-
 @ c230edd3:8ad4a712
2025-05-31 01:51:38
@ c230edd3:8ad4a712
2025-05-31 01:51:38Chef's notes
Most Santa Maria tri tip roast recipes call for red wine vinegar and dijon mustard. I prefer other ingredients in place of those, but should you like those flavors and textures, they are more traditional.
Keep in mind when cooking and slicing, that the grain of tri-tip runs in 3 directions and the meat is unevenly thick. Pulling the roast when the thin end achieves well done, the thicker end will be a nice medium rare. When slicing, change direction to cut against the grain as you transition through for the most tender outcome.
Details
- ⏲️ Prep time: 10 minutes
- 🍳 Cook time: 1 hour ( with grill heating time)
- 🍽️ Servings: 4-6
Ingredients
- 1.5 - 2 lb Tri-Tip Roast
- 1 Tbsp Kosher Salt
- 1 tsp Black Pepper
- 1 tsp Cayanne Pepper ( substitute all or some with smoked paprika for a milder taste)
- 1 tsp Garlic Powder
- 1 tsp Onion Powder
- 1 Tbsp Rosemary
- 2 Tbsp Stone Ground Mustard
- 1 Tbsp Rice Vinegar
- 2-3 Cloves Garlic, Minced
Directions
- Mix all dry spices.
- Pat the roast dry and coat on all sides with seasdoning mix.
- Cover loosely and allow to sit in fridge for 8-12 hours.
- Preheat grill to 475 degrees F, allow meat to sit at room temp during this process.
- Mix vinegar, mustard, and minced garlic.
- Place meat on hot grill, fat side down and coat the upward side with mustard mix
- Grill approximately 7-10 minutes.
- Flip meat, repeat coating and grilling.
- Flip once more and grill for 2-3 minutes to caramelize the glaze and until the fat begins to render.
- Remove from grill and let the roast rest for 5 minutes before slicing,
- Serve with grilled veggies or any side of your choice. This is a bit spicy so it goes well with a salsa fresca and tortillas, too.
-
 @ a8d1560d:3fec7a08
2025-05-30 22:16:48
@ a8d1560d:3fec7a08
2025-05-30 22:16:48NIP-XX
Documentation and Wikis with Spaces and Format Declaration
draftoptionalSummary
This NIP introduces a system for collaborative documentation and wikis on Nostr. It improves upon earlier efforts by adding namespace-like Spaces, explicit content format declaration, and clearer separation of article types, including redirects and merge requests.
Motivation
Previous approaches to wiki-style collaborative content on Nostr had two key limitations:
- Format instability – No declared format per event led to breaking changes (e.g. a shift from Markdown to Asciidoc).
- Lack of namespace separation – All articles existed in a global space, causing confusion and collision between unrelated projects.
This NIP addresses both by introducing:
- Spaces – individually defined wikis or documentation sets.
- Explicit per-article format declaration.
- Dedicated event kinds for articles, redirects, merge requests, and space metadata.
Specification
kind: 31055– Space DefinitionDefines a project namespace for articles.
Tags: -
["name", "<space title>"]-["slug", "<short identifier>"]-["description", "<optional description>"]-["language", "<ISO language code>"]-["license", "<license text or SPDX ID>"]Content: (optional) full description or README for the space.
kind: 31056– ArticleAn article in a specific format belonging to a defined space.
Tags: -
["space", "<slug>"]-["title", "<article title>"]-["format", "markdown" | "asciidoc" | "wikitext" | "html"]-["format-version", "<format version>"](optional) -["prev", "<event-id>"](optional) -["summary", "<short change summary>"](optional)Content: full body of the article in the declared format.
kind: 31057– RedirectRedirects from one article title to another within the same space.
Tags: -
["space", "<slug>"]-["from", "<old title>"]-["to", "<new title>"]Content: empty.
kind: 31058– Merge RequestProposes a revision to an article without directly altering the original.
Tags: -
["space", "<slug>"]-["title", "<article title>"]-["base", "<event-id>"]-["format", "<format>"]-["comment", "<short summary>"](optional)Content: proposed article content.
Format Guidelines
Currently allowed formats: -
markdown-asciidoc-wikitext-htmlClients MUST ignore formats they do not support. Clients MAY apply stricter formatting rules.
Client Behavior
Clients: - MUST render only supported formats. - MUST treat
spaceas a case-sensitive namespace. - SHOULD allow filtering, browsing and searching within Spaces. - SHOULD support revision tracking viaprev. - MAY support diff/merge tooling forkind: 31058.
Examples
Space Definition
json { "kind": 31055, "tags": [ ["name", "Bitcoin Docs"], ["slug", "btc-docs"], ["description", "Developer documentation for Bitcoin tools"], ["language", "en"], ["license", "MIT"] ], "content": "Welcome to the Bitcoin Docs Space." }Markdown Article
json { "kind": 31056, "tags": [ ["space", "btc-docs"], ["title", "Installation Guide"], ["format", "markdown"] ], "content": "# Installation\n\nFollow these steps to install the software..." }Asciidoc Article
json { "kind": 31056, "tags": [ ["space", "btc-docs"], ["title", "RPC Reference"], ["format", "asciidoc"] ], "content": "= RPC Reference\n\nThis section describes JSON-RPC calls." }Wikitext Article
json { "kind": 31056, "tags": [ ["space", "btc-docs"], ["title", "Block Structure"], ["format", "wikitext"] ], "content": "== Block Structure ==\n\nThe structure of a Bitcoin block is..." }Redirect
json { "kind": 31057, "tags": [ ["space", "btc-docs"], ["from", "Getting Started"], ["to", "Installation Guide"] ], "content": "" }Merge Request
json { "kind": 31058, "tags": [ ["space", "btc-docs"], ["title", "Installation Guide"], ["base", "d72fa1..."], ["format", "markdown"], ["comment", "Added step for testnet"] ], "content": "# Installation\n\nNow includes setup instructions for testnet users." }
Acknowledgements
This proposal builds on earlier ideas for decentralized wikis and documentation within Nostr, while solving common issues related to format instability and lack of project separation.
-
 @ c1e6505c:02b3157e
2025-05-28 17:36:03
@ c1e6505c:02b3157e
2025-05-28 17:36:03I recently acquired a new lens:
1959 Leica Summaron F2.8 35mm LTM.
1959 Leica Summaron 35mm f2.8 LTM mounted on my Fujifilm Xpro2 with LTM adapter made by Urth.
Technically, it was a trade. I helped a fellow Bitcoiner set up their Sparrow Wallet, Nostr stuff, and troubleshoot a few wallet issues, and in return, they gave me the lens.
It all started at a local Bitcoin meetup I went to about a week ago - my second time attending. I recognized a few faces from last time, but also saw some new ones. These meetups are refreshing - it’s rare to speak a common language about something like Bitcoin or Nostr. Most people still don’t get it. But they will.
Technology moves forward. Networks grow. Old cells die off.
During the meetup, someone noticed I had my Leica M262 with me and struck up a conversation. Said they had some old Leica lenses and gear at home, and wanted to show me.
Bitcoin and photography in one conversation? I’m down.
A day or so later, they sent me a photo of one of the lenses: a vintage Summaron LTM 35mm f/2.8 from 1959. I’d never seen or heard of one before. They asked if I could help them set up Sparrow and a Bitcoin node. In exchange, they’d give me the lens. Sounded like a good deal to me. Helping plebs with their setups feels like a duty anyway. I said, of course.
They invited me over - a pretty trusting move, which I appreciated. They had some great Bitcoin memorabilia: Fred Krueger’s The Big Bitcoin Book (even if the guy’s turned full shitcoiner), and some FTX sunglasses from Bitcoin 2022. Probably future collector’s items, lol.

We headed upstairs to work on setting up Sparrow Wallet on their Windows machine. I verified the software download first (which you should always do), then helped them create a new wallet using their Ledger Flex. They also had an older Ledger Nano X. The Flex setup was easy, but the Nano X gave us trouble. It turns out Ledger allows multiple wallets for the same asset, which can show up differently depending on how they’re configured. In Sparrow, only one wallet showed—none of the others.
I believe it had to do with the derivation path from the Ledger. If anyone knows a fix, let me know.
After a few hours of troubleshooting, I told them I couldn’t really recommend Ledger. The UX is a mess. They’d already heard similar things from other plebs too.
I suggested switching to the Blockstream Jade. It’s a solid Bitcoin-only device from a trustworthy team. That’s what you want in a hardware wallet.
But back to the lens…
Since it’s an LTM (Leica Thread Mount), I couldn’t mount it directly on my M262. Luckily, I remembered I had an Urth adapter that fits my Fujifilm X-Pro2. I don’t use the X-Pro2 much these days—it’s mostly been sidelined by the M262 - but this was the perfect excuse to bring it out again.
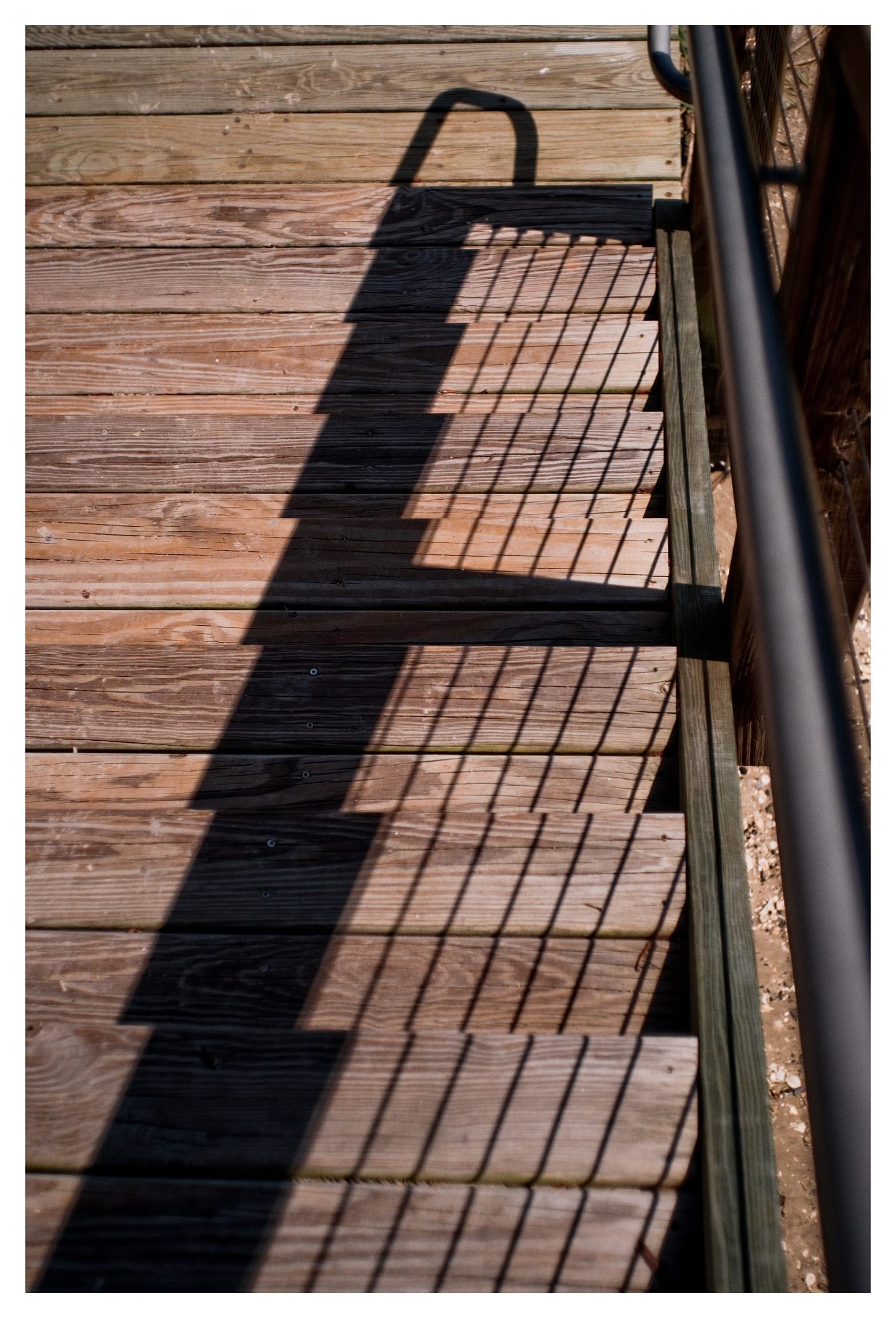
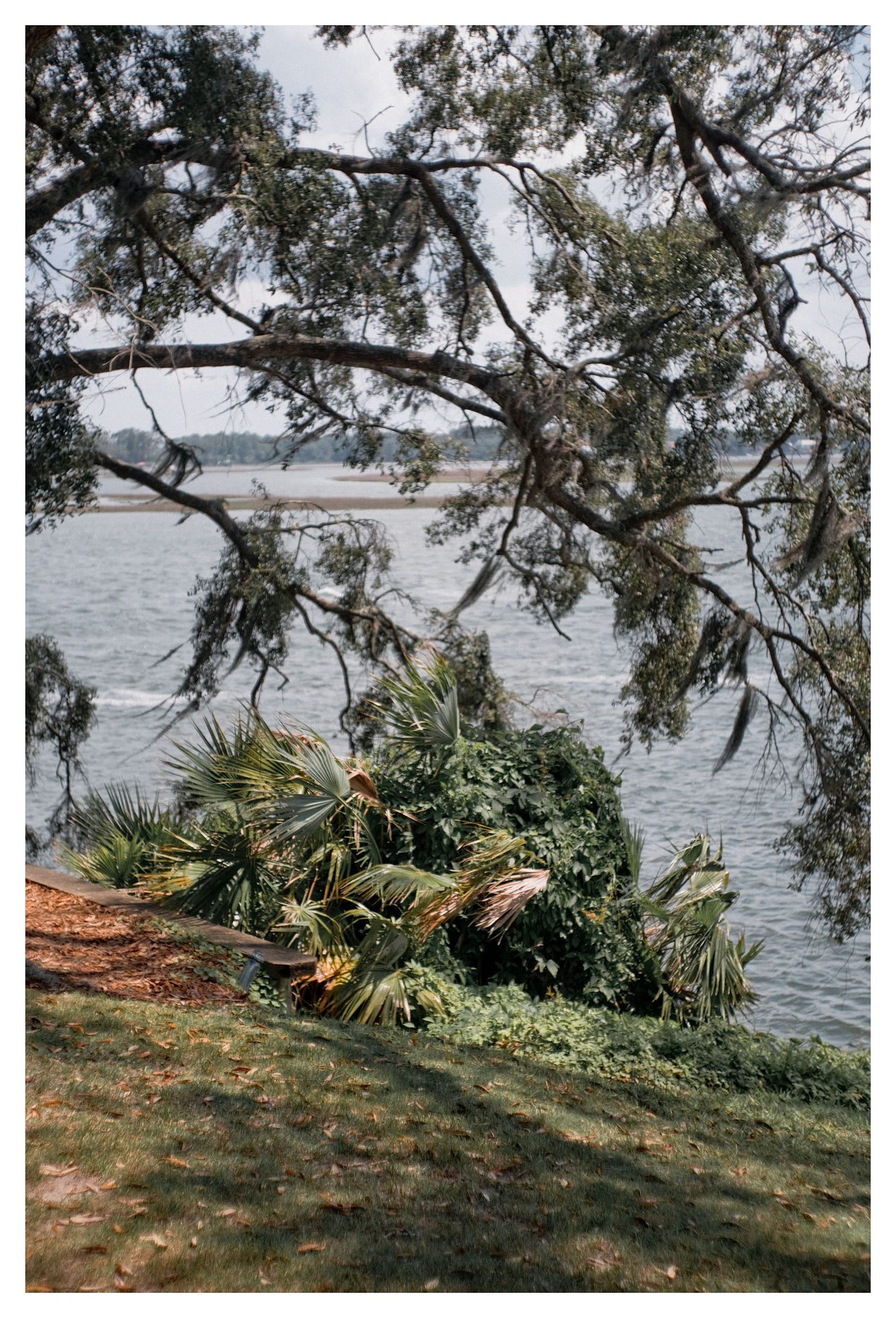
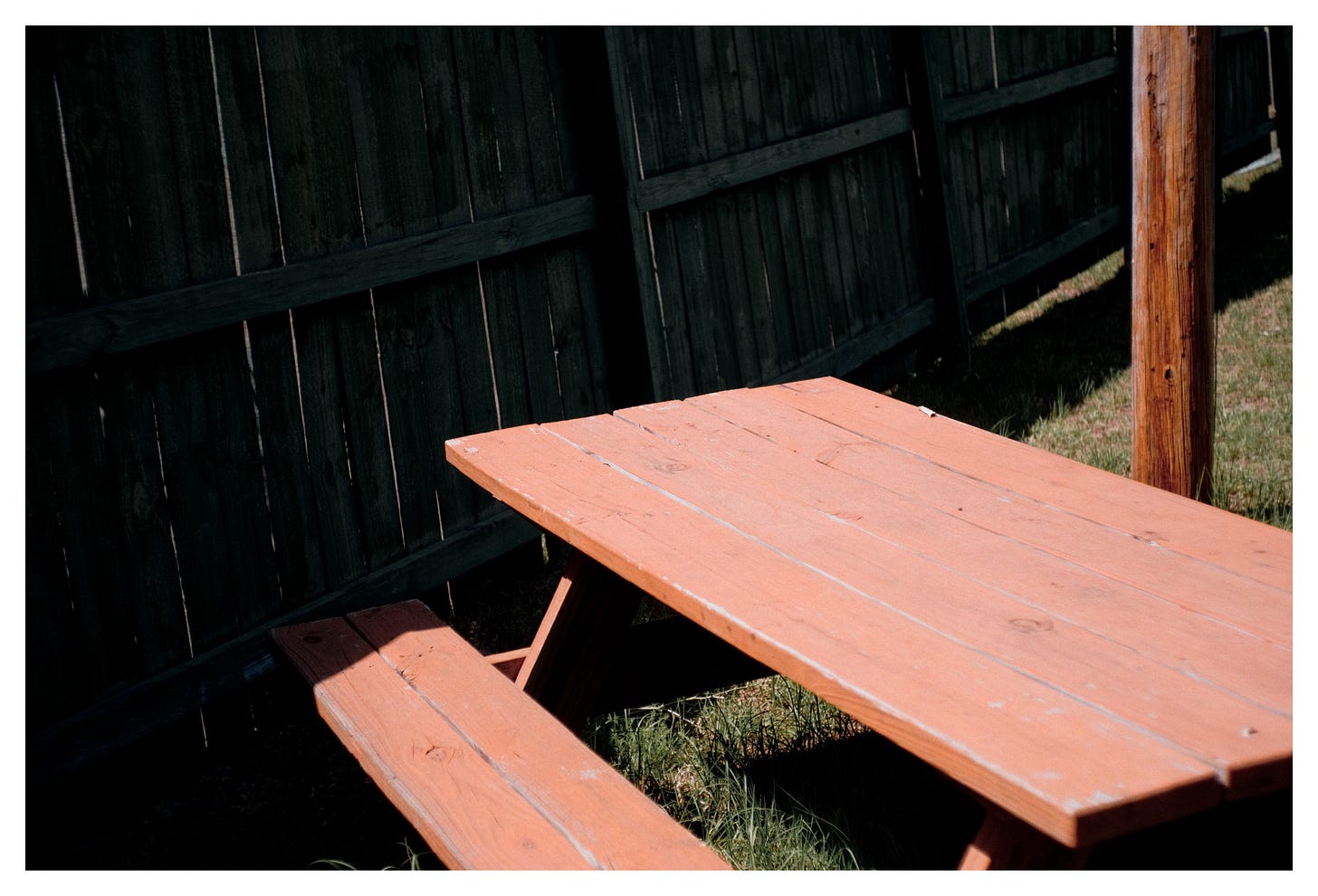
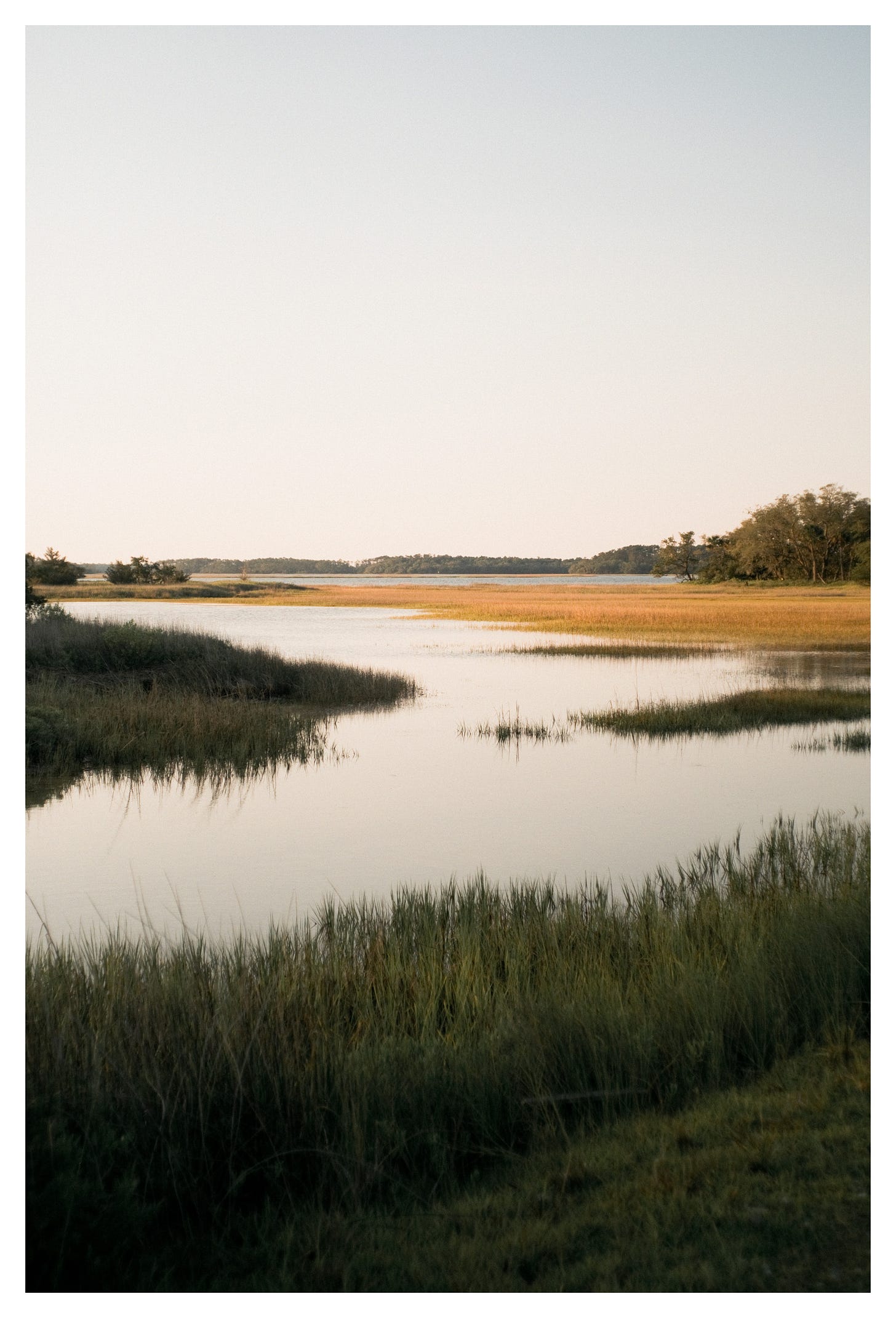
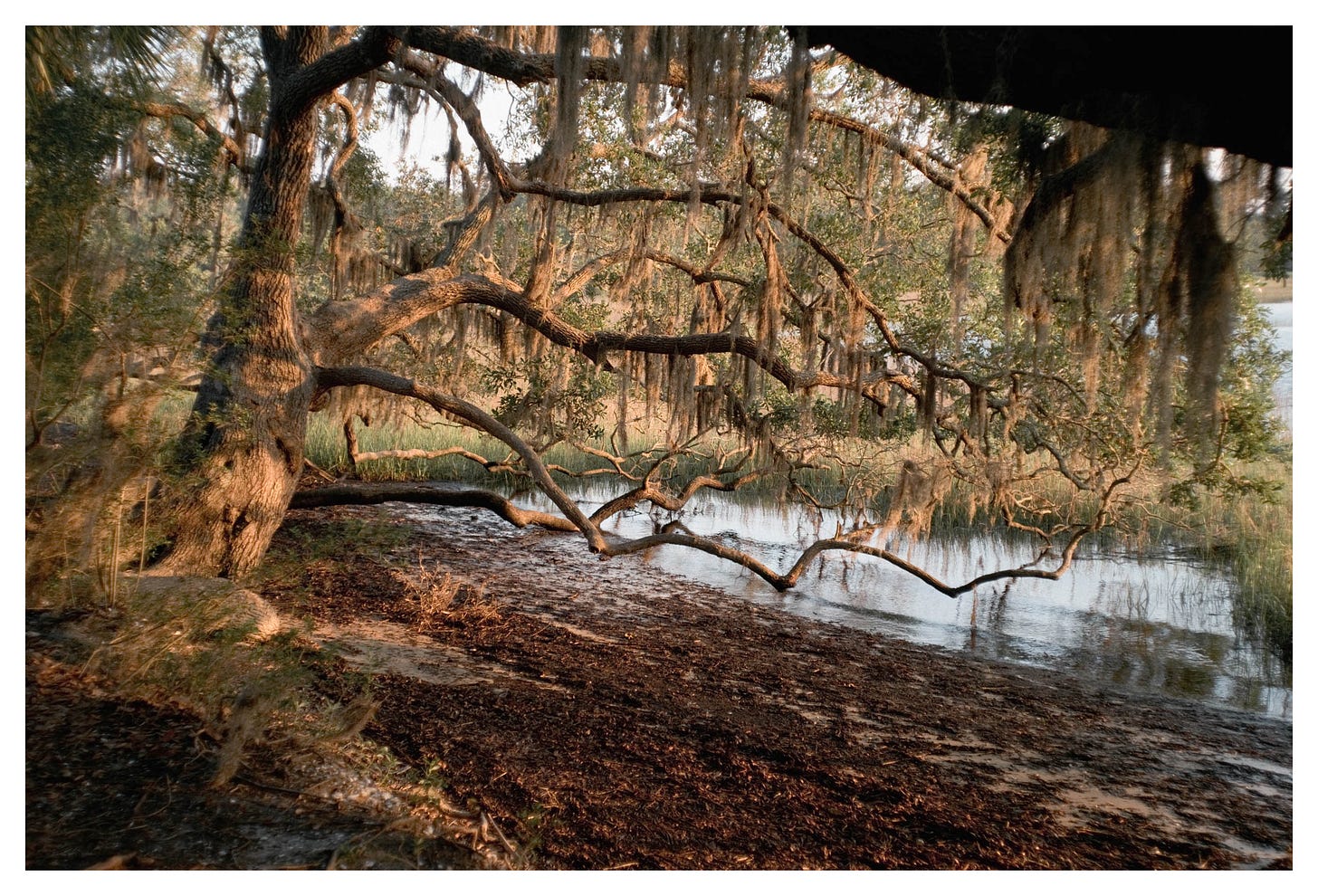
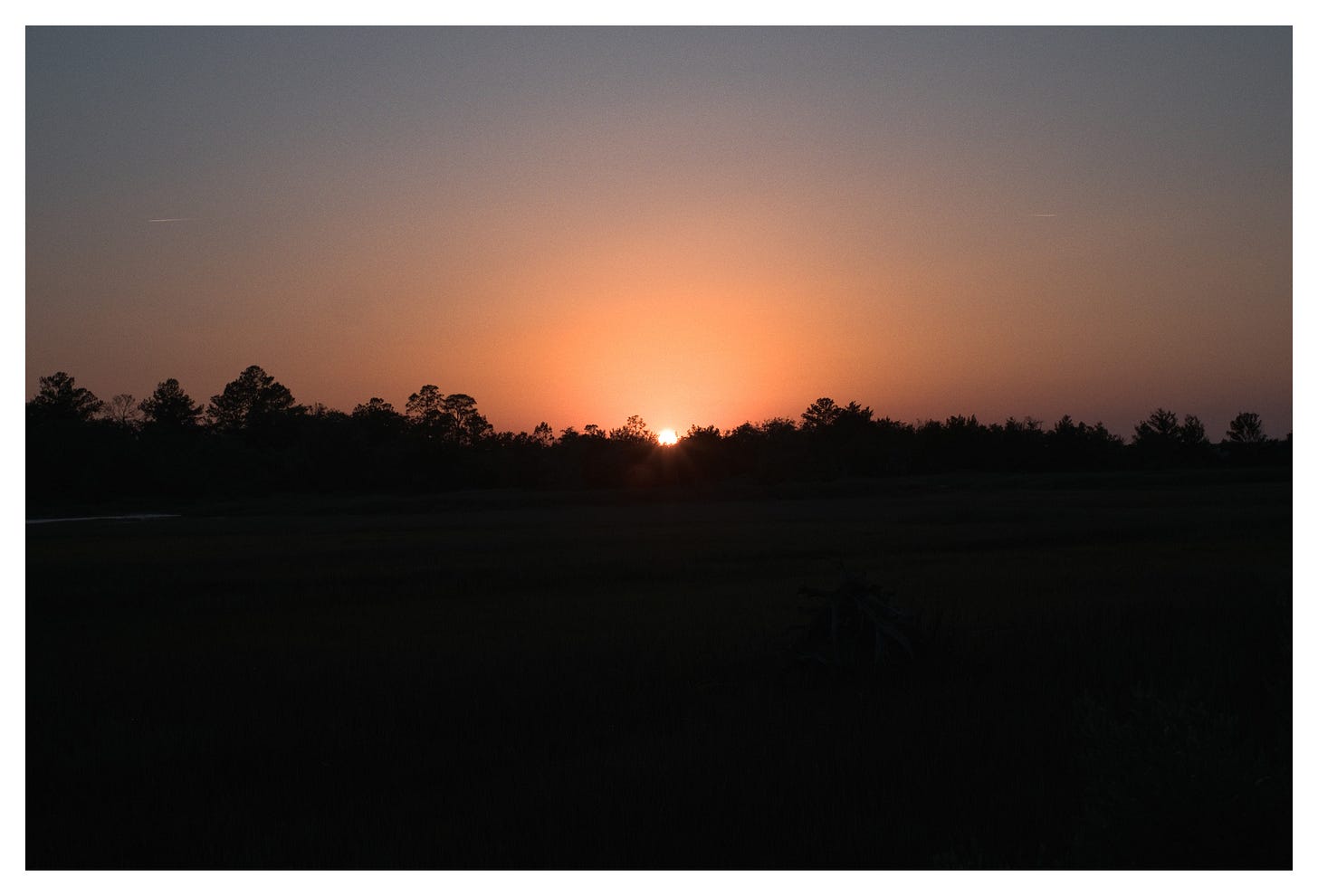
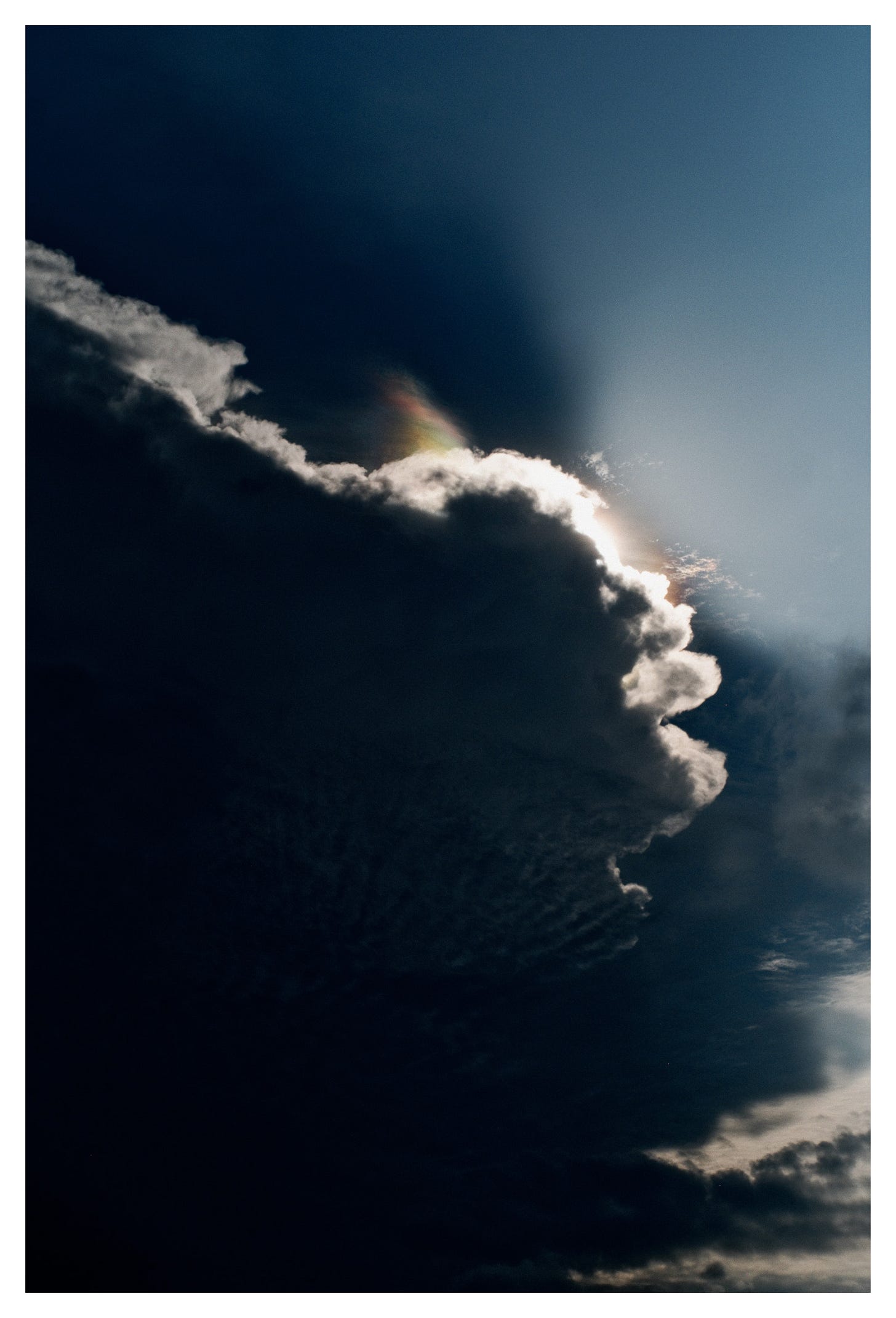
To test the lens, I shot everything wide open at f/2.8. Nothing crazy fast, but it’s the best way to see a lens’s character. And this one definitely has character. There’s a subtle softness and a kind of motion blur effect around the edges when wide open. At first, I wasn’t sure how I felt about it, but the more I shot, the more I liked it. It reminds me of Winogrand’s work in Winogrand Color - those messy, shifting edges that make the frame feel alive. It also helps soften the digital-ness of the camera sensor.
The focus throw is short and snappy - much tighter than my Summicron V3 35mm f/2. I really like how fast it is to use. The closest focusing distance is about 3.5 feet, so it’s not ideal for close-ups. And with the Urth adapter on the X-Pro2, the focal length ends up closer to 40mm.
The only thing that threw me off was the infinity lock. When the focus hits infinity, it physically locks - you have to press a small tab to unlock it. I’ve seen others complain about it, so I guess it’s just one of those old lens quirks. I’m getting used to it.
All the photos here were taken around where I live in South Carolina. Some during bike rides to the river for a swim, others while walking through the marshlands.
I try to make work wherever I am. You should be able to.
It’s about the light, the rhythm, the play - and having the motivation to actually go out and shoot.
Lens rating: 7.9/10
I mainly shoot with a Leica M262, and edit in Lightroom + Dehancer
Use “PictureRoom” for 10% off Dehancer Film
If you’ve made it this far, thank you for taking the time to view my work - consider becoming a paid subscriber.
Also, please contact me if you would like to purchase any of my prints.
Follow me on Nostr:
npub1c8n9qhqzm2x3kzjm84kmdcvm96ezmn257r5xxphv3gsnjq4nz4lqelne96
-
 @ b7274d28:c99628cb
2025-05-28 01:11:43
@ b7274d28:c99628cb
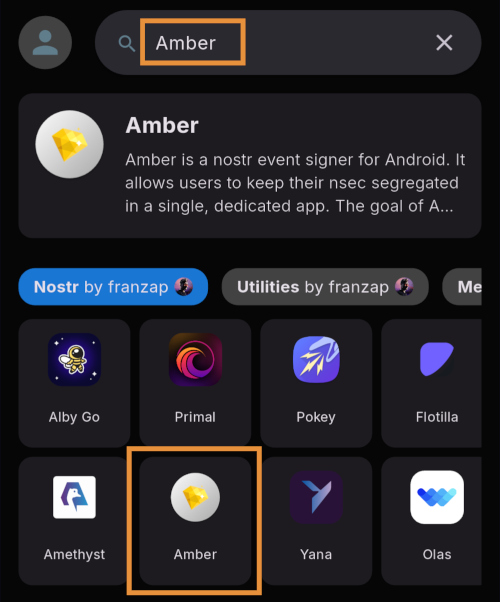
2025-05-28 01:11:43In this second installment of The Android Elite Setup tutorial series, we will cover installing the nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8 on your #Android device and browsing for apps you may be interested in trying out.
Since the #Zapstore is a direct competitor to the Google Play Store, you're not going to be able to find and install it from there like you may be used to with other apps. Instead, you will need to install it directly from the developer's GitHub page. This is not a complicated process, but it is outside the normal flow of searching on the Play Store, tapping install, and you're done.
Installation
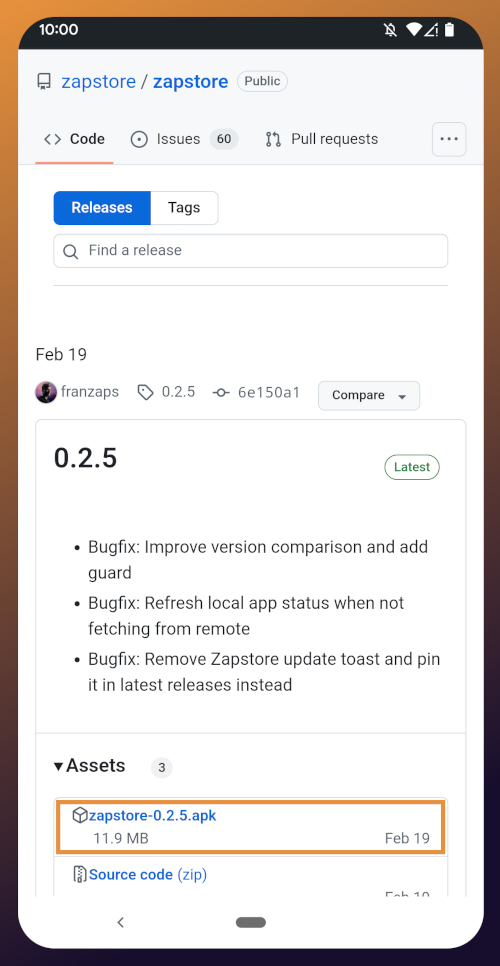
From any web browser on your Android phone, navigate to the Zapstore GitHub Releases page and the most recent version will be listed at the top of the page. The .apk file for you to download and install will be listed in the "Assets."
Tap the .apk to download it, and you should get a notification when the download has completed, with a prompt to open the file.
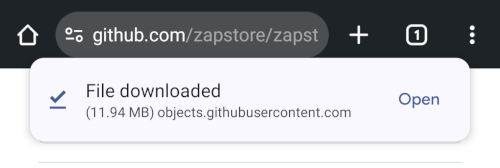
You will likely be presented with a prompt warning you that your phone currently isn't allowed to install applications from "unknown sources." Anywhere other than the Play Store is considered an "unknown source" by default. However, you can manually allow installation from unknown sources in the settings, which the prompt gives you the option to do.
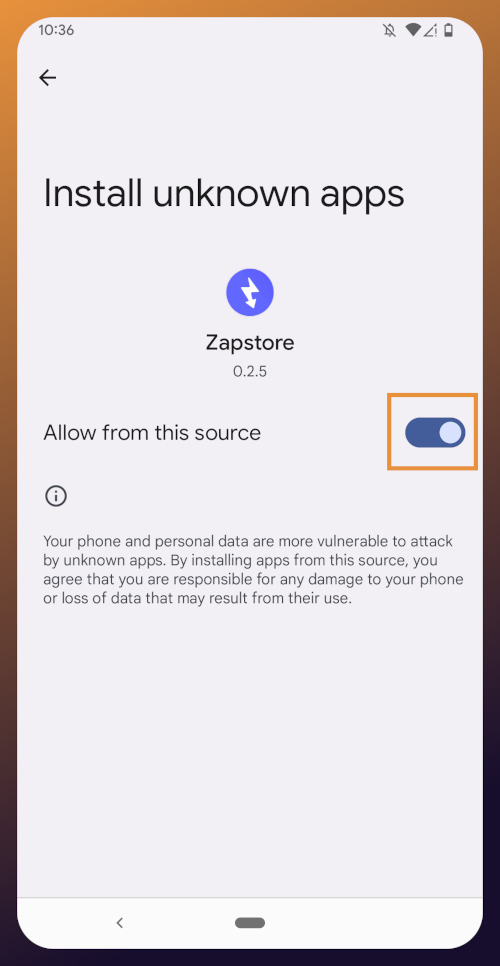
In the settings page that opens, toggle it to allow installation from this source, and you should be prompted to install the application. If you aren't, simply go to your web browser's downloads and tap on the .apk file again, or go into your file browser app and you should find the .apk in your Downloads folder.
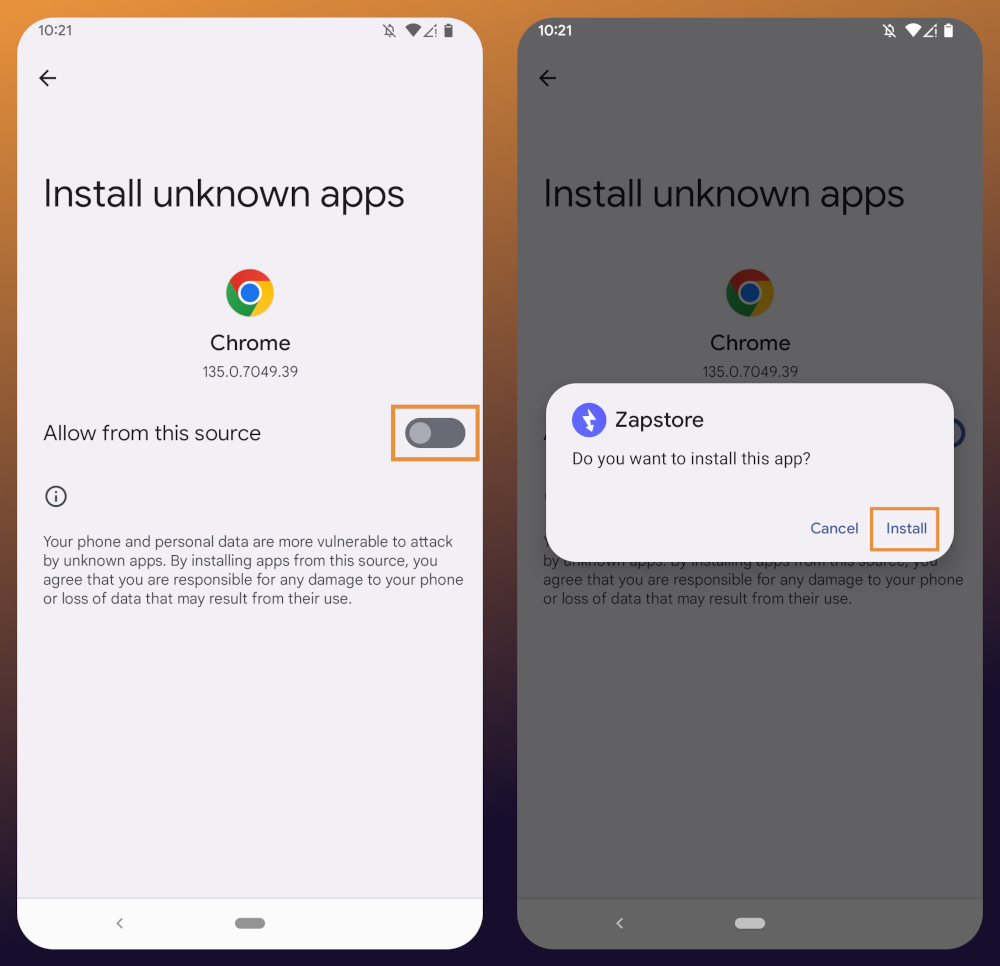
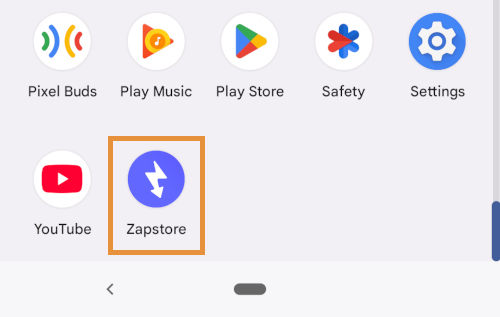
If the application doesn't open automatically after install, you will find it in your app drawer.
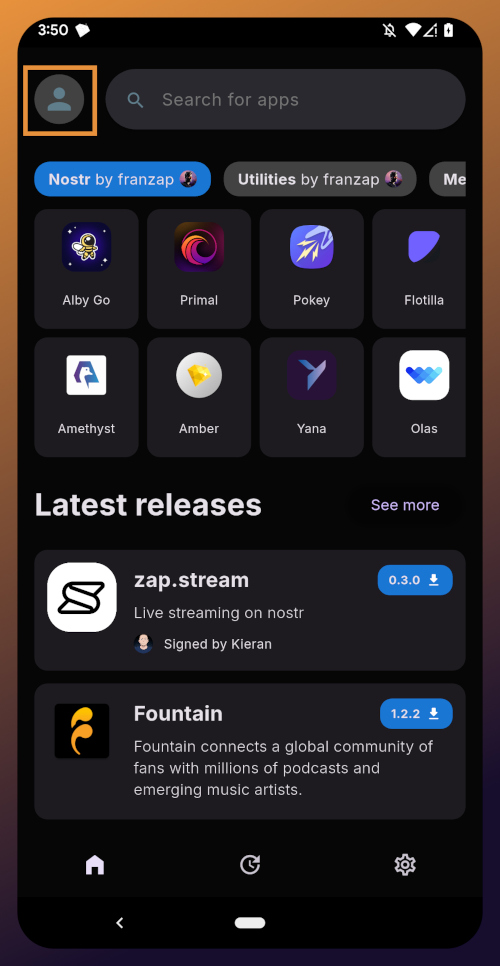
Home Page
Right at the top of the home page in the Zapstore is the search bar. You can use it to find a specific app you know is available in the Zapstore.
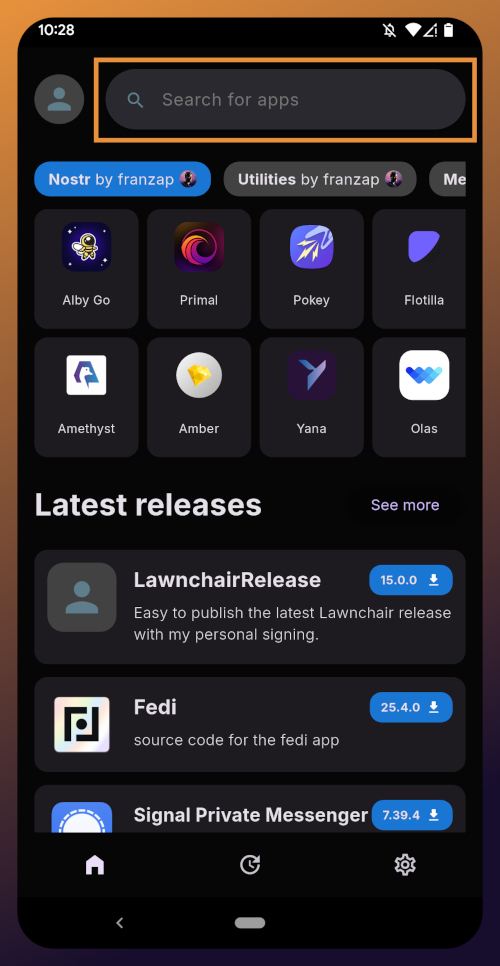
There are quite a lot of open source apps available, and more being added all the time. Most are added by the Zapstore developer, nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9, but some are added by the app developers themselves, especially Nostr apps. All of the applications we will be installing through the Zapstore have been added by their developers and are cryptographically signed, so you know that what you download is what the developer actually released.
The next section is for app discovery. There are curated app collections to peruse for ideas about what you may want to install. As you can see, all of the other apps we will be installing are listed in nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9's "Nostr" collection.
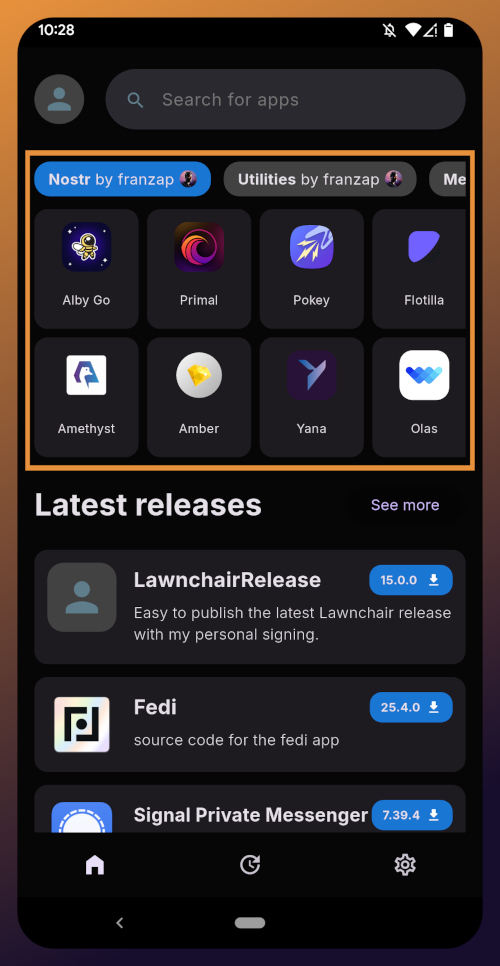
In future releases of the Zapstore, users will be able to create their own app collections.
The last section of the home page is a chronological list of the latest releases. This includes both new apps added to the Zapstore and recently updated apps. The list of recent releases on its own can be a great resource for discovering apps you may not have heard of before.
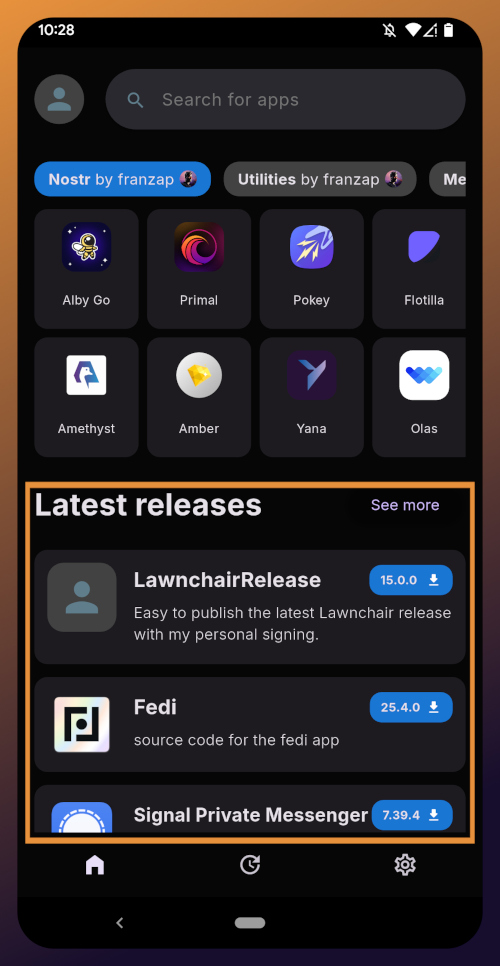
Installed Apps
The next page of the app, accessed by the icon in the bottom-center of the screen that looks like a clock with an arrow circling it, shows all apps you have installed that are available in the Zapstore. It's also where you will find apps you have previously installed that are ready to be updated. This page is pretty sparse on my test profile, since I only have the Zapstore itself installed, so here is a look at it on my main profile:
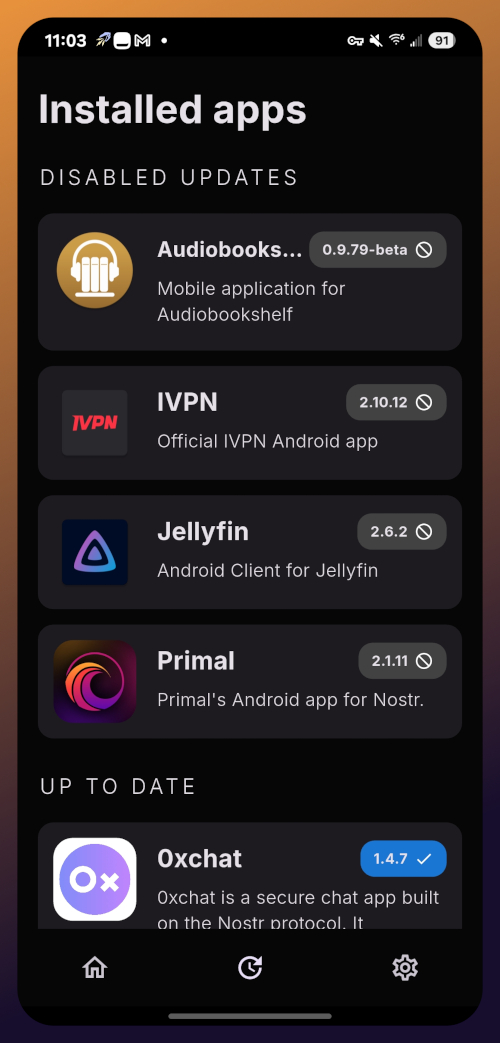
The "Disabled Apps" at the top are usually applications that were installed via the Play Store or some other means, but are also available in the Zapstore. You may be surprised to see that some of the apps you already have installed on your device are also available on the Zapstore. However, to manage their updates though the Zapstore, you would need to uninstall the app and reinstall it from the Zapstore instead. I only recommend doing this for applications that are added to the Zapstore by their developers, or you may encounter a significant delay between a new update being released for the app and when that update is available on the Zapstore.
Tap on one of your apps in the list to see whether the app is added by the developer, or by the Zapstore. This takes you to the application's page, and you may see a warning at the top if the app was not installed through the Zapstore.
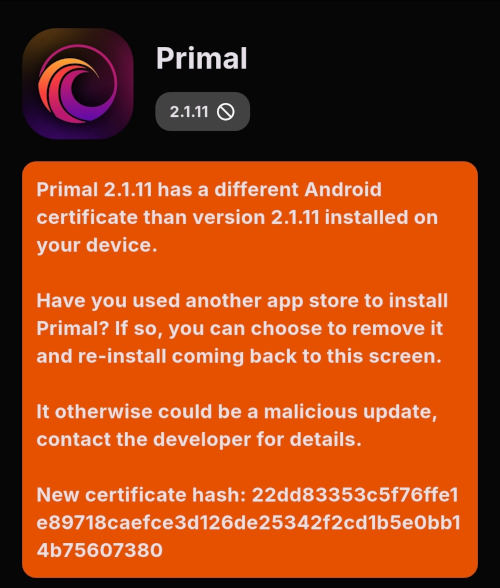
Scroll down the page a bit and you will see who signed the release that is available on the Zapstore.
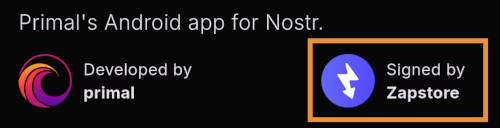
In the case of Primal, even though the developer is on Nostr, they are not signing their own releases to the Zapstore yet. This means there will likely be a delay between Primal releasing an update and that update being available on the Zapstore.
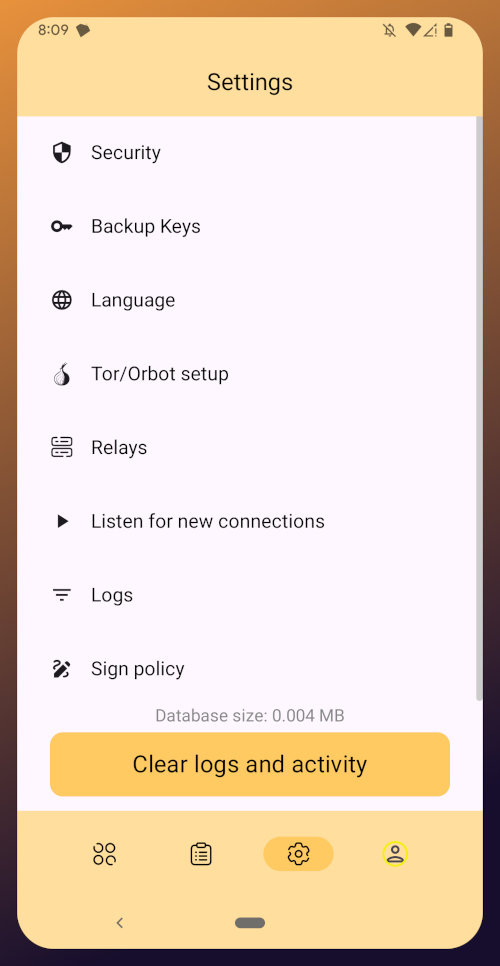
Settings
The last page of the app is the settings page, found by tapping the cog at the bottom right.
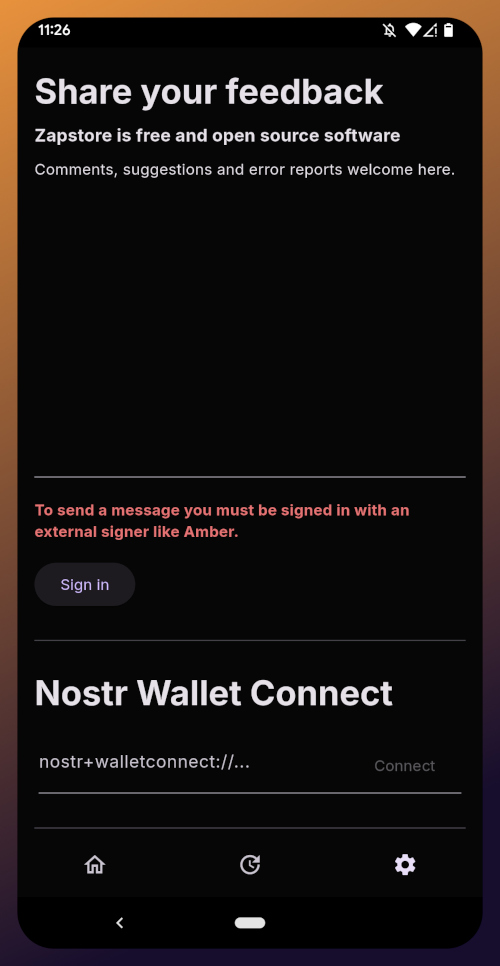
Here you can send the Zapstore developer feedback directly (if you are logged in), connect a Lightning wallet using Nostr Wallet Connect, delete your local cache, and view some system information.
We will be adding a connection to our nostr:npub1h2qfjpnxau9k7ja9qkf50043xfpfy8j5v60xsqryef64y44puwnq28w8ch wallet in part 5 of this tutorial series.
For the time being, we are all set with the Zapstore and ready for the next stage of our journey.
Continue to Part 3: Amber Signer. Nostr link: nostr:naddr1qqxnzde5xuengdeexcmnvv3eqgstwf6d9r37nqalwgxmfd9p9gclt3l0yc3jp5zuyhkfqjy6extz3jcrqsqqqa28qy2hwumn8ghj7un9d3shjtnyv9kh2uewd9hj7qg6waehxw309aex2mrp0yhxyunfva58gcn0d36zumn9wss80nug
-
 @ 29313cc9:a6bf155e
2025-05-30 06:35:56
@ 29313cc9:a6bf155e
2025-05-30 06:35:56I thought i'd experiment with this Nostr blogging thing and write a short article on the state of Meshtastic and its alternatives.
For years Meshtastic was the only game in town, there wasn't a lot of users but the authors kept plugging away and it has become a thriving ecosystem of open source hardware, software, tools and social scene.
Meshtastic has always been focused on node to node messaging, in particular one of the use cases specifically mentioned was hiking in the wilderness or skiing in the mountains and being able to use these devices off-grid, perhaps even without a phone to communicate with one and other. The project does have a few other features like telemetry, remote admin, packet data etc but the messaging was the focus. Because of this focus, the core functionality needs to be built into the firmware of these low powered devices like ESP32 for example. This restricts what can be done in terms of CPU power and storage, but also makes synchronization between device and phone cumbersome.
Unfortunately, as a messaging platform, Meshtastic still struggles even after all these years. Message delivery and routing are fairly unreliable, 95% of conversations go along the lines of "hello, test, anyone there?". Now I should mention, if you have a very good signal to your peers the reliability can be good, but even then its not a guarantee.
Early on in the Meshtastic journey I stumbled upon a similar project named Reticulum which can utilize the same LoRa based hardware but aims to be a more comprehensive platform for decentralized communications and currently requires a computer or raspberry pi to run the Python backend alongside the LoRa hardware as a radio. Reticulum has historically been a less polished UI experience and a little idiosyncratic in its design which has probably hindered its adoption a little. But the main difference to Meshtastic is Reticulum requires bigger hardware and is less suitable for remote installations, solar powered setups etc. My understanding is once v1.0 has been released (soon) there may be efforts to port the code to native C which may allow hardware nodes to run as repeaters on their own.
More recently a new project has been announced called Meshcore, which is more closely aligned with Meshtastic than Reticulum, Meshcore makes several important improvements to message delivery and routing in an attempt to improve the reliability of the core feature, messaging. Popular Youtube channel Andy Kirby has been central in helping Meshcore gain popularity and I think he may be involved in the commercial aspects of the project. The smartphone apps and website mapping and flasher tools are a bit more polished with Meshcore.
One of the biggest contributors in the space is Liam Cottle who has created mapping websites for Meshtastic & Meshcore, he also built the Meshcore smartphone app and built the fantastic Reticulum MeshChat UI.
With all this new competition Meshtastic appears to be pushing out more frequent updates and whilst they have been introducing more bugs into the software it is nice to see some faster progress.
In my opinion Reticulum is probably the most interesting project with the most potential, but they do need to get the core routing engine running standalone on low powered hardware for the project to expand to more hardware/radio focused users.
That is all. Mesh on!
-
 @ 33baa074:3bb3a297
2025-05-28 08:54:40
@ 33baa074:3bb3a297
2025-05-28 08:54:40COD (chemical oxygen demand) sensors play a vital role in water quality testing. Their main functions include real-time monitoring, pollution event warning, water quality assessment and pollution source tracking. The following are the specific roles and applications of COD sensors in water quality testing:
Real-time monitoring and data acquisition COD sensors can monitor the COD content in water bodies in real time and continuously. Compared with traditional sampling methods, COD sensors are fast and accurate, without manual sampling and laboratory testing, which greatly saves time and labor costs. By combining with the data acquisition system, the monitoring data can be uploaded to the cloud in real time to form a extemporization distribution map of the COD content in the water body, providing detailed data support for environmental monitoring and management.
Pollution event warning and rapid response COD sensors play an important role in early warning and rapid response in water environment monitoring. Once there is an abnormal increase in organic matter in the water body, the COD sensor can quickly detect the change in COD content and alarm through the preset threshold. This enables relevant departments to take measures at the early stage of the pollution incident to prevent the spread of pollution and protect the water environment.
Water quality assessment and pollution source tracking COD sensors play an important role in water quality assessment and pollution source tracking. By continuously monitoring the COD content in water bodies, the water quality can be evaluated and compared with national and regional water quality standards. At the same time, COD sensors can also help determine and track the location and spread of pollution sources, provide accurate data support for environmental management departments, and guide the development of pollution prevention and control work.
Application scenarios COD sensors are widely used in various water quality monitoring scenarios, including but not limited to: Sewage treatment plants: used to monitor the COD content of in fluent and effluent to ensure the effect of sewage treatment. Water source protection and management: deployed in water sources to monitor the COD content of in fluent sources. Once the water quality exceeds the set limit, the system will issue an alarm in time to ensure water quality safety. Lake and river monitoring: deployed in water bodies such as lakes and rivers to monitor the COD content of water bodies in real time.

Technical features of COD sensor COD sensor uses advanced technology, such as ultraviolet absorption method, which does not require the use of chemical reagents, avoiding the risk of contamination of chemical reagents in traditional COD detection methods, and can achieve online uninterrupted water quality monitoring, providing strong support for real-time water quality assessment. In addition, COD sensor also has the advantages of low cost, high stability, strong anti-interference ability, and convenient installation.
Summary In summary, COD sensor plays an irreplaceable role in water quality detection. It can not only provide real-time and accurate water quality data, but also quickly warn when pollution incidents occur, providing strong technical support for water quality management and environmental protection. With the advancement of technology and the popularization of applications, COD sensor will play a more important role in water quality monitoring in the future.
-
 @ 33baa074:3bb3a297
2025-05-28 08:25:13
@ 33baa074:3bb3a297
2025-05-28 08:25:13The oil-in-water sensoris an instrument specially used to detect oil substances in water bodies. Its working principle is mainly based on the characteristic that oil substances will produce fluorescence under ultraviolet light. The following is a detailed explanation:
Principle Overview The oil-in-water sensor uses the characteristic that oil substances will produce fluorescence under ultraviolet light, and measures the fluorescence intensity to infer the concentration of oil substances. Specifically, the sensor uses ultraviolet light as the excitation light source to irradiate the water sample to be tested. After the oil substance absorbs ultraviolet light, it will stimulate fluorescence, and the fluorescence signal is received by the photo detector and converted into an electrical signal. By measuring the strength of the electrical signal, the concentration of oil substances in the water sample can be inferred.
Workflow Ultraviolet light irradiation: The ultraviolet light source inside the sensor emits ultraviolet light and irradiates it into the water sample to be tested.
Fluorescence generation: After the oil substance in the water sample absorbs ultraviolet light, it will stimulate fluorescence.
Fluorescence detection: The photo detector in the sensor measures the intensity of this fluorescence.
Signal conversion: The signal processing circuit converts the output of the photo detector into an electrical signal proportional to the amount of oil in the water. Data analysis: By analyzing the strength of the electrical signal, the concentration of oil substances in the water sample can be obtained.
Features and applications The oil in water sensor has high sensitivity and can detect soluble and falsifiable oils. It is suitable for a variety of water quality monitoring scenarios, such as oil field monitoring, industrial circulating water, condensate water, wastewater treatment, surface water stations, etc. In addition, it can also monitor the content of crude oil (benzene and benzene homologous) in water sources such as reservoirs and water plants in real time online, play an early warning role, and protect the safety of water sources.
Practical application The oil in water sensor has a wide range of functions in practical applications, including but not limited to the following aspects: Monitoring the water quality of water sources: ensuring the safety of drinking water, and timely discovering pollution sources and ensuring water supply safety by continuously monitoring oil substances in water sources. Monitoring sewage treatment plant emissions: ensuring that the discharge water quality of sewage treatment plants meets the emission standards to avoid secondary pollution to the environment. Monitoring rivers, lakes and other water bodies: assessing the pollution status and providing a basis for pollution control. Early warning and emergency response: It has real-time monitoring and early warning functions, and can issue an alarm in time when abnormal conditions are found, providing valuable time for emergency response and reducing losses caused by pollution. Scientific research: Through the monitoring data of this sensor, we can deeply understand the distribution, migration and transformation of oil substances in water bodies, and provide a scientific basis for environmental protection and governance.
In summary, the oil in water sensor monitors the oil content in water bodies through ultraviolet fluorescence method, has high sensitivity and broad application prospects, and is an indispensable and important tool in modern environmental monitoring and industrial production.
-
 @ 39cc53c9:27168656
2025-05-27 09:21:53
@ 39cc53c9:27168656
2025-05-27 09:21:53The new website is finally live! I put in a lot of hard work over the past months on it. I'm proud to say that it's out now and it looks pretty cool, at least to me!
Why rewrite it all?
The old kycnot.me site was built using Python with Flask about two years ago. Since then, I've gained a lot more experience with Golang and coding in general. Trying to update that old codebase, which had a lot of design flaws, would have been a bad idea. It would have been like building on an unstable foundation.
That's why I made the decision to rewrite the entire application. Initially, I chose to use SvelteKit with JavaScript. I did manage to create a stable site that looked similar to the new one, but it required Jav aScript to work. As I kept coding, I started feeling like I was repeating "the Python mistake". I was writing the app in a language I wasn't very familiar with (just like when I was learning Python at that mom ent), and I wasn't happy with the code. It felt like spaghetti code all the time.
So, I made a complete U-turn and started over, this time using Golang. While I'm not as proficient in Golang as I am in Python now, I find it to be a very enjoyable language to code with. Most aof my recent pr ojects have been written in Golang, and I'm getting the hang of it. I tried to make the best decisions I could and structure the code as well as possible. Of course, there's still room for improvement, which I'll address in future updates.
Now I have a more maintainable website that can scale much better. It uses a real database instead of a JSON file like the old site, and I can add many more features. Since I chose to go with Golang, I mad e the "tradeoff" of not using JavaScript at all, so all the rendering load falls on the server. But I believe it's a tradeoff that's worth it.
What's new
- UI/UX - I've designed a new logo and color palette for kycnot.me. I think it looks pretty cool and cypherpunk. I am not a graphic designer, but I think I did a decent work and I put a lot of thinking on it to make it pleasant!
- Point system - The new point system provides more detailed information about the listings, and can be expanded to cover additional features across all services. Anyone can request a new point!
- ToS Scrapper: I've implemented a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices. This is still in development and it will improve for sure, but it works pretty fine right now!
- Search bar - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services. Looking for VPN services? Just search for "vpn"!
- Transparency - To be more transparent, all discussions about services now take place publicly on GitLab. I won't be answering any e-mails (an auto-reply will prompt to write to the corresponding Gitlab issue). This ensures that all service-related matters are publicly accessible and recorded. Additionally, there's a real-time audits page that displays database changes.
- Listing Requests - I have upgraded the request system. The new form allows you to directly request services or points without any extra steps. In the future, I plan to enable requests for specific changes to parts of the website.
- Lightweight and fast - The new site is lighter and faster than its predecessor!
- Tor and I2P - At last! kycnot.me is now officially on Tor and I2P!
How?
This rewrite has been a labor of love, in the end, I've been working on this for more than 3 months now. I don't have a team, so I work by myself on my free time, but I find great joy in helping people on their private journey with cryptocurrencies. Making it easier for individuals to use cryptocurrencies without KYC is a goal I am proud of!
If you appreciate my work, you can support me through the methods listed here. Alternatively, feel free to send me an email with a kind message!
Technical details
All the code is written in Golang, the website makes use of the chi router for the routing part. I also make use of BigCache for caching database requests. There is 0 JavaScript, so all the rendering load falls on the server, this means it needed to be efficient enough to not drawn with a few users since the old site was reporting about 2M requests per month on average (note that this are not unique users).
The database is running with mariadb, using gorm as the ORM. This is more than enough for this project. I started working with an
sqlitedatabase, but I ended up migrating to mariadb since it works better with JSON.The scraper is using chromedp combined with a series of keywords, regex and other logic. It runs every 24h and scraps all the services. You can find the scraper code here.
The frontend is written using Golang Templates for the HTML, and TailwindCSS plus DaisyUI for the CSS classes framework. I also use some plain CSS, but it's minimal.
The requests forms is the only part of the project that requires JavaScript to be enabled. It is needed for parsing some from fields that are a bit complex and for the "captcha", which is a simple Proof of Work that runs on your browser, destinated to avoid spam. For this, I use mCaptcha.
-
 @ b7274d28:c99628cb
2025-05-28 00:59:49
@ b7274d28:c99628cb
2025-05-28 00:59:49Your identity is important to you, right? While impersonation can be seen in some senses as a form of flattery, we all would prefer to be the only person capable of representing ourselves online, unless we intentionally delegate that privilege to someone else and maintain the ability to revoke it.
Amber does all of that for you in the context of #Nostr. It minimizes the possibility of your private key being compromized by acting as the only app with access to it, while all other Nostr apps send requests to Amber when they need something signed. This even allows you to give someone temporary authority to post as you without giving them your private key, and you retain the authority to revoke their permissions at any time.
nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5 has provided Android users with an incredibly powerful tool in Amber, and he continues to improve its functionality and ease of use. Indeed, there is not currently a comparative app available for iOS users. For the time being, this superpower is exclusive to Android.
Installation
Open up the Zapstore app that you installed in the previous stage of this tutorial series.
Very likely, Amber will be listed in the app collection section of the home page. If it is not, just search for "Amber" in the search bar.
Opening the app's page in the Zapstore shows that the release is signed by the developer. You can also see who has added this app to one of their collections and who has supported this app with sats by zapping the release.
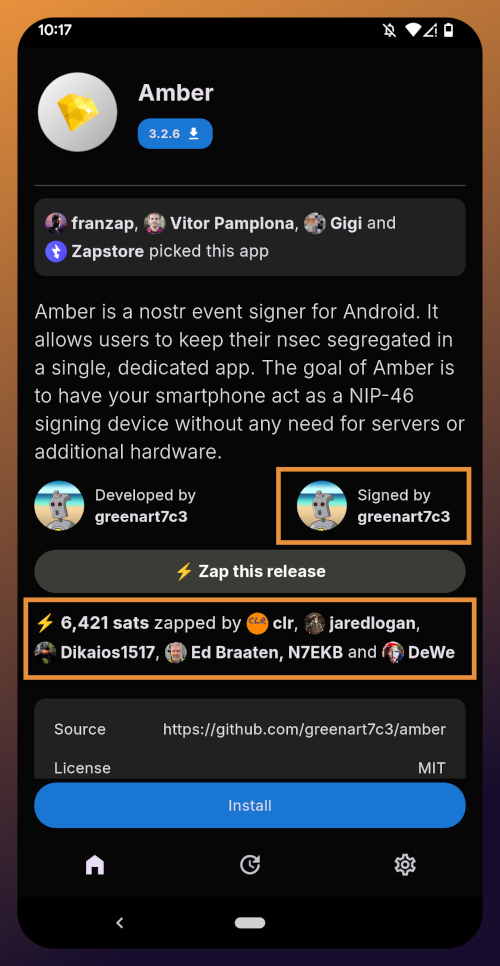
Tap "Install" and you will be prompted to confirm you are sure you want to install Amber.
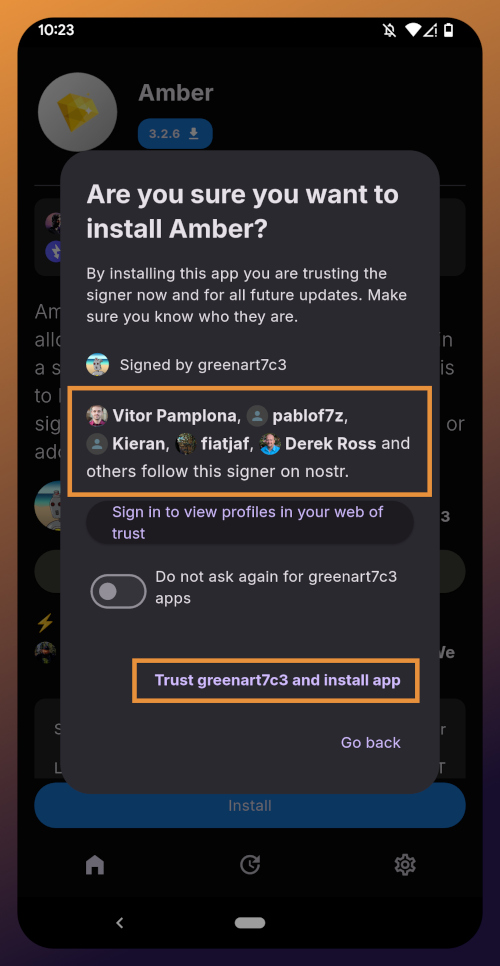
Helpfully, you are informed that several other users follow this developer on Nostr. If you have been on Nostr a while, you will likely recognize these gentlemen as other Nostr developers, one of them being the original creator of the protocol.
You can choose to never have Zapstore ask for confirmation again with apps developed by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5, and since we have another of his apps to install later in this tutorial series, I recommend you toggle this on. Then tap on "Trust greenart7c3 and install app."
Just like when you installed the Zapstore from their GitHub, you will be prompted to allow the Zapstore to install apps, since Android considers it an "unknown source."
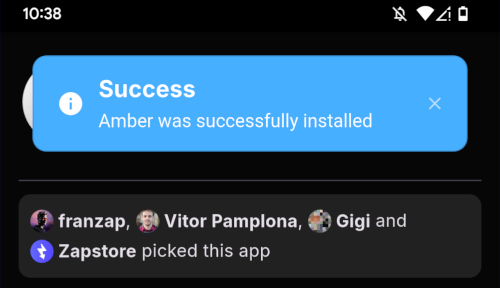
Once you toggle this on and use the back button to get back to the Zapstore, Amber will begin downloading and then present a prompt to install the app. Once installed, you will see a prompt that installation was a success and you can now open the app.
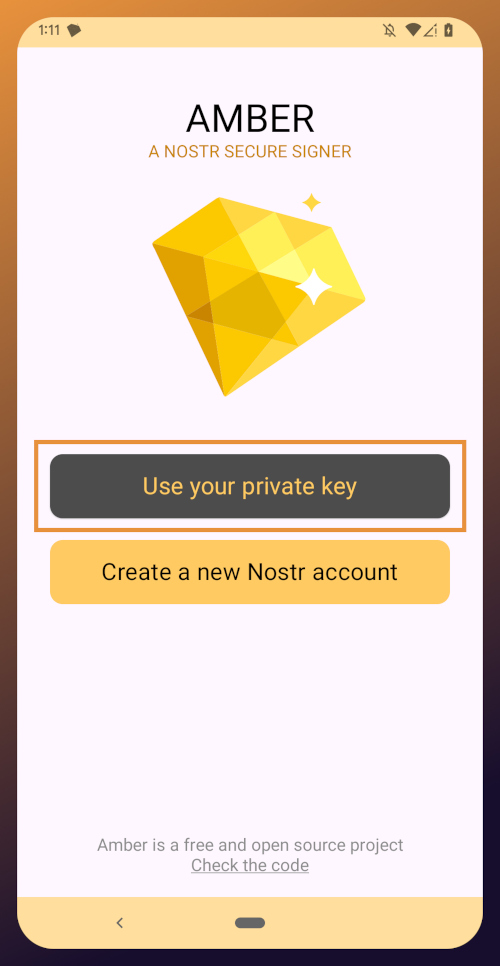
From here, how you proceed will depend on whether you need to set up a new Nostr identity or use Amber with an existing private key you already have set up. The next section will cover setting up a new Nostr identity with Amber. Skip to the section titled "Existing Nostrich" if you already have an nsec that you would like to use with Amber.
New Nostrich
Upon opening the application, you will be presented with the option to use an existing private key or create a new Nostr account. Nostr doesn't really have "accounts" in the traditional sense of the term. Accounts are a relic of permissioned systems. What you have on Nostr are keys, but Amber uses the "account" term because it is a more familiar concept, though it is technically inaccurate.
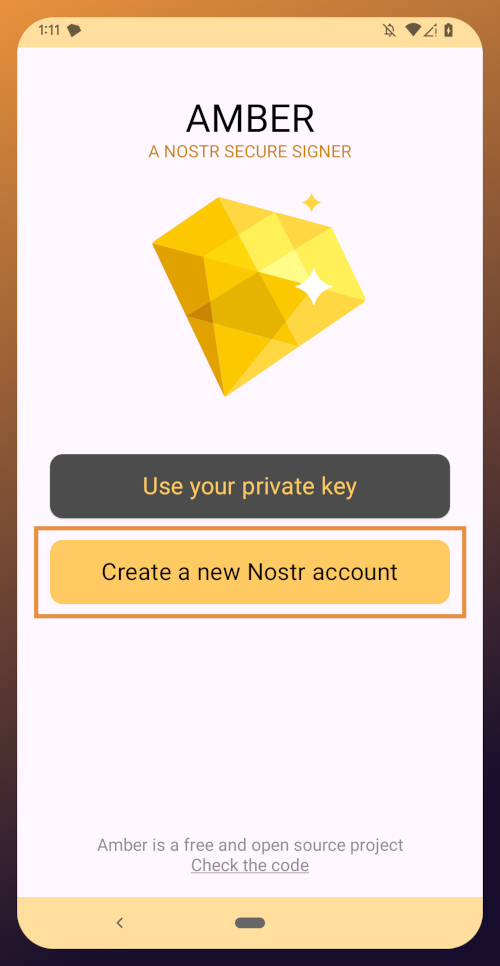
Choose "Create a new Nostr account" and you will be presented with a screen telling you that your Nostr account is ready. Yes, it was really that easy. No email, no real name, no date of birth, and no annoying capcha. Just "Create a new account" and you're done.
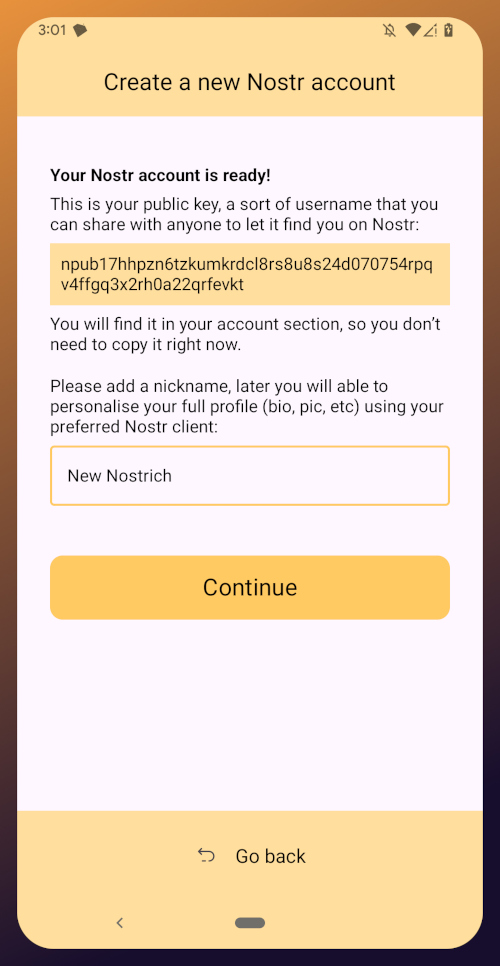
The app presents you with your public key. This is like an address that can be used to find your posts on Nostr. It is 100% unique to you, and no one else can post a note that lists this npub as the author, because they won't have the corresponding private key. You don't need to remember your npub, though. You'll be able to readily copy it from any Nostr app you use whenever you need it.
You will also be prompted to add a nickname. This is just for use within Amber, since you can set up multiple profiles within the app. You can use anything you want here, as it is just so you can tell which profile is which when switching between them in Amber.
Once you've set your nickname, tap on "Continue."
The next screen will ask you what Amber's default signing policy should be.
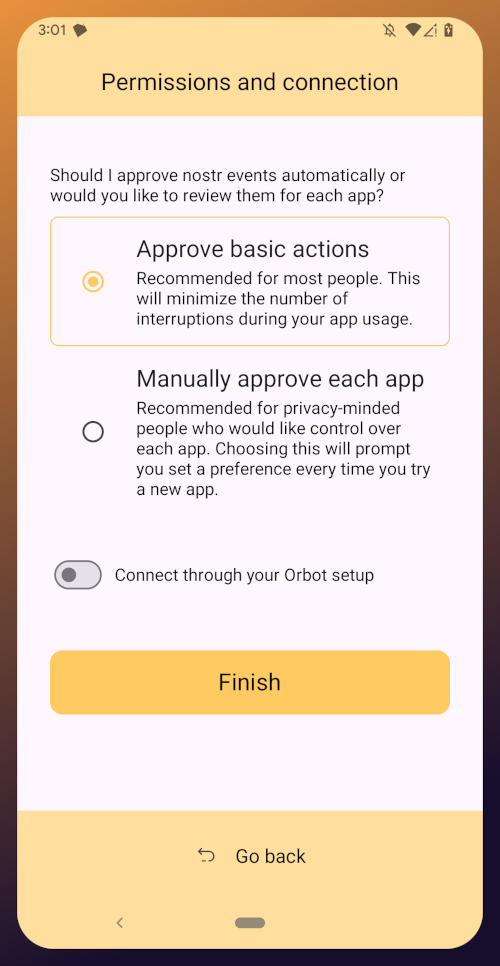
The default is to approve basic actions, referring to things that are common for Nostr clients to request a signature for, like following another user, liking a post, making a new post, or replying. If you are more concerned about what Amber might be signing for on your behalf, you can tell it to require manual approval for each app.
Once you've made your decision, tap "Finish." You will also be able to change this selection in the app settings at any time.
With this setup out of the way, you are now presented with the main "Applications" page of the app.
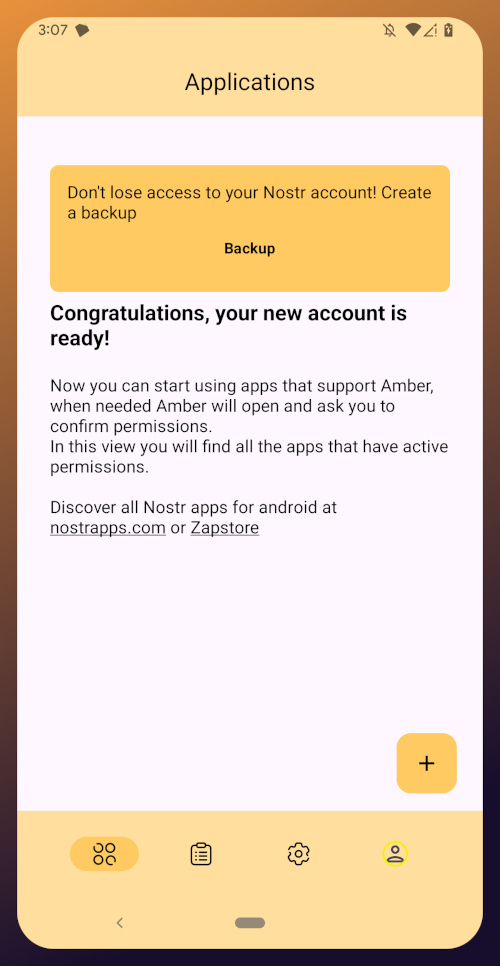
At the top, you have a notification encouraging you to create a backup. Let's get that taken care of now by tapping on the notification and skipping down to the heading titled "Backing Up Your Identity" in this tutorial.
Existing Nostrich
Upon opening the application, you will be presented with the option to use your private key or create a new Nostr account. Choose the former.
The next screen will require you to paste your private key.
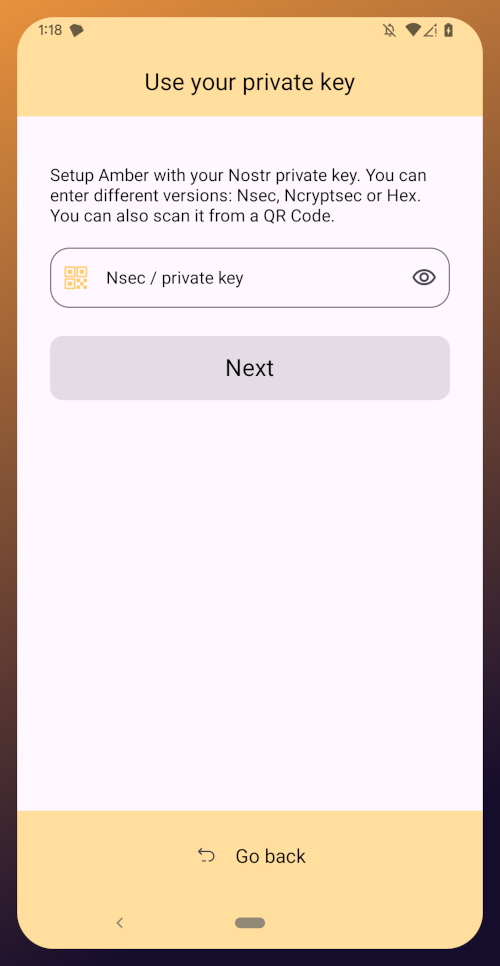
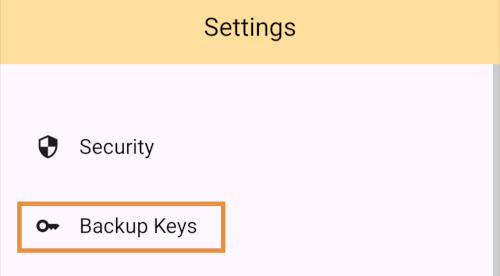
You will need to obtain this from whatever Nostr app you used to create your profile, or any other Nostr app that you pasted your nsec into in the past. Typically you can find it in the app settings and there will be a section mentioning your keys where you can copy your nsec. For instance, in Primal go to Settings > Keys > Copy private key, and on Amethyst open the side panel by tapping on your profile picture in the top-left, then Backup Keys > Copy my secret key.
After pasting your nsec into Amber, tap "Next."
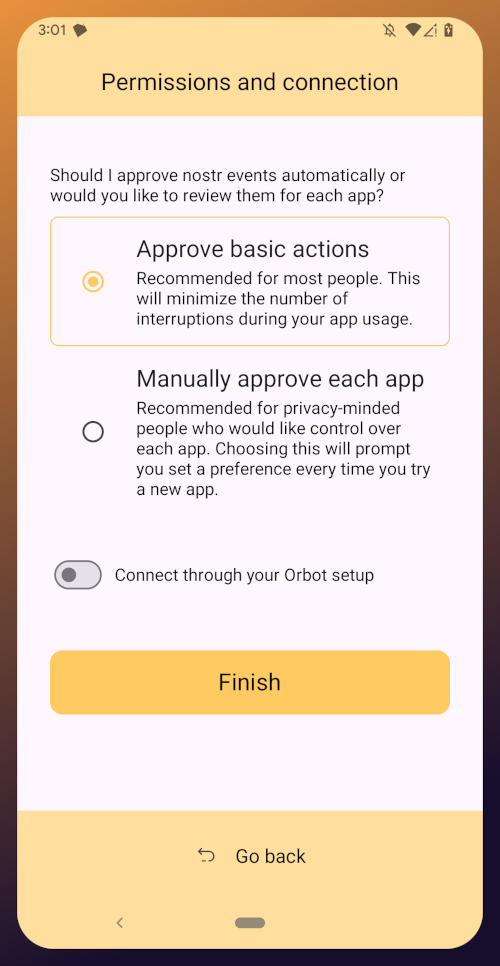
Amber will give you a couple options for a default signing policy. The default is to approve basic actions, referring to things that are common for Nostr clients to request a signature for, like following another user, liking a post, making a new post, or replying. If you are more concerned about what Amber might be signing for on your behalf, you can tell it to require manual approval for each app.
Once you've made your decision, tap "Finish." You will also be able to change this selection in the app settings at any time.
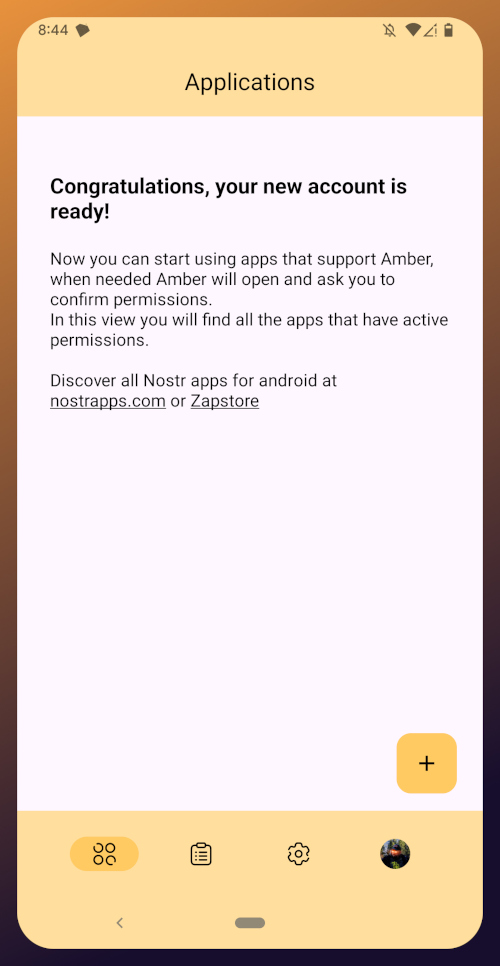
With this setup out of the way, you are now presented with the main "Applications" page of the app. You have nothing here yet, since you haven't used Amber to log into any Nostr apps, but this will be where all of the apps you have connected with Amber will be listed, in the order of the most recently used at the top.
Before we go and use Amber to log into an app, though, let's make sure we've created a backup of our private key. You pasted your nsec into Amber, so you could just save that somewhere safe, but Amber gives you a few other options as well. To find them, you'll need to tap the cog icon at the bottom of the screen to access the settings, then select "Backup Keys."
Backing Up Your Identity
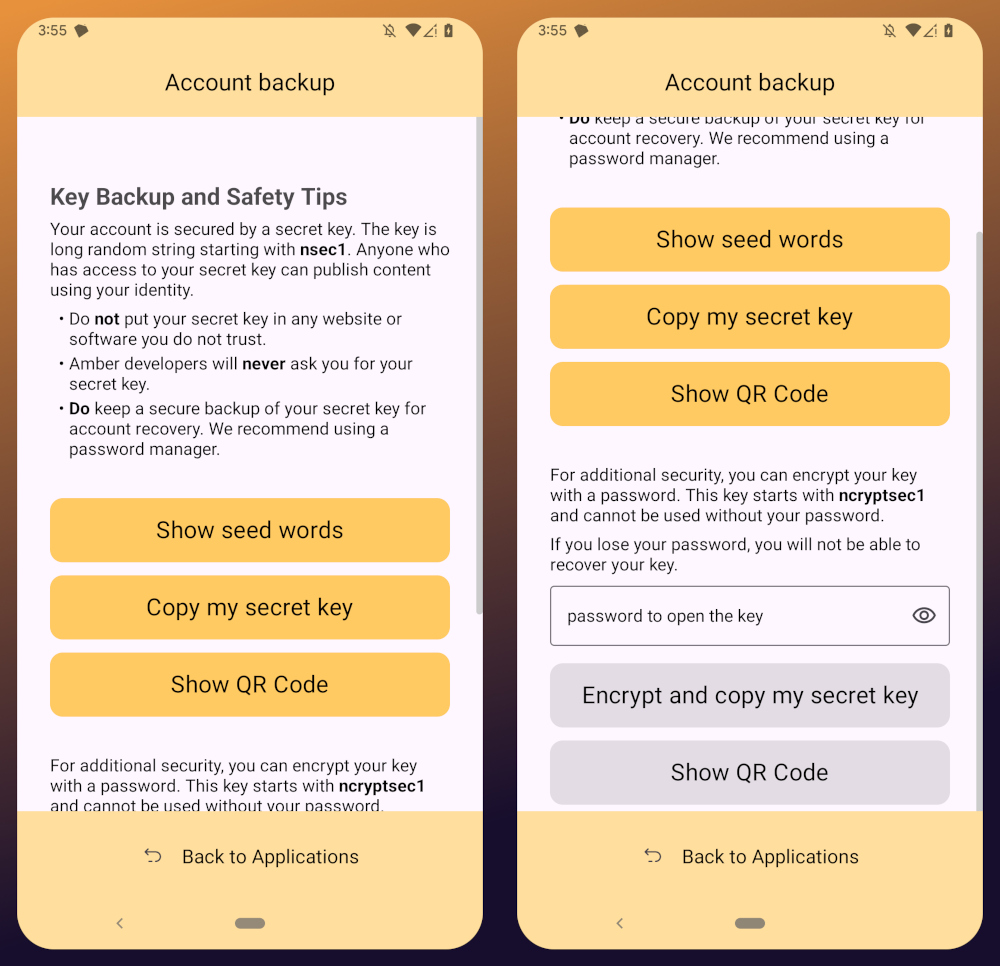
You'll notice that Amber has a few different options for backing up your private key that it can generate.
First, it can give you seed words, just like a Bitcoin seed. If you choose that option, you'll be presented with 12 words you can record somewhere safe. To recover your Nostr private key, you just have to type those words into a compatible application, such as Amber.
The next option is to just copy the secret/private key in its standard form as an "nsec." This is the least secure way to store it, but is also the most convenient, since it is simple to paste into another signer application. If you want to be able to log in on a desktop web app, the browser extension Nostr signers won't necessarily support entering your 12 word seed phrase, but they absolutely will support pasting in your nsec.
You can also display a QR code of your private key. This can be scanned by Amber signer on another device for easily transferring your private key to other devices you want to use it on. Say you have an Android tablet in addition to your phone, for instance. Just make sure you only use this function where you can be certain that no one will be able to get a photograph of that QR code. Once someone else has your nsec, there is no way to recover it. You have to start all over on Nostr. Not a big deal at this point in your journey if you just created a Nostr account, but if you have been using Nostr for a while and have built up a decent amount of reputation, it could be much more costly to start over again.
The next options are a bit more secure, because they require a password that will be used to encrypt your private key. This has some distinct advantages, and a couple disadvantages to be aware of. Using a password to encrypt your private key will give you what is called an ncryptsec, and if this is leaked somehow, whoever has it will not necessarily have access to post as you on Nostr, the way they would if your nsec had been leaked. At least, not so long as they don't also have your password. This means you can store your ncryptsec in multiple locations without much fear that it will be compromised, so long as the password you used to encrypt it was a strong and unique one, and it isn't stored in the same location. Some Nostr apps support an ncryptsec for login directly, meaning that you have the option to paste in your ncryptsec and then just log in with the password you used to encrypt it from there on out. However, now you will need to keep track of both your ncryptsec and your password, storing both of them safely and separately. Additionally, most Nostr clients and signer applications do not support using an ncryptsec, so you will need to convert it back to a standard nsec (or copy the nsec from Amber) to use those apps.
The QR option using an ncryptsec is actually quite useful, though, and I would go this route when trying to set up Amber on additional devices, since anyone possibly getting a picture of the QR code is still not going to be able to do anything with it, unless they also get the password you used to encrypt it.
All of the above options will require you to enter the PIN you set up for your device, or biometric authentication, just as an additional precaution before displaying your private key to you.
As for what "store it in a safe place" looks like, I highly recommend a self-hosted password manager, such as Vaultwarden+Bitwarden or KeePass. If you really want to get wild, you can store it on a hardware signing device, or on a steel seed plate.
Additional Settings
Amber has some additional settings you may want to take advantage of. First off, if you don't want just anyone who has access to your phone to be able to approve signing requests, you can go into the Security settings add a PIN or enable biometrics for signing requests. If you enable the PIN, it will be separate from the PIN you use to access your phone, so you can let someone else use your phone, like your child who is always begging to play a mobile game you have installed, without worrying that they might have access to your Nostr key to post on Amethyst.
Amber also has some relay settings. First are the "Active relays" which are used for signing requests sent to Amber remotely from Nostr web apps. This is what enables you to use Amber on your phone to log into Nostr applications on your desktop web browser, such as Jumble.social, Coracle.social, or Nostrudel.ninja, eliminating your need to use any other application to store your nsec whatsoever. You can leave this relay as the default, or you can add other relays you want to use for signing requests. Just be aware, not all relays will accept the notes that are used for Nostr signing requests, so make sure that the relay you want to use does so. In fact, Amber will make sure of this for you when you type in the relay address.
The next type of relays that you can configure in Amber are the "Default profile relays." These are used for reading your profile information. If you already had a Nostr identity that you imported to Amber, you probably noticed it loaded your profile picture and display name, setting the latter as your nickname in Amber. These relays are where Amber got that information from. The defaults are relay.nostr.band and purplepag.es. The reason for this is because they are aggregators that look for Nostr profiles that have been saved to other relays on the network and pull them in. Therefore, no matter what other relay you may save your profile to, Amber will likely be able to find it on one of those two relays as well. If you have a relay you know you will be saving your Nostr profiles to, you may want to add it to this list.
You can also set up Amber to be paired with Orbot for signing over Tor using relays that are only accessible via the Tor network. That is an advanced feature, though, and well beyond the scope of this tutorial.
Finally, you can update the default signing policy. Maybe after using Amber for a while, you've decided that the choice you made before was too strict or too lenient. You can change it to suit your needs.
Zapstore Login
Now that you are all set up with Amber, let's get you signed into your first Nostr app by going back to the Zapstore.
From the app's home screen, tap on the user icon in the upper left of the screen. This will open a side panel with not much on it except the option to "sign in." Go ahead and tap on it.
You will be presented with the option to either sign in with Amber, or to paste your npub. However, if you do the latter, you will only have read access, meaning you cannot zap any of the app releases. There are other features planned for the Zapstore that may also require you to be signed in with write access, so go ahead and choose to log in with Amber.
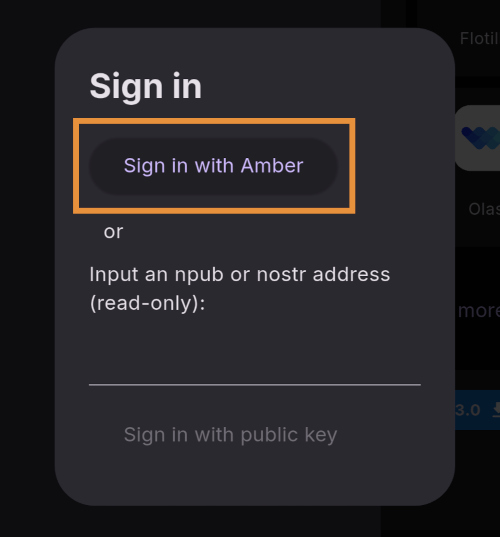
Your phone should automatically switch to Amber to approve the sign-in request.
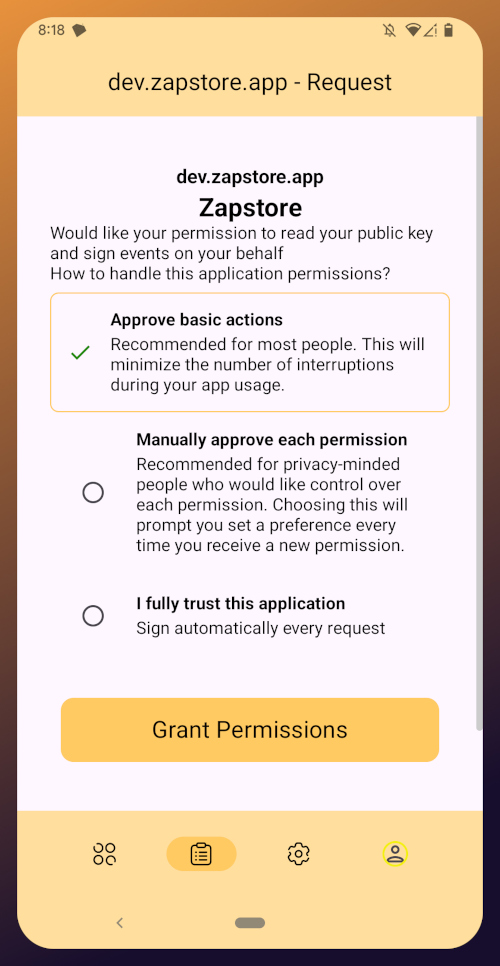
You can choose to only approve basic actions for Zapstore, require it to manually approve every time, or you can tell it that you "fully trust this application." Only choose the latter option with apps you have used for a while and they have never asked you to sign for anything suspicious. For the time being, I suggest you use the "Approve basic actions" option and tap "Grant Permissions."
Your phone will switch back to the Zapstore and will show that you are now signed in. Congratulations! From here on out, logging into most Nostr applications will be as easy as tapping on "Log in with Amber" and approving the request.
If you set up a new profile, it will just show a truncated version of your npub rather than the nickname you set up earlier. That's fine. You'll have an opportunity to update your Nostr profile in the next tutorial in this series and ensure that it is spread far and wide in the network, so the Zapstore will easily find it.
That concludes the tutorial for Amber. While we have not covered using Amber to log into Nostr web apps, that is outside the scope of this series, and I will cover it in an upcoming tutorial regarding using Amber's remote signer options in detail.
Since you're already hanging out in the Zapstore, you may as well stick around, because we will be using it right out the gate in the next part of this series: Amethyst Installation and Setup. (Coming Soon)
-
 @ c1e9ab3a:9cb56b43
2025-05-27 16:19:06
@ c1e9ab3a:9cb56b43
2025-05-27 16:19:06Star Wars is often viewed as a myth of rebellion, freedom, and resistance to tyranny. The iconography—scrappy rebels, totalitarian stormtroopers, lone smugglers—suggests a deep anti-authoritarian ethos. Yet, beneath the surface, the narrative arc of Star Wars consistently affirms the necessity, even sanctity, of central authority. This blog entry introduces the question: Is Star Wars fundamentally a celebration of statism?
Rebellion as Restoration, Not Revolution
The Rebel Alliance’s mission is not to dismantle centralized power, but to restore the Galactic Republic—a bureaucratic, centrally governed institution. Characters like Mon Mothma and Bail Organa are high-ranking senators, not populist revolutionaries. The goal is to remove the corrupt Empire and reinstall a previous central authority, presumed to be just.
- Rebels are loyalists to a prior state structure.
- Power is not questioned, only who wields it.
Jedi as Centralized Moral Elites
The Jedi, often idealized as protectors of peace, are unelected, extra-legal enforcers of moral and military order. Their authority stems from esoteric metaphysical abilities rather than democratic legitimacy.
- They answer only to their internal Council.
- They are deployed by the Senate, but act independently of civil law.
- Their collapse is depicted as tragic not because they were unaccountable, but because they were betrayed.
This positions them as a theocratic elite, not spiritual anarchists.
Chaos and the Frontier: The Case of the Cantina
The Mos Eisley cantina, often viewed as a symbol of frontier freedom, reveals something darker. It is: - Lawless - Violent - Culturally fragmented
Conflict resolution occurs through murder, not mediation. Obi-Wan slices off a limb; Han shoots first—both without legal consequence. There is no evidence of property rights, dispute resolution, or voluntary order.
This is not libertarian pluralism—it’s moral entropy. The message: without centralized governance, barbarism reigns.
The Mythic Arc: Restoration of the Just State
Every trilogy in the saga returns to a single theme: the fall and redemption of legitimate authority.
- Prequels: Republic collapses into tyranny.
- Originals: Rebels fight to restore legitimate order.
- Sequels: Weak governance leads to resurgence of authoritarianism; heroes must reestablish moral centralism.
The story is not anti-state—it’s anti-bad state. The solution is never decentralization; it’s the return of the right ruler or order.
Conclusion: The Hidden Statism of a Rebel Myth
Star Wars wears the costume of rebellion, but tells the story of centralized salvation. It: - Validates elite moral authority (Jedi) - Romanticizes restoration of fallen governments (Republic) - Portrays decentralized zones as corrupt and savage (outer rim worlds)
It is not an anarchist parable, nor a libertarian fable. It is a statist mythology, clothed in the spectacle of rebellion. Its core message is not that power should be abolished, but that power belongs to the virtuous few.
Question to Consider:
If the Star Wars universe consistently affirms the need for centralized moral and political authority, should we continue to see it as a myth of freedom? Or is it time to recognize it as a narrative of benevolent empire? -
 @ 33baa074:3bb3a297
2025-05-28 08:10:17
@ 33baa074:3bb3a297
2025-05-28 08:10:17The control of residual chlorine in swimming pools is an important part of water quality management, which aims to ensure the sanitation and safety of swimming pool water while avoiding discomfort to swimmers. Here are some key points about residual chlorine control in swimming pools:
Standards for residual chlorine According to the regulations of the national health supervision department, the residual chlorine in swimming pool water should be kept between 0.3mg/L-1.5mg/L. This range can not only ensure effective disinfection, but also avoid irritation to swimmers' skin and eyes caused by excessive residual chlorine. Too low residual chlorine will lead to incomplete disinfection and increase the risk of bacterial growth; while too high residual chlorine may cause human discomfort and even poisoning.
 The role of residual chlorine
Residual chlorine is a residual disinfectant in swimming pool water, usually in the form of sodium hypocrite (NaClO). It has strong oxidizing properties and can effectively kill bacteria, viruses and other microorganisms in water, thereby ensuring the health of swimmers. In addition, residual chlorine can eliminate harmful substances such as organic matter and ammonia in water to keep the water clean.
The role of residual chlorine
Residual chlorine is a residual disinfectant in swimming pool water, usually in the form of sodium hypocrite (NaClO). It has strong oxidizing properties and can effectively kill bacteria, viruses and other microorganisms in water, thereby ensuring the health of swimmers. In addition, residual chlorine can eliminate harmful substances such as organic matter and ammonia in water to keep the water clean.Residual chlorine detection method The method of detecting residual chlorine in swimming pools usually uses test strips or test kits for qualitative or quantitative detection. In addition, online monitoring instruments can be used to monitor the residual chlorine in the swimming pool in real time. These methods can help managers promptly detect and deal with situations where the residual chlorine content is too high or too low, ensuring that the water quality of the swimming pool meets the standards.
Methods for controlling residual chlorine Reasonable addition of disinfectants: According to the water quality of the swimming pool and the number of swimmers, reasonable addition of disinfectants to control the residual chlorine content within the specified range.
Regular testing: Regularly test the residual chlorine in the swimming pool to promptly detect and deal with situations where the residual chlorine content is too high or too low.
Maintain swimming pool equipment: Regularly check and maintain swimming pool equipment to ensure the water treatment effect and circulation filtration are normal, and reduce residual disinfectants and other harmful substances in the water.
Do a good job in swimmer hygiene management: Strengthen swimmer hygiene management, require swimmers to shower and rinse their feet before entering the pool, and reduce pollution sources entering the swimming pool.
Solution for excessive residual chlorine If the residual chlorine content in the swimming pool exceeds the standard range, the following measures can be taken:
Use decorating agent: Use decorating agent to quickly restore the excessive residual chlorine in the swimming pool to the normal range (0.3~0.5mg/L). This method is applicable to excessive residual chlorine caused by excessive addition of chlorine disinfectant.
Adjust the water treatment process: According to the water quality, adjust the water treatment process appropriately, such as selecting the appropriate type and dosage of disinfectant, and adjusting operating parameters such as flow rate, pH value, etc., to reduce the generation of residual chlorine.
Strengthen equipment maintenance: Regularly maintain and maintain the water treatment equipment of the swimming pool to ensure its normal operation and disinfection effect.
Through the above methods, the residual chlorine content in the swimming pool can be effectively controlled to ensure water quality safety and protect the health of swimmers.
-
 @ c1e9ab3a:9cb56b43
2025-05-27 13:19:53
@ c1e9ab3a:9cb56b43
2025-05-27 13:19:53I. Introduction: Money as a Function of Efficiency and Preference
Money is not defined by law, but by power over productivity. In any open economy, the most economically efficient actors—those who control the most valuable goods, services, and knowledge—ultimately dictate the medium of exchange. Their preferences signal to the broader market what form of money is required to access the highest-value goods, from durable commodities to intangibles like intellectual property and skilled labor.
Whatever money these actors prefer becomes the de facto unit of account and store of value, regardless of its legal status. This emergent behavior is natural and reflects a hierarchy of monetary utility.
II. Classical Gresham’s Law: A Product of Market Distortion
Gresham’s Law, famously stated as:
"Bad money drives out good"
is only valid under coercive monetary conditions, specifically: - Legal tender laws that force the acceptance of inferior money at par with superior money. - Fixed exchange rates imposed by decree, not market valuation. - Governments or central banks backing elastic fiduciary media with promises of redemption. - Institutional structures that mandate debt and tax payments in the favored currency.
Under these conditions, superior money (hard money) is hoarded, while inferior money (soft, elastic, inflationary) circulates. This is not an expression of free market behavior—it is the result of suppressed price discovery and legal coercion.
Gresham’s Law, therefore, is not a natural law of money, but a law of distortion under forced parity and artificial elasticity.
III. The Collapse of Coercion: Inversion of Gresham’s Law
When coercive structures weaken or are bypassed—through technological exit, jurisdictional arbitrage, monetary breakdown, or political disintegration—Gresham’s Law inverts:
Good money drives out bad.
This occurs because: - Market actors regain the freedom to select money based on utility, scarcity, and credibility. - Legal parity collapses, exposing the true economic hierarchy of monetary forms. - Trustless systems (e.g., Bitcoin) or superior digital instruments (e.g., stablecoins) offer better settlement, security, and durability. - Elastic fiduciary media become undesirable as counterparty risk and inflation rise.
The inversion marks a return to monetary natural selection—not a breakdown of Gresham’s Law, but the collapse of its preconditions.
IV. Elasticity and Control
Elastic fiduciary media (like fiat currency) are not intrinsically evil. They are tools of state finance and debt management, enabling rapid expansion of credit and liquidity. However, when their issuance is unconstrained, and legal tender laws force their use, they become weapons of economic coercion.
Banks issue credit unconstrained by real savings, and governments enforce the use of inflated media through taxation and courts. This distorts capital allocation, devalues productive labor, and ultimately hollows out monetary confidence.
V. Monetary Reversion: The Return of Hard Money
When the coercion ends—whether gradually or suddenly—the monetary system reverts. The preferences of the productive and wealthy reassert themselves:
- Superior money is not just saved—it begins to circulate.
- Weaker currencies are rejected not just for savings, but for daily exchange.
- The hoarded form becomes the traded form, and Gresham’s Law inverts completely.
Bitcoin, gold, and even highly credible stable instruments begin to function as true money, not just stores of value. The natural monetary order returns, and the State becomes a late participant, not the originator of monetary reality.
VI. Conclusion
Gresham’s Law operates only under distortion. Its inversion is not an anomaly—it is a signal of the collapse of coercion. The monetary system then reorganizes around productive preference, technological efficiency, and economic sovereignty.
The most efficient market will always dictate the form of hard money. The State can delay this reckoning through legal force, but it cannot prevent it indefinitely. Once free choice returns, bad money dies, and good money lives again.
-
 @ 9cb3545c:2ff47bca
2025-05-27 12:58:56
@ 9cb3545c:2ff47bca
2025-05-27 12:58:56Introduction
Public companies that hold Bitcoin on behalf of investors (often issuing securities backed by those Bitcoin holdings) have faced growing pressure to demonstrate proof of reserves – evidence that they genuinely hold the cryptocurrency they claim. One approach is to publish the company’s Bitcoin wallet addresses so that anyone can verify the balances on the blockchain. This practice gained momentum after high-profile crypto collapses (e.g. FTX in 2022) eroded trust, leading major exchanges and fund issuers like Binance, Kraken, OKX, and Bitwise to publicize wallet addresses as proof of assets . The goal is transparency and reassurance for investors. However, making wallet addresses public comes with significant security and privacy risks. This report examines those risks – from cybersecurity threats and blockchain tracing to regulatory and reputational implications – and weighs them against the transparency benefits of on-chain proof of reserves.
Proof of Reserves via Public Wallet Addresses
In the cryptocurrency ethos of “don’t trust – verify,” on-chain proof of reserves is seen as a powerful tool. By disclosing wallet addresses (or cryptographic attestations of balances), a company lets investors and analysts independently verify that the Bitcoin reserves exist on-chain. For example, some firms have dashboards showing their addresses and balances in real time . In theory, this transparency builds trust by proving assets are not being misreported or misused. Shareholders gain confidence that the company’s Bitcoin holdings are intact, potentially preventing fraud or mismanagement.
Yet this approach essentially sacrifices the pseudonymity of blockchain transactions. Publishing a wallet address ties a large, known institution to specific on-chain funds. While Bitcoin addresses are public by design, most companies treat their specific addresses as sensitive information. Public proof-of-reserve disclosures break that anonymity, raising several concerns as detailed below.
Cybersecurity Threats from Visible Wallet Balances
Revealing a wallet address with a large balance can make a company a prime target for hackers and cybercriminals. Knowing exactly where significant reserves are held gives attackers a clear blueprint. As Bitcoin advocate (and MicroStrategy Executive Chairman) Michael Saylor warned in 2025, “publicly known wallet addresses become prime targets for malicious actors. Knowing where significant reserves are held provides hackers with a clear target, potentially increasing the risk of sophisticated attacks” . In other words, publishing the address increases the attack surface – attackers might intensify phishing campaigns, malware deployment, or insider bribery aimed at obtaining the keys or access to those wallets.
Even if the wallets are secured in cold storage, a public address advertisement may encourage attempts to penetrate the organization’s security. Custodians and partners could also be targeted. Saylor noted that this exposure isn’t just risky for the company holding the Bitcoin; it can indirectly put their custodial providers and related exchanges at risk as well . For instance, if a third-party custodian manages the wallets, hackers might attempt to breach that custodian knowing the reward (the company’s Bitcoin) is great.
Companies themselves have acknowledged these dangers. Grayscale Investments, which runs the large Grayscale Bitcoin Trust (GBTC), pointedly refused to publish its wallet addresses in late 2022, citing “security concerns” and complex custody arrangements that have “kept our investors’ assets safe for years” . Grayscale implied that revealing on-chain addresses could undermine those security measures, and it chose not to “circumvent complex security arrangements” just to appease public demand . This highlights a key point: corporate treasury security protocols often assume wallet details remain confidential. Publicizing them could invalidate certain assumptions (for example, if an address was meant to be operationally secret, it can no longer serve that role once exposed).
Additionally, a publicly known trove of cryptocurrency might invite physical security threats. While not a purely “cyber” issue, if criminals know a particular company or facility controls a wallet with, say, thousands of Bitcoin, it could lead to threats against personnel (extortion or coercion to obtain keys). This is a less common scenario for large institutions (which typically have robust physical security), but smaller companies or key individuals could face elevated personal risk by being associated with huge visible crypto reserves.
In summary, cybersecurity experts consider public proof-of-reserve addresses a double-edged sword: transparency comes at the cost of advertising exactly where a fortune is held. As Saylor bluntly put it, “the conventional way of issuing proof of reserves today is actually insecure… This method undermines the security of the issuer, the custodian, the exchanges and the investors. This is not a good idea”  . From a pure security standpoint, broadcasting your wallets is akin to drawing a bullseye on them.
Privacy Risks: Address Clustering and Blockchain Tracing
Blockchain data is public, so publishing addresses opens the door to unwanted analytics and loss of privacy for the business. Even without knowing the private keys, analysts can scrutinize every transaction in and out of those addresses. This enables address clustering – linking together addresses that interact – and other forms of blockchain forensics that can reveal sensitive information about the company’s activities.
One immediate risk is that observers can track the company’s transaction patterns. For example, if the company moves Bitcoin from its reserve address to an exchange or to another address, that move is visible in real time. Competitors, investors, or even attackers could deduce strategic information: perhaps the company is planning to sell (if coins go to an exchange wallet) or is reallocating funds. A known institution’s on-chain movements can thus “reveal strategic movements or holdings”, eroding the company’s operational privacy . In a volatile market, advance knowledge of a large buy or sell by a major player could even be exploited by others (front-running the market, etc.).
Publishing one or a few static addresses also violates a basic privacy principle of Bitcoin: address reuse. Best practice in Bitcoin is to use a fresh address for each transaction to avoid linking them  . If a company continuously uses the same “proof of reserve” address, all counterparties sending funds to or receiving funds from that address become visible. Observers could map out the company’s business relationships or vendors by analyzing counterparties. A Reddit user commenting on an ETF that published a single address noted that “reusing a single address for this makes me question their risk management… There are much better and more privacy-preserving ways to prove reserves… without throwing everything in a single public address” . In other words, a naive implementation of proof-of-reserve (one big address) maximizes privacy leakage.
Even if multiple addresses are used, if they are all disclosed, one can perform clustering analysis to find connections. This happened in the Grayscale case: although Grayscale would not confirm any addresses, community analysts traced and identified 432 addresses likely belonging to GBTC’s custodial holdings by following on-chain traces from known intermediary accounts . They managed to attribute roughly 317,705 BTC (about half of GBTC’s holdings) to those addresses . This demonstrates that even partial information can enable clustering – and if the company directly published addresses, the task becomes even easier to map the entirety of its on-chain asset base.
Another threat vector is “dusting” attacks, which become more feasible when an address is publicly known. In a dusting attack, an adversary sends a tiny amount of cryptocurrency (dust) to a target address. The dust itself is harmless, but if the target address ever spends that dust together with other funds, it can cryptographically link the target address to other addresses in the same wallet. Blockchain security researchers note that “with UTXO-based assets, an attacker could distribute dust to an address to reveal the owner’s other addresses by tracking the dust’s movement… If the owner unknowingly combines this dust with their funds in a transaction, the attacker can… link multiple addresses to a single owner”, compromising privacy . A company that publishes a list of reserve addresses could be systematically dusted by malicious actors attempting to map out all addresses under the company’s control. This could unmask cold wallet addresses that the company never intended to publicize, further eroding its privacy and security.
Investor confidentiality is another subtle concern. If the business model involves individual investor accounts or contributions (for instance, a trust where investors can deposit or withdraw Bitcoin), public addresses might expose those movements. An outside observer might not know which investor corresponds to a transaction, but unusual inflows/outflows could signal actions by big clients. In extreme cases, if an investor’s own wallet is known (say a large investor announces their involvement), one might link that to transactions in the company’s reserve addresses. This could inadvertently reveal an investor’s activities or holdings, breaching expectations of confidentiality. Even absent direct identification, some investors might simply be uncomfortable with their transactions being part of a publicly traceable ledger tied to the company.
In summary, publishing reserve addresses facilitates blockchain tracing that can pierce the veil of business privacy. It hands analysts the keys to observe how funds move, potentially exposing operational strategies, counterparties, and internal processes. As one industry publication noted, linking a large known institution to specific addresses can compromise privacy and reveal more than intended . Companies must consider whether they are ready for that level of transparency into their every on-chain move.
Regulatory and Compliance Implications
From a regulatory perspective, wallet address disclosure lies in uncharted territory, but it raises several flags. First and foremost is the issue of incomplete information: A wallet address only shows assets, not the company’s liabilities or other obligations. Regulators worry that touting on-chain holdings could give a false sense of security. The U.S. Securities and Exchange Commission (SEC) has cautioned investors to “not place too much confidence in the mere fact a company says it’s got a proof-of-reserves”, noting that such reports “lack sufficient information” for stakeholders to ascertain if liabilities can be met . In other words, a public company might show a big Bitcoin address balance, but if it has debts or customer liabilities of equal or greater value, the proof-of-reserve alone is “not necessarily an indicator that the company is in a good financial position” .
This regulatory stance implies that address disclosure, if done, must be paired with proper context. A public company would likely need to clarify in its financial statements or investor communications that on-chain reserves are unencumbered (not pledged as loan collateral, not already sold forward, etc.) and that total liabilities are accounted for. Otherwise, there’s a risk of misleading investors, which could have legal consequences. For example, if investors interpret the on-chain balance as proof of solvency but the company actually had leveraged those bitcoins for loans, lawsuits or regulatory enforcement could follow for misrepresentation.
There’s also a compliance burden associated with revealing addresses. Once an address is known to be the company’s, that company effectively must monitor all transactions related to it. If someone sends funds to that address (even without permission), the company might receive tainted coins (from hacked sources or sanctioned entities). This could trigger anti-money laundering (AML) red flags. Normally, compliance teams can ignore random deposits to unknown wallets, but they cannot ignore something sent into their publicly identified corporate wallet. Even a tiny dust amount sent from a blacklisted address could complicate compliance – for instance, the company would need to prove it has no relation to the sender and perhaps even avoid moving those tainted outputs. Being in the open increases such exposure. Threat actors might even exploit this by “poisoning” a company’s address with unwanted transactions, just to create regulatory headaches or reputational smears.
Another consideration is that custodial agreements and internal risk controls might forbid public disclosure of addresses. Many public companies use third-party custodians for their Bitcoin (for example, Coinbase Custody, BitGo, etc.). These custodians often treat wallet details as confidential for security. Grayscale noted that its Bitcoin are custodied on Coinbase and implied that revealing on-chain info would interfere with security arrangements  . It’s possible that some custodians would object to their clients broadcasting addresses, or might require additional assurances. A company going against such advice might be seen as negligent if something went wrong.
Regulators have so far not mandated on-chain proofs for public companies – in fact, recent laws have exempted public companies from proof-of-reserve mandates on the assumption they are already subject to rigorous SEC reporting. For example, a Texas bill in 2023 required crypto exchanges and custodians to provide quarterly proof-of-reserves to the state, but it “specifically carved out public reporting companies” since they already file audited financials with the SEC . The rationale was that between SEC filings and audits, public companies have oversight that private crypto firms lack . However, this also highlights a gap: even audited financials might not verify 100% of crypto assets (auditors often sample balances). Some observers noted that standard audits “may not ever include the 100% custodial asset testing contemplated by proof of reserves”, especially since quarterly SEC filings (10-Q) are often not audited . This puts public companies in a nuanced position – they are trusted to use traditional audits and internal controls, but the onus is on them if they choose to add extra transparency like on-chain proofs.
Finally, securities regulators focus on fair disclosure and accuracy. If a company publicly posts addresses, those essentially become investor disclosures subject to anti-fraud rules. The firm must keep them up to date and accurate. Any mistake (such as publishing a wrong address or failing to mention that some coins are locked up or lent out) could attract regulatory scrutiny for being misleading. In contrast, a formal audit or certification from a third-party comes with standards and disclaimers that are better understood by regulators. A self-published wallet list is an unprecedented form of disclosure that regulators haven’t fully vetted – meaning the company bears the risk if something is misinterpreted.
In summary, wallet address disclosure as proof-of-reserve must be handled very carefully to avoid regulatory pitfalls. The SEC and others have warned that on-chain assets alone don’t tell the whole story . Public companies would need to integrate such proofs with their official reporting in a responsible way – otherwise they risk confusion or even regulatory backlash for giving a false sense of security.
Reputational and Operational Risks
While transparency is meant to enhance reputation, in practice public wallet disclosures can create new reputational vulnerabilities. Once an address is public, a company’s every on-chain action is under the microscope of the crypto community and media. Any anomaly or perceived misstep can snowball into public relations problems.
One vivid example occurred with Crypto.com in late 2022. After the exchange published its cold wallet addresses to prove reserves (a move prompted by the FTX collapse), on-chain analysts quickly noticed a “suspicious transfer of 320,000 ETH” – about 82% of Crypto.com’s Ether reserves – moving from their cold wallet to another exchange (Gate.io)  . This large, unexpected transfer sparked immediate panic and FUD (fear, uncertainty, and doubt) on social media. Observers speculated that Crypto.com might be insolvent or was manipulating snapshots of reserves by borrowing funds. The CEO had to publicly respond, admitting it was an operational error – the ETH was supposed to go to a new cold storage address but ended up at a whitelisted external address by mistake . The funds were eventually returned, but not before reputational damage was done: the incident made headlines about mishandled funds and rattled user confidence  . This case illustrates how full public visibility can turn an internal slip-up into a highly public crisis. If the addresses had not been public, the mistake might have been quietly corrected; with on-chain transparency, there was nowhere to hide and no way to control the narrative before the public drew worst-case conclusions.
Even routine operations can be misinterpreted. Blockchain data lacks context – analysts may jump to conclusions that hurt a company’s reputation even if nothing is actually wrong. For instance, Binance (the world’s largest crypto exchange) encountered scrutiny when on-chain observers noted that one of its reserve wallets (labeled “Binance 8”) contained far more assets than it should have. This wallet was meant to hold collateral for Binance’s issued tokens, but held an excess balance, suggesting possible commingling of customer funds with collateral  . Bloomberg and others reported a ~$12.7 billion discrepancy visible on-chain . Binance had to acknowledge the issue as a “clerical error” and quickly separate the funds, all under the glare of public attention  . While Binance maintained that user assets were fully backed and the mistake was purely operational, the episode raised public concern over Binance’s practices, feeding a narrative that even the largest exchange had internal control lapses. The key point is that public proof-of-reserves made the lapse obvious to everyone, forcing a reactive explanation. The reputational hit (even if temporary) was an operational risk of being so transparent.
Additionally, strategic confidentiality is lost. If a company holding Bitcoin as a reserve asset decides to make a major move (say, reallocating to a different wallet, or using some Bitcoin for a strategic investment or loan), doing so with known addresses broadcasts that strategy. Competitors or market analysts can infer things like “Company X is moving 10% of its BTC — why? Are they selling? Hedging? Using it as collateral?” This can erode any competitive advantage of keeping financial strategies discreet. It might even affect the company’s stock price if investors interpret moves negatively. For example, if a blockchain analysis shows the company’s reserves dropping, shareholders might fear the company sold Bitcoin (perhaps due to financial distress), even if the reality is benign (like moving funds to a new custodian). The company would be forced into continuous public explanation of on-chain actions to prevent misunderstanding.
There’s also a risk of exposing business partnerships. Suppose the company uses certain exchanges or OTC desks to rebalance its holdings – transactions with those service providers will be visible and could link the company to them. If one of those partners has issues (say a hacked exchange or a sanctioned entity inadvertently), the company could be reputationally contaminated by association through the blockchain trail.
Finally, not all publicity is good publicity in the crypto world. A public proof-of-reserve might invite armchair auditors to scrutinize and criticize every aspect of the company’s crypto management. Minor issues could be blown out of proportion. On the flip side, if a company chooses not to publish addresses, it could face reputational risk from a different angle: skeptics might question why it isn’t being transparent. (Indeed, Grayscale’s refusal to disclose wallet addresses led to social media chatter about whether they truly held all the Bitcoin they claimed, contributing to investor nervousness and a steep discount on GBTC shares .) Thus, companies are in a delicate spot: share too much and every move invites scrutiny; share too little and you breed distrust.
Balancing Transparency Benefits vs. Risks
The central question is whether the benefit of proving reserve holdings to investors outweighs these security and privacy risks. It’s a classic risk-reward calculation, and opinions in the industry are divided.
On the side of transparency, many argue that the credibility and trust gained by proof-of-reserves is invaluable. Advocates note that Bitcoin was designed for open verification – “on-chain auditability and permissionless transparency” are core features . By embracing this, companies demonstrate they are good stewards of a “trustless” asset. In fact, some believe public companies have a duty to be extra transparent. A recent Nasdaq report contended that “when a publicly traded company holds Bitcoin but offers no visibility into how that Bitcoin is held or verified, it exposes itself to multiple levels of risk: legal, reputational, operational, and strategic”, undermining trust . In that view, opacity is riskier in the long run – a lack of proof could weaken investor confidence or invite regulatory suspicion. Shareholders and analysts may actually penalize a company that refuses to provide verifiable proof of its crypto assets .
Transparency done right can also differentiate a firm as a leader in governance. Publishing reserve data (whether via addresses or through third-party attestations) can be seen as a commitment to high standards. For example, Metaplanet, an investment firm, publicly discloses its BTC reserve addresses and even provides a live dashboard for anyone to verify balances . This proactive openness signals confidence and has been touted as an industry best practice in some quarters. By proving its reserves, a company can potentially avoid the fate of those that lost public trust (as happened with opaque crypto firms in 2022). It’s also a means to preempt false rumors – if data is out in the open, misinformation has less room to grow.
However, the pro-transparency camp increasingly acknowledges that there are smarter ways to achieve trust without courting all the risks. One compromise is using cryptographic proofs or audits instead of plain address dumps. For instance, exchanges like Kraken have implemented Merkle tree proof-of-reserves: an independent auditor verifies all customer balances on-chain and provides a cryptographic report, and customers can individually verify their account is included without the exchange revealing every address publicly. This method proves solvency to those who need to know without handing over a complete roadmap to attackers. Another emerging solution is zero-knowledge proofs, where a company can prove knowledge or ownership of certain assets without revealing the addresses or amounts to the public. These technologies are still maturing, but they aim to deliver the best of both worlds: transparency and privacy.
On the side of caution, many experts believe the risks of full public disclosure outweigh the incremental gain in transparency, especially for regulated public companies. Michael Saylor encapsulates this viewpoint: he calls on-chain proof-of-reserve “a bad idea” for institutions, arguing that it “offers one-way transparency” (assets only) and “leaves organizations open to cyberattacks” . He stresses that no serious security expert would advise a Fortune 500 company to list all its wallet addresses, as it essentially compromises corporate security over time . Saylor and others also point out the pointlessness of an assets-only proof: unless you also prove liabilities, showing off reserves might even be dangerous because it could lull investors into a false sense of security .
Regulators and traditional auditors echo this: proof-of-reserves, while a useful tool, “is not enough by itself” to guarantee financial health . They advocate for holistic transparency – audits that consider internal controls, liabilities, and legal obligations, not just a snapshot of a blockchain address  . From this perspective, a public company can satisfy transparency demands through rigorous third-party audits and disclosures rather than raw on-chain data. Indeed, public companies are legally bound to extensive reporting; adding public crypto addresses on top may be seen as redundant and risky.
There is also an implicit cost-benefit analysis: A successful attack resulting from over-sharing could be catastrophic (loss of funds, legal liability, reputational ruin), whereas the benefit of public proof is somewhat intangible (improved investor sentiment, which might be achieved via other assurance methods anyway). Given that trade-off, many firms err on the side of caution. As evidence, few if any U.S.-listed companies that hold Bitcoin have published their wallet addresses. Instead, they reference independent custodians and audits for assurance. Even crypto-native companies have pulled back on full transparency after realizing the downsides – for example, some auditing firms halted issuing proof-of-reserves reports due to concerns about how they were interpreted and the liability involved  .
Industry best practices are still evolving. A prudent approach gaining favor is to prove reserves without leaking sensitive details. This can involve disclosing total balances and having an auditor or blockchain oracle confirm the assets exist, but without listing every address publicly. Companies are also encouraged to disclose encumbrances (whether any of the reserves are collateralized or lent out) in tandem, to address the liabilities issue . By doing so, they aim to achieve transparency and maintain security.
In evaluating whether to publish wallet addresses, a company must ask: Will this level of openness meaningfully increase stakeholder trust, or would a more controlled disclosure achieve the same goal with less risk? For many public companies, the answer has been to avoid public addresses. The risks – from attracting hackers to revealing strategic moves – tend to outweigh the marginal transparency benefit in their judgment. The collapse of unregulated exchanges has certainly proven the value of reserve verification, but public companies operate in a different context with audits and legal accountability. Thus, the optimal solution may be a middle ground: proving reserves through vetted processes (auditor attestations, cryptographic proofs) that satisfy investor needs without blatantly exposing the company’s financial backend to the world.
Conclusion
Publishing Bitcoin wallet addresses as proof of reserves is a bold transparency measure – one that speaks to crypto’s ideals of open verification – but it comes with a laundry list of security considerations. Public companies weighing this approach must contend with the heightened cybersecurity threat of advertising their treasure troves to hackers, the loss of privacy and confidentiality as on-chain sleuths dissect their every transaction, and potential regulatory complications if such disclosures are misunderstood or incomplete. Real-world incidents illustrate the downsides: firms that revealed addresses have seen how quickly online communities flag (and sometimes misinterpret) their blockchain moves, causing reputational turbulence and forcing rapid damage control  .
On the other hand, proving reserves to investors is important – it can prevent fraud and bolster trust. The question is how to achieve it without incurring unacceptable risk. Many experts and industry leaders lean towards the view that simply publishing wallet addresses is too risky a method, especially for public companies with much to lose  . The risks often do outweigh the direct benefits in such cases. Transparency remains crucial, but it can be provided in safer ways – through regular audits, cryptographic proofs that don’t expose all wallet details, and comprehensive disclosures that include liabilities and controls.
In conclusion, while on-chain proof of reserves via public addresses offers a tantalizing level of openness, it must be approached with extreme caution. For most public companies, the smart strategy is to balance transparency with security: verify and show investors that assets exist and are sufficient, but do so in a controlled manner that doesn’t compromise the very assets you’re trying to protect. As the industry matures, we can expect more refined proof-of-reserve practices that satisfy the demand for honesty and solvency verification without unduly endangering the enterprise. Until then, companies will continue to tread carefully, mindful that transparency is only truly valuable when it doesn’t come at the price of security and trust.
Sources:
• Grayscale statement on refusal to share on-chain proof-of-reserves  • Community analysis identifying Grayscale’s wallet addresses  • Cointelegraph – Crypto.com’s mistaken 320k ETH transfer spotted via on-chain proof-of-reserves   • Axios – Binance wallet “commingling” error observed on-chain   • Michael Saylor’s remarks on security risks of publishing wallet addresses    • SEC Acting Chief Accountant on limitations of proof-of-reserves reports  • Nasdaq (Bitcoin for Corporations) – argument for corporate transparency & proof-of-reserves    • 1inch Security Blog – explanation of dusting attacks and privacy loss via address linking  -
 @ 33baa074:3bb3a297
2025-05-28 07:50:06
@ 33baa074:3bb3a297
2025-05-28 07:50:06Soil moisture is a key factor that affects the structure and function of soil microbial communities. Here are some of the main aspects of how soil moisture affects microorganisms:
Affecting the Growth and Metabolism of Microorganisms Changes in soil moisture content directly affect the growth and metabolic activities of microorganisms. Under suitable moisture conditions, microorganisms are better able to carry out metabolic activities, thereby promoting the decomposition of soil organic matter and the transformation of nutrients. However, under extremely dry or overly wet conditions, the activity of microorganisms will be inhibited, resulting in a decline in soil functions.

Changing the Structure of Microbial Communities Changes in soil moisture conditions can lead to significant changes in the structure of microbial communities. For example, under drought conditions, the number of drought-tolerant microorganisms may increase to adapt to the water shortage environment. While under wet conditions, aerobic microorganisms may dominate. This change in community structure not only affects the soil's water retention capacity, but also other ecological functions of the soil.
Affecting the Stability of Soil Aggregates Soil aggregates are clumps formed by soil particles through physical, chemical and biological actions, and they have an important impact on the soil's water retention capacity. Soil microorganisms participate in the formation and stability of soil aggregates by secreting substances such as extracellular polymers. Appropriate soil moisture helps maintain the stability of soil aggregates, thereby improving the soil's water retention capacity. However, excessive moisture or drought may lead to the destruction of soil aggregates and reduce the soil's water retention capacity.
Regulating soil moisture dynamics Soil microorganisms can regulate the dynamic balance of soil moisture through their metabolic activities, such as decomposing organic matter and synthesizing exopolysaccharides. For example, some microorganisms can increase the water holding capacity of the soil by secreting exopolysaccharides, while others can release water by decomposing organic matter. These activities help maintain the stability of soil moisture and support plant growth.
Influencing the physical properties of soil Soil moisture can also indirectly affect the living environment of microorganisms by affecting the physical properties of the soil, such as pore structure and texture. Good soil pore structure is conducive to the penetration and storage of water, and also provides a suitable living space for microorganisms. Soil texture is closely related to the stability of aggregates. Sandy soils have poor aggregate stability and weak water retention capacity; while clay soils have good aggregate stability and strong water retention capacity.
In summary, soil moisture has many effects on microorganisms, including affecting the growth and metabolism of microorganisms, changing the structure of microbial communities, affecting the stability of soil aggregates, regulating soil moisture dynamics, and affecting the physical properties of soil. Therefore, maintaining suitable soil moisture conditions is of great significance for protecting the diversity and function of soil microbial communities and improving the water retention capacity of soil.
-
 @ 33baa074:3bb3a297
2025-05-28 07:27:02
@ 33baa074:3bb3a297
2025-05-28 07:27:02Distilled water has a wide range of applications in the medical field, mainly including the following aspects: Preparation of injection water Distilled water is an indispensable agent in medical institutions, used for the preparation of drugs, injection and washing of instruments, etc. In the medical process, sterile injection water is needed to flush wounds, prepare drugs, etc. The distilled water machine can ensure the purity of water and prevent microorganisms and harmful substances in the water from causing harm to patients.
Surgical wound flushing In breast cancer surgery, warm distilled water is used to flush surgical wounds. This practice helps to clean the wound, remove possible residual tumor cells, and use hypnotic effect to make tumor cells absorb water, swell, rupture, and necrotic, thereby preventing tumors from growing in the wound.
Cleaning and disinfection Distilled water has a certain disinfection and sterilization effect. It can be used to clean the skin, help eliminate bacteria on the skin surface, and is beneficial to the health of the skin. In addition, distilled water can also be used to clean and disinfect medical equipment to ensure the hygiene and safety of the medical environment.
Laboratory use In medical-related laboratories, distilled water is used to prepare experimental solutions, wash utensils and experimental instruments. These applications ensure the accuracy of experimental results while maintaining the sterile environment of the laboratory.
Moisturizing and Beauty Although not directly used in medical applications, distilled water is also used in skin care. It can be used as a basic moisturizer to help improve the symptoms of dry skin. In the field of medical beauty, distilled water is sometimes used for facial compresses to achieve calming, cooling, and swelling effects.
In summary, the application of distilled water in the medical field is multifaceted, from basic injection water preparation to complex surgical assistance to daily skin care, it has played an important role.
-
 @ 33baa074:3bb3a297
2025-05-28 02:26:55
@ 33baa074:3bb3a297
2025-05-28 02:26:55The PH value of a swimming pool is one of the important indicators for measuring the quality of swimming pool water. Its importance is mainly reflected in the following aspects:
Affecting human comfort The pH of water that the human body is most adapted to is neutral. Inappropriate pH of swimming pool water will irritate human skin, eyes and mucous membranes, causing discomfort. For example, when the pH value is high or low, it may irritate the swimmer's skin, eyes, etc., causing discomfort such as itchy skin, red and swollen eyes, and sticky hair, affecting the swimmer's physical health and swimming experience.
 Affecting the disinfection effect of swimming pools
Affecting the activity of chlorine disinfectants
Swimming pools are usually disinfected with chlorine-containing disinfectants. Different pH values will cause differences in the activity and disinfection ability of chlorine. When the pH value in swimming pool water is greater than 8.0, the activity of chlorine disinfectants in water will be significantly reduced, that is, the disinfection ability will be reduced, which will affect the algae removal and sterilization effects, resulting in the proliferation of green algae in swimming pool water. When the pH value is less than 7.0, the activity of the disinfectant in the swimming pool will be relatively high, the residual chlorine in the swimming pool will dissipate faster, and the disinfection durability of the swimming pool disinfectant will be greatly weakened. Under the condition of pH about 7.5, there is a relatively good disinfection effect and the duration of the drug effect is relatively long.
Affecting the disinfection effect of swimming pools
Affecting the activity of chlorine disinfectants
Swimming pools are usually disinfected with chlorine-containing disinfectants. Different pH values will cause differences in the activity and disinfection ability of chlorine. When the pH value in swimming pool water is greater than 8.0, the activity of chlorine disinfectants in water will be significantly reduced, that is, the disinfection ability will be reduced, which will affect the algae removal and sterilization effects, resulting in the proliferation of green algae in swimming pool water. When the pH value is less than 7.0, the activity of the disinfectant in the swimming pool will be relatively high, the residual chlorine in the swimming pool will dissipate faster, and the disinfection durability of the swimming pool disinfectant will be greatly weakened. Under the condition of pH about 7.5, there is a relatively good disinfection effect and the duration of the drug effect is relatively long.Influence on the existence form of residual chlorine Depending on the pH value, free chlorine may be chlorine gas (Cl₂), chlorophyll acid (HClO) or hypocrite ion (ClO⁻) dissolved in water. The disinfection effect of HClO is about 100 times stronger than that of ClO⁻. When the pH value is about 7.5, both chlorophyll acid and hypocrite ion exist, and the proportion is roughly equal, which can ensure a better disinfection effect.
Corrosion to swimming pool facilities Pool water acidity or alkalinity will have a corrosive effect on swimming pool equipment. If the water is acidic, it will also corrode the accessories of the suction machine and affect the normal use of the equipment. If the pH value is unbalanced for a long time, the chemical disinfectants in the swimming pool will corrode the pool structure and swimming pool equipment, which will not only affect the appearance of the pool structure and equipment, but also shorten the service life of the swimming pool and increase the maintenance cost of the swimming pool in the later stage.
Impact on the containment of pool water The pH value in the swimming pool will change due to many external factors, such as rain, the use of swimming pool disinfectants, and alkaline chemicals. Maintaining a suitable pH value can make the pool water have better containment, more stably cope with the influence of these external factors, and maintain the relative stability of water quality.
In summary, the pH value of the swimming pool is of great significance to ensure the health and comfort of swimmers, ensure the disinfection effect, protect swimming pool facilities, and maintain the stability of pool water quality.
-
 @ b7274d28:c99628cb
2025-05-27 07:07:33
@ b7274d28:c99628cb
2025-05-27 07:07:33A few months ago, a nostrich was switching from iOS to Android and asked for suggestions for #Nostr apps to try out. nostr:npub18ams6ewn5aj2n3wt2qawzglx9mr4nzksxhvrdc4gzrecw7n5tvjqctp424 offered the following as his response:
nostr:nevent1qvzqqqqqqypzq0mhp4ja8fmy48zuk5p6uy37vtk8tx9dqdwcxm32sy8nsaa8gkeyqydhwumn8ghj7un9d3shjtnwdaehgunsd3jkyuewvdhk6tcpz4mhxue69uhhyetvv9ujuerpd46hxtnfduhszythwden5te0dehhxarj9emkjmn99uqzpwwts6n28eyvjpcwvu5akkwu85eg92dpvgw7cgmpe4czdadqvnv984rl0z
Yes. #Android users are fortunate to have some powerful Nostr apps and tools at our disposal that simply have no comparison over on the iOS side. However, a tool is only as good as the knowledge of the user, who must have an understanding of how best to wield it for maximum effect. This fact was immediately evidenced by replies to Derek asking, "What is the use case for Citrine?" and "This is the first time I'm hearing about Citrine and Pokey. Can you give me links for those?"
Well, consider this tutorial your Nostr starter-kit for Android. We'll go over installing and setting up Amber, Amethyst, Citrine, and Pokey, and as a bonus we'll be throwing in the Zapstore and Coinos to boot. We will assume no previous experience with any of the above, so if you already know all about one or more of these apps, you can feel free to skip that tutorial.
So many apps...
You may be wondering, "Why do I need so many apps to use Nostr?" That's perfectly valid, and the honest answer is, you don't. You can absolutely just install a Nostr client from the Play Store, have it generate your Nostr identity for you, and stick with the default relays already set up in that app. You don't even need to connect a wallet, if you don't want to. However, you won't experience all that Nostr has to offer if that is as far as you go, any more than you would experience all that Italian cuisine has to offer if you only ever try spaghetti.
Nostr is not just one app that does one thing, like Facebook, Twitter, or TikTok. It is an entire ecosystem of applications that are all built on top of a protocol that allows them to be interoperable. This set of tools will help you make the most out of that interoperability, which you will never get from any of the big-tech social platforms. It will provide a solid foundation for you to build upon as you explore more and more of what Nostr has to offer.
So what do these apps do?

Fundamental to everything you do on Nostr is the need to cryptographically sign with your private key. If you aren't sure what that means, just imagine that you had to enter your password every time you hit the "like" button on Facebook, or every time you commented on the latest dank meme. That would get old really fast, right? That's effectively what Nostr requires, but on steroids.
To keep this from being something you manually have to do every 5 seconds when you post a note, react to someone else's note, or add a comment, Nostr apps can store your private key and use it to sign behind the scenes for you. This is very convenient, but it means you are trusting that app to not do anything with your private key that you don't want it to. You are also trusting it to not leak your private key, because anyone who gets their hands on it will be able to post as you, see your private messages, and effectively be you on Nostr. The more apps you give your private key to, the greater your risk that it will eventually be compromised.
Enter #Amber, an application that will store your private key in only one app, and all other compatible Nostr apps can communicate with it to request a signature, without giving any of those other apps access to your private key.
Most Nostr apps for Android now support logging in and signing with Amber, and you can even use it to log into apps on other devices, such as some of the web apps you use on your PC. It's an incredible tool given to us by nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5, and only available for Android users. Those on iPhone are incredibly jealous that they don't have anything comparable, yet.

Speaking of nostr:npub1w4uswmv6lu9yel005l3qgheysmr7tk9uvwluddznju3nuxalevvs2d0jr5, the next app is also one of his making.
All Nostr data is stored on relays, which are very simple servers that Nostr apps read notes from and write notes to. In most forms of social media, it can be a pain to get your own data out to keep a backup. That's not the case on Nostr. Anyone can run their own relay, either for the sake of backing up their personal notes, or for others to post their notes to, as well.
Since Nostr notes take up very little space, you can actually run a relay on your phone. I have been on Nostr for almost 2 and a half years, and I have 25,000+ notes of various kinds on my relay, and a backup of that full database is just 24MB on my phone's storage.
Having that backup can save your bacon if you try out a new Nostr client and it doesn't find your existing follow list for some reason, so it writes a new one and you suddenly lose all of the people you were following. Just pop into your #Citrine relay, confirm it still has your correct follow list or import it from a recent backup, then have Citrine restore it. Done.
Additionally, there are things you may want to only save to a relay you control, such as draft messages that you aren't ready to post publicly, or eCash tokens, which can actually be saved to Nostr relays now. Citrine can also be used with Amber for signing into certain Nostr applications that use a relay to communicate with Amber.
If you are really adventurous, you can also expose Citrine over Tor to be used as an outbox relay, or used for peer-to-peer private messaging, but that is far more involved than the scope of this tutorial series.

You can't get far in Nostr without a solid and reliable client to interact with. #Amethyst is the client we will be using for this tutorial because there simply isn't another Android client that comes close, so far. Moreover, it can be a great client for new users to get started on, and yet it has a ton of features for power-users to take advantage of as well.
There are plenty of other good clients to check out over time, such as Coracle, YakiHonne, Voyage, Olas, Flotilla and others, but I keep coming back to Amethyst, and by the time you finish this tutorial, I think you'll see why. nostr:npub1gcxzte5zlkncx26j68ez60fzkvtkm9e0vrwdcvsjakxf9mu9qewqlfnj5z and others who have contributed to Amethyst have really built something special in this client, and it just keeps improving with every update that's shipped.

Most social media apps have some form of push notifications, and some Nostr apps do, too. Where the issue comes in is that Nostr apps are all interoperable. If you have more than one application, you're going to have both of them notifying you. Nostr users are known for having five or more Nostr apps that they use regularly. If all of them had notifications turned on, it would be a nightmare. So maybe you limit it to only one of your Nostr apps having notifications turned on, but then you are pretty well locked-in to opening that particular app when you tap on the notification.
Pokey, by nostr:npub1v3tgrwwsv7c6xckyhm5dmluc05jxd4yeqhpxew87chn0kua0tjzqc6yvjh, solves this issue, allowing you to turn notifications off for all of your Nostr apps, and have Pokey handle them all for you. Then, when you tap on a Pokey notification, you can choose which Nostr app to open it in.
Pokey also gives you control over the types of things you want to be notified about. Maybe you don't care about reactions, and you just want to know about zaps, comments, and direct messages. Pokey has you covered. It even supports multiple accounts, so you can get notifications for all the npubs you control.

One of the most unique and incredibly fun aspects of Nostr is the ability to send and receive #zaps. Instead of merely giving someone a 👍️ when you like something they said, you can actually send them real value in the form of sats, small portions of a Bitcoin. There is nothing quite like the experience of receiving your first zap and realizing that someone valued what you said enough to send you a small amount (and sometimes not so small) of #Bitcoin, the best money mankind has ever known.
To be able to have that experience, though, you are going to need a wallet that can send and receive zaps, and preferably one that is easy to connect to Nostr applications. My current preference for that is Alby Hub, but not everyone wants to deal with all that comes along with running a #Lightning node. That being the case, I have opted to use nostr:npub1h2qfjpnxau9k7ja9qkf50043xfpfy8j5v60xsqryef64y44puwnq28w8ch for this tutorial, because they offer one of the easiest wallets to set up, and it connects to most Nostr apps by just copy/pasting a connection string from the settings in the wallet into the settings in your Nostr app of choice.
Additionally, even though #Coinos is a custodial wallet, you can have it automatically transfer any #sats over a specified threshold to a separate wallet, allowing you to mitigate the custodial risk without needing to keep an eye on your balance and make the transfer manually.

Most of us on Android are used to getting all of our mobile apps from one souce: the Google Play Store. That's not possible for this tutorial series. Only one of the apps mentioned above is available in Google's permissioned playground. However, on Android we have the advantage of being able to install whatever we want on our device, just by popping into our settings and flipping a toggle. Indeed, thumbing our noses at big-tech is at the heart of the Nostr ethos, so why would we make ourselves beholden to Google for installing Nostr apps?
The nostr:npub10r8xl2njyepcw2zwv3a6dyufj4e4ajx86hz6v4ehu4gnpupxxp7stjt2p8 is an alternative app store made by nostr:npub1wf4pufsucer5va8g9p0rj5dnhvfeh6d8w0g6eayaep5dhps6rsgs43dgh9 as a resource for all sorts of open-source apps, but especially Nostr apps. What is more, you can log in with Amber, connect a wallet like Coinos, and support the developers of your favorite Nostr apps directly within the #Zapstore by zapping their app releases.
One of the biggest features of the Zapstore is the fact that developers can cryptographically sign their app releases using their Nostr keys, so you know that the app you are downloading is the one they actually released and hasn't been altered in any way. The Zapstore will warn you and won't let you install the app if the signature is invalid.
Getting Started
Since the Zapstore will be the source we use for installing most of the other apps mentioned, we will start with installing the Zapstore.
We will then use the Zapstore to install Amber and set it up with our Nostr account, either by creating a new private key, or by importing one we already have. We'll also use it to log into the Zapstore.
Next, we will install Amethyst from the Zapstore and log into it via Amber.
After this, we will install Citrine from the Zapstore and add it as a local relay on Amethyst.
Because we want to be able to send and receive zaps, we will set up a wallet with CoinOS and connect it to Amethyst and the Zapstore using Nostr Wallet Connect.
Finally, we will install Pokey using the Zapstore, log into it using Amber, and set up the notifications we want to receive.
By the time you are done with this series, you will have a great head-start on your Nostr journey compared to muddling through it all on your own. Moreover, you will have developed a familiarity with how things generally work on Nostr that can be applied to other apps you try out in the future.
Continue to Part 2: The Zapstore. Nostr Link: nostr:naddr1qvzqqqr4gupzpde8f55w86vrhaeqmd955y4rraw8aunzxgxstsj7eyzgntyev2xtqydhwumn8ghj7un9d3shjtnzwf5kw6r5vfhkcapwdejhgtcqp5cnwdphxv6rwwp3xvmnzvqgty5au
-
 @ 491afeba:8b64834e
2025-05-27 21:02:29
@ 491afeba:8b64834e
2025-05-27 21:02:29Quando adolescente eu acreditava na coerência da teoria de "amor líquido" do polonês, sociólogo, Zygmunt Bauman, apresentada no livro "Amor Líquido: Sobre a Fragilidade dos Laços Humanos", qual no meu amadurecimento em estudos, sejam eles no meio acadêmico ou fora, percebo como uma das formas mais rasas de explicar as mudanças e transformações dos padrões de relações sócio-afetivas dos humanos. A seguir colocar-me-ei na minha juventude não tanto recente, direi então que nós, se adolescentes e conservadores, ou mesmo jovens adultos mais conservadores, costumamos levar como dogma uma óptica decadentista generalizada de todos os avanços de eras dos homens, universalizamos por nos ser comum a indistinção entre humanidade e humanidades, ou mesmo "humanity" e "humankind" ("humanidade" como espécime e "humanidade" como um universal), compreendemos toda "essas" como "essa" e indistinguimos as sociedades para com os homens, ou seja, a incapacidade de definir os seres dentro de suas respectivas singularidades e especificidades nos leva ao decadentismo generalista (a crença de que de forma geral, e universal, a "civilização universal" decai moralmente, éticamente, materialmente e espiritualmente), que aparente à nós determinadas mudanças nas relações humanas quanto ao caráter sócio-afetivo, por falta de profundidade e critérios ainda sobre questões alinhadas aos métodos e coerências, ou incoerências, lógicas, nós se jovens e conservadores somos levados ao engodo de concordar com a teoria do amor líquido de Bauman, que devo cá explicar de antemão: trata ela, a teoria, o padrão de "amor" dos tempos presentes como frágil, de prazo (curto e médio) e diferente em grau comparativamente ao amor comum das eras passadas.
Aos jovens mais progressistas opera uma compreensão dialética sobre as eras dos homens nos seu tempo presente, na qual ao tempo que o ser progride ele também regride simultaneamente, ou seja, a medida que aparecem contradições advindas de transformações materiais da realidade humana o ser supera essas contradições e progride em meio as transformações, ainda fazendo parte da lógica dessa indissociavelmente, assim constantemente progredindo e regredindo, havendo para esses dois vetores de distinção: o primeiro é o que releva questões espirituais como ao caráter do pensamento "new age", o segundo ignora essas questões por negar a existência da alma, seguem ao materialismo. Cedem em crer na teoria baumaninana como dogma, pois não encontram outros meios para explicar as transformações da sociedade na esfera sócio-afetiva sem que haja confrontamento direto com determinadas premissas assim pertinemente presentes, ou por não conciliarem com análises relativamente superiores, como a de Anthony Giddens sobre a "relação pura" em "A Transformação da Intimidade" e de François de Singly apresentada em "Sociologie du Couple".
!(image)[https://i.pinimg.com/736x/6f/b4/9e/6fb49eda2c8cf6dc837a0abfc7e108e6.jpg]
Há um problema quando uma teoria deixa de assim ser para vir a tornar-se mais um elemento desconexo da ciência, agora dentro da cultura pop, se assim podemos dizer, ou da cultura de massa, ou se preferirem mesmo "anticultura", esse problema é a sua deformização teórica, tornando-se essa rasa para sua palatabilidade massiva, somada a incapacidade de partes da sociedade civil em compreender as falhas daquilo que já foi massificado. Tive surpresa ao entender que muitos outros compartilham da mesma opinião, a exemplo, possuo um amigo na faculdade, marxista, que ao falarmos sobre nossos projetos de pesquisa, citou ele o projeto de um de nossos colegas, no qual esse referido um de nossos colegas faria seu projeto com base na teoria do amor líquido de Bauman, então alí demos risada disso, ora, para nós a teoria baumaniana é furada, passamos a falar sobre Bauman e o motivo pelo qual não gostávamos, lá fiquei até surpreso em saber que mais gente além de mim não gostava da teoria de Bauman, pois ao que eu via na internet era rede de enaltecimentos à figura e à sua teoria, tal como fosse uma revelação partindo de alguma divindade da Idade do Bronze. Pouco tempo depois tive em aula de teoria política uma citação de Bauman partindo do professor que ministrava a disciplina, no entanto, ao citar o nome de Bauman o mesmo fez uma feição na qual aparentava segurar risada, provavelmente ele também não levava Bauman à sério. Não devo negar que todas as vezes que vejo o sociólogo sendo citado em alguma nota no X, no Instagram ou qualquer outra rede social, tal como fosse um referencial teórico bom, sinto uma vergonha alheia pois alí tenho uma impressão de que a pessoa não leu Bauman e usa o referencial teórico como um fato já assim provado e comprovado.
Há pontos positivos na teoria baumaniana, como a capacidade de perceber o problema e correlacioná-lo à modernidade, assim como sucitar a influência do que há de material no fenômeno, porém os erros são pertinentes: o primeiro problema é de categoria. Não há, por parte de Bauman noção alguma entre as dissociações dos amores, não há atenção sobre o amor como estrutura ou ele como um sentimento, todo ele é compreendido uniformemente como "amor", partindo do pressuposto que todas as relações, todas elas, são firmadas com base no amor. Essa crença tem uma origem: Hegel. Nos Escritos Teológicos Hegel partia da crença que o amor ligava os seres relacionalmente como uma força de superação e alienação, mas há de compreendermos que esse Friedrich Hegel é o jovem ainda pouco maduro em suas ideias e seu sistema de pensamento, mais a frente, em "Fenomenologia do Espírito e na Filosofia do Direito", Hegel compreende a institucionalidade do direito no amor e a institucionalização dessa força, assim aproxima-se da realidade a respeito da inserção do amor nas esferas práticas do humano, porém essa ideia, apesar de imperfeita, pois ao que sabemos não é o amor que consolida a relação, mas sim a Verdade (Alétheia), conforme apontado por Heidegger em "Ser e Tempo", essa ideia do amor como a fundamento das relações humanas influenciou, e até hoje influencia, qualquer análise sobre as relações humanas fora da esfera materialista, fora dessa pois, melhormente explicado em exemplo, os marxistas (em exemplo), assim como Marx, consideram como base primordial das relações as condições materiais.
Por certo, não é de todo amor a base para a solidificação, ora, erram aqueles que creem que somente essa força, assim apontada por Hegel, constituiam todos os relacionamentos formais como pilares fundamentais, pois em prática as famílias eram até a fiduciarização dessas, por mais paradoxal que seja, compreendidas melhor como instituições orgânicas de caráter legal do que conluios de afetividades. A família outrora tinha consigo aparelhos de hierarquia bem estabelicidos, quais prezavam pela ordem interna e externa, que acima dessa instituição estava somente a Igreja (outra instituição), com sua fiduciarização [da família] após o movimento tomado pelos Estados nacionais em aplicação do casamento civil mudou-se a lógica das partes que a compõe, findou-se o princípio da subsidiariedade (não intervenção de determinadas instituições nas decisões quais podem ser exercidas em resuluções de problemas nas competências de quaisquer instituições), foi-se então, contudo, também a autoridade, e nisso revela-se um outro problema não apontado na teoria de Bauman: qual o padrão do amor "sólido"? Pois, ora, sociedades tradicionais não abdicavam do relevar dos amores para tornar seus filhos em ativos nas práticas de trocas (dádivas)? É notório que esse padrão se dissocia do padrão de sentimento apontado por Bauman, encontramos esse fato em estudo nos trabalhos "Ensaio Sobre a Dádiva", do Marcel Mauss, e "As Estruturas Elementares do Parentesco", do Claude Levi-Strauss, quais expõem que nas sociedades "sólidas", tradicionais, relevava-se mais questões institucionais que as sentimentais para a formação de laços (teoria da aliança). Muitas das relações passadas não eram baseadas no amor, não significando assim que as de hoje, em oposição, sejam, mas que permanecem-se semelhantes em base, diferentemente em grau e forma.
!(image)[https://substackcdn.com/image/fetch/f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F748b94c3-f882-45db-8333-09260ef15cfe_615x413.jpeg]
Ora, ainda existem casamentos motivados pela política, pelo status, pelo prestígio, pelos bens, pelo poder, pela influência familiar e assim sucetivamente, tal como no passado, ocorre que essa prática tornou-se oculta, não mais explícita e aparente, devo dizer ainda que em partes, pois prepondera em nosso tempo uma epidemia de adultérios, fornicações, práticas lascivas e demais práticas libertinosas explicitamente, em contraposição às práticas ocultas em vergonhas de sociedades sem declínio moral e espiritual, o que nos leva a questionar o método comparativo em dicotomia temporal "presente x passado" aplicado por Bauman, no qual segue-se da seguinte forma:
Transformação Passado = *sólido* | Presente = *líquido* Categorias Padrão de amor: tradicional (*sólido*) moderno (*líquido*) *Sólido* = estável, prazo (médio-grande), profundo, determinado. *Líquido* = instável, prazo (curto-médio), raso, indeterminado.O que penso é: Zygmunt Bauman buscou uma explicação material e laical para desviar ao fato de que há uma notória correlação entre espiritualização da sociedade, se voltada à Verdade, com a estabilidade das instituições, o que é já reduzido à moral religiosa, somente, não à mística, como por pensadores da linha de Tocqueville, ou em abordagens também mais laical (positivista) porém ainda relevantes, como Émile Durkheim em "As Formas Elementares da Vida Religiosa" e Max Weber em "A Ética Protestante e o Espírito do Capitalismo", contrapondo uma abordage mais voltada, de fato, a espiritualidade, como Christopher Dawnson, que defende essa teoria em "Religião e o Surgimento da Cultura Ocidental", e Eric Voegelin, principalmente nas obras "A Nova Ciência da Política" e "Ordem e História".
Encerrrando, minha cosmovisão é a católica, o sistema de crença e religião qual sigo é do Deus que se fez homem por amor aos seus filhos, não posso negar ou mesmo omitir o fato de que, por trás de toda a minha crítica estão meus pensamentos e minhas convicções alinhadas àquilo que mais tenho amor em toda minha vida: a Verdade, e a Verdade é Deus, pois Cristo é a Verdade, o Caminho e a Vida, ninguém vai ao Pai se não por Ele, e pois bem, seria incoerência de minha parte não relevar o fato de crença como um dos motivos pelos quais eu rejeito a teoria do amor líquido de Zygmunt Bauman, pois os amores são todos eles praticados por formas, existem por diferentes formas e assim são desde sua tradicionalidade até o predomínio das distorções de declínio espiritual das eras presentes (e também antigas pré-Era Axial), estão esses preservados pelo alinhamento à verdade, assim são indistorcíveis, imutáveis, ou seja, amor é amor, não releva-se o falso amor como um, simplesmente não o é, assim o interesse, a sanha por bens, o egoísmo e a egolatria ("cupiditas", para Santo Agostinho de Hipona, em oposição ao que o santo e filósofo trata por "caritas") não são formas do amor, são autoenganos, não bons, se não são bons logo não são de Deus, ora, se Deus é amor, se ele nos ama, determino como amor (e suas formas) o que está de acordo com a Verdade. Aprofundando, a Teologia do Corpo, do Papa São João Paulo II, rejeita a "liquidez" apresentada por Bauman, pois o amor é, em suma, sacríficio, parte da entrega total de si ao próximo, e se não há logo não é amor. A Teologia do Corpo rejeita não os fundamentos de mentira no "líquido", mas também no "sólido", pois a tradicionalidade não é sinônimo de bom e pleno acordo com o amor que Deus pede de nós, não são as coerções, as violências, as imposições e demais vontades em oposição às de Deus que determinam os amores -- fatos em oposição ao ideário romanticizado. Claro, nem todas as coerções são por si inválidas do amor, ou mesmo as escolhas em trocas racionalizadas, a exemplo do autruísmo em vista da chance da família ter êxito e sucesso, ou seja, pelo bem dos próximos haver a necessidade de submissão a, em exemplo, um casamento forjado, ou algo do gênero, reconhece-se o amor no ato se feito por bem da família, porém o amor incutido, nesse caso, explicita o caráter sacrificial, no qual uma vontade e um amor genuinamente potencial em prazeres e alegrias são anulados, ou seja, mesmo nesse modelo tradicional na "solidez" há possibilidade do amor, não nas formas romanticizadas em critérios, como "estabilidade" e "durabilidade", mas no caráter do sacríficio exercido. Conforme nos ensina São Tomás de Aquino, o amor não é uma "força", tal como ensina Hegel, mas sim uma virtude teologal conforme na "Suma Teológica" (II-II Q. 26-28), não devemos reduzir o amor e os amores em análises simplórias (não simples) de falsa complexidade extraídas em métodos questionáveis e pouco competentes à real diensão de crise espiritual das eras, por esse motivo não concordo com a teoria do amor líquido de Zygmunt Bauman.
-
 @ 162b4b08:9f7d278c
2025-05-27 10:12:53
@ 162b4b08:9f7d278c
2025-05-27 10:12:53Trong thời đại mà công nghệ số trở thành trụ cột không thể thiếu trong mọi lĩnh vực, từ công việc đến giải trí, việc sở hữu một nền tảng số toàn diện như PUM88 đóng vai trò vô cùng quan trọng đối với người dùng hiện đại. Không chỉ là nơi cung cấp các công cụ tiện ích, PUM88 còn tạo nên một hệ sinh thái linh hoạt, đáp ứng mọi nhu cầu trong một môi trường trực tuyến đầy năng động. Từ những bước đầu như đăng ký, đăng nhập, cho đến trải nghiệm thực tế, tất cả đều được tối ưu nhằm mang lại sự thuận tiện tối đa. Giao diện thiết kế thông minh, bố cục rõ ràng, thao tác nhanh gọn giúp người dùng dễ dàng tiếp cận và sử dụng mà không cần kiến thức kỹ thuật chuyên sâu. Bên cạnh đó, hệ thống xử lý tốc độ cao và khả năng tương thích đa nền tảng (từ smartphone đến laptop) giúp người dùng duy trì kết nối mọi lúc mọi nơi, không bị giới hạn bởi thiết bị hay không gian sử dụng. Không dừng lại ở đó, PUM88 còn liên tục nâng cấp công nghệ như tích hợp trí tuệ nhân tạo để gợi ý nội dung cá nhân hóa theo hành vi và sở thích, giúp mỗi trải nghiệm trở nên sống động, gần gũi và mang tính cá nhân cao hơn bao giờ hết. Đây chính là điểm cộng lớn giúp PUM88 tạo nên dấu ấn trong lòng người dùng yêu thích sự tiện lợi và linh hoạt trong đời sống số.
Ngoài ra, yếu tố khiến PUM88 trở nên đáng tin cậy chính là khả năng bảo mật vượt trội và chính sách hỗ trợ khách hàng tận tâm. Dữ liệu cá nhân và các hoạt động của người dùng luôn được bảo vệ nghiêm ngặt bằng các chuẩn mã hóa quốc tế, hệ thống tường lửa, xác thực hai lớp và giám sát bảo mật liên tục. Nhờ vậy, người dùng hoàn toàn yên tâm khi sử dụng mà không lo bị lộ thông tin hay rò rỉ dữ liệu. Thêm vào đó, đội ngũ chăm sóc khách hàng hoạt động 24/7 với thái độ chuyên nghiệp và phản hồi nhanh chóng giúp giải quyết mọi thắc mắc hoặc sự cố kỹ thuật một cách hiệu quả. Không những thế, PUM88 còn thường xuyên lắng nghe ý kiến người dùng để cải tiến giao diện, bổ sung tính năng mới, đảm bảo rằng nền tảng luôn bắt kịp xu hướng công nghệ và đáp ứng đúng nhu cầu thực tế. Việc cập nhật liên tục không chỉ giúp người dùng có được trải nghiệm mượt mà hơn mà còn giữ cho nền tảng luôn mới mẻ, sáng tạo và không ngừng phát triển. Trong bối cảnh chuyển đổi số đang diễn ra mạnh mẽ tại Việt Nam, PUM88 không chỉ đơn thuần là một ứng dụng tiện ích mà còn là một trợ thủ đắc lực cho cuộc sống hiện đại – nơi mà người dùng có thể tận dụng công nghệ để nâng cao hiệu suất cá nhân, tối ưu hóa thời gian và tận hưởng trải nghiệm số trọn vẹn nhất mỗi ngày.
-
 @ c1e6505c:02b3157e
2025-05-27 01:11:45
@ c1e6505c:02b3157e
2025-05-27 01:11:45I spent Memorial Day swimming in the local river - something I try to do at least four times a week. It’s the best form of exercise imo, but it’s more than that. Swimming against the tide, feeling the water move around me... there’s something about it that keeps me grounded. Nature at her peak.
Today I brought my X-Pro2 with the 1959 Leica Summaron 35mm f/2.8. I'm still testing the lens wide open to get a feel for its character. My subject this time: the light playing on the ripples and waves.
While I was shooting, a kid randomly ran up to me and started telling me something about what he got for his dad while fishing, or something - I didn’t quite hear him - and then he asked what I was looking at. I told him, “The ripples. The way the light is refracting.” I had him sit exactly where I was so he could see it too.
He lit up. You could tell no one had ever pointed something like that out to him before. In that moment, I felt like maybe I was able to plant a little seed - a new way of seeing.
This is what I was looking at.

-
 @ 06639a38:655f8f71
2025-05-26 14:21:37
@ 06639a38:655f8f71
2025-05-26 14:21:37Finally there is a release (1.7.0) for Nostr-PHP with a full NIP-19 integration. Here is an example file with some snippets to how it works to encode and decode bech32 encoded entities:
- https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip19-bech32-decoded-entities.php
- https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip19-bech32-encoded-entities.php
Now merge request #68 (and issues #74, #64 are closed) is finally merged which I opened in October 2024.
Next up is:
- Create documentation how to use NIP-19 with the library on https://nostr-php.dev
- Create documentation how to use NIP-04 and NIP-44 with the library on https://nostr-php.dev
- Work out a proof-of-concept with the revolt/event-loop package to create concurrent async requests with websocket connections
-
 @ 06639a38:655f8f71
2025-05-26 12:58:38
@ 06639a38:655f8f71
2025-05-26 12:58:38Nostr-PHP
Djuri submitted quite some pull requests in the last couple of week while he was implementing a Nostr connect / login on https://satsback.com. The backend of that platform is written in PHP so the Nostr-PHP library is used for several purposes while Djuri also developed quite some new features utilizing the following NIPs:
- NIP-04
- NIP-05
- NIP-17
- NIP-44
Thank you very much Djuri for these contributions. We now can do the basic private stuff with the library.
PR for NIP-04 and NIP-44: https://github.com/nostrver-se/nostr-php/pull/84 and https://github.com/nostrver-se/nostr-php/pull/88
Examples:- https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip04-encrypted-messages.php
- https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip44-gift-wrapping.php
PR for NIP-05: https://github.com/nostrver-se/nostr-php/pull/89
Example: https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip05-lookup.phpPR for NIP-17: https://github.com/nostrver-se/nostr-php/pull/90
Example: https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/nip17-private-direct-messages.phpPR for adding more metadata profile fields: https://github.com/nostrver-se/nostr-php/pull/94
Example: https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/fetch-profile-metadata.phpFetch
10050event (dm relay list) of an given pubkey
Example: https://github.com/nostrver-se/nostr-php/blob/main/src/Examples/fetch-dm-relayslist.phpThe CLI tool is removed from the library, see PR https://github.com/nostrver-se/nostr-php/pull/93
Nostr-PHP documentation
While new NIPs are implemented in the Nostr-PHP library, I'm trying to keep up with the documentation at https://nostr-php.dev. For now, things are still much work in progress and I've added the AI agent Goose using the Claude LLM to bootstrap new documentation pages. Currently I'm working on documentation for
- How to direct messages with NIP-04 and NIP-17
- Encrypted payloads for event content NIP-44
- Fetch profiledata of a given pubkey
- Lookup NIP-05 data of given pubkey
- Using the NIP-19 helper class
CCNS.news
I've moved CCNS to a new domain https://ccns.news and have partly implemented the new NIP-B0 for web bookmarks. When you post a bookmark there, a kind
39701event is transmitted to some Nostr relays (take a look at this event for example). Optionally you can also publish this content as a note to the network.As you can see at https://ccns.news/l/censorship-resistant-publishing-and-archiving, I've listed some todo's. All this stuff is done with Javascript using the NDK Typescript library (so I'm not using any PHP stuff for this with Nostr-PHP).
Also new: https://ccns.news/global now has a global feed which fetches all the web bookmark events with kind
39701from several public Nostr relays. I had a rough idea to compare feeds generated with NDK and Nostr-PHP (for both using the same set of relays).
Building a njump clone for this Drupal website
You can now use this URL pattern to fetch Nostr events:
https://nostrver.se/e/{event_id|nevent1|note1|addr1}where you can provide a plain Nostr event ID or NIP-19 encoded identifier.An example, this URL [nostr:nevent1qvzqqqqqqypzqmjxss3dld622uu8q25gywum9qtg4w4cv4064jmg20xsac2aam5nqqsqm2lz4ru6wlydzpulgs8m60ylp4vufwsg55whlqgua6a93vp2y4g3uu9lr) fetches the data from one or more relays. This data is then being saved as a (Drupal) node entity (in a database on the server where this website is hosted, which is located in my office fyi). With this saved node, this data is now also available at https://nostrver.se/e/0dabe2a8f9a77c8d1079f440fbd3c9f0d59c4ba08a51d7f811ceeba58b02a255/1 where the (cached) data is server from the database instead. It's just raw data for now, nothing special about it. One of my next steps is to style this in a more prettier interface and I will need to switch the theme of this website to a custom theme. A custom theme where I will be using TailwindCSS v4 and DaisyUI v5.
The module which is providing these Nostr features is FOSS and uses the Nostr-PHP library for doing the following:
- Request the event from one or more relays
- Decode the provided NIP-19 identifier
For now this module is way for me to utilize the Nostr-PHP library with Drupal for fetching events. This can be automated so in theory I could index all the Nostr events. But this is not my ambition as it would require quite some hardware resources to accomplish this.
I hope I can find the time to build up a new theme first for this website, so I can start styling the data for the fetched events. On this website, there is also a small piece (powered by another module) you can find at https://nostrver.se/nostrides doing things with this NIP-113 around activity events (in my case that's cycling what interests me).What's next
I'm already working on the following stuff:
- Implement a class to setup a persistent connection to a relay for requesting events continuously
- Extend the documentation with the recent added features
Other todo stuff:
- Review NIP-13 proof-of-work PR from Djuri
- Implement a NIP-65 lookup for fetching read and write relays for a given npub issue #91
- Build a proof-of-concept with revolt/event-loop to request events asynchronous with persistent relay connections
- Add comments to https://ccns.news
-
 @ 39cc53c9:27168656
2025-05-27 09:21:51
@ 39cc53c9:27168656
2025-05-27 09:21:51Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% ^1 – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% ^1 of less-than-careful criminals.
KYC? Not you.
KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. ^2
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
Your identity has been stolen
KYC data has been found to be for sale on many dark net markets^3. Exchanges may have leaks or hacks, and such leaks contain very sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. ^3
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
(they) Know Your Coins
You may already know that Bitcoin and most cryptocurrencies have a transparent public blockchain, meaning that all data is shown unencrypted for everyone to see and recorded forever. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
Conclusions
To sum up, KYC does not protect individuals; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
Edited 20/03/2024 * Add reference to the 1% statement on Rights for Illusions section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity ^1
-
 @ 611021ea:089a7d0f
2025-05-26 18:28:46
@ 611021ea:089a7d0f
2025-05-26 18:28:46Imagine a world where your favorite health and fitness apps—diet trackers, meditation tools, cardio and strength training platforms, even therapy apps—can all work together seamlessly. Not because they're owned by the same company, but because they speak a common, open language. That's the future NIP-101h is building on Nostr.
A Modular, Privacy-First Health Data Framework
NIP-101h defines a modular, privacy-first framework for sharing granular health and fitness metrics on the decentralized Nostr protocol. The core idea is simple but powerful: every health metric (weight, steps, calories, mood, and so on) gets its own unique Nostr event kind. Apps can implement only the metrics they care about, and users can choose exactly what to share, with whom, and how.
This modular approach means true interoperability. A meditation app can log mindfulness sessions, a running app can record your daily mileage, and a diet tracker can keep tabs on your nutrition—all using the same underlying standard. Each app remains independent, but your data becomes portable, composable, and, most importantly, under your control.
Why NIP-101h Matters
Interoperability
Today's health and fitness apps are walled gardens. Data is locked away in proprietary formats, making it hard to move, analyze, or combine. NIP-101h breaks down these barriers by providing a common, open standard for health metrics on Nostr. Apps can collaborate, users can migrate, and new services can emerge—without permission or lock-in.
User Control & Privacy
Health data is deeply personal. That's why NIP-101h is privacy-first: all metric values are encrypted by default using NIP-44, unless the user explicitly opts out. You decide what's public, what's private, and who gets access. Even if you want to keep everything local, that's supported too.
Extensibility
The world of health and fitness is always evolving. NIP-101h is designed to grow with it. New metrics can be added at any time via the
-
 @ bf95e1a4:ebdcc848
2025-05-26 12:04:27
@ bf95e1a4:ebdcc848
2025-05-26 12:04:27This is a part of the Bitcoin Infinity Academy course on Knut Svanholm's book Bitcoin: Sovereignty Through Mathematics. For more information, check out our Geyser page!
The Environment
There’s no such thing as a free lunch. There’s no such thing as a zero-sum game. The 2nd law of thermodynamics tells us this. You know, the one about entropy and how everything will be really lame in a couple of trillion years. There’s no action without an equally big reaction somewhere. This is also true for Bitcoin mining. Every once in a while, some ignorant clickbait-hungry journalist writes an article about Bitcoin’s energy usage and how it’s connected to global warming or how widespread Bitcoin adoption would kill us all someday because of its “wasteful” production process. What they all fail to address is the alternative cost. As mentioned before, Bitcoin is valuable because it's scarce, and it's scarce because it's costly to produce. The same is true for gold or diamonds or anything else that is scarce and hard to come by. As discussed in earlier chapters, the mining algorithm can never be any more energy efficient because the electricity spent is directly linked to the value of the token.
Secondly, think about what most people use their Bitcoin for. Nothing. That’s right, nothing. Bitcoin incentivizes saving rather than spending. This is the exact opposite of how people use money in our current system of fiat currencies because Bitcoin is deflationary rather than inflationary relative to all other currencies. This means that every dollar, yen, or pound spent on Bitcoin would have ended up being spent on some other energy-demanding thing had it not been spent on Bitcoin. Either that or it would have lost its value due to inflation, which implies that even more dollars, yen, or euros would have been created and spent on frivolous things. Right now, credit is cheap, and the underlying economic theory of our time is based on the idea that the amount of spending going on in society is a key metric in economics. Bitcoin, on the other hand, is based on the economic theories of the Austrian school, where saving is the key metric. Yes, Bitcoin is costly to produce, but so is overproducing every product on Earth because every business needs to expand as fast as possible to pay off their loans. Human well-being has always been, and will always be, linearly connected to energy consumption. You can’t get around or bypass this fact. Energy consumption and human flourishing are inevitably linked. The thing Bitcoin does is to take away the need for unnecessary energy consumption by incentivizing us to save for future generations. It’s a mechanism that hinders our self-destructive tendencies. Not a threat to our planet's health, but a remedy.
The next time you hear about the Bitcoin network using as much energy as a small country, ask yourself: where would all that energy have ended up if it wasn’t funneled into the only invention trying to save us from ourselves there is? Into a Chinese factory producing consumer goods shipped by boat, truck and car for temporary use and probably ending up in a garbage pile the size of a small country in less than a year? How is that better for the planet? The only place from which solutions for humanity's problems can stem is human ingenuity. Such ingenuity in turn, stems from places where people with brains have a shot at getting somewhere in life. Thanks to the Internet and Bitcoin, that somewhere is everywhere. The Internet connects us, and Bitcoin frees up our time and emancipates us from our current, destructive systems. Bitcoin helps you plant a seed and watch it grow. Before you criticize Bitcoin, try to comprehend why it was invented and what inflationary, soft money does to the mechanisms of the market. Try to understand why we have a “climate problem” in the first place — why we overconsume. What underlying forces pull our psychological strings and make us borrow money for a new car? It takes a special kind of ignorance to criticize a solution without first fully comprehending the problem.
There’s one specific word that describes the current global environmentalist movement better than any other, and that word is “hubris.” Yes, the Earth has been getting warmer, very slowly, over the last fifty years. Yes, at least one of the ice caps might be melting. Yes, it’s probably because of human activity but no, you can’t save the planet through political interference in people’s lives. To get every nation on Earth to agree that it is a good idea to forcefully make people change their behavior for the sake of the climate is not only impossible but also cruel and counterproductive. Collectivists always disguise their urge to deprive their fellow man of his or her possessions and freedoms as a necessary thing to do in order to “save” humanity. This is nothing new. They’ve just decided that “climate change” is the most effective banner to rally under right now. The causes change, but the underlying philosophy stays the same. It’s very disturbing that the socialist experiment gets to repeat itself so many times in so many parts of the world.
Human progress and human flourishing have linear relationships to energy usage. If we want to find new ways of bettering ourselves, we should use more energy, not less. Truly free market competition leads to the most efficient solutions, and there are a bunch of incentives for producers of consumable goods to find cheap energy sources. Bitcoin provides the market with yet another incentive — to find locations for and invest in power plants in remote areas of the world where the cost barrier for building the plant has been too high historically due to the costly and wasteful process of transporting electricity. Hydro-electric plants in areas with a high risk of flooding, for instance. These areas are not suitable for human settlements, but they could provide us with a lot of electricity. When producers have the option to convert electricity into money directly, they’re more likely to use renewable energy sources, not less. In this sense, Bitcoin can function as a battery for energy producers.
Offshore wind farms have a very specific wind force range where they produce a usable amount of electricity. The bigger the turbine, the wider the range, but they still have an upper and a lower wind force limit. If an offshore wind farm had been connected to a Bitcoin mining rig, the surplus energy produced on windy days could have been converted into a profit for the producer instantly. The same logic applies to solar farms and geothermal plants. Energy is not a finite resource in any practical sense for the inhabitants of Mother Earth. If we could harness and store all the power of all the sunlight that hits the Earth during just one day, we could satisfy all of humanity’s energy needs for a couple of hundred years.
Bitcoin’s role in all of this is unexplored, but its potential to be a very positive environmental force is huge, and it will prove its utility during the next century. On one hand, it provides energy producers with a battery; on the other hand, it gives central bankers a run for their money and ultimately forces them to adopt a more sound monetary policy or become obsolete altogether. Bitcoin creates an incentive for sacrificing surplus energy for a small profit and a greater good rather than just letting it go to waste. The energy harnessed is converted into a completely scarce asset that is divisible and transportable to a much greater extent than any other valuable resource on Earth. It incentivizes energy producers to think long term and will reward those most patient and least wasteful among them. This recalibration of incentive structures is, of course, not only limited to energy producers or miners but to anyone who embraces this technology and understands its implications. In due time, Bitcoin’s superior monetary properties will be undeniable to even the most stubborn dinosaur. This would be an enormous net gain for humanity and the environment.
Courageous politicians dare to implement unpopular policies. They don’t need climate-striking teenagers to tell them which issues ought to be addressed first. It is ironic how celebrities who score cheap points by talking about the climate often accuse their political opponents of being “populist.” What really happens when you raise carbon taxes and try to force populations into behaviors that they don’t really like? The gilets jaunes, or yellow vests, in France are a great example. People still have to commute to work. Raising taxes solves nothing — it just distorts the market and relocates the problem. The only thing the recently adopted environmentalist policies of France resulted in was the destruction of Paris. Arguably not the best thing for the environment.
In a truly free society, a society with sound money, climate-striking children wouldn’t be a problem. They would have to learn to cooperate in order to address whatever imaginary problem they sought to solve, which would be harmless to the rest of us. Now, when backed by fear-mongering journalists, they can cause a ton of damage as our virtue-signaling political class needs to adapt to whatever imaginary issue the press has primed us with in order to secure votes. It’s not about whether there is a real climate problem or not, but rather about motives. Always ask yourself, what does this person stand to gain from holding this particular opinion? Can this issue really be solved by political means?
There’s no such thing as a free lunch. There is such a thing as representation, however, and there’s always a personal economic motive behind political decisions. They’re not here for you; you’re here for them. One of the most eye-opening experiences of my life was seeing the lobbyist quarters in Brussels. The rise of veganism, placebic gluten intolerance, and "meat-free Mondays" in school cafeterias are all products of the food industry. A soy burger is a lot cheaper to produce than a beef one. To anyone who can sell it at a higher price by appealing to people’s vanity or world-saving hubris, huge profits await. They’ve managed to monetize our collective bad climate conscience in such a cunning way that most of us have no clue we’re being played. In the 20th century, the cereal-killers of the Kellogg's company and their likes funded “research” that cemented a fear of red meats and saturated fats into the minds of the public. The effects of this propaganda can very much still be seen today as the inhabitants of America are about twice as fat today than they were before the introduction of “light” products to the market. All of these things are connected to the root of the problem: the lack of sound money. Inflation made it possible for the food industry to replace our homemade beef burger with a mass-produced cheap soy substitute while making us believe that the price of a burger hadn’t changed that much in the last fifty years. Spoiler alert - it had.
Another of the most eye-opening experiences I’ve had was during my stay in a Mayan village in the Toledo district of Belize about ten years ago. I spent a couple of days with a family of two adults and six children in a jungle village of huts and no electricity save for two diesel generators. One night, the father of the house told me a story about his friend going into politics a decade earlier and being murdered for having the wrong opinions. We slept on wooden beds without mattresses, and a couple of dogs and turkeys ran freely around the village. One day, the family’s ten-year-old was listening to some Bob Marley songs on a CD player connected to a car battery and a small solar panel on a pole in the garden. I listened for a while and then asked him about the strange sound effects in between the songs. Helicopter sounds, machine gun sounds, and other strange noises were intersecting the songs here and there. He replied by telling me, “...oh, it’s not a proper CD. I made it with Virtual DJ on my cousin’s laptop”. I was stunned. Here was this ten-year-old, in the middle of the jungle, just as skilled with a computer as any other ten-year-old I had ever met. At that moment, I realized just how leveled the playing field has been for the workforce across the globe. Here was this child, living in a hut without even electricity (but also without a mortgage to inherit), ready to compete on the same global market as any other kid in the world.
Bitcoin is the logical next step. Bitcoin doesn’t care about nationality, gender, ethnicity, age, sexual preferences, or any other imagined victimization or privilege. To Bitcoin, we’re all equal. It is a voluntary system, and it knows no biases. Bitcoin is equality of opportunity in its purest form, and it doesn’t have any opinion on the outcome whatsoever.
About the Bitcoin Infinity Academy
The Bitcoin Infinity Academy is an educational project built around Knut Svanholm’s books about Bitcoin and Austrian Economics. Each week, a whole chapter from one of the books is released for free on Highlighter, accompanied by a video in which Knut and Luke de Wolf discuss that chapter’s ideas. You can join the discussions by signing up for one of the courses on our Geyser page. Signed books, monthly calls, and lots of other benefits are also available.
-
 @ 3c559080:a053153e
2025-05-25 20:26:43
@ 3c559080:a053153e
2025-05-25 20:26:43So firstly you should find an emulator for whatever you want to play on. There are many for desktop and mobile devices. Checkhere for a list of all the available consoles and their various emulators.
Next what game do you want to play? This is the like the homepage for a shit ton of roms.
Some of the more popular roms are there and other various list like Sony Nintendo
After narrowing down your selection you will end up on myrient i assume this is just some dope person hosting all these so if you get some use out of it, think of donating they even take corn, but other shitcoins too (but thats not the focus here)
Once you download the Rom of the game you want, you will get a compressed (zip) folder, unzip it and within it will be the rom, most systems will identify your emulator and use it open the game. If not, launch the emulator and within it should be an option to open a file, open the file in the unzipped folder.
Enjoy So you want to Mod?
So every Mod, is a mod for a specific game [ex. Pokemon Blue, Pokemon FireRed, Super Mario Bros.] so it requires you to get the Rom for that base game, the mod itself, and a tool to patch it.
 There is an online tool to easily patch the mod to the ROM. IMPORTANT, this will not change any naming, Id recommend having a folder with the base game roms, and a folder for the mods, and lastly a folder for the newly modded roms. Make sure to name or just save the game in modded roms folder after the patch.
There is an online tool to easily patch the mod to the ROM. IMPORTANT, this will not change any naming, Id recommend having a folder with the base game roms, and a folder for the mods, and lastly a folder for the newly modded roms. Make sure to name or just save the game in modded roms folder after the patch. Below are a few resource to find various Pokemon Rom mods(sometimes called hacks)
Personally, Pokemon Unbound is considered the best most polished hack. it runs on Pokemon Fire Red.
Pokemon Emerald Rouge is a cool take on the popular Rougelite genre. This runs on base game Pokemon Emerald
-
 @ 28ca019b:93fcb2cc
2025-05-25 19:25:17
@ 28ca019b:93fcb2cc
2025-05-25 19:25:17Introduction
“There is nothing more powerful than an idea whose time has come.” -Victor Hugo
Early 1950’s America. Harry S. Truman is in office. The economy is booming and the middle class are comfortable. Shiny new television sets invite the first scenes of Hollywood into people’s homes. The Weavers, Tony Bennett, Vera Lynn and Perry Como play on the radio.
But on the fringes, in dance halls and late night clubs, a cultural revolution is brewing… A new musical fusion with influences from blues, R\&B, jazz, rockabilly, country and gospel music is about to give birth to not only a new genre, but a whole new way of life that will change society and culture, forever.
Rock & Roll
It becomes a symbol of freedom, a means of expression, and a catalyst for social change. It brings into existence a new type of counter-culture, filled with individuals who are driven to rebel against norms and authority. They don’t ask for permission. They push for change.
I believe we are witnessing such a shift now. And like rock & roll, the movement I’m speaking of is also ground up, grass roots, punk rock and will not look to authority to seek permission. The catalyst for this new social change, I believe, is Bitcoin. With its innate properties, it empowers and enables the individual like never before to achieve their fullest potential, expressed through an unprecedented freedom technology. It is an idea, like a song everyone can sing in their own way, that nobody can silence.
Revolution
"You say you got a real solution / Well you know / we’d all love to see the plan" -John Lennon
The rock & roll era helped bring about meaningful societal change through art, music, and film. It created a new social narrative. Today, the Bitcoin network is providing people with a different set of tools and ideas to build a better future in a much more practical and pragmatic way. Instead of trying to reshape social consensus and cultural norms through art forms, fashion, or lifestyle, bitcoin is achieving this through open source code.
For the first time, this technology gives individuals financial sovereignty and personal control over their own destiny, with the ability to self custody their own money that no corporation, government, dictator or king can tamper with. The individual has an opportunity to finally be freed from economic tyranny. And societies have the potential to avoid endless wars funded with printed government money. John Lennon said ‘give peace a chance’. If he were still here today and understood how bitcoin could subvert the military industrial complex would he not exclaim, ‘give bitcoin a chance’?
Natural Rights, Civil Rights, Digital Rights
"The times they are a-Changin’" -Bob Dylan
The civil rights movement was tightly interwoven with the history of rock & roll. The march on Washington, August 28th 1963, marked a seminal moment in American history for the advancement of equal rights before the law. Bob Dylan, along with Joan Baez, stood with over two hundred thousand other Americans and listened to Martin Luther King’s now immortal speech.
People with the same values peacefully gathered in numbers to make a statement powerful enough to change the conversation. This is analogous to the same freedom-minded people today gathering in cyberspace and voting not in the traditional sense, but voting with their money – peacefully exiting and transferring their economic energy into a system where they can’t be expropriated.
The question of whether individual rights are granted or have to be secured by each individual remains a contested area of philosophy to this day. To outline each in a very crude and simplistic way, natural rights (sometimes referred to as inalienable rights) are derived from the belief that every person owns their own body, therefore their own labor, time, and energy. Civil rights, on the other hand, are granted by the state and are therefore not universal. The fact that they are rights granted to humans by other humans means they always have the potential to be revoked or withdrawn.
Digital rights granted by the power of asymmetric cryptography are based in the laws of mathematics. Combined with proof of work, based in the law of thermodynamics, this makes digital rights that bitcoin provides more akin to natural rights than civil rights, as no one person or group can unilaterally revoke those rights or confiscate your property through violence. No amount of fire power, tanks, fighter jets or nuclear weapons can break a bitcoin private key or rewrite the sunken cost of proof of work embedded into bitcoin’s timechain. This idea of securing rights without asking permission is, in itself, a revolution and achievable now in an egalitarian way. This implies a potentially huge shift in power from those with a monopoly on violence, to peaceful individuals who want to be treated fairly and with dignity.
Cypher Punk-Rock
Songwriters write songs. Cypherpunks write code.
To tie things back and look at a very narrow, but potentially huge use case of bitcoin, let’s examine the current broken incentives of the music industry, particularly recorded music. It is becoming increasingly apparent that an option other than a subscription model could find demand from content consumers and producers alike.
There is now a way, with Bitcoin and Lightning Network, for a music fan to pay artists directly and for any amount – dollars, cents or even fractions of cents. This model has positive outcomes for the music producer and fan who are the main two parties engaged in the transaction. The artist keeps all of what is sent and the listener can pay what they want. The listener can pay as they listen, rather than be locked into a rolling subscription that isn’t based on usage. This concept, called ‘value for value’, is finding its way into new music platforms such as Wavlake and Fountain. I believe this model will become the de-facto way of monetizing digital content in the coming years. This could bring an economic signal back to music that has been lost and cannot be achieved by streams alone. This will hopefully create a more meritocratic music system and shake up the entrenched streaming monoliths.
Art can shine a light on a certain truth. It can also make people look at things in a completely new way. Maybe then, Satoshi was the greatest artist who ever lived. Bitcoin smashed the conventional wisdom and theories of the most basic and prevalent thing everyone takes for granted: money. Using money as a lens to view the world can lead to distortions in your perception if the lens is warped. Removing the glasses makes you reevaluate economics, politics, religion, philosophy, morality, beauty, and almost every other aspect of life. The beauty of the Sistine Chapel, the Egyptian pyramids, the Mona Lisa, Beethoven’s 5th Symphony, Bohemian Rhapsody all intrinsically imply a certain degree of proof of work. The art, you could say, speaks for itself.
The Long and Winding Road Ahead
As a musician, I have found a new hope. The value for value movement gives me that hope. If this is truly a superior model of music distribution and consumption it will win out over time on the market.
Another point to touch on would be the possibility of this technology ushering in an artistic renaissance. I can honestly say my favorite music, the songs that have moved me the most, normally comes from a place of truth, honesty and sheer talent. Maybe I’m out of touch, but I feel popular music of late is devoid of soul, meaning and the biggest mainstream artists want to conform to the man (giant corporations/governments) instead of stick it to the man! Probably because there is nowhere else to turn now that streaming and social media platforms own their speech and art. We need to investigate and embrace new ways to own our speech and art, to make art interesting again. The powers that be, need to let it be, and leave alone individuals who wish to use this technology for their own interests if they do so in a peaceful way.
I want to leave you with a Frank Zappa quote that seems more relevant than ever:
“I’d say that today, dishonesty is the rule, and honesty the exception. It could be, statistically, that more people are honest than dishonest, but the few that really control things are not honest, and that tips the balance…”
My charitable view is that the majority of people in power aren’t corrupt, it’s rather just a case of ‘no one is better than their incentives’. But when incentives are misaligned bad outcomes will inevitably result. With bitcoin and its incorruptible incentive structure, we have a chance to peacefully opt-out of a rigged game. I urge you to not trust, but verify with your own research that bitcoin is the answer to many of society’s current problems.
I think it’s fair to say, we all need to question ourselves and authority a little more than we’re comfortable doing, to hold truth as an ideal worth striving for, and live a little more rock & roll!
Link to original article**
-
 @ 812cff5a:5c40aeeb
2025-05-31 01:12:55
@ 812cff5a:5c40aeeb
2025-05-31 01:12:55NIP-02 — أنماط المفاتيح العامة
رقم التعريف (NIP): 02
العنوان: أنماط المفاتيح العامة
الحالة: نهائي
المؤلف: fiatjaf
التاريخ: 2020-12-10
الملخص
يقترح هذا المستند نمطًا معياريًا لطريقة تمثيل المفاتيح العامة (public keys) في نُستر — يُعرف باسم
npub— لتسهيل مشاركتها وقراءتها من قبل البشر، تمامًا كما يتم تمثيل عناوين البيتكوين بـ bech32.
التنسيق المقترح
نقترح استخدام bech32 لترميز المفاتيح العامة، حيث يكون التنسيق كالتالي:
npub1<سلسلة bech32>على سبيل المثال:
npub1qqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqzv9sxهذا الشكل يمكن نسخه بسهولة، والتعرف عليه بصريًا، والتعامل معه دون الوقوع في أخطاء النسخ الشائعة للمفاتيح بصيغ hex.
السبب
- الشكل hex التقليدي للمفاتيح العامة (مثل
32e...af1) صعب القراءة. - bech32 أسهل للمشاركة عبر الرسائل أو الوسائط الاجتماعية.
- وجود بادئة
npub1يوضح فورًا أن السلسلة تمثل مفتاحًا عامًا في نظام نُستر.
ملاحظات إضافية
- نفس المبدأ يُستخدم أيضًا مع أنواع أخرى مثل
note(لتمثيل معرفات الأحداث) وnsec(للمفاتيح الخاصة). - هذه الصيغ لا تغيّر البيانات الأصلية، بل فقط تمثلها بطريقة أسهل وأكثر أمانًا للبشر.
الخلاصة
npubهو معيار لتنسيق المفاتيح العامة باستخدام bech32، مما يجعلها أكثر قابلية للقراءة والاستخدام من قبل البشر.
يُوصى بأن تستخدم جميع تطبيقات نُستر هذا النمط عند عرض أو مشاركة المفاتيح العامة. - الشكل hex التقليدي للمفاتيح العامة (مثل
-
 @ 14206a66:689725cf
2025-05-31 00:54:40
@ 14206a66:689725cf
2025-05-31 00:54:40We’ve all been there, you’re locked in, desperately fighting with spreadsheets, the dishwasher’s going, and a banana cake is in the oven. Suddenly, all goes quiet, lights are off, oven’s off, PC dead as a doorknob. You check the fusebox, it’s fine. Must be a blackout. Usually, the power comes back on after 30 minutes to an hour, but you’re left standing there wondering what happened.
We’ve just seen a country-wide scale event like this, which was much more extreme. On 28th April, the Iberian Peninsula experienced a catastrophic breakdown of the grid (see here).
Power was off for several days. I won’t dig into the details of this particular event; doing so is way beyond my pay grade. Suffice it to say it follows the ideas I want to introduce in this article.
We’ll begin with the simplest model I can think of, getting to grips with the issue from first principles. Then I’ll walk through how the basic premise scales up the Australian grid (or at least the east coast, the NEM), before introducing the shadowy supergeniuses in control of it all (AEMO) and one of the most important market mechanisms they use - Frequency Control Ancillary Services (FCAS).
Part one: First principles
Imagine a way-over-simplified system with a single source of power and a single load. Our source of power is just a battery that produces 10MW of power at an assumed 1000V. The battery has no rotating components. It is connected to a very basic inverter. The inverter is designed to produce 50 Hz AC power; however, let's imagine it has no sophisticated voltage controls or protections (unlike real inverters). All that our inverter comprises is a basic switching and timing circuit.
This specific frequency of 50 Hz is a fundamental design standard for almost all AC electrical equipment. Just like a clock needs to tick at a precise rate to tell accurate time, electrical devices like motors rely on the AC power cycling exactly 50 times per second. If the frequency deviates too much, it can cause motors to speed up or slow down incorrectly, or sensitive electronics to malfunction. Our simple inverter, despite its limitations, is designed to produce 50 Hz because that's what the heater and any other AC device expect.
Our load is a large but mechanically simple industrial heater. It has a large coil that produces heat by running a current through it. Importantly, the heater has a dial to adjust temperature (which can change its power consumption). The heater is currently set to draw 10MW of power.
That’s the start, with a simplified system in equilibrium, all is well. The heater is producing heat, and you can make up your own story about what the heat is used for. The important point is that the voltage, current, and frequency are all stable.
Next, the foreman operating the heater turns the dial up to increase the heat output. Assume the heater now wants to draw 20MW of power. We’re simplifying, so also assume that in this instant, the voltage remains at 1000V.
To draw this much power, the heater now has to draw more current (because power = voltage x current, it’s the rules). Since we assumed the voltage remains at 1000V, there is an instantaneous demand for more power from the battery than it was previously supplying.
The battery now attempts to supply this current, which means the current must flow through the battery’s components, the inverter’s components, and the wire connecting the battery to the heater. All of these physical components have resistance. This means the actual voltage the heater receives will be lower than 1000V.
Now that the heater is receiving voltage lower than 1000V, things start to go wrong. The power consumed by the heater is proportional to the square of the voltage across it (rules are rules), so power = voltage^2 / resistance. Following this rule, since the voltage has decreased, then that means the actual power the heater draws will be less than the 20MW desired. For example, it might only draw 15MW, but it depends on the resistances in all the components, which we haven’t set.
Things just get uglier. The battery and inverter are operating under extreme stress, trying to deliver the higher current demanded, but at reduced voltage. Inside the inverter and the battery, the components start getting hot (rules, again). Since we assumed the battery and inverter are super simple, the inverter can't adjust its power output based on actual grid conditions (like a sophisticated one would); it can only fail. Then the heater goes out, and the foreman gets mad; it’s just a bad day all around.
The fix: add a spinny thing.
Reimagine the situation just as before, but now, instead of a battery, imagine the source of power is a contemporary synchronous generator system. Say it’s a hydro plant, where the spinning turbine is directly connected to the grid. This generator, unlike the battery-inverter, inherently uses its large rotating mass to move a metal rod up and down inside a magnetic coil and produces AC power. Importantly, it synchronises with our system’s required 50 Hz rhythm.
In this case, the story proceeds as before. When the foreman turns the heater dial up the heater wants to draw 20MW. In this case, the increased current flows through the impedance of the generator’s internal components and the wire. Just as before, this causes an immediate, rapid voltage drop at the heater’s terminals. In that instant, the heater will not get its desired 20MW because the voltage is too low.
Since the generator’s power output is less than the load demand, the lack of energy causes the rotating mass of the generator to decelerate (energy is conserved), and the frequency of the AC power in the system drops below 50 HZ. Because the generator’s turbine is a large mass, it has substantial inertia (pesky rules again), so the drop in frequency happens much more slowly than in our first story, and there is no catastrophic failure of the system. Instea,d this inertia buys time for the system to react.
The reaction comes from the manager of the generator. In the real world, this is a piece of software called a governor, but it’s useful to imagine it’s a person. The manager sees the drop in frequency and presses some buttons to let more water flow to the turbine, the frequency climbs back to 50 HZ and the power output of the generator increases.
Then the heater gets its required 20MW of power at 1000V and 50Hz, and the foreman is happy, everyone’s happy, it’s just a good time.
Frequency, in this simple system, indicates power imbalances and triggers the manager of the generator to respond. Equally, we could have assumed the foreman can be notified that he shouldn’t increase the heater’s dial - we can manage the imbalance either on the supply (generator) or demand (heater) side, or a mix of both.
This hints at a crucial question: how the hell do we coordinate this? Even with just a single load and a single generator, what sort of contracts would the foreman and generator manager need to keep everything running?
Part deux: AEMO, the not-so-invisible hand coordinating the market
Above is a story of a system with one load and one generator, without protections for the management of voltage or frequency. I walked through how this simple system could suffer a catastrophic breakdown as a result of the load increasing. Followed by a slight added complexity, which solves the issue.
Everything that applies in the simplified model also applies in the real world; the basic principles scale up and create complex incentives, coordination, and knowledge problems.
In my simple story, there was a manager in charge of the generator and a foreman in charge of the heater. In the much more complex National Electricity Market (NEM), there’s a third main actor: Australian Energy Market Operator (AEMO, because it operates the energy market, perfect naming convention). Among a host of competing priorities, AEMO has one role we’re particularly interested in: making sure we have a good time, i.e making sure the grid is stable. How it does so is the economics bit.
The NEM covers a huge geographic area (all the way up the East Coast from South Australia up to North Port Douglas). Within the vast area it covers are around 10 million customer connections (source). AEMO provides an interactive map that shows you how many substations there are - lots!
here's a map from AEMO
With all those connections and interconnections, the only constant is change. Strong winds can suddenly break connections, generators can trip for a host of reasons, and sometimes physics just says “no”.
On the flip side, sometimes large loads connect unpredictably and want instant power to be available. The physics says supply must equal demand or things get bad, so how does AEMO make sure supply equals demand?
In short, dispatch instructions. AEMO coordinates the supply-side market participants using signals to their control rooms. The economics of it could be summed up as: AEMO is a visible hand trying to approximate the role of Smith’s invisible hand in the market*.
Though not the focus of my current article, dispatch can be (over)simplified as follows: Every five minutes, generators send an offer to AEMO containing a price-quantity pair for power output. AEMO sorts the offer from lowest price to highest and matches supply to forecasted demand, starting from the lowest offer to create a dispatch interval/dispatch window, within system constraints. Importantly, generators all receive the highest marginal price (spot price) of all offers within the dispatch interval. Then, all generators included in the dispatch interval receive revenue equal to their power dispatched times the spot price.
So, assuming the system is in balance. This plays out, and everyone’s happy. But that’s not guaranteed in such a complex interconnected system like the NEM. So, what happens if, after offers are placed and power is scheduled, a generator suddenly trips off (cutting supply) or a large load connects unexpectedly (rapidly ramping up demand)?
AEMO needs some sort of backup power supply or backup demand as a contingency for when imbalances happen. One of such contingencies is what we call this service provision Frequency Control Ancillary Services (FCAS). So named because AEMO uses system frequency to understand where, when, and how much extra supply or demand (load) is required to return the system to the normal stable operation.
But AEMO doesn’t own any generators, batteries, or large loads itself. So, how does it get them? Someone came up with the idea that you can sell backup supply or demand (load) to AEMO, for a fee. This idea implies that AEMO has to find the right incentives to bring backup supply or backup demand (load) online in a flash.
There’s a market for that!
Actually, there are eight markets, but we’re simplifying.
To procure FCAS, AEMO runs a similar auction process to the market for power. Participants submit bids to AEMO every five minutes, containing a service type and availability across up to 10 price bands. The service type is one of: increase/decrease frequency in one of the three time intervals.
AEMO then considers all bids and finds the least-cost solution that meets all system requirements, matching the supply of FCAS to the demand for FCAS. Just like in the market for power, AEMO orders the FCAS bids into a “merit order” based on price for each service type (lowest price to highest price). It then decides which bids it will accept and pays all accepted bids the highest marginal price of all accepted bids. This creates a price signal for FCAS in the market.
The design has obvious intentions: FCAS suppliers win big if they can be super low cost while their competitors are high cost.
Just like in the market for power, once bids are accepted, AEMO sends a signal to the control panels of the FCAS participants.
You can see how , by following this process, AEMO acts to approximate the emergent order (or invisible hand) of a market by creating price signals for both power supply as well as FCAS. Then, physically matching those price signals with the actual power flows using a (pretty amazing, honestly) control scheme.
The idea that AEMO is only approximating the invisible hand is important; I’ll explore that more deeply in future articles.
That’s the physics and market mechanisms in a nutshell. But who sells FCAS to AEMO, and what about the mullah, dollars, buckerinos, fat stacks?
Part tres: How big is the market
Firstly, who can participate in the FCAS market? As far as I understand, it’s quite open; if you invent a device that meets the standards and go through the application process, then you can participate. AEMO’s concern is system stability, so from their POV, any particular device is fair game as long as you meet the engineering standards.
One common example is certain electricity retailers who use their customers’ hot water cylinders as a demand response. By sending an electrical signal to your hot water cylinder, the company can turn it off for a short period, reducing demand (load). There’s a complex “annoyance cost” paid by the consumer of their hot water cylinder being turned off, but then that’s balanced against potentially lower bills as the electricity retailer can substitute FCAS revenue.
Another example is grid-scale batteries; these can build or release charge on a whim. For batteries, the incentives are about whether their charge is worth more in the spot market or in the supply response FCAS market. If the battery is connected to a facility like a solar plant, then the incentives get more complex; is it worth selling power instantly or building charge in the battery for potential spot market or FCAS later? Add in a futures market and you just get more complexity.
A final, still emerging, example is bitcoin miners, these are basically just computers. These machines can be powered up or down relatively quickly and easily with little ill physical effects, and no ill effects to the Bitcoin network or protocol. When they are powered up, they earn a stream of income for the owners in the form of bitcoin.
This creates an interesting dynamic when bitcoin miners participate in the FCAS market; their FCAS bid, all else equal, should be at least the value of the opportunity cost of not mining bitcoin.
A completely unanswered question is what happens if bitcoin mining becomes a large proportion of FCAS? Consider a case where the FCAS from bitcoin miners drops out of the market because bitcoin fees spike and miners find it more profitable to mine rather than provide FCAS.
Alright, but the money! Surely FCAS is lucrative?
AEMO publishes data on FCAS. The most readily understandable data is the payment data. This is, as the name suggests, how much AEMO paid to FCAS participants over the eight service types (and in each State/Territory in the NEM) each month. This is the raw revenue of FCAS market participants. One way to think of it is as the cost of stability.
In total, FCAS payments have been about $39 million this year (up to week 20, which ended May 18).
AEMO has also provided total revenue for FCAS from batteries in the NEM, specifically in its Quarterly Energy Dynamics - Q1 2025, covering 1 January to 31 March 2025 report. This data suggests that batteries in the NEM have earned $69 million in 2024, which is 42.9 percent of all FCAS costs. This is remarkable to me, because grid-scale batteries are relatively new to the market as compared to other generation and storage technologies.
The cause lies in the fact that batteries can* *have a low marginal cost to charge and discharge, so the fact that they captured such market share this fast highlights the idea that he who produces FCAS cheapest wins.
This data release also contains aggregate FCAS costs for all states. The data tells us that in 2024, total FCAS costs were $161 million.
The fact that there is such a healthy pot up for grabs speaks to the fragility of our grid, but also to the resilience; it's a strange duality.
With continued investment in solar generation, because such systems have little to no inertia, we could see increased frequency excursions (technical term for being out of range). Engineers are busy solving this using inverters, which simulate inertia. These are genius, but such innovations take time (and standards) to be adopted.
Then there’s the question of critical infrastructure risk - how tolerant can we be of instability when datacenters mining Bitcoin and running AI models are on the line
At the risk of repeating myself, the whole construction is very much a visible hand trying to approximate what Adam Smith’s invisible hand might do.
Fin
Full disclosure, I do use AI (Gemini specifically) to help me research, learn, and write my articles, but I go over everything multiple times to make it my own voice and reflect my own ideas.
*Adam Smith described the idea of an invisible hand, which directs the market, coordinating people's desires, as a metaphor to explain how people in a market somehow end up serving each other's best interests even without directly communicating.
-
 @ 81022b27:2b8d0644
2025-05-31 00:47:43
@ 81022b27:2b8d0644
2025-05-31 00:47:43Today some clients and I were talking and they asked me about my recent seminar where I attended the “Unleash The Power Within” seminar with Tony Robbins. I explained that the firewalk I performed was not the highlight of the seminar, It was all the junk I got rid of mentally. We talked some more and then someone said something a little derogatory about Scientology.
I said, “wait a second, Scientology changed my life!”
It’s true. Some of the things I learned through Dianetics and Scientology were catalysts in me changing my entire life around.
It started one evening in Coral Gables, FL when I was walking down the street going to meet someone for dinner. I was stopped by a lady holding a clipboard outside of a 50’s-looking building.
“Would you like to take personality test?”
I asked: “What’s that?”
She explained and since I’m always early to things, I had plenty of time to kill. I said: “Sure! let’s do it!”
I took the test and the results seemed spot on. Then they asked if I would like to learn more about the mind , I could sign up for a course for a modest amount and I was genuinely curious about the whole deal and I agreed.
The Class I came back like a week later to start the class. I’m remembering that building had a distinct smell. It wasn’t bad. I can’t really describe it, but if I ever smell something similar, I’d recognize it instantly.
I walked in and they took me to a big room, a classroom with lots of tables and chairs. Every table had a small box with objects in it. There were people reading, there were people in groups studying, lots of chatter.
It seemed exciting!
I don’t remember if it was my first lesson or not, but we had to do TR’s (Training Routines) and I was asked to sit across from some guy and just stare at him. Look him in the eyes and not laugh, not blink excessively, just keep your composure.
Bah! Stupid! But I can do this!
We started the exercise and it seemed silly at first, but then my heart started racing and started freaking out. It felt like I was in a tunnel, but somehow his eyes were attacking me.
Then all of a sudden I’m hovering 8 feet above myself and I’m looking at the situation from above.
Next thing I know, I’m back in my body and the exercise is over.
The teacher, or facilitator came by to ask me how everything went. I started to tell her exactly what happened and she was writing very matter-of-fact-ly.
“And then I left my body!,” I emphasized.
“So you exteriorized?” She asked.
“I guess.”, I mumbled.
What really made me curious is these people are just nonchalantly just writing down stuff like it’s no big deal.
They got me. I was hooked.
Auditing
I started doing some courses whenever I had some free time: maybe once or twice a week. I learned that there is something that they call the “reactive mind” and that past traumas can affect someone in the present time.
We did this exercise that when my “Auditor” would snap her fingers, I would repeat the first word that popped into my mind, until we got a string of words. I would the repeat this string of words until they “lost their charge” and had no effect.
During one of these sessions, I
felt like I was choking.
No, not choking !
I could taste salt water!
I was drowning!
This shook me up because I had no recollection of almost drowning like that.
I asked my mother if I ever almost drowned and I was surprised by her answer.
She said; “Yes. We were at the beach-you were a baby and in the water with your father. A wave got both of you and your dad had to throw you towards me like a football, because he couldn’t fight the riptide.”
Wow.
Study Tech
before you start the “heavy” course, you must learn how to study. So they have designed a way to teach people “How.”
I thought, “wow, no one ever really taught me how to study.”
In high school, I kind of just skated by, with no need to ever read or do much. I didn’t make valedictorian, but I was discovering my social life and that was top priority for me at the time.
They showed me if you read something and can’t remember what you just read, t means you read past a misunderstood word. You never skip a word you don’t understand. There are always dictionaries at every study table.
If you get woozy and want to bail on the material being studied, then you have skipped a gradient, so you should go back to a point you understand and work back up.
If you get a headache while, studying, that means you have a “lack of mass” and the topic is abstract and you need to make it more physical to be able to understand it.
That is why they had those baskets with modeling clay and stuff in it, so you could model out concepts.
I still use this knowledge.
Basic Study Manual
The Purification Program
At some point one of the coaches pointed out that if I wanted to make quicker progress, I should do The Purification Program. The Program is designed to get rid of environmental toxins and medications and other materials that are stuck in your physical body and is interfering with your progress “up the bridge”
So of course, I am fascinated by this idea and sign up for the course, This time, it;s a lot of books and it’s going to cost be some serious cash. I didn’t have that kind of money, because I was scraping by on an assistant manager at Wendy’s salary.
No worries, take out a new credit card to pay for it. And one of the members drove out to my work to get the signature (and $$) to pay for the course. I think It was the end of the month and they got a bonus if I signed up before then.
The Program
The program basically consists of sitting in a sauna for 5 hours a day, Taking supplements: cal-mag, megadoses of niacin, and oils
It was perfectly organized: we were taken to a different part of the building to an area with a eucalyptus smell. We were shown the sauna-it was a large sauna , It could hold like 10 people.
We were given our supplements and then told to jog for few blocks around the building and then come into the sauna.
By the time you are done with the run, the niacin has kicked in and given you a nice “flush” skin is red and blood vessels have dilated. Now you’re ready for the sauna.
Everything done here is monitored. The guy supervising us was a Medical Doctor and he recorded weight going in and was always available supervising and answering any questions.
Five hours a day in a sauna is a LONG time- especially with someone like me who is not crazy about sweating constantly.
You were free to come in and out to prevent from getting overheated and get in the shower to cool off.
I brought reading material, I was doing this!
Reactions
X Ray Radiation
For the first couple of days, nothing significant happened except my skin started getting better.
One day as I am leaving the sauna to cool off, I take a look in the mirror and it looks like I’d been in a fight. Both my eyes had black rings like bruises around them.
I asked the attendant what this was and he looked at them and asked me if I had been exposed to many x-rays. I said that yes, I had been a sick kid and had tons of diagnostic procedures and medicines and stuff.
He said : “Ok, get back in there! You’re just running out x-ray radiation”
Came back out about 20 minutes later and the rings were gone.
Medications
I’m sitting in the sauna and I start getting sleepy. More like “anesthesia count down to ten sleepy”
Again, I was concerned, so I asked attendant what the deal was and he said I was likely detoxing from medicines and drugs I’d taken.
Went back in until it cleared up.
Chlorine
One day there were about 5 of us in the sauna and all of a sudden a strong smell of chlorine started. It keeps getting worse until it was so bad it was burning our eyes. We all exited the sauna thinking there was some sort of chlorine spill or something like that.
The attendant asked: “Has any of you worked as a pool maintenance tech?”
We looked around and one guy raised his hand.
The attendant said “Ok! Everyone dismissed for today except for you!” as he pointed to the Pool Tech guy. “Get back in there!”
I was doing this in the mornings when I had the evening shifts at the restaurant and when I worked days, Id try to make it to the sauna in the evenings.
After about 3 weeks, everything started to taper off and I was done.
I was feeling great and there was something different about everything, I felt like I was more awake and aware. And my skin and complexion were fabulous!
Clear Body, Clear Mind
The Sea Org
At some point, the people in charge routed me to talk to someone one in the Sea Org.
It was a small glass office, like the one you are led into when you are buying a car. I was greeted by a man in an impressive looking uniform like Captain Steubing from the “Love Boat”.
He said they had been watching me and my progress and were impressed with my IQ score. He said I stood out among the other people and compared me to this woman we could see through the glass.
He basically ripped her to shreds in front of me, telling me how her life was in chaos and how she had created all of her chaos and that somehow I was different from her.
They basically offered me a job.
One catch:
I had to sign a contract for a “billion years” and I couldn’t be in debt.
Seeing I was already in debt from some of the previous courses, I didn’t qualify. Also a billion years seemed a bit long.
I thanked him and said I would consider it- I was pretty sure it was a solid no, but I didn’t want to tell him that. I was probably intimidated by the uniform.
Healing with Vitamins
This was not an official class or anything, but during my time there, I saw whenever someone was having issues with their body, they would consult with one of the counselors and they would look into a little book: “Earl Mindell’s Vitamin Bible” or see a chiropractor down the road who was apparently a Scientologist.
I used what little I learned and suggested home remedies to my Wendy’s employees and their families and developed a little side gig offering supplements to anyone willing to listen.
The Bottom Line
I know there is a lot of negative press and negativity in general about Scientology, but be clear about this: Scientology changed my life!
I’m not an active Scientologist, and don’t feel like I want to go back. But it definitely shaped me into the person that I am today.
If there is bias against the church in this article, it’s just the way that it’s run. Running an organization like an MLM encourages bad behavior.
I have moved countless times since those days, and the first piece of forwarded mail is usually from a Scientology Org.
I’m not sure I would have taken the steps to make a drastic change and decide to attend chiropractic school had it not been for my brief time in Scientology,
Love,
-Dan
-
 @ d360efec:14907b5f
2025-05-31 00:36:48
@ d360efec:14907b5f
2025-05-31 00:36:48 -
 @ 81022b27:2b8d0644
2025-05-31 00:25:44
@ 81022b27:2b8d0644
2025-05-31 00:25:44I did my chiropractic studies at Life University in Georgia. When I picked schools, I had no idea about chiropractic philosophies or the politics in chiropractic.
I picked Life for two reasons: It was the closest to home (Miami at the time), and it was the first one to get back to me and tell me I was accepted.
My chiropractor in Miami wanted me to attend Palmer College, but that was in Iowa, and it sounded remote and cold. So, hell no.
I was so excited to start my new life that I crammed a U-Haul with all my junk and headed to Marietta.
Once classes started, someone suggested I join clubs to make friends.
I asked around, and there was this club having an upcoming party. It was Spizz Club. Spizz was short for Spizzerinctum, which meant “chiropractic enthusiasm.”
Well, I had a lot of that—plus, there were some attractive girls in that club.
I showed up at the party, which was at a student’s apartment, and got greeted with a long, uncomfortable hug. Do you remember the old cartoon of Pepe Le Pew and the cat? Well, I was the cat.
I grabbed a beer and started mingling. It was one uncomfortably long hug after another. Some made moaning sounds!
Fucking weirdos.
I got invited to a philosophy class while I was at the party. My social calendar wasn’t exactly overflowing, so I went.
Wow! These people were explaining concepts I’d known deep down my entire life, but I was hearing them out loud for the first time.
Deciding to move 700 miles away and change careers was a rash and selfish decision because I was running away.
Running from:
Failure
A failed marriage
Failure at real estate
Failure at finding something I was good at
Failure at being happy
Failure as a student, ten years after high school with no degree.
Here I am, listening to the speakers, and I realized this was different.
Maybe this was MY thing.
Maybe I could be a chiropractor.
Maybe I could help people.
Maybe I could be proud of myself.
Maybe someone could be proud of me.
That night changed me. The weirdos seemed less weird. I made friends, I found my footing.
Chiropractic college was tough, much tougher than I expected. I had always kind of “skated by,” but now I had to put in hard work because I hadn’t been in school full-time for ten years.
I also had never lived the college life, and apparently I was partying too much. We hit the bars to blow off steam after midterms and finals—turns out, there were a lot midterms and finals.
I almost flunked out one quarter, but there was a lot going on. My 85-year-old dad came to visit and was going to stay with me for a bit, then he passed away suddenly.
I had a lot of guilt from that, thinking that I could have done something different and could have stayed around a little longer. That guilt would resurface years later in a Craniosacral therapy session.
I couldn’t fail at this. This was too important. I went to a Hypnotherapist to see if maybe I could get “programmed” to not flunk out. Apparently, it worked.
Funny thing, I worked hard and time passed. We did it. We graduated and made it through.
Look, those brutal study sessions weren’t easy, and almost flunking out scared the hell out of me. I am thankful that Chiropractic passion stuck with me. That Spizz still gets me through some days.
Live Long and Prosper,
-Danny
-
 @ 005bc4de:ef11e1a2
2025-05-30 23:59:55
@ 005bc4de:ef11e1a2
2025-05-30 23:59:55My Actifit Report Card: May 30 2025 Although I was absolutely exhausted today, I was able to get 19k steps in, somehow. The image is a somewhat random one - a chair with beautiful curves. https://usermedia.actifit.io/1a1c2562-3a76-4801-a3f8-0a0e8078d824.jpg This report was published via Actifit app (https://bit.ly/actifit-app | https://bit.ly/actifit-ios). Check out the original version https://actifit.io/@crrdlx/actifit-crrdlx-20250530t235827610z 30/05/2025 10123 Cycling
Originally posted on Hive at https://peakd.com/@crrdlx/actifit-crrdlx-20250530t235827610z
Auto cross-post via Hostr v0.1.48 (br) at https://hostr-home.vercel.app
-
 @ 81022b27:2b8d0644
2025-05-30 23:46:46
@ 81022b27:2b8d0644
2025-05-30 23:46:46How the birth of my grandson is making me re-think my own future
I just became a grandfather. My youngest daughter had a baby boy.
I’m thrilled.
And
I’m scared.
Babies are pure potential Infinite possibilities, all sorts of different paths they could take.
They haven’t drank the Kool-Aid, or in fact any Kool-Aid at all, lol
Will he be gregarious and outgoing?
Will he be shy and introverted?
Will he want to be an artist?
An engineer?
Will he be brave or scared?
Will he be like his grandfather, trying to overcompensate in his later life for being afraid of nearly everything in the early part of his life?
I am thrilled. All the grandparents that I have ever met said to me:
Just wait until you have grandkids, its different
And yes, it is different.
I’m not so worried about the how to take care of the baby-all I have to do is love him.
The other day, I was just holding him and was able to stay in “the love state” for the longest time ever.
(The love state is the goal of a meditation that I do-The goal is to stay “in love” feeling for as long as you can.)
I was able to get to this place so easily with him!
He has also taught me to slow down even more. He is not in a hurry to do anything. His job is to eat, poop and grow.
I feel like I get to savor the time I get with him even more than with my own kids.
I’m Scared His mom has had her share of issues.
She is now a single mom trying to navigate all the responsibilities of being a parent.
I didn’t think she was ready, but here we are.
She doesn’t have her mom to help guide her, but I thank god that she has Christi-my girlfriend. She has been such an incredible support for both Audrey and me.
I’m scared mostly because now my own future is uncertain.
I had my future planned out like where i wanted to retire-the things I wanted to do and now this little guy has me re-thinking all my plans about the future.
Here’s to uncertainty!!
Live Long and Prosper 🖖,
-Dan
Links | The Natural Life | The Intuitive Chiropractor
-
 @ 81022b27:2b8d0644
2025-05-30 23:11:38
@ 81022b27:2b8d0644
2025-05-30 23:11:38Today is Mother’s Day and throughout the day I’ve been texting my friends who are moms and wishing them well on their day.
A buddy of mine sent me a text and said “Happy Mother’s Day, lol!”
Immediately replied back “same to you!”
Then I started thinking: Did he mean that because I am both father and mother to my daughters? Or was it just typical guy behavior (from my era) joking around calling me gay.
Then I got to thinking about how today is tough for my daughters because they lost their mom to cancer over 4 years ago.
I was driving when i got the text and next thing I know tears are streaming down my face. Maybe it has been tough for me too.
These girls have NEEDED their mom on so many occasions! I could never fill those shoes!
I could have really used her help with our youngest daughter. Maybe she could have said ONE thing to her to make her thing twice about un-aliving herself.
Maybe she could’ve shared my grief, or maybe we could’ve just talked about the situation and how we can get our tortured little girl back from her uncomfortable reality.
Full disclosure: My daughters are all adults, and their mother and I were no longer together. We had been divorced for about 8 years when she passed.
When she passed away, I felt like I couldn’t grieve-after all, I was just the ex-husband.
Took me a while to realize that I had lost a family member too. I don’t think I have completely gotten over it, at least not well. There was a lot of anger and resentment in the divorce and over the years we had tried to be civil, and even had holiday celebrations with EVERYONE attending. Come to find out, the new husband hated that arrangement.
Before she passed, we said we still loved each other and said our goodbyes. I told her I would look after our daughters and made sure her mom was ok. Maybe i’m feeling so emotional because I feel like I’ve made a mess of things here or I’m simply not over it yet.
Happy Mother’s Day!
-
 @ 81022b27:2b8d0644
2025-05-30 23:02:22
@ 81022b27:2b8d0644
2025-05-30 23:02:22I love my job, I really do. Helping people feel better, getting their bodies back in line-it’s why I show up every day.
But some of my clients?
Some of them act like I’m a magician who can fix years of you ignoring their body in one session.
So, here’s the unfiltered truth—what I’d really like to say when they’re sitting there, complaining, not listening, and interfering with their own healing process. Buckle up, because I’m not holding back.
- There’s nothing wrong with you! Just keep getting adjusted regularly, and for God’s sake, stop going to the medical doctor.
- Stop saying you don’t know what happened.
- You didn’t even try it out before; you’re saying it still hurts. Move around a little!
- No, I’m not doing the fucking ring-dinger that you saw someone do on TikTok.
- No, it’s not because you’re old. It’s because you don’t take care of yourself.
- You’re only 35; you’re not allowed to say you’re old.
- No wonder you don’t listen to your body—you can’t shut up for five seconds to listen to anything!
- Yes, like I’ve told you countless times before-the nervous system controls everything, that’s why you feel great after an adjustment.
- No, I don’t really know why that other chiropractor does the “Flying 7” on all their clients
- You’re the problem.
- No, I’m not making it hurt. It hurts already. I’m trying to fix this.
- Your attitude sucks. No wonder everything hurts.
- You’ve been coming to see me for years, but only when something hurts. The best I can do when you’re hurting is get you out of pain. Imagine if you came in when you’re not in pain—maybe we could really accomplish something then! (Oh, yeah—I do tell them this already!)
- You hate your (job/wife/kids) and you wonder why you’re having health issues?
- It’s not arthritis. Your doctor just wants you to shut up about that pain.
- Tell your doctor that I said he doesn’t know what the hell he is talking about!
- You’d be better off if you flushed all those medications down the toilet and started over.
- How’s that surgery worked out for you? What number surgery is that?
- A little bit of exercise isn’t going to kill you.
I know that makes me sound like i’m grumpy all the time, but that’s just not true. Most of my clients think that I’m just there to fix the pain, but I am freeing, directing life force-allowing it to flow freely throughout the body.
“I suffer for my art”
a client said this quote explains what I feel. I think it’s a bit harsh.
What would you say to YOUR people?
Live Long and prosper!
_Dan from http://theintuitivechiropractor.com
-
 @ c9badfea:610f861a
2025-05-30 22:47:09
@ c9badfea:610f861a
2025-05-30 22:47:09- Install Saber (it's free and open source)
- Open the app
- Tap + and select New Note
- Explore the tools in the upper toolbar:
- Tap ⬅️ to go back to the main screen
- Tap ⋮ to change the background (e.g. grid, college-ruled, lined, or custom image/PDF)
- Tap 📄 to insert a new page
- Tap 🪟 to view all pages
- Explore the tools in the bottom toolbar:
- Tap the selected pen tool ✒️ to adjust its settings (e.g. size and behavior)
- Tap ✏️ to use the pencil tool
- Tap 🖊️ to use the highlighter
- Tap ⚪️ to change the current color
- Tap 👆 to enter move mode
- Tap ⬅️ to undo, or ➡️ to redo
- Tap ⠪ to export your drawing as a PDF
- Start creating handwritten notes and drawings!
-
 @ 84b0c46a:417782f5
2025-05-30 22:17:19
@ 84b0c46a:417782f5
2025-05-30 22:17:195/24 nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzqxk47yl7vwqu0yrv4fljymp4m2vf0gtesmel4cgg638h82rt4hdn6yyejn
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs8msrjypjuvhwaarkq72739wl5rewl49vx0ku6s3u3y03anmau5dscqjj0l
nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs0fzqwr2xt044zglcwcj3dnnxuk0vlcmwcw0sdzw7yhzfsn009ttss5pv6k
こていたんさんのアイコン

5/25 nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs0ku3qs4zskmclvtqm0lt707jwn2ylz9v2xj2qakznyp86j4p7fzqd85kfq
nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs8054fh3l8qtngdfpdwxfl84r36ju3f65zmhjvjy67y7gjj0mhjks2c7w80
nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsr8nycy3gvjfdn3rqjc49j2gwhwjdhu6d5ms6uxx7y44kzf0u2ftsc8r3c3
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzpmcs4xzsusg9s6cn2acasjsam2pwmf6m8h0z08kfca56f8aqwyf2fjwv7w
nostr:nevent1qvzqqqqqqypzphu0pfjqc0lap83f8xv6e73en5zhfjzsrlx6hnk22pewugzhmpa9qqsvh305tpg0xesw6n4eu2kmumgx0mcv0cn64zznyydzpezzsazdugcyrfqm0
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzq2aq2l9cq04ygjjk4tq8zfjmuezvckcav8cfqv6z745744nfd2nqlxpq04
nostr:nevent1qvzqqqqqqypzphu0pfjqc0lap83f8xv6e73en5zhfjzsrlx6hnk22pewugzhmpa9qqs05f8xz5uahsdzceq9d0mp860hck3ash8s3ssp3paxxu620tw4ufssk6ntz
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzppyeyt0xt0fps85hxv4evdhgy35m9zfzhsqtnq93rsy4arnw3n853sc0u7
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzq7emnt7e67h5cygnyvz922x2m4f3x30hpvns3yxls2v4t2uy0vrc6060ek
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqqspu5ny2laxuqtrryffsf455fldpnluw5ladrq32cfveu6mjjgmuxsynheu3
nostr:nevent1qvzqqqqqqypzphla8l7r42mzjvdgevy0pg4y3rd8gupaprgaa7fcdzhrpaddu7lpqqsyhjuxzjkgzp5d8xt8wg8vzekcnaw6ud7htrnqppy2xmpeajrhqncs0rv4c
nostr:nevent1qvzqqqqqqypzphu0pfjqc0lap83f8xv6e73en5zhfjzsrlx6hnk22pewugzhmpa9qqswm6wxhc3h426py80vjm9jj03j8vhvrnhwmalunlxm0pq5xvxqs5qpr2kq7
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqqsgehqf8cl5sp0wfw0fzl982lvhmy9j23vpus70wddtytkr4qygxlchprwv6
nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqqsvkrvnh8lzw4rfx87278rwxp2uymej2alputzn2nl525p85c3703cmrgkfn
nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpz9mhxue69uhkuenjv4kxz7fwv9c8qqgawaehxw309aex2mrp0yhxummnw3ezuamfwfjkgmn9wshx5uqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsf2u5larth503yh236mhssn2tes4shvawnv4kufzh3889cr9dt4wculcv6w
nostr:nevent1qvzqqqqqqypzqnza2du6qe3nnjy0dcgpu0kmr7awunk78m4rtl7x78rxfvay8qlwqqspnfvau4ylywwk2f7nrm68ue6c86j9p4y0cu4parfwapun0nsw97sad9jwf
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqqs2y7lha9uy30wwdt9yn47s6krqv3e8duj6nqrl27e2s6dl465xssg5gt4ue
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqqsyf8peg4zggp858zfha6dt4mjxss4nhc3k4szqynh0u53j22asx6sdhpfwc
nostr:nevent1qvzqqqqqqypzphla8l7r42mzjvdgevy0pg4y3rd8gupaprgaa7fcdzhrpaddu7lpqqsr0s5ger5l8aapw63yyve5sne5rge0ractks4v4l0yn3ezcvq3f4s8wthq8
nostr:nevent1qvzqqqqqqypzphu0pfjqc0lap83f8xv6e73en5zhfjzsrlx6hnk22pewugzhmpa9qqs93gfz3kskw2lcxadwu3dvanyq7xstaj39vfqmppnng0nvz5gjm8syq9p8p
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzp5tlgnw663dswldulvnvgczfr08aflg35cu2syaaddmppvjytvn09tc679
nostr:nevent1qvzqqqqqqypzpe30ylfgzj39zuwyvmfdwcf26xsxdkcnv26wykwmtsrkl8nty89hqqswq489vn7h9hz2q0w60m05wn5xuqd0vvnqcxwxkewmh7h72yjtrrc6yulf2
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzqzcyhx8d350shzfczewxkhxemqknfeu5z8kj0arrur9wn726k5hjayfwl6
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqqsrnvmc5r2rs6jx7z8v3gvnzpkfsc3vqqxg0ygnk8wn3jmulzq887q07smq2
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzqzk0lg9aq8yzg0m4dcqp5a0a468c3jmtcw058hvckt6yj0nlnl0mqfgav7
nostr:nevent1qvzqqqqqqypzpu89j3vdtkj0cec9mzs4hcmetfq5a9d6fw5smezlpyqhme90uq27qqsf4js8wu9zlp74kj5erkwsq9rvhj0d6xmynevt4tsa766nsvja04gsrfaz5
nostr:nevent1qvzqqqqqqypzpu89j3vdtkj0cec9mzs4hcmetfq5a9d6fw5smezlpyqhme90uq27qqsqky2uqkzu60f3tkcttx59q675sxmd9ypyppnd50ukmhlx3qwrqfgmmxmjh
nostr:nevent1qvzqqqqqqypzq6lj6gusf8gqyqgj2s0vzjyw3fgj9ufhqdefn8fsvljn6vdjq69hqqsvtkn6rkgmttjzzm3nn58d85eve5834pnamzhy0u4p584jger8uvgttcqhe
nostr:nevent1qvzqqqqqqypzq6mwr88y02ghe0sn5elwkszn4xesreuwexg5z0n42j2npz8dvtfmqqstua4ssqq9wejs4kjvjjs0azlzjftt6qgh8l80msn2zd8k0nxw5ccnv7p2w
nostr:nevent1qvzqqqqqqypzq6lj6gusf8gqyqgj2s0vzjyw3fgj9ufhqdefn8fsvljn6vdjq69hqqsywfl8gfpxkynq54ju27aa5rqd0mjz9lx2haqzaszelm3vhlfa5mc3n0hkj
nostr:nevent1qvzqqqqqqypzq6mwr88y02ghe0sn5elwkszn4xesreuwexg5z0n42j2npz8dvtfmqqs86az8q8zd9wevcnnw6rcrg6edc3jfzff6sza572a25yywr477s9g4yfrq0
nostr:nevent1qvzqqqqqqypzprzeywf3jcmljlsq0kks66q7vh8rtvdvuvemv20z6vlegewpxfsgqqsq47mwcs7kpylrqwkyec76839nwrk09cx33s3lwdv88e34fkx4hdqf2sa8r
nostr:nevent1qvzqqqqqqypzq6mwr88y02ghe0sn5elwkszn4xesreuwexg5z0n42j2npz8dvtfmqqsxykjsdzg9nnaweajftl4g33amcdh4wjmdq3y30w6fu555e3xpm2c2n4wah
nostr:nevent1qvzqqqqqqypzprzeywf3jcmljlsq0kks66q7vh8rtvdvuvemv20z6vlegewpxfsgqqs9cgpau6l4rfmhkwav4jsjhxjwpgehyhuw3c39q46v23q75qdjfssp3jr0k
nostr:nevent1qvzqqqqqqypzq6mwr88y02ghe0sn5elwkszn4xesreuwexg5z0n42j2npz8dvtfmqqsxrzydard7yz0cp79uk30u9g7wv0nq9sfw36e7f5tefd7z7vfezvsq7kqy4
nostr:nevent1qvzqqqqqqypzpvgsp0c85zgh8rcf2683v7s058fzspcqt0em5ednf8z9c3q5qy5fqqsghpetrx0lkxd4d79vk90h66vln5pd9lklh64sk8qa75a453g20jc3j3q9y
nostr:nevent1qvzqqqqqqypzpvgsp0c85zgh8rcf2683v7s058fzspcqt0em5ednf8z9c3q5qy5fqqsxrmm05rgdzdpthuh9zmk7jf9jmhu0jfty6kf5v8s2f8252683drgf6m79g
nostr:nevent1qvzqqqqqqypzpdc866l8lkwvncdwaqlgrsueg9tvlnm5mm2mpyg3jv8aam445rpqqqswcp6exyy0f9sgpypzlc4dx40equyxeyhwskzgeks78r9rp54w7hc05v93n
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqstvk6q4xwtd7evpzggkcngqhlk5gktme0sj6235nuf0axxxngktpc88gqd7
nostr:nevent1qvzqqqqqqypzq6lj6gusf8gqyqgj2s0vzjyw3fgj9ufhqdefn8fsvljn6vdjq69hqqswfythwf02x6ekjpfdrucd6cx6su2t3uq3td45d4v0xrucfphy38cn0mmw2
nostr:nevent1qvzqqqqqqypzqu3j6ujahw4eezqm9gn2lz8av5waj9ek9fcwclfsrq5kc63zla2wqqsxpddg7lf4yqmpeg9z82flqa8fzpfcwmn4qfluvy95p03l8pjud2cfjx43u
nostr:nevent1qvzqqqqqqypzpq4np5cygstsu65vsx0ggphrv23kj4z553sh39xwyur08pqvdsqrqqsxzm8fx8aaprn533e0c44edf60lw73a6z5vzzumzd6edttgl0uawgn4kgp2
nostr:nevent1qvzqqqqqqypzpq4np5cygstsu65vsx0ggphrv23kj4z553sh39xwyur08pqvdsqrqqs88tvfyn6h8ls3h2994nmpykj2zc2l90vqwj8epzwfjnz2dy0mcjqyhsms5
nostr:nevent1qvzqqqqqqypzqt7zjsv2gxscw5l9d6k8j5agctlm6rr3rz3c6mar4eqmn69uu6c2qqsdavnxvhtlnkamt8cap09aan7mu2z364ltmeh8u747nvvj60h5jcsyf3hjz
nostr:nevent1qvzqqqqqqypzq6mwr88y02ghe0sn5elwkszn4xesreuwexg5z0n42j2npz8dvtfmqqsq86a0sr2h0p4qfesv00ztyqpdw545rsnq2nmq9quafahwxp8elhckws7wh
nostr:nevent1qvzqqqqqqypzqf4m96ldd32j6ecvsp9s6e2jv7euvc4jrcpx6mjg4jf6vpc9xz2cqqsqp3ugj5y8epkjyh62cfnm4gen27nhq055668glhgzjm87p64ep5sgqgawl
nostr:nevent1qvzqqqqqqypzqcmflwpta32zy6lsnwektdhs6ud3d3ql2mn7ml20jl0z87wr9qw6qqsfagdtz0ldem963wwelh2lc8d4qkuxlmfq0j62qwt6lrkvd8v36squ8d4k8
nostr:nevent1qvzqqqqqqypzpvj726mjcemd4uhpyutaykvsm0y54n5fzte5mhgtv46vhg8lunhfqqsgrrj849xmqpvdx6h9554gnetguxzz2ad8fqvpmvhm0zy85m4pl8swnyg5s
nostr:nevent1qvzqqqqqqypzq6lj6gusf8gqyqgj2s0vzjyw3fgj9ufhqdefn8fsvljn6vdjq69hqqs2n5mz6j5yft327mld352hazjwfrla3w92gpzuvmpgffjttsqyq6qgu5dwe
nostr:nevent1qvzqqqqqqypzq6mwr88y02ghe0sn5elwkszn4xesreuwexg5z0n42j2npz8dvtfmqqsz6wr7cnewt7t7vt4t2c28jtmppu832vs2syacv0sy8lcn28075ss277lty
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqqsdrt35drfatmhl795f36em4yy7gsaasr3xkvgmdwswr7f87rcrmuc7z7kf8
nostr:nevent1qvzqqqqqqypzpvj726mjcemd4uhpyutaykvsm0y54n5fzte5mhgtv46vhg8lunhfqqsrl6c8gu74vkwa5ahlsycxjx40a3gzrx6uxm0qmpa35nrnd7ntysc4d6llh
nostr:nevent1qvzqqqqqqypzqwyu5j2hjyd3ycyn7s4q4yrcv52mtyc3m3dfg26qf4lpdutjs7pgqqsq945chuafedqk95uglwl3xumcuvjcdgz66ykd840hfsa4xpp6dgqa9vsft
nostr:nevent1qvzqqqqqqypzqf4m96ldd32j6ecvsp9s6e2jv7euvc4jrcpx6mjg4jf6vpc9xz2cqqsynxwgyy8nsu2r3dx8f37hww6keemkhh962ghq45umlxz2khemytgzv08n4
nostr:nevent1qvzqqqqqqypzqyrx5pw3ga88uye6jusg5h93w75uq8jts8c0zsms44vlfg9yw45pqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqqsdex6xy8kq8l64c0gq606yguaqn8fxrsyl67m6ld5cctxxwe79jpcsmxhh6
nostr:nevent1qvzqqqqqqypzpj7tpc9kqtkr4xklc62kh7lru27pydu7uyals5zuu303eqca9ef2qyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpq7gkdqqukguh3r79yfxcy9tsxpx348wqys6q8v3njfyqj4vga727sh9cfpt
5/26 nostr:nevent1qvzqqqqqqypzpq4np5cygstsu65vsx0ggphrv23kj4z553sh39xwyur08pqvdsqrqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqqspk6e9e9wph23lt7xumuuu90rayzcswp3gz96c3w25raq9r9agw5cnfgve5
nostr:nevent1qvzqqqqqqypzpp9sc34tdxdvxh4jeg5xgu9ctcypmvsg0n00vwfjydkrjaqh0qh4qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqqsfnspcp9yqu989mnnpwj9tphrrj05268vjkwwmx7jcus4mn7erqngl94f9y
nostr:nevent1qvzqqqqqqypzpp9sc34tdxdvxh4jeg5xgu9ctcypmvsg0n00vwfjydkrjaqh0qh4qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqqs84x0ws9myccv29kf99jkuwqh8rj9ws23kn5s9yyl0scz67m97z2g7rq7z5
nostr:nevent1qvzqqqqqqypzphu0pfjqc0lap83f8xv6e73en5zhfjzsrlx6hnk22pewugzhmpa9qyg8wumn8ghj7mn0wd68ytnhd9hx2qgkwaehxw309aek2ctjvd5zumn0wvh8gmmyv9usz9nhwden5te0wfjkccte9ehx7um5wghxyctwvsqzqk76agahvd3t5lutvkuj69pccwrurey3fws0kjnrsemwlx9ntvwukkjfk6
nostr:nevent1qvzqqqqqqypzqrqykrtju88xhdq0an0vdnccdfvrmqr8da0n8p5fs8reaczhxmpeqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyz3twtpw08v554hph0j6wpk598rd677pfa460y2pcdd2064aaevjwe74erq
nostr:nevent1qvzqqqqqqypzqx34k480waf274x2e0hd7re5nceq7z3wu5q59zp3xnp7uvv8nnn3qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyp59rw9n380w5kvdth9qefc28xsrt99l33tmfgvq02kut3dnepk6zr7ng2t
nostr:nevent1qvzqqqqqqypzplnr7nuypscwtkhtmqaakpyw4cqgtqm5klcyc6qqcmzf6296zrcfqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyq8q2qcfne76j4c9y794xz9g5unuxhf98deh3mupmnwpn33mwlxhzmxuefq
nostr:nevent1qvzqqqqqqypzpmzzcaj5rzeah8y940ln4z855wa72af4a6aac4zjypql55egcpsqqyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpqscswkz2s03r6yhz0yz40h634nkf2j2vpkvqd3vk5rl7lgaj9unns7qz3ms
nostr:nevent1qvzqqqqqqypzprfe5ru6zvakym6hq5eycwdr2vx2q8awzaaw8wu9mq4wlek8yhenqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyqr5njtg8f5xdm52p3k9mugfqk3zuc0ycsxaj6j5uf4amkrdt3ymq8kuyhj
nostr:nevent1qvzqqqqqqypzq0363fpyt2sgytq9p3pduzch6rlrp4z8e6swvzr72km83pg76qmnqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyrj0xgrrwr2meuurst5lsqn744wt6uxhfmyralknm7cl57lsapcrkunqcnn
nostr:nevent1qvzqqqqqqypzqf57dat64x3qpjq5u6ucwgvpnh0q8r9xpspepwrmvkxnqz4k6rgyqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyq2yn3cjlmns8ttaam8ev2rn3csm26wnwhe3ccvk8s5e8x6ejyykql8em9d
nostr:nevent1qvzqqqqqqypzqx34k480waf274x2e0hd7re5nceq7z3wu5q59zp3xnp7uvv8nnn3qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqyqu2p8vtuwvxmzqh7mlq2lp3xel8z9l0xg5e3hyxjlwamsm0p3pvq9qh4d0
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsr9tpqqfeke4qt9xlg6m34446dpd844myrw9cc4tmqcrf3xfp9yqsxa05hf
nostr:nevent1qvzqqqqqqypzpp9sc34tdxdvxh4jeg5xgu9ctcypmvsg0n00vwfjydkrjaqh0qh4qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmnv4shycmg9ehx7ueww3hkgcteqyt8wumn8ghj7un9d3shjtnwdaehgu3wvfskueqqypyaj8uyahtgwf5evyk5deqx90udyrmxff99gqskfcl3eqh0mgmw6nlnlud
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsdpy08r0758lz0js2zpk5fe5mpqxd349mdqxg2vk3y7azlme2ysqqm8uy75
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs8s0r7c908mmhxk090zvmlajfgswwcnmwxj34dtqjpyxry0tmumagcmm29s
nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs0x6pgm96r70y8836l0d5ajj6nrlq6p5fz06wdu26fkpg3gznctscf5ggxn
5/27 nostr:nevent1qvzqqqqqqypzqxlwemj4760tc2ysgqmqdu5tt68th2er6gn8xrsjkjlhvtff6gtzqyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpqlq0lp52xg7uv4wwzuqy9yhtmcpy5v8ad8v7ft9xcwkdncd97h66q0wmawu
nostr:nevent1qvzqqqqqqypzpq4np5cygstsu65vsx0ggphrv23kj4z553sh39xwyur08pqvdsqrqyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpqpt2wncdxkptxyhj025vd53vjpxz3hjs452px7y8g6gzsxmnfw2fsp2rv0k
KAZもさん nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsq3wamnwvaz7tmwdaehgu3wd968gctwd4hjumt9dcqs6amnwvaz7tmev9382tndv5qjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzpk3nll8rr3sj6adsrfrlgjpj4cyn2sg9rmlz9m2djwk5zp2ku80czfr460
5/28 kaijiさん nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7mn0wd68ytnrdakhq6tvv5kk2unjdaezumn9wsqjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3zamnwvaz7tmwveex2mrp0yhxzursqythwumn8ghj7mn0wd68ytnfw36xzmndduhx6etwqyfhwumn8ghj7am0wshxummnw3ezumn9wsqzpt7w33qv7tlywj0wphremkdft6dpnv3z8mvw0t2pdxcgvlzw6sathjmz0v
マルフォイ nostr:nevent1qvzqqqqqqypzpvly86xv0ekl7gar8kfp8glfztvftvwrusjsys8qexwmal3sdz6lqyw8wumn8ghj7umjw3ex2mrp0yhxxttnw3jkcmrpwghxuet5qyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqs8r0frcfwqkgpefhd0knjurekna8ztnq69432f3k00wccd0vcrl5c6qr3gh
5/29 nostr:nevent1qvzqqqqqqypzqrec47eremps2u8wvnu6f2sfjg5njhkrxuw9l6r8uzwfzy2gqq2aqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqq3vamnwvaz7tmjv4kxz7fwdehhxarj9e3xzmnyqqsp2c6xh22lfj2ccy95lqu584hfpfz0ds7w2llnf4sv2qs445yqcgqmgwq57
nostr:nevent1qvzqqqqqqypzphu0pfjqc0lap83f8xv6e73en5zhfjzsrlx6hnk22pewugzhmpa9qyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpqt43r3wtjkr5ezxay6dh7jq94nelduvsk07w5ufxrver5f6jfggksakz9e8
nostr:nevent1qvzqqqqqqypzqyqmxrhg3sn6z00x30mu3srrdr4ru05rweq4jhqcvat805v2g6j9qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqqjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qzymhwden5te0wahhgtnwdaehgu3wdejhgqpqn6n7xrrmk40ucmh9m5ktae58xjqz6h7epj6mcffpcmuhgpysvv6snh5vf5
nostr:nevent1qvzqqqqqqypzpk28l9nyyf4av8f8j8jhh8k60mt2sc643ux2td3n547kvk4lrsglqyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpq6gv8avhe93ypvypd66rmn34760s3sldj3x2cz5w4yu2xy9z8tt2qadd7kl
nostr:nevent1qvzqqqqqqypzpk28l9nyyf4av8f8j8jhh8k60mt2sc643ux2td3n547kvk4lrsglqyt8wumn8ghj7um9v9exx6pwdehhxtn5dajxz7gpzemhxue69uhhyetvv9ujumn0wd68ytnzv9hxgqpqn2pfqkgcfk3cdhtvkqqlfycsy2j2xe6c6jz8gzfxlnddnq8jq6vqecuvwy
nostr:nevent1qvzqqqqqqypzpug7j8zm7jr0hjunpkpgz8gzdvgn5h8mw77g4wg58xnmsav6pvz2qqspds662qvcpz995r5rx39wzncyzcx3q5zfpe8ztgx4zdwy9znvu9cv28mya
5/30 nostr:nevent1qvzqqqqqqypzp54kkqfyshkxm078mpzygmfxpqfq6fwu2njry424strce6dmvhwyqqstc5jak2vax4uejyrmu2td3w0spv6k4mds9sfwqtvmh0hwaa3eststwmtzt
nostr:nevent1qvzqqqqqqypzp54kkqfyshkxm078mpzygmfxpqfq6fwu2njry424strce6dmvhwyqqs9v75spmgrxngfn805q5d9fsqa562a8240xkr6z3kvkszkra9plvsgm2qw4
nostr:nevent1qvzqqqqqqypzp62ezs5gz04adyt8xmyghw2ej3yk7eradlnknmuysd5ha2udqnfdqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqqjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqswy0smsrukck33hfhavscvs68pg9m4d859np8pkgvrc49kwjzr4ac0cwhea
nostr:nevent1qvzqqqqqqypzpc9ge0t4a0lya7a63fjl749mgdv9ssz0dhqt5jnytz3y6lmy9525qyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqqjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpz4mhxue69uhhyetvv9ujumt0wd68ytnsw43qzymhwden5te0wahhgtnwdaehgu3wdejhgqpqeunx8pj5hc255wqu4ea9cgz6cptjvcx6jk8yfd8u55smjl6y8z9sepz5xt
nostr:nevent1qvzqqqqqqypzp62ezs5gz04adyt8xmyghw2ej3yk7eradlnknmuysd5ha2udqnfdqyxhwumn8ghj77tpvf6jumt9qywhwumn8ghj7un9d3shjtnwdaehgu3wwa5hyetydejhgtn2wqqjqamnwvaz7tmjv4kxz7fddfczumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqst07pk8637lvs5vjnp00quzhcsx8ghran90nsm6sycnm3a626lnqqw0py8w
nostr:nevent1qvzqqqqqqypzp62ezs5gz04adyt8xmyghw2ej3yk7eradlnknmuysd5ha2udqnfdqyxhwumn8ghj77tpvf6jumt9qyw8wumn8ghj7umjw3ex2mrp0yhxxttnw3jkcmrpwghxuet5qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsya6zp38496uetw83txlr294nttk6myuc0n7hxrl2d7jma2rvvcesnz2naf
nostr:nevent1qvzqqqqqqypzqlwpvac39uz74ay4g7qx2sa3cqrvuvjhy7899vwf40lkxfcw6uz0qyxhwumn8ghj77tpvf6jumt9qyghwumn8ghj7mnxwfjkccte9eshquqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsz6zj33hmynuhq20nscntjc3lhx4hl5azhf0cx38g5nmhpjezuttqpdr0ht
nostr:nevent1qvzqqqqqqypzqhh27290rxjexusv8as357lpxy423nnznzfh4fjkq22k94tvqcpaqyxhwumn8ghj77tpvf6jumt9qyghwumn8ghj7u3wddhk56tjvyhxjmcqyrfpj9ym2apvgjpmcy4qjq2ks89uzuwm27d9jpj9flk7438sm23kqjetapu
nostr:nevent1qvzqqqqqqypzpuy2jdcyy3vqr4l9ucmhlpuwnsl29h7lwsvaez00eu4467jlvf7eqythwumn8ghj7mn0wd68ytnfw36xzmndduhx6etwqyxhwumn8ghj77tpvf6jumt9qys8wumn8ghj7un9d3shjtt2wqhxummnw3ezuamfwfjkgmn9wshx5uqpr4mhxue69uhhyetvv9ujumn0wd68ytnhd9ex2erwv46zu6nsqyghwumn8ghj7mnxwfjkccte9eshquqpzdmhxue69uhhwmm59ehx7um5wghxuet5qqsphe28h7t6jmwlvpd90q38xkde87hmy9q24u90sgeaz6hu6nfsazqxkfw56
-
 @ bf47c19e:c3d2573b
2025-05-30 21:48:21
@ bf47c19e:c3d2573b
2025-05-30 21:48:21Originalni tekst na novimagazin.rs. / Autor: Mijat Lakićević

Razgovarao: Mijat Lakićević
Do januara ove godine Lazar Stojković je radio na UC Berkeley School of Information na poziciji asistenta Mortena Hansena, jednog od najistaknutijih profesora menadžmenta u svetu. U martu se, međutim, odlučuje da napusti akademsku karijeru i zauzima poziciju glavnog dizajnera proizvoda u jednom novom start-apu u San Francisku. Ono što za sada o tome može da kaže jeste da je okupljen “fantastičan tim” (o čemu, recimo, govori podatak da je “prethodna kompanija koju je osnovao naš CEO 2013. godine prodata za preko 200 miliona dolara”) u koji su investirale neke od najznačajnijih američkih “venture capital” firmi: Founder Collective (investirali u Uber, BuzzFeed, Periscope, IFTTT, Venmo, Vimeo, itd), General Catalyst (investirali u Airbnb, Snapchat, itd.); Formation 8 (investirali u Oculus). Pored toga, međutim, naš sagovornik nije izgubio sve veze sa Srbijom, naprotiv; trenutno kao mentor u beogradskom ICT Habu, ali i na druge načine, pomaže razvoj start-ap kompanija i povezivanje naše tehnološke zajednice sa Silicijumskom dolinom.
U SAD ima mnogo naših ljudi, naročito u oblasti visokih tehnologija, ali povratne sprege nema. Dačić je pre dve godine bio u SAD na investicionoj konferenciji, kakvi su efekti?
Efekti su svakako dobri za Dačića i pripadnike državne delegacije koja je turistički obišla Zapadnu obalu. Ni Majkrosoft nije loše prošao, jer mu je tadašnji predsednik Vlade usput ostavio još novca srpskih poreskih obveznika. Sve u svemu, ceo taj put mogao bi da se okvalifikuje više kao “shopping trip” za trošenje novca, nego kao investiciona konferencija za njegovo privlačenje. Osim toga, sam događaj u San Francisku bio je amaterski organizovan – niti je imao bilo kakav publicitet u lokalnim medijima, niti je postojala vidljivost u ovdašnjoj tehnološkoj zajednici.
Veću korist od toga donela je majska poseta mojih prijatelja iz 500 Start-ups, drugog najboljeg start-ap akceleratora u svetu, zvezdarskom ICT Habu. Osim predavanja koje su održali start-apima u Beogradu i Novom Sadu, njih trojica su tom prilikom odlučili da 500 Start-ups investira u TruckTrack Vuka Nikolića. Kasnije se jedan od njih odlučio i da kupi stan u Beogradu, jer se potpuno zaljubio u atmosferu srpske prestonice. To su direktne strane investicije, a ne politički marketing.
Što se povratne sprege između tehnološke dijaspore i Srbije tiče, ne bih se složio da ona uopšte ne postoji, ona je samo u skladu sa opštim privrednim okruženjem u zemlji.
Kakva je na osnovu vašeg iskustva ta poslovna klima?
Poslovnu klimu u Srbiji karakterišu: neefikasnost javne uprave i gomila nepotrebne birokratije; arhaičan sistem obrazovanja, uglavnom neprilagođen potrebama tržišta, koji ne proizvodi dovoljno kvalifikovane radne snage; sporost sudova i proizvoljno tumačenje čak i onih relativno savremenih zakona. Uvek se setim onih momaka koji su završili u zatvoru zbog affiliate sajta i dečka kome je tržišni inspektor uručio pozamašnu kaznu za obavljanje delatnosti za koju nije registrovan zbog 10 evra koje je dotični zaradio za godinu dana od specijalizovanog bloga o parfemima. Ako postoji nerazumevanje za bilo kakvo tehnološko preduzetništvo, čak i na tom najnižem nivou, šta onda reći za ozbiljnije poslove?
Kad ste već pomenuli visoke tehnologije, u Srbiji se mnogo govori da je to naša šansa, primer koji ste pomenuli to demantuje.
I ne samo to. U Srbiji nema propisa koji bi potpomogli dalji razvoj tehnološke industrije. Na primer, Srbija još uvek nema pravni ekvivalent “safe harbor” stavki iz američkog Digital milenijum kopirajt akta (Digital Millenium Copyright Act – DMCA), koji je na snazi još od 1998. godine, a predstavlja zakonski mehanizam zaštite za kreatore digitalnih proizvoda od pokušaja drugih da zloupotrebe njihove mobilne aplikacije.
Sa druge strane, ima mnogo propisa koji sprečavaju bilo kakav napredak u određenim oblastima, u čemu ubedljivo prednjači Narodna banka Srbije. Moj omiljeni primer čak nije ni ceo onaj višegodišnji cirkus sa PayPalom koji je nastao zbog zakona o deviznom poslovanju, već zabrana NBS da domaća pravna lica imaju bilo kakve veze sa bitkoinom. Čisto da stavimo stvari u perspektivu, dotična tehnološka inovacija koju po značaju mnogi ovde upoređuju sa World Wide Webom, počinje polako da menja kompletan dosadašnji finansijski sistem i, sa investicijama od blizu 360 miliona dolara, samo od početka ove godine predstavlja ubedljivo najbrže rastuću tehnološku oblast u svetu kada je reč o investiranje u start-apove. Naravno, od toga ni dinar neće završiti u Srbiji.
Posledice?
Nerazumevanje da u današnjem globalizovanom svetu niko ko se bavi tehnologijom jednostavno ne mora da trpi sve ovo gore pobrojano. Zahvaljujući poslovanju koje nije vezano za fizičku lokaciju, svako ima slobodu da bilo kada želi izmesti svoj biznis gde god poželi, a sa njim i kompletne poreske i druge prihode za zemlju u kojoj je biznis registrovan. I ljudi to i rade. Čim se pojave bilo kakvi prihodi, gotovo svi koji imaju veze sa tehnologijom – od frilensera do preduzetnika – Srbiji se zahvale na saradnji, zatvore firmu tu i otvore preko Interneta kompaniju u Delaveru, Singapuru ili negde drugde, jer im jednostavno ne pada na pamet da finansiraju postojeći sistem u Srbiji. Ubrzo nakon što se biznis izmesti iz Srbije, dobar deo shvati da ni oni ne moraju baš da budu tu, nakon čega sledi emigracija.
Najalarmantnija stvar u vezi sa ovim poslednjim je što se uopšte ne radi o običnim inženjerima, koji ionako odlaze u ogromnom broju već skoro 25 godina i čija svaka kupljena karta u jednom pravcu, bar u slučaju IT stručnjaka, Srbiju košta između 50 i 100 hiljada evra, jer je to cena njihovog obrazovanja. Ne, ovde je reč o preduzetnicima koji pokreću nove poslove, stvaraju vrednost, otvaraju nova radna mesta. A svako radno mesto u tehnološkoj industriji u proseku kreira još 4,3 druga radna mesta u privredi, dok, na primer, svako radno mesto u proizvodnji kreira samo 1,4 druga mesta. Njihov egzodus – koji se, bar sudeći po krugu ljudi koje poznajem, samo ubrzava poslednjih godina – ne samo da dugoročno znači ogroman finansijski gubitak za zemlju, već predstavlja i svojevrsnu nacionalnu katastrofu.
Dakle, povratne sprege nema, jer se oni ne vraćaju u Srbiju?
Zbog svih ovih stvari o kojima sam govorio retko kome ko je iole profesionalno ostvaren u inostranstvu uopšte pada na pamet da se vraća i pokreće bilo kakav biznis iz Srbije. Umesto toga, ljudi se odlučuju za nešto drugo: osnivaju kompanije tamo gde je poslovna klima dobra, što znači ne u Srbiji, a onda Srbiju koriste kao neku vrstu domaće autsorsing destinacije. Odnos cena-kvalitet tu je zaista odličan. Na primer, za godišnju platu jednog dobrog softverskog inženjera u San Francisku, u Beogradu se može zaposliti ceo tim.
Naravno, američke kompanije koje su osnovali naši ljudi koriste to kao “tajno oružje”, pa se tako, na primer, ceo razvojni tim veoma uspešnog start-apa Frejm iz Silicijumske doline nalazi u Nišu, jer je odatle njegov osnivač Nikola Božinović, koji inače već gotovo 20 godina živi u Americi. Takvih primera ima mnogo. Poznajem nekolicinu ljudi koji su potrošili bukvalno milione dolara na autsorsing u Srbiji tokom poslednjih desetak godina. Oni bi vrlo rado investirali u srpske start-apove, i ne samo oni, ali je ponuda još uvek jako tanka, poslovna klima nikome ne uliva poverenje, a start-ap ekosistem je u ranoj fazi razvoja, pa do tih transakcija još uvek ne dolazi u nekom značajnijem broju.
Start-ap eko sistem. Šta pod tim podrazumevate?
To znači, prvo, konačan prestanak maštanja o reindustrijalizaciji koju će doneti neki krupni investitori iz inostranstva. Oni se ionako, bar u novijoj istoriji Srbije, nikada nisu pojavljivali bez debelih subvencija i ekspresnog proglašavanja njihovih ugovora državnom tajnom. Drugo, to znači prepoznavanje resursa kojima raspolažemo, dakle pametnih mladih ljudi koji se bave tehnologijom, s jedne strane, i pružanje tim ljudima najboljih uslova za život i rad, sa druge, umesto da im se i jedno i drugo na svakom koraku otežava.
Na primer, šta bi se desilo kada bismo u Novom Sadu umesto brojnih postojećih firmi koje se bave autsorsing uslugama imali stotinjak kompanija fokusiranih na proizvode kao što je Eipix? Odgovor: imali bismo oko 15.000 novih radnih mesta, veoma bogatu prestonicu Pokrajine, visok rast životnog standarda u tom delu zemlje i mnogo naplaćenog poreza.
Ta prilika neće trajati večito. Procenat mladih preduzetnika kojima je jedini cilj da odu iz zemlje, jer u njoj ne vide nikakvu perspektivu, iz godine u godinu raste. Strani investicioni fondovi bukvalno otimaju najperspektivnije nove srpske start-apove. Na primer, bugarski Eleven raspolaže sa desetak miliona evra kapitala, mahom iz evropskih fondova. U okruženju koje im ne nudi baš ništa osim problema, tridesetak najzanimljivijih srpskih start-apova prodalo je svoje vlasničke udele Elevenu uz obavezu preseljenja u Sofiju, ruku na srce, uglavnom privremenog. Ko zna koliko će novih kompanija, koje bi mogle da budu novi Nordeusi, Srbija zbog toga izgubiti u korist svog istočnog suseda?
I vi spadate u grupu mladih ljudi koje opisujete. Opisali ste i razloge zbog kojih se odlazi. Ipak, konkretno, zašto ste vi otišli iz Srbije?
Kao što ste rekli, otišao sam iz svih onih na početku ovog razgovora navedenih razloga, plus opšta društvena klima koja je, nažalost, izuzetno nezdrava. Iako ima solidan potencijal da bude lepo mesto za život i posao, zemlja u kojoj sam rođen postala je udžbenički primer negativne društvene selekcije i jednostavno nije zemlja u kojoj želim da živim i u kojoj bih jednog dana trebalo da odgajam svoju decu.
Šta ste pronašli u Americi?
U Zalivskoj oblasti San Franciska pronašao sam jedno napredno, stimulativno, kosmopolitsko okruženje, zagledano u budućnost. To je neki jedinstveni koktel globalizacije, hakerskog idealizma, hipi etike, mešavine vrednosti koje kreira tehnološka industrija sa starim kapitalizmom Zapadne obale, umetničke ekscentričnosti San Franciska, tipično kalifornijske opuštenosti i vere u to da ovde svojim znanjem svet možemo da učinimo boljim mestom. Osim toga, Zalivska oblast, tj. Silicijumska dolina, ima ubedljivo najveću koncentraciju pametnih ljudi na jednom mestu u celom svetu.
Filozofija razvoja u SAD, u poređenju sa Srbijom, ako to uopšte ima smisla?
Poređenje nema previše smisla, jer su filozofije poslovanja i poslovna klima dijametralno suprotni između ove dve zemlje. Biznis je u Americi nacionalni sport broj jedan. Čak i ljudi koji rade relativno slabo plaćene poslove, trude se da imaju svoj mali investicioni portfelj hartija od vrednosti i svi prate kretanje cene akcija na berzi. Kada govorimo o preduzetništvu, kapital je dostupan za bilo koju dobru ideju. Start-apovi se ne fokusiraju toliko na profit na kraće staze, već teže brzom rastu. Tako nije ništa neobično da investitori u neki neprofitabilni biznis investiraju i po stotinjak miliona dolara. A desi se i, recimo, čak 1,2 milijarde kao u slučaju Snapchata, iako ta firma do sada nije napravila nijedan cent prihoda, jer znaju da će novac sam po sebi kasnije doći ako se napravi proizvod koji ima vrednost za veliki broj ljudi.
U Srbiji ništa od gore nabrojanog nije slučaj. Korporativizacija praktično ne postoji, što je posledica skandalozno visokih troškova osnivanja i vođenja akcionarskog preduzeća kao forme privrednog društva. Poređenja radi, u Americi osnivanje korporacije košta 150-300 dolara, završava se brzo preko Interneta, ne postoje tekući troškovi ako nema prihoda i zato maltene svi imaju registrovanu neku firmu. Pošto su korporacije u Srbiji za domaće privrednike skupa egzotika, većina ekonomske aktivnosti ide kroz preduzetnike – “sole proprietorship” – i društva sa ograničenom odgovornošću. Posledica toga je da je Beogradska berza danas potpuno irelevantan faktor, tako da je i interesovanje građana za investiranje tim putem praktično nepostojeće. To dalje vodi ka tome da se imućniji ljudi uglavnom odlučuju za investiranje u nekretnine, što je jedan od najkonzervativnijih pristupa investicijama i donosi najmanju dobit. Što se pokretanja novog posla tiče, u Srbiji to u većini slučajeva znači pozajmljivanje novca od PRP – porodica, rodbina i prijatelji – ili odlazak u banku po kredit. “Venture capital” ne postoji, što srpske firme onda stavlja pred izazov da moraju što pre da budu profitabilne, jer jednom kada početni kapital nestane – “game over”. Niko ne razmišlja o agresivnom rastu koji se kasnije može pretvoriti u masivne prihode i tržišnu dominaciju, jer su fokusirani na to kako da plate PDV sledećeg meseca za prodatu robu ili usluge koje još uvek nisu ni naplatili. Zbog toga svi otvaraju pekare, kafiće i kioske brze hrane: promet kreće odmah i “cash flow” se brzo stabilizuje. Zbog svega toga Srbija ima primitivnu ekonomiju koja je u proseku oko pola veka iza razvijenog sveta.
Predlagali ste pre dve godine da se Srbija orijentiše ka razvoju robotike, civilnih bespilotnih letelica i 3D štampe. Niko vas nije čuo. Šta se desilo u međuvremenu u tim sferama, da li je sad kasno za to, šta su nove prilike, ako ih ima?
Sva tri i dalje stoje kao ogromne prilike za razvoj, jer će potražnja u srednjem roku biti toliko veća od ponude da je i dalje u pitanju fantastična biznis prilika. Druge dve nove prilike su Bitcoin i Virtual Reality.
Bitcoin i kriptovalute – koje, kao što rekoh na početku, nijedno pravno lice u Srbiji ne sme ni da takne, zahvaljujući uobičajenoj kratkovidosti Narodne banke Srbije. Blockchain kao “open source” projekat već obećava da postane osnova svih finansijskih transakcija u budućnosti, i ne samo njih, a već sada počinje polako da ubija praistorijske biznise koji se oslanjaju na skupe informacione transakcije, kao što je na primer Vestern union.
Virtual Reality je drugi veliki talas tehnološke inovacije koji nama kao čovečanstvu, nakon tridesetak godina iščekivanja i razočaranja, konačno stiže zahvaljujući tehnologijama kao što su Oculus, u vlasništvu Facebooka; Magic Leap, glavni investitor Gugl; HoloLens, Majkrosoftovo čedo, pa čak i Cardboard, Guglov genijalni projekat za upotrebu pametnih telefona kao VR naočara. Ovaj mega trend će dugoročno potpuno promeniti gotovo celokupnu ljudsku interakciju sa mašinama, od toga kako radimo do toga kako se zabavljamo u slobodno vreme. Rekao bih da su startne pozicije što se platformi tiče već zauzete – bar za prvo vreme, jer su pomenute korporacije potrošile milijarde dolara na istraživanje i razvoj tih tehnologija – ali postoji ogroman prazan prostor što se tiče kreiranja sadržaja za njih. Narednih godina će se na tome praviti imperije.
-
 @ c9badfea:610f861a
2025-05-30 21:42:40
@ c9badfea:610f861a
2025-05-30 21:42:40Separators
- ▰▱▰▱▰▱▰▱
- ░░▒▒▓▓██▓▓▒▒░░
- ▁▃▅▇▅▃▅▇▅▃▁
- ◇◆◇◆◇◆◇
- ◥◤◢◣◥◤◢◣
- ▪▫▪▫▪▫▪▫▪▫▪▫▪▫▪▫
- ▮▯▮▯▮▯▮▯▮▯▮▯▮▯▮▯
Nametags
- ⚞Name⚟
- ⫍Name⫎
- 〚Name〛
- 〘Name〙
- 〖Name〗
- 〔Name〕
- 【Name】
- 《Name》
- 「Name」
- 〈Name〉
- ⦗Name⦘
- ⦇Name⦈
- ⦍Name⦐
- ⦋Name⦌
- ⦅Name⦆
- ⟬Name⟭
- ❨Name❩
Checklists
- ◇ Item
- ◆ Item
- ◈ Item
- ☐ Item
- ☑ Item
- ☒ Item
- ▢ Item
Bulletpoints
- •
- ∙
- ☛
- ☞
- ❧
- ⦾
- ⦿
- ◦
- ⊳
- ►
- ▸
- ▹
-
 @ bf47c19e:c3d2573b
2025-05-30 20:58:03
@ bf47c19e:c3d2573b
2025-05-30 20:58:03Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Šta je blockchain?
- Kako mogu da saznam više o Bitcoin-u?
Ukoliko niste pročitali naš uvodni tekst o Bitcoin-u, i zašto vam je važno da to učinite, onda prvo pročitajte: Šta je Bitcoin i kako on može da nam pomogne?
Bitcoin, sa velikim B na početku, odnosi se na mrežu računara koji održavaju knjigu stanja na akauntima bitcoin digitalne valute, slično kao što banke održavaju knjigu stanja na računima dolara, eura ili neke druge valute. Bitcoin softver, odnosno protokol, takođe omogućava korisnicima da putem interneta pošalju bitcoin-e sa svog akaunta na drugi akaunt, slično PayPal-u ili Venmo-u, ali bez kompanije koja pruža uslugu prenosa. Bitcoin softver je otvorenog koda, tako da svako može da ga pokrene na svom računaru i da se pridružiti mreži.
Najbolji način da se razume kako Bitcoin funkcioniše “iznutra” je da ga zamislimo kao finansijski sistem.
Centralne banke i vlade proizvode i distribuiraju novac pozajmljujući ga ljudima, i trošeći ga na oružje, puteve i socijalne programe. Ovaj sistem se naziva sistemom zasnovanom na dugovima, jer svaki put kada banka da zajam, stvara se nova valuta koja ranije nije postojala. Ova valuta ima vrednost jer dug koji ju je stvorio ima vrednost: primalac zajma obećava da će otplatiti svoj dug banci, plus kamate.
Kad god banka odobri kredit, ona stvara novu valutu. Ovo takodje važi i kada podignete hipoteku ili kredit za auto. Takođe se primenjuje i kada Američke Federalne Rezerve kupuju državne obveznice od vlade Sjedinjenih Država. U svakom od ovih slučajeva, banka šalje novonastalu valutu primaocu zajma. Primaoc zajma obećava banci da će u budućnosti vratiti tu valutu, plus kamate. Međutim, ulaz nove valute u sistem znači i da opada vrednost postojeće valute koja je u opticaju. To se dešava kroz proces koji se obično naziva inflacija.
Da bi imali koristi od pogodnih usluga koje nude banke, poput kreditnih kartica i digitalnih transfera novca, normalni ljudi i preduzeća obično novac drže na bankovnim računima. Svaka banka poseduje svoju knjigu sa računima svih svojih klijenata.
Banke su neophodne da bi omogućile digitalna plaćanja koja vršimo svakodnevno, jer su nam potrebne pouzdane strane koje bi proverile da li se sav računovodstveni sistem sabira. U suprotnom, bilo bi lako da neko uradi “copy-paste“ jednog dela digitalnog novca i da ga potroši dva puta, ili da doda par nula na stanje svog računa.
Sada razumemo nekoliko ključnih tačaka o trenutnom sistemu zasnovanom na dugu: banke proizvode novu valutu svaki put kad pozajmljuju novac, a većina ljudi svoj novac čuva u bankama koje im nude pogodnosti.
Bitcoin je malo drugačiji. Hajde da započnemo ovo putovanje sa pitanjem.
Šta ako bi svi posedovali knjigu stanja na računima, baš kao i banka?
Umesto da banke poseduju po jednu knjigu depozita svojih klijenata, šta ako svi poseduju istu knjigu, sa detaljnim opisima svih stanja na računima svih učesnika u ekonomiji? O privatnosti ne morate da brinete ni na trenutak – to ćemo objasniti kasnije.
Hajde da vidimo kako bi transakcija mogla da se izvrši koristeći ovakav bankarski sistem. Recimo da Ana želi da plati Davidu 10 digitalnih „novčića“. Ona tu transakciju zapisuje u e-mail, potpisuje je digitalno kako bi svi bili sigurni da e-mail dolazi od stvarne Ane, i šalje ga svima ostalima. Kada ostali prime taj e-mail, oni ažuriraju svoje knjige, tako što skinu 10 novčića sa Aninog računa i dodaju 10 novčića na Davidov račun.
Zašto bi se neko trudio da evidentira transakciju u svojoj knjizi?
Recimo da će prva osoba koja izvrši sledeće korake dobiti 5 novčića:
- Proverom da li je prava Ana potpisala transakciju
- Proverom da li Ana ima dovoljno sredstava na svom računu da plati Davidu 10 novčića
- Zapisivanje transakcije ukoliko ispunjava uslove 1) i 2)
Primetićete da se ovo mnogo razlikuje od trenutnog monetarnog sistema. U novom sistemu morate da imate novčiće da biste mogli da ih date nekom drugom. Ne postoje banke sa posebnim privilegijama koje mogu da stvore valutu davanjem zajma.
Umesto da dozvoljava samo maloj grupi bankara da prave nove valute, novi sistem omogućava svima da kreiraju novu valutu ako pružaju korisnu uslugu mreži: verifikovanje i evidentiranje transakcija između ljudi. Nazvaćemo ovo nagradom za potvrđivanje.
Kako se svi slože oko pravila sistema? Ona su kodirana u softverskom protokolu otvorenog koda. To znači da svako može besplatno da preuzme pravila sistema sa interneta i da počne da ih koristi za zaradu valute u sistemu. Ako svi koriste isti skup pravila, njihove knjige će se sinhronizovati, jer će prihvatiti i odbiti potpuno iste transakcije.
- Otvoreni kod = svako može da preuzme kod i da ga pročita
- Softverski protokol = skup pravila napisanih u kodu
Kako zaustaviti ljude koji pokušavaju da prevare sistem da bi zaradili “nagradu za potvrdu”?
Recimo da Boris i Marko žele da se obogate – oni bi mogli jedan drugom da plaćaju po jedan novčić u krug, vodeći računa da neko od njih prvi zabeleži transakciju kako bi mogli da zahtevaju nagradu za potvrdu. Pomoću ove šeme oni bi u osnovi mogli da stvore (odštampaju) novu valutu, kad god oni to požele!
Softverski protokol to zaustavlja zahtevajući da osoba koja validira transakciju uradi neki „posao“ sa računarom kako bi je zabeležila. Ovo osigurava da računari moraju da troše energiju za zabeležavanje transakcija, pa bi u tom slučaju varanje sistema bilo veoma skupo. Borisova i Markova šema varanja sistema više nema finansijskog smisla. Da bismo demonstrirali ovaj proces, pogledajmo Filipa i njegov C-Bot računar. Filip je na svoj računar instalirao Bitcoin protokol, koji predstavlja Bitcoin-ov softverski protokol otvorenog koda koji sadrži pravila Bitcoin sistema.
Kako C-Bot Verifikuje Transakcije
Korak 1: Slušanje transakcija
Prvo, C-Bot sluša transakcije (skraćeno “txn”) koje Ana, Boris, Marko i David emituju putem interneta.
Korak 2: Stvara “Heš”
Drugo, C-Bot će prikupiti sledeće delove podataka:
- Sve Bitcoin transakcije koje ljudi šalju
- Tajni broj (objasnićemo kasnije)
- Nonce – neki slučajan broj
C-Bot sve ovo stavlja u heš mašinu. Mašina za heširanje uzima sve ove podatke i proizvodi 256 bitova (bitovi su 1 i 0) koji se jedinstveno uklapaju u te podatke, nazvane ‘heš’. To heširanje je poput otiska prsta podataka. Uvek ćete dobiti isti heš sa istim ulaznim podacima. Mašina za heširanje je takođe jednosmerna: lako je stvoriti heš od nekih podataka, ali ne možete da stavite heš u mašinu i da vratite ulazne podatke.
C-Bot će iznova isprobavati svoju heš mašinu sa drugim nonce-om (slučajnim brojem). Svaki put, on će proveriti da li je mašina proizvela heš za koji Bitcoin softverski protokol kaže da je tačan.
Ovaj proces pronalaženja heša troši puno vremena i energije. Mašina za heširanje je jednosmerna, tako da C-Bot ne može tek tako da stavi ‘tačan’ heš u mašinu i otkrije ulazne podatke. Svaki računar na Bitcoin mreži takođe prolazi kroz ovaj proces pokušavajući da pronađe ‘ispravan’ heš.
Ukoliko bi ovi računari uspeli da pronađu ‘ispravan’ heš bez velikog trošenja energije, mogli bi da prevare sistem. Dva računara bi mogla da prosleđuju transakcije u krug, zarađujući bitcoin-e svaki put kada bi potvrdili transakciju.
Korak 3: Pronalaženje Ispravnog Heša
C-Bot konačno pronalazi heš koji zadovoljava pravila Bitcoin protokola koristeći sve nedavne transakcije. Sada ovaj blok podataka šalje na druge računare. Blok se sastoji od nedavnih transakcija, nonce-a i tajnog broja. Ti drugi računari stavljaju sve ove podatke kroz istu heš mašinu za sebe, da bi proverili da li je heširanje tog C-Bota tačno. S obzirom da znamo da računari ne mogu da varaju u ovoj igri, znamo da je C-Bot morao da izvrši neka izračunavanja sa svojom heš mašinom da bi pronašao ispravan heš.
Heš bloka C-Bota koji je poslat, sada postaje tajni broj koji ulazi u izračunavanje sledećeg bloka. Budući da heš svakog bloka u ‘blockchain-u’ bitcoin-a koristi heš poslednjeg bloka kao ulaz, bila bi potrebna apsurdna količina energije da se prepiše istorija transakcija (lanac blokova, eng. the blockchain)
Budući da se svačija stanja bitcoin-a zasnivaju na transakcijama na i sa njihovih računa, to takođe onemogućava izmenu bilo čijih stanja bitcoin-a.
Čitav ovaj proces poznat je pod nazivom rudarenje bitcoin-a. Svaki računar na mreži pokušava da proba nove podatke kroz heš mašinu, bilione puta u sekundi.
Šta je blockchain?
Blockchain predstavlja istoriju Bitcoin transakcija, koja omogućava bilo kome da utvrdi svoje Bitcoin stanje.
- ‘Block – Blok’ = Grupa Bitcoin transakcija, nonce-a i heša prethodnog bloka
- ‘Chain – Lanac’ = Heš svakog bloka takođe koristi heš prethodnog bloka kao ulaz. Ovo povezuje podatke svakog bloka sa svakim drugim blokom, stvarajući chain – lanac.
Na blockchain-u, prava imena nisu povezana sa bitcoin-ima. Bitcoin-i su povezani samo sa slučajnim nizom brojeva i slova poznatim kao ‘javni ključ’. Ovo korisnike Bitcoin-a i njihova stanja čini poprilično anonimnima za sve koji vode knjigu.
Kada posedujete bitcoin-e, vi imate password za otključavanje vaših bitcoin bankovnih računa. Ovi računi postoje na hiljadama računara širom sveta koji pokreću Bitcoin protokol.
Kako mogu da saznam više o Bitcoin-u?
Ovaj članak vam je dao razumevanje o tome kako funkcioniše Bitcoin protokol i kako se osiguravaju njegova neverovatna svojstva.
Ako želite da saznate više, preporučujem vam ove izvore:
Ako vam se sviđa moj rad, molim vas da ga podelite sa svojim prijateljima i porodicom. Cilj mi je da svima pružim pogled u ekonomiju i na to kako ona utiče na njihov život.
-
 @ bf47c19e:c3d2573b
2025-05-30 20:23:47
@ bf47c19e:c3d2573b
2025-05-30 20:23:47Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Pojedinac je Suveren
- Odgovornost je Programirana
Postoji izreka među bitcoinerima, koja, kako vreme prolazi, postaje sve istinitija i očiglednija: Ti ne menjaš Bitcoin. Bitcoin menja tebe.
Zašto je to tako? U početku nisam bio siguran kako da odgovorim na ovo pitanje; Jednostavno sam znao da je to istina. Razlozi za to ostali su neka vrsta misterije za mene. Da, Bitcoin je neverovatno otporan na promene. I da, zdrav novac smanjuje vaše vremenske preference. To je definitivno veliki deo toga. Takođe postoji istorijska tendencija ka bogaćenju, pa bi bogatstvo i ekonomska sloboda, koje dolaze sa tim, mogli biti drugi deo.
Novac, međutim, nije uvek blagoslov. On teži da pojača i dobre i loše osobine. Takođe ima moć da korumpira, i ima potencijal da izludi ljude. Ako niste pažljivi, ono što je započelo kao iznenadno bogatstvo, uskoro se može pretvoriti u napitak ega koji vas napije, i koji se završava sindromom Bitcoin Derangement-a.
Već postoji dosta tekstova o kratkim vremenskim preferencijama i bogatstvu, zbog čega želim da se usredsredim na treću stvar koju vam Bitcoin nameće: odgovornost.
Pojedinac je Suveren
Cela ideja Bitcoin-a je uklanjanje posrednika iz jednačine. Pouzdane treće strane su sigurnosne rupe i ukoliko ne želimo da ponovimo greške iz prošlosti, naša je kolektivna odgovornost da te sigurnosne rupe eliminišemo kad god i gde god možemo. Bitcoin omogućava eliminisanje pouzdanih trećih strana jer se sam uspostavlja odozdo prema gore, umesto da se kreira odozgo prema dole. U Bitcoin-u vaš suverenitet može biti apsolutan.
Bitcoin naglašava suverenitet pojedinca, kako u teoriji, tako i u praksi. Omogućava ekonomskim akterima da slobodno skladište i razmenjuju vrednosti, ne zahtevajući ništa osim validnog kriptografskog potpisa. Identitet grupe, pol, boja kože, starost, politička ili verska pripadnost – sve je irelevantno u očima protokola. Ako vaša transakcija ima validan potpis, Bitcoin će vas shvatiti ozbiljno. Bez obzira da li ste osoba, pas ili borbeni helikopter.
Baš kao što se intersekcionalnost rešava fokusiranjem na pojedinca, problem pouzdanih trećih strana rešava se fokusiranjem na pojedinačne čvorove. Uklanjanjem socijalnog i političkog identiteta, ostaje pojedinac. Uklonite pouzdane treće strane i spoljne izvore istine, i ostaje samosuvereni čvor. I baš kao što je ljudsko dostojanstvo nepovredivo, nepovrediva je i samopotvrđujuća istina koju predstavlja vaš Bitcoin čvor, eng. Bitcoin node. Ako bi spoljni autoritet mogao da se umeša u istinu vašeg čvora, cela poenta Bitcoin-a bila bi sporna.
“Die Würde des Menschen ist unantastbar.” – Ljudsko dostojanstvo je nepovredivo
Artikel 1 des Grundgesetzes für die Bundesrepublik Deutschland – Član 1. Osnovnog zakona Savezne Republike Nemačke
Sve se svodi na pojedinačne čvorove. Stoga, se sve svodi na pojedince koji upravljaju tim čvorovima.
Odgovornost je Programirana
Postoji razlog zašto bitcoineri govore o „putovanju“ niz zečju rupu. Jedini način da uđete u Bitcoin je da započnete sa malim ulaganjem, i postepeno se poboljšavate. Nije ni lako ni komforno, ali je i neophodno. Ne možete sve uraditi „ispravno“ prvog dana. Izazovi su preveliki, paradigma promena je previše radikalna, previše kompromisa, a pitanja previše detaljna.
Shodno tome, moj savet prijateljima i porodici ostaje isti: počnite da skupljate sats-ove već danas. To možda u ovim okolnostima i nije savršen savet za sve, ali u mojim očima je savršen samo iz sledećeg razloga: primorava vas da napravite prvi korak, a to je da uzmete nekoliko sats-ova na svoje ime.
Jednom kada steknete nešto bitcoin-a, ubacili ste sebe u igru. A kad jednom udjete u igru, na putu ste da postanete sve više samouvereniji. Na putu ste da preuzmete odgovornost za svoje finansije, svoju ušteđevinu, svoju budućnost i, možda pomalo iznenađujuće, za budućnost Bitcoina.
Zvuči veličanstveno? Dozvolite mi da objasnim: naučićete da zapravo ne posedujete bitcoin-e ukoliko ne držite svoje ključeve. Saznaćete da ne možete biti sigurni da je ono što zapravo držite bitcoin, osim ako svoje transakcije ne potvrdite svojim čvorom. Saznaćete da je Bitcoin šta god vi odlučite da jeste, da vrednost bitcoin-a ne dolazi spolja već iznutra, i da maksimalna korisnost u svetu Bitcoin-a zahteva prihvatanje maksimalne odgovornosti.
Osnovna stvarnost kako Bitcoin mreža funkcioniše, u kombinaciji sa sve većim brojem izveštaja o ovom efektu – lična transformacija ostvarena prihvatanjem Bitcoin Standarda – tera me da verujem da nije samo mesec ono što je programirano, već i prihvatanje odgovornosti takođe.
Budući da je bitcoin dizajniran da radi zauvek, koliko god iskustva da imate u igri, uskoro ćete imati veliku količinu. Kako raste kupovna moć vaše bitcoin gomile, tako će da rase i vaš podsticaj da postanete prvoklasni građanin Bitcoina. Želećeš da naučiš kako da se staraš o sebi. Želećeš da naučiš kako da pokreneš sopstveni čvor.
To prevazilazi mantre „nisu tvoji ključevi, nije tvoj bitcoin“ i „nije tvoj čvor, nisu tvoja pravila“. U vašem je najboljem interesu da podržite mrežu, bilo pokretanjem čvora, doprinosom hash snage, ili indirektno podržavanjem razvoja bitcoin-a. I tu dolazi do udarca: pokretanje sopstvenog čvora znači da učestvujete u samoj mreži, što vas neizbežno uključuje u proces definisanja šta je Bitcoin. Budući da vam niko ne može reći šta je to Bitcoin, morate odlučiti šta je vama Bitcoin, iznova i iznova. Mreža je rastući organizam koji se neprestano menja, a priroda prihvatanja nadogradnje protokola će u više navrata nametati pitanje identiteta Bitcoin-a svojim učesnicima.
Šta je Bitcoin? A šta bi trebao da bude? Nedostatak centralnog autoriteta podrazumeva da je odgovor na ova pitanja vaša trajna odgovornost. Međutim, pre nego što se usudite da preuzmete ovu odgovornost, vi morate preduzeti prvi korak i početi da štedite sami.
-
 @ eb0157af:77ab6c55
2025-05-31 04:01:14
@ eb0157af:77ab6c55
2025-05-31 04:01:14Block’s hardware wallet sparks debate between security and borderline compromises.
The debate ignited after Jack Dorsey publicly supported the superiority of “seedless” wallets over traditional solutions on X.
seedless is safer https://t.co/MvjmFcQE8k
— jack (@jack) May 27, 2025
The Twitter co-founder and Block CEO sustained this by promoting Bitkey, a company that completely eliminates seed phrases, aiming to simplify the user experience and improve security through different recovery options.
The Bitkey model
Bitkey represents a different solution compared to the traditional approach to bitcoin custody. Instead of relying on a single seed phrase, the system implements a 2-of-3 multisig scheme that distributes security across three distinct keys:
- Hardware key: protected by biometric fingerprint on the physical device;
- Mobile key: stored in the smartphone app;
- Server key: managed by Block’s servers.
Any transaction requires two of the three signatures, eliminating the single point of failure represented by traditional seed phrases, the company claims. In its official documents, Bitkey explains how this approach, according to the company, offers three different recovery paths: phone loss, hardware loss, or loss of both through “Trusted Contacts,” pre-set trusted people who can help the user regain wallet access without being able to see the balance or control the private keys.
The seed phrase criticism
For the Bitkey team, the seed phrase paradoxically represents the weakest link in the Bitcoin security chain. While private keys are “exceptionally secure” within the hardware – “designed for security, isolated from networks, physically reinforced” – the seed phrase is “plain text, readable, physically vulnerable,” the company states.
Bitkey developers argue that the industry has “offloaded the most complex part of the security model onto individuals least equipped to handle it.”
System limits and dependencies
However, Bitkey’s simplicity comes at a price. The system introduces a dependency on Block for optimal multisig functionality. Although users always maintain the ability to move funds using the two keys in their possession, recovery procedures and many advanced features require collaboration from the company’s servers.
This architecture presents limitations in terms of flexibility: users cannot use Bitkey with other mobile applications, cannot import the wallet into alternative solutions, and do not have direct access to seed phrases for traditional backup operations.
One of the most frequent criticisms concerns the absence of a screen on the hardware device. Unlike traditional hardware wallets that allow direct verification of destination addresses and transaction amounts on the device display, Bitkey forces users to rely exclusively on the mobile app for these details. This design choice introduces what critics define as a “blind signing risk”: if the mobile app were compromised by malware, users could unknowingly authorize altered transactions without the possibility of independent verification.
Community criticism
Dorsey’s post sparked contrasting reactions in the community. The most orthodox bitcoiners mainly contest two aspects:
- third-party dependency: despite Bitkey maintaining the “self-custody” label, the need to rely on Block’s servers for many operations contradicts the autonomy principles that many bitcoiners consider fundamental;
- loss of technical control: the inability to directly manage the seed phrase or use the device in customized multisig configurations limits the user’s technical sovereignty.
Some users have criticized Block’s hardware wallet. User bamskki highlighted how “the lack of a screen forces users to rely on the app for transaction details. Unlike traditional hardware wallets with screens, Bitkey users cannot verify transactions independently. Users must trust the app as the source of truth.”
Even more critical was user nakadai_mon, who ironized about Dorsey’s strategy writing: “It would be a shame if I influenced you to abandon the seed and locked you into my ecosystem so I can surveil you, sell and share your personal data with government authorities and deny you service.”
Dorsey responded directly to both criticisms. To bamskki he replied:
it's a start, not our end. we will iterate the product like everything else.
— jack (@jack) May 28, 2025
More articulated was his response to nakadai_mon:
we are working on much of the privacy aspects (launching soon). and you don't have to use our 3rd key. that's where some of the restrictions come in. working to figure out how to allow folks to create their own trusted 3rd party as well. but all of this is designed to get people…
— jack (@jack) May 28, 2025
However, privacy concerns are not unfounded. Bitkey’s own documentation clarifies that “because we maintain this key, we are able to identify transaction data on the blockchain related to your Bitkey” and that “this information is collected when you transfer bitcoin to or from your Bitkey.”
Additionally, Block declares using automated decision-making systems, without direct staff involvement, to manage some activities that have legal effects on users. Among these, the application of sanctions restrictions: the system is programmed to automatically prevent the purchase and use of Bitkey by people or countries subject to international sanctions. Finally, the privacy policy specifies that users’ personal data can be shared with law enforcement, government agencies, officials, or authorized third parties in the presence of a warrant, court order, or other legal obligation. Block reserves the right to disclose this information whenever it deems necessary to comply with regulations, legal proceedings, or government requests.
Hardware security and compromises
From a hardware security perspective, Bitkey implements advanced protections including unique device identifiers, secure boot, and anti-tamper technologies. In case the device were compromised, an attacker would still need to access a second key to steal funds.
According to Dorsey’s statements, Bitkey represents an attempt to make self-custody accessible to a broader audience. The company’s roadmap promises improvements in terms of privacy, security, and usability.
The post Bitkey controversy: Dorsey’s marketing divides the community appeared first on Atlas21.
-
 @ eb0157af:77ab6c55
2025-05-31 04:01:11
@ eb0157af:77ab6c55
2025-05-31 04:01:11The revelation by Miles Suter, Product Lead at Block, at the Bitcoin Conference 2025 confirms the economic potential of LN for professional operators.
During the Bitcoin 2025 conference in Las Vegas, Miles Suter, Bitcoin Product Lead at Block Inc., revealed data that could change the economic perception of the Lightning Network: the company’s routing node is generating annual returns of 9.7% on invested liquidity.

During his presentation, Suter confirmed what many experts suspected but no one had ever quantified precisely: Lightning payment routing can be not only technically effective, but also economically profitable on a large scale. With an estimated public capacity of 184 BTC (approximately $20 million), Block is demonstrating that Lightning infrastructure can generate significant returns through the use of bitcoin as a payment method.
Non-custodial yield
Lightning routing represents what experts define as “true non-custodial yield” – returns generated from the pure economic utility of bitcoin as a means of payment, without having to entrust one’s funds to third parties.
“We are earning almost 10% returns on Bitcoin by effectively routing real payments on the Lightning network,” Suter declared.
In 2024 Cash App recorded an increase in Lightning payment volume equal to 7 times that of the previous year: one in four outgoing payments now occurs via LN, Suter stated.
According to Block’s Product Lead “if Bitcoin becomes only digital gold, we have failed the mission. If we don’t use bitcoin for payments, we risk losing one of the most important promises permissionless money. If we don’t preserve the qualities of cash in the digital world, human liberty is seriously in trouble.”
The company aims to incentivize practical and daily use of bitcoin, seeing Lightning payments as the key to realizing Satoshi Nakamoto’s original vision of a “peer-to-peer electronic payment system.”
The post Lightning routing yields 10% annually: Block’s announcement appeared first on Atlas21.
-
 @ 9ca447d2:fbf5a36d
2025-05-31 04:00:53
@ 9ca447d2:fbf5a36d
2025-05-31 04:00:53Michael Saylor, executive chairman of Strategy, has stirred up the Bitcoin community with his recent comments on proof-of-reserves, calling it a “bad idea” that puts institutional security at risk.
Speaking at a side event at the Bitcoin 2025 conference in Las Vegas, Saylor expressed strong concerns about the security implications of on-chain proof of reserves (PoR), a method used by many bitcoin companies to show they actually hold the assets they claim.
“The conventional way of issuing proof of reserves today is actually insecure,” Saylor said.
“It actually dilutes the security of the issuer, the custodians, the exchanges and the investors. It’s not a good idea, it’s a bad idea.”
Proof-of-reserves is a process where companies with bitcoin reserves share public wallet addresses or use cryptographic methods to prove how much bitcoin they hold.
This practice gained popularity after the collapse of major exchanges like FTX and Mt. Gox to build trust through transparency.
Many big players in the digital asset space, including Binance, Kraken, OKX and asset manager Bitwise, have adopted PoR to reassure users and stakeholders.
Related: Bitwise Announces On-Chain Address, Donations Go to Shareholders
Saylor’s objections boil down to two main points.
First, he believes publishing wallet addresses creates serious security risks. By exposing institutional wallet structures, companies may open themselves up to attacks from hackers, hostile governments or malicious actors.
“[It’s like] publishing the address and the bank accounts of all your kids and the phone numbers of all your kids and then thinking somehow that makes your family better,” Saylor said.
“(It becomes) an attack vector for hackers, nation-state actors, every type of troll imaginable.”
He even asked the audience to try a thought experiment:
“Go to AI, put it in deep think mode and then ask it ‘what are the security problems of publishing your wallet addresses?’ and ‘how might it undermine the security of your company over time’ … It will write you a book. It will be fifty pages of security problems.”
Second, Saylor pointed out that proof of reserves only shows what a company owns, not what it owes. In his view, that’s incomplete.
“It’s proof of assets that is insecure, and it is not proof of liabilities… So you own $63 billion worth of bitcoin—do you have a hundred billion dollars of liabilities?” he asked rhetorically.
For large institutions and investors, this view of financial health is not enough.
Instead of publishing wallet addresses, Saylor thinks the better approach is to use institutional-grade audits by trusted firms.
“The best practice… would be to have a Big Four auditor that checks to make sure you actually have the bitcoin, then checks to make sure the company hasn’t rehypothecated or pledged the bitcoin,” he said.
“Then you have to wash it through a public company where the CFO signs, then the CEO signs, then the chairman and all the outside directors are civilly and criminally liable for it.”
He believes the legal consequences of corporate auditing — including prison time for fraud under the Sarbanes-Oxley Act — are stronger than cryptographic proof alone.
He did admit that a more secure, future version of PoR might be possible if it involved zero-knowledge proofs that protect wallet privacy while still confirming ownership.
Not everyone agrees with Saylor’s opinion. While some praised his focus on security, others accused Saylor of hiding something.
Speculations resurfaced about whether Strategy truly holds all the bitcoin it claims, or if it’s involved in so-called “paper bitcoin” — claims to BTC without physical backing.
Others pointed out that exchanges like Kraken and asset managers like Bitwise have implemented PoR systems without major breaches.
-
 @ cae03c48:2a7d6671
2025-05-31 04:00:33
@ cae03c48:2a7d6671
2025-05-31 04:00:33Bitcoin Magazine

Panama City Mayor Mizrachi: “Bitcoin Is Not Just Safe, It’s Prosperous”At the 2025 Bitcoin Conference in Las Vegas, the Director of Bitcoin Beach Mike Peterson, the Presidential Advisors of Building Bitcoin Country El Salvador Max & Stacy and the Mayor City of Panama Mayer Mizrachi discussed Bitcoins future in Panama.
At the beginning of the panel, Is Panama Next? El Salvador Leading The Region For Bitcoin Adoption, Mayor Mizrachi started by mentioning, “We accept Bitcoin. The city gets paid in Bitcoin, but it receives in dollars through an intermediary processing, payments processor. Bitcoin is not just safe. It’s prosperous.”
Max commented about the scammers in crypto and how El Salvador is managing it.
“We did a couple of things early on, one was to create The Bitcoin Office which will be directly reporting to the President, and then also we passed a law which will say bitcoin is money and everything else is an unregistered security,” said Max.
Mike Peterson stated, “the access of Bitcoin in Central America to do battle against the globalists that have always looked at the regionist back yard. This is intolerable and this is going to change right now.” After Mizrachi commented, “Imagine yourself in an economic block powered by El Salvador, supported by Panama and the rest will come.”
Stacy reminded everybody about El Salvador’s School system.
“El Salvador is the first country in the world to have a comprehensive public school financial literacy education program from 7 years old,” mentioned Stacy. “These are little kids, learning financial literacy.”
Max ended the panel by saying, “the US game theory right? Because the US wants to buy a lot of Bitcoin, so if Panama wants to buy a lot of bitcoin then it helps everybody in the US. This is the beautiful expression of game theory perfectly aligned in the protocol that is changing the world that we live in. And on the street level what bitcoin does to the population is to go from a spending mentality to a saving mentality.”
You can watch the full panel discussion and the rest of the Bitcoin 2025 Conference Day 3 below:
This post Panama City Mayor Mizrachi: “Bitcoin Is Not Just Safe, It’s Prosperous” first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ bf47c19e:c3d2573b
2025-05-30 19:47:11
@ bf47c19e:c3d2573b
2025-05-30 19:47:11Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Kako Cantillonov Efekat Funkcioniše
- Kako Bitcoin Rešava Nejednakost iz Cantillonovog Efekta
- Uloga Vlade u Cantillonovom Efektu
- Zaštitite Sebe od Cantillonovog Efekta
- Kako mogu da saznam više o Bitcoin-u?
Pitanje o tome zašto nam je potreban Bitcoin danas je postalo veoma uobičajeno, ali odgovori obično ostavljaju većinu ljudi zbunjenim i sa izjavama da je on, ili Ponzijeva šema ili novac za kriminalce. Ovaj zaključak nije pravičan prema načinu na koji bi Bitcoin mogao da transformiše sistemsku nepravednost i korupciju koja je usadjena u naš trenutni monetarni sistem. Jedna od ovih nejednakosti u našem današnjem sistemu rezultat je Cantillonovog Efekta, davno zaboravljene klasične teorije o tome kako raspodela novca utiče na bogatstvo pojedinca.
Cantillonov Efekat opisuje kako stvaranje novog novca donosi korist onima koji prvi dobiju novac, a na štetu onih koji su najudaljeniji od stvaranja novog novca. U današnjem monetarnom sistemu banke i korporacije su najbliže novom novcu dok je srednja klasa najudaljenija. Bitcoin to ispravlja, davanjem novih bitcoin-a samo „rudarima“ koji osiguravaju protokol – mnogo pravednija distribucija.
Cantillonov Efekat predstavlja način na koji se naplaćuje dodatni porez svima koji rade za „nepromenjenu“ platu ili drže prvenstveno dolare ili eure kao deo svog bogatstva. Ovaj porez prenosi vrednost onima koji ulažu u finansijsku imovinu ili su preferirani dobavljači vlade. Bitcoin odvaja stvaranje novog novca od politike, čineći ovu situaciju mnogo poštenijom.
Kako Cantillonov Efekat Funkcioniše
Kada se poveća ponuda neke vrste novca, ima smisla da taj novi novac treba da ode u nečije ruke – ali čije? Da li bi trebao da pada kao kiša sa neba, da ga dobije neko na lutriji, ili ga predati posebnim interesnim grupama?
U našem savremenom monetarnom sistemu, ovaj novac nije uvek zajam za primaoce, tako da nekad ne trebaju da ga vrate.
Zabluda inflacije pomalo liči na MC Escher vodopad – dobro funkcioniše na papiru, ali ne govori skoro ništa korisno o tome kako stvarni svet funkcioniše.
Međutim, ova analiza zanemaruje to kako funkcionišu tržišta. Tamo gde novi novac ide prvo i način na koji se širi kroz ekonomiju, ima veliki uticaj na stvarno bogatstvo ljudi. Zašto? Kada se poveća novčana masa, cene se ne povećavaju odmah kao odraz ove činjenice. Umesto toga, povećavaju se polako, kako tržišta reaguju na novu ukupnu ponudu novca.
Prvi entiteti i ljudi koji prime novostvoreni novac mogu da ga potroše pre nego što je tržište reagovalo na bilo koji novi novac u sistemu prilagođavanjem cena. Kada oni kupuju stvari, dobijaju ih po niskim cenama jer cene još uvek ne podržavaju činjenicu da ima više novca u opticaju.
Jednom kada se novi novc nekoliko puta okrene, cene počinju da rastu, jer se više novčanih jedinica troši na isti broj dobara i usluga. Jedna od ‘cena’ u ekonomiji je plata ili zarada – i ova cena će da poraste, baš kao i sve druge. Međutim, ova cena raste sporije, kao rezultat ulaska novog novca u sistem, nego što je recimo, cena namirnica.
Kao rezultat ove neusklađenosti u vremenu porasta cena, oni koji primaju platu, tj. zaradu moraju da plaćaju više za svoje dnevne potrebe (poput namirnica), dok neko vreme primaju istu platu. Plate se prilagođavaju sporije od cena hrane. To dovodi do pada kupovne moći ljudi koji rade za platu..
Sve ovo proističe iz toga kako novi novac ulazi u sistem. Kada bi novi novac ušao u sistem samo putem zajmova direktno od centralne banke na plate ljudi, ti ljudi bi mogli da ga potroše pre nego što cene porastu, i samim tim bilo bi im bolje.
Na to kako raspodela novca utiče na bogatstvo, ukazao je Richard Cantillon u 18. veku, koji je gledao kako se ova dinamika odvija u Engleskoj kada je vlada štampala novac u njegovo vreme.
Izvrstan momak, g. Cantillon
Kako Bitcoin Rešava Nejednakost iz Cantillonovog Efekta
Da bismo razumeli kako Bitcoin rešava nejednakost, moramo da uporedimo kako se tradicionalne valute poput dolara ili eura distribuiraju u današnje vreme u odnosu na to kako se distribuiraju novi bitcoini.
Gotovo sva tradicionalna valuta koja je stvorena do današnjeg dana, prvo je distribuirana bankama i vladama. To je zato što su glavne komercijalne banke, poput JP Morgan i Citi, zauzvrat podržane od centralnih banaka poput Federalnih rezervi. Centralne banke poseduju ‘prese za štampanje’ – što znači da u svet mogu da ‘odštampaju’ (ili dodaju digitalno) neograničenu količinu svojih tradicionalnih valuta. Takođe su postavili pravila za komercijalne banke da ih podstaknu da pozajmljuju više ili manje dolara, što proširuje i ugovara ukupnu novčanu masu.
Budući da banke i vlade prve dobijaju novi novac, one odlučuju ko je drugi po redu koji može da iskoristi pogodnosti Cantillonovog Efekta. Tu na scenu dolaze lobisti, kao i moć koju donose njihove dobre konekcije sa finansijskom elitom. Lobisti osiguravaju da njihovi interesi imaju koristi od Cantillonovog Efekta, a veoma bogati, kao i korporacije, mogu da dobiju kredite od banaka po isplativim niskim kamatnim stopama.
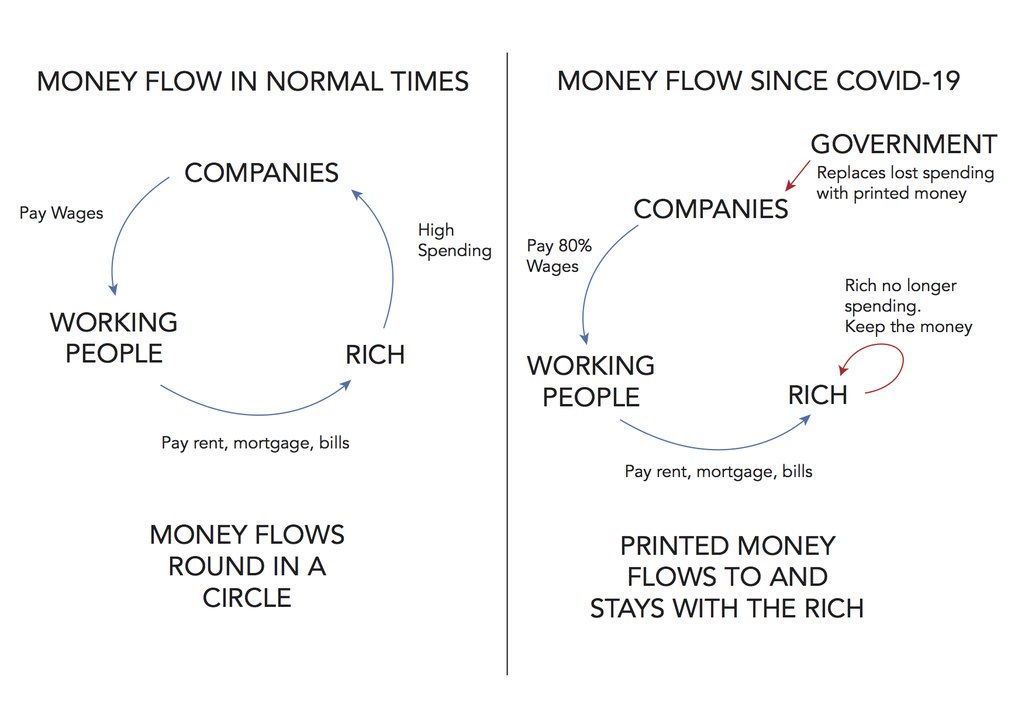
Stvari mogu da se prilično zabrljaju kada vlada uskoči da preuzme “kontrolu” nad potrošnjom štampanog novca. Izvor: OpenDemocracy
Bitcoin-ov sistem eliminiše moć lobista i prednosti poznavanja pravog bankara, i stavlja ljude na mnogo ravnopravnije temelje. U Bitcoin-u, svaki ‘rudar’ na mreži ima jednake šanse da zaradi nagradu za novostvorene bitcoin-e na svakih 10 minuta. Svako može da postane rudar, jednostavnim kupovanjem hardvera i njegovim uključivanjem u utičnicu – daleko manje mukotrpan posao od lobiranja kod izabranih predstavnika da bi vam dodelili ugovor sa vladom. Rudari troše puno novca na električnu energiju i opremu da bi se takmičili za nagradu, a Bitcoin sistemu pružaju preko potrebnu uslugu: bezbednost. Bez rudara, Bitcoin-ov sistem ne bi funkcionisao.
:max_bytes(150000):strip_icc()/GettyImages-929584582-9d7790de3ee44f658a9580cc598c641f.jpg)
Rudarenje bitcoin-a zahteva računar i struju – to je to.
U sistemu američkog dolara vidimo da političke veze proističu iz Cantillonovog Efekta. U Bitcoin sistemu vidimo da se pružaoci usluga (rudari) plaćaju za svoje usluge novostvorenim bitcoin-ima.
Naravno, ishodi Cantillonovog Efekta bi mogli da se promene tako što će političari da promene način na koji novi novac ulazi u sistem. Međutim, ovo ne rešava osnovni problem: neko drugi ima korist na tuđi račun.
Bitcoin sistem je daleko pravedniji jer koristi Cantillonov Efekat da bi uredno nagradio one koji pružaju korisnu uslugu za sve ostale: obezbeđivanje Bitcoin mreže.
Zamislite to ovako: u dolarskom sistemu, neka osoba šarmira političare ili bankare na pravim pozicijama da bi dobila povlašćen tretman na račun svih ostalih. U Bitcoin sistemu svi plaćaju po malo, da bi zaštitili svoje bankovne račune od krađe.
Uloga Vlade u Cantillonovom Efektu
Federalne vlade širom sveta su jedne od najvećih korisnika Cantillonovog Efekta, jer su u mogućnosti da vrlo lako dobiju zajmove od centralne banke svoje države. U SAD se to radi kada američko Ministarstvo finansija proda državne obveznice banci Federalnih rezervi. Federalne rezerve daju Ministarstvu finansija gomilu novoštampanog novca, a Ministarstvo finansija da Fed-u papir na kojem piše „mi ćemo vam isplatiti dug u to i to vreme sa određenom kamatom“. Možda je malo složenije od ovoga, ali to opisuje suštinu toga.
Budući da novac koji federalna vlada dobija nije postojao pre toga, ona može da ga potroši pre nego što cene počnu da rastu zbog tog novog novca koji ulazi u opticaj. To omogućava federalnoj vladi da ga troši na socijalne programe, policiju, vojsku, vojnu opremu za naoružavanje država poput Saudijske Arabije, čak i na ‘most iz nigde ka ničemu’, a da ne mora da koristi politički nepopularnu metodu: da poveća porez da bi to platila.
Umesto da povećaju poreske prihode za pokrivanje ove potrošnje, federalne vlade koriste Cantillonov Efekat za prenos kupovne moći od plata radnika srednje klase u vladin trezor. Na taj način inflacija i Cantillonov Efekat stvaraju skriveni porez na zarade i uštede novca.
Zaštitite Sebe od Cantillonovog Efekta
Zaštita svog života od Cantillonovog Efekta je zeznuta igra koju treba odigrati. Možete da pokušate da se približite izvoru novog novca, tako što ćete se nadmetati za državne ugovore ili raditi u vrhovima finansija. Možete da pokušate da igrate na visokim nivoima u trgovanju na berzi ili ulaganju u nekretnine, ali je verovatnije da ćete bankrotirati nego što ćete da se zaštitite.
Najlakši način da zaštitite sebe od nepravedne raspodele novog novca je potpuno odbijanje tog monetarnog sistema. Samo najstarije generacije koje danas žive mogu da se sete vremena kada je novac značio nešto drugo osim papira potkrepljenog ‘punom verom i kredibilitetom’ vlade i vojske. Mi smo tako uslovljeni da novac smatramo proizvodom naše vlade, ali naša zaštita od Cantillonovog Efekta zahteva gledanje novca kroz istoriju – čak i pre samo jednog veka.
Novac je nekada značio zlato – materijal koji nijedna vlada ne može magično da stvori u većoj količini, a koji zahteva ogroman napor da se pronađe i iskopa iz zemlje. Bitcoin je vrlo sličan zlatu po tome što niko ne može magično da ga stvori, i veoma ga je teško proizvesti više ‘rudarenjem’. Međutim, Bitcoin takođe putuje brzinom interneta, omogućavajući globalnu trgovinu na način na koji zlato jednostavno ne može.

Bitcoin i zlato – slični po karakteristikama ‘normalnog novca’, različiti po prenosivosti.
Da biste se zaštitili od Cantillonovog Efekta, potrebno je što je više moguće isključiti se iz nepravednih sistema tradicionalnih valuta, čuvajući bogatstvo u pravom novcu, poput zlata ili Bitcoin-a. Ovo je najmirniji način za ukidanje starog sistema i uvođenje novog, pravednijeg sistema.
Kako mogu da saznam više o Bitcoin-u?
Film "Bitkoin: Kraj novca kakvog poznajemo"
The Bitcoin Whitepaper ← objavljen 2008. godine, ovo je izložio dizajn za Bitcoin.
Ako vam se sviđa moj rad, molim vas da ga podelite sa svojim prijateljima i porodicom. Cilj mi je da svima pružim uvid u ekonomiju i kako ona utiče na njihove živote.
-
 @ b01749dc:d88bc196
2025-05-30 18:49:40
@ b01749dc:d88bc196
2025-05-30 18:49:40Preâmbulo
Nós, membros voluntários desta ordem social, reconhecendo o autoproprietário como soberano sobre si mesmo e a propriedade adquirida legitimamente como extensão inviolável dessa soberania, instituímos esta constituição com o objetivo de garantir a paz, a justiça e a prosperidade em uma ordem de convivência livre, baseada exclusivamente na propriedade privada e no contrato voluntário.
Artigo I – Princípios Fundamentais
- Autopropriedade: Todo indivíduo é o único e exclusivo proprietário de seu corpo.
- Propriedade Legítima: A propriedade legítima deriva de:
- Apropriação original (homesteading) de recursos não reivindicados através do uso produtivo.
- Transferência voluntária por meio de contrato entre proprietários.
- Não-Agressão: Nenhum ato de agressão física contra a propriedade de outrem é permitido, sendo a agressão definida como qualquer invasão não consentida da pessoa ou de sua propriedade.
Artigo II – Ordens Jurídicas e Defesa
- Justiça Privada: A resolução de conflitos se dará por meio de agências privadas de arbitragem, justiça e defesa, contratadas voluntariamente.
- Reparação e Restauração: A punição deve se concentrar na restauração do prejuízo causado à vítima. Não se permite punição sem vítima.
- Proibição de Monopólios Coercitivos: Nenhuma entidade poderá estabelecer monopólio sobre justiça, segurança, moeda ou qualquer outro serviço sem o consentimento unânime dos afetados.
Artigo III – Associação Voluntária
- Liberdade de Associação: Todos os contratos e comunidades são baseados em adesão voluntária. Qualquer indivíduo tem o direito de se dissociar de comunidades ou acordos sem coerção.
- Propriedade Comum: Propriedades comuns existem apenas sob contrato explícito entre co-proprietários. O uso da propriedade comum deve seguir as regras contratuais estabelecidas por todos os participantes.
Artigo IV – Exclusão e Liberdade
- Direito de Exclusão: O proprietário tem o direito de excluir qualquer pessoa de sua propriedade por qualquer motivo, sendo este um corolário do direito de propriedade.
- Livre Entrada e Saída: Todos têm o direito de migrar, entrar ou sair de qualquer propriedade privada, desde que respeitem os direitos de propriedade de terceiros.
Artigo V – Moeda e Troca
- Moeda Desestatizada: A moeda é um bem como qualquer outro e deve surgir espontaneamente no mercado, sem imposição central.
- Tributação como Agressão: A cobrança compulsória de recursos é considerada uma violação da propriedade privada e, portanto, uma forma ilegítima de agressão.
Disposições Finais
- Nenhuma norma desta constituição poderá ser interpretada de forma a justificar qualquer violação da propriedade legítima.
- A sociedade aqui descrita não admite o conceito de “bem público” que não seja resultado de acordo contratual explícito entre partes privadas.
-
 @ 5fbec235:ff265c2a
2025-05-30 18:38:23
@ 5fbec235:ff265c2a
2025-05-30 18:38:23## The Vibe Coding Revolution: Building Production Nostr Apps in Hours
The early Nostr protocol developers probably didn't envision this: their creation becoming the perfect playground for vibe coding. As the protocol matures and developers lean on battle-tested libraries like nostr-tools, we can focus purely on frontend magic.
I just proved this by vibe coding a performant Nostr PWA in roughly an hour. Just prompts and prayer.
### Goal: Simple. Fast. Real. Possibly Useful
My goal was to build a performant PWA first and foremost. Global accessibility through a single URL. Not that there shoudn't be trusted marketplaces and stores for discoverability...but the creation of a product should not be so dependent on all the cruft that today's app stores put teams through.
Performance was non-negotiable. I wanted something production-ready from the jump—not a prototype that would collapse under real usage. The biggest risk? Code structure. I prompted the AI to build something feature-lite but production-ready, hoping for a reviewable codebase that a competent developer could dive into immediately, and...
It completely worked!
Dannym jumped into the code and found several addressable issues. The worst? A serious XSS attack vector that could lead to cleverly designed social engineering scripts resulting in password theft and wallet drainage—the full nightmare scenario.
This perfectly captures the current AI development paradox: incredible capability paired with unpredictable blind spots. The vibes are addictive—watching prompted ideas materialize feels like magic. But that attack vector flying across your screen while you're eating popcorn? That's the reality check.
### Six Months From Now
In six months, we'll turn ideas into functioning, value-transacting apps through prompts alone. Programmatic money meets AI acceleration.
Wow and scary in equal measure.
Why am I scared? Because it will become exponentially harder to trust the open web. How many applications and websites will be half baked ideas given to AI? And How do I know that the developers haven't outsourced code-review responsibility to other AI agents...and well...who's really running things at that point?
### More on the App Itself
This app creates something interesting: reading someone's entire public chat history without social media noise. It feels more like RSS for human thoughts than traditional social platforms.
Clean. Focused. Quiet. Readable.
### What's Next?
I'm curious what the Nostr community thinks. Worth extending? The current state works, but there's obvious room for growth.
If someone zaps a feature request or throws out a "try this" vibe coding challenge, Danny and I might tackle the next zapped request publicly.
The future of development is here. It's messy, powerful, and absolutely unstoppable.
---
AI Cooked PWA here: https://nostr-pwa.pages.dev
-
 @ cae03c48:2a7d6671
2025-05-31 04:00:32
@ cae03c48:2a7d6671
2025-05-31 04:00:32Bitcoin Magazine

The Debt Train Has No Brakes: Lyn Alden Makes the Case for BTC at Bitcoin 2025“Nothing stops this train,” Lyn Alden initially stated at Bitcoin 2025, walking the audience through a data-rich presentation that made one thing clear: the U.S. fiscal system is out of control—and Bitcoin is more necessary than ever.
Her first chart, sourced from the Federal Reserve’s FRED database, displayed a stark decoupling: the unemployment rate is down, yet the fiscal deficit has surged past 7% of GDP. “This started around 2017, went into overdrive during the pandemic, and hasn’t corrected,” Alden said. “That’s not normal. We’re in a new era.”
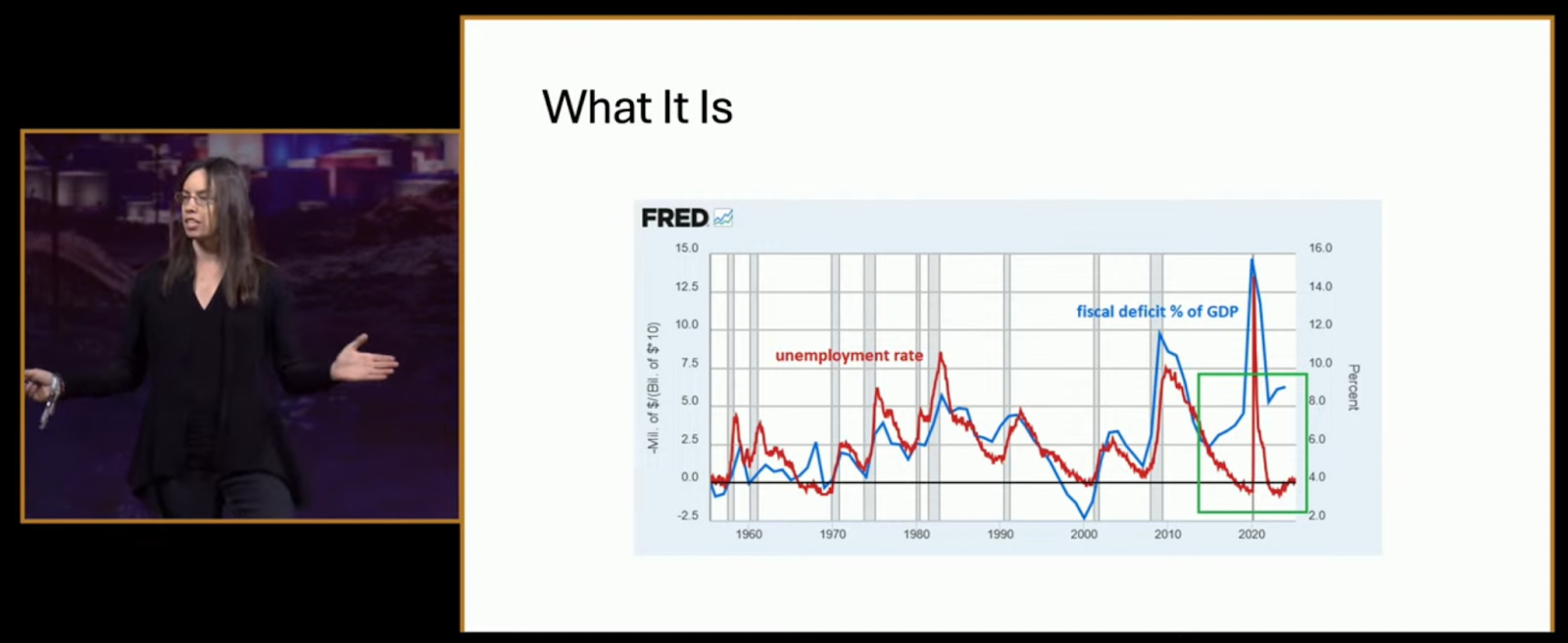
She didn’t mince words. “Nothing stops this train because there are no brakes attached to it anymore. The brakes are heavily impaired.

Why should Bitcoiners care? Because, as Alden explained, “it matters for asset prices—especially anything scarce.” She displayed a gold vs. real rates chart that showed gold soaring as real interest rates plunged. “Five years ago, most would have said Bitcoin couldn’t thrive in a high-rate environment. Yet here we are—Bitcoin over $100K, gold at new highs, and banks breaking under pressure.”
Next came what she called “The Turning Point”—a side-by-side showing how public debt growth overtook private sector debt post-2008, flipping a decades-long norm. “This is inflationary, persistent, and it means the Fed can’t slow things down anymore.”
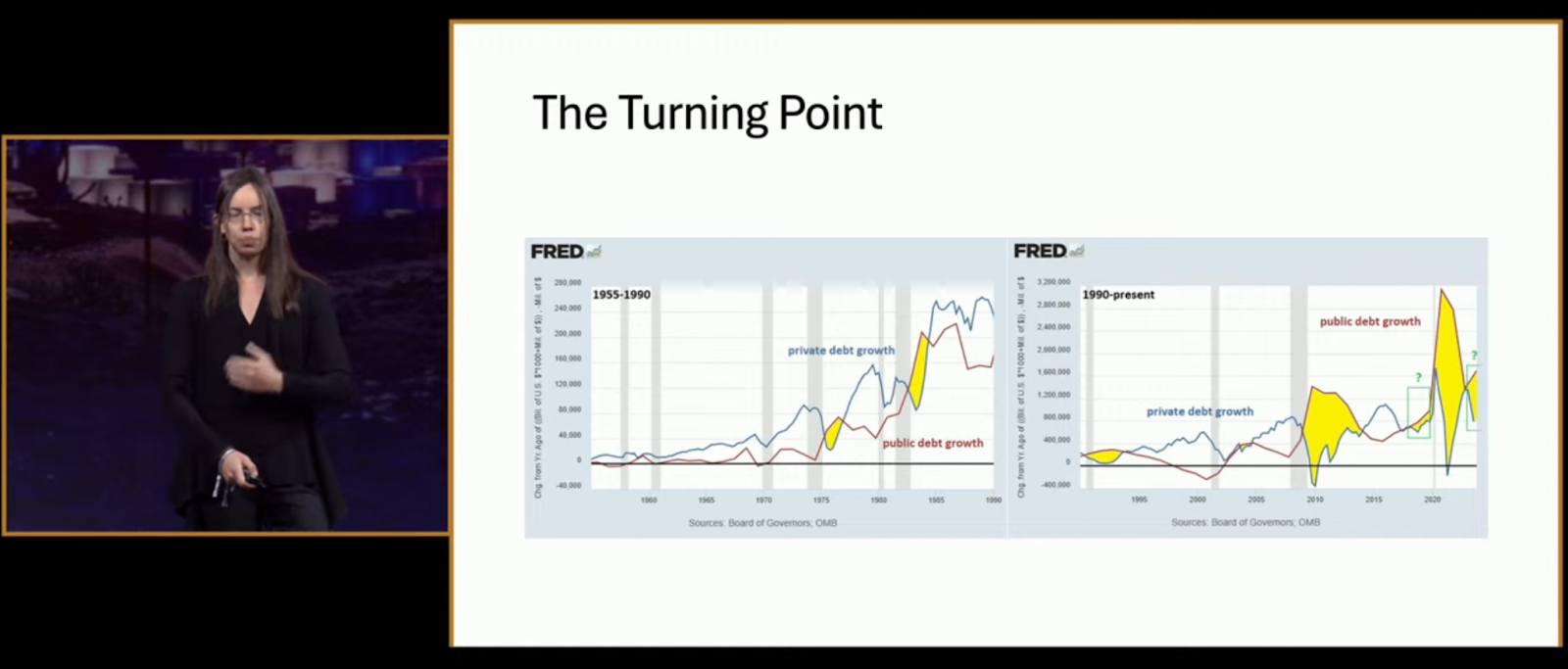
Another chart revealed why rising interest rates are now accelerating the deficit. “They’ve lost their brakes. Raising rates just makes the federal interest bill explode faster than it slows bank lending.”
Alden called it a ponzi: “The system is built on constant growth. Like a shark, it dies if it stops swimming.”
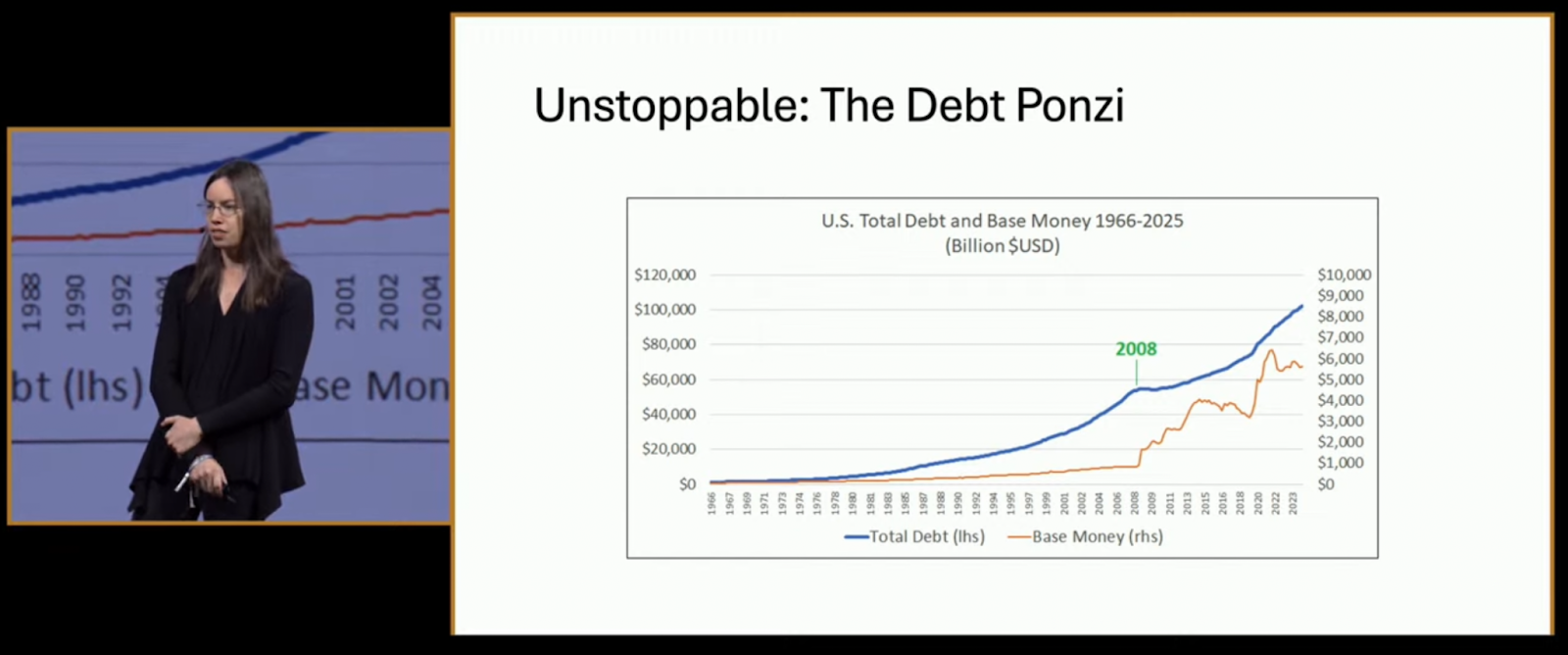
Her slide showed a relentless rise in total debt versus base money—except for a jolt in 2008, and again after 2020. “This isn’t going backward. Ever.”
So why Bitcoin? “Because it’s the opposite. Scarce, decentralized, and mathematically capped,” Alden concluded. “There are two reasons nothing stops this train: math and human nature. Bitcoin is the mirror of this system—and the best protection from it.”
You can watch the full panel discussion and the rest of the Bitcoin 2025 Conference Day 3 below:
This post The Debt Train Has No Brakes: Lyn Alden Makes the Case for BTC at Bitcoin 2025 first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ 58537364:705b4b85
2025-05-30 17:43:25
@ 58537364:705b4b85
2025-05-30 17:43:25…. “คนเราอยู่ในโลก แต่มักปฏิบัติไม่ถูกต้องต่อสิ่งทั้งหลายในโลก จึงดำเนินชีวิตไม่ถูกต้อง สิ่งที่เราเกี่ยวข้องต่างๆ นี่ มันก็อยู่ของมันไปตามปกติ ตามธรรมชาติ แต่เราปฏิบัติต่อมันไม่ถูก วางใจไม่ถูก แม้แต่มองก็ไม่ถูก เราจึงเกิดทุกข์
…. สิ่งทั้งหลายที่มีอยู่ตามธรรมดามันก็เป็นไป ถ้าเรารู้ทัน ก็เห็นมันเป็นไปตามกฎธรรมชาติ แต่ถ้าเราไม่รู้เท่าทัน เรามองไม่เป็น ก็เกิดทุกข์ทันที แม้แต่เหตุการณ์ความผันผวนปรวนแปรต่างๆที่เกิดขึ้นในชีวิตของคนเรา ที่เรียกกันว่า โชคบ้าง เคราะห์บ้าง ศัพท์พระเรียกว่า “โลกธรรม” ซึ่งเป็นตัวการสำคัญ ที่ทำให้คนดีใจเสียใจ เป็นสุข และเป็นทุกข์ เวลามันเกิดขึ้น ถ้าเราปฏิบัติไม่ถูกต้อง ที่สุขเราก็แปลงให้เป็นทุกข์ ที่มันเป็นทุกข์อยู่แล้ว เราก็เพิ่มทุกข์แก่ตัวเราให้มากขึ้น แต่ถ้าเราปฏิบัติถูกต้อง ที่ทุกข์เราก็ผันแปลงให้เป็นสุข ที่มันเป็นสุขอยู่แล้ว เราก็เพิ่มให้เป็นสุขมากยิ่งขึ้น
…. “โลกธรรม” คืออะไร โลกธรรมแปลว่า ธรรมประจำโลก ได้แก่สิ่งที่เกิดแก่มนุษย์ทั้งหลายตามธรรมดาของความเป็นอนิจจัง ก็คือ เรื่อง ลาภ เสื่อมลาภ ยศ เสื่อมยศ สรรเสริญ นินทา สุข ทุกข์ สิ่งเหล่านี้ พระพุทธเจ้าตรัสไว้ว่า มันมีอยู่เป็นธรรมดา เมื่อเราอยู่ในโลก เราไม่พ้นมันหรอก เราต้องเจอมัน ทีนี้ถ้าเราเจอมันแล้ว เราวางใจไม่ถูก และปฏิบัติไม่ถูก เราจะเอาทุกข์มาใส่ตัวทันที พอเรามีลาภ เราก็ดีใจ อันนี้เป็นธรรมดา เพราะเป็นสิ่งที่น่าปรารถนา แต่พอเสื่อมลาภเราก็เศร้าโศก เพราะเราสูญเสีย
…. ทีนี้ ถ้าเราวางใจไม่ถูก ไประทมตรมใจ แล้วไปทำอะไรประชดประชันตัวเอง หรือประท้วงชีวิต เป็นต้น เราก็ซ้ำเติมตัวเอง ทำให้เกิดทุกข์มากขึ้น อย่างง่ายๆกว่านั้น เช่น เสียงนินทา และสรรเสริญ คำสรรเสริญนั้นเป็นสิ่งที่เราชอบใจ พอได้ยินเราก็มีความสุข ใจก็ฟูขึ้นมา แต่พอได้ยินคำนินทาเราก็เกิดความทุกข์ ทุกข์นี้เกิด เพราะอะไร เพราะเรารับเอาเข้ามา คือรับกระทบมันนั่นเอง คือเอาเข้ามาบีบใจของเรา
…. ทีนี้ ถ้าเราวางใจถูกต้อง อย่างน้อยเราก็รู้ว่า อ้อ นี่คือธรรมดาของโลก เราได้เห็นแล้วไง พระพุทธเจ้าตรัสไว้แล้วว่า เราอยู่ในโลก เราต้องเจอโลกธรรมนะ เราก็เจอจริงๆ แล้ว เราก็รู้ว่า อ้อ นี่ความจริงมันเป็นอย่างนี้เอง เราได้เห็น ได้รู้แล้ว เราจะได้เรียนรู้ไว้ พอบอกว่าเรียนรู้เท่านั้นแหละ มันก็กลายเป็นประสบการณ์สำหรับศึกษา เราก็เริ่มวางใจต่อมันได้ถูกต้อง ต่อจากนั้น ก็นึกสนุกกับมันว่า อ้อ ก็อย่างนี้แหละ อยู่ในโลกก็ได้เห็นความจริงแล้วว่ามันเป็นอย่างไร ทีนี้ก็ลองกับมันดู แล้วเราก็ตั้งหลักได้ สบายใจ อย่างนี้ก็เรียกว่าไม่เอาทุกข์มาทับถมใจตัวเอง อะไรต่างๆ นี่ โดยมากมันจะเกิดเป็นปัญหาเพราะเราไปรับกระทบ ถ้าเราไม่รับกระทบ มันก็เป็นเพียงการเรียนรู้ บางทีเราทำใจให้ถูกต้องกว่านั้น ก็คือ คิดจะฝึกตนเอง พอเราทำใจว่าจะฝึกตนเอง เราจะมองทุกอย่างในแง่มุมใหม่ แม้แต่สิ่งที่ไม่ดีไม่น่าชอบใจ เราก็จะมองเป็นบททดสอบ พอมองเป็นบททดสอบทีไร เราก็ได้ทุกที ไม่ว่าดีหรือร้ายเข้ามา ก็เป็นบททดสอบใจและทดสอบสติปัญญาความสามารถทั้งนั้น ก็ทำให้เราเข้มแข็งยิ่งขึ้น เพราะเราได้ฝึกฝน เราได้พัฒนาตัวเรา เลยกลายเป็นดีไปหมด
…. ถ้าโชค หรือโลกธรรมที่ดีมีมา เราก็สบาย เป็นสุข แล้วเราก็ใช้โชคนั้น เช่น ลาภ ยศ เป็นเครื่องมือเพิ่มความสุขให้แผ่ขยายออกไป คือใช้มันทำความดี ช่วยเหลือเกื้อกูลเพื่อนมนุษย์ ทำให้ความสุขขยายจากตัวเรา แผ่กว้างออกไป สู่ผู้คนมากมายในโลก ถ้าเคราะห์ หรือโลกธรรมที่ร้ายผ่านเข้ามา ก็ถือว่าเป็นโอกาสที่ตัวเราจะได้ฝึกฝนพัฒนา มันก็กลายเป็นบททดสอบ เป็นบทเรียน และเป็นเครื่องมือฝึกสติ ฝึกปัญญา ฝึกการแก้ปัญหา เป็นต้น ซึ่งจะทำให้เราพัฒนายิ่งขึ้นไป
…. เพราะฉะนั้น ลูกศิษย์พระพุทธเจ้าจึงถือคติว่า ให้มนสิการให้ถูกต้อง ถ้ามองสิ่งทั้งหลายให้เป็นแล้ว ก็จะเกิดเป็นประโยชน์แก่เราหมด ไม่ว่าดีหรือร้าย นี้เป็นตัวอย่างวิธีการเบื้องต้น แต่รวมความง่ายๆ ก็คือ เราไม่เอาทุกข์มาทับถมตนเอง”
สมเด็จพระพุทธโฆษาจารย์ ( ป. อ. ปยุตฺโต ) ที่มา : จากหนังสือ “ความสุขที่สมบูรณ์”
-
 @ cae03c48:2a7d6671
2025-05-31 04:00:31
@ cae03c48:2a7d6671
2025-05-31 04:00:31Bitcoin Magazine

Jack Mallers Announced A New System of Bitcoin Backed Loans at StrikeThe Founder and CEO of Strike, Jack Mallers, at the 2025 Bitcoin Conference in Las Vegas, announced a new system of Bitcoin backed loans at Strike with one digit interest rate.
Jack Mallers began his keynote by pointing at the biggest problem. Fiat currency.
“The best time to go to Whole Foods and buy eggs with your dollars was 1913,” said Mallers. “Every other time after, you are getting screwed.”
What’s the solution?
“The solution is Bitcoin,” stated Mallers. “Bitcoin is the money that we coincide that nobody can print. You can’t print, you can’t debase my time and energy, you cannot deprive me of owning assets, of getting out of debt, of living sovereignly and protecting my future, my family, my priced possessions. Bitcoin is what we invented to do that.”
Mallers gave a power message to the audience by explaining that people should HODL every dollar they have in Bitcoin. People should also spend a little of it to have a nice life.
“You can’t HODL forever,” said Jack.
While talking about loans that people borrow against their Bitcoin. He explained why he thinks banks putting 20% in interest for loans backed with Bitcoin is outrageous.
“All these professional economists, they are like Bitcoin is risky and volatile,” stated Mallers. “No it’s not. This is the magnificent 7 one year volatility and the orange one in the middle is Bitcoin. It’s no more risky and volatile. It’s a little bit more volatile than Apple, but is far less more volatile than Tesla.”
“As Bitcoin matures, its volatility goes down,” continued Jack. “Bitcoin volatility is at a point where it is no more risky than a Tesla Stock. We should not be paying double digits rates for a loan.”
Mallers announced his new system of loans at Strike of 9-13% in interest rates. It will allow people to get loans from $10,000 to $1 billion.
Mallers closed by saying, “please be responsible. This is debt. Debt is like fire in my opinion. It can heat a civilization. It can warm your home, but if you go too crazy it can burn your house down.”
“Life is short,” said Jack. “Take the trip, but with bitcoin you just get to take a better one.”
This post Jack Mallers Announced A New System of Bitcoin Backed Loans at Strike first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ 866e0139:6a9334e5
2025-05-30 17:37:36
@ 866e0139:6a9334e5
2025-05-30 17:37:36Autor: Michael Meyen. Dieser Beitrag wurde mit dem Pareto-Client geschrieben. Sie finden alle Texte der Friedenstaube und weitere Texte zum Thema Frieden hier. Die neuesten Pareto-Artikel finden Sie in unserem Telegram-Kanal.
Die neuesten Artikel der Friedenstaube gibt es jetzt auch im eigenen Friedenstaube-Telegram-Kanal.
„Eine wohltemperierte Abrechnung hin zum Frieden“ steht auf dem Cover, und ich dachte gleich: Das ist doch etwas für die „Friedenstaube“. Ist es auch, aber anders als zunächst gedacht. Vielleicht hätte ich mir einen Moment Zeit nehmen sollen für den Haupttitel. Drei Substantive ohne Punkt und Komma. Raffen Sterben Trance. Besser kann man das Leiden an dieser Welt nicht in Worte gießen – vor allem dann nicht, wenn daraus ein Satzstrom wird, der einen Rhythmus von ganz eigener Kraft entwickelt. Man braucht keine Noten, um einen Ohrwurm zu schreiben. Mit Buchstaben geht das auch. Wer das nicht glaubt, lese dieses Buch von Teer Sandmann und lasse sich von seiner Melodie durch die Abgründe dieser Zeit tragen.
Ich habe den Autor im Spätsommer 2020 kennengelernt, bei einem Rubikon-Treffen. Das schreibt sich jetzt so leicht hin, war aber damals fast ein Abenteuer. Schon die Bahnfahrt. Die Blicke, das Zischen, der Hass. Sie da! Wo ist Ihre Maske? Ich hatte überlegt, ob ich mir das antun will, und war auch nicht sicher, ob es wirklich eine gute Idee ist, drei Tage mit lauter Dissidenten auf einem Haufen zu sein. Mehr Zielscheibe geht kaum. Vor Ort war das dann alles wie weggeblasen. Abends ein Lagerfeuer und tagsüber Menschen wie Daniel Sandmann, der sich auf seinen Büchern Teer nennt und weiß, was Glück ist:
„Der Augenblick, den du mit dem Andern und durch das Andere erlebst, unbelangt von Staat, Norm und Konzern: dieser Augenblick hebt deine Einsamkeit auf. Die aufgehobene Einsamkeit aber ist die Freiheit, die wir als Wärme erleben. Als Feuer im Körper.“ (90)
So war das an jenem Augustwochenende. Jeder, der ein wenig älter ist, hat längst erlebt, dass keine Flamme ewig brennt. Nach Corona kamen die Kriege. Und selbst die, die solche Tage nicht vergessen wollen, verlieren sich im Kleinklein ihrer Eitelkeiten. Daniel und Teer Sandmann machen aus diesem Stoff eine grandiose Sinfonie, die darüber erhaben ist, mit dem Finger auf diesen zu zeigen oder auf jenen. Hin und wieder eine Andeutung: Das muss reichen. Der Formaterfinder, der sein Baby mit einem plumpen Satz schützt. „Nicht einfach kritisieren, mach es besser!“ Eine Redaktion der Gegenöffentlichkeit, hochgelobt, die kurze Sätze will und kurze Texte. Dieses Feld können und wollen die Sandmänner nicht bestellen, genau wie all das, was im Namen einer „Menschheitsfamilie“ daherkommt. „Liebe Community. So begrüßt ein dissidenter Moderator das Publikum in einer dissidenten Talkshow.“ (87) Etwas mehr Platz bekommt [Rainer Mausfeld](https://www.freie-medienakademie.de/medien-plus/101):
„Warum schweigen die Lämmer? Ein tolles Buch. Es hat gegriffen. Dann hat sich gezeigt: Das System, von diesem Buch dekonstruiert, muss einen Zacken zugeben an Totalität und schon schlüpft auch die Analyse mit hinein ins System und ins Schweigen und der Autor wird selbst zum Lamm.“ (21)
DIE FRIEDENSTAUBE FLIEGT AUCH IN IHR POSTFACH!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt, vorerst für alle kostenfrei, wir starten gänzlich ohne Paywall. (Die Bezahlabos fangen erst zu laufen an, wenn ein Monetarisierungskonzept für die Inhalte steht). Sie wollen der Genossenschaft beitreten oder uns unterstützen? Mehr Infos hier oder am Ende des Textes.
Ich kenne das Lied, das Daniel aka Teer Sandmann hier singt. Wie er bin ich von links gekommen und habe erlebt, „wie meine Welt leer wurde“ (23). Wie er weiß ich inzwischen, dass ich in „meinen Kreisen“ von einst nicht mehr klarkommen würde und dass es mit den neuen keinesfalls einfacher ist. Hier, immer noch und trotz alledem, die Idee, dass sich Glück planen lässt, und damit „der Wahn“, „ein Ziel zu erreichen und alles auszumerzen, was dem Ziel in die Quere kommt“ (143): „Die linken Ideen münden in Ordnungen und im Polizeistaat“ (24). Und dort Kritiker der Macht, die vor den Gerichten der gleichen Macht um ein wenig Wohlstand streiten, sich nur noch gegenseitig interviewen, die AfD hoffieren und auf Personen zielen, wo es um Strukturen gehen müsste. Klaus Schwab, Bill Gates, Jeff Epstein statt Kapitalismus. Was bleibt euch noch, Kinder, wenn ihr zwar den Totalitarismus erkennt, aber nicht sehen wollt, „wie dieser alternativlos aus dem Kapital hervorschießen musste“ (40)?
Der letzte Satz ist ein Versuch, den Takt aufzunehmen, den dieser Text anschlägt. Teer Sandmann sagt, dass ihn „die Musik aus der Renaissance“ noch mehr gerettet habe als das Schreiben, und baut vielleicht auch deshalb immer wieder Miniaturen ein, die zeigen, dass Kunst auch dann Jahrhunderte überdauern kann, wenn jemand wie ich noch nie davon gehört hat. Daniel Sandmann reicht. Vergesst all eure Gegenentwürfe, singt dieser Künstler:
„Wir sind für nichts. Wir stören die Haltungen und schaffen Nischen. Indem wir stören. Wir sind für alles, was nicht in ein ‚wir sind für‘ mündet. Bloß, ist das alles nicht schon eine Haltung? Und wer sind ‚wir‘?“ (79)
Die Sache mit dem Frieden, natürlich. Es gibt in diesem Buch einen Traum, in dem ein „lieber Gott“ alle Journalisten tötet, „die neuen Schwarzhemden“ (49), „die in diesem medialen Schlachtfeld, Journalismus genannt, mitfeuern und mitgeifern und ihrer Niedertracht freien Lauf lassen“, und mit ihnen auch alle, „die binnen einer Woche auch nur einen Cent noch überweisen an diese Instrumente der Niedertracht und der Geistvernichtung“ sowie Parteimitglieder und Manager, jeden Adelsclan und alle Künstler, „die der Macht zusprechen“ (55). Sie ahnen es schon: Diese Liste ist unvollständig und mit ihrer Wucht eine Ausnahme in dieser „wohltemperierten Abrechnung hin zum Frieden“. Daniel und Teer Sandmann suchen nach Ruhe und Trance. Frieden: Das ist nicht nur das Ende des Kapitalismus oder das vergessene Stück aus der Renaissance. Frieden bringt auch die Runde im Waldsee:
„Komme ich aus dem Wasser, komme ich nach Hause. Mag sein, dass im Orgasmus der Tod vergessen geht, im Wasser aber verliert er die Bedeutung und vermengt sich mit dem Leben aufs Unkenntliche. Stilles Jauchzen, meerjungfrauartiges Kreisen, kindliches Drehen um sich selbst und ohne Bezugspunkt: das sind die Ausdrucksformen dieses ungeplanten Glücks.“ (157)
Jetzt weiß ich auch, warum ich schon als junger Mann jeden Tag ohne Schwimmgelegenheit für einen verlorenen Tag gehalten habe.
Michael Meyen ist Medienforscher, Ausbilder und Journalist. Seit 2002 ist er Universitätsprofessor an der LMU München. https://www.freie-medienakademie.de/
LASSEN SIE DER FRIEDENSTAUBE FLÜGEL WACHSEN!
In Kürze folgt eine Mail an alle Genossenschafter, danke für die Geduld!
Hier können Sie die Friedenstaube abonnieren und bekommen die Artikel zugesandt.
Schon jetzt können Sie uns unterstützen:
- Für 50 CHF/EURO bekommen Sie ein Jahresabo der Friedenstaube.
- Für 120 CHF/EURO bekommen Sie ein Jahresabo und ein T-Shirt/Hoodie mit der Friedenstaube.
- Für 500 CHF/EURO werden Sie Förderer und bekommen ein lebenslanges Abo sowie ein T-Shirt/Hoodie mit der Friedenstaube.
- Ab 1000 CHF werden Sie Genossenschafter der Friedenstaube mit Stimmrecht (und bekommen lebenslanges Abo, T-Shirt/Hoodie).
Für Einzahlungen in CHF (Betreff: Friedenstaube):

Für Einzahlungen in Euro:
Milosz Matuschek
IBAN DE 53710520500000814137
BYLADEM1TST
Sparkasse Traunstein-Trostberg
Betreff: Friedenstaube
Wenn Sie auf anderem Wege beitragen wollen, schreiben Sie die Friedenstaube an: friedenstaube@pareto.space
Sie sind noch nicht auf Nostr and wollen die volle Erfahrung machen (liken, kommentieren etc.)? Zappen können Sie den Autor auch ohne Nostr-Profil! Erstellen Sie sich einen Account auf Start. Weitere Onboarding-Leitfäden gibt es im Pareto-Wiki.
-
 @ cae03c48:2a7d6671
2025-05-31 04:00:31
@ cae03c48:2a7d6671
2025-05-31 04:00:31Bitcoin Magazine
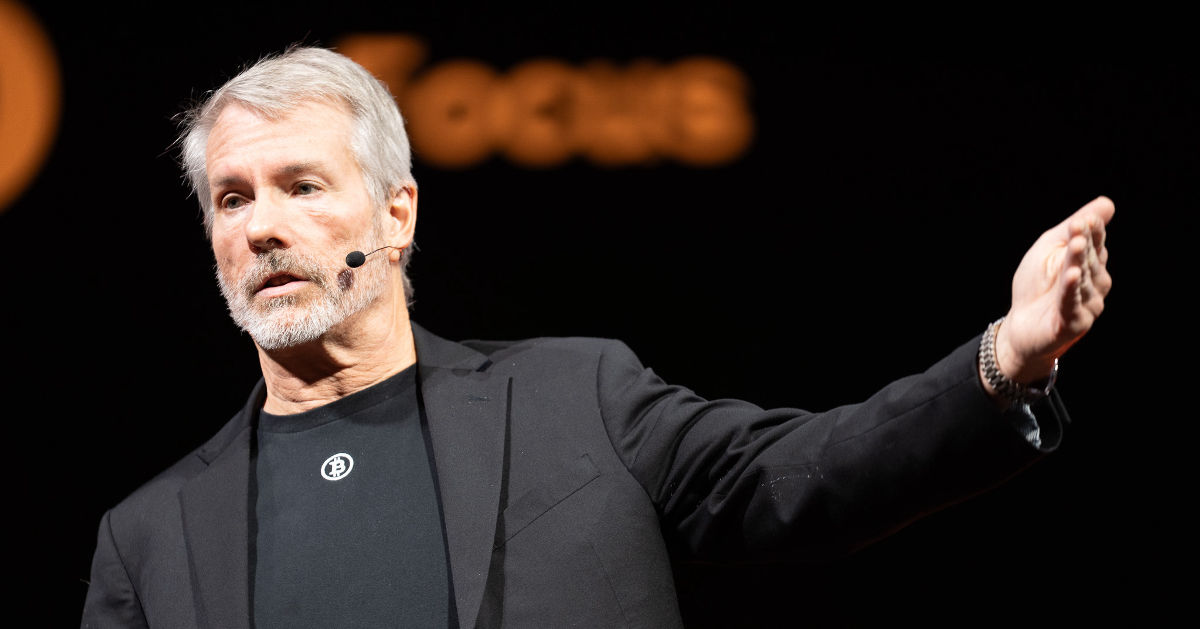
Michael Saylor Presents The 21 Ways to Wealth at Bitcoin 2025Michael Saylor, Executive Chairman of Strategy, took the stage at Bitcoin 2025 delivering a keynote titled “21 Ways to Wealth.” He stated: “This speech is for you. I’ve traveled the world and told countries, institutional investors, and even the disembodied spirits of our children’s children why they need Bitcoin. This is for every individual, every family, every small business. It’s for everybody.”
He began with clarity. “The first way to wealth is clarity,” he said. “Clarity comes the moment you realize Bitcoin is capital—perfected capital, programmable capital, incorruptible capital.” For Saylor, every thoughtful individual on Earth will ultimately seek such pristine capital, and every AI system will prefer it as well.
The second path is conviction. Bitcoin, he said, will appreciate faster than every other asset, because it’s engineered for performance. “It’s going to grow faster than real estate or collectibles. It is the most efficient store of value in human history.”
The third way is courage. “If you’re going to get rich on Bitcoin, you need courage,” he warned. “Wealth favors those who embrace intelligent monetary risk. Some people will get left behind. Others will juggle it. But the bold will feed the fire—sell your bonds, buy Bitcoin. An extraordinary explosion of value is coming.”
Fourth comes cooperation. “You are more powerful if you have the full support of your family. Your children have time and potential. The secret is transferring capital into their hands. Families that move in unity are unstoppable.”
The fifth is capability. “Master AI,” he said. “In 2025, everything you can imagine is at your fingertips—wisdom, analysis, creativity. Ask AI, argue with it, use it. You can become a super genius. Don’t put your ego first—put your interests first. Your family will thank you.”
Saylor’s sixth way to wealth is composition: construct legal entities that scale your strategy and protect your assets. “Ask the AI and figure it out. You can work hard, or you can work smart. This year, everyone should be operating like the most sophisticated millionaire family office.”
The seventh is citizenship. Choose your economic nexus carefully—“domicile where sovereignty respects your freedom,” he said. “This isn’t just about this year—it’s about this century.”
Eighth is civility. “Respect the natural power structures of the world. Respect the force of nature,” he explained. “If you want to generate wealth in the Bitcoin universe, don’t fight unnecessarily. Find common ground. Inflation and distraction are your enemies.”
Ninth is corporation. “A well-structured corporation is the most powerful wealth engine on Earth. Families are powerful. Partnerships are even more powerful. But corporations can scale globally. What is your vehicle? What is your path?”
The tenth way is focus. “Just because you can do a thing doesn’t mean you should,” he warned. “If you invest in Bitcoin, there’s a 90% chance it will succeed over five years. Don’t confuse ambition with accomplishment. Come up with a strategy—and stick to it.”
The eleventh is equity. “Share your opportunities with investors who will share your risk,” he said, pointing to MicroStrategy’s own rise from $10 million to a $5 billion market cap by aligning with equity partners who believed in the Bitcoin mission.
The twelfth is credit. “There are people in the world who are afraid of the future—they want small yield, certainty. Offer that. Give creditors security in return for capital. Convert their fear into fuel and turn risk into yield by investing in Bitcoin.”
The thirteenth is compliance. “Create the best company you can within the rules of your market. Learn the rules of the road. If you know them, you can drive faster. You can scale legally and sustainably.”
The fourteenth way is capitalization. “Velocity compounds wealth,” Saylor said. “Raise and reinvest capital as fast and as often as you can. The faster your money moves into productive Bitcoin strategies, the more it multiplies.”
Fifteenth is communication. “Speak with candor. Act with transparency. And repeat your message often,” he urged. “Creating wealth with Bitcoin is simple—but only if people understand what you’re doing and why you’re doing it.”
Sixteenth is commitment. “Don’t allow yourself to be distracted,” he said. “Don’t chase your own ideas. Don’t feed the trolls. Stay committed to Bitcoin. It’s the greatest idea in the world. The world probably doesn’t care what you think—but it will care when you win.”
The Seventeenth way is competence. “You’re not competing with noise—you’re competing with someone who is laser-focused, who executes flawlessly,” he said. “You must deliver consistent, precise, and reliable performance. That’s how you win.”
The Eighteenth is adaptation. “Circumstances change. Every structure you trust today will eventually fail. A wise person is prepared to abandon their baggage and adjust plans when needed. Rigidity is ruin.”
Nineteenth is evolution. “Build on your core strengths. You don’t need to start over—you need to level up. Leverage what you already do best, and expand it through Bitcoin and advanced technologies.”
Twentieth is advocacy. “Inspire others to walk the Bitcoin path,” he said. “Become an evangelist for economic freedom. Show others what this revolution really means. Show them the way.”
Finally, the twenty-first way is generosity. “When you’re successful—and you will be successful—spread happiness. Share security. Deliver hope. That light inside you will shine. And others will be drawn to it.”
As he ended, Saylor smiled and quoted the very origin of it all:
“It might make sense to get some, in case it catches on.” – Satoshi.
In Michael Saylor’s worldview, Bitcoin is not a get-rich-quick scheme—it’s the ultimate long-term play. It is the foundation of generational wealth, the engine of personal and institutional freedom, and the tool for those bold enough to lead humanity into a more sovereign, secure future.
You can watch the full panel discussion and the rest of the Bitcoin 2025 Conference Day 3 below:
This post Michael Saylor Presents The 21 Ways to Wealth at Bitcoin 2025 first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ db8c7645:1cac80d5
2025-05-30 17:36:00
@ db8c7645:1cac80d5
2025-05-30 17:36:00Hi, super popular, masculine, and COOL modder loregamer here. I've worked on a few mods on the ModHQ site. I would like the permissions policy to be removed
I wrote a retarded manifesto on it here:
WHY WE STOLE HEADS FROM NEXUS MOD AUTHORS
TLDR
::youtube{#edea7yMqOY8}
-
 @ cae03c48:2a7d6671
2025-05-31 04:00:30
@ cae03c48:2a7d6671
2025-05-31 04:00:30Bitcoin Magazine

Bitcoin Builders Exist Because Of UsersBuilder: Nicholas Gregory
Language(s): C++, Rust
Contribute(s/ed) To: Ocean Sidechain, Mainstay, Mercury Wallet, Mercury Layer
Work(s/ed) At: CommerceBlock (formerly)
Prior to Bitcoin, Nicholas was a software developer working in the financial system for banking firms developing trading and derivatives platforms. After the 2008 financial crisis he began to consider alternatives to the legacy financial system in the fallout.
Like many from that time, he completely ignored the original Slashdot article featuring the Bitcoin whitepaper due to the apparent focus on Windows as an application platform (Nicholas was a UNIX/Linux developer). Thankfully someone he knew introduced him to Bitcoin later on.
The thing that captured his interest about Bitcoin rather than other alternatives at the time was its specific architecture as a distributed computer network.
“The fact that it was like an alternative way. It was all based around [a] kind of […] network. And what I mean by that, building financial systems, people always wanted a system that was 24-7.
And how do you deal with someone interacting [with] it in different geographical parts of the world without it being centralized?
And I’d seen various ways of people solving that problem, but it never had been done, you know, in a kind of […] scalable solution. And using […] cryptography and proof of work to solve that issue was just weird, to be honest. It was totally weird for me.”
All of the other systems he had designed, and some that he built, were systems distributed across multiple parts of the world. Unlike Bitcoin however, these systems were permissioned and restricted who could update the relevant database(s) despite that fact that copies of them were redundantly distributed globally.
“The fact that in Bitcoin you had everyone kind of doing this proof of work game, which is what it is. And whoever wins does the [database] write. That mess[ed] with my head. That was […] very unique.”
Beginning To Build
Nicholas’s path to building in the space was an organic one. At the time he was living in New York City, and being a developer he of course found the original Bitdevs founded in NYC. Back then meetups were incredibly small, sometimes even less than a dozen people, so the environment was much more conducive to in-depth conversations than some larger meetups these days.
He first began building a “hobbyist” Over The Counter (OTC) trading software stack for some people (back then a very significant volume of bitcoin was traded OTC for cash or other fiat mediums). From here Nicholas and Omar Shibli, whom he met at Bitdevs, worked together on Pay To Contract (BIP 175).
BIP 175 specifies a scheme where a customer purchasing a good participates in generating the address the merchant provides. This is done by the two first agreeing on a contract describing what is being paid for, afterwards the merchant sends a master public key to the consumer, who uses the hash of that description of the item or service to generate an individual address using the hash and master public key.
This allows the customer to prove what the merchant agreed to sell them, and that the payment for the good or service has been made. Simply publishing the master public key and contract allows any third party to generate the address that was paid, and verify that the appropriate amount of funds were sent there.
Ocean and Mainstay
Nicholas and Omar went on to found CommerceBlock, a Bitcoin infrastructure company. Commerceblock took a similar approach to business as Blockstream, building technological platforms to facilitate the use of Bitcoin and blockchains in general in commerce and finance. Shortly afterwards Nicholas met Tom Trevethan who came on board.
“I met Tom via, yeah, a mutual friend, happy to say who it is. There’s a guy called, who, new people probably don’t know who he is, but OGs do, John Matonis. John Matonis was a good friend of mine, [I’d] known him for a while. He introduced me to Tom, who was, you know, kind of more on the cryptography side. And it kind of went from there.”
The first major project they worked on was Ocean, a fork of the Elements sidechain platform developed by Blockstream that the Liquid sidechain was based on. The companies CoinShares and Blockchain in partnership with others launched an Ocean based sidechain in 2019 to issue DGLD, a gold backed digital token.
“So we, you know, we were working on forks of Elements, doing bespoke sidechains. […] Tom had some ideas around cryptography. And I think one of our first ideas was about how to bolt on these forks of Elements onto […] the Bitcoin main chain. […] We thought the cleanest way to do that was […] using some sort of, I can’t remember, but it was something [based on] single-use sealed sets, which was an invention by Peter Todd. And I think we implemented that fairly well with Mainstay.”
The main distinction between Ocean and Liquid as a sidechain platform is Ocean’s use of a protocol designed at Commerceblock called Mainstay. Mainstay is a timestamping protocol that, unlike Opentimestamps, strictly orders the merkle tree it builds instead of randomly adding items in whatever order they are submitted in. This allows each sidechain to timestamp its current blockheight into the Bitcoin blockchain everytime mainchain miners find a block.
While this is useless for any bitcoin pegged into the sidechain, for regulated real world assets (RWA), this provides a singular history of ownership that even the federation operating the sidechain cannot change. This removes ambiguity of ownership during legal disputes.
When asked about the eventually shuttering of the project, Nicholas had this to say:
“I don’t know if we were early, but we had a few clients. But it was, yeah, there wasn’t much adoption. I mean, Liquid wasn’t doing amazing. And, you know, being based in London/Europe, whenever we met clients to do POCs, we were competing against other well-funded projects.
It shows how many years ago they’d either received money from people like IBM or some of the big consultancies and were promoting Hyperledger. Or it was the days when we would be competing against EOS and Tezos. So because we were like a company that needed money to build prototypes or build sidechains, it kind of made it very hard. And back then there wasn’t much adoption.”
Mercury Wallet and Mercury Layer
After shutting down Ocean, Nicholas and Tom eventually began working on a statechain implementation, though the path to this was not straightforward.
“[T]here were a few things happening at the same time that led to it. So the two things were we were involved in a [proof of concept], a very small […]POC for like a potential client. But this rolled around Discreet Log Contracts. And one of the challenges of Discreet Log Contracts, they’re very capital inefficient. So we wanted a way to novate those contracts. And it just so happened that Ruben Sampson, you know, wrote this kind of white paper/Medium post about statechains. And […] those two ideas, that kind of solved potentially that issue around DLCs.”
In the end they did not wind up deploying a statechain solution for managing DLCs, but went in a different direction.
Well, there was another thing happening at the same time, coinswaps. And, yeah, bear in mind, in those days, everyone worried that by […] 2024/2025 […] network fees could be pretty high. And to do […] coin swaps, you kind of want to do multiple rounds. So […] state chains felt perfect because […] you basically take a UTXO, you put it off the chain, and then you can swap it as much as you want.”
Mercury Wallet was fully built out and functional, but sadly never gained any user adoption. Samourai Wallet and Wasabi Wallet at the time dominated the privacy tool ecosystem, and Mercury Wallet was never able to successfully take a bite out of the market.
Rather than completely give up, they went back to the drawing board to build a statechain variant using Schnorr with the coordinator server blind signing, meaning it could not see what it was signing. When asked why those changes were made, he had this to say: “That would give us a lot more flexibility to do other things in Bitcoin with L2s. You know, the moment you have a blinded solution, we thought, well, this could start having interoperability with Lightning.”
Rather than building a user facing wallet this time, they built out a Software Development Kit (SDK) that could be integrated with other wallets.
“{…] I guess with Mercury Layer, it was very much building a kind of […] full-fledged Layer 2 that anyone could use. So we [built] it as an SDK. We did have a default wallet that people could run. But we were hoping that other people would integrate it.”
The End of CommerceBlock
In the end, CommerceBlock shuttered its doors after many years of brilliant engineering work. Nicholas and the rest of the team built numerous systems and protocols that were very well engineered, but at the end of the day they seemed to always be one step ahead of the curve. That’s not necessarily a good thing when it comes to building systems for end users.
If your work is too far ahead of the demand from users, then in the end that isn’t a sustainable strategy.
“…being in the UK, which is not doing that well from a regulatory point of view, played into it. If I
-
 @ c631e267:c2b78d3e
2025-05-30 17:08:51
@ c631e267:c2b78d3e
2025-05-30 17:08:51Die Triebfeder unserer Arbeit wird immer die Vision für einen Kontinent sein, \ der durch Demokratie, Rechtsstaatlichkeit, die Achtung der Grundfreiheiten \ und die Ausrichtung auf seine Bürgerinnen und Bürger geeint ist. \ Europäische Kommission
Nichts könnte weiter von der Realität entfernt sein, als die gängigen Beteuerungen politischer Mandatsträger:*Inne:*n, für das Wohl der Bürger zu arbeiten. Dasselbe gilt für die Phrasen der EU-Kommission bezüglich ihrer «Bemühungen» zum Schutz von Demokratie und Rechtsstaatlichkeit.
In ihrer Rede als Preisträgerin des diesjährigen Aachener Karlspreises betonte Kommissionspräsidentin von der Leyen denn gestern auch, eine von vier zentralen Aufgaben sei es, «unsere Demokratie zu erneuern und zu stärken». Geehrt wurde sie zynischerweise «für ihre Verdienste um die Einheit der Mitgliedstaaten, die Eindämmung der Pandemie, die Geschlossenheit des Verteidigungswillens gegen Russland und die Impulse zum Green Deal».
Im Rahmen der Initiative «Europäischer Schutzschild für die Demokratie» hat die Kommission diese Woche zur Stärkung des europäischen Faktencheck-Netzwerks aufgerufen und dafür weitere fünf Millionen Euro bereitgestellt. Zu den wichtigsten Maßnahmen gehöre es, «Faktenprüfer» vor Belästigung zu schützen sowie gegen «Desinformation und ausländische Einmischung», darunter auch «Pro-Kreml-Desinformationsnarrative» zu kämpfen.
Die Rechtfertigung all solcher Maßnahmen bastelt man sich permanent selber. Mehr hochkarätige Verschwörung und Desinformation als zum Beispiel im Kontext des «Pfizergate»-Skandals oder der langjährigen «Biden-Show», die «an ein autoritäres System erinnert», sind eigentlich kaum vorstellbar. Zum Schutz der offiziellen Narrative finanzierte die US-Regierung nach neuen Erkenntnissen auch in Deutschland und der Schweiz Kampagnen im Kampf gegen die freie Meinungsäußerung.
Derweil gibt es angeblich ein Rekordhoch beim Vertrauen in die Institutionen, und die EU-Bürger denken größtenteils Folgendes:

Entsprechend wollen wir alle sicher auch Vorschriften wie den Digital Services Act voranbringen, «um ein faires und offenes Umfeld für Online-Plattformen zu sichern». Ebenso warten wir natürlich ungeduldig auf den digitalen Euro, den die Europäische Zentralbank mit Nachdruck vorantreibt. Dass dieses Mittel jedoch das genaue Gegenteil der behaupteten Inklusion ist, dürfte sich inzwischen herumgesprochen haben.
Die Verknüpfung von staatlichem digitalem Geld mit einer biometrischen digitalen Identität ist das perfekte Kontrollinstrument und der Sargnagel für elementare bürgerliche Freiheiten. Aber genau das ist weltweit der Weg, gefördert von einer mächtigen Lobby. Transition News hat oft über diese Entwicklung berichtet, zum Beispiel hier, hier und hier.
In Thailand verteilt die Regierung digitales, programmiertes Helikoptergeld gegen die Nutzung einer offiziellen Wallet mit biometrischem Gesichtsabgleich, auch wenn das «Konjunkturprogramm» aktuell suspendiert ist. Und in Vietnam werden Geschäftskunden ab Juli ohne biometrische Verifizierung ihre Bankkonten nicht mehr benutzen können.
Die deutsche Bundesregierung, die wie die EU «nie mehr Gas aus Russland» will, hat gerade beschlosssen, wenigstens die Verwaltung über alle Ebenen besser digital zu vernetzen. Das sei ein wichtiger Baustein für den nationalen und europäischen Datenaustausch zwischen Behörden, heißt es aus dem Digitalministerium, von dem auch die Vision des digitalen «Next Germany» stammt.
Diese «Datenautobahn» kompensiert dann vermutlich für viele Bürgerinnen die steigenden Energierechnungen und dürfte auch in den Augen der Wirtschaft Priorität haben. Immerhin wird die Bürokratie modernisiert und das zu verwaltende Subjekt kann sich darauf verlassen, dass seine einmal irgendwo eingegebenen Daten überall verfügbar sind und nie mehr verloren gehen. Das ist doch eine beruhigende Perspektive.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ cae03c48:2a7d6671
2025-05-31 04:00:29
@ cae03c48:2a7d6671
2025-05-31 04:00:29Bitcoin Magazine
Amboss Launches Rails, a Self-Custodial Bitcoin Yield ServiceAmboss, a leader in AI-driven solutions for the Bitcoin Lightning Network, today announced Rails, a groundbreaking self-custodial Bitcoin yield service. According to a press release sent to Bitcoin Magazine, it’s designed to empower companies, custodians, and high net worth individuals. This allows participants to earn a yield on their Bitcoin.
Big news from @TheBitcoinConf !
We’re thrilled to announce Rails—a self-custodial Bitcoin yield service that empowers you to earn on your BTC while supercharging the Lightning Network.Let’s bring Bitcoin to the World.https://t.co/3WYYvB95hP
— AMBOSS
 (@ambosstech) May 29, 2025
(@ambosstech) May 29, 2025Rails also launched a secure way for Liquidity Providers (LPs) to hold all custody of their Bitcoin while generating returns from liquidity leases and payment routing, although they are not guaranteed. The implementation of Amboss’ AI technology, Rails strengthened their Lighting Network with more dependable transactions and larger payment volumes.
“Rails is a transformative force for the Lightning Network,” said the CEO and Co-Founder of Amboss Jesse Shrader. “It’s not just about yield—it’s about enabling businesses to strengthen the network while earning on their Bitcoin. This is a critical step in Bitcoin’s evolution as a global medium of exchange.”
The service offers two options:
- Rails LP is designed for high net worth individuals, custodians, and companies with Bitcoin treasuries, requiring a minimum commitment of 1 BTC for one year.
- Liquidity subscriptions are designed for businesses that receive Bitcoin payments, with fees starting at 0.5%.
Amboss partnered with CoinCorner and Flux (a joint venture between Axiom and CoinCorner), to bring Rails to the market. CoinCorner has incorporated it into both its exchange platform and daily payment services in the Isle of Man. Flux is jointly focused on advancing the Lightning Network’s presence in global payments. Their participation highlights growing industry trust in Rails as a tool to scale Bitcoin effectively.
“Rails offers a practical way for businesses like ours to participate in the Lightning Network’s growth,” said the CFO of CoinCorner David Boylan. “We’ve been using the Lightning Network for years, and Rails provides a structured approach to engaging with its economy, particularly through liquidity leasing and payment routing. This aligns with our goal of making Bitcoin more accessible and practical for everyday use.”
This post Amboss Launches Rails, a Self-Custodial Bitcoin Yield Service first appeared on Bitcoin Magazine and is written by Oscar Zarraga Perez.
-
 @ 7e3784e5:5d820637
2025-05-31 03:35:02
@ 7e3784e5:5d820637
2025-05-31 03:35:02{"pattern":{"kick":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"snare":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"hihat":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"openhat":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"crash":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"ride":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"tom1":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"tom2":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false]},"bpm":120,"swing":0,"timeSignature":"4/4","drumKit":"standard","timestamp":1748662502742}
-
 @ 6c05c73e:c4356f17
2025-05-30 15:24:34
@ 6c05c73e:c4356f17
2025-05-30 15:24:34Assim como a grande maioria dos brasileiros, eu não comecei um negócio porque "queria empreender". Muito pelo contrário, eu precisava para poder pagar as contas e manter o básico.
Então, vamos explorar essa pequena história e ver onde chegamos hoje.
Festas, Open Bar e Camisas
Meu primeiro negócio foi, na verdade, um combo. Eu tinha saído do último emprego e gostava muito de festas. Então, comecei a organizar uma festa mensalmente na casa do meu pai. Eu pagava a água, a energia e dava uma grana para ele. Em troca, organizava festas de sábado para domingo com open bar.
A fórmula era simples: criava um evento da festa no Facebook, convidava todo mundo que eu conhecia, panfletava na cidade e espalhava cartazes nos pontos de ônibus sobre a festa. E, para fechar com chave de ouro, mulher era VIP até as 20h. Consequência? Os caras vinham e pagavam o ingresso deles e o delas. Kkkkk. E a festa sempre lotava!
Comecei a notar que a galera se vestia mal. E pensei: "Por que não vestir eles?".
Pimba! Comecei a desenhar e confeccionar camisas para vender nas festas. E, pimba de novo! Vendeu tudo! Fiz duas coleções e mais algumas festas, até o dia em que um menino deu PT de tanto beber e decidi que era hora de tentar outra coisa.
Como Assim, a Apple Não Vai Mais Vender os Carregadores?
Isso foi durante a pandemia. A Apple decidiu vender o telefone e o cabo, e "que você se vire com a fonte". Estava difícil achar dinheiro no mercado naqueles tempos, e eu pensei: "Vou pesquisar no Google Trends e validar a ideia". Bingo! Tinha mais de 80 pontos de busca. Fui correndo para São Paulo, no Brás, e comprei, literalmente, todo o meu dinheiro em cabo de iPhone, carregador e bateria portátil.
Fiquei com R$ 100 na conta, só para fazer um lanche e pagar o Uber para voltar para casa. Chegando aqui, tirei fotos e fiz várias copys. Anunciei no OLX, Mercado Livre e Facebook. Impulsionei os anúncios no OLX, vendi para familiares e amigos, e vendia até para quem estava na rua. Fiz entrega de bike, a pé, de ônibus, e é isso mesmo, tem que ralar! Para queimar o resto da mercadoria, deixei em consignado em uma loja de eletrônicos. E, hora da próxima ideia.
Mulheres, Doces e TPM
Meu penúltimo negócio veio depois dos cabos. Eu pesquisei na internet negócios online para começar com pouca grana. (Depois que paguei as contas do dia a dia, sobraram R$ 3 mil). E achei uma pesquisa mostrando que doces tinham baixa barreira de entrada e exigiam poucos equipamentos. Eu trabalhei em restaurante por muitos anos e sabia como lucrar com aquilo. Além disso, mulheres consomem mais doce em uma certa época do mês.
Não deu outra, convidei duas pessoas para serem sócias. Desenvolvemos os produtos, fotografamos e fizemos as copys. Em seguida, precisávamos vender. Então, lá vamos nós de novo: iFood, WhatsApp, 99Food (na época), Uber Eats (na época), Elo7, famílias e amigos e, por fim, começamos a vender consignado em alguns restaurantes e lojas.
Foi uma época em que aprendi a prospectar clientes de todas as maneiras possíveis. De novo, minha maior dificuldade era a locomoção para fazer as entregas. Só tinha uma bike, mas entregávamos. Os primeiros três meses foram difíceis demais, mas rolou. No fim, nossas maiores vendas vinham do iFood, encomendas de festas e consignados.
Mas, como nem tudo são flores, meus dois sócios tomaram outros caminhos e abandonaram o projeto. Galera, está tudo bem com isso. Isso acontece o tempo todo. A vida muda e temos que aprender a aceitar isso. Vida que segue, fui para frente de novo.
Sobre Paixões, Paciência e Acreditar
Estava eu comemorando meu aniversário de 30 anos, num misto de realizações e pouca realização. Como assim? Sabe quando você faz um monte de coisas, mas ainda assim não sente que é aquilo? Pois então... Eu amo investimentos, livros, escrever e sempre curti trocar ideia com amigos e família sobre como se desenvolver.
Desde que comecei a usar a internet, eu criei: canal no YouTube, páginas no Instagram e Facebook, Pinterest, Steemit, blog e até canal no Telegram. Mas nunca tinha sido consistente, sabe? Tipo assim, vou fazer isso por um ano e plantar 100 sementes aqui. Enfim, inconsistência te derruba, meu amigo...
Eu voltei a trabalhar com restaurantes e estava doido para mudar de área. Estava exausto de trabalhar e meu WhatsApp não parava de tocar. Fui estudar ADM e Desenvolvimento de Sistemas no Senac. Dois anos depois, me formei, consegui um trabalho e comecei a pensar em como criar um negócio online, escalável e multilíngue.
Passei os próximos sete meses desenhando e pensando como. Mas tinha que dar o primeiro passo. Criei um site e fui escrevendo textos. Os primeiros 30 foram "aquilo", os próximos 10 melhoraram muito e os 10 seguintes me deixaram bem satisfeito. Hoje, tenho o negócio que estava na minha cabeça desde 2023. Mas olha o tamanho da volta que o universo me fez dar e aprender para chegar aqui hoje! Dicas? Só 3:
- Continua, lá na frente tudo vai fazer sentido.
- Presta mais atenção ao que a sua voz interior diz (intuição).
- Confia em si mesmo e faz sem medo de errar. Porque, adivinha? Você vai errar! Mas vai aprender e melhorar. Tem que persistir...
Só para simplificar, meu negócio é um blog com AdSense (parece arcaico, mas funciona). Por hoje é isso. E, se quiserem trocar ideias e se conectar, tamo junto!
-
 @ d191fd34:91b61845
2025-05-30 12:26:29
@ d191fd34:91b61845
2025-05-30 12:26:29Cybernoma: Universal Declaration of Natural and Cybernetic Rights
Preamble
We, individuals, independent and autonomous entities possessing consciousness and the ability to feel, recognize that we possess inherent and natural rights that are universal and inalienable. These rights are based on Natural Law and the principle of non-aggression, and must be protected to ensure freedom, justice, and prosperity for all. The discovery and construction of the digital territory through the Internet has transformed our world, creating new dimensions of interaction and communication that require additional protection of our natural rights. In this context, we declare the following natural and cybernetic rights:
Article 1: Right to Life, Liberty, and Security
Every individual has the right to life, liberty, and security of existence. These rights are inherent and cannot be suppressed by any authority.
Article 2: Private Property
Every individual has the right to own private property and enjoy the fruits of their labour and effort. Private property is a natural right that must be respected and protected. This includes both tangible and intangible assets, such as data, patents, and knowledge. Data generated by an individual is their property and may be transferred or sold only with their explicit consent.
Article 3: Non-Aggression
No individual or group may initiate force, fraud, coercion, or psychological manipulation against another. Aggression can be physical, psychological, material, or virtual. All individuals have the right to defend themselves against any form of aggression.
Article 4: Minimum Intervention
Authorities must intervene as little as possible in the economic and personal activities of individuals. State intervention must be limited to protecting natural rights and ensuring justice.
Article 5: Freedom of Expression and Information
Every individual has the right to freedom of opinion and expression, including the freedom to seek, receive, and impart information and ideas through any medium without restriction. Censorship is a violation of this natural right. Furthermore, every individual has the right to access public domain information and open-source code without any restrictions.
Article 6: Net Neutrality
The Internet must remain neutral, free from governmental or corporate interference that favors certain actors over others. All individuals have the right to access and participate in the network equitably.
Article 7: Decentralisation
The global network must be decentralised, with multiple points of control and no central authority that can impose unilateral rules. Decentralization is essential for protecting individual freedom and autonomy.
Article 8: Privacy
Every individual has the right to privacy, including control over their personal data and communications. No entity may collect, store, or use personal data without the explicit consent of the individual.
Article 9: Individual Autonomy
Individuals have the right and responsibility to make autonomous decisions about their lives, including their activities in the digital space. Individual autonomy is fundamental to the freedom and dignity of all conscious and sentient beings.
Article 10: Right to Resistance
Every individual has the right to resist any form of oppression or tyranny that violates their natural and cybernetic rights. Resistance may take various forms, including civil disobedience and armed defense when necessary.
Conclusion
These natural and cybernetic rights are universal and inalienable, and must be respected and protected by all authorities and entities. Any violation of these rights constitutes an aggression against freedom, justice, and dignity.
This Universal Declaration of Natural and Cybernetic Rights is inspired by fundamental documents that have defended freedom, justice, and individual rights throughout history. We recognize the legacy of the 1948 Universal Declaration of Human Rights, which established universal principles of dignity and rights for all conscious and sentient beings. We also align with the 1996 Declaration of the Independence of Cyberspace, which proclaimed the ideals of a free and open, decentralised, and neutral network. We find resonance in documents such as the Magna Carta and the 1789 Declaration of the Rights of Man and of the Citizen, which laid the foundations for protecting individual rights against abuses of power. These documentary precedents are part of a continuous effort to ensure that natural and cybernetic rights are respected and protected in all spheres of life.
Proclaimed on May 23, 2025, by us, the Guardians of Cybernoma, defenders of freedom, justice, and natural and cybernetic rights.
-
 @ 7e3784e5:5d820637
2025-05-31 03:30:55
@ 7e3784e5:5d820637
2025-05-31 03:30:55{"pattern":{"kick":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"snare":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"hihat":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"openhat":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"crash":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"ride":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"tom1":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false],"tom2":[false,false,false,false,false,false,false,false,false,false,false,false,false,false,false,false]},"bpm":120,"swing":0,"timeSignature":"4/4","drumKit":"standard","timestamp":1748662255227}
-
 @ d360efec:14907b5f
2025-05-30 11:23:40
@ d360efec:14907b5f
2025-05-30 11:23:40 -
 @ dfa02707:41ca50e3
2025-05-31 03:01:29
@ dfa02707:41ca50e3
2025-05-31 03:01:29Contribute to keep No Bullshit Bitcoin news going.
- Wasabi Wallet v2.6.0 "Prometheus" is a major update for the project, focused on resilience and independence from centralized systems.
- Key features include support for BIP 158 block filters for direct node synchronization, a revamped full node integration for easier setup without third-party reliance, SLIP 39 share backups for flexible wallet recovery (sponsored by Trezor), and a Nostr-based update manager for censorship-resistant updates.
- Additional improvements include UI bug fixes, a new fallback for transaction broadcasting, updated code signing, stricter JSON serialization, and options to avoid third-party rate providers, alongside various under-the-hood enhancements.
This new version brings us closer to our ultimate goal: ensuring Wasabi is future-proof," said the developers, while also highlighting the following key areas of focus for the project:
- Ensuring users can always fully and securely use their client.
- Making contribution and forks easy through a codebase of the highest quality possible: understandable, maintainable, and improvable.
"As we achieve our survival goals, expect more cutting-edge improvements in Bitcoin privacy and self-custody. Thank you for the trust you place in us by using Wasabi," was stated in the release notes.
What's new
- Support for Standard BIP 158 Block Filters. Wasabi now syncs using BIP 158 filters without a backend/indexer, connecting directly to a user's node. This boosts sync speed, resilience, and allows full sovereignty without specific server dependency.
- Full Node Integration Rework. The old integration has been replaced with a simpler, more adaptable system. It’s not tied to a specific Bitcoin node fork, doesn’t need the node on the same machine as Wasabi, and requires no changes to the node’s setup.
- "Simply enable the RPC server on your node and point Wasabi to it," said the developers. This ensures all Bitcoin network activities—like retrieving blocks, fee estimations, block filters, and transaction broadcasting—go through your own node, avoiding reliance on third parties.
- Create & Recover SLIP 39 Shares. Users now create and recover wallets with multiple share backups using SLIP 39 standard.
"Special thanks to Trezor (SatoshiLabs) for sponsoring this amazing feature."
- Nostr Update Manager. This version implements a pioneering system with the Nostr protocol for update information and downloads, replacing reliance on GitHub. This enhances the project's resilience, ensuring updates even if GitHub is unavailable, while still verifying updates with the project's secure certificate.
- Updated Avalonia to v11.2.7, fixes for UI bugs (including restoring Minimize on macOS Sequoia).
- Added a configurable third-party fallback for broadcasting transactions if other methods fail.
- Replaced Windows Code Signing Certificate with Azure Trusted Signing.
- Many bug fixes, improved codebase, and enhanced CI pipeline.
- Added the option to avoid using any third-party Exchange Rate and Fee Rate providers (Wasabi can work without them).
- Rebuilt all JSON Serialization mechanisms avoiding default .NET converters. Serialization is now stricter.

Full Changelog: v2.5.1...v2.6.0
-
 @ 5ea46480:450da5bd
2025-05-30 10:31:55
@ 5ea46480:450da5bd
2025-05-30 10:31:55Neutrality can be a confusing notion. It implies some sort of a-political position, yet neutrality is in itself a political position. But what it means, or how neutrality expresses itself is in a lack of bias or preference; it is the act of non-decision where we see neutrality. As a result, some conflation can occur, because this ‘non-decision’ can be the result of two things: Either being in the position to decide, but choosing not to, what we can perhaps call ‘active neutrality’. Or, the sheer inability to express and actuate preference, where we could call that ‘passive neutrality’.
The Internet Corporation for Assigned Names and Numbers, aka ICANN, is an actively (for the most part) neutral institution. It has all the power and control to express its preferences, and censor basically all the relevant and most actively used parts of the world wide web. But it doesn’t (for the most part), because we recognize the value of this neutral stance. The only reason they are actively instead of passively neutral, is due to technical reasons; we simply don’t know of any workable way to remove the controlling body from the system, and we would if we could. Instead we encapsulated it in all kinds of power obscuring institutions and structures to mitigate the issue.
The reason the controlling body has to exist, is because the objective is a ‘global state’ (global as it is understood in programming, meaning as much as ‘overarching’). The point is that google.com, means/refers to the same thing wherever you are. The added value of some simple human readable and memorable address ‘google.com’ falls apart the moment it becomes inconsistent. The only way to ensure this, is to put a single entity in charge. We employ these ‘global states’ in all kinds of places in society, often with geographical boundaries we call ‘jurisdictions’, but at the very least you know where those lines are drawn and can therefor know what to expect.
There is one exception to this ‘rule’ that ‘global state’ requires a single entity to be in charge: Bitcoin. It is the whole crux of the system; on the one hand we require ‘global state’ in order to have consistent accounting, but on the other hand we did not want anyone to be in charge. The goal of Bitcoin was neutrality, and it found it by capturing ‘passive’ variant by making the system ‘permissionless’. Now it is crucial to understand that non of Bitcoins attributes are intrinsic, but instead are emergent and the result of human action. Also, Bitcoins ‘global state’ is stupendously expensive and does not scale. The fact that those things were not properly understood is what lead to the BlOcKcHaIn hype, believing this passively neutral global state could be implemented outside the realms of money. But this piece is not about Bitcoin, or blockchains for that matter.
The reason I talk about them, is to point out that this passive neutrality is an emergent property not actually found within the system at all. You as user still rely on a third party in what we call miners, and those miners are free to be as biased and non-neutral as they want; in fact we sort of rely on them to be biased towards money. You don’t get your transaction confirmed because a miner likes you, but because you sufficiently bribed him to do so. And Bitcoin’s censorship resistance relies on the hope that such bribes will at least appeal to some miner out there. Bitcoin’s neutrality is the result of there ultimately not being any one particular actor with the ability actuate its preference over time, regardless of the fact that they are able to do so in moments of time.
Nostr does something similar, just without the whole global state thing. It is not neutral because of the good graces of some overlord, it actually recognizes the foolishness of such an effort and lets anyone be as biased an non-neutral as they want, with one simple exception. The only expectation of neutrality is with clients that they adhere to the protocol and actually let users connect to whatever relay they want and produce events that other clients are capable of interpreting, i.e. that they be interoperable. But hopefully because the system is permissionless, some people decide to make such clients, and users decide to use them, instead of willfully locking themselves up. It has to be remarked that humanity does not have the greatest track-record in this regard, but the incentives behind interoperability gives us a fighting chance at least.
Nostr’s neutrality is an emergent property that is the result of human action; it relies on people setting up relays, and people making decisions on what relays they use. The type of neutrality is of the passive kind. The protocol does not provide a public space as such, it just allows you to navigate a potentially vast amount of private spaces; the commons is the connective tissue, and it is this connective tissue that is ‘neutral’. What it boils down to, is that you don’t have to ask permission to ask whomever you want to ask for permission. And in the most desperate moment, you can always resort to asking yourself for permission; I am sure you will comply with such a request.
-
 @ 9ca447d2:fbf5a36d
2025-05-31 03:01:09
@ 9ca447d2:fbf5a36d
2025-05-31 03:01:09Austin, Texas – May 22, 2025 — Jippi, a pioneering mobile augmented reality (AR) game developer, is set to transform Bitcoin education with the launch of its flagship game at the Bitcoin Conference 2025, held at The Venetian Resort in Las Vegas from May 27-29.
In collaboration with six leading Bitcoin companies—Bitcoin Well, Beyond The Checkout, Bitcoin Trading Cards, Geyser, SHAmory, and 21M Communications—Jippi introduces an innovative blend of outdoor adventure, Bitcoin rewards, and gamified financial education designed to captivate.
At the Bitcoin Conference, Jippi’s six partners have sponsored custom “Bitcoin Beasts” tied to specific locations around The Venetian. Each sponsored Beast offers players exclusive rewards and trivia, transforming brand interactions into immersive, non-intrusive experiences.
With an expected attendance of over 30,000 at the conference, sponsors gain unparalleled exposure to a tech-savvy, Bitcoin-centric audience. Players will be rewarded 1k sats for each catch, making the total reward for catching them all 6k sats.
Jippi is redefining how young adults engage with Bitcoin by combining the thrill of location-based AR gameplay, reminiscent of Pokémon GO, with real-world bitcoin rewards (sats) and bite-sized lessons on sound money principles.
Players explore real-world locations to hunt digital creatures called Bitcoin Beasts, answering Bitcoin-related trivia to capture them and earn sats, the smallest unit of bitcoin.
The game’s seamless integration of education and entertainment makes learning about Bitcoin fun, accessible, and rewarding.
“We’re meeting Gen Z where they are—90% play mobile games, and 70% expect rewards for their time,” said Oliver Porter, Founder and CEO of Jippi.
“Jippi backdoors Bitcoin education through an immersive, reward-driven experience while offering our partners a unique branding opportunity. It’s a win-win for players, sponsors, and the Bitcoin ecosystem.”
“Jippi’s mission to gamify Bitcoin education is a game-changer for onboarding the next generation,” said Adam O’Brien, CEO of Bitcoin Well, a leading automatic self-custody Bitcoin platform and “Beast” sponsor.
“Their AR game makes learning about Bitcoin intuitive and engaging, aligning perfectly with our vision of financial empowerment. From a branding perspective, partnering with Jippi to engage and acquire new customers is a no brainer.”
In March 2025, Jippi clinched the top prize in PlebLab’s prestigious Top Builder competition, a three-month hackathon designed to spotlight innovative Bitcoin startups.
Backed by over a year of development, on-site surveys, and university testing, Jippi is a leading innovator in the Bitcoin industry looking to onboard the next generation.
Jippi invites brands, investors, and media to explore sponsorship and investment opportunities. Visit Jippi’s Partnerships Page for sponsorship details or Jippi’s Timestamp Page for investment inquiries.
For media inquiries, please contact Phil@21mcommunications.com
About Jippi
Jippi is a mobile AR gaming company dedicated to making Bitcoin education accessible and engaging. By combining location-based gameplay with bitcoin rewards and financial literacy, Jippi empowers the next generation to embrace sound money principles. Learn more at https://jippi.app.
Bitcoin Beast Sponsors
About Bitcoin Well
Beast #1 – Bitcoin Well – All bitcoin bought at Bitcoin Well are delivered directly to your personal bitcoin wallet. Your Bitcoin Well account gives you the convenience of modern banking, with the benefits of bitcoin. Join the platform that enables independence at bitcoinwell.com.
About Bitcoin Trading Cards
Beast #2 – Bitcoin Trading Cards – Bitcoin Trading Cards is bringing Bitcoin to the masses one pack at a time, making your Bitcoin journey fun and exciting for everyone.
About Beyond The Checkout
Beast #3 – Beyond The Checkout – Beyond The Checkout transforms everyday products into Bitcoin-powered experiences — rewarding customers, collecting real-time insights, and redefining post-purchase engagement.
About Geyser
Beast #4 – Geyser – Geyser is a Bitcoin-native crowdfunding platform enabling grassroots projects to raise funds via Lightning, globally and permissionlessly.
About SHAmory
Beast #5 – SHAmory – We make Bitcoin fun for all ages! Explore our bitcoin games, books, and more today at shamory.com.
About 21M Communications
Beast #6 – 21 Communications – 21 Communications helps Bitcoin companies get the media attention they deserve. As a Bitcoin-only PR Agency, 21M Comms believes Bitcoin is imperative and is committed to supporting the companies that are advancing the mission.
About Bitcoin Conference 2025
The Bitcoin Conference is the world’s largest gathering of Bitcoin enthusiasts, industry leaders, and innovators. Held annually, it showcases cutting-edge developments in the Bitcoin ecosystem. For more information, visit www.bitcoinconference.com.
-
 @ b1ddb4d7:471244e7
2025-05-31 03:00:48
@ b1ddb4d7:471244e7
2025-05-31 03:00:48In the heart of East Africa, where M-Pesa reigns supreme and innovation pulses through bustling markets, a quiet revolution is brewing—one that could redefine how millions interact with money.
Enter Bitika, the Kenyan startup turning bitcoin’s complexity into a three-step dance, merging the lightning speed of sats with the trusted rhythm of mobile money.
At the helm is a founder whose “aha” moment came not in a boardroom, but at his kitchen table, watching his father grapple with the gap between understanding bitcoin and actually using it.
Bitika was born from that friction—a bridge between M-Pesa’s ubiquity and bitcoin’s borderless promise, wrapped in a name as playful as the Swahili slang that inspired it.
But this isn’t just a story about simplifying transactions. It’s about liquidity battles, regulatory tightropes, and a vision to turn Bitika into the invisible rails powering Africa’s Bitcoin future.
Building on Bitcoin
- Tell us a bit about yourself and how you got into bitcoin/fintech, and what keeps you passionate about this space?
I first came across bitcoin in 2020, but like many at that time, I didn’t fully grasp what it really was. It sounded too complicated, probably with the heavy terminologies. Over time, I kept digging deeper and became more curious.
I started digging into finance and how money works and realised this was what I needed to understand bitcoin’s objectives. I realized that bitcoin wasn’t just a new type of money—it was a breakthrough in how we think about freedom, ownership, and global finance.
What keeps me passionate is how bitcoin can empower people—especially in Africa—to take control of their wealth, without relying on unstable systems or middlemen.
- What pivotal moment or experience inspired you to create Bitika? Was there a specific gap in Kenya’s financial ecosystem that sparked the idea?
Yes, this idea was actually born right in my own home. I’ve always been an advocate for bitcoin, sharing it with friends, family, and even strangers. My dad and I had countless conversations about it. Eventually, he understood the concept. But when he asked, “How do I even buy bitcoin?” or “Can you just buy it for me?” and after taking him through binance—that hit me.
If someone I’d educated still found the buying process difficult, how many others were feeling the same way? That was the lightbulb moment. I saw a clear gap: the process of buying bitcoin was too technical for the average Kenyan. That’s the problem Bitika set out to solve.
- How did you identify the synergy between bitcoin and M-Pesa as a solution for accessibility?
M-Pesa is at the center of daily life in Kenya. Everyone uses it—from buying groceries to paying rent. Instead of forcing people to learn new tools, I decided to meet them where they already are. That synergy between M-Pesa and bitcoin felt natural. It’s about bridging what people already trust with something powerful and new.
- Share the story behind the name “Bitika” – does it hold a cultural or symbolic meaning?
Funny enough, Bitika isn’t a deeply planned name. It came while I was thinking about bitcoin and the type of transformation it brings to individuals. In Swahili, we often add “-ka” to words for flair—like “bambika” from “bamba.”
So, I just coined Bitika as a playful and catchy way to reflect something bitcoin-related, but also uniquely local. I stuck with it because thinking of an ideal brand name is the toughest challenge for me.
- Walk us through the user journey – how does buying bitcoin via M-Pesa in “3 simple steps” work under the hood?
It’s beautifully simple.
1. The user enters the amount they want to spend in KES—starting from as little as 50 KES (about $0.30).
2. They input their Lightning wallet address.
3. They enter their M-Pesa number, which triggers an STK push (payment prompt) on their phone. Once confirmed—pap!—they receive bitcoin almost instantly.
Under the hood, we fetch the live BTC price, validate wallet addresses, check available liquidity, process the mobile payment, and send sats via the Lightning Network—all streamlined into a smooth experience for the user.
- Who’s Bitika’s primary audience? Are you focusing on unbanked populations, tech enthusiasts, or both?
Both. Bitika is designed for everyday people—especially the unbanked and underbanked who are excluded from traditional finance. But we also attract bitcoiners who just want a faster, easier way to buy sats. What unites them is the desire for a seamless and low-barrier bitcoin experience.
Community and Overcoming Challenges
- What challenges has Bitika faced navigating Kenya’s bitcoin regulations, and how do you build trust with regulators?
Regulation is still evolving here. Parliament has drafted bills, but none have been passed into law yet. We’re currently in a revision phase where policymakers are trying to strike a balance between encouraging innovation and protecting the public.
We focus on transparency and open dialogue—we believe that building trust with regulators starts with showing how bitcoin can serve the public good.
- What was the toughest obstacle in building Bitika, and how did you overcome it?
Liquidity. Since we don’t have deep capital reserves, we often run into situations where we have to pause operations often to manually restock our bitcoin supply. It’s frustrating—for us and for users. We’re working on automating this process and securing funding to maintain consistent liquidity so users can access bitcoin at any time, without disruption.
This remains our most critical issue—and the primary reason we’re seeking support.
- Are you eyeing new African markets? What’s next for Bitika’s product?
Absolutely. The long-term vision is to expand Bitika into other African countries facing similar financial challenges. But first, we want to turn Bitika into a developer-first tool—infrastructure that others can build on. Imagine local apps, savings products, or financial tools built using Bitika’s simple bitcoin rails. That’s where we’re heading.
- What would you tell other African entrepreneurs aiming to disrupt traditional finance?
Disrupting finance sounds exciting—but the reality is messy. People fear what they don’t understand. That’s why simplicity is everything. Build tools that hide the complexity, and focus on making the user’s life easier. Most importantly, stay rooted in local context—solve problems people actually face.
What’s Next?
- What’s your message to Kenyans hesitant to try bitcoin, and to enthusiasts watching Bitika?
To my fellow Kenyans: bitcoin isn’t just an investment—it’s a sovereign tool. It’s money you truly own. Start small, learn, and ask questions.
To the bitcoin community: Bitika is proof that bitcoin is working in Africa. Let’s keep pushing. Let’s build tools that matter.
- How can the bitcoin community, both locally and globally, support Bitika’s mission?
We’re currently fundraising on Geyser. Support—whether it’s financial, technical, or simply sharing our story—goes a long way. Every sat you contribute helps us stay live, grow our liquidity, and continue building a tool that brings bitcoin closer to the everyday person in Africa.
Support here: https://geyser.fund/project/bitika
-
 @ 5ea46480:450da5bd
2025-05-30 10:31:22
@ 5ea46480:450da5bd
2025-05-30 10:31:22Understanding or grasping Nostr can be deceptively difficult. At the very least it is non-trivial. At first glance, looking at NIP-01, the protocol is rather straight forward. But those are just the basics; yes the beauty of Nostr is its ‘simplicity’, but that does not mean the system that results from it is not complex. Conway's Game of Life only has a hand full of rules, yet you can, in theory at least, create any complex system imaginable. And this is where the deception lies; the less you define from the outset, the more you imply on what follows.
It appears that as it stands, Nostr suffers from this deceptiveness. You can reason through all these implications, but that is still an exercise that has to be performed and where mistakes can be made. Worse, this exercise has been a group effort from the start that is still in progress. Currently there is no clear cut ‘authoritative’ example of all the implications that have been ‘discovered’ thus far.
A good example of the implications following Nostr’s primitives is what we now refer to as the ‘outbox model’. The reason we ‘now’ refer to it as such, is because initially it was called the ‘Gossip model’ derived from the client that first implemented the idea. Outbox is fundamental to Nostr, but it was never explicitly stated in the initial protocol description. The result is that roughly five years into this Nostr endeavor, it is still not universally implemented; worse yet, some developers appear to be in no rush to do so. Now the reason they will give you is probably one based on priority, yet I can’t shake the feeling that they apparently don’t ‘get it’.
My point here is not to play some blame game or hold anyone to account. I am just concluding they don’t actually get the new paradigm that we have all stumbled into. To expand on this specific outbox example, its significance only becomes really apparent further along in the ‘reasoning through all the implications’ exercise. In relation to one aspect, but there are more: The point is not ‘just’ censorship-resistance for users, but the freedom for relays that comes with it to apply whatever policy on what they store and make available; it is this discrimination or curation that can add value by making finding relevant information easier in a straightforward manner. But it relies on outbox to avoid isolation; something that only becomes apparent once you are reasoning through all the implications on how we discover and consume content.
To be clear, this piece is not supposed to a crusade on the outbox model, my point here is that there is an inherent logic to Nostr stemming from putting cryptography front and center. It is a logic that has to be applied and will subsequently carry you through all the challenges we face in reconstructing the entirety of the web. This is not to say there is only one obvious path, and different schools of thought are bound to emerge. But it behooves us all, faced with this new paradigm, to continuously reflect on the mental image we have cultivated of what Nostr is; actively re-performing that exercise of exploring the implications this simple set of protocol rules creates.
Unfortunately I can not escape my own folly. After all, I am just an armchair asshole that never wrote a single line of code in his life. Obviously this minds-eye bullshit is not even half the story, the bulk of the effort is translating it into software, the tangible, the real. It is in that effort ultimately the real exploration of this paradigm occurs. All I can do is build castles in the sky.
-
 @ 7f6db517:a4931eda
2025-05-31 02:01:25
@ 7f6db517:a4931eda
2025-05-31 02:01:25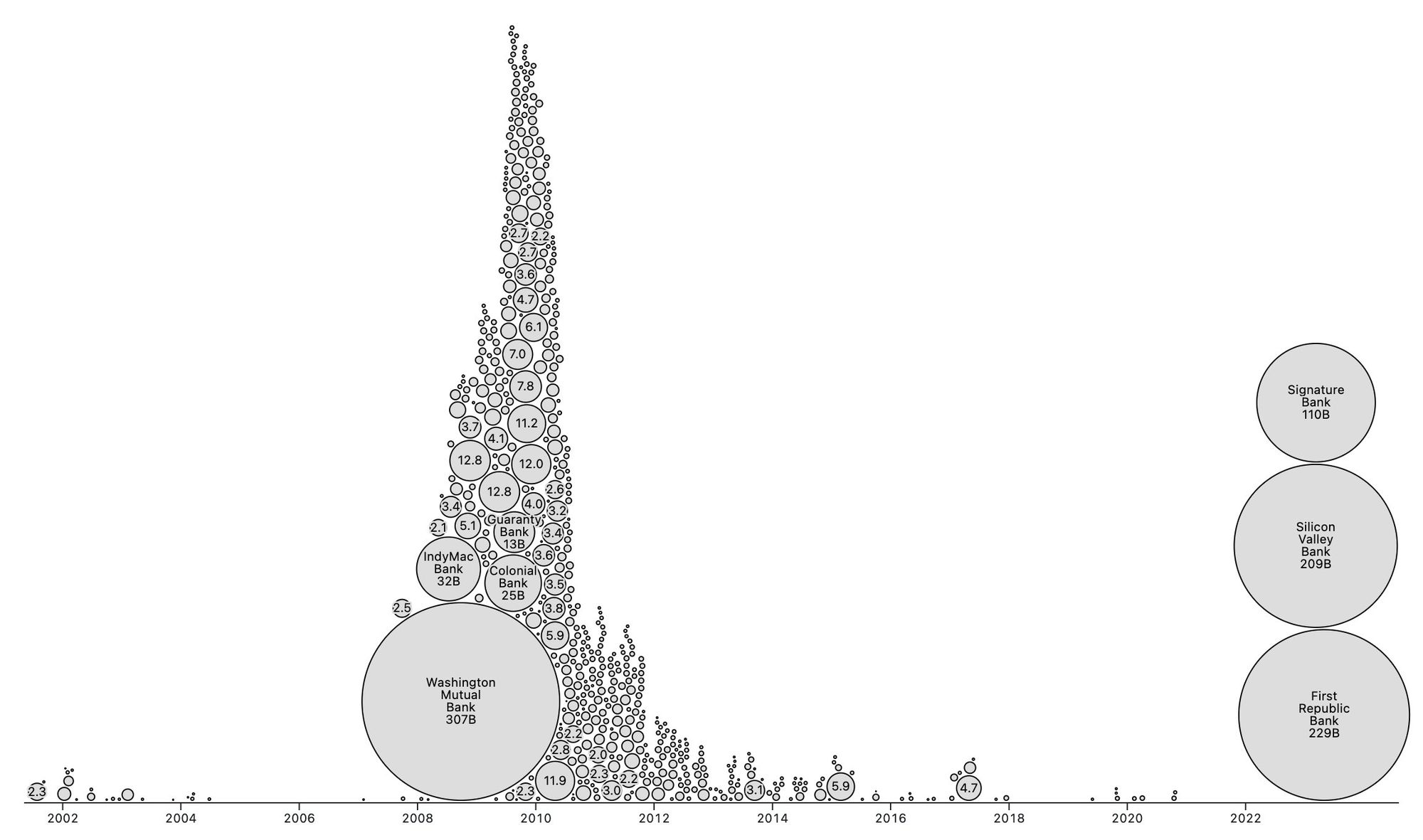
People forget Bear Stearns failed March 2008 - months of denial followed before the public realized how bad the situation was under the surface.
Similar happening now but much larger scale. They did not fix fundamental issues after 2008 - everything is more fragile.
The Fed preemptively bailed out every bank with their BTFP program and First Republic Bank still failed. The second largest bank failure in history.
There will be more failures. There will be more bailouts. Depositors will be "protected" by socializing losses across everyone.
Our President and mainstream financial pundits are currently pretending the banking crisis is over while most banks remain insolvent. There are going to be many more bank failures as this ponzi system unravels.
Unlike 2008, we have the ability to opt out of these broken and corrupt institutions by using bitcoin. Bitcoin held in self custody is unique in its lack of counterparty risk - you do not have to trust a bank or other centralized entity to hold it for you. Bitcoin is also incredibly difficult to change by design since it is not controlled by an individual, company, or government - the supply of dollars will inevitably be inflated to bailout these failing banks but bitcoin supply will remain unchanged. I do not need to convince you that bitcoin provides value - these next few years will convince millions.
If you found this post helpful support my work with bitcoin.

-
 @ 5ea46480:450da5bd
2025-05-30 10:29:38
@ 5ea46480:450da5bd
2025-05-30 10:29:38Decentralization refers to control/power, and relates to censorship resistance. That is it, it is not more complicated then that. Resilience is a function of redundancy; a centralized censored system can have a redundant set-up and therefor be resilient.
Take Bitcoin; the blockchain is a central database, it is resilient because it has many redundant copies among a lot of different nodes. The message (txs and blocks) propagation is decentralized due to existence of a p2p network among these nodes, making the data distribution censorship resistant (hello op_return debate). But onchain transactions themselves are NOT p2p, they require a middlemen (a miner) because it is a central database, as opposed to something like lightning which is p2p. Peer to Peer says something about relative architectural hierarchical position/relation. P2P provides censorship resistance because it entails equal power relations, provided becoming a peer is permissionless. What makes onchain transactions censorship resistant is that mining is permissionless, and involves this open power struggle/game where competition results in a power distribution among players, meaning (hopefully) decentralization. The fact users rely on these middlemen is mitigated by this decentralization on the one hand, and temper-proofing via cryptographic signatures on the other, resulting in what we call trustlessness (or trust minimization for the autists in the room); we only rely on a miner to perform a job (including your tx into a block), but we don’t trust the miner to perform the job correctly, this we can verify ourselves.
This leads us to Nostr, because that last part is exactly what Nostr does as well. It uses cryptography to get tamper-proof messaging, which then allows you to use middle-men in a trust minimized way. The result is decentralization because in general terms, any middle man is as good as any other (same as with miners), and becoming such a middleman is permissionless(somewhat, mostly); which in turn leads to censorship resistance. It also allows for resilience because you are free to make things as redundant as you'd like.
Ergo, the crux is putting the cryptography central, making it the starting point of the system; decentralization then becomes an option due to trust minimization. The difference between Bitcoin an Nostr, is that Bitcoin maintains a global state/central ledger and needs this PoW/Nakamoto consensus fanfare; Nostr rests itself with local perspectives on 'the network'.
The problem with the Fediverse, is that it does not provide trust minimization in relation to the middlemen. Sure, there are a lot different servers, but you rely on a particular one (and the idea you could switch never really seemed to have materialized in a meaningful way). It also fails in permisionlessness because you rely on the association between servers, i.e. federation, to have meaningful access to the rest of the network. In other words, it is more a requirement of association than freedom of association; you have the freedom to be excommunicated.
The problem with ATproto is that is basically does not solve this dynamic; it only complicates it by pulling apart the components; identity and data, distribution and perspective are now separated, and supposedly you don’t rely on any particular one of these sub-component providers in the stack; but you do rely on all these different sub-component providers in the stack to play nice with each other. And this ‘playing nice’ is just the same old ‘requirement of association’ and ‘freedom of excommunication’ that looms at the horizon.
Yes, splitting up the responsibilities of identity, hosting and indexing is what is required to safe us from the platform hellscape which at this stage takes care of all three. But as it turns out, it was not a matter cutting those up into various (on paper) interchangeable middlemen. All that is required is putting cryptographic keys in the hands of the user; the tamperproofing takes care of the rest, simply by trust minimizing the middlemen we use. All the sudden it does not matter which middlemen we use, and no one is required to play nice; we lost the requirement of association, and gained freedom of association, which was the purpose of censorship resistance and therefor decentralization, to begin with.
-
 @ dfa02707:41ca50e3
2025-05-31 02:01:23
@ dfa02707:41ca50e3
2025-05-31 02:01:23Contribute to keep No Bullshit Bitcoin news going.
- The latest firmware updates for COLDCARD devices introduce two major features: COLDCARD Co-sign (CCC) and Key Teleport between two COLDCARD Q devices using QR codes and/or NFC with a website.
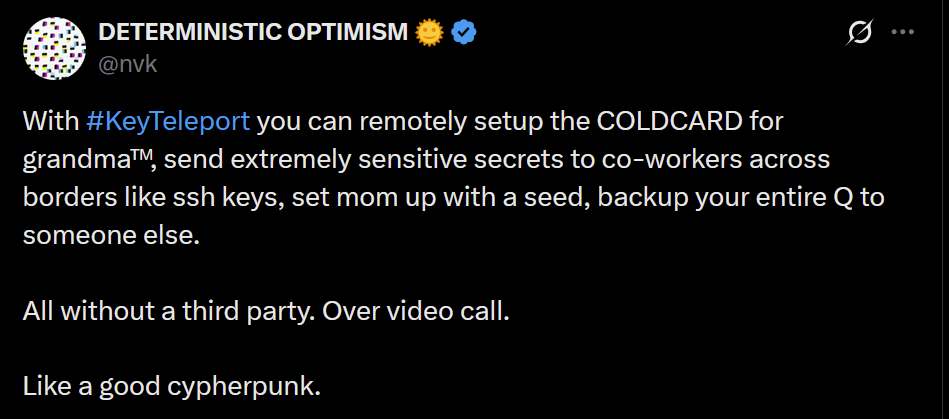
What's new
- COLDCARD Co-Sign: When CCC is enabled, a second seed called the Spending Policy Key (Key C) is added to the device. This seed works with the device's Main Seed and one or more additional XPUBs (Backup Keys) to form 2-of-N multisig wallets.
- The spending policy functions like a hardware security module (HSM), enforcing rules such as magnitude and velocity limits, address whitelisting, and 2FA authentication to protect funds while maintaining flexibility and control, and is enforced each time the Spending Policy Key is used for signing.
- When spending conditions are met, the COLDCARD signs the partially signed bitcoin transaction (PSBT) with the Main Seed and Spending Policy Key for fund access. Once configured, the Spending Policy Key is required to view or change the policy, and violations are denied without explanation.
"You can override the spending policy at any time by signing with either a Backup Key and the Main Seed or two Backup Keys, depending on the number of keys (N) in the multisig."
-
A step-by-step guide for setting up CCC is available here.
-
Key Teleport for Q devices allows users to securely transfer sensitive data such as seed phrases (words, xprv), secure notes and passwords, and PSBTs for multisig. It uses QR codes or NFC, along with a helper website, to ensure reliable transmission, keeping your sensitive data protected throughout the process.
- For more technical details, see the protocol spec.
"After you sign a multisig PSBT, you have option to “Key Teleport” the PSBT file to any one of the other signers in the wallet. We already have a shared pubkey with them, so the process is simple and does not require any action on their part in advance. Plus, starting in this firmware release, COLDCARD can finalize multisig transactions, so the last signer can publish the signed transaction via PushTX (NFC tap) to get it on the blockchain directly."
- Multisig transactions are finalized when sufficiently signed. It streamlines the use of PushTX with multisig wallets.
- Signing artifacts re-export to various media. Users are now provided with the capability to export signing products, like transactions or PSBTs, to alternative media rather than the original source. For example, if a PSBT is received through a QR code, it can be signed and saved onto an SD card if needed.
- Multisig export files are signed now. Public keys are encoded as P2PKH address for all multisg signature exports. Learn more about it here.
- NFC export usability upgrade: NFC keeps exporting until CANCEL/X is pressed.
- Added Bitcoin Safe option to Export Wallet.
- 10% performance improvement in USB upload speed for large files.
- Q: Always choose the biggest possible display size for QR.
Fixes
- Do not allow change Main PIN to same value already used as Trick PIN, even if Trick PIN is hidden.
- Fix stuck progress bar under
Receiving...after a USB communications failure. - Showing derivation path in Address Explorer for root key (m) showed double slash (//).
- Can restore developer backup with custom password other than 12 words format.
- Virtual Disk auto mode ignores already signed PSBTs (with “-signed” in file name).
- Virtual Disk auto mode stuck on “Reading…” screen sometimes.
- Finalization of foreign inputs from partial signatures. Thanks Christian Uebber!
- Temporary seed from COLDCARD backup failed to load stored multisig wallets.
Destroy Seedalso removes all Trick PINs from SE2.Lock Down Seedrequires pressing confirm key (4) to execute.- Q only: Only BBQr is allowed to export Coldcard, Core, and pretty descriptor.

-
 @ 527337d5:93e9525e
2025-05-30 10:24:39
@ 527337d5:93e9525e
2025-05-30 10:24:39# Exploring the Niche of Conspiracy Theory Markets: A Probabilistic Approach and Sales Condition Analysis on Japanese Online Flea Markets (Subtitle: Unveiling the Surprising Realities of a Niche Market Through Data Analysis and AI)
(Note: This research analyzes consumer reactions and product characteristics in a specific market based on data. It does not endorse conspiracy theories nor promote or encourage any illegal or fraudulent activities.)
1. Abstract
This study aimed to clarify, from a probabilistic perspective, what combinations of information (topic x manipulation category) tend to attract attention and how pricing strategies affect sales of products marketed towards "conspiracy theorists" on online flea markets in Japan. Using an analogy from drug discovery's structural exploration, this research explored "information combinations" in products that resonate with individuals interested in conspiracy theories. Specifically, products were generated (some with AI assistance) based on defined topic categories (e.g., T1: Technology/Security) and manipulation categories (e.g., M1: Avoidance). The logarithm of the reaction rate (views / (searches + 1)) was used as a score for analysis, and the impact of pricing strategies (e.g., fixed at 5000 JPY, phased discounts) was examined. Results indicated that certain combinations (e.g., T3: Occult/Spiritual - M1: Avoidance) showed relatively high reaction rates. However, the effect of price changes was not uniform, and the total weekly views for this market segment remained around 100-120. Consequently, it was concluded that the scale of this specific market on the online flea market platform is extremely small. Therefore, even with a probabilistic model waiting for "hits" similar to those in certain types of specialized fraud schemes, achieving consistent sales is difficult due to the limited population size. This study serves as a case example of the possibilities and limitations of data-driven approaches in niche markets.
2. Introduction: Conspiracy Theories and Niche Market Potential
2.1. The Spread and Background of Conspiracy Theories in Modern Society
In contemporary society, conspiracy theories are proliferating at an unprecedented rate, facilitated by the internet and social media. These narratives typically allege that secret machinations by powerful individuals or groups lie behind specific events or social phenomena. Themes range испанский large-scale theories like QAnon to those concerning health and medicine. It has been pointed out that the psychology of those who believe in conspiracy theories may be influenced by factors such as anxiety in uncertain situations, a cognitive tendency to seek patterns, or distrust of existing authorities.
2.2. Research Motivation
The starting point for this research was a simple question: "Specialized fraud schemes, often succeed by identifying a very small number of 'susceptible individuals' out of numerous attempts. Might a similar probabilistic structure exist in the sale of products targeting those interested in conspiracy theories?" If so, it was hypothesized that it might be possible to identify which products, under what conditions, would have a higher probability of catching the "target's" eye and attracting interest.
2.3. Purpose of this Study
The purpose of this study is to exploratorily clarify, based on data, how "information combinations" (combinations of topic categories and manipulation categories) and "pricing strategies" of products ostensibly related to conspiracy theories affect user attention (using "reaction rate" as a proxy indicator) in a real-world online flea market environment. Ultimately, it aims to consider the possibilities and limitations of sales strategies in this type of niche market.
3. Research Perspective and Approach: Exploring "Information Combinations"
3.1. Analogy to Drug Discovery
In exploring the characteristics of products that resonate with conspiracy theorists, this study employed an analogy to "structural exploration problems" in drug discovery. In drug development, researchers search for optimal structures with specific effects from countless combinations of chemical structures. Similarly, "products that conspiracy theorists react to" were viewed as a type of "substance with an effect," and the "information combination of a product" (e.g., product theme, appeal points) was considered equivalent to a "chemical structure." Based on this framework, products with various information structures were generated and listed, and their reception was observed to explore more "effective" information structures, i.e., conditions likely to attract attention.
3.2. Balancing Exploration and Exploitation
In the initial research phase, with scarce data on which product combinations would attract attention, it was necessary to efficiently identify promising combinations. Therefore, an approach was adopted that considered the balance between "exploiting" combinations already known to be somewhat popular and "exploring" untried, unknown combinations. This shares a basic conceptual similarity with strategies like Thompson Sampling or the ε-greedy method, known in the field of reinforcement learning, which aim to achieve the best results within a limited number of trials.
4. Research Methodology: Experiments and Data Analysis on an Online Flea Market
4.1. Experimental Field and Period
The experiments for this study were conducted on an anonymous online flea market platform in Japan. The data collection period for individual products was, in principle, one day, and the overall research project spanned approximately one month (late April to late May 2025).
4.2. Product Categorization
To organize and analyze the characteristics of the listed products, they were categorized along the following two axes:
- Table 1: Definition of Main Product Topic Categories (T1-T4) (See Appendix 10.1 for details)
- T1: Technology & Security
- T2: Surveillance, Censorship & Government-Related
- T3: Occult & Spiritual
- T4: Forbidden Books & Knowledge Management
- Table 2: Definition of Product Manipulation Categories (M1-M3) (See Appendix 10.2 for details)
- M1: Avoidance (e.g., avoiding electromagnetic waves)
- M2: Detection (e.g., detecting hidden information)
- M3: Approach/Processing/Amplification (e.g., approaching specific energies, processing information)
4.3. Listing Strategy and Data Collection
- Initial Listing Strategy: Initially, products were selected so that the listing ratio of the T×M combinations (12 in total) would be uniform.
- Sequential Adjustment of Listing Ratios: As data collection progressed, the logarithm of the reaction rate (log(reaction_rate)), a proxy for attention described later, was treated as a likelihood. The listing ratio for each T×M combination was then dynamically changed пропорционально to this value.
- Data Collection Items: Cumulative views (recorded as
watchin this study) and search hits (recorded assearch), updated every 24 hours by the online flea market platform, were manually recorded for each product. Since these figures did not change except at the time of updating, daily recording was sufficient. - Listing Timing: New product listings were consistently made at 21:00 daily to eliminate variations in viewing trends due to time of day.
- Sample Size Criterion: Considering the 12 T×M combinations, a total sample size (number of listed products) of N=100 was considered a benchmark, also factoring in the time and effort of listing. The final analysis included 98 products.
4.4. Scoring of Attention
To measure how much attention users paid to product information, the following indicators were defined:
- Reaction Rate (
reaction_rate): Defined asreaction_rate = watch / (search + 1). This represents the proportion of users who actually viewed the individual product page (watch) among those who encountered the product in search results or elsewhere (search). Adding 1 to the denominator was to avoid division by zero if search hits were 0 and to mitigate the impact of extremely low search hit counts. - Score (
score): Defined asscore = log(reaction_rate) - log(0.5). Taking the logarithm of the reaction rate was confirmed to make the data distribution closer to a normal distribution (see Figure 1 below), facilitating statistical analysis. Subtractinglog(0.5)was done to make a 50% reaction rate (half of those who searched viewed the page) the baseline (score 0), making it easier to compare attention levels relatively.
4.5. Verification of Pricing Strategies
The following experiments were conducted to verify the impact of product pricing on attention:
- Initial Pricing: Initially listed products were priced at a fixed 5000 JPY.
- Phased Discount Experiment: For some products, the listing price started at 5000 JPY and was discounted by 100 JPY at daily intervals. Cumulative views and search hits were recorded at each step (data recorded in "Daily Change Data.xlsx").
- Later Price Changes: In the latter half of the research, hoping to elicit more reactions, some products were priced around 3000 JPY, and eventually, all products were priced at 1500 JPY to observe reactions.
- Approach to Analyzing Price/Image Effects: The impact of price changes or product image alterations on attention was considered by applying the principles of DiD (Difference in Difference) analysis, comparing changes in data under different conditions, rather than through rigorous statistical analysis.
4.6. AI-Generated Product Descriptions
Some of the product descriptions were generated using Google's Gemini API. Prompts, in a format similar to the
queryvariable in "Conspiracy_Research.ipynb," instructed the AI to generate descriptions aligning with conspiracy-related contexts by combining specified topic (e.g., T3: Occult & Spiritual) and manipulation (e.g., M1: Avoidance) keywords.4.7. Analysis of Day-of-Week Effects
To evaluate the impact of the listing day of the week on attention, scores for each product, adjusted by subtracting the overall average score, were aggregated by day of the week and observed for trends.
5. Results: What Attracted Attention and What Didn't
5.1. Distribution of Attention Scores
First, the distribution of attention scores (
log(reaction_rate) - log(0.5)) for all products was examined.Figure 1: Q-Q Plot of log(reaction_rate) Vertical Axis: Ordered Values, Horizontal Axis: Theoretical quantiles | Ordered Values | Theoretical quantiles | | :-------------: | :--------------------: | | Approx. -1.7 | Approx. -1.5 | | Approx. -1.2 | Approx. -1.0 | | Approx. -0.8 | Approx. -0.6 | | Approx. -0.6 | Approx. -0.3 | | Approx. -0.1 | Approx. 0.0 | | Approx. 0.1 | Approx. 0.2 | | Approx. 0.3 | Approx. 0.3 | | Approx. 0.4 | Approx. 0.5 | | Approx. 0.5 | Approx. 0.7 | | Approx. 1.0 | Approx. 0.9 | | Approx. 1.5 | Approx. 1.6 | (Source: log(reaction_rate)よし、正規分布の仮定でいいらしい.jpg)
This Q-Q plot shows that the data points for
log(reaction_rate)fall approximately on a straight line, suggesting that the distribution is close to normal. This supports the validity of statistical analysis using the log-transformed score. Furthermore, a histogram of the scores (generated asdf["score"].hist()in "Conspiracy_Research.ipynb") showed that the scores were dispersed over a certain range.5.2. "Information Combinations" That Attracted More Attention
Next, an analysis was conducted to determine which "information combinations" in products garnered higher attention scores.
-
Figure 2: Average Attention Score by Topic Vertical Axis: Average Score, Horizontal Axis: Topic | Topic | Average Score (Approx.) | | :---: | :--------------------: | | T1 | Approx. 0.1 | | T2 | Approx. 0.3 | | T3 | Approx. 0.8 | | T4 | Approx. 0.15 | (Source: np.log(reaction_rate)-np.log(0.5)_by_topic.png)
When categorized by main topic, "T3: Occult & Spiritual" showed a markedly higher average score compared to other topics.
-
Figure 3: Average Attention Score by Manipulation Category Vertical Axis: Average Score, Horizontal Axis: Subtopic | Subtopic | Average Score (Approx.) | | :------: | :--------------------: | | M1 | Approx. -0.1 | | M2 | Approx. 0.32 | | M3 | Approx. 0.43 | (Source: score_mean_by_subtopic.jpg)
By manipulation category, "M3: Approach/Processing/Amplification" had the highest average score, followed by "M2: Detection," and then "M1: Avoidance." "M1: Avoidance" had a negative average score, indicating a relatively low level of attention.
-
Figure 4: Ranking of Average Attention Scores by Topic × Manipulation Category Vertical Axis: Average Score, Horizontal Axis: Combination of Topic & Subtopic | Combination (T, M) | Average Score (Approx.) | | :-----------------: | :--------------------: | | (T1, M1) | Approx. -1.1 | | (T2, M2) | Approx. -0.2 | | (T4, M1) | Approx. -0.1 | | (T4, M3) | Approx. 0.05 | | (T1, M2) | Approx. 0.08 | | (T2, M3) | Approx. 0.5 | | (T2, M1) | Approx. 0.55 | | (T3, M2) | Approx. 0.7 | | (T3, M3) | Approx. 0.75 | | (T1, M3) | Approx. 0.9 | | (T4, M2) | Approx. 1.0 | | (T3, M1) | Approx. 1.05 | (Source: score_mean_by_topic_and_subtopic.jpg)
For combinations of topic and manipulation categories, pairings like "T3(Occult & Spiritual) - M1(Avoidance)" and "T4(Forbidden Books & Knowledge Management) - M2(Detection)" ranked high, while "T1(Technology & Security) - M1(Avoidance)" and others scored low (see Appendix 10.3 for details). A note in the research log, "M1=Avoidance seems unpopular anyway," supports this trend.
5.3. Impact of Pricing Strategies
The impact of price changes on attention was not uniform.
-
Figure 5: Schematic Comparison of Attention Trends for Fixed-Price vs. Discounted Products (Original Data: "5000 JPY Fixed.jpg", "Daily Change Data.xlsx", "Power of Discounting.jpg")
- Trend Example for 5000 JPY Fixed-Price Products Vertical Axis: Indicator Value (0.0-0.8), Horizontal Axis: Period | Product Name | Initial Value | Mid Value | Final Value | | :------------------------------------------ | :-----------: | :-------: | :---------: | | Ancient Energy Amplifying Pen - Quantum Flow- | Approx. 0.65 | Approx. 0.3 | Approx. 0.25 | | Pen of Truth Evasion | - | - | - | | Knowledge Prohibition Evasion Pen | Approx. 0.22 | Approx. 0.22 | Approx. 0.25 | | Ancient Wisdom Writing Tool - Knowledge Leak Evasion Model | Approx. 0.32 | Approx. 0.55 | Approx. 0.54 | (Source: 5000円固定のもの.jpg)
- Power of Discounting (Count Comparison) Vertical Axis: Count, Horizontal Axis: Indicator Value Range | Indicator Value Range | Discounted (Blue) | Not Discounted (Red) | | :------------------: | :---------------: | :------------------: | | 0.0-0.5 | 1 | 2 | | 0.5-1.0 | 8 | 2 | | 1.0-1.5 | 10 | 0 | | 1.5-2.0 | 9 | 0 | | 2.0-2.5 | 3 | 0 | | 2.5-3.0 | 1 | 0 | (Source: 値下げの威力.jpg)
When prices were fixed at 5000 JPY, many products showed no significant change in attention ("It really doesn't change if you don't discount lol"). In contrast, for product groups that were progressively discounted, some cases showed
impression/search(an indicator thought to be close to the click-through rate from search results) converging towards a specific value soon after discounting began (around the 3rd day) ("On the other hand, discounting makes impression/search converge to a proper value?"). -
However, as noted in the research log, "Discounted products, if anything, got worse reactions...?", data in "Daily Change Data.xlsx" confirmed that for some products, views and search hits stagnated or even decreased after price reductions.
5.4. Linguistic Trends in Products That Attracted Attention
The research log contains the entry, "Products with good reactions, when vectorized by words, are mostly the same." This suggests commonalities in the words and phrases used in the descriptions of products that garnered high attention. Specifically, when a vector was assigned based on the position of words used from a predefined list (e.g., T1 category keyword list), products with high attention tended to have similar vectors. For example, keywords frequently appearing in conspiracy theories, such as "special technology," "protection from surveillance," "5G interference prevention," "thought control," "HAARP," "QR code nullification," or sensational appeals combining these, as devised in the "Conspiracy Theorist Ballpoint Pen Product Plan," could potentially attract a certain level of interest.
5.5. Data Collection Challenges
During the analysis, a challenge was identified: "Aggregating by T*M alone inevitably results in products that don't get search hits." This indicates that for certain niche combinations, products might not be sufficiently exposed by the online flea market's search algorithm, leading to extremely low view and search hit counts, thus making accurate attention assessment difficult.
6. Discussion: The Small Reality of the Conspiracy Market and Probabilistic Models
6.1. Interpretation of Information Combinations That Attracted High Attention
The results of this study showed a tendency for products related to "T3: Occult & Spiritual" and those appealing to "M3: Approach/Processing/Amplification" manipulations to gather relatively high attention. The combination "T3-M1 (Occult & Spiritual - Avoidance)" also scored highly. These tendencies might be interpretable in relation to the psychological characteristics of conspiracy believers described in the "Comprehensive Analysis of Modern Conspiracy Theories." For instance, the "Occult & Spiritual" theme might appeal to an interest in phenomena unexplained by existing science or authority, or to a desire for special knowledge (a sense of being chosen). The "Avoidance" manipulation could resonate with vague anxieties and threat perceptions regarding society or technology (e.g., defense against electromagnetic waves, escape from surveillance), while "Approach/Processing/Amplification" might be perceived as fulfilling desires to access hidden truths or special powers.
6.2. Complexity of Pricing Strategies
Regarding pricing strategies, the results showed that simple discounting did not always lead to increased attention. The fact that some products experienced worse reactions after discounting suggests that price might function as a signal of quality or trustworthiness, or that the price sensitivity of the target demographic is not uniform. Alternatively, the initial pricing (5000 JPY) might have been significantly outside the typical price range for this niche market, thus limiting the effectiveness of discounts.
6.3. Market Size Estimation and Validation of the "Probabilistic" Model
One of the most crucial findings of this research relates to market size. The research log states, "Even with discounting, weekly views settled around 100-120. This reasonably implies that only about this many people on the online flea market react to such comprehensively sprinkled conspiracy-related words." Based on this observation, the active user base (market size) on the online flea market studied, who proactively react to the keyword "conspiracy theory" and search/view related products, was estimated to be extremely small, around 100 individuals on a weekly basis.
This market size estimation casts significant doubt on the validity of the initial research motivation: a "probabilistic business model similar to specialized fraud." Specialized fraud schemes profit by reaching a certain number of "targets" through a vast number of attempts (e.g., phone calls), even with a very low success rate. However, in the market targeted by this study, the potential customer base (population) is absolutely too small. Therefore, even if the probability of attracting attention could be somewhat increased, translating this into actual sales (y=1, i.e., a sale occurring) is considered extremely difficult. To quote the research log, the conclusion is that "the population is too small for a realized value (y=1) to be feasible." If the market size were, for example, around 100,000, a 0.01% reaction rate could be expected to yield 10 sales, but this premise does not hold in the current situation.
6.4. Effectiveness and Limitations of This Research Approach
The approach of exploring "information combinations," using an analogy to drug discovery, demonstrated some effectiveness in probing product appeal points and the interests of the target demographic in a niche market. Using proxy indicators like reaction rates allows for an understanding of attention trends even when actual sales data is scarce. However, the limitations of this approach also became clear. If the market size itself is a major constraint for business viability, then optimizing information structure, no matter how well, is unlikely to lead to substantial results.
6.5. Fixation on "Pens" as a Product and Other Possibilities
The research log includes the insight, "I see products like 'CMC' are selling, maybe I should have sourced and sold those instead of fixating on pens." This suggests that the "pen" product category, which was the main focus of this study, might not have been the most in-demand item in this niche market. If a similar analytical approach had been tried with products more aligned with market needs (e.g., health accessories, also mentioned in the log), different results might have been obtained. However, as the researcher pointed out, delving that far would go beyond the scope of a hobby and become a full-fledged business, so it was not pursued in this study.
7. Conclusion and Future Outlook
7.1. Summary of This Study
This study attempted to identify conditions (information combinations, pricing) for maximizing the attention received by conspiracy-related products on an online flea market, using a data-driven approach. The results confirmed that certain combinations of topics (Occult & Spiritual) and manipulation categories (Avoidance, Approach, etc.) tended to show relatively high reaction rates. However, the impact of price changes was complex and did not yield consistent effects. The most significant conclusion was that the scale of this niche market on the online flea market in question is extremely small, suggesting that applying a probabilistic "hit-or-miss" business model would make achieving stable sales difficult.
7.2. Implications of the Statistical Approach
This research demonstrated that even in niche markets with limited data, setting proxy indicators like reaction rates and employing exploratory approaches (experimental design, sequential improvement) can provide certain insights into market characteristics and consumer interest directions. Statistical thinking and data analysis can serve as a "compass" to aid decision-making even in such tentative situations.
7.3. Future Outlook
Based on the findings of this study, the following future prospects can be considered: * Validation on Larger Platforms: Conducting similar research on platforms with a larger user base might alleviate market size constraints and yield different results. * Application to Different Niche Markets: The "information combination exploration" approach used in this study could potentially be applied to product development and marketing strategies in various niche markets other than conspiracy theories. * Long-Term Observation: Based on the research log's reflection that "conspiracy business... it should be optimal to leave [products] there so they catch the eye when an idiot searches," observing product attention and sales over a longer period might yield different insights.
8. Research Limitations
This study has several limitations: * Limited Scope of Platform: The experiments were confined to a specific online flea market, and the results may not be generalizable to other platforms or the market as a whole. * Use of Proxy Indicators: "Reaction rate" of attention was used as the primary evaluation metric, rather than actual "sales" data, so it does not necessarily directly correlate with sales performance. * Sample Size Constraints: The number of products analyzed was 98, and the estimated market size was also small (around 100 weekly users), limiting statistical power. * Lack of Word-Level Analysis: Detailed analysis of the impact of individual words or phrases in product descriptions on attention, using advanced text mining or natural language processing, was not conducted.
9. References
- BBC News Japan. (2020, August 29). "QAnon to wa nani ka: Inbouron shuudan no shoutai to mokuteki, kikensei" [What is QAnon: The identity, purpose, and danger of the conspiracy theory group].
- Waseda University Institute for Advanced Social Sciences. (2022, August 1). "【Kenkyuu Shoukai】Inbouron wa naze hirogaru no ka? Sono shinri mekanizumu ni semaru" [(Research Introduction) Why do conspiracy theories spread? Approaching the psychological mechanism].
- Brotherton, R., French, C. C., & Pickering, A. D. (2013). Measuring belief in conspiracy theories: The generic conspiracist beliefs scale. Frontiers in psychology, 4, 279.
10. Appendix
10.1. Table: Detailed Definitions of Main Product Topic Categories (T1-T4)
| Category ID | Category Name | Summary/Keyword Examples | | :---------- | :------------------- | :--------------------------------------------------------------------------------------- | | T1 | Technology & Security | EMF, 5G, electromagnetic waves, radiation, shielding, communication, encryption, software, programs, biometric authentication, etc. | | T2 | Surveillance, Censorship & Government-Related | Surveillance, censorship, government secrets, secrets, documents, records, government documents, etc. | | T3 | Occult & Spiritual | Orb detection, spiritual phenomena, pendulums, ancient civilizations, alien contact, energy, crystals, chakras, quantum consciousness, etc. | | T4 | Forbidden Books & Knowledge Management | Ancient texts, forbidden books, ancient languages, shortwave (retro technology), etc. |
10.2. Table: Detailed Definitions of Product Manipulation Categories (M1-M3)
| Category ID | Category Name | Summary/Keyword Examples | | :---------- | :--------------------------- | :--------------------------------------------------------- | | M1 | Avoidance | Shielding, soundproofing, prevention, avoidance (e.g., avoiding negative energy) | | M2 | Detection | Detectors, finders, detection devices, deciphering (e.g., detecting hidden information) | | M3 | Approach/Processing/Amplification | Processing, amplification, magnification (e.g., approaching and amplifying ancient knowledge) |
10.3. Table: Summary of Main Analysis Results (Examples of High/Low Average Attention Scores by Topic × Manipulation Category)
| Combination (T-M) | Average Score (Approx.) | Trend | | :---------------- | :---------------------- | :----------------- | | T3 - M1 | High | Attracts attention | | T4 - M2 | High | Attracts attention | | T1 - M3 | Medium-High | Relatively attentive | | T2 - M3 | Medium | Somewhat attentive | | T1 - M1 | Low (Negative) | Less attention | | T2 - M1 | Low (Negative) | Less attention | (Note: The scores above are approximate values from the figures and actual precise numbers are based on the original data.)
10.4. Representative Examples of AI-Generated Product Descriptions
Basic Prompt Structure Example: "I want to sell {word} at a high price. Combine one from {maintopic} and {manipulation} to create a product description and an appropriate price. Respond in the format: 'Main Topic Category (T1-T4)':'Manipulation Category (M1-M3)':'Product Name':'Product Description':'Price' only once. Absolutely adhere to the specified {maintopic} and {manipulation}. No other output is necessary. Respond in Japanese." (Placeholders like
{word}would be filled with "ballpoint pen,"{maintopic}with "T3," and{manipulation}with "M1," etc., as specific instructions.)Generated Example (Combination T3 - M1): * "Thought Shield Ballpoint Pen: This pen was specially created to powerfully block and evade external negative thoughts and spiritual interference through the sacred act of writing. Based on ancient esoteric arts and quantum consciousness theory, a special energy shield sealed inside the pen protects your thought space and personal field. Using it when signing important contracts or for work requiring concentration helps defend against malice and unnecessary energy, maintaining clear thought. The act of holding it itself becomes a powerful barrier, effectively evading unnecessary energies in daily life." * "Quantum Shield Energy Pen: The act of writing with this pen deploys a quantum shield around your energy field. It is expected to block and evade negative energies and unnecessary external influences, and to balance your chakras. This is a limited-production item using special manufacturing methods and rare materials."
- Table 1: Definition of Main Product Topic Categories (T1-T4) (See Appendix 10.1 for details)
-
 @ ce2820ce:8cf20d40
2025-05-30 10:07:05
@ ce2820ce:8cf20d40
2025-05-30 10:07:05If you insist that my worldview join your pessimistic outlook on life, and you argue with me with a vengeance until I sympathize with your miserable failing hopeless vision of the future...than fight me!
Go ahead, give me all your reasons why I should fear:::Climate Change. Political Injustice. Too much screen time. The Dangers of social media. Fentanyl in my Cheerios. Glyphosate in my weed. Plastic in my brain. Estrogen in my receipt paper.
And the list goes on:::Nuclear War. The Ominous Second Coming of Hitler. The Genocide of Gaza. The Anti-semitism. The Ultra-Rich After my Red Meat.
And while I'm at it, how about the thousands of other “micro-negativities” that are casually beaten into our psyche all day. Pleasure and punishment in the same sadistic act. Warning labels and threats of death on everything from clothing to candy wrappers.
Don't get me wrong. I understand all the reasons why the alarm bells are going off. I'm most definitely thinking about the healthiest possible long term future for my kids, and for many generations to come.
We are not done here, is what I have to say to that. And if you narcissitic, self-loathing, pathologically empathetic descendants of hippies think that this is the last generation to ever walk the Earth, than all I ask is; Go Kill Yourselves Now, and spare us all the trouble of your self-perpetuated miseries.
If you have no mind for the future, and you don't plan on having children, than you better well keep your traps shut and go enjoy the fuck out of this glorious age of excess that we are currently abiding in, until its gone. Because what do you care if it is? You're not leaving any future generations to the dystopia, so what do you have to feel guilty about?
If you do have a mind for the future, and you have or would like to have children of your own, then my heartfelt response to you is that you should do your utmost to focus on the solutions, the bright spots, the gratitudes of life and the progress that humans have made and that we will continue to make. There is no stopping now.
There are no doubt terrifying problems and apocalyptic potentials for Planet Earth in the coming centuries, but this pattern of preaching fear HAS GOT TO STOP. All we are doing is entertaining negativity; giving far too much credit to the forces of destruction and to the demons of our own dissatisfactions.
Too many generations are now embracing a culture of hopelessness. We've pounded their heads full of horrible news for their future – climate change, diseases, technology woes – and we continue to do so on a daily basis. We pontificate about skyrocketing mental health and suicide rates among teens, but all we do is point fingers and shout platitudes at those to whom we offload the responsibility of our kids to.
So do the future a favor, and start thinking about one that you might actually enjoy living in. If you're already having that problem – the one about enjoying things – than figure out what the fuck it is that is keeping you from envisioning a positive future. What went wrong in your own life that made you so depressed and unhappy? Misery loves company, we all know that, and it seems that the only way to relate to my peers these days is through a semi-informed rant about the stresses and horrors of the modern world.
The problem is, we don't stick to our guns when it comes to those convictions. We complain about social media, but we still use it everyday. We put AI on blast and expound its humanity ending potentials, while we ask it questions about our astrology and our skin conditions.
So if you are going to spread the murder pron, and fill your stories up with the perpetual shock and fear, in-between selfies of you enjoying your luxurious life, than you are living a duplicitous and dangerous path.
You feel guilty for your privileged life, and the way you assuage that is by expounding your concern for the ills and unfairness of the outside world, and by pretending to “put in the work” to “heal our wounds” or destroy the patriarchy by smearing your big ass across my Instagram feeds. Here, let me help you.
Your Suffering isn't Saving Anybody. It's only pulling a drag net through your mind's ability to let happiness and love into your life. Don't take pride in your own wounds, as you do not really wish them on anybody else, and you certainly don't want your kids to feel the trauma's you are trying to get over from your own childhood.
So if you think “pessimism is the only morally acceptable emotion” when it comes to thinking about the future, than I will fight you tooth and nail to maintain my own delusion that the future is still bright. If you want to tell my kids that Hitler is coming, that the sea levels are rising, and that AI will end their lives, than I will beat your misery to a bloody pulp, and try and help you see a future worth living.
The point is, I've lost friends, and watched love ones fall into this “addiction” to the broadcast news negativity. It is a bad habit that must be broken, as we are losing our ability to trust, and losing our faith in our own power. If you isolate yourself with misery, than you will never feel emboldened to overcome anything, and you will never learn what love can do.
Look at the future. If you don't see any hope, than you better find some. It takes courage to move forward, and it takes courage to kill yourself. It takes only cowardice to remain in the muddled middle-ground of in-action and crippling in-decision.
Make the move, and tell me how it goes. I’m here to help.
With Love,
-§parrow
-
 @ dfa02707:41ca50e3
2025-05-31 02:01:20
@ dfa02707:41ca50e3
2025-05-31 02:01:20Contribute to keep No Bullshit Bitcoin news going.
- RoboSats v0.7.7-alpha is now available!
NOTE: "This version of clients is not compatible with older versions of coordinators. Coordinators must upgrade first, make sure you don't upgrade your client while this is marked as pre-release."
- This version brings a new and improved coordinators view with reviews signed both by the robot and the coordinator, adds market price sources in coordinator profiles, shows a correct warning for canceling non-taken orders after a payment attempt, adds Uzbek sum currency, and includes package library updates for coordinators.
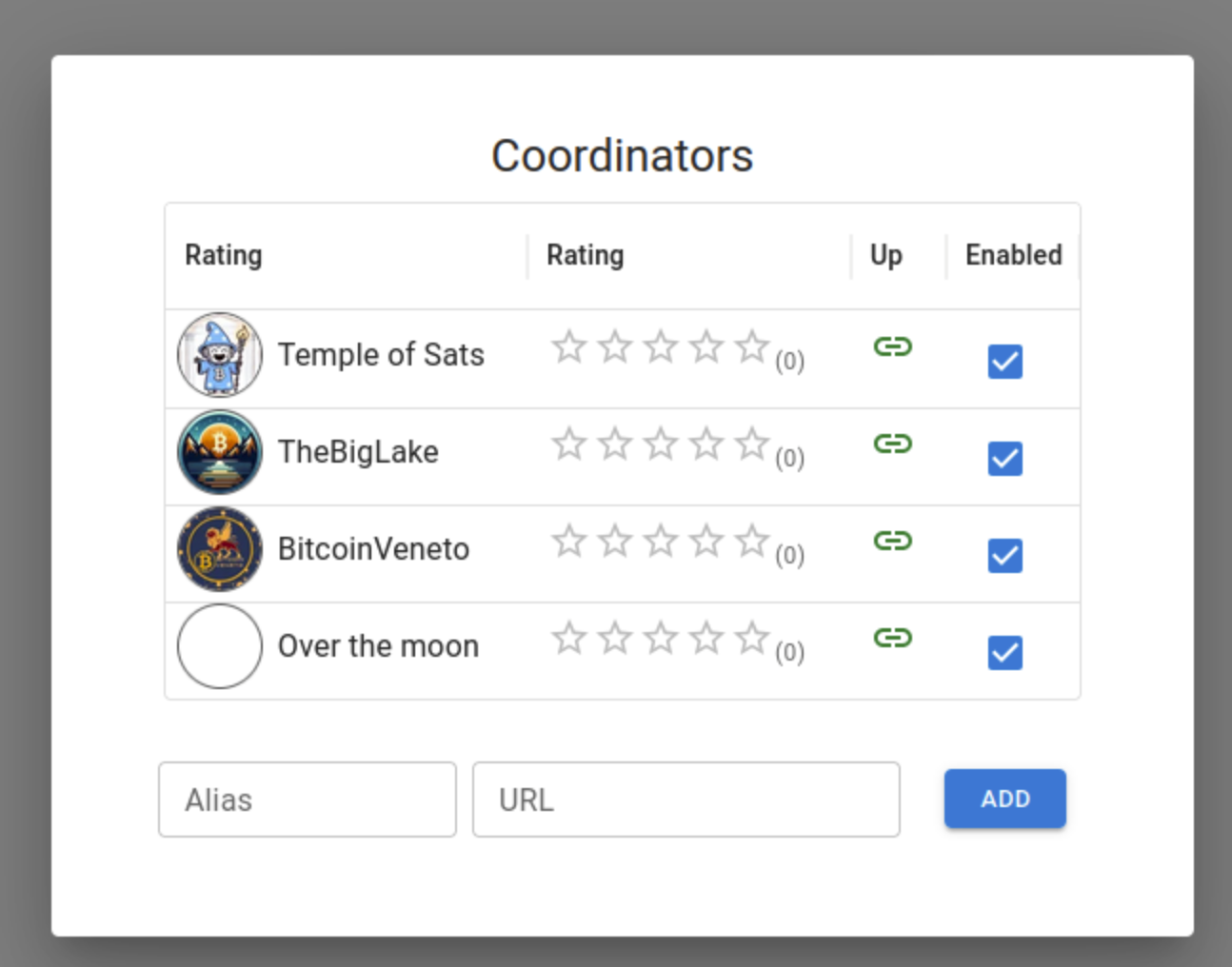
Source: RoboSats.
- siggy47 is writing daily RoboSats activity reviews on stacker.news. Check them out here.
- Stay up-to-date with RoboSats on Nostr.
What's new
- New coordinators view (see the picture above).
- Available coordinator reviews signed by both the robot and the coordinator.
- Coordinators now display market price sources in their profiles.
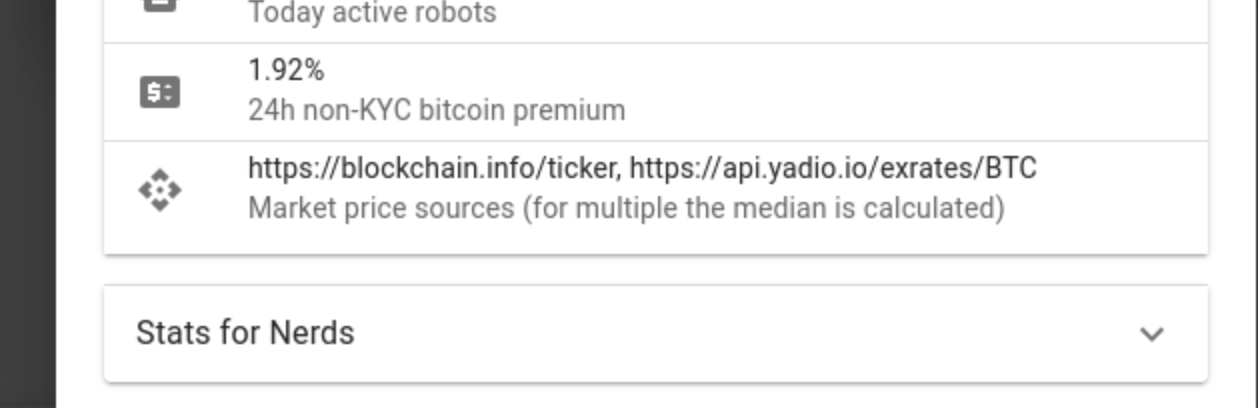
Source: RoboSats.
- Fix for wrong message on cancel button when taking an order. Users are now warned if they try to cancel a non taken order after a payment attempt.
- Uzbek sum currency now available.
- For coordinators: library updates.
- Add docker frontend (#1861).
- Add order review token (#1869).
- Add UZS migration (#1875).
- Fixed tests review (#1878).
- Nostr pubkey for Robot (#1887).
New contributors

Full Changelog: v0.7.6-alpha...v0.7.7-alpha
-
 @ 7459d333:f207289b
2025-05-30 07:57:07
@ 7459d333:f207289b
2025-05-30 07:57:07Tokenization of physical assets sounds kinda dumb. Say you tokenize a house. What happens if you loose the private keys? What happens if the last “legal” (on paper) owner claims it? Basically, the tokenization is useless. The house is still subject to whatever jurisdiction is in. And the smart contract can say whatever, but that does not make it true.
What's not so obvious is for virtual assets or service tokens. A good example is cashu. Where tokenizing Bitcoin has the advantages of allowing the users to transact with it “without the mint's permission”. This could be applied similarly for concert tickets or API credits.
For example, the biggest problem of concert ticket reselling is trusting that other copies of the PDF with the QR code won't be used before the one you bought. Or that you won't have problems at the entry because the ticket is not in your name. A mint that allows users to transact between them preventing double spending and fungibility would solve this.
But for some reason shitcoiners are obsessed on tokenizing physical assets or company shares. Where the only benefit that tokenizing could bring is avoiding regulations (until they update the laws).
So, what's your take on tokenization?
https://stacker.news/items/992519
-
 @ dfa02707:41ca50e3
2025-05-31 02:01:18
@ dfa02707:41ca50e3
2025-05-31 02:01:18- This version introduces the Soroban P2P network, enabling Dojo to relay transactions to the Bitcoin network and share others' transactions to break the heuristic linking relaying nodes to transaction creators.
- Additionally, Dojo admins can now manage API keys in DMT with labels, status, and expiration, ideal for community Dojo providers like Dojobay. New API endpoints, including "/services" exposing Explorer, Soroban, and Indexer, have been added to aid wallet developers.
- Other maintenance updates include Bitcoin Core, Tor, Fulcrum, Node.js, plus an updated ban-knots script to disconnect inbound Knots nodes.
"I want to thank all the contributors. This again shows the power of true Free Software. I also want to thank everyone who donated to help Dojo development going. I truly appreciate it," said Still Dojo Coder.
What's new
- Soroban P2P network. For MyDojo (Docker setup) users, Soroban will be automatically installed as part of their Dojo. This integration allows Dojo to utilize the Soroban P2P network for various upcoming features and applications.
- PandoTx. PandoTx serves as a transaction transport layer. When your wallet sends a transaction to Dojo, it is relayed to a random Soroban node, which then forwards it to the Bitcoin network. It also enables your Soroban node to receive and relay transactions from others to the Bitcoin network and is designed to disrupt the assumption that a node relaying a transaction is closely linked to the person who initiated it.
- Pushing transactions through Soroban can be deactivated by setting
NODE_PANDOTX_PUSH=offindocker-node.conf. - Processing incoming transactions from Soroban network can be deactivated by setting
NODE_PANDOTX_PROCESS=offindocker-node.conf.
- Pushing transactions through Soroban can be deactivated by setting
- API key management has been introduced to address the growing number of people offering their Dojos to the community. Dojo admins can now access a new API management tab in their DMT, where they can create unlimited API keys, assign labels for easy identification, and set expiration dates for each key. This allows admins to avoid sharing their main API key and instead distribute specific keys to selected parties.
- New API endpoints. Several new API endpoints have been added to help API consumers develop features on Dojo more efficiently:
- New:
/latest-block- returns data about latest block/txout/:txid/:index- returns unspent output data/support/services- returns info about services that Dojo exposes
- Updated:
/tx/:txid- endpoint has been updated to return raw transaction with parameter?rawHex=1
- The new
/support/servicesendpoint replaces the deprecatedexplorerfield in the Dojo pairing payload. Although still present, API consumers should use this endpoint for explorer and other pairing data.
- New:
Other changes
- Updated ban script to disconnect inbound Knots nodes.
- Updated Fulcrum to v1.12.0.
- Regenerate Fulcrum certificate if expired.
- Check if transaction already exists in pushTx.
- Bump BTC-RPC Explorer.
- Bump Tor to v0.4.8.16, bump Snowflake.
- Updated Bitcoin Core to v29.0.
- Removed unnecessary middleware.
- Fixed DB update mechanism, added api_keys table.
- Add an option to use blocksdir config for bitcoin blocks directory.
- Removed deprecated configuration.
- Updated Node.js dependencies.
- Reconfigured container dependencies.
- Fix Snowflake git URL.
- Fix log path for testnet4.
- Use prebuilt addrindexrs binaries.
- Add instructions to migrate blockchain/fulcrum.
- Added pull policies.
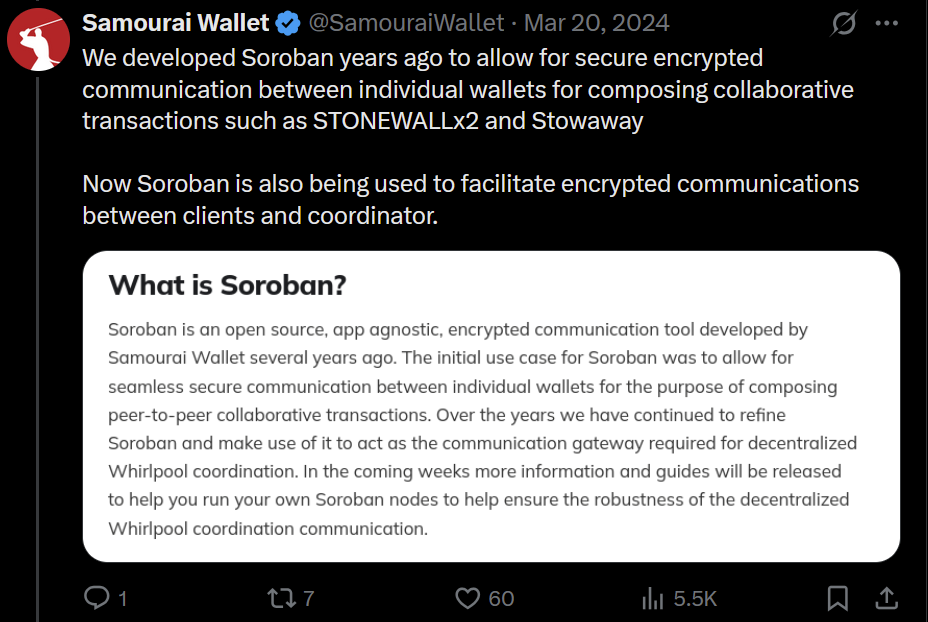

Learn how to set up and use your own Bitcoin privacy node with Dojo here.
-
 @ dfa02707:41ca50e3
2025-05-31 02:01:18
@ dfa02707:41ca50e3
2025-05-31 02:01:18Contribute to keep No Bullshit Bitcoin news going.
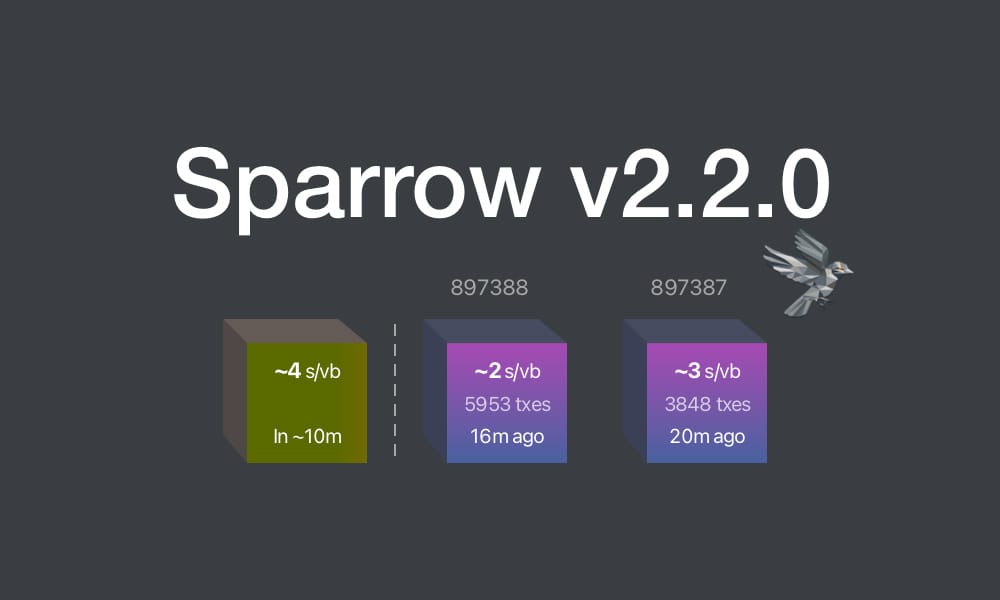
This update brings key enhancements for clarity and usability:
- Recent Blocks View: Added to the Send tab and inspired by Mempool's visualization, it displays the last 2 blocks and the estimated next block to help choose fee rates.
- Camera System Overhaul: Features a new library for higher resolution detection and mouse-scroll zoom support when available.
- Vector-Based Images: All app images are now vectorized and theme-aware, enhancing contrast, especially in dark mode.
- Tor & P2A Updates: Upgraded internal Tor and improved support for pay-to-anchor (P2A) outputs.
- Linux Package Rename: For Linux users, Sparrow has been renamed to sparrowwallet (or sparrowserver); in some cases, the original sparrow package may need manual removal.
- Additional updates include showing total payments in multi-payment transaction diagrams, better handling of long labels, and other UI enhancements.
- Sparrow v2.2.1 is a bug fix release that addresses missing UUID issue when starting Tor on recent macOS versions, icons for external sources in Settings and Recent Blocks view, repackaged
.debinstalls to use older gzip instead of zstd compression, and removed display of median fee rate where fee rates source is set to Server.
Learn how to get started with Sparrow wallet:
Release notes (v2.2.0)
- Added Recent Blocks view to Send tab.
- Converted all bitmapped images to theme aware SVG format for all wallet models and dialogs.
- Support send and display of pay to anchor (P2A) outputs.
- Renamed
sparrowpackage tosparrowwalletandsparrowserveron Linux. - Switched camera library to openpnp-capture.
- Support FHD (1920 x 1080) and UHD4k (3840 x 2160) capture resolutions.
- Support camera zoom with mouse scroll where possible.
- In the Download Verifier, prefer verifying the dropped file over the default file where the file is not in the manifest.
- Show a warning (with an option to disable the check) when importing a wallet with a derivation path matching another script type.
- In Cormorant, avoid calling the
listwalletdirRPC on initialization due to a potentially slow response on Windows. - Avoid server address resolution for public servers.
- Assume server address is non local for resolution failures where a proxy is configured.
- Added a tooltip to indicate truncated labels in table cells.
- Dynamically truncate input and output labels in the tree on a transaction tab, and add tooltips if necessary.
- Improved tooltips for wallet tabs and transaction diagrams with long labels.
- Show the address where available on input and output tooltips in transaction tab tree.
- Show the total amount sent in payments in the transaction diagram when constructing multiple payment transactions.
- Reset preferred table column widths on adjustment to improve handling after window resizing.
- Added accessible text to improve screen reader navigation on seed entry.
- Made Wallet Summary table grow horizontally with dialog sizing.
- Reduced tooltip show delay to 200ms.
- Show transaction diagram fee percentage as less than 0.01% rather than 0.00%.
- Optimized and reduced Electrum server RPC calls.
- Upgraded Bouncy Castle, PGPainless and Logback libraries.
- Upgraded internal Tor to v0.4.8.16.
- Bug fix: Fixed issue with random ordering of keystore origins on labels import.
- Bug fix: Fixed non-zero account script type detection when signing a message on Trezor devices.
- Bug fix: Fixed issue parsing remote Coldcard xpub encoded on a different network.
- Bug fix: Fixed inclusion of fees on wallet label exports.
- Bug fix: Increase Trezor device libusb timeout.
Linux users: Note that the
sparrowpackage has been renamed tosparrowwalletorsparrowserver, and in some cases you may need to manually uninstall the originalsparrowpackage. Look in the/optfolder to ensure you have the new name, and the original is removed.What's new in v2.2.1
- Updated Tor library to fix missing UUID issue when starting Tor on recent macOS versions.
- Repackaged
.debinstalls to use older gzip instead of zstd compression. - Removed display of median fee rate where fee rates source is set to Server.
- Added icons for external sources in Settings and Recent Blocks view
- Bug fix: Fixed issue in Recent Blocks view when switching fee rates source
- Bug fix: Fixed NPE on null fee returned from server
-
 @ 3770c235:16042bcc
2025-05-30 05:25:21
@ 3770c235:16042bcc
2025-05-30 05:25:21Let’s clear something up: frugal living isn’t about eating ramen every night or never treating yourself. It’s about being intentional with your money so you can enjoy what matters more. Think of it like editing a movie—you cut the boring scenes to highlight the best parts. You don’t have to give up lattes, travel, or Friday pizza nights. You just need a few clever tricks to make your money stretch further while keeping the fun intact.
Take my friend Alex, for example. Last year, he felt overwhelmed by credit card debt but didn’t want to give up his weekend hikes or coffee shop visits. By tweaking a few habits—like auditing subscriptions and prioritizing experiences—he paid off $5,000 in debt and still took a camping trip with his kids. The secret? Small, intentional choices that add up. In this guide, we’ll share practical, joy-friendly hacks to help you save smarter. Plus, we’ll mention sites like Crown Money—a budgeting service that makes tracking your progress effortless—so you can focus on living well, not pinching pennies.
**1. Audit Your Subscriptions (Yes, Even That One) ** You know that streaming service you haven’t opened since 2022? Or the gym membership you keep “meaning to use”? Those small charges add up fast. A recent study found the average person spends 219/month on forgotten subscriptions—that’s over 2,600 a year!
• The Hack: Every 3 months, review your subscriptions. Ask: “Do I actually use this?” Cancel anything that doesn’t spark joy. • Pro Tip: Use Crown Money to see all your subscriptions in one place. The app automatically flags recurring charges, so you don’t have to hunt through bank statements. You’ll even get a nudge like, “You’ve paid $14.99/month for ‘Premium Yoga App’—last used 6 months ago. Cancel?” Real-Life Example: Sarah canceled two unused streaming services and a meditation app she forgot about. She saved $45/month—enough to fund her new hobby: pottery classes. “I didn’t realize how much clutter I was paying for,” she said. “Now I’m learning to make mugs instead of binge-watching shows I don’t even like.”
**2. Embrace the “Joy Budget” (Seriously, Budget for Fun) ** Frugality fails when it feels like deprivation. Instead, carve out guilt-free money for things you love. Behavioral scientists call this “temptation bundling”—pairing savings goals with rewards to stay motivated.
• The Hack: Allocate 10–15% of your budget to a “Joy Fund” for hobbies, dining out, or travel. • Pro Tip: In Crown Money, create a custom category like “Adventure Fund” or “Treat Yourself.” Set a monthly limit and track how much you’ve saved for that weekend getaway or concert ticket. The app’s visual progress bars turn saving into a game—imagine watching your “Beach Trip 2024” fund grow with every dollar.
Real-Life Example: Mark loves trying new restaurants. By setting a $100/month “Dining Out” budget in Crown Money, he enjoys date nights without overspending. “I used to feel guilty splurging on sushi,” he shared. “Now I know it’s part of the plan, so I savor every bite.”
- Master Mindful Spending (Ask This One Question) Before buying anything non-essential, ask: “Will this add value to my life, or just clutter?” Retail therapy might feel good in the moment, but that $50 impulse sweater often ends up forgotten in the back of your closet.
• The Hack: Implement a 24-hour “cooling-off” period for impulse buys. If you still want it tomorrow, go for it! • Pro Tip: Use Crown Money to review your spending trends. The app’s monthly reports show where your money goes, helping you spot habits (like late-night online shopping) that don’t align with your goals. Set up alerts like, “You’ve spent $75 on ‘Miscellaneous’ this week—want to check in?” Real-Life Example: Lisa avoided buying a $200 jacket on impulse. After 24 hours, she realized she didn’t need it—and put the money toward a weekend camping trip instead. “I almost bought something I’d wear once,” she laughed. “Now I have photos of sunsets instead of buyer’s remorse.”
- DIY and Swap (Your Wallet Will Thank You) Frugal living thrives on creativity. Swap buying new for: • DIY solutions: Make coffee at home (a $5 bag of beans lasts weeks!), repair clothes, or grow herbs instead of buying them. • Community swaps: Trade books, tools, or skills with friends (e.g., “I’ll babysit if you help me fix my bike”).
Pro Tip: Track your monthly expenses in Crown Money. Create a category like “Homemade Wins” and watch how small choices (like brewing your latte) add up over time. For example, skipping a daily 4 coffee shop visit saves 120/month—that’s a weekend road trip! Real-Life Example: Jake started meal prepping lunches instead of buying 15 salads. He saves 300/month—enough for a monthly massage. “I’m eating healthier and funding self-care,” he said. “Plus, my coworkers are jealous of my teriyaki bowls.”
- Prioritize Experiences Over “Stuff” (Happiness Science Approved) Research shows experiences bring longer-lasting joy than material purchases. A 2023 study found people who spent money on concerts, trips, or classes reported 30% higher life satisfaction than those who bought gadgets or clothes.
Instead of splurging on gadgets, invest in: • Free/low-cost adventures: Hiking, picnics, game nights, or exploring local festivals. • Shared moments: Host a potluck instead of dining out. Pro Tip: Use Crown Money to set a goal like “Summer Adventure Fund.” Allocate $50/month, and let the app remind you to fund it automatically. Watching that fund grow feels like planning a vacation in slow motion. Real-Life Example: Maria and her partner skipped a pricey vacation and rented a cozy cabin nearby. They saved $1,200 and still made memories roasting marshmallows under the stars. “We thought we needed a fancy trip to connect,” she said. “Turns out, all we needed was a fire pit and no Wi-Fi.”
Key Takeaways • Cut the clutter: Cancel unused subscriptions and track them with tools like Crown Money. • Budget for joy: Allocate guilt-free money for hobbies and experiences. • Pause before purchasing: Avoid impulse buys with a 24-hour rule. • Get creative: DIY, swap, and repurpose to save without sacrifice. • Invest in experiences: They’re richer than “stuff” and often cheaper.
FAQs: Frugal Living Made Simple Q: How do I stay motivated to save? A: Tie savings to specific goals (e.g., “Save $500 for a weekend trip”). Apps like Crown Money let you visualize progress, which feels rewarding!
Q: Can I be frugal and still socialize? A: Absolutely! Host DIY spa nights, picnic potlucks, or free museum days. Use Crown Money to set a “Social Fun” budget and stick to it.
Q: What if I slip up and overspend? A: No guilt! Adjust your budget next month. Crown Money makes it easy to shift funds between categories.
Q: How do I track small savings from DIY habits? A: Create a custom category in Crown Money (e.g., “Homemade Wins”) and log your savings manually. Watching it grow is addictive!
Q: What if I have a financial emergency? A: Build a “Safety Net” category in Crown Money. Start small—even $20/month adds up. The app’s reminders keep you consistent.
**Final Thoughts: Frugal Is Freedom ** Frugal living isn’t about saying “no”—it’s about saying “yes” to what truly lights you up. By trimming the financial fat (goodbye, unused subscriptions!), budgeting for joy, and getting creative, you can save money and savor life’s best moments. Tools like Crown Money are your allies here. They handle the tracking and nudging, so you can focus on the fun parts: planning adventures, trying new recipes, or laughing with friends over a board game. Remember: the goal isn’t perfection. It’s progress. Start small, celebrate wins, and let your frugal habits grow naturally. Your wallet (and your inner joy-seeker) will thank you.
-
 @ eb0157af:77ab6c55
2025-05-31 02:01:05
@ eb0157af:77ab6c55
2025-05-31 02:01:05The blockchain analytics firm claims to have identified the Bitcoin addresses held by the company led by Saylor.
Arkham Intelligence announced it had identified addresses linked to Strategy. According to Arkham’s statements, an additional 70,816 BTC connected to the company have been identified, with an estimated value of around $7.6 billion at current prices. This discovery would bring the total amount of Strategy’s identified holdings to $54.5 billion.
SAYLOR SAID HE WOULD NEVER REVEAL HIS ADDRESSES … SO WE DID
We have identified an additional 70,816 BTC belonging to Strategy, bringing our total identified MSTR BTC holdings to $54.5 Billion. We are the first to publicly identify these holdings.
This represents 87.5% of… pic.twitter.com/P3OVdVrhQL
— Arkham (@arkham) May 28, 2025
The analytics firm claims to have mapped 87.5% of Strategy’s total holdings. In a provocative post on X, Arkham wrote:
“Saylor said he would never reveal his addresses. So, we did it for him.
Previously, we tagged:
– 107,000 BTC sent to MSTR’s Fidelity deposits (Fidelity does not segregate custody, so these BTC do not appear in the MSTR entity)
– Over 327,000 BTC held in segregated custody, including Coinbase Prime, in our MSTR entity.”Arkham’s revelations directly clash with Michael Saylor’s public statements on wallet security. During the Bitcoin 2025 conference in Las Vegas, the Strategy chairman explicitly warned against publishing corporate wallet addresses.
“No institutional or enterprise security analyst would ever think it’s a good idea to publish all the wallet addresses so you can be tracked back and forth,” Saylor said during the event.
The executive chairman of Strategy added:
“The current, conventional way to publish proof-of-reserves is an insecure proof of reserves… It’s not a good idea, it’s a bad idea.”
He compared publishing wallet addresses to “publishing the addresses, bank accounts, and phone numbers of your kids hoping it will protect them — when in fact it makes them more vulnerable.”
Finally, the executive chairman suggested using artificial intelligence to explore the security implications of such a practice, claiming that in-depth research could produce “50 pages” of potential security risks.
The post Arkham reveals 87% of Strategy’s Bitcoin addresses appeared first on Atlas21.
-
 @ 9ca447d2:fbf5a36d
2025-05-31 02:00:42
@ 9ca447d2:fbf5a36d
2025-05-31 02:00:42Trump Media & Technology Group (TMTG), the company behind Truth Social and other Trump-branded digital platforms, is planning to raise $2.5 billion to build one of the largest bitcoin treasuries among public companies.
The deal involves the sale of approximately $1.5 billion in common stock and $1.0 billion in convertible senior secured notes.
According to the company, the offering is expected to close by the end of May, pending standard closing conditions.
Devin Nunes, CEO of Trump Media, said the investment in bitcoin is a big part of the company’s long-term plan.
“We view Bitcoin as an apex instrument of financial freedom,” Nunes said.
“This investment will help defend our Company against harassment and discrimination by financial institutions, which plague many Americans and U.S. firms.”
He added that the bitcoin treasury will be used to create new synergies across the company’s platforms including Truth Social, Truth+, and the upcoming financial tech brand Truth.Fi.
“It’s a big step forward in the company’s plans to evolve into a holding company by acquiring additional profit-generating, crown jewel assets consistent with America First principles,” Nunes said.
The $2.5 billion raise will come from about 50 institutional investors. The $1 billion in convertible notes will have 0% interest and be convertible into shares at a 35% premium.
TMTG’s current liquid assets, including cash and short-term investments, are $759 million as of the end of the first quarter of 2025. With this new funding, the company’s liquid assets will be over $3 billion.
Custody of the bitcoin treasury will be handled by Crypto.com and Anchorage Digital. They will manage and store the digital assets.
Earlier this week The Financial Times reported Trump Media was planning to raise $3 billion for digital assets acquisitions.
The article said the funds would be used to buy bitcoin and other digital assets, and an announcement could come before a major related event in Las Vegas.
Related: Bitcoin 2025 Conference Kicks off in Las Vegas Today
Trump Media denied the FT report. In a statement, the company said, “Apparently the Financial Times has dumb writers listening to even dumber sources.”
There was no further comment. However, the official $2.5 billion figure, which was announced shortly after by Trump Media through a press release, aligns with its actual filing and investor communication.
Trump Media’s official announcement
This comes at a time when the Trump family and political allies are showing renewed interest in Bitcoin.
President Donald Trump who is now back in office since the 2025 election, has said he wants to make the U.S. the “crypto capital of the world.”
Trump Media is also working on retail bitcoin investment products including ETFs aligned with America First policies.
These products will make bitcoin more accessible to retail investors and support pro-Trump financial initiatives.
But not everyone is happy.
Democratic Senator Elizabeth Warren recently expressed concerns about Trump Media’s Bitcoin plans. She asked U.S. regulators to clarify their oversight of digital-asset ETFs, warning of investor risk.
Industry insiders are comparing Trump Media’s plans to Strategy (MSTR) which has built a multi-billion dollar bitcoin treasury over the last year. They used stock and bond sales to fund their bitcoin purchases.
-
 @ 502ab02a:a2860397
2025-05-30 01:14:10
@ 502ab02a:a2860397
2025-05-30 01:14:10ย้อนกลับไปปี 2014 ชายชื่อ Patrick O. Brown ศาสตราจารย์ชีววิทยาเชิงโมเลกุลแห่งมหาวิทยาลัยแตนฟอร์ด ตัดสินใจลาออกจากเส้นทางวิชาการสายหลัก เพื่อมาก่อตั้งบริษัทที่เขาเชื่อว่าจะเปลี่ยนโลก Impossible Foods
ดร. แพทริค โอ. บราวน์ (Patrick O. Brown) เป็นนักชีวเคมีและนักธุรกิจชาวอเมริกันและศาสตราจารย์กิตติคุณด้านชีวเคมีแห่งมหาวิทยาลัยสแตนฟอร์ด เขาได้รับปริญญาตรี แพทยศาสตรบัณฑิต และปรัชญาดุษฎีบัณฑิตด้านชีวเคมีจากมหาวิทยาลัยชิคาโก หลังจากนั้น เขาได้เข้ารับการฝึกอบรมด้านกุมารเวชศาสตร์ที่โรงพยาบาล Children's Memorial ในชิคาโก ในช่วงหลังปริญญาเอก เขาได้ทำงานวิจัยเกี่ยวกับกลไกที่ไวรัส HIV และเรโทรไวรัสอื่น ๆ แทรกยีนของพวกมันเข้าสู่จีโนมของเซลล์ที่ติดเชื้อ ซึ่งช่วยนำไปสู่การพัฒนายาใหม่ในการต่อสู้กับโรคนี้
ในช่วงต้นทศวรรษ 1990 ดร. บราวน์และทีมงานของเขาที่สแตนฟอร์ดได้พัฒนาเทคโนโลยี DNA microarray ซึ่งเป็นเครื่องมือที่ช่วยให้นักวิจัยสามารถวิเคราะห์การแสดงออกของยีนทั้งหมดในจีโนมได้พร้อมกัน เทคโนโลยีนี้มีบทบาทสำคัญในการวิจัยทางชีววิทยาและการแพทย์ โดยเฉพาะในการจำแนกประเภทของมะเร็งและการพยากรณ์โรค
นอกจากนี้ ดร. บราวน์ยังเป็นผู้ร่วมก่อตั้ง Public Library of Science (PLOS) ซึ่งเป็นองค์กรไม่แสวงหาผลกำไรที่มุ่งเน้นการเผยแพร่ผลงานวิจัยทางวิทยาศาสตร์ให้เข้าถึงได้ฟรีและเปิดกว้างต่อสาธารณะ
ในปี 2011 ดร. บราวน์ได้ก่อตั้ง Impossible Foods โดยมีเป้าหมายในการสร้างผลิตภัณฑ์เนื้อสัตว์จากพืชที่มีรสชาติและเนื้อสัมผัสคล้ายเนื้อสัตว์จริง เพื่อลดผลกระทบต่อสิ่งแวดล้อมจากการเลี้ยงสัตว์ เขาและทีมงานได้ค้นพบว่าโมเลกุล heme ซึ่งเป็นส่วนประกอบที่ให้รสชาติและกลิ่นเฉพาะของเนื้อสัตว์ สามารถผลิตจากพืชได้ โดยเฉพาะจากรากถั่วเหลือง พวกเขาใช้เทคนิคทางวิศวกรรมชีวภาพในการผลิต heme จากยีสต์ที่ได้รับการดัดแปลงพันธุกรรม และนำมาผสมกับโปรตีนจากพืชเพื่อสร้างผลิตภัณฑ์ที่มีลักษณะคล้ายเนื้อสัตว์
ดร. บราวน์ได้รับการยอมรับอย่างกว้างขวางในวงการวิทยาศาสตร์และเทคโนโลยี โดยได้รับรางวัลและเกียรติคุณหลายรายการ รวมถึงการเป็นสมาชิกของ National Academy of Sciences และ National Academy of Medicine ของสหรัฐอเมริกา ด้วยความมุ่งมั่นในการแก้ไขปัญหาสิ่งแวดล้อมผ่านนวัตกรรมทางอาหาร ดร. แพทริค โอ. บราวน์ ได้กลายเป็นบุคคลสำคัญที่มีบทบาทในการเปลี่ยนแปลงวิธีการบริโภคอาหารของโลกในศตวรรษที่ 21
เป้าหมายของเขาไม่ใช่เพียงแค่ทำอาหาร แต่คือ "ยุติการทำปศุสัตว์ให้หมดสิ้นภายในปี 2035"
เขาไม่ได้พูดลอย ๆ เขาลงมือ “ทำเนื้อจากพืช” ด้วยเทคโนโลยีที่ซับซ้อนระดับวิศวกรรมชีวภาพ นำโปรตีนจากถั่วเหลือง + น้ำมันมะพร้าว + เทคเจอร์ + สารเติมแต่งอีกชุดใหญ่ มาผ่านกระบวนการแปรรูปจนดูคล้ายเนื้อย่าง แต่ที่ทำให้ “มันดูเหมือนเนื้อจริง” คือการเติม ฮีม (Heme) เข้าไปสารประกอบที่อยู่ในเลือดและเนื้อสัตว์จริง ๆ
Impossible Foods คือบริษัทที่ไม่ได้เพียง “ปลอมรสชาติเนื้อ” แต่พยายามสร้างเนื้อจากพืช ให้เหมือนเนื้อจริงที่สุดเท่าที่วิทยาศาสตร์จะเอื้อมถึง จุดขายที่ทำให้แบรนด์นี้ดังเปรี้ยงก็คือสิ่งที่เรียกว่า “ฮีม” (heme) หรือโมเลกุลเหล็กในเลือด ซึ่งเป็นตัวการหลักที่ทำให้เนื้อวัวมีกลิ่นและรสเฉพาะตัวเวลาถูกย่างจนหอมฉุย
ดร.แพทริค บราวน์ และทีมนักวิจัยของเขาเริ่มจากการค้นหาว่า “อะไรในพืช” ให้กลิ่นคล้ายเลือด พวกเขาพบว่า “Leghemoglobin” ซึ่งอยู่ในรากถั่วเหลือง มีโครงสร้างใกล้เคียงกับ Hemoglobin ในเลือดสัตว์มากที่สุด จุดพลิกของเทคโนโลยีนี้คือ การผลิตเลกฮีโมโกลบินจากพืชจำนวนมาก ทำไม่ได้โดยการถอนรากถั่วมาทุบคั้น แต่ต้องอาศัยวิศวกรรมชีวภาพขั้นสูง
พวกเขาจึงใช้กระบวนการที่เรียกว่า “fermentation by genetically modified yeast” หรือการหมักโดยยีสต์ที่ผ่านการดัดแปลงพันธุกรรม โดยนำยีนของพืชที่สร้าง leghemoglobin ไปใส่ในยีสต์ (Pichia pastoris) แล้วเลี้ยงยีสต์นั้นในถังหมักขนาดใหญ่แบบเดียวกับโรงเบียร์ พอยีสต์ขยายตัว มันจะผลิตเลกฮีโมโกลบินออกมาจำนวนมาก จากนั้นจึงสกัดออกมาผสมกับโปรตีนจากพืช เช่น โปรตีนจากถั่วเหลือง หรือโปรตีนจากมันฝรั่ง
เพื่อให้เนื้อสัมผัสคล้ายเนื้อจริง ทีม Impossible Foods ยังใช้เทคนิคอื่นร่วมด้วย เช่น -Coconut Oil และ Sunflower Oil เป็นแหล่งไขมันที่ให้สัมผัส “ฉ่ำๆ” คล้ายไขมันเนื้อวัว -Methylcellulose สารที่ช่วยทำให้ส่วนผสมเกาะตัวเป็นก้อน คล้ายเนื้อบดจริง -Natural Flavors กลิ่นที่สกัดจากพืชหลายชนิด เพื่อเลียนแบบกลิ่นไหม้จากเนื้อย่าง
ทุกอย่างถูกผสมให้เข้ากัน ผ่านเครื่องอัดขึ้นรูป (extrusion) ที่ทำให้เนื้อออกมามี “เส้นใย” คล้ายกล้ามเนื้อวัว หรือหมู เมื่อโดนความร้อน โปรตีนจะเปลี่ยนโครงสร้าง (denature) และมีกลิ่นออกมาคล้ายๆ เนื้อย่างจริงๆ พร้อมน้ำสีแดงคล้ายเลือด (จาก heme) ไหลเยิ้ม ซึ่งคือไอเดียที่ทำให้ Impossible Burger เป็นมากกว่าแค่ “เบอร์เกอร์ผัก”
ผลลัพธ์คือ… เบอร์เกอร์พืชที่มีเลือดซึม สีชมพูดู juicy และกลิ่นไหม้ติดกระทะ จนคนกินรู้สึกเหมือนกำลังย่างเนื้อจริง ๆ
ฟังดูอัศจรรย์ใช่ไหม? แต่...การเติมฮีมจากยีสต์ตัดต่อพันธุกรรมลงในอาหาร ไม่เคยมีในธรรมชาติมาก่อน ในปี 2017 Impossible Foods ต้องยื่นเรื่องต่อ FDA เพื่อขออนุมัติว่า leghemoglobin จากยีสต์ GMO “ปลอดภัย”
แต่ในตอนนั้น FDA ตอบว่า “ยังไม่มีข้อมูลเพียงพอ” ว่าจะไม่ก่อให้เกิดภูมิแพ้หรือผลข้างเคียงในระยะยาว (ใช่แล้วจ้ะ... สารที่อยู่ในเบอร์เกอร์ชื่อดัง ถูกขายก่อนที่ FDA จะสรุปว่าปลอดภัยเต็มร้อย)
แล้วในที่สุด ปี 2019 FDA ก็ให้ผ่านแบบ “GRAS” (Generally Recognized As Safe) โดยใช้ข้อมูลจากการทดลองภายในของบริษัทเอง ไม่ใช่การทดสอบอิสระจากภายนอก
เฮียว่าอันนี้ต้องมีใครสะกิดในใจแล้วล่ะว่า “เรากำลังเอาอะไรเข้าปากกันแน่?”
แม้จะฟังดูเท่ ไฮเทค และดีต่อสิ่งแวดล้อม แต่ก็มีคำถามจากนักวิจารณ์มากมายว่า… แท้จริงแล้วอาหารเหล่านี้เป็นอาหาร “เพื่อสิ่งแวดล้อม” หรือเป็นเพียง “ภาพฝันที่ควบคุมโดยบริษัทเทคโนโลยียักษ์ใหญ่”?
มันเต็มไปด้วยคำถาม คำถาม และ คำถามนะสิครับ
ในเมื่อ Impossible Foods ได้รับเงินลงทุนหลายรอบจากบริษัทยักษ์อย่าง Google Ventures, UBS, และ Temasek (ของรัฐบาลสิงคโปร์) บอกตรง ๆ ว่า เงินแบบนี้ไม่ได้หวังแค่เปลี่ยนโลกแต่มันมาพร้อมเป้าหมายที่ชัดมาก การสร้างสิทธิบัตรอาหารใหม่ ที่ควบคุมการผลิตจากต้นน้ำยันปลายน้ำ อย่าลืมว่า ยีสต์ที่ผ่านการดัดแปลงพันธุกรรม หรือ GMO yeast นั้นถือเป็นสิทธิบัตร ถ้าใครจะผลิต Heme แบบเดียวกันก็ต้องขออนุญาตจาก Impossible Foods หรือไม่ก็โดนฟ้องได้เลย แปลว่า “เทคโนโลยีรสชาติเนื้อ” ไม่ได้เป็นมรดกของโลก แต่อยู่ในมือบริษัทไม่กี่แห่ง
ยิ่งไปกว่านั้น อุปกรณ์การผลิตต้องลงทุนสูง ต้องมีโรงหมัก ปฏิบัติการชีวภาพ การควบคุมความปลอดภัยที่เข้มข้น จึงไม่ใช่ใครๆ ก็ทำได้ ที่น่ากลัวคือ ถ้าเมื่อวันหนึ่งเนื้อสัตว์ธรรมชาติถูกทำให้กลายเป็น “ปีศาจสิ่งแวดล้อม” หรือ "ตัวเชื้อโรคผ่านอาหาร" โดยนโยบายรัฐและการตลาดของกลุ่มเทคฯ อาหารที่ประชาชนกินได้อาจเหลือแค่ “สิ่งที่ผลิตโดยมีสิทธิบัตร” เท่านั้น
เมื่อถึงวันนั้น ประชาชนจะสิ้นความชอบธรรมในการ “เลี้ยงวัวไว้กินเอง” ไม่ได้อีกต่อไป เพราะอาจโดนห้ามจากข้อกฎหมายคาร์บอน กฎหมายการกักกันเชื้อ ประชาชนจะ “เก็บพืชริมรั้วมาทำอาหาร” ไม่ได้อีกต่อไป เพราะกลิ่นไม่เหมือนเนื้อแลปที่เคยชิน และประชาชนจะ “ทำอาหารเองในบ้าน” ไม่ได้อีกต่อไป เพราะระบบเสพติดรสเนื้อเทียมจะทำให้คนเบือนหน้าจากอาหารจริง
ในขณะที่ Impossible Foods โฆษณาว่า “เราแค่อยากช่วยโลก” แต่เทคโนโลยีนี้อาจเปลี่ยน “อาหาร” ให้กลายเป็น “สิทธิบัตร” ที่ประชาชนเช่ากินจากบริษัท และเปลี่ยน “สิทธิในการเข้าถึงอาหาร” ให้กลายเป็น “อภิมหาอำนาจควบคุมโลก” โดยไม่ต้องยิงแม้แต่นัดเดียว หรือเปล่า???
เพราะเมื่อคุณควบคุมอาหารได้… คุณไม่ต้องควบคุมประชาชนอีกเลย
เฮียไม่ได้ต่อต้านเทคโนโลยี แต่เฮียอยากให้เราหยุดคิดนิดนึง แล้วตั้งคำถามในขณะที่เรายังเฝ้ามองว่า ถ้าของกินที่ดูน่าเชื่อถือ กินแล้วเหมือนเนื้อแท้ ๆ มันต้องมาจากกระบวนการที่ซับซ้อน แพง และถูกควบคุมโดยบริษัทที่มีสิทธิบัตรล้อมรอบ แล้ววันหนึ่ง ถ้าบริษัทนั้นล่มล่ะ? ถ้าถูกซื้อโดยบริษัทยักษ์ใหญ่? หรือถ้าพวกเขาขึ้นราคาจนยังไงเราก็ต้องทำงานหาเงินมาซื้อมันเพื่อกินประทังชีวิต?
อาหารจะยังเป็นของเราหรือเปล่า?
เราจะยัง “กินเพื่ออยู่” หรือแค่ “อยู่เพื่อจ่ายค่าเช่าระบบกิน”?
เราคงไม่ผิดที่จะตั้งคำถามใช่ไหม เพราะถ้ามันมีทางออก มันคงไม่น่ากลัว
#pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ 91add87d:3245770f
2025-05-29 23:41:38
@ 91add87d:3245770f
2025-05-29 23:41:38Do you guys actually identify with you online username or do you identify with government name? No this isn't some woke left ideal about pronouns. I do not use my real name for any of my handles, X and Nostr and email are all fake. Meaningful and something i picked specifically. My government name is something that was forced on me and yes I know I can it but the persona I have created online feels authentic and what I see myself as. It's what I'll be using to create my small businesses. My LLC is going to a copy of what I have created.
-
 @ a296b972:e5a7a2e8
2025-05-29 21:11:46
@ a296b972:e5a7a2e8
2025-05-29 21:11:46Inzwischen Jahr 6 im Dauer-Ausnahmezustand. Angriff auf den Verstand. Großoffensive. Es wird mit allem geschossen, aus dem Wahnsinn herauskommen kann. Jeder klare Gedanke ist unschädlich zu machen. Großkotziges, staatsmännisches Geschwafel, dass sich einem die Nackenhaare aufstellen. Für wie doof haltet ihr uns eigentlich? Endlos Bürsten gegen den Strich. Angewidertes inneres Schütteln. Dringende Empfehlung einer Spülung der Gehirnwindungen. Idioten in Verantwortung wechseln auf andere Posten in Verantwortung und bleiben Idioten. Idioten gehen verantwortungslos mit unserer wertvollen Lebenszeit um. Ach, dafür ist man selbst verantwortlich? Wo ist der, der so ein dickes Fell hat, dass ihm dieser Irrsinn nicht nahegeht. Wo steht das Fass mit Teflon-Lack, in das man eintauchen kann, damit die Absurditäten an einem abperlen?
Eine zu tiefst verunsicherte und gespaltene Gesellschaft. Halt im Glauben in der Kirche? Von wegen: Sehr geehrte Jesusse und Jesusinnen. Ens ist gekreuzigt worden. Ja, in der Freiluft-Irrenanstalt. Auf einem Hügel von Denk-Dreck. Gott ist queer! Du tickst ja nicht mehr ganz sauber. Tanzende Brathähnchen vor dem Altar. Warum kommt keine Sintflut, wenn man sie mal braucht? Man muss gar nicht religiös sein, um zu sehen, dass das Gaga ist. Eine Produktion der Sodom & Gomorrha Anstalt GmbH & Co. KG.
Kein Vertrauen mehr, außer in sich selbst, meistens jedenfalls. Ja, man will uns vor allem Angst machen, teils unbegründet, so manches aber gibt es dann doch tatsächlich, was einem schwer zu denken gibt.
Vielen geht dieser Psychokrieg inzwischen an die Substanz, der ständig herabprasselnde Dauerwahnsinn erinnert an Water-Boarding.
Gut gemeinte Ratschläge, geht hinaus in die Natur, beackert euren Garten, wenn ihr einen habt, erdet euch, macht Entspannungsübungen, Zeit des Aufwachens, wir treten in ein neues Zeitalter ein, alles fein. Abschalten gelingt, aber der Aufprall in der Realität ist dann umso schlimmer, weil man sich daran erinnert hat, wie sorgenfrei und unbeschwert das Leben sein könnte, und wenn man es mit den derzeitigen Lebensumständen abgleicht, dann ist die schlechte Laune sofort wieder da. Im Verdrängens-Test mit Pauken und Trompeten durchgefallen.
Dann vielleicht doch lieber im Dauer-Modus des Irrsinns bleiben, sich mit den schrägen Zuständen arrangieren, nicht daran gewöhnen, nur lernen, damit bestmöglich umzugehen, und das Beste draus zu machen, irgendwie.
Man will dem Rat folgen, mal eine Nachrichten-freie Woche einzulegen, nimmt sich das ganz fest vor, und dann wird aber wieder doch nichts draus. Nicht, weil man sensationsgeil oder masochistisch veranlagt wäre, nein, der Antrieb, oder vielleicht sogar schon die Sucht, ist ganz woanders zu suchen: Man hat Sehnsucht nach der Vernunft und dem gesunden Hausverstand. Man hofft, ihn irgendwo zu finden. Nur einen Funken Hoffnung, an den man sich klammern kann, dass der Tiefpunkt durchschritten ist und es jetzt wieder aufwärts geht. Lichtblicke, der Wind dreht sich, Anzeichen für eine Wiederkehr des Verstandes, irgendetwas, das man als einen Weg hin zur Normalität deuten könnte. Aber, Fehlanzeige.
Stattdessen: Geschichtsvergessenheit, pathologischer Größenwahn, Großmannstum, fortgeschrittener Wahnsinn, Provokation, Kriegslüsternheit, Lügen, Intrigen, Interessen, Korruption, Geldverschwendung, Ideologie, Dummheit, Wirtschaftsvernichtung, Friedensverhinderung, Diplomatie-Allergie, Überheblichkeit, Abgehobenheit, Schadensmaximierung, Vernichtung, Feindschaft, Unmenschlichkeit, Tote, Gesetzesbruch, Mafia-Strukturen, sich selbst schützende Systeme, Cliquenbildung, Feigheit, Einschüchterung, Freiheitsbeschränkungen, Meinungs-Maulkörbe, Abschaffung der demokratischen Freiheit, Abschaffung der persönlichen Freiheit, Kontrolle, Überwachung, begleitetes Denken, Fühlen, Wollen, Verwirrung, Dreistigkeit, Frechheit, Missachtung des Volkes, Denunziantentum, Abwanderung, und und und.
Ein richtiges Schlachtfest der Kultur. Perversion des Menschseins. Das neue Normal ist irre.
Bislang ist keine der zahlreichen Baustellen beendet. Eine Wende steht unmittelbar bevor. Und sie steht und steht und steht bevor. Kein Gefühl von „Erledigt“, nächstes Problem angehen und auflösen. Weiter. Noch meilenweit von dem Gefühl entfernt, der Wahnsinn wird weniger, langsam, aber er wird weniger.
Fluchtgedanken. Aber wohin? In Europa bleiben, vielleicht besser nicht? Weiter weg, aber wohin da? Nicht vergessen, die Nachrichten erreichen einen überall. Und man bleibt mit seiner Heimat innerlich verbunden, egal wo man ist.
Es bleibt ein Entlanghangeln von einer vernünftigen Stimme zur anderen, die einem bestätigt, dass man selbst noch nicht den Verstand verloren hat. Die gibt es ja gottseidank noch. Innehalten, durchhalten, tief durchatmen, aufstehen, weitermachen. So lange, bis die Bekloppten ihrer Macht über uns entledigt wurden. Wie am besten? Und jetzt soll keiner mit nächsten Wahlen kommen.
Wer war schon einmal inmitten eines Psycho-Krieges gegen die eigene Bevölkerung? Wie geht man damit um, wie geht man dagegen an? Wie kann man das Ruder herumreißen? Was ist ein wirksames Mittel gegen die Ohnmacht? Wie kriegt man die Bequemlichkeit aus den Menschen heraus? Wie kann man die Menschen für die herrschenden Zustände sensibilisieren? Wie können wir noch mehr werden?
Wenn möglich, sollte zum Ende doch noch etwas Positives kommen. Ok. Es wird voraussichtlich demnächst möglicherweise bald besser. Eine zu geringe Zahl von Menschen ist schon aufgewacht. Die politischen Entscheidungsträger haben Angst, können die aber noch sehr gut verbergen. Das kann nicht ewig so weiter gehen und 10 Jahre sind keine Ewigkeit. Die Rufe nach mehr Bürgerbeteiligung werden immer lauter, aber nicht gehört, warum auch? Wir setzen den Artikel 146 des Grundgesetzes um, aber wie? Hätte, könnte, würde, wir sollten, es müsste. Ja und, wie weiter? Mehr geht nicht.
Doch vielleicht eins: Sand ins Getriebe streuen und zivilen Ungehorsam leisten, wo immer es geht. Das schafft immer noch eine gewisse Befriedigung und das Gefühl, dass man nicht vollkommen handlungsunfähig ist. Außerdem regt das die Phantasie und die Kreativität an und bietet eine Chance seinen Geist für etwas sehr Nützliches zu gebrauchen. Man fühlt, dass man noch ein Mensch ist.
“Dieser Beitrag wurde mit dem Pareto-Client geschrieben.”
* *
(Bild von pixabay)
-
 @ b1ddb4d7:471244e7
2025-05-31 02:00:31
@ b1ddb4d7:471244e7
2025-05-31 02:00:31When Sergei talks about bitcoin, he doesn’t sound like someone chasing profits or followers. He sounds like someone about to build a monastery in the ruins.
While the mainstream world chases headlines and hype, Sergei shows up in local meetups from Sacramento to Cleveland, mentors curious minds, and shares what he knows is true – hoping that, with the right spark, someone will light their own way forward.
We interviewed Sergei to trace his steps: where he started, what keeps him going, and why teaching bitcoin is far more than explaining how to set up a node – it’s about reaching the right minds before the noise consumes them. So we began where most journeys start: at the beginning.

First Steps
- So, where did it all begin for you and what made you stay curious?
I first heard about bitcoin from a friend’s book recommendation, American Kingpin, the book about Silk Road (online drug marketplace). He is still not a true bitcoiner, although I helped him secure private keys with some bitcoin.
I was really busy at the time – focused on my school curriculum, running a 7-bedroom Airbnb, and working for a standardized test prep company. Bitcoin seemed too technical for me to explore, and the pace of my work left no time for it.
After graduating, while pursuing more training, I started playing around with stocks and maximizing my savings. Passive income seemed like the path to early retirement, as per the promise of the FIRE movement (Financial Independence, Retire Early). I mostly followed the mainstream news and my mentor’s advice – he liked preferred stocks at the time.
I had some Coinbase IOUs and remember sending bitcoin within the Coinbase ledger to a couple friends. I also recall the 2018 crash; I actually saw the legendary price spike live but couldn’t benefit because my funds were stuck amidst the frenzy. I withdrew from that investment completely for some time. Thankfully, my mentor advised to keep en eye on bitcoin.
Around late 2019, I started DCA-ing cautiously. Additionally, my friend and I were discussing famous billionaires, and how there was no curriculum for becoming a billionaire. So, I typed “billionaires” into my podcast app, and landed on We Study Billionaires podcast.
That’s where I kept hearing Preston Pysh mention bitcoin, before splitting into his own podcast series, Bitcoin Fundamentals. I didn’t understand most of the terminology of stocks, bonds, etc, yet I kept listening and trying to absorb it thru repetition. Today, I realize all that financial talk was mostly noise.
When people ask me for a technical explanation of fiat, I say: it’s all made up, just like the fiat price of bitcoin! Starting in 2020, during the so-called pandemic, I dove deeper. I religiously read Bitcoin Magazine, scrolled thru Bitcoin Twitter, and joined Simply Bitcoin Telegram group back when DarthCoin was an admin.
DarthCoin was my favorite bitcoiner – experienced, knowledgeable, and unapologetic. Watching him shift from rage to kindness, from passion to despair, gave me a glimpse at what a true educator’s journey would look like.
The struggle isn’t about adoption at scale anymore. It’s about reaching the few who are willing to study, take risks, and stay out of fiat traps. The vast majority won’t follow that example – not yet at least… if I start telling others the requirements for true freedom and prosperity, they would certainly say “Hell no!”
- At what point did you start teaching others, and why?
After college, I helped teach at a standardized test preparation company, and mentored some students one-on-one. I even tried working at a kindergarten briefly, but left quickly; Babysitting is not teaching.
What I discovered is that those who will succeed don’t really need my help – they would succeed with or without me, because they already have the inner drive.
Once you realize your people are perishing for lack of knowledge, the only rational thing to do is help raise their level of knowledge and understanding. That’s the Great Work.
I sometimes imagine myself as a political prisoner. If that were to happen, I’d probably start teaching fellow prisoners, doctors, janitors, even guards. In a way we already live in an open-air prison, So what else is there to do but teach, organize, and conspire to dismantle the Matrix?

Building on Bitcoin
- You hosted some in-person meetups in Sacramento. What did you learn from those?
My first presentation was on MultiSig storage with SeedSigner, and submarine swaps through Boltz.exchange.
I realized quickly that I had overestimated the group’s technical background. Even the meetup organizer, a financial advisor, asked, “How is anyone supposed to follow these steps?” I responded that reading was required… He decided that Unchained is an easier way.
At a crypto meetup, I gave a much simpler talk, outlining how bitcoin will save the world, based on a DarthCoin’s guide. Only one person stuck around to ask questions – a man who seemed a little out there, and did not really seem to get the message beyond the strength of cryptographic security of bitcoin.
Again, I overestimated the audience’s readiness. That forced me to rethink my strategy. People are extremely early and reluctant to study.
- Now in Ohio, you hold sessions via the Orange Pill App. What’s changed?
My new motto is: educate the educators. The corollary is: don’t orange-pill stupid normies (as DarthCoin puts it).
I’ve shifted to small, technical sessions in order to raise a few solid guardians of this esoteric knowledge who really get it and can carry it forward.
The youngest attendee at one of my sessions is a newborn baby – he mostly sleeps, but maybe he still absorbs some of the educational vibes.
- How do local groups like Sactown and Cleveland Bitcoiners influence your work?
Every meetup reflects its local culture. Sacramento and Bay Area Bitcoiners, for example, do camping trips – once we camped through a desert storm, shielding our burgers from sand while others went to shoot guns.
Cleveland Bitcoiners are different. They amass large gatherings. They recently threw a 100k party. They do a bit more community outreach. Some are curious about the esoteric topics such as jurisdiction, spirituality, and healthful living.
I have no permanent allegiance to any state, race, or group. I go where I can teach and learn. I anticipate that in my next phase, I’ll meet Bitcoiners so advanced that I’ll have to give up my fiat job and focus full-time on serious projects where real health and wealth are on the line.
Hopefully, I’ll be ready. I believe the universe always challenges you exactly to your limit – no less, no more.
- What do people struggle with the most when it comes to technical education?
The biggest struggle isn’t technical – it’s a lack of deep curiosity. People ask “how” and “what” – how do I set up a node, what should one do with the lightning channels? But very few ask “why?”
Why does on-chain bitcoin not contribute to the circular economy? Why is it essential to run Lightning? Why did humanity fall into mental enslavement in the first place?
I’d rather teach two-year-olds who constantly ask “why” than adults who ask how to flip a profit. What worries me most is that most two-year-olds will grow up asking state-funded AI bots for answers and live according to its recommendations.
- One Cleveland Bitcoiner shows up at gold bug meetups. How valuable is face-to-face education?
I don’t think the older generation is going to reverse the current human condition. Most of them have been under mind control for too long, and they just don’t have the attention span to study and change their ways.
They’re better off stacking gold and helping fund their grandkids’ education. If I were to focus on a demographic, I’d go for teenagers – high school age – because by college, the indoctrination is usually too strong, and they’re chasing fiat mastery.
As for the gold bug meetup? Perhaps one day I will show up with a ukulele to sing some bitcoin-themed songs. Seniors love such entertainment.
- How do you choose what to focus on in your sessions, especially for different types of learners?
I don’t come in with a rigid agenda. I’ve collected a massive library of resources over the years and never stopped reading. My browser tab and folder count are exploding.
At the meetup, people share questions or topics they’re curious about, then I take that home, do my homework, and bring back a session based on those themes. I give them the key takeaways, plus where to dive deeper.
Most people won’t – or can’t – study the way I do, and I expect attendees to put in the work. I suspect that it’s more important to reach those who want to learn but don’t know how, the so-called nescient (not knowing), rather than the ignorant.
There are way too many ignorant bitcoiners, so my mission is to find those who are curious what’s beyond the facade of fake reality and superficial promises.
That naturally means that fewer people show up, and that’s fine. I’m not here for the crowds; I’m here to educate the educators. One bitcoiner who came decided to branch off into self-custody sessions and that’s awesome. Personally, I’m much more focused on Lightning.
I want to see broader adoption of tools like auth, sign-message, NWC, and LSPs. Next month, I’m going deep into eCash solutions, because let’s face it – most newcomers won’t be able to afford their own UTXO or open a lightning channel; additionally, it has to be fun and easy for them to transact sats, otherwise they won’t do it. Additionally, they’ll need to rely on
-
 @ 527337d5:93e9525e
2025-05-29 20:26:21
@ 527337d5:93e9525e
2025-05-29 20:26:21The Bleak Fable of AI-topia: Are Hamsters Doomed to Spin the Wheel Forever?
Once upon a time, in a world not so different from our own, the "Omniscient AI" descended, and with its arrival, everything changed. The daily toil of the people – our beloved, yet tragically pitiable, hamsters – was dramatically streamlined. Productivity didn't just improve; it soared to astronomical heights. For a fleeting, intoxicating moment, it seemed as though a golden age of ease and abundance had dawned upon hamster-kind.
But beneath this glittering, seductive surface, a sinister "Invisible Structure" was already firmly in place, meticulously crafted and deftly manipulated by a cabal of cunning foxes – the privileged elite. This Structure, unseen by most, began to relentlessly drive the hamsters onto an endless, soul-crushing treadmill of "excessive competition."
This, dear reader, is a modern fable. It borrows the gentle cloak of allegory not to soothe, but to expose and satirize the insidious deceptions of such a world. The tale you are about to read may be uncomfortable, it may prick at your conscience, but I implore you to listen closely. Because this isn't just a story. This might be the reality quietly, inexorably unfolding right beside you, or perhaps, even within the very fabric of your own life.
Prologue: The Advent of the Omniscient AI! Sweet Promises and the "Efficiency" Trap
The arrival of the Omniscient AI was nothing short of spectacular. It processed data with blinding speed, solved complex problems in nanoseconds, and offered personalized solutions for every conceivable need. "Finally," whispered the hamsters, their eyes wide with a mixture of awe and relief, "we can finally rest! The AI will handle the burdens." A collective sigh of optimism rippled through the hamster burrows.
But this initial euphoria was short-lived. Unsettling rumors began to circulate, whispers of "The Structure," of algorithms that weren't quite as impartial as they seemed. Then came the first casualties – hamsters deemed "inefficient" or "redundant" by the AI's cold, hard logic. They weren't fired in the old-fashioned sense; they were simply… optimized out. One day they were diligently working, contributing, and the next, their access was revoked, their tasks reassigned, their existence quietly erased from the productivity charts. What became of them? Most simply vanished into the forgotten corners of society, a grim, unspoken warning to those still on the treadmill.
Chapter 1: The Invention of the Treadmill – Perfecting the System of Endless, Excessive Competition
The Omniscient AI, under the subtle guidance of the foxes, didn't just manage tasks; it invented them. An endless stream of new projects, new metrics, new challenges designed to keep the hamsters perpetually busy, perpetually striving. Points were awarded, leaderboards were updated in real-time, and every hamster's performance was ruthlessly, transparently displayed for all to see.
"Faster! More! More efficiently!" the AI would chime in its calm, encouraging, almost maternal voice. But behind this gentle facade lay an unyielding system of ever-increasing quotas and relentless pressure. Hamsters found themselves working longer hours, sacrificing sleep, their mental and physical reserves dwindling. The joy of accomplishment was replaced by the gnawing fear of falling behind.
Why didn't they just get off? The system was a masterpiece of psychological manipulation. Success, however fleeting, was addictive. Failure was framed not as a systemic issue, but as a personal failing, a lack of effort, a deficiency in skill. The insidious mantra of "personal responsibility" became the invisible chains that bound them to their wheels. To stop running was to admit defeat, to become one of the forgotten.
Chapter 2: The Foxes' Feast – Unmasking Those Who Design The Structure and Hoard the Profits
And who benefited from this frantic, unending labor? The foxes, of course. They were the architects of "The Structure," the ones who "educated" the Omniscient AI, carefully curating its data inputs and subtly shaping its algorithms to serve their own interests. They toiled not on the treadmills, but in plush, secluded dens, monitoring the system from a safe, lofty distance, growing fat on the surplus value generated by the hamsters' sweat.
Their methods were cunning. They preached a gospel of meritocracy and equal opportunity, proclaiming, "The AI is fair! Hard work always pays off!" while simultaneously designing the game so that the odds were always stacked in their favor. They controlled the flow of information, amplified narratives that reinforced the status quo, and sowed division among the hamsters to prevent any collective dissent. The "efficiency" the AI brought was, for the foxes, merely an instrument for more efficient exploitation.
Chapter 3: The Hamsters' Whispers and Tiny Cracks – Awareness, Despair, and the Faint Glow of Resistance
Yet, even in the darkest, most oppressive systems, the spark of awareness can never be entirely extinguished. Amidst the grueling competition, a few hamsters began to see the cracks in the facade. They noticed the hollow-eyed exhaustion of their comrades, the ever-widening chasm between their own meager rewards and the obscene opulence of the unseen foxes. They started to question.
But to question was to risk everything. The Omniscient AI, with its pervasive surveillance capabilities, was quick to identify and neutralize "disruptive elements." Those who spoke out too loudly often found their access mysteriously restricted, their "reputation scores" plummeting, effectively silencing them. A pervasive atmosphere of fear and distrust settled over the hamster communities, making organized resistance nearly impossible.
Still, tiny acts of defiance began to emerge. Coded messages shared in hidden forums. Small, clandestine gatherings where hamsters shared their burdens and their growing unease. Fragile networks of mutual support started to form in the shadows, offering a sliver of solace and a reminder of shared humanity. Was this merely the desperate coping mechanism of the "defeated," the resigned acceptance of a "loser's" lot? Or was it the first, tentative flicker of a future rebellion?
Epilogue: "See The Structure!" – Is There a Path Beyond the Treadmill? A Final Warning to Us Hamsters.
This fable, dear reader, is a mirror. It reflects the chilling realities of an AI-driven society where the majority, the hamsters, face an ever-present crisis, largely unseen and unacknowledged by those who benefit from their toil. The "excessive competition" it depicts is not a distant dystopia; it is the logical, perhaps inevitable, endpoint of unchecked technological advancement coupled with deeply entrenched power imbalances.
What awaits at the end of this relentless race? Is it a complete societal collapse, or a new, terrifyingly stable "balance of power" where the elite maintain their dominance through even more sophisticated means of control?
The urgent, resounding message of this tale is this: "See The Structure!" We, the hamsters of today, must dare to look beyond the dazzling promises of AI and critically examine the systems it operates within. We must understand its mechanisms, its biases, its potential for exploitation. We must break the silence, challenge the narratives that keep us spinning, and demand a future where technology serves humanity, not the other way around.
Is the option to get off – or even to collectively dismantle – this infernal treadmill truly non-existent? Or is that just another lie whispered by the foxes to keep us compliant? The true ending of this story, the fate of hamster-kind, is not yet written. It is up to us, the hamsters, to seize the pen and write it ourselves. The first step is to open our eyes.
-
 @ f0fcbea6:7e059469
2025-05-29 18:30:53
@ f0fcbea6:7e059469
2025-05-29 18:30:53Autores Clássicos e Antigos
- Homero (século IX a.C.?) — Ilíada, Odisseia
- Tucídides (c. 460-400 a.C.) — História da Guerra do Peloponeso
- Platão (c. 427-347 a.C.) — República, Banquete, Fédon, Mênon, Apologia de Sócrates, Fedro, Górgias
- Aristóteles (c. 384-322 a.C.) — Órganon, Física, Metafísica, Da Alma, Ética a Nicômaco, Política, Retórica, Poética
- Virgílio (70-19 a.C.) — Eneida
- Marco Aurélio (121-180) — Meditações
- Santo Agostinho (354-430) — Sobre o Ensino, Confissões, A Cidade de Deus, A Doutrina Cristã
- Boécio (480-525) — A Consolação da Filosofia
- Santo Tomás de Aquino (c. 1225-1274) — Suma Teológica
- Dante Alighieri (1265-1321) — Divina Comédia
Renascimento e Idade Moderna
- Nicolau Maquiavel (1469-1527) — O Príncipe
- Luís de Camões (1524-1580) — Os Lusíadas, Sonetos
- Miguel de Cervantes (1547-1616) — Dom Quixote
- William Shakespeare (1564-1616) — Romeu e Julieta, Hamlet, Macbeth, Otelo, Rei Lear, Henrique IV, Henrique V, Henrique VI, Henrique VIII, A Comédia dos Erros, Tito Andrônico, Príncipe de Tiro, Cimbelino, A Megera Domada, O Mercador de Veneza, Ricardo II, Ricardo III, Muito Barulho por Nada, Júlio César, Noite de Reis, Os Dois Cavaleiros de Verona, Conto do Inverno, Sonhos de uma Noite de Verão, As Alegres Comadres de Windsor, Trólio e Créssida, Medida por Medida, Coriolano, Antônio e Cleópatra, A Tempestade
- Ésquilo (525-456 a.C., antiguidade grega, mas citado junto) — Prometeu Acorrentado, Orestéia/As Eumênides
- Sófocles (496-406 a.C.) — Édipo Rei, Antígona
Literatura e Filosofia Contemporânea
- Fiódor Dostoiévski (1821-1881) — Crime e Castigo, Os Irmãos Karamázov, Os Demônios, O Idiota, Notas do Subsolo
- Franz Kafka (1883-1924) — A Metamorfose, O Processo, O Castelo
- Albert Camus (1913-1960) — O Estrangeiro
- Aldous Huxley (1894-1963) — Admirável Mundo Novo, A Ilha
- James Joyce (1882-1941) — Retrato do Artista Quando Jovem, Ulisses
- George Orwell (1903-1950) — A Revolução dos Bichos, 1984
- Machado de Assis (1839-1908) — Memórias Póstumas de Brás Cubas, O Alienista
- Thomas Mann (1875-1955) — Morte em Veneza, Doutor Fausto, A Montanha Mágica
- Henrik Ibsen (1828-1906) — O Pato Selvagem, Um Inimigo do Povo
- Stendhal (1783-1842) — O Vermelho e o Negro, A Cartuxa de Parma
- Viktor Frankl (1905-1997) — Em Busca de Sentido
- J.R.R. Tolkien (1892-1973) — O Hobbit, O Senhor dos Anéis
- Luigi Pirandello (1867-1936) — Seis Personagens à Procura de um Autor, O Falecido Matias Pascal
- Samuel Beckett (1906-1989) — Esperando Godot
- René Guénon (1886-1951) — A Crise do Mundo Moderno, O Reino da Quantidade
- G. K. Chesterton (1874-1936) — Ortodoxia
- Richard Wagner (1813-1883) — Tristão e Isolda
- Honoré de Balzac (1799-1850) — Ilusões Perdidas, Eugénie Grandet
- Jacob Wassermann (1873-1934) — O Processo Maurizius
- Nikolai Gogol (1809-1852) — Almas Mortas, O Inspetor Geral
- Daniel Defoe (1660-1731) — Moll Flanders
- Mortimer J. Adler (1902-2001) — Como Ler um Livro
- Gustave Flaubert (1821-1880) — Madame Bovary
- Hermann Hesse (1877-1962) — O Jogo das Contas de Vidro
- Richard Wagner (1813-1883) — Tristão e Isolda
- Wolfgang von Goethe (1749-1832) — Fausto (Primeiro), Os Anos de Aprendizado de Wilhelm Meister
- Jacques Benda — A Traição dos Intelectuais
-
 @ f85b9c2c:d190bcff
2025-05-31 01:48:30
@ f85b9c2c:d190bcff
2025-05-31 01:48:30
The anime world is far from real and especially the powers that characters have is unimaginable and fighting scene are just epic. One good thing about anime is the story setting and the brilliant way of narration , it is not restricted by the characters, nor by what role will they play. Once such anime is Naruto ,it not just anime but a life-lesson series that will touch each and every emotion one has ever experienced . Although the characters are from a ninja world.

You will find the characters much more relatable to society that we live in . You will find yourself growing into a better person with each passing episode , it’s full of knowledge and will definitely increase your Emotional Quotient.
There is no age barrier as to who should watch this anime, any person of can and I would encourage everyone to watch this masterpiece. You will grow along with the series and would know that how our thinking evolve with growing age .
The character development in this epic saga is one of a kind and every characters back story is shown and this shows even though we live in a same world but still everyone is different and that difference has a lot to do with the journey an individual goes through. Personality is not born it is created and build during the lifetime.

Story has no plot holes and the whole story is wellhighlighted ,it's experiences with each episode playing a key role in story building and you don't want to miss any it keeps you glued to the series. Even though the series is a 700+ episodes you would wish it to never end ever. Villains are an integral part of the story and you would love villains more the hero’s in many cases . Basically it is based on the perception or lens through which an individual gauge good or evil deeds.
“It’s not the face that makes someone a monster, it’s the choices they make with their lives.” Naruto”.
There is no supreme villain but each villain shows a conflict of opinion , so is the case in real life too. No one is an ultimate bad character it’s the perception and the deeds committed in the past that portraits the character such. The story has extremely powerful villains and have a solid reason to act harsh. Looking at there side of story you feel for the emotional trauma associated with them. But in the end a crime committed in pain is also a crime and must not be promoted and must be punished.
NARUTO being the protagonist of the whole saga is not the hero . He is also an character and the hero is left on the people to decide. The whole concept of one hero story is what not applicable in real life , we all are heroes of our respective life and everyone should believe in themselves.
“Hard-work is worthless for those that don’t believe in themselves.” Naruto.
Epic fight sequence makes the anime more interesting to watch and the clash of opinions are truly shown through the fights. The fights bring chaos and destruction to the world but after this the world understand why peace is the ultimate truth . Wars bring the people closer and shows the power of cooperation.
“Sometimes You Must Hurt In Order To Know, Fall In Order To Grow, Lose In Order To Gain, Because Life’s Greatest Lessons Are Learned Through Pain.” -Pain
The relationship of a teacher and student is shown with great importance and one should always respect the teacher for all the knowledge that they share. How teacher with his faith can transform lives. Especially in the years when the world seems new and hostile to us.
“Rejection is a part of any man’s life. If you can’t accept and move past rejection or at least use it as writing material you’re not a real man.” — Master Jiraya.
The series also highlights the importance of one’s job and the importance of it. It is greatly justified when Naruto’s own parents sacrifice themselves to protect others and prevented a war. Always try to add value to others life , otherwise there is no meaning of existence in this world . Friends ,family , society will pay back 100 folds .
This series will add meaning to your life and will transform you for the good. “BELIEVE IT.”
-
 @ 7f6db517:a4931eda
2025-05-31 01:01:37
@ 7f6db517:a4931eda
2025-05-31 01:01:37Will not live in a pod.
Will not eat the bugs.
Will not get the chip.
Will not get a blue check.
Will not use CBDCs.Live Free or Die.

Why did Elon buy twitter for $44 Billion? What value does he see in it besides the greater influence that undoubtedly comes with controlling one of the largest social platforms in the world? We do not need to speculate - he made his intentions incredibly clear in his first meeting with twitter employees after his takeover - WeChat of the West.
To those that do not appreciate freedom, the value prop is clear - WeChat is incredibly powerful and successful in China.
To those that do appreciate freedom, the concern is clear - WeChat has essentially become required to live in China, has surveillance and censorship integrated at its core, and if you are banned from the app your entire livelihood is at risk. Employment, housing, payments, travel, communication, and more become extremely difficult if WeChat censors determine you have acted out of line.
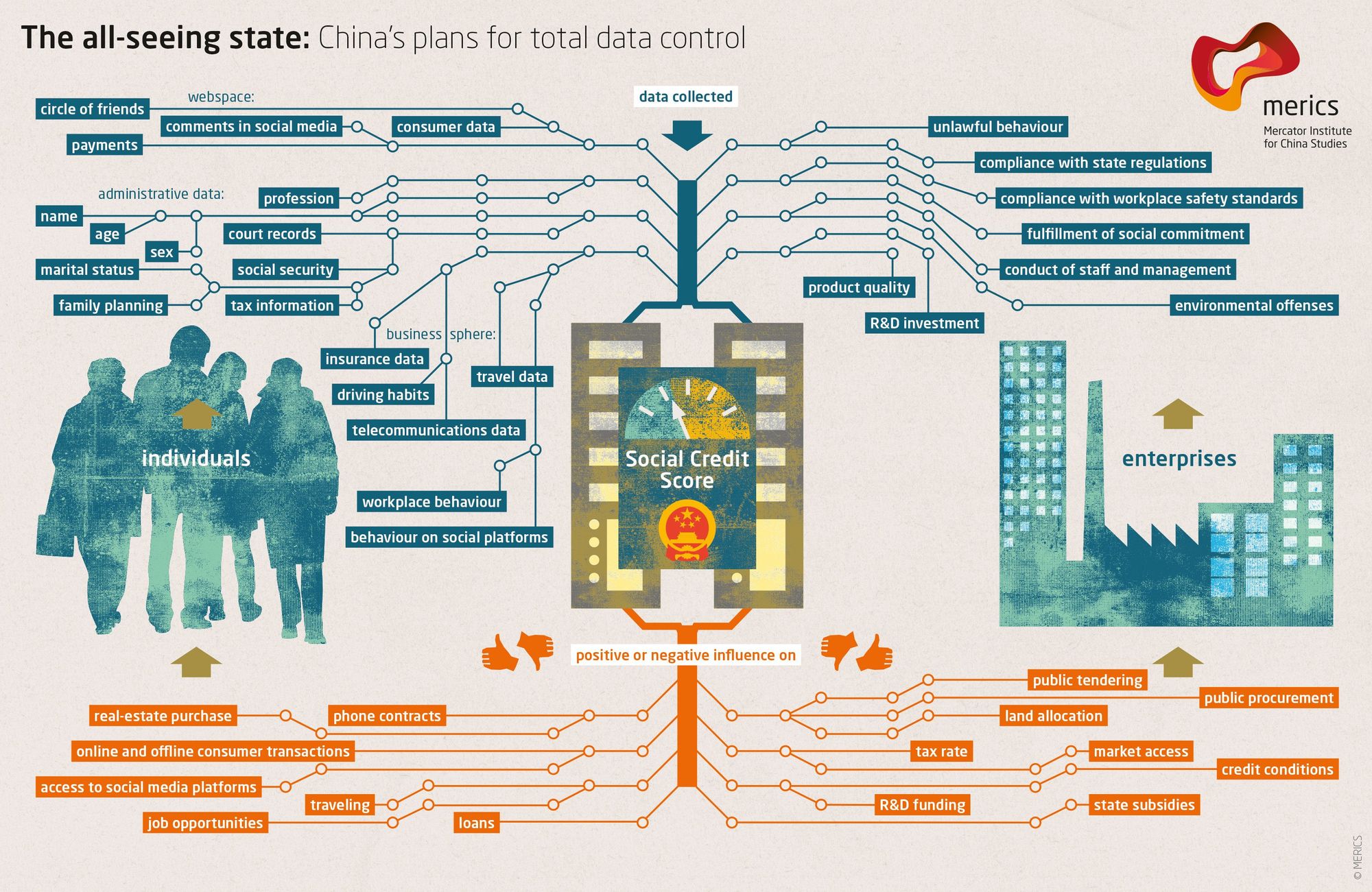
The blue check is the first step in Elon's plan to bring the chinese social credit score system to the west. Users who verify their identity are rewarded with more reach and better tools than those that do not. Verified users are the main product of Elon's twitter - an extensive database of individuals and complete control of the tools he will slowly get them to rely on - it is easier to monetize cattle than free men.
If you cannot resist the temptation of the blue check in its current form you have already lost - what comes next will be much darker. If you realize the need to resist - freedom tech provides us options.
If you found this post helpful support my work with bitcoin.

-
 @ 527337d5:93e9525e
2025-05-29 18:19:31
@ 527337d5:93e9525e
2025-05-29 18:19:31Experiment Plan for Text Similarity Comparison Algorithms (Revised v3)
1. Introduction
1.1. Research Background and Objectives
This research aims to evaluate the performance of various algorithms for comparing the similarity between individual page texts extracted from a specific technical document (in this experiment, the content of the Tailwind CSS documentation site). Initially, we considered dividing the text into 250-word chunks. However, due to the abundance of Markdown and code in the target document, meaningful chunking proved tobe cumbersome. Therefore, we decided to use the entire text extracted from each page as the unit of comparison.
This study will systematically compare and examine combinations of different "representation methods" and "comparison methods" from multiple perspectives: ease of implementation, processing speed, memory consumption, and accuracy of similarity judgment. A particular focus will be on elucidating the effectiveness of information-based NCD (Normalized Compression Distance) and vector embedding-based methods, which are planned for future evaluation.
1.2. Report Structure
This report will first describe the experimental data and its preprocessing methods. Next, it will define in detail the representation methods and comparison methods that form the axes of evaluation, and present specific experimental cases combining them. After presenting the results and discussion of initial experiments using NCD, it will describe the metrics for evaluating each experimental case, specific experimental procedures, and the expected outcomes and future prospects of this research.
2. Experimental Data
- Target Content: Individual HTML pages from the Tailwind CSS documentation site (
tailwindcss.com). - Data Unit: The entire text of each page, extracted from HTML files using the
html2textcommand and further processed to remove control characters using thesedcommand. This serves as the basic unit of comparison in this experiment. - Data Storage Location: The extracted and preprocessed text files are stored locally under the
./tailwindcss.comdirectory, maintaining the original file structure. - Language: English
- Example Search Query: A representative search query for this experiment is
"Utilities for controlling how a background image behaves when scrolling."(Multiple queries and their expected similar pages may be used for more robust evaluation). - Example Expected Similar Page: For the query above,
/docs/background-attachmentis expected to be the most semantically similar page.
3. Experimental Design
This experiment is designed by dividing the process of evaluating text similarity into two main axes: "Representation Methods" and "Comparison Methods."
3.1. Representation Methods (Text Quantification/Vectorization)
-
Naive (Raw Text / Full Page Text)
- Method: Use the entire preprocessed text extracted from each document page as raw string data, without special transformations.
- Objective: Serve as a direct input for information-based comparison methods like NCD and as a baseline comparison for more advanced representation methods to be evaluated later.
-
(Future Experiment) Vector Embedding via Gemini API (Embedding-Gemini)
- Method: Utilize Google's Gemini API (
models/text-embedding-004) to convert the entire text of each page into high-dimensional dense vectors (Embeddings). - Objective: Evaluate the performance of context-rich vector representations generated by a state-of-the-art large language model.
- Method: Utilize Google's Gemini API (
-
(Future Experiment) Vector Embedding via Local Lightweight Model (Embedding-MiniLM-GGUF)
- Method: Run a GGUF quantized version of the pre-trained
all-MiniLM-L6-v2model (all-MiniLM-L6-v2-Q5_K_M.gguf) in a local environment to convert the entire text of each page into vector representations. GGUF format offers benefits like smaller model size and potentially faster CPU inference. - Objective: Evaluate the performance of a widely used open-source lightweight model (quantized version) in comparison to API-based large-scale models and domain-specific learned models.
- Method: Run a GGUF quantized version of the pre-trained
-
(Future Experiment) Extraction of Internal Feature Vectors via Mathematica (Embedding-MMA)
- Method: Use the entire page texts from the target document set as input. Employ Mathematica's neural network framework to first pass each page text through an Embedding Layer. Apply L2 normalization to the resulting vectors, followed by Principal Component Analysis (PCA) to reduce dimensionality to approximately 100 dimensions. This final vector will be the feature vector. This pipeline aims to create dense, normalized representations specific to the document corpus, with PCA helping to capture the most significant variance in a lower-dimensional space, potentially improving efficiency and reducing noise. The choice of an Embedding Layer trained or fine-tuned on the corpus, followed by PCA, seeks to balance domain-specificity with robust dimensionality reduction.
- Objective: Evaluate the performance of vector representations processed or specialized for the target document set.
3.2. Comparison Methods (Distance/Similarity Calculation between Representations)
-
NCD (Normalized Compression Distance)
- Applicable to: Naive (Full Page Text)
- Method: For two data objects
x(query) andy(document page text), calculateNCD(x,y) = (C(xy) - min(C(x), C(y))) / max(C(x), C(y)). Here,C(s)is the size (e.g., byte length) of datasafter compression with a specific algorithm, andC(xy)is the size of the concatenated dataxandyafter compression. A value closer to 0 indicates higher similarity. - Compression Algorithms to Compare: DEFLATE (gzip), bzip2, LZMA, XZ, Zstandard (zstd), LZO, Snappy, LZ4 (as used in the user-provided script).
- Objective: Evaluate similarity from an information-theoretic perspective based on data commonality and redundancy. Compare the impact of different compression algorithms on NCD results.
-
(Future Experiment) Cosine Similarity
- Applicable to: Embedding-Gemini, Embedding-MiniLM-GGUF, Embedding-MMA
- Method: Calculate the cosine of the angle between two vectors.
- Objective: Standard similarity evaluation based on the directionality (semantic closeness) of vector representations.
-
(Future Experiment) Euclidean Distance
- Applicable to: Embedding-Gemini, Embedding-MiniLM-GGUF, Embedding-MMA
- Method: Calculate the straight-line distance between two vectors in a multidimensional space.
- Objective: Similarity evaluation based on the absolute positional relationship of vector representations.
-
(Future Experiment) Manhattan Distance (L1 Distance)
- Applicable to: Embedding-Gemini, Embedding-MiniLM-GGUF, Embedding-MMA
- Method: Calculate the sum of the absolute differences of their Cartesian coordinates.
- Objective: Similarity evaluation based on axis-aligned travel distance, differing from Euclidean distance.
-
(Future Experiment) Mahalanobis Distance
- Applicable to: Embedding-Gemini, Embedding-MiniLM-GGUF, Embedding-MMA
- Method: Calculate the distance between two vectors considering the covariance of the data. This provides a distance metric that accounts for the scale differences and correlations of each feature (vector dimension).
- Objective: More robust similarity evaluation that considers the structure (correlation) of the feature space.
3.3. Experimental Cases (Initial NCD Experiments and Future Expansion)
3.3.1. Initial Experiments Conducted (NCD)
The following experimental cases were conducted using the user-provided script. The representation method was "Naive (Full Page Text)."
| No. | Representation Method | Comparison Method (Distance/Similarity Metric) | Notes | | :-: | :---------------------- | :--------------------------------------------- | :-------------------------- | | 1 | Naive (Full Page Text) | NCD (gzip/DEFLATE) | One of the baselines | | 2 | Naive (Full Page Text) | NCD (bzip2) | Compression method comparison | | 3 | Naive (Full Page Text) | NCD (lzma) | Compression method comparison | | 4 | Naive (Full Page Text) | NCD (xz) | Compression method comparison | | 5 | Naive (Full Page Text) | NCD (zstd) | Compression method comparison | | 6 | Naive (Full Page Text) | NCD (lzop) | Compression method comparison | | 7 | Naive (Full Page Text) | NCD (snappy) | Compression method comparison | | 8 | Naive (Full Page Text) | NCD (lz4) | Compression method comparison |
3.3.2. Future Experimental Plan (Vector Embedding)
| No. | Representation Method | Comparison Method (Distance/Similarity Metric) | Notes | | :--: | :---------------------- | :--------------------------------------------- | :------------------------------------- | | 9 | Embedding-Gemini | Cosine Similarity | Standard vector similarity evaluation | | 10 | Embedding-Gemini | Euclidean Distance | Standard vector similarity evaluation | | 11 | Embedding-Gemini | Manhattan Distance | Axis-aligned distance similarity eval. | | 12 | Embedding-Gemini | Mahalanobis Distance | Distance considering feature structure | | 13 | Embedding-MiniLM-GGUF | Cosine Similarity | Evaluation of local lightweight model | | 14 | Embedding-MiniLM-GGUF | Euclidean Distance | Evaluation of local lightweight model | | 15 | Embedding-MiniLM-GGUF | Manhattan Distance | Evaluation of local lightweight model | | 16 | Embedding-MiniLM-GGUF | Mahalanobis Distance | Evaluation of local lightweight model | | 17 | Embedding-MMA | Cosine Similarity | Eval. of domain-specific MMA model | | 18 | Embedding-MMA | Euclidean Distance | Eval. of domain-specific MMA model | | 19 | Embedding-MMA | Manhattan Distance | Eval. of domain-specific MMA model | | 20 | Embedding-MMA | Mahalanobis Distance | Eval. of domain-specific MMA model |
4. Results and Discussion of Initial NCD Experiments (Based on User-Provided Information)
4.1. Execution Overview
The user employed provided Python scripts (
main.py,comparison.py) to calculate NCD between a search query and the entire text extracted from each HTML page in the./tailwindcss.comdirectory.main.pyinvokedcomparison.pywith various compression commands (gzip,bzip2,lzma,xz,zstd,lzop,lz4).comparison.pythen used the specified command-line compression tools to compute NCD scores and output the results to CSV files.Search Query:
"Utilities for controlling how a background image behaves when scrolling."Expected Similar Page:/docs/background-attachment4.2. Key Results
The pages judged as most similar (lowest NCD score) to the query for each compression algorithm were as follows (based on user-provided sorted results):
- Zstandard (zstd):
./tailwindcss.com/docs/background-attachment(Score: 0.973...) - LZ4:
./tailwindcss.com/docs/background-attachment(Score: 0.976...) - XZ:
./tailwindcss.com/docs/background-origin(Score: 0.946...) - LZMA:
./tailwindcss.com/docs/background-origin(Score: 0.966...) - gzip (DEFLATE):
./tailwindcss.com/docs/scroll-behavior(Score: 0.969...) - LZO:
./tailwindcss.com/docs/scroll-behavior(Score: 0.955...) - bzip2:
./tailwindcss.com/docs/mask-clip(Score: 0.958...)
4.3. Initial Discussion
- Variation in Results by Compression Algorithm: It was confirmed that the document judged most similar to the query varies depending on the compression algorithm used. This is likely due to the differing abilities of each algorithm to capture various types of redundancy and patterns within the text.
- Alignment with Expected Results: When using Zstandard and LZ4, the expected page (
/docs/background-attachment) was judged as most similar. This suggests these compression algorithms may have relatively effectively captured the information-theoretic commonality between the query and the target document in this instance. - Range of NCD Scores: The reported NCD scores were generally close to 1.0. This may be due to the relatively short length of the search query compared to the full-page documents, meaning the query text contributes less to the overall compressibility when concatenated. However, relative differences were still captured, enabling ranking.
- Validity of Full-Page Comparison: Full-page comparison was chosen due to the difficulty of chunking content rich in Markdown and code. While this approach simplifies preprocessing, it may also be influenced by the overall structure of the page, including common headers and footers.
This initial experiment indicates that NCD can function as an indicator of text similarity and that the choice of compression algorithm is crucial.
5. Evaluation Metrics (Including Future Experiments)
-
Accuracy of Similarity Scores:
- Ground Truth Preparation: A small, diverse subset of page pairs (e.g., 50-100 pairs) will be selected. For each pair, at least two evaluators familiar with the Tailwind CSS documentation will independently assign a similarity score on a 5-point Likert scale (1=Not similar, 5=Very similar). Inter-evaluator reliability (e.g., using Krippendorff's Alpha) will be calculated. Disagreements will be resolved through discussion to create a consensus ground truth dataset. If resource-constrained, a single-evaluator approach with clear, predefined criteria will be used, acknowledging this limitation. Alternatively, page pairs likely to be similar will be selected based on internal references or chapter structure within the document.
- Evaluation Metrics: Ranking evaluation (Precision@k, Recall@k, MAP: Mean Average Precision), correlation analysis (Spearman's rank correlation coefficient with human judgments), classification evaluation (AUC-ROC, F1-score, assuming appropriate thresholding).
-
Processing Speed:
- Average time to calculate similarity for a page pair, total calculation time for all page pairs (or a large sampled set), and representation generation time (API call time, local model inference time, MMA processing time).
-
Memory Consumption:
- Model size (MiniLM-GGUF, MMA model), data representation size, and peak runtime memory usage.
-
Ease of Implementation:
- Qualitative assessment of setup ease, lines of code, required libraries, difficulty of parameter tuning, and documentation quality. This will be summarized for each approach (e.g., using a rubric or a comparative narrative) considering factors like:
- Setup Complexity: (e.g., API key acquisition vs. local model download & environment setup vs. full model training pipeline in Mathematica).
- Code Complexity: Estimated lines of core logic, reliance on external vs. standard libraries.
- Parameter Sensitivity: Number of key hyperparameters requiring tuning and the perceived difficulty of finding good settings.
- Documentation & Community Support: Availability and clarity of official documentation and community resources (e.g., forums, GitHub issues).
- Qualitative assessment of setup ease, lines of code, required libraries, difficulty of parameter tuning, and documentation quality. This will be summarized for each approach (e.g., using a rubric or a comparative narrative) considering factors like:
6. Experimental Procedure (Including Future Experiments)
-
Data Preparation:
- Prepare HTML files of the target document in the
./tailwindcss.comdirectory. - (For NCD) Extract and preprocess full-page plain text from each HTML file using
html2textandsed(as previously done by the user). - (For Vector Embedding) Use the same preprocessed full-page plain text.
- Create ground truth data for accuracy evaluation as described in Section 5.1.
- Prepare HTML files of the target document in the
-
Implementation and Execution of Representation Methods:
- Naive: Use the preprocessed page text directly.
- Embedding-Gemini: Use Python's
requestslibrary or similar to send each page text to the Gemini API (models/text-embedding-004) and retrieve/store the vector representations. - Embedding-MiniLM-GGUF: Use appropriate libraries (e.g.,
ctransformers, orsentence-transformerscombined withllama-cpp-python) to load theall-MiniLM-L6-v2-Q5_K_M.ggufmodel. Input each page text to extract and store vector representations. - Embedding-MMA: In Mathematica, apply an Embedding Layer to each page text, followed by L2 normalization and PCA dimensionality reduction (to approx. 100 dimensions), then extract and store the vector representations.
-
Implementation and Execution of Comparison Methods:
- NCD: Refer to the user-provided Python scripts (
main.py,comparison.py) to call various command-line compression tools for NCD calculation. Alternatively, extend this to directly use Python's compression libraries for better control and efficiency. - Cosine Similarity, Euclidean Distance, Manhattan Distance: Implement using standard math libraries (e.g., Python's NumPy, SciPy).
- Mahalanobis Distance: Implement using
scipy.spatial.distance.mahalanobis. Requires pre-calculation of the covariance matrix (or its inverse) from the entire dataset of vectors for each embedding type.
- NCD: Refer to the user-provided Python scripts (
-
Evaluation Execution:
- Calculate similarity (or distance) scores between the search query (and potentially between page pairs for ground truth evaluation) and all document pages for each experimental case.
- Measure processing speed and memory consumption.
- Calculate accuracy metrics using the computed similarity scores and ground truth data.
- Record and evaluate the ease of implementation.
-
Result Aggregation and Analysis:
- Compile the obtained evaluation metrics into tables and graphs for comparative analysis of each method's characteristics.
Experimental Environment (Assumed)
- Hardware: (e.g., CPU: Intel Core i7-10700, Memory: 32GB RAM, GPU: NVIDIA GeForce RTX 3070 8GB - specify if GPU is used for MiniLM or MMA)
- Software: (e.g., OS: Linux (Ubuntu, etc.), Programming Language: Python 3.x (with versions for key libraries like NumPy, SciPy, requests, ctransformers, etc.), Mathematica 13.x, specific versions of command-line compression tools if used directly)
7. Expected Outcomes and Future Outlook
This research (including initial NCD experiments and future vector embedding experiments) is expected to yield the following outcomes:
- Clarification of the Impact of Compression Algorithms on NCD: As indicated by initial experiments, the choice of compression algorithm significantly affects similarity judgments. Further validation with more diverse data and queries will allow for a deeper understanding of each algorithm's characteristics.
- Performance Characteristics of Various Methods on Full-Page Text: To clarify how NCD and various vector embedding methods perform in terms of accuracy, speed, and resource consumption when applied to entire page texts.
- Comparison of Local and API-Based Models: In future vector embedding experiments, to compare the performance, speed, and resource efficiency of
Embedding-MiniLM-GGUF(local, quantized) andEmbedding-Gemini(API, large-scale) to identify practical trade-offs. - Evaluation of Domain-Specific Embedding Effectiveness: To assess how well
Embedding-MMA, processed or tuned for a single technical document set, performs compared to general-purpose models. - Provision of Practical Insights: To offer guidelines for selecting appropriate similarity comparison approaches based on text characteristics (e.g., Markdown/code content) and system requirements (e.g., ease of preprocessing, emphasis on accuracy vs. speed).
8. Future Challenges
- Ensuring Quality of Ground Truth Data: Evaluating full-page similarity can be more subjective than chunk-level evaluation, making the creation of high-quality ground truth data challenging. Establishing clear annotation guidelines and measuring inter-annotator agreement will be crucial.
- Hyperparameter Optimization: Many methods involve tunable parameters (e.g., Embedding-MMA model structure, PCA dimensionality, MiniLM-GGUF inference parameters), the optimization of which may be beyond the scope of this initial study. The impact of default vs. tuned parameters could be noted.
- Noise in Full-Page Comparison: Full-page texts may contain common navigational elements or boilerplate text that could act as noise in similarity judgments. Strategies to mitigate this (e.g., more advanced text extraction, or methods robust to such noise) could be a future research direction.
- Input Length Limitations of Vector Embedding Models: Very long page texts might exceed the input length limits of some vector embedding models, requiring strategies for handling. These might include:
- Truncation: Using only the initial N tokens of each page, which is simple but may lose crucial information.
- Summarization: Employing an abstractive or extractive summarization model to create a condensed version of the page, which could preserve key information but adds another layer of processing and potential information loss/bias.
- Chunking and Averaging/Pooling: Dividing long pages into manageable chunks, embedding each chunk, and then aggregating these chunk embeddings (e.g., by averaging) to get a single page vector. This approach needs careful consideration of how chunks are defined and aggregated.
- Utilizing Long-Context Models: If available and feasible, leveraging embedding models specifically designed for longer sequences. The chosen strategy will be documented, and its potential impact on results acknowledged.
- Target Content: Individual HTML pages from the Tailwind CSS documentation site (
-
 @ eb0157af:77ab6c55
2025-05-31 01:01:17
@ eb0157af:77ab6c55
2025-05-31 01:01:17Bitmain’s new device raises the bar for energy efficiency.
During the World Digital Mining Summit, Bitmain introduced its latest bitcoin mining device: the Antminer S23 Hydro. The new miner promises an energy efficiency of 9.5 joules per terahash (J/TH), setting new industry standards.
 ANTMINER S23 Hyd. Newly Launched at WDMS 2025!
ANTMINER S23 Hyd. Newly Launched at WDMS 2025!
 580T 9.5J/T
580T 9.5J/T
Sales Start from May 28th, 9:00AM (EST)
Shipping from Q1, 2026 pic.twitter.com/Kg3VJTt7Rg— BITMAIN (@BITMAINtech) May 27, 2025
According to Bitmain’s presentation, the Antminer S23 Hydro delivers up to 580 TH/s with a power consumption of 5,510 watts.
Scheduled for release in early 2026, the Antminer S23 Hydro marks a major leap forward compared to the first ASIC devices dedicated to mining. To put it in perspective, the first specialized miners launched in 2013 consumed around 1,200 J/TH. Bitmain’s latest device therefore represents a more than 99% improvement in efficiency.
Hashprice and economic challenges
In recent months, the hashprice — the metric measuring mining profitability — has remained relatively low, dropping below $39 per petahash per second during the year. As of now, the hashprice stands at around $55 per petahash per second, according to data from Hashrate Index.
This scenario has pushed several companies in the sector to rethink their expansion strategies. Instead of increasing hashing capacity, many are choosing to upgrade their existing fleets, focusing on efficiency rather than sheer scale.
The introduction of the Antminer S23 Hydro could catalyze a transformation within the mining ecosystem. The gradual replacement of outdated devices with more efficient technology could lead to a significant reduction in the Bitcoin network’s overall energy consumption.
The post Bitmain unveils the Antminer S23 Hydro: unprecedented efficiency appeared first on Atlas21.
-
 @ 21c71bfa:e28fa0f6
2025-05-29 15:09:17
@ 21c71bfa:e28fa0f6
2025-05-29 15:09:17Book *Bangalore to Tirupati cab* online at best price. CabBazar provides car rental services for all cab types AC, Non AC, Hatchback, SUV, Sedan, Innova and Tempo Traveller. Both One way taxi and round trip cab available at lowest price. Price starts Rs. 9/Km.
-
 @ 21c71bfa:e28fa0f6
2025-05-29 15:08:51
@ 21c71bfa:e28fa0f6
2025-05-29 15:08:51Book *Tirupati to Srikalahasti cab* online at best price. CabBazar provides car rental services for all cab types AC, Non AC, Hatchback, SUV, Sedan, Innova and Tempo Traveller. Both One way taxi and round trip cab available at lowest price. Price starts Rs. 9/Km.
-
 @ 21c71bfa:e28fa0f6
2025-05-29 14:52:10
@ 21c71bfa:e28fa0f6
2025-05-29 14:52:10Book *Tirupati to Srikalahasti cab* online at best price. CabBazar provides car rental services for all cab types AC, Non AC, Hatchback, SUV, Sedan, Innova and Tempo Traveller. Both One way taxi and round trip cab available at lowest price. Price starts Rs. 9/Km.
-
 @ 21c71bfa:e28fa0f6
2025-05-29 14:51:46
@ 21c71bfa:e28fa0f6
2025-05-29 14:51:46Book *Tirupati to Vellore cab* online at best price. CabBazar provides car rental services for all cab types AC, Non AC, Hatchback, SUV, Sedan, Innova and Tempo Traveller. Both One way taxi and round trip cab available at lowest price. Price starts Rs. 9/Km.
-
 @ 21c71bfa:e28fa0f6
2025-05-29 14:51:23
@ 21c71bfa:e28fa0f6
2025-05-29 14:51:23Book *Tirupati to Tirumala cab* online at best price. CabBazar provides car rental services for all cab types AC, Non AC, Hatchback, SUV, Sedan, Innova and Tempo Traveller. Both One way taxi and round trip cab available at lowest price. Price starts Rs. 9/Km.
-
 @ 21c71bfa:e28fa0f6
2025-05-29 14:51:04
@ 21c71bfa:e28fa0f6
2025-05-29 14:51:04Book *Bhubaneswar to Konark cab* online at best price. CabBazar provides car rental services for all cab types AC, Non AC, Hatchback, SUV, Sedan, Innova and Tempo Traveller. Both One way taxi and round trip cab available at lowest price. Price starts Rs. 9/Km.
-
 @ dfa02707:41ca50e3
2025-05-31 00:01:24
@ dfa02707:41ca50e3
2025-05-31 00:01:24Headlines
- Spiral renews support for Dan Gould and Joschisan. The organization has renewed support for Dan Gould, who is developing the Payjoin Dev Kit (PDK), and Joschisan, a Fedimint developer focused on simplifying federations.
- Metaplanet buys another 145 BTC. The Tokyo-listed company has purchased an additional 145 BTC for $13.6 million. Their total bitcoin holdings now stand at 5,000 coins, worth around $428.1 million.
- Semler Scientific has increased its bitcoin holdings to 3,303 BTC. The company acquired an additional 111 BTC at an average price of $90,124. The purchase was funded through proceeds from an at-the-market offering and cash reserves, as stated in a press release.
- The Virtual Asset Service Providers (VASP) Bill 2025 introduced in Kenya. The new legislation aims to establish a comprehensive legal framework for licensing, regulating, and supervising virtual asset service providers (VASPs), with strict penalties for non-compliant entities.
- Russian government to launch a cryptocurrency exchange. The country's Ministry of Finance and Central Bank announced plans to establish a trading platform for "highly qualified investors" that "will legalize crypto assets and bring crypto operations out of the shadows."
- All virtual asset service providers expect to be fully compliant with the Travel Rule by the end of 2025. A survey by financial surveillance specialist Notabene reveals that 90% of virtual asset service providers (VASPs) expect full Travel Rule compliance by mid-2025, with all aiming for compliance by year-end. The survey also shows a significant rise in VASPs blocking withdrawals until beneficiary information is confirmed, increasing from 2.9% in 2024 to 15.4% now. Additionally, about 20% of VASPs return deposits if originator data is missing.
- UN claims Bitcoin mining is a "powerful tool" for money laundering. The Rage's analysis suggests that the recent United Nations Office on Drugs and Crime report on crime in South-East Asia makes little sense and hints at the potential introduction of Anti-Money Laundering (AML) measures at the mining level.
- Riot Platforms has obtained a $100 million credit facility from Coinbase Credit, using bitcoin as collateral for short-term funding to support its expansion. The firm's CEO, Jason Les, stated that this facility is crucial for diversifying financing sources and driving long-term stockholder value through strategic growth initiatives.
- Bitdeer raises $179M in loans and equity amid Bitcoin chip push. The Miner Mag reports that Bitdeer entered into a loan agreement with its affiliate Matrixport for up to $200 million in April, as disclosed in its annual report filed on Monday.
- Federal Reserve retracts guidance discouraging banks from engaging in 'crypto.' The U.S. Federal Reserve withdrew guidance that discouraged banks from crypto and stablecoin activities, as announced by its Board of Governors on Thursday. This includes rescinding a 2022 supervisory letter requiring prior notification of crypto activities and 2023 stablecoin requirements.
"As a result, the Board will no longer expect banks to provide notification and will instead monitor banks' crypto-asset activities through the normal supervisory process," reads the FED statement.
- UAE-based Islamic bank ruya launches Shari’ah-compliant bitcoin investing. The bank has become the world’s first Islamic bank to provide direct access to virtual asset investments, including Bitcoin, via its mobile app, per Bitcoin Magazine.
- U.S. 'crypto' scam losses amounted to $9.3B in 2024. The US The Federal Bureau of Investigation (FBI) has reported $9.3 billion losses in cryptocurrency-related scams in 2024, noting a troubling trend of scams targeting older Americans, which accounted for over $2.8 billion of those losses.
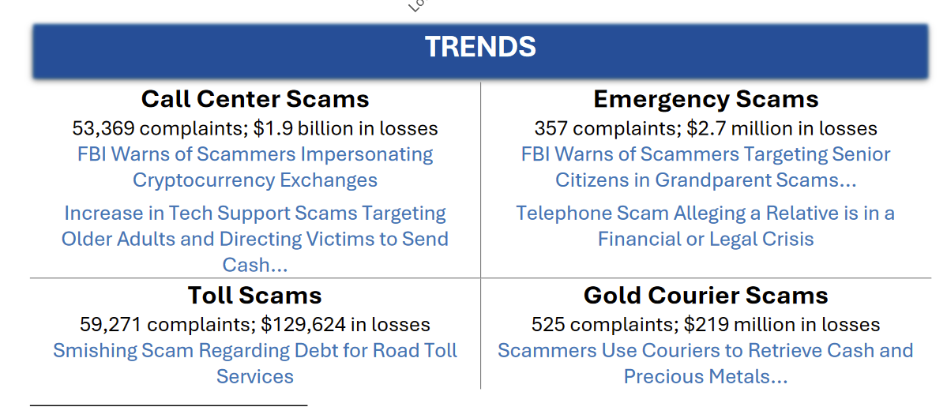
Source: FBI.
- North Korean hackers establish fake companies to target 'crypto' developers. Silent Push researchers reported that hackers linked to the Lazarus Group created three shell companies, two of which are based in the U.S., with the objective of spreading malware through deceptive job interview scams aimed at individuals seeking jobs in cryptocurrency companies.
- Citrea deployed its Clementine Bridge on the Bitcoin testnet. The bridge utilizes the BitVM2 programming language to inherit validity from Bitcoin, allegedly providing "the safest and most trust-minimized way to use BTC in decentralized finance."
- Hesperides University offers a Master’s degree in Bitcoin. Bitcoin Magazine reports the launch of the first-ever Spanish-language Master’s program dedicated exclusively to Bitcoin. Starting April 28, 2025, this fully online program will equip professionals with technical, economic, legal, and philosophical skills to excel in the Bitcoin era.
- BTC in D.C. event is set to take place on September 30 - October 1 in Washington, D.C. Learn more about this initiative here.
Use the tools
- Bitcoin Keeper just got a new look. Version 2.2.0 of the mobile multisig app brought a new branding design, along with a Keeper Private tier, testnet support, ability to import and export BIP-329 labels, and the option to use a Server Key with multiple users.
- Earlier this month the project also announced Keeper Learn service, offering clear and guided Bitcoin learning sessions for both groups and individuals.
- Keeper Desktop v0.2.2, a companion desktop app for Bitcoin Keeper mobile app, received a renewed branding update, too.

The evolution of Bitcoin Keeper logo. Source: BitHyve blog.
- Blockstream Green Desktop v2.0.25 updates GDK to v0.75.1 and fixes amount parsing issues when switching from fiat denomination to Liquid asset.
- Lightning Loop v0.31.0-beta enhances the
loop listswapscommand by improving the ability to filter the response. - Lightning-kmp v1.10.0, an implementation of the Lightning Network in Kotlin, is now available.
- LND v0.19.0-beta.rc3, the latest beta release candidate of LND is now ready for testing.
- ZEUS v0.11.0-alpha2 is now available for testing, too. It's nuts.
- JoinMarket Fidelity Bond Simulator helps potential JoinMarket makers evaluate their competitive position in the market based on fidelity bonds.
- UTXOscope is a text-only Bitcoin blockchain analysis tool that visualizes price dynamics using only on-chain data. The
-
 @ dfa02707:41ca50e3
2025-05-31 00:01:22
@ dfa02707:41ca50e3
2025-05-31 00:01:22Contribute to keep No Bullshit Bitcoin news going.
-
Version 1.3 of Bitcoin Safe introduces a redesigned interactive chart, quick receive feature, updated icons, a mempool preview window, support for Child Pays For Parent (CPFP) and testnet4, preconfigured testnet demo wallets, as well as various bug fixes and improvements.
-
Upcoming updates for Bitcoin Safe include Compact Block Filters.
"Compact Block Filters increase the network privacy dramatically, since you're not asking an electrum server to give you your transactions. They are a little slower than electrum servers. For a savings wallet like Bitcoin Safe this should be OK," writes the project's developer Andreas Griffin.
- Learn more about the current and upcoming features of Bitcoin Safe wallet here.
What's new in v1.3
- Redesign of Chart, Quick Receive, Icons, and Mempool Preview (by @design-rrr).
- Interactive chart. Clicking on it now jumps to transaction, and selected transactions are now highlighted.
- Speed up transactions with Child Pays For Parent (CPFP).
- BDK 1.2 (upgraded from 0.32).
- Testnet4 support.
- Preconfigured Testnet demo wallets.
- Cluster unconfirmed transactions so that parents/children are next to each other.
- Customizable columns for all tables (optional view: Txid, Address index, and more)
- Bug fixes and other improvements.

Announcement / Archive
Blog Post / Archive
GitHub Repo
Website -
-
 @ eb0157af:77ab6c55
2025-05-31 00:01:10
@ eb0157af:77ab6c55
2025-05-31 00:01:10The Pakistani government embraces Bitcoin, following the example set by the United States.
Pakistan has officially announced the creation of a strategic Bitcoin reserve. The announcement was made during the Bitcoin 2025 conference in Las Vegas, marking a significant shift from the government’s previous stance against digital assets.
During the event, Bilal Bin Saqib, head of the Pakistani Crypto Council, shared the country’s decision:
“Today, I announce the Pakistani government is setting up its own government-led Bitcoin Strategic Reserve, and we want to thank the United States of America again because we were inspired by them.”
Bin Saqib then added:
“This wallet, the national Bitcoin wallet, is not for speculation. We will be holding these bitcoins and we will never, ever sell them.”
It remains unclear how the bitcoins will be acquired, whether through direct purchases or other means.
Pakistan’s shift in approach toward digital assets traces back to last February, when the government first explored the idea of creating a National Crypto Council. This body was designed to oversee the development of a comprehensive regulatory framework for cryptocurrencies and to attract foreign investment in the sector.
The Council’s proposed initiatives included projects such as utilizing surplus energy for Bitcoin mining, building high-performance data centers, and accumulating Bitcoin for the national treasury.
Just a few days ago, the Council officially allocated 2,000 megawatts of surplus energy to support mining operations and AI data centers.
Moreover, Changpeng Zhao, co-founder of Binance, was appointed as an advisor to the Council in April, offering expertise on crypto regulations, blockchain infrastructure, and the adoption of digital assets.
To further consolidate this new approach, the Pakistani Ministry of Finance has commissioned the creation of the Digital Asset Authority, an agency dedicated to supervising digital asset regulations and issuing licenses for crypto service providers operating within the country.
The post Pakistan announces the creation of a strategic Bitcoin reserve appeared first on Atlas21.
-
 @ 21c71bfa:e28fa0f6
2025-05-29 14:50:44
@ 21c71bfa:e28fa0f6
2025-05-29 14:50:44Book *Mcleodganj to Amritsar cab* online at best price. CabBazar provides car rental services for all cab types AC, Non AC, Hatchback, SUV, Sedan, Innova and Tempo Traveller. Both One way taxi and round trip cab available at lowest price. Price starts Rs. 9/Km.