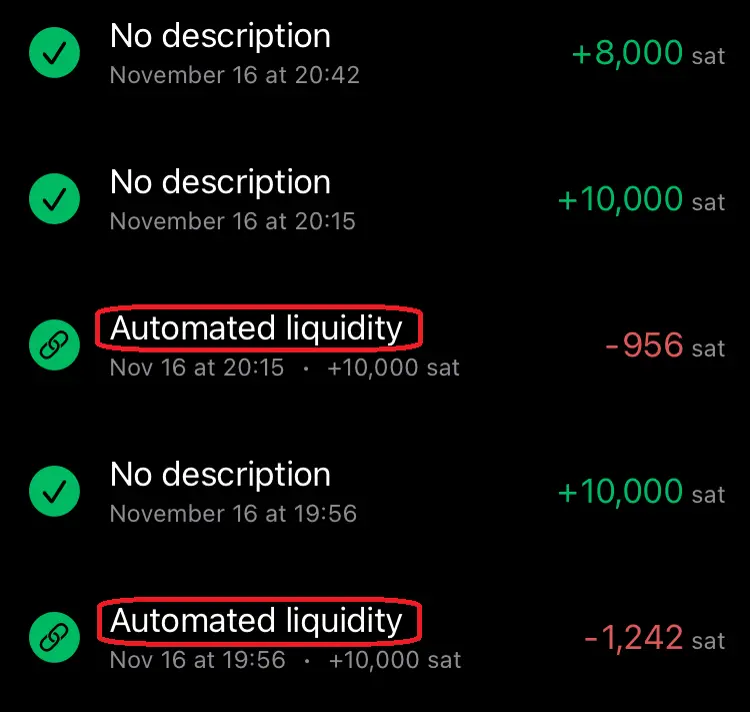
上記の8,000satsを受け取っている時には手数料が発生していませんね。これはチャネル拡張が必要ないギリギリの金額を狙って送金したためです。送金前は8,859satsの余裕がありました。送金後は1,719satsに減っています。(余裕分がぴったり8,000sats減るわけではないようです。このへんの仕組みはよくわかりません。) (画面は左上⚙️マークの設定からPayment channelsから。)
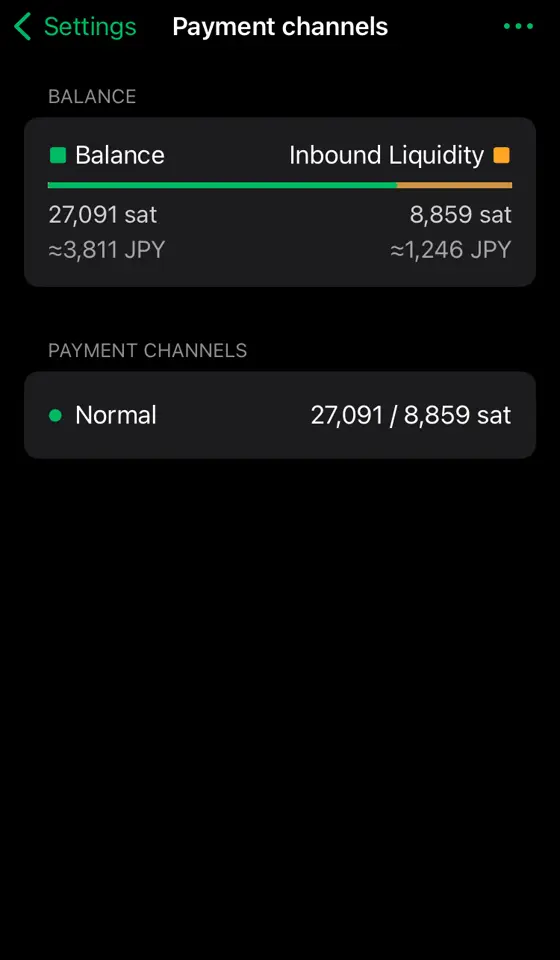
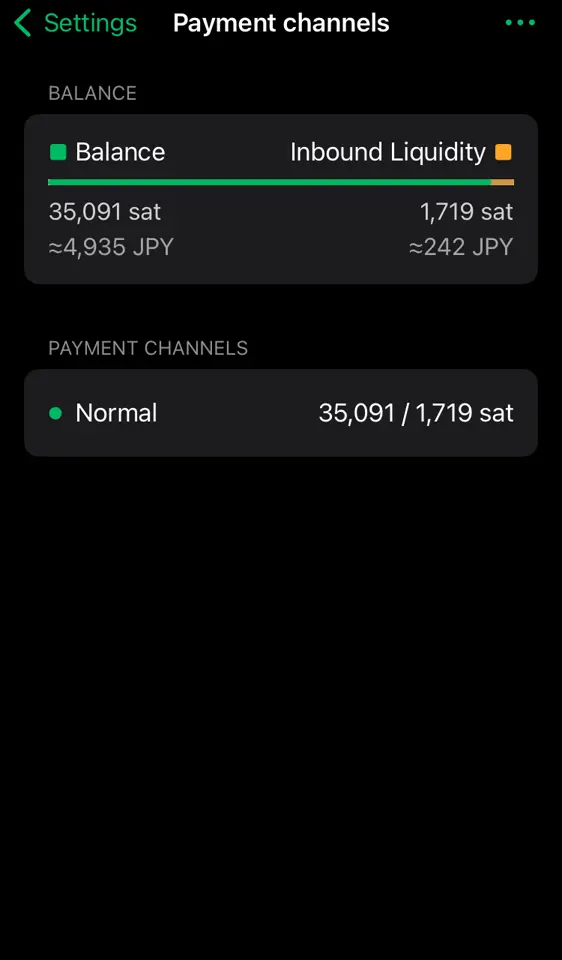
財布が軽くなると余裕が増える?
逆にPhoenixからWoSに5,000satsほど送金してみます。(手数料として24satsほど余計に抜かれました)
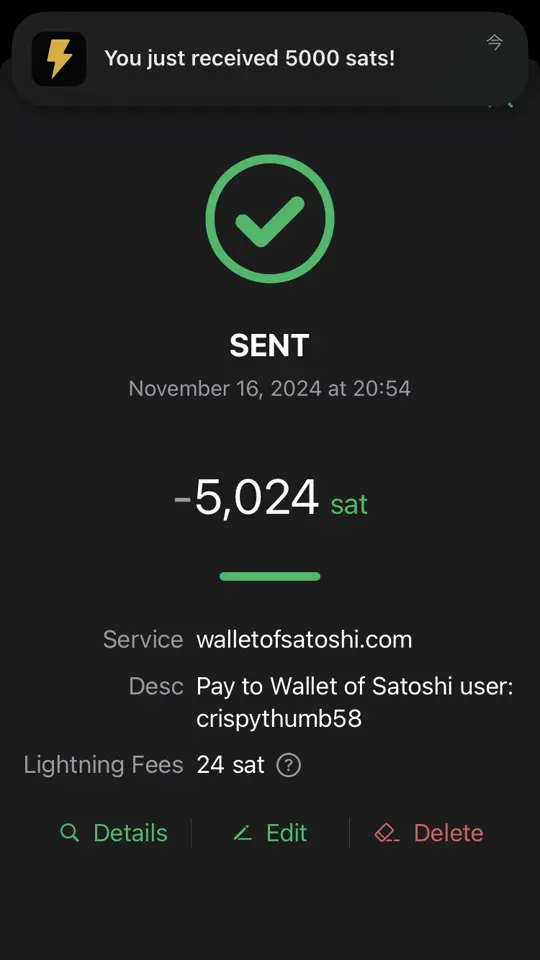
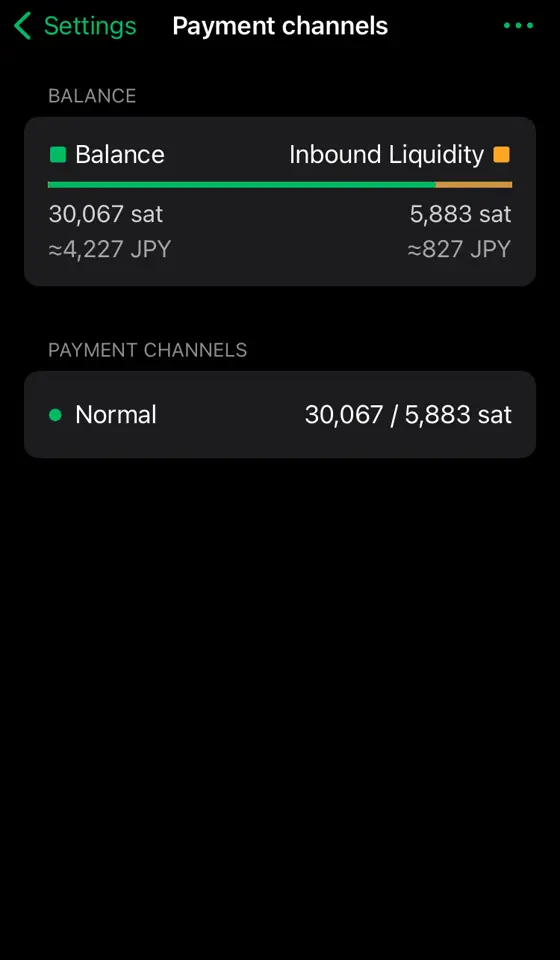
余裕(Inbound Liquidity)が5,883satsまで復活しています。受け取るばかりでなく、バランスよく送ることで財布を重たくしなければチャネル拡張せずに使い続けることができそうです。(太くしたチャネルは永遠に残るわけではなく、1年までらしいです)
自動でチャネル拡張にsatsを使われたくない!
自動チャネル拡張を設定で無効化できます。左上⚙️マークの設定から
Channel managementから。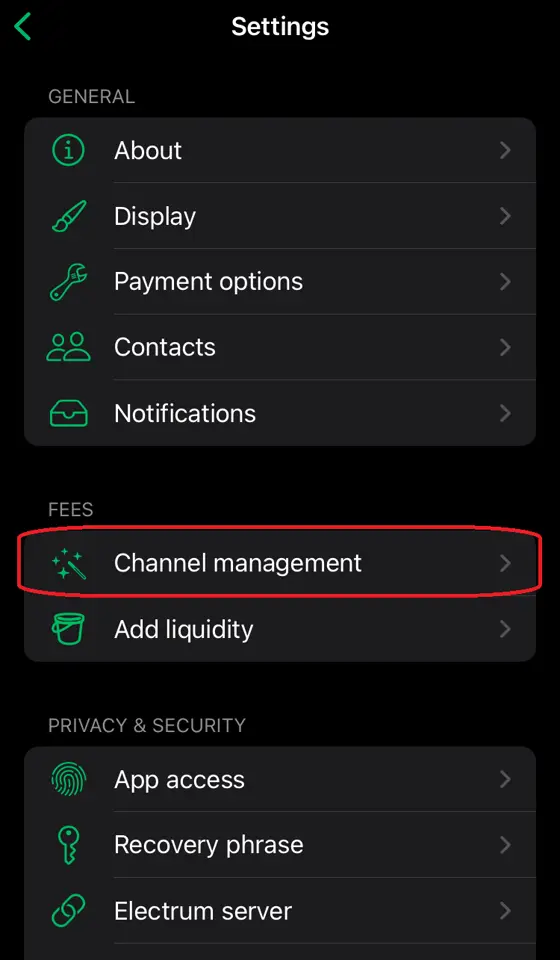
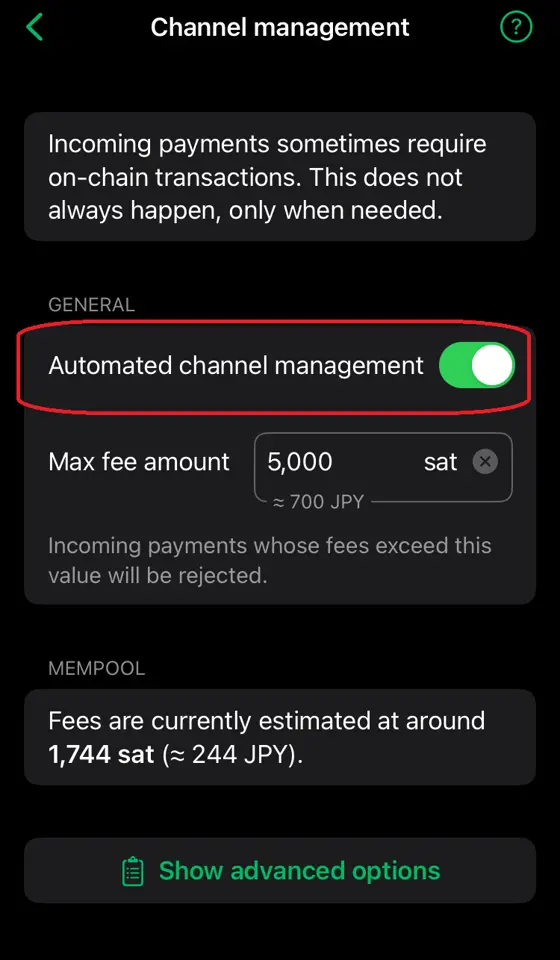
これでチャネル拡張が必要なほどの金額を送金しようとするとエラーになり失敗します。
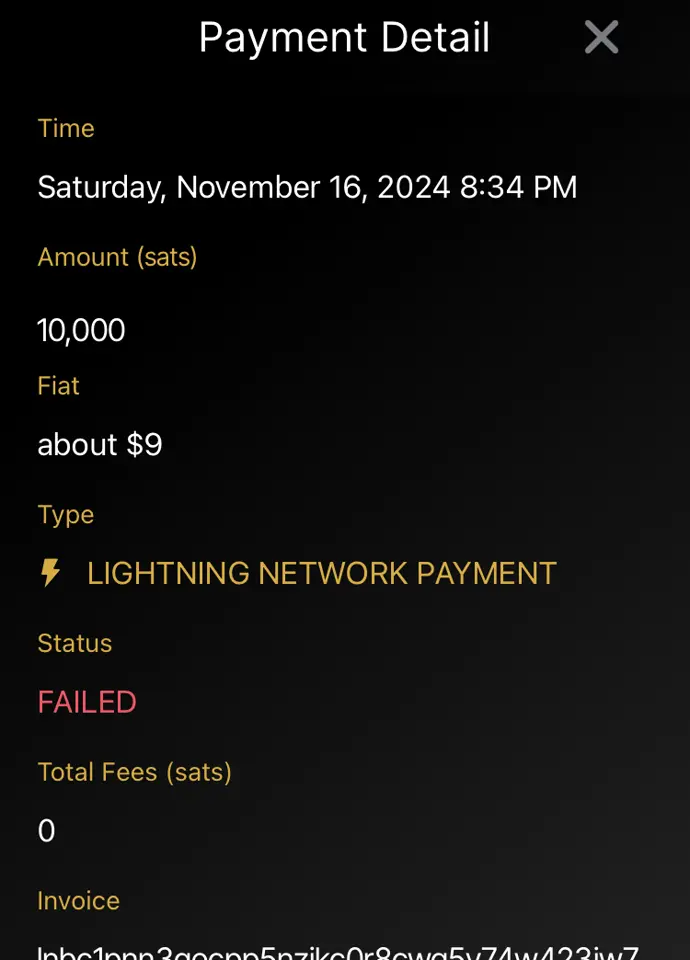
まとめ
セルフカストディアルウォレットならではの概念があり、謎の手数料が発生したりして怖いイメージがありましたが、どういう理由で手数料が発生するのかを知り、設定でのコントロールの仕方を習得することである程度怖いイメージを払拭することができました。 しかしカストディアルウォレット(特にWoS)の使いやすさを再認識することにもなりました。ただ自分で管理することの重要性も理解していますので、徐々に知識を深めていこうと思います。
参考/謝辞
- Phoenix wallet(フェニックスウォレット)の使い方!ビットコインのセルフカストディができるアプリを解説 - 知っとこ!ビットコイン図鑑
- nostr:npub10zeurmg22wc89l8m3npw9cyu45cun0lvs6w3ep69cdpa25pna65s0994qz 様
-
 @ ec42c765:328c0600
2024-10-21 07:42:48
@ ec42c765:328c0600
2024-10-21 07:42:482024年3月
フィリピンのセブ島へ旅行。初海外。

Nostrに投稿したらこんなリプライが
nostr:nevent1qqsff87kdxh6szf9pe3egtruwfz2uw09rzwr6zwpe7nxwtngmagrhhqc2qwq5
nostr:nevent1qqs9c8fcsw0mcrfuwuzceeq9jqg4exuncvhas5lhrvzpedeqhh30qkcstfluj
(ビットコイン関係なく普通の旅行のつもりで行ってた。というか常にビットコインのこと考えてるわけではないんだけど…)
そういえばフィリピンでビットコイン決済できるお店って多いのかな?
海外でビットコイン決済ってなんかかっこいいな!
やりたい!
ビットコイン決済してみよう! in セブ島
BTCMap でビットコイン決済できるところを探す
本場はビットコインアイランドと言われてるボラカイ島みたいだけど
セブにもそれなりにあった!

なんでもいいからビットコイン決済したいだけなので近くて買いやすい店へ
いざタピオカミルクティー屋!

ちゃんとビットコインのステッカーが貼ってある!

つたない英語とGoogle翻訳を使ってビットコイン決済できるか店員に聞いたら
店員「ビットコインで支払いはできません」
(えーーーー、なんで…ステッカー貼ってあるやん…。)
まぁなんか知らんけどできないらしい。
店員に色々質問したかったけど質問する英語力もないのでする気が起きなかった
結局、せっかく店まで足を運んだので普通に現金でタピオカミルクティーを買った
タピオカミルクティー
話題になってた時も特に興味なくて飲んでなかったので、これが初タピオカミルクティーになった
法定通貨の味がした。

どこでもいいからなんでもいいから
海外でビットコイン決済してみたい
ビットコイン決済させてくれ! in ボラカイ島
ビットコインアイランドと呼ばれるボラカイ島はめちゃくちゃビットコイン決済できるとこが多いらしい
でもやめてしまった店も多いらしい
でも300もあったならいくつかはできるとこあるやろ!
nostr:nevent1qqsw0n6utldy6y970wcmc6tymk20fdjxt6055890nh8sfjzt64989cslrvd9l
行くしかねぇ!
ビットコインアイランドへ
フィリピンの国内線だぁ

``` 行き方: Mactan-Cebu International Airport ↓飛行機 Godofredo P. Ramos Airport (Caticlan International Airport, Boracay Airport) ↓バスなど Caticlan フェリーターミナル ↓船 ボラカイ島
料金: 飛行機(受託手荷物付き) 往復 21,000円くらい 空港~ボラカイ島のホテルまで(バス、船、諸経費) 往復 3,300円くらい (klookからSouthwest Toursを利用)
このページが色々詳しい https://smaryu.com/column/d/91761/ ```
空港おりたらSouthwestのバスに乗る
事前にネットで申し込みをしている場合は5番窓口へ

港!

船!(めっちゃ速い)

ボラカイついた!

ボラカイ島の移動手段
セブの移動はgrabタクシーが使えるがボラカイにはない。
ネットで検索するとトライシクルという三輪タクシーがおすすめされている。
 (トライシクル:開放的で風がきもちいい)
(トライシクル:開放的で風がきもちいい)トライシクルの欠点はふっかけられるので値切り交渉をしないといけないところ。
最初に300phpくらいを提示され、行き先によるけど150phpくらいまでは下げられる。
これはこれで楽しい値切り交渉だけど、個人的にはトライシクルよりバスの方が気楽。
Hop On Hop Off バス:
https://www.hohoboracay.com/pass.php
一日乗り放題250phpなので往復や途中でどこか立ち寄ったりを考えるとお得。
 バスは現金が使えないので事前にどこかでカードを買うか車内で買う。
バスは現金が使えないので事前にどこかでカードを買うか車内で買う。私は何も知らずに乗って車内で乗務員さんから現金でカードを買った。
バスは狭い島内を数本がグルグル巡回してるので20~30分に1本くらいは来るイメージ。
逆にトライシクルは待たなくても捕まえればすぐに乗れるところがいいところかもしれない。
現実
ボラカイ島 BTC Map
 BTC決済できるとこめっちゃある
BTC決済できるとこめっちゃあるさっそく店に行く!
「bitcoin accepted here」のステッカーを見つける!
店員にビットコイン支払いできるか聞く!
できないと言われる!
もう一軒行く
「bitcoin accepted here」のステッカーを見つける
店員にビットコイン支払いできるか聞く
できないと言われる
5件くらいは回った
全部できない!
悲しい
で、ネットでビットコインアイランドで検索してみると
旅行日の一か月前くらいにアップロードされた動画があったので見てみた
要約 - ビットコイン決済はpouch.phというスタートアップ企業がボラカイ島の店にシステムを導入した - ビットコインアイランドとすることで観光客が10%~30%増加つまり数百~千人程度のビットコインユーザーが来ると考えた - しかし実際には3~5人だった - 結果的に200の店舗がビットコイン決済を導入しても使われたのはごく一部だった - ビットコイン決済があまり使われないので店員がやり方を忘れてしまった - 店は関心を失いpouchのアプリを消した
https://youtu.be/uaqx6794ipc?si=Afq58BowY1ZrkwaQ
なるほどね~
しゃあないわ
聖地巡礼
動画内でpouchのオフィスだったところが紹介されていた
これは半年以上前の画像らしい

現在はオフィスが閉鎖されビットコインの看板は色あせている
 おもしろいからここに行ってみよう!となった
おもしろいからここに行ってみよう!となったで行ってみた
看板の色、更に薄くなってね!?

記念撮影
 これはこれで楽しかった
これはこれで楽しかった場所はこの辺
https://maps.app.goo.gl/WhpEV35xjmUw367A8
ボラカイ島の中心部の結構いいとこ
みんな~ビットコイン(の残骸)の聖地巡礼、行こうぜ!
最後の店
Nattoさんから情報が
なんかあんまりネットでも今年になってからの情報はないような…https://t.co/hiO2R28sfO
— Natto (@madeofsoya) March 22, 2024
ここは比較的最近…?https://t.co/CHLGZuUz04もうこれで最後だと思ってダメもとで行ってみた なんだろうアジア料理屋さん?

もはや信頼度0の「bitcoin accepted here」

ビットコイン払いできますか?
店員「できますよ」
え?ほんとに?ビットコイン払いできる?
店員「できます」
できる!!!!
なんかできるらしい。
適当に商品を注文して
印刷されたQRコードを出されたので読み取る
ここでスマートに決済できればよかったのだが結構慌てた
自分は英語がわからないし相手はビットコインがわからない
それにビットコイン決済は日本で1回したことがあるだけだった
 どうもライトニングアドレスのようだ
どうもライトニングアドレスのようだ送金額はこちらで指定しないといけない
店員はフィリピンペソ建ての金額しか教えてくれない
何sats送ればいいのか分からない
ここでめっちゃ混乱した
でもウォレットの設定変えればいいと気付いた
普段円建てにしているのをフィリピンペソ建てに変更すればいいだけだった
設定を変更したら相手が提示している金額を入力して送金
送金は2、3秒で完了した
やった!
海外でビットコイン決済したぞ!
ログ

PORK CHAR SIU BUN とかいうやつを買った
 普通にめっちゃおいしかった
普通にめっちゃおいしかったなんかビットコイン決済できることにビビッて焦って一品しか注文しなかったけどもっと頼めばよかった
ここです。みなさん行ってください。
Bunbun Boracay
https://maps.app.goo.gl/DX8UWM8Y6sEtzYyK6
めでたしめでたし
以下、普通の観光写真
セブ島
ジンベエザメと泳いだ

スミロン島でシュノーケリング

市場の路地裏のちょっとしたダウンタウン?スラム?をビビりながら歩いた

ボホール島
なんか変な山

メガネザル

現地の子供が飛び込みを披露してくれた

ボラカイ島
ビーチ


夕日

藻

ボラカイ島にはいくつかビーチがあって宿が多いところに近い南西のビーチ、ホワイトビーチは藻が多かった(時期によるかも)
北側のプカシェルビーチは全然藻もなく、水も綺麗でめちゃくちゃよかった

プカシェルビーチ



おわり!
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28LessPass remoteStorage
LessPass is a nice idea: a password manager without any state. Just remember one master password and you can generate a different one for every site using the power of hashes.
But it has a very bad issue: some sites require just numbers, others have a minimum or maximum character limits, some require non-letter characters, uppercase characters, others forbid these and so on.
The solution: to allow you to specify parameters when generating the password so you can fit a generated password on every service.
The problem with the solution: it creates state. Now you must remember what parameters you used when generating a password for each site.
This was a way to store these settings on a remoteStorage bucket. Since it isn't confidential information in any way, that wasn't a problem, and I thought it was a good fit for remoteStorage.
Some time later I realized it maybe would be better to have a centralized repository hosting all weird requirements for passwords each domain forced on its users, and let LessPass use data from that central place when generating a password. Still stateful, not ideal, not very far from a centralized password manager, but still requiring less trust and less cryptographic assumptions.
- https://github.com/fiatjaf/lesspass-remotestorage
- https://addons.mozilla.org/firefox/addon/lesspass-remotestorage/
- https://chrome.google.com/webstore/detail/lesspass-remotestorage/aogdpopejodechblppdkpiimchbmdcmc
- https://lesspass.alhur.es/
See also
-
 @ 6bcc27d2:b67d296e
2024-10-21 03:54:32
@ 6bcc27d2:b67d296e
2024-10-21 03:54:32yugoです。 この記事は「Nostrasia2024 逆アドベントカレンダー」10/19の分です。Nostrasiaの当日はリアルタイムで配信を視聴していました。Nostrを使ってアプリケーションの再発明をすべきという発表を聴き、自分だったらどんなものを作ってみたいかを考えて少し調べたり試みたりしたのでその記録を書きます。また、超簡単なものですがおそらく世界初となるvisionOS対応のNostrクライアントをつくってみたので最後の方に紹介します。
アプリケーションを再発明する話があったのは、「What is Nostr Other Stuff?」と題したkaijiさんの発表でした。
Nostrプロトコルを使って既存のアプリケーションを再発明することで、ユーザ体験を損なわずにゆるやかな分散を促すことができ、プロトコルとしてのNostrも成長していくというような内容でした。
自分はまだNostrで何かをつくった経験はなかったので、実装に必要な仕様の知識がほとんどない状態からどのようなアプリケーションをつくってみたいかを考えました。
最初に思いついたのは、Scrapboxのようなネットワーク型のナレッジベースです。自分は最近visionOS勉強会をやっており、勉強会でナレッジを共有する手段としてScrapboxの導入を検討していました。
Nostrコミュニティにも有志によるScrapboxがありますが、Nostrクライアントがあればそれを使うだろうから同じくらいの実用性を備えたクライアントはまだ存在しないのではないかという見立てでした。
長文投稿やpublic chatなどの機能を組み合わせることで実現できるだろうか。そう思っていた矢先、NIP-54のWikiという規格があることを知りました。
https://github.com/nostr-protocol/nips/blob/master/54.md
まだちゃんとは読めていないですが、Scrapboxもwikiソフトウェアだし参考になりそうと思っています。正式な仕様に組み込まれていないようで、採用しているクライアントはfiatjafによるリファレンス実装(?)のwikistrくらいしか見つかりませんでした。
Scrapboxのようなナレッジベースを志向するNostrクライアントがあれば、後述するvisionOS対応クライアントの存在もありアカウントを使いまわせて嬉しいので試してみたいです。もし他にも似たようなサービスをどなたか知っていたら教えてください。
また現在は、勉強会やワークショップ、ハッカソンなどのコラボレーションワークを支援するためのツールを自分たちでも開発しています。Apple Vision Proに搭載されているvisionOSというプラットフォームで動作します。
https://image.nostr.build/14f0c1b8fbe5ce7754825c01b09280a4c22f87bbf3c2fa6d60dd724f98919c34.png
この画面で自分が入りたいスペースを選んで共有体験を開始します。
スライドなどのコンテンツや自らのアバターを同期させることで、遠隔地にいてもまるでオフラインかのように同じ空間を共有することが可能になります。
https://image.nostr.build/cfb75d3db2a9b9cd39f502d6426d5ef4f264b3d5d693b6fc9762735d2922b85c.jpg
ということなので、急遽visionOS対応のクライアントを作ってみました。検索しても1つも事例が出てこなかったので多分まだ世界で実装しているアプリはないのではないでしょうか。
とはいえ、クライアントを名乗っているもののまだ大した機能はなく、リレーからデータを取得するだけの読み取り専用です。
https://image.nostr.build/96e088cc6a082528682989ccc12b4312f9cb6277656e491578e32a0851ce50fe.png
画像では自分のプロフィールデータをリレーから取得しています。
まだどのライブラリもvisionOSに対応していなかったりで手こずったものの仕様の勉強になりました。
ただvisionOSアプリはiOSアプリ同様NIP-7が使えないので秘密鍵を自分で保管しなくてはならず、今後どう対処すべきかわかりかねています。これから時間ある時に少しずつ調べていこうと思っていますが、ネイティブアプリの秘密鍵周りはあまりリソースが多くないようにも感じました。もしどなたかその辺の実装に詳しい方いたら教えていただけると嬉しいです。
準備ができたらそのうちコードも公開したいと思っています。
これから少しずつ色んな機能を実装しながらNostrで遊んでいきたいです!
-
 @ fa0165a0:03397073
2024-10-23 17:19:41
@ fa0165a0:03397073
2024-10-23 17:19:41Chef's notes
This recipe is for 48 buns. Total cooking time takes at least 90 minutes, but 60 minutes of that is letting the dough rest in between processing.
The baking is a simple three-step process. 1. Making the Wheat dough 2. Making and applying the filling 3. Garnishing and baking in the oven
When done: Enjoy during Fika!
PS;
-
Can be frozen and thawed in microwave for later enjoyment as well.
-
If you need unit conversion, this site may be of help: https://www.unitconverters.net/
-
Traditionally we use something we call "Pearl sugar" which is optimal, but normal sugar or sprinkles is okay too. Pearl sugar (Pärlsocker) looks like this: https://search.brave.com/images?q=p%C3%A4rlsocker
Ingredients
- 150 g butter
- 5 dl milk
- 50 g baking yeast (normal or for sweet dough)
- 1/2 teaspoon salt
- 1-1 1/2 dl sugar
- (Optional) 2 teaspoons of crushed or grounded cardamom seeds.
- 1.4 liters of wheat flour
- Filling: 50-75 g butter, room temperature
- Filling: 1/2 - 1 dl sugar
- Filling: 1 teaspoons crushed or ground cardamom and 1 teaspoons ground cinnamon (or 2 teaspoons of cinnamon)
- Garnish: 1 egg, sugar or Almond Shavings
Directions
- Melt the butter/margarine in a saucepan.
- Pour in the milk and allow the mixture to warm reach body temperature (approx. + 37 ° C).
- Dissolve the yeast in a dough bowl with the help of the salt.
- Add the 37 ° C milk/butter mixture, sugar and if you choose to the optional cardamom. (I like this option!) and just over 2/3 of the flour.
- Work the dough shiny and smooth, about 4 minutes with a machine or 8 minutes by hand.
- Add if necessary. additional flour but save at least 1 dl for baking.
- Let the dough rise covered (by a kitchen towel), about 30 minutes.
- Work the dough into the bowl and then pick it up on a floured workbench. Knead the dough smoothly. Divide the dough into 2 parts. Roll out each piece into a rectangular cake.
- Stir together the ingredients for the filling and spread it.
- Roll up and cut each roll into 24 pieces.
- Place them in paper molds or directly on baking paper with the cut surface facing up. Let them rise covered with a baking sheet, about 30 minutes.
- Brush the buns with beaten egg and sprinkle your chosen topping.
- Bake in the middle of the oven at 250 ° C, 5-8 minutes.
- Allow to cool on a wire rack under a baking sheet.
-
-
 @ 30ceb64e:7f08bdf5
2025-01-05 16:11:46
@ 30ceb64e:7f08bdf5
2025-01-05 16:11:46Hey Freaks,
Another round of songs I've been listening to lately.
Un Sospiro slaps. Wind Tunnel hits me in the childhood.
https://music.youtube.com/watch?v=50A-Mssm6w8&si=OFa8UA-0o71k4ETK
https://music.youtube.com/watch?v=eMnxjdGTK4w&si=STFc4APblXLEp1Ig
https://music.youtube.com/watch?v=RpsN6b95DAQ&si=ixMQY5ZnyuPeum2O
https://music.youtube.com/watch?v=W91-jAQ2ijM&si=MhluAXuU1v_a86yW
https://music.youtube.com/watch?v=LMAhXhRsRXA&si=jo-UPFILXvZd8pS7
https://music.youtube.com/watch?v=53FDkWb7Mv4&si=lp4ikhtx39UqHzSA
https://music.youtube.com/watch?v=rrYMiAoGnVg&si=ya0qnGtbwCdyQ676
https://music.youtube.com/watch?v=Lk9Xwj0mnsI&si=OFMyBaXSO-Jyufxl
https://music.youtube.com/watch?v=057A1RdssoU&si=4lueg4C8Y3ac3LCE
https://music.youtube.com/watch?v=ghxzLw2wRis&si=wjgwjaPOJwo6-Cu2
https://music.youtube.com/playlist?list=PLmYfnnK_Qs5hOiZazXiwEoCdg1RiUvBBv&si=X4opO4goVt2K1T4D
Thanks, Hustle
originally posted at https://stacker.news/items/838006
-
 @ 101b30ee:18a46a45
2024-10-15 00:30:33
@ 101b30ee:18a46a45
2024-10-15 00:30:33背景
Junさんが山形県在住で、車で色々案内いただけることになりました。
メンバー (敬称略)
- Jun (nostr:npub1nlnjcakw6xfkpuhx9kym3d20sr774pm6rue5kk93uj7lrca9lypqgqj7fd)
- りら (nostr:npub1tuqsl6l8xzly95vv80um7wsnt7gxy8w9wgt4khp4wyv4xwhfw44slm93e9)
- あめ (nostr:npub1eqw8nx0hya3cwvtc0rje6lpjzzf6gvuh0mngz898dhp6juuwrp5s5uzduw)
- Don (nostr:npub1dv9xpnlnajj69vjstn9n7ufnmppzq3wtaaq085kxrz0mpw2jul2qjy6uhz)
- 横谷加奈子 (nostr:npub1sd2zns7qsfster7vcyjcqkert4cev2rzfeuus0d8hnfdh74t6g7su0p4c6)
- 発火大根 (nostr:npub1zqdnpm5gcfap8hngha7gcp3k363786phvs2etsvxw4nh6x9ydfzsuyk6mn)
スケジュール
10/12
11:00 - 11:30 霞城セントラル 日本酒めぐりツアー
500円で3コインもらえて、1コインでカップ1杯分の試飲ができるシステムのようです。
山形はフルーツも有名で、日本酒だけでなくワインなども試飲できました。個人的には、梨ベースのお酒が飲み口すっきりしていておいしかったです。
名前は忘れました ()霞城公園セントラル
https://yamagatakanko.com/attractions/detail_13443.html
nostr:nevent1qqszfgt4vef3ncyw7cy9yykuwv06pq5v9znaf2xeehfpp6s5j27ncqg2val6m nostr:nevent1qqsvfknrdtwsyvmztdzx40adzvtx8nztxu3vscgkljzzk2zr8kfmfnce54ke0
11:30 - 12:30 霞城公園散策
東北屈指の戦国大名・最上義光(もがみよしあき)公 (1546-1614)が礎を築いた「山形城」を復原整備した都市公園らしいです。
Junさんに聞いたところ、最上義光の妹が伊達政宗の母・義姫 (よしひめ)で、息子の伊達政宗を毒殺しようとしたことで有名らしいです。
後で調べたところ、毒殺事件が捏造だったとする記事もあり、真偽はいかに。また、これもJunさんに聞いたのですが山形藩は幕府重役から失脚した左遷の地と呼ばれているようです。
ちょっと悲しい。
後に調べたところ、山形藩は計12家が収めており、入れ替わりも激しかったようです。
まぁ、左遷だったとしても自然豊かな地でスローライフを過ごすのもアリかもしれない。個人的には、最上義光像が精巧に出来ているなぁと感動しました。
構図がナポレオンに似ていたので、もしかして身長が低かった?と思いましたが
後で調べたところ、180cm以上の長身だったとする文献があるようです。山形藩
https://ja.wikipedia.org/wiki/%E5%B1%B1%E5%BD%A2%E8%97%A9
義姫の毒殺事件について
https://bushoojapan.com/bushoo/date/2024/08/12/76725
最上義明の身長
http://iiwarui.blog90.fc2.com/blog-entry-13581.html
霞城公園セントラル
https://yamagatakanko.com/attractions/detail_2304.html
nostr:nevent1qqsp78jf76yudrwf6w88szq4x50t0zpeht77adkmk5pj5xsg6wplcmcv25e3g nostr:nevent1qqsfvw828mus5ek44m5myuya5ndpvj8mjhlltzx4y6ha93932cvzaxgwqwah3 nostr:nevent1qqs9sd8m43lj6pmd7hzu0quf4v0s7rm4uaq83aqp5jn5sqfy8aw6f8skg0sgv
12:30 - 13:30 旧済生館
済生館は1878年(明治11年)に山形県立病院として建設され、東北地方で最も早く西洋医学を取り入れたことで有名のようです。
建物内部の展示物の写真撮影は禁じられていたので写真は取れていませんが、あの有名な杉田玄白の訳書「解体新書」や、明治時代の医療器具などが展示されていました。私は工業高校出身で電気科だったので、昔の医療電気機器の展示などは見ていて飽きないものがありました。
旧済生館
https://www100.pref.yamagata.jp/110001/sangyo/sangyoushinkou/him_top/him_maincat1/him_15.html
13:30 - 14:30 山寺付近に移動・ランチ
山寺付近に車で移動後、玉こんにゃくを食べながら山寺方面に徒歩移動。
玉こんにゃくは名産らしく、山形のいたるところで売っていました。途中で近場のお店でランチ(蕎麦)を食べました。
ランチを食べながら映画 (オッペンハイマー)の話とかビットコインの話をしてました。
ちなみに私はオッペンハイマー見れてません。
あめさんはオッペンハイマーを見に県外 (奈良 -> 大阪)まで行ったらしい。
行動力すげぇ。nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpgqwakh6t2vm0ufy82rmwjqa2ld2z9jdl9l90v0ds7afwe6n5myl5uf5p7 nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpqq570ak2p9wx9q09xafjnlnulshwg2wc5c66q37z884m0pselu36sz5k7jk nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpp8xy7nktvyq87d676pkh6hjpftm5s703fq8e8c52l2l9xupe55wyhfc0p nostr:nevent1qvzqqqqqqypzq6c2vr8l8m9952e9qhxt8acn8kzzypzuhm6q70fvvxylkzu49e75qyshwumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5up0qy08wumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqhsqgqthnr72cp92yqv9upzg2fyplvt6eazf6kxe24h6ea6syg3mthsl5tc3r26
14:30 - 16:00 山寺 (宝珠山立石寺)
宝珠山立石寺 (愛称:山寺)は山形屈指の観光スポットで、松尾芭蕉が「閑さや岩にしみ入る蝉の声」の名句を紀行文「おくのほそ道」に残したことでも知られているそうです。
展望台付近まで登りましたが、前日2時間程度しか寝れてなかった からか、途中で何回か力尽きました。
何気にずっと階段だったのが厳しかった。w
展望台から見る景色が超綺麗でした。達成感あった。途中でDonさんが「松尾芭蕉も山寺登ってますよ!」と励ましてくれましたが、松尾芭蕉は服部半蔵だったのでは、といわれる説が頻繁に出るくらい、体力おばけです ()
#### 山寺・宝珠山立石寺 https://yamagatakanko.com/attractions/detail_2352.html
松尾芭蕉が忍者服部半蔵ではないかと言われる都市伝説の理由5つ
https://spirituabreath.com/matuobasyou-hattorihannzou-5207.html
nostr:nevent1qvzqqqqqqypzp8l893mva5vnvrewvtvfhz65lq8aa2rh58enfdvtre9a7836t7gzqqs2jsu0efm0s0xnp9exv0m4xkxaw07nsraxhfjqrl6rmjd977aqcycfaf05e nostr:nevent1qvzqqqqqqypzp8l893mva5vnvrewvtvfhz65lq8aa2rh58enfdvtre9a7836t7gzqqsxmrsa8h6y6z8hmt7hzg8cmspvc373gnjjs67vlrdp24lud8wm8ncp682ev nostr:nevent1qvzqqqqqqypzq6c2vr8l8m9952e9qhxt8acn8kzzypzuhm6q70fvvxylkzu49e75qyshwumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5up0qy08wumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqhsqgq3a6ehlurcsmpzlc4vghnnu7tnk5tekwm2kxn7e9rkrq7uslqmlu9sg6vl nostr:nevent1qvzqqqqqqypzp8l893mva5vnvrewvtvfhz65lq8aa2rh58enfdvtre9a7836t7gzqqs9lp9n8yjwjx56khduh7sqehtpgfs20d5w7x9lnjpnlt3vmqkpnmq7xfcef nostr:nevent1qvzqqqqqqypzp8l893mva5vnvrewvtvfhz65lq8aa2rh58enfdvtre9a7836t7gzqqsx4m8un5h952d6f7zuq9yraucs82lcah2p2lk4z6n9u0lduje2pcs40zhkz nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzq5pf4h2je6jkpypup9kj2k66qtlcmce3gcg9q39xpv5388u50sun6ku45d nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpqkdwwjagam6rcxmakpcgsylu95zkm8s0qkvae8j2km6e5l5sr9alsm8vrfn nostr:nevent1qvzqqqqqqypzq6c2vr8l8m9952e9qhxt8acn8kzzypzuhm6q70fvvxylkzu49e75qyshwumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5up0qy08wumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqhsqg9cqvgzvegmdsnc6xc5mhwnvsn9unyx4nx6megwcqxlheaddffc8ckpk3qj
16:00 - 18:30 山形駅でりらさん合流・産業科学館
車で山形駅まで戻り、りらさんと合流。
山形駅内の産業科学館を見て回りました。産業科学館は子供向けの知育ブースや山形県民向けの各種企業ブースもあり、見ていて飽きないものが沢山展示されていました。
発電機を回してミニカーを動かすゼネコンレーシングが楽しかった。
また、各種企業ブースを回りながら、Junさんに山形県民憧れの就職先などを聞いていました。産業科学館
http://y-sunka.org/
nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpx0ykjd6egvded9jksguphr4deluxlz56dm4rpw9n68npx9wt3hx976mcl nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpek5k3fygrx8y0024mmmnhqxdnd7jmqed7gf7sqt2tnushcv8xu7dwwctd nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyzzfwt63psqw4w5x7s33al0k0ms2v80p88vjjjd4rx7f8t4juppkux27ek7 nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpqgj58fqpvpngr2vafhdcqtf5vn264960dad73kqfrem3m27hr6mpstqgs5t nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyrnaxmkc47f5p46p36v8qnf4pr5ktm5algd86fsgzw9de96n9yp4qxu6dl8 nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqypehj7clkzll3yf7yftcp5t9k6dfnetvrpl943q4jd8ccy39neq66nyavjs nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzqnc3mmp8sg4lysfkcz7x4ft3c6rrulne8aetvd8lwkzz86k8fp9lt040df nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzqgdms2ltla34u9qr4whzlz69r3mpsj7e3jlpv935yltn799xsk89d3a6g4
18:30 - 20:40 旅館チェックイン、夕食
私 / あめさん / りらさんで、喜三郎という温泉旅館に泊まりました。
ここの温泉の泉質は芒硝泉(リウマチ・高血圧・切り傷・婦人病に効くとのこと)で、保養温泉として親しまれているそうです。
夕食のしゃぶしゃぶ、サザエ、釜めし、芋煮、... 全部旨かった!!!
夕食を食べていたら意外と時間ギリギリになり、露天風呂は朝入ることにして爆速で風呂に入りました。温泉旅館 (喜三郎)
https://kisaburo.jp/
nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyqr9wgwca9jknh88c83nq3n5nnqtflrrd4v5d7uhuh9d47a2qsl870yprel nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyr6yt65e79gqh4dp8pll2kfgaw837xulq2jh2x3y9zd4udk47lkn55pqkzm nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpqwdv2aa4n5z5r5k8q3z2retc9zgujytx9z36xmpsw6h9npc97250qkne529 nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzp2rhy02kfw73jtzq7t7sp2njn2gnt9elta7nm09u55csld8kg5t39lh49r nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyzv32r03thal6tvjqh4wgxk6xv6x2tkuwngw6kfv6ar49rg2yq55jc8arsp nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpqy2duq6xsl8jwns0r7qxgpf6703uwvawrhhlanytrepd082mnyugqxnxpj3
20:40 - 23:00 二次会
二次会の居酒屋でJunさん、Donさんと再度合流。
Junさんの奥さんで漫画家をされている、横谷先生も来てくれました。山形の地酒を飲みながら、Nostrasia 2024での思い出 / 山形の特産品 / Junさん夫妻が東京にくるタイミングはいつか など話していました。
横谷先生はM3やコミティアなど東京に来られるタイミングがいくつかありそうでしたが、Junさんが東京に来るタイミングはなかなか無さそう。
山形にまた会いにいくか、東京で面白いイベントをやって呼ぶしかない!また、山形には「ほや」と呼ばれる海産物が有名という話を聞きました。
ほや、結局食べ損ねてしまった。山形うまいものと地酒 母家
https://r.gnavi.co.jp/t846900/?sc_lid=smp_top_01
横谷先生の読み切り : 遠い日の陽
https://comic-days.com/episode/14079602755391426482
nostr:nevent1qvzqqqqqqypzq6c2vr8l8m9952e9qhxt8acn8kzzypzuhm6q70fvvxylkzu49e75qyshwumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5up0qy08wumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqhsqgplnrvwhk6hsl9rk979u6qtmnmrpgywdgexruznhmtkmyevsaua8s8cy2pq nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpkwu2t5zgug7wlwqh8nfh4zyma3f6tlacx9dag4kawnq7nynkxr33rdgaz nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpq8szzc33567mtsjnvajzgur9n8us3fuv2ckx86y0et3c7kddqd37uxuz0
23:00 - 旅館に戻る・就寝
旅館まで車で送ってもらい、旅館で就寝。
翌日も朝早いので、恒例(?)の枕投げやトランプをして遊ぶこともなく、12時に消灯しました。10/13
6:00 - 起床・露天風呂 ~ 7:30 朝食 ~ 8:30 チェックアウト
前日に入れなかった露天風呂に入るため、早めに起きて露天風呂に入りました。
旅館の窓を開けると須川が流れていて、天然のASMRを感じられました。nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzpz260lg35sg06h758y7eppvrwzypv5kc3yj4n0t8jyx5q4f82mse3ung9s nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpqt6cyt5hmatsuct2plneae7t0apnkkrxm38hvee3auhu0h3hljjgs943h27 nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzp2qq9lv0d3umyxprne6xpjj70af6flzcfs2qpgsx2r347q7ukpdm2rwml4 nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzqgaugf683lhlww8ynlgd7qfhgj2d3zlkecm72td35lfw6m4tkvhke4k8jt nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyz750rwdqdk0x8r08m96fcyf5l4wp9pmc0rz8mle02ygtrdzdhf0gjwc823 nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzqq36wgay36wz58kmjvsucple6whamvd28pqrhu082wsdkkpvxzht34tq02
8:30 - 移動・買い物 ~ 9:40 Junさんの家に移動・芋煮会開始
近隣のスーパーで芋煮会用の買い物を済ませたあと、Junさんの家に移動して芋煮会を始めました。 あめさんが帰宅の関係上、山形駅を11:11に出ねばならず、芋をよく煮るために爆速で芋煮を作る必要がありました。
皆で協力して爆速で芋煮を作り、しっかり煮えた状態の芋煮をあめさんに持って帰ってもらうことができました!nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qy0hwumn8ghj7mn0wd68yttjv4kxz7fwdehkkmm5v9ex7tnrdakj7qg6waehxw309aex2mrp0ykk5upwwd5xjmn0xvhxuet59uqzqe03zqdcpjzakz3u7jjs07crz05y024lvgmjuvh0zysf4zal9q0la8772q nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpq6xaa2etzypq7hlm8zs3rkrjsc0wh5c29huupe9mfxqqeu5uanttq39l9w6 nostr:nevent1qqs0zkh2t2crsv8ljxzvmy3ndwzncyl6wwz67hfy4p09tacem3pjzwg2h4ac8 nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpq3ugypvt2fw886375nzltef4fzlasvk7nzj5n9tpuunwrr4p9etasskzqd6 nostr:nevent1qvzqqqqqqypzpjqu0xvlwfmrsuchs789n47ryyyn5seewlhxsyw2wmwr49ecuxrfqyv8wumn8ghj7mn0wd68ytnxd46zuamf0ghxy6t69uq3uamnwvaz7tmwdaehgu3dwp6kytnhv4kxcmmjv3jhytnwv46z7qpq9u5559ucupe755xnlm00vm5wcj7rpu3wwc3wvrdjxxdcadcwumzqjg8e6r
芋煮ビルド過程
nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqypn3w96w3wu375rz5hwhwhnmvrc664dltaudzvt578s6dh6kzq205u0m44v nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqypc0nxkt4ht0ku9l4hjmvtlv9rh5lt496r7s3755clg7q45fypnxkjms92t nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqypdfx9umwcyupt4cx38klfhl0f3saf3ar47jr7rcyj69dzyxve7tqk8wmcm nostr:nevent1qqsve084cxu5kw3gvqhjaehfge202z2nyddft89ufn9j73wyynwzhwczwz8j2 nostr:nevent1qqs26rp3gc2dhz4yznynym0y3c6y257kt2u773dvaaf87uf40fzjmcqk2zxxm nostr:nevent1qqsf3jx69s6guydhfxqstcw2m5aaw0zpum74aawe79nhz3xyg7p7dks0x9gn5 nostr:nevent1qqswtgfxseqwnt424ay668ps782drdmxkyyqj8uk8lfxs264gayfnkg3ls82a nostr:nevent1qqsqd257ng55ynkrwe3v2skcx29xalz85qcgn3ghj8ug4lqt9ewqvwgshz303 nostr:nevent1qqsw04zd3wgd3c5ztave9yhhavupl7pc3e4rcke5qn4azn8gpctz23cm7e5p8 nostr:nevent1qqsv8kqnr36jyhj9tnc602p6njakhgcuf6klm0xfrsngjrxlej9068s9vz3jg nostr:nevent1qvzqqqqqqypzqhcppl47wv97gtgccwlehuapxhusvgwu2ushtdwr2uge2vawjattqyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcpy9mhxue69uhhyetvv9uj66ns9ehx7um5wgh8w6tjv4jxuet59e48qtcqyrpm5t3gxyjxnfw6y8eu2j0mpgf8acj83c86ueykdqke6nxchjku63rl6q5
11:20 - 14:30 Junさんの家でまったり・ねるねるねるね
Junさんにあめさんを駅に送ってもらった後は、残ったメンバーでテレビを見たり、ねるねるねるねを作って皆で食べたりしていました。
りらさんが仙台に行くため、14:30で帰っていきました。nostr:nevent1qqsya6u4r9amxs32m4k45s9203ph3kwmtlyddq283zrtyufk3z7tk9gaw3dyv nostr:nevent1qqs0nr6xznhxr4hfrczatlgy26lcrlup3zg8ey6j6ldthxnu9fy3mfq7tauam
14:30 - 16:30 伺かレクチャーを受ける
Junさんにりらさんを送ってもらっている途中、せっかく伺かベテランのDonさんがいるので
伺かを始めました。
※元々伺かやSSTPには興味があった
Donさんに伺かの基礎や「Nostr x 伺か」のOSSの機能などをレクチャーしてもらいながら、
Nostrと伺かで出来ることを話し合っていました。個人的に驚いたのは、一方通行で喋らせるだけだと思っていた伺かが、SSTPを通じてデスクトップマスコットとシーケンシャルに「やりとりができる」ことです。
非常に拡張性が高く、Nostrと同じで無限に遊べそうな雰囲気を感じました。伺か (うかがか) とは
2000年5月25日に初公開されたデスクトップ常駐型のフリーウェアで、24年間色んな人が発展・メンテナンスしています。
SSTP (Sakura Script Transfer Protocol) と呼ばれるプロトコルで指定のポート番号 (9801番)あてにメッセージを送ると、デスクトップマスコットを喋らせたり色んなことができます。
プロトコル仕様が公開されており、SSTPクライアントやサーバー、ベースウェアまで自作することが可能です。詳細 https://dic.nicovideo.jp/a/%E4%BC%BA%E3%81%8B
伺か参考 (ばぐとら研究所)
現在デファクトスタンダードとなっているベースウェア、SSPがここからダウンロードできます。 https://ssp.shillest.net/
nostr:nevent1qqsyrz64vff9fjkpj297qyr278d2a58l3fuysgknsm8jwyuwy6v8hcgvmn4mt nostr:nevent1qqsdzfjfvxxk5ph49x40s3hf8pdgazzq2x5xekd6ztqnqw4y4z3r8as4pdywy nostr:nevent1qqsr8sdds33g53asp7c45v3eems3vj3qhtxayvku9nxext95aauuuaq4d6t0x
16:30 - 17:30 四谷ラボの配信アーカイブを見る・帰宅
Nostrasia 2024やBluesky meetup、Nostr勉強会の配信アーカイブを見ながら、当時の思い出やNostrの未来について語っていました。
こういうのを忘年会や新年会でやっても面白いかもしれない。
18時の山形駅発の新幹線を取っていたので、18時にJunさんに駅まで送ってもらい、山形を去りました。四谷ラボの配信アーカイブ
https://www.youtube.com/@428-lab
終わりに
私は1泊2日でしたが、山形を味わい尽くしてリフレッシュすることが出来ました!
今回、Junさんには企画だけでなく車で色々連れて行ってもらったりと、本当にお世話になりました。
次に直接お会いしたら、何かしらもてなしたい。また、Donさんに直接会えて色々話せたのは本当に貴重でした。聞くところによると、Nostrのオフ会だけでなく、歴の長い伺か仲間とのオフ会も出たことがないらしいです。
また山形に行きたい!と思えるようなオフ会でした。
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28idea: Custom multi-use database app
Since 2015 I have this idea of making one app that could be repurposed into a full-fledged app for all kinds of uses, like powering small businesses accounts and so on. Hackable and open as an Excel file, but more efficient, without the hassle of making tables and also using ids and indexes under the hood so different kinds of things can be related together in various ways.
It is not a concrete thing, just a generic idea that has taken multiple forms along the years and may take others in the future. I've made quite a few attempts at implementing it, but never finished any.
I used to refer to it as a "multidimensional spreadsheet".
Can also be related to DabbleDB.
-
 @ 6ad3e2a3:c90b7740
2025-01-05 14:26:34
@ 6ad3e2a3:c90b7740
2025-01-05 14:26:34Maybe it’s because I watched The Omen at way too young an age, or maybe it’s because the Book of Revelation’s “mark of the beast” allegory is playing out too literally for my tastes, but having already written about the Second Coming, it only follows I should speculate as to its counterpart.
As I mentioned in The Second Coming, it’s dangerous to take the myths from our ancestors too literally. They used the symbols of their times, and we should be careful not to confuse the mental maps they had of their world with reality itself. That said, we should also not be dismissive — Mozart didn’t have fancy music editing software, but his genius using the modalities of the time was real. To the extent our forebears offered us their wisdom about the nature of man and forces within him we should endeavor to understand it. The technology and the symbols may have changed, but our essential nature is ever the same.
Just as the second coming of Christ would free man from tyranny, the Antichrist would be its imposition. And just as I speculated that Jesus might not return in the form of a person, it’s likely neither would his counterpart. But if Satoshi, Bitcoin’s pseudonymous creator, can be the face, so to speak, representing the movement toward freedom and God, who and what would represent its antithesis? Let’s speculate.
It would have to be someone charismatic, a person the multitudes would want to follow and in whom to look for reassurance. That eliminates villains du jour like Bill Gates, Klaus Schwab and Vladimir Putin. If that’s who Satan is sending, he’s not sending his best. What about Donald Trump? More charismatic, much more popular appeal. He’s a better choice than the first group, but while street-smart, he lacks refined intelligence and is too despised by wide swaths of the population. He’s also probably too old.
For a while, I would have said Barack Obama was the best candidate, and even some hard-core right wingers agreed (it’s hilarious that this claim was actually fact-checked! — you can’t fact-check whether someone is the Antichrist!) Obama was relatively young, vital enough, popular, charismatic and intelligent. But he’s faded from view the last few years and has been a surprisingly inconsequential former president.
That leaves one person of whom I can think with the qualities and societal position to fill the role. Regrettably it’s someone I like, but of course I would like the Antichrist! If he weren’t likable he wouldn’t be the Antichrist.
That person is Elon Musk.
Musk is the richest person in the world, among the most followed on Twitter, has a borderline worshipful fanbase and big plans for improving humanity. Musk is young enough, he’s probably a genius and considering a private takeover of arguably the world’s most important communications network. He’s also a big player in satellites, energy, transportation and internet provision.
Musk says lots of sensible things with which I agree about free speech and rights. He is the perfect foil to the out-of-central-casting Schwab supervillain. As Edward Dowd speculated:
 But, you might object, if Musk is the foil to Schwab’s terrible ideas, isn’t that good for humanity? How could the Antichrist be for free speech, renewable energy, population expansion? Again, of course, the Antichrist is going to have good, sensible ideas! But as Marshall McLuhan said, “The medium is the message.”
But, you might object, if Musk is the foil to Schwab’s terrible ideas, isn’t that good for humanity? How could the Antichrist be for free speech, renewable energy, population expansion? Again, of course, the Antichrist is going to have good, sensible ideas! But as Marshall McLuhan said, “The medium is the message.”Or, more aptly, the top-down messianic complex is the message.
Musk has long discussed saving humanity via expansion into space and sustainable energy. But in order to save humanity, one must exert some control over it. While Musk’s Twitter takeover from the ineffectual woke scolds is getting most of the press, this is also going on:
 Klaus Schwab’s pitch to own nothing and eat bugs is weak, but Musk, via brain implant, could potentially create a more satisfying virtual experience than most could hope to achieve in reality. And what could be more tantamount to complete control than letting someone else get the keys to the very organ of perception itself?
Klaus Schwab’s pitch to own nothing and eat bugs is weak, but Musk, via brain implant, could potentially create a more satisfying virtual experience than most could hope to achieve in reality. And what could be more tantamount to complete control than letting someone else get the keys to the very organ of perception itself?
Well don’t get the implant then. Just get in your Tesla and drive away. But electric cars don’t work that way — they are attached to the grid, trackable and capable of being shut down remotely. And that’s before we consider driverless cars in which there would be even less privacy and autonomy. Moreover, Teslas track the driver’s movements already to an extent combustion-engine cars do not, ostensibly to inform the developing AI, but uses for technology evolve over time — sending email and paying bills over the internet was commonplace in 2000, but now people are micro-tracked by Facebook and Google.
One could object that Musk has, to-date, used his influence for good. But that makes it no less dangerous to entrust him with so much power: J.R.R. Tolkien understood this clearly:
“You are wise and powerful. Will you not take the Ring?”
“No!” cried Gandalf, springing to his feet. “With that power I should have power too great and terrible. And over me the Ring would gain a power still greater and more deadly.” His eyes flashed and his face was lit as by a fire within. “Do not tempt me! For I do not wish to become like the Dark Lord himself. Yet the way of the Ring to my heart is by pity, pity for weakness and the desire of strength to do good. Do not tempt me! I dare not take it, not even to keep it safe, unused. The wish to wield it would be too great for my strength. I shall have such need of it. Great perils lie before me.”
-- The Lord of the Rings
Beyond Neuralink, Musk also seems to have a strong utilitarian bent:
 In this paper Nick Bostrom makes the case that delaying technological advancement could cost humanity astronomical amounts of well-being because every moment we delay, stars are burning out, useful energy is being sucked into black holes, irreversible entropy is happening apace, depriving us of future potential. Bostrom translates it into potential human lives lost (or more aptly, never having been born) on account of this permanent loss.
In this paper Nick Bostrom makes the case that delaying technological advancement could cost humanity astronomical amounts of well-being because every moment we delay, stars are burning out, useful energy is being sucked into black holes, irreversible entropy is happening apace, depriving us of future potential. Bostrom translates it into potential human lives lost (or more aptly, never having been born) on account of this permanent loss.While Bostrom’s framework seems benign — who is against collective human happiness in the form of more worthwhile lives? — it’s actually a form of utilitarianism that tries to sum the totality of human happiness over the entire species rather than to consider, as Immanuel Kant would, each individual as an end in himself. This viewing of the collective good as the optimal outcome has been used to justify many of history’s worst atrocities. To create a master race, to make sure everyone gets the same amount, to protect the world from covid, we must do whatever it takes!
If, per Bostrom’s math, one harnessed black hole were worth quadrillions of lives, it would, for example, seem an easy call to sacrifice a bunch of selfish losers on earth who stood in the way of creating the technology for doing so. Utilitarianism, ironically, winds up failing miserably by its own metric because (a) it can so easily be manipulated by whoever is maintaining the “greater good” spread sheet, which just happens to coincide with one’s ambitions; and (b) because it’s absurd to think you can calculate aggregate good for octillions of lives so far into an unknowable future. As such, while Musk’s pitch is more persuasive than Schwab’s or Gates’, it’s ultimately part of the same dangerous philosophy which is: “Let me optimize for total human happiness on your behalf.”
Contrast Musk’s top-down humanity-saving endeavors with Bitcoin which is purely opt-in, works with simple incentives and imposes no value judgments on its users. It’s a truth-recording clock, impervious to fraud and cooption by the powerful. No matter how wealthy or powerful a person is, he cannot control the network or get treated with special privileges. Bitcoin’s finite supply means governments cannot print more of it, cannot finance unpopular wars or massive giveaways to the military and pharmaceutical industrial complexes. Instead of trusting any particular powerful person (the president, Elon Musk, Bill Gates) to be good, it simply removes the incentives toward and reduces the capacity for evil.
The supreme good is like water, which nourishes all things without trying to. It is content with the low places that people disdain. Thus it is like the Tao.
From the Tao Te Ching (Lao Tse — translated by Stephen Mitchell)
We simply need the right conditions, the proper axioms on which to build. Just as the US Constitution created the framework for the most prosperous society in the history of the world, bitcoin will provide the axioms for peace, the harnessing of stranded energy and the low-time preference required for a more prosperous future.
But it won’t be the future brought to you by Elon Musk, and ultimately I foresee a clash between the two. One tell is his otherwise inexplicable promotion of Dogecoin as a possible currency for Tesla purchases. Dogecoin was literally a joke from its creator and of course has none of the security, decentralization or censorship resistance of bitcoin. Musk is too smart not to know that — he put a couple billion dollars of Tesla’s balance sheet in bitcoin already and almost certainly understands the value proposition. That he still cites Doge seriously would be a clever way to muddy the waters about what bitcoin is vs what blockchain-based “crypto” is. And of course the Antichrist would avail himself of bitcoin, if only to obfuscate his real intentions and also to be able to crash the price by selling, if necessary, at an opportune time.
The Klaus Schwab-Bill Gates-WEF set have already lost. They are widely despised, central banks are flailing, once-trusted institutions like the legacy media, major science and medical journals, the WHO, CDC and FDA are hemorrhaging influence. People are unhappy and looking for someone or something to trust. Elon Musk could fill that void, and if he does, he will be The Final Boss, the last false idol that needs to be discarded before humanity can, through its own efforts, enjoy a new era of prosperity, the Second Coming, so to speak.
I actually suspect Musk is genuine in his desire to help humanity via his vision and am pretty sure he doesn’t have 666 embedded in his scalp — in any case even Damian in The Omen neither knew who he was nor wanted to be the Antichrist! But the most dangerous people for humanity are those with the biggest plans for it.
Or put more succinctly:

-
 @ 7cc328a0:2a247c0e
2024-10-12 15:54:42
@ 7cc328a0:2a247c0e
2024-10-12 15:54:42relay.tools quarterly report
October, 2024
Project Updates
Milestone: Relay.tools is celebrating 1 year of OpenSats! Cheers to everyone that made this possible.
Relays were very popular this quarter. Scaling efforts were prioritized! This is a good indicator for relay.tools as it means that it's healthily growing. Development was executed well, completing one project at a time across the whole stack.
Relay Discovery
I've been working with @sandwich from nostr.watch on NIP66.
NIP66 will be an ABSOLUTE GAMECHANGER for clients in finding of their relays. This was always a vision for relay.tools and I am honored to be working with @sandwich on what is a pretty amazing solution. We are now in a phase of client outreach, to gather client feedback and help them implement/understand the overall goal of the NIP.
TLDR: the goal is to create a distributed version of the nostr.watch data, using nostr events.
- [x] implemented NIP66 draft7 (the 'final' design) in monitorlizard
- [x] started shipping events to the monitor relay(s) in collab with nostr.watch backends and relay.tools backends.
- [x] fixed bugs and released new binaries for monitorlizard (a NIP66 data reporting tool)
Auth Proxy Rollout
The NIP42 Auth Proxy project went really well this quarter. It's now serving tons of traffic and most bugs with clients have been squashed and the proxy hardened. This has become a very popular feature on the relays, as AUTH has many benefits beyond protecting of DMs.
- [x] testing vs. NIP17 and bugs fixed
- [x] cluster operations (multiple proxies)
UI/UX
A huge milestone this quarter was the release of the settings wizard. This is a walkthrough for new (and current) users of all the available settings for different 'relay types'. A lot of work over the last year has gone into the culmination of these settings and the wizard was a major step forward to help users understand what their options are when running a relay.
Another major UI change was the introduction of a relay feed to the landing page for a relay. This is called the relay explorer. The idea was to move to a single page app, and re-do navigation for easy relay browsing and discovery.
- [x] settings wizard released
- [x] relay explorer v2
Installer
The installer had lots of good effort put in by me and some nice contributors. We did a couple iterations on documentation and facilitated in the creation of 2-3 new relay hubs that are using this installer infrastructure.
Some additions to the installer were:
- [x] docs for building self-hosted machine images and installing on a VPS
- [x] FULLY AUTOMATIC SSL certificate handling for multiple domains with certbot
- [x] self-hosted influxDB (for relay metrics)
- [x] fix bugs with auto-deploy upgrade
Billing/Invoicing/Support
The billing system had some improvements this quarter and many invoices were sent. :) It now has better super-admin tools to notify users of past-due balances via nostr (With NDK). This took a few iterations of deciding the best way to contact users of nostr and figuring out why they don't respond to messages. It's a learning experience all the way around and the billing system will evolve over time in ways that are conducive to remaining 100% nostr for user communication and support.
The support system also showed signs of life, and people were able to use it to contact me with their questions via the various help-desk methods that I've been rolling out. (A relay, a support npub, DMs, NIP17 DMs, simplex)
Scaling!
Relay.tools successfully completed the first scale-out event. This is HUGE. Relays take more and more bandwidth and resources as they establish themselves, while at the same time needing a reasonable low-cost environment to grow in. To meet their demands the horizontal scaling is important. This will scale on commodity hardware or VPSs with ZERO vendor lock-in.
- [x] multi-server clustering with ZERO cloud vendor lock-in
- [x] deployment pipeline and capacity planning
- [x] HAproxy and additional AUTH proxies fronting all services
- [x] internal/external network support
-
 @ 7f29628d:e160cccc
2025-01-07 11:50:30
@ 7f29628d:e160cccc
2025-01-07 11:50:30Der gut informierte Bürger denkt bei der Pandemie sofort an Intensivstationen, an die Bilder aus Bergamo und erinnert sich an die Berichterstattung damals – also muss es wohl ein Maximum gewesen sein. Manche Skeptiker behaupten jedoch das Gegenteil. Klarheit sollte ein Blick nach Wiesbaden, zum Statistischen Bundesamt, schaffen. Schließlich sitzen dort gut bezahlte Profis, die seit vielen Jahrzehnten die Sterbestatistik pflegen und veröffentlichen. Jeder Todesfall wird in Deutschland über die Standesämter exakt erfasst.
Doch die Überraschung: Das Statistische Bundesamt liefert uns auf diese einfache Frage zwei extrem unterschiedliche Antworten – ein Minimum und ein Maximum. Das Ergebnis hängt davon ab, wie tief man in die Veröffentlichungen des Bundesamtes eintaucht. Betrachtet man nur die Webseiten und Pressemitteilungen, erhält man den Eindruck eines Maximums. Schaut man jedoch etwas tiefer in die Tabellen und Rohdaten, zeigt sich plötzlich ein Minimum. Aber wie kann das sein? Beides gleichzeitig geht ja wohl kaum. Wer lügt hier – die Tabellen des Amtes oder die Pressemitteilungen? Gehen wir dieser Frage Schritt für Schritt auf den Grund.
2020: Ein historisches Maximum?
Schauen wir uns die vielen Hundert Veröffentlichungen des Statistischen Bundesamtes aus dieser Zeit an. Oder wir kürzen ab und fragen ChatGPT, da die KI auf diesen Daten trainiert wurde und das gesamte Material kennt. Die Frage an ChatGPT lautet also: Wie war das Sterbegeschehen im Jahr 2020 im Vergleich zu den Vorjahren?
ChatGPT antwortet: »Im Jahr 2020 war die Sterblichkeit in Deutschland höher als in den Jahren zuvor. Es gab eine Übersterblichkeit von etwa 982.000 Todesfällen, das sind rund 46.000 mehr als der Durchschnitt der Vorjahre (2016 bis 2019). Dieser Anstieg wurde überwiegend im Zusammenhang mit der COVID-19-Pandemie gesehen. Während die Sterbezahlen in den Vorjahren schwankten, war ein solch signifikanter Anstieg wie 2020 bisher nicht zu beobachten.«
Wir fragen konkreter: Ist es ein Fakt, dass wir eine so ernste Lage im Sterbegeschehen wie im Frühjahr 2020 noch nie erlebt haben?
ChatGPT bestätigt: »Ja, die COVID-19-Pandemie führte im Frühjahr 2020 zu einer außergewöhnlichen Situation im Sterbegeschehen in Deutschland. Die dramatische Übersterblichkeit, die ab der 13. Kalenderwoche auftrat, veranlasste das Statistische Bundesamt, besonders eindringliche Warnungen zu veröffentlichen. Der damalige Vizepräsident des Amtes und andere führende Stimmen wiesen öffentlich darauf hin, dass die Todesfallzahlen stark vom Durchschnitt abwichen. Diese klare Warnung richtete sich an die Öffentlichkeit und die Politik gleichermaßen. Die Medien berichteten intensiv über diese Warnungen, was das Bewusstsein für die Schwere der Pandemie erheblich schärfte. In den vergangenen Jahrzehnten hatte es keine vergleichbare Übersterblichkeit gegeben, die eine solch umfangreiche Kommunikation durch das Statistische Bundesamt erforderlich gemacht hätte.«
Ein gut informierter Zeitungsleser wird sich an dieser Stelle bestätigt fühlen: Ja, so war es damals. Ein Maximum im Sterbegeschehen – wegen der Pandemie. Oder etwa nicht?
2020: Ein historisches Minimum?
Tauchen wir in die Rohdaten des Statistischen Bundesamtes ein. Die Tabellen, die das Amt seit Jahrzehnten verlässlich veröffentlicht, nennen sich Sterbetafeln. Diese werden jährlich bereitgestellt und stehen auf der Website des Bundesamtes zum Download bereit. Ein erster Blick in die Sterbetafeln mag den Laien abschrecken, doch mit einer kurzen Erklärung wird alles verständlich. Wir gehen schrittweise vor.
Nehmen wir die Sterbetafel des Jahres 2017. Sie enthält zwei große Tabellen – eine für Männer und eine für Frauen. Jede Zeile der Tabelle steht für einen Jahrgang, zum Beispiel zeigt die Zeile 79 die Daten der 79-jährigen Männer. Besonders wichtig ist nun die zweite Spalte, in der der Wert 0,05 eingetragen ist. Das bedeutet, dass 5 Prozent der 79-jährigen Männer im Jahr 2017 verstorben sind. Das ist die wichtige Kennzahl. Wenn wir diesen exakten Wert, den man auch als Sterberate bezeichnet, nun in ein Säulendiagramm eintragen, erhalten wir eine leicht verständliche visuelle Darstellung (Grafik 1).
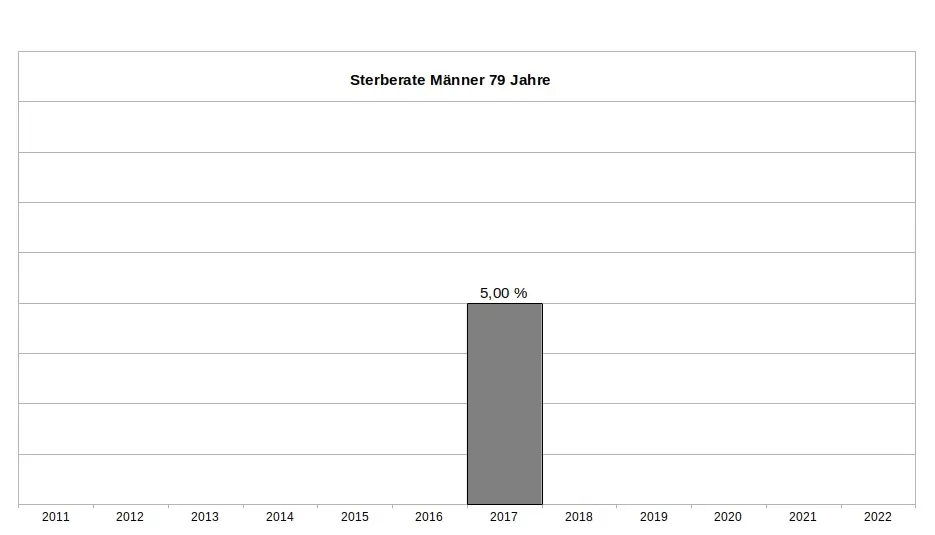
Es ist wichtig zu betonen, dass dieser Wert weder ein Schätzwert noch eine Modellrechnung oder Prognose ist, sondern ein exakter Messwert, basierend auf einer zuverlässigen Zählung. Sterberaten (für die Fachleute auch Sterbewahrscheinlichkeiten qx) sind seit Johann Peter Süßmilch (1707–1767) der Goldstandard der Sterbestatistik. Jeder Aktuar wird das bestätigen. Fügen wir nun die Sterberaten der 79-jährigen Männer aus den Jahren davor und danach hinzu, um das Gesamtbild zu sehen (Grafik 2). Und nun die entscheidende Frage: Zeigt das Jahr 2020 ein Maximum oder ein Minimum?
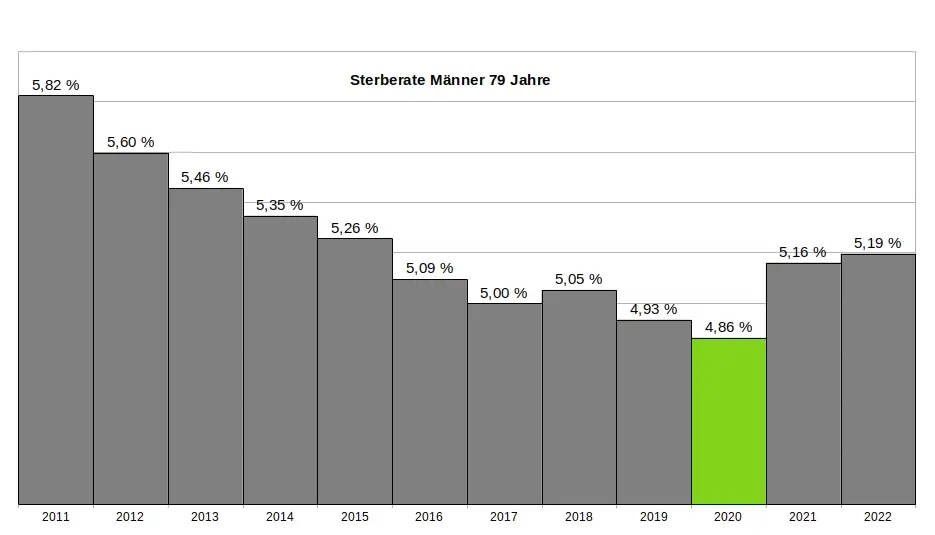
Ein kritischer Leser könnte vermuten, dass die 79-jährigen Männer eine Ausnahme darstellen und andere Jahrgänge im Jahr 2020 ein Maximum zeigen würden. Doch das trifft nicht zu. Kein einziger Jahrgang verzeichnete im Jahr 2020 ein Maximum. Im Gegenteil: Auch die 1-Jährigen, 2-Jährigen, 3-Jährigen, 9-Jährigen, 10-Jährigen, 15-Jährigen, 18-Jährigen und viele weitere männliche Jahrgänge hatten ihr Minimum im Jahr 2020. Dasselbe gilt bei den Frauen. Insgesamt hatten 31 Jahrgänge ihr Minimum im Jahr 2020. Wenn wir schließlich alle Jahrgänge in einer einzigen Grafik zusammenfassen, ergibt sich ein klares Bild: Das Minimum im Sterbegeschehen lag im Jahr 2020 (Grafik 3).
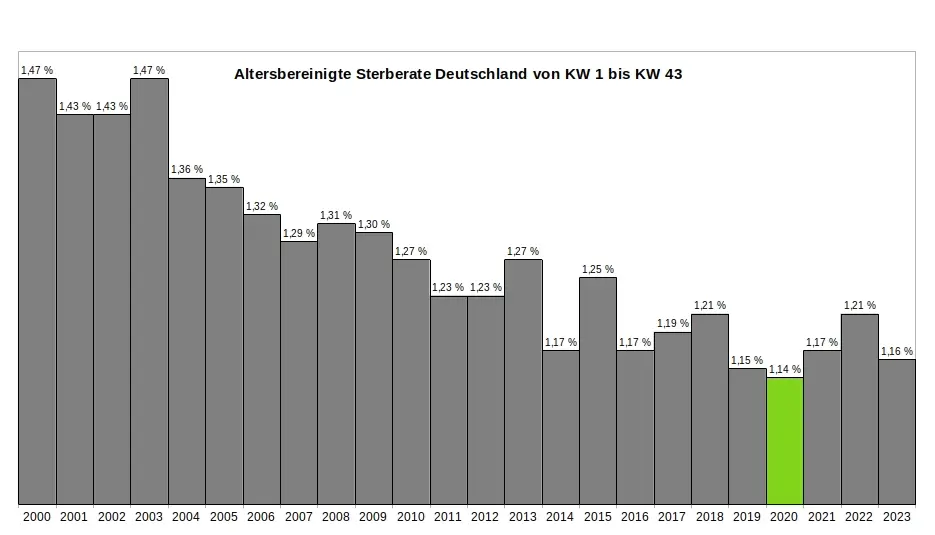
Ein kritischer Leser könnte nun wiederum vermuten, dass es innerhalb des Jahres 2020 möglicherweise starke Ausschläge nach oben bei einzelnen Jahrgängen gegeben haben könnte, die später durch Ausschläge nach unten ausgeglichen wurden – und dass diese Schwankungen in der jährlichen Übersicht nicht sichtbar sind. Doch auch das trifft nicht zu. Ein Blick auf die wöchentlichen Sterberaten zeigt, dass die ersten acht Monate der Pandemie keine nennenswerten Auffälligkeiten aufweisen. Es bleibt dabei: Die Rohdaten des Statistischen Bundesamtes bestätigen zweifelsfrei, dass die ersten acht Monate der Pandemie das historische Minimum im Sterbegeschehen darstellen. (Für die Fachleute sei angemerkt, dass im gleichen Zeitraum die Lebenserwartung die historischen Höchststände erreicht hatte – Grafik 4.)
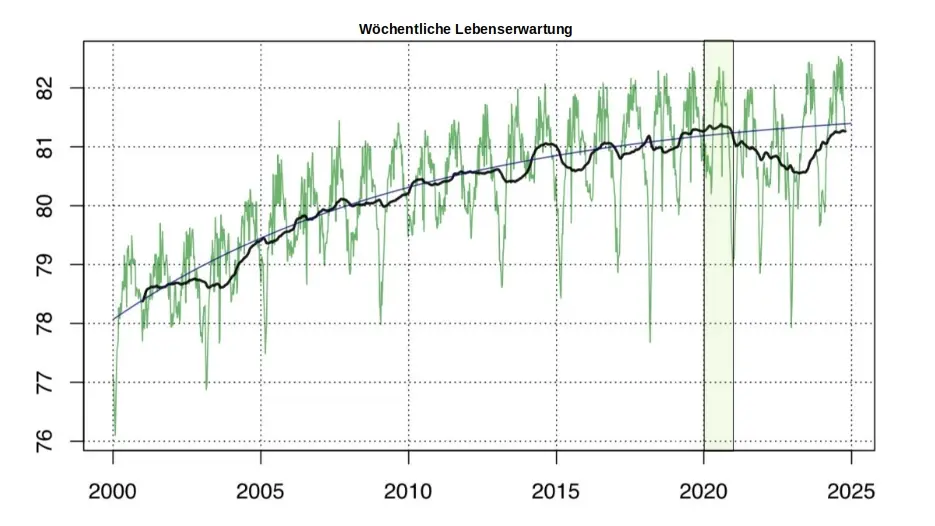
So konstruierte das Amt aus einem Minimum ein Maximum:
Zur Erinnerung: Die Rohdaten des Statistischen Bundesamtes, die in den jährlichen Sterbetafeln zweifelsfrei dokumentiert sind, zeigen für das Jahr 2020 eindeutig ein Minimum im Sterbegeschehen. Aus diesen »in Stein gemeißelten« Zahlen ein Maximum zu »konstruieren«, ohne die Rohdaten selbst zu verändern, scheint auf den ersten Blick eine unlösbare Aufgabe. Jeder Student würde an einer solchen Herausforderung scheitern. Doch das Statistische Bundesamt hat einen kreativen Weg gefunden - ein Meisterstück gezielter Manipulation. In fünf Schritten zeigt sich, wie diese Täuschung der Öffentlichkeit umgesetzt wurde:
(1) Ignorieren der Sterberaten: Die präzisen, objektiven und leicht verständlichen Sterberaten aus den eigenen Sterbetafeln wurden konsequent ignoriert und verschwiegen. Diese Daten widersprachen dem gewünschten Narrativ und wurden daher gezielt ausgeklammert.
(2) Fokus auf absolute Todeszahlen: Die Aufmerksamkeit wurde stattdessen auf die absolute Zahl der Todesfälle gelenkt. Diese wirkt allein durch ihre schiere Größe dramatisch und emotionalisiert die Diskussion. Ein entscheidender Faktor wurde dabei ignoriert: Die absolute Zahl der Todesfälle steigt aufgrund der demografischen Entwicklung jedes Jahr an. Viele Menschen verstehen diesen Zusammenhang nicht und verbinden die steigenden Zahlen fälschlicherweise mit der vermeintlichen Pandemie.
(3) Einführung der Übersterblichkeit als neue Kennzahl: Erst ab Beginn der „Pandemie“ wurde die Kennzahl "Übersterblichkeit" eingeführt – und dies mit einer fragwürdigen Methode, die systematisch überhöhte Werte lieferte. Diese Kennzahl wurde regelmäßig, oft monatlich oder sogar wöchentlich, berechnet und diente als ständige Grundlage für alarmierende Schlagzeilen.
(4) Intensive Öffentlichkeitsarbeit: Durch eine breit angelegte Kampagne wurden die manipulativen Kennzahlen gezielt in den Fokus gerückt. Pressemitteilungen, Podcasts und öffentliche Auftritte konzentrierten sich fast ausschließlich auf die absoluten Todeszahlen und die Übersterblichkeit. Ziel war es, den Eindruck einer dramatischen Situation in der Öffentlichkeit zu verstärken.
(5) Bekämpfen kritischer Stimmen: Kritiker, die die Schwächen und manipulativen Aspekte dieser Methoden aufdeckten, wurden systematisch diskreditiert. Ihre Glaubwürdigkeit und Kompetenz wurden öffentlich infrage gestellt, um das sorgsam konstruierte Narrativ zu schützen.
Ohne diesen begleitenden Statistik-Betrug wäre das gesamte Pandemie-Theater meiner Meinung nach nicht möglich gewesen. Wer aus einem faktischen Minimum ein scheinbares Maximum "erschafft", handelt betrügerisch. Die Folgen dieses Betruges sind gravierend. Denken wir an die Angst, die in der Bevölkerung geschürt wurde – die Angst, bald sterben zu müssen. Denken wir an Masken, Abstandsregeln, isolierte ältere Menschen, Kinderimpfungen und all die Maßnahmen, die unter anderem auf diese falsche Statistik zurückgehen.
Wollen wir Bürger uns das gefallen lassen?
Wenn wir als Bürger zulassen, dass ein derart offensichtlicher und nachprüfbarer Täuschungsversuch ohne Konsequenzen bleibt, dann gefährdet das nicht nur die Integrität unserer Institutionen – es untergräbt das Fundament unserer Gesellschaft. In der DDR feierte man öffentlich Planerfüllung und Übererfüllung, während die Regale leer blieben. Damals wusste jeder: Statistik war ein Propagandainstrument. Niemand traute den Zahlen, die das Staatsfernsehen verkündete.
Während der Pandemie war es anders. Die Menschen vertrauten den Mitteilungen des Statistischen Bundesamtes und des RKI – blind. Die Enthüllungen durch den "RKI-Leak" haben gezeigt, dass auch das Robert-Koch-Institut nicht der Wissenschaft, sondern den Weisungen des Gesundheitsministers und militärischen Vorgaben folgte. Warum sollte es beim Statistischen Bundesamt anders gewesen sein? Diese Behörde ist dem Innenministerium unterstellt und somit ebenfalls weisungsgebunden.
Die Beweise für Täuschung liegen offen zutage. Es braucht keinen Whistleblower, keine geheimen Enthüllungen: Die Rohdaten des Statistischen Bundesamtes sprechen für sich. Sie sind öffentlich einsehbar – klar und unmissverständlich. Die Daten, die Tabellen, die Veröffentlichungen des Amtes selbst – sie sind die Anklageschrift. Sie zeigen, was wirklich war. Nicht mehr und nicht weniger.
Und wir? Was tun wir? Schweigen wir? Oder fordern wir endlich ein, was unser Recht ist? Wir Bürger dürfen das nicht hinnehmen. Es ist Zeit, unsere Behörden zur Rechenschaft zu ziehen. Diese Institutionen arbeiten nicht für sich – sie arbeiten für uns. Wir finanzieren sie, und wir haben das Recht, Transparenz und Verantwortung einzufordern. Manipulationen wie diese müssen aufgearbeitet werden und dürfen nie wieder geschehen. Die Strukturen, die solche Fehlentwicklungen in unseren Behörden ermöglicht haben, müssen offengelegt werden. Denn eine Demokratie lebt von Vertrauen – und Vertrauen muss verdient werden. Jeden Tag aufs Neue.
.
.
MARCEL BARZ, Jahrgang 1975, war Offizier der Bundeswehr und studierte Wirtschafts- und Organisationswissenschaften sowie Wirtschaftsinformatik. Er war Gründer und Geschäftsführer einer Softwarefirma, die sich auf Datenanalyse und Softwareentwicklung spezialisiert hatte. Im August 2021 veröffentlichte Barz den Videovortrag »Die Pandemie in den Rohdaten«, der über eine Million Aufrufe erzielte. Seitdem macht er als "Erbsenzähler" auf Widersprüche in amtlichen Statistiken aufmerksam.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28A estrutura lógica do livro didático
Todos os livros didáticos e cursos expõem seus conteúdos a partir de uma organização lógica prévia, um esquema de todo o conteúdo que julgam relevante, tudo muito organizadinho em tópicos e subtópicos segundo a ordem lógica que mais se aproxima da ordem natural das coisas. Imagine um sumário de um manual ou livro didático.
A minha experiência é a de que esse método serve muito bem para ninguém entender nada. A organização lógica perfeita de um campo de conhecimento é o resultado final de um estudo, não o seu início. As pessoas que escrevem esses manuais e dão esses cursos, mesmo quando sabem do que estão falando (um acontecimento aparentemente raro), o fazem a partir do seu próprio ponto de vista, atingido após uma vida de dedicação ao assunto (ou então copiando outros manuais e livros didáticos, o que eu chutaria que é o método mais comum).
Para o neófito, a melhor maneira de entender algo é através de imersões em micro-tópicos, sem muita noção da posição daquele tópico na hierarquia geral da ciência.
- Revista Educativa, um exemplo de como não ensinar nada às crianças.
- Zettelkasten, a ordem surgindo do caos, ao invés de temas se encaixando numa ordem preexistentes.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Zettelkasten
https://writingcooperative.com/zettelkasten-how-one-german-scholar-was-so-freakishly-productive-997e4e0ca125 (um artigo meio estúpido, mas útil).
Esta incrível técnica de salvar notas sem categorias, sem pastas, sem hierarquia predefinida, mas apenas fazendo referências de uma nota à outra e fazendo supostamente surgir uma ordem (ou heterarquia, disseram eles) a partir do caos parece ser o que faltava pra eu conseguir anotar meus pensamentos e idéias de maneira decente, veremos.
Ah, e vou usar esse tal
neuronque também gera sites a partir das notas?, acho que vai ser bom. -
 @ 7cc328a0:2a247c0e
2024-10-12 15:33:58
@ 7cc328a0:2a247c0e
2024-10-12 15:33:58relay.tools quarterly report
January, 2024
Project updates
UI design
Relay.tools spent quite a bit of time working on UI design this quarter. Since UI is time intensive and there are many other aspects of the project that need work, I time-boxed this work to 3-4 weeks total.
I engaged with @Daniel from #nostrdesign and a freelance UI developer @freecritter. We setup a penpot instance for relay.tools and practiced using that instead of closed-source figma. We learned that penpot is not as friendly as figma from a designers point of view, but is workable. From the perspective of a frontend engineer it is no different than figma and using penpot is a big opensource win.
The following designs were implemented this quarter. There is still much to do in this area and some aspects have been brainstormed but put on hold due to other priorities.
Relay branding and directory
I wanted to give the relays personality and branding, here is a list of improvements in this area:
- [x] The home page now prominently displays the public relays that have chosen to advertise.
- [x] Relay 'Badges' were re-designed to have better contrast and fit.
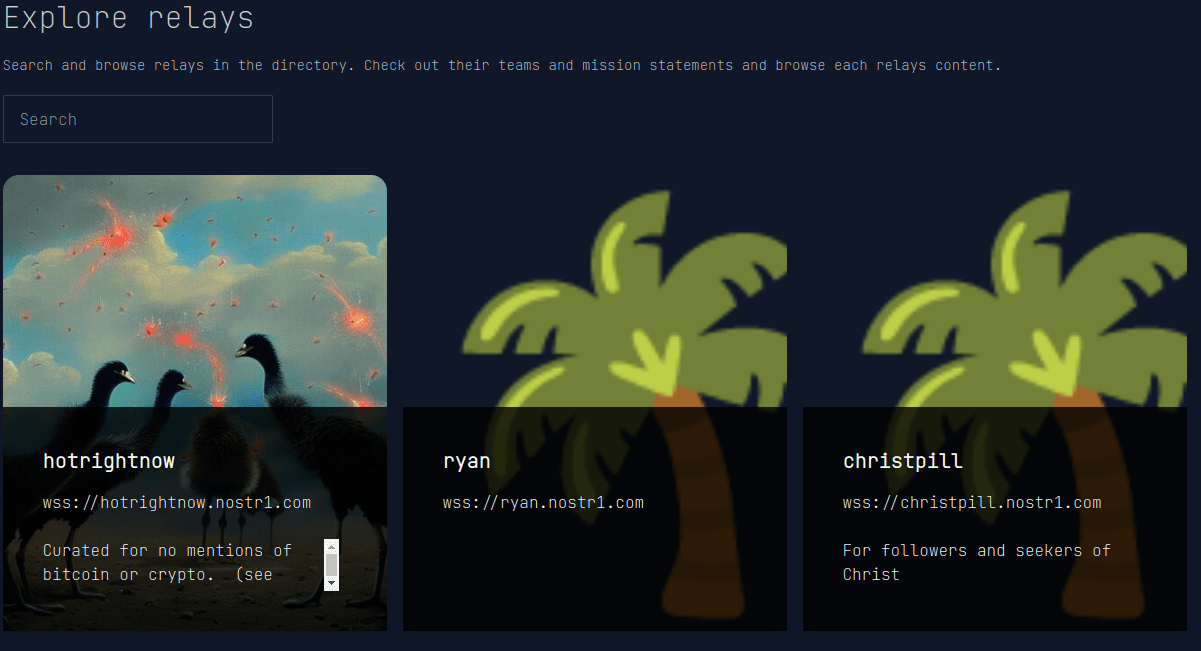
- [x] Relays have a custom direct landing page at their domain. eg. frogathon.nostr1.com
### 'Paid relay' support
Relays now support lightning payments to the relay.tools operator. This helps with combating spam and allowing the relay owners to subsidize their monthly cost.
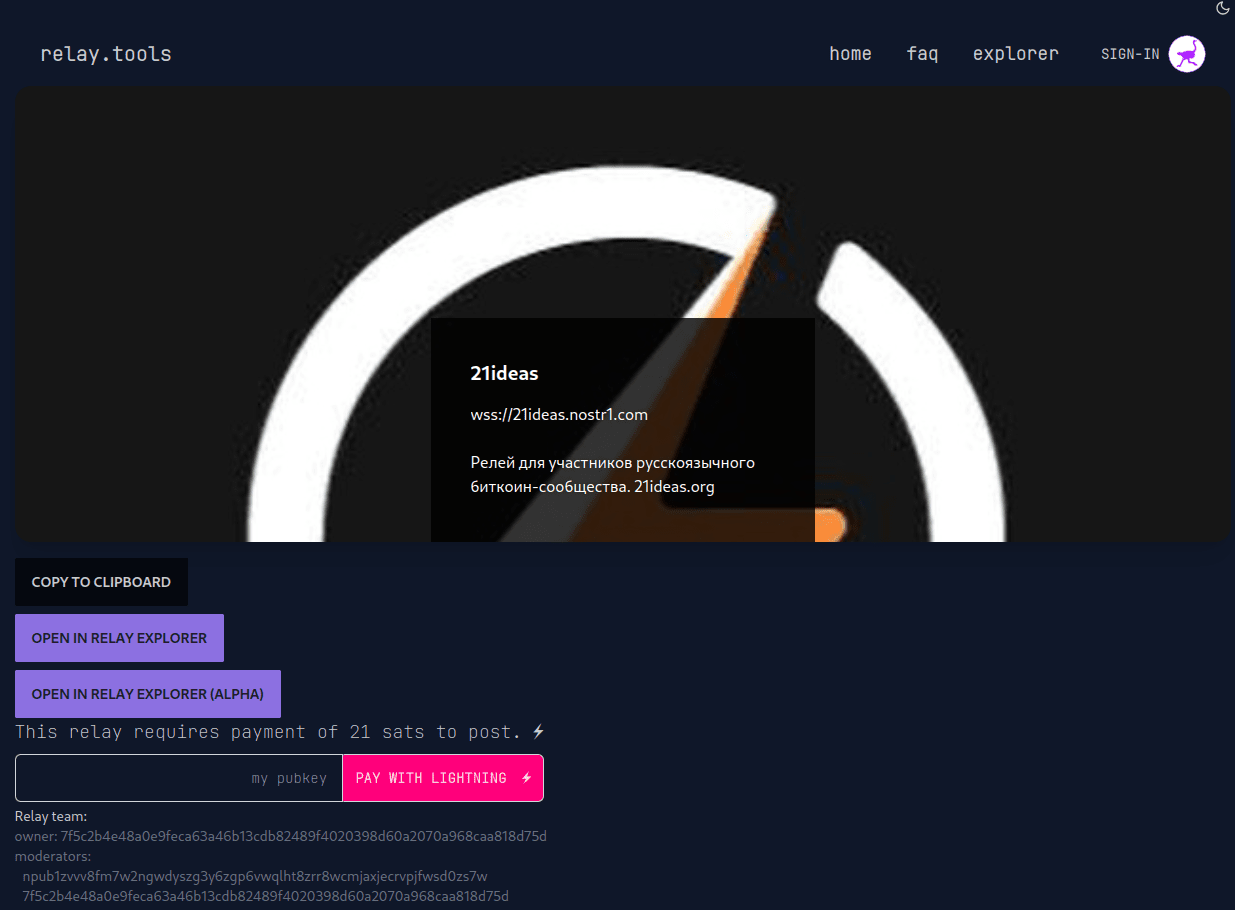
Layout / theme
The frontend code has been modified so that it is responsive on mobile/desktop using columns. The menu was re-designed to be responsive on mobile and shows user hints for login as well as additional links (explore, FAQ). Theme switcher bugs for light/dark modes have been fixed. (Nextjs bleeding edge workaround was required).
Relay Explorer Alpha
The Relay Explorer Alpha is a mini-client for interacting with a single relay. The following improvements were made:
- [x] Moderation capabilities added: Mods can delete messages, block pubkeys, and delete+block directly from the explorer.
- [x] Image and Link parsing / optional loading.
- [x] Replies implemented.
Example screenshot showing these features:
Installer
Another main focus this quarter was to implement an installer for the relay.tools software so that anyone can easily self-host this on a generic VPS.
The installer will be a simple shell script that asks the user a few questions (like their domain name) and then automatically installs the entire stack.
A new code repository was created for this called relay-tools-images
- [x] Main architecture to match production (systemd and nspawn).
- [x] Common Base OS image builds (Debian).
- [x] Haproxy, Strfry, Relaycreator and Mysql image builds.
- [x] Auto-updating of application code (including database migrations).
This is still in-progress and will be part of next quarter's priorities to finish the first stage. (described in plans for next quarter)
Lightning Node
A decent amount of time was spent managing a Bitcoin+Lightning+LnBits node and building a second node for testing and standby purposes.
I had some node issues this quarter and have been learning, re-building the node, upgrading, and aquiring more inbound liquidity to support relay operations.
Relay Management / daily operations
Relay.tools growth last quarter exceeded expectations and lots of work in the ladder part of this quarter went into daily operations.
It grew so fast that I have paused any advertising so that I have time to implement some important growth related features (as described in the plans for next quarter).
- number of relays currently running: 63
- number of unique admins/mods: 207
- events processed in last 30d: 5,091,724
- gigabytes sent/received in last 30d: 1,651GB / 175GB
Monitoring
Daily operations include checking in on the relay activity to get a feel for what's going on. I've implemented an InfluxDB integration for the strfry plugin, which helps with daily operations and in the future will provide owners, mods, and users with stats showing relay performance and event counts. This greatly improves visibility into the relays and is the backbone of data analysis for the platform.
Events by Kind (7d)
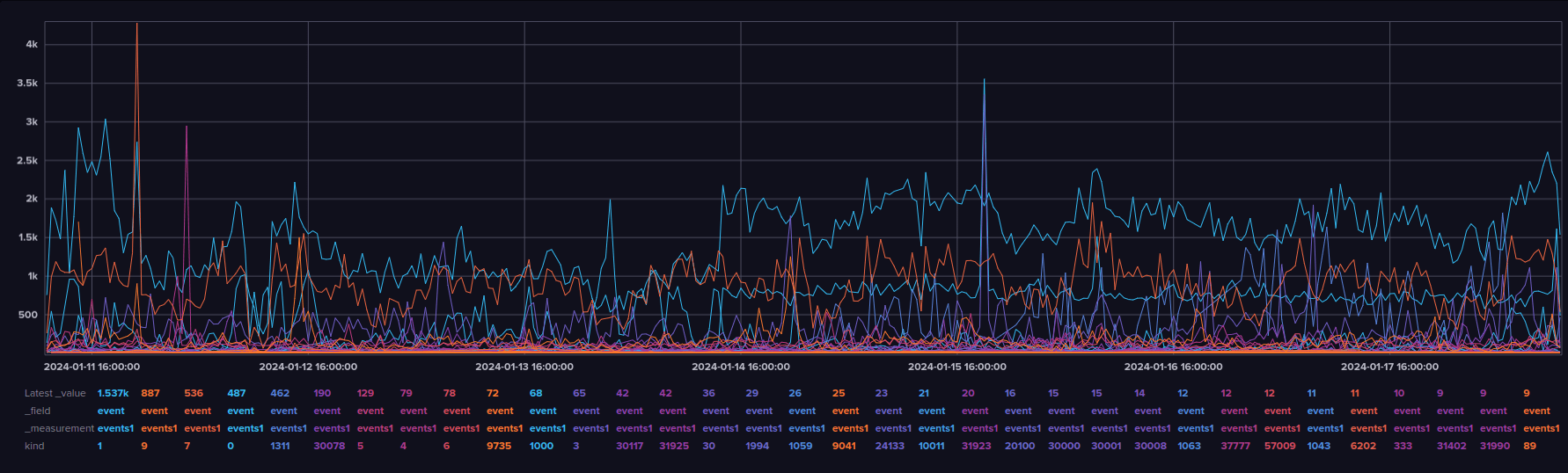
Events by Relay (7d)
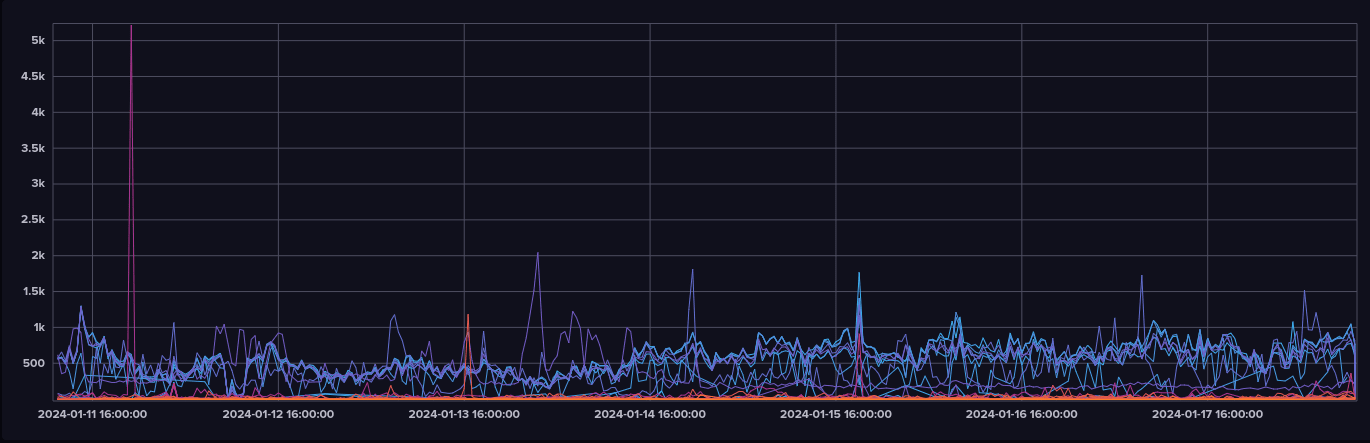
Data Explorer View (single relay, kind 3)
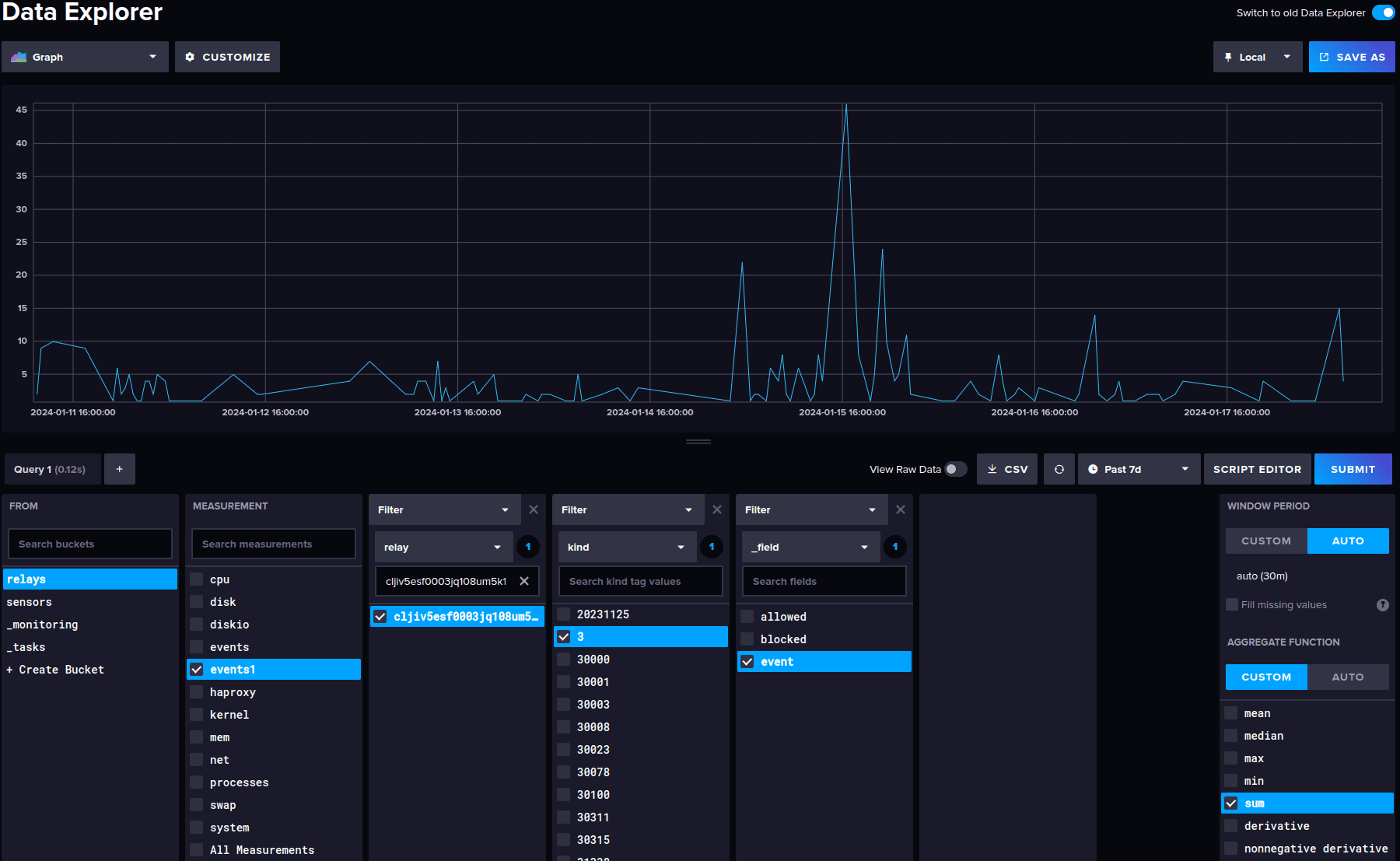
Moderation
Daily operations time is also spent ensuring relays meet our TOS. That includes browsing the relays content for anything that does not meet the TOS and performing mitigation when necessary. This can be time consuming. I will be adding super-moderator capability so that others can assist as we grow (as described in the plans for next quarter).
Training / Feedback / Community
I promoted the use of event specific relays for nostr community events. Feedback was very positive and showed that people enjoy having event specific relays even if client support is minimal. * Nostrasia * Frogathon
Plans for next Quarter
Finish the installer - [ ] SSL certificate management with certbot. - [ ] Nostr key generation for API credentials. - [ ] install.sh script for interactive -and- config file based one-shot installation. - [ ] Publish pre-built images and integrate their use with the installer.
Re-Occuring Billing (+ tools for interacting with community of relay runners) - [ ] Implement re-occuring billing using a credits system and lightning payments. - [ ] Implement user notification(s) for billing cycle notifications. - [ ] Implement user feedback / support channel.
Additional visibility and moderation tools - [ ] Implement super-moderator capability for TOS violations. - [ ] Engage with community to help support moderation
-
 @ a42048d7:26886c32
2025-01-04 22:32:52
@ a42048d7:26886c32
2025-01-04 22:32:52OP_CAT, Coffee, and keeping an open mind to Bitcoin soft forks by an 80 IQ BTC Maxi Pleb
TLDR: CAT is both low risk and low appeal to the broader non-dev BTC community. I don’t care and you shouldn’t either. If I am an 80 IQ HODL pleb or a company that caters to that group, can you please give me 2-4 fifth grade level coherent english sentences that explain why I should support CAT? I’m still waiting… CTV or LNHANCE on the other hand have broad appeal.
Five years ago in the office we got a fancy $6,000 coffee maker. It was hooked up to wifi, showed TV on a giant screen, and could make every type of coffee/milkshake you could think of. I was captivated… for about 1 day. After trying a few times I realized almost all the drinks it made were of low quality. The wifi connection actually ended up just being annoying. Half the time I wanted a coffee, only had a 5 minute break, and the machine displayed some inscrutable error. I went back to the proverbial grind un-caffeinated and frustrated wishing we had the old reliable boring coffee maker back. I also found myself only coming back to the 2 drinks I really cared about, espresso and maybe an occasional cappuccino. It was “cool” that new machine could make over 60 different drinks, but when I sat back and thought about it all I really needed or wanted were a few key options that I used constantly. Especially as those extra bells and whistles seemed to be the usual suspect in the coffee machine constantly breaking. I would’ve loved them upgrading from burnt starbucks coffee beans to a local specialty roaster, that would’ve greatly enhanced my daily coffee. Echoing this realization, my coffee setup at home became a simple machine that could only make espresso and a hand crank coffee bean grinder. Still have them years later and they work great. They’re robust and fit exactly what I wanted with no nonsense that created more headache than everyday value. As you probably suspected, this is a loose comparison to OP_CAT. I’ve listened to podcast after podcast, read blog after blog, and sat through every CAT pitch I could find. I genuinely tried to approach with an open mind. However, ultimately what every pro OP_CAT argument boils down to is that there is no simple left curve elevator pitch a pleb will understand or care about. “But we can get this really cool ZK Rollup and have infinite DEFI bridging to altcoin chains! Look we sort of did it on this other altcoin chain.” And they did, they aren’t lying. They have live software on a shitcoin chain like ETH or SOL that does some modest volume. But the story quickly falls apart in the face of a few basic left curve questions: “Why should I, as an 80 IQ left curve BTC maxi give a shit?” “Does this enhance my everyday experience holding and using BTC?” “Why do you have a non-BTC token for your rollup/sidechain/glorified multisig that is totally centralized?” “Why is there only a hard to understand often ill-defined path to de-centralization? Why isn’t it just already decentralized?” “What is a clear use case that the typical non-technical everyday BTC holder can understand and rally behind?” “Why should I care about bridging to ETH, SOL, or whatever shitcoin chain? I only want BTC and don’t want to participate in all that shitcoin bullshit. Bitcoin is a store of value and money to me and it doesn’t help with those use cases in a clear direct way. It sounds like it maybe, kinda, sorta does help with a lot of caveats, ifs, and steps that I struggle to understand.” Sorry yeah I know, that one got a little personal. I’ll try to do better going forward guys.
ZK proofs or other Pro-CAT arguments, are undoubtedly cool and do factually enable potential cool new stuff. It just happens to all be stuff that sounds complex, esoteric, and unappealing to an 80 IQ HODL pleb - let alone a miner, ETF investor, or exchange exec. I don’t mean to say ZK or other tech has no potential and that we won’t eventually move there, but just to say that it’s not in the cards as currently dealt.
I really went out trying to keep an open mind and steelman the case for CAT. I came back firmly believing:
1 Support is deep in the developer community, but nonexistent everywhere else. I have yet to find a single person that supports CAT who is not a dev or working at or sponsored by a company that stands to directly profit from something CAT enables. Which is fine, but I reserve the right to be skeptical of your direct incentive. I acknowledge rough consensus is very hard to judge, and am open to changing my mind on this over time but feel this is a currently accurate assessment.
2 To get a soft fork you need rough consensus. Most people in that potential consensus are not highly technical developers. They care mostly or exclusively about BTC’s store of value use case. No one has yet articulated a clear compelling store of value enhancing use case that they can understand and care about. Without pull demand from potential users and paying customers, CAT will inevitably stall.
3 Lots of factually inaccurate FUD has been thrown at CAT. People saw the Taproot Wizards or shitcoiners pushing CAT, and immediately dismiss CAT as an evil psyop without any real consideration for its technical merits. Frankly most people just hate Udi and say “Fuck CAT” based solely on that. Maybe not fair, but true.
4 CAT is low risk, and it is not a catastrophe waiting to happen. Anything bad it potentially enables is enabled in such an inefficient and/or use hostile way that it is highly unlikely to pose any issues to Bitcoin. CAT’s technical risk is low and this is consistently proven by other chains enabling CAT and having no issues with it, such as Liquid.
5 Lots of people who have no idea wtf they are talking about falsely claim CAT is the apocalypse without any ability whatsoever to explain why. Imho you are no better than Udi and the shitcoiners if you are willing to lie about CAT just because you dislike them. We as the BTC community need the ability to have a rational discussion on technical merits, and not to devolve into a cult of personality based political battle. The question should be, “Is CAT good or bad and why?” and not “I just hate Udi, therefore its a no from me dog.”
Summarizing CAT using TradFi language: those pushing CAT have technology in search of a problem and no clear product market fit. They are pushing their technology to an apathetic audience. Pushers of CAT are not pulled forward by customer demand. In the tech world these are some of the quintessential red flags that every good investor knows mean you need to sit this one out.
CTV or LNHANCE on the other hand are soft fork proposals that have clear use cases you can quickly explain to a broad swathe of the Bitcoin ecosystem: “Hey HOLD pleb, worried about losing your coins? Wouldn’t it be nice to have a simple vault that reduces the chances your coins are lost or stolen? Let’s make self custody and BTC’s store of value use case strictly better, specifically without enabling any shitcoin-ery.” “Hey Blackrock, Van Eck, ARK, Franklin Templeton, and every ETF investor - it would really suck if Coinbase lost all your Bitcoin and that ETF went to zero, right? What it we could create vaults to make that Bitcoin more secure?” “Like Lightning but find it hard to use self-custodially? Let’s make Lightning better, easier, and more scalable with fewer onchain transactions and lower fees.” “Tried or seen the ARK demos yet? They have real working code even without covenants. With covenants we get big ARK volumes and scaling while also making it easier.”
Signing off: See the difference? I, an 80 IQ pleb, can steelman multiple use cases for CTV/LNHANCE that have broad appeal. I have yet to see any such case for CAT, and until then I don’t think it’ll go anywhere.
*Pro-CAT Sources I’ve digested and would encourage others to consider: https://en.bitcoin.it/wiki/Covenants_support https://www.youtube.com/watch?v=no_Nj-MX53w https://www.youtube.com/watch?v=_yp4eYK9S6M
Pro-CTV/LNHANCE sources to consider which have CLEAR use cases with widespead appeal: https://github.com/jamesob/simple-ctv-vault https://github.com/stutxo/op_ctv_payment_pool https://lnhance.org/ https://bitcoinmagazine.com/technical/how-ctv-can-help-scale-bitcoin
-
 @ eac63075:b4988b48
2025-01-04 19:41:34
@ eac63075:b4988b48
2025-01-04 19:41:34Since its creation in 2009, Bitcoin has symbolized innovation and resilience. However, from time to time, alarmist narratives arise about emerging technologies that could "break" its security. Among these, quantum computing stands out as one of the most recurrent. But does quantum computing truly threaten Bitcoin? And more importantly, what is the community doing to ensure the protocol remains invulnerable?
The answer, contrary to sensationalist headlines, is reassuring: Bitcoin is secure, and the community is already preparing for a future where quantum computing becomes a practical reality. Let’s dive into this topic to understand why the concerns are exaggerated and how the development of BIP-360 demonstrates that Bitcoin is one step ahead.
What Is Quantum Computing, and Why Is Bitcoin Not Threatened?
Quantum computing leverages principles of quantum mechanics to perform calculations that, in theory, could exponentially surpass classical computers—and it has nothing to do with what so-called “quantum coaches” teach to scam the uninformed. One of the concerns is that this technology could compromise two key aspects of Bitcoin’s security:
- Wallets: These use elliptic curve algorithms (ECDSA) to protect private keys. A sufficiently powerful quantum computer could deduce a private key from its public key.
- Mining: This is based on the SHA-256 algorithm, which secures the consensus process. A quantum attack could, in theory, compromise the proof-of-work mechanism.
Understanding Quantum Computing’s Attack Priorities
While quantum computing is often presented as a threat to Bitcoin, not all parts of the network are equally vulnerable. Theoretical attacks would be prioritized based on two main factors: ease of execution and potential reward. This creates two categories of attacks:
1. Attacks on Wallets
Bitcoin wallets, secured by elliptic curve algorithms, would be the initial targets due to the relative vulnerability of their public keys, especially those already exposed on the blockchain. Two attack scenarios stand out:
-
Short-term attacks: These occur during the interval between sending a transaction and its inclusion in a block (approximately 10 minutes). A quantum computer could intercept the exposed public key and derive the corresponding private key to redirect funds by creating a transaction with higher fees.
-
Long-term attacks: These focus on old wallets whose public keys are permanently exposed. Wallets associated with Satoshi Nakamoto, for example, are especially vulnerable because they were created before the practice of using hashes to mask public keys.
We can infer a priority order for how such attacks might occur based on urgency and importance.
 Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)
Bitcoin Quantum Attack: Prioritization Matrix (Urgency vs. Importance)2. Attacks on Mining
Targeting the SHA-256 algorithm, which secures the mining process, would be the next objective. However, this is far more complex and requires a level of quantum computational power that is currently non-existent and far from realization. A successful attack would allow for the recalculation of all possible hashes to dominate the consensus process and potentially "mine" it instantly.
 Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin Attacks
Satoshi Nakamoto in 2010 on Quantum Computing and Bitcoin AttacksRecently, Narcelio asked me about a statement I made on Tubacast:
https://x.com/eddieoz/status/1868371296683511969
If an attack became a reality before Bitcoin was prepared, it would be necessary to define the last block prior to the attack and proceed from there using a new hashing algorithm. The solution would resemble the response to the infamous 2013 bug. It’s a fact that this would cause market panic, and Bitcoin's price would drop significantly, creating a potential opportunity for the well-informed.
Preferably, if developers could anticipate the threat and had time to work on a solution and build consensus before an attack, they would simply decide on a future block for the fork, which would then adopt the new algorithm. It might even rehash previous blocks (reaching consensus on them) to avoid potential reorganization through the re-mining of blocks using the old hash. (I often use the term "shielding" old transactions).
How Can Users Protect Themselves?
While quantum computing is still far from being a practical threat, some simple measures can already protect users against hypothetical scenarios:
- Avoid using exposed public keys: Ensure funds sent to old wallets are transferred to new ones that use public key hashes. This reduces the risk of long-term attacks.
- Use modern wallets: Opt for wallets compatible with SegWit or Taproot, which implement better security practices.
- Monitor security updates: Stay informed about updates from the Bitcoin community, such as the implementation of BIP-360, which will introduce quantum-resistant addresses.
- Do not reuse addresses: Every transaction should be associated with a new address to minimize the risk of repeated exposure of the same public key.
- Adopt secure backup practices: Create offline backups of private keys and seeds in secure locations, protected from unauthorized access.
BIP-360 and Bitcoin’s Preparation for the Future
Even though quantum computing is still beyond practical reach, the Bitcoin community is not standing still. A concrete example is BIP-360, a proposal that establishes the technical framework to make wallets resistant to quantum attacks.
BIP-360 addresses three main pillars:
- Introduction of quantum-resistant addresses: A new address format starting with "BC1R" will be used. These addresses will be compatible with post-quantum algorithms, ensuring that stored funds are protected from future attacks.
- Compatibility with the current ecosystem: The proposal allows users to transfer funds from old addresses to new ones without requiring drastic changes to the network infrastructure.
- Flexibility for future updates: BIP-360 does not limit the choice of specific algorithms. Instead, it serves as a foundation for implementing new post-quantum algorithms as technology evolves.
This proposal demonstrates how Bitcoin can adapt to emerging threats without compromising its decentralized structure.
Post-Quantum Algorithms: The Future of Bitcoin Cryptography
The community is exploring various algorithms to protect Bitcoin from quantum attacks. Among the most discussed are:
- Falcon: A solution combining smaller public keys with compact digital signatures. Although it has been tested in limited scenarios, it still faces scalability and performance challenges.
- Sphincs: Hash-based, this algorithm is renowned for its resilience, but its signatures can be extremely large, making it less efficient for networks like Bitcoin’s blockchain.
- Lamport: Created in 1977, it’s considered one of the earliest post-quantum security solutions. Despite its reliability, its gigantic public keys (16,000 bytes) make it impractical and costly for Bitcoin.
Two technologies show great promise and are well-regarded by the community:
- Lattice-Based Cryptography: Considered one of the most promising, it uses complex mathematical structures to create systems nearly immune to quantum computing. Its implementation is still in its early stages, but the community is optimistic.
- Supersingular Elliptic Curve Isogeny: These are very recent digital signature algorithms and require extensive study and testing before being ready for practical market use.
The final choice of algorithm will depend on factors such as efficiency, cost, and integration capability with the current system. Additionally, it is preferable that these algorithms are standardized before implementation, a process that may take up to 10 years.
Why Quantum Computing Is Far from Being a Threat
The alarmist narrative about quantum computing overlooks the technical and practical challenges that still need to be overcome. Among them:
- Insufficient number of qubits: Current quantum computers have only a few hundred qubits, whereas successful attacks would require millions.
- High error rate: Quantum stability remains a barrier to reliable large-scale operations.
- High costs: Building and operating large-scale quantum computers requires massive investments, limiting their use to scientific or specific applications.
Moreover, even if quantum computers make significant advancements, Bitcoin is already adapting to ensure its infrastructure is prepared to respond.
Conclusion: Bitcoin’s Secure Future
Despite advancements in quantum computing, the reality is that Bitcoin is far from being threatened. Its security is ensured not only by its robust architecture but also by the community’s constant efforts to anticipate and mitigate challenges.
The implementation of BIP-360 and the pursuit of post-quantum algorithms demonstrate that Bitcoin is not only resilient but also proactive. By adopting practical measures, such as using modern wallets and migrating to quantum-resistant addresses, users can further protect themselves against potential threats.
Bitcoin’s future is not at risk—it is being carefully shaped to withstand any emerging technology, including quantum computing.
-
 @ 82b30d30:40c6c003
2024-10-09 03:51:41
@ 82b30d30:40c6c003
2024-10-09 03:51:41[3]
[4]
[5]
[6]
[7]
[8]
[9]
[10]
[11]
[12]
[13]
[14]
[15]
[16]
[17]
[18]
[19]
[20]
[21]
[22]
[23]
[24]
[25]
[26]
[27]
[28]
[29]
[30]
[31]
[32]
[33]
[34]
-
 @ 460c25e6:ef85065c
2024-10-10 13:22:06
@ 460c25e6:ef85065c
2024-10-10 13:22:06In the early days of Nostr, developers often competed to see who could implement the most NIPs. Although all were optional (except NIP-01), it became a point of pride and vital for the ecosystem's growth. Back then, there were only a few dozen relatively simple NIPs to implement. Fast forward to today, with nearly 100 NIPs, maintaining and implementing everything has become nearly impossible. Yet, the drive among developers to "code all things Nostr" remains as strong as ever.
nostr:nprofile1qqsrhuxx8l9ex335q7he0f09aej04zpazpl0ne2cgukyawd24mayt8gprfmhxue69uhhq7tjv9kkjepwve5kzar2v9nzucm0d5hszxmhwden5te0wfjkccte9emk2um5v4exucn5vvhxxmmd9uq3xamnwvaz7tmhda6zuat50phjummwv5hsx7c9z9 raised the point that everyone, even I, agrees:
nostr:nevent1qqsqqqp2zrs7836tyjlsfe7aj9c4d97zrxxqyayagkdwlcur96t4laspzemhxue69uhhyetvv9ujumt0wd68ytnsw43z7q3q80cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsxpqqqqqqzgcrrrp
But how big is too big? How can we better understand the range of options available for devs out there?
I went out for a hunt in my own brain to figure out how to clarify the situation. I came up with the following 4 categories for Nostr Clients: - Super Clients: These apps merge vastly different domains into a single application, offering basic support for reading, writing, configuration, and data management for each use case within each domains. An example would be an app that combines a Marketplace and Live Streams under one roof.
-
Clients: These apps provide comprehensive support for a single domain, handling all its use cases in a single home. They manage the complete set of reading, writing, configuration, and long-term data management within that domain. An example is a marketplace app that helps users manage product catalogs, process orders, collect payments, and handle fulfillment and reports.
-
Mini Clients: These apps focus on read and write functionality for a single use case, including configuration management and any actions related to that specific task. For example, a fulfillment app that helps users view orders placed from another client to then pack and ship them.
-
Micro Clients: These apps have a single interface and perform one specific action. Viewing and creating a record is handled by separate micro apps. An example is an app that simply scans an order's QR code and marks it as shipped.
Based on my made-up categories described at the end, this is how I would split our most known apps.
Super Clients - amethyst - nostrudel - coracle
Clients - damus - twitter - primal - twitter - snort - twitter - gossip - twitter - lume - twitter - ditto - twitter - rabbit - twitter - freefrom - twitter - nos - twitter - flycat - twitter - straylight - twitter - nostter - twitter - iris - twitter - nostur - twitter - nostrmo - twitter - yana - twitter - openvibe - twitter - freerse - twitter - 0xchat - chats - cornychat - chats - coop - chats - nostrchat - chats - blowater - chats - habla - blogs - yakihonne - blogs - highlighter - blogs - blogstack - blogs - stemstr - music - wavlake - music - fountain - podcasts - zap.stream - live streaming - shopstr - marketplace - plebeian.market - marketplace - flotilla - communities - satellite - communities - zapddit - communities - nostr.kiwi - communities - hivetalk - video calls - flare - long-form videos - nostrnests - audio spaces - wherostr - location - yondar - location - stacker.news - news - flockstr - events - nostrocket - issue tracker - docstr - docs - satshoot - freelance - wikifreedia - wiki - formstr - forms - chesstr - chess - memestr - meme feed - npub.cash - wallet - npub.pro - websites - gitworkshop - dev tools - onosendai - metaverse - degmods - games - turdsoup - prompts
Mini Clients - amber - signer - alby - signer - nos2x - signer - nsec.app - signer - keys.band - signer - nostrame - signer - nokakoi - anon - zap.cooking - recipes - anonostr - anon - getwired - anon - lowent - anon - creatr - exclusive content - lightning.video - exclusive content - zaplinks - slides - listr - lists - zap.store - app store - badges.page - badges - oddbean - news - dtan - torrents - nosta - user pages - pinstr - pinterest - pollerama - polls - swarmstr - trending - nostrapp - apps manager - noogle - search - ostrich.work - job postings - emojito - emoji manager - nostree - links - citrine - local relay - joinstr - coinjoins - heya - crowdfunding - zapplepay - zaps - nosbin - clipboard - shipyard - scheduler - tunestr - live streams - filestr - files - nostrcheck.me - media hosting - sheetstr - spreadsheets - crafters - curriculum vitae
Micro Clients - w3 - url shortener - nosdrive - backups - zaplife - zaps dashboard - zapper.fun - payments - nostrends - trends - zephyr - trends - wavman - music player - nostrrr - relay info - nosdump - relay info - notestack - blogs - nostr.build - media hosting - nostr.watch - relay info - nostr hours - use reports - lazereyes - vision prescriptions - snakestr - games - deletestr - deletion requests - 2048str - games - nostrqr - qr generator - notanostrclient - anon
Super apps will try to do everything, but can't really do most things super well. Regular-sized Clients will try to manage most of a given domain but are likely to centralize users on themselves, an unwanted effect inside of Nostr. If we want Nostr to grow in a decentralized fashion, we have to start betting on and using more Mini and Micro clients.
-
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Boardthreads
This was a very badly done service for turning a Trello list into a helpdesk UI.
Surprisingly, it had more paying users than Websites For Trello, which I was working on simultaneously and dedicating much more time to it.
The Neo4j database I used for this was a very poor choice, it was probably the cause of all the bugs.
-
 @ c6f7077f:ad5d48fd
2024-09-08 01:24:03
@ c6f7077f:ad5d48fd
2024-09-08 01:24:03“The more you learn about something, the more you realize you know nothing.” This saying resonates deeply with me. The truth is, no one really has all the big answers. Many in the scientific community seem to pretend they do. Let’s explore this further.
Consider the Most Fundamental Questions
- The Origin of the Universe
- The Origin of Life on Earth
The Origin of the Universe
You might think we have a solid answer: the Big Bang. However, this explanation has its limitations, and calling it a “start” can be misleading. In fact, this theory might be entirely wrong. New research challenges the Big Bang theory, and I highly recommend listening to Sir Roger Penrose for a deeper understanding.
The only substantial evidence we have is the universe's expansion. Penrose proposes a different hypothesis: the endless expansion and contraction of the universe. This idea doesn’t contradict our current understanding.
Thus, the evidence for the Big Bang and Penrose’s theory are both radically different, yet neither can be definitively proven over the other. This highlights the limitations of our current understanding.
The Origin of Life on Earth
The origin of life is even more complex. Life requires three essential components: - Proteins for basic functioning - RNA for storing and replicating genes - Lipids (cell walls) to create separation from the environment
Mathematical models suggest that while proteins and lipids have a reasonable probability of forming, the creation of RNA seems nearly impossible through random mutations in a short time frame. The best explanations indicate that we either lack crucial information or that these RNA molecules—and life as a whole—might have come from outside sources. Some scholars even question the entire random mutation model.
The Question of Certainty
If scientists don’t know the answers, why do they pretend they do? In my humble opinion, It seems they do this to distance science from religion and to close the discussion before the wealthiest can fit God into the narrative, Interestingly, I’m not alone in believing they closed the books too early.
Reclaiming Control of Science and Education
The best way to reclaim control of science and education is to learn. If you’re looking for a starting point, I highly recommend: - “A Brief History of Time” by Stephen Hawking for physics - “Sapiens” or “The Selfish Gene” for evolutionary biology
All three are excellent starting points—densely packed with information and covering a wide range of topics in a concise and accessible manner.
-
 @ 5f010feb:3ae9756b
2024-10-03 13:28:13
@ 5f010feb:3ae9756b
2024-10-03 13:28:13[3]
[4]
[5]
[6]
[7]
[8]
[9]
[10]
[11]
[12]
[13]
[14]
[15]
[16]
[17]
[18]
[19]
[20]
[21]
[22]
[23]
[24]
[25]
[26]
[27]
[28]
[29]
[30]
[31]
[32]
[33]
[34]
[35]
[36]
[37]
[38]
[39]
[40]
[41]
[42]
[43]
[44]
[45]
[46]
[47]
[48]
[49]
[50]
[51]
[52]
[53]
[54]
[55]
[56]
[57]
[58]
[59]
[60]
[61]
[62]
[63]
[64]
[65]
[66]
[67]
[68]
[69]
[70]
[71]
[72]
[73]
[74]
[75]
[76]
[77]
[78]
[79]
[80]
[81]
[82]
[83]
[84]
[85]
[86]
[87]
[88]
[89]
[90]
[91]
[92]
[93]
[94]
[95]
[96]
[97]
[98]
[99]
[100]
[101]
[102]
[103]
[104]
[105]
[106]
[107]
[108]
[109]
[110]
[111]
[112]
[113]
[114]
[115]
[116]
[117]
[118]
[119]
[120]
[121]
[122]
[123]
[124]
[125]
[126]
[127]
[128]
[129]
[130]
[131]
[132]
[133]
[134]
[135]
[136]
[137]
[138]
[139]
[140]
[141]
[142]
[143]
[144]
[145]
[146]
[147]
[148]
[149]
[150]
[151]
[152]
[153]
[154]
[155]
[156]
[157]
[158]
[159]
[160]
[161]
[162]
[163]
[164]
[165]
[166]
[167]
[168]
[169]
[170]
[171]
[172]
[173]
[174]
[175]
[176]
[177]
[178]
[179]
[180]
[181]
[182]
[183]
[184]
-
 @ 101b30ee:18a46a45
2024-10-01 04:08:22
@ 101b30ee:18a46a45
2024-10-01 04:08:22昨日 (2024/9/30), お世話になった会社を退職しました。
2023/7/1入社のため、在籍期間は1年3か月でした。どんな会社だったの?
会社名は伏せますが、BtoBtoCのサブスク課金型Webサービスを展開している会社のインフラエンジニアをやっていました。
職務内容は多岐にわたり、
- 開発・商用環境の構築
- サービスのデプロイ
- DNS関連の設定
- サービス加入時や解約時の定期作業
- 社内のセキュリティ意識向上のための啓蒙
- 情シス業務
- サービスのバックエンド(PHP)のリファクタ
- OS含めた各種ソフトウェアのバージョン移行などなど。
インフラエンジニアという職種ではあったものの、開発系のタスクも多く経験させてもらいました。なぜ退職したの?
売上が芳しくなく業務縮小することになり、退職しないかと勧められました。
この希望退職は私だけではなく、ほとんどの社員に話がいっていたようです。
実際、社員数は半分以下になっていたようで、統合により消えた部署や、1人しか残らなくなった部署もあります。
個人的にはまだ1年少ししか在籍しておらず少し未練はあったものの、これをチャンスと捉えて希望退職に乗ることにしました。
幸い、いくつかコミュニティ活動をしているので、リファラルで声をかけて頂いている会社様が何社かあります。会社の良かった所
大きなカンファレンスで複数回登壇されているような凄い方と一緒に仕事が出来たり、レンタル出来る技術書が多かったり、月一で社内LT大会兼交流会があって会社経費でピザや寿司が食えたり、良かった所は沢山ありました!
最後に参加したLT会は、これで最後かと思うとちょっと泣きそうになりました。
ちなみに、私は社内LT会の運営をやったり、LT自体もこの1年で4回ほど行いました。これから
色々ありましたが、会社への恨みのようなものは全くありません。感謝しかないです。
ただ、自社の仕事がもう少し楽になるような土台を作りたかったな、というのは心残りではあります。
人数も減って状況は厳しくなっていると思いますが、V字回復してくれることを祈るばかりです。次の会社も、自社開発系の企業でバックエンドないしインフラ系の職種で働けたらと考えています。
今日 (2024/10/1)から無職です!会社受けまくります!頑張るぞい! -
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Channels without HTLCs
HTLCs below the dust limit are not possible, because they're uneconomical.
So currently whenever a payment below the dust limit is to be made Lightning peers adjust their commitment transactions to pay that amount as fees in case the channel is closed. That's a form of reserving that amount and incentivizing peers to resolve the payment, either successfully (in case it goes to the receiving node's balance) or not (it then goes back to the sender's balance).
SOLUTION
I didn't think too much about if it is possible to do what I think can be done in the current implementation on Lightning channels, but in the context of Eltoo it seems possible.
Eltoo channels have UPDATE transactions that can be published to the blockchain and SETTLEMENT transactions that spend them (after a relative time) to each peer. The barebones script for UPDATE transactions is something like (copied from the paper, because I don't understand these things):
OP_IF # to spend from a settlement transaction (presigned) 10 OP_CSV 2 As,i Bs,i 2 OP_CHECKMULTISIGVERIFY OP_ELSE # to spend from a future update transaction <Si+1> OP_CHECKLOCKTIMEVERIFY 2 Au Bu 2 OP_CHECKMULTISIGVERIFY OP_ENDIFDuring a payment of 1 satoshi it could be updated to something like (I'll probably get this thing completely wrong):
OP_HASH256 <payment_hash> OP_EQUAL OP_IF # for B to spend from settlement transaction 1 in case the payment went through # and they have a preimage 10 OP_CSV 2 As,i1 Bs,i1 2 OP_CHECKMULTISIGVERIFY OP_ELSE OP_IF # for A to spend from settlement transaction 2 in case the payment didn't went through # and the other peer is uncooperative <now + 1day> OP_CHECKLOCKTIMEVERIFY 2 As,i2 Bs,i2 2 OP_CHECKMULTISIGVERIFY OP_ELSE # to spend from a future update transaction <Si+1> OP_CHECKLOCKTIMEVERIFY 2 Au Bu 2 OP_CHECKMULTISIGVERIFY OP_ENDIF OP_ENDIFThen peers would have two presigned SETTLEMENT transactions, 1 and 2 (with different signature pairs, as badly shown in the script). On SETTLEMENT 1, funds are, say, 999sat for A and 1001sat for B, while on SETTLEMENT 2 funds are 1000sat for A and 1000sat for B.
As soon as B gets the preimage from the next peer in the route it can give it to A and them can sign a new UPDATE transaction that replaces the above gimmick with something simpler without hashes involved.
If the preimage doesn't come in viable time, peers can agree to make a new UPDATE transaction anyway. Otherwise A will have to close the channel, which may be bad, but B wasn't a good peer anyway.
-
 @ 6be5cc06:5259daf0
2024-12-29 19:54:14
@ 6be5cc06:5259daf0
2024-12-29 19:54:14Um dos padrões mais bem estabelecidos ao medir a opinião pública é que cada geração tende a seguir um caminho semelhante em termos de política e ideologia geral. Seus membros compartilham das mesmas experiências formativas, atingem os marcos importantes da vida ao mesmo tempo e convivem nos mesmos espaços. Então, como devemos entender os relatórios que mostram que a Geração Z é hiperprogressista em certos assuntos, mas surpreendentemente conservadora em outros?
A resposta, nas palavras de Alice Evans, pesquisadora visitante na Universidade de Stanford e uma das principais estudiosas do tema, é que os jovens de hoje estão passando por um grande divergência de gênero, com as jovens mulheres do primeiro grupo e os jovens homens do segundo. A Geração Z representa duas gerações, e não apenas uma.
Em países de todos os continentes, surgiu um distanciamento ideológico entre jovens homens e mulheres. Milhões de pessoas que compartilham das mesmas cidades, locais de trabalho, salas de aula e até casas, não veem mais as coisas da mesma maneira.
Nos Estados Unidos, os dados da Gallup mostram que, após décadas em que os sexos estavam distribuídos de forma relativamente equilibrada entre visões políticas liberais e conservadoras, as mulheres entre 18 e 30 anos são agora 30 pontos percentuais mais liberais do que os homens dessa faixa etária. Essa diferença surgiu em apenas seis anos.
A Alemanha também apresenta um distanciamento de 30 pontos entre homens jovens conservadores e mulheres jovens progressistas, e no Reino Unido, a diferença é de 25 pontos. Na Polônia, no ano passado, quase metade dos homens entre 18 e 21 anos apoiou o partido de extrema direita Confederation, em contraste com apenas um sexto das jovens mulheres dessa mesma idade.
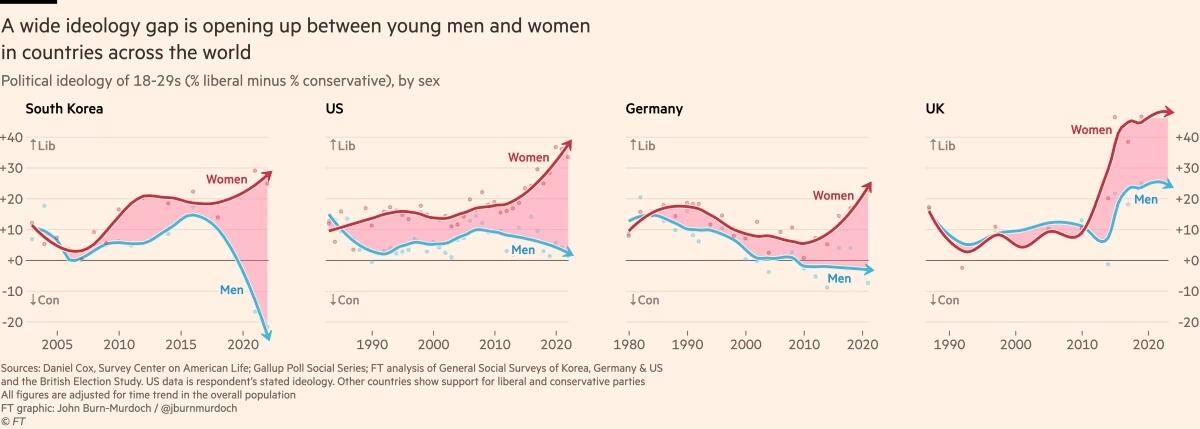
Fora do Ocidente, há divisões ainda mais acentuadas. Na Coreia do Sul, há um enorme abismo entre homens e mulheres jovens, e a situação é semelhante na China. Na África, a Tunísia apresenta o mesmo padrão. Vale notar que em todos os países essa divisão drástica ocorre principalmente entre a geração mais jovem, sendo muito menos pronunciada entre homens e mulheres na faixa dos 30 anos ou mais velhos.
O movimento # MeToo foi o principal estopim, trazendo à tona valores feministas intensos entre jovens mulheres que se sentiram empoderadas para denunciar injustiças de longa data. Esse estopim encontrou especialmente terreno fértil na Coreia do Sul, onde a desigualdade de gênero é bastante visível e a misoginia explícita é comum. (palavras da Financial Times, eu só traduzi)
Na eleição presidencial da Coreia do Sul em 2022, enquanto homens e mulheres mais velhos votaram de forma unificada, os jovens homens apoiaram fortemente o partido de direita People Power, enquanto as jovens mulheres apoiaram o partido liberal Democratic em números quase iguais e opostos.
A situação na Coreia é extrema, mas serve como um alerta para outros países sobre o que pode acontecer quando jovens homens e mulheres se distanciam. A sociedade está dividida, a taxa de casamento despencou e a taxa de natalidade caiu drasticamente, chegando a 0,78 filhos por mulher em 2022, o menor número no mundo todo.
Sete anos após a explosão inicial do movimento # MeToo, a divergência de gênero em atitudes tornou-se autossustentável.
Dados das pesquisas mostram que em muitos países, as diferenças ideológicas vão além dessa questão específica. A divisão progressista-conservadora sobre assédio sexual parece ter causado ou pelo menos faz parte de um alinhamento mais amplo, em que jovens homens e mulheres estão se organizando em grupos conservadores e liberais em outros assuntos.
Nos EUA, Reino Unido e Alemanha, as jovens mulheres agora adotam posturas mais liberais sobre temas como imigração e justiça racial, enquanto grupos etários mais velhos permanecem equilibrados. A tendência na maioria dos países tem sido de mulheres se inclinando mais para a esquerda, enquanto os homens permanecem estáveis. No entanto, há sinais de que os jovens homens estão se movendo para a direita na Alemanha, tornando-se mais críticos em relação à imigração e se aproximando do partido de extrema direita AfD nos últimos anos.
Seria fácil dizer que tudo isso é apenas uma fase passageira, mas os abismos ideológicos apenas crescem, e os dados mostram que as experiências políticas formativas das pessoas são difíceis de mudar. Tudo isso é agravado pelo fato de que o aumento dos smartphones e das redes sociais faz com que os jovens homens e mulheres agora vivam em espaços separados e tenham culturas distintas.
As opiniões dos jovens frequentemente são ignoradas devido à baixa participação política, mas essa mudança pode deixar consequências duradouras, impactando muito mais do que apenas os resultados das eleições.
Retirado de: https://www.ft.com/content/29fd9b5c-2f35-41bf-9d4c-994db4e12998
-
 @ 5f010feb:3ae9756b
2024-09-30 13:57:10
@ 5f010feb:3ae9756b
2024-09-30 13:57:10こんにちは。小牧りらです。 こちらは「Nostrasia2024 逆アドベントカレンダー」2日目の記事です。 1日目はしのさんの「Nostrasia イベントレポート #1」です。
この記事はオタクなら一度は考える夢、「コスプレ」(主語デカ)を夢見ていたオタクの、人生初のコスプレを記録したものです。
Nostrasia2024の開催が現実味を帯びる
2024年7月、四谷ラボDiscordで「Nostrasiaをもう一度。」と高まっていた機運が動き出しました。 Nostrasia2024の始動です。テイザーサイトの作成、サイトやNostr、Connpasでの告知に始まり、会場の選定、当日のタイムラインの作成など、7月〜9月前半でNostrasiaはその全貌を顕にしていきました。私はDiscordには入っているものの、仕事が忙しく(という言い訳)特に貢献もしないままグループを眺めていました。そんな中当日スタッフとして協力させていただけることとなり、何か盛り上がりに貢献できないか?と考えた結果、「コスプレするしかない」との結論に至りました。
1週間前に動き出すコスプレ製作記
以前から技術書典など「Nostr関連のイベントでNostr関連キャラクターのコスプレができたらな〜」、という思いや、「オタクたるもの人生で一度はちゃんとしたコスプレをしたい!」、という思いを抱えていた私。ではこのNostrasia2024で誰のコスプレをするか?が課題となっていきます。自律分散型コミュニティのNostr、日本人コミュニティも成立から1年以上が経過し、実に多くのキャラクターが生み出されてきました。その中でも直近で話題沸騰中のキャラクター、「りとりん」のコスプレをしよう!と思い、生みの親であるかすてらふぃさんとたーごいるさんの許可を得て製作に取り掛かりました。女オタクの聖地、池袋に繰り出しウィッグや毛糸などの買い出しを行いました(この時点で1週間前)。池袋は新しくなったアニメイトにコスプレコーナーがあったり、今回は入っていないですがウィッグ専門店のアシストウィッグさん、そしてユザワヤなどの手芸店に100均などコスプレに必要な資材を購入する店舗に事欠きません。3時間近く店舗を渡り歩いた結果、アニメイトとダイソーで必要な資材を揃えました。
資材一覧
<アニメイト>
・ピンクのウィッグ
・水色の毛束
・耳を取り付けるためのピン
・ピンクのアイブロウ
・ウィッグ固定用の両面テープ
<ダイソー>
・ピンクの毛糸(耳としっぽ)
・針金(耳としっぽの芯)
・ヘアアクセサリー(ヘアピン、ヘアゴム)
・ウィッグネット
・ペット用ブラシ
Nostrasia当日
平日仕事終わりに作業を進める時間もなく、前日、前々日の土日でぶっつけ本番のウィッグ製作に取り掛かりました。ミディアムボブのウィッグを、動画やメイキング記事を見ながら切ったり、毛束をつけたり、結んだり…。失敗したら即終了の緊張感が走る中、慎重に作業を進めていきます。並行してアクリル毛糸と針金でけも耳・けもしっぽを作りました。ペット用ブラシをガシガシして毛並みを作っていく作業、そしてその過程で発生した抜け毛はもはやリアル。膝の上にりとりんが居るのではないか、と思いながら作業を進めました。最終的に当日スタートのギリギリまで作業し(会場でポニテにしたり耳を取り付けたりしていました)、ギリギリオープニングには間に合いました。ウィッグを付けた瞬間は「重い!暑い!」となりましたが、意外と室内半日であれば耐えられるな、という感想でした。
 これはマグロを心待ちにするりとりん
これはマグロを心待ちにするりとりんまとめ
・とりあえず池袋に行けばなんとかなる
・ウィッグの構造に驚く
・ネットで調べれば扱い方、作り方が分かる
・製作には余裕を持って(当日会場で作業するな)
おわりに
Nostrasiaとりとりんというビッグウェーブに乗りながら、オタクとしての夢であったコスプレが実現できたこと、とても良い経験になりました!そして世の中のだいたいのものごとは調べてやったらなんとかなると感じました。次回、Nostr関連でコスプレする機会があればさらにバージョンアップしたりとりんをやりたい!という気持ちと、衣装製作も楽しめるキャラクターをやりたい!という気持ちが湧き上がってきました。その時はちゃんと工程管理します…。
3日目はjunさんの「Nostr のフォロワーネットワークにおけるクラスタリング係数」です。
-
 @ 76c71aae:3e29cafa
2024-08-13 04:30:00
@ 76c71aae:3e29cafa
2024-08-13 04:30:00On social media and in the Nostr space in particular, there’s been a lot of debate about the idea of supporting deletion and editing of notes.
Some people think they’re vital features to have, others believe that more honest and healthy social media will come from getting rid of these features. The discussion about these features quickly turns to the feasibility of completely deleting something on a decentralized protocol. We quickly get to the “We can’t really delete anything from the internet, or a decentralized network.” argument. This crowds out how Delete and Edit can mimic elements of offline interactions, how they can be used as social signals.
When it comes to issues of deletion and editing content, what matters more is if the creator can communicate their intentions around their content. Sure, on the internet, with decentralized protocols, there’s no way to be sure something’s deleted. It’s not like taking a piece of paper and burning it. Computers make copies of things all the time, computers don’t like deleting things. In particular, distributed systems tend to use a Kafka architecture with immutable logs, it’s just easier to keep everything around, as deleting and reindexing is hard. Even if the software could be made to delete something, there’s always screenshots, or even pictures of screens. We can’t provably make something disappear.
What we need to do in our software is clearly express intention. A delete is actually a kind of retraction. “I no longer want to associate myself with this content, please stop showing it to people as part of what I’ve published, stop highlighting it, stop sharing it.” Even if a relay or other server keeps a copy, and keeps sharing it, being able to clearly state “hello world, this thing I said, was a mistake, please get rid of it.” Just giving users the chance to say “I deleted this” is a way of showing intention. It’s also a way of signaling that feedback has been heard. Perhaps the post was factually incorrect or perhaps it was mean and the person wants to remove what they said. In an IRL conversation, for either of these scenarios there is some dialogue where the creator of the content is learning something and taking action based on what they’ve learned.
Without delete or edit, there is no option to signal to the rest of the community that you have learned something because of how the content is structured today. On most platforms a reply or response stating one’s learning will be lost often in a deluge of replies on the original post and subsequent posts are often not seen especially when the original goes viral. By providing tools like delete and edit we give people a chance to signal that they have heard the feedback and taken action.
The Nostr Protocol supports delete and expiring notes. It was one of the reasons we switched from secure scuttlebutt to build on Nostr. Our nos.social app offers delete and while we know that not all relays will honor this, we believe it’s important to provide social signaling tools as a means of making the internet more humane.
We believe that the power to learn from each other is more important than the need to police through moral outrage which is how the current platforms and even some Nostr clients work today.
It’s important that we don’t say Nostr doesn’t support delete. Not all apps need to support requesting a delete, some might want to call it a retraction. It is important that users know there is no way to enforce a delete and not all relays may honor their request.
Edit is similar, although not as widely supported as delete. It’s a creator making a clear statement that they’ve created a new version of their content. Maybe it’s a spelling error, or a new version of the content, or maybe they’re changing it altogether. Freedom online means freedom to retract a statement, freedom to update a statement, freedom to edit your own content. By building on these freedoms, we’ll make Nostr a space where people feel empowered and in control of their own media.
-
 @ 91687725:a0de48ea
2024-08-24 05:40:14
@ 91687725:a0de48ea
2024-08-24 05:40:14こんにちは。Kateです。
最近ちょっとお休みしていますが、日本でビットコインを専門に扱うDiamond Hands Magazineに寄稿したりしてます。
私がビットコインと出会ったのは2011年、まだビットコイン利用者はとても少なかった時代です。たまたま身内にビットコイン界隈の人がいました。もしかしたら今でいうビト妻だったかも?
まだビットコインが1ドル以下でおもちゃみたいな存在だった頃に知ったわけですが、その後勢いづいて、100ドル、1000ドルと価値が上がっていきました。
それを見て、ビットコインを少しずつ買って貯めておけば、将来リタイヤの蓄えになるかもと思ってお小遣い程度のビットコインを積立してました。でも、アクシデントで失くしちゃったんですよね。
その後、身内のごたごたで自分の生活が天地がひっくり返るように一変し、気がつけばカナダでただお金がないアジア系移民シングルマザー、しかも周りに家族が誰もいないという、非常にマイノリティな立場になりました。
人生、何事も経験。一度ビットコインを失くし、傷心もあり、数年はビットコインから離れました。でも気がつけばビットコインは冬の時代を終えて、また元気になっていたんですね。自分は海外でひとり子育てに追われ、なんとか生きてた感じですが!
ビットコインが500ドルくらいになっていた時に困窮していた私は、ふとペーパーウォレットと呼ばれた当時の携帯可能ウォレット?に0.5btc 残っていたのを発見して速攻換金しましたね。悔やまれます。
その後、2017年頃、カナダで当時大手の割と使い勝手のいい取引所があることを知って、再度ビットコイン貯蓄にチャレンジしました。2年ほどで、ほぼ1ビットコインと10ETHくらいあったんですけどね、今度は取引所の代表者が行方不明になり、またもやビットコインを失くしました。
ふつうだったら、もうやめますよね。2回もなくしたら。
けれど、自分はかつてインターネットが始まったころのワクワクを経験していました。90年代半ば、新宿にできたばかりのインターネットカフェで、GIFがかろうじて表示できるグレーのブラウザ画面と対面しました。世界を変える技術を体験した時の感動は今でも忘れられません。
(こう書くと立派なオバサンなのがバレちゃいますね。ビットコインネイティブ世代の中では年長者)
それから15年以上たって、初めてサトシナカモトのホワイトペーパーを読んだ時に、同じ衝撃を受けたのです。初めて実用化されたインターネット上で世界の誰とでも送り合えるマネー。その可能性は無限∞。
そのビットコインの進化を、実際に買ってみたり、使ってみたり、なくしたりしつつ、より深く知ろうと付き合ってきた自分は、いつの間にかビットコインを通して世の中のいろいろを見て考えるようになりました。
ビットコインが生まれ、実験段階を経て、すでに15年が経ちます。けれども、ビットコインは今でも多くの人から最も誤解されている技術・発明のように見えます。ここまで来たら、自分が生きている間に、ビットコインが世界とどう関わっていくのか見届けたいと思います!
そして、私自身がビットコインを知ることで発見した世界や新しい価値観を、誰かに伝えられたらいいなと願って、このブログをスタートすることにしました。
今回は自己紹介という形になりましたが、私がビットコインを通して学んだことや気づいたことをこれから少しづつアップしてみます!
週1くらいのペースで投稿が目標です。よろしくお願いします。
-
 @ 0e8c41eb:95ff0faa
2024-07-08 14:36:14
@ 0e8c41eb:95ff0faa
2024-07-08 14:36:14Chef's notes
Sprinkle a pinch of salt in a bowl. Sift 275 grams of flour above it. Make a well in the center of the flour and sprinkle the yeast into it. Add 50 grams of butter, 25 grams of sugar, and the egg. Pour in the milk and knead the dough with the mixer or by hand into a smooth dough. If necessary, add a bit more flour if the dough is too sticky. Form the dough into a ball. Let the dough rise covered with cling film at room temperature for 1 hour.
Peel the apples. Cut the apples and apricots into pieces. Cook the fruit with 150 grams of sugar and 50 ml of water in 15 minutes into a thick compote. Let this fruit filling cool.
Knead the dough again briefly and roll it out to a round sheet of about 28-30 cm in diameter, so that it fits well over the baking tin. Press the dough into the tin and press it well into the corners. Let the dough rise again for 10 minutes and cut off the excess edges.
Spread the fruit filling over the dough.
Mix the rest of the flour with the remaining 100 grams of butter and 100 grams of sugar and knead it with your fingers into a crumbly mixture. Sprinkle this crumble mixture over the fruit filling. Bake the tart in the preheated oven at 200°C for about 30 minutes until golden brown.
Variations: Only apple? Make this tart with 1 kilo of apples. High or low? You can also bake the crumble tart in a low tart tin of 30 cm diameter. If the fruit filling is a bit too voluminous, you can make double the crumble mixture and sprinkle it over the larger surface area.
Additional needs: Mixer with dough hooks or food processor Cling film Round baking tin with a diameter of 28-30 cm, greased
Details
- ⏲️ Prep time: 45 min + 1 hour Rising
- 🍳 Cook time: 30 minutes
- 🍽️ Servings: 8
Ingredients
- 375 grams flour
- 1 packet dried yeast (7 grams)
- 125 grams unsalted butter, at room temperature
- 275 grams sugar
- 1 egg
- 100 ml milk, at room temperature
- 500 grams apples
- 500 grams apricots (fresh or from a can)
Directions
- Sprinkle a pinch of salt in a bowl. Sift 275 grams of flour above it. Make a well in the center of the flour and sprinkle the yeast into it. Add 50 grams of butter, 25 grams of sugar, and the egg. Pour in the milk and knead the dough with the mixer or by hand into a smooth dough. If necessary, add a bit more flour if the dough is too sticky. Form the dough into a ball. Let the dough rise covered with cling film at room temperature for 1 hour.
- Peel the apples. Cut the apples and apricots into pieces. Cook the fruit with 150 grams of sugar and 50 ml of water in 15 minutes into a thick compote. Let this fruit filling cool.
- Knead the dough again briefly and roll it out to a round sheet of about 28-30 cm in diameter, so that it fits well over the baking tin. Press the dough into the tin and press it well into the corners. Let the dough rise again for 10 minutes and cut off the excess edges.
- Spread the fruit filling over the dough.
-
 @ dd664d5e:5633d319
2024-06-24 06:05:05
@ dd664d5e:5633d319
2024-06-24 06:05:05The new Great Library
We have all heard tales of Amazon or other booksellers banning customers from their bookstores or censoring/editing purchased books. The famous Project Gutenberg, and similar organizations, are performing a good work, to help protect many of our precious books from this fate, but it is merely a centralized website and therefore not censorship resistant. Also, it mostly posts books in English or German.
So, we at nostr:npub1s3ht77dq4zqnya8vjun5jp3p44pr794ru36d0ltxu65chljw8xjqd975wz have decided to move Project Gutenberg to Nostr and house it in the most distributed way possible: on relays. Specifically, our new, public Citadel relay for out-of-print books (and other documents), but also on any relay, anywhere.
And, because we are a very humble group, we're naming the effort "Alexandria". And the first book to be printed on Nostr is the Bible because obviously.
Why on relays?
Well, why not on relays? Relays are one of the few widely-distributed databases for documentation in existence. The relay database spans the entire globe and anyone can maintain their own relay on their personal computer or mobile phone.
That means that anyone can house their own books. Which books are their own? Any books they have in their own possession. Any books someone would have to physically pry out of their cold, dead, computer.
Notes are perfect for publishing
Once we begin generating eBooks from notes with an associated header (which will be quite easy to do, so long as they are written in markdown or similar), they will also be readable, downloadable, and storable in ePub format (see Pandoc). And it is, after all, only a matter of time until someone enterprising makes an ePaper Nostr client for calmer reading of notes, and then you can download and read them, without having to bother converting beforehand, which maintains their Nostr-navigation.
The new event kind 30040 allows us to take any sort of note containing any sort of characters and create a type of "note collection" or "book of notes", "journal of notes", "magazine of notes". And it can be nested or embedded in other notes, creating any sort of note-combination and note-hierarchy you can think of, only limited in size by the ability of your computer to processes the relationships.
Save the Zettels
The associated kind 30041 adds the prospect of breaking longer texts or articles up into sections or snippets (called "Zettel" in German). We can then collect or refer to particular bits of a longer text (like a chart, elegant paragraph or definition, data table), directly. Anyone can create such snippets, even of texts they didn't write, as they can add a reference to the original publication in the tags of the new event.
This means we no longer have to "copy-paste" or quote other people's works, we can simply tie them in. If we worry about them being deleted, we can fork them to create our own, digitally-linked version, and then tie that in. This means that source material can be tied to the new material, and you can trace back to the source easily (using Nostr IDs and tags, which are signed identifiers) and see who else is branching out from that source or discussing that source.
It's gonna be HUGE!
We are making a big, beautiful library... and you are going to build it for us. Anyone, anywhere can therefore publish or republish any document they wish, with Nostr, and store it wherever they have a relay, and view it on any client willing to display it.
You will own something and be happy.
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28comentário pertinente de Olavo de Carvalho sobre atribuições indevidas de acontecimentos à "ordem espontânea"
Eis aqui um exemplo entre outros mil, extraído das minhas apostilas de aulas, de como se analisam as relações entre fatores deliberados e casuais na ação histórica. O sr, Beltrão está INFINITAMENTE ABAIXO da possibilidade de discutir essas coisas, e por isso mesmo me atribui uma simploriedade que é dele próprio e não minha:
Já citei mil vezes este parágrafo de Georg Jellinek e vou citá-lo de novo: “Os fenômenos da vida social dividem-se em duas classes: aqueles que são determinados essencialmente por uma vontade diretriz e aqueles que existem ou podem existir sem uma organização devida a atos de vontade. Os primeiros estão submetidos necessariamente a um plano, a uma ordem emanada de uma vontade consciente, em oposição aos segundos, cuja ordenação repousa em forças bem diferentes.”
Essa distinção é crucial para os historiadores e os analistas estratégicos não porque ela é clara em todos os casos, mas precisamente porque não o é. O erro mais comum nessa ordem de estudos reside em atribuir a uma intenção consciente aquilo que resulta de uma descontrolada e às vezes incontrolável combinação de forças, ou, inversamente, em não conseguir enxergar, por trás de uma constelação aparentemente fortuita de circunstâncias, a inteligência que planejou e dirigiu sutilmente o curso dos acontecimentos.
Exemplo do primeiro erro são os Protocolos dos Sábios de Sião, que enxergam por trás de praticamente tudo o que acontece de mau no mundo a premeditação maligna de um número reduzidos de pessoas, uma elite judaica reunida secretamente em algum lugar incerto e não sabido.
O que torna essa fantasia especialmente convincente, decorrido algum tempo da sua publicação, é que alguns dos acontecimentos ali previstos se realizam bem diante dos nossos olhos. O leitor apressado vê nisso uma confirmação, saltando imprudentemente da observação do fato à imputação da autoria. Sim, algumas das idéias anunciadas nos Protocolos foram realizadas, mas não por uma elite distintamente judaica nem muito menos em proveito dos judeus, cuja papel na maioria dos casos consistiu eminentemente em pagar o pato. Muitos grupos ricos e poderosos têm ambições de dominação global e, uma vez publicado o livro, que em certos trechos tem lances de autêntica genialidade estratégica de tipo maquiavélico, era praticamente impossível que nada aprendessem com ele e não tentassem por em prática alguns dos seus esquemas, com a vantagem adicional de que estes já vinham com um bode expiatório pré-fabricado. Também é impossível que no meio ou no topo desses grupos não exista nenhum judeu de origem. Basta portanto um pouquinho de seletividade deformante para trocar a causa pelo efeito e o inocente pelo culpado.
Mas o erro mais comum hoje em dia não é esse. É o contrário: é a recusa obstinada de enxergar alguma premeditação, alguma autoria, mesmo por trás de acontecimentos notavelmente convergentes que, sem isso, teriam de ser explicados pela forca mágica das coincidências, pela ação de anjos e demônios, pela "mão invisível" das forças de mercado ou por hipotéticas “leis da História” ou “constantes sociológicas” jamais provadas, que na imaginação do observador dirigem tudo anonimamente e sem intervenção humana.
As causas geradoras desse erro são, grosso modo:
Primeira: Reduzir as ações humanas a efeitos de forças impessoais e anônimas requer o uso de conceitos genéricos abstratos que dão automaticamente a esse tipo de abordagem a aparência de coisa muito científica. Muito mais científica, para o observador leigo, do que a paciente e meticulosa reconstituição histórica das cadeias de fatos que, sob um véu de confusão, remontam às vezes a uma autoria inicial discreta e quase imperceptível. Como o estudo dos fenômenos histórico-políticos é cada vez mais uma ocupação acadêmica cujo sucesso depende de verbas, patrocínios, respaldo na mídia popular e boas relações com o establishment, é quase inevitável que, diante de uma questão dessa ordem, poucos resistam à tentação de matar logo o problema com duas ou três generalizações elegantes e brilhar como sábios de ocasião em vez de dar-se o trabalho de rastreamentos históricos que podem exigir décadas de pesquisa.
Segunda: Qualquer grupo ou entidade que se aventure a ações histórico-políticas de longo prazo tem de possuir não só os meios de empreendê-las, mas também, necessariamente, os meios de controlar a sua repercussão pública, acentuando o que lhe convém e encobrindo o que possa abortar os resultados pretendidos. Isso implica intervenções vastas, profundas e duradouras no ambiente mental. [Etc. etc. etc.]
(no facebook em 17 de julho de 2013)
-
 @ bcea2b98:7ccef3c9
2025-01-03 22:31:38
@ bcea2b98:7ccef3c9
2025-01-03 22:31:38originally posted at https://stacker.news/items/835751
-
 @ 3bf0c63f:aefa459d
2024-01-14 13:55:28
@ 3bf0c63f:aefa459d
2024-01-14 13:55:28Um algoritmo imbecil da evolução
Suponha que você queira escrever a palavra BANANA partindo de OOOOOO e usando só alterações aleatórias das letras. As alterações se dão por meio da multiplicação da palavra original em várias outras, cada uma com uma mudança diferente.
No primeiro período, surgem BOOOOO e OOOOZO. E então o ambiente decide que todas as palavras que não começam com um B estão eliminadas. Sobra apenas BOOOOO e o algoritmo continua.
É fácil explicar conceber a evolução das espécies acontecendo dessa maneira, se você controlar sempre a parte em que o ambiente decide quem vai sobrar.
Porém, há apenas duas opções:
- Se o ambiente decidir as coisas de maneira aleatória, a chance de você chegar na palavra correta usando esse método é tão pequena que pode ser considerada nula.
- Se o ambiente decidir as coisas de maneira pensada, caímos no //design inteligente//.
Acredito que isso seja uma enunciação decente do argumento "no free lunch" aplicado à crítica do darwinismo por William Dembski.
A resposta darwinista consiste em dizer que não existe essa BANANA como objetivo final. Que as palavras podem ir se alterando aleatoriamente, e o que sobrar sobrou, não podemos dizer que um objetivo foi atingido ou deixou de sê-lo. E aí os defensores do design inteligente dirão que o resultado ao qual chegamos não pode ter sido fruto de um processo aleatório. BANANA é qualitativamente diferente de AYZOSO, e aí há várias maneiras de "provar" que sim usando modelos matemáticos e tal.
Fico com a impressão, porém, de que essa coisa só pode ser resolvida como sim ou não mediante uma discussão das premissas, e chega um ponto em que não há mais provas matemáticas possíveis, apenas subjetividade.
Daí eu me lembro da minha humilde solução ao problema do cão que aperta as teclas aleatoriamente de um teclado e escreve as obras completas de Shakespeare: mesmo que ele o faça, nada daquilo terá sentido sem uma inteligência de tipo humano ali para lê-las e perceber que não se trata de uma bagunça, mas sim de um texto com sentido para ele. O milagre se dá não no momento em que o cão tropeça no teclado, mas no momento em que o homem olha para a tela.
Se o algoritmo da evolução chegou à palavra BANANA ou UXJHTR não faz diferença pra ela, mas faz diferença para nós, que temos uma inteligência humana, e estamos observando aquilo. O homem também pensaria que há //algo// por trás daquele evento do cão que digita as obras de Shakespeare, e como seria possível alguém em sã consciência pensar que não?