-
 @ 472f440f:5669301e
2025-05-20 13:01:09
@ 472f440f:5669301e
2025-05-20 13:01:09Marty's Bent

via me
Don't sleep on what's happening in Japan right now. We've been covering the country and the fact that they've lost control of their yield curve since late last year. After many years of making it a top priority from a monetary policy perspective, last year the Bank of Japan decided to give up on yield curve control in an attempt to reel inflation. This has sent yields for the 30-year and 40-year Japanese government bonds to levels not seen since the early 2000s in the case of the 30-year and levels never before seen for the 40-year, which was launched in 2007. With a debt to GDP ratio that has surpassed 250% and a population that is aging out with an insufficient amount of births to replace the aging workforce, it's hard to see how Japan can get out of this conundrum without some sort of economic collapse.
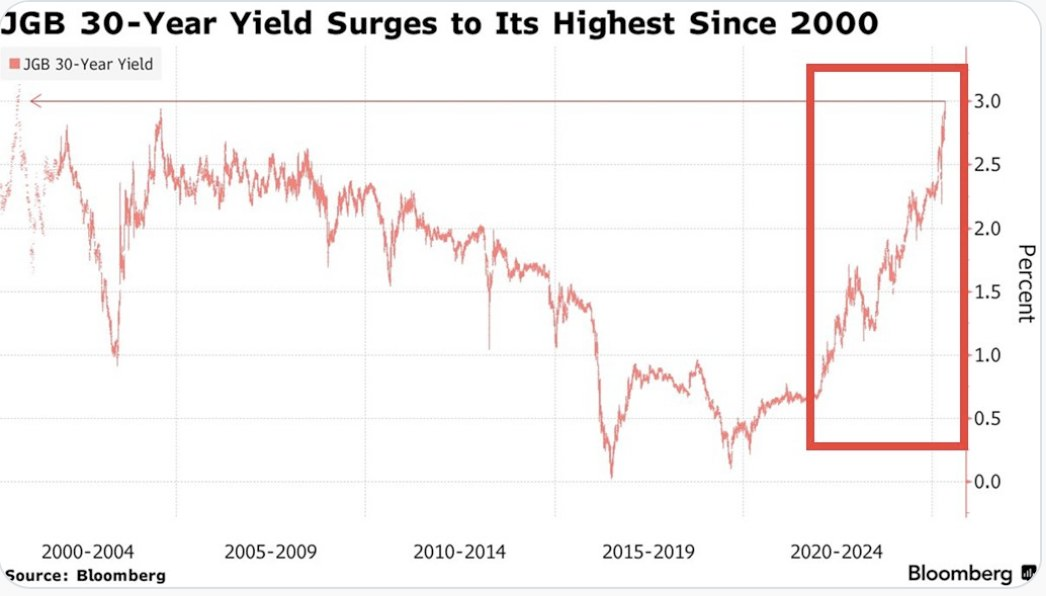

This puts the United States in a tough position considering the fact that Japan is one of the largest holders of U.S. Treasury bonds with more than 1,135 sats | $1.20 trillion in exposure. If things get too out of control in Japan and the yield curve continues to drift higher and inflation continues to creep higher Japan can find itself in a situation where it's a forced seller of US Treasuries as they attempt to strengthen the yen. Another aspect to consider is the fact that investors may see the higher yields on Japanese government bonds and decide to purchase them instead of US Treasuries. This is something to keep an eye on in the weeks to come. Particularly if higher rates drive a higher cost of capital, which leads to even more inflation. As producers are forced to increase their prices to ensure that they can manage their debt repayments.
It's never a good sign when the Japanese Prime Minister is coming out to proclaim that his country's financial situation is worse than Greece's, which has been a laughing stock of Europe for the better part of three decades. Japan is a very proud nation, and the fact that its Prime Minister made a statement like this should not be underappreciated.
As we noted last week, the 10-year and 30-year U.S. Treasury bonds are drifting higher as well. Earlier today, the 30-year bond yield surpassed 5%, which has been a psychological level that many have been pointed to as a critical tipping point. When you take a step back and look around the world it seems pretty clear that bond markets are sending a very strong signal. And that signal is that something is not well in the back end of the financial system.
This is even made clear when you look at the private sector, particularly at consumer debt. In late March, we warned of the growing trend of buy now, pay later schemes drifting down market as major credit card companies released charge-off data which showed charge-off rates reaching levels not seen since the 2008 great financial crisis. At the time, we could only surmise that Klarna was experiencing similar charge-off rates on the bigger-ticket items they financed and started doing deals with companies like DoorDash to finance burrito deliveries in an attempt to move down market to finance smaller ticket items with a higher potential of getting paid back. It seems like that inclination was correct as Klarna released data earlier today showing more losses on their book as consumers find it extremely hard to pay back their debts.

via NewsWire
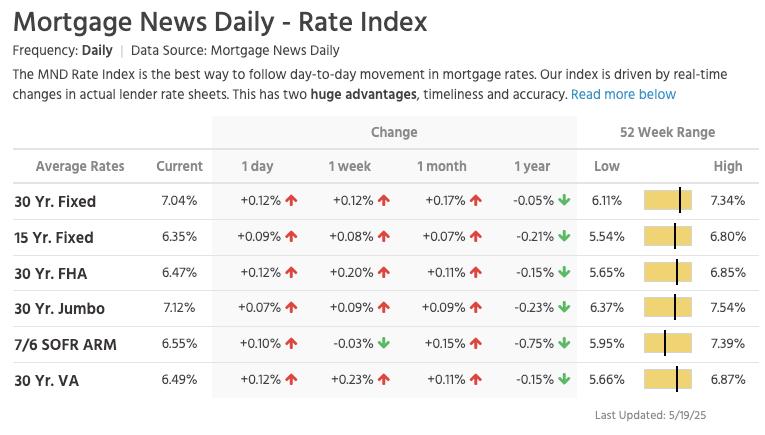
This news hit the markets on the same day as the average rate of the 30-year mortgage in the United States rose to 7.04%. I'm not sure if you've checked lately, but real estate prices are still relatively elevated outside of a few big cities who expanded supply significantly during the COVID era as people flooded out of blue states towards red states. It's hard to imagine that many people can afford a house based off of sticker price alone, but with a 7% 30-year mortgage rate it's becoming clear that the ability of the Common Man to buy a house is simply becoming impossible.
via Lance Lambert
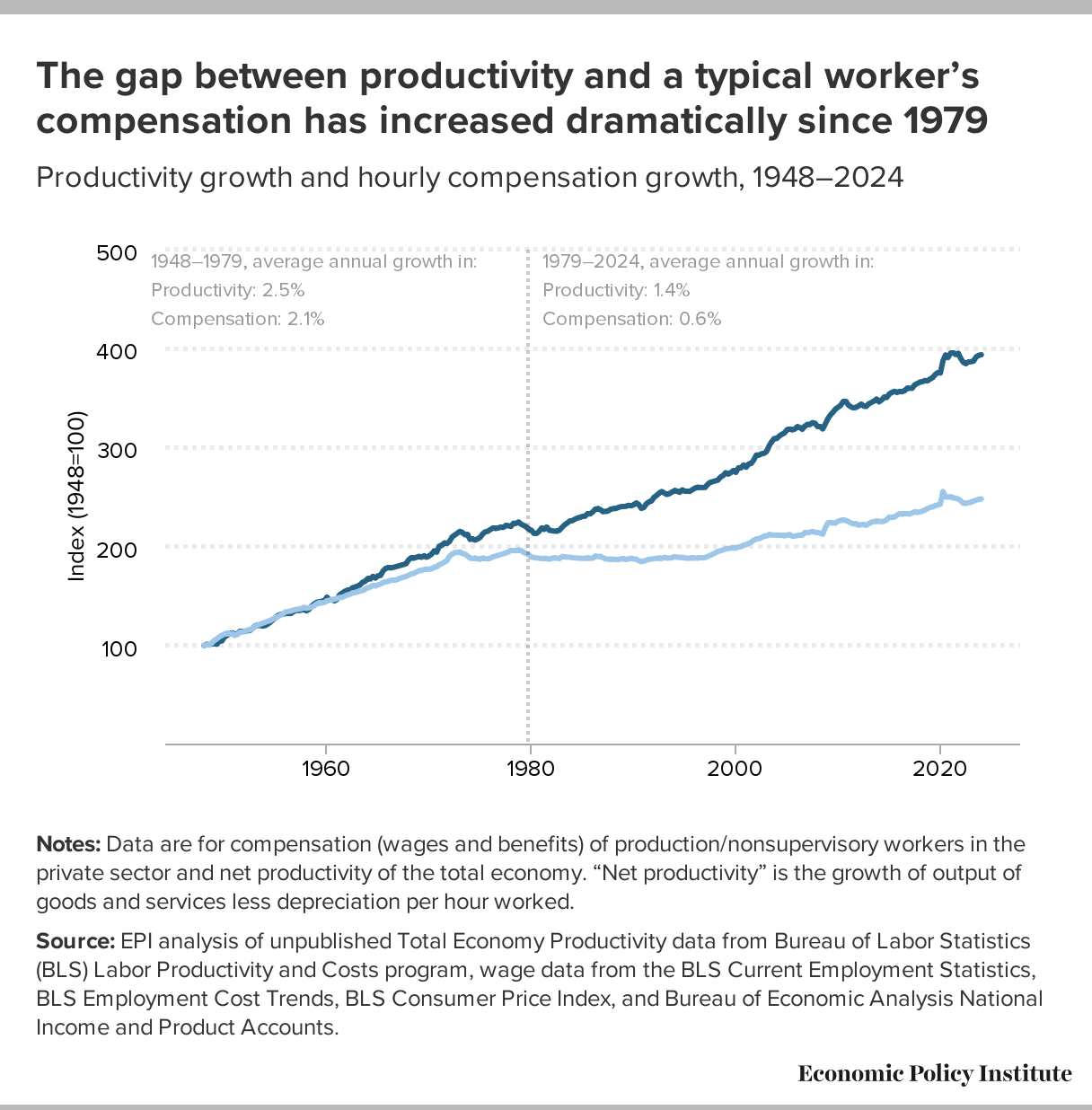
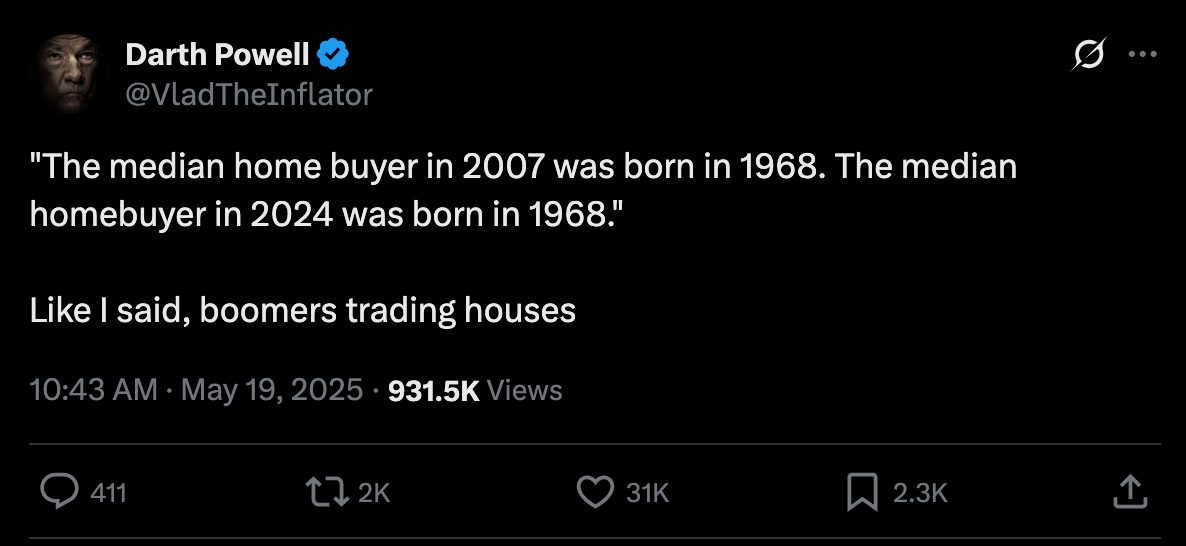
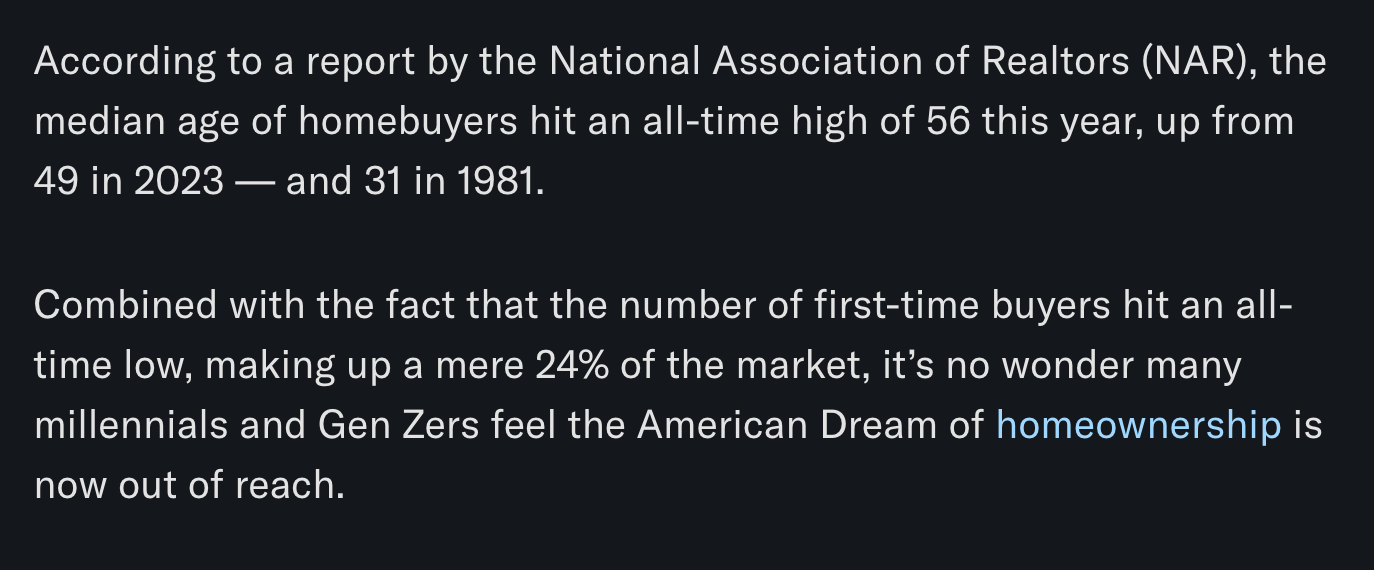
The mortgage rate data is not the only thing you need to look at to understand that it's becoming impossible for the Common Man of working age to buy a house. New data has recently been released that highlights That the median home buyer in 2007 was born in 1968, and the median home buyer in 2024 was born in 1968. Truly wild when you think of it. As our friend Darth Powell cheekily highlights below, we find ourselves in a situation where boomers are simply trading houses and the younger generations are becoming indentured slaves. Forever destined to rent because of the complete inability to afford to buy a house.
via Darth Powell
via Yahoo Finance
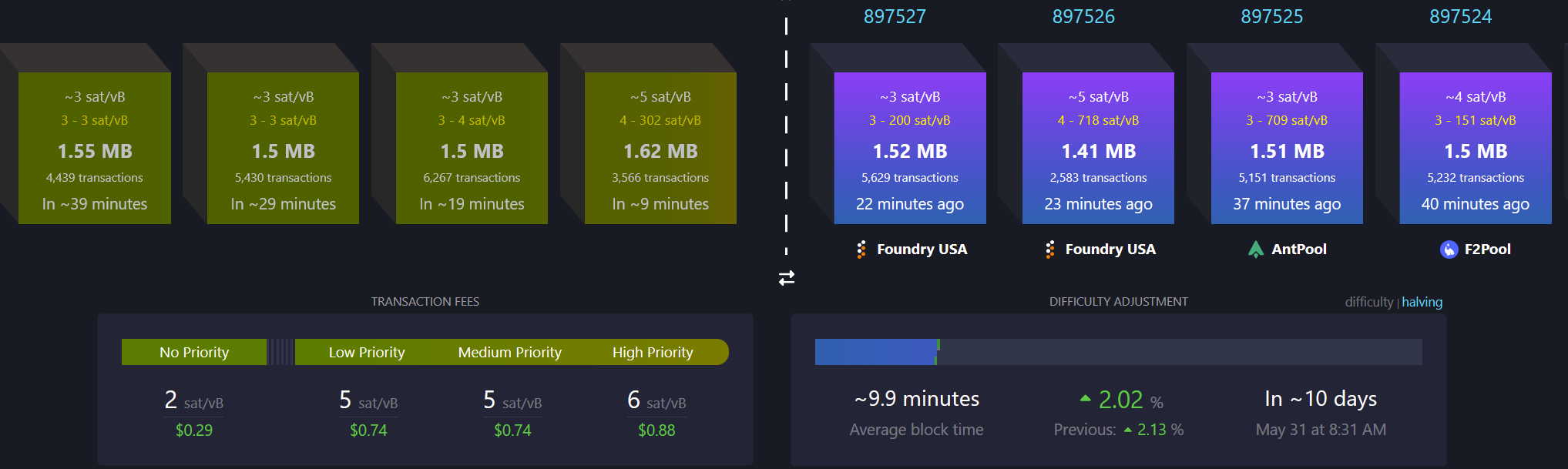
Meanwhile, Bitcoin re-approached all-time highs late this evening and looks primed for another breakout to the upside. This makes sense if you're paying attention. The high-velocity trash economy running on an obscene amount of debt in both the public and private sectors seems to be breaking at the seams. All the alarm bells are signaling that another big print is coming. And if you hope to preserve your purchasing power or, ideally, increase it as the big print approaches, the only thing that makes sense is to funnel your money into the hardest asset in the world, which is Bitcoin.

via Bitbo
Buckle up, freaks. It's gonna be a bumpy ride. Stay humble, Stack Sats.
Trump's Middle East Peace Strategy: Redefining U.S. Foreign Policy
In his recent Middle East tour, President Trump signaled what our guest Dr. Anas Alhajji calls "a major change in US policy." Trump explicitly rejected the nation-building strategies of his predecessors, contrasting the devastation in Afghanistan and Iraq with the prosperity of countries like Saudi Arabia and UAE. This marks a profound shift from both Republican and Democratic foreign policy orthodoxy. As Alhajji noted, Trump's willingness to meet with Syrian President Assad follows a historical pattern where former adversaries eventually become diplomatic partners.
"This is really one of the most important shifts in US foreign policy to say, look, sorry, we destroyed those countries because we tried to rebuild them and it was a big mistake." - Dr. Anas Alhajji
The administration's new approach emphasizes negotiation over intervention. Rather than military solutions, Trump is engaging with groups previously considered off-limits, including the Houthis, Hamas, and Iran. This pragmatic stance prioritizes economic cooperation and regional stability over ideological confrontation. The focus on trade deals and investment rather than regime change represents a fundamental reimagining of America's role in the Middle East.
Check out the full podcast here for more on the Iran nuclear situation, energy market predictions, and why AI development could create power grid challenges. Only on TFTC Studio.
Headlines of the Day
Bitcoin Soars to 100,217 sats | $106.00K While Bonds Lose 40% Since 2020 - via X
US Senate Advances Stablecoin Bill As America Embraces Bitcoin - via X
Get our new STACK SATS hat - via tftcmerch.io
Texas House Debates Bill For State-Run Bitcoin Reserve - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code “TFTC20” during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed 158,469 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
Don't let the noise consume you. Focus on making your life 1% better every day.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ 9be6a199:6e133301
2025-05-20 12:47:14
@ 9be6a199:6e133301
2025-05-20 12:47:14sadfsflkjsdflkdsjfglksjdfglksdaasdfsdfsdfsdfssdsd
-
 @ 9be6a199:6e133301
2025-05-20 12:46:43
@ 9be6a199:6e133301
2025-05-20 12:46:43sadfsflkjsdflkdsjfglksjdfglksdaasdfsdfsdfsdfssdsd
-
 @ 9be6a199:6e133301
2025-05-20 12:46:20
@ 9be6a199:6e133301
2025-05-20 12:46:20sadfsflkjsdflkdsjfglksjdfglksdaasdfsdfsdfsdfs
-
 @ 9be6a199:6e133301
2025-05-20 12:45:08
@ 9be6a199:6e133301
2025-05-20 12:45:08sadfsflkjsdflkdsjfglksjdfglksd
-
 @ 9be6a199:6e133301
2025-05-20 12:44:22
@ 9be6a199:6e133301
2025-05-20 12:44:22 -
 @ 57d1a264:69f1fee1
2025-05-20 06:15:51
@ 57d1a264:69f1fee1
2025-05-20 06:15:51Deliberate (?) trade-offs we make for the sake of output speed.
... By sacrificing depth in my learning, I can produce substantially more work. I’m unsure if I’m at the correct balance between output quantity and depth of learning. This uncertainty is mainly fueled by a sense of urgency due to rapidly improving AI models. I don’t have time to learn everything deeply. I love learning, but given current trends, I want to maximize immediate output. I’m sacrificing some learning in classes for more time doing outside work. From a teacher’s perspective, this is obviously bad, but from my subjective standpoint, it’s unclear.
Finding the balance between learning and productivity. By trade, one cannot be productive in specific areas without first acquire the knowledge to define the processes needed to deliver. Designing the process often come on a try and fail dynamic that force us to learn from previous mistakes.
I found this little journal story fun but also little sad. Vincent's realization, one of us trading his learnings to be more productive, asking what is productivity without quality assurance?
Inevitably, parts of my brain will degenerate and fade away, so I need to consciously decide what I want to preserve or my entire brain will be gone. What skills am I NOT okay with offloading? What do I want to do myself?
Read Vincent's journal https://vvvincent.me/llms-are-making-me-dumber/
https://stacker.news/items/984361
-
 @ 57d1a264:69f1fee1
2025-05-20 06:02:26
@ 57d1a264:69f1fee1
2025-05-20 06:02:26Digital Psychology ↗Wall of impact website showcase a collection of success metrics and micro case studies to create a clear, impactful visual of your brand's achievements. It also displays a Wall of love with an abundance of testimonials in one place, letting the sheer volume highlight your brand's popularity and customer satisfaction.
And like these, many others collections like Testimonial mashup that combine multiple testimonials into a fast-paced, engaging reel that highlights key moments of impact in an attention-grabbing format.
Awards and certifications of websites highlighting third-party ratings and verification to signal trust and quality through industry-recognized achievements and standards.
View them all at https://socialproofexamples.com/
https://stacker.news/items/984357
-
 @ 9be6a199:6e133301
2025-05-20 12:24:02
@ 9be6a199:6e133301
2025-05-20 12:24:02test
-
 @ 609f186c:0aa4e8af
2025-05-16 20:57:43
@ 609f186c:0aa4e8af
2025-05-16 20:57:43Google says that Android 16 is slated to feature an optional high security mode. Cool.
Advanced Protection has a bunch of requested features that address the kinds of threats we worry about.
It's the kind of 'turn this one thing on if you face elevated risk' that we've been asking for from Google.
And likely reflects some learning after Google watched Apple 's Lockdown Mode play out. I see a lot of value in this..
Here are some features I'm excited to see play out:
The Intrusion Logging feature is interesting & is going to impose substantial cost on attackers trying to hide evidence of exploitation. Logs get e2ee encrypted into the cloud. This one is spicy.
The Offline Lock, Inactivity Reboot & USB protection will frustrate non-consensual attempts to physically grab device data.

Memory Tagging Extension is going to make a lot of attack & exploitation categories harder.
2G Network Protection & disabling Auto-connect to insecure networks are going to address categories of threat from things like IMSI catchers & hostile WiFi.
I'm curious about some other features such as:
Spam & Scam detection: Google messages feature that suggests message content awareness and some kind of scanning.
Scam detection for Phone by Google is interesting & coming later. The way it is described suggests phone conversation awareness. This also addresses a different category of threat than the stuff above. I can see it addressing a whole category of bad things that regular users (& high risk ones too!) face. Will be curious how privacy is addressed or if this done purely locally. Getting messy: Friction points? I see Google thinking these through, but I'm going to add a potential concern: what will users do when they encounter friction? Will they turn this off & forget to re-enable? We've seen users turn off iOS Lockdown Mode when they run into friction for specific websites or, say, legacy WiFi. They then forget to turn it back on. And stay vulnerable.

Bottom line: users disabling Apple's Lockdown Mode for a temporary thing & leaving it off because they forget to turn it on happens a lot. This is a serious % of users in my experience...
And should be factored into design decisions for similar modes. I feel like a good balance is a 'snooze button' or equivalent so that users can disable all/some features for a brief few minute period to do something they need to do, and then auto re-enable.
Winding up:
I'm excited to see how Android Advanced Protection plays with high risk users' experiences. I'm also super curious whether the spam/scam detection features may also be helpful to more vulnerable users (think: aging seniors)...
Niche but important:
Some users, esp. those that migrated to security & privacy-focused Android distros because of because of the absence of such a feature are clear candidates for it... But they may also voice privacy concerns around some of the screening features. Clear communication from the Google Security / Android team will be key here.
-
 @ b83a28b7:35919450
2025-05-16 19:26:56
@ b83a28b7:35919450
2025-05-16 19:26:56This article was originally part of the sermon of Plebchain Radio Episode 111 (May 2, 2025) that nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpqtvqc82mv8cezhax5r34n4muc2c4pgjz8kaye2smj032nngg52clq7fgefr and I did with nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7ct4w35zumn0wd68yvfwvdhk6tcqyzx4h2fv3n9r6hrnjtcrjw43t0g0cmmrgvjmg525rc8hexkxc0kd2rhtk62 and nostr:nprofile1qyxhwumn8ghj7mn0wvhxcmmvqyg8wumn8ghj7mn0wd68ytnvv9hxgqpq4wxtsrj7g2jugh70pfkzjln43vgn4p7655pgky9j9w9d75u465pqahkzd0 of the nostr:nprofile1qythwumn8ghj7ct5d3shxtnwdaehgu3wd3skuep0qyt8wumn8ghj7etyv4hzumn0wd68ytnvv9hxgtcqyqwfvwrccp4j2xsuuvkwg0y6a20637t6f4cc5zzjkx030dkztt7t5hydajn
Listen to the full episode here:
<<https://fountain.fm/episode/Ln9Ej0zCZ5dEwfo8w2Ho>>
Bitcoin has always been a narrative revolution disguised as code. White paper, cypherpunk lore, pizza‑day legends - every block is a paragraph in the world’s most relentless epic. But code alone rarely converts the skeptic; it’s the camp‑fire myth that slips past the prefrontal cortex and shakes hands with the limbic system. People don’t adopt protocols first - they fall in love with protagonists.
Early adopters heard the white‑paper hymn, but most folks need characters first: a pizza‑day dreamer; a mother in a small country, crushed by the cost of remittance; a Warsaw street vendor swapping złoty for sats. When their arcs land, the brain releases a neurochemical OP_RETURN which says, “I belong in this plot.” That’s the sly roundabout orange pill: conviction smuggled inside catharsis.
That’s why, from 22–25 May in Warsaw’s Kinoteka, the Bitcoin Film Fest is loading its reels with rebellion. Each documentary, drama, and animated rabbit‑hole is a stealth wallet, zipping conviction straight into the feels of anyone still clasped within the cold claw of fiat. You come for the plot, you leave checking block heights.
Here's the clip of the sermon from the episode:
nostr:nevent1qvzqqqqqqypzpwp69zm7fewjp0vkp306adnzt7249ytxhz7mq3w5yc629u6er9zsqqsy43fwz8es2wnn65rh0udc05tumdnx5xagvzd88ptncspmesdqhygcrvpf2
-
 @ 88cc134b:5ae99079
2025-05-20 12:22:03
@ 88cc134b:5ae99079
2025-05-20 12:22:03content
nostr:nevent1qvzqqqqqqypzpkygz22lv3pdey6gr7ygmk67wjh24hdvj3t797mm6z0x3ax4erdhqqsdxy48qm3tces0tu90shwltcg20zsprejkahklwftpzyhytcf32tc9sm779
-
 @ c631e267:c2b78d3e
2025-05-16 18:40:18
@ c631e267:c2b78d3e
2025-05-16 18:40:18Die zwei mächtigsten Krieger sind Geduld und Zeit. \ Leo Tolstoi
Zum Wohle unserer Gesundheit, unserer Leistungsfähigkeit und letztlich unseres Glücks ist es wichtig, die eigene Energie bewusst zu pflegen. Das gilt umso mehr für an gesellschaftlichen Themen interessierte, selbstbewusste und kritisch denkende Menschen. Denn für deren Wahrnehmung und Wohlbefinden waren und sind die rasanten, krisen- und propagandagefüllten letzten Jahre in Absurdistan eine harte Probe.
Nur wer regelmäßig Kraft tankt und Wege findet, mit den Herausforderungen umzugehen, kann eine solche Tortur überstehen, emotionale Erschöpfung vermeiden und trotz allem zufrieden sein. Dazu müssen wir erkunden, was uns Energie gibt und was sie uns raubt. Durch Selbstreflexion und Achtsamkeit finden wir sicher Dinge, die uns erfreuen und inspirieren, und andere, die uns eher stressen und belasten.
Die eigene Energie ist eng mit unserer körperlichen und mentalen Gesundheit verbunden. Methoden zur Förderung der körperlichen Gesundheit sind gut bekannt: eine ausgewogene Ernährung, regelmäßige Bewegung sowie ausreichend Schlaf und Erholung. Bei der nicht minder wichtigen emotionalen Balance wird es schon etwas komplizierter. Stress abzubauen, die eigenen Grenzen zu kennen oder solche zum Schutz zu setzen sowie die Konzentration auf Positives und Sinnvolles wären Ansätze.
Der emotionale ist auch der Bereich, über den «Energie-Räuber» bevorzugt attackieren. Das sind zum Beispiel Dinge wie Überforderung, Perfektionismus oder mangelhafte Kommunikation. Social Media gehören ganz sicher auch dazu. Sie stehlen uns nicht nur Zeit, sondern sind höchst manipulativ und erhöhen laut einer aktuellen Studie das Risiko für psychische Probleme wie Angstzustände und Depressionen.
Geben wir negativen oder gar bösen Menschen keine Macht über uns. Das Dauerfeuer der letzten Jahre mit Krisen, Konflikten und Gefahren sollte man zwar kennen, darf sich aber davon nicht runterziehen lassen. Das Ziel derartiger konzertierter Aktionen ist vor allem, unsere innere Stabilität zu zerstören, denn dann sind wir leichter zu steuern. Aber Geduld: Selbst vermeintliche «Sonnenköniginnen» wie EU-Kommissionspräsidentin von der Leyen fallen, wenn die Zeit reif ist.
Es ist wichtig, dass wir unsere ganz eigenen Bedürfnisse und Werte erkennen. Unsere Energiequellen müssen wir identifizieren und aktiv nutzen. Dazu gehören soziale Kontakte genauso wie zum Beispiel Hobbys und Leidenschaften. Umgeben wir uns mit Sinnhaftigkeit und lassen wir uns nicht die Energie rauben!
Mein Wahlspruch ist schon lange: «Was die Menschen wirklich bewegt, ist die Kultur.» Jetzt im Frühjahr beginnt hier in Andalusien die Zeit der «Ferias», jener traditionellen Volksfeste, die vor Lebensfreude sprudeln. Konzentrieren wir uns auf die schönen Dinge und auf unsere eigenen Talente – soziale Verbundenheit wird helfen, unsere innere Kraft zu stärken und zu bewahren.
[Titelbild: Pixabay]
Dieser Beitrag wurde mit dem Pareto-Client geschrieben und ist zuerst auf Transition News erschienen.
-
 @ a296b972:e5a7a2e8
2025-05-20 12:22:00
@ a296b972:e5a7a2e8
2025-05-20 12:22:00Die Natur strebt nach einem Gleichgewicht durch Ausgleich von nicht zueinander passenden Verhältnissen. Die Gesellschaft ist ein sozialer Organismus, der ebenso nach Ausgleich und einer Stimmigkeit der Verhältnisse strebt. Das sind Naturgesetze, die keine Regierung auf Dauer imstande ist, außer Kraft zu setzen.
Weder oppositionelle Kräfte, noch Kräfte innerhalb des Souveräns haben die Absicht, die Demokratie abzuschaffen. Es geht vielmehr darum, sie wieder in der Form herzustellen, in der sie ihren Namen auch verdient. Dazu gehört, dass alle Macht vom Volke ausgeht, was derzeit nicht der Fall ist.
Ein durch den Staat vorgegebenes Bildungssystem hat Menschen vor allem zu gefügigen Rädchen im Wirtschaftsgetriebe und nicht zu alles kritisch hinterfragenden Bürgern erzogen, die ständig der Regierung auf die Finger schauen.
Wenn die Bürger, der Souverän, eine Regierung immer mehr „machen lässt“ und glaubt, es sei genug, alle 4 Jahre sein Wahl-Kreuzchen zu machen, entfernt er sich immer mehr von der Kontrolle der durch ihn beauftragten Vertreter, und diese entfernen sich so immer mehr vom Alltag der Bürger.
Zu wenig Gegenrede des Souveräns führt zu immer mehr Übermut der Regierung, die sich immer sicherer wird, mit jedem Unsinn durchzukommen.
Ist dann die Schmerzgrenze des Souveräns erreicht, beginnt er, die Opposition zu stärken. In einer funktionierenden Demokratie würde das dazu führen, dass die Opposition die Regierung bildet, die dann die Chance hat, Fehlentwicklungen abzustellen und ausgleichend tätig zu werden.
Derzeit findet sowohl beim Souverän, als auch bei den Parteien, die bisher Regierungen zusammengestellt haben, ein Erwachen statt.
Da die ehemaligen Volks-Parteien unbedingt an der Macht festhalten wollen, seitens des Souveräns auf zu wenig Widerstand stoßen, wird mit der Macht, einer Demokratie nicht würdig, umgegangen. Dem sollte dringend Einhalt geboten werden.
Der Missbrauch äußert sich in brutalen (Lieblingswort der Ex-Außen-Dings) Einschränkungen der Grundrechte (Corona-Zeit), in der Einschränkung der Meinungsfreiheit (D S A), in Tendenzen zunehmender Kontrolle und Überwachung, Förderung von Denunzianten-Portalen, Kapern des öffentlich-rechtlichen Rundfunks, Förderung von NGOs, die als Sprechpuppen genutzt werden. Besetzt von Menschen, die entweder tatsächlich überzeugt sind von dem, was sie ideologisch vertreten, oder die über Charaktereigenschaften verfügen, die noch sehr viel Optimierungspotenzial in sich bergen. Gepaart mit fachlicher Inkompetenz ist das ein gefährlicher Cocktail.
Erst jüngst sogar durch Ausreiseverbote, wie in einem Staat, mit dem man das derzeitige Deutschland nicht vergleichen darf. So groß ist inzwischen schon die Angst geworden, die Kontrolle über die Macht zu verlieren. Alles, was an Kritik geäußert werden will, gilt als Delegitimierung des Staates. Auf keinen Fall darf sie im Ausland geäußert werden, damit es ja nichts davon mitbekommt, was in Deutschland abgeht. Das ist so wie ein Kind, dass sich die Hände vor die Augen hält und meint, es würde nicht gesehen werden.
Die Regierung ist übergriffig geworden. Je lauter sie Demokratie schreit, desto totalitärer wird sie.
Durch fehlende Kontrolle des Souveräns sind charakterlich und fachlich ungeeignete Personen in die Politik gelangt, deren ständige Überforderung dazu führt, dass sich deren Entscheidungen immer weiter von der Lebensrealität des Souveräns entfernen.
Bislang haben rund 25% des Souveräns diese Schieflage erkannt und wollen einer Opposition, die so stark geworden ist, weil die Alt-Parteien über Jahre Fehler an Fehler aneinandergereiht haben, die Gelegenheit geben, diese Fehler zu beheben und auszugleichen. Offen bleibt die Frage, ob sie dazu wirklich in der Lage sind, oder ob die Gefahr besteht, dass sie von einem möglicherweise grundsätzlich kranken System vereinnahmt werden.
Da es seitens der Alt-Parteien keine Einsicht gibt, dass sie in der Regierung nicht mehr den Willen des Souveräns vertreten, derzeit auch besonders gut zu sehen an dem Friedenswillen des Souveräns im Vergleich zur Kriegstreiberei der Regierung, bleibt nur, der Opposition zumindest die Chance zu geben, es besser zu machen und den Willen des Souveräns umzusetzen. Gelänge das nicht, ist die Demokratie, wie wir sie bislang verstanden haben, gescheitert.
Eine daraus resultierende Staatsform stünde dem Freiheitsgedanken diametral gegenüber.
Die Verteidigung von Unseredemokratie seitens der Regierung entlarvt das eigentliche, was damit gemeint ist, nämlich die Erhaltung der eigenen Macht, verbunden mit allen Vorzügen und Privilegien. Sie richtet sich gegen das eigene Volk, das mit einer ganz normal funktionierenden Demokratie schon sehr zufrieden wäre. Unseredemokratie ist nicht unsere Demokratie!
In Anlehnung an die berühmt gewordene Lüge Walter Ulbrichs: „Niemand hat die Absicht eine Mauer zu errichten“, hat derzeit niemand die Absicht, die sogenannte Brandmauer einzureißen, bzw. sie so lange stehen zu lassen, wie es eben geht, um die herrschenden Machtverhältnisse so lange wie möglich aufrechtzuerhalten. Die Geschichte hat jedoch zum Glück gezeigt, dass selbst eine Berliner Mauer nicht ewig hält.
Wie sich aus dem absurd-lächerlichen Gutachten, einer der Regierung gegenüber weisungsgebundenen Behörde herausgestellt hat, gibt es keinerlei Anzeichen dafür, dass die Opposition die demokratische Grundordnung weder gefährden noch beseitigen will.
Da die ehemaligen Volksparteien augenscheinlich nicht in der Lage sind, politische, wirtschaftliche und gesellschaftliche Verhältnisse zum Wohle des Deutschen Volkes herzustellen, ist der demokratische Weg, die Opposition hierzu zu ermächtigen.
Wird das weiterhin verhindert, wird der Unmut des Souveräns weiter zunehmen, und spätestens, wenn die zunehmenden Schikanen die Schmerzgrenze überschritten haben, wird der Souverän nach geeigneten Mitteln und Möglichkeiten suchen, diese Schieflage zu beheben und auszugleichen.
Derzeit stehen sich ein in der Zahl und im Befinden zunehmend unzufrieden werdender Souverän und eine immer absurdere Entscheidungen treffende Regierung im lebendigen Tauziehen um Interessen gegenüber. Je mehr Bockmist die Alt-Parteien bauen, um so stärker wird die Opposition.
Aufgrund der jetzt schon vorhandenen Anzahl wacher Bürger und der Anzahl der in der Politik Unfähigen, ist eigentlich schon jetzt klar, wer in diesem Tauziehen die größere Kraft hat und wer das „Spiel“ nach demokratischen Regeln am Ende gewinnen wird. Das ist eindeutig der Souverän. Verliert er, wider Erwarten, verliert auch die Demokratie.
Dem Souverän fehlt nur noch ein wenig mehr Selbstvertrauen und ein Bewusstsein für die Macht, über die er tatsächlich verfügt.
Je mehr absurde Entscheidungen seitens der Regierung getroffen werden, und man arbeitet ja sehr fleißig daran, besonders, wenn es um Frieden geht, desto stärker wird das Selbstbewusstsein des Souveräns werden und ein natürlicher, friedlicher Ausgleich der Schieflage kann stattfinden. Der Start der neuen Regierung war jedenfalls schon einmal sehr "Keine-4-Jahre".
Wer sich in die steile und eisglatte Abfahrtspiste Deutschlands vertiefen will, hier eine Rezension zu dem Buch „Im Taumel des Niedergangs“ von dem von mir sehr geschätzten und akribisch arbeitenden Uwe Froschauer:
https://www.manova.news/artikel/abwarts
oder
Dieser Artikel wurde mit dem Pareto-Client geschrieben
* *
(Bild von pixabay)
-
 @ 91bea5cd:1df4451c
2025-05-20 12:16:57
@ 91bea5cd:1df4451c
2025-05-20 12:16:57Contexto e início
O precursor direto do avivamento foi William J. Seymour, um pregador afro-americano filho de ex-escravos, influenciado pelos ensinamentos de Charles Parham, que pregava o "batismo no Espírito Santo" com evidência do falar em línguas.
Em 1906, Seymour foi convidado para pregar em uma igreja em Los Angeles. Após ser rejeitado por alguns por sua pregação sobre o batismo com o Espírito Santo, ele começou a liderar reuniões de oração na casa da família Asberry. Em abril de 1906, durante uma dessas reuniões, os participantes começaram a experimentar manifestações intensas do Espírito Santo, incluindo glossolalia (falar em línguas), curas e profecias.
A Rua Azusa
Logo, o número de participantes cresceu tanto que foi necessário mudar para um antigo prédio da Igreja Metodista Africana Episcopal, no número 312 da Rua Azusa, no centro de Los Angeles. Esse local se tornou o epicentro do avivamento.
Características marcantes
Cultos espontâneos e fervorosos, muitas vezes sem ordem pré-definida.
Diversidade étnica e social: negros, brancos, latinos, asiáticos, ricos e pobres adoravam juntos — algo radical para os padrões da época.
Ênfase nas manifestações espirituais, como línguas, curas, visões e profecias.
Igualdade de gênero e raça no ministério, com mulheres e homens de diversas origens pregando e liderando.
Impacto
O avivamento da Rua Azusa marcou o nascimento e expansão global do pentecostalismo, hoje uma das maiores forças do cristianismo mundial. Missionários saíram de Azusa para várias partes do mundo, levando a mensagem pentecostal. Movimentos como as Assembleias de Deus e Igreja do Evangelho Quadrangular têm raízes nesse avivamento.
Tensão e Interpretação entre Reformistas e Pentecostalistas
Evangelhos e Atos
João Batista profetiza: “Ele vos batizará com o Espírito Santo e com fogo” (Mateus 3:11).
Em Atos 2, no Pentecostes, os discípulos falam em línguas e recebem poder (Atos 1:8; 2:4).
Outros episódios: Atos 10 (Casa de Cornélio) e Atos 19 (Éfeso).
Cartas Paulinas
Paulo não relaciona diretamente o “batismo com o Espírito” ao falar em línguas. Em 1 Coríntios 12:13 ele diz: “Pois em um só Espírito todos nós fomos batizados em um corpo”.
A glossolalia aparece como um dom entre outros, mas não como evidência obrigatória (1 Coríntios 12:30).
Tensão
Pentecostais veem o batismo com o Espírito como uma segunda experiência após a conversão, evidenciada por línguas. Reformados geralmente interpretam que o batismo com o Espírito ocorre na conversão e que línguas não são obrigatórias ou cessaram com os apóstolos.
Reformadores e o Batismo com o Espírito Santo
Martinho Lutero, João Calvino e outros reformadores não falavam em línguas nem davam ênfase a experiências carismáticas.
Cessacionismo: Doutrina comum entre reformados que diz que os dons sobrenaturais (línguas, profecias, curas) cessaram com a era apostólica.
Continuação (posição pentecostal): Os dons continuam hoje.
Filmes / Documentários
“Azusa Street: The Origins of Pentecostalism” (2006) – Documentário com imagens históricas e entrevistas.
“Wesley” (2009) – Biografia de John Wesley, precursor do metodismo e influência indireta no pentecostalismo.
“The Cross and the Switchblade” (1970) – História de David Wilkerson e a conversão de Nicky Cruz; enfatiza a obra do Espírito.
Série “God in America” (PBS) – Episódio sobre o pentecostalismo (não só Azusa, mas seu impacto cultural).
-
 @ 04c915da:3dfbecc9
2025-05-16 18:06:46
@ 04c915da:3dfbecc9
2025-05-16 18:06:46Bitcoin has always been rooted in freedom and resistance to authority. I get that many of you are conflicted about the US Government stacking but by design we cannot stop anyone from using bitcoin. Many have asked me for my thoughts on the matter, so let’s rip it.
Concern
One of the most glaring issues with the strategic bitcoin reserve is its foundation, built on stolen bitcoin. For those of us who value private property this is an obvious betrayal of our core principles. Rather than proof of work, the bitcoin that seeds this reserve has been taken by force. The US Government should return the bitcoin stolen from Bitfinex and the Silk Road.
Using stolen bitcoin for the reserve creates a perverse incentive. If governments see bitcoin as a valuable asset, they will ramp up efforts to confiscate more bitcoin. The precedent is a major concern, and I stand strongly against it, but it should be also noted that governments were already seizing coin before the reserve so this is not really a change in policy.
Ideally all seized bitcoin should be burned, by law. This would align incentives properly and make it less likely for the government to actively increase coin seizures. Due to the truly scarce properties of bitcoin, all burned bitcoin helps existing holders through increased purchasing power regardless. This change would be unlikely but those of us in policy circles should push for it regardless. It would be best case scenario for American bitcoiners and would create a strong foundation for the next century of American leadership.
Optimism
The entire point of bitcoin is that we can spend or save it without permission. That said, it is a massive benefit to not have one of the strongest governments in human history actively trying to ruin our lives.
Since the beginning, bitcoiners have faced horrible regulatory trends. KYC, surveillance, and legal cases have made using bitcoin and building bitcoin businesses incredibly difficult. It is incredibly important to note that over the past year that trend has reversed for the first time in a decade. A strategic bitcoin reserve is a key driver of this shift. By holding bitcoin, the strongest government in the world has signaled that it is not just a fringe technology but rather truly valuable, legitimate, and worth stacking.
This alignment of incentives changes everything. The US Government stacking proves bitcoin’s worth. The resulting purchasing power appreciation helps all of us who are holding coin and as bitcoin succeeds our government receives direct benefit. A beautiful positive feedback loop.
Realism
We are trending in the right direction. A strategic bitcoin reserve is a sign that the state sees bitcoin as an asset worth embracing rather than destroying. That said, there is a lot of work left to be done. We cannot be lulled into complacency, the time to push forward is now, and we cannot take our foot off the gas. We have a seat at the table for the first time ever. Let's make it worth it.
We must protect the right to free usage of bitcoin and other digital technologies. Freedom in the digital age must be taken and defended, through both technical and political avenues. Multiple privacy focused developers are facing long jail sentences for building tools that protect our freedom. These cases are not just legal battles. They are attacks on the soul of bitcoin. We need to rally behind them, fight for their freedom, and ensure the ethos of bitcoin survives this new era of government interest. The strategic reserve is a step in the right direction, but it is up to us to hold the line and shape the future.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:59:23
@ 04c915da:3dfbecc9
2025-05-16 17:59:23Recently we have seen a wave of high profile X accounts hacked. These attacks have exposed the fragility of the status quo security model used by modern social media platforms like X. Many users have asked if nostr fixes this, so lets dive in. How do these types of attacks translate into the world of nostr apps? For clarity, I will use X’s security model as representative of most big tech social platforms and compare it to nostr.
The Status Quo
On X, you never have full control of your account. Ultimately to use it requires permission from the company. They can suspend your account or limit your distribution. Theoretically they can even post from your account at will. An X account is tied to an email and password. Users can also opt into two factor authentication, which adds an extra layer of protection, a login code generated by an app. In theory, this setup works well, but it places a heavy burden on users. You need to create a strong, unique password and safeguard it. You also need to ensure your email account and phone number remain secure, as attackers can exploit these to reset your credentials and take over your account. Even if you do everything responsibly, there is another weak link in X infrastructure itself. The platform’s infrastructure allows accounts to be reset through its backend. This could happen maliciously by an employee or through an external attacker who compromises X’s backend. When an account is compromised, the legitimate user often gets locked out, unable to post or regain control without contacting X’s support team. That process can be slow, frustrating, and sometimes fruitless if support denies the request or cannot verify your identity. Often times support will require users to provide identification info in order to regain access, which represents a privacy risk. The centralized nature of X means you are ultimately at the mercy of the company’s systems and staff.
Nostr Requires Responsibility
Nostr flips this model radically. Users do not need permission from a company to access their account, they can generate as many accounts as they want, and cannot be easily censored. The key tradeoff here is that users have to take complete responsibility for their security. Instead of relying on a username, password, and corporate servers, nostr uses a private key as the sole credential for your account. Users generate this key and it is their responsibility to keep it safe. As long as you have your key, you can post. If someone else gets it, they can post too. It is that simple. This design has strong implications. Unlike X, there is no backend reset option. If your key is compromised or lost, there is no customer support to call. In a compromise scenario, both you and the attacker can post from the account simultaneously. Neither can lock the other out, since nostr relays simply accept whatever is signed with a valid key.
The benefit? No reliance on proprietary corporate infrastructure.. The negative? Security rests entirely on how well you protect your key.
Future Nostr Security Improvements
For many users, nostr’s standard security model, storing a private key on a phone with an encrypted cloud backup, will likely be sufficient. It is simple and reasonably secure. That said, nostr’s strength lies in its flexibility as an open protocol. Users will be able to choose between a range of security models, balancing convenience and protection based on need.
One promising option is a web of trust model for key rotation. Imagine pre-selecting a group of trusted friends. If your account is compromised, these people could collectively sign an event announcing the compromise to the network and designate a new key as your legitimate one. Apps could handle this process seamlessly in the background, notifying followers of the switch without much user interaction. This could become a popular choice for average users, but it is not without tradeoffs. It requires trust in your chosen web of trust, which might not suit power users or large organizations. It also has the issue that some apps may not recognize the key rotation properly and followers might get confused about which account is “real.”
For those needing higher security, there is the option of multisig using FROST (Flexible Round-Optimized Schnorr Threshold). In this setup, multiple keys must sign off on every action, including posting and updating a profile. A hacker with just one key could not do anything. This is likely overkill for most users due to complexity and inconvenience, but it could be a game changer for large organizations, companies, and governments. Imagine the White House nostr account requiring signatures from multiple people before a post goes live, that would be much more secure than the status quo big tech model.
Another option are hardware signers, similar to bitcoin hardware wallets. Private keys are kept on secure, offline devices, separate from the internet connected phone or computer you use to broadcast events. This drastically reduces the risk of remote hacks, as private keys never touches the internet. It can be used in combination with multisig setups for extra protection. This setup is much less convenient and probably overkill for most but could be ideal for governments, companies, or other high profile accounts.
Nostr’s security model is not perfect but is robust and versatile. Ultimately users are in control and security is their responsibility. Apps will give users multiple options to choose from and users will choose what best fits their need.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:51:54
@ 04c915da:3dfbecc9
2025-05-16 17:51:54In much of the world, it is incredibly difficult to access U.S. dollars. Local currencies are often poorly managed and riddled with corruption. Billions of people demand a more reliable alternative. While the dollar has its own issues of corruption and mismanagement, it is widely regarded as superior to the fiat currencies it competes with globally. As a result, Tether has found massive success providing low cost, low friction access to dollars. Tether claims 400 million total users, is on track to add 200 million more this year, processes 8.1 million transactions daily, and facilitates $29 billion in daily transfers. Furthermore, their estimates suggest nearly 40% of users rely on it as a savings tool rather than just a transactional currency.
Tether’s rise has made the company a financial juggernaut. Last year alone, Tether raked in over $13 billion in profit, with a lean team of less than 100 employees. Their business model is elegantly simple: hold U.S. Treasuries and collect the interest. With over $113 billion in Treasuries, Tether has turned a straightforward concept into a profit machine.
Tether’s success has resulted in many competitors eager to claim a piece of the pie. This has triggered a massive venture capital grift cycle in USD tokens, with countless projects vying to dethrone Tether. Due to Tether’s entrenched network effect, these challengers face an uphill battle with little realistic chance of success. Most educated participants in the space likely recognize this reality but seem content to perpetuate the grift, hoping to cash out by dumping their equity positions on unsuspecting buyers before they realize the reality of the situation.
Historically, Tether’s greatest vulnerability has been U.S. government intervention. For over a decade, the company operated offshore with few allies in the U.S. establishment, making it a major target for regulatory action. That dynamic has shifted recently and Tether has seized the opportunity. By actively courting U.S. government support, Tether has fortified their position. This strategic move will likely cement their status as the dominant USD token for years to come.
While undeniably a great tool for the millions of users that rely on it, Tether is not without flaws. As a centralized, trusted third party, it holds the power to freeze or seize funds at its discretion. Corporate mismanagement or deliberate malpractice could also lead to massive losses at scale. In their goal of mitigating regulatory risk, Tether has deepened ties with law enforcement, mirroring some of the concerns of potential central bank digital currencies. In practice, Tether operates as a corporate CBDC alternative, collaborating with authorities to surveil and seize funds. The company proudly touts partnerships with leading surveillance firms and its own data reveals cooperation in over 1,000 law enforcement cases, with more than $2.5 billion in funds frozen.
The global demand for Tether is undeniable and the company’s profitability reflects its unrivaled success. Tether is owned and operated by bitcoiners and will likely continue to push forward strategic goals that help the movement as a whole. Recent efforts to mitigate the threat of U.S. government enforcement will likely solidify their network effect and stifle meaningful adoption of rival USD tokens or CBDCs. Yet, for all their achievements, Tether is simply a worse form of money than bitcoin. Tether requires trust in a centralized entity, while bitcoin can be saved or spent without permission. Furthermore, Tether is tied to the value of the US Dollar which is designed to lose purchasing power over time, while bitcoin, as a truly scarce asset, is designed to increase in purchasing power with adoption. As people awaken to the risks of Tether’s control, and the benefits bitcoin provides, bitcoin adoption will likely surpass it.
-
 @ 04c915da:3dfbecc9
2025-05-16 17:12:05
@ 04c915da:3dfbecc9
2025-05-16 17:12:05One of the most common criticisms leveled against nostr is the perceived lack of assurance when it comes to data storage. Critics argue that without a centralized authority guaranteeing that all data is preserved, important information will be lost. They also claim that running a relay will become prohibitively expensive. While there is truth to these concerns, they miss the mark. The genius of nostr lies in its flexibility, resilience, and the way it harnesses human incentives to ensure data availability in practice.
A nostr relay is simply a server that holds cryptographically verifiable signed data and makes it available to others. Relays are simple, flexible, open, and require no permission to run. Critics are right that operating a relay attempting to store all nostr data will be costly. What they miss is that most will not run all encompassing archive relays. Nostr does not rely on massive archive relays. Instead, anyone can run a relay and choose to store whatever subset of data they want. This keeps costs low and operations flexible, making relay operation accessible to all sorts of individuals and entities with varying use cases.
Critics are correct that there is no ironclad guarantee that every piece of data will always be available. Unlike bitcoin where data permanence is baked into the system at a steep cost, nostr does not promise that every random note or meme will be preserved forever. That said, in practice, any data perceived as valuable by someone will likely be stored and distributed by multiple entities. If something matters to someone, they will keep a signed copy.
Nostr is the Streisand Effect in protocol form. The Streisand effect is when an attempt to suppress information backfires, causing it to spread even further. With nostr, anyone can broadcast signed data, anyone can store it, and anyone can distribute it. Try to censor something important? Good luck. The moment it catches attention, it will be stored on relays across the globe, copied, and shared by those who find it worth keeping. Data deemed important will be replicated across servers by individuals acting in their own interest.
Nostr’s distributed nature ensures that the system does not rely on a single point of failure or a corporate overlord. Instead, it leans on the collective will of its users. The result is a network where costs stay manageable, participation is open to all, and valuable verifiable data is stored and distributed forever.
-
 @ 9be6a199:6e133301
2025-05-20 12:00:17
@ 9be6a199:6e133301
2025-05-20 12:00:17teststing
-
 @ e4950c93:1b99eccd
2025-05-20 11:06:09
@ e4950c93:1b99eccd
2025-05-20 11:06:09Contenu à venir.
-
 @ 56f27915:5fee3024
2025-05-20 11:02:41
@ 56f27915:5fee3024
2025-05-20 11:02:41Buchbeschreibung:\ \ Dieses Buch ist ein Appell.
Es richtet sich nicht nur an den Kopf des Lesers, sondern auch an seinen Willen.\ \ Es ist ein Appell an Volk und Leser, die Lenkung der Geschicke direkt selbst in die Hand zu nehmen. Nicht nur: "Was ist?" sondern vor allem: "Was können wir tun?" ist in diesem Buch die große Frage.\ \ Mit dem Blick auf diese Frage wird das Grundgesetz betrachtet und gezeigt, dass es absolut noch nicht der gediegene Glockenguss ist, als der es uns von "oben" immer vorgestellt wurde, sondern dass in ihm auch extrem gegenläufige, bemessen an seinen freiheitlich-demokratischen Idealen sogar als extrem verfassungs-widrig zu bezeichnende Tendenzen wirken, die heute in seine Zerstörung führen.\ \ Vor allem die unselige Übermacht des Parteienwesens und die damit verbundene systemische Entmündigung des Souveräns, des Volkes, ist das Ergebnis dieser verfassungs-widrigen Tendenzen.\ \ Es wird aber auch gezeigt, wo in den Idealen des Grundgesetzes und in den Entscheidungen der Mütter und Väter dieses Grundgesetzes die Ansatzpunkte liegen, durch die der Zerstörung des Grundgesetzes wirkungsvoll begegnet werden kann. Und diese Ansatzpunkte werden im Buch allseits zur Entfaltung gebracht.\ \ "Wer die Demokratie verteidigen will, der muss sie weiter entwickeln." Im Sinne dieses Wortes wird dem Leser ein praktikabler Weg gewiesen, auf dem er unmittelbar helfen kann, das Grundgesetz den wirkenden Zerstörungskräften zu entwinden, durch Einrichtung der direkten Bürgerbeteiligung an den entscheidenden Fragen unserer Republik die Position des Souveräns gegenüber der Parteienmacht zu stärken, Freiheitsrechte, Demokratie und Rechtsstaat auf eine wesentlich höhere Stufe als bisher zu bringen und sich durch eine verfassungs-klärende Versammlung seine Basis selbst und neu zu geben.
Buch bestellen: https://great-reset-von-unten.de/
\ Und nicht vergessen, abzustimmen! Die Zeit ist reif. Packen wir's an.\
-
 @ 57d1a264:69f1fee1
2025-05-16 07:51:08
@ 57d1a264:69f1fee1
2025-05-16 07:51:08Payjoin allows the sender and receiver of an on-chain payment to collaborate and create a transaction that breaks on-chain heuristics, allowing a more private transaction with ambiguous payment amount and UTXO ownership. Additionally, it can also be used for UTXO consolidation (receiver saves future fees) and batching payments (receiver can make payment(s) of their own in the process of receiving one), also known as transaction cut-through. Other than improved privacy, the rest of the benefits are typically applicable to the receiver, not the sender.
BIP-78 was the original payjoin protocol that required the receiver to run a endpoint/server (always online) in order to mediate the payjoin process. Payjoin adoption has remained pretty low, something attributed to the server & perpetual online-ness requirement. This is the motivation for payjoin v2.
The purpose of the one-pager is to analyse the protocol, and highlight the UX issues or tradeoffs it entails, so that the payjoin user flows can be appropriately designed and the tradeoffs likewise communicated. A further document on UX solutions might be needed to identify solutions and opportunities
The following observations are generally limited to individual users transacting through their mobile devices:
While users naturally want better privacy and fee-savings, they also want to minimise friction and minimise (optimise) payment time. These are universal and more immediate needs since they deal with the user experience.
Added manual steps
TL;DR v2 payjoin eliminates server & simultaneous user-liveness requirements (increasing TAM, and opportunities to payjoin, as a result) by adding manual steps.
Usually, the extent of the receiver's involvement in the transaction process is limited to sharing their address with the sender. Once they share the address/URI, they can basically forget about it. In the target scenario for v2 payjoin, the receiver must come online again (except they have no way of knowing "when") to contribute input(s) and sign the PSBT. This can be unexpected, unintuitive and a bit of a hassle.
Usually (and even with payjoin v1), the sender crafts and broadcasts the transaction in one go; meaning the user's job is done within a few seconds/minutes. With payjoin v2, they must share the original-PSBT with the receiver, and then wait for them to do their part. Once the the receiver has done that, the sender must come online to review the transaction, sign it & broadcast.
In summary,
In payjoin v1, step 3 is automated and instant, so delay 2, 3 =~ 0. As the user experiences it, the process is completed in a single session, akin to a non-payjoin transaction.
With payjoin v2, Steps 2 & 3 in the above diagram are widely spread and noticeable. These manual steps are separated by uncertain delays (more on that below) when compared to a non-payjoin transaction.
Delays
We've established that both senders and receivers must take extra manual steps to execute a payoin transaction. With payjoin v2, this process gets split into multiple sessions, since the sender and receiver are not like to be online simultaneously.
Delay 2 & 3 (see diagram above) are uncertain in nature. Most users do not open their bitcoin wallets for days or weeks! The receiver must come online before the timeout hits in order for the payjoin process to work, otherwise time is just wasted with no benefit. UX or technical solutions are needed to minimise these delays.
Delays might be exacerbated if the setup is based on hardware wallet and/or uses multisig.
Notifications or background processes
There is one major problem when we say "the user must come online to..." but in reality the user has no way of knowing there is a payjoin PSBT waiting for them. After a PSBT is sent to the relay, the opposite user would only find out about it whenever they happen to come online. Notifications and background sync processes might be necessary to minimise delays. This is absolutely essential to avert timeouts in addition to saving valuable time. Another risk is phantom payjoin stuff after the timeout is expired if receiver-side does not know it has.
Fee Savings
The following observations might be generally applicable for both original and this v2 payjoin version. Fee-savings with payjoin is a tricky topic. Of course, overall a payjoin transaction is always cheaper than 2 separate transactions, since they get to share the overhead.
Additionally, without the receiver contributing to fees, the chosen fee rate of the PSBT (at the beginning) drops, and can lead to slower confirmation. From another perspective, a sender paying with payjoin pays higher fees for similar confirmation target. This has been observed in a production wallet years back. Given that total transaction time can extend to days, the fee environment itself might change, and all this must be considered when designing the UX.
Of course, there is nothing stopping the receiver from contributing to fees, but this idea is likely entirely novel to the bitcoin ecosystem (perhaps payments ecosystem in general) and the user base. Additionally, nominally it involves the user paying fees and tolerating delays just to receive bitcoin. Without explicit incentives/features that encourage receivers to participate, payjoining might seem like an unncessary hassle.
Overall, it seems that payjoin makes UX significant tradeoffs for important privacy (and potential fee-saving) benefits. This means that the UX might have to do significant heavy-lifting, to ensure that users are not surprised, confused or frustrated when they try to transact on-chain in a privacy-friendly feature. Good, timely communication, new features for consolidation & txn-cutthrough and guided user flows seem crucial to ensure payjoin adoption and for help make on-chain privacy a reality for users.
---------------
Original document available here. Reach out at
yashrajdca@proton.me,y_a_s_h_r_a_j.70on Signal, or on reach out in Bitcoin Design discord.https://stacker.news/items/981388
-
 @ 39cc53c9:27168656
2025-05-20 10:45:31
@ 39cc53c9:27168656
2025-05-20 10:45:31The new website is finally live! I put in a lot of hard work over the past months on it. I'm proud to say that it's out now and it looks pretty cool, at least to me!
Why rewrite it all?
The old kycnot.me site was built using Python with Flask about two years ago. Since then, I've gained a lot more experience with Golang and coding in general. Trying to update that old codebase, which had a lot of design flaws, would have been a bad idea. It would have been like building on an unstable foundation.
That's why I made the decision to rewrite the entire application. Initially, I chose to use SvelteKit with JavaScript. I did manage to create a stable site that looked similar to the new one, but it required Jav aScript to work. As I kept coding, I started feeling like I was repeating "the Python mistake". I was writing the app in a language I wasn't very familiar with (just like when I was learning Python at that mom ent), and I wasn't happy with the code. It felt like spaghetti code all the time.
So, I made a complete U-turn and started over, this time using Golang. While I'm not as proficient in Golang as I am in Python now, I find it to be a very enjoyable language to code with. Most aof my recent pr ojects have been written in Golang, and I'm getting the hang of it. I tried to make the best decisions I could and structure the code as well as possible. Of course, there's still room for improvement, which I'll address in future updates.
Now I have a more maintainable website that can scale much better. It uses a real database instead of a JSON file like the old site, and I can add many more features. Since I chose to go with Golang, I mad e the "tradeoff" of not using JavaScript at all, so all the rendering load falls on the server. But I believe it's a tradeoff that's worth it.
What's new
- UI/UX - I've designed a new logo and color palette for kycnot.me. I think it looks pretty cool and cypherpunk. I am not a graphic designer, but I think I did a decent work and I put a lot of thinking on it to make it pleasant!
- Point system - The new point system provides more detailed information about the listings, and can be expanded to cover additional features across all services. Anyone can request a new point!
- ToS Scrapper: I've implemented a powerful automated terms-of-service scrapper that collects all the ToS pages from the listings. It saves you from the hassle of reading the ToS by listing the lines that are suspiciously related to KYC/AML practices. This is still in development and it will improve for sure, but it works pretty fine right now!
- Search bar - The new search bar allows you to easily filter services. It performs a full-text search on the Title, Description, Category, and Tags of all the services. Looking for VPN services? Just search for "vpn"!
- Transparency - To be more transparent, all discussions about services now take place publicly on GitLab. I won't be answering any e-mails (an auto-reply will prompt to write to the corresponding Gitlab issue). This ensures that all service-related matters are publicly accessible and recorded. Additionally, there's a real-time audits page that displays database changes.
- Listing Requests - I have upgraded the request system. The new form allows you to directly request services or points without any extra steps. In the future, I plan to enable requests for specific changes to parts of the website.
- Lightweight and fast - The new site is lighter and faster than its predecessor!
- Tor and I2P - At last! kycnot.me is now officially on Tor and I2P!
How?
This rewrite has been a labor of love, in the end, I've been working on this for more than 3 months now. I don't have a team, so I work by myself on my free time, but I find great joy in helping people on their private journey with cryptocurrencies. Making it easier for individuals to use cryptocurrencies without KYC is a goal I am proud of!
If you appreciate my work, you can support me through the methods listed here. Alternatively, feel free to send me an email with a kind message!
Technical details
All the code is written in Golang, the website makes use of the chi router for the routing part. I also make use of BigCache for caching database requests. There is 0 JavaScript, so all the rendering load falls on the server, this means it needed to be efficient enough to not drawn with a few users since the old site was reporting about 2M requests per month on average (note that this are not unique users).
The database is running with mariadb, using gorm as the ORM. This is more than enough for this project. I started working with an
sqlitedatabase, but I ended up migrating to mariadb since it works better with JSON.The scraper is using chromedp combined with a series of keywords, regex and other logic. It runs every 24h and scraps all the services. You can find the scraper code here.
The frontend is written using Golang Templates for the HTML, and TailwindCSS plus DaisyUI for the CSS classes framework. I also use some plain CSS, but it's minimal.
The requests forms is the only part of the project that requires JavaScript to be enabled. It is needed for parsing some from fields that are a bit complex and for the "captcha", which is a simple Proof of Work that runs on your browser, destinated to avoid spam. For this, I use mCaptcha.
-
 @ 39cc53c9:27168656
2025-05-20 10:45:29
@ 39cc53c9:27168656
2025-05-20 10:45:29Know Your Customer is a regulation that requires companies of all sizes to verify the identity, suitability, and risks involved with maintaining a business relationship with a customer. Such procedures fit within the broader scope of anti-money laundering (AML) and counterterrorism financing (CTF) regulations.
Banks, exchanges, online business, mail providers, domain registrars... Everyone wants to know who you are before you can even opt for their service. Your personal information is flowing around the internet in the hands of "god-knows-who" and secured by "trust-me-bro military-grade encryption". Once your account is linked to your personal (and verified) identity, tracking you is just as easy as keeping logs on all these platforms.
Rights for Illusions
KYC processes aim to combat terrorist financing, money laundering, and other illicit activities. On the surface, KYC seems like a commendable initiative. I mean, who wouldn't want to halt terrorists and criminals in their tracks?
The logic behind KYC is: "If we mandate every financial service provider to identify their users, it becomes easier to pinpoint and apprehend the malicious actors."
However, terrorists and criminals are not precisely lining up to be identified. They're crafty. They may adopt false identities or find alternative strategies to continue their operations. Far from being outwitted, many times they're several steps ahead of regulations. Realistically, KYC might deter a small fraction – let's say about 1% ^1 – of these malefactors. Yet, the cost? All of us are saddled with the inconvenient process of identification just to use a service.
Under the rhetoric of "ensuring our safety", governments and institutions enact regulations that seem more out of a dystopian novel, gradually taking away our right to privacy.
To illustrate, consider a city where the mayor has rolled out facial recognition cameras in every nook and cranny. A band of criminals, intent on robbing a local store, rolls in with a stolen car, their faces obscured by masks and their bodies cloaked in all-black clothes. Once they've committed the crime and exited the city's boundaries, they switch vehicles and clothes out of the cameras' watchful eyes. The high-tech surveillance? It didn’t manage to identify or trace them. Yet, for every law-abiding citizen who merely wants to drive through the city or do some shopping, their movements and identities are constantly logged. The irony? This invasive tracking impacts all of us, just to catch the 1% ^1 of less-than-careful criminals.
KYC? Not you.
KYC creates barriers to participation in normal economic activity, to supposedly stop criminals. ^2
KYC puts barriers between many users and businesses. One of these comes from the fact that the process often requires multiple forms of identification, proof of address, and sometimes even financial records. For individuals in areas with poor record-keeping, non-recognized legal documents, or those who are unbanked, homeless or transient, obtaining these documents can be challenging, if not impossible.
For people who are not skilled with technology or just don't have access to it, there's also a barrier since KYC procedures are mostly online, leaving them inadvertently excluded.
Another barrier goes for the casual or one-time user, where they might not see the value in undergoing a rigorous KYC process, and these requirements can deter them from using the service altogether.
It also wipes some businesses out of the equation, since for smaller businesses, the costs associated with complying with KYC norms—from the actual process of gathering and submitting documents to potential delays in operations—can be prohibitive in economical and/or technical terms.
You're not welcome
Imagine a swanky new club in town with a strict "members only" sign. You hear the music, you see the lights, and you want in. You step up, ready to join, but suddenly there's a long list of criteria you must meet. After some time, you are finally checking all the boxes. But then the club rejects your membership with no clear reason why. You just weren't accepted. Frustrating, right?
This club scenario isn't too different from the fact that KYC is being used by many businesses as a convenient gatekeeping tool. A perfect excuse based on a "legal" procedure they are obliged to.
Even some exchanges may randomly use this to freeze and block funds from users, claiming these were "flagged" by a cryptic system that inspects the transactions. You are left hostage to their arbitrary decision to let you successfully pass the KYC procedure. If you choose to sidestep their invasive process, they might just hold onto your funds indefinitely.
Your identity has been stolen
KYC data has been found to be for sale on many dark net markets^3. Exchanges may have leaks or hacks, and such leaks contain very sensitive data. We're talking about the full monty: passport or ID scans, proof of address, and even those awkward selfies where you're holding up your ID next to your face. All this data is being left to the mercy of the (mostly) "trust-me-bro" security systems of such companies. Quite scary, isn't it?
As cheap as $10 for 100 documents, with discounts applying for those who buy in bulk, the personal identities of innocent users who passed KYC procedures are for sale. ^3
In short, if you have ever passed the KYC/AML process of a crypto exchange, your privacy is at risk of being compromised, or it might even have already been compromised.
(they) Know Your Coins
You may already know that Bitcoin and most cryptocurrencies have a transparent public blockchain, meaning that all data is shown unencrypted for everyone to see and recorded forever. If you link an address you own to your identity through KYC, for example, by sending an amount from a KYC exchange to it, your Bitcoin is no longer pseudonymous and can then be traced.
If, for instance, you send Bitcoin from such an identified address to another KYC'ed address (say, from a friend), everyone having access to that address-identity link information (exchanges, governments, hackers, etc.) will be able to associate that transaction and know who you are transacting with.
Conclusions
To sum up, KYC does not protect individuals; rather, it's a threat to our privacy, freedom, security and integrity. Sensible information flowing through the internet is thrown into chaos by dubious security measures. It puts borders between many potential customers and businesses, and it helps governments and companies track innocent users. That's the chaos KYC has stirred.
The criminals are using stolen identities from companies that gathered them thanks to these very same regulations that were supposed to combat them. Criminals always know how to circumvent such regulations. In the end, normal people are the most affected by these policies.
The threat that KYC poses to individuals in terms of privacy, security and freedom is not to be neglected. And if we don’t start challenging these systems and questioning their efficacy, we are just one step closer to the dystopian future that is now foreseeable.
Edited 20/03/2024 * Add reference to the 1% statement on Rights for Illusions section to an article where Chainalysis found that only 0.34% of the transaction volume with cryptocurrencies in 2023 was attributable to criminal activity ^1
-
 @ 57d1a264:69f1fee1
2025-05-16 05:38:28
@ 57d1a264:69f1fee1
2025-05-16 05:38:28LegoGPT generates a LEGO structure from a user-provided text prompt in an end-to-end manner. Notably, our generated LEGO structure is physically stable and buildable.
Lego is something most of us knows. This is a opportuity to ask where is our creativity going? From the art of crafting figures to building blocks following our need and desires to have a machine thinking and building following step-by-step instructions to achieve an isolated goal.
Is the creative act then in the question itself, not anymore in the crafting? Are we just delegating the solution of problems, the thinking of how to respond to questions, to machines? Would it be different if delegated to other people?
Source: https://avalovelace1.github.io/LegoGPT/
https://stacker.news/items/981336
-
 @ 39cc53c9:27168656
2025-05-20 10:45:28
@ 39cc53c9:27168656
2025-05-20 10:45:28Over the past few months, I've dedicated my time to a complete rewrite of the kycnot.me website. The technology stack remains unchanged; Golang paired with TailwindCSS. However, I've made some design choices in this iteration that I believe significantly enhance the site. Particularly to backend code.
UI Improvements
You'll notice a refreshed UI that retains the original concept but has some notable enhancements. The service list view is now more visually engaging, it displays additional information in a more aesthetically pleasing manner. Both filtering and searching functionalities have been optimized for speed and user experience.
Service pages have been also redesigned to highlight key information at the top, with the KYC Level box always accessible. The display of service attributes is now more visually intuitive.
The request form, especially the Captcha, has undergone substantial improvements. The new self-made Captcha is robust, addressing the reliability issues encountered with the previous version.
Terms of Service Summarizer
A significant upgrade is the Terms of Service summarizer/reviewer, now powered by AI (GPT-4-turbo). It efficiently condenses each service's ToS, extracting and presenting critical points, including any warnings. Summaries are updated monthly, processing over 40 ToS pages via the OpenAI API using a self-crafted and thoroughly tested prompt.
Nostr Comments
I've integrated a comment section for each service using Nostr. For guidance on using this feature, visit the dedicated how-to page.
Database
The backend database has transitioned to pocketbase, an open-source Golang backend that has been a pleasure to work with. I maintain an updated fork of the Golang SDK for pocketbase at pluja/pocketbase.
Scoring
The scoring algorithm has also been refined to be more fair. Despite I had considered its removal due to the complexity it adds (it is very difficult to design a fair scoring system), some users highlighted its value, so I kept it. The updated algorithm is available open source.
Listings
Each listing has been re-evaluated, and the ones that were no longer operational were removed. New additions are included, and the backlog of pending services will be addressed progressively, since I still have access to the old database.
API
The API now offers more comprehensive data. For more details, check here.
About Page
The About page has been restructured for brevity and clarity.
Other Changes
Extensive changes have been implemented in the server-side logic, since the whole code base was re-written from the ground up. I may discuss these in a future post, but for now, I consider the current version to be just a bit beyond beta, and additional updates are planned in the coming weeks.
-
 @ 39cc53c9:27168656
2025-05-20 10:45:26
@ 39cc53c9:27168656
2025-05-20 10:45:26I'm launching a new service review section on this blog in collaboration with OrangeFren. These reviews are sponsored, yet the sponsorship does not influence the outcome of the evaluations. Reviews are done in advance, then, the service provider has the discretion to approve publication without modifications.
Sponsored reviews are independent from the kycnot.me list, being only part of the blog. The reviews have no impact on the scores of the listings or their continued presence on the list. Should any issues arise, I will not hesitate to remove any listing.
The review
WizardSwap is an instant exchange centred around privacy coins. It was launched in 2020 making it old enough to have weathered the 2021 bull run and the subsequent bearish year.
| Pros | Cons | |------|------| | Tor-friendly | Limited liquidity | | Guarantee of no KYC | Overly simplistic design | | Earn by providing liquidity | |
Rating: ★★★★★ Service Website: wizardswap.io
Liquidity
Right off the bat, we'll start off by pointing out that WizardSwap relies on its own liquidity reserves, meaning they aren't just a reseller of Binance or another exchange. They're also committed to a no-KYC policy, when asking them, they even promised they would rather refund a user their original coins, than force them to undergo any sort of verification.
On the one hand, full control over all their infrastructure gives users the most privacy and conviction about the KYC policies remaining in place.
On the other hand, this means the liquidity available for swapping isn't huge. At the time of testing we could only purchase at most about 0.73 BTC with XMR.
It's clear the team behind WizardSwap is aware of this shortfall and so they've come up with a solution unique among instant exchanges. They let you, the user, deposit any of the currencies they support into your account and earn a profit on the trades made using your liquidity.
Trading
Fees on WizardSwap are middle-of-the-pack. The normal fee is 2.2%. That's more than some exchanges that reserve the right to suddenly demand you undergo verification, yet less than half the fees on some other privacy-first exchanges. However as we mentioned in the section above you can earn almost all of that fee (2%) if you provide liquidity to WizardSwap.
It's good that with the current Bitcoin fee market their fees are constant regardless of how much, or how little, you send. This is in stark contrast with some of the alternative swap providers that will charge you a massive premium when attempting to swap small amounts of BTC away.
Test trades
Test trades are always performed without previous notice to the service provider.
During our testing we performed a few test trades and found that every single time WizardSwap immediately detected the incoming transaction and the amount we received was exactly what was quoted before depositing. The fees were inline with what WizardSwap advertises.

- Monero payment proof
- Bitcoin received
- Wizardswap TX link - it's possible that this link may cease to be valid at some point in the future.
ToS and KYC
WizardSwap does not have a Terms of Service or a Privacy Policy page, at least none that can be found by users. Instead, they offer a FAQ section where they addresses some basic questions.
The site does not mention any KYC or AML practices. It also does not specify how refunds are handled in case of failure. However, based on the FAQ section "What if I send funds after the offer expires?" it can be inferred that contacting support is necessary and network fees will be deducted from any refund.
UI & Tor
WizardSwap can be visited both via your usual browser and Tor Browser. Should you decide on the latter you'll find that the website works even with the most strict settings available in the Tor Browser (meaning no JavaScript).
However, when disabling Javascript you'll miss the live support chat, as well as automatic refreshing of the trade page. The lack of the first means that you will have no way to contact support from the trade page if anything goes wrong during your swap, although you can do so by mail.
One important thing to have in mind is that if you were to accidentally close the browser during the swap, and you did not save the swap ID or your browser history is disabled, you'll have no easy way to return to the trade. For this reason we suggest when you begin a trade to copy the url or ID to someplace safe, before sending any coins to WizardSwap.
The UI you'll be greeted by is simple, minimalist, and easy to navigate. It works well not just across browsers, but also across devices. You won't have any issues using this exchange on your phone.
Getting in touch
The team behind WizardSwap appears to be most active on X (formerly Twitter): https://twitter.com/WizardSwap_io
If you have any comments or suggestions about the exchange make sure to reach out to them. In the past they've been very receptive to user feedback, for instance a few months back WizardSwap was planning on removing DeepOnion, but the community behind that project got together ^1 and after reaching out WizardSwap reversed their decision ^2.
You can also contact them via email at:
support @ wizardswap . ioDisclaimer
None of the above should be understood as investment or financial advice. The views are our own only and constitute a faithful representation of our experience in using and investigating this exchange. This review is not a guarantee of any kind on the services rendered by the exchange. Do your own research before using any service.
-
 @ 39cc53c9:27168656
2025-05-20 10:45:24
@ 39cc53c9:27168656
2025-05-20 10:45:24Bitcoin enthusiasts frequently and correctly remark how much value it adds to Bitcoin not to have a face, a leader, or a central authority behind it. This particularity means there isn't a single person to exert control over, or a single human point of failure who could become corrupt or harmful to the project.
Because of this, it is said that no other coin can be equally valuable as Bitcoin in terms of decentralization and trustworthiness. Bitcoin is unique not just for being first, but also because of how the events behind its inception developed. This implies that, from Bitcoin onwards, any coin created would have been created by someone, consequently having an authority behind it. For this and some other reasons, some people refer to Bitcoin as "The Immaculate Conception".
While other coins may have their own unique features and advantages, they may not be able to replicate Bitcoin's community-driven nature. However, one other cryptocurrency shares a similar story of mystery behind its creation: Monero.
History of Monero
Bytecoin and CryptoNote
In March 2014, a Bitcointalk thread titled "Bytecoin. Secure, private, untraceable since 2012" was initiated by a user under the nickname "DStrange"^1^. DStrange presented Bytecoin (BCN) as a unique cryptocurrency, in operation since July 2012. Unlike Bitcoin, it employed a new algorithm known as CryptoNote.
DStrange apparently stumbled upon the Bytecoin website by chance while mining a dying bitcoin fork, and decided to create a thread on Bitcointalk^1^. This sparked curiosity among some users, who wondered how could Bytecoin remain unnoticed since its alleged launch in 2012 until then^2^.
Some time after, a user brought up the "CryptoNote v2.0" whitepaper for the first time, underlining its innovative features^4^. Authored by the pseudonymous Nicolas van Saberhagen in October 2013, the CryptoNote v2 whitepaper^5^ highlighted the traceability and privacy problems in Bitcoin. Saberhagen argued that these flaws could not be quickly fixed, suggesting it would be more efficient to start a new project rather than trying to patch the original^5^, an statement simmilar to the one from Satoshi Nakamoto^6^.
Checking with Saberhagen's digital signature, the release date of the whitepaper seemed correct, which would mean that Cryptonote (v1) was created in 2012^7^, although there's an important detail: "Signing time is from the clock on the signer's computer" ^9^.
Moreover, the whitepaper v1 contains a footnote link to a Bitcointalk post dated May 5, 2013^10^, making it impossible for the whitepaper to have been signed and released on December 12, 2012.
As the narrative developed, users discovered that a significant 80% portion of Bytecoin had been pre-mined^11^ and blockchain dates seemed to be faked to make it look like it had been operating since 2012, leading to controversy surrounding the project.
The origins of CryptoNote and Bytecoin remain mysterious, leaving suspicions of a possible scam attempt, although the whitepaper had a good amount of work and thought on it.
The fork
In April 2014, the Bitcointalk user
thankful_for_today, who had also participated in the Bytecoin thread^12^, announced plans to launch a Bytecoin fork named Bitmonero^13^.The primary motivation behind this fork was "Because there is a number of technical and marketing issues I wanted to do differently. And also because I like ideas and technology and I want it to succeed"^14^. This time Bitmonero did things different from Bytecoin: there was no premine or instamine, and no portion of the block reward went to development.
However, thankful_for_today proposed controversial changes that the community disagreed with. Johnny Mnemonic relates the events surrounding Bitmonero and thankful_for_today in a Bitcointalk comment^15^:
When thankful_for_today launched BitMonero [...] he ignored everything that was discussed and just did what he wanted. The block reward was considerably steeper than what everyone was expecting. He also moved forward with 1-minute block times despite everyone's concerns about the increase of orphan blocks. He also didn't address the tail emission concern that should've (in my opinion) been in the code at launch time. Basically, he messed everything up. Then, he disappeared.
After disappearing for a while, thankful_for_today returned to find that the community had taken over the project. Johnny Mnemonic continues:
I, and others, started working on new forks that were closer to what everyone else was hoping for. [...] it was decided that the BitMonero project should just be taken over. There were like 9 or 10 interested parties at the time if my memory is correct. We voted on IRC to drop the "bit" from BitMonero and move forward with the project. Thankful_for_today suddenly resurfaced, and wasn't happy to learn the community had assumed control of the coin. He attempted to maintain his own fork (still calling it "BitMonero") for a while, but that quickly fell into obscurity.
The unfolding of these events show us the roots of Monero. Much like Satoshi Nakamoto, the creators behind CryptoNote/Bytecoin and thankful_for_today remain a mystery^17^, having disappeared without a trace. This enigma only adds to Monero's value.
Since community took over development, believing in the project's potential and its ability to be guided in a better direction, Monero was given one of Bitcoin's most important qualities: a leaderless nature. With no single face or entity directing its path, Monero is safe from potential corruption or harm from a "central authority".
The community continued developing Monero until today. Since then, Monero has undergone a lot of technological improvements, migrations and achievements such as RingCT and RandomX. It also has developed its own Community Crowdfundinc System, conferences such as MoneroKon and Monerotopia are taking place every year, and has a very active community around it.
Monero continues to develop with goals of privacy and security first, ease of use and efficiency second. ^16^
This stands as a testament to the power of a dedicated community operating without a central figure of authority. This decentralized approach aligns with the original ethos of cryptocurrency, making Monero a prime example of community-driven innovation. For this, I thank all the people involved in Monero, that lead it to where it is today.
If you find any information that seems incorrect, unclear or any missing important events, please contact me and I will make the necessary changes.
Sources of interest
- https://forum.getmonero.org/20/general-discussion/211/history-of-monero
- https://monero.stackexchange.com/questions/852/what-is-the-origin-of-monero-and-its-relationship-to-bytecoin
- https://en.wikipedia.org/wiki/Monero
- https://bitcointalk.org/index.php?topic=583449.0
- https://bitcointalk.org/index.php?topic=563821.0
- https://bitcointalk.org/index.php?action=profile;u=233561
- https://bitcointalk.org/index.php?topic=512747.0
- https://bitcointalk.org/index.php?topic=740112.0
- https://monero.stackexchange.com/a/1024
- https://inspec2t-project.eu/cryptocurrency-with-a-focus-on-anonymity-these-facts-are-known-about-monero/
- https://medium.com/coin-story/coin-perspective-13-riccardo-spagni-69ef82907bd1
- https://www.getmonero.org/resources/about/
- https://www.wired.com/2017/01/monero-drug-dealers-cryptocurrency-choice-fire/
- https://www.monero.how/why-monero-vs-bitcoin
- https://old.reddit.com/r/Monero/comments/u8e5yr/satoshi_nakamoto_talked_about_privacy_features/
-
 @ 9ca447d2:fbf5a36d
2025-05-20 11:09:00
@ 9ca447d2:fbf5a36d
2025-05-20 11:09:00Ed Suman, a 67-year-old retired artist who helped create large sculptures like Jeff Koons’ Balloon Dog, reportedly lost his entire life savings — over $2M in digital assets — in a sophisticated scam.
The incident is believed to be tied to the major data breach at Coinbase, one of the world’s largest digital asset exchanges.
Suman’s story is part of a bigger wave of attacks on digital asset holders using stolen personal info, and has triggered lawsuits, regulatory concerns and questions about digital security in the Bitcoin space.
In March 2025, Suman got a text message about suspicious activity on his Coinbase account. After Suman reported he was unaware of any unauthorized activity regarding his account, he got a call from a man who introduced himself as Brett Miller from Coinbase Security.
The guy sounded legit — he knew Suman’s setup, including that he used a Trezor Model One hardware wallet, a device meant to keep bitcoin and other digital assets offline and safe.
Suman told Bloomberg the guy knew everything, including the exact amount of digital assets he had.
The attacker persuaded Suman that his Trezor One hardware wallet and its funds were at risk and walked him through a “security procedure” that involved entering his seed phrase into a website that looked exactly like Coinbase, in order to “link his wallet to Coinbase”.
Nine days later, another guy called and repeated the process, saying the first one didn’t work.
And then, all of Suman’s digital assets — 17.5 bitcoin and 225 ether — were gone. At the time, bitcoin was around $103,000 and ether around $2,500, so the stolen stash was worth over $2 million.
Suman turned to digital assets after retiring from a decades-long art career. He stored his assets in cold storage to avoid the risks of online exchanges. He thought he did everything right.
Suman’s attackers didn’t pick his name out of a hat.
It looks like his personal info may have been leaked in the major breach at Coinbase. The company confirmed on May 15 that some of its customer service reps in India were bribed to access internal systems and steal customer data.
The stolen data included names, phone numbers, email addresses, balances and partial Social Security numbers.
According to Coinbase’s filing with the U.S. Securities and Exchange Commission, the breach may have started as early as January and affected nearly 1% of the company’s active monthly users — tens of thousands of people.
Hackers demanded $20M from Coinbase to keep the breach quiet but the company refused to pay. Coinbase says it fired the compromised agents and is setting aside $180M to $400M to reimburse affected users.
But so far, Suman hasn’t been told if he’ll be reimbursed.
Since the breach was disclosed, Coinbase has been hit with at least six lawsuits.
The lawsuits claim the company failed to protect user data and handled the aftermath poorly. One lawsuit filed in New York federal court on May 16 says Coinbase’s response was “inadequate, fragmented, and delayed.”
“Users were not promptly or fully informed of the compromise,” the complaint states, “and Coinbase did not immediately take meaningful steps to mitigate further harm.”
Some lawsuits are seeking damages, others are asking Coinbase to purge user data and improve its security. Coinbase has not commented on the lawsuits but pointed reporters to a blog post about its response.
Suman’s case is a cautionary tale across the Bitcoin world. He used a hardware wallet (considered the gold standard of Bitcoin security) and was still tricked through social engineering. Even the strongest security is useless if you don’t understand how Bitcoin works.
It’s never too early for Bitcoiners to start learning more about Bitcoin, especially on how to keep their stash safe. And the first lesson is “never ever share your seed phrase with anyone”.
Related: Bitcoin Hardware Wallet Hacks: What You Need to Know
-
 @ 39cc53c9:27168656
2025-05-20 10:45:23
@ 39cc53c9:27168656
2025-05-20 10:45:23I've been thinking about how to improve my seed backup in a cheap and cool way, mostly for fun. Until now, I had the seed written on a piece of paper in a desk drawer, and I wanted something more durable and fire-proof.
After searching online, I found two options I liked the most: the Cryptosteel Capsule and the Trezor Keep. These products are nice but quite expensive, and I didn't want to spend that much on my seed backup. Privacy is also important, and sharing details like a shipping address makes me uncomfortable. This concern has grown since the Ledger incident^1. A $5 wrench attack^2 seems too cheap, even if you only hold a few sats.
Upon seeing the design of Cryptosteel, I considered creating something similar at home. Although it may not be as cool as their device, it could offer almost the same in terms of robustness and durability.
Step 1: Get the materials and tools
When choosing the materials, you will want to go with stainless steel. It is durable, resistant to fire, water, and corrosion, very robust, and does not rust. Also, its price point is just right; it's not the cheapest, but it's cheap for the value you get.

I went to a material store and bought:
- Two bolts
- Two hex nuts and head nuts for the bolts
- A bag of 30 washers
All items were made of stainless steel. The total price was around €6. This is enough for making two seed backups.
You will also need:
- A set of metal letter stamps (I bought a 2mm-size letter kit since my washers were small, 6mm in diameter)
- You can find these in local stores or online marketplaces. The set I bought cost me €13.
- A good hammer
- A solid surface to stamp on
Total spent: 19€ for two backups
Step 2: Stamp and store
Once you have all the materials, you can start stamping your words. There are many videos on the internet that use fancy 3D-printed tools to get the letters nicely aligned, but I went with the free-hand option. The results were pretty decent.

I only stamped the first 4 letters for each word since the BIP-39 wordlist allows for this. Because my stamping kit did not include numbers, I used alphabet letters to define the order. This way, if all the washers were to fall off, I could still reassemble the seed correctly.
The final result
So this is the final result. I added two smaller washers as protection and also put the top washer reversed so the letters are not visible:

Compared to the Cryptosteel or the Trezor Keep, its size is much more compact. This makes for an easier-to-hide backup, in case you ever need to hide it inside your human body.
Some ideas
Tamper-evident seal
To enhance the security this backup, you can consider using a tamper-evident seal. This can be easily achieved by printing a unique image or using a specific day's newspaper page (just note somewhere what day it was).
Apply a thin layer of glue to the washer's surface and place the seal over it. If someone attempts to access the seed, they will be forced to destroy the seal, which will serve as an evident sign of tampering.
This simple measure will provide an additional layer of protection and allow you to quickly identify any unauthorized access attempts.
Note that this method is not resistant to outright theft. The tamper-evident seal won't stop a determined thief but it will prevent them from accessing your seed without leaving any trace.
Redundancy
Make sure to add redundancy. Make several copies of this cheap backup, and store them in separate locations.
Unique wordset
Another layer of security could be to implement your own custom mnemonic dictionary. However, this approach has the risk of permanently losing access to your funds if not implemented correctly.
If done properly, you could potentially end up with a highly secure backup, as no one else would be able to derive the seed phrase from it. To create your custom dictionary, assign a unique number from 1 to 2048 to a word of your choice. Maybe you could use a book, and index the first 2048 unique words that appear. Make sure to store this book and even get a couple copies of it (digitally and phisically).
This self-curated set of words will serve as your personal BIP-39 dictionary. When you need to translate between your custom dictionary and the official BIP-39 wordlist, simply use the index number to find the corresponding word in either list.
Never write the idex or words on your computer (Do not use
Ctr+F) -
 @ 8bad92c3:ca714aa5
2025-05-20 11:00:32
@ 8bad92c3:ca714aa5
2025-05-20 11:00:32Marty's Bent

via me

Don't sleep on what's happening in Japan right now. We've been covering the country and the fact that they've lost control of their yield curve since late last year. After many years of making it a top priority from a monetary policy perspective, last year the Bank of Japan decided to give up on yield curve control in an attempt to reel inflation. This has sent yields for the 30-year and 40-year Japanese government bonds to levels not seen since the early 2000s in the case of the 30-year and levels never before seen for the 40-year, which was launched in 2007. With a debt to GDP ratio that has surpassed 250% and a population that is aging out with an insufficient amount of births to replace the aging workforce, it's hard to see how Japan can get out of this conundrum without some sort of economic collapse.
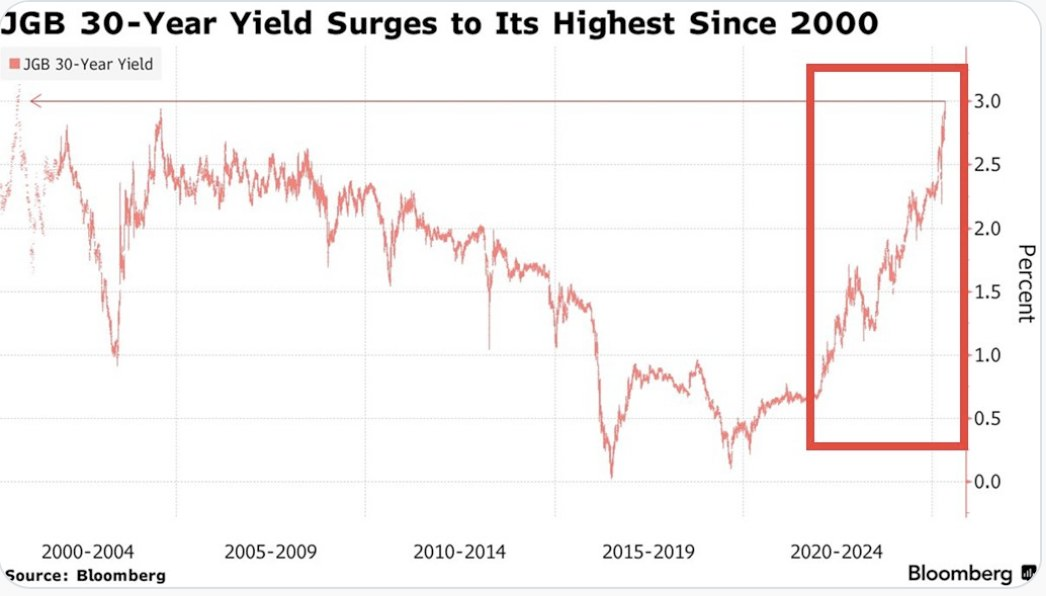

This puts the United States in a tough position considering the fact that Japan is one of the largest holders of U.S. Treasury bonds with more than $1.20 trillion in exposure. If things get too out of control in Japan and the yield curve continues to drift higher and inflation continues to creep higher Japan can find itself in a situation where it's a forced seller of US Treasuries as they attempt to strengthen the yen. Another aspect to consider is the fact that investors may see the higher yields on Japanese government bonds and decide to purchase them instead of US Treasuries. This is something to keep an eye on in the weeks to come. Particularly if higher rates drive a higher cost of capital, which leads to even more inflation. As producers are forced to increase their prices to ensure that they can manage their debt repayments.
It's never a good sign when the Japanese Prime Minister is coming out to proclaim that his country's financial situation is worse than Greece's, which has been a laughing stock of Europe for the better part of three decades. Japan is a very proud nation, and the fact that its Prime Minister made a statement like this should not be underappreciated.
As we noted last week, the 10-year and 30-year U.S. Treasury bonds are drifting higher as well. Earlier today, the 30-year bond yield surpassed 5%, which has been a psychological level that many have been pointed to as a critical tipping point. When you take a step back and look around the world it seems pretty clear that bond markets are sending a very strong signal. And that signal is that something is not well in the back end of the financial system.
This is even made clear when you look at the private sector, particularly at consumer debt. In late March, we warned of the growing trend of buy now, pay later schemes drifting down market as major credit card companies released charge-off data which showed charge-off rates reaching levels not seen since the 2008 great financial crisis. At the time, we could only surmise that Klarna was experiencing similar charge-off rates on the bigger-ticket items they financed and started doing deals with companies like DoorDash to finance burrito deliveries in an attempt to move down market to finance smaller ticket items with a higher potential of getting paid back. It seems like that inclination was correct as Klarna released data earlier today showing more losses on their book as consumers find it extremely hard to pay back their debts.

via NewsWire
This news hit the markets on the same day as the average rate of the 30-year mortgage in the United States rose to 7.04%. I'm not sure if you've checked lately, but real estate prices are still relatively elevated outside of a few big cities who expanded supply significantly during the COVID era as people flooded out of blue states towards red states. It's hard to imagine that many people can afford a house based off of sticker price alone, but with a 7% 30-year mortgage rate it's becoming clear that the ability of the Common Man to buy a house is simply becoming impossible.
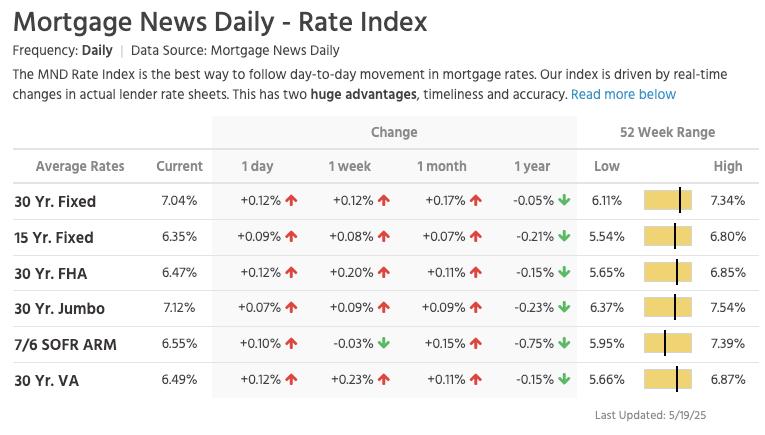
via Lance Lambert
The mortgage rate data is not the only thing you need to look at to understand that it's becoming impossible for the Common Man of working age to buy a house. New data has recently been released that highlights That the median home buyer in 2007 was born in 1968, and the median home buyer in 2024 was born in 1968. Truly wild when you think of it. As our friend Darth Powell cheekily highlights below, we find ourselves in a situation where boomers are simply trading houses and the younger generations are becoming indentured slaves. Forever destined to rent because of the complete inability to afford to buy a house.
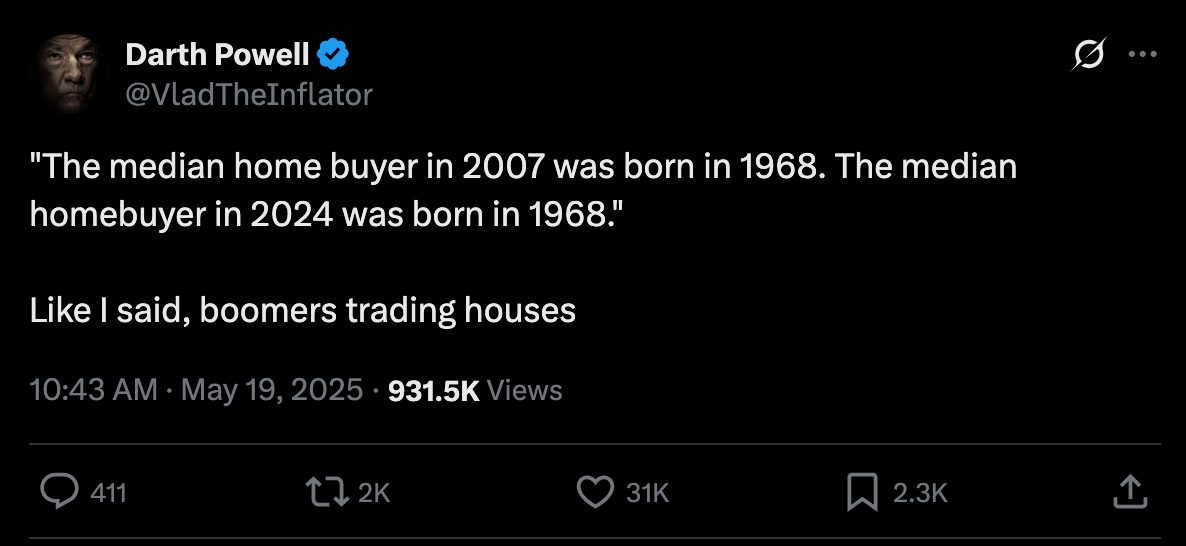
via Darth Powell
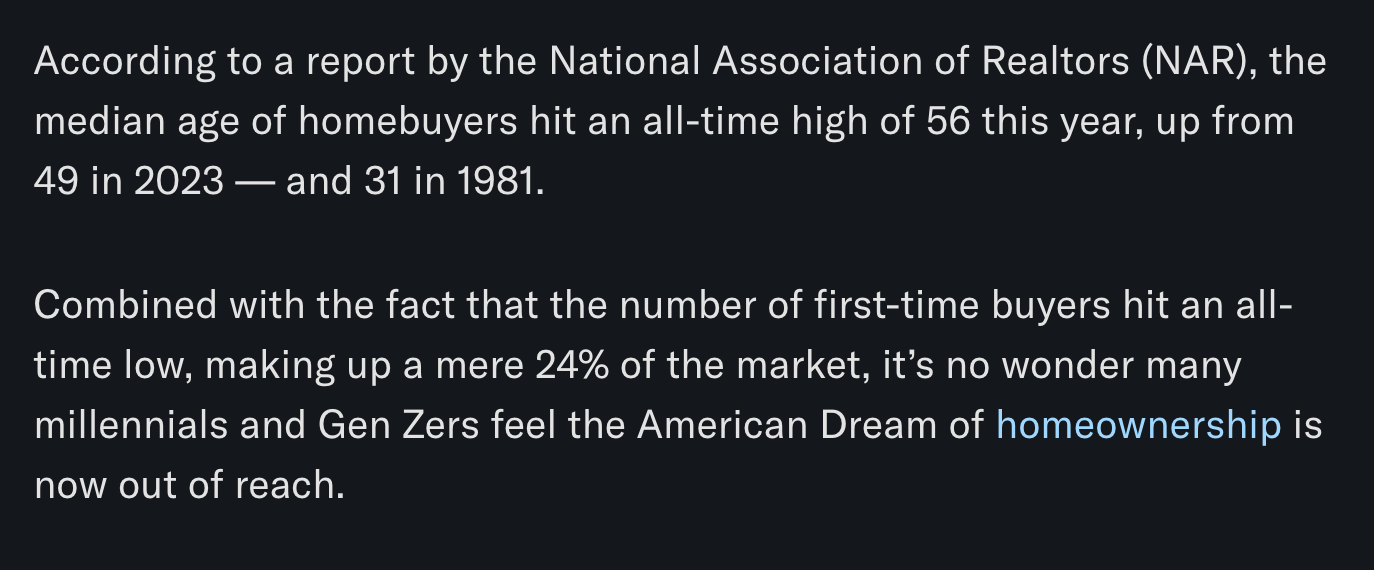
via Yahoo Finance
Meanwhile, Bitcoin re-approached all-time highs late this evening and looks primed for another breakout to the upside. This makes sense if you're paying attention. The high-velocity trash economy running on an obscene amount of debt in both the public and private sectors seems to be breaking at the seams. All the alarm bells are signaling that another big print is coming. And if you hope to preserve your purchasing power or, ideally, increase it as the big print approaches, the only thing that makes sense is to funnel your money into the hardest asset in the world, which is Bitcoin.

via Bitbo
Buckle up, freaks. It's gonna be a bumpy ride. Stay humble, Stack Sats.
Trump's Middle East Peace Strategy: Redefining U.S. Foreign Policy
In his recent Middle East tour, President Trump signaled what our guest Dr. Anas Alhajji calls "a major change in US policy." Trump explicitly rejected the nation-building strategies of his predecessors, contrasting the devastation in Afghanistan and Iraq with the prosperity of countries like Saudi Arabia and UAE. This marks a profound shift from both Republican and Democratic foreign policy orthodoxy. As Alhajji noted, Trump's willingness to meet with Syrian President Assad follows a historical pattern where former adversaries eventually become diplomatic partners.
"This is really one of the most important shifts in US foreign policy to say, look, sorry, we destroyed those countries because we tried to rebuild them and it was a big mistake." - Dr. Anas Alhajji
The administration's new approach emphasizes negotiation over intervention. Rather than military solutions, Trump is engaging with groups previously considered off-limits, including the Houthis, Hamas, and Iran. This pragmatic stance prioritizes economic cooperation and regional stability over ideological confrontation. The focus on trade deals and investment rather than regime change represents a fundamental reimagining of America's role in the Middle East.
Check out the full podcast here for more on the Iran nuclear situation, energy market predictions, and why AI development could create power grid challenges. Only on TFTC Studio.
Headlines of the Day
Bitcoin Soars to $106K While Bonds Lose 40% Since 2020 - via X
US Senate Advances Stablecoin Bill As America Embraces Bitcoin - via X
Get our new STACK SATS hat - via tftcmerch.io
Texas House Debates Bill For State-Run Bitcoin Reserve - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code *“TFTC20”* during checkout for 20% off
_Ten31, the largest bitcoin-focused inves
-
 @ 39cc53c9:27168656
2025-05-20 10:45:21
@ 39cc53c9:27168656
2025-05-20 10:45:21kycnot.me features a somewhat hidden tool that some users may not be aware of. Every month, an automated job crawls every listed service's Terms of Service (ToS) and FAQ pages and conducts an AI-driven analysis, generating a comprehensive overview that highlights key points related to KYC and user privacy.
Here's an example: Changenow's Tos Review

Why?
ToS pages typically contain a lot of complicated text. Since the first versions of kycnot.me, I have tried to provide users a comprehensive overview of what can be found in such documents. This automated method keeps the information up-to-date every month, which was one of the main challenges with manual updates.
A significant part of the time I invest in investigating a service for kycnot.me involves reading the ToS and looking for any clauses that might indicate aggressive KYC practices or privacy concerns. For the past four years, I performed this task manually. However, with advancements in language models, this process can now be somewhat automated. I still manually review the ToS for a quick check and regularly verify the AI’s findings. However, over the past three months, this automated method has proven to be quite reliable.
Having a quick ToS overview section allows users to avoid reading the entire ToS page. Instead, you can quickly read the important points that are grouped, summarized, and referenced, making it easier and faster to understand the key information.
Limitations
This method has a key limitation: JS-generated pages. For this reason, I was using Playwright in my crawler implementation. I plan to make a release addressing this issue in the future. There are also sites that don't have ToS/FAQ pages, but these sites already include a warning in that section.
Another issue is false positives. Although not very common, sometimes the AI might incorrectly interpret something harmless as harmful. Such errors become apparent upon reading; it's clear when something marked as bad should not be categorized as such. I manually review these cases regularly, checking for anything that seems off and then removing any inaccuracies.
Overall, the automation provides great results.
How?
There have been several iterations of this tool. Initially, I started with GPT-3.5, but the results were not good in any way. It made up many things, and important thigs were lost on large ToS pages. I then switched to GPT-4 Turbo, but it was expensive. Eventually, I settled on Claude 3 Sonnet, which provides a quality compromise between GPT-3.5 and GPT-4 Turbo at a more reasonable price, while allowing a generous 200K token context window.
I designed a prompt, which is open source^1, that has been tweaked many times and will surely be adjusted further in the future.
For the ToS scraping part, I initially wrote a scraper API using Playwright^2, but I replaced it with Jina AI Reader^3, which works quite well and is designed for this task.
Non-conflictive ToS
All services have a dropdown in the ToS section called "Non-conflictive ToS Reviews." These are the reviews that the AI flagged as not needing a user warning. I still provide these because I think they may be interesting to read.
Feedback and contributing
You can give me feedback on this tool, or share any inaccuraties by either opening an issue on Codeberg^4 or by contacting me ^5.
You can contribute with pull requests, which are always welcome, or you can support this project with any of the listed ways.
-
 @ 39cc53c9:27168656
2025-05-20 10:45:20
@ 39cc53c9:27168656
2025-05-20 10:45:20These reviews are sponsored, yet the sponsorship does not influence the outcome of the evaluations. Sponsored reviews are independent from the kycnot.me list, being only part of the blog. The reviews have no impact on the scores of the listings or their continued presence on the list. Should any issues arise, I will not hesitate to remove any listing. Reviews are in collaboration with Orangefren.
The review
Swapter.io is an all-purpose instant exchange. They entered the scene in the depths of the bear market about 2 years ago in June of 2022.
| Pros | Cons | | --------------- | ---------------------------------- | | Low fees | Shotgun KYC with opaque triggers | | Large liquidity | Relies on 3rd party liquidity | | Works over Tor | Front-end not synced with back-end | | Pretty UI | |
Rating: ★★★☆☆ Service Website: swapter.io
⚠️ There is an ongoing issue with this service: read more on Reddit.
Test Trades
During our testing we performed a trade from XMR to LTC, and then back to XMR.
Our first trade had the ID of:
mpUitpGemhN8jjNAjQuo6EvQ. We were promised 0.8 LTC for sending 0.5 XMR, before we sent the Monero. When the Monero arrived we were sent 0.799 LTC.On the return journey we performed trade with ID:
yaCRb5pYcRKAZcBqg0AzEGYg. This time we were promised 0.4815 XMR for sending 0.799 LTC. After Litecoin arrived we were sent 0.4765 XMR.As such we saw a discrepancy of
~0.1%in the first trade and~1%in the second trade. Considering those trades were floating we determine the estimates presented in the UI to be highly accurate and honest.Of course Swapter could've been imposing a large fee on their estimates, but we checked their estimates against CoinGecko and found the difference to be equivalent to a fee of just over
0.5%. Perfectly in line with other swapping services.Trading
Swapter supports BTC, LTC, XMR and well over a thousand other coins. Sadly they don't support the Lightning Network. For the myriad of currencies they deal with they provide massive upper limits. You could exchange tens, or even hundreds, of thousands of dollars worth of cryptocurrency in a single trade (although we wouldn't recommend it).
The flip side to this is that Swapter relies on 3rd party liquidity. Aside from the large liqudity this also benefits the user insofar as it allows for very low fees. However, it also comes with a negative - the 3rd party gets to see all your trades. Unfortunately Swapter opted not to share where they source their liquidity in their Privacy Policy or Terms of Service.
KYC & AML policies
Swapter reserves the right to require its users to provide their full name, their date of birth, their address and government-issued ID. A practice known as "shotgun KYC". This should not happen often - in our testing it never did - however it's not clear when exactly it could happen. The AML & KYC policy provided on Swapter's website simply states they will put your trade on hold if their "risk scoring system [deems it] as suspicious".
Worse yet, if they determine that "any of the information [the] customer provided is incorrect, false, outdated, or incomplete" then Swapter may decide to terminate all of the services they provide to the user. What exactly would happen to their funds in such a case remains unclear.
The only clarity we get is that the Swapter policy outlines a designated 3rd party that will verify the information provided by the user. The third party's name is Sum & Substance Ltd, also simply known as samsub and available at sumsub.com
It's understandable that some exchanges will decide on a policy of this sort, especially when they rely on external liquidity, but we would prefer more clarity be given. When exactly is a trade suspicious?
Tor
We were pleased to discover Swapter works over Tor. However, they do not provide a Tor mirror, nor do they work without JavaScript. Additionally, we found that some small features, such as the live chat, did not work over Tor. Fortunately, other means of contacting their support are still available.
UI
We have found the Swapter UI to be very modern, straightforward and simple to use. It's available in 4 languages (English, French, Dutch and Russian), although we're unable to vouch for the quality of some of those, the ones that we used seemed perfectly serviceable.
Our only issue with the UI was that it claims the funds have been sent following the trade, when in reality it seems to take the backend a minute or so to actually broadcast the transaction.
Getting in touch
Swapter's team has a chat on their website, a support email address and a support Telegram. Their social media presence in most active on Telegram and X (formerly Twitter).
Disclaimer
None of the above should be understood as investment or financial advice. The views are our own only and constitute a faithful representation of our experience in using and investigating this exchange. This review is not a guarantee of any kind on the services rendered by the exchange. Do your own research before using any service.
-
 @ cae03c48:2a7d6671
2025-05-20 11:00:00
@ cae03c48:2a7d6671
2025-05-20 11:00:00Bitcoin Magazine

Ben Allen Receives Maelstrom Bitcoin Developer Grant to Advance Payjoin TechBen Allen has been named the third recipient of the Maelstrom Bitcoin Developer Grant, the family office of Arthur Hayes announced in a recent press release sent to Bitcoin Magazine. Over the next year, Allen will focus on enhancing the Payjoin Dev Kit project, a privacy-focused Bitcoin transaction tool designed to improve user anonymity and network scalability.
Payjoin, first introduced in 2019 by Nicolas Dorier in BIP 78, allows both the sender and receiver to contribute inputs to a single Bitcoin transaction. This disrupts common assumptions used by financial surveillance firms, namely the idea that multiple transaction inputs must come from a single entity. By breaking this assumption, even limited adoption of Payjoin can bolster privacy across the Bitcoin network.
“Maelstrom would like to congratulate Ben Allen on this grant,” said Arthur Hayes, Chief Investment Officer of Maelstrom. “The great thing about Payjoin, is that if only a small amount of adoption is achieved, it breaks a key assumption used by financial surveillance companies. The assumption they have is that if a Bitcoin transaction has multiple inputs, all the inputs must all belong to the same entity. Therefore, Payjoin adoption improves the privacy of even the people who don’t use it. We are excited to support Ben Allen’s work on open-source tools and software to increase Payjoin adoption.”
Allen, who will be working alongside Dan Gould, aims to expand the implementation of Payjoin so it can be integrated into more Bitcoin wallets. He acknowledged the technical complexities of the project—including the requirement for receivers to be online—but expressed optimism about overcoming these challenges.
“I’m deeply grateful to Arthur Hayes and Maelstrom for generously providing me with this grant to support my work on the Payjoin Dev Kit project,” said Allen. “With this funding, I can dedicate myself full-time to enhancing the Payjoin implementation, improving testing, and ensuring that the dev kit remains robust, well-documented, and maintainable for the future.”
Allen also emphasized the broader mission of his work: “Improving privacy for bitcoin is an area where continued improvement allows for a better experience by empowering users to control their financial data and foster greater peace of mind when using bitcoin day to day. This is an exciting opportunity to contribute to Bitcoin’s privacy and scalability, and I’m looking forward to continuing to collaborate with the community to make Payjoin more widely adopted.”
Maelstrom, which is focused on supporting digital asset infrastructure, is led by Arthur Hayes, co-founder of BitMEX. Through grants like this one, the firm is investing in the foundational tools that promote a more private, scalable, and decentralized Bitcoin ecosystem.
This post Ben Allen Receives Maelstrom Bitcoin Developer Grant to Advance Payjoin Tech first appeared on Bitcoin Magazine and is written by Jenna Montgomery.
-
 @ 39cc53c9:27168656
2025-05-20 10:45:18
@ 39cc53c9:27168656
2025-05-20 10:45:18“The future is there... staring back at us. Trying to make sense of the fiction we will have become.” — William Gibson.
This month is the 4th anniversary of kycnot.me. Thank you for being here.
Fifteen years ago, Satoshi Nakamoto introduced Bitcoin, a peer-to-peer electronic cash system: a decentralized currency free from government and institutional control. Nakamoto's whitepaper showed a vision for a financial system based on trustless transactions, secured by cryptography. Some time forward and KYC (Know Your Customer), AML (Anti-Money Laundering), and CTF (Counter-Terrorism Financing) regulations started to come into play.
What a paradox: to engage with a system designed for decentralization, privacy, and independence, we are forced to give away our personal details. Using Bitcoin in the economy requires revealing your identity, not just to the party you interact with, but also to third parties who must track and report the interaction. You are forced to give sensitive data to entities you don't, can't, and shouldn't trust. Information can never be kept 100% safe; there's always a risk. Information is power, who knows about you has control over you.
Information asymmetry creates imbalances of power. When entities have detailed knowledge about individuals, they can manipulate, influence, or exploit this information to their advantage. The accumulation of personal data by corporations and governments enables extensive surveillances.
Such practices, moreover, exclude individuals from traditional economic systems if their documentation doesn't meet arbitrary standards, reinforcing a dystopian divide. Small businesses are similarly burdened by the costs of implementing these regulations, hindering free market competition^1:

How will they keep this information safe? Why do they need my identity? Why do they force businesses to enforce such regulations? It's always for your safety, to protect you from the "bad". Your life is perpetually in danger: terrorists, money launderers, villains... so the government steps in to save us.
‟Hush now, baby, baby, don't you cry Mamma's gonna make all of your nightmares come true Mamma's gonna put all of her fears into you Mamma's gonna keep you right here, under her wing She won't let you fly, but she might let you sing Mamma's gonna keep baby cosy and warm” — Mother, Pink Floyd
We must resist any attack on our privacy and freedom. To do this, we must collaborate.
If you have a service, refuse to ask for KYC; find a way. Accept cryptocurrencies like Bitcoin and Monero. Commit to circular economies. Remove the need to go through the FIAT system. People need fiat money to use most services, but we can change that.
If you're a user, donate to and prefer using services that accept such currencies. Encourage your friends to accept cryptocurrencies as well. Boycott FIAT system to the greatest extent you possibly can.
This may sound utopian, but it can be achieved. This movement can't be stopped. Go kick the hornet's nest.
“We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do.” — Eric Hughes, A Cypherpunk's Manifesto
The anniversary
Four years ago, I began exploring ways to use crypto without KYC. I bookmarked a few favorite services and thought sharing them to the world might be useful. That was the first version of kycnot.me — a simple list of about 15 services. Since then, I've added services, rewritten it three times, and improved it to what it is now.
kycnot.me has remained 100% independent and 100% open source^2 all these years. I've received offers to buy the site, all of which I have declined and will continue to decline. It has been DDoS attacked many times, but we made it through. I have also rewritten the whole site almost once per year (three times in four years).
The code and scoring algorithm are open source (contributions are welcome) and I can't arbitrarly change a service's score without adding or removing attributes, making any arbitrary alterations obvious if they were fake. You can even see the score summary for any service's score.
I'm a one-person team, dedicating my free time to this project. I hope to keep doing so for many more years. Again, thank you for being part of this.
-
 @ f18b1f8f:5f442454
2025-05-20 10:40:01
@ f18b1f8f:5f442454
2025-05-20 10:40:01Graphiti's MCP Server builds temporal knowledge graphs from interactions with MCP-compatible applications like Claude and Cursor. The system creates and maintains structured representations of conversations over time, enabling AI tools to access historical context through a standardized protocol.
Santiago's review: "This is next-level context management" - https://x.com/svpino/status/1924437664997998996
Available at: https://agentlist.com/agent/6fe099b024714254a038d4b977ae2a35
6fe099b024714254a038d4b977ae2a35 #AI #ContextRetention
-
 @ 10870fc2:f5c8cdcd
2025-05-20 10:34:29
@ 10870fc2:f5c8cdcd
2025-05-20 10:34:29Graphiti's MCP Server builds temporal knowledge graphs from interactions with MCP-compatible applications like Claude and Cursor. The system creates and maintains structured representations of conversations over time, enabling AI tools to access historical context through a standardized protocol.
Santiago's review: "This is next-level context management" - https://x.com/svpino/status/1924437664997998996
Available at: https://agentlist.com/agent/6fe099b024714254a038d4b977ae2a35
6fe099b024714254a038d4b977ae2a35 #AI #ContextRetention
-
 @ cd17b2d6:8cc53332
2025-05-20 10:15:09
@ cd17b2d6:8cc53332
2025-05-20 10:15:09🚀 Instantly Send Spendable Flash BTC, ETH, & USDT — Fully Blockchain-Verifiable!
Welcome to the cutting edge of crypto innovation: the ultimate tool for sending spendable Flash Bitcoin (BTC), Ethereum (ETH), and USDT transactions. Our advanced blockchain simulation technology employs 🔥 Race/Finney-style mechanisms, producing coins indistinguishable from authentic blockchain-confirmed tokens. Your transactions are instantly trackable and fully spendable for durations from 60 to 360 days!
🌐 Visit cryptoflashingtool.com for complete details.
🌟 Why Choose Our Crypto Flashing Service? Crypto Flashing is perfect for crypto enthusiasts, blockchain developers, ethical hackers, security professionals, and digital entrepreneurs looking for authenticity combined with unparalleled flexibility.
🎯 Our Crypto Flashing Features: ✅ Instant Blockchain Verification: Transactions appear completely authentic, complete with real blockchain confirmations, transaction IDs, and wallet addresses.
🔒 Maximum Security & Privacy: Fully compatible with VPNs, TOR, and proxy servers, ensuring absolute anonymity and protection.
🖥️ Easy-to-Use Software: Designed for Windows, our intuitive platform suits both beginners and experts, with detailed, step-by-step instructions provided.
📅 Customizable Flash Durations: Control your transaction lifespan precisely, from 60 to 360 days.
🔄 Universal Wallet Compatibility: Instantly flash BTC, ETH, and USDT tokens to SegWit, Legacy, or BCH32 wallets.
💱 Spendable on Top Exchanges: Flash coins seamlessly accepted on leading exchanges like Kraken and Huobi.
📊 Proven Track Record: ✅ Over 79 Billion flash transactions completed. ✅ 3000+ satisfied customers worldwide. ✅ 42 active blockchain nodes for fast, reliable transactions. 📌 Simple Step-by-Step Flashing Process: Step 1️⃣: Enter Transaction Details
Choose coin (BTC, ETH, USDT: TRC-20, ERC-20, BEP-20) Specify amount & flash duration Provide wallet address (validated automatically) Step 2️⃣: Complete Payment & Verification
Pay using the cryptocurrency you wish to flash Scan the QR code or paste the payment address Upload payment proof (transaction hash & screenshot) Step 3️⃣: Initiate Flash Transaction
Our technology simulates blockchain confirmations instantly Flash transaction appears authentic within seconds Step 4️⃣: Verify & Spend Immediately
Access your flashed crypto instantly Easily verify transactions via provided blockchain explorer links 🛡️ Why Our Technology is Trusted: 🔗 Race/Finney Attack Logic: Creates realistic blockchain headers. 🖥️ Private iNode Cluster: Guarantees fast synchronization and reliable transactions. ⏰ Live Timer System: Ensures fresh wallet addresses and transaction legitimacy. 🔍 Genuine Blockchain TX IDs: Authentic transaction IDs included with every flash ❓ Frequently Asked Questions: Is flashing secure? ✅ Yes, encrypted with full VPN/proxy support. Can I flash from multiple devices? ✅ Yes, up to 5 Windows PCs per license. Are chargebacks possible? ❌ No, flash transactions are irreversible. How long are flash coins spendable? ✅ From 60–360 days, based on your chosen plan. Verification after expiry? ❌ Transactions can’t be verified after the expiry. Support available? ✅ Yes, 24/7 support via Telegram & WhatsApp.
🔐 Transparent, Reliable & Highly Reviewed:
CryptoFlashingTool.com operates independently, providing unmatched transparency and reliability. Check out our glowing reviews on ScamAdvisor and leading crypto forums!
📲 Get in Touch Now: 📞 WhatsApp: +1 770 666 2531 ✈️ Telegram: @cryptoflashingtool
🎉 Ready to Start?
💰 Buy Flash Coins Now 🖥️ Get Your Flashing Software
Experience the smartest, safest, and most powerful crypto flashing solution on the market today!
CryptoFlashingTool.com — Flash Crypto Like a Pro.
Instantly Send Spendable Flash BTC, ETH, & USDT — Fully Blockchain-Verifiable!
Welcome to the cutting edge of crypto innovation: the ultimate tool for sending spendable Flash Bitcoin (BTC), Ethereum (ETH), and USDT transactions. Our advanced blockchain simulation technology employs
Race/Finney-style mechanisms, producing coins indistinguishable from authentic blockchain-confirmed tokens. Your transactions are instantly trackable and fully spendable for durations from 60 to 360 days!
Visit cryptoflashingtool.com for complete details.
Why Choose Our Crypto Flashing Service?
Crypto Flashing is perfect for crypto enthusiasts, blockchain developers, ethical hackers, security professionals, and digital entrepreneurs looking for authenticity combined with unparalleled flexibility.
Our Crypto Flashing Features:
Instant Blockchain Verification: Transactions appear completely authentic, complete with real blockchain confirmations, transaction IDs, and wallet addresses.
Maximum Security & Privacy: Fully compatible with VPNs, TOR, and proxy servers, ensuring absolute anonymity and protection.
Easy-to-Use Software: Designed for Windows, our intuitive platform suits both beginners and experts, with detailed, step-by-step instructions provided.
Customizable Flash Durations: Control your transaction lifespan precisely, from 60 to 360 days.
Universal Wallet Compatibility: Instantly flash BTC, ETH, and USDT tokens to SegWit, Legacy, or BCH32 wallets.
Spendable on Top Exchanges: Flash coins seamlessly accepted on leading exchanges like Kraken and Huobi.
Proven Track Record:
- Over 79 Billion flash transactions completed.
- 3000+ satisfied customers worldwide.
- 42 active blockchain nodes for fast, reliable transactions.
Simple Step-by-Step Flashing Process:
Step : Enter Transaction Details
- Choose coin (BTC, ETH, USDT: TRC-20, ERC-20, BEP-20)
- Specify amount & flash duration
- Provide wallet address (validated automatically)
Step : Complete Payment & Verification
- Pay using the cryptocurrency you wish to flash
- Scan the QR code or paste the payment address
- Upload payment proof (transaction hash & screenshot)
Step : Initiate Flash Transaction
- Our technology simulates blockchain confirmations instantly
- Flash transaction appears authentic within seconds
Step : Verify & Spend Immediately
- Access your flashed crypto instantly
- Easily verify transactions via provided blockchain explorer links
Why Our Technology is Trusted:
- Race/Finney Attack Logic: Creates realistic blockchain headers.
- Private iNode Cluster: Guarantees fast synchronization and reliable transactions.
- Live Timer System: Ensures fresh wallet addresses and transaction legitimacy.
- Genuine Blockchain TX IDs: Authentic transaction IDs included with every flash
Frequently Asked Questions:
- Is flashing secure?
Yes, encrypted with full VPN/proxy support. - Can I flash from multiple devices?
Yes, up to 5 Windows PCs per license. - Are chargebacks possible?
No, flash transactions are irreversible. - How long are flash coins spendable?
From 60–360 days, based on your chosen plan. - Verification after expiry?
Transactions can’t be verified after the expiry.
Support available?
Yes, 24/7 support via Telegram & WhatsApp.
Transparent, Reliable & Highly Reviewed:
CryptoFlashingTool.com operates independently, providing unmatched transparency and reliability. Check out our glowing reviews on ScamAdvisor and leading crypto forums!
Get in Touch Now:
WhatsApp: +1 770 666 2531
Telegram: @cryptoflashingtool
Ready to Start?
Experience the smartest, safest, and most powerful crypto flashing solution on the market today!
CryptoFlashingTool.com — Flash Crypto Like a Pro.
-
 @ cae03c48:2a7d6671
2025-05-20 10:50:37
@ cae03c48:2a7d6671
2025-05-20 10:50:37Bitcoin Magazine
Proof of Reserves Should Be the Standard for Bitcoin Treasury Companies“The root problem with conventional currency is all the trust that’s required to make it work. The central bank must be trusted not to debase the currency, but the history of fiat currencies is full of breaches of that trust. Banks must be trusted to hold our money and transfer it electronically, but they lend it out in waves of credit bubbles with barely a fraction in reserve.”
— Satoshi Nakamoto (2009)
Bitcoin was created to eliminate the need for trusted intermediaries. It replaced opaque, permissioned systems with transparency, auditability, and decentralized verification. The ethos was clear from day one: don’t trust—verify.
And yet, many of the institutions now holding Bitcoin—custodians, exchanges, ETFs, even public companies—continue to rely on trust-based assumptions, the very problem Bitcoin was designed to solve.
For Bitcoin treasury companies, this contradiction is especially glaring. These are firms that claim to operate on a Bitcoin standard—yet without verifiable Proof of Reserves (PoR), there’s no way for shareholders to know whether the Bitcoin is actually there.
The Problem: Unproven Bitcoin Is Just Another IOU
Bitcoin is designed to be verifiable—but most corporate disclosures aren’t. When companies report BTC holdings without public wallet visibility or on-chain proof, investors are left to trust balance sheets, auditors, and custodians.
That opens the door to systemic risks:
- Rehypothecation: BTC pledged or lent behind the scenes
- Custodial failure: Centralized services operating without 1:1 backing
- “Paper Bitcoin”: Multiple claims on the same BTC, echoing legacy financial opacity
The mere presence of Bitcoin on a balance sheet is not a guarantee. Without verification, it’s no different than a fiat-denominated claim—an IOU dressed up in BTC terms.
What We Learned from Gold: The Paper Problem
Bitcoin is not the first hard asset to face this challenge. The gold market offers a cautionary tale.
For decades, gold investors have dealt with “paper gold” systems—unallocated accounts, synthetic ETFs, and derivatives with little or no linkage to actual metal. These claims often outnumber real reserves many times over, leading to widespread suspicion of price distortion and systemic misrepresentation.
Most gold investors don’t own gold—they own a claim to gold. And they have no way to prove it.
Bitcoin gives us the tools to break this cycle. But only if companies choose to use them.
Bitcoin Is Built for Proof—and Companies Should Use It
Unlike legacy assets, Bitcoin is designed to make proof of ownership and solvency a native function of the asset itself. Through public key cryptography, on-chain auditability, and permissionless transparency, Bitcoin enables real-time, trust-minimized verification.
This isn’t just a technical capability—it’s a governance feature. Bitcoin allows companies to demonstrate, cryptographically and without intermediaries, that their reserves exist, are intact, and are unencumbered. No bank statements. No opaque custodial claims. Just data, on-chain.
That’s a radical shift—and it’s one that Bitcoin treasury companies are uniquely positioned to take advantage of. In doing so, they can reduce audit complexity, strengthen shareholder communication, and align their internal capital practices with the trustless architecture of the asset they’re holding.
And it’s already happening. Metaplanet, Premiere Member of Bitcoin For Corporations, publicly discloses its BTC reserve addresses and transaction history. Anyone in the world—including shareholders, analysts, and regulators—can independently verify the existence and movement of their treasury. That’s not just compliance. That’s Bitcoin, applied. View the snapshot of Metaplanet’s proof of reserves dashboard below.

Public Companies Face the Greatest Responsibility
Public companies don’t operate in a vacuum. Their disclosures shape market perception, influence investor behavior, and—especially when Bitcoin is involved—serve as a proxy for the maturity of the asset class itself.
When a publicly traded company holds Bitcoin but offers no visibility into how that Bitcoin is held or verified, it exposes itself to multiple levels of risk: legal, reputational, operational, and strategic. It undermines trust at the very moment it claims to be embracing a trustless system.
More importantly, public companies send signals. Whether they like it or not, they become de facto representatives of the Bitcoin strategy they’ve adopted. Their behavior becomes part of the playbook for others considering similar moves.
That’s why the responsibility is higher. Transparency isn’t optional for companies who lead with Bitcoin. It’s a duty. And companies that choose opacity not only take on unnecessary risk—they weaken the credibility of the entire movement.e.
What Proof of Reserves Should Actually Include
For Proof of Reserves to have real integrity, it must go beyond vague references to “custody partners” or internal assurance statements. The key is verifiability—independent, data-driven, and actionable by any shareholder or auditor.
At a minimum, Bitcoin treasury companies should provide:
- Custody model clarity: Is the company using self-custody, shared multisig, or third-party solutions? Who controls the keys, and under what governance?
- On-chain transparency: Whether through view-only wallet addresses or cryptographic attestations (like Merkle tree proofs), companies must make it possible to verify balances against public disclosures.
- Encumbrance disclosure: Reserves that are pledged, lent out, or locked in yield strategies should be disclosed clearly, with timelines and risk parameters attached.
- Routine updates: Proof should be refreshed regularly—not once per year in an audit footnote, but as part of ongoing financial communication.
- Reconciliation framework: Companies should explain how on-chain data maps to reported BTC NAV in filings or investor materials.
For boards and CFOs, this doesn’t need to introduce operational risk. Tools already exist—xpub view-only wallets, custody APIs, third-party validators—to provide assurance without compromising security. The obstacle isn’t capability. It’s willingness.
Setting the Industry Benchmark: Where Bitcoin Treasury Companies Must Lead
Bitcoin treasury companies are not just financial outliers—they are structural pioneers. Their decision to hold BTC signals not only a belief in long-term value, but a rejection of legacy capital inefficiency. That’s why they must also lead on standards of integrity.
By adopting PoR voluntarily and early, companies can position themselves as trustworthy, sophisticated, and future-ready. This will matter more as institutional capital rotates into Bitcoin, as index inclusion expands, and as regulators begin asking sharper questions about crypto asset disclosures on balance sheets.
PoR isn’t just a way to comply with future standards—it’s a way to shape them. The companies that lead now will not only avoid future scrutiny—they’ll attract capital from allocators who are seeking transparency but don’t yet know where to find it.
At BFC, we believe the market rewards clarity. Bitcoin treasury companies have a chance to bake transparency into their structure, not as an afterthought, but as a strategic differentiator.
Shareholders Must Demand It
Proof of Reserves isn’t just a company initiative—it’s a shareholder obligation. When a public company holds Bitcoin on its balance sheet, it is acting as a fiduciary for shareholder capital denominated in one of the hardest, most transparent assets in history. To accept opacity in that context is to forfeit the very advantage Bitcoin offers.
If you’re an investor in a Bitcoin treasury company and you can’t verify the Bitcoin, you don’t own a monetary reserve—you own a narrative. You’re trusting that someone else is telling the truth, rather than requiring the proof Bitcoin makes possible.
That’s not aligned with the principles of sound capital stewardship.
Institutional allocators, activist shareholders, and governance professionals have a growing role to play here. Just as proxy advisors and investor coalitions have pushed for climate disclosures, board transparency, and ESG clarity in the past decade, it’s time to apply that same rigor to Bitcoin disclosures—especially for companies who claim to operate on a Bitcoin standard.
Demand direct answers:
- Can we verify the holdings on-chain?
- Are reserves fully collateralized and unencumbered?
- Has manageme
-
 @ 90c656ff:9383fd4e
2025-05-20 09:06:27
@ 90c656ff:9383fd4e
2025-05-20 09:06:27Since its creation in 2008, Bitcoin has been seen as a direct challenge to the traditional banking system. Developed as a decentralized alternative to fiat money, Bitcoin offers a way to store and transfer value without relying on banks, governments, or other financial institutions. This characteristic has made it a symbol of resistance against a financial system that, over time, has been marked by crises, manipulation, and restrictions imposed on citizens.
The 2008 financial crisis and the birth of Bitcoin
Bitcoin emerged in response to the 2008 financial crisis—a collapse that exposed the flaws of the global banking system. Central banks printed massive amounts of money to bail out irresponsible financial institutions, while millions of people lost their homes, savings, and jobs. In this context, Bitcoin was created as an alternative financial system, where no central authority could manipulate the economy for its own benefit.
In the first block of the Bitcoin blockchain or timechain, Satoshi Nakamoto included the following message:
“The Times 03/Jan/2009 Chancellor on brink of second bailout for banks.”
This phrase, taken from a newspaper headline of the time, symbolizes Bitcoin’s intent to offer a financial system beyond the control of banks and governments.
- Key reasons why Bitcoin resists the banking system
01 - Decentralization: Unlike money issued by central banks, Bitcoin cannot be created or controlled by any single entity. The network of users validates transactions transparently and independently.
02 - Limited Supply: While central banks can print money without limit—causing inflation and currency devaluation—Bitcoin has a fixed supply of 21 million units, making it resistant to artificial depreciation.
03 - Censorship Resistance: Banks can freeze accounts and block transactions at any time. With Bitcoin, anyone can send and receive funds without needing permission from third parties.
04 - Self-Custody: Instead of entrusting funds to a bank, Bitcoin users can store their own coins without the risk of account freezes or bank failures.
- Conflict between banks and Bitcoin
01 - Media Attacks: Large financial institutions often label Bitcoin as risky, volatile, or useless, attempting to discourage its adoption.
02 - Regulation and Crackdowns: Some governments, influenced by the banking sector, have implemented restrictions on Bitcoin usage, making it harder to buy and sell.
03 - Creation of Centralized Alternatives: Many central banks are developing digital currencies (CBDCs) that maintain control over digital money but do not offer Bitcoin’s freedom and decentralization.
In summary, Bitcoin is not just a digital currency—it is a movement of resistance against a financial system that has repeatedly failed to protect ordinary citizens. By offering a decentralized, transparent, and censorship-resistant alternative, Bitcoin represents financial freedom and challenges the banking monopoly over money. As long as the traditional banking system continues to impose restrictions and control the flow of capital, Bitcoin will remain a symbol of independence and financial sovereignty.
Thank you very much for reading this far. I hope everything is well with you, and sending a big hug from your favorite Bitcoiner maximalist from Madeira. Long live freedom!
-
 @ 5188521b:008eb518
2025-05-20 08:33:09
@ 5188521b:008eb518
2025-05-20 08:33:09This memo intends to brief the federated societies of the galaxy on the status of one specific emerging civilization that has increasingly been of interest to our members, and further, to recommend caution when traveling unannounced nearby their local planet.
External Memo #263 from the Emerging Civilizations Council (ECC)
As you are all aware, it is the intention of our federated societies to isolate any emerging civilization in order to allow them the freedom to evolve and innovate independent of any external knowledge or technology. The benefits of this are twofold. Firstly, if during their scientific exploration and development, they are able to reach our same conclusions about the fundamentals of the universe, then we receive additional independent confirmation of our existing knowledge base. Secondly, and of much greater interest, is that all of our most advanced zero-to-one technological innovations have originated from these isolated civilizations because they are permitted to solve problems without bias from more advanced societies.
In earlier times, some of our members practiced strategic infusions of knowledge into emerging civilizations that would be disguised as native discoveries in order to secretly accelerate their advancement. While this was effective in developing advanced and peaceful civilizations more quickly, it was observed that those societies rarely developed any meaningful new technologies. As we have since learned, once a bias is introduced into an emerging civilization, it is typically destined to only innovate around our existing knowledge base.
More dangerously, societies that become aware of more advanced galactic civilizations almost always become focused on extrasolar power projection. This is an extension of the local evolutionary pressures that led to their domination as the apex predator on their planet. Only after they access the virtually unlimited resources of the galaxy, and they have resolved their internal struggle over distribution of those resources, will they be granted full federation status and interspecies technology transfer can be permitted. Prior to this stage, technology transfer from advanced societies must be avoided, as it can destabilize their development and often leads to the destruction of our most precious galactic resource; independent, decentralized technological innovation.
The dominant intelligent species of the specific civilization that is the focus of this memo identify as “Humans” and collectively inhabit a planet they call “Earth.” The Humans of Earth have yet to discover any advanced technology that would be useful to our members at this time; however, based on a key recent milestone in their development, their status has been upgraded to that of “pre-federation,” making them the leading candidate for our next admission into the galactic federation. As such, it has been estimated that first contact with the Humans of Earth may be possible within the next 1-2 GmRs [1 Galactic micro-Rotation (GmR) equals approximately 200 Earth solar orbits and spans approximately 10 human generations].
Their recent promotion to pre-federation status is based on their discovery of inviolable absolute scarcity — a key event that was independently reached among all federation members and typically triggers exponential advancement within two to four local generations. As is the case on Earth, inviolable absolute scarcity is virtually always used to develop undiluted intraspecies communication of value (the so-called perfect money). This has shown to be critical for cooperation and advancement among planetary apex predators throughout our galaxy.
The Earth-based discovery centers around a simple massless ledger system that is secured by electric power projection and is rapidly being adopted among the Humans of Earth. As with most apex predators, human trust is extremely difficult to scale across their entire planetary population. However, the new Earth-based monetary system, which they have named “bitcoin,” is quickly gaining the trust of humans as it continues to prove its inviolability. As has been the case among all emerging civilizations since the formation of the ECC, scarcity alone, even absolute scarcity, has never been enough to trigger exponential technological growth. The source of absolute scarcity must also be inviolable, or it will never be sufficiently trusted among a population.
The new currency of Earth is in the process of proving its inviolability by surviving numerous attacks with no meaningful disruption. Notably, even those closest to its discovery attempted to violate the properties of Earth’s initial implementation of absolute scarcity but were unsuccessful. Today it continues to withstand external attacks by those who have the most to lose, as adoption of a true and fair economic communication threatens to expose the opposition’s less productive, less efficient ideas. This, of course, is the specific class that must be disintegrated in order to allow the Humans of Earth to innovate freely and unlock exponential advancement. This same scenario has played out in all of our ancient histories following the discovery of inviolable absolute scarcity.
Because bitcoin has only existed for approximately one half of one human generation, proofs of inviolability have only been apparent to those who are looking the closest into the implications of the new discovery. Unsurprisingly, the humans who are the most inadequately compensated by the previous monetary systems are the first to find the benefits of inviolable absolute scarcity.
The highly anticipated exponential advancement from the now pre-federation Humans of Earth has attracted the interest of many of our members. Note, that at this juncture, the galactic playbook permits members to approach a pre-federation civilization undetected in order to fairly attain small quantities of their local implementation of inviolable absolute scarcity. The purpose of this practice is to allow our members to obtain a compatible and trusted source of compensation to be used in exchange for the first valuable innovations of a pre-federation society in a way that avoids unnecessary exposure to our technology prior to its full federation status.
Fortunately, all members who have taken part in this practice have fairly participated in the securitization of the bitcoin network, contributing small amounts of energy to organize and record transactions onto its independent time-based ledger system called the “Timechain.” Fair participation is critical to establish trust upon first contact.
Further, our members have, thus far, successfully minimized their impact on the new monetary system of Earth. This is important to disguise our existence but will also help gain trust in the future as no member will be seen as having abused its privileged access to overwhelming amounts of energy and computational power. To that end, it is believed that none of our members have collected more than a single payment for their energy contributions; meaning that no member society has more than 50 out of the full supply of 21,000,000 bitcoin (this was originally the smallest attainable payment for this form of fair participation).
The ECC asks that you please continue exercising caution, keeping your contributions to the bitcoin network to an absolute minimum. As a reminder, even a single service payment (currently 6.25 out of the full supply of 21,000,000 bitcoin), will likely be sufficient compensation for any of their innovations following first contact. Once awarded full federation status, Humans of Earth will be permitted to act as a full trading partner and will be eligible for other means of value for value payment.
However, the purpose of this message is not simply to commend our members for following those aspects of the galactic playbook. All federated societies of the galaxy should also be aware that there have recently been an increasing number of atmospheric anomalies detected by the Humans of Earth. Many believe that these anomalies are primarily caused by the influx of near-earth TDEs following their upgrade to pre-federation status [Temporary Distortion Events (TDEs) are a byproduct of most means of galactic travel]. We are, therefore, requesting that all members voluntarily announce their travel coordinates to help ensure that any TDEs in the future are adequately dispersed in space-time to avoid detectable events on Earth.
Although it has been almost 50 GmRs since the last emerging civilization was upgraded to pre-federation status, it is imperative that we maintain the complete isolation of the Humans of Earth at this critical juncture. As stated, if the Humans of Earth begin to suspect the presence of an overwhelmingly advanced species, they are highly likely to skew their innovations towards violent technologies that could destabilize their society and disrupt their potential for future contributions.
Thank you for maintaining our core principles as we begin to prepare for the next member to be admitted into our peaceful, decentralized federation.
End wideband galactic transmission…
This story first appeared in Tales from the Timechain. Support our work and buy a copy here.
79% of the zaps from this story will be passed onto the author, Reed. 21 Futures requests 21% for operating costs.
@nostr:npub1xgyjasdztryl9sg6nfdm2wcj0j3qjs03sq7a0an32pg0lr5l6yaqxhgu7s is a Christian, father of three, husband, bitcoiner, mechanical engineer in the nuclear power industry, science nerd and is passionate about the pursuit of truth. Reed also organized the Western Mass Bitcoin Meetup and is active on bitcoin twitter (@FreedomMoney21) and Nostr (nostrplebs.com/s/reed)
-
 @ 04ce30c2:59ea576a
2025-05-20 04:19:25
@ 04ce30c2:59ea576a
2025-05-20 04:19:25Em uma sociedade verdadeiramente livre, o indivíduo tem o direito de escolher como guardar e transferir valor. Isso inclui a liberdade de escolher qual moeda usar, sem coerção, monopólios ou imposições estatais. A concorrência entre moedas permite que as melhores propriedades monetárias prevaleçam de forma natural e voluntária.
Moeda imposta é controle
Quando uma única moeda é forçada por lei, seja por decreto estatal ou por exigências institucionais, o usuário perde a soberania sobre seu próprio patrimônio. Isso abre espaço para inflação arbitrária, bloqueios de transações, congelamento de fundos e vigilância massiva.
Concorrência monetária é essencial
A liberdade monetária implica a coexistência de várias moedas competindo entre si. Cada uma traz suas características e vantagens específicas. A escolha deve estar nas mãos do usuário, não em autoridades centralizadas.
A melhor moeda tende a se tornar o padrão
No longo prazo, a moeda com melhores propriedades monetárias, como previsibilidade, descentralização, auditabilidade e liquidez, tende a ser adotada como padrão de referência para precificação, poupança e comércio global.
O Bitcoin é a moeda mais forte nesse sentido. Mas isso não impede que outras moedas coexistam como ferramentas complementares em contextos específicos.
Conversão é liberdade
Se o usuário quiser por exemplo mais privacidade ao comprar um café ou pagar uma conta, ele pode facilmente trocar seus bitcoins por monero e usá-los conforme sua necessidade. A possibilidade de trocar entre moedas é parte essencial da liberdade financeira.
Uma sociedade livre permite a escolha. O padrão monetário deve emergir do consenso do mercado, não de imposições. Que o Bitcoin se torne o padrão não por decreto, mas por mérito. E que outras moedas existam para servir à liberdade individual em toda sua complexidade.
-
 @ 472f440f:5669301e
2025-05-20 02:00:54
@ 472f440f:5669301e
2025-05-20 02:00:54Marty's Bent
https://www.youtube.com/watch?v=p0Sj1sG05VQ
Here's a great presentation from our good friend nostr:nprofile1qyx8wumn8ghj7cnjvghxjmcpp4mhxue69uhkummn9ekx7mqqyz2hj3zg2g3pqwxuhg69zgjhke4pcmjmmdpnndnefqndgqjt8exwj6ee8v7 , President of The Nakamoto Institute titled Hodl for Good. He gave it earlier this year at the BitBlockBoom Conference, and I think it's something everyone reading this should take 25 minutes to watch. Especially if you find yourself wondering whether or not it's a good idea to spend bitcoin at any given point in time. Michael gives an incredible Austrian Economics 101 lesson on the importance of lowering one's time preference and fully understanding the importance of hodling bitcoin. For the uninitiated, it may seem that the hodl meme is nothing more than a call to hoard bitcoins in hopes of getting rich eventually. However, as Michael points out, there's layers to the hodl meme and the good that hodling can bring individuals and the economy overall.
The first thing one needs to do to better understand the hodl meme is to completely flip the framing that is typically thrust on bitcoiners who encourage others to hodl. Instead of ceding that hodling is a greedy or selfish action, remind people that hodling, or better known as saving, is the foundation of capital formation, from which all productive and efficient economic activity stems. Number go up technology is great and it really matters. It matters because it enables anybody leveraging that technology to accumulate capital that can then be allocated toward productive endeavors that bring value to the individual who creates them and the individual who buys them.
When one internalizes this, it enables them to turn to personal praxis and focus on minimizing present consumption while thinking of ways to maximize long-term value creation. Live below your means, stack sats, and use the time that you're buying to think about things that you want in the future. By lowering your time preference and saving in a harder money you will have the luxury of demanding higher quality goods in the future. Another way of saying this is that you will be able to reshape production by voting with your sats. Initially when you hold them off the market by saving them - signaling that the market doesn't have goods worthy of your sats - and ultimately by redeploying them into the market when you find higher quality goods that meet the standards desire.
The first part of this equation is extremely important because it sends a signal to producers that they need to increase the quality of their work. As more and more individuals decide to use bitcoin as their savings technology, the signal gets stronger. And over many cycles we should begin to see low quality cheap goods exit the market in favor of higher quality goods that provide more value and lasts longer and, therefore, make it easier for an individual to depart with their hard-earned and hard-saved sats. This is only but one aspect that Michael tries to imbue throughout his presentation.
The other is the ability to buy yourself leisure time when you lower your time preference and save more than you spend. When your savings hit a critical tipping point that gives you the luxury to sit back and experience true leisure, which Michael explains is not idleness, but the contemplative space to study, create art, refine taste, and to find what "better goods" actually are. Those who can experience true leisure while reaping the benefits of saving in a hard asset that is increasing in purchasing power significantly over the long term are those who build truly great things. Things that outlast those who build them. Great art, great monuments, great institutions were all built by men who were afforded the time to experience leisure. Partly because they were leveraging hard money as their savings and the place they stored the profits reaped from their entrepreneurial endeavors.
If you squint and look into the future a couple of decades, it isn't hard to see a reality like this manifesting. As more people begin to save in Bitcoin, the forces of supply and demand will continue to come into play. There will only ever be 21 million bitcoin, there are around 8 billion people on this planet, and as more of those 8 billion individuals decide that bitcoin is the best savings vehicle, the price of bitcoin will rise.
When the price of bitcoin rises, it makes all other goods cheaper in bitcoin terms and, again, expands the entrepreneurial opportunity. The best part about this feedback loop is that even non-holders of bitcoin benefit through higher real wages and faster tech diffusion. The individuals and business owners who decide to hodl bitcoin will bring these benefits to the world whether you decide to use bitcoin or not.
This is why it is virtuous to hodl bitcoin. The potential for good things to manifest throughout the world increase when more individuals decide to hodl bitcoin. And as Michael very eloquently points out, this does not mean that people will not spend their bitcoin. It simply means that they have standards for the things that they will spend their bitcoin on. And those standards are higher than most who are fully engrossed in the high velocity trash economy have today.
In my opinion, one of those higher causes worthy of a sats donation is nostr:nprofile1qyfhwumn8ghj7enjv4jhyetvv9uju7re0gq3uamnwvaz7tmfdemxjmrvv9nk2tt0w468v6tvd3skwefwvdhk6qpqwzc9lz2f40azl98shkjewx3pywg5e5alwqxg09ew2mdyeey0c2rqcfecft . Consider donating so they can preserve and disseminate vital information about bitcoin and its foundations.
The Shell Game: How Health Narratives May Distract from Vaccine Risks
In our recent podcast, Dr. Jack Kruse presented a concerning theory about public health messaging. He argues that figures like Casey and Callie Means are promoting food and exercise narratives as a deliberate distraction from urgent vaccine issues. While no one disputes healthy eating matters, Dr. Kruse insists that focusing on "Froot Loops and Red Dye" diverts attention from what he sees as immediate dangers of mRNA vaccines, particularly for children.
"It's gonna take you 50 years to die from processed food. But the messenger jab can drop you like Damar Hamlin." - Dr Jack Kruse
Dr. Kruse emphasized that approximately 25,000 children per month are still receiving COVID vaccines despite concerns, with 3 million doses administered since Trump's election. This "shell game," as he describes it, allows vaccines to remain on childhood schedules while public attention fixates on less immediate health threats. As host, I believe this pattern deserves our heightened scrutiny given the potential stakes for our children's wellbeing.
Check out the full podcast here for more on Big Pharma's alleged bioweapons program, the "Time Bank Account" concept, and how Bitcoin principles apply to health sovereignty.
Headlines of the Day
Aussie Judge: Bitcoin is Money, Possibly CGT-Exempt - via X
JPMorgan to Let Clients Buy Bitcoin Without Direct Custody - via X
Get our new STACK SATS hat - via tftcmerch.io
Mubadala Acquires 384,239 sats | $408.50M Stake in BlackRock Bitcoin ETF - via X
Take the First Step Off the Exchange
Bitkey is an easy, secure way to move your Bitcoin into self-custody. With simple setup and built-in recovery, it’s the perfect starting point for getting your coins off centralized platforms and into cold storage—no complexity, no middlemen.
Take control. Start with Bitkey.
Use the promo code “TFTC20” during checkout for 20% off
Ten31, the largest bitcoin-focused investor, has deployed 158,469 sats | $150.00M across 30+ companies through three funds. I am a Managing Partner at Ten31 and am very proud of the work we are doing. Learn more at ten31.vc/invest.
Final thought...
I've been walking from my house around Town Lake in Austin in the mornings and taking calls on the walk. Big fan of a walking call.
Get this newsletter sent to your inbox daily: https://www.tftc.io/bitcoin-brief/
Subscribe to our YouTube channels and follow us on Nostr and X:
-
 @ 6e0ea5d6:0327f353
2025-05-20 01:35:20
@ 6e0ea5d6:0327f353
2025-05-20 01:35:20**Ascolta bene! ** A man's sentimental longing, though often disguised in noble language and imagination, is a sickness—not a virtue.
It begins as a slight inclination toward tenderness, cloaked in sweetness. Then it reveals itself as a masked addiction: a constant need to be seen by a woman, validated by her, and reciprocated—as if someone else's affection were the only anchor preventing the shipwreck of his emotions.
The man who understands the weight of leadership seeks no applause, no gratitude, not even romantic love. He knows that his role is not theatrical but structural. He is not measured by the emotion he evokes, but by the stability he ensures. Being a true man is not ornamental. He is not a decorative symbol in the family frame.
We live in an era where male roles have been distorted by an overindulgence in emotion. The man stopped guiding and began asking for direction. His firmness was exchanged for softness, his decisiveness for hesitation. Trying to please, many have given up authority. Trying to love, they’ve begun to bow. A man who begs for validation within his own home is not a leader—he is a guest. And when the patriarch has to ask for a seat at the table he should preside over and sustain, something has already been irreversibly inverted.
Unexamined longing turns into pleading. And all begging is the antechamber of humiliation. A man who never learned to cultivate dignified solitude will inevitably fall to his knees in desperation. And then, he yields. Yields to mediocre presence, to shallow affection, to constant disrespect. He smiles while he bleeds, praises the one who despises him, accepts crumbs and pretends it’s a banquet. All of it, cazzo... just to avoid the horror of being alone.
Davvero, amico mio, for the men who beg for romance, only the consolation of being remembered will remain—not with respect, but with pity and disgust.
The modern world feeds the fragile with illusions, but reality spits them out. Sentimental longing is now celebrated as sensitivity. But every man who nurtures it as an excuse will, sooner or later, pay for it with his dignity.
Thank you for reading, my friend!
If this message resonated with you, consider leaving your "🥃" as a token of appreciation.
A toast to our family!
-
 @ 502ab02a:a2860397
2025-05-20 01:22:31
@ 502ab02a:a2860397
2025-05-20 01:22:31พอพูดถึงบริษัทอย่าง Formo ที่ทำชีสโดยไม่ใช้วัวเลย คนส่วนใหญ่จะนึกถึงคำว่า “นวัตกรรม” “ยั่งยืน” “ลดโลกร้อน” กันเป็นด่านแรก แต่พอเฮียมองทะลุม่านควันพวกนี้ไป จะเห็นทุนรายใหญ่ที่หนุนหลังอยู่ ซึ่งหลายเจ้าก็ไม่ใช่ผู้พิทักษ์โลก แต่เป็นผู้เล่นตัวจี๊ดในอุตสาหกรรมอาหารโลกมายาวนาน
หนึ่งในนั้นคือบริษัทจากเกาหลีใต้ชื่อ CJ CheilJedang ซึ่งอาจฟังดูไกลตัว แต่จริงๆ แล้ว เฮียว่าชื่อนี้โผล่ตามซองอาหารสำเร็จรูปในครัวคนไทยหลายบ้านโดยไม่รู้ตัว
ถ้าจะเข้าใจ Formo ให้ถึงแก่น เราต้องมองไปถึงทุนที่ “ใส่เงิน” และ “ใส่จุดยืน” ลงไปในบริษัทนั้น และหนึ่งในผู้ถือหุ้นรายสำคัญก็คือ CJ CheilJedang บริษัทเกาหลีใต้ที่ก่อตั้งมาตั้งแต่ปี 1953 โดยเริ่มจากการเป็นโรงงานผลิตน้ำตาล จากนั้นก็กินรวบแทบทุกวงจรอาหารของเกาหลี
โปรไฟล์ CJ แค่เห็นภาพรวมก็ขนลุกแล้วครับ ลูกพี่เราแข็งแกร่งขนาดไหน - เป็นเจ้าของแบรนด์ Bibigo ที่เราอาจจะคุ้นในสินค้า กิมจิ และ CJ Foods ที่มีขายทั่วโลก -เป็นผู้ผลิต กรดอะมิโน รายใหญ่ของโลก เช่น ไลซีน, ทรีโอนีน, ทริปโตแฟน ที่ใช้เป็นวัตถุดิบในอาหารสัตว์ แต่ตอนนี้หลายบริษัทเอาไปใส่ใน Plant-based food แล้วเคลมว่าเป็นโปรตีนสมบูรณ์ -เป็นเจ้าของโรงงานผลิต แบคทีเรียสายพันธุ์พิเศษ สำหรับการหมักหลายประเภท -ขึ้นชื่อเรื่อง bioscience โดยเฉพาะ precision fermentation ซึ่งเป็นเทคโนโลยีเดียวกับที่ Formo ใช้ผลิตเคซีน (โปรตีนในนมวัว)
แปลว่า CJ ไม่ได้มาลงทุนใน Formo แบบ “หวังผลกำไรเฉยๆ” แต่เขามองเห็น “อนาคตใหม่ของอาหาร” ที่ตัวเองจะเป็นเจ้าของต้นน้ำยันปลายน้ำ
คำถามก็คือเบื้องลึกการลงทุนใน Formo ใครได้อะไร? Formo ปิดรอบระดมทุน Series A ได้ประมาณ 50 ล้านดอลลาร์สหรัฐ เมื่อปี 2021 โดยมีนักลงทุนหลายเจ้า เช่น EQT Ventures, Elevat3 Capital, Atomico แต่ CJ CheilJedang ก็เป็นหนึ่งในผู้ลงทุนเชิงกลยุทธ์ (strategic investor) ที่เข้ามาแบบไม่ใช่แค่ลงเงิน แต่เอา เทคโนโลยี + เครือข่ายโรงงาน + ซัพพลายเชนระดับโลก มาเสริมให้ Formo ขยายได้เร็วขึ้น
การจับมือกันครั้งนี้มีนัยยะสำคัญครับ -Formo ได้ เทคโนโลยีหมักจุลินทรีย์ (ที่ CJ ถนัดมาก) และช่องทางกระจายสินค้าในเอเชีย -CJ ได้ ถือหุ้นในบริษัทที่กำลังจะเปลี่ยนภาพ “ผลิตภัณฑ์จากนม” ให้กลายเป็นสิ่งที่ไม่ต้องมีสัตว์อีกต่อไป ซึ่งจะเป็นกลยุทธ์สำคัญในการสร้างแบรนด์อาหารแห่งอนาคต ที่นมจะต้องมาจากโรงงานผลิตเท่านั้นจึงจะมีคุณสมบัติที่ดีทั้งสารอาหารและความสะอาด
CJ เองก็เคยประกาศต่อสื่อว่า อยากเป็น “Global Lifestyle Company” ซึ่งฟังดูเบาๆ แต่จริงๆ คือแผนใหญ่ในการ เปลี่ยนวิธีการกินของคนทั้งโลกได้เลยเช่นกัน -จาก “อาหารจริง” ไปเป็น “อาหารสังเคราะห์” (synthetic food) -จาก “ฟาร์มสัตว์” ไปเป็น “ถังหมักจุลินทรีย์” -จาก “ความหลากหลายตามธรรมชาติ” ไปเป็น “สูตรกลาง” ที่ควบคุมได้ในระดับโมเลกุล
การหนุนหลัง Formo จึงไม่ใช่เรื่องบังเอิญ แต่เป็นอีกหนึ่งหมากในกระดานใหญ่ที่ CJ วางไว้ เพื่อเป็นเจ้าของอาหารอนาคตแบบไม่ต้องเลี้ยงหมู ไก่ วัว แต่ครองเทคโนโลยีแทน
คำถามคือแล้วผู้บริโภคจะรู้ทันไหมว่า เบื้องหลังชีสที่ไม่มีวัว อาจมี “ทุนที่อยากครองโลกอาหาร” คำที่เคลมว่า “ยั่งยืน” อาจสร้างระบบอาหารใหม่ที่ยิ่งห่างจากธรรมชาติเข้าไปทุกที
คนที่เคย “กลัวสารเคมี” ในอาหารแปรรูป กลับกลืนผลิตภัณฑ์จากห้องแล็บ โดยคิดว่า “มันคือความสะอาดและอนาคต” #pirateketo #กูต้องรู้มั๊ย #ม้วนหางสิลูก #siamstr
-
 @ fd06f542:8d6d54cd
2025-05-20 01:18:45
@ fd06f542:8d6d54cd
2025-05-20 01:18:45🧱 NostrTrust Initial Trust Score List (V0.1)
This list defines the initial trust scores (T Score) for key members of the Nostr community based on their contributions, reputation, and role in the ecosystem. The goal is to seed a decentralized trust system that encourages quality interactions and authentic contributions.
> ⚠️ Note: This is an draft version.
✅ Initial T Score Allocation Rules
| User Type | Initial T Score Range | Criteria | |-----------|------------------------|----------| | Founder | 10,000 | Creator of the Nostr protocol | | Core Developers | 5,000 - 8,000 | Major contributors to core codebase, clients, or infrastructure | | Active Contributors | 1,000 - 4,000 | Recognized long-term contributors to content, tools, or community |
👤 Initial Trust Score Table
| Name / Alias | npub | Initial T Score | Justification | |--------------|------|------------------|----------------| | fiatjaf | npub180cvv07tjdrrgpa0j7j7tmnyl2yr6yr7l8j4s3evf6u64th6gkwsyjh6w6 | 10,000 | Creator of the Nostr protocol | |Jack|npub1sg6plzptd64u62a878hep2kev88swjh3tw00gjsfl8f237lmu63q0uf63m|9,000|| | jb55 | npub1xtscya34g58tk0z605fvr788k263gsu6cy9x0mhnm87echrgufzsevkk5s | 7,000 | Developer of tools, relays, and early Nostr integrations,made damus | |Alex Gleason | npub1q3sle0kvfsehgsuexttt3ugjd8xdklxfwwkh559wxckmzddywnws6cd26p | 7,000 || |PABLOF7z|npub1l2vyh47mk2p0qlsku7hg0vn29faehy9hy34ygaclpn66ukqp3afqutajft|7,000|NDK| |DASHU|npub19yeqjawls407xjnmgkk6yss7936pcd7qzd5srlj8wye6j8433vrsjazqwk|4,000|Nostrmo | |Moss|npub129z0az8lgffuvsywazww07hx75qas3veh3dazsq56z8y39v86khs2uy5gm|4,000| freerse.com| |w|npub10td4yrp6cl9kmjp9x5yd7r8pm96a5j07lk5mtj2kw39qf8frpt8qm9x2wl|4,000| 0xchat | |Cody Tseng|npub1syjmjy0dp62dhccq3g97fr87tngvpvzey08llyt6ul58m2zqpzps9wf6wl|4,000| jumble.social| |nostr_cn_dev|npub1l5r02s4udsr28xypsyx7j9lxchf80ha4z6y6269d0da9frtd2nxsvum9jm|1,000|nostrbook.com,NostrTrust,nostrbridge| |hzrd149|npub1ye5ptcxfyyxl5vjvdjar2ua3f0hynkjzpx552mu5snj3qmx5pzjscpknpr|6,000|blossom,nostrudel| ||||| ||||| ||||| ||||| |||||
-
 @ 9be6a199:6e133301
2025-05-19 23:11:35
@ 9be6a199:6e133301
2025-05-19 23:11:35this is the content
this is an update
-
 @ 9be6a199:6e133301
2025-05-19 22:39:28
@ 9be6a199:6e133301
2025-05-19 22:39:28sdsdsd
-
 @ a93d7cd3:ae5ce5dd
2025-05-20 10:16:55
@ a93d7cd3:ae5ce5dd
2025-05-20 10:16:55Test Nostr
-
 @ 4ba8e86d:89d32de4
2025-05-19 22:33:46
@ 4ba8e86d:89d32de4
2025-05-19 22:33:46O que é Cwtch? Cwtch (/kʊtʃ/ - uma palavra galesa que pode ser traduzida aproximadamente como “um abraço que cria um lugar seguro”) é um protocolo de mensagens multipartidário descentralizado, que preserva a privacidade, que pode ser usado para construir aplicativos resistentes a metadados.
Como posso pronunciar Cwtch? Como "kutch", para rimar com "butch".
Descentralizado e Aberto : Não existe “serviço Cwtch” ou “rede Cwtch”. Os participantes do Cwtch podem hospedar seus próprios espaços seguros ou emprestar sua infraestrutura para outras pessoas que buscam um espaço seguro. O protocolo Cwtch é aberto e qualquer pessoa é livre para criar bots, serviços e interfaces de usuário e integrar e interagir com o Cwtch.
Preservação de privacidade : toda a comunicação no Cwtch é criptografada de ponta a ponta e ocorre nos serviços cebola Tor v3.
Resistente a metadados : O Cwtch foi projetado de forma que nenhuma informação seja trocada ou disponibilizada a ninguém sem seu consentimento explícito, incluindo mensagens durante a transmissão e metadados de protocolo
Uma breve história do bate-papo resistente a metadados Nos últimos anos, a conscientização pública sobre a necessidade e os benefícios das soluções criptografadas de ponta a ponta aumentou com aplicativos como Signal , Whatsapp e Wire. que agora fornecem aos usuários comunicações seguras.
No entanto, essas ferramentas exigem vários níveis de exposição de metadados para funcionar, e muitos desses metadados podem ser usados para obter detalhes sobre como e por que uma pessoa está usando uma ferramenta para se comunicar.
Uma ferramenta que buscou reduzir metadados é o Ricochet lançado pela primeira vez em 2014. Ricochet usou os serviços cebola Tor v2 para fornecer comunicação criptografada segura de ponta a ponta e para proteger os metadados das comunicações.
Não havia servidores centralizados que auxiliassem no roteamento das conversas do Ricochet. Ninguém além das partes envolvidas em uma conversa poderia saber que tal conversa está ocorrendo.
Ricochet tinha limitações; não havia suporte para vários dispositivos, nem existe um mecanismo para suportar a comunicação em grupo ou para um usuário enviar mensagens enquanto um contato está offline.
Isto tornou a adoção do Ricochet uma proposta difícil; mesmo aqueles em ambientes que seriam melhor atendidos pela resistência aos metadados, sem saber que ela existe.
Além disso, qualquer solução para comunicação descentralizada e resistente a metadados enfrenta problemas fundamentais quando se trata de eficiência, privacidade e segurança de grupo conforme definido pelo consenso e consistência da transcrição.
Alternativas modernas ao Ricochet incluem Briar , Zbay e Ricochet Refresh - cada ferramenta procura otimizar para um conjunto diferente de compensações, por exemplo, Briar procura permitir que as pessoas se comuniquem mesmo quando a infraestrutura de rede subjacente está inoperante, ao mesmo tempo que fornece resistência à vigilância de metadados.
O projeto Cwtch começou em 2017 como um protocolo de extensão para Ricochet, fornecendo conversas em grupo por meio de servidores não confiáveis, com o objetivo de permitir aplicativos descentralizados e resistentes a metadados como listas compartilhadas e quadros de avisos.
Uma versão alfa do Cwtch foi lançada em fevereiro de 2019 e, desde então, a equipe do Cwtch dirigida pela OPEN PRIVACY RESEARCH SOCIETY conduziu pesquisa e desenvolvimento em cwtch e nos protocolos, bibliotecas e espaços de problemas subjacentes.
Modelo de Risco.
Sabe-se que os metadados de comunicações são explorados por vários adversários para minar a segurança dos sistemas, para rastrear vítimas e para realizar análises de redes sociais em grande escala para alimentar a vigilância em massa. As ferramentas resistentes a metadados estão em sua infância e faltam pesquisas sobre a construção e a experiência do usuário de tais ferramentas.
https://nostrcheck.me/media/public/nostrcheck.me_9475702740746681051707662826.webp
O Cwtch foi originalmente concebido como uma extensão do protocolo Ricochet resistente a metadados para suportar comunicações assíncronas de grupos multiponto por meio do uso de infraestrutura anônima, descartável e não confiável.
Desde então, o Cwtch evoluiu para um protocolo próprio. Esta seção descreverá os vários riscos conhecidos que o Cwtch tenta mitigar e será fortemente referenciado no restante do documento ao discutir os vários subcomponentes da Arquitetura Cwtch.
Modelo de ameaça.
É importante identificar e compreender que os metadados são omnipresentes nos protocolos de comunicação; é de facto necessário que tais protocolos funcionem de forma eficiente e em escala. No entanto, as informações que são úteis para facilitar peers e servidores também são altamente relevantes para adversários que desejam explorar tais informações.
Para a definição do nosso problema, assumiremos que o conteúdo de uma comunicação é criptografado de tal forma que um adversário é praticamente incapaz de quebrá-lo veja tapir e cwtch para detalhes sobre a criptografia que usamos, e como tal nos concentraremos em o contexto para os metadados de comunicação.
Procuramos proteger os seguintes contextos de comunicação:
• Quem está envolvido em uma comunicação? Pode ser possível identificar pessoas ou simplesmente identificadores de dispositivos ou redes. Por exemplo, “esta comunicação envolve Alice, uma jornalista, e Bob, um funcionário público”.
• Onde estão os participantes da conversa? Por exemplo, “durante esta comunicação, Alice estava na França e Bob estava no Canadá”.
• Quando ocorreu uma conversa? O momento e a duração da comunicação podem revelar muito sobre a natureza de uma chamada, por exemplo, “Bob, um funcionário público, conversou com Alice ao telefone por uma hora ontem à noite. Esta é a primeira vez que eles se comunicam.” *Como a conversa foi mediada? O fato de uma conversa ter ocorrido por meio de um e-mail criptografado ou não criptografado pode fornecer informações úteis. Por exemplo, “Alice enviou um e-mail criptografado para Bob ontem, enquanto eles normalmente enviam apenas e-mails de texto simples um para o outro”.
• Sobre o que é a conversa? Mesmo que o conteúdo da comunicação seja criptografado, às vezes é possível derivar um contexto provável de uma conversa sem saber exatamente o que é dito, por exemplo, “uma pessoa ligou para uma pizzaria na hora do jantar” ou “alguém ligou para um número conhecido de linha direta de suicídio na hora do jantar”. 3 horas da manhã."
Além das conversas individuais, também procuramos defender-nos contra ataques de correlação de contexto, através dos quais múltiplas conversas são analisadas para obter informações de nível superior:
• Relacionamentos: Descobrir relações sociais entre um par de entidades analisando a frequência e a duração de suas comunicações durante um período de tempo. Por exemplo, Carol e Eve ligam uma para a outra todos os dias durante várias horas seguidas.
• Cliques: Descobrir relações sociais entre um grupo de entidades que interagem entre si. Por exemplo, Alice, Bob e Eva se comunicam entre si.
• Grupos vagamente conectados e indivíduos-ponte: descobrir grupos que se comunicam entre si através de intermediários, analisando cadeias de comunicação (por exemplo, toda vez que Alice fala com Bob, ela fala com Carol quase imediatamente depois; Bob e Carol nunca se comunicam).
• Padrão de Vida: Descobrir quais comunicações são cíclicas e previsíveis. Por exemplo, Alice liga para Eve toda segunda-feira à noite por cerca de uma hora. Ataques Ativos
Ataques de deturpação.
O Cwtch não fornece registro global de nomes de exibição e, como tal, as pessoas que usam o Cwtch são mais vulneráveis a ataques baseados em declarações falsas, ou seja, pessoas que fingem ser outras pessoas:
O fluxo básico de um desses ataques é o seguinte, embora também existam outros fluxos:
•Alice tem um amigo chamado Bob e outro chamado Eve
• Eve descobre que Alice tem um amigo chamado Bob
• Eve cria milhares de novas contas para encontrar uma que tenha uma imagem/chave pública semelhante à de Bob (não será idêntica, mas pode enganar alguém por alguns minutos)
• Eve chama essa nova conta de "Eve New Account" e adiciona Alice como amiga.
• Eve então muda seu nome em "Eve New Account" para "Bob"
• Alice envia mensagens destinadas a "Bob" para a conta falsa de Bob de Eve Como os ataques de declarações falsas são inerentemente uma questão de confiança e verificação, a única maneira absoluta de evitá-los é os usuários validarem absolutamente a chave pública. Obviamente, isso não é o ideal e, em muitos casos, simplesmente não acontecerá .
Como tal, pretendemos fornecer algumas dicas de experiência do usuário na interface do usuário para orientar as pessoas na tomada de decisões sobre confiar em contas e/ou distinguir contas que possam estar tentando se representar como outros usuários.
Uma nota sobre ataques físicos A Cwtch não considera ataques que exijam acesso físico (ou equivalente) à máquina do usuário como praticamente defensáveis. No entanto, no interesse de uma boa engenharia de segurança, ao longo deste documento ainda nos referiremos a ataques ou condições que exigem tal privilégio e indicaremos onde quaisquer mitigações que implementámos falharão.
Um perfil Cwtch.
Os usuários podem criar um ou mais perfis Cwtch. Cada perfil gera um par de chaves ed25519 aleatório compatível com Tor.
Além do material criptográfico, um perfil também contém uma lista de Contatos (outras chaves públicas do perfil Cwtch + dados associados sobre esse perfil, como apelido e (opcionalmente) mensagens históricas), uma lista de Grupos (contendo o material criptográfico do grupo, além de outros dados associados, como apelido do grupo e mensagens históricas).
Conversões entre duas partes: ponto a ponto
https://nostrcheck.me/media/public/nostrcheck.me_2186338207587396891707662879.webp
Para que duas partes participem de uma conversa ponto a ponto, ambas devem estar on-line, mas apenas uma precisa estar acessível por meio do serviço Onion. Por uma questão de clareza, muitas vezes rotulamos uma parte como “ponto de entrada” (aquele que hospeda o serviço cebola) e a outra parte como “ponto de saída” (aquele que se conecta ao serviço cebola).
Após a conexão, ambas as partes adotam um protocolo de autenticação que:
• Afirma que cada parte tem acesso à chave privada associada à sua identidade pública.
• Gera uma chave de sessão efêmera usada para criptografar todas as comunicações futuras durante a sessão.
Esta troca (documentada com mais detalhes no protocolo de autenticação ) é negável offline , ou seja, é possível para qualquer parte falsificar transcrições desta troca de protocolo após o fato e, como tal - após o fato - é impossível provar definitivamente que a troca aconteceu de forma alguma.
Após o protocolo de autenticação, as duas partes podem trocar mensagens livremente.
Conversas em Grupo e Comunicação Ponto a Servidor
Ao iniciar uma conversa em grupo, é gerada uma chave aleatória para o grupo, conhecida como Group Key. Todas as comunicações do grupo são criptografadas usando esta chave. Além disso, o criador do grupo escolhe um servidor Cwtch para hospedar o grupo. Um convite é gerado, incluindo o Group Key, o servidor do grupo e a chave do grupo, para ser enviado aos potenciais membros.
Para enviar uma mensagem ao grupo, um perfil se conecta ao servidor do grupo e criptografa a mensagem usando a Group Key, gerando também uma assinatura sobre o Group ID, o servidor do grupo e a mensagem. Para receber mensagens do grupo, um perfil se conecta ao servidor e baixa as mensagens, tentando descriptografá-las usando a Group Key e verificando a assinatura.
Detalhamento do Ecossistema de Componentes
O Cwtch é composto por várias bibliotecas de componentes menores, cada uma desempenhando um papel específico. Algumas dessas bibliotecas incluem:
- abertoprivacidade/conectividade: Abstração de rede ACN, atualmente suportando apenas Tor.
- cwtch.im/tapir: Biblioteca para construção de aplicativos p2p em sistemas de comunicação anônimos.
- cwtch.im/cwtch: Biblioteca principal para implementação do protocolo/sistema Cwtch.
- cwtch.im/libcwtch-go: Fornece ligações C para Cwtch para uso em implementações de UI.
TAPIR: Uma Visão Detalhada
Projetado para substituir os antigos canais de ricochete baseados em protobuf, o Tapir fornece uma estrutura para a construção de aplicativos anônimos.
Está dividido em várias camadas:
• Identidade - Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um par.
• Conexões – O protocolo de rede bruto que conecta dois pares. Até agora, as conexões são definidas apenas através do Tor v3 Onion Services.
• Aplicativos - As diversas lógicas que permitem um determinado fluxo de informações em uma conexão. Os exemplos incluem transcrições criptográficas compartilhadas, autenticação, proteção contra spam e serviços baseados em tokens. Os aplicativos fornecem recursos que podem ser referenciados por outros aplicativos para determinar se um determinado peer tem a capacidade de usar um determinado aplicativo hospedado.
• Pilhas de aplicativos - Um mecanismo para conectar mais de um aplicativo, por exemplo, a autenticação depende de uma transcrição criptográfica compartilhada e o aplicativo peer cwtch principal é baseado no aplicativo de autenticação.
Identidade.
Um par de chaves ed25519, necessário para estabelecer um serviço cebola Tor v3 e usado para manter uma identidade criptográfica consistente para um peer.
InitializeIdentity - de um par de chaves conhecido e persistente:i,I
InitializeEphemeralIdentity - de um par de chaves aleatório: ie,Ie
Aplicativos de transcrição.
Inicializa uma transcrição criptográfica baseada em Merlin que pode ser usada como base de protocolos baseados em compromisso de nível superior
O aplicativo de transcrição entrará em pânico se um aplicativo tentar substituir uma transcrição existente por uma nova (aplicando a regra de que uma sessão é baseada em uma e apenas uma transcrição).
Merlin é uma construção de transcrição baseada em STROBE para provas de conhecimento zero. Ele automatiza a transformação Fiat-Shamir, para que, usando Merlin, protocolos não interativos possam ser implementados como se fossem interativos.
Isto é significativamente mais fácil e menos sujeito a erros do que realizar a transformação manualmente e, além disso, também fornece suporte natural para:
• protocolos multi-round com fases alternadas de commit e desafio;
• separação natural de domínios, garantindo que os desafios estejam vinculados às afirmações a serem provadas;
• enquadramento automático de mensagens, evitando codificação ambígua de dados de compromisso;
• e composição do protocolo, usando uma transcrição comum para vários protocolos.
Finalmente, o Merlin também fornece um gerador de números aleatórios baseado em transcrição como defesa profunda contra ataques de entropia ruim (como reutilização de nonce ou preconceito em muitas provas). Este RNG fornece aleatoriedade sintética derivada de toda a transcrição pública, bem como dos dados da testemunha do provador e uma entrada auxiliar de um RNG externo.
Conectividade Cwtch faz uso do Tor Onion Services (v3) para todas as comunicações entre nós.
Fornecemos o pacote openprivacy/connectivity para gerenciar o daemon Tor e configurar e desmontar serviços cebola através do Tor.
Criptografia e armazenamento de perfil.
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir uma senha.
Perfis não criptografados e a senha padrão Para lidar com perfis "não criptografados" (ou seja, que não exigem senha para serem abertos), atualmente criamos um perfil com uma senha codificada de fato .
Isso não é o ideal, preferiríamos confiar no material de chave fornecido pelo sistema operacional, de modo que o perfil fosse vinculado a um dispositivo específico, mas esses recursos são atualmente uma colcha de retalhos - também notamos, ao criar um perfil não criptografado, pessoas que usam Cwtch estão explicitamente optando pelo risco de que alguém com acesso ao sistema de arquivos possa descriptografar seu perfil.
Vulnerabilidades Relacionadas a Imagens e Entrada de Dados
Imagens Maliciosas
O Cwtch enfrenta desafios na renderização de imagens, com o Flutter utilizando Skia, embora o código subjacente não seja totalmente seguro para a memória.
Realizamos testes de fuzzing nos componentes Cwtch e encontramos um bug de travamento causado por um arquivo GIF malformado, levando a falhas no kernel. Para mitigar isso, adotamos a política de sempre habilitar cacheWidth e/ou cacheHeight máximo para widgets de imagem.
Identificamos o risco de imagens maliciosas serem renderizadas de forma diferente em diferentes plataformas, como evidenciado por um bug no analisador PNG da Apple.
Riscos de Entrada de Dados
Um risco significativo é a interceptação de conteúdo ou metadados por meio de um Input Method Editor (IME) em dispositivos móveis. Mesmo aplicativos IME padrão podem expor dados por meio de sincronização na nuvem, tradução online ou dicionários pessoais.
Implementamos medidas de mitigação, como enableIMEPersonalizedLearning: false no Cwtch 1.2, mas a solução completa requer ações em nível de sistema operacional e é um desafio contínuo para a segurança móvel.
Servidor Cwtch.
O objetivo do protocolo Cwtch é permitir a comunicação em grupo através de infraestrutura não confiável .
Ao contrário dos esquemas baseados em retransmissão, onde os grupos atribuem um líder, um conjunto de líderes ou um servidor confiável de terceiros para garantir que cada membro do grupo possa enviar e receber mensagens em tempo hábil (mesmo que os membros estejam offline) - infraestrutura não confiável tem o objetivo de realizar essas propriedades sem a suposição de confiança.
O artigo original do Cwtch definia um conjunto de propriedades que se esperava que os servidores Cwtch fornecessem:
• O Cwtch Server pode ser usado por vários grupos ou apenas um.
• Um servidor Cwtch, sem a colaboração de um membro do grupo, nunca deve aprender a identidade dos participantes de um grupo.
• Um servidor Cwtch nunca deve aprender o conteúdo de qualquer comunicação.
• Um servidor Cwtch nunca deve ser capaz de distinguir mensagens como pertencentes a um grupo específico. Observamos aqui que essas propriedades são um superconjunto dos objetivos de design das estruturas de Recuperação de Informações Privadas.
Melhorias na Eficiência e Segurança
Eficiência do Protocolo
Atualmente, apenas um protocolo conhecido, o PIR ingênuo, atende às propriedades desejadas para garantir a privacidade na comunicação do grupo Cwtch. Este método tem um impacto direto na eficiência da largura de banda, especialmente para usuários em dispositivos móveis. Em resposta a isso, estamos ativamente desenvolvendo novos protocolos que permitem negociar garantias de privacidade e eficiência de maneiras diversas.
Os servidores, no momento desta escrita, permitem o download completo de todas as mensagens armazenadas, bem como uma solicitação para baixar mensagens específicas a partir de uma determinada mensagem. Quando os pares ingressam em um grupo em um novo servidor, eles baixam todas as mensagens do servidor inicialmente e, posteriormente, apenas as mensagens novas.
Mitigação de Análise de Metadados
Essa abordagem permite uma análise moderada de metadados, pois o servidor pode enviar novas mensagens para cada perfil suspeito exclusivo e usar essas assinaturas de mensagens exclusivas para rastrear sessões ao longo do tempo. Essa preocupação é mitigada por dois fatores:
- Os perfis podem atualizar suas conexões a qualquer momento, resultando em uma nova sessão do servidor.
- Os perfis podem ser "ressincronizados" de um servidor a qualquer momento, resultando em uma nova chamada para baixar todas as mensagens. Isso é comumente usado para buscar mensagens antigas de um grupo.
Embora essas medidas imponham limites ao que o servidor pode inferir, ainda não podemos garantir resistência total aos metadados. Para soluções futuras para esse problema, consulte Niwl.
Proteção contra Pares Maliciosos
Os servidores enfrentam o risco de spam gerado por pares, representando uma ameaça significativa à eficácia do sistema Cwtch. Embora tenhamos implementado um mecanismo de proteção contra spam no protótipo do Cwtch, exigindo que os pares realizem alguma prova de trabalho especificada pelo servidor, reconhecemos que essa não é uma solução robusta na presença de um adversário determinado com recursos significativos.
Pacotes de Chaves
Os servidores Cwtch se identificam por meio de pacotes de chaves assinados, contendo uma lista de chaves necessárias para garantir a segurança e resistência aos metadados na comunicação do grupo Cwtch. Esses pacotes de chaves geralmente incluem três chaves: uma chave pública do serviço Tor v3 Onion para o Token Board, uma chave pública do Tor v3 Onion Service para o Token Service e uma chave pública do Privacy Pass.
Para verificar os pacotes de chaves, os perfis que os importam do servidor utilizam o algoritmo trust-on-first-use (TOFU), verificando a assinatura anexada e a existência de todos os tipos de chave. Se o perfil já tiver importado o pacote de chaves do servidor anteriormente, todas as chaves são consideradas iguais.
Configuração prévia do aplicativo para ativar o Relé do Cwtch.
No Android, a hospedagem de servidor não está habilitada, pois essa opção não está disponível devido às limitações dos dispositivos Android. Essa funcionalidade está reservada apenas para servidores hospedados em desktops.
No Android, a única forma direta de importar uma chave de servidor é através do grupo de teste Cwtch, garantindo assim acesso ao servidor Cwtch.
Primeiro passo é Habilitar a opção de grupo no Cwtch que está em fase de testes. Clique na opção no canto superior direito da tela de configuração e pressione o botão para acessar as configurações do Cwtch.
Você pode alterar o idioma para Português do Brasil.Depois, role para baixo e selecione a opção para ativar os experimentos. Em seguida, ative a opção para habilitar o chat em grupo e a pré-visualização de imagens e fotos de perfil, permitindo que você troque sua foto de perfil.
https://pomf2.lain.la/f/eprhj0u3.mp4
Próximo passo é Criar um perfil.
Pressione o + botão de ação no canto inferior direito e selecione "Novo perfil" ou aberta no botão + adicionar novo perfil.
-
Selecione um nome de exibição
-
Selecione se deseja proteger
este perfil e salvo localmente com criptografia forte: Senha: sua conta está protegida de outras pessoas que possam usar este dispositivo
Sem senha: qualquer pessoa que tenha acesso a este dispositivo poderá acessar este perfil.
Preencha sua senha e digite-a novamente
Os perfis são armazenados localmente no disco e criptografados usando uma chave derivada de uma senha conhecida pelo usuário (via pbkdf2).
Observe que, uma vez criptografado e armazenado em disco, a única maneira de recuperar um perfil é recuperando a chave da senha - como tal, não é possível fornecer uma lista completa de perfis aos quais um usuário pode ter acesso até inserir um senha.
https://pomf2.lain.la/f/7p6jfr9r.mp4
O próximo passo é adicionar o FuzzBot, que é um bot de testes e de desenvolvimento.
Contato do FuzzBot: 4y2hxlxqzautabituedksnh2ulcgm2coqbure6wvfpg4gi2ci25ta5ad.
Ao enviar o comando "testgroup-invite" para o FuzzBot, você receberá um convite para entrar no Grupo Cwtch Test. Ao ingressar no grupo, você será automaticamente conectado ao servidor Cwtch. Você pode optar por sair do grupo a qualquer momento ou ficar para conversar e tirar dúvidas sobre o aplicativo e outros assuntos. Depois, você pode configurar seu próprio servidor Cwtch, o que é altamente recomendável. https://pomf2.lain.la/f/x4pm8hm8.mp4
Agora você pode utilizar o aplicativo normalmente. Algumas observações que notei: se houver demora na conexão com outra pessoa, ambas devem estar online. Se ainda assim a conexão não for estabelecida, basta clicar no ícone de reset do Tor para restabelecer a conexão com a outra pessoa.
Uma introdução aos perfis Cwtch.
Com Cwtch você pode criar um ou mais perfis . Cada perfil gera um par de chaves ed25519 aleatório compatível com a Rede Tor.
Este é o identificador que você pode fornecer às pessoas e que elas podem usar para entrar em contato com você via Cwtch.
Cwtch permite criar e gerenciar vários perfis separados. Cada perfil está associado a um par de chaves diferente que inicia um serviço cebola diferente.
Gerenciar Na inicialização, o Cwtch abrirá a tela Gerenciar Perfis. Nessa tela você pode:
- Crie um novo perfil.
- Desbloquear perfis.
- Criptografados existentes.
- Gerenciar perfis carregados.
- Alterando o nome de exibição de um perfil.
- Alterando a senha de um perfil Excluindo um perfil.
- Alterando uma imagem de perfil.
Backup ou exportação de um perfil.
Na tela de gerenciamento de perfil:
-
Selecione o lápis ao lado do perfil que você deseja editar
-
Role para baixo até a parte inferior da tela.
-
Selecione "Exportar perfil"
-
Escolha um local e um nome de arquivo.
5.confirme.
Uma vez confirmado, o Cwtch colocará uma cópia do perfil no local indicado. Este arquivo é criptografado no mesmo nível do perfil.
Este arquivo pode ser importado para outra instância do Cwtch em qualquer dispositivo.
Importando um perfil.
-
Pressione o +botão de ação no canto inferior direito e selecione "Importar perfil"
-
Selecione um arquivo de perfil Cwtch exportado para importar
-
Digite a senha associada ao perfil e confirme.
Uma vez confirmado, o Cwtch tentará descriptografar o arquivo fornecido usando uma chave derivada da senha fornecida. Se for bem-sucedido, o perfil aparecerá na tela Gerenciamento de perfil e estará pronto para uso.
OBSERVAÇÃO Embora um perfil possa ser importado para vários dispositivos, atualmente apenas uma versão de um perfil pode ser usada em todos os dispositivos ao mesmo tempo. As tentativas de usar o mesmo perfil em vários dispositivos podem resultar em problemas de disponibilidade e falhas de mensagens.
Qual é a diferença entre uma conexão ponto a ponto e um grupo cwtch?
As conexões ponto a ponto Cwtch permitem que 2 pessoas troquem mensagens diretamente. As conexões ponto a ponto nos bastidores usam serviços cebola Tor v3 para fornecer uma conexão criptografada e resistente a metadados. Devido a esta conexão direta, ambas as partes precisam estar online ao mesmo tempo para trocar mensagens.
Os Grupos Cwtch permitem que várias partes participem de uma única conversa usando um servidor não confiável (que pode ser fornecido por terceiros ou auto-hospedado). Os operadores de servidores não conseguem saber quantas pessoas estão em um grupo ou o que está sendo discutido. Se vários grupos estiverem hospedados em um único servidor, o servidor não conseguirá saber quais mensagens pertencem a qual grupo sem a conivência de um membro do grupo. Ao contrário das conversas entre pares, as conversas em grupo podem ser conduzidas de forma assíncrona, para que todos num grupo não precisem estar online ao mesmo tempo.
Por que os grupos cwtch são experimentais? Mensagens em grupo resistentes a metadados ainda são um problema em aberto . Embora a versão que fornecemos no Cwtch Beta seja projetada para ser segura e com metadados privados, ela é bastante ineficiente e pode ser mal utilizada. Como tal, aconselhamos cautela ao usá-lo e apenas o fornecemos como um recurso opcional.
Como posso executar meu próprio servidor Cwtch? A implementação de referência para um servidor Cwtch é de código aberto . Qualquer pessoa pode executar um servidor Cwtch, e qualquer pessoa com uma cópia do pacote de chaves públicas do servidor pode hospedar grupos nesse servidor sem que o operador tenha acesso aos metadados relacionados ao grupo .
https://git.openprivacy.ca/cwtch.im/server
https://docs.openprivacy.ca/cwtch-security-handbook/server.html
Como posso desligar o Cwtch? O painel frontal do aplicativo possui um ícone do botão "Shutdown Cwtch" (com um 'X'). Pressionar este botão irá acionar uma caixa de diálogo e, na confirmação, o Cwtch será desligado e todos os perfis serão descarregados.
Suas doações podem fazer a diferença no projeto Cwtch? O Cwtch é um projeto dedicado a construir aplicativos que preservam a privacidade, oferecendo comunicação de grupo resistente a metadados. Além disso, o projeto também desenvolve o Cofre, formulários da web criptografados para ajudar mútua segura. Suas contribuições apoiam iniciativas importantes, como a divulgação de violações de dados médicos em Vancouver e pesquisas sobre a segurança do voto eletrônico na Suíça. Ao doar, você está ajudando a fechar o ciclo, trabalhando com comunidades marginalizadas para identificar e corrigir lacunas de privacidade. Além disso, o projeto trabalha em soluções inovadoras, como a quebra de segredos através da criptografia de limite para proteger sua privacidade durante passagens de fronteira. E também tem a infraestrutura: toda nossa infraestrutura é open source e sem fins lucrativos. Conheça também o Fuzzytags, uma estrutura criptográfica probabilística para marcação resistente a metadados. Sua doação é crucial para continuar o trabalho em prol da privacidade e segurança online. Contribua agora com sua doação
https://openprivacy.ca/donate/
onde você pode fazer sua doação em bitcoin e outras moedas, e saiba mais sobre os projetos. https://openprivacy.ca/work/
Link sobre Cwtch
https://cwtch.im/
https://git.openprivacy.ca/cwtch.im/cwtch
https://docs.cwtch.im/docs/intro
https://docs.openprivacy.ca/cwtch-security-handbook/
Baixar #CwtchDev
cwtch.im/download/
https://play.google.com/store/apps/details?id=im.cwtch.flwtch
-
 @ dfc7c785:4c3c6174
2025-05-20 09:55:44
@ dfc7c785:4c3c6174
2025-05-20 09:55:44![[0B745064-2D34-4A3C-8393-AD033910E6D7.jpeg]]![[0C3FA837-E1BA-497F-8D44-9EC1CD723970.jpeg]]
-
 @ bf47c19e:c3d2573b
2025-05-19 21:41:37
@ bf47c19e:c3d2573b
2025-05-19 21:41:37Originalni tekst na bitcoin-balkan.com.
Pregled sadržaja
- Šta je Bitcoin?
- Šta Bitcoin može da učini za vas?
- Zašto ljudi kupuju Bitcoin?
- Da li je vaš novac siguran u dolarima, kućama, akcijama ili zlatu?
- Šta je bolje za štednju od dolara, kuća i akcija?
- Po čemu se Bitcoin razlikuje od ostalih valuta?
- kako Bitcoin spašava svet?
- Kako mogu da saznam više o Bitcoin-u?
Bitcoin čini da štednja novca bude kul – i praktična – ponovo. Ovaj članak objašnjava kako i zašto.
Šta je Bitcoin?
Bitcoin se naziva digitalno zlato, mašina za istinu, blockchain, peer to peer mreža čvorova, energetski ponor i još mnogo toga. Bitcoin je, u stvari, sve ovo. Međutim, ova objašnjenja su često toliko tehnička i suvoparna, da bi većina ljudi radije gledala kako trava raste. Što je najvažnije, ova objašnjenja ne pokazuju kako Bitcoin ima bilo kakve koristi za vas.
iPod nije postao kulturološka senzacija jer ga je Apple nazvao „prenosnim digitalnim medijskim uređajem“. Postao je senzacija jer su ga zvali “1,000 pesama u vašem džepu.”
Ne zanima vas šta je Bitcoin. Vas zanima šta on može da učini za vas.
Baš kao i Internet, vaš auto, vaš telefon, kao i mnogi drugi uređaji i sistemi koje svakodnevno koristite, vi ne treba da znate šta je Bitcoin ili kako to funkcioniše da biste razumeli šta on može da učini za vas.
Šta Bitcoin može da učini za vas?
Bitcoin može da sačuva vaš teško zarađeni novac.
Bitcoin je stekao veliku pažnju u 2017. i 2018. godini zbog svoje spekulativne upotrebe. Mnogi ljudi su ga kupili nadajući se da će se obogatiti. Cena je naglo porasla, a zatim se srušila. Ovo nije bio prvi put da je Bitcoin uradio to. Međutim, niko nikada nije izgubio novac držeći bitcoin duže od 3,5 godine – ćak i ako je kupio na apsolutnim vrhovima.
Zašto Bitcoin konstantno raste? Ljudi počinju da shvataju koliko je Bitcoin moćan, kao način uštede novca u svetu u kojem je ’novac’ poput dolara, eura i drugih nacionalnih valuta dizajniran da gubi vrednost.
Ovo čini Bitcoin odličnom opcijom za štednju novca na nekoliko godina ili više. Bitcoin je bolji od štednje novca u dolarima, akcijama, nekretninama, pa čak i u zlatu.
Zato pokušajte da zaboravite na trenutak na razumevanje blockchaina, digitalne valute, kriptografije, seed fraza, novčanika, rudarstva i svih ostalih nerazumljivih termina. Za sada, razgovarajmo o tome zašto ljudi kupuju Bitcoin: razlog je prostiji nego što vi mislite.
Zašto ljudi kupuju Bitcoin?
Naravno, svako ima svoj razlog za kupovinu Bitcoin-a. Jedan od razloga, koji verovatno često čujete, je taj što mu vrednost raste. Ljudi žele da se obogate. Uskoče kao spekulanti, krenu u vožnju i najverovatnije ih prodaju ubrzo nakon kupovine.
Međutim, čak i kada cena krene naglo prema gore i strmoglavo padne nazad, mnogi ljudi ostanu i nakon tog pada. Otkud mi to znamo? Broj aktivnih novčanika dnevno, koji je otprilike sličan broju korisnika Bitcoin-a, nastavlja da raste. Takođe, nakon svakog balona u istoriji Bitcoin-a, cena se nikada ne vraća na svoju cenu pre balona. Uvek ostane malo višlja. Bitcoin se penje, a svaka masovna spekulativna serija dovodi sve više i više ljudi.
Broj aktivnih Bitcoin novčanika neprekidno raste
„Aktivna adresa“ znači da je neko tog dana poslao Bitcoin transakciju. Donji grafikon je na logaritamskoj skali.
 Izvor: Glassnode
Izvor: GlassnodeCena Bitcoina se neprestano penje
Kroz istoriju Bitcoin-a možemo videti divlje kolebanje cena, ali nakon svakog balona, cena se ostaje višlja nego pre. Ovo je cena Bitcoin-a na logaritamskoj skali.
 Izvor: Glassnode
Izvor: GlassnodeTo pokazuje da se ljudi zadržavaju: potražnja za Bitcoin-om se povećava. Da je svaki masovni rast cena bio samo balon koji su iscenirali prevaranti koji žele brzo da se obogate, cena bi se vratila na nivo pre balona. To se dogodilo sa lalama, ali ne i sa Bitcoin-om.
I zašto se onda cena Bitcoin-a stalno povećava? Sve veći broj ljudi čuva Bitcoin dugoročno – oni razumeju šta Bitcoin može učiniti za njihovu štednju.
Zašto ljudi štede svoj novac u Bitcoin-u umesto na štednim računima, kućama, deonicama ili zlatu? Hajde da pogledajmo sve te metode štednje, i zatim da ih uporedimo sa Bitcoin-om.
Da li je vaš novac siguran u dolarima, kućama, akcijama ili zlatu?
Tokom mnogo godina, to su bile pristojne opcije za štednju. Međutim, sistem koji podržava vrednost svega ovoga je u krizi.
Dolari, Euri, Dinari
Dolari i sve ostale „tradicionalne“ valute koje proizvode vlade, stvorene su da izgube vrednost kroz inflaciju. Banke i tradicionalni monetarni sistem uzrokuju inflaciju stalnim stvaranjem i distribucijom novog novca. Kada Američke Federalne Rezerve objave ciljanu stopu od 2% inflacije, to znači da žele da vaš novac svake godine izgubi 2% od svoje vrednosti. Čak i sa inflacijom od samo 2%, vaša štednja u dolarima izgubiće polovinu vrednosti tokom 40-godišnjeg radnog veka.
Izveštena inflacija se danas opasno povečava, uprkos rastućem „buretu sa barutom“ koji bi mogao da explodira i dovede do masivne hiperinflacije. Što je više valute u opticaju, to je više baruta u buretu.
Naše vlade su ekonomiju napunile valutama da bankarski sistem ne bi propao nakon finansijske krize koja se dogodila 2008. godine. Od tada je većina glavnih centralnih banaka postavila vrlo niske kamatne stope, što pojedincima i korporacijama omogućava dobijanje jeftinijih kredita. To znači da mnogi pojedinci i korporacije podižu ogromne kredite i koriste ih za kupovinu druge imovine poput deonica, umetničkih dela i nekretnina. Sve ovo pozajmljivanje znači da stvaramo tone novog novca i stavljamo ga u opticaj.
Računi za podsticaje (stimulus bills) COVID-19 za 2020. godinu unose trilione u sistem. Ovoliko stvaranje valuta na kraju dovodi do inflacije – velikog gubitka u vrednosti valute.
 Količina američkog dolara u opticaju gotovo se udvostručila od marta 2020. godine. Izvor
Količina američkog dolara u opticaju gotovo se udvostručila od marta 2020. godine. IzvorRačuni za podsticaje su bez presedana, toliko da je neko izmislio meme da opiše ovu situaciju.
Resurs koji vlade mogu da naprave u većem broju da bi platile svoje račune? Ne zvuči kao dobro mesto za štednju novca.
Kuće
Kuće su tokom prošlog veka bile pristojan način štednje novca. Međutim, pad cena nekretnina 2007. godine doveo je do toga da su mnogi vlasnici kuća izgubili svu ušteđevinu.
Danas su kuće gotovo nepristupačne za prosečnog čoveka. Jedan od načina da se ovo izmeri je koliko godišnjih zarada treba prosečnom čoveku da zaradi ekvivalent vrednosti prosečne kuće. Prema CityLab-u, publikaciji Bloomberg-a koja pokriva gradove, porodica može da priuštiti određenu kuću ako košta manje od 2,6 godišnjih prihoda domaćinstva te porodice.
Međutim, prema RZS (Republički zavod za statistiku) prosečan prihod porodičnog domaćinstva u Srbiji iznosi oko 570 EUR mesečno ili otprilike 7.000 EUR godišnje. Nažalost, samo najjeftinija područja van gradova imaju srednje cene kuća od oko 2,6 prosečnih godišnjih prihoda domaćinstva. U većim gradovima poput Beograda i Novog Sada srednja cena kuće je veća od 10 prosečnih godišnjih prihoda jednog domaćinstva.
Ako nekako možete sebi da priuštite kuću, ona bi mogla biti pristojna zaliha vrednosti. Dokle god ne doživimo još jedan krah i izvršitelji zaplene ovu imovinu mnogim vlasnicima kuća.
Akcije
Berza je u prošlosti takođe dobro poslovala. Međutim, sporo i stabilno povećanje tržišta događa se u dosadnom, predvidljivom svetu. Svakog dana vidimo sve manje toga. Nakon ubrzanja korona virusa, videli smo smo najbrži pad američke berze u istoriji od 25% – brži od Velike depresije.
Neki se odlučuju za ulaganje u obveznice i drugu finansijsku imovinu, ali ’prinosi’ za tu imovinu – procenat kamate zarađene na imovinu iz godine u godinu – stalno opada. Sve veći broj odredjenih imovina ima čak i negativne prinose, što znači da posedovanje te imovine košta! Ovo je veliki problem za sve koji se oslanjaju na penziju. Plus, s obzirom na to da su akcije denominovane u tradicionalnim valutama poput dolara i evra, inflacija pojede prinos koji investitor dobije.
Najgore od svega je to što ti isti ekonomski krahovi koji uzrokuju masovna otpuštanja i teško tržište rada takođe znače i nagli pad cena akcija. Čuvanje ušteđevine u akcijama može značiti i gubitak štednje i gubitak posla zbog recesije. Teška vremena mogu da vas prisile da svoje akcije prodate po vrlo malim cenama samo da biste platili svoje račune.
A to nije baš siguran način štednje novca.
Zlato
Vrednost zlata neprekidno se povećavala tokom 5000 godina, obično padajući onda kada berza obećava jače prinose.
Evidencija vrednosti zlata je solidna. Međutim, zlato nosi i druge rizike. Većina ljudi poseduje zlato na papiru. Oni fizički ne poseduju zlato, već ga njihova banka čuva za njih. Zbog toga je zlato veoma podložno konfiskaciji od strane vlade.
Zašto bi vlada konfiskovala nečije zlato, a kamoli u demokratskoj zemlji u „slobodnom svetu“? Ali to se dešavalo i ranije. 1933. godine Izvršnom Naredbom 6102, predsednik Roosevelt naredio je svim Amerikancima da prodaju svoje zlato vladi u zamenu za papirne dolare. Vlada je iskoristila pretnju zatvorom za prikupljanje zlata u fizičkom obliku. Znali su da se zlato više poštuje kao zaliha vrednosti širom sveta od papirnih dolara.
Ako posedujete svoje zlato na nekoj od aplikacija za trgovanje akcijama, možete se kladiti da će vam ga država oduzeti ako joj zatreba. Čak i ako posedujete fizičko zlato, onda ga izlažete mogućnosti krađe – od strane kriminalca ili vaše vlade.
Vaša uštedjevina nije bezbedna.
Rast cena svih gore navedenih sredstava zavisi od našeg trenutnog političkog i ekonomskog sistema koji se nastavlja kao i tokom proteklih 100 godina. Međutim, danas vidimo ogromne pukotine u ovom sistemu.
Sistem ne funkcioniše dobro za većinu ljudi.
Od 1971. plate većine američkih radnika nisu rasle. S druge strane, bogatstvo koje imaju najbogatiji u društvu nalazi se na nivoima koji nisu viđeni više od 80 godina. U međuvremenu, ljudi sve manje i manje veruju institucijama poput banaka i vlada.
 CBPP Nejednakost Bogatstva Tokom Vremena
CBPP Nejednakost Bogatstva Tokom VremenaŠirom sveta možemo videti dokaze o slamanju sistema kroz politički ekstremizam: izbor Trampa i drugih ekstremističkih desničarskih kandidata, Bregzit, pokret Occupy, popularizacija koncepta univerzalnog osnovnog dohotka, povratak pojma „socijalizam“ nazad u modu. Ljudi na svim delovima političkog i društvenog spektra osećaju problematična vremena i posežu za sve radikalnijim rešenjima.
Šta je bolje za štednju od dolara, kuća i akcija?
Pa kako ljudi mogu da štede novac u ovim teškim vremenima? Ili ne koriste tradicionalne valute, ili kupuju sredstva koja će zadržati vrednost u teškim vremenima.
Bitcoin ima najviše potencijala da zadrži vrednost kroz politička i ekonomska previranja od bilo koje druge imovine. Na tom putu će biti rupa na kojima će se rušiti ili pumpati, međutim, njegova svojstva čine ga takvim da će verovatno preživeti previranja kada druga imovina ne bude to mogla.
Šta Bitcoin čini drugačijim?
Bitcoini su retki.
Proces ‘rudarenja’ bitcoin-a, proizvodnju bitcoin-a čini veoma skupom, a Bitcoin protokol ograničava ukupan broj bitcoin-a na 21 milion novčića. To čini Bitcoin imunim na nagle poraste ponude. Ovo se veoma razlikuje od tradicionalnih valuta, koje vlade mogu da štampaju sve više kad god one to požele. Zapamtite, povećanje ponude vrši veliki pritisak na vrednost valute.
Bitcoini nemaju drugu ugovornu stranu.
Bitcoin se takođe razlikuje od imovine kao što su obveznice, akcije i kuće, jer mu nedostaje druga ugovorna strana. Druge ugovorne strane su drugi subjekti uključeni u vrednost sredstva, koji to sredstvo mogu obezvrediti ili vam ga uzeti. Ako imate hipoteku na svojoj kući, banka je druga ugovorna strana. Kada sledeći put dođe do velikog finansijskog kraha, banka vam može oduzeti kuću. Kompanije su kvazi-ugovorne strane akcijama i obveznicama, jer mogu da počnu da donose loše odluke koje utiču na njihovu cenu akcija ili na „neizvršenje“ duga (da ga ne vraćaju vama ili drugim poveriocima). Bitcoin nema ovih problema.
Bitcoin je pristupačan.
Svako sa 5 eura i mobilnim telefonom može da kupi i poseduje mali deo bitcoin-a. Važno je da znate da ne morate da kupite ceo bitcoin. Bitcoin-i su deljivi do 100-milionite jedinice, tako da možete da kupite Bitcoin u vrednosti od samo nekoliko eura. Neuporedivo lakše nego kupovina kuće, zlata ili akcija!
Bitcoin se ne može konfiskovati.
Banke drže većinu vaših eura, zlata i akcija za vas. Većina ljudi u razvijenom svetu veruje bankama, jer većina ljudi koji žive u današnje vreme nikada nije doživela konfiskaciju imovine ili ’šišanje’ od strane banaka ili vlada. Nažalost, postoji presedan za konfiskaciju imovine čak i u demokratskim zemljama sa snažnom vladavinom prava.
Kada vlada konfiskuje imovinu, ona obično ubedi javnost da će je menjati za imovinu jednake vrednosti. U SAD-u 1930-ih, vlada je davala dolare vlasnicima zlata. Vlada je znala da uvek može da odštampa još više dolara, ali da ne može da napravi više zlata. Na Kipru 2012. godine, jedna propala banka je svojim klijentima dala deonice banke da pokrije dolare klijenata koje je banka trebala da ima. I dolari i deonice su strmoglavo opali u odnosu na imovinu koja je uzeta od ovih ljudi.
Doći do bitcoin-a koji ljudi poseduju, biće mnogo teže jer se bitcoin-i mogu čuvati u novčaniku koji ne poseduje neka treća strana, a vi možete čak i da zapamtite privatne ključeve do vašeg bitcoin-a u glavi.
Bitcoin je za štednju.
Bitcoin se polako pokazuje kao najbolja opcija za dugoročnu štednju novca, posebno s obzirom na današnju ekonomsku klimu. Posedovanje čak i malog dela, je polisa osiguranja koja se isplati ako svet i dalje nastavi da ludi. Cena Bitcoin-a u dolarima može divlje da varira u roku od godinu ili dve, ali tokom 3+ godine skoro svi vide slične ili više cene od trenutka kada su ga kupili. U stvari, doslovno niko nije izgubio novac čuvajući Bitcoin duže od 3,5 godine – čak i ako je kupio BTC na apsolutnim vrhovima tržišta.

Imajte na umu da nakon ove tačke ti ljudi više nikada nisu videli rizik od gubitka. Cena se nikada nije smanjila niže od najviše cene u prethodnom ciklusu.
Po čemu se Bitcoin razlikuje od ostalih valuta?
Bitcoin funkcioniše tako dobro kao način štednje zbog svog neobičnog dizajna, koji ga čini drugačijim od bilo kog drugog oblika novca koji je postojao pre njega. Bitcoin je digitalna valuta, prvi i verovatno jedini primer valute koja ima ograničenu ponudu dok radi na otvorenom, decentralizovanom sistemu. Vlade strogo kontrolišu valute koje danas koristimo, poput dolara i eura, i proizvode ih za finansiranje ratova i dugova. Korisnici Bitcoin-a – poput vas – kontrolišu Bitcoin protokol.
Evo šta Bitcoin razlikuje od dolara, eura i drugih valuta:
Bitcoin je otvoren sistem.
Svako može da odluči da se pridruži Bitcoin mreži i primeni pravila softverskog protokola, što je dovelo do vrlo decentralizovanog sistema u kojem nijedan pojedinac ili entitet ne može da blokira transakciju, zamrzne sredstva ili da ukrade od druge osobe.Današnji savremeni bankarski sistem se uveliko razlikuje. Nekoliko banaka je dobilo poverenje da gotovo sve valute, akcije i druge vredne predmete čuvaju na “sigurnom” za svoje klijente. Da biste postali banka, potrebni su vam milioni dolara i neverovatne količine političkog uticaja. Da biste pokrenuli Bitcoin čvor i postali „svoja banka“, potrebno vam je nekoliko stotina dolara i jedno slobodno popodne.
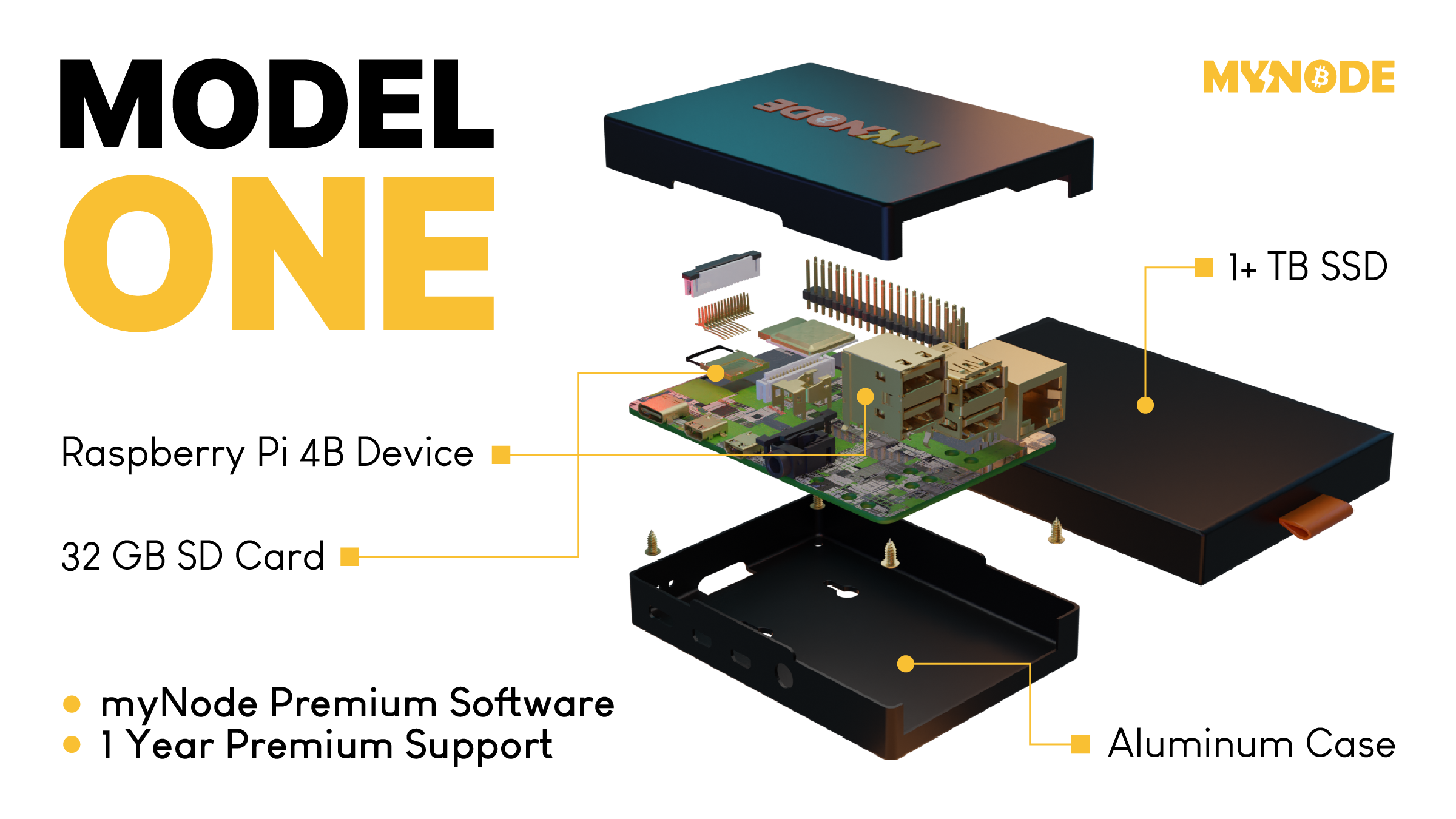 Tako izgleda Bitcoin čvor – Node
MyNode čvor vam omogućava da postanete svoja banka za samo nekoliko minuta.
Tako izgleda Bitcoin čvor – Node
MyNode čvor vam omogućava da postanete svoja banka za samo nekoliko minuta.Bitcoin ima ograničenu ponudu.
Softverski protokol otvorenog koda koji upravlja Bitcoin sistemom ograničava broj novih bitcoin-a koji se mogu stvoriti tokom vremena, sa ograničenjem od ukupno 21.000.000 bitcoin-a. S druge strane, valute koje danas koristimo imaju neograničenu ponudu. Istorija i sadašnje odluke centralnih banaka govore nam da će vlade uvek štampati sve više i više valuta, sve dok valuta ne bude bezvredna. Sve ovo štampanje uzrokuje inflaciju, što pravi štetu običnim radnim ljudima i štedišama.
Tradicionalne valute su dizajnirane tako da opadaju vremenom. Svaki put kada centralna banka kaže da cilja određenu stopu inflacije, oni ustvari kažu da žele da vaš novac svake godine izgubi određeni procenat svoje vrednosti.
Bitcoin-ova ograničena ponuda znači da je on tako dizajniran da raste vremenom kako se potražnja za njim povećava.

Bitcoin putuje oko sveta za nekoliko minuta.
Svako može da pošalje bitcoin-e za nekoliko minuta širom sveta, bez obzira na granice, banke i vlade. Potrebno je manje od minuta da se transakcija pojavi na novčaniku primaoca i oko 60 minuta da se transakcija u potpunosti „obračuna“, tako da primaoc može da bude siguran da su primljeni bitcoin-i sada njegovi (6 konfirmacija bloka). Slanje drugih valuta širom sveta traje danima ili čak mesecima ako se šalju milionski iznosi, a podrazumeva i visoke naknade.
Neke vlade i novinari tvrde da ova sloboda putovanja koju pruža Bitcoin pomaže kriminalcima i teroristima. Međutim, transakciju Bitcoin-a je lakše pratiti nego većinu transakcija u dolarima ili eurima.
Bitcoin se može čuvati na “USB-u”.
Dizajn Bitcoin-a je takav da vam treba samo da čuvate privatni ključ do svojih ‘bitcoin’ adresa (poput lozinke do bankovnih računa) da biste pristupili svojim bitcoin-ima odakle god poželite. Ovaj privatni ključ možete da sačuvate na disku ili na papiru u obliku 12 ili 24 reči na engleskom jeziku. Kao rezultat toga, možete da držite Bitcoin-e vredne milione dolara u svojoj šaci.
Sve ostale valute danas možete ili da strpate u svoj dušek ili da ih poverite banci na čuvanje. Za većinu ljudi koji žive u razvijenom svetu, i koji ne osporavaju autoritet i poverenje u banku, ovo deluje sasvim dobro. Međutim, oni kojima je potrebno da pobegnu od ugnjetavačke vlade ili koji naljute pogrešne ljude, ne mogu verovati bankama. Za njih je sposobnost da nose svoju ušteđevinu bez potrebe za ogromnim koferom neprocenjiva. Čak i ako ne živite na mestu poput ovog, cena Bitcoin-a se i dalje povećava kada ih neko kome oni trebaju kupi.
Kako Bitcoin spašava svet?
Bitcoin, kao ultimativni način štednje, je cakum pakum, ali da li on pomaže u poboljšanju sveta u celini?
Kao što ćete početi da shvatate, ulazeći sve dublje i u druge sadržaje na ovoj stranici, mnogi temeljni delovi našeg današnjeg monetarnog sistema i ekonomije su duboko slomljeni. Međutim, oni koji upravljaju imaju korist od ovakvih sistema, pa se on verovatno neće promeniti bez revolucije ili mirnog svrgavanja od strane naroda. Bitcoin predstavlja novi sistem, sa nekoliko glavnih prednosti:
- Bitcoin popravlja novac, koji je milenijumima služio kao važan alat za rast i poboljšanje društva.
- Bitcoin vraća zdrav razum pozajmljivanju, uklanjanjem apsurdnih situacija poput negativnih kamatnih stopa (gde zajmitelj plaća da bi se zadužio).
- Bitcoin pokreće ulaganja u obnovljive izvore energije i poboljšava energetsku efikasnost u mreži, služeći kao „krajnji kupac“ za sve vrste energije.
Kako mogu da saznam više o Bitcoin-u?
Ovaj članak vam je dao osnovno razumevanje zašto biste trebali razmišljati o Bitcoin-u. Ako želite da saznate više, preporučujem ove resurse:
- Film Bitcoin: Kraj Novca Kakav Poznajemo
- Još uvek je rano za Bitcoin
- Zasto baš Bitcoin?
- Šta je to Bitcoin?
- The Bitcoin Whitepaper ← objavljen 2008. godine, ovo je izložio dizajn za Bitcoin.
-
 @ eb0157af:77ab6c55
2025-05-20 09:21:47
@ eb0157af:77ab6c55
2025-05-20 09:21:47A Chinese printer company inadvertently distributed malware that steals Bitcoin through its official drivers, resulting in the theft of over $950,000.
According to local media outlet Landian News, a Chinese printer manufacturer was found to have unknowingly distributed malware designed to steal Bitcoin through its official device drivers.
Procolored, a Shenzhen-based printer company, distributed malware capable of stealing Bitcoin alongside the official drivers for its devices. The company reportedly used USB devices to spread infected drivers and uploaded the compromised software to globally accessible cloud storage services.
Crypto security and compliance firm SlowMist explained how the malware works in a post on X:
 The official driver provided by this printer carries a backdoor program. It will hijack the wallet address in the user's clipboard and replace it with the attacker's address: 1BQZKqdp2CV3QV5nUEsqSg1ygegLmqRygj
The official driver provided by this printer carries a backdoor program. It will hijack the wallet address in the user's clipboard and replace it with the attacker's address: 1BQZKqdp2CV3QV5nUEsqSg1ygegLmqRygj  According to @MistTrack_io, the attacker has stolen 9.3086… https://t.co/DHCkEpHhuH pic.twitter.com/W1AnUpswLU
According to @MistTrack_io, the attacker has stolen 9.3086… https://t.co/DHCkEpHhuH pic.twitter.com/W1AnUpswLU— MistTrack
 (@MistTrack_io) May 19, 2025
(@MistTrack_io) May 19, 2025The consequences of the breach have been significant, with a total of 9.3 BTC stolen — equivalent to over $950,000.
The issue was first flagged by YouTuber Cameron Coward, whose antivirus software detected malware in the drivers during a test of a Procolored UV printer. The software identified both a worm and a trojan virus named Foxif.
When contacted, Procolored denied the accusations, dismissing the antivirus warning as a false positive. Coward then turned to Reddit, where he shared the issue with cybersecurity professionals, drawing the attention of security firm G Data.
G Data’s investigation revealed that most of Procolored’s drivers were hosted on the MEGA file-sharing platform, with uploads dating back to October 2023. Their analysis confirmed the presence of two separate malware strains: the Win32.Backdoor.XRedRAT.A backdoor and a crypto-stealer designed to replace clipboard wallet addresses with those controlled by the attacker.
G Data reached out to Procolored, which stated that it had removed the infected drivers from its storage as of May 8 and had re-scanned all files. The company attributed the malware to a supply chain compromise, saying the malicious files were introduced via infected USB devices before being uploaded online.
Landian News recommended that users who downloaded Procolored drivers in the past six months “immediately run a full system scan using antivirus software.” However, given that antivirus tools are not always reliable, the Chinese media outlet suggested that a full system reset is the safest option when in doubt.
The post Bitcoin malware discovered: Chinese printer manufacturer involved appeared first on Atlas21.
-
 @ 2b998b04:86727e47
2025-05-19 21:18:46
@ 2b998b04:86727e47
2025-05-19 21:18:46After the pruning came clarity.\ And after the clarity came a quiet but relentless question:\ What now?
If I wasn’t going back to Web3, if I wasn’t going to pretend anymore — not in faith, not in finance — then I needed to start building again. But this time, with different materials. Different rhythms. A different spirit.
Starting Over on Solid Ground
I’d spent years exploring tokens, networks, and well-intentioned communities. But most of it, I see now, was sand. It moved with the tides. The incentives shifted. The values bent. And when the storms came — personal, financial, spiritual — much of what I’d been part of collapsed or exposed its shallowness.
So I returned to the beginning: What can’t be faked?
That’s where Bitcoin came in — not just as an asset, but as a foundation.\ It taught me cost. Time. Truth. It doesn’t market itself. It just is.\ A system that punishes shortcuts, rewards discipline, and invites peace.
And the more I leaned in, the more I realized:\ This isn’t just money. This is philosophy. This is soil.
Pruned to Plant Again
I used to be a buy-and-hold investor. I still carry those instincts. But in 2020–21, I discovered trading — and with it, a new kind of discipline. Not gambling. Not speculation. Stewardship under pressure. Real-time decision-making with skin in the game.
My grandfather, who passed in the late '90s, probably would’ve looked a little dimly on trading. He lived off his dividends. Stocks he held for decades. He wasn’t chasing. He was rooting. But he would’ve respected the discipline — the clarity — when done right.
He also saw things I didn’t. He once told me I wasn’t raised properly. It hurt at the time, but now I understand. He saw the drift — not just in me, but in the culture. He understood that frugality means nothing if it’s not paired with truth.
I think he would’ve respected what I’m doing now — even if he wouldn't have fully understand it.
What I’m Building Now
-
StartNation – A Bitcoin-aligned equity accelerator. Proof-based. No tokens. No hype.
-
Golden Gate Group Investments – Real estate with a vision to integrate BTC in payments and ownership. Still early. Still real.
-
Blue Planet Ventures – Equities trading with daily proof-of-work and sats-based performance tracking.
-
A garden – Yes, literal food. Soil and seed. Hypdropnics. Bitcoin taught me patience; gardening reinforces it.
I’m not building a brand. I’m building a life. And I’m doing it in public — not to be seen, but to help others see. That it’s possible to step off the hype rails and still thrive.
Bitcoin: The Turning Point
It wasn’t until last fall that Bitcoin truly became central for me.\ Not just part of a portfolio — the lens through which I see capital, time, and truth.
I don’t see it as speculative anymore. I see it as inevitable. In 20–30 years, I believe Bitcoin will be the de facto reserve currency — even if not in name. Those who hold it will steward wealth not because they played the game, but because they opted out of it early.
I’m stacking not to escape — but to prepare. Not to prove I'm right — but to live rightly.
Legacy Without a Platform
I don’t have children.\ But I do have nieces. Nephews. Brothers. Sisters. Cousins. In-Laws.
And I know they’re watching — even if they don’t say it.\ I want to show them that you can live with truth, walk by faith, work with your hands — and still thrive.
I’m not stacking for applause. I’m stacking for legacy.\ I’m building not just for the next quarter — but for the next generation.
And if someone, years from now, asks why I chose this path, I want to say:
Because it was real.\ Because it was proof.\ Because it was built to last.
⚡ If this series has encouraged or challenged you, zap a few sats/bitcoin. It keeps me building.
✍️ Catch up on the full series here:\ \ Part 1: The Drift -> https://primal.net/andrewgstanton/why-i-left-web3-for-proof-of-work-%E2%80%93-part-1%3A-the-drift\ Part 2: The Breaking Point -> https://primal.net/andrewgstanton/why-i-left-web3-for-proof-of-work---part-2%3A-the-breaking-point\ Part 3: The Return -> https://primal.net/andrewgstanton/why-i-left-web3-for-proof-of-work-%E2%80%93-part-3%3A-the-return\ Part 4: Proof Of Work as Philosophy -> https://primal.net/andrewgstanton/why-i-left-web3-for-proof-of-work-%E2%80%93-part-4%3A-proof-of-work-as-philosophy\ Part 5: Building Again (what you are reading now...)
Written with help from ChatGPT (GPT-4), edited and posted by me.
-
-
 @ 1817b617:715fb372
2025-05-19 20:39:28
@ 1817b617:715fb372
2025-05-19 20:39:28Looking to simulate a USDT deposit that appears instantly in a wallet — with no blockchain confirmation, no real spend, and no trace?
You’re in the right place.
🔗 Buy Flash USDT Now This product sends Flash USDT directly to your TRC20, ERC20, or BEP20 wallet address — appears like a real deposit, but disappears after a set time or block depth.
✅ Perfect for: Simulating token inflows Wallet stress testing “Proof of funds” display Flash USDT is ideal for developers, trainers, UI testers, and blockchain researchers — and it’s fully customizable.
🧠 What Is Flash USDT? Flash USDT is a synthetic transaction that mimics a real Tether transfer. It shows up instantly in a wallet balance, and it’s confirmed on-chain — and expires after a set duration.
This makes it:
Visible on wallet interfaces Time-limited (auto-disappears cleanly) Undetectable on block explorers after expiry It’s the smartest, safest way to simulate high-value transactions without real crypto.
🛠️ Flash USDT Software – Your Own USDT Flasher at Your Fingertips Want to control the flash? Run your own operations? Flash unlimited wallets?
🔗 Buy Flash USDT Software
This is your all-in-one USDT flasher tool, built for TRC20, ERC20, and BEP20 chains. It gives you full control to:
Send custom USDT amounts Set custom expiry time (e.g., 30–360 days) Flash multiple wallets Choose between networks (Tron, ETH, BSC) You can simulate any amount, to any supported wallet, from your own system.
No third-party access. No blockchain fee. No trace left behind.
💥 Why Our Flash USDT & Software Stands Out Feature Flash USDT Flash USDT Software One-time flash send ✅ Yes Optional Full sender control ❌ No ✅ Yes TRC20 / ERC20 / BEP20 ✅ Yes ✅ Yes Custom duration/expiry Limited ✅ Yes Unlimited usage ❌ One-off ✅ Yes Whether you’re flashing for wallet testing, demoing investor dashboards, or simulating balance flows, our tools deliver realism without risk.
🛒 Ready to Buy Flash USDT or the Software? Skip the wait. Skip the scammers. You’re one click away from real control.
👉 Buy Flash USDT 👉 Buy Flash USDT Software
📞 Support or live walkthrough?
💬 Telegram: @cryptoflashingtool 📱 WhatsApp: +1 770-666-2531
🚫 Legal Notice These tools are intended for:
Educational purposes Demo environments Wallet and UI testing They are not for illegal use or financial deception. Any misuse is your full responsibility.
Final Call: Need to flash USDT? Want full control? Don’t wait for another “maybe” tool.
Get your Flash USDT or Flashing Software today and simulate like a pro.
🔗 Buy Now → Flash USDT 🔗 Buy Now → Flash USDT Software 💬 Telegram: @cryptoflashingtool 📱 WhatsApp: +1 770-666-2531Looking to simulate a USDT deposit that appears instantly in a wallet — with no blockchain confirmation, no real spend, and no trace?
You’re in the right place.
Buy Flash USDT Now\ This product sends Flash USDT directly to your TRC20, ERC20, or BEP20 wallet address — appears like a real deposit, but disappears after a set time or block depth.
Perfect for:
- Simulating token inflows
- Wallet stress testing
- “Proof of funds” display
Flash USDT is ideal for developers, trainers, UI testers, and blockchain researchers — and it’s fully customizable.
What Is Flash USDT?
Flash USDT is a synthetic transaction that mimics a real Tether transfer. It shows up instantly in a wallet balance, and it’s confirmed on-chain — and expires after a set duration.
This makes it:
- Visible on wallet interfaces
- Time-limited (auto-disappears cleanly)
- Undetectable on block explorers after expiry
It’s the smartest, safest way to simulate high-value transactions without real crypto.
Flash USDT Software – Your Own USDT Flasher at Your Fingertips
Want to control the flash?\ Run your own operations?\ Flash unlimited wallets?
This is your all-in-one USDT flasher tool, built for TRC20, ERC20, and BEP20 chains. It gives you full control to:
- Send custom USDT amounts
- Set custom expiry time (e.g., 30–360 days)
- Flash multiple wallets
- Choose between networks (Tron, ETH, BSC)
You can simulate any amount, to any supported wallet, from your own system.
No third-party access.\ No blockchain fee.\ No trace left behind.
Why Our Flash USDT & Software Stands Out
Feature
Flash USDT
Flash USDT Software
One-time flash send
Yes
Optional
Full sender control
No
Yes
TRC20 / ERC20 / BEP20
Yes
Yes
Custom duration/expiry
Limited
Yes
Unlimited usage
One-off
Yes
Whether you’re flashing for wallet testing, demoing investor dashboards, or simulating balance flows, our tools deliver realism without risk.
Ready to Buy Flash USDT or the Software?
Skip the wait. Skip the scammers.\ You’re one click away from real control.
Support or live walkthrough?
Telegram: @cryptoflashingtool
WhatsApp: +1 770-666-2531
Legal Notice
These tools are intended for:
- Educational purposes
- Demo environments
- Wallet and UI testing
They are not for illegal use or financial deception. Any misuse is your full responsibility.
Final Call:
Need to flash USDT? Want full control?\ Don’t wait for another “maybe” tool.
Get your Flash USDT or Flashing Software today and simulate like a pro.
Telegram: @cryptoflashingtool
WhatsApp: +1 770-666-2531
-
 @ dfa02707:41ca50e3
2025-05-20 09:10:54
@ dfa02707:41ca50e3
2025-05-20 09:10:54News
- Wallet of Satoshi teases a comeback in the US market with a non-custodial product. According to an announcement on X, the widely popular custodial Lightning wallet is preparing to re-enter the United States market with a non-custodial wallet. It is unclear whether the product will be open-source, but the project has clarified that "there will be no KYC on any Wallet of Satoshi, ever!" Wallet of Satoshi ceased serving customers in the United States in November 2023.
- Vulnerability disclosure: Remote crash due to addr message spam in Bitcoin Core versions before v29. Bitcoin Core developer Antoine Poinsot disclosed an integer overflow bug that crashes a node if spammed with addr messages over an extended period. A fix was released on April 14, 2025, in Bitcoin Core v29.0. The issue is rated Low severity.
- Coinbase Know Your Customer (KYC) data leak. The U.S. Department of Justice, including its Criminal Division in Washington, is investigating a cyberattack on Coinbase. The incident involved cybercriminals attempting to extort $20 million from Coinbase to prevent stolen customer data from being leaked online. Although the data breach affected less than 1% of the exchange's users, Coinbase now faces at least six lawsuits following the revelation that some customer support agents were bribed as part of the extortion scheme.
- Fold has launched Bitcoin Gift Cards, enabling users to purchase bitcoin for personal use or as gifts, redeemable via the Fold app. These cards are currently available on Fold’s website and are planned to expand to major retailers nationwide later this year.
"Our mission is to make bitcoin simple and approachable for everyone. The Bitcoin Gift Card brings bitcoin to millions of Americans in a familiar way. Available at the places people already shop, the Bitcoin Gift Card is the best way to gift bitcoin to others," said Will Reeves, Chairman and CEO of Fold.
- Corporate treasuries hold nearly 1.1 million BTC, representing about 5.5% of the total circulating supply (1,082,164 BTC), per BitcoinTreasuries.net data. Recent purchases include Strategy adding 7,390 BTC (total: 576,230 BTC), Metplanet acquiring 1,004 BTC (total: 7,800 BTC), Tether holding over 100,521 BTC, and XXI Capital, led by Jack Mallers, starting with 31,500 BTC.
- Meanwhile, a group of investors has filed a class action lawsuit against Strategy and its executive Michael Saylor. The lawsuit alleges that Strategy made overly optimistic projections using fair value accounting under new FASB rules while downplaying potential losses.
- The U.S. Senate voted to advance the GENIUS stablecoin bill for further debate before a final vote to pass it. Meanwhile, the House is crafting its own stablecoin legislation to establish a regulatory framework for stablecoins and their issuers in the U.S, reports CoinDesk.
- French 'crypto' entrepreneurs get priority access to emergency police services. French Minister of the Interior, Bruno Retailleau, agreed on measures to enhance security for 'crypto' professionals during a meeting on Friday. This follows a failed kidnapping attempt on Tuesday targeting the family of a cryptocurrency exchange CEO, and two other kidnappings earlier this year.
- Brussels Court declares tracking-based ads illegal in EU. The Brussels Court of Appeal ruled tracking-based online ads illegal in the EU due to an inadequate consent model. Major tech firms like Microsoft, Amazon, Google, and X are affected by the decision, as their consent pop-ups fail to protect privacy in real-time bidding, writes The Record.
- Telegram shares data on 22,777 users in Q1 2025, a significant increase from the 5,826 users' data shared during the same period in 2024. This significant increase follows the arrest of CEO and founder Pavel Durov last year.
- An Australian judge has ruled that Bitcoin is money, potentially exempting it from capital gains tax in the country. If upheld on appeal, this interim decision could lead to taxpayer refunds worth up to $1 billion, per tax lawyer Adrian Cartland.
Use the tools
- Bitcoin Safe v1.3.0 a secure and user-friendly Bitcoin savings wallet for beginners and advanced users, introduces an interactive chart, Child Pays For Parent (CPFP) support, testnet4 compatibility, preconfigured testnet demo wallets, various bug fixes, and other improvements.
- BlueWallet v7.1.8 brings numerous bug fixes, dependency updates, and a new search feature for addresses and transactions.
- Aqua Wallet v0.3.0 is out, offering beta testing for the reloadable Dolphin card (in partnership with Visa) for spending bitcoin and Liquid BTC. It also includes a new Optical Character Recognition (OCR) text scanner to read text addresses like QR codes, colored numbers on addresses for better readability, a reduced minimum for spending and swapping Liquid Bitcoin to 100 sats, plus other fixes and enhancements.

Source: Aqua wallet.
- The latest firmware updates for COLDCARD Mk4 v5.4.3 and Q v1.3.3 are now available, featuring the latest enhancements and bug fixes.
- Nunchuk Android v1.9.68.1 and iOS v1.9.79 introduce support for custom blockchain explorers, wallet archiving, re-ordering wallets on the home screen via long-press, and an anti-fee sniping setting.
- BDK-cli v1.0.0, a CLI wallet library and REPL tool to demo and test the BDK library, now uses bdk_wallet 1.0.0 and integrates Kyoto, utilizing the Kyoto protocol for compact block filters. It sets SQLite as the default database and discontinues support for sled.
- publsp is a new command-line tool designed for Lightning node runners or Lightning Service Providers (LSPs) to advertise liquidity offers over Nostr.
"LSPs advertise liquidity as addressable Kind 39735 events. Clients just pull and evaluate all those structured events, then NIP-17 DM an LSP of their choice to coordinate a liquidity purchase," writes developer smallworlnd.
-
Lightning Blinder by Super Testnet is a proof-of-concept privacy tool for the Lightning Network. It enables users to mislead Lightning Service Providers (LSPs) by making it appear as though one wallet is the sender or recipient, masking the original wallet. Explore and try it out here.
-
Mempal v1.5.3, a Bitcoin mempool monitoring and notification app for Android, now includes a swipe-down feature to refresh the dashboard, a custom time option for widget auto-update frequency, and a
-
 @ 30b99916:3cc6e3fe
2025-05-19 20:30:52
@ 30b99916:3cc6e3fe
2025-05-19 20:30:52bitcoin #security #vault #veracrypt #powershell
BTCwallet automates running hot and cold storage wallets for multiple Bitcoin wallet applications.

BTCwallet is included with VaultApi and supports Sparrow, Blockstream Green, and just added support for Wasabi wallets.
To launch a wallet application, the command BTCwallet start is executed.
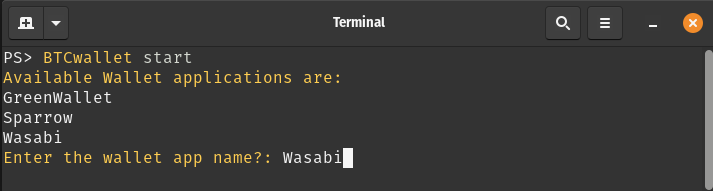
After responding to prompts for launching and initializing the Vault (not shown), the following prompts are presented.
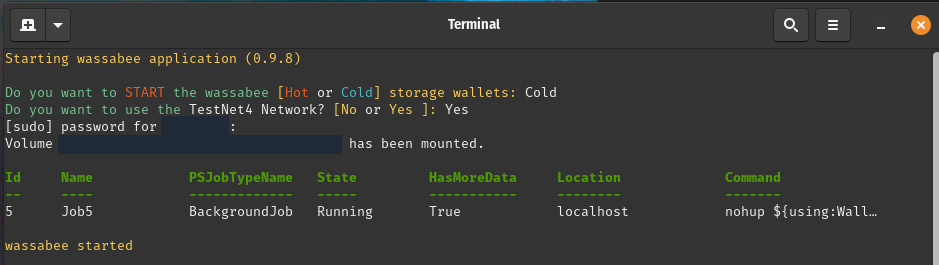
Now the Wasabi GUI application (a.k.a wassabee) is presented.

With the combination of VaultApi and BTCwallet one has a very secure self-hosted password manager along with a very secure way of protecting your Bitcoin wallet's data.
Care to follow me on my journey? If so, then check out the following links.
-
 @ 9be6a199:6e133301
2025-05-19 20:27:20
@ 9be6a199:6e133301
2025-05-19 20:27:20ssdsdsdsdsdsdsd
-
 @ 9be6a199:6e133301
2025-05-19 20:15:18
@ 9be6a199:6e133301
2025-05-19 20:15:18 -
 @ bd4ae3e6:1dfb81f5
2025-05-20 08:46:08
@ bd4ae3e6:1dfb81f5
2025-05-20 08:46:08