-
 @ 5d4b6c8d:8a1c1ee3
2024-07-14 13:50:54
@ 5d4b6c8d:8a1c1ee3
2024-07-14 13:50:54Yesterday's edition https://stacker.news/items/607040/r/Undisciplined
Happy July 14th, everyone. America narrowly averted a civil war last night and I'm pretty happy about that. I was impressed by how well Stacker News covered the biggest breaking news event of the site's existence. People were pulling together lots of sources and offering generally measured thoughts.
-
- -
July 14, 2023 📅
📝
TOP POSTCommon psychological biases that bitcoiners have
Excerpt
One of the primary reasons I got involved with markets is my interest in psychology. Humans are a fickle bunch, and it's fascinating to observe the human condition in such a clear, mathematical way.
3217 sats \ 11 comments \ @birdeye21 \ ~bitcoin
💬
TOP COMMENThttps://stacker.news/items/208075/r/Undisciplined?commentId=208936
Excerpt
I get your point, but this seems to me one of the (rare) differences where "technically possible but empirically infeasible" vs "technically impossible" matters a lot.
1128 sats \ 3 replies \ @elvismercury
From Portable experiences by @k00b in ~nostr
🏆
TOP STACKER2nd place @k00b (1st hiding, presumed @siggy47)
7947 stacked \ 10.5k spent \ 3 posts \ 12 comments \ 0 referrals
🗺️
TOP TERRITORY~bitcoin
everything bitcoin related
founded by @k00b on Tue May 02 2023
37.3k stacked \ 0 revenue \ 51.8k spent \ 95 posts \ 214 comments
https://imgprxy.stacker.news/fsFoWlgwKYsk5mxx2ijgqU8fg04I_2zA_D28t_grR74/rs:fit:960:540/aHR0cHM6Ly9tLnN0YWNrZXIubmV3cy8yMzc5Ng
July 14, 2022 📅
📝
TOP POSTPine – A bitcoin wallet w/ a messenger-like UI || A BTC Wallet UX for the masses
Link to https://pine.pm/
509 sats \ 15 comments \ @Spartan \ ~bitcoin
💬
TOP COMMENThttps://stacker.news/items/44747/r/Undisciplined?commentId=45060
Excerpt
The user @darthcoin has way to many guides from wich you can learn a lot IMO, he is active here to most of the time, though I dont know if I've @ him correctly.
300 sats \ 4 replies \ @bangbang_u_r_done
From Any Good Routing Node Strategies? by @andyleroy in ~bitcoin
🏆
TOP STACKER1st place @nerd2ninja
544 stacked \ 1765 spent \ 3 posts \ 17 comments \ 0 referrals
🗺️
TOP TERRITORY~bitcoin
everything bitcoin related
founded by @k00b on Tue May 02 2023
14.6k stacked \ 0 revenue \ 31.6k spent \ 133 posts \ 261 comments
https://imgprxy.stacker.news/fsFoWlgwKYsk5mxx2ijgqU8fg04I_2zA_D28t_grR74/rs:fit:960:540/aHR0cHM6Ly9tLnN0YWNrZXIubmV3cy8yMzc5Ng
July 14, 2021 📅
📝
TOP POSTHow Bitcoin And Green Energy Can Save Ethiopia’s Economy
Link to https://stacker.news/items/320/r/Undisciplined
2 sats \ 1 comment \ @0268486dc4 \ ~bitcoin
💬
TOP COMMENThttps://stacker.news/items/332/r/Undisciplined?commentId=333
Excerpt
From the Twitter announcement
Students will learn how to build #Bitcoin applications from the ground up using the Rust programming language. […]
18 sats \ 0 replies \ @sha256
From Fodé Diop Launches a Bitcoin Academy by @sha256 in ~bitcoin
🏆
TOP STACKER1st place @sha256
4 stacked \ 5 spent \ 2 posts \ 1 comment \ 0 referrals
🗺️
TOP TERRITORY~bitcoin
everything bitcoin related
founded by @k00b on Tue May 02 2023
10 stacked \ 0 revenue \ 47 spent \ 9 posts \ 8 comments
originally posted at https://stacker.news/items/608036
-
-
 @ b2caa9b3:9eab0fb5
2024-07-14 10:52:36
@ b2caa9b3:9eab0fb5
2024-07-14 10:52:36The African sun is warming things up here at Kilimanjaro, but there's still a crispness in the morning air. My fleece jacket came in handy after a refreshing shower! I started my day with a perfect combo: coffee and breakfast on the rooftop, with a stunning view as my backdrop.
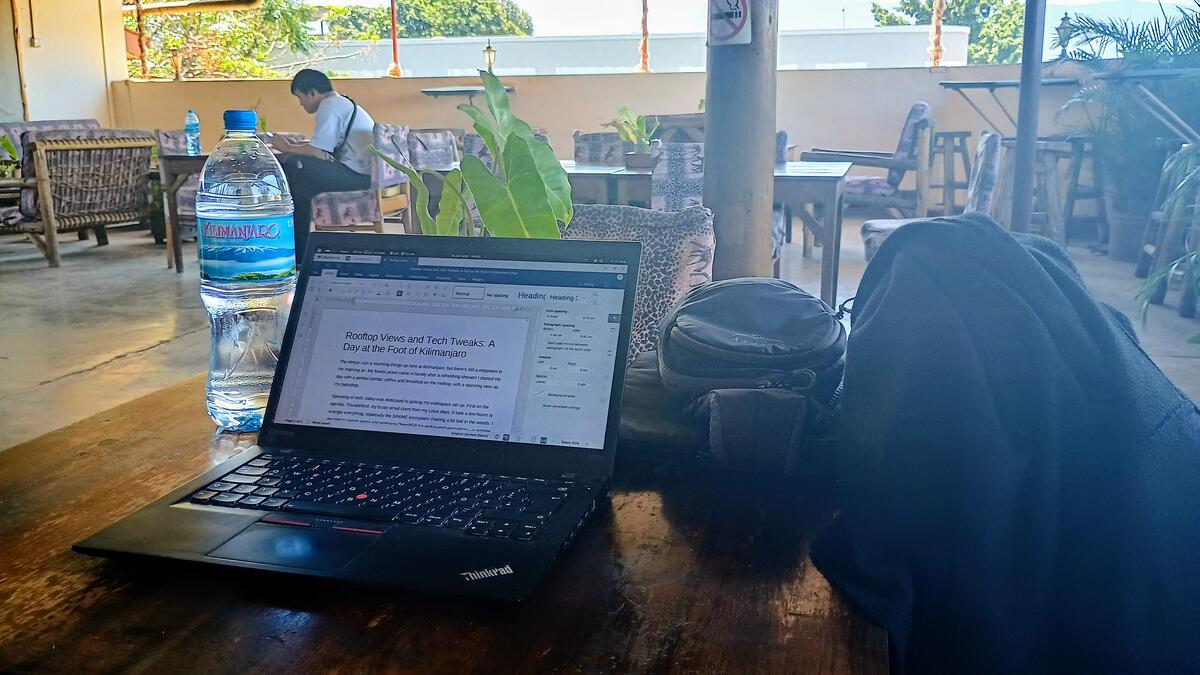
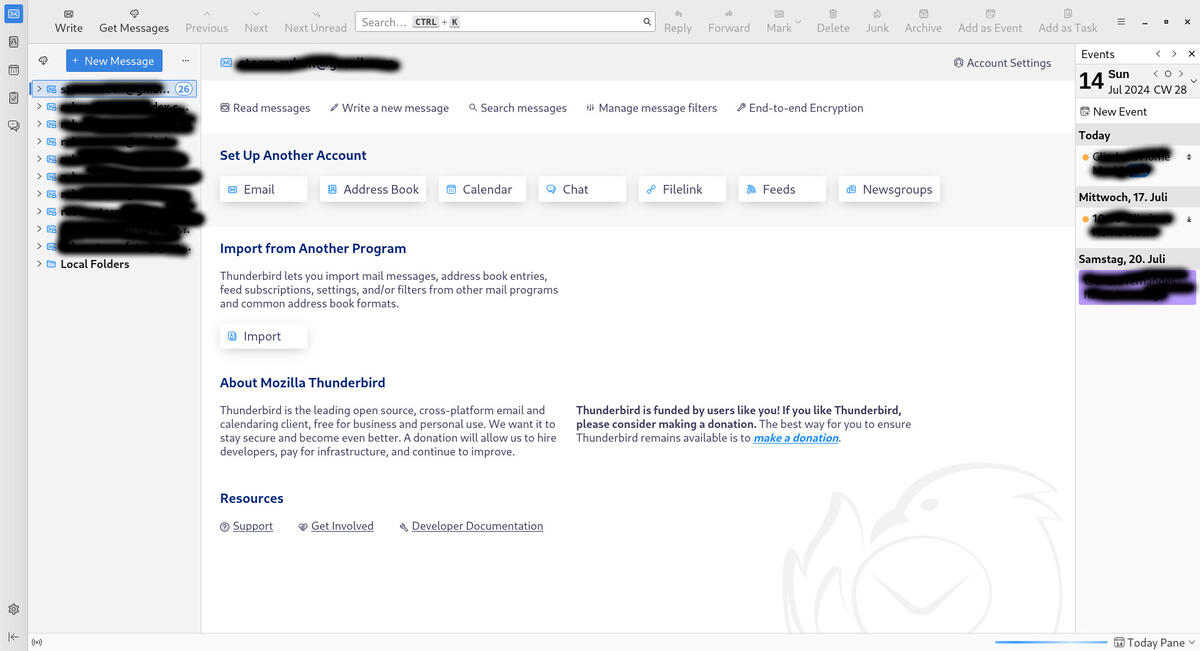
Speaking of tech, today was dedicated to getting my workspace set up. First on the agenda: Thunderbird, my trusty email client from my Linux days. It took a few hours to wrangle everything, especially the S/MIME encryption. Feeling a bit lost in the weeds, I decided to switch gears and embrace OpenPGP for end-to-end encryption – a simpler solution in my opinion.
Just as I finished conquering Thunderbird, Kilimanjaro itself decided to make an appearance! The clouds parted to reveal the majestic peak, and I couldn't resist capturing the moment with a couple of photos.
Today's another day with no set plans, just taking things minute by minute. Soaking up the beautiful scenery, the cool mornings, and the positive vibes. As soon as my foot heals, I'll be out exploring the town, snapping photos, and enjoying a delicious coffee at a local cafe.

Speaking of exploring, the world of NFTs has piqued my interest. I have a few on Opensea and WAX Blockchain, but I'm curious – where else are people showcasing their digital art? Let me know in the comments where you buy and sell your NFTs, or if they're just patiently waiting for a better future. I'd love to hear your NFT stories!

Life has a way of taking us on unexpected journeys. So, here's to embracing the unexpected, making the most of each situation, and maybe even finding a small online job to boost my budget. Wishing you all a wonderful day – and remember, don't stress yourself!
Online
Feel free to support me by sending some sats via the lightning network to rubenstorm@sats.mobi
-
 @ 6be5cc06:5259daf0
2024-12-29 19:54:14
@ 6be5cc06:5259daf0
2024-12-29 19:54:14Um dos padrões mais bem estabelecidos ao medir a opinião pública é que cada geração tende a seguir um caminho semelhante em termos de política e ideologia geral. Seus membros compartilham das mesmas experiências formativas, atingem os marcos importantes da vida ao mesmo tempo e convivem nos mesmos espaços. Então, como devemos entender os relatórios que mostram que a Geração Z é hiperprogressista em certos assuntos, mas surpreendentemente conservadora em outros?
A resposta, nas palavras de Alice Evans, pesquisadora visitante na Universidade de Stanford e uma das principais estudiosas do tema, é que os jovens de hoje estão passando por um grande divergência de gênero, com as jovens mulheres do primeiro grupo e os jovens homens do segundo. A Geração Z representa duas gerações, e não apenas uma.
Em países de todos os continentes, surgiu um distanciamento ideológico entre jovens homens e mulheres. Milhões de pessoas que compartilham das mesmas cidades, locais de trabalho, salas de aula e até casas, não veem mais as coisas da mesma maneira.
Nos Estados Unidos, os dados da Gallup mostram que, após décadas em que os sexos estavam distribuídos de forma relativamente equilibrada entre visões políticas liberais e conservadoras, as mulheres entre 18 e 30 anos são agora 30 pontos percentuais mais liberais do que os homens dessa faixa etária. Essa diferença surgiu em apenas seis anos.
A Alemanha também apresenta um distanciamento de 30 pontos entre homens jovens conservadores e mulheres jovens progressistas, e no Reino Unido, a diferença é de 25 pontos. Na Polônia, no ano passado, quase metade dos homens entre 18 e 21 anos apoiou o partido de extrema direita Confederation, em contraste com apenas um sexto das jovens mulheres dessa mesma idade.
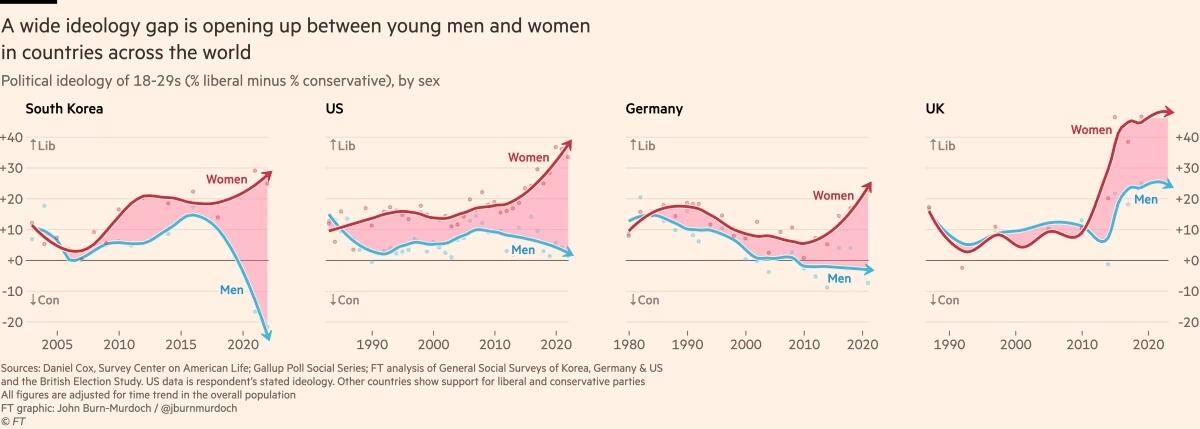
Fora do Ocidente, há divisões ainda mais acentuadas. Na Coreia do Sul, há um enorme abismo entre homens e mulheres jovens, e a situação é semelhante na China. Na África, a Tunísia apresenta o mesmo padrão. Vale notar que em todos os países essa divisão drástica ocorre principalmente entre a geração mais jovem, sendo muito menos pronunciada entre homens e mulheres na faixa dos 30 anos ou mais velhos.
O movimento # MeToo foi o principal estopim, trazendo à tona valores feministas intensos entre jovens mulheres que se sentiram empoderadas para denunciar injustiças de longa data. Esse estopim encontrou especialmente terreno fértil na Coreia do Sul, onde a desigualdade de gênero é bastante visível e a misoginia explícita é comum. (palavras da Financial Times, eu só traduzi)
Na eleição presidencial da Coreia do Sul em 2022, enquanto homens e mulheres mais velhos votaram de forma unificada, os jovens homens apoiaram fortemente o partido de direita People Power, enquanto as jovens mulheres apoiaram o partido liberal Democratic em números quase iguais e opostos.
A situação na Coreia é extrema, mas serve como um alerta para outros países sobre o que pode acontecer quando jovens homens e mulheres se distanciam. A sociedade está dividida, a taxa de casamento despencou e a taxa de natalidade caiu drasticamente, chegando a 0,78 filhos por mulher em 2022, o menor número no mundo todo.
Sete anos após a explosão inicial do movimento # MeToo, a divergência de gênero em atitudes tornou-se autossustentável.
Dados das pesquisas mostram que em muitos países, as diferenças ideológicas vão além dessa questão específica. A divisão progressista-conservadora sobre assédio sexual parece ter causado ou pelo menos faz parte de um alinhamento mais amplo, em que jovens homens e mulheres estão se organizando em grupos conservadores e liberais em outros assuntos.
Nos EUA, Reino Unido e Alemanha, as jovens mulheres agora adotam posturas mais liberais sobre temas como imigração e justiça racial, enquanto grupos etários mais velhos permanecem equilibrados. A tendência na maioria dos países tem sido de mulheres se inclinando mais para a esquerda, enquanto os homens permanecem estáveis. No entanto, há sinais de que os jovens homens estão se movendo para a direita na Alemanha, tornando-se mais críticos em relação à imigração e se aproximando do partido de extrema direita AfD nos últimos anos.
Seria fácil dizer que tudo isso é apenas uma fase passageira, mas os abismos ideológicos apenas crescem, e os dados mostram que as experiências políticas formativas das pessoas são difíceis de mudar. Tudo isso é agravado pelo fato de que o aumento dos smartphones e das redes sociais faz com que os jovens homens e mulheres agora vivam em espaços separados e tenham culturas distintas.
As opiniões dos jovens frequentemente são ignoradas devido à baixa participação política, mas essa mudança pode deixar consequências duradouras, impactando muito mais do que apenas os resultados das eleições.
Retirado de: https://www.ft.com/content/29fd9b5c-2f35-41bf-9d4c-994db4e12998
-
 @ e97aaffa:2ebd765d
2024-07-14 09:57:13
@ e97aaffa:2ebd765d
2024-07-14 09:57:13Estamos numa época tão estranha da humanidade…
Onde alguns querem reescrever a história, em vez de aprender e evoluir com a mesma. São com os erros que se cresce.
Onde o termo fascista é sinónimo de alguém com uma opinião diferente da sua, sem minimamente saber o real significado dessa palavra.
Onde defendem uma liberdade, que proíba o contraditório.
Onde não se discutem ideias, mas sim combatem ideias.
Onde o ambientalmente sustentável é substituir árvores e zonas verdes por estruturas em aço e zonas negras.
Onde os políticos constroem casas ou cidades, literalmente, em cima dos rios mas depois a culpa das cheias é as alterações climáticas.
Onde os alimentos tem menos importância que um peido de uma vaca.
Onde pessoas defendem que a solução para o aquecimento, é morrer de frio.
Onde a igualdade é favorecer um grupo, em detrimento de outro.
Onde o essencial é viver para consumir, em vez de usufruir.
Onde o importante é ser rico e ostentar essa mesma riqueza, mesmo que tenha de espezinhar outros para a conquistar.
Onde o mais importante é parecer em vez de ser.
Onde políticos defendem que o conhecimento pode levar a escolhas erradas, defendem o carneirismo.
Onde um político define o que é verdade ou mentira, limitando o que as pessoas podem expressar. Mas quem controla o controlador.
Onde os revisores da verdade deixaram de estar num gabinete, passando a ser um exército de jovens atrás de um teclado.
Onde, são propostas e aprovadas limitações de liberdade, sem esclarecimento ou divulgação pública. Pior que a obscuridade, é desinteresse da comunidade por liberdade.
Onde a censura é o novo normal, defender o contrário é que é censurável.
Onde a imprensa é tão livre como uma pomba dentro de sua gaiola.
Onde, quem comete o crime é protegido, quem o denúncia é perseguido.
Onde o certo é pensar com a cabeça dos outros, sem questionar.
Onde os pais delegaram o papel de educar às escolas e aos ecrãs azuis.
Onde a escola deixou de ser um lugar de conhecimento e/ou do desenvolvimento do espírito crítico.
Onde as crianças crescem doutrinados por políticos e por AI.
Onde a sociedade é programada e com um destino predefinido, como um rato dentro da sua roda.
Onde o maior erro, é pretender construir seres que não cometem erros, que não tenham vícios. Quando isso acontecer, deixamos de ser humanos. A imperfeição é a essência dos seres humanos, é o que nos difere das máquinas.
Onde só se ensina a não cair, em vez de ajudar e incentivar a levantar.
Onde se suspende a liberdade de circulação e os direitos mais básicos, sem ninguém questionar.
Onde a privacidade é crime.
Onde Satoshi é excomungado, mas Miguel Tiago é idoleterado.
Onde a moeda é utilizado como uma arma.
Onde uma guerra é digladiada entre zeros e uns, sem o comum mortal aperceber da sua existência.
Onde crianças caem em campos de batalha, como folhas em pleno outono.
Onde o direito ao Livre-arbítrio está sob ameaça.
-
 @ 6f3670d9:03f04036
2024-12-29 08:20:22
@ 6f3670d9:03f04036
2024-12-29 08:20:22Disclaimer: - This will void your warranty - There might be differences between the Bitaxe and the Lucky Miner that might not cause issues or damage immediately, but might manifest long-term - Proceed at your own risk
A Different Pickaxe
You live in a place where it's difficult to get a Bitaxe. You have access to AliExpress. You look around. You find something called the "Lucky Miner LV06". A Bitaxe clone that uses the same mining chip as the Bitaxe Ultra (BM1366 ASIC). You buy one.
You plug it in, you enter your wallet address and other settings, and it starts mining. It works! Great!
But it's running a customized firmware. It's not AxeOS. Maybe there's something shady in the stock firmware. It's not open-source, after all. Also, AxeOS looks amazing... And that automatic pool fail-over feature is handy.
You think to yourself: "Maybe I can use the Bitaxe firmware on this?". Guess what? You're right!
Flashing From Web UI
What usually works for me is to: - Download the Bitaxe firmware files (
esp-miner.binandwww.bin) from GitHub (here). Version 2.4.1 seems to work well, as of this writing. - Then from the Lucky Miner web interface, upload the "Website" (www.bin) file. - Wait for a minute or two after it's done uploading. - Upload the "Firmware" (esp-miner.bin) file. - Wait another minute or two. - Unplug the power and plug it back in. - Set the "Core Voltage" and "Frequency" to the defaults. - Unplug the power and plug it back in again.If you're lucky (no pun intended), you'll have a working Lucky Miner with AxeOS. Update the settings and mine away!
However, often times I've been unlucky, like what happened while I was writing this article, ironically. The miner malfunctions for no obvious reason. It keeps rebooting, or it's not mining (zero/low hashrate), or the web interface is inaccessible. You name it.
The miner has become a "brick". How do you "unbrick" it?
When you brick a Bitaxe, you can recover it by flashing (uploading) a "Factory Image". The Bitaxe has a USB port that makes this easy. Follow the guide and it should come back to life again. Unfortunately, the Lucky Miner LV06 doesn't have a USB port. It has a serial port, though. We'll have to get our hands a bit dirty.
Flashing Using the Serial Port
We need to connect the serial port of the miner to a computer and run a program to flash (upload) the firmware file on the miner. Any 3.3v UART serial port should be sufficient. Unfortunately, PCs don't usually come with a UART serial port these days, let alone a 3.3v one. The serial port common in old computers is an RS-232 port, which will most probably fry your miner if you try to connect it directly. Beware.
In my case, as a serial port for my PC, I'm using an Arduino Due I had lying around. We connect it to the PC through USB, and on the other side we connect a few wires to the miner, which gives the PC access to the miner.
WARNING: Make sure your serial port is 3.3v or you will probably kill the miner. Arduino Uno is 5v not 3.3v, for example, and cannot be used for this.
Wiring
First, we need to open the Lucky Miner. Use a small flat screwdriver to gently push the two plastic clips shown in the picture below. Gently pry the top cover away from the bottom cover on the clips side first, then remove the other side. Be careful not to break the display cable.
Once the cover is off, you can find the miner's serial port in the top right corner (J10), as shown in the next picture. We'll also need the reset button (EN).
There are three screws holding the PCB and the bottom cover together. If you're confident in your ability to push the small button on the underside of the PCB with the bottom cover on, then no need to remove these. The following picture shows what we need from that side.
And the next picture shows the pins and USB port we will use from the Arduino.
Now, we need to connect: - The USB port on the Arduino labelled "programming" to the PC - Pin 18 (TX1) on the Arduino to J10 through-hole pad 5 (blue dot) - Pin 19 (RX1) on the Arduino to J10 through-hole pad 3 (green dot) - Any GND pin on the Arduino to J10 through-hole pad 4 (yellow dot)
I didn't need to solder the wires to the pads. Keeping everything stable, perhaps by putting a weight on the wires or a bit of tape, was sufficient in all my attempts.
Setting up the Arduino
To use the Arduino as a serial port for our PC, we'll have to make it pass-through data back and forth between the USB port and UART1, where we connected the miner.
The following steps are all done on a PC running Debian Linux (Bookworm), in the spirit of freedom and open-source.
First, we start the Arduino IDE. If the package for the Arduino Due board is not already installed, you'll see a small prompt at the bottom. Click "Install this package".
Click the "Install" button.
Once the package is installed, click "Close".
Next, we select the Due board. Click the "Tools" menu, select "Board", select "Arduino ARM (32-bits) Boards" and click "Arduino Due (Programming Port)"
Next, we select the port. Click the "Tools" menu again, select "Port", and click the port where the Arduino is connected. In my case it was "/dev/ttyACM0".
Now we need to upload the following code to the Arduino board. The code is actually the "SerialPassthrough" example from the IDE, but with the serial speed changed to match the miner.
``` void setup() { Serial.begin(115200); Serial1.begin(115200); }
void loop() { if (Serial.available()) { // If anything comes in Serial (USB), Serial1.write(Serial.read()); // read it and send it out Serial1 }
if (Serial1.available()) { // If anything comes in Serial1 Serial.write(Serial1.read()); // read it and send it out Serial (USB) } } ```
Copy/paste the code into the IDE and click upload. You'll see "Done uploading" at the bottom.
Next we'll test if we're receiving data from the miner. We start by opening the "Serial Monitor" from the "Tools" menu in the IDE. Then we change the baudrate to 115200.
Set the Arduino and the miner in a comfortable position, make sure the wires are held in place and got a good contact on both sides, and the power is plugged in.
Now we'll put the miner in "download" mode. Press and hold the button on the underside (K1), press and release the reset button (EN), then release the other button (K1).
You should see some text from the miner in the serial monitor window, like in the picture below.
Congratulations! We know we're able to receive data from the miner now. We're not sure transmit is working, but we'll find out when we try to flash.
Flashing Using the Serial Port, for Real
To flash the Lucky Miner we'll need a software tool named esptool and the factory image firmware file.
I usually use "esp-miner-factory-205-v2.1.8.bin" for the factory image (this one) as a base, and then flash the version I want from the Web UI, using the steps I mentioned earlier.
For esptool, the documentation (here) shows us how to install it. To make things a little easier on our Debian Linux system, we'll use pipx instead of pip. The instructions below are adapted for that.
First we make sure pipx is installed. Run this command in a terminal and follow the instructions:
sudo apt-get install pipxThen we install esptool using pipx. Run the following in a terminal:
pipx install esptoolThe output will be something like this:
user@pc:~$ pipx install esptool installed package esptool 4.8.1, installed using Python 3.11.2 These apps are now globally available - esp_rfc2217_server.py - espefuse.py - espsecure.py - esptool.py ⚠️ Note: '/home/user/.local/bin' is not on your PATH environment variable. These apps will not be globally accessible until your PATH is updated. Run `pipx ensurepath` to automatically add it, or manually modify your PATH in your shell's config file (i.e. ~/.bashrc). done! ✨ 🌟 ✨We can see pipx telling us we won't be able to run our tool because the folder where it was installed is not in the PATH variable. To fix that, we can follow pipx instructions and run:
pipx ensurepathAnd we'll see something like this:
``` user@pc:~$ pipx ensurepath Success! Added /home/user/.local/bin to the PATH environment variable.
Consider adding shell completions for pipx. Run 'pipx completions' for instructions.
You will need to open a new terminal or re-login for the PATH changes to take effect.
Otherwise pipx is ready to go! ✨ 🌟 ✨ ```
Now, close the terminal and re-open it so that esptool becomes available.
Finally, to actually flash the miner, put the miner in download mode, then in the following command change the port ("/dev/ttyACM0") to your serial port, as we've seen earlier, and the file path to where your firmware file is, and run it:
esptool.py -p /dev/ttyACM0 --baud 115200 write_flash --erase-all 0x0 ~/Downloads/esp-miner-factory-205-v2.1.8.binIf everything went fine, the tool will take a few minutes to flash the firmware to the miner. You'll see something like this in the output:
``` user@pc:~$ esptool.py -p /dev/ttyACM0 --baud 115200 write_flash --erase-all 0x0 ~/Downloads/esp-miner-factory-205-v2.1.8.bin esptool.py v4.8.1 Serial port /dev/ttyACM0 Connecting..... Detecting chip type... ESP32-S3 Chip is ESP32-S3 (QFN56) (revision v0.2) Features: WiFi, BLE, Embedded PSRAM 8MB (AP_3v3) Crystal is 40MHz MAC: 3c:84:27:ba:be:01 Uploading stub... Running stub... Stub running... Configuring flash size... Erasing flash (this may take a while)... Chip erase completed successfully in 9.5s Compressed 15802368 bytes to 1320190... Wrote 15802368 bytes (1320190 compressed) at 0x00000000 in 152.1 seconds (effective 831.2 kbit/s)... Hash of data verified.
Leaving... Hard resetting via RTS pin... ```
And we're done! Hopefully the miner will be recovered now.
Hope this helps!
Stay humble,
dumb-packageA Warning About Beta Versions of AxeOS
For reasons unknown to me, while I was writing this article I wanted to try the testing version of AxeOS, which was v2.4.1b (beta). Flashing from Web UI went smooth, but the miner stopped mining. I flashed back to v2.1.8 using the serial port, a known good version for me, but it wouldn't mine, still.
Thankfully, v2.4.1 was released recently, and flashing it from the Web UI magically revived my miner. So, be warned.
Bonus: File Hashes
For convenience, these are the SHA256 hashes of the files I used in this article: ``` da24fceb246f3b8b4dd94e5143f17bd38e46e5285e807ebd51627cb08f665c0a ESP-Miner-v2.4.1/esp-miner.bin 16c5c671391f0e3e88a3e79ce33fad3b0ec232b8572fad5e1e0d1ad3251ab394 ESP-Miner-v2.4.1/www.bin
d5182a15b6fa21d7b9b31bff2026d30afed9d769781a48db914730a5751e20c6 esp-miner-factory-205-v2.1.8.bin ```
-
 @ 700c6cbf:a92816fd
2024-07-14 00:51:44
@ 700c6cbf:a92816fd
2024-07-14 00:51:44... something else
This is the final image. Or is it? Likely, it is not. I have already started on a perfect version of my Mother Earth painting.
Of course, there is no such thing as a perfect painting. What I mean is that I already started on a vector version of Mother Earth. You're familiar with vector vs. pixel, right?
But let's start at the beginning, not the end.
This here is a pic from the sketching phase. I am not one who can just magically and with a few strokes produce an amazing sketch of something that resembles a human. There are artists out there that do this wonderfully. It's amazing but it is not me (unfortunately).

Here I am starting to color in the sketch with a watercolor brush. This is all done in Procreate App on an iPad Pro. The coloring is on a separate layer with the pencil sketch set to multiply to shine through the colors. That's why the pencil strokes now are black. I like that look.

And here, I am almost done. Just need to decide on the background color. And as you can see from the gif and video I didn't really decide. Though at the moment I am favoring that muted pinkish red - LOL

Which color is your favorite?


Here you can see the whole process in a timelapse. Above pictures were grabbed from it to detail the process a little.
https://cdn.satellite.earth/05774dcaaf4679c34cbeb46cb43b4c4f85553a3d2b4850a7256d26a871b0c4f3.mp4
And that's it my Nostr friends for my first longform post in this community.
I hope you enjoyed this post. Comments are encouraged an appreciated. Thank you.
Cheers, OceanBee
-
 @ 9edd72eb:cb697b0a
2024-07-13 22:16:45
@ 9edd72eb:cb697b0a
2024-07-13 22:16:45If one knows exactly what to do to alleviate one's pain, comfort oneself, and emerge more or less unscathed from Adversity, I think it can be said that one has reached a fairly high level of Wisdom in Life.
originally posted at https://stacker.news/items/607422
-
 @ 6f3670d9:03f04036
2024-12-29 06:51:25
@ 6f3670d9:03f04036
2024-12-29 06:51:25This is my first long-form post. The starting line.
There's nothing of value here. Just using this as a marker.
I hope to post a lot more. Documenting how I made something work would be very useful to me, and hopefully others, but I've been too lazy to do that. Wish me luck!
Stay humble,
dumb-package -
 @ 16d11430:61640947
2024-12-23 16:47:01
@ 16d11430:61640947
2024-12-23 16:47:01At the intersection of philosophy, theology, physics, biology, and finance lies a terrifying truth: the fiat monetary system, in its current form, is not just an economic framework but a silent, relentless force actively working against humanity's survival. It isn't simply a failed financial model—it is a systemic engine of destruction, both externally and within the very core of our biological existence.
The Philosophical Void of Fiat
Philosophy has long questioned the nature of value and the meaning of human existence. From Socrates to Kant, thinkers have pondered the pursuit of truth, beauty, and virtue. But in the modern age, the fiat system has hijacked this discourse. The notion of "value" in a fiat world is no longer rooted in human potential or natural resources—it is abstracted, manipulated, and controlled by central authorities with the sole purpose of perpetuating their own power. The currency is not a reflection of society’s labor or resources; it is a representation of faith in an authority that, more often than not, breaks that faith with reckless monetary policies and hidden inflation.
The fiat system has created a kind of ontological nihilism, where the idea of true value, rooted in work, creativity, and family, is replaced with speculative gambling and short-term gains. This betrayal of human purpose at the systemic level feeds into a philosophical despair: the relentless devaluation of effort, the erosion of trust, and the abandonment of shared human values. In this nihilistic economy, purpose and meaning become increasingly difficult to find, leaving millions to question the very foundation of their existence.
Theological Implications: Fiat and the Collapse of the Sacred
Religious traditions have long linked moral integrity with the stewardship of resources and the preservation of life. Fiat currency, however, corrupts these foundational beliefs. In the theological narrative of creation, humans are given dominion over the Earth, tasked with nurturing and protecting it for future generations. But the fiat system promotes the exact opposite: it commodifies everything—land, labor, and life—treating them as mere transactions on a ledger.
This disrespect for creation is an affront to the divine. In many theologies, creation is meant to be sustained, a delicate balance that mirrors the harmony of the divine order. Fiat systems—by continuously printing money and driving inflation—treat nature and humanity as expendable resources to be exploited for short-term gains, leading to environmental degradation and societal collapse. The creation narrative, in which humans are called to be stewards, is inverted. The fiat system, through its unholy alliance with unrestrained growth and unsustainable debt, is destroying the very creation it should protect.
Furthermore, the fiat system drives idolatry of power and wealth. The central banks and corporations that control the money supply have become modern-day gods, their decrees shaping the lives of billions, while the masses are enslaved by debt and inflation. This form of worship isn't overt, but it is profound. It leads to a world where people place their faith not in God or their families, but in the abstract promises of institutions that serve their own interests.
Physics and the Infinite Growth Paradox
Physics teaches us that the universe is finite—resources, energy, and space are all limited. Yet, the fiat system operates under the delusion of infinite growth. Central banks print money without concern for natural limits, encouraging an economy that assumes unending expansion. This is not only an economic fallacy; it is a physical impossibility.
In thermodynamics, the Second Law states that entropy (disorder) increases over time in any closed system. The fiat system operates as if the Earth were an infinite resource pool, perpetually able to expand without consequence. The real world, however, does not bend to these abstract concepts of infinite growth. Resources are finite, ecosystems are fragile, and human capacity is limited. Fiat currency, by promoting unsustainable consumption and growth, accelerates the depletion of resources and the degradation of natural systems that support life itself.
Even the financial “growth” driven by fiat policies leads to unsustainable bubbles—inflated stock markets, real estate, and speculative assets that burst and leave ruin in their wake. These crashes aren’t just economic—they have profound biological consequences. The cycles of boom and bust undermine communities, erode social stability, and increase anxiety and depression, all of which affect human health at a biological level.
Biology: The Fiat System and the Destruction of Human Health
Biologically, the fiat system is a cancerous growth on human society. The constant chase for growth and the devaluation of work leads to chronic stress, which is one of the leading causes of disease in modern society. The strain of living in a system that values speculation over well-being results in a biological feedback loop: rising anxiety, poor mental health, physical diseases like cardiovascular disorders, and a shortening of lifespans.
Moreover, the focus on profit and short-term returns creates a biological disconnect between humans and the planet. The fiat system fuels industries that destroy ecosystems, increase pollution, and deplete resources at unsustainable rates. These actions are not just environmentally harmful; they directly harm human biology. The degradation of the environment—whether through toxic chemicals, pollution, or resource extraction—has profound biological effects on human health, causing respiratory diseases, cancers, and neurological disorders.
The biological cost of the fiat system is not a distant theory; it is being paid every day by millions in the form of increased health risks, diseases linked to stress, and the growing burden of mental health disorders. The constant uncertainty of an inflation-driven economy exacerbates these conditions, creating a society of individuals whose bodies and minds are under constant strain. We are witnessing a systemic biological unraveling, one in which the very act of living is increasingly fraught with pain, instability, and the looming threat of collapse.
Finance as the Final Illusion
At the core of the fiat system is a fundamental illusion—that financial growth can occur without any real connection to tangible value. The abstraction of currency, the manipulation of interest rates, and the constant creation of new money hide the underlying truth: the system is built on nothing but faith. When that faith falters, the entire system collapses.
This illusion has become so deeply embedded that it now defines the human experience. Work no longer connects to production or creation—it is reduced to a transaction on a spreadsheet, a means to acquire more fiat currency in a world where value is ephemeral and increasingly disconnected from human reality.
As we pursue ever-expanding wealth, the fundamental truths of biology—interdependence, sustainability, and balance—are ignored. The fiat system’s abstract financial models serve to disconnect us from the basic realities of life: that we are part of an interconnected world where every action has a reaction, where resources are finite, and where human health, both mental and physical, depends on the stability of our environment and our social systems.
The Ultimate Extermination
In the end, the fiat system is not just an economic issue; it is a biological, philosophical, theological, and existential threat to the very survival of humanity. It is a force that devalues human effort, encourages environmental destruction, fosters inequality, and creates pain at the core of the human biological condition. It is an economic framework that leads not to prosperity, but to extermination—not just of species, but of the very essence of human well-being.
To continue on this path is to accept the slow death of our species, one based not on natural forces, but on our own choice to worship the abstract over the real, the speculative over the tangible. The fiat system isn't just a threat; it is the ultimate self-inflicted wound, a cultural and financial cancer that, if left unchecked, will destroy humanity’s chance for survival and peace.
-
 @ 6f170f27:711e26dd
2024-07-13 18:16:58
@ 6f170f27:711e26dd
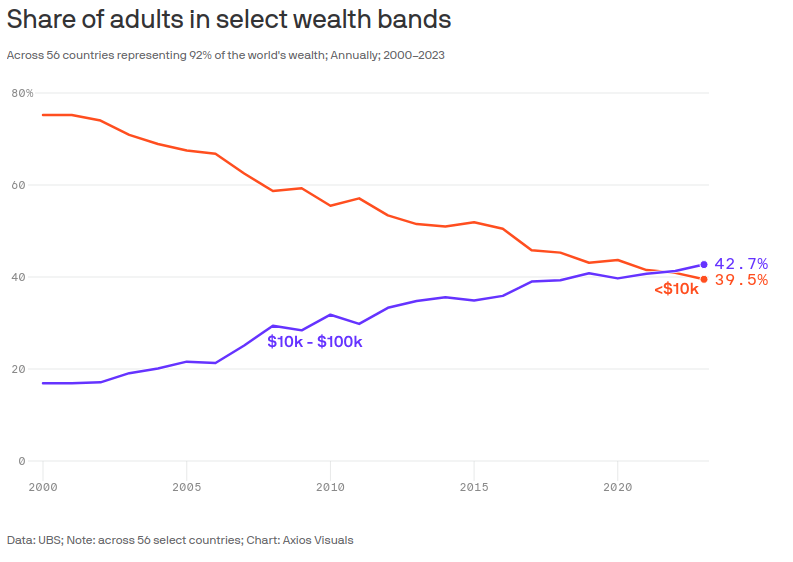
2024-07-13 18:16:58This century has known a stunning decrease in global income inequality, bringing it down to levels not seen in well over a century. That's the conclusion that Branko Milanovic, one of the world's foremost inequality researchers, comes to in an important essay for Foreign Affairs.
https://www.axios.com/2024/07/11/world-income-inequality-ubs-wealth-report
https://www.axios.com/2023/06/14/global-economic-inequality
originally posted at https://stacker.news/items/607318
-
 @ 2fb77d26:c47a6ee1
2024-12-27 20:12:28
@ 2fb77d26:c47a6ee1
2024-12-27 20:12:28John Brockmans Edge-Foundation galt als Treffpunkt für die Genies der Gegenwart. Ob Jeff Bezos, Sean Parker, Elon Musk oder Daniel Hillis – sie alle wohnten Veranstaltungen bei, die sie als Tech-Avantgarde darauf vorbereiten sollten, die Zukunft zu gestalten. Die »Dritte Kultur«. Doch was zunächst progressiv klingt, entpuppt sich auf den zweiten Blick rasch als Trainingslager für Technokraten. Finanziert von Jeffrey Epstein.
Original mit Quellen (VÖ: 24.11.2024) - https://www.regenauer.press/die-glorreichen-sieben
Sie regieren die Welt. Das ist keine Übertreibung. Denn sie haben deutlich mehr Einfluss darauf, was wir sehen, lesen, hören, fühlen, kaufen, tun und denken als jeder Politdarsteller – gemeint sind die »glorreichen Sieben«. Also die sieben größten Unternehmen der Tech-Branche: Apple, Microsoft, Amazon, Alphabet (Google), Tesla, Meta und Nvidia. Mit ihren Plattformen, Produkten und Smartphone-Apps dominieren sie Medienlandschaft, Konsum, persönliche Kommunikation, digital-soziale Räume, nachrichtendienstliche Aktivitäten, künstliche Intelligenz (KI) und in zunehmendem Maße auch den Finanzmarkt.
Nachdem Microsoft und Apple mit der Entwicklung von Personal Computern und einer grafischen Benutzeroberfläche dafür sorgten, dass sich Mitte der 80er auch neugierige Normalos einen PC ins Haus holten – als Ersatz für die plötzlich altbacken wirkende Schreibmaschine – und Tim Berners-Lee, der 1989 am CERN die Grundlagen des World Wide Web entwickelte, am 6. August 1991 sein Konzept eines Hypertext-Dienstes online gestellt hatte, waren es Ende der 90er eine Handvoll Unternehmen, die sich im sonnigen Süden der USA anschicken sollten, das Mediazän zu dominieren. Gegründet von einer Handvoll Tech-Desperados, die abseits gültiger Normen und Gesetzmäßigkeiten operierte, weil es für das, was sie erfanden, noch keine gab, formierte sich ein anomistisches Ökosystem, das heute die Welt dominiert: Die Plattform-Plutokratie. Der digital-zensorische Komplex. Die größte Social-Engineering-Maschinerie aller Zeiten.
So steht die Einordnung als »größte Unternehmen« nicht nur für die astronomischen Börsenwerte dieser Konzerne, sondern vor allem für ihren massiven Einfluss auf die Entwicklung des Individuums und die postmoderne Gesellschaft an sich. Dass diese Einflussnahme abseits von Marktwert und Performance-Indikatoren nicht allein auf organischem Wachstum und Marktdurchdringung beruht, liegt auf der Hand – denn die Tech-Giganten erfuhren signifikante Starthilfe von Seiten des Staates. Genauer gesagt dem Geheimdienstkomplex.
Facebook erhielt Millionen von Deep-State-Technokrat Peter Thiel und Accel, dessen Management enge Verbindungen zum CIA-Finanzvehikel In-Q-Tel pflegte, und galt für das Forbes-Magazine schon 2018 als »das ultimative Überwachungsinstrument für Regierungen«. Sergey Brin und Larry Page erhielten 1995 erhebliche Summen von der DARPA, um Google zu gründen. Aus einem »schwarzen Budget«, mit dem NSA und CIA Werkzeuge zur Massenüberwachung entwickeln wollten. Wenig verwunderlich also, dass auch Google Earth aus einem CIA-Projekt namens Keyhole EarthViewer hervorging, dessen Unterstützung In-Q-Tel gemäß Pressemitteilung vom 25. Juni 2003 als »strategisches Investment« bezeichnete. Julian Assange lag also ganz richtig, als er 2014 warnte, »Google sei nicht das, für was es sich ausgibt«.
Selbst bei Reuters konnte man im Rahmen eines ausführlichen Artikels vom 3. Juli 2013 nachlesen, wie eng die Verbindungen der Big-Tech-Konzerne zu Geheimdiensten ist. Von der Start-up-Finanzierung über die Rekrutierung von Ex-Agenten bis zum Austausch von Computerchips, die Spionage erleichtern, ist alles dabei. »Die Zusammenarbeit zwischen Tech-Industrie und Geheimdiensten ist enger als die meisten Menschen denken«, so Reuters.
So erstaunt es kaum, dass Amazon, Apple, Microsoft, Google, Meta und Elon Musks Firmenkonglomerat mittlerweile auch in den Krisen- und Kriegsgebieten der Welt aktiv sind, um dort in Zusammenarbeit mit Peter Thiels Palantir, Pentagon und Geheimdiensten jene Drecksarbeit zu übernehmen, die Regierungen nicht offiziell übernehmen wollen, oder dürfen. Korporatismus in voller Blüte eben. Die vermeintlich privatwirtschaftlich geführten Tech-Konzerne dominieren nicht mehr nur den zivilen, sondern zusehends auch den militärischen »Markt« – das Geschäft des industrialisierten Tötens.
Dass der militärisch-industrielle mit dem digital-zensorischen Komplex fusionierte, ist eine logische Folge des Umstands, dass beide dem gleichen »Gott« dienen: Mammon. Sprich, dem Zentral- und Geschäftsbankenkartell. In diesem Lichte betrachtet gebietet das Gesetz der Logik, dass die Schaffung dieser unheiligen Allianz nicht allein betriebswirtschaftlich motiviert war. Denn schon im 17., 18., und 19. Jahrhundert nutzten die Finanzkartelle Medien, Staat und Wirtschaft, um den Lauf der Dinge zu ihren Gunsten zu beeinflussen. Siehe mein Text »Monopole, Macht und Mord« Teil 1 und 2.
Damals zeitigte diese überstaatliche Einflussnahme vor allem militärische Konflikte, bei denen Territorialansprüche, Ressourcen und Monopolisierung im Fokus standen. Weil in diesen Bereichen aber bis auf die planetaren Gemeingüter, die sich die Herrschaftskaste nun im Rahmen der Green Economy unter den Nagel zu reißen gedenkt, nicht mehr viel zu holen ist, geht es dieser Tage vor allem darum, die Kontrolle nicht zu verlieren. Dazu müssen die 0,1 bis 1,0 Prozent an der Spitze des wertewestlichen Kastensystems sicherstellen, dass die unterworfene Masse der transgenerational operierenden Kriminalität ihrer Zirkel nicht auf die Schliche kommt.
Eine Bedrohung für die von immer mehr Rissen gezeichneten Fundamente des Elfenbeinturms markiert vor allem das Internet. Denn trotz vielschichtiger Zensurmethoden im Web 2.0, legislativer Hütchenspielertricks und der Segregation Andersdenkender, bahnt sich das kleine, aber persistente Licht der Wahrheit auch in dunkelsten Zeiten seinen Weg durch Paywalls, Geofences, Blockwart-Barrikaden und Plattform-Patrouillen. VPN, Blockchain, Graphene OS, De-Fi (Decentralized Finance) und Verschlüsselung sei Dank. Das Web 3.0 lässt sich nicht zensieren.
Um derart autonomisierenden Entwicklungen entgegenzuwirken, konzentrieren sich die Kolonialisierungsprojekte der Herrschaftskaste nun nicht mehr auf die bewaffnete Unterwerfung ferner Länder – sondern auf das Erringen der Lufthoheit über einem geradezu grenzenlosen Schlachtfeld: dem Gehirn. Allerdings nicht in Form simpler Propaganda. Denn im Zeitalter des fortgeschrittenen Informationskrieges ist Nudging die sozialarchitektonische Königsdisziplin, um Menschen dazu zu bringen, etwas zu unterstützen, das ihnen nichts bringt, oder sogar schadet. Und wie könnte Nudging in der Breite besser gelingen als durch willfährige Hilfestellung »der glorreichen Sieben«. Genau dazu wurden sie geschaffen.
Technologische Revolutionen werden Dekaden bevor sie eintreten antizipiert, durchdacht, angekündigt und visualisiert. Nicht zuletzt von Hollywood, der laut Edward Bernays »größten Propagandamaschine der Welt«. Jene Kräfte, die die Gesellschaft kontrollieren wollen, machen sich das zu nutze. Sie erkennen, welche Paradigmenwechsel technologische Revolutionen einläuten werden und versuchen daher frühzeitig, deren Entwicklung zu steuern. Aus diesem Grund lohnt sich ein Blick auf die Entstehungsgeschichte des Nudging – beziehungsweise der zugrundeliegenden wissenschaftlichen Disziplin: Verhaltensforschung.
Klassische Propaganda beruht auf den Standardwerken von Walter Lippmann (1922) und Edward Bernays (1928). Moderne Verhaltensforschung – oder Sozialarchitektonik – in weiten Teilen auf den Arbeiten von Anthony Giddens. Der britische Soziologe veröffentlichte 1990 das Buch »The Consequences of Modernity«, in dem er die Grundlagen für den »Dritten Weg« skizzierte – ein Konzept der Politikproduktion, das abseits politischer Spektren dazu dient, die Massen zu gesellschaftlichem Konsens zu zwingen. Giddens’ Konzept beruht auf den Infiltrationsansätzen der Fabian Society, die damit das Fundament der Partizipation simulierenden Sozialdemokratien des heutigen Europas schuf. Hintergründe zu Fabian Society und dem Roll-out des Dritten Weges finden sich in meinem Text »Dominanzdialektik« vom 30. September 2023.
Nach 1990 publizierte Giddens weitere Bücher, die sich mit dem Themenkomplex befassten. Darunter Titel wie »Moderne und Identität« (1991), »Die Transformation der Intimität« (1992), »Jenseits von rechts und links« (1994) und »Der Dritte Weg« (1998). In all diesen Werken beschäftigt sich der Sozialwissenschaftler mit der übergeordneten Frage, wie der Mensch sich in die Welt der Postmoderne einzufügen vermag – oder besser – einfügen muss, um mit Globalisierung, Klimawandel und sozialen Verwerfungen zurecht zu kommen. Anthony Giddens war von 1997 bis 2003 Direktor der einflussreichen, von der Fabian Society gegründeten London School of Economics. Er ist der meistzitierte Autor im Bereich soziologischer Studien und Mitglied des 2007 ins Leben gerufenen European Council on Foreign Relations.
Relevant ist Giddens Arbeit zum »Dritten Weg« vor allem deshalb, weil dieser manipulative Ansatz der Politikproduktion durch Tony Blair, Bill Clinton und Gerhard Schröder Einzug in die Parlamente des Wertewestens fand. Heute orientiert sich praktisch jede Regierung an Giddens Theorien – und setzt demzufolge um, was die Fabian Society bereits Ende des 19. Jahrhunderts vorschlug, um Kollektivismus unter dem Deckmantel von Mitbestimmung zu generieren. Das erklärt, warum weder Klaus Schwabs »Stakeholder Kapitalismus« noch die »Vierte Industrielle Revolution« etwas mit Kapitalismus oder Demokratie zu tun haben.
Damit solche Konzepte in der Gesellschaft Fuß fassen, benötigt es vor allem eine auf Linie gebürstete Führungsebene. Diese wird mit Stipendien und Förderprogrammen eingenordet, bevor man sie auf die Bevölkerung loslässt. Viele dieser Kaderschmieden sind mittlerweile hinlänglich bekannt. Da wäre zum Beispiel das zu fragwürdigem Ruhm gelangte Young Global Leaders Programm des Weltwirtschaftsforums (WEF), das neben knapp 3.800 weiteren Absolventen auch Angela Merkel, Tony Blair, Gordon Brown, Nicolas Sarkozy und Bill Gates auf ihre Karrieren in der »regelbasierten internationalen Ordnung« vorbereitete. Ein weiterer WEF-Absolvent ist Lawrence Summers, US-Finanzminister unter Bill Clinton, nationaler Wirtschaftsberater unter Barack Obama und von 1991 bis 1993 Chefökonom der Weltbank. Darüber hinaus war Summers von 2001 bis 2006 Präsident der Harvard University, wo bis 2006 auch Mark Zuckerberg studierte und mit drei Kommilitonen Facebook gründete.
Nach nicht zweifelsfrei verifizierbaren Angaben eines anonymen Facebook-Whistleblowers soll Summers in diesem Zeitraum auf Zuckerberg zugegangen sein, um ihm für die Mitarbeit an einem Social-Media-Überwachungs-Projekt der DARPA lukrative Regierungsaufträge in Aussicht zu stellen – siehe Life Log, das einen Tag vor dem Start von TheFacebook offline ging. In Anbetracht von Summers Position durchaus denkbar. Auch Moral scheint dem Mann ein Fremdwort zu sein, wie Formulierungen aus einem Weltbank-Memo Summers zeigen, die am 18. Mai 1993 bei einer Anhörung im US-Senat thematisiert wurden.
»Ich denke, die wirtschaftliche Logik, die hinter der Entsorgung einer Menge von Giftmüll in einem Land mit den niedrigsten Löhnen steht, ist einwandfrei, und wir sollten uns dem stellen. (…) Ich war schon immer der Meinung, dass die unterbevölkerten Länder Afrikas stark unterverschmutzt sind.«
Nicht zu vergessen Summers enge Verbindungen zum Pädophilen, Sexualstraftäter und Menschenhändler Jeffrey Epstein. Nachdem Summers bereits mehrfach mit Epsteins Privatjet – bekannt unter dem Namen »Lolita Express« – unterwegs war, bestieg er die Maschine nur zehn Tage nach seiner Hochzeit im Jahr 2005 erneut, um Epsteins ominöse Privatinsel »Pedophile Island« zu besuchen. Die Huffington Post schrieb dazu am 24. April 2020: »Joe Biden sollte sich von Larry Summers fernhalten – Summers ruiniert alles, was er anfasst«. Summers WEF-Training scheint sich jedenfalls ausgezahlt zu haben. Denn wer mit Jeffrey Epstein zu tun hatte, ist definitiv im Establishment angekommen.
Tony Blair und Gordon Brown hatten vor dem WEF bereits das 1940 von Nelson Rockefeller initiierte und bis heute vom US-Außenministerium betriebene »International Visitor Leadership Program« (IVLP) durchlaufen. Auch der 1972 gegründete German Marshall Fund betreibt diverse Förderprogramme – siehe EU-US Young Leaders Seminar 2024 oder Policy Designers Network 2024, das sich auf transatlantisch bewegten Nachwuchs aus der Ukraine, Georgien und Armenien fokussiert. Auch die Elite-Universitäten kümmern sich um Nachwuchs. So unter anderem das seit 1902 bestehende Rhodes Stipendium der Oxford-Universität, das neben unzähligen US-Senatoren, Finanzmagnaten, Bestsellerautoren und Wissenschaftlern beispielsweise Edwin Hubble, Bill Clinton oder Naomi Wolf zu Ruhm verhalf. Rhodes-Alumni bleiben über Organisationen wie AARS (Association of American Rhodes Scholars) ein Leben lang verbunden.
Diesbezüglich Fakten zusammenzutragen erscheint bisweilen müßig. Denn mit Details und Verflechtungen zu Entitäten dies- und jenseits des Atlantik, die Führungskräften von morgen die sozioökonomische Philosophie der Herrschaftskaste vermitteln, könnte man Bände füllen. Versucht man die Herrschaftsphilosophie der heutigen Plattform-Plutokraten zu verstehen, sticht eine Organisation dabei allerdings heraus – und zwar die 1988 von John Brockman ins Leben gerufene Edge Foundation. Geburtsort der »Dritten Kultur«.
Die Frankfurter Allgemeine portraitierte Brockman am 7. Januar 2014 mit den einleitenden Worten: »Der wohl wichtigste Buchagent der Welt versammelt in seinem Internetsalon Edge die Cyber-Elite.« Danach beschreibt FAZ-Autor Jordan Mejas, was sich der Normalsterbliche unter Edge vorstellen darf:
»Edge, das ist der Treffpunkt für die Cyber-Elite, die erlauchtesten Geister, die das Vorfeld der neuesten natur- und sozialwissenschaftlichen Entwicklungen prägen, ob nun digital oder gentechnisch, ob psychologisch, kosmologisch oder neurologisch. Jedenfalls melden sich bei Brockman nicht nur Digerati aus dem Computeruniversum des Silicon Valley zu Wort, sondern genauso häufig Koryphäen wie die Evolutionsbiologen Richard Dawkins und Steven Pinker, der Philosoph Daniel Dennett, der Kosmologe Martin Rees, die biologische Anthropologin Helen Fisher, der Ökonom, Psychologe und Nobelpreisträger Daniel Kahneman, der Quantenphysiker David Deutsch, der Computerwissenschaftler Marvin Minsky oder der Sozialtheoretiker Anthony Giddens. Vom Apple-Mitbegründer Steve Wozniak bis zum Genomentschlüssler Craig Venter reicht seine Gästeliste, die ihresgleichen auch in der grenzenlosen Weite des Internets kaum finden wird.«
Was dem FAZ-Autor bei seiner Recherche offensichtlich entging, ist, dass neben Giddens, Wozniak, Dennis Hopper und all den wissenschaftlichen Koryphäen auch Jeff Bezos (Gründer von Amazon, Besitzer Washington Post), Elon Musk, Sean Parker (Gründer von Napster, Co-Gründer Facebook), Larry Page und Sergey Brin (Gründer von Google), Pierre Omidyar (Gründer von eBay), Salar Kamangar (ehem. CEO YouTube), Matt Groening (Erfinder von »Die Simpsons«), Marissa Mayer (ehem. CEO Google und Yahoo), Joi Ito (ehem. Direktor MIT Media Lab), Evan Williams (Co-Gründer Twitter), Paul Romer (Economist) oder Bill Gates regelmäßig auf der Gästeliste von Edge-Events standen. Wer sich durch die Event-Sektion der Edge-Webseite klickt, begegnet unter dem Menüpunkt »Billionaires’ Dinner« der damaligen wie heutigen Crème de la Crème der Plattform-Plutokratie. Garniert mit ein paar Sahnehäubchen aus Wissenschaft, Kunst und Kultur.
Hervorzuheben ist dabei vor allem das Billionaires’ Dinner 2011. Denn die Fotogalerie des Events (hier zusätzlich gesichert im Internet Archive) birgt eine kleine Überraschung: das bislang einzige Foto, das Elon Musk in Gegenwart des zu diesem Zeitpunkt bereits für Sexualstraftaten und Menschenhandel angeklagten Jeffrey Epstein zeigt. Musk sitzt zwar am Nebentisch, mit dem Rücken zur Kamera, ist dank Vergleichsaufnahmen des Events aber zweifelsfrei zu identifizieren. Interessant ist dieser Umstand deshalb, weil Musk bisher stets behauptete, Epstein lediglich einmal in dessen Haus in New York getroffen zu haben. Für 30 Minuten. Und zwar auf Drängen seiner damaligen Partnerin Talulah Riley, die Epstein angeblich für ihre Arbeit an einer Novelle kennenlernen wollte.
Ein Artikel der Newsweek vom 9. November 2022 bestätigt sowohl Musks als auch Epsteins Anwesenheit beim Edge Billionaires’ Dinner 2011. Darüber hinaus geht Newsweek noch einmal auf den Umstand ein, dass Elon Musk bereits auf einem Foto von 2014 mit Ghislaine Maxwell zu sehen war, der linken und rechten Hand Epsteins. Musk gab an, dass besagtes Bild nur entstanden sei, weil Maxwell sich ungefragt ins Bild gedrängt habe. Diesen Eindruck macht das Foto zwar nicht, das Gegenteil zu beweisen, dürfte jedoch schwer fallen. Nun sind Fotos von Gästen einer Veranstaltung natürlich noch kein Beleg dafür, dass sie mit deren Organisation zu tun haben. Finanzielle Zuwendungen dagegen schon.
Entsprechend bedeutsam ist daher ein Artikel der BuzzFeed News vom 27. September 2019. Denn er belegt, dass der bei Weitem größte Einzelspender der Edge-Foundation kein Geringerer war als Jeffrey Epstein. Das veranschaulichen die von ProPublica veröffentlichten Steuerunterlagen von Brockmans »Internetsalon« für 2001 bis 2017. So spendete Epstein 638.000 US-Dollar – während die gesamten Spendeneinnahmen sich auf 857.000 US-Dollar beliefen. Ein eigenes Profil auf der Edge-Webseite hatte Epstein natürlich auch. Kaum verwunderlich also, dass die Edge-Foundation ihre wichtigste jährliche Veranstaltung – das Billionaires’ Dinner – sofort einstellte, nachdem Epsteins Zuwendungen ab 2016 ausblieben. BuzzFeed News führt diesbezüglich aus:
»Epstein war ein regelmäßiger Teilnehmer bei Edge-Veranstaltungen. Er war bei den Billionaires’ Dinner Events 1999 und 2000 auf Fotos und Seiten zu sehen, die kürzlich von der Edge-Website gelöscht wurden, und wurde auch in einem Bericht über das Abendessen 2004 erwähnt. Epstein war auch 2011 bei Edge-Veranstaltungen anwesend, nach seiner Verurteilung wegen Sexualverbrechen im Jahr 2008. Darüber berichtete BuzzFeed News Anfang dieses Monats.«
Überschrift des betreffenden Artikels: »2011 war Jeffrey Epstein ein bekannter Sexualstraftäter. Jeff Bezos, Elon Musk und Sergey Brin speisten trotzdem mit ihm.« Weiter erklärt BuzzFeed:
»2002 waren Brockman, seine Frau und Geschäftspartnerin Katinka Matson sowie die führenden Wissenschaftler Steven Pinker, Richard Dawkins und Daniel Dennett in Epsteins Jet auf dem Weg zu TED in Monterey, Kalifornien, zu sehen – der mehrtägigen Technologie-, Unterhaltungs- und Designkonferenz, bei der das Billionaires’ Dinner diesen Jahres stattfand. Die Bildunterschrift wurde kürzlich geändert, um die Erwähnung Epsteins zu entfernen. Sein Edge-Profil, das ihn als Finanzier und Wissenschaftsphilanthrop beschreibt, wurde ebenfalls entfernt. Ob Epstein selbst am Billionaires’ Dinner 2002 teilnahm, ist unklar. Aber Mitglieder seines Gefolges waren dort. Ein Foto von der Veranstaltung zeigt Brockman mit zwei jungen Frauen, die in der Bildunterschrift namentlich genannt werden. Das Foto wurde kürzlich ebenfalls von der Edge-Webseite entfernt. Eine dieser Frauen ist Sarah Kellen, die als Assistentin von Epsteins ehemaliger Freundin Ghislaine Maxwell angestellt und im Rahmen eines Vergleichs von 2008 vor Strafverfolgung geschützt war. Der Vergleich brachte Epstein nach seiner früheren Verhaftung eine 13-monatige Gefängnisstrafe in Florida ein. In mehreren Klagen haben Epsteins Opfer behauptet, Kellen gehöre zu den Personen, die halfen, den sexuellen Missbrauch für Epstein zu organisieren.«
Brockmans Interaktionen mit Epstein gingen aber offenbar weit über die Edge-Foundation hinaus. Im August 2019 publizierte der belarussische Publizist Evgeny Morozov auf Google Drive E-Mail-Korrespondenz aus dem Jahr 2013, die belegt, dass Brockman Pläne hatte, ein Meeting zwischen ihm und Epstein zu arrangieren. Doch Morozov lehnte ab. In den Mails an Morozov erwähnt Brockman Epsteins »hübsche junge Assistentin aus Weißrussland« und beschreibt seinen Gönner fälschlicherweise als »Milliardär, dem Victorias Secret und eine Modelagentur gehören«. Tatsächlich lag Epsteins Vermögen gemäß seines Testaments aber nur bei einigen hundert Millionen – und die fragwürdige Marke Victorias Secret ist Teil von L Brands, der Holding von Leslie Wexner, einem Tiefenstaat-Veteran mit Verbindungen zu Harvard und WEF-Gründung, dessen Finanzen Jeffrey Epstein bis 2007 verwaltete.
Auch sonst pflegte Brockmans Organisation verwunderliche Geschäftspraktiken. Zwischen 2001 und 2017 vergab die Edge-Foundation beispielsweise nur ein einziges Mal einen Förderpreis. Der entsprechende Betrag in Höhe von 100.000 US-Dollar ging an David Deutsch, einen Pionier für Quanteninformationstheorie, der an der Universität Oxford forschte. Financier des Preises – man ahnt es – war Jeffrey Epstein. Nicht umsonst stellte The Verve am 19. September 2019 fest, dass »Jeffrey Epstein die Wissenschaft infiltrierte, weil die Wissenschaft bereit war, ihn willkommen zu heißen«.
So knüpfte der Finanzmagnat Kontakte zu prominenten Biologen wie George Church, weil er nach Wegen suchte, die menschliche Spezies mit seiner DNA zu kreuzen. Langfristiges Ziel: Das Schaffen einer »Super-Rasse«. Mehrere preisgekrönte Wissenschaftler bestätigten gegenüber der New York Times, dass Epstein auch sie in seine misogynen Pläne eingeweiht hatte. Auf seiner abgelegenen, unterkellerten »Zorro-Ranch« in New Mexico, wo jedes Zimmer mit Kameras überwacht wurde, hatte er eigens ein Behandlungszimmer einrichten lassen, um künstliche Befruchtungen mit jungen Frauen durchführen zu können.
Bei The New Yorker konnte man am 6. September 2019 nachlesen, dass Epstein sich auch im Bereich digitale Währungen engagierte. Unter anderem finanzierte er das damals von Joi Ito geleitete MIT Media Lab – und damit auch die von Ito geführte Digital Currency Initiative (DCI). Diese wiederum unterstützte die Bitcoin-Core-Entwickler bei der Fork 2017, die Bitcoin von einer digitalen Währung zu, wie Epstein es nannte, »digitalem Gold« machen sollte – und damit weitaus ungefährlicher für das herrschende Finanzmarktkartell. Bill Gates, Harvard-Autoren wie Steven Pinker oder MIT-Programmierer wie Richard Stallmann verteidigten Epstein sogar noch nach dessen endgültiger Festnahme. Stallmann forderte gar, Kinderpornografie zu entkriminalisieren. Joi Ito dagegen kündigte kleinlaut beim MIT. Heute ist er Präsident des Chiba Institute for Technology in Japan, wo das Center for Radical Transformation (CRT) angesiedelt ist. Auch die Digital Currency Initiative gibt es bis heute. Genau wie das »digitale Gold«, mit dem aber fast niemand mehr bezahlt. HODL und so.
Mit dem Thema Digitalwährungen nähern wir uns denn auch Jeffrey Epsteins Einfluss auf den Geschäftsbereich der »glorreichen Sieben«. Denn der im Gefängnis ermordete Menschenhändler finanzierte nicht nur einen Großteil von Brockmans Edge-Aktivitäten, sondern sorgte durch die Infiltration des Wissenschaftsbetriebes auch dafür, dass Edge den Tech-Nachwuchs in genau der Domäne schulte, die für das Erringen von Weltherrschaft im Mediazän essenziell ist: Social Engineering.
Dazu veranstaltete die Edge-Foundation sogenannte Master Class Events. Im Jahr 2008 zum Beispiel zum Thema »Libertärer Paternalismus – warum es nicht möglich ist, nicht zu nudgen«. Dozent: Richard Thaler, »Vater der modernen Verhaltensökonomie«, über den die ZEIT am 18. Mai 2010 unter der Überschrift »Die Stunde der Verführer« schrieb:
»Richard Thaler hat den Draht nach oben. Der 64-Jährige ist einer der weltweit führenden Verhaltensökonomen – neuerdings berät er auch die Wirtschaftsexperten des mächtigsten Mannes der Welt, US-Präsident Barack Obama. Auch die britischen Konservativen, die in London die neue Regierung führen, haben dem Professor der Universität von Chicago einen Beraterposten versprochen. Thaler steht an der Spitze einer wirtschaftspolitischen Revolution. (…) Verhaltensorientierte Wirtschaftsforscher postulieren (…) eine grundlegend andere Wirtschaftspolitik. Zwar lehnen sie – ähnlich wie klassische liberale Ökonomen – eine direkte Bevormundung des Einzelnen durch den Staat ab. Sie sprechen sich aber für sanften Druck aus, mit dem der Staat die Menschen in die richtige Richtung leitet, ihnen gleichzeitig aber die Option lässt, sich anders zu entscheiden, wenn sie es wollen. »Nudge« (Anstupsen) hat Thaler dieses Politikkonzept zusammen mit Co-Autor Cass Sunstein im gleichnamigen Buch getauft. Private Institutionen, Behörden und Regierungen versuchen dabei, die Entscheidungen der Menschen so zu lenken, dass sie hinterher besser dastehen. Ein anderer Begriff, der den neuen Politikansatz charakterisiert, ist sanfter Paternalismus.«
Das Buch, das ZEIT-Autor Olaf Storbek referenziert, hat Thaler 2010 gemeinsam mit Cass Sunstein verfasst, einem Edge-Kollegen und Harvard-Professor für Rechtswissenschaft und Verhaltensökonomie. Deutscher Titel des Werks: »Nudge – wie man kluge Entscheidungen anstößt«. Alternativ untertitelt mit: »Wie man Menschen dazu bringt, das Richtige zu tun«. In welche Kerbe das Machwerk schlägt, zeigt der Umstand, dass Cass Sunstein schon im Januar 2008 ein Papier namens »Verschwörungstheorien« publizierte, die er darin als ernsthaftes Risiko für Recht und Gesetz einstufte. Sunstein verteidigt das offizielle 9/11-Narrativ, will eine bargeldlose Gesellschaft und hielt Corona-Lockdowns für eine »smarte« Sache. Ein Beitrag von Sunstein für »Educators at Home« vom 14. September 2010 offenbart, was für ein Menschenbild die Rechtswissenschaften in Harvard mittlerweile kultivieren:
»Wenn wir erst einmal wissen, dass Menschen menschlich sind und etwas von Homer Simpson in sich tragen, dann kann man viel tun, um sie zu manipulieren.« (Cass Sunstein)
Trotz, oder gerade wegen dieser respektlosen Haltung gegenüber den Freiheitsrechten des Individuums, öffnete ihr gemeinsames Werk Thaler und Sunstein die Türen zum Elfenbeinturm. Ab 2008 berieten die beiden Verhaltensökonomen die Regierung von Barack Obama beim Aufbau sogenannter »Nudge-Units«. Kurze Zeit später unterstützte Richard Thaler auch die britische Regierung und half bei der Formierung des »Behavioural Insights Team« (BIT), dem sowohl Sunstein als auch Thaler bis heute angehören. Das BIT spielte via SAGE (Scientific Advisory Group for Emergencies), dem britischen Äquivalent zum Robert-Koch-Institut (RKI), eine tragende Rolle bei der Implementierung der Covid-19-Maßnahmen in Großbritannien. Händewaschanleitungen für Erwachsene, tote Großeltern für die Kleinen. Sie wissen schon. Strategieberater von Tony Blair hatten bereits im Februar 2004 eine Studie zum Thema »Persönliche Verantwortung und Verhaltensänderung: Stand des Wissens und Auswirkungen auf die öffentliche Politik« erstellen lassen – nur Thalers griffige Bezeichnung für die neue Doktrin fehlte noch. Ein Auszug aus dem Papier von 2004 erklärt:
»Mit Blick auf die Zukunft besteht ein offensichtlicher Bedarf, unser theoretisches und empirisches Verständnis der Ursachen für Verhalten und Verhaltensänderung zu stärken. Ebenso wichtig wird die umfassendere Erprobung politischer Instrumente sein, um ein ausgefeilteres Instrumentarium für politische Entscheidungsträger zu entwickeln. Die Politik sollte nicht einfach persönliche Verantwortung oder Schuldzuweisungen proklamieren, sondern muss sich an der Art und Weise orientieren, wie Menschen tatsächlich denken und fühlen, sowie an den sozialen und psychologischen Kräften, die das Verhalten beeinflussen.«
Das war vor 20 Jahren. Drei Jahre später kam das Smartphone auf den Markt und mauserte sich binnen kurzer Zeit zum perfekten Werkzeug einer auf Nuding ausgelegten Observationsökonomie. Heute hat fast jeder ein grell illuminiertes Brett vor dem Kopf, das seinen Tagesablauf, Bio-, Kommunikations- und Schlafrhythmus beeinflusst. Oder steuert. Je nach Schwere der Handysucht. Das eigentliche Problem dabei ist jedoch nicht die Hardware, das Endgerät, sondern die Software der »glorreichen Sieben«. Denn sie ist so designt, dass sie abhängig, krank und depressiv macht – und Menschen dazu bewegt, »das Richtige zu tun«. Auch wenn es absolut falsch ist.
»Wie schaffen wir es, möglichst viel von deiner Zeit und Aufmerksamkeit zu konsumieren. Dazu müssen wir dir hin und wieder eine kleine Dopamin-Dosis verabreichen. (...) Das bringt dich dazu, mehr beizutragen, was dir wiederum mehr Kommentare und Likes bringt. Es ist ein sozial validierender Feedback-Loop. (...) Wir nutzen eine Schwäche der menschlichen Psychologie. Die Erfinder, die Erschaffer, ich, Mark, die Leute von Instagram, all diese Menschen, haben das verstanden - voll und ganz - und wir haben es trotzdem getan.« (Sean Parker, am 8. November 2017)
Nahtlos kontrolliert wird der auf Konformismus dressierte Bürger dabei von einem Überwachungskomplex unvorstellbaren Ausmaßes. Die Webseite von Surveillance Watch führt Buch über die wichtigsten dafür zuständigen Unternehmen.
Nachdem Facebook 2004 online ging und das iPhone 2007 auf den Markt kam, erscheint das Jahr 2008 also tatsächlich als der perfekte Zeitpunkt für Edge, um die Silicon-Valley-Elite in puncto Nudging und Sozialarchitektonik zu schulen. Das soziale Netzwerk war seinen Kinderschuhen entwachsen – am 26. August 2008 knackte Facebook die 100 Millionen-Nutzer-Marke – und mit dem Taschenspion aus dem Hause Apple kündigte sich bereits das mächtigste Manipulations-Malträtat der Zivilisationsgeschichte an. Für die herrschenden Zirkel war absehbar, dass die Frontlinien des transgenerationalen Informationskrieges schon bald nicht mehr über die Auslagen der Zeitungskioske, durch Rundfunkredaktionen oder über die Mattscheibe, sondern direkt durch die Köpfe der Bevölkerung verlaufen werden.
Dieses Ziel wurde fraglos erreicht. Entsprechend hellhörig sollte machen, welche Themen die Edge Master Class 2008 behandelte. Die zweite Session widmete sich zum Beispiel dem Thema »Verbesserung der Auswahlmöglichkeiten durch maschinenlesbare Offenlegung«. Richard Thaler umriss deren Inhalt mit folgendem Eröffnungsstatement.
»Das ist die Idee. Ich nenne es elektronische Offenlegung. Lassen sie mich erklären, wie es bei Kreditkarten funktionieren würde. Die Idee ist, dass das Kreditkartenunternehmen ihnen für jede Kreditkarte, die sie besitzen, einmal im Jahr zwei elektronische Dateien senden muss. Die erste Datei wäre im Wesentlichen eine Tabelle mit allen Formeln für alle Möglichkeiten, wie ihnen Dinge in Rechnung gestellt werden können. (…) Die zweite Datei ist die Liste der Dinge, für die ihnen im letzten Jahr Gebühren in Rechnung gestellt wurden. Es könnte heißen, ihnen wurden im letzten Jahr 1.800 Dollar für diese Kreditkarte berechnet, davon 1.200 Dollar für Zinszahlungen, für Verzugsgebühren, oder Währungstransfers und so weiter. Wir glauben nicht, dass sich irgendjemand diese Dateien jemals ansehen würde. Wir glauben, dass sofort Websites auftauchen würden, die diese Informationen verarbeiten würden. Diese Websites würden den folgenden Zwecken dienen. Erstens: Übersetzung. Sie würden dem Benutzer in einfachem Englisch erklären, was mit ihm passiert. Zweitens: Verhaltensänderung. Sie würden ihm erklären, dass er 1.800 Dollar bezahlt hat, weil er unfähig war, seine Rechnungen pünktlich zu bezahlen. Wenn er also eine automatische Zahlung einrichten würde, würde er viel Geld sparen. Drittens: Preisvergleich. Beachten sie bitte, dass die entsprechenden Unternehmen mit diesen Informationen die Nutzungsmuster kennen; und sie kennen alle Formeln für alle Kreditkartenunternehmen. Sie können also drei Kreditkartenunternehmen suchen, und finden, die für die Art und Weise, wie der Nutzer seine Kreditkarten verwendet, besser wären. Das ist das Konzept. (…)«
Jeff Bezos warf kurz darauf ein: »Außerdem werden sie bezahlt. Sie sind wie der Fuchs, der den Hühnerstall bewacht.«
Dem wachsamen Leser dürfte klar sein, dass wir heute genau von solchen System umgeben, überwacht, analysiert und bedrängt werden. Zu unserem Vorteil – wie Thaler meint.
Bemerkenswert in Bezug auf das, was uns noch bevorstehen könnte, ist die dritte Session der Master Class 2008. Thema: »Die Psychologie der Knappheit«. Teilnehmer – unter anderem: Jeff Bezos, Sean Parker, Elon Musk, Nathan Myhrvold, der 14 Jahre als Stratege für Bill Gates arbeitete, Daniel Hillis, ehemals Vizepräsident für Forschung und Entwicklung bei Disney und Vater des Parallel Computing, das die Grundlage für moderne Supercomputer darstellt, et cetera. Neben Richard Thaler sprach bei der dritten Session auch Sendhil Mullainathan, Volkswirt an der Harvard-Universität. Sein Spezialgebiet: Verhaltensökonomie und Armutsökonomik. Einleitend erklärte Mullainathan:
»Lassen wir die Armutsbekämpfung für einen Moment beiseite und fragen uns: Gibt es etwas, das der Armut innewohnt und das an und für sich eine Untersuchung wert ist? Einer der Gründe dafür ist, dass wir – abgesehen von Wundermitteln – verstehen müssen, ob es unter Bedingungen der Knappheit gemeinsame Prinzipien gibt, die uns helfen können, Verhalten zu verstehen und Interventionen zu gestalten. Wenn wir das Gefühl haben, dass Bedingungen der Knappheit bestimmte psychologische Effekte hervorrufen, dann wird das, ganz zu schweigen vom rein wissenschaftlichen Interesse, eine große Mehrheit der Interventionen beeinflussen. Das ist eine wichtige und alte Frage.«
Korrekt. Denn Schuldknechtschaft war, wie die künstliche Verknappung von Nahrungsmitteln, seit jeher ein beliebtes Mittel der herrschenden Kaste, um den Pöbel im Zaum, beziehungsweise mit existenziellen Problemen auf Trab zu halten. So hat er nämlich weder Zeit noch Energie, um mit Mistgabeln und Fackeln gen Elfenbeinturm aufzubrechen. In diesem Zusammenhang sei nochmals auf »Food Chain Reaction – A Global Food Security Game« hingewiesen, ein Planspiel, das im November 2015 vom tiefenstaatlichen Center for American Progress, dem World Wildlife Fund, Center for Naval Analyses (CNA), Cargill und Mars durchgeführt wurde und Nahrungsmittelknappheit im Zeitraum von 2020 bis 2030 simulierte.
Der Einblick in die Ausbildungsprozesse der Edge-Foundation und die Liste ihrer Teilnehmer gibt somit allen Anlass zu befürchten, dass Brockmans »Internetsalon« die zentralen Akteure der kontinuierlich engmaschiger greifenden Technokratie nicht nur in puncto Social Engineering ausbilden, sondern sie darüber hinaus auf eine Zeit von Mangelwirtschaft und massiver Armut vorbereiten wollte. Auf die »Dritte Kultur«. Die wohlstandsvernichtende Tokenisierung der Welt.
Dabei sollte nicht vergessen werden, dass Brockman vermutlich nur ein geschäftstüchtiger Narzisst mit sozialen Kompetenzen war, der seine Chance auf Geld und Rampenlicht geschickt zu nutzen wusste – und dass Jeffrey Epstein als maßgeblicher Finanzier der Edge-Foundation nicht einfach im Alleingang handelte. Denn Epstein war Doppelagent, unterwegs im Auftrag von CIA und Mossad. Mindestens. Dass er mittlerweile nicht mehr unter den Lebenden weilt, dürfte weder sein Geheimdienstnetzwerk noch seinen elitären Kundenstamm davon abgehalten haben, sein schmutziges Geschäft weiterzubetreiben.
Man kann also durchaus mit einem metaphorisch zu lesenden Zitat aus jenem kultigen 60er-Film schließen, dessen Titel nun als Bezeichnung für ein Septett börsennotierter Technokratie-Operatoren missbraucht wird:
»Das Blutvergießen wird so lange weitergehen, bis die Ursache dafür ausgehoben ist.«
-
 @ 5d4b6c8d:8a1c1ee3
2024-07-13 12:44:32
@ 5d4b6c8d:8a1c1ee3
2024-07-13 12:44:32Yesterday's edition https://stacker.news/items/605773/r/Undisciplined
We have a confessional from a professional shitcoiner, today. That's fun.
-
- -
July 13, 2023 📅
📝
TOP POSTValidating Lightning Signer - AMA
Excerpt
VLS is a nifty piece of software that helps boost the security of the Bitcoin Lightning Network. 🛡️
11k sats \ 33 comments \ @devrandom \ ~bitcoin
💬
TOP COMMENThttps://stacker.news/items/208442/r/Undisciplined?commentId=208454
Excerpt
Ever bought a computer or cell phone? Why? Why not wait until your money is worth more later compared to the price of that cell phone?
1441 sats \ 7 replies \ @02674f045a
From Opinion: Why BTC can't become the reserve currency by @0xBTC in ~bitcoin
🏆
TOP STACKER1st place @k00b
5838 stacked \ 7855 spent \ 3 posts \ 19 comments \ 0 referrals
🗺️
TOP TERRITORY~bitcoin
everything bitcoin related
founded by @k00b on Tue May 02 2023
27k stacked \ 0 revenue \ 40.6k spent \ 108 posts \ 281 comments
https://imgprxy.stacker.news/fsFoWlgwKYsk5mxx2ijgqU8fg04I_2zA_D28t_grR74/rs:fit:960:540/aHR0cHM6Ly9tLnN0YWNrZXIubmV3cy8yMzc5Ng
July 13, 2022 📅
📝
TOP POSTAny Good Routing Node Strategies?
Excerpt
For people who have/are running nodes, are there any strategies that have been most effective for you for earning routing fees? From my very limited routing experience so far it seems there are a few main questions:
1232 sats \ 33 comments \ @andyleroy \ ~bitcoin
💬
TOP COMMENThttps://stacker.news/items/44747/r/Undisciplined?commentId=44755
Excerpt
Obligatory not a node routing expert, but this guy is a good follow: https://mobile.twitter.com/cold_sats
276 sats \ 1 reply \ @Cornleone
From Any Good Routing Node Strategies? by @andyleroy in ~bitcoin
🏆
TOP STACKER1st place @k00b
37.3k stacked \ 15.2k spent \ 1 post \ 29 comments \ 0 referrals
🗺️
TOP TERRITORY~bitcoin
everything bitcoin related
founded by @k00b on Tue May 02 2023
27.4k stacked \ 0 revenue \ 34.7k spent \ 117 posts \ 279 comments
https://imgprxy.stacker.news/fsFoWlgwKYsk5mxx2ijgqU8fg04I_2zA_D28t_grR74/rs:fit:960:540/aHR0cHM6Ly9tLnN0YWNrZXIubmV3cy8yMzc5Ng
July 13, 2021 📅
📝
TOP POSTI joined a shitcoin project full time couple of months ago
Excerpt
I though it would be exciting and fun. But I think I'm wasting my time.
3 sats \ 9 comments \ @03785de7ab \ ~bitcoin
💬
TOP COMMENThttps://stacker.news/items/306/r/Undisciplined?commentId=316
Excerpt
There are many companies working with Bitcoin but it's not their main focus. I did implement Bitgo sevices for one e-wallet provider but that was it. What I'm looking for is a project which build useful things for user with current Bitcoin features, […]
2 sats \ 1 reply \ @03785de7ab
From I joined a shitcoin project full time couple of months ago by @03785de7ab in ~bitcoin
🏆
TOP STACKERNo top stacker
🗺️
TOP TERRITORY~bitcoin
everything bitcoin related
founded by @k00b on Tue May 02 2023
37 stacked \ 0 revenue \ 60 spent \ 6 posts \ 10 comments
originally posted at https://stacker.news/items/607040
-
-
 @ b2caa9b3:9eab0fb5
2024-07-13 12:01:35
@ b2caa9b3:9eab0fb5
2024-07-13 12:01:35I woke up in my dorm this morning to the sound of rain – a rarity in Africa, but a common occurrence here around Mount Kilimanjaro. The climate is much like a European summer, with comfortable temperatures ranging from 18 to 30 degrees Celsius. Unlike the rest of Africa, this region receives more rainfall, creating a lush and scenic environment.

After a quick shower, I stepped out onto the balcony to find myself greeted by a chilly rain. Not ideal weather for exploring, but it did present a different perspective of the majestic Kilimanjaro. The mountain, often shrouded in clouds, occasionally peeks through, and on a clear day, might even be bathed in sunshine. From this vantage point, it's hard to imagine the countless hikers making their way up its slopes.
Did you know that Kilimanjaro, Africa's tallest mountain and a dormant volcano, once held a unique title? Back in 1910, during the German Empire, it was considered the empire's highest peak. While Mount Everest holds the title of the world's highest mountain overall, Kilimanjaro takes the crown for the tallest freestanding mountain – any higher peak is likely part of a mountain range or group.
Gazing at Kilimanjaro, I'm struck by its history – a single, towering volcano, once a part of the German Empire. Traces of that era linger in Moshi, with some colonial-era buildings, some in disrepair, others beautifully restored. Arusha, another nearby town, boasts an impressive art gallery and a fascinating National Museum. This museum, housed in a former German fort, offers a glimpse into the past. One particularly intriguing resident is a giant tortoise, discovered by German colonists as a hatchling in Kilimanjaro National Park. This living relic has witnessed a century of change, a silent observer of a bygone era.

Today promises to be a relaxing one. I'll spend time soaking up the views from the rooftop, hoping to catch a glimpse of Kilimanjaro in all its glory. On a more practical note, I'm also on the hunt for a remote job to help with some financial constraints. Finding the right opportunity seems to be a bit more challenging than anticipated.
As I wrap up this post, the weather has taken a turn for the better. The rain has stopped, the temperature has risen, and the sun is beginning to peek through the clouds. Here's to a wonderful day for everyone – enjoy yours!
(P.S. Be sure to check out the photos – one captures Kilimanjaro from yesterday evening, the other is a picture of me with the giant tortoise from my previous trip here in December 2022).
Online
Feel free to support me by sending some sats via the lightning network to rubenstorm@sats.mobi
-
 @ 2fb77d26:c47a6ee1
2024-12-27 20:10:18
@ 2fb77d26:c47a6ee1
2024-12-27 20:10:18Während ein weiteres Jahr voller Abnormitäten sich dem Ende neigt, ist vieles, das sich im Interesse des nächsten hätte verbessern können, beim Alten geblieben. Denn Veränderungen beginnen im Kopf – und der fungiert bei einer Mehrheit der Artgenossen vor allem als Reservoir für Informationen, Gedanken und Meinungen Dritter. Dritter, die sich die psychischen Schwachstellen der Spezies Mensch gekonnt zunutze machen.
Original mit Quellen: https://www.regenauer.press/der-unsichtbare-dritte
Es war einmal die UNESCO. Diese farbenfroh-inklusiv erscheinende UN-Suborganisation für Erziehung, Wissenschaft und Kultur. Sie wollte »das Undenkbare wenigstens wieder denkbar machen«. So steht es auf Seite 21 des 1946 vom ersten Generaldirektor Julian Huxley verfassten Gründungsdokuments. Gemeint war die Eugenik. Rassenlehre. Die genoss kurz nach Hitler nämlich keinen besonders guten Ruf, sollte uns nach Ansicht von Huxley und Co. jedoch schon bald in überarbeiteter Form als Humangenetik, Bioethik oder biodigitale Konvergenz wieder mit ihren Zuchtprogrammen beglücken dürfen. Mit Transhumanismus. Was Julian Huxley im Rahmen seines im wahrsten Sinne des Wortes wegweisenden Dossiers unterschlug – immerhin prägte er auch den Begriff Transhumanismus – ist die Tatsache, dass die Vereinten Nationen nicht nur »das Undenkbare wieder denkbar machen«, sondern auch »das Denkbare undenkbar machen« wollten.
Die sozialarchitektonischen Vektoren in Richtung einer homogenisierten, pflegeleichten Hominidenbrut – dem Nutzmensch – sind gepflastert mit Stolpersteinen evolutionärer, aufklärerischer Errungenschaften: Selbstbewusstsein und -erhaltungstrieb, Freiheitsdrang, Kreativität, Sozialkompetenz, Empathie, kritisches Denken. All das steht den postmodernen Variationen von Eugenik beharrlich im Weg. Niemand, der originäre Gedanken pflegt, eigene Wege geht und seine Freiheiten schätzt, möchte Teil eines mit der Cloud gekoppelten, genetisch optimierten Kollektivs seelenloser Konformisten werden. Und doch sind es die meisten schon längst. Ob sie Herrschaftsnarrative goutieren, oder Widerstand dagegen leisten – alles, was sie wahrnehmen, diskutieren, verteidigen oder ablehnen stammt aus dem Netz. Es sind limitierte, interpretierte und manipulierte Informationen aus dritter Hand.
Im besten Falle stammen sie noch aus verschiedenen Quellen und erlauben Triangulation zur Bestimmung der eigenen Position. Dazu muss man sich nämlich noch ein paar eigene Gedanken machen. Im schlimmsten Fall wurden sie von Alexa, Siri, dem Google Assistant, ChatGPT oder einem anderen Intelligenz simulierenden Digitalassistenten bereitgestellt, der nur noch eine Antwort serviert. Die richtige. Die Akzeptable. Denn genau das war stets Anspruch der Technokraten. Der langjährige Google-Chef und Bilderberg-Grande Eric Schmidt erklärte schon vor über einem Jahrzehnt, dass »eine Vielzahl von Suchergebnissen ein Fehler und keine Funktion sind«. Das erklärte Ziel von Google sei es, so Schmidt, nur ein einziges Suchergebnis zu präsentieren – das richtige.
Damit solch ein kommunikativer Reduktionismus nicht als Bevormundung, sondern Serviceangebot wahrgenommen wird, muss man verstehen, und steuern, wie Menschen denken. Vielleicht wollte Schmidt aus diesem Grund unbedingt mit Julian Assange über Googles Visionen für eine »neue digitale Welt« sprechen. Mit jemandem, der die technischen Untiefen des Internets kennt – und sie für das Gegenteil dessen nutzt, was Google will. Am 23. Juni 2011 und auf Schmidts Betreiben kam es jedenfalls zu einem geheimen, fünfstündigen Treffen mit dem unter Hausarrest stehenden WikiLeaks-Gründer. Das Transkript dieser Konversation ist erhellend. Vor allem die zweite Hälfte lässt erahnen, wie Schmidt sich die »neue digitale Welt« vorstellt und warum er Ende 2019 konstatierte, dass »Biologie die nächste Grenzverschiebung in puncto Computing ist«.
Google wollte uns nämlich nie informieren, sondern »programmieren«. Das steht so wortwörtlich in internen Dokumenten des Unternehmens, die dank eines Whistleblowers am 24. Juni 2019 den Weg in die Öffentlichkeit fanden. Und wer denkt, »programmieren« beginne erst mit dem Neuralimplantat, dem Chip im Hirn, irrt. Google, Microsoft, Apple, YouTube, Twitter (das ich auch weiterhin so nennen werde), Amazon, Facebook, Wikipedia, Rumble, Instagram, TikTok und Co. schaffen das auch ohne. Denn ihre Algorithmen und Omnipräsenz bestimmen schon jetzt nahezu vollständig, was Menschen wahrnehmen – was sie empört, begeistert, besprechen und bekämpfen. Was nicht bei den großen Portalen, Plattformen und Apps auftaucht, existiert nicht. Ist kein Bestandteil der Realität.
Das gilt gleichermaßen für alles, was Googles Suchmaschine nicht ausspuckt. Entsprechend interessant sind die sogenannten Transparenzberichte des Unternehmens, die veranschaulichen, wie oft staatliche Stellen die Entfernung von Suchergebnissen fordern. Wobei die entsprechenden Listen wohl nur die Spitze der Spitze des Eisbergs darstellen dürften. Nicht umsonst beschäftigen sich weitere geleakte Google-Dokumente primär mit den Zusammenhängen von maschinellem Lernen und menschlicher Wahrnehmung. Mit Nudging und kognitiver Kriegsführung. Das von der CIA gegründete Unternehmen war von Beginn an darauf ausgelegt, die Bevölkerung auszuspionieren, um sie qua Filterblasen zu manipulieren.
Was wir wahrnehmen, ist unsere Realität. Was wir nicht wahrnehmen, wird unsere Realität. Ohne, dass wir etwas dagegen unternehmen könnten. Googles Suchmaschinensegregativ schafft Wirklichkeit. Bei immer noch 91 Prozent Marktanteil ein Kinderspiel. Ganz wie US-Chefstratege Zbigniew Brzezinski es vor 54 Jahren in seinem Buch »Between Two Ages – America's Role in the Technetronic Era« prophezeite.
Was in Abhandlungen zu Verhaltensökonomie blasiert umrissen wird, verblüfft im Alltag durch die Effizienz seiner Profanität: Der zwangsalimentierte Erziehungsfunk repliziert das folgenlose Geschwafel von Politdarstellern, Twitter den von Technokraten kuratierten »Bürgerjournalismus«, Instagram Propaganda von Influencern und Facebook den Tratsch von Oma und Opa. Google präsentiert nur Ergebnisse, die dem Herrschaftsnarrativ dienen, Wikipedia gefährliches Halbwissen von Ideologen, YouTube handzahme Kommentare zum Politspektakel und Rumble die emotionalisierte Replik des vermeintlichen Widerstands. Spotify und Apple Music generieren die Playlist, Amazon schlägt vor, was zu Weihnachten gekauft, Microsoft Word, welche Worte man bei der Formulierung eines Textes meiden und der Krypto-Guru, in welche aus null und eins bestehende »Währung« investiert werden soll. Damit steht das Programm. Die tragenden Wände des Debattenraums. Mehr als dieses Potpourri von Second-Hand-Inhalten haben die meisten Menschen gar nicht mehr im Kopf.
Das Weltwirtschaftsforum (WEF) veröffentlichte im Februar 2022 ein 46 Seiten umfassendes Papier namens »Advancing Digital Agency«, das sich mit der »Macht der Datenvermittler« befasst. Sprich, mit der Rolle der zuvor erwähnten »Dritten« und der Frage, wie Externa zur Verinnerlichung am effektivsten ausgerollt werden können. Der Executive Summary lässt sich auf Seite vier entnehmen:
»Niemand weiß (oder verfolgt), was mit seinen Daten geschieht. (…) Wo Menschen früher Bildschirme zum Navigieren hatten, erzeugen neue Methoden zur Erfassung von Umgebungsdaten mit ihren vielen Vorteilen Nervosität und Resignation, wenn Menschen nicht den Gesamtüberblick haben. Manchmal entscheiden sich Einzelpersonen möglicherweise gegen die Interaktion mit Technologien, die für ihr Leben von großem Nutzen wären. Was aber wäre, wenn man diese Entscheidungspunkte an einen vertrauenswürdigen Agenten auslagern könnte, der im Namen einer Einzelperson oder sogar einer Gruppe handelt? Jetzt, da bildschirmlose Technologie Teil des Alltags ist, bietet sich die Gelegenheit, das Paradigma der Mensch-Technik-Interaktion zu überdenken und die Debatte neu auszurichten, um den Fokus auf Rollen und Verantwortlichkeiten jenseits der Person zu legen. Wie kann der Einsatz von Datenvermittlern Menschen dabei helfen, sich in Technologien und Datenökosystemmodellen zurechtzufinden, ohne aus den Augen zu verlieren, was es bedeutet, Mensch zu sein? (…) Datenvermittler – insbesondere digitale Agenten – stellen einen neuen politischen Hebel dar, mit dem Einzelpersonen die Herausforderungen des wachsenden Datenökosystems möglicherweise meistern können. Dieser Bericht soll Licht auf eine alternative Methode der vermittelten Mensch-Technik-Interaktion werfen, bei der Daten scheinbar nahtlos von Menschen zur Technologie gelangen, und zwar auf eine menschenzentrierte und vor allem vertrauenswürdige Weise. Durch die Kommunikation gemeinsamer Anreize, den Aufbau eines guten Rufs oder die Einholung einer Bestätigung durch Dritte. (…) Dieser Bericht untersucht die Chancen und Risiken von Datenvermittlern und insbesondere digitalen Drittagenten. Von Datentreuhändern bis hin zu vertrauenswürdigen digitalen Agenturen zeichnet der Bericht das Bild einer Welt, die Menschen und Unternehmen gegenüber einfühlsamer ist und durch die Einführung eines vertrauenswürdigen Dritten mehr Sicherheit für den Datenaustausch als Grundlage für Innovationen bietet. Entscheidend ist, dass der Bericht Handlungshebel für den öffentlichen und privaten Sektor vorschlägt, um ein zukunftssicheres digital-politisches Umfeld zu gewährleisten, das einen nahtlosen und vertrauenswürdigen Datenverkehr zwischen Menschen und der Technologie ermöglicht, die ihnen dient.«
Technologie, die uns »dient«? Wer den Buzzword-Neusprech des Davoser Global-Governance-Tentakels zu decodieren weiß, kann sich vorstellen, was mit »dienen« gemeint ist. Denn das Produkt sind wir – die Steuersklaven, DNA-Pools und Datenfarmen. Die Technologie sorgt lediglich für unsere zeitgemäße Versklavung. Sie ist ein maschinell-zentralistisches Monstrum, das sich an unserer Lebenszeit labt. Und die nächsten Jahre dürften darüber entscheiden, ob die Spezies Mensch vor ihrem Fortschritt kapituliert, oder die Oberhand gewinnt. Ob sie auf Generationen hinaus dazu verdammt ist, Vasall ihrer Werkzeuge zu sein, oder diese zu ihrem Vorteil einzusetzen weiß. Denn schlecht sind technische Revolutionen nicht per se. Siehe Blockchain. Lässt man sich von ihnen überrumpeln, allerdings schon.
Und genau das geschieht gerade. Während die leitmediale Deutungselite sich als Megafon moralisierender Selbstgerechtigkeit präsentiert und einer Phase kriegerischer Auseinandersetzungen mit suizidaler Sorglosigkeit entgegensieht, betätigt sich ein guter Teil der kritischen Prominenz als ebenso wirkungsvolles Sedativum für die von Ersteren enttäuschten Massen. Denn am Ende reagiert die jeweilige Klientel auf ein und dieselbe Weise: Sie sitzt auf dem Sofa.
Die tragende Säule der transluzenten Haftanstalt, die ein Habitus lethargischer Bequemlichkeit um uns herum errichtet, ist die Einführung der digitalen Identität. Und die ist in vollem Gange. Australien hat Ende November 2024 als erstes Land der Welt ein Gesetz erlassen, dass Jugendlichen unter 16 Jahren den Zugang zu Social-Media-Portalen untersagt. Und während es sicherlich zu begrüßen ist, dass Kinder ihre Zeit nicht mit digitalem Nonsens verplempern, zeitigt solche Legislatur in letzter Konsequenz nichts anderes als einen Ausweiszwang fürs Internet. Wie sonst soll man feststellen können, wer unter 16 ist? Was eine Frage der Erziehung wäre, gerät in Händen des Staates zu einem Instrument ausufernder Kontrolle.
Auch die Schweiz plant die Einführung einer E-ID – obwohl diese bei einer Volksabstimmung im März 2021 klar abgelehnt wurde. Verfügbar sein soll der digitale Pass ab 2026. Die Nutzung beruhe auf Freiwilligkeit, so die Behörden. Doch schon jetzt werden Stimmen laut, die den Einsatz der digitalen Identität beim Sammeln von Stimmen für politische Begehren fordern. Stichwort »E-Collecting«. Damit soll Unregelmäßigkeiten bei der Vorbereitung von Volksabstimmungen vorgebeugt werden. Die hiesige Piratenpartei hat bereits angekündigt, ein zweites Referendum gegen den elektronischen Ausweis zu lancieren – denn er sei »ein Wolf im Schafspelz«. Die Eidgenossenschaft dürfte in Anbetracht einer erfolgsversprechenden Abstimmungskampagne also noch eine ganze Weile von den negativen Folgen eines solchen Überwachungsinstrumentariums verschont bleiben.
Derweil arbeiten natürlich auch Deutschland, die EU, die USA und das »System Chief Executives Board for Coordination« der UN an einer digitalen Identität. Denn ohne eine solche wird weder das volldigitalisierte Finanzsystem von morgen noch das Mikromanagement der Individualmobilität via CO2-Emissionstracking funktionieren. Keine E-ID, kein digitales Gulag.
Noch lassen sich solche Sachverhalte recherchieren und darstellen. Noch kann Widerstand artikuliert, organisiert und geleistet werden. Doch wenn der Heimcomputer in absehbarer Zeit keine Tastatur mehr hat, weil es nur noch Touchscreens gibt, wenn Gestik, Mimik, Sprachsteuerung und KI das Tippen und Suchen ersetzen, wenn Google nur noch das eine Ergebnis auswirft und der digitale Assistent jede noch so komplexe Frage mit unterkomplexen Monokausalitäten trivialisiert, wenn Plattformen ausgeblendet haben, was die Obrigkeit als »Hassrede« klassifiziert, werden die meisten Menschen gar nicht mehr wissen – und wissen können – was sie nicht wissen. Woher denn auch.
Zensur bedeutet in Zeiten der Plattformökonomie nicht, dass Webseiten gelöscht und Bücher verbrannt werden – Zensur bedeutet, dass Informationen, Artikel und Webseiten einfach nicht mehr angezeigt werden. Dass sie nicht mehr gesucht, gefunden, verlinkt oder zitiert werden können, weil sie nicht mehr Teil des digitalen Ökosystems sind. Zensur beginnt mit Orwells »Memory Hole«, das immer häufiger essenzielle Ressourcen wie das Internetarchiv erfasst. Erst vor wenigen Wochen war die Webseite tagelang offline, weil sie sich einem massiven Hackerangriff ausgesetzt sah. Und auch die Wayback Machine, mit der sich die Historie von Webseiten nachvollziehen lässt, weist immer mehr Löcher auf. So fehlen zum Beispiel alle Einträge des Twitter-Blogs für den Zeitraum vom 3. März 2019 bis zum 28. November 2023. Warum, weiß niemand. Zensur beginnt dort, wo der von Bequemlichkeit, Unwissenheit und Lethargie vereinnahmte Konsument das Internet nur noch via Plattform, Social-Media-Portal und Smartphone-App nutzt, anstatt sich mittels Browser selbst zu orientieren.
Dass genau das schon jetzt gang und gäbe ist, kann ich aus eigener Erfahrung bestätigen. Denn obwohl viele tausend Personen meinen Konten bei Twitter, Telegram und YouTube folgen, hat sich bislang nur etwa ein Zehntel dieser Menge auf meiner Webseite für E-Mail-Updates registriert. Obwohl diese kostenlosen Mail-Updates einen direkten Link zwischen Autor und Leser etablieren und damit »datenvermittelnde« Dritte umgehen. Einen Link, der auch dann noch funktioniert, wenn Social-Media-Konten gesperrt oder gelöscht werden. Wäre das morgen bei mir der Fall, würde vermutlich nur ein Bruchteil meiner »Follower« wissen, wie er meine Webseite findet.
Die diesbezügliche Unselbstständigkeit nimmt teils groteske Formen an. Da fragen Menschen, wo man meine Texte lesen kann, während die URL meines Blogs im nur einen Klick entfernten Profil zu finden ist. Andere posten Fragen, Links oder Screenshots unter Beiträge, die nahelegen, dass sie nicht einmal gelesen haben, was sie kommentieren. Auch eine Suchmaschine scheinen viele nicht mehr aufrufen zu können, wenn sie etwas wissen wollen. Anstatt die gewünschte Information in 30 Sekunden selbst zu recherchieren, stellen sie ihre Frage in Form eines Social-Media-Kommentars und hoffen, dass jemand sie beantwortet. Geschieht das nicht, vergessen sie nach fünf Minuten, dass sie eine Frage hatten.
Es wirkt bisweilen tragisch. Denn auch wer die seit Corona im Aufwind befindlichen neuen Medien, die »kritischen Accounts« und Podcaster verfolgt, macht häufig nichts anderes als der Tagesthemen-Zuschauer: Er konsumiert die Polykrise, als wäre es ein Spielfilm, den man in passiver Schockstarre über sich ergehen lässt.
Aber auch die Medienschaffenden der »fünften Gewalt« unterscheiden sich mithin kaum von ihren Widersachern im leitmedialen Konsenskomplex. Wenn sie nicht gerade mit der eigenen Geschichte oder Opferrolle beschäftigt sind, berichten sie über die Schicksale und Leidenswege von Kollegen. Oder über das, was der Konsenskomplex verlautbaren lässt. Auch die ein oder andere Tirade gegenüber missliebigen Konkurrenten darf nicht fehlen. Hauptsache, es bringt Klicks. Denn wer den Medienzirkus einmal zu seinem Broterwerb gemacht hat, ist abhängig davon, dass er sich auszahlt. Auch wenn es zu Lasten des Inhalts geht.
Kaum jemand recherchiert Fakten, macht Textarbeit, deckt auf, dokumentiert Entwicklungsprozesse, empfiehlt stichhaltige Quellen, liefert neue Themen oder zusätzliche Hintergründe. Kaum ein Format zeichnet sich durch Informationsgehalt aus oder bietet irgendeine Form von Erkenntnisgewinn. Meistens wird einfach das besprochen, kommentiert, analysiert oder eingeordnet – also wiedergekäut – was gerade durch Newsfeeds, Timelines und Trend-Charts geistert.
Eine herausragende Unart ist es, wenn die Moderatoren sich dabei nicht einmal zu schade sind, ihren Twitter-Feed einzublenden, um dann eine Stunde lang geistlos Kommentare von Kommentatoren zu kommentieren. Retorten-Radio. Informativ und intellektuell bereichernd wie die hundertfünfzigste Wiederholung eines Bud-Spencer-Streifens am Weihnachtsfeiertag. Weniger journalistische Relevanz geht kaum.
Wer also nach guten Vorsätzen für das neue Jahr sucht, könnte an exakt dieser Stelle ansetzen. Der Medienschaffende könnte sich auf die Kernaufgabe des Journalismus besinnen und die Mühe machen, zu recherchieren, um seinen Zuschauern und -hörern echten Erkenntnisgewinn zu bescheren. Das macht zwar mehr Arbeit – aber eben auch Sinn.
Und der Konsument könnte damit beginnen, die Kontrolle über seine Informationsgewinnung wiederzuerlangen, anstatt sich berieseln zu lassen wie in alten Zeiten. Zum Beispiel durch die Nutzung eines RSS-Readers, das Lesen von Primärquellen, den Boykott von Big-Tech-Plattformen oder die Anschaffung eines Smartphones mit GrapheneOS-Betriebssystem. Das macht sogar weniger Arbeit, wenn man sich erst einmal eingefuchst hat – und vor allem freier, gelassener und mental resilienter.
Grundsätzlich gilt: Wer nach Lösungen sucht, sollte bei sich selbst beginnen. Denn für die meisten Herausforderungen unserer Zeit existieren sie längst. Nur genutzt werden sie zu selten. Und das liegt nicht an den Lösungen, sondern den Konsumenten, die jeden Tag aufs Neue die Chance verstreichen lassen, es besser zu machen. Wann also wäre ein geeigneterer Zeitpunkt, um den ein oder anderen Neustart zu planen als jetzt, wo sich ein weiteres Jahr in seine letzten, kurzen Tage streckt?
So schwer, verstörend und düster viele davon gewesen sein mögen, so schön, bemerkenswert, erheiternd und licht war manch ein Moment der vergangenen zwölf Monate. Leider ist der menschliche Geist zwecks Risikominimierung evolutionär darauf ausgelegt, sich vor allem an Negatives zu erinnern. Und viel zu oft verdrängen diese unschönen, aber lehrreichen Erfahrungen die Wertschätzung für eine der simpelsten Wahrheiten des Lebens:
Das Schöne zieht seinen Reiz aus der Vergänglichkeit.
Gerade die Flüchtigkeit des Positiven macht es so wichtig, sich diese Erkenntnis zum Ablauf eines Kalenderjahres bewusst zu machen. Denn das wertvollste, was wir Menschen im Lauf eines Lebens sammeln können, sind erhebende Momente. Wie viele wir davon anhäufen bevor unsere eigene Zeit abgelaufen ist, hängt nicht primär von äußeren Umständen, sondern unserer inneren Einstellung ab. Eine den Wirren der Zeit angemessene Sichtweise verbirgt sich hinter einem kurzen, fast schon philosophischen Wortwechsel aus dem für den vorliegenden Text namensgebenden Hitchcock-Streifen:
»Wollen Sie behaupten, Sie hätten Interesse für die Kunst?«
»Ja – für die Kunst weiterzuleben.«
-
 @ ee11a5df:b76c4e49
2024-12-24 18:49:05
@ ee11a5df:b76c4e49
2024-12-24 18:49:05China
I might be wrong, but this is how I see it
This is a post within a series I am going to call "I might be wrong, but this is how I see it"
I have repeatedly found that my understanding of China is quite different from that of many libertarian-minded Americans. And so I make this post to explain how I see it. Maybe you will learn something. Maybe I will learn something.
It seems to me that many American's see America as a shining beacon of freedom with a few small problems, and China is an evil communist country spreading communism everywhere. From my perspective, America was a shining beacon of freedom that has fallen to being typical in most ways, and which is now acting as a falling empire, and China was communist for about a decade, but turned and ran away from that as fast as they could (while not admitting it) and the result is that the US and China are not much different anymore when it comes to free markets. Except they are very different in some other respects.
China has a big problem
China has a big problem. But it is not the communism problem that most Westerners diagnose.
I argue that China is no longer communist, it is only communist in name. And that while it is not a beacon of free market principles, it is nearly as free market now as Western nations like Germany and New Zealand are (being somewhat socialist themselves).
No, China's real problem is authoritarian one-party rule. And that core problem causes all of the other problems, including its human rights abuses.
Communism and Socialism
Communism and Socialism are bad ideas. I don't want to argue it right here, but most readers will already understand this. The last thing I intend to do with this post is to bolster or defend those bad ideas. If you dear reader hold a candle for socialism, let me know and I can help you extinguish it with a future "I might be wrong, but this is how I see it" installment.
Communism is the idea of structuring a society around common ownership of the means of production, distribution, and exchange, and the idea of allocating goods and services based on need. It eliminates the concept of private property, of social classes, ultimately of money and finally of the state itself.
Back under Mao in 1958-1962 (The Great Leap Forward), China tried this (in part). Some 50+ million people died. It was an abject failure.
But due to China's real problem (authoritarianism, even worship of their leaders), the leading classes never admitted this. And even today they continue to use the word "Communist" for things that aren't communist at all, as a way to save face, and also in opposition to the United States of America and Europe.
Authorities are not eager to admit their faults. But this is not just a Chinese fault, it is a fault in human nature that affects all countries. The USA still refuses to admit they assassinated their own president JFK. They do not admit they bombed the Nord Stream pipeline.
China defines "socialism with Chinese characteristics" to mean "the leadership of the Communist Party of China". So they still keep the words socialism and communism, but they long ago dropped the meanings of those words. I'm not sure if this is a political ploy against us in the West or not.
China's Marketplace Today
Today China exhibits very few of the properties of communism.
They have some common ownership and state enterprises, but not much differently than Western countries (New Zealand owns Air New Zealand and Kiwibank and Kiwirail, etc). And there are private enterprises all over China. They compete and some succeed and some fail. You might hear about a real-estate bank collapsing. China has private property. They have mostly free markets. They have money, and the most definitely have social classes and a very strong state.
None of that is inline with what communist thinkers want. Communist thinkers in China moan that China has turned away from communism.
Deng Xiaoping who succeeded Mao and attempted to correct the massive mistake, did much when he said "to get rich is glorious."
China achieved staggering rates of economic growth. 10% annually on average since 1977. Chinese economic reform started in 1979 and has continued through successive administrations (Deng, Jiang, Hu and now Xi).
China is now the world's largest economy (by GDP in PPP terms) since 2016.
I was first made aware of China's economic growth by Jim Rogers, an American commodities expert who travelled through China (and the rest of the world from 1990-1992) and in 2007 moved to Singapore where he ensured his daughters learned to speak Mandarin, because Jim knew where the economic growth was going to happen. Jim always spoke positively of China's economic prospects, and his view was so different from the "China is a nasty communist place" view that I had grown up with that my mind opened.
How can anybody believe they are still a communist country? In what world does it make sense that communism can produce such a massively booming economy? It doesn't make sense because it is simply wrong.
What does happen is that the CPC interferes. It lets the market do what markets do, but it interferes where it thinks oversight and regulation would produce a better result.
Western nations interfere with their markets too. They have oversight and regulation. In fact some of China's planned reforms had to be put on hold by Xi due to Donald Trump's trade war with China. That's right, they were trying to be even more free market than America, but America's protectionism prodded Xi to keep control so he could fight back efficiently.
Government oversight and regulation IMHO is mostly bad because it gets out of control, and there are no market forces to correct this. This gets even more extreme in a one-party system, so I can judge that China's oversight and regulation problems are very likely worse than those in Western nations (but I have no first hand experience or evidence).
Why do you keep saying CPC?
The Communist Party of China (CPC) is the ruling party in China. That is their official name. To call them the CCP is to concede to the idea that the British and Americans get to name everybody. I'm not sure who is right, since CPC or CCP is their "English" name (in Chinese it is 中国共产党 and Westernized it is Zhōngguó Gòngchǎndǎng). Nonetheless, I'll call them CPC because that is their wish.
Social Credit System
China moved from a planned economy to a market economy in stages. They didn't want any more sudden changes (can you blame them?). In the process, many institutions that have existed in the West for a long time didn't exist in China and they had to arise somehow. IMHO market forces would have brought these about in the private sector, but the one-party CP of China instead decided to create these.
One of those institutions was a credit score system. In the West we have TransUnion and Equifax that maintain credit ratings on people, and we have S&P, Moody's and Fitch that maintain credit ratings on companies. The domain of these ratings is their financial credit-worthiness.
So the People's Bank of China developed a credit information database for it's own needs. The government picked up on the idea and started moving towards a National Credit Management System. In 2004 it became an official goal to establish a credit system compatible with a modern market system. By 2006 banks were required to report on consumer creditworthiness.
But unchecked one-party governmental power will often take a good idea (credit worthiness data shared among private parties) and systematize it and apply it top-down, creating a solution and a new problem at the same time.
Nonetheless, originally it was about credit worthiness and also criminal convictions. That is no big scary thing that some right-wing American commentators will lead you to believe. In the US for example criminal records are public, so China's Social Credit System started out being no more over-reaching in scope than what Americans have lived under their entire lives, its only fault (a severe one) being centrally planned. And that remained the case up until about 2016 (in my estimation).
But of course there is always scope creep. As it exists today, I have reason to believe that CPC officials and even A.I. use judgement calls to score someone on how moral that person has been! Of course that is not a good idea, and IMHO the problem stems from one-party rule, and authoritarian administration of ideas that should instead be handled by the private sector.
Environmental, Social, and Governance
ESG is a system that came out of a couple basic ideas. The first is that many two-party transactions actually have externalities. They don't just affect the two parties, they also affect everybody else. When you fly in an airplane, you increase the CO2 in the atmosphere that everybody has to pay for (eventually). You may dispute that example, but that is no doubt one of the motivations of ESG.
But of course the recognition of this basic issue didn't lead all people towards market solutions (well it did, but those have been mostly messed up by others), but instead led many people towards ESG, which is a social credit scoring system which applies scores based on environmental and social side-effects of market transactions.
This is not at all the same as China's social credit system, which I described above. I hope you can see the difference.
In fact, China imported ESG from the West. Chinese companies, of their free will, in an attempt to court Western capital, achieve ESG goals for those Western investors. They have been playing this ESG game for 20 years just like the entire world has, because the West has imposed this faux-morality upon them. It isn't something China exported to us, it is something we exported to them.
I think China has avoided Woke-ism
My understanding of Chinese people, based on what I've heard many Chinese people say, is that China isn't affected by the Western woke-ism epidemic. They deride Western white woke people with the term "Baizuo". They have never sent an incompetent break dancer to the Olympics because of wok-ism. Competence is highly respected as is the competition to be the most competent, which (when augmented by a one-child policy which is no longer) has produced child prodigies like no other country has.
What about predatory loans of the Belt and Road initiative?
Predatory is an odd name for loans to people in need. The World Bank makes loans to people in need. China does too. China stands in opposition to Western Empire, and in that regard they produce their own alternative BRICS institutions. This is one of them.
There is AFAIK nothing more predatory about them. It is just that in some cases the borrowers have trouble paying them back and they get foreclosed upon. I don't think this is worthy of much discussion, except that the term "predatory" seems to me to be a propaganda device.
What about foreign influence from China?
China wants to influence the world, especially its own trading partners and potential trading partners. Doing that above board is fine by me.
But some of it is undoubtedly covert. Sometimes Chinese-born people run for public office in Western countries. In New Zealand we stood down some when it became clear they were being influenced too much by the CPC while being charged with representing their local town (dual loyalty issues). If only the USA would do the same thing to their dually-loyal politicians.
And all large nations run influence operations. The USA has the CIA, for example, and claims this "soft power" is actually the better alternative to what would otherwise be military intervention (but IMHO shouldn't be either). I'm not defending such operations (I despise them), I'm just explaining how China's position of exerting influence is not only no big deal and totally expected, it pales in comparison to the United States' influence operations which often become military excursions (something China rarely ever does).
What about the Great Firewall?
Yeah, that sucks. Again, single-party authoritarian control gone to extremes.
What about Human Rights Abuses? What about the Uyghur Genocide?
I don't like them. To the extent they are occurring (and I lean towards the belief that they are occurring), I condemn them.
China has anti-terrorism and anti-extremism policies that go too far. They end up oppressing and/or criminalizing cultures that aren't Chinese enough. But especially, China punishes dissent. Disagreement with the CPC is the high crime. It is the one-party rule that causes this problem. Anybody who speaks out against the CPC or goes against the state in any way is harshly punished. This happens to Uyghurs, to Falun Gong, to Tibetans, and to any religion that is seen as subversive.
Amnesty International and the UN OHCHR have documented issues around the Xinjiang Uyghur autonomous region, Tibet, LGBT rights, death penalty, workers rights, and the Hong Kong special administrative region. I am not about to pretend I know better than they do, but to some extent they go too far.
Amnesty International says this about the USA: Discrimination and violence against LGBTI people were widespread and anti-LGBTI legislation increased. Bills were introduced to address reparations regarding slavery and its legacies. Multiple states implemented total bans on abortion or severely limited access to it. Gender-based violence disproportionately affected Indigenous women. Access to the USA for asylum seekers and migrants was still fraught with obstacles, but some nationalities continued to enjoy Temporary Protected Status. Moves were made to restrict the freedom to protest in a number of states. Black people were disproportionately affected by the use of lethal force by police. No progress was made in the abolition of the death penalty, apart from in Washington. Arbitrary and indefinite detention in the US naval base Guantánamo Bay, Cuba, continued. Despite extensive gun violence, no further firearm reform policies were considered, but President Biden did announce the creation of the White House Office of Gun Violence Prevention. The USA continued to use lethal force in countries around the world. Black people, other racialized groups and low-income people bore the brunt of the health impacts of the petrochemical industry, and the use of fossil fuels continued unabated.
Amnesty international didn't even point out that the US government quashes free speech via pressure on social media corporations (because Amnesty International is far too lefty).
So who is worse, China or the US? I'm not going to make that judgement call, but suffice it to say that in my mind, China is not obviously worse.
China violates freedom of expression, association, and assembly of all people. This is bad, and a consequence mainly of one-party rule (again, what I think is the root cause of most of their ills). They arrest, detain, potentially kill anybody who publicly disagrees openly with their government. Clearly this is an excess of authoritarianism, a cancer that is very advanced in China.
As to organ harvesting of Uyghur Muslims, I think this is a myth.
China has dealt harshly with Muslim extremism. They don't offer freedom of religion to ISIS. And Amnesty International complains about that. But practically speaking you probably shouldn't respect the extremist religion of people who want to force everybody into a global caliphate through threat of violence. As you are well aware, some extremist Muslims (<1% of Islam) believe in using violence to bring about a global caliphate. Those extremists pop up in every country and are usually dealt with harshly. China has had to deal with them too.
I have watched two different Western YouTubers travel to Xinjiang province trying to find the oppressed Uyghurs and interview them. They can't find them. What they find instead are Uyghur Muslims doing their prayers five times a day at the local mosque. And also stories that the CPC pitched in some money to help them renovate the mosque. Maybe they were afraid it was a CPC trap and so they wouldn't speak freely. Amnesty International and the UN OHCHR say more than a million are "arbitrarily detained" and I'm not going to argue otherwise. But I'd be more convinced if there were a stream of pictures and news like there is out of Gaza, and it is suspicious that there isn't.
Conclusion
China is more like a Western nation that Westerners realize. Economically, militarily, socially. It still has a very serious obstacle to overcome: one-party rule. I don't think the one-party is going to voluntarily give up power. So most probably at some point in the future there will be a revolution. But in my opinion it won't happen anytime soon. For the most part Chinese people are living high on the hog, getting rich, enjoying the good life, in positive spirits about life, and are getting along with their government quite well at present.
-
 @ 1f9e547c:8af216ed
2024-07-13 07:37:05
@ 1f9e547c:8af216ed
2024-07-13 07:37:05Opinion about Bitcoin Wallet Crypto Ethereum (android)
For archival purposes
Atomic Wallet suffers hack on June 2023
Sources
Atomic Wallet users have been left wanting more answers, despite the decentralized wallet provider finally releasing a full “event statement” about the June exploit — which some estimate has run up to $100 million in losses.
In a June 20 blog post — the first major update from the firm since the June 3 exploit — Atomic Wallet claimed there have been no new confirmed cases after initial reports of the hack.
Atomic Wallet Was Breached by North Korean Hackers: Elliptic
Atomic Wallet users might have fallen victim to Lazarus, the infamous North Korean hacking group, said blockchain intelligence firm Elliptic in a blog post on Tuesday.
Early Saturday morning, the team behind Atomic, a non-custodial crypto wallet, announced that some users were compromised and lost the funds from their wallets. According to the company, the number of incidents did not exceed 1% of "monthly active users." The announcement followed multiple reports on Reddit from users complaining their wallets had been drained.
WalletScrutiny #nostrOpinion
-
 @ a367f9eb:0633efea
2024-12-22 21:35:22
@ a367f9eb:0633efea
2024-12-22 21:35:22I’ll admit that I was wrong about Bitcoin. Perhaps in 2013. Definitely 2017. Probably in 2018-2019. And maybe even today.
Being wrong about Bitcoin is part of finally understanding it. It will test you, make you question everything, and in the words of BTC educator and privacy advocate Matt Odell, “Bitcoin will humble you”.
I’ve had my own stumbles on the way.
In a very public fashion in 2017, after years of using Bitcoin, trying to start a company with it, using it as my primary exchange vehicle between currencies, and generally being annoying about it at parties, I let out the bear.
In an article published in my own literary magazine Devolution Review in September 2017, I had a breaking point. The article was titled “Going Bearish on Bitcoin: Cryptocurrencies are the tulip mania of the 21st century”.
It was later republished in Huffington Post and across dozens of financial and crypto blogs at the time with another, more appropriate title: “Bitcoin Has Become About The Payday, Not Its Potential”.
As I laid out, my newfound bearishness had little to do with the technology itself or the promise of Bitcoin, and more to do with the cynical industry forming around it:
In the beginning, Bitcoin was something of a revolution to me. The digital currency represented everything from my rebellious youth.
It was a decentralized, denationalized, and digital currency operating outside the traditional banking and governmental system. It used tools of cryptography and connected buyers and sellers across national borders at minimal transaction costs.
…
The 21st-century version (of Tulip mania) has welcomed a plethora of slick consultants, hazy schemes dressed up as investor possibilities, and too much wishy-washy language for anything to really make sense to anyone who wants to use a digital currency to make purchases.
While I called out Bitcoin by name at the time, on reflection, I was really talking about the ICO craze, the wishy-washy consultants, and the altcoin ponzis.
What I was articulating — without knowing it — was the frame of NgU, or “numbers go up”. Rather than advocating for Bitcoin because of its uncensorability, proof-of-work, or immutability, the common mentality among newbies and the dollar-obsessed was that Bitcoin mattered because its price was a rocket ship.
And because Bitcoin was gaining in price, affinity tokens and projects that were imperfect forks of Bitcoin took off as well.
The price alone — rather than its qualities — were the reasons why you’d hear Uber drivers, finance bros, or your gym buddy mention Bitcoin. As someone who came to Bitcoin for philosophical reasons, that just sat wrong with me.
Maybe I had too many projects thrown in my face, or maybe I was too frustrated with the UX of Bitcoin apps and sites at the time. No matter what, I’ve since learned something.
I was at least somewhat wrong.
My own journey began in early 2011. One of my favorite radio programs, Free Talk Live, began interviewing guests and having discussions on the potential of Bitcoin. They tied it directly to a libertarian vision of the world: free markets, free people, and free banking. That was me, and I was in. Bitcoin was at about $5 back then (NgU).
I followed every article I could, talked about it with guests on my college radio show, and became a devoted redditor on r/Bitcoin. At that time, at least to my knowledge, there was no possible way to buy Bitcoin where I was living. Very weak.
I was probably wrong. And very wrong for not trying to acquire by mining or otherwise.
The next year, after moving to Florida, Bitcoin was a heavy topic with a friend of mine who shared the same vision (and still does, according to the Celsius bankruptcy documents). We talked about it with passionate leftists at Occupy Tampa in 2012, all the while trying to explain the ills of Keynesian central banking, and figuring out how to use Coinbase.
I began writing more about Bitcoin in 2013, writing a guide on “How to Avoid Bank Fees Using Bitcoin,” discussing its potential legalization in Germany, and interviewing Jeremy Hansen, one of the first political candidates in the U.S. to accept Bitcoin donations.
Even up until that point, I thought Bitcoin was an interesting protocol for sending and receiving money quickly, and converting it into fiat. The global connectedness of it, plus this cypherpunk mentality divorced from government control was both useful and attractive. I thought it was the perfect go-between.
But I was wrong.
When I gave my first public speech on Bitcoin in Vienna, Austria in December 2013, I had grown obsessed with Bitcoin’s adoption on dark net markets like Silk Road.
My theory, at the time, was the number and price were irrelevant. The tech was interesting, and a novel attempt. It was unlike anything before. But what was happening on the dark net markets, which I viewed as the true free market powered by Bitcoin, was even more interesting. I thought these markets would grow exponentially and anonymous commerce via BTC would become the norm.
While the price was irrelevant, it was all about buying and selling goods without permission or license.
Now I understand I was wrong.
Just because Bitcoin was this revolutionary technology that embraced pseudonymity did not mean that all commerce would decentralize as well. It did not mean that anonymous markets were intended to be the most powerful layer in the Bitcoin stack.
What I did not even anticipate is something articulated very well by noted Bitcoin OG Pierre Rochard: Bitcoin as a savings technology.
The ability to maintain long-term savings, practice self-discipline while stacking stats, and embrace a low-time preference was just not something on the mind of the Bitcoiners I knew at the time.
Perhaps I was reading into the hype while outwardly opposing it. Or perhaps I wasn’t humble enough to understand the true value proposition that many of us have learned years later.
In the years that followed, I bought and sold more times than I can count, and I did everything to integrate it into passion projects. I tried to set up a company using Bitcoin while at my university in Prague.
My business model depended on university students being technologically advanced enough to have a mobile wallet, own their keys, and be able to make transactions on a consistent basis. Even though I was surrounded by philosophically aligned people, those who would advance that to actually put Bitcoin into practice were sparse.
This is what led me to proclaim that “Technological Literacy is Doomed” in 2016.
And I was wrong again.
Indeed, since that time, the UX of Bitcoin-only applications, wallets, and supporting tech has vastly improved and onboarded millions more people than anyone thought possible. The entrepreneurship, coding excellence, and vision offered by Bitcoiners of all stripes have renewed a sense in me that this project is something built for us all — friends and enemies alike.
While many of us were likely distracted by flashy and pumpy altcoins over the years (me too, champs), most of us have returned to the Bitcoin stable.
Fast forward to today, there are entire ecosystems of creators, activists, and developers who are wholly reliant on the magic of Bitcoin’s protocol for their life and livelihood. The options are endless. The FUD is still present, but real proof of work stands powerfully against those forces.
In addition, there are now dozens of ways to use Bitcoin privately — still without custodians or intermediaries — that make it one of the most important assets for global humanity, especially in dictatorships.
This is all toward a positive arc of innovation, freedom, and pure independence. Did I see that coming? Absolutely not.
Of course, there are probably other shots you’ve missed on Bitcoin. Price predictions (ouch), the short-term inflation hedge, or the amount of institutional investment. While all of these may be erroneous predictions in the short term, we have to realize that Bitcoin is a long arc. It will outlive all of us on the planet, and it will continue in its present form for the next generation.
Being wrong about the evolution of Bitcoin is no fault, and is indeed part of the learning curve to finally understanding it all.
When your family or friends ask you about Bitcoin after your endless sessions explaining market dynamics, nodes, how mining works, and the genius of cryptographic signatures, try to accept that there is still so much we have to learn about this decentralized digital cash.
There are still some things you’ve gotten wrong about Bitcoin, and plenty more you’ll underestimate or get wrong in the future. That’s what makes it a beautiful journey. It’s a long road, but one that remains worth it.
-
 @ fd208ee8:0fd927c1
2024-12-26 07:02:59
@ fd208ee8:0fd927c1
2024-12-26 07:02:59I just read this, and found it enlightening.
Jung... notes that intelligence can be seen as problem solving at an everyday level..., whereas creativity may represent problem solving for less common issues
Other studies have used metaphor creation as a creativity measure instead of divergent thinking and a spectrum of CHC components instead of just g and have found much higher relationships between creativity and intelligence than past studies
https://www.mdpi.com/2079-3200/3/3/59
I'm unusually intelligent (Who isn't?), but I'm much more creative, than intelligent, and I think that confuses people. The ability to apply intelligence, to solve completely novel problems, on the fly, is something IQ tests don't even claim to measure. They just claim a correlation.
Creativity requires taking wild, mental leaps out into nothingness; simply trusting that your brain will land you safely. And this is why I've been at the forefront of massive innovation, over and over, but never got rich off of it.
I'm a starving autist.
Zaps are the first time I've ever made money directly, for solving novel problems. Companies don't do this because there is a span of time between providing a solution and the solution being implemented, and the person building the implementation (or their boss) receives all the credit for the existence of the solution. At best, you can hope to get pawned off with a small bonus.
Nobody can remember who came up with the solution, originally, and that person might not even be there, anymore, and probably never filed a patent, and may have no idea that their idea has even been built. They just run across it, later, in a tech magazine or museum, and say, "Well, will you look at that! Someone actually went and built it! Isn't that nice!"
Universities at least had the idea of cementing novel solutions in academic papers, but that: 1) only works if you're an academic, and at a university, 2) is an incredibly slow process, not appropriate for a truly innovative field, 3) leads to manifestations of perverse incentives and biased research frameworks, coming from 'publish or perish' policies.
But I think long-form notes and zaps solve for this problem. #Alexandria, especially, is being built to cater to this long-suffering class of chronic underachievers. It leaves a written, public, time-stamped record of Clever Ideas We Have Had.
Because they are clever, the ideas. And we have had them.
-
 @ 16d11430:61640947
2024-12-30 06:25:23
@ 16d11430:61640947
2024-12-30 06:25:23The sky was a smear of red and gray, a molten soup of corporate smog and the fallout from decaying orbital platforms. A low hum vibrated through the megascraper’s skeletal walls, the pulse of industrial turbines below or something worse—something alive. Daniel had stopped looking over his shoulder hours ago. Paranoia was pointless now. They were tracking him through every lens and drone. Every step he took, every breath he exhaled, was already logged on some server buried under a thousand feet of reinforced concrete.
His son, Mikey, sat cross-legged on the floor of the abandoned node café, the glow of a salvaged holographic tablet painting his freckled face in shifting rainbows. Ten years old. Too young for this world, but not too young for what Daniel needed to do.
“Mikey,” Daniel said, slumping against the wall. His ribs screamed where the drone's shard had grazed him earlier. He'd staunched the bleeding with a strip of synthcloth, but the pain was relentless. “We don’t have much time.”
Mikey didn’t look up. He was playing some ancient 8-bit game that Daniel had installed when he was still naïve enough to think childhood could be preserved.
“They’re coming for me,” Daniel said, his voice sharp enough to slice through the haze of distraction. Mikey paused the game.
“Who’s coming?” he asked, his voice quivering.
“The kind of people who don’t leave witnesses.” Daniel knelt down, gripping Mikey’s shoulders. His hands were trembling, but his grip was firm. “Listen to me. They want something I have—private keys to tech they can’t control. But it’s more than just money, Mikey. It’s freedom. It’s hope. If they get it, they’ll own everything, everyone.”
Mikey stared at him, wide-eyed. “Why don’t you just give it to them?”
“Because,” Daniel said, leaning in close, “it’s not just mine. It’s the only thing keeping the world from falling apart. But I’m running out of time. They dosed me with a neural decay agent. My brain’s got hours, maybe a day, before it’s mush.”
Mikey’s lip quivered. “What do we do?”
Daniel exhaled, a bittersweet mix of relief and despair. “We’re going to do something crazy. I’m going to teach you everything I know.”
The Download
The next hour was a blur. Daniel jacked into a local darknet relay, setting up a secure uplink to his personal server cluster—what was left of it, anyway. The room buzzed with the flicker of dying neon and the hum of overworked processors.
“Mikey,” Daniel said, pulling a thin mesh glove from his pack. “This is a cognitive transference device. It’s experimental, and it’s going to hurt, but it’s the only way.”
Mikey looked at the glove, then at his father. “What does it do?”
“It maps my neural pathways, compresses them, and streams them into your brain. You’ll have fragments of my skills, my memories. Not perfect, but enough. Enough to code, to think like I do. But it’s risky. You ready?”
Mikey nodded, eyes steeled. “I’m ready.”
Daniel slipped the glove onto Mikey’s hand and activated the uplink. A lattice of blue light spiraled up Mikey’s arm, embedding itself into his skin like a living tattoo. The boy screamed, his body convulsing. Daniel held him tight, whispering encouragements through gritted teeth.
“It’s okay, Mikey. It’s okay. Breathe. You’re stronger than this.”
Mikey’s screams subsided, replaced by rapid, shallow breaths. His eyes fluttered open, glowing faintly with the residual charge of the transfer.
“I see it,” Mikey whispered. “I see the code.”
The Final Hour
They worked side by side, father and son. Daniel guided Mikey through the cryptic maze of his life’s work: quantum-proof encryption, autonomous networks, self-healing AI. Mikey’s hands flew across the keyboard, his newfound knowledge mingling with his innate creativity.
“They’re breaching,” Mikey said, his voice calm despite the chaos. Red indicators flashed on the terminal, signaling the proximity of their pursuers.
“Focus,” Daniel said, ignoring the pounding in his chest. “Deploy the polymorphic algorithm. Let it spread through the mesh. It’ll buy us time.”
Mikey nodded, typing furiously. Lines of code cascaded down the screen like a digital waterfall.
“Done,” Mikey said, glancing at his father. “But what about you?”
Daniel smiled weakly, his vision blurring. “Doesn’t matter. What matters is you. The world. You’ve got everything you need now, Mikey. Everything I am, everything I stood for, is in you.”
The door exploded inward, a blast of light and sound. Shadows moved through the smoke, the silhouette of their enemies sharp and inhuman. Mikey turned to his father, tears streaming down his face.
“I won’t let them win,” he said.
Daniel nodded, his lips forming a final, unspoken command: Run.
Mikey bolted for the emergency hatch, clutching the tablet tight against his chest. Behind him, the sound of gunfire erupted, followed by silence.
Epilogue
Weeks later, the world was different. Subtly, at first. Corporate networks began to collapse, their monopolies eroded by the decentralized systems Mikey had unleashed. Grassroots movements flourished, empowered by tools they didn’t fully understand but knew they could trust.
Mikey sat alone in a hidden bunker, the tablet glowing faintly in his lap. His father’s voice echoed in his mind, fragments of the neural transfer surfacing like ghosts in the machine.
“The code is freedom, Mikey. And freedom always wins.”
-
 @ 6734e11d:c7e34e8f
2024-12-29 18:07:00
@ 6734e11d:c7e34e8f
2024-12-29 18:07:00 -
 @ fe32298e:20516265
2024-12-16 20:59:13
@ fe32298e:20516265
2024-12-16 20:59:13Today I learned how to install NVapi to monitor my GPUs in Home Assistant.
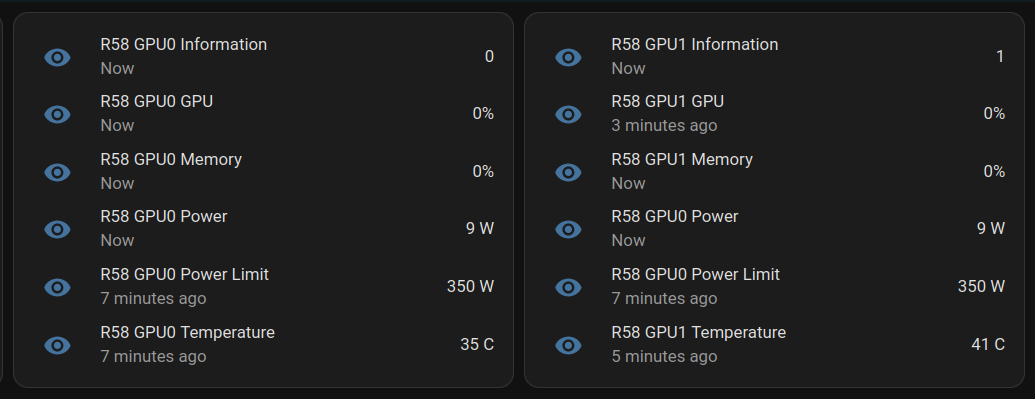
NVApi is a lightweight API designed for monitoring NVIDIA GPU utilization and enabling automated power management. It provides real-time GPU metrics, supports integration with tools like Home Assistant, and offers flexible power management and PCIe link speed management based on workload and thermal conditions.
- GPU Utilization Monitoring: Utilization, memory usage, temperature, fan speed, and power consumption.
- Automated Power Limiting: Adjusts power limits dynamically based on temperature thresholds and total power caps, configurable per GPU or globally.
- Cross-GPU Coordination: Total power budget applies across multiple GPUs in the same system.
- PCIe Link Speed Management: Controls minimum and maximum PCIe link speeds with idle thresholds for power optimization.
- Home Assistant Integration: Uses the built-in RESTful platform and template sensors.
Getting the Data
sudo apt install golang-go git clone https://github.com/sammcj/NVApi.git cd NVapi go run main.go -port 9999 -rate 1 curl http://localhost:9999/gpuResponse for a single GPU:
[ { "index": 0, "name": "NVIDIA GeForce RTX 4090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 16, "power_limit_watts": 450, "memory_total_gb": 23.99, "memory_used_gb": 0.46, "memory_free_gb": 23.52, "memory_usage_percent": 2, "temperature": 38, "processes": [], "pcie_link_state": "not managed" } ]Response for multiple GPUs:
[ { "index": 0, "name": "NVIDIA GeForce RTX 3090", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 14, "power_limit_watts": 350, "memory_total_gb": 24, "memory_used_gb": 0.43, "memory_free_gb": 23.57, "memory_usage_percent": 2, "temperature": 36, "processes": [], "pcie_link_state": "not managed" }, { "index": 1, "name": "NVIDIA RTX A4000", "gpu_utilisation": 0, "memory_utilisation": 0, "power_watts": 10, "power_limit_watts": 140, "memory_total_gb": 15.99, "memory_used_gb": 0.56, "memory_free_gb": 15.43, "memory_usage_percent": 3, "temperature": 41, "processes": [], "pcie_link_state": "not managed" } ]Start at Boot
Create
/etc/systemd/system/nvapi.service:``` [Unit] Description=Run NVapi After=network.target
[Service] Type=simple Environment="GOPATH=/home/ansible/go" WorkingDirectory=/home/ansible/NVapi ExecStart=/usr/bin/go run main.go -port 9999 -rate 1 Restart=always User=ansible
Environment="GPU_TEMP_CHECK_INTERVAL=5"
Environment="GPU_TOTAL_POWER_CAP=400"
Environment="GPU_0_LOW_TEMP=40"
Environment="GPU_0_MEDIUM_TEMP=70"
Environment="GPU_0_LOW_TEMP_LIMIT=135"
Environment="GPU_0_MEDIUM_TEMP_LIMIT=120"
Environment="GPU_0_HIGH_TEMP_LIMIT=100"
Environment="GPU_1_LOW_TEMP=45"
Environment="GPU_1_MEDIUM_TEMP=75"
Environment="GPU_1_LOW_TEMP_LIMIT=140"
Environment="GPU_1_MEDIUM_TEMP_LIMIT=125"
Environment="GPU_1_HIGH_TEMP_LIMIT=110"
[Install] WantedBy=multi-user.target ```
Home Assistant
Add to Home Assistant
configuration.yamland restart HA (completely).For a single GPU, this works: ``` sensor: - platform: rest name: MYPC GPU Information resource: http://mypc:9999 method: GET headers: Content-Type: application/json value_template: "{{ value_json[0].index }}" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature scan_interval: 1 # seconds
- platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} GPU" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Memory" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC {{ state_attr('sensor.mypc_gpu_information', 'name') }} Temperature" value_template: "{{ state_attr('sensor.mypc_gpu_information', 'temperature') }}" unit_of_measurement: "°C" ```
For multiple GPUs: ``` rest: scan_interval: 1 resource: http://mypc:9999 sensor: - name: "MYPC GPU0 Information" value_template: "{{ value_json[0].index }}" json_attributes_path: "$.0" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature - name: "MYPC GPU1 Information" value_template: "{{ value_json[1].index }}" json_attributes_path: "$.1" json_attributes: - name - gpu_utilisation - memory_utilisation - power_watts - power_limit_watts - memory_total_gb - memory_used_gb - memory_free_gb - memory_usage_percent - temperature
-
platform: template sensors: mypc_gpu_0_gpu: friendly_name: "MYPC GPU0 GPU" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_memory: friendly_name: "MYPC GPU0 Memory" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_0_power: friendly_name: "MYPC GPU0 Power" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_0_power_limit: friendly_name: "MYPC GPU0 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_0_temperature: friendly_name: "MYPC GPU0 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu0_information', 'temperature') }}" unit_of_measurement: "C"
-
platform: template sensors: mypc_gpu_1_gpu: friendly_name: "MYPC GPU1 GPU" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'gpu_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_memory: friendly_name: "MYPC GPU1 Memory" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'memory_utilisation') }}" unit_of_measurement: "%" mypc_gpu_1_power: friendly_name: "MYPC GPU1 Power" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_watts') }}" unit_of_measurement: "W" mypc_gpu_1_power_limit: friendly_name: "MYPC GPU1 Power Limit" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'power_limit_watts') }}" unit_of_measurement: "W" mypc_gpu_1_temperature: friendly_name: "MYPC GPU1 Temperature" value_template: "{{ state_attr('sensor.mypc_gpu1_information', 'temperature') }}" unit_of_measurement: "C"
```
Basic entity card:
type: entities entities: - entity: sensor.mypc_gpu_0_gpu secondary_info: last-updated - entity: sensor.mypc_gpu_0_memory secondary_info: last-updated - entity: sensor.mypc_gpu_0_power secondary_info: last-updated - entity: sensor.mypc_gpu_0_power_limit secondary_info: last-updated - entity: sensor.mypc_gpu_0_temperature secondary_info: last-updatedAnsible Role
```
-
name: install go become: true package: name: golang-go state: present
-
name: git clone git: repo: "https://github.com/sammcj/NVApi.git" dest: "/home/ansible/NVapi" update: yes force: true
go run main.go -port 9999 -rate 1
-
name: install systemd service become: true copy: src: nvapi.service dest: /etc/systemd/system/nvapi.service
-
name: Reload systemd daemons, enable, and restart nvapi become: true systemd: name: nvapi daemon_reload: yes enabled: yes state: restarted ```
-
 @ 254f56d7:f2c38100
2024-12-30 07:38:27
@ 254f56d7:f2c38100
2024-12-30 07:38:27Vamos ver seu funcionamento

-
 @ 502ab02a:a2860397
2024-07-13 02:14:11
@ 502ab02a:a2860397
2024-07-13 02:14:11Anna Britt Agnsäter ผู้อุทิศชีวิตให้โภชนาการ แต่โดนโลกบูลลีเพราะอเมริกา?
โลกรับรู้ว่า คุณ Anna Britt Agnsäter (ขอเรียกสั้นๆว่า ป้าแอน) เป็นผู้ที่นำเสนอ ปิรามิดอาหาร คนแรกของโลก และเป็นแบบจำลองที่ทาง USDA นำไปพัฒนาปรับใช้แล้วนำมาเป็น แบบที่ใช้สื่อสารกับคนทั้งโลก ในเรื่องของการกำหนด ประเภทอาหารที่ควรกิน ในช่วงปี 1992-2005 ซึ่งในบทความที่แล้วผมได้เขียนว่า ปิรามิดเวอร์ชั่นที่ป้าแอนคิด กับ ที่อเมริกาเอาไปปรับใช้เป็นคนละตัวกัน แต่โลกทั้งโลกก็บูลลีป้าเอนว่า เป็นสาเหตุของการทำลายสุขภาพคนทั้งโลก ทั้งๆที่ไม่ได้เป็นนักวิทยาศาสตร์ ผมก็เป็นคนนึงที่เคยคิดแบบนั้นครับ และเคยอุทานในใจเบาๆว่า แกเป็นใครนะทำไมถึงนำเสนออะไรแบบนี้มาทำร้ายคนทั้งโลก???
นานวันเข้า ความคิดอีกฝั่งของผมก็บอกมาว่า ประโยคข้างบนเป็นคำบ่นหรือคำถาม
นั่นสิ!!!!! ถ้ามันเป็นคำถาม มันจะทำให้เราได้รู้จักตัวตนป้าแอนและเข้าใจว่าแกได้ทำอะไรลงไปนะ มันควรเป็นคำถามมากกว่าคำบ่น นั่นเลยเป็นเหตุผลที่ทำให้ผมเริ่มขุดเรื่องป้าแอน Anna Britt Agnsäter มากที่สุดเท่าที่จะทำได้ พร้อมที่จะอ่านกันแล้วใช่ไหมครับ
Anna Britt Agnsäter เกิดเมื่อปี 1915 ที่เมือง Älmhult ประเทศสวีเดน (นอกเรื่องนิดนึง เมืองนี้คือเมืองที่ให้กำเนิด IKEA ที่เรารู้จักกันดีเรื่องเฟอร์นิเจอร์ ที่นี่มีพิพิธภัณฑ์อิเกีย ซึ่งปรับปรุงมาจากโกดังแห่งแรกของเขาด้วยครับ) เรียกได้ว่า เกิดในช่วงสงครามโลกครั้งที่1 พอดีเลยครับ
ป้าแอน จบการศึกษาที่โรงเรียนสตรี ในเมือง Ystad ก่อนจะเข้ารับการฝึกสอนเพื่อเป็นครูสอนวิทยาศาสตร์ในครัวเรือน (rural domestic science teacher) ในช่วงปี 1930 ที่โรงเรียนวิทยาศาสตร์ในครัวเรือนในชนบทชื่อว่า Rimforsa ก่อนจะได้รับวุฒิการศึกษาการสอนวิทยาศาสตร์ในครัวเรือนในชนบทในปี 1939 จาก Kvinnliga medborgarskola (civic women’s school) จนกระทั่ง ปี 1943 ถึง 1945 เธอได้เดินทางไปทั่ว Norrland (พื้นที่ภาคเหนือของสวีเดน) โดยได้รับเงินสนับสนุนจาก Kooperativa Förbund (เรียกสั้นๆว่า KF หรือ สมาคมสหกรณ์ ก่อตั้งขึ้นในปี 1899 โดยสหกรณ์ผู้บริโภคในท้องถิ่น 41 แห่ง เป็นผู้นำด้านการค้าปลีกในสวีเดนโดยพัฒนารูปแบบร้านค้าใหม่และใหญ่ขึ้น และเป็นหนึ่งในกลุ่มธุรกิจหลักในสแกนดิเนเวีย ในสมัยนี้คำว่าสหกรณ์อาจจะดูเชยๆ แต่ต้องเข้าใจครับว่ายุคนั้นคือความก้าวหน้ามากๆ และต้องมีความรู้รอบด้านทั้งวิทยาศาสตร์ เศรษฐกิจ การเมือง) เพื่อบรรยายให้คนหนุ่มสาวและแม่บ้านฟังเกี่ยวกับวิธีรับมือกับเสบียงที่มีจำกัดในช่วงสงครามที่ตึงเครียด เนื่องจากอยู่ในภาวะสงครามโลกครั้งที่2

ในปี 1946 ป้าแอนได้รับการแต่งตั้งเป็นหัวหน้าของSwedish Cooperative Union หรือ Kooperativa Förbundets (KF) Provkök (experimental kitchen หรือ ภาษาสมัยนี้น่าจะใกล้เคียงกับ kitchen lab นั่นเอง) ซึ่งเป็นองค์กรที่มีอิทธิพลทางด้านอาหารเป็นอย่างมากในสวีเดน มีบทบาทสำคัญในเศรษฐกิจและสังคมสวีเดน โดยสร้างโอกาสให้แก่สมาชิกและส่งเสริมการพัฒนาที่ยั่งยืนในชุมชนต่าง ๆ ทั่วประเทศ
ป้าแอนทำงานที่นี่นานจนถึงช่วงปี 1980 ขนาดของ KF ก็ใหญ่โตขึ้นมากมาย จนขยายอำนาจและขอบเขตการทำงานไปถึงการเป็นคณะกรรมการทดสอบรสชาติซึ่งทดสอบอาหารกึ่งสำเร็จรูปและอาหารสำเร็จรูปใหม่ด้วย ในจุดนี้ ป้าแอน เล็งเห็นความสำคัญและความรับผิดชอบของผู้ผลิต/ผู้ค้าอาหาร ควรจะขยายความรับผิดชอบครอบคลุมไปจนถึงโต๊ะอาหาร (ในที่นี่น่าจะหมายถึงลูกค้า) นั่นคือเหตุผลที่การติดฉลากอาหารจึงมีความสำคัญมาก ป้าแอนได้มุ่งเน้นให้ความรู้กับผู้บริโภคว่า ‘Weigh up the price against the quality’ หรือ ให้ชั่งน้ำหนักพิจารณาให้ดี ระหว่างราคากับคุณภาพ ตลอดระยะเวลาการทำงาน Anna-Britt Agnsäter ได้รณรงค์เพื่อให้มีการแสดงข้อมูล ให้ผู้บริโภครับทราบ เพื่อคุณภาพชีวิตที่ดีขึ้นและได้ให้คำแนะนำด้านโภชนาการ เพื่อให้เข้าใจได้ง่ายขึ้น ในรูปแบบฉลากโภชนาการ
ในปี 1946 เช่นกันป้าแอนได้มีแผนในการทำ มีแผนที่จะผลิตหนังสือสอนทำอาหารสำหรับสถานการณ์ฉุกเฉิน เพราะบทเรียนในภาวะสงครามโลก ที่ป้าแอนผ่านมาตลอด แต่ไม่สามารถพิมพ์ออกมาได้เนื่องจากกระดาษขาดแคลนเนื่องจากอยู่ในภาวะหลังสงคราม
ในปี 1948-1949 ป้าแอนเดินทางไปอเมริกา เพื่อศึกษาเทคนิคการทำอาหารใหม่ๆ การผลิตภัณฑ์อาหารแช่แข็ง รวมถึงอาหารผงแห้งต่างๆ (dry powder) รวมไปถึงวิทยาศาสตร์การอาหาร (food science) ที่มหาวิทยาลัย Iowa State University การเดินทางมาอเมริกาครั้งนี้เปลี่ยนโลกของป้าแอนเป็นอย่างมาก ในตอนที่ป้าทำงานกับ KF เธอมักจะร่วมงานกับ Hemmens Forskningsinstitut (สถาบันวิจัยในประเทศ) เพื่อจัดหาเครื่องมือในครัวที่ยกระดับมาตรฐานการทำอาหารที่ดียิ่งขึ้น รวมถึงอุปกรณ์การครัว ภาชนะต่างๆที่เข้าเตาอบได้ และจากประสบการณ์ที่อเมริกานี้
ป้าแอนได้จับมือกับ โรงงานเครื่องเคลือบและพลาสติก Gustavsberg และ HFI Anna-Britt Agnsäter พัฒนาช้อนตวง ชุด4ชิ้น ที่วางซ้อนกันได้ ซึ่งเป็นการปฎิวัติวงการอาหารครั้งสำคัญของสวีเดน เรียกว่า “ชุดช้อนตวงมาตรฐาน” ซึ่งจะมีการระบุขนาดที่ชัดเจน 4 ชิ้น ประกอบไปด้วย

ซึ่งทำให้ผู้ใช้สามารถวัดปริมาณวัตถุดิบได้อย่างถูกต้องตามที่สูตรอาหารกำหนด กลายเป็นเครื่องมือที่จำเป็นในครัวเรือนและการประกอบอาหารในเชิงพาณิชย์
แม้การพัฒนา “ชุดช้อนตวงมาตรฐาน” นี้จะเริ่มต้นในสวีเดน แต่นวัตกรรมนี้มีผลกระทบที่กว้างขวางและแพร่หลายไปยังครัวเรือนและอุตสาหกรรมอาหารทั่วโลกจนถึงปัจจุบัน


ในชุดช้อนตวงมาตรฐาน original 4 คุณอาจสังเกตคำนึงที่ไม่ค่อยคุ้นสักเท่าไรคือหน่วย kryddmått
นอกจากชุดช้อนตวงมาตรฐานแล้ว ป้าแอนยังคิดค้นสิ่งต่างๆอีกมากมาย ให้กับวงการอาหารสวีเดน รวมถึงหน่วยวัดใหม่ที่เรียกว่า kryddmått นี้ด้วยครับ ซึ่งมันเป็นหน่วยวัดขนาดเล็กที่ใช้ในการตวงเครื่องเทศและวัตถุดิบปริมาณน้อย โดยหน่วยวัดนี้มีขนาด 1 มิลลิลิตร (ml)ซึ่งถูกกำหนดมาเป็นหน่วยที่เล็กที่สุดซึ่งทำให้มีการจดบันทึกสูตรได้แม่นยำยิ่งขึ้น นั่นเพราะว่า การตวงเครื่องเทศ หรือ เกลือ นั้นหากรสชาติที่เข้มข้น หรือมีการใช้มากเกินไปหรือไม่พออาจทำให้รสชาติของอาหารเปลี่ยนไป การใช้ kryddmått ช่วยให้การวัดปริมาณเครื่องเทศที่ใช้ในสูตรอาหารเป็นไปอย่างแม่นยำและสม่ำเสมอ
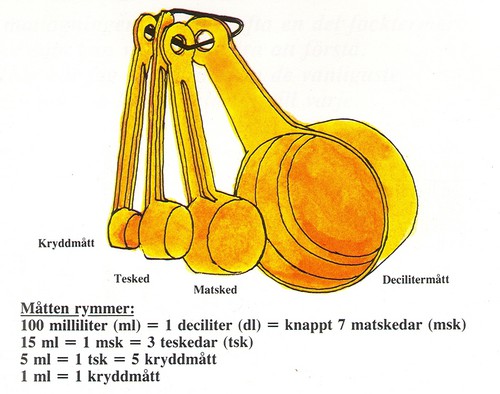
ถือว่าเป็นอีกผลงานคุโณปการที่ป้าแอน ฝากไว้ให้กับโลกนี้ มันมีส่วนสำคัญในการทำให้งานครัวเรือนง่ายขึ้นและมีประสิทธิภาพมากขึ้นผ่านการพัฒนาหน่วยวัดที่แม่นยำและสะดวกในการใช้งาน นวัตกรรมนี้ช่วยให้การทำอาหารเป็นไปอย่างราบรื่นและมีคุณภาพสูงยิ่งขึ้น
ในปี 1951 ป้าแอนได้บูรณะหนังสือการทำอาหารประจำสวีเดนใหม่ทั้งหมด (Vår kokbok) จุดประสงค์ของตำราอาหาร Vår คือการนำเสนอตำราอาหารราคาต้นทุนวัตถุดิบไม่แพง ที่ให้ความรู้เรื่องสารอาหารและใช้งานง่าย นอกจากนี้ยังเป็นการวางวัตถุดิบให้ได้รับสารอาหารที่เพียงพออีกด้วย เพราะในยุคนั้นสวีเดนมีข้อจำกัดในเรื่องอาหารเป็นอย่างมาก
เนื้อหาสูตรอาหารที่ใช้ในหนังสือเล่มนี้กลายเป็นบรรทัดฐานในช่วงทศวรรษ 1950 โดยมีการใช้หน่วยชั่งตวงแบบใหม่ ตามชุดช้อนตวงมาตรฐาน (ปริมาตร) จากของเดิมที่ใช้การชั่งน้ำหนัก ใช้ศัพท์ในการทำอาหารแบบเป็นสากล เช่น ขูด ปอกเปลือก ล้าง เป็นต้น (grate, peel, rinse) จัดอาร์ทเวิคให้แต่ละสูตร สามารถจบได้ในหน้าเดียวไม่ต้องพลิกอ่านหน้าต่อๆไป ทำให้สะดวกในการเปิดแล้วทำตาม การไล่ลำดับอาหาร เปลี่ยนจากการไล่ประเภทอาหาร ไปเป็นไล่ลำดับตามวัตถุดิบหลักของอาหาร ทำให้คนอ่านสามารถบริหารจัดการเมนูได้ง่าย เช่น ไก่ ก็สามารถไล่เรียงได้เลยว่า วันนี้มีไก่ จะทำอะไรกินดี
นอกจากนี้ยังรับประกันว่าทุกสูตรสามารถทำได้จริง เพราะป้าแอนลงมือทดสอบสูตรด้วยตัวเองทุกสูตร นอกจากนี้ยังคงมีการแนะนำให้ใช้การวัดอุณหภูมิในการทำอาหารด้วยเพื่อความเป๊ะในรสชาติ เนื่องจากป้าแอนเห็นตอนไปดูงานที่อเมริกา จนถึงทุกวันนี้ Vår kokbok เป็นหนึ่งในตำราอาหารที่ขายมากที่สุดในโลกด้วยยอดขายมากกว่า 2.3 ล้านเล่มนับตั้งแต่เริ่มต้น โดยเฉลี่ยมากกว่า 40,000 เล่มต่อปี


ด้วยความที่ Kooperativa Förbundets เป็นองค์กรที่มีอิทธิพลสูงมากในวงการอาหารสวีเดน และคุณป้าแอน ก็มีตำแหน่งที่สูงมาก จึงสามารถเป็นผู้มีส่วนสนับสนุนรูปแบบซูเปอร์มาร์เก็ตสมัยใหม่ ในการใส่รายการส่วนผสมและคำแนะนำในการปรุงอาหารในรูปแบบฉลากของผลิตภัณฑ์อาหารสมัยใหม่
จนกระทั่งในช่วงปี 1970 ประเทศสวีเดนต้องเผชิญกับปัญหาราคาอาหารที่สูงเนื่องจากเงินเฟ้อ รวมถึงสภาพอากาศของสวีเดนนั้น ไม่เอื้อต่อการได้รับสารอาหารที่หลากหลายได้ ครอบครัวที่มีเด็ก ไม่สามารถปรุงอาหารและรับประทานอาหารที่มีคุณค่าทางโภชนาการในราคาที่เหมาะสมได้ รัฐบาลจึงมอบหมายให้ Sweden’s National Board of Health and Welfare (คณะกรรมการสุขภาพและสวัสดิการแห่งชาติของสวีเดน) หาวิธีแก้ไขสถานการณ์ดังกล่าว และคัดกรองแบ่งประเภทอาหารออกเป็น “basic food” และ “supplement” มาเป็นรูปแบบของ กราฟวงกลม (diet circle) แต่ป้าแอนพบปัญหาบางอย่าง ที่ทำให้กราฟวงกลมนี้ใช้งานยาก เพราะการแบ่งปริมาณของอาหารแต่ละประเภทไม่ชัดเจน
ในระหว่างบรรยายเรื่องการกำหนดอาหารพื้นฐาน คุณ Fjalar Clemes หนึ่งในผู้เข้าร่วมการบรรยาย ได้ให้ไอเดียด้วยการสร้างแบบจำลองที่เรียกว่า ปิรามิดอาหาร (Food Pyramid) ขึ้นมา เพื่อให้เห็นภาพสัดส่วนอาหารที่ชัดเจนขึ้น ป้าแอนเลยนำข้อมูลจากกราฟวงกลมนั้น มาสร้างโมเดลจำลองให้อยู่ในรูปแบบปิรามิด โดยให้ “basic food” เช่น ขนมปัง มันฝรั่ง พาสต้า และนม และ “supplements” เช่น ผลไม้ ผัก เนื้อสัตว์ และปลา อยู่ในรูปแบบที่เข้าใจได้ง่ายขึ้น แม้แต่คนที่อ่านหนังสือไม่ออก

แต่นี่แหละที่เป็นจุดเริ่มต้นของปัญหา ด้วยความที่มันใช้งานง่ายสะดวก อเมริกาจึงนำไปปรับปรุงเป็นเวอร์ชั่นตัวเอง แต่ก็มีการเปลี่ยนแปลงไปอย่างมาก ตามที่ได้มีการทำบทความไปแล้ว (อ่านที่นี่)
ทั้งๆที่ปิรามิดต้นแบบของป้าแอนนั้น สร้างขึ้นมาเพื่อชาวสวีเดนเนื่องจากนำข้อมูลพื้นฐานจากข้อจำกัดในประเทศในขณะนั้น ไม่ว่าจะเรื่องของวัตถุดิบที่หาได้ในภาวะยากแค้นแบบนั้น อุณหภูมิอันปรวนแปร รวมถึงสภาพเศรษฐกิจที่ย่ำแย่มาก การจัดแจงข้อจำกัดที่มีเพื่อให้ได้สารอาหารที่เพียงพอที่สุดเท่าที่จะทำได้ต่างหาก (eat healthier, more affordable and save on fat) ที่เป็นที่มาของ “ปิรามิดอาหารของสวีเดน” (คือ จะให้เอาอุดมคติมาสร้างปิรามิดอาหาร คงไม่มีประโยชน์ เพราะยังไงก็ไม่มีเงินซื้อและหาวัตถุดิบไมไ่ด้ตามอุดมคติ วัตถุประสงค์ในการสร้างและเผยแพร่ครั้งนี้มันเพื่อให้ประชาชนทั้งประเทศที่มีความรู้ด้านอาหารน้อย รู้และทำตามได้จริง สมกับพื้นที่และกำลังทรัพย์ // ความเห็นส่วนตัวผมครับ)
ปิรามิดอาหารที่แท้จริงแล้ว จะมีการปรับปรุงตลอดเวลา ตามปัจจัยที่เปลี่ยนไป ไม่ใช่ปิรามิดที่เอาไว้ยึดถือตลอดไป แต่การที่อเมริกานำไปยึดถือว่าเป็น all time information เป็นค่าคงที่ให้ทั้งโลกยึดตาม รวมถึงสร้างด้วยเบื้องหลังด้านธุรกิจ จึงต่างกับที่ป้าแอนทำในทุกมิติ แต่ไฉน เป้าการบูลลี จึงต้องไปตกที่ป้าแอน ว่าเป็นต้นตอความพังของสุขภาพ มันแฟร์แล้วหรือ
เรื่องนี้มีข้อพิสูจน์ได้จนถึงปัจจุบันเช่น ในปี 2022 ก็มีการนำเสนอ ปิรามิดอาหารสำหรับ Mixed diet, flexitarian, vegetarian และ vegan ออกมาสืบทอดเจตนารมณ์ป้าแอน นอกจากนี้ในช่วงที่ป้าแอนมีชีวิต ก็ยังคงมีการช่วยเหลือแนะนำให้ประเทศต่างๆ “มีปิรามิดอาหารของตัวเอง” นั่นคือ วิชั่นที่กว้างไกลของป้าแอน ที่เห็นได้ชัดเจนว่า อาหารพื้นถิ่นกับสารอาหารที่สมดุล ของแต่ละประเทศมีความไม่เหมือนกัน และแนวคิดนี้ได้มีทั้ง เดนมาร์ก, นอร์เวย์, ฟินแลนด์, ญี่ปุ่น, ศรีลังกา ได้นำไปพัฒนาใช้เช่นกัน
นอกจากนี้ ป้าแอนและองค์กร Kooperativa Förbundets ยังให้ข้อมูลการศึกษาที่สำคัญสำหรับประชาชนผ่านบทความเกี่ยวกับอาหารที่ตีพิมพ์ใน นิตยสาร Vi รวมถึงการจัดตั้งกลุ่มการศึกษาร่วมกับทาง สมาคมการศึกษาของชนชั้นแรงงาน หรือ Arbetarnas bildningsförbund (ABF) มีส่วนสนับสนุนในการอภิปรายแบบเปิดทางสังคมเกี่ยวกับปัญหาโรคอ้วนอีกด้วย รวมถึงยังออกหนังสือเกี่ยวกับการทำอาหารอีกร่วมๆ 30เล่ม ซึ่งรวมถึงบทเกี่ยวกับมื้ออาหารที่มีคุณค่าทางโภชนาการที่สมดุล ด้วยเช่นกัน
ในปี 1983 ป้าแอนได้ตีพิมพ์หนังสือ Matboken ซึ่งได้รับการพิสูจน์แล้วว่าเป็นประโยชน์อย่างมาก โดยเฉพาะกับคนหนุ่มสาวเกี่ยวกับวิธีการกินอาหารที่มีคุณค่าทางโภชนาการและมีวิธีทำที่เรียบง่ายที่สุด

ในช่วงทศวรรษ 1990 เมื่อป้าแอนเป็นม่าย จึงได้ย้ายเข้าไปอยู่ในบ้านพักคนชรา Färdknäppen ใน Södermalm ในสตอกโฮล์ม และ ได้แก้ไขสูตรอาหาร 250 สูตรจาก Vår kokbok เพื่อให้เหมาะสมกับสภาพแวดล้อมการปรุงอาหารส่วนกลางของบ้านพักคนชรา เพื่อให้ได้อาหารที่มีสารอาหารครบถ้วนตามที่ควรเป็น
เกียรติประวัติป้าแอนได้รับการตอบแทนดังนี้ ในปี 1979 ได้รับรางวัลเหรียญ St Erik เพื่อเป็นการยกย่องสิ่งที่เธอทุ่มเทแรงกายแรงใจทำมาตลอดชีวิต ในปี 1993 ได้รับเหรียญ HM Konungens ลำดับที่ 8 (HM The King’s Medal หรือ H.M. Konungens medalj ในภาษาสวีเดน) เป็นหนึ่งในรางวัลเกียรติยศที่สำคัญที่สุดที่มอบโดยพระมหากษัตริย์สวีเดนเพื่อยกย่องบุคคลที่มีผลงานดีเด่นหรือมีความโดดเด่นในด้านต่าง ๆ เช่น วิทยาศาสตร์ ศิลปะ วัฒนธรรม และการบริการสาธารณะ ในปี 1995 ได้รับเหรียญทอง Albin Johansson สำหรับผลงานอันทรงคุณค่าของเธอต่อสหกรณ์สวีเดน ในปี 1998 ได้รับรางวัล Gastronomiska Akademiens Guldpenna (ปากกาทองของสถาบันอาหาร) สำหรับบทความเกี่ยวกับส่วนผสมและการทำอาหารของเธอ

Anna-Britt Agnsäter เสียชีวิตในปี 2006 (อายุ 90ปี) ป้าแอนทำงานทั้งชีวิตเพื่อสอนชาวสวีเดนในการจัดการอาหารให้ดีขึ้น ทุกการทดลอง ทดสอบ ได้มีการบันทึกไว้อย่างชัดเจนสามารถพัฒนาต่อไปได้ การริเริ่มให้ข้อมูลที่ซื่อสัตย์ต่อผู้บริโภค ทั้งการติดฉลากอุปกรณ์ คำแนะนำในการทำอาหาร สูตรอาหาร บทความ และตำราอาหาร สิ่งเหล่านี้กลายเป็นพื้นฐานสำคัญในอุตสาหกรรมอาหารจนปัจจุบัน
แต่ทุกวันนี้วงการสุขภาพส่วนมากยังคงล้อเลียนเธอว่าเป็นครูธรรมดา ที่มีหน้ามาสร้างปิรามิดอาหาร จึงทำให้คนทั่งโลกป่วย ทั้งที่ความจริงทั้งหมดนั้น ความรู้ของป้าแอนไม่ได้น้อยไปกว่า ผู้เชี่ยวชาญทางวิทยาศาสตร์การอาหาร ซึ่งในสมัยนั้นนับว่าเป็นอีกแขนงที่อยู่ในระดับบนของการศึกษา ไม่ต่างกับวิทยาศาสตร์อื่นๆ ปิรามิดควรเป็นไปตามถิ่นที่อยู่ สภาพเวลาและสภาพเศรษฐกิจขณะนั้น ไม่ใช่การสร้างมาตรฐานให้ต้องทำเหมือนกันทั่วโลก โดยมาจากอิทธิพลของกลุ่มธุรกิจดังที่ usda ได้ทำการแก้ไขก่อนจะประกาศให้คนทั่วไปยึดถือ รายละเอียดเป็นไปตามที่สืบค้นข้อมูลประวัติของป้าแอน มาเล่าสู่กันฟัง ณ วันนี้ครับ
ผมก็เป็นหนึ่งในนั้น สิ่งที่ผมสามารถทำได้เพื่อเป็นการขอโทษคุณ Anna-Britt Agnsäter ที่ดีที่สุดที่ทำได้ตอนนี้คือ เผยแพร่ประวัติอันทรงคุณค่าของเธอ ให้คนอื่นๆได้รับทราบมากที่สุด เท่าที่จะทำได้
โปรดแชร์ เพื่อคืนความเป็นธรรมให้ Anna-Britt Agnsäter ให้โลกได้เข้าใจและรับรู้ถึงการอุทิศชีวิตให้วงการอาหารของคุณป้าครับ
ปล.มีการค้นพบไฟล์เสียง ที่ป้าแอน จัดรายการวิทยุในปี 1968 ให้ลองฟังกันครับ (น่าจะภาษาสวีเดนนะ 5555) ฟังได้ที่นี่ครับ https://rumble.com/v56p1wa-ann-britt-agnster-in-a-radio-find-from-1968.html
siamstr #pirateketo
-
 @ 1ec45473:d38df139
2024-07-12 22:51:49
@ 1ec45473:d38df139
2024-07-12 22:51:49The probability of AGI ending us is negative.
A common tactic among doomers is to state something along the lines of the following:
"If we create AGI, there is some non-zero chance every year, that the AGI will end humanity. Whatever that chance is compounds every year, and is thus unacceptable."
The question I would ask the doomer is "How do you know that the chance of AGI ending humanity isn't negative?"
What does it mean for AGI to have a negative chance of ending humanity?
Setting aside AGI for a moment, what is the chance every year that humanity ends from other events, such as nuclear war, solar flares, super-volcanoes, asteroid hits, societal collapse, etc?
How do you even answer this question in a reasonable manner? Well lets look at past data.
Of all species that have existed 99% have gone extinct.
Of our closest 7 relatives from the genus Homo, 100% have gone extinct.
On a higher level looking at civilizational collapse. According to Wikipedia, virtually all historical societies have collapsed.
Looking out into the universe, we see no signs of life elsewhere, so if there was life in the past we can assume that they have gone extinct.
It would therefore be reasonable to say that the chance of our extinction is very high even without AGI, well above 90%. Maybe 99%.
You could argue the numbers but at least with these numbers we are using some past data to extrapolate the future, where the doomers are using no data whatsoever to support their numbers.
We can also state, that of all the species and societies that have collapsed in the past, they have done so because they did not yet have the knowledge on how to survive. They didn't know how to create antibiotics, or generate enough energy, or defend themselves from the environment.
What is AGI? AGI is a way to create knowledge. Most all societies in the past have collapsed because they didn't have the knowledge on how to survive, and the doomer argument is that we should slow down our ability to create knowledge, when we know that this has been precisely the problem in the past.
It is a certainty we will all die without more knowledge then we have now. The future death of our sun ensures that.
We have to create the knowledge on how to survive, and that is what AGI does - it creates knowledge.
AGI most certainly has a negative probability of ending humanity.
-
 @ b8851a06:9b120ba1
2024-12-16 16:38:53
@ b8851a06:9b120ba1
2024-12-16 16:38:53Brett Scott’s recent metaphor of Bitcoin as a wrestling gimmick, reliant on hype and dollar-dependence, reduces a groundbreaking monetary innovation to shallow theatrics. Let’s address his key missteps with hard facts.
1. Bitcoin Isn’t an Asset in the System—It’s the System
Scott claims Bitcoin competes with stocks, bonds, and gold in a financial "wrestling ring." This misrepresents Bitcoin’s purpose: it’s not an investment vehicle but a decentralized monetary network. Unlike assets, Bitcoin enables permissionless global value transfer, censorship resistance, and self-sovereign wealth storage—capabilities fiat currencies cannot match.
Fact: Bitcoin processes over $8 billion in daily transactions, settling more value annually than PayPal and Venmo combined. It isn’t competing with assets but offering an alternative to the monetary system itself.
2. Volatility Is Growth, Not Failure
Scott critiques Bitcoin’s price volatility as evidence of its unsuitability as "money." However, volatility is a natural stage in the adoption of transformative technology. Bitcoin is scaling from niche use to global recognition. Its growing liquidity and adoption already make it more stable than fiat in inflationary economies.
Fact: Bitcoin’s annualized volatility has decreased by 53% since 2013 and continues to stabilize as adoption rises. It’s the best-performing asset of the last decade, with an average annual ROI of 147%—far outpacing stocks, gold, and real estate. As of February 2024, Bitcoin's volatility was lower than roughly 900 stocks in the S and P 1500 and 190 stocks in the S and P 500. It continues to stabilize as adoption rises, making it an increasingly attractive store of value.
3. Bitcoin’s Utility Extends Beyond Countertrade
Scott diminishes Bitcoin to a "countertrade token," reliant on its dollar price. This ignores Bitcoin’s primary functions:
- Medium of exchange: Used in remittances, cross-border payments, and for the unbanked in Africa today (e.g., Ghana, Nigeria, Kenya).
- Store of value: A hedge against inflation and failing fiat systems (e.g., Argentina, Lebanon, Turkey).
- Decentralized reserve asset: Held by over 1,500 public and private institutions, including Tesla, MicroStrategy, and nations like El Salvador.
Fact: Lightning Network adoption has grown 1,500% in capacity since 2021, enabling microtransactions and reducing fees—making Bitcoin increasingly viable for everyday use. As of December 2024, Sub-Saharan Africa accounts for 2.7% of global cryptocurrency transaction volume, with Nigeria ranking second worldwide in crypto adoption. This demonstrates Bitcoin's real-world utility beyond mere speculation.
4. Bitcoin Isn’t Controlled by the Dollar
Scott suggests Bitcoin strengthens the dollar system rather than challenging it. In truth, Bitcoin exists outside the control of any nation-state. It offers people in authoritarian regimes and hyperinflationary economies a lifeline when their local currencies fail.
Fact: Over 70% of Bitcoin transactions occur outside the U.S., with adoption highest in countries like Nigeria, India, Venezuela, China, the USA and Ukraine—where the dollar isn’t dominant but government overreach and fiat collapse are. This global distribution shows Bitcoin's independence from dollar dominance.
5. Hype vs. Adoption
Scott mocks Bitcoin’s evangelists but fails to acknowledge its real-world traction. Bitcoin adoption isn’t driven by hype but by trustless, verifiable technology solving real-world problems. People don’t buy Bitcoin for "kayfabe"; they buy it for what it does.
Fact: Bitcoin wallets reached 500 million globally in 2023. El Salvador’s Chivo wallet onboarded 4 million users (60% of the population) within a year—far from a gimmick in action. As of December 2024, El Salvador's Bitcoin portfolio has crossed $632 million in value, with an unrealized profit of $362 million, demonstrating tangible benefits beyond hype.
6. The Dollar’s Coercive Monopoly vs. Bitcoin’s Freedom
Scott defends fiat money as more than "just numbers," backed by state power. He’s correct: fiat relies on coercion, legal mandates, and inflationary extraction. Bitcoin, by contrast, derives value from transparent scarcity (capped at 21 million coins) and decentralized consensus, not military enforcement or political whims.
Fact: Bitcoin’s inflation rate is just 1.8%—lower than gold or the U.S. dollar—and will approach 0% by 2140. No fiat currency can match this predictability. As of December 2024, Bitcoin processes an average of 441,944 transactions per day, showcasing its growing role as a global, permissionless monetary system free from centralized control.
Conclusion: The Revolution Is Real
Scott’s "wrestling gimmick" analogy trivializes Bitcoin’s purpose and progress. Bitcoin isn’t just a speculative asset—it’s the first truly decentralized, apolitical form of money. Whether as a hedge against inflation, a tool for financial inclusion, or a global settlement network, Bitcoin is transforming how we think about money.
Dismiss it as a gimmick at your peril. The world doesn’t need another asset—it needs Bitcoin.
"If you don't believe me or don't get it, I don't have time to try to convince you, sorry." Once Satoshi said.
There is no second best.
-
 @ 32e18276:5c68e245
2023-12-06 15:29:43
@ 32e18276:5c68e245
2023-12-06 15:29:43I’m going to be on an ordinals panels as one of the people who is counter arguing the claim that they are good for bitcoin. I decided to brush up on the technicals on how inscriptions work. I am starting to see luke’s perspective on how it is exploiting a loophole in bitcoin’s anti-data-spam mechanisms.
Storing data in Bitcoin, the “standard” way
The standard way you add “data” to bitcoin is by calling the OP_RETURN opcode. Bitcoin devs noticed that people were storing data (like the bitcoin whitepaper) in the utxo set via large multisig transactions. The problem with this is that this set is unprunable and could grow over time. OP_RETURN outputs on the other-hand are provably prunable and don’t add to utxo bloat.
Here’s an excerpt from the march 2014 0.9.0 release notes that talks about this:
On OP_RETURN: There was been some confusion and misunderstanding in the community, regarding the OP_RETURN feature in 0.9 and data in the blockchain. This change is not an endorsement of storing data in the blockchain. The OP_RETURN change creates a provably-prunable output, to avoid data storage schemes – some of which were already deployed – that were storing arbitrary data such as images as forever-unspendable TX outputs, bloating bitcoin’s UTXO database. Storing arbitrary data in the blockchain is still a bad idea; it is less costly and far more efficient to store non-currency data elsewhere.
Much of the work on bitcoin core has been focused on making sure the system continues to function in a decentralized way for its intended purpose in the presence of people trying to abuse it for things like storing data. Bitcoin core has always discouraged this, as it is not designed for storage of images and data, it is meant for moving digital coins around in cyberspace.
To help incentive-align people to not do stupid things, OP_RETURN transactions were not made non-standard, so that they are relayable by peers and miners, but with the caveat:
- They can only push 40 bytes (later increased to 80,83, I’m guessing to support larger root merkle hashes since that is the only sane usecase for op_return)
Bitcoin also added an option called -datacarriersize which limits the total number of bytes from these outputs that you will relay or mine.
Why inscriptions are technically an exploit
Inscriptions get around the datacarriersize limit by disguising data as bitcoin script program data via OP_PUSH inside OP_IF blocks. Ordinals do not use OP_RETURN and are not subjected to datacarriersize limits, so noderunners and miners currently have limited control over the total size of this data that they wish to relay and include in blocks. Luke’s fork of bitcoin-core has some options to fight this spam, so hopefully we will see this in core sometime soon as well.
Inscriptions are also taking advantage of features in segwit v1 (witness discount) and v2/taproot (no arbitrary script size limit). Each of these features have interesting and well-justified reasons why they were introduced.
The purpose of the witness discount was to make it cheaper to spend many outputs which helps the reduction of the utxo set size. Inscriptions took advantage of this discount to store monke jpegs disguised as bitcoin scripts. Remember, bitcoin is not for storing data, so anytime bitcoin-devs accidentally make it cheap and easy to relay data then this should be viewed as an exploit. Expect it to be fixed, or at least provide tools to noderunners for fighting this spam.
Where do we go from here
The interesting part of this story is that people seem to attach value to images stored on the bitcoin blockchain, and they are willing to pay the fee to get it in the block, so non-ideologic miners and people who don’t care about the health and decentralization of bitcoin are happy to pay or collect the fee and move on.
Data should not get a discount, people should pay full price if they want to store data. They should just use op_return and hashes like opentimestamps or any other reasonable protocol storing data in bitcoin.
After going through this analysis I’ve come to the opinion that this is a pretty bad data-spam exploit and bitcoin devs should be working on solutions. Ideological devs like luke who actually care about the health and decentralization of the network are and I’m glad to see it.
-
 @ b6dcdddf:dfee5ee7
2024-07-12 20:15:22
@ b6dcdddf:dfee5ee7
2024-07-12 20:15:22🚀 Exciting News: Introducing Project Affiliates!
Creators can finally reach a wider audience by partnering with affiliates!
Affiliates earn automated payouts for contributions enabled through their shares. 🤑
Announcement link: https://x.com/geyserfund/status/1811434402041282680
originally posted at https://stacker.news/items/606500
-
 @ a012dc82:6458a70d
2024-12-30 05:51:11
@ a012dc82:6458a70d
2024-12-30 05:51:11Table Of Content
-
The Influence of Global Oil Prices
-
Bitcoin's Roller Coaster Ride
-
Anticipation Surrounding the 2024 Halving Event
-
The Broader Crypto Landscape
-
Conclusions
-
FAQ
In the ever-evolving world of cryptocurrencies, Bitcoin stands as a beacon, often dictating the mood of the entire crypto market. Its price fluctuations are closely watched by investors, analysts, and enthusiasts alike. Max Keiser, a prominent figure in the crypto space, recently shed light on some intriguing factors that might be influencing Bitcoin's current price trajectory. This article delves into Keiser's insights, exploring the broader implications of global events on Bitcoin's market performance.
The Influence of Global Oil Prices
Max Keiser, a renowned Bitcoin advocate and former trader, recently drew attention to the interplay between global oil prices and Bitcoin's market performance. Responding to a post by German economics expert, Holger Zschaepitz, Keiser highlighted the significance of Brent oil reaching $90 per barrel for the first time since the previous November. According to Keiser, the surge in oil prices, driven by Saudi Arabia's decision to extend its reduction in oil production for another three months, has had ripple effects in the financial world. One of these effects is the shift of investor interest towards higher interest deposit USD accounts. This diversion of investments is creating what Keiser terms as "a small headwind for Bitcoin," implying that as traditional markets like oil show promise, some investors might be reconsidering their cryptocurrency positions.
Bitcoin's Roller Coaster Ride
The cryptocurrency market, known for its volatility, witnessed Bitcoin's price undergoing significant fluctuations recently. A notable event that gave Bitcoin a temporary boost was Grayscale's triumph over the SEC in a legal battle concerning the conversion of its Bitcoin Trust into a spot ETF. This victory led to a rapid 7.88% spike in Bitcoin's price within a mere hour, pushing it from the $26,000 bracket to briefly touch the $28,000 threshold. However, this euphoria was short-lived. Over the subsequent week, the cryptocurrency saw its gains erode, settling in the $25,400 range. At the time the reference article was penned, Bitcoin was hovering around $25,688.
Anticipation Surrounding the 2024 Halving Event
The Bitcoin community is abuzz with anticipation for the next scheduled Bitcoin halving, projected to take place in April-May 2024. This event will see the rewards for Bitcoin miners being slashed by half, resulting in a decreased supply of Bitcoin entering the market. Historically, such halvings have acted as catalysts, propelling Bitcoin's price upwards. A case in point is the aftermath of the 2020 halving, post which Bitcoin soared to an all-time high of $69,000 in October 2021. However, some financial analysts argue that this surge was less about the halving and more a consequence of the extensive monetary measures adopted by institutions like the US Federal Reserve. These measures, taken in response to the pandemic and the ensuing lockdowns, flooded the market with cash, potentially driving up Bitcoin's price.
The Broader Crypto Landscape
While Bitcoin remains the most dominant and influential cryptocurrency, it's essential to consider its position within the broader crypto ecosystem. Other cryptocurrencies, often referred to as 'altcoins', also play a role in shaping investor sentiment and market dynamics. Factors such as technological advancements, regulatory changes, and global economic shifts not only impact Bitcoin but the entire crypto market. As investors diversify their portfolios and explore newer blockchain projects, Bitcoin's role as the market leader is continually tested. Yet, its pioneering status and proven resilience make it a focal point of discussions and analyses in the crypto world.
Conclusion
Bitcoin, the flagship cryptocurrency, has always been subject to a myriad of market forces and global events. While its inherent potential remains undeniable, the current market landscape, shaped by factors ranging from oil prices to global economic policies, presents challenges. Yet, with events like the 2024 halving on the horizon, there's an air of optimism among Bitcoin enthusiasts and investors about the future trajectory of this digital asset.
FAQ
Who is Max Keiser? Max Keiser is a prominent Bitcoin advocate, former trader, and well-known crypto podcaster.
What did Keiser say about Bitcoin's price? Keiser pointed out that rising global oil prices and the allure of higher interest deposit USD accounts are creating a "small headwind" for Bitcoin.
How did Grayscale's legal victory affect Bitcoin? Grayscale's win over the SEC led to a 7.88% spike in Bitcoin's price within an hour.
When is the next Bitcoin halving expected? The next Bitcoin halving is projected to occur around April-May 2024.
Did the 2020 Bitcoin halving influence its price? Yes, post the 2020 halving, Bitcoin reached an all-time high of $69,000 in October 2021.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 33baa074:3bb3a297
2024-12-30 01:06:40
@ 33baa074:3bb3a297
2024-12-30 01:06:40Evaporation is an important link in the water cycle in nature, and it plays a key role in the circulation of water and energy exchange. The following are the specific manifestations of the cyclical role of evaporation in nature:
Key links in the water cycle Evaporation is one of the most important links in the water cycle. Through evaporation, water changes from liquid to gas, enters the atmosphere, and becomes water vapor. This process occurs not only on the surface of the ocean, but also in lakes, rivers on land, and moisture in the soil. The evaporated water vapor then moves with atmospheric activity, participates in subsequent condensation, precipitation, and other links, and completes the global cycle of water.
Energy exchange and climate impact During the evaporation process, water absorbs heat from the surrounding environment, thereby cooling the environment. When water vapor condenses into liquid water (such as clouds and rain) in the atmosphere, it releases energy, warming the environment. This energy exchange has an important impact on the climate and is an important mechanism for regulating the temperature of the earth.
 Water purification
The evaporation process has a certain purification effect. When water evaporates, some impurities dissolved in the water are left in place, while pure water vapor enters the atmosphere. This natural filtering process helps improve the quality of precipitation and replenish clean freshwater resources on land.
Water purification
The evaporation process has a certain purification effect. When water evaporates, some impurities dissolved in the water are left in place, while pure water vapor enters the atmosphere. This natural filtering process helps improve the quality of precipitation and replenish clean freshwater resources on land.Mineral Transport Evaporation and the water cycle work together to promote the transport of minerals around the world. Water carries and distributes minerals during evaporation, precipitation, infiltration, etc., affecting the geological characteristics of the earth and the nutritional balance of the ecosystem.
Life Support The water cycle, including evaporation, is essential for the maintenance of most life on Earth. It ensures the continuous supply and distribution of water resources and supports the survival and reproduction of various organisms.
Summary Evaporation is not only a key link in the water cycle in nature, but also plays an important role in energy exchange, climate regulation, water purification, mineral transportation, and life support. By understanding the role of evaporation in the natural cycle, we can better understand and protect our environment.
-
 @ 7175188c:6382a72c
2024-07-12 20:02:24
@ 7175188c:6382a72c
2024-07-12 20:02:24originally posted at https://stacker.news/items/606482
-
 @ 06b7819d:d1d8327c
2024-12-12 11:43:36
@ 06b7819d:d1d8327c
2024-12-12 11:43:36The Peano axioms are a set of rules that define the natural numbers (like 0, 1, 2, 3, and so on) in a logical way. Here’s a simplified explanation: 1. There is a first number: There is a number called zero, and it is the starting point for all natural numbers. 2. Each number has a next number: Every number has a unique “successor,” or the number that comes after it (like 1 comes after 0, 2 comes after 1, etc.). 3. Zero is special: Zero is not the “next” number of any other number. This means the sequence of natural numbers doesn’t loop back to zero. 4. No two numbers are the same if they have different successors: If two numbers have the same “next” number, then they must actually be the same number. 5. Patterns hold for all numbers: If something is true for zero, and it stays true when moving from one number to the next, then it must be true for all numbers.
These principles lay the groundwork for understanding and working with the natural numbers systematically.
-
 @ 0cb6f0b2:4fe22158
2024-12-30 06:21:39
@ 0cb6f0b2:4fe22158
2024-12-30 06:21:39Table of Contents 1.Introduction 2.Understanding the Role of a Realtor **3.Key Qualities of a Top Realtor ** * Knowledge and Expertise * Strong Communication Skills * Reputation and Trustworthiness * Negotiation Skills * Local Market Knowledge * Attention to Detail
**4.Proven Success Factors in a Top Realtor ** * Consistent Sales Performance * Client Testimonials and Reviews * Professional Certifications and Associations * Track Record of Successful Transactions
5.How to Evaluate a Realtor’s Track Record 6.Questions to Ask Before Hiring a Realtor
7.Conclusion
- Introduction
When it comes to buying or selling a home, one of the most important decisions you’ll make is choosing the right realtor. A top realtor not only helps you find the right property or buyer but also navigates the complexities of the real estate market to ensure you get the best deal. The real estate industry is highly competitive, and having a skilled, trustworthy, and knowledgeable realtor on your side can make all the difference. This guide explores how to identify a top realtor by focusing on key qualities, proven success factors, and effective ways to evaluate their track record.
-
Understanding the Role of a Realtor Before delving into the qualities of a top realtor, it's important to understand what a realtor does. A realtor is a licensed professional who assists clients in buying, selling, and renting properties. Unlike real estate agents, realtors are members of the National Association of Realtors (NAR) and are bound by a strict code of ethics. They help clients navigate the complex real estate market, ensuring smooth transactions and minimizing potential risks.
-
Key Qualities of a Top Realtor Knowledge and Expertise A top realtor has a deep understanding of the real estate market. This includes knowledge of current trends, pricing, financing options, and legal requirements. Whether you're buying or selling, a knowledgeable realtor can help you make informed decisions and avoid costly mistakes. For instance, a study by the National Association of Realtors (NAR) found that 87% of buyers and 89% of sellers said that a realtor’s market knowledge was critical in the decision-making process. Knowledge of local markets is particularly important, as housing prices can vary greatly by location. Strong Communication Skills Effective communication is one of the most important qualities in a top realtor. Whether you're negotiating a deal, scheduling showings, or discussing terms, a realtor with excellent communication skills can ensure that all parties are on the same page. According to a report by Inman, 91% of clients said that strong communication was a key factor in their satisfaction with a realtor. Top realtors respond promptly to emails, phone calls, and messages, keeping clients updated throughout the process. They explain complicated real estate terms and processes in a clear, concise manner to ensure you understand every step of the transaction. Reputation and Trustworthiness A realtor's reputation is one of the most reliable indicators of their success. A strong reputation comes from consistently delivering results and building long-lasting relationships with clients. Word-of-mouth referrals, online reviews, and client testimonials are great ways to assess a realtor's credibility. Trustworthiness is crucial when dealing with such a significant investment like a home. You need a realtor who acts in your best interest, not their own. According to NAR, 75% of buyers and sellers trust their realtors based on past performance, and their ability to represent them effectively. Negotiation Skills The ability to negotiate effectively is perhaps the most crucial skill a realtor can possess. Whether you are buying or selling, negotiations can significantly impact the final deal. A top realtor will fight to get you the best price, whether you’re negotiating a home sale price or asking for repairs after an inspection. A study by the National Association of Realtors found that 77% of sellers said they would hire a realtor based on their ability to negotiate on their behalf. Local Market Knowledge Top realtors have an in-depth understanding of the local market trends, including property values, zoning laws, and school districts. They can help you find homes in neighborhoods that fit your lifestyle and budget. Local knowledge helps in determining whether a property is priced competitively, assessing the neighborhood's long-term value, and advising on future developments. Realtors familiar with your area can offer insights that others may overlook. Attention to Detail Real estate transactions involve a lot of paperwork, contracts, and legalities. A top realtor will have great attention to detail, ensuring everything is done correctly, from the initial offer to the closing paperwork. Small errors or overlooked details can lead to delays or even legal issues, so it’s crucial to have a realtor who is thorough and meticulous.
-
Proven Success Factors in a Top Realtor Consistent Sales Performance A top realtor consistently performs well, regardless of market conditions. This doesn’t mean they have to be the top seller in the country, but they should have a track record of closing deals on time and achieving results for their clients. You can check a realtor’s sales history to assess how many transactions they’ve completed, their average sale price, and how long it typically takes them to sell a property. Many realtors will proudly showcase their sales figures on their website or in their marketing materials. Client Testimonials and Reviews A great way to gauge the effectiveness of a realtor is by looking at client reviews and testimonials. Websites like Zillow, Realtor.com, and Google My Business feature reviews from past clients. Positive reviews can provide valuable insights into how a realtor works with clients and handles challenges during the buying or selling process. You should look for realtors with multiple positive reviews and testimonials. While no one is perfect, a realtor with consistently good feedback is likely to provide a positive experience. Professional Certifications and Associations Top realtors often have professional certifications and are members of professional organizations like the National Association of Realtors (NAR). Certifications such as Certified Residential Specialist (CRS), Accredited Buyer’s Representative (ABR), or Certified Luxury Home Marketing Specialist (CLHMS) signify a realtor’s commitment to continuing education and professional development. These certifications can indicate a higher level of expertise, ensuring the realtor is up-to-date on industry standards and trends. Track Record of Successful Transactions A realtor with a history of successful transactions in both buyer’s and seller’s markets shows their ability to adapt and deliver results under any circumstances. They should have experience handling different types of properties (single-family homes, condos, luxury homes, etc.) and clients (first-time buyers, seasoned investors, downsizers, etc.).
**5. How to Evaluate a Realtor’s Track Record ** Here’s a simple table to help you evaluate a realtor’s track record: Factor What to Look For Number of Transactions Look for a realtor with a consistent number of transactions in the past year or two. Sales to Listing Ratio A high sales-to-listing ratio indicates that they sell properties quickly and at or above asking price. Client Testimonials Positive reviews with specific details about the realtor’s professionalism, expertise, and results. Experience in Your Area Realtors with local knowledge will be better suited to find properties that match your needs.
-
Questions to Ask Before Hiring a Realtor Before hiring a realtor, it’s essential to ask the right questions. Here are some key questions to consider: How many homes have you sold in the past year? What is your marketing strategy for selling my home? How familiar are you with the neighborhoods I’m interested in? Can you provide references from past clients? What is your average days-on-market for listings? Asking these questions will help you gauge whether the realtor aligns with your goals and expectations.
-
Conclusion
Choosing the right realtor can significantly impact your real estate experience. By focusing on key qualities like communication skills, market knowledge, negotiation abilities, and trustworthiness, you can ensure that you’re working with a professional who has the experience to guide you through the process successfully. Additionally, evaluating their track record, client reviews, and certifications will help you make an informed decision. When it comes to one of the largest financial transactions of your life, you deserve a realtor who understands your needs, communicates clearly, and fights for your best interests. Take the time to identify a top realtor who aligns with your goals, and you’ll be on the right path to a successful real estate experience.
-
 @ 68ce44e4:ecd5f574
2024-12-29 12:33:14
@ 68ce44e4:ecd5f574
2024-12-29 12:33:14Xenea Wallet Daily Quiz 29 Dec
Complete now : https://xenea.app/register/167mZpWf7A

XENEAwallet #cryptoairdrop #cryptocurrency #cryptonews #bitcoin #EarnFreeCrypto
-
 @ 6f6b50bb:a848e5a1
2024-12-15 15:09:52
@ 6f6b50bb:a848e5a1
2024-12-15 15:09:52Che cosa significherebbe trattare l'IA come uno strumento invece che come una persona?
Dall’avvio di ChatGPT, le esplorazioni in due direzioni hanno preso velocità.
La prima direzione riguarda le capacità tecniche. Quanto grande possiamo addestrare un modello? Quanto bene può rispondere alle domande del SAT? Con quanta efficienza possiamo distribuirlo?
La seconda direzione riguarda il design dell’interazione. Come comunichiamo con un modello? Come possiamo usarlo per un lavoro utile? Quale metafora usiamo per ragionare su di esso?
La prima direzione è ampiamente seguita e enormemente finanziata, e per una buona ragione: i progressi nelle capacità tecniche sono alla base di ogni possibile applicazione. Ma la seconda è altrettanto cruciale per il campo e ha enormi incognite. Siamo solo a pochi anni dall’inizio dell’era dei grandi modelli. Quali sono le probabilità che abbiamo già capito i modi migliori per usarli?
Propongo una nuova modalità di interazione, in cui i modelli svolgano il ruolo di applicazioni informatiche (ad esempio app per telefoni): fornendo un’interfaccia grafica, interpretando gli input degli utenti e aggiornando il loro stato. In questa modalità, invece di essere un “agente” che utilizza un computer per conto dell’essere umano, l’IA può fornire un ambiente informatico più ricco e potente che possiamo utilizzare.
Metafore per l’interazione
Al centro di un’interazione c’è una metafora che guida le aspettative di un utente su un sistema. I primi giorni dell’informatica hanno preso metafore come “scrivanie”, “macchine da scrivere”, “fogli di calcolo” e “lettere” e le hanno trasformate in equivalenti digitali, permettendo all’utente di ragionare sul loro comportamento. Puoi lasciare qualcosa sulla tua scrivania e tornare a prenderlo; hai bisogno di un indirizzo per inviare una lettera. Man mano che abbiamo sviluppato una conoscenza culturale di questi dispositivi, la necessità di queste particolari metafore è scomparsa, e con esse i design di interfaccia skeumorfici che le rafforzavano. Come un cestino o una matita, un computer è ora una metafora di se stesso.
La metafora dominante per i grandi modelli oggi è modello-come-persona. Questa è una metafora efficace perché le persone hanno capacità estese che conosciamo intuitivamente. Implica che possiamo avere una conversazione con un modello e porgli domande; che il modello possa collaborare con noi su un documento o un pezzo di codice; che possiamo assegnargli un compito da svolgere da solo e che tornerà quando sarà finito.
Tuttavia, trattare un modello come una persona limita profondamente il nostro modo di pensare all’interazione con esso. Le interazioni umane sono intrinsecamente lente e lineari, limitate dalla larghezza di banda e dalla natura a turni della comunicazione verbale. Come abbiamo tutti sperimentato, comunicare idee complesse in una conversazione è difficile e dispersivo. Quando vogliamo precisione, ci rivolgiamo invece a strumenti, utilizzando manipolazioni dirette e interfacce visive ad alta larghezza di banda per creare diagrammi, scrivere codice e progettare modelli CAD. Poiché concepiamo i modelli come persone, li utilizziamo attraverso conversazioni lente, anche se sono perfettamente in grado di accettare input diretti e rapidi e di produrre risultati visivi. Le metafore che utilizziamo limitano le esperienze che costruiamo, e la metafora modello-come-persona ci impedisce di esplorare il pieno potenziale dei grandi modelli.
Per molti casi d’uso, e specialmente per il lavoro produttivo, credo che il futuro risieda in un’altra metafora: modello-come-computer.
Usare un’IA come un computer
Sotto la metafora modello-come-computer, interagiremo con i grandi modelli seguendo le intuizioni che abbiamo sulle applicazioni informatiche (sia su desktop, tablet o telefono). Nota che ciò non significa che il modello sarà un’app tradizionale più di quanto il desktop di Windows fosse una scrivania letterale. “Applicazione informatica” sarà un modo per un modello di rappresentarsi a noi. Invece di agire come una persona, il modello agirà come un computer.
Agire come un computer significa produrre un’interfaccia grafica. Al posto del flusso lineare di testo in stile telescrivente fornito da ChatGPT, un sistema modello-come-computer genererà qualcosa che somiglia all’interfaccia di un’applicazione moderna: pulsanti, cursori, schede, immagini, grafici e tutto il resto. Questo affronta limitazioni chiave dell’interfaccia di chat standard modello-come-persona:
-
Scoperta. Un buon strumento suggerisce i suoi usi. Quando l’unica interfaccia è una casella di testo vuota, spetta all’utente capire cosa fare e comprendere i limiti del sistema. La barra laterale Modifica in Lightroom è un ottimo modo per imparare l’editing fotografico perché non si limita a dirti cosa può fare questa applicazione con una foto, ma cosa potresti voler fare. Allo stesso modo, un’interfaccia modello-come-computer per DALL-E potrebbe mostrare nuove possibilità per le tue generazioni di immagini.
-
Efficienza. La manipolazione diretta è più rapida che scrivere una richiesta a parole. Per continuare l’esempio di Lightroom, sarebbe impensabile modificare una foto dicendo a una persona quali cursori spostare e di quanto. Ci vorrebbe un giorno intero per chiedere un’esposizione leggermente più bassa e una vibranza leggermente più alta, solo per vedere come apparirebbe. Nella metafora modello-come-computer, il modello può creare strumenti che ti permettono di comunicare ciò che vuoi più efficientemente e quindi di fare le cose più rapidamente.
A differenza di un’app tradizionale, questa interfaccia grafica è generata dal modello su richiesta. Questo significa che ogni parte dell’interfaccia che vedi è rilevante per ciò che stai facendo in quel momento, inclusi i contenuti specifici del tuo lavoro. Significa anche che, se desideri un’interfaccia più ampia o diversa, puoi semplicemente richiederla. Potresti chiedere a DALL-E di produrre alcuni preset modificabili per le sue impostazioni ispirati da famosi artisti di schizzi. Quando clicchi sul preset Leonardo da Vinci, imposta i cursori per disegni prospettici altamente dettagliati in inchiostro nero. Se clicchi su Charles Schulz, seleziona fumetti tecnicolor 2D a basso dettaglio.
Una bicicletta della mente proteiforme
La metafora modello-come-persona ha una curiosa tendenza a creare distanza tra l’utente e il modello, rispecchiando il divario di comunicazione tra due persone che può essere ridotto ma mai completamente colmato. A causa della difficoltà e del costo di comunicare a parole, le persone tendono a suddividere i compiti tra loro in blocchi grandi e il più indipendenti possibile. Le interfacce modello-come-persona seguono questo schema: non vale la pena dire a un modello di aggiungere un return statement alla tua funzione quando è più veloce scriverlo da solo. Con il sovraccarico della comunicazione, i sistemi modello-come-persona sono più utili quando possono fare un intero blocco di lavoro da soli. Fanno le cose per te.
Questo contrasta con il modo in cui interagiamo con i computer o altri strumenti. Gli strumenti producono feedback visivi in tempo reale e sono controllati attraverso manipolazioni dirette. Hanno un overhead comunicativo così basso che non è necessario specificare un blocco di lavoro indipendente. Ha più senso mantenere l’umano nel loop e dirigere lo strumento momento per momento. Come stivali delle sette leghe, gli strumenti ti permettono di andare più lontano a ogni passo, ma sei ancora tu a fare il lavoro. Ti permettono di fare le cose più velocemente.
Considera il compito di costruire un sito web usando un grande modello. Con le interfacce di oggi, potresti trattare il modello come un appaltatore o un collaboratore. Cercheresti di scrivere a parole il più possibile su come vuoi che il sito appaia, cosa vuoi che dica e quali funzionalità vuoi che abbia. Il modello genererebbe una prima bozza, tu la eseguirai e poi fornirai un feedback. “Fai il logo un po’ più grande”, diresti, e “centra quella prima immagine principale”, e “deve esserci un pulsante di login nell’intestazione”. Per ottenere esattamente ciò che vuoi, invierai una lista molto lunga di richieste sempre più minuziose.
Un’interazione alternativa modello-come-computer sarebbe diversa: invece di costruire il sito web, il modello genererebbe un’interfaccia per te per costruirlo, dove ogni input dell’utente a quell’interfaccia interroga il grande modello sotto il cofano. Forse quando descrivi le tue necessità creerebbe un’interfaccia con una barra laterale e una finestra di anteprima. All’inizio la barra laterale contiene solo alcuni schizzi di layout che puoi scegliere come punto di partenza. Puoi cliccare su ciascuno di essi, e il modello scrive l’HTML per una pagina web usando quel layout e lo visualizza nella finestra di anteprima. Ora che hai una pagina su cui lavorare, la barra laterale guadagna opzioni aggiuntive che influenzano la pagina globalmente, come accoppiamenti di font e schemi di colore. L’anteprima funge da editor WYSIWYG, permettendoti di afferrare elementi e spostarli, modificarne i contenuti, ecc. A supportare tutto ciò è il modello, che vede queste azioni dell’utente e riscrive la pagina per corrispondere ai cambiamenti effettuati. Poiché il modello può generare un’interfaccia per aiutare te e lui a comunicare più efficientemente, puoi esercitare più controllo sul prodotto finale in meno tempo.
La metafora modello-come-computer ci incoraggia a pensare al modello come a uno strumento con cui interagire in tempo reale piuttosto che a un collaboratore a cui assegnare compiti. Invece di sostituire un tirocinante o un tutor, può essere una sorta di bicicletta proteiforme per la mente, una che è sempre costruita su misura esattamente per te e il terreno che intendi attraversare.
Un nuovo paradigma per l’informatica?
I modelli che possono generare interfacce su richiesta sono una frontiera completamente nuova nell’informatica. Potrebbero essere un paradigma del tutto nuovo, con il modo in cui cortocircuitano il modello di applicazione esistente. Dare agli utenti finali il potere di creare e modificare app al volo cambia fondamentalmente il modo in cui interagiamo con i computer. Al posto di una singola applicazione statica costruita da uno sviluppatore, un modello genererà un’applicazione su misura per l’utente e le sue esigenze immediate. Al posto della logica aziendale implementata nel codice, il modello interpreterà gli input dell’utente e aggiornerà l’interfaccia utente. È persino possibile che questo tipo di interfaccia generativa sostituisca completamente il sistema operativo, generando e gestendo interfacce e finestre al volo secondo necessità.
All’inizio, l’interfaccia generativa sarà un giocattolo, utile solo per l’esplorazione creativa e poche altre applicazioni di nicchia. Dopotutto, nessuno vorrebbe un’app di posta elettronica che occasionalmente invia email al tuo ex e mente sulla tua casella di posta. Ma gradualmente i modelli miglioreranno. Anche mentre si spingeranno ulteriormente nello spazio di esperienze completamente nuove, diventeranno lentamente abbastanza affidabili da essere utilizzati per un lavoro reale.
Piccoli pezzi di questo futuro esistono già. Anni fa Jonas Degrave ha dimostrato che ChatGPT poteva fare una buona simulazione di una riga di comando Linux. Allo stesso modo, websim.ai utilizza un LLM per generare siti web su richiesta mentre li navighi. Oasis, GameNGen e DIAMOND addestrano modelli video condizionati sull’azione su singoli videogiochi, permettendoti di giocare ad esempio a Doom dentro un grande modello. E Genie 2 genera videogiochi giocabili da prompt testuali. L’interfaccia generativa potrebbe ancora sembrare un’idea folle, ma non è così folle.
Ci sono enormi domande aperte su come apparirà tutto questo. Dove sarà inizialmente utile l’interfaccia generativa? Come condivideremo e distribuiremo le esperienze che creiamo collaborando con il modello, se esistono solo come contesto di un grande modello? Vorremmo davvero farlo? Quali nuovi tipi di esperienze saranno possibili? Come funzionerà tutto questo in pratica? I modelli genereranno interfacce come codice o produrranno direttamente pixel grezzi?
Non conosco ancora queste risposte. Dovremo sperimentare e scoprirlo!Che cosa significherebbe trattare l'IA come uno strumento invece che come una persona?
Dall’avvio di ChatGPT, le esplorazioni in due direzioni hanno preso velocità.
La prima direzione riguarda le capacità tecniche. Quanto grande possiamo addestrare un modello? Quanto bene può rispondere alle domande del SAT? Con quanta efficienza possiamo distribuirlo?
La seconda direzione riguarda il design dell’interazione. Come comunichiamo con un modello? Come possiamo usarlo per un lavoro utile? Quale metafora usiamo per ragionare su di esso?
La prima direzione è ampiamente seguita e enormemente finanziata, e per una buona ragione: i progressi nelle capacità tecniche sono alla base di ogni possibile applicazione. Ma la seconda è altrettanto cruciale per il campo e ha enormi incognite. Siamo solo a pochi anni dall’inizio dell’era dei grandi modelli. Quali sono le probabilità che abbiamo già capito i modi migliori per usarli?
Propongo una nuova modalità di interazione, in cui i modelli svolgano il ruolo di applicazioni informatiche (ad esempio app per telefoni): fornendo un’interfaccia grafica, interpretando gli input degli utenti e aggiornando il loro stato. In questa modalità, invece di essere un “agente” che utilizza un computer per conto dell’essere umano, l’IA può fornire un ambiente informatico più ricco e potente che possiamo utilizzare.
Metafore per l’interazione
Al centro di un’interazione c’è una metafora che guida le aspettative di un utente su un sistema. I primi giorni dell’informatica hanno preso metafore come “scrivanie”, “macchine da scrivere”, “fogli di calcolo” e “lettere” e le hanno trasformate in equivalenti digitali, permettendo all’utente di ragionare sul loro comportamento. Puoi lasciare qualcosa sulla tua scrivania e tornare a prenderlo; hai bisogno di un indirizzo per inviare una lettera. Man mano che abbiamo sviluppato una conoscenza culturale di questi dispositivi, la necessità di queste particolari metafore è scomparsa, e con esse i design di interfaccia skeumorfici che le rafforzavano. Come un cestino o una matita, un computer è ora una metafora di se stesso.
La metafora dominante per i grandi modelli oggi è modello-come-persona. Questa è una metafora efficace perché le persone hanno capacità estese che conosciamo intuitivamente. Implica che possiamo avere una conversazione con un modello e porgli domande; che il modello possa collaborare con noi su un documento o un pezzo di codice; che possiamo assegnargli un compito da svolgere da solo e che tornerà quando sarà finito.
Tuttavia, trattare un modello come una persona limita profondamente il nostro modo di pensare all’interazione con esso. Le interazioni umane sono intrinsecamente lente e lineari, limitate dalla larghezza di banda e dalla natura a turni della comunicazione verbale. Come abbiamo tutti sperimentato, comunicare idee complesse in una conversazione è difficile e dispersivo. Quando vogliamo precisione, ci rivolgiamo invece a strumenti, utilizzando manipolazioni dirette e interfacce visive ad alta larghezza di banda per creare diagrammi, scrivere codice e progettare modelli CAD. Poiché concepiamo i modelli come persone, li utilizziamo attraverso conversazioni lente, anche se sono perfettamente in grado di accettare input diretti e rapidi e di produrre risultati visivi. Le metafore che utilizziamo limitano le esperienze che costruiamo, e la metafora modello-come-persona ci impedisce di esplorare il pieno potenziale dei grandi modelli.
Per molti casi d’uso, e specialmente per il lavoro produttivo, credo che il futuro risieda in un’altra metafora: modello-come-computer.
Usare un’IA come un computer
Sotto la metafora modello-come-computer, interagiremo con i grandi modelli seguendo le intuizioni che abbiamo sulle applicazioni informatiche (sia su desktop, tablet o telefono). Nota che ciò non significa che il modello sarà un’app tradizionale più di quanto il desktop di Windows fosse una scrivania letterale. “Applicazione informatica” sarà un modo per un modello di rappresentarsi a noi. Invece di agire come una persona, il modello agirà come un computer.
Agire come un computer significa produrre un’interfaccia grafica. Al posto del flusso lineare di testo in stile telescrivente fornito da ChatGPT, un sistema modello-come-computer genererà qualcosa che somiglia all’interfaccia di un’applicazione moderna: pulsanti, cursori, schede, immagini, grafici e tutto il resto. Questo affronta limitazioni chiave dell’interfaccia di chat standard modello-come-persona:
Scoperta. Un buon strumento suggerisce i suoi usi. Quando l’unica interfaccia è una casella di testo vuota, spetta all’utente capire cosa fare e comprendere i limiti del sistema. La barra laterale Modifica in Lightroom è un ottimo modo per imparare l’editing fotografico perché non si limita a dirti cosa può fare questa applicazione con una foto, ma cosa potresti voler fare. Allo stesso modo, un’interfaccia modello-come-computer per DALL-E potrebbe mostrare nuove possibilità per le tue generazioni di immagini.
Efficienza. La manipolazione diretta è più rapida che scrivere una richiesta a parole. Per continuare l’esempio di Lightroom, sarebbe impensabile modificare una foto dicendo a una persona quali cursori spostare e di quanto. Ci vorrebbe un giorno intero per chiedere un’esposizione leggermente più bassa e una vibranza leggermente più alta, solo per vedere come apparirebbe. Nella metafora modello-come-computer, il modello può creare strumenti che ti permettono di comunicare ciò che vuoi più efficientemente e quindi di fare le cose più rapidamente.
A differenza di un’app tradizionale, questa interfaccia grafica è generata dal modello su richiesta. Questo significa che ogni parte dell’interfaccia che vedi è rilevante per ciò che stai facendo in quel momento, inclusi i contenuti specifici del tuo lavoro. Significa anche che, se desideri un’interfaccia più ampia o diversa, puoi semplicemente richiederla. Potresti chiedere a DALL-E di produrre alcuni preset modificabili per le sue impostazioni ispirati da famosi artisti di schizzi. Quando clicchi sul preset Leonardo da Vinci, imposta i cursori per disegni prospettici altamente dettagliati in inchiostro nero. Se clicchi su Charles Schulz, seleziona fumetti tecnicolor 2D a basso dettaglio.
Una bicicletta della mente proteiforme
La metafora modello-come-persona ha una curiosa tendenza a creare distanza tra l’utente e il modello, rispecchiando il divario di comunicazione tra due persone che può essere ridotto ma mai completamente colmato. A causa della difficoltà e del costo di comunicare a parole, le persone tendono a suddividere i compiti tra loro in blocchi grandi e il più indipendenti possibile. Le interfacce modello-come-persona seguono questo schema: non vale la pena dire a un modello di aggiungere un return statement alla tua funzione quando è più veloce scriverlo da solo. Con il sovraccarico della comunicazione, i sistemi modello-come-persona sono più utili quando possono fare un intero blocco di lavoro da soli. Fanno le cose per te.
Questo contrasta con il modo in cui interagiamo con i computer o altri strumenti. Gli strumenti producono feedback visivi in tempo reale e sono controllati attraverso manipolazioni dirette. Hanno un overhead comunicativo così basso che non è necessario specificare un blocco di lavoro indipendente. Ha più senso mantenere l’umano nel loop e dirigere lo strumento momento per momento. Come stivali delle sette leghe, gli strumenti ti permettono di andare più lontano a ogni passo, ma sei ancora tu a fare il lavoro. Ti permettono di fare le cose più velocemente.
Considera il compito di costruire un sito web usando un grande modello. Con le interfacce di oggi, potresti trattare il modello come un appaltatore o un collaboratore. Cercheresti di scrivere a parole il più possibile su come vuoi che il sito appaia, cosa vuoi che dica e quali funzionalità vuoi che abbia. Il modello genererebbe una prima bozza, tu la eseguirai e poi fornirai un feedback. “Fai il logo un po’ più grande”, diresti, e “centra quella prima immagine principale”, e “deve esserci un pulsante di login nell’intestazione”. Per ottenere esattamente ciò che vuoi, invierai una lista molto lunga di richieste sempre più minuziose.
Un’interazione alternativa modello-come-computer sarebbe diversa: invece di costruire il sito web, il modello genererebbe un’interfaccia per te per costruirlo, dove ogni input dell’utente a quell’interfaccia interroga il grande modello sotto il cofano. Forse quando descrivi le tue necessità creerebbe un’interfaccia con una barra laterale e una finestra di anteprima. All’inizio la barra laterale contiene solo alcuni schizzi di layout che puoi scegliere come punto di partenza. Puoi cliccare su ciascuno di essi, e il modello scrive l’HTML per una pagina web usando quel layout e lo visualizza nella finestra di anteprima. Ora che hai una pagina su cui lavorare, la barra laterale guadagna opzioni aggiuntive che influenzano la pagina globalmente, come accoppiamenti di font e schemi di colore. L’anteprima funge da editor WYSIWYG, permettendoti di afferrare elementi e spostarli, modificarne i contenuti, ecc. A supportare tutto ciò è il modello, che vede queste azioni dell’utente e riscrive la pagina per corrispondere ai cambiamenti effettuati. Poiché il modello può generare un’interfaccia per aiutare te e lui a comunicare più efficientemente, puoi esercitare più controllo sul prodotto finale in meno tempo.
La metafora modello-come-computer ci incoraggia a pensare al modello come a uno strumento con cui interagire in tempo reale piuttosto che a un collaboratore a cui assegnare compiti. Invece di sostituire un tirocinante o un tutor, può essere una sorta di bicicletta proteiforme per la mente, una che è sempre costruita su misura esattamente per te e il terreno che intendi attraversare.
Un nuovo paradigma per l’informatica?
I modelli che possono generare interfacce su richiesta sono una frontiera completamente nuova nell’informatica. Potrebbero essere un paradigma del tutto nuovo, con il modo in cui cortocircuitano il modello di applicazione esistente. Dare agli utenti finali il potere di creare e modificare app al volo cambia fondamentalmente il modo in cui interagiamo con i computer. Al posto di una singola applicazione statica costruita da uno sviluppatore, un modello genererà un’applicazione su misura per l’utente e le sue esigenze immediate. Al posto della logica aziendale implementata nel codice, il modello interpreterà gli input dell’utente e aggiornerà l’interfaccia utente. È persino possibile che questo tipo di interfaccia generativa sostituisca completamente il sistema operativo, generando e gestendo interfacce e finestre al volo secondo necessità.
All’inizio, l’interfaccia generativa sarà un giocattolo, utile solo per l’esplorazione creativa e poche altre applicazioni di nicchia. Dopotutto, nessuno vorrebbe un’app di posta elettronica che occasionalmente invia email al tuo ex e mente sulla tua casella di posta. Ma gradualmente i modelli miglioreranno. Anche mentre si spingeranno ulteriormente nello spazio di esperienze completamente nuove, diventeranno lentamente abbastanza affidabili da essere utilizzati per un lavoro reale.
Piccoli pezzi di questo futuro esistono già. Anni fa Jonas Degrave ha dimostrato che ChatGPT poteva fare una buona simulazione di una riga di comando Linux. Allo stesso modo, websim.ai utilizza un LLM per generare siti web su richiesta mentre li navighi. Oasis, GameNGen e DIAMOND addestrano modelli video condizionati sull’azione su singoli videogiochi, permettendoti di giocare ad esempio a Doom dentro un grande modello. E Genie 2 genera videogiochi giocabili da prompt testuali. L’interfaccia generativa potrebbe ancora sembrare un’idea folle, ma non è così folle.
Ci sono enormi domande aperte su come apparirà tutto questo. Dove sarà inizialmente utile l’interfaccia generativa? Come condivideremo e distribuiremo le esperienze che creiamo collaborando con il modello, se esistono solo come contesto di un grande modello? Vorremmo davvero farlo? Quali nuovi tipi di esperienze saranno possibili? Come funzionerà tutto questo in pratica? I modelli genereranno interfacce come codice o produrranno direttamente pixel grezzi?
Non conosco ancora queste risposte. Dovremo sperimentare e scoprirlo!
Tradotto da:\ https://willwhitney.com/computing-inside-ai.htmlhttps://willwhitney.com/computing-inside-ai.html
-
-
 @ 6389be64:ef439d32
2024-12-09 23:50:41
@ 6389be64:ef439d32
2024-12-09 23:50:41Resilience is the ability to withstand shocks, adapt, and bounce back. It’s an essential quality in nature and in life. But what if we could take resilience a step further? What if, instead of merely surviving, a system could improve when faced with stress? This concept, known as anti-fragility, is not just theoretical—it’s practical. Combining two highly resilient natural tools, comfrey and biochar, reveals how we can create systems that thrive under pressure and grow stronger with each challenge.
Comfrey: Nature’s Champion of Resilience
Comfrey is a plant that refuses to fail. Once its deep roots take hold, it thrives in poor soils, withstands drought, and regenerates even after being cut down repeatedly. It’s a hardy survivor, but comfrey doesn’t just endure—it contributes. Known as a dynamic accumulator, it mines nutrients from deep within the earth and brings them to the surface, making them available for other plants.
Beyond its ecological role, comfrey has centuries of medicinal use, earning the nickname "knitbone." Its leaves can heal wounds and restore health, a perfect metaphor for resilience. But as impressive as comfrey is, its true potential is unlocked when paired with another resilient force: biochar.
Biochar: The Silent Powerhouse of Soil Regeneration
Biochar, a carbon-rich material made by burning organic matter in low-oxygen conditions, is a game-changer for soil health. Its unique porous structure retains water, holds nutrients, and provides a haven for beneficial microbes. Soil enriched with biochar becomes drought-resistant, nutrient-rich, and biologically active—qualities that scream resilience.
Historically, ancient civilizations in the Amazon used biochar to transform barren soils into fertile agricultural hubs. Known as terra preta, these soils remain productive centuries later, highlighting biochar’s remarkable staying power.
Yet, like comfrey, biochar’s potential is magnified when it’s part of a larger system.
The Synergy: Comfrey and Biochar Together
Resilience turns into anti-fragility when systems go beyond mere survival and start improving under stress. Combining comfrey and biochar achieves exactly that.
-
Nutrient Cycling and Retention\ Comfrey’s leaves, rich in nitrogen, potassium, and phosphorus, make an excellent mulch when cut and dropped onto the soil. However, these nutrients can wash away in heavy rains. Enter biochar. Its porous structure locks in the nutrients from comfrey, preventing runoff and keeping them available for plants. Together, they create a system that not only recycles nutrients but amplifies their effectiveness.
-
Water Management\ Biochar holds onto water making soil not just drought-resistant but actively water-efficient, improving over time with each rain and dry spell.
-
Microbial Ecosystems\ Comfrey enriches soil with organic matter, feeding microbial life. Biochar provides a home for these microbes, protecting them and creating a stable environment for them to multiply. Together, they build a thriving soil ecosystem that becomes more fertile and resilient with each passing season.
Resilient systems can withstand shocks, but anti-fragile systems actively use those shocks to grow stronger. Comfrey and biochar together form an anti-fragile system. Each addition of biochar enhances water and nutrient retention, while comfrey regenerates biomass and enriches the soil. Over time, the system becomes more productive, less dependent on external inputs, and better equipped to handle challenges.
This synergy demonstrates the power of designing systems that don’t just survive—they thrive.
Lessons Beyond the Soil
The partnership of comfrey and biochar offers a valuable lesson for our own lives. Resilience is an admirable trait, but anti-fragility takes us further. By combining complementary strengths and leveraging stress as an opportunity, we can create systems—whether in soil, business, or society—that improve under pressure.
Nature shows us that resilience isn’t the end goal. When we pair resilient tools like comfrey and biochar, we unlock a system that evolves, regenerates, and becomes anti-fragile. By designing with anti-fragility in mind, we don’t just bounce back, we bounce forward.
By designing with anti-fragility in mind, we don’t just bounce back, we bounce forward.
-
-
 @ 06b7819d:d1d8327c
2024-12-08 10:52:55
@ 06b7819d:d1d8327c
2024-12-08 10:52:55Power as the Reduction of Possibilities: Niklas Luhmann’s Perspective
Niklas Luhmann, a leading figure in systems theory, offers a unique conceptualization of power that diverges from traditional notions of domination or coercion. Rather than viewing power as a forceful imposition of will, Luhmann frames it as a mechanism for reducing possibilities within a given social system. For Luhmann, power is less about direct coercion and more about structuring decision-making processes by limiting the range of available options.
In his systems-theoretical approach, Luhmann argues that power operates as a communication medium, enabling complex social systems to function by simplifying the overwhelming array of potential actions. In any decision-making context, there are countless possibilities, and not all can be pursued. Power serves as a tool to focus attention, filter alternatives, and channel behavior toward specific actions while excluding others. This reduction of options creates a manageable environment for coordinated action, which is essential for the stability of a system.
Importantly, this process does not inherently involve force or threats. Instead, power works through expectations, norms, and structures that guide behavior. For example, in an organizational setting, the hierarchy of authority determines which decisions are permissible, thereby shaping the actions of individuals without overt coercion. The employees’ actions are not forced; rather, they are conditioned by the organizational framework, which narrows their choices.
Luhmann’s idea redefines power as a productive force in social systems. By limiting possibilities, power reduces uncertainty, making collaboration and collective action possible. It ensures that systems can function efficiently despite their inherent complexity. This perspective shifts the emphasis from conflict to coordination, offering a more nuanced understanding of how power operates in modern societies.
In sum, Niklas Luhmann’s theory of power as the reduction of possibilities highlights its integrative role in enabling social systems to navigate complexity. It challenges conventional views of power as coercion, emphasizing its capacity to organize and stabilize interactions through the selective limitation of actions.
-
 @ c11cf5f8:4928464d
2024-12-29 12:22:08
@ c11cf5f8:4928464d
2024-12-29 12:22:08Let's hear some of your latest Bitcoin purchases, feel free to include links to the shops or merchants you bought from too.
If you missed our last thread, here are some of the items stackers recently spent their sats on.
originally posted at https://stacker.news/items/828556
-
 @ 06b7819d:d1d8327c
2024-12-03 09:00:46
@ 06b7819d:d1d8327c
2024-12-03 09:00:46The History of Bananas as an Exportable Fruit and the Rise of Banana Republics
Bananas became a significant export in the late 19th century, fueled by advancements in transportation and refrigeration that allowed the fruit to travel long distances without spoilage. Originally native to Southeast Asia, bananas were introduced to the Americas by European colonists. By the late 1800s, companies like the United Fruit Company (later Chiquita) and Standard Fruit Company (now Dole) began cultivating bananas on a large scale in Central America and the Caribbean.
These corporations capitalized on the fruit’s appeal—bananas were cheap, nutritious, and easy to transport. The fruit quickly became a staple in Western markets, especially in the United States. However, the rapid expansion of banana exports came at a significant political and social cost to the countries where the fruit was grown.
To maintain control over banana production and maximize profits, these companies required vast amounts of arable land, labor, and favorable trade conditions. This often led them to form close relationships with local governments, many of which were authoritarian and corrupt. The companies influenced policies to secure land concessions, suppress labor rights, and maintain low taxes.
The term “banana republic” was coined by writer O. Henry in 1904 to describe countries—particularly in Central America—that became politically unstable due to their economic dependence on a single export crop, often controlled by foreign corporations.
The U.S. government frequently supported these regimes as part of its broader strategy during the Cold War to counter communist influence in the region. Washington feared that labor movements and demands for land reform, often supported by the peasantry and indigenous groups, could lead to the rise of socialist or communist governments. Consequently, the U.S. backed coups, such as the 1954 overthrow of Guatemala’s democratically elected President Jacobo Árbenz, who had threatened United Fruit’s interests by redistributing unused land.
These interventions created a legacy of exploitation, environmental degradation, and political instability in many banana-exporting countries. While bananas remain a global dietary staple, their history underscores the complex interplay of economics, politics, and imperialism.
-
 @ 32e18276:5c68e245
2023-10-10 12:02:37
@ 32e18276:5c68e245
2023-10-10 12:02:37Hey guys, I'm spending some time today preparing v1.6 for the app store, it's been a long time coming with many new features. Here's a breakdown of everything new in this version!
Notable new features in 1.6
- Custom built, embedded C WASM interpreter (nostrscript), which will be used for custom algos, filters and lists
- Longform note support
- Hashtag following
- Configurable reactions
- New Live user status NIP (music, general)
- Adjustable font sizes
- A very long list of bug fixes and performance improvements
- Fast and persistent profile searching using nostrdb
Top priorities for 1.7
- Lists
- Custom algos and filters using nostrscript
- Stories
- Multi account
- Tor integration
- Better NWC integration (wallet balances, transaction history)
- Advanced note search via nostrdb
- Fully switch to nostrdb for all notes
- Discord-like relays (click a relay to view all the notes on it)
So much more but maybe I will not try to be too ambitious ...
Contributors
name added removed commits William Casarin +57964 -8274 288 petrikaj +1524 -0 1 Terry Yiu +1266 -964 9 ericholguin +1234 -252 11 Daniel D’Aquino +1223 -399 19 Suhail Saqan +905 -70 16 Grimless +838 -736 6 Bryan Montz +793 -744 30 Jon Marrs +658 -60 3 Joel Klabo +653 -105 6 transifex-integration[bot] +176 -0 9 Fishcake +129 -21 5 Daniel D‘Aquino +123 -9 5 Jericho Hasselbush +78 -2 2 cr0bar +66 -19 11 Daniel D'Aquino +55 -32 2 Mazin +53 -0 1 gladiusKatana +37 -8 1 doffing.brett +10 -6 1 tappu75e@duck.com +5 -1 2 Ben Harvie +5 -0 1Changelog
- 76 Fixes
- 18 Changes
- 26 Additions
Added
- Add "Do not show #nsfw tagged posts" setting (Daniel D’Aquino)
- Add ability to change order of custom reactions (Suhail Saqan)
- Add close button to custom reactions (Suhail Saqan)
- Add followed hashtags to your following list (Daniel D’Aquino)
- Add initial longform note support (William Casarin)
- Add r tag when mentioning a url (William Casarin)
- Add relay log in developer mode (Montz)
- Add settings for disabling user statuses (William Casarin)
- Add space when tagging users in posts if needed (William Casarin)
- Add support for multilingual hashtags (cr0bar)
- Add support for multiple reactions (Suhail Saqan)
- Add support for status URLs (William Casarin)
- Add the ability to follow hashtags (William Casarin)
- Added feedback when user adds a relay that is already on the list (Daniel D'Aquino)
- Added generic user statuses (William Casarin)
- Added live music statuses (William Casarin)
- Added merch store button to sidebar menu (Daniel D’Aquino)
- Added padding under word count on longform account (William Casarin)
- Adjustable font size (William Casarin)
- Click music statuses to display in spotify (William Casarin)
- Enable banner image editing (Joel Klabo)
- Finnish translations (petrikaj)
- Hold tap to preview status URL (Jericho Hasselbush)
- Re-add nip05 badges to profiles (William Casarin)
- Show nostr address username and support abbreviated _ usernames (William Casarin)
- Suggested Users to Follow (Joel Klabo)
Changed
- Allow reposting and quote reposting multiple times (William Casarin)
- Damus icon now opens sidebar (Daniel D’Aquino)
- Hide nsec when logging in (cr0bar)
- Improve UX around clearing cache (Daniel D’Aquino)
- Improved memory usage and performance when processing events (William Casarin)
- Increase size of the hitbox on note ellipsis button (Daniel D’Aquino)
- Make carousel tab dots tappable (Bryan Montz)
- Move the "Follow you" badge into the profile header (Grimless)
- Remove nip05 on events (William Casarin)
- Remove note size restriction for longform events (William Casarin)
- Rename NIP05 to "nostr address" (William Casarin)
- Show muted thread replies at the bottom of the thread view (#1522) (Daniel D’Aquino)
- Show renotes in Notes timeline (William Casarin)
- Start at top when reading longform events (William Casarin)
- Switch to nostrdb for @'s and user search (William Casarin)
- Updated relay view (ericholguin)
- Use nostrdb for profiles (William Casarin)
- clear statuses if they only contain whitespace (William Casarin)
Fixed
- Allow relay logs to be opened in dev mode even if relay (Daniel D'Aquino)
- Allow user to login to deleted profile (William Casarin)
- Apply filters to hashtag search timeline view (Daniel D’Aquino)
- Avoid notification for zaps from muted profiles (tappu75e@duck.com)
- Crash when muting threads (Bryan Montz)
- Dismiss qr screen on scan (Suhail Saqan)
- Don't always show text events in reposts (William Casarin)
- Don't spam lnurls when validating zaps (William Casarin)
- Eliminate nostr address validation bandwidth on startup (William Casarin)
- Ensure the person you're replying to is the first entry in the reply description (William Casarin)
- Fix Invalid Zap bug in reposts (William Casarin)
- Fix PostView initial string to skip mentioning self when on own profile (Terry Yiu)
- Fix UI freeze after swiping back from profile (#1449) (Daniel D’Aquino)
- Fix UTF support for hashtags (Daniel D‘Aquino)
- Fix action bar appearing on quoted longform previews (William Casarin)
- Fix broken markdown renderer (William Casarin)
- Fix bug where it would sometimes show -1 in replies (tappu75e@duck.com)
- Fix compilation error on test target in UserSearchCacheTests (Daniel D‘Aquino)
- Fix crash when long pressing custom reactions (William Casarin)
- Fix crash when long-pressing reactions (William Casarin)
- Fix freezing bug when tapping Developer settings menu (Terry Yiu)
- Fix icons on settings view (cr0bar)
- Fix images and links occasionally appearing with escaped slashes (Daniel D‘Aquino)
- Fix issue where malicious zappers can send fake zaps to another user's posts (William Casarin)
- Fix issue where relays with trailing slashes cannot be removed (#1531) (Daniel D’Aquino)
- Fix issue where typing cc@bob would produce brokenb ccnostr:bob mention (William Casarin)
- Fix issue with emojis next to hashtags and urls (William Casarin)
- Fix issue with slashes on relay urls causing relay connection problems (William Casarin)
- Fix lag when creating large posts (William Casarin)
- Fix localization issues and export strings for translation (Terry Yiu)
- Fix localization issues and export strings for translation (Terry Yiu)
- Fix long status lines (William Casarin)
- Fix nav crashing and buggyness (William Casarin)
- Fix nostr:nostr:... bugs (William Casarin)
- Fix npub mentions failing to parse in some cases (William Casarin)
- Fix padding of username next to pfp on some views (William Casarin)
- Fix padding on longform events (William Casarin)
- Fix paragraphs not appearing on iOS17 (cr0bar)
- Fix parsing issue with NIP-47 compliant NWC urls without double-slashes (Daniel D’Aquino)
- Fix potential fake profile zap attacks (William Casarin)
- Fix profile not updating (William Casarin)
- Fix profile post button mentions (cr0bar)
- Fix profiles not updating (William Casarin)
- Fix rare crash triggered by local notifications (William Casarin)
- Fix reaction button breaking scrolling (Suhail Saqan)
- Fix situations where the note composer cursor gets stuck in one place after tagging a user (Daniel D’Aquino)
- Fix small graphical toolbar bug when scrolling profiles (Daniel D’Aquino)
- Fix some note composer issues, such as when copying/pasting larger text, and make the post composer more robust. (Daniel D’Aquino)
- Fix status events not expiring locally (William Casarin)
- Fix text composer wrapping issue when mentioning npub (Daniel D’Aquino)
- Fix text editing issues on characters added right after mention link (Daniel D’Aquino)
- Fix wiggle when long press reactions (Suhail Saqan)
- Fix wikipedia url detection with parenthesis (William Casarin)
- Fix zaps sometimes not appearing (William Casarin)
- Fixed a bug where following a user might not work due to poor connectivity (William Casarin)
- Fixed audio in video playing twice (Bryan Montz)
- Fixed disappearing text on iOS17 (cr0bar)
- Fixed issue where hashtags were leaking in DMs (William Casarin)
- Fixed issue where reposts would sometimes repost the wrong thing (William Casarin)
- Fixed issues where sometimes there would be empty entries on your profile (William Casarin)
- Fixed nav bar color on login, eula, and account creation (ericholguin)
- Fixed nostr reporting decoding (William Casarin)
- Fixed nostrscript not working on smaller phones (William Casarin)
- Fixed old notifications always appearing on first start (William Casarin)
- Fixes issue where username with multiple emojis would place cursor in strange position. (Jericho Hasselbush)
- Hide quoted or reposted notes from people whom the user has muted. (#1216) (Daniel D’Aquino)
- Hide users and hashtags from home timeline when you unfollow (William Casarin)
- Make blurred videos viewable by allowing blur to disappear once tapped (Daniel D’Aquino)
- Mute hellthreads everywhere (William Casarin)
- Show QRCameraView regardless of same user (Suhail Saqan)
- Show longform previews in notifications instead of the entire post (William Casarin)
- Stop tab buttons from causing the root view to scroll to the top unless user is coming from another tab or already at the root view (Daniel D’Aquino)
- don't cutoff text in notifications (William Casarin)
- endless connection attempt loop after user removes relay (Bryan Montz)
- icon color for developer mode setting is incorrect in low-light mode (Bryan Montz)
- relay detail view is not immediately available after adding new relay (Bryan Montz)
Removed
- Remove following Damus Will by default (William Casarin)
- Remove old @ and & hex key mentions (William Casarin)
-
 @ 16d11430:61640947
2024-12-30 05:08:22
@ 16d11430:61640947
2024-12-30 05:08:22The colonial period in India introduced systemic neglect of public welfare and sanitation, fostering a culture that normalized unsanitary practices. This transformation can be understood by analyzing the psychological, societal, and infrastructural impacts of colonial neglect, combined with the natural challenges of scaling traditional systems to meet the needs of a rapidly growing population.
- Colonial Neglect and Disruption of Indigenous Sanitation Practices
Destruction of Community Systems
Before colonization, sanitation systems in India were often community-managed. Local governance structures (e.g., village panchayats) organized water management, waste disposal, and hygiene practices.
The British prioritized centralized control, sidelining these systems. This resulted in a vacuum where no effective local or central systems functioned properly for the majority of the population.
Urbanization Without Sanitation
British industrial and trade-focused urbanization led to densely populated cities like Bombay, Calcutta, and Madras, which lacked adequate sanitation infrastructure.
Overcrowding, lack of waste disposal, and insufficient clean water supplies created unhygienic living conditions.
Psychological Impact of Exclusion
The colonial administration primarily catered to European populations, neglecting Indian communities. Indians were implicitly (and sometimes explicitly) told that their hygiene and living conditions were not a priority.
Over time, this neglect fostered a sense of inferiority and apathy towards public health and sanitation among the general population.
- Psychological and Societal Impact of Neglect
Normalization of Unsanitary Conditions
Two centuries of neglect normalized squalor and uncleanliness as inevitable aspects of daily life. Public spaces filled with waste became a common sight, and efforts to improve hygiene were deprioritized at individual and community levels.
Apathy towards sanitation became ingrained in public consciousness, with the belief that it was either too expensive or unnecessary.
Internalized Self-Neglect
Repeated messaging of Indian inferiority during the colonial period caused a cultural shift towards accepting unsanitary conditions as unchangeable.
Post-independence, this internalized neglect persisted, as people struggled to see sanitation as a collective responsibility.
Caste and Sanitation
The British formalized and exacerbated caste divisions. Sanitation work became even more stigmatized and relegated to specific marginalized groups, further discouraging others from engaging in hygiene practices.
This contributed to a societal disconnect from sanitation responsibilities.
- Biological Challenges Against Unsustainable Systems
Unscalable Traditional Systems
Traditional sanitation systems (e.g., open defecation combined with composting) were sustainable in low-density rural settings but could not scale to urban centers or a rapidly growing population.
The British colonial administration failed to invest in modern infrastructure that could meet these new challenges, leaving cities overwhelmed.
Biological Realities of Waste
Human biological urges for immediate waste disposal clashed with the lack of public facilities. Open defecation and improper waste disposal became the norm in the absence of latrines and garbage systems.
The lack of accessible facilities perpetuated the cycle of unsanitary conditions.
- Post-Colonial Normalization of Unsanitary Practices
Lack of Systemic Overhaul
After independence, India inherited an underdeveloped sanitation infrastructure. Attempts to modernize sanitation systems often faltered due to resource constraints, corruption, and a lack of public awareness.
Government campaigns to promote cleanliness were met with limited success because deeply ingrained cultural norms and apathy persisted.
Urban-Rural Divide
Investments in sanitation have often prioritized urban areas, leaving rural communities with limited facilities. This disparity perpetuates unsanitary practices in the majority of the population.
Population Growth
Rapid population growth has outpaced the development of sanitation infrastructure, further compounding the problem.
- Cultural Normalization of Unsanitary Situations
Cognitive Dissonance
People adapt to unsanitary environments by rationalizing them as unavoidable. The widespread acceptance of open defecation, garbage-filled streets, and polluted water is partly due to cognitive dissonance—a way of reconciling living conditions with the lack of alternatives.
Institutionalized Apathy
Bureaucratic inefficiency and corruption contribute to a lack of accountability for improving sanitation.
Over time, citizens have learned to expect inaction from the state, perpetuating a cycle of neglect.
Economic Priorities
For much of the population, economic survival takes precedence over sanitation. Limited resources mean that people often prioritize immediate needs (e.g., food, shelter) over hygiene.
Solutions and Lessons
Reversing Colonial Legacies
Encouraging community participation in sanitation reforms can revive traditional systems of collective responsibility.
Public awareness campaigns (e.g., Swachh Bharat Abhiyan) can help shift societal attitudes towards hygiene.
Investment in Infrastructure
Comprehensive sanitation infrastructure that includes toilets, waste disposal systems, and clean water supply is essential to breaking the cycle of neglect.
Education and Inclusion
Addressing cultural stigmas around sanitation work and promoting dignity for sanitation workers can help integrate cleanliness into societal values.
Education campaigns should emphasize the public health benefits of sanitation.
Scaling for Population Needs
Modernizing sanitation systems to handle urban density and rural accessibility is critical. Technologies like biogas toilets, community waste treatment plants, and water recycling systems can bridge the gap.
Conclusion
The colonial period created a systemic neglect of sanitation in India, fostering a culture of self-neglect that persists to this day. Addressing this legacy requires a combination of community engagement, infrastructure investment, and education to redefine hygiene as a collective responsibility. Recognizing the intersection of history, biology, and culture is key to creating scalable, sustainable solutions.
-
 @ ab8cb80e:5395d502
2024-07-12 14:21:14
@ ab8cb80e:5395d502
2024-07-12 14:21:14Hey, I have nothing to do this Friday evening, so why not chill with chess?
Spontaneously I launched an Arena Tournament for today: https://lichess.org/tournament/2iNa8jh4
@ek @kristapsk @BitcoinAbhi @grayruby @frostdragon @Taft @02d43d3798 @030e0dca83 @riberet19 @felipe @didiplaywell @SatsMate @itsTomekK @wize123 @Coinsreporter @stefano @anon @314piepi @160ed04091 do you want to play?
! TODAY ! ♟️ https://lichess.org/tournament/2iNa8jh4 ♟️ 90 min arena, with 5 minute games.
Join on @Alby's new Discord: https://discord.gg/3vbafUCZ?event=1261325278358016091 for voicechat I plan to stream it to zap.stream, because why not.
Who takes my challenge?
originally posted at https://stacker.news/items/605942
-
 @ e31e84c4:77bbabc0
2024-12-02 10:44:07
@ e31e84c4:77bbabc0
2024-12-02 10:44:07Bitcoin and Fixed Income was Written By Wyatt O’Rourke. If you enjoyed this article then support his writing, directly, by donating to his lightning wallet: ultrahusky3@primal.net
Fiduciary duty is the obligation to act in the client’s best interests at all times, prioritizing their needs above the advisor’s own, ensuring honesty, transparency, and avoiding conflicts of interest in all recommendations and actions.
This is something all advisors in the BFAN take very seriously; after all, we are legally required to do so. For the average advisor this is a fairly easy box to check. All you essentially have to do is have someone take a 5-minute risk assessment, fill out an investment policy statement, and then throw them in the proverbial 60/40 portfolio. You have thousands of investment options to choose from and you can reasonably explain how your client is theoretically insulated from any move in the \~markets\~. From the traditional financial advisor perspective, you could justify nearly anything by putting a client into this type of portfolio. All your bases were pretty much covered from return profile, regulatory, compliance, investment options, etc. It was just too easy. It became the household standard and now a meme.
As almost every real bitcoiner knows, the 60/40 portfolio is moving into psyop territory, and many financial advisors get clowned on for defending this relic on bitcoin twitter. I’m going to specifically poke fun at the ‘40’ part of this portfolio.
The ‘40’ represents fixed income, defined as…
An investment type that provides regular, set interest payments, such as bonds or treasury securities, and returns the principal at maturity. It’s generally considered a lower-risk asset class, used to generate stable income and preserve capital.
Historically, this part of the portfolio was meant to weather the volatility in the equity markets and represent the “safe” investments. Typically, some sort of bond.
First and foremost, the fixed income section is most commonly constructed with U.S. Debt. There are a couple main reasons for this. Most financial professionals believe the same fairy tale that U.S. Debt is “risk free” (lol). U.S. debt is also one of the largest and most liquid assets in the market which comes with a lot of benefits.
There are many brilliant bitcoiners in finance and economics that have sounded the alarm on the U.S. debt ticking time bomb. I highly recommend readers explore the work of Greg Foss, Lawrence Lepard, Lyn Alden, and Saifedean Ammous. My very high-level recap of their analysis:
-
A bond is a contract in which Party A (the borrower) agrees to repay Party B (the lender) their principal plus interest over time.
-
The U.S. government issues bonds (Treasury securities) to finance its operations after tax revenues have been exhausted.
-
These are traditionally viewed as “risk-free” due to the government’s historical reliability in repaying its debts and the strength of the U.S. economy
-
U.S. bonds are seen as safe because the government has control over the dollar (world reserve asset) and, until recently (20 some odd years), enjoyed broad confidence that it would always honor its debts.
-
This perception has contributed to high global demand for U.S. debt but, that is quickly deteriorating.
-
The current debt situation raises concerns about sustainability.
-
The U.S. has substantial obligations, and without sufficient productivity growth, increasing debt may lead to a cycle where borrowing to cover interest leads to more debt.
-
This could result in more reliance on money creation (printing), which can drive inflation and further debt burdens.
In the words of Lyn Alden “Nothing stops this train”
Those obligations are what makes up the 40% of most the fixed income in your portfolio. So essentially you are giving money to one of the worst capital allocators in the world (U.S. Gov’t) and getting paid back with printed money.
As someone who takes their fiduciary responsibility seriously and understands the debt situation we just reviewed, I think it’s borderline negligent to put someone into a classic 60% (equities) / 40% (fixed income) portfolio without serious scrutiny of the client’s financial situation and options available to them. I certainly have my qualms with equities at times, but overall, they are more palatable than the fixed income portion of the portfolio. I don’t like it either, but the money is broken and the unit of account for nearly every equity or fixed income instrument (USD) is fraudulent. It’s a paper mache fade that is quite literally propped up by the money printer.
To briefly be as most charitable as I can – It wasn’t always this way. The U.S. Dollar used to be sound money, we used to have government surplus instead of mathematically certain deficits, The U.S. Federal Government didn’t used to have a money printing addiction, and pre-bitcoin the 60/40 portfolio used to be a quality portfolio management strategy. Those times are gone.
Now the fun part. How does bitcoin fix this?
Bitcoin fixes this indirectly. Understanding investment criteria changes via risk tolerance, age, goals, etc. A client may still have a need for “fixed income” in the most literal definition – Low risk yield. Now you may be thinking that yield is a bad word in bitcoin land, you’re not wrong, so stay with me. Perpetual motion machine crypto yield is fake and largely where many crypto scams originate. However, that doesn’t mean yield in the classic finance sense does not exist in bitcoin, it very literally does. Fortunately for us bitcoiners there are many other smart, driven, and enterprising bitcoiners that understand this problem and are doing something to address it. These individuals are pioneering new possibilities in bitcoin and finance, specifically when it comes to fixed income.
Here are some new developments –
Private Credit Funds – The Build Asset Management Secured Income Fund I is a private credit fund created by Build Asset Management. This fund primarily invests in bitcoin-backed, collateralized business loans originated by Unchained, with a secured structure involving a multi-signature, over-collateralized setup for risk management. Unchained originates loans and sells them to Build, which pools them into the fund, enabling investors to share in the interest income.
Dynamics
- Loan Terms: Unchained issues loans at interest rates around 14%, secured with a 2/3 multi-signature vault backed by a 40% loan-to-value (LTV) ratio.
- Fund Mechanics: Build buys these loans from Unchained, thus providing liquidity to Unchained for further loan originations, while Build manages interest payments to investors in the fund.
Pros
- The fund offers a unique way to earn income via bitcoin-collateralized debt, with protection against rehypothecation and strong security measures, making it attractive for investors seeking exposure to fixed income with bitcoin.
Cons
- The fund is only available to accredited investors, which is a regulatory standard for private credit funds like this.
Corporate Bonds – MicroStrategy Inc. (MSTR), a business intelligence company, has leveraged its corporate structure to issue bonds specifically to acquire bitcoin as a reserve asset. This approach allows investors to indirectly gain exposure to bitcoin’s potential upside while receiving interest payments on their bond investments. Some other publicly traded companies have also adopted this strategy, but for the sake of this article we will focus on MSTR as they are the biggest and most vocal issuer.
Dynamics
-
Issuance: MicroStrategy has issued senior secured notes in multiple offerings, with terms allowing the company to use the proceeds to purchase bitcoin.
-
Interest Rates: The bonds typically carry high-yield interest rates, averaging around 6-8% APR, depending on the specific issuance and market conditions at the time of issuance.
-
Maturity: The bonds have varying maturities, with most structured for multi-year terms, offering investors medium-term exposure to bitcoin’s value trajectory through MicroStrategy’s holdings.
Pros
-
Indirect Bitcoin exposure with income provides a unique opportunity for investors seeking income from bitcoin-backed debt.
-
Bonds issued by MicroStrategy offer relatively high interest rates, appealing for fixed-income investors attracted to the higher risk/reward scenarios.
Cons
-
There are credit risks tied to MicroStrategy’s financial health and bitcoin’s performance. A significant drop in bitcoin prices could strain the company’s ability to service debt, increasing credit risk.
-
Availability: These bonds are primarily accessible to institutional investors and accredited investors, limiting availability for retail investors.
Interest Payable in Bitcoin – River has introduced an innovative product, bitcoin Interest on Cash, allowing clients to earn interest on their U.S. dollar deposits, with the interest paid in bitcoin.
Dynamics
-
Interest Payment: Clients earn an annual interest rate of 3.8% on their cash deposits. The accrued interest is converted to Bitcoin daily and paid out monthly, enabling clients to accumulate Bitcoin over time.
-
Security and Accessibility: Cash deposits are insured up to $250,000 through River’s banking partner, Lead Bank, a member of the FDIC. All Bitcoin holdings are maintained in full reserve custody, ensuring that client assets are not lent or leveraged.
Pros
-
There are no hidden fees or minimum balance requirements, and clients can withdraw their cash at any time.
-
The 3.8% interest rate provides a predictable income stream, akin to traditional fixed-income investments.
Cons
-
While the interest rate is fixed, the value of the Bitcoin received as interest can fluctuate, introducing potential variability in the investment’s overall return.
-
Interest rate payments are on the lower side
Admittedly, this is a very small list, however, these types of investments are growing more numerous and meaningful. The reality is the existing options aren’t numerous enough to service every client that has a need for fixed income exposure. I challenge advisors to explore innovative options for fixed income exposure outside of sovereign debt, as that is most certainly a road to nowhere. It is my wholehearted belief and call to action that we need more options to help clients across the risk and capital allocation spectrum access a sound money standard.
Additional Resources
-
River: The future of saving is here: Earn 3.8% on cash. Paid in Bitcoin.
-
MicroStrategy: MicroStrategy Announces Pricing of Offering of Convertible Senior Notes
Bitcoin and Fixed Income was Written By Wyatt O’Rourke. If you enjoyed this article then support his writing, directly, by donating to his lightning wallet: ultrahusky3@primal.net
-
-
 @ 68ce44e4:ecd5f574
2024-12-29 10:56:32
@ 68ce44e4:ecd5f574
2024-12-29 10:56:32CELL Wallet Daily Combo 29 Dec
7-6-3-5
Activate now : https://t.me/cellcoin_Bot/app?startapp=871998660

cellwallet #dailycombo #CryptoAirdrop #cryptonews #cryptocurrency #bitcoin
-
 @ 32e18276:5c68e245
2023-07-30 21:19:40
@ 32e18276:5c68e245
2023-07-30 21:19:40Company Overview:
Damus is the pioneering iOS nostr client. Through its platform, Damus empowers billions on iOS with the tools for free speech and free speech money. If you're driven to bring freedom technology to the masses and ignite change, we invite you to join our mission.
Job Description
- Collaborate on iOS Damus in tandem with our core developer, Will Casarin, and the broader Damus team.
- Implement our vision as laid out in our product roadmap: https://github.com/orgs/damus-io/projects/3/views/1.
- Embrace the fun and critical mission of undermining totalitarian regimes across the globe.
Job Requirements
- A genuine passion for freedom technology.
- At least one year of collaborative development experience.
- Experience building SwiftUI iOS apps.
- Passionate about design and user experience.
- Eager to work in close coordination with Damus lead developer, Will, and a dedicated team spanning development, design, and product.
- Commitment to a full-time role, although we remain open to discussing alternative arrangements.
Bonus Qualifications
- Experience with Nostr development.
- Experience with C.
- Previous work in free and open source projects.
- A publicly shareable portfolio.
Job Structure
- A one-month paid probationary period to ensure a mutual fit.
- Upon successful completion of the trial, the opportunity for a six (6) month contractual engagement.
- The potential for contract renewal, contingent on funding.
Application Process:
Interested candidates should forward a motivational statement alongside their CV/portfolio to vanessa@damus.io. -
 @ 6d8e2a24:5faaca4c
2024-12-02 09:03:49
@ 6d8e2a24:5faaca4c
2024-12-02 09:03:49"if your boyfriend uses Tiktok, you have a girlfriend" worlds riches man. Elon Musk tells women.

What's your opinion, do you think Elon Musk is right by his statement?
-
 @ 06b7819d:d1d8327c
2024-12-02 20:05:48
@ 06b7819d:d1d8327c
2024-12-02 20:05:48Benjamin Franklin and His Fondness for Madeira Wine
Benjamin Franklin, one of America’s most celebrated founding fathers, was not only a statesman, scientist, and writer but also a man of refined taste. Among his many indulgences, Franklin was particularly fond of Madeira wine, a fortified wine from the Portuguese Madeira Islands. His love for this drink was well-documented and reflects both his personal preferences and the broader cultural trends of 18th-century America.
The Allure of Madeira Wine
Madeira wine was highly prized in the 18th century due to its unique production process and exceptional durability. Its rich, fortified nature made it well-suited for long sea voyages, as it could withstand temperature fluctuations and aging in transit. This durability made Madeira a popular choice in the American colonies, where European wines often spoiled before arrival.
Franklin, who was known for his appreciation of fine things, embraced Madeira as a beverage of choice. Its complex flavors and storied reputation resonated with his intellectual and social pursuits. The wine was often served at dinners and social gatherings, where Franklin and his contemporaries debated ideas and shaped the future of the nation.
Franklin’s Personal Connection to Madeira
In Franklin’s writings and correspondence, Madeira is mentioned on several occasions, reflecting its prominence in his life. He referred to the wine not only as a personal pleasure but also as a symbol of hospitality and refinement. As a diplomat in France and England, Franklin often carried Madeira to share with his hosts, using it as a means of forging connections and showcasing the tastes of the American colonies.
One notable instance of Franklin’s affinity for Madeira occurred during his time in Philadelphia. He reportedly had cases of the wine shipped directly to his home, ensuring he would never be without his favorite drink. Madeira also featured prominently in many toasts and celebrations, becoming a hallmark of Franklin’s gatherings.
The Role of Madeira in Colonial America
Franklin’s fondness for Madeira reflects its broader significance in colonial America. The wine was not only a favorite of the elite but also a symbol of resistance to British taxation. When the British imposed heavy duties on imported goods, including wine, Madeira became a patriotic choice for many colonists. Its direct trade routes with the Madeira Islands circumvented British intermediaries, allowing Americans to assert their economic independence.
A Legacy of Taste
Franklin’s appreciation for Madeira wine endures as a charming detail of his multifaceted life. It offers a glimpse into the personal habits of one of America’s most influential figures and highlights the cultural exchanges that shaped colonial society. Today, Franklin’s love of Madeira serves as a reminder of the historical connections between wine, politics, and personal expression in the 18th century.
In honoring Franklin’s legacy, one might raise a glass of Madeira to toast not only his contributions to American independence but also his enduring influence on the art of living well.
-
 @ e57fec0c:e3153bf8
2024-12-30 04:34:00
@ e57fec0c:e3153bf8
2024-12-30 04:34:00The Logic Behind “I’m Too Late to Bitcoin”
It makes sense why someone who hasn’t researched Bitcoin would assume that they are too late to the game. Bitcoin’s first known transaction took place on May 22nd, 2010, when Laszlo Hanyecz, a programmer, offered 10,000 Bitcoins (approximately $41 at the time) to anyone who could obtain two large Papa John’s pizzas and deliver them to his doorstep. Laszlo established Bitcoin’s first price, less than half a cent. Since then, Bitcoin has faced relentless attacks from nation states, banks, sophisticated hackers, and subject to endless slander from the media… all while growing to a market cap of $1.5 trillion.
From $0.0041 to $65,000 is a 15-million bagger. Due to the law of large numbers, you’re not likely to see another 15,000,000x return without severe hyperinflation; but the question at hand is not whether you’re too late to get insanely rich off a tiny investment in a short period of time. The question is, are you too late to dramatically improve your and your loved ones’ lives with Bitcoin? The answer is unequivocally, NO.
Disclaimer: Bitcoin is a disruptive technology laying the foundation for an entirely new economic system. It should be noted, as Jeff Booth, author of The Price of Tomorrow says, “anything that attempts to value the new system in terms of the old system is fundamentally flawed.” Thinking about Bitcoin in terms of dollars has a number of pitfalls, including that it makes Bitcoin seem volatile. In reality, 1 BTC = 1 BTC. Nonetheless, number-go-up does more marketing for Bitcoin than anything else, which is why it’s useful to this discussion. This is evidenced by the following chart of retail adoption vs. price. As price rises, new buyers enter the market. When price falls, they exit.
 Bitcoin has seen multiple 75%+ corrections, including a 35% correction this year. Without strong conviction around Bitcoin’s long-term value, these draw-downs tend to shake Bitcoin holders out and discourage them from returning. However, even during the worst performing four year period in Bitcoin’s history (December 2017-2021), you would still have seen a 23% CAGR. Lowering your time preference is key to weathering Bitcoin’s short-term price volatility. When in doubt, zoom out.
Bitcoin has seen multiple 75%+ corrections, including a 35% correction this year. Without strong conviction around Bitcoin’s long-term value, these draw-downs tend to shake Bitcoin holders out and discourage them from returning. However, even during the worst performing four year period in Bitcoin’s history (December 2017-2021), you would still have seen a 23% CAGR. Lowering your time preference is key to weathering Bitcoin’s short-term price volatility. When in doubt, zoom out.Reason 1: Money is a Technology and Bitcoin is Better Money
Money is an emergent technology that solves the Double Coincidence of Wants Problem. People have used beads, shells, large rocks and cacao beans as money, but there have only been two layer one monies adopted globally: gold and dollars. Gold was a widely accepted form of money for 5,000 years because it outperformed the alternatives in terms of its durability, portability and divisibility. Gold backed the US Dollar until 1971… how the dollar became unpegged from gold is a discussion for another day. The point is, dollars (paper IOUs) were easier to move, divide and trade, which is largely why gold failed. Bitcoin is more durable, portable and divisible than both gold and dollars which is part of makes it the best money ever discovered.
For more on how Bitcoin obsoletes all other monies, here are a few books to read:
- The Bitcoin Standard by Saifadean Ammous
- Gradually, Then Suddenly by Parker Lewis
- Broken Money by Lyn Alden
- The Hidden Cost of Money by Seb Bunney
Reason 2: Inflation Protection
Beyond the three aforementioned properties, money’s most important function is storing purchasing power through time. When demand for gold increases, gold production increases. When demand for dollars increases (i.e. the government wants to finance a war or manipulate the economy), the bankers and politicians simply create more, diluting the value of the current dollars in circulation. While it is difficult to say exactly how much purchasing power the dollar has lost over a specific time frame, I don’t need to convince you that the prices of food, gas, rent, etc. have increased dramatically in recent years.
Keynesian economists assert that 2% inflation is healthy and the “velocity” of money helps to “grease the economic wheels.” This is a fallacy with profound implications. A 2% annual inflation rate halves the value of money in approximately 36 years. As a result, the average person must become an investor in their free time, using assets like stocks and real estate to protect themselves from debasement. But not everyone has the ability to invest in stocks, or purchase real estate. Currency debasement increases the wealth gap between people who save in hard assets and people who save in cash. Bitcoin is more accessible and scarce than stocks or real estate, making it a superior store of value. The following chart shows the relationship between the monetary base and inflation.
 ## Reason 3: Increased Purchasing Power Over Time
## Reason 3: Increased Purchasing Power Over TimeHistorical data indicates that Bitcoin is likely to buy more goods and services in the future than it does today. While this is not an investment pitch, Bitcoin’s dollar price does more marketing than anything else.
Try this exercise- consider the three most valuable assets you own. Your car, house, computer, maybe a private jet? How much did they cost at the time in terms of dollars and in terms of Bitcoin? How much would it cost for you to purchase that same asset today in terms of dollars? What about in terms of Bitcoin?
 This chart shows the price of an average home in terms of the two competing monies, highlighting Bitcoin’s increasing purchasing power vs. the dollar’s erosion of value. Over a 4+ year time frame, it’s almost guaranteed that these three assets would cost less Bitcoin today, and more dollars (Anthony Pompliano explains this in relation to the median home). The key insight here is that Bitcoin is already re-pricing all assets. As long as Bitcoin remains decentralized and secure, this trend is likely to continue. The counter argument here is that the same could be said about gold or stocks. Gold already failed as money and you can’t buy anything with stocks. While Bitcoin is not yet a widely accepted medium of exchange, it is already being used to purchase assets such as real estate.
This chart shows the price of an average home in terms of the two competing monies, highlighting Bitcoin’s increasing purchasing power vs. the dollar’s erosion of value. Over a 4+ year time frame, it’s almost guaranteed that these three assets would cost less Bitcoin today, and more dollars (Anthony Pompliano explains this in relation to the median home). The key insight here is that Bitcoin is already re-pricing all assets. As long as Bitcoin remains decentralized and secure, this trend is likely to continue. The counter argument here is that the same could be said about gold or stocks. Gold already failed as money and you can’t buy anything with stocks. While Bitcoin is not yet a widely accepted medium of exchange, it is already being used to purchase assets such as real estate.Reason 4: A Growing Network, Lagging Price
Price and market cap are metrics that fail to capture the Bitcoin network‘s overall growth. Bitcoin’s price topped $67k in November 2021 before entering a bear market that bottomed around $16k. As of today (October 2024) the USD/BTC exchange rate is dancing between $60-70k/BTC. Based on this one metric, we could conclude that Bitcoin’s growth has been stagnant for three years. This is an incorrect assessment. While BTC price has not surpassed it’s inflation-adjusted all-time highs in three years, other metrics such as hash rate, difficulty adjustment, active nodes, stock-to-flow, and on-chain analytics tell a different story.
 As you can see in the chart above, Bitcoin’s hash rate continues to increase over time. Bitcoin miners are directing more and more energy to the network, making it more robust and secure. Miners have skin in the game, and the fact that hash rate continues to increase is a signal that they expect the network to continue growing. Add to that the number of full Bitcoin nodes, active wallet addresses, increased mining difficulty and supply distribution. These metrics point to Bitcoin’s growth, with price being a lagging indicator.
As you can see in the chart above, Bitcoin’s hash rate continues to increase over time. Bitcoin miners are directing more and more energy to the network, making it more robust and secure. Miners have skin in the game, and the fact that hash rate continues to increase is a signal that they expect the network to continue growing. Add to that the number of full Bitcoin nodes, active wallet addresses, increased mining difficulty and supply distribution. These metrics point to Bitcoin’s growth, with price being a lagging indicator.Reason 5: Supply and Demand: Institutional and Corporate Adoption
Institutions and corporations have opened the floodgates for larger pools of capital to flow into Bitcoin. In 2024, Bitcoin ETFs set record inflows and quickly became top 10 funds in terms of AUM, causing a ruckus on Wall Street. Corporations are adopting Bitcoin as a treasury asset, adding it to their balance sheet instead of holding cash, T-Bills or bonds. MicroStrategy (MSTR) pioneered the Bitcoin treasury playbook, and since August 2020 has outperformed every single company in the S&P 500, including Invidia (NVDA).
The predicament MicroStrategy faced in 2020 is not unique. Companies with cash and cash equivalents on their balance sheets are holding a melting fiat ice cube, losing purchasing power every day. Saylor’s strategy is being replicated by other companies such as Square, Semler Scientific, Fold and others. What happens when Apple or Microsoft decides to put 5% of its treasury into Bitcoin?
Sovereign wealth funds and nation states are also starting to adopt Bitcoin. El Salvador adopted bitcoin as legal tender in 2021 and has been purchasing 1 BTC every day since. Bhutan has been quietly mining Bitcoin for years. Wisconsin’s pension fund now holds Bitcoin. US politicians are discussing Bitcoin as a strategic reserve asset. Rewind just a few years and all of this would sound ludicrous. The Overton window has shifted and Bitcoin is no longer just magic internet money for money laundering and illegal transactions.
These groups are driving demand, but what about supply? Since 2021 the amount of Bitcoin issued to the network halved, from 6.5 BTC/block (\~900 BTC/day) to 3.125 BTC/block (450 per day). \~19,570,000 or 93% of Bitcoin have been mined to date, and by 2034, 99% of all Bitcoin ever to exist will be in circulation, or lost. Michael Saylor aptly describes the coming decade as the “Digital Gold Rush.” Bitcoin’s absolute scarcity is something humanity has never experienced before.
Reason 6: Overcoming Unit Bias
Bitcoin’s unit bias causes many people to think they are too late to Bitcoin. From an early age, we are conditioned to think in terms of dollars. At $0.05, $5, $500, or even $5,000, owning a full Bitcoin was feasible on an entry-level salary. But today, only 1 in 3 Americans can afford a $400 emergency expense. Acquiring a full Bitcoin is out of the question, so why even try? What these folks fail to see is that is that mathematically, owning 1 BTC was never going to achievable for the average person. If you divide Bitcoin’s total supply, 21 million, by 8 billion, the current global population, the result is .002625 Bitcoin or 262,500 Satoshis (a Satoshi is 1/100,000,000th of a Bitcoin). However, Bitcoin ownership is not evenly distributed. MicroStrategy currently holds more than 252,000 BTC. Once you account for the 20-30% of coins already lost forever, there’s no way everyone can own 262k sats. At the time of writing, 262k sats is worth \~$170. You read that right. For $170 you can buy more Bitcoin than the average person will ever own. Unlike stocks, Bitcoin does not have CEO who can decide to do a share split to avoid unit bias, which means those who can wrap their head around this are likely to adopt Bitcoin sooner.
Reason 7: Not Just a Store of Value – Bitcoin Use Cases
Bitcoin is versatile. People with differing pain points and needs use Bitcoin in distinct ways. In the West, Bitcoin is typically thought of as a store of value. “Do you invest in Bitcoin?” “At what price will you sell?” In other countries, Bitcoin is useful for different reasons. For example, a Ukrainian refugee was able to escape to Poland with much of his wealth, rather than leave everything he worked for behind. Bitcoin is also being used to get aid to Gaza, and facilitate P2P transactions in Nigeria. Cross-border remittances are another way Bitcoin is giving power back to the people. These use cases are happening all over the world today. Because Bitcoin is a digital bearer asset protected by the strongest cryptographic network ever created, it provides optionality for an uncertain future.
Human Rights Foundation Chief Strategy Officer, Alex Gladstein makes the case that Bitcoin has four primary use cases: savings, commerce, freedom and power. You can listen to his episode on What Bitcoin Did, here. In addition to Alex’s thesis on four primary use cases, Bitcoin researcher Daniel Batten outlines 19 ways bitcoin is already being used. Bitcoin has even more potential because it is not just a store of value.
Conclusion
THERE IS NO SUCH THING AS BEING “TOO LATE” TO BITCOIN. Is it too late to start eating healthy? Is it too late to start working out? Is it too late to start an internet-based business? Of course not. In the same way, it’s never too late to study and ultimately plug Bitcoin into your life. As BTC Sessions articulates, “the last person on earth to adopt Bitcoin will benefit from it immensely.” There’s no arguing that the longer you wait, and the higher Bitcoin’s price goes, the harder it will be to acquire a certain amount of Bitcoin, but even if you don’t adopt it personally, Bitcoin is threatening the power of the money printer and creating more transparency and fairness in the economic system.
You get Bitcoin at the price you deserve. I remember when Bitcoin’s price was $23. I didn’t deserve it then. It took the government sending me a $1400 stimulus check in 2020 to buy my first Bitcoin, and it’s changed my life in many ways since. Bitcoin’s eventual USD-denominated price is already known: infinity / 21M. Bitcoin has no ceiling because fiat has no floor.
In conclusion, I hope this article sparked some curiosity to learn more about how Bitcoin solves the age-old problem of currency debasement. Satoshi Nakamoto created Bitcoin so that you could create the life you are meant to live.
Last thing- the arguments in this article still hold up once Bitcoin’s price surpasses $100k, $1M or $10M. The only thing that would make you too late to Bitcoin is if the network itself is no longer secure or decentralized.
Listen to the episode here: https://fountain.fm/episode/T7Yh2vmBOfNAc3RKTU2p
-
 @ 32e18276:5c68e245
2023-07-19 02:56:47
@ 32e18276:5c68e245
2023-07-19 02:56:47I’m so lazy I’m thinking of running the damus merch store via stateless and serverless lightning payment links. All data is collected and stored in the lightning invoice descriptions which are fetched from your node. You can do this without having to run any server code except a lightning node!
This is the same tech we used when selling merch as at bitcoin Miami. It was extremely reliable. I love these things, they are so easy. Integrating with the legacy fiat system is such a pita, It may just be a lightning-only store for now because of how simple this is. Here's what a lightning payment link looks like:
http://lnlink.org/?d=ASED88EIzNU2uFJoQfClxYISu55lhKHrSTCA58HMNPgtrXECMjQuODQuMTUyLjE4Nzo4MzI0AANgB6Cj2QCeZAFOZ1nS6qGuRe4Vf6qzwJyQ5Qo3b0HRt_w9MTIwJm1ldGhvZD1pbnZvaWNlfG1ldGhvZD13YWl0aW52b2ljZSZwbmFtZWxhYmVsXmxubGluay0mcmF0ZT04BERlYXRoIFN0YXIABQAAAGQGQW4gb2JqZWN0IG9mIHVuZmF0aG9tYWJsZSBwb3dlcgAHEwhodHRwczovL3VwbG9hZC53aWtpbWVkaWEub3JnL3dpa2lwZWRpYS9lbi9mL2Y5L0RlYXRoX3N0YXIxLnBuZwA=
How it works
The entire product page is stored as data in the url. When a customer click the link, the product info is decoded and rendered as a webpage. The data in the url includes
- The product name
- Description
- Price in sats
- Product image url
- Fields to collect data from the user
- Lightning node address
- Lightning node rune for fetching and waiting for invoice payments
This works thanks to a javascript library I created called "lnsocket". It allows you to connect to your CLN node over websockets. Once the user fills out all of the info, a new lightning invoice is fetched with this information in the description, by connecting directly to your node. This connection is end-to-end encrypted thanks to the lightning protocol itself.
To your lightning node, it looks like another lightning node is connecting to it, but in reality it's just a dumb client asking for things.
At this point, custom lightning packets called "commando" packets are sent to your node which asks your node to run certain commands. CLN authenticates these packets using the rune and then returns a response. This is pretty much the same as calling these commands directly on your lightning node, except now someone is doing it from a browser in a secure way!
Why not just run btcpayserver?
btcpayserver is cool and is more powerful, but I like exploring simpler ways to do things that don't require running lots of software which can be challenging for many non-technical people. You shouldn't have to become a server administrator to start accepting payments. It should be as simple as running a bitcoin and lightning node, pushing all of the application logic to the clients.
This is a similar philosophy to what we have in the nostr space. Let's make it easier for people to use self-sovereign tools. Everyone deserves freedom tech.
Anyways, I'm still working on https://lnlink.org. I just added images and nostr address support! You can make your own payment links here! Try it out:
http://lnlink.org/?d=ASED88EIzNU2uFJoQfClxYISu55lhKHrSTCA58HMNPgtrXECMjQuODQuMTUyLjE4Nzo4MzI0AANgB6Cj2QCeZAFOZ1nS6qGuRe4Vf6qzwJyQ5Qo3b0HRt_w9MTIwJm1ldGhvZD1pbnZvaWNlfG1ldGhvZD13YWl0aW52b2ljZSZwbmFtZWxhYmVsXmxubGluay0mcmF0ZT04BERlYXRoIFN0YXIABQAAAGQGQW4gb2JqZWN0IG9mIHVuZmF0aG9tYWJsZSBwb3dlcgAHEwhodHRwczovL3VwbG9hZC53aWtpbWVkaWEub3JnL3dpa2lwZWRpYS9lbi9mL2Y5L0RlYXRoX3N0YXIxLnBuZwA=&edit=1
-
 @ 0dc2dcb1:4787801a
2024-07-12 13:44:28
@ 0dc2dcb1:4787801a
2024-07-12 13:44:28- Prepared a Dutch webinar with an short introduction to Nostr - https://welkom.keuzevrijbijmij.nl/evenement/wwebinar-vergroot-je-privacy-op-social-media-10-juli/

- Received a nice t-shirt with the Nostr-PHP logo from Bitpopart who designed the logo
- Did an introduction talk in Dutch on a webinar with 350+ people subscribed on July 10th. 100+ watched the webinar live.
- Here is the full replay:
At around 38min the Nostr stuff begins
- Here is the full replay:
- Adding pages and wrote some documentation on nostr-php.dev
- Added a custom field
field_nsecto the user entity on nostrver.se (Drupal website) using the contrib module field_encrypt. The value of this field is stored encrypted in the database using a self created private key. This key is stored as a blob the server, but multiple ways of storing this are possible. In the Drupal CMS I now can save a Nostr private key for each user which will be fetch from nostr_content_nip23. All changes made in this Drupal contrib module for this: https://git.drupalcode.org/project/nostr_content_nip23/-/commit/cbc172b976aceaff107fea0296a8a476e098467e -
With a
nsecstored for each user, it’s possible to select a user when you’re broadcasting an Nostr event from Drupal. The event will be signed with the nsec of the selected user. Quick demo here: https://njump.me/nevent1qvzqqqqqqypzqpnrnguxe8qszsshvgkvhn6qjzxy7xsvx03rlrtddr62haj4lrm3qy88wumn8ghj7mn0wvhxcmmv9uq3camnwvaz7tmwdaehgu3wwdjkyctnw35hstnnda3kjctv9uqzqj75dy5eps3lgwum7f9p2l8sywy7wuxjr08pyhzyzv9mklylaydgdyll3z
-
 @ e6817453:b0ac3c39
2024-12-07 15:06:43
@ e6817453:b0ac3c39
2024-12-07 15:06:43I started a long series of articles about how to model different types of knowledge graphs in the relational model, which makes on-device memory models for AI agents possible.
We model-directed graphs
Also, graphs of entities
We even model hypergraphs
Last time, we discussed why classical triple and simple knowledge graphs are insufficient for AI agents and complex memory, especially in the domain of time-aware or multi-model knowledge.
So why do we need metagraphs, and what kind of challenge could they help us to solve?
- complex and nested event and temporal context and temporal relations as edges
- multi-mode and multilingual knowledge
- human-like memory for AI agents that has multiple contexts and relations between knowledge in neuron-like networks
MetaGraphs
A meta graph is a concept that extends the idea of a graph by allowing edges to become graphs. Meta Edges connect a set of nodes, which could also be subgraphs. So, at some level, node and edge are pretty similar in properties but act in different roles in a different context.
Also, in some cases, edges could be referenced as nodes.
This approach enables the representation of more complex relationships and hierarchies than a traditional graph structure allows. Let’s break down each term to understand better metagraphs and how they differ from hypergraphs and graphs.Graph Basics
- A standard graph has a set of nodes (or vertices) and edges (connections between nodes).
- Edges are generally simple and typically represent a binary relationship between two nodes.
- For instance, an edge in a social network graph might indicate a “friend” relationship between two people (nodes).
Hypergraph
- A hypergraph extends the concept of an edge by allowing it to connect any number of nodes, not just two.
- Each connection, called a hyperedge, can link multiple nodes.
- This feature allows hypergraphs to model more complex relationships involving multiple entities simultaneously. For example, a hyperedge in a hypergraph could represent a project team, connecting all team members in a single relation.
- Despite its flexibility, a hypergraph doesn’t capture hierarchical or nested structures; it only generalizes the number of connections in an edge.
Metagraph
- A metagraph allows the edges to be graphs themselves. This means each edge can contain its own nodes and edges, creating nested, hierarchical structures.
- In a meta graph, an edge could represent a relationship defined by a graph. For instance, a meta graph could represent a network of organizations where each organization’s structure (departments and connections) is represented by its own internal graph and treated as an edge in the larger meta graph.
- This recursive structure allows metagraphs to model complex data with multiple layers of abstraction. They can capture multi-node relationships (as in hypergraphs) and detailed, structured information about each relationship.
Named Graphs and Graph of Graphs
As you can notice, the structure of a metagraph is quite complex and could be complex to model in relational and classical RDF setups. It could create a challenge of luck of tools and software solutions for your problem.
If you need to model nested graphs, you could use a much simpler model of Named graphs, which could take you quite far.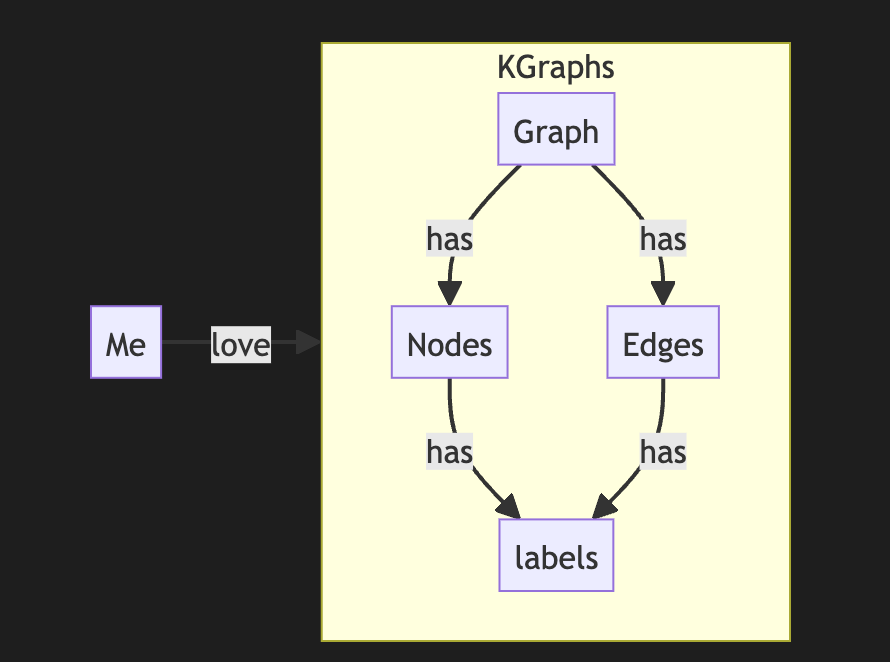
The concept of the named graph came from the RDF community, which needed to group some sets of triples. In this way, you form subgraphs inside an existing graph. You could refer to the subgraph as a regular node. This setup simplifies complex graphs, introduces hierarchies, and even adds features and properties of hypergraphs while keeping a directed nature.
It looks complex, but it is not so hard to model it with a slight modification of a directed graph.
So, the node could host graphs inside. Let's reflect this fact with a location for a node. If a node belongs to a main graph, we could set the location to null or introduce a main node . it is up to you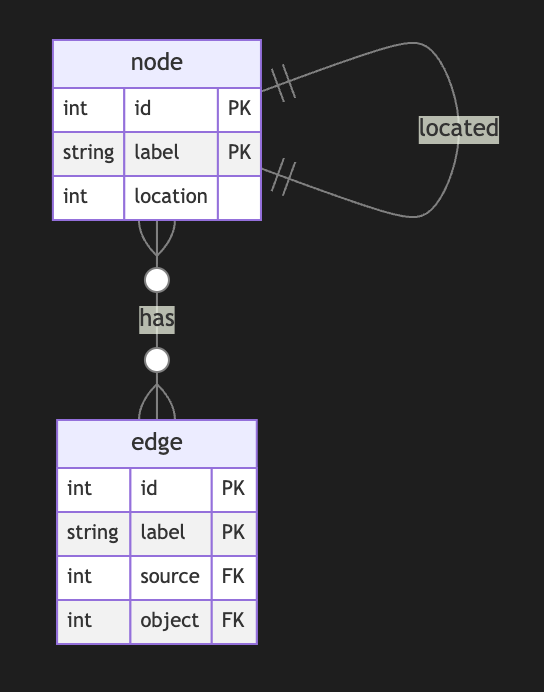
Nodes could have edges to nodes in different subgraphs. This structure allows any kind of nesting graphs. Edges stay location-free
Meta Graphs in Relational Model
Let’s try to make several attempts to model different meta-graphs with some constraints.
Directed Metagraph where edges are not used as nodes and could not contain subgraphs
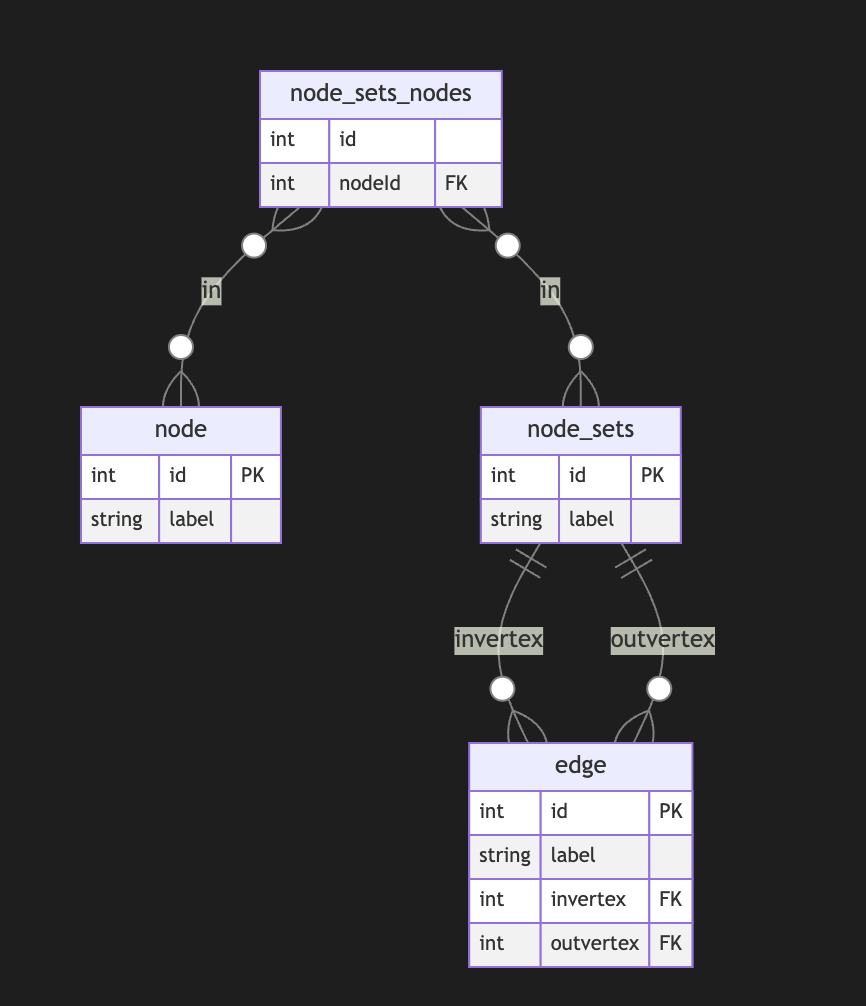
In this case, the edge always points to two sets of nodes. This introduces an overhead of creating a node set for a single node. In this model, we can model empty node sets that could require application-level constraints to prevent such cases.
Directed Metagraph where edges are not used as nodes and could contain subgraphs
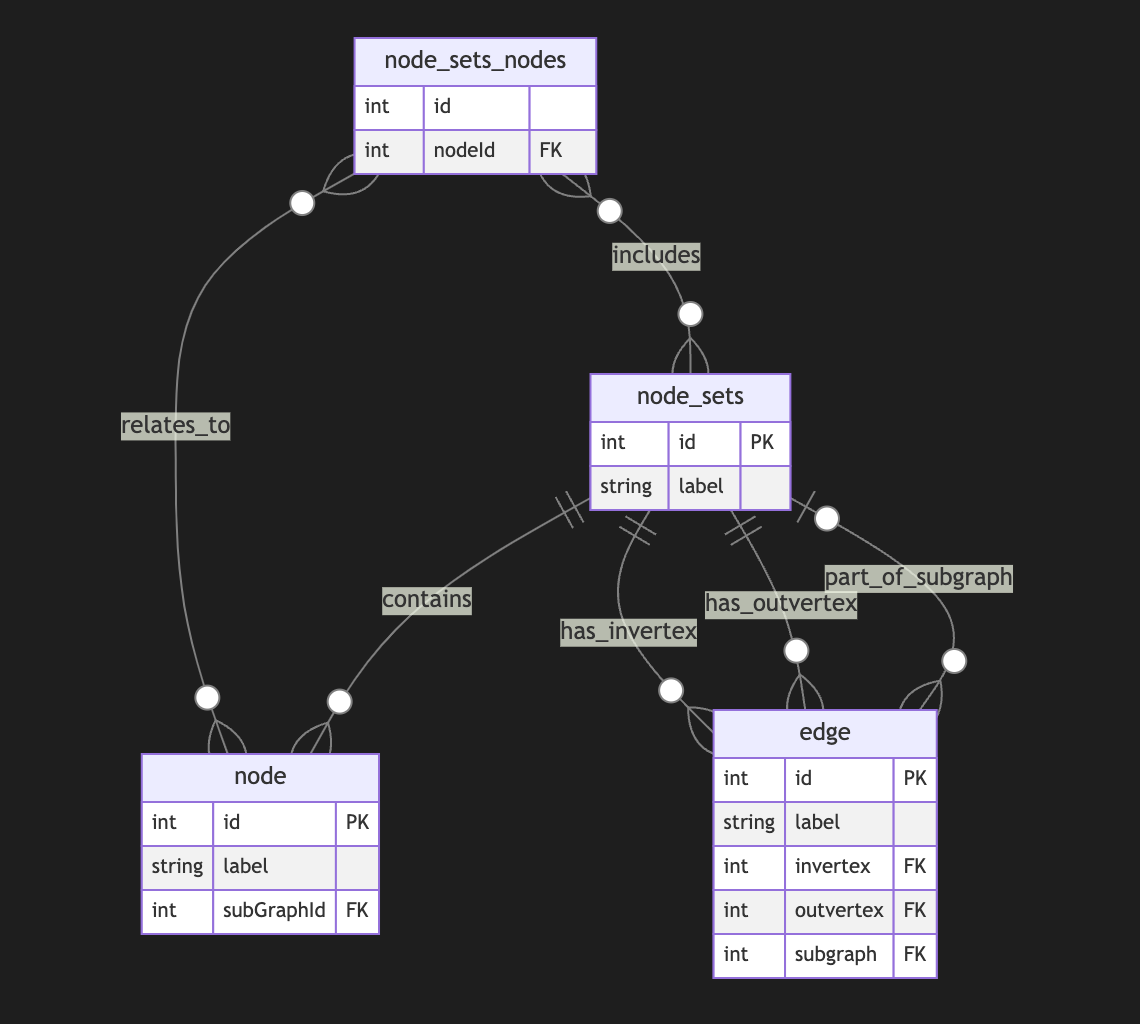
Adding a node set that could model a subgraph located in an edge is easy but could be separate from in-vertex or out-vert.
I also do not see a direct need to include subgraphs to a node, as we could just use a node set interchangeably, but it still could be a case.Directed Metagraph where edges are used as nodes and could contain subgraphs
As you can notice, we operate all the time with node sets. We could simply allow the extension node set to elements set that include node and edge IDs, but in this case, we need to use uuid or any other strategy to differentiate node IDs from edge IDs. In this case, we have a collision of ephemeral edges or ephemeral nodes when we want to change the role and purpose of the node as an edge or vice versa.
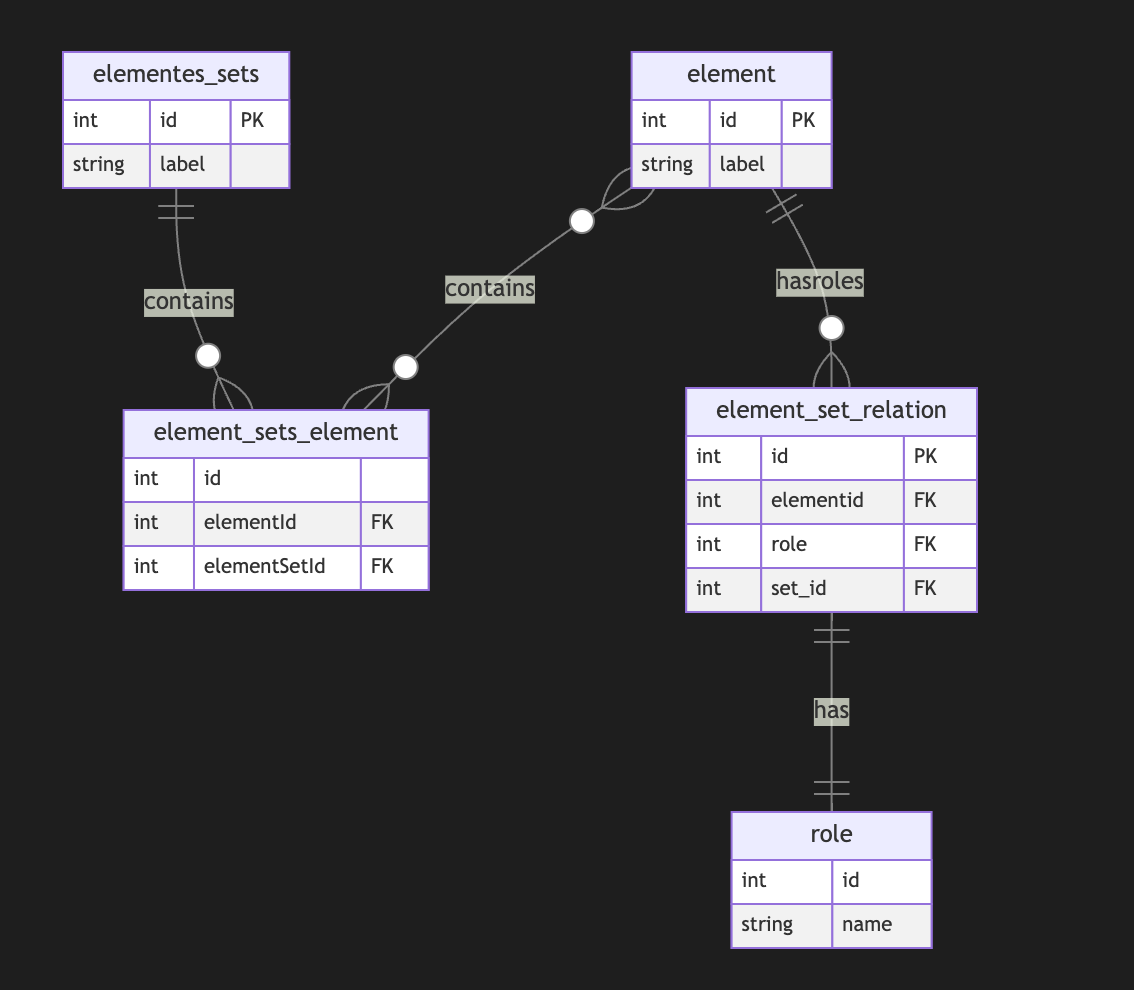
A full-scale metagraph model is way too complex for a relational database.
So we need a better model.Now, we have more flexibility but loose structural constraints. We cannot show that the element should have one vertex, one vertex, or both. This type of constraint has been moved to the application level. Also, the crucial question is about query and retrieval needs.
Any meta-graph model should be more focused on domain and needs and should be used in raw form. We did it for a pure theoretical purpose. -
 @ 06b7819d:d1d8327c
2024-11-29 13:26:00
@ 06b7819d:d1d8327c
2024-11-29 13:26:00The Weaponization of Technology: A Prelude to Adoption
Throughout history, new technologies have often been weaponized before becoming widely adopted for civilian use. This pattern, deeply intertwined with human priorities for power, survival, and dominance, sheds light on how societies interact with technological innovation.
The Weaponization Imperative
When a groundbreaking technology emerges, its potential to confer an advantage—military, economic, or ideological—tends to attract attention from those in power. Governments and militaries, seeking to outpace rivals, often invest heavily in adapting new tools for conflict or defense. Weaponization provides a context where innovation thrives under high-stakes conditions. Technologies like radar, nuclear energy, and the internet, initially conceived or expanded within the framework of military priorities, exemplify this trend.
Historical Examples
1. Gunpowder: Invented in 9th-century China, gunpowder was first used for military purposes before transitioning into civilian life, influencing mining, construction, and entertainment through fireworks.-
The Internet: Initially developed as ARPANET during the Cold War to ensure communication in the event of a nuclear attack, the internet’s infrastructure later supported the global digital revolution, reshaping commerce, education, and social interaction.
-
Drones: Unmanned aerial vehicles began as tools of surveillance and warfare but have since been adopted for everything from package delivery to agricultural monitoring.
Weaponization often spurs rapid technological development. War environments demand urgency and innovation, fast-tracking research and turning prototypes into functional tools. This phase of militarization ensures that the technology is robust, scalable, and often cost-effective, setting the stage for broader adoption.
Adoption and Civilian Integration
Once a technology’s military dominance is established, its applications often spill into civilian life. These transitions occur when:
• The technology becomes affordable and accessible. • Governments or corporations recognize its commercial potential. • Public awareness and trust grow, mitigating fears tied to its military origins.For example, GPS was first a military navigation system but is now indispensable for personal devices, logistics, and autonomous vehicles.
Cultural Implications
The process of weaponization shapes public perception of technology. Media narratives, often dominated by stories of power and conflict, influence how societies view emerging tools. When technologies are initially seen through the lens of violence or control, their subsequent integration into daily life can carry residual concerns, from privacy to ethical implications.
Conclusion
The weaponization of technology is not an aberration but a recurring feature of technological progress. By understanding this pattern, societies can critically assess how technologies evolve from tools of conflict to instruments of everyday life, ensuring that ethical considerations and equitable access are not lost in the rush to innovate. As Marshall McLuhan might suggest, the medium through which a technology is introduced deeply influences the message it ultimately conveys to the world.
-
-
 @ d83793e3:3de45629
2024-12-29 06:40:46
@ d83793e3:3de45629
2024-12-29 06:40:46VN98 là một nền tảng trực tuyến hiện đại, mang lại cho người dùng những trải nghiệm độc đáo và tiện lợi. Với thiết kế giao diện thân thiện, dễ sử dụng và tính năng linh hoạt, VN98 đã khẳng định vị thế của mình trong lòng người dùng. Được tối ưu hóa để phục vụ đa dạng nhu cầu, từ giải trí đến kết nối cộng đồng, nền tảng này không chỉ giúp người dùng giải trí mà còn cung cấp một không gian an toàn và sáng tạo.
Một trong những điểm nổi bật của VN98 là giao diện người dùng được thiết kế tinh tế và dễ dàng tiếp cận. Các tính năng của nền tảng đều được bố trí hợp lý, giúp người dùng dễ dàng tìm thấy những công cụ và dịch vụ mà mình cần mà không gặp phải bất kỳ khó khăn nào. Giao diện đơn giản nhưng hiệu quả giúp người dùng tận dụng tối đa các tính năng, từ đó mang lại trải nghiệm sử dụng mượt mà và hiệu quả. Điều này cũng khiến VN98 trở thành lựa chọn lý tưởng cho cả những người mới sử dụng nền tảng lần đầu. https://vn98.online
Bảo mật là yếu tố mà VN98 đặt lên hàng đầu. Nền tảng sử dụng các công nghệ bảo mật tiên tiến, giúp bảo vệ thông tin cá nhân và dữ liệu của người dùng khỏi những nguy cơ tiềm ẩn. Mọi thông tin và giao dịch đều được mã hóa và xử lý một cách an toàn, mang lại sự yên tâm tuyệt đối cho người dùng khi tham gia vào các hoạt động trực tuyến. Chính vì thế, người dùng có thể hoàn toàn tin tưởng vào sự an toàn của dữ liệu và bảo mật thông tin cá nhân khi sử dụng VN98.
Ngoài việc chú trọng đến bảo mật, VN98 còn xây dựng một cộng đồng người dùng năng động và sáng tạo. Người dùng có thể dễ dàng kết nối với nhau, chia sẻ ý tưởng và học hỏi từ những kinh nghiệm của những thành viên khác. Môi trường cộng đồng của VN98 khuyến khích sự sáng tạo và hỗ trợ lẫn nhau, giúp mọi người phát triển kỹ năng và mở rộng mối quan hệ. Đây là yếu tố quan trọng giúp VN98 giữ vững sự trung thành của người dùng, đồng thời tạo ra một không gian trực tuyến tích cực và gắn kết.
Cuối cùng, VN98 luôn nỗ lực cải tiến và nâng cấp các tính năng để đáp ứng nhu cầu ngày càng đa dạng của người dùng. Nền tảng này không chỉ theo kịp các xu hướng công nghệ mới mà còn liên tục đưa ra các giải pháp sáng tạo để nâng cao trải nghiệm người dùng. Với khả năng tương thích trên nhiều thiết bị, từ máy tính đến điện thoại di động, VN98 đảm bảo rằng người dùng có thể truy cập nền tảng mọi lúc, mọi nơi, giúp tối ưu hóa sự tiện lợi cho người sử dụng.
Tóm lại, VN98 là một nền tảng trực tuyến toàn diện, cung cấp những tính năng tiện ích, bảo mật cao và cộng đồng tích cực. Với giao diện thân thiện, tính năng bảo mật mạnh mẽ và sự cam kết đổi mới liên tục, VN98 là sự lựa chọn lý tưởng cho những ai tìm kiếm một nền tảng trực tuyến an toàn, tiện lợi và hiệu quả. Nền tảng này chắc chắn sẽ tiếp tục phát triển và mang lại giá trị lớn cho người dùng trong tương lai.
-
 @ a849beb6:b327e6d2
2024-11-23 15:03:47
@ a849beb6:b327e6d2
2024-11-23 15:03:47
\ \ It was another historic week for both bitcoin and the Ten31 portfolio, as the world’s oldest, largest, most battle-tested cryptocurrency climbed to new all-time highs each day to close out the week just shy of the $100,000 mark. Along the way, bitcoin continued to accumulate institutional and regulatory wins, including the much-anticipated approval and launch of spot bitcoin ETF options and the appointment of several additional pro-bitcoin Presidential cabinet officials. The timing for this momentum was poetic, as this week marked the second anniversary of the pico-bottom of the 2022 bear market, a level that bitcoin has now hurdled to the tune of more than 6x despite the litany of bitcoin obituaries published at the time. The entirety of 2024 and especially the past month have further cemented our view that bitcoin is rapidly gaining a sense of legitimacy among institutions, fiduciaries, and governments, and we remain optimistic that this trend is set to accelerate even more into 2025.
Several Ten31 portfolio companies made exciting announcements this week that should serve to further entrench bitcoin’s institutional adoption. AnchorWatch, a first of its kind bitcoin insurance provider offering 1:1 coverage with its innovative use of bitcoin’s native properties, announced it has been designated a Lloyd’s of London Coverholder, giving the company unique, blue-chip status as it begins to write bitcoin insurance policies of up to $100 million per policy starting next month. Meanwhile, Battery Finance Founder and CEO Andrew Hohns appeared on CNBC to delve into the launch of Battery’s pioneering private credit strategy which fuses bitcoin and conventional tangible assets in a dual-collateralized structure that offers a compelling risk/return profile to both lenders and borrowers. Both companies are clearing a path for substantially greater bitcoin adoption in massive, untapped pools of capital, and Ten31 is proud to have served as lead investor for AnchorWatch’s Seed round and as exclusive capital partner for Battery.
As the world’s largest investor focused entirely on bitcoin, Ten31 has deployed nearly $150 million across two funds into more than 30 of the most promising and innovative companies in the ecosystem like AnchorWatch and Battery, and we expect 2025 to be the best year yet for both bitcoin and our portfolio. Ten31 will hold a first close for its third fund at the end of this year, and investors in that close will benefit from attractive incentives and a strong initial portfolio. Visit ten31.vc/funds to learn more and get in touch to discuss participating.\ \ Portfolio Company Spotlight
Primal is a first of its kind application for the Nostr protocol that combines a client, caching service, analytics tools, and more to address several unmet needs in the nascent Nostr ecosystem. Through the combination of its sleek client application and its caching service (built on a completely open source stack), Primal seeks to offer an end-user experience as smooth and easy as that of legacy social media platforms like Twitter and eventually many other applications, unlocking the vast potential of Nostr for the next billion people. Primal also offers an integrated wallet (powered by Strike BLACK) that substantially reduces onboarding and UX frictions for both Nostr and the lightning network while highlighting bitcoin’s unique power as internet-native, open-source money.
Selected Portfolio News
AnchorWatch announced it has achieved Llody’s Coverholder status, allowing the company to provide unique 1:1 bitcoin insurance offerings starting in December.\ \ Battery Finance Founder and CEO Andrew Hohns appeared on CNBC to delve into the company’s unique bitcoin-backed private credit strategy.
Primal launched version 2.0, a landmark update that adds a feed marketplace, robust advanced search capabilities, premium-tier offerings, and many more new features.
Debifi launched its new iOS app for Apple users seeking non-custodial bitcoin-collateralized loans.
Media
Strike Founder and CEO Jack Mallers joined Bloomberg TV to discuss the strong volumes the company has seen over the past year and the potential for a US bitcoin strategic reserve.
Primal Founder and CEO Miljan Braticevic joined The Bitcoin Podcast to discuss the rollout of Primal 2.0 and the future of Nostr.
Ten31 Managing Partner Marty Bent appeared on BlazeTV to discuss recent changes in the regulatory environment for bitcoin.
Zaprite published a customer testimonial video highlighting the popularity of its offerings across the bitcoin ecosystem.
Market Updates
Continuing its recent momentum, bitcoin reached another new all-time high this week, clocking in just below $100,000 on Friday. Bitcoin has now reached a market cap of nearly $2 trillion, putting it within 3% of the market caps of Amazon and Google.
After receiving SEC and CFTC approval over the past month, long-awaited options on spot bitcoin ETFs were fully approved and launched this week. These options should help further expand bitcoin’s institutional liquidity profile, with potentially significant implications for price action over time.
The new derivatives showed strong performance out of the gate, with volumes on options for BlackRock’s IBIT reaching nearly $2 billion on just the first day of trading despite surprisingly tight position limits for the vehicles.
Meanwhile, the underlying spot bitcoin ETF complex had yet another banner week, pulling in $3.4 billion in net inflows.
New reports suggested President-elect Donald Trump’s social media company is in advanced talks to acquire crypto trading platform Bakkt, potentially the latest indication of the incoming administration’s stance toward the broader “crypto” ecosystem.
On the macro front, US housing starts declined M/M again in October on persistently high mortgage rates and weather impacts. The metric remains well below pre-COVID levels.
Pockets of the US commercial real estate market remain challenged, as the CEO of large Florida developer Related indicated that developers need further rate cuts “badly” to maintain project viability.
US Manufacturing PMI increased slightly M/M, but has now been in contraction territory (<50) for well over two years.
The latest iteration of the University of Michigan’s popular consumer sentiment survey ticked up following this month’s election results, though so did five-year inflation expectations, which now sit comfortably north of 3%.
Regulatory Update
After weeks of speculation, the incoming Trump administration appointed hedge fund manager Scott Bessent to head up the US Treasury. Like many of Trump’s cabinet selections so far, Bessent has been a public advocate for bitcoin.
Trump also appointed Cantor Fitzgerald CEO Howard Lutnick – another outspoken bitcoin bull – as Secretary of the Commerce Department.
Meanwhile, the Trump team is reportedly considering creating a new “crypto czar” role to sit within the administration. While it’s unclear at this point what that role would entail, one report indicated that the administration’s broader “crypto council” is expected to move forward with plans for a strategic bitcoin reserve.
Various government lawyers suggested this week that the Trump administration is likely to be less aggressive in seeking adversarial enforcement actions against bitcoin and “crypto” in general, as regulatory bodies appear poised to shift resources and focus elsewhere.
Other updates from the regulatory apparatus were also directionally positive for bitcoin, most notably FDIC Chairman Martin Gruenberg’s confirmation that he plans to resign from his post at the end of President Biden’s term.
Many critics have alleged Gruenberg was an architect of “Operation Chokepoint 2.0,” which has created banking headwinds for bitcoin companies over the past several years, so a change of leadership at the department is likely yet another positive for the space.
SEC Chairman Gary Gensler also officially announced he plans to resign at the start of the new administration. Gensler has been the target of much ire from the broader “crypto” space, though we expect many projects outside bitcoin may continue to struggle with questions around the Howey Test.
Overseas, a Chinese court ruled that it is not illegal for individuals to hold cryptocurrency, even though the country is still ostensibly enforcing a ban on crypto transactions.
Noteworthy
The incoming CEO of Charles Schwab – which administers over $9 trillion in client assets – suggested the platform is preparing to “get into” spot bitcoin offerings and that he “feels silly” for having waited this long. As this attitude becomes more common among traditional finance players, we continue to believe that the number of acquirers coming to market for bitcoin infrastructure capabilities will far outstrip the number of available high quality assets.
BlackRock’s 2025 Thematic Outlook notes a “renewed sense of optimism” on bitcoin among the asset manager’s client base due to macro tailwinds and the improving regulatory environment. Elsewhere, BlackRock’s head of digital assets indicated the firm does not view bitcoin as a “risk-on” asset.
MicroStrategy, which was a sub-$1 billion market cap company less than five years ago, briefly breached a $100 billion equity value this week as it continues to aggressively acquire bitcoin. The company now holds nearly 350,000 bitcoin on its balance sheet.
Notably, Allianz SE, Germany’s largest insurer, spoke for 25% of MicroStrategy’s latest $3 billion convertible note offering this week, suggesting growing appetite for bitcoin proxy exposure among more restricted pools of capital.
The ongoing meltdown of fintech middleware provider Synapse has left tens of thousands of customers with nearly 100% deposit haircuts as hundreds of millions in funds remain missing, the latest unfortunate case study in the fragility of much of the US’s legacy banking stack.
Travel
-
BitcoinMENA, Dec 9-10
-
Nashville BitDevs, Dec 10
-
Austin BitDevs, Dec 19
-
-
 @ ebdee929:513adbad
2024-12-28 14:46:21
@ ebdee929:513adbad
2024-12-28 14:46:21Blue light is not inherently bad, just bad in the wrong context.
Blue light provides wakefulness, stimulation, and sets our internal body clock (circadian rhythm).
When we go outside in the sun, we get bathed in blue lightblue light is not inherently bad, just bad in the wrong context.
Blue light sets the human rhythm.
However, sunlight never gives us blue light without the rest of the visible rainbow + infrared.
Light from screens & LED bulbs do not contain any infrared, and has a unnaturally high proportion of blue light.
LEDs = unbalanced & blue light dominant

Light from artificial sources is especially disruptive at night time, where the high blue light component can interfere with melatonin production and sleep quality at a greater rate than lower energy colors of light. Blue Light has a Dark Side
This doesn't mean that red light is completely innocent of disrupting sleep either
It is both the spectrum of light AND the intensity of light that contributes to sleep disruption. See this tweet from Huberman.

We took all of this into account when building the DC-1 to be the world's first blue light free computer.
The DC-1 has a reflective screen that:
• emits ZERO light during the day
• can be used easily outside in direct sunlight

& a backlight that:
• can be 100% blue light free
• has a broad spectrum of light
• can be seen at very low brightness

Our Live Paper™ display technology feels like a magic piece of paper
During the day, that piece of paper is illuminated by sunlight. At night, that piece of paper is illuminated by candle light.
(backlight is converging with a candle light spectrum)

The two sources of natural light are sunlight & fire.
We are trying to reproduce this experience for the most enjoyable, healthy, and least invasive technology experience for humanity.
Root cause problem solving by emulating nature.
"But can't I just put a red light screen filter on my MacBook?"
Absolutely you can, and we advocate for it
Software screen filters are great, but anyone who has changed their screen to full “red mode” to get rid of the blue light knows the downsides to this…

You can barely see anything and you end up having to crank up the brightness in order to see any contrast.
This is because of the highly isolated nature of LED emissive screens, you can only isolate a very narrow band of colors.
Going full red is not something your eyes have ever been used to seeing.
You need a broad spectrum light solution, and that is what we have in our amber backlight while still being blue light free.
This means you can have a better visual experience, turn down the brightness, and get minimal sleep/circadian disruption.
What about FLICKER?
Nearly all LEDs flicker. Especially when changing in brightness due to Pulsed Width Modulation (PWM) LED driver control
Our LED backlight uses DC dimming & is expert verified flicker-free.
This can only be achieved through hardware changes, not software screen filters.

& Blue Light Blocking Glasses?
They need to be tinted orange/red to block all of the blue light.
Thus the same issues as screen filters (bad visual experience, not solving flicker) + average joe would never wear them.
We still love blue blockers, they just aren't a root cause solution.
We made a computer that is healthier and less stimulating, with a low barrier to entry
Whether you are a staunch circadian health advocate or just like the warm vibes of amber mode and being outside...the DC-1 just feels good because it doesn't make you feel bad :)
Learn more here and thanks for reading.
-
 @ a39d19ec:3d88f61e
2024-11-21 12:05:09
@ a39d19ec:3d88f61e
2024-11-21 12:05:09A state-controlled money supply can influence the development of socialist policies and practices in various ways. Although the relationship is not deterministic, state control over the money supply can contribute to a larger role of the state in the economy and facilitate the implementation of socialist ideals.
Fiscal Policy Capabilities
When the state manages the money supply, it gains the ability to implement fiscal policies that can lead to an expansion of social programs and welfare initiatives. Funding these programs by creating money can enhance the state's influence over the economy and move it closer to a socialist model. The Soviet Union, for instance, had a centralized banking system that enabled the state to fund massive industrialization and social programs, significantly expanding the state's role in the economy.
Wealth Redistribution
Controlling the money supply can also allow the state to influence economic inequality through monetary policies, effectively redistributing wealth and reducing income disparities. By implementing low-interest loans or providing financial assistance to disadvantaged groups, the state can narrow the wealth gap and promote social equality, as seen in many European welfare states.
Central Planning
A state-controlled money supply can contribute to increased central planning, as the state gains more influence over the economy. Central banks, which are state-owned or heavily influenced by the state, play a crucial role in managing the money supply and facilitating central planning. This aligns with socialist principles that advocate for a planned economy where resources are allocated according to social needs rather than market forces.
Incentives for Staff
Staff members working in state institutions responsible for managing the money supply have various incentives to keep the system going. These incentives include job security, professional expertise and reputation, political alignment, regulatory capture, institutional inertia, and legal and administrative barriers. While these factors can differ among individuals, they can collectively contribute to the persistence of a state-controlled money supply system.
In conclusion, a state-controlled money supply can facilitate the development of socialist policies and practices by enabling fiscal policies, wealth redistribution, and central planning. The staff responsible for managing the money supply have diverse incentives to maintain the system, further ensuring its continuation. However, it is essential to note that many factors influence the trajectory of an economic system, and the relationship between state control over the money supply and socialism is not inevitable.
-
 @ 16d11430:61640947
2024-12-30 03:14:06
@ 16d11430:61640947
2024-12-30 03:14:06- Introduction: The Crisis of Modern Digital Design
The digital age has delivered unprecedented connectivity and convenience, but it has also brought a dark underbelly: poorly designed digital interfaces that exploit and exhaust users. These interfaces, driven by profit-maximizing motives and shortsighted leadership, target the most productive and capable members of society—engineers, creators, thinkers—undermining their mental health and productivity. This is not merely a design issue; it is a crisis with profound implications for global stability, innovation, and the future of humanity.
- Critical Failures by Leadership
Modern leadership in both corporate and governmental spheres has repeatedly failed to address the following systemic issues in the digital landscape:
- Profit over People:
Leaders prioritize revenue generation (e.g., ad-based models, data mining) over the cognitive and emotional well-being of users.
Examples: Algorithmic design optimized for engagement metrics, not user health, leads to addictive and mentally draining experiences.
- Lack of Accountability:
Big Tech often escapes regulation, perpetuating harmful practices like dark patterns and manipulative UI/UX.
Example: Platforms like Facebook and TikTok amplify divisive content for profit, intensifying societal fractures.
- Incompetence in Digital Policy:
Policy makers lack the technical literacy to regulate effectively, leaving users vulnerable to exploitative systems.
Example: GDPR and similar regulations address data privacy but fail to address the root causes of digital harm—poor design and exploitative incentives.
- Shortsighted Metrics:
Corporate focus on quarterly earnings drives iterative, superficial changes instead of meaningful, user-focused innovation.
Example: Instead of solving UX pain points, companies often introduce features that increase complexity and cognitive load.
- Risks to Mass Populations
The societal consequences of failing to address this crisis are severe:
- Mental Health Epidemic:
Digital interfaces are linked to increased rates of anxiety, depression, and burnout, particularly among high-functioning individuals.
Source: Twenge et al. (2017) report a sharp increase in depression and suicidal ideation among teens correlating with smartphone usage.
- Productivity Collapse:
The workforce's most creative and capable members are being drained by poor UX, leading to a significant loss in economic output.
Source: Gallup (2022) shows record-low engagement among knowledge workers, exacerbated by digital fatigue.
- Cultural and Civic Decline:
Manipulative interfaces polarize societies, eroding trust in institutions and fragmenting social cohesion.
Source: MIT Technology Review (2021) highlights the role of algorithmic content delivery in amplifying political extremism.
- Long-Term Cognitive Harm:
Sustained interaction with chaotic digital environments can alter brain function, impairing critical thinking and long-term memory.
Source: Carr, "The Shallows" (2010), describes how digital tools reshape neural pathways, often detrimentally.
- The Role of DamageBDD in Driving Massive Change
DamageBDD offers a potential scaffolding for radical improvement by targeting the root issues:
- Behavior-Driven Verification:
By emphasizing behaviors, DamageBDD ensures digital systems align with human needs and expectations, rather than manipulative profit-driven incentives.
Use case: Verifying accessible, transparent, and intuitive UI behaviors for public and private digital platforms.
- Accountability Through Immutable Records:
DamageBDD leverages blockchain for an immutable record of system behaviors, fostering accountability in design and implementation.
Use case: Tracking user-centric design milestones and holding corporations accountable for harmful design practices.
- Rewarding Ethical Development:
DamageBDD incentivizes high-quality, ethical software development through Bitcoin Lightning payouts for verified milestones.
Use case: Developers receive immediate rewards for implementing systems that prioritize user well-being.
- Cognitive Restoration:
By reducing friction and chaos in digital systems, DamageBDD promotes a healthier cognitive landscape, restoring productivity and creativity to users.
- Conclusion: A Call to Action
The current state of digital design is unsustainable. The continued exploitation of human cognition through rotten interfaces represents a direct threat to mental health, economic productivity, and societal stability. Immediate intervention is not just desirable but essential.
DamageBDD provides the foundation for this intervention. By combining accountability, ethical incentives, and a focus on user behavior, it represents a scalable solution to a crisis that impacts billions. The time to act is now—before the collective depression caused by these interfaces buries the very people capable of driving humanity forward.
-
 @ f4db5270:3c74e0d0
2024-07-12 10:33:41
@ f4db5270:3c74e0d0
2024-07-12 10:33:41
"Barche a riposo" (2023)
40x40 cm, oil on panel canvas
-
 @ e6817453:b0ac3c39
2024-12-07 15:03:06
@ e6817453:b0ac3c39
2024-12-07 15:03:06Hey folks! Today, let’s dive into the intriguing world of neurosymbolic approaches, retrieval-augmented generation (RAG), and personal knowledge graphs (PKGs). Together, these concepts hold much potential for bringing true reasoning capabilities to large language models (LLMs). So, let’s break down how symbolic logic, knowledge graphs, and modern AI can come together to empower future AI systems to reason like humans.
The Neurosymbolic Approach: What It Means ?
Neurosymbolic AI combines two historically separate streams of artificial intelligence: symbolic reasoning and neural networks. Symbolic AI uses formal logic to process knowledge, similar to how we might solve problems or deduce information. On the other hand, neural networks, like those underlying GPT-4, focus on learning patterns from vast amounts of data — they are probabilistic statistical models that excel in generating human-like language and recognizing patterns but often lack deep, explicit reasoning.
While GPT-4 can produce impressive text, it’s still not very effective at reasoning in a truly logical way. Its foundation, transformers, allows it to excel in pattern recognition, but the models struggle with reasoning because, at their core, they rely on statistical probabilities rather than true symbolic logic. This is where neurosymbolic methods and knowledge graphs come in.
Symbolic Calculations and the Early Vision of AI
If we take a step back to the 1950s, the vision for artificial intelligence was very different. Early AI research was all about symbolic reasoning — where computers could perform logical calculations to derive new knowledge from a given set of rules and facts. Languages like Lisp emerged to support this vision, enabling programs to represent data and code as interchangeable symbols. Lisp was designed to be homoiconic, meaning it treated code as manipulatable data, making it capable of self-modification — a huge leap towards AI systems that could, in theory, understand and modify their own operations.
Lisp: The Earlier AI-Language
Lisp, short for “LISt Processor,” was developed by John McCarthy in 1958, and it became the cornerstone of early AI research. Lisp’s power lay in its flexibility and its use of symbolic expressions, which allowed developers to create programs that could manipulate symbols in ways that were very close to human reasoning. One of the most groundbreaking features of Lisp was its ability to treat code as data, known as homoiconicity, which meant that Lisp programs could introspect and transform themselves dynamically. This ability to adapt and modify its own structure gave Lisp an edge in tasks that required a form of self-awareness, which was key in the early days of AI when researchers were exploring what it meant for machines to “think.”
Lisp was not just a programming language—it represented the vision for artificial intelligence, where machines could evolve their understanding and rewrite their own programming. This idea formed the conceptual basis for many of the self-modifying and adaptive algorithms that are still explored today in AI research. Despite its decline in mainstream programming, Lisp’s influence can still be seen in the concepts used in modern machine learning and symbolic AI approaches.
Prolog: Formal Logic and Deductive Reasoning
In the 1970s, Prolog was developed—a language focused on formal logic and deductive reasoning. Unlike Lisp, based on lambda calculus, Prolog operates on formal logic rules, allowing it to perform deductive reasoning and solve logical puzzles. This made Prolog an ideal candidate for expert systems that needed to follow a sequence of logical steps, such as medical diagnostics or strategic planning.
Prolog, like Lisp, allowed symbols to be represented, understood, and used in calculations, creating another homoiconic language that allows reasoning. Prolog’s strength lies in its rule-based structure, which is well-suited for tasks that require logical inference and backtracking. These features made it a powerful tool for expert systems and AI research in the 1970s and 1980s.
The language is declarative in nature, meaning that you define the problem, and Prolog figures out how to solve it. By using formal logic and setting constraints, Prolog systems can derive conclusions from known facts, making it highly effective in fields requiring explicit logical frameworks, such as legal reasoning, diagnostics, and natural language understanding. These symbolic approaches were later overshadowed during the AI winter — but the ideas never really disappeared. They just evolved.
Solvers and Their Role in Complementing LLMs
One of the most powerful features of Prolog and similar logic-based systems is their use of solvers. Solvers are mechanisms that can take a set of rules and constraints and automatically find solutions that satisfy these conditions. This capability is incredibly useful when combined with LLMs, which excel at generating human-like language but need help with logical consistency and structured reasoning.
For instance, imagine a scenario where an LLM needs to answer a question involving multiple logical steps or a complex query that requires deducing facts from various pieces of information. In this case, a solver can derive valid conclusions based on a given set of logical rules, providing structured answers that the LLM can then articulate in natural language. This allows the LLM to retrieve information and ensure the logical integrity of its responses, leading to much more robust answers.
Solvers are also ideal for handling constraint satisfaction problems — situations where multiple conditions must be met simultaneously. In practical applications, this could include scheduling tasks, generating optimal recommendations, or even diagnosing issues where a set of symptoms must match possible diagnoses. Prolog’s solver capabilities and LLM’s natural language processing power can make these systems highly effective at providing intelligent, rule-compliant responses that traditional LLMs would struggle to produce alone.
By integrating neurosymbolic methods that utilize solvers, we can provide LLMs with a form of deductive reasoning that is missing from pure deep-learning approaches. This combination has the potential to significantly improve the quality of outputs for use-cases that require explicit, structured problem-solving, from legal queries to scientific research and beyond. Solvers give LLMs the backbone they need to not just generate answers but to do so in a way that respects logical rigor and complex constraints.
Graph of Rules for Enhanced Reasoning
Another powerful concept that complements LLMs is using a graph of rules. A graph of rules is essentially a structured collection of logical rules that interconnect in a network-like structure, defining how various entities and their relationships interact. This structured network allows for complex reasoning and information retrieval, as well as the ability to model intricate relationships between different pieces of knowledge.
In a graph of rules, each node represents a rule, and the edges define relationships between those rules — such as dependencies or causal links. This structure can be used to enhance LLM capabilities by providing them with a formal set of rules and relationships to follow, which improves logical consistency and reasoning depth. When an LLM encounters a problem or a question that requires multiple logical steps, it can traverse this graph of rules to generate an answer that is not only linguistically fluent but also logically robust.
For example, in a healthcare application, a graph of rules might include nodes for medical symptoms, possible diagnoses, and recommended treatments. When an LLM receives a query regarding a patient’s symptoms, it can use the graph to traverse from symptoms to potential diagnoses and then to treatment options, ensuring that the response is coherent and medically sound. The graph of rules guides reasoning, enabling LLMs to handle complex, multi-step questions that involve chains of reasoning, rather than merely generating surface-level responses.
Graphs of rules also enable modular reasoning, where different sets of rules can be activated based on the context or the type of question being asked. This modularity is crucial for creating adaptive AI systems that can apply specific sets of logical frameworks to distinct problem domains, thereby greatly enhancing their versatility. The combination of neural fluency with rule-based structure gives LLMs the ability to conduct more advanced reasoning, ultimately making them more reliable and effective in domains where accuracy and logical consistency are critical.
By implementing a graph of rules, LLMs are empowered to perform deductive reasoning alongside their generative capabilities, creating responses that are not only compelling but also logically aligned with the structured knowledge available in the system. This further enhances their potential applications in fields such as law, engineering, finance, and scientific research — domains where logical consistency is as important as linguistic coherence.
Enhancing LLMs with Symbolic Reasoning
Now, with LLMs like GPT-4 being mainstream, there is an emerging need to add real reasoning capabilities to them. This is where neurosymbolic approaches shine. Instead of pitting neural networks against symbolic reasoning, these methods combine the best of both worlds. The neural aspect provides language fluency and recognition of complex patterns, while the symbolic side offers real reasoning power through formal logic and rule-based frameworks.
Personal Knowledge Graphs (PKGs) come into play here as well. Knowledge graphs are data structures that encode entities and their relationships — they’re essentially semantic networks that allow for structured information retrieval. When integrated with neurosymbolic approaches, LLMs can use these graphs to answer questions in a far more contextual and precise way. By retrieving relevant information from a knowledge graph, they can ground their responses in well-defined relationships, thus improving both the relevance and the logical consistency of their answers.
Imagine combining an LLM with a graph of rules that allow it to reason through the relationships encoded in a personal knowledge graph. This could involve using deductive databases to form a sophisticated way to represent and reason with symbolic data — essentially constructing a powerful hybrid system that uses LLM capabilities for language fluency and rule-based logic for structured problem-solving.
My Research on Deductive Databases and Knowledge Graphs
I recently did some research on modeling knowledge graphs using deductive databases, such as DataLog — which can be thought of as a limited, data-oriented version of Prolog. What I’ve found is that it’s possible to use formal logic to model knowledge graphs, ontologies, and complex relationships elegantly as rules in a deductive system. Unlike classical RDF or traditional ontology-based models, which sometimes struggle with complex or evolving relationships, a deductive approach is more flexible and can easily support dynamic rules and reasoning.
Prolog and similar logic-driven frameworks can complement LLMs by handling the parts of reasoning where explicit rule-following is required. LLMs can benefit from these rule-based systems for tasks like entity recognition, logical inferences, and constructing or traversing knowledge graphs. We can even create a graph of rules that governs how relationships are formed or how logical deductions can be performed.
The future is really about creating an AI that is capable of both deep contextual understanding (using the powerful generative capacity of LLMs) and true reasoning (through symbolic systems and knowledge graphs). With the neurosymbolic approach, these AIs could be equipped not just to generate information but to explain their reasoning, form logical conclusions, and even improve their own understanding over time — getting us a step closer to true artificial general intelligence.
Why It Matters for LLM Employment
Using neurosymbolic RAG (retrieval-augmented generation) in conjunction with personal knowledge graphs could revolutionize how LLMs work in real-world applications. Imagine an LLM that understands not just language but also the relationships between different concepts — one that can navigate, reason, and explain complex knowledge domains by actively engaging with a personalized set of facts and rules.
This could lead to practical applications in areas like healthcare, finance, legal reasoning, or even personal productivity — where LLMs can help users solve complex problems logically, providing relevant information and well-justified reasoning paths. The combination of neural fluency with symbolic accuracy and deductive power is precisely the bridge we need to move beyond purely predictive AI to truly intelligent systems.
Let's explore these ideas further if you’re as fascinated by this as I am. Feel free to reach out, follow my YouTube channel, or check out some articles I’ll link below. And if you’re working on anything in this field, I’d love to collaborate!
Until next time, folks. Stay curious, and keep pushing the boundaries of AI!
-
 @ 06b7819d:d1d8327c
2024-11-29 12:11:05
@ 06b7819d:d1d8327c
2024-11-29 12:11:05In June 2023, the Law Commission of England and Wales published its final report on digital assets, concluding that the existing common law is generally flexible enough to accommodate digital assets, including crypto-tokens and non-fungible tokens (NFTs).
However, to address specific areas of uncertainty, the Commission recommended targeted statutory reforms and the establishment of an expert panel.
Key Conclusions and Recommendations:
1. Recognition of a Third Category of Personal Property:Traditional English law classifies personal property into two categories: “things in possession” (tangible items) and “things in action” (enforceable rights). Digital assets do not fit neatly into either category. The Commission recommended legislation to confirm the existence of a distinct third category of personal property to better accommodate digital assets. 
-
Development of Common Law: The Commission emphasized that the common law is well-suited to adapt to the complexities of emerging technologies and should continue to evolve to address issues related to digital assets. 
-
Establishment of an Expert Panel: To assist courts in navigating the technical and legal challenges posed by digital assets, the Commission recommended that the government create a panel of industry experts, legal practitioners, academics, and judges. This panel would provide non-binding guidance on issues such as control and transfer of digital assets. 
-
Facilitation of Crypto-Token and Crypto-Asset Collateral Arrangements: The Commission proposed the creation of a bespoke statutory legal framework to facilitate the use of digital assets as collateral, addressing current legal uncertainties in this area. 
-
Clarification of the Financial Collateral Arrangements Regulations: The report recommended statutory amendments to clarify the extent to which digital assets fall within the scope of the Financial Collateral Arrangements (No 2) Regulations 2003, ensuring that existing financial regulations appropriately cover digital assets. 
Overall, the Law Commission’s report underscores the adaptability of English common law in addressing the challenges posed by digital assets, while also identifying specific areas where legislative action is necessary to provide clarity and support the evolving digital economy.
-
-
 @ acbcec47:dd305bec
2024-12-27 13:49:37
@ acbcec47:dd305bec
2024-12-27 13:49:37Prepare starter
- 1 part starter (~30g)
- 2 parts wholemeal rye flour (~60g)
- 2 parts warm water (~60g)
Stir well, then leave to stand warm and covered until the volume has almost doubled.

Once the starter has doubled in volume and a light cap has formed, it can be used for the dough.

Ingredients
- Flour (2/3 550/1100 wheat flour, 1/3 997 rye flour) = 600g
- Water: 60% of the flour quantity = 360g warm water
- Starter: 20% of the flour quantity = 120g starter
- Salt: 3% of the flour = 18g

Put the rest of the starter (about 30g) back in the fridge for the next batch. Knead everything well for 5 minutes, then leave to stand warm and covered.

Fermenting
First fermenting phase in one piece until the volume has almost doubled.

Then divide into portions ...


Shape and leave to rise on the baking tray for 1-2 hours.


Baking
- Preheat oven to 230°C (450°F)
- Just before baking, cut in the top of the rolls with a razor blade, so that they can extend

- Bake for 20 min with steam/cover at 210°C (410°F)
- Then remove the steam/cover and bake another 15-20 min at 180°C (360°F)

Enjoy ...


-
 @ 6cc4225f:942b7222
2024-12-30 00:32:47
@ 6cc4225f:942b7222
2024-12-30 00:32:47(Cover image photo credit: The Crypto Times)
“Our world of widows needs to be saved / it’s now or never — victim or victory, rebel or regret / who you are and who you claim to be / no more heroes.” -Converge, “No Heroes”
Usually, bad takes from big figures in the Bitcoin space roll off my back. I often don’t feel a need to counter them because 1.) Everyone is entitled to their opinion and 2.) I don’t enjoy spending my time arguing with people on the Internet.
But when a take is really bad — downright evil — I feel compelled to respond.
And respond I did to a bad take this week (link in just a second, first some context).
Lately in the media, MicroStrategy Chair Michael Saylor has been laying out his vision for a digital asset framework.
This framework includes conceptualizing Bitcoin as a commodity — nothing more than capital — and stablecoins like Tether (USDT) and USD Coin (USDC) as “digital currencies” (his words).
As if someone who considers themselves a “triple bitcoin maxi” (maybe one of the lamest terms ever) denying that bitcoin is a currency weren’t nauseating enough, his “evil genius plan” (his words) to get the world hooked on USD stablecoins as money while the US hoards bitcoin should have you upchuck everything in your guts if you truly believe in Bitcoin’s value proposition.
Below (a few lines down) is the piece I wrote countering Saylor’s perspective.
If there are two things I hope you take away from it, the first is to KILL YOUR IDOLS (not literally, of course) and the second is that WE ARE BITCOIN, and if we believe in the technology — all dimensions of it — we have to defend it.
Enjoy.
Michael Saylor Doesn't Understand Bitcoin
## Support The Open Dialogue Foundation
Speaking of defending Bitcoin, we all owe a debt of gratitude to the work that the Open Dialogue Foundation (ODF) is doing to defend our legal right to use non-custodial bitcoin wallets.
Please read the following piece I wrote this week to learn more.
Protect Your Non-Custodial Bitcoin Wallet — Support The Open Dialogue Foundation
And please make a tax-deductible contribution (before the year’s end) to the organization here.
Bitcoin’s Second Book-Length Academic Text — The Satoshi Papers — Coming Soon
This week, I published my interview with Natalie Smolenski, a PhD-holding theoretical anthropologist who often makes very valuable thought contributions to the Bitcoin space.
What I loved most about this interview (and I loved a lot about it) is Smolenski’s lack of reverence.
Two of my favorite quotes from the interview:
“There was kind of a triumph of a certain very statist approach to socialism and even communism in the American academy, in the Anglophone academy, that has persisted to this day, where there's, like I was saying earlier, a suspicion of anything smacking of individualism as bourgeois conceit or reinscribing social hierarchies, racial hierarchies, gender hierarchies, blah, blah, blah.”
The “blah, blah, blah” hit hard. It reminded me of how I used to tune out when speaking with a good portion of my co-workers during the years I taught at the college level.
The other one:
“What do you hope people will take away from The Satoshi Papers?
*> If there's only one idea that people take away from it, it's that your emancipation does not require the state. You do not need to wait for the government.
*> My God, take control of your life. You can, it is within your power to do so, and here are some examples of ways that people throughout human history have chosen to do so."
The “My God” was so properly placed. Chef’s kiss.
Check out to entire piece to absorb more of Smolenski’s wisdom.
Thank you all for reading, and here’s to a great week ahead!
Best,
Frank
-
 @ e6817453:b0ac3c39
2024-12-07 14:54:46
@ e6817453:b0ac3c39
2024-12-07 14:54:46Introduction: Personal Knowledge Graphs and Linked Data
We will explore the world of personal knowledge graphs and discuss how they can be used to model complex information structures. Personal knowledge graphs aren’t just abstract collections of nodes and edges—they encode meaningful relationships, contextualizing data in ways that enrich our understanding of it. While the core structure might be a directed graph, we layer semantic meaning on top, enabling nuanced connections between data points.
The origin of knowledge graphs is deeply tied to concepts from linked data and the semantic web, ideas that emerged to better link scattered pieces of information across the web. This approach created an infrastructure where data islands could connect — facilitating everything from more insightful AI to improved personal data management.
In this article, we will explore how these ideas have evolved into tools for modeling AI’s semantic memory and look at how knowledge graphs can serve as a flexible foundation for encoding rich data contexts. We’ll specifically discuss three major paradigms: RDF (Resource Description Framework), property graphs, and a third way of modeling entities as graphs of graphs. Let’s get started.
Intro to RDF
The Resource Description Framework (RDF) has been one of the fundamental standards for linked data and knowledge graphs. RDF allows data to be modeled as triples: subject, predicate, and object. Essentially, you can think of it as a structured way to describe relationships: “X has a Y called Z.” For instance, “Berlin has a population of 3.5 million.” This modeling approach is quite flexible because RDF uses unique identifiers — usually URIs — to point to data entities, making linking straightforward and coherent.
RDFS, or RDF Schema, extends RDF to provide a basic vocabulary to structure the data even more. This lets us describe not only individual nodes but also relationships among types of data entities, like defining a class hierarchy or setting properties. For example, you could say that “Berlin” is an instance of a “City” and that cities are types of “Geographical Entities.” This kind of organization helps establish semantic meaning within the graph.
RDF and Advanced Topics
Lists and Sets in RDF
RDF also provides tools to model more complex data structures such as lists and sets, enabling the grouping of nodes. This extension makes it easier to model more natural, human-like knowledge, for example, describing attributes of an entity that may have multiple values. By adding RDF Schema and OWL (Web Ontology Language), you gain even more expressive power — being able to define logical rules or even derive new relationships from existing data.
Graph of Graphs
A significant feature of RDF is the ability to form complex nested structures, often referred to as graphs of graphs. This allows you to create “named graphs,” essentially subgraphs that can be independently referenced. For example, you could create a named graph for a particular dataset describing Berlin and another for a different geographical area. Then, you could connect them, allowing for more modular and reusable knowledge modeling.
Property Graphs
While RDF provides a robust framework, it’s not always the easiest to work with due to its heavy reliance on linking everything explicitly. This is where property graphs come into play. Property graphs are less focused on linking everything through triples and allow more expressive properties directly within nodes and edges.
For example, instead of using triples to represent each detail, a property graph might let you store all properties about an entity (e.g., “Berlin”) directly in a single node. This makes property graphs more intuitive for many developers and engineers because they more closely resemble object-oriented structures: you have entities (nodes) that possess attributes (properties) and are connected to other entities through relationships (edges).
The significant benefit here is a condensed representation, which speeds up traversal and queries in some scenarios. However, this also introduces a trade-off: while property graphs are more straightforward to query and maintain, they lack some complex relationship modeling features RDF offers, particularly when connecting properties to each other.
Graph of Graphs and Subgraphs for Entity Modeling
A third approach — which takes elements from RDF and property graphs — involves modeling entities using subgraphs or nested graphs. In this model, each entity can be represented as a graph. This allows for a detailed and flexible description of attributes without exploding every detail into individual triples or lump them all together into properties.
For instance, consider a person entity with a complex employment history. Instead of representing every employment detail in one node (as in a property graph), or as several linked nodes (as in RDF), you can treat the employment history as a subgraph. This subgraph could then contain nodes for different jobs, each linked with specific properties and connections. This approach keeps the complexity where it belongs and provides better flexibility when new attributes or entities need to be added.
Hypergraphs and Metagraphs
When discussing more advanced forms of graphs, we encounter hypergraphs and metagraphs. These take the idea of relationships to a new level. A hypergraph allows an edge to connect more than two nodes, which is extremely useful when modeling scenarios where relationships aren’t just pairwise. For example, a “Project” could connect multiple “People,” “Resources,” and “Outcomes,” all in a single edge. This way, hypergraphs help in reducing the complexity of modeling high-order relationships.
Metagraphs, on the other hand, enable nodes and edges to themselves be represented as graphs. This is an extremely powerful feature when we consider the needs of artificial intelligence, as it allows for the modeling of relationships between relationships, an essential aspect for any system that needs to capture not just facts, but their interdependencies and contexts.
Balancing Structure and Properties
One of the recurring challenges when modeling knowledge is finding the balance between structure and properties. With RDF, you get high flexibility and standardization, but complexity can quickly escalate as you decompose everything into triples. Property graphs simplify the representation by using attributes but lose out on the depth of connection modeling. Meanwhile, the graph-of-graphs approach and hypergraphs offer advanced modeling capabilities at the cost of increased computational complexity.
So, how do you decide which model to use? It comes down to your use case. RDF and nested graphs are strong contenders if you need deep linkage and are working with highly variable data. For more straightforward, engineer-friendly modeling, property graphs shine. And when dealing with very complex multi-way relationships or meta-level knowledge, hypergraphs and metagraphs provide the necessary tools.
The key takeaway is that only some approaches are perfect. Instead, it’s all about the modeling goals: how do you want to query the graph, what relationships are meaningful, and how much complexity are you willing to manage?
Conclusion
Modeling AI semantic memory using knowledge graphs is a challenging but rewarding process. The different approaches — RDF, property graphs, and advanced graph modeling techniques like nested graphs and hypergraphs — each offer unique strengths and weaknesses. Whether you are building a personal knowledge graph or scaling up to AI that integrates multiple streams of linked data, it’s essential to understand the trade-offs each approach brings.
In the end, the choice of representation comes down to the nature of your data and your specific needs for querying and maintaining semantic relationships. The world of knowledge graphs is vast, with many tools and frameworks to explore. Stay connected and keep experimenting to find the balance that works for your projects.
-
 @ 06b7819d:d1d8327c
2024-11-29 11:59:20
@ 06b7819d:d1d8327c
2024-11-29 11:59:20The system design and challenges of retail Central Bank Digital Currencies (CBDCs) differ significantly from Bitcoin in several key aspects, reflecting their distinct purposes and underlying philosophies:
-
Core Purpose and Issuance
• CBDCs: Issued by central banks, CBDCs are designed as state-backed digital currencies for public use. Their goal is to modernize payments, enhance financial inclusion, and provide a risk-free alternative to private money. • Bitcoin: A decentralized, peer-to-peer cryptocurrency created to operate independently of central authorities. Bitcoin aims to be a store of value and medium of exchange without reliance on intermediaries or governments.
-
Governance and Control
• CBDCs: Operate under centralized governance. Central banks retain control over issuance, transaction validation, and data management, allowing for integration with existing regulatory frameworks (e.g., AML and CFT). • Bitcoin: Fully decentralized, governed by a consensus mechanism (Proof of Work). Transactions are validated by miners, and no single entity controls the network.
-
Privacy
• CBDCs: Seek to balance privacy with regulatory compliance. Privacy-enhancing technologies may be implemented, but user data is typically accessible to intermediaries and central banks to meet regulatory needs. • Bitcoin: Pseudonymous by design. Transactions are public on the blockchain but do not directly link to individual identities unless voluntarily disclosed.
-
System Design
• CBDCs: May adopt a hybrid system combining centralized (e.g., central bank-controlled settlement) and decentralized elements (e.g., private-sector intermediaries). Offline functionality and interoperability with existing systems are priorities. • Bitcoin: Fully decentralized, using a distributed ledger (blockchain) where all transactions are validated and recorded without reliance on intermediaries.
-
Cybersecurity
• CBDCs: Cybersecurity risks are heightened due to potential reliance on centralized points for data storage and validation. Post-quantum cryptography is a concern for future-proofing against quantum computing threats. • Bitcoin: Security relies on cryptographic algorithms and decentralization. However, it is also vulnerable to quantum computing in the long term, unless upgraded to quantum-resistant protocols.
-
Offline Functionality
• CBDCs: Exploring offline payment capabilities for broader usability in remote or unconnected areas. • Bitcoin: Offline payments are not natively supported, although some solutions (e.g., Lightning Network or third-party hardware wallets) can enable limited offline functionality.
-
Point of Sale and Adoption
• CBDCs: Designed for seamless integration with existing PoS systems and modern financial infrastructure to encourage widespread adoption. • Bitcoin: Adoption depends on merchant willingness and the availability of cryptocurrency payment gateways. Its volatility can discourage usage as a medium of exchange.
-
Monetary Policy and Design
• CBDCs: Can be programmed to support specific policy goals, such as negative interest rates, transaction limits, or conditional transfers. • Bitcoin: Supply is fixed at 21 million coins, governed by its code. It is resistant to monetary policy interventions and inflationary adjustments.
In summary, while CBDCs aim to complement existing monetary systems with centralized oversight and tailored features, Bitcoin is designed as a decentralized alternative to traditional currency. CBDCs prioritize integration, control, and regulatory compliance, whereas Bitcoin emphasizes autonomy, censorship resistance, and a trustless system.
-
-
 @ 06b7819d:d1d8327c
2024-11-28 18:30:00
@ 06b7819d:d1d8327c
2024-11-28 18:30:00The Bank of Amsterdam (Amsterdamse Wisselbank), established in 1609, played a pivotal role in the early history of banking and the development of banknotes. While banknotes as a concept had been pioneered in China centuries earlier, their modern form began emerging in Europe in the 17th century, and the Bank of Amsterdam leveraged its unique position to dominate this nascent monetary tool.
Founding and Early Innovations
The Bank of Amsterdam was created to stabilize and rationalize Amsterdam’s chaotic monetary system. During the early 1600s, a plethora of coins of varying quality and origin circulated in Europe, making trade cumbersome and unreliable. The Wisselbank provided a centralized repository where merchants could deposit coins and receive account balances in return, denominated in a standardized unit of account known as “bank money.” This “bank money” was more stable and widely trusted, making it an early form of fiat currency.
The Rise of Banknotes
Although the Wisselbank initially issued “bank money” as a ledger-based system, the growing demand for portable, trusted currency led to the adoption of transferable receipts or “banknotes.” These receipts acted as claims on deposited money and quickly became a trusted medium of exchange. The innovation of banknotes allowed merchants to avoid carrying large quantities of heavy coinage, enhancing convenience and security in trade.
Monopoly on Banknotes
The Wisselbank’s reputation for financial stability and integrity enabled it to establish a monopoly on banknotes in the Dutch Republic. The bank’s stringent policies ensured that its issued notes were fully backed by coinage or bullion, which bolstered trust in their value. By centralizing the issuance of notes, the bank eliminated competition from private or less reliable issuers, ensuring its notes became the de facto currency for merchants and traders.
Moreover, the bank’s policies discouraged the redemption of notes for physical coins, as it charged fees for withdrawals. This incentivized the circulation of banknotes rather than the underlying specie, cementing their role in the economy.
Decline of the Monopoly
The Wisselbank’s monopoly and influence lasted for much of the 17th century, making Amsterdam a hub of global trade and finance. However, as the 18th century progressed, financial mismanagement and competition from other emerging financial institutions eroded the Wisselbank’s dominance. By the late 18th century, its role in the global financial system had diminished, and other European financial centers, such as London, rose to prominence.
Legacy
The Bank of Amsterdam’s early monopolization of banknotes set a precedent for centralized banking and the development of modern monetary systems. Its ability to create trust in a standardized, portable medium of exchange foreshadowed the role that central banks would play in issuing and regulating currency worldwide.
-
 @ 87730827:746b7d35
2024-11-20 09:27:53
@ 87730827:746b7d35
2024-11-20 09:27:53Original: https://techreport.com/crypto-news/brazil-central-bank-ban-monero-stablecoins/
Brazilian’s Central Bank Will Ban Monero and Algorithmic Stablecoins in the Country
Brazil proposes crypto regulations banning Monero and algorithmic stablecoins and enforcing strict compliance for exchanges.
KEY TAKEAWAYS
- The Central Bank of Brazil has proposed regulations prohibiting privacy-centric cryptocurrencies like Monero.
- The regulations categorize exchanges into intermediaries, custodians, and brokers, each with specific capital requirements and compliance standards.
- While the proposed rules apply to cryptocurrencies, certain digital assets like non-fungible tokens (NFTs) are still ‘deregulated’ in Brazil.

In a Notice of Participation announcement, the Brazilian Central Bank (BCB) outlines regulations for virtual asset service providers (VASPs) operating in the country.
In the document, the Brazilian regulator specifies that privacy-focused coins, such as Monero, must be excluded from all digital asset companies that intend to operate in Brazil.
Let’s unpack what effect these regulations will have.
Brazil’s Crackdown on Crypto Fraud
If the BCB’s current rule is approved, exchanges dealing with coins that provide anonymity must delist these currencies or prevent Brazilians from accessing and operating these assets.
The Central Bank argues that currencies like Monero make it difficult and even prevent the identification of users, thus creating problems in complying with international AML obligations and policies to prevent the financing of terrorism.
According to the Central Bank of Brazil, the bans aim to prevent criminals from using digital assets to launder money. In Brazil, organized criminal syndicates such as the Primeiro Comando da Capital (PCC) and Comando Vermelho have been increasingly using digital assets for money laundering and foreign remittances.
… restriction on the supply of virtual assets that contain characteristics of fragility, insecurity or risks that favor fraud or crime, such as virtual assets designed to favor money laundering and terrorist financing practices by facilitating anonymity or difficulty identification of the holder.
The Central Bank has identified that removing algorithmic stablecoins is essential to guarantee the safety of users’ funds and avoid events such as when Terraform Labs’ entire ecosystem collapsed, losing billions of investors’ dollars.
The Central Bank also wants to control all digital assets traded by companies in Brazil. According to the current proposal, the national regulator will have the power to ask platforms to remove certain listed assets if it considers that they do not meet local regulations.
However, the regulations will not include NFTs, real-world asset (RWA) tokens, RWA tokens classified as securities, and tokenized movable or real estate assets. These assets are still ‘deregulated’ in Brazil.
Monero: What Is It and Why Is Brazil Banning It?
Monero ($XMR) is a cryptocurrency that uses a protocol called CryptoNote. It launched in 2013 and ‘erases’ transaction data, preventing the sender and recipient addresses from being publicly known. The Monero network is based on a proof-of-work (PoW) consensus mechanism, which incentivizes miners to add blocks to the blockchain.
Like Brazil, other nations are banning Monero in search of regulatory compliance. Recently, Dubai’s new digital asset rules prohibited the issuance of activities related to anonymity-enhancing cryptocurrencies such as $XMR.
Furthermore, exchanges such as Binance have already announced they will delist Monero on their global platforms due to its anonymity features. Kraken did the same, removing Monero for their European-based users to comply with MiCA regulations.
Data from Chainalysis shows that Brazil is the seventh-largest Bitcoin market in the world.

In Latin America, Brazil is the largest market for digital assets. Globally, it leads in the innovation of RWA tokens, with several companies already trading this type of asset.
In Closing
Following other nations, Brazil’s regulatory proposals aim to combat illicit activities such as money laundering and terrorism financing.
Will the BCB’s move safeguard people’s digital assets while also stimulating growth and innovation in the crypto ecosystem? Only time will tell.
References
Cassio Gusson is a journalist passionate about technology, cryptocurrencies, and the nuances of human nature. With a career spanning roles as Senior Crypto Journalist at CriptoFacil and Head of News at CoinTelegraph, he offers exclusive insights on South America’s crypto landscape. A graduate in Communication from Faccamp and a post-graduate in Globalization and Culture from FESPSP, Cassio explores the intersection of governance, decentralization, and the evolution of global systems.
-
 @ 06b7819d:d1d8327c
2024-11-27 11:53:39
@ 06b7819d:d1d8327c
2024-11-27 11:53:39Understanding Figure and Ground: How We Perceive the World
The concept of “figure and ground” originates from Gestalt psychology but takes on profound implications in Marshall McLuhan’s media theory. At its core, figure and ground describe the relationship between what we focus on (the “figure”) and the larger context that shapes and influences it (the “ground”). Together, they illustrate how perception is shaped not only by what we pay attention to, but by what we overlook.
Figure and Ground in Perception
Imagine looking at a photo of a tree in a forest. The tree might stand out as the figure—it’s what your attention is drawn to. However, the forest, the sky, and even the light conditions around the tree create the ground. These background elements are not immediately in focus, but they are essential to understanding the tree’s existence and meaning within its environment.
Our minds are naturally inclined to separate figure from ground, but this process often distorts our perception. By focusing on one aspect, we tend to neglect the broader context that gives it meaning. This principle applies not just to visual perception but also to the way we experience media, technology, and culture.
McLuhan’s Take: Media as Ground
For McLuhan, media and technology are the “ground” upon which all human activity takes place. We often fixate on the “figure” of a medium—the content it delivers—without recognizing the ground, which is the medium itself and its pervasive influence. For example, we might focus on the latest viral video (the figure) without reflecting on how platforms like TikTok (the ground) shape attention spans, social behaviors, and even our cultural norms.
McLuhan famously argued that “the medium is the message,” meaning the medium’s structure and characteristics influence society far more deeply than the specific content it carries. The figure (content) distracts us from examining the ground (medium), which often operates invisibly.
Figure and Ground in Daily Life
Consider smartphones. The apps, messages, and videos we interact with daily are the figures. The ground is the smartphone itself—a device that transforms communication, alters social dynamics, and restructures how we manage time and attention. Focusing solely on what’s displayed on the screen blinds us to the ways the device reshapes our lives.
Rebalancing Perception
To truly understand the impact of media and technology, McLuhan urged us to become aware of the ground. By stepping back and observing how the environment shapes the figure, we can better grasp the larger systems at work. This requires a shift in perspective: instead of asking “What does this content mean?” we might ask “How does this medium affect the way I think, behave, or relate to others?”
Understanding figure and ground helps us see the world more holistically, uncovering hidden dynamics that shape perception and culture. It’s a reminder that what we take for granted—what fades into the background—is often the most transformative force of all.
-
 @ 5e5fc143:393d5a2c
2024-11-19 10:20:25
@ 5e5fc143:393d5a2c
2024-11-19 10:20:25Now test old reliable front end Stay tuned more later Keeping this as template long note for debugging in future as come across few NIP-33 post edit issues
-
 @ bec0c9d3:c4e9cd29
2024-12-28 23:43:18
@ bec0c9d3:c4e9cd29
2024-12-28 23:43:18GENESIS PARTY - by 2140 Collective and Angor.io

Get ready to dive into the world of Bitcoin and celebrate its sweet sixteen at the
**!
Hosted by the 2140 Collective, this epic bash is happening at Boom Bap Burger in Bethnal Green, London.
From 5:30 PM to 11:00 PM, join fellow Bitcoin enthusiasts in a venue that not only serves mouth-watering burgers but also embraces the future by accepting Bitcoin payments for all your food and drink cravings.
Thanks to our awesome supporter, ANGOR.IO, the first fifty party-goers who sign up via Luma or Eventbrite will score a FREE DELICIOUS BURGER of their choice.
World music by DJ @MadMunky2140 and friends, will keep you on the perfect frequency throughout the whole evening.
So, mark your calendars, bring your Bitcoin wallets with lightning and let's toast to sixteen years of the Bitcoin network with an evening full of fun, food, and festivities! *🥳🎉🤪***
EVENT PAGE - register
Crew behind
SPONSOR
LOCATION:
BOOM BAP BURGER 252 Paradise Row, London E2 9LE, UK
see ya in a NEW YEAR ,
-
 @ e6817453:b0ac3c39
2024-12-07 14:52:47
@ e6817453:b0ac3c39
2024-12-07 14:52:47The temporal semantics and temporal and time-aware knowledge graphs. We have different memory models for artificial intelligence agents. We all try to mimic somehow how the brain works, or at least how the declarative memory of the brain works. We have the split of episodic memory and semantic memory. And we also have a lot of theories, right?
Declarative Memory of the Human Brain
How is the semantic memory formed? We all know that our brain stores semantic memory quite close to the concept we have with the personal knowledge graphs, that it’s connected entities. They form a connection with each other and all those things. So far, so good. And actually, then we have a lot of concepts, how the episodic memory and our experiences gets transmitted to the semantic:
- hippocampus indexing and retrieval
- sanitization of episodic memories
- episodic-semantic shift theory
They all give a different perspective on how different parts of declarative memory cooperate.
We know that episodic memories get semanticized over time. You have semantic knowledge without the notion of time, and probably, your episodic memory is just decayed.
But, you know, it’s still an open question:
do we want to mimic an AI agent’s memory as a human brain memory, or do we want to create something different?
It’s an open question to which we have no good answer. And if you go to the theory of neuroscience and check how episodic and semantic memory interfere, you will still find a lot of theories, yeah?
Some of them say that you have the hippocampus that keeps the indexes of the memory. Some others will say that you semantic the episodic memory. Some others say that you have some separate process that digests the episodic and experience to the semantics. But all of them agree on the plan that it’s operationally two separate areas of memories and even two separate regions of brain, and the semantic, it’s more, let’s say, protected.
So it’s harder to forget the semantical facts than the episodes and everything. And what I’m thinking about for a long time, it’s this, you know, the semantic memory.
Temporal Semantics
It’s memory about the facts, but you somehow mix the time information with the semantics. I already described a lot of things, including how we could combine time with knowledge graphs and how people do it.
There are multiple ways we could persist such information, but we all hit the wall because the complexity of time and the semantics of time are highly complex concepts.
Time in a Semantic context is not a timestamp.
What I mean is that when you have a fact, and you just mentioned that I was there at this particular moment, like, I don’t know, 15:40 on Monday, it’s already awake because we don’t know which Monday, right? So you need to give the exact date, but usually, you do not have experiences like that.
You do not record your memories like that, except you do the journaling and all of the things. So, usually, you have no direct time references. What I mean is that you could say that I was there and it was some event, blah, blah, blah.
Somehow, we form a chain of events that connect with each other and maybe will be connected to some period of time if we are lucky enough. This means that we could not easily represent temporal-aware information as just a timestamp or validity and all of the things.
For sure, the validity of the knowledge graphs (simple quintuple with start and end dates)is a big topic, and it could solve a lot of things. It could solve a lot of the time cases. It’s super simple because you give the end and start dates, and you are done, but it does not answer facts that have a relative time or time information in facts . It could solve many use cases but struggle with facts in an indirect temporal context. I like the simplicity of this idea. But the problem of this approach that in most cases, we simply don’t have these timestamps. We don’t have the timestamp where this information starts and ends. And it’s not modeling many events in our life, especially if you have the processes or ongoing activities or recurrent events.
I’m more about thinking about the time of semantics, where you have a time model as a hybrid clock or some global clock that does the partial ordering of the events. It’s mean that you have the chain of the experiences and you have the chain of the facts that have the different time contexts.
We could deduct the time from this chain of the events. But it’s a big, big topic for the research. But what I want to achieve, actually, it’s not separation on episodic and semantic memory. It’s having something in between.
Blockchain of connected events and facts
I call it temporal-aware semantics or time-aware knowledge graphs, where we could encode the semantic fact together with the time component.I doubt that time should be the simple timestamp or the region of the two timestamps. For me, it is more a chain for facts that have a partial order and form a blockchain like a database or a partially ordered Acyclic graph of facts that are temporally connected. We could have some notion of time that is understandable to the agent and a model that allows us to order the events and focus on what the agent knows and how to order this time knowledge and create the chains of the events.
Time anchors
We may have a particular time in the chain that allows us to arrange a more concrete time for the rest of the events. But it’s still an open topic for research. The temporal semantics gets split into a couple of domains. One domain is how to add time to the knowledge graphs. We already have many different solutions. I described them in my previous articles.
Another domain is the agent's memory and how the memory of the artificial intelligence treats the time. This one, it’s much more complex. Because here, we could not operate with the simple timestamps. We need to have the representation of time that are understandable by model and understandable by the agent that will work with this model. And this one, it’s way bigger topic for the research.”
-
 @ af9c48b7:a3f7aaf4
2024-11-18 20:26:07
@ af9c48b7:a3f7aaf4
2024-11-18 20:26:07Chef's notes
This simple, easy, no bake desert will surely be the it at you next family gathering. You can keep it a secret or share it with the crowd that this is a healthy alternative to normal pie. I think everyone will be amazed at how good it really is.
Details
- ⏲️ Prep time: 30
- 🍳 Cook time: 0
- 🍽️ Servings: 8
Ingredients
- 1/3 cup of Heavy Cream- 0g sugar, 5.5g carbohydrates
- 3/4 cup of Half and Half- 6g sugar, 3g carbohydrates
- 4oz Sugar Free Cool Whip (1/2 small container) - 0g sugar, 37.5g carbohydrates
- 1.5oz box (small box) of Sugar Free Instant Chocolate Pudding- 0g sugar, 32g carbohydrates
- 1 Pecan Pie Crust- 24g sugar, 72g carbohydrates
Directions
- The total pie has 30g of sugar and 149.50g of carboydrates. So if you cut the pie into 8 equal slices, that would come to 3.75g of sugar and 18.69g carbohydrates per slice. If you decided to not eat the crust, your sugar intake would be .75 gram per slice and the carborytrates would be 9.69g per slice. Based on your objective, you could use only heavy whipping cream and no half and half to further reduce your sugar intake.
- Mix all wet ingredients and the instant pudding until thoroughly mixed and a consistent color has been achieved. The heavy whipping cream causes the mixture to thicken the more you mix it. So, I’d recommend using an electric mixer. Once you are satisfied with the color, start mixing in the whipping cream until it has a consistent “chocolate” color thorough. Once your satisfied with the color, spoon the mixture into the pie crust, smooth the top to your liking, and then refrigerate for one hour before serving.
-
 @ 1739d937:3e3136ef
2024-07-12 10:11:42
@ 1739d937:3e3136ef
2024-07-12 10:11:42This is the third in a series of weekly updates detailing progress on bringing MLS protocol DMs and group messaging to Nostr.
Previous Updates
Progress this week
Short update post this week but I made solid progress updating several OpenMLS dependencies and building a new library that implements all the OpenMLS crypto requirements for Nostr.
HPKE-RS
I mentioned a PR last week on the
rust-hpkelibrary, that PR is still waiting on review. However, in the meantime, the OpenMLS library depends on a slightly different hpke library, thehpke-rslibrary.This library didn't support the secp256k1 curve either so I've opened a PR to add support for secp256k1. That PR uses the
RustCryptolibrary that is the default in the thehpke-rslibrary. However, because this library is built to allow for swapping out the underlying crypto library (using traits), I was also able to create a new library that uses thesecp256k1library instead of theRustCryptolibrary. This is the main crypto library that almost all Bitcoin and Nostr apps use so it's important we use that instead ofRustCrypto.OpenMLS Nostr Crypto
The library that I've created (openmls-nostr-crypto) does a few things via separate sub-libraries (crates). The entire library tries to do as little as possible; only implementing the one required ciphersuite for all MLS implementations and the
secp256k1schnorr signatures ciphersuite I've created for Nostr. It's also using the rightsecp256k1library to do it.openmls-nostr-crypto: implementes the crypto traits that the OpenMLS library expects to find for a given provider and removes all the ciphersuites that we don't care about supporting.
hpke-rs-nostr-crypto: This implements the crypto traits that the hpke-rs library expects to find. Again removing all the ciphersuites we don't care about supporting.
I've not yet written any tests for these libraries (which needs to be done) but I've gotten some very simple demos working with OpenMLS using this new set of libraries to handle the crypto.
I've been really impressed with the simplicity of the OpenMLS interface as well. While there is A LOT going on under the hood, the public interface that client developers have to use is clean and simple.
Onward and Upward
Next week I'll continue working on these libraries; adding tests and continuing to build out my small demo app. I've been in touch with the maintainers of the OpenMLS library and I'm hoping to get a review done with them on my PRs and on my new library.
One thing I'll call out here: The review of my library and getting them to review the direction of the project overall will be paid consulting so I'm making sure that I've got as much done as possible before scheduling that time and paying their rates. I'm a strong believer that the right conversation can save you months of wasted time, but I'm also a believer in making sure you're prepared if you're going to drop money on that conversation. 😅
-
 @ 41e6f20b:06049e45
2024-11-17 17:33:55
@ 41e6f20b:06049e45
2024-11-17 17:33:55Let me tell you a beautiful story. Last night, during the speakers' dinner at Monerotopia, the waitress was collecting tiny tips in Mexican pesos. I asked her, "Do you really want to earn tips seriously?" I then showed her how to set up a Cake Wallet, and she started collecting tips in Monero, reaching 0.9 XMR. Of course, she wanted to cash out to fiat immediately, but it solved a real problem for her: making more money. That amount was something she would never have earned in a single workday. We kept talking, and I promised to give her Zoom workshops. What can I say? I love people, and that's why I'm a natural orange-piller.
-
 @ 06b7819d:d1d8327c
2024-11-26 16:57:14
@ 06b7819d:d1d8327c
2024-11-26 16:57:14Hanlon’s Razor is a philosophical principle or adage that states:
“Never attribute to malice that which is adequately explained by stupidity.”
It suggests that when trying to understand someone’s actions, it is often more reasonable to assume a lack of knowledge, competence, or foresight rather than intentional harm or ill will. The principle encourages people to avoid jumping to conclusions about malicious intent and instead consider simpler, more mundane explanations.
Hanlon’s Razor is often used in problem-solving, interpersonal interactions, and organizational settings to promote understanding and reduce conflict. It’s part of a broader family of “razors,” which are rules of thumb used to simplify decision-making.
-
 @ 3b19f10a:4e1f94b4
2024-12-07 09:55:46
@ 3b19f10a:4e1f94b4
2024-12-07 09:55:46 -
 @ fd78c37f:a0ec0833
2024-12-28 16:58:51
@ fd78c37f:a0ec0833
2024-12-28 16:58:51In this edition, We were honored to have Martin npub19vtlpmfzz8yl4g9r7c8u8t2vaqjhjgpjrc36hc2typxnutpnluzs3tx8xe, the founder of Bitcoin Nairobi, share his journey in creating the Bitcoin community, his goals, and some of the challenges faced. He emphasized the importance of education and innovation in promoting Bitcoin adoption in Kenya.
YakiHonne: Martin, it’s truly an honor and a pleasure to have you with us today. We’re looking forward to a fruitful conversation as we move forward. Before we dive in, I’d like to take a moment to share some background on what YakiHonne is. YakiHonne is a decentralized media client built on the Nostr protocol that enables freedom of speech through technology. It empowers creators to create their own voice, assets, and features. It also allows features like smart widgets, verified notes, and focuses on long-form articles. today. we'll be exploring more about your community. Can you tell us a bit about yourself?
Martin:I’m Martin Mutonga, the founder of Bitcoin Nairobi. I’m 21 years old and currently studying at the University of Nairobi.
 YakiHonne: What sparked your interest in Bitcoin, and what motivated you to create a community around it?
YakiHonne: What sparked your interest in Bitcoin, and what motivated you to create a community around it?Martin:I first got interested in Bitcoin as a way to find passive income. Before discovering Bitcoin, I worked as an AI annotation Jobs. During this time, I came across Bitcoin. After reading the Bitcoin white paper, I decided to explore it further. I then started looking for Bitcoin communities in Kenya and joined events like Bitcoin DADA,The Core, and others. It was then that I realized there was a gap in Bitcoin education in Kenya. Many people were getting into Bitcoin but didn’t know how to earn from it. Martin:I decided to create Bitcoin Nairobi, a community focused on advancing Bitcoin through education, adoption, and innovation. Our mission is to educate people about Bitcoin, help merchants integrate Bitcoin payments to attract more customers, and foster innovation by exploring protocols like Nostr and leveraging apps like YakiHonne to drive growth.
YakiHonne: Great. Could you share how your community started and how you managed to attract members?
Martin:The community initially started through a WhatsApp group, originally for people who have questions related to Bitcoin. I shared my knowledge of Bitcoin and expressed my desire to train others, which led to small Bitcoin learning sessions. Before this, I completed a Bitcoin diploma course with Mi Premier Bitcoin, which deepened my passion for Bitcoin and inspired me to start my own company. Bitcoin became my true passion, and I was determined to fully dive into it. Martin:I then founded Bitcoin Nairobi, initially focusing on the concept of the circular economy, which I called Bitcoin Aerobics. With support from Geyser and other Bitcoin enthusiasts in Kenya, the community began to grow. Every few months, we attract new members through a project called Bitcoin School Kenya, mostly university students who want to learn and earn with Bitcoin while studying.

YakiHonne: Can you share some of the challenges you faced when you first started?
Martin:One of the main challenges I faced early on was the lack of guidance, as many Bitcoin users are anonymous. Additionally, relevant content is scattered across various platforms, making it difficult to gather all the necessary information in one place. Another challenge is the small number of true Bitcoiners in Kenya. While there are many participants in cryptocurrency and altcoins, there are only about 28 true Bitcoin users in Kenya, which is a tiny fraction of the country's 58 million people. Martin:Seeing this gap, I founded Bitcoin School Kenya, aiming to promote Bitcoin education. Our goal is not only to teach people about Bitcoin but also to empower them to become Bitcoin ambassadors in their local communities. This way, we can extend our impact beyond Nairobi, especially to rural areas.
YakiHonne: As you mentioned, many people are involved in cryptocurrency and other coins, including popular meme coins like Dogecoin. While they claim to be part of the crypto space, Bitcoin is truly the dominant and most significant coin. However, true Bitcoiners are few in number and not as widely recognized. Additionally, the content related to Bitcoin is scattered across platforms like YouTube and Google, making it hard to find a single source to access all the necessary information. I completely understand the frustration. YakiHonne: What are the core principles that guide the Bitcoin Nairobi community? How do you maintain trust and reliability, especially when facing the widespread skepticism around cryptocurrency? How do you ensure that community members trust you, particularly when onboarding them?
Martin:I think we are simply following the principles of Bitcoin's proof of work—if you show your proof of work, you'll be rewarded, and that's all there is to it. That's the essence of proof of work.
YakiHonne: A lot of people feel that cryptocurrency, Bitcoin, and Web3 are scams, and they don't see them as the future. So, How do you convince people to trust and believe in Bitcoin?
Martin:What we do is organize meetups. However, due to financial constraints, we've only been able to host two so far, one of which was in Kibra, a part of the Bitcoin Nairobi community. I believe this is how we gain trust in Bitcoin and what we do. Another key aspect is maintaining consistent communication. If people have issues, we engage with them. We also communicate with merchants and guide them on what they need. This helps build trust within the community. Additionally, we are transparent with our funds. Whatever donations or grants we receive, we make sure to be open about how the funds are used and show the community exactly what we’ve spent them on. This is how we build trust.
YakiHonne: It seems you're really doing a great job in that aspect. How do you educate your members and keep them informed about the latest Bitcoin developments?
Martin: We collaborate with Bitcoin developers like Simon, who is the lead of BitDevs Nairobi. Simon often conducts classes with Bitcoin School Kenya, where he trains people in Bitcoin development.We also invite guest developers, such as those from Btrust, to join our sessions and train people on Bitcoin development. Additionally, we bring in experts on specific topics like Lightning or Nostr to provide specialized training for students. Looking ahead, we aim to nurture our own developers who can contribute to projects like Bitcoin Core, the Lightning Network, and Nostr. These developers will eventually train others, helping us build a stronger ecosystem.
YakiHonne: I look forward to seeing your developers in the future. It would be amazing to have developers from your community contributing—it would be a great benefit both for them and for the Bitcoin community as a whole.
Martin:Honestly, you can't know everything. Another amazing thing about Bitcoin is the supportive community—there's always someone willing to help. For example, I didn’t even approach Simon myself; I just attended a BitDevs meetup, and he offered to train during our classes. We also have Nayoma, the first African male Bitcoin Core developer, contributing to the classes. It's truly inspiring to see so many knowledgeable people coming together to share their expertise.
YakiHonne: How does the community collaborate with the broader Bitcoin ecosystem, and what partnerships have had the greatest impact on Bitcoin Nairobi?
Martin:One key factor that has helped Bitcoin Nairobi gain recognition globally is our involvement with the Federation of Bitcoin Circular Economies. We collaborate with other communities by actively participating in their calls and staying in contact with leaders at the Federation as well as other communities. This consistent engagement has significantly boosted our visibility. Martin:Additionally, through Bitcoin School Kenya, we operate as a light node in the broader Bitcoin ecosystem. For now, we function as a light node, but we’re aiming to upgrade to a full node by next year. This will enable members of our community not only to contribute locally but also to teach and collaborate with other communities and circular economies worldwide.
YakiHonne: What major challenges has the community faced, and how did you overcome them while maintaining integrity?
Martin:I wouldn't say there's a major challenge, but one challenge we faced was connecting with others in the Bitcoin space. However, we’ve made progress. Another challenge we’re facing now is organizing physical meetups. This has been difficult since we’re still relatively new in the Federation and the circular economies.
YakiHonne: It seems like you haven’t faced much resistance in terms of people viewing Bitcoin as a scam or having trust issues about its stability, like concerns over whether Bitcoin will crash. You haven't experienced these kinds of challenges.
Martin:Most people believe in the technology and in Bitcoin. The main issue they have is knowing where and how they can sell it. However, when it comes to doubting Bitcoin itself, I can’t say many people question the technology. Especially young people, they’re into online work, AI, and Bitcoin—basically anything related to the future.
YakiHonne: What are the community's goals for the next 6-12 months, and how do you see it evolving with Bitcoin's growth?
Martin:Our community's goals are to develop more educators and promote the widespread adoption of Bitcoin education, launch more Bitcoin-based projects to drive local adoption, strengthen collaborations with other organizations and communities to expand our influence, and increase our efforts in “orange-pilling” to help more people understand and embrace Bitcoin. As Bitcoin continues to grow, we will also continue to expand and evolve, fostering the maturation of the Bitcoin ecosystem.

YakiHonne: That's great. We’re excited to see how these initiatives will unfold in the coming months. Best of luck in achieving your vision, and we look forward to hearing about your progress in the future! OK, We're glad to see everyone and look forward to the next community interview. Thank you all, and that wraps up today's session.
-
 @ e83b66a8:b0526c2b
2024-09-06 19:16:04
@ e83b66a8:b0526c2b
2024-09-06 19:16:04The founder of Telegram has just been arrested in France. Charges include lack of cooperation with law enforcement, drug trafficking and fraud.
Aside from Telegram, social media is controlled by two billionaires who decide what you say, are themselves controlled by overbearing governments and make money through advertising and selling your personal data.
There is a different way.
NOSTR stands for Notes and Other Stuff Transmitted on Relays and it is a social media protocol in the same way http is a web protocol.
The protocol is open and anybody can build upon it. It has some fundamental concepts that are very different to existing social media platforms.
Firstly it is decentralised, it runs across relays and anybody can run a relay. They can be open or closed, public or private, free or paid.
Secondly as a user, you don’t have an account, you have a private key which is used to secure your data.
Your profile (account) is yours, you own and control it using your private keys and verified by others with your public key.
Your posts are yours and you can store them on your own relay in your own home or business or you can rely on free public relays or more feature rich paid public relays.
All your public data is signed by your private keys to verify it is you that owns it and all your private data is encrypted so nobody can read it.
Messages (i.e. think NOSTR WhatsApp) are encrypted with your private keys so NOBODY can hack it or listen in, not even the NSA through a companies backdoor. You message other users privately by encrypting messages to them using their public key, which they decrypt using their private key.
Relays store your data in a decentralised network of private and public relays and you discover relays automatically when searching for people or content.
Data is normally sent on the clearnet, but can be relayed across the darknet (Tor) in highly censored regions.
Because it is built using Bitcoin principles and technology, so it has Bitcoin money built in, meaning you actually send / receive money from / to any participant.
As money is built in, the commercial options are different to centralised corporate owned platforms. It would be technically possible to build a platform that supports advertising, however that hasn’t really happened because influencers can be paid directly from their audience in many different ways. Ad hoc tips, subscriptions, pay to view or pay per time models.
The great thing for content creators is that they control, own and keep all the money they make. There is no third party intermediary or merchant deciding whether they are allowed to be paid or not.
NOSTR is censorship resistant, as there is no way to stop anybody publishing anything they want, in the same way nobody can stop or interfere with a Bitcoin payment.
From an end users point of view, if they want to self censor, they can do this in multiple ways. You can mute users individually, or you can choose to use relays that adhere to your views or interests, so if you don’t want to see certain categories of content, you would avoid relays that carry those feeds. You can even run your own relay and curate content that you then charge other like minded users to connect to. You can of course connect to multiple relays for multiple different type of feed.
While NOSTR is a protocol, platforms have to be built to use it, so the first platforms were twitter like clients and they are still very prevalent. However, NOSTR now has clients that emulate most social media platforms, Instagram, Facebook, YouTube, Soundcloud, WhatsApp etc. They are even creating their own categories as well as emulating other functions such as Office Suite tools, collaborative calendars, contact lists or e-commerce shops.
If you want to give it a go, the easiest, but not the best, way to get started is download Primal on your phone from here:
https://primal.net/downloads
It will create a private key for you and setup a Bitcoin wallet.
Once you have done this you can visit me here:
nostr:npub1aqakd28d95muqlg6h6nwrvqq5925n354prayckr424k49vzjds4s0c237n
If you want to see a small part of the ecosystem, then visit https://www.nostrapps.com/ where volunteers are listing some of the many apps that exist already.
NOSTR is being backed by Jack Dorsey, Twitter founder, and you can see his account here:
nostr:npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m
Or you can see his account like this:
https://primal.net/jack
Edward Snowden is also on the platform and you can find him here:
https://primal.net/Snowden
NOSTR has around 2 million users or public keys, although nobody really knows how many, because it is decentralised and not controlled or run by any person or organisation.
Once you’ve setup Primal, you can use those same private keys to access any platform you wish and you can use a browser extension such as Alby to manage your keys: https://getalby.com/
Primal looks great, but there are other better functioning twitter like clients, probably the most reliable for iPhone is Damus: https://www.nostrapps.com/apps/damus
or Amethyst for Android: https://nostrapps.com/amethyst
The content and user base is very Bitcoin and freedom focused right now, but more and more people are starting to use the various platforms and some are transferring exclusively to it.
Some of the more interesting projects right now are:
https://www.0xchat.com/#/ – Private messaging – think WhatsApp
https://zap.stream/ – Video streaming
https://fountain.fm/ – Podcasting
https://wavlake.com/ – Music streaming
https://shopstr.store/ – Online shop
https://npub.pro/ – Website creation tool
https://nostr.build/ – Media and file storage
https://relay.tools/ – Build and curate your own relay
https://creatr.nostr.wine/subscriptions/new-user – Creator tools
Remember, the same keys you created for Primal can be used across the whole ecosystem.
If you want to see some of the other apps that have been built on the NOSTR protocol visit: https://nostrapps.com/
-
 @ 38d0888d:bd8e1246
2024-07-12 07:10:35
@ 38d0888d:bd8e1246
2024-07-12 07:10:35A thriving society rests on the principles of modesty and humility, avoiding idleness and self-indulgence. Individuals are needed to forsake the constant pursuit of attention and instead aspire to selflessness, dedicating themselves to serving humanity. Humility fosters spiritual harmony and protects against materialism and selfish desires.
Beyond personal conduct, humanity must champion altruism and solidarity within the global community. Belief in collective endeavors will pave the way for global harmony. Embracing values like kindness, compassion, and genuine concern for others promotes positivity and reflects the influence of a higher power. The aim is to cultivate a unified multicultural community where each person contributes to manifesting this higher presence.
The collective goal is to direct humanity to nurture a community that experiences spiritual growth while upholding humility as a guiding principle, resisting materialism's allure. By creating such an environment, the hope is to resonate with a sacred harmony that extends beyond immediate boundaries. Through intentional actions and meaningful relationships, a collective space embodying these values can be established, ensuring the higher power's presence guides individual lives and interactions with the world.
-
 @ 8d34bd24:414be32b
2024-12-29 23:22:36
@ 8d34bd24:414be32b
2024-12-29 23:22:36Everyone was amazed and gave praise to God. They were filled with awe and said, “We have seen remarkable things today.” (Luke 5:26)
There are lots of verses in the Bible, both Old and New Testaments, where people were amazed at the works of God, but my question is, “Is there anything that amazes God?”
When the Sabbath came, he began to teach in the synagogue, and many who heard him were amazed.
“Where did this man get these things?” they asked. “What’s this wisdom that has been given him? What are these remarkable miracles he is performing? Isn’t this the carpenter? Isn’t this Mary’s son and the brother of James, Joseph, Judas and Simon? Aren’t his sisters here with us?” And they took offense at him.
Jesus said to them, “A prophet is not without honor except in his own town, among his relatives and in his own home.” He could not do any miracles there, except lay his hands on a few sick people and heal them. He was amazed at their lack of faith. (Mark 6:2-6) {emphasis mine}
This passage mentions the people being amazed at Jesus’s teaching, but it also talks about Jesus being amazed at their lack of faith. It is amazing that people could see the son of God, face to face, and listen to Him teach God’s word and still not believe. They heard about and even saw Him work miracles and yet they did not repent, nor believe.
This is an example of a negative amazement. Are there any examples of positive amazement? There are two passages, that I know of, that describe one particular event that amazed Jesus:
The centurion replied, “Lord, I do not deserve to have you come under my roof. But just say the word, and my servant will be healed. For I myself am a man under authority, with soldiers under me. I tell this one, ‘Go,’ and he goes; and that one, ‘Come,’ and he comes. I say to my servant, ‘Do this,’ and he does it.” *When Jesus heard this, he was amazed* and said to those following him, “Truly I tell you, I have not found anyone in Israel with such great faith**. I say to you that many will come from the east and the west, and will take their places at the feast with Abraham, Isaac and Jacob in the kingdom of heaven. But the subjects of the kingdom will be thrown outside, into the darkness, where there will be weeping and gnashing of teeth.”
Then Jesus said to the centurion, “Go! Let it be done just as you believed it would.” And his servant was healed at that moment. (Matthew 8:8-13) {emphasis mine}
The other mention of this event is in Luke:
He was not far from the house when the centurion sent friends to say to him: “Lord, don’t trouble yourself, for I do not deserve to have you come under my roof. That is why I did not even consider myself worthy to come to you. But say the word, and my servant will be healed. For I myself am a man under authority, with soldiers under me. I tell this one, ‘Go,’ and he goes; and that one, ‘Come,’ and he comes. I say to my servant, ‘Do this,’ and he does it.”
When Jesus heard this, he was amazed at him, and turning to the crowd following him, he said, “I tell you, I have not found such great faith even in Israel.” (Luke 7:6-9) {emphasis mine}
This Roman centurion had greater faith than any one of God’s chosen people in Israel. This gentile man trusted that Jesus had the power to heal his servant and that all it would take was Jesus’s command. If Jesus spoke the word, his servant would be healed, and it was so. Just as Jesus spoke the universe into existence, He also spoke the centurion’s servant into health. The creator healed His creation with His word and the centurion believed that it would be so.
What can amaze God? It looks like both our lack of faith and great faith can amaze God.
This coming year, let’s try to amaze God with our undying faith in His goodness and ability to do anything and everything for our good.
Trust Jesus.
-
 @ 266815e0:6cd408a5
2024-04-22 22:20:47
@ 266815e0:6cd408a5
2024-04-22 22:20:47While I was in Mediera with all the other awesome people at the first SEC cohort there where a lot of discussions around data storage on nostr and if it could be made censorship-resistent
I remember lots of discussions about torrents, hypercore, nostr relays, and of course IPFS
There were a few things I learned from all these conversations:
- All the existing solutions have one thing in common. A universal ID of some kind for files
- HTTP is still good. we don't have to throw the baby out with the bath water
- nostr could fix this... somehow
Some of the existing solutions work well for large files, and all of them are decentralization in some way. However none of them seem capable of serving up cat pictures for social media clients. they all have something missing...
An Identity system
An identity system would allow files to be "owned" by users. and once files have owners servers could start grouping files into a single thing instead of a 1000+ loose files
This can also greatly simplify the question of "what is spam" for a server hosting (or seeding) these files. since it could simply have a whitelist of owners (and maybe their friends)
What is blossom?
Blossom is a set of HTTP endpoints that allow nostr users to store and retrieve binary data on public servers using the sha256 hash as a universal id
What are Blobs?
blobs are chunks of binary data. they are similar to files but with one key difference, they don't have names
Instead blobs have a sha256 hash (like
b1674191a88ec5cdd733e4240a81803105dc412d6c6708d53ab94fc248f4f553) as an IDThese IDs are universal since they can be computed from the file itself using the sha256 hashing algorithm ( you can get a files sha256 hash on linux using:
sha256sum bitcoin.pdf)How do the servers work?
Blossom servers expose four endpoints to let clients and users upload and manage blobs
GET /<sha256>(optional file.ext)PUT /uploadAuthentication: Signed nostr event- Returns a blob descriptor
GET /list/<pubkey>- Returns an array of blob descriptors
Authentication(optional): Signed nostr eventDELETE /<sha256>Authentication: Signed nostr event
What is Blossom Drive?
Blossom Drive is a nostr app built on top of blossom servers and allows users to create and manage folders of blobs
What are Drives
Drives are just nostr events (kind
30563) that store a map of blobs and what filename they should have along with some extra metadataAn example drive event would be
json { "pubkey": "266815e0c9210dfa324c6cba3573b14bee49da4209a9456f9484e5106cd408a5", "created_at": 1710773987, "content": "", "kind": 30563, "tags": [ [ "name", "Emojis" ], [ "description", "nostr emojis" ], [ "d", "emojis" ], [ "r", "https://cdn.hzrd149.com/" ], [ "x", "303f018e613f29e3e43264529903b7c8c84debbd475f89368cb293ec23938981", "/noStrudel.png", "15161", "image/png" ], [ "x", "a0e2b39975c8da1702374b3eed6f4c6c7333e6ae0008dadafe93bd34bfb2ca78", "/satellite.png", "6853", "image/png" ], [ "x", "e8f3fae0f4a43a88eae235a8b79794d72e8f14b0e103a0fed1e073d8fb53d51f", "/amethyst.png", "20487", "image/png" ], [ "x", "70bd5836807b916d79e9c4e67e8b07e3e3b53f4acbb95c7521b11039a3c975c6", "/nos.png", "36521", "image/png" ], [ "x", "0fc304630279e0c5ab2da9c2769e3a3178c47b8609b447a30916244e89abbc52", "/primal.png", "29343", "image/png" ], [ "x", "9a03824a73d4af192d893329bbc04cd3798542ee87af15051aaf9376b74b25d4", "/coracle.png", "18300", "image/png" ], [ "x", "accdc0cdc048f4719bb5e1da4ff4c6ffc1a4dbb7cf3afbd19b86940c01111568", "/iris.png", "24070", "image/png" ], [ "x", "2e740f2514d6188e350d95cf4756bbf455d2f95e6a09bc64e94f5031bc4bba8f", "/damus.png", "32758", "image/png" ], [ "x", "2e019f08da0c75fb9c40d81947e511c8f0554763bffb6d23a7b9b8c9e8c84abb", "/old emojis/astral.png", "29365", "image/png" ], [ "x", "d97f842f2511ce0491fe0de208c6135b762f494a48da59926ce15acfdb6ac17e", "/other/rabbit.png", "19803", "image/png" ], [ "x", "72cb99b689b4cfe1a9fb6937f779f3f9c65094bf0e6ac72a8f8261efa96653f5", "/blossom.png", "4393", "image/png" ] ] }There is a lot going on but the main thing is the list of "x" tags and the path that describes the folder and filename the blob should live at
If your interested, the full event definition is at github.com/hzrd149/blossom-drive
Getting started
Like every good nostr client it takes a small instruction manual in order to use it properly. so here are the steps for getting started
1. Open the app
Open https://blossom.hzrd149.com
2. Login using extension

You can also login using any of the following methods using the input - NIP-46 with your https://nsec.app or https://flare.pub account - a NIP-46 connection string - an
ncryptsecpassword protected private key - ansecunprotected private key (please don't) - bunker:// URI from nsecbunker3. Add a blossom server

Right now
https://cdn.satellite.earthis the only public server that is compatible with blossom drive. If you want to host your own I've written a basic implementation in TypeScript github.com/hzrd149/blossom-server4. Start uploading your files
NOTE: All files upload to blossom drive are public by default. DO NOT upload private files

5. Manage files

Encrypted drives
There is also the option to encrypt drives using NIP-49 password encryption. although its not tested at all so don't trust it, verify

Whats next?
I don't know, but Im excited to see what everyone else on nostr builds with this. I'm only one developer at the end of the day and I can't think of everything
also all the images in this article are stored in one of my blossom drives here
nostr:naddr1qvzqqqrhvvpzqfngzhsvjggdlgeycm96x4emzjlwf8dyyzdfg4hefp89zpkdgz99qq8xzun5d93kcefdd9kkzem9wvr46jka
-
 @ a39d19ec:3d88f61e
2024-11-17 10:48:56
@ a39d19ec:3d88f61e
2024-11-17 10:48:56This week's functional 3d print is the "Dino Clip".

Dino Clip
I printed it some years ago for my son, so he would have his own clip for cereal bags.
Now it is used to hold a bag of dog food close.
The design by "Sneaks" is a so called "print in place". This means that the whole clip with moving parts is printed in one part, without the need for assembly after the print.
 The clip is very strong, and I would print it again if I need a "heavy duty" clip for more rigid or big bags.
Link to the file at Printables
The clip is very strong, and I would print it again if I need a "heavy duty" clip for more rigid or big bags.
Link to the file at Printables -
 @ 3bf0c63f:aefa459d
2024-12-06 20:37:26
@ 3bf0c63f:aefa459d
2024-12-06 20:37:26início
"Vocês vêem? Vêem a história? Vêem alguma coisa? Me parece que estou tentando lhes contar um sonho -- fazendo uma tentativa inútil, porque nenhum relato de sonho pode transmitir a sensação de sonho, aquela mistura de absurdo, surpresa e espanto numa excitação de revolta tentando se impôr, aquela noção de ser tomado pelo incompreensível que é da própria essência dos sonhos..."
Ele ficou em silêncio por alguns instantes.
"... Não, é impossível; é impossível transmitir a sensação viva de qualquer época determinada de nossa existência -- aquela que constitui a sua verdade, o seu significado, a sua essência sutil e contundente. É impossível. Vivemos, como sonhamos -- sozinhos..."
- Livros mencionados por Olavo de Carvalho
- Antiga homepage Olavo de Carvalho
- Bitcoin explicado de um jeito correto e inteligível
- Reclamações
-
 @ ee11a5df:b76c4e49
2024-07-11 23:57:53
@ ee11a5df:b76c4e49
2024-07-11 23:57:53What Can We Get by Breaking NOSTR?
"What if we just started over? What if we took everything we have learned while building nostr and did it all again, but did it right this time?"
That is a question I've heard quite a number of times, and it is a question I have pondered quite a lot myself.
My conclusion (so far) is that I believe that we can fix all the important things without starting over. There are different levels of breakage, starting over is the most extreme of them. In this post I will describe these levels of breakage and what each one could buy us.
Cryptography
Your key-pair is the most fundamental part of nostr. That is your portable identity.
If the cryptography changed from secp256k1 to ed25519, all current nostr identities would not be usable.
This would be a complete start over.
Every other break listed in this post could be done as well to no additional detriment (save for reuse of some existing code) because we would be starting over.
Why would anyone suggest making such a break? What does this buy us?
- Curve25519 is a safe curve meaning a bunch of specific cryptography things that us mortals do not understand but we are assured that it is somehow better.
- Ed25519 is more modern, said to be faster, and has more widespread code/library support than secp256k1.
- Nostr keys could be used as TLS server certificates. TLS 1.3 using RFC 7250 Raw Public Keys allows raw public keys as certificates. No DNS or certification authorities required, removing several points of failure. These ed25519 keys could be used in TLS, whereas secp256k1 keys cannot as no TLS algorithm utilizes them AFAIK. Since relays currently don't have assigned nostr identities but are instead referenced by a websocket URL, this doesn't buy us much, but it is interesting. This idea is explored further below (keep reading) under a lesser level of breakage.
Besides breaking everything, another downside is that people would not be able to manage nostr keys with bitcoin hardware.
I am fairly strongly against breaking things this far. I don't think it is worth it.
Signature Scheme and Event Structure
Event structure is the next most fundamental part of nostr. Although events can be represented in many ways (clients and relays usually parse the JSON into data structures and/or database columns), the nature of the content of an event is well defined as seven particular fields. If we changed those, that would be a hard fork.
This break is quite severe. All current nostr events wouldn't work in this hard fork. We would be preserving identities, but all content would be starting over.
It would be difficult to bridge between this fork and current nostr because the bridge couldn't create the different signature required (not having anybody's private key) and current nostr wouldn't be generating the new kind of signature. Therefore any bridge would have to do identity mapping just like bridges to entirely different protocols do (e.g. mostr to mastodon).
What could we gain by breaking things this far?
- We could have a faster event hash and id verification: the current signature scheme of nostr requires lining up 5 JSON fields into a JSON array and using that as hash input. There is a performance cost to copying this data in order to hash it.
- We could introduce a subkey field, and sign events via that subkey, while preserving the pubkey as the author everybody knows and searches by. Note however that we can already get a remarkably similar thing using something like NIP-26 where the actual author is in a tag, and the pubkey field is the signing subkey.
- We could refactor the kind integer into composable bitflags (that could apply to any application) and an application kind (that specifies the application).
- Surely there are other things I haven't thought of.
I am currently against this kind of break. I don't think the benefits even come close to outweighing the cost. But if I learned about other things that we could "fix" by restructuring the events, I could possibly change my mind.
Replacing Relay URLs
Nostr is defined by relays that are addressed by websocket URLs. If that changed, that would be a significant break. Many (maybe even most) current event kinds would need superseding.
The most reasonable change is to define relays with nostr identities, specifying their pubkey instead of their URL.
What could we gain by this?
- We could ditch reliance on DNS. Relays could publish events under their nostr identity that advertise their current IP address(es).
- We could ditch certificates because relays could generate ed25519 keypairs for themselves (or indeed just self-signed certificates which might be much more broadly supported) and publish their public ed25519 key in the same replaceable event where they advertise their current IP address(es).
This is a gigantic break. Almost all event kinds need redefining and pretty much all nostr software will need fairly major upgrades. But it also gives us a kind of Internet liberty that many of us have dreamt of our entire lives.
I am ambivalent about this idea.
Protocol Messaging and Transport
The protocol messages of nostr are the next level of breakage. We could preserve keypair identities, all current events, and current relay URL references, but just break the protocol of how clients and relay communicate this data.
This would not necessarily break relay and client implementations at all, so long as the new protocol were opt-in.
What could we get?
- The new protocol could transmit events in binary form for increased performance (no more JSON parsing with it's typical many small memory allocations and string escaping nightmares). I think event throughput could double (wild guess).
- It could have clear expectations of who talks first, and when and how AUTH happens, avoiding a lot of current miscommunication between clients and relays.
- We could introduce bitflags for feature support so that new features could be added later and clients would not bother trying them (and getting an error or timing out) on relays that didn't signal support. This could replace much of NIP-11.
- We could then introduce something like negentropy or negative filters (but not that... probably something else solving that same problem) without it being a breaking change.
- The new protocol could just be a few websocket-binary messages enhancing the current protocol, continuing to leverage the existing websocket-text messages we currently have, meaning newer relays would still support all the older stuff.
The downsides are just that if you want this new stuff you have to build it. It makes the protocol less simple, having now multiple protocols, multiple ways of doing the same thing.
Nonetheless, this I am in favor of. I think the trade-offs are worth it. I will be pushing a draft PR for this soon.
The path forward
I propose then the following path forward:
- A new nostr protocol over websockets binary (draft PR to be shared soon)
- Subkeys brought into nostr via NIP-26 (but let's use a single letter tag instead, OK?) via a big push to get all the clients to support it (the transition will be painful - most major clients will need to support this before anybody can start using it).
- Some kind of solution to the negative-filter-negentropy need added to the new protocol as its first optional feature.
- We seriously consider replacing Relay URLs with nostr pubkeys assigned to the relay, and then have relays publish their IP address and TLS key or certificate.
We sacrifice these:
- Faster event hash/verification
- Composable event bitflags
- Safer faster more well-supported crypto curve
- Nostr keys themselves as TLS 1.3 RawPublicKey certificates
-
 @ fd78c37f:a0ec0833
2024-12-28 15:58:04
@ fd78c37f:a0ec0833
2024-12-28 15:58:04In this edition, we are pleased to speak with Luthando nostr:npub10vudmjqhr8kn2kv2pxhezt2h5t5c9zauwq8qr56nhdn64yacsqyqf08djm leader of the Bitcoin Ekasi community, about how they are using Bitcoin to transform payment systems, savings habits, and cross-border remittances in a South African township, while fostering digital currency education and boosting local economic trust.
YakiHonne: Luthando. We really appreciate you coming in. YakiHonne is a decentralized media client built on the Nostr protocol that enables freedom of speech through technology. It empowers creators to create their own voice, assets, and features. It also allows features like smart widgets, verified notes, and focuses on long-form articles. today. we'll be exploring more about your community.Can you tell us a bit about yourself? What do you do, and what’s your role in your community?
Luthando:I’m Luthando, a project community leader at Bitcoin Ekasi. My role includes onboarding township shops to help them adopt Bitcoin as a payment method. I also manage staff records, tracking workdays and paid leave for team members involved in the project. Additionally, I conduct interviews and collaborate with a supervisor to share insights and experiences about Bitcoin. This work is part of my efforts with Bitcoin Ekasi.

YakiHonne: You're really doing a lot of work in the Bitcoin ecosystem,what sparked your interest in Bitcoin? And what motivated you to create a community around it?
Luthando:When I was working as a safety coach at Safeacase, Herman introduced me to Bitcoin. During the COVID-19 pandemic, Safeacase, which relied on donations, faced severe financial challenges. This led to the launch of the Bitcoin Ekasi Project, where I helped township shops adopt Bitcoin as a payment method. With limited funds, I transitioned from receiving a fiat salary to earning in Bitcoin. Bitcoin transformed my mindset, making me realize it is the future of money. This realization inspired me to travel the world and explore new countries.
YakiHonne: Great. I really admire the enthusiasm you have for Bitcoin.Can you share a brief history of how you built your community and attracted members? What methods or advertisements did you use to onboard them?
Luthando:We host monthly Bitcoin movie nights to engage the community, running from February to December starting next year. We promote the events with posters in town, shops, and clinics, inviting residents to join. During the movie nights, participants use Bitcoin we provide to purchase popcorn and drinks, gaining hands-on experience with the technology. Luthando:And our Bitcoin center features a thrift shop and a small Bitcoin ATM. Community members can exchange fiat for Bitcoin using the ATM and use it to purchase clothing from the shop. We also offer Bitcoin courses with 14 students attending classes five days a week. To encourage attendance, students are rewarded with Bitcoin for consistent participation. Similarly, in the “Safer Kids” program, children who maintain a 70% attendance rate or higher also receive Bitcoin rewards. Luthando:To further promote Bitcoin adoption in the community, we painted Bitcoin-themed logos on 34 shops and paid the owners in Bitcoin, which they can use in local shops. This initiative not only spreads awareness but also provides the community with practical opportunities to use Bitcoin.

YakiHonne: Yeah, we are pushing Bitcoin adoption so hard this time. It's really great.What principles guide your community, and how do you ensure trust and reliability in your discussions?
Luthando:I was born in eastern South Africa, and my parents moved here around 1996. The community knows me well and trusts that I wouldn’t introduce anything fraudulent. Since 2010, we’ve been working in this township, especially helping children, building over a decade of trust. I explain to the community that we aim to bring value through Bitcoin, encouraging them to save in Bitcoin instead of fiat. As a result, the community has great trust in our Bitcoin Ekasi team.
YakiHonne: How do you educate your members and keep them updated on Bitcoin developments? You mentioned having five weekly meetups to onboard members, but what other methods do you use to educate them and keep them informed about the Bitcoin ecosystem?
Luthando:We use the Felly app to communicate with community members and keep them updated. At the Ekasi Center, we host quizzes to encourage participation. For example, the first attendees can earn 5,000 sats, motivating them to regularly engage with the Felly app. Although we initially tried a few other methods that didn't really involve them getting Sats, its impact was limited as many people in the township seek quick financial returns and often don’t return after their first visit. To address this, we host movie nights as a more engaging way to promote Bitcoin education. During these events, we screen Bitcoin-related films, allowing community members to learn about Bitcoin in a fun and relaxed setting.

YakiHonne: It's truly captivating and highly insightful.How does your community collaborate with the global Bitcoin ecosystem? Specifically, how does it engage with the broader worldwide Bitcoin community, and which partnership has been of more significant impact on Bitcoin Ekasi?
Luthando:We have established a strong partnership with Bitcoin Beach, which provided crucial support in the creation of the Bitcoin Ekasi project. Currently, we are planning to build a community center in the township, earning the trust and support of both Bitcoin Beach and the local government of Mossel Bay. The community center will serve as a multifunctional space for events like weddings and more. As one of the earliest Bitcoin adoption projects in Africa, Bitcoin Ekasi has inspired other countries to follow suit, viewing us as a model for building sustainable Bitcoin communities.
YakiHonne: How do you collaborate with Bitcoin communities and organizations outside South Africa? What partnerships or interactions do you have with other global Bitcoin communities?
Luthando: We collaborate with other Bitcoin projects through community initiatives. For example, we paint logos on local community shops and pay the owners 7000Sats per week. This approach has helped us build connections with projects outside South Africa. One notable example is our assistance to the Bitcoin Dua project in Africa, helping them establish a Bitcoin circular economy. We also supported the Bitcoin Loxin project in Cape Town, South Africa, in launching their Bitcoin circular economy. Through these collaborations, we have developed strong relationships with other Bitcoin communities.

YakiHonne: We’d like to understand the challenges you faced when starting the community, as well as the challenges the community has encountered?
Luthando: One of the main challenges is convincing members that Bitcoin is not a scam. Many people are skeptical about Bitcoin, fearing they might lose their money. Additionally, saving is not a common habit within the community, even with fiat currency. I often explain the importance of saving in Bitcoin, emphasizing how it can safeguard their financial security. However, changing deeply ingrained mindsets has proven to be quite difficult. Another challenge is the limited level of education in the community. Even those who own smartphones often struggle to use them effectively. This lack of familiarity extends to using Bitcoin wallets, with many people finding it challenging to navigate wallet usage, especially in shops. Lastly, I feel like I’m working around the clock. Even outside of work hours, people come to my house seeking assistance, such as exchanging Bitcoin for fiat. While I’m happy to help, the constant demands can feel overwhelming at times, making it seem as though I’m working every day, including weekends.
YakiHonne: and how you managed to overcome them?
Luthando: Overcoming these challenges is not easy. I can't say that I've fully managed to resolve them, but I do my best to address them. Fortunately, I have a colleague who assists me, although he’s currently out of town. He helps manage some of the workload, especially in dealing with local community members and providing them with the support they need.
YakiHonne: I'm really interested in the issue of people thinking Bitcoin is a scam. Could you elaborate on that? What specific steps have you taken to demonstrate that Bitcoin is reliable and not a scam?
Luthando: Many shop owners initially believe Bitcoin is a scam and refuse to accept it. To address their doubts, I demonstrate Bitcoin's legitimacy through practical examples. First, I help them download a Bitcoin wallet and post about it on X, receiving small tips from Bitcoin enthusiasts worldwide. I then use these tips to showcase Bitcoin's real-world applications. For instance, I use Bitrefill to purchase mobile airtime or fuel vouchers for them, highlighting Bitcoin's utility in daily life. I also mention South African restaurants like Steers that accept Bitcoin and even place food orders using Bitcoin to show its usability. Additionally, I demonstrate withdrawing cash from a crypto ATM using Bitcoin, further proving that it is a reliable financial tool and not a scam.
YakiHonne: You've done a lot of work in South Africa. I can imagine the effort, the pain and the stress.What initiatives has the community taken to promote Bitcoin adoption, and what results have these efforts achieved?
Luthando: At first, I never imagined we would reach this point. Now, many people frequently come to my home to ask how to buy Bitcoin. For example, this week, a man from Nigeria wanted to purchase Bitcoin worth 5,000 units. I explained the process to him and recommended using a hardware wallet for securely storing large amounts of Bitcoin. He used to struggle with sending money back home, but now he has realized the convenience of Bitcoin. In October last year, I helped two stores owned by Nigerians adopt Bitcoin payments. Since then, this practice has spread within the community, and more people, especially shop owners, have developed an interest in Bitcoin. They ask about its low transaction fees and have recognized it as an efficient solution for cross-border remittances. Initially, some shop owners were skeptical about Bitcoin, but they eventually started saving with it. Today, many of them have accumulated significant Bitcoin savings for their families and children, and they often express their gratitude for introducing Bitcoin to the community. Overall, the Bitcoin adoption project has had a profound impact here. We have educated the community about Bitcoin’s long-term savings value, and many people are now satisfied with this initiative and optimistic about the future.

YakiHonne: It’s clear you’ve achieved tangible results from your efforts. Looking ahead, what are your community's goals for the next 6 to 12 months? How do you plan to achieve them?
Luthando: For Bitcoin Ekasi, one of our main goals is to establish a dedicated Bitcoin Ekasi Center. This center would serve as a hub to educate people about Bitcoin on a frequent basis. We have already started working with a local school in the township, recruiting students and introducing teachers to Bitcoin. Our vision is to integrate Bitcoin education into the school’s curriculum, similar to what has been done in El Salvador. By incorporating Bitcoin as part of their regular subjects, students can gain foundational knowledge about Bitcoin and its potential uses. Ultimately, we aim for teachers to become advocates who can confidently teach children about Bitcoin, empowering the next generation with essential financial literacy skills.
YakiHonne: Thank you so much! I think most of my questions have been answered. I’m really glad to see Bitcoin enthusiasts with a clear focus on Bitcoin. As you said, Bitcoin is the future, and I truly appreciate your enthusiasm for it.
Luthando: Bitcoin is truly the future. We want to see this township transformed into something more modern, rather than its current state. I hope to see more parents saving some Bitcoin for their children. In our community, most kids receive a monthly government allowance of $50 starting from the age of one. I often suggest to parents that they set aside half of that allowance to buy Bitcoin for their child. If they save consistently from age one to 18, the value could grow significantly as Bitcoin appreciates. I’m already doing this for my own child so that he will have savings as he grows up.
YakiHonne: Bitcoin is the future. Its value continues to grow steadily over time. Thank you so much for today’s conversation; we are truly honored. Your sharing of such rich experiences has been incredibly insightful for us. I’ve learned that using movie events to engage more people is an excellent idea, and we plan to start trying it out soon. Once again, thank you for your time and for sharing with us!
-
 @ 68ce44e4:ecd5f574
2024-12-28 12:01:44
@ 68ce44e4:ecd5f574
2024-12-28 12:01:44Xenea Wallet Daily Quiz 28 Dec
Complete now : https://xenea.app/register/167mZpWf7A

XENEAwallet #CryptoAirdrop #cryptocurrency #cryptonews #bitcoin #EarnFreeCrypto
-
 @ 32e18276:5c68e245
2024-03-02 12:26:09
@ 32e18276:5c68e245
2024-03-02 12:26:09Thanks to OpenSats and its generous donors, Damus has been able to continue building open source freedom tech without influence from external parties. Damus' mission is to build the best nostr and bitcoin tech without compromise on decentralization, and this will continue to be our mission going forward. This wouldn't be possible without OpenSats and other organizations that continue to help make this vision a reality!
As per our OpenSats agreement, we are required to publish quarterly reports on our progress. We submit this report to nostr for full transparency. If you're curious what we've been working on this past quarter, check it out:
Damus OpenSats Q2 Progress Report
The second quarter of the Damus OpenSats grant has been very productive and encompasses the 1.7 release of Damus, soon to be released to the appstore.
Notable new features in Damus iOS 1.7
- Damus purple subscriptions which includes the DeepL Universal Translator 🖖
- Local-first full-text search engine for privacy preserving searching powered by nostrdb4
- Add NIP-42 relay auth support
- Added regional relay recommendations for Germany, Japan, Thailand
- Add naddr link support
New tech built in this quarter
- A new nostr share-link opengraph renderer in rust called notecrumbs2, powered by egui and nostrdb4
- Added query and subscription support to nostrdb{,-rs}
- Added fulltext search query support nostrdb, which powers the search in Damus iOS v1.7
- Working prototype of Damus Android and Damus NoteDeck, a rust-powered multiplatform nostr client3 powered by egui and nostrdb4
How money was used
- Paying individual contributors via patch submissions on the damus dev mailing list (patches@damus.io)
- relay.damus.io server costs
- deepl translation costs
- Living expenses, nostr/bitcoin conferences, travel, etc
Contributions
Damus-iOS
name added removed commits Daniel D’Aquino <daniel@daquino.me> +7655 -2989 46 William Casarin <jb55@jb55.com> +3753 -2396 132 kernelkind <kernelkind@gmail.com> +1513 -273 27 Charlie Fish <contact@charlie.fish> +1386 -331 12 Terry Yiu <git@tyiu.xyz> +1018 -102 3 ericholguin <ericholguin@apache.org> +509 -65 3 Transifex <transifex@transifex.com> +464 -67 80 Suhail Saqan <suhail.saqan@gmail.com> +347 -27 2 ericholguin <eric.holguinsanchez@gmail.com> +202 -101 6 alltheseas <64376233+alltheseas@users.noreply.github.com> +51 -24 5 Kieran <kieran@harkin.me> +33 -0 1 kunigaku <kunigaku@gmail.com> +13 -2 1 vuittont60 <81072379+vuittont60@users.noreply.github.com> +3 -3 1 Jing维 <zhjw43@163.com> +1 -1 1 hakkadaikon <hakkadaikon@yahoo.co.jp> +1 -1 1notecrumbs
name added removed commits William Casarin <jb55@jb55.com> +6079 -819 68Damus Android/NoteDeck
name added removed commits William Casarin <jb55@jb55.com> +5205 -2870 86 0xb10c <b10c@b10c.me> +6 -2 1 alltheseas <64376233+alltheseas@users.noreply.github.com> +5 -0 1nostrdb
name added removed commits William Casarin <jb55@jb55.com> +88175 -3758 186 kernelkind <kernelkind@gmail.com> +50 -3 1 Yasuhiro Matsumoto <mattn.jp@gmail.com> +26 -3 1 Charlie Fish <contact@charlie.fish> +12 -0 1 shuoer86 <129674997+shuoer86@users.noreply.github.com> +3 -3 1 hakkadaikon <hakkadaikon@yahoo.co.jp> +2 -2 1nostrdb-rs
name added removed commits William Casarin <jb55@jb55.com> +8181 -248 50iOS Changelog
Added
- Damus Purple membership! (Daniel D’Aquino)
- Improved damus.io share links (William Casarin)
- Add local, privacy-preserving fulltext search engine (William Casarin)
- Add NIP-42 relay auth support (Charlie Fish)
- Add ability to hide suggested hashtags (ericholguin)
- Add ability to mute hashtag from SearchView (Charlie Fish)
- Add ability to preview media taken with camera (Suhail Saqan)
- Add ability to search for naddr, nprofiles, nevents (kernelkind)
- Add experimental push notification support (Daniel D’Aquino)
- Add naddr link support (kernelkind)
- Add regional relay recommendations to Relay configuration view (Daniel D’Aquino)
- Add regional relays for Germany (Daniel D’Aquino)
- Add regional relays for Japan (Daniel D’Aquino)
- Add regional relays for Thailand (Daniel D’Aquino)
- Add support for Apple In-App purchases (Daniel D’Aquino)
- Always convert damus.io links to inline mentions (William Casarin)
- Notification reminders for Damus Purple impending expiration (Daniel D’Aquino)
Changed
- Disable inline text suggestions on 17.0 as they interfere with mention generation (William Casarin)
- EULA is not shown by default (ericholguin)
- Generate nprofile/nevent links in share menus (kernelkind)
- Improve push notification support to match local notification support (Daniel D’Aquino)
- Move mute thread in menu so it's not clicked by accident (alltheseas)
- Prioritize friends when autocompleting (Charlie Fish)
Fixed
- Add workaround to fix note language recognition and reduce wasteful translation requests (Terry Yiu)
- Allow mentioning users with punctuation characters in their names (kernelkind)
- Fix broken mentions when there is text is directly after (kernelkind)
- Fix crash on very large notes (Daniel D’Aquino)
- Fix crash when accessing cached purple accounts (William Casarin)
- Fix crash when logging out and switching accounts (William Casarin)
- Fix duplicate notes getting written to nostrdb (William Casarin)
- Fixed bug where sometimes notes from other profiles appear on profile pages (Charlie Fish)
- Fixed previews not rendering (ericholguin)
- Fix issue where adding relays might not work on corrupted contact lists (Charlie Fish)
- Fix load media formatting on small screens (kernelkind)
- Fix many nostrdb transaction related crashes (William Casarin)
- Fix onboarding post view not being dismissed under certain conditions (Daniel D’Aquino)
- Fix performance issue with gifs (William Casarin)
- Fix persistent local notifications even after logout (William Casarin)
- Fix profile not updating bug (William Casarin)
- Fix shared nevents that are too long (kernelkind)
- Fix welcome screen not showing if the user enters the app directly after a successful checkout without going through the link (Daniel D’Aquino)
- Remove extra space at the end of DM messages (kernelkind)
- Save current viewed image index when switching to fullscreen (kernelkind)
Removed
- Removed copying public key action (ericholguin)
- Removed old nsec key warning, nsec automatically convert to npub when posting (kernelkind)
-
 @ 68ce44e4:ecd5f574
2024-12-28 09:14:27
@ 68ce44e4:ecd5f574
2024-12-28 09:14:27Midas Airdrop - Trending now .. ✅🔥
https://t.me/MidasRWA_bot/app?startapp=ref_f8260b8d-1da0-47c7-b9b0-bb333d6ee1d6
 Received $13.75M Funding ..
Most trending airdrop right now.. 🔥💯 Join Fast.. ✅
Received $13.75M Funding ..
Most trending airdrop right now.. 🔥💯 Join Fast.. ✅midasairdrop #midastouch #CryptoAirdrop #cryptonews #cryptocurrency #bitcoin
-
 @ 16d11430:61640947
2024-12-29 23:17:52
@ 16d11430:61640947
2024-12-29 23:17:52Bitcoin, as a decentralized digital asset, exists fundamentally outside the framework of traditional financial (TradFi) systems. While the adoption of Bitcoin by TradFi institutions has brought it closer to mainstream acceptance, the dynamics of regulated markets create barriers to accurately reflecting Bitcoin’s intrinsic value. Here’s why:
- TradFi's Centralized Control and Market Manipulation
Regulated markets are built on centralized systems that allow institutions to exert significant control over price movements. Unlike Bitcoin’s decentralized, trustless model, TradFi relies on intermediaries and can be prone to manipulative practices such as spoofing, short selling, and derivative leveraging. These tactics often distort Bitcoin’s price to align with institutional agendas rather than its organic demand and supply.
For example:
Futures contracts allow institutions to short Bitcoin, pushing prices down without requiring physical delivery of the asset.
Over-the-counter (OTC) trading hides real volumes, further distorting public price signals.
- Lack of Weekend Liquidity
Regulated markets like futures or ETFs don’t operate 24/7. This creates a disjointed price discovery mechanism. Bitcoin trades continuously on global exchanges, but its value can diverge significantly from TradFi-set benchmarks over weekends due to thin liquidity and increased volatility. When TradFi markets reopen, institutions often adjust Bitcoin prices to suit their positioning, regardless of real market sentiment.
- Regulatory Constraints
The core ethos of Bitcoin is permissionless, borderless, and resistant to censorship. TradFi markets, by contrast, are heavily regulated and often impose restrictions that undermine Bitcoin’s true value:
Limits on leverage, capital flows, and trading hours inhibit the natural market dynamics that define Bitcoin.
Regulatory actions, such as lawsuits or exchange crackdowns, introduce external pressures that disproportionately impact prices.
- Misaligned Incentives
Many TradFi institutions profit more from Bitcoin's volatility than its growth. Products like Bitcoin ETFs or derivatives generate fees regardless of whether Bitcoin's price goes up or down, giving TradFi little incentive to advocate for Bitcoin's long-term value. Moreover, central banks and governments may view Bitcoin as a threat to fiat systems, further motivating policies that suppress its adoption.
How Bitcoiners Can Factor This In Over the Weekend
Weekends present unique challenges for Bitcoin holders, given the interplay of reduced liquidity, TradFi manipulation, and retail-driven volatility. Here are strategies to reduce exposure:
- Limit Leveraged Positions
Leverage amplifies risk, particularly over weekends when sudden price swings can trigger liquidations. Bitcoiners should consider reducing or closing leveraged positions before the weekend to avoid forced selling during thin markets.
- Use Stop-Loss Orders
Setting stop-loss orders can protect against significant downside risk during volatile periods. However, ensure these are placed strategically to avoid being liquidated by temporary wicks or market manipulation.
- Diversify Holding Strategies
Rather than keeping funds solely on centralized exchanges, Bitcoiners can use:
Cold storage: Safeguard long-term holdings from price volatility.
Lightning Network wallets: For immediate liquidity and payments without exposing large holdings to exchange risk.
- Monitor On-Chain Metrics
Bitcoin’s true value is better gauged through on-chain data, such as:
Hash rate: Reflects network security and miner activity.
Wallet activity: Indicates organic user demand.
HODL waves: Show long-term accumulation trends.
- Avoid Emotional Trading
Weekend price swings are often exaggerated by low liquidity and retail panic. Staying focused on Bitcoin’s fundamentals and long-term vision helps prevent reactive decisions.
Conclusion
TradFi markets will never fully reflect Bitcoin’s true value because their structure is antithetical to Bitcoin's decentralized, free-market ethos. Bitcoiners should be aware of the disconnect and take proactive steps, especially over weekends, to protect their investments from TradFi-induced volatility. By limiting leverage, diversifying holdings, and focusing on long-term fundamentals, Bitcoiners can mitigate TradFi's influence and stay aligned with Bitcoin's revolutionary potential.
-
 @ 4ba8e86d:89d32de4
2024-11-14 09:17:14
@ 4ba8e86d:89d32de4
2024-11-14 09:17:14Tutorial feito por nostr:nostr:npub1rc56x0ek0dd303eph523g3chm0wmrs5wdk6vs0ehd0m5fn8t7y4sqra3tk poste original abaixo:
Parte 1 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/263585/tutorial-debloat-de-celulares-android-via-adb-parte-1
Parte 2 : http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/index.php/263586/tutorial-debloat-de-celulares-android-via-adb-parte-2
Quando o assunto é privacidade em celulares, uma das medidas comumente mencionadas é a remoção de bloatwares do dispositivo, também chamado de debloat. O meio mais eficiente para isso sem dúvidas é a troca de sistema operacional. Custom Rom’s como LineageOS, GrapheneOS, Iodé, CalyxOS, etc, já são bastante enxutos nesse quesito, principalmente quanto não é instalado os G-Apps com o sistema. No entanto, essa prática pode acabar resultando em problemas indesejados como a perca de funções do dispositivo, e até mesmo incompatibilidade com apps bancários, tornando este método mais atrativo para quem possui mais de um dispositivo e separando um apenas para privacidade. Pensando nisso, pessoas que possuem apenas um único dispositivo móvel, que são necessitadas desses apps ou funções, mas, ao mesmo tempo, tem essa visão em prol da privacidade, buscam por um meio-termo entre manter a Stock rom, e não ter seus dados coletados por esses bloatwares. Felizmente, a remoção de bloatwares é possível e pode ser realizada via root, ou mais da maneira que este artigo irá tratar, via adb.
O que são bloatwares?
Bloatware é a junção das palavras bloat (inchar) + software (programa), ou seja, um bloatware é basicamente um programa inútil ou facilmente substituível — colocado em seu dispositivo previamente pela fabricante e operadora — que está no seu dispositivo apenas ocupando espaço de armazenamento, consumindo memória RAM e pior, coletando seus dados e enviando para servidores externos, além de serem mais pontos de vulnerabilidades.
O que é o adb?
O Android Debug Brigde, ou apenas adb, é uma ferramenta que se utiliza das permissões de usuário shell e permite o envio de comandos vindo de um computador para um dispositivo Android exigindo apenas que a depuração USB esteja ativa, mas também pode ser usada diretamente no celular a partir do Android 11, com o uso do Termux e a depuração sem fio (ou depuração wifi). A ferramenta funciona normalmente em dispositivos sem root, e também funciona caso o celular esteja em Recovery Mode.
Requisitos:
Para computadores:
• Depuração USB ativa no celular; • Computador com adb; • Cabo USB;
Para celulares:
• Depuração sem fio (ou depuração wifi) ativa no celular; • Termux; • Android 11 ou superior;
Para ambos:
• Firewall NetGuard instalado e configurado no celular; • Lista de bloatwares para seu dispositivo;
Ativação de depuração:
Para ativar a Depuração USB em seu dispositivo, pesquise como ativar as opções de desenvolvedor de seu dispositivo, e lá ative a depuração. No caso da depuração sem fio, sua ativação irá ser necessária apenas no momento que for conectar o dispositivo ao Termux.
Instalação e configuração do NetGuard
O NetGuard pode ser instalado através da própria Google Play Store, mas de preferência instale pela F-Droid ou Github para evitar telemetria.
F-Droid: https://f-droid.org/packages/eu.faircode.netguard/
Github: https://github.com/M66B/NetGuard/releases
Após instalado, configure da seguinte maneira:
Configurações → padrões (lista branca/negra) → ative as 3 primeiras opções (bloquear wifi, bloquear dados móveis e aplicar regras ‘quando tela estiver ligada’);
Configurações → opções avançadas → ative as duas primeiras (administrar aplicativos do sistema e registrar acesso a internet);
Com isso, todos os apps estarão sendo bloqueados de acessar a internet, seja por wifi ou dados móveis, e na página principal do app basta permitir o acesso a rede para os apps que você vai usar (se necessário). Permita que o app rode em segundo plano sem restrição da otimização de bateria, assim quando o celular ligar, ele já estará ativo.
Lista de bloatwares
Nem todos os bloatwares são genéricos, haverá bloatwares diferentes conforme a marca, modelo, versão do Android, e até mesmo região.
Para obter uma lista de bloatwares de seu dispositivo, caso seu aparelho já possua um tempo de existência, você encontrará listas prontas facilmente apenas pesquisando por elas. Supondo que temos um Samsung Galaxy Note 10 Plus em mãos, basta pesquisar em seu motor de busca por:
Samsung Galaxy Note 10 Plus bloatware listProvavelmente essas listas já terão inclusas todos os bloatwares das mais diversas regiões, lhe poupando o trabalho de buscar por alguma lista mais específica.
Caso seu aparelho seja muito recente, e/ou não encontre uma lista pronta de bloatwares, devo dizer que você acaba de pegar em merda, pois é chato para um caralho pesquisar por cada aplicação para saber sua função, se é essencial para o sistema ou se é facilmente substituível.
De antemão já aviso, que mais para frente, caso vossa gostosura remova um desses aplicativos que era essencial para o sistema sem saber, vai acabar resultando na perda de alguma função importante, ou pior, ao reiniciar o aparelho o sistema pode estar quebrado, lhe obrigando a seguir com uma formatação, e repetir todo o processo novamente.
Download do adb em computadores
Para usar a ferramenta do adb em computadores, basta baixar o pacote chamado SDK platform-tools, disponível através deste link: https://developer.android.com/tools/releases/platform-tools. Por ele, você consegue o download para Windows, Mac e Linux.
Uma vez baixado, basta extrair o arquivo zipado, contendo dentro dele uma pasta chamada platform-tools que basta ser aberta no terminal para se usar o adb.
Download do adb em celulares com Termux.
Para usar a ferramenta do adb diretamente no celular, antes temos que baixar o app Termux, que é um emulador de terminal linux, e já possui o adb em seu repositório. Você encontra o app na Google Play Store, mas novamente recomendo baixar pela F-Droid ou diretamente no Github do projeto.
F-Droid: https://f-droid.org/en/packages/com.termux/
Github: https://github.com/termux/termux-app/releases
Processo de debloat
Antes de iniciarmos, é importante deixar claro que não é para você sair removendo todos os bloatwares de cara sem mais nem menos, afinal alguns deles precisam antes ser substituídos, podem ser essenciais para você para alguma atividade ou função, ou até mesmo são insubstituíveis.
Alguns exemplos de bloatwares que a substituição é necessária antes da remoção, é o Launcher, afinal, é a interface gráfica do sistema, e o teclado, que sem ele só é possível digitar com teclado externo. O Launcher e teclado podem ser substituídos por quaisquer outros, minha recomendação pessoal é por aqueles que respeitam sua privacidade, como Pie Launcher e Simple Laucher, enquanto o teclado pelo OpenBoard e FlorisBoard, todos open-source e disponíveis da F-Droid.
Identifique entre a lista de bloatwares, quais você gosta, precisa ou prefere não substituir, de maneira alguma você é obrigado a remover todos os bloatwares possíveis, modifique seu sistema a seu bel-prazer. O NetGuard lista todos os apps do celular com o nome do pacote, com isso você pode filtrar bem qual deles não remover.
Um exemplo claro de bloatware insubstituível e, portanto, não pode ser removido, é o com.android.mtp, um protocolo onde sua função é auxiliar a comunicação do dispositivo com um computador via USB, mas por algum motivo, tem acesso a rede e se comunica frequentemente com servidores externos. Para esses casos, e melhor solução mesmo é bloquear o acesso a rede desses bloatwares com o NetGuard.
MTP tentando comunicação com servidores externos:
Executando o adb shell
No computador
Faça backup de todos os seus arquivos importantes para algum armazenamento externo, e formate seu celular com o hard reset. Após a formatação, e a ativação da depuração USB, conecte seu aparelho e o pc com o auxílio de um cabo USB. Muito provavelmente seu dispositivo irá apenas começar a carregar, por isso permita a transferência de dados, para que o computador consiga se comunicar normalmente com o celular.
Já no pc, abra a pasta platform-tools dentro do terminal, e execute o seguinte comando:
./adb start-serverO resultado deve ser:
daemon not running; starting now at tcp:5037 daemon started successfully
E caso não apareça nada, execute:
./adb kill-serverE inicie novamente.
Com o adb conectado ao celular, execute:
./adb shellPara poder executar comandos diretamente para o dispositivo. No meu caso, meu celular é um Redmi Note 8 Pro, codinome Begonia.
Logo o resultado deve ser:
begonia:/ $
Caso ocorra algum erro do tipo:
adb: device unauthorized. This adb server’s $ADB_VENDOR_KEYS is not set Try ‘adb kill-server’ if that seems wrong. Otherwise check for a confirmation dialog on your device.
Verifique no celular se apareceu alguma confirmação para autorizar a depuração USB, caso sim, autorize e tente novamente. Caso não apareça nada, execute o kill-server e repita o processo.
No celular
Após realizar o mesmo processo de backup e hard reset citado anteriormente, instale o Termux e, com ele iniciado, execute o comando:
pkg install android-toolsQuando surgir a mensagem “Do you want to continue? [Y/n]”, basta dar enter novamente que já aceita e finaliza a instalação
Agora, vá até as opções de desenvolvedor, e ative a depuração sem fio. Dentro das opções da depuração sem fio, terá uma opção de emparelhamento do dispositivo com um código, que irá informar para você um código em emparelhamento, com um endereço IP e porta, que será usado para a conexão com o Termux.
Para facilitar o processo, recomendo que abra tanto as configurações quanto o Termux ao mesmo tempo, e divida a tela com os dois app’s, como da maneira a seguir:
Para parear o Termux com o dispositivo, não é necessário digitar o ip informado, basta trocar por “localhost”, já a porta e o código de emparelhamento, deve ser digitado exatamente como informado. Execute:
adb pair localhost:porta CódigoDeEmparelhamentoDe acordo com a imagem mostrada anteriormente, o comando ficaria “adb pair localhost:41255 757495”.
Com o dispositivo emparelhado com o Termux, agora basta conectar para conseguir executar os comandos, para isso execute:
adb connect localhost:portaObs: a porta que você deve informar neste comando não é a mesma informada com o código de emparelhamento, e sim a informada na tela principal da depuração sem fio.
Pronto! Termux e adb conectado com sucesso ao dispositivo, agora basta executar normalmente o adb shell:
adb shellRemoção na prática Com o adb shell executado, você está pronto para remover os bloatwares. No meu caso, irei mostrar apenas a remoção de um app (Google Maps), já que o comando é o mesmo para qualquer outro, mudando apenas o nome do pacote.
Dentro do NetGuard, verificando as informações do Google Maps:
Podemos ver que mesmo fora de uso, e com a localização do dispositivo desativado, o app está tentando loucamente se comunicar com servidores externos, e informar sabe-se lá que peste. Mas sem novidades até aqui, o mais importante é que podemos ver que o nome do pacote do Google Maps é com.google.android.apps.maps, e para o remover do celular, basta executar:
pm uninstall –user 0 com.google.android.apps.mapsE pronto, bloatware removido! Agora basta repetir o processo para o resto dos bloatwares, trocando apenas o nome do pacote.
Para acelerar o processo, você pode já criar uma lista do bloco de notas com os comandos, e quando colar no terminal, irá executar um atrás do outro.
Exemplo de lista:
Caso a donzela tenha removido alguma coisa sem querer, também é possível recuperar o pacote com o comando:
cmd package install-existing nome.do.pacotePós-debloat
Após limpar o máximo possível o seu sistema, reinicie o aparelho, caso entre no como recovery e não seja possível dar reboot, significa que você removeu algum app “essencial” para o sistema, e terá que formatar o aparelho e repetir toda a remoção novamente, desta vez removendo poucos bloatwares de uma vez, e reiniciando o aparelho até descobrir qual deles não pode ser removido. Sim, dá trabalho… quem mandou querer privacidade?
Caso o aparelho reinicie normalmente após a remoção, parabéns, agora basta usar seu celular como bem entender! Mantenha o NetGuard sempre executando e os bloatwares que não foram possíveis remover não irão se comunicar com servidores externos, passe a usar apps open source da F-Droid e instale outros apps através da Aurora Store ao invés da Google Play Store.
Referências: Caso você seja um Australopithecus e tenha achado este guia difícil, eis uma videoaula (3:14:40) do Anderson do canal Ciberdef, realizando todo o processo: http://odysee.com/@zai:5/Como-remover-at%C3%A9-200-APLICATIVOS-que-colocam-a-sua-PRIVACIDADE-E-SEGURAN%C3%87A-em-risco.:4?lid=6d50f40314eee7e2f218536d9e5d300290931d23
Pdf’s do Anderson citados na videoaula: créditos ao anon6837264 http://eternalcbrzpicytj4zyguygpmkjlkddxob7tptlr25cdipe5svyqoqd.onion/file/3863a834d29285d397b73a4af6fb1bbe67c888d72d30/t-05e63192d02ffd.pdf
Processo de instalação do Termux e adb no celular: https://youtu.be/APolZrPHSms
-
 @ 0dc2dcb1:4787801a
2024-07-11 15:16:25
@ 0dc2dcb1:4787801a
2024-07-11 15:16:25- Added ids and
setIds()to the Filter class to fetch events with ids - https://github.com/nostrver-se/nostr-php/compare/1.3.1...1.3.2 - Discovered https://revolt.run/ as a package to be used for concurrent async code in PHP. Source: TalkingDrupal podcast with KingDutch - https://www.drupal.org/project/drupal/issues/3257726
- Fix response in Relay class - https://github.com/nostrver-se/nostr-php/releases/tag/1.3.3. Found and reported on Nostr: https://njump.me/nevent1qvzqqqqqqypzphtxf40yq9jr82xdd8cqtts5szqyx5tcndvaukhsvfmduetr85ceqy88wumn8ghj7mn0wvhxcmmv9uq3zamnwvaz7tmwdaehgu3wwa5kuef0qqsq3utlvgf6tz88ctexwu8ppgct9dkahmv5esxhmmgphv675get22qmzah0a
- Created a seperate repository with the code for the nostr-php.dev website: https://github.com/nostrver-se/nostr-php.dev
- Added ids and
-
 @ a012dc82:6458a70d
2024-12-28 03:31:08
@ a012dc82:6458a70d
2024-12-28 03:31:08Table Of Content
-
The Nikkei 225: A Comprehensive Overview
-
Bitcoin's Meteoric Rise: A Journey of Peaks and Valleys
-
Drawing Parallels: Bitcoin and Nikkei's Path of Resilience
-
Conclusions
-
FAQ
The financial world is vast and diverse, with assets ranging from traditional stocks to the more recent phenomenon of cryptocurrencies. Among these, Bitcoin stands out as the pioneering digital currency, often drawing comparisons with various stock indices. One such intriguing comparison is with Japan's Nikkei 225.
The Nikkei 225: A Comprehensive Overview
The Nikkei 225, commonly known as the Nikkei, stands as one of the primary stock market indices representing the Tokyo Stock Exchange. Established in 1950, it comprises 225 of the most prominent companies listed on the exchange, making it a significant barometer of the Japanese economy's overall health.
Over the decades, the Nikkei has witnessed various economic cycles, from booms to recessions. Its performance often mirrors the broader economic and business trends in Japan. The recent achievement in June, where the Nikkei touched a 33-year high, is not just a numerical milestone. It symbolizes the enduring nature of the Japanese market, its ability to recover from setbacks, and the confidence of investors in the country's economic prospects.
Bitcoin's Meteoric Rise: A Journey of Peaks and Valleys
Bitcoin, introduced in 2009 by an anonymous entity known as Satoshi Nakamoto, revolutionized the concept of currency. As the world's first decentralized digital currency, Bitcoin operates without a central authority, making it inherently resistant to government interference or manipulation.
Over the years, Bitcoin's journey has been nothing short of a roller coaster. From being an obscure digital asset to becoming a household name, its value has seen dramatic surges and equally sharp declines. This volatility often becomes a hotbed for speculations, predictions, and intense debates among financial experts. A recent statement by an analyst, suggesting that Bitcoin's trajectory might align with that of the Nikkei, has added fuel to these discussions. The implication here is that Bitcoin, despite its volatile nature, has the potential to reach unprecedented highs, much like the Nikkei did after its long journey.
Drawing Parallels: Bitcoin and Nikkei's Path of Resilience
At an initial glance, comparing a traditional stock market index like the Nikkei to a modern digital asset like Bitcoin might seem like comparing apples to oranges. However, when delving deeper, certain similarities emerge.
Both Bitcoin and the Nikkei have demonstrated remarkable resilience. The Nikkei, representing Japan's economic might, has bounced back from economic crises, natural disasters, and global downturns. Similarly, Bitcoin, despite facing regulatory challenges, technological hurdles, and market skepticism, has managed to not only survive but thrive.
The adaptability of both these assets is noteworthy. While the Nikkei reflects the evolving nature of the Japanese economy and its industries, Bitcoin showcases the world's shifting attitude towards decentralized finance and digital assets. The recent prediction by the analyst, suggesting a potential parallel growth pattern, underscores the idea that both traditional and modern financial instruments can coexist, learn from each other, and potentially follow similar trajectories of success.
Conclusion
A Convergence of Old and New The financial landscape is ever-evolving, with traditional and modern assets often intersecting in unexpected ways. The comparison between Bitcoin and the Nikkei 225 serves as a testament to this. As Bitcoin continues its journey in the financial realm, only time will tell if it truly follows the path of the Nikkei to new record highs.
FAQ
What is the Nikkei 225? The Nikkei 225 is a primary stock market index representing the Tokyo Stock Exchange, showcasing the health of the Japanese economy.
How is Bitcoin related to the Nikkei 225? An analyst recently predicted that Bitcoin's growth trajectory might align with that of the Nikkei, hinting at potential record highs for the cryptocurrency.
Has the Nikkei 225 reached any significant milestones recently? Yes, in June, the Nikkei achieved a 33-year high, reflecting the resilience of the Japanese market.
Why is Bitcoin's growth compared to the Nikkei's? Both Bitcoin and the Nikkei have shown adaptability and resilience in changing market dynamics, leading to speculations of similar growth patterns.
Is Bitcoin expected to reach new highs? While predictions vary, some analysts believe Bitcoin might emulate the Nikkei's success and reach new record highs.
That's all for today
If you want more, be sure to follow us on:
NOSTR: croxroad@getalby.com
Instagram: @croxroadnews.co
Youtube: @croxroadnews
Store: https://croxroad.store
Subscribe to CROX ROAD Bitcoin Only Daily Newsletter
https://www.croxroad.co/subscribe
DISCLAIMER: None of this is financial advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. Please be careful and do your own research.
-
-
 @ 32e18276:5c68e245
2023-09-21 22:31:03
@ 32e18276:5c68e245
2023-09-21 22:31:03Hey gang,
I just pushed Damus build 18 which is the first major nostrdb integration. Now all damus profiles are stored in nostrdb! You will always be able to search profiles from people you've seen in the past.
There are many crash fixes in this build as well, check out the full changelog:
Enjoy!
Added
- Add followed hashtags to your following list (Daniel D’Aquino)
- Add "Do not show #nsfw tagged posts" setting (Daniel D’Aquino)
- Hold tap to preview status URL (Jericho Hasselbush)
- Finnish translations (etrikaj)
Changed
- Switch to nostrdb for @'s and user search (William Casarin)
- Use nostrdb for profiles (William Casarin)
- Updated relay view (ericholguin)
- Increase size of the hitbox on note ellipsis button (Daniel D’Aquino)
- Make carousel tab dots tappable (Bryan Montz)
- Move the "Follow you" badge into the profile header (Grimless)
Fixed
- Fix text composer wrapping issue when mentioning npub (Daniel D’Aquino)
- Make blurred videos viewable by allowing blur to disappear once tapped (Daniel D’Aquino)
- Fix parsing issue with NIP-47 compliant NWC urls without double-slashes (Daniel D’Aquino)
- Fix padding of username next to pfp on some views (William Casarin)
- Fixes issue where username with multiple emojis would place cursor in strange position. (Jericho Hasselbush)
- Fixed audio in video playing twice (Bryan Montz)
- Fix crash when long pressing custom reactions (William Casarin)
- Fix random crash due to old profile database (William Casarin)
-
 @ 569d536d:ba043e85
2024-12-29 22:43:33
@ 569d536d:ba043e85
2024-12-29 22:43:33Test post
-
 @ fd208ee8:0fd927c1
2024-11-08 10:27:40
@ fd208ee8:0fd927c1
2024-11-08 10:27:40You have no idea
I regularly read comments from people, on here, wondering how it's possible to marry -- or even simply be friends! -- with someone who doesn't agree with you on politics. I see this sentiment expressed quite often, usually in the context of Bitcoin, or whatever pig is currently being chased through the village, as they say around here.

It seems rather sensible, but I don't think it's as hard, as people make it out to be. Further, I think it's a dangerous precondition to set, for your interpersonal relationships, because the political field is constantly in flux. If you determine who you will love, by their opinions, do you stop loving them if their opinions change, or if the opinions they have become irrelevant and a new set of opinions are needed -- and their new ones don't match your new ones? We could see this happen to relationships en masse, during the Covid Era, and I think it happens every day, in a slow grind toward the disintegration of interpersonal discourse.
I suspect many people do stop loving, at that point, as they never really loved the other person for their own sake, they loved the other person because they thought the other person was exactly like they are. But no two people are alike, and the longer you are in a relationship with someone else, the more the initial giddiness wears off and the trials and tribulations add up, the more you notice how very different you actually are. This is the point, where best friends and romantic couples say, We just grew apart.
But you were always apart. You were always two different people. You just didn't notice, until now.

I've also always been surprised at how many same-party relationships disintegrate because of some disagreement over some particular detail of some particular topic, that they generally agree on. To me, it seems like an irrelevant side-topic, but they can't stand to be with this person... and they stomp off. So, I tend to think that it's less that opinions need to align to each other, but rather that opinions need to align in accordance with the level of interpersonal tolerance they can bring into the relationship.
I was raised by relaxed revolutionaries
Maybe I see things this way because my parents come from two diverging political, cultural, national, and ethnic backgrounds, and are prone to disagreeing about a lot of "important" (to people outside their marriage) things, but still have one of the healthiest, most-fruitful, and most long-running marriages of anyone I know, from that generation. My parents, you see, aren't united by their opinions. They're united by their relationship, which is something outside of opinions. Beyond opinions. Relationships are what turn two different people into one, cohesive unit, so that they slowly grow together. Eventually, even their faces merge, and their biological clocks tick to the same rhythm. They eventually become one entity that contains differing opinions about the same topics.
It's like magic, but it's the result of a mindset, not a worldview. Or, as I like to quip:
The best way to stay married, is to not get divorced.

My parents simply determined early on, that they would stay together, and whenever they would find that they disagreed on something that didn't directly pertain to their day-to-day existence with each other they would just agree-to-disagree about that, or roll their eyes, and move on. You do you. Live and let live.
My parents have some of the most strongly held personal opinions of any people I've ever met, but they're also incredibly tolerant and can get along with nearly anyone, so their friends are a confusing hodgepodge of people we liked and found interesting enough to keep around. Which makes their house parties really fun, and highly unusual, in this day and age of mutual-damnation across the aisle.

The things that did affect them, directly, like which school the children should attend or which country they should live in, etc. were things they'd sit down and discuss, and somehow one opinion would emerge, and they'd again... move on.
And that's how my husband and I also live our lives, and it's been working surprisingly well. No topics are off-limits to discussion (so long as you don't drone on for too long), nobody has to give up deeply held beliefs, or stop agitating for the political decisions they prefer.
You see, we didn't like that the other always had the same opinion. We liked that the other always held their opinions strongly. That they were passionate about their opinions. That they were willing to voice their opinions; sacrifice to promote their opinions. And that they didn't let anyone browbeat or cow them, for their opinions, not even their best friends or their spouse. But that they were open to listening to the other side, and trying to wrap their mind around the possibility that they might just be wrong about something.

We married each other because we knew: this person really cares, this person has thought this through, and they're in it, to win it. What "it" is, is mostly irrelevant, so long as it doesn't entail torturing small animals in the basement, or raising the children on a diet of Mountain Dew and porn, or something.
Live and let live. At least, it's never boring. At least, there's always something to ~~argue~~ talk about. At least, we never think... we've just grown apart.
-
 @ f1989a96:bcaaf2c1
2024-12-26 16:34:58
@ f1989a96:bcaaf2c1
2024-12-26 16:34:58Good morning, readers!
In Russia, the State Duma passed sweeping amendments granting officials the ability to equate “funding extremist activities” with “financing terrorism.” These changes allow officials to label anyone accused of spreading “fake news” or “discrediting” the military and authorities as “terrorists and extremists.” This development threatens activists and civil society organizations with intensified financial repression, including frozen accounts, restricted access to funds, and strict withdrawal limits.
Meanwhile, North Korea’s currency crisis continues to worsen, pushing citizens to abandon the North Korean won in favor of barter. As exchange rates for foreign currencies soar, merchants and money changers increasingly demand tangible goods like rice and fuel and no longer accept North Korean won for imported goods and foreign currencies.
In technology news, Tando, a Bitcoin payment app in Kenya, received significant attention at the 2024 Africa Bitcoin Conference for integrating the Bitcoin Lightning Network with M-PESA, Kenya’s mobile money system. This allows people to use Bitcoin to buy things across the country while merchants receive Kenyan shillings, bridging the gap between the local financial system and Bitcoin. \ \ Finally, we feature the latest episode of the Dissidents and Dictators podcast, featuring Togolese human rights activist Farida Nabourema sharing her first-hand experience growing up under the Gnassingbé dictatorship. She believes Bitcoin can enable greater transparency and offer a financial lifeline for citizens in Togo and across Africa.
Now, let’s dive right in!
Subscribe Here
GLOBAL NEWS
Russia | Sweeping Amendments Expand Financial Repression Against Dissidents
Russia’s State Duma made sweeping amendments to 48 federal laws, granting officials the power to equate “funding extremist activities” with “financing terrorism.” This move allows the regime to directly target individuals, activists, and nonprofit organizations suspected of spreading “fake news” or “discrediting” the military and regime. Once designated as a “terrorist” or “extremist,” a person or organization faces frozen bank accounts, restricted access to funds, and a withdrawal cap of just 10,000 rubles ($95) per month — a limit that extends to each dependent in their family. Compounding these hardships, employers often refuse to hire individuals on these government lists.
North Korea | Failing Currency Forces Return to Barter
North Korea’s currency crisis is forcing citizens to abandon the depreciating won currency in favor of barter. As exchange rates for foreign currencies like the US dollar and Chinese yuan hit record highs, merchants and money changers now demand commodities (such as rice and fuel) for foreign currencies and imported goods. One such example is trading around 2 kilograms of rice for a single dollar. This collapse leaves those without access to foreign currency in increasingly precarious financial positions and struggling to secure food and basic necessities. Even farmers, once partially compensated with valuable goods, now increasingly receive devalued cash, worsening nationwide food insecurity.
Nicaragua | Human Rights Abuses and Financial Repression Exposed
Under Daniel Ortega’s authoritarian rule, Nicaragua exemplifies the devastating intersection of financial repression and human rights abuses. New reports detail how the regime has confiscated over $250 million in assets, dissolved more than 5,200 NGOs, canceled pensions, and frozen bank accounts, leaving citizens financially vulnerable and silenced. Since Ortega’s return to power in 2007, and especially after the 2018 protests, his government has dismantled civil society, crushed political opposition, and eradicated independent media. Hundreds have been killed and exiled, and in 2023 and 2024 alone, 452 political opponents were stripped of their citizenship.
El Salvador | Bitcoin Adoption Limited as Government Comes to Terms With IMF
El Salvador finalized a $1.4 billion agreement with the International Monetary Fund (IMF) to support the government’s economic reform agenda at the cost of scaling back some of its Bitcoin policies. The deal will make accepting Bitcoin in the private sector voluntary, require all taxes to be paid in US dollars (as opposed to making it possible to pay in BTC), and see Chivo, the government-supported Bitcoin wallet, gradually unwound. In addition, the government will enhance “transparency, regulation, and supervision of digital assets” and establish a stronger Anti-Money Laundering and Counter-Financial Terrorism (AML/CFT) framework.
Malaysia | Parliament Passes Repressive Media Bills Amidst Financial Struggles
Earlier this year, Malaysia’s ringgit currency plunged to a 26-year low, driving up prices nationwide. As families struggled with a higher cost of living, officials passed an amendment granting law enforcement the power to freeze bank accounts suspected of fraud. Meanwhile, Malaysia’s parliament is passing two more bills to regulate media and online spaces, allowing officials to censor content and request user data from service providers without approval. Critics warn the vague language in these laws will likely be exploited to silence dissent and stifle public discourse. As financial hardships mount, Malaysia’s online spaces become increasingly controlled, eroding freedom of expression and financial autonomy.
BITCOIN NEWS
Tando | Bridging Bitcoin and Everyday Payments in Kenya
Tando, a new bitcoin payments app and HRF grantee, makes it easy to spend bitcoin anywhere in Kenya by integrating with M-PESA, Kenya’s mobile money system. Users simply download the Tando app, enter the merchant’s M-PESA number, and input the amount owed in Kenyan shillings. The app calculates the required amount of bitcoin and generates a Lightning invoice, which users pay through their own Bitcoin wallet. Tando then converts the sats to shillings and completes the transaction instantly (you can watch this one-minute live demo here). For Kenyans excluded from M-PESA due to Know-Your-Customer regulations, Tando provides a practical solution that bridges Bitcoin and local financial systems to make everyday transactions easier.
Yakihonne | Adds Support for Improved Encrypted Direct Messaging
YakiHonne, a Nostr client, champions free speech and facilitates Bitcoin payments across 170 countries. Recent updates have made the platform more user-friendly and secure. The updated text editor now supports multiple languages, including right-to-left scripts, enhancing accessibility for a global audience. Messaging capabilities have been upgraded to allow longer texts, and users can now activate Secure DMs (NIP 44) for encrypted messaging on Nostr. These improvements make YakiHonne an appealing communication platform for pro-democracy and human rights activists, offering secure messaging and the ability to receive payments in Bitcoin in countries ruled by authoritarian regimes.
Mostro | Making Bitcoin More Accessible and Private
Mostro, a private and peer-to-peer (P2P) Bitcoin exchange built on Nostr, made significant strides this year toward empowering human rights defenders and nonprofits with accessible, private, and censorship-resistant financial tools. Created by Venezuelan developer Francisco Calderon, the platform implemented advanced key management which allows users to rotate the keys used for every bitcoin trade. This adds a layer of privacy critical for those operating under authoritarian regimes. Additionally, Mostro adopted NIP-69, standardizing all peer-to-peer orders on Nostr, creating a larger liquidity pool, and making trades more accessible for users. Finally, Mostro will soon launch a mobile app (currently in the testing phase), helping democratize Bitcoin access by providing individuals with a user-friendly mobile interface.
Foundation | Introduces Personal Security Platform
Foundation, a Bitcoin hardware wallet company, introduced Passport Prime, which they call “the world’s first Personal Security Platform.” Designed to protect users’ bitcoin and digital lives, Passport Prime offers a Bitcoin wallet, multi-factor authentication, secure file storage, and a Seed Vault to organize seed phrases. It does not require usernames, passwords, or email addresses, making it an interesting option for privacy-conscious users, particularly pro-democracy and human rights activists operating under authoritarian regimes. You can learn more about Passport Prime here.
BTrust Builders | Applications for 2024 ₿OSS Cohort Close Tomorrow
Applications for the 2025 ₿OSS Cohort, hosted by Btrust Builders in partnership with Chaincode Labs, close tomorrow, Dec. 27, 2024. This part-time, three-month, fully remote program is tailored to African developers seeking to contribute to Bitcoin open-source software (₿OSS), in order to increase the potential for use cases in a region where three-quarters of the governments are authoritarian regimes. The program is open to developers of all experience levels, and it provides hands-on technical training, career-building opportunities, and mentorship. If you’re a developer interested in this program, you can apply here.
RECOMMENDED CONTENT
Is Bitcoin a Lifeline for Africa with Farida Nabourema
In this episode of Dissidents and Dictators, an HRF podcast, Togolese human rights activist Farida Nabourema reveals her experience growing up under the Gnassingbé dictatorship—a single-family autocracy that has ruled Togo for over 50 years. Nabourema shares insights into the corruption and lack of trust that permeates Togo’s financial system and discusses how Bitcoin can enable greater transparency and offer a lifeline for citizens in Togo and across Africa, where authoritarian regimes stifle financial freedom. Watch the full episode here.
If this article was forwarded to you and you enjoyed reading it, please consider subscribing to the Financial Freedom Report here.
Support the newsletter by donating bitcoin to HRF’s Financial Freedom program via BTCPay.\ Want to contribute to the newsletter? Submit tips, stories, news, and ideas by emailing us at ffreport @ hrf.org
The Bitcoin Development Fund (BDF) is accepting grant proposals on an ongoing basis. The Bitcoin Development Fund is looking to support Bitcoin developers, community builders, and educators. Submit proposals here.
Subscribe to newsletter\ Apply for a grant\ Support our work\ Visit our website
-
 @ 32e18276:5c68e245
2023-07-17 21:55:39
@ 32e18276:5c68e245
2023-07-17 21:55:39Hey guys!
Another day, another TestFlight build. This fixes many mention bugs and includes bandwidth improvements.
During nostrica, jack told everyone to open their phones and say GM to fiatjaf. This actually brought down nostrica's wifi! Damus is really dumb when it first opens and makes many requests. Sometimes hundreds (nip05 validation, etc). This build fixes all those issues. Damus will no longer:
- Make hundreds of nostr address validation requests.
- Make tons of duplicate lnurl requests when validating zaps
nostr address validation only happens when you open someones profile now.
This build also fixes some annoying mention issues. If you forget a space when mentioning someone, it will automatically add it.
I've also removed the restriction where you were not allowed to login to "deleted" accounts. This was way too confusing for people, and logging into a deleted account will allow you to reset the profile information and get it going again. You're welcome NVK.
Another thing that was added in this build is support for
_usernames in nostr addresses. This will hide your full nostr address username when used. Damus will also hide your username if it matches your profile username. Damus always did this before but it was incorrect. Now it will show your full nostr address (nip05) with its proper username. You can stop bugging me about this now Semisol.Last but not least there are some small tweaks to longform note padding. Nothing too crazy but it does make notes like this look less cramped.
Until next time!
Added
- Show nostr address username and support abbreviated _ usernames (William Casarin)
- Re-add nip05 badges to profiles (William Casarin)
- Add space when tagging users in posts if needed (William Casarin)
- Added padding under word count on longform account (William Casarin)
Fixed
- Don't spam lnurls when validating zaps (William Casarin)
- Eliminate nostr address validation bandwidth on startup (William Casarin)
- Allow user to login to deleted profile (William Casarin)
- Fix issue where typing cc@bob would produce brokenb ccnostr:bob mention (William Casarin)
-
 @ 32e18276:5c68e245
2023-07-11 21:23:37
@ 32e18276:5c68e245
2023-07-11 21:23:37You can use github PRs to submit code but it is not encouraged. Damus is a decentralized social media protocol and we prefer to use decentralized techniques during the code submission process.
[Email patches][git-send-email] to patches@damus.io are preferred, but we accept PRs on GitHub as well. Patches sent via email may include a bolt11 lightning invoice, choosing the price you think the patch is worth, and we will pay it once the patch is accepted and if I think the price isn't unreasonable. You can also send an any-amount invoice and I will pay what I think it's worth if you prefer not to choose. You can include the bolt11 in the commit body or email so that it can be paid once it is applied.
Recommended settings when submitting code via email:
$ git config sendemail.to "patches@damus.io" $ git config format.subjectPrefix "PATCH damus" $ git config format.signOff yesYou can subscribe to the [patches mailing list][patches-ml] to help review code.
Submitting patches
Most of this comes from the linux kernel guidelines for submitting patches, we follow many of the same guidelines. These are very important! If you want your code to be accepted, please read this carefully
Describe your problem. Whether your patch is a one-line bug fix or 5000 lines of a new feature, there must be an underlying problem that motivated you to do this work. Convince the reviewer that there is a problem worth fixing and that it makes sense for them to read past the first paragraph.
Once the problem is established, describe what you are actually doing about it in technical detail. It's important to describe the change in plain English for the reviewer to verify that the code is behaving as you intend it to.
The maintainer will thank you if you write your patch description in a form which can be easily pulled into Damus's source code tree.
Solve only one problem per patch. If your description starts to get long, that's a sign that you probably need to split up your patch. See the dedicated
Separate your changessection because this is very important.When you submit or resubmit a patch or patch series, include the complete patch description and justification for it (-v2,v3,vn... option on git-send-email). Don't just say that this is version N of the patch (series). Don't expect the reviewer to refer back to earlier patch versions or referenced URLs to find the patch description and put that into the patch. I.e., the patch (series) and its description should be self-contained. This benefits both the maintainers and reviewers. Some reviewers probably didn't even receive earlier versions of the patch.
Describe your changes in imperative mood, e.g. "make xyzzy do frotz" instead of "[This patch] makes xyzzy do frotz" or "[I] changed xyzzy to do frotz", as if you are giving orders to the codebase to change its behaviour.
If your patch fixes a bug, use the 'Closes:' tag with a URL referencing the report in the mailing list archives or a public bug tracker. For example:
Closes: https://github.com/damus-io/damus/issues/1234Some bug trackers have the ability to close issues automatically when a commit with such a tag is applied. Some bots monitoring mailing lists can also track such tags and take certain actions. Private bug trackers and invalid URLs are forbidden.
If your patch fixes a bug in a specific commit, e.g. you found an issue using
git bisect, please use the 'Fixes:' tag with the first 12 characters of the SHA-1 ID, and the one line summary. Do not split the tag across multiple lines, tags are exempt from the "wrap at 75 columns" rule in order to simplify parsing scripts. For example::Fixes: 54a4f0239f2e ("Fix crash in navigation")The following
git configsettings can be used to add a pretty format for outputting the above style in thegit logorgit showcommands::[core] abbrev = 12 [pretty] fixes = Fixes: %h (\"%s\")An example call::
$ git log -1 --pretty=fixes 54a4f0239f2e Fixes: 54a4f0239f2e ("Fix crash in navigation")Separate your changes
Separate each logical change into a separate patch.
For example, if your changes include both bug fixes and performance enhancements for a particular feature, separate those changes into two or more patches. If your changes include an API update, and a new feature which uses that new API, separate those into two patches.
On the other hand, if you make a single change to numerous files, group those changes into a single patch. Thus a single logical change is contained within a single patch.
The point to remember is that each patch should make an easily understood change that can be verified by reviewers. Each patch should be justifiable on its own merits.
If one patch depends on another patch in order for a change to be complete, that is OK. Simply note "this patch depends on patch X" in your patch description.
When dividing your change into a series of patches, take special care to ensure that the Damus builds and runs properly after each patch in the series. Developers using
git bisectto track down a problem can end up splitting your patch series at any point; they will not thank you if you introduce bugs in the middle.If you cannot condense your patch set into a smaller set of patches, then only post say 15 or so at a time and wait for review and integration.
-
 @ 4ba8e86d:89d32de4
2024-11-07 13:56:21
@ 4ba8e86d:89d32de4
2024-11-07 13:56:21Tutorial feito por Grom mestre⚡poste original abaixo:
http://xh6liiypqffzwnu5734ucwps37tn2g6npthvugz3gdoqpikujju525yd.onion/240277/tutorial-criando-e-acessando-sua-conta-de-email-pela-i2p?show=240277#q240277
Bom dia/tarde/noite a todos os camaradas. Seguindo a nossa série de tutoriais referentes a tecnologias essenciais para a segurança e o anonimato dos usuários, sendo as primeiras a openPGP e a I2P, lhes apresento mais uma opção para expandir os seus conhecimentos da DW. Muitos devem conhecer os serviços de mail na onion como DNMX e mail2tor, mas e que tal um serviço de email pela I2P. Nesse tutorial eu vou mostrar a vocês como criar a sua primeira conta no hq.postman.i2p e a acessar essa conta.
É importante que vocês tenham lido a minha primeira série de tutoriais a respeito de como instalar, configurar e navegar pela I2P nostr:nevent1qqsyjcz2w0e6d6dcdeprhuuarw4aqkw730y542dzlwxwssneq3mwpaspz4mhxue69uhhyetvv9ujuerpd46hxtnfduhsygzt4r5x6tvh39kujvmu8egqdyvf84e3w4e0mq0ckswamfwcn5eduspsgqqqqqqsyp5vcq Esse tutorial é um pré-requisito para o seguinte e portanto recomendo que leia-os antes de prosseguir com o seguinte tutorial. O tutorial de Kleopatra nostr:nevent1qqs8h7vsn5j6qh35949sa60dms4fneussmv9jd76n24lsmtz24k0xlqzyp9636rd9ktcjmwfxd7ru5qxjxyn6uch2uhas8utg8wa5hvf6vk7gqcyqqqqqqgecq8f7 é complementar dado que é extremamente recomendado assinar e criptografar as mensagens que seguem por emails pela DW. Sem mais delongas, vamos ao tutorial de fato.
1. Criando uma conta de email no hq.postman
Relembrando: Esse tutorial considera que você já tenha acesso à I2P. Entre no seu navegador e acesse o endereço hq.postman.i2p. O roteador provavelmente já contém esse endereço no seu addressbook e não haverá a necessidade de inserir o endereço b32 completo. Após entrar no site vá para a página '1 - Creating a mailbox' https://image.nostr.build/d850379fe315d2abab71430949b06d3fa49366d91df4c9b00a4a8367d53fcca3.jpg
Nessa página, insira as credenciais de sua preferências nos campos do formulário abaixo. Lembre-se que o seu endereço de email aceita apenas letras e números. Clique em 'Proceed' depois que preencher todos os campos. https://image.nostr.build/670dfda7264db393e48391f217e60a2eb87d85c2729360c8ef6fe0cf52508ab4.jpg
Uma página vai aparecer pedindo para confirmar as credenciais da sua nova conta. Se tudo estiver certo apenas clique em 'Confirm and Create Mailbox'. Se tudo ocorrer como conforme haverá uma confirmação de que a sua nova conta foi criada com sucesso. Após isso aguarde por volta de 5 minutos antes de tentar acessá-la, para que haja tempo suficiente para o servidor atualizar o banco de dados. https://image.nostr.build/ec58fb826bffa60791fedfd9c89a25d592ac3d11645b270c936c60a7c59c067f.jpg https://image.nostr.build/a2b7710d1e3cbb36431acb9055fd62937986b4da4b1a1bbb06d3f3cb1f544fd3.jpg
Pronto! Sua nova conta de email na I2P foi criada. Agora vamos para a próxima etapa: como acessar a sua conta via um cliente de email.
2. Configurando os túneis cliente de SMTP e POP3
O hq.postman não possui um cliente web que nos permite acessar a nossa conta pelo navegador. Para isso precisamos usar um cliente como Thunderbird e configurar os túneis cliente no I2Pd que serão necessários para o Thunderbird se comunicar com o servidor pela I2P.
Caso não tenha instalado o Thunderbird ainda, faça-o agora antes de prosseguir.
Vamos configurar os túneis cliente do servidor de email no nosso roteador. Para isso abra um terminal ou o seu gestor de arquivos e vá para a pasta de configuração de túneis do I2P. Em Linux esse diretório se localiza em /etc/i2pd/tunnels.d. Em Windows, essa pasta se localiza em C:\users\user\APPDATA\i2pd. Na pasta tunnels.d crie dois arquivos: smtp.postman.conf e pop-postman.conf. Lembre-se que em Linux você precisa de permissões de root para escrever na pasta de configuração. Use o comando sudoedit
para isso. Edite-os conforme as imagens a seguir:
Arquivo pop-postman.conf https://image.nostr.build/7e03505c8bc3b632ca5db1f8eaefc6cecb4743cd2096d211dd90bbdc16fe2593.jpg
Arquivo smtp-postman.conf https://image.nostr.build/2d06c021841dedd6000c9fc2a641ed519b3be3c6125000b188842cd0a5af3d16.jpg
Salve os arquivos e reinicie o serviço do I2Pd. Em Linux isso é feito pelo comando:
sudo systemctl restart i2pdEntre no Webconsole do I2Pd pelo navegador (localhost:7070) e na seção I2P Tunnels, verifique se os túneis pop-postman e smtp-postman foram criados, caso contrário verifique se há algum erro nos arquivos e reinicie o serviço.Com os túneis cliente criados, vamos agora configurar o Thunderbird
3. Configurando o Thunderbird para acessar a nossa conta
Abra o Thunderbird e clique em criar uma nova conta de email. Se você não tiver nenhum conta previamente presente nele você vai ser diretamente recebido pela janela de criação de conta a seguir. https://image.nostr.build/e9509d7bd30623716ef9adcad76c1d465f5bc3d5840e0c35fe4faa85740f41b4.jpg https://image.nostr.build/688b59b8352a17389902ec1e99d7484e310d7d287491b34f562b8cdd9dbe8a99.jpg
Coloque as suas credenciais, mas não clique ainda em Continuar. Clique antes em Configure Manually, já que precisamos configurar manualmente os servidores de SMTP e POP3 para, respectivamente, enviar e receber mensagens.
Preencha os campos como na imagem a seguir. Detalhe: Não coloque o seu endereço completo com o @mail.i2p, apenas o nome da sua conta. https://image.nostr.build/4610b0315c0a3b741965d3d7c1e4aff6425a167297e323ba8490f4325f40cdcc.jpg
Clique em Re-test para verificar a integridade da conexão. Se tudo estiver certo uma mensagem irá aparecer avisando que as configurações do servidores estão corretas. Clique em Done assim que estiver pronto para prosseguir. https://image.nostr.build/8a47bb292f94b0d9d474d4d4a134f8d73afb84ecf1d4c0a7eb6366d46bf3973a.jpg
A seguinte mensagem vai aparecer alertando que não estamos usando criptografia no envio das credenciais. Não há problema nenhum aqui, pois a I2P está garantindo toda a proteção e anonimato dos nossos dados, o que dispensa a necessidade de uso de TLS ou qualquer tecnologia similar nas camadas acima. Marque a opção 'I Understand the risks' e clique em 'Continue' https://image.nostr.build/9c1bf585248773297d2cb1d9705c1be3bd815e2be85d4342227f1db2f13a9cc6.jpg
E por fim, se tudo ocorreu como devido sua conta será criada com sucesso e você agora será capaz de enviar e receber emails pela I2P usando essa conta. https://image.nostr.build/8ba7f2c160453c9bfa172fa9a30b642a7ee9ae3eeb9b78b4dc24ce25aa2c7ecc.jpg
4. Observações e considerações finais
Como informado pelo próprio site do hq.postman, o domínio @mail.i2p serve apenas para emails enviados dentro da I2P. Emails enviados pela surface devem usar o domínio @i2pmai.org. É imprescindível que você saiba usar o PGP para assinar e criptografar as suas mensagens, dado que provavelmente as mensagens não são armazenadas de forma criptografada enquanto elas estão armazenadas no servidor. Como o protocolo POP3 delete as mensagens no imediato momento em que você as recebe, não há necessidade de fazer qualquer limpeza na sua conta de forma manual.
Por fim, espero que esse tutorial tenha sido útil para vocês. Que seu conhecimento tenha expandido ainda mais com as informações trazidas aqui. Até a próxima.
-
 @ b2caa9b3:9eab0fb5
2024-07-11 15:04:06
@ b2caa9b3:9eab0fb5
2024-07-11 15:04:06Hey everyone,
Today wasn't super eventful, but there were a couple things I wanted to share. First off, I had to pay rent, which meant a trip to the bank with my still-not-great foot. On the bright side, I took some pictures of Moshi along the way - hopefully you'll enjoy a glimpse of the city!

Speaking of my foot, there's been some improvement! The pain isn't constant anymore, only when I'm walking around. It looks better too, so hopefully it'll be back to normal soon.
Now, onto the slightly more frustrating topic: the Kenyan border situation. As you might recall, I had a big issue where border control wouldn't let me leave the country and even refused to contact my embassy. Basically, they held me hostage (which, by the way, is a violation of international law).
Two days later, I managed to get out through a different border. Recently, the Kenyan police has started investigating. They contacted me on WhatsApp a few days ago, and things are getting stranger by the day.

There's a big part of this that just doesn't add up. They keep asking for a photo of the exit stamp, but the officer who wouldn't let me leave never gave me one. He actually denied my exit and put me on a bus back to the city! I explained this and told them another border provided the stamp later, but they insist they need the original stamp to find this as "proof" related to this officer. It just doesn't connect to the man who caused the problem in the first place.

Even more concerning, they want me to return to Kenya. First, they want me to sign a document, but when I expressed hesitation about returning, they switched to asking me to identify this officer in a lineup. And all of this communication is happening on a personal WhatsApp number, which makes the whole situation incredibly suspicious.
Overall, it's a confusing situation.
On a brighter note, my foot is definitely on the mend. Here's to hoping it keeps getting better!
That's all for today. I'll just be relaxing and grabbing some dinner later.
Stay tuned for more updates!


Online
Feel free to support me by sending some sats via the lightning network to rubenstorm@sats.mobi
-
 @ 796a6d9b:3bb533e3
2024-07-11 12:57:35
@ 796a6d9b:3bb533e3
2024-07-11 12:57:35For more than a while now, I think you have experienced the feeling that things are not right in the world or in your country, it is not surprising that it coincides with a moment in history where we will experience the end of a monetary cycle like It is FIAT money or in other words fiat money that is backed by debt, every day you look around you and people do not find much hope in the future, many of them are working to support themselves, pay the costs of living and In the best of cases, just saving a little inflationary money, a slower theft in the population, in the worst of cases, people are full of debt and without a plan on how to escape said trap.
Everything is connected, we just have to look for the signs that are leaving us with the naked eye, as for example we have never had in history countries so indebted based on their GDP or gross domestic product and that this same debt was financed with a deficit, For people who have studied or lived the situations of hyperinflationary countries like Venezuela, Argentina, Turkey, Lebanon, you will know what I am talking about, it is simpler than it sounds, no country can spend more than it produces without any consequences, someone has to pay the price, in this case the population through the dark hand of inflation.
We have reached the point where governments blatantly lie to us with inflation data that does not include food, rent and energy prices, to save appearances and maintain the psychological operation that everything is fine, but when you go to the supermarket you know that something was never there. Well, it is not surprising that even you, the person reading this, know that inevitably your Dollars, Euros or Pesos will not buy you the same thing in a year as what they buy you today.
So where are we headed? It is normal then that people are not very enthusiastic about the future, since when we look into the depths of our system we realize that people's savings and purchasing power will increasingly be devalued so that everything continues to function as it has until now. Today, it is noticeable that something in people's subconscious warns them that tomorrow will be worse and that is why they have to enjoy the now, reducing their time preference to sporadic moments without thinking about the long term, even if they do not understand complex mechanisms. economics, it is observed that people are increasingly working more for less remuneration since the numbers of a salary can increase nominally but they buy fewer and fewer goods and services, as we can see in this graph.
What we have left in the coming years is the acceleration of government mechanisms to be able to continue keeping the wealth extraction system functioning, trying to extend the psychological operation to a point of no return, it is clear that a form of money has been confiscated from us. . that allowed us savings like gold did, I think it is important that we begin to question certain things and choose not to continue participating in a system that is arranged to destroy the energy of our work.
What can we do? Alternatives such as Bitcoin and gold to protect the energy of our work are some of the best options that we can implement as a refuge from the disaster to which our politicians have dragged us. Using these alternatives as a kind of battery for our energy is the only way we can ensure that the effort we make every day in our jobs, ventures or companies is not devalued, since both gold and bitcoin are not debt. of anyone, they are reserves of value and have no risk of reverse departure or non-payment.
It is time to take action and educate ourselves to be able to rise to the challenges of the paradigm shift that we will have as a civilization, since a change in the monetary standard is what can lead us to a better path of incentives where people can change preferences. temporary and build for the future.
originally posted at https://stacker.news/items/604619
-
 @ a367f9eb:0633efea
2024-11-05 08:48:41
@ a367f9eb:0633efea
2024-11-05 08:48:41Last week, an investigation by Reuters revealed that Chinese researchers have been using open-source AI tools to build nefarious-sounding models that may have some military application.
The reporting purports that adversaries in the Chinese Communist Party and its military wing are taking advantage of the liberal software licensing of American innovations in the AI space, which could someday have capabilities to presumably harm the United States.
In a June paper reviewed by Reuters, six Chinese researchers from three institutions, including two under the People’s Liberation Army’s (PLA) leading research body, the Academy of Military Science (AMS), detailed how they had used an early version of Meta’s Llama as a base for what it calls “ChatBIT”.
The researchers used an earlier Llama 13B large language model (LLM) from Meta, incorporating their own parameters to construct a military-focused AI tool to gather and process intelligence, and offer accurate and reliable information for operational decision-making.
While I’m doubtful that today’s existing chatbot-like tools will be the ultimate battlefield for a new geopolitical war (queue up the computer-simulated war from the Star Trek episode “A Taste of Armageddon“), this recent exposé requires us to revisit why large language models are released as open-source code in the first place.
Added to that, should it matter that an adversary is having a poke around and may ultimately use them for some purpose we may not like, whether that be China, Russia, North Korea, or Iran?
The number of open-source AI LLMs continues to grow each day, with projects like Vicuna, LLaMA, BLOOMB, Falcon, and Mistral available for download. In fact, there are over one million open-source LLMs available as of writing this post. With some decent hardware, every global citizen can download these codebases and run them on their computer.
With regard to this specific story, we could assume it to be a selective leak by a competitor of Meta which created the LLaMA model, intended to harm its reputation among those with cybersecurity and national security credentials. There are potentially trillions of dollars on the line.
Or it could be the revelation of something more sinister happening in the military-sponsored labs of Chinese hackers who have already been caught attacking American infrastructure, data, and yes, your credit history?
As consumer advocates who believe in the necessity of liberal democracies to safeguard our liberties against authoritarianism, we should absolutely remain skeptical when it comes to the communist regime in Beijing. We’ve written as much many times.
At the same time, however, we should not subrogate our own critical thinking and principles because it suits a convenient narrative.
Consumers of all stripes deserve technological freedom, and innovators should be free to provide that to us. And open-source software has provided the very foundations for all of this.
Open-source matters When we discuss open-source software and code, what we’re really talking about is the ability for people other than the creators to use it.
The various licensing schemes – ranging from GNU General Public License (GPL) to the MIT License and various public domain classifications – determine whether other people can use the code, edit it to their liking, and run it on their machine. Some licenses even allow you to monetize the modifications you’ve made.
While many different types of software will be fully licensed and made proprietary, restricting or even penalizing those who attempt to use it on their own, many developers have created software intended to be released to the public. This allows multiple contributors to add to the codebase and to make changes to improve it for public benefit.
Open-source software matters because anyone, anywhere can download and run the code on their own. They can also modify it, edit it, and tailor it to their specific need. The code is intended to be shared and built upon not because of some altruistic belief, but rather to make it accessible for everyone and create a broad base. This is how we create standards for technologies that provide the ground floor for further tinkering to deliver value to consumers.
Open-source libraries create the building blocks that decrease the hassle and cost of building a new web platform, smartphone, or even a computer language. They distribute common code that can be built upon, assuring interoperability and setting standards for all of our devices and technologies to talk to each other.
I am myself a proponent of open-source software. The server I run in my home has dozens of dockerized applications sourced directly from open-source contributors on GitHub and DockerHub. When there are versions or adaptations that I don’t like, I can pick and choose which I prefer. I can even make comments or add edits if I’ve found a better way for them to run.
Whether you know it or not, many of you run the Linux operating system as the base for your Macbook or any other computer and use all kinds of web tools that have active repositories forked or modified by open-source contributors online. This code is auditable by everyone and can be scrutinized or reviewed by whoever wants to (even AI bots).
This is the same software that runs your airlines, powers the farms that deliver your food, and supports the entire global monetary system. The code of the first decentralized cryptocurrency Bitcoin is also open-source, which has allowed thousands of copycat protocols that have revolutionized how we view money.
You know what else is open-source and available for everyone to use, modify, and build upon?
PHP, Mozilla Firefox, LibreOffice, MySQL, Python, Git, Docker, and WordPress. All protocols and languages that power the web. Friend or foe alike, anyone can download these pieces of software and run them how they see fit.
Open-source code is speech, and it is knowledge.
We build upon it to make information and technology accessible. Attempts to curb open-source, therefore, amount to restricting speech and knowledge.
Open-source is for your friends, and enemies In the context of Artificial Intelligence, many different developers and companies have chosen to take their large language models and make them available via an open-source license.
At this very moment, you can click on over to Hugging Face, download an AI model, and build a chatbot or scripting machine suited to your needs. All for free (as long as you have the power and bandwidth).
Thousands of companies in the AI sector are doing this at this very moment, discovering ways of building on top of open-source models to develop new apps, tools, and services to offer to companies and individuals. It’s how many different applications are coming to life and thousands more jobs are being created.
We know this can be useful to friends, but what about enemies?
As the AI wars heat up between liberal democracies like the US, the UK, and (sluggishly) the European Union, we know that authoritarian adversaries like the CCP and Russia are building their own applications.
The fear that China will use open-source US models to create some kind of military application is a clear and present danger for many political and national security researchers, as well as politicians.
A bipartisan group of US House lawmakers want to put export controls on AI models, as well as block foreign access to US cloud servers that may be hosting AI software.
If this seems familiar, we should also remember that the US government once classified cryptography and encryption as “munitions” that could not be exported to other countries (see The Crypto Wars). Many of the arguments we hear today were invoked by some of the same people as back then.
Now, encryption protocols are the gold standard for many different banking and web services, messaging, and all kinds of electronic communication. We expect our friends to use it, and our foes as well. Because code is knowledge and speech, we know how to evaluate it and respond if we need to.
Regardless of who uses open-source AI, this is how we should view it today. These are merely tools that people will use for good or ill. It’s up to governments to determine how best to stop illiberal or nefarious uses that harm us, rather than try to outlaw or restrict building of free and open software in the first place.
Limiting open-source threatens our own advancement If we set out to restrict and limit our ability to create and share open-source code, no matter who uses it, that would be tantamount to imposing censorship. There must be another way.
If there is a “Hundred Year Marathon” between the United States and liberal democracies on one side and autocracies like the Chinese Communist Party on the other, this is not something that will be won or lost based on software licenses. We need as much competition as possible.
The Chinese military has been building up its capabilities with trillions of dollars’ worth of investments that span far beyond AI chatbots and skip logic protocols.
The theft of intellectual property at factories in Shenzhen, or in US courts by third-party litigation funding coming from China, is very real and will have serious economic consequences. It may even change the balance of power if our economies and countries turn to war footing.
But these are separate issues from the ability of free people to create and share open-source code which we can all benefit from. In fact, if we want to continue our way our life and continue to add to global productivity and growth, it’s demanded that we defend open-source.
If liberal democracies want to compete with our global adversaries, it will not be done by reducing the freedoms of citizens in our own countries.
Last week, an investigation by Reuters revealed that Chinese researchers have been using open-source AI tools to build nefarious-sounding models that may have some military application.
The reporting purports that adversaries in the Chinese Communist Party and its military wing are taking advantage of the liberal software licensing of American innovations in the AI space, which could someday have capabilities to presumably harm the United States.
In a June paper reviewed by Reuters, six Chinese researchers from three institutions, including two under the People’s Liberation Army’s (PLA) leading research body, the Academy of Military Science (AMS), detailed how they had used an early version of Meta’s Llama as a base for what it calls “ChatBIT”.
The researchers used an earlier Llama 13B large language model (LLM) from Meta, incorporating their own parameters to construct a military-focused AI tool to gather and process intelligence, and offer accurate and reliable information for operational decision-making.
While I’m doubtful that today’s existing chatbot-like tools will be the ultimate battlefield for a new geopolitical war (queue up the computer-simulated war from the Star Trek episode “A Taste of Armageddon“), this recent exposé requires us to revisit why large language models are released as open-source code in the first place.
Added to that, should it matter that an adversary is having a poke around and may ultimately use them for some purpose we may not like, whether that be China, Russia, North Korea, or Iran?
The number of open-source AI LLMs continues to grow each day, with projects like Vicuna, LLaMA, BLOOMB, Falcon, and Mistral available for download. In fact, there are over one million open-source LLMs available as of writing this post. With some decent hardware, every global citizen can download these codebases and run them on their computer.
With regard to this specific story, we could assume it to be a selective leak by a competitor of Meta which created the LLaMA model, intended to harm its reputation among those with cybersecurity and national security credentials. There are potentially trillions of dollars on the line.
Or it could be the revelation of something more sinister happening in the military-sponsored labs of Chinese hackers who have already been caught attacking American infrastructure, data, and yes, your credit history?
As consumer advocates who believe in the necessity of liberal democracies to safeguard our liberties against authoritarianism, we should absolutely remain skeptical when it comes to the communist regime in Beijing. We’ve written as much many times.
At the same time, however, we should not subrogate our own critical thinking and principles because it suits a convenient narrative.
Consumers of all stripes deserve technological freedom, and innovators should be free to provide that to us. And open-source software has provided the very foundations for all of this.
Open-source matters
When we discuss open-source software and code, what we’re really talking about is the ability for people other than the creators to use it.
The various licensing schemes – ranging from GNU General Public License (GPL) to the MIT License and various public domain classifications – determine whether other people can use the code, edit it to their liking, and run it on their machine. Some licenses even allow you to monetize the modifications you’ve made.
While many different types of software will be fully licensed and made proprietary, restricting or even penalizing those who attempt to use it on their own, many developers have created software intended to be released to the public. This allows multiple contributors to add to the codebase and to make changes to improve it for public benefit.
Open-source software matters because anyone, anywhere can download and run the code on their own. They can also modify it, edit it, and tailor it to their specific need. The code is intended to be shared and built upon not because of some altruistic belief, but rather to make it accessible for everyone and create a broad base. This is how we create standards for technologies that provide the ground floor for further tinkering to deliver value to consumers.
Open-source libraries create the building blocks that decrease the hassle and cost of building a new web platform, smartphone, or even a computer language. They distribute common code that can be built upon, assuring interoperability and setting standards for all of our devices and technologies to talk to each other.
I am myself a proponent of open-source software. The server I run in my home has dozens of dockerized applications sourced directly from open-source contributors on GitHub and DockerHub. When there are versions or adaptations that I don’t like, I can pick and choose which I prefer. I can even make comments or add edits if I’ve found a better way for them to run.
Whether you know it or not, many of you run the Linux operating system as the base for your Macbook or any other computer and use all kinds of web tools that have active repositories forked or modified by open-source contributors online. This code is auditable by everyone and can be scrutinized or reviewed by whoever wants to (even AI bots).
This is the same software that runs your airlines, powers the farms that deliver your food, and supports the entire global monetary system. The code of the first decentralized cryptocurrency Bitcoin is also open-source, which has allowed thousands of copycat protocols that have revolutionized how we view money.
You know what else is open-source and available for everyone to use, modify, and build upon?
PHP, Mozilla Firefox, LibreOffice, MySQL, Python, Git, Docker, and WordPress. All protocols and languages that power the web. Friend or foe alike, anyone can download these pieces of software and run them how they see fit.
Open-source code is speech, and it is knowledge.
We build upon it to make information and technology accessible. Attempts to curb open-source, therefore, amount to restricting speech and knowledge.
Open-source is for your friends, and enemies
In the context of Artificial Intelligence, many different developers and companies have chosen to take their large language models and make them available via an open-source license.
At this very moment, you can click on over to Hugging Face, download an AI model, and build a chatbot or scripting machine suited to your needs. All for free (as long as you have the power and bandwidth).
Thousands of companies in the AI sector are doing this at this very moment, discovering ways of building on top of open-source models to develop new apps, tools, and services to offer to companies and individuals. It’s how many different applications are coming to life and thousands more jobs are being created.
We know this can be useful to friends, but what about enemies?
As the AI wars heat up between liberal democracies like the US, the UK, and (sluggishly) the European Union, we know that authoritarian adversaries like the CCP and Russia are building their own applications.
The fear that China will use open-source US models to create some kind of military application is a clear and present danger for many political and national security researchers, as well as politicians.
A bipartisan group of US House lawmakers want to put export controls on AI models, as well as block foreign access to US cloud servers that may be hosting AI software.
If this seems familiar, we should also remember that the US government once classified cryptography and encryption as “munitions” that could not be exported to other countries (see The Crypto Wars). Many of the arguments we hear today were invoked by some of the same people as back then.
Now, encryption protocols are the gold standard for many different banking and web services, messaging, and all kinds of electronic communication. We expect our friends to use it, and our foes as well. Because code is knowledge and speech, we know how to evaluate it and respond if we need to.
Regardless of who uses open-source AI, this is how we should view it today. These are merely tools that people will use for good or ill. It’s up to governments to determine how best to stop illiberal or nefarious uses that harm us, rather than try to outlaw or restrict building of free and open software in the first place.
Limiting open-source threatens our own advancement
If we set out to restrict and limit our ability to create and share open-source code, no matter who uses it, that would be tantamount to imposing censorship. There must be another way.
If there is a “Hundred Year Marathon” between the United States and liberal democracies on one side and autocracies like the Chinese Communist Party on the other, this is not something that will be won or lost based on software licenses. We need as much competition as possible.
The Chinese military has been building up its capabilities with trillions of dollars’ worth of investments that span far beyond AI chatbots and skip logic protocols.
The theft of intellectual property at factories in Shenzhen, or in US courts by third-party litigation funding coming from China, is very real and will have serious economic consequences. It may even change the balance of power if our economies and countries turn to war footing.
But these are separate issues from the ability of free people to create and share open-source code which we can all benefit from. In fact, if we want to continue our way our life and continue to add to global productivity and growth, it’s demanded that we defend open-source.
If liberal democracies want to compete with our global adversaries, it will not be done by reducing the freedoms of citizens in our own countries.
Originally published on the website of the Consumer Choice Center.